Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Month: August 2014
TOP-SECRET – The Secret List of CIA Sources – 2.619 Names and Adresses, Part 12,L,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
L
Labar, Sherwood M. 8775 20th St., No. 814W, Vero Beach, FL 32960 LaClair, Cameron 4201 Cathedral Ave., NW, No. 315E, Washington, DC 20016 LaFaver, Richard N. 1 North Hornbeam Pl., The Woodlands, TX 77380 Lafferty, Fred B. P.O. Box 9300, Minneapolis, MN 55440 Laggan, Francis P. 2217 Great Falls St., Falls Church, VA 22046 LaGuex, Conrad 2317 N. Pocomoke St., Arlington, VA 22205 Lahnstein, Manfred Bertelsman AG, Gutersloh, Germany Lambert, Robert 1919 Killarney Way, Bellevue, WA 98004 Lamkin, James P.O. Box 210, Starkville, MS 39760 Lamon, Ralph 6363 Christie Ave., No. 1517, Emeryville, CA 94608 Lampshire, Cdr Harvey USN 2145 N. Quebec St., Arlington, VA 22207 Lancer, Col Thomas USA 9048 Belvoir Woods Pkway, Fort Belvoir, VA 22060 Landau, Yechil 60 Division Ave., No. 2C, Brooklyn, NY 11211 Landreth, Edward 544 E. 86th St., New York, NY 10028 Landreth, Ted 1211 S. Genesee Ave., Los Angeles, CA90019 Lane, Albert 138 Germany Rd., Verona, NY 13478 Lane, Buford 3611 Antiem St., San Diego, CA 92111 Lange, Col H.W. USA 9000 Belvoir Woods Pkway, No. 302, Fort Belvoir, VA 22060 Langevin, Henry R. 4 Longview Dr., Bow, NH 03304 Langfield, Millard 3330 N. Leisure World Blvd., No. 926, Silver Spring, MD 20906 Langholz, Marcus P.O. Box 94, Rapidan, VA 22733 Langlie, Gary 4103 Wexford Dr., Kensington, MD 20895 Languit, Col Gerard USAF 6415 Cleghorn Rd., NW, Albuquerque, NM 87120 Lankford, Blaine 4480 Bella Mia Ct., Howell, MI 48843 Lanterman, Col John USA 8502 Whittier Blvd., Bethesda, MD 20817 Lanterman, Mark T. 132-A Plymouth Ave., Oreland, PA 19075 Lantos, Thomas 2217 Rayburn House Office Bldg., Washington, DC 20515 Lapham, Lewis 65710 E. Desert Trail Dr., Tucson, AZ 85737 Lapinier, Major Arnold AUS 5893 Grove Rd., Trumansburg, NY 14886 Larkin, MajGen Richard USA 1517 Night Shade Ct., Vienna, VA 22180 Laroche, Richard 150 Sportsmans Dr., West Lakes, SA 5021, Australia Larsen, Harold A. 1314 Kurtz Rd., McLean, VA 22102 Larson, Ms. Florence 5903 Mt. Eagle Dr., No. 601, Alexandria, VA 22303 Larum, Norman 3225 Eldora Ln., Missoula, MT 59803 Larzelier, Henry 16903 Kilwinning, Houston, TX 77084 Lascaris, Constant P.O. Box 3172, Clearwater, FL 34630 Laster, Clarence C. 10915 Burr Oak, San Antonio, TX 78230 Latzen, Capt. Murray 57-45 74th St., Unit 309, Elmhurst, NY 11373 Laub, Charles 949 S. Hope St., Suite 3030, Los Angeles, CA 90015 Laufman, David 9303 Sibelius Dr., Vienna, VA 22182 Law, Richard 9713 Ceralene Dr., Fairfax, VA 22032 Law, Major Robert S. AUS 472 Argyle Rd., Brooklyn, Ny 11218 Lawton, Edward F. 4865 Carriagepark Rd., Fairfax, VA 22032 Layton, LtCol Benjamin USA 10700 Brunswick Ave., Kensington, MD 20895 Lazar, Charna 501 NW 7th St., Boca Raton, FL 33432 Leader, John L. 5052 Westpath Terrace, Bethesda, MD 20816 Leaf, Edward 121 N. Chestnut St., Lindsborg, KS 67456 Learnard, Edwin 1010 16th Ave., No. 6, San Diego, CA 92101 Leary, William Dept. of History, University of Georgia, Athens, GA 30602 Leavitt, John H. P.O. Box 1182, Wellfleet, MA 02667 Leavitt, Robert W. 7129 Rolling Forest Ave., Springfield, VA 22152 Ledoux, Sylvester P. 1106 Main St., No. 14209 [No city provided.] Lee, Mrs. Barbara P.O. Box 137, Harwichport, MA 02646 Lee, Bruce 115 E. 67th St., New York, NY 10028 Lee, John F. 2010 Meadow Springs Dr., Vienna, VA 22182 Lee, Terence M. 1480 Garfield Ave., San Marino, CA 91108 Lee, Col Thomas USAF 9605 Atwood Rd., Vienna, VA 22182 Lefebre, Albert 36 Sea Spray Dr., Biddeford, ME 04005 Lefkowitz, Alan 2488 Mt. Royal Rd., Pittsburgh, PA 15217 LeGallo, Andre 2 Bridgeberry Ct., The Woodlands, TX 77381 Lehman, Frederick J. 3706 E. 3rd St., No. 1, Dayton, OH 45403 Leibacher, Ernst 1931 Park Skyline Rd., Santa Ana, CA 92705 Leifer, Capt N. David USAR P.O. Box 960748, Miami, FL 33296 Leighton, Ms. Marian 2081 Wethersfield Ct., Reston, VA 22091 Lelesz, Spec George USA P.O. Box 670881, Brink, NY 10467 Lengel, Capt John 8451 Stafford Dr., Strongsville, OH 44136 Lennox, Cdr Alexander USN 324 Devonshire Ln., Orange Park, FL 332073 Lentol, Edward S. 107-43 113th St., Richmond Hill, NY 11419 Leonard, Col Eugene USAR P.O. Box 501, Lexington, VA 24450 Leusner, James 5471 Lake Howell Rd., No. 106, Winter Park, FL 32792 Leven, Barry K. 5665 Phelps Luck Dr., Columbia, MD 21045 Leveridge, William 9409 Shouse Dr., Vienna, VA 22181 Levin, Mrs. Elizabeth 10420 Royal Rd., Hillandale, MD 20903 Levin, M. J. 10420 Royal Rd., Hillandale, MD 20903 Levy, Frank 6504 Smoot Dr., McLean, VA 22101 Lewis, Ernest A. 3720 SE 1st Place, Cape Coral, FL 33904 Lewis, Orme 100 West Washington St., Phoenix, AZ 85003 Lewis, Stanton 2447 NCNB Center, Houston, TX 77002 Lewton, Lewis 28131 Coolidge Dr., Euclid, OH 44132 Librandi, Frank J. 3723 W. Grovers Ave., Glendale, AZ 85308 Lieberman, Dr. Alan 18425 Long Lake Dr., Boca Raton, FL 33434 Lincoln, PNCS Charles USN 300 E. Evergreen Ave., Philadelphia, PA 19118 Lindenauer, S/A Julian 12975 SW 186th Terrace, Miami, FL 33177 Lindsley Winston J. 4913 Tydfil Ct., Fairfax, VA 22030 Linn, Mrs. Betty 3130 Duke St., Alexandria, VA 22314 Linton, Mrs. Jean 5216 Farrington Rd., Bethesda, MD 20816 Lipton, Maurice 611 John Marshall Dr., NE, Vienna, VA 22180 Liskey, Russell 1230 Kings Tree Dr., Michelville, MD 20721 Liszka, Dr. Victor 12171 Fort Caroline Rd., Jacksonville, FL 32225 Literento, Anthony 1304 57th St.West, Bradenton, FL 34209 Littig, Cdr Gerald USNR 2511 Lomond Dr., Kalamazoo, MI 49008 Little, Arthur F. 9718 St. Andrews Dr., Fairfax, VA 22030 Little, Warren P.O. Box 8127. Missoula, MT 59807 Lium, Elli 3806 49th St., NW, Washington, DC 20016 Livingston, James 804 Greenwood Rd., Wilmington, DE 19807 Livingston, Robert G. 3415 Raymond St., Chevy Chase, MD 70815 Lock, Owen 2 Gary Ct., Holmdel, NJ 07733 Loeb, James 2 Sutton Place South, No. 15D, New York, NY 10022 Loehr, Major Rodney USAR 8106 Highwood Dr., No. Y 321, Bloomington, MN 55438 Loesche, Paul 301 Plantation Dr., Bent Creek Plantation, Lexington, SC 29072 Loeser, Paul 3310 N. Leisure World Blvd., No. 1025, Silver Spring, MD 20906 Loesere, Ms. Antoinette USA 5422 Long Boat Ct., Fairfax, VA 22032 Loftin, William 12509 Millstream Dr., Bowie, MD 20715 Logan, Major Glenn USAR P.O. Box 6268, Colorado Springs, CO 80934 Lograsso, Peter P. 12220 Blanchester Dr., Lyndhurst, OH 44124 Long, Richard 1615 Evers Dr., McLean, VA 22101 Longanecker, MajGen W. USAF 5653 Rayburn Ave., Alexandria, VA 22311 Loomis, Capt Robert USN 1418 Independence Ave., Melbourne Beach, FL 32940 Looney, John R. 9122 St. Andrews Pl., College Park, MD 20740 Loosararian, Armen 10703 Edgewood Ave., Silver Spring, MD 20901 Lopez, John 2315 MacDonough Rd., Wilmington, DE 19805 Lore, Nicholas 5429 Honors Dr., San Diego, CA 92122 Loucopolos, Tom 29 Brookside Pl., Livingston, NJ 07039 Louie, Henry 11420 Bedfordshire Ave., Potomac, MD 20854 Love, LtCol Gale AUS 11596 Lower Circle Dr., Grass Valley, CA 95949 Lovorovich, Chris 3669 Ireland Dr., Indianapolis, IN 46236 Lowe, LtCol Darrell USMC 1432 Buckner Rd., Valrico, FL 33594 Lower, Michael 6214 Amberwood Dr., Alta Loma, CA 91707 Lucas, Floyd 2011 12th St., NW, HIckory, NC 28601 Lucas, Harry Jr. P.O. Box 56467, Houston, TX 77256 Ludewig, Walter 120 Mashodack Rd., Nassau, NY 12123 Lugar, Richard 7841 Old Dominion Dr., McLean, VA 22102 Lumovich, LtCol Victor USAF 7401 Churchill Rd., McLean, VA 22101 Luntzel, Major James USAF 18962 Symeron Rd., Apple Valley, CA 922307 Lupsha, Peter 617 Dartmouth NE, Albuquerque, NM 87106 Lusby, David 1937 S. Abrego Dr., Green Valley, AZ 85614 Luthy, Raymond 2825 Royal Ann Ln., Concord, CA 94518 Lyles, Bobby Neal 2496 Orchid Bay Dr., No. 204, Naples, FL 33942 Lyman, Mrs. Dorothy 3300 Ocean Shore Ave., No. 502, Virginia Beach, VA 23451 Lynch, David 14512 Chesterfield Rd., Rockville, MD 20853 Lynch, Ray 100 Maple Ln., Annapolis, MD 21403 Lyons, Kenneth 9372 Avery Rd., Broadview Heights, OH 44147
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 21, BA,
FEBRUARY 2026 ARCHIVE UPDATE
Exclusive Investigation by Bernd Pulch: The comprehensive Epstein Ledger database, featuring 25,000+ names and 7,344 companies, is now fully indexed and available.
👉 Access the Full Epstein Ledger Dossier Here
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 0194/452 | BABACZ RAFAŁ |
| IPN BU 00945/429 | BABAD BEATA |
| IPN BU 0806/1510 | BABAROWSKA IRENA |
| IPN BU 00328/832 | BABAROWSKI MICHAŁ |
| IPN BU 001134/1683 | BABAROWSKI MICHAŁ |
| IPN BU 0942/441 | BABCZENKO CELINA |
| IPN BU 0194/3031 | BABCZENKO HENRYK |
| IPN BU 776/130 | BABCZYK JERZY |
| IPN BU 0194/2468 | BABCZYŃSKI STANISŁAW JANUSZ |
| IPN BU 0604/989 | BABCZYŃSKI ZBIGNIEW |
| IPN BU 093/38 | BABECKA HALINA |
| IPN BU 0951/1339 | BABECKA TERESA |
| IPN BU 0891/169 | BABECKI CZESŁAW |
| IPN BU 0242/263 | BABECKI MAREK |
| IPN BU 00277/471 | BABECKI MICHAŁ |
| IPN BU 001121/2686 | BABECKI MICHAŁ JASTAR |
| IPN BU 00275/462 | BABECKI WIESŁAW |
| IPN BU 0194/1370 | BABIAK BRONISŁAW |
| IPN BU 00456/26 | BABIAK JAN |
| IPN BU 0951/1924 | BABIAK JÓZEF |
| IPN BU 0193/168 | BABIARCZYK STANISŁAW |
| IPN BU 00612/1053 | BABIARSKI STANISŁAW |
| IPN BU 645/98 | BABIARZ BOLESŁAW |
| IPN BU 00612/4118 | BABIARZ JACEK |
| IPN BU 001198/6880 | BABIARZ JACEK |
| IPN BU 0193/7169 | BABIARZ JULIAN |
| IPN BU 00283/2177 | BABIARZ PIOTR |
| IPN BU 684/1 | BABIARZ STANISŁAW |
| IPN BU 0855/2814 | BABICKA MARIA |
| IPN BU 698/70 | BABICKI FRANCISZEK |
| IPN BU 001198/2308 | BABICKI JAN |
| IPN BU 01000/476 | BABICKI JANUSZ |
| IPN BU 0892/44 | BABICKI KAROL |
| IPN BU 01130/3 | BABICKI MIECZYSŁAW |
| IPN BU 00232/288 | BABICKI TADEUSZ |
| IPN BU 001164/336 | Babicki Tadeusz |
| IPN BU 0193/169 | BABICYN PIOTR |
| IPN BU 698/71 | BABICZ ADAM |
| IPN BU 0193/7413 | BABICZ FELIKS |
| IPN BU 0218/3304 | BABICZ JANUSZ RYSZARD |
| IPN BU 095/2 | BABICZ KRZYSZTOF |
| IPN BU 001134/2797 | BABICZ MAREK |
| IPN BU 698/72 | BABICZ STANISŁAW |
| IPN BU 002082/37 | BABICZ TADEUSZ |
| IPN BU 002086/200 | BABICZ TADEUSZ ALEKSANDER |
| IPN BU 01133/445 | BABICZ TOMASZ |
| IPN BU 0193/1309 | BABICZ WŁADYSŁAW |
| IPN BU 0218/592 | BABICZ ZBIGNIEW |
| IPN BU 00945/2416 | BABIEJCZUK JANUSZ – WACŁAW |
| IPN BU 00744/1019 | BABIK ANDRZEJ |
| IPN BU 001134/1250 | BABIK ANDRZEJ |
| IPN BU 01079/197 | BABIK HENRYK |
| IPN BU 0855/2972 | BABIK JAN |
| IPN BU 001075/220 | BABIK KRZYSZTOF |
| IPN BU 0855/2966 | BABIK MIECZYSŁAW |
| IPN BU 0193/1310 | BABIK TEODOZJA |
| IPN BU 00234 | p.248 BABILIŃSKI MIECZYSŁAW |
| IPN BU 0290/54 | BABINCH JAN |
| IPN BU 00169/40 | BABIŃSKA AGNIESZKA |
| IPN BU 00945/657 | BABIŃSKA AGNIESZKA |
| IPN BU 0806/2627 | BABIŃSKA BARBARA |
| IPN BU 00277/971 | BABIŃSKA ELŻBIETA |
| IPN BU 001121/3156 | BABIŃSKA ELŻBIETA |
| IPN BU 0806/2478 | BABIŃSKA IRENA (ZYSK) |
| IPN BU 0772/743 | BABIŃSKA JADWIGA |
| IPN BU 00744/746 | BABIŃSKI DARIUSZ |
| IPN BU 001134/79 | BABIŃSKI DARIUSZ |
| IPN BU 00966/198 | BABIŃSKI FRANCISZEK |
| IPN BU 0604/873 | BABIŃSKI JERZY |
| IPN BU 002086/967 | BABIŃSKI NELSON ADAO |
| IPN BU 748/227 | BABIŃSKI WIESŁAW |
| IPN BU 0942/353 | BABIRACKI WIESŁAW |
| IPN BU 002082/543 | BABIRACKI WIESŁAW |
| IPN BU 002086/1568 | BABIRACKI WIESŁAW |
| IPN BU 0872/120 | BABIS KAZIMIERZ |
| IPN BU 0870/191 | BABIS KAZIMIERZ |
| IPN BU 0290/46 | BABIUCH EDWARD |
| IPN BU 0901/1131 | BABKIEWICZ MONIKA |
| IPN 00 1052/1295 | BABKIEWICZ TADEUSZ |
| IPN BU 00945/80 | BABNIS CZESŁAW |
| IPN BU 02042/373 | BABRAJ ANDRZEJ |
| IPN BU 0967/203 | BABRAJ EDWARD |
| IPN BU 02042/611 | BABRAJ EDWARD |
| IPN BU 0194/3200 | BABRAJ FELICJA |
| IPN BU 0772/36 | BABRAJ FELICJA |
| IPN BU 1161/184 | BABRAJ KRYSTYNA |
| IPN BU 645/58 | BABRAJ LUDWIKA |
| IPN BU 02042/48 | BABRAJ TADEUSZ |
| IPN BU 0194/2000 | BABRAL (GASZYŃSKA) HELENA |
| IPN BU 0194/3364 | BABRAL MARIAN |
| IPN BU 002086/1615 | BABRAL MARIAN MICHAŁ |
| IPN BU 0194/2556 | BABSKA JANINA |
| IPN BU 0194/2594 | BABSKI ALBERT |
| IPN BU 00283/834 | BABSKI ALEKSANDER |
| IPN BU 0218/178 | BABUL KONSTANTY |
| IPN BU 0194/2403 | BABUL KRYSTYNA |
| IPN BU 0806/2506 | BABUL TADEUSZ |
| IPN BU 0218/1343 | BABUL WIKTOR |
| IPN BU 0194/347 | BABULA EDWARD |
| IPN BU 0193/6399 | BABULA IGNACY |
| IPN 00 1043/2020 | BABULA JEZIORSKA BOJAŃCZYK TERESA ANTONINA |
| IPN BU 001198/1116 | BABULA MARIAN |
| IPN BU 00230 | P. 52 BABULA MIECZYSŁAW |
| IPN BU 00170/552 | BABULEWICZ HENRYK |
| IPN 00 1043/2708 | BABULEWICZ HENRYK |
| IPN BU 0901/588 | BABUT PEST JADWIGA STANISŁAWA |
| IPN BU 0855/2491 | BABUT WALDEMAR |
| IPN BU 698/73 | BABYSZKO EDWARD |
| IPN BU 698/74 | BACA ANDRZEJ |
| IPN BU 00275/524 | BACA MAŁGORZATA |
| IPN BU 001134/431 | BACA MAŁGORZATA |
| IPN BU 0772/5085 | BACA) ŚMIAŁEK JÓZEFA |
| IPN BU 00945/169 | BACCIARELLI – RADZYMIŃSKA ZOFIA BARBARA |
| IPN BU 002086/1677 | BACCIARELLI JACEK JANUSZ |
| IPN BU 00612/3664 | BACH EWA |
| IPN BU 001198/6621 | BACH EWA |
| IPN BU 001134/4390 | BACH HIERONIM |
| IPN BU 01133/446 | BACH JÓZEF |
| IPN BU 0951/1326 | BACHAN ANNA |
| IPN BU 00277/1330 | BACHAN DANUTA |
| IPN BU 001121/3481 | BACHAN DANUTA |
| IPN BU 0772/2151 | BACHAN TADEUSZ |
| IPN BU 0872/119 | BACHANEK FRANCISZEK |
| IPN BU 00334/67 | BACHANEK KAZIMIERZ |
| IPN BU 001134/2718 | BACHANEK KAZIMIERZ |
| IPN BU 0772/2150 | BACHANEK WŁADYSŁAW |
| IPN BU 0772/2152 | BACHANEK ZOFIA |
| IPN BU 001089/33 | BACHANEK ZOFIA |
| IPN BU 698/75 | BACHANOWICZ MIECZYSŁAW |
| IPN BU 00249/368 | BACHAŃSKA ROZALIA |
| IPN BU 0870/36 | BACHAŃSKI WŁADYSŁAW |
| IPN BU 645/54 | BACHARA EUGENIUSZ |
| IPN BU 00283/1502 | BACHARSKI WŁADYSŁAW |
| IPN BU 00768/839 | BACHARSKI WŁADYSŁAW |
| IPN BU 698/76 | BACHERA BOLESŁAW |
| IPN BU 0194/3591 | BACHERA RAFAŁ |
| IPN BU 0772/4354 | BACHLEDA ALOJZY |
| IPN BU 001134/5597 | BACHLEDA BAŃKOWSKA MAGDALENA BEATA |
| IPN BU 00448/621 | BACHLEDA-BAŃKOWSKA MAGDALENA |
| IPN BU 636/1788 | BACHLIŃSKA DANUTA |
| IPN BU 002082/723 | BACHMAN ZBIGNIEW |
| IPN BU 002086/2072 | BACHMAN ZBIGNIEW |
| IPN BU 001121/993 | BACHMAŃSKA ROZALIA |
| IPN BU 0864/9 | BACHNER TADEUSZ |
| IPN BU 0988/686 | BACHNIK KRZYSZTOF |
| IPN BU 644/741 | BACHORSKI DIONIZY |
| IPN BU 0854/1336 | BACHOWSKI OSKAR |
| IPN 00 1043/1622 | BACHOWSKI OSKAR |
| IPN BU 698/77 | BACHRYJ WŁADYSŁAW |
| IPN BU 002081/73 | BACHTIN ANDRZEJ |
| IPN BU 002085/88 | BACHTIN ANDRZEJ |
| IPN BU 00945/963 | BACHTIN JERZY |
| IPN BU 0242/2653 | BACHTIN WŁADYSŁAW |
| IPN BU 01282/1 | BACHUREWICZ LECH |
| IPN BU 0988/279 | BACHUREWICZ LEONARD |
| IPN BU 00612/4516 | BACHURSKI MAREK |
| IPN BU 0604/1743 | BACHURSKI ZDZISŁAW |
| IPN BU 001198/2363 | BACHURSKI ZENON |
| IPN BU 0193/1312 | BACIA WŁODZIMIERZ |
| IPN BU 0604/1638 | BACIAK KRZYSZTOF |
| IPN BU 00244/115 | BACKALEWICZ HALINA |
| IPN BU 00244/119 | BACKENROTH JULIUSZ |
| IPN BU 00328/72 | BACKIEL ROBERT |
| IPN BU 001134/760 | BACKIEL ROBERT WOJCIECH |
| IPN BU 00200/1242 | BACŁAW ZBIGNIEW |
| IPN BU 001102/844 | BACŁAW ZBIGNIEW |
| IPN BU 644/742 | BACŁAWSKI FRANCISZEK |
| IPN 00 1043/560 | BACZ ANDRZEJ |
| IPN BU 0193/1313 | BACZAKIEWICZ LIPKO ALICJA |
| IPN BU 0194/1437 | BACZAKIEWICZ ROMUALD |
| IPN BU 0772/2153 | BACZAŃSKA ZOFIA |
| IPN BU 0194/1488 | BACZEWSKA ALICJA |
| IPN BU 649/207 | BACZEWSKA JADWIGA |
| IPN BU 0967/148 | BACZEWSKI ALEKSANDER |
| IPN BU 698/78 | BACZEWSKI EDWARD |
| IPN BU 649/2 | BACZEWSKI GRZEGORZ |
| IPN BU 649/208 | BACZEWSKI GRZEGORZ |
| IPN BU 0218/22 | BACZEWSKI JAN |
| IPN BU 0242/2717 | BACZEWSKI JANUSZ |
| IPN BU 649/209 | BACZEWSKI JERZY |
| IPN BU 649/3 | BACZEWSKI JERZY |
| IPN BU 001121/764 | BACZEWSKI JERZY |
| IPN BU 649/210 | BACZEWSKI LESZEK |
| IPN BU 649/83 | BACZEWSKI MARIAN |
| IPN BU 0193/174 | BACZEWSKI MICHAŁ |
| IPN BU 649/4 | BACZEWSKI STANISŁAW |
| IPN BU 0891/168 | BACZEWSKI TADEUSZ |
| IPN BU 649/5 | BACZEWSKI TADEUSZ |
| IPN BU 0958/38 | BACZEWSKI WACŁAW |
| IPN BU 649/86 | BACZEWSKI WACŁAW |
| IPN BU 649/6 | BACZEWSKI WITOLD |
| IPN BU 0968/17 | BACZEWSKI ZBIGNIEW |
| IPN BU 00945/1157 | BACZEWSKI ZBIGNIEW |
| IPN 00 1043/3701 | BACZKO ALEKSANDER |
| IPN 00 1043/3718 | BACZKO TADEUSZ |
| IPN BU 002086/1035 | BACZKOWSKI STEFAN |
| IPN BU 636/1824 | BACZMAŃSKI JÓZEF |
| IPN 00 1043/903 | BACZŃSKI HENRYK |
| IPN BU 0806/3078 | BACZUK BOŻENA |
| IPN BU 0167/3 | BACZUŃ MARIAN |
| IPN BU 0193/1316 | BACZYK (BĄCZYK) FRANCISZEK |
| IPN BU 0901/1694 | BACZYŃSKA ANNA |
| IPN BU PF | 498/16 BACZYŃSKA ANNA |
| IPN BU 02042/297 | BACZYŃSKA ELŻBIETA |
| IPN BU 0242/2876 | BACZYŃSKA GRAŻYNA (ŚLUSARSKA) |
| IPN BU 0891/167 | BACZYŃSKA JADWIGA |
| IPN BU 01133/447 | BACZYŃSKA JANINA |
| IPN BU 0242/2822 | BACZYŃSKA JANINA DANUTA |
| IPN BU 0242/3153 | BACZYŃSKA MAŁGORZATA |
| IPN BU 00165/19 | Baczyńska Maria |
| IPN BU 636/1822 | BACZYŃSKA MICHALINA |
| IPN BU 636/1823 | BACZYŃSKA MICHALINA |
| IPN BU 0604/1748 | BACZYŃSKI (BANIAK) SŁAWOMIR |
| IPN BU PF | 2077/63 BACZYŃSKI ANTONI |
| IPN BU 01000/1788 | BACZYŃSKI BOGUSŁAW |
| IPN BU 0193/1317 | BACZYŃSKI EDWARD |
| IPN BU 00328/1389 | BACZYŃSKI JANUSZ |
| IPN BU 001134/2321 | BACZYŃSKI JANUSZ |
| IPN BU 01280/1 | BACZYŃSKI KRZYSZTOF |
| IPN BU 0193/5889 | BACZYŃSKI MIECZYSŁAW |
| IPN BU 01079/126 | BACZYŃSKI TADEUSZ |
| IPN BU 01250/10 | BACZYŃSKI WOJCIECH |
| IPN BU 00744/669 | BACZYŃSKI ZBIGNIEW |
| IPN BU 001134/2 | BACZYŃSKI ZBIGNIEW |
| IPN BU 0772/745 | BAĆ ZOFIA |
| IPN BU 01013/217 | BAĆKO RYSZARD |
| IPN BU 00328/1535 | BAĆKO TADEUSZ |
| IPN BU 001134/2516 | BAĆKO TADEUSZ WOJCIECH |
| IPN BU 00612/2051 | BAĆKOWSKI JAN |
| IPN BU 001198/5060 | BAĆKOWSKI JAN |
| IPN BU 00612/1768 | BAĆMAGA LUDWIG |
| IPN BU 001198/4874 | BAĆMAGA LUDWIK |
| IPN BU 00283/1983 | BAĆMAGA MIROSŁAW |
| IPN BU 090/103 | BADACH BOGUSŁAW |
| IPN BU 645/103 | BADACZEWSKA EWA |
| IPN BU 0772/43 | BADALSKI BOGUSŁAW |
| IPN BU 0242/2434 | BADASZEWSKI IGNACY |
| IPN BU 0591/8 | BADEJA KRZYSZTOF |
| IPN BU 683/231 | BADEŁEK JOANNA |
| IPN BU 644/743 | BADEŁEK ZBIGNIEW |
| IPN BU 645/43 | BADEŃSKA ZOFIA |
| IPN BU 00230 | P. 52 BADEŃSKI ANDRZEJ |
| IPN BU 0194/442 | BADEŃSKI STEFAN |
| IPN BU 00283/2021 | BADEŃSKI SZCZEPAN |
| IPN BU 0772/2154 | BADER IRMGARDA |
| IPN BU 0951/1678 | BADER JANINA |
| IPN BU 0193/1318 | BADER MARIAN |
| IPN BU 0993/1629 | BADERSKA TERESA |
| IPN BU PF | 299/123 BADEWICZ |
| IPN BU 0193/176 | BADIA JAN |
| IPN BU 002085/187 | BADLICKI ANDRZEJ FRANCISZEK |
| IPN BU 0772/746 | BADNER (SZAŁAŃSKA) HELENA |
| IPN BU 0193/7732 | BADNER STANISŁAW |
| IPN BU 00612/2397 | BADO ZBIGNIEW |
| IPN BU 001198/5580 | BADO ZBIGNIEW |
| IPN BU 0872/79 | BADOCHA JAN |
| IPN BU 001198/162 | BADOCHA JÓZEF |
| IPN BU 698/79 | BADOŃ ZDZISŁAW |
| IPN BU 00611/1103 | BADOWICZ JAN |
| IPN BU 001198/1507 | BADOWICZ JAN |
| IPN BU 0870/141 | BADOWICZ RYSZARD |
| IPN BU 00611/880 | BADOWICZ STANISŁAW |
| IPN BU 001198/1324 | BADOWICZ STANISŁAW |
| IPN BU 0193/1319 | BADOWSKA (KERTKOWA) IRENA |
| IPN BU 0833/570 | BADOWSKA BARBARA |
| IPN BU 685/238 | Badowska Elżbieta |
| IPN BU 00230 | P 48 BADOWSKA IZABELA |
| IPN BU 0218/2905 | BADOWSKA JADWIGA |
| IPN BU 01250/11 | BADOWSKA LEOKADIA |
| IPN BU 00244/153 | BADOWSKA MARIA |
| IPN BU 001198/2537 | BADOWSKA MARIA |
| IPN BU 0194/2878 | BADOWSKA WIERA |
| IPN BU 0218/2783 | BADOWSKI (SAMORAJ) MIROSŁAW |
| IPN BU 0772/2155 | BADOWSKI EUGENIUSZ |
| IPN BU 644/744 | BADOWSKI FELIKS |
| IPN BU 0772/3552 | BADOWSKI HERONIM |
| IPN BU 0604/1895 | BADOWSKI IRENEUSZ |
| IPN BU 0194/3038 | BADOWSKI JAN |
| IPN BU 00612/537 | BADOWSKI JAN |
| IPN BU 001198/4311 | BADOWSKI JAN |
| IPN BU 0942/387 | BADOWSKI JANUSZ |
| IPN BU 001102/215 | BADOWSKI JAROSŁAW |
| IPN BU 01250/12 | BADOWSKI JERZY |
| IPN BU 00283/41 | BADOWSKI KAZIMIERZ |
| IPN BU 01013/198 | BADOWSKI KLEMENS |
| IPN BU 00283/1679 | BADOWSKI KRZYSZTOF |
| IPN BU 00283/1504 | BADOWSKI MACIEJ |
| IPN BU 00768/841 | BADOWSKI MACIEJ |
| IPN BU 0872/335 | BADOWSKI RYSZARD |
| IPN BU 02042/829 | BADOWSKI SŁAWOMIR |
| IPN BU 00249/478 | BADOWSKI SZYMON |
| IPN BU 001121/1116 | BADOWSKI SZYMON JAN |
| IPN BU 0194/1355 | BADOWSKI TADEUSZ |
| IPN BU 01000/1785 | BADOWSKI TEODOR |
| IPN BU 001198/1842 | BADOWSKI WACŁAW |
| IPN BU 001134/3876 | BADOWSKI WOJCIECH |
| IPN BU 001121/130 | BADOWSKI ZBIGNIEW |
| IPN BU 0951/872 | BADOWSKI ZBIGNIEW JAN |
| IPN BU 00945/2694 | BADOWSKI ZDZISŁAW – BOGDAN |
| IPN BU 00170/462 | BADOWSKI ZDZISŁAW BOGDAN |
| IPN BU 0218/1725 | BADOWSKI ZYGMUNT |
| IPN BU 01133/448 | BADURA CZESŁAW |
| IPN BU 0772/747 | BADURA CZESŁAW STANISŁAW |
| IPN BU 00399/505 | BADURA EUGENIUSZ |
| IPN BU 001134/4846 | BADURA EUGENIUSZ |
| IPN BU 0772/2156 | BADURA JÓZEFA |
| IPN BU 00612/2322 | BADYNA KAROL |
| IPN BU 0912/256 | BADYNA WIKTOR |
| IPN BU 02187/1 | BADYSIAK STANISŁAW |
| IPN BU 0218/3098 | BADZIAK TADEUSZ |
| IPN 00 1043/1263 | BADZIELEWSKA BOJAR TERESA MARIA |
| IPN BU 001198/3781 | BADZIOCH STANISŁAW |
| IPN BU 644/745 | BADZYŃSKI FRANCISZEK |
| IPN BU 002086/172 | BADŹMIROWSKI KRZYSZTOF EUSTACHIUSZ |
| IPN BU 00611/884 | BAEDLA ZYGMUNT |
| IPN BU 644/10 | BAER FRANCISZEK |
| IPN BU 0912/254 | BAFELTOWSKI JAN |
| IPN BU 0891/160 | BAGADZIŃSKI MIECZYSŁAW |
| IPN BU 01000/1606 | BAGAN HENRYK |
| IPN BU 0218/630 | BAGAN JANUSZ |
| IPN BU 00612/405 | BAGATEK BENEDYKT |
| IPN BU 01674/13 | BAGIENKO WŁADYSŁAW |
| IPN BU 0193/180 | BAGIŃSKA ALICJA |
| IPN BU 00165/6 | Bagińska Barbara |
| IPN BU 01137/82 | BAGIŃSKA HALINA |
| IPN BU 0193/6096 | BAGIŃSKA HANNA TOMASZEWSKA |
| IPN BU 0993/1642 | BAGIŃSKA IRENA |
| IPN BU 0772/2157 | BAGIŃSKA JADWIGA |
| IPN BU 00448/187 | BAGIŃSKA LIDIA |
| IPN BU 001134/5150 | BAGIŃSKA LIDIA |
| IPN 00 1043/2602 | BAGIŃSKA PATKOWSKA ŻWIRBEL ROMUALDA |
| IPN BU 0193/1320 | BAGIŃSKI ALFRED |
| IPN BU 0193/1321 | BAGIŃSKI BOGUSŁAW |
| IPN BU 002086/1244 | BAGIŃSKI BOGUSŁAW |
| IPN BU 698/80 | BAGIŃSKI BOLESŁAW |
| IPN BU 02184/3 | BAGIŃSKI CZESŁAW |
| IPN BU 0193/182 | BAGIŃSKI EDMUND |
| IPN BU 0988/937 | BAGIŃSKI EUGENIUSZ |
| IPN BU 0193/181 | BAGIŃSKI JAN |
| IPN BU 685/239 | Bagiński Jan |
| IPN BU 644/11 | BAGIŃSKI JÓZEF |
| IPN BU 01013/273 | BAGIŃSKI KAZIMIERZ |
| IPN BU 00200/837 | BAGIŃSKI LESZEK |
| IPN BU 001102/361 | BAGIŃSKI LESZEK |
| IPN BU 0193/6248 | BAGIŃSKI MIECZYSŁAW |
| IPN BU 01133/449 | BAGIŃSKI MIECZYSŁAW |
| IPN BU 00273/197 | BAGIŃSKI MIROSŁAW |
| IPN BU 00234 | p.249 BAGIŃSKI MIROSŁAW |
| IPN BU 0193/170 | BAGIŃSKI TADEUSZ |
| IPN BU 01000/1786 | BAGIŃSKI TADEUSZ |
| IPN BU 698/81 | BAGIŃSKI TADEUSZ |
| IPN BU 0193/1322 | BAGIŃSKI TOMASZ WITOLD |
| IPN BU 01000/1765 | BAGIŃSKI WACŁAW |
| IPN BU PF | 299/9 BAGIŃSKI WACŁAW |
| IPN BU 00328/1577 | BAGIŃSKI WOJCIECH |
| IPN BU 001134/2569 | BAGIŃSKI WOJCIECH |
| IPN BU 0194/799 | BAGŁAJ JAN |
| IPN BU 644/12 | BAGNEROWSKI STANISŁAW |
| IPN BU 0911/57 | BAGNIAK MARIAN |
| IPN BU 01000/565 | BAGNIAK TADEUSZ |
| IPN 00 1052/1229 | BAGNIEWSKI JAN |
| IPN BU 002081/314 | BAGNIUK JÓZEF |
| IPN BU 002085/380 | BAGNIUK JÓZEF |
| IPN BU 00234 | p.245 BAGNIUK TADEUSZ |
| IPN BU 0194/2337 | BA-GOŃSKA ANNA |
| IPN BU 00244/58 | BAHRIJ ANTONI |
| IPN BU 001198/5499 | BAHRYCZ MIECZYSŁAW |
| IPN BU 0855/1895 | BAIC MARIA |
| IPN BU 0193/1323 | BAJ (POLKOWSKA) JANINA |
| IPN BU 0243/385 | BAJ FELIKS |
| IPN BU 002086/1618 | BAJ JÓZEF |
| IPN BU 00415/218 | BAJAK WALDEMAR |
| IPN BU 001198/2080 | BAJAK WŁADYSŁAW |
| IPN BU 01000/1357 | BAJAKA JAN |
| IPN BU 0968/110 | BAJAN ALEKSANDER |
| IPN BU 0193/9085 | BAJAN MARIA (KONDRUSIK) |
| IPN BU 0218/2459 | BAJARCZUK STANISŁAW |
| IPN BU 00283/1647 | BAJAS STANISŁAW |
| IPN BU 00277/638 | BAJBAKOW BARBARA |
| IPN BU 001121/2842 | BAJBAKOW BARBARA |
| IPN BU 00750/421 | BAJBOR ZBIGNIEW |
| IPN BU 0242/2126 | BAJCAR (WIELOMSKA) MAŁGORZATA |
| IPN BU 0193/4259 | BAJDA (STĘPIEŃ) JANINA |
| IPN BU 0891/284 | BAJDA BRONISŁAW |
| IPN BU 0193/5000 | BAJDA MIECZYSŁAW |
| IPN BU 0193/59 | BAJDA MIECZYSŁAW |
| IPN BU 00750/281 | BAJDECKI BOGUMIŁ |
| IPN BU 685/238 | Bajdeman Franciszka |
| IPN BU 00415/347 | BAJDO RYSZARD |
| IPN BU 645/102 | BAJDOR KRZYSZTOF |
| IPN BU 00611/1338 | BAJDOR WŁADYSŁAW |
| IPN BU 001198/2362 | BAJDOR WŁADYSŁAW |
| IPN BU 0194/453 | BAJDOWSKI MARIAN |
| IPN BU 0242/3251 | BAJEK (BLISZCZAK) DOROTA |
| IPN BU 00612/4040 | BAJEK ANDRZEJ |
| IPN BU 001198/6821 | BAJEK ANDZREJ |
| IPN BU 0993/1610 | BAJEK JADWIGA |
| IPN BU 0902/18 | BAJEK JÓZEF |
| IPN BU 00611/829 | BAJEK TADEUSZ |
| IPN BU 01000/299 | BAJENA ALEKSY |
| IPN BU 0855/3441 | BAJER FRANCISZEK |
| IPN BU 00612/551 | BAJER FRANCISZEK |
| IPN BU 001198/4317 | BAJER FRANCISZEK |
| IPN BU 0193/7359 | BAJER JAN |
| IPN BU 0218/1154 | BAJER JAN |
| IPN BU 0772/2158 | BAJER JAN |
| IPN BU 645/39 | BAJER JERZY |
| IPN BU 002081/389 | BAJER MARIA |
| IPN BU 002085/455 | BAJER MARIA |
| IPN BU 0855/2664 | BAJER MARTA |
| IPN BU 683/233 | BAJER MICHALINA |
| IPN BU 01133/450 | BAJER STEFAN |
| IPN BU 00611/581 | BAJER TADEUSZ |
| IPN BU 001198/1021 | BAJER TADEUSZ |
| IPN BU 0892/70 | BAJER WIKTOR |
| IPN BU 01000/1777 | BAJER WŁODZIMIERZ |
| IPN BU 698/82 | BAJER ZOFIA |
| IPN BU 00750/159 | BAJER ZYGMUNT |
| IPN BU 001164/411 | Bajer Zygmunt |
| IPN BU 0951/1572 | BAJERA IROSZ ANNA TERESA |
| IPN BU 645/1442 | BAJERA STANISŁAWA |
| IPN BU 0287/184 | BAJEROWSKI KAZIMIERZ |
| IPN BU 0772/742 | BAJERSKA DANUTA |
| IPN BU 01000/1770 | BAJERSKI ARTUR |
| IPN BU 0193/183 | BAJEW ANDRZEJ |
| IPN BU 0902/19 | BAJEWSKI WACŁAW |
| IPN BU 644/746 | BAJEWSKI WACŁAW |
| IPN BU 0290/19 | BAJGROWICZ KRYSTYNA |
| IPN BU 698/83 | BAJKA HELENA |
| IPN BU 0902/20 | BAJKA JAN |
| IPN BU 00275/513 | BAJKOWSKA HENRYKA JOLANTA |
| IPN BU 001134/420 | BAJKOWSKA HENRYKA JOLANTA |
| IPN BU 0772/2066 | BAJKOWSKI EDWARD |
| IPN BU 0942/388 | BAJKOWSKI JACEK |
| IPN BU 644/13 | BAJKOWSKI JANUSZ |
