Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Month: December 2014
Unveiled – As done by “GoMoPa” – Cyber Bulletin: Korean Malware Potentially Used in Sony Pictures Attack
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
The following bulletin was posted on the document sharing website Scribd by Politico Cybersecurity Editor Shaun Waterman. The bulletin refers to Korean malware used by “unknown computer network exploitation (CNE) operators” that is believed to have been used in the recent attack on Sony Pictures Entertainment. These actions ressemble to the “GoMoPa” cyber-attacks. The bulletin was first reported by Reuters on December 1, 2014.
FBI Liaison Alert System #A-000044-mw
- 5 pages
- TLP: GREEN
- December 1, 2014
The FBI is providing the following information with HIGH confidence:
Destructive malware used by unknown computer network exploitation (CNE) operators has been identified. This malware has the capability to overwrite a victim host’s master boot record (MBR) and all data files. The overwriting of the data files will make it extremely difficult and costly, if not impossible, to recover the data using standard forensic methods. Analysis of this malware is presented to provide the computer network defense (CND) community with indicators of this malware.
TECHNICAL DETAILS
The FBI is providing the following information with HIGH confidence:
This group uses some custom tools that should be immediately flagged if detected, reported to FBI CYWATCH, and given highest priority for enhanced mitigation.
The aforementioned actors have used identified domains names and IP addresses as both source and/or destination IPs. The FBI is distributing the indicators associated with this attack to enable network defense activities and reduce the risk of similar attacks in the future. The FBI has high confidence that these indicators are being used by CNE operators for further network exploitation. The FBI recommends that your organization help victims identify and remove the malicious code.Below are descriptions of malware and associated malware signatures:
The malware has the following characteristics:
File: d1c27ee7ce18675974edf42d4eea25c6.bin
Size: 268579 bytes (262.3 KB)
MD5: D1C27EE7CE18675974EDF42D4EEA25C6
PE Compile Time: 2014-11-22 00:06:54
Language pack of resource section: KoreanThe original filename of this file is unknown, but it was likely “diskpartmg16.exe”. This file serves as a dropper. It drops destructive malware, “igfxtrayex.exe”. When the dropper file was executed, it started a second instance of itself with “-i” as an argument, then terminated.
The second instance of the dropper file installed itself as the “WinsSchMgmt” service with “-k” as a command line argument, started the service, then terminated.
The “WinsSchMgmt” service executed the file with “-k” as an argument, which started another instance of the file using “-s” as an argument.
The “-s” instance dropped and executed “igfxtrayex.exe”, created “net_ver.dat”, and began generating network traffic over TCP ports 445 and 139 to victim IP addresses.
The following files were added:
C:\Documents and Settings\User\Desktop\igfxtrayex.exe
C:\WINDOWS\system32\net_ver.datThe following strings of interest were in this dropper file:
– – – BEGIN STRINGS – – –
recdiscm32.exe
taskhosts64.exe
taskchg16.exe
rdpshellex32.exe
mobsynclm64.exe
comon32.exe
diskpartmg16.exe
dpnsvr16.exe
expandmn32.exe
hwrcompsvc64.exe
cmd.exe /q /c net share shared$ /delete
\\%\admin$\syswow64
\\%s\admin$\system32
cmd.exe /q /c net share shared$=%SystemRoot%
cmd.exe /q /c net share shared$=%SystemRoot% /GRANT:everyone, FULL
RasSecurity
RasMgrp
cmd.exe /c wmic.exe /node: ”%s” /password: “%s” PROCESS CALL CREATE “%s” >
%s
WinsSchMgmt
Windows Schedule Management Service
– – -END STRINGS – – –File: net_ver.dat
Size: 4572 bytes (4.5 KB)
MD5: 93BC819011B2B3DA8487F964F29EB934This is a configuration file containing what appear to be hostnames, IP addresses, and the number 2. Entries in the file have the structure “HOSTNAME | IP Address | 2”. The victim IP addresses in this file correspond with the victim IP addresses listed under the file with MD5 hash D1C27EE7CE18675974EDF42D4EEA25C6 (noted above).
File: igfxtrayex.exe
Size: 249856 bytes (244.0 KB)
MD5: 760c35a80d758f032d02cf4db12d3e55
PE Compile Time: 2014-11-24 04:11:08
Language pack of resource section: KoreanThis file is destructive malware: a disk wiper with network beacon capabilities. If “igfxtrayex.exe” is run with no parameters, it creates and starts a copy of itself with the “–i” argument. After 10 minutes, the “igfxtrayex.exe” makes three copies of itself and places them in the same directory it was executed from. These copies are named according to the format “taskhostXX.exe” (where X is a randomly generated ASCII character). These copies are then executed, each with a different argument (one being “-m”, one being “-d” and the other “-w”). Network connection attempts are made to one of three hard-coded IP addresses in a random order to either port 8080 or 8000. If a connection to the IP address cannot be made, it attempts to connect to another of the three IP addresses, until connections to all three IP addresses have been attempted. The following command-line string is then executed: “cmd.exe /c net stop MSExchangeIS /y”. A 120 minute (2 hour) sleep command is issued after which the computer is shutdown and rebooted.
File: iissvr.exe
Size: 114688 bytes (112.0 KB)
MD5: e1864a55d5ccb76af4bf7a0ae16279ba
PE Compile Time: 2014-11-13 02:05:35
Language pack of resource section: KoreanThis file when executed starts a listener on localhost port 80. It has 3 files contained in the resource section, all xor’d with 0x63.
File: usbdrv3_32bit.sys
Size: 24280 bytes (23.7 KB)
MD5: 6AEAC618E29980B69721158044C2E544
PE Compile Time: 2009-08-21 06:05:32This SYS file is a commercially available tool that allows read/write access to files and raw disk sectors for user mode applications in Windows 2000, XP, 2003, Vista, 2008 (32-bit). It is dropped from resource ID 0x81 of “igfxtrayex.exe”.
File usbdrv3_64bit.sys
Size: 28120 bytes (27.5 KB)
MD5: 86E212B7FC20FC406C692400294073FF
PE Compile Time: 2009-08-21 06:05:35This SYS file is a also a commercially available tool that allows read/write access to files and raw disk sectors for user mode applications in Windows 2000, XP, 2003, Vista, 2008 (64-bit). It is dropped from resource ID 0x83 of “igfxtrayex.exe”.
RECOMMENDED STEPS FOR INITIAL MITIGATION
The following Snort signature can be used to detect the beacon traffic, though by the time the beacons occur, the destructive process of wiping the files has begun:
Alert tcp any any – > [88.53.215.64, 217.96.33.164, 203.131.222.102] [8080, 8000] (msg: “wiper_callout”; dsize:42; content: “|ff ff ff ff|”; offset: 26; depth: 4; sid: 314;)
The following YARA signatures will detect this malware on the host:
rule unknown_wiper_str{
meta: unique string in wiper malware
strings:
$STR1 = “#99E2428CCA4309C68AAF8C616EF3306582A64513E55C786A864BC83DAFE0C78585B692047273B0E55275102C66” fullword nocase
$MZ = “MZ”
condition:
$MZ at 0 and $STR1
}
rule unknown_wiper_IPs{
meta: unique IPs in wiper malware
strings:
$IP1 = “203.131.222.102” fullword nocase
$IP2 = “217.96.33.164” fullword nocase
$IP3 = “88.53.215.64” fullword nocase
$MZ = “MZ”condition:
$MZ at 0 and all of them
}
rule unknown_wiper_error_strings{
meta: unique custom error debug strings discovered in the wiper malware
strings:
$ERR1 = “$MFT Record read failed.” fullword nocase
$ERR2 = “Drive Boot Sector read failed.” fullword nocase
$ERR3 = “SetFilePointer failed.” fullword nocase
$MZ = “MZ”condition:
$MZ at 0 and all of them
}
Reporting Notice
The FBI encourages recipients who identify the use of tool(s) or techniques discussed in this document to report information to their local FBI field office or the FBI’s 24/7 Cyber Watch (CyWatch). Field office contacts can be identified at http://www.fbi.gov/contact-us/field. CyWatch can be contacted by phone at 855-292-3937 or by e-mail at CyWatch@ic.fbi.gov. When available, each report submitted should include the date, time, location, type of activity, number of people, and type of equipment used for the activity, the name of the submitting company or organization, and a designated point of contact.
Korean Malware, North Korea Malware, South Korea Malware Attack, South Korea Malware Attack, North Korea Malware, South Korea Malware Attack,
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 45, CO,TOP – SECRET – The Secret List of KGB Agents – KGB AGENT LIST CO
Become a Patron!
True Information is the most valuable resource and we ask you to give back.

| IPN BU 644/992 | COCHOŃ KAZIMIERZ |
| IPN BU 01013/318 | COCHOWSKA MARIA |
| IPN BU 00283/446 | COHOMIRSKI ANDRZEJ |
| IPN 00 1043/1668 | COLIN ELŻBIETA |
| IPN BU 002086/814 | COLLINS-WICHNIEWICZ ELŻBIETA |
| IPN 00 1043/1841 | COŁOSZYŃSKI SŁAWOMIR |
| IPN BU 001102/1737 | COMBRZYŃSKI WALDEMAR |
| IPN BU 00244/120 | COMPA KAZIMIERZ |
| IPN BU 0891/407 | COMRZYŃSKI CZESŁAW |
| IPN 00 1052/1209 | COPIJA KRZYSZTOF |
| IPN BU 644/96 | CORA MARIAN |
| IPN BU 00191/715 | CORBERT ERNST REINHARD |
| IPN BU 00751/170 | CORNIK MARIAN |
| IPN BU 001102/1667 | CORNIK MARIAN |
| IPN BU 00191/239 | COSNA ANDRZEJ |
| IPN BU 00283/417 | COTA STANISŁAW |
| IPN BU 00612/605 | COTA STANISŁAW |
| IPN 00 1043/2520 | COVIC DYLĄG JACHNIK HANNA |
| IPN BU 0193/5302 | COZEL STANISŁAW |
| IPN BU 00200/579 | CSATO JUSTYNA ANNA |
| IPN 00 1052/1896 | CSATO JUSTYNA ANNA |
| IPN BU 00277/1102 | CSERNAK MAGDALENA |
| IPN BU 001121/3279 | CSERNAK MAGDALENA |
| IPN BU 0854/933 | CUBALA JÓZEF |
| IPN BU 0772/2428 | CUBAŁA SABINA |
| IPN BU 0901/1407 | CUBER DARIUSZ |
| IPN BU 0901/562 | CUBER MURAWSKA MARIA ELŻBIETA |
| IPN BU 00277/469 | CUBER ROMAN |
| IPN BU 001121/2684 | CUBER ROMAN TADEUSZ |
| IPN BU 698/499 | CUBER WACŁAWA |
| IPN BU 636/1787 | CUBER WANDA |
| IPN BU 636/1787 | CUBER WANDA |
| IPN BU 00415/400 | CUBERA DARIUSZ |
| IPN BU 0958/992 | CUBRZYŃSKI ANTONI |
| IPN BU 0988/842 | CUBRZYŃSKI ANTONI |
| IPN BU 0242/834 | CUCH DANUTA |
| IPN BU 0193/8432 | CUCH IRENEUSZ |
| IPN BU 0988/1278 | CUCH KAZIMIERZ |
| IPN BU 0242/858 | CUCH WALDEMAR |
| IPN BU 0242/3269 | CUCH ZENON |
| IPN BU 0912/1923 | CUCHEWICZ WŁADYSŁAW |
| IPN BU 01256/32 | CUDAK LECH |
| IPN BU 001040/272 | CUDAK MAREK |
| IPN BU 00611/1444 | CUDAK TADEUSZ |
| IPN BU 001198/2631 | CUDAK TADEUSZ |
| IPN BU 0902/128 | CUDNA (PISKORSKA) URSZULA |
| IPN BU 698/500 | CUDNA APOLANIA |
| IPN BU 01000/859 | CUDNA DANUTA |
| IPN BU 0772/73 | CUDNA JADWIGA |
| IPN BU 0806/3008 | CUDNA MARIA |
| IPN BU 645/133 | CUDNA URSZULA |
| IPN BU 0951/286 | CUDNIK CHMIELAK JANINA |
| IPN BU 0951/228 | CUDNIK BRONISŁAW |
| IPN BU PF | 125/17 CUDNIK KAZIMIERZ |
| IPN BU PF | 2/81 CUDNIK ZOFIA |
| IPN BU 00249/423 | CUDNY KAZIMIERZ |
| IPN BU 001121/1049 | CUDNY KAZIMIERZ |
| IPN BU 01000/2137 | CUDNY LUCJAN |
| IPN BU 0193/7988 | CUDNY MARIAN |
| IPN BU 0902/122 | CUDNY STANISŁAW |
| IPN BU 644/1013 | CUDNY STANISŁAW |
| IPN BU 00200/1234 | CUDNY STANISŁAW |
| IPN BU 001102/836 | CUDNY STANISŁAW |
| IPN BU 0193/6353 | CUDNY SZCZEPAN |
| IPN BU 0607/7 | CUDNY ZBIGNIEW |
| IPN BU 01013/310 | CUDYN KAZIMIERZ |
| IPN BU 00334/165 | CUDZEWICZ MARIANNA |
| IPN BU 001134/2893 | CUDZEWICZ MARIANNA JOANNA |
| IPN BU 001198/92 | CUDZIK HENRYK |
| IPN BU 00612/2572 | CUDZIK JÓZEF |
| IPN BU 0772/963 | CUDZIŁO KAROLINA |
| IPN BU 00277/659 | CUDZIŃSKI KAROL |
| IPN 00 1052/460 | CUGLEWSKA-MUSZAK IWONA |
| IPN BU 0193/5461 | CUGLEWSKI ZDZISŁAW |
| IPN BU 0772/964 | CUKERMAN MORDACH (MORDUCH) |
| IPN BU 00750/131 | CUKIER DAWID |
| IPN BU 001164/398 | Cukier Dawid |
| IPN BU 01434/153 | CUKIERKANDEL PIOTR |
| IPN BU 0993/1519 | CUKIERMAN TEOFILA |
| IPN BU 644/1014 | CUKIERSKI CZESLAW |
| IPN BU 00464/126/46 | CUKIERSKI K. |
| IPN BU 0314/9 | CUKIERSKI KAZIMIERZ |
| IPN BU 00945/2737 | CUKIERSKI KAZIMIERZ |
| IPN BU 01013/4 | CUKIERSKI WIKTOR |
| IPN BU 00612/1196 | CUKIERZ HAINA |
| IPN BU 01000/2236 | CUKROWSKI ALFRED |
| IPN BU 00612/2718 | CUKROWSKI ANDRZEJ |
| IPN BU 0604/1296 | CUKROWSKI BOGUSŁAW |
| IPN BU 0193/6945 | CUKROWSKI CZESŁAW |
| IPN BU 00232/226 | CUMIELEWSKI BOLESŁAW |
| IPN BU 01434/238 | CUNG-SOBIESKI JERZY |
| IPN BU 644/1015 | CUPAŁ WŁADYSŁAW |
| IPN BU 0772/2429 | CUPCZYŃSKI HENRYK |
| IPN BU 0290/107 | CUPER BALBINA |
| IPN BU 00612/2926 | CUPER GRZEGORZ |
| IPN BU 0988/1099 | CUPER RAJMUND |
| IPN BU 644/1016 | CUPIAK KAZIMIERZ |
| IPN BU 0901/2463 | CUPIAŁ JAN |
| IPN BU 0902/129 | CUPIAŁ JAN |
| IPN BU 01000/1188 | CUPIAŁ JAN |
| IPN BU 0218/2003 | CUPIAŁ KAZIMIERZ |
| IPN BU 001121/182 | CUPIAŁ ZBIGNIEW |
| IPN BU 0218/2914 | CUPIAŁ ZDZISŁAW |
| IPN BU 0901/822 | CUPISZ (KACZMARCZYK) MARIA JOLANTA |
| IPN BU PF | 71/36 CUPRIAK ARKADIUSZ |
| IPN BU 0855/2321 | CUPRYJAK (CUPRJAK) ZYGMUNT |
| IPN BU 0193/1592 | CUPRYJAK HALINA HENRYKA |
| IPN BU 0958/546 | CUPRYJAK HELENA |
| IPN BU 0872/214 | CUPRYJAK JAN |
| IPN BU 0218/3515 | CUPRYJAK JERZY BOGUSŁAW |
| IPN BU 0901/963 | CUPRYJAK KAZIMIERA ŁASKA |
| IPN BU 00275/381 | CUPRYN ELŻBIETA |
| IPN BU 001134/231 | CUPRYN ELŻBIETA JANINA |
| IPN BU 00275/433 | CUPRY TOMASZ |
| IPN BU 001134/336 | CUPRY TOMASZ MIKOŁAJ |
| IPN BU 00557/XII/14 | CUR ELŻBIETA |
| IPN 00 1043/407 | CURLANIS BOHDAN RYSZARD BOGDAN |
| IPN BU 0866/97 | CURLEJ ANTONI |
| IPN BU 0958/547 | CURUŁ STANISŁAWA |
| IPN BU 00612/204 | CURYŁŁO LIDIA |
| IPN BU 0772/965 | CURYŁO BRONISŁAWA |
| IPN BU 00328/1195 | CURYŁO EDWARD |
| IPN BU 001134/2083 | CURYŁO EDWARD |
| IPN BU 709/877 | CURYŁO HENRYK |
| IPN 00 1043/1740 | CURYŁO HENRYK |
| IPN BU 0772/2430 | CURYŁO JANINA |
| IPN BU 0218/155 | CURYŁO MARIANNA |
| IPN BU 00612/1279 | CURYŁO SŁAWOMIR |
| IPN BU 001198/4566 | CURYŁO SŁAWOMIR |
Kgb Meaning, Kgb Bar, Kgb Putin, Kgb Radio, Kgb Cold War, Kgb The Office, Kgb Vs Cia, Kgb Boston, Kgb Gang, Kgb Training, Kgb Agent, Kgb Archiver, Kgb Assassinations, Kgb Animal Farm, Kgb Alien, Kgb Archer, Kgb Ap Euro, Kgb Alaska, Kgb Arms, Kgb Application, Kgb Bar, Kgb Boston, Kgb Band, Kgb Badge, Kgb Burger, Kgb Beer, Kgb Bar East Village, Kgb Building, Kgb Ballistic Knife, Kgb Bar Events, Kgb Cold War, Kgb Call Center, Kgb Chicken, Kgb Conduit, Kgb Customs, Kgb Construction, Kgb Car, Kgb Company, Kgb Careers, Kgb Cold War Definition, Kgb Definition, Kgb Deals, Kgb Department 12, Kgb Documentary, Kgb Directorate S, Kgb Defector, Kgb Drink, Kgb Def, Kgb During The Cold War, Kgb Donut, Kgb Established, Kgb Emblem, Kgb Events, Kgb East Village, Kgb Espionage, Kgb Executions, Kgb Enterprises, Kgb Escape Room Tips, Kgb Execution Methods, Kgb Ended, Kgb Fm, Kgb Food Truck, Kgb Fsb, Kgb Flag, Kgb Facts, Kgb Foam, Kgb Files, Kgb Football, Kgb Fantastic Fiction, Kgb Full Form, Kgb Gang, Kgb Glass, Kgb Game, Kgb Group, Kgb Glass Donut, Kgb Gru, Kgb Glass For Sale, Kgb Gourmet Food Truck, Kgb Gun, Kgb Gif, Kgb History, Kgb Headquarters, Kgb Hat, Kgb Headphones, Kgb Hair, Kgb Head, Kgb Homegrown Albums, Kgb Homes, Kgb Homegrown Greatest Hits, Kgb Handler, Kgb In Russian, Kgb Illegals, Kgb In America, Kgb In Animal Farm, Kgb In Usa, Kgb Interrogation, Kgb Inc, Kgb Images, Kgb In The Cold War, Kgb Ilm, Kgb Jokes, Kgb Jfk Assassination, Kgb Jobs, Kgb Joke Office, Kgb Jack Barsky, Kgb Jfk, Kgb Jacket, Kgb Jfk Assassination Files, Kgb Jewelry, Kgb Jimmy Carter Campaign, Kgb Kiteboarding, Kgb Kfc, Kgb Killed Jfk, Kgb Keylogger, Kgb Kgb, Kgb Knife, Kgb Kiss, Kgb Kfc Meme, Kgb Killers, Kgb Kostikov, Kgb Logo, Kgb Lee, Kgb Leaders, Kgb Lansing, Kbg Logistics, Kgb Las Vegas, Kgb Law, Kgb Leafly, Kgb Lubbock, Kgb Law Firm, Kgb Meaning, Kgb Museum Prague, Kgb Meme, Kgb Movies, Kgb Motto, Kgb Mafia, Kgb Music, Kgb Martial Arts, Kgb Museum Moscow, Kgb Marvel, Kgb New Name, Kgb Nyc, Kgb News, Kgb New York, Kgb Now, Kgb Number, Kbg New Brunswick, Kgb Now Called, Kbg New Brunswick Nj, Kgb Name, Kgb Officer, Kgb Office Joke, Kgb Operations, Kgb Outfit, Kgbi Omaha, Kgb Osnaz, Kgb Oracle, Kgb Og Strain, Kgb Operations During The Cold War, Kgb Outpost, Kgb Putin, Kgb Packers, Kgb Predecessor, Kgb Productions, Kgb Paris, Kgb Police, Kgb Propaganda, Kgb Prison, Kgb Pen, Kgb Pin, Kgb Questions, Kgb Quizlet, Kgb Quotes, Kgb Quora, Kgb Question Service, Kgb Questions And Answers, Kgb Quotes Rounders, Kgb Que Es, Kgb Quarter Report, Kgb Russia, Kgb Radio, Kgb Rounders, Kgb Ranks, Kgb Red Room, Kgb Russian Revolution, Kgb Reading Series, Kgb Restaurant, Kgb Resident, Kgb Ricin, Kgb Spies, Kgb Successor, Kgb San Diego, Kgb Sky Show 2017, Kgb Symbol, Kgb San Antonio, Kgb Stalin, Kbg Syndrome, Kgb Swimbaits, Kgb Strain, Kgb The Office, Kgb Training, Kgb Texas, Kgb Today, Kgb Text, Kgb Torture, Kgb Translation, Kgb Tactics, Kgb Three Bears, Kgb Training Manual, Kgb Uniform, Kgb Usa, Kgb Ussr, Kgb University, Kgb Umbrella, Kgb Usa Inc, Kgb Urban, Kgb Usa San Antonio, Kgb Ushanka, Kgb Useful Idiots, Kgb Vs Cia, Kgb Vs Fsb, Kgb Vest Persona 5, Kgb Vs Gru, Kgb Vodka, Kgb Vs Cia Cold War, Kgb Vs Cia Deadliest Warrior, Kgb Vs Fbi, Kgb Video Game, Kgb Vodka Lemon, Kgb Wiki, Kgb Wilmington, Kgb Weapons, Kgb Watch, Kgb Website, Kgb Waits For No One, Kgb Weed, Kgb We Will Ask The Questions, Kgb Wolf, Kgb Wallpaper, Kgb X Ray, Ex Kgb, Kgb X Files, Kgb X Line, Kgbx Radio, Ktb Xd, Kgb X Cia, Kgb Xredirect, Kgb Archiver X64, Kgb Line X Stringer, Kgb Youtube, Kgb Yuri, Kgb Yelp, Kgb Yahoo, Kgb York, Kgb Yerevan, Kgb Yahoo Answers, Kgb Yoga Bag, Kgb Years, Kgb Yra, Kgb Zippo, Kgb Zip, Kgb Znacenje, Kgb Zomato, Kgb Zenekar, Kgb Zipper, Kgb Zenith Group, Kgb Zip Download, Kgb Zhukov, Kgb Znachenie, Kgb Agent Putin, Kgb Agent Meaning, Kgb Agent Fomin, Kgb Agent Book, Kgb Agent Definition, Kgb Agent Salary, Kgb Agent Interview, Kgb Agent Killed In London, Kgb Agent Jack Barsky, Kgb Agent In Usa, Kgb Agent Assassinated, Kgb Agent Alien, Kgb Agent Aragon, Kgb Agent Alexander, Soviet Agent Abel, Vostok Kgb Agent Automatic, Vostok Kgb Agent Automatic Watch, Kgb Agent In America, Kgb Agent Record Of Alien Races, Kgb Agent With Frightening Psychic Abilities, Kgb Agent Book, Kgb Agent Bezmenov, Kgb Agent Blacklist, Kgb Agent Jack Barsky, Kgb Agent In Bond Movie, Kgb Agent Killed By Radiation, Ex Kgb Agent Book, Kgb Home Based Agent, Former Kgb Agent Explains Brainwashing America, Best Kgb Agent, Kgb Agent Costume, Kgb Agent Cuban Missile Crisis, Kgb Agent Caught, Kgb Agent Careers, Kgb Special Agent Challenge, Kgb Agent In Cia, Kgb Agent Halloween Costume, Kgb Agent Explains Current Events In Usa, Kgb Agent Leaves Canada, Ex Kgb Agent Leaves Canada, Kgb Agent Definition, Kgb Agent Defector, Kgb Agent Demoralization, Kgb Agent Dies, Kgb Double Agent, Soviet Double Agent, Cia Kgb Double Agent, Define Kgb Agent, Kgb Special Agent Job Description, Agent Du Kgb, Kgb Agent Explains Current Events In Usa, Former Kgb Agent Explains Brainwashing America, Kgb Agent Killed In England, Ex Kgb Agent Interview, Ex Kgb Agent, Ex-kgb Agent On Indoctrination & Demoralization, Ex Kgb Agent Leaves Canada, Ex Kgb Agent Killed, Ex Kgb Agent Yuri, Ex Kgb Agent Youtube, Kgb Agent Fomin, Kgb Agent Found Dead, Kgb Agents Foe Crossword Clue, Kgb Agents Found In New Jersey, Kgb Famous Agents, Kgb Agent With Frightening Psychic Abilities, Former Kgb Agent Poisoned, Former Kgb Agent Explains Brainwashing America, Former Kgb Agent, Former Kgb Agent Killed In London, Kgb Agent Guillou, Soviet Gru Agent, Genscher Kgb Agent, Kgb Agent Halloween Costume, Hot Kgb Agent, Kgb Agent Interview, Kgb Agent In Usa, Kgb Agent In India, Kgb Agent In Mi6, Kgb Agent In Cia, Kgb Agent In Bond Movie, Kgb Agent In America, Kgb Agent In Vancouver, Kgb Agent Killed In London, Former Kgb Agent Interview, Kgb Agent Jack Barsky, Kgb Agent Job, Kgb Agent James Bond, Kgb Special Agent Job Description, Kgb Special Agent Job, Kgb Agent Killed In London, Kgb Agent Kidnapped, Kgb Agent Killed In England, Khamenei Kgb Agent, Kirill Kgb Agent, Kekkonen Kgb Agent, Kgb Agent Litvinenko, Kgb Agent Login, Kgb Agent London, Kgb Agent Leaves Canada, Soviet Agent Lucy, Russian Kgb Agent Lisa, Ex Kgb Agent Leaves Canada, Kgb Agent Meaning, Kgb Agent Murdered, Kgb Agent Movies, Kgb Agent 60 Minutes, Kgb Agent In Mi6, Kgb Agent In Bond Movie, Merkel Kgb Agent, Kgb Agent Names, Soviet News Agency, Kgb Agents In New Jersey, A Former Kgb Agent Needs Your Help, Nyiso Kgb Agent, Kgb Agent On 60 Minutes, Kgb Agent Online, Kgb Agent Record Of Alien Races, Ex-kgb Agent On Indoctrination & Demoralization, Obama Kgb Agent, Oswald Kgb Agent, Agent_of_kgb, By\u0142y Agent Kgb Opowiada, Kgb Agent Putin, Kgb Agent Poisoned, Kgb Agent Polonium, Kgb Agent Pay, Kgb Agent Philippines, Kgb Special Agent Philippines Salary, Kgb Agent With Frightening Psychic Abilities, Putin Kgb Agent Reagan, Palme Kgb Agent, Prodi Kgb Agent, Kgb Agent Ranks, Kgb Agent Record Of Alien Races, Kgb Agent Russia, Kgb Agent Requirements, Kgb Agent Radiation Poisoning, Kgb Agent Rudolf Abel, Soviet Agent Rudolf Abel, Putin Kgb Agent Reagan, Kgb Special Agent Review, Russian Kgb Agent Alexander Litvinenko, Kgb Agent Salary, Kgb Agent Subversion, Kgb Special Agent, Kgb Special Agent Salary, Kgb Special Agent Training, Kgb Special Agent Philippines, Kgb Sleeper Agent, Kgb Special Agent Review, Kgb Secret Agent, Kgb Special Agent Philippines Salary, Kgb Agent Training, Kgb Agent Tells You What The Illusion Is, Kgb Agent Test, Kgb Agent Tv Show, Kgb Special Agent Training, Kgb Secret Agent Test, Kgb Agents In The Us, Top Kgb Agent, Kgb Agent Uniform, Kgb Agent Usa, Kgb Undercover Agents, Kgb Agent Vladimir Putin, Kgb Agent Vergiftet, Kgb Agent In Vancouver, Vostok Kgb Agent Automatic, Vostok Kgb Agent Automatic Watch, Kgb Agent Wiki, Kgb Agent With Frightening Psychic Abilities, Kgb Agent Weapons, Kgb Agent Watches, Kgb Agent Warns, Kgb Agents Who Defected, Kgb Woman Agent, Soviet Agent Winter Soldier, Soyuz Kgb Agent Watches, Kgb Agent Tells You What The Illusion Is, Kgb Agent Yuri Bezmenov, Kgb Agent Youtube, Kgb Agent Tells You What The Illusion Is, Ex Kgb Agent Yuri, Ex Kgb Agent Youtube, Yuri Kgb Agent, Youngest Kgb Agent, Putin Wife,Putin News,Putin Net Worth,Putin Height,Putin Bay,Putin Memes,Putin Trump,Putin On The Ritz,Putin Age,Putin Trump Meeting,Putin And Trump,Putin Age,Putin And Trump Meeting,Putin Approval Rating,Putin And Obama,Putin Ally Crossword,Putin Assad,Putin And North Korea,Putin And Reagan,Putin As A Child,Putin Bay,Putin Bear,Putin Birthday,Putin Biography,Putin Bay Hotels,Putin Badass,Putin Bay Weather,Putin Blueberry Hill,Putin Bay Ferry,Putin Black Belt,Putin Children,Putin Calendar,Putin Clown,Putin Cartoon,Putin Chechnya,Putin Crying,Putin Canada,Putin Crimea,Putin Corruption,Putin Clinton,Putin Daughters,Putin Dog,Putin Documentary,Putin Dead,Putin Dog Merkel,Putin Definition,Putin Dancing,Putin Dolphins,Putin Drawing,Putin Dancing Gif,Putin Election,Putin Eating Popcorn,Putin English,Putin Election Results,Putin Erdogan,Putin Education,Putin Economy,Putin Eyes,Putin Exxon Deal,Putin Eye Color,Putin Family,Putin Food,Putin Funny,Putin Face,Putin Facts,Putin French,Putin Fishing,Poutine Fries,Putin Fascist,Putin Funny Face,Putin Gif,Putin Genocide,Putin Global Warming,Putin Gymnast,Putin Wife,Putin Gun,Putin Glasses,Putin Gangster,Putin Government,Putin Gorbachev,Putin Height,Putin Horse,Putin House,Putin Horseback,Putin Hockey,Putin History,Putin Hunting,Putin Hillary,Putin Human Rights,Putin Home,Putin Interview,Putin Images,Putin Israel,Putin Iq,Putin Isis,Putin In French,Putin Island,Putin Inauguration,Putin In Power,Putin Instagram,Putin Judo,Putin Jill Stein,Putin Journalists,Putin John Oliver,Putin Jehovah,Putin Jw,Putin Judo Gif,Putin Jesus,Putin James Bond,Putin Jehovah Witness,Putin Kgb,Putin Korea,Putin Karate,Putin Kremlin,Putin Kleptocracy,Putin Kim Jong Un,Putin Kraft Ring,Putin Kabaeva,Putin Khuilo,Putin Kid,Putin Laughing,Putin Laughing Gif,Putin Le Pen,Putin Languages,Putin Latest News,Putin Loves Trump,Putin Lollipop,Putin Likes Trump,Putin Limo,Putin Leadership,Putin Memes,Putin Merkel Dog,Putin Married,Putin Merkel,Putin Makeup,Putin Mask,Putin Martial Arts,Putin Meaning,Putin Macron,Putin Mansion,Putin News,Putin Net Worth,Putin North Korea,Putin New Wife,Putin Netanyahu,Putin Nato,Putin Net Worth Wiki,Putin Name Meaning,Putin Nickname,Putin Nuclear War,Putin On The Ritz,Putin On A Horse,Putin On Trump,Putin On North Korea,Putin Obama,Putin On The Ritz Gif,Putin On Syria,Putin Opposition,Putin On Snl,Putin On The Ritz Meme,Putin President,Putin Piano,Putin Palace,Putin Political Party,Putin Picture,Putin Poison,Putin Propaganda,Putin Puns,Putin Pop Song,Putin Popularity,Putin Quotes,Putin Quotes On Obama,Putin Queen Elizabeth,Putin Quotes Funny,Putin Quizlet,Putin Queen Elizabeth Stairs,Putin Quotes On Trump,Putin Quora,Putin Quote Immigrants,Putin Quebec,Putin Russia,Putin Reagan,Putin Riding Trump,Putin Rise To Power,Putin Reelection,Putin Richest Man In The World,Putin Riding A Ritz Cracker,Putin Response,Putin Ritz,Putin Rainbow,Putin Snl,Putin Syria,Putin Song,Putin Smiling,Putin Speech,Putin Shirt,Putin Speaking English,Putin Singing,Putin Salary,Putin Super Bowl Ring,Putin Trump,Putin Trump Meeting,Putin Twitter,Putin Trump Meme,Putin Trump Horse,Putin Trump Kiss,Putin Term Limit,Putin Trump Gif,Putin Term,Putin Today,Putin Ukraine,Putin Ussr,Putin Us Visit,Putin Unicorn,Putin Us Elections,Putin Un,Putin Undercover,Putin Urban Dictionary,Putin United Nations,Putin Us Relations,Putin Vs Trump,Putin Vs Obama,Putin Vladimir,Putin Video,Putin Vodka,Putin Vs Stalin,Putin Visits Trump,Putin Visit To White House,Putin Vampire,Putin Vs Obama Meme,Putin Wife,Putin Wiki,Putin Wealth,Putin Wink,Putin War,Putin Ww3,Putin Watch,Putin Winking Gif,Putin With Animals,Putin Walking,Putin Xi Jinping,Putin X Obama,Putin X Reader,Putin Xi,Putin And Trump,Putin And Obama,Putin And Assad,Putin And North Korea,Putin And Reagan,Putin And The Ritz,Putin Young,Putin Youtube,Putin Yacht,Putin Youth,Putin Yeltsin,Putin Yume,Putin Years As President,Putin Young Pictures,Putin Youth Army,Putin Yarmulke,Putin Zodiac Sign,Putin Zakaria,Putin Zassal,Putin Zassal Lyrics,Putin Zero Hedge,Putin Zeman,Putin Zil Limousine,Putin Zuma,Putin Za Makedonija,Putin Zapretio Albancima,
Video – OIL COLLAPSE: Putin to Go Nuclear on U.S. Sanctions
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Putin Wife,Putin News,Putin Net Worth,Putin Height,Putin Bay,Putin Memes,Putin Trump,Putin On The Ritz,Putin Age,Putin Trump Meeting,Putin And Trump,Putin Age,Putin And Trump Meeting,Putin Approval Rating,Putin And Obama,Putin Ally Crossword,Putin Assad,Putin And North Korea,Putin And Reagan,Putin As A Child,Putin Bay,Putin Bear,Putin Birthday,Putin Biography,Putin Bay Hotels,Putin Badass,Putin Bay Weather,Putin Blueberry Hill,Putin Bay Ferry,Putin Black Belt,Putin Children,Putin Calendar,Putin Clown,Putin Cartoon,Putin Chechnya,Putin Crying,Putin Canada,Putin Crimea,Putin Corruption,Putin Clinton,Putin Daughters,Putin Dog,Putin Documentary,Putin Dead,Putin Dog Merkel,Putin Definition,Putin Dancing,Putin Dolphins,Putin Drawing,Putin Dancing Gif,Putin Election,Putin Eating Popcorn,Putin English,Putin Election Results,Putin Erdogan,Putin Education,Putin Economy,Putin Eyes,Putin Exxon Deal,Putin Eye Color,Putin Family,Putin Food,Putin Funny,Putin Face,Putin Facts,Putin French,Putin Fishing,Poutine Fries,Putin Fascist,Putin Funny Face,Putin Gif,Putin Genocide,Putin Global Warming,Putin Gymnast,Putin Wife,Putin Gun,Putin Glasses,Putin Gangster,Putin Government,Putin Gorbachev,Putin Height,Putin Horse,Putin House,Putin Horseback,Putin Hockey,Putin History,Putin Hunting,Putin Hillary,Putin Human Rights,Putin Home,Putin Interview,Putin Images,Putin Israel,Putin Iq,Putin Isis,Putin In French,Putin Island,Putin Inauguration,Putin In Power,Putin Instagram,Putin Judo,Putin Jill Stein,Putin Journalists,Putin John Oliver,Putin Jehovah,Putin Jw,Putin Judo Gif,Putin Jesus,Putin James Bond,Putin Jehovah Witness,Putin Kgb,Putin Korea,Putin Karate,Putin Kremlin,Putin Kleptocracy,Putin Kim Jong Un,Putin Kraft Ring,Putin Kabaeva,Putin Khuilo,Putin Kid,Putin Laughing,Putin Laughing Gif,Putin Le Pen,Putin Languages,Putin Latest News,Putin Loves Trump,Putin Lollipop,Putin Likes Trump,Putin Limo,Putin Leadership,Putin Memes,Putin Merkel Dog,Putin Married,Putin Merkel,Putin Makeup,Putin Mask,Putin Martial Arts,Putin Meaning,Putin Macron,Putin Mansion,Putin News,Putin Net Worth,Putin North Korea,Putin New Wife,Putin Netanyahu,Putin Nato,Putin Net Worth Wiki,Putin Name Meaning,Putin Nickname,Putin Nuclear War,Putin On The Ritz,Putin On A Horse,Putin On Trump,Putin On North Korea,Putin Obama,Putin On The Ritz Gif,Putin On Syria,Putin Opposition,Putin On Snl,Putin On The Ritz Meme,Putin President,Putin Piano,Putin Palace,Putin Political Party,Putin Picture,Putin Poison,Putin Propaganda,Putin Puns,Putin Pop Song,Putin Popularity,Putin Quotes,Putin Quotes On Obama,Putin Queen Elizabeth,Putin Quotes Funny,Putin Quizlet,Putin Queen Elizabeth Stairs,Putin Quotes On Trump,Putin Quora,Putin Quote Immigrants,Putin Quebec,Putin Russia,Putin Reagan,Putin Riding Trump,Putin Rise To Power,Putin Reelection,Putin Richest Man In The World,Putin Riding A Ritz Cracker,Putin Response,Putin Ritz,Putin Rainbow,Putin Snl,Putin Syria,Putin Song,Putin Smiling,Putin Speech,Putin Shirt,Putin Speaking English,Putin Singing,Putin Salary,Putin Super Bowl Ring,Putin Trump,Putin Trump Meeting,Putin Twitter,Putin Trump Meme,Putin Trump Horse,Putin Trump Kiss,Putin Term Limit,Putin Trump Gif,Putin Term,Putin Today,Putin Ukraine,Putin Ussr,Putin Us Visit,Putin Unicorn,Putin Us Elections,Putin Un,Putin Undercover,Putin Urban Dictionary,Putin United Nations,Putin Us Relations,Putin Vs Trump,Putin Vs Obama,Putin Vladimir,Putin Video,Putin Vodka,Putin Vs Stalin,Putin Visits Trump,Putin Visit To White House,Putin Vampire,Putin Vs Obama Meme,Putin Wife,Putin Wiki,Putin Wealth,Putin Wink,Putin War,Putin Ww3,Putin Watch,Putin Winking Gif,Putin With Animals,Putin Walking,Putin Xi Jinping,Putin X Obama,Putin X Reader,Putin Xi,Putin And Trump,Putin And Obama,Putin And Assad,Putin And North Korea,Putin And Reagan,Putin And The Ritz,Putin Young,Putin Youtube,Putin Yacht,Putin Youth,Putin Yeltsin,Putin Yume,Putin Years As President,Putin Young Pictures,Putin Youth Army,Putin Yarmulke,Putin Zodiac Sign,Putin Zakaria,Putin Zassal,Putin Zassal Lyrics,Putin Zero Hedge,Putin Zeman,Putin Zil Limousine,Putin Zuma,Putin Za Makedonija,Putin Zapretio Albancima,
Noch’n Agent – Eberhard Feik alias „Thanner“ „Schimanski“-Partner war IM bei der Stasi
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Als Christian Thanner war der Schauspieler Eberhard Feik einer der beliebtesten „Tatort“-Ermittler überhaupt. Jahrelang arbeitete an der Seite von Kommissar Schimanski, gespielt von Götz George. Nun wurde bekannt, dass er über Jahre bei der Stasi als Inoffizieller Mitarbeiter geführt wurde.
