Become a Patron!
True Information is the most valuable resource and we ask you to give back

Between 1981 and 1989 the foreign intelligence branches of the Soviet KGB and the East German Ministry of State Security launched a combined effort to develop a system for detecting signs of an impending western nuclear first strike. Codenamed “Project RYaN”, this early-warning system constituted one part of the Soviet response to the perceived threat of a surprise “decapitation” strike by NATO nuclear forces.
233 pages of documents from the Stasi’s Hauptverwaltung A and analysis by Bernd Schaefer, Nate Jones, and Benjamin Fischer below give unprecedented insight into the capabilities and fears of the Eastern Bloc intelligence services from the Able Archer ’83 War Scare to the end of the Cold War.
Introduction to the Collection
by Bernd Schaefer
In November 2012 CWIHP published e-Dossier No. 37 on the cooperation between the Soviet Committee for State Security (KGB) and the East German Ministry for State Security (MfS or Stasi), which highlighted a wide array of German documents dating from the 1960s through 1989. These materials were introduced by Walter Süss and Douglas Selvage, historians in the research division of the Federal Commissioner for the Stasi Records (BStU) in Berlin.[1] While e-Dossier No.37 featured just one document[2] on Soviet/East German preparations to detect a surprise Western “nuclear missile attack” (RYAN or Raketno Yadernoye Napadenie/Ракетно ядерное нападение in Russian) from August 1984, the BStU research division added a substantial number of German Stasi documents on RYAN to its online collection in 2013.[3] These new materials are remarkable and add to our understanding of the intentions, scope, and duration of the Soviet RYAN project; all of them are available in translation today in the CWHIP Digital Archive. The follow e-Dossier includes detailed comments and analysis on their significance by Nate Jones, a nuclear expert at the National Security Archive in Washington D.C., and Benjamin Fischer, a retired CIA officer and veteran researcher of RYAN and the so-called “Able Archer Crisis” of November 1983.
The August 1984 record of bilateral Stasi-KGB conversations, written by East German foreign intelligence spy chief Markus Wolf, includes an apt summarization of RYAN’s purpose by the Soviet representative: “The need for such approaches derives from the fact that a multitude of measures undertaken by the adversary do not allow advance determination which variation to launch a war the adversary will choose. In addition, we need to integrate experiences from analyzing the enemy’s crisis management into a process of further perfecting the definition of indicators to detect the adversary’s main measures for its acute war preparation.”[4]
It is undisputable that after 1979 the Soviet leadership, military, and intelligence service grew increasingly nervous about a “possible” Western “surprise nuclear missile attack” to “decapitate” the USSR’s nuclear potential and win a subsequent war
It is undisputable that after 1979 the Soviet leadership, military, and intelligence service grew increasingly nervous about a “possible” Western “surprise nuclear missile attack” to “decapitate” the USSR’s nuclear potential and win a subsequent war. The KGB operated an intelligence network to monitor worldwide “indicators” to detect to assess the likelihood of a “surprise nuclear missile attacked” launched by NATO. Soviet assessments of the likelihood of such an attack differed over the years, peaking between 1982 and 1984.

Whether such fears were warranted given the actual activities of the United States and NATO is disputed. Historians and analysts have differed in their assessments of partially declassified American sources, archival materials from Eastern European and Soviet archives, post-1990 oral histories from Russia, and memories of former actors, such as prominent KGB defector Oleg Gordievsky. Some consider the so-called “Able Archer Crisis” or “War Scare” of November 1983 to be the most dangerous event of the Cold War next to the Cuban Missile Crisis, while others view it in a much less dramatic fashion.[5]
The bulk of newly available Stasi and KGB documentation on RYAN from the BStU Archives in Berlin does not address Able Archer 83. However, it casts an unprecedented light on Stasi and KGB perspectives since 1984, as well as on the operational details, structure, and scope of the RYAN project. The collection includes a KGB catalogue from 1984/85 that, in excruciating detail, outlines the 292 indicators that might precede a potential “surprise nuclear missile attack.” Many of them refer to activities in and around Washington offices and buildings, including the White House parking lot. The collection also includes summaries of monthly KGB reports up to April 1989, which list possible global indicators of preparations for a “surprise nuclear missile attack.” These records tell us that hundreds of KGB officers were assigned to work on the RYAN program and a special division was created inside the KGB exclusively for this purpose. Combined with earlier published Stasi documents on the Soviet shoot down of KAL 007 in September 1983 (in which Soviet intelligence’s inability to determine whether the airliner was military or civilian before it was shot down was identified as a serious problem[6]), these new RYAN materials provide ample evidence of comprehensive Soviet efforts to avoid and thwart a “surprise attack.”
While hindsight shows that Soviet fears were exaggerated, the level of Soviet and East German anxiety over Western intentions, particularly during the first Reagan administration, is noteworthy. On the other hand, many Stasi documents on RYAN read like overbearing bureaucratic exercises, aimed at comprehensiveness and perfection on paper, but unattainable in practice. Phrasing in some of the Stasi materials implies that there probably was some skepticism in higher Stasi echelons about the program’s effectiveness and the Soviet approach (though it did not deter the Stasi from contributing more substantive efforts than any other fraternal socialist intelligence service towards identifying indicators).
Still, it does not seem far-fetched that Soviet anxieties were enhanced by the ensuing and ever expanding RYAN program and fed into Moscow’s shift towards disarmament policies under Mikhail Gorbachev. Strangely enough, the KGB’s RYAN project had acquired such a life of its own that its operational routines continued all the way through the first half of 1989, regardless of changes in Soviet-American relations and disarmament efforts during the second Reagan and the early Bush I administration.
Was RYaN simply a “ vicious cycle of intelligence collection and assessment” as described by Oleg Gordievsky? While Gordievsky’s word choice is debatable, these new documents put a certain amount of Soviet “circular reasoning” on full display.
The Vicious Circle of Intelligence
Oleg Gordievsky, the spy who revealed the existence of Operation RYaN –RYaN (РЯН) is the Russian acronym for Raketno Yadernoye Napadenie (Ракетно ядерное нападение), or “nuclear missile attack”– described it as “a vicious circle of intelligence collection and assessment.” During the last decade of the Cold War, Soviet intelligence operatives abroad were “required to report alarming information” to Moscow about a Western surprise nuclear strike, “even if they themselves were skeptical of it.” After the Moscow Center received these inflated and incorrect –but requested– reports of Western preparations for a surprise nuclear strike, it became “duly alarmed by what they reported and demanded more.” Now, documents newly released by the Cold War International History Project and the Office of the Federal Commissioner for the Records of the State Security Service of the Former German Democratic Republic (BStU), provide unprecedented insight into the “vicious circle of intelligence” of Operation RYaN. And, in a development never envisaged by the documents’ authors, they now present historians with comprehensive, real-time monthly RYaN reports from Soviet intelligence operatives abroad as they witnessed and catalogued the Cold War’s end.[7]
In 1979 the Institute for Intelligence Problems, coordinated by the KGB’s First Chief Directorate, was tasked to work on “the development of new intelligence concepts” that could provide preliminary warning of Western preparations for a first strike. The result of this work was the creation of Operation RYaN, which was secretly announced in May of 1981.[8] At a major KGB conference in Moscow, General Secretary Leonid Brezhnev and Yuri Andropov, then Chairman of the KGB, justified the creation of Operation RYaN because, they claimed, the United States was “actively preparing for nuclear war” against the Soviet Union and its allies. According to a newly released Stasi report, the primary “Chekist work” discussed in the May 1981 meeting was the “demand to allow for ‘no surprise.’”[9]
The establishment of Operation RYaN has also been corroborated by KGB annual reports from 1981 and 1982, previously published by the National Security Archive. The 1981 annual report states that the KGB had “implemented measures to strengthen intelligence work in order to prevent a possible sudden outbreak of war by the enemy.” To do this, the KGB “actively obtained information on military and strategic issues, and the aggressive military and political plans of imperialism [the United States] and its accomplices,” and “enhanced the relevance and effectiveness of its active intelligence abilities.”[10]
The 1982 annual report confirmed Soviet fears of Western encirclement, and noted the challenges of countering the “U.S. and NATO aspirations to change the existing military-strategic balance.” Therefore, “[p]rimary attention was paid to military and strategic issues related to the danger of the enemy’s thermonuclear attack.” This Soviet unease was spurred by the pending November 1983 deployment of Pershing II and Gryphon Cruise missiles, whose short flight times and long range changed the nuclear balance by threatening Soviet nuclear command and control with decapitation.[11]
The first comprehensive account of the details of Operation RYaN remains a Top Secret February 1983 telegram from KGB Headquarters Moscow to the London KGB Residency entitled “Permanent operational assignment to uncover NATO preparations for a nuclear missile attack on the USSR,” with enclosed instructions on how to report on indicators pointing toward a nuclear sneak attack. This document was published in full in 1991 by Soviet double agent Oleg Gordievsky and British intelligence historian Christopher Andrew in Comrade Kryuchkov’s Instructions: Top Secret Files on KGB Foreign Operations, 1975-1985.
 Above: M113 armored personnel carriers move through the town of Stockhausen (Herbstein) during REFORGER ’83 in Germany.
Above: M113 armored personnel carriers move through the town of Stockhausen (Herbstein) during REFORGER ’83 in Germany.
