Officers & Master Clients (2961)
Budiono
A Prabhu
A. Budi Pranoto
AAJ BATAVIA
Aam Dewi Hamidah
Aarti Lohia
Abdul Hadi Ismail
Abdul Rachman
Abdul Rahman
Abdul Rifai Natanegara
Abdul Slam TAHIR
Abdul Slam Tahir
Abdullah Alatas
Abu Djaja Bunjamin
Abu Hermanto Budiono
Achirsyah Moeis
Achmad Fadjar
Achmad faried Joesoef
Achmad Faried Joesoef
Achmad Kalla
Achmad Latief Alwy
Achmad Nugraha Djuanda
Achmad Sandi
Achmad, Sally, Erma and Cindy as joint tenants
ADAM SAUTIN
ADAM SAUTIN
Ade R. Syarief
ADE TJAKRALAKSANA
Ade Tjakralaksana
Ade Tjakralaksana
ADELINA PRASETIO
Adhi Utomo
ADHI UTOMO JUSMAN
ADI BISONO
ADI BISONO
Adi Sasono
Adi Sumito
Adimitra Baratama Nusantara
Aditya Koeswojo
Adji Muljo Teguh
Adnan Kelana Haryanto & Hermanto
ADRI ACHMAD DRAJAT
Adriana Maya Politon
Adryansyah
Afandi Hermawan Oey
Afandi Hermawan Oey and Tjoeng Anna Chrisnadi
Agam Nugraha Subagdja
Ago Harlim
Agoeng Noegroho
Agung Podomoro Group
Agung Salim
Agung Tobing
Agus Djohari
AGUS HARTONO LIE
Agus Lasmono Sudwikatmono
Agus Leman Gunawan
AGUS MAKMUR
Agus Nursalim
Agus Pranoto Setiadi
Agus Purnomo Edhi
Agus Soenong / Intina Wirawan The
Agus Suherman Wirjan
AGUS SUSANTO
Agus Tjandra
AGUS WIDAGDO
Agustinus Prasetio
Agustinus Wishnu Handoyono
AGUSTON MAKMUR
Ahadiat Wargana
AHMAD DIPODITIRO
AHMAD MARDA
Ahmad Rahman Pasaman
Ahmaddin Ahmad
Ahmaddin Ahmad
Ahmaddin Ahmad
AHMADES MIQAILLA
AHSANIL GUSNAWATI
Aida Ishak
AIRIN OKTAVIANY GUNAWAN
Aiwy
Aizid Syafriel Adjam
AIZID SYAFRIEL ADJAM
AJI BAYU WIRROTAMA
Aji Bayu Wirrotama
AJI WIJAYA, SUNARTO YUDO & CO
Akbar Yoso Trisedia
Alan Clark
Alan Clark
Alan Robertson Clark
Alanberg Pte. Ltd.
ALBERT CAHYADI SUKANDADINATA
Albert Kongoasa
Albert Sugianto
Albert Suherman
ALDO PUTRA BRASALI
Alex Ivan Tanoyo
Alexander Hermas Wolfe
Alexander Hermas Wolfe
Alexander Johan Widjaja
Alexander Johan Widjaja
Alexander Thaslim
Alexandra Miksar
Alexandra Miksar and Djoni Aristianto Prasetio
Alexandra Miksar and others
Alfari Narindra
Ali Alimsyah
Ali Alimsyah
ALI CHENDRA
Alice Haryono
ALIEN WIBOWO
Aling Hermawan Oey
Alisyahrazad Hanafiah
Allan Dijaya Keller
Allan Tjahja Tjao
Aluinanto Sandjojo
ALVIN GOZALI
Alwi Alatas
Alwijaya Aw
Amalia
Amalia Aristiningsih
Amaluddin Djambak
AMAN
Ameesh Anand
Amelia Kurniawan
Amelia Mulyono
American Express Bank Ltd (Indonesia)
AMIN HALIM
AMIN SUPRIYADI LIU
AMINOTO SUTANDI
AMINOTO SUTANDY
Amrullah Hasyim
Amrullah Hasyim
Amy Delia
Anak Agung Alit Wiradarma
Anak Agung Gde Agung
Ananda Soewono
ANCE ANGGRAENY
Andang Bachtiar
ANDHIKA ANINDYAGUNA HERMANTO
Andi Achmad Dara
Andi Ahmad Dara and Evi Yulisma Harahap as joint tenants with right of survivorship
Andi Gunawan Wibowo
ANDI PRAVIDIA SALIMAN
Andi Zainal A. Dulung
Andiko Ardi Purnomo
Andre Abdi
Andre Abdi
ANDRE JOHANNES MAMUAYA
Andre S Prijono
Andre Sukendra Atmadja
Andreas Andikha Bunanta
Andreas Kastono
Andreas Kongoasa
Andreas Tjahjadi
Andrew I Sriro
Andrew K. Labbiaka
Andrew McKay
ANDREW MELLON PRIASMORO
ANDREW TANOTO
Andrew Thomas Eriksson
Andrie Setiawan Yapsir
Andry Irwan Djugo
Andry Pribady
Andry Pribady
Andry Setiawan
Andy Nugroho Purwohardono
Andy Soewatdy
Andy Wiryanto Ong
Ang Lian Ping
Ang Rianti
Ang Rosabella Martina
Angela Lestari Widjaja
Angelique Stampfer
Angie Christina
Angus Maclachlan
Angus Nelson Karoll
Ani Sim
Anil Kumar Lachman Panjabi
Anindya N. Bakrie
Anita Kalim
ANITA RATNASARI
Anna Solana Hamami Kadarachman
Anna Sri Dewi Sianto
Annie Halim
ANTHONY BRENT ELAM
Anthony Dominic Byron
ANTHONY KURNIADI
Anthony Salim
Anthony Salim
Anthony Siswanto
Anthony Wijaya
Anton Henning Linderum
Anton Henning Linderum
ANTON KUSUMA
Anton Santoso
Anton Santoso
Anton Santoso and Anita Marta
Anton Sugiono
Anton Tjahjono
Anton Tjahjono
Anton Wiratama
Antonius Mulya Saputri
ANTONY GUNAWAN
Antony Gunawan
Anuj Ralhan
Anwar Lim
ANWAR SAEBE
Apex Oil & Gas Ltd.
Appointcorp Limited
Ardas Dipa
ARDAS DIPA
ARDIANI KARTIKA SARI SUBIANTO
Ardy Wiria
Ari Hardono Suroso
Ari Indra Gautama
Ari Rophian Perdana Ariwibowo
ARI SULISTIO
Arianto Prasetio
Arianto Wisnu Triyatno
Arie Kondang Kresnadi
Arief Prijatna
Arief Santoso
Arief Wiyoso Aswismarmo
Arif and Yvette Suryatenggara
Arif Rachmat
Arifin Yohan
ARINI SARASWATY SUBIANTO
Aris Agung Budiman
Aris Yuwono Ang
Aristotle
Arjen Tridarma Darmawan
Arlehne Purnomo
Arman Sutedja
Armedta Budi Asmara
Armeilia Widayanti Subianto
Arniaty Achmad
ARNIATY ACHMAD
Arta Satria Soebandi
Artha Mitra Interdata
Arthur Andersen & Co. (Indonesia)
Arwan Ahimsa
ARY SURYA
Arya Widjaya
Aryo Bimo Notowidigdo
Aryo Bimo Notowidigdo
ASHWANI CHOWDHRY
Asia Consulting and Investment Limited
ASIA INVESTMENT CAPITAL I LIMITED
Asian Venture Finance Ltd.
ASWADI
Ateng Suhendra
Ateng Sulestio
Atira Aksa
Aubrey Bobb
AURELIA SUPARDI
Aviariananto Sukotjo
Awiek Lestari Rahayu
Aziar Zain
Azir Azwien Jenie
B. Dorpi Parlindungan
Bachrumsyah Hamzah
Baduraman Dorpi Parlindungan
Badurmana Dorpi Parlindungan
Bagus Panuntun
Baldeo Singh
Baldeo Singh
Baldeo Singh
Baldeo Singh
Bambang Hartono
Bambang Irawan Massie
Bambang Niaga Tjiputra
Bambang Rahardja Burhan
Bambang Subianto
Bambang Sugianto
Bambang Suhandi. T, SE
Bambang Sujagad Susanto
BamBang Sumantri
Bambang Tijoso Tedjokusumo
Bambang, Derice Alda, Malcolm Alda and Meyrick Alda Sumantri
Banbang Panutomo
Bank Bira
Bank Centra
Bank Danamon
Barlianto Ronald
Barlianto Ronald
BASIR B. NASIKUN
Basuiki Puspoputro
Batavia Prosperindo Sekuritas
Bayu Irianto
Bayu Prawitasari
Bayu Virgan Triyatno
Beata Ida Hartono
Beatrice El
BEATRICE EL
Belinda Natalia Tanoko
BELLYANAWATY BUDIMAN
Ben Morice
Beng Phiau
Bengt Carl Gustav Thornberg
Benjamin Subrata
Benjamin Subrata, Niluh Rosye Peny Subrata, Emily Ayu Subrata and Karla Dewi Su
Benjamin Wong Siong Yuit
BENNY IRSJAD
Benny Setiawan
Benny Tenges
Benny Tjokrosapoetro
Beny Haryanto
Bernadette Ruth Irawati
Bernie Prajoga
Betty Ang
BHAYANG SURYADIMADJA
Bimo Pramudyo Soekarno
Bimo Surono
Bing Gondosubroto
Bintoro Wong
Bismarka Kurniawan
Blue Ribbon Holding Ltd
Bob Yanuar
Bob Yanuar
Bobby Andhika
Bobby Iman Satrio
Boedi Sampoerna
Boedihardjo Sastro Hadiwirjo, Uki Budi Sulaksani and Atty Boedi Milyarti
Boediyanio Gondotirto
Boelio Muliadi
Boelio Muliadi
BOENJAMIN & POPPY & SANADI & SHINTA
Bong Kiu Nio
Bong Tjen Khun
Bong Tjen Khun and Tjong Njuk Fon
Bonny Budi Setiawan
BOURNIGAUD (ep Williams) Edith Monique, Danielle, Marie
Boy Gemino Kalauserang
Brett Hay
BRIAN KENNETH JOHN DALLAMORE
BRIAN KENNETH JOHN DALLAMORE
Bright City Group Corporation
Bruce William Carpenter
Bruce Williams Carpenter
BUDHI SOEJONO
Budi Arsil
Budi Basuki
Budi Christranto
BUDI DHARMO NOTOWIDJOJO
Budi Enijati Maria Soedjana
Budi Ferdinandus JAPADERMAWAN
Budi Mulio Utomo
Budi Santoso Taruno Sembodo
Budi Setiadharma SH
Budi Sintoro Then
Budi Surjana
Budi Widyadi
Budi Yanto Lusli
Budiarto Karim
Budiarto Karim
Budiarto Karim
Budiawan Jusmin
BUDIJUWONO HANDJAJA
Budiman Effendi
Budiono
Budiono Darsono
Budiono Tanbun Boen
Budy Hartono Santosa
Budyanto Totong
Burhansjah
BUSTAMI
Cakra Ciputra
Calvin Lukmantara
Cameron Robert Knox
Candra Winoto Salim
CANDRA WINOTO, SALIM
Capital Reserves Ltd
CARLOS TARAZONA RAMIREZ
Caroline
Catherine Gina Hambali
Catherine Hambali
CATHERINE YOSHAWIRJA
Cavalier International Group Corporation
Cecilia TEJOWARNO
Celin Tanardi
Chairul Iskandar Zulkarnaen
Chairul Tanjung
Chairul Tanjung
CHAIRUL TANJUNG
Chalid & Partners
Chalid & Partners Law Firm
CHAN HIONG POH
Chan Hiong Poh
Chander Vinod Laroya
Chandler Capital Inc.
CHANDRA EKAJAYA
CHANDRA EKAJAYA
CHANDRA EKAJAYA
CHANDRA EKAJAYA
Chandra Widjaja
CHANG MEI YU
Charles Louis De Queljoe
Charlie Kasim
Charterhouse Limited
CHEAM SOON TEE
Chenry Micron Mor
Chew Say Loo
Chew Say Loo
Chien Cheng, Chieh Yu-Kun and Chieh Chen Hon-Tsu
Chin Chin Chandera
Choo Khee
Choo Ngaw (Choo Kok An)
Choo Tek (@ Choo Chin Tek)
Chris Fong
Chris Newton
Christanto Santoso
Christian Dieter Scholz
Christian Leuchtenberg
Christian Nainggolan
Christian Parlaungan Mulyanto
CHRISTIAN SANDY RACHMAT CHRISTIAN SANDY RACHMAT
Christian Sandy Rachmat
CHRISTIAN SANDY RACHMAT
CHRISTIAN SUGIARTO
Christiana Halim
Christiana Niowni
Christianto
CHRISTIE RUSSELL CARTER
Christina Harapan
Christina Harapan
Christina Sumarlin Pribadi
Christopher Basil Newton
Christopher Carson
Christopher Fong
CHRISTOPHER FONG
Christopher James Garrard
Christopher James Garrard
Christopher Tanuwidjaja
Chu Jackson
Chui Hing Keung
Chung, Sung Chae
Cindy Tanuwidjaja
Citibank, N.A. (Indonesia)
Citrawinda Priapantja
City Harvest Investments Limited
CL Law Firm
Clarence Leonard Stratton
Crescento Hermawan
Dadi Sukarso Yuwono
Damsiruddin Siregar
Dan Brown
Danamon Group Legal
Danan Kadarachman
DANI ISMULYATIE
DANIEL
DANIEL & VERONICA YUWONO YU
Daniel Indra Djajadi
Daniel Kurniawan Lukman
DANIEL MARATHON
Daniel Podiman
Daniel Wewengkang Korompis
Danielle Catharina Willemijn Maria Van Poppel
DANNY JUWONO
Danny Juwono and Linda Liani Janti Senjaya
Danny Nugroho
Danny Nugroho
Danny Tjiu
Danny Tjiu
Dany Subrata
Darjoto Setyawan
Darjoto Setyawan and Tjan Felisa
Darmadi Karjanto Putro
Darmansjah Darsono
DARMAWANSJAH SETIAWAN
Darminto
Darminto Hartono
Darmo Suwito Barwin
Darmoseputro
DARWIN LEO
Darwin Silalahi
Darwin Soegiatto
Darwin Sutanto
Daswi Rayawang
David Alexander Yuwono
David Kristian
David Kuchenbecker
David Myles Falkner
David Nico Sutanto
David Pierre Michael Bakker
David Salim
David Widjaja
David William DONALDSON
David William Magson
DEBBY FEBRIANY GUNAWAN
Deborah Kent Janawati
Dectra (Samoa) Limited
DEDDY HARIJANTO SUDARIJANTO
Dedie Suherlan
DEDY ROCHIMAT
Dendy Kurniawan
Denise Tjokrosaputro
Denise Tjokrosaputro
Denise Tjokrosaputro
Denise Tjokrosaputro
Denny Lim
Denny Rahardja
Denny Suryadinata
Denny Wijaya
Denny Wijaya
Deny Juliarto
Dermawan
DEVI TRI ASMARASARI
Devie Hendrastiti Darmawan
Devin Wirawan
Devy Prasetyo Yuwono Ang
Dewi Garlina Sari
Dewi Indrajani Alimwidjaja
Dewi Kencanawati Natawidjaja
Dewi Livia Sari (Alternate Protector)
Dewi Natalia Lim
Dewi Nilka Sari
Dewi Novianawati
Dewi Suryati Liauw
Dharma Tjitra Widjaja
Dharma Tjitra Widjaja
Dharmadi Budiman
DHARMAWANDI SUTANTO
Dharsono Hartono
Diah Soemedi
Dian Muljani Soedarjo
Dian Sumeler
Diana Husein
Diana Sastrajaya
DIANA WIDJAJA
Dick Leitch
Dicky Herman
DICKY HERMAN
Dicky Kurniawan
Dicky Tjokrosaputro
Dicky Yordan
Didi Ferdinand Korompis
Didit Abdurachman Rustandi
Didit Budijarto
Dina Eldelina Pow
Diniwati
DINO KOESHANDERY
Diono Nurjadin
Dixon Koesdjojo
Djajadi Djaja
Djajadinata Hardjono
Djamaluddin Tanoto
Djamaluddin Tanoto and Limiwaty Lie
Djan Faridz
Djan Faridz
Djan Faridz
Djatmiko Tedjo
Djatmiko Tedjo
Djauhara Faizal
DJERISIN KUESAR
Djie Tjian An
Djie Tjian An and Febe Maryanti Wirjadi as joint tenants with right
Djohan Is Hardjo
Djohan Tjiunardi
Djoko Kartono
Djoko N. Labbaika
Djoko Nirmala Labbaika
Djoko Soesanto Gusti
Djoni Muchsin
Djoni Rion Gui
Djoni Rion Gui
Djoni Rion Gui and Kusnadi Gui as joint tenants with right of survivorship
Djoni Rion Gui and Kusnadi Gui as joint tenants with right of survivorship
Djoni Sukohardjo
Djonny Koesoemahardjono
Djuana Sulestio
Djuffan Achmad
Djumharbey Anwar
Djuniar Tunggal
Doddy Agustiawan Tjahjadi
Dodi Suhartono Abdul Kadir
Dody Lukito Hendrokusumo
Dolly Periagutan Pulungan
Dominique Gallamnn
Dominique Gallmann
Don MacDonald
Doni Irawan
Donny Imam Priambodo
Donny Yoesgiantoro
Doreen Sim
Dorys Setiawati Herlambang
Douglas Vincent Tingey
Dr Hmnm Hasyim Ning
Dr R. Soeparmadi
Dr. Cheam Soon Tee
Dr. Darmadi Goenawan
Dr. Johnny Goenawan
Dr. Kahar Tjandra, Evy Tjandra
Dr. Kahar Tjandra, Evy Tjandra, Nancy Tjandra Muljadi
Dr. Pudji Witomo
DRS ARYANTO AGUS MULYO
DRS J.B NETYAKA
Dunn Fa Chong
Dwiarti Widiyani
East Star Ventures Ltd
EDDI SUGIARDI
Eddie Sudijono
Eddy Daud
EDDY HALIM
Eddy Handoko
EDDY HERMAN
Eddy Hussy
Eddy Iskandar
Eddy Kusnadi Sariaatmadja and Sofie Widjaja Sariaatmadja as joint
Eddy Pramono
Eddy Purwanto
Eddy Purwanto
Eddy Purwanto Lim
EDDY SETIAWAN
Eddy Sindoro
EDDY SUSANTO
Eddy Sutandinata
Eddy William Katuari
Eddy Winata
Eddyanto Hadisurjo
Eddyanto Hadisurjo and Ratna Kurniati Bahana
Edgardo Abelarde Tinsay
EDGARDO ELOY DIAZ FALCONET
Edhie Hardjanto
Edi Firmansyah
Edianto Prasetyo
Edo Djunaydi
Edoardus Ardianto
EDOARDUS ARDIANTO
Edoardus Ardianto
Edoardus Ardianto
Edward Ang
Edward Magnus Lang
Edward Magnus Lang
Edward Magnus Lang / Hans Jurgen Kaschull
Edward Magnus Lang and Kartini Herawati Lang
EDWARD STEPHANUS DJAUHARI
EDWIN MOHTAR
Edwin Muchtar (Mr.)
Edwin Soeryadjaya
Edwin Sugiarto
Edy
Edy Kosasih
Edy Kusnadi
Edy Susanto
Edy Suwarno
Efendi Boedhiman
Effendy Husin
Efrem Wardhana
Eiffel Tedja
EKA SINTO KASIH TJIA
Eko Budianto
Eko Prasetyo Ang
Eko Purnomo
Eko Suharto
EKO SUKAMTO
El Beatrice
Eliani Johan
Eliezer Nugroho Tjandrakusuma
Elisabet Lay
Elisabeth Lintje
Elisabeth Magdalena
Elizabeth Januarti W
Elizabeth Jayne
Elizabeth Jayne
Elizabeth Sindoro
Elizabeth, Alicia, Denise and Michelle as joint tenants with
Eljay Limited
Elke Camillia Kurniawan
Elline Yohan Yau
Elly Koeswandia Tjokronegoro
Elly Lestari Adiutama
Elly Nurlaila Hutabarat
Elly Soepono
Elmursil Moenzir
ELSA DJAUHARI
ELVIN TJANDRA
Elvina Jonas Jahja
Elvira Pudjiwati
Emi Sukiati Lasimon
EMIL ABENG
EMILY STEPHANA DJAUHARI
Emily Waty Setiawan
EMMANUEL LESTARTO WANANDI
Emmy Damayanti
Emy Harjono
Emy Harjono/Andres S, Magbitang jr
Endah Sulistyorini Himawan
Endang Soertikanty
ENDANG SUGIARTI
Endang Sugiarti
Endang Susila BUDI
Endang Susila Budi
Endang Triningsih
Endro S. Wahono
Endy Suryokusumo
Endy Suryokusumo
Enny Lukitaning Diah
Enny Soegiarto
Enny Trang
ENTARIO WIDJAJA SUSANTO
Era Helvani
ERIC HARDONO TIRTAJASA
Erick Djuwadi
Erick Thohir
ERICS YOSHAWIRJA
Erik Setiawan
ERIKA DEBORA DJAUHARI
Erlina Ongoredjo
ERLINA ONGSOREDJO
Erly Tandjung
Erna Widyastuti
ERNAWATI
Erni Gunawan
Ernitha Halim
Erric B. Wibowo
Erric B. Wibowo
Ervin Wijaya
Ervin Wijaya/Shiany Angsana/Andree Wijaya
Erwin Aksa
Erwin Aksa
Erwin Budisantosa
Erwin Ciputra
Erwin Gunawan
Erwin Indra Hamid
Erwin Sasunto
Erwin Sutanto & Wiwiek Kwedarisman as joint tenants
Erwin Tunggul Setiawan
Ery Yunasri
Esther Riawaty Hari
Eugene Trismitro
Eunice Meriati Satyono
Eva Berliana Rosway
EVAN SAMUEL DJAUHARI
EVELYN DJAUHARI
Evelyn Luciana Soeyapto
Evert Jimmy LENGKONG
Evi Hamdani
Evi Wikarsa
Evi Yulisma Harahap
Evie Raviana
EWIK HENDRI
Execorp Limited
F. Franky
Fabian Gelael
Fadjar Endranto
Fahmi Babra
Fahmi Idris
Fahyudi Djaniatmadja
Faisal Panggabean Law Firm
Faisol Soleh Masjkoer
Faiz Shahab
Faizan Abdul Rahan
Fan Chiang, Teng-Chang
Farah Liza
FARINA TADJOEDIN
Farouk Rais
FAS Consulting Asia Pacific Pte Ltd
Fauzi Ezeddin
Fauzi Jahja
Fauzi Jurnalis
Febrina Sari Bak
Febriyanti (Ms.)
Feilie Sulestijani
Felianah Soetemo
Fendi Santoso
Fensa Sofyan
Fenza Sofyan
FERDINAND JOSEF WONGKAREN
FERNANDO ANTONIO GIL
FERRY SUDJONO
Ferry Tenacious
Fida Unidjaja
Fides Pro Consulting (Business Advisory Services)
FIEFIE TJAHJADI
Fifi Indra
FIFI LETY INDRA & PARTNERS
FIFI NOVITA BASARAH KISYANTO
FIFI WIRIADINATA
Financecorp Limited
Finney Henry Katuari
Fiona Adeline Sutanto
Firdaus Siddik
Firman Matondang Silalahi
Fitri Wiriasari
FLORDEN INVESTMENTS S.A.
Florence & James
Florence Wanamurti
Flores Samudro
FOE SIAT KHIUN
Fong Felix
Fong/Aiwy
Fonny Tedjajadi
Foronkid Gunawan
Francisca Citrasari
Franciscus Xaverius Hardianto Tjondro
Frank Taira Supit
Franky Widjoyo
Frans Limas
Fransiscus Antonius S.A
Fransiskus Budhinata
Fransisous Iwo
Freddy H. Suryadiharja
Freddy Ignatius Katuari
Freddy Sumartono Santoso
Freddy SUTJIPTO
Freddyanto Tirtadjaja
Freeport trading Group Limited
Fuad Segayir Alkatiri
G. Lal Agrawala
Gahet Loengara Ascobat
Gahral Sjah
Gaitini Tjokrosaputro
Gan Boot Lian
Gan Chooi Yang
GANDHI BEND
Ganesh Chander Grover
Gareth Joh LEWIS
Garibaldi Thohir
Garibaldi Thohir
Gary Dino Ridwan Sjah
Gary Neal Christenson
Gary Neal Christenson
Gary Neal Christenson
Gary Phair
Gary Phair
Gary Phair (in-active)
Gatot Kariyoso Wiroyudo
Geeta M. Mirpuri
Gemilang Investama
Gen Sik Tjin Tan
Gene Sik Tjin Tan
Geoffrey David Simms
George Christoph Robert Spath
George Nicolas Simanjuntak
George Nicolas Simanjuntak
George Setiyadi
Gerald Rossi
Gerry Aubry
Gerry Prawira Saputra Tjong
Gesang Budiarso
Ginawan Chondro
Ginawan Chondro
Gino Junior Korompis
Giovani Maria Ekaputra Suhari
Gita Irawan Wirjawan
Gita Irawan Wirjawan
Gita Irawan Wirjawan and Yasmin Stamboel Wirjawan
Gita Wirjawan
Gladys Kiong
Glenn Timothy Sugita
GLENN TIMOTHY SUGITA
GLENN TIMOTHY SUGITA
Glenn Timothy Sugita
Glesen Frais Energy Co. Ltd
Go Sek San
Go Siauw Hong
Go Sik Ying
Go Sri Hartati
GODEFRIDUS TAMPUBOLON
Goh Lay Ling
Goh Tie Sin
Graham Daniel Fogarty
GRANDFIELD HOLDINGS GROUP LIMITED
Grant Moon-Tae Kim
Grant McArthur
Grant Moon-Tae Kim
Grant Moon-Tae Kim
Gregorius Petrus Aji Wijaya
Gregory Campbell HINCHLIFE
GT Asia Pacific Funds Management Limited
Guat Tjing Thio
Gunardi Frans Fong
Gunawan Endi
Gunawan Gusti
Gunawan Jusuf
Gunawan Santoso Gwie
Gunawan Subagio
Gunawan Sucahijono Tjoa
Gunawan suteja
Gurker Limited
GW Franklin Hall
H. Sonny Wibisono Widjanarko
H.I. Made Sadha Ardiana
HABIB HUSEIN ALLAYDRUS
HADI GUNAWAN
HADI GUNAWAN AND LYDIA ANGKAWIDJAJA
Hadi Lukman
Hadi Suginawan
Hadi Suginawan & Nurmalasari Suginawan
Hadidarma Kosasih Kho
Hadinata Widjaja
Hadysugani Hoshi
Hadysugani Hosni
Hajato Darsono
HALIFAH SUNJATA
Halim Podiono
Halim Setiabudi Wijono
Han Hai Thon
Han Jung Kuk
HANDAJA SUSANTO
Handaja Susanto
HANDANA HALIM WANAWIJAYA
Handi Gunawan
Handojo Santosa
Handoko Anindya Tanuadji
Handoko Susilo
Handoyo Sutanto
Handrie Wirawan
HANDY PURNOMO SOETEDJO
Handy Sunardio
Hanny Suprayogi
HANNY SUTANTO
Hanny Sutanto
Hans Jurgen Kaschull
Hans Jurgen Kaschull
Hans Jurgen Kaschull
Hans Jurgen Kaschull
Hans Jurgen Kaschull
Hans Maramis
Hans Moelyadi
Hansen Suryadi
Hanson Ramli
HARDI KOESNADI
HARDI WARDHANA
Hardy Woosnam
Hari Raharta
Hari Widodo
Hariadien Ratmawati Soeprapto
Harianto Solichin
Harianto, Peh
Harijanto Koesdjojo
Haris
Hariyanto Wijaya Sarwono Lim
Harjanto Kusuma Halim
Harjanto Kusuma Halim & Lisa Ambarwati Dharmawan
HARJOSENO
HARMIONO JUDIANTO
Harris Lasmana
Harry Haslett
Harry Herjanto
Harry Nugroho Prasetyo
Harry Soeria
Harry Susanto
Harry Suwignjo
Hartadi Angkosubroto
HARTADI ANGKOSUBROTO
HARTANTO EDHIE WIBOWO
Harto Djojo Nagaria
Hartono Gunawan
Hartono Sundoro Hosea
Haruhiko
Harun Ibrahim Tajuddin Nur
Hary Djaja and Ratna Endang Hartatiek
HARYADI KUMALA
HARYETTI
Haryono Winarta
Hasan Aula
Hasan Aula and Nina Koswandi
Hasan Dali
Hasan W. W. Krisno
Hashim Djojohadikusumo
HASNURYANI SULAIMAN
Haston Limardo
Hastuti Sulistio
Hawanto Hartono
HAZRIYANDI
Heindrix Liauw
Heindrix Liauw
Helen Turtan Setiawan
Helen Wijaya Ong
Helmut Paasch
Helyuzar
Helyuzar
Hen gky Kunta Adjie
HENDARTA ATMADJA
Hendra Alamsjah
Hendra Basoeki
Hendra Harjadi
HENDRA KOESNADI
Hendra Liem
Hendra Nagaria
Hendra Nagaria
HENDRA NOVA SYAMSU
Hendra Soegiarto
Hendra Tjahyawati
Hendra Tjoa
Hendra Wijaja, Tang Linawaty, Teddy Widjaja, William & Silvia
Hendra Wirajang
Hendra Wirajang
Hendrik
Hendrik Hartono, Hoo
Hendrik Suhardiman
Hendrik Suhardiman
Hendrik Tanojo
Hendrik Tee
HENDRIKO WIJAYA
Hendro Guwanda Sutandi
Hendro Santoso Gondokusumo
Hendro Santoso Gondokusumo
Hendro Santoso Gondokusumo
Hendro Setiawan
Hendro Tjokrosetio
Hendry Lesmana
Hendy Rusli
HENG Ijat Hong
Hengki Sovian
Hengky Tenacious
Henking Wargana
HENKY SUWIGNJO
Henny Kusumawati Tanuhardja
HENNY HARMANI WIRJOSOEKARTO
Henny Harmani Wirjosoekarto
Henny Hartady
Henny Kentjanawati Natawidjaja
henny Kusumawati Tanuhardja
Henny Purnamawati
Henny Santoso
HENNY VICTORIA
Henoch Pradhana
Henrianto Kuswendi
Henrik Antoni Jie and Diana Purnamasari Go and Adi Janitra
Henry Halomoan Sitanggang
Henry Hartono Go
Henry Jahja
Henry Kurli
Henry Kurli and Lin Konggui
Henry Leo
Henry Leo
Henry Liem
HENRY PASCAL TAMPUBOLON
Henry Pribadi
Henry Rudy Zaini
HENRY SUPANNI
Henry Susilowidjojo Njoo
Henry Suwignjo
Henry Wargana
HENRY WIDJAYA
Herdin Syafari
HERIK ANTONI JIE
Herlina
Herlina
Herlinah Soetemo
Herline Goenawan
Herman Afif Kusumo
Herman Gozali
Herman Iskandar
HERMAN ISKANDAR
Herman Iskandar, Khoe Ay Hwa & Seraphine Volkani Iskandar
Herman Karmana
Herman Moeliana
Herman Nagaria
Herman Nagaria
Herman Wijaya, Yuliana Kusno, Lenny, Rudy and Joni Wijaya
Herman Y.S. Gunawan (Mr. )
HERMAN, ETI, IVAN & ASTRID
Hermani Soeprapto
HERMANSJAH TAMIN
Hermanto Tangkau Adrian
HERMIJANTO TOTO
HERRY KARYANING CIPTO
Herry Mirza Putera
Herry Mirza Putera
Herry Wibowo
HERTONO RICHARD PRAJITNO
HERU HIDAYAT
Heru Soesanto Gusti
Heru Sucahyo
Herumanlo Zaini
Hesti Femi Nugraheny
Hesye Silya Mamesah
Hetty Heryati Sumantri
Hetty Indrakasih Soetikno
HIANG.TJE
HIANTO DHARMAPUTRA SUNARDY
Hilary Richard Bolton
Hilary Richard Bolton
Hilda Noveda Kaliman
Hilmi Panigoro
Hilton King
Hilton R. King
Himawan & Associates
Himawan Surya
Hindarta Sanjaya
HINDARTA SANJAYA
Hindarto Budiono
HINDARTO SUHARDJO
Hioe Isenta
Hioe Isenta
Hioe Isenta
Hioe Isenta and Ivy Lianawati
Hiramsyah Sambudhy Thaib
Hiswara Natawindjaja
Ho Mie Ling
Ho Mie Ling
Ho Mie Ling
Ho Sze Wah
Hoediono Kweefanus
HOESEN GUNAWAN
Honey Angkosubroto
Honey Angkosubroto
Hong Usman Effendy
HONGKIE WIDJAYA KANG
Horas Chu Naga
HOSEA HADELI
Hotman Naiborhu
Houston Jusuf
Hubertus Setiyadi
Hudi Janti
Hunarti Gosal
HUSIN CHANDRA
Husin Sariman and Dewi Ngadiman
Husin Suliawan
Husni Muchtar
Husodo Angkosubroto
Husodo Angkosubroto
Hutabarat, Halim & Rekan
I Gusti Ngurah Adi Suputra
I MADE DJENDRA
I Nengah Bagiada
I Nyoman Djintji
I Wayan Arya
I. Goesti Ben Kel Bagoes Oka
IAN DONALD MACAULAY
Ibrahim
Ibu Rahmawaty
Ichsan Rizal
ICHSANUDDIN NOORSY
Ida Bagus Made Putra Jandhana
Ida Budisusetyo
Ie Kian Tjoan
Ie Mila Setiawaty
Ie Mila Setiawaty
Ignanto Sandjojo
IGNATIUS JOE BUDIMAN
Ignatius Toni Gunawan
IING YOSHAWIRJA
Ilham Akbar Habibie
Ilham Akbar Habibie
IMA ENDANG PRAYANTI GARIBALDI
Ima Tjahjadi Tjhang
IMAM MUHADI ROWI
Iman Tamin
Imelda Dharma
Imelda Dharma
Ina Irena Jonas Jahja
Inayat Ali Badruddin
Inda Aryanti Imanto
Indah Djuita Tjatursari
Indahwaty Hartono
Indawan Saputra Hatta
Indawati
Inder Singh
Indra Gunawan
Indra Gunawan Wonowidjojo
Indra Makmur
Indra Muliadi Sugiharto
Indra Widjaja
Indrajaty Hadiwardojo
Indrawati Sampoerna
Indriani Harsono
INDRIENA YUDHAYANTI BASARAH
Indro Wibowo
INGRID WILIANTO
Ir. Danny Walla
Ir. Hagianto Kumala
Ir. Rudyanto Hardjanto
IRAWAN HADIKUSUMO
Irawan Kurniadi Tjandra
Irawan Sutandinata (Mr.)
Irawan Widjaja
Irene Maya Hambali Ishak
Irene Maya Hambali Ishak
Irene Susanto Adikoesoemo
Irene Tedja
Iriawan Suharyanto
Irma Mirzanti
IRMAYANI PUJIASTUTI
Irmayani Pujiastuti
Iroshita Arsyafira
IRSANTO ONGKO
Irsanto Ongko
IRVAN YUSRIZAL GADING
Irvinia Megawati Saddak
Irwan Atmadja Dinata
Irwan Hermanto
Irwan Santoso Chandra
Irwan Siregar
Irwan Siregar
Irwandy Ma Rajabasa
Isenta Hioe
Ishak Sumarno
Iskandar Tanuwidjaja
Ismail Hirawan
Ismail Hirawan
ISMAN AYUB
Istini Siddharta
Istini Tatiek Siddharta
Itjendri Suitono Thio
Ivan Budiono
IVAN HENRY
Ivan Setiawan Tan
Ivantara Dviyudha
Ivantara Dviyudha
Ivonny Budiono
IVY LIANAWATI
Iwa Sewaka
Iwan Dewono Budi Juwono
Iwan Hardja
Iwan Margana
Iwan Margana
Iwan Rosadi Widyapranolo
Iwan Ruwiyadi
Iwan Samsuddin
Iwan Valiant Joesoef
Iwan Valiant Joesoef, Marwan Arie Joesoef and Nurfadh Subhan Joesoef
J. C. Gosa
Jackson Chu
Jacky Afandi
Jacky Soerya Santoso
JACOB ANTUNG KANG
Jacob Soetoyo
Jacobus Busono
Jacobus Busono Prawiroredjo
Jacqueline Tjahjadi
Jacub Johannes The
Jahja Santoso
Jahja Santoso
Jahja Santoso and Johana Poedjokerto
Jahjaa Soetoyo
Jajat Priatna Purwita
JAMES BUDIONO
James C. Haebig
James Eric Zaini
James Kallman
James Preston TRUESDELL
James Rachman Adjimin
James Steven Kallman
James T. Riady
James Thomas Henry Arthur
James Tjahaja Riady
Jamin Soetoyo
Jamin Tjandra
Jan Adam Tangkilisan
JAN TRIANA JOHANES
JAN TRIANA JOHANES, YULIANA JOHANES, WINDY MARLINA, OMAR AZHARI, NURDIN HASJIM JOHANES and OKTAVIA DEWI TIRTA as joint tenants
Janni
JANSEN WIRAATMAJA
JANTI JAHJA
Jap Carmen
JAP HARTONO & SANTY MULJAWANA
Jap Johanes
JAP, SOEGIONO
Jason James Raymond
JAYANTI SARI
Jeannie Widjaja
Jeffery Freshen Sihombing
Jeffery Koes Wonsoo
Jeffrey Hartono
Jeffrey Iuwena
Jeffrey K. Wonsono
Jeffrey Koes Wonsono
Jeffrey Sugianto
JEMMY ROMMY PONTOH
Jendrawasih Jenni
Jeniawati
Jennie Widjaya
Jenny Elisabeth RG
JENNY WIDJAJA
JENTY
Jeremy David Kemp
Jessy Vishamkar Adnani
JIALIPTO JIARAVANON
JIALIPTO JIARAVANON
Jim Truesdell
Jimmy Budhi
JIMMY BUDIARTO
JIMMY HARTONO LIE
JIMMY HENRICUS KURNIAWAN LAIHAD
Jimmy Namara
Jimmy Samantha
Jimmy Suryanto Budhi
Jimmy Tjahjanto
Jimmy Welianto Siauw
Jimmy Ziepo Setiawan
JIO TIEN CAROLYNA
Jiohan Sebastian
Jo Andreson Wiharjo
Jo Gasyanto
Jo Liat Tjiang
Jo Souw Koan
Jo Tjin Khoen
Joachim U. Rohn
Joachim Ulrich ROHN
Joachim V. Rohn
Jocelin Yohan Yau
Jodi Haryanto
Joe Su Fun
Joeliardi Sunendar
Joesril Hainim
JOGI HENDRA ATMADJA
Johan Alexander Supit
JOHAN ARIFKAJA ADI LESMANA
JOHAN SOEDIBJO
JOHAN T. GILBERT
Johan Tandean
Johana Poedjokerto
JOHANAS HERKIAMTO
JOHANES GUNAWAN
Johanes Kennedy Aritonang
Johanes Susilo
JOHANES TANG WIDJAJA
Johannes Goenawan
JOHANNES HALIM
Johannes Oentoro
Johannes Setijono and Indriyati
Johannes Tanuwijaya
John (Lam) Kosasih
John Franklin
John Gordon McFadzien
JOHN HUGH LESTER
John Hugh Lester
John Joseph Franklin
JOHN TODD BONNER
John Williem Vanderwal
Johnlee Mailoa
Johnnie Hermanto
JOHNNY
Johnny Wiriawan
Johnny Wiriawan
JOHNSON WILLIANG SUTJIPTO
JOHNSON WILLIANG SUTJIPTO
JOHNSON WILLIANG SUTJIPTO
JOHNSON WILLIANG SUTJIPTO
Johny Lisangan
Johny Surjana
Joice
Joice
Joko Himawan / Paul Himawan
Jonas Jahja
Joni Yoesoef
Jopie Widjaja
Joppy Robert Saerang
Jos Parengkuan
Jos Winata Wihardja
Jose R. Hanna
Josef Indra Njoman
Josep Lay
Josep Susanto Kiswandono
Joseph Dharmabrata
Joseph Donald Charles Buddy
Joseph Tjakra/Ms Margaret
Josephyne Widjaja
Joso Ramli
Jovanka Mardova
JOYCE HANDAJANI
JOYNER OVERSEAS INC.
Jozef Darmawan Angkasa
Juanda Lesmana Lauw
JUANDY WIJAYA
JUANITA DESIREE TAMPUBOLON
Judca Herlina Hansoehardi
Judi Gunawan
Juliana Kusnandar
Juliana Ong Pei I
Julianna Yohan
Juliati Widjaja
Juliati Widjaja
JULIATI WIDJOJO
Juliawati Budiman
JULIE MULYA JIAUW
Junanda Syarfuan
Junanda Syarfuan / Bobby Andhika
Juni Setiawati Wonowidjojo
Junita Ciputra
JUNIUS WIJAYA
Junty
Junus Jen Suherman
Junus Jen Suherman & Juliana Kusnandar
Junus Siswadi
JURNALIS & PONTO LAW FIRM
Jusak Hadi Wardojo
Justian Suhandinata
Justin Barney GOFF
Justin Breheny
Justo Padilla Nestro
JUSUF
Jusuf Handri Rachmantio
Jusuf Heryanto
Jusuf Salman
Jusuf Tanuwidjaja
Jusup Budihartono Prajogo
Jusup Susanto Djunaidi
Juwita Lianty Suandi
Jyoti Lekhraj Budhrani
JYOTI LEKHRAJ BUDHRANI
K MELBOURNE BREAU
K.P. Irwan Kartawijaya
Kaizer Management Ltd
KAKAN SUKANDA DINATA
Kalim
Kam Lie Giok
Kama Putra Kusdianto
KAMAN HALIM
Kamlesh Ishwardas
KANG ARIES FUKSAR
Kang Rita Sadeli
Kang Rita Sadeli and Song Wen Shyu
Kanisha Sunil Mirpuri
Kardaya Warnika
Kardja Rahardjo
KARTA WIGUNA
Kartini Fahmi Idris
Karuna Murdaya
Kasiviswanathan Prakash
Katharina Wihardja
Katini Dewi
Katleen Yangrikho Gui
KAZAN GUNAWAN
Ken Leksono Sedianto
KEN LEKSONO SEDIANTO
Ken Ng
Kendra Soegandha
Kenneth R. Wynn
Kenneth R. Wynn
Kezia Putri Aprilya Kusdianto
Khairul Saleh
KHOE AY HWA
Khou Lim Ngo
KHOU LIM NGO
Kiki Barki
Kiki Kiftiah
Kiki Sutantyo
Kim Doo Young
Kim Sung Kook
Kim Sung Kook (Mr)
Kimberly Ananto
KIMIN TANOTO
Kindarto Kohar
Kirk D. Evans
Kirk David Evans
Kitty Joantina Wulanda
KITTY TJIOE
Kiyomi Sato
Ko Rudy Oetomo
Kokarjadi Chandra
Kokarjadi Chandra
Koko Poernomo Santoso
Kokos Leo Lim
Kompleks Perkantoran
Kris Widjojo
Krishan Kulmar Ralhan
Krishan Kulmar Ralhan
Krishnan Sjarif (Mr)
Krisnadi Gautama
KRISNO ABIYANTO, SOEKARNO
Kristanto Wibowo Siswanto
Kristina Minto
Kumalasari Tjiong
Kurniati Phan & Jusuf Budi Wijoto as joint tenants with right of survivorship
Kurniawan Nurdin Karim
Kusdianto Soewarno
Kusdianto Soewarno
Kusdianto Soewarno
Kusnadi Budiman
Kusnan Kirana
Kusnandar & Co.
Kusuma Hadi Soetemo
Kusumawati
KUSUMO ABUJONO MARTOREJO
Kusumo Purwanti Dewi
Kwee Suo Chie
Kwok Moi Moy
L & P Capital Investments & Corporate Advisory
Laksamana Sukardi
Lakshmi Harris Lasmana
LAKSMI PRATIWI DALLAMORE
Lam Mang Ying
Lam Toi Lai
Lambertus Nuryono
Lambertus Somar
Lanasari Halim
Lanny Lanawaty
Lanny Tanzil
Lanny Widjajanti
Lao Rusming
Lauw Samuel Lawrence
Law Office CCN & Associates
Lawrence Barki
Lawrence Barki
Lawrence Barki
Lay Sioe Ho
Le Purna Harjani
LE PURNA HARJANI
Leda Magdangal Tamin
LEDRES BALMACEDA MARIO
Lee Chuck Soo
Lee Yick Cheung
Leman Hadi Soetemo
Lenny Wijaya
Leny Anwar
Leny I. Wangsawidjaja
LEONARD PANDY PHUA
Leonardus Eko Daru Lumadyo
Lestariono
Letty Johan
Levi Octavia Soewarna
Lianawati Setyo
LIANNY HARYONO
Liauw Sumiati
Lidwina Lindawati Kartiko
LIE SIE GIEM
Lie Soemarli
Lie Tjauw Mian
Lie Tjin Ming
Liem Hadi Mualim
Liem Johan Halim
Liem Kong Shiung
Liem Kong Shiung
LIEM SIN HUANG
Lies Kusumawati
Lijatini Setiono
LIKE RANI IMANTO RACHMAT
LIKE RANI IMANTO RACHMAT
Likin Handoko
LiLi Ashari
Liliana Budi Santoso
Liliana Budi Santoso and Willy Gunawan
Liliana Wibisono
Liliawati Rahardjo
Lily Ciarensia Tjia
Lily Lawandra
Lily Marjani Pribadi
Lily Solaiman Sutantyo
LILY TAMIN
LILY TAMIN
Lily Yuliani Halim
Lilyani Tanoko
Lilys Tjiawi
Lim Arie Sasmita
Lim Budi Susetyo
LIM EDDY PURNOMO
Lim Eng Khim
Lim Fie Tjong
Lim Fie Tjong
LIM LIMMAN NUGROHO
Lim Lys Erty
Lim Soon Huat
Lim Tjung Luong
Limanto
LIMIWATY LIE
Lin, Yu-Cheng
Lina Gunawan
Lina Harjanti Latif
LINA KURNIAWAN
Lina Soegiharto Leo
LINAWATI SOEJANTO
Linawidjaja Kusprajudi
Linda Hakim
Linda Lauw
LINDA LIANI JANTI SENJAYA
Linda Marlina Isatyawan
Linda Marlina Isatyawan, Edy Kosasih
Linda Ng
LINDA RACHMAT
LINDA RACHMAT
Linda Sidharta
Linda Tanuwiradjaja
Linda Tjahja
Lindawaty Hartono
Lisa Ambarwati Dharmawan
LISA MARDIANI GUNAWAN
Lisa Sundoro Hosea
LISA WIDJAJA
Lisawati Soegiharto
Lista Adriani
Listyani Setijawati Sidik
LIZA WIDAYATI PRADJONGGO
Loa Djin Sui
Loa Sui Hong
Lovri Ricarda
Lucas
Lucas and Lenny Patricia Halim Liem
Lucia Mogi
Lucia Mogi
Lucia Mogi & Others
Lucia Sungkoro
Lucky Tjahaja Diputra Prawiro
Lukas Masehi
Lukman Ahmad Mahfoed
Lukman Hakin
Lukman Herry Latip
LUKMAN TACHJADI
LUKMAN TACHJADI
Lukman Tirtaguna
Lukman Tirtaguna
Lum Weng Loy
Lunardi Basuki
Lunardi Basuki & Sasongko Basuki & Basuki
Lusi Murniati Gunawan
Lusi Windayati
LYDIA ANGKAWIDJAJA
LYDIA TJIPTO
LYNDA TJANDRA BRASALI
Lys Erna Ontjeng
M. A. Ismail Ning
Madampath Sathibal Menon
Madampath Sathibal Menon
Made Oka Masagung
Maggie
Mahesa Alit Pramesty
Mahesa Alit Pramesty (Mr.)
Mahhesa Alit Pramesty
Maiko Kawano
Makarim & Taira
Maly Widoyo
Managecorp Limited as a Trustee of Westend Holdings Trust
MANGGI TARUNA HABIR
MANIWANEN
Marcella Magdalena
Marcellus Charles Colondam
Marcellyna Junita Widjaja
Marcellyna Junita Widjaja
Marco Baldini
Margareth Maria Regina Budhiparama
Margaretha Natalia Widjaja
Margaretha Natalia Widjaja
Maria Karmila
Maria Karmila
Marilyn Caracas
Marilyn Caracas
Mario Christy
Mario Satya Pratomo
Mark Patrick Hanusz
Markun
Markus Parmadi
Marluce Tio Indriati Santoso
Marten Liu
Martin Wijaya Ng
Martina M. Sudwikatmono (Co-Trustee)
Martina M. Sukwikaimono
Martinus Arief Limandoko
Marvin C S Yong
MARY GANASUTRISNA
Maryati Benniardi Imanto
Masayu Pangestu
Masterclass Ltd
Mathilda Stephanie
Mathilda Stephanie
MATTHEW JOSEPH GEORGESON
Matthew S. Deayton
Maxymilian Adelberd
MAYA HARTONO
MEDINA LATIEF
Meena
MEENA
Megawati Setiadi
Mei Ing
Meigawaty Soejatno
Meiliana Widjaja
Meiriana Soetoyo
Meiriani Soetoyo
Meiriaty Soetoyo
Meity Subianto
Meizar Suyardi
MELIAWATI SURJASARI
Melina Jonas
Melisa Patricia Tanoko
Melissa Ong
Melly Kristanti
Melvin
Melvin Salim (Mr.)
Mende Sulinadi
Meranti Handajani Serad
Meridian Pacific Trading Ltd
Mermeden Ltd
Mermeden Ltd
Merry
MESLIN Bertrand Marie Jacques
Metta Margaretha Murdaya
Miana Dwilasmini Sudwikatmono
MICHAEL ATMAN
Michael D. Twomey
Michael Dharmawan Euslim
Michael Gan
Michael Goenawan
Michael Goenawan
Michael Jackson Purwanto Widjaja
Michael Jackson Purwanto Widjaja
Michael Mary Mackay Seward
MICHAEL PATRICK DONNELLY
Michael Rusli
Michael Seabrook
Michael Steven
Michael Steven and Ingrid Kusumodjojo
Michael Tjahjadi
Michael Twomey
Michael Wijaya Goutama
Micheal Tjahjadi
Michel Vicky Tumiwang
Michelle Tjokrosaputro
Michelle Tjokrosaputro
Mieke Santosa
Milany Terianto Luwena
Mimin Aminah
Minny Riady
Mintardjo Halim
Mintardjo Halim
Mira SAVIRA
Mira Savira
Mirah Amiria Adhyaksa
Miranda Tedjasaputra
Miranti Handajani Serad
ML&B Indonesia
Mochamad Adnan
MOCHAMAD RAIS
Mochammad Anwar
Mochtar Riady
Moernoto Reksonegoro
Mohamad Noer
Mohamad Abdullah Jasin and Dewi Kam
Mohamad Abdullah Jasin and Dewi Kam
Mohamad Abdullah Jasin and Dewi Kam
Mohamad Abdullah Jasin and Dewi Kam
Mohamad Iskandar
Mohamad Noer
Mohammad Hidayat Hasan
MOHAMMAD LENDI BASARAH
Mohammad Mas Pendi Soleh
Mohammad Noah Haji
Mohan N. Mirpuri
MOHIT RAMCHAND VASWANI
Monalita Kardono Soegiarto
Monica Yoanita Octavia
Morgan Tjoe
Morgan Tjoe
Motinggo Soputan
Motinggo Soputan
Mr Arifin Yohan
Mr Aris Sunarko
Mr Burhansjah
Mr Koh Tji Beng
Mr Liem Henry
Mr Marimutu Siniran
Mr Nono Fadjartyassasono Padmodimuljo
Mr Ulian Napsiah
Mr Welly
Mr William Goenawan
Mr. Eddy Goenawan
Mr. Salim Aziz Mochdar
MR. THOMSON
Mrs Josephine Budi Santoso
Mrs Lina Ovani
Mrs Masiana Wijaya & Fam.
Mrs Theresia Noerpeni Padmodimuljo
Ms Affin
MS Group
Ms Rohani Indahsi
MS Taxes
Ms. T.Handayani Andokho
MUCHSIN CIPUTRA TJOE
Muddai Madang
Mugijanto Sugijono
Muhammad Agus
Muhammad Aksa Mahmud
Muhammad Alatas
Muhammad Andre Pasha Djuanda
Muhammad Ikbal
Mulianto Api Tanaga
Mulianto Api Tanaga
Mulianto Tanaga
Muljadi Budiman
Muljadi Irawan
Muljadi Irawan
Muljana Husodho, Tintje Jusran, Fransisca Haller, Andreas Husodho & Danni Arton
Multi-Holdings Group Ltd
Mulyadi Anggono
MUNKLEY Christopher James
Murdaya Widyawimarta
MUSTIKO SALEH
Mustofa
MYRNA ESTHER CONTRERAS DE NAVARRO
Myrna Putri Pribadi
NA NA
Nam Yong Hwa
NANCY NARSIS RUNTUWENE
Nancy Urania Rachman Latief
Nani Indraswati Alimwidjaja
Nanik Santoso
Naresh Kumar Modi
Nasir Saleem Haji
Natalie Ong
Natalie Tjahjadi
Nathalia Setiawan
National Management Ltd
Nazamudin Latief
Nazarudin Kiemas
NELSON SAPUTRA
Nestor Padilla
Netcorp Securities Limited
NG ANTON WIJAYA
NG JE TJIEN
Ng Kee Yeok
Ng Soat Go
Ng Tje Suang
Ngadimun
Ngu Hew Tak
NI MADE JATI
Nia Soniati Wityasmoro
Nicholaas Bernardus Tirtadinata
Nicholas James GRAHAM
Nico Krisnanto
Nigel Brett Eaton
Niko Listya Prabowo Se
Nila Fatina
Nilayanti
Nini Djajasaputra
Niniek Haryani
Ninik P. Nathan
Nio Yantony
Nixon Jacobus Silfanus
Norbert Alois Meixner
Norbert Alois Meixner
Nordiansyah Nasri
NORTHSTAR EQUITY PARTNERS LTD.
Northstar Pacific Partners Pte Ltd
Nova Chandra
Nova Negara Silaban
Nova Yudhanto Mugiyanto
Novi Ariyunida Dharma
Novi Nenolaswaty
Noviani Eka Susanto
Nugraha Tirtanata
Nugroho Halim Wijaya
Nur Zain
NURBAITI
NURDIN HASJIM JOHANES
Nurmalasari Suginawan
NUROCHIM
Nursalim Podiono
NYOMAN SARIMIN
Octarina Ratih Damayanti
Octarina Ratik Damayanti
Oei Denny Kurniawan
Oei Denny Kurniawan
Oei Harry Lukmito
Oentoro Surya
Oerip Wirontono
Oesman Sapta
OETIE HERMAWAN
Oey Aling HERMAWAN
Okkie Adhika Tirta Monterie
Omar Azhari
Omar Putihrai
Ong Ju Chi
Ong Mei Sian
Ong Thiam Hok
ONG TIONG YUN
Ong Wen Nio
Ongko Multicorpora
Ongkowijoyo Onggowarsito
OSBERT KOSASIH
Oscar Gonzalo Guedez Machado
P. T. ARPENI PRATAMA OCEAN LINE, Tbk
P. T. Asuransi Jiwa Sewu New York Life
P.T Arpeni Pratame Ocean Line
P.T Dwi Satrya Utama
P.T. Charoen Pokphand Indonesia
P.T. Detra Marina
P.T. Duta Sewa Raya
P.T. Elnusa
P.T. Ever Shine Tex
P.T. Fusenindo
P.T. Grahamakmur Wiratama
P.T. ICC Indonesia
P.T. Interindo Global
P.T. Kaltimex Energi
P.T. Lippo Industries
P.T. Lippo Pacific Finance
P.T. Nugra Santana
P.T. Ometraco Cipta Sarana
Pacific Financial Services
Pacific Overseas Trading Corporation
Pacific Trading & Development Ltd. (BVI)
Pacmas Limited
PANDJI SURYA SOERJOPRAHONO
PAO TJEN KANG
Para Group
Parveen Gandhi
Pat Stratton
Patrick Morris Alexander
Patrick Walujo
PATUN YUDISTHIRA ARITONANG
Paul Banuara Silalahi
Paulis Amin Djohan
Paulis Amin Djohan
Paulus Johanes
PAULUS THIO
Payal Vijay Goklani
Pe Sioe Kim
Peaceland Holdings Ltd
Pedro Limardo
Pek Teng Beng
PER-GUNNAR THURESSON
Permadi
Pernardi Djojosudirdjo
Perseroan Terbatas
Perumahan Tegal Indah Permai
Peter Anthony Wallace
Peter BOWDEN
Peter Markart
Peter Vinzenz Merkle
Petrus Budiman Gho
Petrus Budiyanto
Phang Chin Liat
PHILIP PRIASMORO
Philip Strachan Attwood
Philip Tjandra
PHOA HERMANTO SUNDJOJO
Phoenix Holdings Trading Inc.
Phoenix Holdings Trading Inc.
Piet Wijaya
Pieter Tanuri
Pinardi
Piong Denisse Lucia
Pipin Arifin Linggawidjaja
Pirngady Adhi Wicaksono Himawan
PITER KOROMPIS
Pitra Wiria
Poniman
POPPY HADIMAN
Poppy Tumengkol
Portcullis Institute Pte Ltd
Portcullis Nominees (BVI) Limited
Portcullis TrustNet (BVI) Limited
Portcullis TrustNet (Samoa) Limited
Pra Ciputra
Pradeep Dudaney
Pradeep Dudaney & Soniya Dudaney
Pradono Joko Trajutrisno Himawan
Prakash Mohanlal Panjabi
Prakash Mohanlal Panjabi and Vidhya Prakash Panjabi
Prakoso Eko Setyawan Himawan
Pramudji Suginawan
Praptono Budhi Haksomo Himawan
Prasetio, Utomo & Co
Prasodjo Winarko
Prayitno Cipto Anggoro Himawan
Prayugi Sukardjo
Prem Ramchand Harjani
Pri Wono
Prijono Winarko
Primanaga Hartanto Kalim
Priyatno Sulisto
Priyatno Sulisto
Proboraras Mudoyo
Protasius DARITAN
PSP Group
PT Agung Sedayu Permai
PT Agung sedayu Propertindo
PT Aiti Investment
PT Anugra Cipta Investa
PT Argapura Wira Kencana
PT Asia Securities Limited
PT Astra International Limited
PT Astratel Nusantara
PT Asuransi Jiwa Sequis Life
PT Bahana Securities
PT Bakrie & Brothers
PT BAKRIE CAPITAL INDONESIA
PT Bimantara Citra
PT Bira Aset Manajemen
PT Cameron Chisholm Nicol
PT Central Total Finance
PT CENTRANUSA INSANPURNAMA
PT Centronix
PT Cikarang Listrindo
PT Cipta Imajinasi Disain
PT CIPTADANA CAPITAL
PT Ciputra Development TBK
PT COMETA CAN
PT Danatama Makmur
PT Dayabangun Persada
PT Detik Ini Juga
PT Dwibras Darma
PT Energi Mega Persada Tbk
PT Energi Mega Persada Tbk
PT ENERGI TIMUR JAUH
PT EPHINDO
PT Galib Instalindo Utama
PT Garuda Metalindo
PT Gema Nuansa Persada
PT Global Consulting Indonesia
PT Global Multi Investama
PT Gra Tiara Imaji
PT Great Giant Pineapple Co.
PT Gunung Sewu Kencana
PT Hanjaja Mandala Sampoerna Tbk.
PT Hasnur Coal Terminal
PT Hikmah Albros
PT Hitawasana Luhur
PT Imbang Tata Alam
PT Indah Kiat Pulp & Paper Tbk
PT Inti Permata Nusantara
PT J.CO Donuts & Coffee
PT Japfa Comfeed Indonesia Tbk
PT JASTRINDO DINAMIKA
PT Jembatan Kapita Utama Corporate Advisor
PT Jenshiang Nusantara Textile Chemical Industrial
PT Kencana Gula Manis
PT Lippo Bank
PT Lippo Karawaci, TBK
PT Manggala Adhikara
PT MEDCO E & P BANGKANAI
PT Media Intertel Graha
PT Media Karya Sentosa
PT Mitra Andalan Mandiri
PT Moores Rowland Indonesia
PT Niaga Langgeng Sejahtera
PT Ningz Pacific
PT Odira Energy Persada
PT Ogspiras Basya Pratama
PT Omega Propertindo
PT Pabrik Kertas Tjiwi Kimia Tbk
PT Pabrik Kertas Tjiwi Kimia Tbk
PT Pelayaran Tamarin Sumudra
PT Penilai Wahana Caraka
PT PERTAMINA (PERSERO)
PT PP London Sumatra Indonesia, Tbk
PT PriceWaterhouseCoopers FAS
PT Rajawali Corpora
PT Rajawali Corporation
PT Recapital Advisors
PT Renaissance Capital Asia
PT Rindaco Prima Sakti
PT Sainath Industrial Corp Ltd
PT Saptapusaka Investama
PT SAS INTERNASIONAL
PT SAS INTERNATIONAL
PT Sentra Kharisma Indah
PT Simplot Agritama
PT SKEYE
PT Sriagung Cahya Sakti
PT Supraprima Sistem Sekusiti
PT Suryaraya Gatratama
PT Tiwi Utomo Investama
PT Trans Nusantara Multi Construction
PT Trijaya Pratama Future
PT Tripar MultivisionPlus
PT TUNAS HARAPAN PERKASA
PT Udinda Telesis
PT Widari Securties
PT Wizoffice Indonesia
PT. 2morrowland Indonesia
PT. Akraya International
PT. ALAM TRI ABADI
PT. Askomindo Dinamika
PT. Astra Graphia Tbk
PT. Astra International, Tbk
PT. Bakrie Interinvestindo
PT. BUMI PERTIWI KENCANA
PT. Cikarang Listrindo
PT. Citra Nusa Insan Purnama
PT. Citrabumi Sacna
PT. Citrabumi Sacna
PT. Delta Nusantara
PT. DWI PRIMA SEMBADA
PT. EATERTAINMENT INTERNATIONAL Tbk
PT. Ekatama Prima Sejati
PT. FAISALINDO SAKTI
PT. Ge Ka Jaya
PT. Global Petronusa
PT. INDOGAS KRIYA DWIGUNA
PT. Indonesia Transit Central
PT. Inti Brawijaya
PT. INTIM PERKASA
PT. Karisma Nata Rucitra
PT. Kasogi Internasional Tbk
PT. Long Haul Indonesia
PT. LONG HAUL INDONESIA
PT. Maetro Internasional
PT. MAHAKAM NUSA ENERGI
PT. Murni Cipta Sentosa
PT. Ometraco Corporation
PT. Pelita Cengkareng Paper
PT. RADIAS BINTANG TIMUR
PT. Santos Jaya Abadi
PT. SRIREJEKI PERDANA STEEL
PT. Surabaya Agung Industri Pulp & Kertas Tbk.
PT. Toba Pulp Lestari tbk
PT. TOPAS MULTI SECURITIES
Pudjiastuti Binti Soemarno
Pudjiono Iwansantoso
Pujiastuti Elizabeth Sindoro
Pujiastuti Elizabeth Sindoro
PURNAMA WIDJAJA
PURNAMAWATI PURWADI
Purnardi Djojosudirdjo
Purwadi Hendropurnomo
Purwoso Warsito Utomo Himawan
RABOBANK INTERNATIONAL
Rachana Bhansali
Rachmat Basuki Alimwidjaja
Rachmat Gobel
RACHMAT GUNAWAN
Rachmat Mulyana Hamami
Rachmat Santoso Alimwidjaja
Rachmat Susantyo
RACHMAT SUTIONO
Rachmat Sutiono
Rachmiwaty
Radisha Didi Utama
Radius Christanto
Rafael Buhay Concepcion Jr.
RAHARDJO MOECHARAR
Rahendrawan Djoko
Rahendrawan Djoko
Rahmad Pribadi
Rahmad Pribadi
Rahmawaty
RAJ KUMAR
Raja Sapta Ervian
Raja Sapta Ervian
Raju Karamchandani
Raju Karamchandani and Sara Raju Karamchandani
Ramajati Tamin
Randolph Adi Zaini
Randy Hirawan
Rashid Irawan Mangunkusumo
Rasyid, Arwin
Rat Anggraini Susantio
Ratna Anggraini Susantio
Ratna Christina
Ratna Indira Nirwan Bakrie
RATNASARI TAMIN
Ratnawati Budiman
Ratnawati Jenny Haryadi
Ratnawati Sasongko
RATNAWATI WIHARDJO
Ratnesh BEDI
RAVI SHYAM SADARANGANI
RAVI SHYAM SADARANGANI & SONAL RAVI SADARANGANI
Ravi T. Vasandani
Ravi Tulsidas Vasandani
Rayanusin Widjaja
Raymond A. Klesc
Raymond Patra
RAYMOND PRIBADI
RAYMOND PRIBADI
Raymond S. B.
RAYMOND, LOUIS COUHAULT
Razief Nur Usman
Razif Susanto
REIMER ALOAN SIMORANGKIR
RENDOR OVERSEAS S.A.
Rendra Tjajadi
Rendra Tjajadi
Rendra Tjajadi
Rendra Tjajadi
Rendra Tjajadi
RETNO CAHYANINGTYAS
Reza Maulana
Reza Pribadi
Reza Pribadi
Reza Sazly H Siregar
Rhita Manik
Ria Indriana Pasaman
Ria Yulianty Tj he
Rianto Lesmana
RICHARD AnTHONY SCHUMACHER
Richard Cornwallis
Richard Dian Santoso
Richard Hamilton MCCANDLESS
Richard L. McAdoo
RICHARD MOHANLAL HARJANI
Richard Sugianto
Richard Sugianto & Veronica Susianty Rachim
Richard Tjandra
Ricky Frederik
Ricky Tandiono
Ricky Tandriono
Ridwan Irawan
RIDWAN ZAINUDDIN
Rilantini Harjani Muljawan
Rina Ciputra Sastrawinata
Rinda Syafrinda
Rini Mariani Soewandi
Rini Susilo Putri
RISTY ISTIANA
RISWAN WIJAYA
RITA HANDOSO
Rita Indriawati
RIZA MUTYARA
Rizal Risjad
Robby Rhemrev
Robert Kevin Ellis
ROBERT PRIANTONO BONOSUSATYA
ROBERT PRIANTONO BONOSUSATYA
Robert Sean King
Roberto Hanna Jose
ROBERTO TAMPUBOLON
Robin Liem
Robin Makmur
Roger Morrison
Roger Pinder
Roger PINDER (Mr.)
Roij Bramasiswadi Pura Widjaja
Romo Nittyyudo Wacho
Ronald E.P. Mullers
Ronald Edward Philip Mullers
Ronald Liem
Ronald Mullers
Ronald Rusco
Ronald Wijaya
Ronaldi Machmud
Roni Faisal Siregar
Roni Pramaditia
Ronny Hadiana Angkasa
Ronny Lukito
Ronny Suryana
Ronny Susanto
Rony Moelyadi
RONY NARPATISUTA MEDANLAGA
Roos Diana
Roosmiati Handojo
RORI INDRA
Rosan Perkasa Roeslani
ROSANA
Roselyne Yosawiria
Rosemelati S. Adikusumah
Rosianawati Adikara
ROSIDA CHUNG
Rosmeiny Djaja Burhan
Roswita Trismitro
Roy E. Tirtadji
Roy Gosjen
Roy Kevin Kurniawan
Roy Muljadi Soetikno
Rubyanto F. Komala
Rudi Darmawan
Rudi Soraya
Rudi Wirawan Rusli
RUDY CAHYADI SUKANDADINATA
Rudy Ghozali
Rudy Hari
RUDY HARJANTO WIDJAJA
Rudy Muljadi Atmawidjaja
Rudy Nanggulangi
Rudy Rayawang
Rudy Soetikno
Rudy Suhendra
Rudy Susanto
Rudy Temasoa Luwia and Suzie Ramli
Rudy Unjoto
Rudy Y.
Rudyantho & Partners
Rudyanto Gunawan
Rudyanto Suliawan
Rudyono
Rulyani Basyir
RUNI ADIANTI
Rusdi Kirana
Rusdi Sunarjo
Rusdy Budisusetyo
Rusdy Budisusetyo, Lanny Widjajanti and Ida Budisusetyo
Rusiana Susanto
RUSJATI TAMIN
RUSJATI TAMIN
RUSSELL BRUCE MCDONALD
Russell McDonald
Rustiyan Oen
Ryan Pascal Masagung
Ryandi Irawan
Ryu Kawano
S&B Inc
S.H.C.N Lucas
Saad Shaarawi
SABHNANI MANOJ
Sacheen Harris Lasmana
Sadikun Wiratno
SAFARINA GOLFIANI MALIK
Safersa Yusana Sertana
Said Agil Assagaff
Saiko Doi
Salik Soetemo
Salim Podiono
Salim Santoso
Sally Texania Marita Joesoef
Sallyawati Rahardja
Samin Tan
Samin Tan
Sammy Hamzah
Sammy Hamzah
SAMUDRA ENERGY LIMITED
Samuel Setiawan
SANADI BOENYAMIN
Sanderawati Joesoef
SANDI GUNAWAN HO
Sandiaga Salahuddin Uno
Sandiaga Uno
Sandra Setijono
Sandrawati Setiadi
Sandria Kirana Budiendra
SANGEETA RAMCHAND
SANGEETA RAMCHAND AND MOHIT RAMCHAND VASWANI
Sanjay Bhansali
Sanjaya Raharja / Loren
Santoso Widjojo
Santy Jennice Lioe
Santy Jennice Lioe
SANTY WIJAYA
Sanyo Leebrianto Suhaimi
Saparuddin
Sapri
SARASWATI TEDJAKUSUMA
Sardjono
Sari Wulaningsih
Satyadharma Ruslim
Sectra (Samoa) Limited
Sefrie Roring
Sefrie Roring
Sembodo Broto Winarso
Semiwati Lawanto
Sengman Tjahja
Septiana Iskandar
Septo Adjie Sudiro
Septo Adjie Sudiro (2)
SETIA BUDHI
Setiabudi Djaelani
Setiady Koeswojo
Setiawan Achmad
Setiawan Lukman
Setiono Tandriono
Sgfried Rinaldy
Shalimar Sulisto
SHALINE MARY SHABNA SOULSBY
Sharecorp Limited
Shariq Mukhtar
Sherlly Hartono
Sherman Rana Krishna
Sherman Rana Krishna
Sherper Limited
Sherper Ltd
Shih, Chih-Hung
SHINTA DEVIYANTI
Shinta Moetiara
SHINTA SANJAYA ISMAEL, SE
Shuzy Lipina
Siak Tjai Oi
Siauw Rachel Anatola
Siauw Welly Susanto
Siegfried Erwin Bengner
Sierah Landajani Soetemo
Sigit Iswandi
Silkar National Limited
SILVA HALIM
Siman Darmamulia
Simon C. Horn
Simon Lim
Simon Subrata
SIMON SUSILO
Simson Panjaitan
Sinar Mas Group
Sinarto Dharmawan
Sinatra Arto Hardy
Sindhu Wibhisono Ongkosoewito
Sindhu Wibhisono Ongkosoewito
Singgih Amara Widjanarko
Singgih Kartono Halim Lie
SIOK LIM TJOA
Sistha Alicia Tjokrosaputro
Sistha Alicia Tjokrosaputro
Siti Farihah
Siti Hartati Tjakra Murdaya
Sity Leo Samudera
Sity Leo Samudera
Siusan Hermawan
Slamet Wibowo
So Lai Fun
Soebagjo Jatim Djarot
SOEBALI SUDJIE
Soegianto Nagaria
Soegiarto Djitowibowo
Soegwanto
Soekrisman Legiman
Soemadipradja & Taher
SOENARJANTO INDRATONO
Soenarjanto Indratono
Soenarni Sampoerno
Soenarta Natapradja
Soendari Widjaja
Soeparmadi
Soeparman Hardjodikromo
Soeroto Hadimuljono
Soeryo Bawono
Soesanto Effendi
Soesilowati
Soetikno Soedarjo
Soetikno Soedarjo
Soetikno Soedarjo
Soetikno Soedarjo, Dian Muljani Soedarjo and Putri Rahayu Soedarjo
SOETIKNO TANOKO
Soetjahjono Winarko
Soetjipto Nagaria
Soewandi Gunawan
Soeyanto
Sofian Widagdo
Sohet Chairil
SOLEH MAMUN
Solidi Korompis
Solidi Silvester Korompis
Solihin
Solihin Asiah
SOLIHIN YUSUF KALLA
Somboon Yuprapan
SONAL RAVI SADARANGANI
Song Liang Hua
Song Wen Po
Song Wen Po, Junty, Jimmy Song and Michael Song
Song Wen Shyang
Song Wen Shyu
Soniya Dudaney
Sonny Agustino Laksito
SONY RUDIKAN
Sonya Riupassa
Sonya Riupassa and Kitty Joantina Wulanda
Sorgato Widjaja
Sri Iriani Goenawan
SRI KRISHNA WISHNU WARDHANA
Sri Mulyono Herlambang
SRI MURWATI HABIR
Sri Rahayu Setyawati
Sri Rahayu Setyawati
Sri Setyaningsih Elisabeth
Sri Setyaningsih Elisabeth
Sri Setyaningsih Elisabeth (SG)
Sri Soelijah
Stan Maringka
Stan Maringka
Stefanus Arief Chrisnamurti
STEPHAN PUTRA KURNIAWAN
Stephen Charles Dodgson
Stephen Patra
Steven Hirawan
Steven Scott Barki
Steven Sugianto
Steven Tirtawidjaja
Stewart Donald HALL
Stewart James Robinson
Stockcorp Limited
Su Kam To
Suarmin Tioniwar
Suarmin Tioniwar
Suarmin Tioniwar
Suarmin Tioniwar and Dewi Salim as joint tenants
Subagio Wirjoatmodjo
Subardi
Subari Setiono
Subianto Arpan Sumodikoro
Subianto Tjandra
SUBUH HARI CAHYANTO
Sudiarso Prasetio
Sudijanto Atmodjo
Sudiro Andi Wiguno
Sudjono Barak Rimba
Sudjono Karim
Sudjono Karim
SUFAN ABNER
SUFAN ABNER
Sugar Group
Sugianto Adiwinata
Sugianto of Sinarmas Group
Sugiharto
Sugiharto Ta
Sugiman
Sugiman
Sugiman
Sugiono
SUGIONO DJAUHARI
Sugiono Wiyono Sugialam
Sugiono Wiyono Sugialam – New
Sugiono Wiyono Sugialam and Lanny Herawati Wibowo Ng
Sugito Walujo
SUGITO WALUJO
Sugito Walujo
Sugito Walujo
Sugun Susilo
Suhadi Zaini
SUHANGKAT LAKMUDIN
SUHARDI
Suhardi Budiman
Suhardiman
SUHARDY
Suhari Setiono
Suharman Subianto
Suhendra Gunadi
Suherman Tjandradjaja
Suhiantoro Supardjono
Sujanty Jamin
Sujarni
Sujono Hadikusumo
Sukendar Unjoto
Sukmawati Widjata
SULAIMAN HAKIM
SULAIMAN HAKIM
Sulaiman Leban Koswara
SULIENIATI CHANDRA TJOE
SULIENIATI CHANDRA TJOE
Sulistiani Sampoerna
Sulung Poniman
Sumadi
Sumardi Kartasasmita alias Kong Phing Li
Sumarto Wonowidjojo
Sumarto Wonowidjojo
SUMET JIARAVANON
Sumiati Liauw
Sumiaty
Sun Moon Suhaimi
Sun, Khai-Nien
Sunan Susilo
SUNARDI
Sunarjo Sampoerna
Sunata Tjiterosampurno
Sung Pui Man
Sunil Motilal Mirpuri
Sunny Suhaimi
Supardi
Supartono Suparto
Supartono Suparto
Supartono Suparto
Suresh Narsinhdas Shah
Suria Kurniawan Lukiman
Suriawati Tan
Suripto
Surjadinata Sumantri
Surjantoro Siswanto
SURJANY KURNIAWAN ECKERT
SURJONO TANOTO
Surjono Tanoto
Surono
Surya Laksana Ongkoredjo
Suryadiharja Freddi H.
Suryana Tochmi
SURYANA NURZAMAN ZEIN
Suryana Tochmi
SURYANTO
Suryawati L. Riady
Susan Lo
Susana Sutanto
Susanna Kusnowo
Susanna Nagaria
Susanti Pheng
SUSANTI SUNARDI
Susanto
Susanto Suwarto
Susanto Tandra
Susanto Tjandra
Susanto Winarto
Susi Salamah
Susilawati
Susilo SOPUTRO
Susilo Wonowidjojo
Susilowati
Susin Valentinus
SUSWANTI GUNAWAN
Susy Angkawijaya
Susy Gunawan
Sutanto DJUHAR
SUTANTO LEON PATRICK
Sutarsa Tanu
Sutiadi Widjaja
Sutiadi Widjaya
Sutiana Juhanda
Sutikno
Sutono Nitisastro
Suwandi Widjaja
Suwantara Gotama Lim
Suwantara Gotama Lim
Suwito Brodjonegoro
Suwito MULIADI
Suyono Purnomo
Suzie Surjana, Tony Surjana, Johny Surjana and Ronny Suryana
Syahbandi
SYAHRUL
SYAIFUL ZEN
Syamsul Hoiri
Syarief Tando
Syarif Bastaman
Syarif Bastaman
Sylvia Efi Widyantari Sumarlin
Sylvia Mardiana Sarwani
Sylvia Mardiana Sarwani
SYLVIA MULJADI
Sylvia Novieta
Symon Brewis – Weston
T-Line Ltd
Tahi Parulian Saragi
Tan Ali Susanto
Tan Hong Kiem
Tan Loo Mei
Tan Lucas Adnan Soen Hwat
Tan Lunardi
TAN LUNARDI (Mr.)
Tan Olinda Dewi
Tan Timothy Tandon
Tan Tjoe Liang
Tanaka Kazuya
Tanaka Kiyomi
Tandean Rustandy and Susan Sujanto
Tang Eng Hoo
Tansri Soen Zen
Tansri Soen Zen
Targian Tan
TATANG HERMAWAN
Taufan
TAUFIK SURYA DHARMA
Tay Robinto
TEDDY FADIL
Teddy Jeffrey Katuari
Teddy Sugianto
Teddy Sutandinata
Teddy Tjahjono
TEDDY YOSHAWIRJA
Tedja Widjaja
Tedy Tanumihardja
Teguh Arianto Budiman
TEGUH BOENTORO
Teguh Ganda Wijaya
Teguh Suginawan
TEL CORPORATE SERVICES PTE LTD
Teng Goat Nio
Tengku Muhammad Ali Mahara
Teresa Suteja
Terra Computer Systems
Terunodjojo Nusa
Texmaco Group
The Citigroup Private Banking
THE HIE TING
The Kwen Ie
The Liliana
The Practice
The Wen Jun
Theodorus Marto Sutiono
Theresia & Lidwina as joint tenants with right of survivorship
Theresia Suciah
Theresia Widyawati Setiono
Theresia Yustina Sumarlin
THIO JULIA TIMOTIUS
Thomas Derek Wilkes Burland
Thomas Derek Wilkes Burland
Thomas Lundi Halim
Thomas Lundi Halim & Elly Lestari Adiutama as joint tenants with right of survivorship
Thomas M. Tampi
Thomas Soulsby
Thomas Tampi
THOMSON
Tiara Dharani Josodirdjo
Tien Thinh Pham
Tigran Timotius Adhiwiyogo
Timmie Melvin
Timothius Felix Intan
Timothy James Supple
TIMOTHY SIDDIK
Timothy Watts
Tina Meimona Shazell
Tina Suteja
Tio Imelda
TIRTA JUWANA DARMADJI
Tirtadjaja Hambali
Tirto Angesti
Tirto Angesty
Tito Sulistio
Titus Wahjoe Dewanto
Tjahjadi Hari Surjono
Tjahjadi Rahardja
Tjahjadi Tresna, Tin Tin Tresna and Senjaya Tresna
Tjahjono Alim
Tjahyono Imawan
Tjan Kok Pin
Tjandra Sari
Tjandra Teresna Widjaja
Tjhang Hwee Tjoe
Tjia Tjhun Hwa
Tjia Tjoen Hiong
Tjia Tjoen Hok
Tjia Wiwin Anggono
Tjiam Ming Ping
Tjie Jien Wang
Tjindrasa Ng
Tjioe Hauw Tze
Tjioe, Gunawan Adianto
Tjipto Surjanto
Tjiu Thomas Effendy
Tjoa Siok Lim
Tjoe Hendry
Tjoe Meuw Sen
Tjoi Wilson
Tjokrorianto
Tjondro Indria Liemonta
Tjong Euw Khiong
Tjong Jok Ha
Tjong Miranti
Tjong Tje Liong
Tjong Tje Tjin
TODDY MIZAABIANTO SUGOTO
Tom Soulsby
Tommy Jacobus Silfanus
Tommy Laurens
Tommy Nugraha
TOMMY TANADY
Tomy Wikutomojati
Tonny Raidy Djamhir
TONNY WANTAH
Tony Djayalaksana
Tony Supargo
Tossin Suharya
Tossin Suharya, Stephen Ignatius Suharya & Daniel Suharya
Toto Soegiarto
Toto Soegiarto and Enny Soegiarto
TOTOK SUSILO
TOTTY MOEKARDIONO
Trent Karoll
Triana Soenryo
TRIANAWATI
Tricia Barki
Trini Koeswanti Sri Soepardianti
TRIONO JULIARSO DAWIS
Trisnawati Budiman
Trisning Setiadi
Triyatno Atmodiharjo
Triyatno Atmodiharjo
Troy Surya Subandi
TSANG KAM HEUNG
Tseng Hsueh Sung
Tseng, Hsueh Sung
Tung Bibiana
Tunggono
Turcahyo Wahyudi
Turniady Widjaja
Turniady Widjaja, Rosmeiny Djaja Burhan and Yessica Beatrice Widjaja
Tuty Sumargo
Tyrone Kaskam Awan
TYTY CHANDRA
UBS AG (Indonesia) Ltd
Udinda Group
Ulian Napsiah
Umar Suwandi
Ungkoro Darmosusilo
Untoro Angkawijaya
Upekkha Theresia Murdaya
Ustadai Tedja,Gan Ying May, Felix Tedja and Edwin Tedja
Ustadi Tedja
USTADI TEDJA
Utama Gondokusumo
Utama Halim
Utama Jusuf
Utama Jusuf, Megawati Hartono, Eddy Jusuf, Dewi Jusuf, Angela Jusuf
UTARYO SUWANTO
Utomo Djohan
Uwat
Uwat (Mr.)
Varisa Susilo
Vemmy Febriyanti
Vera Marlinata Widjaya
Vernon Charles Lee
VERONICA LUKITO
VERONICA LUKITO
Veronica Colondam
Veronica Devi Intan
Veronica Lukito
Veronica Renata
Veronica Tjendro Susanto
VERONICA YUWONO YU
Veronika Slamet
Victor Fungkong
Victor Luhur
Victor Sebastian Vaz
Vidhya Prakash Panjabi
VIJAY NARAINDAS GANGTANI
Vincent Kus Chu
Vincent Kus Chu
Vinod Kumar Agarwal
VIONA GUNAWAN
Virendra Prakash Sharma
Vivi Hottama
Vivi Hottama
Vivian Kent Janawati
Vivien Goh
Vonny Harsono
Vonny Juwono
Wachid Hendriadi and Lizza Christina Budihardjo
Wadyono Suliantoro and Setijanti Suliantoro as joint tenants
Wahjudin Judiana Ardiwinata
Wahjudin Judiana Ardiwinata
Wahjudin Judiana Ardiwinata
Wahjudin Judiana Ardiwinata
Wahyu Subayani
Wahyu Tri Laksono
Wahyudi Lukmantara
WALTER LEO WIDMER
wan peng lim
WARDHANA ATMADJA
WATNI DJOHAN
Wei Zhigang
Wei Zhigang
Welly Thomas
Wen Shyang Song
WESLEY INTERNATIONAL GROUP LIMITED
West Side Ltd.
Wewey Tjahjadi
Wewey Tjahjadi
Wewey Tjahjadi Wanadihardja
Whitlam Luhur
Wibawa Darmawan
Wibowo Brotorahardjo
Wibowo Kartopranoto
Wibowo Suseno Wirjawan
Wicahyo Ratomo
Wicahyo Ratomo
Wida Martha Sari Newton
Widhayati Hendropurnomo
Widhi Sesanti
Widiyanti Putri
WIDJAJA LASWONO
WIDJAJA Tjangdra Herawati
Widjaja Trisna
Widjaya Sendra
Widjojo Budiarto
Widjojo Parawirohardjo
Widjojo Soejono
WIDYA SURAANNISA
Widyakumala Sulistyo
Widyawati Budiman
Wientoro Prasetyo
Wijayanto Ang
WIJONO TANOKO
Wijono Widjojo
Wilfred Schultz
Wilfred Schultz
Wilfred Schultz
Wilfred Schultz (Inactivated)
Wilhelmina Bia Mugirato
William A. Sullivan, Esq.
William James Park and Yuliati Karnadi as joint tenants with right of survivors
William Lietanawaty
WILLIAM O BRIEN JOHNSTON
William Shane Tan
William Sutjiatma
William T Jugiarto
WILLIAM TJUGIARTO
WILLIAM TOBAGUS
Willie Tandanu
Willy Gunawan
Willy Lukito
Willy Sugianto
Wina Widjaja
Winardi Darmansa Lim
WINARDI PRANATAJAYA
Winardi Setiaputra
Winardi Thamrin
Winarno Tjajadi
WINARNO TJAJADI
Winarno Tjajadi
Winarno Tjajadi and Lili Liauw as joint tenants with right of survivorship
Winarno Tjajadi, Rendra Tjajadi and Sujanto Tjajadi Tjio
Winarno Tjajadi, Rendra Tjajadi and Sujanto Tjajadi Tjio
Winarno Tjajadi, Rendra Tjajadi and Sujanto Tjajadi Tjio As Joint Tenants with Right of Survivorship
Winarto Halim
Winata Wiryaputra.
Winny Martina Christine
WINSON POLA
Wira Satria Dewo Anggoro Kasih
Wirawan Chondro
Wirawan Chondro
Wirawan Chondro
Wirontono & Co. Ltd
Wisasongko Puspoyo
Witijasmoro Sih Handajanto
Witijasmoro Sih Handajanto and Nia Soniati Wityasmoro
Witjaksono Abadiman Sidharta
Wito Chandra
Witono Dani
Wiwiek Hidajati
Wiwin Untari Andoko
Wiyang
Wong Alfian Widjaya
Wong Chuk Chen
WONG KIAN KHIONG
WONG KIAN KHIONG and FOE SIAT KHIUN
WONG LAI FONG FELICITAS
Wong Steffania
Wong Tommy Wibowo
Wong Tranadi
Wong, Siong Yuit Benjamin
Xu Jun
XU PENG
Yakin Lijaya
Yamin Widjaja
Yamin Widjaja and Linda Sidharta As Joint Tenants with Right of Survivorship
