 010468410172;99;99;99;;::;;;7575,00
010468410172;99;99;99;;::;;;7575,00
250768415330;99;99;99;;::;;;7575,00
221169411538;99;99;99;;::;;;7575,00
150369401312;99;99;99;;::;;;7575,00
141169403212;99;99;99;;::;;;7575,00
070570408217;99;99;99;;::;;;7575,00
020537425052;99;99;99;;::;;;7548,39
021268400619;99;99;99;;::;;;7575,00
160168402414;99;99;99;;::;;;7483,71
271269428236;99;99;99;;::;;;7561,29
020667415311;99;99;99;;::;;;7560,00
250866400837;99;99;99;;::;;;7560,00
230170413236;99;99;99;;::;;;7550,00
030169407545;99;99;99;;::;;;7550,00
280667418521;99;99;99;;::;;;7550,00
041169402246;99;99;99;;::;;;7575,00
070966407616;99;99;99;;::;;;7425,00
231066422727;99;99;99;;::;;;7425,00
121067430270;99;99;99;;::;;;7425,00
200567420314;99;99;99;;::;;;7425,00
291267430242;99;99;99;;::;;;7425,00
270667430169;99;99;99;;::;;;7425,00
180666430176;99;99;99;;::;;;7425,00
250768406717;99;99;99;;::;;;7486,13
080967403720;99;99;99;;::;;;7425,00
140263404022;99;99;99;;::;;;7425,00
051067422798;99;99;99;;::;;;7425,00
020568408546;99;99;99;;::;;;7425,00
010358400862;99;99;99;;::;;;7417,50
150267416214;99;99;99;;::;;;7400,00
040368429228;99;99;99;;::;;;7400,00
290268413933;99;99;99;;::;;;7200,00
100766430330;99;99;99;;::;;;7425,00
100533530146;99;99;99;;::;;;7440,00
201169419312;99;99;99;;::;;;7595,00
210644408810;99;99;99;;::;;;7481,86
150568418512;99;99;99;;::;;;7480,00
171164417727;99;99;99;;::;;;7480,00
161255429724;99;99;99;;::;;;7475,00
300332402726;99;99;99;;::;;;7470,00
131267401326;99;99;99;;::;;;7425,00
090568412215;99;99;99;;::;;;7452,50
290962408915;99;99;99;;::;;;7425,00
231069424015;99;99;99;;::;;;7436,13
200857416217;99;99;99;;::;;;7431,25
020265404417;99;99;99;;::;;;7429,00
210866411513;99;99;99;;::;;;7425,00
150568430255;99;99;99;;::;;;7425,00
310368430103;99;99;99;;::;;;7425,00
040568411014;99;99;99;;::;;;7486,13
300538416824;99;99;99;;::;;;7466,66
280966400938;99;99;99;;::;;;7729,55
140666430305;99;99;99;;::;;;7750,00
140468414718;99;99;99;;::;;;7750,00
130429530012;99;99;99;;::;;;7750,00
040866430184;99;99;99;;::;;;7750,00
040437507622;99;99;99;;::;;;7750,00
290864407310;99;99;99;;::;;;7749,00
060268400899;99;99;99;;::;;;7729,55
020568401547;99;99;99;;::;;;7729,55
270162407318;99;99;99;;::;;;7755,00
011267400837;99;99;99;;::;;;7729,55
270568400212;99;99;99;;::;;;7729,55
010167400042;99;99;99;;::;;;7729,55
191267400766;99;99;99;;::;;;7729,55
150467400268;99;99;99;;::;;;7729,55
130641502713;99;99;99;;::;;;7583,34
070368401329;99;99;99;;::;;;7729,55
101066413710;99;99;99;;::;;;7800,00
241267422917;99;99;99;;::;;;6600,00
010168406446;99;99;99;;::;;;6600,00
131266413747;99;99;99;;::;;;7800,00
030468421216;99;99;99;;::;;;7800,00
130168413028;99;99;99;;::;;;7800,00
300368429250;99;99;99;;::;;;7800,00
211166428247;99;99;99;;::;;;7750,00
180446420312;99;99;99;;::;;;7800,00
111137530041;99;99;99;;::;;;7750,00
261129506918;99;99;99;;::;;;7786,45
270638512229;99;99;99;;::;;;7786,09
230268427548;99;99;99;;::;;;7775,00
171126412212;99;99;99;;::;;;7775,00
040457409536;99;99;99;;::;;;7762,50
160954518414;99;99;99;;::;;;7755,00
031067401323;99;99;99;;::;;;7729,55
201067403432;99;99;99;;::;;;7800,00
200429530013;99;99;99;;::;;;7625,00
060767411410;99;99;99;;::;;;7685,00
311267400719;99;99;99;;::;;;7684,55
100365406735;99;99;99;;::;;;7684,50
251166417747;99;99;99;;::;;;7683,71
100153415373;99;99;99;;::;;;7680,00
080569402415;99;99;99;;::;;;7677,50
170168406756;99;99;99;;::;;;7729,55
200729430014;99;99;99;;::;;;7631,25
280927415395;99;99;99;;::;;;7687,50
250468418919;99;99;99;;::;;;7625,00
080929407536;99;99;99;;::;;;7622,91
101266413037;99;99;99;;::;;;7614,00
211233511519;99;99;99;;::;;;7600,80
081267402748;99;99;99;;::;;;7600,00
291167401719;99;99;99;;::;;;7400,00
260769410012;99;99;99;;::;;;7640,00
160461402624;99;99;99;;::;;;7700,00
030468400861;99;99;99;;::;;;7729,55
280468429228;99;99;99;;::;;;7729,55
260667401326;99;99;99;;::;;;7729,55
110767407326;99;99;99;;::;;;7725,00
040368408523;99;99;99;;::;;;7725,00
040463411114;99;99;99;;::;;;7713,75
010138411519;99;99;99;;::;;;7687,50
220551426349;99;99;99;;::;;;7700,00
130930430023;99;99;99;;::;;;7687,50
070863409117;99;99;99;;::;;;7700,00
050568412112;99;99;99;;::;;;7700,00
020868410410;99;99;99;;::;;;7700,00
260866405338;99;99;99;;::;;;7690,00
101028430034;99;99;99;;::;;;7687,50
290128430029;99;99;99;;::;;;7687,50
200166430175;99;99;99;;::;;;7594,00
150261419633;99;99;99;;::;;;7711,91
070658530030;99;99;99;;::;;;7299,63
300667409524;99;99;99;;::;;;7400,00
101267413418;99;99;99;;::;;;7320,00
290529422775;99;99;99;;::;;;7312,50
171142429719;99;99;99;;::;;;7312,50
110332400811;99;99;99;;::;;;7312,50
120967424947;99;99;99;;::;;;7308,06
310567419329;99;99;99;;::;;;7320,00
120568405132;99;99;99;;::;;;7300,00
090966400236;99;99;99;;::;;;7320,00
011166409111;99;99;99;;::;;;7295,17
301166415330;99;99;99;;::;;;7295,00
200268425035;99;99;99;;::;;;7295,00
080468400824;99;99;99;;::;;;7295,00
300636407219;99;99;99;;::;;;7294,35
280331427010;99;99;99;;::;;;7287,50
110954429811;99;99;99;;::;;;7302,50
110468421216;99;99;99;;::;;;7325,00
050768426818;99;99;99;;::;;;7350,00
221167402435;99;99;99;;::;;;7345,00
291067414547;99;99;99;;::;;;7345,00
080267412132;99;99;99;;::;;;7344,00
301266414714;99;99;99;;::;;;7344,00
290366403640;99;99;99;;::;;;7344,00
130167409510;99;99;99;;::;;;7320,00
190268413038;99;99;99;;::;;;7325,00
201167426711;99;99;99;;::;;;7258,06
221267407938;99;99;99;;::;;;7325,00
211167421020;99;99;99;;::;;;7325,00
120966418318;99;99;99;;::;;;7325,00
220767428044;99;99;99;;::;;;7325,00
041165430274;99;99;99;;::;;;7325,00
020967430302;99;99;99;;::;;;7325,00
110966417164;99;99;99;;::;;;7344,00
290866413052;99;99;99;;::;;;7200,00
011267430075;99;99;99;;::;;;7207,26
100234506111;99;99;99;;::;;;7204,16
310867413623;99;99;99;;::;;;7200,00
310867410318;99;99;99;;::;;;7200,00
310867424939;99;99;99;;::;;;7200,00
310168420533;99;99;99;;::;;;7200,00
240168413113;99;99;99;;::;;;7278,87
300468430128;99;99;99;;::;;;7200,00
070666415366;99;99;99;;::;;;7225,00
280767412215;99;99;99;;::;;;7200,00
280567420536;99;99;99;;::;;;7200,00
290667417763;99;99;99;;::;;;7200,00
271267424717;99;99;99;;::;;;7200,00
290268400833;99;99;99;;::;;;7200,00
281267426236;99;99;99;;::;;;7200,00
300867403426;99;99;99;;::;;;7200,00
050632500812;99;99;99;;::;;;7250,00
230967420214;99;99;99;;::;;;7350,00
160867420531;99;99;99;;::;;;7257,00
230767411014;99;99;99;;::;;;7255,81
300338429727;99;99;99;;::;;;7250,00
290268407066;99;99;99;;::;;;7250,00
220831503716;99;99;99;;::;;;7250,00
080264430132;99;99;99;;::;;;7208,00
050745422419;99;99;99;;::;;;7250,00
050268413244;99;99;99;;::;;;7225,00
040242529725;99;99;99;;::;;;7250,00
031242530043;99;99;99;;::;;;7250,00
280268409556;99;99;99;;::;;;7225,00
251066402513;99;99;99;;::;;;7225,00
210867406134;99;99;99;;::;;;7225,00
121067404152;99;99;99;;::;;;7225,00
120126409515;99;99;99;;::;;;7274,19
100832530277;99;99;99;;::;;;7250,00
160367400147;99;99;99;;::;;;7400,00
210368422412;99;99;99;;::;;;7400,00
110267419013;99;99;99;;::;;;7400,00
181267417745;99;99;99;;::;;;7400,00
091268407515;99;99;99;;::;;;7400,00
180667418611;99;99;99;;::;;;7400,00
090567401514;99;99;99;;::;;;7400,00
041066400838;99;99;99;;::;;;7400,00
071167400615;99;99;99;;::;;;7400,00
120367424978;99;99;99;;::;;;7400,00
070766430344;99;99;99;;::;;;7400,00
151267400727;99;99;99;;::;;;7400,00
061267430169;99;99;99;;::;;;7400,00
230667402110;99;99;99;;::;;;7400,00
041167409428;99;99;99;;::;;;7400,00
091266409517;99;99;99;;::;;;7350,00
171167430054;99;99;99;;::;;;7400,00
010568401919;99;99;99;;::;;;7400,00
030966416727;99;99;99;;::;;;7400,00
030766430153;99;99;99;;::;;;7400,00
020867425039;99;99;99;;::;;;7400,00
260667406717;99;99;99;;::;;;7400,00
020468405313;99;99;99;;::;;;7400,00
260667405810;99;99;99;;::;;;7400,00
110667424989;99;99;99;;::;;;7400,00
241267407426;99;99;99;;::;;;7400,00
220667424062;99;99;99;;::;;;7400,00
240966430030;99;99;99;;::;;;7400,00
150965421838;99;99;99;;::;;;7400,00
241067407624;99;99;99;;::;;;7400,00
240268430121;99;99;99;;::;;;7400,00
130665400113;99;99;99;;::;;;7400,00
230167430019;99;99;99;;::;;;7400,00
180767430095;99;99;99;;::;;;7400,00
020168416248;99;99;99;;::;;;7400,00
040367424994;99;99;99;;::;;;7370,00
310766402722;99;99;99;;::;;;7375,00
081266430077;99;99;99;;::;;;7375,00
250666425044;99;99;99;;::;;;7375,00
150838529715;99;99;99;;::;;;7375,00
291167402519;99;99;99;;::;;;7375,00
240566422015;99;99;99;;::;;;7375,00
220368409516;99;99;99;;::;;;7400,00
010367403133;99;99;99;;::;;;7375,00
080767427728;99;99;99;;::;;;7388,71
250167421823;99;99;99;;::;;;7362,90
190367415434;99;99;99;;::;;;7360,00
260867428216;99;99;99;;::;;;7360,00
120767400019;99;99;99;;::;;;7350,00
261046416044;99;99;99;;::;;;7350,00
280268427412;99;99;99;;::;;;7400,00
040867419630;99;99;99;;::;;;7375,00
280167418816;99;99;99;;::;;;7400,00
300668401516;99;99;99;;::;;;7400,00
161066418452;99;99;99;;::;;;7400,00
281167416217;99;99;99;;::;;;7400,00
240766417712;99;99;99;;::;;;7400,00
200967430060;99;99;99;;::;;;7400,00
180168430093;99;99;99;;::;;;7400,00
081166400823;99;99;99;;::;;;7375,00
230168420314;99;99;99;;::;;;7400,00
151066407017;99;99;99;;::;;;7375,00
271167404727;99;99;99;;::;;;7400,00
260766406456;99;99;99;;::;;;7400,00
241267416736;99;99;99;;::;;;7400,00
241266430106;99;99;99;;::;;;7400,00
040967415397;99;99;99;;::;;;7396,77
131267424616;99;99;99;;::;;;7395,00
110867415323;99;99;99;;::;;;7350,00
151067407318;99;99;99;;::;;;7400,00
030168405716;99;99;99;;::;;;6600,00
020667423813;99;99;99;;::;;;6600,00
070568407127;99;99;99;;::;;;6600,00
030268406142;99;99;99;;::;;;6600,00
070667407915;99;99;99;;::;;;6600,00
030267428278;99;99;99;;::;;;6600,00
070668428216;99;99;99;;::;;;6600,00
070867418424;99;99;99;;::;;;6600,00
070368422787;99;99;99;;::;;;6600,00
030168407017;99;99;99;;::;;;6600,00
070467403426;99;99;99;;::;;;6600,00
021067424219;99;99;99;;::;;;6600,00
070467405616;99;99;99;;::;;;6600,00
021067403610;99;99;99;;::;;;6600,00
061267430142;99;99;99;;::;;;6600,00
021066410616;99;99;99;;::;;;6600,00
030167424720;99;99;99;;::;;;6600,00
030168415324;99;99;99;;::;;;6600,00
160568408516;99;99;99;;::;;;6640,00
070868409212;99;99;99;;::;;;6625,00
241067406429;99;99;99;;::;;;6625,00
240867422748;99;99;99;;::;;;6625,00
311267407312;99;99;99;;::;;;6622,00
230666414814;99;99;99;;::;;;6615,00
030168416212;99;99;99;;::;;;6600,00
250429430026;99;99;99;;::;;;6604,84
061167428117;99;99;99;;::;;;6600,00
030268401923;99;99;99;;::;;;6600,00
070568427216;99;99;99;;::;;;6600,00
030168426226;99;99;99;;::;;;6600,00
070767409539;99;99;99;;::;;;6600,00
030168417741;99;99;99;;::;;;6600,00
070867413957;99;99;99;;::;;;6600,00
011229430015;99;99;99;;::;;;6612,90
060667422833;99;99;99;;::;;;6600,00
060468419332;99;99;99;;::;;;6600,00
020666408910;99;99;99;;::;;;6600,00
060468428212;99;99;99;;::;;;6600,00
020568402515;99;99;99;;::;;;6600,00
060468409310;99;99;99;;::;;;6600,00
020767430076;99;99;99;;::;;;6600,00
061167425012;99;99;99;;::;;;6600,00
020766423827;99;99;99;;::;;;6600,00
021166418420;99;99;99;;::;;;6600,00
020667405738;99;99;99;;::;;;6600,00
060568422782;99;99;99;;::;;;6600,00
020766416010;99;99;99;;::;;;6600,00
060667414219;99;99;99;;::;;;6600,00
020568416220;99;99;99;;::;;;6600,00
060267406148;99;99;99;;::;;;6800,00
060467415356;99;99;99;;::;;;6600,00
061067416223;99;99;99;;::;;;6600,00
090568413947;99;99;99;;::;;;6653,33
021067410538;99;99;99;;::;;;6600,00
061267430353;99;99;99;;::;;;6600,00
021167424929;99;99;99;;::;;;6600,00
070168427428;99;99;99;;::;;;6600,00
020967426936;99;99;99;;::;;;6600,00
020966422837;99;99;99;;::;;;6600,00
020967427111;99;99;99;;::;;;6600,00
060468414515;99;99;99;;::;;;6600,00
020967411945;99;99;99;;::;;;6600,00
060867425035;99;99;99;;::;;;6600,00
021167408216;99;99;99;;::;;;6600,00
060965407914;99;99;99;;::;;;6600,00
020966416031;99;99;99;;::;;;6600,00
060967427134;99;99;99;;::;;;6600,00
021067423611;99;99;99;;::;;;6600,00
061066409822;99;99;99;;::;;;6600,00
270368422046;99;99;99;;::;;;6775,00
240468400867;99;99;99;;::;;;6800,00
280168429218;99;99;99;;::;;;6800,00
260767408517;99;99;99;;::;;;6800,00
260767403011;99;99;99;;::;;;6800,00
200468413127;99;99;99;;::;;;6795,00
220666413927;99;99;99;;::;;;6775,00
140941530336;99;99;99;;::;;;6758,40
270967417740;99;99;99;;::;;;6775,00
210568407321;99;99;99;;::;;;6800,00
240568402413;99;99;99;;::;;;6775,00
270767407513;99;99;99;;::;;;6775,00
151167424828;99;99;99;;::;;;6775,00
141267404518;99;99;99;;::;;;6775,00
230767413714;99;99;99;;::;;;6762,90
200568414258;99;99;99;;::;;;6640,00
160567430164;99;99;99;;::;;;6775,00
111268418914;99;99;99;;::;;;6800,00
220167424410;99;99;99;;::;;;6800,00
060268430043;99;99;99;;::;;;6800,00
200367421718;99;99;99;;::;;;6800,00
051167408926;99;99;99;;::;;;6800,00
171067411411;99;99;99;;::;;;6800,00
050568415372;99;99;99;;::;;;6800,00
031067412946;99;99;99;;::;;;6800,00
041067401314;99;99;99;;::;;;6800,00
150766407435;99;99;99;;::;;;6800,00
040766424334;99;99;99;;::;;;6800,00
221266405615;99;99;99;;::;;;6800,00
031267425020;99;99;99;;::;;;6800,00
190167420124;99;99;99;;::;;;6800,00
120767407317;99;99;99;;::;;;6800,00
110867429215;99;99;99;;::;;;6800,00
021067421042;99;99;99;;::;;;6755,00
141167422874;99;99;99;;::;;;6800,00
110468400538;99;99;99;;::;;;6700,00
210568428253;99;99;99;;::;;;6745,00
120632430085;99;99;99;;::;;;6741,94
150862430213;99;99;99;;::;;;6737,50
120760511023;99;99;99;;::;;;6728,10
200967406810;99;99;99;;::;;;6725,00
190653429829;99;99;99;;::;;;6720,00
140866428015;99;99;99;;::;;;6760,00
211066424919;99;99;99;;::;;;6700,00
240167401321;99;99;99;;::;;;6747,17
050924417738;99;99;99;;::;;;6691,81
070568402422;99;99;99;;::;;;6675,00
160767410117;99;99;99;;::;;;6675,00
140468413811;99;99;99;;::;;;6675,00
231070418819;99;99;99;;::;;;6660,00
060168404323;99;99;99;;::;;;6600,00
100168400414;99;99;99;;::;;;6700,00
291027428012;99;99;99;;::;;;6750,00
080168419910;99;99;99;;::;;;6750,00
141127430028;99;99;99;;::;;;6750,00
300129412216;99;99;99;;::;;;6750,00
140445430088;99;99;99;;::;;;6750,00
290435417115;99;99;99;;::;;;6750,00
120733409541;99;99;99;;::;;;6750,00
291166421718;99;99;99;;::;;;6745,00
171138507227;99;99;99;;::;;;6750,00
081166426839;99;99;99;;::;;;6745,00
280927430018;99;99;99;;::;;;6750,00
220842430057;99;99;99;;::;;;6750,00
120924412217;99;99;99;;::;;;6750,00
110526420028;99;99;99;;::;;;6750,00
070329426910;99;99;99;;::;;;6750,00
031226420311;99;99;99;;::;;;6750,00
230568408023;99;99;99;;::;;;6650,00
280429424926;99;99;99;;::;;;6750,00
040368424021;99;99;99;;::;;;6600,00
060766424973;99;99;99;;::;;;6600,00
011066406933;99;99;99;;::;;;6600,00
040168421520;99;99;99;;::;;;6600,00
011067427357;99;99;99;;::;;;6600,00
040468410137;99;99;99;;::;;;6600,00
011067415321;99;99;99;;::;;;6600,00
011067409829;99;99;99;;::;;;6600,00
010867416037;99;99;99;;::;;;6600,00
040268407523;99;99;99;;::;;;6600,00
011067408316;99;99;99;;::;;;6600,00
040168422128;99;99;99;;::;;;6600,00
010468429252;99;99;99;;::;;;6600,00
031066413736;99;99;99;;::;;;6600,00
010568422816;99;99;99;;::;;;6600,00
031267408052;99;99;99;;::;;;6600,00
040468415149;99;99;99;;::;;;6600,00
010867411156;99;99;99;;::;;;6600,00
010867409320;99;99;99;;::;;;6600,00
040767410110;99;99;99;;::;;;6600,00
010967430127;99;99;99;;::;;;6600,00
040766424959;99;99;99;;::;;;6600,00
010967416923;99;99;99;;::;;;6600,00
040667405314;99;99;99;;::;;;6600,00
040368411212;99;99;99;;::;;;6600,00
040568422215;99;99;99;;::;;;6600,00
010568406146;99;99;99;;::;;;6600,00
040568417328;99;99;99;;::;;;6600,00
010967416835;99;99;99;;::;;;6600,00
040767411914;99;99;99;;::;;;6600,00
011066414829;99;99;99;;::;;;6600,00
040168424975;99;99;99;;::;;;6600,00
010967427710;99;99;99;;::;;;6600,00
011066418619;99;99;99;;::;;;6600,00
010268412296;99;99;99;;::;;;6600,00
010267402117;99;99;99;;::;;;6600,00
030967426222;99;99;99;;::;;;6600,00
010267416447;99;99;99;;::;;;6600,00
030767410023;99;99;99;;::;;;6600,00
010368427110;99;99;99;;::;;;6600,00
030867429231;99;99;99;;::;;;6600,00
010468427310;99;99;99;;::;;;6600,00
030967421210;99;99;99;;::;;;6600,00
030967417414;99;99;99;;::;;;6600,00
030866415049;99;99;99;;::;;;6600,00
030568412253;99;99;99;;::;;;6600,00
100368416816;99;99;99;;::;;;7125,00
280866416625;99;99;99;;::;;;7400,00
010367402536;99;99;99;;::;;;6600,00
030568422785;99;99;99;;::;;;6600,00
010168405718;99;99;99;;::;;;6600,00
010667400866;99;99;99;;::;;;6600,00
040866424024;99;99;99;;::;;;6600,00
031267403411;99;99;99;;::;;;6600,00
010568413119;99;99;99;;::;;;6600,00
031267405310;99;99;99;;::;;;6600,00
010468410113;99;99;99;;::;;;6600,00
031067408939;99;99;99;;::;;;6600,00
030967424710;99;99;99;;::;;;6600,00
030967404824;99;99;99;;::;;;6600,00
010368416438;99;99;99;;::;;;6600,00
030766422778;99;99;99;;::;;;6600,00
010667402538;99;99;99;;::;;;6600,00
030766403614;99;99;99;;::;;;6600,00
010367417754;99;99;99;;::;;;6600,00
030767412125;99;99;99;;::;;;6600,00
010367417738;99;99;99;;::;;;6600,00
031267407017;99;99;99;;::;;;6600,00
010467403114;99;99;99;;::;;;6600,00
020268400884;99;99;99;;::;;;6600,00
020468419029;99;99;99;;::;;;6600,00
051266401711;99;99;99;;::;;;6600,00
020267404824;99;99;99;;::;;;6600,00
051166427017;99;99;99;;::;;;6600,00
020468400838;99;99;99;;::;;;6600,00
051167413039;99;99;99;;::;;;6600,00
050368414228;99;99;99;;::;;;6600,00
050766417758;99;99;99;;::;;;6600,00
051067425024;99;99;99;;::;;;6600,00
050867425001;99;99;99;;::;;;6600,00
011267418412;99;99;99;;::;;;6600,00
050668409519;99;99;99;;::;;;6600,00
011267414825;99;99;99;;::;;;6600,00
050667422033;99;99;99;;::;;;6600,00
040667424937;99;99;99;;::;;;6600,00
020468428320;99;99;99;;::;;;6600,00
020568420916;99;99;99;;::;;;6600,00
020867427544;99;99;99;;::;;;6600,00
060268413526;99;99;99;;::;;;6600,00
020667422837;99;99;99;;::;;;6600,00
060267407116;99;99;99;;::;;;6600,00
020867409215;99;99;99;;::;;;6600,00
060268404734;99;99;99;;::;;;6600,00
050967408022;99;99;99;;::;;;6600,00
060367409514;99;99;99;;::;;;6600,00
020368430028;99;99;99;;::;;;6600,00
060367405337;99;99;99;;::;;;6600,00
020568424722;99;99;99;;::;;;6600,00
060168430329;99;99;99;;::;;;6600,00
020468413938;99;99;99;;::;;;6600,00
051267412244;99;99;99;;::;;;6600,00
020468426931;99;99;99;;::;;;6600,00
011167425068;99;99;99;;::;;;6600,00
020568417418;99;99;99;;::;;;6600,00
050168424210;99;99;99;;::;;;6600,00
050168413933;99;99;99;;::;;;6600,00
010867407528;99;99;99;;::;;;6600,00
050268411820;99;99;99;;::;;;6600,00
010767410519;99;99;99;;::;;;6600,00
050168422426;99;99;99;;::;;;6600,00
010967409838;99;99;99;;::;;;6600,00