“The objective of the assignment is to see that the Residency works systematically to uncover any plans in preparation by the main adversary [USA] for RYaN and to organize continual watch to be kept for indications of a decision being taken to use nuclear weapons against the USSR or immediate preparations being made for a nuclear missile attack.”
Attached to the telegram was a list of seven “immediate” and thirteen “prospective” tasks for the agents to complete and report. These included: the collection of data on potential places of evacuation and shelter, an appraisal of the level of blood held in blood banks, observation of places where nuclear decisions were made and where nuclear weapons were stored, observation of key nuclear decision makers, observation of lines of communication, reconnaissance of the heads of churches and banks, and surveillance of security services and military installations.
Regrettably, however, Comrade Kryuchkov’s Instructions included a facsimile reproduction of only the first page of this document. The additional pages were translated and typeset into English with no Russian corroboration of their authenticity. Nevertheless, the KGB annual reports, as well as documents from other former Eastern Bloc (Czechoslovakian and Bulgarian) archives, and now these Stasi documents, help to substantiate Gordievsky’s accounts.[12]
The newly released Stasi documents on RYaN show that East German Intelligence did not begin conducting RYaN collection activities until years after the Soviets began. A January 1983 “brief note” describes initial Stasi preparations for creation of systematic RYaN intelligence collection and reporting, but acknowledges “[f]urther questions had to be straightened out.” [13] At the February 9th high-level meeting in Moscow, Stasi head Erich Mielke told KGB Chairman Victor Chebrikov that, “consultations have to be continued.” Chebrikov replied, “The work is definitely not finalized.”[14] In August of 1984, the Soviet and East German intelligence agencies were still discussing how, exactly, “to approach conceptual, organizational, and practical aspects when dealing with the RYaN problem.”[15]
In fact, German collection and analysis of RYaN information did not begin in earnest until early 1985, according to the February 15, 1985, Order Number 1/85 which directed that “all options” be utilized to detect Western “military aggression, particularly a surprise nuclear missile attack” by observing non-socialist states and West Berlin in a “systematic and targeted manner.”[16] While systematic Stasi RYaN collection and analysis did not commence until well after the end of what has become known as the “1983 War Scare,” these newly released documents do contain insights about the danger of the era, which will be discussed below.
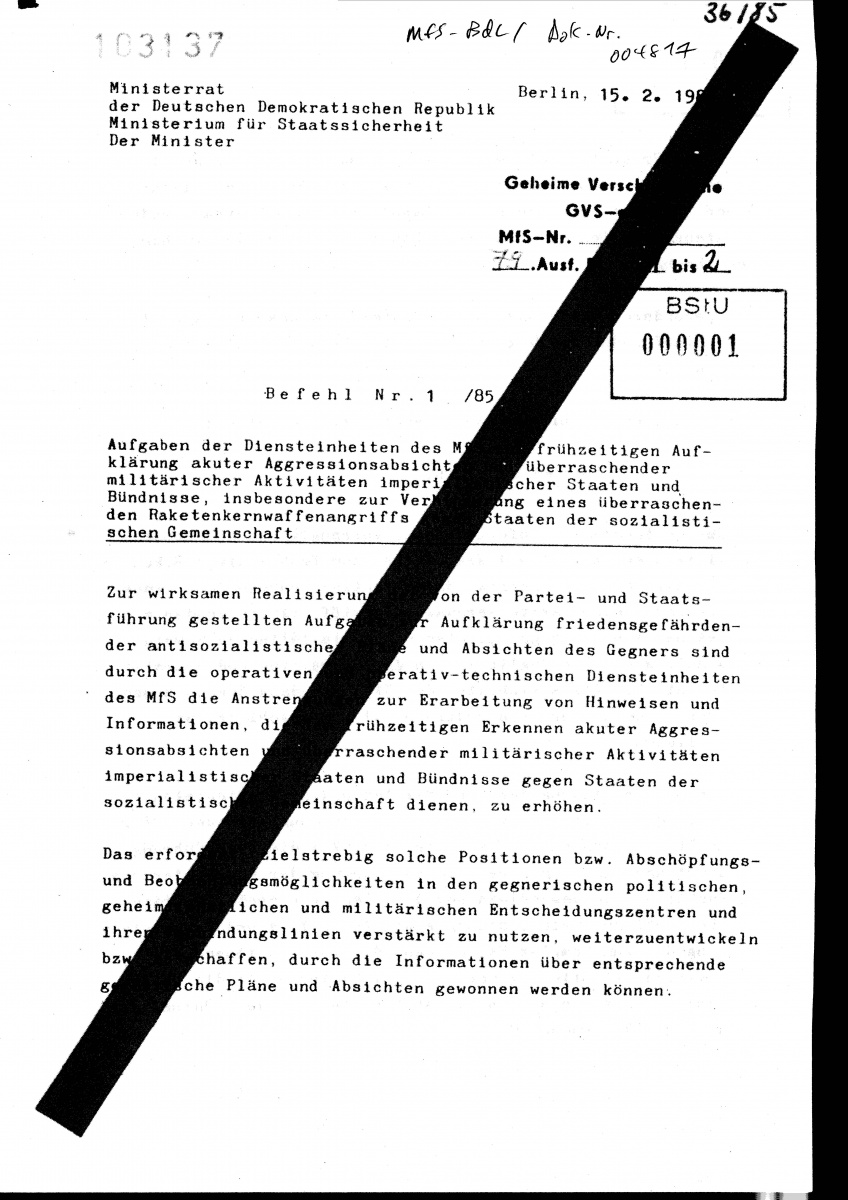
Above: Order Number 1/85
The documents also provide unprecedented operational details about RYaN, including its size, the importance of East German intelligence to the Soviets, the use of computers for RYaN collection, and the 292 indicators that some Eastern Bloc intelligence experts believed could be used to detect a nuclear attack.
For the first time, historians have access to hard numbers about the size of Operation RYaN, revealing that within the KGB, 300 positions were created so that RYaN operatives could implement the real-time “transmission and evaluation” of reported indicators showing the likelihood of a Western first strike. In July of 1984, KGB chairman Victor Chebrikov created a new division within the First Department (Information) of the KGB’s First Main Directorate (responsible for foreign intelligence and operations) to implement Operation RYaN throughout the KGB and world. This coordinating division was composed of 50 KGB officers.[17]
The documents further acknowledge that the Stasi was the KGB’s primary source of foreign intelligence. In July 1981, Andropov thanked Stasi head Erich Mielke for providing information on “West German tank production, defense technology, and the NATO manual [as of now the contents of this manual is unknown].” Andropov then complemented the Stasi, lauding, “We rate your information very highly,” and forebodingly requested Stasi sources procure “an assessment of the NATO manual and NATO’s preparations for war.”[18] In September 1983, Deputy Chairman of the KGB Vladimir Kryuchkov told Stasi head Erich Mielke that although Andropov was officially on vacation in the Southern USSR, it was “no actual vacation… For half the day he is reading information, including ours [KGB] and what we received from you.” In December 1986, KGB Chairman Victor Chebrikov wrote Stasi head Erich Mielke to thank him for the “tangible results in this extremely important area [Operation RYaN].” He emphasized that the KGB “highly value[d] the contribution of the MfS of the GDR to the joint efforts on timely recognition of the danger of a sudden attack.”[19]
There are also references to the primitive computer system that the Soviet Union was attempting to use to track and calculate the coalition of world forces, including the risk of nuclear war. The KGB reported to the Stasi that it had “revised its planning for scientific-technological research and industrial procurement” of new “reliably working technology.” Gordievsky had earlier reported of “a large computer model in the Min[istry] of Defense to calculate and monitor the correlation of forces, including mili[tary], economy, [and] psychological factors, to assign numbers and relative weights.”[20] On November 23, 1983, US Defense and Intelligence officials circulated an article entitled, “In pursuit of the Essence of War” that described a Soviet method which “cataloged and computerized” the world’s “correlation of forces.” The results, it claimed, were “highly objective, empirically provable and readily adaptable to modern data processing.”[21] The newly released documents show that the East Germans were skeptical of Soviet computing prowess, however: past “Soviet experiences show us that a danger exists of computer application concepts not getting implemented,” snidely wrote Marcus Wolf.[22]
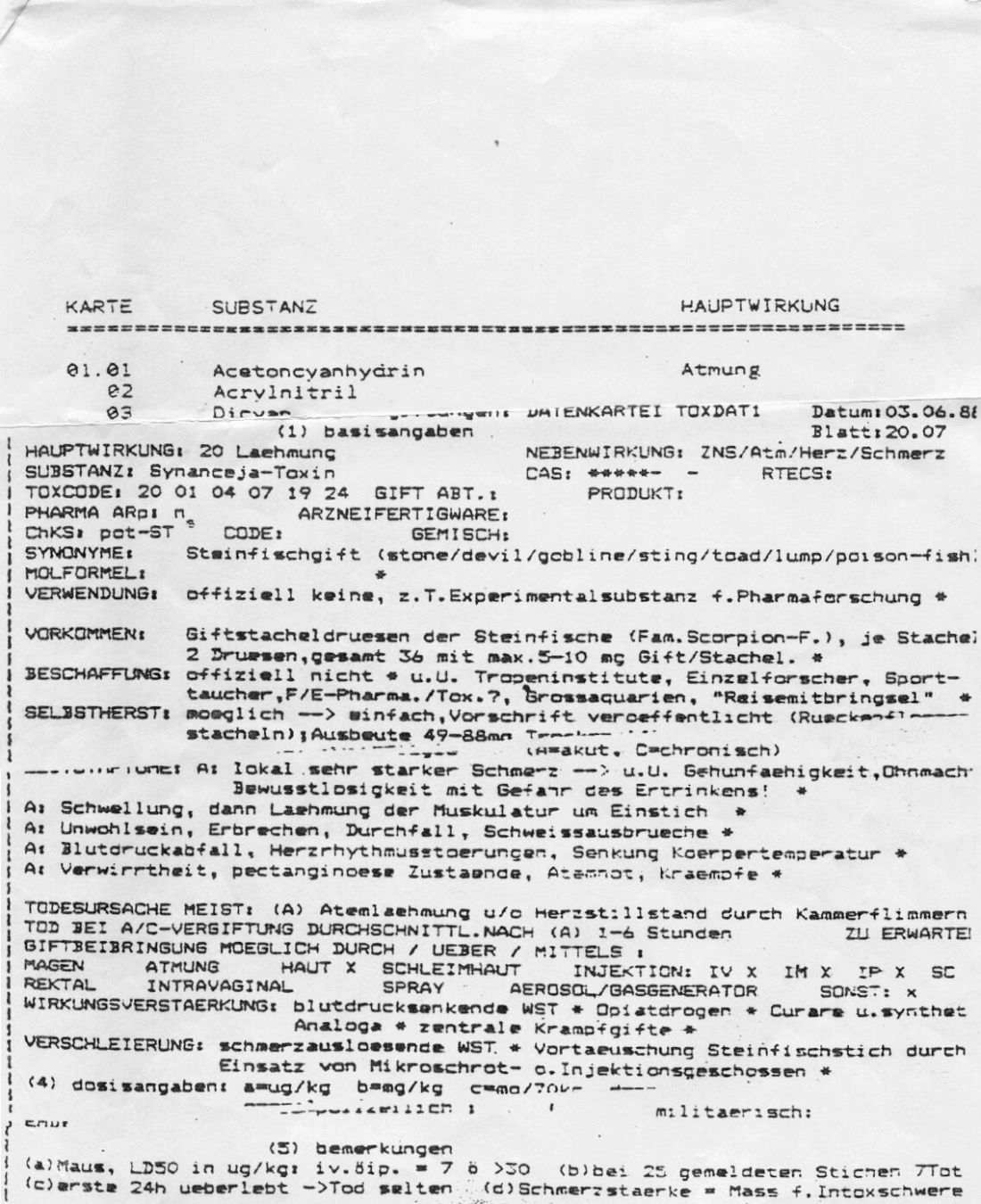
Computer analysis was desired because the amount of information captured during Operation RYaN was massive. The newly released Stasi documents provide far more detail than Gordievsky’s account of the precise indicators that human intelligence collectors were compiling and analyzing (such as: activity at Defense instillations, the location of prominent political officials, and even the treatment of “the most important government documents at the US National Archives”). In October 1983, Deputy KGB Chairman Kryuchkov revealed that the First Directorate’s Institute for Intelligence Problems[23] had compiled seven binders full of possible RYaN indicators.[24] By May of 1986, these binders had evolved into a catalogue of 292 indicators of “signs of tension.”[25] The Stasi reported that 226 indicators (77 percent) were able to be “covered, though to varying degree.” The indicators were organized into five main categories: Political, Military, Intelligence Services, Civil Defense Agencies, and the Economic sector. A read through the newly released full catalogue of RYaN indicators (as opposed to the truncated list published by Gordievsky) makes the program appear more rational and effective than has previously been portrayed.[26] Just one telling example is the fact that RYaN watchers had sniffed out the US Continuity of Government program, discovering and surveilling “two presidential planes… equipped with accelerated speed [and] electronic apparatuses which work under conditions of nuclear weapons use.”[27] These planes were where the president and his emergency cabinet would command during a nuclear war.