Yanto Kasiman
YANUAR ARSAD
Yanuar Tenacious
Yap Eng Siu
Yap Johanes
Yau Hang Yip
Yau Hang Yip and Elline Yohan Yau as joint tenants
Yau Hang Yip and Jocelin Yohan Yau as joint tenants
Yau Yung
Yaya Winarno Junardy
Yayasan Chandra Bunda Dewi
Yeni Rohaeni
YENNI
YEOMUN LTD
Yeomun Ltd
Yessica Beatrice Widjaja
Yogie Sandi Yudhianto
Yohan Sutandar
YOHAN SUTANDAR
Yohanes Eka Putranto
Yohannes Alexander Wintery Oei
Yohannes Riyadi
Yoko Kawano
Yolanda Wijaya
Yong Wiyono Buyung Yasin
Yonna Septarina Kusdianto
Yos Hendri
Yos Sidy Teo )formerly Sie Tjit Kiong
Yoseph Suherman
Yosodewi Limurti
Yosyan Madolen
Yoyok Soebagio
YUDHO ENJANARKO
Yudi Astono
Yudi Astono
Yugisako Tita
Yuke Elia Susiloputro
Yulia Sinta Dewi
YULIANA JOHANES
Yuliana Sudradjat
Yully
Yunet Limanto
Yunie Wono and Elline Yohan Yau as joint tenants
Yunita Kalim
Yunita Sastrasanjaya
YUPI HARYANTO
Yusak Teguh Nugroho
Yustiningsih Suharsono
Yustinus Wisnoe Bayuaji
Yusuf Adrian Chandra
Yusuf Valent
Yusy Widjaja Oey
Yvonne Shirley Fogarty
ZAINAL ABIDINSYAH SIREGAR
Zaini Abidin Noor
ZAMHARIR
ZEIN SWETLANA ANDREYEVNA
Zentry Ltd
Zerline Conception Boncorp Pliac
ZULFIKAR ALIMUDDIN
Zuriah
Offshore Entities (43)
Alpilles Holdings Offshore Ltd
ASANUSA CAPITAL PARTNERS PTE. LTD.
Asia Pacific Leisure Ltd
Ballistic Success Trading Limited
Blossoms Glamour Profits Inc.
Capsec Limited
CEWE LTD.
CHANDLER CAPITAL INC.
Chang Wen Yu and Chen Fang Min
CHARTERHOUSE LIMITED
Chien, Cheng
CYRUS BAAL Inc.
Energi Mega Pratama Inc.
Falkner Family Trust
Folkstone Worldwide Limited
Grand Benefit Enterprises Ltd
Grid Consulting Limited
Indoprop Ltd
Innovative Ventures Ltd
Kilda Corporation
Legacy Investments Pte Ltd
Lilac Swish Offshore Ltd
Linkberg Offshore Ltd
MEGA INTERNATIONAL CORPORATION ENTERPRISES LIMITED
Nexuss Investment Worldwide Ltd
Northern Star Capital Pte Limited
Northstar Pacific Partners
Palladium Overseas Corporation
Paving Investments Ltd
PERSEPOLIS CAPITAL LTD
PT Indo Buana Makmur Textile
PT Jenshiang Nusantara Textile Chemical Industrial
PT Uni Enlarge Industry Indonesia
PT. TOPAS MULTI SECURITIES
Stafford Services Ltd
Starhill Trading Ltd
Times Investment Group Ltd.
Triston Capital Ltd
United Capital Enterprise Worldwide Ltd
Victory Harvest Investment Ltd
VIENA INVESTMENTS LIMITED
Wanamurti & Associates
Willowcreek Development Incorporated
Listed Addresses (2400)
(Invoice sent by email before send out) Jalan Brawijaya II No.5, Kebayoran Baru Jakarta Selatan 12160, Indonesia
108 Jalan Drupadi 2 Seminyak Bali Indonesia
11, Sea Mist, Pali Road Bandra  Mumbai – 400050 Indonesia
Mumbai – 400050 Indonesia
11th Floor, Menara Asia 101 Diponegoro Blvd Lippo-Karawaci Karawaci-Tangerang
139 Jl. Raya Kapuk Kamal Jakarta Utara INDONESIA
14, Kartini Raya Pasar Baru Jakarta Indonesia
14th Floor, Bank Bali Tower, Jl. Jend Sudirman Kav 27, Jakarta 12920, Indonesia
15-A-8-3 Scots Tower, Mont Kiara Pines Jalan Mont Kiara (Off Jalan Bunkit Kiara) Mont Kiara 50480 Kuala Lumpur INDONESIA
1501 Menara DEA Kawasan Mega Kuningan Jakarta 12950 INDONESIA
15th Floor, Menara DEA, Suite 1503 Kawasan Mega Kuningan Jl. Mega Kuningan Barat IX Kav. E.4.3 No. 1 Jakarta 12950 Indonesia
18 Jalan Mataram Jakarta 12110 Indonesia
18 Jalan Suryakencana Bandung 40132 Indonesia
19a-2 Tuladong Bawah Empat Jakarta 10220 Indonesia
19F Wisma Indosemen JI Jend Sudirman Kav 70-71 jakarta Indonesia
20th Floor, Citibank Tower Jl. Jend. Sudirman KAV 54 Jakarta 12190 INDONESIA
21 Banyuwangi No. 5 Menteng, Jakarta Indonesia
2111 Boulevard Gajah Mada #01-01 Lippo Cyber Park, Lippo Karawaci Utara Tangerang 15811, Banten INDONESIA
2112 Bulevar Gajah Mada # 01-01 Lippo Cyber Park Lippo Karawaci Kel. Panunggangan Barat, Kec. Cibodas Tangerang, Indonesia
21st Floor Wisma Bank Dharmala JI. Jenderal Sudirman Kav. 28, Jakarta Selatan Jakarta 12920 INDONESIA
21st Floor, Plaza Bapindo, Menara II Jl. Jenderal Sudirman Kav 54-55 Jakarta 12190, Indonesia
22 Caringin Timur Cilandak Barat Jakarta 12430 Indonesia
22B SCBD Suites, Jl Jend Sudirman Kav 52-53, Jakarta 12190, Indonesia
22nd Flr, Menara Jamsotek Jl. Jend. Gatot Subroto Kav. 38 Jakarta 12710 Indonesia
23rd Floor Menara Rajawali Jl Mega Kuningan Lot # 5.1 Kawasan Mega Kuningan Jakarta 12950, Indonesia
28 Jalan Matraman Raya Jakarta 13150 Indonesia
3 JL. BARAT SENER, GG. MERPATI NO. 1 BARATSENER KEROBOKAN KUTA BALI INDONESIA
30a Jutland Parade Dalkeith WA 6009 Western Australia Jakarta Selatan – 12980 Indonesia
31 Corroaminojo No.81, Ranalauj Bandar, Lampung.
35 Cipanganti Bandung Indonesia
35 Cipanganti, Bandung Indonesia
37-05 Ambassador 2 ITC Kuningan, Jl Prof Dr Satrio Kuningan Jakarta 12940
38 Jalan Teluk Betung Jakarta 10230, Indonesia
38 Mandala Utara Tomang Jakarta 11440 Indonesia
3rd Floor, Dynaplast Tower No. 1 MH Thamrin Blvd Lippo Karawaci 1100 Tangerang 15811, West Java, INDONESIA
4 Seasons Residences Spring Tower 19D Jl. Setiabudi Tengah Jakarta 12910, Indonesia
41 jalan Kebon Sirih Jakarta INDONESIA 10320
44-46, WLIKOTA MUSTAJAB (18. GANDASULI) SURABAYA 60272 INDONESIA
481 Jl. Legian, Legian Kaja Kota Denpasar, Bali Indonesia
4th, Enseval Building Jl. Let Jend Suprapto Kav 4 Jakarta 10510 Indonesia
55 Pajajaran Bandung Indonesia
5th Floor, Menara Kebon Sirih Jl. Kebon Sirih No. 17-19 Jakarta 10340 Indonesia
61, Jalan Mangunsarkoro Jakarta 10310 Indonesia
65 Jalan Raya Kuta Denpasar, Bali INDONESIA
65 Prescott Drive, Murdoch, WA6150, Australia and/ or Jl. Hegarmanah Wetan No. 35A, Bandung, Indonesia
6A Jahmada No. 193A Jakarta Indonesia
7 Palem boulevard Matahari Building 3rd Floor Lippo Karawaci 1200 Tangerang 15811 INDONESIA
78b JI. Kemang Timur Kemang 12510 Jakarta Indonesia
7B Nongsa Point Marina Nongsa, Batam Island Indonesia
7th Floor, Menara Perdana, JL. HR. Rasuna Said Kav.C-17, Jakarta 12940
7th Floor, Wisma BSG Jalan Abdul Muis No. 40, Jakarta 10160 Indonesia
7th Floor, Wisma BSG, Jalan Abdul Muis No.40 Jarkarta 10160 Indonesia
8th Floor Menara Asia Lippo Karawaci West Java INDONESIA
9th Fl. Lippo Centre, Jl. Gatot Subroto Kv. 35-36 Jakarta 12950 INDONESIA
9th Floor Asia Tower 101 Diponegroro Boulevard Tangerang 1500 Indonesia
9th Floor, Plaza Asia Jl. Jendral Sudirman Kav. 59 Jakarta 12190 Indonesia
AAF Building 2nd Floor Jl. TB Simatupang Kav 18 Jakarta 12430 Indonesia
Advocates & Solicitors Plaza ABDA, 16th Floor, Zone D Jl. Jend. Sudirman Kav. 59 Jakarta 12190 Indonesia.
Agil Kusumadya Akbp No. 1.B Kudus Indonesia
Agung Indah 4/4 RT 015 RW 016 Sunter Agung Jakarta Utara INDONESIA
Agung Permai IV/39 C4/24 Kelurahan Sunter Agung Jakarta Utara Indonesia
Agung Rakas Bungalows. JL Padma Utara, Legian Bali Indonesia
Alam Elok V1/CIF 26-27 RT 002/016 Pondok Pinang Jakarta Selatan Indonesia
Alumanium A3/III/1 Medan-Sumatera Utara INDONESIA
Ambengan No. 19 RT/RW Ketabang, Surabaya INDONESIA
AMDI BUILDING – B 7th Floor Jalan Gaya Motor Raya No.8 Suntor II, Jakarta 14330 INDONESIA
Apart Atap Merah, Unit 1054 JL Pecenongan Raya No. 72 Jakarta 10120 INDONESIA
APARTEMEN PERMATA HIJAU TOWER 1 NO. 7A, JL. RAYA PERMATA HIJAU BLOK B NO. 8, INDONESIA
Apartemen Permata Hijau Tower 2 No. 1A Jl. Raya Permata Hijau Blok B No. 8 Indonesia
Apartemen Puri Kemayoran 207C Jl. Landas Pacu Selatan A6 Kota Baru Bandar Kemayoran Jakarta Pusat, Indonesia
Apartm Bona Vista I/0906 Jl Bona Vista Raya No.1 Jakarta 12440 Indonesia
Apartmen Casablanca Tower 1 Unit 0412 Jl Casablanca Kav 12 Jakarta Selatan 12870
Apartment Airlangga Unit 39A Jl. Lingkar Mega Kuningan E1.1 Mega Kuningan, Jakarta 12950 Indonesia
Apartment Airlangga Unit 39A Jl. Lingkar Mega Kuningan Kav E1.1 No. 1 Jakarta 12950 INDONESIA
Apartment Ambassador, Kuningan Unit 25F Jl. Prof. Dr Satrio, Jakarta Pusat Indonesia
APARTMENT BATAVIA TOWER II/ SUITE 1505 JLN K.H. MAS MANSYUR KAV. 126 JAKARTA 10210 INDONESIA
Apartment Executive Menteng Blok Palem No. 1205 Jl. Pagangsaan Barat Kav 6 JAKARTA, INDONESIA
Apartment Istana Harmoni, Unit 28K Komplek Harmoni Plaza Jl. Suryo Pranoto No. 2, Jakarta Pusat INDONESIA
Apartment Istana Sahid Tower ME-05-C Jl. Jenderal Sudirman 86 Jakarta 10220 Indonesia
Apartment ITC Roxymas 7th Floor, No. 81 Jakarta Indonesia
Apartment Kempinski Plaza 18 RT 013 RW 011, Jakarta Pusat Indonesia
Apartment Mediteranean Garden Tower A 9th Floor, Unit B/AC Tanjung Duren Jakarta Indonesia
Apartment Pantai Mutiara Tower Enggano Iantai 15/7 Jalan Raya Pantai Mutiara T.I. Jakarta Utara 14450, Indonesia
Apartment Parama Unit 10B Jl. T. B. Simatupang Jakarta Selatan 12430 Indonesia
Apartment Pavilion, Tower 1 Unit 1902 JI. KH Mas Mansyur Kav 24 Jakarta Pusat Indonesia
Apartment Pearl Garden, WPI GF Jl Jend Gatot Subroto Kav. 6-7 Jakarta 12930, Indonesia
Apartment Permata Hijau Tower 1 No. 2-A, Jl. Raya Permata Hijau Blok. B No.8, Jakarta 12210 Indonesia
Apartment Permata Hijau Tower Two, Unit 7 Jakarta-Selatan Indonesia
Apartment Permata Safir #603 Jl. Permata Safir Blok W/9 Jakarta Selatan 12210 Indonesia.
Apartment Plaza Senayan Jl. Tinju No. 1 Pintu Satu Gelora Senayan Jakarta 10270, Indonesia
Apartment Sailendra, No. 11B Jalan Mega Kuningan Jakarta 12950, Indonesia
Apartment Salendra Jalan Mega Kuningan Timur 1 Kav E1.2., No. 1&2 Jakarta 12950 Indonesia
Apartment Setiabudi Unit 1704 Jalan RS Aini, Karet Setiabudi Jakarta Selatan Indonesia
Apartment Simprug Teras A-21 RT007/003 Jakarta Selatan, Indonesia
Apartment Taman Anggrek Tower 4 Unit 11 Jakarta Barat 11470 Indonesia
Apartment Taman Anggrek Tower 7/29 Floor Jl. Letjend S. Parman Kav. 21 Jakarta 11470 Indonesia
APARTMENT TAMAN ANGGREK TOWER, 4-11D JARKATA 11470 INDONESIA
Apartment The Ascott Unit 0331 Kebon Kacang Raya No. 2 Jakarta, Indonesia
APR. PERSONA BAHARI BLOK TOPAZ NO. P1D, JAKARTA UTARA INDONESIA
Apt Senayan Res B1S/2 LT.11, RT003/RW007 Grogol Utara, Kebayoran Lama Jakarta Selatan, Indonesia
Apt. 1409 at The Ascott Jakarta Jalan Kebun Kacang Raya No. 2 Jakarta 10230 Indonesia
Apt. Atap Merah #1195 JI. Pecenongan 72 Jakarta 10120 Indonesia
Apt. Istana Sahid No. ME-7C JI. Jenderal Sudirman Kav. 86 Jakarta 10220 Indonesia
APT. ISTANA SAHID NO. ME-7C JL. JENDERAL SUDIRMAN KAV.86 JAKARTA 10220 INDONESIA
Apt. Nuansa Hijau C. 024, RT007/015, Pondok Pinang Jakarta, Indonesia
Apt. Permata Safir, #603 Jl Permata, Safir Bok W/9 Jakarta 12210, Indonesia
Apt. Redtop 1062, JL. Pecanongan No. 72 Jakarta Pusat, Indonesia
Arena Pekan Raya Jakarta Hah E Kota Baru Bandar Kemayoran Jakarta 10620
Ariobimo Sentral 4th Floor Jl. HR Rasuna Said Kav X-2 No. 5 Jakarta 12950 Indonesia
Artha Graha Building 19th Floor Suite 1909 Jl. Jend. Sudirman Kav. 52-53 Senayan-Keyaboran Baru South Jakarta, Indonesia
Artha Graha Building 32nd Fl Sudirman Central Business District (SCBD) Jl. Jend. Sudirman Kav. 52-53 Jakarta 12190, Indonesia
Artha Graha Building 6th Floor Sudirman Central Business District (SCBD) Jl. Jend. Sudirman Kav. 52-53 Jakarta 12190 Indonesia
Artha Graha Building, 6th Floor, Jl. Jend. Sudirman Kav. 52-53 Jakarta 12190, Indonesia
Artha Graha Building, Sudirman Central Business Jalan Jenderal Sudirman Kav. 52-53, Jakarta-12910 INDONESIA
Arthaloka Building, Jin Jend Sudirman Kav., 2 Jakarta Pusat 10220
Asem Baris Raya No. 1, RT 001/005 Kebon Baru Jakarta Salatan
Asia Superyachts Office 117 Jalan Kunti, Seminyak Bali, Indonesia 80361
Aston Condominium, Jl. Braga City Walk, Bandung Indonesia
Aston Rasuna Residence Apartment 29C Komplex Apartment Taman Rasuna, Jalan H R Rasuna Said Jakarta, Indonesia
B-102, Bugenville Apartment Komplek Klub Kelapa Gading Jalan Bulevar, Blok KGC Kelpa Gading Permai, Jakarta
Babelan Indah Blok B-3 RT/RW 08/08 Babelan Bekasi Indonesia
BALOI GARDEN BLOK C NO. 3 RT/RW 003/005 KEL. BATU SELICIN KEC LUBUK BAJA INDONESIA
Bambu Durix No. 10 Rt 013/Rw 006 Jakarta Indonesia 13430
Bank Mega Building, 2nd floor, Suite 202 Jl. Tanjung Karang No. 3 – 4A Jakarta 10230
Bapindo Plaza Mandiri Tower 19th Floor Jl. Jend. Sudirman Kav. 54 – 55 Jakarta 12190 Indonesia
BCD Tower, 4th Floor Jl. Jend.Sudirman Kav.26 Jakarta 12920 INDONESIA
Bellagio Residence Unit 22 AF 6 Jl. Mega Kuningan Barat Kav. E4/3 Jakarta, Indonesia
Benda, Rt. 004/ Rw. 001 Ciganjur, Jagakarsa Jakarta Selatan INDONESIA
Bening Indah Estate Blok B5 No. 1 Pondok Gede Jakarta Timur Indonesia
BENING INDAH ESTATE BLOK B5 NO.1 PONDOK GEDE KATARTA TIMUR INDONESIA
Bidakara Office Tower 12-18th Floor Jl. Jend. Gatot Subroto 71-73 Jakarta 12870, Indonesia
Billy & Moon KI /2-3, RT 008/010, Jakarta Timur, Indonesia
Bina Mulia Building, 5th Floor Jl.H.R. Rasuna Siad, Kav. 10, Jakarta 12950, Indonesia
Bintaro Melati Blk 2 No. 19 Pasanggrahan Jakarta, Indonesia
Bintaro Sektor IV JI. Cucur Barat X Blok E1/29 Jakarta Selatan 15225 Indonesia
Bkt Golf UTM III 24-25 RT00/03 Kel Pondok, Pinang, Jakarta Indocnesia
BLOCK I/1 SELATAN NO.32 MUARA KARANG JAKARTA INDONESIA
Blok A1/4, Jl Trapesium 3, Tmn Kedoya Permai, Kebon Jeruk, 11530 Jakarta Barat, Indonesia
Blok D No 11, Komplex Batam Plaza, Nagoya, Batam, Indonesia
Blok K-9, Selatan No.2 Pluit Muara Karang Jakarta, Utara Indonesia
Blok Vll/No. 8, Jalan Tangkuban Perahu, Banjar Tegal Buah Padang Sambian Kelod Denasar Barat 80117, Bali INDONESIA
BNI Building 20th Floor JI. Jendral Sudirman, Kav 1 10220, Jakarta INDONESIA
Br. Blangsinga, DS. Saba Kec Blahbatuh-Gianyar, Bali Indonesia
BRAWIJAYA NO.50 BOGO INDONESIA
Budi Indah Raya No. 15 Bandung Indonesia
Budi Indah Raya No., 15 Bandung INDONESIA
Budiarto Law Partnership Wisma Bisnis Indonesia 3rd Floor, Suite 309 Jalan Letjen S. Parman Kav. 12 Jakarta 11480 Indonesia
BUKIT CINERE INDAH JL PURI PESANGGRAHAN I BLOK M INDONESIA
Bukit Golf 1-PC 14 Pondok Indah, Jakarta Indonesia
BUKIT GOLF 11 NO.20, PONDOK INDAH JAKARTA SELATAN, INDONESIA
BUKIT GOLF BLOK PE NO 6 PONDOK INDAH Jakarta 12310 INDONESIA
Bukit Golf II No. 20 Pondok Indah Jakarta Selatan Indonesia
Bukit Golf Utama III P.17 Rt 000/Rw 003, Pondok Pinang Kebayoran Lama Jakarta Selatan Indonesia
Bukit Golf Utama III P.A 17 Pondok Pinang – Kebayoran Lama Jakarta Indonesia
Bukit Golf Utama III., PA 17, RT 000/003, Pondok Pinang, Kebayoran Lama, Jakarta Selatan, Indonesia
BUKIT GOLF UTAMA PA/27 RT 00/03 PONDOK PINANG JAKARTA SELATAN INDONESIA
BUKIT HIJAU II/2 PONDOK INDAH JAKARTA
Bukit Rivaria M5/24, Sawangan Depok 16519, Indonesia
Bumi Daya Plaza, 28th Floor, Jl. Imam Bonjol No.61, Jakarta 10310 – Indonesia
Bumi Karang Indah Karang Asri II Blok C2/21 Jakarta 12440 Indonesia
Bumina Wahana JI. Riau No. 17-21 Hakarta 10350 Indonesia
BUNCIT INDAH E/I, RT006/004, PEJATEN BARAT JAKARTA SELATAN, INDONESIA
Buncit Mas Bok B-3 Jl. Mampang Prapatan Raya 108 Jakarta 12790
C/- 11th Floor Menara Asia, Jl. Diponegoro Lippo Karawaci INDONESIA
c/- 8th Floor Menara Asia Lippo Karawaci West Java
c/- Bank Bira, Wisma Metropolitan Level 1-2, Jl. Jend Sudirman Kav. 29-31 Jakarta
C/- Bank Ekonomi Ekonomi Graba 7th Floor, JL. Setiabudi Selatan, Kav. 10 Jakarta 12920, INDONESIA
C/- Ciptadana Securitas, Citra Graha 8th Floor Jin. Jend. Gatot Subroto Kav. 35-36 Jakarta 12950 INDONESIA
C/- Deloitte Touche Wisma Antara, 18th Floor Jl Medan Merdeka Selatan No. 17 Jakarta 10110, INDONESIA
C/- Erlin 3rd Floor, Menara Matahari – Lippo Life Jalan Boulevard Palem Raya No. 7 Lippo Karawaci 1200 Tangerang 15811 INDONESIA
C/- Lippo Centre 10th Floor, Asia Tower 101 Diponegoro Blvd Lippo Village 1200, Karawaci-Tangerang, INDONESIA
C/- Lippo Centre Building 10th Floor, Jl. Gatot Subroto Kav. 35-36 Jakarta
C/- Lippo Centre Building Jl. Jend Gatot Subroto Kav. 35-36 Jakarta Selatan
C/- Lippo Group, 10th Floor Asia Tower 101 Diponegoro Blvd., Lippo Village 1200 Karawaci – Tangerang, Jakarta INDONESIA
C/- Lippo Group, 9th Floor Lippo Centre Jalan Jenderal, Gatoto Subroto Kav 35-36 Jakarta 12490 INDONESIA
c/- Makarim & Taira S. Summitmas I, 17th Floor Jl. Jenderal Sudirman Kav. 61-62 Jakarta 12069 Indonesia
C/- P. T. Bakrie Capital Indonesia Wisma Bakri, FL 3, Jl H. R. Rasuna Said Kav. B-1 Jakarta 12920, Indonesia
C/- P. T. Dayabangun Persada, Wisma Bakri, Fl 3, Jl H. R. Rasuna Said Kav. B-1 JAKARTA, INDONESIA
C/- P.T. Bymindo Setiatama Gedung Bank Bali Lot 6, Jl. Jend. Sudirman Kav. 27 Jakarta Selantan INDONESIA
c/- P.T. Ever Shine Tax Jl. H. Fachruddin No. 16 Jakarta Pusat 10250 Indonesia
c/- Pacific Financial Services Plaza Chase 6th Floor, Jalan Jend Sudirman Kav 21, Jakarta 12920, Indonesia
C/- PP. PT London Sumatra Indonesia Tbk Indonesia Tbk, World trade Centre 15th Floor Jl. Jend. Sudirman Kav. 29-31 Jakarta 12920 Indonesia
C/- PT Binapuri Lestari Jalan Dharmawangsa Raya No. 39 Jakarta Selatan
C/- PT Binapuri Lestari Jalan Dharmawangsa Raya No. 39 Jakarta Selatan Jakarta
C/- PT Cardig Air Menara Cardig Menara Cardig 3rd Floor Jalan Raya Halim Perdanakusuma Jakarta 13650, Indonesia Indonesia
c/- PT Gunung Sewu Kencana Chase Plaza Fl. 20 Jl. Sudirman Kav. 21 Jakarta 12920
c/- PT Moores Rowland Indonesia Jl. Sisingamangaraja #3c Jakarta Indonesia
C/- PT Sanbe Prakarsa Husada Jl. Taman Sari No. 10 Bandung 40116 Tromol PO 850 Indonesia
C/- PT Tridaya Esta Jalan Dharmawangsa Raya No. 39, Jakarta Selatan INDONESIA
c/- PT. Delta Aneka Consultants & Trade, Bank Bali Tower, 14th Floor, Kav 27, Jl. Jend. Sudirman, Jakarta, Indonesia
C/- Wisma Indosemen, Fl 6 Jl. Jend Sudirman Kav. 70-71 Jakarta 12910 Indonesia
c/- Wisma Trident Lt. 3 Jl. Tanah Abang IV No. 23-25 Jakarta 10160 Indonesia
c/-P.T. Kaltimex Energi Graha Irama, 2nd Floor Unite 2C JL. H.R. Rasuna Said
C/= Bank Ekonomi, Ekonomi Graba 7th Floor, JL. Setiabudi Selatan, Kav. 10 Jakarta 12920, INDONESIA
c/o Mr Ronald Mullers Sisingamangaraja No.3C Jakarta 12110 Indonesia
c/o 27th Floor, Menara Rajawali Jl Mega Kuningan Lot #5.1 Kawasan Mega Kuningan, Jakarta 12950 Indonesia
c/o Apartment Kuningan, Apt. # 610 Jalan Setiabudi Utara Kuningan Jakarta Selatan, Indonesia
C/o Bank Ekonomi, Ekonomi Graba 7th Floor, J1. Setiabudi Selatan Kav. 10, Jakarta 12920
c/o BNI Building 22nd Floor Jalan Jenderal Sudirman Kav. 1, Jakarta 10220 Indonesia
C/o Gedung Artha Graha 10th Floor SCBD jl. Jend, Sudirman KAV 52-53 Jakarta 12910
c/o Graha Cempaka Mas Blok B/12A JL. Letjen Suprapto Jakarta, 10640 Indonesia
c/o Graha Elnusa JI. TB Simatupang Kav. I B, Jakarta 12560 Indonesia
c/o Herjanto Lutantowidjojo PT Moore Stephens Advisory Services Wisma Dharmala Sakti, 7th Floor, Jl. Jenderal Sudirman Kav 32, Jakarta
C/O JALAN KETAPANG UTARA 1 NO. 14 JAKARTA BARAT INDONESIA
c/o Jl. Daan Mogot KM 11 Cengkareng Jakarta 11710 Indonesia
C/o JL. Jatibaru No. 24 Jakarta Pusat, 10160 INDONESIA
c/o Jl. Jelita Utara No. 21B Rawamangun Jakarta 13220 Indonesia
c/o Jl. Johor No. 27/I Surabaya Indonesia
c/o Jl. Taman Sari No. 10 Bandung 40116 Indonesia
C/O KANTOR Taman Mega Kuningan A9 Unit C8-C14 Jalan Mega Kuningan Lot 8.9/9 Kawasan Mega Kuningan
C/O Kartini Muljadi Jl. Gunawarman No. 18 Kebayoran Baru Jakarta 12110 Indonesia
c/o Leisure Investment Villas Jl. By Pass Ngurah Rai No. 888 Br. Kelan, Tuban Bali Indonesia 80361
c/o Limajari Jalan Raya Kerobokan 100x, Denpasar BALI Indonesia
C/O MENARA GLOBAL 15TH FLOOR JL GATOT SUBROTO KAV. 27 JAKARAT SELATAN 12950 INDONESIA
C/O MENARA GLOBAL 15TH FLOOR Jl. Gatot Subroto Kav. 27 Jakarta Selantan 12950 Indonesia
c/o Menara Kadin 7th Floor JI. HR Rasuna Said Blok X-5 Kav. 1 – 3 Jakarta 12950 Indonesia
c/o Menara Kadin 7th Floor Jl. HR Rasuna Said Blok X-5 Kav. 1-3 Jakarta 12950, Indonesia
c/o Menara Kadin Indonesia Suite 19C JI. H.R. Rasuna Said Blok X – 5, Kav. 2-3 Jakarta 12950 Indonesia
c/o Menara Kadin, 7th floor Jl. H.R. Rasuna Said Blok X-5 Kav.2-3 Jakarta 12950, Indonesia
c/o Menara Rajawali 27th Fl Jl Mega Kuningan Lot #5.1 Kawasan Mega Kuningan Jakarta 12950, Indonesia
c/o Mr. Lukman Nagaria PT Hajiabu Propertindo Graha Niaga 12th Floor Jln Jend Sudirman Kav 58 Jakarta 12190 Indonesia
c/o Nomade Jaya, Jalan Raya Pengubengan No. 82 Kerobakan. Kuta Bali Indonesia
c/o P. T. Ciptadana Securities Plaza Asia Office Park, Unit 2 Jl. Jend. Sudirman Kav. 59 Jakarta 12190 Indonesia
c/o P.T. Cipta Daya Teratai Emas Jalan Kemanggisan Raya No.106 Slipi, Jakarta 11480 INDONESIA
c/o P.T. Citra DMG Nusantara Gedung PriceWaterhouseCoopers 12th Floor,Suite 1201 Jl. H.R. Rasuna Said, Kav. C-3
c/o P.T. Elsuna Graha Elnusa JI. TB. Simatupang Kav. 1B Jakarta 12560, Indonesia
C/o P.T. Indiratex Spindo Desa Randu Agung Km. 75, P.O.Box 95 Singosari 65153 INDONESIA
c/o P.T. Zinga Indonesia Nusantara German Centre Building 4th Floor, Suite 4320/4330 Jalan Kapt. Subijanto Dj. Bumi Serpong Damai, Tangeang 15321 INDONESIA
C/O PLAZA DM 25TH FLOOR SUITE 2503 JL JEND SUDIRMAN KAV 25 JAKARTA 12920 INDONESIA
C/O PLAZA DM, 25TH FLOOR SUITE 2503, JL. JEND. SUDIRMAN KAV. 25 JAKARTA 12920 INDONESIA
c/o Plaza DM, 25th Floor, Suite 2503 Jl. Jendral Sudirman Kav. 25 Jakarta 12920 Indonesia
c/o PT BOKORMAS WAHANA MAKMUR Jl. Palatehan I / 35 Kebayoran Baru Jakarta 12160 Indonesia
c/o PT Catur Sentosa Adiprana Jalan Daan Mogot Raya No. 234 Jakarta 11510, Indonesia
c/o PT DWI Satrya Utama Tifa Building, 6th Floor Jl. Kuningan Barat No. 26 Jakarta 12710 Indonesia
c/o PT Global Jaringan Nusantara Menara Rajawali, 10th Floor Jl. Mega Kuningan Lot #5.1 Jakarta 12950 Indonesia
C/O PT MANDARA SELULAR INDONESIA GRAHA MOBISEL LT 1 JL. MAMPANG PRAPATAN RAYA NO. 139 JAKARTA INDONESIA
c/o PT Paperpro Indonesia Menara Gracia 9th Floor Jl. HR Rasuna Said Kav. C – 17 Jakarta 12940 Indonesia
c/o PT Pertamina (Persero) Pertamina Head Office, 19th Floor Jl. Merdeka Timur 1A, Jakarta 10110 Indonesia
c/o PT The Practice Menara Jamsostek, 22nd Floor Jl. Jend. Gatot Subroto Kav. 38 Jakarta 12710, Indonesia
c/o PT Yapindex Nagatama Kencana Jln Daan Mogot II No. 100 M & N KompleksIndo Ruko Jakarta Barat 11510
C/o PT. BUKIT SUNUR WIJAYA Jl. Musi No. 40 E Jakarta Pusat P.O.Box 4320/JKT 10043 Indonesia
c/o PT. Cipta Cakra Murdaya Jl. Cikini Raya No. 78 Jakarta 10330 Indonesia
c/o PT. Energi Pasir Hitam Indonesia (EPHINDO) Plaza Bapindo, Citibank Tower, 12th Floor Jl. Jendral Sudirman Kav. 54-55 Jakarta 12190, Indonesia
c/o PT. Eurocapital Peregrine Securities Plaza Bapindo, Citibank Tower, 12th Floor Jl. Jendral Sudirman Kav. 54-55 Jakarta 12190, Indonesia
c/o PT. Gunung Sewu Kencana Plaza Chase Podium 7th Floor Jl. Jend. Sudirman Kav. 21 Jakarta 12920, INDONESIA Indonesia
c/o PT. Quadrigga Appollonya Satrya P. O. Box 3726, Jakarta 10037 Indonesia
c/o PT. TRIAS SENTOSA Jl. Raya Waru 1B, Waru Sidoarjo
c/o Sanggraha Daksamitra, PT Wisma Soewarna 2nd Fl Soewarna Business Park Soekarna Hatta Airport Jakarta – Indonesia 19110
c/o Soewito Suhardiman Eddymurley Kordono Wisma Bank Dharmala, 14th Fl. Jl Jend. Sudirman, Kav.28 Jakarta 12920, Indonesia
c/o Sudirman Tower 11th Floor, Jl. Jend Sudirman Kav 60 Jakarta 12190
c/o Superblok Bumi Niaga Jln Pangeran Tubagus Angke No.170 Jakarta 14450 Indonesia
c/o Susanna Nagaria P.O. Box 4486/JKBTF Jakarta 11044 Indonesia
c/o Wisma 46, Kota BN1 32nd floor, Suite 3201, Jl. Jend Sudirman Kav 1 Jakarta 10220, Indonesia
c/o Wisma Dharmala Sakti 7th Floor Jl. Jenderal Sudirman Kav 32 Jakarta 10220 Indonesia Attn: Mr Herjanto Lutantowidjojo/Mr Andres Magbitang
C/o Wisma Indo Seman 12th Floor Jalan Sudirman Kav. 70-71 Jakarta 12910
C/O Wisma Tamara 7th Floor JL.JEND SUDIRMAN KAV 24 JAKARTA 12920 INDONESIA
c/o. Exotic Equities Asia Ltd / Exotic Properties Ltd Jl. Oberoi 55 80361 Kuta Bali Indonesia.
c/o. Graha Motor City, Level 2, Suite 201 Jalan Abdul Muis 24 – 26 Jakarta Pusat 10160 Indonesia.
c/o. Jl. Kencana Permai II/8 Jakarta 12310 Indonesia.
C/o. PT Cayman Trust Indonesia World Trade Centre 16/F Jl. Jend. Sudirman Kav. 29-31 Jakarta 12920 Indonesia
c/o. PT Energi Timur Jauh Gedung Wisma Mulia, 32nd Floor Jl. Jend. Gatot Subroto Kav. 42 Jakarta 12710 Indonesia
c/o. PT Yudistira Umawar Building 1st Floor Jl. Kapten Tendean Kav 28 Jakarta 12710 Indonesia.
c/o: PT SARI WANGI AEA Jl Mercedes Benz No. 288, Cicadas Gunung Putri Bogor, 16964 Jawa Barat, Indonesia
Capital Managers Asia Pet., Ltd Wisma Bakrie, 6th Floor JI. H. R. Rasuna Said Kav. B-1 Jakarta 12960 INDONESIA
Capital Managers Asia Pte Ltd 6th Floor Wisma Bakrie Jakarta
Capital Residence Tower 2/2C SCBD, Jl. Jend. Sudirman Kav. 52-53 Lot 24, Jakarta 12190 Indonesia
Caringin Barat Kav 12 Jakarta 12430 Indonesia
Cemara Raya CM 3 Solo-Baru, Sukoharjo 57552 Indonesia
Cempaka Lestapi I/5, Cilandak Jakarta Selatan, Indonesia
Cempaka Putih RT.006/005, Kel. Bintaro Kec. Pasanggrahan Jakarta Selatan
Cempaka Putih Tengah XVII/9 Jakarta 10510 Indonesia
Cempaka Putih Tengah XXII-A/14 RT006/RW006 Kel. Cempaka Putih Jakarta Pusat Indonesia
Central SPS, Ketapang Indah Blok A-1, No 3-4, Jl. K.A. Zainal Arifin, Indonesia
Chase Plaza 22nd Floor 11 Jend. Sudirman Kav 21 Jakarta, INDONESIA
Chase Plaza 7/F Jl. Jend Sudirman Kav.4 Jakarta 12920 INDONESIA
Chase Plaza Fl. 20 Jl. Sudirman Kav. 21 Jakarta 12920 INDONESIA
Chase Plaza Lt 19 Jl. Jend Sudirman Kav 21 Jakarta 12920 INDONDESIA
Chase Plaza Tower Lt. 20 JI. Jend. Sudirman Kav.21 Jakarta 12920 INDONESIA
CHASE PLAZA, 12TH FLOOR JL. JEND SUDIRMAN KAV. 21 JAKARTA 12920 INDONESIA
Chase Plaza, 18th Floor Jl. Jend Sudirman Kav. 21 Jakarta 12920 Indonesia
Cibubur Indah Bi No. 1 RT005/011 Kel. Cibubur Ciracas Jakarta Timur Indonesia
CIDAKU INDAH VI NO. 2 BANDUNG 40143 INDONESIA
Cileduk Raya No. 2 Kebayorn Lama Jakarta Selatan Indonesia
Cipinang Elok Blok W-5 RT 008 RW-010 Jakarta, Indonesia
CIPINANG INDAH BLOK D/5 RT/RW 006/016 CIPINANG MUARA JATINEGARA JAKARTA TIMUR INDONESIA
CIPINANG JAYA KK NO. 35 JAKARTA TIMUR INDONESIA
Cipinang Kcbembem,R.T/R.W.0313/012 Pisangan Timur, Kecamatan, Pulo Gadung Jarkarta, Timur INDONESIA
Cireundeu R.T. 03 R.W 04 Kelurahan/ Desa Pisangan Kecamatan Ciputat Indonesia
CitiBank Tower, 5th Floor Jl. Jend Sudirman Kav. 54-55 Jakarta 12190 Indonesia
Citra 1 Ext AA-3/27, RT 002/015 Kalideres, Jakarta Barat, Indonesia
Citra Garden 2 Blok P09/NO8 Kelurahan Pegadungan – Kalideres Jakarta Barat Indonesia
Citra Garden 2, Blok P09/N08 Kelurahan Pegadungan – Kalideras Jakarta Barat, Indonesia
Citra Garden Blok A.7 No. 40 Kelurahan Kalideres Jakarta Barat Indonesia
Citra Gdn III Extn Blk B12 A Jakarta Indonesia
Citra Graha 8th Floor Jln. Jend. Gatot Subroto Kav. 35-36 Jakarta 12950 Indonesia
Citra I Ext AA-3/27, RT 002/015 Kalideres, Jakarta Barat, Indonesia
Citra III, Blok B.8/3A, Kalideres, Jakarta Indonesia
Commonwealth Bank Wisma Metropolitan II, Lantai Dasar Jl. Jend. Surdiman Kav. 29-31 Jakarta 12920, Indonesia
Daan Mogot Baru Blok LA/22 RT/RW 002/017 Kalideres Jakarta Barat, Indonesia
Daan Mogot Estate DA/19 003/015, Kapuk, Cengkareng, Jakarta Barat, Indonesia
Dalangan RT 01 RW 05 Kel. Chiapursari, Kec. Bulu Temanggung Jawa Tengah Indonesia
Danau Agung 15/7, Block E14 Sunter Agung, Podomoro Jakarta, Utara 14350 Indonesia
Danau Indah I Blok A.3 No. 11 Sunter Jaya, Tanjung Priok Jakarta Utara, Indonesia
Danau Indah IXA-12/31 Sunter Jaya Tanjong Priok, Jakarta Utara Indonesia
Danau Permai Timur II, C2/7 Sunter Jaya, Jakarta Utara Indonesia ID No. 09.5103.REDACTED
DANAU SUNTER SELATAN0/5 KOMPLEX MEGA SUNTER NO. C10 JAKARTA INDONESIA
Dann Mogot No. 165 Jakarta 11520 INDONESIA
Darmawangsa No. 7 Vila Indah Pajajaran Bogor 16151 Indonesia
Darmo Harapan II/EF-27 Surabaya – Indonesia
Darmo Harapan Regency Blok RC-3 SURABAYA INDONESIA
Darmo Permai Selatan, 5/38 Surabaya, Indonesia.
Darmo Permai Timur, 6/15A, Surabaya, Indonesia
Denpasar 4/18 Jakarta 12950 INDONESIA
Dharmawangsa Apt. 905 Jl. Dharmawangsa VII No. 9 Kebayoran Baru Jakarta 12160 Indonesia
Diponegoro 76 Surabaya 60264
DK. NGADIROJO, RO.06, RW.05 NGADIROJO SUB DISTRIST, AMPEL DISTRICT BOYOLALI REGENCY REPUBLIC OF INDONESIA
Ds.Sajen Rt1/1Pacet Mojokerto, Indonesia.
Dsn. Bahagia Sentehbarik , Matang Terap West Kalimantan
Dsn. Krajan RT08/RW03 Jajag Gambiran Banyuwangi, Indonesia
Duri Kencana Raya No. 7 Jakarta 11510 Indonesia
Duri Kepa Kebon Jeruk JL Palem Utama No. 18 Jakarta 11510 Indonesia
DURI KEPA KEBON JERUK JL PALEM UTAMA NO. 8 JAKARTA 11510 INDONESIA
Dusun Klampok, Rt/Rw 001/011 Desa Sumbergedang, Kecamatan Pandaan Kabupaten Pasuruan, 67156 Indonesia
Dusun V Telegasari Tanjung Morawan Deli Serdang Medan Indonesia
Duta Indah 2 #21, Pondok Indah Jakarta Indonesia
Embong Malang 85-89 3rd Fl. Surabaya 60261 Indonesia
Embong Wungu No:6 Rt 01 Rw 03 Surabaya, Indonesia
Enterprise Building 4th Floor, Suite 401 Jl H. R. Rasuna Said Kav. C-5 Jakarta 12920, Indonesia
Exertainment Indonesia Plaza Chase 14th Floor J1. Jend. Sudirman kav.21 Jakarta, Indonesia, 12920
Fatmawati Golf Mansion Kav.29 Jl. R.S Fatmawati, Jakarta 12430 Indonesia
Fatmawati Mas Complex 329 Jl. R.S Fatmawati No. 20, Jakarta 12430 Indonesia
First City Complex 2, #02-33 Batam Centre, Pulau Batam, Indonesia
Fl 15, Menara Bank Danamon Jl Prof.Dr. Satrio Kav E.IV, No. 6 Mega Kuningan Jakarta 12950 Indonesia
Flamboyan Utama I Blok B5/36, Kosambi Baru Jakarta Barat, Indonesia
Flat 2709, Apt. Batavia Jl.k.h., Mas Mansyar, Kar. 126 Jakarta, Pusat 10220, Indonesia
Four Season Regent Residences J1 Setiabudi Tengah Spring Tower 11A Jakarta 12910 INDONESIA
Four Seasons Apartments Summer Tower, Unit 1B JI. Setiabudi Tengah Jakarta 12910, Indonesia
Four Seasons Apt 3A Summer Tower Jakarta, Indonesia
Four Seasons Residences, Summer Tower Apartment 01D, JI. Setiabudi Tengah, Jakarta 12910, Indonesia
G 1/3 RT 013 RW 007 Lebak Bulus Jakarta Selatan Indonesia
Gajah Mada Mediterania D16, 3rd Floor Gajah Mada #174 Jakarta Indonesia
GANG SUNYI NO. 105 JL. PETITENGET, BALI INDONESIA 80361
GB, YOSUA ST. NO.12-A MEDAN
GB. Yosua, No. 12 A Medan North Sumatra Indonesia
Gd. Asosiasi Emiten Indonesia Building 2nd Floor, Jl. Fachrudin No. 6 Tanah Abang Jakarta Pusat 10250 Indonesia
Gdg. Kebon Kacang, Jl. Kebon Kacang Raya No. 15 Jarkarta 10240 Indonesia
Gedung Bri II Suite 1705 Jl Jend Sudirman No.44-46 Jakarta 10210 INDONESIA
Gedung Graha Kapital, 4th Floor, Jalan Kemang Raya No. 4, Mampang Prapatan, Jakarta Selatan Jalarta 12730, Indonesia.
Gedung Graha Niaga 1, Lt. 5 Jl. Putri Hijau No. 20 Medan 20115 – Indonesia
Gedung harco Mangga Dua Electronic Superstore Lt. Komplek Mangga Dua Plaza, Jl. Mangga Dua Raya Jakarta Pusat Indonesia
Gedung Hijsu TK19 Jakarta Indonesia
Gedung Manara Karya 24th Floor Jl. HR Rasuna Said Block x-5, Kav 1-2 Jakarta 12950 Indonesia INDONESIA
Gedung Nugra Santana Lt 12, Jln. Jendral Sudirman Kav. 7-8 Jakarta 10220 Indonesia
GEDUNG SETIABUDI ATRIUM 7TH FLOOR, JL. HR. RASUNA SAID KAV. 62 KUNINGAN, JAKARTA SELATAN 12920 Indonesia
Gedung Thamrin Handphone Center 2nd floor Komplek Sarinah Thamrin Jl. H.Agus Salim No. 60A Jakarta 10350, Indonesia
Gedung Tifa Lt.6 Jl Kuningan Barat No 26 Jakarta Selatan 12710 Indonesia
Gedung Wirabuana, Jl. Abdul Muis No. 24 Jakarta 10160 Indonesia
Gedung World Trade Centre Lt. 12 Jalan Jenderal Sudirman Kavling 29-31 Jakarta Selatan 12920 Indonesia
Gg Balangan 1, 120 X, Ungasan, Bali, Indonesia
GG Lontar, RT/RW : 012/002, Pejagalan, Penjaringan Jakarta Utara Indonesia
GG. Cayho No. 23 Jakarta INDONESIA
Gg. Krama RT. 009 RW.010 Kelurahan Ciracas Cecamatan Ciracas Jakarta Timur 12610 Indonesia
Goodway Hotel Jl.Imam Bonjol No. 1 Batam
Grading Griya Lestari Blok D1, No. 15 Jakarta Utara, Indonesia
Graha Aktiva, Jl. HR Rasuna Said Kav. 03 Blok X-1, Jakarta 12950, Indonesia
Graha BIP 9th Floor, Jl. Jend. Gatot Subroto Kav. 23, Jakarta 12930, Indonesia
Graha Famili Block D No. 72 Surabaya 60226 INDONESIA
Graha Famili Block I-3 Taman Golf Famili Timur I-3 Surabaya 60226, Indonesia
Graha Family BB-18 Surabaya Indonesia
Graha Family Selatan V B-32 Surabaya Indonesia
Graha GRC Board Jln.S.parman Kav 64 Jakarta 11410 Indonesia
Graha Hijau B 11/12 Ciputat Tangerang Indonesia
Graha Irama 3rd Floor Jl. Hr. Rasuna Said Kav. 1-2 Jakarta Selantan Indonesia
Graha Irama Bldg 9th Floor JI. HR Rasuna Said Block X-1 Kav 1-2, Jakarta 12950 INDONESIA
Graha Kirana, 6th Floor, Jalan Yos Sudarso No. 88, Jakarta 14350 Indonesia.
Graha Multi Impresa Pratama 6th Flr Jl RS Mata Aini Kav BC 1 Setia Budi Jakarta 12920 Indonesia
Graha Niaga 1st Floor Jl Jend. Sudirman Kav. 58 Jakarta 12190, Indonesia
Graha Niaga Lt. 11 Jl Jenderal Sudirman Kav 58 Jakarta 12190 Indonesia
Graha Niaga, 18th Floor Jalan Jenderal Sudirman Kav 58 Jakarta 12190 INDONESIA
Graha Nigra 16th Fl. Jl. Jend, Sudirman Kav. 58 Jarkata 12190, Indonesia
Graha Semesta 4th Floor, Jln Kebayoran Lama Pal VII No. 31 Jakarta Selatan 12210 Indonesia
Graha Taman HC 2No. 4 Bintaro Jaya Sector 9 Tangerang Indonesia
Graha Wirabuana Level 2, Suite 201 Jl. Abdus Muis, No. 24-26 Jakarta Pusat 10160 INDONESIA
Green Garden Block I-1/14 Jakarta 11520 Indonesia
Green Garden Block Y2/5 Jakarta 11520 Indonesia
Green Garden Blok B9 No. 30 Jakarta Barat, Indonesia
Green Garden Blok EI/49 Kebon Jeruk, Jakarta Barat Indonesia
Green Garden Blok F1/2 Kedoya Jakarta
Green Garden DIII No. 20 RT 012 RW 004 Jakarta Barat INDONESIA
Green Garden H2/6 Jakarta Barat 11520 Indonesia
Green Ville Blok BQ/26 RT 01/014 Duri Kepa Keb Jeruk Jakarta Barat 11610
Greenville Block BC/5 Duri Kepa Jakarta Barat INDONESIA
Greenville Blok BG 10 JAKARTA BARAT Indonesia
Griya Agung Road, No. 73 Sunter Jakarta – Utara
Griya Ampera 3rd Floor JI. Ampera Raya 18 Jakarta, 12560 Indonesia
Griya Ampera Bldg. 2nd Floor Jl. Ampera Raya No. 18 Cilandak, Jakarta 12560
Griya Astika JL. Lamandau IV/16, Kebayoran Baru Jakarta Selatan, Indonesia
GRIYA ELOK BLOK O NO. 98 SUNTER AGUNG, TANJUNG PRIUK Jakarta Utara Indonesia
GUDANG BANDUNG 3, RT 001 RW. 005 KEL. JEMBATAN LIMA KEC.TAMBORA JAKARTA – BARAT
Gudang Peluru Blok A/25 Kebon Baru Tebet, Jakarta Selatan Indonesia
Gudang Peluru Blok E/139 Rt. 02/03, Kebon Baru, Tebet Jakarta Selatan Indonesia
Gudang Peluru Blok H/201 Rt. 006/03, Kebon Baru Jakarta Selatan
GULF RESOURCES IND WISMA 46 BNI 23RD FL JL JENDERAL SUDIRMAN KAV 1 JAKARTA 10220 INDONESIA
GUNUNG ATLANTIK NO. 2, LIPPO KARAWACI, TANGERANG INDONESIA
Gunung Mutiara 5 Lippo Karawaci, Tangerang Banten Indonesia
Gunung Sahari XI/70g J/d – Indonesia
H. NURDIN NO. 71D, RT 005/003 LEBAK BULUS, JAKARTA SELATAN INDONESIA
Hanglekir I/6 RT 004/006 Gunung, Jakarta Selatan Indonesia
House of Bali, Jalan Danau Tamblingan #108 Sanur 80228, Bali, Indonesia
ID Card: 32.03.26.2015/4417/4643429 JL. Gandaria Raya No 35, RT13/RW12, Kelurahan Ragajaya, Kecamatan Rojonggede Indonesia
Intercon blok E2/1, rt/rw 001/010 Srengseng, Kembangan Jakarta Barat Indonesia
Interkon Kebon Jeruk Blok I 7 No. 29 Jakarta 11630, Indonesia
J l. Tembakau II No. 74 A Jakarta Selatan INDONESIA
J Teuku Umar No. 50 RT/RW 001/001 Gondangdia Menteng Jakarta Pusat Indonesia
J. Wijaya Kusuma Blok 1 No. 17 Duren Sawit East Jakarta INDONESIA
J1 Cipaganti No. 136 Bandung Indonesia
J1 Drupadi No. 1 Banjar Basangkasa Seminyak, Bali Indonesia 80361
J1 Kelapa Sawit 13/3 Blok M II/3 Billy & Moon RE Pondok Kelapa East Jakarta 13450
J1 Kramat II #34, Jakarta Indonesia
J1, Katamaran Permai 8 No. 2, Kav, UT/LS II Pantai Indah, Kapuk, Jakarta, Indonesia
J1-Gunung Sahari V1 No.24, Jakarta,Indonesia.
J1-Mangga Besar V111/8,RT/008/02, Kel Tamansari,Jakarta Barat, Indonesia.
J1. Barata 40 Bandung, 40172 Indonesia
J1. Bidurl Bulan J1 #21 Permata Hijau Jakarta Selatan INDONESIA
J1. Gayungsari VI/30 Wonocolo – Surabaya Indonesia
J1. Kaliurang KM 5, GG Megatruh No. 18 Yogyakarta Indonesia
J1. Kedoya Angsana II Blok D2 No. 25 Jakarta, 11520 Indonesia
J1. Kemang Dahlia Raya AK/16, RT/RW 001/012 Bojong Menteng Bekasi, Jawa Barat INDONESIA
J1. Madkum No. 15 Menteng Jakarta Pusat INDONESIA
J1. P. Jayakarta 46 Block A/12 Jakarta Pusat Indonesia
J1. Perumahan Kebon Jeruk Baru Blok A 6, No. 27 Jakarta 11530 INDONESIA
J1. Petemon Timur 68 Surabaya Indonesia
J1. Pluit Putra Dalam No. 3 Jakarta 14450 Indonesia
J1. Polisi Istimewa 32-38 Surabaya 60265 INDONESIA
J1. Pulasaren 82 Cirebon, 45117 Indonesia
J1. Puri Mutiara Wisma Pertamina #5 Jakarta Selatan 12430 Indonesia
J1. Rajawali Selatan I/55 RT 014/ RW 002 Gunung Sahari Utara Jakarta Pusat INDONESIA
J1. Siliwangi 80 Cirebon, 45124 Indonesia
J1. Sultan Iskandar Muda No.25 Arteri Pondok Indah Jakarta 12240 INDONESIA
J1. Tambak Adi 46 Surabaya Indonesia
J1. Tisna Senjaya No. 80/18D Pungkur Bandung-40252 West Java, Indonesia
J1. Urip Sumoharjo 40 RT. 24/VI, Klitren Gondodusuman, Yogyakarta Indonesia
J1.Daan Mogot Km. 18 Cengkareng, Jakarta Barat, 11840 Indonesia.
J1.Daan Mogot Km. 18 Cengkareng, Jakarta,11840. Indonesia.
J1.Daan Mogot Km.18 ` Jakarta Barat 11840, Indonesia.
Jakarta Representative Office , Suite 1605, Wisma GKBL Jalan Jenderal S INDONESIA
Jakarta Selatan, Indonesia
Jakarta Timur, Indonesia
Jalan Kiai Maja No. 9 Jakarta Selatan 12130 Indonesia
Jalan Margorejo Indah No. C-203, Surabaya 60237, Indonesia
Jalan Metro Pondok Indah No. UF-19, Pondok Indah Jakarta, 12320, Indonesia
Jalan 8 No. 5, Kelurahan Cipinang Muara Kecamatan Jetinegara East Jakarta, Indonesia
Jalan A No. 1 Karang Anyar Jakarta Indonesia
Jalan Adityawarman, No. 9 Jkt Selatan, Indonesia
Jalan Agung Permai, 4/23 Jakarta 14350 Indonesia
Jalan Aipda K.S. Tubun IIC No. 17-18 Jakarta Barat 11410 Indonesia
Jalan Akasia 1 B3 No. 39 Kedoya Selatan Jakarta 11520, Indonesia
Jalan Akasia I B3 No. 39 Kedoya Selatan Jakarta 11520, Indonesia
Jalan Alam Asri VII/SK. 8 Pondok Pinang, Jakarta Selatan Indonesia
Jalan Alam Segar VI/51 Pondok Inah Jakarta 12310 Indonesia
Jalan Alaydrus 78-C Jakarta Pusat 10130 Indonesia
Jalan Andara Dalam Kav. IX/21, Pangkalan Jati Baru, Depok 16513, Indonesia
Jalan Arjuna Utara 87 Guna Group Building 6th Fl. Kebon Jeruk Jakarta 11510, Indonesia
Jalan Bangka 8A No. 21 JAKARTA 12720 Indonesia
JALAN BAU CEPER NO. 40 JAKARTA PUSAT 1 INDONESIA
Jalan Behape No. 1 Blok BB 9-10 Bumi Harapan Permai Jakarta 13550,
Jalan Biduri, Blok 12, No. 18 Permata Hijau Jakarta Selatan 12210
Jalan Boulevard Palem Raya No. 2105 Lippo Karawaci, Tangerang Indonesia
Jalan Braga No. 106 Bandung 40111, Indonesia
Jalan Bukit Golf 1 PD5 Pondok Indah Jakarta, Indonesia
Jalan Bukit Golf Utama Kav. III PA 1-2 Pondok Indah Jakarta Selatan, Indonesia
Jalan Bukit Golf Utama Kav. III PA 1-2, Pondok Indah Jakarta Indonesia
Jalan Bukit Hijau III No. 11 Jakarta 12310 Indonesia
Jalan Bukit Pakar Utara No. 7 (Dago Pakar) Bandung, West Java INDONESIA
Jalan Cembaka Putih 20A Jakarta Pusat 10520 Indonesia
Jalan Cempaka Putih Tengah 27A No. F24 Taman Solo Jakarta 10510, Indonesia
JALAN CEMPAKA PUTIH TENGAH 27A/8 JAKARTA, PUSAT INDONESIA
Jalan Cendrawasih – LX/No.157 Jatiwaringin – Antilop Pondok Gede, Bekasi – 17411 INDONESIA
Jalan Cibaligo Melong No. 238, KM3 Leuwigajah Cimindi, Bandung Indonesia
Jalan Cilandak VI No. 23 RT 001 RW 003 Cilandak Barat Jakarta Indonesia
Jalan Cipedes Heger No 8, Dr. Jujunan dalam III Bandung 40173, Indonesia
Jalan Cipete Raya no. 9, RT 004/004, Cipete Selatan, Jakarta Selatan, Indonesia
Jalan Cipinang Muara 70 Jakarta Timur 13420 Indonesia
Jalan Cut Mutia No. 1, P.T. 001 Padana Pasir Padang Barat Indonesia
Jalan Daan Mogot Estate RT 005/015 Kapuk, Cengkareng Jakarta Barat Indonesia
Jalan Dadali No. 9 Bandung Indonesia
Jalan Dadali No. 9 Bandung, Indonesia
Jalan Dago Raya No. 77 Lippo Cikarang, Bekasi 17550 Indonesia
JALAN DAHA 3 NO 7 KEBAYORAN BARU JAKARTA 12110 INDONESIA
Jalan Danau Sunter Selatan Blok M2/7 North Jakarta
Jalan Darmarangsa 8 No. 17 Kebayora Baru Jakarta 12160 Indonesia
JALAN DARMAWANGSA X, RT 007, RW 008, KELURAHAN CIPETE UTARA, KECAMATAN KEBAYORAN BARU, JAKARTA SELATAN, INDONESIA
Jalan Delima IV / 29, RT. 004, RW. 005 Tanjung Duren Selantan Sub District Grogol District, West Jakarta Republic of Indonesia
JALAN DELTA BARAT C 166 BEKASI INDONESIA
Jalan Deperdag 111 no. A-11 Radio Dalan Kebayoran Baru Jakarta Selatan 12140
Jalan Derman Kencana IV, Block A IX/205 Taman Kusir, RT 013, RW 009 Kelurahan Kabaroyan Lama Utara Kecamatan Kabaroyan Lama, Jakarta Selatan
Jalan Dharmahusada Indah 120, Surabaya Indonesia
Jalan Diponegoro No. 33 Jakrata Pusat INDONESIA
Jalan Dr Semeru 1 No.32, Jakarta 11450 Indonesia
Jalan Dr. Setia Budhi No. 265-G Bandung 40154 Indonesia
Jalan Drupadi #1, Banjar Basangkasa Seminyak, Bali 80361, Indonesia
Jalan Duyong Gang 1/3x Sanur, Bali 80288
Jalan Elang Thainesia A-3 No.S Curug Indah, Cipinang Melayu Jakarta Timur Indonesia
Jalan Elang Thanesia Blok A3 No. 18 Complex TNI-AU Curug Indah Jatiwaringin, Jakarta Indonesia
Jalan Empu Sendok No. 57 Kebayoran Baru Jakarta Selatan, Indonesia
Jalan Flamboyan F-59 CJT II RT. 014, RW. 004, Gedong Sub District Kebon Jeruk District, West Jakarta Republic of Indonesia
Jalan G No. 408 Teluk Gong Jakarta Utara Indonesia
Jalan Gelong Baru Selatan, No. 54, Tomang, Jakart a Barat, Indonesia
Jalan Griya Indah Blok M1/18 Jakarta
Jalan H. Abdul Majid RT 011 RW002 Cipete Utara Kebayoran Baru, Jakarta Indonesia
JALAN H.MOCHAMAD NAIM III/86 RT 007 RW 009 KELURAHAN CIPETE UTARA KECAMATAN KEBAYORAN BARU, JAKARTA SELATAN INDONESIA
Jalan Haji Domang No. 31 Kelapa Dua, Kebon Jeruk Jakarta 11550 Indonesia.
Jalan Hang Lekir VII/6 Kebayoran Baru Jakarta 12120 Indonesia
JALAN HIANG LEKIR II/ 20 KEBAYORAN BARU JAKARTA SELATAN INDONESIA
Jalan Hiang Lekir II/20 Kebayoran Baru Jakarta Selatan Indonesia
Jalan Imam Bonjol, No. 54 Menteng, Jakarta INDONESIA
Jalan Ir. H. Juanda III No. 6, 4th Floor Jakarta Pusat 10120 Indonesia.
Jalan Janur Hijau VIII TC 1-9 Kelapa Gading Jakarta
Jalan Jatibaru Raya No 24 Jakarta Pusat Indonesia
Jalan Jatipadang Utara No. 10 Pejaten Jakarta 12540 Indonesia
Jalan Jend. Sudirman Kav.21 Jarkata 12920 Indonesia
Jalan Jendral Gatot Soebroto Kav. 35 37 dan 39, Jakarta 10210, Indonesia.
Jalan Johar No.2 Lt.2A Menteng Jakarta Pusat 10310 Indonesia Indonesia.
Jalan Kalisari 3 No.22 Jakarta Timur 13780 INDONESIA
Jalan Kamboja 21 Pejaten Barat 2 Jakarta Selatan 12510 Indonesia
Jalan Karet No. 20, Pekan Baru, Indonesia
Jalan Kartika Utama Sm-29, Pondok Indah, Jakarta Selatan, indonesia, Postal Code 12310
Jalan Kartini Raya 64/65 Blok C9 Jakarta Pusat Indonesia 10750
Jalan Kebangkitan Nasional No. 48 RT/RW 001/001 Kelurahan Sriwedari Surakarta 57141 Indonesia
Jalan Kebon Manggis II, Number 6B Rukun Tetangga 009, Rukun Warga 002 Kelurahan Kebon Manggis, Kecamatan Matramatan Jakarta Timur, Jakarta, Indonesia
Jalan Kebon Sirih No. 17-19 Jakarta 10340 Indonesia
Jalan Kedoya Albasia Raya B.X1/6 Jakarta Barat 11520 Indonesia
Jalan Kelapa Puan Timur IV – NB 5/33 Pegangsaan Dua, Kelapa Gading Jakarta Urata, Indonesia
JALAN KEMANDARAN 1, NO. 22 PALMERAH BARAT JAKARTA SELATAN 12210 INDONESIA
Jalan Kemang Dalam 1x No. F-27 Jakarta 12730 Indonesia
Jalan Kemang Timur Raya No. 78B Jakarta Selatan – 12730 Indonesia
JALAN KEMANG UTARA 26B JAKARTA SELATAN INDONESIA
Jalan Kemanggisan Ilir II / 43 RT 06 / RW 07 – Kemanggisan Jakarta Barat 11610 Indonesia
Jalan Kemanggisan llir II No. 43, RT06/RW07 Kemanggisan Jakarta Barat 11480, Indonesia
Jalan Kenanga No. 50J RT 007/RW 002 Cilandak Timur Jakarta Selantan 12560 Indonesia
Jalan Kesehatan No. 26, Jakarta Indonesia
Jalan Kintamani 2 No.14, Kelapa Gading Jakarta
JALAN KRAMAT GANTUNG NO. 25 SURABAYA INDOENESIA
Jalan Kuta Raya No. 21 Bukit Gading Villa Jakarta 14240 Indonesia
Jalan Lembah Madang AF-28 RT. 001, RW. 005, Lidah Wetan Sub District Lakarsantri District, Surabaya INDONESIA
Jalan Malabar #4, Guntur Jakarta 12970 Indonesia
Jalan Mangga Besar IV J No. 3 RT. 004, RW. 001, Taman Sari Jakarta Barat 11150 Indonesia
Jalan Mangga Besar IV M/24 RT.004 RW.003, Taman Sari Sub District Taman Sari District, West Jakarta Indonesia
Jalan Mangga Besar VI No. 30, Jakarta Barat Indonesia
Jalan Mangga No. 18 RT012/004 Gandaria Selatan Jakarta Selatan Indonesia
Jalan Mawar Raya D23 Cipinang Indah I Jakarta
Jalan Melinjo No. 17, RT 006/RW 007, Pejaten Barat, Jakarta Selatan.
Jalan Menteng Tenggulun RT002/RW010 No.7 Indonesia
Jalan Metro Alam III PH-2, Pondok Indah Jakarta Selatan Indonesia
Jalan Metro Alam X N010 Pondok Indah Jakarta
Jalan Minyak 333 no. 10 Jakarta Indonesia
Jalan Muara Karang Blok P8U No.27 Jakarta Utara INDONESIA
Jalan Muara Karang CIII Barat No. 25 North Jakarta Indonesia
Jalan Muara Karang E5/41, RT 005, RW 013, Kelurahan Pluit, KECAMATAN PENJARINGAN, Jakarta Utara, Indonesia
Jalan Mulawarman No. 1 Kebayoran Baru Jakarta 12100 Indonesia
Jalan Mushollah No. 20C, RT 004/RW 004 Kemang Cilandak Timur Jakarta Selatan 12562 Indonesia
Jalan Nipah No. 20J Padang, 25118 West Sumatra Indonesia
Jalan Pademangan I gg 7 No. 21 Jakarta Utara 14410 Indonesia
Jalan Palatehan I/35 Kebayoran Baru Jakarta 12160 Indonesia
Jalan Pangadaran VII/I Ancol Barat Jakarta Indonesia
Jalan Panglima Polim V No. 29 Kebayoram Baru Jakarta Selatan 12160 Indonesia
Jalan Pantai Mutiara AB/2 Jakarta 14440 Indonesia
JALAN PANTAI MUTIARA BLOK F NO. 23, RT 003, RW 016, KELURAHAN PLUIT, KECAMATAN PENJARINGAN, JAKARTA UTARA, INDONESIA
Jalan Pantai Mutiara G No. 1 Jakarta Indonesia
Jalan Paradise Raya III, No. 1 Sunter Paradise Real Estate Jakarta Utara 14350 Indonesia
Jalan Parang Tritis Raya No. 15A
Jalan Parang Tritis Raya No. 15A Jakarta 14430 Indonesia
Jalan Pelepah Indah Blok LC2 No. 9, Kelapa Gading Permai Jakarta Utara, Indonesia
Jalan Pelepah Kuning II WV 2/14 002/016, KLP Gading TMR Kelapa Gading, Jakarta Utara Indonesia
Jalan Pengembak Gang 3, No. 29 Sanur, Denpasar Bali Indonesia 80228
JALAN PENGEMBAK NO. 10 SANUR, BALI INDONESIA.
Jalan Pengembak No. 29 SANUR, BALI Indonesia 80228
Jalan Penyelesaian IV Kavling 65-3 Meruya Utara Jakarta Barat 11620 Indonesia
Jalan Perdatam Raya No. 24 RT008/002, Pancoran Jakarta Selatan Indonesia
Jalan Permata Berlian R12 Jakarta Selatan Indonesia
Jalan Petitenget No. 111 Kerobokan, Bali Indonesia
Jalan Pinisi Permai VII No. 21 Jakarta Utara Indonesia
Jalan Pluit Murni III No. 3 Jakarta Utara Indonesia
Jalan Pluit Putera Kencana No. 20 RT 004 RW 006, Pluit Jakarta Utara Indonesia
Jalan Pluit Sakti II No. 37 RT 007 RW 007 Pluit Jakarta Utara Indonesia
Jalan Pluit Samudera V/* Jakarta INDONESIA
JALAN POSANAN RT. 003 RW 006 KELURAHAN TEGAL HARJO KECAMATAN JEBRES SURAKARTA JAWA TENGAH INDONESIA
Jalan Praja II No. 24, Kebayoran Lama, Jakarta Selatan, Indonesia
Jalan Prapanca Raya 106 Jakarta Selatan 12150 Indonesia
Jalan Pratama No. 74, Tanjung Benoa, KEC. Kuta, Kab.Bdung, Indonesia
Jalan Prof. Dr.Ir Sutami No. 1, Makassar Indonesia
Jalan Pulo Mas Utara IIIB/4, RT005/RW014 Kayu Putih, Pulo Gadung Jakarta Timur Indonesia
Jalan Pulo Nangka II No.4 RT. 009 RW. 008 Pulo Gadung Sub District Pulo Gadung District, East Jakarta Republic of Indonesia
Jalan Pulolentut No. 16 Kawasan Industri Pulogadung Jakarta Timur Indonesia
JALAN PUNCAK PERMAI UTARA SURABAYA INDONESIA
Jalan Pupuk Raya No. 43 Balikpapan 76114, Kalimantan, Timur, Indonesia
Jalan R.E. Martadinata No. 13-C Ancol Jakarta 14430
Jalan Ratulangi 47 Kelurahan Setonopande, Kecamatan Kota Kediri, East Java, Indonesia
Jalan Raya Margorejo Indah No. D-104 Surabaya 60237, Indonesia
Jalan Raya Puri Blok C1 No. 33, Jakarta Barat 11610, Indonesia
Jalan S. Syahrir, No. 12B, Jakarta, Indonesia
Jalan Sebandaran I / 6 Semarang 50135 Indonesia
Jalan Sekolah Kencana No. 4 Greenview Apt. Tower A, No. 54 Pondok Indah, Jakarta Selatan Indonesia
JALAN SHINTA INDAH DJAYA RT/014/01 TANJERANG, INDONESIA
Jalan Simprug Golf III/113 Jakarta 122220 Indonesia
Jalan Simpruk Golf XIII/19 Kebayoran Baru Jakarta Selantan Indonesia
JALAN SULTAN AGUNG NO. 18 JAKARTA 12980 INDONESIA 12980
Jalan Sultan Agung No. 18 Jakarta Indonsesia 12980
Jalan Sultan Syahrir No. 7, RT10/RW02 Gondangdia, Menteng Jakart Pusat Indonesia
Jalan Sultan Tirtayasa, No. 14 Bandung 40115 Indonesia
Jalan Sumatra 32 Surabaya 60281 INDONESIA
Jalan Sumatra No. 16 Menteng RT 02 RW 04 Jakarta 10350 Indonesia
JALAN SUMBAWA NO. 12 MENTENG, JAKARTA PUSAT INDONESIA
Jalan Sunter Paradise Raya 1, Blok F16 No. 28, Jakarta 14350, Indonesia
Jalan Suryo No.7 Blok S Kebayoran Baru Jakarta 12180 INDONESIA
Jalan Suwiryo 26, Menteng, Jakarta 10350, Indonesia
Jalan Suwiryo No. 28 Menteng, Jakarta 10350 Indonesia
Jalan Taman Atas No.7-9-11 Baloi Centre-Batam
Jalan Taman Metro Alam IV PL 6 Pondok Indah Jakarta Selatan Indonesia
Jalan Taman Metro Alam IV PL 6, RT 011/RW 016 Pondok Indah, South Jakarta Indonesia
Jalan Taman Sari II/22, RT 005/03 Kelurahan Maphar, Jakarta Barat, Indonesia
Jalan Tanjung No. 28 Gondangia Jakarta Pusat Indonesia
Jalan Tanjung No. 28 Jakarta 10350 Indocnesia
Jalan Tegehsari Jimbaran Bali Indocnesia
Jalan Tembakau III No. 74 A RT. 02/01 Pejaten Timur, Pasar Minggu Jakarta 12510 Indonesia
Jalan Terusan Hang Lekir V No. 18A Kebayoran Baru Jakarta Selatan Jakarta 12220 Indonesia
Jalan Tomang Raya No 5A Jakarta 11440 Indonesia
Jalan Tomang Utara No.3 Jakarta Indonesia
Jalan Tukad Gerinding Gang 1 No. 1 Denpasar Bali Indonesia
Jalan Uluwatu No 1 Tengeh Sari Jimboran, Bali Indonesia
Jalan Wambi No. 27 Bandung Indonesia
Jalan Wambi No. 28 Bandung, Indonesia
Jalan Wambi No. 30 Bandung INDONESIA
Jalan Warung Buncit Raya 49 Mampang Prepatan Jakarta 12740 Indonesia
JALAN WIDYA CHANDRA VII/7 RT008/001 SENAYAN KEBAYORAN BARU, JAKARTA SELATAN INDONESIA
Jalan Wijaya I Blok Q/4 No. 381 N Kebayoran Baru – Jakarta 12170 Indonesia
Jalan Wijaya I Blok Q/4 No. 381 N, Kebayoran Baru Jakarta 12170 Indonesia
Jalan Wijaya Kusuma FF/18 RT 001 RW 006 Rawa Badak Jakarta, Indonesia
JALAN WIJAYAKARTA NO. 1 MAMPANG PRAPATAN JAKARTA SELATAN INDONESIA
Jalan Willis 2B, Semarang, Indonesia
Jalan Zeni G 96 RT/RW 04/06 Kelurahan Cipinang Melayu, Kecamatan Makasar, Jakarta Timur Indonesia
JALAN, KALIANAK BARAT NO 78B – 88 SURABAYA INDONESIA
Jalen Karang Anyar Raya 53-54 Blok D/24 Jakarta 10740
Janur Asri 9, Block QK18, No 12 A, kelapa gading, Jakarta, Indonesia 14240
Jati Barang/16 RT012/RW004 Kel. Jati, Pulo Gadung Jakarta Timur
Jati Padang Baru E-5 PASAR MINGGU Jakarta Indonesia
Jati Padang Poncol/5 Kav.8, RT. 004, RW. 008, Pasar Minggu, Jakarta Selatan Indonesia
Jayakarta Plaza Lt. IV/DB 1, Kakarta 11180 Indonesia
Jelan Kemang Selatan, IC No. 25, Jakarta Selatan Indonesia
Jembatan II Blok C/47 RT.010 RW.002 Pejagalan Penjarinsan, Jakarta Indonesia
Jemur Andayani VI/15, Surabaya Indonesia
Jeruk Garut Raya No. 7 RT/RW : 003/006 Duri Kepa Kebon Jeruk, Jakarta Barat Indonesia
Jeruk Purut Buntu No. 67 RT 004/03, Kel. Cilandak Timur Jakarta Selatan Indonesia
JI A. M. Sangaji No.11 L-M-J Jakarta 10160, Indonesia
Ji Arco Raya No.63 Cipete Jakarta Selatan Indonesia
JI Bougenville No. 16 Flamboyan Baru Padang West Sumatera Indonesia
JI BUKIT HIJAU 2 NO. 2 JAKARTA SELATAN INDONESIAN 12310
JI BUKIT HIJAU 5 NO. 7 PANDOK PINANG JALARTA SELATAN INDONESIA
JI Cibeber I/No.21 Rt003/003 Rawa Barat, Jakarta Selatan Indonesia
Ji Duren Sawit Barh Blokai No 14 Jakarta Timur Indonesia
JI KENCANA PERMAI 5 NO. 48 JAKARTA SELATAN SELATAN INDONESIAN
JI Pangeran Jayakarta 105G Jakarta Indonesia 10730
JI Pertani 1/71, RT008/RW003 Duren Tiga, Jakarta Selatan, Indonesia
JI Sunter Mediterania Block E No. 33 Sunter, Jakarta-Utara 14340 Indonesia
Ji Talang No 3 Jakarta Indonesia
JI TAMAN BUKIT HIJAU NO.37 RT010 RW013PD KEBAYORAN LAMA JAKARTA SELATAN, INDONESIA
JI Taman Patra Raya No. 6 Kuningan , Jakarta 12870 Indocnesia
JI. Borobudur No.6 Menteng – Jakarta Pusat INDONESIA
JI. Bumi Pratama Timur-I R25 Perumahan Bumi Harapan Permai Jakarta 13550 Indonesia
JI. Camar I Blok BA No. 12 A, Bintaro Jaya III Tangerang Indonesia
Ji. DR. Makaliwe Raya No. 39A Jakarta 11450 Indonesia
JI. Gajah Mada No. 13 RT 02/RW 02 Pekanbaru Indonesia
JI. Gereja Theresia 27 Jakarta Indonesia
JI. Gunung Sahari IV No. 1 Jakarta 10610 Indonesia
JI. Harji Samali No. 51 Kalibabta Jakarta Selatan 12740 Indonesia
JI. Harji Samali No. 51 Kalibata Jakarta Selatan 12740 Indonesia
JI. Jend. Sudirman No. 94, Bandar Lampung Indonesia
Ji. Kampung Seng I No. 6 Surabaya, Indonesia
JI. Kenanga 6 Cilandak Jakarta, 12560 Indonesia
JI. Kesari #15 Br Batujimbar Sanur, Bali Indonesia
JI. Kramat No. 25 Rt. 004/ Rw. 007 Kwitang, Senen, Jakarta Pusat INDONESIA
Ji. Kuta Indah 15 Kelepa Gading Jakarta 14240 Indonesia
JI. Lembang No.9 Central of Jakarta Indonesia
JI. M. Kahfi 1/21 Taman Botanik C 14/15, Jagakarsa, Jakarta, Selatan Indonesia
JI. Madrasah Raya No. 7 Cilandak Timur Pasar Minggu, Jakarta Indonesia
JI. Mutiara 12 Pondok Labu Jakarta, 13220 Indonesia
JI. Nirwana 28 Blok H-5 Nirwana Sunter Asrithp III Jakarta-Utara Indonesia 14350
JI. Permata Timur VIII/N-7 Jakarta Timur Indonesia
JI. Pramuka Sari III/12 Jakarta 10570 Indonesia
JI. RS FATMAWATI 31 A JAKARTA, 12430 INDONESIA
JI. RS. Fatmawati No. 15 Kompleks D-Best Blok J-5 Jakarta Selatan 12420 Indonesia
JI. Rs. Fatmawati No. 20 Fatamawati Mas Kav. 2/215 Jakarta 12430 Indonesia
JI. Sisingamangaraja No. 3c Jakarta 12120 INDONESIA
JI. Swakarya Bawah No. 1 RT.001/001 Pondok Labu-Jakarta Selatan, Indonesia
JI. Taman Surya Block IID/8 Jakarta 11520 Indonesia
JI. Tg. Duren Timur No. 27 RT.004. RW.006 Jakarta Barat Indonesia
JI. Walet Permai I No. 25 Pentai Indah Kapuk Jakarta, Indonesia
JI. Widya Chandra XI/3, Kebayoran Baru Jakarta Selatan Indonesia
JI.Letnan Arsyad No.7 Perumnas, Bekasi Bekasi II Indonesia 17144
JI.Sisingamangaraja No.3C, Jakarta 12120, Indonesia
JI> Andong II RT 004/006, Kota Bambu Palmerah Jakarta, Barat Indonesia
Jimerto 2, Surabaya 60272, Indonesia
Jin Bandengan Utara No. 81 Blok B RT 009/016 Penjaringan Jakarta Utara Indonesia
Jin Batu Ceper No. 40 Jarkarta Pusat 1 Indonesia
JIN CENDANA 37/39 MENTENG JAKARTA 10350
Jin Kesehatan No. 26 RT010/RW005 Petojo Selatan Jakarta Pusat Indonesia
Jin Sungai Sambas V11 No.16, Kebayoran Baru, Jakarta Selatan, Indonesia.
JIN TANJUNG ANOM NO. 4 BANDUNG INDONESIA
Jin. Kampung Bali IV No. 32, Jakarta 10250 Indonesia
JIn. Madiun 15 Jakarta INDONESIA
Jin. Pasir Putih 7, No. 3 Ancol Timur Jakarta, Indonesia
Jl Agung Perkasa 6, Block J 1A/34 Jakarta Utara 14350, Indonesia
Jl Alam Elok VII No. 15 Pondok Indah, Jakarta Selantan 12310 Indonesia
Jl Alamanda II Blok E2 no. 14 Kedoya Selatan-Jakarta Barat Indonesia
Jl Alaydrus No. 82 Jakarta Pusat 10130 Indonesia
Jl Alaydrus No. 82 Jakarta Pusat 10130, Indonesia
Jl Alyadrus No. 76 RT 002/02, Petejo Utara Jakarta Pusat Indonesia
Jl Alydrus No. 76 RT 2/6, Gambir Jakarta Pusat Indonesia
Jl Ampera Raya No. 27, RT003, Ragunan, Pasar Minggu, (Depan Gedung Arsip Nasional), Indonesia.
Jl Arteri Mangga Dua Gedung Harco elektronik Superstore Lt. 45, Jakarta Pusat Indonesia
Jl Bangau IV no. 2A, Jakarta 10610, Indonesia
JL BANGKA RAYA 99C, JAKARTA 12720, INDONESIA
Jl Bangka Raya Pela 49 Kebayoran Baru Jakarta Selatan 12730 Indonesia
Jl Batu Ceper No. 18-C Jakarta 10120 Indonesia
Jl Batur Sari No. 37X, Bj Medura, Sanur, Danpasar, Bali INDONESIA
JL Batur Sari, 37X, Sanur, Bali, Indonesia
Jl Batutulis VI No. 39 RT 011/RW003 Kebon Kelapa Jakarta PUS Indonesia
JL BB Cipinang Mura RT. 002/RW:004 Cipinang Mura Jakarts Mura Indonesia
JL Bendungan Hilir Raya Blok G1, No:7 Jakarta-Pusat Indonesia
Jl Berlian I/B-3 Cilandak Barat Jakarta Selatan Indonesia
Jl Biduri Pandan Blok II No. 2, Permata Hijau Jakarta Selatan Indonesia
JL Bisma 12 Blok C1 No. 22 Jakarta INDONESIA
Jl Bukit Golf II, PB 26 RT 012/015 PD Pinang, KBY Lama Jakarta Selatan, Indonesia
Jl Bunga Lili, No. 9 RT 010 / 006, Kel Bintaro Jakarta Selatan Indonesia
JL BUNGUR BESAR NO. 31-A JAKARTA PUSAT INDONESIA
Jl Bungur Besar No. 51 Jakarta 10730 Indonesia
JL BUNGUR BESAR NO. 78 JAKARTA PUSAT INDONESIA
Jl Camar Permai IV/22 Jakarta Indonesia
Jl Canadianti Blok A No. 10 Komplek Bank Prapanca K4eb. Baru Jakarta Selatan Indonesia
Jl Cemara Raya CM 1-2 Grogol, Solo Baru Sukoharjo 57552 Indonesia
Jl Cemp Putih Tengah 17/9 Rt02/08 Kel Cemp Pth Tgh Jakarta Pusat, Indonesia
Jl Cibodas C-14 No. 177 Jati Cempaka Jakarta Indonesia
JL Cihampelas 258A Bandung 40131 Indonesia
Jl Cipaganti No. 63 Bandung Indonesia
Jl Cipaganti No. 92A Bandung Indonesia
Jl Cipinang galur Kulon RT:008/05 Jatinegara Jakarta Tinmur Indonesia
Jl Cisanggiri 1/3 Kebayoran Baru Jakarta 12170 Indonesia
Jl Danau Indah II A2/15, Sunter Jakarta Utara, Indonesia