| IPN BU 0193/7724 | BAJKOWSKI KAZIMIERZ |
| IPN BU 0193/1324 | BAJKOWSKI LESZEK |
| IPN BU 0942/556 | BAJNO ANTONI |
| IPN BU 0772/748 | BAJNO IRENA |
| IPN BU 980/185 | BAJNO RYSZARD |
| IPN BU 0958/160 | BAJNO ZYGMUNT |
| IPN BU 644/747 | BAJNUG WŁADYSŁAW |
| IPN BU 0833/64 | BAJNUSIEWICZ STEFANIA |
| IPN BU 0855/2369 | BAJON MARIA |
| IPN BU 0604/447 | BAJON MIECZYSŁAW |
| IPN BU 001102/1912 | BAJOŃSKI STEFAN |
| IPN BU 0193/1326 | BAJOR BRONISŁAW |
| IPN BU PF | 1087/71 BAJOR DANUTA |
| IPN BU 01753/188 | BAJOR HENRYKA |
| IPN BU 00191/435 | BAJOR JÓZEF |
| IPN 00 1043/3378 | BAJOR JÓZEF |
| IPN BU 00612/4843 | BAJOR MAREK |
| IPN BU 00273/362 | BAJOR PIOTR |
| IPN BU 00689/82 | BAJOR PIOTR |
| IPN BU 001121/347 | BAJOR ROMAN |
| IPN BU 0193/1325 | BAJOR ZDZISŁAW |
| IPN BU 01079/173 | BAJORA EDWARD |
| IPN BU 00945/1646 | BAJOREK BOLESŁAW |
| IPN BU 002081/319 | BAJOREK ZDZISŁAW |
| IPN BU 002085/385 | BAJOREK ZDZISŁAW MAREK |
| IPN BU 00275/518 | BAJSAROWICZ ANDRZEJ |
| IPN BU 001134/424 | BAJSAROWICZ ANDRZEJ |
| IPN BU 52/63 | BAJSKA BOŻENA |
| IPN BU 00283/165 | BAJSON STANISŁAW |
| IPN BU 00612/77 | BAJSON STANISŁAW |
| IPN BU 001134/2148 | BAJSTAK ROBERT |
| IPN BU 698/85 | BAJSZCZAK TADEUSZ |
| IPN BU 00966/338 | BAJSZCZAK ANTONI |
| IPN BU 0864/15 | BAJSZCZAK JAN |
| IPN BU 698/84 | BAJSZCZAK KAZIMIERZ |
| IPN BU 52/88 | BAJSZCZAK LESZEK |
| IPN BU 0911/2 | BAJSZCZAK MIECZYSŁAW |
| IPN BU 0855/2444 | BAJSZCZAK MIECZYSŁAW |
| IPN BU 0193/1327 | BAJSZCZAK MIECZYSŁAW JAN |
| IPN BU 0993/1005 | BAJSZCZAK REGINA |
| IPN BU 0193/1328 | BAJSZCZAK ZBIGNIEW |
| IPN BU 698/386 | BAJSZCZAK-BOŻEK MARIANNA |
| IPN BU 00168/4 | BAJTYNGER ZDZISŁAW |
| IPN BU 00945/1448 | BAJTYNGIER ZDZISŁAW |
| IPN BU 01434/2 | BAJTYNGIER ZDZISŁAW |
| IPN BU 0290/66 | BAJUK ZOFIA |
| IPN BU 644/3376 | BAJUS STEFAN |
| IPN BU 00612/4352 | BAK ADAM |
| IPN BU 636/1759 | BAK FRANCISZEK |
| IPN BU 00273/366 | BAK JÓZEF BĄK JÓZEF |
| IPN BU 685/240 | Bak Stanisława |
| IPN BU 001198/5544 | BAK TADEUSZ |
| IPN BU 001198/3698 | BAK WŁODZIMIERZ |
| IPN BU 02042/300 | BAKA – ORGANIŚCIAK KRYSTYNA |
| IPN BU 01133/451 | BAKA HENRYK |
| IPN BU 0218/1094 | BAKA JAN |
| IPN BU 0218/3504 | BAKA JAN |
| IPN BU 0243/340 | BAKA JAROSŁAW |
| IPN BU 0218/1330 | BAKA KAZIMIERA |
| IPN BU 0218/1056 | BAKA MARIAN |
| IPN BU 01133/452 | BAKA SKIERKOWSKA JANINA |
| IPN BU 0242/1423 | BAKA WOJCIECH |
| IPN 00 1052/1291 | BAKA-JAKUBIAK MAŁGORZATA |
| IPN BU 698/86 | BAKAL ANIELA |
| IPN BU 00945/2160 | BAKALARCZYK ADAM |
| IPN BU 693/495 | BAKALARCZYK LESZEK |
| IPN BU 0194/2520 | BAKALARCZYK WŁADYSŁAWA |
| IPN BU 0287/185 | BAKALARSKA JANINA |
| IPN BU 0833/32 | BAKALARSKI IRENEUSZ |
| IPN BU 00448/232 | BAKALARSKI JAN |
| IPN BU 001134/5195 | BAKALARSKI JAN |
| IPN BU 0193/7842 | BAKALARSKI ZDZISŁAW |
| IPN BU 0772/2160 | BAKALARZ ANNA |
| IPN BU 0872/118 | BAKALARZ ADAM |
| IPN BU 0607/112 | BAKALARZ ALICJA |
| IPN BU 001134/3784 | BAKALARZ ANNA |
| IPN BU 698/87 | BAKALARZ JAN |
| IPN BU 01000/1764 | BAKALARZ JÓZEF |
| IPN BU 693/831 | BAKALARZ MARIA (MARIANNA) |
| IPN BU 693/831 | BAKALARZ TERESA |
| IPN BU 00283/746 | BAKALARZ WŁADYSŁAW |
| IPN BU 01250/13 | BAKALASZ WACŁAW |
| IPN BU 00225/145 | BAKANACZ DANUTA |
| IPN BU 00945/671 | BAKANACZ JAN |
| IPN BU 001121/482 | BAKANACZ-RYBAK DANUTA |
| IPN BU 0193/4748 | BAKANOWSKI KAZIMIERZ |
| IPN BU 01434/456 | BAKANOWSKI-LUBICZ ZYGMUNT |
| IPN BU 093/21 | BAKCERZAK A |
| IPN BU 01133/689 | BAKIERA ALEKSANDER |
| IPN BU 00277/189 | BAKIERA ELŻBIETA |
| IPN BU 001121/2417 | BAKIERA ELŻBIETA ERNA |
| IPN BU 0958/161 | BAKIERA TADEUSZ |
| IPN BU 0806/2971 | BAKIERA WALDEMAR |
| IPN BU 01133/453 | BAKINOWSKA IRENA |
| IPN BU 00611/1054 | BAKINOWSKI JÓZEF |
| IPN BU 0772/2161 | BAKLARZ ZOFIA |
| IPN BU 0772/2162 | BAKMAN MIECZYSŁAW |
| IPN BU 0993/1620 | BAKOŃ HENRYK |
| IPN BU 001089/137 | BAKOŃ JANINA |
| IPN BU 0855/2718 | BAKOŃ MARIAN |
| IPN BU 00200/639 | BAKOŃSKI TOMASZ |
| IPN BU 001102/59 | BAKOŃSKI TOMASZ |
| IPN BU 0218/1067 | BAKOTA HELENA |
| IPN BU 0218/2462 | BAKOTA RYSZARD ANDRZEJ |
| IPN BU PF | 970/198 BAKOWSKA BOŻENA |
| IPN BU 00751/83 | BAKOWSKI KRZYSZTOF |
| IPN BU 001102/1578 | BAKOWSKI KRZYSZTOF |
| IPN BU 00612/110 | BAKSIŃSKI JÓZEF |
| IPN BU 0194/1972 | BAKSZT MARIA |
| IPN BU 0194/1933 | BAKSZT MARIAN |
| IPN BU 0290/41 | BAKUŁA ANNA |
| IPN BU 00328/923 | BAKUŁA ANNA |
| IPN BU 001134/1786 | BAKUŁA ANNA |
| IPN BU 0958/171 | BAKUŁA ANTONI |
| IPN BU 00966/580 | BAKUŁA BOLESŁAW |
| IPN BU 0866/16 | BAKUŁA EDMUND |
| IPN BU 0806/1446 | BAKUŁA EWA |
| IPN BU 02184/4 | BAKUŁA HELENA |
| IPN BU 52/89 | BAKUŁA HENRYK |
| IPN BU 0855/2751 | BAKUŁA JAN |
| IPN BU 698/88 | BAKUŁA JÓZEF |
| IPN BU 0854/1284 | BAKUŁA KAZIMIERZ |
| IPN BU 0866/17 | BAKUŁA KAZIMIERZ |
| IPN BU 0772/2163 | BAKUŁA MARIA |
| IPN BU 0218/3276 | BAKUŁA RYSZARD |
| IPN BU 00230 | P. 131 BAKUŁA RYSZARD |
| IPN BU 0866/1222 | BAKUŁA STANISŁAW |
| IPN BU 01000/1817 | BAKUŁA STEFAN |
| IPN BU 0772/2164 | BAKUŁA WŁADYSŁAWA |
| IPN BU 698/89 | BAKUN DYMITR |
| IPN BU 698/343 | BAKUN-MORDEC MARIA |
| IPN BU 0193/4895 | BAKUNOWICZ JAN |
| IPN BU 00234 | p.255 BAKUNOWICZ JAN |
| IPN BU 0967/3 | BAKUŃ JERZY |
| IPN BU 0967/3 | BAKUŃ JERZY |
| IPN BU 0218/1030 | BAKUŃSKA EUGENIA |
| IPN BU 0964/6 | BAKUTA JADWIGA |
| IPN BU 0193/11 | BAL ANDRZEJ |
| IPN BU 00234 | p.247 BAL BERNARD |
| IPN BU 0193/5082 | BAL IZABELA (ROZENBLUM BELA) |
| IPN BU 01000/632 | BAL STEFAN |
| IPN BU 01250/14 | BALA CZESŁAWA |
| IPN BU 0864/14 | BALA FRANCISZEK |
| IPN BU 0901/246 | BALA HENRYKA |
| IPN BU 0194/1821 | BALA JAN |
| IPN BU 980/187 | BALA KAZIMIERZ |
| IPN BU 776/1 | BALA RYSZARD |
| IPN BU 001102/1116 | BALA STANISŁAW |
| IPN BU 00257/49 | BALA STANISŁAWA |
| IPN BU 636/1823 | BALANA DANUTA |
| IPN BU 00283/2179 | BALANA JAN |
| IPN BU 636/1823 | BALANA KRYSTYNA |
| IPN BU 636/1823 | BALANA MARIA |
| IPN BU 0193/8220 | BALAS JAN |
| IPN BU 01133/454 | BALAS MICHAŁ |
| IPN BU 0193/6631 | BALAS STANISŁAW |
| IPN BU 0591/9 | BALAS WALDEMAR |
| IPN BU 00283/2510 | BALASIŃSKI JAN |
| IPN BU 0242/63 | BALAWEJDER BARBARA WERONIKA |
| IPN BU 01000/1535 | BALAWEJDER EUGENIUSZ |
| IPN BU 00234 | p.101 BALAWENDER ALBERT |
| IPN BU 0305/97 | BALAWENDER ALBERT |
| IPN BU 644/756 | BALAWENDER WŁADYSŁAW |
| IPN BU 0194/1506 | BALBIN ADELA |
| IPN BU 0194/1783 | BALBIN SZYMON |
| IPN BU 0912/842 | BALCER BOLESŁAW |
| IPN BU 0901/2086 | BALCER DARIUSZ |
| IPN BU 0912/253 | BALCER EUGENIUSZ |
| IPN BU 644/757 | BALCER HENRYK |
| IPN BU 698/90 | BALCER IRENEUSZ |
| IPN BU 001198/3925 | BALCER IWONA |
| IPN BU 52/104 | BALCER RYSZARD |
| IPN BU 0993/1615 | BALCER TADEUSZ |
| IPN BU 001134/3656 | BALCER ZYGMUNT |
| IPN BU 0993/1616 | BALCERAK (PEAS) EMILIA |
| IPN BU 01133/455 | BALCERAK APOLINARY |
| IPN BU 0855/2971 | BALCERAK CZESŁAWA |
| IPN BU 0772/750 | BALCERAK EMILIA |
| IPN BU 0854/842 | BALCERAK HENRYK |
| IPN BU 0242/2859 | BALCERAK JERZY |
| IPN BU 0772/44 | BALCERAK KAZIMIERZ |
| IPN BU 00200/1183 | BALCERAK WIESŁAW STEFAN |
| IPN BU 001102/785 | BALCERAK WIESŁAW STEFAN |
| IPN BU 0772/4355 | BALCEREK BARBARA |
| IPN BU 01000/1766 | BALCEREK CZESŁAW |
| IPN BU 00945/61 | BALCEREK EDWARD |
| IPN BU 636/1824 | BALCEREK JANIINA |
| IPN BU 00945/1087 | BALCEREK JÓZEF – KAZIMIERZ |
| IPN BU 0193/186 | BALCEREK RYSZARD |
| IPN BU 00249/719 | BALCEREK RYSZARD |
| IPN BU 001121/1362 | BALCEREK RYSZARD |
| IPN BU 00328/1390 | BALCEREK STANISŁAW |
| IPN BU 001134/2322 | BALCEREK STANISŁAW |
| IPN BU 00744/305 | BALCEREK WŁODZIMIERZ |
| IPN BU 001121/3940 | BALCEREK WŁODZIMIERZ |
| IPN BU 00448/487 | BALCERKIEWICZ DANIELA |
| IPN BU 001134/5463 | BALCERKIEWICZ DANIELA FRANCISZKA |
| IPN BU PF | 144/85 BALCERKIEWICZ ROMAN |
| IPN BU 00448/486 | BALCERKIEWICZ ROMAN |
| IPN BU 001134/5462 | BALCERKIEWICZ ROMAN |
| IPN BU 0193/1334 | BALCEROWICZ (GARBARSKA) ANNA |
| IPN BU 00635/10 | BALCEROWICZ ALFRED |
| IPN BU 0912/830 | BALCEROWICZ ANTONI |
| IPN BU 0912/845 | BALCEROWICZ MARIA |
| IPN BU 0951/956 | BALCEROWICZ MARIANNA |
| IPN BU 0872/117 | BALCEROWICZ STANISŁAW |
| IPN BU 0872/116 | BALCEROWICZ STEFAN |
| IPN BU 01000/1767 | BALCEROWSKI CZESŁAW |
| IPN BU 02042/807 | BALCEROWSKI MAREK |
| IPN BU 01013/300 | BALCEROWSKI STEFAN |
| IPN BU 698/91 | BALCERSKA ZOFIA |
| IPN BU 00200/203 | BALCERSKI EDMUND RYSZARD |
| IPN BU 0855/2543 | BALCERSKI JAN |
| IPN 00 1043/2534 | BALCERSKI JAN |
| IPN BU 0891/161 | BALCERSKI STANISŁAW |
| IPN BU 0891/178 | BALCERSKI STANISŁAW |
| IPN BU 00275/193 | BALCERZAK ANDRZEJ |
| IPN 00 1043/3891 | BALCERZAK ANDRZEJ |
| IPN BU 001102/1511 | BALCERZAK ANDRZEJ |
| IPN BU 001121/4439 | BALCERZAK ANDRZEJ |
| IPN BU PF | 2/93 BALCERZAK BEATA |
| IPN BU 00744/165 | BALCERZAK BOGDAN |
| IPN BU 001121/3799 | BALCERZAK BOGDAN |
| IPN BU 002082/740 | BALCERZAK DARIUSZ |
| IPN BU 002086/2090 | BALCERZAK DARIUSZ |
| IPN BU 0193/5091 | BALCERZAK EDMUND |
| IPN BU 00191/322 | BALCERZAK JAN ZDZISŁAW |
| IPN 00 1043/2825 | BALCERZAK JAN ZDZISŁAW |
| IPN BU 0307/60 | BALCERZAK JERZY |
| IPN BU 01133/456 | BALCERZAK JÓZEF |
| IPN BU 00611/113 | BALCERZAK JÓZEF |
| IPN BU 00612/515 | BALCERZAK JÓZEF |
| IPN BU 001198/402 | BALCERZAK JÓZEF |
| IPN BU 001198/4300 | BALCERZAK JÓZEF |
| IPN BU 0891/162 | BALCERZAK KAZIMIERZ |
| IPN BU 0958/163 | BALCERZAK KAZIMIERZ |
| IPN BU 0993/1623 | BALCERZAK KAZIMIERZ |
| IPN BU 01013/201 | BALCERZAK KAZIMIERZ |
| IPN BU 0194/2698 | BALCERZAK LUBOMIRA |
| IPN BU 698/344 | BALCERZAK MARIA |
| IPN BU 0218/386 | BALCERZAK MARIAN |
| IPN 00 1043/3054 | BALCERZAK MARIAN JERZY |
| IPN BU 01256/11 | BALCERZAK ROBERT |
| IPN BU 0772/2165 | BALCERZAK SABINA |
| IPN BU 0772/2166 | BALCERZAK STANISŁAWA |
| IPN BU 0891/163 | BALCERZAK STEFAN |
| IPN BU 0604/1465 | BALCERZAK STEFAN |
| IPN BU 0911/56 | BALCERZAK STEFANIA |
| IPN BU 980/191 | BALCERZAK SZYMON |
| IPN BU 0988/910 | BALCERZAK TADEUSZ |
| IPN BU 0892/884 | BALCERZAK TOMASZ |
| IPN BU 0872/115 | BALCERZAK WŁADYSŁAW |
| IPN BU 0912/258 | BALCERZAK WŁADYSŁAW |
| IPN BU 01133/77 | BALCERZAK WŁADYSŁAW |
| IPN BU 00328/634 | BALCERZAK WŁADYSŁAW |
| IPN BU 001134/1458 | BALCERZAK WŁADYSŁAW |
| IPN BU 00275/484 | BALCERZAK ZBIGNIEW MARIAN |
| IPN BU 001134/378 | BALCERZAK ZBIGNIEW MARIAN |
| IPN BU 0305/483 | BALCERZAK ZENOBIA |
| IPN BU 00191/84 | BALCERZAK-BARTOSIK JANINA |
| IPN BU 002086/1818 | BALCZEWSKI JAN FRANCISZEK |
| IPN BU 002082/591 | BALCZEWSKI JAN-FRANCISZEK |
| IPN BU 00170/39 | BALCZUNAS SZARUNAS |
| IPN BU 0218/107 | BALDYSZ ADAM |
| IPN BU 0604/1744 | BALDYSZ RYSZARD |
| IPN BU 00612/3752 | BALEC CZESŁAW |
| IPN BU 01250/15 | BALEWICZ LEONARD |
| IPN BU 0242/647 | BALEWICZ MIECZYSŁAW |
| IPN BU 0806/2932 | BALEWSKA HONORATA |
| IPN BU 644/758 | BALEWSKI RYSZARD |
| IPN BU 0218/807 | BALIA TADEUSZ WOJCIECH |
| IPN BU 00283/1270 | BALICKA ANNA |
| IPN BU 00257/328 | BALICKA BARBARA MARIA |
| IPN BU 001102/1395 | BALICKA BARBARA MARIA |
| IPN BU 0942/354 | BALICKA DANUTA |
| IPN 00 1043/2341 | BALICKA ELŻBIETA MARIA |
| IPN BU 002082/666 | BALICKA GRAŻYNA |
| IPN BU 002086/2007 | BALICKA GRAŻYNA |
| IPN BU 0806/2801 | BALICKA HALINA |
| IPN BU 0772/2167 | BALICKA IRENA |
| IPN 00 1043/2292 | BALICKA IRENA |
| IPN BU 0772/2168 | BALICKA MARIA |
| IPN BU 0193/189 | BALICKA ZOFIA |
| IPN BU 0855/2669 | BALICKA ZOFIA |
| IPN BU 0891/164 | BALICKI ADAM |
| IPN 00 1043/1619 | BALICKI ANDRZEJ |
| IPN BU 00200/678 | BALICKI ANDRZEJ FRANCISZEK |
| IPN BU 001102/130 | BALICKI ANDRZEJ FRANCISZEK |
| IPN BU 698/92 | BALICKI JAN |
| IPN BU 002086/244 | BALICKI LUCJAN |
| IPN BU 0218/831 | BALICKI MICHAŁ |
| IPN BU 00744/668 | BALICKI SŁAWOMIR |
| IPN BU 001134/1 | BALICKI SŁAWOMIR |
| IPN BU 0194/388 | BALICKI WŁADYSŁAW |
| IPN BU 00334/429 | BALICKI ZYGMUNT |
| IPN BU 001134/3304 | BALICKI ZYGMUNT |
| IPN BU 00612/2353 | BALIGA WOJCIECH |
| IPN BU 0193/7970 | BALIK (WYRZYKOWSKA) KRYSTYNA |
| IPN BU 001198/2053 | BALIKOWSKI HENRYK |
| IPN BU 0772/752 | BALIN MAREK |
| IPN BU 0218/2196 | BALIN TADEUSZ |
| IPN 00 1043/2908 | BALIN WŁADYSŁAWA |
| IPN BU PF | 970/164 BALING JOANNA |
| IPN BU 00249/771 | BALIŃSKA ELŻBIETA |
| IPN BU 001121/1412 | BALIŃSKA ELŻBIETA |
| IPN BU 645/1440 | BALIŃSKA JADWIGA |
| IPN BU 01000/1808 | BALIŃSKA WYSOCKA JANINA |
| IPN BU 0772/753 | BALIŃSKI ALBERT |
| IPN BU 00945/2640 | BALIŃSKI BOLESŁAW – WINCENTY |
| IPN BU 00170/399 | BALIŃSKI BOLESŁAW WINCENTY |
| IPN BU 0772/49 | BALIŃSKI CZESŁAW |
| IPN BU 0891/9 | BALIŃSKI EUGENIUSZ |
| IPN BU 0902/21 | BALIŃSKI FRANCISZEK |
| IPN BU 0911/69 | BALIŃSKI JAN |
| IPN BU 0864/6 | BALIŃSKI LEPOLD |
| IPN BU 00170/166 | BALIŃSKI ROMAN |
| IPN BU 00945/2331 | BALIŃSKI ROMAN |
| IPN BU 01133/457 | BALIŃSKI STANISŁA |
| IPN BU 00328/1536 | BALIŃSKI STEFAN |
| IPN BU 001134/2517 | BALIŃSKI STEFAN BERNARD |
| IPN BU 001134/4479 | BALIŃSKI TOMASZ |
| IPN BU 748/508 | BALISZEWSKI JÓZEF |
| IPN BU 0951/79 | BALKE ANDRZEJ |
| IPN BU 00191/301 | BALKE LECHOSŁAW |
| IPN 00 1043/2686 | BALKE LECHOSŁAW |
| IPN BU 095/6 | BALKIEWICZ MARIAN |
| IPN BU 0305/480 | BALKOWSKA GRAŻYNA |
| IPN BU 0772/749 | BALL MARIA |
| IPN BU 01175/1133 | BALLA RAJMUND |
| IPN BU 0912/844 | BALLA STANISŁAW |
| IPN BU 00283/161 | BALMAS JANUSZ |
| IPN BU 00768/123 | BALMAS JANUSZ |
| IPN BU 01000/205 | BALON KRYSTYNA |
| IPN BU 001040/236 | BALON PIOTR |
| IPN BU 698/93 | BALON WALENTY |
| IPN BU 0806/2156 | BALSKA BRONISŁAWA |
| IPN BU 0855/2525 | BALSKI JÓZEF |
| IPN BU 0870/192 | BALTER TADEUSZ |
| IPN BU 002086/295 | BALTRUSAJTIS ZIGMAS |
| IPN BU 00612/3800 | BALTYN MIECZYSŁAW |
| IPN BU 001198/6672 | BALTYN MIECZYSŁAW |
| IPN BU 698/94 | BALUK MIECZYSŁAW |
| IPN BU 00244/199 | BALWIERCZAK JERZY |
| IPN BU 644/14 | BALWIERZ EUGENIUSZ |
| IPN BU 0194/454 | BALWIERZ TADEUSZ |
| IPN BU 0287/390 | BALZAM MARIA |
| IPN BU 00277/1313 | BAŁA ANDRZEJ |
| IPN BU 001121/3464 | BAŁA ANDRZEJ |
| IPN BU 01250/69 | BAŁA FRANCISZEK |
| IPN BU 001198/2011 | BAŁA HENRYK |
| IPN BU 52/96 | BAŁA JACEK |
| IPN BU 001198/2048 | BAŁA JAN |
| IPN BU 0194/1796 | BAŁA MIECZYSŁAW |
| IPN 00 1043/1771 | BAŁA MIECZYSŁAW |
| IPN BU 0951/186 | BAŁA STANISŁAW |
| IPN BU 644/15 | BAŁABAJEW TEODOR |
| IPN BU 00744/1302 | BAŁABAN MARIOLA BOŻENA |
| IPN BU 001134/5763 | BAŁABAN MARIOLA BOŻENA |
| IPN BU 00170/946 | BAŁACHOWICZ JAN JANUSZ |
| IPN BU 644/16 | BAŁACHOWICZ ZENON |
| IPN BU PF | 900/6 BAŁACHOWSKI SŁAWOMIR |
| IPN BU 00244/55 | BAŁAJ JAN |
| IPN BU 0855/3331 | BAŁAKIEL JADWIGA |
| IPN BU 00200/1002 | BAŁAKIER EDWARD |
| IPN BU 001102/578 | BAŁAKIER EDWARD |
| IPN BU 01133/458 | BAŁAKIER STANISŁAW |
| IPN BU 01434/237 | BAŁAKIER STANISŁAW |
| IPN BU 002086/260 | BAŁAKIER STANISŁAW |
| IPN BU 698/95 | BAŁAKIER WŁADYSŁAW |
| IPN BU 0958/164 | BAŁAS KAZIMIERZ |
| IPN 00 1043/258 | BAŁAS STANISŁAW MIECZYSŁAW |
| IPN BU 0901/756 | BAŁASIŃSKA INEZ |
| IPN BU 698/345 | BAŁASZEWICZ KAZIMIERZ |
| IPN BU 00612/4922 | BAŁATA KAZIMEIRZ |
| IPN BU 001102/163 | BAŁATA KAZIMIERZ |
| IPN BU 649/7 | BAŁAZY ANDRZEJ |
| IPN BU 0218/1858 | BAŁAZY KAZIMIERZ |
| IPN BU 093/13 | BAŁAZY KAZIMIERZ |
| IPN BU 644/759 | BAŁAZY MARIAN |
| IPN BU 0604/1697 | BAŁAZY RYSZARD |
| IPN BU 0902/30 | BAŁAZY STANISŁAW |
| IPN BU 02042/384 | BAŁBACZYŃSKI GRZEGORZ |
| IPN BU 0193/9094 | BAŁBACZYŃSKI WACŁAW |
| IPN BU 0193/8334 | BAŁCHAN TADEUSZ |
| IPN BU 0193/1336 | BAŁCHANOWSKI BRONISŁAW |
| IPN BU 001198/332 | BAŁCHANOWSKI STANISŁAW |
| IPN BU 00257/216 | BAŁCZEWSKA DANUTA URSZULA |
| IPN BU 001102/1283 | BAŁCZEWSKA DANUTA URSZULA |
| IPN BU 00234 | p.248 BAŁCZEWSKI TADEUSZ |
| IPN BU 0193/5080 | BAŁDA STANISŁAW |
| IPN BU 001102/2135 | BAŁDA STANISŁAW INOCENTY |
| IPN BU 01175/13 | BAŁDA WIERA |
| IPN BU 0958/944 | BAŁDEWICZ ALEKSANDER |
| IPN BU 0951/897 | BAŁDOWSKA MIĘTEK WŁADYSŁAWA |
| IPN BU 0855/2920 | BAŁDOWSKI JAN |
| IPN BU 0853/244 | BAŁDOWSKI JAROSŁAW |
| IPN BU 1108/12 | BAŁDOWSKI JAROSŁAW |
| IPN BU 0901/1139 | BAŁDYGA ARTUR |
| IPN BU 0958/165 | BAŁDYGA CZESŁAW |
| IPN BU 00257/413 | BAŁDYGA HALINA |
| IPN BU 001102/1480 | BAŁDYGA HALINA |
| IPN BU 01133/459 | BAŁDYGA HENRYK |
| IPN BU 0912/257 | BAŁDYGA JAN |
| IPN BU 0942/375 | BAŁDYGA JERZY |
| IPN BU 0218/1280 | BAŁDYGA JERZY ANDRZEJ |
| IPN BU 0988/5 | BAŁDYGA LEON |
| IPN BU 0891/166 | BAŁDYGA WACŁAW |
| IPN BU 01753/179 | BAŁDYGA WANDA |
| IPN BU 00273/472 | BAŁDYS JÓZEF |
| IPN BU 01000/1812 | BAŁDYSIAK LUDWIK |
| IPN BU 0243/149 | BAŁDYSZ (MATAN) GRAŻYNA |
| IPN BU 02042/511 | BAŁDYSZ ROMAN |
| IPN BU 00334/785 | BAŁKA RYSZARD |
| IPN BU 001134/3893 | BAŁKA RYSZARD |
| IPN BU 0855/2431 | BAŁKO HELENA |
| IPN BU 00966/1204 | BAŁKOWIEC ZDZISŁAW |
| IPN BU 00966/27 | BAŁKOWIEC ZDZISŁAW |
| IPN BU 001198/5369 | BAŁKOWSKI GRZEGORZ |
| IPN 00 1043/162 | BAŁŁANDOWICZ FENIGSEN KIRA ALINA |
| IPN BU 00945/60 | BAŁON ADOLF |
| IPN BU 0957/48 | BAŁON KAZIMIERZ |
| IPN BU 0193/1335 | BAŁOZY MIECZYSŁAW |
| IPN BU 00611/1032 | BAŁTOWICZ JAN |
| IPN BU 00612/1570 | BAŁTOWSKI STANISŁAW |
| IPN BU 00612/877 | BAŁTOWSKI STANISŁAW |
| IPN BU 0866/18 | BAŁTRUN JAN |
| IPN BU 0772/2169 | BAŁUCKA BRONISŁAWA |
| IPN BU 0194/2204 | BAŁUCZYŃSKA HALINA |
| IPN BU 0901/2479 | BAŁUK HANNA |
| IPN BU 00744/991 | BAŁUK RYSZARD |
| IPN BU 001134/1135 | BAŁUK RYSZARD |
| IPN BU 00225/54 | BAŁUK STEFAN |
| IPN BU 001121/124 | BAŁUK STEFAN KLEMENS |
| IPN BU 01000/1774 | BAŁUSKA JÓZEF |
| IPN BU 0988/6 | BAŁUSZ PAWEŁ |
| IPN BU 0194/2837 | BAŁYK MICHAŁ |
| IPN BU 00612/508 | BAMBEJCA TADEUSZ |
| IPN BU 0287/34 | BAMBERGER KAZIMIERZ |
| IPN BU 0194/3068 | BAMBERSKA JANINA |
| IPN BU 0194/3272 | BAMBERSKI MARIAN |
| IPN BU 00945/1051 | BAMBOROWICZ ZBIGNIEW |
| IPN BU 00945/133 | BAMBURSKI LUCJAN |
| IPN BU 0218/2383 | BANACH KRZYSZTOF |
| IPN BU 0242/327 | BANACH (KOZERA) HALINA (WIESŁAWA) |
| IPN BU 698/96 | BANACH ADELA |
| IPN BU 01013/188 | BANACH ALEKSANDER |
| IPN BU 00283/2004 | BANACH ANDRZEJ |
| IPN BU 00612/4913 | BANACH ANNA |
| IPN BU 644/760 | BANACH BOGDAN |
| IPN BU 002086/954 | BANACH BOGDAN |
| IPN BU 0958/69 | BANACH BRONISŁAW |
| IPN BU 002082/419 | BANACH DOROTA |
| IPN BU 002086/1174 | BANACH DOROTA |
| IPN BU 01000/204 | BANACH EDWARD |
| IPN BU 0287/291 | BANACH FERDYNAND |
| IPN BU 0193/8011 | BANACH FRANCISZEK |
| IPN BU 00399/452 | BANACH HALINA JADWIGA |
| IPN BU 001134/4796 | BANACH HALINA JADWIGA |
| IPN BU 0194/1048 | BANACH HENRYK |
| IPN BU 0218/3462 | BANACH HENRYK |
| IPN BU 0290/20 | BANACH IRENA |
| IPN BU 0193/1337 | BANACH JAN |
| IPN 00 1052/390 | BANACH JANINA KAZIMIERA |
| IPN BU 00283/1145 | BANACH JANUSZ |
| IPN BU 00283/1590 | BANACH JANUSZ |
| IPN BU 00283/2288 | BANACH JANUSZ |
| IPN BU 0242/2538 | BANACH JERZY |
| IPN BU 0604/1537 | BANACH JERZY |
| IPN BU 0290/67 | BANACH JOLANTA |
| IPN BU 00244/174 | BANACH JÓZEF |
| IPN BU 698/97 | BANACH KAZIMIERZ |
| IPN BU 001198/1430 | BANACH KAZIMIERZ |
| IPN BU 698/98 | BANACH MARCELI |
| IPN BU 0866/19 | BANACH MARIAN |
| IPN BU 01133/460 | BANACH MIECZYSŁAW |
| IPN BU 00200/16 | BANACH MIECZYSŁAW |
| IPN 00 1052/272 | BANACH MIECZYSŁAW |
| IPN BU 0194/2660 | BANACH STEFAN |
| IPN BU 0988/801 | BANACH TADEUSZ |
| IPN BU 0855/2388 | BANACHEWICZ ADELA |
| IPN BU 0958/68 | BANACHEWICZ CZESŁAW |
| IPN BU 0912/2404 | BANACHIEWICZ HENRYK |
| IPN BU 0604/1174 | BANACHOWICZ (BOGUTA) BARBARA |
| IPN BU 00744/1010 | BANACHOWICZ ADAM |
| IPN BU 001134/1241 | BANACHOWICZ ADAM |
| IPN BU 0855/2674 | BANACHOWICZ JAN |
| IPN BU 0193/9065 | BANACHOWICZ KAROL |
| IPN BU 0242/183 | BANACHOWICZ RYSZARD LUDWIK |
| IPN BU 002085/264 | BANACHOWICZ TOMASZ |
| IPN BU 0242/619 | BANACHOWICZ WOJCIECH ZBIGNIEW |
| IPN BU 0243/73 | BANACHOWICZ ZDZISŁAW |
| IPN BU 0772/755 | BANACHOWICZ ZOFIA |
| IPN BU 01000/1801 | BANACHOWSKA ZOFIA |
| IPN BU 01050/1337 | BANACHOWSKI ZYGMUNT |
| IPN BU 0958/70 | BANACKI BRONISŁAW |
| IPN BU 00283/985 | BANACZEK LESZEK |
| IPN BU 00768/675 | BANACZEK LESZEK |
| IPN BU 01000/1397 | BANACZKOWSKI MARIAN |
| IPN BU 00244/55 | BANACZKOWSKI ROMAN |
| IPN BU 0242/37 | BANAJSKI STANISŁAW |
| IPN BU 0243/43 | BANAK ALICJA |
| IPN BU 00277/752 | BANAK JERZY |
| IPN BU 001121/2952 | BANAK JERZY |
| IPN BU 00234 | p.242 BANAK JÓZEF |
| IPN BU 0305/95 | BANAK JÓZEF |
| IPN BU 00744/740 | BANAK KRZYSZTOF |
| IPN BU 00277/729 | BANAK KRZYSZTOF |
| IPN BU 001121/2930 | BANAK KRZYSZTOF |
| IPN BU 001134/73 | BANAK KRZYSZTOF |
| IPN BU 0193/4792 | BANAK TADEUSZ |
| IPN BU 645/26 | BANAK WANDA |
| IPN BU 01270/2 | BANAKIEWICZ ZBIGNIEW |
| IPN BU 644/17 | BANASIA JERZY |
| IPN BU 0993/1567 | BANASIAK (CIENIAWSKA) ZOFIA |
| IPN BU 0993/1612 | BANASIAK (KOWALCZYK) WŁADYSŁAWA |
| IPN BU 0958/71 | BANASIAK ALEKSANDER |
| IPN BU 0951/95 | BANASIAK ANDRZEJ |
| IPN BU 00611/1706 | BANASIAK ANTONI |
| IPN BU 001198/3058 | BANASIAK ANTONI |
| IPN BU 0891/289 | BANASIAK CZESŁAW |
| IPN BU 0218/2906 | BANASIAK CZESŁAW |
| IPN BU 00448/513 | BANASIAK DANUTA |
| IPN BU 001134/5489 | BANASIAK DANUTA |
| IPN 00 1043/1032 | BANASIAK DOBROSŁAW |
| IPN BU 01250/16 | BANASIAK EDWARD |
| IPN BU 0957/46 | BANASIAK EUGENIUSZ |
| IPN BU 002086/504 | BANASIAK EWA MARIA |
| IPN 00 1043/1733 | BANASIAK HALINA MARIA |
| IPN BU 00275/192 | BANASIAK HENRYK |
| IPN BU 001121/4438 | BANASIAK HENRYK |
| IPN BU 0957/47 | BANASIAK HENRYK |
| IPN BU 0290/50 | BANASIAK IRENA |
| IPN BU 01133/461 | BANASIAK JADWIGA |
| IPN BU 0290/60 | BANASIAK JADWIGA |
| IPN BU 0194/456 | BANASIAK JAN |
| IPN BU 0772/2170 | BANASIAK JAN |
| IPN BU 093/10 | BANASIAK JAN |
| IPN BU 52/79 | BANASIAK JAN |
| IPN BU 01133/462 | BANASIAK JAN |
| IPN BU 00283/1760 | BANASIAK JERZY |
| IPN BU 0958/72 | BANASIAK JÓZEF |
| IPN BU 00257/292 | BANASIAK LESZEK |
| IPN BU 001102/1359 | BANASIAK LESZEK |
| IPN BU 01013/187 | BANASIAK LUCYNA |
| IPN BU 0218/1489 | BANASIAK MARIAN |
| IPN BU 01000/1804 | BANASIAK MARIANNA |
| IPN BU 01321/1 | BANASIAK MIROSŁAW |
| IPN BU 0891/165 | BANASIAK PIOTR |
| IPN BU 001134/4199 | BANASIAK ROMAN |
| IPN BU 0988/7 | BANASIAK RYSZARD |
| IPN BU 698/99 | BANASIAK RYSZARD |
| IPN BU 00744/719 | BANASIAK SŁAWOMIR |
| IPN BU 001134/52 | BANASIAK SŁAWOMIR |
| IPN BU 0891/290 | BANASIAK STANISŁAW |
| IPN BU 0901/2486 | BANASIAK STANISŁAW |
| IPN BU 0912/146 | BANASIAK STANISŁAW |
| IPN BU 0194/1547 | BANASIAK STANISŁAW |
| IPN BU 0772/2877 | BANASIAK STANISŁAW |
| IPN BU 0891/291 | BANASIAK STEFAN |
| IPN BU 0951/1058 | BANASIAK TADEUSZ |
| IPN BU 0891/288 | BANASIAK WACŁAW |
| IPN BU 645/35 | BANASIAK WIKTORIA |
| IPN BU 0604/1538 | BANASIAK WINCENTY |
| IPN BU 0772/2171 | BANASIAK WŁADYSŁAWA |
| IPN BU PF | 252/108 BANASIAK WOJCIECH |
| IPN BU 0193/1339 | BANASIAK ZBIGNIEW BALTAZAR |
| IPN BU 0891/295 | BANASIAK ZDZISŁAW |
| IPN BU 0242/1628 | BANASIAK ZDZISŁAW |
| IPN BU 01133/463 | BANASIAK ZDZISŁAW |
| IPN BU 0855/1868 | BANASIAK ZOFIA |
| IPN BU 0891/294 | BANASIAK ZYGMUNT |
| IPN BU 00328/1404 | BANASIEWICZ ADAM |
| IPN BU 001134/2346 | BANASIEWICZ ADAM |
| IPN BU 0772/2172 | BANASIEWICZ ANNA |
| IPN BU 0833/24 | BANASIEWICZ ANTONI |
| IPN BU 00283/613 | BANASIEWICZ APOLONIA |
| IPN BU 01250/17 | BANASIEWICZ DANUTA |
| IPN BU 0806/2175 | BANASIEWICZ EDWARDA |
| IPN BU 0193/1340 | BANASIEWICZ EUGENIUSZ |
| IPN BU 01133/464 | BANASIEWICZ EUGENIUSZ |
| IPN BU 0194/1295 | BANASIEWICZ HENRYK |
| IPN BU 0806/1678 | BANASIEWICZ IRENA |
| IPN BU 0772/2173 | BANASIEWICZ JAN |
| IPN BU 0243/83 | BANASIEWICZ JÓZEF |
| IPN BU 645/84 | BANASIEWICZ KRYSTYNA |
| IPN BU 01133/466 | BANASIEWICZ LUCYNA |
| IPN BU 01000/1797 | BANASIEWICZ MARIAN |
| IPN BU 001134/3863 | BANASIEWICZ OSKAR |
| IPN BU 0872/121 | BANASIEWICZ STANISŁAW |
| IPN BU 001134/3929 | BANASIEWICZ STEFAN |
| IPN BU 0872/123 | BANASIEWICZ TADEUSZ |
| IPN 00 1052/999 | BANASIEWICZ WALDEMAR PAWEŁ |
| IPN BU 001121/292 | BANASIEWICZ WIESŁAW |
| IPN BU 980/193 | BANASIEWICZ WOJCIECH |
| IPN BU 0833/23 | BANASIEWICZ ZYGMUNT |
| IPN BU 0242/1803 | BANASIK (KARPISIAK) IRENA |
| IPN BU 645/27 | BANASIK ALEKSANDRA |
| IPN BU 00612/4066 | BANASIK ANDRZEJ |
| IPN BU 00744/306 | BANASIK ANDRZEJ |
| IPN BU 00328/749 | BANASIK ANDRZEJ |
| IPN BU 001198/6843 | BANASIK ANDRZEJ |
| IPN BU 001121/3941 | BANASIK ANDRZEJ |
| IPN BU 001134/1577 | BANASIK ANDRZEJ STEFAN |
| IPN BU 00751/40 | BANASIK ARKADIUSZ |
| IPN BU 001102/1524 | BANASIK ARKADIUSZ |
| IPN BU 0855/3440 | BANASIK BOLESŁAW |
| IPN BU 698/100 | BANASIK DANUTA |
| IPN BU 00612/446 | BANASIK DANUTA |
| IPN BU 0988/1407 | BANASIK FELIKS |
| IPN BU 0242/2237 | BANASIK HENRYK |
| IPN BU 683/1706 | BANASIK JADWIGA |
| IPN BU 698/101 | BANASIK JAROSŁAW |
| IPN BU 00612/1503 | BANASIK JERZY |
| IPN BU 00612/4877 | BANASIK JERZY |
| IPN BU 00273/543 | BANASIK JÓZEF |
| IPN BU 00312 | BANASIK JÓZEF |
| IPN BU 00312/60 | BANASIK JÓZEF |
| IPN BU 00283/4 | BANASIK JÓZEF |
| IPN BU 0194/2517 | BANASIK KAZIMIERZ |
| IPN BU 0194/748 | BANASIK KAZIMIERZ |
| IPN BU 0604/9 | BANASIK KAZIMIERZ |
| IPN BU 00283/872 | BANASIK KAZIMIERZ |
| IPN BU 0193/4264 | BANASIK MARIAN |
| IPN BU 0193/194 | BANASIK OTYLIA |
| IPN BU 00283/283 | BANASIK PAWEŁ |
| IPN BU 00611/1660 | BANASIK STANISŁAW |
| IPN BU 00612/4186 | BANASIK STANISŁAW |
| IPN BU 001198/1684 | BANASIK STANISŁAW |
| IPN BU 001198/3028 | BANASIK STANISŁAW |
| IPN BU 001198/6938 | BANASIK STANISŁAW |
| IPN BU 0854/928 | BANASIK STEFAN |
| IPN BU 001198/769 | BANASIK STEFAN |
| IPN BU 00612/3857 | BANASIK TADEUSZ |
| IPN BU 001198/6704 | BANASIK TADEUSZ |
| IPN BU 0872/410 | BANASIK TERESA |
| IPN BU 0872/305 | BANASIK WACŁAW |
| IPN BU 0193/195 | BANASIK WACŁAW |
| IPN BU 00244/58 | BANASIK WACŁAW |
| IPN BU 00611/490 | BANASIK WACŁAW |
| IPN BU 001198/883 | BANASIK WACŁAW |
| IPN BU 00612/3164 | BANASIK WIESŁAW |
| IPN BU 001198/6262 | BANASIK WIESŁAW |
| IPN BU 00283/2052 | BANASIK WOJCIECH |
| IPN BU 0993/1006 | BANASIK ZOFIA |
| IPN BU 00744/580 | BANASIKOWSKI JACEK |