011267411413;99;99;99;;::;;;6600,00
010766424927;99;99;99;;::;;;6600,00
020168424416;99;99;99;;::;;;6600,00
010966415312;99;99;99;;::;;;6600,00
041067412275;99;99;99;;::;;;6600,00
010965428947;99;99;99;;::;;;6600,00
040866400516;99;99;99;;::;;;6600,00
010766419319;99;99;99;;::;;;6600,00
010268422056;99;99;99;;::;;;6600,00
041267413715;99;99;99;;::;;;6600,00
050367424969;99;99;99;;::;;;6600,00
050368405110;99;99;99;;::;;;6600,00
011167409316;99;99;99;;::;;;6600,00
050568428229;99;99;99;;::;;;6600,00
011166420118;99;99;99;;::;;;6600,00
050567412276;99;99;99;;::;;;6600,00
011267422219;99;99;99;;::;;;6600,00
020168419721;99;99;99;;::;;;6600,00
020168400414;99;99;99;;::;;;6600,00
041167424919;99;99;99;;::;;;6600,00
020168409523;99;99;99;;::;;;6600,00
050367416037;99;99;99;;::;;;6600,00
020168411113;99;99;99;;::;;;6600,00
050568426311;99;99;99;;::;;;6600,00
020168426315;99;99;99;;::;;;6600,00
050168406418;99;99;99;;::;;;6600,00
010967401967;99;99;99;;::;;;6600,00
050367406162;99;99;99;;::;;;6600,00
090666420016;99;99;99;;::;;;7000,00
010268409214;99;99;99;;::;;;7000,00
120167406118;99;99;99;;::;;;7000,00
111067421711;99;99;99;;::;;;7000,00
110568413926;99;99;99;;::;;;7000,00
110567402539;99;99;99;;::;;;7000,00
110268420518;99;99;99;;::;;;7000,00
041067427119;99;99;99;;::;;;7000,00
091167411232;99;99;99;;::;;;7000,00
120568427913;99;99;99;;::;;;7000,00
090167406113;99;99;99;;::;;;7000,00
080568430035;99;99;99;;::;;;7000,00
070440412218;99;99;99;;::;;;7000,00
060568412242;99;99;99;;::;;;7000,00
060766427728;99;99;99;;::;;;7000,00
240867419637;99;99;99;;::;;;7000,00
101066430019;99;99;99;;::;;;7000,00
031267413732;99;99;99;;::;;;7000,00
290735507518;99;99;99;;::;;;6960,00
190967422865;99;99;99;;::;;;7000,00
181228430015;99;99;99;;::;;;7000,00
180830430021;99;99;99;;::;;;7000,00
180567409523;99;99;99;;::;;;7000,00
171267424954;99;99;99;;::;;;7000,00
120568408018;99;99;99;;::;;;7000,00
170967417419;99;99;99;;::;;;7000,00
010168430294;99;99;99;;::;;;7000,00
160368407420;99;99;99;;::;;;7000,00
031166414517;99;99;99;;::;;;7000,00
130667414850;99;99;99;;::;;;7000,00
030268402774;99;99;99;;::;;;7000,00
120766424510;99;99;99;;::;;;7000,00
020867425100;99;99;99;;::;;;7000,00
040667404020;99;99;99;;::;;;7000,00
040467430208;99;99;99;;::;;;7000,00
010667419049;99;99;99;;::;;;6975,00
230967410817;99;99;99;;::;;;6975,00
230967428259;99;99;99;;::;;;6975,00
241066403111;99;99;99;;::;;;6975,00
271167401542;99;99;99;;::;;;6975,00
280567410127;99;99;99;;::;;;6975,00
040767409216;99;99;99;;::;;;6975,00
050430430019;99;99;99;;::;;;7000,00
021167417737;99;99;99;;::;;;6975,00
150368419617;99;99;99;;::;;;6975,00
010667404242;99;99;99;;::;;;6975,00
200867400040;99;99;99;;::;;;6975,00
090568412282;99;99;99;;::;;;6966,13
220766400859;99;99;99;;::;;;6966,00
200965412117;99;99;99;;::;;;6966,00
131252417755;99;99;99;;::;;;6960,00
040368430085;99;99;99;;::;;;6975,00
200230503819;99;99;99;;::;;;6993,95
111167408928;99;99;99;;::;;;7000,00
130168402513;99;99;99;;::;;;7000,00
120368418318;99;99;99;;::;;;7000,00
120368420530;99;99;99;;::;;;7000,00
140168403224;99;99;99;;::;;;7000,00
010268410338;99;99;99;;::;;;7000,00
050167422053;99;99;99;;::;;;6975,00
170168420718;99;99;99;;::;;;7000,00
171167407436;99;99;99;;::;;;6975,00
230367417134;99;99;99;;::;;;6990,00
090568418916;99;99;99;;::;;;6990,00
270566405650;99;99;99;;::;;;6988,74
051166422742;99;99;99;;::;;;6975,00
061167413046;99;99;99;;::;;;6975,00
081155412220;99;99;99;;::;;;6975,00
241267430124;99;99;99;;::;;;7000,00
010268417548;99;99;99;;::;;;7000,00
120153425019;99;99;99;;::;;;7038,97
200967402510;99;99;99;;::;;;7050,00
180367412250;99;99;99;;::;;;7050,00
080767402619;99;99;99;;::;;;7050,00
080468413916;99;99;99;;::;;;7050,00
070668405516;99;99;99;;::;;;7050,00
120767405522;99;99;99;;::;;;7045,00
130468404123;99;99;99;;::;;;7017,74
040660415368;99;99;99;;::;;;7040,00
091066423824;99;99;99;;::;;;7060,00
190967428036;99;99;99;;::;;;7025,00
190368421318;99;99;99;;::;;;7025,00
180566430048;99;99;99;;::;;;7025,00
140667400116;99;99;99;;::;;;7025,00
270768404816;99;99;99;;::;;;7022,24
191067410329;99;99;99;;::;;;7000,00
250861400811;99;99;99;;::;;;7040,00
240867419020;99;99;99;;::;;;7075,00
081267405324;99;99;99;;::;;;7125,00
071167416617;99;99;99;;::;;;7125,00
080462416622;99;99;99;;::;;;7122,50
231040407246;99;99;99;;::;;;6800,00
291268421831;99;99;99;;::;;;7110,00
230570402333;99;99;99;;::;;;7110,00
230750510315;99;99;99;;::;;;7050,00
110470418219;99;99;99;;::;;;7110,00
270367400427;99;99;99;;::;;;7050,00
190668400826;99;99;99;;::;;;7075,00
131066415318;99;99;99;;::;;;7075,00
080468424930;99;99;99;;::;;;7075,00
040168416422;99;99;99;;::;;;7075,00
270267430290;99;99;99;;::;;;7066,93
171067422786;99;99;99;;::;;;7060,00
281059408025;99;99;99;;::;;;7012,50
130470413926;99;99;99;;::;;;7110,00
250767420322;99;99;99;;::;;;7000,00
250468419321;99;99;99;;::;;;7000,00
210967428920;99;99;99;;::;;;7000,00
250168408014;99;99;99;;::;;;7000,00
210467415023;99;99;99;;::;;;7000,00
240967420547;99;99;99;;::;;;7000,00
200467430275;99;99;99;;::;;;7000,00
111168409316;99;99;99;;::;;;7019,35
200667424216;99;99;99;;::;;;7000,00
220368424011;99;99;99;;::;;;7000,00
200168410717;99;99;99;;::;;;7000,00
250368422128;99;99;99;;::;;;7000,00
200168405336;99;99;99;;::;;;7000,00
241067424918;99;99;99;;::;;;7000,00
221267403822;99;99;99;;::;;;7000,00
250767401746;99;99;99;;::;;;7000,00
230268403423;99;99;99;;::;;;7000,00
270866427528;99;99;99;;::;;;7000,00
130468419341;99;99;99;;::;;;7003,63
300568421712;99;99;99;;::;;;7000,00
300568424614;99;99;99;;::;;;7000,00
300467426813;99;99;99;;::;;;7000,00
290967403312;99;99;99;;::;;;7000,00
290666403837;99;99;99;;::;;;7000,00
211167426331;99;99;99;;::;;;7000,00
271066514716;99;99;99;;::;;;7000,00
250866422737;99;99;99;;::;;;7000,00
270667403427;99;99;99;;::;;;7000,00
270667407014;99;99;99;;::;;;7000,00
260368406127;99;99;99;;::;;;7000,00
220567430174;99;99;99;;::;;;7000,00
220567401517;99;99;99;;::;;;7000,00
250667428271;99;99;99;;::;;;7000,00
160168410828;99;99;99;;::;;;7120,00
290343516212;99;99;99;;::;;;7000,00
270168409525;99;99;99;;::;;;6845,00
211265415353;99;99;99;;::;;;6850,00
060967404717;99;99;99;;::;;;6850,00
290967420323;99;99;99;;::;;;6850,00
250568423619;99;99;99;;::;;;6850,00
290567418515;99;99;99;;::;;;6850,00
220168417511;99;99;99;;::;;;6850,00
030667404523;99;99;99;;::;;;6800,00
310568417544;99;99;99;;::;;;6845,00
201167419052;99;99;99;;::;;;6875,00
230967426616;99;99;99;;::;;;6845,00
200368420522;99;99;99;;::;;;6845,00
140666428221;99;99;99;;::;;;6845,00
070568420321;99;99;99;;::;;;6840,00
101063424510;99;99;99;;::;;;6806,25
310556417512;99;99;99;;::;;;6900,00
150767428115;99;99;99;;::;;;6850,00
030468418615;99;99;99;;::;;;6895,00
190667428210;99;99;99;;::;;;6900,00
150655407512;99;99;99;;::;;;6900,00
111267407623;99;99;99;;::;;;6900,00
100741519013;99;99;99;;::;;;6895,16
290468415028;99;99;99;;::;;;6895,00
250268416724;99;99;99;;::;;;6895,00
010368418812;99;99;99;;::;;;6862,80
070666401925;99;99;99;;::;;;6895,00
190427422717;99;99;99;;::;;;6875,00
010165404314;99;99;99;;::;;;6888,50
130166400813;99;99;99;;::;;;6885,00
211264427037;99;99;99;;::;;;6885,00
111168426810;99;99;99;;::;;;6876,13
240740529716;99;99;99;;::;;;6875,00
230427412213;99;99;99;;::;;;6875,00
281267401338;99;99;99;;::;;;6800,00
120468421522;99;99;99;;::;;;6895,00
071167425054;99;99;99;;::;;;6800,00
090268413814;99;99;99;;::;;;6800,00
191267403246;99;99;99;;::;;;6800,00
080368421046;99;99;99;;::;;;6800,00
180767402537;99;99;99;;::;;;6800,00
080568401517;99;99;99;;::;;;6800,00
160368414524;99;99;99;;::;;;6800,00
280967430063;99;99;99;;::;;;6800,00
150168402757;99;99;99;;::;;;6800,00
211067400126;99;99;99;;::;;;6800,00
070867406714;99;99;99;;::;;;6800,00
060966421232;99;99;99;;::;;;6800,00
110867422056;99;99;99;;::;;;6800,00
120433429719;99;99;99;;::;;;6937,50
070467403223;99;99;99;;::;;;6800,00
120568430119;99;99;99;;::;;;6800,00
071167413723;99;99;99;;::;;;6800,00
110667400012;99;99;99;;::;;;6800,00
020766407018;99;99;99;;::;;;6800,00
280468416910;99;99;99;;::;;;6800,00
020767402411;99;99;99;;::;;;6800,00
261266401530;99;99;99;;::;;;6800,00
020468430244;99;99;99;;::;;;6800,00
260667416915;99;99;99;;::;;;6800,00
201067401525;99;99;99;;::;;;6800,00
260666406184;99;99;99;;::;;;6800,00
090468422803;99;99;99;;::;;;6800,00
230967426229;99;99;99;;::;;;6800,00
110268421035;99;99;99;;::;;;6800,00
230168401519;99;99;99;;::;;;6800,00
100866420316;99;99;99;;::;;;6800,00
220767400818;99;99;99;;::;;;6800,00
091067406719;99;99;99;;::;;;6800,00
140367406137;99;99;99;;::;;;6800,00
010468401524;99;99;99;;::;;;6800,00
040967406159;99;99;99;;::;;;6920,00
120866418919;99;99;99;;::;;;6925,00
061267413414;99;99;99;;::;;;6925,00
020167415032;99;99;99;;::;;;6925,00
020167415331;99;99;99;;::;;;6925,00
100967417124;99;99;99;;::;;;6920,00
100867411956;99;99;99;;::;;;6920,00
311067407027;99;99;99;;::;;;6920,00
180568410526;99;99;99;;::;;;6925,00
291167416910;99;99;99;;::;;;6920,00
040567407224;99;99;99;;::;;;6920,00
270468413235;99;99;99;;::;;;6920,00
110268413115;99;99;99;;::;;;6920,00
270367417413;99;99;99;;::;;;6920,00
240468402723;99;99;99;;::;;;6920,00
041267400826;99;99;99;;::;;;6920,00
211224407218;99;99;99;;::;;;6937,50
230528430066;99;99;99;;::;;;6937,50
080457430171;99;99;99;;::;;;6900,00
030328419042;99;99;99;;::;;;6937,50
200630430049;99;99;99;;::;;;6937,50
101043429728;99;99;99;;::;;;6937,50
190429430024;99;99;99;;::;;;6937,50
140667407211;99;99;99;;::;;;6925,00
120730430011;99;99;99;;::;;;6937,50
010367430123;99;99;99;;::;;;6925,00
110435429713;99;99;99;;::;;;6937,50
290345430084;99;99;99;;::;;;6933,34
151266414254;99;99;99;;::;;;6925,00
220168411523;99;99;99;;::;;;6925,00
210667403836;99;99;99;;::;;;6925,00
270229412219;99;99;99;;::;;;6937,50
160542429730;99;99;99;;::;;;6937,50
050468415367;99;99;99;;::;;;6920,00
150767403217;99;99;99;;::;;;6920,00
050667417322;99;99;99;;::;;;6920,00
130467412236;99;99;99;;::;;;6920,00
211266412912;99;99;99;;::;;;6920,00
160467412946;99;99;99;;::;;;6920,00
141266424015;99;99;99;;::;;;6920,00
051167408029;99;99;99;;::;;;6920,00
050568408420;99;99;99;;::;;;6920,00
300168419648;99;99;99;;::;;;6920,00
041167418519;99;99;99;;::;;;6920,00
291167400812;99;99;99;;::;;;6920,00
221167411411;99;99;99;;::;;;6920,00
110329530025;99;99;99;;::;;;6937,50
250634517710;99;99;99;;::;;;6905,24
080568424612;99;99;99;;::;;;6912,50
251267421112;99;99;99;;::;;;6920,00
150468408018;99;99;99;;::;;;6920,00
200568417520;99;99;99;;::;;;6920,00
090667430160;99;99;99;;::;;;6920,00
210168411815;99;99;99;;::;;;6920,00
090468405720;99;99;99;;::;;;6920,00
300467424017;99;99;99;;::;;;6900,65
081167408034;99;99;99;;::;;;6920,00
190668411824;99;99;99;;::;;;6920,00
080767424738;99;99;99;;::;;;6920,00
080568427717;99;99;99;;::;;;6920,00
130867413131;99;99;99;;::;;;6920,00
090967401943;99;99;99;;::;;;6920,00
070767402521;99;99;99;;::;;;6920,00
080667418111;99;99;99;;::;;;6920,00
231266413438;99;99;99;;::;;;6920,00
130367430111;99;99;99;;::;;;6920,00
151264424715;99;99;99;;::;;;6920,00
010158450080;97;07;00;;::;;;0,00
110761406146;94;11;00;;::;;;20295,00
310161401727;94;11;00;;::;;;19477,50
120870423817;90;65;40;;::;;;8955,00
190261402328;94;11;00;;::;;;18252,50
140857419061;94;11;00;;::;;;21850,00
101069422786;90;65;40;;::;;;2700,00
140161406131;94;11;00;;::;;;19636,13
241263401326;94;11;00;;::;;;16720,00
030552518328;94;11;00;;::;;;16652,50
100847404011;94;11;00;;::;;;24562,50
050762400078;00;00;00;;::;;;0,00
050442415115;00;00;00;;::;;;0,00
070667400019;00;00;00;;::;;;0,00
120259410317;00;00;00;;::;;;0,00
060548416211;00;00;00;;::;;;0,00
120962400436;00;00;00;;::;;;0,00
070156420827;00;00;00;;::;;;0,00
041028430016;00;00;00;;::;;;0,00
130268400873;00;00;00;;::;;;0,00
020768424911;00;00;00;;::;;;0,00
020465406134;00;00;00;;::;;;0,00
080457430139;00;00;00;;::;;;0,00
100565500427;00;00;00;;::;;;0,00
181229406121;00;00;00;;::;;;0,00
120147406145;00;00;00;;::;;;0,00
180966415402;00;00;00;;::;;;0,00
110829516211;00;00;00;;::;;;0,00
180562400423;00;00;00;;::;;;0,00
101251429714;00;00;00;;::;;;0,00
171259405112;00;00;00;;::;;;0,00
130129406124;00;00;00;;::;;;0,00
140654400838;00;00;00;;::;;;0,00
100948413427;00;00;00;;::;;;26125,00
140546417536;00;00;00;;::;;;0,00
090940415114;00;00;00;;::;;;0,00
131251512275;00;00;00;;::;;;0,00
090367413238;00;00;00;;::;;;0,00
081160423629;00;00;00;;::;;;0,00
020658504515;00;00;00;;::;;;0,00
080662528776;00;00;00;;::;;;0,00
100336411228;00;00;00;;::;;;0,00
050845414731;00;00;00;;::;;;5125,00
070367400615;00;00;00;;::;;;680,00
140270400214;00;00;00;;::;;;680,00
180362418610;00;00;00;;::;;;1292,50
230769405339;00;00;00;;::;;;2177,66
300968415346;00;00;00;;::;;;2355,00
280169430325;00;00;00;;::;;;2400,00
091166510028;00;00;00;;::;;;3396,87
010739429140;00;00;00;;::;;;0,00
051065500123;00;00;00;;::;;;4545,96
010767400118;00;00;00;;::;;;0,00
200868400237;00;00;00;;::;;;5600,00
240153405110;00;00;00;;::;;;6716,00
210369405710;00;00;00;;::;;;8850,00
110166430125;00;00;00;;::;;;9197,00
191066500410;00;00;00;;::;;;9695,18
251062511114;00;00;00;;::;;;13083,79
300462413431;00;00;00;;::;;;15812,50
260633500828;00;00;00;;::;;;3750,00
020253429828;00;00;00;;::;;;0,00
010264424310;00;00;00;;::;;;0,00
040926530065;00;00;00;;::;;;0,00
010330406138;00;00;00;;::;;;0,00
151027530258;00;00;00;;::;;;0,00
010662430046;00;00;00;;::;;;0,00
150958503720;00;00;00;;::;;;0,00
151256407325;00;00;00;;::;;;0,00
290370425447;00;00;00;;::;;;680,00
160250420929;00;00;00;;::;;;0,00
030642407613;00;00;00;;::;;;0,00
160751429817;00;00;00;;::;;;0,00
020349411956;00;00;00;;::;;;0,00
010168400415;00;00;00;;::;;;0,00
020159516917;00;00;00;;::;;;0,00
010668526524;00;00;00;;::;;;0,00
010765404422;00;00;00;;::;;;0,00
030868400019;00;00;00;;::;;;0,00
011068415016;00;00;00;;::;;;0,00
020836430142;00;00;00;;::;;;0,00
150320500010;00;00;00;;::;;;0,00
300648426820;00;00;00;;::;;;0,00
240447402222;00;00;00;;::;;;0,00
230852424928;00;00;00;;::;;;0,00
231065410310;00;00;00;;::;;;0,00
230565401512;00;00;00;;::;;;0,00
230442513418;00;00;00;;::;;;0,00
220660511200;00;00;00;;::;;;0,00
240564512244;00;00;00;;::;;;0,00
150252417759;00;00;00;;::;;;0,00
241134405144;00;00;00;;::;;;0,00
141262500850;00;00;00;;::;;;0,00
141253401519;00;00;00;;::;;;0,00
220265400623;00;00;00;;::;;;0,00
270463406116;00;00;00;;::;;;0,00
270471406431;00;00;00;;::;;;0,00
270767428015;00;00;00;;::;;;0,00
270652511433;00;00;00;;::;;;0,00
070663423635;00;00;00;;::;;;0,00
150333400115;00;00;00;;::;;;0,00
260360401516;00;00;00;;::;;;0,00
220152517315;00;00;00;;::;;;0,00
220145410819;00;00;00;;::;;;0,00
091251424730;00;00;00;;::;;;0,00
100256407616;00;00;00;;::;;;0,00
261236400617;00;00;00;;::;;;0,00
261157440741;00;00;00;;::;;;0,00
260952416615;00;00;00;;::;;;0,00
240764430235;00;00;00;;::;;;0,00
260248429711;00;00;00;;::;;;0,00
310750405136;00;00;00;;::;;;0,00
260351510315;00;00;00;;::;;;0,00
260264410818;00;00;00;;::;;;0,00
251160430326;00;00;00;;::;;;0,00
250526400216;00;00;00;;::;;;0,00
250521406117;00;00;00;;::;;;0,00
250359411718;00;00;00;;::;;;0,00
250366407215;00;00;00;;::;;;0,00
250266415445;00;00;00;;::;;;0,00
260466414825;00;00;00;;::;;;0,00
071162401512;00;00;00;;::;;;0,00
271045422011;00;00;00;;::;;;0,00
210244415018;00;00;00;;::;;;0,00
200963401537;00;00;00;;::;;;0,00
100363442214;00;00;00;;::;;;0,00
090451524694;00;00;00;;::;;;0,00
060951412245;00;00;00;;::;;;0,00
110328421513;00;00;00;;::;;;0,00
210862430055;00;00;00;;::;;;0,00
200853413115;00;00;00;;::;;;0,00
150662509218;00;00;00;;::;;;0,00
110963400623;00;00;00;;::;;;0,00
100856412275;00;00;00;;::;;;0,00
190669411113;00;00;00;;::;;;0,00
091265430189;00;00;00;;::;;;0,00
190451427913;00;00;00;;::;;;0,00
161256400210;00;00;00;;::;;;0,00
190264430252;00;00;00;;::;;;0,00
190867412256;00;00;00;;::;;;0,00
261251442110;00;00;00;;::;;;0,00
280960407522;00;00;00;;::;;;0,00
291048400836;00;00;00;;::;;;0,00
290931530125;00;00;00;;::;;;0,00
300862402141;00;00;00;;::;;;0,00
271034434121;00;00;00;;::;;;0,00
291056430154;00;00;00;;::;;;0,00
280254504229;00;00;00;;::;;;0,00
291031417711;00;00;00;;::;;;0,00
210356424015;00;00;00;;::;;;0,00
300170412226;00;00;00;;::;;;0,00
190562430357;00;00;00;;::;;;0,00
300862430089;00;00;00;;::;;;0,00
281161403423;00;00;00;;::;;;0,00
310554414713;00;00;00;;::;;;0,00
281056421128;00;00;00;;::;;;0,00
311260412223;00;00;00;;::;;;0,00
090964410828;00;00;00;;::;;;0,00
060567400012;00;00;00;;::;;;0,00
051262405918;00;00;00;;::;;;0,00
280556430173;00;00;00;;::;;;0,00
191064401312;00;00;00;;::;;;0,00
130637430147;90;65;40;;1/72,;;;0,00
261030400718;01;00;50;;1022/84, :;;;29250,00
151140430208;96;15;00;;1029/67, J:;;;26937,50
080630430248;96;15;00;;1041/67, M:;;;30158,33
230232430067;15;00;41;;1041/70, :;;;25995,83
290455415379;96;15;00;;1043/84, A:;;;19745,00
120636430234;96;15;00;;1046/67, M:;;;26375,00
110163405936;96;15;00;;1047/82, M:;;;17820,00
290350403611;90;65;40;;1058/86, :;;;22511,29
080861413445;96;15;00;;1078/81, F:;;;2800,00
091033429736;96;15;00;;1087/84, U:;;;27300,00
220351530117;96;15;00;;109/78, J:;;;21161,85
020728401344;01;00;47;;1110/73, :;;;22500,00
220441500114;01;18;00;;1119/79, :;;;20722,50
031141429712;96;15;00;;112/76, M:;;;25500,00
270541426834;96;15;00;;113/74, L:;;;22820,00
300358406426;96;15;00;;113/75, F:;;;19745,00
310828405620;15;18;00;;1143/70, :;;;24480,00
151060428220;90;65;40;;1153/86, :;;;19430,00
260666406125;90;65;40;;1159/89, :;;;15326,84
280267426223;90;65;40;;1160/89, :;;;15108,00
050666422787;90;65;40;;1161/89, :;;;16291,90
310352419719;96;15;00;;121/69/35, AB:;;;25677,16
070152408513;96;15;00;;1226/70, F:;;;21833,22
220538430132;96;15;00;;12487/60, A:;;;25500,00
120644430103;94;11;00;;1276/73, :;;;25080,00
250240430348;96;15;00;;128/68, F:;;;23062,50
060129429237;96;15;00;;12904/60, U:;;;35250,00
210351402124;15;06;00;;1299/85, :;;;24960,00
141038430077;96;15;00;;1305/68, P:;;;30000,00
270734430039;96;15;00;;13222/60, X:;;;27000,00
210739430260;96;15;00;;1331/63, T:;;;24750,00
291132429711;15;18;00;;1341/83, :;;;27052,08
210361505629;96;15;00;;1346/85/1, F:;;;8731,70
100730430013;96;15;00;;1347/85, F:;;;42000,00
230833430118;96;15;00;;1348/85, F:;;;37500,00
111142530150;96;15;00;;1351/89, N:;;;19980,00
260344413437;15;06;00;;1352/75, :;;;30000,00
270461430155;90;65;40;;1356/84, :;;;18480,00
050645422745;96;15;00;;136/71, J:;;;21390,00
140232430076;96;15;00;;1362/60, J:;;;25746,65
260857416035;96;15;00;;1371/77, F:;;;21040,00
120743406432;96;15;00;;1381/89, M:;;;31580,00
160747421011;96;15;00;;1382/89, M:;;;30625,00