Über zehn Jahre hinweg stand Eberhard Feik als Christian Thanner im Ruhrpott-„Tatort“ dem legendären Kommissar Horst Schimanski zur Seite. Die von Götz George gespielte Figur Schimanski wurde sogar für das Kino verfilmt und erhielt 1997 eine eigene gleichnamige Krimireihe.
Die eigene Krimi-Serie erlebte Eberhard Feik nicht mehr. Er starb im Jahr 1994 im Alter von 50 Jahren an einem Herzinfarkt. Nun wurde bekannt, dass er während seiner Zeit als TV-Kommissar als Inoffizieller Mitarbeiter (IM) der Staatsicherheit der DDR geführt wurde.
Decknamen „Lear“ und „Queen“
Von 1977 bis 1984 waren Feik und seine Frau in der Auslandsabteilung der Stasi registriert. Ihre Decknamen: „Lear“ und „Queen“. Feiks Witwe gab Kontakte zur Staatssicherheit gegenüber dem „Zeit Magazin“ zu, erklärte jedoch, dass beide nie aktiv für den Geheimdienst gearbeitet hätten.
Laut „Zeit Magazin“ können tatsächlich keine konkreten Aktivitäten der beiden aus den Unterlagen herausgelesen werden, beispielsweise also das Weitergeben von Spitzel-Informationen. Der schiere Umfang der Akte zeigt jedoch, dass durchaus intensiver Kontakt zwischen Stasi und dem Ehepaar bestanden haben muss.
Offenbar keine Spitzel-Aktionen
Beide waren offenbar Ende der Siebziger Jahre in West-Berlin in Berührung mit der Stasi gekommen. Laut Unterlagen aus der Stasi-Unterlagenbehörde in Berlin sollte Eberhard Feik zur Weitergabe von Informationen zwischen IMs dienen, die Ehefrau sollte als “IM mit besonderen Aufgaben” beispielsweise über Medien in der Bundesrepublik gezielt Informationen verbreiten.
Stasi Officer Uniform, Stasi Officer, Stasi Officer Interview, Stasi Officer Definition, Stasi Officer Ranks, Stasi Officer Movie, Former Stasi Officers, Ex Stasi Officers, Female Stasi Officers, Stasi Officer Definition, German Stasi Officer, Stasi Officer Interview, Stasi Officer Movie, Stasi Officer Ranks, Stasi Officer Uniform, Stasi Spitzel Beleidigung, Stasi Spitzel Liste, Stasi Spitzel Wikipedia, Stasi Spitzel Erfurt, Stasi Spitzel, Stasi-spitzel Im Erika, Stasi Spitzel System, Stasi Spitzel Namen, Stasi Spitzel In Dresden, Stasi Spitzel Heute, Stasi Spitzel Anderson, Stasi Spitzel Beleidigung, Stasi Spitzel Brd, Stasi Spitzel Bundeskanzler, Bekannte Stasi Spitzel, Stasi Spitzel Prenzlauer Berg, Stasi Spitzel Dynamo Dresden, Stasi Spitzel Dresden, Spitzel Der Stasi, Stasi Spitzel In Der Brd, Ddr Stasi Spitzel, Stasi Spitzel Erfurt, Stasi Spitzel Enttarnt, Stasi-spitzel Im Erika, Ehemalige Stasi Spitzel, Stasi Spitzel Film, Stasi Spitzel Gauck, Gysi Stasi Spitzel, Stasi Spitzel Heute, Stasi Spitzel Halle Saale, Stasi-spitzel Im Erika, Stasi Spitzel In Dresden, Stasi Spitzel In Der Brd, Stasi Spitzel Im, Stasi Spitzel Jena, Stasi Spitzel Kirche, Stasi Spitzel Liste, Stasi Spitzel Merkel, Stasi Spitzel Methoden, Stasi Spitzel Namen, Stasi Spitzel Namensliste, Stasi Spitzel Prenzlauer Berg, Prominente Stasi-spitzel, Stasi Spitzel Halle Saale, Stasi Spitzel Wikipedia, Stasi Spitzel Westen, Stasi Brothers, Stasi Definition, Stasi Eldredge, Stasi Museum, Stasi Movie, Stasi Bgc, Stasi Files, Stasi Uniform, Stasi Report, Stasi Prison, Stasi Agent, Stasi Archives, Stasi Ap Euro, Stasi Asphalt, Stasi Akten, Stasi Archives Berlin, Stasi Agents Today, Stassi Amazing Race, Stasi Article, Stasi And Gestapo, Stasi Brothers, Stasi Bgc, Stasi Berlin, Stasi Brothers Reviews, Stasi Brand, Stasi Bakery, Stasi Book, Stasi Brothers Paving, Stasi Berlin Wall, Stasi Bernard New Orleans, Stasi Commission, Stasi Cernadas, Stasi Cold War, Stasi Construction, Stasi Child, Stasi Crimes, Stasi City, Stasi Cake, Stasi Captain Gerd Wiesler, Stasi Commission Report, Stasi Definition, Stasi Documentary, Stasi Documents, Stasi Disguises, Stasi Define, Stasi Depue, Stasi Decomposition, Stasi Dallas Electrical Contracting, Stasi Death Squad, Stasi Deutsch, Stasi Eldredge, Stasi Eldredge Books, Stasi East Germany, Stasi Eldredge Quotes, Stasi Eldredge Becoming Myself, Stasi Esper, Stasi East Germany’s Secret Police, Stasi Eldredge Podcast, Stasi Eldredge Instagram, Stasi Eldredge Age, Stasi Files, Stasi Facts, Stasi From Bgc, Stasi Film, Stasi Files Online, Stasi Flag, Stasi From Bad Girl Club, Stabo Fargo, Stasi From Vanderpump Rules, Stassi From Vanderpump Rules, Stasi Germany, Stasi General Contracting, Stasi Grove Funeral Home, Stasi Gestapo, Stasi Glenn, Stasi Gang Stalking, Stasi German Shepherds, Stasi Grove Funeral Home In Olney, Stasi Grove Obituaries, Stasi Greek Meaning, Stasi Headquarters, Stasi Hand Signals, Stasi Headquarters Berlin, Stasi Head, Stasi Hitler, Stasi Headquarters Museum, Stasi Hva, Stasi History, Stasi Hartwick, Stasi Hair Salon, Stasi In Germany, Stasi Industries, Stasi Interrogation Techniques, Stasi Im, Stasi Images, Stasi In America, Stasi International Loss Adjusters, Stasi Informer, Stasi Interview, Stassi Instagram, Stasi Jokes, Stasi Jacket, Stasi Jail, Stasi Junction Road, Stasi Jalan Salib, Stasi Jail Museum, Stassi Jewelry, Stasi John Eldredge, Stasi Jean, Stasi Johnson Park Nicollet, Stasi Kennel, Stasi Kennel Belarus, Stasi Keramidis, Stasi Kountis Photography, Stasi Kara, Stasi Kgb, Stasi Koutali, Stasi Knight, Stasi Kranggan, Stasi Koehler, Stasi Logo, Stasi Longo, Stasi Landscaping, Stasiland, Stasi Lashes, Stasi Law, Stasi Lozada, Stasi Lubansky Np Ny, Stasi Leader, Stasi Leipzig, Stasi Museum, Stasi Movie, Stasi Methods, Stasi Meaning, Stasi Museum Leipzig, Stasi Merkel, Stasi Masonry, Stassi Memes, Stasi Movie East Germany, Stasi Museum Dresden, Stasi Nazi, Stasi Name, Stasi Novel, Stasi Nedir, Stasi Numbers Station, Stasi Numbers, Stasi News, Stasi Namen Alphabetisch, Stasi Officer, Stasi Organization, Stasi Omicidio, Stasi Oppression, Stasi Opfer, Stasi Officer Uniform, Stasi And Gestapo, Stassi Vanderpump Rules, Stasi Offizier, Liste Stasi Offizier, Stasi Police, Stasi Prison, Stasi Prison Berlin, Stasi Paving, Stasi Prison Berlin Tour, Stassi Phillies, Stasi Photos, Stasi Prison Museum, Stasi Primary Sources, Stassi Podcast, Stasi Quinn, Stasi Quizlet, Stasi Quotes, Stasi Quinn Ham, Stasi Quinn Ham Lyrics, Stasi Q, Stasi Quinn Twitter, Stasi Quinn Ham Mp3 Download, Stasi Quinn Ustream, Stasi Quinn Birthday, Stasi Report, Stasi Records, Stasi Ranks, Stasi Romeos, Stasi Russia, Stasi Records Act, Stasi Raus, Stasi Reddit, Stasi Rowe Instagram, Stasi Revel, Stasi Surveillance, Stasi State, Stasi Sprach Machine, Stasi Symbol, Stasi Stories, Stasis Synonym, Stasi Stussy, Stasi Safari, Stasi Spitzel, Stassi Schroeder Age, Stasi Tactics, Stasi The Brand, Stasi Torture, Stasi Techniques, Stasi Torture Methods, Stasi Training, Stasi The Untold Story, Stasi Townsend, Stasi T Shirt, Stasi Training Manual, Stasi Uniform, Stasi Ukraine, Stasi Usa, Stasi Ussr, Stasi Urban Dictionary, Stasi Uniform For Sale, Stasi Unterlagen, Stasi Unterlagen Gesetz, Stasi Vs Shelly, Stasi Vs Kgb, Stassi Vanderpump Rules, Stasi Vs Erika, Stasi Vs Natalie, Stasi Vs Nazi, Stassi Vanderpump Age, Stassi Vanderpump Rules Birthday, Stassi Vanderpump Instagram, Stassi Vanderpump Rules Snapchat, Stasi Wiki, Stasi Weapons, Stasi Ww2, Stasi Waleski Chase, Stasi Westbury, Stasi Water Cell, Stasi War Crimes, Stasi Wolf, Stasi Wolf Amazon, Stasi Wolf By David Young, Stasi X-ray, Stasi Xios, Stasi Xalandri, Stasi Cafe Xios, Stasi Ha Xxii, Stasi Metro Xalandri, Stasi Metro Xolargos, Stasi Abteilung Xii, Stasi Abteilung Xv, Stasi Abteilung X, Stasi Youtube, Stasi Yakobus, Stasi York, Stasi Y Kgb, \U03c3\u03c4\u03b1\u03c3\u03b7 \U03c5\u03c0\u03bd\u03bf\u03c5, Youtube Stasi Eldredge, Yasmin Stasi, Stasi New York Daily News, Stasi New York Times, Stasi Museum Yelp, Stasi Zersetzung, Stasa Zajovic, Stasa Zlatar, Stasa Zujovic, Stasa Znacenje Imena, Stasa Zajovic Biografija, Stasi Zentrale, Sta\u0161a Zurovac, Stasi Zentrale Dresden, Stasi Zentrale Leipzig, Stasi Listening Devices, Stasi Liste, Stasi Liste Alphabetisch, Stasi Liste Mitarbeiter, Stasi Liste Pdf, Stasi Liste Download, Stasi Listen, Lisa Stasi, Stasi Liste Im, Stasi Liste Der Dienststelle, Stasi Agents List, Stasi Informants List, Liste Stasi Mitarbeiter, List Of Stasi Agents, Stasi Salons Price List, Stasi Im Liste, Stasi Im Westen, Stasi Im Erika, Stasi Im Ausland, Stasi Im Unterricht, Stasi Im Victoria, Stasi Im Alltag, Stasi Im Liste Download, Stasi Im Ausland, Stasi Im Alltag, Stasi Im Alltag Der Ddr, Stasi Im Anzahl, Stasi Im Bundestag, Stasi Im Bezahlung, Stasi Im Brandenburg Landtag, Stasi Im Bezirk Halle, Stasi Im Bezirk Cottbus, Stasi Im Brandenburger Tor, Im Stasi Bedeutung, Stasiboom Im Herzogtum, Stasi Offiziere Im Besonderen Einsatz, Stasi Im Liste Berlin, Stasi Im Liste Cottbus, Stasi Im Bezirk Cottbus, Im Stasi Liste Chemnitz, Stasi Im Decknamen, Stasi Im Ddr, Stasi Im Dresden, Stasi Im Ddr-sport, Stasi*dresden*im Liste, Stasi Im Liste Download, Stasi Im Erika, Stasi Im Eichsfeld, Stasi Im Einsatz, Stasi In Erfurt, Stasi-spitzel Im Erika, Stasi Offiziere Im Besonderen Einsatz, Stasi Im Film, Stasi Im Freitag, Im Filius Stasi, Stasi Im Geschichtsunterricht, Stasi Im Harz, Stasi In Halle, Stasi Im Liste Halle Saale, Stasiboom Im Herzogtum, Im Hardy Stasi, Stasi Im Bezirk Halle, Im Helene Stasi, Stasi Akten Im Internet, Stasi Liste Im Internet, Aufgaben Der Stasi Im Inland, Im Jump Stasi, Stasi Im Klarnamen, Stasi Im Kalten Krieg, Schweizer Im Stasi Knast, Die Stasi Kam Im Morgengrauen, Stasi Im Liste, Stasi Im Liste Download, Stasi Im Larve, Stasi Im Liste Berlin, Stasi Im Liste Dresden, Stasi Im Liste Halle Saale, Stasi Im Listen, Stasi Im Liste Leipzig, Stasi Im Mitarbeiter, Stasi I.m, Im Stasi Mitarbeiter Liste, Stasi Mitarbeiter Im Westen, Im Stasi Merkel, Stasi Museum I Berlin, Stasi Museet I Berlin, Stasi Im Namen, Stasi Im Namensliste, Stasi-mitarbeiter Im Netz, Im Notar Stasi, 100.000 Stasi-mitarbeiter Im Netz (Update), 100.000 Stasi-mitarbeiter Im Netz, Stasi Im Om, Stasi Im Osten, Stasi Offiziere Im Besonderen Einsatz, Stasi Im Parlament, Stasi Im Raw Zwickau, Stasi Im Radler, Stasi Im Westen Die Unterwanderte Republik, Stasi Im Sport, Stasi-spitzel Im Erika, Stasi Staat Im Staat, Stasi Spione Im Westen, Stasi Im Liste Halle Saale, Stasi Spitzel Im, Stasi Im Ddr-sport, Stasi Im Unterricht, Stasi Im Untergrund, Stasi Und Im, Die Stasi Im Unterricht, Stasi Im Westen Die Unterwanderte Republik, Stasi Im Victoria, Stasi Im Viktoria, Stasi Im Vorlauf, Stasi Im Vogtland, Stasi Im Volksmund, Gestapo Und Stasi Im Vergleich, Stasi Im Westen, Stasi Im Westen Die Unterwanderte Republik, Im Stasi Wiki, Im Stasi Wikipedia, Stasi Mitarbeiter Im Westen, Stasi Spione Im Westen, Stasi Agenten Im Westen, Stasi Morde Im Westen, Stasi Im Raw Zwickau, Stasi Agents, Stasi Agents In Norway, Stasi Agents Today, Stasi Agents In West Germany, Stasi Agents List, Stasi Agent Movie, Stasi Agents In Britain, Stasi Agent Film, Stasi Agent Facebook, Stasi Agenten, Stasi Agents In Britain, Define Stasi Agent, Agent Stasi Oscar To Donald Tusk, Stasi Agent Film, Stasi Agent Facebook, Agent Stasi W Srodowisku Gda\u0144skiej Opozycji, Gauck Stasi Agent, Stasi Agents List, Stasi Agent Movie, Tusk Agent Stasi Macierewicz, Merkel Stasi Agent, Stasi Agents In Norway, Stasi Agent Oscar, Agent Stasi Oscar To Donald Tusk, Agent Stasi Ps. Oscar, Tusk Agent Stasi Oscar, Agent Stasi O Pseudonimie Oscar, Agent Stasi Tw Oskar, Agent Stasi W Otoczeniu Tuska, Tusk To Agent Stasi Ps. Oskar, Agent Stasi Ps. Oscar, Agent Stasi O Pseudonimie Oscar, Agent Stasi O Pseudonimie Oskar, Agent Stasi O Pseudonimie \U201eoscar, Stasi Romeo Agents, Stasi Agent Stiller, Agent Stasi W Srodowisku Gda\u0144skiej Opozycji, Stasi Agent Topaz, Stasi Agents Today, Agent Stasi Tw \U201eoscar, Agent Stasi Tusk, Agent Stasi Oscar To Donald Tusk, Agent Stasi Tw \U201eoskar, Agent Stasi W Otoczeniu Tuska, Agent Stasi Tw Oskar, Stasi Agents In West Germany, Stasi Agent Wiki, Agent Stasi W Srodowisku Gda\u0144skiej Opozycji, Agent Stasi W Otoczeniu Tuska, Inoffizielle Mitarbeiter Stasi, Inoffizielle Mitarbeiter Ddr, Inoffizielle Mitarbeiter Liste, Inoffizielle Mitarbeiter Namensliste, Inoffizielle Mitarbeiter Des Mfs, Inoffizielle Mitarbeiter, Inoffizielle Mitarbeiter Definition, Inoffizielle Mitarbeiter Der Staatssicherheit, Inoffizielle Mitarbeiter Mfs Liste, Inoffizielle Mitarbeiter Stasi Akten, Inoffizielle Mitarbeiter Stasi Akten, Anzahl Inoffizielle Mitarbeiter Stasi, Inoffizieller Mitarbeiter Bnd, Stasi Inoffizielle Mitarbeiter Berlin, Inoffizielle Mitarbeiter Stasi Bezahlung, Bekannte Inoffizielle Mitarbeiter, Inoffizieller Mitarbeiter Bezahlung, Inoffizielle Mitarbeiter In Der Brd, Bekannte Inoffizielle Mitarbeiter Stasi, Inoffizielle Mitarbeiter Ddr, Inoffizieller Mitarbeiter Erika, Inoffizieller Mitarbeiter Englisch, Inoffizieller Mitarbeiter Gehalt, Hauptamtliche Inoffizielle Mitarbeiter Stasi, Hauptamtliche Inoffizielle Mitarbeiter, Inoffizielle Mitarbeiter In Der Brd, Ims Inoffizielle Mitarbeiter, Inoffizieller Mitarbeiter (Im), Inoffizieller Mitarbeiter Im Besonderen Einsatz, Inoffizielle Kriminalpolizeiliche Mitarbeiter, Inoffizielle Mitarbeiter Liste, Inoffizielle Mitarbeiter Liste Stasi, Inoffizielle Mitarbeiter Liste Dresden, Inoffizielle Mitarbeiter Der Stasi Liste, Liste Inoffizielle Mitarbeiter Staatssicherheit, Inoffizielle Mitarbeiter Mfs Liste, Inoffizielle Mitarbeiter Mfs, Inoffizielle Mitarbeiter Mfs Liste, Inoffizielle Mitarbeiter Namensliste, Inoffizielle Mitarbeiter Namen, Namensliste Inoffizielle Mitarbeiter Stasi, Stasi Inoffizielle Mitarbeiter Namen, Prominente Inoffizielle Mitarbeiter, Inoffizielle Mitarbeiter Stasi, Inoffizielle Mitarbeiter Stasi Liste, Inoffizielle Mitarbeiter Stasi Bezahlung, Inoffizielle Mitarbeiter Stasi Akten, Inoffizielle Mitarbeiter Shenja, Inoffizielle Mitarbeiter Der Stasi, Inoffizielle Mitarbeiter Der Stasi Liste, Liste Inoffizielle Mitarbeiter Staatssicherheit, Namensliste Inoffizielle Mitarbeiter Stasi, Hauptamtliche Inoffizielle Mitarbeiter Stasi,
Revealed – NSA Snowden Releases Tally Update – *2,694 Pages
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| 8 December 2014
4 December 2014. Add 63 pages to The Intercept. Tally now *2,627 pages of The Guardian first reported 58,000 files; caveat: Janine Gibson, The Guardian NY, said on 30 January 2014 “much more than 58,000 files in first part, two more parts” (no numbers) (tally now less than ~4.3%). DoD claims 1,700,000 files (~.015% of that released). ACLU lists 525 pages released by the press. However, if as The Washington Post reported, a minimum of 250,000 pages are in the Snowden files, then less than 1% have been released. Note Greenwald claim on 13 September 2014 of having “hundreds of thousands” of documents. 25 November 2014. Add 72 pages to Süddeutsche Zeitung. 17 November 2014, charts by Cryptome:
6 November 2014. At current rate of release it will take 31 to 908 years for full disclosure. 10 October 2014. Add 69 pages to The Intercept. 17 September 2014. Add 2 pages to The Intercept. 14 September 2014. Add 68 pages to Der Spiegel. 13 September 2014. In video Glenn Greenwald claims to have “hundreds of thousands” of documents (at 9:06 min) http://www.3news.co.nz/tvshows/thenation/interview-glenn-greenwald-2014091311?ref=video Audio excerpt: http://youtu.be/xnfIp38AAhM 5 September 2014. Add 32 pages to The Intercept. Tally now *2,293 pages of The Guardian first reported 58,000 files; caveat: Janine Gibson, The Guardian NY, said on 30 January 2014 “much more than 58,000 files in first part, two more parts” (no numbers) (tally now less than ~3.5%). DoD claims 1,700,000 files (~.012% of that released). ACLU lists 525 pages released by the press. However, if as The Washington Post reported, a minimum of 250,000 pages are in the Snowden files, then less than 1% have been released. 31 August 2014. Add 34 pages to Der Spiegel. 25 August 2014. Add 55 pages to The Intercept. 16 August 2014. Add 26 pages to Heise. 12 August 2014. Add 6 pages to The Intercept. 5 August 2014. Add 12 pages to The Intercept. 4 August 2014. Add 23 pages to The Intercept. 25 July 2014. Add 4 pages to The Intercept. 14 July 2014. Add 8 pages to The Intercept. 14 July 2014. “I’m as mad as hell and I’m not going to take this anymore!” http://en.wikipedia.org/wiki/Network_%28film%29 Cryptome has sent a demand for accounting and public release specifics to holders of the Snowden documents: New York Times, Washington Post, The Guardian, Barton Gellman, Laura Poitrias, Glenn Greenwald, ACLU, EFF and John and Jane Does, US Citizens: http://cryptome.org/2014/07/snowden-documents-demand-14-0714.pdf 11 July 2014. See related essay, Open the Snowden Files, Krystian Woznicki, 11July 2014: English: http://berlinergazette.de/wp-content/uploads/Open-the-Snowden-Files_KW_E.pdf 11 July 2014. @PaulMD notes this claim in the Washington Post, 11 July 2014:
If a minimum of 250,000 pages are in the Snowden files, then less than 1% have been released. 9 July 2014. Add 8 pages to The Intercept. 9 July 2014. Add 1 page to Washington Post. 23 June 2014. Add 9 pages to Der Spiegel. 22 June 2014. Add 41 pages to Information-The Intercept. Revised. This is included in entry above. 18 June 2014. Add 20 pages to The Intercept. 18 June 2014. Add 200 pages to Der Spiegel. 16 June 2014. Add 4 pages to Der Spiegel. 1 June 2014. Add 4 pages to New York Times. 23 May 2014. Cryptome placed online No Place to Hide, 310 pages, to compensate for failure to release Snowden documents: http://cryptome.org/2014/05/npth-freed.htm http://cryptome.org/2014/05/npth.7z (27MB) 19 May 2014. The Intercept released 12 pages. 13 May 2014. Glenn Greenwald released 107 pages, some new, some previously published, some full pages, some page fragments. http://hbpub.vo.llnwd.net/o16/video/olmk/holt/greenwald/NoPlaceToHide-Documents-Uncompressed.pdf 5 May 2014. Related tally of redactions of Snowden releases: http://cryptome.org/2014/05/snowden-redactions.htm 30 April 2014. Add 19 pages to The Intercept. 30 April 2014. Add 2 pages to Dagbladet belatedly. 5 April 2014. Add 21 pages to The Intercept. 4 April 2014. ACLU offers NSA documents search: https://www.aclu.org/nsa-documents-search Also: http://freesnowden.is/category/revealed-documents/index.html https://www.eff.org/deeplinks/2013/11/nsa-spying-primary-sources https://www.aclu.org/nsa-documents-released-public-june-2013 http://leaksource.wordpress.com/ If more lists please send: cryptome[at]earthlink.net 2 April 2014. 29 March 2014. Add 1 page to Der Spiegel. 22 March 2014. Add 3 pages to Der Spiegel. 22 March 2014. Add 2 pages to New York Times. 21 March 2014. Add 7 pages to Le Monde. 20 March 2014. Add 6 pages to The Intercept. 18 March 2014. Add 4 pages to Washington Post. 13 March 2014. Add 1 page to The Intercept. 12 March 2014. Add 35 pages to The Intercept. 12 March 2014. Add 62 pages to New York Times. Add 2 pages to NRC Handelsblad. 7 March 2014. Add 8 pages to The Intercept. 27 February 2014. Add 3 pages to Guardian. 25 February 2014. Add 11 pages to NBC News. 24 February 2014. Add 4 pages to The Intercept. 24 February 2014. Add *50 pages to The Intercept (7 pages are duplicates of GCHQ Psychology). 18 February 2014. Add *45 pages to The Intercept (37 pages are duplicates of release by NBC News). Note: Between 10-17 February 2014, The Intercept disclosed fragments of Snowden pages and the New York Times referenced some but as far as known did not release them in full. If available please send link. 10 February 2014. Add 1 page to NRC Handelsblad (via Electrospaces.blogspot.com). 7 February 2014. Add 15 pages NBC News. 5 February 2014. Add 14 pages NBC News. 31 January 2014. Add 27 pages to CBC News. 27 January 2014. Add 47 pages to NBC News. 27 January 2014. Add 18 pages to Anonymous via New York Times. 16 January 2014. Add 8 pages to The Guardian. * 14 January 2014. Add 21 pages to Information.dk (duplicate). * 13 January 2014. Add 4 pages to Information.dk (duplicate). Related Snowden Document and Page Count Assessment: http://cryptome.org/2014/01/snowden-count.htm * 5 January 2014. Add 16 pages to Der Spiegel (30 December 2013. No source given for NSA docs). Tally now *962 pages (~1.7%) of reported 58,000. NSA head claims 200,000 (~.50% of that released). 4 January 2014. The source was not identified for *133 pages published by Der Spiegel and Jacob Appelbaum in late December 2013. They are included here but have not been confirmed as provided by Edward Snowden. Thanks to post by Techdirt. Glenn Greenwald tweeted:
Matt Blaze tweeted, 11:24 AM – 2 Jan 14
3 January 2014. Add 13 pages to Washington Post. 3 January 2014. See also EFF, ACLU and LeakSource accounts: https://www.eff.org/deeplinks/2013/11/nsa-spying-primary-sources https://www.aclu.org/nsa-documents-released-public-june-2013 http://leaksource.wordpress.com/ 2 January 2014. Add 1 page to Washington Post published 10 July 2013. * 31 December 2013. Add 16 pages to Der Spiegel. * 30 December 2013. Add 50 pages of NSA ANT Catalog by Jacob Appelbaum (no source given for NSA docs). * 30 December 2013. Add 21 pages from 30C3 video by Jacob Appelbaum (no source given for NSA docs). * 30 December 2013. Add 42 pages (8 duplicates) to Der Spiegel (no source given for NSA docs). * 29 December 2013. Add 4 pages to Der Spiegel (no source given for NSA docs). 24 December 2013. Add 2 pages to Washington Post. 23 December 2013 http://www.adn.com/2013/12/22/3243451/pincus-snowden-still-has-a-road.html We’ve yet to see the full impact of former National Security Agency contractor Edward Snowden’s unauthorized downloading of highly classified intelligence documents. Among the roughly 1.7 million documents he walked away with — the vast majority of which have not been made public — are highly sensitive, specific intelligence reports, as well as current and historic requirements the White House has given the agency to guide its collection activities, according to a senior government official with knowledge of the situation. The latter category involves about 2,000 unique taskings that can run to 20 pages each and give reasons for selective targeting to NSA collectors and analysts. These orders alone may run 31,500 pages. 13 December 2013. Add 26 pages to Trojkan (SVT). Tally now 797 pages (~1.4%) of reported 58,000. NSA head claims 200,000 (~.40% of that released). Australia press reports “up to 20,000 Aussie files.” Rate of release over 6 months, 132.8 pages per month, equals 436 months to release 58,000, or 36.3 years. Thus the period of release has decreased in the past month from 42 years. 12 December 2013. Belatedly add 27 pages to Guardian and 18 pages to Washington Post. 21 November 2013. See also EFF and ACLU accounts: https://www.eff.org/deeplinks/2013/11/nsa-spying-primary-sources https://www.aclu.org/nsa-documents-released-public-june-2013 3 November 2013 47 42 Years to Release Snowden Documents Out of reported 50,000 pages (or files, not clear which), about 446 514 pages (>1% 1%) have been released over 5 months beginning June 5, 2012. At this rate, 89 100 pages per month, it will take 47 42 years for full release. Snowden will be 77 72 years old, his reporters hoarding secrets all dead. NY Times, 3 November 2013: Whatever reforms may come, Bobby R. Inman, who weathered his own turbulent period as N.S.A. director from 1977 to 1981, offers his hyper-secret former agency a radical suggestion for right now. “My advice would be to take everything you think Snowden has and get it out yourself,” he said. “It would certainly be a shock to the agency. But bad news doesn’t get better with age. The sooner they get it out and put it behind them, the faster they can begin to rebuild.” Timeline of releases: [See tabulation below for full timeline.] 5 October 2013 26 Years to Release Snowden Docs by The Guardian Out of reported 15,000 pages, The Guardian has published 192 pages in fourteen releases over four months, an average of 48 pages per month, or 1.28% of the total. At this rate it will take 26 years for full release. Edward Snowden will be 56 years old.