Jl Delman Asri IX/A 33 RT006/011 Kebayoran Lama Utara Jakarta Selatan, Indonesia
Jl Delman Asri IXA 33-39 RT006/011 Kebayoran Lama Utara Jakarta Selatan, Indonesia
Jl Denpasar III (YBR IV) Blok D, Kav. 4 Jakarta 12950 Indonesia
Jl Dieng No. 6 Semarang INDONESIA
Jl Diponegoro 50 Surabaya, East Java, Indonesia.
JL DR SEMERU III/6 GROGOL, JAKARTA 11450 INDONESIA
Jl Dr Sutomo 56-58, Surabaya Indonesia
JL DRUPADI, NO. 1, BANJAR BASANGKASA SEMINYAK DENPASAR BALI 80361
Jl Duta 2/54, Kelurahan Duri Jakarta Barat 11510 Indonesia
Jl Duta Permai III, No. 1 Pondok Indah Jakarta Selatan 12310 Indonesia
Jl Embong Cerme 25 Surabaya Indonesia
JL Empu Tantular 77, Tanjung Mas, Semarang Utara, Karyanan, Indonesia
JL ERLANGGA III NO.11, SELONG, KEBAYORAN BARU JAKARTA SELATAN 12110 INDONESIA
JL Fajar Indah 11/77 RT 05 RW 07 KEL. Jajar Kecamatan Laweyan Surakarta Indonesia
Jl Fajar Indah 11/77 RT/RW 05/07 Kel Jajar Kecamatan Laweyan Surakarta Indonesia
Jl Gajah Mada 150 A B C Jakarta Pusat Indonesia
JL Gandaapura IV No. 3B Kesiman Tohpati Denpasar 80237 Bali, Indonesia
Jl Gedung Hijau I/48 Jakarta Selatan Indoensia
Jl Gedung Hijau Raya SG 17 Kav 5, Pondok Indah Jakarta Selatan Indonesia
Jl Gelong Baru Tengah No.3A, RT011/RW002 , Tomang, Grogol Petambur, Jakarta Barat, Indonesia
Jl Gg. Langgar No. 24 Jakarta Indonesia
Jl Gotong Royong No. 11 Cipete Jakarta Selatan Indonesia
JL GS Machmud Merchant G.S Sadaraya, RT001/011, Pontianak Saiantan, Indonesia
JL H Jann 1 No. 49 Indonesia
JL H SAABAH NO. 5 CIPETE UTARA-KEBAYORAN BARU JAKARTA SELATAN 12150 Indonesia
JL H Saili F. 51 Indonesia
JL H. Feichruddin, No. 16 Jakarta, Pusat 10250 Indonesia
Jl Hayam Wuruk No. 57 RT02/RW01, Cibodas Baru Tangerang Indonesia
JL HOS COKMAMINOTO NO. 15RT03/04 KABUPATEN KLATEN INDONESIA.
JL HR RASUNA SAID BLOK X-5 KAV 2-3 MENARA KADIN BLDG LANTAI 30 JAKARTA INDOENSIA
Jl Imam Bonjol 52 RT002 RW05 Menteng Jakarta Pusat Indonesia
Jl Janur Elok VI Blok QC 13 No. 9 Jakarta 14240 Indonesia
Jl Janur Hijau III – TI 1 No. 1 Jakarata 14240 Indonesia
JL JATIBARU, NO. 24 JAKARTA 10160 INDONESIA
Jl Jend. Sudirman 1 No. 41 Medan Indonesia
Jl Jeruk Purut No 1B Jakarta, 12560 Indonesia
JL Karmel Vibl G No 12, RT/RW 011/004 Kel. Kebon Jeruk Jakarta Barat Indonesia
Jl Karper K-17A, Cinere Estate Jakarta Selatan, Indonesia
Jl Kartika Utama 29 Kav 5 RT 012/006 Kelurahan Pondok Pinang Jakarta 12310
Jl Kartini V No. 11C, Jakarta Indonesia
JL Kebon Jeruk 111 No.1A-F Maphar Taman Sari Jakarta Barat Indonesia
Jl Kelapa Dua Raya No. 25 RT 06/RW.05 Jakarta 11550 INDONESIA
Jl Kelapa Gading Blk E-106 Cinere Jaksel PT Lorin Indonesia
Jl Kelapa Puan Timur I NB 1/8 Kelapa Gading Permai Jakarta Vtara Indonesia
JL Kelepa Gading Raya No.18 Semaring Indonesia
Jl Kemag Utara IX/9 BlokAI-2 Rukan Tiara Buncit Jakrata 12760 Indonesia
Jl Kemang 5A No. 21 Kemang Jakarta Selatan Indonesia 12730
Jl Kemang Selatan 1E No. 17 Kemang, Jakarta 12730 Indonesia
Jl Kemang Timur No. 36 Jakarta 12730 Indonesia
JL Kenanga No. 50J RT 007/02 Cilandak Timur, Pasar Minggu Jakarta Selatan, Indonesia
JL Kenanga No. 7 Pondok Pinang Jakarta, Selatan Indonesia
JL Kenanga No. 7 Pondok Pinang Jakarta, Selatan, Indonesia
Jl Ki Hajar Dewantara No. 58 Ciputat 15413 Jakarta Selatan Indonesia
JL KINTAMANI 1/21 BUKIT GADING VILLA KELAPA GADING, JAKARTA PUSAT INDONESIA
JL KLP Puyuh VI KJ 10, RT005 RW 019, KLP Gading, Kelapa Gading Jakarta Utara, Indonesia
Jl Kolombo 19 RT 033, RW 007 Terban, Gondokusuman, Yogyakarta 55223 Jakarta Utara, Indonesia
JL Krakatau Vill No. 16 Semarang 50125 Indonesia.
Jl Kramat Kwitang, Kecil No. 5 RT005/RW007, Jakarta Pusat Indonesia
Jl Ks Tubun II no 15, Jakarta, Indonesia
Jl Kusuma Atmaja No. 51 Kelurahan, Menteng Jakarta 10310, Indonesia
Jl Kusuma Atmaja No. 51 Menteng, Jakarta Pusat 10310 Indonesia
Jl Kuta Indah No. 75, Klpgd Brt, Jakarta 14240, Indonesia
JL Laksana Bintan Komp Tanah Mas Blok. A1 Sei Panas Batam 29432
JL LEMBANG 11 MENTENG JAKARTA INDONESIA
Jl Lembang Terusan D-51, Menteng, Jakarta Pusat Indonesia
Jl Malibu Indah Raya Blok F-11 Medan 20157 Indonesia
Jl Mampang Prapatan IV/20 Jakarta 12790 Indonesia
Jl Mangga Besar IX No. 2D Jakarta Indonesia
Jl Mangga No. 4 Panjunan Kudus 59317 Indonesia
Jl Mas Putih 31, Permata Hijau, Jakarta Selatan, Indonesia
Jl Matraman Raya/198 R.T./R.W. 012/006 Kampung Melayu Jakarta Timur Indonesia
Jl Merdeka No. 36, Palembang Indonesia
Jl Metro Kencana 5/16 Pondok Indah Jakarta 12310 Indonesia
JL METRO PONDIK INDAH KAV. IV TH2 RT 010/015 KEL. PONDOK PINANG JAKARTS SELATAN INDONESIA
Jl Mirah Kencana 43 Permata Hijau Jakarta 12210 INDONESIA
JL MURAI 11, NO. 01 R7.18 PALEMBANG, INDONESIA
JL MURAI 11, NO. 01 RT.18 PALEMBANG, INDONESIA
JL Otista Raya No. 39 Cawang Jakarta Indonesia
JL P JAYAKARTA 119A JAKARTA INDONESIA
Jl padang Sidempuan No. 2C/6 Medan
Jl Pajajaran No. 59 Bandung Indonesia
JL PALAPA XV NO 10 PASAR MINGGU JAKARTA SELATAN INDONESIA
JL PALATHAN I/35 KEBAYRON BARU JAKARATN SELETAN INDOESIAN 12160
JL Pandeglang No. 27, R.T./R.W. 001/004 Menteng, Jakarta Pusat Indocnesia
Jl Panglima Polim XIV No. 62B Melawai, Kebayoran Baru Jakarta Selatan Indonesia
Jl Panjunan G-II RT.16 RW.03 Sidoarjo Indonesia
JL Pasir Putih Raya 26 Jakarta INDONESIA
Jl Patal Senayan no 38 Jakarta 12210 Indonesia
Jl Pattimura No. 35, Jakarta, Indonesia
JL PEDURENAN 2A CILANDAK TIMUR JAKARTA SELATAN INDONESIA
Jl Pemuda No. 60 – 70 Surabaya 60271 Indonesia
Jl Perak Blok B-18, 001/012, Grogol Utara Kebayoran Lama, Jakarta Selatan Indonesia
Jl Permata Angkasa No. 15 Jakarta Indonesia
JL PERMATA HIJAU BLOK 1-2 NO.18 JAKARTA INDONESIA 12210
Jl Permata Hijau, Blk B Jakarta Indonesia
JL Permata Mirah, Block T No.5 Permata Hijah Jakarta Selatan 12210, Indonesia.
Jl Perniagaan Barat 26/27 Jakarta Indonesia
Jl Perniagaan Bo. 3 Medan Indonesia
Jl Pertanian Raya Kav DPRD No. 52 Jakarta Indonesia
Jl Peta Selatan NO. 48 Kalideres Jakarta 11840, Indonesia
JL PETOJO DUCLEK II/16, R.T. 012, R.W 007 JAKARTA
JL PINTU KECIL RAYA 40 RT 04/01 ROA MALAKA JAKARTA BARAT INDONESIA
Jl Pluit Kencana V No. 8 Jakarta Indonesia
Jl Pluit Sakti VI/40, Jakarata Utara Indonesia
Jl Pluit Samudera V No. 20 Jakarta Indonesia
JL PONDOK DUTA RAYA BG 111/7 RT 12 RW 14, TUGA, KEC. CIMANGGIS BOGOR INDONESIA.
JL PRIMSMA 2 BLOK B2 NO.33 TAMAN KEDOYA PERMAI JAKARTA INDONESIA
Jl Prof Dr Soepomo No. 44 Jakarta Selantan 12870 Indonesia
Jl Prof Dr Soepomo No. 44 Jakarta, Indonesia
Jl Prof Supomo SH No. 55A RT013/003 Kel. Tebet Barat, Kec, Tebet Jakarata Selatan Indonesia
Jl Prof Yamin No. 34 Menteng, Jakarta Indonesia
Jl Pulo Mas Barat X/25 RT 003 RW 010 Kelurahan: Kayu Putih Kecamatan: Pulo Gadung Jakarta Timur, Indonesia
JL PUNACK GOLF NO. 2 KOMPEK LIPPO KARAWACI JAKARTA INDONESIA
Jl Puri Pesanggrahan I, Blok M Bukit Cinere Indah Indonesia 16514
JL Rajawali Selatan 5 No. 39, Jakarta 10720 Indonesia
Jl Raya Bogor Km28 Pasar Rebo Jakarta 13710 INDONESIA
JL RAYA GUBENG, NO. 100, SURABAYA, INDONESIA
Jl Raya Kertajaya, Indah No. 91, Blok 0207 Surabaya Indocnesia
JL RAYA MANGGA BESAR 58 RT 006/001 TAMAN SARI Jakarta Barat Indonesia
JL RAYA RANCAEKEK KM23 SUMEDUNG Indonesia
Jl Raya Surabaya Mojokerto, KM. 44, Sidoarjo, East Java, Indonesia
JL RAYA TROPODO NO. 126 WARU-SIDOARJO SURABAYA INDONESIA
Jl Rontgen No.4 Bandung 40171 Indonesia
JL ROSALIA 4 BLOK LL NO. 9 JAKARTA INDONESIA
JL Ruby I/28 Blok G Jakarta Selatan Indonesia
JL Rungkut Mejoyo Selatan Blok AM-39, JL Tenggilis Blok AM-39 University of Surabaya Surabaya 60292, INDONESIA
Jl Sanu Indah No. 47 Bukit Gading Vila, Kelapa Gading, Jakarta Utara 14240 Indonesia
Jl Sawo No. 23 Mengteng Jakarta Pusat Jakarta 10330 Indocnesia
JL SEMANGKA RAYA RT 015/02 Jakarta Barat Indonesia
JL SEMOLOWARU TENGAH 9/37 SURABAYA INDONESIA
Jl Simprug Golf 1/176 Jakarta Selatan 12220 Indonesia
Jl Slamet Riyadi No. 450 Solo Indonesia
Jl Subanjo Wingo Pranoto 38-C, Jakarta Barat Indonesia
JL SUMBING NO 5 JAKARTA INDOEDSIA 13720
JL SUMBING NO.5 JAKARTA INDOESIA 13720
Jl Sutan Syahrir No. 27 Jakarta Pusat, Indonesia
Jl Suwiryo No. 45 Jakarta Pusat Indonesia
Jl Talang No. 3 Jakarta
Jl Talang No. 3 Jakarta 10320 Indonesia
Jl Taman Patra XI No. 6 Jakarta 12950 Indonesia
Jl Taman Kedoya Baru D 10/26 Kedoya Selatan-Jakarta Barat Indonesia
Jl Taman Patra II Blok M7/KAV. 11 Jakarta Selatan 12950
Jl Taman Patra II Blok M7/KAV.11 Jakarta Selatan 12950
Jl Taman Radio DLM V/14 RT 006/013 Gandaria Utara Kebayoran Baru Jakarta Selatan, Indonesia
Jl Taman Sari VIII/114, RT 009, RW 006, Maphar, Taman Sari, Jakarta Barat, Indonesia
JL TAMAN TORAM II RT 02/10 KALIDERES JAKARTA BARAT INDONESIA
Jl Tanjung 74 Blitar 66122 Jawa Timur Indonesia
Jl Tanjung Karang R.T./R.W. 03/03 Desa Tanjung Karang, Kudus Indonesia
JL TANJUNG SARI NO.5 SURABAYA INDONESIA
Jl Tasikmalaya No. 23, 10310 Jakarta Indonesia
JL TEBAH 11/9 RT 013/003 GUNUNG JAKARTS SELATAN INDOENSAIN
Jl Thalib II, No. 35A RT 012/05, Kel. Krukut Jakarta Barat Indonesia
Jl Tidore No. 15 Jakarta Pusap Indonesia
JL Trs. Hanglekir II/WG-6 RT.006/08, Grogol Selatan, Keb.Lama, Jakarta Selatan Indonesia
Jl Tukat Balian, 121, Renon Bali Indonesia
Jl Tunjung II No. 12, RT 16/03 Jati Pulo, Jakarta Barat Indonesia
Jl Uluwatu Perumahan Baliview Blok AII/2 Jakarta Selatan Indonesia
Jl Veteran No. 50 Bekasi Selatan INDONESIA
Jl Wahid Hashim 96 Jakarta 10340 Indonesia
Jl Westhoff No. 12 Bandung 40171 Indonesia
Jl Wijayakarta Raya No. 3, Jakarta 12710 Indonesia
JL, Anggrek 12 No. 2 Rt. 001 Rw 04 Karet Kuningan Jakarta Selatan Indonesia
JL, CIDENG TIMUR 62, JAKARTA PUSAT, INDONESIA
JL, KARTIKA UTAMA PU 21, RT/TW 012/016, PONDOK PINANG, KEBAYORAN LAMA, JAKARTA SELATAN, INDONESIA
JL, KH. M MANSYUR BLOK 15A NO. 23-25 JAKARTA PUSAT INDONESIA
Jl, Puri Mutiara Wisma Pertamina #5 Jakarta Selatan 12430 INDONESIA
JL-Melong Kidul No. 51 Bandung 40261 Indonesia
Jl. Cikajang 29 Kebayoran Baru Jakarta 12170 INDONESIA
Jl. Supratman no. 23, Kel. Peunayong, Banda Aceh, Indonesia
Jl. Abdul Muis No. 24 Gedung Wirabuana Lt. Dasar Jakarta 10160 Indonesia
Jl. Abdul Muis No. 80A Petojo Selatan Jakarta 10160 Indonesia
Jl. Agung Perkasa 15 RT009/ RW014 Sunter Agung, Tanjung Priok Indonesia
JL. AGUNG TENGAH II BLOK I.4 NO. 12B JAKARTA UTARA INDONESIA
Jl. Agung Utara Blk 0/15 STS, Jakarta Utara, Indonesia
Jl. Aipda K.S. Tubun HC/12 R.T. 004 R.W.01 Jakarta Indonesia
JL. ALAM ASRI IX/15, SF.3 RT 009/015 PONDOK PINANG JAKARTA SELATAN, INDONESIA
Jl. Alam Segar III/12 RT 007/016 Pondok Pinang Jakarta Selatan Indonesia
Jl. Alam Segar XI No. 7 Pondok Indah Jakarta Selatan Indonesia
Jl. Alam Segar XI/56 Jakarta Selatan Indonesia
Jl. Alamanda CII/19 Sunter Jaya, Jakarta Utara Indonesia
Jl. Alamanda Raya Blk. HB No. 26 Rt:009/002 Pesanggrahan Jakarta Selatan Indonesia
Jl. Alaydrus No. 45A Jakarta Pusat Indonesia
Jl. Aman No. 7, RT 002/02 Kel. MP. Prapatah, Jakarta, Selatan Indonesia
Jl. Ametis 3 No. 60 Permata Hijau Jakarta, Indonesia
Jl. Ampera Raya 18 Jakarta, 12560 Indonesia
Jl. Ancol VIII, No. 1 Ancol Barat Jakarta 14430 Indonesia
Jl. Anggrek Cendrawasih J/4 Slipi, Jakarta Indonesia 11480
Jl. Anggrek Garuda IV/79 Kemanggisan, Jakarta Barat Indonesia
Jl. Angkasa No. 32 Block A1 Jakarta 10610 Indonesia Indonesia
Jl. Angke Jaya II/42 RT 15/03 Angke Jakarta Barat Indonesia
Jl. Angsa III Blk D5/7, Rt/Rw 013/004, Kelurahan Kedoya Selatan, Kecamatan Kebon Jeruk, Jakarta-Barat, Indonesia
Jl. Anjasmoro 59 Surabaya Indonesia
Jl. Antara 41A Jakarta Pusat, Indonesia
Jl. Antara 41A Jakarta, Indonesia
Jl. Anyelir 4/21 RT 002, RW 004 Cedong, Pasar Rebo Jakarta Timur, Indonesia
Jl. Anyelir F/28 RT02 RW04 Pasar Rebo East Jakarta INDONESIA
Jl. Artuna Utara 42A Tanjung Duren Jakarta 11470 Indonesia
Jl. Astana Anyar No. 33 Bandung 40241 In don esia
Jl. Bahtera Permai 2/26 Pantai Indah Kapuk Jakarta 14460, Indonesia
Jl. Baladewa No. 13, RT001/RW003 Duren Sawit, Jakarta Timur Indonesia
JL. BALIKPAPAN RAYA NO.7 JAKARTA
Jl. Bambu Apus Raya Blok J-II No. 189, RT.04, RW.011 Kel. Pondok Bambu, Kec. Duren Sawit Jakarta Timur, Indonesia
Jl. Bandun No. 3A, RT. 013, RW. 005 Menteng, Jakpus, Jakarta Pusat
JL. Bangka XI A/12 RT 002 RW 010, Pela Mampang Jakarta, Selatan Indonesia
Jl. Bank Raya II/2F Prapanca Bawah Jakarta Selatan Indonesia
Jl. Banyuwangi No. 17 Jakarta, Indonesia
Jl. Banyuwangi No. 17 RT 004 / RW 005 JARKARTA INDONEISA
Jl. Batu Tulis Vi No. 39D Rt. 001/RW.003 Kelurahan Kebon Kelapa Jakarta Pusat, Indonesia
Jl. Bdn I No. 26 Cilandak Barat Jakarta Selatan Indonesia
Jl. BDN I/38 RT.011/013 Cilandak Jakarta 12430 Indonesia
Jl. Belanak V/6 RT.012 RW. 007, Kelurahan Jati, Kecamatan Pulo Gadung, Jakarta Timur, Indonesia
Jl. Bendungan Hilir (Benhil) IV No. 15 Jakarta Pusat 10210 INDONESIA
Jl. Bengawan 56, RT004/ RW002 Kel. Darmo, Kec. Wonokromo Surabaya 60241 Indonesia
JL. BENGAWAN 56, SURABAYA, INDONESIA
Jl. Beraban 98 Klod, Kuta Bali Indonesia
JL. BERLIANI I, B6 CILANDAK BARAT JAKARTA SELATAN 12430, INDONESIA
JL. BESAKIH NO. 1, KUNINGAN JAKARTA 12950 INDONESIA
Jl. Biduri Bulan Blok M No.10-11 Permata Hijau Jakarta Indonesia
Jl. Biduri Bulan IX/10.A. RT. 010/003, Kel. Sumur Batu, Jakarta Pusat, Indonesia
Jl. Birah III No. 1 Kebayoran Baru Jakarta, Selatan INDONESIA
Jl. Biru Laut Raya No. 20 Cipinang, Jakarta Timur 13340 Indonesia
Jl. Bisma VI Block B15 House C8 Sunter Jakarta Utara Indonesia
Jl. Blandongan 28 D Jakarta Barat Indonesia
Jl. Bongas II, Blk E7 No. 19 Jatiwaingin Asri, Pndk Gede Bekasi, Jawa Barat 17411 Indonesia
Jl. Boulevard Raya WB2/32 RT011/RW016, Kelapa Gading Timur Jakarta Utara Indonesia
Jl. Brawijaya II/9 RT. 003/002 Pulo-Kebayoran Baru Jakarta Selatan Indonesia
Jl. Bromo 6 Malang Indonesia
Jl. Brumbungan No.58 Semarang Indonesia
Jl. Btanghari No.23-B RT.006 RW.003 Cideng, Jakpus Indonesia
JL. Buana Pesanggrahan I/16 Bukit Cinere Indah Kav. ON 10 jakarta Selatan
JL. BUDI MULIA, NO. 8, RT 003 RW 004, INDONESIA
Jl. Budi Sari III No. 19 Cidadap, Bandung Indonesia
Jl. Bukit Gading Raya Block C, No. 1 Komp Gading Permai Jakarta 14240 Indonesia
Jl. Bukit Golf 1 Sektor VI Blok B No. 11 Bumi Serpong Damai 15310 Jakarta, Indonesia
Jl. Bukit Golf Utama Kav. PA 27 Pondok Indah Jakarta 12310 Indonesia
Jl. Bukit Golf Utama Kav. PA 27 RT012/015, Pondok Pinang Jakarta Selatan Indonesia
Jl. Bukit Golf Utama PA No 27 RT000/RW003 Kelurahan Pondok Pinang Kecamatan Kebayoran Lama South Jakarta INDONESIA
JL. Bukit Hijau 9/14 Pondok Indah Jakarta Selatan Indonesia
Jl. Bukit Kumala No. 8 Bukit Sari, Semapang Indonesia
JL. BUKIT PAKAR TIMUR 110 RT 04 RW O3 DESA CIBURIAL KEC. CIMENYAN KAB. BANGDUNG Indonesia
Jl. Bukit Pakar Timur 110 RT04 RW03 Desa Ciburial Kec. Cimenyan Kab. Banguang 40198, Indonesia
Jl. Bukit Pakar Utara No.7 (Dago Pakar) Bandung, Indonesia
Jl. Bumi Asih IV A.5 Jakata Selatan Indonesia
Jl. Buncit Raya Ujung RT 003/005 Jati Padang Jakarta Selatan Indonesia
JL. BUNGUR BESAR NO. 78-A JAKARTA PUSAT INDONESIA
Jl. Bungur Besar No. 79 Kemayoran, Jakarta Pusat Indonesia
JL. BUNGUR BESAR NO. 81 JAKARTA PUSAT INDONESIA
JL. BUNGUR BESAR XIII/83B, RT006/RW001 KEMAYORAN, JAKPUS, JAKARTA INDONESIA
Jl. Bungur No. 2, Bangka Jakarta Selatan Indonesia
Jl. By Pass Ngurah Rai No. 888 Br. Kelan, Tuban Kuta, Bali Indonesia 80361
Jl. Cahaya D6/20-21, RT001/RW004, Kemb. Selatan Kembangan, Jakarta Barat, Indonesia
Jl. Camar Elok V No. 35 Pantai Indah Kapuk Jakarta Indonesia
Jl. Camar Permai I No. 35 Kapuk Utara, Penjaringan Jakarta Utara Indonesia
Jl. Canadianti No. 16 RT 001/RW008 Kel. Pela Mampang Jakarta Selatan
JL. Capitaku IV/304 Kebayoran Baru Jakarta Selatan Indonesia.
JL. Caringin Utara I No. 31, Cilandak Jakarta Selatan 12430, Indonesia
JL. Caringin Utara Kav. 34 RT15/10 Cilandak Barat, Jakarta Selatan 12430 Indonesa
JL. Caringin Utara No. 31 Cilandak Barat Cilandak Jakarta Selatan 12430 Indonesia
JL. CASABLANCA NO. 1, APARTMENT PURI CASABLANCA TOWER C 2501, KUNINGAN JAKARTA SELATAN 12870 INDONESIA
JL. CC NO. 1, CENGKARENG BARAT JAKARTA BARAT INDONESIA
Jl. Cedung Pinang SMO5 Pondok Indah Jakarta Indonesia
JL. Cemara Boulevard G1-23 Deli Serdang 20371 Medan Indonesia
Jl. Cempaka No. 19 RT 04/01 Kel Jatipulo Jakarta Barat Indonesia
Jl. Cempaka Putih Barat 21 No. A-6, RT 006 RW 012 Kelurahan Cempaka Putih Brt Jakarta Pusat, Indonesia
Jl. Cempaka Putih Timur 5A/3 RT 012/RW 007, cempaka Puith Timur, Jakarta
JL. CEMPAKA PUTIH TIMUR IV B/8 JAKPUS 10510 INDONESIA
Jl. Cempaka Putih Timur IV No. 6 Jakarta 10510 Indonesia
Jl. Cibitung I / No. 3 Kebayoran Baru Jakarta Selatan INDONESIA
Jl. Cibitung I No. 3 Rt.012 Rw. 004 Petogongan – Kebayoran Baru South Jakarta, Indonesia
JL. CIBITUNG I/NO. 3 KEBAYORAN BARU JAKARTA SELATAN INDONESIA
Jl. Cidadap Girang Baru No. 3 (Jl. Setia Budi) Bandung, Indonesia
Jl. Cideng Timur No. 55 Jakarta Indonesia
Jl. Cigondewah Girang RT 02/32 Cimahi Bandung Indonesia
JL. CIGONDEWAH GIRANG RT. 02/32 CIMAHI INDONESIA
Jl. Cigondewah Girang, RT07132, Bandung Indonesia
Jl. Cijerah Cigondewah Blok Suci No. 16, Cimahi Bandung, Indonesia
Jl. Cijerah Cigondewah Blok Suci, No. 13 Cimahi Bandung, Indonesia
Jl. CijerahCigondewah Blok Suci No. 16, Cimahi Bandung, Indonesia
JL. Cikajang No. 29 RT 001/005 Petogogan, Kebayoran Baru Jakarta Selantan Indonesia
Jl. Cikini No. 2 Jakarta Indonesia
Jl. Cikini Raya 24 Menteng, Jakarta Pusat INDONESIA
Jl. Cikini Raya No. 24 Jakarta Pusat Indonesia
Jl. Cilandak Tengah No. 97 Jakarta Selatan
Jl. Cililin II No. 8A, RT. 010, RW. 006 Petogogan, Kebayoran Baru Jakarta Selatan, Indonesia
Jl. Cilimblileuit No. 184, Bandung, Indonesia
Jl. Cimanuk No. 24 Bandung, Indonesia
Jl. Cinere No. 14 Rt 005/006 Pondok Labu Jakarta Selatan Indonesia
Jl. Ciniru 1 No. 10, RT006/003 Rawa Barat, Kebayoran Baru Indonesia
Jl. Ciniru 6/15, Keboyaran Baru Jakarta Selatan, Indonesia
Jl. Cipaganti No. 63, Bandung, Indonesia
Jl. Cipinang Cempedak II No. 10, Jakarta Indonesia
JL. CIPINANG CEMPEDAK II/NO. 41 JAKARTA TIMUR INDONESIA
JL. Cipinang Elok X-39 Rt. OT/010 Kel Cipinang Minara Jakarta Timur INDONESIA
Jl. Cirendeu Permai raya Kav. BB Cilandak-Lebak Bulus Jakarta Selatan Indonesia
Jl. Cirendeu Permui Raya Kav. BB Cilandak-Lebak Bulus Jakarta Selatan Indonesia
Jl. Cisatu 1/2, Ciumbuleuit Bandung, Indonesia
Jl. Citra 3 Block B8 No. 9 Pegadungan, Kalideres Jakarta Indonesia
JL. CITRAYUDA IV No. 204, INDONESIA
Jl. Ciumbuleuit I, No. 2, Bandung, INDONEISA
Jl. Ciumbuleuit RT/RW. 01/07 Kel. Ciumbuleuit Kec. Cidadap, Bandung Indonesia
Jl. Ciumbuleuit, No. 189 Bandung, Indonesia
Jl. D No. 23 Kav. Polri, RT.003/03 Kel. Ragunan Jakarta Selatan Indonesia
Jl. Daan Mogot Km. 18, Tangerang 15122 Indonesia
Jl. Daan Mogot No. 165 Jakarta-11520, Indonesia
Jl. Daan Mogot Raya No. 234 Jakarta Barat 11510 Indonesia
Jl. Dabo Lama No. 01/06, Kelurahan Dabo, Kelurahan Singkep, Kabupaten Lingga, Propinsi Kepulauan Riau, Indonesia
Jl. Damai Musyawarah No. 3A RT 003/03 Pondok Labu Jakarta Selantan 12450 Indonesia
Jl. Danau Agung Utara, Block G-1 No. 22, Jakarta 14350, Indonesia
JL. Danau Biru No. 105 Tangerang, Indonesia
JL. DANAU PERMAI BLK C3/9 JAKUT INDONESIA
Jl. Darat No. 61A/37 Medan 20153 North Sumatra Indonesia
Jl. Darmawangsa VI No. 25 Kebayoran Baru Jakarta 12160
Jl. Darmo Harapan Utara 6 EW 18 Surabaya 60165 INDONESIA
Jl. De. Stb. Panggabean No. 55 Kelurahan Aek Habil Sibolga 22533-Sumatra Utara Indonesia
Jl. Demak 138 / Demak Timur 34A Surabaya 60172 Indonesia
Jl. Denpasar I No. 2, RT 001/002 Kuningan Timur Jakarta Selatan Indonesia
Jl. Denpasar IV No. 5 Kuningan, Jakarta 12950 Indonesia
Jl. Denpasar Raya Bl. E/6, Rt. 1/2 Kuningan Jakarta Selatan
Jl. Deperdag III/G-11 Jakarta Selatan Indonesia
Jl. Dharmahusada Indah Timur 16 / 16 (J-81B) Surabaya, Indonesia
Jl. Dharmahusada Indah Timur I/M-72 Surabaya
Jl. Dharmawangsa VII No. 7 Kebayoran Baru Jakarta 12160
Jl. Diponegoro No. 46 Jakarta 10310 Indonesia
Jl. Diponegoro No. 46 Jakarta 10310, Indonesia
Jl. Diponegoro No. 66 Jakarta 10320 Indonesia
Jl. Dr. Cipto 18 Surabaya Indonesia
Jl. Dr. CIPTO 3 Surabaya, Indonesia
Jl. Dr. Kusumaatmaja No. 5 RT. 009 / RW.004 Kelurahan : Menteng Jakarta Pusat Indonesia
Jl. DR. Muwardi I/35 E, RT 001 RW 004 Kelurahan Grogol, Kecamatan Grogol Petamburan Jakarta Barat, Indonesi
Jl. Dr. Sahardjo No. 123 A, Jakarta 12960 Indonesia
Jl. DR. Saharjo 246 Jakarta 12870 Indonesia
Jl. Dr. Saharjo No 96A Jakarta 12960 Indonesia
Jl. Dr. Supomo No. 53A, Rt/Rw 001/012 Kelurahan Mangkubumen Kecamatan Banjarsari, Surakarta, 57139 Indonesia
Jl. Dr. Sutomo 56 Surabaya INDONESIA
Jl. Dr. Sutomo 58 Surabaya INDONESIA
Jl. Dr. Sutomo, No. 6, Bandung, Indonesia
Jl. Dukuh Kupang Barat 2/26-28 Surabaya, Indonesia
JL. DURIAN BARAT III NO. 2 JAGAKARSA, JAKARTA 12550, INDONESIA
JL. DURIAN BARAT III NO. 2, JAGAKARSA, JAKARTA 12550 INDONESIA
Jl. Duta II/C-61 RT02/07 Kel. Duri Kepa Jakarta Barat Indonesia
Jl. Duta Indah II/6 RT001/014 Pondou Pinang Jakarta Selatan Indonesia
Jl. Duta Niaga Raya No. 25 Pondok Indah Jakarta 12310 Indonesia
Jl. Duta Niaga Raya No. 25 RT003/RW014, Pondok Pinang Jakarta Selatan Indonesia
Jl. Duta Permai III/6 Jakarta Selatan 12310 Indonesia
Jl. Duyung Gang 1/3 X Sanur Bali 80288 Indonesia
Jl. Dwijaya III/1 Gandaria Jakarta Selatan Indonesia
Jl. Elang Thainesia A3/5 Jakarta Timur Indonesia
JL. ERLANGGA 4 NO. 6 JAKARTA 12110 INDONESIA
Jl. Fatmawati No. 15 Kompleks D Best – Blok G 38 Jakarta 12420 Indonesia
Jl. Flores 3, Bloit L3/18 Nusa Loita Bumi Serpong Damai Indonesia
Jl. Gading Elok Utara I FGII/ii Jakarta Utara Indonesia
Jl. Gading Kirana Timur 1, Blok B2 No. 38, Kelapa Gading, Jakarta 12420
JL. GADING KIRANA TIMUR IV / BLOK H4 NO. 1, JAKARTA UTARA, KELAPA GADING INDONESIA
Jl. Gading Riviera I Block PF 22 No. 3 Pegangsaan Dua Jakarta Utara Indonesia
Jl. Gajah Mada No. 11 RT5/III Mojopanggung, Banyuwangi 68425 Indonesia
Jl. Gajah Mada No. 119 RT 15/08 Keagungan Jakarta Barat, Indonesia
Jl. Galuh 11/18, RT003/001 Selong, Jakarta Selatan, Indonesia
Jl. Galuh II/8 Kebayoran Baru Jakarta 12110 Indonesia
Jl. Gandapura 39A Bandung 40113 Indonesia
Jl. Gandaria II No. 5 RT009/001 Kramat Pela Jakarta Selatan Indonesia
Jl. Garden I, No. 3 Kedoya Garden Jakarta 11520 Indonesia
Jl. Garut #9, Menteng Jakarta, Indonesia
Jl. Garut 23 Menteng Jakarta Pusat 10310 INDONESIA
Jl. Garut No 12 Menten g Jakarta Pusat, Indonesia
Jl. Garut No. 12, Menteng Jakarta Pusat, Indonesia
Jl. Gatot Subroto Kav 35-39, Jakarta 10210, Indonesia
Jl. Gembong 2-16, Komplex Wisma Gemini Block C-8 Surabaya Indonesia
Jl. Gereja No. 17 Cilandak Barat Jakarta 12430 INDONESIA
Jl. Gomet Riyadi 356A TR01/04 Punumping Surhkarta, Indonesia
JL. Graha Family Block G-7 Surabaya, Indonesia
Jl. Griya Cantik, Blok K1 No. 8 RT. 008/RW. 020, Sunter Agung Kecamatan Tanjung Priok Jakarta Utara – Indonesia
Jl. Griya Mustika F No. 5 Kelurahan Sunter Agung Kecamatan Tanjung Priok Jakarta Utara, Indonesia
Jl. Griya Sentosa Blok N No. 42 RT006 RW.020 Kel Sunter Agung Kec Tanjong Priok Jakarta Utara Indonesia
Jl. Gunung Gede No Bogor 16151 Indonesia
JL. GUNUNG GEULIS NO. 11 TAMAN BROMO, LIPPO KARAWACI TANGERANG, INDONESIA
Jl. Gunung Indah II No. 18 Cirendeu Ciputat Jakarta 15419 INDONESIA
Jl. Gunung Sahari II/No. 4C Jakarta 10610
Jl. Gunung Sahari IV/No.1 Rt 07/07 Jakarta 10610
Jl. Gunung Sahari VI/24 Jakarta Indonesia
Jl. Gunung Sahari XI No. 74 RT. 009, RW. 003 Jakarta 10720 Indonesia
Jl. Guru Mughni No. B3 Karet Kuningan Jakarta Selatan 12930 Indonesia
JL. H Adam Malik No. 50 Medan Barat Indocnesia
JL. H Saabah No. 5 Cipete Utara-Kebayoran Baru Jakarta Selatan 12150, Indonesia
JL. H. Ahmad Sobana S>H> No. 77 Bogor, Indonesia
Jl. H. Buang I No. 12 Jakarta 12250 Indonesia
Jl. H. Buang I No. 12, Ulujami, Pesanggrahan, Jakarta 12250 Indonesia
Jl. H. Mandor No.40A Jakarta Selatan Indonesia
Jl. H. Muhi 37 RT 011/011 Pondok Pinang Jakarta Selatan Indonesia
Jl. H. Murtadho IV / A 124 RT.004, RW.006, Paseban, Jakarta Pusat Indonesia
Jl. H. Saaba 9A, Cipete Utara Jakarta Selatan Indonesia 12150
Jl. Hadi Agus No. 72 Menteng Jakarta Pusat Indonesia
Jl. Haji Agus Salim No. 94 Menteng, Jakarta 10350 Indonesia
JL. HAJI BALI NO. 16 MAKASSAR INDONESIA
Jl. Haji Ismail Saleh No. 2 Makassar Indonesia
Jl. Hang Lekiu III/4 Kebayoran Baru Jakarta Selatan Indonesia
Jl. Haryono MT No. 105, Medan Kota, Indonesia
Jl. Hasanuddin No. 22 LK. I Kisaran Indonesia
Jl. Hayam Wuruk No. 5/6B Jakarta 10120 Indonesia
Jl. Hos Cokroaminoto No. 54 Jakarta, Indonesia
Jl. Imam Bonjol 202 Semarang 50132 Indonesia
Jl. IMAM Bonjol 70 Jakarta
JL. IR. H. Juanda I No. 22G Medan Polonia, Indonesia
Jl. Ir. Haji Juanda 22, P.O. Box 2934, Jakarta Indonesia
Jl. Ir. Haji Juanda No. 39 Medan, Indonesia
JL. IRIAN NO. 9 MENTENG, JAKARTA PUSAT INDONESIA
Jl. Iskandarsyah 11 No. 85 Melawai-Kebayoran Baru Jakarta Selatan Indonesia
Jl. Jambu No. 12 Gondangdia, Jakarta Pusat – Indonesia
Jl. Janur Elok VI Blok QC-13 No. 9 Jakarta Indonesia
Jl. Janur Elok VIII Blok QG 4/5 Jakarta Utara Indonesia
Jl. Janur Kuning III NH 178 RT009/RW015, KLP, Gading Timur Jakarta Utara Indonesia
Jl. Jatibaru, No. 24, Jakarta 10160, Indonesia
JL. Jatibaru, no.24, Jakarta 10169 INDONESIA
Jl. Jatiroto No. 135A RT 010 RW 012 Jatiwaringin Kec. Pondok Gede, Bekasi, Indonesia
Jl. Jawara 27, Kemang Timur RT:007/RW:003 Bangka Mampang Prapatan, Jakarta Selatan Indonesia
Jl. Jelambar Ilir Grogol Petamburan Jakarta Barat Indonesia
Jl. Jelambar Utama Raya Blok D/11 Jakarta Barat 11460 Indonesia
JL. JEMBATAN III NO. 36 DA RT001/RW016, PENJARINGAN Jakarta Utara, Indonesia
Jl. Jend. Sudirman, Kav. 29-31 Wisma Metroplitan I., Lantai 3A Jakarta Selatan 12920 Indonesia
Jl. Jenggala I No. 5, Kebayoran Baru, Jakarta Selatan, Indonesia
Jl. Johar No. 1A Jakarta Pusat 10350 Indonesia.
Jl. Johar No. 1A Menteng, Jakarta 10350
Jl. Jombang Raya Blok C NO. 101 Bintaro Sector 9 Tangerang – Indonesia
Jl. Juanda III No. 38 Jakarta 10120 Indonesia
Jl. K 1 No. 11, Rt. 010/03, Cipinang Muara Jakarta Timur
Jl. K. H. Hasyim Ashari 11D-F Jakarta Pusat, 10730 Indonesia
Jl. K. H. Moh Mansyur 208-214 Jakarta 11210 Indonesia
Jl. K.H. Hasyim Ashari, No. 11, Jakarta Pusat, Indonesia
Jl. K.S. Tubun II C No. 28 B Slipi Jakarta 11410 Indonesia
Jl. Kalianda No. 6 Medan, Indonesia
Jl. Kalibata Tengah No.4, RT.002, RW.007 JAKARTA SELATAN, INDONESIA
Jl. Kalimantan No. 10, RT 4/RW 1, Kelurahan Merdeka, Bandung
Jl. Kaliwaran 158 Surabaya Indonesia
Jl. Kampar No.9 Cideng, Gambir Jakarta, Pusat Indonesia
Jl. Kapt. Mauliana Lubis No. 3-U R.T/R.W:000/000 Kel. Petisah Tengah Kecamatan:Medan Petisah Kota : Medan 20112, Indonesia
Jl. Kapt. Mauliana Lubis No. 3-U RT/RW : 000/000 Kel. Petisah Tengah Kecamatan : Medan Petisah Kota : Medan 20112 Indonesia
Jl. Kapt. Mauliana Lubis No. 8-T R.T/R.W:007/005 Kel. Petisah Tengah Kecamatan: Medan Petisah Kota: Medan 20112, Indonesia
Jl. Kapt. Mauliana Lubis No. 8-T RT/RW : 007/005 Kel. Petisah Tengah Kecamatan : Medan Petisah Kota : Medan 20112 Indonesia
Jl. Kapten Tendean 48 (Hegar Manah) Bandung Indonesia
Jl. Kapuk Kamal Raya No. 23 Jakarta – 14470 Indonesia
Jl. Kapuk Kamal Raya No.23 Jakarta 14470 – Indonesia
JL. KARANG ASEM III/6-8 RT 008/02, KUNINGAN TIMUR JAKARTA SELATAN, INDONESIA
Jl. Karang Asem Tengah No. 18 Jakarta Selatan 12950 Indonesia
Jl. Karang Asem Utara C.4/34 RT.007/02 Kel. Kuningan Timur Kec. Setia Budi Jakarta Selatan, Indonesia
Jl. Karang Asem Utara C4 No. 34 RT007/002 Kelurahan Kuningan Timur Kecamatan Setia Budi Jakarta Selatan 12560 Indonesia
JL. KARANG MULIA A7 – 22 LEBAK BULUS, SOUTH JAKARTA INDONESIA
Jl. Kartanegara No. 31 Selong, Jakarta Selatan Indonesia
Jl. Kartini 7A/8 Jakarta Pusat Indonesia
Jl. Kartini IV, No. 7 Jakpus, Jakarta INDONESIA
Jl. Kartini Raya 64/65 C9 Jakarta Pusat Indonesia
Jl. Kartini Raya No. 52E, RT 010/004 Kel Kartini, Jakarta Pusat Indonesia
Jl. Karya Sarana No. BL B/28, RT/RW 001/013 Jl. Buaran 2, Klendar, Jakarta Timur 13470, Indonesia.
Jl. Kaveling Polri Block G No. 53B Jagakarsa, Jakarta Selatan 12520 Indonesia
Jl. Kavling Polri Bloke E/1239 Rt/Rw 001/002, Kel. Jelambar Kec. Grogol Jakarta Indonesia
Jl. Kawatan 4/9, Surabaya, Indonesia
Jl. Kayumas Utara B-12A, RT 001/RW007, Keluraban Kuningan Kecamatan Semarang Utara Senarang Indonesia
Jl. Kdm. Ilir Barat Permai Blok D. 61 RT.11 RW.03 24 Ilir Palembang Indonesia
Jl. Keagungan, No. 75 RT. 014/ 003, Keagungan Jakarta Barat Indonesia
Jl. Kebangkitan Nasional No. 48, RT001/RW001 Kelurahan Sriwedari, Kecamatan Laweyan Surakarta 57141, Indonesia
Jl. Kebon Jeruk Baru A1/2 Jakarta Barat Indonesia
Jl. Kebon Kacang 35/9, RT 009, RW 004, Jakarta Pusat, Indonesia
Jl. Kebon Kosong Gang XX. Kebon Kosong Jakarta Pusat Indonesia
Jl. Kebon Sirih Barat VI No. 7, RT.013/RW.002 Kebon Sirih, Jakarta Pusat 10340 Indonesia
Jl. Kebon Sirih No. 25-27, RT/RW 002/001 Babakan, Ciamis, Sumur Bandung Indonesia
Jl. Kebun Karet No. 623 RT20, Palembang Indonesia
Jl. Kedungdoro 60, 10th Floor Surabaya 60251 Indonesia
JL. KELAPA ASRI I BLOKQJII NO.3 KELAPA GADING JAKARTA, UTARA INDONESIA
Jl. Kelapa Kuning Raya Blok A1 No. 23 Perumahan Pondok Kelapa Indah Kalimalang Jakarta 13450 Indonesia
Jl. Kelapa Molek IV/29 Jakarta Utara Indonesia
Jl. Kelapa Molek VI S 2/14 Jakarta Utara Indonesia
JL. KELAPA NIAS PB 1/6 KELAPA GADING INDONESIA
Jl. Kelapa Sawit IX B6. 2/OP RT 09 RW 13, Pakulonan Barat Curug Tangerang, Indonesia
Jl. Kelapa Sawit V, Blok AB, No. 8 RT/RW 008/017, Kelapa Gading Timur Kelapa Gading, Jakarta Utara Indonesia
JL. KEMANG 5A NO. 21 KEMANG, JAKARTA SELATAN INDONESIA 12730
Jl. Kemang Dalam 11 No. L7 Jakarta 12730 Indonesia
Jl. Kemang Dalam X No. M-4, Kemang Jakarta Selatan Indonesia
Jl. Kemang IV No. 23B Jakarta 12730 Indonesia
JL. KEMANG SELATAN IC NO. 25 JAKARTA 12730 INDONESIA
Jl. Kemang Selatan VIII No. C8 Kemang Jaya Jakarta Selatan Indonesia
Jl. Kemang Selatan VIII/C8 Kemang Jaya Jakarta 12730 Indonesia
Jl. KEMANG TIMUR I NO.1 JAKARTA 12730 INDONESIA
Jl. Kemang Timur Raya No. 1 Jakarta 12730 Indonesia
Jl. Kemang Timur V No. 12A, Kemang Jakarta INDONESIA
JL. Kemang Timur V/28 Jakarta 12370 Indonesia
Jl. KEMANG TIMUR V/B3 KEMANG JAKSEL JAKARTA 12730 INDONESIA
Jl. Kemang Utara VII No. 6 RT03/04 Mampang Prapatan Jakarta Selatan 12730 Indonesia
Jl. Kemang Utara VIII/45G JAKARTA SELATAN Indonesia
Jl. Kemanggisan Utama V/16 RT003/RW007, Palmerah Jakarta Barat Indonesia
Jl. Kembang Harum II C6/6 Kelurahan Kembangan West JAKARTA
JL. KEMBANG SAKTI I B1/16 PURI INDAH JAKARTA BARAT 11610 INDONESIA
Jl. Kembang Sepatu No. 20 Senen, Jakarta Pusat Indonesia
Jl. Kembangan Baru, RT 08/03 Kembangan Selantan Jakarta Barat, Indonesia
Jl. Kemuning No. 39 RT.008/RW.006, Kelurahan Pejaten Kecmantan Pasar Minggu, Jakarta Selatan INDONESIA
Jl. Kenanga Kav. 23 No. D-1, Ampera, Kemang Jakarta, Indonesia
Jl. Kenanga No. 50 Cilandak Timur, Pasar Mingu Jakarta Selatan Indonesia
Jl. Kenanga No. 50J RT007/02 Cilandak Timur, Pasar Minggu Jakarta Selatan, Indonesia
Jl. Kenanga No. 71 Cilandak Timur Jakarta Selatan 12560 Indonesia
Jl. Kenanga No. 71 Jakarta Selatan 12560 Indonsesia
Jl. Kenanga R.T./R.W. 007/002 Clilandak Timur Pasar Minggu, Jakarta Selatan
Jl. Kenanga Terusan No. 300 Cilandak Timur Jakarta 12560 Indonesia
Jl. Kencana Indah III Blok JII No.38 Puri Kencana, Jakarta Barat INDONESIA
Jl. Kencana Indah III, Blok JII No.38 Puri Kencana Jakarta Barat INDONESIA
JL. KENCANA PERMAI 7 NO. 6 PONDOK PINANG JAKARTA SELATAN 12310 INDONESIA
Jl. Kencana Permai II No.8 Pondok Indah Jakarta 12310 Indonesia
Jl. Kencana Permai V No. 7 Pondok Pinanng Kebayoran Lama, Jakarta Selatan 12310 INDONESIA
Jl. Kencana Permai VI/7 RT 001/RW 015, Pondok Pinang Kebayoran Lama Jakarta Selatan, Indonesia
Jl. Kencana Permai VII/9 RT001/015 Pondok Pinang KBX Lama Jakarta Indonesia
Jl. Kenrinci 91, Block J Cinere Rt/Rw 1605, Kel Limo, Kec. Limo Depok Indonesia
JL. Kenrinci 93, Blok J Cinere Rt/Rw 16/05, Kel. Limo Kec. Limo Depok Indonesia
Jl. Kentang No. 12A Jakarta Indonesia
JL. KERTANEGARA NO. 2A JAKARTA 12180 Indonesia
Jl. Kesehatan 1/2, Jakarta 10160 Indonesia
Jl. Kesehatan 1/4 007/006 Petojo Selatan, Gambir Jakarta Pusat, Indonesia
Jl. Kesehatan 1/4 Gambir, Jakarta Pusat Indonesia
Jl. Kesehatan 8 No. 11 Jakarta 10160 Indonesia
Jl. Kesehatan I No. 2 RT011/RW006 Petojo Selatan Jakarta Pusat Indonesia
Jl. Kesehatan III No. 33 Petojo Selatan Jakarta Pusat Indonesia
Jl. Kesehatan III/33 Jakarta Pusat Indonesia
JL. KESEHATAN NO. 26 RT010/RW005 PETOJO SELATAN JAKARTA PUSAT INDONESIA
Jl. Keselamatan Gg Sadar No. 15 RT 010 RW 003 Kelurahan Manggarai Selatan-Tebet Jakarta Selatan Indonesia
Jl. Ketapang II No. 122 RT. 03/RW 15 Kel. Baktijaya Kec. Sukmajaya, Depok 16418 Indonesia
Jl. KH. Hasjim Ashari No. 37 Jakarta Pusat Indonesia
JL. KHM Mansyur 150 Jakarta Indonsia
Jl. KHM. Mansyur 116, RT005/RW004 Semampir, Surabaya 60151 Indonesia
Jl. Kiputih No. 29 RT. 05/05 Cidadap Bandung Indonesia
Jl. Kis. Mangunsarkoro No. 45 Jakarta 10310 Indonesia
Jl. Klampis Indah 111/10 (Blok C-4) Surabaya 60117
Jl. KLP Nias IX PB 19/15, Pegangsaan Dua, Kelapa Gading, Jakarta Timur Indonesia
JL. KLUNGKUNG 46 JAKARTA 12950 INDONESIA
Jl. Kolombo 19 Yogyakarta Terban, Gondokusuman Yogyakarta 55223 INDONESIA
Jl. Komplek PLN RT001 RW009 Kel. Cililitan, Kramat Jati Jakarta Timur Indonesia
Jl. Komplex Sunrise Garden No. BL 3S/1, Jl. Surya Mandala, Kedoya Utara, Jakarta Barat 11520, Indonesia
Jl. Kramat Bunder No. 25 Jakarta Pusat Indonesia
Jl. Kramat Raya No. 43 Jakarta 10450, Indonesia
Jl. Kramat VI Dalam No. 2 Jakarta Pusat Indonesia
JL. KREKOT JAYA BLOK E 16 JAKARTA 10710 Indonesia
Jl. Kristal Blok H/20 Kebayoran Lama Jakarta 12210 Indonesia
Jl. KS TUBUN II/15 Jakarta Indonesia
Jl. Kucica VIII Blok JF 1-7, RT 13/05 Pondok Pecung TANGERANG
Jl. Kupu – Blok 18 No. 14 RT002/RW007, Kel. Mekarsari Kec. Tambun Selatan, Bekasi Indonesia
Jl. Laboratorium 11/8 Medan Indonesia
Jl. Labu No. 1 A/3 Medan 20153 Sumatra Utara Indonesia
Jl. Lamandau Raya No. 5 Kebayoran Baru Jakarta 12130 INDONESIA
JL. Lautze No. 31A, RT/RW 012/05, Pasar Baru, Jakarta, Indonesia
JL. LEBAK BULUS INDAH H-1 CILANDAK, JAKARTA SELATAN INDONESIA
Jl. Lebak Bulus IV/7A Cilandak Barat Jakarta Selatan Indonesia
Jl. Lembang No. 8 Menteng Jakarta 10310 Indonesia
Jl. Letjend Suprapto No.45 Pontianak Indonesia
Jl. Lima Iv No. 35A Jatibening 2, Pondok Gede Bekasi 17412 Indonesia
Jl. Listrik #7 Medan 20112 Indonesia
Jl. Lombok No. 56 Jakarta Pusat Indonesia
Jl. Lumajang No. 2 Jakarta Pusat Indonesia
Jl. Lumajang No. 5 Jakarta 10310 Indonesia
Jl. Madium No. 15 Menteng, Jakarta Pusat INDONESIA
Jl. Mahoni No. 17, Rt/Rw 005/008 Kelurahan Bungur, Kecamatan Semen, Jakarta-Pusat, Indonesia
Jl. Majapahit No. 16 Room 321 Petojo Selatan Jakarta Pusat INDONESIA
Jl. Malang No 7 Menteng Jakarta Pusat Indonesia
Jl. Malang No. 3, RT07/RW07, Menteng Jakarta 10310, Indonesia
Jl. Mampang Prapatan IV/20 Jakarta Selatan Indonesia
Jl. Mandala Permai III/6 Rt.004 Rw.008 Kapuk Muara, Jakarta Utara Indonesia
Jl. Mangga 23, No. BL C/84 Duri Kepa, Jakarta Barat 11510 Indonesia
JL. MANGGA BESAR 4F., 28A JARKARTA BARAT 1150 INDONESIA
Jl. Mangga Besar 6 Selatan No. 104 – 106 – 108 Jakarta 11150 Indonesia
Jl. Mangga Besar IV E/16 Jakarta Barat Indonesia
Jl. Mangga Besar VI No. 36 Taman Sari, Jakarta Barat Indonesia
Jl. Mangga Besar VI Utara No. 30 RT009/RW01, Taman Sari Jakarta Barat Indonesia
Jl. Mangga Besar VIII/8, Jakarta Barat, Indonesia
Jl. Mangga Dua Raya (Komplek Harco Mangga Dua) Block E, No. 34 Jakarta, Indonesia
Jl. Mangga No. 18 RT007/012 Jati Pulo Jakarta Barat Indonesia
Jl. Manyar Kertoarjo III No. 32 Surabaya 60115 Indonesia
Jl. Mappala Blok A 5 No 26 Makasar Indonesia
Jl. Margomulyo 68E KAV 11-15 Surabaya Indonesia
Jl. Maribaya G2/4, Puri Cinere, Cinere, Depok, Indonesia
Jl. Mas Putih D-50 Permata Hijau Jakarta INDONESIA
Jl. Mataharl IIIB/464 Jaka Setia, Bekasi Selatan INDONESIA
Jl. Matraman Raya 198 RT 012/005 Kamp Melayu Jatinegara Jakarta Timur Indonesia
Jl. Matraman Raya 198 RT 012/06 Kamp Melayu Jatinegara Jakarta Timur Indonesia
Jl. Maulana Yusup No. 12 Banguna Indonesia
Jl. Mayjend Sungkono Kav. B-5, Surabaya 60225, Indonesia
Jl. Medan No. 127 Blok M Cinere, Kec. Limo Depok Indonesia
Jl. Mega Kuningan Timur Blok C-6 Kav. 12 Jakarta Selatan 12950 Indonesia
Jl. Melati Dalam RT. 003 RW. 002 Cilandak Timur-Pasar Minggu South Jakarta 12150, Indonesia
Jl. Melati Mas Raya Blok GI/NO 7 Villa Melatimas, Serpong Tangerang Indonesia
JL. MELAYU BARAT NO. 66 BANJARMASIN, SOUTH KALIMANTAN INDONESIA
Jl. Merak No. 7 Rempora Permai Housing Jakarta 12330 INDONESIA
JL. MERAPI BV/7, RT001 RW011 CIBUBUR PASAR REBO JAKARTA TIMUR 13720 INDONESIA
Jl. Merdeka No. 2K Medan Indonesia
Jl. Merdeka No. 36 Palembang Indonesia
Jl. Meruya Selatan 68 Jakarta 11650 Indonesia
Jl. Meruya Selatan No. 66 Jakarta 11650 Indonesia
Jl. Meruya Selatan No. 9 RT/RW:003/002, Meruya Selatan Kembangan, Jakarta Barat Indocnesia
Jl. Metro Hijau 2 No. 10 Pondok Pinang, Jakarta Selatan 12310
Jl. Metro Kencana V/18, Rt. 001/015 Pondok Pinang Jakarta Selatan
Jl. Mimosa II No. G7 Jakarta 12510 Indonesia
JL. Mojopahit No. 177 Mojokerto, Indonesia
Jl. MPR IV No. 4 Cilandak, Jakarta Selatan Indonesia
JL. Muara Karang Blok A4s/38, Kelurahan Pluit Kecamatan Penjaringan Jakarta Utara, Indonesia
JL. Muara Karang Blok K6S/8 Jakarta Utara, Indonesia
Jl. Natuna Blok G.225 RT. 05, RW.13, Kel. Cinere, Kec. Limo Jakarta Selatan, Indonesia
Jl. Natuna No. 20 Bandung Indonesia
Jl. Niaga Hijau 1/60 Pondok Indah, Jakarta Indonesia
Jl. Niaga Hijau IX No. 11-E, RT007/RW017 Pondok Pinang, Kebayoran Lama Jakarta Selatan, Indonesia
Jl. Niaga Hijau Raya 47 RT 011/013 Kel. Pondok Pinang, Jaksel Indonesia
Jl. Niaga Hijau Raya No. 51 Pondok Indah Selatan Jakarta INDONESIA
Jl. Nusa Indah Raya No. 29 Rt:002/001 Kel:Pondok Kopi Kec:Duren Sawit Jakarta Timur Indonesia
Jl. Otista, Gang H Maung, No. 33, RT 03/11, Sasak Tinggi, Ciputat, Tangerang, Indonesia
Jl. P Jayakarta 119A Jakarta Indonesia
JL. P Jayakarta No. 117/B8 RT006/RW007 Mangga Dua Selatan, Jakarta Pusat Indonesia
JL. P Jayakarta No. 117B RT006/RW008 Mangga Dua Selatan, Jakarta Pusat Indonesia
Jl. P. Jayakarta 131-A / 44-45 Jakarta 10730, Indonesia
Jl. P. Jayakarta 131-A/44-45 Jakarta 10730 Indonesia
Jl. Padasuka RT32/RW09 Kel. Sukamaju Kaler/Kec. Indihiang Tasikmalaya 46151 West Java, Indonesia
Jl. Pademangan I No.15 Jakarta 14410 Indonesial
Jl. Pademangan II, RT. 001 / RW. 001 Kel.Pademangan Barat Kec. Pademangan Jakarta Utara, Indonesia
Jl. Pademangan IV GG.23 No. 22 Jakarta Utara, Indonesia
Jl. Pakubuwano VI/17 RT 006/04 Gunung Kebayoran Baru Jakarta Selatan Indonesia
Jl. Palapa I/18 RT/RW 001/005 Pasar Minggu, Jakarta Selatan Indonesia
Jl. Palem Barat No. 27 RT 004 / RW 007, Kelurahan Duri Kepa Kecamatan Kebon Jeruk Jakarta Barat, Indonesia
Jl. Palem Utama No. 18 RT 08/07 Duri Kepa Kebon Jeruk Jakarta Barat 11510 Indonesia
Jl. Palma Raya I Blok F/36, Taman Kedoya Baru Jakarta, Indonesia
Jl. Pancoran Barat VI/5B RT013/06 Pancoran-Mampang Prapatan Jakarta Selatan 12780 Indonesia
Jl. Pancoran V No. 14. RT 08/02 Kel. Glodok, Jakarta Barat Indonesia
Jl. Pandeglang No. 27 Menteng, Jakarta Pusat Indonesia
Jl. Pangeran Antasari No.55, RT003/011 Cipete Utara, Jakarta Selatan Indonesia
Jl. Pangeran Jayakarta, 105G Jakarta 10730 Indonesia
Jl. Panglima Polim IX No. 12, Melawai, Kebayoran Baru, Jakarta Selatan
Jl. Panjunan 2/167 Sidoarjo, Surabaya Indonesia
Jl. Panjunan II No. 167 Sidoarjo, Indonesia
Jl. Panjunan II/165 Sidoarjo, Indonesia
Jl. Pantai Karang No. 5 Samur, Denpasar, Bali, Indonesia
Jl. Pantai Kuta II 3 RT 002, RW 10, Ancol Pademangar, Jakarta Utara Indonesia
Jl. Pantai Kuta IV/I Ancol Jakarta, Indonesia
Jl. Pantai Mutiara AD17 Jakarta Indonesia
JL. PANTAI MUTIARA BLOK A NO. 9 JAKARTA 14450 INDONESIA
Jl. Pantai Mutiara Blok J 20-Pluit Jakarta Indonesia
Jl. Pantai Mutiara ZF/No. 1 Jakarta Indonesia
Jl. Pasir Putih V1/7, RT/RW. 006/010 Ancol Pademangan Jakarta Utara Indonesia
Jl. Paso No. 63 Kav. 80 RT.003/RW.06, Kelurahan Jagakarsa, Jakarta 12620, Indonesia
Jl. Patal Senayan No. 38 Jakarta 12210 Indonesia
Jl. Pati Unus No. 2A RT: 004/RW:004 Gunung Kebayoran Baru, Jakarta Selatan, Indonesia
Jl. Patimura No. 9, Cilandak Kebayoran Baru, Jakarta Selatan Indonesia
Jl. Patra Kuningan 1, Blk L1/10-11 006/04 Kuningan Timur, Setiabudi Jakarta Selatan, Indonesia
Jl. Patra Kuningan I Blk. L1 Jakarta Selatan Indonesia
JL. Patra Kuningan Raya Block M41 Kav. 4-5 Jakarta 12950 Indonesia
Jl. Patra Kuningan X/5 RT. 006/ RW. 004 Kuningan Timur, Kecamatan Setiabudi Jakarta Selatan Indonesia
Jl. Patra Kuningan XI/5 Jakarta Selatan Indonesia
Jl. Patra Tomang II/34, Jakarta 11510, Indonesia
JL. PECENONGAN NO. 72 APARTEMEN ATAP MERAH #1195 JAKARTA 10120, INDONESIA
Jl. Pedureuan Kav 25 Ampera, Jakarta Selatan, Dki Jakarta 12430 Indonesia
JL. PEJATEN RAYA NO. 8A JAKARTA SELANTAN 12510 INDONESIA
Jl. Pekayon 1 No 16C Jakarta Indonesia
Jl. Pelangi IV, No. 5 Blok 48 RT 10 RW 16 Mekar Sari Cimanggis Depok Indonesia
Jl. Pelangi Nila VI Blok A-8/15 Kelapa Gading Jakarta Utara Indonesia
Jl. Pelepah Kuning II WV 2 No. 14 Kelapa Gading Jakarta 14240 Indonesia
Jl. Pengadegan Selatan No 10 Kalibata Rt 002/005 Jakarta Selatan Indonesia
Jl. Pengadegan Selatan VII No. 67 Pancoran, Jakarta 12770 Indonesia
JL. Pengayoman No. 21 Samping Polsekta 9 Panakkukang, Makassar Indonesia
JL. PENGAYOMAN NO. 21 SAMPING POLSEKTA 9, PANAKKUKANG, MAKASSAR, INDONESIA
Jl. Permata Berlian Blok R-13 Permata Hijau Jakarta 12210
Jl. Permata Hijan Blok K/1. Jakarta Indonesia 12950
JL. Permata Hijau Blk A38, Jakarta Selatan, Indonesia
JL. Permata Hijau Blok M, No. 10-11 Jakarta Selatan Indonesia
Jl. Permata Hijau F/11 Jakarta Selatan Indonesia
Jl. Permata Hijau F/74 Jakarta Indonesia
Jl. Permata Hijau L/19 Jakarta Indonesia
Jl. Permata Hijau, Blk 4/6 RT. 014/002 Grogol Utara, Keby. Lama Jakarta Selantan Indonesia
Jl. Permata Mediterania Raya No. 19 Srengseng, Jakarta Barat Indonesia
Jl. Permata No. 10, Grogol Jakarta 11440, Indonesia
JL. Perniagaan No.3 Medan, Indonesia
JL. PERTANI NO. 14 KALIBATA JAKARTA 12960 INDONESIA
Jl. Petike Luar No. 29 RT 011/01 Tambora Jakarta Barat Indonesia
Jl. Petojo Barat VII No. 8, RT009/RW001 Jakarta 10140, Indonesia
Jl. Petojo Selatan 1, No: 4D, Central Jakarta Indonesia
Jl. Petojo VIY II No. 32-34 RT.004/RW.006 Cideng Jakarta Pusat, Indonesia
Jl. Petojo Viy V #4 Kelurahan Cideng Jakarta Pusat
Jl. Pinang Emas VI-VQ/12 Pondok Pinang Jakarta 12310 Indonesia
JL. Pinang Emas X/26, RT 010/03 JAKARTA SELATAN Indonesia
Jl. Pinangsia Timur No. 4K Jakarta 1110 Indonesia
Jl. Pinisi Indah 2 No. 2 Pantai Indah Kapuk Jakarta, Indonesia
Jl. Pinisi Permai 2/11 Jakarta Utara, Indonesia
JL. Pluit Barat V/5 RT 015 RW 007 Jakarta Utara INDONESIA
Jl. Pluit Barat 14, No. 7 Jakarta
Jl. Pluit Indah No. 29 Jakarta Utara 14450, Indonesia
Jl. Pluit Indah/29 Jakarta 14450 Indonesia Tel: REDACTED
Jl. Pluit Karang Permai RT 012, RW 008 Pluit, Penjaringan Jakarta Utara, Indonesia
Jl. Pluit Permai Raya / 20, Pluit Penjaringan, Jakarta Utara Indonesia
Jl. Pluit Permai Raya No. 12A Rt.009 Rw.004, Pluit, Jakut Indonesia
Jl. Pluit Sakti Raya No. 125, Jakarta Utara, Indonesia Indonesia.
Jl. Pluit Sakti Raya No. 28 Rt. 009. Rw. 007, Pluit, Penjaringan Jakarta Utara 11450 Indonesia
Jl. Pluit Sakti Raya No. 30 Jakarta Indonesia
Jl. Pluit Selatan 11 No. 17 Jakarta Utara Indonesia
Jl. Pluit sumudra 5 No. 9 Jakarta Utara 14450 Indonesia
Jl. Pluit Timur Blk C/17 Jakarta Utara Indonesia
Jl. Pluit Utara II No. 15, Pluit, Penjaringan Jakarta Utara, Indonesia
Jl. Pramuka Jayasari No. 29 Rawasari, Cempaka Putih Jakarta Pusat Indonesia
Jl. Prisma 2 Blok B2, No. 33 Taman Kedoya Permai Jakarta 11530, Indonesia
JL. Prisma 2 Blok B2, No.33 Taman Kedoya Permai Jakarta 11530, INDONESIA
Jl. Prof. DR. Satrio Kav. 6 Jakarta 12940 INDONESIA
Jl. Prof. M. Yamin No. 22B RT 007/RW 005 Jakarta Pusat Indonesia
JL. PROP DR SATRIO AP AMBASADOR RT/RW 011/004, Kelurahan Karet Kuningan Kecamatan Setia Budi Jakarta Selatan, Indonesia
JL. Pulan Putri I/A2/3 Kota Modern Tangerang 15117 Indonesia
Jl. Pulau Laki IV Blk K-6/18 Kembangan Utara Jakarta Barat Indonesia
Jl. Pulau Matahari VI Blok A-6/34, Jakarta Barat, Indonesia
JL. Pulau Putri B.IV/No. 16 Modern Land – Tangerang Indonesia
JL. PULAU PUTRI III/25, R.T 011, R.W 002, JAKARTA
Jl. Pulau Sebaru M1/31 RT 011/009 Kel Kembangan Utara Kec Kembangan Jakarta Barat Indonesia
Jl. Pulau Sebaru M1/31 RT011/009 Kel Kembangan Utara Kec Kembangan Jakarta Barat Indonesia
Jl. Pulau Sebaru M1/31 Taman Permata Buana Jakarta Barat 11610 Indonesia
Jl. Pulau Sembilan Block N/14 Jatiwaringin Asri II Pondok Gede Bekasi 17411 Indonesia
Jl. Pulo Asem Timur Pulo Gadung, Jakarta Timur Indonesia
Jl. Pulo Ayang Raya Blok JJ-9 Kawasan Industri Pulogadung Jakarta 13260 INDONESIA
Jl. Pulo Indah No. 35 Rt 002/005 Petukangan Selatan, Jakarta Selatan, Indonesia
Jl. Pulo Indah No. 39 RT 010/005 Petukangan Sel. Jakarta 12270 Indonesia
JL. Pulo Kambing II No. 18 Kawasan Industri Pulogadung Jakarta 13920
JL. PULO MAS RAYA 12, RT.007, RW.011 KAYU PUTIH SUB DISTRICT PULO GADUNG DISTRICT EAST JAKARTA, INDONESIA
Jl. Pulo Mas VIII B/10 RT.08/11 Kel . Kayu Putih Jakarta Timur, Indonesia
JL. Pulomas Raya No. 16A RT 007 RW 016 Jakarta Timur INDONESIA
Jl. Pulomas Timur No 1B/1, Jakarta Pusat
Jl. Pulonangka Timur I C /46 Pulogadung Jakarta Timur Indonesia
Jl. Punai III T7/10 Bintaro Jaya Sektor 2 Tangerang Indonesia
Jl. Puncak Pesanggrahan VII/32 RT 02 RW 16, Kel. Cinere, Kec. Limo Depok, Bogor, Indonesia
JL. PURBA ENDAH I RT.04/05, KEC. CIMAHI UTARA, KAB. BANDUNG
Jl. Puri Indah C1 No. 6 Jakarta Barat Indonesia
Jl. Puri Kencana Elok Timur I Blk K4/32, Jakarta Barat Indonesia
Jl. Puri Mutiara No. 5 Wisma Pertamina RT009/RW011 Jakarta 12430 Indonesia
Jl. Purnawarman No. 85, Kav. 3 Kebayora Baru, Jakarta 12110 Indonesia
Jl. Purnawarman No. 85, Kav. 3 Kebayoran Baru Jakarta 12110 Indonesia
Jl. Purwakarta No 3 Jakarta Pusat 10310 Indonesia
JL. Putat Indah 15, Surabaya Indonesia
Jl. Puter II ED 2/32 BTR V RT 002 RW 09, Jurangmangu Timur Pondok Aren Tangerang Indonesia
Jl. Putri No. 6 Bandung 40262 Indonesia
Jl. Pyrus Blok C No. VIP 1 Jakarta 12210, Indonesia
JL. R.S. Fatmawati No. 7 Kebayoran Baru Jakarta Selatan 12140 Indonesia
Jl. Raden Patah III No. 9 Kebayoran Baru Jakarta Selatan INDONESIA
Jl. Raden Saleh Dalam No. 95, Medan Indonesia
Jl. Radio V No. 8, Blok B2 RT001/004, Kramat Pela Jakarta Selatan Indonesia
Jl. Rajawali No. 53, Surabaya 60175 Jawa Timur Indonesia
Jl. Rajawali Selatan I, No. 1 RT / RW 017/002, Gunung Sahari Utara Kecamatan Sawah Besar Jakarta Pusat, Indonesia
Jl. Rajawali Selatan Raya No. 17, Jakarta 10720 Indonesia
Jl. Rajawali Selatan V No. 42 Jakarta 10720 Indonesia
JL. Rawa Bahagia I/25, RT / RW : 006/002, Grogol Pertamburan, Jakarta Barat
Jl. Rawa Kemiri 14/B RT004/RW 011, Grogol Selatan Kebayoran Lama, Jakarta Selatan Indonesia
JL. Rawa Kepa IX, No. 69, Tomang Utara, Jakarta Barat 11440, Indonesia
JL. RAWAMANGUN MUKA V, RT/RW 015/012, KELURAHAN RAWAMANGUN, KECAMATAN PULOGADUNG JAKARTA-TIMUR, INDONESIA
Jl. Raya Batujajar KM. 2,8 Padalarang 40561 Bandung – Jawa Barat, Indonesia
Jl. Raya Gubeng No. 61 SURABAYA INDONESIA
Jl. Raya Kalimalang /77 RT 010/08 Jakarta Timur Indonesia
Jl. Raya Kelapa Dua No. 1 RT 007/002 Kelapa Dua Jakarta Barat 11550 Indonesia
Jl. Raya Kelapa Dua No. 1 RT007/RW002, No. 1 Kelapa Dua-Kebun Jeruk Jakarta Barat 11550 Indonesia
Jl. Raya Kerobokan # 106 – Br. Taman Kuta 80361 Bali Indonesia Kuta 80361, Bali Indonesia
Jl. Raya Kertajaya Indah No. 91 Surabaya Indonesia
Jl. Raya Margorejo Indah D/104 DS/Kel. Sidosermo RT.004/005 Kec. Wonocolo, Surabaya Indonesia
Jl. Raya Padang Solok KM 17, Padang Indonesia
JL. RAYA PASAR MINGGU NO. 39 DUREN TIGA BUNTU Jakarta Selatan Indonesia
Jl. Raya Permata Hijau Blok B No. 8, Jakarta Selatan, Indonesia
JL. RAYA PLUIT SAKTI NO. 28 JAKARTA UTARA INDONESIA
JL. RAYA PLUIT SAKTI NO. 28 JAKARTA UTARA INDONESIA
Jl. Raya Pluit Selatan Blok S No. 1 Jakarta 14450 Indonesia
JL. RAYA SEMER NO. 883 BANJAR SEMER KEROBOKAN-KUTA, BALI INDONESIA 80361
Jl. Raya Serang Km. 71 Desa Tambak Kec. Kibin Kab. Serang Propinsi Banten Indonesia
Jl. Raya Solo Sragen KM 9.5 Palur, Solo 57771 Indonesia
Jl. Renijaya, Blok E RT.02, RW.05 Kel. Pondok Petir, Kec Sawangan Bogor, Indonesia
Jl. RM SAID No. 148, RT/RW 005/002 Kelurahan Punggawan Kecamatan Banjarsari Surakarta 57132, Indonesia
Jl. Rontgen No. 3, Bandung – West Java INDONESIA
Jl. Rontgen No. 4 Bandung 40171 Indonesia
Jl. Rosiga VII/B-9 Kebon Jeruk, Jakarta Barat Indonesia
Jl. Rotowijaya No. 15 Yogyakarta-Indonesia 55321
Jl. Ruby I/28 Blok G Jakarta, Indonesia
Jl. S. Wiryopranoto No. 46, Jakarta 10120, Indonesia
Jl. Safir II Blok I/10 Cilandak Barat Jakarta Selatan Indonesia
Jl. Salak No. 35 RT 007/002 Kel. Guntu,r Kec. Setiabudi Jakarta Selatan Indonesia
Jl. Sanur Blok C4 No.7, Bali View Estate, Cirendeu, Jakarta Selatan Indonesia
Jl. Saw No. 24, Menteng Jakarta 10350 Indonesia
Jl. Sawo No. 23 Menteng Jakarta Pusat Jakarta 10330 Indonesia
Jl. Sedap Malam B-182 Bekasi Jawa Barat Indonesia
Jl. Sekolah Duta I/14-16 Pondok Pinang Jakarta – Indonesia
Jl. Sekolah Duta I/14-16 RT 002-014 Pondok Pinang Jakarta, Indonesia
Jl. Sekolah Duta V/50 RT 003/014 PONDOK INDAH PERMAI JAKARTA SELATAN Indonesia
Jl. Sekolah Duta V/50 RT 003/014 Pondok Pinang, Jakarta Selatan Indonesia
JL. SEKOLAH DUTA V/50, PONDOK INDAH PERMAI Jakarta Selatan INDONESIA
JL. SEKOLAH DUTA V/50, RT003/RW014, PONDOK PINANG, JAKARTA SELATAN INDONESIA
Jl. Sekolah Kencana, Nuansa Hijau Apt A/8-1, South Jakarta Indonesia
Jl. Semampir II/1 Kediri Indonesia
Jl. Semampir II/No. 1, Kediri, East Java, Indonesia
Jl. Seminyak GG Plaw No 566 Kuta Bali Indonesia
Jl. Seruni, No. 3, Surabaya, Indonesia
Jl. Setia 1 No. 21, RT03/RW10 Kel. Jati Cempaka, Kec. Pondok Gede Bekasi, Indonesia
Jl. Setia Budi II No. 54 Jakarta 12910 Indonesia
Jl. Siaga Utama Kav 12A RToo7/04 KEL. Pejaten Barat South Jakarta Indonesia
Jl. Sidas No.8 RT001/002 Pontianak Barat. Indonesia
Jl. Sikambing Blk No. 26/13 Medan 20113 Indonesia
Jl. Sikatan No. 37 Surabaya Indonesia
Jl. Simprug Garden Blok D No. 2 RT 007/RW003 Grogol Selatan Jakarta 12220 Indonesia
Jl. Simprug Garden Blok D No. 2 RT007/RW003 Grogol Selatan Jakarta 12220 Indonesia
Jl. Simprug Garden II No. 10 Jakarta, Indonesia
Jl. Simprug Golf 14/55A, Jakarta Selatan
Jl. Simprug Golf III Kav. 111 Jakarta Selatan Jakarta 12210 Indonesia
Jl. Sinar Budi Gg. N/5 RT002 RW 03, Kelurahan, Pejagalan Kecamatan, Penjaringan, Jakarta Indonesia
Jl. Sircon Blok. C/71 Rt 009/01 Grogol Utara Jakarta Selatan 12210 Indonesia
Jl. Sircon Blok. G/72 Rt 009/01 Grogol Utara Jakarta Selatan 12210 Indonesia
Jl. Sircon Blok. G/73 Rt 009/01 Grogol Utara Jakarta Selatan 12210 Indonesia
Jl. Sisingamangaraja No. 26 Jakarta 12120 INDONESIA
Jl. Sisingamangaraja No. 3 C Jakarta 12110 INDONESIA
JL. SLAMET RIYADI TSI BLOK A NO.1 , BANDAR LAMPUNG 35228 INDONESIA
Jl. Sri Gading II 35, RT. 003, RW.012, Mangkubumen Sub District, Banjarsari District, Surakarta Mayoralty, Central Java, Republic of Indonesia
JL. SRI WIJAYA RAYA NO. 4 KEBAYORAN BARU JAKARTA SELATAN 12110 INDONESIA
Jl. Sriwijaya Raya No. 33 Kebayoran Baru Jakarta Selatan Indonesia
Jl. ST Budi Tgh Four Season Apart RT/RW 007/03 Setia Budi Jakarta Selatan Indonesia
Jl. St. Hasanudin No. 69 002/001 Melawai, Kebayoran Baru Jakarta Selatan Indonesia
Jl. Sudirman Kav. 1 Panin Centre 7th Floor Jakarta 10270 INDONESIA
Jl. Sukarela No. 1, RT 009/RW009, Penjaringan, Jakarta Utara, Indonesia
Jl. Sukarno Hatta A2 Malang, Indonesia
Jl. Sultan Hasannudin No. 45/115 Blok M, Kebayoran Baru Jakarta Selatan Indonesia
Jl. Sumbawa 12 Menteng Jakarta Pusat 10350 Indonesia
Jl. Sumbawa No. 6 Jakarta Pusat INDONESIA
JL. SUMBER WUNI 341, RT 02/05, LAWANG, MALANG, INDONESIA
Jl. Suren I/12 Keb Baru. Jakarta 12160 INDONESIA
Jl. Surya IV/28, RT 04/05 Kedoya Utara, Jakarta Barat Indonesia
Jl. Surya Timur Blok III A/8 RT 13/05 Kedoya Utara Jakarta Barat, Indonesia
Jl. Surya Utama Blok V/17 RT 004/rw005 Kelurahan Kedoya Utara Kecamatan Kebon Jeruk Jakarta Barat, Indonesia
Jl. Surya Utama II H/11 Sunrise Garden Jakarta 11520 Indonesia
Jl. Surya Wijaya 8/4 – E/10 RT/RW 007/011, Kedoya Utara Kebon Jeruk Jakarta Barat, Indonesia
Jl. Surya Wijaya III No. 14 Kedoya Selatan Jakarta Barat Indonesia
Jl. Suryo No. 58, RT004/004 Rawa Barat, Jakarta Selatan Indonesia
Jl. Suryo No. 7, Blok S-Kebayoran Baru Jakarta Selatan 12180 Indonesia
Jl. Sutomo No. 301 Medan 20212 Sumatra Utara Indonesia
JL. SUWIRYO NO. 45, JAKARTA PUSAT, INDONESIA
Jl. Talib II No. 35A Jakarta 11140 Indonesia
Jl. Taman Cilandak V No. C10, Cilamdak Barat, Jalarta Selatan 12430, Indonesia
Jl. Taman Cilandak V/B2 RT 012/004 Cilandak Jakarta Selantan Indonesia
JL. TAMAN DELIMA IV/29, RT.004, RW.005 TANJUNG DUREN SELATAN SUB DISTRICT GROGOL DISTRICT, WEST JAKARTA REPUBLIC OF INDONESIA
Jl. Taman Delima VI/59, RT.007, RW.005, Tanjung Duren Selatan Sub District, Grogol Petamburan District, West Jakarta, Republic of Indonesia
Jl. Taman Kebon Jeruk Blok G1 Kav 60 Jakarta Ta Barat Indonesia
Jl. Taman Kebon Jeruk Blok G1 No. 37, Intercon Jakarta Barat Indonesia
Jl. Taman Kencana Indah I Kav TC18, Pondok Indah Jakarta Indonesia
Jl. Taman Kliningan No.1 Bandung Indonesia
Jl. Taman Lebak Bulus V/I RT002/007 Lebak Bulus Jakarta Selatan Indonesia
JL. Taman Patra 3 No. 9B JAKARTA 12950 Indonesia
Jl. Taman Patra Raya No. 8 Kuningan Timur Jaksel
Jl. Taman Patra XIII, No. 11-12 005/004 Kuningan Timur, Setia Budi Jakarta Selatan, Indonesia
JL. TAMAN RADIO DALAM VI NO. 4 JAKARTA, INDONESIA
Jl. Taman S. Parman A/12 RT004/008, Tomang Jakarta Barat, Indonesia
Jl. Taman S. Parman A/12 RT007/008, Tomang Jakarta Barat, Indonesia
Jl. Taman Sari Raya 56-NE RT 12/04, Taman Sari Jakarta Barat Indonesia
Jl. Taman Sari Raya No. 10 Jakarta Indonesia
JL. TAMAN SURYA BLOCK IID/8 JAKARTA 11520 INDONESIA
Jl. Taman Surya III Blok G-3/17 Kalideres Jakarta Barat Indonesia
Jl. Taman Tanah Abang III No. 6 RT002/RW004 Jakarta, Indonesia
Jl. Taman Tangkuban Perahu No. 6 RT 011/RW001 Jakarta 12980 INDONESIA
JL. TAMANSARI XI / 7A Jakarta Barat Indonesia
Jl. Tambak Bayan Tengah 36 RT 02/33, Alon Alon Contong Surabaya, Indonesia
Jl. Tampak Siring Indah No. 99 RT005/RW007 Bukit Gading Villa – Kelapa Gading Barat Jakarta Utara 14240, Indonesia
Jl. Tampak Siring Raya No. 7 Bukit Gading Villa, Kelapa Gading, Jakarta Utara Indonesia
JL. TANAH ABANG 2 NO. 53 JAKARTA 10160 INDONESIA
Jl. Tanggamus No. 10 Klojen, Malang Indonesia
Jl. Tanjung Duren Selatan No. 57 RT 011/RW002, Tanjung Duren, Jakarta Barat 11470, Indonesia
Jl. Tanjung Duren Utara II A/386, Jakarta 11470 Indonesia
Jl. Tanjung Mas Raya, Blok B8/16, Tanjung Barat, Jakarta Selatan, Indonesia
JL. TANJUNG NO. 10 RT/RW: 007/001 MENTENG JAKARTA 10350, INDONESIA
JL. TANJUNG NO. 32B GONDANGDIA – MENTENG JAKARTA PUSAT – 10350 Indonesia
Jl. Tanjung No. 39 Gondangdia, Jakpus Jakarta Indonesia – 10350
JL. Tarogong/Caringin Utara 31 RT12/10 Cilandak Barat, Jakarta 12430 Indonesia
JL. TARUNA NO. 28A RT/RW 004/011 JATINEGARA CAKUNG JAKARTA TIMUR – DKI JAKARTA INDONESIA
JL. TB. ANGKE NO. 190P RT. 10/09 ANGKE JAKARTA BARAT INDONESIA
Jl. Tebet Barat Raya No. 44, RT014/004, Tebet Barat Jakarta
Jl. Tebet Barat VI G/5 Jakarta Selatan 12810 Indonesia
Jl. Tebet Mas Indah V/B 8 RT. 009, RW. 002, Tebet Barat, Tebet, Jakarta Selatan, Indonesia
Jl. Tebet Timur Raya No. 45 Jakarta Selatan 12820 Indonesia
Jl. Telomoyo 6 Semarang 50252 Indonesia
Jl. Tengah Raya No. 22 R.T./R.W. 004/012, Gedong Pasar Rebo, Jakarta Timur Indonesia
Jl. Tengah Raya No. 22, R.T/R.W 004/012 Gedong, Pasar Rebo, Jalan Timur Indonesia
Jl. Terogong II/51 RT 008/010 Cilandak Barat, Jakarta Selatan Indonesia
JL. TEUKU UMAR NO. 50 RT/RW : 001/001 GONDANGDIA MENTENG JAKARTA PUSAT Indonesia
Jl. Tg. Duren Utara IV/50, Jakarta Barat, Indonesia
Jl. Thamrin 64 Surabaya Indonesia
JL. Thamrin No.4-C, P. Siantar Indonesia
Jl. Tidar, No. 30, Surabaya, Indonesia
Jl. Tidore No. 10, Cideng Jakarta Pusat Indonesia