160544430102;96;15;00;;1391/86, M:;;;30000,00
110130400821;01;06;00;;1397/86, :;;;29250,00
150860426915;96;15;00;;1433/85, J:;;;2900,00
070141426716;14;00;54;;1435/89, *:;;;33750,00
040454419085;96;15;00;;1439/89, F:;;;16280,00
110444417749;96;15;00;;1472/87, F:;;;30135,00
041250430068;96;15;00;;1476/87, F:;;;34980,00
250253417118;96;15;00;;1477/87, F:;;;26400,00
091251416247;96;15;00;;1478/87, F:;;;35040,00
230245424010;15;00;47;;1484/82, :;;;25854,17
200241419823;96;15;00;;1492/86, F:;;;33000,00
250537422752;96;15;00;;1498/87, F:;;;36450,00
190457430021;90;65;40;;1508/80,;;;0,00
210252429882;90;65;40;;1514/75,;;;0,00
041150424015;94;11;00;;1515/75, :;;;23200,00
161156409832;96;15;00;;1525/75, F:;;;23100,00
270248400715;96;15;00;;1528/87, M:;;;30000,00
290147429728;96;15;00;;1529/87, M:;;;30000,00
180730430198;96;15;00;;153/72, J:;;;28500,00
300532400821;01;18;00;;1530/70, :;;;25200,00
070750424548;96;15;00;;1530/87, M:;;;31282,50
191243413925;96;15;00;;1531/87, M:;;;37500,00
271151500722;94;11;00;;1533/87, M:;;;16038,00
220259427213;90;65;40;;1548/80,;;;0,00
130159404111;90;65;40;;1549/80,;;;0,00
251056417754;90;65;40;;1551/80,;;;0,00
200650422791;96;15;00;;1555/87, F:;;;27840,00
021252402118;96;15;00;;1565/86, M:;;;28800,00
120244409524;96;15;00;;1566/86, M:;;;30750,00
250552417329;96;15;00;;157/85, M:;;;28000,00
030232404823;96;15;00;;1573/85, K:;;;33000,00
040861403419;96;15;00;;1577/86, F:;;;18421,00
071152408948;06;40;00;;1587/87, :;;;24150,00
280244403416;96;15;00;;1587/87, F:;;;30750,00
290530430027;96;15;00;;1593/86, U:;;;35250,00
130736400736;96;15;00;;1594/75, M:;;;26250,00
111159403617;90;65;40;;1598/81,;;;0,00
050742420311;94;11;00;;1601/68, :;;;26250,00
080230426354;96;15;00;;1601/75, M:;;;27000,00
281050426913;96;15;00;;1603/75, M:;;;23265,00
200454500510;90;65;40;;1603/76,;;;0,00
290946406944;90;65;40;;1604/76,;;;0,00
141152404817;90;65;40;;1607/76,;;;0,00
300754401520;94;11;00;;1607/88, :;;;21600,00
140161500224;94;11;00;;1607/88/1, :;;;16252,50
061039401366;01;00;44;;1608/70, :;;;23040,00
270240430215;90;65;40;;1608/76,;;;0,00
071054400731;94;11;00;;1608/88, :;;;25290,00
220952529242;94;11;00;;1608/88/1, :;;;18000,00
100130430132;96;15;00;;1610/69, B:;;;33000,00
160236430282;96;15;00;;1611/69, Q:;;;30750,00
270941430170;90;65;40;;1611/76,;;;0,00
171052426346;14;08;00;;163, :;;;1980,00
270951416612;96;15;00;;1635/84, O:;;;28080,00
280943429738;96;15;00;;1640/88, F:;;;31491,93
140764430317;90;65;40;;1642/85, :;;;17850,00
120644430066;96;15;00;;1643/68, O:;;;27750,00
101047430080;96;15;00;;1644/69, F:;;;25200,00
300459424973;94;11;00;;1649/82, :;;;20625,00
270136430047;96;15;00;;1653/87, F:;;;35250,00
260265402721;96;15;00;;1656/69/2, P:;;;11220,00
220349427719;14;08;00;;166, :;;;1920,00
040342400611;96;15;00;;166/77, M:;;;30000,00
220355427213;14;08;00;;167, :;;;1920,00
200747409817;96;15;00;;167/78, K:;;;25920,00
060249420720;96;15;00;;1670/84, J:;;;23100,00
241045406815;96;15;00;;1671/87, F:;;;34800,00
180437529711;96;15;00;;1672/84, A:;;;22687,50
240740429715;96;15;00;;1675/84, C:;;;25500,00
120341529712;96;15;00;;1675/84/1, C:;;;21000,00
290951406113;96;15;00;;1679/88, E:;;;25530,00
161051427321;14;08;00;;168, :;;;1860,00
200761423615;96;15;00;;1680/88, F:;;;17016,00
200131430175;96;15;00;;1685/87, F:;;;39900,00
201142430132;90;65;40;;1687/76,;;;0,00
120653426237;14;08;00;;169, :;;;1860,00
281051421719;90;65;40;;1690/76,;;;0,00
300152402139;90;65;40;;1692/76,;;;0,00
200945403424;94;11;00;;17/71, :;;;24750,00
150256413739;94;11;00;;1709/89, :;;;22252,50
220830400838;01;18;00;;171/70, :;;;23250,00
030158430133;94;11;00;;1710/89, :;;;21844,43
240460409525;94;11;00;;1711/89, :;;;21762,50
100160411223;94;11;00;;1712/89, :;;;21562,50
180558519819;94;11;00;;1712/89/1, :;;;10780,00
161162423825;94;11;00;;1713/89, :;;;18656,79
230156412210;96;15;00;;1715/89, M:;;;26125,00
241164407618;96;15;00;;1716/89, T:;;;11220,00
140562422036;14;08;00;;172, :;;;1292,50
021258403824;96;15;00;;1738/87, F:;;;26730,00
120260503625;96;15;00;;1738/87/1, F:;;;8706,48
021066428285;14;08;00;;174, :;;;1215,00
261151421726;96;15;00;;174/79, M:;;;26640,00
280651422817;96;15;00;;1746/89, E:;;;28325,80
130547417782;94;11;00;;1748/75, :;;;24000,00
251141416238;01;06;00;;1748/89, :;;;27000,00
020867419616;14;08;00;;175, :;;;13860,00
091152428242;96;15;00;;175/75, F:;;;25817,50
300640428266;96;15;00;;1750/72, M:;;;30000,00
161052426929;90;65;40;;1753/80,;;;0,00
170151428270;14;08;00;;176, :;;;1687,50
190145419915;94;11;00;;176/72, :;;;24000,00
040944404820;96;15;00;;1762/89, N:;;;28500,00
150249426814;90;65;40;;1763/76,;;;0,00
230562514212;96;15;00;;1763/88, E:;;;15952,66
111140430164;90;65;40;;1769/71,;;;0,00
130355528322;14;08;00;;177, :;;;1351,25
230357430087;90;65;40;;1775/78,;;;0,00
160649424833;96;15;00;;1779/71, F:;;;26910,00
150341428222;14;08;00;;178, :;;;1750,00
110357415403;90;65;40;;1787/81,;;;0,00
160857401919;90;65;40;;1788/78,;;;0,00
041154426325;14;08;00;;179, :;;;1495,00
271138406926;94;11;00;;179/78, :;;;24750,00
030537430213;96;15;00;;18/67, S:;;;28500,00
130261427416;14;08;00;;180, :;;;1408,75
040938402749;96;15;00;;180/73, M:;;;33120,00
220135430082;90;65;40;;1807/72,;;;0,00
061058426614;14;08;00;;181, :;;;1667,50
140528430198;96;15;00;;181/73, M:;;;28500,00
170159413137;94;11;00;;1819/87, :;;;21390,00
290867427210;14;08;00;;182, :;;;13244,00
101241428953;94;11;00;;182/70, :;;;24000,00
060936429719;96;15;00;;1826/88, A:;;;30000,00
260528430143;96;15;00;;18264/60, Y:;;;36750,00
260156401914;90;65;40;;1840/79,;;;0,00
260259530137;94;11;00;;1844/88, :;;;19616,55
260529430129;96;15;00;;18500/60, F:;;;33000,00
240534430061;96;15;00;;18554/60, T:;;;28687,50
200631430171;96;15;00;;18556/60, E:;;;27750,00
200557430017;90;65;40;;1856/86, :;;;19830,00
161235430066;96;15;00;;1858/89, F:;;;32062,50
111037430211;96;15;00;;186/77, J:;;;28500,00
060744401543;96;15;00;;1863/89, M:;;;34920,00
090356402410;90;65;40;;1864/78,;;;0,00
090151425045;96;15;00;;1864/89, M:;;;27720,00
230230530064;94;11;00;;1866/69/2, :;;;20880,00
100137430178;94;11;00;;1868/69, :;;;33000,00
141150400839;96;15;00;;1870/87, L:;;;25530,00
070356415336;96;15;00;;1881/88, A:;;;24056,59
260752411019;90;65;40;;1883/81,;;;0,00
010555528320;90;65;40;;1884/81,;;;0,00
240451530032;90;65;40;;1885/81,;;;0,00
240438400866;01;18;00;;189/71, :;;;23040,00
260459412231;94;11;00;;1894/87, :;;;21390,00
260162512266;94;11;00;;1894/87/1, :;;;17490,00
120151428128;96;15;00;;19/76, F:;;;15697,50
160459420532;96;15;00;;19/81, F:;;;19305,00
090148400824;96;15;00;;1902/72, F:;;;27600,00
210145422773;94;11;00;;1903/72, :;;;24000,00
080448402128;94;11;00;;1904/72, :;;;24000,00
100851417712;96;15;00;;1904/73, F:;;;27600,00
270951418423;90;65;40;;1906/71,;;;0,00
280434430044;15;18;00;;1911/78, :;;;21248,00
110743417722;96;15;00;;192/73, X:;;;25380,00
260429430017;96;15;00;;1920/75, J:;;;34092,06
101149530218;90;65;40;;1922/76,;;;0,00
281153429789;90;65;40;;1926/76,;;;0,00
300451424987;96;15;00;;1938/75, F:;;;13800,00
250327406113;96;15;00;;19522/60, X:;;;26250,00
121054417747;96;15;00;;1960/75, M:;;;25920,00
130133430047;96;15;00;;19666/60, E:;;;29250,00
100738529720;96;15;00;;19666/60/1, E:;;;25500,00
150241415133;96;15;00;;1967/64, A:;;;27750,00
271259400416;90;65;40;;1985/79,;;;0,00
090651429245;90;65;40;;1988/76,;;;0,00
121037404434;96;15;00;;1990/72, M:;;;25200,00
130254419725;90;65;40;;1990/76,;;;0,00
260743430066;90;65;40;;1991/69,;;;0,00
300445424948;96;15;00;;1996/73, A:;;;23760,00
110749530101;90;65;40;;1997/77,;;;0,00
230455425003;90;65;40;;1999/77,;;;0,00
270941407632;15;19;00;;1O91/79, :;;;26424,00
031141410616;96;15;00;;200/66, F:;;;30000,00
141154524927;90;65;40;;2002/87, :;;;6130,34
090846423628;90;65;40;;2006/67,;;;0,00
240746414717;90;65;40;;2007/67,;;;0,00
280246420316;90;65;40;;2009/67,;;;0,00
180547408718;90;65;40;;2010/67,;;;0,00
300355413110;90;65;40;;2012/78,;;;0,00
240160530219;90;65;40;;2015/80,;;;0,00
140353403824;94;11;00;;2026/86, :;;;24480,00
110353401944;90;65;40;;2028/79,;;;0,00
090947424814;96;15;00;;2032/72, J:;;;22980,00
101235407611;94;11;00;;2046/64, :;;;26250,00
160160430082;96;15;00;;205/84, F:;;;20642,50
240239406130;90;65;40;;2075/76,;;;0,00
260563426713;90;65;40;;2080/82,;;;0,00
141043419614;96;15;00;;209/81, F:;;;30750,00
250351416426;94;11;00;;2093/72, :;;;23040,00
110650428262;90;65;40;;2094/72,;;;0,00
290633429731;96;15;00;;21/77, F:;;;32214,58
120146430151;96;15;00;;2105/73, O:;;;27202,50
190828430021;96;15;00;;2110/73, Z:;;;35250,00
020659430183;96;15;00;;2110/84, F:;;;21820,31
150843425048;96;15;00;;2111/72, F:;;;27600,00
281137424961;96;15;00;;2111/73, A:;;;24937,50
090446426811;90;65;40;;2112/66,;;;0,00
160551417731;96;15;00;;2112/72, F:;;;26580,00
160951429715;96;15;00;;2113/72, F:;;;24500,00
151053416942;96;15;00;;2113/89, E:;;;25530,00
161146428116;90;65;40;;2114/66,;;;0,00
120145427129;96;15;00;;2124/89, F:;;;36937,50
200458430046;90;65;40;;2129/78,;;;0,00
131239430066;96;15;00;;2133/73, A:;;;8864,91
121129430146;96;15;00;;2142/73, L:;;;25500,00
061166425109;96;15;00;;2143/86, A:;;;11016,00
070326430076;96;15;00;;2148/72, U:;;;33000,00
130834400860;01;02;00;;2162/88, :;;;28500,00
240451421346;96;15;00;;2163/73, F:;;;26910,00
190853429743;96;15;00;;2164/73, F:;;;23402,50
150434430225;15;20;00;;219/76, :;;;27739,58
101157422778;90;65;40;;2195/82,;;;0,00
060731403216;96;15;00;;221/75, M:;;;24750,00
190136530240;96;15;00;;2221/70, J:;;;24000,00
190250421355;96;15;00;;2224/86, O:;;;31500,00
071037430058;94;11;00;;2233/66, :;;;24000,00
221038422763;96;15;00;;2245/73, M:;;;35250,00
090130507519;96;15;00;;225/78, U:;;;23250,00
280841400897;01;29;00;;2254/84, :;;;26250,00
250452429787;96;15;00;;2256/73, F:;;;26910,00
080950414757;96;15;00;;2257/70, F:;;;27600,00
301146430082;96;15;00;;2259/73, M:;;;26820,00
240941430077;94;11;00;;2260/66, :;;;24000,00
250444429744;90;65;40;;2262/87, :;;;21750,00
100261530096;96;15;00;;2264/86, U:;;;17118,00
260953406435;96;15;00;;227/85, F:;;;26162,50
120650409239;90;65;40;;2279/74/1,;;;0,00
240647506915;90;65;40;;2286/74,;;;0,00
270236404815;96;15;00;;2295/70, U:;;;27750,00
150751422034;96;15;00;;23/77, F:;;;24420,00
230354427421;94;11;00;;2305/85, :;;;23040,00
300456408943;96;15;00;;2306/74, F:;;;21807,50
271149426332;90;65;40;;2309/73,;;;0,00
220947401340;96;15;00;;231/75, M:;;;25500,00
120249420722;96;15;00;;231/78, J:;;;24322,50
240531429719;96;15;00;;2310/88, E:;;;37500,00
070736529722;96;15;00;;2310/88/1, E:;;;21750,00
280654420219;96;15;00;;2311/88, O:;;;24660,00
050753407526;90;65;40;;2319/84, :;;;21135,00
250136422751;96;15;00;;2332/73, M:;;;25200,00
020752429830;96;15;00;;234/73, F:;;;25920,00
110137430150;94;11;00;;235/65, :;;;35250,00
270357406112;96;15;00;;235/79, M:;;;22990,00
121054407311;96;15;00;;2354/88, M:;;;27700,00
060444415396;96;15;00;;2355/88, M:;;;37500,00
030134430075;96;15;00;;2367/73, U:;;;31680,00
241235425099;94;11;00;;237/70, :;;;24750,00
141052403614;96;15;00;;237/73, F:;;;28740,00
040256429215;96;15;00;;2378/88, F:;;;25000,00
171150412212;94;11;00;;2382/74, :;;;23040,00
270443516414;94;11;00;;239/85, :;;;21750,00
160632530058;94;11;00;;2390/70, :;;;22500,00
171247413916;96;15;00;;2394/85, J:;;;27360,00
290756410619;90;65;40;;2403/78,;;;0,00
310153419054;94;11;00;;2414/88, :;;;25200,00
161055417737;94;11;00;;2415/88, :;;;20850,00
140261417743;94;11;00;;2416/88, :;;;20770,00
060661430146;94;11;00;;2417/88, :;;;17820,00
291252418515;96;15;00;;2427/74, F:;;;25702,50
140347515328;96;15;00;;2428/79, O:;;;17796,25
140247415418;96;15;00;;2429/79, O:;;;28800,00
061053422235;96;15;00;;2429/88, M:;;;28080,00
121140430163;90;65;40;;2437/60,;;;0,00
030131429714;94;11;00;;246/77, :;;;24000,00
040857430115;96;15;00;;2472/79, F:;;;19800,00
280854429832;96;15;00;;2477/75, F:;;;20350,00
020638402722;96;15;00;;2477/85, F:;;;38700,00
260934429711;96;15;00;;2481/88, F:;;;22687,50
040838530268;96;15;00;;2481/88/1, F:;;;21312,50
150250429780;96;15;00;;2482/88, F:;;;28380,00
231057406928;90;65;40;;2487/77,;;;0,00
060444403635;94;11;00;;2496/74, :;;;24000,00
140434427115;96;15;00;;250/81, M:;;;31500,00
200952427117;96;15;00;;2501/77, F:;;;25160,00
140952427254;96;15;00;;2503/77, F:;;;26392,50
071246430097;96;15;00;;2505/65, G:;;;21000,00
110250422048;96;15;00;;2511/77, M:;;;28080,00
150254418616;96;15;00;;2518/88, F:;;;28020,00
061126430149;96;15;00;;252/74, U:;;;29250,00
250253422777;90;65;40;;2528/82,;;;0,00
160159421023;94;11;00;;2528/88, :;;;22080,00
251256521046;96;15;00;;2528/88/1, F:;;;20074,92
091248419818;90;65;40;;255/73,;;;0,00
111148430118;96;15;00;;2553/80, P:;;;28800,00
030546430047;15;00;41;;2562/80, :;;;23785,83
030459522744;94;11;00;;2563/86, :;;;16353,75
260556424912;90;65;40;;2564/86, :;;;21210,00
200252406147;96;15;00;;2565/88, O:;;;28800,00
250362404412;90;65;40;;2567/87, :;;;16665,00
040851422421;96;15;00;;2570/79, O:;;;25702,50
181251414523;96;15;00;;2576/77, F:;;;24420,00
190932430144;96;15;00;;2580/65, K:;;;35812,50
051141430260;90;65;40;;2582/65,;;;0,00
270831405628;96;15;00;;2588/77, P:;;;20250,00
080758400822;96;15;00;;2592/80, F:;;;24150,00
140555422126;96;15;00;;2596/79, J:;;;21102,50
180439430205;96;15;00;;2607/84, F:;;;31500,00
201058422738;96;15;00;;2611/84, F:;;;20625,00
080363430285;96;15;00;;2612/84, F:;;;16800,00
220659430091;96;15;00;;2613/84, E:;;;20700,00
270761430042;96;15;00;;2614/84, F:;;;11220,00
040854429776;96;15;00;;2616/80, U:;;;20325,00
190744430139;90;65;40;;2626/65,;;;0,00
250529430015;96;15;00;;2637/77, S:;;;28687,50
270862410032;96;15;00;;2637/84, M:;;;14245,00
110853422741;96;15;00;;2639/79, J:;;;21540,00
240238429736;96;15;00;;2649/80, F:;;;44400,00
130850424934;94;11;00;;2649/82, :;;;23040,00
030440529727;96;15;00;;2650/80, F:;;;26400,00
160961430218;96;15;00;;2657/80, M:;;;16852,35
221144407516;96;15;00;;2660/79, M:;;;26937,50
041144405344;01;00;50;;2678/70, :;;;25637,50
280458412246;96;15;00;;2686/79, F:;;;12760,00
310129430165;96;15;00;;269/68, P:;;;30000,00
151157424947;96;15;00;;2691/80, F:;;;23460,00
130548414313;94;11;00;;270/74, :;;;23187,50
130656429715;96;15;00;;2708/78, F:;;;24365,00
210742424929;94;11;00;;271/68, :;;;24750,00
140247424939;90;65;40;;271/74,;;;0,00
211264413946;90;65;40;;2729/86, :;;;16335,00
240355421127;96;15;00;;2729/89, A:;;;27400,00
190754403433;96;15;00;;2730/89, F:;;;16280,00
151051416818;94;11;00;;2741/77, :;;;23040,00
150648411214;94;11;00;;2747/79, :;;;24000,00
060739424986;96;15;00;;2756/84, G:;;;27750,00
260953529857;96;15;00;;2758/78, J:;;;17681,25
250739530233;94;11;00;;2758/89, :;;;21750,00
100164412223;94;11;00;;2759/89, :;;;16704,03
210262413235;96;15;00;;2766/84, F:;;;14245,00
160267400027;96;15;00;;2767/89, F:;;;8262,00
300959406915;96;15;00;;2769/84, F:;;;24150,00
250652429802;96;15;00;;2769/87, F:;;;25530,00
280865430257;96;15;00;;2778/76/1, T:;;;11067,00
020852522776;96;15;00;;2779/84, O:;;;18794,02
030551426819;96;15;00;;2784/72, U:;;;23700,00
050653407422;96;15;00;;2784/73, F:;;;25530,00
260258424244;94;11;00;;2794/87, :;;;21562,50
180254423922;94;11;00;;2795/87, :;;;23040,00
150255421219;94;11;00;;2797/87, :;;;22720,00
021234430086;96;15;00;;2806/78, F:;;;37500,00
151258404611;94;11;00;;2806/89, :;;;20642,50
230752418336;90;65;40;;2808/79,;;;0,00
160961502517;96;15;00;;2816/80, O:;;;15446,82
180355429899;96;15;00;;2817/80, M:;;;26780,00
240239415379;96;15;00;;2824/84, X:;;;30000,00
270248529738;01;08;00;;2832/85, :;;;25500,00
160464400835;96;15;00;;2833/87, M:;;;21228,22
030467403438;96;15;00;;2842/89, J:;;;12929,00
300352515402;96;15;00;;2850/78, J:;;;21045,00
200343406433;96;15;00;;2856/80, M:;;;23250,00
040664424966;96;15;00;;2858/84, F:;;;11220,00
030629406712;96;15;00;;2859/68, M:;;;25920,00
230362430153;96;15;00;;2859/84, U:;;;17509,94
041050428246;96;15;00;;2879/78, J:;;;21505,00
110743430257;94;11;00;;288/67, :;;;24000,00
080151426372;94;11;00;;2895/77, :;;;23360,00
110739417770;94;11;00;;2899/68, :;;;26250,00
180644430140;90;65;40;;2900/66,;;;0,00
130241424023;90;65;40;;2901/66,;;;0,00
200759430066;96;15;00;;2912/78, F:;;;22715,00
200138430063;96;15;00;;2929/61, F:;;;30750,00
131257430166;90;65;40;;2955/79,;;;0,00
120459430099;90;65;40;;2958/79,;;;0,00
220258415325;90;65;40;;2959/79,;;;0,00
060356402413;96;15;00;;2963/78, F:;;;21065,00
260857412237;90;65;40;;2966/79,;;;0,00
130341410614;96;15;00;;2968/87, M:;;;31500,00
160641510614;96;15;00;;2969/87, M:;;;21000,00
190252422773;96;15;00;;2970/87, M:;;;26910,00
080753429247;96;15;00;;2972/76, F:;;;21065,00
030267407522;90;65;40;;2976/86, :;;;15876,00
270439430108;15;18;00;;2978/81, :;;;28960,00
080349414414;96;15;00;;2987/77, J:;;;24420,00
180240417724;96;15;00;;2990/76, M:;;;27000,00
200739425083;96;15;00;;30/70, A:;;;24375,00
051260430052;90;65;40;;3002/80,;;;0,00
111150428930;15;20;00;;3003/84, :;;;24633,55
080938422850;96;15;00;;3009/89, M:;;;26250,00
Diese Liste beinhaltet die Namen von 90.598 Mitarbeitern des Ministeriums für Staatssicherheit der DDR. Die Liste ist nicht vollständig. Insbesondere Mitarbeiter der Führungsebene sind nicht enthalten.
This is a list of 90.598 members of the secret police of East Germany (Ministry for State Security), the list isn’t complete, because the most of the high Officiers lieke Colonel and higher have destroyed the personal Informations in the last days of Eastern Germany.
| Listen der Stasimitarbeiter-hier findest Du sie! Was bedeuten die Zahlen? |
|
1.Listen der Stasi-Diensteinheiten!
Bem.:hier kannst du die Nr.(6-stellig) der Dienststellen heraussuchen.
2.Liste der Stasi-Mitarbeiter (Hauptamtlich)
Bem.:Hoffentlich hast Du einen guten Rechner, denn die Liste ist erschreckend lang. Die ersten 6 Ziffern sind das Geburtsdatum + die nächsten 6 Ziffern = Dienstausweisnummer! Die zwei Ziffern hinter dem Geburtsdatum geben das Geschlecht an: 41 und 42 = Männlich, 51 und 52 = Weiblich! Wichtig für suchen und finden, sind die sechs Ziffern in den Semikolon vor den Namen: z.B. ;07;00;44; ! Das ist die Nummer der Dienststelle !
Also du suchst in der Liste der Dienststellen, die Nummer der Dienststelle, die Dich interessiert. Damit gehst Du in die Liste der Mitarbeiter und suchst Dir alle Mitarbeiter der entsprechenden Dienststelle heraus. Ich habe das für mein Wohnort getan und so alle Mitarbeiter gefunden. Ob die Liste Vollständig ist kann ich nicht einschätzen, aber zumindest er/kannte ich einige Exverräter vom Namen her.
3.Liste der OibE (Offiziere im besonderen Einsatz) |