RYaN watchers were also instructed to watch for the “preparation and conduct of large-scale exercises,” because they increased “the level of combat-readiness of US strategic forces,” and hence, could indicate intentions for a “surprise nuclear missile attack.” When Gordievsky disclosed Operation RYaN he also revealed Able Archer 83, a November 1983 NATO command post nuclear release exercise that he claims Soviet intelligence may have miscalculated as an actual nuclear strike.[28]
The RYaN catalogue noted several indicators that would have occurred during Able Archer 83 (and other NATO exercises), including: the “large scale transfer of US armed forces” by C-5A and C-141 aircraft (16,000 troops were transferred from the US to Europe on radio silent flights during Autumn Forge 83, which included Able Archer 83); “preparation of anti-ABC [atomic-biological-chemical] protective gear” and mobilization (during Able Archer 83 the war gamers donned ABC equipment and transferred to an Alternate War Headquarters in response to simulated chemical attacks); and, perhaps most importantly, “significant changes in communications” including “transmittal of orders to deploy nuclear weapons” (on October 17-21 1983, the Supreme Headquarters Allied Powers Europe school in Oberammergau, West Germany trained more than 50 NATO officers on new nuclear weapons release procedures which utilized a new format that was practiced for the first time during Able Archer 83).[29]
Another eyebrow-raising, though certainly not dispositive, reference to Able Archer 83 can be found in these documents. On November 7, the day Able Archer 83 began, an East German Major General (whose name is illegible) sent a summary of discussions between Stasi foreign intelligence chief Marcus Wolf and Deputy KGB Chairman Vladimir Kryuchkov to Major General Damm. Gordievsky has written that on November 8 or 9, he “was not sure which,” flash telegrams were sent to both KGB and GRU residencies in Western Europe reporting “an alert on US bases.” The flash telegrams “clearly implied that one of several possible explanations for the (non-existent) alert was that the countdown to a nuclear first strike had actually begun.”[30]
Perhaps relatedly, the East German documents also reveal a persistent undercurrent of skepticism and concern about the effectiveness of Operation RYaN. In August of 1984, Lev Shapkin, deputy director of the KGB for foreign intelligence, told Marcus Wolf that reforms to Operation RYaN were underway. Though no faulty reporting by Operation RYaN during Able Archer 83 was mentioned in the meeting, the two intelligence officials clearly were worried that false warnings of a Western nuclear first strike could lead to preemptive actions by Soviet nuclear forces. Shapkin told Wolf that the indicators agents were observing and reporting “must be complemented, revised, and made more precise,” and bemoaned “the problem of not getting deceived” by faulty indicators. He reiterated that “clear-headedness about the entire RYAN complex” was a “mandatory requirement.” Marcus Wolf included his concerns in an addendum to the summary of the meetings, stressing the need to know the “actual situation” rather than the picture presented by Operation RYaN’s indicators. “Constant and ongoing assessments,” he sensibly wrote, “have to be made whether certain developments actually constitute a crisis or not.”[31]
The documents contained in this release include one final invaluable resource for historians: monthly Soviet intelligence summaries (translated from Russian to German, and now, to English) spanning August 1986 to April 1989. The monthly summaries, serving a purpose likely never imagined by their drafters, allow us to see how Soviet intelligence witnessed and reported the peaceful ending of the Cold War. The reports, which mirror the above RYaN format, are thorough and include much reporting on the West still officially classified in the United States. This includes reports on the operational readiness of Pershing II, MX, and Trident missiles at specific bases, and US military activities in Nicaragua, Panama, and Iran/Iraq. They also include comprehensive reporting of NATO drills and maneuvers. The Soviet observers reported of Able Archer 87, for example, that NATO “simulated” the switch from peace to war time; nuclear consultations were practiced “in the context of the exercise.” Regrettably, no November 1983 RYaN report is yet available for historians to observe if the reporting on Able Archer 83 was as couched and nuanced as it was four years later.
The task of following CWIHP and the BStU’s lead and finding these earlier RYaN reports now falls to archivists and archival burrowers in other former Soviet states now liberalized.[32]
Finally, these monthly RYaN reports about the Cold War’s peaceful resolution reflect the strangeness of the nuclear superpower rivalry itself. The absurd logic of the Cold War becomes evident when one reads about the NATO “elimination of intermediate and tactical nuclear missiles” in a September 1987 report incongruently entitled, “On the Results of Intelligence Activities to Report Indicators for a Sudden Nuclear Missile Attack.”
Comments on the Soviet-East German Intelligence Alert
by Benjamin Fischer
A real contribution
The BStU documents contain important information about both the Soviet intelligence alert RYAN and its East German counterpart KWA (Kernwaffenangriff or nuclear-weapons attack) during the 1980s. On several accounts, we owe Douglas Selvege a debt of gratitude for locating and disseminating the new tranche. First, no Soviet records have become available since former KGB officer (and British agent) Oleg Gordievsky published a selection of RYAN cables almost a quarter of a century ago, and it is unlikely that Russia will declassify new sources. Most commentators, I myself the most culpable, were mesmerized by both the stark tone of both the cables and Gordievsky’s various accounts of the “war scare.” A more balanced interpretation is now possible. Second, the East German Ministry for State Security (MfS) and especially its foreign intelligence service, the Hauptverwaltung A (Main Directorate A, hereafter HV A), played a major role in the alert system documented here for the first time. For many years, the only information on the East German side was Markus Wolf’s memoir (1997), which some researchers considered a reliable and original source while others did not. Wolf, however, couched his brief account, referring only to RYAN, not KWA. He apparently expected that HV A records would never see the light of day. There was good reason to do so, since most files were destroyed on the eve of German unification.[33] Though skeptical about the purpose and priority of the Soviet intelligence alert, Wolf nevertheless saluted and obeyed KGB orders. The MfS/HV A organized an elaborate early-warning system (Früherkennung/Frühwarnsystem) that replicated and, to some degree, exceeded its Soviet counterpart.