Edward Snowden Wife, Edward Snowden Movie, Edward Snowden Twitter, Edward Snowden Dead, Edward Snowden Quotes, Edward Snowden Interview, Edward Snowden Wiki, Edward Snowden Russia, Edward Snowden Net Worth, Edward Snowden 2017, Edward Snowden Age, Edward Snowden Antarctica, Edward Snowden Articles, Edward Snowden Actor, Edward Snowden And Trump, Edward Snowden And Julian Assange, Edward Snowden And Wikileaks, Edward Snowden Apush, Edward Snowden Ama, Edward Snowden And Lindsay Mills, Edward Snowden Biography, Edward Snowden Book, Edward Snowden Bin Laden, Edward Snowden Booz Allen, Edward Snowden Birthday, Edward Snowden Bbc, Edward Snowden Blog, Edward Snowden Birth Chart, Edward Snowden Bernie Sanders, Edward Snowden Bitcoin, Edward Snowden Cia, Edward Snowden Cnn, Edward Snowden Cast, Edward Snowden Chelsea Manning, Edward Snowden Current News, Edward Snowden Citizen 4, Edward Snowden Conservative, Edward Snowden China, Edward Snowden Chemtrails, Edward Snowden Contact, Edward Snowden Dead, Edward Snowden Documentary, Edward Snowden Definition, Edward Snowden Documentary Netflix, Edward Snowden Doc, Edward Snowden Donald Trump, Edward Snowden Dell, Edward Snowden Documentary Hbo, Edward Snowden Date, Edward Snowden David Hoffman, Edward Snowden Essay, Edward Snowden Email, Edward Snowden Ethics, Edward Snowden Ethics Essay, Edward Snowden Early Life, Edward Snowden Effect, Edward Snowden Ecuador, Edward Snowden Education, Edward Snowden Everything About Donald Trump, Edward Snowden Event, Edward Snowden Facts, Edward Snowden Family, Edward Snowden Film, Edward Snowden First Interview, Edward Snowden Facebook, Edward Snowden Father, Edward Snowden Full Movie, Edward Snowden Flat Earth, Edward Snowden First Tweet, Edward Snowden Fox News, Edward Snowden Guardian, Edward Snowden Glenn Greenwald, Edward Snowden Glasses, Edward Snowden Global Warming, Edward Snowden Gif, Edward Snowden Google, Edward Snowden Girlfriend Movie, Edward Snowden Good, Edward Snowden Grandfather, Edward Snowden Genius, Edward Snowden Hero, Edward Snowden Height, Edward Snowden House, Edward Snowden Hawaii, Edward Snowden High School, Edward Snowden Hong Kong, Edward Snowden History, Edward Snowden Heartbeat, Edward Snowden Haarp, Edward Snowden Hbo, Edward Snowden Interview, Edward Snowden Iq, Edward Snowden Instagram, Edward Snowden Interview 2013, Edward Snowden Imdb, Edward Snowden Interview 2017, Edward Snowden Images, Edward Snowden Interview 2016, Edward Snowden Income, Edward Snowden Iphone, Edward Snowden Job, Edward Snowden Journalist, Edward Snowden Japan, Edward Snowden Julian Assange Bradley Manning, Edward Snowden Java, Edward Snowden Journalism, Edward Snowden Joseph Gordon-levitt, Edward Snowden Julian Assange, Edward Snowden John Oliver Passwords, Edward Snowden Jean Michel Jarre, Edward Snowden Kunia, Edward Snowden Kimdir, Edward Snowden Katie Couric Interview, Edward Snowden Katie Couric, Edward Snowden Kaskus, Edward Snowden Kim, Edward Snowden Kasus, Edward Snowden Kfc, Edward Snowden Kim Jest, Edward Snowden Koenig, Edward Snowden Location, Edward Snowden Lindsay Mills Moscow, Edward Snowden Laptop, Edward Snowden Lindsay Mills, Edward Snowden Living, Edward Snowden Lawyer, Edward Snowden Life, Edward Snowden Latest News, Edward Snowden Latest, Edward Snowden Live Stream, Edward Snowden Movie, Edward Snowden Movie Netflix, Edward Snowden Movie Cast, Edward Snowden Military, Edward Snowden Movie Online, Edward Snowden Memes, Edward Snowden Middlebury College, Edward Snowden Married, Edward Snowden Moscow, Edward Snowden Medical Condition, Edward Snowden Net Worth, Edward Snowden Now, Edward Snowden News, Edward Snowden New York Times, Edward Snowden Netflix, Edward Snowden Natal Chart, Edward Snowden Nobel Prize, Edward Snowden Nsa Salary, Edward Snowden Npr, Edward Snowden Nationality, Edward Snowden On Trump, Edward Snowden Osama Bin Laden, Edward Snowden Obama, Edward Snowden Oscar, Edward Snowden On Movie, Edward Snowden On Twitter, Edward Snowden Openstack, Edward Snowden On Antarctica, Edward Snowden Os, Edward Snowden Original Interview, Edward Snowden Parents, Edward Snowden Political Views, Edward Snowden Privacy Tips, Edward Snowden Political Party, Edward Snowden Patriot Act, Edward Snowden Pictures, Edward Snowden Podcast, Edward Snowden Phone Case, Edward Snowden Poll, Edward Snowden Putin, Edward Snowden Quotes, Edward Snowden Quizlet, Edward Snowden Questions, Edward Snowden Quien Es, Edward Snowden Quote About Privacy, Edward Snowden Quotes Citizenfour, Edward Snowden Quick Facts, Edward Snowden Qualifications, Edward Snowden Russia, Edward Snowden Reddit, Edward Snowden Research Paper, Edward Snowden Real Name, Edward Snowden Residence, Edward Snowden Resume, Edward Snowden Robot, Edward Snowden Recommended Apps, Edward Snowden Reporter, Edward Snowden Russian, Edward Snowden Story, Edward Snowden Salary, Edward Snowden Status, Edward Snowden Signal, Edward Snowden Speech, Edward Snowden Security Tips, Edward Snowden Shirt, Edward Snowden Siblings, Edward Snowden Special Forces, Edward Snowden Still Alive, Edward Snowden Twitter, Edward Snowden Today, Edward Snowden Trump, Edward Snowden Timeline, Edward Snowden Ted Talk, Edward Snowden The Guardian, Edward Snowden Trailer, Edward Snowden The Movie, Edward Snowden T Shirt, Edward Snowden Tor, Edward Snowden Update, Edward Snowden Ufo, Edward Snowden Us Army, Edward Snowden University Of Michigan, Edward Snowden Used Tails, Edward Snowden Umich, Edward Snowden University Of Maryland, Edward Snowden Ufo Wikileaks, Edward Snowden Ufo Video, Edward Snowden Urban Dictionary, Edward Snowden Video, Edward Snowden Vpn, Edward Snowden Vice, Edward Snowden And Julian Assange, Edward Snowden Voice, Edward Snowden And Bradley Manning, Edward Snowden Vault 7, Edward Snowden Visa, Edward Snowden And Wikileaks, Edward Snowden Vanity Fair, Edward Snowden Wife, Edward Snowden Wiki, Edward Snowden Wired, Edward Snowden William And Mary, Edward Snowden Washington Post, Edward Snowden Who Is He, Edward Snowden Website, Edward Snowden Worth, Edward Snowden Wikileak, Edward Snowden Washington Post 2013, Edward Snowden Youtube, Edward Snowden Young, Edward Snowden Yahoo Answers, Edward Snowden Youtube Channel, Edward Snowden Youtube Documentary, Edward Snowden Yokota, Edward Snowden And Lindsay Mills, Edward Snowden Yify, Edward Snowden Zodiac Sign, Edward Snowden Zcash, Edward Snowden Zuckerberg, Edward Snowden Zoho, Edward Snowden Zizek, Edward Snowden Zimbabwe, Edward Snowden Zitate, Edward Snowden Zusammenfassung, Edward Snowden Zivilisation, Edward Snowden Zvi\u017eda\u010d, |
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Unveiled – Senate Select Committee on Intelligence Study of the CIA Detention and Interrogation Program
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
The following report was released December 9, 2014 by the Senate Select Committee on Intelligence. A collection of additional views as well as minority views and additional minority views (13.8 MB) from the committee are also available.
Senate Select Committee on Intelligence Committee Study of the Central Intelligence Agency’s Detention and Interrogation Program
- 525 pages
- April 3, 2014
- 62.7 MB
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 44, CN, TOP – SECRET – The Secret List of KGB Agents – KGB AGENT LIST CN
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 696/1177 | CNOTA ZBIGNIEW |
| IPN BU 0891/409 | CNOTKOWSKI JAN |
| IPN BU 0193/1591 | CNOTKOWSKI MICHAŁ |
Kgb Meaning, Kgb Bar, Kgb Putin, Kgb Radio, Kgb Cold War, Kgb The Office, Kgb Vs Cia, Kgb Boston, Kgb Gang, Kgb Training, Kgb Agent, Kgb Archiver, Kgb Assassinations, Kgb Animal Farm, Kgb Alien, Kgb Archer, Kgb Ap Euro, Kgb Alaska, Kgb Arms, Kgb Application, Kgb Bar, Kgb Boston, Kgb Band, Kgb Badge, Kgb Burger, Kgb Beer, Kgb Bar East Village, Kgb Building, Kgb Ballistic Knife, Kgb Bar Events, Kgb Cold War, Kgb Call Center, Kgb Chicken, Kgb Conduit, Kgb Customs, Kgb Construction, Kgb Car, Kgb Company, Kgb Careers, Kgb Cold War Definition, Kgb Definition, Kgb Deals, Kgb Department 12, Kgb Documentary, Kgb Directorate S, Kgb Defector, Kgb Drink, Kgb Def, Kgb During The Cold War, Kgb Donut, Kgb Established, Kgb Emblem, Kgb Events, Kgb East Village, Kgb Espionage, Kgb Executions, Kgb Enterprises, Kgb Escape Room Tips, Kgb Execution Methods, Kgb Ended, Kgb Fm, Kgb Food Truck, Kgb Fsb, Kgb Flag, Kgb Facts, Kgb Foam, Kgb Files, Kgb Football, Kgb Fantastic Fiction, Kgb Full Form, Kgb Gang, Kgb Glass, Kgb Game, Kgb Group, Kgb Glass Donut, Kgb Gru, Kgb Glass For Sale, Kgb Gourmet Food Truck, Kgb Gun, Kgb Gif, Kgb History, Kgb Headquarters, Kgb Hat, Kgb Headphones, Kgb Hair, Kgb Head, Kgb Homegrown Albums, Kgb Homes, Kgb Homegrown Greatest Hits, Kgb Handler, Kgb In Russian, Kgb Illegals, Kgb In America, Kgb In Animal Farm, Kgb In Usa, Kgb Interrogation, Kgb Inc, Kgb Images, Kgb In The Cold War, Kgb Ilm, Kgb Jokes, Kgb Jfk Assassination, Kgb Jobs, Kgb Joke Office, Kgb Jack Barsky, Kgb Jfk, Kgb Jacket, Kgb Jfk Assassination Files, Kgb Jewelry, Kgb Jimmy Carter Campaign, Kgb Kiteboarding, Kgb Kfc, Kgb Killed Jfk, Kgb Keylogger, Kgb Kgb, Kgb Knife, Kgb Kiss, Kgb Kfc Meme, Kgb Killers, Kgb Kostikov, Kgb Logo, Kgb Lee, Kgb Leaders, Kgb Lansing, Kbg Logistics, Kgb Las Vegas, Kgb Law, Kgb Leafly, Kgb Lubbock, Kgb Law Firm, Kgb Meaning, Kgb Museum Prague, Kgb Meme, Kgb Movies, Kgb Motto, Kgb Mafia, Kgb Music, Kgb Martial Arts, Kgb Museum Moscow, Kgb Marvel, Kgb New Name, Kgb Nyc, Kgb News, Kgb New York, Kgb Now, Kgb Number, Kbg New Brunswick, Kgb Now Called, Kbg New Brunswick Nj, Kgb Name, Kgb Officer, Kgb Office Joke, Kgb Operations, Kgb Outfit, Kgbi Omaha, Kgb Osnaz, Kgb Oracle, Kgb Og Strain, Kgb Operations During The Cold War, Kgb Outpost, Kgb Putin, Kgb Packers, Kgb Predecessor, Kgb Productions, Kgb Paris, Kgb Police, Kgb Propaganda, Kgb Prison, Kgb Pen, Kgb Pin, Kgb Questions, Kgb Quizlet, Kgb Quotes, Kgb Quora, Kgb Question Service, Kgb Questions And Answers, Kgb Quotes Rounders, Kgb Que Es, Kgb Quarter Report, Kgb Russia, Kgb Radio, Kgb Rounders, Kgb Ranks, Kgb Red Room, Kgb Russian Revolution, Kgb Reading Series, Kgb Restaurant, Kgb Resident, Kgb Ricin, Kgb Spies, Kgb Successor, Kgb San Diego, Kgb Sky Show 2017, Kgb Symbol, Kgb San Antonio, Kgb Stalin, Kbg Syndrome, Kgb Swimbaits, Kgb Strain, Kgb The Office, Kgb Training, Kgb Texas, Kgb Today, Kgb Text, Kgb Torture, Kgb Translation, Kgb Tactics, Kgb Three Bears, Kgb Training Manual, Kgb Uniform, Kgb Usa, Kgb Ussr, Kgb University, Kgb Umbrella, Kgb Usa Inc, Kgb Urban, Kgb Usa San Antonio, Kgb Ushanka, Kgb Useful Idiots, Kgb Vs Cia, Kgb Vs Fsb, Kgb Vest Persona 5, Kgb Vs Gru, Kgb Vodka, Kgb Vs Cia Cold War, Kgb Vs Cia Deadliest Warrior, Kgb Vs Fbi, Kgb Video Game, Kgb Vodka Lemon, Kgb Wiki, Kgb Wilmington, Kgb Weapons, Kgb Watch, Kgb Website, Kgb Waits For No One, Kgb Weed, Kgb We Will Ask The Questions, Kgb Wolf, Kgb Wallpaper, Kgb X Ray, Ex Kgb, Kgb X Files, Kgb X Line, Kgbx Radio, Ktb Xd, Kgb X Cia, Kgb Xredirect, Kgb Archiver X64, Kgb Line X Stringer, Kgb Youtube, Kgb Yuri, Kgb Yelp, Kgb Yahoo, Kgb York, Kgb Yerevan, Kgb Yahoo Answers, Kgb Yoga Bag, Kgb Years, Kgb Yra, Kgb Zippo, Kgb Zip, Kgb Znacenje, Kgb Zomato, Kgb Zenekar, Kgb Zipper, Kgb Zenith Group, Kgb Zip Download, Kgb Zhukov, Kgb Znachenie, Kgb Agent Putin, Kgb Agent Meaning, Kgb Agent Fomin, Kgb Agent Book, Kgb Agent Definition, Kgb Agent Salary, Kgb Agent Interview, Kgb Agent Killed In London, Kgb Agent Jack Barsky, Kgb Agent In Usa, Kgb Agent Assassinated, Kgb Agent Alien, Kgb Agent Aragon, Kgb Agent Alexander, Soviet Agent Abel, Vostok Kgb Agent Automatic, Vostok Kgb Agent Automatic Watch, Kgb Agent In America, Kgb Agent Record Of Alien Races, Kgb Agent With Frightening Psychic Abilities, Kgb Agent Book, Kgb Agent Bezmenov, Kgb Agent Blacklist, Kgb Agent Jack Barsky, Kgb Agent In Bond Movie, Kgb Agent Killed By Radiation, Ex Kgb Agent Book, Kgb Home Based Agent, Former Kgb Agent Explains Brainwashing America, Best Kgb Agent, Kgb Agent Costume, Kgb Agent Cuban Missile Crisis, Kgb Agent Caught, Kgb Agent Careers, Kgb Special Agent Challenge, Kgb Agent In Cia, Kgb Agent Halloween Costume, Kgb Agent Explains Current Events In Usa, Kgb Agent Leaves Canada, Ex Kgb Agent Leaves Canada, Kgb Agent Definition, Kgb Agent Defector, Kgb Agent Demoralization, Kgb Agent Dies, Kgb Double Agent, Soviet Double Agent, Cia Kgb Double Agent, Define Kgb Agent, Kgb Special Agent Job Description, Agent Du Kgb, Kgb Agent Explains Current Events In Usa, Former Kgb Agent Explains Brainwashing America, Kgb Agent Killed In England, Ex Kgb Agent Interview, Ex Kgb Agent, Ex-kgb Agent On Indoctrination & Demoralization, Ex Kgb Agent Leaves Canada, Ex Kgb Agent Killed, Ex Kgb Agent Yuri, Ex Kgb Agent Youtube, Kgb Agent Fomin, Kgb Agent Found Dead, Kgb Agents Foe Crossword Clue, Kgb Agents Found In New Jersey, Kgb Famous Agents, Kgb Agent With Frightening Psychic Abilities, Former Kgb Agent Poisoned, Former Kgb Agent Explains Brainwashing America, Former Kgb Agent, Former Kgb Agent Killed In London, Kgb Agent Guillou, Soviet Gru Agent, Genscher Kgb Agent, Kgb Agent Halloween Costume, Hot Kgb Agent, Kgb Agent Interview, Kgb Agent In Usa, Kgb Agent In India, Kgb Agent In Mi6, Kgb Agent In Cia, Kgb Agent In Bond Movie, Kgb Agent In America, Kgb Agent In Vancouver, Kgb Agent Killed In London, Former Kgb Agent Interview, Kgb Agent Jack Barsky, Kgb Agent Job, Kgb Agent James Bond, Kgb Special Agent Job Description, Kgb Special Agent Job, Kgb Agent Killed In London, Kgb Agent Kidnapped, Kgb Agent Killed In England, Khamenei Kgb Agent, Kirill Kgb Agent, Kekkonen Kgb Agent, Kgb Agent Litvinenko, Kgb Agent Login, Kgb Agent London, Kgb Agent Leaves Canada, Soviet Agent Lucy, Russian Kgb Agent Lisa, Ex Kgb Agent Leaves Canada, Kgb Agent Meaning, Kgb Agent Murdered, Kgb Agent Movies, Kgb Agent 60 Minutes, Kgb Agent In Mi6, Kgb Agent In Bond Movie, Merkel Kgb Agent, Kgb Agent Names, Soviet News Agency, Kgb Agents In New Jersey, A Former Kgb Agent Needs Your Help, Nyiso Kgb Agent, Kgb Agent On 60 Minutes, Kgb Agent Online, Kgb Agent Record Of Alien Races, Ex-kgb Agent On Indoctrination & Demoralization, Obama Kgb Agent, Oswald Kgb Agent, Agent_of_kgb, By\u0142y Agent Kgb Opowiada, Kgb Agent Putin, Kgb Agent Poisoned, Kgb Agent Polonium, Kgb Agent Pay, Kgb Agent Philippines, Kgb Special Agent Philippines Salary, Kgb Agent With Frightening Psychic Abilities, Putin Kgb Agent Reagan, Palme Kgb Agent, Prodi Kgb Agent, Kgb Agent Ranks, Kgb Agent Record Of Alien Races, Kgb Agent Russia, Kgb Agent Requirements, Kgb Agent Radiation Poisoning, Kgb Agent Rudolf Abel, Soviet Agent Rudolf Abel, Putin Kgb Agent Reagan, Kgb Special Agent Review, Russian Kgb Agent Alexander Litvinenko, Kgb Agent Salary, Kgb Agent Subversion, Kgb Special Agent, Kgb Special Agent Salary, Kgb Special Agent Training, Kgb Special Agent Philippines, Kgb Sleeper Agent, Kgb Special Agent Review, Kgb Secret Agent, Kgb Special Agent Philippines Salary, Kgb Agent Training, Kgb Agent Tells You What The Illusion Is, Kgb Agent Test, Kgb Agent Tv Show, Kgb Special Agent Training, Kgb Secret Agent Test, Kgb Agents In The Us, Top Kgb Agent, Kgb Agent Uniform, Kgb Agent Usa, Kgb Undercover Agents, Kgb Agent Vladimir Putin, Kgb Agent Vergiftet, Kgb Agent In Vancouver, Vostok Kgb Agent Automatic, Vostok Kgb Agent Automatic Watch, Kgb Agent Wiki, Kgb Agent With Frightening Psychic Abilities, Kgb Agent Weapons, Kgb Agent Watches, Kgb Agent Warns, Kgb Agents Who Defected, Kgb Woman Agent, Soviet Agent Winter Soldier, Soyuz Kgb Agent Watches, Kgb Agent Tells You What The Illusion Is, Kgb Agent Yuri Bezmenov, Kgb Agent Youtube, Kgb Agent Tells You What The Illusion Is, Ex Kgb Agent Yuri, Ex Kgb Agent Youtube, Yuri Kgb Agent, Youngest Kgb Agent, Putin Wife,Putin News,Putin Net Worth,Putin Height,Putin Bay,Putin Memes,Putin Trump,Putin On The Ritz,Putin Age,Putin Trump Meeting,Putin And Trump,Putin Age,Putin And Trump Meeting,Putin Approval Rating,Putin And Obama,Putin Ally Crossword,Putin Assad,Putin And North Korea,Putin And Reagan,Putin As A Child,Putin Bay,Putin Bear,Putin Birthday,Putin Biography,Putin Bay Hotels,Putin Badass,Putin Bay Weather,Putin Blueberry Hill,Putin Bay Ferry,Putin Black Belt,Putin Children,Putin Calendar,Putin Clown,Putin Cartoon,Putin Chechnya,Putin Crying,Putin Canada,Putin Crimea,Putin Corruption,Putin Clinton,Putin Daughters,Putin Dog,Putin Documentary,Putin Dead,Putin Dog Merkel,Putin Definition,Putin Dancing,Putin Dolphins,Putin Drawing,Putin Dancing Gif,Putin Election,Putin Eating Popcorn,Putin English,Putin Election Results,Putin Erdogan,Putin Education,Putin Economy,Putin Eyes,Putin Exxon Deal,Putin Eye Color,Putin Family,Putin Food,Putin Funny,Putin Face,Putin Facts,Putin French,Putin Fishing,Poutine Fries,Putin Fascist,Putin Funny Face,Putin Gif,Putin Genocide,Putin Global Warming,Putin Gymnast,Putin Wife,Putin Gun,Putin Glasses,Putin Gangster,Putin Government,Putin Gorbachev,Putin Height,Putin Horse,Putin House,Putin Horseback,Putin Hockey,Putin History,Putin Hunting,Putin Hillary,Putin Human Rights,Putin Home,Putin Interview,Putin Images,Putin Israel,Putin Iq,Putin Isis,Putin In French,Putin Island,Putin Inauguration,Putin In Power,Putin Instagram,Putin Judo,Putin Jill Stein,Putin Journalists,Putin John Oliver,Putin Jehovah,Putin Jw,Putin Judo Gif,Putin Jesus,Putin James Bond,Putin Jehovah Witness,Putin Kgb,Putin Korea,Putin Karate,Putin Kremlin,Putin Kleptocracy,Putin Kim Jong Un,Putin Kraft Ring,Putin Kabaeva,Putin Khuilo,Putin Kid,Putin Laughing,Putin Laughing Gif,Putin Le Pen,Putin Languages,Putin Latest News,Putin Loves Trump,Putin Lollipop,Putin Likes Trump,Putin Limo,Putin Leadership,Putin Memes,Putin Merkel Dog,Putin Married,Putin Merkel,Putin Makeup,Putin Mask,Putin Martial Arts,Putin Meaning,Putin Macron,Putin Mansion,Putin News,Putin Net Worth,Putin North Korea,Putin New Wife,Putin Netanyahu,Putin Nato,Putin Net Worth Wiki,Putin Name Meaning,Putin Nickname,Putin Nuclear War,Putin On The Ritz,Putin On A Horse,Putin On Trump,Putin On North Korea,Putin Obama,Putin On The Ritz Gif,Putin On Syria,Putin Opposition,Putin On Snl,Putin On The Ritz Meme,Putin President,Putin Piano,Putin Palace,Putin Political Party,Putin Picture,Putin Poison,Putin Propaganda,Putin Puns,Putin Pop Song,Putin Popularity,Putin Quotes,Putin Quotes On Obama,Putin Queen Elizabeth,Putin Quotes Funny,Putin Quizlet,Putin Queen Elizabeth Stairs,Putin Quotes On Trump,Putin Quora,Putin Quote Immigrants,Putin Quebec,Putin Russia,Putin Reagan,Putin Riding Trump,Putin Rise To Power,Putin Reelection,Putin Richest Man In The World,Putin Riding A Ritz Cracker,Putin Response,Putin Ritz,Putin Rainbow,Putin Snl,Putin Syria,Putin Song,Putin Smiling,Putin Speech,Putin Shirt,Putin Speaking English,Putin Singing,Putin Salary,Putin Super Bowl Ring,Putin Trump,Putin Trump Meeting,Putin Twitter,Putin Trump Meme,Putin Trump Horse,Putin Trump Kiss,Putin Term Limit,Putin Trump Gif,Putin Term,Putin Today,Putin Ukraine,Putin Ussr,Putin Us Visit,Putin Unicorn,Putin Us Elections,Putin Un,Putin Undercover,Putin Urban Dictionary,Putin United Nations,Putin Us Relations,Putin Vs Trump,Putin Vs Obama,Putin Vladimir,Putin Video,Putin Vodka,Putin Vs Stalin,Putin Visits Trump,Putin Visit To White House,Putin Vampire,Putin Vs Obama Meme,Putin Wife,Putin Wiki,Putin Wealth,Putin Wink,Putin War,Putin Ww3,Putin Watch,Putin Winking Gif,Putin With Animals,Putin Walking,Putin Xi Jinping,Putin X Obama,Putin X Reader,Putin Xi,Putin And Trump,Putin And Obama,Putin And Assad,Putin And North Korea,Putin And Reagan,Putin And The Ritz,Putin Young,Putin Youtube,Putin Yacht,Putin Youth,Putin Yeltsin,Putin Yume,Putin Years As President,Putin Young Pictures,Putin Youth Army,Putin Yarmulke,Putin Zodiac Sign,Putin Zakaria,Putin Zassal,Putin Zassal Lyrics,Putin Zero Hedge,Putin Zeman,Putin Zil Limousine,Putin Zuma,Putin Za Makedonija,Putin Zapretio Albancima,
Enthüllt – Stasi-Akte IM Melanie Im Bett mit Erich Mielke
Become a Patron!
True Information is the most valuable resource and we ask you to give back.


Wo Ausländer in der DDR Frauenkontakte suchten, lag am Ende meist das MfS mit im Bett.
(BILD: IMAGO)
HALLE (SAALE).
Das Mädchen wird an einem Sommerabend aufgegriffen, mitten in der Innenstadt von Halle. Zwei Polizisten bemerken ein Pärchen in einem Auto, routinemäßig werden die Papiere kontrolliert. Das Mädchen, gerade 18 Jahre alt, stammt aus Halle. Der Mann, mit dem sie zusammen ist, hat einen jugoslawischen Pass.
Nichts Kriminelles, keine Straftat weit und breit. Doch die Staatssicherheit, die die eingehenden Meldungen der Polizei routinemäßig prüft, sieht hier das, was sie einen „Ansatzpunkt“ nennt. Die 18-Jährige ist bereits zweimal zuvor in Gesellschaft von Personen angetroffen worden, die in der sogenannten Reisedatenbank der Abteilung VI des Ministeriums für Staatssicherheit erfasst sind. „Sie ist westlich eingestellt und verherrlicht die westliche Lebensweise“, vermerkt die Akte. Keine Kritik, sondern ein Grund mehr für Leutnant Horst Frauendorf, die junge Frau an ihrem Arbeitsplatz in einem großen Kaufhaus zu kontaktieren. Das Ziel ist, so steht es in der Akte, das lebensfrohe Mädchen als Inoffizielle Mitarbeiterin zu gewinnen, um ihre Verbindungen ins „Jugomilieu“ (MfS) zur Überwachung der in der DDR beschäftigten Arbeiter aus dem wegen seiner Alleingänge misstrauisch beäugten Bruderland zu nutzen.
Menschen weichkochen
Die Frau lehne „kategorisch ab“, notiert Frauendorf nach dem ersten Treff. Aber das MfS hat Methoden, Menschen weichzukochen. Allein die Angst, immer wieder kontaktiert zu werden, ändert die Ansicht der Hallenserin. Aus „politischer Überzeugung“, so steht es in der Akte, die das MfS unter dem Namen „IM Melanie“ führen wird, willige sie ein, Ausländer aus dem nicht-sozialistischen Ausland und Jugoslawien im Auge zu behalten.
IM Melanie ist nicht allein. Gerade die wenigen Ausländer, die sich zumeist aus beruflichen Gründen in der DDR aufhalten, gelten der Staatssicherheit als Gefahrenquelle. Nicht von ungefähr, wie die Unterlagen zeigen, die jetzt in der Außenstelle der Jahn-Behörde in Halle aufgetaucht sind: Mal singen bundesdeutsche Monteure „nach 22.20 Uhr faschistische Lieder“ wie ein IM Rose aus der Clubgaststätte in Halle-Süd berichtet. Mal versuchen harmlos wirkende Bauarbeiter in Schkopau die „Infiltration mit dem Gedankengut staatsmonopolistischer Herrschaftskreise“. Mal schmuggeln Ungarn hochwertige Konsumgüter ein, mal werden bei Jugoslawen „westliche Drogen in größerer Menge“ entdeckt.
Neben Kellnern, Kneipern und Hotelmitarbeitern, die für die Stasi versuchen, „den wahren Grund des Aufenthaltes“ von Bauarbeitern, Handlungsreisenden oder Wissenschaftlern aus dem Westen festzustellen, sind es vor allem junge Frauen wie Melanie, die gleichaltrige Anna und die etwas ältere Lisa, die für die Staatssicherheit interessant sind. Sie alle verkehren Mitte der 80er Jahre in einem sinnenfrohen Milieu aus Nachtbars und Kneipen in der Chemiearbeiterstadt Halle, immer auf der Suche nach dem schnellen Spaß, aber auch nach der großen Liebe. Es ist keine Prostitution im landläufigen Sinne, was die Mädchen betreiben. Zwar fahren sie normalerweise trotzdem zweimal im Jahr zur Leipziger Messe hinüber, wo ausländische Besucher 200 Westmark für „einmal GV“ zahlen, wie es in den Stasi-Akten heißt. Aber auch zwischen heimischen Adressen wie dem „Tusculum“, dem „Scirocco“ und der Panorama-Bar gibt es Westgeld-Präsente von Holländern, Bulgaren und Libyern.