 A Roman Catholic priest and former prison chaplain who ministered to Chicago mob boss Frank Calabrese, Sr., was indicted earlier this month for illegally passing jailhouse messages from Calabrese and plotting with his associates on the outside—a sobering reminder of how deeply organized crime can reach into the community, even from behind bars.
A Roman Catholic priest and former prison chaplain who ministered to Chicago mob boss Frank Calabrese, Sr., was indicted earlier this month for illegally passing jailhouse messages from Calabrese and plotting with his associates on the outside—a sobering reminder of how deeply organized crime can reach into the community, even from behind bars.











![[Image]](https://i0.wp.com/cryptome.org/2012-info/femen-wef/pict6.jpg) Activists of the Ukrainian feminist nudity group FEMEN clash with Swiss police during a protest at the 42nd Annual Meeting of the World Economic Forum, WEF, in Davos, Switzerland, Saturday, Jan. 28, 2012. (Jean-Christophe Bott)
Activists of the Ukrainian feminist nudity group FEMEN clash with Swiss police during a protest at the 42nd Annual Meeting of the World Economic Forum, WEF, in Davos, Switzerland, Saturday, Jan. 28, 2012. (Jean-Christophe Bott)![[Image]](https://i0.wp.com/cryptome.org/2012-info/femen-wef/pict7.jpg) EDS NOTE NUDITY Topless Ukrainian protesters demonstrate at the entrance to the congress center where the World Economic Forum takes place in Davos, Switzerland Saturday, Jan. 28, 2012. The activists are from the group Femen, which has have become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)
EDS NOTE NUDITY Topless Ukrainian protesters demonstrate at the entrance to the congress center where the World Economic Forum takes place in Davos, Switzerland Saturday, Jan. 28, 2012. The activists are from the group Femen, which has have become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)![[Image]](https://i0.wp.com/cryptome.org/2012-info/femen-wef/pict5.jpg) Topless Ukrainian protesters climb up a fence at the entrance to the congress center where the World Economic Forum takes place in Davos, Switzerland Saturday, Jan. 28, 2012. The activists are from the group Femen, which has have become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)
Topless Ukrainian protesters climb up a fence at the entrance to the congress center where the World Economic Forum takes place in Davos, Switzerland Saturday, Jan. 28, 2012. The activists are from the group Femen, which has have become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)![[Image]](https://i0.wp.com/cryptome.org/2012-info/femen-wef/pict4.jpg) EDS NOTE NUDITY – Topless Ukrainian protesters demonstrate at the entrance to the congress center where the World Economic Forum takes place in Davos, Saturday, Jan. 28, 2012. The activists are from the group Femen, which has become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)
EDS NOTE NUDITY – Topless Ukrainian protesters demonstrate at the entrance to the congress center where the World Economic Forum takes place in Davos, Saturday, Jan. 28, 2012. The activists are from the group Femen, which has become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)![[Image]](https://i0.wp.com/cryptome.org/2012-info/femen-wef/pict3.jpg) EDS NOTE NUDITY- A topless Ukrainian protester is arrested by Swiss police after climbing up a fence at the entrance to the congress center where the World Economic Forum takes place in Davos, Saturday, Jan. 28, 2012. The activists are from the group Femen, which has become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)
EDS NOTE NUDITY- A topless Ukrainian protester is arrested by Swiss police after climbing up a fence at the entrance to the congress center where the World Economic Forum takes place in Davos, Saturday, Jan. 28, 2012. The activists are from the group Femen, which has become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)![[Image]](https://i0.wp.com/cryptome.org/2012-info/femen-wef/pict2.jpg) Topless Ukrainian protesters demonstrate at the entrance to the congress center where the World Economic Forum takes place in Davos, Switzerland Saturday, Jan. 28, 2012. The activists are from the group Femen, which has have become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)
Topless Ukrainian protesters demonstrate at the entrance to the congress center where the World Economic Forum takes place in Davos, Switzerland Saturday, Jan. 28, 2012. The activists are from the group Femen, which has have become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)![[Image]](https://i0.wp.com/cryptome.org/2012-info/femen-wef/pict0.jpg) A topless Ukrainian protester is arrested by Swiss police after climbing up a fence at the entrance to the congress center where the World Economic Forum takes place in Davos, Switzerland Saturday, Jan. 28, 2012. The activists are from the group Femen, which has have become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)
A topless Ukrainian protester is arrested by Swiss police after climbing up a fence at the entrance to the congress center where the World Economic Forum takes place in Davos, Switzerland Saturday, Jan. 28, 2012. The activists are from the group Femen, which has have become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)![[Image]](https://i0.wp.com/cryptome.org/2012-info/femen-wef/pict1.jpg) Topless Ukrainian protesters demonstrate at the entrance to the congress center where the World Economic Forum takes place in Davos, Saturday, Jan. 28, 2012. The activists are from the group Femen, which has have become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)
Topless Ukrainian protesters demonstrate at the entrance to the congress center where the World Economic Forum takes place in Davos, Saturday, Jan. 28, 2012. The activists are from the group Femen, which has have become popular in Ukraine for staging small, half-naked protests against a range of issues including oppression of political opposition. (Anja Niedringhaus)![[Image]](https://i0.wp.com/cryptome.org/2012-info/femen-wef/pict11.jpg) An activist from Ukrainian feminist group FEMEN shouts slogans as she is arrested by Swiss police during a topless protest on January 28, 2012, against the World Economic Forum (WEF) annual meeting on January 28, 2012 in the Swiss resort of Davos. Getty
An activist from Ukrainian feminist group FEMEN shouts slogans as she is arrested by Swiss police during a topless protest on January 28, 2012, against the World Economic Forum (WEF) annual meeting on January 28, 2012 in the Swiss resort of Davos. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/femen-wef/pict10.jpg) An activist from Ukrainian feminist group FEMEN shouts slogans as she is arrested by Swiss police during a topless protest on January 28, 2012, against the World Economic Forum (WEF) annual meeting on January 28, 2012 in the Swiss resort of Davos. Getty
An activist from Ukrainian feminist group FEMEN shouts slogans as she is arrested by Swiss police during a topless protest on January 28, 2012, against the World Economic Forum (WEF) annual meeting on January 28, 2012 in the Swiss resort of Davos. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/femen-wef/pict9.jpg) Attivist from Ukrainian feminist group ‘ Femen ‘ is arrested by Swiss police as they make a topless protest on January 28, 2012, against the World Economic Forum (WEF) in the center of the Swiss resort of Davos. The global elite has talked itself into an upbeat frame of mind as the Davos forum nears its climax on Saturday, but the Greek debt crisis still hangs heavily over proceedings. Getty
Attivist from Ukrainian feminist group ‘ Femen ‘ is arrested by Swiss police as they make a topless protest on January 28, 2012, against the World Economic Forum (WEF) in the center of the Swiss resort of Davos. The global elite has talked itself into an upbeat frame of mind as the Davos forum nears its climax on Saturday, but the Greek debt crisis still hangs heavily over proceedings. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/femen-wef/pict8.jpg) EDS NOTE : NUDITY – A member of the Ukrainian FEMEN women’s rights group is detained by policemen after a protest at the 42nd Annual Meeting of the World Economic Forum, WEF, in Davos, Switzerland, Saturday, Jan. 28, 2012. In freezing temperatures three topless Ukrainian protesters were detained Saturday while climbing a security fence outside the economic forum to draw attention to the needs of the world’s poor. The protesters had their papers checked and will be released later from custody.
EDS NOTE : NUDITY – A member of the Ukrainian FEMEN women’s rights group is detained by policemen after a protest at the 42nd Annual Meeting of the World Economic Forum, WEF, in Davos, Switzerland, Saturday, Jan. 28, 2012. In freezing temperatures three topless Ukrainian protesters were detained Saturday while climbing a security fence outside the economic forum to draw attention to the needs of the world’s poor. The protesters had their papers checked and will be released later from custody.



