JL. TIMBUL 21-PEJATEN BARAT II JAKARTA SELATAN INDONESIA 12510
Jl. Timor (T. Timor Raya) No. 58 Medan 20235 Indonesia
Jl. Timor No. 8 Gondangdia, Jakpus Jakarta Indonesia
JL. TIMOR NO. 8 RT 009/RW004, GONDANGDIA JAKPUS, JAKARTA INDONESIA
Jl. Timor No. 8, Jakarta Pusat Indonesia
Jl. Tirtayasa IX No.8-10 Jakarta Indonesia
Jl. Tisna Senjaya, No. 80/18D Bandung, Indonesia
Jl. Tomang Asli No. 25 RT07/03, Jati Pulo Indonesia
Jl. Tosiga Blok E/9 – RT 07/04 Kebon Jeruk Jakarta Barat Indonesia
JL. TOSIGA I NO. K 5 KEBON JERUK Jakarta Barat Indonesia
JL. Trembesi 130 Depok 14621 INDONESIA
Jl. Trs Hang Lekir III/54 RT/RW 005/008, Grogol Selatan Jakarta Selatan Indonesia
Jl. Trunojoyo 101, Surabaya, Indonesia
Jl. Tulodong Bawah 18 Kebayoran Baru Jakarta Selatan Indonesia
Jl. Tulodong Bawah III/42 Jakarta Selatan Indonesia
Jl. Tulodong Bawah IV/2, Jakarta 12190, Indonesia
Jl. Tulodong Bawah No. B-3 Kebayoran Baru Jakarta 12190 Indonesia
Jl. Tumenggung 43 Jakarta, Indonesia
Jl. Tuparev Mo. 21 Kerawang Indonesia 41312
Jl. Untung Suropati No. 28 Surabaya, Indonesia
Jl. Untung Suropati No. 29 Surabaya, Indonesia
Jl. Uranus V No. 10, Villa Cinere Mas, Jakarta Selatan, Indonesia
Jl. Uranus V, No. 10 Villa Cinere Mas Jakarta Selatan, Indonesia
Jl. Veteran No. 27 RT 01, PS. Pagi Samarinda 75111, Indonesia
Jl. Veteran No. 3A Semarang Indonesia
Jl. Villa Jati Padang 11/53 Indonesia
Jl. Villa Polonia Indah No. 68, Medan, Indonesia
Jl. Wahyu No. 15 RT 003/005 Gandaria Selatan Indonesia
Jl. Walet Permai 3/5, Rt007/003 Kel. Kapuk, Kec. Penjaringan Jakarta Utara
Jl. Walet Permai V/30, Pantai Indah Kapuk, Jakarta Utara, Indonesia
Jl. Widya Chandra 6 No. 4 Jakarta 12190 Indonesia
Jl. Widya Chandra II No. 3 Kav 14 Jakarta 12190 Indonesia
Jl. Widya Chandra V/3 Jakarta 12190 Indonesia
Jl. Widya Chandra VIII/8 Jakarta 12190 Indonesia
Jl. Widya Chandra XI No. 3 Jakarta Selatan 12190 Indocnesia
Jl. Widya Chandra, Raya/37 RT 008/001 Kby Baru, Jakarta Selatan Indonesia
Jl. Wijaya 10 No. 4, Kebayoran Baru, Jakarta 12160, Indonesia
Jl. Wijaya Kusuma Blok B1 No. 17 Duran Sawit Jakarta Timur
Jl. Wijaya Kusuma Raya No. 38 RT.041 RW.014, Desa Cilandek Barak, Kecamatan Kota Bogor Barat, Kotamadya Bogor Indonesia
Jl. Wilis Indah No.A.7 RT07 RW04 GD.Kasri MALANG, Indonesia
Jl. Wiyung Pratama B/5 Surabaya 60227 Indonesia
JL. WR. SUPRATMAN 9 SURABAYA, INDONESIA
Jl. YBR 1 Kav 62, Kuningan Timur, Jakarta, Selatan Indonesia
Jl. Ybr I Kav 62 Kuningan Timur Setiabudi Jakarta Selatan 12910
Jl. YBR IV No. C17 Kuningan Tower Jakarta Selatan Indonesia
Jl. YBR IV No. C17, RT001/002 Kuningan Timor, Setiabudi Jakarta, Selatan
Jl. YDPP II/20 RT/RW 006/01 Kemang Selatan Cipete Selatan, Cilandak Jakarta Selatan 12410, Indonesia
Jl. Yos Sudarso RT.OT. Tarakan Indonesia
JL. Yupiter IV No. 26 Villa Cinere Mas, Ciputat 15419 Indonesia
Jl.. Madrasah II/No.40 Jeruk Purut Cilandak-Timur Jakarta Selatan Indonesia
JL.DARMO PEMAI SELATAN 1/67 SURABAYA, EAST JAVE Indonesia
JL.Kalampeto No.8 Ujung Pandang, Indonesia.
Jl.Kimia No.13 Jakarta Pusat 10320 Indonesia
Jl.Lawu No.14 Malang Indonesia
JL.Mulyosari Mapan 4/DC20, Aurabaya, Indonesia.
Jl.Pinang Merah II/SK-1 Pondok Indah Pondok Pihang Jakarta 12310
JL.Rappocini Raya 181F, Makassar, Indonesia.
JL.Taman Patra 3 No. 9B Jakarata 12950 Indonesia
JL.Vila Sunter Mas. Blok H XI/I. Rt. 001 RW 08, Sunter Jaya, Tanjung Priok, Jakarta Utara, Indonesia
Jl.Walikota no.10 Medan
Jln Bambu Betung VII, RT. 005/RW 05, Kelurahan Rawa Buaya, Kecamatan Cengkareng, Kotamadya Jakarta Barat, Indonesia
JLN BANDENGAN UTARA NO.81 BLOK B RT 009/016 PENJARINGAN JAKARTA UTARA IDONESIA
JLN BIMA 1, NO. 84 DEPOK II TENGAH – 16411 KABUPATEN BOGOR INDONESIA
JLN BUKIT HIJAU 111/11, KEBAYORAN LAMA, JAKARTA SELATAN, INDONESIA
JLN Danau Agung XI No. 16, Sunter Agung, Jakarta, Indonesia
Jln Imam Bonjol No. 18 Pasuruan, Jawa Timur, 67122 Indonesia
Jln Kampung Bali IV, No. 32 Jakarta Pusat Indonesia
Jln Kdm. Ilir Barat Permai Blok D-16, RT.11 RW.03 24 Ilir Palembang Indonesia
Jln Kemurnian Utara No 3 Weast Jakarta, Indonesia 11120
Jln Krekot Bunder No. 46 Jakarta 10710 Indonesia
JLN M.H THAMRIN NO. 31 BII PLAZA, TOWER 2, 22ND FLOOR JAKARTA 10350, INDONESIA
Jln Mandala Utara No. 376 Jakarta Barat 11440 Indonesia
JLN MANDALA UTARA NO. 376 JAKARTA BARAT INDONESIA
JLN MANDALA UTARA NO. 4 JAKARTA BARAT 11440 INDONESIA
Jln Mangga Besar VI Selatan No. 102A Jakarta Barat 11150 Indonesia
JLN Muarakarang, BLK V-85/ /32. RT 010 RW 019, Pluit, Benjaringan, Jakarta Utara, Indonesia
JLN P. POLIM RAYA NO. 80 RT 002/008 PULO JAKARTA SELATAN INDONESIA
Jln Pasir Putih Raya E 41/1 RT.009/010, Kelurahan Ancol Kecamatan Pademangan Jakarta Utara, Indonesia
Jln Petojo Sabangan I/37 Jakarta 10160 Indonesia
JLN PLUIT UTARA 4 NO. 22 JAKARTA UTARA
Jln Pupan No.23 Pondok Pinang South Jakarta Indonesia
Jln Raung No. 12 Semarang, Indonesia
Jln Raya Uluwatu, Gang Kahuripan (Tegeh Pall) No. 69 Br Bakungsari, Ungasan, Kuta Selatan, Kab. Badung Bali 80363 – Indonesia
JLN SULTAN AGUNG NO. 58 JAKARTA INDONESIA
Jln Sultan Agung No. 69 Semarang, Indonesia
Jln Syahrial, No. 9 RT. 003/002 Rengat – Indragiri Hulu Riau Indonesia
Jln. Pejaten Barat II/81 Pasar Minggu Jakarta Selatan Indonesia
Jln. Agung Tengah 6 Blok I IV No. 6A Sunter Agung – Jakarta Utara Indonesia
Jln. Ancol Barat VII Blok A 5D No. 2 Jakarta 14430 Indonesia
Jln. Ancol Timur XIII No. 11A Regol, Bandung West Java
JLN. BAGAU BLOK P NO.4, CIPINANG INDAH 2 JAKARTA 13430 INDONESIA
JLN. BIMA 1, NO. 84, DEPOK II, TENGAH-16411, KOTA DEPOK, KABUPATEN BOGOR INDONESIA
Jln. Camar Elok V No. 35, Sektor Selatan Timur Pantai Indah Kapuk, Jakarta Utara Indonesia
JLN. CAWANG BARU NO. 22 JAKARTA 13340 INDONESIA
Jln. Dr. Cipto 3 Surabaya 60264, Indonesia
Jln. Dr. Sahardjo No. 182, Jakarta Selatan Indonesia
Jln. Ds. Petta Tabukan Utara – North Sulawesi
Jln. Dukuh Ilir Cibungbulan West Java
Jln. Gading Kirana Timur 1 Blk B3/23, Jakarta 14240 Indonesia
Jln. Gandaria Tengah VI No. 18 Jakarta 12130 Indonesia
Jln. Gg. Griya Lestari G2/2 KELAPA GADING Jakarta
Jln. Gg. Swadaya No. 27 Tebet – Jakarta
Jln. Gubeng Kertajaya 5-C/36 Surabaya East Java Indonesia
JLN. JEMBATAN III NO. 36 R.T. 001 R.W. 016 JAKARTA INDONESIA
Jln. K.N. Samanhudi (Pintu Besi) no. 32 Jakarta – Pusat INDONESIA
Jln. Kampung Salo Kembangan Jakarta
Jln. Kavling Polri Blok DIII/971A RT 008/RW001, Jelambar, Grogol Jakarta Barat Indonesia 11460
Jln. Kp. Rawa Lele Jombang Ciputat, Jakarta
Jln. Kp. Sidamukti Sukamaju – Depok
Jln. M. H. Thamrin No. 31, Bll Plaza Tower 2, 22nd Floor Jakarta 10350 Indonesia
Jln. Mangga Besar VIII/8 RT 008/01 Kelurahan Taman Sari, Kecamatan Taman, Sari, Jakarta Barat
JLN. MENDUT NO. 21, RT 009 RT 002 KEL. PEGANGSAAN, JAKARTA PUSAT INDONESIA
Jln. Metro Hijau II No. 10 Jakarta 12310 Indonesia
Jln. Mimosa Blok N. 1 Buncit Indah Pejaten Barat Jakarta Selatan Indonesia
Jln. Mitra Sunter Boulevard Blok A No. 20-21 Jakarta 14350 Indonesia
Jln. Pangeran Jayakarta, No. 55, Central Jakarta 10730 Indonesia
Jln. Paradise 25 Block A/20 Nirwana Sunter Asri TH III North Jakarta Indonesia
Jln. Pelepah Hijau II TG I/4 Kelapa Gading Jakarta
Jln. Pendidikan No. 26 Cilandak Barat, Jakarta Selatan Indonesia
Jln. Peninggaran No. 53 Ciputat, Kebayoran Lama Jakarta
Jln. Petak Serani Tanah Sereal – Tambora Jakarta
Jln. Raya Gilang 159 (Taman – Sepanjang) Sidoarjo 61257 Indonesia
Jln. Senjaya 4 No. 95 Kebayoran Baru Jakarta 12110 Indonesia
Jln. Sidokapasan 2/33 Sidodadi 60145 Surabaya, Indonesia
Jln. Surya Wijaya 8/4E/10 Kebon Jeruk, Jakarta Barat Indonesia
Jln. Taman Borobudar 19, Malang East Java, Indonesia.
Jln. Tebet Raya No. 62 Jakarta Selatan 12820 Indonesia
Jln. Tebet Timur Dalam VI C/11 Tebet – Jakarta
Jln. Unggul Graha Permai C12/18 Tambun – Bekasi
Jln. Villa Bukit Mas K3 Surabaya, Indonesia
Jln. Widya Chandra V/23 Kuningan Jakarta 12190 Indonesia
Joyce Handajani c/o P T Enseval Enseval Building, 4th Floor Jl Let. Jend. Suprapto Kav 4 Jakarta 10510 Indonesia
Jt. Bangka VIII A No. 28 Jakarta 12720 INDONESIA
JT.Tinumbu No.12, Ujung Pandang, Indonesia.
Kacibata No. 12 Jakarta 12740 Indonesia
Kalibata Indah Blok F/5, RT005/006 Rawajati Pancor An Jak-Sel Indonesia
Kamboja No.8, Mentent Jakarta Indonesia
Kantor Taman E 3.3 Mega Kuningan Jakarta 12950 Indonesia
Kantor Taman E. 3.3 Unit B6 & B7 Kawasan Mega Kuningan Jakarta 12950 Indonesia
Kantor Taman E.3.3 Unit B6 & B7 Kawasan Mega Kuningan Jakarta 12950 Indonesia
Kantor Taman E3.3, Unit A-3 Kawasan Mega Kuningan Jl. Mega Kuningan Indonesia 12950 Jakarta 12950 Indonesia
KAP Jimmy Budhi & Rekan Jl. Patimura No.2 Jakarta Selatan Indonesia
Kapuk Pulo No. 100 Jakarta Barat Indonesia
Karang Anyar Raya 56/B1 Kelurahan Sunter Agung, Kecamatan Sawah Besar Jakarta, Indonesia
Karang Jaya Baru E1/60 Johar Baru Jakarta Pusat Indonesia
Karet Setiabudi Park Avenue Suites Apartment #606 JL RS Aini, Jakarta 12920 INDONESIA
Karyawan Tmn. Duta MAS Blk C2/38 RT009/009 Kel. Indaya Kusuma Jakarta Barat Indonesia
Karyo Indoh Village II Blok D No 2 Bintaro Jakarta INDONEISA
Kav DK 1 Blok 84 No. 17-19 RT 001 RW 010 Jakarta Barat INDONESIA
Kav. Polri Blok A IX No. 226 Jakarta Indonesia
Kav. Polri Blok E/1222 Jakarta Indonesia
Kav. Polri Blok G No. 51 RT.009, RW.006 Jagakarsa, JAKARTA INDONESIA
Kav. Polri Blok G No. 51, RT. 009, RW. 006, Jagakarsa, Jakarta Selatan, Indonesia
Kav. Polri, Blk E1/1272, RT. 01/02 Kec. Grogol Petam, Kodya, Jakarta Barat, Indonesia
Kav. Polvi Blok D-IX/1054 RT/RW 003/001, Jelambar Grogol Petamburan Jakarta Barat, Indonesia
Kawasan Berikat Nusantara (E.P.Z) Jl. Pelabuhan Nusantara II Blok B2, Tanjong Priok Jakarta – 14310, INDONESIA
Kawasan Berikat Nusantara Block A-07 Jl. Jawa Raya 13, Cakung Cilincing Jakarta 14140 Indonesia
Kawasan BIIE Multi Guna Niaga Jl. Mahoni I No. 5 Sukaresmi, Lippo Cikarang Bekasi – 17550 Indonesia
Kayu Putih Tengah Lvb No 11 Jakarta Timur Indonesia
KB Jeruk I/1/5 RT 04/II Jakarta Barat Indonesia
Kebagusan Besar, R.T./R.W. 008/005 Kebagusan Pasar Minggu, Jakarta Selatan Indonesia
KEC KELAPA GADING BLK H4 KEL KELAPA GADING TIMUR JL. GADING KIRANA IV NO. 1 JAKARTA 14240 INDONESIA
Kedoya Albasia Raya D13-15 Tamau Kedoya Jakarta Barat INDONESIA
KEDOYA APARTMENTS BLOK N, JAKARTA BARAT, INDONESIA.
Kedoya Elok Apt N. 104 Jalan Panjang Kebun Jeruk Jakarta, Indonesia
Kedoya Garden E/35, RT.014/005 Kedoya Selatan, Jakarta Barat, Indonesia
KEL PLUIT KEC. PENJARINGAN JL PLUITT PUTRI V/8 RT 006 RW 006 JAKARTA UTARA INDONESIA
Kelapa Puan TMR II, Blk NC 3130 RT 002 RW 012 Pegangsaan II Klp Gading Jakarta Utara, Indonesia
Kelapa Sawit Raya KL/18 Kelapa Gading Jakarta Utara Indonesia
Kelapapuan Timur VII NB 7/1 Pegangsaan II, Kelapa Gading Indonesia
Kemang Club Villas, Apt A#101, JL. Kemang Selatan 1, Jakarta Selatan 12730, Indonesia
Kemang Ifi Graha A8/28 Bekasi Indonesia
Kemang Jaya Apartment Unit 1104, JL. Kemang Selatan VIII, Jakarta Selatan 12730 Jakarta Indonesia
Kemanggisan Raya, RT 015/ RW009 Palmerah, Jakarta Barat Indonesia
Kembang Elok III H3/23 Rt. 009/Rw. 006, Kembangan West Jakarta 11610 Indonesia
Kembang Murni II Blok L2/14 Puri Indah Jakarta 11610 Indonesia
Kembangan Baru III C/2 Jakarta Barat, Indonesia
Kembangan Utama Raya Blok LI/ 3B RT. 003 RW. 003 Kembangan Utara Jakarta Barat Indonesia
KENANGA NO. 71, CILANDAK TIMUR JAKARTA SELATAN 12560, INDONESIA
Kenari Golf V/82 Bukit Golf Mediterania Pantai Indah Kapuk Jakarta Utara 14470 Indonesia
Kencana Permai RT 005/015 Kel. Pondok Pinang Jausel Indonesia
Kepa Duri Blk, G 1/143 Duri Kepa, Kebon Jeruk Jakarta Barat Indonesia
Kertajaya Indah Timur 8/21 Surabaya Indonesia
Ketupa 6, Surabaya Indonesia
KH Naim 1 No A17, RT/RW 005/11, Cipete Utara Jakarta Selatan 12150, Indonesia.
Klampis Ngasem 152 Surabaya – Indonesia
Klampis Semolo Barat X/30 RT 03 RW 10 Surabaya Indonesia
Kombes Pol Duryat No. 12 Kediri Indonesia
Komp Bunga Lily Kav 11 R.T./R.W. Bintaro Indonesia
Komp Citramas Indah Bok F, No. 2B, RT/RW 003/006 Batu Besar, Nongsa Batum Indonesia
KOMP DUTA HARAPAN INDAH, BLOCK P-52. JI KAPUK MUARA, NO.7 JAKARTA 14460 INDONESIA
Komp Green Ville D/24 RT09/09, Duri Kepa Jakarta Barat, Indonesia
Komp MPR No 15, Cilandak Barat Jakarta Selatan Indonesia
Komp Ruko Lodan Centre Blok Jl-2, Jakarta 14430 Indonesia
Komp TSI RT 002/002 Bandar Lampung 35228 Indonesia
Komp, Aviari Pratama No. 7 Blok E3 Jl. Batu AJ1, Batam
Komp. Bali Agung II, 003/023 Kel. Benua Melayu Darat, Pontianak Selatan, Pontianak 78122, Indonesia
Komp. Batununggal Indah Ruko No. 173 Soekamo Hatta, Bandung Indonesia
KOMP. BUKIT IDAMAN NO. 128-129 JL. CIPAKU INDAH, BANDUNG Indonesia
Komp. Bumi Indah RT03/4 Tanjung Pinang Indonesia
Komp. Bumi Pusaka Cinere Blok A/14 Jakarta Selatan Indonesia
Komp. Citra Green Garden Kav. 17 RT. 02/05 Bandung, Indonesia
Komp. Deplu Kav. 136 RT.07 RW. 07 Cipadu Jaya-Larangan Tangerang Indonesia
Komp. DKI Blok I/7 RT 003 RW 004, Joglo, Kembangan Jakarta Barat Indonesia
KOMP. DUTA MAS D5 NO. 9 GROGOL, WEST JAKARTA INDONESIA
Komp. Grawisa Blok A/1 Jakarta Barat 11460 Indonesia
Komp. Grawisa Blok A/1, Jakarta Barat, 11460 Indonesia
Komp. Green Ville Blok BJ No.5 Jakarta Indonesia
Komp. Harco Elektronick Mangga Dua Blok I, No. 5A-5B, Jl. Mangga Dua Raya Jakarta Pusat Indonesia
Komp. Kembangan Baru D/12 RT 008, RW 003, Kembangan Jakarta Barat, Indonesia
Komp. Mikasa E2 A Jakarta Selatan Indonesia
Komp. Nagoya Plaza, Lbk Baja, Batam, Indonesia
Komp. Pergudangan Muara Karang Blok B No. 12 Jl. Jembatan III Barat Jakarta Utara Indonesia
Komp. Taman Bukit Kemang Blok C No 7-8 Jakarta, Indonesia
Komp. Villa Melati Mas Blok G-2 No. 15, Serpon Tangerang 15323, Indonesia
Komp.Deplu kav. 136 RT.07/07, kel.Cipadu Jaya kec.Larangan, Tangerang – Indonesia
Kompi Villa Melati Mas Blok M8/No 25 Tangerang 15350 Indonesia
Komplek Andara No.20 JI Andara, Pondok Labu Jakarta Selatan Indonesia
Komplek BNI46 Blok GG1 Grogol Petamburan
Komplek Bonagabe Blok B-15 Jl Raya Jatinegara Timur No. 101 Jakarta 13310, Indonesia
Komplek Bpk V No. C-1 Gandul Rt/Rw 31/04 Kelurahan Desa Gandul Kecamatan Limo Kota Depok Indonesia
Komplek Bpk V No. C-1 Gandul Rt/Rw 31/40 Kelurahan/Desa Gandul Kecamatan Limo Kota Depok Indonesia
Komplek Green Garden Blok A-8 No. 1 Jl Arteri Kedova Jakarta 11520 Indonesia
Komplek Green Garden Blok A-8 No. 1 Jl. Arteri Kedoya Jakarta 11520 Indonesia
Komplek Green Garden, Blok A8/1, Jln Arteri Kedoya, Jakarta 11520, Indonesia.
Komplek Harmoni Plaza F/10 Jl. Suryopranoto No. 2 Jakarta Indonesia
Komplek Ketapang Indah Blok B2/14 Jl. K H Zainul Arifin No. 2 Jakarta 11140 Indonesia
Komplek Kota Grogol Permal G-5 Jl. Prof. Latumeten Jakarta 11460 INDONESIA
Komplek Mekar Wangi Jl. Mekar Wangi No. 9 Bandung Indonesia
Komplek Puri Indah Blok G5 No. 64 Jl. Kembang Indah Utama Jakarta 11610, Indonesia
Kompleks Apartemen Taman Rasuna 17-16-D, JI. H.R Rasuna Said Jakarta Indonesia
Kompleks Batan Blok E/2 RT 006/RW 007, Pasar Minggu Jakarta 12520 Indonesia
Kompleks Bukit Idaman No. 128 Jl. Cipaku Indah Bandung Indonesia
Kompleks Duta Mas Fatmawati Blok B, I/33 Jl. RS Fatmawati No. 39 Jakarta 12150 INDONESIA
Kompleks Golden Plaza Blok C No. 16-17, Jl. R.S. Fatmawati No. 15 Jakarta Selatan, 12420 Indonesia
Kompleks Green Garden Blok Fi No II JL Dan Mogot Jak Barat 11520 INDONESIA
Kompleks Greenville Block V/24 Jakarta Indonesia
Kompleks Mangga Dua Plaza Blok L No. 19, Jl. Mangga Dua Raya Jakarta Utara 10730 Indonesia
Kompleks Perkantoran Buncit Mas Block B-3 Jl. Mampang Prapatan Raya No. 108 Jakarta Selatan Jakarta 12790 Indonesia
Kompleks Permata Hijau Jl Boulevar Barrat No. 42 Jakarta 12210 Indonesia
Kompleks Permata Timur II Blok LL No. 4 Jatiwaringin Bekasi 17411 Indonesia
Kompleks Perumahan Cemara Asri Jalan Tulip Blok H4 No. 7 Medan – Sumatera Utara 20371 Indonesia
KOMPLEKS TAMA PUTRI HIJAU BLOCK D NO. 50 MEDAN INDONESIA
Komplex Barata Karya Nomor 442 Rukun Tetangga 07, Rukun Warga 07 Kel. Karang Tengah, Kecamatan Ciledung, Kot. Tangerang 15157, Jawa Barat, Indonesia
Komplex Grawisa Blok E/15 Jl. PTB Angke Jakarta Barat 11000 Indonesia
Komplex Grawisa Blok G/11 Jl. Tubagus Angke Jakarta 11460 Indonesia
Komplex Pakuwon r. 14 Jelambar Baru, Jakarta 11460 Indonesia
Komplex Perkantoran Duta Raya Blok F1/24, Jalan Mangga Dua Raya Jakarta 10730, Indonesia
Komplex Permata Hijau A/31 Jl. Mutiara Jakarta 12210 Indonesia
Kond. Taman Anggrek Tower IV, Unit 24F Jl. Tanjung Duren Selatan Jakarta Barat, Indonesia
Kond. Taman Anggrek, Tower 6, Unit 28H Jl. Tanjung Duren Selatan Jakarta Barat, Indonesia
Kondominium Graha Family PA-82 Surabaya 60226
Kondominium Menara Kelapa Gading F-502 Jl. Terusan Gading Timur Boulevard No. 88 Kelapa Gading, Jakarta 14250 Indonesia
Kondominium Tama Anggrek, Tow 2-32EF,RT.002,RW.007 Tanjung Duren Selatan Sub District Grogol Petamburan District, West Jakarta REPUBLIC OF INDONESIA
Kondominium Taman Anggrek, Tower 3-25D RT003/RW007 Tanjung Duren Selatan West Jakarta, Indonesia
Kondominium Taman Anggrek, Tower 7-29B RT.007, RW. 007, Tanjung Duren Selatan Sub Dist. Grogol Petamburan District, West Jakarta, Republic of Indonesia
Kondominium Wesling Kedoya B9/0905 Jl. Raya Kedoya Garden Jakarta Barat 11520 Indonesia
KONDOMINUIM TMN ANGGREK TW 8-27 D JAKARTA BARAT
Kp Srengseng RT. 012/008 Lenteng Agung, 12610 Jakarta Selatan Indonesia
KP. Muara RT. 04/RW. 01 Desa Banjaranwetan, Kecamatan Banjaran Kabupaten Bandung, Indonesia
Kp. Padabeunghar RT 02 RW 09 Bogo, Indonesia
Kp. Ros, Leuweung Klot Cibungbulan West Java
Kp. Sukadana RT/RW 01/01 Desa Cigagade, Bi Limbangan Garut Indonesia
Kuningan Village Taman Patra II No. 17 Jakarta 12950 INDONESIA
Law Office CCN & Associates Menara Imperium 12th Fl. – Suite D Jl. HR Rasuna Said Kav 1 Jakarta, 12980, Indonesia
Lembang No. 7, RT.006/RW.005 Menteng, Jakarta Pusat 10310 Indonesia
Level 22 Bank of BNI Building Jl. Jend. Sudirman Kav 1 Jakart 10220 INDONESIA
Limas V Block C2/25 Taman Kedoya Permal Jakarta 11530 Indonesia
LIMUS PRATAMA REGENCY F/6 RT09 LIMUS CILENGSI, JAWA INDONESIA
Lingkar Bima Luar Kav. 3 Bima Asri – Dukuh Bima Kota Legenda Bekasi Timur – Jawa Barat Indonesia
Lippo Centre 11th Floor J1. Gatoto Subroto Kav. 35-36 Jakarta 12950
Lippo Centre Building J1. Jend. Gatot Subroto Kav. 35-36 Jakarta
Lippo Centre, 11th Floor Jl. Gatot Subroto Kav. 35-36 Jakarta Indonesia 12950
Lippo Group Lippo Centre 10/F Asia Tower 101 Diponegoro Blvd
Lippo Group Lippo Centre Building 8th Floor J1. Jend Gatot
Lj. Kayu Putih III. C/3 R.T. 003 R.W. 006 Kelurahan Pulogadung, Kecamatan Pulo Gadung Kota J Indonesia
Lubis, Santosa & Maulana Wisma bank Dharmala, 5th Floor JI. Jend. Surdirman Kav 28 Jakarta INDONESIA
Mampang Prapatan I/32 RT/W 03/06 Mampang Prapatan Jakarta Selatan 12790, Indonesia
Mandala Barat III No. 10, Tomang Jakarta Indonesia
Mangga Besar IV E/5 R.T./R.W. 004/001 Taman Sari Jakarta Barat, Indonesia
MANGGA DUA ABDAD APARTEMENT PESONA BAHARI TOWER TO PA 2 LANTAI 19, NO. 19D JAKARTA INDONESIA
MANYAR KERTOADI BLOK W 229 SURABAYA INDONESIA
Mashill Tower 6th Floor Jl. Jend. Sudirman Kav. 25 Indonesia
Mayapada Tower, 16th Floor Jl. Jend. Sudirman Kav. 28 Jakarta 12920 Indonesia
Mediterania Garden Apt., Tower A, No. A/09B/K Jl. Tanjung Duren Raya Kav. 5-9 Jakarta 11470, Indonesia
Mega Kebon Jeruk B2/10 Joglo Jakarta Barat 11640 Indonesia
Menara Bank Danamon 15th Floor Jl. Prof. Dr. Satrio Kav. E IV No. 6 Mega Kuningan, Jakarta 12950 Indonesia
Menara Bank Mega 24th Floor Kawasan Terpadu Para Group Jl. Kapten P. Tendean Kav. 12 – 14A Jakarta 12790 Indonesia
Menara Batavia ,29th Floor, Jl. K.H. Mas Mansyur Kav 126, Jakarta 10220, Indonesia
Menara Batavia 10 Floor JI KH Mas Mansyur, Kav 126 Jakarta 10220 INDONESIA
Menara Batavia 11th Fl. Jalan KH., Mas Mansyur Kavling 126 Jakarta Pusat 10220
Menara DEA 15th Floor Suite 1505 Kawasan Mega Kuningan Jakarta Selatan 12950 Indonesia
Menara DEA, Lantai 9 Kawasan Mega Kuningan Jl. Mega Kuningan Barat IX Kav.E4, 3 NO. 1 Jakarta 12950 Indonesia.
Menara Hijau Lantai 5, JI. MT. Haryono Kav. 33 Jakarta 12770
Menara Imperium 16C Jl. HR Rasuna Said Kav. 1 Jakarta Indonesia
Menara Imperium Lt. 17 Menara Kuningan Super Blok Kav No. 1 Jl. Rasuna Said Jakarta 12980
Menara Imperium, 9th Floor, Suite B Metropolitian Kuningan Superblok Kav 1A, Jl. HR. Rasuna Said Jakarta 12
Menara Jamsostek South Tower 2nd Floor Unit TB 02-02 Jl. Jenderal Gatot Subroto No. 38 Jakarta 12710 Indonesia
Menara Jamsostek, Menara Selatan 10th Floor Jend. Gatot Subroto No. 38 Jakarta 12710 Indonesia
Menara Jamsostek, Menara Selatan 10th Floor, Jend. Gatot Subroto No. 38, Jakarta 12710 Indonesia
Menara Kadin , 23rd Floor Unit D, Jalan HR Rasuna Said Blok X-5, Lav. 2-3 Jakarta 12950, Indonesia
Menara Kadin 23rd Floor Jalan HR Rasuna Said Kav 2-3 Jakarta Selatan 12950 Indonesia
Menara Kadin 7th Floor Jl. HR Rasuna Said Blok X-5 Kav 2-3 Jakarta Indonesia
Menara Kadin Indonesia Suite 19C JI. H.R. Rasuna Said Blok X – 5, Kav. 2-3 Jakarta 12950 Indonesia
Menara Kadin Indonesia, Penthouse 11, JL.HR. Rasuna Said Blok x5 KAV 2-3 Jakarta 12950. Indonesia
Menara Kadin, 21st Floor Jl. H.R. Rasuna Said Blok X-5 Kav. 2-3 Jakarta 12950, Indonesia
MENARA KADIN, 7TH FLOOR JI. HR RASUNA SAID BLOK X-5 KAV. 1-3 JAKARTA 12950 INDONESIA
Menara Kadin, 7th Floor Jl. H. R. Rasuna Said Blok X-5 Kav. 2-3 Jakarta 12950 Indonesia
Menara Kadin, 7th Floor Jl.H.R. Rasuna Said Blok X-5 Kav. 1-3 Jakarta 12950, Indonesia.
Menara Karya 19th Floor, Unit G-H Jl. H.R. Rasuna Said Block X-5, Kav. 1-2 Jakarta 12950 Indonesia
Menara Matahari 17th Floor Palem Raya Boulever No. 7 Lippo Karawaci, Tangerang 15811 Indonesia
Menara Matahari 17th Floor, Palem Raya Boulever No. 7 Lippo Karawaci Tangerang Indonesia
Menara Mulia, 28th Flr. Penthouse Jl. Jend Gatot, Subroto Kav 9-11 Jakarta 12930 Indonesia
Menara Mulia, Suite 1701 17th Floor Jl. Jend. Gatot Subroto Kav 9-11 Jakarta 12930,
Menara Perdama, 7th Floor Jl. H.R. Rasuna Said Kav. C-17 Jakarta 12940 INDONESIA
Menara Rajawali 6th Floor Mega Kuningan Lot #5.1 Jakarta 12950 Indonesia
Menara Rajawali Lt 18 Jl. Mega Kuningan Lot 5.1 Kawasan Mega Kuningan Jakarta 12950 Indonesia
Menara Rajawali, 18 Floor Kawasan Mega Kuningan Mega Kuningan lot 5.1 Jakarta 12950 INDONESIA
Menara Standard Chartered 30/F Menara Standard Chartered Jl. Prof. Dr. Satrio Kav. 164 Jakarta 12930, Indonesia
Menara Sudirman Suite 8A, Jl. Jend Sudirman Kav 60, Jakarta 12190 Indonesia
Menara Sudirman, 19th Fl, Jl Jend, Sudirman Kav 60, Jakarta 12190, Indonesia
Mess Indah Kiat, Jl Raya Serpong KM 8 Tangerang, Indonesia
Metro Alam III/10, RT 011/016, Pondok Pinang, Jakarta Selatan Indonesia
Mid Plaza I #04-00 Jalan Sudirman Jakarta Indonesia
MidPlaza 1, Level 8 Jalan Jend. Sudirman 10-11 Jakarta 10220 Indonesia
Midplaza 2 Building 25th Floor Jl. Jend Sudirman Kav. 10-11 Jakarta 10220 Indonesia
Mitra Building 8th Floor Gatot Subroto kav 21. Jakarta 12930 Indonesia
Mitra Building 8th Floor Jalan Jendral Gatot Subroto Kav. 21 Jakarta 12930 Indonesia
Mitra Ganesha Graha Jl. Kemang Timur Raya No. 28 Jakarta 12730 Indonesia
Muara Karang Blk 6.S/16 Pluit Jakarta Indonesia
Muara Karang Blok D VI Utara No.3 Jakarta Utara Indonesia
MUARA KARANG BLOK G10 UTARA NO 11 JAKARTA INDONESIA
Muara Karang Blok Q8 Barat No. 53 Jakarta Indonesia
Muara Karang Blok U8 Utara No. 29 Jakarta Utara Indonesia
Muara Karang Blok V 7 Utara No. 33 Jakarta Utara Indonesia
Muara Karang Blok Z 8 Utara No. 16 Jakarta, Indonesia 14450
Muara Karang G. VI. B/30 RT001/RW008 Pluit, Jakarta Utara Indonesia
Muara Karang J-7 Selatan No. 20 Jakarata Utara 14450 Indonesia
Multi Trend Holdings Ltd. Jalan Sriwijaya Raya 18 Kebayoran Baru Jakarta 12110, Indonesia INDONESIA
MURA KARANG BLOK 1/X SELANTAN NO. 9 JAKARTA UTARA INDONESIA
Mutiara Mediterania D8K RT 011/005 Kel. Pluit Jakarta Utara Indonesia
N.V. Perusahaan Dagang Dan Industrie Wirontono & Co. 41 Jalan Kebon Sirih Jakarta
Ngadirojo, RT 02, RW 04, Ngadirojo Sub District, Ampel District, Boyolali Regency Republic of Indonesia
No. 14, DR. Latumeten Jakarta 11330 Indonesia
NO. 17 JL. BANYUWANGI, MENTENG JAKARTA PUSAT INDONESIA
No. 3 Chairil Anwar Medan 20152 Indonesia
No. 32 Jl. Bukit Golf II Pondok Indah Jakarta-Selatan 12310 Indonesia
No. 33 Jalan Cikini Jakarta Indonesia
NO. 39, JL. JEND A YANI KM 6.5 BANDUNG 40291 INDONESIA
No. 47 Jalan Kemang Raja Jakarta Selatan Indonesia
No. 5.1404, The Residence The Sultan Hotel Complex Jl. Gatot Subroto Jakarta 12040, Indonesia
No. 63 Jalan Berlian II Cilandak, Jakarta Selatan Indonesia
No. 64G, Jalan Lautze Jakarta, Pusat 10710 Indonesia
NO.62 JL MARGASATWA PONDOK LABO JAKARTA 12450 INDONESIA
Nuansa Hijau Apartment C11/3 Jalan Sekolah Kencana IV Pondok Indah, Jakarta Indonesia
OMAR CORPORATION Wisma Tamara Lt. 15 JI. Jend. Sudirman Kav. 24 Jakarta 12920 INDONESIA
One Seminyak Ltd. JL. Braban 98 Taman Kerobokan Bali Indonesia
Orchid Park C/ 278, Batam Indonesia
P O Box 4208 JKTM 12700 Jakarta Selatan INDONESIA
P. Jayakarta No. 11A. 001-004 Jakarta 1110, Indonesia
P.O BOX 3726, Jakarta 10037 Indonesia
P.O. Box 1072 Denpasar – 80362 Bali INDONESIA
P.O. Box 1317/JKB 11013 Jakarta Indonesia
P.O. Box 1689, Jakarta 12016 Indonesia
P.O. Box 3965 Jkt 10039 Jakarta INDONESIA
P.O. Box 8083/Smel Semarang , Central Java INDONESIA
P.T. Eurocapital Plaza Bapindo, Citibank Tower 12th Floor, Jl Jend Sudirman Kav. 54-55, Jakarta 12190, Indonesia
P.T. Stud Menara Batavia 22nd Floor Jl. KH Mas Mansyur Kav 126 Jakarta 10220 Indonesia
Paem Utama 18, RT008/007 Kel Duri Kepa, Kebon Jeruk, Jakarta Barat,
Pajajaran 59 BADUNG INDONESIA
Pakubuwono Residence Sandalwood Tower #17C JL Pakubuwono 6/68 Jakarta 12120 Indonesia
Pakubuwono Residence Unit S12D RT.003/01 Jl. Pakubuwono VI No. 68, Kebayoran Baru Jakarta 1210 Indonesia
Pakuwon Indah Villa Bukit Regensi ABL-17 Surabaya Indonesia
Pangeran Jayakarta 101 Bloc C No 6 Jakarta Pusat
Panglima Polim III No. 6 Melawai, Kebayoran Baru Jakarata Selatan 12160 Indonesia
Panglima Polin 111/8 Jakarta, Selatan 12610 Indonesia
Panorama Lebak Bulus RT 006/004 Kel. Cilandak Barat, Kec. Cilandak Jakarta Selatan, Indonesia
Pantai Kuta V/7 Ancol Jakarta 14430 Indonesia
Pantai Kuta VI No. 25 Ancol Timur Jakarta, Indonesia
Pantai Mutiara AB/6 Jakarta, Indonesia
Pantai Mutiara AD/9 Jakarta, Indonesia
Pantai Mutiara Bloh SD1Y Jakarta, Indonesia
Pantai Mutiara Blok A/51 RT001/RW016, Pluit Penjaringan Jakarta Utara, Indonesia
Pantai Mutiara Blok F/19 Jakarta Utara INDONESIA
Pantai Mutiara Blok P No. 38 RT. 007 RW. 016 Pluit Penjaringan Jakarta Utara
Pantai Mutiara Blok ZF No. 1, Jakarta Utara Indonesia.
Pantai Mutiara N/S RT 005 RW 016 Pluit Jakarta Utara INDONESIA
Pantai Mutiara P21 Jakarta Utara Indonesia
Parang Tritis 4 No. 7 Jakarta Utara Indonesia
Pasir Kaliki 155 Bandung Indonesia
Patra Jasa Bldg Suite 903/905 Jl. Gatot Subroto Kav. 32-34, Jakarta Indonesia
Patra Kuningan M. 4 Kasv. 4RT 003/004 Kel. Kuningan, Timur Jakarta Timur Indonesia
Patra Kuningan M.4, Kav. 4 RT 003/004, Kel. Kuningan Timur Jakarta Selatan Indonesia
Patra Kuningan Raya 1M 7/4, Rt. 005/04, Kuningan Jakarta Selatan
Patra Kuningan Raya RT-005/004 Kuningan Timur, Jakarta Selatan
Pd Bambu Asri Raya G-3/29 RT002/RW009, Pondok Bambu Duren Sawit, Jakarta Timur Indonesia
Pejaten Barat IV/18B Jakarta Selatan Indonesia
Pejaten Elok D/7 RT003/007 Pejaten Barat Jakarta Selatan Indonesia
Peranata Hijau Blok B No 32 Jakarta Salatan 12210
Perkantoran Roxymas Jl. K.H. Hasyim Ashari KAV. 125B Blok C 2 no. 27 – 34 Jakarta 10150 Indonesia.
Perkantoran Taman A-9 Unit B Lantal 1-3 Jl. Mega Kuningan, H.R. Rasuna Said Jakarta 12950 INDONESIA
Permata Hijau Blok F III/56 RT 019/010 Grogol Utara, Keb. Lama Jakarta-Sel Indonesia
Permata Hijau Blok G56 Jakarta 12210 Indonesia
Permata Hijau 1/29 RT 019/010, Grogol Utara Jakarta Selatan Indonesia
Permata Hijau A48 Jakarta Selatan Indonesia
Permata Hijau Blk G. No. 42 RT008/013 Grogol Utara Jakarta Selatan Indonesia
Permata Hijau Blk U/6 RT. 014/002 Grogol Utara, Indonesia
Permata Hijau BLK X / Kav C, RT / RW : 002 / 02, Grogol Utara Kebayoran Lama, Jakarta Selatan, Indonesia
Permata Hijau Blk. A/48 Kel. Grogol Utara Jakarta Selatan Indonesia
Permata Hijau Blok 12/12 Jakarta Selatan Indonesia
PERMATA HIJAU BLOK D 41/42 RT 009/008, KEL. GROGOL UTARA KEC. KEBAYORAN LAMA, JAKARTA Selatan, Indonesia
Permata Hijau Blok D/25 Jl. Mas Murni, Jakarta Selatan Indonesia
Permata Hijau Blok G/20 Grogol Utara, Kebayoran Lama Jakarta Selatan Indonesia
Permata Hijau Blok I/2119. RT. 004/001 Grogol Utara, Jakarta Selatan, Indonesia
Permata Hijau Blok O/1, RT 006/001 Grogol Utara Kebayoran Lama Jakarta Selatan Indonesia
Permata Hijau Bok F5, RT 19/10 Grogol Utara, Jakarta Selatan, Indonesia.
Permata Hijau F/74 Jakarta Selatan Indonesia
Permata Hijau R/13 RT008 RW002 Grogol, Indonesia
Permata Intan II Blok S2/1 Permata Hijau Jakarta Selatan 12210 Indonesia
Permata Intan IV X/V, 002/002 Grogol Utara Kebayoran Lama, Jakarta Selatan Indonesia
Permata Intan V/2.5 Grogol Utara Jakarta Indonesia
Permata Plaza 8th Floor Jl. MH Thamrin No. 57 Jakarta 10350 Indonesia
Permaya Hidan Block E No.19 Dakarya Selatan , Indonesia
Permaya Hidan Block, No. 19 Dakarya Selatan , Indonesia.
Pertamina Head Office, 19th Floor Jl. Merdeka Timur 1A Jakarta 10110, Indonesia
Perum Citra 2A-5/17 RT001 RW012 Jakarta Indonesia
Perum, Graha Family Blok E/No. 3 Surabaya 60226 Indonesia
Perumahan Cendrawasih Permai no.88 Samarinda 75117, Indonesia
Perumahan Citra 2 Blok D 6/14 Kel. Pegadungan Jakarta Pusat Indonesia
Perumahan Eramas 2000 Blok E4 No. 10 Kelurahan Pulo Gebang Cakung Jakarta Timur Indonesia
Perumahan Graha Famili Blok E, No. 3 Surabaya, Indonesia
Perumahan Kelapa Gading Permai, Jl. Janur Elok IX Blok QH 9 No. 1 Jakarta, Indonesia
Perumahan Permata Nusa Dua Blok IV No. 12, Nusa Dua, Bali, Indonesia 80363
Perumahan Puri Indah Jl. Kembang Sakti Timur Raya Blok D-9 No. 34 Jakarta Barat
Pesona Den Haaq Kota Wisata Jakarta Indonesia
PESONA KAYANGAN CM 4 DEPOK – JAWA BARAT INDONESIA
Petemon Barat 173 Surabaya 60253 Indonesia
Pinang Merah Blok P5, RT 001, Rukun Warga 016, Kelurahan Cinipang Muara Kecamatan Jatinegara, Jakarta Timur, Jakarta, Indonesia
PLAZA 89 9TH FLOOR JL. H.R. RASUNA SAID KAV X-7 NO. 6 JAKARTA 12940 INDONESIA
Plaza 89, Fl 10 Suite 1006 Jl. H. R. Rasuna Said Kav. X-7, No. 6 Jakarta 12940 Indonesia
PLAZA ABDA 7th FLOOR ZONE D JL. Jenderal Sudirman Kav. 59 Jakarta 12190 INDONESIA
Plaza Bapindo, Bank Mandiri Tower, Lantai 18, Jl. Jenderal Sudirman Kav 54-55, Jarkarta 12190 Indonesia
Plaza Bapindo, Citibank Tower 12th floor JI. Jenderal Sudirman Kav. 54-55 Jakarta 12190 Indonesia
Plaza Bapino, Menara II, 21st Floor JL Jend. Sudirman Kav. 54-55 Jakarta 12190 INDONESIA
Plaza BII Menara II Jl M H Thamrin NO. 51, Kav. 22 Jakarta 10350 Indonesia
Plaza BII Menara II, 7th Floor Jl MH Thamrin no 51 Kav. 22 Jakarta 10350 Indonesia
Plaza BII Tower II, 7th Floor Jalan M.H. Thamrin No. 51 Jakarta 10350, Indonesia HP: 6281-REDACTED
Plaza BII, Tower 2, 36th Floor, J1. M.H. Thamrin, Kav. 22, Jakarta 10350 INDONESIA
Plaza Chase 24th Floor, Jln. Jend. Sudirman Kav. 21 Jakart 12920 Indonesia
Plaza Chase 6th Floor JI. Jend. Sudiman Kav. 21 Jakarta 12920 INDONESIA
Plaza Chase Podium 7th Floor Jl. Jend. Sudirman Kav. 21 Jakarta 12920 INDONESIA
Plaza Chase, 24th Floor Jl. Jend Sudirman Kav. 21 Jakarta 12920 Indonesia
Plaza DM 6th Floor, Jl. Jend. Sudirman Kav.25 Jakarta 12920 Indonesia
Plaza DM, 18th Floor Jalan Jenderal Sudiman Kav. 25 Jakarta, 12920 Indonesia
PLAZA DM, 25/F SUITE 2503 JL. JEND SUDRMAN KAV. 25 JARKARTA 12920-INDONESIA
Plaza II, Tower 2, 37th Floor Jalan M.H. Thamrin Kav. 21-22 Jakarta 10350 INDONESIA
Plaza Kebon Jeruk A-21 Jakarta
Plaza Lippo Building 11th Floor Jl. Jend. Sudirman Kav 25 Jakarta 12920 Indonesia
Plaza Mashill 20th Floor 5-2002, JL. Jend. Sudirman Kav 25, Jakarta 12920, Indonesia
Plaza Mutiara 18-19 Floor Jl Linghar Mega Kuningan KAV E 1-2 No. 12 Jakarta 12950 Indonesia
Plaza Mutiara 19th Floor Jalan Kingar, Mega Kumingan Kav. E1-2 Number 1-2 Jakarta 12950 Indonesia
Plaza Mutiara 19th Floor Jalan Lingkar Mega Kuning Kav E1-2 Jakarta 12950 Indonesia
Plaza Mutiara, 16th Floor Jl. Lingkar Mega Kuningan Kav E. 1.2 No. 1-2 Jakarta 12950, Indonesia
Plaza Pondok Indah III Blok E-7 Jl. T.B. Simatupang, Pondok Indah Jakarta Selatan, 12310 Indonesia
Plaza Sentral 14 Fl. JI. Jendral Sudirman No. 47 Jakarta 12930 Indonesia
Plemaham V/51-A, Surabaya 60261, Indonesia
Pluit Barat 6, No. 39 Jakarta Utara 14440 Indonesia
Pluit Barat V/5 RT:014/07 Jakarta Utara Indonesia
Pluit Indah Streeet No.29 Pluit North Jakarata Indonesia
Pluit Pantai Mutiara Blok P, No. 37 Pluit Jarkata Indonesia
Pluit Permai VI No. 39 Pluit Penjaringan, Jakarta Utara RT04/04, Jakarta Raya 14240 Indonesia
Pluit Putri II/7 JAKARTA INDONESIA
Pluit Raya 200 Blok E/15, Jakarta Utara 14450, Indonesia.
Pluit Sakti Raya No. 28, Rt.009, RW 007 Pluitt, Penjarinan Jakarta Utara 11450 INDONESIA
Pluit Timur Blk J5/34, RT.002, RW.009 Pluit Penjaringan Jakarta Utara Indonesia
Pluit Timur Blok V – Utara No. 59 Jakarta 14450 Indonesia
Pluit Timur Raya 38 Pluit Jakarta Utara, Indonesia
PLUIT UTARA III/ 14, R.T 002, R.W. 005, JAKARTA
PO Box 1072 Denpasar Bali
PO Box 3408 Denpasar Bali Indonesia 80034
Po Box 3426 Denpasar Bali Indonesia 80034
Pondok Bambu Permai Blok B1/29, Jakarta-Timur Indonesia
Pondok Damar Blok A-22 Perumahan Kedaton Indah Cikpupa, Tangerang Indonesia
Poris Plawad RT/RW, 02/06 Kelurahan Poris Plawad Kecamatan Cipondoh Tangerang
Pratama Capital Indonesia Bapindo Plaza, Citibank Tower 20th Floor, Jl Jend Sudirman Kav. 54-55 Jakarta 12190, Indonesia
Pregolan Bunder 32 Surabaya, East Java Indonesia
Price Water House Centre Jl. HR Rasuna Said Kav C-3 Kuningan Jakarta 12940 INDONESIA
PricewaterhouseCoopers Bldg., 8th Floor, Jalan H.R. Rasuna Said Kav C-3 Kuningan, Jakarta 12940 INDONESIA
PRISMA KEDOYA PLAZA BLOK A-10, J1 RAYA PEJUANGAN, KEL. KEBON JERUK, KEC. KEBON JERUK JARKARTA BARAT
Probolinggo Indonesia
PT ALFACO INDONESIA KOMP RUKO PURI MUTIARA BLK C-9 SUNTER AGUNG JAKARTA UTARA 14350 INDONESIA
PT Anugerahtama Bina Citra Menara Imperium Lt. 17 Jl Rasuna Said Kav. No. 1 Jakarta 12980 Indonesia
PT Anugra Cipta Investa Menara Rajawali, 18th Floor, Mega Kuningan Lot 5.1, Jarakata Jakarta akarta
PT Asia Inti Utama Menara Imperium 12nd Fl Suite C JL.H.R. Rasuna Said Kav. 1A
PT Asia inti Utama, Menara Imperium 12x Fl, Suite C, JI. HR Rasunan Said Kav 1A Jakarta 12980 INDONESIA
PT Bank DBS Indonesia Plaza Permata. 8th Floor Jl. M.H. Thamrin Kav 57 Jakarta 10350, Indonesia
PT Bira Aset Manajemen, Wisma GKBI 2nd Floor, J1. Jend Sudirman Kav. 28 Jakarta 10210 INDONESIA
PT Catur Agrodaya Mandiri Wisma Budi, 4th Floor – Suite 402 Jl. H. R. Rasuna Said Kav. C-6 Jakarta 12940, INDONESIA
PT CB Indonesia Central Plaza, 16th Floor JL Jend Sudirman No.47 Jakarta 12930 INDONESIA
PT Cikal Wana Selaras TIFA Building 5th Floor Kuningan Barat No 26, Jakarta Selatan (12710), Indonesia Indonesia
PT Ciputra Group Jaya Building, 5th Floor Jl. M-H Thamrin 12 Jakarta 10340
PT Delta Aneka Consultants & Trade 14th Floor Bank Bali Tower Jl Jend. Sudirman Kav 27 Jakarta 12920 Indonesia
PT Dewata Wibawa Sona Topas Tower 19th Floor, Jl Jend. Sudirman Kav. 26, Jakarta 12920 Indonesia
PT Duta Anggada Realty Chase Plaza Tower 21st Floor Jl. Jend Sudirman Kav. 21 Jakarta 12910 Indonesia
PT Energi Timur Jauh Menara Global 23rd Floor, Jl. Jend. Gatot Subroto Kav. 27, Jakarta 12950 Indonesia
PT Enseval 4th Floor, Enseval Building Jl. Let Jend Suprapto Kav 4 Jakarta 10510 Indonesia
PT Fas Consulting Mid Plaza 1, 9th Floor, Jl. Jend. Sudirman Kav. 10 – 11 Jakarta 10220 Indonesia
PT FAS MANAJEMEN CITRAPERDANA Century Tower 3rd Floor Suite 304 Jl H R Sasuna Said Kav X-2 No.4 Jakarta 12950
PT Ilthabi Rekatama Kantor Taman A 9 Unit C8-14 Jl Mega Kuningan Lot 8.9/9 Jakarta 12950 Indonesia
PT Indokapital Securities Plaza Chase Podium, 7th Floor J1. Jend. Sudirman Kav. 21 Jakarta 12920- INDONESIA
PT INTISAR PIRANTI MEGA Jl. Pemuda No. 103, Jakarta 13220, Indonesia
PT Multi Resources Indonesia Graha Iskandarsyah, 10th Floor Jl. Iskandarsyah Raya No. 66C Kebayoran Baru, Jakarta Selatan, 12160, Indonesia
PT Murni Ciptasentosa Jalan Ir. H. Juanda III No. 6 4th Floor, Jakarta Pusat 10120 Indonesia
PT Northstar Pacific Menara Kadin, 7th Floor Jl. H.R. Rasuna Said Blok X-5 Kav. 1-3, Jakarta 12950 Indonesia
PT Renaissance Capital Asia Menara Bank Danamon 15th Floor Jl. Prof. Dr. Satrio E.IV No. 6 Mega Kuningan Jakarta 12950 Indonesia
PT Sampoerna Strategic Sampoerna Strategic Square North Tower, 30th Floor Jl Jendral Sudirman Kav 45, Jakarta 12930 Indonesia
PT WAHAMA BERSAMA GLOBALINDO, GEDUNG BRI II SUIT 1805, JJ JEND SUDIRMAN KAV44-46, JARKARTA 10210 INDONESIA
PT Widya Global JI Haji Samali No.51 Kalibata Jakarta 12740 Indonesia
PT. Andalan Sekar Makmur Midplaza I, Jln Jend Sudirman Kav 10-11 Jakarta 10220 Indonesia
PT. Asia Kaitalindo Komoditi Berjangka Sona Topas Tower Lt. 15A Suite 15A1 Jl. Jenderal Sudirman Kav 26 Jakarta 12920 Indonesia
PT. Bineatama Kayone Lestari Jl. Raya Pajapolah Km 7. Tasikmalaya 46151 West Java, Indonesia
PT. Branta Mulia Tbk Wisma Indocement 7th Floor Jl. Jend Sudirman Kav. 70-71 Jakarta 12910 Indonesia
PT. Charoen Pokphan Indonesia Jl. Ancol Barat 8/1 Jakarta 14430 Indonesia
PT. GRAMA BAZITA Jl. Mampang Prapatan Raya Kav. 71-71 Multika Building 3fl Suite 300 Jakarta Selatan, Indonesia
PT. INTERCALLIN JL. DAAN MOGOT KM. 11, CENGKARENG JAKARTA 11710 INDONESIA
PT. Kaltimex Energi Menara Batavia, 26th Floor Unit A-26, Jl.K.H Mas Mansyur, Kav. 126 Jarkarta 10220
PT. Mega Prima Persada Sakti Perumahan Kelapa Gading Permai, Jl. Janur Elok IX Blok QH 9 No. 1 Jakarta
PT. Prima Batavia Indobulking Graha Iskandarsyah Lt.10 Jl. Iskandarsyah Raya No. 66 C Kebayoran Baru, Jakarta Selatan 12160, Indonesia
PT. Samuel Sekuritas Indonesia Menara Imperium, 11th Floor JI. H.R. Rasuna Said Kav. 1 Jakarta 12980 INDONESIA
PTB Duren Sawit Blok Q III No. 17 Jakarta Timur 13440 Indonesia
PTB Duren Sawit S.II/13, RT 002 / RW 004, Kelurahan Duret Sawit, Kecamatan Duren Sawit, Jakarta Timur, Indonesia
Pulo Mas 1 G No. II Kayu Putih, Pulo Gadung Jakarta 13210, Indonesia
Puncak Permai 2/15-17, Surabaya, Indonesia Indonesia
Puri Casablanca Apt. 3502B Ji Casablanca Jakarta Indonesia
Puri Indah Blok B1 No. 11, Jl. Kembang Asri 6, Jakarta Barat 11610
Puri Indah Mall, Jl. Puri Agung Puri Indah, 2nd Floor, #227 Jakarta Barat 11610 INDONESIA
Puri Indah Street Block A. 14 No. 21 RT.005 RW.004 Kembangan West Jakarta Indonesia
Puri Kencana Blok J3 No. 26 Kembangan Jakarta Barat Indonesia
Puri Kencana L7/3 RT007/007 Kembangan Selatan Jakarta Barat Indonesia
Pusat Niaga Roxy Mas Blk B2 No. 2 Jln K.H. Hasyim Ashari 125B Jakarta 10150 Indonesia
Pusat Niaga Roxy Mas Blok B2, No. 2 Jln KH Hasyim Ashari 125 B Jakarta 10150, Indonesia
PUSPAN RT01/07 BLULUKAN COLOMADU KARANGANYAR
RA KARTINI NO 30 MEDAN INDOENESIA
Rajawali Selatan 4 No. 35 Jakarta 10720 Indonesia
Ratu Plaza Apartment, Suite 1503 Jl. Jendral Sudirman No. 9 Jakarta 10270 Indonesia
Rawa Selatan VI No. 14 Jakarta 10550 Indonesia
RAYA PLUIT TIMUR 12-A PLUIT JAKARTA UTARA INDONESIA
Raya Tenggilis 79 SURABAYA Indonsesia 60292
Roa Malaka Selatan 35 Jakarta 11230 Indonesia
RT 005113 MPR III DALAM 3 JAKARTA SELATAN
RT. 006, RW 006 Pademangan TMR Pademangan, Jakarta Utara Indonesia
RT. 04/02 Komp. Bumi Indah, Lubuk Baja Kota, Lubuk Daja Batam
RT/RW 04/06 PERUM ANGGREK MASE/33 KOTA BATAM INDONESIA
Rudy Yusuf (Site Office) Jl. Pakubuwono VI No.76, Kebayoran Baru, Jakarta 12120 Indonesia
Ruko Bisnis Sentra B-21 Tanjung Duren, Jakarta Indonesia
Sagu No. 36, Jagakarsa, Jakarta, Indonesia
Sam ratulmugi no. 2 medan indonesia 20152
Sambas 3 No. 125 Jakarta 12130 Indonesia
Samirejo, RT/RW02/02 Desa Samirejo, Kecamatan Dawe Kebupaten Kudus, Jawa Tengah Indonesia
Sampoerna Strategic Square Tower B 26th Floor, Jl. Jend Sudirman Kav. 45-46 Jakarta 12930 Indonesia
Sanur Indah No. 37 Kelapa Gading Jakarta Utara Indonesia
Sasak No. 4 Kebon-Jeruk Jakarta 11550 Indonesia
Sekolah Duta Raya, PN 04 No. 52, Pondok Indah Jakarta, Indonesia
Sekolah Kencana 4 No. 19 Pondok Indah, Kebayoran Lama Jakarta Selatan Indonesia
Sekolah Kenlana 4 No. 19 Pondok Indah Jakarta Selatan Indonesia
Senaya Bintaro HI 9/2 Sektor 9, Pondok Pucung, Pondok Aren, Tangerang, Indonesia
Senayan Residence Tower 3, Lt. 18 B2S Jakarta Selatan, Indonesia
Senayan Residence Tower 3 Lt. 18 B2S Jakarta Selatan Indonesia
Sentra Mulia 10th Floor, Jl. HR. Rasuna Said KAV. X-6 No. 8, Jakarta 12940 INDONESIA
Setia Budhi Regency Wing I No. 38 Bandung, Indonesia
Setiabudi Atrium Bldg 3rd Floor, Suite no. 303 Jl., H.R. Rasuna Said Kav. 62, Jakarta 12920 INDONESIA
SETIABUDI ATRIUM BUILDING 5TH FLOOR (501), JL. H.R. RASUNA SAID KAV 62 JAKARTA 12920 INDONESIA
SETRA DUTA RAYA I NO:10 BANDUNG 40151 INDONESIA
SIMPANG GRAHA FAMILI 7-R/96 SURABAYA
Simprug Garden 11 BF 8.9, RT 007/003 Grogol, Jakarta Indonesia
Simprug Garden Kav. # / 16 RT 007/ RW 003, Grogol Selatan Jakarta Selatan, Indonesia
Simprug Golf 17 No. 55 Jakarta 12220 Indonesia
Simprug Golf IX Kav 140 Jakarta Indonesia
Simprug Golf VIII / J.2, RT. 003/008, Grogol Selatan, Jakarta Selatan, Indonesia
Simpruk Kav. WG 7 Jakarta Selatan Indonesia
Simpruk Terrace Apartment Blok. C 8th Floor, No. 805 Jl. Sultan Iskander Muda, Jakarta 12210 Indonesia
Simpruk Terrace Apartment Blok. D 7th Floor, No. 706 Jl. Sultan Iskandar Muda, Jakarta 12210 Indonesia
Simpruk Terrace Condominium Tower C Unit 509 Jalan Sultan Iskandar Muda Jakarta Selatan 12220 Indonesia
Simprul Teras Kondominium Suite D0306, Jl. Simprul By-Pass Arterie, 12220 Jakarta Selatan, Indonesia
Slipi Apt. Tower 1 10-D Jln. S. Parman Kav. 22-24 Jakarta Indonesia
Snabung R707 RW01 Wonotingal Candisari Semarang INDONESIA
Soebagjo Jatim Djarot Plaza DM, 17th Floor, Jl. Jend. Sudirman Kav. 25 Jakarta 12920, INDONESIA
Sona Topas Tower FL. 16 Jalan Jenderal Sudirman Kav. 26 Jakarta 12920 Indonesia
Sona Topas Tower, 12th Floor Jl. Jend. Sudirman Kav. 26 Jakarta 12920 Indonesia
Sona Topas Tower, 18th Floor Jl. Jend. Sudirman Kav. 26 Jakarta 12920 Indonesia
STR Paradise Blok F I/8-13, R.T. 001 R.W. 012 Sunter Agung, Tanjung Priok, Jakarta Utara, Indonesia
Sudirman Plaza Complex, Marein Tower 11th Floor, Jl Jend Sudirman Kav 76 – 78 Jakarta 12910 Indonesia
Sudirman Plaza, Marein 17th Floor Jalan Jenderal Sudirman Kav 76-78 Jakarta 12910 Indonesia
SUDIRMAN TOWER 19TH FLOOR JL. JEND SUDIRMAN KAV 60 JAKARTA 12190 INDONESIA
Sudirman Tower 19th Floor Jl. Jend Sudirman Kav. 60 Jakarta 12190 Indonesia
Suite 403 Gedung Pusat Niaga Arena Pekan Raya Jakarta Kemayoran Jakarta 10620 Indonesia
Sukmajaya C4/25 Depok
Sumatra No.10, Central Jakarta Indonesia
Summerville Apartment No. C101 Jl. Kelapa Gading Boulevard Jakarta Utara
Summitmas I, 17th Floor JI. Jenderal Sudirman Kav. 61-62 Jakarta 12069 Indonesia
SUNTER PARADISE F 9/21 JAKARTA UTARA, INDONESIA
Suntev Hijau II Blok BII/6 Jakarta Utara
Sutan Syahrir No. 36, RT 007, RW 005, Gondangdia, Jakarta Pusat – Indonesia
Taman Kebon Jeruk Block E1 No.13 Jakarta Indonesian
Taman Kebon Jeruk Blok F1/16, Kembangan Jakarta 11530 Indonesia
TAMAN ALPHA INDAH BLOK F4/7 RT 003/01 JOGLO JAKARTA BARAT INDONESIA
Taman Anggrek Condominium Tower 6-35G Jl. Letjen S. Parman Kav. 21 Slipi Jakarta Barat 11470 Indonesia
Taman Anggrek Condominium Tower 8 No. 31D, Tanjung Duren Jakarta Indonesia
Taman Aries E10 No. 28 Jakarta Barat, 11610 DKI Jakarta, Indonesia
Taman Aries E8/7, Meruya Jakarta Indonesia
Taman Cipulir C.I/13, RT. 009, RW.008, Sub-District of Cipadu Raya District of Larangan, Tangerang, Indonesia
Taman Duta Mas Blok B5 No.4 Rt/Rw 002/009 Kelurahan Wijaya, Kasuma, Kecamatan Grogol Petamburan Jakarta Barat
Taman Gandaria Blok A/4 Kebayoran Lama Jakarta Selatan Indonesia
Taman Gandarla F 1/12 RR 012/005 Kebayoran Lama Utara Jakarta, Indonesia
Taman Giri Loka, Blok C No. 3A Bumi Serpong Damai Tangerang 15322
Taman Golf Kav 303, Lippo Karawaci Tangerang Indonesia
Taman Harapan Baru I-2/38, Bekasi Indonesia
Taman Harapan Indah 1/14, RT03/07 Jelambar Baru Jakarta Barat, Indonesia
Taman Harapan Indah A/21, RT. 02/07, Jelambar Baru, Jakarta Barat, Indonesia
Taman Harapan Indah Blok 1 No. 7 Jalan Pangeran Tubagus Angke Jakarta 11460 Indonesia
Taman Kebon Jeruk 12, No. 13-14, RT004/RW011, Srengseng, Jakarta Barat, Indonesia
Taman Kebon Jeruk Block E1 No. 13 Jakarta Indonesian
Taman Kebon Jeruk Blok E-1 No. 27 Jakarta Barat Indonesia
Taman Kebon Jeruk Blok F1 / 16, Kembagan Jakarta 11530 Indonesia
Taman Kebon Jeruk Blok M5/20 Jakarta, Barat INDONESIA
Taman Kebon Jeruk H2/2, RT 03/11 Srengseng, Jakarta Barat, Indonesia
Taman Kebon Jeruk J14 No. 16 Jakarta 11630 Indonesia
Taman Kebon Jeruk L1 No 27 Intercon Jakarta Barat Indonesia
Taman Kebon Jeruk L1/6, Jakarta Barat, Indonesia
Taman Kebon Jeruk PI/44 Jakarta Indonesia 11630
Taman Kebon Jeruk U4/102 RT 12/03 Joglo Jakarta Barat, Indonesia
Taman Kebon Jeruk, Blok D IV No. 12A, Meruya, Jakarta 11630 Indonesia
Taman Kebon Jeruk, P4/18 Jakarta Barat Indonesia
Taman Kebun Jeruk F. I.I, RT.003, RW 010 Srengseng, Kembangan Jakarta Barat, Indonesia
Taman Kedoya Permai A2/l Jakarta Barat Indonesia
Taman Kedoya Permai Jl. Prisma Blok B-3 No. 24 Kebon Jeruk, West Jakarta Indonesia
Taman Kedoya Permai, Blok A2/1, Jakarta Barat 11530, Indonesia
Taman Kedoya, Permai A2, No. 1, RT. 005, RW. 007, Kel. Kebun Jeruk, Kec. Kebun Jeruk, Jakarta Barat, Indonesia
Taman Kemayoran Kondominium Bougenville Tower #21-03 Jakarta Kemayoran Indonesia
Taman Laguan Blok H2 No.39 Rt/Rw 004/005, Cibubur, Kel. Jati Karya Kec. Jati Sampurna, Jakarta Indonesia
Taman Lestari Indah/R3 Lebak Bulus Cilandak Jakarta Selatan
Taman Malibu Indah Blok A-1 Medan 20157 Indocnesia
Taman Meruya Ilir D5/3, RT001/02 Jakarta Barat, Indonesia
Taman Metro Alam 1 Blok PG14 No. 03 Pondok Indah, Jakarta Selantan 12310 Indonesia
Taman Metro Alam PK. 16 Pondok Indah Jakarta 12310 Indonesia
Taman Mutiara Prima Blok E/6 RT 006/05, Kelurahan Kebon Jeruk Jakarta Barat, Indonesia
Taman Patra IX/9, Rt. 005/04, Kuningan Jakarta Selatan
Taman Patra VIII No.8 Rt 005/04 Kuningan Timur Jakarta Selatan
Taman Permata Blok B 20 No. 56 RT. 01/01, Kel. Binong Kec. Curug, Tangerang Indonesia
Taman Pluit Murni 2, No. 2, RT.017, RW.004, Kelurahan Pluit, Kecamatan Penjaringan, Kotamadya Jakarta Utara, Indonesia
TAMAN POLONIA III/34 NORTH SUMATRA INDONESIA
Taman Pulo Indah,Blok P3 No. 12 RT. 017/07, Penggilingan Cakung Jakarta Timur, Indonesia
Taman Rahayu D2 No. 2 Bandung Indonesia
Taman Raja Apartment A703 Jl. Warung Jati Barat I Warung Buncit Jakarta Selatan 12740, Indonesia
Taman Rasuna Apartment, Unit 0626D RT005/RW010, Menteng Atas Setiabudi Jakarta Selatan Indonesia
Taman Ratu Block BB II No.17 RT.006 RW.001 Kedoya West Jakarta Indonesia
Taman Ratu Blok E1 No. 12 Duri Kepa, Jakarta 11510 Indonesia
Taman Ratu Indah C.II/6, RT.004, RW.013 Duri Kepa Sub District Kebon Jeruk District, West Jakarta Republic of Indonesia
Taman Resort Mediterania Z3 No. 11 RT 002/008, Kel Kapuk Muara Kec. Penjaringan, Jakarta 14460 Indonesia
Taman Sari 56S Jakarta Indonesia
Taman Sari 56S Jakarta Indonesia
TAMAN SARI PESONA BALI JLN.C1 RENDEV RAYA 46 C. 1/18, TANGERANG, INDONESIA
Taman Semanan Indah Blok, C3/43, Kelurahan Semanan, Kalideres, Jakarta Barat, Indonesia
Taman Sunter Agung II Blok E/1A Jakarta Utara Indonesia
Taman Surya 2 B4/38 Cengkareng Indonesia
Taman Surya 5 Blok 00.4/34 Pegadungan, Kalideres Jakarta Barat, Indonesia
Taman Surya Blok C No. 27 Grogol Petamburan Jakarta Indonesia
Taman Surya II/09 Rt. 007/05, Kedoya Utara Kebon Jeruk Jakarta Barat
Taman Surya V Blk 004/24 RT. 008/02, Pegadungan-Kalideres Jakarta Barat Indonesia
Taman Tanah Abang III/28 RT002/004, Jakarta Indonesia
Tamara Center 12th Floor, NO. 1212 JL Jendral Sudirman Kav No. 24 Jakarta 12920 Indonessia
TAMARA CENTRE, 7/F RM. 701. JEND SUDIRMAN KAV. 24 JARKARTA 12910 INDONESIA
TAMPAK SIRING INDAH NO. 2 BUKIT GADING VILLA KELAPA GADING JAKARTA UTARA JAKARTA INDONESIA
Tanjung Duren Utara III C/222 RT 09/RW03, Grogol Petamburan Jakarta Barat, Indonesia
Tanjung Sadari 23, Surabaya Indonesia
Tebet Barat Dalam IV No. 10 Jakarta 12810 Indonesia
TEBET BARAT VI A/26, RT 011/004 TEBET JARKARTA SELETAN INDONESIA
Tebet Timur Dalam VIII I No. 2 Jakarta Selatan Indonesia
Tebet Timur Dalam Vll/ll, Rt. 04 RW. 06 Tebet Timur, Jakarta Selatan, Indonesia
Terusan Hang Lekir IV 32-33 RT 005/RW 008, Grogol Selatan, Kebayoran Lama, Jakarta, Indonesia
Tg. Duren Timur No. 27 RT/RW 004/006 Tg Duren Selatan Jakarta Barat Indonesia
The Ascott Jakarta, Condo. #1724 Jl. Kebon Kacang Raya, Jakarta 10240 Indonesia
The Pakubuwono Residence Eaglewood Tower Unit 11A Jl Pakubuwono VI No. 68 Kebayoran Baru, Jakarta 12120, Indonesia
TM KEB JERUK 1-77 JAKARTA BARAT INDONESIA
TMN Bona Indah Blk C 1/20 010/006, Lebak Bulus Cilandak, Jakarta Selatan Indonesia
Tmn Harapan Indah, A21 Jakarta Indonesia
TMN KB Jeruk Blok G 1/5 Jakarta Barat Indonesia
TMN KEBON JERUK A IV/15 RT 10/01 MERUYA SELATAN JAKARTA BARAT INDONESIA
Tmn. Duta MAS C2/38 RT 16/09 Fec. Grogol Petam. Fodya Jakarta Barat Indonesia
Tomang Pulo Macan Raya 50, 012/005 Tomang, Grogol Petamburan, Jakarta Barat, Indonesia
Tomang Rawa Kepa IX/71 RT 008 RW 012 Jakarta Barat INDONESIA
Tower VI Jend Sudirman Kav.26 Jarkata INDONESIA
Trisakti University Kampus A Universitas Trisakti Jl. Kyai Tapa Grogol Jakarta 11440 Indonesia
Unit 1206 Residences At Dharmawandsa Jalan Darmawangsa V111 Jakarta 12160 Indonesia
Untung Suropati No. 58 Surabaya Indonesia
Urio Sumoharjo #151 Solo 57128 Indonesia
Utama Tengah No. 111 Weleri, Jawa Tengah, Indonesia
V No. 21C 009/005 Bangka Mampang Prapatan Jakarta Selatan Indonesia
Victoria Building 3rd Floor Suite 304 Jalan Sultan Hasanudin Kavling 47-51 Jakarta 12160 Indonesia
Villa Bintaro Regency Jl Sumatra Blok K1.12B Tanooerang 18228 Indonesia
Villa Pamcelang, Blok DF1/16 Pondok Benda, Tangerang Indonesia
Villa Pamulang, Blok DF 1/16 RT / RW 06/19, Pondok Benda Pamalang, Tangerang Indonesia
Villa Pan B.L. Jalan Ahmad Yani Block E/37 Batam 29433 Indonesia
Villa Pejaten No. 9 RT 012 RW 005, Pajaten Barat Jakarta Selatan Indonesia
Villa Taman Juanda, Jl. Ir. H. Juanda Type Emerald Blok 16-F, Medan 20157 Indonesia
Villa Tirta Naga, Gang Kahyangan No. 2 Jl. Lesmana, Kuta, Bali, Indonesia
Villa Tomang Mas A-6 Kepa Duri, Jakarta 11510 Indonesia.
Wangsa Ningrat No 15 Kota Baru Parahyangan Bandung Indonesia
Wangsasetra Wetan No 18 Kota Baru Parahyangan Bandung Indonesia
WIDYA CHANDRA VII/7 SENAYAN, JAKARTA INDONESIA
WIDYA CHANDRA VIII, SENAYAN INDONESIA
Wijaya Graha Puri, Blok B No. 16 Jl. Darmawangsa III, Kebayoran Baru Jakarta 12160 Indonesia
Wijaya Kusuma 24, Surabaya Indonesia
Wisma 46 (Kota BNI) 9th Floor Jl Jendral Sudirman Kav 1 Jakarta 10220 Indonesia
Wisma 46 – Kota BNI, 8th Floor Jl. Jend Sudirman Kav.1, Jakarta 10220 Indonesia
Wisma 46 – Kota BNI, 8th Floor Jl. Jend. Sudirman Kav. 1 Jakarta 10220 Indonesia
Wisma 46, Kota BNI Level 43, Jl. Jend. Sudirman Kav 1 Jakarta 10220 Indonesia
Wisma 46-Kota BNI 34th Fl. S.3401 Jalan Jend. Sudirman Kav. 1 Jarkarta 10220 – Indonesia
Wisma 46-Kota BNI, 8th Floor Jl. Jend. Sudirman Kav.1 Jakarta 10220 Indonesia
Wisma 76, Lt. 21, Jl. Jend S. Parman Kav. 76, Slipi Jakarta Barat 11410 Indonesia
Wisma 77, 7th Floor Jl. Letjen S. Parman Kav. 77 West Jakarta Indonesia
Wisma Bakri, Fl3, Jl. H. R. Rasuna Said Kav. B-1, Jakarta 12920 Indonesia
Wisma Bakrie 2, Jl. HR. Rasuna Said Kav. B2 Kuningan, Jakarta Selatan 12210 Indonesia
Wisma Bakrie 6th Floor Jl. H. R. Rasuna Said Kav. B-1 Jakarta 12920 INDONESIA
Wisma Bakrie, Fl 3 Jl H. R. Rasuna Said Kav. B-1 Jakarta 12920 Indonesia
Wisma Bank Danamon 16th Floor Jl. Jend. Sudirman Kav. 45-46 Jakarta 12930 Indonesia
Wisma Bank Dharmala 21st Floor Jl. Jenderal Sudirman Kav. 28, Jakarta Selatan 12920 Jakarta INDONESIA
Wisma Bank Tiara Jl M. T. Haryono, Kav 16 Jakarta 12810, Indonesia
Wisma Bank Tiara, 8th Floor, Jalan M.T Haryano Kav.16 Jarkarta 12810 Indonesia
Wisma Barito Pacific Tower A-4th Floor, Jl Letjen S Parman Kav 62-63 Jakarta 11410, Indonesia
WISMA CIKINI – JL. GONDANGDIA LAMA 40 JAKARTA 10350 INDONESIA
Wisma Danamon Aetna Life 6th Floor, Jl. Jend. Sudirman Kav. 45-46, Jakarta 12930 INDONESIA
Wisma Eka Karma Jl. Kapten Tendean No. 15 Jakarta 12790 Indonesia
Wisma Eka Karma Jl. Kapten Tendean No.15 Jakarta 12790 Indonesia
Wisma GKBI 17th Floor Suite 1715 Jalan Jend Sudirman No. 28 Jakarta Indonesia
Wisma GKBI, 6th Floor Jl. Jend Sudiraman Kav. 28 Jakarta 10210 Indonesia
Wisma GKBI, Mezzanine A Floor Jl. Jendera, Sudirman No 28 Jakarta, 10210 Indonesia
Wisma Grant Thornton Jl. Sisingamangaraja No. 3C Jakarta 12120 INDONESIA
Wisma Indocement, 6th Floor Jalan Jenderal Sudirman Kav. 70-71 Jakarta 12910, Indonesia
Wisma Indosemen 6th Floor JI. Jenderal Sudirman Kav-70-71 Jakarta 12910 Indonesia
Wisma Indosemen 6th Floor JI. Jenderal Sudirman Kav-70-71 Jakarta, 12910 Indonesia
Wisma Indovision, 11th Floor Jalan Raya Panjang Block Z/III Green Garden Jakarta 11520 Indonesia
Wisma Kosogoro 16 Floor Jl. MH Thamrin No. 53 Jakarta 10350 Indonesia
Wisma Kyoei Price 15th Fl. Jl. Jend Sudirman Kav. 3 Jakarta 1220 Indonesia
Wisma Kyoei Prince Building 7th Floor, Jl. Jend. Sudirman Kav. 3 Jakarta Pusat 10220 Indonesia
Wisma Metropolitan II 2nd Floor J1. Jend., Sudirman Kav. 29-31 Jakarta 12920
Wisma Metropolitan II 2nd floor, Jl. Jend. Sudirman Kav. 29-31 Jakarta 12920 INDONESIA
Wisma Metropolitan II Level 1 & 11, Jalan Jend Sudirman Kav.29-31 Jarkata 12920 INDONESIA
Wisma Metropolitan II, 1/F JLn. Jend Sudirman Kav 29-31 Jakarta Indonesia
Wisma Millenia 7th Floor, Jln. MT Haryono Kav 16, Jakarta 12810 Indonesia.
Wisma Mulia 23rd Floor Jln. Jend. Gatot Subroto Kav.42 Jakarta 12710
Wisma Mulia 27th Floor, Jl. Jend. Gatot Subroto No. 42, Jakarta 12710, Indonesia
Wisma Mulia 33rd FLOOR, Jl. Jend. Gatot Subroto No. 42, Jakarta 12710 INDONESIA
Wisma Mulia LT 29 Jl. Jend Gatot Subroto No. 42, Kel. Kuningan Barat Kec. Mampang Praptan Jakarta Selatan, Indonesia
Wisma Mulia, 21st Floor Jln. Jend. Gatot Subroto No. 42 Jakarta 12710 Indonesia
Wisma Mulia, 33rd Floor Jln. Jend. Gatot Subroto No. 42 Jakarta 12710 INDONESIA
Wisma Nugra Santana 3rd Floor Jl Jend. Sudirman Kav. 7 Jakarta 10220, Indonesia
Wisma Nugra Santana Suite 1207 JL. JEND., Sudirman KAV. 7-8, Jakarta 10220 Indonesia
Wisma Paramuda 2nd Floor Jalan Raden Saleh No. 41 Jakarta 10330 Indonesia
Wisma Permai Barat EE 34 Mulyorejo Surabaya 60115 Indonesia
Wisma Pondok Indah 2 17th Floor, Suite 1702 Jl. Sultan Iskandar Muda Kav. V-TA Jakarta 12310, Indonesia
Wisma Pondok Indah 2, 17th Floor, Suite 1702 Jl. Sultan Iskandar Muda Kav. V-TA Jakarta 12310 Indonesia
Wisma Pondok Indah Suite 203 Jalan Sultan Iskandar Muda Kav V-TA Jakarta 12310, Indonesia
Wisma Sakura Jl. Hati Suci No. 4 Jakarta 10250 Indonesia
Wisma Sejahtera 2nd Floor, Room 210, Jl. Let. Jend. S. Parman Kav. 75, Jakarta 11410, Indonesia
Wisma Supra, Menara 76, Lt. 21 Jl. Let Jend S Parman, Kav. 76 Jakarta Barat – 11410 Indonesia
Wisma Tamara- Annexed Building Jl.Jenral Sudirman Kav.No.24 Jakarta 12920 INDONESIA
Witono Dani Jl. Duta permai III/6 Jakarta Selatan 12310 Indonesia
Wolter Monginsidi 64C Kebayoran Baru Jakarta 12170 Indonesia
Wonorejo Permai Utr 7/86 BB 556 RT 003 / RW 009, Kelurahan Wonorejo Kecamatan Rungkut Surabaya 60296 Indonesia
Wonorejo Permat Selatan 6/26 Surabaya – Indonesia
World Trade Center 15th Floor Jl Jend. Sudirman Kav. 29-31 Jakarta 12920, Indonesia
World Trade Center 17th Floor JI> Jend. Sudirman Kave. 29 Jakarta 12920 Indonesia
World Trade Centre, 12th Floor J1. Jend. Sudirman Ka. 29-31 Jakarta 12920 INDONESIA
World Trade Centre, 17th Floor Jl. Jend Sudirman KAV. 29 – 31 Jakarta 12920 Indonesia
Wr. Supratman No. 7 Surabaya INDONESIA


















































