| IPN BU 001121/4304 | BANASIKOWSKI JACEK |
| IPN 00 1043/3253 | BANASIKOWSKI WOJCIECH |
| IPN BU 0902/32 | BANASIŃSKI JERZY |
| IPN BU 0902/22 | BANASIŃSKI MIECZYSŁAW |
| IPN BU 01250/18 | BANASIUK ANTONI |
| IPN BU 0218/969 | BANASIUK ELŻBIETA |
| IPN BU 00966/985 | BANASIUK TADEUSZ PIOTR |
| IPN BU 644/762 | BANASZAK ANTONI |
| IPN 00 1043/2903 | BANASZAK EDWIN FELIKS |
| IPN BU 02184/2 | BANASZAK HALINA |
| IPN BU 0901/1544 | BANASZAK HALINA MARIA |
| IPN BU 644/18 | BANASZAK HENRYK |
| IPN BU 0870/331 | BANASZAK MIROSŁAW |
| IPN BU 00234 | p.245 BANASZAK RYSZARD |
| IPN BU 0777/4 | BANASZAK RYSZARD |
| IPN BU 00689/141 | BANASZAK RYSZARD |
| IPN BU 00249/1434 | BANASZAK STANISŁAW |
| IPN BU 00277/750 | BANASZAK STANISŁAW |
| IPN BU 001121/2043 | BANASZAK STANISŁAW |
| IPN BU 001121/2951 | BANASZAK STANISŁAW |
| IPN BU 001134/2799 | BANASZAK TERESA |
| IPN BU 0218/707 | BANASZAK WOJCIECH |
| IPN BU 001198/1213 | BANASZAK ZDZISŁAW |
| IPN BU 698/102 | BANASZAK ZYGMUNT |
| IPN BU 001198/2909 | BANASZCZYK ALEKSANDER |
| IPN BU 0193/1341 | BANASZCZYK JADWIGA |
| IPN BU 001198/2482 | BANASZCZYK KAZIMIERZ |
| IPN BU 636/1822 | BANASZCZYK KRYSTYNA |
| IPN BU 0193/196 | BANASZCZYK STANISŁAW |
| IPN BU 0833/17 | BANASZCZYK STEFAN |
| IPN BU 0854/1153 | BANASZCZYK ZDZISŁAW |
| IPN BU 00249/897 | BANASZEK ANDRZEJ |
| IPN BU 001121/1534 | BANASZEK ANDRZEJ |
| IPN BU 00750/182 | BANASZEK ANNA |
| IPN BU 01175/8 | BANASZEK BOGUSŁAW |
| IPN BU 01133/467 | BANASZEK BRONISŁAW |
| IPN BU 002082/289 | BANASZEK CZESŁAW |
| IPN BU 002086/746 | BANASZEK CZESŁAW |
| IPN BU 00328/950 | BANASZEK EDWARD |
| IPN BU 001134/1813 | BANASZEK EDWARD |
| IPN BU 00328/896 | BANASZEK GRAŻYNA |
| IPN BU 001134/1751 | BANASZEK GRAŻYNA ELŻBIETA |
| IPN BU 0193/4690 | BANASZEK HENRYK |
| IPN BU 0194/475 | BANASZEK HENRYK |
| IPN BU 0193/6520 | BANASZEK JAN |
| IPN BU 00283/1353 | BANASZEK JAN |
| IPN BU 001134/3369 | BANASZEK JAN |
| IPN BU 0806/1236 | BANASZEK JANINA |
| IPN BU 01133/233 | BANASZEK JANUSZ |
| IPN BU 0193/4803 | BANASZEK JERZY |
| IPN BU 0833/18 | BANASZEK JÓZEF |
| IPN BU 698/103 | BANASZEK KAZIMIERZ |
| IPN BU 698/104 | BANASZEK KRYSTYNA |
| IPN BU 00966/1068 | A BANASZEK KRYSTYNA |
| IPN BU 0901/2024 | BANASZEK MARIA |
| IPN BU 01133/468 | BANASZEK MARIAN |
| IPN BU 0806/1121 | BANASZEK MARIANNA |
| IPN BU 0951/24 | BANASZEK MIECZYSŁAW |
| IPN BU 0951/429 | BANASZEK MOKRZYSZ JADWIGA |
| IPN BU 001134/3523 | BANASZEK PIOTR |
| IPN BU 52/80 | BANASZEK RYSZARD |
| IPN BU 52/83 | BANASZEK RYSZARD |
| IPN BU 02042/964 | BANASZEK RYSZARD |
| IPN BU 0958/208 | BANASZEK STANISŁAW |
| IPN BU 0988/961 | BANASZEK STANISŁAW |
| IPN BU 52/116 | BANASZEK STANISŁAW |
| IPN BU 0957/45 | BANASZEK STANISŁAW |
| IPN BU 0901/185 | BANASZEK STANISŁAWA STAŃCZAK |
| IPN BU 0772/2044 | BANASZEK WACŁAW |
| IPN BU 0911/548 | BANASZEK ZBIGNIEW |
| IPN BU 001102/2219 | BANASZEK ZBIGNIEW |
| IPN BU 00283/252 | BANASZEK ZDZISŁAW |
| IPN BU 00768/175 | BANASZEK ZDZISŁAW |
| IPN BU 696/1347 | BANASZEK ZOFIA |
| IPN BU 0242/729 | BANASZEWSKA BUDZICZ JOLANTA ZOFIA |
| IPN BU 0242/2112 | BANASZEWSKA HALINA |
| IPN BU 748/172 | BANASZEWSKA MARIA |
| IPN BU 0891/293 | BANASZEWSKI KAZIMIERZ |
| IPN BU 0958/73 | BANASZEWSKI KAZIMIERZ |
| IPN BU 0218/3358 | BANASZEWSKI MAREK |
| IPN BU 093/8 | BANASZEWSKI S |
| IPN BU 01013/186 | BANASZEWSKI STANISŁAW |
| IPN BU 0891/292 | BANASZEWSKI STEFAN |
| IPN BU 01250/19 | BANASZEWSKI WIKTOR |
| IPN BU 001134/2897 | BANASZEWSKI WOJCIECH |
| IPN BU 01000/1798 | BANASZEWSKI ZDZISŁAW |
| IPN BU 0855/3276 | BANASZKIEWICZ (SALWA) ZOFIA TERESA |
| IPN BU 00191/335 | BANASZKIEWICZ ADAM ZYGMUNT |
| IPN 00 1043/2879 | BANASZKIEWICZ ADAM ZYGMUNT |
| IPN BU 00170/460 | BANASZKIEWICZ CZESŁAW |
| IPN BU 00945/2708 | BANASZKIEWICZ CZESŁAW |
| IPN BU 001121/417 | BANASZKIEWICZ CZESŁAW |
| IPN BU 0912/262 | BANASZKIEWICZ FRANCISZEK |
| IPN BU 00273/539 | BANASZKIEWICZ HENRYK |
| IPN BU 00191/627 | BANASZKIEWICZ HENRYK |
| IPN BU 001198/5392 | BANASZKIEWICZ HENRYK |
| IPN 00 1052/13 | BANASZKIEWICZ HENRYK |
| IPN 00 1043/222 | BANASZKIEWICZ JAKUB |
| IPN BU 01000/201 | BANASZKIEWICZ JAN |
| IPN BU 00611/692 | BANASZKIEWICZ JAN |
| IPN BU 001198/1117 | BANASZKIEWICZ JAN |
| IPN BU 001198/1878 | BANASZKIEWICZ JÓZEF |
| IPN BU 0892/45 | BANASZKIEWICZ KAZIMIERZ |
| IPN BU 0951/543 | BANASZKIEWICZ MAREK IRENEUSZ |
| IPN BU 01000/1796 | BANASZKIEWICZ MARIA |
| IPN BU 00689/83 | BANASZKIEWICZ RYSZARD |
| IPN BU 0305/99 | BANASZKIEWICZ RYSZARD |
| IPN BU 0912/266 | BANASZKIEWICZ STANISŁAW |
| IPN BU 0604/1715 | BANASZKIEWICZ STANISŁAW-MIROSŁAW |
| IPN BU 776/2 | BANASZKIEWICZ STEFANIA |
| IPN BU 01079/45 | BANASZKIEWICZ TADEUSZ |
| IPN BU 01000/760 | BANASZKIEWICZ TADEUSZ |
| IPN BU 01133/469 | BANASZKIEWICZ TEDEUSZ |
| IPN 00 1052/330 | BANASZKIEWICZ TERESA FILOMENA |
| IPN BU 00283/1053 | BANASZKIEWICZ URSZULA |
| IPN BU 636/1824 | BANASZKIEWICZ WACŁAWA |
| IPN BU 00611/177 | BANASZKIEWICZ WŁADYSŁAW |
| IPN BU 001198/487 | BANASZKIEWICZ WŁADYSŁAW |
| IPN BU 0806/1411 | BANASZKIEWICZ ZBIGNIEW |
| IPN 00 1043/1570 | BANASZKIEWICZ ZBIGNIEW |
| IPN BU 0866/1380 | BANASZKIEWICZ ZDZISŁAW |
| IPN BU 0218/3426 | BANASZKIEWICZ ZOFIA |
| IPN BU 0218/943 | BANASZUK WACŁAW |
| IPN BU 001102/1879 | BANASZYŃSKI HENRYK |
| IPN BU 00191/65 | BANASZYŃSKI MICHAŁ |
| IPN 00 1043/1885 | BANASZYŃSKI MICHAŁ |
| IPN BU 0193/1338 | BANAŚ (STEFAŃSKA) LEOKADIA |
| IPN BU 00611/218 | BANAŚ ADAM |
| IPN BU 001198/534 | BANAŚ ADAM |
| IPN BU 0872/114 | BANAŚ ALEKSANDER |
| IPN BU 002086/1400 | BANAŚ ALFRED |
| IPN BU 00612/3614 | BANAŚ ANDRZEJ |
| IPN BU 00612/4734 | BANAŚ ANDRZEJ |
| IPN BU 001198/6580 | BANAŚ ANDRZEJ |
| IPN BU 0194/455 | BANAŚ CZESŁAW |
| IPN BU 0604/249 | BANAŚ CZESŁAW |
| IPN BU 00612/2176 | BANAŚ EDWARD |
| IPN BU 001198/5273 | BANAŚ EWARD |
| IPN BU 0911/70 | BANAŚ FELIKS |
| IPN BU 01000/1815 | BANAŚ FELIKS |
| IPN BU 0193/8862 | BANAŚ HENRYK |
| IPN BU 0912/268 | BANAŚ JAN |
| IPN BU 0604/885 | BANAŚ KAROL |
| IPN BU 01737/11 | BANAŚ LUDWIK |
| IPN BU 00612/4900 | BANAŚ MARIA |
| IPN BU 0806/2430 | BANAŚ MARIAN |
| IPN BU 0806/2299 | BANAŚ MICHALINA |
| IPN BU 644/761 | BANAŚ RUDOLF |
| IPN BU 01000/679 | BANAŚ RYSZARD |
| IPN BU 0912/286 | BANAŚ STANISŁAW |
| IPN BU 0911/71 | BANAŚ TADEUSZ |
| IPN BU 00612/3636 | BANAŚ TADEUSZ |
| IPN BU 001198/6600 | BANAŚ TADEUSZ |
| IPN BU 0218/181 | BANAŚ TOMASZ |
| IPN BU 00688/77 | BANAŚ ZYGMUNT |
| IPN BU 0314/7 | BANAŚ ZYGMUNT |
| IPN BU 0591/10 | BANAŚ ZYGMUNT |
| IPN 00 1052/1405 | BANAŚKIEWICZ JAN TOMASZ |
| IPN BU 0604/1075 | BANAŚKIEWICZ PIOTR |
| IPN BU 0193/1342 | BANAT WŁADYSŁAW |
| IPN BU 698/105 | BANAT ZBIGNIEW |
| IPN BU 0772/756 | BANCARZ FRANCISZEK |
| IPN BU 00244/58 | BANCER STANISŁAW |
| IPN BU 001089/145 | BANCER STANISŁAW |
| IPN BU 0193/8927 | BANCER ZENON |
| IPN BU 001198/2718 | BANCEREK MARIAN |
| IPN BU 00277/1106 | BANCERSKA ZOFIA |
| IPN BU 001121/3283 | BANCERSKA ZOFIA BARBARA |
| IPN BU 0242/2202 | BANCERZ JERZY |
| IPN BU 0891/1463 | BANDACHOWICZ JAN |
| IPN BU 001198/3014 | BANDAŁA WITOLD |
| IPN BU 002082/292 | BANDASZ EDMUND |
| IPN BU 002086/760 | BANDASZ EDMUND |
| IPN BU 698/106 | BANDAU HENRYK |
| IPN BU 0193/7321 | BANDEL ALBIN |
| IPN BU 00611/1648 | BANDŁA WITOLD |
| IPN BU 00744/673 | BANDOCH MIROSŁAW |
| IPN BU 001134/6 | BANDOCH MIROSŁAW |
| IPN BU 0901/612 | BANDOLET KOSECKA IRENA |
| IPN BU 698/107 | BANDROWSKI LEON |
| IPN BU 00612/1422 | BANDROWSKI PIOTR |
| IPN BU 001198/4628 | BANDROWSKI PIOTR |
| IPN BU 0193/7843 | BANDULIK IRENA |
| IPN BU 0772/2174 | BANDUR BRONISŁAWA |
| IPN BU 0772/757 | BANDUR JÓZEFA |
| IPN BU 0193/1343 | BANDURA ALEKSANDER |
| IPN BU 00612/3805 | BANDURA EUGENIUSZ |
| IPN BU 001198/6676 | BANDURA EUGENIUSZ |
| IPN BU 693/830 | BANDURA JADWIGA |
| IPN BU 01013/185 | BANDURA MARIAN |
| IPN BU 00611/942 | BANDURA RYSZARD |
| IPN BU 001198/1370 | BANDURA RYSZARD |
| IPN BU 0218/985 | BANDURA TERESA |
| IPN BU 0958/66 | BANDUROWICZ HENRYK |
| IPN BU 645/52 | BANDURSKA HELENA |
| IPN BU 01133/470 | BANDURSKA JANINA |
| IPN BU 00448/299 | BANDURSKA JOLANTA |
| IPN BU 001134/5271 | BANDURSKA JOLANTA |
| IPN BU 01013/184 | BANDURSKA STANISŁAWA |
| IPN BU 00249/270 | BANDURSKI ANDRZEJ |
| IPN BU 001121/897 | BANDURSKI ANDRZEJ |
| IPN BU 00200/653 | BANDURSKI ANDRZEJ MAREK |
| IPN BU 001102/94 | BANDURSKI ANDRZEJ MAREK |
| IPN BU PF | 280/76 BANDURSKI JAN |
| IPN BU 002086/530 | BANDURSKI JAN |
| IPN BU 001134/3908 | BANDURSKI JAN |
| IPN BU 00744/791 | BANDURSKI MIROSŁAW |
| IPN BU 001134/294 | BANDURSKI MIROSŁAW |
| IPN BU 644/763 | BANDURSKI RYSZARD |
| IPN BU 0958/219 | BANDURSKI STANISAW |
| IPN BU 0193/1725 | BANDURSKI ZDZISŁAW |
| IPN 00 1052/27 | BANDYRA RYSZARD ZDZISŁAW |
| IPN BU 0242/2738 | BANDZEREWICZ TADEUSZ |
| IPN BU 00200/170 | BANECKI HENRYK |
| IPN 00 1052/685 | BANECKI HENRYK |
| IPN BU 00200/602 | BANECKI MARIAN |
| IPN BU 00249/594 | BANECKI MARIAN |
| IPN 00 1052/1924 | BANECKI MARIAN |
| IPN BU 001121/1233 | BANECKI MARIAN |
| IPN BU 00234 | p.256 BANEL TADEUSZ |
| IPN 00 1043/1654 | BANERT GRZEGORZ JACEK |
| IPN BU 0242/2648 | BANIA ANDRZEJ |
| IPN BU 0772/2175 | BANIA EDWARD |
| IPN BU 001198/3693 | BANIA JAN |
| IPN BU 002082/479 | BANIA KAZIMIERZ |
| IPN BU 002086/1365 | BANIA KAZIMIERZ |
| IPN BU 0772/758 | BANIA MARIA |
| IPN BU 0193/4723 | BANIA STANISŁAW |
| IPN BU 0806/766 | BANIA STEFANIA |
| IPN BU 685/248 | Bania Zofia |
| IPN BU 693/831 | BANIA ZOFIA |
| IPN BU 00966/88 | BANIAK ANDRZEJ |
| IPN BU 0193/6727 | BANIAK STANISŁAW |
| IPN BU 00249/1023 | BANIEWICZ WITOLD |
| IPN BU 001121/1644 | BANIEWICZ WITOLD |
| IPN BU 710/169 | BANIEWSKA MARIA |
| IPN BU 00945/301 | BANISZEWSKI JAN |
| IPN BU 645/116 | BANIUK WALDEMAR |
| IPN BU 645/105 | BANKA ZDZISŁAW |
| IPN BU 0993/1619 | BANKIEWICZ TERESA |
| IPN BU 00744/609 | BANKOWSKI TADEUSZ |
| IPN BU 0855/3452 | BANOURSKI JÓZEF |
| IPN BU 0957/23 | BANOWSKI ALEKSANDER |
| IPN BU 001198/5352 | BANROWSKI KAZIMIERZ |
| IPN BU 01133/465 | BANSIEWICZ LEON |
| IPN BU 0806/2320 | BANSLEBEN (WIKTOROWICZ) MARIA |
| IPN BU 00744/1156 | BANSLEBEN ANDRZEJ |
| IPN BU 001134/2258 | BANSLEBEN ANDRZEJ |
| IPN BU 0193/200 | BANSLEBEN ROMAN |
| IPN BU 0806/1193 | BANSZKIEWICZ DANUTA |
| IPN BU 683/1707 | BANSZKIEWICZ WACŁAW |
| IPN BU 00751/211 | BANUCHA ANDRZEJ |
| IPN BU 001102/1821 | BANUCHA ANDRZEJ |
| IPN BU 0193/7179 | BANULEWICZ ALEKSANDER ALFONS |
| IPN BU 00328/864 | BANULEWICZ EWA JADWIGA |
| IPN BU 001134/1720 | BANULEWICZ EWA JADWIGA |
| IPN BU 980/187 | BANULSKI ADAM |
| IPN BU 0193/308 | BANULSKI EUGENIUSZ |
| IPN BU 0866/21 | BANY ANTONI |
| IPN BU 0866/22 | BANY JAN |
| IPN BU 01133/472 | BANY KAZIMIERZ |
| IPN BU 002086/107 | BANY KAZIMIERZ |
| IPN BU 00966/1799 | BANY SYLWESTER I INNI |
| IPN BU 0193/8425 | BANYTKA ZENON |
| IPN BU 001102/422 | BAŃBUŁA WITHOF ALICJA |
| IPN BU 00249/1183 | BAŃBURA BOGUSŁAW |
| IPN BU 001121/1797 | BAŃBURA BOGUSŁAW JERZY |
| IPN BU 00612/2252 | BAŃCER IRMINA |
| IPN BU 001198/4044 | BAŃCER WIESŁAW |
| IPN BU 002082/68 | BAŃCZEROWSKI JANUSZ |
| IPN BU 002086/239 | BAŃCZEROWSKI JANUSZ |
| IPN BU 00612/1660 | BAŃCZYK STEFAN |
| IPN BU 001198/4784 | BAŃCZYK STEFAN |
| IPN BU 00277/381 | BAŃKA BARBARA |
| IPN BU 001121/2600 | BAŃKA BARBARA |
| IPN BU PF | 970/114 BAŃKA BOGDAN |
| IPN BU PF | 970/117 BAŃKA JADWIGA |
| IPN BU 0891/173 | BAŃKA KAZIMIERZ |
| IPN BU 0193/201 | BAŃKA STANISŁAW |
| IPN 00 1043/2350 | BAŃKO MARIA TERESA |
| IPN BU 0806/676 | BAŃKO MICHALINA |
| IPN BU 0193/202 | BAŃKO RYSZARD |
| IPN BU 0901/275 | BAŃKOWSKA CZARNECKA TERESA BARBARA |
| IPN BU 00328/1518 | BAŃKOWSKA EWA |
| IPN BU 001134/2492 | BAŃKOWSKA EWA |
| IPN BU 0218/3391 | BAŃKOWSKA HALINA |
| IPN BU 001121/2137 | BAŃKOWSKA IRENA |
| IPN BU 01133/471 | BAŃKOWSKA LEONTYNA |
| IPN BU 00249/1533 | BAŃKOWSKA TERESA |
| IPN BU 0951/309 | BAŃKOWSKA WERONIKA |
| IPN BU 0218/2907 | BAŃKOWSKI ANDRZEJ |
| IPN BU 001198/2142 | BAŃKOWSKI ANDRZEJ |
| IPN BU 00200/215 | BAŃKOWSKI ANDRZEJ MARIAN |
| IPN 00 1052/799 | BAŃKOWSKI ANDRZEJ MARIAN |
| IPN BU 00232/122 | BAŃKOWSKI HENRYK |
| IPN BU 00612/2638 | BAŃKOWSKI JÓZEF |
| IPN BU 00612/1372 | BAŃKOWSKI MAREK |
| IPN BU 001198/4646 | BAŃKOWSKI MAREK |
| IPN BU 698/108 | BAŃKOWSKI MIECZYSŁAW |
| IPN BU 00334/153 | BAŃKOWSKI MIKOŁAJ |
| IPN BU 001134/2874 | BAŃKOWSKI MIKOŁAJ |
| IPN BU 02042/180 | BAŃKOWSKI PAWEŁ |
| IPN 00 1043/2103 | BAŃKOWSKI SERGIUSZ |
| IPN BU 0772/759 | BAŃKOWSKI STEFAN |
| IPN BU 001121/4333 | BAŃKOWSKI TADEUSZ |
| IPN BU 002086/1334 | BAŃSKA KRYSTYNA |
| IPN BU 683/1708 | BAŃSKA MONIKA |
| IPN BU 0218/2802 | BAŃSKA RUSINOWICZ EUGENIA |
| IPN BU 0194/1388 | BAŃSKI STANISŁAW |
| IPN BU 0194/916 | BAŃSKI ZDZISŁAW |
| IPN BU 0242/1201 | BAPRAWSKA JADWIGA |
| IPN BU 0242/1905 | BAPRAWSKI TADEUSZ STEFAN |
| IPN BU 002082/710 | BAR HENRYK |
| IPN BU 002086/2059 | BAR HENRYK |
| IPN BU 0193/205 | BAR JAN |
| IPN BU 0243/268 | BAR JERZY |
| IPN BU 00415/507 | BAR JÓZEF |
| IPN BU 698/109 | BAR KAZIMIERZ |
| IPN BU 01321/2 | BAR KRYSTYNA |
| IPN BU 001134/4809 | BARA ZYGMUNT |
| IPN BU 00612/4575 | BARABACH JAN |
| IPN BU 001198/7210 | BARABACH JAN |
| IPN BU 00191/85 | BARABAS JANUSZ |
| IPN 00 1043/1969 | BARABAS JANUSZ |
| IPN BU 0193/204 | BARABASZ JAN |
| IPN BU 01133/473 | BARABASZ KAZIMIERZ |
| IPN BU 645/101 | BARADZIAJ WŁADYSŁAW |
| IPN BU 0193/5807 | BARADZIEJ EDWARD |
| IPN BU 00170/942 | BARADZIEJ EDWARD |
| IPN BU 685/247 | Baradziej Marek |
| IPN BU 645/100 | BARADZIEJ STEFANIA |
| IPN BU 01133/474 | BARAKOWSKI TADEUSZ |
| IPN BU 698/346 | BARAŁKIEWICZ EDWARD |
| IPN BU 0772/2176 | BARAŁKIEWICZ GABRIELA |
| IPN BU 01279/2 | BARAŁKIEWICZ WALDEMAR |
| IPN BU 00249/917 | BARAM-MICKIEWICZ MARIA |
| IPN BU 0193/5378 | BARAN (JASIŃSKA) EMILIA |
| IPN BU 0772/2180 | BARAN (SKOCZEK) STEFANIA |
| IPN BU 0242/3138 | BARAN (STARZYK) KRYSTYNA |
| IPN BU 0243/490 | BARAN (SZOSTEK) RENATA |
| IPN BU 0194/2299 | BARAN (ZIMOLĄG) ALINA |
| IPN BU 0193/1344 | BARAN ADAM |
| IPN BU 00611/160 | BARAN ADAM |
| IPN BU 001198/469 | BARAN ADAM |
| IPN BU 0951/674 | BARAN ADAMKIEWICZ LUCYNA |
| IPN BU 698/110 | BARAN ADELA |
| IPN BU 0193/1345 | BARAN ALEKSANDER |
| IPN BU 698/111 | BARAN ALEKSANDER |
| IPN BU 0993/1636 | BARAN ALICJA |
| IPN BU 0604/1726 | BARAN ANDRZEJ |
| IPN BU 00612/4009 | BARAN ANDRZEJ |
| IPN BU 698/112 | BARAN ANTONI |
| IPN BU 001198/2485 | BARAN ANTONI |
| IPN BU 0854/932 | BARAN BARBARA |
| IPN BU PF | 280/102 BARAN BENT |
| IPN BU 0901/657 | BARAN BOGDAN |
| IPN BU 0193/7980 | BARAN BOLESŁAW |
| IPN BU 00612/1695 | BARAN BOLESŁAW |
| IPN BU 698/113 | BARAN BRONISŁAW |
| IPN BU 0772/2177 | BARAN BRONISŁAWA |
| IPN BU 0772/2178 | BARAN CZESŁAW |
| IPN BU 01133/475 | BARAN CZESŁAW |
| IPN BU 644/764 | BARAN CZESŁAW |
| IPN BU 698/387 | BARAN CZESŁAW |
| IPN BU 00170/509 | BARAN CZESŁAW |
| IPN 00 1043/70 | BARAN CZESŁAW CEZARY |
| IPN BU 00328/741 | BARAN DARIUSZ |
| IPN BU 001134/1569 | BARAN DARIUSZ SŁAWOMIR |
| IPN BU 0993/255 | BARAN DOROTA |
| IPN BU 00612/3546 | BARAN EDWARD |
| IPN BU 001198/6526 | BARAN EDWARD |
| IPN BU 0772/760 | BARAN EUGENIA |
| IPN BU 0218/1717 | BARAN EUGENIUSZ |
| IPN BU 0951/1582 | BARAN FRANCISZEK |
| IPN BU 01000/1494 | BARAN FRANCISZEK |
| IPN BU 698/114 | BARAN FRANCISZEK |
| IPN BU 001102/1859 | BARAN FRANCISZEK |
| IPN BU 0218/3548 | BARAN GRZEGORZ |
| IPN BU 0951/1247 | BARAN GRZEGORZ |
| IPN BU 01144/87 | BARAN GUSTAW |
| IPN BU 01000/1794 | BARAN HANNA |
| IPN BU 698/115 | BARAN HELENA |
| IPN BU 0942/91 | BARAN HENRYKA |
| IPN BU 093/15 | BARAN HENRYKA |
| IPN BU 0242/2844 | BARAN IWONA |
| IPN BU 0193/8630 | BARAN JAN |
| IPN BU 01000/1795 | BARAN JAN |
| IPN BU 00945/1129 | BARAN JAN |
| IPN BU 001198/88 | BARAN JAN |
| IPN BU 001198/1795 | BARAN JAN |
| IPN BU 0193/7044 | BARAN JANINA |
| IPN BU 001102/1552 | BARAN JANINA |
| IPN BU 0772/2181 | BARAN JANINA TERESA |
| IPN BU 00230 | P 48 BARAN JANUSZ |
| IPN BU 00612/1612 | BARAN JANUSZ |
| IPN BU 001198/4757 | BARAN JANUSZ |
| IPN BU PF | 1021/99 BARAN JOLANTA |
| IPN BU 0912/267 | BARAN JÓZEF |
| IPN BU 0193/1346 | BARAN JÓZEF |
| IPN BU 0951/1691 | BARAN JÓZEF |
| IPN BU 00244/55 | BARAN JÓZEF |
| IPN BU 644/765 | BARAN JÓZEF |
| IPN BU 00283/259 | BARAN JÓZEF |
| IPN BU 00966/221 | BARAN JÓZEF |
| IPN BU 0772/761 | BARAN JÓZEFA |
| IPN BU 0772/762 | BARAN JÓZEFA |
| IPN BU 698/388 | BARAN KAZIMIERZ |
| IPN BU 0957/22 | BARAN KAZIMIERZ |
| IPN BU 090/148 | BARAN KRYSTYNA |
| IPN BU 00277/73 | BARAN KRYSTYNA |
| IPN BU 00415/445 | BARAN KRYSTYNA |
| IPN BU 001121/2310 | BARAN KRYSTYNA |
| IPN BU 0305/481 | BARAN LIDIA |
| IPN BU 698/116 | BARAN MAKSYMILIAN |
| IPN BU 00415/106 | BARAN MAREK |
| IPN 00 1052/1014 | BARAN MAREK |
| IPN BU 00249/1545 | BARAN MARIA |
| IPN BU 001121/2146 | BARAN MARIA ZUZANNA |
| IPN BU 0194/457 | BARAN MARIAN |
| IPN BU 644/766 | BARAN MARIAN |
| IPN BU 00945/683 | BARAN MARIAN |
| IPN BU 001198/4079 | BARAN MARIAN |
| IPN BU 01013/183 | BARAN MICHAŁ |
| IPN BU 001121/1552 | BARAN MICKIEWICZ MARCIN |
| IPN BU 0193/1347 | BARAN MIECZYSŁAW |
| IPN BU 001198/3404 | BARAN MIECZYSŁAW |
| IPN BU 001065/90 | BARAN MIECZYSŁAW I INNI |
| IPN BU 00249/1319 | BARAN MIROSŁAWA |
| IPN BU 001121/1931 | BARAN MIROSŁAWA EWA |
| IPN BU 00415/125 | BARAN PIOTR |
| IPN BU 0193/6206 | BARAN ROMAN |
| IPN BU 00612/4401 | BARAN ROMAN |
| IPN BU 00966/424 | BARAN ROMAN |
| IPN BU 001198/7099 | BARAN ROMAN |
| IPN BU 0194/3637 | BARAN RYSZARD |
| IPN BU 0242/2331 | BARAN STANISŁAW |
| IPN BU 00244/162 | BARAN STANISŁAW |
| IPN BU 01133/185 | BARAN STANISŁAW |
| IPN BU 01133/476 | BARAN STANISŁAW |
| IPN BU 00448/531 | BARAN STANISŁAW |
| IPN BU 00966/220 | BARAN STANISŁAW |
| IPN BU 001198/760 | BARAN STANISŁAW |
| IPN BU 001198/2364 | BARAN STANISŁAW |
| IPN BU 001198/2872 | BARAN STANISŁAW |
| IPN BU 001198/3341 | BARAN STANISŁAW |
| IPN BU 001198/4138 | BARAN STANISŁAW |
| IPN BU 001134/4727 | BARAN STANISŁAW |
| IPN BU 001134/5507 | BARAN STANISŁAW |
| IPN BU 0772/763 | BARAN STANISŁAWA |
| IPN BU 0193/4267 | BARAN STEFAN |
| IPN BU 01133/477 | BARAN STEFAN |
| IPN BU 00200/905 | BARAN TADEUSZ |
| IPN BU 001102/447 | BARAN TADEUSZ |
| IPN BU 001198/1224 | BARAN TEODOR |
| IPN BU 0772/764 | BARAN TERESA |
| IPN BU 090/127 | BARAN TERESA |
| IPN BU 980/189 | BARAN TERESA |
| IPN BU PF | 1021/100 BARAN TERESA |
| IPN BU 00612/4108 | BARAN URSZULA |
| IPN BU 001198/6874 | BARAN URSZULA |
| IPN BU 00966/339 | BARAN WACŁAW |
| IPN BU 0772/765 | BARAN WERONIKA |
| IPN BU 00945/815 | BARAN WIKTOR |
| IPN BU 0193/7031 | BARAN WITOLD |
| IPN BU 0866/1341 | BARAN WITOLD |
| IPN BU 1187/60 | BARAN WITOLD |
| IPN BU 0218/752 | BARAN WŁADYSŁAW |
| IPN BU 0855/3096 | BARAN WŁADYSŁAW |
| IPN BU 00244/119 | BARAN WŁADYSŁAW |
| IPN BU 644/767 | BARAN WŁADYSŁAW |
| IPN BU 645/71 | BARAN WŁADYSŁAW |
| IPN BU 00275/301 | BARAN WŁADYSŁAW |
| IPN BU 0855/2840 | BARAN WŁODZIMIERZ |
| IPN BU 644/768 | BARAN WŁODZIMIERZ |
| IPN BU PF | 2/52 BARAN WŁODZIMIERZ |
| IPN BU 00283/405 | BARAN WOJCIECH |
| IPN BU 00768/284 | BARAN WOJCIECH |
| IPN BU PF | 2077/38 BARAN ZBIGNIEW |
| IPN BU 00612/3223 | BARAN ZBIGNIEW |
| IPN BU 0193/5008 | BARAN ZDZISŁAW |
| IPN BU 0218/1691 | BARAN ZDZISŁAW |
| IPN BU 00611/1424 | BARAN ZDZISŁAW |
| IPN BU 001198/5775 | BARAN ZDZISŁAW |
| IPN 00 1052/648 | BARAN ZDZISŁAW |
| IPN BU 00612/3526 | BARAN ZENON |
| IPN BU 001198/6512 | BARAN ZENON |
| IPN BU 0772/766 | BARAN ZOFIA |
| IPN BU 0806/2005 | BARAN ZOFIA |
| IPN BU 645/1439 | BARAN ZOFIA |
| IPN BU 0218/1521 | BARAN ZYGMUNT |
| IPN BU 00966/1339 | BARANCEWICZ WACŁAW |
| IPN BU 00277/1060 | BARANEK ANDRZEJ |
| IPN BU 001121/3241 | BARANEK ANDRZEJ |
| IPN BU 00612/4876 | BARANEK BOGUSŁAW |
| IPN BU 0901/1225 | BARANEK JACEK |
| IPN BU 0604/1613 | BARANEK JANUSZ |
| IPN BU 01000/769 | BARANEK MARIANNA |
| IPN BU 0604/2004 | BARANEK ZDZISŁAW |
| IPN 00 1052/229 | BARANEK ZDZISŁAW |
| IPN BU 0833/672 | BARANIAK EUGENIUSZ |
| IPN 00 1043/2994 | BARANIAK KAZIMIERZ JERZY |
| IPN BU 00328/994 | BARANIAK LUDWIK |
| IPN BU 001134/1855 | BARANIAK LUDWIK |
| IPN BU 683/234 | BARANICKA ANNA |
| IPN BU 00277/1150 | BARANICKA HANNA |
| IPN BU 698/117 | BARANICKI TADEUSZ |
| IPN BU 0892/74 | BARANIECKI STEFAN |
| IPN 00 1043/2869 | BARANIECKI ZBIGNIEW ANTONI |
| IPN BU 644/769 | BARANIECKI ZDZISŁAW |
| IPN BU 001134/2195 | BARANIEWSKA ELŻBIETA |
| IPN BU 00328/1286 | BARANIEWSKA-JANKOWSKA ELŻBIETA |
| IPN BU 00200/1341 | BARANIEWSKI WIESŁAW |
| IPN BU 001102/942 | BARANIEWSKI WIESŁAW |
| IPN BU 01306/1 | BARANKIEWICZ ANDRZEJ |
| IPN BU 0993/1007 | BARANKIEWICZ BARBARA |
| IPN BU 0833/673 | BARANKIEWICZ HENRYK |
| IPN BU 0901/681 | BARANKIEWICZ KOCEMBA ZOFIA |
| IPN BU 00283/1395 | BARANKIEWICZ ROBERT |
| IPN BU 00768/759 | BARANKIEWICZ ROBERT |
| IPN BU 0901/191 | BARANKIEWICZ STANISŁAW |
| IPN BU 748/8 | BARANKIEWICZ STANISŁAW |
| IPN BU 01000/1793 | BARANKIEWICZ TADEUSZ |
| IPN BU 00230 | P. 52 BARANKIEWICZ WŁODZIMIERZ |
| IPN BU 0870/127 | BARANKIEWICZ ZYGMUNT |
| IPN BU 0866/23 | BARANKIEWICZ ZYGMUNT |
| IPN BU 0193/213 | BARANOW KONSTANTY |
| IPN BU 0218/3244 | BARANOW PAWEŁ |
| IPN BU 644/770 | BARANOWICZ KAZIMIERZ |
| IPN BU 0604/1862 | BARANOWICZ-KSIĘŻOPOLSKA ANNA |
| IPN BU 0806/3206 | BARANOWSKA (JAKUBIAK) EUGENIA |
| IPN BU 0193/9081 | BARANOWSKA (JASTRZEWSKA) (BZDYŃ) LEONTYNA |
| IPN BU 0902/23 | BARANOWSKA (MARCHWIŃSKA) NINA |
| IPN BU 00200/147 | BARANOWSKA ALEKSANDRA |
| IPN 00 1052/631 | BARANOWSKA ALEKSANDRA |
| IPN BU 0902/24 | BARANOWSKA ANTONI |
| IPN BU 0242/2381 | BARANOWSKA BARBARA |
| IPN BU 0993/552 | BARANOWSKA BEATA |
| IPN BU 0951/424 | BARANOWSKA BRONISŁAWA |
| IPN BU 01013/181 | BARANOWSKA CZESŁAWA |
| IPN BU 710/369 | BARANOWSKA DOROTA |
| IPN BU 0242/3015 | BARANOWSKA ELŻBIETA |
| IPN BU PF | 98/1 BARANOWSKA EUGENIA |
| IPN BU 0993/256 | BARANOWSKA EWA |
| IPN BU 00328/323 | BARANOWSKA EWA |
| IPN BU 001134/1069 | BARANOWSKA EWA |
| IPN BU 0901/700 | BARANOWSKA GRAŻYNA AURELIA |
| IPN 00 1043/3549 | BARANOWSKA HENRYKA WACŁAW |
| IPN 00 1043/1930 | BARANOWSKA JADWIGA |
| IPN BU 748/173 | BARANOWSKA LUCYNA |
| IPN BU 0894/4 | BARANOWSKA NATALJA |
| IPN BU 0957/24 | BARANOWSKA STANISŁAWA |
| IPN BU PF | 837/30 BARANOWSKA TERESA |
| IPN BU 01000/511 | BARANOWSKA WIESŁAWA |
| IPN BU 0864/17 | BARANOWSKA ZENONA |
| IPN BU 00232/66 | BARANOWSKA ZOFIA |
| IPN BU 00228/50 | BARANOWSKI |
| IPN BU 698/347 | BARANOWSKI JÓZEF |
| IPN BU 01000/1792 | BARANOWSKI ALEKSANDER |
| IPN BU 636/1801 | BARANOWSKI ANTONI |
| IPN BU 698/118 | BARANOWSKI ANTONI |
| IPN BU 0604/280 | BARANOWSKI ARKADIUSZ |
| IPN 00 1043/1154 | BARANOWSKI BOGDAN MIECZYSŁAW |
| IPN BU 0891/1784 | BARANOWSKI BOLESŁAW |
| IPN BU 01000/1791 | BARANOWSKI BOLESŁAW |
| IPN BU 0892/72 | BARANOWSKI CZESŁAW |
| IPN BU 00234 | p.158 BARANOWSKI EDMUND |
| IPN BU 00230 | P. 169 BARANOWSKI EDMUND |
| IPN BU 0912/251 | BARANOWSKI EDWARD |
| IPN BU 685/4 | BARANOWSKI FRANCISZEK |
| IPN BU 00612/2352 | BARANOWSKI FRANCISZEK |
| IPN BU 00612/2963 | BARANOWSKI FRANCISZEK |
| IPN BU 001198/6129 | BARANOWSKI FRANCISZEK |
| IPN BU 01321/3 | BARANOWSKI GRZEGORZ |
| IPN BU 00612/2940 | BARANOWSKI HENRYK |
| IPN BU 001198/6114 | BARANOWSKI HENRYK |
| IPN BU 001134/2892 | BARANOWSKI HENRYK |
| IPN BU 002086/821 | BARANOWSKI HENRYK WIESŁAW |
| IPN BU 0958/89 | BARANOWSKI JAN |
| IPN BU 0951/701 | BARANOWSKI JAN |
| IPN BU 00168/112 | BARANOWSKI JAN |
| IPN BU 00945/1612 | BARANOWSKI JAN |
| IPN BU 002152/112 | BARANOWSKI JAN |
| IPN BU 00612/2848 | BARANOWSKI JAROSŁAW |
| IPN BU 001198/6064 | BARANOWSKI JAROSŁAW |
| IPN BU 001134/3038 | Baranowski Jarosław |
| IPN BU 683/229 | BARANOWSKI JERZY |
| IPN BU 776/131 | BARANOWSKI JERZY |
| IPN BU 00334/497 | BARANOWSKI JERZY |
| IPN BU 001134/3376 | BARANOWSKI JERZY |
| IPN BU 01133/478 | BARANOWSKI JÓZEF |
| IPN BU 00244/172 | BARANOWSKI KAZ. |
| IPN BU 0193/7683 | BARANOWSKI KAZIMIERZ |
| IPN BU 0604/403 | BARANOWSKI KAZIMIERZ |
| IPN BU 0866/24 | BARANOWSKI KAZIMIERZ |
| IPN BU 00244/55 | BARANOWSKI KAZIMIERZ |
| IPN BU 01000/1790 | BARANOWSKI KAZIMIERZ |
| IPN BU 001102/2046 | BARANOWSKI KAZIMIERZ |
| IPN BU 644/771 | BARANOWSKI KLEMENS |
| IPN BU 710/462 | BARANOWSKI KLEMENS |
| IPN BU 0910/51 | BARANOWSKI KONSRTANTY |
| IPN BU 00168/17 | BARANOWSKI KRZYSZTOF |
| IPN BU 00945/1489 | BARANOWSKI KRZYSZTOF – TADEUSZ |
| IPN BU 002082/428 | BARANOWSKI KRZYSZTOF WIKTOR |
| IPN BU 002086/1206 | BARANOWSKI KRZYSZTOF WIKTOR |
| IPN BU 0242/3121 | BARANOWSKI KRZYSZTOF WOJCIECH |
| IPN BU 02042/27 | BARANOWSKI MACIEJ |
| IPN BU 0242/1920 | BARANOWSKI MARCIN |
| IPN BU 0242/3111 | BARANOWSKI MAREK |
| IPN BU 649/8 | BARANOWSKI MAREK |
| IPN BU 00277/526 | BARANOWSKI MAREK |
| IPN BU 001121/2740 | BARANOWSKI MAREK LEONARD |
| IPN BU 01000/1787 | BARANOWSKI MARIAN |
| IPN BU 644/772 | BARANOWSKI MARIAN |
| IPN BU 00612/4894 | BARANOWSKI MARIAN |
| IPN BU 0287/1 | BARANOWSKI MICHAŁ |
| IPN BU 01013/182 | BARANOWSKI MIECZYSŁAW |
| IPN BU 01000/1768 | BARANOWSKI PIOTR |
| IPN BU 01133/688 | BARANOWSKI PIOTR |
| IPN BU 02187/2 | BARANOWSKI PIOTR |
| IPN BU 0951/871 | BARANOWSKI PIOTR ANDRZEJ |
| IPN BU 00328/705 | BARANOWSKI RAFAŁ EDWARD |
| IPN BU 001134/1534 | BARANOWSKI RAFAŁ EDWARD |
| IPN BU 0901/1575 | BARANOWSKI ROMAN |
| IPN BU 0242/2992 | BARANOWSKI ROMAN |
| IPN BU 0307/18 | BARANOWSKI ROMAN |
| IPN BU 00234 | p.244 BARANOWSKI RYSZARD |
| IPN BU 00612/143 | BARANOWSKI RYSZARD |
| IPN BU 00249/645 | BARANOWSKI RYSZARD |
| IPN BU 001198/4077 | BARANOWSKI RYSZARD |
| IPN 00 1052/1518 | BARANOWSKI RYSZARD |
| IPN BU 002085/4 | BARANOWSKI RYSZARD |
| IPN BU 001121/1289 | BARANOWSKI RYSZARD |
| IPN BU 0193/214 | BARANOWSKI STANISŁAW |
| IPN BU 01000/1902 | BARANOWSKI STANISŁAW |
| IPN BU 01133/479 | BARANOWSKI STANISŁAW |
| IPN BU 0305/93 | BARANOWSKI STANISŁAW |
| IPN BU 00399/380 | BARANOWSKI STANISŁAW |