 Preet Bhrara, Verfasser der Anklage
Preet Bhrara, Verfasser der Anklage

![[Image]](https://i0.wp.com/cryptome.org/info/belarus-protest/pict64.jpg) Belarus plainclothes policemen detain protesters during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)
Belarus plainclothes policemen detain protesters during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)![[Image]](https://i0.wp.com/cryptome.org/info/belarus-protest/pict63.jpg) Belarus plainclothes policemen detain a protester during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)
Belarus plainclothes policemen detain a protester during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)![[Image]](https://i0.wp.com/cryptome.org/info/belarus-protest/pict68.jpg) Belarus plainclothes policemen detain protesters during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko.
Belarus plainclothes policemen detain protesters during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko.![[Image]](https://i0.wp.com/cryptome.org/info/belarus-protest/pict69.jpg)
![[Image]](https://i0.wp.com/cryptome.org/info/belarus-protest/pict72.jpg) Detained protesters show V-signs as they sit in a police van during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)
Detained protesters show V-signs as they sit in a police van during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)![[Image]](https://i0.wp.com/cryptome.org/info/belarus-protest/pict60.jpg) A detained protester showsa V-sign as he sits in a police van during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)
A detained protester showsa V-sign as he sits in a police van during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)![[Image]](https://i0.wp.com/cryptome.org/info/belarus-protest/pict58.jpg) Belarus plainclothes policemen detain a protester during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)
Belarus plainclothes policemen detain a protester during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)![[Image]](https://i0.wp.com/cryptome.org/info/belarus-protest/pict66.jpg) Belarus plainclothes policemen detain a protester during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)
Belarus plainclothes policemen detain a protester during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)![[Image]](https://i0.wp.com/cryptome.org/info/belarus-protest/pict67.jpg) A Belarus plainclothes policeman, left, detains protesters during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)
A Belarus plainclothes policeman, left, detains protesters during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)![[Image]](https://i0.wp.com/cryptome.org/info/belarus-protest/pict57.jpg) A woman protects her husband from a plainclothes policeman, left, during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)
A woman protects her husband from a plainclothes policeman, left, during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)![[Image]](https://i0.wp.com/cryptome.org/info/belarus-protest/pict59.jpg) A woman argues with plainclothes policemen as they push back protesters during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)
A woman argues with plainclothes policemen as they push back protesters during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)![[Image]](https://i0.wp.com/cryptome.org/info/belarus-protest/pict71.jpg) Belarus plainclothes policemen push back protesters during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)
Belarus plainclothes policemen push back protesters during an action “Revolution via social network” in Minsk, Belarus, Wednesday, June 29, 2011. Police in Belarus have violently quashed a peaceful anti-government rally, detaining dozens of people protesting the authoritarian regime of President Alexander Lukashenko. (Sergei Grits)![[Image]](https://i0.wp.com/cryptome.org/info/belarus-protest/pict62.jpg) Youths applaud as they participate in a peaceful rally to protest the authoritarian regime of President Alexander Lukashenko, Minsk, Belarus, Wednesday, June 29, 2011. Belarusian police violently dispersed a peaceful rally Wednesday by thousands of people protesting the authoritarian regime of President Alexander Lukashenko and the country’s worst financial crisis since the fall of the Soviet Union two decades ago. (Sergei Grits)
Youths applaud as they participate in a peaceful rally to protest the authoritarian regime of President Alexander Lukashenko, Minsk, Belarus, Wednesday, June 29, 2011. Belarusian police violently dispersed a peaceful rally Wednesday by thousands of people protesting the authoritarian regime of President Alexander Lukashenko and the country’s worst financial crisis since the fall of the Soviet Union two decades ago. (Sergei Grits)![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict18.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict16.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict0.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict4.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict12.jpg) FILE – In this June 1, 2009 file photo, reviewed by the U.S. military, Chinese Uighur detainees, who at the time were cleared for release, show a home-made note to visiting members of the media in Camp Iguana detention facility at the Guantanamo Bay U.S. Naval Base in Cuba.
FILE – In this June 1, 2009 file photo, reviewed by the U.S. military, Chinese Uighur detainees, who at the time were cleared for release, show a home-made note to visiting members of the media in Camp Iguana detention facility at the Guantanamo Bay U.S. Naval Base in Cuba.![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict2.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict6.jpg) FILE – In this May 14, 2009 file photo, reviewed by the U.S. military, detainees pray before dawn near a fence of razor-wire inside Camp 4 detention facility at the Guantanamo Bay U.S. Naval Base in Cuba.
FILE – In this May 14, 2009 file photo, reviewed by the U.S. military, detainees pray before dawn near a fence of razor-wire inside Camp 4 detention facility at the Guantanamo Bay U.S. Naval Base in Cuba.![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict14.jpg) FILE – In this May 13, 2009 file photo, reviewed by the U.S. military, a detainee stands at his cell window yelling after seeing a group of journalists who were visiting Camp 5 maximum-security detention facility at the Guantanamo Bay U.S. Naval Base in Cuba.
FILE – In this May 13, 2009 file photo, reviewed by the U.S. military, a detainee stands at his cell window yelling after seeing a group of journalists who were visiting Camp 5 maximum-security detention facility at the Guantanamo Bay U.S. Naval Base in Cuba.![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict1.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict10.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict3.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict13.jpg) FILE – In this Dec. 4, 2006 file photo, reviewed by a U.S. Department of Defense official, a detainee shields his face as he peers out through the so-called “bean hole” which is used to pass food and other items into detainee cells, in Camp Delta detention facility at the Guantanamo Bay U.S. Naval Base in Cuba.
FILE – In this Dec. 4, 2006 file photo, reviewed by a U.S. Department of Defense official, a detainee shields his face as he peers out through the so-called “bean hole” which is used to pass food and other items into detainee cells, in Camp Delta detention facility at the Guantanamo Bay U.S. Naval Base in Cuba.![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict5.jpg) FILE – In this Sept. 19, 2006 file photo, reviewed by a U.S. Department of Defense official, a detainee stands at a fence holding Islamic prayer beads in Camp Delta detention facility at the Guantanamo Bay U.S. Naval Base in Cuba.
FILE – In this Sept. 19, 2006 file photo, reviewed by a U.S. Department of Defense official, a detainee stands at a fence holding Islamic prayer beads in Camp Delta detention facility at the Guantanamo Bay U.S. Naval Base in Cuba.![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict8.jpg) FILE – In this Sept. 19, 2006 file photo, reviewed by a U.S. Department of Defense official, military personnel stand inside the brand new Camp 6 maximum security detention facility at the Guantanamo Bay U.S. Naval Base in Cuba.
FILE – In this Sept. 19, 2006 file photo, reviewed by a U.S. Department of Defense official, military personnel stand inside the brand new Camp 6 maximum security detention facility at the Guantanamo Bay U.S. Naval Base in Cuba.![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict9.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict11.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict7.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict23.jpg) Members of the Turkish Communist Party (TKP) chant slongans against French president during a protest outside the French consulate in Istanbul, on January 24, 2012. The French Senate on Monday approved, by 127 votes to 86, the measure which makes it an offence punishable by jail in France to deny that the 1915 massacre of Armenians by Ottoman Turk forces amounted to genocide. French President Nicolas Sarkozy, whose right-wing UMP party put forward the bill, now has sign it into law. Getty
Members of the Turkish Communist Party (TKP) chant slongans against French president during a protest outside the French consulate in Istanbul, on January 24, 2012. The French Senate on Monday approved, by 127 votes to 86, the measure which makes it an offence punishable by jail in France to deny that the 1915 massacre of Armenians by Ottoman Turk forces amounted to genocide. French President Nicolas Sarkozy, whose right-wing UMP party put forward the bill, now has sign it into law. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict24.jpg) Monica a German trucker gestures on the Turin highway during a truckers’ protest against the government’s deregulation plans in Turin January 23, 2012. Truckers blocked roads throughout Italy and taxi drivers resumed a strike on Monday as opposition mounted to fuel tax rises and economic reforms aimed at opening up competition in protected sectors including transport and pharmacies. Reuters
Monica a German trucker gestures on the Turin highway during a truckers’ protest against the government’s deregulation plans in Turin January 23, 2012. Truckers blocked roads throughout Italy and taxi drivers resumed a strike on Monday as opposition mounted to fuel tax rises and economic reforms aimed at opening up competition in protected sectors including transport and pharmacies. Reuters![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict25.jpg) Pro-life activists protest at the March for Life rally on January 23, 2012 in Washington, DC. Pro-life activists gather each year to protest on the anniversary of the Roe v. Wade Supreme Court decision that legalized abortion. Getty
Pro-life activists protest at the March for Life rally on January 23, 2012 in Washington, DC. Pro-life activists gather each year to protest on the anniversary of the Roe v. Wade Supreme Court decision that legalized abortion. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict26.jpg) An ‘Occupy WEF’ protester cuts firewood during a protest against the World Economic Forum (WEF) at the Swiss resort of Davos on January 23, 2012. Some 1,600 economic and political leaders, including 40 heads of states and governments, will be asked to urgently find ways to reform a capitalist system that has been described as ‘outdated and crumbling as they converge at eastern Switzerland’s chic ski station of Davos for the 42nd edition of the five-day World Economic Forum (WEF) which opens on January 25, 2012. Getty
An ‘Occupy WEF’ protester cuts firewood during a protest against the World Economic Forum (WEF) at the Swiss resort of Davos on January 23, 2012. Some 1,600 economic and political leaders, including 40 heads of states and governments, will be asked to urgently find ways to reform a capitalist system that has been described as ‘outdated and crumbling as they converge at eastern Switzerland’s chic ski station of Davos for the 42nd edition of the five-day World Economic Forum (WEF) which opens on January 25, 2012. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict27.jpg) Members of a leftist Turkish party waves party flags and hold a banner reading ‘Armenian allegations are part of a new Treaty of Sevres (which would have divided Turkey) by the USA and EU’ as they protest outside the French embassy in Ankara on January 23, 2012. Turkey threatened France with new sanctions over a bill criminalising the denial of the Armenian genocide as the French Senate prepared to vote on the legislation. Getty
Members of a leftist Turkish party waves party flags and hold a banner reading ‘Armenian allegations are part of a new Treaty of Sevres (which would have divided Turkey) by the USA and EU’ as they protest outside the French embassy in Ankara on January 23, 2012. Turkey threatened France with new sanctions over a bill criminalising the denial of the Armenian genocide as the French Senate prepared to vote on the legislation. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict2.jpg) Cambodian victims hold a demonstration to mark the third anniversary of a forced eviction in the Dey Krahorm community, Tuesday, Jan. 24, 2012, in Phnom Penh, Cambodia. Three years ago residents were forcibly evicted from their homes and told by local authorities that the land was owned by others. (Heng Sinith)
Cambodian victims hold a demonstration to mark the third anniversary of a forced eviction in the Dey Krahorm community, Tuesday, Jan. 24, 2012, in Phnom Penh, Cambodia. Three years ago residents were forcibly evicted from their homes and told by local authorities that the land was owned by others. (Heng Sinith)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict3.jpg) AIDS protestors are seen outside the FDA building on Monday Jan. 23, 2012, in Silver Spring, MD. (Larry French)
AIDS protestors are seen outside the FDA building on Monday Jan. 23, 2012, in Silver Spring, MD. (Larry French)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict1.jpg) A Hungarian protestor covers her mouth with a mask during a protest in support of the largest opposition radio station ‘Klub Radio’ which recently lost its radio frequency in Budapest, Hungary, Sunday, Jan. 22, 2012. Thousands gathered to protest against the government’s controversial media law and to help the ‘Klub Radio’. (Bela Szandelszky)
A Hungarian protestor covers her mouth with a mask during a protest in support of the largest opposition radio station ‘Klub Radio’ which recently lost its radio frequency in Budapest, Hungary, Sunday, Jan. 22, 2012. Thousands gathered to protest against the government’s controversial media law and to help the ‘Klub Radio’. (Bela Szandelszky)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict28.jpg) The Ladies in White, a group of family members of imprisoned dissidents, protest during their weekly march in Havana January 22, 2012. The opposition group “Ladies in White” accused the Cuban government on Sunday of “murdering” by neglect a 31-year-old dissident who died last week following a hunger strike in prison. Ladies in White leader Berta Soler said Wilman Villar Mendoza died because the government did not respect his rights and that he was only the latest such victim to die for the same reason. Reuters
The Ladies in White, a group of family members of imprisoned dissidents, protest during their weekly march in Havana January 22, 2012. The opposition group “Ladies in White” accused the Cuban government on Sunday of “murdering” by neglect a 31-year-old dissident who died last week following a hunger strike in prison. Ladies in White leader Berta Soler said Wilman Villar Mendoza died because the government did not respect his rights and that he was only the latest such victim to die for the same reason. Reuters![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict4.jpg) Anti-government protesters shout as they carry portraits of several prisoners during a rally organized by the pro-democracy 20th February movement in Casablanca, Morocco, Sunday, Jan. 22 2012. Like the rest of the region, Morocco was once shaken by pro-democracy protests but the king has succeeded in blunting them by holding early elections and amending the constitution and the numbers of protesters have dwindled.
Anti-government protesters shout as they carry portraits of several prisoners during a rally organized by the pro-democracy 20th February movement in Casablanca, Morocco, Sunday, Jan. 22 2012. Like the rest of the region, Morocco was once shaken by pro-democracy protests but the king has succeeded in blunting them by holding early elections and amending the constitution and the numbers of protesters have dwindled.![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict5.jpg) Demonstrators, dressed as workers, holds a sign that reads in Spanish ‘I don’t want apartheids in Chile’ during a protest in support of maids and workers outside the gated community “El Algarrobal II” in Chicureo, Chile, Saturday, Jan. 21, 2012. According to community rules, workers are forbidden to walk along the residential development.
Demonstrators, dressed as workers, holds a sign that reads in Spanish ‘I don’t want apartheids in Chile’ during a protest in support of maids and workers outside the gated community “El Algarrobal II” in Chicureo, Chile, Saturday, Jan. 21, 2012. According to community rules, workers are forbidden to walk along the residential development.![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict30.jpg) Topless activists of Ukraine’s protest group Femen punch reporters in front of the Bulgarian Parliament in Sofia, on Saturday, Jan 21, 2012. Ukrainian female rights activists FEMEN staged a protest in Sofia against the domestic violence on women and children and against human trafficking. (Valentina Petrova)
Topless activists of Ukraine’s protest group Femen punch reporters in front of the Bulgarian Parliament in Sofia, on Saturday, Jan 21, 2012. Ukrainian female rights activists FEMEN staged a protest in Sofia against the domestic violence on women and children and against human trafficking. (Valentina Petrova)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict7.jpg) An anti-government protester holds a banner that reads ‘I love democracy’ while posing in front of a group of riot police in combat gear in Bucharest, Romania, early Saturday, Jan. 21, 2012. Police on Sunday clashed with a small contingent of around 1,000 protesters in the capital, after demonstrations against austerity measures turned violent. (Vadim Ghirda)
An anti-government protester holds a banner that reads ‘I love democracy’ while posing in front of a group of riot police in combat gear in Bucharest, Romania, early Saturday, Jan. 21, 2012. Police on Sunday clashed with a small contingent of around 1,000 protesters in the capital, after demonstrations against austerity measures turned violent. (Vadim Ghirda)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict8.jpg) Occupy protester Julie Searle chains herself to fellow protesters blocking a Bank of America branch entrance on Friday, Jan. 20, 2012, in San Francisco. Anti-Wall Street demonstrators across the U.S. planned rallies Friday in front of banks and courthouses. (Noah Berger)
Occupy protester Julie Searle chains herself to fellow protesters blocking a Bank of America branch entrance on Friday, Jan. 20, 2012, in San Francisco. Anti-Wall Street demonstrators across the U.S. planned rallies Friday in front of banks and courthouses. (Noah Berger)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict9.jpg) Children chant slogans during an anti-Syrian regime demonstration at the mountain resort town of Zabadani, Syria, near the Lebanese border, on Friday Jan. 20, 2012. President Bashar Assad’s forces attacked Zabadani, some 17 miles (27 kilometers) west of the capital, for six days, sparking fierce fighting that involved heavy bombardments and clashes with army defectors.
Children chant slogans during an anti-Syrian regime demonstration at the mountain resort town of Zabadani, Syria, near the Lebanese border, on Friday Jan. 20, 2012. President Bashar Assad’s forces attacked Zabadani, some 17 miles (27 kilometers) west of the capital, for six days, sparking fierce fighting that involved heavy bombardments and clashes with army defectors.![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict10.jpg) Protesters hold signs that read in Spanish “English get out of Malvinas” outside the British embassy in Buenos Aires, Argentina, Friday Jan. 20, 2012. A small crowd of demonstrators turned out Friday after British Prime Minister David Cameron accused Argentina of being “much more than colonialist” for asserting its claims to the islands.
Protesters hold signs that read in Spanish “English get out of Malvinas” outside the British embassy in Buenos Aires, Argentina, Friday Jan. 20, 2012. A small crowd of demonstrators turned out Friday after British Prime Minister David Cameron accused Argentina of being “much more than colonialist” for asserting its claims to the islands.![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict11.jpg) A demonstrator chants as she holds up a poster with the image of Chile’s Interior Minister Rodrigo Hinzpeter, during a protest against a proposed plan on new ways to crack down on unauthorized social protests, in Santiago, Chile, Thursday Jan. 19, 2012. “Hinzpeter Law,” had included enabling police to seize images from media without court orders but Hinzpeter is backing away from that idea.
A demonstrator chants as she holds up a poster with the image of Chile’s Interior Minister Rodrigo Hinzpeter, during a protest against a proposed plan on new ways to crack down on unauthorized social protests, in Santiago, Chile, Thursday Jan. 19, 2012. “Hinzpeter Law,” had included enabling police to seize images from media without court orders but Hinzpeter is backing away from that idea.![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict12.jpg) Half naked and caged activists of the animal rights group ‘Igualdad Animal’ (Equality Animal) symbolically sit in cages to denounce the slaying of animals to make fur coats, in Barcelona, Spain, Thursday, Jan. 19, 2012. (Manu Fernandez)
Half naked and caged activists of the animal rights group ‘Igualdad Animal’ (Equality Animal) symbolically sit in cages to denounce the slaying of animals to make fur coats, in Barcelona, Spain, Thursday, Jan. 19, 2012. (Manu Fernandez)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict13.jpg) Bulgarian environmental activist wears a gas mask and carries Bulgarian national flag during a protest in Sofia, on Wednesday, Jan 18, 2012. Though the Bulgarian parliament banned on Wednesday shale oil and gas exploration through hydraulic fracturing or fracking hundreds activists gathered to protest against the environmental policy of the government. (Valentina Petrova)
Bulgarian environmental activist wears a gas mask and carries Bulgarian national flag during a protest in Sofia, on Wednesday, Jan 18, 2012. Though the Bulgarian parliament banned on Wednesday shale oil and gas exploration through hydraulic fracturing or fracking hundreds activists gathered to protest against the environmental policy of the government. (Valentina Petrova)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict14.jpg) Israeli Ethiopian girls have their faces painted as they take part in a demonstration against racism and discrimination in Jerusalem, Wednesday, Jan. 18, 2012. Thousands of young Ethiopian immigrants and other supporters gathered on Wednesday outside the Israeli parliament, to protest what they say is racism directed at them. (Sebastian Scheiner)
Israeli Ethiopian girls have their faces painted as they take part in a demonstration against racism and discrimination in Jerusalem, Wednesday, Jan. 18, 2012. Thousands of young Ethiopian immigrants and other supporters gathered on Wednesday outside the Israeli parliament, to protest what they say is racism directed at them. (Sebastian Scheiner)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict15.jpg) An anti-government protester draped in a Bahraini flag argues with riot police who told her to go inside as police dispersed a banned demonstration Wednesday, Jan. 18, 2012, in Manama, Bahrain. Opposition groups, led by al-Wefaq society, had called for a march through central Manama, but turned the protest into a sit-in when police who turned out in large numbers blocked their way.
An anti-government protester draped in a Bahraini flag argues with riot police who told her to go inside as police dispersed a banned demonstration Wednesday, Jan. 18, 2012, in Manama, Bahrain. Opposition groups, led by al-Wefaq society, had called for a march through central Manama, but turned the protest into a sit-in when police who turned out in large numbers blocked their way.![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict16.jpg) Workers demonstrate at the request of the CGT union (General Confederation of Work), in Marseille, southern France, Wednesday, Jan. 18, 2012, against what they describe as anti social government measures. Labor unions insist workers shouldn’t have to pay the cost of the financial crisis at a time when many French companies are still making profits, and accuse unpopular conservative leader President Nicolas Sarkozy of putting together a slap-dash solution ahead of elections.
Workers demonstrate at the request of the CGT union (General Confederation of Work), in Marseille, southern France, Wednesday, Jan. 18, 2012, against what they describe as anti social government measures. Labor unions insist workers shouldn’t have to pay the cost of the financial crisis at a time when many French companies are still making profits, and accuse unpopular conservative leader President Nicolas Sarkozy of putting together a slap-dash solution ahead of elections.![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict17.jpg) Occupy London protesters chant anti-corporate slogans as they gather on the steps of St. Paul’s Cathedral, in central London, Wednesday, Jan. 18, 2012. Britain’s High Court decided Wednesday, Occupy London protest camp an be evicted from outside St. Paul’s Cathedral. (Lefteris Pitarakis)
Occupy London protesters chant anti-corporate slogans as they gather on the steps of St. Paul’s Cathedral, in central London, Wednesday, Jan. 18, 2012. Britain’s High Court decided Wednesday, Occupy London protest camp an be evicted from outside St. Paul’s Cathedral. (Lefteris Pitarakis)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict18.jpg) Occupy Congress protesters arrives for a day of demonstrations and activities on Capitol Hill in Washington, Tuesday, Jan. 17, 2012. (J. Scott Applewhite)
Occupy Congress protesters arrives for a day of demonstrations and activities on Capitol Hill in Washington, Tuesday, Jan. 17, 2012. (J. Scott Applewhite)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict19.jpg) Protester, holds a black cross to symbolically mourn the death of PSI (Private Sector Involvement) and CDS (Credit Default Swaps) during a rally in central Athens, Tuesday, Jan. 17, 2012. Strikes and demonstrations over austerity measures hit the Greek capital of Athens on Tuesday, as international debt inspectors returned to resume their scrutiny of the country’s reforms. (Dimitri Messinis)
Protester, holds a black cross to symbolically mourn the death of PSI (Private Sector Involvement) and CDS (Credit Default Swaps) during a rally in central Athens, Tuesday, Jan. 17, 2012. Strikes and demonstrations over austerity measures hit the Greek capital of Athens on Tuesday, as international debt inspectors returned to resume their scrutiny of the country’s reforms. (Dimitri Messinis)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict20.jpg) International Indignados movement demonstrators chash with Italian police officers as they try to move out of St. Peter’s Square at the Vatican, in Rome, Saturday, Jan. 13, 2012. The Indignados staged a sit-in and tried to place tents and climb the Vatican Christmas tree as a protest. (Andrew Medichini)
International Indignados movement demonstrators chash with Italian police officers as they try to move out of St. Peter’s Square at the Vatican, in Rome, Saturday, Jan. 13, 2012. The Indignados staged a sit-in and tried to place tents and climb the Vatican Christmas tree as a protest. (Andrew Medichini)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict21.jpg) Border guards, fire brigade officers and prison guards blow horns as they protest demanding monthly wage increases of 300 zlotys (US dollar 85, euro 66) , just like those recently given to the police and armed forces, in Warsaw, Poland, Thursday, Jan. 12, 2012. Similar protests took place simultaneously in Warsaw, Gdansk, Poznan and Wroclaw, the four Polish towns that will host the Euro 2012 soccer championships games. (Alik Keplicz)
Border guards, fire brigade officers and prison guards blow horns as they protest demanding monthly wage increases of 300 zlotys (US dollar 85, euro 66) , just like those recently given to the police and armed forces, in Warsaw, Poland, Thursday, Jan. 12, 2012. Similar protests took place simultaneously in Warsaw, Gdansk, Poznan and Wroclaw, the four Polish towns that will host the Euro 2012 soccer championships games. (Alik Keplicz)![[Image]](https://i0.wp.com/cryptome.org/2012-info/women-protest11/pict22.jpg) Indigenous women rest after protesting the Conga gold and silver mining project in Cajamarca, Peru, Tuesday Jan. 3, 2012. Demonstrators in Peru resumed their protests against plans to develop a $4.8 billion gold mine, saying they fear the mine will will taint their water and affect a major aquifer. The mine is majority owned by U.S.-based Newmont Mining Corp. (Karel Navarro)
Indigenous women rest after protesting the Conga gold and silver mining project in Cajamarca, Peru, Tuesday Jan. 3, 2012. Demonstrators in Peru resumed their protests against plans to develop a $4.8 billion gold mine, saying they fear the mine will will taint their water and affect a major aquifer. The mine is majority owned by U.S.-based Newmont Mining Corp. (Karel Navarro)




























 George Kennan of the Department of State could be considered the godfather of NCFE. He – more than any other official – pressed the National Security Council to reorganize covert action planning and management. This resulted in the creation of the Office of Policy Coordination (OPC) at the CIA in September 1948 and the appointment of the visionary OSS veteran Frank G. Wisner as its chief.
George Kennan of the Department of State could be considered the godfather of NCFE. He – more than any other official – pressed the National Security Council to reorganize covert action planning and management. This resulted in the creation of the Office of Policy Coordination (OPC) at the CIA in September 1948 and the appointment of the visionary OSS veteran Frank G. Wisner as its chief.




![[Image]](https://i0.wp.com/cryptome.org/2012-info/megaupload/pict73.jpg) Megaupload.com employees Bram van der Kolk, also known as Bramos, left, Finn Batato,second from left, Mathias Ortmann and founder, former CEO and current chief innovation officer of Megaupload.com Kim Dotcom (also known as Kim Schmitz and Kim Tim Jim Vestor), right, appear in North Shore District Court in Auckland, New Zealand, Friday, Jan. 20, 2012.
Megaupload.com employees Bram van der Kolk, also known as Bramos, left, Finn Batato,second from left, Mathias Ortmann and founder, former CEO and current chief innovation officer of Megaupload.com Kim Dotcom (also known as Kim Schmitz and Kim Tim Jim Vestor), right, appear in North Shore District Court in Auckland, New Zealand, Friday, Jan. 20, 2012. German Internet millionaire Kim Schmitz arrives for. a trial at a district court in Munich in these May 27, 2002 file photos. New Zealand police broke through electronic locks and cut their way into a mansion safe room to arrest the alleged kingpin of an international Internet copyright theft case and seize millions of dollars worth of cars, artwork and other goods. German national Schmitz, also known as Kim Dotcom, was one of four men arrested in Auckland on January 20, 2012, in an investigation of the Megaupload.com website led by the U.S. Federal Bureau of Investigation. Reuters
German Internet millionaire Kim Schmitz arrives for. a trial at a district court in Munich in these May 27, 2002 file photos. New Zealand police broke through electronic locks and cut their way into a mansion safe room to arrest the alleged kingpin of an international Internet copyright theft case and seize millions of dollars worth of cars, artwork and other goods. German national Schmitz, also known as Kim Dotcom, was one of four men arrested in Auckland on January 20, 2012, in an investigation of the Megaupload.com website led by the U.S. Federal Bureau of Investigation. Reuters![[Image]](https://i0.wp.com/cryptome.org/2012-info/megaupload/pict75.jpg) In this April 30, 2007 file photo, attorney Robert Bennett speaks in Washington. Bennett, one of the nation’s most prominent defense lawyers will represent file-sharing website Megaupload on charges that the company used its popular site to orchestrate a massive piracy scheme that enabled millions of illegal downloads of movies and other content. (J. Scott Applewhite)
In this April 30, 2007 file photo, attorney Robert Bennett speaks in Washington. Bennett, one of the nation’s most prominent defense lawyers will represent file-sharing website Megaupload on charges that the company used its popular site to orchestrate a massive piracy scheme that enabled millions of illegal downloads of movies and other content. (J. Scott Applewhite)![[Image]](https://i0.wp.com/cryptome.org/2012-info/megaupload/pict72.jpg) Tow trucks wait to remove vehicles from Kim Dotcom’s house in Coatesville, north west of Auckland, New Zealand Friday, Jan. 20, 2012. Police arrested founder Kim Dotcom and three employees of Megaupload.com, a giant Internet file-sharing site, on U.S. accusations that they facilitated millions of illegal downloads of films, music and other content costing copyright holders at least $500 million in lost revenue. (Natalie Slade)
Tow trucks wait to remove vehicles from Kim Dotcom’s house in Coatesville, north west of Auckland, New Zealand Friday, Jan. 20, 2012. Police arrested founder Kim Dotcom and three employees of Megaupload.com, a giant Internet file-sharing site, on U.S. accusations that they facilitated millions of illegal downloads of films, music and other content costing copyright holders at least $500 million in lost revenue. (Natalie Slade)![[Image]](https://i0.wp.com/cryptome.org/2012-info/megaupload/pict78.jpg) A general view shows the Dotcom Mansion, home of Megaupload founder Kim Dotcom, in Coatesville, Auckland, January 21, 2012. The U.S. government shut down the Megaupload.com content sharing website, charging its founders and several employees with massive copyright infringement, the latest skirmish in a high-profile battle against piracy of movies and music. The U.S. Department of Justice announced the indictment and arrests of four company executives in New Zealand on Friday as debate over online piracy reaches fever pitch in Washington where lawmakers are trying to craft tougher legislation. Reuters
A general view shows the Dotcom Mansion, home of Megaupload founder Kim Dotcom, in Coatesville, Auckland, January 21, 2012. The U.S. government shut down the Megaupload.com content sharing website, charging its founders and several employees with massive copyright infringement, the latest skirmish in a high-profile battle against piracy of movies and music. The U.S. Department of Justice announced the indictment and arrests of four company executives in New Zealand on Friday as debate over online piracy reaches fever pitch in Washington where lawmakers are trying to craft tougher legislation. Reuters![[Image]](https://i0.wp.com/cryptome.org/2012-info/megaupload/pict79.jpg) A broken intercom system is seen after a police raid at Dotcom Mansion, home of accused Kim Dotcom, who founded the Megaupload.com site and ran it from the $30 million mansion in Coatesville, Auckland January 21, 2012. The U.S. government shut down the Megaupload.com content sharing website, charging its founders and several employees with massive copyright infringement, the latest skirmish in a high-profile battle against piracy of movies and music. New Zealand police on Friday raided a mansion in Auckland and arrested Kim Dotcom, also known as Kim Schmitz, 37, a German national with New Zealand residency. Reuters
A broken intercom system is seen after a police raid at Dotcom Mansion, home of accused Kim Dotcom, who founded the Megaupload.com site and ran it from the $30 million mansion in Coatesville, Auckland January 21, 2012. The U.S. government shut down the Megaupload.com content sharing website, charging its founders and several employees with massive copyright infringement, the latest skirmish in a high-profile battle against piracy of movies and music. New Zealand police on Friday raided a mansion in Auckland and arrested Kim Dotcom, also known as Kim Schmitz, 37, a German national with New Zealand residency. Reuters![[Image]](https://i0.wp.com/cryptome.org/2012-info/megaupload/pict77.jpg) An entrance to Megaupload’s office at a hotel in Hong Kong is seen in this Hong Kong government handout photo released late January 20, 2012. The Hong Kong government said on Friday over HK$300 million ($38.4 million) worth of proceeds from Megaupload were seized in the country in joint operations by Hong Kong customs and U.S. authorities. The U.S. government shut down the Megaupload.com content sharing website, charging its founders and several employees with massive copyright infringement, the latest skirmish in a high-profile battle against piracy of movies and music. Reuters
An entrance to Megaupload’s office at a hotel in Hong Kong is seen in this Hong Kong government handout photo released late January 20, 2012. The Hong Kong government said on Friday over HK$300 million ($38.4 million) worth of proceeds from Megaupload were seized in the country in joint operations by Hong Kong customs and U.S. authorities. The U.S. government shut down the Megaupload.com content sharing website, charging its founders and several employees with massive copyright infringement, the latest skirmish in a high-profile battle against piracy of movies and music. Reuters![[Image]](https://i0.wp.com/cryptome.org/2012-info/megaupload/pict74.jpg) In this photo taken Friday, Jan. 20,2012, provided by the Government Information Service in Hong Kong, large-scale high-speed servers set up at Megaupload’s office are shown inside a hotel room in Hong Kong. Customs officials said they seized more than $42.5 million in assets from the Hong Kong based company. The U.S. government shut down Megaupload’s file-sharing website on Thursday, alleging that the company facilitated illegal downloads of copyrighted movies and other content.
In this photo taken Friday, Jan. 20,2012, provided by the Government Information Service in Hong Kong, large-scale high-speed servers set up at Megaupload’s office are shown inside a hotel room in Hong Kong. Customs officials said they seized more than $42.5 million in assets from the Hong Kong based company. The U.S. government shut down Megaupload’s file-sharing website on Thursday, alleging that the company facilitated illegal downloads of copyrighted movies and other content.![[Image]](https://i0.wp.com/cryptome.org/2012-info/megaupload/pict76.jpg) A masked hacker, part of the Anonymous group, hacks the French presidential Elysee Palace website on January 20, 2012 near the eastern city of Lyon. Anonymous, which briefly knocked the FBI and Justice Department websites offline in retaliation for the US shutdown of file-sharing site Megaupload, is a shadowy group of international hackers with no central hierarchy. On the left screen, an Occupy mask is seen. Getty
A masked hacker, part of the Anonymous group, hacks the French presidential Elysee Palace website on January 20, 2012 near the eastern city of Lyon. Anonymous, which briefly knocked the FBI and Justice Department websites offline in retaliation for the US shutdown of file-sharing site Megaupload, is a shadowy group of international hackers with no central hierarchy. On the left screen, an Occupy mask is seen. Getty