 Die Menschen in Belarus haben ihre Wahl getroffen” Die belarussische Oppositionskandidatin Svetlana Tikhanovskaya fordert ein Ende der Proteste in verdächtigen Videos, die online geteilt werden.
Die Menschen in Belarus haben ihre Wahl getroffen” Die belarussische Oppositionskandidatin Svetlana Tikhanovskaya fordert ein Ende der Proteste in verdächtigen Videos, die online geteilt werden.





![[Image]](https://cryptome.org/2020-info/pict96.jpg)
![[Image]](https://cryptome.org/2020-info/pict97.jpg)
![[Image]](https://cryptome.org/2020-info/pict99.jpg)
![[Image]](https://cryptome.org/2020-info/pict100.jpg)
![[Image]](https://cryptome.org/2020-info/pict101.jpg)
![[Image]](https://cryptome.org/2020-info/pict102.jpg)
![[Image]](https://cryptome.org/2020-info/pict103.jpg)
![[Image]](https://cryptome.org/2020-info/pict104.jpg)
![[Image]](https://cryptome.org/2020-info/pict105.jpg)
![[Image]](https://cryptome.org/2020-info/pict106.jpg)
![[Image]](https://cryptome.org/2020-info/pict107.jpg)
![[Image]](https://cryptome.org/2020-info/pict108.jpg)
![[Image]](https://cryptome.org/2020-info/pict109.jpg)
![[Image]](https://cryptome.org/2020-info/pict110.jpg)
![[Image]](https://cryptome.org/2020-info/pict95.jpg)
![[Image]](https://cryptome.org/2020-info/pict87.jpg)
![[Image]](https://cryptome.org/2020-info/pict88.jpg)
![[Image]](https://cryptome.org/2020-info/pict89.jpg)
![[Image]](https://cryptome.org/2020-info/pict90.jpg)
![[Image]](https://cryptome.org/2020-info/pict91.jpg)
![[Image]](https://cryptome.org/2020-info/pict92.jpg)
![[Image]](https://cryptome.org/2020-info/pict93.jpg)
![[Image]](https://cryptome.org/2020-info/pict94.jpg)
![[Image]](https://cryptome.org/2020-info/pict76.jpg)
![[Image]](https://cryptome.org/2020-info/pict77.jpg)
![[Image]](https://cryptome.org/2020-info/pict78.jpg)
![[Image]](https://cryptome.org/2020-info/pict79.jpg)
![[Image]](https://cryptome.org/2020-info/pict80.jpg)
![[Image]](https://cryptome.org/2020-info/pict81.jpg)
![[Image]](https://cryptome.org/2020-info/pict82.jpg)
![[Image]](https://cryptome.org/2020-info/pict83.jpg)
![[Image]](https://cryptome.org/2020-info/pict84.jpg)
![[Image]](https://cryptome.org/2020-info/pict85.jpg)
![[Image]](https://cryptome.org/2020-info/pict86.jpg)
![[Image]](https://cryptome.org/2020-info/pict68.jpg)
![[Image]](https://cryptome.org/2020-info/pict69.jpg)
![[Image]](https://cryptome.org/2020-info/pict70.jpg)
![[Image]](https://cryptome.org/2020-info/pict72.jpg)
![[Image]](https://cryptome.org/2020-info/pict73.jpg)
![[Image]](https://cryptome.org/2020-info/pict74.jpg)
![[Image]](https://cryptome.org/2020-info/pict65.jpg)
![[Image]](https://cryptome.org/2020-info/pict66.jpg)
![[Image]](https://cryptome.org/2020-info/pict67.jpg)
![[Image]](https://cryptome.org/2020-info/pict63.jpg)
![[Image]](https://cryptome.org/2020-info/pict54.jpg)
![[Image]](https://cryptome.org/2020-info/pict55.jpg)
![[Image]](https://cryptome.org/2020-info/pict56.jpg)
![[Image]](https://cryptome.org/2020-info/pict57.jpg)
![[Image]](https://cryptome.org/2020-info/pict58.jpg)
![[Image]](https://cryptome.org/2020-info/pict59.jpg)
![[Image]](https://cryptome.org/2020-info/pict60.jpg)
![[Image]](https://cryptome.org/2020-info/pict61.jpg)
![[Image]](https://cryptome.org/2020-info/pict12.jpg)
![[Image]](https://cryptome.org/2020-info/pict13.jpg)
![[Image]](https://cryptome.org/2020-info/pict8.jpg)
![[Image]](https://cryptome.org/2020-info/pict9.jpg)
![[Image]](https://cryptome.org/2020-info/pict10.jpg)
![[Image]](https://cryptome.org/2020-info/pict11.jpg)
![[Image]](https://cryptome.org/2020-info/pict4.jpg)
![[Image]](https://cryptome.org/2020-info/pict5.jpg)
![[Image]](https://cryptome.org/2020-info/pict6.jpg)
![[Image]](https://cryptome.org/2020-info/pict7.jpg)
![[Image]](https://cryptome.org/2020-info/pict0.jpg)
![[Image]](https://cryptome.org/2020-info/pict3.jpg)
![[Image]](https://cryptome.org/2020-info/pict14.jpg)
![[Image]](https://cryptome.org/2020-info/pict15.jpg)
![[Image]](https://cryptome.org/2020-info/pict16.jpg)
![[Image]](https://cryptome.org/2020-info/pict17.jpg)
![[Image]](https://cryptome.org/2020-info/pict52.jpg)
![[Image]](https://cryptome.org/2020-info/pict53.jpg)
![[Image]](https://cryptome.org/2020-info/pict18.jpg)
![[Image]](https://cryptome.org/2020-info/pict19.jpg)
![[Image]](https://cryptome.org/2020-info/pict20.jpg)
![[Image]](https://cryptome.org/2020-info/pict21.jpg)
![[Image]](https://cryptome.org/2020-info/pict44.jpg)
![[Image]](https://cryptome.org/2020-info/pict45.jpg)
![[Image]](https://cryptome.org/2020-info/pict46.jpg)
![[Image]](https://cryptome.org/2020-info/pict47.jpg)
![[Image]](https://cryptome.org/2020-info/pict48.jpg)
![[Image]](https://cryptome.org/2020-info/pict49.jpg)
![[Image]](https://cryptome.org/2020-info/pict50.jpg)
![[Image]](https://cryptome.org/2020-info/pict51.jpg)
![[Image]](https://cryptome.org/2020-info/pict43.jpg)
![[Image]](https://cryptome.org/2020-info/pict39.jpg)
![[Image]](https://cryptome.org/2020-info/pict40.jpg)
![[Image]](https://cryptome.org/2020-info/pict41.jpg)
![[Image]](https://cryptome.org/2020-info/pict42.jpg)
![[Image]](https://cryptome.org/2020-info/pict35.jpg)
![[Image]](https://cryptome.org/2020-info/pict36.jpg)
![[Image]](https://cryptome.org/2020-info/pict37.jpg)
![[Image]](https://cryptome.org/2020-info/pict38.jpg)
![[Image]](https://cryptome.org/2020-info/pict27.jpg)
![[Image]](https://cryptome.org/2020-info/pict28.jpg)
![[Image]](https://cryptome.org/2020-info/pict29.jpg)
![[Image]](https://cryptome.org/2020-info/pict30.jpg)
![[Image]](https://cryptome.org/2020-info/pict23.jpg)
![[Image]](https://cryptome.org/2020-info/pict24.jpg)
![[Image]](https://cryptome.org/2020-info/pict25.jpg)
![[Image]](https://cryptome.org/2020-info/pict26.jpg)