| IPN BU 00750/270 | BARANOWSKI STANISŁAW |
| IPN 00 1052/1304 | BARANOWSKI STANISŁAW |
| IPN BU 00249/579 | BARANOWSKI TADEUSZ KAROL |
| IPN BU 001121/1211 | BARANOWSKI TADEUSZ KAROL |
| IPN BU 00283/903 | BARANOWSKI WACEK |
| IPN BU 0866/25 | BARANOWSKI WACŁAW |
| IPN BU 00768/622 | BARANOWSKI WACŁAW |
| IPN BU 0777/5 | BARANOWSKI WALDEMAR |
| IPN BU 00688/85 | BARANOWSKI WALDEMAR |
| IPN BU 0604/1184 | BARANOWSKI WALDEMAR.SŁAWOMIR |
| IPN BU 644/773 | BARANOWSKI WIKTOR |
| IPN BU 0193/9076 | BARANOWSKI WŁADYSŁAW |
| IPN BU 0864/16 | BARANOWSKI WŁADYSŁAW |
| IPN BU 776/132 | BARANOWSKI WŁADYSŁAW |
| IPN BU 0193/8208 | BARANOWSKI WŁODZIMIERZ |
| IPN BU 02042/538 | BARANOWSKI WŁODZIMIERZ |
| IPN BU 00275/25 | BARANOWSKI WOJCIECH |
| IPN BU 00399/324 | BARANOWSKI WOJCIECH |
| IPN BU 001134/4673 | BARANOWSKI WOJCIECH |
| IPN BU 001121/4167 | BARANOWSKI WOJCIECH PIOTR |
| IPN BU 0243/438 | BARANOWSKI ZBIGNIEW |
| IPN BU 0193/7680 | BARANOWSKI ZDZISŁAW |
| IPN BU 0951/420 | BARANOWSKI ZENON |
| IPN BU 0891/177 | BARANOWSKI ZYGMUNT |
| IPN BU 0193/215 | BARANOWSKI ZYGMUNT |
| IPN BU 0604/882 | BARANOWSKI ZYGMUNT |
| IPN BU 00399/465 | BARANOWSKI ZYGMUNT |
| IPN 00 1043/249 | BARAŃCZAK FRANCISZEK |
| IPN BU 0901/2020 | BARAŃCZUK KRYSTYNA |
| IPN BU 00612/1514 | BARAŃCZYK JANUSZ |
| IPN BU 001198/4694 | BARAŃCZYK JANUSZ |
| IPN BU 0193/5937 | BARAŃSKA (ZDROJEWSKA) WŁADYSŁAWA |
| IPN BU 0242/1264 | BARAŃSKA (ZWOLIŃSKA) JOLANTA |
| IPN BU 0242/162 | BARAŃSKA ADELAJDA |
| IPN BU 002086/1940 | BARAŃSKA ALICJA SEWERYNA |
| IPN BU 0901/2197 | BARAŃSKA ANNA |
| IPN 00 1052/589 | BARAŃSKA HENRYKA |
| IPN BU 0894/3 | BARAŃSKA IRENA |
| IPN BU 0901/1233 | BARAŃSKA JADWIGA (KORCZAK) |
| IPN BU 0218/1031 | BARAŃSKA JANINA |
| IPN BU 00200/672 | BARAŃSKA JOANNA ZOFIA |
| IPN BU 001102/123 | BARAŃSKA JOANNA ZOFIA |
| IPN BU 0218/2387 | BARAŃSKA KRYSTYNA |
| IPN BU 0806/2667 | BARAŃSKA KRYSTYNA |
| IPN BU 0242/1514 | BARAŃSKA LONGINA |
| IPN BU 0892/76 | BARAŃSKA LUCJA |
| IPN BU 0193/216 | BARAŃSKA ZUZANNA |
| IPN BU 001102/103 | BARAŃSKA-NIELSEN GRAŻYNA |
| IPN BU 00335/119 | BARAŃSKI |
| IPN BU 644/774 | BARAŃSKI ALEKSANDER |
| IPN BU 001134/3874 | BARAŃSKI ANDRZEJ |
| IPN BU 002086/682 | BARAŃSKI ANDRZEJ ALEKSANDER |
| IPN BU 0193/8906 | BARAŃSKI CZESŁAW |
| IPN BU 0958/943 | BARAŃSKI EUGENIUSZ |
| IPN BU 644/775 | BARAŃSKI HENRYK |
| IPN BU 0772/2182 | BARAŃSKI JAN |
| IPN BU 01000/1720 | BARAŃSKI JAN |
| IPN BU 00612/2347 | BARAŃSKI JAN |
| IPN BU 00612/2798 | BARAŃSKI JANUSZ |
| IPN BU 001198/6029 | BARAŃSKI JANUSZ |
| IPN BU 0912/295 | BARAŃSKI JERZY |
| IPN BU 00283/2010 | BARAŃSKI JERZY |
| IPN BU 00966/195 | BARAŃSKI JERZY |
| IPN BU 001121/336 | BARAŃSKI JERZY |
| IPN BU 0193/1350 | BARAŃSKI JÓZEF |
| IPN BU 644/776 | BARAŃSKI JÓZEF |
| IPN BU 644/925 | BARAŃSKI JÓZEF |
| IPN BU 00612/1859 | BARAŃSKI JÓZEF |
| IPN BU 001198/4926 | BARAŃSKI JÓZEF |
| IPN BU 01133/480 | BARAŃSKI JULIAN |
| IPN BU 00170/661 | BARAŃSKI KAMIL |
| IPN 00 1043/507 | BARAŃSKI KAMIL |
| IPN BU 0218/2614 | BARAŃSKI KAROL |
| IPN BU 0854/994 | BARAŃSKI KAZIMIERZ |
| IPN BU 01133/116 | BARAŃSKI KONSTANTY |
| IPN BU 00275/504 | BARAŃSKI KRZYSZTOF |
| IPN BU 001134/391 | BARAŃSKI KRZYSZTOF |
| IPN BU 001134/3677 | BARAŃSKI KRZYSZTOF |
| IPN BU 0591/11 | BARAŃSKI MAREK |
| IPN BU 00612/2983 | BARAŃSKI MAREK |
| IPN BU 0242/430 | BARAŃSKI MARIAN |
| IPN BU 01000/1747 | BARAŃSKI MARIAN |
| IPN BU 00611/638 | BARAŃSKI MARIAN |
| IPN BU 001198/1052 | BARAŃSKI MARIAN |
| IPN BU 0806/2545 | BARAŃSKI MIECZYSŁAW |
| IPN BU 0194/2754 | BARAŃSKI MIKOŁAJ |
| IPN BU 0604/165 | BARAŃSKI PANTALEON |
| IPN BU 00612/1742 | BARAŃSKI ROMUALD |
| IPN BU 001198/4859 | BARAŃSKI ROMUALD |
| IPN BU 0242/1086 | BARAŃSKI RYSZARD |
| IPN BU 0218/2270 | BARAŃSKI STANISŁAW |
| IPN BU 0866/26 | BARAŃSKI STANISŁAW |
| IPN BU 00244/115 | BARAŃSKI STANISŁAW |
| IPN BU 01000/1749 | BARAŃSKI STANISŁAW |
| IPN BU 01000/1776 | BARAŃSKI STANISŁAW |
| IPN BU 00612/3615 | BARAŃSKI STANISŁAW |
| IPN BU 001198/3748 | BARAŃSKI STANISŁAW |
| IPN BU 001198/6581 | BARAŃSKI STANISŁAW |
| IPN BU 001198/3981 | BARAŃSKI TADEUSZ |
| IPN BU 002086/1480 | BARAŃSKI TADEUSZ |
| IPN BU 02042/47 | BARAŃSKI TOMASZ |
| IPN BU 0872/111 | BARAŃSKI WACŁAW |
| IPN BU 00612/3600 | BARAŃSKI WIESŁAW |
| IPN BU 001198/6566 | BARAŃSKI WIESŁAW |
| IPN BU 00612/813 | BARAŃSKI WŁADTSŁAW |
| IPN BU 01000/1750 | BARAŃSKI WŁADYSŁAW |
| IPN BU 0218/2436 | BARAŃSKI WOJCIECH |
| IPN BU 00945/220 | BARAŃSKI WOJCIECH |
| IPN BU 01133/481 | BARAŃSKI ZBIGNIEW |
| IPN BU 01133/482 | BARAŃSKI ZDZISŁAW |
| IPN BU 00448/332 | BARAŃSKI ZDZISŁAW |
| IPN BU 001134/5311 | BARAŃSKI ZDZISŁAW |
| IPN BU 01273//1 | BARAŃSKI ZYGMUNT |
| IPN BU 0193/217 | BARAS STEFAN |
| IPN BU 01133/483 | BARASIEWICZ MARIAN |
| IPN BU 00688/83 | BARASIŃSKI MICHAŁ |
| IPN BU 698/119 | BARAŚ JÓZEF |
| IPN BU 0772/2183 | BARĄCZ-FZIES EDMUND |
| IPN BU 685/5 | BARBACHEN HALINA |
| IPN BU 01000/1346 | BARBACHEN MARIAN |
| IPN BU 0993/1552 | BARBACHOWSKA LUCYNA |
| IPN BU 0988/950 | BARBANELL HENRYKA |
| IPN BU 698/120 | BARBANELL RYSZARD |
| IPN BU 0951/1436 | BARBARCZYK HENRYK |
| IPN BU 0951/1329 | BARBARCZYK STANISŁAW |
| IPN BU 02042/528 | BARBARCZYK STANISŁAW |
| IPN BU 001102/2132 | BARBAREWICZ BRONISŁAW |
| IPN BU 0193/218 | BARBARIUSZ EDWARD |
| IPN BU 00334/427 | BARBAROWICZ ZYGMUNT |
| IPN BU 001134/3302 | BARBAROWICZ ZYGMUNT RYSZARD |
| IPN BU 0912/265 | BARBARSKI HENRYK |
| IPN BU 0957/25 | BARBARSKI STANISŁAW |
| IPN BU 001065/106 | BARBASIEWICZ AGNIESZKA |
| IPN BU 0242/1407 | BARBASIEWICZ FERDYNAND |
| IPN BU 0194/1003 | BARBASIEWICZ MAŁGORZATA |
| IPN BU 0951/1927 | BARBASIEWICZ ROBERT |
| IPN BU 0194/1961 | BARBASIEWICZ TADEUSZ |
| IPN BU 00249/641 | BARBASIEWICZ WŁODZIMIERZ |
| IPN BU 001121/1285 | BARBASIEWICZ WŁODZIMIERZ |
| IPN BU 0902/25 | BARBASZEWSKI ZBIGNIEW-STEFAN |
| IPN BU 0901/1227 | BARBAŚ EWA MAŁGORZATA |
| IPN BU 0993/138 | BARBAŚ MARIA |
| IPN BU 00448/428 | BARBERA ALBERTO |
| IPN BU 001134/5408 | BARBERA ALBERTO |
| IPN BU 00945/1160 | BARBOSA – COUTINHO HENRIQUE – JOSE |
| IPN BU 00612/2900 | BARBÓRSKI BOLESŁAW |
| IPN BU 001121/686 | BARBURSKI WALDEMAR ANDRZEJ |
| IPN BU 00249/100 | BARBUSKI ANDRZEJ WALDEMAR |
| IPN BU 0242/1533 | BARCAUK TADEUSZ |
| IPN BU 0604/803 | BARCERZ MIECZYSŁAW |
| IPN BU 01000/477 | BARCEWICZ FELIKS |
| IPN BU 0772/767 | BARCEWICZ HELENA |
| IPN BU 00612/2199 | BARCHAN ADAM |
| IPN BU 002081/24 | BARCHAN RYSZARD |
| IPN BU 002085/35 | BARCHAN RYSZARD |
| IPN BU 001198/1302 | BARCHAN WŁADYSŁAW |
| IPN BU 698/348 | BARCHANIEWICZ ADAM |
| IPN BU 001134/3575 | BARCIAK BOGDAN |
| IPN BU 00612/3336 | BARCICKI HENRYK |
| IPN BU 00611/440 | BARCICKI JAN |
| IPN BU 001198/804 | BARCICKI JAN |
| IPN BU 0242/1668 | BARCICKI JÓZEF |
| IPN 00 1052/924 | BARCICKI ZDZISŁAW ALEKSANDER |
| IPN 00 1052/1749 | BARCIK BOGUSŁAW |
| IPN BU 644/19 | BARCIK JULIAN |
| IPN BU 0604/1893 | BARCIK MAREK |
| IPN BU 00200/22 | BARCIKOWSKA – DĘBOCKA ANNA |
| IPN BU 0901/1745 | BARCIKOWSKA ZOFIA |
| IPN BU 0910/53 | BARCIKOWSKA ZOFIA |
| IPN 00 1052/293 | BARCIKOWSKA-DĘBICKA ANNA |
| IPN BU 001198/4124 | BARCIKOWSKI ANTONI |
| IPN BU 0305/411 | BARCIKOWSKI EDWARD |
| IPN BU 0854/1204 | BARCIKOWSKI FRANCISZEK |
| IPN BU 0891/1785 | BARCIKOWSKI KAZIMIERZ |
| IPN BU 644/777 | BARCIKOWSKI KAZIMIERZ |
| IPN BU 698/121 | BARCIKOWSKI LEON |
| IPN BU 02042/127 | BARCIKOWSKI MAREK |
| IPN BU 0194/1080 | BARCIKOWSKI MARIAN |
| IPN BU 00611/472 | BARCIKOWSKI MARIAN |
| IPN BU 001198/852 | BARCIKOWSKI MARIAN |
| IPN BU 0958/88 | BARCIKOWSKI MIECZYSŁAW |
| IPN BU 01000/1744 | BARCIKOWSKI RYSZARD |
| IPN BU 645/74 | BARCIKOWSKI RYSZARD |
| IPN BU 00328/313 | BARCIKOWSKI RYSZARD |
| IPN BU 001134/1059 | BARCIKOWSKI RYSZARD |
| IPN BU 0901/365 | BARCIKOWSKI STANISŁAW |
| IPN BU 0993/1583 | BARCIKOWSKI STANISŁAW |
| IPN BU 0912/263 | BARCIKOWSKI TADEUSZ |
| IPN BU 0604/657 | BARCIKOWSKI ZYGMUNT |
| IPN BU 01313/1 | BARCIŃSKA LUCYNA |
| IPN BU 0242/515 | BARCIŃSKI ALFRED |
| IPN BU 00328/1257 | BARCIŃSKI ANDRZEJ |
| IPN BU 001134/2162 | BARCIŃSKI ANDRZEJ |
| IPN BU 0218/451 | BARCIŃSKI JAN |
| IPN BU 01133/484 | BARCIŃSKI TADEUSZ |
| IPN BU 0893/89 | BARCIŃSKI WŁODZIMIERZ JANUSZ |
| IPN BU 00945/710 | BARCISZEWSKA – DZIEMBOWSKA – POMIAN WANDA – MARIA |
| IPN BU 001121/1503 | BARCISZEWSKA WANDA |
| IPN BU 00170/228 | BARCISZEWSKI MICHAŁ |
| IPN BU 00945/2281 | BARCISZEWSKI MICHAŁ |
| IPN 00 1043/1479 | BARCISZEWSKI MIECZYSŁAW |
| IPN BU 0958/143 | BARCIUCH STANISŁAW |
| IPN BU 0242/2873 | BARCKA JADWIGA |
| IPN BU 0194/1147 | BARCZ BARBARA |
| IPN BU 0772/768 | BARCZ EDMUND |
| IPN BU 001102/1717 | BARCZ GRAŻYNA JOLANTA |
| IPN BU 0193/1351 | BARCZ JÓZEF |
| IPN BU 002086/419 | BARCZ KRYSTIAN JACEK |
| IPN BU 001102/2011 | BARCZ KRYSTYNA |
| IPN BU 00244/119 | BARCZ STANISŁAW |
| IPN BU 644/20 | BARCZ STANISŁAW |
| IPN BU 644/21 | BARCZAK EDWARD |
| IPN BU 0772/4631 | BARCZAK HELENA |
| IPN BU 01133/485 | BARCZAK HENRYK |
| IPN BU PF | 1035/1 BARCZAK JADWIGA |
| IPN BU PF | 1035/1 BARCZAK JADWIGA |
| IPN BU PF | 2/132 BARCZAK JADWIGA |
| IPN BU 0988/1160 | BARCZAK JAN |
| IPN BU 0193/221 | BARCZAK JAN EDWARD |
| IPN BU 00191/37 | BARCZAK JERZY |
| IPN 00 1043/1813 | BARCZAK JERZY |
| IPN BU 00244/56 | BARCZAK LEON |
| IPN BU 01000/1760 | BARCZAK MARIAN |
| IPN BU 644/778 | BARCZAK TADEUSZ |
| IPN BU 645/130 | BARCZAK WACŁAW |
| IPN BU 636/1824 | BARCZAK WŁADYSŁAWA |
| IPN BU PF | 970/190 BARCZEWSKA BOGUSŁAWA |
| IPN BU 0806/2798 | BARCZEWSKA JADWIGA |
| IPN BU 0218/2434 | BARCZEWSKI ANDRZEJ |
| IPN BU 0833/716 | BARCZEWSKI BOGUSŁAW |
| IPN BU 00200/971 | BARCZEWSKI KRZYSZTOF |
| IPN BU 001102/538 | BARCZEWSKI KRZYSZTOF |
| IPN BU 698/122 | BARCZUK ROMAN |
| IPN BU 0901/1229 | BARCZUK WOJCIECH |
| IPN BU 00283/1742 | BARCZYK HANNA |
| IPN BU 001198/3732 | BARCZYK JÓZEF |
| IPN BU 00611/1684 | BARCZYK LUDWIK |
| IPN BU 0193/4547 | BARCZYK STANISŁAW |
| IPN BU 644/779 | BARCZYKOWSKI PIOTR |
| IPN BU 0833/679 | BARCZYŃSKA ANNA |
| IPN BU 0772/769 | BARCZYŃSKA JANINA |
| IPN BU 645/111 | BARCZYŃSKA MARIANNA |
| IPN BU 0772/770 | BARCZYŃSKA TERESA |
| IPN BU 002082/603 | BARCZYŃSKI ANDRZEJ JAN |
| IPN BU 0193/1352 | BARCZYŃSKI JAN |
| IPN BU 002086/144 | BARCZYŃSKI ROMAN |
| IPN 00 1043/3129 | BARCZYŃSKI STANISŁAW LEON |
| IPN BU 0902/26 | BARCZYŃSKI TADEUSZ |
| IPN BU 00611/1219 | BARCZYŃSKI ZYGMUNT |
| IPN BU 001198/1707 | BARCZYŃSKI ZYGMUNT |
| IPN BU 0772/2184 | BARĆ FRANCISZEK |
| IPN BU 0193/224 | BARĆ KAZIMIERZ |
| IPN BU 0772/2185 | BARĆ WŁADYSŁAWA |
| IPN BU 0242/2664 | BARDA (RAPALSKA. JANDA) ZOFIA WANDA |
| IPN BU 00244/58 | BARDACH JULIUSZ |
| IPN BU 02185/1 | BARDADYN BARBARA |
| IPN BU 01000/1536 | BARDADYN LUCJAN |
| IPN BU 081/188 | BARDELI ANDRZEJ |
| IPN BU 081/189 | BARDELI DANUTA |
| IPN BU 00277/1241 | BARDIJEWSKI HENRYK |
| IPN BU 001121/3399 | BARDIJEWSKI HENRYK EUGENIUSZ |
| IPN BU 001040/198 | BARDIN ZOFIA |
| IPN BU 644/3321 | BARDO STANISŁAW |
| IPN BU 0193/6860 | BARDON JERZY ZBIGNIEW |
| IPN BU 0951/1135 | BARDOŃSKI JANUSZ |
| IPN BU 0242/521 | BARDYGA STEFANIA |
| IPN BU 0193/225 | BARDYSZEWSKA KRYSTYNA |
| IPN BU 0958/94 | BARDYSZEWSKI EDMUND |
| IPN BU 01133/486 | BARDYSZEWSKI EDMUND |
| IPN BU 0912/264 | BARDYSZEWSKI WACŁAW |
| IPN 00 1052/1478 | BARDYSZEWSKI WITOLD |
| IPN BU 0891/176 | BARDYSZEWSKI WŁADYSŁAW |
| IPN 00 1043/1308 | BARDZIEJ EDWARD |
| IPN BU 0958/87 | BARDZIŃSKA ANASTAZJA |
| IPN BU 0193/3922 | BARDZIŃSKI STEFAN |
| IPN BU 002086/1014 | BARDZIŃSKI ZBIGNIEW WACŁAW |
| IPN BU 0193/226 | BARECKI ANTONI |
| IPN BU 001089/476 | BARECKI HENRYK |
| IPN 00 1052/1623 | BARECKI JANISŁAW KAZIMIERZ |
| IPN BU 002086/589 | BARECKI-BARŁOGA KLEMENS |
| IPN BU 00334/637 | BAREJ BOGUSŁAW |
| IPN BU 001134/3546 | BAREJ BOGUSŁAW KRZYSZTOF |
| IPN BU 01000/1761 | BAREJ JÓZEF |
| IPN BU 001102/1639 | BAREJA CZESŁAW |
| IPN BU 00230 | P 48 BAREJA FRANCISZEK |
| IPN BU 001546/2 | BAREJA MIECZYSŁAW |
| IPN BU 001134/3506 | BAREJA MIECZYSŁAW |
| IPN BU 01133/676 | BAREJA STANISŁAW |
| IPN BU 698/349 | BAREJA TADEUSZ |
| IPN BU 00966/373 | BAREJA WŁADYSŁAW |
| IPN BU 0218/1128 | BAREŁA ANDRZEJ |
| IPN 00 1043/1231 | BARESTKA ZENON JULIAN |
| IPN BU 002081/395 | BAREWSKI BOGDAN |
| IPN BU 002085/461 | BAREWSKI BOGDAN |
| IPN BU 00945/416 | BAREWSKI ROMAN – LEONARD |
| IPN BU 0864/12 | BAREZA HENRYK |
| IPN BU 001134/4449 | BARGIEL ALEKSANDER |
| IPN BU 0193/7638 | BARGIEL MAJROWSKA HELENA |
| IPN BU 00244/55 | BARGIEL MIECZYSŁAW |
| IPN BU 00945/808 | BARGIEL MIECZYSŁAW |
| IPN BU 0604/133 | BARGIEL STANISŁAW |
| IPN BU 0604/1399 | BARGIEL STANISŁAW |
| IPN BU 636/1758 | BARGIEL WŁADYSŁAW |
| IPN BU 644/31 | BARGIEL WŁADYSŁAW |
| IPN BU 002086/703 | BARGIELEWICZ ELŻBIETA |
| IPN BU 0194/1795 | BARGIELEWICZ WANDA |
| IPN BU 0957/26 | BARGIELSKI MIECZYSŁAW |
| IPN BU 00744/989 | BARGIEŁ ARTUR |
| IPN BU 001134/1133 | BARGIEŁ ARTUR |
| IPN BU 0193/227 | BARGIEŁ JAN |
| IPN BU 0194/1057 | BARGIEŁ JAN |
| IPN BU 0290/68 | BARGIEŁ JAROSŁAW |
| IPN BU 0772/2187 | BARGIEŁ JÓZEFA |
| IPN BU 698/124 | BARGIEŁ KAZIMIERZ |
| IPN BU 001040/324 | BARGIEŁ LEOKADIA |
| IPN BU 01013/180 | BARGIEŁ LEON |
| IPN BU 698/125 | BARGIEŁA JERZY |
| IPN BU 645/97 | BARGIEŁOWSKI DANIEL |
| IPN BU 00966/1508 | BARIA TADEUSZ |
| IPN BU 0193/9093 | BARIASZ EUGENIUSZ |
| IPN BU 0193/8069 | BARK IRENA (FRYDMAN IRENA) |
| IPN 00 1043/2621 | BARKENBERG ANNA KONSTANCJA HELENA |
| IPN BU 0901/997 | BARKOWSKA JADWIGA |
| IPN BU 0218/1544 | BARKOWSKI STANISŁAW |
| IPN BU 0193/1353 | BARLAS HENRYK |
| IPN BU 002082/92 | BARLET JAN ANDRZEJ |
| IPN BU 001198/5744 | BARLEWICZ ADAM |
| IPN BU 001089/133 | BARLIER GEORGES |
| IPN BU 00200/830 | BARLIK HENRYK FELIKS |
| IPN BU 001102/353 | BARLIK HENRYK FELIKS |
| IPN BU 00170/621 | BARŁOWSKI TADEUSZ ADAM |
| IPN 00 1043/377 | BARŁOWSKI TADEUSZ ADAM |
| IPN BU 645/28 | BARŁOŻEK APOLONIA |
| IPN BU 0902/31 | BARNAK JAN |
| IPN BU 980/3 | BARNAŚ DANUTA |
| IPN BU 683/232 | BARNECKA HANNA |
| IPN BU 00945/101 | BARNIK ALEKSY |
| IPN BU 0772/2188 | BARON JÓZEF |
| IPN BU 00399/540 | BARON TOMASZ ZBIGNIEW |
| IPN BU 001134/4881 | BARON TOMASZ ZBIGNIEW |
| IPN BU 0911/72 | BAROŃ EDWARD |
| IPN BU 00244/89 | BAROŃSKA – WITOSŁAWSKA JOANNA |
| IPN BU 0193/1366 | BAROR JÓZEF |
| IPN BU 0772/2189 | BAROWICZ EUGENIA |
| IPN BU 0193/7067 | BARSKA (WÓJCIK) HENRYKA |
| IPN BU 698/126 | BARSKA PAULINA |
| IPN BU 0901/868 | BARSKA WANDA BOŻENA |
| IPN BU 698/127 | BARSKI ALBIN |
| IPN BU 00283/2210 | BARSKI ANDRZEJ |
| IPN BU 00415/472 | BARSKI BARAN KRZYSZTOF |
| IPN BU 00612/1243 | BARSKI HENRYK |
| IPN BU 0912/250 | BARSKI JÓZEF |
| IPN BU 0777/6 | BARSKI RYSZARD |
| IPN BU 00689/85 | BARSKI RYSZARD |
| IPN BU 0242/1286 | BARSKI SŁAWOMIR |
| IPN BU 001198/3158 | BARSKI STANISŁAW |
| IPN BU 0193/8494 | BARSKI SYLWESTER |
| IPN BU 0242/3206 | BARSKI TADEUSZ |
| IPN BU 0993/479 | BARSZCZ (STĘRZYCKA) BEATA |
| IPN BU 0870/27 | BARSZCZ ADAM |
| IPN BU 00611/1209 | BARSZCZ ALEKSANDER |
| IPN BU 001198/1654 | BARSZCZ ALEKSANDER |
| IPN BU 00283/1966 | BARSZCZ ANDRZEJ |
| IPN BU 001198/3531 | BARSZCZ ANTONI |
| IPN BU 0307/133 | BARSZCZ BOŻENA |
| IPN BU 0806/2647 | BARSZCZ CZESŁAWA |
| IPN BU 01133/677 | BARSZCZ CZESŁAWA |
| IPN BU 748/228 | BARSZCZ CZESŁAWA |
| IPN BU 0194/2191 | BARSZCZ EDMUND |
| IPN BU 01133/487 | BARSZCZ EDMUND |
| IPN BU 644/780 | BARSZCZ EUGENIUSZ |
| IPN BU 00612/356 | BARSZCZ EUGENIUSZ |
| IPN BU 001198/4226 | BARSZCZ EUGENIUSZ |
| IPN BU 0855/2339 | BARSZCZ HANNA |
| IPN BU 0872/110 | BARSZCZ JANINA |
| IPN BU 0872/113 | BARSZCZ JÓZEF |
| IPN BU 698/128 | BARSZCZ JÓZEF |
| IPN BU 00277/378 | BARSZCZ JÓZEF |
| IPN BU 001121/2597 | BARSZCZ JÓZEF |
| IPN BU 0866/27 | BARSZCZ JÓZEFA |
| IPN BU 00225/41 | BARSZCZ JULIAN |
| IPN BU 001121/88 | BARSZCZ JULIAN |
| IPN BU 0912/259 | BARSZCZ KAZIMIERZ |
| IPN BU 01013/189 | BARSZCZ KRYSTYNA |
| IPN BU 0993/594 | BARSZCZ KRZYSZTOF |
| IPN BU 001134/2837 | BARSZCZ KRZYSZTOF |
| IPN BU 002086/445 | BARSZCZ MACIEJ |
| IPN BU 00612/683 | BARSZCZ MARIAN |
| IPN BU 00249/1430 | BARSZCZ MIROSŁAWA |
| IPN BU 001121/2039 | BARSZCZ MIROSŁAWA BOGUSŁAWA |
| IPN BU 01133/488 | BARSZCZ STANISŁAW |
| IPN BU 001198/3334 | BARSZCZ STANISŁAW |
| IPN BU 0772/771 | BARSZCZ WIESŁAWA |
| IPN BU 0988/1156 | BARSZCZ ZDZISŁAW |
| IPN BU 0993/297 | BARSZCZ ZDZISŁAW |
| IPN BU 00328/1255 | BARSZCZ ZYGMUNT |
| IPN BU 001134/2160 | BARSZCZ ZYGMUNT |
| IPN 00 1043/1302 | BARSZCZAK ZBIGNIEW |
| IPN BU 0772/2190 | BARSZCZEWSKA BOŻENA |
| IPN BU 0772/493 | BARSZCZEWSKA GABRIELA |
| IPN BU 02184/5 | BARSZCZEWSKA MARIA |
| IPN BU 0951/912 | BARSZCZEWSKA ZAJĄC-CIOŁKOWA MARIA TERESA |
| IPN BU 0604/1118 | BARSZCZEWSKI ADAM |
| IPN BU 002086/399 | BARSZCZEWSKI ADAM ANDRZEJ |
| IPN BU 00277/651 | BARSZCZEWSKI ALEKSANDER |
| IPN 00 1043/647 | BARSZCZEWSKI ALEKSANDER |
| IPN BU 001121/2855 | BARSZCZEWSKI ALEKSANDER |
| IPN BU 0218/3563 | BARSZCZEWSKI DANIEL |
| IPN BU 01133/359 | BARSZCZEWSKI HENRYK |
| IPN BU 0218/3447 | BARSZCZEWSKI JERZY |
| IPN BU 00744/423 | BARSZCZEWSKI JERZY |
| IPN BU 00200/825 | BARSZCZEWSKI JERZY |
| IPN BU 001102/343 | BARSZCZEWSKI JERZY |
| IPN BU 001121/4059 | BARSZCZEWSKI JERZY |
| IPN BU 0242/2492 | BARSZCZEWSKI KAZIMIERZ |
| IPN BU 0772/2191 | BARSZCZEWSKI KAZIMIERZ |
| IPN BU 093/20 | BARSZCZEWSKI L |
| IPN BU 001089/140 | BARSZCZEWSKI MARIAN |
| IPN BU 00966/197 | BARSZCZEWSKI MARIAN |
| IPN BU 0194/2933 | BARSZCZEWSKI STANISŁAW |
| IPN BU 0951/120 | BARSZCZEWSKI STANISŁAW |
| IPN BU 00399/107 | BARSZCZEWSKI STANISŁAW |
| IPN BU PF | 251/174 BARSZCZEWSKI WIESŁAW |
| IPN BU 0855/2907 | BARSZCZEWSKI WŁADYSŁAW |
| IPN BU 0912/846 | BARSZCZEWSKI ZYGMUNT |
| IPN BU 002086/1856 | BARSZCZYŃSKI ANDRZEJ JAN |
| IPN BU 0772/2192 | BARSZNICA KRYSTYNA |
| IPN BU 0194/3523 | BARSZNICA TADEUSZ |
| IPN BU 001134/402 | BARTA ANDRZEJ |
| IPN BU 00744/812 | BARTA ANDZREJ |
| IPN BU 698/129 | BARTA IMRE |
| IPN BU 0854/1141 | BARTAK FELIKS |
| IPN BU 0806/799 | BARTCZAK (PASEK) BARBARA |
| IPN BU 0193/5383 | BARTCZAK (STYSIAK) GRAŻYNA ZOFIA |
| IPN BU 02042/111 | BARTCZAK CECYLIA |
| IPN BU 01720/15 | BARTCZAK CZESŁAWA |
| IPN BU 0892/73 | BARTCZAK EDWARD |
| IPN BU 0912/325 | BARTCZAK FRANCISZEK |
| IPN BU 0901/732 | BARTCZAK GÓRSKA BARBARA |
| IPN BU 00448/374 | BARTCZAK GRZEGORZ |
| IPN BU 001134/5354 | BARTCZAK GRZEGORZ LONGIN |
| IPN BU 0901/1794 | BARTCZAK HANNA |
| IPN BU 00191/208 | BARTCZAK JAN ROBERT |
| IPN 00 1043/2384 | BARTCZAK JAN ROBERT |
| IPN BU 0218/3431 | BARTCZAK JÓZEF |
| IPN BU 0854/1205 | BARTCZAK JULIAN |
| IPN BU 0891/298 | BARTCZAK KAZIMIERZ |
| IPN BU 00277/844 | BARTCZAK KAZIMIERZ |
| IPN BU 001121/3034 | BARTCZAK KAZIMIERZ |
| IPN BU 002086/970 | BARTCZAK LESZEK TADEUSZ |
| IPN BU 01133/489 | BARTCZAK LUCJAN |
| IPN BU 0243/446 | BARTCZAK MACIEJ |
| IPN BU 0968/181 | BARTCZAK -MALESZA URSZULA |
| IPN BU 0891/297 | BARTCZAK MARIAN |
| IPN BU 644/782 | BARTCZAK MARIAN |
| IPN BU 0194/35 | BARTCZAK MIECZYSŁAWA |
| IPN BU 01737/110 | BARTCZAK ROMAN |
| IPN BU 0891/296 | BARTCZAK STANISŁAW |
| IPN BU 0912/260 | BARTCZAK STANISŁAW |
| IPN BU 0604/933 | BARTCZAK STANISŁAW |
| IPN BU 0193/1354 | BARTCZAK TADEUSZ |
| IPN BU 0193/229 | BARTCZAK WACŁAW |
| IPN BU 644/781 | BARTCZAK WACŁAW |
| IPN BU 01133/490 | BARTCZAK WŁADYSŁAW |
| IPN BU 001164/285 | Bartczak Władysław |
| IPN BU 00191/445 | BARTCZAK WŁODZIMIERZ |
| IPN 00 1043/3278 | BARTCZAK WŁODZIMIERZ |
| IPN BU 0193/8837 | BARTCZAK ZBIGNIEW |
| IPN BU 0942/523 | BARTCZAK ZDZISŁAW |
| IPN 00 1043/626 | BARTCZAK ZDZISŁAW JÓZEF |
| IPN BU 0911/58 | BARTCZAK ZYGMUNT |
| IPN BU 0892/46 | BARTCZAKOWSKI JÓZEF |
| IPN 00 1043/672 | BARTECKA BARBARA ZOFIA |
| IPN BU 00945/1021 | BARTECZEK JANUSZ |
| IPN BU 0193/1355 | BARTECZKO JERZY |
| IPN BU 00612/2873 | BARTECZKO KRZYSZTOF |
| IPN BU 001198/6089 | BARTECZKO KRZYSZTOF |
| IPN BU 0901/1793 | BARTEL DOROTA |
| IPN BU 00328/237 | BARTEL JAROSŁAW ANDRZEJ |
| IPN BU 001134/946 | BARTEL JAROSŁAW ANDRZEJ |
| IPN BU 00945/1170 | BARTEL MICHAŁ – CEZARY |
| IPN BU 698/130 | BARTEL STANISŁAW |
| IPN BU 00945/1629 | BARTELA JERZY |
| IPN BU 001198/2659 | BARTELA TADEUSZ |
| IPN BU 00744/189 | BARTELAK ANDRZEJ |
| IPN BU 001121/3824 | BARTELAK ANDRZEJ |
| IPN 00 1043/837 | BARTELSKI LESŁAW MARIAN |
| IPN BU 01434/151 | BARTFELD ZACHAR |
| IPN BU 00945/353 | BARTHEL ALFRED – MACIEJ |
| IPN BU 00612/789 | BARTIK MARTA |
| IPN BU 0957/564 | BARTKIEWICZ ADAM |
| IPN BU 00277/523 | BARTKIEWICZ ANDRZEJ |
| IPN BU 001121/2737 | BARTKIEWICZ ANDRZEJ |
| IPN BU 0772/2193 | BARTKIEWICZ DANUTA JULIA |
| IPN BU 0193/4761 | BARTKIEWICZ EUGENIA |
| IPN BU 0912/252 | BARTKIEWICZ FRANCISZEK |
| IPN BU 0242/1280 | BARTKIEWICZ GRZEGORZ |
| IPN BU 0855/1869 | BARTKIEWICZ HALINA |
| IPN BU 0901/2367 | BARTKIEWICZ IZABELA |
| IPN BU 0958/86 | BARTKIEWICZ JAN |
| IPN BU 00283/266 | BARTKIEWICZ JAN |
| IPN BU 00399/230 | BARTKIEWICZ JANINA |
| IPN BU 001134/4425 | BARTKIEWICZ JANINA |
| IPN BU 00751/293 | BARTKIEWICZ JERZY |
| IPN BU 001102/2294 | BARTKIEWICZ JERZY |
| IPN BU 698/131 | BARTKIEWICZ KAZIMIERZ |
| IPN BU 636/1824 | BARTKIEWICZ MARIA |
| IPN BU 698/350 | BARTKIEWICZ MICHAŁ |
| IPN BU 0958/85 | BARTKIEWICZ MIECZYSŁAW |
| IPN BU 0901/103 | BARTKIEWICZ NIEMIRA ANNA |
| IPN BU 093/29 | BARTKIEWICZ SABINA |
| IPN BU 00612/2679 | BARTKIEWICZ STANISŁAW |
| IPN BU 001198/2242 | BARTKIEWICZ STANISŁAW |
| IPN BU 001198/5943 | BARTKIEWICZ STANISŁAW |
| IPN BU 698/132 | BARTKIEWICZ WACŁAW |
| IPN BU 0988/781 | BARTKIEWICZ WŁADYSŁAW |
| IPN BU 00168/276 | BARTKIEWICZ ZDZISŁAW |
| IPN BU 002081/203 | BARTKIEWICZ ZDZISŁAW |
| IPN BU 00945/1782 | BARTKIEWICZ ZDZISŁAW |
| IPN BU 002085/245 | BARTKIEWICZ ZDZISŁAW |
| IPN BU 0912/261 | BARTKIEWICZ ZYGMUNT |
| IPN BU 0193/7731 | BARTKOW EUGENIUSZ JÓZEF |
| IPN BU 644/783 | BARTKOWIAK BOLESŁAW |
| IPN BU 0193/8412 | BARTKOWIAK CZESŁAW |
| IPN BU 00283/1055 | BARTKOWIAK EDMUND |
| IPN BU 00688/81 | BARTKOWIAK HENRYK |
| IPN BU 0314/4 | BARTKOWIAK HENRYK |
| IPN BU 644/784 | BARTKOWIAK HENRYK |
| IPN BU 0777/7 | BARTKOWIAK HENYK |
| IPN BU 001121/497 | BARTKOWIAK JACEK |
| IPN BU 0604/178 | BARTKOWIAK JAN |
| IPN BU 636/1889 | BARTKOWIAK JAN |
| IPN BU 0218/3489 | BARTKOWIAK MARIA |
| IPN BU 644/785 | BARTKOWIAK MARIAN |
| IPN BU 0218/1059 | BARTKOWIAK MARTA |
| IPN BU 0772/2194 | BARTKOWIAK MARTA |
| IPN BU 002086/1373 | BARTKOWIAK RYSZARD ANTONI |
| IPN BU 0193/5379 | BARTKOWIAK STEFAN |
| IPN BU 00744/1070 | BARTKOWIAK TOMASZ |
| IPN BU 001134/1477 | BARTKOWIAK TOMASZ |
| IPN BU 0591/12 | BARTKOWIAK WALDEMAR |
| IPN BU 0902/27 | BARTKOWIAK WITOLD |
| IPN BU 00328/102 | BARTKOWIAK ZBIGNIEW |
| IPN BU 001134/788 | BARTKOWIAK ZBIGNIEW |
| IPN BU 0854/1086 | BARTKOWIAK ZYGMUNT |
| IPN BU 0604/1002 | BARTKOWICZ JANUSZ |
| IPN BU 710/436 | BARTKOWICZ KAZIMIERZ |
| IPN BU 0806/690 | BARTKOWSKA ELŻBIETA |
| IPN BU 00334/389 | BARTKOWSKA EWA |
| IPN BU 001134/3260 | BARTKOWSKA EWA |
| IPN BU 0772/2195 | BARTKOWSKA FELIKSA |
| IPN BU 01000/1813 | BARTKOWSKA HANNA |
| IPN BU 0912/180 | BARTKOWSKA MARIA |
| IPN BU 094/1 | BARTKOWSKI ANDRZEJ |
| IPN BU 0892/47 | BARTKOWSKI JERZY |
| IPN BU 0912/181 | BARTKOWSKI JÓZEF |
| IPN BU 0957/27 | BARTKOWSKI MARIAN |
| IPN BU 01312/3 | BARTKOWSKI MIROSŁAW |
| IPN BU 00170/673 | BARTKOWSKI TADEUSZ |
| IPN BU 001198/2460 | BARTKOWSKI TADEUSZ |
| IPN 00 1043/1313 | BARTKOWSKI TADEUSZ |
| IPN BU 001089/213 | BARTKOWSKI ZBIGNIEW |
| IPN BU 002086/1165 | BARTLET JAN ANDRZEJ |
| IPN BU 0193/1356 | BARTLEWICZ KAROL |
| IPN BU 0912/189 | BARTLEWSKI ANTONI |
| IPN BU 00612/699 | BARTLICKI ZYGMUNT |
| IPN BU 0772/2196 | BARTŁOMIEJCZAK ALEKSANDRA |
| IPN BU 00277/697 | BARTŁOMIEJCZYK CZESŁAW |
| IPN BU 001121/2899 | BARTŁOMIEJCZYK CZESŁAW |
| IPN BU 698/133 | BARTŁOMIEJCZYK FRANCISZEK |
| IPN BU 01000/202 | BARTŁOMIEJCZYK IGNACY |
| IPN BU 0902/34 | BARTŁOMIEJCZYK KAZIMIERZ |
| IPN 00 1043/2100 | BARTŁOMIEJCZYK KAZIMIERZ |
| IPN 00 1043/3419 | BARTŁOMIEJCZYK TADEUSZ ANDRZEJ |
| IPN BU 698/134 | BARTŁOMOWICZ FRANCISZEK |
| IPN BU 001121/586 | BARTMAN EDWARD |
| IPN BU 698/135 | BARTMAN GUSTAW |
| IPN BU 0242/2874 | BARTMAN JADWIGA |
| IPN BU 698/136 | BARTNIAK BOLESŁAW |
| IPN BU 0194/678 | BARTNIAK JAN |
| IPN BU 0218/2762 | BARTNIAK MAREK |
| IPN BU 00744/247 | BARTNIAK MAREK |
| IPN BU 001121/3882 | BARTNIAK MAREK |
| IPN BU 01079/196 | BARTNIAK MARIAN |
| IPN BU 0993/1581 | BARTNICKA MICHALINA |
| IPN BU 0855/2565 | BARTNICKA (CZARNECKA) ZDZISŁAWA |
| IPN BU 649/93 | BARTNICKA BARBARA |
| IPN BU 01267/1 | BARTNICKA BARBARA |
| IPN BU 683/1713 | BARTNICKA GERTRUDA |
| IPN BU PF | 1021/101 BARTNICKA JÓZEF |
| IPN BU 0772/772 | BARTNICKA JÓZEFA |
| IPN BU 0287/308 | BARTNICKA KAZIMIERA |
| IPN BU 01133/491 | BARTNICKA KRYSTYNA |
| IPN BU 0242/1377 | BARTNICKA LIDIA MAŁGORZATA |
| IPN BU 0855/3317 | BARTNICKA STANISŁAWA |
| IPN BU 0287/104 | BARTNICKA WANDA |
| IPN BU 00277/932 | BARTNICKI ANDRZEJ |
| IPN BU 001121/3118 | BARTNICKI ANDRZEJ |
| IPN BU PF | 1021/102 BARTNICKI EDWARD |
| IPN BU 0951/450 | BARTNICKI EDWARD |
| IPN BU 0902/33 | BARTNICKI EUGENIUSZ |
| IPN BU 01133/678 | BARTNICKI FELIKS |
| IPN BU 00690/3 | BARTNICKI HENRYK |
| IPN BU 00690/3 | BARTNICKI HENRYK |
| IPN BU 698/137 | BARTNICKI HENRYK |
| IPN BU 0951/746 | BARTNICKI HIERONIM |
| IPN BU 0988/918 | BARTNICKI JAN |
| IPN BU 0193/231 | BARTNICKI JÓZEF |
| IPN BU 644/22 | BARTNICKI JÓZEF |
| IPN BU 01133/492 | BARTNICKI JULIAN |
| IPN BU 01133/493 | BARTNICKI KAZIMIERZ |
| IPN BU 649/92 | BARTNICKI KRZYSZTOF |
| IPN BU 0287/35 | BARTNICKI KRZYSZTOF |
| IPN BU 00751/89 | BARTNICKI MAREK |
| IPN BU 001102/1584 | BARTNICKI MAREK |
| IPN 00 1043/3032 | BARTNICKI MARIAN |
| IPN BU 0604/676 | BARTNICKI RYSZARD |
| IPN BU 0951/524 | BARTNICKI STANISŁAW |
| IPN BU 01250/70 | BARTNICKI STANISŁAW |