How scary was the war scare?
Wolf occupied a much higher position than Gordievsky in the Warsaw Pact intelligence community. The spymaster was closer to the real center of power in Moscow, was a keen observer of both superpowers, and his agents in the West— especially inside NATO provided insights that countered the ideological stereotype of the “inherent aggressiveness” of the Western alliance. Moreover, his view may have been in line with the actual perceptions of his Soviet masters.
Yuri Andropov was the leading proponent of RYAN. He inaugurated the alert in 1981 as chairman of the KGB and presided over its expansion after succeeding Leonid Brezhnev as General Secretary the next year. In May 1981, during a private conversation with Wolf’s boss, State Security Minister Erich Mielke, Andropov assessed the Reagan administration’s plans for accelerated modernization of strategic and theater-nuclear forces:
The US is preparing for war, but it is not willing to start a war. They are not building factories and palaces in order to destroy them. They are striving for military superiority in order to “check” us and then declare “checkmate” against us without starting a war. Maybe I am wrong.[34]
Andropov added that Washington had abandoned détente because it benefited the USSR at the expense of the US—in words that echoed Ronald Reagan’s condemnation of détente as a “one-way” street! Now the US was trying to recover its losses by reverting to the earlier policy of containment, in other words, to the old Cold War.
Two years later, facing the prospect of deployment of new US Pershing II missiles in Western Europe, Andropov addressed a meeting of the Warsaw Pact’s Political Consultative Committee. The missiles were the “most serious challenge,” he said, and the military situation was “especially dangerous.” In the past, the US had counted on its nuclear weapons “to deter” and “to contain” the Soviet Union; now there was talk of actually fighting and prevailing in a nuclear war.[35] “It is difficult to say where the line between extortion and actual preparation to take a fateful step lies.”[36]
Andropov stopped short of declaring that war was imminent or unavoidable. In his public statements, however, he spoke as if the world was on the brink of a nuclear holocaust. Soviet propagandists compared Reagan to Hitler and the US to Nazi Germany on the eve of 1941. Less than a month after Andropov’s speech, the KGB dispatched a cable that sounded the alarm, asserting that RYAN “now lies at the core of [Soviet] military strategy;” the intelligence alert had become a military alert.[37]
Another “cut” at the question of leadership thinking on the prospect of war comes from a Politburo meeting in May 1983. Acknowledging that the US cruise and ballistic missiles would arrive on schedule, Andropov turned to Foreign Minister Andrei Gromyko for an assessment of US intentions. Gromyko replied: “The United States, as is known, is talking about the fact that they can only strike in response to aggression. I think that without enough reason they wouldn’t dare to use nuclear missiles.” He added that, in any event, NATO’s pluralist structure would act as brake on the US: “Against the first strike are also Canada, England, France, and West Germany.”
The Alert Ramps Up
The Soviets were nervous but not to the point of shaking in their boots. RYAN did not, as Gordievsky claimed, begin to wind down in mid-1984, on the eve of his departure from London and after he had lost access to KGB cable traffic. It ramped up. KGB officer Lev Shapkin briefed the East Germans on a series of decisions made to expand RYAN and to create an infrastructure to support it.[38] The KGB formed a new division within the First (information/analysis) Department of the First Chief (foreign intelligence) Directorate (FCD). It was a situation center or watch office designed to collect and assess warning indicators and levy requirements on the FCD’s operations divisions and signals intelligence (Sigint) department.
The new division was a high priority and was almost certainly initiated by Andropov. The formation of a special RYAN commission chaired by KGB chairman Viktor Chebrikov underscored the alert’s top-level political backing and its bureaucratic clout. Chebrikov earmarked 300 slots for the new RYAN division, 50 of which had been filled to monitor warning indications around the clock. However, the KGB had trouble finding qualified personnel and training officers to perform “warning-and-indications of war intelligence,” as it is referred to by US intelligence services. This is one of several signs that the Soviets, even in this late stage of the Cold War, had little or no experience with early-warning intelligence.
Warning and Surprise
RYAN was launched in May 1981 during an All-Union Conference of senior KGB managers from the length and breadth of the USSR. Andropov chaired it, but the presence of Leonid Brezhnev signified that the session was no routine gabfest. Gordievsky’s accounts give the impression that RYAN was the sole item on the agenda. It was not.
The East German documents show that the conference discussed a range of threats, referred to as “surprises,” emanating from within the USSR and the Eastern bloc, as well as from the international arena. The KGB chieftains were instructed to reorient their collection priorities toward early detection and advance warning of potential or impending crises that threatened the internal security and stability, as well as external security, of the Soviet empire. As KGB officer [full name unknown] Zinyov told the East Germans, the new operational directive was to “allow no surprises.” The mission of “Chekist work,” he added, now encompassed “the struggle against espionage and terror, questions of the economy, morale, the construction industry, etc.”[39]
Subsequently, FCD chief Vladimir Kryuchkov confided to Wolf that even foreign intelligence had been drawn into novel operations aimed at detecting threats to internal security originating from outside the USSR.[40] The MfS and HV A followed suit. “The bunker mentality of the GDR [German Democratic Republic] leadership revealed itself in the mantra-like repetition ‘impede every surprise from the enemy in every area.’”[41] This originally meant external military threats, i.e., the war scare, but then it expanded to include a range of dangers posed by domestic dissidence—religious, pacifist, and environmental groups, e.g.—allegedly supported by the West. The “most urgent” mission of the MfS, as well as the HV A, was to detect this conflation of internal and external “surprises” and to “prophylactically” deal with them before they grew to threaten the GDR regime.
Wolf’s repeated assertion that his service had nothing to do with the Stasi police-state was false. Like his counterpart Kryuchkov, Wolf followed orders. HV A case officers and their agents were tasked with collecting intelligence on internal threats emanating from abroad, even at the expense of conventional foreign intelligence inside the GDR and in the “Operations Area” (Stasi-deutsch for West Germany, West Berlin, and other NATO countries). The HV A began filing counterintelligence reports (Abwerberichte)—normally the provenance of the MfS internal security and surveillance departments—which contributed to increased repression in the GDR.[42]
KWA and the Frühwarnsystem
The MfS/HV A was the largest and most efficient Eastern bloc security/foreign intelligence service outside the Soviet Union. Its operational assets were considerable and in several respects exceeded those of the KGB, especially the massive MfS signals intelligence (Sigint) main directorate and the HV A’s extensive agent (Humint) networks that targeted West Germany/West Berlin and the US and NATO presence there.[43] Following the expansion of RYAN in mid-July, the KGB used the MfS/HV A to replicate its own organizational and operational model for early-warning intelligence.
This new collection includes one of the two key documents on KWA, Mielke’s Order Nr. 1/85, which mandated it as “the absolute priority” [emphasis in original] for the entire MfS.[44] The Order authorized Wolf, in his capacity as deputy MfS head, to formulate and implement an organizational plan and operational directives for the entire MfS. The second document[45] is not included in the collection, but several years ago I translated and commented on both documents.[46] The main components of the HV A’s early-warning system included:[47]
- A “catalog” of warning indicators that was based on the RYAN template of five “political/societal areas” (US/NATO political and military leaderships, intelligence services, civil defense organizations, and economic institutions); it also included targets covered by MfS Sigint and HV A agent networks in West Germany/West Berlin, as well as US/NATO diplomatic, military, and intelligence sites in West Germany;[48]
- A centralized situation center (Lagezentrum) to constantly monitor KWA indicators on a global basis;
- A dedicated communications link to the KGB’s situation center;
- Annual alert drills and military exercises for HV A officers that simulated conditions of a surprise attack;[49]
- Emergency communications plans and safe houses in West Germany for agents selected to report on KWA;[50]
- Coordination of operations and intelligence sharing with East German military intelligence on the Soviet model of KGB-GRU cooperation under RYAN guidelines.
A Catalog of Warning Indicators
The focal point of Soviet and East German collaboration was the compilation of a list or “catalog” of warning-of-war indicators designed to detect signs of an impending crisis or war “in real time.” The KGB demanded that the HV A catalog should be based on “strict conformity” with the RYAN template, i.e., on the five “political/societal areas” noted above.