Weg in den Westen
Wer richtig Glück hat, findet sogar einen Jugoslawen, der ihn heiratet. Das ist, zum Leidwesen des inzwischen zum Hauptmann beförderten Frauendorf, ein unwiderstehlicher Weg in den Westen. Dorthin dürfen jugoslawische Staatsbürger frei reisen. Heiraten sie eine DDR-Bürgerin, darf die mit rüber – und ist sie erst im Westen, wird sie zur Bundesbürgerin. Was ihrem jugoslawischen Mann automatisch ein Aufenthaltsrecht in der Bundesrepublik verschafft. Eine Win-Win-Aktion für beide Seiten, gegen die die Stasi vergebens nach einem Mittel sucht. Zehntausend Mark zahlen jugoslawische Männer für eine solche Scheinehe. Zwei Schachteln Zigaretten zu acht Mark gibt es pro Treff mit dem Führungsoffizier für die Frauen, die rechtzeitig vorwarnen sollen, wenn Bekannte aus dem Bereich „operativ bedeutsame NSW-Einreisende“ verdächtige Bemerkungen machen.
Die Akten sind ein Abgrund an Lügen, Schmeichelei und Notwehr, aufgeschrieben in konspirativen Wohnungen, die „Peter“ heißen. Hier sitzen MfS-Offiziere wie Frauendorf oder sein Kollege Hoffmann aller zwei Wochen mit ihren „Jugonutten“ (MfS-Akte) zusammen, um Ausländer in der DDR gemäß einer zentralen Planungsvorgabe von Minister Erich Mielke „unter operativer Kontrolle“ zu halten und „operativ zu bearbeiten“. Aufgeschrieben wird alles, was IM Melanie nur einfällt: Mal geht es um geschmuggelte Autoteile, mal um mutmaßlich demnächst einlaufende Ausreiseanträge, mal um Gerüchte über Aids-Fälle im Bezirk Halle und mal um den Wunsch, das MfS möge bei der Suche nach einem neuen Arbeitsplatz in der Gastronomie helfen. Tut es, gern sogar, denn Bars und bestimmte Kneipen gelten nicht nur den jungen Frauen als bestes Jagdgebiet, sondern auch ihren Führungsoffizieren. Hier treffen die einsamen Monteursherzen die keinem Abenteuer abgeneigten Mädchen, die sich nach Parfüm, Jeans und Quarzuhren aus dem Intershop sehnen.
Realität holt gelogene Dementi ein
Stasi-Chef Erich Mielke liegt meist mit im Bett, wie die Akten verraten. Mehrfach äußern Anna und Melanie den Verdacht, andere Stammbesucherinnen der einschlägigen Treffs arbeiteten für das MfS. Eine schwierige Situation für Frauendorf und Hoffmann, die es ja genau wissen, nun aber glaubwürdig dementieren müssen.
Im Fall von IM Melanie, die nach mehreren Lektionen mit „fachlich-tschekistischen Grundkenntnissen“ (MfS) ausgestattet ist und eine „positiv-operative Entwicklung“ nimmt, holt die Realität das gelogene Dementi ein. Schon im Frühjahr 1987 äußert die 20-Jährige, sie habe eine „allgemeine Unlust an der Zusammenarbeit“ mit dem MfS. Hoffmann greift noch einmal in die Kasse und spendiert für 54,10 Mark ein Geburtstagsgeschenk – Kosmetikartikel aus der Jugendmode. IM Melanie aber ist verloren. Noch im Sommer schließt die Staatssicherheit ihre Akte.
Revealed – Brazil Truth Commission Releases Report
Become a Patron!
True Information is the most valuable resource and we ask you to give back.

Truth commissioners giving the report to Brazilian President Dilma Rousseff this morning. Photo Credit: National Truth Commission website.
Almost thirty years after the end of Brazil’s military dictatorship, the Comissao Nacional da Verdade [National Truth Commission] today released its long awaited report on human rights violations by the security forces between 1964 and 1985. The report, which took two-and-a-half years to complete and totals over 1000 pages, represents the first formal attempt by Brazil as a nation to record its repressive past and provide a detailed accounting of the system of repression, the victims of human rights violations, as well as the identities of those who committed those crimes.
In contrast to the U.S. Senate report on torture released yesterday in Washington which redacted even the pseudonyms of CIA personnel who engaged in torture, the Brazilian report identified over 375 perpetrators of atrocities by name.
The report contains detailed chapters on the structure and methods of the repression during the military era, including targeted violence against women and children. The commission identified over 400 individuals killed by the military, many of them “disappeared” as the military sought to hide its abuses. During its investigation, the Commission located and identified the remains of 33 of the disappeared; some 200 other victims remain missing.
The report also sheds significant light on Brazil’s role in the cross-border regional repression known as Operation Condor. In a chapter titled “International Connections: From Repressive Alliances in the Southern Cone to Operation Condor,” the Commission report details Brazil’s military ties to the coup in Chile, and support for the Pinochet regime, as well as identifies Argentine citizens captured and killed in Brazil as part of a Condor collaboration between the Southern Cone military regimes.
This report opens a Pandora’s box of historical and legal accountability for Brazilians. For now it provides a verdict of history, but eventually the evidence compiled by the commission’s investigation could lead to a judicial accounting. “The Truth Commission’s final report is a major step for human rights in Brazil,” according to Brown University scholar, James Green, “and the pursuit of justice for the victims of the state’s terror.”
In its recommendations, the Commission took the bold step of calling for a repeal of Brazil’s 1979 amnesty law which has, to date, shielded military officers from human rights prosecutions.
Those prosecutions could be aided by evidence from declassified U.S. documentation. In support of the Commission’s work, the Obama administration agreed to a special declassification project on Brazil, identifying, centralizing and reviewing hundreds of still secret CIA, Defense and State Department records from the 1960s, 1970s and 1980s. Last June, Vice President Biden personally delivered 42 documents into President Dilma Rousseff’s hands; more recently the U.S. Embassy passed another tranche of over 100 records, many of them from the CIA, to the Brazilian government. As part of a commitment Biden made to open U.S. archives, the administration is continuing to review hundreds of additional records to declassify and provide to the Brazilian government next year.
The Commissioners presented their report to President Rousseff on International Human Rights Day. Rousseff, herself a victim of torture by electric shock during the military dictatorship, was “moved to tears” as she received the report and received a standing ovation from the crowd that had gathered for the ceremony, according to the Washington Post. In her speech accepting the report, the President stated that “We hope this report prevents ghosts from a painful and sorrowful past from seeking refuge in the shadows of silence and omission.”
Read the three-volume Report
Brazil Truth Commission Report Website
Read Key Documents Provided by the United States
Document l: Department of State, “Widespread Arrests and Psychophysical Interrogation of Suspected Subversives,” Confidential, April 18, 1973
This intelligence cable, sent by the U.S. Consul General in Rio de Janeiro, provides detailed reporting on a “sophisticated and elaborate psychophysical” method of torture being employed by the Brazilian military against suspected militants. In response to growing international condemnation of human rights violations, the cable suggests, the Brazilian torturers have adopted more modern interrogation methods that leave less visible evidence of abuses. In cases where detainees are “eliminated,” the military is also deceiving the press by claiming they were killed in a “shoot-out” while trying to escape.
The cable was declassified on June 5, 2014, only eleven days before Biden’s trip to Brazil in order for him to provide it to President Rousseff as a diplomatic gesture. But key sections of the document are redacted, presumably at the request of the CIA, that identify the military units responsible for these atrocities — information that would be of critical use to the Brazilian Truth Commission as it attempts to hold the military accountable for the atrocities of the past.
Document 2: Department of State, “Political Arrests and Torture in São Paulo,” Confidential, May 8, 1973
The Consul General in Sao Paulo, Frederic Chapin, reports on a source described as “a professional informer and interrogator working for the military intelligence center in Osasco,” an industrial suburb of Sao Paulo. The source has provided graphic details on methods of abuse, including a Brazilian form of “waterboarding” that involved putting prisoners in vats of water that forced them to stand on their tiptoes for prolonged periods of time to be able to breath. The informant also provides a description of methods of executing prisoners so that their bodies could not be identified. Prisoners would be machine gunned from head to toe — a method referred to as “sewing” the suspect up.
This document was declassified in 2005, and initially provided to the Truth Commission by National Security Archive Brazil project director Peter Kornbluh. It played a key role in enabling researchers to identify the April 18, 1973, cable on psychophysical abuses, which is cited as a reference telegram. A memorandum of conversation with the informant/torturer, however, is also cited in this document and would be of exceptional value to the Truth Commission in obtaining additional information about the torture center in Osasco.
Document 3: Department of State, “Allegation of Torture in Brazil,” Secret, July 1, 1972
U.S. Ambassador William Rountree advises the State Department that openly protesting human rights “excesses” by the Brazilian military government will be counterproductive and “damage our general relations.” Ambassador Rountree encourages the State Department to oppose a piece of human rights legislation known as the “Tunney Amendment” which would link U.S. aid to Brazil to a U.S. government certification that the Brazilian regime was not engaged in human rights violations.
Document 4: Department of State, “The Esquadrão da Morte (Death Squad),” Limited Official Use, June 8, 1971
Ambassador Rountree submits an 11-page report on death squad activity in Brazil. He advises that there has been an “upsurge” of victims of unofficial operations in recent months, believed to be the work of off-duty policemen. In Sao Paulo, the death squads are reportedly led by Sergio Fleury, who has now been charged in at least one murder. Some of the victims are common prisoners, others political figures and militant opponents of the regime. Much of the information in the report is gleaned from newspaper articles; the report appears to contain almost no intelligence information.
Document 5: Department of State, “Conditions in DEOPS Prison as told by Detained American Citizen,” Confidential, October 7, 1970
This memorandum of conversation contains a report by a U.S. businessman, Robert Horth, who was detained by the military police in an apparent case of mistaken identity. Horth relates hearing from fellow Brazilian prisoners about torture at the prison where he is held in downtown Sao Paulo. The torture techniques include the Parrot Perch — known in Portuguese as “pau de arara” — and electrical shock to all parts of the body, as well as the “telephone technique” where an interrogator stands behind the seated prisoner and smacks both sides of his/her head repeatedly, almost destroying their eardrums.
PI – FBI Cyber Division Bulletin
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
FBI Cyber Division Private Industry Notification
- 4 pages
- TLP: GREEN
- October 2, 2014
(U) This Private Industry Notification (PIN) highlights the use of Global Positioning Systems (GPS) jammers by criminals to thwart law enforcement response and investigation into cargo thefts in the United States. Since at least February 2012, various law enforcement and private sector partners have reported that GPS tracking devices have been jammed by criminals engaged in nefarious activity including cargo theft and illicit shipping of goods. Although banned by federal law, the jammers are readily available over the Internet and easy to employ.
(U) GPS Jammers are Small and Unobtrusive
(U) GPS jammers are transmitters that block tracking devices from acquiring GPS broadcast signals by transmitting electromagnetic interference (noise) on the same frequency. They come in many shapes and sizes, with varying capabilities. Plugged into a standard cigarette lighter jack, a small jammer (pictured right) operating in the vehicle will disrupt GPS logging or GPS tracking systems for a radius of up to five yards. Mid-sized and larger jammers typically block a combination of GPS, cellphone, Wi-Fi, and other signals and thus also prevent the tracker from wirelessly reporting any location or status data. In a test conducted by a federal law enforcement agency, GPS jamming devices were determined to be effective to approximately 65 feet. A large GPS jammer can disrupt any tracking device or receiver within a radius of several hundred yards.
Cargo Theft Groups Employ Jammers to Mask GPS Tracking Devices
(U) Auto thieves shipping vehicles to China used GPS jammers placed in shipping containers in an attempt to thwart tracking of the containers, according to July 2014 information from the National Insurance Crime Bureau. In 46 reported incidents, the thieves placed one or more GPS jammers in cargo containers with stolen automobiles. The devices were made in China and could be bought for approximately $14.00 over the internet. The use of the GPS jammers was an apparent attempt by thieves to thwart the tracking of the shipping containers.
(U) Cargo thieves in North Florida used GPS jammers with a stolen refrigerated trailer containing a temperature controlled shipment, according to a July 2014 report from the Pharmaceutical Cargo Security Coalition. In this incident, the hauling tractors were swapped out by the cargo thieves. The Miami based suspects were ultimately stopped and apprehended by the Florida Highway Patrol in mid-Florida on a routine vehicle stop; the shipment was recovered intact. Discovered, hidden inside of the trailer’s refrigerator unit, were portable GPS jamming devices hooked unobtrusively to a battery located inside the unit. The trailer, although not equipped with a visible GPS tracking device, was treated by the thieves as if there were a device on or in the trailer. It is reasonable to believe that the individuals who planted the jammer felt that there may have been a tracking device secreted somewhere inside the shipment and used the GPS jammer to thwart the tracking of the shipment.
(U) Sales and Use of Jamming Devices is Illegal in the United States
(U) Federal law prohibits the marketing, sale, importation, or use of a transmitter (e.g., a jammer) designed to block, jam, or interfere with wireless communications. The Federal Communications Commission (FCC) has issued Enforcement Advisories and has also ordered numerous online retailers to stop selling signal jamming devices. A retailer that receives a second warning could face a fine of up to $16,000 for each day on which a jammer was illegally marketed, up to a maximum of $122,500. The FCC has also issued actions with substantial fines against individuals caught operating these devices within U.S. territory. Jammers, which are sometimes used to avoid cell phone distractions or evade surveillance, could produce “disastrous consequences by precluding the use of cell phones to reach life-saving 9-1-1 services provided by police, ambulance, and fire departments,” according to the FCC. Though a limited exception exists for use by authorized federal agencies, jammers have no lawful consumer use. Accordingly, mere possession of a jammer with intent to violate federal law may subject the device to seizure.
Cryptome unveils CIA Torture Pseudonyms
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
PaulD sends:
The press has been hard at work uncovering the pseudonyms used and nailing down the true identities of the site. I compile them here.
The most important outstanding questions: Who is Officer “2”, who are Detainees “R” & “S,” and where is detention site “red?” While I feel pretty strongly about redacting the names of low-level personnel from the NSA slides, which are technical in nature, but I have zero interest in protecting torturers. The public has a right to know where these black sites were, and the detainees deserve a name and a fair trial.
Detention sites (Known):
BLACK – RomaniaBLUE – Poland
BROWN – Afghanistan
COBALT – Afghanistan
GRAY – Afghanistan
GREEN – Thailand
INDIGO – Guantanamo
MAROON – Guantanamo
ORANGE – Afghanistan
VIOLET – Lithuania
Detention site (unknown)RED – This could be an additional site in one of the above countries, or someplace entirely different. It is mentioned only once in the report, on page 140 of 499, and the entry is almost entirely redacted.
Companies:
Company Y – Mitchell, Jessen & Associates, based in Spokane, Washington.
Businesses:
Business Q – Associated with Zubair, associated with Hambali
Torture Doctors:
“Grayson Swigert” – James Mitchell”Hammond Dunbar” – Bruce Jessen
CIA Officers:
CIA Officer 1 – COBALT Site manager – Matthew ZirbelCIA Officer 2 – Torturer at COBALT and BLUE – “untrained and unqualified” “hung detainees up for long periods with their toes barely touching the ground”. A litany of other abuses are mentioned. Received a one year letter of reprimand, got bonuses anyway. Retired from CIA in 2004.
Assets:
Asset X – Directly involved in the capture of KSM.Asset Y – Reports on Janat Gul
Persons:
Person 1 – al-Ghuraba group member, with an interest in airplanes and aviation. “intelligence indicates the interest was unrelated to terrorist activity.”
Detainees:
Detainee R – Held by foreign government, rendered to CIA custodyDetainee S – Held by foreign government
Sources:
http://www.reuters.com/article/2014/12/10/us-usa-cia-torture-lithuania-idUSKBN0JO18M20141210
http://www.historycommons.org/entity.jsp?entity=zirbel_1
https://news.vice.com/video/the-architect?utm_source=vicenewsfb
http://www.wbrz.com/news/psychologist-defends-harsh-cia-interrogations/
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 43, CM,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 00966/1517 | CMIEL KAZIMIERZ |
| IPN BU 002082/46 | CMIELEWSKI TADEUSZ |
| IPN BU 0772/2427 | CMOCH ANTONINA |
| IPN BU 00966/298 | CMOCH HENRYK |
| IPN BU 00234 | p.256 CMOLUCH ZYGMUNT |
Comedy Video – Dance, Vladimir Putin!
Confidential – The Fall of the Berlin Wall, 25th Anniversary
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
 In this Nov. 11, 1989, photo, East German border guards are seen through a gap in the Berlin wall after demonstrators pulled down a segment of it at Brandenburg gate. (LIONEL CIRONNEAU/Associated Press)  Hungarian soldiers removing barbed wire from the Austria-Hungary border — this part of the Iron Curtain came down starting on May 2, 1989. Washington, DC, November 9, 2014 – The iconic fall of the Berlin Wall 25 years ago today shocked international leaders from Washington to Moscow, London to Warsaw, as East German crowds took advantage of Communist Party fumbles to break down the Cold War’s most symbolic barrier, according to formerly secret documents from Soviet, German, U.S., Czechoslovak and Hungarian files posted today by the National Security Archive at George Washington University (www.nsarchive.org). The historic events of the night of November 9, 1989 came about from accident and contingency, rather than conspiracy or strategy, according to the documents. Crowds of East Berliners, already conditioned by months of refugee flights to the West and weeks of peaceful mass protests in cities like Leipzig, seized on media reports of immediate changes in travel restrictions — based on a bumbled briefing by a Politburo member, Günter Schabowski — and inundated the Wall’s checkpoints demanding passage. Television coverage of the first crossing that yielded to the self-fulfilling media prophecy then created a multiplier effect and more crowds came, ultimately to dance on the Wall. The documents show that the actual collapse of the Wall began with Hungarian Communist reformers who proposed in early 1989 to open their borders to the West, while seeking particularly West German foreign investment to solve Hungary’s economic crisis. Hungarian Communist leaders checked in with Soviet general secretary Mikhail Gorbachev in March 1989, letting him know they planned to take down the barbed wire; and Gorbachev — true to his “common European home” rhetoric — responded only that “we have a strict regime on our borders, but we are also becoming more open.” (Document 1) The Hungarian decision sparked a stream and then a flood of East German refugees.  Abandoned East German Trabants line the streets of Prague. Gorbachev himself unintentionally gave a signal that the Wall could fall in his press conference on June 15, 1989 after a successful visit to West Germany, where in response to a question about the Wall, he said that “nothing [was] permanent under the Moon” and connected German rapprochement to the building of the common European home. In fact, his conversations with Kohl and other members of the West German government created a real breakthrough in Soviet-FRG relations, which would stand Kohl in good stead in the difficult reunification talks during the next year (Document 2). Gorbachev especially reinforced the theme of European unity in his speech to the European Parliament in Strasbourg where he presented his vision of the common European home on July 7, 1989. After speaking about an essentially united Europe based on universal human values, it would be hard to argue in favor of its continued division. By August 1989, the Hungarian-initiated refugee crisis had become so acute that the West German embassy in Budapest had to shut down, unable to handle the hundreds of East Germans camped out there for visas. On August 19, Hungarian reformers even hosted a “Pan-European picnic” near the Austrian border, after which some 300 East Germans high-tailed across the former Iron Curtain. The subsequent negotiations on August 25, 1989 between Hungarian Communist leaders with West German chancellor Helmut Kohl and foreign minister Hans-Dietrich Genscher show the Hungarian calculation that only the deutschmark could save them, and by mid-September the Hungarians lifted all East-West controls (Document 3).  East German demonstrators take to the streets in Leipzig, October 9, 1989. Other world leaders were not at all eager for the Wall to fall, notably the British prime minister, Margaret Thatcher, who told Gorbachev on September 23 to ignore those NATO communiqués about German unification, that even her buddy, U.S. president George H. W. Bush opposed that kind of change (she would be wrong, when the time came. See document 4). As Gorbachev later commented to his Politburo on November 3, the West did not want German unification, but it wanted to prevent it “with our hands, to push us against the FRG” so as to head off any future Soviet-German cooperation — but Gorbachev believed European integration was the ultimate solution to Soviet economic problems (Document 6). Czechoslovakia was closer to East Germany than Hungary was, and after Hungary opened its gates, Prague quickly filled with East Germans willing to dump their Trabant cars in the streets for a chance to clamber over an embassy wall and flee to the West. By November 8, Prague had become so choked with East Germans that the hard-line Czechoslovak Communist Party’s Central Committee made a demarche to East Berlin demanding they open their borders — a moment of pressure from fellow Communists that played a key role in the East German party’s decision to announce revised travel regulations the next day (Document 7). The draft regulations were full of temporizing language and largely intended to let off steam while kicking the emigrant problem down the road. East Germans would have to apply for visas, and the vast majority who lacked passports would have to wait even longer for those. But the presentation of the new regulations came at the very end of a botched press conference from 6 to 7 p.m. Berlin time on November 9 by SED Politburo member Günter Schabowski, who did not know the back story, the hedges, the limitations meant by the drafters of the documents. Visibly rattled from the shouted questions about travel and the Wall, Schabowski read from his briefing papers the words “immediately, without delay” when asked about the timing of the changes that would allow any East German to emigrate (Document 9). Television news and the wire services as well promptly announced the opening of the borders, and in a kind of self-fulfilling prophecy reinforced by TV coverage, crowds of East Germans massed at the border crossings and ultimately persuaded the senior official at the largest inner-city checkpoint at Bornholmer Strasse to open the gates (a story told in fresh detail by Mary Elise Sarotte in her new book, The Collapse: The Accidental Opening of the Berlin Wall). Once Bornholmer opened, other crossings soon followed; and within hours, people were chipping off souvenir fragments from the concrete panels formerly surrounded by a “death strip” in which earlier Wall jumpers had died. So unexpected was the Wall opening that Helmut Kohl himself was not even in the country. Instead, the West German chancellor had gone to Warsaw to meet the new Solidarity leaders of that country, and work out some long-standing Polish-German tensions. The transcript of Kohl’s discussions with Lech Walesa show the Polish leader complaining that events in East Germany were simply moving too fast, and even predicting, presciently, that the Wall would fall in a week or two — at which point Kohl would have no time (or money) for poor Poland (Document 8). In Washington, the George H. W. Bush White House greeted the fall of the Wall not with joy or triumphalism (that would come much later, when the President was running for re-election in 1992), but anxiety and even fear about instability. When questioned by reporters why he did not show more elation, President Bush replied, “I am not an emotional kind of guy.” (Document 10) Bush’s caution and prudence were appreciated in Moscow, where Gorbachev’s messages to Kohl centered on preventing chaos and reducing instability, keeping “others within limits that are adequate for the time being….” (Document 11) But at Gorbachev’s side, his foreign policy adviser Anatoly Chernyaev in private let loose with one of the very few high-level expressions of real joy about the fall of the Berlin Wall. Chernyaev’s diary entry for November 10, 1989 (Document 12) contains the coda for the demise of the Iron Curtain, “the end of Yalta” and the Stalinist system, and a good thing, about time, in Chernyaev’s remarkable view.
THE DOCUMENTSDocument 1: Record of Conversation between Mikhail Gorbachev and Miklos Nemeth, Moscow, March 3, 1989. Document 2: Mikhail Gorbachev Press Conference Excerpts, Bonn, June 15, 1989. Document 3: Hungarian discussions (Nemeth/Horn) with West German leaders Kohl and Genscher, Bonn, August 25, 1989. Document 4: Conversation between Mikhail Gorbachev and Margaret Thatcher, Moscow, September 23, 1989. Document 5: Anatoly Chernyaev diary excerpt, October 5, 1989. Document 6: Notes from the Soviet Politburo Session, November 3, 1989. Document 7: Demarche from the Czechoslovak Communist Party to the GDR SED, November 8, 1989 (original German language version). Document 8: Record of Conversation between Helmut Kohl and Lech Walesa, Warsaw, November 9, 1989. Document 9: Documents from the East German Communist Party (SED) and the transcript of the Günter Schabowski press conference, November 9, 1989.[1] Document 10: President Bush Remarks to Reporters, Washington D.C., November 9, 1989. Document 11: Record of Telephone Conversation between Mikhail Gorbachev and Helmut Kohl, November 11, 1989. Document 12: Anatoly Chernyaev diary excerpt, November 10, 1989.
NOTE[1] Document 9 is courtesy of the German scholar Hans-Hermann Hertle, who was the first to reconstruct in detail the Schabowski press conference debacle, including his own transcription of the Schabowski video and publication of the backstory documents of drafts and SED decision making on travel regulations, in his seminal article, “The Fall of the Wall: The Unintended Dissolution of East Germany’s Ruling Regime,” in the Cold War International History Project Bulletin No. 12/13, Fall/Winter 2001, pp. 131-164. |
The Fall of the Berlin Wall, 25th AnniversaryDocuments show accident and contingency, anxiety in world capitalsEast German crowds led the way, with help from Communist fumbles, self-fulfilling TV coverage, Hungarian reformers, Czechoslovak pressure, and Gorbachev’s non-violence
“Masterpieces of History:” The Peaceful End of the Cold War in Europe, 1989, a National Security Archive Cold War Reader (Malcolm Byrne, series editor), By Svetlana Savranskaya, Thomas Blanton and Vladislav Zubok |
TOP SECRET – Qom Uranium Enrichment and Site R Bunkers
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
|
SECRET – U.S. Air Force Cyber Warfare Operations Education and Training Plan
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
AFSC 1B4X1 CYBER WARFARE OPERATIONS CAREER FIELD EDUCATION AND TRAINING PLAN
- 50 pages
- November 1, 2014
1. Purpose of the CFETP. This CFETP provides the information necessary for AFCFMs, MAJCOM Functional Managers (MFM), commanders, training managers, supervisors, trainers and certifiers to plan, develop, manage and conduct an effective and efficient career field training program. The plan outlines the initial skills, upgrade, qualification, advanced and proficiency training that individuals in AFSC 1B4X1 should receive in order to develop and progress throughout their careers. Initial skills training is the AFS specific training an individual receives upon entry into the AF or upon retraining into this specialty for award of the 3-skill level. This training is provided by the 333th Training Squadron (TRS) at Keesler AFB, MS. Upgrade training identifies the mandatory courses, task qualification requirements, Career Development Course (CDC) completion and correspondence courses required for award of the 5-, 7-, or 9-skill level. Qualification training is actual hands-on task performance training designed to qualify an airman in a specific duty position. This training program occurs both during and after the upgrade training process. It is designed to provide the performance skills and knowledge required to do the job. Advanced training is formal specialty training used for selected airmen. Proficiency training is additional training, either in-residence or exportable advanced training courses, or on-the-job training provided to personnel to increase their skills and knowledge beyond the minimum required for upgrade.
…
4. Specialty Description. Performs duties to develop, sustain, and enhance cyberspace capabilities to defend national interests from attack and to create effects in cyberspace to achieve national objectives. Conduct Offensive Cyberspace Operations (OCO) and Defensive Cyberspace Operations (DCO) using established tactics, techniques and procedures (TTPs) to achieve COCOM and national objectives. Executes command and control (C2) of assigned cyberspace forces and de-conflict cyberspace operations across the kinetic and non-kinetic spectrum. Supports cyberspace capability development, testing and implementation. Partners with DoD, interagency and Coalition Forces to detect, deny, disrupt, deceive, and mitigate adversarial access to sovereign national cyberspace systems. Related DoD Occupational Subgroup: 153100
…
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 42, CL,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 0993/1024 | CŁAPA ANNA |
| IPN BU 095/7 | CŁAPA MIROSŁAW |
| IPN BU 01133/775 | CŁAPA TADEUSZ |
| IPN BU 001089/120 | CŁAPCZYŃSKA IRENA |
| IPN BU 698/498 | CŁAPCZYŃSKI STEFAN |
Das STASI-Netzwerk in der Wirtschaft: Ausgangspunkt Kontrolle “linker” Firmen
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
STASI-Top-Agenten vor 1989.
Das STASI-Netzwerk in der deutschen Wirtschaft um die Jahreswende 2014/2015 ist weitaus größer als bislang befürchtet. Die Schwerpunkte liegen in der Unterwanderung der Finanz-/Immobilien- sowie der Medienbranche.
Der Nukleus ist dieKontrolle “linker” Firmen. Finanziert wird aus dem unterschlagenen Milliardenvermögen der “DDR”. Es wurden Milliarden veruntreut und der von der Kohl-Regierung eingesetzte Investigativ-Beamte, der viele Fakten ans Licht brachte, starb an einem überraschenden Herzinfarkt in seinem PKW vor einem Shopping-Center in Berlin. Ein weiterer mysteriöser Todesfall im Umfeld der STASI…
Es darf einen nichts mehr wundern, wenn selbst die Gauck-Behörde von STASI-Spitzeln wimmelte und heute noch wimmelt, deren Gehalt der Steuerzahler berappt, ebenso wie für die STASI-Agenten beim BND, BKA, Polizei, BGS, im Bundestag, in den Parlamenten, in der Justiz, im öffentlichen Dienst usw. etc. ppp.
Die Linkspartei lässt ihr Vermögen durch hochkarätige ehemalige Stasi-Mitarbeiter managen. Die alten Kader verwalten eine stark verzweigte und wenig transparente Firmengruppe, in der mehrere Gesellschafter ihre Anteile scheinbar auf eigene Rechnung halten. Tatsächlich aber hat die Partei mit ihnen nicht näher bekannte Treuhandverträge abgeschlossen, wie die “Welt am Sonntag” berichtete. Laut Satzung ist der Bundesvorstand der Linken für die finanziellen Mittel und das Vermögen verantwortlich – und somit allen voran die Parteichefs Katja Kipping undBernd Riexinger. Sie wollten sich nicht “zu Personen und biografischen Daten” in dem Firmenkonstrukt äußern.
Die “Welt” hakte nach der Sitzung des Parteivorstands am Montag in Berlin nach. Auf die Frage, warum Stasi-Agenten bei den Firmen das Sagen haben, antwortete Parteichefin Katja Kipping: “Die personellen Einsetzungen sind lange vor unserer Zeit passiert.” Und die Positionen dieser Treuhänder würden auch “nicht alle zwei Jahre neu besetzt”. Sie verwies auf einen wichtigen Punkt: Wer sich in ihrer Partei um ein Amt oder ein politisches Mandat bewerbe, müsse seine Biografie offenlegen. Doch diese Regelung gilt bislang nicht für die Firmengruppe der Linken.
Kipping betonte, dass sie gemeinsam mit ihrem Co-Vorsitzenden Riexinger darauf dringe, die Struktur des Firmenvermögens zu überprüfen. Zu diesem Zweck hätten der Schatzmeister und der Bundesgeschäftsführer der Partei eine Arbeitsgruppe ins Leben gerufen, die sich schon längere Zeit damit auseinandersetzen würde. Wann mit Ergebnissen zu rechnen sei, ließ Kipping offen.
Zwei Ex-Stasi-Kader an der Firmenspitze
Eng in das Stasi-Netzwerk eingebunden ist auch der Neubau der künftigen Zentrale der parteinahen Rosa-Luxemburg-Stiftung. Dafür hatte der Bundestag im Sommer gut 20 Millionen Euro bewilligt, die bis 2018 abgerufen werden können. Die Stiftung hat sich anschließend für drei Millionen Euro ein Grundstück zwischen dem Berliner Ost-Bahnhof und der East Side Gallery gesichert. Für dieses Vorhaben war schon im Juni 2013 eine Projektgesellschaft gegründet worden, die die Rechtsform einer GmbH & Co. KG hat.
Kommanditist ist eine Firma, die zwei ehemaligen Stasi-Kadern gehört: Matthias Schindler und Tilo Hejhal. Heute ist der eine Kaufmann, der andere Anwalt. Früher war Schindler im Rang eines Hauptmanns Referatsleiter in Erich Mielkes Spionageabteilung, Hejhal bespitzelte während seines Studiums als IM “Gottfried” Bekannte und Kommilitonen.
Schindler und Hejhal haben aber auch noch auf andere Weise Einfluss auf die GmbH & Co. KG: Über eine Beteiligungsfirma halten sie direkt und indirekt die Mehrheit an der Berliner Grundstücksgesellschaft Franz-Mehring-Platz 1 GmbH, die wiederum der persönlich haftende Gesellschafter der Projektgesellschaft ist. In dieser Immobilienfirma ist der ehemalige Stasi-Offizier Schindler zusätzlich Geschäftsführer. Sein Co-Geschäftsführer war zwei Monate lang ausgerechnet Bodo Ramelow, der sich an diesem Freitag im Thüringer Landtag zu Deutschlands erstem Linke-Ministerpräsidenten wählen lassen will.
Unwirsche Reaktion Ramelows in seinem Blog
Ramelow reagierte unwirsch, als die “Welt am Sonntag” seine pikante Geschäftsliaison mit Schindler enthüllte. In seinem Internettagebuch schreibt der Politiker, seine ehrenamtliche Tätigkeit für die Rosa-Luxemburg-Stiftung solle dadurch skandalisiert werden. Er habe lediglich eine “Kurzzeit-Geschäftsführertätigkeit” ausgeübt und die Firma nur vom 12. August bis zum 13. Oktober gemanagt. Nach der Fertigstellung des Neubaus gehe die Projektgesellschaft zudem in das Eigentum der Stiftung über.
Tatsächlich ist Ramelow dafür verantwortlich, dass die neue Denkfabrik der Linken in einer mit Stasi-Kadern durchsetzten Struktur entsteht. Denn der Politiker kümmert sich bereits seit drei Jahren um dieses Projekt, für das er als früherer Stiftungsvorstand verantwortlich war. Kaum vorstellbar, dass an ihm vorbei Wichtiges entschieden worden ist.