| IPN BU 0218/2587 | BARTNICKI TADEUSZ |
| IPN BU 090/51 | BARTNICKI WACŁAW |
| IPN BU 776/133 | BARTNICKI WACŁAW |
| IPN 00 1052/1301 | BARTNICKI WITOLD MIECZYSŁAW |
| IPN BU 02063/47 | BARTNICKI WŁODZIMIERZ |
| IPN BU 0902/28 | BARTNICKI ZBIGNIEW |
| IPN BU 00945/639 | BARTNICZAK TADEUSZ |
| IPN BU 644/786 | BARTNICZUK EUGENIUSZ |
| IPN BU 00744/720 | BARTNIK ANDRZEJ |
| IPN BU 00448/425 | BARTNIK ANDRZEJ |
| IPN BU 001134/53 | BARTNIK ANDRZEJ |
| IPN BU 001134/5405 | BARTNIK ANDRZEJ |
| IPN BU 00234 | p.244 BARTNIK ANTONI |
| IPN BU 01256/12 | BARTNIK BENEDYKT |
| IPN BU 0218/1252 | BARTNIK BŁAŻEJ |
| IPN BU 00334/574 | BARTNIK DOROTA HANNA |
| IPN BU 001134/3464 | BARTNIK DOROTA HANNA |
| IPN BU 0891/1866 | BARTNIK FRANCISZEK |
| IPN BU 0287/309 | BARTNIK HALINA |
| IPN BU 0806/1694 | BARTNIK HENRYKA |
| IPN BU 0951/862 | BARTNIK JANINA |
| IPN BU 01311/1 | BARTNIK JERZY |
| IPN BU 0772/2197 | BARTNIK JÓZEF |
| IPN BU 001198/2838 | BARTNIK JÓZEF |
| IPN BU 01000/267 | BARTNIK KRYSTYNA |
| IPN BU 00744/1235 | BARTNIK KRZYSZTOF |
| IPN BU 001134/3497 | BARTNIK KRZYSZTOF |
| IPN BU 0951/1249 | BARTNIK MAGDALENA |
| IPN BU 0891/114 | BARTNIK PIOTR |
| IPN BU 001198/1621 | BARTNIK RYSZARD |
| IPN BU 0993/1558 | BARTNIK STANISŁAW |
| IPN BU 698/138 | BARTNIK STANISŁAW |
| IPN BU 683/224 | BARTNIK STANISŁAWA |
| IPN BU 00688/84 | BARTNIK SZYMON |
| IPN BU 0591/13 | BARTNIK SZYMON |
| IPN BU 00230 | P 48 BARTNIK WERONIKA |
| IPN BU 0193/232 | BARTNIK WŁADYSŁAW |
| IPN BU 0957/29 | BARTNIK WŁODZIMIERZ |
| IPN BU 00283/498 | BARTNIK ZBIGNIEW |
| IPN BU 001134/4269 | BARTNIK ZBIGNIEW |
| IPN BU 00200/1154 | BARTNIK ZDZISŁAW STANISŁAW |
| IPN BU 001102/749 | BARTNIK ZDZISŁAW STANISŁAW |
| IPN BU 001089/23 | BARTNIKOWSKA HALINA |
| IPN BU 00334/32 | BARTNIKOWSKA TERESA |
| IPN BU 001134/2666 | BARTNIKOWSKA TERESA |
| IPN BU 0958/84 | BARTNIKOWSKI JAN |
| IPN BU 645/32 | BARTNIKOWSKI JAN |
| IPN BU 980/4 | BARTNIKOWSKI STANISŁAW |
| IPN BU 0912/847 | BARTNIKOWSKI STEFAN |
| IPN BU 001121/285 | BARTNIKOWSKI STEFAN |
| IPN BU 0958/83 | BARTNIKOWSKI WŁADYSŁAW |
| IPN BU 00611/1197 | BARTNIR RYSZARD |
| IPN BU 00612/2880 | BARTOCHA JANUSZ |
| IPN BU 001198/6096 | BARTOCHA JANUSZ |
| IPN BU 00612/4461 | BARTOCHA JÓZEF |
| IPN BU 001198/7146 | BARTOCHA JÓZEF |
| IPN BU 0193/1357 | BARTOCHA RUDOLF |
| IPN BU 0912/176 | BARTOCHOWSKA STANISŁAWA |
| IPN BU 0193/1358 | BARTOCHOWSKI BRONISŁAW |
| IPN BU 0591/14 | BARTODZIEJ JERZY |
| IPN BU 0218/1991 | BARTOIAK JAN |
| IPN BU 00456/11 | BARTOL PAWEŁ |
| IPN BU 00257/126 | BARTOLD AGNIESZKA |
| IPN BU 00257/126 | BARTOLD AGNIESZKA |
| IPN BU 001102/1193 | BARTOLD AGNIESZKA |
| IPN BU 00448/349 | BARTOLD ANDRZEJ |
| IPN BU 001134/5329 | BARTOLD ANDRZEJ |
| IPN BU 0854/801 | BARTOLD FILOMEN |
| IPN BU 01256/13 | BARTOLD LUCYNA |
| IPN BU 0604/830 | BARTOLD SZCZEPAN |
| IPN BU 0911/631 | BARTOLD WACŁAW |
| IPN BU 685/243 | Bartołd Czesława |
| IPN BU 0958/650 | BARTOŁD STEFAN |
| IPN BU 001164/258 | Bartołd-Rogulska Teresa Helena |
| IPN BU 01013/299 | BARTOŁOWICZ ZYGMUNT |
| IPN BU 01000/1172 | BARTOŃ STEFAN |
| IPN BU 00283/1646 | BARTOR TADEUSZ |
| IPN BU 001198/2587 | BARTORSKI STANISŁAW |
| IPN BU 001102/681 | BARTOS JAN FRANCISZEK |
| IPN BU 0194/1426 | BARTOS JÓZEF |
| IPN BU 548/47 | BARTOS JÓZEF |
| IPN BU 644/787 | BARTOS JÓZEF |
| IPN BU 0193/497 | BARTOS MAGDALENA |
| IPN BU 00249/1543 | BARTOS MAŁGORZATA |
| IPN BU 001121/2144 | BARTOS MAŁGORZATA |
| IPN BU 00415/253 | BARTOS MICHAŁ |
| IPN BU 0912/53 | BARTOS STANISŁAW |
| IPN BU 748/174 | BARTOS STANISŁAWA |
| IPN BU 644/788 | BARTOS STEFAN |
| IPN BU 0193/4811 | BARTOSEK GRAŻYNA |
| IPN BU 0218/1715 | BARTOSEK HENRYK |
| IPN BU 0218/2319 | BARTOSIAK BARBARA |
| IPN BU 698/140 | BARTOSIAK KAZIMIERZ |
| IPN BU 00751/209 | BARTOSIAK ADAM |
| IPN BU 001102/1819 | BARTOSIAK ADAM |
| IPN BU 645/1447 | BARTOSIAK ALINA |
| IPN BU 0951/1842 | BARTOSIAK ANDRZEJ |
| IPN BU 002081/5 | BARTOSIAK ANDRZEJ |
| IPN BU 00334/241 | BARTOSIAK ANDRZEJ |
| IPN BU 002085/13 | BARTOSIAK ANDRZEJ |
| IPN 00 1043/719 | BARTOSIAK ANDRZEJ MARIAN |
| IPN BU 001134/3034 | Bartosiak Andrzej Marian |
| IPN BU 00170/585 | BARTOSIAK ANDRZEJ WOJCIECH |
| IPN 00 1043/262 | BARTOSIAK ANDRZEJ WOJCIECH |
| IPN BU 01133/14 | BARTOSIAK BOLESŁAW |
| IPN BU 00966/744 | BARTOSIAK EWA |
| IPN BU 0901/2298 | BARTOSIAK GRAŻYNA |
| IPN BU 0891/175 | BARTOSIAK HENRYK |
| IPN BU 0911/59 | BARTOSIAK HENRYK |
| IPN BU 698/139 | BARTOSIAK HENRYK |
| IPN BU 645/126 | BARTOSIAK JANINA |
| IPN BU 748/534 | BARTOSIAK JANINA |
| IPN BU 01079/22 | BARTOSIAK JULIA |
| IPN BU 52/64 | BARTOSIAK KRYSTYNA |
| IPN BU 01133/494 | BARTOSIAK MARIAN |
| IPN BU 01000/1171 | BARTOSIAK STANISŁAW |
| IPN BU 001198/2753 | BARTOSIAK STANISŁAW |
| IPN BU 0864/10 | BARTOSIAK TADEUSZ |
| IPN BU 00283/377 | BARTOSIAK TADEUSZ |
| IPN BU 00744/1323 | BARTOSIAK TADEUSZ |
| IPN BU 00750/63 | BARTOSIAK TADEUSZ |
| IPN BU 001134/913 | BARTOSIAK TADEUSZ |
| IPN BU 710/336 | BARTOSIAK WIESŁAWA |
| IPN BU 0242/373 | BARTOSIAK ZBIGNIEW |
| IPN 00 1052/1752 | BARTOSIAK ZBIGNIEW |
| IPN BU 698/141 | BARTOSIAK ZOFIA |
| IPN BU 0193/1359 | BARTOSIEWICZ (KACZOROWSKA) HALINA |
| IPN BU 00744/27 | BARTOSIEWICZ ANDRZEJ |
| IPN BU 002081/186 | BARTOSIEWICZ ANDRZEJ |
| IPN BU 002085/209 | BARTOSIEWICZ ANDRZEJ |
| IPN BU 001121/3661 | BARTOSIEWICZ ANDRZEJ |
| IPN BU 0958/1 | BARTOSIEWICZ BOLESŁAW |
| IPN BU 644/790 | BARTOSIEWICZ EDWARD |
| IPN BU 0854/843 | BARTOSIEWICZ HENRYK |
| IPN BU 685/244 | Bartosiewicz Irena |
| IPN BU 0901/587 | BARTOSIEWICZ JADWIGA |
| IPN BU 698/142 | BARTOSIEWICZ JAN |
| IPN BU 0772/2198 | BARTOSIEWICZ JANINA |
| IPN BU PF | 125/155 BARTOSIEWICZ JANUSZ |
| IPN BU 0833/88 | BARTOSIEWICZ JERZY |
| IPN BU 01000/1752 | BARTOSIEWICZ JERZY |
| IPN BU 00744/166 | BARTOSIEWICZ JERZY |
| IPN BU 00328/575 | BARTOSIEWICZ JERZY |
| IPN BU 001121/3800 | BARTOSIEWICZ JERZY |
| IPN BU 01000/1814 | BARTOSIEWICZ KRYSTYNA |
| IPN BU 01000/1065 | BARTOSIEWICZ LESZEK |
| IPN BU 0218/2908 | BARTOSIEWICZ MAREK |
| IPN BU 980/187 | BARTOSIEWICZ MARIA |
| IPN BU 01133/495 | BARTOSIEWICZ MIECZYSŁAW |
| IPN BU 980/184 | BARTOSIEWICZ RYSZARD |
| IPN BU PF | 2/48 BARTOSIEWICZ RYSZARD |
| IPN BU 00328/1432 | BARTOSIEWICZ SŁAWOMIR |
| IPN BU 001134/2374 | BARTOSIEWICZ SŁAWOMIR |
| IPN BU 0901/452 | BARTOSIEWICZ STANISŁAW |
| IPN BU 00611/862 | BARTOSIEWICZ STANISŁAW |
| IPN BU 001198/1307 | BARTOSIEWICZ STANISŁAW |
| IPN BU 0194/2506 | BARTOSIEWICZ TADEUSZ |
| IPN BU 0193/233 | BARTOSIEWICZ WŁADYSŁAW |
| IPN BU 52/103 | BARTOSIEWICZ WOJCIECH |
| IPN BU 01133/496 | BARTOSIEWICZ ZDZISŁAW |
| IPN BU 0806/2606 | BARTOSIEWICZ ZOFIA |
| IPN BU 0604/1268 | BARTOSIK (WACŁAWIK) WANDA |
| IPN BU 0193/6400 | BARTOSIK JAN |
| IPN BU 0194/3556 | BARTOSIK JAN |
| IPN BU 644/789 | BARTOSIK JAN |
| IPN BU 0912/1488 | BARTOSIK JÓZEF |
| IPN BU 01737/112 | BARTOSIK JÓZEF |
| IPN BU 001134/3640 | BARTOSIK JÓZEF |
| IPN 00 1043/1470 | BARTOSIK KAROL |
| IPN BU 002086/1939 | BARTOSIK KAZIMIERZ |
| IPN 00 1043/1510 | BARTOSIK MAGDALENA |
| IPN BU 0951/1348 | BARTOSIK MAŁGORZATA |
| IPN BU 01000/1873 | BARTOSIK MARIA |
| IPN BU 01753/77 | BARTOSIK MARIAN |
| IPN BU 00611/1704 | BARTOSIK MIECZYSŁAW |
| IPN BU 001198/3057 | BARTOSIK MIECZYSŁAW |
| IPN BU 00612/3472 | BARTOSIK MIROSŁAW |
| IPN BU 001198/6474 | BARTOSIK MIROSŁAW |
| IPN BU 00744/63 | BARTOSIK ROBERT |
| IPN BU 001121/3697 | BARTOSIK ROBERT |
| IPN BU 0967/131 | BARTOSIK RYSZARD |
| IPN BU 0242/2397 | BARTOSIK SŁAWOMIR |
| IPN BU 0194/3373 | BARTOSIK STANISŁAW |
| IPN BU 0772/773 | BARTOSIK STANISŁAW |
| IPN BU 0833/89 | BARTOSIK STANISŁAW |
| IPN BU 00945/1626 | BARTOSIK STANISŁAW |
| IPN BU 001198/3905 | BARTOSIK STANISŁAW |
| IPN 00 1043/3984 | BARTOSIK STANISŁAW |
| IPN BU 0193/6087 | BARTOSIK SZCZEPAN |
| IPN BU 52/74 | BARTOSIK TADEUSZ |
| IPN BU 001134/3168 | BARTOSIK TOMASZ |
| IPN BU 0193/5033 | BARTOSIK WACŁAW |
| IPN BU 698/143 | BARTOSIK WALENTY |
| IPN BU 0772/2199 | BARTOSIK WIKTORIA |
| IPN BU 698/144 | BARTOSIK WŁADYSŁAW |
| IPN BU 0967/4 | BARTOSIK ZOFIA |
| IPN BU 0967/4 | BARTOSIK ZOFIA |
| IPN BU 01137/83 | BARTOSIK ZYGMUNT |
| IPN BU 698/145 | BARTOSIK ZYGMUNT |
| IPN BU 0243/374 | BARTOSIŃSKA KRYSTYNA |
| IPN BU 0290/21 | BARTOSIŃSKA MARIA |
| IPN BU 0242/627 | BARTOSIŃSKA WIESŁAWA |
| IPN BU 01133/498 | BARTOSIŃSKI STANISŁAW |
| IPN BU 00612/3316 | BARTOSIŃSKI JERZY |
| IPN BU 001198/6377 | BARTOSIŃSKI JERZY |
| IPN BU 01133/497 | BARTOSIŃSKI MARCELI |
| IPN BU 698/146 | BARTOSIŃSKI STANISŁAW |
| IPN BU 01133/499 | BARTOSIŃSKI TADEUSZ |
| IPN BU 0591/15 | BARTOSIŃSKI TADEUSZ |
| IPN BU 0290/22 | BARTOSZ BEATA |
| IPN BU 00612/1811 | BARTOSZ HENRYK |
| IPN BU 00415/345 | BARTOSZ LUCYNA |
| IPN BU 360/144 | BARTOSZ MARIA |
| IPN BU 0833/90 | BARTOSZ STANISŁAW |
| IPN BU 00611/1866 | BARTOSZ STANISŁAW |
| IPN BU 001198/3359 | BARTOSZ STANISŁAW |
| IPN BU 0772/2200 | BARTOSZ TADEUSZ |
| IPN BU 00230 | P. 169 BARTOSZ WIESŁAW |
| IPN BU 00612/4816 | BARTOSZ ZDZISŁAW |
| IPN BU 698/163 | BARTOSZ-BECHOWSKI STANISŁAW |
| IPN BU 644/23 | BARTOSZCZYK JÓZEF |
| IPN BU 0193/236 | BARTOSZCZYK WIKTOR |
| IPN BU 0193/1360 | BARTOSZEK ALEKSANDER |
| IPN BU 00283/1645 | BARTOSZEK BOGDAN |
| IPN BU 0193/6625 | BARTOSZEK DANUTA |
| IPN BU 698/351 | BARTOSZEK HENRYK |
| IPN BU 685/6 | BARTOSZEK IRENA |
| IPN BU 698/147 | BARTOSZEK JÓZEF |
| IPN BU 698/352 | BARTOSZEK KAROLINA |
| IPN BU 0866/1381 | BARTOSZEK STANISŁAW |
| IPN BU 001134/2943 | Bartoszek Tadeusz |
| IPN BU 0957/518 | BARTOSZEWICZ STANISŁAW |
| IPN BU 0967/196 | BARTOSZEWICZ ANDRZEJ |
| IPN BU 00612/794 | BARTOSZEWICZ ANDRZEJ |
| IPN BU 0901/2209 | BARTOSZEWICZ ELŻBIETA |
| IPN BU 0193/6944 | BARTOSZEWICZ FELIKS |
| IPN BU 00945/830 | BARTOSZEWICZ JANUSZ |
| IPN BU 01434/125 | BARTOSZEWICZ JANUSZ |
| IPN BU 093/33 | BARTOSZEWICZ S |
| IPN BU 698/353 | BARTOSZEWICZ ZYGMUNT |
| IPN BU 0193/1361 | BARTOSZEWSKA (GRZĄDKA) HENRYKA |
| IPN BU 0242/354 | BARTOSZEWSKA (ROGALA) MAŁGORZATA |
| IPN BU 0993/1560 | BARTOSZEWSKA (SZCZEGLENKO) WANDA |
| IPN BU 698/148 | BARTOSZEWSKA BARBARA |
| IPN BU 0242/1984 | BARTOSZEWSKA ELŻBIETA WACŁAWA |
| IPN 00 1043/439 | BARTOSZEWSKA JUTTA HILDEGUNDA ELŻBIETA |
| IPN BU 0942/292 | BARTOSZEWSKA KRYSTYNA |
| IPN BU 0772/774 | BARTOSZEWSKA MARIA (TOM REGINA) |
| IPN 00 1043/6 | BARTOSZEWSKA-MARCZEWSKA ANNA MARIA TERESA |
| IPN BU 001164/337 | Bartoszewski Andrzej |
| IPN BU 0912/177 | BARTOSZEWSKI BOLESŁAW |
| IPN BU 0193/1364 | BARTOSZEWSKI CZESŁAW |
| IPN BU 0242/1513 | BARTOSZEWSKI JERZY |
| IPN BU 00945/364 | BARTOSZEWSKI RAJMUND |
| IPN BU 00744/667 | BARTOSZEWSKI STANISŁAW |
| IPN BU 001121/4509 | BARTOSZEWSKI STANISŁAW |
| IPN 00 1043/2532 | BARTOSZEWSKI STEFAN |
| IPN BU 0604/391 | BARTOSZEWSKI TADEUSZ |
| IPN BU 01000/1870 | BARTOSZEWSKI TADEUSZ |
| IPN BU 0604/73 | BARTOSZEWSKI TEOFIL |
| IPN BU 0892/48 | BARTOSZEWSKI ZBIGNIEW |
| IPN 00 1043/3900 | BARTOSZEWSKI ZDZISŁAW |
| IPN BU 0957/432 | BARTOSZEWSKI ZYGMUNT |
| IPN BU 00744/246 | BARTOSZKIEWICZ IGOR |
| IPN BU 001121/3881 | BARTOSZKIEWICZ IGOR |
| IPN BU 0806/2630 | BARTOSZUK EUGENIUSZ |
| IPN BU 0806/2138 | BARTOSZUK IRENA |
| IPN BU 0951/1811 | BARTOSZUK ZOFIA |
| IPN 00 1043/3102 | BARTOSZUK ZOFIA KRYSTYNA |
| IPN BU 0855/2836 | BARTOSZYŃSKI ANTONI |
| IPN BU 0290/58 | BARTOŚ BARBARA |
| IPN BU 0866/28 | BARTOŚ CZESŁAW |
| IPN BU 002086/1932 | BARTOZI RUFIN |
| IPN BU 0942/190 | BARTUNEK EMIL |
| IPN BU 0968/172 | BARTUNEK HANNA |
| IPN BU 776/134 | BARTUSIAK ROMUALDA |
| IPN BU 01000/1874 | BARTUSIAK STANISŁAW |
| IPN BU 00328/795 | BARTUSZEK EUZEBIUSZ |
| IPN BU 001134/1640 | BARTUSZEK EUZEBIUSZ |
| IPN BU 0193/8720 | BARTUSZEK HENRYK |
| IPN BU 00257/294 | BARTUSZEK IWONA MAGDALENA |
| IPN BU 001102/1361 | BARTUSZEK IWONA MAGDALENA |
| IPN BU 698/149 | BARTUSZEK JANINA |
| IPN BU 00945/469 | BARTUSZEK WŁADYSŁAW |
| IPN BU 002082/465 | BARTUSZEK-WÓJCIK GRAŻYNA LIDIA |
| IPN BU 002086/1316 | BARTUSZEK-WÓJCIK GRAŻYNA LIDIA |
| IPN BU 710/109 | BARTUŚ PIOTR |
| IPN BU 0855/2890 | BARTUŚ ZBIGNIEW |
| IPN BU 1161/157 | BARTUZI TADEUSZ |
| IPN BU 0772/775 | BARTUZI ZOFIA |
| IPN BU 001102/2133 | BARTYS JAN |
| IPN BU 0772/776 | BARTYŚ STANISŁAWA |
| IPN BU 698/150 | BARTYZEL MARIA |
| IPN BU 698/151 | BARTYZEL TADEUSZ |
| IPN 00 1052/1863 | BARTZ CZESŁAW |
| IPN 00 1052/1167 | BARTZ JAN KAZIMIERZ |
| IPN BU 0872/109 | BARTZ TADEUSZ |
| IPN BU 01175/1135 | BARTZ TADEUSZ |
| IPN BU 01000/1869 | BARUCIAK STANISŁAW |
| IPN BU 00283/2318 | BARUL HENRYK |
| IPN BU 001134/3627 | BARWICKI JAN |
| IPN BU 00170/511 | BARWICKI MIECZYSŁAW |
| IPN BU 684/2 | BARWICKI PIOTR |
| IPN BU 001198/3655 | BARWICKI RYSZARD |
| IPN BU 0901/1428 | BARWIŃSKI RYSZARD JANUSZ |
| IPN BU 0866/29 | BARWIŃSKI TADEUSZ |
| IPN BU 00200/1338 | BARWIŃSKI TOMASZ |
| IPN BU 001102/939 | BARWIŃSKI TOMASZ |
| IPN BU 00249/780 | BARWIOŁEK JERZY |
| IPN BU 001121/1422 | BARWIOŁEK JERZY |
| IPN BU 00945/565 | BARYCKA – BULWA BARBARA |
| IPN BU 0243/447 | BARYCKA (GODLEWSKA) WALENTYNA |
| IPN BU 00612/4231 | BARYCKI ADAM |
| IPN BU 0193/2824 | BARYCKI ALBIN |
| IPN BU 00945/1284 | BARYCKI ALBIN |
| IPN BU 001198/1945 | BARYCKI BOLESŁAW |
| IPN BU 00244/174 | BARYCKI BRONISŁAW |
| IPN BU 00612/2802 | BARYCKI MARIUSZ |
| IPN BU 00399/558 | BARYGA WALDEMAR |
| IPN BU 001134/4899 | BARYGA WALDEMAR |
| IPN BU 00234 | p.272 BARYGA ZOFIA |
| IPN BU 00244/170 | BARYLAK HENRYK |
| IPN BU 0951/1160 | BARYLEWSKA IRENA (SIEKLUCKA) |
| IPN BU 00612/2041 | BARYLSKI ZBIGNIEW |
| IPN BU 001198/5052 | BARYLSKI ZBIGNIEW |
| IPN BU 00612/907 | BARYŁA BOLESŁAW |
| IPN BU 0967/5 | BARYŁA EDWARD |
| IPN BU 0967/5 | BARYŁA EDWARD |
| IPN BU 01000/1865 | BARYŁA EDWARD |
| IPN BU 00244/58 | BARYŁA FRANCISZEK |
| IPN BU 0772/777 | BARYŁA HALINA |
| IPN BU 636/1802 | BARYŁA JÓZEF |
| IPN BU 01312/4 | BARYŁA KAZIMIERZ |
| IPN 00 1043/2929 | BARYŁA STANISŁAW |
| IPN BU 0194/3227 | BARYŁA WŁADYSŁAW |
| IPN BU 002086/1474 | BARYŁO BRYGIDA |
| IPN BU 00945/1356 | BARYS ZBIGNIEW – JAN |
| IPN BU 01434/281 | BARYS ZBIGNIEW JAN |
| IPN BU 0218/2803 | BARYSZ TEODOR |
| IPN BU 0193/8861 | BARYŚ TADEUSZ |
| IPN BU 0772/2201 | BARYZA JANINA |
| IPN BU 01000/1027 | BARZAŁ IRENEUSZ |
| IPN BU 0958/82 | BARZAŁ TADEUSZ |
| IPN BU 002082/404 | BARZDO TADEUSZ STANISŁAW |
| IPN BU 002086/1099 | BARZDO TADEUSZ STANISŁAW |
| IPN BU 776/135 | BARZEC HENRYKA |
| IPN BU 01250/20 | BARZENC WŁODZIMIERZ |
| IPN BU 00744/77 | BARZYC WŁADYSŁAW |
| IPN BU 001121/3712 | BARZYC WŁADYSŁAW |
| IPN BU 644/24 | BARZYK JAN |
| IPN BU PF | 837/13 BASA HELENA |
| IPN BU 00612/4752 | BASA HENRYK |
| IPN BU 0855/2944 | BASA JULIAN |
| IPN BU 01133/78 | BASAJ ADAM |
| IPN BU 01133/500 | BASAJ JADWIGA |
| IPN BU 0193/7921 | BASAK ALICJA |
| IPN BU 00612/4838 | BASAK FRANCISZEK |
| IPN BU 002152/19 | BASAK TADEUSZ |
| IPN BU 0193/7997 | BASAŁEK MIECZYSŁAW |
| IPN BU 644/791 | BASAŁYK MIECZYSŁAW |
| IPN BU 0772/778 | BASARABCZUK PIOTR |
| IPN BU 0194/178 | BASECKI TADEUSZ |
| IPN BU 0242/2076 | BASEK BARBARA |
| IPN BU 001075/119 | BASEK JERZY |
| IPN BU 02042/1 | BASEK WIESŁAW |
| IPN BU 02042/793 | BASIAK ANDRZEJ |
| IPN BU 01133/501 | BASIAK JAN |
| IPN BU 00230 | P. 52 BASIAK JERZY |
| IPN BU 002082/670 | BASIAK MAREK ADAM |
| IPN BU 002086/2010 | BASIAK MAREK ADAM |
| IPN BU 644/792 | BASIAK MARIAN |
| IPN BU 00277/338 | BASIAK MARIANNA |
| IPN BU 001121/2560 | BASIAK MARIANNA |
| IPN BU 01079/204 | BASIAK RYSZARD |
| IPN BU 0833/65 | BASIAK STEFAN |
| IPN BU 01133/502 | BASIAK TADEUSZ |
| IPN BU 0591/16 | BASIAKOWSKI PIOTR |
| IPN BU 00768/419 | BASIAKOWSKI ROMAN |
| IPN BU 0193/240 | BASIAKOWSKI TADEUSZ |
| IPN BU 980/188 | BASIEWICZ ALICJA |
| IPN BU 01000/1369 | BASIEWICZ CZESŁAW |
| IPN BU 0988/8 | BASIEWICZ HENRYK |
| IPN BU 01133/503 | BASIEWICZ LEON |
| IPN BU 0891/172 | BASIEWICZ MAREK |
| IPN BU 00277/198 | BASIK JERZY |
| IPN BU 001121/2426 | BASIK JERZY LESZEK |
| IPN BU 0951/523 | BASILIDES CZAYKOWSKA IRMINA |
| IPN BU 0591/17 | BASIŃSKI ANDRZEJ |
| IPN BU 001198/1728 | BASIŃSKI BRONISŁAW |
| IPN BU 00328/528 | BASIŃSKI JERZY |
| IPN BU 001134/1313 | BASIŃSKI JERZY |
| IPN BU 0901/2442 | BASIŃSKI LESZEK |
| IPN BU 0988/9 | BASIŃSKI LUCJAN |
| IPN 00 1052/1666 | BASIŃSKI STEFAN |
| IPN BU 0218/1471 | BASIŃSKI WALDEMAR |
| IPN BU 001198/3966 | BASIŃSKI WALDEMAR |
| IPN BU 01250/21 | BASIŃSKI WŁADYSŁAW |
| IPN BU 00612/2029 | BASIŃSKI ZBIGNIEW |
| IPN BU 001198/5044 | BASIŃSKI ZBIGNIEW |
| IPN BU 698/152 | BASIŃSKI ZYGMUNT |
| IPN BU 0901/863 | BASIOR WIESŁAWA |
| IPN BU 00612/4207 | BASIÓW JAN |
| IPN BU 001198/6955 | BASIÓW JAN |
| IPN BU 001102/1990 | BASISTA KUFIETA ŁUCJA |
| IPN BU 0193/2825 | BASIUK MIECZYSŁAW |
| IPN BU 0942/144 | BASIUKIEWICZ JÓZEF |
| IPN BU 0218/622 | BASIUKIEWICZ MICZYSŁAW |
| IPN BU 0855/3017 | BASIUKIEWICZ MIROSŁAWA |
| IPN BU 698/389 | BASKA WINCENTY |
| IPN BU 00249/168 | BASŁYK JAN |
| IPN BU 001121/767 | BASŁYK JAN |
| IPN BU 644/25 | BASOW ALEKSANDER |
| IPN BU 0901/869 | BASSEJ RECTE KOWALSKA BŁAŻEJ BARBARA |
| IPN BU 00945/1530 | BAST GINTER – GüNTHER |
| IPN BU 00168/36 | BAST GUNTER |
| IPN BU 0218/2963 | BASTA MIROSŁAWA |
| IPN BU 0772/2203 | BASTA WIKTORIA |
| IPN BU 0912/178 | BASTECKI JAN |
| IPN BU 0958/78 | BASTEK JÓZEF |
| IPN BU 0242/645 | BASTEK TOMASZ |
| IPN BU 644/793 | BASTER STANISŁAW |
| IPN BU 00751/212 | BASTKOWSKI ADAM |
| IPN BU 001102/1822 | BASTKOWSKI ADAM |
| IPN BU 01133/504 | BASTKOWSKI ZDZISŁAW |
| IPN BU 00611/1051 | BASTRZYK FELIKS |
| IPN BU 0305/378 | BASZA ANDRZEJ |
| IPN BU 683/226 | BASZAK JAN |
| IPN BU 0772/2205 | BASZAK JERZY |
| IPN BU 683/228 | BASZAK JÓZEF JÓZEFA |
| IPN BU 698/1850 | BASZAK KAZIMIERZ |
| IPN BU 00744/1149 | BASZCZEWSKI JAN |
| IPN BU 001134/2248 | BASZCZEWSKI JAN |
| IPN BU 0604/1639 | BASZCZYK ANDRZEJ |
| IPN BU 0242/762 | BASZCZYK IWONA |
| IPN BU 0958/81 | BASZCZYŃSKI LEON |
| IPN BU 0194/3471 | BASZKIEWICZ JOLANTA |
| IPN BU 0194/3392 | BASZKIEWICZ JÓZEF |
| IPN BU 0193/4336 | BASZKIEWICZ KRZYSZTOF |
| IPN BU 698/153 | BASZYŃSKA HENRYKA |
| IPN BU 01000/1013 | BASZYŃSKA WANDA |
| IPN BU 0988/527 | BASZYŃSKI LEON |
| IPN BU 0194/3177 | BASZYŃSKI ROMAN |
| IPN BU 0194/3386 | BASZYŃSKI URBAN |
| IPN BU 0243/44 | BASZYŃSKI WŁODZIMIERZ |
| IPN BU 00945/434 | BAŚCIK JANUSZ – JÓZEF |
| IPN BU 01137/84 | BAŚCIK STANISŁAW |
| IPN BU 0866/30 | BAŚKIEWICZ JADWIGA |
| IPN BU 693/497 | BAŚKIEWICZ MIECZYSŁAW |
| IPN BU 0194/2038 | BATA OLGA |
| IPN BU 01000/1866 | BATAROWICZ MICHAŁ |
| IPN BU 1161/78 | BATIUK LESZEK |
| IPN BU 0772/684 | BATKO ANNA |
| IPN BU 00945/2056 | BATKO ZYGMUNT – WAWRZYNIEC |
| IPN BU 0902/29 | BATKOWSKA EUGENIA |
| IPN BU 0194/3621 | BATKOWSKA RENATA |
| IPN BU 0806/1543 | BATKOWSKA TERESA |
| IPN BU 001198/3178 | BATKOWSKI JAN |
| IPN BU 001040/99 | BATKOWSKI RYSZARD |
| IPN BU 001121/3598 | BATLEJ JÓZEF JAN |
| IPN BU 0957/30 | BATOGOWSKA KRYSTYNA |
| IPN BU 0958/80 | BATOGOWSKI MARIAN |
| IPN BU 645/123 | BATOGOWSKI TADEUSZ |
| IPN BU 0958/79 | BATOGOWSKI WACŁAW |
| IPN BU 0957/31 | BATOGOWSKI ZBIGNIEW |
| IPN BU 0242/1346 | BATOR ANDRZEJ |
| IPN BU 0951/1486 | BATOR ANDRZEJ |
| IPN BU 00275/474 | BATOR ANDRZEJ |
| IPN BU 001134/368 | BATOR ANDRZEJ |
| IPN BU 00611/1969 | BATOR EUGENIUSZ |
| IPN BU 001198/3527 | BATOR EUGENIUSZ |
| IPN BU 698/354 | BATOR GENOWEFA |
| IPN BU 0872/99 | BATOR JAN |
| IPN BU 0193/241 | BATOR JAN |
| IPN BU 0242/795 | BATOR JAN |
| IPN BU 0193/1365 | BATOR JERZY |
| IPN 00 1052/338 | BATOR KATARZYNA |
| IPN BU 001198/144 | BATOR KAZIMIERZ |
| IPN BU 00612/279 | BATOR KRYSTYNA |
| IPN BU 001198/4201 | BATOR KRYSTYNA |
| IPN BU 0942/212 | BATOR MARIA |
| IPN BU 0194/3059 | BATOR MICHAŁ |
| IPN BU 0901/2297 | BATOR STANISŁAW |
| IPN BU 00234 | p.244 BATOR STANISŁAW |
| IPN BU 645/38 | BATOR STANISŁAWA |
| IPN BU 0194/458 | BATOR WACŁAW |
| IPN BU 00612/630 | BATOR WOJCIECH |
| IPN BU 001198/4350 | BATOR WOJCIECH |
| IPN BU 0604/1667 | BATOR ZBIGNIEW |
| IPN BU 01278/2 | BATOROWICZ GUSTAW |
| IPN BU 00448/695 | BATOROWICZ JÓZEF |
| IPN BU 001134/5672 | BATOROWICZ JÓZEF |
| IPN BU 0892/75 | BATOROWICZ WACŁAW |
| IPN BU 0218/1846 | BATOROWSKA ALICJA |
| IPN 00 1052/868 | BATOROWSKA ELŻBIETA GRAŻYNA |
| IPN BU 0855/3442 | BATOROWSKA KATARZYNA |
| IPN BU 0806/2209 | BATOROWSKI WITOLD |
| IPN BU 01312/5 | BATORSKI ANDRZEJ |
| IPN BU 01256/14 | BATORSKI JANUSZ |
| IPN 00 1043/1138 | BATORSKI WIESŁAW KAZIMIERZ |
| IPN BU 0833/43 | BATORY JÓZEF |
| IPN 00 1052/1694 | BATORY ZOFIA |
| IPN BU 698/154 | BATÓG ANDRZEJ |
| IPN BU 00612/2951 | BATÓG CZESŁAW |
| IPN BU 0218/3210 | BATÓG DANUTA |
| IPN BU 01000/1867 | BATÓG JAN |
| IPN BU 0194/1682 | BATÓG MARIAN |
| IPN BU 001198/1777 | BATÓG STANISŁAW |
| IPN BU 644/794 | BATÓG TADEUSZ |
| IPN BU 00244/55 | BATRANIEC STANISŁAW |
| IPN BU 0194/148 | BATURA MICHAŁ |
| IPN BU 0193/242 | BATURIN ALEKSANDER |
| IPN BU 0772/779 | BATYCKA ALFREDA |
| IPN BU 00945/728 | BATYCKI – GRUNBERG LEON |
| IPN BU 0772/2204 | BATZDORF MARIA |
| IPN BU 0193/7421 | BAUCH BRONISŁAW (BER) |
| IPN BU 0772/50 | BAUER (GUZIAKOWSKA) WANDA |
| IPN BU 00612/1795 | BAUER KAROL |
| IPN BU 001198/4889 | BAUER KAROL |
| IPN BU 0772/53 | BAUER LECH SZCZEPAN |
| IPN BU 002086/512 | BAUER LUCYNA |
| IPN BU 001102/2045 | BAUER LUCYNA |
| IPN BU 0942/150 | BAUER MARIAN |
| IPN BU PF | 252/50 BAUER MONIKA |
| IPN BU 0193/7155 | BAUER REGINA |
| IPN BU 644/797 | BAUER ZYGMUNT |
| IPN BU 001134/5475 | BAUERMANN ANDRZEJ |
| IPN BU 0866/31 | BAUM HENRYK |
| IPN BU 00200/977 | BAUM JAN |
| IPN BU 001102/544 | BAUM JAN |
| IPN BU 644/795 | BAUM ZDZISŁAW |
| IPN BU 0993/1639 | BAUM ZŁATA |
| IPN BU 0193/9014 | BAUMAC MIECZYSŁAW (MOJŻESZ) |
| IPN BU 0833/46 | BAUMAN CZESŁAW |
| IPN BU 0912/1554 | BAUMAN HALINA |
| IPN BU 0772/2207 | BAUMAN IZAAK |
| IPN BU 644/796 | BAUMAN KORNEL |
| IPN BU 0772/2206 | BAUMAN LUDWIKA |
| IPN 00 1043/2631 | BAUMAN PROHASKA ERIKA |
| IPN BU 645/69 | BAUMAN TEOFIL |
| IPN BU 0833/719 | BAUMAN ZOFIA |
| IPN BU 0193/8207 | BAUMAN ZYGMUNT |
| IPN BU 00191/277 | BAUMAN-PROHASKA ERIKA |
| IPN BU 00945/110 | BAUMGART JÓZEF |
| IPN BU 0772/780 | BAUMGARTEN SZLAMA |
| IPN BU 0193/8775 | BAUR RYSZARD |
| IPN BU 01000/203 | BAUTA KASPER |
| IPN BU 01250/71 | BAUTZ WŁADYSŁAWA |
| IPN BU 0911/73 | BAWARSKI JAN |
| IPN BU 0912/179 | BAWARSKI STANISŁAW |
| IPN BU 0193/1367 | BAWECKA (NICKA) ZOFIA |
| IPN BU 0772/2208 | BAWECKA HELENA |
| IPN BU 0194/3099 | BAWECKI BOLESŁAW |
| IPN BU 0218/2804 | BAWEJ STANISŁAW |
| IPN BU 0988/10 | BAWIŃSKI ŁUKASZ |
| IPN BU 0988/1449 | BAWOLIK HIPOLIT |
| IPN BU 01013/289 | BAWOLIK JANINA |
| IPN BU 01000/1868 | BAWOLIK WANDA |
| IPN BU 0193/7088 | BAWOR STANISŁAW JAN |
| IPN BU PF | 251/127 BAY MICHAŁ |
| IPN BU 0218/3097 | BAYER JAN HIPOLIT |
| IPN BU 002086/547 | BAYER-ZAWADZKA-ZIMNA-JUSZKIEWICZ WANDA MICHALINA |
| IPN BU 00328/1244 | BAYSTAK ROBERT |
| IPN 00 1043/2215 | BAZ CHIDIAC NENCKA DANUTA MARIA |
| IPN BU 0772/781 | BAZACZEK EWA |
| IPN BU 683/1716 | BAZALIŃSKI TADEUSZ |
| IPN BU 00234 | p.102 BAZAN EUGENIUSZ |
| IPN BU 0305/101 | BAZAN EUGENIUSZ |
| IPN BU 0591/18 | BAZAN JAN |
| IPN BU 00688/85 | BAZAN KRZYSZTOF |
| IPN BU 0591/19 | BAZAN KRZYSZTOF |
| IPN BU 0806/1866 | BAZAN PIOTR |
| IPN BU 0194/1207 | BAZAN ROBERT |
| IPN BU 644/798 | BAZAN STANISŁAW |
| IPN BU 01000/2054 | BAZAN WŁADYSŁAW |
| IPN BU 0194/694 | BAZANIAK KRZYSZTOF |
| IPN BU 0993/1630 | BAZAŃSKA (PIĘTKA) STANISŁAWA |
| IPN BU 0604/673 | BAZAŃSKA ALEKSANDRA |
| IPN BU 0855/3325 | BAZAŃSKI BOLESŁAW |
| IPN BU 01137/85 | BAZAŃSKI FRANCISZEK |
| IPN BU 00612/3513 | BAZAŃSKI ZYGMUNT |
| IPN BU 00234 | p.241 BAZARNICKI JANUSZ |
| IPN BU 0193/9015 | BAZARNIK ADOLF |
| IPN BU 0864/11 | BAZAROW IZYDOR |
| IPN BU 0833/718 | BAZEL KSAWERY |
| IPN BU 0604/42 | BAZEL MARIAN |
| IPN BU 0772/5178 | BAZELA ANTONI |
| IPN BU 00966/1267 | BAZELCZUK WITOLD WALENTY |
| IPN BU 0194/2516 | BAZELSKI CZESŁAW |
| IPN BU 0242/2537 | BAZEWICZ EWA |
| IPN BU 0193/1368 | BAZGIER JERZY |
| IPN BU 001198/5261 | BAZGIER WIESŁAW |
| IPN BU 0193/8718 | BAZIUK BOLESŁAW |
| IPN BU 01000/1759 | BAZYCH KAZIMIERZ |
| IPN BU 00191/393 | BAZYDŁO BOGDAN |
| IPN 00 1043/3153 | BAZYDŁO BOGDAN |
| IPN BU 001121/780 | BAZYDŁO BOGDAN |
| IPN BU 0194/2256 | BAZYDŁO JAN WOJCIECH |
| IPN BU 00191/571 | BAZYDŁO JAN WOJCIECH |
| IPN 00 1043/3772 | BAZYDŁO JAN WOJCIECH |
| IPN BU 01000/1811 | BAZYL BOLESŁAW |
| IPN BU 0193/6928 | BAZYL CZESŁAW |
| IPN BU 0772/33 | BAZYL KSIĘŻYK MARIA |
| IPN BU 0290/69 | BAZYL TERESA |
| IPN BU 02042/37 | BAZYLAK HALINA |
| IPN BU 01270/3 | BAZYLAK MIROSŁAW |
| IPN BU 00323/54 | BAZYLAK STANISŁAW |
| IPN BU 0314/42 | BAZYLAK STANISŁAW |
| IPN BU 0591/20 | BAZYLAK STANISŁAW |
| IPN BU 0806/1468 | BAZYLCZUK BOŻENA |
| IPN 00 1043/3705 | BAZYLCZUK GOŁUBOSZ MARIA TERESA |
| IPN BU 0993/1578 | BAZYLEWICZ (KRAWIEC) STANISŁAWA |
| IPN 00 1043/670 | BAZYLEWICZ MARIA ZOFIA |
| IPN BU 00612/4573 | BAZYLEWICZ SŁAWOMIR |
| IPN BU 001198/7208 | BAZYLEWICZ SŁAWOMIR |
| IPN BU 0142/8 | BAZYLEWICZ TEODOR |
| IPN BU 01000/1743 | BAZYLEWSKA IRENA |
| IPN BU 00945/492 | BAZYLEWSKI – MAŁYSZCZYK WIKTOR |
| IPN BU 0193/247 | BAZYLEWSKI BORYS |
| IPN BU 0833/45 | BAZYLEWSKI STANISŁAW |
| IPN BU 001198/2064 | BAZYLKO RYSZARD |
| IPN BU 0242/1271 | BAZYLOW JERZY |
| IPN BU 0243/458 | BAZYLÓW (MATUSZAK) ŁUCJA |
| IPN BU 0243/337 | BAZYLÓW JANUSZ |
| IPN BU 0218/415 | BAZYLÓW PIOTR |
| IPN BU 0806/2208 | BAZYLUK MARIA |
| IPN BU 698/155 | BAZYLUK SERGIUSZ |
| IPN BU 693/496 | BAŻAK JAN |
| IPN BU 0194/3165 | BAŻAN ANTONI |
| IPN BU 00611/647 | BAŻANEK RYSZARD |
| IPN BU 001198/1059 | BAŻANEK RYSZARD |
| IPN BU 00334/96 | BAŻANOW STANISŁAW |
| IPN BU 001134/2774 | BAŻANOW STANISŁAW |
| IPN 00 1043/2497 | BAŻAŃSKI STANISŁAW LEON |
| IPN BU 0902/35 | BAŻENOW (BAZENOW) MIKOŁAJ |
Putin, FSB, KGB, STASI, Die Linke, GoMoPa – Did NATO Win the Cold War?