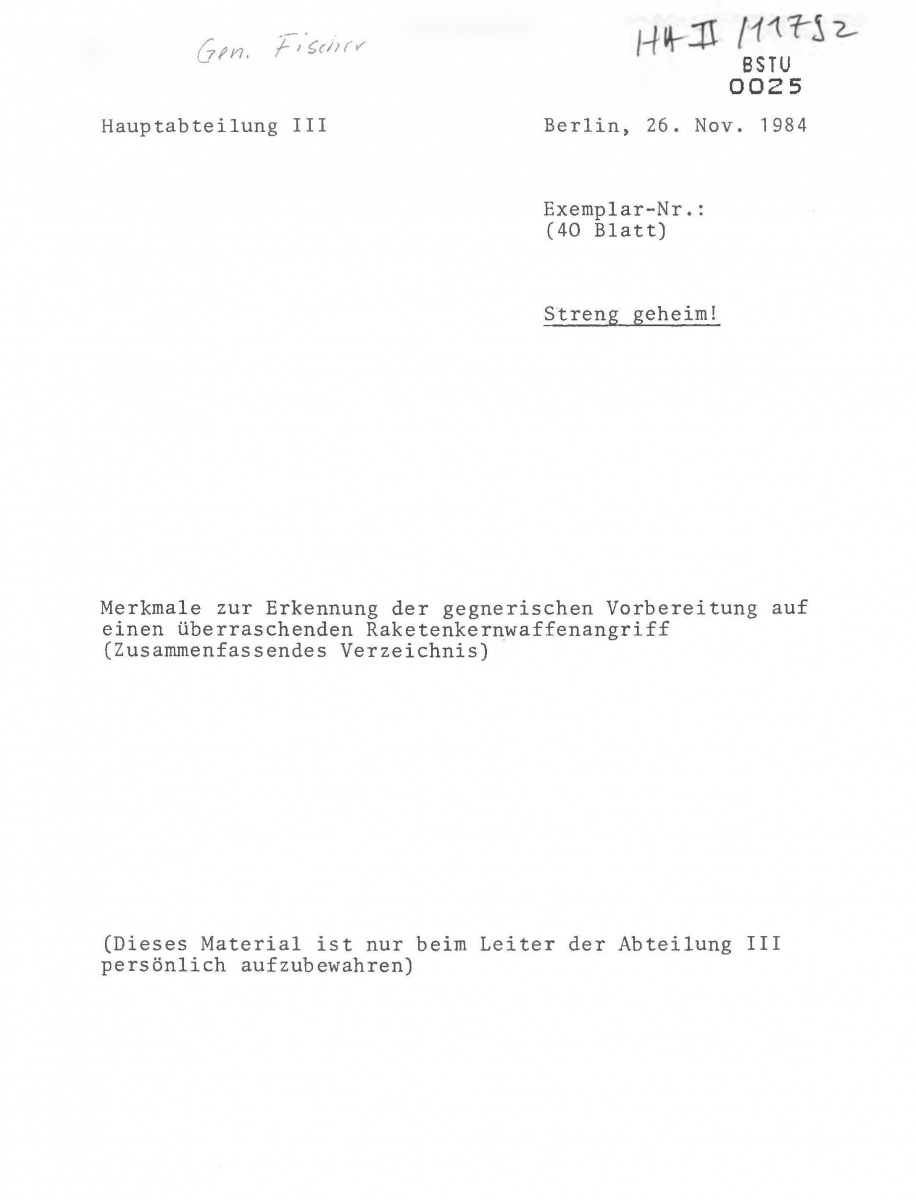
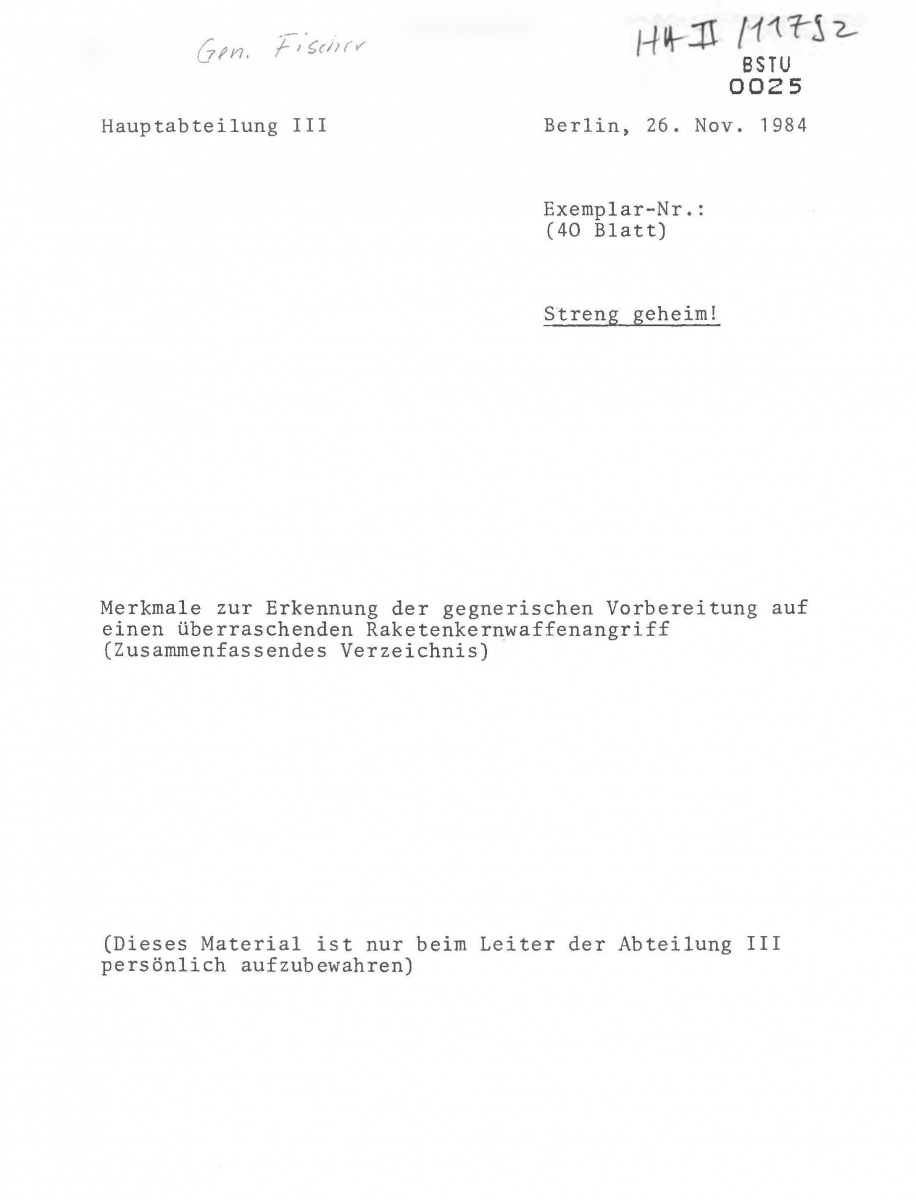 Above: Cover page from the HA III copy of the Project RYaN catalog of indicators.
Above: Cover page from the HA III copy of the Project RYaN catalog of indicators.
MfS/HV A records reveal that both services devoted considerable effort to conceptualizing, defining, and operationalizing warning indicators, yet they also seemed to have encountered problems that were never fully resolved. The main objective was agent penetration of “the enemy’s decision-making centers” and acquisition of “documents” on a political decision for war. The Soviet-East German intelligence reach, however, exceeded its grasp. The overriding goal was to obtain advance warning of a US decision to launch strategic nuclear forces, an urgent requirement since one-third of those forces remained on permanent alert, and the rest could be readied on short notice. A 1986 HV A report noted that “at the moment” this had not been accomplished.[51]
The second string to the RYAN/KWA bow was an extensive list of indirect indicators that, it was assumed, would reveal the implementation of alert procedures and mobilization plans that could not be concealed from intelligence surveillance and monitoring. The KGB and HV A were forced to resort to “observable intelligence,” i.e., things that can be seen and counted, in lieu of “message-like” intelligence, which relies on well-placed agents with access to plans, decisions, and intentions.[52] RYAN/KWA signified that the neither the KGB nor the HV A had such agents in place. The questionable methodological assumption was that overt or visible deviations from peacetime norms in the five political/societal areas could reveal a decision to attack the USSR and Warsaw Pact countries.
The one place where both services had well-placed agents was NATO headquarters. The KGB cables Gordievsky published, as well as the East German documents[EMP1] , reveal detailed knowledge of the alliance’s alert procedures and early-warning capabilities, especially NATO’s “crisis management” system. The KGB and HV A did not, however, find it reassuring that NATO arrangements were designed to warn of a Warsaw Pact attack in time to mount a defense. They simply declared that “crisis management” was dual-purpose concept that could be used to attack as well as warn.
The whole RYAN/KWA framework was anachronistic, seemingly more appropriate for the pre-nuclear age when states required lead times to mobilize armed forces and prepare populations for war. The template came from the KGB’s Institute for Research on Operational Problems. One explanation is that with little knowledge or experience to draw on, the Institute was dusting off old lessons learned from a previous surprise attack, namely Hitler’s Operation Barbarossa.
Some of the indicators were based on a mirror-image of how the Warsaw Pact would prepare for war, such as the stockpiling of mineral oil and mass slaughter of cattle. HV A case officers, for example, were instructed to look for:
“Confirmation of deviations in the behavior of prominent personalities and other persons in possession of classified information as well as their family members and persons close to them, which can be viewed as measures for protecting their own security (among other things, sudden moving into specially equipped secure accommodations, unexpected departure from normal residential areas and from border zones at home and abroad).”