![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict40.jpg) President Barack Obama and Orlando, Fla. Mayor Buddy Dyer, right, walk over to greet onlookers after arriving at Orlando International Airport in Orlando, Fla., Thursday, Jan. 19, 2012. (Haraz N. Ghanbari)
President Barack Obama and Orlando, Fla. Mayor Buddy Dyer, right, walk over to greet onlookers after arriving at Orlando International Airport in Orlando, Fla., Thursday, Jan. 19, 2012. (Haraz N. Ghanbari)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict41.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict42.jpg) President Barack Obama shakes hands with people waiting to greet him on the tarmac as he steps off of Air Force One at Hickam Air Force Base in Friday, Dec. 23, 2011, in Honolulu. (Carolyn Kaster)
President Barack Obama shakes hands with people waiting to greet him on the tarmac as he steps off of Air Force One at Hickam Air Force Base in Friday, Dec. 23, 2011, in Honolulu. (Carolyn Kaster)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict43.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict44.jpg) President Barack Obama visits with patron at PetsMart, Wednesday, Dec. 21, 2011, in Alexandria, Va., where he shopped with his dog Bo. (Carolyn Kaster)
President Barack Obama visits with patron at PetsMart, Wednesday, Dec. 21, 2011, in Alexandria, Va., where he shopped with his dog Bo. (Carolyn Kaster)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict50.jpg) President Barack Obama, accompanied by his security personnel, walks through a White House gate prior to crossing Pennsylvania Avenue heading to the Blair House to attend a holiday party, Friday, Dec. 9, 2011, in Washington. (Carolyn Kaster)
President Barack Obama, accompanied by his security personnel, walks through a White House gate prior to crossing Pennsylvania Avenue heading to the Blair House to attend a holiday party, Friday, Dec. 9, 2011, in Washington. (Carolyn Kaster)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict51.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict52.jpg) President Barack Obama greets people on the tarmac upon his arrival at Kansas City International Airport, Tuesday, Dec. 6, 2011, in Kansas City , Mo. (Carolyn Kaster)
President Barack Obama greets people on the tarmac upon his arrival at Kansas City International Airport, Tuesday, Dec. 6, 2011, in Kansas City , Mo. (Carolyn Kaster)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict46.jpg) In this Nov. 30, 2011, file photo, President Barack Obama walks to his motorcade with members of security after visiting with Patrick and Donna Festa in their Scranton, Pa. home.
In this Nov. 30, 2011, file photo, President Barack Obama walks to his motorcade with members of security after visiting with Patrick and Donna Festa in their Scranton, Pa. home.
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict47.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict48.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict53.jpg) President Barack Obama greets members of the Towson University football team during half time as he and first lady Michelle Obama, not seen, attend the Oregon State versus Towson NCAA college basketball game at Towson University Saturday, Nov. 26, 2011, in Towson, Md. (Carolyn Kaster)
President Barack Obama greets members of the Towson University football team during half time as he and first lady Michelle Obama, not seen, attend the Oregon State versus Towson NCAA college basketball game at Towson University Saturday, Nov. 26, 2011, in Towson, Md. (Carolyn Kaster)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict54.jpg) As Secret Service agents watch, President Barack Obama embraces a girl following an address where he remarked on the American Jobs Act, Tuesday, Nov. 22, 2011, at Central High School in Manchester, N.H. (Charles Krupa)
As Secret Service agents watch, President Barack Obama embraces a girl following an address where he remarked on the American Jobs Act, Tuesday, Nov. 22, 2011, at Central High School in Manchester, N.H. (Charles Krupa)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict55.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict56.jpg) President Barack Obama arrives in Manchester, N.H., Tuesday, Nov. 22, 2011. President Obama will travel to Manchester High School Central to discuss the American Jobs Act. (Cheryl Senter)
President Barack Obama arrives in Manchester, N.H., Tuesday, Nov. 22, 2011. President Obama will travel to Manchester High School Central to discuss the American Jobs Act. (Cheryl Senter)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict57.jpg) U.S. President Barack Obama walks as he attends the East Asia Summit at Nusa Dua, Bali, Indonesia on Saturday Nov. 19, 2011. (Aaron Favila)
U.S. President Barack Obama walks as he attends the East Asia Summit at Nusa Dua, Bali, Indonesia on Saturday Nov. 19, 2011. (Aaron Favila)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict58.jpg) President Barack Obama greets Australian troops during a visit to the Royal Army Air Force Base in Darwin, Australia, Thursday, Nov. 17, 2011. (Charles Dharapak)
President Barack Obama greets Australian troops during a visit to the Royal Army Air Force Base in Darwin, Australia, Thursday, Nov. 17, 2011. (Charles Dharapak)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict59.jpg) President Barack Obama talks with Medal of Honor recipient John Baca before the start of the Carrier Classic NCAA basketball game between North Carolina and Michigan State on the flight deck of the USS Carl Vinson in Coronado, Calif., Friday, Nov. 11, 2011. (Susan Walsh)
President Barack Obama talks with Medal of Honor recipient John Baca before the start of the Carrier Classic NCAA basketball game between North Carolina and Michigan State on the flight deck of the USS Carl Vinson in Coronado, Calif., Friday, Nov. 11, 2011. (Susan Walsh)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict60.jpg) President Barack Obama and French President Nicolas Sarkozy walk together after arriving at an event outside City Hall in Cannes, France, Friday, Nov. 4, 2011. The two leaders were at a memorial to World Wars I and II. (Susan Walsh)
President Barack Obama and French President Nicolas Sarkozy walk together after arriving at an event outside City Hall in Cannes, France, Friday, Nov. 4, 2011. The two leaders were at a memorial to World Wars I and II. (Susan Walsh)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict61.jpg) President Barack Obama arrives to speak about managing student debt during an event at the University of Colorado Denver Downtown Campus in Denver, Wednesday, Oct. 26, 2011. Denver is the final stop on a three-day trip to the West Coast for fundraising and speeches promoting his American Jobs Act. (Susan Walsh)
President Barack Obama arrives to speak about managing student debt during an event at the University of Colorado Denver Downtown Campus in Denver, Wednesday, Oct. 26, 2011. Denver is the final stop on a three-day trip to the West Coast for fundraising and speeches promoting his American Jobs Act. (Susan Walsh)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict62.jpg) President Barack Obama walks out of Roscoe’s House of Chicken and Waffles in Los Angeles, Monday, Oct. 24, 2011, with Rep. Karen Bass, D-Calif., after ordering a snack. Obama is on a three-day trip to the West Coast. (Susan Walsh)
President Barack Obama walks out of Roscoe’s House of Chicken and Waffles in Los Angeles, Monday, Oct. 24, 2011, with Rep. Karen Bass, D-Calif., after ordering a snack. Obama is on a three-day trip to the West Coast. (Susan Walsh)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict63.jpg) President Barack Obama greets after exiting Air Force One after arriving at McCarran International Airport in Las Vegas Monday, Oct. 24, 2011. (John Gurzinski)
President Barack Obama greets after exiting Air Force One after arriving at McCarran International Airport in Las Vegas Monday, Oct. 24, 2011. (John Gurzinski)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict64.jpg) President Barack Obama talks on the phone as he greets people outside the Reid’s House Restaurant in Reidsville, N.C., Tuesday, Oct. 18, 2011. Obama is on a three-day bus tour promoting the American Jobs Act. (Susan Walsh)
President Barack Obama talks on the phone as he greets people outside the Reid’s House Restaurant in Reidsville, N.C., Tuesday, Oct. 18, 2011. Obama is on a three-day bus tour promoting the American Jobs Act. (Susan Walsh)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict66.jpg) President Barack Obama poses for a photo after speaking at West Wilkes High School in Millers Creek, N.C., on Monday, Oct. 17, 2011. (Terry Renna)
President Barack Obama poses for a photo after speaking at West Wilkes High School in Millers Creek, N.C., on Monday, Oct. 17, 2011. (Terry Renna)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict67.jpg) President Barack Obama walks to his bus after stopping at the Countryside Barbeque in Marion in N.C., Monday, Oct. 17, 2011. Obama is on a three-day bus tour promoting the American Jobs Act. (Susan Walsh)
President Barack Obama walks to his bus after stopping at the Countryside Barbeque in Marion in N.C., Monday, Oct. 17, 2011. Obama is on a three-day bus tour promoting the American Jobs Act. (Susan Walsh)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict68.jpg) President Barack Obama walks around his bus at Asheville Regional Airport in Fletcher, N.C., Monday, Oct. 17, 2011, to begin his three-day bus tour promoting the American Jobs Act. (Susan Walsh)
President Barack Obama walks around his bus at Asheville Regional Airport in Fletcher, N.C., Monday, Oct. 17, 2011, to begin his three-day bus tour promoting the American Jobs Act. (Susan Walsh)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect45/pict69.jpg)







![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict29.jpg) Italian naval divers approach the cruise ship Costa Concordia Tuesday, Jan. 17, 2012, after running aground on the tiny Tuscan island of Giglio, Italy, on Friday evening. Italian naval divers on Tuesday exploded holes in the hull of a cruise ship grounded off a Tuscan island to speed the search for 29 missing people while seas were still calm. One official said there was still a “glimmer of hope” that survivors could be found.
Italian naval divers approach the cruise ship Costa Concordia Tuesday, Jan. 17, 2012, after running aground on the tiny Tuscan island of Giglio, Italy, on Friday evening. Italian naval divers on Tuesday exploded holes in the hull of a cruise ship grounded off a Tuscan island to speed the search for 29 missing people while seas were still calm. One official said there was still a “glimmer of hope” that survivors could be found.![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict30.jpg) Italian naval divers work on the cruise ship Costa Concordia Tuesday, Jan. 17, 2012, after running aground on the tiny Tuscan island of Giglio, Italy, on Friday evening.
Italian naval divers work on the cruise ship Costa Concordia Tuesday, Jan. 17, 2012, after running aground on the tiny Tuscan island of Giglio, Italy, on Friday evening.![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict31.jpg) The cruise ship Costa Concordia leans on its side Tuesday, Jan. 17, 2012, after running aground on the tiny Tuscan island of Giglio, Italy, on Friday evening.
The cruise ship Costa Concordia leans on its side Tuesday, Jan. 17, 2012, after running aground on the tiny Tuscan island of Giglio, Italy, on Friday evening.![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict32.jpg) Italian navy divers approach the cruise ship Costa Concordia in the tiny Tuscan island of Giglio, Italy, Tuesday, Jan. 17, 2012.
Italian navy divers approach the cruise ship Costa Concordia in the tiny Tuscan island of Giglio, Italy, Tuesday, Jan. 17, 2012.![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict12.jpg) Oil removal ships near the cruise ship Costa Concordia leaning on its side Monday, Jan. 16, 2012, after running aground near the tiny Tuscan island of Giglio, Italy, last Friday night. The rescue operation was called off mid-afternoon Monday after the Costa Concordia shifted a few inches (centimeters) in rough seas. The fear is that if the ship shifts significantly, some 500,000 gallons of fuel may begin to leak into the pristine waters. (Gregorio Borgia)
Oil removal ships near the cruise ship Costa Concordia leaning on its side Monday, Jan. 16, 2012, after running aground near the tiny Tuscan island of Giglio, Italy, last Friday night. The rescue operation was called off mid-afternoon Monday after the Costa Concordia shifted a few inches (centimeters) in rough seas. The fear is that if the ship shifts significantly, some 500,000 gallons of fuel may begin to leak into the pristine waters. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict24.jpg) The cruise ship Costa Concordia leans on its side Monday, Jan.16, 2012, after running aground near the tiny Tuscan island of Giglio, Italy, last Friday. The rescue operation was called off mid-afternoon Monday after the Costa Concordia shifted a few inches (centimeters) in rough seas. The fear is that if the ship shifts significantly, some 500,000 gallons of fuel may begin to leak. (Gregorio Borgia)
The cruise ship Costa Concordia leans on its side Monday, Jan.16, 2012, after running aground near the tiny Tuscan island of Giglio, Italy, last Friday. The rescue operation was called off mid-afternoon Monday after the Costa Concordia shifted a few inches (centimeters) in rough seas. The fear is that if the ship shifts significantly, some 500,000 gallons of fuel may begin to leak. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict22.jpg) In this underwater photo released by the Italian Coast Guard Monday, Jan. 16, 2012 the cruise ship Costa Concordia leans on its side, after it ran aground near the tiny Tuscan island of Isola del Giglio, Italy. (Italian Coast Guard)
In this underwater photo released by the Italian Coast Guard Monday, Jan. 16, 2012 the cruise ship Costa Concordia leans on its side, after it ran aground near the tiny Tuscan island of Isola del Giglio, Italy. (Italian Coast Guard)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict23.jpg) In this underwater photo taken on Jan. 13 and released by the Italian Coast Guard Monday, Jan. 16, 2012 a view of the cruise ship Costa Concordia, after it ran aground near the tiny Tuscan island of Giglio, Italy. Italian rescue officials say a passenger’s body has been found in the wreckage of the Costa Concordia cruise ship, raising to six the number of confirmed dead in the disaster. Sixteen people remain unaccounted-for. (Italian Coast Guard)
In this underwater photo taken on Jan. 13 and released by the Italian Coast Guard Monday, Jan. 16, 2012 a view of the cruise ship Costa Concordia, after it ran aground near the tiny Tuscan island of Giglio, Italy. Italian rescue officials say a passenger’s body has been found in the wreckage of the Costa Concordia cruise ship, raising to six the number of confirmed dead in the disaster. Sixteen people remain unaccounted-for. (Italian Coast Guard)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict17.jpg) In this photo released by the Italian Coast Guard Monday, Jan. 16, 2012 a coast guard scuba diver makes his way through floating pieces of furniture inside the cruise ship Costa Concordia Sunday Jan. 15. 2012,after it run aground off the tiny Tuscan island of Giglio, Italy. Italian rescue officials say a passenger’s body has been found in the wreckage of the Costa Concordia cruise ship, raising to six the number of confirmed dead in the disaster. Sixteen people remain unaccounted-for.
In this photo released by the Italian Coast Guard Monday, Jan. 16, 2012 a coast guard scuba diver makes his way through floating pieces of furniture inside the cruise ship Costa Concordia Sunday Jan. 15. 2012,after it run aground off the tiny Tuscan island of Giglio, Italy. Italian rescue officials say a passenger’s body has been found in the wreckage of the Costa Concordia cruise ship, raising to six the number of confirmed dead in the disaster. Sixteen people remain unaccounted-for.![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict15.jpg) Italian rescue personnel are seen atop the Costa Concordia cruise liner, two days after it ran aground off the tiny Tuscan island of Giglio, Italy, Monday, Jan. 16, 2012. The captain of a cruise liner that ran aground and capsized off the Tuscan coast faced accusations from authorities and passengers that he abandoned ship before everyone was safely evacuated as rescuers found another body on the overturned vessel. (Gregorio Borgia)
Italian rescue personnel are seen atop the Costa Concordia cruise liner, two days after it ran aground off the tiny Tuscan island of Giglio, Italy, Monday, Jan. 16, 2012. The captain of a cruise liner that ran aground and capsized off the Tuscan coast faced accusations from authorities and passengers that he abandoned ship before everyone was safely evacuated as rescuers found another body on the overturned vessel. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict25.jpg) Italian firefighters scuba divers work on the cruise ship Costa Concordia two days after it run aground the tiny Tuscan island of Giglio, Italy, Monday, Jan. 16, 2012. Italian rescue officials say a passenger’s body has been found in the wreckage of the Costa Concordia cruise ship, raising to six the number of confirmed dead in the disaster. Sixteen people remain unaccounted-for. (Gregorio Borgia)
Italian firefighters scuba divers work on the cruise ship Costa Concordia two days after it run aground the tiny Tuscan island of Giglio, Italy, Monday, Jan. 16, 2012. Italian rescue officials say a passenger’s body has been found in the wreckage of the Costa Concordia cruise ship, raising to six the number of confirmed dead in the disaster. Sixteen people remain unaccounted-for. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict26.jpg) Italian rescue divers approach the Costa Concordia cruise liner, two days after it run aground off tiny Tuscan island of Giglio, Italy, Monday, Jan. 16, 2012. The captain of a cruise liner that ran aground and capsized off the Tuscan coast faced accusations from authorities and passengers that he abandoned ship before everyone was safely evacuated as rescuers found another body on the overturned vessel. (Gregorio Borgia)
Italian rescue divers approach the Costa Concordia cruise liner, two days after it run aground off tiny Tuscan island of Giglio, Italy, Monday, Jan. 16, 2012. The captain of a cruise liner that ran aground and capsized off the Tuscan coast faced accusations from authorities and passengers that he abandoned ship before everyone was safely evacuated as rescuers found another body on the overturned vessel. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict8.jpg) Italian Firefighters scuba divers work aboard the luxury cruise ship Costa Concordia which ran aground off the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. Firefighters worked Sunday to rescue a crew member with a suspected broken leg from the overturned hulk of the cruise liner, 36 hours after it ran aground. More than 40 people are still unaccounted-for. (Remo Casilli)
Italian Firefighters scuba divers work aboard the luxury cruise ship Costa Concordia which ran aground off the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. Firefighters worked Sunday to rescue a crew member with a suspected broken leg from the overturned hulk of the cruise liner, 36 hours after it ran aground. More than 40 people are still unaccounted-for. (Remo Casilli)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict16.jpg) Italian firefighters approach the luxury cruise ship Costa Concordia which ran aground off the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. (Remo Casilli)
Italian firefighters approach the luxury cruise ship Costa Concordia which ran aground off the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. (Remo Casilli)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict11.jpg) Italian firefighters’ scuba divers approach the luxury cruise ship Costa Concordia which ran aground off the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. (Gregorio Borgia)
Italian firefighters’ scuba divers approach the luxury cruise ship Costa Concordia which ran aground off the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict6.jpg) Italian firefighters scuba divers approach the cruise ship Costa Concordia leaning on its side, the day after running aground the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. A helicopter on Sunday airlifted a third survivor from the capsized hulk of a luxury cruise ship 36 hours after it ran aground off the Italian coast, as prosecutors confirmed they were investigating the captain for manslaughter charges and abandoning the ship. (Gregorio Borgia)
Italian firefighters scuba divers approach the cruise ship Costa Concordia leaning on its side, the day after running aground the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. A helicopter on Sunday airlifted a third survivor from the capsized hulk of a luxury cruise ship 36 hours after it ran aground off the Italian coast, as prosecutors confirmed they were investigating the captain for manslaughter charges and abandoning the ship. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict33.jpg) Italian Navy scuba divers approach the cruise ship Costa Concordia leaning on its side, the day after running aground the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. A helicopter on Sunday airlifted a third survivor from the capsized hulk of a luxury cruise ship 36 hours after it ran aground off the Italian coast, as prosecutors confirmed they were investigating the captain for manslaughter charges and abandoning the ship. (Gregorio Borgia)
Italian Navy scuba divers approach the cruise ship Costa Concordia leaning on its side, the day after running aground the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. A helicopter on Sunday airlifted a third survivor from the capsized hulk of a luxury cruise ship 36 hours after it ran aground off the Italian coast, as prosecutors confirmed they were investigating the captain for manslaughter charges and abandoning the ship. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict7.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict13.jpg) Investigators approach the luxury cruise ship Costa Concordia which leans on its starboard side after running aground in the tiny Tuscan island of Isola del Giglio, Italy, Sunday, Jan. 15, 2012. The Costa Concordia cruise ship ran aground off the coast of Tuscany, sending water pouring in through a 160-foot (50-meter) gash in the hull and forcing the evacuation of some 4,200 people from the listing vessel early Saturday, the Italian coast guard said. (Gregorio Borgia)
Investigators approach the luxury cruise ship Costa Concordia which leans on its starboard side after running aground in the tiny Tuscan island of Isola del Giglio, Italy, Sunday, Jan. 15, 2012. The Costa Concordia cruise ship ran aground off the coast of Tuscany, sending water pouring in through a 160-foot (50-meter) gash in the hull and forcing the evacuation of some 4,200 people from the listing vessel early Saturday, the Italian coast guard said. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict14.jpg) Firefighters work on the luxury cruise ship Costa Concordia the day after it run aground off the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. The Italian Coast Guard says its divers have found two more bodies aboard the stricken Costa Concordia cruise ship. The discovery of the bodies brings to five the number of known dead after the luxury ship ran aground with some 4,200 people aboard on Friday night. (Andrea Sinibaldi)
Firefighters work on the luxury cruise ship Costa Concordia the day after it run aground off the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. The Italian Coast Guard says its divers have found two more bodies aboard the stricken Costa Concordia cruise ship. The discovery of the bodies brings to five the number of known dead after the luxury ship ran aground with some 4,200 people aboard on Friday night. (Andrea Sinibaldi)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict28.jpg) The cruise ship Costa Concordia leans on its side, after it ran aground off the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. A helicopter on Sunday airlifted a third survivor from the capsized hulk of a luxury cruise ship 36 hours after it ran aground off the Italian coast, as prosecutors confirmed they were investigating the captain for manslaughter charges and abandoning the ship. (Gregorio Borgia)
The cruise ship Costa Concordia leans on its side, after it ran aground off the tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. A helicopter on Sunday airlifted a third survivor from the capsized hulk of a luxury cruise ship 36 hours after it ran aground off the Italian coast, as prosecutors confirmed they were investigating the captain for manslaughter charges and abandoning the ship. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict27.jpg) Italian Navy scuba divers prepare to search the wreck of the luxury cruise ship Costa Concordia that ran aground in the tiny Tuscan island of Isola del Giglio, Italy, Sunday, Jan. 15, 2012. The Costa Concordia cruise ship ran aground off the coast of Tuscany, sending water pouring in through a 160-foot (50-meter) gash in the hull and forcing the evacuation of some 4,200 people from the listing vessel early Saturday, the Italian coast guard said. (Gregorio Borgia)
Italian Navy scuba divers prepare to search the wreck of the luxury cruise ship Costa Concordia that ran aground in the tiny Tuscan island of Isola del Giglio, Italy, Sunday, Jan. 15, 2012. The Costa Concordia cruise ship ran aground off the coast of Tuscany, sending water pouring in through a 160-foot (50-meter) gash in the hull and forcing the evacuation of some 4,200 people from the listing vessel early Saturday, the Italian coast guard said. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict21.jpg) An Italian firefighter helicopter lifts up a person from the luxury cruise ship Costa Concordia which ran aground the off tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. Firefighters worked Sunday to rescue a crew member with a suspected broken leg from the overturned hulk of the luxury cruise liner Costa Concordia, 36 hours after it ran aground. More than 40 people are still unaccounted-for. (Gregorio Borgia)
An Italian firefighter helicopter lifts up a person from the luxury cruise ship Costa Concordia which ran aground the off tiny Tuscan island of Giglio, Italy, Sunday, Jan. 15, 2012. Firefighters worked Sunday to rescue a crew member with a suspected broken leg from the overturned hulk of the luxury cruise liner Costa Concordia, 36 hours after it ran aground. More than 40 people are still unaccounted-for. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict34.jpg) Italian Coast guard personnel recovers the black box of the luxury cruise ship Costa Concordia after running aground the tiny Tuscan island of Giglio, Italy, Saturday, Jan. 14, 2012. A luxury cruise ship ran aground off the coast of Tuscany, sending water pouring in through a 160-foot (50-meter) gash in the hull and forcing the evacuation of some 4,200 people from the listing vessel early Saturday, the Italian coast guard said. (Gregorio Borgia)
Italian Coast guard personnel recovers the black box of the luxury cruise ship Costa Concordia after running aground the tiny Tuscan island of Giglio, Italy, Saturday, Jan. 14, 2012. A luxury cruise ship ran aground off the coast of Tuscany, sending water pouring in through a 160-foot (50-meter) gash in the hull and forcing the evacuation of some 4,200 people from the listing vessel early Saturday, the Italian coast guard said. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict36.jpg) Passengers of the luxury ship that ran aground off the coast of Tuscany board a bus in Porto Santo Stefano, Italy, Saturday, Jan. 14, 2012. A luxury cruise ship ran aground off the coast of Tuscany, gashing open the hull and taking on water, forcing some 4,200 people aboard to evacuate aboard lifeboats to a nearby island early Saturday. At least three were dead, the Italian coast guard said. Three bodies were recovered from the sea, said Coast Guard Cmdr. Francesco Paolillo. (Gregorio Borgia)
Passengers of the luxury ship that ran aground off the coast of Tuscany board a bus in Porto Santo Stefano, Italy, Saturday, Jan. 14, 2012. A luxury cruise ship ran aground off the coast of Tuscany, gashing open the hull and taking on water, forcing some 4,200 people aboard to evacuate aboard lifeboats to a nearby island early Saturday. At least three were dead, the Italian coast guard said. Three bodies were recovered from the sea, said Coast Guard Cmdr. Francesco Paolillo. (Gregorio Borgia)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict18.jpg) This photo acquired by the Associated Press from a passenger of the luxury ship that ran aground off the coast of Tuscany shows rescued passengers arriving at the Giglio island harbor, Saturday, Jan. 14, 2012. A luxury cruise ship ran aground off the coast of Tuscany, gashing open the hull and taking on water, forcing some 4,200 people aboard to evacuate aboard lifeboats to a nearby island early Saturday. At least three were dead, the Italian coast guard said.
This photo acquired by the Associated Press from a passenger of the luxury ship that ran aground off the coast of Tuscany shows rescued passengers arriving at the Giglio island harbor, Saturday, Jan. 14, 2012. A luxury cruise ship ran aground off the coast of Tuscany, gashing open the hull and taking on water, forcing some 4,200 people aboard to evacuate aboard lifeboats to a nearby island early Saturday. At least three were dead, the Italian coast guard said.![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict42.jpg) This photo acquired by the Associated Press from a passenger of the luxury ship that ran aground off the coast of Tuscany shows fellow passengers wearing life-vests on board the Costa Concordia as they wait to be evacuated, Saturday, Jan. 14, 2012. A luxury cruise ship ran aground off the coast of Tuscany, sending water pouring in through a 160-foot (50-meter) gash in the hull and forcing the evacuation of some 4,200 people from the listing vessel early Saturday, the Italian coast guard said.
This photo acquired by the Associated Press from a passenger of the luxury ship that ran aground off the coast of Tuscany shows fellow passengers wearing life-vests on board the Costa Concordia as they wait to be evacuated, Saturday, Jan. 14, 2012. A luxury cruise ship ran aground off the coast of Tuscany, sending water pouring in through a 160-foot (50-meter) gash in the hull and forcing the evacuation of some 4,200 people from the listing vessel early Saturday, the Italian coast guard said.![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict35.jpg) In this photo released by the Guardia di Finanza (Border Police), the luxury cruise ship Costa Concordia leans on its side after running aground off the tiny Tuscan island of Giglio, Italy, Saturday, Jan. 14, 2012. The luxury cruise ship ran aground off the coast of Tuscany, sending water pouring in through a 160-foot (50-meter) gash in the hull and forcing the evacuation of some 4,200 people from the listing vessel early Saturday, the Italian coast guard said. (Guardia di Finanza)
In this photo released by the Guardia di Finanza (Border Police), the luxury cruise ship Costa Concordia leans on its side after running aground off the tiny Tuscan island of Giglio, Italy, Saturday, Jan. 14, 2012. The luxury cruise ship ran aground off the coast of Tuscany, sending water pouring in through a 160-foot (50-meter) gash in the hull and forcing the evacuation of some 4,200 people from the listing vessel early Saturday, the Italian coast guard said. (Guardia di Finanza)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict40.jpg) In this photo released by the Guardia di Finanza (border Police), the luxury cruise ship Costa Concordia leans on its side after running aground off the tiny Tuscan island of Giglio, Italy, Saturday, Jan. 14, 2012. The luxury cruise ship ran aground off the coast of Tuscany, sending water pouring in through a 160-foot (50-meter) gash in the hull and forcing the evacuation of some 4,200 people from the listing vessel early Saturday, the Italian coast guard said. [Costa Concordia yellow lifeboats at lower right.]
In this photo released by the Guardia di Finanza (border Police), the luxury cruise ship Costa Concordia leans on its side after running aground off the tiny Tuscan island of Giglio, Italy, Saturday, Jan. 14, 2012. The luxury cruise ship ran aground off the coast of Tuscany, sending water pouring in through a 160-foot (50-meter) gash in the hull and forcing the evacuation of some 4,200 people from the listing vessel early Saturday, the Italian coast guard said. [Costa Concordia yellow lifeboats at lower right.]![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict10.jpg) The luxury cruise ship Costa Concordia leans after it ran aground off the coast of the Isola del Giglio island, Italy, gashing open the hull and forcing some 4,200 people aboard to evacuate aboard lifeboats to the nearby Isola del Giglio island, early Saturday, Jan. 14, 2012. About 1,000 Italian passengers were onboard, as well as more than 500 Germans, about 160 French and about 1,000 crew members. (Giorgio Fanciulli)
The luxury cruise ship Costa Concordia leans after it ran aground off the coast of the Isola del Giglio island, Italy, gashing open the hull and forcing some 4,200 people aboard to evacuate aboard lifeboats to the nearby Isola del Giglio island, early Saturday, Jan. 14, 2012. About 1,000 Italian passengers were onboard, as well as more than 500 Germans, about 160 French and about 1,000 crew members. (Giorgio Fanciulli)![[Image]](https://i0.wp.com/cryptome.org/2012-info/costa-concordia/pict19.jpg) The luxury cruise ship Costa Concordia sails from Limassol, Cyprus in this April 2009 photo. The ship ran aground off the coast of Isola del Giglio island, Italy, gashing open the hull and forcing some 4,200 people aboard to evacuate aboard lifeboats to the nearby Isola del Giglio island, early Saturday, Jan. 14, 2012.
The luxury cruise ship Costa Concordia sails from Limassol, Cyprus in this April 2009 photo. The ship ran aground off the coast of Isola del Giglio island, Italy, gashing open the hull and forcing some 4,200 people aboard to evacuate aboard lifeboats to the nearby Isola del Giglio island, early Saturday, Jan. 14, 2012.