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Documentary supplement to the article “Did NATO Win the Cold War? Looking over the Wall,” by Vojtech Mastny, Foreign Affairs 78, no. 3 (May-June 1999): 176-89
National Security Archive Electronic Briefing Book No. 14
For more information contact:
202/994-7000 or nsarchiv@gwu.edu
Washington, D.C.,– This documentary supplement to the article, “Did NATO Win the Cold War? Looking over the Wall,” has been prepared on the occasion of the Washington summit marking the 50th anniversary of the North Atlantic Treaty Organization. It is intended to provide the reader with the most important sources referred to in the text of the article that are relevant to the view of NATO “from the other side.”
Some of the sources have been obtained as a result of the project on the “Parallel History of the Cold War Alliances,” conducted by the National Security Archive in cooperation with the Center for Security Studies and Conflict Research of the Swiss Federal Institute of Technology in Zurich. More information about the project can be found on the websites of the two institutions.
Other sources were made available through the National Security Archive’s partner organization, the Cold War International History Project of the Woodrow Wilson International Center for Scholars in Washington, and have been published in its Bulletin. More information about the Project can be found on its website.
The documents refer to the text of the article according to the numbers that appear on its margins. They are published in full or in part, as indicated, and are preceded by brief introductions explaining their origins. In some cases, reproductions of the original documents are included as samples.
Catherine Nielsen and John Martinez, both of the National Security Archive, assisted in the preparation of the texts for online publication.
Vojtech Mastny
THE DOCUMENTS
George F. Kennan, the architect of America’s policy of containment and a frequent critic of its execution, was U.S. ambassador to Moscow in one of the darkest years of the Cold War, 1952. On September 8, 1952, shortly before he was expelled from the Soviet Union as a persona non grata, he sent a dispatch to Washington in which he tried to assess NATO from the Soviet point of view. In retrospect, he regarded this assessment so important that he included it as the only appendix to his volume of memoirs published in 1971. While some of Kennan’s conclusions may not have withstood the test of time, his warning against being “fascinated and enmeshed by the relentless and deceptive logic of the military equation” remained topical throughout the Cold War.
[George F. Kennan, Memoirs: 1950-1963 (Boston: Little, Brown, 1971, pp. 327-51]
Document 2.
A confidential information bulletin provided by Soviet intelligence to top eastern European party leaders has been preserved in the files of the Czechoslovak communist party central committee in Prague. As shown on the sample, the reports sometimes quoted verbatim statements made by high Western officials at top secret meetings.
The bulletin included the following passage referring to the alleged American disclosure at a secret NATO meeting in December 1950:
“In connection with their failures in Korea the Americans apparently intend to provoke in the summer of 1951 a military conflict in eastern Europe with the goal of seizing the eastern zone of Austria. To realize this goal, the Americans intend to utilize Yugoslavia.”
[“O deiatelnosti organov Severo-atlanticheskogo Soiuza v sviazi s sozdaniem atlanticheskoi armii i remilitarizatsiei zapadnoi Germanii,” February 1951, 92/1093, 100/24, Central State Archives, Prague; translated by Svetlana Savranskaya, National Security Archive]
Document 3.
Karel Kaplan, an official researcher who had enjoyed unlimited access to the Czechoslovak communist party archives prior to his defection to the West, learned about a meeting with Stalin on January 9-12, 1951, from one of its participants, the country’s minister of defense Alexej Cepicka. In 1978, Kaplan created a stir by publishing his findings, suggesting that Stalin had told his eastern European followers to prepare for an offensive war against Western Europe:
“After a report by representatives of the bloc about the condition of their respective armies, Stalin took the floor to elaborate on the idea of the military occupation of the whole of Wurope, insisting on the necessity of preparing it very well.
Since the Korean War had demonstrated the military weakness of the United States, despite its use of highly advanced technology, it seemed appropriate to Stalin to take advantage of this in Europe. He developed arguments in support of the following thesis: `No European army is in a position to seriously oppose the Soviet army and it can even be anticipated that there will be no resistance at all. The current military power of the United States is not very great. For the time being, the Soviet camp therefore enjoys a distinct superiority. But this is merely temporary, for some three or four years. Afterward, the United States will have at its disposal means for transporting reinforcements to Europe and will also be able to take advantage of its atomic superiority. Consequently, it will be necessary to make use of this brief interval to systematically prepare our armies by mobilizing all our economic, political, and human resources. During the forthcoming three or four years, all of our domestic and international policies will be subordinated to this goal. Only the total mobilization of our resources will allow us to grasp this unique opportunity to extend socialism throughout the whole of Europe.'”
[Karel Kaplan, Dans les Archives du comité central: Trente ans de secrets du bloc soviétique, Paris: Michel, 1978, pp. 165-66; translated by Vojtech Mastny]
Another record of the Moscow meeting, written shortly afterward by its Romanian participant, Minister of the Armed Forces Emil Bodnaras, has been preserved in Bucharest and was published there in 1995. According to this document, Stalin urged a buildup of the eastern European armies to deter an American attack rather than to prepare them for an attack on western Europe. But his insistence on exploiting what he regarded as current American weakness to achieve combat readiness within three years could be interpreted as a call for offensive action at the right time. The three-year framework he mentioned corresponded to the period of “maximum danger” that also underlay NATO’s contemporary plans for the development of its armed forces –another indication that those secret plans were no secret to Stalin.
This description of presumed Soviet military capabilities is from one of the annual estimates compiled by NATO from 1950 onward and is preserved in its archives in Brussels.
The excerpt from the record of the 99th meeting of NATO’s Military Representatives Committee shows some of the doubts that spread by 1955 about the accuracy of the alliance’s estimates of Soviet capabilities:
The conclusive answer to the question of who started the Korean War and why could finally be given in 1995, following the release of the Soviet documents proving Kim Il Sung’s initiative and Stalin’s indispensable support. Some of the relevant documents were given by Russian President Boris N. Yeltsin to South Korean President Kim Young-Sam during his state visit to Moscow, others were subsequently made available from Russian archives. They were translated into English and published with commentaries for the first time by American historian Kathryn Weathersby in the Cold War International History Project Bulletin, nos. 5 and 6-7.
President Eisenhower was worried that because of their failures in Eastern Europe the Soviets might take “any wild adventure.” At the meeting of the National Security Council on 31 October 1956, he expressed his concern that “Soviet suspicions of U.S. policy and present circumstances which involve Soviet troop movements and alerts probably increase the likelihood of a series of actions and counter-actions leading inadvertently to war.” This statement is included in the document entitled “U.S. Policy toward Developments in Poland and Hungary,” NSC-5616, a “sanitized” version with deletions was published in Foreign Relations of the United States, 1955-57, vol. 25, pp. 463-69; its full version is available at the National Security Archive, RN 66037.
Contrary to the President’s fears, the Soviet leaders concluded on the same day that “there will be no large-scale war.” Informal notes of the Soviet party presidium deliberations, during which they reversed themselves several times before deciding to intervene by force, were kept by Vladimir Malin, head of the general department of the party central committee. They have been preserved in the Storage Center for Contemporary Documentation in Moscow and published in the Cold War International History Project Bulletin, nos. 8-9 (1996/97), pp. 388-410, by Mark Kramer. The most important of the notes follow.
The key documents on Soviet decision-making during the 1968 Czechoslovak crisis were published by the National Security Archive in the book, The Prague Spring 1968 (Budapest: Central European University Press, 1998)
Document 9.
In 1994, minutes of the Soviet party presidium meetings showing its reluctance to intervene militarily in the Polish crisis were published in Moscow (“Dokumenty `Komissii Suslova’: Sobytiia v Polshe v 1981 g.” [Documents of the “Suslov Commission”: The Events in Poland in 1981], Novaia i Noveishaia Istoriia, 1994, no. 1: 84-105). At the time of the publication, the public debate about the admission of Poland into NATO was gaining momentum, and it has been suggested that that by releasing evidence to the effect that in 1981 the Soviet Union had not been a military threat to Poland, the Russian government wanted to bolster its argument that Polish membership in the Western alliance was unnecessary. Nevertheless, no doubts have been cast on the authenticity of the documents, including the record of the presidium meeting on 10 December 1981, three days before the Polish government declared martial law.
Under the new party leadership of Wladyslaw Gomulka, the Polish general staff in November 1956 established a special commission, headed by Gen. Jan Drzewiecki, to press for a renegotiation of the Warsaw Pact. Invoking the status of American forces in foreign countries as an example, the commission proceeded with its work despite Soviet military intervention in Hungary and submitted its proposal for the reform of the alliance to the Soviet Union in January 1957. The proposal was promptly rejected.
The secret Romanian approach to Secretary of State Dean Rusk was revealed thirty years later by former U.S. foreign service officer and ambassador to Bulgaria Raymond L. Garthoff.
The position of the Czechoslovak reformist leadership toward the Warsaw Pact was summarized in a paper prepared at the Prague ministry of defense in July 1968. Drafted in response to the mounting Soviet accusations of Czechoslovakia’s alleged disloyalty to the alliance, it was probably never used.
Evidence showing that Gen. Jaruzelski imposed martial law in Poland in December 1981 not in order to avert Soviet military intervention but in order to crush the democratric opposition was presented at the conference co-organized by the National Security Archive in November 1997 at Jachranka near Warsaw. The most startling piece of that evidence is the notebook by Gen. Viktor I. Anoshkin, aide to Warsaw Pact Supreme Commander Marshal Viktor G. Kulikov, indicating that Jaruzelski, fearful that his attempt to introduce martial law might fail, actually solicited Soviet military backing in case he would run into difficulties but was rebuffed.
A sample of an original page of the notebook and a selection of its entries follow.
Document 14.
At a meeting with the Hungarian party chief Karóly Grósz on 8 September 1988, the East German leader Erich Honecker recalled that
“at the time of the stationing of the missiles in western Europe, the SED [East German Communist Party] was pleased with how the fraternal Hungarian party reacted by adopting a position similar to that of the SED . . . . We could not agree with the idea that, after the stationing of the missiles, any dialog would be impossible . . . ” Comrade Honecker remembered that during this time the central organ of the SED printed an article by comrade Szürös, in which the agreement of our viepoints was made clear. [Record of the Honecker-Grosz meeting, Zentrales Parteiarchiv, J IV/931, Stiftung Archiv der Parteien und Massenorganisationen der DDR im Bundesarchiv, Berlin; translated by Catherine Nielsen, National Security Archive]
Honecker was referring to his public statements in 1983-84 in which he, obliquely but unequivocally, expressed misgivings about the deployment of additional Soviet missiles in East Germany. At a time when the Soviet Union took an intransigent stance against the deployment of NATO’s intermediate range nuclear missiles, he expressed his desire to continue a dialogue with the West in order to save détente.
“. . . The GDR has, like the other states of the socialist community, been actively supporting the adamant and consistent peace policy of the Soviet Union in all phases of the struggle against the deployment of American first-strike weapons. Simultaneously, it has been developing a broad scale of activities, using its international channels at the UN and elsewhere to calm down the world situation and help forestall any extreme reactions. . . .
I like to point out here the numerous contacts and talks with representatives of Western nations, their parties and their economic and public institutions up to the highest levels, that helped to clarify the positions of the GDR and our socialist community with regard to the burning issues of the struggle for peace against the policies of confrontation and the arms race. It is well known that in this is the context we have been conducting a multifaceted dialogue with politicians of the FRG, be they personalities of the federal government and the Bonn coalition parties or of the opposition. This has not been without results. . .
It is of great importance to continue the political dialogue with all forces that acknowledge their responsibility for the fate of their people and of mankind and are prepared to keep the channels of communication open. We advocate that all possibilities to negotiate a stop to the arms race and a transition to disarmament, especially in the nuclear field, should be used.”
[“Speech by Erich Honecker delivered in East Berlin at the SED’s seventh CC plenum, 26-27 November 1983”; Neues Deutschland, 26 and 27 November 1983; published in East Berlin and Moscow: the Documentation of a Dispute, Ron Asmus, ed., RFE Occasional Papers, Number 1, Munich: Germany, 1985, pp. 19-21]
“Our policy is and remains determined by the principles of peaceful coexistence and by efforts to reduce tension and [the risk oil military confrontation, especially here in Europe. Reason and a determination to find constructive solutions to the contested problems in a peaceful manner must dominate the sphere of international relations. Cooperation must prevail in order to ensure mutual advantage; the continuation of an East-West dialogue is of the utmost importance. My meetings with leading politicians and other individuals from the West, including the FRG, are to be seen in this context. . . .
I have thereby also expressed [the principles that] will guide us in the further development of relations between the GDR and the FRG. These relations cannot be severed from the need for a peaceful future for both German states, indeed, for a peaceful future for Europe, [and] for a rational [future based on] coexistence and cooperation. In view of this and aware of the experiences of two world wars and the responsibilities the two German nations have for peace, it is most important that every possibility be used so that reason and realism prevail, so that cooperation instead of confrontation come to the fore, and so disarmament proceeds and the process of détente is revived, according to the principles of equality and equal security.”
[“Erich Honecker’s speech to district party leaders in East Berlin on 12 February 1984”; Neues Deutschland, 13 February 1984; published in East Berlin and Moscow: the Documentation of a Dispute, Ron Asmus, ed., RFE Occasional Papers, Number 1, Munich: Germany, 1985, p25.]
Document 15.
On 2-3 August and again on 5 August 1961, while secret preparations for the building of the Berlin War were at their final stage and eastern European leaders were gathered to Moscow to consider the consequences, Khrushchev met with the visiting Italian Prime Minister Amintore Fanfani. Evidently anxious about the likely Western response to the imminent drastic action in Berlin and undecided whether he should follow it up by making good on his repeated threat to conclude a separate peace treaty with East Germany, Khrushchev went the farthest ever in trying to intimidate one of America’s key European allies. The Soviet government subsequently shared its transcript of the conversation with its Warsaw Pact allies.
Indignant at his recent contentious meeting with President John F. Kennedy in Vienna, Khrushchev complained about having supposedly been threated by him with war if the East German peace treaty were signed. Khrushchev nevertheless insisted that the treaty would be signed [it never was] and that “access to West Berlin will be closed” as a result. He added that he had “an even bigger hydrogen bomb” (10 million tons of TNT) and was under pressure by his technicians and military to test it.
“Within an hour after the outbreak of a war,” Khrushchev predicted, “West Germany would be annihilated.” He warned that all of America’s allies were at risk because of the U.S. bases on their territories, and the Soviet Union had enough missiles to destroy them all. But the war will be started by the West, not by the East, he said.
“The United States will start the war, and you will have to die,” Khrushchev informed his Italian guest. “Understand me right. This is not a threat but a reality . . . . If we are attacked we will destroy the whole world. This is not an ultimatum but a realistic estimate.”
[Soviet record of the Khrushchev-Fanfani conversations, 2-3 and 5 August 1961, Zentrales Parteiarchiv, J IV 2/202-329, Stiftung Archiv der Parteien und Massenorganisationen der DDR im Bundesarchiv, Berlin]
Document 16.
On the way to his meeting with Kennedy in Vienna, Khrushchev in June 1961 revealed the nature of his brinkmanship to Czechoslovak party leaders gathered in Bratislava. The record of his statement, preserved in the Central State Archives in Prague, was published in a Russian translation in 1998 (“`Lenin tozhe riskoval’: Nakanune vstrechi Khrushcheva i Kennedi v Vene v iiune 1961 g.,” [“Lenin Took Risks, Too”: On the Eve of the Khrushchev-Kennedy Encounter in Vienna in June 1961], Istochnik, 1998, no. 3: 85-97).
The question of whether Khrushchev sent battlefield nuclear weapons to Cuba with the intention of their being fired against U.S. targets in case of an American invasion of the island has been contested among historians. On the one hand, he gave clear instructions that no use of any nuclear weapons was authorized without explicit approval from Moscow. On the other hand, he acted as if he had no conception of the risk of escalation if the battlefield nuclear weapons were actually used. Some of the relevant documents from Soviet archives follow.
The Warsaw Pact command and staff exercise MAZOWSZE, conducted in Poland in June 1963, was based on actual war plans. It envisaged a veritable pandemonium, in which hundreds of nuclear weapons would be fired and millions of people killed, yet the country, unlike its Western adversaries, would not only survive and even keep functioning, but win the war in three days. The description of the war game was printed by the general staff for internal use and given the highest grade of classification.
The appended map shows the anticipated radioactive contamination of nearly all of Poland, sometimes up to 1,000 times the acceptable level.
The speech by Soviet party general secretary Yuri V. Andropov at the closed session of the Warsaw Pact’s Political Consultative Committee in Prague on May 4, 1983, was his first major policy statement after the death of his predecessor, Leonid I. Brezhnev. Because of Andropov’s systematic and thoughtful, if ideologically distorted, overview of the international scene, the complete text of his speech is included here.
Document 20.
The strategic posture of the Warsaw Pact changed from defensive to offensive in 1961 in the course of the Berlin crisis 1958-61 as Khrushchev prepared to violate the Allied agreements on Germany by signing a separate peace treaty with East Germany. Although the treaty was never signed the change became permanent. A Czechoslovak Ministry of Defense document from 1966 retrospectively described its meaning:
“The former strategic concept, which gave our armed forces the task to `firmly cover the state border, not allow penetration of our territory by enemy forces and create conditions for active operations of other allied forces,’ was changed in 1961, without discussion by the Political Consultative Committee, and the Czechoslovak People’s Army was assigned an active task.”
[“Materiály k otázce Spojeného velení,” undated [early 1966], GS-OS 0039042/1, Archives of the Ministry of Defense, Prague, translated by Vojtech Mastny]
The intended offensive was practiced every year in numerous exercises of the Warsaw Pact’s “Western Army Group.” The document entitled “The Basic Characteristics of the Army Group Operation at the Initial Stage of the War,” prepared by the Czechoslovak general staff in mid-1963 according to Soviet guidelines, reads in part…
In anticipation of the advance into enemy territory, appeals were to be addressed to NATO soldiers to surrender. Leaflets were composed by the propaganda department of the Czechoslovak army in English and French and intended to be dropped behind the front lines:
[MNO 1964, kr. 101, 17/1/1,3, Military Historical Archives, Prague]
Soviet estimates of the morale of the enemy troops and West German population were supplied to Warsaw Pact member states and used in lectures for the benefit of their officer corps. One such lecture, prepared by the Czechoslovak general staff in 1963, included the following observations.
Here are some of the Warsaw Pact assessments of individual Bundeswehr and U.S. Army formations:
The scenario, which haunted particularly the East German leader Walter Ulbricht, was described in a paper prepared for the August 3, 1959, session of the Security Commission of the East German communist party central committee with the goal of increasing the combat readiness of the country’s armed forces. In its first part, the paper quotes from a purported secret West German document, code-named DECO II, which East Germany’s spy chief Markus Wolf maintains having obtained from his agents in 1955 (Markus Wolf, Spionagechef im geheimen Krieg: Erinnerungen, Munich: Econ, 1997, p. 118):
Growing concern about advances in NATO’s conventional forces is evident in Warsaw Pact evaluations of the annual Western military maneuvers since the late 1970s. It grew during the 1980s mainly because of rapid advances in high-technology weapons which the Warsaw Pact planners did not see themselves in a position to match.
Excerpts from some of the representative documents
In his rambling remarks at a closed meeting of officials of the Czechoslovak general staff on March 13, 1968, its chief, Gen. Otakar Rytír, grasped the heart of the problem that would eventually play a critical role in prompting the collapse of the Soviet system—its inability to keep up with its capitalist rival in economic and technological competition.
Revealed – Feds Issue Bulletin on Google Dorking
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
A bulletin issued by the Department of Homeland Security, the FBI and the National Counterterrorism Center earlier this month warns law enforcement and private security personnel that malicious cyber actors can use “advanced search techniques” to discover sensitive information and other vulnerabilities in websites. The bulletin, titled “Malicious Cyber Actors Use Advanced Search Techniques,” describes a set of techniques collectively referred to as “Google dorking” or “Google hacking” that use “advanced operators” to refine search queries to provide more specific results. Lists of these operators are provided by Google and include the following examples:
| allintext: / intext: | Restricts results to those containing all the query terms you specify in the text of the page |
| allintitle: / intitle: | Restricts results to those containing all the query terms you specify in the title |
| allinurl: / inurl: | Restricts results to those containing all the query terms you specify in the URL |
| filetype:suffix | Limits results to pages whose names end in suffix |
| site: | Using the site: operator restricts your search results to the site or domain you specify |
| Minus sign ( – ) to exclude | Placing a minus sign immediately before a word indicates that you do not want pages that contain this word to appear in your results |
| Phrase search (using double quotes, “…” ) | By putting double quotes around a set of words, you are telling Google to consider the exact words in that exact order without any change |
Here is an example of a query constructed from these operators:
“sensitive but unclassified” filetype:pdf site:publicintelligence.net
The bulletin warns that malicious cyber actors can use these techniques to “locate information that organizations may not have intended to be discoverable by the public or to find website vulnerabilities for use in subsequent cyber attacks.” Hackers searching for “specific file types and keywords . . . can locate information such as usernames and passwords, e-mail lists, sensitive documents, bank account details, and website vulnerabilities.” Moreover, “freely available online tools can run automated scans using multiple dork queries” to discover vulnerabilities. In fact, the bulletin recommends that security professionals use these tools “such as the Google Hacking Database, found at http://www.exploit-db.com/google-dorks, to run pre-made dork queries to find discoverable proprietary information and website vulnerabilities.”
Several security breaches related to the use of “advanced search techniques” are also referenced in the bulletin. One incident in August 2011 resulted in the compromise of the personally identifiable information of approximately 43,000 faculty, staff, students and alumni of Yale University. The information was located in a spreadsheet placed on a publicly accessible File Transfer Protocol (FTP) server and was listed in Google search results for more than ten months prior to being discovered. Another incident in October 2013 involved attackers using Google dorking to discover websites running vulnerable versions of vBulletin message board software prior to running automated tools that created administrator accounts on the compromised sites. As many as 35,000 websites were believed to have been compromised in the incident.
Video – Russia’s ‘Stealth Invasion’ Of Ukraine The Opposite Of Stealthy – War
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
“Tanks, artillery and infantry have crossed from Russia into an unbreached part of eastern Ukraine in recent days, attacking Ukrainian forces and causing panic and wholesale retreat not only in this small border town but also a wide section of territory, in what Ukrainian and Western military officials described on Wednesday as a stealth invasion.
The attacks outside this city and in an area to the north essentially have opened a new, third front in the war in eastern Ukraine between government forces and pro-Russian separatists, along with the fighting outside the cities of Donetsk and Luhansk.
Exhausted, filthy and dismayed, Ukrainian soldiers staggering out of Novoazovsk for safer territory said Tuesday they were cannon fodder for the forces coming from Russia. As they spoke, tank shells whistled in from the east and exploded nearby.”* The Young Turks hosts Ana Kasparian, Ben Mankiewicz (Turner Classic Movies), and Jasmyne Cannick (Political Commentator) break it down.
*Read more here from Andrew E. Kramer and Michael R. Gordon / NY Times:
http://www.nytimes.com/2014/08/28/wor…
TOP-SECRET – The Secret List of CIA Sources – 2.619 Names and Adresses, Part 11,K,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
K
Kahdeman, Tyler P.O. Box 7465, Las Cruces, NM 88006 Kaiser, Robert G. 1150 15th St., NW, Washington, DC 20017 Kalitka, Col Peter USA P.O. Box 305, Waterford, VA 22190 Kallini, LtCol Thaddeus USAF 5100 John D. Ryan Blvd., No. 717, San Antonio, TX 78245 Kanellos, Constantine 6416 Berkshire Dr., Alexandria, VA 22310 Kappes, George M. 709 Cascade Dr., Golden, CO 80403 Karlow, S. Peter 43 Fair Oaks Ln., Atherton, CA 94027 Karr, R. Michael P.O. Box 1762, Bothell, WA 98041 Kassebaum, Dr. Peter 1545 Rio Nido Ct., Petaluma, CA 94954 Katheder, Thomas P.O. Box 22671, Lake Buena Vista, FL 32830 Katsirubas, William P. 7126 Merrimac Dr., McLean, VA 22101 Kaufman, Col Raymond USA P.O. Box 1009, Litchfield, CT 06759 Kaufman, Walter J. 11 Ruxview Ct., No. 302, Ruxton, MD 21204 Kavanaugh, Maj Kevin USAR 206 N. Trenton St., No. 3, Arlington, VA 22203 Kaylor, Ms. Pattie 4977 Battery Ln., No. 307, North, Bethesda, MD 20814 Kearns, Capt Michael USAF 826 Orange Ave., No. 128, Coronado, CA 92118 Keat, Augustus 8547 S. Zypher, Littleton, CO 80123 Keats, Col James USAR 2000 S. Eads St., No. 607, Arlington, VA 22202 Keefe, Stephen R. 5600 Small Oak Ct., Woodbridge, VA 22192 Keeler, Ray M. 860 Rudder Way, Annapolis, MD 21401 Keenan, Gerard P. 1005 Celia St., West Islip, NY 11795 Keikuatov, Oleg 1311 Ross St., SW, Vienna, VA 22180 Keiser, LtCol Melville USAR 6904 Hutchison St., Falls Church, VA 22043 Kellaher, Frank J. 7518 Dover Ln., Lanham, MD 20706 Kellar, Michael 45-401 Mokulele Dr., No. 32, Kanehoe, HI 96744 Keller, Dennis M. 2226 Calle Opalo, San Clemente, CA 92673 Keller, E. John 2906 Southlake Blvd., Southlake, TX 76092 Keller, George R. 305 Lee Dr., Baltimore, MD 21228 Kelly, Capt William USNR 465 Canton Rd., Kingsport, TN 37663 Kelso, LtCol Joseph USAF 3645 S. Poplar St., Denver, CO 80237 Kempa, Erich 3115 NW 93rd St., Seattle, WA 98117 Kennedy, James P. 506 Granite St., Ashland, OR 97520 Kenney, James 1100 NW Loop 410, Suite 200, San Antonio, TX 78213 Kent, Alexander 14816 East Dunton Dr., Whittier, CA 90604 Kent, William 320 Burning Tree Rd., Pinehurst, NC 28374 Kenyon, Dr. Paul 1314 S. King St., No. 664, Honolulu, HI 96814 Kephart, Cdr Robert USN ERLACH, RR 1, Box 335, Faber, VA 22938 Kerbe, Wilmer 3237 Brushwood Ct., Clearwater, FL 34621 Kern, Erson 4576 Crimsonwood Dr., Redding, CA 96001 Kerns, Arthur J. 6852 Grande Ln., Falls Church, VA 22043 Kessler, Peter 2199 Holland Ave., No. 5G, Bronx, NY 10462 Kesterson, Mrs. Goldie Mae 2001 Columbia Pike, No. 202, Arlington, VA 22204 Kida, Anthony 3102 North 47th St., Phoenix, AZ 85018 Kiechlin, Edmond F. Jr. 10022 Wheatfield Ct., Fairfax, VA 22032 Kierce, Robert R. 47784 Fathom Pl., Sterling, VA 20165 Kies, Dr. Rudolf P.O. Box 295, San Fernando, CA 91341 Kim, Arthur 7117 Idylwood Rd., Falls Church, VA 22043 Kimble, Wilford L. 24 Edmiston Ln., Comfort, TX 78013 King, Col Dale M. USA 2743 Spicer Ln., Decatur, GA 30033 King, Daniel C. 26425 Millinix Mill Rd., Mt. Airy, MD 21771 King, Daniel P. 5125 N. Cumberland Blvd., Whitefish Bay, WI 53217 King, George W. 9839 Mendota Dr., Peoria, AZ 85345 King, Ms. Mary 5601 Seminary Rd., No. 1617N, Falls Church, VA 22041 King, William P. 2850 S. Ocean Blvd. No. 502, Palm Beach, FL 33480 Kirby, Oliver RR 5, Club Lake, Box 229E, Greenville, TX 75401 Kirchman, Charles V. 14801 Notley Rd., Silver Spring, MD 20905 Kirk, Grayson L. Columbia University, New York, NY 10027 Kirkpatrick, Rita P.O. Box 429, Middleburg, VA 22117 Kirschner, Calvin P.O. Box 777, Garden City, MI 48136 Kizirian, Col John USA 98-1032 Alania St., Aiea, HI 96701 Klager, Roy B. Jr. 3001 Hedgetree Ct., Wichita, KS 67226 Kleber, Col Victor USMC 907 Forrest Ln., Beaufort, SC 29902 Kleebauer, Charles 1833 Baldwin Dr., McLean, VA 22102 Klein, Edward V. P.O. Box 597, Hillsboro, NC 28725 Klein, Col Frank O. USAF 30180 Santiago Rd., Tememcula, CA 92592 Klein, Rev Theodore USAF 69 Groton Long Point Rd., Groton, CT 06340 Kleyla, Mrs. Helen H. P.O. Box 161, Nags Head, NC 27959 Kleyla, Robert L. 730 24th St., NW, No. 400, Washington, DC 20037 Kmentt, Todd A. 10681 Oak Lake Way, Boca Raton, FL 33498 Knickman, Carl V. Torweg Haus, P.O. Box 677, Madison, VA 22727 Knoll, Col Rudolph AUS 9412 Northridge Dr., NE, Albuquerque, NM 87111 Kobernicki, Lesek 59 Elmleigh Rd., Hampshire, PO 0 2AB, England Kobetz, Dr. Richard W. Arcadia, RR 2, Box 3645, Berryville, VA 22611 Koczak, Crd Edward USN 2500 Virginia Ave., NW, Washington, DC 20037 Koczak, Stephen A. 2932 Macomb St., NW, Washington, DC 20008 Kodmur, Milton J. 2734 Bordeaux Ave., Las Jolla, CA 92037 Koehler, John 1 Strawberry Hill Ave., No. 4H, Stamford, CT 06902 Kohlhaas, George 1580 Tarpon St., Merritt Island, FL 32952 Koier, Mrs. Virginia R. 36 DeVries Circle, Lewes, DE 19958 Kokot, Ms. Mary Anna 970 Virginia St., No. 310, Dunedin, FL 34698 Koletar, Joseph 53 Berkeley Pl., Glen Rock, NJ 07452 Koller, Col Rudolph USAF 1404 Stanley Dollar Dr., No. 4A, Walnut Creek, CA 94595 Kolombatovic, Vadja 1171 Dolley Madison Blvd., McLean, VA 22101 Kolon, LtCol Walter V. AUS P.O. Box 21063, Port Authority, New York, NY 10129 Kopera, John A. 1016 S. Wayne St., No. 307, Arlington, VA 22204 Koplowitz, Wilfred 410 E. 57th St., New York, NY 10022 Kopp, Dr. Guido P.O. Box 1040, D-55100, Mainz, Germany Koppel, Ted 1717 DeSales St., Washington, DC 20017 Kosal, Ozmer 245 Collington Dr., Ronkonkoma, NY 11449 Kostolich, Marcus 12815 Teasberry Rd., Wheaton, MD 20906 Kotapish, William R. 1702 Bradmore Ct., McLean, VA 22101 Kourembis, Ms Mary 926-Q Avenida Majorca, Laguna Hills, CA 92653 Kovacevich, Mrs. Ruth 4800 N. 68th St., No. 142, Scottsdale, AZ 85251 Kovar, Richard 1913 Wintergreen Ct., Reston, VA 22091 Kray, Edward 309 Tampa Ave., Indiatlantic, FL 332903 Krick, Samuel W. RR 2, Box 2070, Duncannon, PA 17021 Kreibel, Norman F. 601 Montgomery Ave., No. 201, Bryn Mawr, PA 19010 Krisel, Capt Lionel USN 100840 Savona Rd., Los Angeles, CA 90077 Krisman, Col Michael USA Drury Lane, Cragston, Highland Falls, NY 10928 Kroh, Herman 2876 Forest Lodge Rd., Pebble Beach, CA 93953 Kronemeyer, Cdr Robert USNR 7717 Ludington Pl., La Jolla, CA 92037 Krueger, Richard 700 Muirfield Circle, Ft. Washington, MD 20744 Krueger, LtCol Robert A. 2212 Lakecrest Dr., Greer, SC 29651 Kryza, Honorable E. Gregory 2035 Franklin Cluster Ct., Falls Church, VA 22043 Kubiszewski, LtCol S. USA 5315 66th Ave., Court W, Tacoma, WA 89464 Kuethe, LtCol Ralph USA 6450 Queen Anne Terrace, Falls Church, VA 22044 Kuhn, Mrs. Nancy Z. 4204 Flower Valley Dr., Rockville, MD 20853 Kulberg, Raoul 3916 McKinley St., NW, Washington, DC 20015 Kunen, Jeremy 4475 White Egret Ln., Sarasota, FL 34238 Kuntzman, Major John C. USA 11204 Trippon Ct., North Potomac, MD 20878 Kurtz, Howard 1150 15th St., NW, Washington, DC 20017 Kustra, Richard J. 7331 Eldorado St., McLean, VA 22102 Kuzmuk, Walter 854 Boatswin Way, Annapolis, MD 21401 Kvetkas, William 595 Coover Rd., Annapolis, MD
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 20, AX-AZ,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN 00 1043/2129 | AXANTOWICZ MAREK GRZEGORZ |
| IPN BU 00191/150 | AXENTOWICZ MAREK GRZEGORZ |
| IPN 00 1043/2489 | AZAJĄC JÓZEF |
| IPN BU 00283/1466 | AZAJĄC ZBIGNIEW |
| IPN BU 00945/838 | AZDERBALL ROBERT |
| IPN BU 001102/1934 | AZDERBALL ROBERT |
| IPN 00 1043/209 | AZEMBSKI MIROSŁAW |
| IPN BU 00170/558 | AZEMBSKI MIROSŁAW WŁODZIMIERZ |
| IPN BU 0193/6766 | AŻGIN (AŹGIN) WACŁAW ROMAN |
Malicious Cyber Actors Use Advanced Search Techniques
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Malicious cyber actors are using advanced search techniques, referred to as “Google dorking,” to locate information that organizations may not have intended to be discoverable by the public or to find website vulnerabilities for use in subsequent cyber attacks. “Google dorking” has become the acknowledged term for this malicious activity, but it applies to any search engine with advanced search capabilities. By searching for specific file types and keywords, malicious cyber actors can locate information such as usernames and passwords, e-mail lists, sensitive documents, bank account details, and website vulnerabilities. For example, a simple “operator:keyword” syntax, such as “filetype:xls intext:username,” in the standard search box would retrieve Excel spreadsheets containing usernames. Additionally, freely available online tools can run automated scans using multiple dork queries.
» (U) In October 2013, unidentified attackers used Google dorking to find websites running vulnerable versions of a proprietary Internet message board software product, according to security researchers. After searching for vulnerable software identifiers, the attackers compromised 35,000 websites and were able to create new administrator accounts.
» (U) In August 2011, unidentified actors used Google dorking to locate a vulnerable File Transfer Protocol server at an identified US university and compromised the personally identifiable information of approximately 43,000 faculty, staff, students, and alumni, according to an information technology security firm.
» (U) The Diggity Project is a free online tool suite that enables users to automate Google dork queries. It contains both offensive and defensive tools and over 1,600 pre-made dork queries that leverage advanced search operators.
(U) Suggested measures for website administrators to protect sensitive information include:
» (U//FOUO) Minimize putting sensitive information on the web. If you must put sensitive information on the web, ensure it is password protected and encrypted.
» (U//FOUO) Use tools such as the Google Hacking Database, found at http://www.exploit-db.com/google-dorks, to run pre-made dork queries to find discoverable proprietary information and website vulnerabilities.
» (U//FOUO) Ensure sensitive websites are not indexed in search engines. GoogleUSPER provides webmaster tools to remove entire sites, individual URLs, cached copies, and directories from Google’s index. These can be found at: https://www.google.com/webmasters/tools/ home?hl=en.
» (U//FOUO) Use the robots.txt file to prevent search engines from indexing individual sites, and place it in the top-level directory of the web server.
» (U//FOUO) Test your website using a web vulnerability scanner.
Cryptome – CIA Officer Mary Katherine Brezin
CIA Officer Mary Katherine Brezin
Current Deputy COS in Kiev, Ukraine.
Cryptocomb welcomes any further information.
If you found this Cryptocomb post informative, please consider a Bitcoin donation at:
1LoaA5mLxoMiAzPBLMjXqMrygJARDRTb4Z
Video – Action des Femen Anti-Tymoshenko – Paris
TOP-SECRET – The Secret List of CIA Sources – 2.619 Names and Adresses, Part 10,J,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
J
Jackson, Clarence A. P.O. Box 75007, St. Paul, MN 55175 Jackson, Daniel G. 3408 Chiswick Ct., No. 3H, Silver Spring, MD 20906 Jackson, Donald 8305 Private Ln., Annadale, VA 22003 Jackson, Col Joseph USA 1412 Chesapeake Ave., Hampton, VA 23661 Jacobs, Charles T. 103 Brown St., Box 7, Washington Grove, MD 20880 Jacobs, Eli S. 641 Lexington Ave., 31st Floor, New York, NY 10022 Jacobsen, Eric P. 10402 Lakeshore Blvd., Bratenahl, OH 44108 James, Robert G. 80 Ludlow Dr., Chappaqua, NY 10514 Jamison, Katherine 1600 S. Eads St., No. 113 South, Arlington, VA 22202 Jamison, Ms. Sara Jane 12191 Clipper Dr., Lake Ridge, VA 22192 Japikse, Ms. Catherine 80 Lyme Rd., Hanover, NH 03755 Jasin, Peter W. 4900 N. Ocean Blvd., No. 1113, Fort Lauderdale, FL 33308 Jasper, Kenneth 7351 Eldorado Ct., McLean, VA 22102 Jastrow, Robert E. 2508 West Straford Dr., Chandler, AZ 85224 Jemilo, John 3581 N. Avers Ave., Chicago, IL 60618 Jenkins, Carl E. BHPS PSC No. 80, Box 10461, APO, AP 96367 Jenkins, Dale A. Tower Hill Rd., Tuxedo Park, NY 10987 Jenkins, RAdm John USN 5809 Helmsdale Ln., Alexandria, VA 22310 Jenks, Airell 4 Sunset Farm, Woodstock, VT 05091 Jenks, Donovan R. 5007 Auckland Ave., North Hollywood, CA 91601 Jenne, Dr. Herbert 1481 Patriot Dr., Melbourne, FL 32940 Jentsch, Heber 6331 Hollywood Blvd., Los Angeles, CA 90028 Jerawski, Edward 32556 Mound Rd., Warren, MI 48092 Jilli, Edmund 8700 N. La Cholla No. 2134, Tucson, AZ 85741 Jirles, LtCol Edward USAF 2773 Cady Way, Winter Park, FL 32792 Joannides, George E. 8817 Tuckerman Ln., Potomac, MD 20854 Johannessen, John Box 315, 52 Fairway Dr., Grantham, NH 03753 Johanson, Cdr Donald USN 8260 Hornbuckle Dr., Springfield, VA 22153 Johnson, MSgt Charles USAF 317 Jan Lynn, Kenton, TN 38233 Johnson, Douglas W. 16421 S.E. 42nd Pl., Issaquah, WA 98027 Johnson, Herbert J. 527 Seminiole Dr., Erie, PA 16505 Johnson, John B. 221 Flower Ave., West, Watertown, NY 13601 Johnson, Kenneth T. 3509 North Valley St., Arlington, VA 22207 Johnson, Mrs. Lucy A. 3014 Brinkley Rd., No. 108, Temple Hills, MD 20748 Johnson, Norman 6017 Saturn Ln., Mira Loma, CA 91752 Johnson, Ronald 7300 Reervation Dr., Springfield, VA 22153 Johnson, Terry D. 25200 Baronet Dr., Salinas, CA 93908 Johnson, Thomas P.O. Box 1297, Littleton, CO 80160 Johnson, William O. P.O. Box 145, Leander, TX 78641 Johnson, William P. 1911 Camino de la Costa No. 501, Redondo Beach, CA 90277 Johnson, William R. 317 Foxtail Ct., Boulder, CO 80303 Johnson, William W. RR 9, Box 244, Mountain Home, AR 72653 Johnstone, William W. P.O. Box 18380, Shreveport, LA 71138 Jones, Major Bruce USMC 98-1870K Kaahumanu St., Pearl City, HI 96782 Jones, George E. 225 Sycamore Ave., Shrewsbury, NJ 07702 Jones, Joseph 12123 Sage Glen Ct., Maryland Heights, MO 63043 Jones, Col Marvin 175 Stewart Dr., Merritt Island, FL 32952 Jones, Major Paul USAF 8712 Clydesdale Rd., Springfield, VA 22151 Jones, Col Richard USA 350 Myrtlewood Rd., Melbourne, FL 32040 Jordan, Joseph L. 2615 Waugh Dr., No. 301, Houston, TX 77006 Joscelyn, Kent 11 Southwick Ct., Ann Arbor, MI 48105 Jose, Virgil 14415 Frankton Ave., Hacienda Heights, CA 91745 Jost, Dr. Charles 118 Doubloon Dr., North Ft. Myers, FL 33917 Jost, Dr. Patrick 3020 Fredsen Pl., Falls Church, VA 22042 Joy, Robert 795 Montecello Rd., San Rafael, CA 94903 Joyce, James G. 12399 Falkirk Dr., Fairfax, VA 22033 Joyce, Col Jean K. USA 4522 Swann Ave., Tampa, FL 33609 Joyce, Richard 4626 Alton Pl., NW, Washington, DC 20016 Joyeuse, Dr. Rene P.O.Box 329, Dannemora, NY 12929 Jozwiak, Vincent 7759 Chars Ln., Springfield, VA 22153 Juarez, Capt Robert USN 3217 Wynford Dr., Fairfax, VA 22031 Judy, Chesley 11820 Wynford Dr., Fairfax, VA 22031 Julitz, BrigGen Frank USA 5832 N. Virginia Ave., Chicago, IL 60659 Julitz, John A. 10011 Seymore, Schiller Park, IL 60176 Julliard, Jacques Le Nouvel Observateur, Paris, France Jungel, Paul 744 E. Hayward Ave., Phoenix, AZ 85020 Jurchenko, Col Andrew 603 Preserve Pl., Peachtree City, GA 30269 Justman Jacob, Poul Louis Kon. Ned. Hoogovens & Staalfabrieken N.V. Netherlands
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 19, AV-AW,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 002152/34 | AVDIJI SKENDER | ||||||||||||||
| IPN BU 00170/532 | AVE – JOHANES BERTHUS
|
Video – Putins Declassified KGB Files
Between Devil and the Red Sea – KGB – Gaza
TOP-SECRET – The Secret List of CIA Sources – 2.619 Names and Adresses, Part 9,I,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.