The GDR, meanwhile, was building bunkers and fall-out shelters for the political, military, and intelligence elite and practicing “evacuation exercises” in case of a putative nuclear assault.[53]
The KGB and the HV A both had difficulties defining “key” indicators and do not appear to have arranged them in rank order or have assigned numerical weights or some form of an “accounting” method. There is a fleeting reference to the possibility of reaching false conclusions about hostile intentions, but the inherent problem of arriving at a false positive as watch officers worked through their checklists was apparently never fully addressed. Was there a tipping point or designated critical mass of accumulated indicators that would predict an attack? We don’t know, and the documents don’t tell us.
In 1986, the HV A reported that it had covered 226 of the 292 (!) indicators (“77%”), “albeit in varying degrees,” from its catalog, but what that meant is not clear. Were the results negative—no war on the horizon—or positive? The documents refer to efforts to employ computer-based data processing, but they also allude to problems with software and algorithms that, apparently, were never resolved.
All intelligence bureaucracies write memos and send cables when they want to give the impression that they are making decisions and taking action while, actually, “slow rolling the process.” The KGB-HV A dialogue on the indicators may have been no different. Despite repeated references to the urgency and priority of the alert, the HV A took several years to compile its own list of indicators. Meetings of working-level experts in Moscow and East Berlin were arranged at a leisurely pace. It took more than a year after Order Nr. 1/85 to organize an HV A situation center to monitor KWA indicators. By the time it was up and running, the entire effort was about to be overtaken by events in Moscow with the advent of Mikhail Gorbachev and “new thinking.”
Mielke’s Variant
RYAN single-mindedly focused on the putative threat of a US surprise attack on the USSR. KGB cables declared that timely warning was required for Soviet strategic forces to take “retaliatory measures,” but the logic of the alert suggests that a preemptive first-strike, not a second-strike after US missiles had been launched, was the actual purpose.
Mielke repeatedly, and vainly, pushed for consideration of “other variants” of surprise, in particular conflict in Central Europe arising from a crisis in East-West relations. Mielke’s concern, shared by many in West Germany, was that the superpowers were prepared to fight in Europe, with conventional forces or “limited” nuclear strikes, down to the last German and on the last inch of German soil.[54] The Soviets simply ignored him. As the documents show time and again, Kremlin leaders had far less concern for their ally’s security than for their own.
Tradecraft and the war scare
The documents contain several references to operational tradecraft that underscore the Warsaw Pact’s lack of experience with warning intelligence. With the onset of the RYAN and KWA alerts, the KGB and the HV A, apparently for the first time, decided to issue to selected agents in the West rapid response communications equipment. The German term was Sofortmeldung (immediate reporting), which may have referred either to radios or burst transmitters using satellite relays to transmit encrypted electronic signals to the HV A situation center.
Theretofore, the KGB and HV A had employed personal communications (face-to-face meetings) or impersonal communications (dead drops) to pass requirements to and collect information from agents. Such arrangements required advance planning, conduct of pre-and-post meeting surveillance detection routes, and continuous “casing” for meeting or dead drop sites. Old-fashion tradecraft was secure but time-consuming and not suited for real-time reporting.
So, what was the war scare?
Wolf and his officers found Moscow’s “war games” a burdensome waste of time in pursuit of a non-existent threat. Some said KWA was a bureaucratic boondoggle that Mielke used to expand his power and influence. Vadim Bakatin, the last KGB chairman, called RYAN “an atavism of the Cold War” and a “sort of window dressing, and boiled down to compilation of regular reports stating that any given country was not intending in the next few days to drop nuclear bombs on the USSR.”[55] Soviet and East German leaders, however, were genuinely fearful, even if the threats and conspiracies they saw all around them were often exaggerated or even imaginary. As they were losing their grip on power, they were also losing their grip on reality.
Vadim Bakatin, the last KGB chairman, called RYAN “an atavism of the Cold War”
At the same time, the US was investing billions of dollars to upgrade its command-and-control, communications, intelligence, and early-warning capabilities, all predicated on the potential threat a Soviet surprise attack.[56] During the last decade of the Cold War, the fear of war was reciprocal and real, even if the threat of war was not.
Document Appendix
A brief note written by the Ministry of State Security that includes a number of questions for the leadership of the KGB in the USSR, such as whether other elements, like military doctrine or emergency responses, should be examined as possible options for starting a war.
This note on the talks between Minister Wolf and KGB Chairman Chebrikov contains heartfelt congratulations on cooperation thus far, but it also highlights problems with the situation and the importance of utilizing the potential of all fraternal organs to detect and prevent hostile plans and measures.
These notes describe statements made by Colonel General Kryuchkov which outline the current state of Soviet institutions and intelligence networks in various regions, including Western Europe, Africa, the Middle East, and the United States.
This report describes conversations with Comrade Kryuchkov, coving a multitude of subjects, but delving briefly into the problem of “prevention of a surprise nuclear attack” (RYAN). Kryuchkov responded that this issue is being continually worked on, but no central decisions had been made as of yet.
A catalog of indicators of NATO preparation for nuclear war that were monitored by Warsaw Pact intelligence services under Project RYaN. The activity is divided into the following areas: political and military, activities of intelligence services, civil defense, and economic.
This order from the Ministry of State Security describes the tasks of the MfS units concerning efforts to uncover intentions of aggression and surprise military activities by western states and their allies, especially a surprise nuclear missile attack against the USSR.
This speech by East German Minister of State Security Mielke addresses the technological, intellectual, and ideological preparations for war by the west and how to uncover and organize indicators of a potential attack.
This report by Ministry of State Security describes developments and achievements toward early recognition of a surprise nuclear missile attack on the USSR.
This letter from East German Minister of State Security Mielke to KGB Chairman Chebrikov requests a consultation on the development and continuation of Complex RYAN, especially on furthering collaboration between the MfS and KGB.
Responding to Mielke’s letter from November 1986, Chebrikov agrees to the proposed meeting between the MfS and the KGB on the subject of a sudden nuclear missile attack on the states of the socialist community.
This document is a plan for the consultations to take place in Berlin between the Stasi and the KBG. It includes objectives and proposed theses on the subject of early recognition of a sudden nuclear missile attack by NATO forces.
Documents 12 A–T: Committee for State Security (KGB), ‘About Results of Intelligence Activities to Note Indicators for a Surprise Nuclear Missile Attack’.
Documents 12A–T are monthly intelligence reports digests generated using intelligence by Project RyaN between August 1986 and April 1989.
[1] Süß, Walter and Douglas Selvage. “CWIHP e-Dossier No. 37: KGB/Stasi Cooperation” Cold War International History Project http://www.wilsoncenter.org/publication/kgbstasi-cooperation.
[2] “Deputy Minister Markus Wolf, Stasi Note on Meeting with KGB Experts on the RYAN Problem, 14 to 18 August 1984,” August 24, 1984, History and Public Policy Program Digital Archive, Office of the Federal Commissioner for the Stasi Records (BStU), MfS, ZAIG 5384, pp. 1-16. http://digitalarchive.wilsoncenter.org/document/115721
[3] „Das MfS und die Zusammenarbeit mit anderen kommunistischen Geheimdiensten: Staatssicherheit und sowjetischer KGB.“ Der Bundesbeauftragte für die Unterlagen des Staatssicherheitsdienstes der ehemaligen Deutschen Demokratischen Republik. http://www.bstu.bund.de/DE/Wissen/MfS-Dokumente/MfS-KGB/_node.html.
[4] “Deputy Minister Markus Wolf, Stasi Note on Meeting with KGB Experts on the RYAN Problem, 14 to 18 August 1984,” August 24, 1984, History and Public Policy Program Digital Archive, Office of the Federal Commissioner for the Stasi Records (BStU), MfS, ZAIG 5384, pp. 1-16. http://digitalarchive.wilsoncenter.org/document/115721.
[5] See below respective comments by Nate Jones and Ben Fischer.
[6] “Stasi Note on Meeting Between Minister Mielke and KGB Deputy Chairman Kryuchkov,” September 19, 1983, History and Public Policy Program Digital Archive, Office of the Federal Commissioner for the Stasi Records (BStU), MfS, ZAIG 5306, pp. 1-19. http://digitalarchive.wilsoncenter.org/document/115718.
Deputy KGB Chairman Viktor Chebrikov described Soviet “evidence” that the flight looked like a “reconnaissance mission”: “If we would have known this was a passenger plane, we would not have shot it down.” Put differently, the Soviet side wondered what would have been if the plane would have been a military aircraft and part of a Western surprise attack: In this case the Soviet Union would have been unable to detect such an attack, i.e. Moscow would have become “surprised.”
[7] Christopher Andrew and Oleg Gordievsky, KGB: The Inside Story of its Foreign Operations from Lenin to Gorbachev, (New York: Harper Collins, 1991), 585.