 „GoMopa“ schreibt:08.09.2008
„GoMopa“ schreibt:08.09.2008
 Rocky J Suhayda(chairman)
Rocky J Suhayda(chairman)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict55.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict64.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict73.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict61.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict54.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict52.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict77.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict78.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict76.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict60.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict74.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict56.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict75.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict57.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict50.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict51.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict79.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict81.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict80.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict59.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict68.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict69.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict66.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict49.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict46.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict47.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict70.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict62.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict72.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict48.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict63.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict65.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict67.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/anti-sopa-pipa/pict71.jpg)



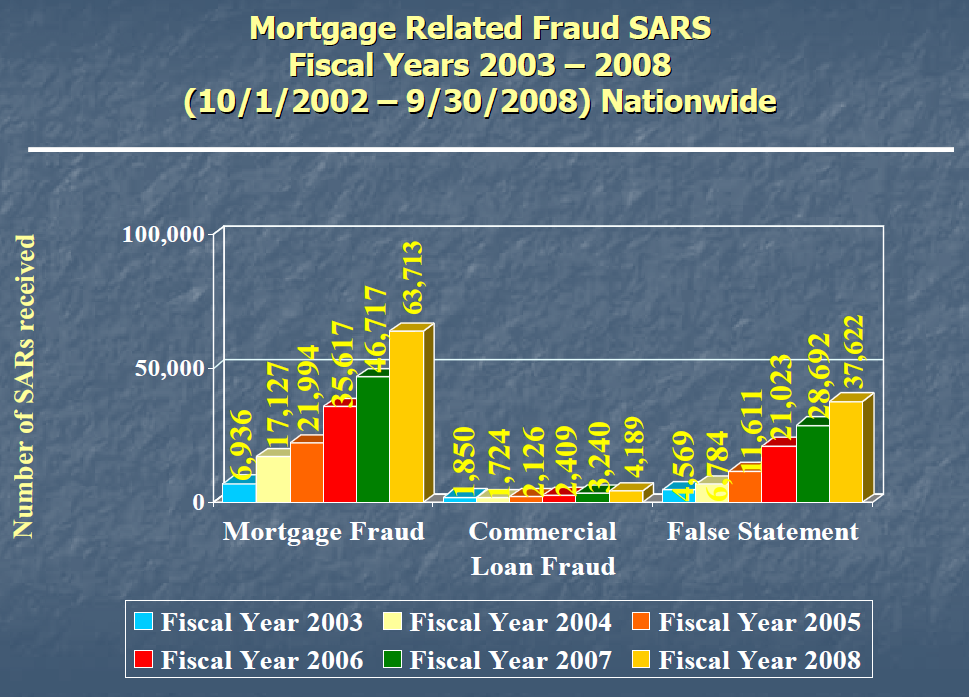
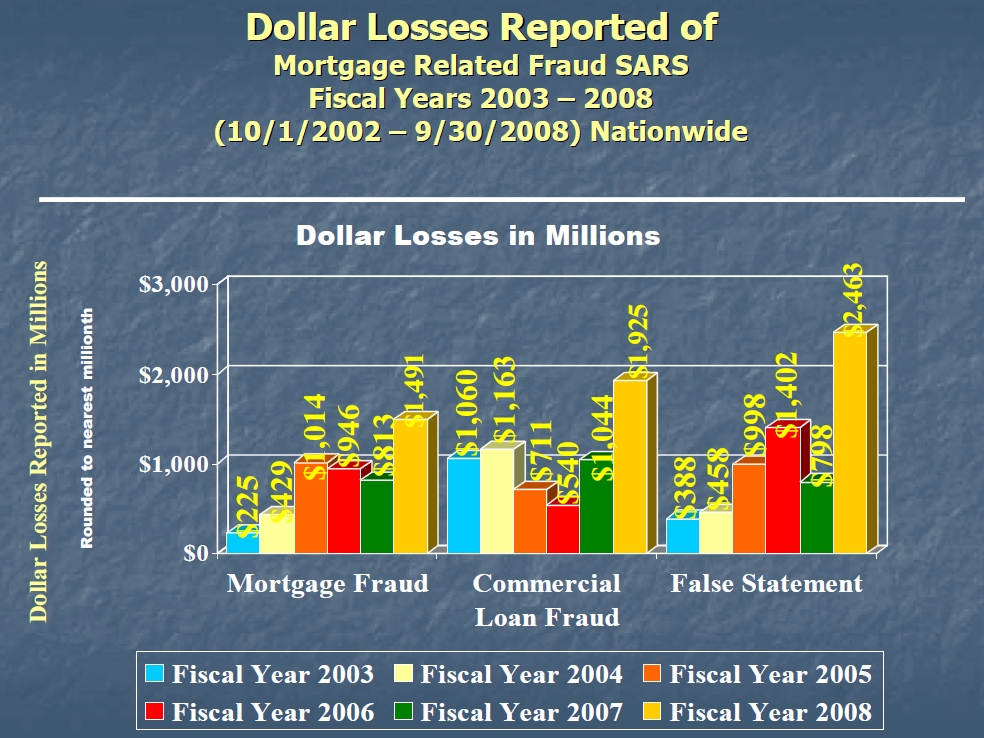
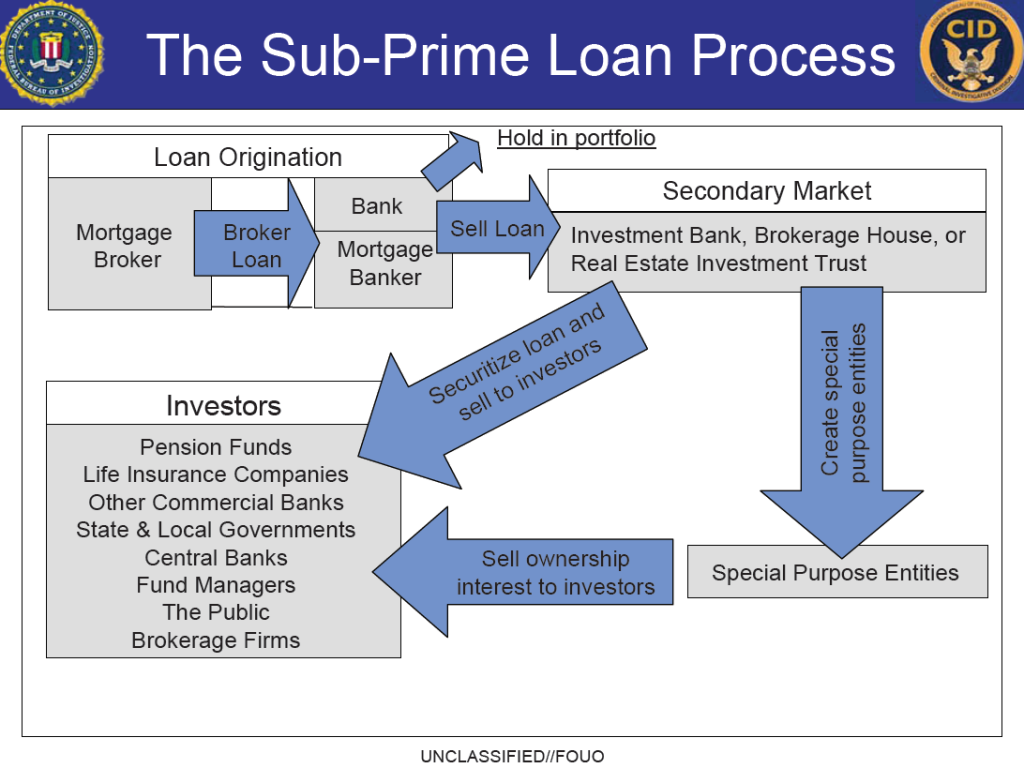
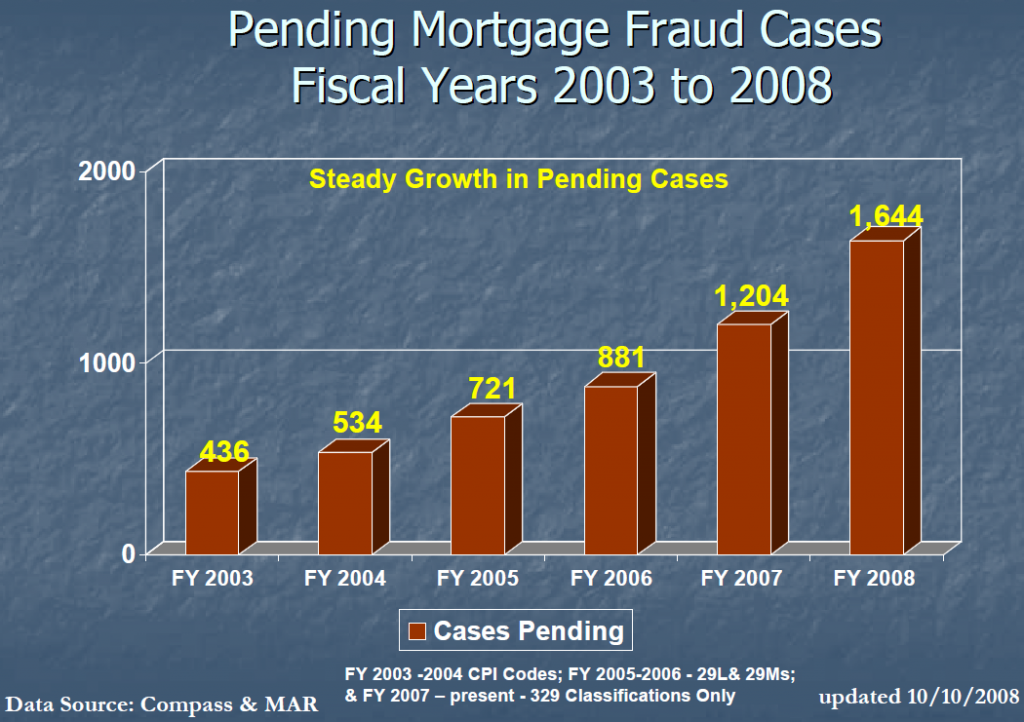
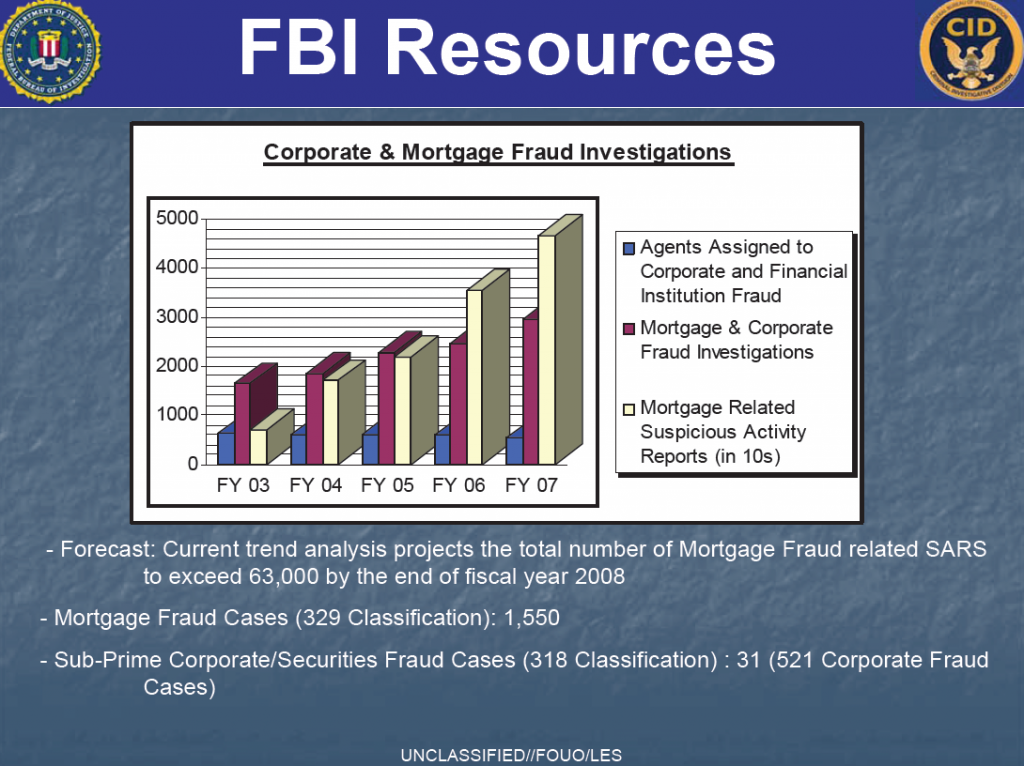
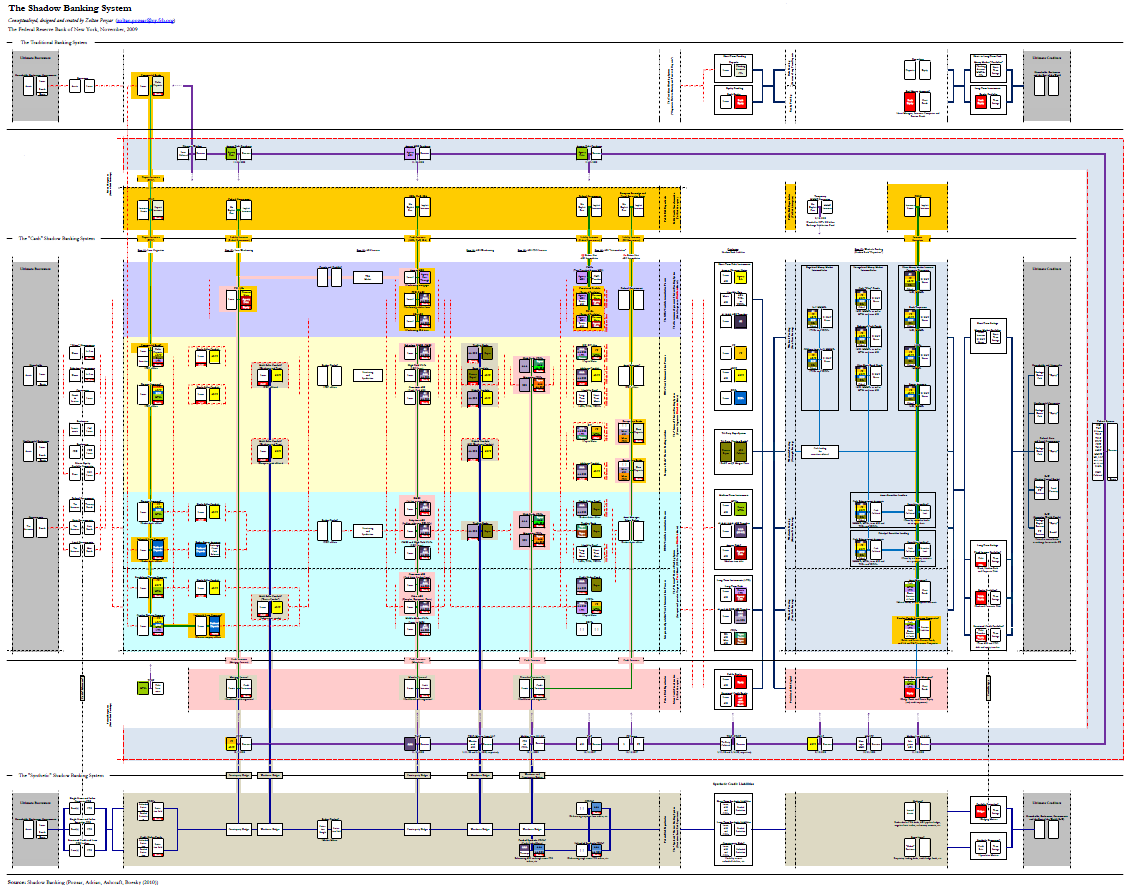