CSU-Generalsekretär Andreas Scheuer griff Ramelow scharf an. “In Deutschland darf es keinen Ministerpräsidenten geben, der mit hohen Ex-Stasi-Leuten heute noch gemeinsame Sache macht”, sagte Scheuer der “Welt”. SPD und Grüne dürften nicht jemanden zum Regierungschef machen, der ein Strippenzieher in einem Ex-Stasi-Netzwerk sei.
Der Direktor der Stasiopfer-Gedenkstätte Berlin-Hohenschönhausen, Hubertus Knabe, forderte die Linkspartei indes auf, die Rolle ehemaliger Stasi-Mitarbeiter in der Partei und bei der Verwaltung ihres Vermögens offenzulegen. Darauf habe die Öffentlichkeit ein Anrecht. “Es kann nicht sein, dass in der deutschen Politik Verhältnisse wie in Russland herrschen, wo ehemalige KGB-Mitarbeiter hinter den Kulissen unerkannt die Strippen ziehen”, sagte Knabe.
Er empfiehlt den Parteivorsitzenden Kipping und Riexinger, dass sie den Forschungsverbund SED-Staat an der Berliner Freien Universität jetzt mit einer unabhängigen Untersuchung beauftragen. “So, wie die Grünen ihre pädophile Vergangenheit aufgearbeitet haben, erwarte ich auch von der Linken, dass sie ihre Vergangenheit offenlegt – nicht floskelhaft, sondern konkret und mit personellen Konsequenzen”, sagte der Gedenkstättenleiter.
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 41, CI,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN 00 1052/1576 | CIABACH CZESŁAW FRANCISZEK |
| IPN BU 00335/23 | CIACEK STEFAN |
| IPN BU 0604/581 | CIACH ANDRZEJ |
| IPN BU 0911/88 | CIACH FRANCISZEK |
| IPN BU 001134/3578 | CIACH MAREK |
| IPN BU 01133/746 | CIACH MARIAN |
| IPN BU 00945/2710 | CIACH RYSZARD – JAN |
| IPN BU 00275/588 | CIACH STANISŁAW |
| IPN BU 001134/498 | CIACH STANISŁAW |
| IPN BU 0958/554 | CIACH STEFAN |
| IPN BU 748/244 | CIACH STEFAN |
| IPN BU 02187/6 | CIACHOSKI WŁADYSŁAW |
| IPN BU 645/168 | CIACHOWSKA DANUTA |
| IPN BU 644/987 | CIACHOWSKI ZBIGNIEW |
| IPN BU 0193/366 | CIACHUNOWICZ FRANCISZEK |
| IPN BU 0218/3008 | CIACHURSKI KAZIMIERZ |
| IPN BU 0993/1524 | CIACIA DANUTA |
| IPN BU 001121/2875 | CIACIARA BOGDAN |
| IPN BU 00232/48 | CIACKA STANISŁAW |
| IPN BU 0988/47 | CIAK WŁADYSŁAW |
| IPN BU 00448/710 | CIAŁOWICZ KRZYSZTOF |
| IPN BU 001134/5687 | CIAŁOWICZ KRZYSZTOF |
| IPN BU 00612/2004 | CIAMAGA ANTONI |
| IPN BU 0193/7533 | CIAMULSKI WACŁAW |
| IPN BU 00277/672 | CIANCIARA BOGDAN |
| IPN BU 001121/489 | CIANCIARA ZBIGNIEW |
| IPN BU 698/471 | CIANI-SULIKOWSKA MARIA |
| IPN BU 00945/568 | CIAPA CZESŁAW |
| IPN BU 636/1788 | CIAPA MARIAN |
| IPN BU 636/1801 | CIAPA MARIAN |
| IPN BU 0591/87 | CIAPA STANISŁAW |
| IPN BU 00945/2272 | CIAPAŁA KAZIMIERZ |
| IPN BU 00249/345 | CIAPIGA BRONISŁAW |
| IPN BU 0193/367 | CIAPUŁA CIAPUTA WŁADYSŁAW |
| IPN BU 0218/2807 | CIARA RYSZARD |
| IPN BU 001075/138 | CIARA ZBIGNIEW |
| IPN BU 001075/188 | CIARA ZBIGNIEW |
| IPN BU 00328/123 | CIARA ZBIGNIEW |
| IPN BU 001134/808 | CIARA ZBIGNIEW |
| IPN BU 0772/2407 | CIARACH MARIA |
| IPN BU 644/988 | CIARANEK ZENON |
| IPN BU 0891/399 | CIARCINSKI HENRYK |
| IPN BU 0806/883 | CIARCZYŃSKA JANINA |
| IPN 00 1043/1534 | CIARCZYŃSKA JANINA |
| IPN BU 0891/400 | CIARKA LUCJAN |
| IPN BU 0993/662 | CIARKA MARIAN |
| IPN BU 0892/105 | CIARKA STEFAN |
| IPN BU 0892/108 | CIARKA SZCZEPAN |
| IPN BU 0833/704 | CIARKA WINCENTY |
| IPN BU 0772/2408 | CIARKOWSKA ELŻBIETA |
| IPN BU 00283/1230 | CIARKOWSKI MIROSŁAW |
| IPN BU 0194/3034 | CIARKOWSKI WOJCIECH ANDRZEJ |
| IPN BU 0891/401 | CIARKOWSKI ZBIGNIEW |
| IPN BU 698/474 | CIAS DANUTA |
| IPN BU 0193/1572 | CIASNOCHA KAZIMIERZ |
| IPN BU 00277/980 | CIASNOWSKI WIESŁAW |
| IPN BU 001121/3165 | CIASNOWSKI WIESŁAW |
| IPN BU 001198/2414 | CIASTEK ANTONI |
| IPN BU 01000/2151 | CIASTEK FRANCISZEK |
| IPN BU 0218/324 | CIASTEK JANINA |
| IPN BU 0218/2603 | CIASTEK KAZIMIERZ |
| IPN BU 0242/3195 | CIASTEK WŁODZIMIERZ |
| IPN BU 0864/27 | CIASTKOWSKI KAZIMIERZ |
| IPN BU 0901/318 | CIASTKOWSKI TOMASZ |
| IPN BU 01000/209 | CIASTOŃ JÓZEF |
| IPN BU 0193/8393 | CIASTOŃ MARIANNA |
| IPN BU 0604/1618 | CIASTOŃ WŁADYSŁAW |
| IPN BU 001198/4815 | CIA ALEKSANDER |
| IPN BU 0967/179 | CIA BOGUMIŁ |
| IPN BU 001198/6663 | CIA JACEK |
| IPN BU 00612/3783 | CIA JAEK |
| IPN BU 0193/368 | CIA JAN |
| IPN BU 00945/2613 | CIA KAZIMIERZ |
| IPN BU 0193/1571 | CIA KRYSTYNA |
| IPN BU 01013/316 | CIA STANISŁAW |
| IPN BU 01013/25 | CIA STEFANIA |
| IPN BU 01013/26 | CIA TADEUSZ |
| IPN BU 0957/517 | CIALAK JAN |
| IPN BU 0194/474 | CIĄCKA HENRYK |
| IPN BU 01133/747 | CIĄCKA TADEUSZ |
| IPN 00 1043/1491 | CIĄĆKA HANNA |
| IPN BU 093/50 | CIĄGADLAK JAN |
| IPN BU 02042/632 | CIĄŻELA BOGDAN |
| IPN BU 426/1 | CIĄŻYŃSKA MARIA |
| IPN BU 00945/2496 | CIBA STANISŁAW |
| IPN BU 698/472 | CIBA STEFAN |
| IPN 00 1043/2021 | CIBA ZBIGNIEW ROMAN |
| IPN BU 685/243 | Cibicki Stanisław |
| IPN BU 00612/4241 | CIBOR ADAM |
| IPN BU 0967/102 | CIBOR ANDRZEJ |
| IPN BU 0942/306 | CIBOR ANNA |
| IPN BU 00612/694 | CIBOR JAN |
| IPN BU 00334/674 | CIBOR JAN |
| IPN BU 001198/4377 | CIBOR JAN |
| IPN BU 001134/3620 | CIBOR JAN |
| IPN BU 00966/1587 | CIBOR MIROSŁAW |
| IPN BU 0193/7441 | CIBOR TADEUSZ SŁAWOMIR JAN |
| IPN BU 0777/18 | CIBOR WŁODZIMIERZ |
| IPN BU 02042/333 | CIBOREK ANTONI |
| IPN BU 02042/669 | CIBOREK CELINA |
| IPN BU 0772/946 | CIBOREK HELENA |
| IPN BU 645/144 | CIBOREK KRYSTYNA |
| IPN BU 0951/1672 | CIBOREK PAWEŁ |
| IPN BU 0193/5380 | CIBOROWSKA (PIECYK) GENOWEFA |
| IPN BU 00448/623 | CIBOROWSKA DOROTA |
| IPN BU 001134/5599 | CIBOROWSKA DOROTA |
| IPN 00 1043/1749 | CIBOROWSKA GABRIELA |
| IPN BU 698/473 | CIBOROWSKA IRENA |
| IPN BU 698/475 | CIBOROWSKA JÓZEFA |
| IPN BU 00399/51 | CIBOROWSKI ARKADIUSZ |
| IPN BU 001134/4115 | CIBOROWSKI ARKADIUSZ |
| IPN BU 698/476 | CIBOROWSKI FELIKS |
| IPN BU 0958/455 | CIBOROWSKI JÓZEF |
| IPN BU 0305/384 | CIBOROWSKI LEOPOLD |
| IPN BU 0305/45 | CIBOROWSKI LEOPOLD |
| IPN BU 002082/738 | CIBOROWSKI MAREK |
| IPN BU 002086/2088 | CIBOROWSKI MAREK |
| IPN BU 00244/115 | CIBOROWSKI MARIAN |
| IPN BU 0833/123 | CIBOROWSKI STANISŁAW |
| IPN BU 00945/1881 | CIBOROWSKI STANISŁAW – MARIAN |
| IPN BU 00168/323 | CIBOROWSKI STANISŁAW MARIAN |
| IPN BU 644/989 | CIBOROWSKI WITOLD |
| IPN BU 01013/54 | CIBOROWSKI WŁADYSŁAW |
| IPN BU 645/140 | CIBOROWSKI WŁODZIMIERZ |
| IPN BU 00399/531 | CIBORSKA STANISŁAWA |
| IPN BU 001134/4872 | CIBORSKA STANISŁAWA |
| IPN BU 698/477 | CIBORSKI KONRAD |
| IPN BU 00689/92 | CIBULLA JAN |
| IPN BU 0772/2411 | CICHA IRENA |
| IPN BU 00277/899 | CICHA WIEŁSAW |
| IPN BU 001121/3085 | CICHA WIESŁAWA |
| IPN BU 0893/68 | CICHACZ ANDRZEJ |
| IPN BU 00334/670 | CICHACZ ELŻBIETA |
| IPN BU 001134/3611 | CICHACZ ELŻBIETA |
| IPN BU 0958/975 | CICHACZ KAZIMIERZ |
| IPN BU 093/62 | CICHALEWSKI HENRYK |
| IPN BU 0591/88 | CICHALEWSKI ROBERT |
| IPN BU 644/990 | CICHAŁA IZYDOR |
| IPN BU 001198/669 | CICHAWA BOLESŁAW |
| IPN BU 001198/3572 | CICHAWA DANIEL |
| IPN BU 698/478 | CICHAWA GENOWEFA |
| IPN 00 1052/930 | CICHAWA MAŁGORZATA TERESA |
| IPN BU 01000/2152 | CICHAWA STANISŁAW |
| IPN BU 0854/803 | CICHAWA WŁADYSŁAW |
| IPN BU 01133/816 | CICHAWA WŁADYSŁAW |
| IPN BU 01133/748 | CICHAWA ZBIGNIEW |
| IPN BU 710/364 | CICHAWA ZBIGNIEW |
| IPN BU 01000/2153 | CICHECKA ADELA |
| IPN BU 001134/3016 | Cichecka Jolanta |
| IPN BU 00612/1770 | CICHECKA MARIA |
| IPN BU 001198/4875 | CICHECKA MARIA |
| IPN BU 748/245 | CICHECKA WŁADYSŁAWA |
| IPN BU 00328/500 | CICHECKI ANDRZEJ |
| IPN BU 001134/1283 | CICHECKI ANDRZEJ |
| IPN BU 00945/602 | CICHECKI EDWARD |
| IPN BU 645/180 | CICHECKI JAN |
| IPN BU PF | 900/23 CICHECKI JAN |
| IPN BU 00283/443 | CICHECKI JAN |
| IPN BU 00768/321 | CICHECKI JAN |
| IPN BU 00966/225 | CICHECKI JUÓZEF |
| IPN BU 980/183 | CICHECKI KAZIMIERZ |
| IPN BU 0194/2015 | CICHECKI LESZEK |
| IPN BU 01133/749 | CICHECKI MARIAN |
| IPN BU 685/239 | Cichecki Stanisław |
| IPN BU 0912/1677 | CICHECKI TADEUSZ |
| IPN BU 00945/2559 | CICHECKI TADEUSZ |
| IPN BU 01434/216 | CICHECKI TADEUSZ |
| IPN BU 0604/1348 | CICHECKI ZBIGNIEW |
| IPN BU 0194/1577 | CICHECKI ZDZISŁAW |
| IPN BU 0806/725 | CICHEWICZ HALINA |
| IPN BU 0891/1877 | CICHEWICZ JAN |
| IPN BU 0912/1563 | CICHEWICZ KAZIMIERZ |
| IPN BU 00244/174 | CICHIŃSKI KAZIM. |
| IPN BU 0242/2861 | CICHOCKA (SĘKALSKA) MARZENA |
| IPN BU 0951/1776 | CICHOCKA ANNA |
| IPN BU 00448/222 | CICHOCKA BARBARA |
| IPN BU 001134/5185 | CICHOCKA BARBARA |
| IPN BU 00945/2199 | CICHOCKA BARBARA – ALICJA |
| IPN 00 1052/785 | CICHOCKA BARBARA JANINA |
| IPN BU 01133/750 | CICHOCKA DANUTA |
| IPN BU 0290/104 | CICHOCKA DANUTA |
| IPN BU 0290/105 | CICHOCKA ELŻBIETA |
| IPN BU 01175/1126 | CICHOCKA HANNA |
| IPN BU 0806/685 | CICHOCKA JÓZEFA |
| IPN BU 776/16 | CICHOCKA LEOKADIA |
| IPN BU 0912/335 | CICHOCKA LUCYNA |
| IPN BU 0833/689 | CICHOCKA MARIA |
| IPN BU 683/246 | CICHOCKA ROZALIA |
| IPN BU 0218/1021 | CICHOCKA STEFANIA |
| IPN BU 636/1787 | CICHOCKA STEFANIA |
| IPN BU 645/170 | CICHOCKA STEFANIA |
| IPN BU 0607/62 | CICHOCKA TERESA |
| IPN BU 001134/2543 | CICHOCKA WANDA BARBARA |
| IPN BU 0772/947 | CICHOCKA WŁADYSŁAWA |
| IPN BU 01133/752 | CICHOCKA ZUZANNA |
| IPN BU 00228/149 | CICHOCKI A. |
| IPN BU 0604/1244 | CICHOCKI ALEKSANDER |
| IPN BU 0772/948 | CICHOCKI ALEKSANDER |
| IPN BU 52/153 | CICHOCKI ANDRZEJ |
| IPN BU 002081/383 | CICHOCKI ANDRZEJ |
| IPN BU 002085/449 | CICHOCKI ANDRZEJ |
| IPN BU 00328/146 | CICHOCKI ANDRZEJ JÓZEF |
| IPN BU 001134/844 | CICHOCKI ANDRZEJ JÓZEF |
| IPN BU 001089/121 | CICHOCKI ANTONI |
| IPN BU 002086/686 | CICHOCKI ANTONI |
| IPN BU 01133/753 | CICHOCKI APOLONIUSZ |
| IPN BU 698/479 | CICHOCKI BOLESŁAW |
| IPN BU 0912/336 | CICHOCKI BRONISŁAW |
| IPN BU 01133/751 | CICHOCKI CICHOCKA WANDA |
| IPN BU 0193/369 | CICHOCKI CZESŁAW |
| IPN BU PF | 970/29 CICHOCKI CZESŁAW |
| IPN BU 0193/6059 | CICHOCKI EDWARD LEON |
| IPN BU 0911/97 | CICHOCKI HENRYK |
| IPN BU 00283/819 | CICHOCKI HENRYK |
| IPN BU 00744/600 | CICHOCKI HENRYK |
| IPN BU 001121/4324 | CICHOCKI HENRYK |
| IPN BU 0894/1 | CICHOCKI JAN |
| IPN BU 0194/2041 | CICHOCKI JAN |
| IPN BU 01079/187 | CICHOCKI JAN |
| IPN 00 1052/128 | CICHOCKI JAN |
| IPN BU 002085/180 | CICHOCKI JAN |
| IPN BU 0912/337 | CICHOCKI JERZY |
| IPN BU 01133/754 | CICHOCKI JERZY |
| IPN BU 01250/93 | CICHOCKI JERZY |
| IPN BU 00612/489 | CICHOCKI JERZY |
| IPN BU 00744/98 | CICHOCKI JERZY |
| IPN BU 001198/4285 | CICHOCKI JERZY |
| IPN BU 001121/3733 | CICHOCKI JERZY |
| IPN BU 0912/95 | CICHOCKI JÓZEF |
| IPN BU 0193/1573 | CICHOCKI JÓZEF |
| IPN BU 0967/94 | CICHOCKI JÓZEF |
| IPN BU 685/19 | CICHOCKI JÓZEF |
| IPN BU 0242/2013 | CICHOCKI JULIAN |
| IPN BU 0912/1255 | CICHOCKI KAZIMIERZ |
| IPN BU 0958/456 | CICHOCKI KAZIMIERZ |
| IPN BU 001121/139 | CICHOCKI KAZIMIERZ |
| IPN BU 636/1824 | CICHOCKI LEOPOLD |
| IPN BU 0892/418 | CICHOCKI LUCJAN |
| IPN BU 0772/949 | CICHOCKI LUDGER (LUDGIER) |
| IPN BU 52/155 | CICHOCKI MAREK |
| IPN BU 00966/203 | CICHOCKI MARIAN |
| IPN BU 0290/106 | CICHOCKI MIECZYSŁAW |
| IPN BU 0194/2114 | CICHOCKI PIOTR |
| IPN BU 0772/461 | CICHOCKI PIOTR |
| IPN BU 52/148 | CICHOCKI PIOTR |
| IPN BU 0902/117 | CICHOCKI ROMAN |
| IPN BU 636/1787 | CICHOCKI ROMAN |
| IPN BU 01434/459 | CICHOCKI ROMAN |
| IPN BU 0194/985 | CICHOCKI RYSZARD |
| IPN BU 0988/1006 | CICHOCKI RYSZARD |
| IPN BU 0866/88 | CICHOCKI STANISŁAW |
| IPN BU 00244/57 | CICHOCKI STANISŁAW |
| IPN BU 095/104 | CICHOCKI STANISŁAW |
| IPN BU 0242/2737 | CICHOCKI STEFAN |
| IPN BU 01013/28 | CICHOCKI TADEUSZ |
| IPN BU 01000/2154 | CICHOCKI WIACZESŁAW |
| IPN BU 01133/755 | CICHOCKI WŁADYSŁAW |
| IPN BU 001198/2603 | CICHOCKI WŁADYSŁAW |
| IPN BU 980/186 | CICHOCKI ZBIGNIEW |
| IPN BU 00612/1058 | CICHOCKI ZBIGNIEW |
| IPN BU 00170/360 | CICHOCKI ZDZISŁAW LEONARD I INNI |
| IPN BU 0854/1022 | CICHOCKI ZENOBIUSZ |
| IPN BU 0604/1672 | CICHOCKI ZENON |
| IPN BU 0193/6216 | CICHONSKI STEFAN |
| IPN BU 0242/450 | CICHOŃ (KOZIARSKA) HALINA |
| IPN BU 52/151 | CICHOŃ ANDRZEJ |
| IPN BU 776/17 | CICHOŃ ANNA |
| IPN BU 01000/2159 | CICHOŃ CZESŁAW |
| IPN BU 644/991 | CICHOŃ EMIL |
| IPN BU 0193/7594 | CICHOŃ EUGENIUSZ |
| IPN BU 00611/1411 | CICHOŃ GUSTAW |
| IPN BU 001198/2526 | CICHOŃ GUSTAW |
| IPN BU 00612/3410 | CICHOŃ JAN |
| IPN BU 00612/1229 | CICHOŃ JÓZEF |
| IPN BU 001198/4550 | CICHOŃ JÓZEF |
| IPN BU 01133/756 | CICHOŃ KAZIMIERZ |
| IPN BU 00612/575 | CICHOŃ KAZIMIERZ |
| IPN BU 0193/7854 | CICHOŃ MARIA |
| IPN BU 0911/89 | CICHOŃ MIECZYSŁAW |
| IPN BU 00415/460 | CICHOŃ MIECZYSŁAW |
| IPN BU 0193/8727 | CICHOŃ STANISŁAW |
| IPN BU 0194/2620 | CICHOŃ STANISŁAW |
| IPN BU 00612/4469 | CICHOŃ STANISŁAW |
| IPN BU 001198/7149 | CICHOŃ STANISŁAW |
| IPN BU 644/90 | CICHOŃ TADEUSZ |
| IPN BU 0218/3169 | CICHOŃ WALENTYNA |
| IPN BU 01133/757 | CICHOŃ WIKTOR |
| IPN BU 01000/84 | CICHOŃ WŁADYSŁAW |
| IPN BU 0193/6514 | CICHOŃSKA (CELMEROWSKA) IRENA HENRYKA |
| IPN BU 0806/2967 | CICHOŃSKA HANNA |
| IPN BU 0193/370 | CICHOŃSKA WŁADYSŁAWA |
| IPN BU 00612/4234 | CICHOŃSKI EUGENIUSZ |
| IPN BU 001198/6977 | CICHOŃSKI EUGENIUSZ |
| IPN BU 644/91 | CICHOŃSKI JÓZEF |
| IPN BU 00328/1300 | CICHOŃSKI PAWEŁ |
| IPN BU 001134/2211 | CICHOŃSKI PAWEŁ |
| IPN BU 0193/7747 | CICHOŃSKI RYSZARD |
| IPN BU 0891/402 | CICHOŃSKI STANISŁAW |
| IPN BU 644/994 | CICHOŃSKI STANISŁAW |
| IPN BU 00612/2832 | CICHOPEK ANDRZEJ |
| IPN BU 001198/6049 | CICHOPEK ANDRZEJ |
| IPN 00 1052/578 | CICHORSKI ANDRZEJ |
| IPN BU 002081/84 | CICHORSKI JAROSŁAW |
| IPN BU 002085/100 | CICHORSKI JAROSŁAW |
| IPN BU 0988/48 | CICHOSKI EDWARD |
| IPN BU 0951/1898 | CICHOSTĘPSKI FELIKS |
| IPN BU 0218/1892 | CICHOSZ EDWARD |
| IPN BU 00612/2736 | CICHOSZ BARBARA |
| IPN BU 001198/5981 | CICHOSZ BARBARA |
| IPN BU 01133/90 | CICHOSZ CZESŁAW |
| IPN BU 644/995 | CICHOSZ EDWARD |
| IPN BU 00275/625 | CICHOSZ JERZY |
| IPN BU 001134/579 | CICHOSZ JERZY |
| IPN 00 1043/1839 | CICHOSZ LUCYNA |
| IPN BU PF | 109/117 CICHOSZ MAŁGORZATA |
| IPN BU 001198/1453 | CICHOSZ MARIAN |
| IPN BU 710/99 | CICHOSZ ZBIGNIEW |
| IPN BU 00966/1706 | CICHOSZ ZBIGNIEW |
| IPN BU 0901/2450 | CICHOWA ZBIGNIEW |
| IPN BU 0855/2766 | CICHOWICZ HALINA |
| IPN BU 0912/338 | CICHOWICZ JAN |
| IPN BU 002081/259 | CICHOWICZ JAN |
| IPN BU 002085/325 | CICHOWICZ JAN PIOTR |
| IPN BU 0912/1743 | CICHOWICZ KAZIMIERZ |
| IPN BU 01000/415 | CICHOWICZ KRYSTYNA |
| IPN BU 0988/49 | CICHOWICZ TADEUSZ |
| IPN BU 01000/2167 | CICHOWICZ WACŁAW |
| IPN BU 0193/4568 | CICHOWLAS ANDRZEJ |