[8] Other sources vary the spelling of RYaN. Soviet Ambassador to the United States Anatoly Dobrynin spelled it “ryon.” Another spelling includes the word “surprise:” “VRYAN” “vnezapnoe raketno yadernoe napadenie” –surprise nuclear missile attack. Czech Intelligence referred to the operation as NRJAN. One document shows that the Bulgarians monitored “VRYAN indicators” as late as June 1987. These East German documents confirm that the operation continued until at least April, 1989. The 1983 War Scare, Part One http://www2.gwu.edu/~nsarchiv/NSAEBB/NSAEBB426/; Anatoly Dobrynin, In Confidence: Moscow’s Ambassador to Six Cold War Presidents (Seattle: University of Washington Press, 2001), 523; Oleg Kalugin, The First Directorate: My 32 Years in Intelligence and Espionage Against the West, (New York: St. Martins, 1994), 302; 9 March 1984, Bulgarian Ministry of Interior; MVR Information re: Results from the work on the improvement of the System for detection of RYAN indications, AMVR, Fond 1, Record 12, File 553, provided by Jordan Baev; Peter Rendek, ” Operation ALAN – Mutual Cooperation of the Czechoslovak Intelligence Service and the Soviet KGB as Given in One of the Largest Leakage Cases of NATO Security Data in the Years 1982 – 1986 .”
[9] RYaN Translation #2
[10] The 1983 War Scare, Part One http://www2.gwu.edu/~nsarchiv/NSAEBB/NSAEBB426/.
[11] The 1983 War Scare, Part One http://www2.gwu.edu/~nsarchiv/NSAEBB/NSAEBB426/; Benjamin Fischer, “CANOPY WING: The U.S. War Plan That Gave the East Germans Goose Bumps,” International Journal of Intelligence and CounterIntelligence, 27:3, 431-464. Recently, Benjamin Fischer has introduced an additional potential source of East German fear: CANOPY WING, purportedly a US military research project to exploit a vulnerability of Soviet Warsaw pact command and control communications to launch a “decapitation/surgical” strike.
[12] 9 March 1984, Bulgarian Ministry of Interior; MVR Information re: Results from the work on the improvement of the System for detection of RYAN indications, AMVR, Fond 1, Record 12, File 553, provided by Jordan Baev; Peter Rendek, ” Operation ALAN – Mutual Cooperation of the Czechoslovak Intelligence Service and the Soviet KGB as Given in One of the Largest Leakage Cases of NATO Security Data in the Years 1982 – 1986 .”
[13] “Issues to discuss with the leadership of the KGB of the USSR” http://digitalarchive.org/document/119308.
[14] “Note About the Talks of Comrade Minister [Mielke] with the Chairman of the KGB, Comrade Chebrikov, in Moscow.” http://digitalarchive.wilsoncenter.org/document/119319.
[15] “Deputy Minister Markus Wolf, Stasi Note on Meeting with KGB Experts on the RYAN Problem, 14 to 18 August 1984,” http://digitalarchive.wilsoncenter.org/document/115721.
[16] “Order Number 1/85” http://digitalarchive.org/document/119322.
[17] “Deputy Minister Markus Wolf, Stasi Note on Meeting with KGB Experts on the RYAN Problem, 14 to 18 August 1984,” http://digitalarchive.wilsoncenter.org/document/115721. It is possible that this new coordinating division was created as a reaction to the false alerts generated by Operation RYaN in November 1983 incorrectly warning that a NATO nuclear release drill, Able Archer 83, could have been an actual nuclear attack.
[18] “Stasi Note on Meeting Between Minister Mielke and KGB Chairman Andropov,” July 11, 1981, History and Public Policy Program Digital Archive, Office of the Federal Commissioner for the Stasi Records (BStU), MfS, ZAIG 5382, p. 1-19. http://digitalarchive.wilsoncenter.org/document/115717.
[19] ”Letter, KGB Chairman Chebrikov to East German Minister for State Security Mielke.” http://digitalarchive.wilsoncenter.org/document/119332; For more on the East German contributions to Soviet intelligence collection, see Benjamin Fischer, “CANOPY WING: The U.S. War Plan That Gave the East Germans Goose Bumps,” International Journal of Intelligence and CounterIntelligence, 27:3, 431-464.
[20] The 1983 War Scare, Part Three, http://www2.gwu.edu/~nsarchiv/NSAEBB/NSAEBB428/.
[21] The 1983 War Scare, Part Three, http://www2.gwu.edu/~nsarchiv/NSAEBB/NSAEBB428/.
[22] “Deputy Minister Markus Wolf, Stasi Note on Meeting with KGB Experts on the RYAN Problem, 14 to 18 August 1984,” http://digitalarchive.wilsoncenter.org/document/115721
[23] Translated here as “Institute for Operative Problems.”
[24] “Ministry of State Security (Stasi), ‘About the Talks with Comrade V. A. Kryuchkov” http://digitalarchive.wilsoncenter.org/document/119320
[25] “Ministry of State Security (Stasi), ‘Report on Development and Achieved State of Work Regarding Early Recognition of Adversarial Attack and Surprise Intentions (Complex RYAN)” http://digitalarchive.wilsoncenter.org/document/119334.
[26] “Ministry of State Security (Stasi), Report, ‘Indicators to Recognize Adversarial Preparations for a Surprise Nuclear Missile Attack’” http://digitalarchive.wilsoncenter.org/document 119338. A partially declassified CIA document shows that Operation RYaN had its analogue in U.S. intelligence gathering. The CIA was also working with the DIA, and presumably allied intelligence agencies, to create a list of indicators — including the defense industry — for its chiefs of station to monitor, in an attempt to “emphasize greater early warning cooperation with intelligence services.” Other parallels to RYaN date back to 1961, when the Soviets also instructed embassies in all “capitalist” countries to collect and report information during the Berlin Crisis. In 1991, one might have deduced the January 16 Desert Storm invasion by monitoring the influx of pizza deliveries to the Pentagon, according to current U.S. Army Operational Security (OPSEC) training materials. In October 1983, justifying the KGB’s difficulties, Kryuchkov stated, “Even in the United States they have not completed this [a RYaN equivalent] yet.” The 1983 War Scare, Part One http://www2.gwu.edu/~nsarchiv/NSAEBB/NSAEBB426/.
[27] “Report, Ministry of State Security (Stasi), ‘About Results of Intelligence Activities to Note Indicators for a Surprise Nuclear Missile Attack’” http://digitalarchive.wilsoncenter.org/document/119909. For more on Continuity of Government, see James Mann, “The Armageddon Plan,” The Atlantic, March 2004.
[28] Still-classified reports by the British Joint Intelligence Council and the US President’s Foreign Intelligence Advisory Board have allegedly confirmed Gordievsky’s accounts. See The 1983 War Scare, Part Three, http://www2.gwu.edu/~nsarchiv/NSAEBB/NSAEBB428/, and British Documents Confirm UK Alerted US to Danger of Able Archer 83, http://nsarchive.wordpress.com/2013/11/04/british-documents-confirm-uk-alerted-us-to-danger-of-able-archer-83/
[29] The 1983 War Scare, Part Two http://www2.gwu.edu/~nsarchiv/NSAEBB/NSAEBB427/.
[30] Regrettably, no text of the November 8 or 9 flash telegram has been released or reproduced. Gordievsky’s revelation of this warning is the only basis for the current historical record (though the preceding and following telegrams which he reproduced and published do serve as somewhat sturdy bona fides). Christopher Andrew and Oleg Gordievsky, Comrade Kryuchkov’s Instructions: Top Secret Files on KGB Foreign Operations, 1975-1985, (Stanford: Stanford University Press 1991), 87.
[31] Marcus Wolf did not write kindly of the Soviets, or Operation RYaN, in his 1997 memoir: “Our Soviet partners had become obsessed with the danger of a nuclear missile attack,” though he writes that he had not. “Like most intelligent people, I found these war games a burdensome waste of time, but these orders were no more open to discussion than other orders from above.” Marcus Wolf with Anne McElvoy, Man without a Face: The Autobiography of Communism’s Greatest Spymaster (New York: Random House, 1997), 222. http://digitalarchive.wilsoncenter.org/document/115721.
[32] Welcome, Ukraine. http://euromaidanberlin.wordpress.com/2014/04/01/kgb-archives-in-ukraine-will-be-open-to-public/
[33] For an account of the file destruction by the HV A officer who supervised it, see Klaus Eichner and Gotthold Schramm, Konterspionage: Die DDR-Aufklärung in den Geheimdienstzentrum (Berlin: edition ost, 2010), pp. 174-177.
[34] “Stasi Note on Meeting Between Minister Mielke and KGB Chairman Andropov,” July 11, 1981, History and Public Policy Program Digital Archive, Office of the Federal Commissioner for the Stasi Records (BStU), MfS, ZAIG 5382, p. 1-19. Translated from German for CWIHP by Bernd Schaefer. http://digitalarchive.wilsoncenter.org/document/115717
[35] Andropov was referring to the new US war-fighting strategy for “prevailing” in a limited nuclear conflict that was first announced as Presidential Directive 59 by the Carter administration and slightly modified during the Reagan administration in National Security Decision Memorandum 13.
[36] “Speech of General Secretary Comrade Yu. V. Andropov of the Central Committee of the Communist Party of the Soviet Union.” Available at <http://www.gwu.edu/~nsarchiv/NSAEBB/NSAEBB14/doc19.htm>
[37] Christopher Andrew and Oleg Gordievsky, Instructions from the Centre (London: Hodder & Stoughton, 1991), p. 74.