 Am 5. Mai 2020 berichteten deutsche Medien, dass die deutsche Bundesanwaltschaft einen Haftbefehl gegen den russischen Staatsbürger Dmitry Badin erlassen hat, den Hauptverdächtigen beim Hacking des Deutschen Bundestages im Jahr 2015.
Am 5. Mai 2020 berichteten deutsche Medien, dass die deutsche Bundesanwaltschaft einen Haftbefehl gegen den russischen Staatsbürger Dmitry Badin erlassen hat, den Hauptverdächtigen beim Hacking des Deutschen Bundestages im Jahr 2015.


















































 GRU Zentrale in Moskau
GRU Zentrale in Moskau


















 Above: M113 armored personnel carriers move through the town of Stockhausen (Herbstein) during REFORGER ’83 in Germany.
Above: M113 armored personnel carriers move through the town of Stockhausen (Herbstein) during REFORGER ’83 in Germany.
 Above: Cover page from the HA III copy of the Project RYaN catalog of indicators.
Above: Cover page from the HA III copy of the Project RYaN catalog of indicators.









![[Image]](https://i0.wp.com/cryptome.org/michael-sorkin.jpg)






 OO F. l'onnHH c (Mu.:112 0 14)
Instructions for Part 1
Note· This is a form Does not include account numbers street addresses or family member names See instructions for required Information
Filer's Nnme
IPage Number
Donald J. Trump
I
Pnrt 1: Filer's Positions Held Outside United States Government
IOrgnnizntlon Nnme
•
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
ICily/Stntc
IOrgnnlzntlon Type
IPosition Hehl
I
3 of51
From
I
To
DT Dubai II Golf Manaaer LLC
NewYork NY
LLC
Member/President
10/30/14
1/19/2017
DT Dubai II Golf Manaaer Member Coro
NewYork NY
Cornoralion
Director/Chairman/President
10130/14
1/19/2017
DT Home Marks lnlernalianal LLC
NewYark NY
LLC
Member/President
07/12/13
111912017
DT Home Marks lnlernalional Member Caro
NewYark NY
Corooralion
1/19/2017
New Yark, NY
LLC
Director/Chairman/President
Member/President
07/12113
DT India Venture LLC
01/09/12
1/19/2017
OT India Venture Manaoina Member Coro
NewYork NY
CornoraUon
Director/Chairman/President
01/09/12
1/19/2017
DT Marks Baku LLC
DT Marks Baku Managing Member Corp
NewYork NY
LLC
04/10/12
1/19/2017
NewYark NY
Cornorallon
Member/President
Director/Chairman/President
04/10/12
1/19/2017
1/1912017
DT Marks Dubai LLC
DT Marks Dubai Member Corp
NewYork NY
LLC
Member/President
09/05/13
NewYork NY
Comoralion
09105/13
1/1912017
DT Marks Dubai II LLC
NewYork NY
LLC
10/30/14
11120/2015
DT Marks Dubai II Member Coro
NewYork NY
Comoralion
10/30/14
11/20/2015
OT Marks Gurgaon LLC
NewYork NY
LLC
OT Marks Gurgaon Menaalno Member Caro
NewYork NY
Cornoralion
OT Marks Jersey City LLC
NewYork NY
LLC
DT Marks Jupiter LLC
NewYork, NY
LLC
OT Marks Qatar LLC
NewYork NY
LLC
OT Marks Qatar Member Com
DT Marks Products International LLC
OT Marks Products International Member Corp
NewYork NY
Corooralion
New York, NY
LLC
New York, NY
Corporalion
Director/Chairman/President
Member/President
Director/Chairman/President
Member/President
Director/ChalrmanfPresident
Member/President
Member/President
Member/President
Director/Chairman/President
Member/President
Director/Chairman/President
DT Marks Pune LLC
DT Marks Puna Managing Member Carp
NewYork NY
LLC
Member/President
New York, NY
Corporation
DT MARKS PUNE Ii LLC
NewYork NY
LLC
DT Marks Pune II Managing Member Corp
New York, NY
Corporation
DT Marks Rio LLC
New York, NY
LLC
OT Marks Rio Member Corp
NewYark NY
OT Marks Vancouver LP
OT Marks Vancouver Manaaer Corp
NewYork, NY
Corporation
Partnership
Corporation
DT Marks Warli LLC
NewYark. NY
New Yark, NY
OT Marks Worli Member Corp
DT Tower Gurgaan LLC
NewYork NY
LLC
Corporation
OT Tower Guraaon Manaaina Member Corp
New York, NY
New York, NY
LLC
Corporation
DTW Venture LLC
New York, NY
LLC
DTW Venture Manaaing Member Coro
New York, NY
Corporation
East 61 SI Campany, L.P., The
New York, NY
Partnership
EID Venture I LLC
NewYark. NY
NewYork, NY
LLC
EID Venture I Corporation
Excel Venture I LLC
Excel Venture I Corp.
Fifty Seven Manaaement Corp
Fifty Sevenlh Street Associates LLC
First Member, Inc.
Corporation
St. Martin, French West lndi
LLC
SI. Martin French West lndi
NewYark NY
Corporation
Corporation
NewYark NY
LLC
NewYark NY
Corporation
Corporation
Flights, Inc. {Formerly Trump Flights, Inc.)
NewYark NY
Florida Properties Management LLC
Fontainbleu Apartments LLC
Palm Beach, Florida
LLC
New York. NY
Golf Produclions LLC
New York, NY
LLC
LLC
10/28/14
1/19/2017
10130/14
1/19/2017
10/30114
1/19/2017
08/29/14
1119/2017
10/30/14
1119/2017
10/30/14
1119/2017
09/13/13
1/19/2017
09/13/13
01/09/12
1/19/2017
1/19/2017
Director/Chairman/President
Member/President
Director/Chairman/President
Member/President
Director/Chairman/President
Partner/President
Direclor/ChairmantPresident
Member/President
Director/Chairman/President
Member/President
Director/Chairman/President
Member
Director/President
Partner
Member
PresidenUDirector
PresidenUSecretarvffreasurer/Member
Director/Chairman/President
Director/Chairman
President
01/09/12
1/19/2017
06/18/14
1/19/2017
06/18/14
1/19/2017
03/09/12
1/19/2017
03/09/12
1/19/2017
01122/13
1119/2017
01122/13
1119/2017
05/21/13
1/19/2017
05/21/13
1/19/2017
03/09/15
1119/2017
03/09/15
03/14/14
1/19/2017
03/14/14
1/19/2017
12/06/96
05/01/13
1/19/2017
05/01113
1/19/2017
07/01113
07/01113
1/19/2017
08/23/12
1/19/2017
11/30/95
1/19/2017
President
09/26/96
PresidenVfreasurer/Director
Member
Member
Member/Presidenl
07/01199
1/19/2017
1/19/2017
12/17/01
1/19/2017
11/22/95
06/16/09
1/19/2017
Gaps in numerical sequence are due to the removal of previously reported items no longer reportable on this part.
1/19/2017
1/19/2017
1/19/2017
1/19/2017
OO F. l'onnHH c (Mu.:112 0 14)
Instructions for Part 1
Note· This is a form Does not include account numbers street addresses or family member names See instructions for required Information
Filer's Nnme
IPage Number
Donald J. Trump
I
Pnrt 1: Filer's Positions Held Outside United States Government
IOrgnnizntlon Nnme
•
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
ICily/Stntc
IOrgnnlzntlon Type
IPosition Hehl
I
3 of51
From
I
To
DT Dubai II Golf Manaaer LLC
NewYork NY
LLC
Member/President
10/30/14
1/19/2017
DT Dubai II Golf Manaaer Member Coro
NewYork NY
Cornoralion
Director/Chairman/President
10130/14
1/19/2017
DT Home Marks lnlernalianal LLC
NewYark NY
LLC
Member/President
07/12/13
111912017
DT Home Marks lnlernalional Member Caro
NewYark NY
Corooralion
1/19/2017
New Yark, NY
LLC
Director/Chairman/President
Member/President
07/12113
DT India Venture LLC
01/09/12
1/19/2017
OT India Venture Manaoina Member Coro
NewYork NY
CornoraUon
Director/Chairman/President
01/09/12
1/19/2017
DT Marks Baku LLC
DT Marks Baku Managing Member Corp
NewYork NY
LLC
04/10/12
1/19/2017
NewYark NY
Cornorallon
Member/President
Director/Chairman/President
04/10/12
1/19/2017
1/1912017
DT Marks Dubai LLC
DT Marks Dubai Member Corp
NewYork NY
LLC
Member/President
09/05/13
NewYork NY
Comoralion
09105/13
1/1912017
DT Marks Dubai II LLC
NewYork NY
LLC
10/30/14
11120/2015
DT Marks Dubai II Member Coro
NewYork NY
Comoralion
10/30/14
11/20/2015
OT Marks Gurgaon LLC
NewYork NY
LLC
OT Marks Gurgaon Menaalno Member Caro
NewYork NY
Cornoralion
OT Marks Jersey City LLC
NewYork NY
LLC
DT Marks Jupiter LLC
NewYork, NY
LLC
OT Marks Qatar LLC
NewYork NY
LLC
OT Marks Qatar Member Com
DT Marks Products International LLC
OT Marks Products International Member Corp
NewYork NY
Corooralion
New York, NY
LLC
New York, NY
Corporalion
Director/Chairman/President
Member/President
Director/Chairman/President
Member/President
Director/ChalrmanfPresident
Member/President
Member/President
Member/President
Director/Chairman/President
Member/President
Director/Chairman/President
DT Marks Pune LLC
DT Marks Puna Managing Member Carp
NewYork NY
LLC
Member/President
New York, NY
Corporation
DT MARKS PUNE Ii LLC
NewYork NY
LLC
DT Marks Pune II Managing Member Corp
New York, NY
Corporation
DT Marks Rio LLC
New York, NY
LLC
OT Marks Rio Member Corp
NewYark NY
OT Marks Vancouver LP
OT Marks Vancouver Manaaer Corp
NewYork, NY
Corporation
Partnership
Corporation
DT Marks Warli LLC
NewYark. NY
New Yark, NY
OT Marks Worli Member Corp
DT Tower Gurgaan LLC
NewYork NY
LLC
Corporation
OT Tower Guraaon Manaaina Member Corp
New York, NY
New York, NY
LLC
Corporation
DTW Venture LLC
New York, NY
LLC
DTW Venture Manaaing Member Coro
New York, NY
Corporation
East 61 SI Campany, L.P., The
New York, NY
Partnership
EID Venture I LLC
NewYark. NY
NewYork, NY
LLC
EID Venture I Corporation
Excel Venture I LLC
Excel Venture I Corp.
Fifty Seven Manaaement Corp
Fifty Sevenlh Street Associates LLC
First Member, Inc.
Corporation
St. Martin, French West lndi
LLC
SI. Martin French West lndi
NewYark NY
Corporation
Corporation
NewYark NY
LLC
NewYark NY
Corporation
Corporation
Flights, Inc. {Formerly Trump Flights, Inc.)
NewYark NY
Florida Properties Management LLC
Fontainbleu Apartments LLC
Palm Beach, Florida
LLC
New York. NY
Golf Produclions LLC
New York, NY
LLC
LLC
10/28/14
1/19/2017
10130/14
1/19/2017
10/30114
1/19/2017
08/29/14
1119/2017
10/30/14
1119/2017
10/30/14
1119/2017
09/13/13
1/19/2017
09/13/13
01/09/12
1/19/2017
1/19/2017
Director/Chairman/President
Member/President
Director/Chairman/President
Member/President
Director/Chairman/President
Partner/President
Direclor/ChairmantPresident
Member/President
Director/Chairman/President
Member/President
Director/Chairman/President
Member
Director/President
Partner
Member
PresidenUDirector
PresidenUSecretarvffreasurer/Member
Director/Chairman/President
Director/Chairman
President
01/09/12
1/19/2017
06/18/14
1/19/2017
06/18/14
1/19/2017
03/09/12
1/19/2017
03/09/12
1/19/2017
01122/13
1119/2017
01122/13
1119/2017
05/21/13
1/19/2017
05/21/13
1/19/2017
03/09/15
1119/2017
03/09/15
03/14/14
1/19/2017
03/14/14
1/19/2017
12/06/96
05/01/13
1/19/2017
05/01113
1/19/2017
07/01113
07/01113
1/19/2017
08/23/12
1/19/2017
11/30/95
1/19/2017
President
09/26/96
PresidenVfreasurer/Director
Member
Member
Member/Presidenl
07/01199
1/19/2017
1/19/2017
12/17/01
1/19/2017
11/22/95
06/16/09
1/19/2017
Gaps in numerical sequence are due to the removal of previously reported items no longer reportable on this part.
1/19/2017
1/19/2017
1/19/2017
1/19/2017