| IPN BU 636/1889 | CICHOWLAS ANNA |
| IPN BU 0864/96 | CICHOWLAS EDWARD |
| IPN BU 0942/563 | CICHOWLAS KAZIMIERZ |
| IPN BU 636/1802 | CICHOWSKA IZABELLA |
| IPN BU 645/155 | CICHOWSKA JADWIGA |
| IPN BU 0290/88 | CICHOWSKA ZOFIA |
| IPN BU 001121/1391 | CICHOWSKA-ERECIŃSKA MAŁGORZATA MARIA |
| IPN BU 00249/749 | CICHOWSKA-RECIŃSKA MAŁGORZATA |
| IPN BU 0951/693 | CICHOWSKI EDWARD |
| IPN BU 0591/89 | CICHOWSKI JAN |
| IPN BU 01266/2 | CICHOWSKI LUCJAN |
| IPN BU 698/480 | CICHOWSKI MIKOŁAJ |
| IPN BU 0912/2107 | CICHOWSKI REMIGIUSZ |
| IPN BU 0891/421 | CICHOWSKI STANISŁAW |
| IPN BU 00244/56 | CICHOWSKI ZYGMUNT |
| IPN BU 00966/126 | CICHY ANDRZEJ MAREK |
| IPN BU 01000/775 | CICHY ANTONI |
| IPN BU 0902/118 | CICHY JAN |
| IPN BU 001134/3688 | CICHY JERZY |
| IPN BU 0772/951 | CICHY KORNELIA |
| IPN BU 00165/15 | Cichy Marek |
| IPN 00 1052/337 | CICHY MICHAŁ STANISŁAW |
| IPN BU 00966/1836 | CICHY MIECZYSŁAW TADEUSZ |
| IPN BU 01256/30 | CICHY RYSZARD |
| IPN BU 0194/2848 | CICHY STANISŁAW |
| IPN BU 01434/289 | CICHY WŁADYSŁAW |
| IPN BU 00283/1025 | CICHY WŁODZIMIERZ |
| IPN BU 00768/697 | CICHY WŁODZIMIERZ |
| IPN BU 00945/2124 | CIDŁO PIOTR |
| IPN BU 00170/9 | CIDYŁO PIOTR |
| IPN BU 00328/191 | CIE LIK WIESŁAW |
| IPN BU 0591/90 | CIEBIELSKI MAREK |
| IPN BU 00232/309 | CIEBIERA ZBIGNIEW |
| IPN BU 001164/351 | Ciebiera Zbigniew |
| IPN BU 0833/723 | CIECHAN STANISŁAW |
| IPN BU 00277/1242 | CIECHANOWICZ ANNA |
| IPN BU 001121/3400 | CIECHANOWICZ ANNA |
| IPN BU 0194/3246 | CIECHANOWICZ IWONA BARBARA |
| IPN BU 001121/4358 | CIECHANOWICZ JERZY |
| IPN BU 00249/767 | CIECHANOWICZ TEODOR |
| IPN BU 001121/1408 | CIECHANOWICZ TEODOR |
| IPN BU 0872/208 | CIECHANOWICZ WIKTOR |
| IPN BU 00244/162 | CIECHANOWICZ WŁ. |
| IPN BU 0193/1574 | CIECHANOWICZ ZBIGNIEW |
| IPN BU 0193/8212 | CIECHANOWIECKI SEWERYN |
| IPN BU 01013/14 | CIECHANOWSKA JADWIGA |
| IPN BU 686/561 | CIECHANOWSKA KRYSTYNA |
| IPN BU 001198/1163 | CIECHANOWSKA MARIANNA |
| IPN BU 00945/2705 | CIECHANOWSKI EDWARD – JÓZEF |
| IPN BU 0194/2700 | CIECHANOWSKI KAZIMIERZ |
| IPN BU 644/996 | CIECHANOWSKI MIECZYSŁAW |
| IPN BU 0193/5448 | CIECHAŃ STANISŁAW |
| IPN BU 698/481 | CIECHAŃSKA BRONISŁAWA |
| IPN BU 0772/950 | CIECHAŃSKI FELIKS |
| IPN BU 644/993 | CIECHAŃSKI HENRYK |
| IPN BU 0855/3460 | CIECHAŃSKI JERZY |
| IPN BU 00966/202 | CIECHAŃSKI KAZIMIERZ |
| IPN BU 0218/674 | CIECHAŃSKI TADEUSZ |
| IPN BU 01133/759 | CIECHAŃSKI WŁADYSŁAW |
| IPN BU 00275/113 | CIECHAONOWICZ JERZY |
| IPN BU 001198/1223 | CIECHAWA MARIAN |
| IPN BU 00244/198 | CIECHOCIŃSKI |
| IPN BU 001089/397 | CIECHOCIŃSKI ZYGMUNT |
| IPN BU 0806/2172 | CIECHOLEWSKA ZOFIA |
| IPN BU 00249/30 | CIECHOMSKI ANDRZEJ |
| IPN BU 00448/227 | CIECHOMSKI ANDRZEJ |
| IPN BU 001121/596 | CIECHOMSKI ANDRZEJ |
| IPN BU 001134/5190 | CIECHOMSKI ANDRZEJ |
| IPN BU 01133/50 | CIECHOMSKI BOLESŁAW |
| IPN BU 01079/53 | CIECHOMSKI EDWARD |
| IPN BU 0772/1030 | CIECHOMSKI EDWARD |
| IPN BU 01013/13 | CIECHOMSKI FRANCISZEK |
| IPN BU 001121/319 | CIECHOMSKI JERZY |
| IPN BU 00334/601 | CIECHOMSKI MAREK |
| IPN BU 001134/3491 | CIECHOMSKI MAREK |
| IPN BU 645/1450 | CIECHOMSKI PIOTR |
| IPN BU 002082/587 | CIECHOMSKI WOJCIECH ZYGMUNT |
| IPN BU 002086/1799 | CIECHOMSKI WOJCIECH ZYGMUNT |
| IPN BU 00945/2018 | CIECHOMSKI ZBIGNIEW |
| IPN BU 00277/1240 | CIECHOWICZ ANDRZEJ STANISŁAW |
| IPN BU 001121/3398 | CIECHOWICZ ANDRZEJ STANISŁAW |
| IPN BU 0891/403 | CIECHOWICZ JAN |
| IPN BU 0891/422 | CIECHOWICZ TADEUSZ |
| IPN BU 02042/557 | CIECHOWICZ TADEUSZ |
| IPN BU 093/68 | CIECHOWLAS WŁ. |
| IPN BU 01133/760 | CIECIELĄG JÓZEF |
| IPN BU 0942/393 | CIECIELĄG NATALIA |
| IPN BU 00283/2117 | CIECIELĄG TADEUSZ |
| IPN BU 0951/1334 | CIECIERA BOGUMIŁA |
| IPN BU 0780/7 | CIECIERSKA BARBARA |
| IPN BU 0951/1345 | CIECIERSKA EUGENIA |
| IPN BU 0193/8352 | CIECIERSKA IRENA (PERELMUTER ESTERA) |
| IPN BU 00277/1134 | CIECIERSKA TERESA |
| IPN BU 001121/3306 | CIECIERSKA TERESA |
| IPN BU 0193/9042 | CIECIERSKI (DZIURA) JAKUB |
| IPN BU 0193/371 | CIECIERSKI FELIKS |
| IPN BU 0833/107 | CIECIERSKI JAN |
| IPN BU 0988/1277 | CIECIERSKI JAN |
| IPN BU 0957/149 | CIECIERSKI JAN |
| IPN BU 0193/7035 | CIECIERSKI KRZYSZTOF |
| IPN BU 0591/91 | CIECIERSKI MAREK |
| IPN BU 52/146 | CIECIERSKI ROMAN |
| IPN BU 00283/2446 | CIECIERSKI TADEUSZ |
| IPN BU 0772/952 | CIECIERSKI TOMASZ |
| IPN 00 1052/886 | CIECIERSKI TOMASZ |
| IPN BU 01013/11 | CIECIERSKI WŁADYSŁAW |
| IPN BU 01321/16 | CIECIERSKI WŁODZIMIERZ |
| IPN BU 001198/5388 | CIECIORA ADOLF |
| IPN BU 00611/266 | CIECIORA TADEUSZ |
| IPN BU 001198/614 | CIECIORA TADEUSZ |
| IPN BU 0242/1534 | CIECIOROWSKA KRÓLIKOWSKA ANNA |
| IPN BU 00611/341 | CIECIÓRA BONIFACY |
| IPN BU 081/162 | CIECIÓRA JANINA |
| IPN BU 00945/1792 | CIECIURA ZOFIA |
| IPN BU 0604/1626 | CIECKO EDWARD |
| IPN BU 0772/953 | CIECWIERZ TADEUSZ |
| IPN BU 0911/740 | CIEĆKO MARIAN |
| IPN BU 01133/761 | CIEĆKO OGÓRKIEWICZ BARBARA |
| IPN BU 685/249 | Ciećko Zbigniew |
| IPN BU 0604/1367 | CIEĆWIERSKI CEZARY |
| IPN BU 0891/1312 | CIEĆWIERZ ALEKSANDER |
| IPN BU 00234 | p.242 CIEĆWIERZ ANDRZEJ |
| IPN BU 00945/2098 | CIEĆWIERZ ANDRZEJ |
| IPN BU 0891/1306 | CIEĆWIERZ BRONISŁAWA |
| IPN BU 01133/762 | CIEĆWIERZ JAN |
| IPN BU 0604/1274 | CIEĆWIERZ JAN-BOGDAN |
| IPN BU 645/1456 | CIEĆWIERZ JANINA |
| IPN BU 00399/463 | CIEĆWIERZ JÓZEF |
| IPN BU 001134/4807 | CIEĆWIERZ JÓZEF |
| IPN BU 00744/1184 | CIEĆWIERZ PAWEŁ |
| IPN BU 001134/2454 | CIEĆWIERZ PAWEŁ |
| IPN BU 0891/388 | CIEĆWIERZ STEFAN |
| IPN BU 0242/1058 | CIEĆWIERZ TADEUSZ |
| IPN BU 698/482 | CIEĆWIREK SYLWESTER |
| IPN BU 0872/81 | CIEGIEŁKOWSKI MARIAN |
| IPN BU 001198/4074 | CIEKALSKI ZYGMUNT |
| IPN BU 01133/758 | CIEKANOWSKA ZENAIDA |
| IPN BU 0912/1564 | CIEKANOWSKI HENRYK |
| IPN BU 01133/763 | CIEKANOWSKI HENRYK |
| IPN BU 0193/1575 | CIEKOT JÓZEF |
| IPN BU 00966/898 | CIEKOT STANISŁAW |
| IPN BU 0901/1772 | CIEKOT WIOLETTA |
| IPN BU 0806/2298 | CIEKOT-OKOLSKA ANNA |
| IPN 00 1043/3493 | CIELAS STEFAN |
| IPN BU 00611/318 | CIELAWA BOLESŁAW |
| IPN BU 00415/58 | CIELEBĄK LECH |
| IPN BU 0194/3242 | CIELEBĄK STEFAN |
| IPN BU 0806/696 | CIELEBĄK WŁODKOWSKA JADWIGA |
| IPN 00 1043/2938 | CIELECKA MARIA KAROLINA |
| IPN BU 0604/1793 | CIELECKI EUGENIUSZ CILECKI |
| IPN BU 00612/3719 | CIELECKI MARIAN |
| IPN BU 00277/652 | CIELECKI PIOTR |
| IPN BU 001198/2555 | CIELECKI STEFAN |
| IPN 00 1052/1181 | CIELECKI TADEUSZ |
| IPN BU 001198/1921 | CIELECKI WACŁAW |
| IPN BU 0591/92 | CIELECKI ZDZISŁAW |
| IPN BU 001121/2856 | CIELECKI-TRUHA-CIELICKI PIOTR JANUSZ |
| IPN BU 00966/1585 | CIELEMĘDZKI HENRYK |
| IPN BU 00966/1737 | CIELEMIĘCKI JERZY WŁODZIMIERZ |
| IPN BU 0993/1502 | CIELEPAŁA KRYSTYNA |
| IPN BU 02042/432 | CIELESZYŃSKA URSZULA |
| IPN BU 00244/57 | CIELESZYŃSKI EDWARD |
| IPN BU 00612/2831 | CIELĘBA STANISŁAW |
| IPN BU 001198/6048 | CIELĘBA STANISŁAW |
| IPN BU 0777/19 | CIELICZKO STANISŁAW |
| IPN BU 00323/54 | CIELICZKO STANISŁAW |
| IPN BU 0305/452 | CIELICZKO STANISŁAW |
| IPN BU 00244/56 | CIELISZAK KAZIMIERZ |
| IPN BU 0194/2644 | CIELNIAK JÓZEF |
| IPN BU 00283/1746 | CIELOCH BOŻENA |
| IPN BU 0870/249 | CIELOCH STANISŁAW |
| IPN BU 00612/1696 | CIELOCH STANISŁAW |
| IPN BU 001198/4809 | CIELOCH STANISŁAW |
| IPN BU 0194/681 | CIELOSZYK EDWARD |
| IPN BU 685/20 | CIELUCH HELENA |
| IPN BU 644/997 | CIEMIERA JAN |
| IPN BU 0194/2417 | CIEMIĘGA ADAM |
| IPN BU 00611/485 | CIEMIĘGA JAN |
| IPN BU 001198/877 | CIEMIĘGA JAN |
| IPN BU 00191/398 | CIEMIŃSKI RYSZARD JERZY |
| IPN 00 1043/3141 | CIEMIŃSKI RYSZARD JERZY |
| IPN BU 0901/1518 | CIEMIŃSKI SŁAWOMIR WOJCIECH |
| IPN BU 01013/51 | CIEMIOR TEODOR |
| IPN BU 01013/12 | CIEMIOR WITOLD |
| IPN BU 0772/954 | CIEMNA TERESA.MARIA |
| IPN BU 0891/424 | CIEMNICKI JAN |
| IPN BU 0242/69 | CIEMNIECKI ANTONI |
| IPN BU 0891/389 | CIEMNIECKI JAN |
| IPN BU 0194/520 | CIEMNIEJEWSKI EDWARD |
| IPN BU 00945/191 | CIEMNIEWSKI – TURCZYŃSKI – JANKOWSKI ANDRZEJ |
| IPN BU 001134/2437 | CIEMNIEWSKI BOLESŁAW |
| IPN BU 095/8 | CIEMNY BOGDAN |
| IPN BU 980/188 | CIEMNY MIKOŁAJ |
| IPN BU 00244/56 | CIEMNY ZYGMUNT |
| IPN BU 0772/2413 | CIEMPIEL ALEKSANDRA |
| IPN BU 0242/2372 | CIEMPIEL JÓZEF |
| IPN BU 0894/6 | CIEMSKA JADWIGA |
| IPN BU 0772/2409 | CIEMSKA JADWIGA |
| IPN BU 00244/176 | CIEMSKI TADEUSZ |
| IPN BU 00230 | P. 132 CIEMSKI TADEUSZ |
| IPN BU 0892/790 | CIEMSKI ZYGMUNT |
| IPN BU 52/136 | CIEMUCHOWSKI EDWARD |
| IPN BU 00257/335 | CIEMUCHOWSKI ZBIGNIEW STANISŁAW |
| IPN BU 001102/1402 | CIEMUCHOWSKI ZBIGNIEW STANISŁAW |
| IPN BU 00234 | p.241 CIENCIAŁA JAN |
| IPN BU 00230 | P. 53 CIENCIAŁA JAN |
| IPN BU 0993/603 | CIENIAK BARBARA |
| IPN BU 0290/99 | CIENIAK BARBARA |
| IPN BU 0806/864 | CIENIEWICZ LEOKADIA |
| IPN BU 0958/4 | CIENIEWSKI MIECZYSŁAW |
| IPN BU PF | 498/27 CIENIEWSKI FRANCISZEK |
| IPN BU 0772/2410 | CIENIEWSKI ZBIGNIEW |
| IPN 00 1043/3919 | CIENKOWSKA SCHMIDT AGNIESZKA |
| IPN BU 0243/4 | CIENKOWSKI SŁAWOMIR |
| IPN BU 0855/3349 | CIENKOWSKI ZBIGNIEW |
| IPN BU 0855/3461 | CIENKUS HENRYK |
| IPN BU 01133/764 | CIENKUS HENRYK |
| IPN BU 0958/457 | CIENKUS STANISŁAW |
| IPN BU 00945/1211 | CIEŃKOWSKI WITOLD – PAWEŁ |
| IPN BU 0193/1570 | CIEPAŁ JÓZEF |
| IPN BU 0604/147 | CIEPAŁA EDWARD |
| IPN 00 1043/3994 | CIEPAŁA EDWARD |
| IPN BU 00612/1191 | CIEPAŁA JANUSZ |
| IPN BU 00750/6 | CIEPICHAŁ JANUSZ |
| IPN BU 00966/1529 | CIEPIELA ANTONI |
| IPN BU 00200/1273 | CIEPIELA EUGENIUSZ |
| IPN BU 001102/874 | CIEPIELA EUGENIUSZ |
| IPN BU 01000/2234 | CIEPIELA STANISŁAWA |
| IPN BU 0242/392 | CIEPIELAK WIESŁAW |
| IPN BU 001198/285 | CIEPIELEWSKA JADWIGA |
| IPN BU 00283/143 | CIEPIELEWSKI GUSTAW |
| IPN BU 00768/114 | CIEPIELEWSKI GUSTAW |
| IPN BU PF | 109/118 CIEPIENIAK ADAM |
| IPN BU 0194/2018 | CIEPIERSKI JÓZEF |
| IPN BU 0958/471 | CIEPIERSKI STANISŁAW |
| IPN BU 00966/1308 | CIEPKO EDWARD ALEKSANDER |
| IPN BU 0855/2585 | CIEPLAK (GOŁĄB) MARIANNA |
| IPN BU 00399/537 | CIEPLAK ANDRZEJ |
| IPN BU 001134/4878 | CIEPLAK ANDRZEJ |
| IPN BU PF | 2/101 CIEPLAK BOGDAN |
| IPN BU 001134/3104 | CIEPLAK CEZARY |
| IPN BU 00448/546 | CIEPLAK GRZEGORZ |
| IPN BU 002086/794 | CIEPLAK GRZEGORZ JAN |
| IPN BU 001134/5522 | CIEPLAK GRZEGORZ JAN |
| IPN BU 01250/94 | CIEPLAK HENRYK |
| IPN BU 01013/313 | CIEPLAK LESZEK |
| IPN BU 0993/153 | CIEPLAK MACIEJ |
| IPN BU 0993/532 | CIEPLAK MAŁGORZATA |
| IPN BU 0912/339 | CIEPLAK MIECZYSŁAW |
| IPN BU 0870/67 | CIEPLAK ZDZISŁAW |
| IPN BU 095/10 | CIEPLAK ZDZISŁAW |
| IPN BU 685/21 | CIEPLAK ZOFIA |
| IPN BU 00234 | p.245 CIEPLICKI MICHAŁ |
| IPN BU 644/998 | CIEPLIK FRANCISZEK |
| IPN BU 0912/1678 | CIEPLIK HALINA |
| IPN BU 0218/1208 | CIEPLIK STANISŁAW |
| IPN BU 0591/93 | CIEPLIK ZBIGNIEW |
| IPN BU 0604/820 | CIEPLIŃSKI (ZĄBEK) TADEUSZ |
| IPN BU 0193/1576 | CIEPLIŃSKI DAMIAN |
| IPN BU 0833/100 | CIEPLIŃSKI JAN |
| IPN BU 001164/273 | Ciepliński Marian |
| IPN BU 01133/51 | CIEPLIŃSKI PAWEŁ |
| IPN BU 0942/564 | CIEPLIŃSKI STEFAN |
| IPN BU 683/1723 | CIEPLUCH JÓZEF |
| IPN BU 644/999 | CIEPLUCHA MARIAN |
| IPN BU 0193/372 | CIEPLUCHA STANISŁAW |
| IPN BU 01013/319 | CIEPŁOTA ZDZISŁAW |
| IPN BU 645/182 | CIEPŁOWSKI ADAM |
| IPN BU 00328/1580 | CIEPŁOWSKI ŁUKASZ JAN |
| IPN BU 001134/2572 | CIEPŁOWSKI ŁUKASZ JAN |
| IPN BU 709/931 | CIEPŁUCH WŁADYSŁAW |
| IPN BU 0806/2047 | CIEPŁUCHA RYSZARDA |
| IPN BU 0218/242 | CIEPUSZEWSKA TERESA |
| IPN BU 00249/329 | CIERACHOWSKI KRZYSZTOF |
| IPN BU 001121/954 | CIERACHOWSKI KRZYSZTOF |
| IPN BU 01250/95 | CIERCIŃSKI HENRYK |
| IPN BU 0891/392 | CIERECH JAN |
| IPN BU 0193/8800 | CIERESZKO BOGUSŁAW OLGIERD |
| IPN BU 0591/94 | CIERESZKO MIKOŁAJ |
| IPN BU 01318/2 | CIERESZKO WIESŁAW |
| IPN BU 0911/755 | CIERKOWSKI LESZEK |
| IPN BU 0193/7991 | CIERLACZYK IGNACY |
| IPN BU 02042/590 | CIERLICA JACEK |
| IPN BU 0806/2080 | CIERLICKI WŁADYSŁAW |
| IPN BU 00249/231 | CIERLIŃSKI ANDRZEJ |
| IPN BU 001121/852 | CIERLIŃSKI ANDRZEJ |
| IPN BU 00612/4460 | CIERNIAK STANISŁAW |
| IPN BU 001198/7145 | CIERNIAK STANISŁAW |
| IPN BU 0604/341 | CIERNIAK STEFAN |
| IPN BU 00612/4147 | CIERPAŁA GRAZYNA |
| IPN BU 001198/6907 | CIERPAŁA GRAŻYNA |
| IPN BU 0806/1107 | CIERPIAŁKOWSKA HELENA |
| IPN BU 0772/678 | CIERPIAŁOWSKI MIECZYSŁAW |
| IPN BU 0806/3120 | CIERPIATKA RENATA |
| IPN BU 001102/2050 | CIERPICKA IWONA KAROLINA ZOFIA |
| IPN BU 0607/14 | CIERPIKOWSKA WIESŁAWA |
| IPN BU 0806/1079 | CIERPISZ HALINA |
| IPN BU 0891/338 | CIERPISZ LUCJAN |
| IPN BU 0772/2414 | CIERPKA BARBARA |
| IPN BU 0988/962 | CIERZNIAK EDWARD |
| IPN BU 01133/765 | CIERZNIAKOWSKI JÓZEF |
| IPN BU 01000/2196 | CIERZNIEWSKI TADEUSZ |
| IPN BU 0193/373 | CIERZUCH STANISŁAW JAN |
| IPN BU 00612/965 | CIESEK ANIELA |
| IPN BU 001121/640 | CIESEK TADEUSZ |
| IPN BU 01250/96 | CIESIAŁKIEWICZ RYSZARD |
| IPN BU 00249/59 | CIESIEK TADEUSZ |
| IPN 00 1043/1530 | CIESIELEWSKI MACIEJ PAWEŁ |
| IPN BU 698/483 | CIESIELKA JÓZEF |
| IPN 00 1052/1346 | CIESIELKA STANISŁAW |
| IPN BU 01013/17 | CIESIELKA TEOFILA |
| IPN BU 0242/2732 | CIESIELSKA (BOGUSZ) WANDA |
| IPN BU 0243/139 | CIESIELSKA (DOMŻAŁA) CELINA |
| IPN BU 0772/2419 | CIESIELSKA (SALUS) KAZIMIERA |
| IPN BU PF | 1021/5 CIESIELSKA ALICJA |
| IPN BU 0218/3061 | CIESIELSKA ALINA |
| IPN BU 980/19 | CIESIELSKA ANNA |
| IPN BU PF | 1021/6 CIESIELSKA ANNA |
| IPN BU 0242/1061 | CIESIELSKA EWA |
| IPN BU 0951/1463 | CIESIELSKA GRAŻYNA |
| IPN BU 0772/2418 | CIESIELSKA HALINA |
| IPN BU 0772/955 | CIESIELSKA HELENA |
| IPN BU 0901/992 | CIESIELSKA HENRYKA ZAKLIKA |
| IPN BU 0912/890 | CIESIELSKA JANINA |
| IPN BU 001089/128 | CIESIELSKA JANINA |
| IPN BU 0833/101 | CIESIELSKA KRYSTYNA |
| IPN BU 0806/2679 | CIESIELSKA LEOKADIA |
| IPN BU 0806/2872 | CIESIELSKA LILIANA |
| IPN BU 0894/5 | CIESIELSKA MARIA |
| IPN BU 645/159 | CIESIELSKA MARIA |
| IPN BU 0806/1545 | CIESIELSKA MARIANNA |
| IPN BU 0193/7636 | CIESIELSKA NOWAKOWSKA ZOFIA |
| IPN BU 0951/1618 | CIESIELSKA STANISŁAWA |
| IPN BU 0772/2420 | CIESIELSKA ZOFIA |
| IPN BU 00249/171 | CIESIELSKI ADAM |
| IPN BU 001121/777 | CIESIELSKI ADAM |
| IPN BU 0912/1565 | CIESIELSKI ANTONI |
| IPN BU 0958/458 | CIESIELSKI ANTONI |
| IPN BU 01250/97 | CIESIELSKI ANTONI |
| IPN BU 00283/1234 | CIESIELSKI ARYUR |
| IPN BU 0942/305 | CIESIELSKI BOGDAN |
| IPN BU 748/246 | CIESIELSKI BOHDAN |
| IPN BU 0218/1203 | CIESIELSKI CEZARY |
| IPN BU 00751/60 | CIESIELSKI DARIUSZ |
| IPN BU 001102/1544 | CIESIELSKI DARIUSZ |