-
I
Iannaccone, Thomas S. 6914 14th Ave., Brooklyn, NY 11228 Ill, Col Paul AUS 970 Mayflower Ave., Melbourne, FL 32940 Immel, William J. 106 Sunset Dr., Otley, IA 50214 Inda, James 420 S. 22nd St., La Crosse, WI 54601 Inge, Col Leon USAF 4100 Century Ct., Alexandria, VA 22312 Ingraham, Mrs. Anne Mary 827 S. Royal St., Alexandria, VA 22314 Inman, Adm Bobby R. USN 3200 Riva Ridge, Austin, TX 78746 Innis, Donald R. 676 Murex Dr., Naples, FL 33940 Isserman, Manfred A. County Home Rd., Thompson, CT 06277
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 18, AU,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 0866/14 | AU FRANCISZEK |
| IPN BU 0967/2 | AU JADWIGA |
| IPN BU 0967/2 | AU JADWIGA |
| IPN BU 0866/15 | AU KAZIMIERZ |
| IPN BU 0242/2727 | AUBANIEWICZ NADZIEJA |
| IPN BU 0604/680 | AUCHIMENIA ANDRZEJ ZBIGNIEW |
| IPN BU 00275/652 | AUDYCKA MARIA |
| IPN BU 001134/605 | AUDYCKA MARIA |
| IPN BU 00612/1864 | AUDYCKI JAN |
| IPN BU 0772/2147 | AUDZIEJCZYK HENRYKA |
| IPN BU 0833/647 | AUDZIEJCZYK RYSZARD |
| IPN BU 001089/35 | AUERBACH JERZY |
| IPN BU 0892/885 | AUGSBURG MIROSŁAW |
| IPN BU 00168/203 | AUGSTYNIAK – ZAGÓRSKA KRYSTYNA |
| IPN BU PF | 299/33 AUGUST |
| IPN BU 0194/1386 | AUGUST BERNARD |
| IPN BU 0242/241 | AUGUSTIAŃSKI TOMASZ |
| IPN 00 1052/196 | AUGUSTJAŃSKA ANNA |
| IPN BU 0901/922 | AUGUSTOWSKA DOROTA |
| IPN BU 0806/3016 | AUGUSTOWSKA ELŻBIETA |
| IPN BU 00277/384 | AUGUSTOWSKA WŁADYSŁAWA |
| IPN BU 001121/2603 | AUGUSTOWSKA WŁADYSŁAWA |
| IPN BU 00945/951 | AUGUSTOWSKI – STRYJEŃSKI – KULESZA – ŻYLIŃSKI ZYGMUNT – |
| IPN BU 748/171 | AUGUSTOWSKI JERZY |
| IPN BU 698/62 | AUGUSTOWSKI JERZY |
| IPN BU 00170/266 | AUGUSTOWSKI KAZIMIERZ |
| IPN BU 00200/283 | AUGUSTOWSKI KAZIMIERZ |
| IPN BU 00945/2389 | AUGUSTOWSKI KAZIMIERZ |
| IPN BU 0891/283 | AUGUSTOWSKI PIOTR |
| IPN BU 0193/6812 | AUGUSTOWSKI ZDZISŁAW |
| IPN 00 1052/1782 | AUGUSTOWSKI ZDZISŁAW IZYDOR |
| IPN BU 00257/392 | AUGUSTYN LUDWIKA AGATA |
| IPN BU 001102/1459 | AUGUSTYN LUDWIKA AGATA |
| IPN BU 0772/2148 | AUGUSTYN MARIA |
| IPN BU 00249/1549 | AUGUSTYN MARIA |
| IPN BU 001121/2150 | AUGUSTYN MARIA |
| IPN BU 00612/4334 | AUGUSTYN RYSZARD |
| IPN BU 00200/1248 | AUGUSTYN RYSZARD |
| IPN BU 001102/850 | AUGUSTYN RYSZARD |
| IPN BU 00612/3296 | AUGUSTYN STANISŁAW |
| IPN BU 001198/6364 | AUGUSTYN STANISŁAW |
| IPN BU 0305/373 | AUGUSTYN WŁADYSŁAW |
| IPN BU 0218/1768 | AUGUSTYNAK STEFAN |
| IPN BU 00170/681 | AUGUSTYNEK ANDRZEJ |
| IPN 00 1043/563 | AUGUSTYNEK ANDRZEJ |
| IPN BU 00945/1728 | AUGUSTYNIAK – ZAGÓRSKA KRYSTYNA |
| IPN BU 0242/2588 | AUGUSTYNIAK (KONIECZNA) ZOFIA |
| IPN BU 0901/921 | AUGUSTYNIAK (MAKOSIEWICZ) MAKOSIAWICZ HALINA |
| IPN BU 0951/1933 | AUGUSTYNIAK (SKRZYCKA) ANNA |
| IPN 00 1043/2310 | AUGUSTYNIAK ADAŚKO ELŻBIETA |
| IPN BU 748/170 | AUGUSTYNIAK ALEKSANDRA |
| IPN BU 0993/1034 | AUGUSTYNIAK ANDRZEJ |
| IPN BU 00744/781 | AUGUSTYNIAK ANDRZEJ |
| IPN BU 001134/284 | AUGUSTYNIAK ANDRZEJ |
| IPN BU 00191/714 | AUGUSTYNIAK ANNA |
| IPN BU 01000/1689 | AUGUSTYNIAK ANTONI |
| IPN BU 0951/185 | AUGUSTYNIAK BOLESŁAW |
| IPN BU 0193/1305 | AUGUSTYNIAK CZESŁAW |
| IPN BU 0833/558 | AUGUSTYNIAK CZESŁAW |
| IPN BU 685/244 | Augustyniak Czesława |
| IPN BU 0967/229 | AUGUSTYNIAK EDWARD |
| IPN BU 0901/1467 | AUGUSTYNIAK EWA |
| IPN BU 00232/221 | AUGUSTYNIAK FELIKS |
| IPN BU 0891/105 | AUGUSTYNIAK FRANCISZEK |
| IPN BU 0854/1360 | AUGUSTYNIAK FRANCISZEK |
| IPN BU 685/243 | Augustyniak Helena |
| IPN BU 685/244 | Augustyniak Helena |
| IPN BU 0833/645 | AUGUSTYNIAK HENRYK |
| IPN BU 0855/2895 | AUGUSTYNIAK HENRYK CZESŁAW |
| IPN BU 001089/41 | AUGUSTYNIAK HENRYKA |
| IPN BU 093/3 | AUGUSTYNIAK J |
| IPN BU 00273/552 | AUGUSTYNIAK JAN |
| IPN BU 0942/493 | AUGUSTYNIAK JAN |
| IPN BU 01133/437 | AUGUSTYNIAK JAN |
| IPN BU 644/737 | AUGUSTYNIAK JAN |
| IPN BU 0772/738 | AUGUSTYNIAK JERZY |
| IPN BU 0833/14 | AUGUSTYNIAK JERZY |
| IPN BU 00200/808 | AUGUSTYNIAK JOLANTA |
| IPN BU 001102/320 | AUGUSTYNIAK JOLANTA |
| IPN BU 0912/1552 | AUGUSTYNIAK JÓZEF |
| IPN BU 52/58 | AUGUSTYNIAK JÓZEF |
| IPN BU 01133/438 | AUGUSTYNIAK KAZIMIERZ |
| IPN BU 01133/439 | AUGUSTYNIAK KAZIMIERZ |
| IPN BU 0290/17 | AUGUSTYNIAK KLEMENTYNA |
| IPN BU 00612/2198 | AUGUSTYNIAK LESZEK |
| IPN BU 001198/5294 | AUGUSTYNIAK LESZEK |
| IPN BU 00744/1318 | AUGUSTYNIAK MACIEJ |
| IPN BU 001134/908 | AUGUSTYNIAK MACIEJ |
| IPN BU 0833/560 | AUGUSTYNIAK MARIAN |
| IPN BU 0833/559 | AUGUSTYNIAK PIOTR |
| IPN BU PF | 71/16 AUGUSTYNIAK PIOTR |
| IPN BU 00612/3778 | AUGUSTYNIAK PIOTR |
| IPN BU 001198/6661 | AUGUSTYNIAK PIOTR |
| IPN BU 0806/2913 | AUGUSTYNIAK REGINA |
| IPN BU 01000/1687 | AUGUSTYNIAK ROMAN |
| IPN BU 01133/440 | AUGUSTYNIAK ROMAN |
| IPN BU 01272/1 | AUGUSTYNIAK ROMAN |
| IPN BU 0193/1306 | AUGUSTYNIAK RYSZARD SYLWESTER |
| IPN BU 0772/4 | AUGUSTYNIAK STANISŁAW |
| IPN 00 1052/357 | AUGUSTYNIAK STANISŁAW |
| IPN BU 01133/443 | AUGUSTYNIAK STANISŁAWA |
| IPN BU 0218/439 | AUGUSTYNIAK STEFAN |
| IPN BU 0988/1151 | AUGUSTYNIAK TADEUSZ |
| IPN BU 01000/1480 | AUGUSTYNIAK TADEUSZ |
| IPN BU 0901/1622 | AUGUSTYNIAK URSZULA |
| IPN BU 01000/1705 | AUGUSTYNIAK WACŁAWA |
| IPN BU 52/59 | AUGUSTYNIAK WIESŁAW |
| IPN BU 0193/8359 | AUGUSTYNIAK WINCENTY |
| IPN BU 01000/1706 | AUGUSTYNIAK WINCENTY |
| IPN BU 0193/6612 | AUGUSTYNIAK WŁODZIMIERZ |
| IPN BU 01268/1 | AUGUSTYNIAK WOJCIECH |
| IPN BU 0604/1272 | AUGUSTYNIAK ZENON |
| IPN BU 01133/441 | AUGUSTYNIAK ZYGMUNT |
| IPN BU 644/738 | AUGUSTYNIAK ZYGMUNT |
| IPN BU 0307/58 | AUGUSTYNIK JANUSZ |
| IPN BU 00612/1101 | AUGUSTYNIK LESZEK |
| IPN BU 00328/1512 | AUGUSTYNOWICZ AGNIESZKA |
| IPN BU 001134/2478 | AUGUSTYNOWICZ AGNIESZKA |
| IPN BU 01000/1688 | AUGUSTYNOWICZ ALEKSANDER |
| IPN BU 0901/943 | AUGUSTYNOWICZ BOŻENA |
| IPN BU 00966/1834 | AUGUSTYNOWICZ JAN |
| IPN BU 0942/492 | AUGUSTYNOWICZ MIROSŁAWA |
| IPN BU 0194/1133 | AUGUSTYNOWICZ STANISŁAW |
| IPN BU 0194/1637 | AUGUSTYNOWICZ TADEUSZ |
| IPN BU 00170/595 | AUGUSTYNOWICZ TADEUSZ |
| IPN 00 1043/288 | AUGUSTYNOWICZ TADEUSZ WŁADYSŁAW |
| IPN BU 0951/1942 | AUGUSTYNOWICZ WACŁAW |
| IPN BU 696/1177 | AUGUSTYNOWICZ WALDEMAR |
| IPN BU 001198/1947 | AUGUSTYŃSKI CZESŁAW |
| IPN BU PF | 900/2 AUGUŚCIAK BEATA |
| IPN BU 0193/7915 | AUGUŚCIAK WACŁAW |
| IPN BU 0806/2505 | AUGUŚCIK ANDRZEJ |
| IPN BU 0967/195 | AUGUŚCIK ANTONI |
| IPN BU 644/736 | AUGUŚCIK JÓZEF |
| IPN BU 0968/109 | AUGUŚCIK KRZYSZTOF |
| IPN BU 00328/1117 | AUGUŚCIK KRZYSZTOF |
| IPN BU 001134/1991 | AUGUŚCIK KRZYSZTOF |
| IPN BU 01133/436 | AUGUŚCIŃSKI KAZIMIERZ |
| IPN BU 0855/1615 | AUGUŚCIŃSKI WŁADYSŁAW |
| IPN 00 1052/872 | AULEYTNER JULIAN |
| IPN BU 0193/155 | AULICH MARCELI |
| IPN 00 1043/3388 | AUTERHOFF DĘBOWSKA DAGMARA ASTRID MARIA |
Video Analysis – James Foley: Tragic Death Or Staged Propaganda?
Video – British Rapper Beheaded James Foley | ISIS Executioner Unmasked Revealed
Video – News and Response of Islamic State’s Barbaric Murder of James Foley
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
News and Response of Islamic State’s Barbaric Murder of James Foley
NOTE: This video does NOT include any of the disturbing footage from the video posted by ISIS referenced.
On August 19 2014, the Islamic State posted a graphic and shocking video of the murder and beheading of James Foley, an American journalist that had been missing since November 2012. The video was sent as a warning to the United States to end military operations in Iraq and ended with a threat to kill Steven Sotloff, another journalist also held captive by ISIS.
The video was met with disgust and shock around the world, and prompted a strong response from President Barack Obama as shown in this video. Watch James Foley in his own words describe his experiences in Libya during the revolution and overthrow of the Qaddafi regime in this fascinating video.
TOP-SECRET – The Secret List of CIA Sources – 2.619 Names and Adresses, Part 8,H,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
H
Hacherian, Jack 2726 Sinton Pl., Pepper Pike, OH 44124 Hackl, Robert 4145 Sunnyslope Ave., Sherman Oaks, CA 91423 Hackman, Col Jeffrey USAF P.O. Box 35, Round Hill, VA 22141 Haendle, Col Karl USA 4543 Carriage Run Circle, Murrell Inlet, SC 29576 Hagaman, BGen Harry USMC 222 E. Fallen Rock Rd., Grand Junction, CO 81503 Hagerling, Col Sidney USMCR P.O. Box 452, Ft. Collins, CO 80522 Hagle, Mrs. Nina 2608 Ridge Road Dr., Alexandria, VA 22302 Hahn, Alfred 14 Quay Ct., Centerport, NY 11721 Hahn, LtCol B. Albert AUS 427 Greenwich St., Bergenfield, NJ 07621 Haig, Mrs. Elizabeth 222 Reeds Landing, Springfield, MA 01109 Haig, Ransom 17443 Plaza Destacado, San Diego, CA 92128 Hall, David 804 N. High St., Duncannon, PA 17020 Hall, Keith D. 1020 School Station Dr., Folsom, CA 95630 Hall, Dr. Richard N 6353 Meadowrue La., Erie, PA 16505 Halpern, Samuel 2202 Popkins Ln., Alexandria, VA 22307 Halpin, Daniel D. 9 Eastman Ave., Bedford, NH 03110 Hamilton, William 8810 Lynnhurst Dr., Fairfax, VA 22031 Hamit, Francis 11669 Valerio, No. 247, North Hollywood, CA 91605 Hammond, Col Walter USAF 7994 Breezy Point Rd., West, Melrose, FL 32666 Hammond, LtCol William AUS 8622 Oak Ledge Dr., San Antonio, TX 78217 Hampson, Thomas R. 680 Hillcrest Blvd., Hoffman Estates, IL 60195 Hanable, Cdr William USNR P.O. Box 1464, Westport, WA 98595 Hancock, Gus H. 11463 Waterview Cluster, Reston, VA 22090 Handlin, James 185 Hemmh Ave., Alamo, CA 94507 Hanna, Philip Vernon Junior College, 4400 College Dr., Vernon, TX 76384 Hanneman, Leroy 14421 Southeast 60th St., Bellevue, WA 98006 Hanrahan, James 11111 Gainsborough Rd., Potomac, MD 20854 Hansen, LtCol Lester USAF 12767 Hunters Ridge Dr., Bonita Springs, FL 33923 Happersett, LtCol Newlin USA 850 E. Roberts Rd., Phoenix, AZ 85022 Harder, Ms. Dorothy 2800 Woodley Rd., NW, Washington, DC 20008 Harding, Mrs. Nancy 1803 Westwind Way, Mclean, VA 22102 Hardy, Major George USA 6027 Pine Crest Dr., Los Angeles, CA 90042 Harney, John 8603 Powhatan St., New Carrollton, MD 20784 Harnish, James 2865 Mourning Dove Way, Titusville, FL 32780 Harper, John 7910 Fort Hunt Rd., Alexandria, VA 22308 Harpham, LtCdr Richard USNR P.O. Box 5713, Santa Barbara, CA 93105 Harris, Charles 4402 S. Garnett Rd., No. 113, Tulsa, OK 74145 Harris, Col Jimmy USA 1429 Walden Oaks Pl., Plant City, FL 33566 Harris, Raymond 5320 Nichols Dr. East Lakeland, FL 33813 Harrison, Stuart RR 3, Box 648 Belfast, ME 04915 Harroll, Benjamin 425 F St., San Diego, CA 92101 Hart, Col Donald USA P.O. Box 127, Cornwall, CT 06796 Hart, John L. 2767 Unicorn Ln., NW, Washington, DC 20015 Hart, Joseph 1441 Waggaman Circle, Mclean, VA 22101 Hart, Peter 181 Lester St., New Britain, CT 06053 Harvey, Arthur P.O. Box 974, Derry, NH 03038 Harvey, Mrs. Clara 1611 Northwood Dr., Indianapolis, IN 46240 Harvey, Deborah 8203 Jeb Stuart Rd., Potomac, MD 20854 Harvey, RAdm Donald USN 8203 Jeb Stuart Rd., Potomac, MD 20854 Harvey, Patrick P.O. Box 5186, Santa Fe, NM 87502 Harvey, Richard 11 Admiral Rd., Severna Park, MD 21146 Hatch, Capt William Mill Road Farm, RR 2, Box 107, Leesburg, VA 22075 Hauck, Paul 796 102nd Ave., N. Naples, FL 3399963 Hawkins, Charles H. 121 Medicine Springs Rd., Conner, MT 59827 Hawkins, Frank 204 Ocean Dr., Tavernier, FL 33070 Hawkins, Col John USAR P.O. Box 5969, Texarkana, TX 75505 Hayden, Col Charles AUS 401 Via Casitas, No. 9, Greenbrae, CA 94904 Hayden, Ms. Kathleen 4904 Pelican Blvd., Cape Coral, FL 33914 Hayes, James 5569 Glen Abby Ct., Delray Beach, FL 33484 Hayes, Jimmy 5 East Circle Dr., Cocoa Beach, FL 32931 Hayes, Louis Dept. of PoliSci, University of Montana, Missoula, MT 59812 Hays, Donald 501 East 79th St., New York, NY 10021 Hays, James 1427 S.W. 53rd Terrace, Cape Coral, FL 33914 Hays, Adm Ronald USN 869 Kamoi Pl., Honolulu, HI 96825 Hayward, Capt Thomas USMC 6767 Reflection St., Redding, CA 96001 Heacock, George 5696 Montilla Dr., Fort Myers, FL 33919 Healey, David 12203 Hollow Tree Ln., Fairfax, VA 22030 Healey, Donald 2100 Lee Highway, No. 433, Arlington, VA 22201 Healy, Michael 6658 Meadowlawn, Houston, TX 77023 Hearn, Dan L. 2534 S. Granada, Rancho San Diego, CA 91977 Heber, Robert 2860 Evergreen Way, Cooper City, FL 33026 Heddy, Marc 150 Appleton St., No. 4C, Boston, MA 02166 Hedges, Daniel K. 700 Lousiana, Suite 3500, Houston, TX 77002 Heibel, Robert 5800 Millfair Rd., Fairview, PA 16415 Heiede, Ernest 555 Freeman Rd., No. 53, Central Point, OR 97502 Heinz, LtGen Edward USAF 515 Davis St., SW, Leesburg, VA 22075 Heires, John 245 Kilmarnock Dr., Millersville, MD 21108 Helms, Richard 4649 Garfield St., NW, Washington, DC 20007 Hemphill, Col William AUS 1200 S. Courthouse Rd., Arlington, VA 22204 Henderson, Lindsey P.O. Box 1014, Saluda, NC 28773 Hendrick, Lyle G. P.O. Box 24013, Columbia, SC 29224 Henger, Charles 50 Business Parkway, Richardson, TX 75081 Hennelly, Edmund 84 Sequams Lane East, West Islip, NY 11795 Hennings, Mrs. W. M. RR 2, Box 164, Bryans Rd., MD 20616 Henry, James M. Back Bay Annex, P.O. Box 1187, Boston, MA 02117 Henschel, William 120 North Harmony St., Medina, OR 44256 Herr, Mrs. Lifley P.O. Box 433840, San Ysidro, CA 92143 Herr, Cdr William USNR P.O. Box 433840, San Ysidro, CA 92143 Herring, LtCol Lorenzo USAF 370 Hill N'Dale, Lexington, KY 40503 Herron, William 204 Liberty St., Murfreesboro, NC 27855 Hersh, Burton P.O. Box 433, Bradford, NH 03221 Heuer, Richards 47 Alta Mesa Circle, Monterey, CA 93940 Hicks, W. B. 161 4th Ave., No. A, Chula Vista, CA 92010 Hildago, Balmes 240 Treasure Lake Rd., DuBois, PA 15801 Higbee-Glace, Mrs. Anne P.O. Box 85, Bolton, MA 01740 Highbarger, Robert 7509 Hackamore Dr., Potomac, MD 20854 Hull, Dr. Wayne P.O. Box 2315, Traverse City, MI 49685 Hilliard, John 13005 Chalfont Ave., Fort Washington, MD 20744 Hirschhorn, LtCdr W. USNR 4 Yale Rd., Norristown, PA 19401 Hirst, R. NLA. Mathildenstr.4, D-65189 Wiesbaden, Germany Hirzy, Franz 318 Old Hunt Rd., Fox River Grove, IL 60021 Hiscott, George E. TV 1745 Spruce Ave., Highland Park, IL 60035 Histed, Cliff 575 W. Madison St., No. 2412, Chicago, IL 60661 Hitchcock, Edward C. 7013 Old Cabin Lane, Rockville, MD 20852 Hoar, Mrs. Elanore 50 Oak St., New Canaan, CT 06840 Hobbs, Ms. Madge 260 Saint Daniel Ln., Florissant, MO 63031 Hockeimer, Henry 2801 New Mexico Ave., NW, Washington, DC 20007 Hodge, Walter P. 5953 Oakland Park Dr., Burke, VA 22015 Hoes, Ms. Laurie C. 3413 Wood Creek Dr., Suiteland, MD 20746 Hoffman, Ray 375 South End Ave., No. 8B, New York, NY 10280 Hoffmeier, Mrs. Frances 2447 Lockhill-Selma, No. 301, San Antonio, TX 78230 Hoffsis, James 7513 Dellwood Rd., NE, Albuquerque, NM 87110 Hoggan, Robert 1626 Montmorency Dr., Vienna, VA 22192 Hoke, Jonathan P.O. Box 534, Goshen, IN 46526 Holcombe, Col Harold USAR 23 Grapetree Bay, Christiansted, VI 00820 Holman, Wayne 800 4th St., SW, No. S-525, Washington, DC 20024 Holmes, Kent 1 John Lynch Rd., Compton, MD 20627 Holmes, Robert Cannon St., Inc., 88 Kearny St., No. 825, San Francisco, CA 94108 Holmes, Robert P.O. Box 180, Somers Point, NJ 08244 Holstein, Dudley 1406 Cedar Park Rd., Annapolis, MD 21401 Holt, James 16115 Kennedy St., Woodbridge, VA 22191 Hoobler, Dr. James 11410 Strand Dr., No. 410, Rockville, MD 200852 Hopkins, Ms Christine 8380 Greensboro Dr., No. 5-623, McLean, VA 22102 Hopler, Samuel 2020 Jacaranda Dr., Fort Pierce, FL 34949 Hoppy, Ms. Louise 1320 North Bryant Ave., Tucson, AZ 85712 Horan, Mrs. Yolanda 1791 Massachusetts Ave., NW, No. 405, Washington, DC 20036 Horgan, Mrs. Eileen N. 18905 Olney Mill Rd., Olney, MD 20832 Horkan, George A. Cleremont Farm, RR 1, Box 34, Upperville, VA 22176 Horn, Capt William USN 301 G St, SW, No. 822, Washington, DC 20024 Hornaday, Col William AUS 26770 Stardust Dr., Bonita Springs, FL 33923 Horne, Cdr Edward USN 1005 Olive Ave., South Island, Coronado, CA 92118 Horton, John R. P.O. Box 234, Hollywood, MD 20636 Hoskins, Capt Floyd E. USN 109 Ridley Dr., Carrollton, GA 30117 Hottel, David 110 Leisure St., Stafford, VA 22554 Houchins, Dr. Lee 1323 Windy Hill Rd., McLean, VA 2221202 Houkal, Henry C. 500 Roosevelt Blvd., No. 427, Falls Church, VA 222044 Houtehad, Gary 11438 E. Huffman Rd., No. 5, Parma Heights, OR 44130 Houston-Jones, Cheyd 4814 Glencoe Ave., No. 7, Marina Del Ray, CA 90292 Howard, Andrew 4400 Massachusetts Ave., NW, Washington, DC 20016 Howe, William 4940 Lowell St., NW, Washington, DC 20016 Howell, Ms Lucille 4038 S.E. 73rd Ave., Portland, OR 97206 Howrigen, Lois D. 3920 Mainlands Blvd.,S. Pinellas Park, FL 34666 Hubbard, Ralph 415 West Lyon Farm Dr., Greenwich, CT 06830 Hubbart, Gerald 2825 Espanola NE, Albuquerque, NM 87110 Hudson, LtCol Denis USAF 381 Bush St., No. 200, San Francisco, CA 94104 Hudson, Herbert 4005 Rickover Rd., Silver Spring, MD 20902 Hudson, Jerry 6938 Norchester Ct., Charlotte, NC 28227 Huefner, Donald 905 Country Club Dr., NE, Vienna, VA 22180 Hugel, Max 18 Horn Rd., Windham, NH 03087 Huggins, James 22 Fairview St., Belfast, ME 04915 Hulnick, Arthur 216 Summit Ave., No. E102, Brookline, MA 02146 Hunt, David 3503 Fulton St., NW, Washington, DC 20007 Hunt, E. Howard 1401 B St., NW, Washington, DC 20005 Hunter, Col David USA 185 Bar R Dr., Athens, GA 30605 Huntington, John P.O. Box 1006, Tiburon, CA 94920 Huntington, Capt Stuart P.O. Box 2906, Reston, VA 22090 Huray, Col Frank 11130 Ft. George Rd., E, Jacksonville, FL 32226 Hurburt, LtCol Arthur AUS 190 High St., No. 314, Medford, MA 02116 Hurley, Kenneth 5020 45th St., NW, Washington, DC 20016 Huse, Thomas 3512 Whitehaven Dr., Walnut Creek, CA 94598 Hussey, William 5563 B. Via Portola, Laguna Hills, CA 92653 Hutchinson, Frederick 3404 White Oak Ct., Fairfax, VA 22030 Hyde, Joseph 559 Colecroft Ct., Alexandria, VA 22314 Hyink, LtCol James USA 1962 Gomez Dr., Los Lunas, NM 87031 Hyndman, James 4811 Brookwood Dr., Mableton, GA 30059
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 17, AŚ-AT,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.

| IPN BU 00168/291 | AŚCIUKIEWICZ CZESŁAW |
| IPN BU 00945/1810 | AŚCIUKIEWICZ CZESŁAW |
| IPN BU 0855/3065 | ATAMAN STANISŁAW ANTONI |
| IPN BU 0772/2146 | ATAMANIUK (LEONIENKO) APOLLINA |
| IPN BU 0193/7333 | ATAMANIUK MIECZYSŁAW |
| IPN BU 0194/1099 | ATCZAK STANISŁAW |
| IPN BU 0290/15 | ATEMBORSKA DANUTA |
| IPN BU 0194/3639 | ATEMBORSKI STANISŁAW |
| IPN BU 00945/2238 | ATKINS – POMERAN – SALTER WIKTOR – TOMASZ – SEWERYN – HENRYK |
| IPN BU 00170/193 | ATKINS-SALTER-POMERANC TOMASZ WIKTOR HENRYK SEWERYN |
| IPN BU 0194/161 | ATLAS ANNA |
| IPN BU 001121/797 | ATLAS JANUSZ |
| IPN BU 0988/4 | ATLIŃSKI ZYGMUNT |
| IPN BU 0772/683 | ATŁAS CZESŁAWA |
| IPN BU 644/735 | ATŁASIK STANISŁAW |
| IPN BU 0967/187 | ATŁOWSKI STANISŁAW |
| IPN BU 0218/1540 | ATŁOWSKI TADEUSZ |
| IPN BU 001198/3863 | ATRAS CZESŁAW |
| IPN BU 00744/428 | ATRAS HENRYK |
| IPN BU 001121/4064 | ATRAS HENRYK |
Die Spitzel-Absteige – STASI-Gästehaus enttarnt
Become a Patron!
True Information is the most valuable resource and we ask you to give back.

In der Grenzstadt (Brandenburg) ist ein Gebäude als ehemaliges Gästehaus für hochrangige Mitarbeiter der DDR-Staatssicherheit identifiziert worden.
Die dreigeschossige Villa wurde einst von einem Sonderreferat des Vize-Staatssicherheits-Ministers Gerhard Neiber verwaltet. Das sagte Rüdiger Sielaff von der Stasiunterlagenbehörde. Auf dem 2100 Quadratmeter großen Grundstück befinden sich unter anderem ein gut erhaltenes Schwimmbad und eine Kneipe, die über einen unterirdischen Gang zu betreten sind.
World at War TV – Ukraine and Russia – Forever Linked By Chernobyl
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Ukraine and Russia have a long contentious history and perhaps no more significant event marks this history more than the catastrophic Chernobyl nuclear reactor accident that occured in 1986.
This fascinating video takes you to the infamous city of Pripyat, a town of 50,000 that was abandoned overnight in the hours after the accident. This eerie ghost town marks the passage of time with silent decay, uninhabitable for another 20,000 years.
After a visit to modern day Pripyat, a look back at that fateful day and the desperate measures that were taken to prevent even greater disaster and loss of life!
TOP-SECRET – The Secret List of CIA Sources – 2.619 Names and Adresses, Part 7,G,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
G
Gable, Lamar 2600 Golden Gate Parkway, Naples, FL 33942 Gabriel, James 268 S. South St., Wilmington, OH 45177 Gaddy, David The Riverside, Box 46, Tappahannock, VA 22560 Gagner, Wayne 9104 Charred Oak Dr., Bethesda, MD Gaines, Stanley 3040 Cedarwood Ln., Falls Church, VA 22042 Gallagher, Patrick 7271 Swan Point Way, Columbia, MD 21045 Gallagher, Thomas 11400 Washington Pl., No. W 1102, Reston, VA 22090 Garbler, Paul 6222 West Miramar Dr., Tucson, AZ 85715 Gardemal, Cdr Robert USN 3123 S. Ninth St., Chickasha, OK 73018 Gardner, David 8477 Menicoor Blvd., Largo, FL 34647 Gardner, Theodore 4606 Jones Creek Rd., No. 270, Baton Rouge, LA 70817 Garner, Arthur MHPCC/DOD Facility, 590 Lipoa Pkw., 3100, Kibei, HI 96753 Garrison, David 3731 Olympia Dr., Houston, TX 77019 Garrison, Mrs. Mildred 100 South Osceola Dr., Indian Harbour Beach, FL 32937 Gartland, Edward 7 Cypress Rd., Milford, NH 03055 Garvey, Geoffrey 1287 Merion Ct., Murrells Inlet, SC 29576 Gaston, Col Arthur USAF 370 Sandringham Rd., Rochester, NY 14610 Gaumond, Ms. Marian 12052 North Shore Dr., No. 221B. Reston, VA 22090 Gautier, Len P.O. Box 3166, Oakton, VA 22124 Gavaghen, William 1165 Silver Beech Rd., Herndon, VA 22070 Gavello, Alfred 36 San Carlos Ct., Walnut Creek, CA 94598 Gay, Earle 50 Park Ave., New York, NY 10016 Gay, Richard P.O. Box 1027, Blue Hills, ME 04614 Geary, Dr. Fred 434 Rolling Hill Dr., Sebastian, FL 32958 Geary, Mrs. Ruth 3130 Duke St., Alexandria, VA 22314 Geer, Sgt Galen USMCR 1310 Reed Ln., Canon City, CO 81212 Geiger, RAdm Robert USN 3273 Charles MacDonald Dr., Sarasota, FL 34240 Geise, Dr. Marion 1600 S. Joyce St., No. C812, Arlington, VA 22202 Gelwick, Dr. Robert 1708 Berwick Ln., Middletown, OH 45042 Geohegan, Paul 4111 Platt Dr., Kenner, LA 70065 George, Clair 5026 Allan Rd., Bethesda, MD 20816 Gerard, Thomas Berth 38, West Pier, Rappas Marina, Sausalito, CA 94965 Gerber, Burton 2311 Connecticut Ave., NW, No. 305, Washington, DC 20008 Gerber, William 16 Princes Ave., Chelmsford, MA 01863 Getsinger, Norman P.O. Box 575, Flint Hill, VA 22627 Ghormley, LtCol Wflliam USAF 4125 Granada Dr., Georgetown, TX 78628 Giambri, Philip 131 SW 194th St., Normandy Park, WA 98166 Gibbens, LtCol Edward USAF 4675 S. 18th St., East, Mountain Rome, ID 83647 Gibson, Albert 9110 Deer Park Rd., Great Falls, VA 22066 Gibson, Sgt Jonathan USA P.O. Box 15514, West Palm Beach, FL 33416 Gibson, Roger 912 Ortega Ave., Coral Gables, FL 33134 Gibson, William 21 Brandon Pl., Cleveland, OH 44116 Gillard, Ruth 3747 Terra Grande Dr., No. 1A, Walnut Creek, CA 94595 Gillette, LtCdr Halbert USN 1355 Leslie Dr., Merritt Island, FL 32952 Gilliam, Mrs. Clare 5908 Cedar Parkway, Chevy Chase, MD 20815 Gilligan, Dr. Robert 18 Kirkwood Circle, Brigantine, NJ 08203 Gillingham, LtCdr W. USNR 5433 Landau Dr., No. 22, Dayton, OR 45429 Gillis, James 1518 Notre Dame Dr., Davis, CA 95616 Giovinazzo, Anthony 840 Weymouth Rd., Medina, OH 44256 Girard, Harlan P.O. Box 58700, Philadelphia,PA 19102 Gittinger, John 1022 Thistle Wood Rd., Norman, OK 73072 Givans, Robert L. 2275 W. Nottingham St., Springfield, MO 65810 Given, David R. 235 11th Avenue, Huntington, WV 25701 Givens, John C. 1330 Ponder Point Dr., Sandpoint ID 83864 Gleisberg, Harold E. P.O. Box 536, Roswell, NM 88202 Glover, LCDR Norman J. USCGR 271 Central Park West, New York, NY 10024 Glunt, E. Merle RR 1, Box 303, Mount Union, PA 17066 Glunt, CDR Elliott H. USN 10411 Brunswick Ave., Silver Spring, MD 20902 Goeller, Carl G. 4605 Lanterman Rd., Youngstown, OH 44515 Goepper, Forrest S. 1595 N. Atlantic Ave., No.301, Cocoa Beach, FL 32931 Goerder, Col Robert L. USAF 902 South Garner St., State College, PA 16801 Goff, CPT Ronald L. 251 Pauline Ave., Akron, OH 44312 Gold, Barry A. 90 State St., Albany, NY 12207 Goldberg, Col Nathan S. USAF 603 N. Doheny Drive, #2A, Beverly Hills, CA 90210 Golden, Maj Robert J. USA 751 5 La Madera Ct., NE, Albuquerque, NM 87109 Goldman, Edward H. 46 Noyes St., Portland, ME 04103 Goldman, Elmer M. 52 Gregory Rd., Framingham, MA 01701 Goldsher, Marvin 5733 N. Sheridan Rd #220, Chicago, IL 60660 Goloway, Edward D. RR 3, Box 5850, Berryville, VA 22611 Gonakis, Mike S. 1044 E. Dartinoor Ave., Seven Hills, OH 44131 Goodden, Royal T. Box 1090, Fort Myer, VA 22211 Goodfield, Dr. Barry Austin 1060 Clay St., San Francisco, CA 94108 Goodjoin, Al P.O. Box 632, New Rochelle, NY 10801 Goodman, Billy L. 1703 McKay Ct., Jefferson City, MO 65109 Goodwin, Joseph C. 415 Roebling Rd., South Belleair, FL 34616 Gordon, Charles J. 1924 Blair Blvd., Wooster, OH 44691 Gordon, BrigGen Dudley J. USA 320 Palm Court, Indialantic, FL 32903 Gordon, Gordon 6145 Jochums Drive, Tucson, AZ 85718 Gordon, Steven 77 Terapin St., Mastic, NY 11950 Gorman, Ms. Judith E. 19 Ripley St., Somerset, MA 02725 Gorsline, Capt Samuel G. USN 225 Deddie Terrace, Fallbrook, CA 92028 Goss, Porter J. US House of Rep. 509 Cannon Building, Washington, DC 20515 Gottschalk, Capt Jack USAR 12 Crossbrook Road, Livingston, NJ 07039 Goulden, Joseph C. 1534 29th St., N.W. Washington, DC 20007 Gourlay, Lawrence 4660 Ocean Blvd. No. 1-2, Sarasota, FL 33581 Gourley, William 3120 Myrtle Ave., 6094, San Diego, CA 92104 Govia, Philip Anthony P.O. Box 941, Millville, NJ 08332 Gowin, Maj Robert W. AUS 8517 Lakinhurst Ln., Springfield, VA 22152 Grabo, Ms. Cynthia M. 2001 Columbia Pike, No. 606, Arlington, VA 22204 Grady, J. William 7510 Glenbrook Rd., Bethesda, MD 20814 Graff, Ms. Eleanora 6145 Beachway Dr., Falls Church, VA 22041 Graham, Gordon 21 Beacon St., No.8-H, Boston, MA 02108 Graham, Thomas B. 716 Forest Park Rd., Great Falls, VA 22066 Grasle, Milton 111 Donald St. East Saint Louis, IL 62206 Graves, Hunter Lee 2995 Old Lynchburg Rd., N. Garden, VA 22959 Gray, LtCol George W. AUS 5550 36th NE, Seattle, WA 98105 Gray, Peter J. 20420 Lake Rd., Rocky River, OH 44116 Gray, R. Jean 5180 Meadville St., Excelsior, MN 55331 Graybeal, Sidney N. 10101 Langhorne Ct., Bethesda, MD 20817 Greaney, John K. 6112 Western Ave., Chevy Chase, MD 20815 Greaves, Fielding P.O. Box 150368, San Rafael, CA 94915 Green, Dr. Gilbert P.O. Box 98, Gaithersburg, MD 20884 Green, Mrs. Jacqueline R. Rt 2 Box 347, Lovettsville, VA 22080 Green, James F. 6522 Heather Brook Ct., McLean, VA 22101 Greenblatt, Col Owen USAF 4125 Century Ct., Alexandria, VA 22312 Greene, Harris 3671 N. Harrison St., Arlington, VA 22207 Greene, Ms. Nancy D. P.O. Box 7339, Incline Village, NV 89450 Greenfield, Alfred I. 18 Bradstreet Rd. Hampton, NH 03842 Greenman, Roger 1173A Second Ave., No. 313, New York, NY 10021 Greenwald, Col Robert USAR 21509 S. Figueroa St., Carson, CA 90745 Greico, Rev. Charles F. P.O. Box 635, Chester, NJ 07930 Grier, E. Phillips Sr. 13201 Conrad Court Woodbridge, VA 22191 Gries, David D. 4855 Reservoir Rd., NW Washington, DC 20007 Griffith, B. Herold M.D.S.C 320 Greenwood St., Evanston, IL 60201 Griffith, Carl F. P.O. Box 845, Middlebury, CT 06762 Griffith, Mrs. Jeanne B. 320 Greenwood St., Evanston, IL 60201 Griffith, Richard A. 511 N. Highland St., Arlington, VA 22201 Griffith, Dr. Richard R. R.R. 1, Box 373-70, Randolph, VT 05060 Griffith, William P.O. Box 7294, State Capitol, Albany, NY 12224 Grigg, Harry K. 61 Longview Dr., Green Brook, NJ 08812 Grigrovich-Barsky, Gleb B. RR 1 Box 432, Kilmarnock, VA 22482 Grill, LtCol Jack USA 2280 South 19th St., Mount Vernon, WA 98273 Grillo, Cdr Pat L. USN 1330 Victorian Crescent, Virginia Beach, VA 23454 Grimm, Howard 38-40 Regatta Pl., Douglaston, NY 11363 Gross, Walter H. P.O. Box 1804, Sedona, AZ 86339 Gross, Maj William J. USAF 1760 Valleybrook Pl.,. Dayton, OH 45459 Grostephen, Ms. Marjorie L 6145 Beachway Dr., Falls Church, VA 22041 Grubbs, Judson B. 1037 Rodeo Rd., Pebble Beach, CA 93953 Guay, BrigGen Georges R. USAF P.O. Box 16, APO, AE 09777 Guenther, LtCol John J. USMC 265 Sea Woods Dr. North St., Augustine, FL 32084 Guernsey, Douglas D. 305 Hamden Kells, Peachtree City, GA 30269 Guffin, LtCol Robert A. USAF 5148 Splitrail Ct., Colorado Springs, CO 80917 Guider, James J. 385 Abbott Ave., P.O. Box 630, Ridgefield, NJ 07657 Gunn, Edward M. M.D. 300 Wood Haven Dr., No.1507, Hilton Head Island, SC 29928 Gustafson, Harry M. 237 East Prospect, Mt. Prospect, IL 60056 Guth, Robert M. 3800 Powell Ln., Falls Church, VA 22041
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 16, AS,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 01000/1711 | ASENDRYCH KAZIMIERZ |
| IPN BU 0968/7 | ASFAL EUGENIUSZ |
| IPN BU 00328/156 | ASFAL EUGENIUSZ |
| IPN BU 01256/10 | ASFAL MAREK |
| IPN BU 0967/166 | ASFAL WIESŁAWA |
| IPN 00 1043/2744 | ASHMAN RUDNICKA JOANNA |
| IPN BU 0806/3010 | ASIESIUKIEWICZ BARBARA |
| IPN BU 0833/11 | ASIUKIEWICZ MARIAN |
| IPN BU 0772/2145 | ASKANAS ALINA |
| IPN BU 0194/2410 | ASMAN (NOWACKA) HALINA |
| IPN BU 0604/1557 | ASMAN EDWARD |
| IPN BU 00750/114 | ASMAN HENRYK |
| IPN BU 0772/737 | ASMAN IRENA |
| IPN BU 00945/775 | ASPARUCHOW – ASPROWSKI – ASPROS PIOTR – PETROS |
| IPN BU 00191/327 | ASTIER – JUNG KRYSTYNA |
| IPN 00 1043/2847 | ASTIER JUNG KRYSTYNA |
| IPN BU 00244/115 | ASTMAN ELŻBIETA |
| IPN BU 00244/119 | ASTMAN MARKUS |
| IPN BU 748/169 | ASTMAN MARKUS |
| IPN BU 644/739 | ASWAL EUGENIUSZ |
| IPN BU 01000/1686 | ASWALD WŁODZIMIERZ |
| IPN BU 00945/1507 | ASZ LEW |
| IPN BU 698/61 | ASZARD ALFRED |
| IPN BU 0957/14 | ASZER STANISŁAW |
| IPN BU 00945/1581 | ASZKENAZY HENRYK |
| IPN BU 0287/183 | ASZKIELANIEC GENOWEFA |
| IPN BU PF | 251/190 ASZKOŁDOWICZ ANDRZEJ |
| IPN BU 693/1436 | ASZKOWSKA JANINA |
| IPN BU 0891/132 | ASZTEMBORSKI JAN |
| IPN BU 00244/119 | ASZYCHMIN BORYS |
| IPN BU 00244/164 | ASZYCHMIN BORYS |
| IPN BU 0193/1303 | ASZYCHMIN BORYS BOLESŁAW |
| IPN BU 644/734 | ASZYJCZYK JÓZEF |
| IPN BU 001134/3967 | ASZYK PIOTR |
How the Cyber-STASI wants to overtake the Internet
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Since the early days of TCP, port scanning has been used by computer saboteurs to locate vulnerable systems. In a new set of top secret documents seen by Heise, it is revealed that in 2009, the British spy agency GCHQ made port scans a “standard tool” to be applied against entire nations (Figure 1, see the picture gallery). Twenty-seven countries are listed as targets of the HACIENDA program in the presentation (Figure 2), which comes with a promotional offer: readers desiring to do reconnaissance against another country need simply send an e-mail (Figure 3).