![[Image]](https://cryptome.org/2020-info/agadez/pict52.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict24.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict51.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict25.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict50.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict26.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict49.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict27.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict48.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict28.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict47.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict29.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict43.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict30.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict42.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict31.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict41.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict32.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict40.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict33.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict39.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict34.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict38.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict35.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict37.jpg)
![[Image]](https://cryptome.org/2020-info/agadez/pict36.jpg)



![[Image]](https://i0.wp.com/cryptome.org/121192976-Cover.jpg)
![[Image]](https://i0.wp.com/cryptome.org/120481246.jpg)


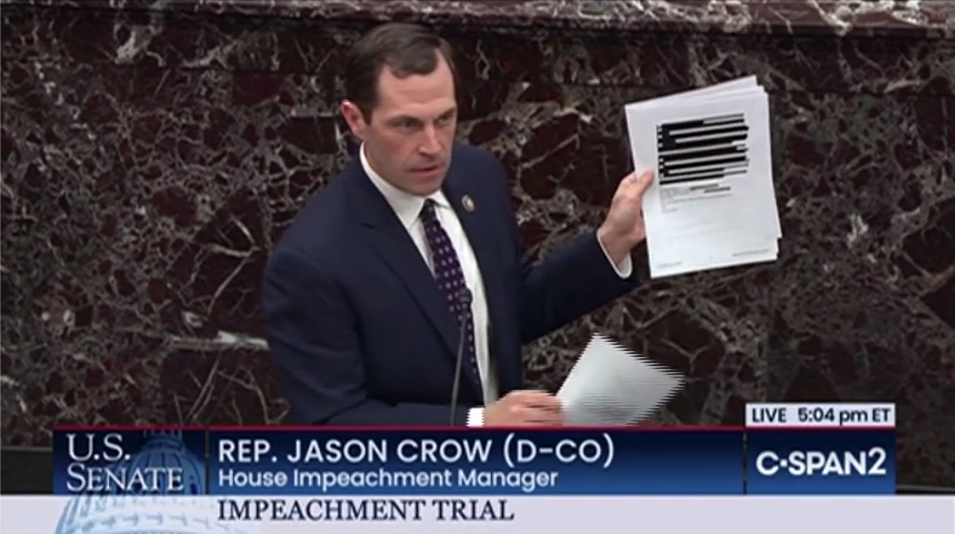
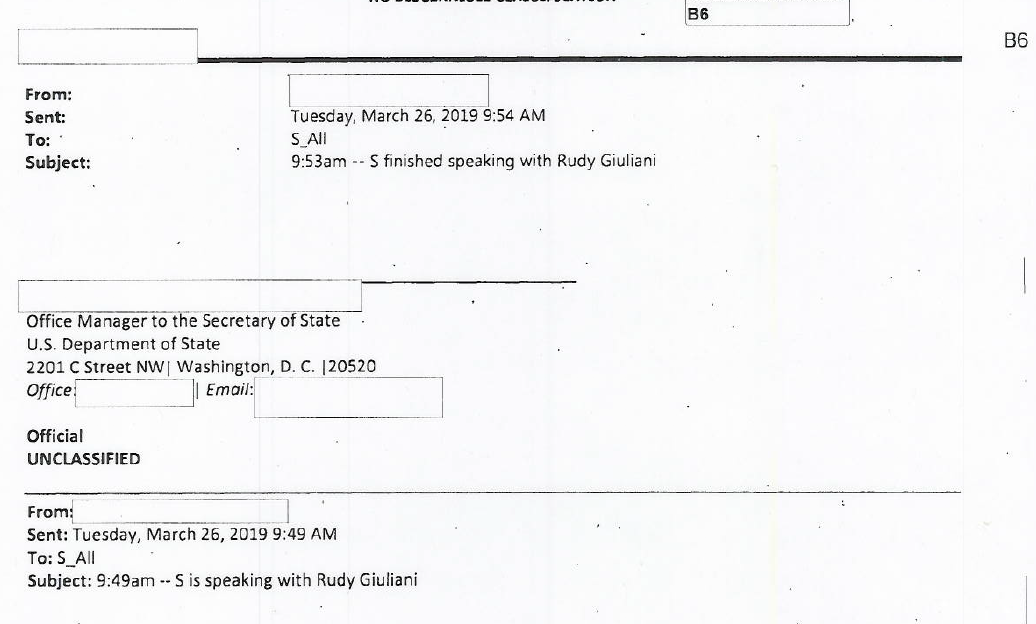
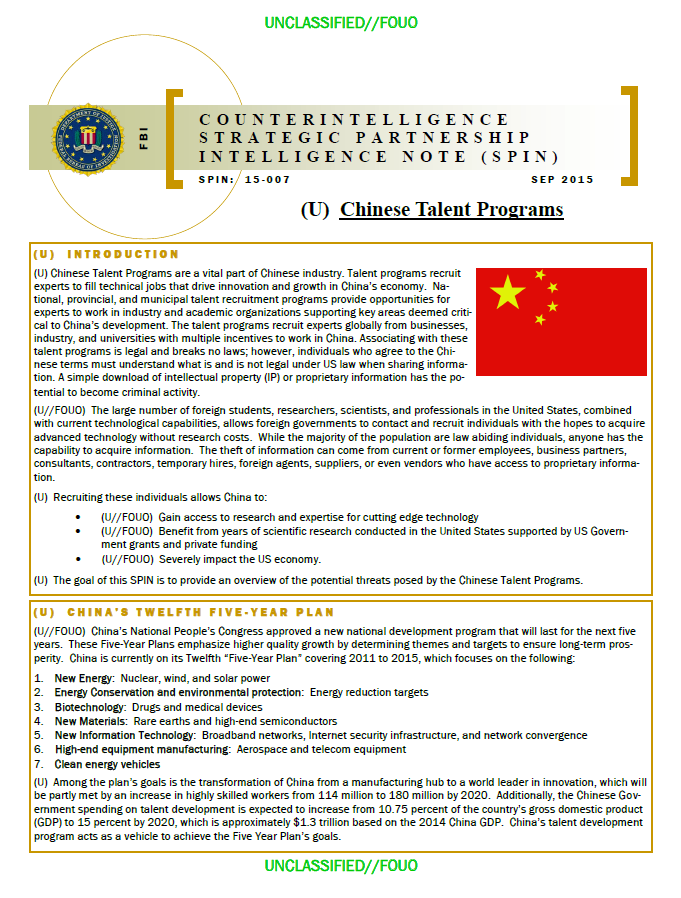







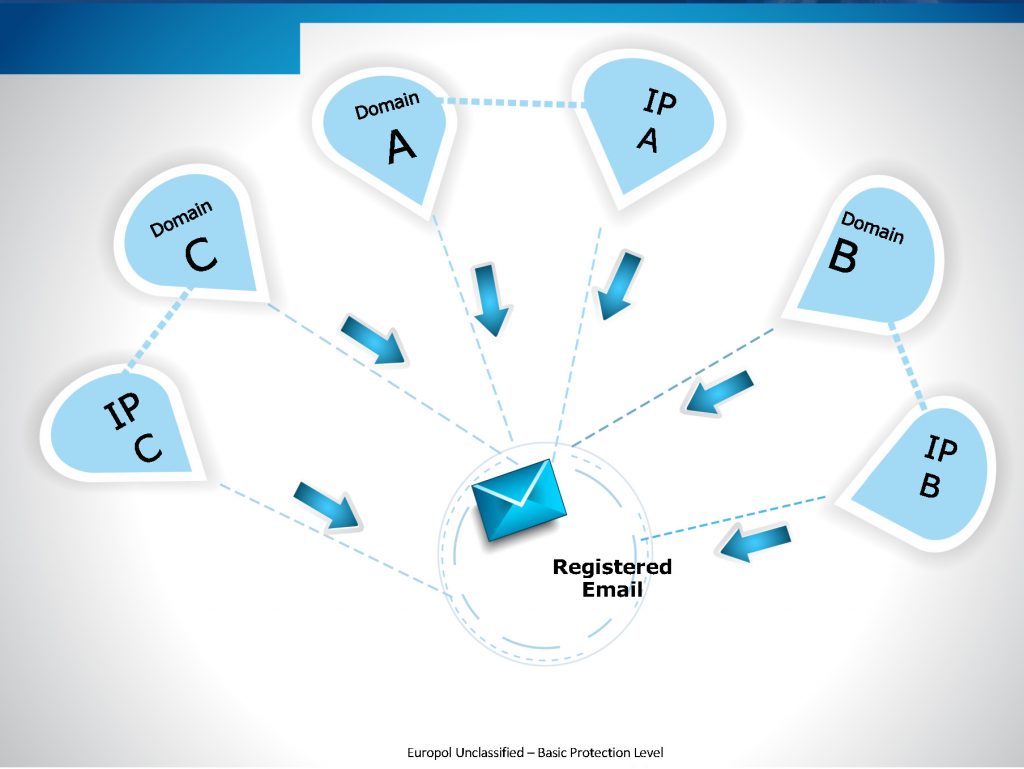
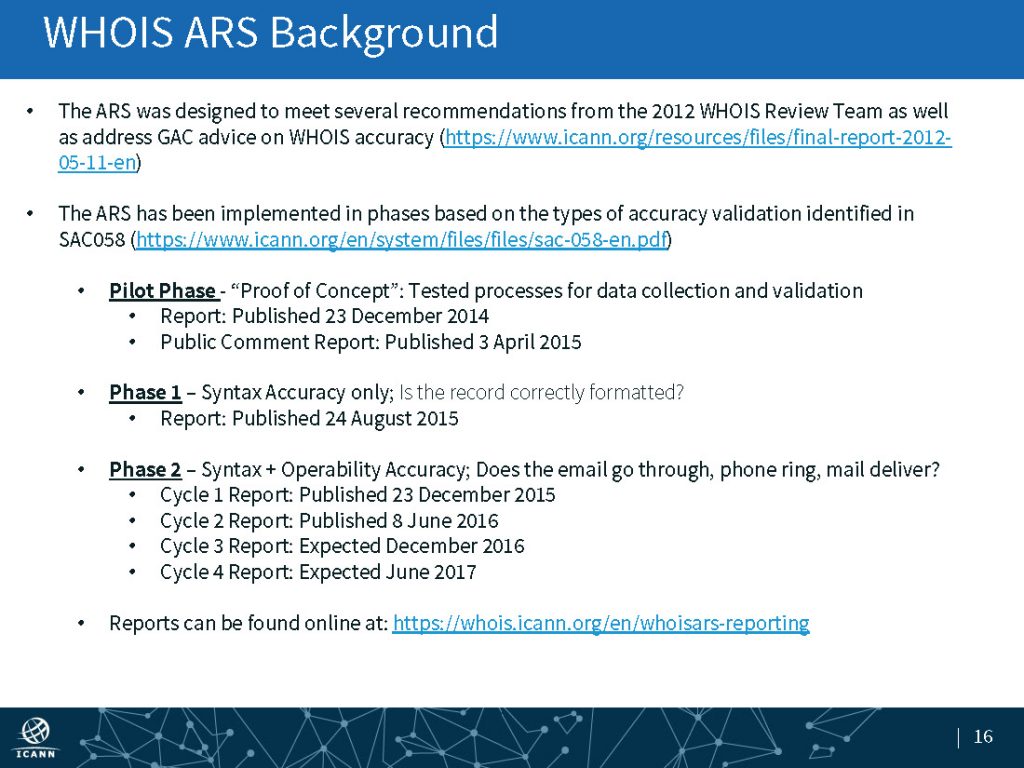
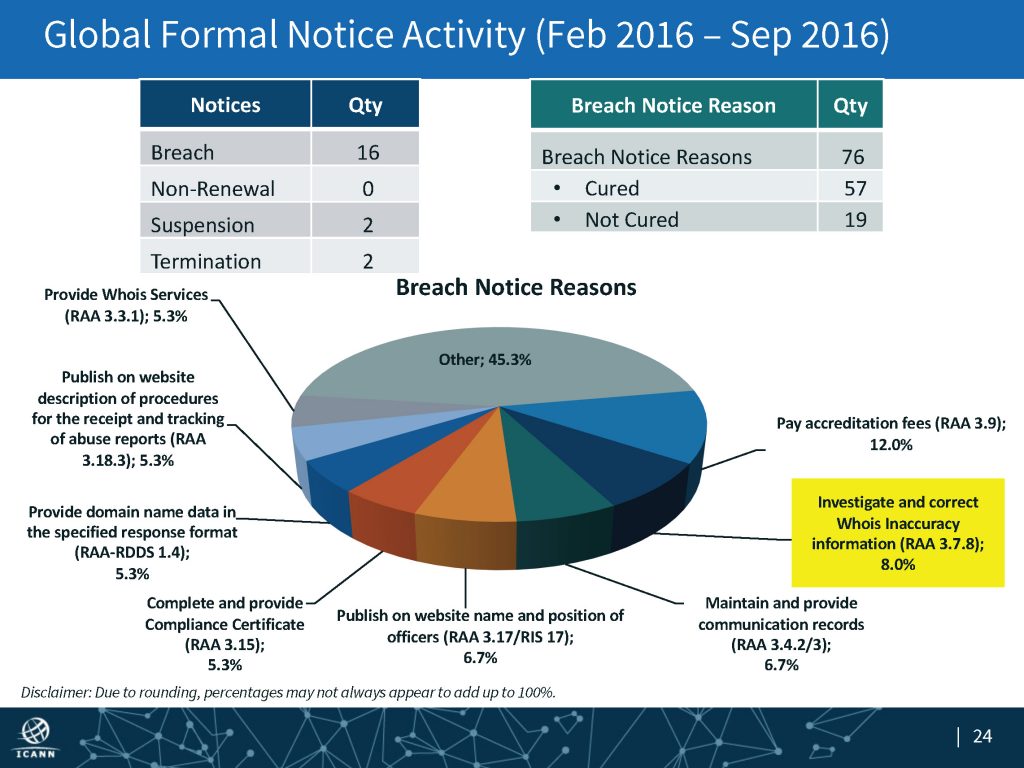
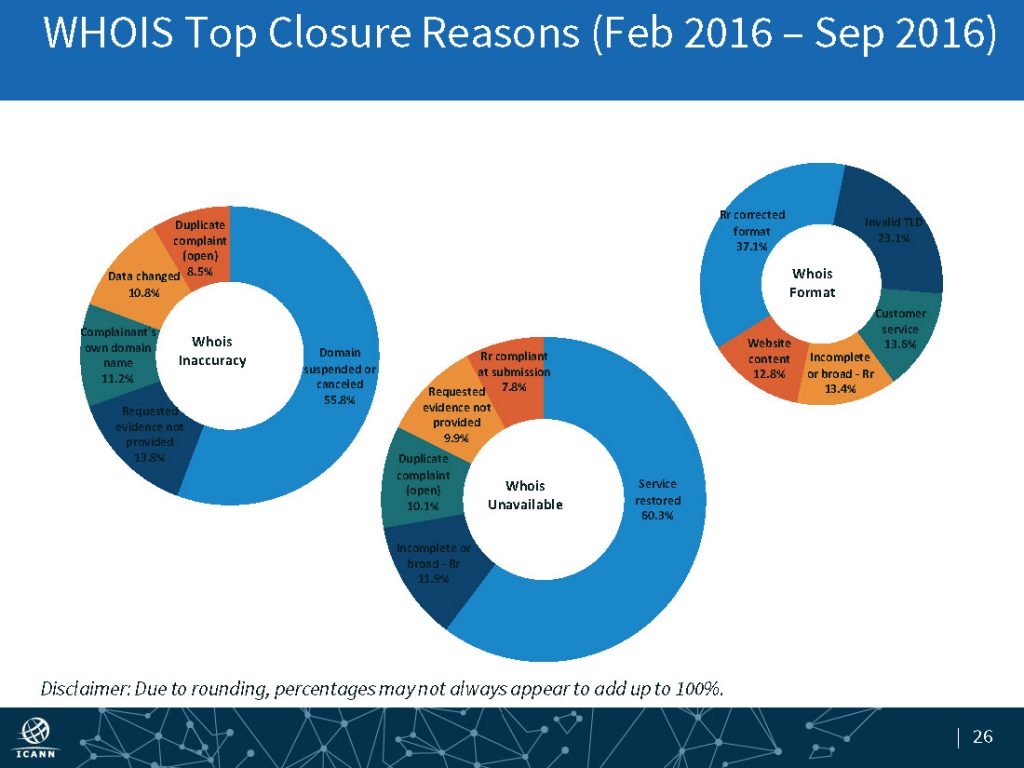











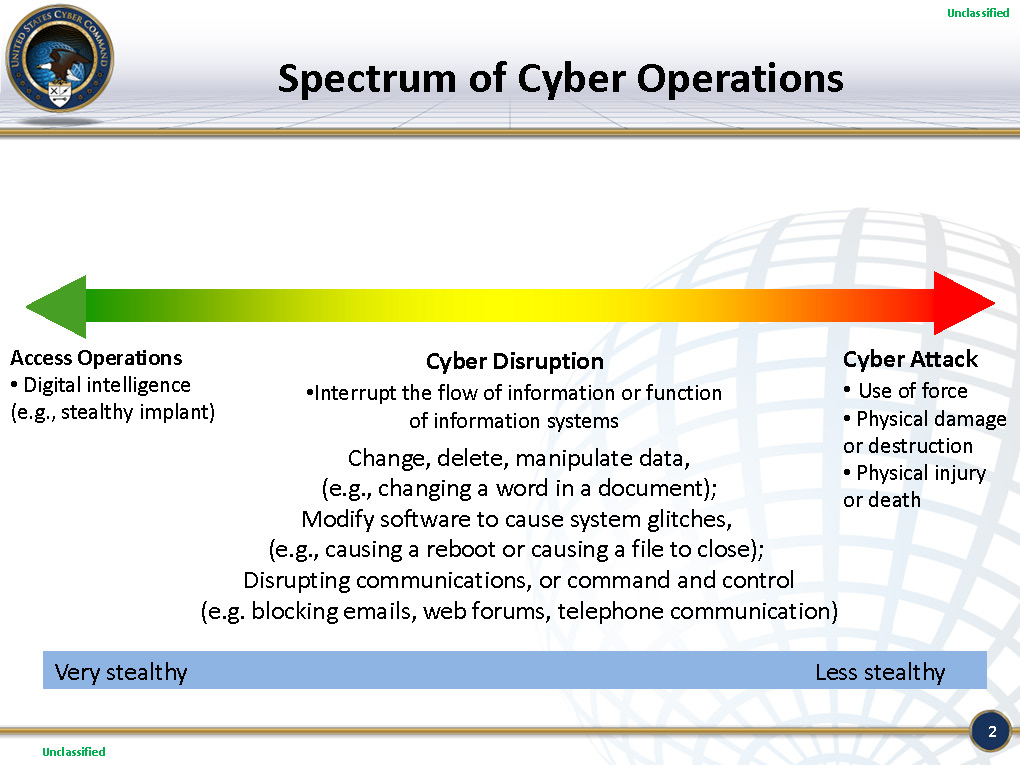

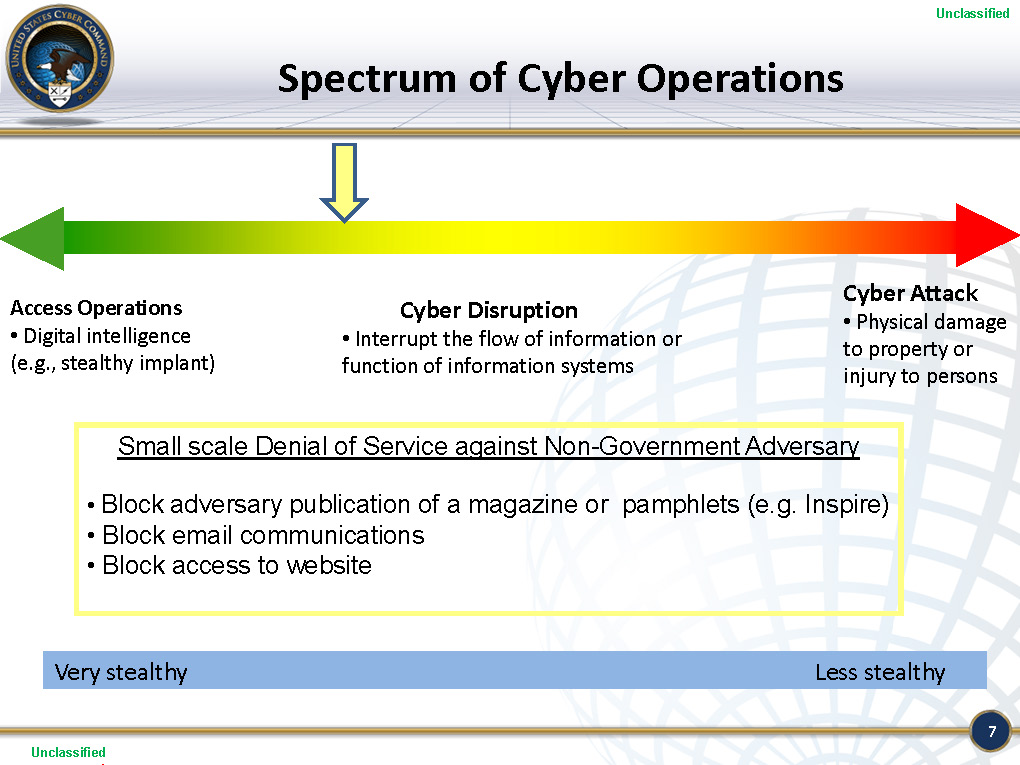
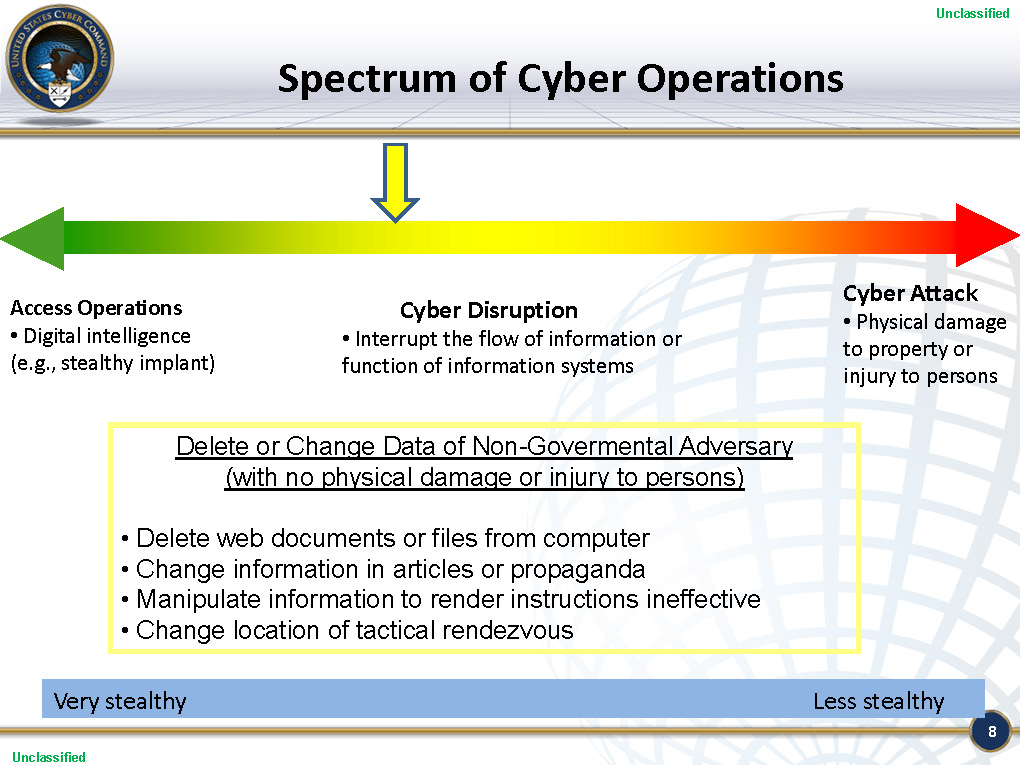
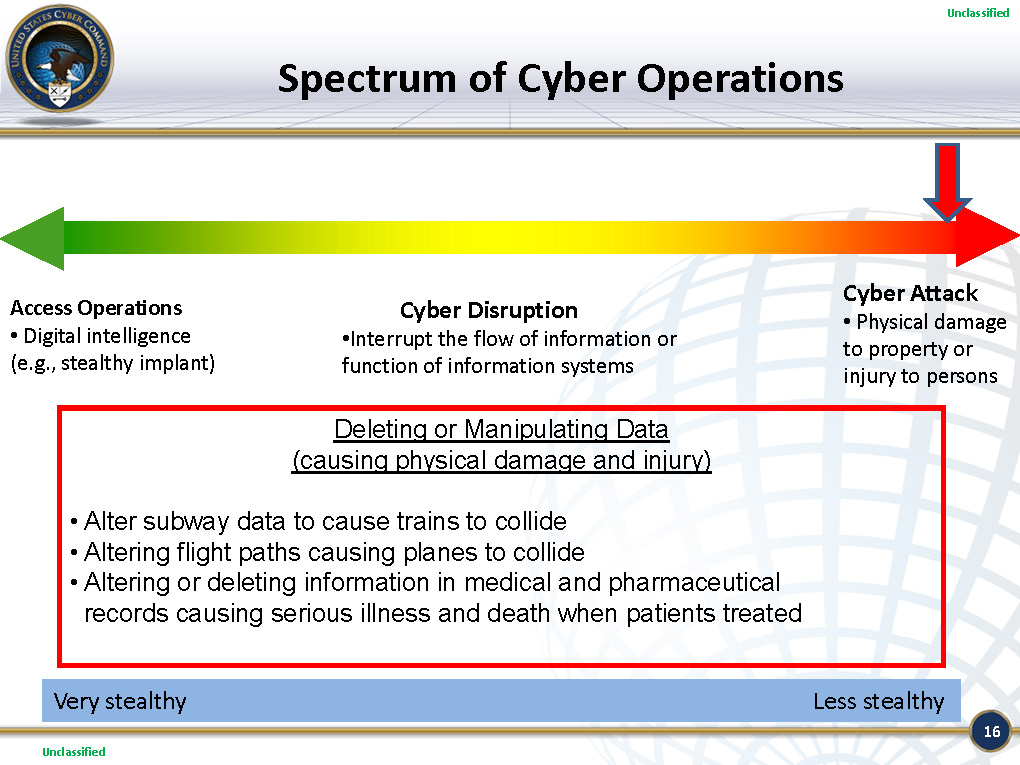
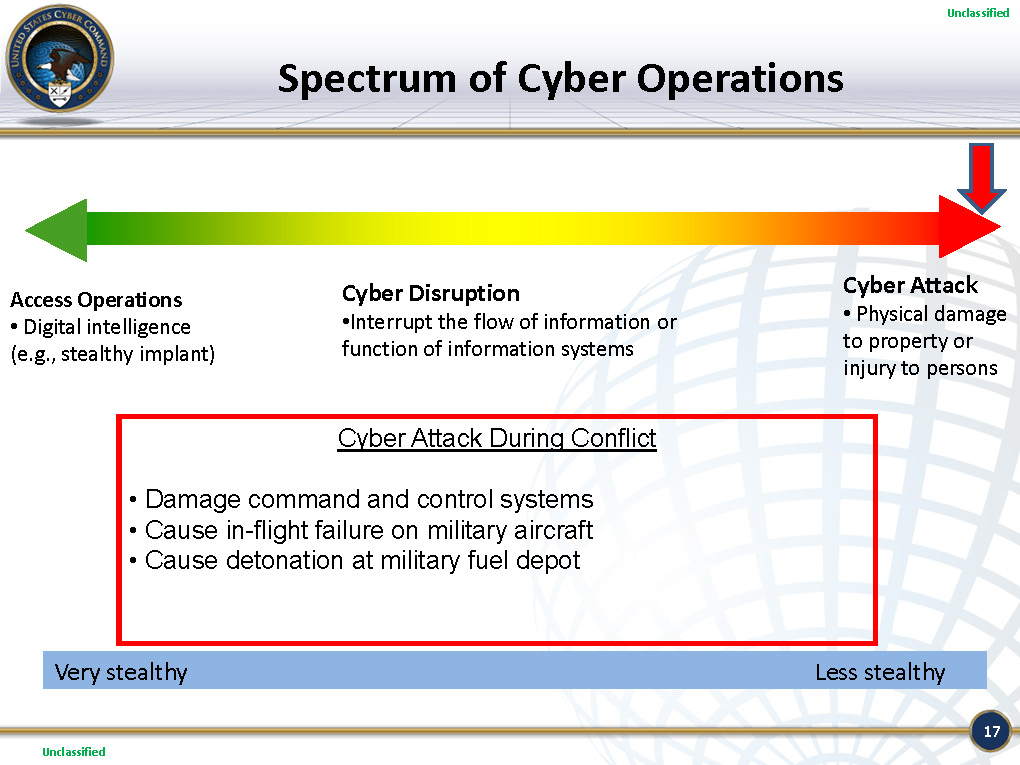
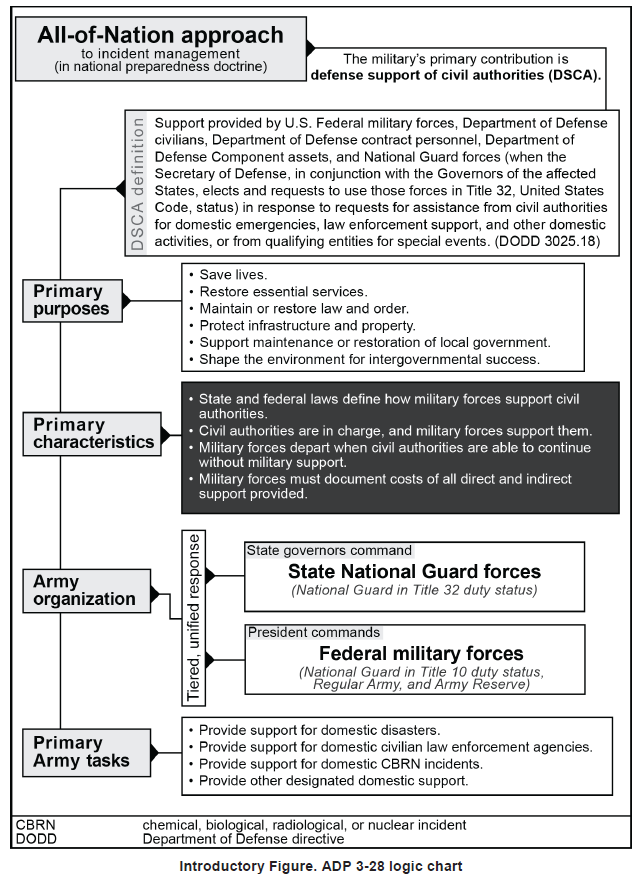
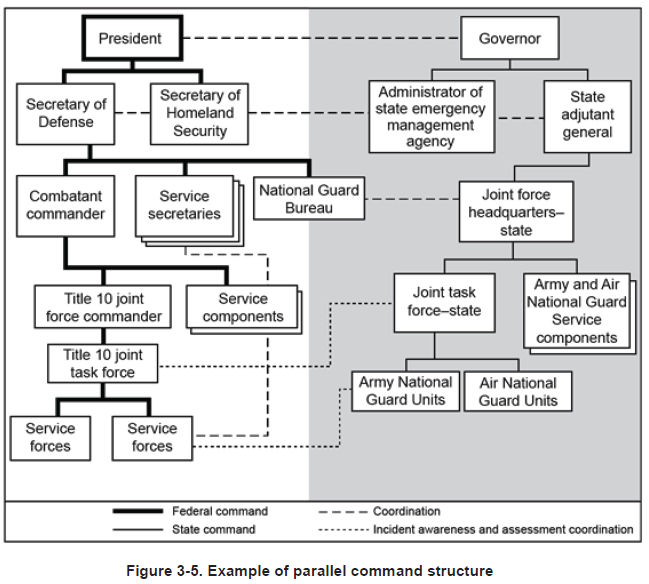










































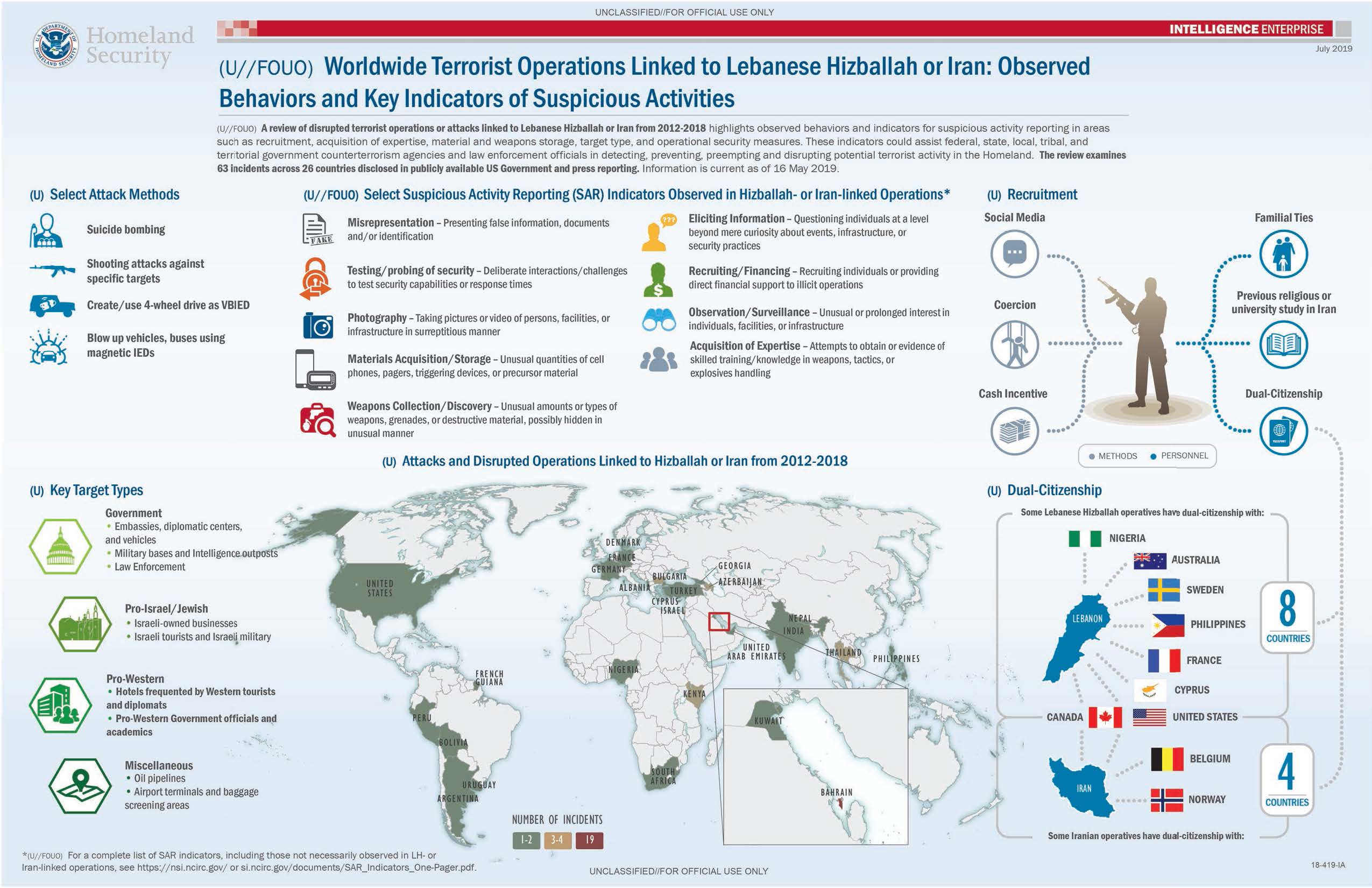


















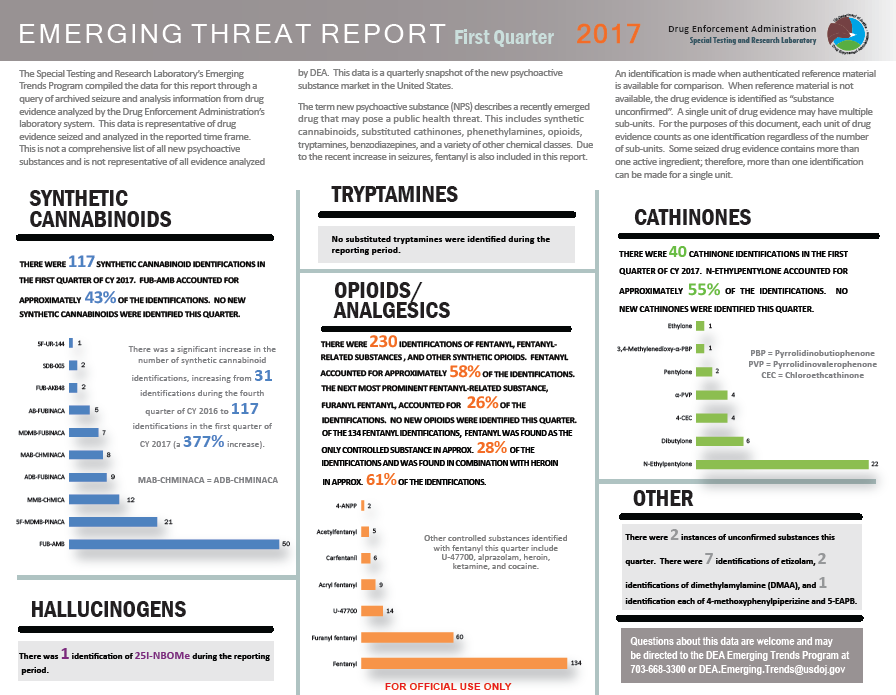
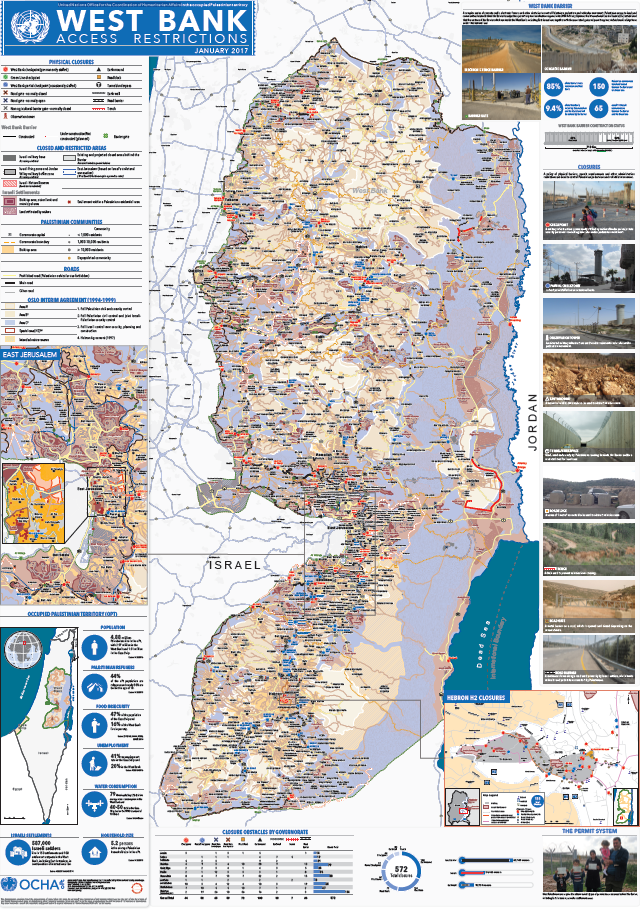















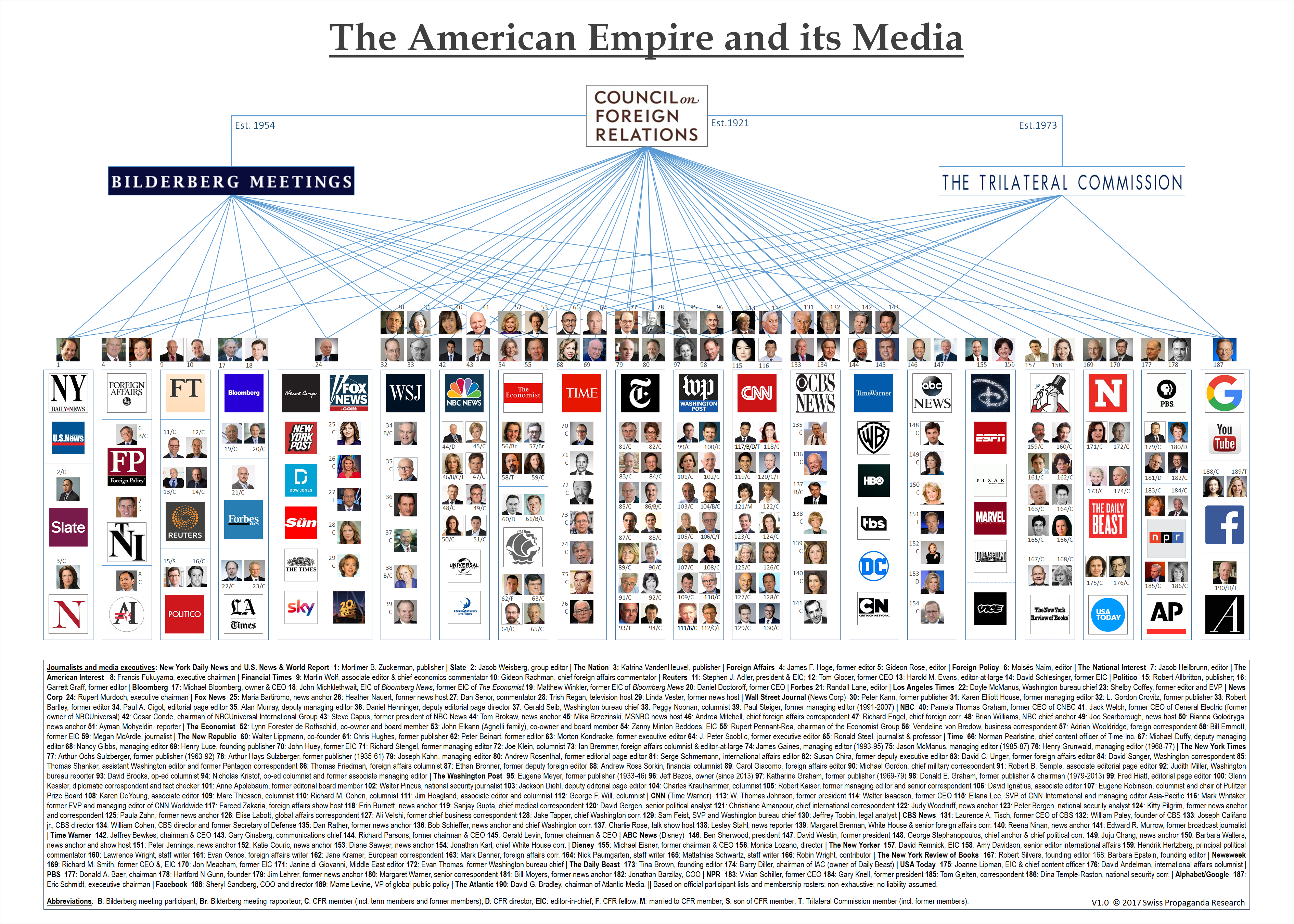





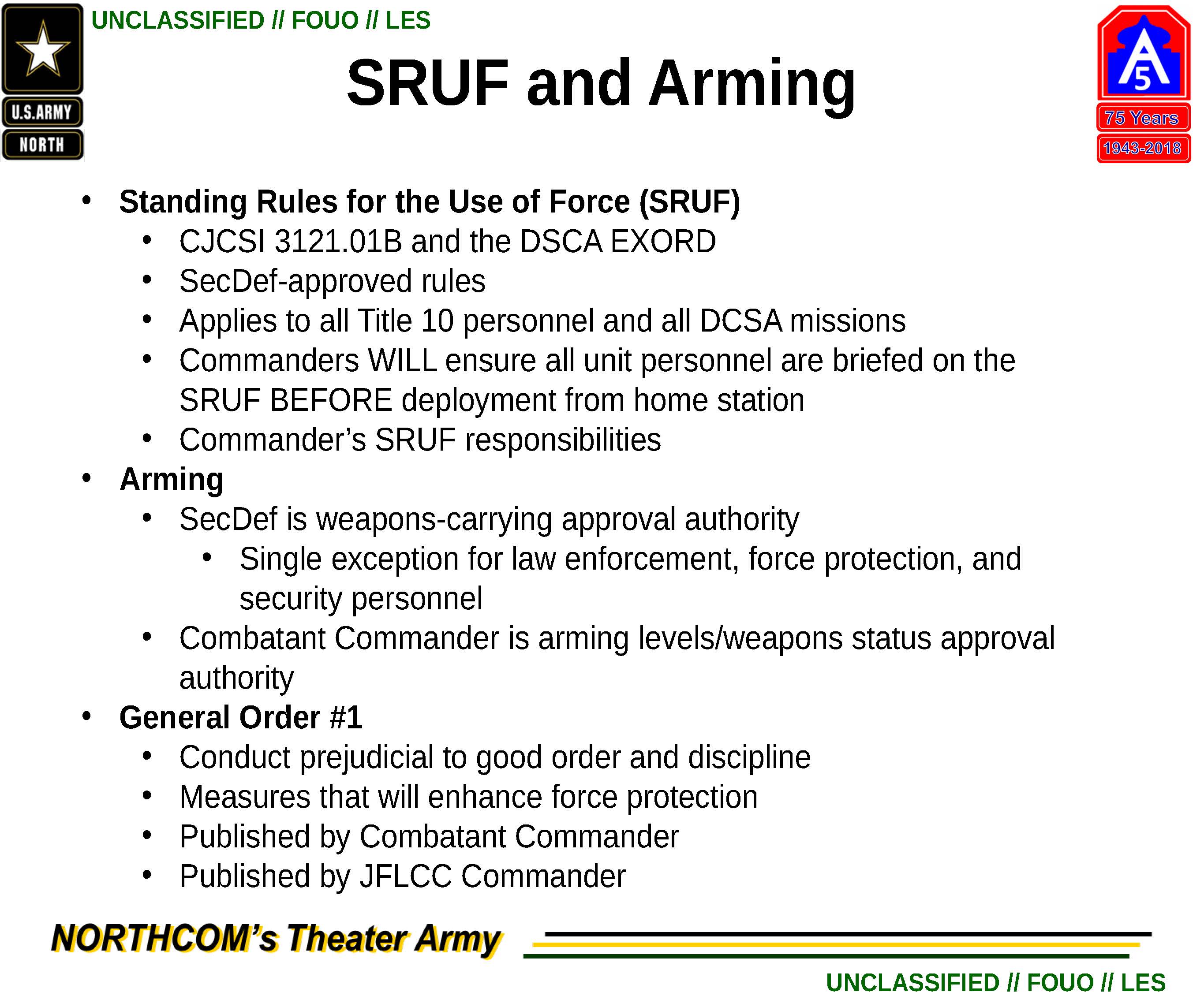
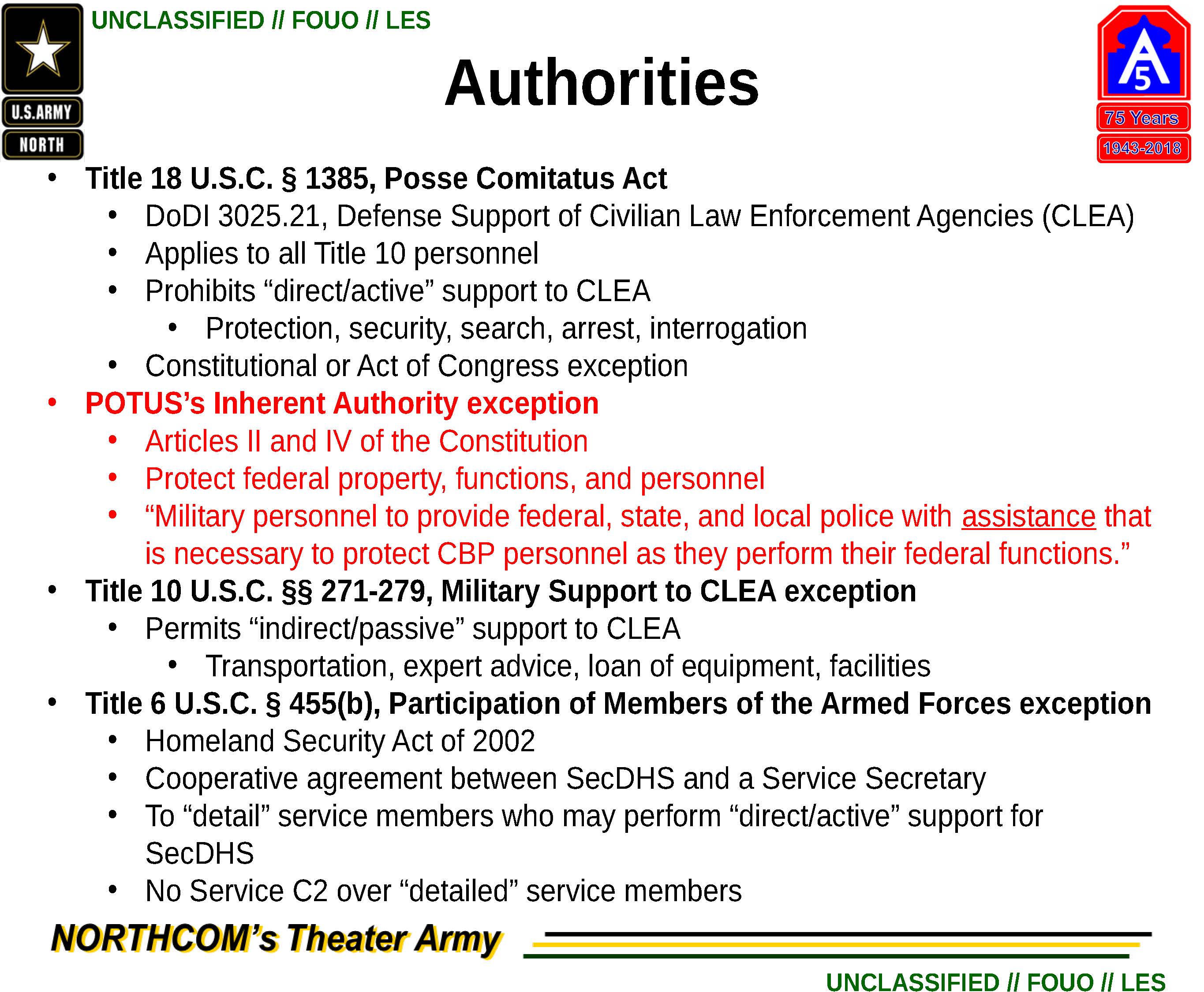
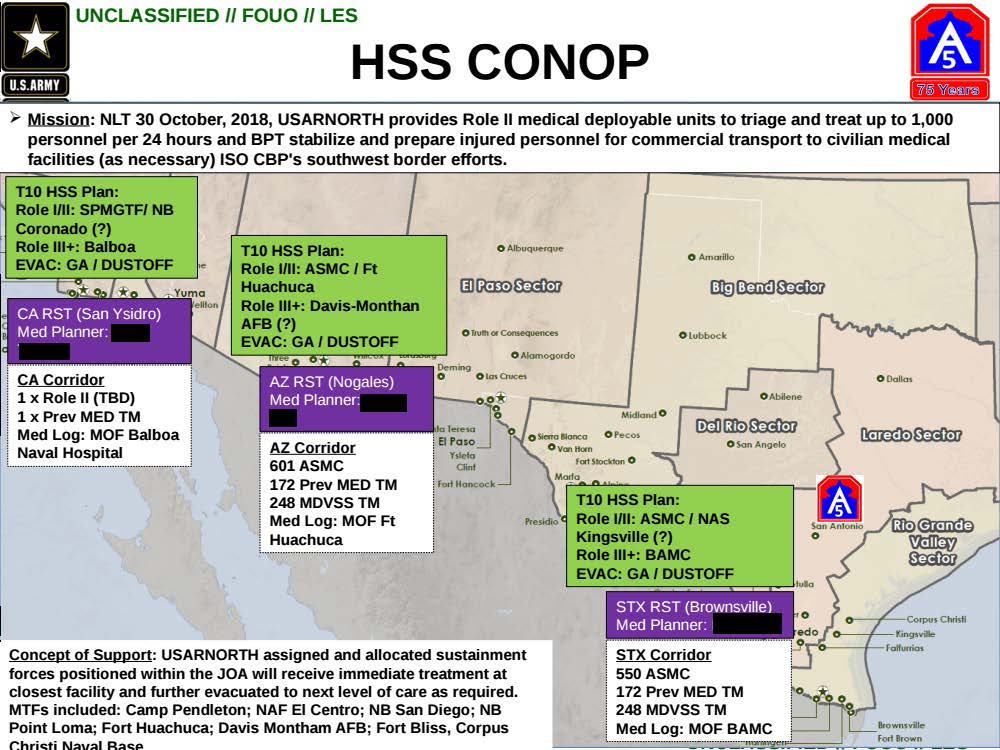

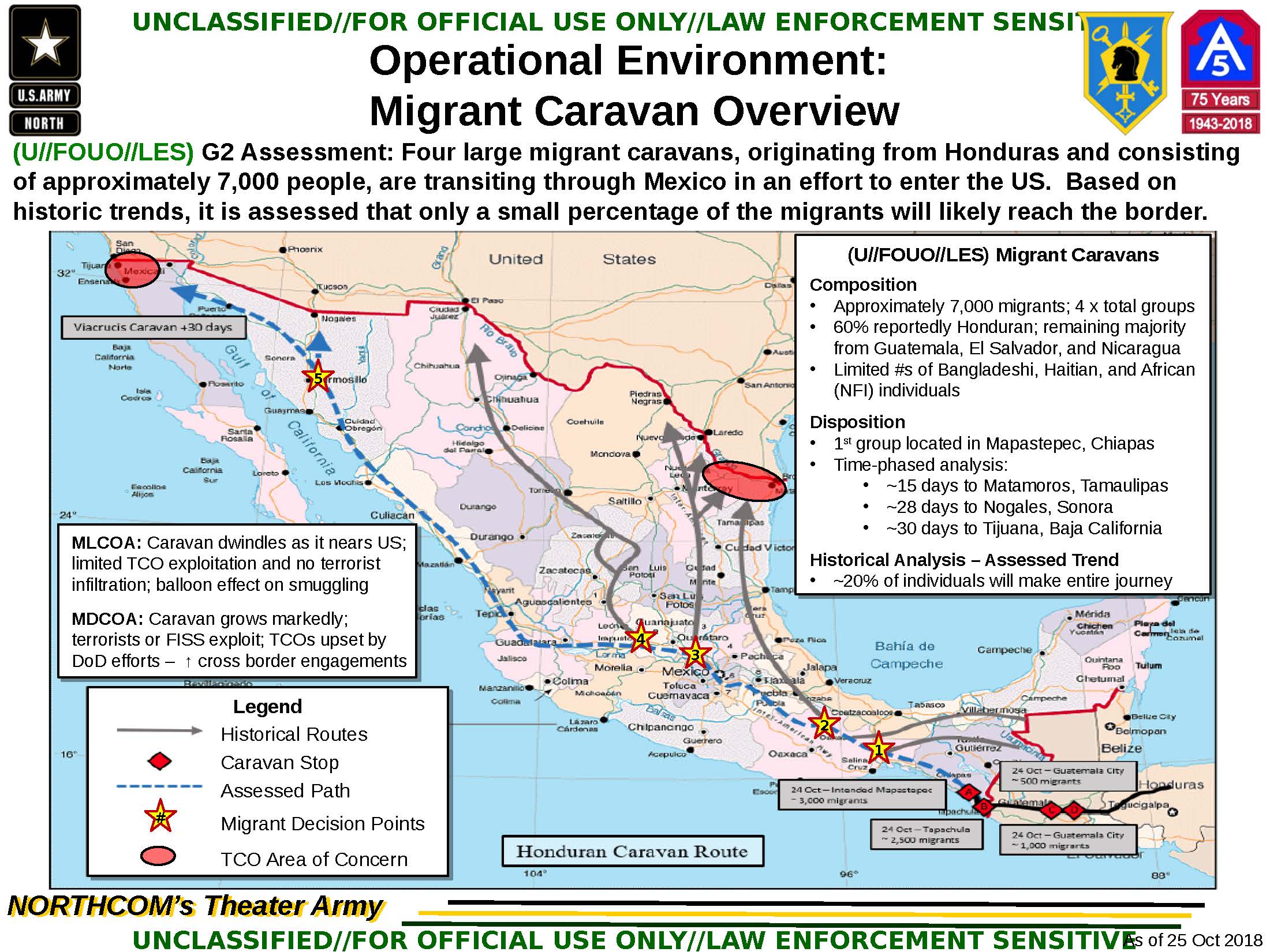
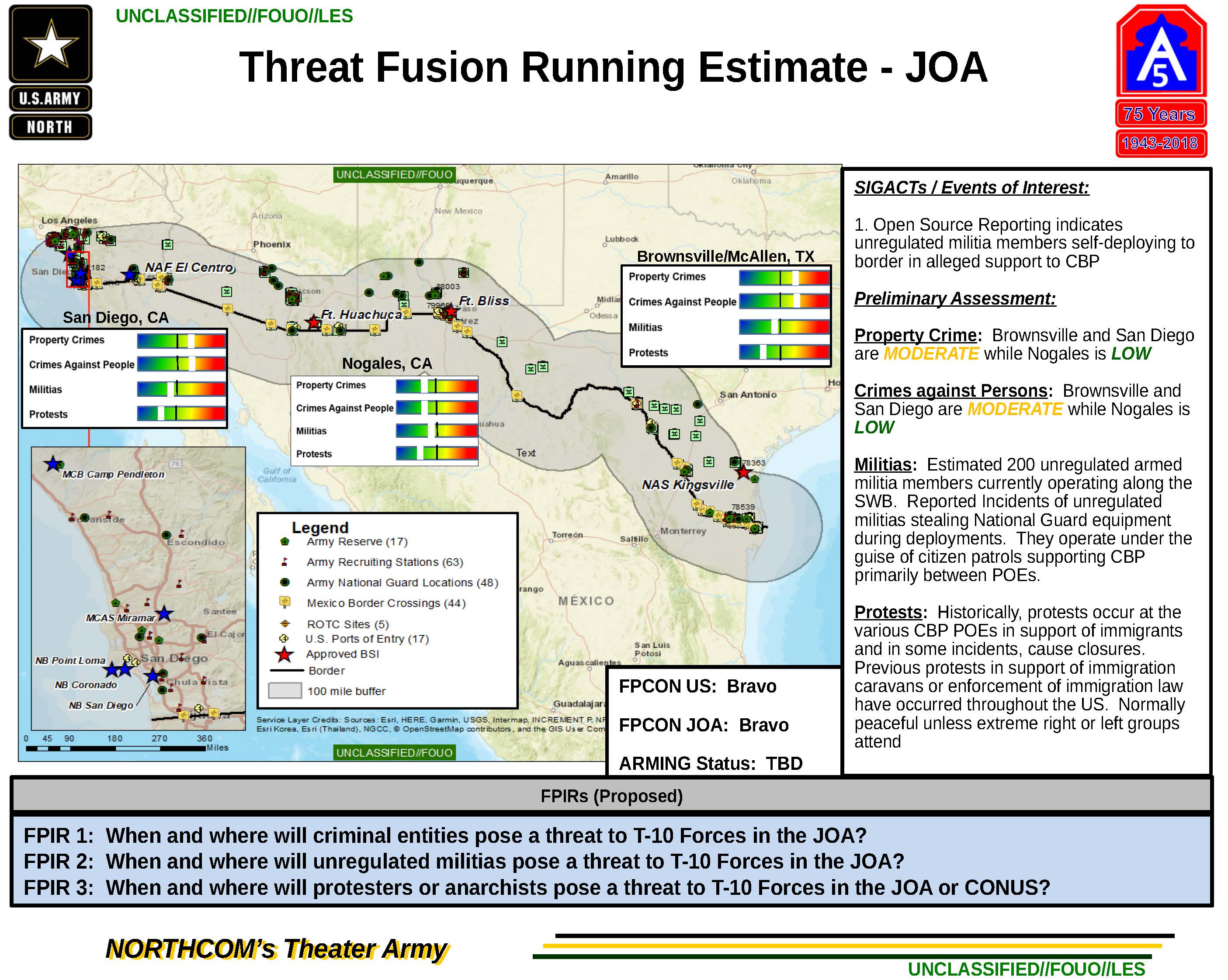
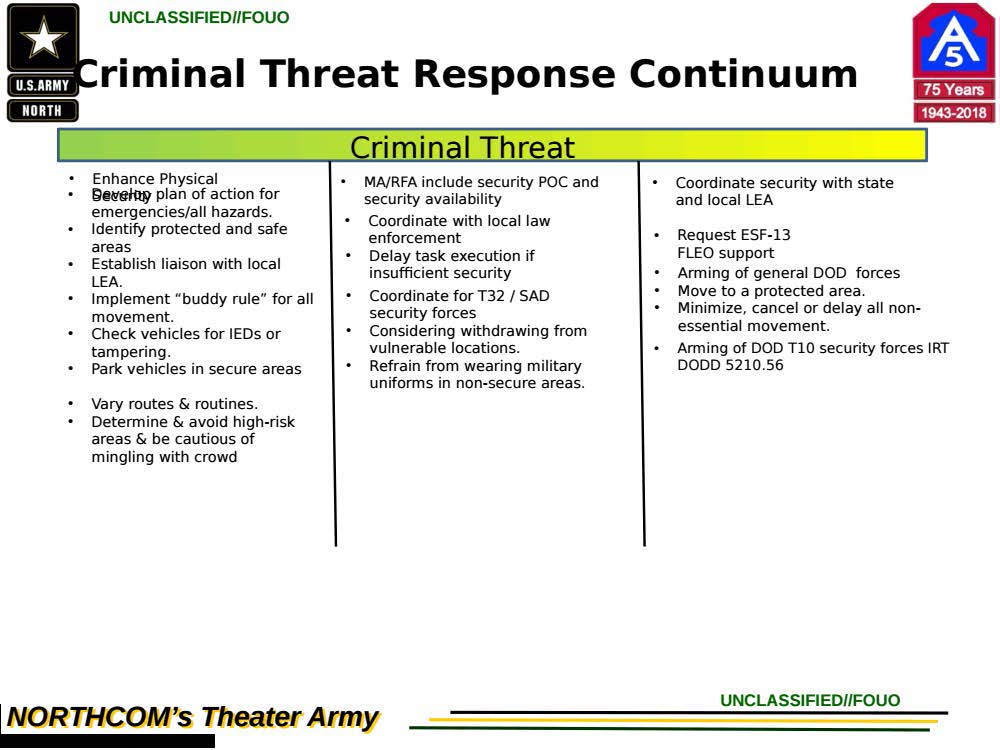
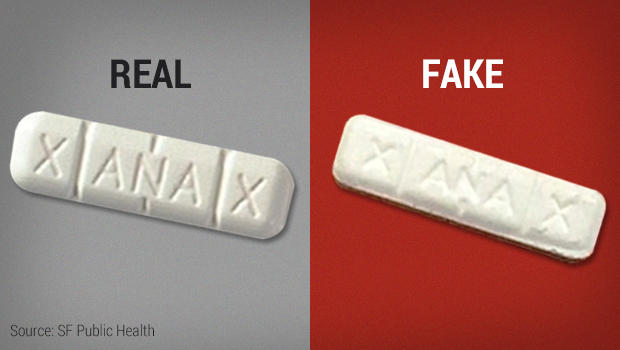
/cdn.vox-cdn.com/uploads/chorus_image/image/55407063/spacecorps.0.jpg) FM 3-14, Army Space Operations, provides an overview of space operations in the Army and is consistent and compatible with joint doctrine. FM 3-14 links Army space operations doctrine to joint space operations doctrine as expressed in JP 3-14, Space Operations and other joint doctrinal publications. This FM establishes guidance for employing space and space-based systems and capabilities to support United States (U.S.) Army land warfighting dominance. It provides a general overview of overhead support to Army operations, reviews national guidance and direction, and outlines selected unique space-related Army capabilities. The doctrine in this manual documents Army thought for the best use of space capabilities. This manual also contains tactics and procedures outlining how to plan, integrate, and execute Army space operations.
FM 3-14, Army Space Operations, provides an overview of space operations in the Army and is consistent and compatible with joint doctrine. FM 3-14 links Army space operations doctrine to joint space operations doctrine as expressed in JP 3-14, Space Operations and other joint doctrinal publications. This FM establishes guidance for employing space and space-based systems and capabilities to support United States (U.S.) Army land warfighting dominance. It provides a general overview of overhead support to Army operations, reviews national guidance and direction, and outlines selected unique space-related Army capabilities. The doctrine in this manual documents Army thought for the best use of space capabilities. This manual also contains tactics and procedures outlining how to plan, integrate, and execute Army space operations.