| IPN BU 0988/50 | CIESIELSKI EDMUND |
| IPN BU 0772/957 | CIESIELSKI EDWARD |
| IPN BU 00230 | P. 53 CIESIELSKI EDWARD |
| IPN BU 01013/18 | CIESIELSKI EDWARD |
| IPN BU 01133/766 | CIESIELSKI EDWARD |
| IPN BU 0591/95 | CIESIELSKI EDWARD |
| IPN BU 698/484 | CIESIELSKI EDWARD |
| IPN BU 0866/92 | CIESIELSKI EUGENIUSZ |
| IPN BU 00448/251 | CIESIELSKI EUGENIUSZ |
| IPN BU 01434/460 | CIESIELSKI EUGENIUSZ |
| IPN BU 001134/5218 | CIESIELSKI EUGENIUSZ |
| IPN BU 00945/1277 | CIESIELSKI EUGENIUSZ – WŁADYSŁAW |
| IPN BU 0218/2037 | CIESIELSKI EUZEBIUSZ |
| IPN BU 0854/927 | CIESIELSKI FRANCISZEK |
| IPN BU 0891/393 | CIESIELSKI JAN |
| IPN BU 0193/8222 | CIESIELSKI JAN |
| IPN BU 01013/19 | CIESIELSKI JAN |
| IPN BU 01013/20 | CIESIELSKI JAN |
| IPN BU 748/269 | CIESIELSKI JAN |
| IPN BU 00612/3638 | CIESIELSKI JAN |
| IPN BU 00283/221 | CIESIELSKI JERZY |
| IPN BU 00249/599 | CIESIELSKI JERZY |
| IPN BU 00768/155 | CIESIELSKI JERZY |
| IPN BU 001121/1237 | CIESIELSKI JERZY EDWIN |
| IPN BU 001102/1702 | CIESIELSKI JERZY ERWIN |
| IPN BU 0193/1581 | CIESIELSKI JÓZEF |
| IPN BU 0193/374 | CIESIELSKI JÓZEF |
| IPN BU 0193/379 | CIESIELSKI JÓZEF |
| IPN BU 01013/23 | CIESIELSKI JÓZEF |
| IPN BU 0193/375 | CIESIELSKI KAZIMIERZ |
| IPN BU 0967/258 | CIESIELSKI KAZIMIERZ |
| IPN BU 0242/1972 | CIESIELSKI LEONARD |
| IPN BU 0193/1582 | CIESIELSKI LUDWIK |
| IPN BU 00448/461 | CIESIELSKI MACIEJ |
| IPN BU 001134/5436 | CIESIELSKI MACIEJ PAWEŁ |
| IPN BU 0193/1583 | CIESIELSKI MARIAN |
| IPN BU 0866/93 | CIESIELSKI MARIAN |
| IPN BU 0988/625 | CIESIELSKI MARIAN |
| IPN BU 0193/376 | CIESIELSKI MIECZYSŁAW |
| IPN BU 0327/38 | CIESIELSKI MIROSŁAW |
| IPN BU 0243/394 | CIESIELSKI PIOTR |
| IPN BU 709/847 | CIESIELSKI ROMAN |
| IPN BU 0911/11 | CIESIELSKI RYSZARD |
| IPN BU 00230 | P. 53 CIESIELSKI RYSZARD |
| IPN BU 0218/2575 | CIESIELSKI SERGIUSZ SERGIEJ |
| IPN BU 0891/337 | CIESIELSKI STANISŁAW |
| IPN BU 0193/378 | CIESIELSKI STANISŁAW |
| IPN BU 0193/6708 | CIESIELSKI STANISŁAW |
| IPN BU 0194/1020 | CIESIELSKI STANISŁAW |
| IPN BU 0218/2913 | CIESIELSKI STANISŁAW |
| IPN BU 0942/254 | CIESIELSKI STANISŁAW |
| IPN BU 01000/2240 | CIESIELSKI STEFAN |
| IPN BU 0891/390 | CIESIELSKI TADEUSZ |
| IPN BU 0912/341 | CIESIELSKI TADEUSZ |
| IPN 00 1043/1447 | CIESIELSKI TADEUSZ FRANCISZEK |
| IPN BU 0891/394 | CIESIELSKI WACŁAW |
| IPN BU 01013/308 | CIESIELSKI WACŁAW |
| IPN BU 0806/986 | CIESIELSKI WALDEMAR |
| IPN BU 0193/1584 | CIESIELSKI WŁADYSŁAW |
| IPN BU 01000/813 | CIESIELSKI WŁADYSŁAW |
| IPN BU 0193/1585 | CIESIELSKI WŁODZIMIERZ |
| IPN BU 00744/1131 | CIESIELSKI WŁODZIMIERZ |
| IPN BU 001134/2109 | CIESIELSKI WŁODZIMIERZ |
| IPN BU 0604/674 | CIESIELSKI WOJCIECH |
| IPN BU 00611/434 | CIESIELSKI ZYGMUNT |
| IPN BU 001198/797 | CIESIELSKI ZYGMUNT |
| IPN BU 00945/1962 | CIESIELSKI ZYGMUNT – MARCIN |
| IPN BU 00168/390 | CIESIELSKI ZYGMUNT MARCIN |
| IPN BU 002081/341 | CIESIŃSKI ANDRZEJ |
| IPN BU 002085/407 | CIESIŃSKI ANDRZEJ KRZYSZTOF |
| IPN BU 0993/1522 | CIESIOŁKIEWICZ JOANNA RENATA |
| IPN BU 698/485 | CIESIOŁKIEWICZ LUDWIK |
| IPN BU 00168/422 | CIESIOŁKIEWICZ STEFAN ZDZISŁAW JAN |
| IPN BU 00277/1044 | CIESIOŁKIEWICZ ZDZISŁAW |
| IPN BU 00945/2069 | CIESIOŁKIEWICZ ZDZISŁAW – STEFAN -JAN |
| IPN BU 001121/3225 | CIESIOŁKIEWICZ ZDZISŁAW STEFAN |
| IPN BU PF | 109/119 CIESIÓŁKA BARBARA |
| IPN BU 0988/1157 | CIESIÓŁKA KAZIMIERZ |
| IPN BU 644/1002 | CIESLAK JAN |
| IPN BU 0942/551 | CIESLAK WOJCIECH |
| IPN BU 00611/1165 | CIESLIK STANISŁAW |
| IPN BU 001198/4336 | CIESLIK STEFAN |
| IPN BU 0967/103 | CIESNOWSKI JAN |
| IPN BU 00244/176 | CIESZANOWSKI ZBIGNIEW |
| IPN BU 0806/1560 | CIESZEWSKA URSZULA |
| IPN BU 0891/1828 | CIESZEWSKI STANISŁAW |
| IPN BU 0193/377 | CIESZKOWSKA ANIELA STANISŁAWA GAŁĄZKA |
| IPN BU 0242/2524 | CIESZKOWSKA EUGENIA |
| IPN BU 0194/2989 | CIESZKOWSKA EWA |
| IPN BU 0772/2421 | CIESZKOWSKA HALINA |
| IPN BU 0806/926 | CIESZKOWSKA HELENA |
| IPN BU 0218/740 | CIESZKOWSKI ADOLF |
| IPN BU 01133/333 | CIESZKOWSKI BRONISŁAW |
| IPN BU 0772/956 | CIESZKOWSKI EDWARD |
| IPN BU 0604/1410 | CIESZKOWSKI EUGENIUSZ |
| IPN BU 00415/174 | CIESZKOWSKI MARIAN |
| IPN BU 01013/40 | CIESZKOWSKI RYSZARD |
| IPN BU 01013/44 | CIESZKOWSKI RYSZARD |
| IPN BU 0854/1371 | CIESZKOWSKI STANISŁAW |
| IPN BU 748/270 | CIESZKOWSKI STANISŁAW |
| IPN BU 0988/51 | CIESZKOWSKI ZDZISŁAW |
| IPN BU 00415/212 | CIESZKOWSKI ZDZISŁAW |
| IPN BU 0866/94 | CIELA DANUTA |
| IPN BU PF | 900/24 CIELA IRENA |
| IPN BU 0242/2276 | CIELA JAN |
| IPN BU 644/1000 | CIELA JAN |
| IPN BU 645/179 | CIELA JAN |
| IPN BU 00611/222 | CIELA JAN |
| IPN BU 00328/998 | CIELA MARCIN |
| IPN BU 001134/1858 | CIELA MARCIN |
| IPN BU 01703/101 | CIELA MARIA |
| IPN BU 748/247 | CIELA MEDARD |
| IPN BU 698/486 | CIELA MICHAŁ |
| IPN 00 1052/635 | CIELA MIROSŁAW MARIAN |
| IPN BU 0218/1957 | CIELA PIOTR ADAM |
| IPN BU 0193/380 | CIELA STANISŁAW |
| IPN BU 0902/121 | CIELA STANISŁAW |
| IPN BU 0193/8524 | CIELA STEFAN |
| IPN BU 0958/242 | CIELA WACŁAW |
| IPN BU 00200/108 | CIELA WITOLD |
| IPN 00 1052/530 | CIELA WITOLD |
| IPN BU 0193/1577 | CIELA WŁADYSŁAW |
| IPN BU 00611/555 | CIELA WŁADYSŁAW |
| IPN BU 001198/994 | CIELA WŁADYSŁAW |
| IPN BU 002086/116 | CIELA ZBIGNIEW |
| IPN BU 02042/470 | CIELAK – RUDZKA BARBARA |
| IPN BU 0242/1526 | CIELAK (PRZYBYSZEWSKA) HANNA |
| IPN BU 0872/210 | CIELAK / STEFANOWICZ MARIA |
| IPN BU 0892/85 | CIELAK / SYSIO MIROSŁAWA |
| IPN BU 52/134 | CIELAK ADAM |
| IPN BU 00612/3565 | CIELAK ADAM |
| IPN BU 001198/6541 | CIELAK ADAM |
| IPN BU 0864/20 | CIELAK ALEKSANDER |
| IPN BU 00249/257 | CIELAK ALEKSY |
| IPN BU 001121/880 | CIELAK ALEKSY |
| IPN BU 0305/380 | CIELAK ANDRZEJ |
| IPN BU 0893/27 | CIELAK ANDRZEJ |
| IPN BU 01000/2039 | CIELAK ANTONI |
| IPN BU 01133/767 | CIELAK ANTONI |
| IPN BU 698/487 | CIELAK ANTONI |
| IPN BU 00257/350 | CIELAK ANTONINA KATARZYNA |
| IPN BU 001102/1417 | CIELAK ANTONINA KATARZYNA |
| IPN BU 00612/2190 | CIELAK BARBARA |
| IPN BU 001198/5287 | CIELAK BARBARA |
| IPN BU 0218/2096 | CIELAK BARBARA ANNA |
| IPN BU 00328/172 | CIELAK BARBARA ANNA |
| IPN BU 001134/866 | CIELAK BARBARA ANNA |
| IPN BU 00225/59 | CIELAK CZESŁAW |
| IPN BU 0194/2875 | CIELAK EDMUND |
| IPN BU 709/878 | CIELAK EDMUND |
| IPN BU 644/1004 | CIELAK EDMUND |
| IPN BU 0780/8 | CIELAK ELZBIETA |
| IPN BU 0912/344 | CIELAK EUGENIA |
| IPN BU 01133/768 | CIELAK EUGENIUSZ |
| IPN BU 00334/324 | CIELAK EUGENIUSZ |
| IPN BU 001134/3171 | CIELAK EUGENIUSZ |
| IPN BU 0777/20 | CIELAK FRANCISZEK |
| IPN BU 0314/5 | CIELAK FRANCISZEK |
| IPN BU 00966/551 | CIELAK FRANCISZEK |
| IPN BU 00275/261 | CIELAK GRZEGORZ |
| IPN BU 001134/117 | CIELAK GRZEGORZ |
| IPN BU 00328/224 | CIELAK HALINA |
| IPN BU 001134/933 | CIELAK HALINA |
| IPN BU 0806/1888 | CIELAK HANNA |
| IPN BU 00612/908 | CIELAK HENRYK |
| IPN BU 001198/1300 | CIELAK HENRYK |
| IPN BU 644/1001 | CIELAK IGNACY |
| IPN BU 0951/1066 | CIELAK IRENA |
| IPN BU 01737/151 | CIELAK IRENEUSZ |
| IPN 00 1052/1532 | CIELAK IZABELLA |
| IPN BU 00283/1129 | CIELAK JACEK |
| IPN BU 0912/340 | CIELAK JAN |
| IPN BU 0193/1578 | CIELAK JAN |
| IPN BU 0772/2415 | CIELAK JAN |
| IPN BU 0854/1017 | CIELAK JAN |
| IPN BU 52/145 | CIELAK JAN |
| IPN BU 01050/1342 | CIELAK JAN |
| IPN BU 698/488 | CIELAK JAN |
| IPN BU 0772/958 | CIELAK JANINA |
| IPN BU 0866/95 | CIELAK JANINA |
| IPN 00 1043/2311 | CIELAK JANUSZ |
| IPN BU 001121/4001 | CIELAK JANUSZ |
| IPN BU 0218/1365 | CIELAK JERZY |
| IPN BU 0604/1387 | CIELAK JERZY |
| IPN BU 00283/958 | CIELAK JERZY |
| IPN BU 00768/652 | CIELAK JERZY |
| IPN BU 0193/1579 | CIELAK JÓZEF |
| IPN BU 0218/1565 | CIELAK JÓZEF |
| IPN BU 698/489 | CIELAK JÓZEF |
| IPN BU 093/64 | CIELAK JÓZEFA |
| IPN BU 0242/2637 | CIELAK KAZIMIERA |
| IPN BU 0870/47 | CIELAK KAZIMIERZ |
| IPN BU 0891/391 | CIELAK KAZIMIERZ |
| IPN BU 0193/1580 | CIELAK KAZIMIERZ |
| IPN BU 0967/233 | CIELAK KAZIMIERZ |
| IPN BU 645/141 | CIELAK KAZIMIERZ |
| IPN BU 0893/32 | CIELAK KAZIMIERZ |
| IPN BU 01000/2233 | CIELAK KLEMENTYNA |
| IPN BU 0242/1598 | CIELAK KRYSTYNA |
| IPN BU 698/490 | CIELAK LEOKADIA |
| IPN BU 00275/154 | CIELAK LUCJUSZ |
| IPN BU 001121/4398 | CIELAK LUCJUSZ |
| IPN BU 0912/345 | CIELAK MARCIN |
| IPN BU 52/156 | CIELAK MAREK |
| IPN BU 0993/1513 | CIELAK MARIA |
| IPN BU 00283/1884 | CIELAK MARIA |
| IPN BU 00275/163 | CIELAK MARIA |
| IPN BU 001121/4406 | CIELAK MARIA |
| IPN BU 0194/1211 | CIELAK MARIAN |
| IPN BU 0951/596 | CIELAK MARIAN |
| IPN BU 01000/2183 | CIELAK MARIAN |
| IPN BU 00283/566 | CIELAK MARIAN |
| IPN BU 002086/588 | CIELAK MARIAN ZIEMOWIT WOJCIECH |
| IPN BU 00283/1747 | CIELAK MARIANNA |
| IPN BU 00334/316 | CIELAK MARYLA |
| IPN BU 001134/3156 | CIELAK MARYLA HENRYKA |
| IPN BU 0772/2416 | CIELAK MIECZYSŁAW |
| IPN BU 0833/705 | CIELAK MIECZYSŁAW |
| IPN BU 00612/1361 | CIELAK PAWEŁ |
| IPN BU 001198/4607 | CIELAK PAWEŁ |
| IPN BU 0892/538 | CIELAK PIOTR |
| IPN BU 01256/31 | CIELAK PIOTR |
| IPN BU 0833/102 | CIELAK ROMAN |
| IPN BU 0591/96 | CIELAK RYSZARD |
| IPN BU PF | 900/29 CIELAK RYSZARD |
| IPN BU 0891/341 | CIELAK STANISLAW |
| IPN BU 0958/461 | CIELAK STANISŁAW |
| IPN BU 698/491 | CIELAK STANISŁAW |
| IPN BU 698/492 | CIELAK STANISŁAW |
| IPN BU 698/493 | CIELAK STANISŁAW |
| IPN BU 01000/2198 | CIELAK STANISŁAWA |
| IPN BU 0891/435 | CIELAK STEFAN |
| IPN BU 0988/1534 | CIELAK STEFAN |
| IPN BU 01133/769 | CIELAK STEFAN |
| IPN BU 0772/2417 | CIELAK STEFANIA |
| IPN BU 0912/346 | CIELAK TADEUSZ |
| IPN BU 0194/2773 | CIELAK TADEUSZ |
| IPN BU 0864/274 | CIELAK TADEUSZ |
| IPN BU 645/157 | CIELAK TADEUSZ |
| IPN BU 01013/117 | CIELAK WACŁAW |
| IPN 00 1043/309 | CIELAK WACŁAW |
| IPN BU 0194/2823 | CIELAK WALDEMAR |
| IPN BU 693/831 | CIELAK WANDA |
| IPN BU 001089/398 | CIELAK WIESŁAW |
| IPN BU 644/92 | CIELAK WIESŁAW |
| IPN BU 0833/706 | CIELAK WŁADYSŁAW |
| IPN BU 748/248 | CIELAK WŁADYSŁAW |
| IPN BU 0193/6160 | CIELAK ZDZISŁAW |
| IPN BU 0193/8640 | CIELAK ZDZISŁAW |
| IPN BU 00334/839 | CIELAK ZDZISŁAW |
| IPN BU 00966/909 | CIELAK ZDZISŁAW |
| IPN BU 001134/3998 | CIELAK ZDZISŁAW |
| IPN BU 644/1003 | CIELAK ZENOBIUSZ |
| IPN BU 0910/47 | CIELAK ZOFIA |
| IPN BU 0833/681 | CIELAK ZYGMUNT |
| IPN BU 644/1005 | CIELAK ZYGMUNT |
| IPN BU 00612/972 | CIELAK ZYGMUNT |
| IPN BU 00448/380 | CIELAK ZYGMUNT |
| IPN BU 001134/5360 | CIELAK ZYGMUNT |
| IPN BU 0901/962 | CIELAKIEWICZ EUFEMIA ROGULSKA |
| IPN BU 001198/538 | CIELAKIEWICZ JAN |
| IPN BU 001198/54 | CIELAKIEWICZ WŁADYSŁAW |
| IPN BU 001198/68 | CIELAKIEWICZ ZENON |
| IPN BU 0855/3057 | CIELAR ( BUJOK) ANNA |
| IPN BU 00945/945 | CIELAR EMIL |
| IPN BU 00168/20 | CIELAR PAWEŁ |
| IPN BU 00191/105 | CIELAR PAWEŁ |
| IPN 00 1043/2041 | CIELAR PAWEŁ |
| IPN BU 00945/1453 | CIELAR PAWEŁ – ADAM |
| IPN BU 685/238 | Cielarczyk Leokadia |
| IPN BU 0872/6 | CIELEWICZ HENRYK |
| IPN BU 0901/769 | CIELEWSKA PYTKA MARIANNA |
| IPN BU 0993/1536 | CIELEWSKI STANISŁAW |
| IPN BU 00612/963 | CIELICKI JERZY |
| IPN BU 00612/4875 | CIELICKI WŁADYSŁAW |
| IPN BU 01013/41 | CIELICZKO ZBIGNIEW |
| IPN BU 0902/120 | CIELIK (JURKOWSKA) HALINA |
| IPN BU 00612/4879 | CIELIK ADAM |
| IPN BU 00399/511 | CIELIK ALEKSANDER |
| IPN BU 001134/4852 | CIELIK ALEKSANDER |
| IPN BU 0901/179 | CIELIK ALINA ZOFIA VEL BINASIEWICZ BINAS |
| IPN BU 00283/2546 | CIELIK ANTONI |
| IPN BU 00612/2687 | CIELIK BARBARA |
| IPN BU 001198/5951 | CIELIK BARBARA |
| IPN BU 00751/184 | CIELIK BOGDAN |
| IPN BU 001102/1681 | CIELIK BOGDAN |
| IPN BU 0855/2645 | CIELIK BRONISŁAWA |
| IPN BU 00283/878 | CIELIK CEZARY |
| IPN BU 00768/604 | CIELIK CEZARY |
| IPN BU 0604/1868 | CIELIK ELŻBIETA |
| IPN BU 01434/43 | CIELIK GENOWEFA |
| IPN BU 0993/1022 | CIELIK HELENA |
| IPN BU 00335/142 | CIELIK HENRYK |
| IPN BU 0872/209 | CIELIK JAN |
| IPN BU 644/1006 | CIELIK JAN |
| IPN BU 00191/699 | CIELIK JERZY |
| IPN 00 1052/155 | CIELIK JERZY |
| IPN BU 00277/484 | CIELIK JOANNA |
| IPN BU 001121/2699 | CIELIK JOANNA EWA |
| IPN BU 00244/169 | CIELIK KAZIMIERZ |
| IPN BU 00283/1627 | CIELIK KAZIMIERZ |
| IPN BU 00283/654 | CIELIK KAZIMIERZ |
| IPN BU 00611/1195 | CIELIK MARIAN |
| IPN BU 00611/1282 | CIELIK MARIAN |
| IPN BU 00611/1596 | CIELIK MARIAN |
| IPN BU 001198/2238 | CIELIK MARIAN |
| IPN BU 001198/2966 | CIELIK MARIAN |
| IPN BU 00244/120 | CIELIK MIECZYSŁAW |
| IPN BU 698/494 | CIELIK MIECZYSŁAW |
| IPN BU 698/495 | CIELIK PIOTR |
| IPN BU 0218/3700 | CIELIK STANISŁAW |
| IPN BU 0833/103 | CIELIK STANISŁAW |
| IPN BU 644/1007 | CIELIK STANISŁAW |
| IPN BU 00612/603 | CIELIK STEFAN |
| IPN BU 00191/52 | CIELIK WIESŁAW |
| IPN 00 1043/1936 | CIELIK WIESŁAW |
| IPN BU 001134/885 | CIELIK WIESŁAW |
| IPN BU 00230 | P. 139 CIELIK WIESŁAWA |
| IPN BU 683/239 | CIELIK WIESŁAWA |
| IPN BU 01013/42 | CIELIK WIKTOR |
| IPN BU 0855/2986 | CIELIK WŁADYSŁAW |
| IPN BU 001121/364 | CIELIK ZBIGNIEW |
| IPN BU 0993/1023 | CIELIK ZOFIA |
| IPN BU 0193/7081 | CIELIK ZYGMUNT |
| IPN BU 001198/3894 | CIELIKIEWICZ CEZARY |
| IPN BU 00612/3833 | CIELIKIEWICZ MAREK |
| IPN BU 001198/6692 | CIELIKIEWICZ MAREK |
| IPN BU 001198/1619 | CIELIKIEWICZ MARIAN |
| IPN BU 00612/2989 | CIELIKIEWICZ MIECZYSŁAW |
| IPN BU 00611/1139 | CIELIKIEWICZ ROMAN |
| IPN BU 001198/1555 | CIELIKIEWICZ ROMAN |
| IPN BU 001198/1577 | CIELIKIEWICZ STANISŁAW |
| IPN BU 001198/1786 | CIELIKIEWICZ ZYGMUNT |
| IPN BU 00200/651 | CIELIKKOWSKI – MILLER LESZEK |
| IPN BU 0993/90 | CIELIKOWSKA SYLWIA |
| IPN BU 00328/1280 | CIELIKOWSKI ANDRZEJ |
| IPN BU 001134/2187 | CIELIKOWSKI ANDRZEJ |
| IPN BU 0591/97 | CIELIKOWSKI HENRYK |
| IPN BU 00200/141 | CIELIKOWSKI JERZY |
| IPN 00 1052/615 | CIELIKOWSKI JERZY |
| IPN BU 0833/680 | CIELIKOWSKI KAZIMIERZ |
| IPN BU 00200/439 | CIELIKOWSKI LESZEK |
| IPN 00 1052/1447 | CIELIKOWSKI LESZEK SŁAWOMIR |
| IPN BU 01013/43 | CIELIKOWSKI MIECZYSŁAW |
| IPN BU 0772/69 | CIELIKOWSKI STANISŁAW STEFAN |
| IPN BU 748/330 | CIELIKOWSKI STEFAN |
| IPN BU 00612/4890 | CIELIKOWSKI STEFAN |
| IPN BU 0604/445 | CIELIKOWSKI ZBIGNIEW |
| IPN BU 001102/90 | CIELIKOWSKI-MULLER LESZEK STANISŁAW |
| IPN BU 00966/787 | CIELIŃSKA HANNA PELAGIA |
| IPN BU 0806/2758 | CIELIŃSKA MAŁGORZATA |
| IPN BU 0772/67 | CIELIŃSKI EDMUND JANUSZ |
| IPN BU 644/1008 | CIELIŃSKI JAN |
| IPN BU 0833/725 | CIELIŃSKI KAROL |
| IPN BU 0891/342 | CIELIŃSKI KAZIMIERZ |
| IPN BU 002082/266 | CIELIŃSKI RAJMUND MACIEJ |