 Über ihre in der Auslandsspionage eingesetzten Spitzel hat die Stasi eine detaillierte Datei angelegt. Diese sogenannte Rosenholz-Datei, die unter mysteriösen Umständen der CIA in die Hände gefallen war, wurde den deutschen Behörden erst im Sommer 2003 zurückgegeben. Anhand dieser Daten schildern die Autoren jetzt erstmals das Ausmaß des Geheimnisverrats. Ob Auswärtiges Amt, Kanzleramt, Verteidigungsministerium oder die Parteizentralen von CDU, SPD, FDP und Grünen – die Schaltstellen der Macht waren von DDR-Agenten durchsetzt. Ein Agententhriller aus der Wirklichkeit, der in spektakulären Fallbeispielen die Arbeitsweise der Spione schildert
Über ihre in der Auslandsspionage eingesetzten Spitzel hat die Stasi eine detaillierte Datei angelegt. Diese sogenannte Rosenholz-Datei, die unter mysteriösen Umständen der CIA in die Hände gefallen war, wurde den deutschen Behörden erst im Sommer 2003 zurückgegeben. Anhand dieser Daten schildern die Autoren jetzt erstmals das Ausmaß des Geheimnisverrats. Ob Auswärtiges Amt, Kanzleramt, Verteidigungsministerium oder die Parteizentralen von CDU, SPD, FDP und Grünen – die Schaltstellen der Macht waren von DDR-Agenten durchsetzt. Ein Agententhriller aus der Wirklichkeit, der in spektakulären Fallbeispielen die Arbeitsweise der Spione schildert
![[Image]](https://i0.wp.com/cryptome.org/0006/cia-john2/pict31.jpg) “This is a composite of several images of the President and his national security team during a series of meetings in the Situation Room of the White House discussing the mission against Osama bin Laden on Sunday, May 1. We put this together so in addition to the previous, now iconic image of this day, people might have a better sense of what it’s like in presidential meetings of historic significance.” (Official White House Photo by Pete Souza)
“This is a composite of several images of the President and his national security team during a series of meetings in the Situation Room of the White House discussing the mission against Osama bin Laden on Sunday, May 1. We put this together so in addition to the previous, now iconic image of this day, people might have a better sense of what it’s like in presidential meetings of historic significance.” (Official White House Photo by Pete Souza)![[Image]](https://i0.wp.com/cryptome.org/0006/cia-john2/pict32.jpg)
![[Image]](https://i0.wp.com/cryptome.org/0006/cia-john2/pict33.jpg)
![[Image]](https://i0.wp.com/cryptome.org/0004/cia-john/pict26.jpg) President Barack Obama and Vice President Joe Biden, along with members of the national security team, receive an update on the mission against Osama bin Laden in the Situation Room of the White House, May 1, 2011. (Official White House Photo by Pete Souza)
President Barack Obama and Vice President Joe Biden, along with members of the national security team, receive an update on the mission against Osama bin Laden in the Situation Room of the White House, May 1, 2011. (Official White House Photo by Pete Souza)
![[Image]](https://i0.wp.com/cryptome.org/0004/cia-john/pict27.jpg)
![[Image]](https://i0.wp.com/cryptome.org/0004/cia-john/pict29.jpg)

![[Image]](https://i0.wp.com/cryptome.org/0004/cia-john/pict28.jpg)
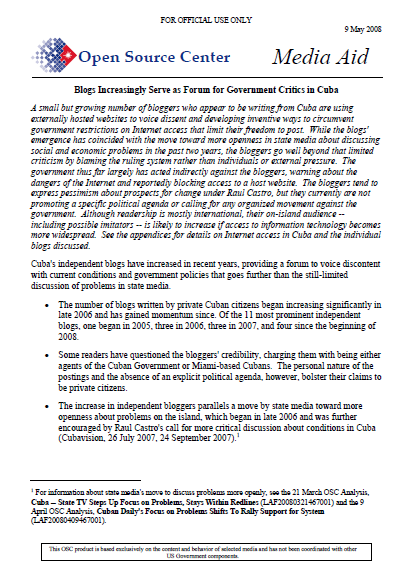


![[Image]](https://i0.wp.com/cryptome.org/2012-info/ows-23/pict6.jpg) Occupy Wall Street protesters read books in Zuccotti Park, Tuesday, Jan.10, 2012, in New York. Barricades were removed by Brookfield Properties, the owners of the park, allowing access once again into the park by the protesters. (Louis Lanzano)
Occupy Wall Street protesters read books in Zuccotti Park, Tuesday, Jan.10, 2012, in New York. Barricades were removed by Brookfield Properties, the owners of the park, allowing access once again into the park by the protesters. (Louis Lanzano)![[Image]](https://i0.wp.com/cryptome.org/2012-info/ows-23/pict7.jpg) Occupy Wall Street protesters gather in Zuccotti Park as security guards stand next to stacks of barricades,Tuesday, Jan. 10, 2012, in New York. The barricades were removed by Brookfield Properties, the owners of the park, allowing access once again into the park by the protesters. (Louis Lanzano)
Occupy Wall Street protesters gather in Zuccotti Park as security guards stand next to stacks of barricades,Tuesday, Jan. 10, 2012, in New York. The barricades were removed by Brookfield Properties, the owners of the park, allowing access once again into the park by the protesters. (Louis Lanzano)![[Image]](https://i0.wp.com/cryptome.org/2012-info/ows-23/pict8.jpg) Occupy Wall Street protesters make signs in Zuccotti Park, Tuesday, Jan.10, 2012, in New York. Barricades were removed by Brookfield Properties, the owners of the park Tuesday, allowing access once again into the park by the protesters. (Louis Lanzano)
Occupy Wall Street protesters make signs in Zuccotti Park, Tuesday, Jan.10, 2012, in New York. Barricades were removed by Brookfield Properties, the owners of the park Tuesday, allowing access once again into the park by the protesters. (Louis Lanzano)![[Image]](https://i0.wp.com/cryptome.org/2012-info/ows-23/pict10.jpg) Police officers guard the perimeter of Zuccotti Park As Occupy Wall Street protesters gather in the park, Tuesday, Jan.10, 2012, in New York. Barricades were removed by Brookfield Properties, the owners of the park, Tuesday, allowing access once again into the park by the protesters. (Louis Lanzano)
Police officers guard the perimeter of Zuccotti Park As Occupy Wall Street protesters gather in the park, Tuesday, Jan.10, 2012, in New York. Barricades were removed by Brookfield Properties, the owners of the park, Tuesday, allowing access once again into the park by the protesters. (Louis Lanzano)![[Image]](https://i0.wp.com/cryptome.org/2012-info/ows-23/pict9.jpg) Occupy Wall Street protesters gather in Zuccotti Park, Tuesday, Jan.10, 2012, in New York. Barricades were removed by Brookfield Properties, the owners of the park, allowing access once again into the park by the protesters. (Louis Lanzano)
Occupy Wall Street protesters gather in Zuccotti Park, Tuesday, Jan.10, 2012, in New York. Barricades were removed by Brookfield Properties, the owners of the park, allowing access once again into the park by the protesters. (Louis Lanzano)![[Image]](https://i0.wp.com/cryptome.org/2012-info/ows-23/pict11.jpg) Security from Brookfield Properties, the owners of Zuccotti Park, watch as Occupy Wall Street protesters gather in the park, Tuesday, Jan.10, 2012, in New York. Barricades were removed by the owners allowing access into the park by the protesters on Tuesday. (Louis Lanzano)
Security from Brookfield Properties, the owners of Zuccotti Park, watch as Occupy Wall Street protesters gather in the park, Tuesday, Jan.10, 2012, in New York. Barricades were removed by the owners allowing access into the park by the protesters on Tuesday. (Louis Lanzano)![[Image]](https://i0.wp.com/cryptome.org/2012/01/0029.jpg)

 Fort Meade, MD. – The National Security Agency (NSA) announced today the launch of “NSA CryptoChallenge,” a mobile cryptograph game app available free of charge from the Apple App Store. The game is the latest digital communications effort designed to educate young adults on career opportunities with NSA and recruit the best and brightest to support NSA’s cybersecurity initiatives.
Fort Meade, MD. – The National Security Agency (NSA) announced today the launch of “NSA CryptoChallenge,” a mobile cryptograph game app available free of charge from the Apple App Store. The game is the latest digital communications effort designed to educate young adults on career opportunities with NSA and recruit the best and brightest to support NSA’s cybersecurity initiatives.

























































![[IMAGE]](https://i0.wp.com/www.gwu.edu/~nsarchiv/nsa/elvis/elnix.gif)













![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-moron/pict2.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-moron/pict3.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-moron/pict4.jpg)







![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict1.jpg) On his first day in office, President Barack Obama speaks with a foreign leader in the Oval Office, Jan. 21, 2009. (Official White House Photo by Pete Souza)
On his first day in office, President Barack Obama speaks with a foreign leader in the Oval Office, Jan. 21, 2009. (Official White House Photo by Pete Souza)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict0.jpg) President Barack Obama places a phone call at his desk in the Oval Office, Jan. 23, 2009. (Official White House Photo by Pete Souza) [This is a Raytheon IST secure phone.
President Barack Obama places a phone call at his desk in the Oval Office, Jan. 23, 2009. (Official White House Photo by Pete Souza) [This is a Raytheon IST secure phone. ![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict4.jpg) President Barack Obama meets with Interior Secretary Ken Salazar aboard Air Force One during a flight to Denver, Col., Feb. 17, 2009. (Official White House Photo by Pete Souza) [Desk phone is a
President Barack Obama meets with Interior Secretary Ken Salazar aboard Air Force One during a flight to Denver, Col., Feb. 17, 2009. (Official White House Photo by Pete Souza) [Desk phone is a ![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict7.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict8.jpg) [Phone at Oval Office seating area] President Obama has a briefing with a staff member prior to a phone call in the Oval Office, March 13, 2009. (Official White House Photo by Pete Souza)
[Phone at Oval Office seating area] President Obama has a briefing with a staff member prior to a phone call in the Oval Office, March 13, 2009. (Official White House Photo by Pete Souza)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict11.jpg) President Barack Obama is seen at a meeting with his staff April 5, 2009, aboard Air Force One on a flight from Prague, Czech Republic en route to Ankara, Turkey. (Official White House Photo by Pete Souza)
President Barack Obama is seen at a meeting with his staff April 5, 2009, aboard Air Force One on a flight from Prague, Czech Republic en route to Ankara, Turkey. (Official White House Photo by Pete Souza)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict12.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict13.jpg) President Barack Obama works with Jon Favreau, director of speechwriting, on the President’s Normandy speech aboard Air Force One enroute to Paris on June 5, 2009. (Official White House photo by Pete Souza)
President Barack Obama works with Jon Favreau, director of speechwriting, on the President’s Normandy speech aboard Air Force One enroute to Paris on June 5, 2009. (Official White House photo by Pete Souza)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict14.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict15.jpg) President Barack Obama confers with Senior Advisor David Axelrod and Press Secretary Robert Gibbs at their hotel in Moscow, Russia, July 6, 2009. (Official White House Photo by Pete Souza) [Enlarged from small image.]
President Barack Obama confers with Senior Advisor David Axelrod and Press Secretary Robert Gibbs at their hotel in Moscow, Russia, July 6, 2009. (Official White House Photo by Pete Souza) [Enlarged from small image.]![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict16.jpg) President Barack Obama meets with John Brennan, Assistant to the President for Counterterrorism and Homeland Security, in the Oval Office, Jan. 4, 2010. (Official White House photo by Pete Souza) [Two phones, top for secure, bottom White House phone system.]
President Barack Obama meets with John Brennan, Assistant to the President for Counterterrorism and Homeland Security, in the Oval Office, Jan. 4, 2010. (Official White House photo by Pete Souza) [Two phones, top for secure, bottom White House phone system.]
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict17.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict18.jpg) “This is a rare look inside the President’s Treaty Room office in the private residence of the White House. He was making a call to Poland Prime Minister Donald Tusk.” (Official White House photo by Pete Souza)
“This is a rare look inside the President’s Treaty Room office in the private residence of the White House. He was making a call to Poland Prime Minister Donald Tusk.” (Official White House photo by Pete Souza)![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict19.jpg) March 29, 2009. “It was a Sunday night in the Oval Office. The auto task force listened to the President before he made phone calls to alert key people about his plan to set deadlines for General Motors and Chrysler overhauls that was to be announced the next morning.” (Official White House photo by Pete Souza)
March 29, 2009. “It was a Sunday night in the Oval Office. The auto task force listened to the President before he made phone calls to alert key people about his plan to set deadlines for General Motors and Chrysler overhauls that was to be announced the next morning.” (Official White House photo by Pete Souza)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict20.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict21.jpg) President Barack Obama meets with Rep. Dennis Kucinich, D-Ohio, aboard Air Force One en route to Cleveland, Ohio, March 15, 2010. (Official White House Photo by Pete Souza) [The desk phone is a
President Barack Obama meets with Rep. Dennis Kucinich, D-Ohio, aboard Air Force One en route to Cleveland, Ohio, March 15, 2010. (Official White House Photo by Pete Souza) [The desk phone is a ![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict22.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict23.jpg) President Barack Obama checks his BlackBerry as he walks along the Colonnade to the Oval Office, March 18, 2010. (Official White House Photo by Pete Souza)
President Barack Obama checks his BlackBerry as he walks along the Colonnade to the Oval Office, March 18, 2010. (Official White House Photo by Pete Souza)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict24.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict25.jpg) President Barack Obama talks on the phone with a Member of Congress while en route to a health care event at George Mason University in Fairfax, Va., March 19, 2010. Assistant to the President for Legislative Affairs Phil Schiliro rides with the President. (Official White House Photo by Pete Souza) [A sends ” [The device between the seats under the seal is unknown. Not all presidential vehicles have it. There is a phone in the console.]
President Barack Obama talks on the phone with a Member of Congress while en route to a health care event at George Mason University in Fairfax, Va., March 19, 2010. Assistant to the President for Legislative Affairs Phil Schiliro rides with the President. (Official White House Photo by Pete Souza) [A sends ” [The device between the seats under the seal is unknown. Not all presidential vehicles have it. There is a phone in the console.]
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict2.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict27.jpg) President Barack Obama talks on the phone in a holding room at Oakley Lindsay Center in Quincy, Ill., April 28, 2010. Mona Sutphen, deputy chief of staff for policy, sits at right. (Official White House Photo by Pete Souza) [Phones are L-3 STE model:
President Barack Obama talks on the phone in a holding room at Oakley Lindsay Center in Quincy, Ill., April 28, 2010. Mona Sutphen, deputy chief of staff for policy, sits at right. (Official White House Photo by Pete Souza) [Phones are L-3 STE model: ![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict28.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict29.jpg) President Barack Obama talks on the phone with German Chancellor Angela Merkel to discuss the economic situation in Europe, prior to the Hampton University commencement in Hampton, Va., Sunday, May 9, 2010. (Official White House Photo by Pete Souza)
President Barack Obama talks on the phone with German Chancellor Angela Merkel to discuss the economic situation in Europe, prior to the Hampton University commencement in Hampton, Va., Sunday, May 9, 2010. (Official White House Photo by Pete Souza)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict30.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict31.jpg) President Barack Obama talks with Alyssa Mastromonaco, director of scheduling and advance, in the Outer Oval Office, May 24, 2010. (Official White House Photo by Pete Souza) [Three types of phones sets, perhaps for three different systems.]
President Barack Obama talks with Alyssa Mastromonaco, director of scheduling and advance, in the Outer Oval Office, May 24, 2010. (Official White House Photo by Pete Souza) [Three types of phones sets, perhaps for three different systems.]![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict32.jpg) President Barack Obama prepares for foreign leader phone calls with Nigerian President Goodluck Jonathan and Japanese Prime Minister designate Naoto Kan, in the Oval Office, Saturday, June 5, 2010. Pictured, from left, are Michelle Gavin, senior director for African Affairs, Puneet Talwar, senior director for Iraq, Iran and the Gulf States, John Buchanan (on phone), director of operations and deputy director of the White House Situation Room, and National Security Advisor Gen. James Jones. (Official White House Photo by Pete Souza) [A phone technician apparently arranging a secure hook-up.]
President Barack Obama prepares for foreign leader phone calls with Nigerian President Goodluck Jonathan and Japanese Prime Minister designate Naoto Kan, in the Oval Office, Saturday, June 5, 2010. Pictured, from left, are Michelle Gavin, senior director for African Affairs, Puneet Talwar, senior director for Iraq, Iran and the Gulf States, John Buchanan (on phone), director of operations and deputy director of the White House Situation Room, and National Security Advisor Gen. James Jones. (Official White House Photo by Pete Souza) [A phone technician apparently arranging a secure hook-up.]





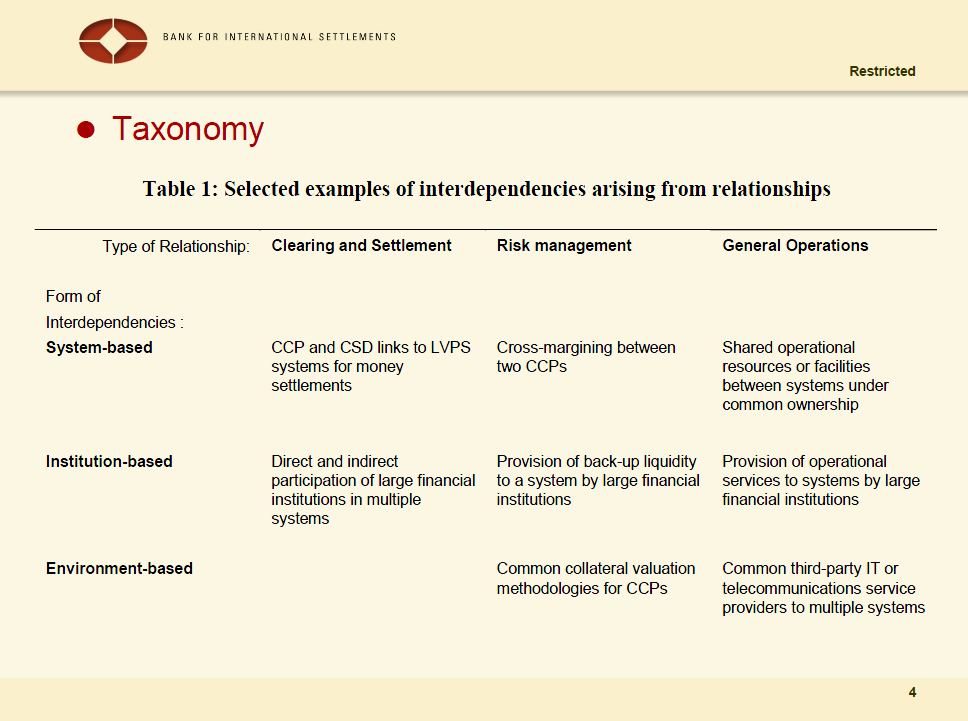
























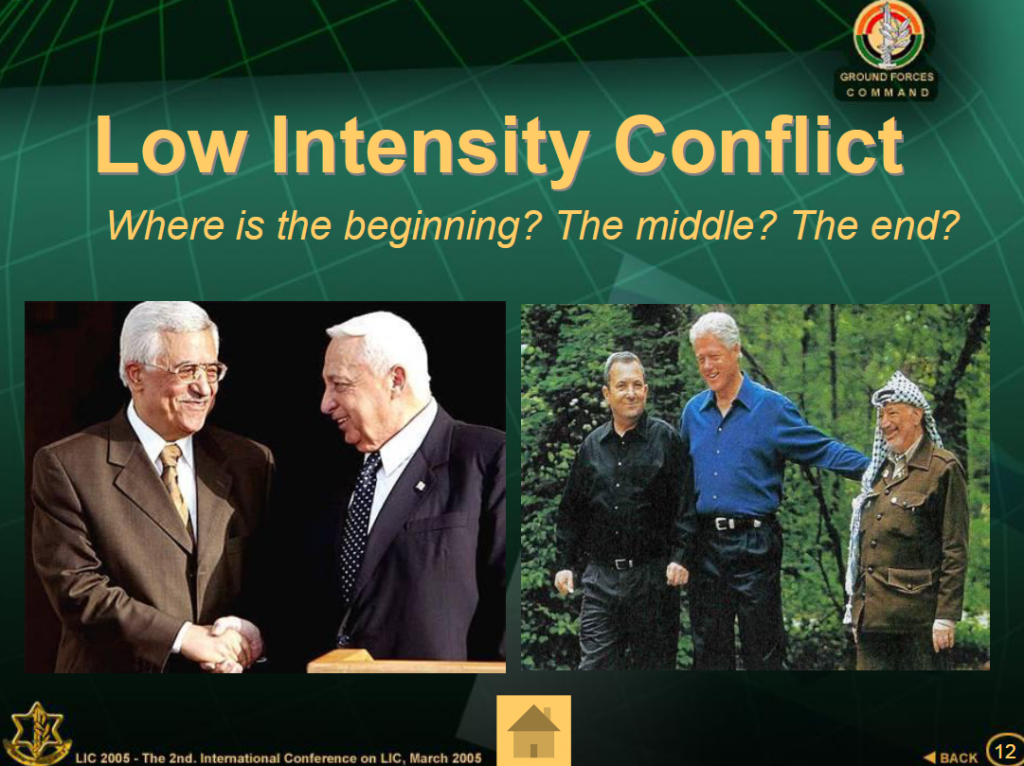











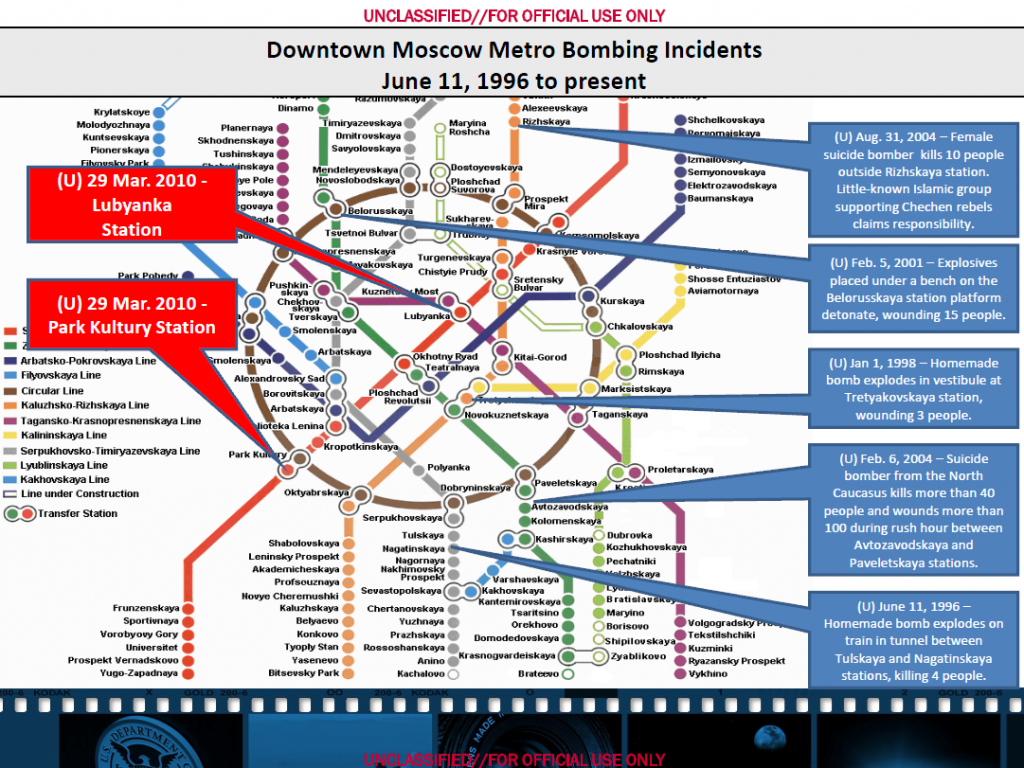
You must be logged in to post a comment.