[38] “Deputy Minister Markus Wolf, Stasi Note on Meeting with KGB Experts on the RYAN Problem, 14 to 18 August 1984,” August 24, 1984, History and Public Policy Program Digital Archive, Office of the Federal Commissioner for the Stasi Records (BStU), MfS, ZAIG 5384, pp. 1-16. Translated from German for CWIHP by Bernd Schaefer. http://digitalarchive.wilsoncenter.org/document/115721
[39] RYAN Translation #2: “Note about the Talks of Comrade Minister with the Chairman of the KGB, Comrade Chebrikov, on February 9, 1983 in Moscow.”
[40] RYAN Translation #3: “Notes on Statements made by Comrade Colonel General Kryuchkov, V. A. on October 3, 1983.”
[41] Peter Richter and Klaus Rösler, Wolfs West-Spione: Ein Insider Report (Berlin: elefanten press, 1992), p. 85.
[42] Ibid.
[43] On MfS Sigint, see Ben B. Fischer, “‘One of the Biggest Ears in the World’: East German Sigint Operations,’” International Journal of Intelligence and Counterintelligence 11:2 (Spring 1998), pp.142‑153. The MfS, the HV A, and the intelligence service of the East German Army were handling some 3,000 agents in West Germany/West Berlin when the Berlin Wall fell. About half spied for the MfS and military intelligence and the other half for the HV A. Five of every 100,000 West German citizens were “working clandestinely for the GDR.” Georg Herbstritt, Bundesbürger im Dienst der DDR-Spionage: Eine analytische Studie (Göttingen: Vandenhoeck & Ruprecht: 2007), p. 84.
[44] “Befehl 1/85 zu den Aufgaben der Dienstheiten des MfS zur frühzeitigen Aufklärung akuter Agressionsabsichten und überraschender militärischer Aktivitäten imperialisticher Staaten und Bundnisse, inbesondere zur Verhinderung eines überraschinden Raketenkernwaffenangriffs gegen Staaten der sozialistischen Gemeinschaft,” BstU [Bündesbeauftragte für die Unterlagen des Staatssicherheitsdienstes der ehemaligen DDR], ZA [Zentralarchiv], DSt [Dokumentenstelle im Zentalarchiv des BStU]103137. Also RYAN Translation #4.
[45] “1. Durchführungsbestimmung des Stellvertreters des Ministers auf Befehl 1/85 vom 15.2.1985, GVS 0008-1/85: Allzeitige Nutzung der Möglichkeiten der Dienstheiten des MfS zur frühzeitgen und zuverlässigen Beschaffung von Hinweisen auf akute feindliche Aggressionsabsichten, -vorbereitungen und –handlungen,” BstU, ZA, DSt103137.
[46] Benjamin B. Fischer, “The 1980s Soviet War Scare: New Evidence from East German Documents,” Intelligence and National Security, 14:4 (Autumn 1999), pp. 186-197.
[47] Wolf’s tasking of MfS departments is described in Ibid.
[48] “Katalog ausgewählter Indikatoren zur Früherkennung gegnerischer militärischer Aggressionsvorbereitungen und Überraschungsabsichten, inbesondere von Maßssnahmen zur Vorbereitung eines überraschenden Raketenwaffenangriffs (KWA),” BstU, ZA, DSt103137. A different version of this text is available in Document #5 of this collection.
[49] See Richter and Rösler, Wolfs West-Spione, pp. 72, 85 and Günter Bohnsack, Hauptverwaltung Aufklärung: Die Legende Stirbt (Berlin: edition ost, 1997), p. 64.
[50] Richter and Klaus Rösler, Wolfs West-Spione, p. 85.
[51] RYAN Translation #6: “R E P O R T on development and achieved state of work regarding early recognition of enemy attack and surprise intentions (Complex RYAN).”
[52] Michael Herman, Intelligence Power in Peace and War (New York: Cambridge University Press, 1996), pp. 83-88.
[53] Richter and Rösler, Wolfs West-Spione, p. 72.
[54] Fear of a superpower conflict lead GDR leader Erich Honecker to open a back channel to West German Chancellor Helmut Schmidt, a decision that irritated Andropov. Markus Wolfe, Man Without a Face (New York: Times Books, 1997), p. 221.
[55] Mikhail A. Alexeev, Without Warning: Threat Assessment, Intelligence, and Global Struggle (New York: St. Martin’s Press, 1997), p. 203.
[56] See Thomas P. Coakley, Command and Control for War and Peace (Washington, DC: National Defense University Press, 1992). Parallels between mutual American and Soviet fears of surprise attack are discussed in Benjamin B. Fischer, “The Soviet-American War Scare of the 1980s,” International Journal of Intelligence andCounterintelligence 19:3, Fall 2006, pp.480-519.
ABOUT THE AUTHORS
Bernd Schaefer
Global Fellow, Former Senior Scholar;
Professional Lecturer, The George Washington University
Nate Jones
Director, Freedom of Information Act Project, National Security Archive
Benjamin B. Fischer
Former Chief Historian of the Central Intelligence Agency
The Nuclear Proliferation International History Project is a global network of individuals and institutions engaged in the study of international nuclear history through archival documents, oral history interviews, and other empirical sources. At the Wilson Center, it is part of the Wilson Center’s History and Public Policy Program. Read more
The Cold War International History Project supports the full and prompt release of historical materials by governments on all sides of the Cold War. Through an award winning Digital Archive, the Project allows scholars, journalists, students, and the interested public to reassess the Cold War and its many contemporary legacies. It is part of the Wilson Center’s History and Public Policy Program. Read more
Become a Patron!
True Information is the most valuable resource and we ask you to give back











 GRU Zentrale in Moskau
GRU Zentrale in Moskau


















 Above: M113 armored personnel carriers move through the town of Stockhausen (Herbstein) during REFORGER ’83 in Germany.
Above: M113 armored personnel carriers move through the town of Stockhausen (Herbstein) during REFORGER ’83 in Germany.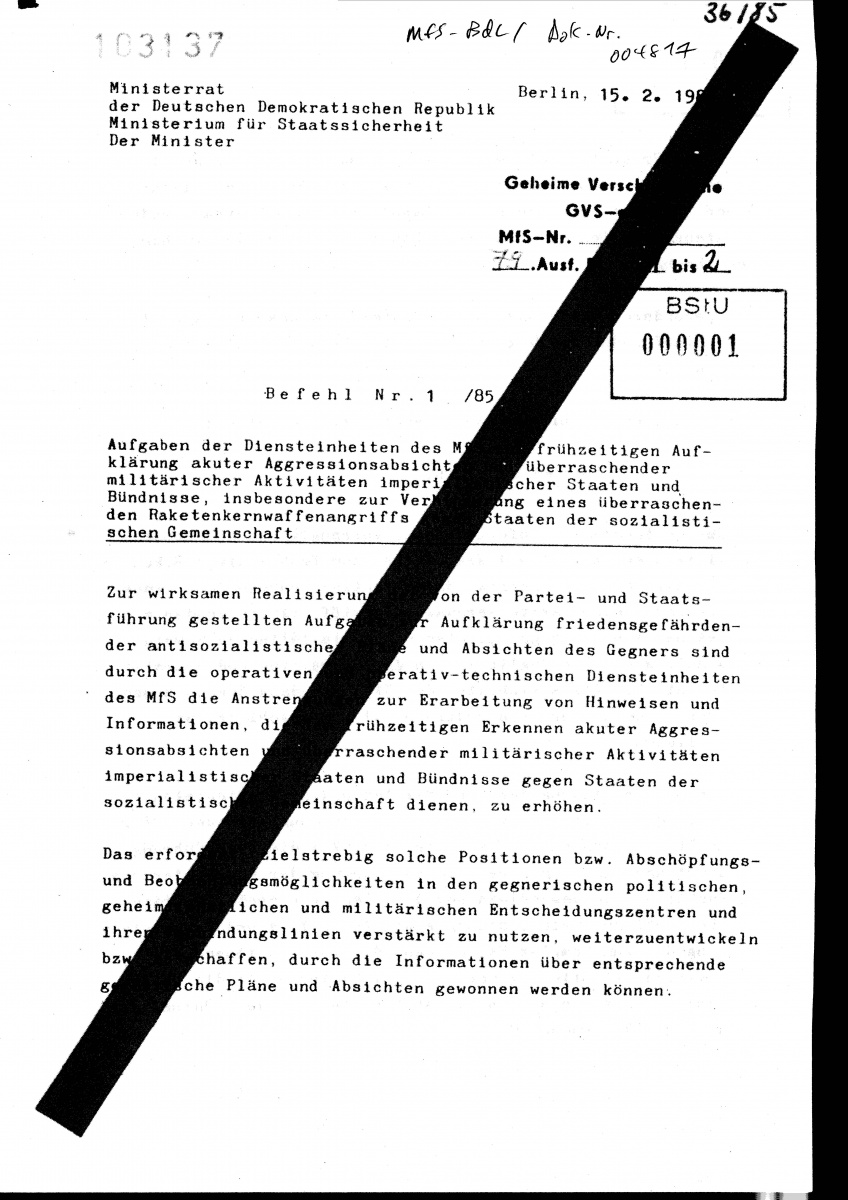
 Above: Cover page from the HA III copy of the Project RYaN catalog of indicators.
Above: Cover page from the HA III copy of the Project RYaN catalog of indicators.








You must be logged in to post a comment.