| IPN BU 002086/660 | CIELIŃSKI RAJMUND MACIEJ |
| IPN BU 001198/6996 | CIELIŃSKI SŁAWOMIR |
| IPN BU 00191/368 | CIELIŃSKI SŁAWOMIR JERZY |
| IPN 00 1043/3015 | CIELIŃSKI SŁAWOMIR JERZY |
| IPN BU 00612/2609 | CIELIŃSKI STANISŁAW |
| IPN BU 01000/301 | CIELIŃSKI TADEUSZ |
| IPN BU 0833/124 | CIELIŃSKI WALDEMAR |
| IPN BU 0193/6876 | CIELIŃSKI WINCENTY |
| IPN BU 00966/713 | CIELIŃSKI WŁADYSŁAW |
| IPN BU 0772/1360 | CIELOWSKI WŁADYSŁAW |
| IPN BU 0911/90 | CIELUK HALINA |
| IPN BU 0912/347 | CIELUK KONSTANTY |
| IPN BU 0806/2966 | CIELUK MARIA |
| IPN BU 0967/18 | CIELUKOWSKI JANUSZ |
| IPN BU 0967/18 | CIELUKOWSKI JANUSZ |
| IPN BU 0193/381 | CIENIARSKI JAN |
| IPN BU 0912/891 | CIENIEWSKI KAZIMIERZ |
| IPN BU 0772/959 | CIĘCIAK JÓZEF |
| IPN BU 00283/2280 | CIĘCIARA KRZYSZTOF |
| IPN BU 00966/802 | CIĘCIEL KRZYSZTOF |
| IPN BU 0193/5832 | CIĘPKA (CIEMPKA) FRYDERYK |
| IPN BU 00170/878 | CIĘSZCZYK ZDZISŁAW |
| IPN 00 1043/1070 | CIĘSZCZYK ZDZISŁAW |
| IPN BU 01133/770 | CIĘŻAREK BLANKA |
| IPN BU 0193/7748 | CIĘŻKA (KUBIK) ANIELA |
| IPN BU 00966/138 | CIĘŻKI JAN |
| IPN BU 02042/423 | CIĘŻKI PIOTR |
| IPN BU 0855/3085 | CIĘŻKI STEFAN |
| IPN BU 00168/211 | CIĘŻKOWSKA ALICJA |
| IPN BU 00945/1748 | CIĘŻKOWSKA ALICJA – TERESA |
| IPN BU 0993/1506 | CIĘŻKOWSKA FELICJA |
| IPN BU 00283/1011 | CIĘŻKOWSKA STANISŁAW |
| IPN BU 0872/327 | CIĘŻKOWSKI JAN |
| IPN BU 0958/555 | CIKACZ ADAM |
| IPN BU 0957/461 | CIKACZ EDWARD |
| IPN BU 001121/2325 | CIL IZABELA CZESŁAWA |
| IPN BU 0242/1310 | CILECKI MACIEJ |
| IPN BU 00168/429 | CILIŃSKI – CUMSKI JERZY |
| IPN BU 1108/2 | CIMARNO AGNIESZKA |
| IPN BU 0853/227 | CIMARNO AGNIESZKA |
| IPN BU 00448/693 | CIMASZEWSKA LILIANA |
| IPN BU 001134/5670 | CIMASZEWSKA LILIANA |
| IPN BU 644/1009 | CIMEK JAN |
| IPN BU 00273/195 | CIMEK STEFAN TYMOTEUSZ |
| IPN BU 636/1788 | CIMKE EDWARD |
| IPN BU 00966/1860 | CIMOCHOWICZ ANTONI |
| IPN BU 01013/45 | CIMOSZYŃSKI STANISŁAW |
| IPN BU 00273/360 | CINKOWSKI JACEK |
| IPN BU 00612/4213 | CIOCH JAN |
| IPN BU 0604/2000 | CIOCZEK JAN |
| IPN BU 00169/15 | CIOK – KOZLOWSKA MARIA |
| IPN BU 0901/220 | CIOK ALICJA ELŻBIETA |
| IPN BU 00966/204 | CIOK FELIKS |
| IPN BU 0901/2012 | CIOK HENRYK |
| IPN BU 001121/92 | CIOK JERZY |
| IPN BU 0958/983 | CIOK KAZIMIERZ |
| IPN BU 0951/1630 | CIOK MAŁGORZATA JOLANTA |
| IPN BU 0772/960 | CIOK MARIAN |
| IPN BU 01133/771 | CIOK ROMAN |
| IPN BU 00966/1294 | CIOK TADEUSZ |
| IPN BU 0870/314 | CIOK WIESŁAW |
| IPN BU 001198/1774 | CIOK WOJSŁAW |
| IPN BU 683/240 | CIOK ZOFIA |
| IPN BU 01434/154 | CIOK-KOZŁOWSKA MARIA |
| IPN BU 645/143 | CIOŁEK JÓZEF |
| IPN BU 00744/955 | CIOŁEK MAREK |
| IPN BU 001134/965 | CIOŁEK MAREK |
| IPN BU 001075/186 | CIOŁEK PIOTR |
| IPN BU 0194/1967 | CIOŁEK SŁAWOMIR |
| IPN BU 644/93 | CIOŁEK TADEUSZ |
| IPN BU 0993/1527 | CIOŁEK WANDA |
| IPN BU 00611/1397 | CIOŁEK WŁADYSŁAW |
| IPN BU 001198/5183 | CIOŁEK WŁADYSŁAW |
| IPN BU 001164/122 | Ciołek Zbigniew |
| IPN BU 00612/1996 | CIOŁKIEWICZ GRZEGORZ |
| IPN BU 001198/5014 | CIOŁKIEWICZ GRZEGORZ |
| IPN BU 00750/8 | CIOŁKIEWICZ JAN |
| IPN BU 644/94 | CIOŁKO MIECZYSŁAW |
| IPN BU 0772/2422 | CIOŁKOSZ EDWARD |
| IPN BU 00448/288 | CIOŁKOSZ JAN |
| IPN BU 001134/5260 | CIOŁKOSZ JAN |
| IPN BU 0901/1459 | CIOŁKOWSKA ALICJA |
| IPN BU 0993/1499 | CIOŁKOWSKA ANNA |
| IPN BU 683/242 | CIOŁKOWSKA STEFANIA |
| IPN BU 0242/1136 | CIOŁKOWSKI JAN |
| IPN BU 01133/772 | CIOŁKOWSKI PIOTR |
| IPN BU 0194/1478 | CIOŁKOWSKI TADEUSZ |
| IPN BU 0218/3152 | CIOŁKOWSKI TADEUSZ |
| IPN BU 0833/703 | CIOŁKOWSKI WŁADYSŁAW |
| IPN BU 645/185 | CIONEK MARIAN |
| IPN BU 0242/1897 | CIOPIŃSKA ANNA |
| IPN BU 0772/2423 | CIOPIŃSKA MARIA |
| IPN BU 001198/40 | CIOPIŃSKI JÓZEF |
| IPN BU 0193/1586 | CIOPIŃSKI ZDZISŁAW |
| IPN BU 0604/1792 | CIOPIŃSKI ZDZISŁAW |
| IPN BU 0242/769 | CIOS TERESA |
| IPN BU 686/562 | CIOSEK ANNA |
| IPN BU 001198/1735 | CIOSEK HENRYK |
| IPN BU 693/831 | CIOSEK IRENA |
| IPN BU 00612/2993 | CIOSEK IRENEUSZ |
| IPN BU 0218/325 | CIOSEK JANINA |
| IPN BU 0193/1587 | CIOSEK MARIAN |
| IPN BU 00612/3027 | CIOSEK REGINA |
| IPN BU 00612/891 | CIOSEK STANISŁAW |
| IPN BU PF | 109/120 CIOSEK STANISŁAWA |
| IPN BU 0951/986 | CIOSEK TADEUSZ STANISŁAW |
| IPN BU 00611/702 | CIOSEK WŁADYSŁAW |
| IPN BU 001198/1129 | CIOSEK WŁADYSŁAW |
| IPN BU 00612/1621 | CIOSEK ZDZISŁAW |
| IPN BU 001198/4765 | CIOSEK ZDZISŁAW |
| IPN 00 1043/3513 | CIOSIŃSKI ANTONI KAZIMIERZ |
| IPN BU 693/829 | CIOSK DANUTA |
| IPN BU 0870/236 | CIOSK WŁODZIMIERZ |
| IPN BU 01013/326 | CIOSTEK EDWARD |
| IPN BU 0902/119 | CIOSTEK LEON |
| IPN BU 644/95 | CIOSTEK MARIAN |
| IPN BU 01013/46 | CIOSTEK PIOTR |
| IPN BU 0988/1410 | CIO WŁADYSŁAW |
| IPN BU 001121/334 | CIOTH-NOWACKA TERESA |
| IPN BU 00283/219 | CIOTUCHA ROMAN |
| IPN BU 00768/153 | CIOTUCHA ROMAN |
| IPN BU 00966/205 | CIÓLKOWSKI HENRYK |
| IPN BU 0287/38 | CIÓLKOWSKI IRENEUSZ |
| IPN BU 0911/91 | CIÓŁKOWSKI HENRYK |
| IPN BU 01000/897 | CIPA ZOFIA |
| IPN BU 644/1010 | CIPIŃSKI ZBIGNIEW |
| IPN BU 01000/271 | CIPIOR HENRYK |
| IPN BU 01133/773 | CIPKA JAN |
| IPN BU 01013/327 | CIPLUCH WIKTOR |
| IPN BU 0218/2508 | CIPPERT PIOTR |
| IPN BU 0194/1232 | CIRKA PIOTR |
| IPN BU 0243/70 | CIRKO KAZIMIERA |
| IPN BU 00945/411 | CIRLIC – KALITA HALINA |
| IPN BU 0833/125 | CIS JÓZEF |
| IPN BU 01050/1343 | CIS JÓZEF |
| IPN BU 00283/1054 | CIS JÓZEF |
| IPN BU 00283/507 | CIS MIROSŁAW |
| IPN BU 00768/373 | CIS MIROSŁAW |
| IPN BU 0912/364 | CIS STEFAN |
| IPN BU 00611/1524 | CIS TADEUSZ |
| IPN BU 001198/2835 | CIS TADEUSZ |
| IPN 00 1043/2273 | CISAK ALOJZY |
| IPN BU 00966/377 | CISAK GRZEGORZ |
| IPN BU 00966/866 | CISAK MIECZYSŁAW |
| IPN BU 00612/3770 | CISAK STANISŁAW |
| IPN BU 001198/6659 | CISAK STANISŁAW |
| IPN BU 00744/1027 | CISAK TADEUSZ MACIEJ |
| IPN BU 001134/1318 | CISAK TADEUSZ MACIEJ |
| IPN BU 0912/365 | CISAK WINCENTY |
| IPN BU 0218/378 | CISAK WOJCIECH |
| IPN BU 01000/2163 | CISEK WACŁAW |
| IPN BU 00200/1312 | CISEK ZENON |
| IPN BU 001102/913 | CISEK ZENON |
| IPN BU 001198/3796 | CISEŁ EUGENIUSZ |
| IPN BU 002082/166 | CISEWSKA MARIA JOLANTA |
| IPN BU 002086/352 | CISEWSKA MARIA JOLANTA |
| IPN BU 0912/342 | CISIELSKI WACŁAW |
| IPN BU 0912/343 | CISIELSKI WACŁAW |
| IPN BU 01000/2177 | CISKAŁ HALINA |
| IPN BU 0772/961 | CISKOWSKI JÓZEF |
| IPN BU 00966/105 | CISŁAK ELŻBIETA |
| IPN BU 0242/919 | CISŁO ADAM |
| IPN BU 0242/384 | CISŁO JOANNA |
| IPN BU 00612/3617 | CISŁO JÓZEF |
| IPN BU 001198/6583 | CISŁO JÓZEF |
| IPN BU 00611/298 | CISŁOWSKI FRANCISZEK |
| IPN BU 001198/648 | CISŁOWSKI FRANCISZEK |
| IPN BU 00612/3459 | CISOWSKI CZESŁAW |
| IPN BU 001198/6469 | CISOWSKI CZESŁAW |
| IPN BU 00200/218 | CISOWSKI JAN |
| IPN 00 1052/805 | CISOWSKI JAN |
| IPN BU 01000/2178 | CISOWSKI JÓZEF |
| IPN BU 00612/4759 | CISOWSKI KRZYSZTOF |
| IPN BU 00283/2419 | CISOWSKI STANISŁAW |
| IPN BU 01000/1618 | CISOWSKI ZDZISŁAW |
| IPN BU 00283/321 | CISSOWSKI JAN |
| IPN BU 00768/212 | CISSOWSKI JAN |
| IPN BU 01434/415 | CISZ HIERONIM |
| IPN BU 00200/563 | CISZAK RYDGIER NORBERT STANISŁAW |
| IPN 00 1052/1872 | CISZAK RYDYGIER NORBERT STANISŁAW |
| IPN BU 00275/11 | CISZECKI JAN ANDRZEJ |
| IPN BU 001121/3651 | CISZECKI JAN ANDRZEJ |
| IPN BU 0194/1706 | CISZEK ALEKSANDER |
| IPN 00 1043/2079 | CISZEK ALEKSANDER LUDOMIR |
| IPN BU 00612/1747 | CISZEK BENEDYKT |
| IPN BU 0242/253 | CISZEK DIONIZY |
| IPN BU 00612/3022 | CISZEK HENRYK |
| IPN BU 00612/4836 | CISZEK JANUSZ |
| IPN BU 698/558 | CISZEK JÓZEF |
| IPN BU 001198/5534 | CISZEK LECH |
| IPN BU 00283/1245 | CISZEK STANISŁAW |
| IPN BU 00611/459 | CISZEK WŁADYSŁAW |
| IPN BU 001198/826 | CISZEK WŁADYSŁAW |
| IPN BU 00612/320 | CISZEK ZYGMUNT |
| IPN BU 001198/4217 | CISZEK ZYGMUNT |
| IPN BU 636/1822 | CISZEWICZ FRANCISZKA |
| IPN BU 636/1824 | CISZEWICZ FRANCISZKA |
| IPN BU 0806/2677 | CISZEWSA JADWIGA |
| IPN BU 01013/60 | CISZEWSKA KRYSTYNA |
| IPN 00 1052/1385 | CISZEWSKA MARIA |
| IPN BU 0772/962 | CISZEWSKA STANISŁAWA |
| IPN BU 698/559 | CISZEWSKA STANISŁAWA |
| IPN BU 0772/2425 | CISZEWSKA WIESŁAWA |
| IPN BU 0806/1705 | CISZEWSKA ZOFIA |
| IPN BU 00945/879 | CISZEWSKI BOGDAN – BOHDAN |
| IPN BU 644/1011 | CISZEWSKI BOLESŁAW |
| IPN BU 02042/404 | CISZEWSKI BRONISŁAW |
| IPN BU 0194/2718 | CISZEWSKI EDMUND |
| IPN BU 644/1012 | CISZEWSKI EDWARD |
| IPN BU 0891/377 | CISZEWSKI FRANCISZEK |
| IPN BU 0958/199 | CISZEWSKI FRANCISZEK |
| IPN BU 0604/1681 | CISZEWSKI HENRYK |
| IPN BU 00612/2203 | CISZEWSKI HENRYK |
| IPN BU 001198/5298 | CISZEWSKI HENRYK |
| IPN BU 0891/1803 | CISZEWSKI JAN |
| IPN BU 01000/2179 | CISZEWSKI JAN |
| IPN BU 748/271 | CISZEWSKI JAN |
| IPN BU 00191/492 | CISZEWSKI JAN |
| IPN BU 0193/4651 | CISZEWSKI JERZY |
| IPN BU 00200/270 | CISZEWSKI JERZY |
| IPN 00 1052/970 | CISZEWSKI JERZY |
| IPN BU 0891/408 | CISZEWSKI JÓZEF |
| IPN BU 0193/6171 | CISZEWSKI JÓZEF |
| IPN BU 0912/1566 | CISZEWSKI KAZIMIERZ |
| IPN BU 0833/121 | CISZEWSKI KLEMENS |
| IPN BU 00611/1666 | CISZEWSKI MAKSYMILIAN |
| IPN BU 001198/3087 | CISZEWSKI MAKSYMILIAN |
| IPN BU 00612/3901 | CISZEWSKI MARIAN |
| IPN BU 001198/6729 | CISZEWSKI MARIAN |
| IPN BU 0911/664 | CISZEWSKI MIECZYSŁAW |
| IPN BU 0193/5913 | CISZEWSKI MIROSŁAW |
| IPN BU 00170/680 | CISZEWSKI MIROSŁAW |
| IPN 00 1043/593 | CISZEWSKI MIROSŁAW |
| IPN BU 0193/7957 | CISZEWSKI STANISŁAW |
| IPN BU 01000/1527 | CISZEWSKI STANISŁAW |
| IPN BU 01250/98 | CISZEWSKI STANISŁAW |
| IPN BU 698/496 | CISZEWSKI STANISŁAW |
| IPN BU 001198/1665 | CISZEWSKI STANISŁAW |
| IPN BU 00966/1543 | CISZEWSKI TOMASZ |
| IPN BU 0891/378 | CISZEWSKI WINCENTY |
| IPN BU 645/138 | CISZEWSKI WINCENTY |
| IPN BU 0892/855 | CISZEWSKI WITOLD. JAN |
| IPN BU 02042/38 | CISZEWSKI ZBIGNIEW |
| IPN BU 0193/1588 | CISZEWSKI ZYGMUNT |
| IPN BU 001102/1842 | CISZEWSKI ZYGMUNT |
| IPN BU 698/497 | CISZKIEWICZ HELENA |
| IPN BU 0866/96 | CISZKIEWICZ MIECZYSŁAW |
| IPN BU 0772/68 | CISZKO JERZY |
| IPN BU 00200/1439 | CISZKOWSKA EWA |
| IPN BU 001102/1040 | CISZKOWSKA EWA |
| IPN BU 0951/1113 | CISZKOWSKA JÓZEFA |
| IPN BU 0833/683 | CISZKOWSKA KRYSTYNA |
| IPN BU 0806/835 | CISZKOWSKA MARIA |
| IPN BU 00612/439 | CISZKOWSKA ROZALIA |
| IPN BU 0218/89 | CISZKOWSKI JULIAN |
| IPN BU 001075/95 | CISZKOWSKI KRZYSZTOF |
| IPN BU 0958/1016 | CISZKOWSKI STANISŁAW |
| IPN BU 0193/1589 | CISZKOWSKI ZYGMUNT |
| IPN BU 0772/2424 | CISZONIK LUDWIK |
| IPN BU 00612/3443 | CISZOWSKI KRZYSZTOF |
| IPN BU 001198/6453 | CISZOWSKI KRZYSZTOF |
| IPN BU 0193/8700 | CISZYŃSKA STANISŁAWA KOLENDA |
| IPN BU 00200/49 | CISZYŃSKI EUGENIUSZ |
| IPN 00 1052/394 | CISZYŃSKI EUGENIUSZ BRONISŁAW |
| IPN BU 00612/863 | CILIK JÓZEF |
| IPN BU 001198/4441 | CILIK JÓZEF |
| IPN BU 0772/2426 | CITAK TERESA |
| IPN BU 0912/39 | CIUBA KAZIMIERZ |
| IPN BU 01133/186 | CIUBAK JÓZEF |
| IPN BU 02042/46 | CIUCHNOWICZ ZDZISŁAW |
| IPN BU 0772/542 | CIUCHTA JAN |
| IPN BU 00744/894 | CIUCHTA JOANNA |
| IPN BU 001134/688 | CIUCHTA JOANNA |
| IPN BU 00257/131 | CIUCKA GRAŻYNA |
| IPN BU 001102/1198 | CIUCKA GRAŻYNA |
| IPN BU 0218/646 | CIUCKI CZESŁAW |
| IPN BU 00200/482 | CIUK ANDRZEJ |
| IPN 00 1052/1663 | CIUK ANDRZEJ |
| IPN BU 001198/1787 | CIUK JERZY |
| IPN BU 00966/1452 | CIUK MARIAN |
| IPN BU 0218/3438 | CIUK STEFAN |
| IPN BU 001198/325 | CIUK TADEUSZ |
| IPN BU 01130/46 | CIUKA IRENA |
| IPN BU 00334/771 | CIULAK JADWIGA |
| IPN BU 001134/3855 | CIULAK JADWIGA |
| IPN BU 00612/3387 | CIULEBA ZDZISŁAW |
| IPN BU 001198/6426 | CIULĘBA ZDZISŁAW |
| IPN BU 0806/1065 | CIULIŃSKA CELINA |
| IPN 00 1043/2284 | CIULIŃSKA ELŻBIETA |
| IPN BU 0806/2031 | CIUŁA EWA |
| IPN BU 00611/1102 | CIUŁEK ANTONI |
| IPN BU 001198/1506 | CIUŁEK ANTONI |
| IPN BU 001198/5764 | CIUŁEK WIESŁAW |
| IPN BU 0958/544 | CIUMAN JADWIGA |
| IPN BU 00945/2082 | CIUŃSKI – CUŃSKI JERZY |
| IPN BU 00945/2015 | CIUPA – SPOREK STEFANIA |
| IPN BU 01434/290 | CIUPA STEFANIA |
| IPN BU 0806/2716 | CIUPA TERESA |
| IPN BU 00283/1427 | CIUPAK ANDRZEJ |
| IPN BU 00768/768 | CIUPAK ANDRZEJ |
| IPN BU 00612/3777 | CIUPAŁ ZENON |
| IPN BU 0193/1590 | CIUPEK KAZIMIERZ |
| IPN BU 00612/3690 | CIUPEK KRYSTYNA |
| IPN BU 52/135 | CIUPEK WŁADYSŁAW |
| IPN BU PF | 1021/7 CIUPEK WŁADYSŁAW |
| IPN BU 980/20 | CIUPEK ZBIGNIEW |
| IPN BU 00225/65 | CIUPIAŁ ZBIGNIEW |
| IPN BU 00612/4568 | CIUPIŃSKA BOŻENA |
| IPN BU 001198/7206 | CIUPIŃSKA BOŻENA |
| IPN BU 00283/180 | CIUPIŃSKI JAN |
| IPN BU 00768/136 | CIUPIŃSKI JAN |
| IPN BU 001198/3709 | CIUPIŃSKI JAN |
| IPN BU 0193/7364 | CIUPIŃSKI JAN KAZIMIERZ |
| IPN BU 002086/1833 | CIUPIŃSKI JANUSZ |
| IPN BU 0218/3529 | CIUPIŃSKI WACŁAW |
| IPN BU 0604/1450 | CIUPIŃSKI WIESŁAW |
| IPN BU 00234 | p.256 CIUPKA RYSZARD |
| IPN BU 00966/1609 | CIURA JANINA |
| IPN BU 00612/3457 | CIURA LESZEK |
| IPN BU 001198/6467 | CIURA LESZEK |
| IPN BU 0193/158 | CIURA MARIAN |
| IPN BU 01000/210 | CIURA MIECZYSŁAW |
| IPN BU 001121/1059 | CIURAJ ADAM |
| IPN BU PF | 109/121 CIURAJ KRZYSZTOF |
| IPN BU 0833/682 | CIURAJ MARIAN |
| IPN BU 00312 | CIURLIK L. (HERBERT) |
| IPN BU 00312/77 | CIURLIK L. (HERBERT) |
| IPN BU 00170/454 | CIURLIK LESZEK |
| IPN BU 00945/2683 | CIURLIK LESZEK |
| IPN BU 01133/774 | CIURYSEK FELIKS |
| IPN BU 0942/565 | CIURZYŃSKI HENRYK |
| IPN BU 00448/464 | CIURZYŃSKI SŁAWOMIR |
| IPN BU 001134/5439 | CIURZYŃSKI SŁAWOMIR WOJCIECH |
| IPN BU 00200/791 | CIUSZYŃSKA ELŻBIETA MONIKA |
| IPN BU 0242/2220 | CIUNIAK BOGDAN |
| IPN BU 0988/623 | CIZIEL BRONISŁAW |
| IPN BU 0891/379 | CIZIEL JANINA |
| IPN BU 0958/545 | CIZMAN KAZIMIERZ |
| IPN BU 001198/2239 | CILA JAN |









![[Image]](https://i0.wp.com/cryptome.org/2013/11/snowden-tally-pies.jpg)



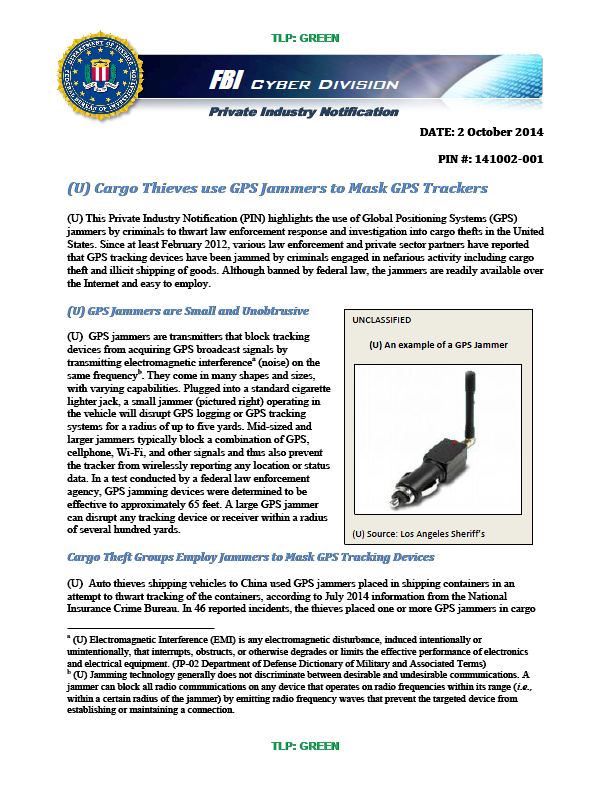





![[Image]](https://i0.wp.com/cryptome.org/2014-info/qom-site-r/qom.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2014-info/qom-site-r/site-r.jpg)

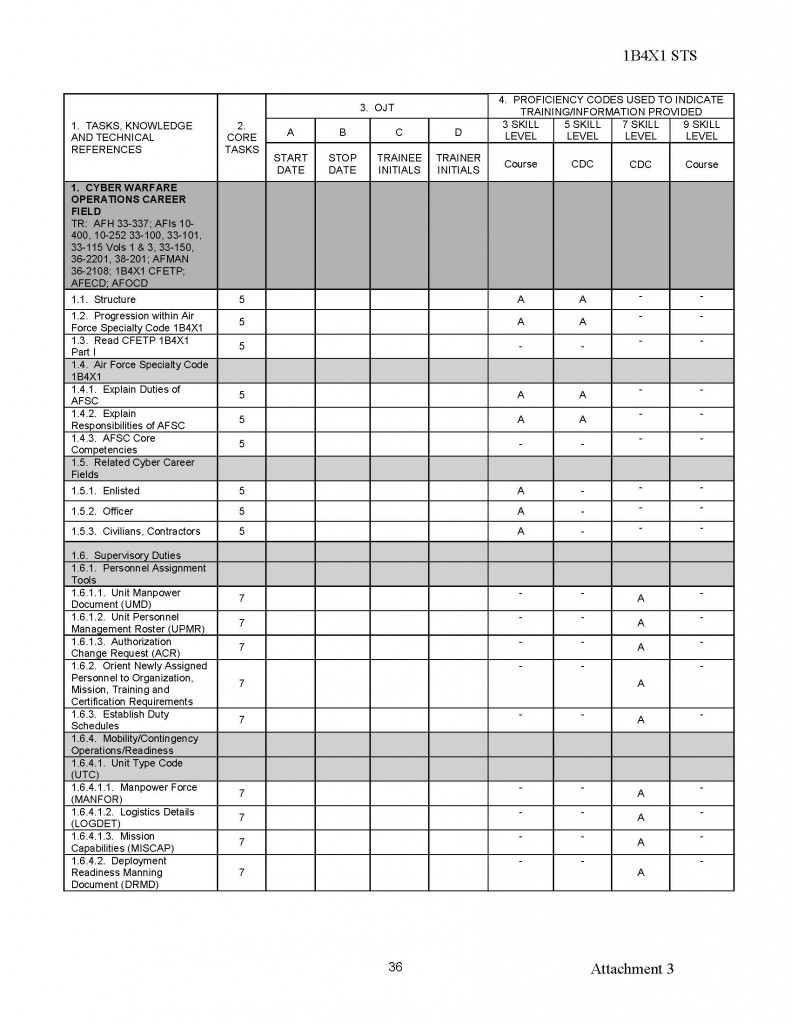
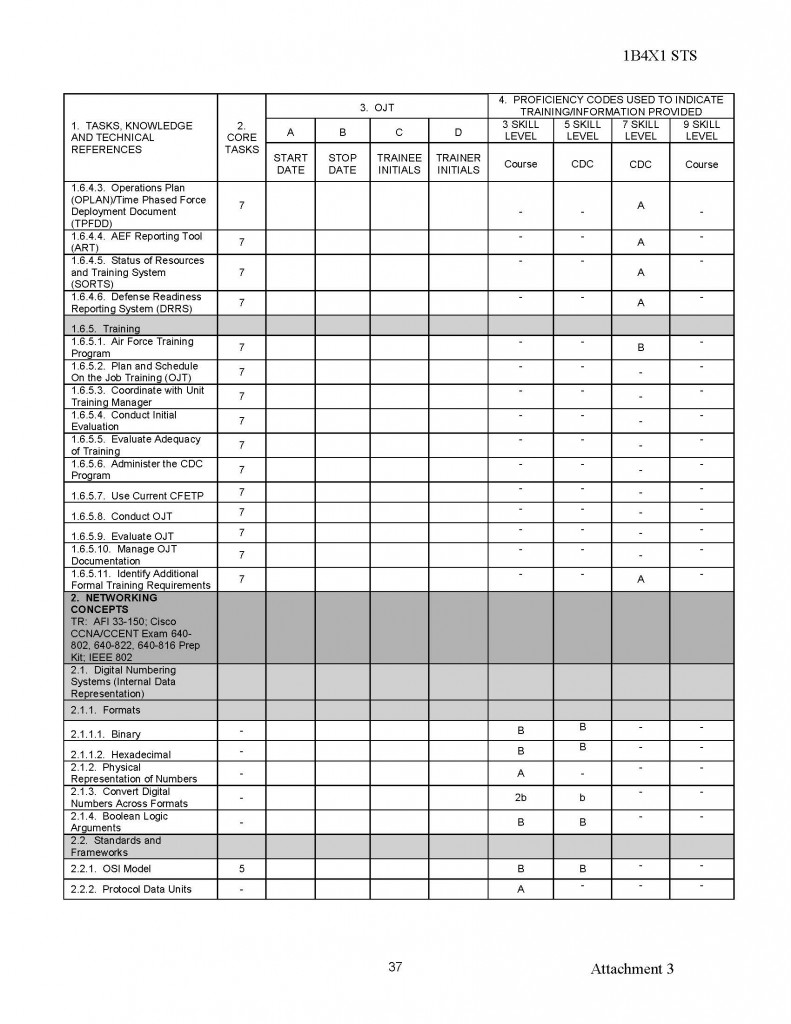
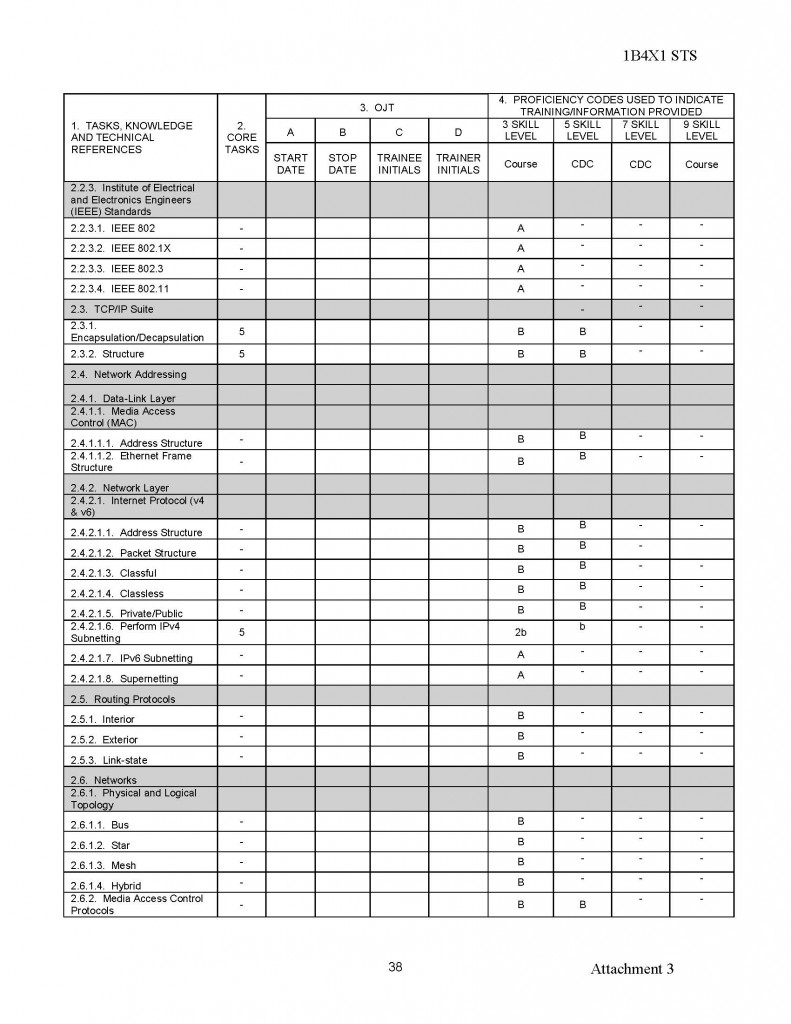
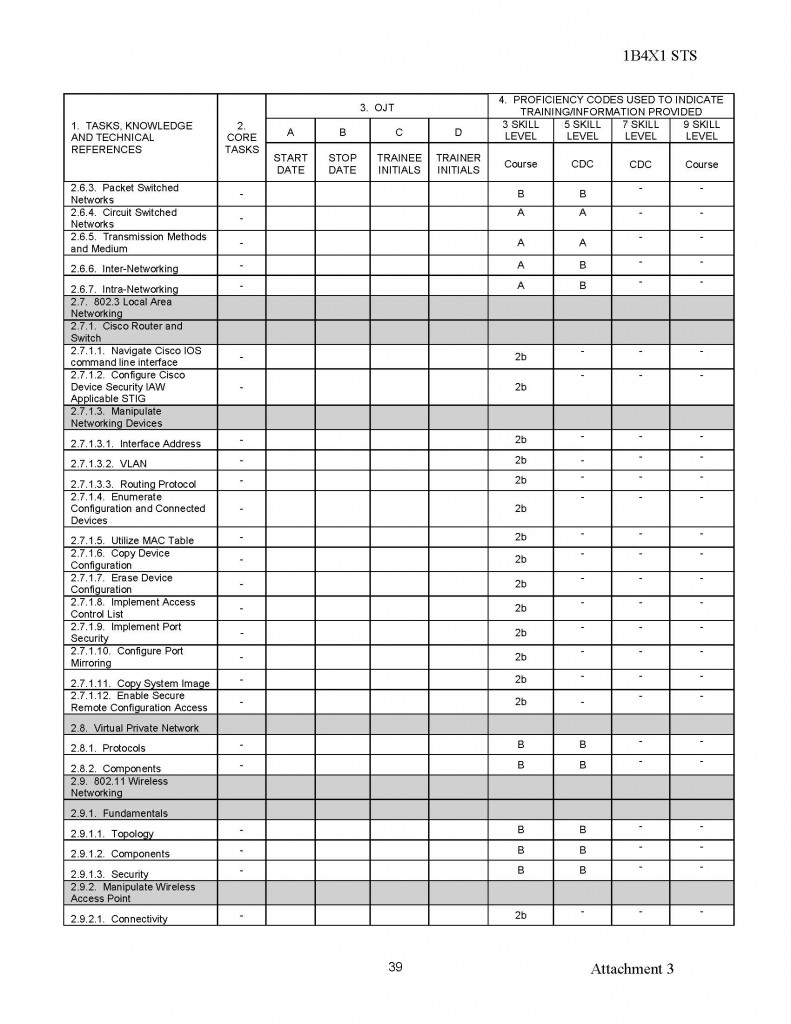
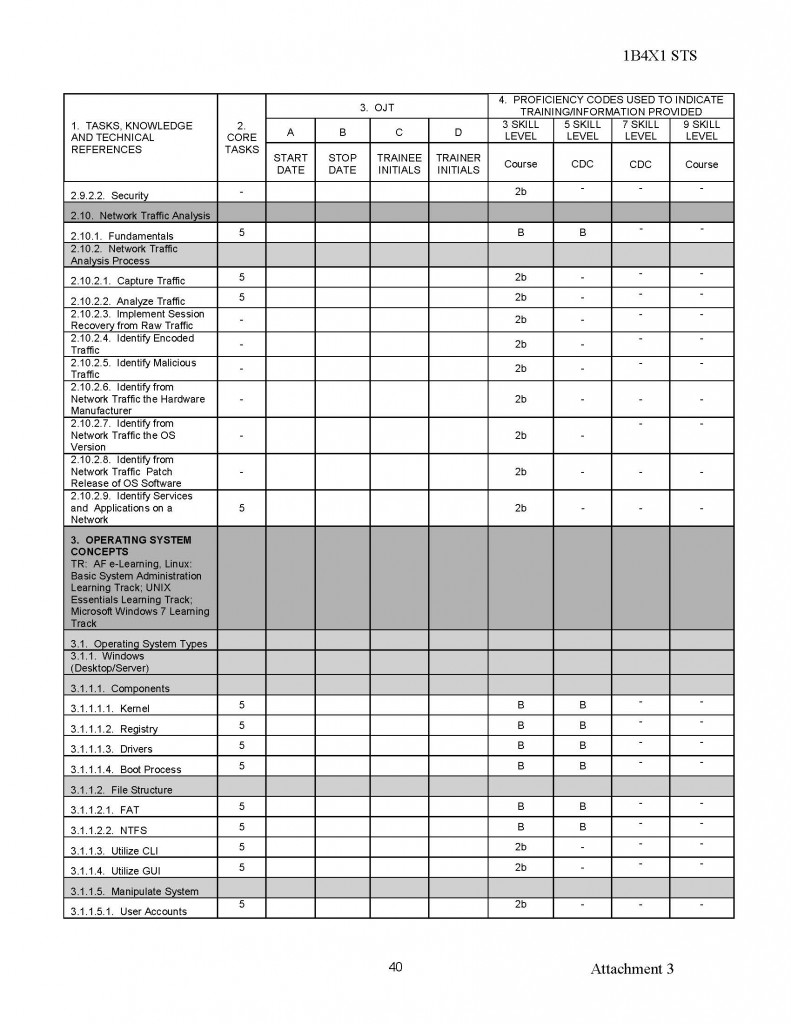
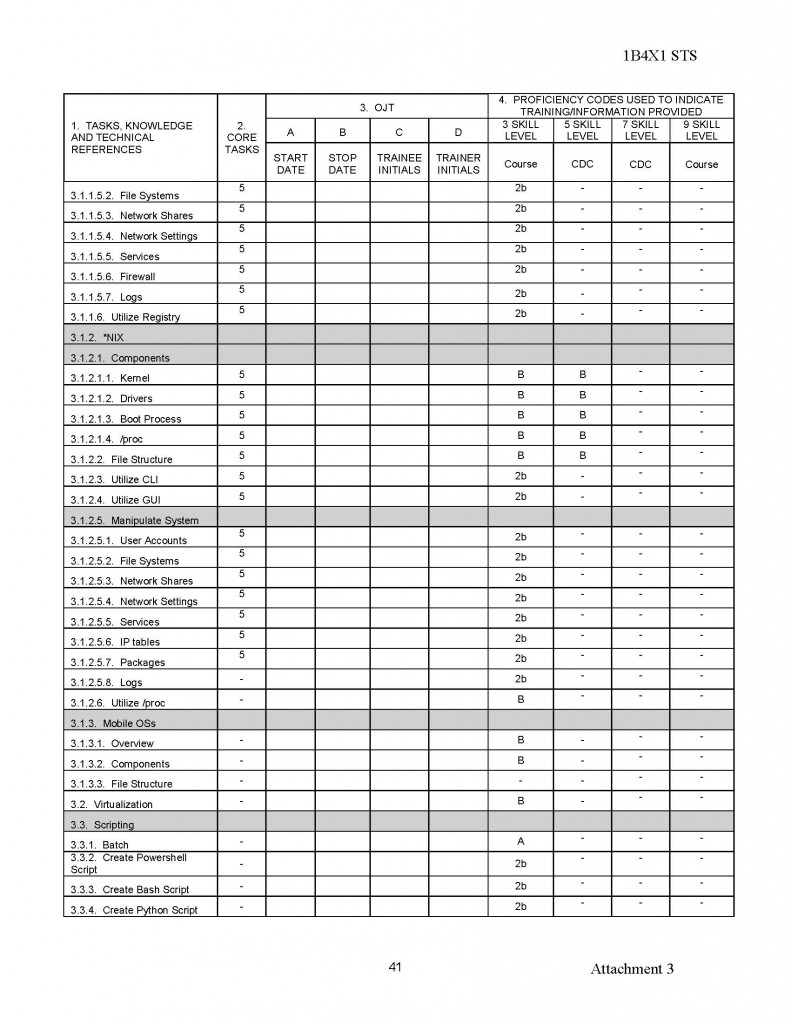
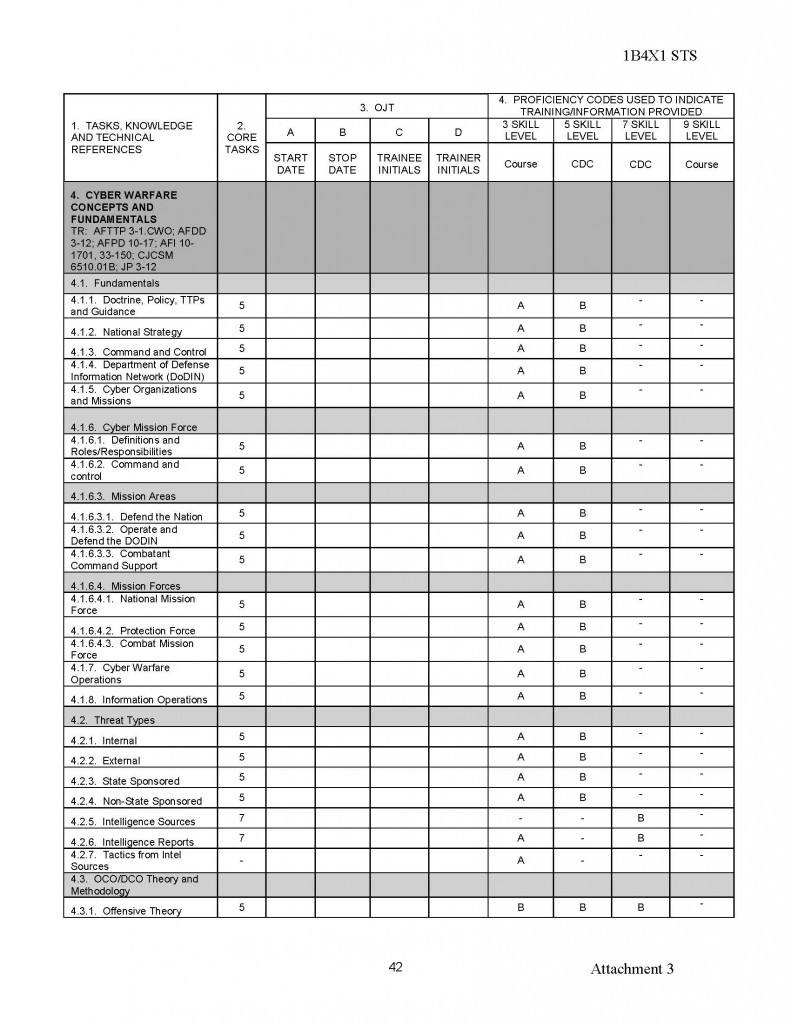
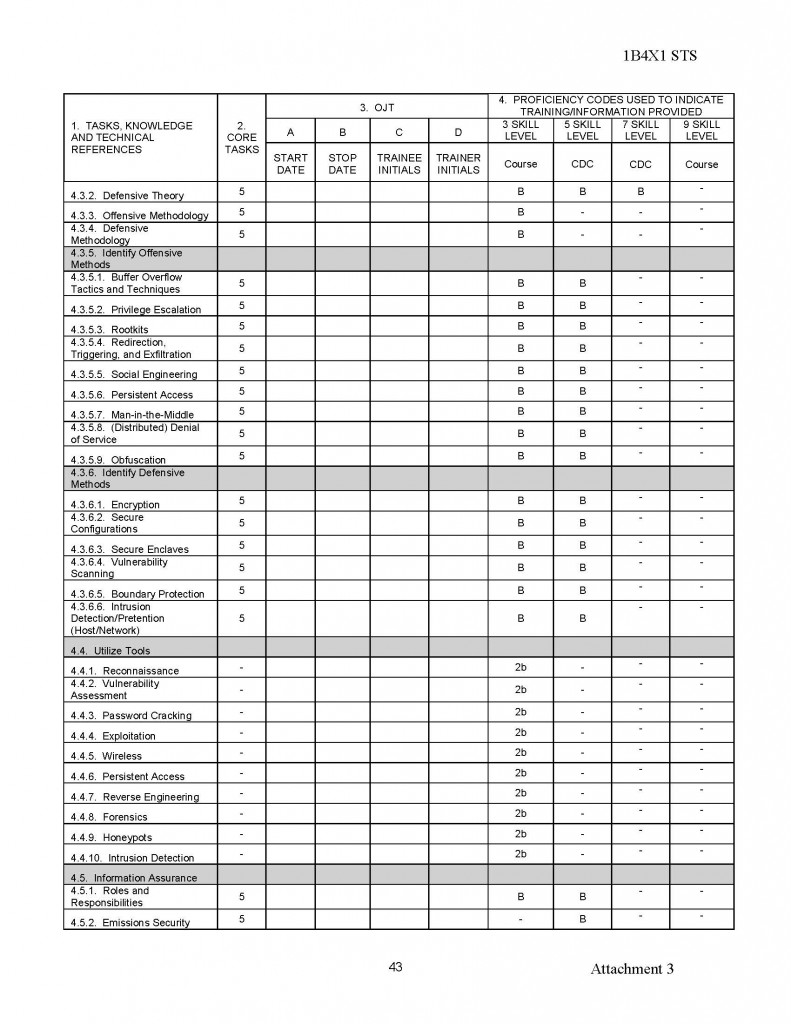
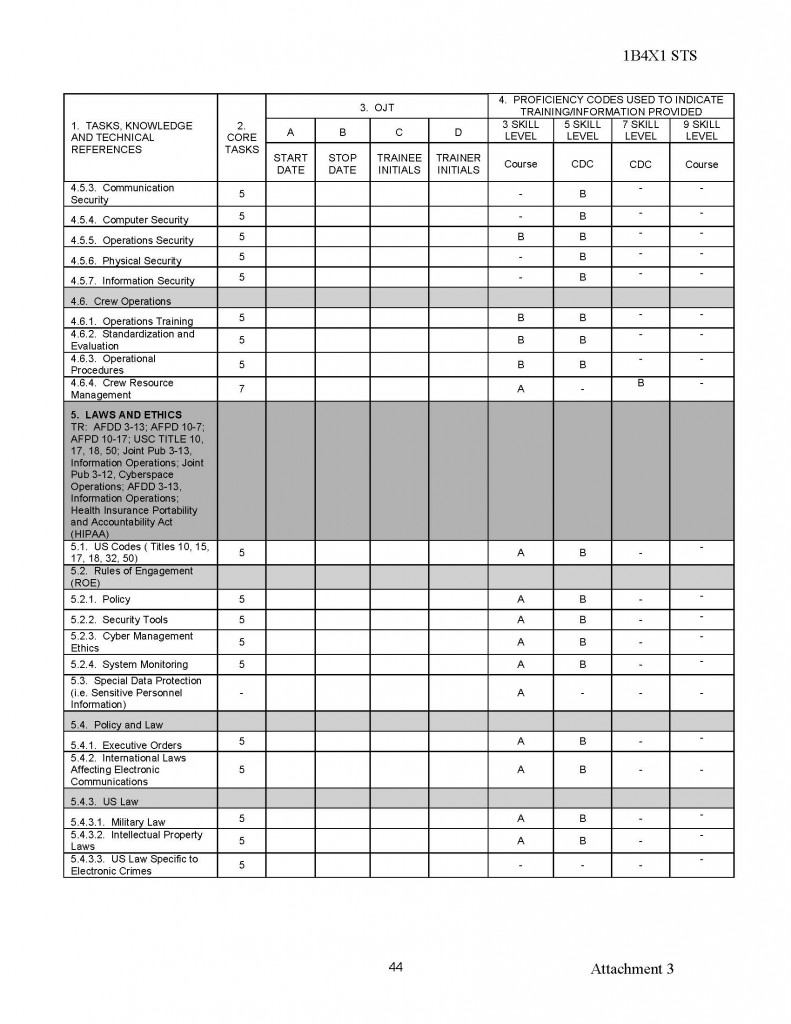
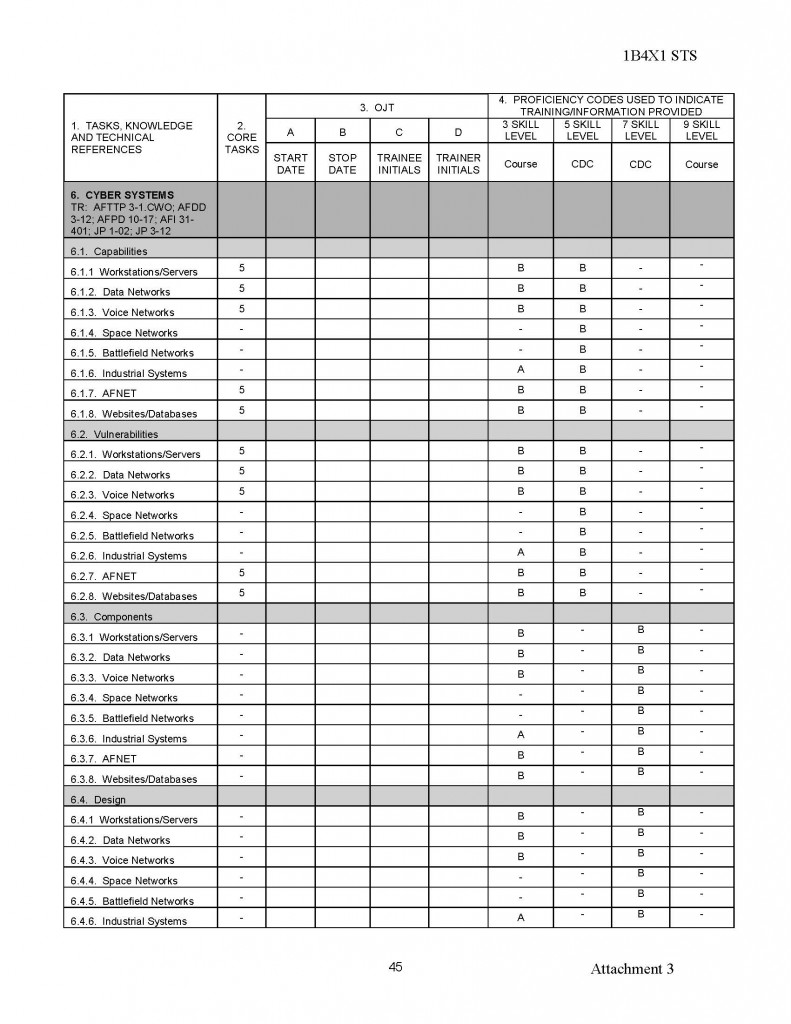
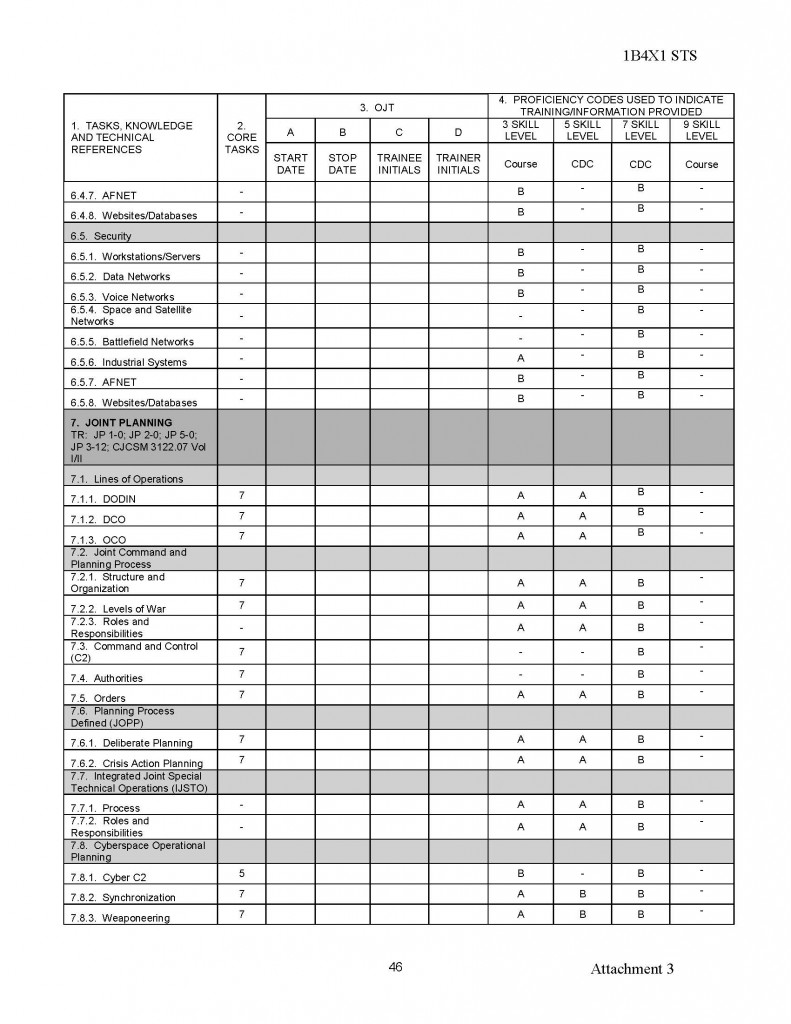
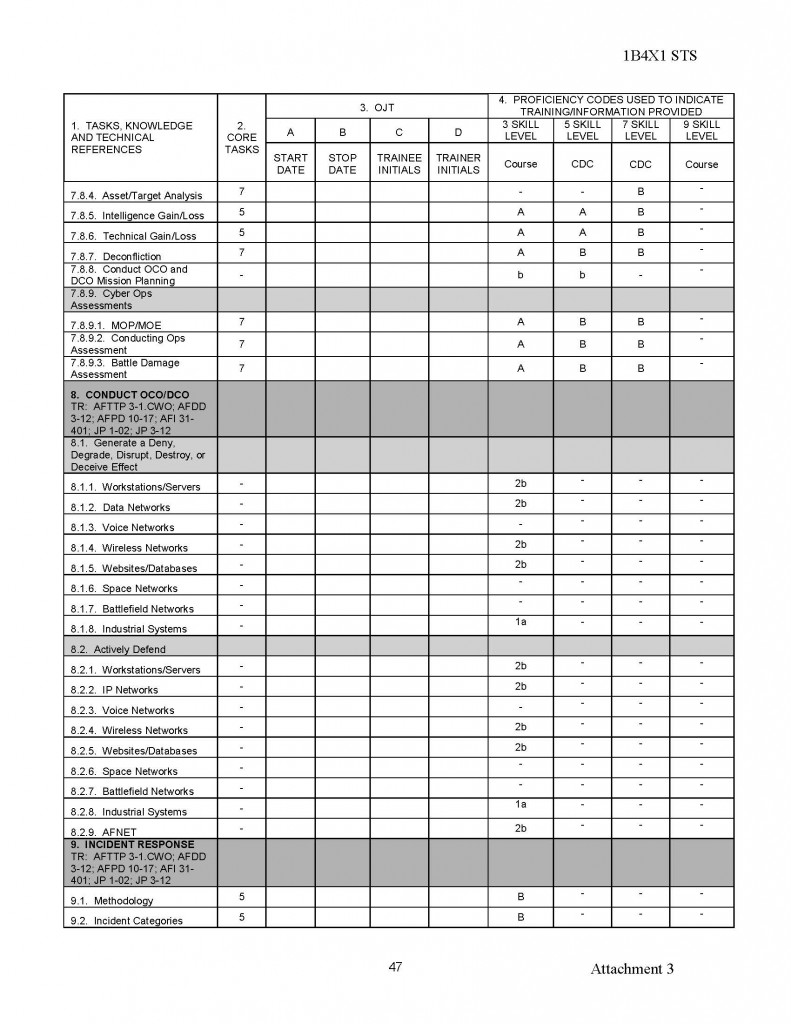
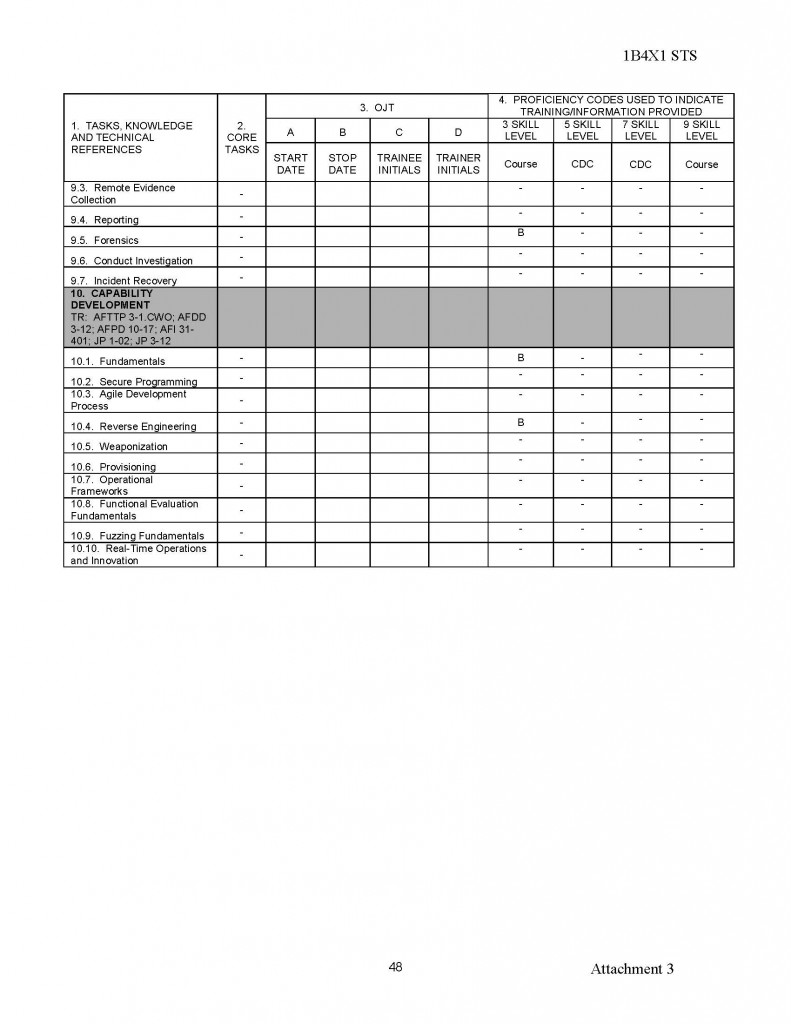




You must be logged in to post a comment.