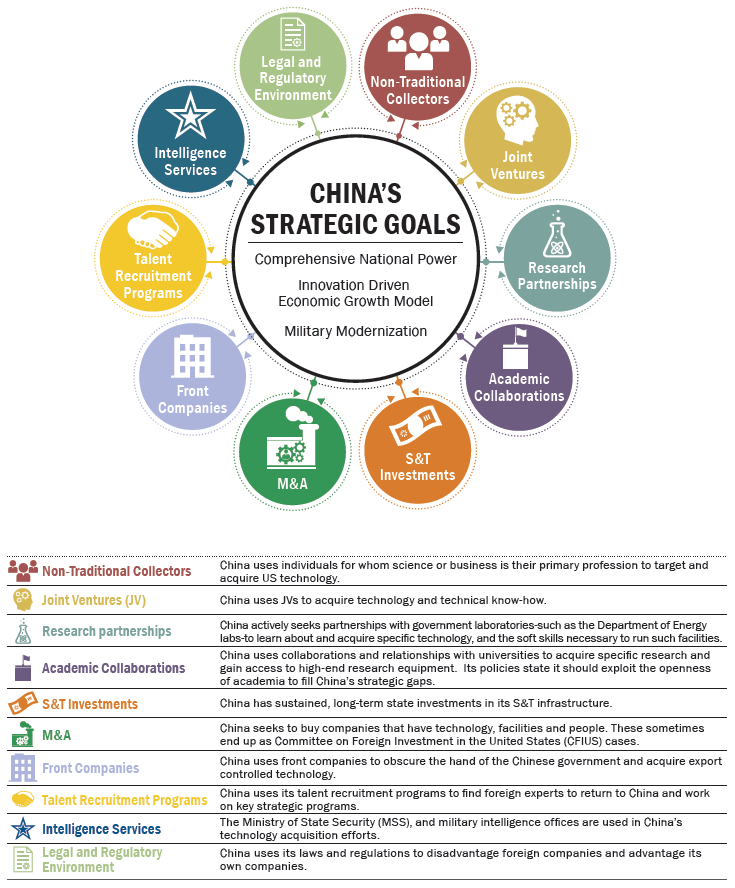

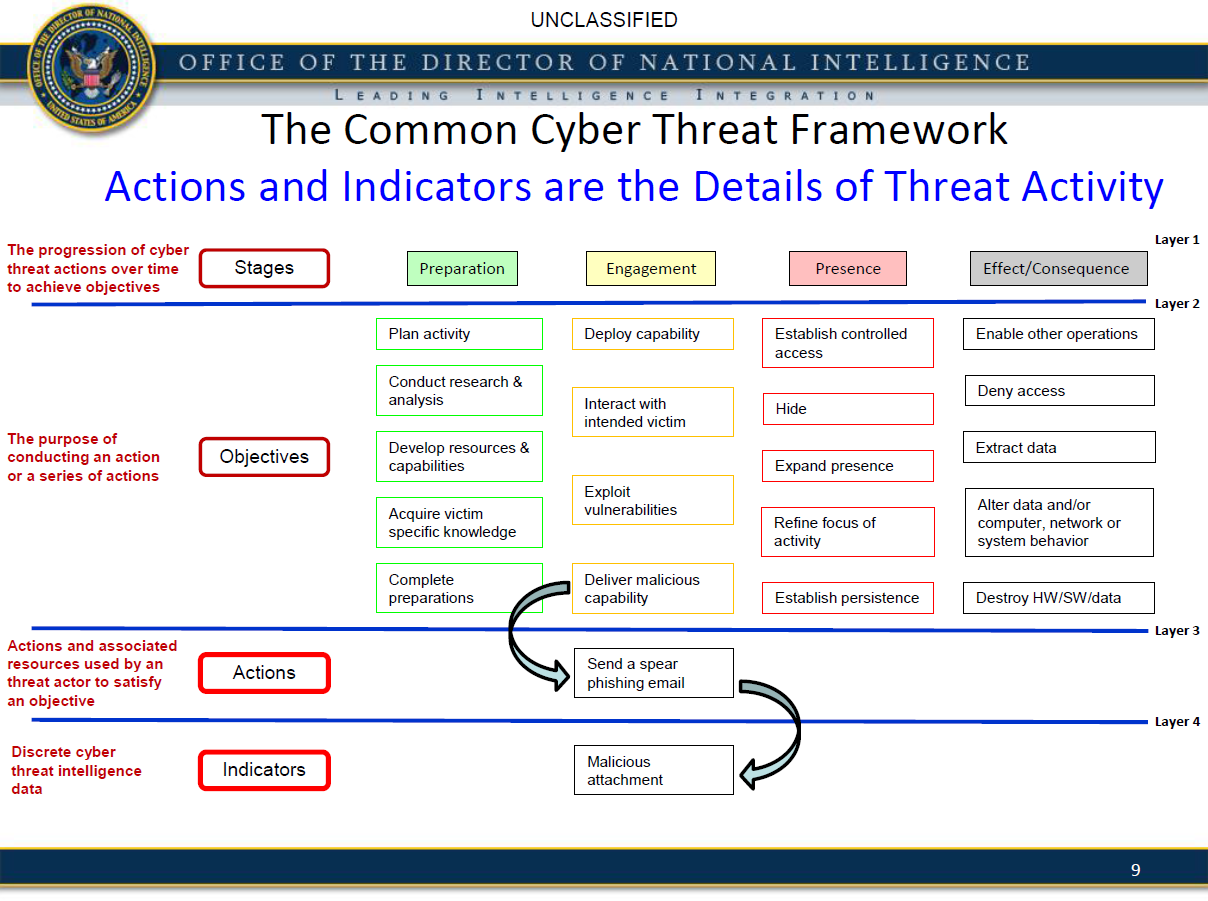
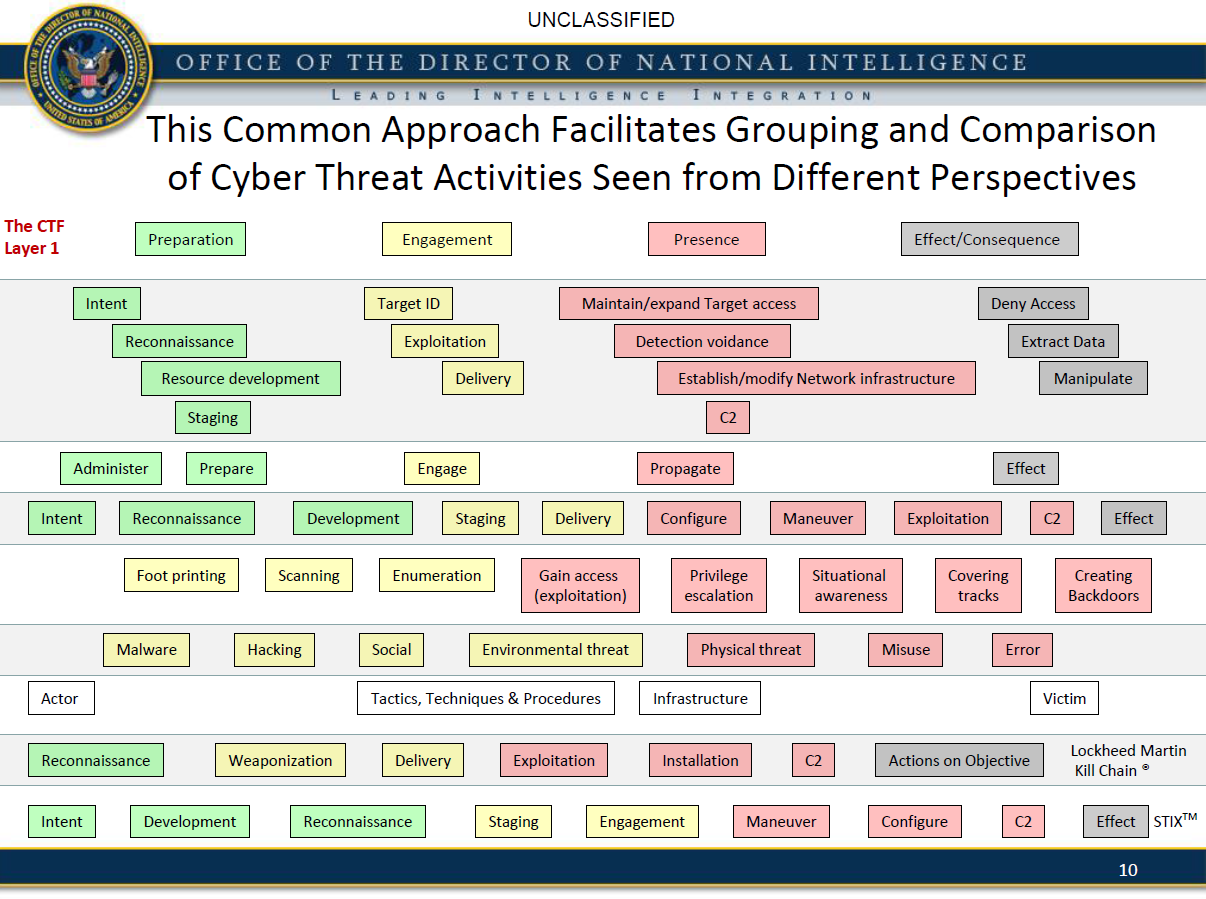




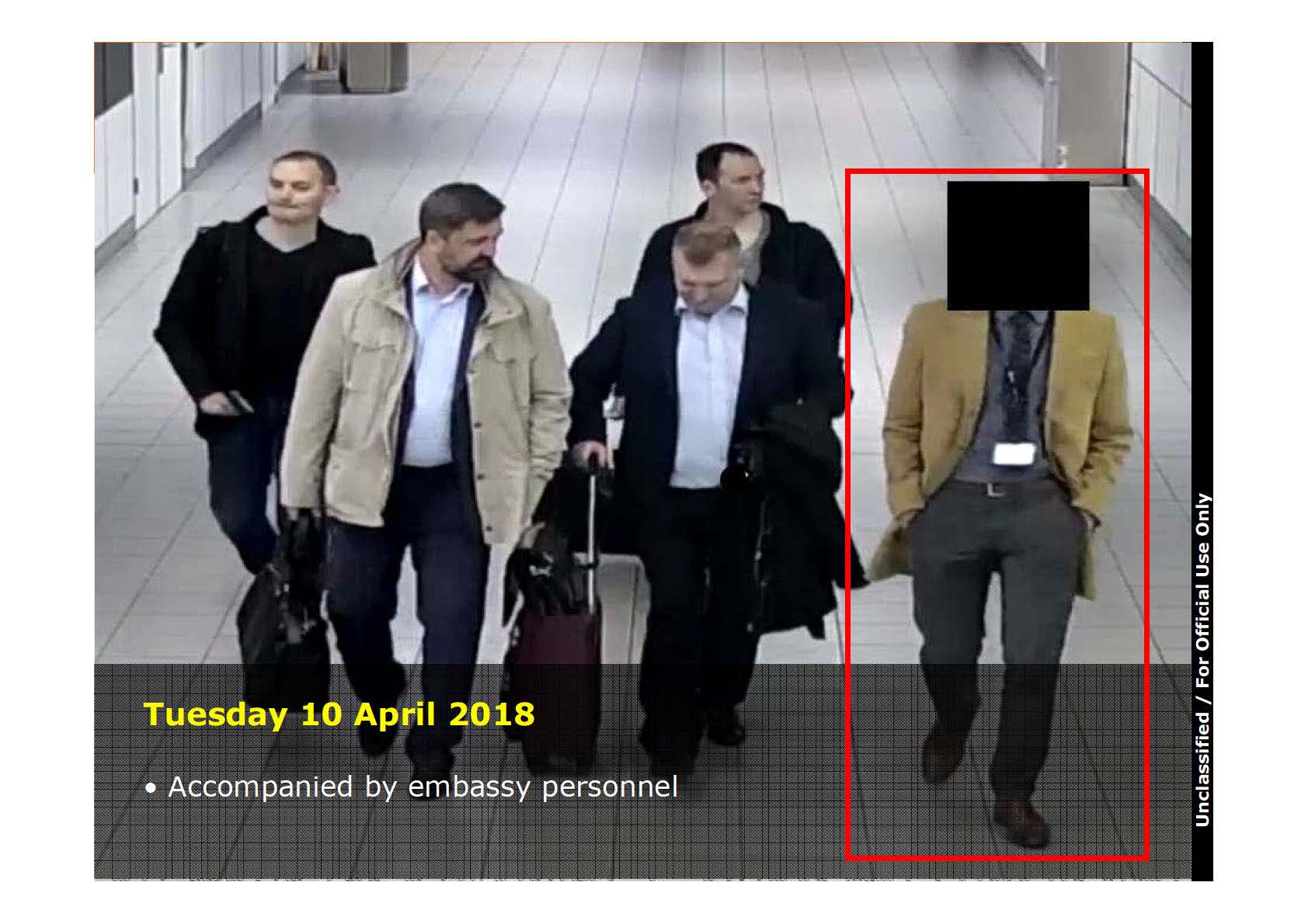
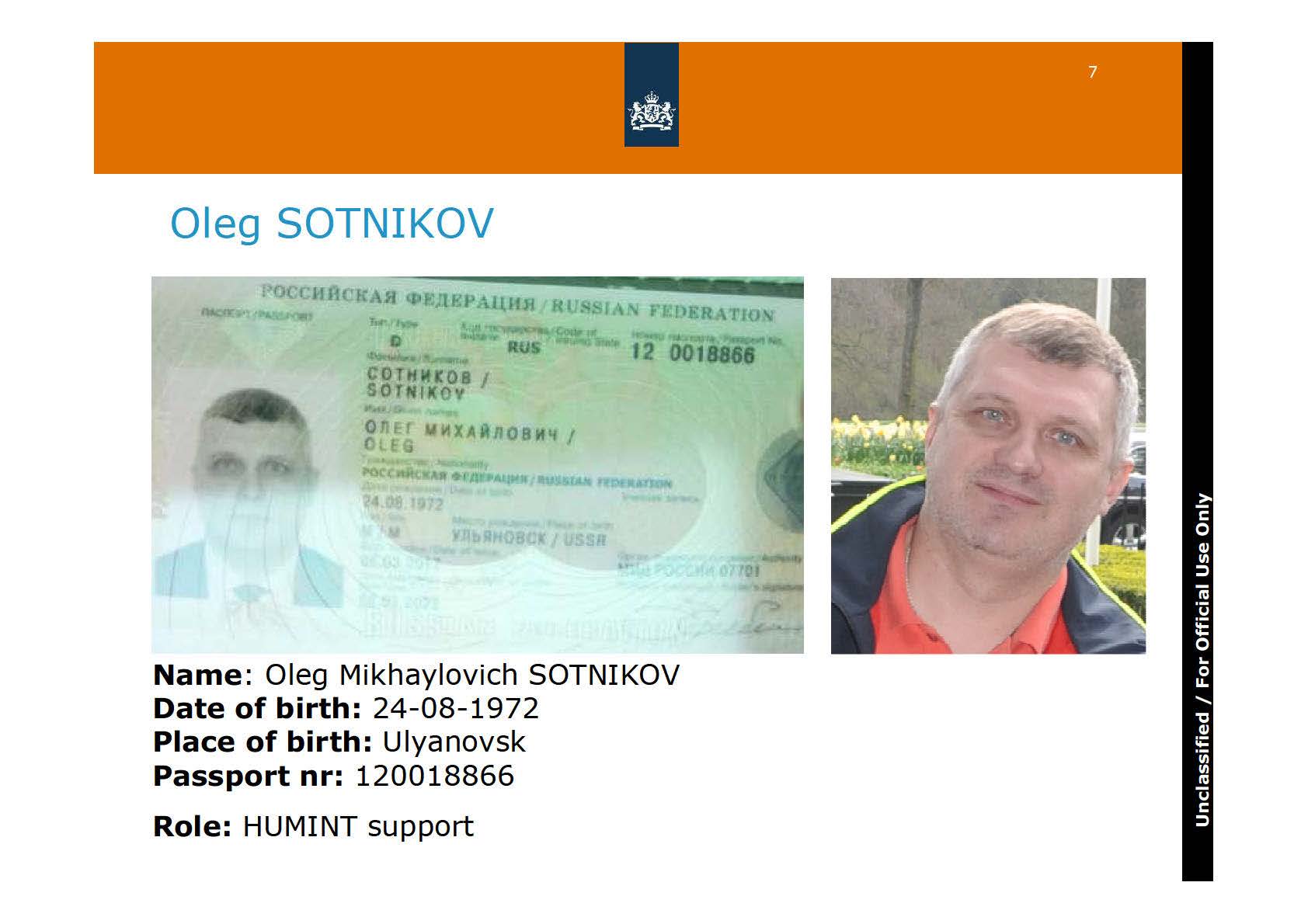
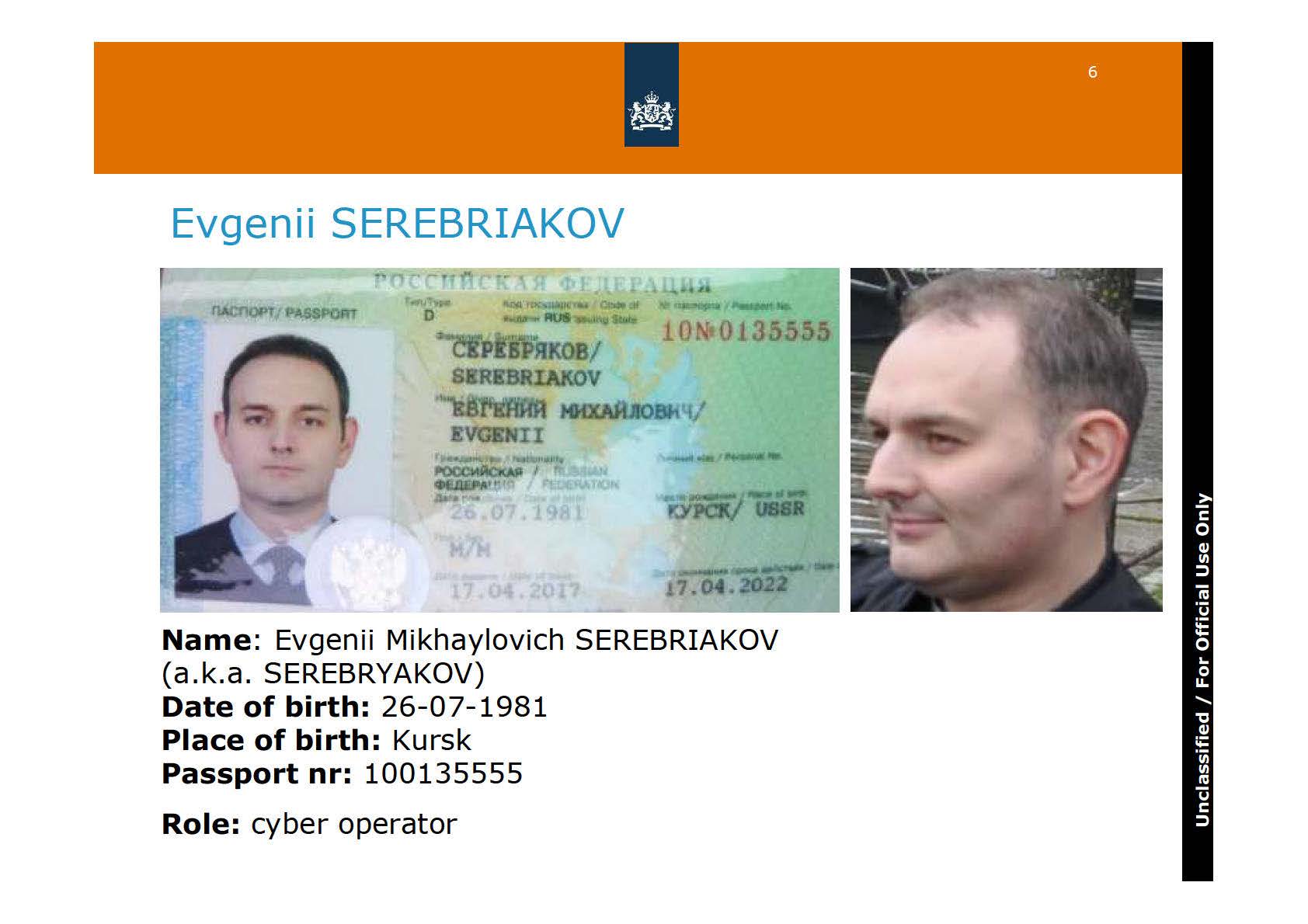

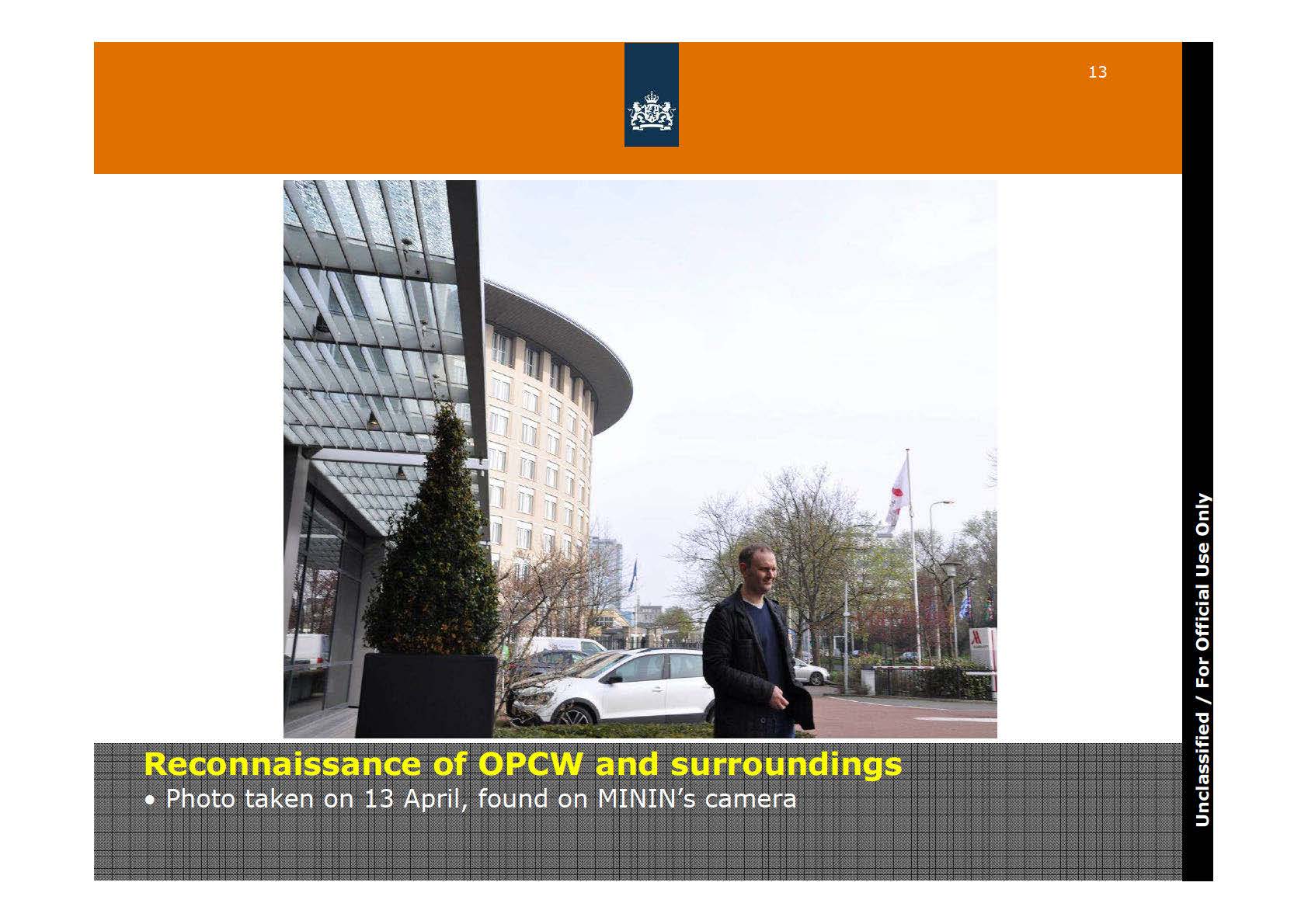
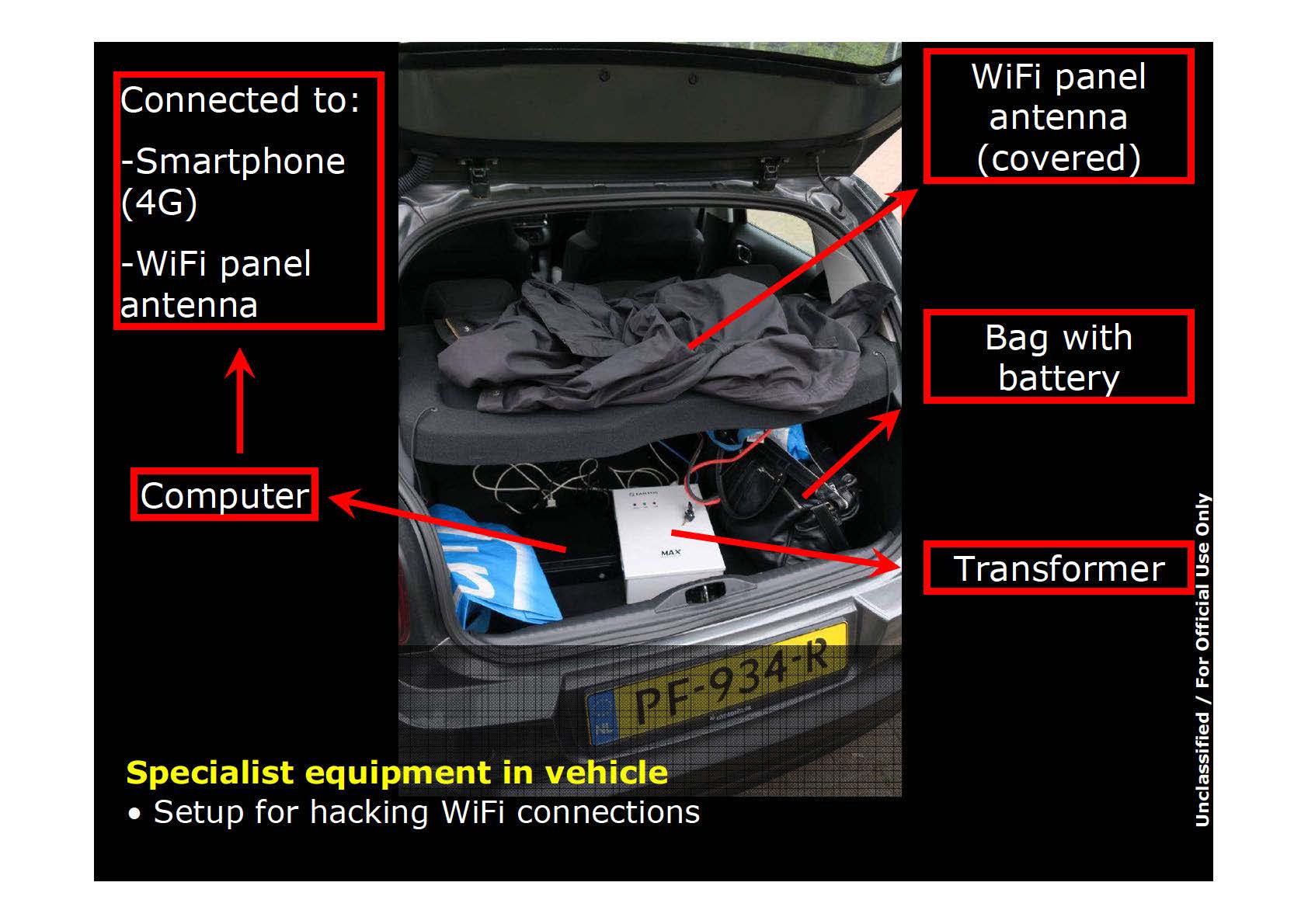
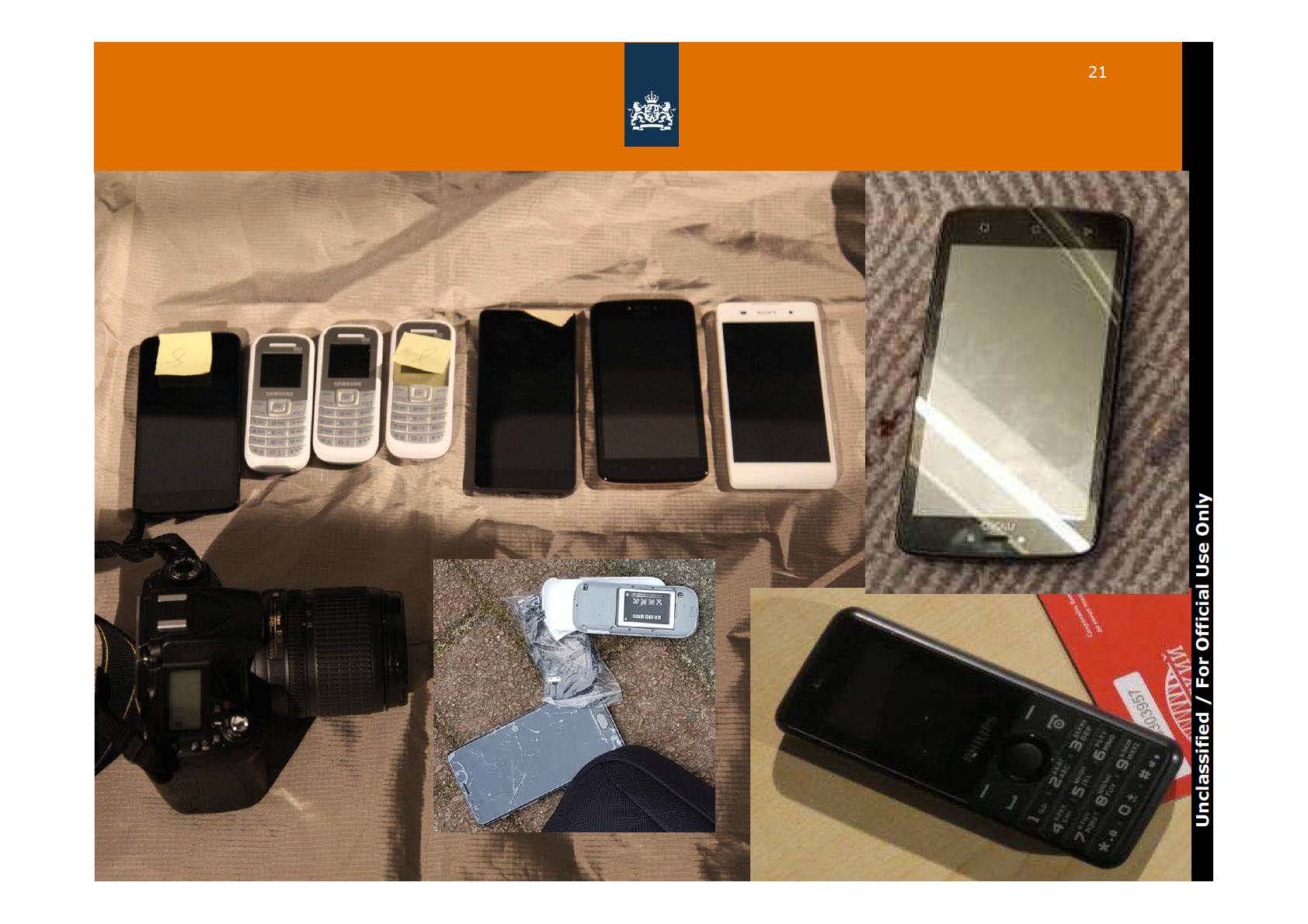
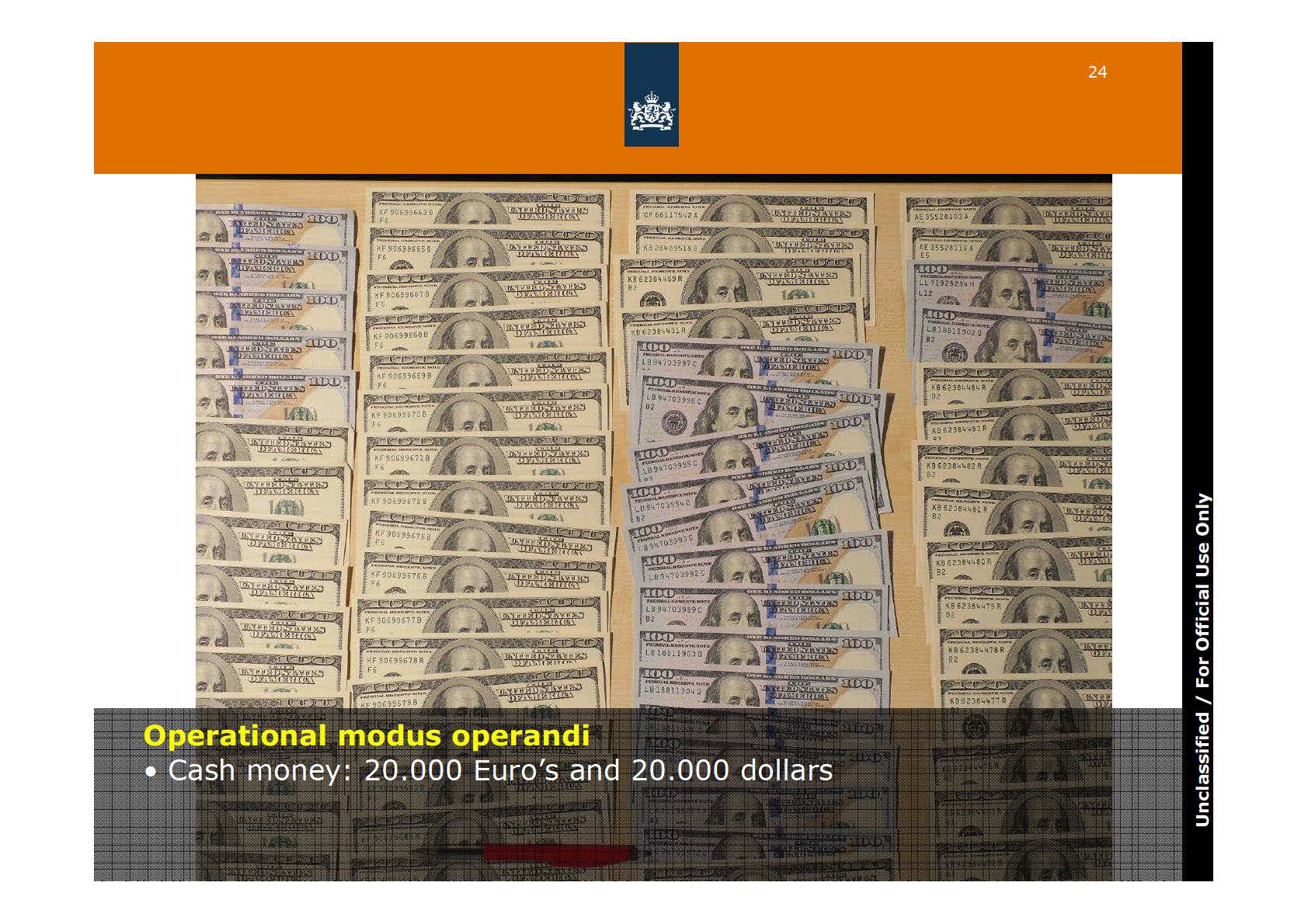
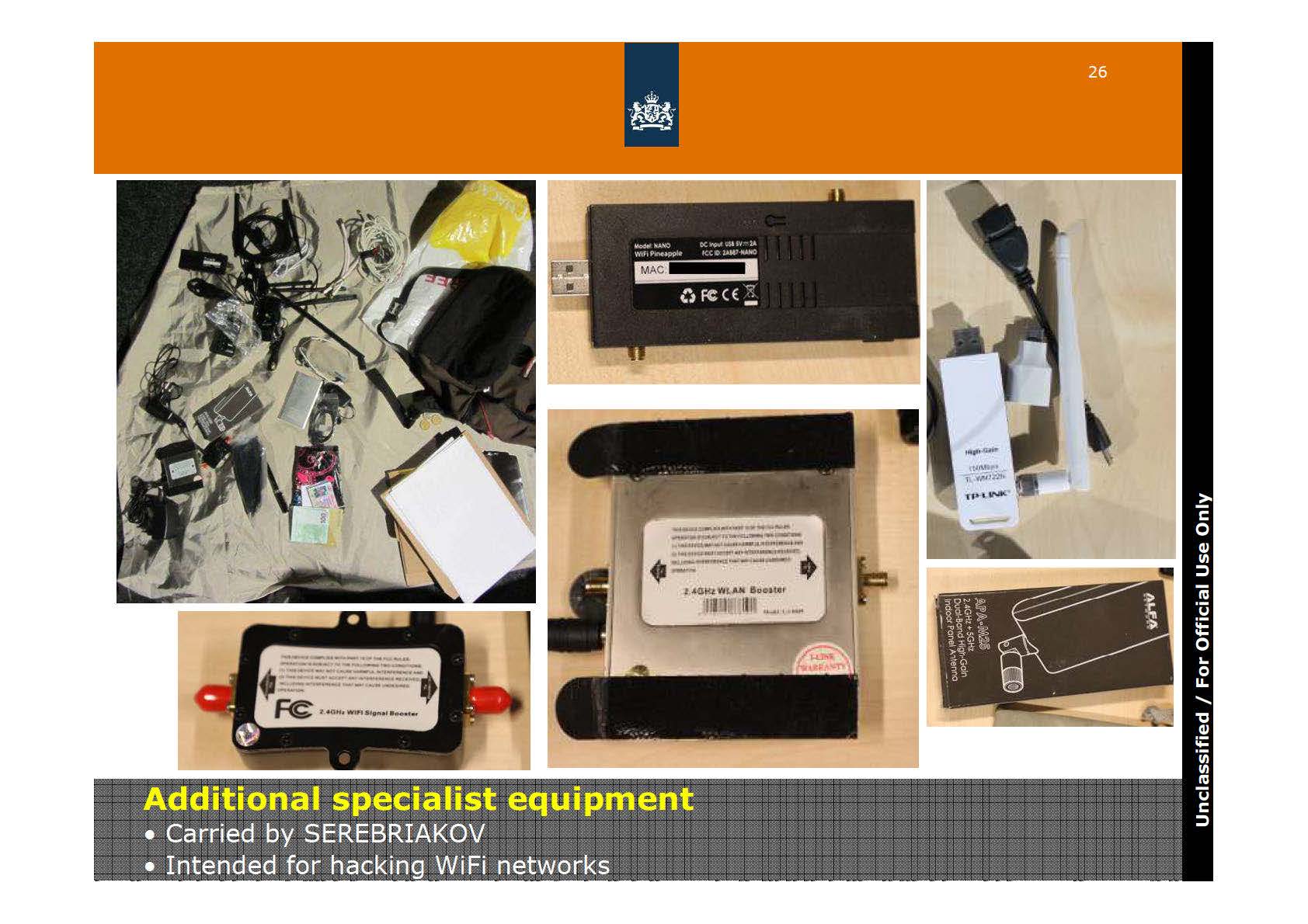
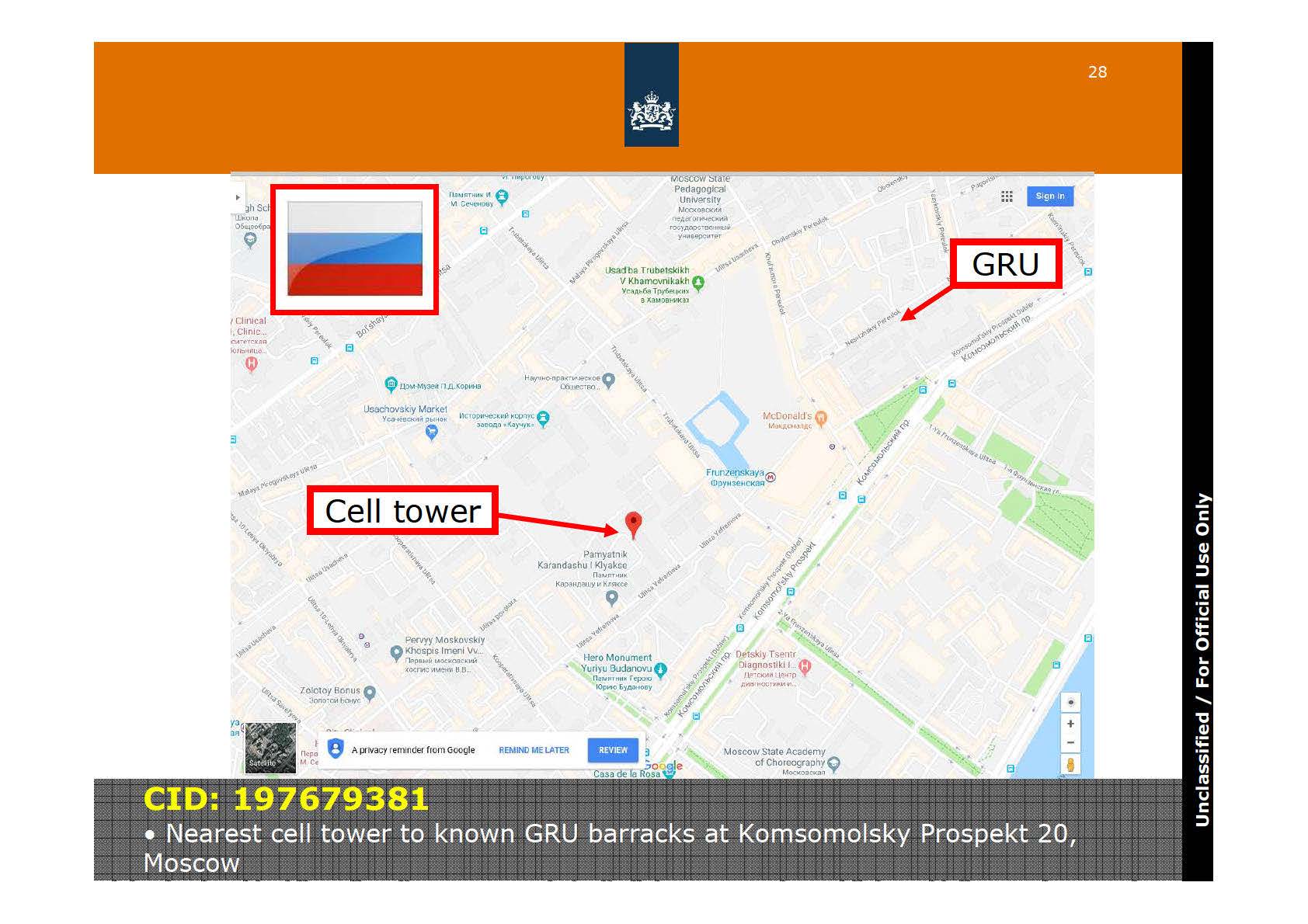





































































































































![[Image]](https://cryptome.org/2018-info/pict5.jpg)
![[Image]](https://cryptome.org/2018-info/pict6.jpg)
![[Image]](https://cryptome.org/2018-info/pict7.jpg)
![[Image]](https://cryptome.org/2018-info/pict8.jpg)
![[Image]](https://cryptome.org/2018-info/pict9.jpg)
![[Image]](https://cryptome.org/2018-info/pict10.jpg)

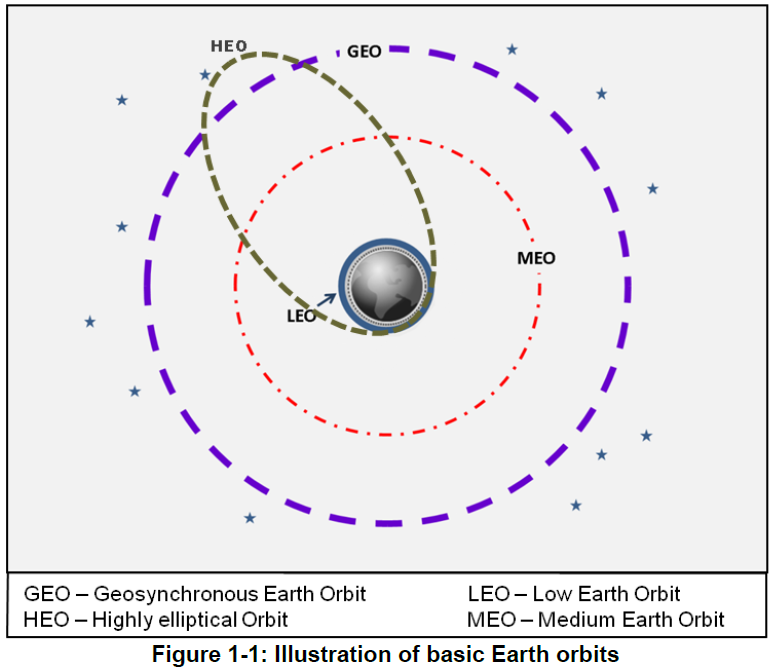
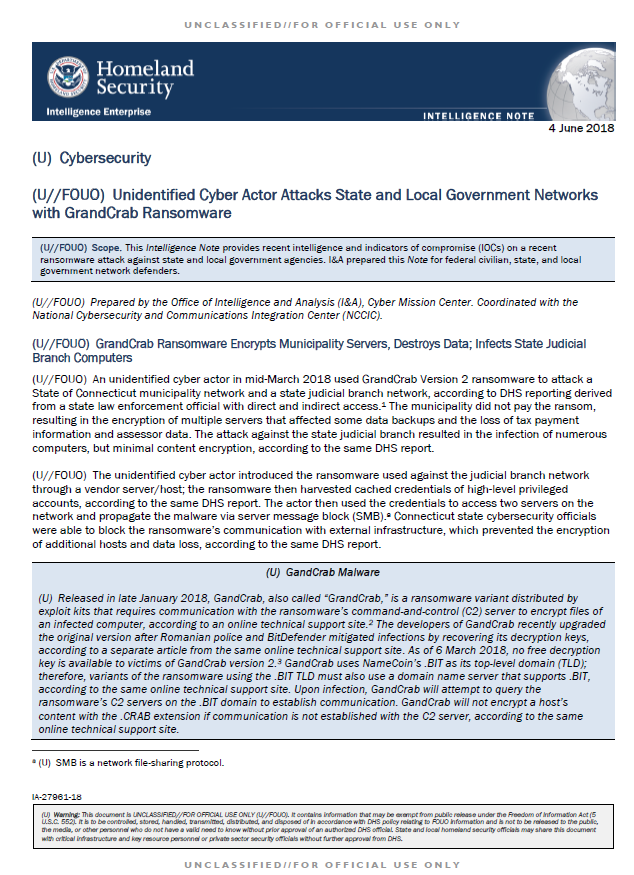









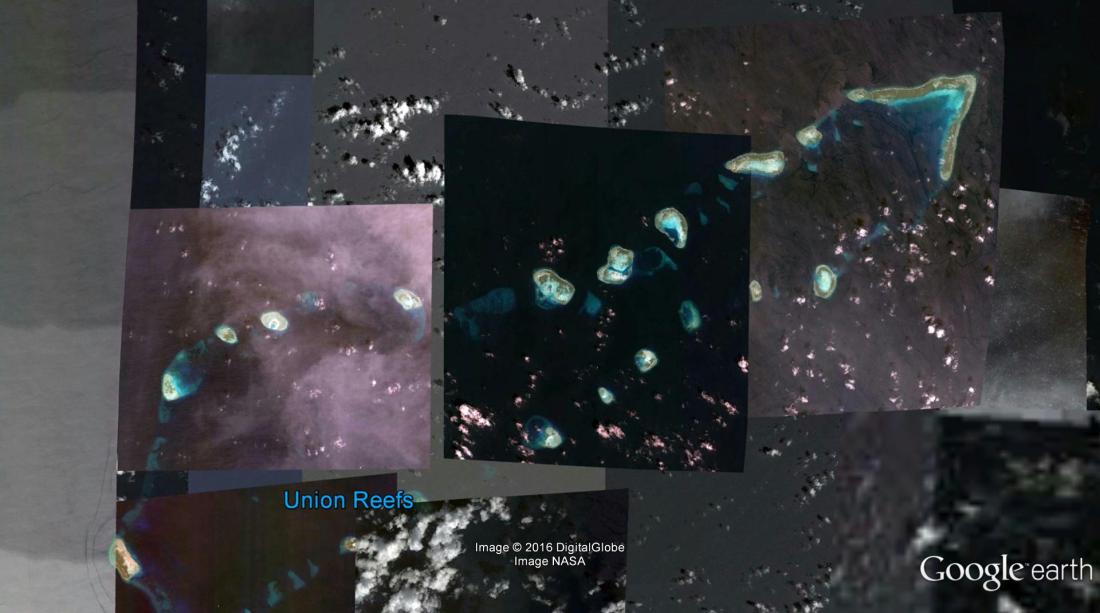




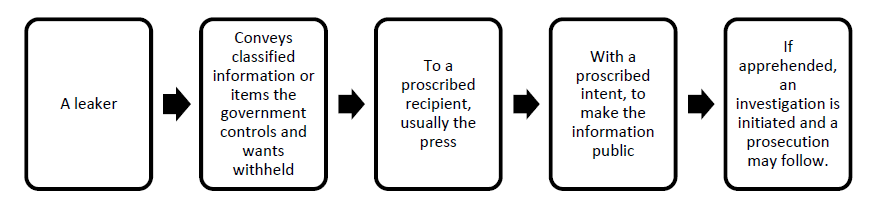
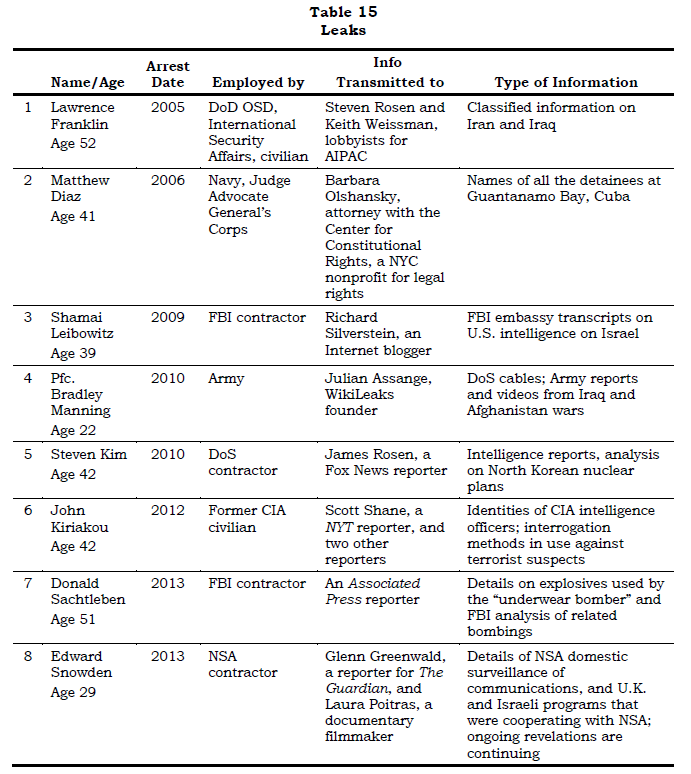

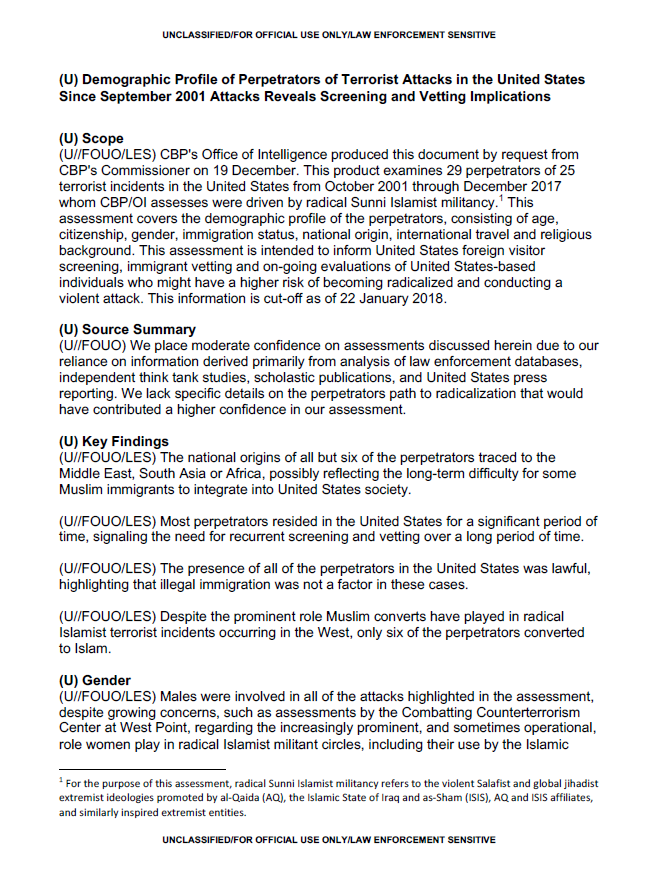















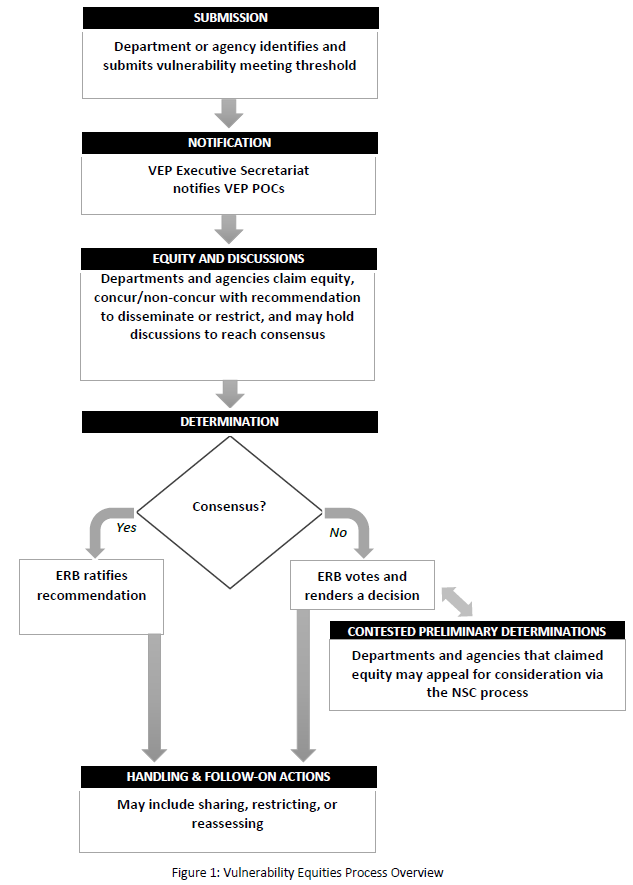



You must be logged in to post a comment.