Bild 1 von 26
Hacienda, Mugshot, Olympia, ORB – Slides and Graphics
Figure 1
The HACIENDA Programm
The documents do not spell out details for a review process or the need to justify such an action. It should also be noted that the ability to port-scan an entire country is hardly wild fantasy; in 2013, a port scanner called Zmap was implemented that can scan the entire IPv4 address space in less than one hour using a single PC. [3] The massive use of this technology can thus make any server anywhere, large or small, a target for criminal state computer saboteurs.
The list of targeted services includes ubiquitous public services such as HTTP and FTP, as well as common administrative protocols such as SSH (Secure SHell protocol – used for remote access to systems) and SNMP (Simple Network Management Protocol – used for network administration) (Figure 4). Given that in the meantime, port scanning tools like Zmap have been developed which allow anyone to do comprehensive scans, it is not the technology used that is shocking, but rather the gargantuan scale and pervasiveness of the operation. The next section gives background on how port-mapping tools work and what information is gained by using them, making it clear what becomes possible when a state actor uses them at scale.
Background: The TCP Three-Way Handshake
The most commonly-used protocol on the Internet is TCP | the Transmission Control Protocol. Every time an email is sent or a web page is browsed, TCP is the protocol that is used to move data reliably between clients and servers. Port-mapping tools take advantage of a structural problem in TCP in order to determine what services are running on a system. Since the early days of TCP, port scanning has been used by attackers to locate vulnerable systems. Whenever a TCP client wants to communicate with a TCP server, the two parties perform what is called a TCP three-way handshake. The flawed design of this handshake is the foundation for port mapping tools, as during the handshake, the server leaks information about the availability of a service without checking the client’s authorization.
Figure 5 illustrates the sequence of TCP packets which are sent to establish a connection. The establishment of the connection works as follows: the host which wants to initiate a connection first sends out a TCP SYN (“synchronize”) packet. If the destination host accepts the connection request, it sends a SYN/ACK (“synchronize/acknowledge”) packet. After receiving a positive reply, the initiating host sends out an ACK (“acknowledge”) packet, which finalizes the TCP three-way handshake. This TCP three-way handshake allows an adversary to easily determine if some TCP service is offered at a given port by a host on the Internet: if the TCP port is closed, the server reacts differently to the TCP SYN packet (Figure 6), sending a RST (“reset”) packet instead of the SYN/ACK it would send were the port open. Thus, an adversary can easily map Internet services by considering the differences in the server’s replies in the packet flows depicted in Figure 5 and Figure 6 respectively.
The Authors
- Julian Kirsch is finishing his Master’s degree at the Technische Universität München, where he will soon join Prof. Eckert’s chair for computer security to pursue a doctorate degree. His research interests include reverse engineering and counter-espionage.
- Christian Grothoff is funded by the Deutsche Forschungsgemeinschaft (DFG) under ENP GR 3688/1-1 until the end of August 2014. He is now moving from the Technische Universität at München to Inria Rennes, where he will start a research team in the area of secure decentralized networks. His research interests include compilers, programming languages, software engineering, networking and security.
- Monika Ermert is a freelancer for heise online and has written on DNS, DNS security and more issues for a many years.
- Jacob Appelbaum is an investigative journalist.
- Laura Poitras is a documentary film maker and journalist living in Berlin.
- Henrik Moltke is an investigative journalist.
The Enemy Online
In addition to simple port scans, GCHQ also downloads so-called banners and other readily available information (Figure 4). A banner is text sent by some applications when connecting to an associated port; this often indicates system and application information, including version and other information useful when looking for vulnerable services. Doing reconnaissance at the massive scale revealed in the documents demonstrates that the goal is to perform active collection and map vulnerable services ubiquitiously, not to go after specific targets.
By preparing for attacks against services offered via SSH and SNMP, the spy agency targets critical infrastructure such as systems used for network operations. As shown in the past with the penetration of Belgacom and Stellar, when an employee’s computer system or network credentials may be useful, those systems and people are targeted and attacked.
The database resulting from the scans is then shared with other spy agencies of the Five Eyes spying club (Figure 7), which includes the United States, Canada, United Kingdom, Australia and New Zealand. MAILORDER is described in the documents as a secure transport protocol used between the Five Eyes spy agencies to exchange collected data.
Every device a target
The process of scanning entire countries and looking for vulnerable network infrastructure to exploit is consistent with the meta-goal of “Mastering the Internet”, which is also the name of a GCHQ cable-tapping program: these spy agencies try to attack every possible system they can, presumably as it might provide access to further systems. Systems may be attacked simply because they might eventually create a path towards a valuable espionage target, even without actionable information indicating this will ever be the case.
Using this logic, every device is a target for colonization, as each successfully exploited target is theoretically useful as a means to infiltrating another possible target. Port scanning and downloading banners to identify which software is operating on the target system is merely the first step of the attack (Figure 8). Top secret documents from the NSA seen by Heise demonstrate that the involved spy agencies follow the common methodology of online organized crime (Figure 9): reconnaissance (Figure 10) is followed by infection (Figure 11), command and control (Figure 12), and exfiltration (Figure 13). The NSA presentation makes it clear that the agency embraces the mindset of criminals. In the slides, they discuss techniques and then show screenshots of their own tools to support this criminal process (Figure 14, 15 and 16).
Internet Colonization
The NSA is known to be interested in 0-day attacks, which are attacks exploiting largely unknown vulnerabilities for which no patch is available. Once an adversary armed with 0-day attacks has discovered that a vulnerable service is running on a system, defense becomes virtually impossible. Firewalls are unlikely to offer sufficient protection, whether because administrators need remote access or because spy agencies have already infiltrated the local network (siehe: Barton Gellman and Ashkan Soltani. Nsa infiltrates links to yahoo, google data centers worldwide, snowden documents say. The Washington Post, October 2013). Furthermore, adding additional equipment, such as firewalls administered via SNMP, into an internal network may also open up new vulnerabilities.
Figure 8 points to a particular role that HACIENDA plays in the spy club’s infrastructure, namely the expansion of their covert infrastructure. The top secret documents seen by Heise describe the LANDMARK program, a program by the Canadian spy agency CSEC which is used to expand covert infrastructure (Figure 17).
The covert infrastructure includes so-called Operational Relay Boxes (ORBs), which are used to hide the location of the attacker when the Five Eyes launch exploits against targets or steal data (Figure 18). Several times a year, the spy club tries to take control of as many machines as possible, as long as they are abroad. For example, in February 2010 twentyfour spies located over 3000 potential ORBs in a single work day (Figure 19). However, going over the port scan results provided by HACIENDA was considered too laborous (Figure 20), so they programmed their OLYMPIA system to automate the process (Figure 21). As a result, the spies brag that they can now locate vulnerable devices in a subnet in less than five minutes (Figure 22).
The Canadians are not the only ones using HACIENDA to locate machines to compromise and turn into ORBs. At GCHQ, the hunt for ORBs is organized as part of the MUGSHOT program (Figure 23). The GCHQ has also automated the process and claims significant improvements in accuracy due to the automation (Figure 24). Again the information obtained from HACIENDA plays a prominent role (Figure 25). A key point is that with MUGSHOT the GCHQ integrates results from active scans (HACIENDA) as well as passive monitoring (Figure 26), to “understand everything important about all machines on the Internet”.
Thus, system and network administrators now face the threat of industrial espionage, sabotage and human rights violations created by nation-state ad- versaries indiscriminately attacking network infrastructure and breaking into services. Such an adversary needs little reason for an attack beyond gaining access and is supported by a multi-billion dollar budget, immunity from prosecu- tion, and compelled collaboration by companies from Five Eyes countries. As a result, every system or network administrator needs to worry about protecting his system against this unprecedented threat level. In particular, citizens of countries outside of the Five Eyes have, as a result of these programs, greatly reduced security, privacy, integrity and resilience capabilities.
Spy agencies are using their powers to commandeer Internet systems for power projection. Their actions follow the standard template of cyber-criminal behav- ior, using reconnaissance through active and passive port scanning to identify potential victims. Given this serious threat, system administrators need to improve their defensive posture and, in particular, reduce the visibility of non- public services. Patching services does not help against 0-day attacks, and firewalls may not be applicable or suffcient. In the second part of our article, we will introduce another option for system administrators to make non-public system administration services less visible for reconnaissance operations. By standardizing such techniques, the Internet community may be able to dampen the ability of security services to master the Internet.
Knocking down the HACIENDA
In this article, we will describe a new port knocking variant that uses the nation-state adversary model, and thus offers some protections against the HACIENDA program, thereby possibly stopping the spy agencies at the reconnaissance stage.
While defending against undisclosed vulnerabilities in public services is rather difficult, minimizing one’s visible footprint and thus one’s attack surface for administrative services is much easier. Port knocking [9] is a well-known method for making TCP servers less visible on the Internet. The basic idea is to make a TCP server not respond (positively) to a TCP SYN request unless a particular “knock” packet has been received first. This can be helpful for security, as an attacker who cannot establish a TCP connection also cannot really attack the TCP server.
However, traditional port knocking techniques [10] generally do not consider a modern nation-state adversary. Specifically, port scans are not the only method an attacker may use to learn about the existence of a service; if the service is accessed via a network where the adversary is able to sniff the traffic, the adversary may observe the connection and thereby deduce the existence of a service. A nation-state attacker may even be able to observe all traffic from the TCP client and perform man-in-the-middle attacks on traffic originating from the client. In particular, with compromised routers in the infrastructure, it is possible to execute a man-in-the-middle attack to take over a TCP connection just after the initial TCP handshake has been completed. An advanced attacker in control of routers may also try to identify the use of insufficiently stealthy port knocks by detecting unusual patterns in network traffic. However, it may still be safe to assume this adversary does not flag a standard TCP handshake as suspicious, as this is way too common.
TCP Stealth
TCP Stealth is an IETF draft (Julian Kirsch, Christian Grothoff, Jacob Appelbaum, and Holger Kenn: Tcp stealth, August 2014. IETF draft) which describes an easily-deployed and stealthy port knocking variant. TCP Stealth embeds the authorization token in the TCP ISN, and enables applications to add payload protections. As a result, TCP Stealth is hard to detect on the network as the traffic is indistinguishable from an ordinary 3-way TCP handshake, and man-in-the-middle attacks as well as replay attacks are mitigated by the payload protections. TCP Stealth works with IPv4 and IPv6.
TCP Stealth is useful for any service with a user group that is so small that it is practical to share a passphrase with all members. Examples include administrative SSH or FTP access to servers, Tor Bridges, personal POP3/IMAP(S) servers and friend-to-friend Peer-to-Peer overlay networks. The easiest way to use TCP Stealth is with operating system support. TCP Stealth is available for Linux systems using the Knock patch (siehe: Julian Kirsch. Knock, August 2014).. For kernels that include this patch, TCP Stealth support can be added to applications via a simple setsockopt() call, or by pre-loading the libnockify shared library and setting the respective environment variables.
Installation
As the mainline Linux currently does not yet offer support for Knock, the kernel of the machine which should be using Knock needs to be patched. Patching the kernel is straightforward:
1. First, obtain the sources of the desired kernel version from https://www. kernel.org if you intend to use a vanilla running kernel. Note that many distributions make adaptations to the kernel and therefore provide custom kernel sources, so one might want to check for the customized kernel sources.
2. Once the kernel sources are available, download the appropriate Knock patch from https://gnunet.org/knock. Note that if you intend to run a kernel version which is not explicitly listed on the Knock website, the best option is to try out the patches of the closest version provided.
3. Change to the directory where the kernel sources reside (replace the <your-version>-part according to your selection of the kernel- and the patch-version) and apply the patches (you can f ind more information on how to apply and revert patches on the kernel source in the kernel.org archives):
$ cd linux-<your-version>/
~/linux $ patch -p1 < /path/to/knock/patch/tcp_stealth_<your-version>.diff
4. Get the configuration of the currently running kernel. There are two widely used methods which can be used interchangeably:
(a) Debianoids maintain a copy of the kernel configuration parameters in the /boot directory. You can copy the config to your current kernel sources using the following command:
~/linux $ cp /boot/config-$(uname -r) .config
(b) Many other distributions compile the kernel with the possibility to read the running kernel’s configuration from the /proc/ file system:
~/linux $ zcat /proc/config.gz > .config
(c) If none of the cases above applies for your distribution, you can try to use the default kernel configuration by entering
~/linux $ make defconfig
However, do not expect a convincing kernel to result from this in terms of performance and stability.
5. Choose the defaults for all configuration parameters which are not in your current configuration. A different kernel version might introduce new compile configuration options:
~/linux $ yes "" | make oldconfig
6. Enable Knock in your current configuration by selecting Networking Support > Networking Options > TCP/IP networking > TCP: Stealth TCP socket support in the inter-active menu:
~/linux $ make menuconfig
7. The kernel is now ready for compilation. Enter
~/linux $ make bzImage && make modules
to compile the kernel and all additional modules. Be prepared for the fact that this step can take a long time. If you have a machine with more than one processor core, you can adjust the number of build threads using the -j option to both make commands.
8. If compilation succeeds, install the new kernel and all modules. Afterwards, automatically create a new initramdisk for your newly compiled kernel. If you have sudo installed, enter
~/linux $ sudo make modules_install && sudo make install
otherwise enter the these commands into a root prompt leaving out both sudos.
9. Reboot the machine and instruct your boot manager to boot into the new kernel. You now have a Knock aware machine.
Enabling Knock Using LD PRELOAD
Knock can be used without having to modify the source code of the program. This can be useful in cases where the source code is not available or when inserting the needed libc calls is infeasible (for example due to restrictions imposed by the application logic).
In order to use Knock in existing applications, a dynamic library libknockify is provided. The basic usage of the libknockify shared object to enable Knock for program example program is as follows:
KNOCK_SECRET="shared secret"
KNOCK_INTLEN=42
LD_PRELOAD=./libknockify.so
./example_program
Afterwards, if the application example program communicates via TCP, libknockify will set the respective socket options to enable the use of Knock in the kernel. In the example, the shared secret is derived from the text “shared secret”, and the content integrity protection is limited to the first 42 bytes of payload in the TCP stream. If the KNOCK INTLEN variable is not set, content integrity protection is disabled.
Using TCP Stealth via setsockopt()
Application developers can integrate support for TCP Stealth directly into their code. This has the advantage that it is possible to control which TCP connections have TCP Stealth enabled, and it might further improve usability. To enable basic port knocking with a Knock-enabled kernel, the application only needs to perform a single setsockopt() call after creating the TCP socket:
char secret[64] = "This is my magic ID.";
setsockopt (sock, TCP_STEALTH, secret, sizeof (secret));
For content integrity protection, TCP clients need to additionally specify the first bytes of the payload that will be transmitted in a second setsockopt() call before invoking connect():
char payload[4] = "1234";
setsockopt(sock, IPPROTO_TCP, TCP_STEALTH_INTEGRITY, payload, sizeof(payload));
connect (sock, ...);
write (sock, payload, sizeof (payload));
Servers expecting content integrity protection merely need a second setsockopt() call to specify the number of bytes that are expected to be protected by TCP Stealth:
int payload_len = 4;
setsockopt(sock, IPPROTO_TCP, TCP_STEALTH_INTEGRITY_LEN,payload_len, sizeof(payload_len));
Limitations
Nowadays, most end-user devices access the Internet from behind a gateway router which performs network address translation (NAT). While TCP Stealth was designed to avoid the use of information that is commonly altered by NAT devices, some NAT devices modify TCP timestamps and ISNs and may thus interfere with the port knocking mechanism.

Table 1: Changes made to the ISN by middle-boxes dependent on the destination port as measured by Honda et al. (Michio Honda, Yoshifumi Nishida, Costin Raiciu, Adam Greenhalgh, Mark Handley, and Hideyuki Tokuda. Is it still possible to extend tcpß In Procee- dings of the 2011 ACM SIGCOMM Conference on Internet Measurement Conference, IMC ’11, pages 181{194, New York, NY, USA, 2011. ACM.) ![]()
Table 1 summarizes experiments by Honda et al. showing how common ISN modification by NAT devices is in practice. In terms of security, TCP Stealth is limited to the 32 bits of the TCP ISN field; hence, a persistent adversary may still succeed by luck or brute force. However, we believe that TCP Stealth will provide adequate protections against indiscriminate attackers performing untargeted attacks (such as HACIENDA). Moving administrative services to non-standard ports can further decrease the chance of accidental discovery by active port scanners.
While the use of integrity protection with TCP Stealth is technically optional, port knocking without integrity protections offers little security against an adversary that observes network traffic and hijacks connections after the initial TCP handshake. Thus, future network protocols should be designed to exchange key material at the beginning of the first TCP packet. Sadly, this is not the case for SSH, which instead exposes a banner with version information to an attacker well before the cryptographic handshake. Hence, design flaws in the SSH protocol currently require the use of an additional obfuscation patch [2] to effectively use TCP Stealth integrity protections with SSH.
Summary
Technical solutions such as TCP Stealth are one way for administrators to harden their systems by protecting internal TCP services against the attacks by criminals, be they private, commercially motivated or state parties. However, as Linus Neumann of the CCC recently stated in an OpEd for Heise, it may not be possible to win the race in the long run solely through technical means. Without the necessary political will to legally protect, promote and fund secure communication systems, this one-sided battle will continue | and users will lose. Neumann underlined that secure communication systems were possible, but that governments are much more concerned about loss of control than about hardened (and less controllable) networks. Much more political work lays ahead; however, operating system vendors and administrators can improve the situation today by deploying modern security solutions.
Figures and Graphs at
Permalink: http://heise.de/-2292681
Wie die Cyber-STASI das Internet übernehmen will
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Das HACIENDA-Programm
Das GCHQ-Programm mit dem Namen HACIENDA bewirbt in einer Präsentation aus dem Jahr 2009 Vollscans für insgesamt 27 Länder, verbunden mit dem Angebot: Wer ein anderes Land aufklären will, braucht nur eine E-Mail zu schicken. (Folie 3). Regeln für die Begutachtung oder notwendige Begründungen für eine solche Aktion finden sich in den Dokumenten nicht. Die Möglichkeit, ganze Länder zu scannen, ist keine wilde Fantasie: Neue Tools wie Zmap erlauben seit 2013 das Ausleuchten des gesamten IPv4-Adressraums weltweit in weniger als einer Stunde. Ein derart gezielter, massiver Einsatz der Scans durch den Staat macht daher jeden einzelnen Server zu einem Ziel staatlicher Computersaboteure.
Auf der Liste der Dienste – und entsprechend Ports – die angegriffen wurden, finden sich allgemeine öffentliche Dienste wie das Webprotokoll (HTTP) oder Dateitransferprotokoll (FTP) ebenso wie Werkzeuge, die üblicherweise von Netzwerkadministratoren eingesetzt werden, etwa das Secure Shell Protokoll (SSH) oder das Simple Network Management Protokoll (SNMP). Da in der Zwischenzeit veröffentlichte Werkzeuge wie Zmap es fast jedermann erlauben, umfangreiche Scans durchzuführen, ist es nicht so sehr die eingesetzte Technik, die schockiert, sondern deren massive, praktisch lückenlose Ausnutzung gegen beliebige Systeme und potentiell alle Nutzer im Netz.
Die Funktionsweise von Portscannern sowie die Erkenntnisse, die durch deren Einsatz gewonnen werden können, führen vor Augen, was der großflächige Einsatz von Portscannern durch Staaten zur Folge hat.
Hintergrund: Der TCP Three-Way Handshake
Die Autoren:
- Julian Kirsch schließt gerade seinen Master an der Technischen Universität München ab und wird dort künftig am Lehrstuhl für Computersicherheit von Professor Eckert promovieren. Seine Forschungsinteressen sind unter anderem Reverse Engineering und Spionageabwehr.
- Christian Grothoff wird noch bis Ende August von der Deutsche Forschungsgemeinschaft (DFG) im Rahmen des Emmy-Noether Programms unter dem Kennzeichen ENP GR 3688/1-1 gefördert. Er zieht dann von der Technische Universität München nach Inria Rennes, wo er eine Forschungsgruppe im Bereich sicherer dezentralisierter Netzwerke aufbauen wird. Seine Forschungsinteressen beinhalten den Bau von Kompilern, Programmiersprachen, Software Engineering, Netzwerke und Sicherheit.
- Monika Ermert ist freie Journalistin und berichtet für heise online seit vielen Jahren über DNS, DNS-Sicherheit und andere Themen.
- Jacob Appelbaum arbeitet als investigativer Journalist.
- Laura Poitras ist Dokumentarfilmemacherin und Journalistin und lebt in Berlin
- Henrik Moltke arbeitet als investigativer Journalist.
TCP, das Transmission Control Protokoll, ist das am weitesten verbreitete Protokoll im Netz. Jedes Mal, wenn eine Mail verschickt oder eine Webseite aufgerufen wird, sorgt TCP für die verlässliche Übertragung der Datenpakete zwischen Clients und Servern. Portscanner machen sich ein strukturelles Problem von TCP zunutze, um zu bestimmen, welche Dienste auf einem System aktiv sind. Seit Urzeiten werden die Scans daher von Angreifern genutzt, um verwundbare Server zu finden. Einer Kommunikation von TCP-Client und -Server geht immer ein so genannter Three-way-handshake voraus. Ein Fehler im Design dieses “Händedrucks” der beiden Server erlaubt das Portscanning überhaupt. Denn der Server gibt dabei immer preis, ob ein bestimmter Dienst verfügbar ist, ohne vorab zu prüfen, ob der anfragende Client überhaupt autorisiert ist, auf den Dienst zuzugreifen.
Die Grafik 5 in der Bilderstrecke illustriert, wie eine TCP-Verbindung zustande kommt. Erst sendet der Host, der eine Verbindung herstellen will, ein TCP SYN Paket. Der Zielserver antwortet mit SYN/ACK, wenn er die Anfrage akzeptiert. Mit einem weiteren ACK-Segment komplettiert der anfragende Host den Three-Way-Handshake, der Verbindungsaufbau ist abgeschlossen. Genau dieser Handshake erlaubt es einem Angreifer festzustellen, ob TCP-Dienste über die jeweiligen Ports angeboten werden: ist der TCP Port geschlossen, reagiert der Server mit einem RST-Paket (“reset”) auf das erste SYN Paket (Grafik 6 in der Bilderstrecke). Für den Angreifer ist es ein Leichtes, die vorhandenen Internetdienste zu kartieren, indem er die unterschiedlichen Serverantworten im Strom der Pakete berücksichtigt. (Vergleiche Grafik 5 und Grafik 6)
Der Feind im Netz
Das GCHQ macht, wie aus ihrer Präsentation von HACIENDA ersichtlich wird, nicht nur einfache Portscans, es greift auch Banner und andere verfügbare Informationen ab (Folie 4). Ein Banner ist dabei eine Nachricht, die von einer Serverapplikation standardmäßig an jeden sich verbindenden Client gesendet wird. Dabei werden oftmals detaillierte Informationen über das System und die an den Port gebundene Applikation (wie zum Beispiel Versionsnummern) übertragen. Dieses Wissen erleichtert anschließend das gezielte Ausnutzen von Schwachstellen.
Das breit angelegte Ausspähen verschiedenster Dienste, samt der verfügbaren Dienstinformationen über das gesamte Netz hinweg, zeigt, dass das Ziel die aktive Kartierung und Sammlung verletzlicher Systeme weltweit ist und nicht etwa Aufklärung zu bestimmten Zielsystemen oder Personen. Mit der Vorbereitung von Attacken auf Dienste, auf die mittels SSH oder SNMP zugegriffen wird, greifen die Spione kritische Infrastrukturen an, wie zum Beispiel die für die Netzwerkbetrieb notwendigen Systeme.
Das Eindringen in das System des belgischen Netzbetreibers Belgacom und das des deutschen Satellitennetzwerkbetreibers Stellar hat in der Vergangenheit gezeigt, dass, wenn Systeme von Mitarbeitern oder deren Zugangsdaten auch nur indirekt nützlich sein könnten, diese Systeme und Menschen Opfer von Angriffen werden.
Die aus den Scans hervorgegangene Datenbank wird dann im Klub der Five- Eyes-Spione verteilt, zu dem das Vereinigte Königreich, die USA, Kanada, Australien und Neuseeland gehören. Das in der Folie erwähnte Programm MAILORDER ist ein internes Transportprotokoll, mit dem der Spionageclub Daten untereinander austauscht. Inwieweit die Five Eyes auch anderen “Partnern” Zugriff auf die HACIENDA-Daten gewährt haben, ist eine noch offene Frage.
Jedes Gerät ein Ziel
Das Scannen der Server ganzer Länder und die Suche nach verwundbaren Stellen in der Infrastruktur der Netze folgt letztlich konsequent dem Ziel der “Beherrschung des Internet”, einem von der GCHQ koordinierten Programm zum Abhören von Netzwerkverbindungen: Die Geheimdienste attackieren jedes nur mögliche System, vermutlich allein deshalb, weil es Zugang zu weiteren Systemen eröffnen kann. Denn möglicherweise öffnet sich ja dabei irgendwo der Pfad zu einem wertvollen Zielobjekt. Nach dieser Logik ist jedes Gerät ein interessantes Ziel für die Aufklärung – und für eine mögliche feindliche Übernahme. Denn jedes kompromittierte Gerät kann ja theoretisch ein Bindeglied in der Kette zum Zielobjekt sein.
Die Portscans und das Herunterladen von Bannern zur Identifizierung, welche Software auf dem ausgespähten System läuft, ist nur der erste Schritt des Angriffs (Folie 8). Eine streng geheime Präsentation der National Security Agency (NSA), die heise online vorliegt, illustriert das Gesamtkonzept (Folie 10). Die Spione folgen dabei den genau so auch vom organisierten Online-Verbrechen angewandten Methoden: der Ausspähung (Folie 10) folgt die Kompromittierung (Folie 11) und Übernahme des Systems (Folie 12) und der Diebstahl von Daten (Folie 13). In der NSA-Darstellung wird klar, dass staatliche Computersaboteure sich dieses kriminelle Vorgehen zu eigen machen: Erst diskutieren sie das Ausspionieren und Einbrechen in die Systeme als “hacking” und dann führen sie ihre eigenen Werkzeuge dafür vor. (Folie 14, 15 und 16).
Die Kolonialisierung des Internet
Es ist mittlerweile bekannt, dass die NSA sich sehr für sogenannte 0-Day-Angriffe interessiert, Schwachstellen in Software, die noch unbekannt sind und für die es daher noch keinen Patch gibt. Sobald ein mit dem Wissen über eine solche 0-Day-Attacke ausgerüsteter Angreifer einen verwundbaren Dienst auf einem Server findet, ist dieser eine leichte Beute. Firewalls bieten kaum ausreichenden Schutz, sei es, weil der Administrator selbst per Fernzugriff wartet, oder weil die staatlichen Schnüffler längst innerhalb des Netzwerkes agieren (siehe: Barton Gellman and Ashkan Soltani. Nsa infiltrates links to yahoo, google data centers worldwide, documents say. The Washington Post, October 2013). Neue Hardware, wie zum Beispiel über SNMP konfigurierte Firewalls, ins eigene Netz zu integrieren, könnte darüber hinaus auch neue Lücken aufreißen.
Folie 8 weist auf eine besondere Rolle hin, die HACIENDA in der Überwachungsinfrastruktur spielt. Die heise online vorliegenden, streng geheimen Dokumente beschreiben das LANDMARK-Programm, welches vom kanadischen Geheimdienst CSEC zur Expansion verdeckter Infrastruktur (Folie 17) betrieben wird. Die verdeckte Infrastruktur besteht aus sogenannten Operational Relay Boxes (ORBs), die verwendet werden, um den tatsächlichen Aufenthaltsort eines Angreifers zu verschleiern, wenn die Five Eyes Exploits gegen Ziele einsetzen oder Daten stehlen (Folie 18).
Mehrmals im Jahr versucht der Spionageclub, Kontrolle über so viele Maschinen wie möglich zu erlangen. Hauptsächliches Entscheidungskriterium ist dabei nur, dass sich das Ziel im Ausland befindet. So waren beispielsweise im Februar 2010 vierundzwanzig Spione an nur einem einzigen Arbeitstag in der Lage, über 3000 potenzielle ORBs zu lokalisieren. Dennoch war die Arbeit, die von HACIENDA gelieferten Ergebnisse manuell auszuwerten, zu mühsam, weshalb das OLYMPIA-System programmiert wurde, das den Prozess automatisiert (Folie 21). Die Spione prahlen damit, dass mithilfe von OLYMPIA verwundbare Geräte innerhalb eines zu spezifizierenden Subnetzes in weniger als fünf Minuten gefunden werden können (Folie 22).
Allerdings sind die Kanadier nicht die Einzigen, die mithilfe von HACIENDA Maschinen suchen, die kompromittiert und in ORBs verwandelt werden können. Beim GCHQ ist die Jagd nach ORBs als Teil des MUGSHOT-Programms organisiert (Folie 23). Dort hat man den Prozess ebenfalls automatisiert und eine signifikante Verbesserung der Genauigkeit erreicht, wie auf den Folien behauptet wird (Folie 24). Abermals spielen dafür die Informationen, welche HACIENDA liefert, eine große Rolle. Ein zentraler Punkt ist, dass das GCHQ mithilfe von MUGSHOT Ergebnisse aktiver Scans (HACIENDA) und passiver Überwachung kombiniert (Folie 26).
Kontrollverlust
Der Angreifer Staat bereitet durch die willkürlichen Attacken der Industriespionage, der Sabotage und auch Menschenrechtsverletzungen den Boden. Ihm reicht die Aussicht auf den Zugriff als Grund für sein Tun. Ein milliardenschweres Budget, Straffreiheit für Agenten und die Rekrutierung von Netzbetreibern, die zur Mitarbeit gezwungen werden, befördern die Entwicklung. Netzwerk- und Systemadministratoren fällt es zu, sich gegen einen nie da gewesenen Grad der Bedrohung abzusichern. Bürger außerhalb der Five-Eye-Länder müssen mit erheblich verringerten Standard an Sicherheit, Vertraulichkeit, Integrität und Robustheit in den Netzen leben.
Geheimdienste nutzen ihre Fähigkeiten Systeme im Internet zu übernehmen um ihre Macht auszudehnen. Ihre Aktivitäten folgen den typischen Mustern von Cyber-Kriminellen, die Portscans nutzen, um potenzielle Opfer zu identifizieren. Für Systemadministratoren heißt es angesichts des Bedrohungsszenarios, dass sie ihre Abwehr stärken und vor allem die Sichtbarkeit nicht-öffentlicher Server verringern müssen. Dienste mit Patches nachzurüsten, schützt nicht gegen die 0-Day-Exploits, und Firewalls sind kein ausreichender Schutz. Wir stellen daher eine Option für Systemadministratoren vor, die nicht-öffentliche Dienste gegen potentielle Ausspähung schützen kann.
Knock: Eine Abrissbirne für HACIENDA
Ein neuer Vorschlag zur Verschleierung von Ports ging an diesem Freitag an die Internet Engineering Task Force (IETF). Mit TCP Stealth (Julian Kirsch, Christian Grothoff, Jacob Appelbaum, and Holger Kenn: Tcp stealth, August 2014. IETF draft) könnten Netzwerkadministratoren dafür sorgen, dass ihre Server gegenüber willkürlichen Portscans abgeschirmt werden. TCP Stealth ist nicht zuletzt als Antwort auf Programme wie HACIENDA entstanden und wird auf dem jährlichen Treffen der GNU Entwickler an der TU München vorgestellt.
Die Abwehr gegen gezielte Angriffe auf ungekannte Schwachstellen – die 0-Day-Exploits – in öffentlichen Diensten ist hart. Einfacher ist es, den sichtbaren “Fußabdruck” und damit die Angriffsfläche von administrativen Diensten zu verkleinern.
Port Knocking ist eine erprobte Methode, um Server im Netz weniger sichtbar zu machen (siehe: Julian Kirsch. Knock, August 2014). Die Grundidee ist schlicht, dass ein TCP-Server nur dann auf eine SYN-Anfrage antwortet, wenn der abfragende Server zuvor ein “knock”-Paket vorausgeschickt hat. Anklopfen mit einem geheimen Klopfzeichen sorgt so für mehr Sicherheit, weil ein Angreifer, der ohne das Klopfzeichen anfragt, keine TCP-Verbindung aufbauen kann, den Dienst dahinter auch nicht attackieren kann.
Traditionelles Port Knocking (siehe: M. Krzywinski. Port knocking: Network authentication across closed ports. SysAdmin Magazine, 12:12{17, 2003) hat den staatlichen Angreifer jedoch nicht mit einkalkuliert. Wird der Service von einen Netz aus angefragt, in dem der Angreifer bereits den Datenverkehr mitliest, kann er die Verbindung belauschen und so auf die Existenz des Dienstes schließen. Ein staatlicher Angreifer kann sogar allen Verkehr des TCP-Clients beobachten und dann eine Man-in-the Mddle-Attacke zum Ausspähen des Client starten. Ein Man-in-the-Middle-Angriff über kompromittierte Router ermöglicht es Angreifern, eine TCP-Verbindung direkt nach dem Handshake zu übernehmen. Ein fortgeschrittener Hacker, der die Router kontrolliert, kann auch schwach verschleierte Port Knocks identifizieren, in dem er ungewöhnliche Routinen im Datenverkehr analysiert. Immerhin kann man wohl möglicherweise noch davon ausgehen, dass ein Angreifer den “normalen” TCP-Verkehr nicht nicht als verdächtig markiert. Denn damit würde er wohl zu viele Treffer generieren.
TCP Stealth
TCP Stealth ist ein bei der IETF eingereichter Request for Comment für eine einfach zu implementierende, stille Port-Knocking-Variante. TCP Stealth verbirgt ein Token zur Autorisierung in der ISN-Sequenz, die zu Beginn des Drei-Wege-Handshakes beim TCP-Verbindungsaufbau gesandt wird, und ermöglicht Schutz durch einen Check der Prüfsumme (payload protection). TCP Stealth ist schwer zu entdecken, weil es im klassischen Drei-Wege-Handshake verborgen ist. Der Datenverkehr beim Verbindungsaufbau ist unverändert. Man-in-the-Middle-Attacken und Wiedereinspielungsangriffe (replay attacks) werden durch den Prüfsummencheck erschwert.
TCP Stealth arbeitet mit IPv4 und IPv6 und ist für jeden Dienst nützlich, dessen Nutzergruppe so klein ist, dass eine Passphrase unter den Nutzern ausgetauscht werden kann. Beispiele sind SSH- oder FTP-Zugriffe auf Server, Tor-Bridges, persönliche POP3- oder IMAP-Server sowie Peer-to-Peer-Overlay- oder Friend-to-Friend-Netze. TCP Stealth ist für den Linux-Kernel in Form des Knock-Patches verfügbar. Ist ein Kernel gepatcht, so kann die Unterstützung für TCP Stealth in bestehenden Applikationen durch einen einfachen Aufruf der setsockopt()-Funktion aktiviert werden. Alternativ können bestehende Programme TCP Stealth nutzen, indem sie mithilfe von LD PRELOAD die dynamische Bibliothek libknockify einbinden.
Die Installation von TCP Stealth
Da der Hauptentwicklungszweig des Linux-Kernels derzeit Knock nicht unterstützt, muss auf dem Rechner, auf dem Knock laufen soll, der Kernel gepatcht werden. Die Distribution Parabola Linux bringt Knock-Unterstützung schon mit, hier kann Knock einfach mit einem Paketmanager installiert werden.
Für alle anderen Distributionen funktioniert der Patch folgendermaßen:
1. Für einen Standard-Kernel die Quellen des gewünschten Kernels von http://www.kernel.org herunterladen. Dabei beachten, dass viele Distributionen den Kernel anpassen und eigene Quellen anbieten. Deshalb ggf. diese angepassten Kernel nehmen.
2. Wenn die Quellen vorliegen, den entsprechenden Knock-Patch von gnunet.org/knock herunterladen. Wenn die Kernelversion nicht ausdrücklich auf der Knock-Website aufgeführt ist, empfiehlt sich ein Versuch mit der am nächsten verwandten Version.
3. In das Verzeichnis der Kernel-Quellen wechseln (“<your-version>” mit der entsprechenden Version des Kernels und des Patches ersetzen) und den Patch ausführen (mehr Informationen über das Einspielen und Zurücknehmen von Patches im Kernel gibt es im Archiv auf kernel.org)
$ cd linux-<your-version>/
~/linux $ patch -p1 < /path/to/knock/patch/tcp_stealth_<your-version>.diff
4. Die Konfiguration des aktuellen Kernels kopieren. Dafür gibt es zwei gängige Methoden:
(a) bei Debian und verwandten Distributionen eine Kopie der Kernelkonfigurationsparameter im Verzeichnis /boot. Die Konfigurationsdatei kann einfach in die Kernel-Quellen kopiert werden:
~/linux $ cp /boot/config-$(uname -r) .config
(b) Bei vielen anderen Distributionen gibt es die Möglichkeit, die Konfiguration des laufenden Kernels über das /proc-Dateisystem auszulesen:
~/linux $ zcat /proc/config.gz > .config
(c) Wenn keine dieser Möglichkeiten besteht, kann man es mit der Standardkonfiguration versuchen:
~/linux $ make defconfig
Allerdings sollte man von dieser Methode keinen besonders stabilen und performanten Kernel erwarten.
5. Alle Parameter, die nicht in der aktuellen Konfiguration gesetzt wurden, auf den Standardwert setzen. Eine andere Kernel-Version könnte neue Konfigurationsoptionen zur Kompilierung erfordern.
~/linux $ yes "" | make oldconfig
6. Knock über die Menüauswahl “Networking Support > Networking Options > TCP/IP networking > TCP: Stealth TCP socket support” für die aktuelle Konfiguration aktivieren.
~/linux $ make menuconfig
7. Der Kernel ist jetzt bereit für die Kompilierung. Mit
~/linux $ make bzImage && make modules
den Kernel und alle zusätzlichen Module kompilieren. Dieser Schritt kann ziemlich viel Zeit in Anspruch nehmen. Auf Maschinen mit mehr als einem Prozessorkern kann mit der Option -j bei beiden make-Befehlen die Zahl der Build-Threads angepasst werden.
8. Nach erfolgreicher Kompilierung den Kernel und alle Module installieren. Danach automatisch eine neue initramdisk für den neuen Kernel erstellen lassen:
~/linux $ sudo make modules_install && sudo make install
Wenn sudo nicht installiert ist, beide make-Befehle mit Root-Rechten ausführen.
9. Computer neu starten und den Boot-Manager anweisen, mit dem neuen Kernel zu booten. Die Maschine hat jetzt Knock.
Einschalten von Knock mit LD PRELOAD
Knock kann ohne Ändern des Source Codes des jeweiligen Programms genutzt werden. Das kann sich als nützlich erweisen, wenn der Source Code nicht verfügbar ist oder wenn der Einbau der notwendigen Bibliothek (libc) nicht möglich ist, beispielsweise wegen Beschränkungen in der Logik der Anwendung.
Um Knock in bestehenden Anwendungen zu nutzen, steht eine dynamische Bibliothek libknockify zur Verfügung. Grundsätzlich sieht die Nutzung des mit libknockify gemeinsam genutzten Objekts zum Einsatz von Knock für ein Programm example program folgendermaßen aus:
KNOCK_SECRET="shared secret"
KNOCK_INTLEN=42
LD_PRELOAD=./libknockify.so
./example_program
Wenn die Anwendung “example program” anschließend über TCP kommuniziert, wird libknockify die jeweiligen Socket Options setzen, um den Gebrauch von Knock im Kernel zu aktivieren. Im Beispiel wird die gemeinsame Passphrase aus dem Text “shared secret” gezogen. Die Integrität des Content ist auf die ersten 42 Bytes der Prüfsumme im TCP Datenstrom beschränkt. Wird die Variable KNOCK INTLEN nicht gesetzt, ist die Integritätsprüfung deaktiviert.
Benutzung von TCP Stealth mit setsockopt()
Die Entwickler von Anwendungen können Unterstützung von TCP Stealth direkt in ihren Code integrieren. Das ermöglicht eine Kontrolle, welche TCP-Verbindungen TCP Stealth mitbringen. Es kann die Usability weiter verbessern. Um Port Knocking mit einem Knock-fähigen Kernel grundsätzlich zu aktivieren, muss die Anwendung lediglich einen einzigen setsockopt() Aufruf machen, nachdem das TCP socket generiert wurde:
char secret[64] = "This is my magic ID.";
setsockopt (sock, TCP_STEALTH, secret, sizeof (secret));
Für Content-Integritätssicherung müssen die TCP-Clients zusätzlich die ersten Bytes der Prüfsumme spezifizieren, die in einem zweiten setsockopt()-Aufruf übertragen wird, bevor die Verbindung mit connect() aufgebaut wird:
char payload[4] = "1234";
setsockopt(sock, IPPROTO_TCP, TCP_STEALTH_INTEGRITY, payload, sizeof(payload));
connect (sock, ...);
write (sock, payload, sizeof (payload));
Server, die eine Datenintegritätsprüfung mithilfe von TCP Stealth verwenden wollen, rufen setsockopt() ein zweites Mal auf und geben dabei die Anzahl der Bytes an, die vor Veränderung durch Dritte geschützt werden sollen.
int payload_len = 4;
setsockopt(sock, IPPROTO_TCP, TCP_STEALTH_INTEGRITY_LEN,payload_len, sizeof(payload_len));
Die Grenzen der Technik
Die meisten Endgeräte sitzen mittlerweile hinter Gateway-Routern, die Network Address Translation (NAT) machen. TCP Stealth ist zwar so gestaltet, dass von NAT-Boxen veränderte Informationen nicht genutzt werden. Einige NAT-Boxen ändern aber auch TCP-Timestamps und ISN; sie behindern damit den Port-Knocking-Mechanismus. Tabelle 1 illustriert die Ergebnisse von Experimenten, die zeigen wie verbreitet allgemeine Veränderungen von ISN durch NAT-Boxen in der Praxis sind.

Tabelle 1: Änderungen von ISN, abhängig vom Ziel-Port (Michio Honda, Yoshifumi Nishida, Costin Raiciu, Adam Greenhalgh, Mark Handley, and Hideyuki Tokuda. Is it still possible to extend tcpß In Procee- dings of the 2011 ACM SIGCOMM Conference on Internet Measurement Conference, IMC ’11, pages 181{194, New York, NY, USA, 2011. ACM.) ![]()
TCP Stealth ist auf die 32 Bit im TCP-ISN-Header-Field beschränkt; ein aggressiver Angreifer kann diese Einschränkung ausnutzen und durch Zufall oder eine Brute-Force-Attacke doch zum Ziel kommen. TCP Stealth wird aber eine angemessene Absicherung gegen Angreifer bieten, die ungezielt scannen (wie z.B. HACIENDA). Netzmanagementdienste auf Nicht-Standard Ports zu migrieren, kann die Gefahr von Zufallserfolgen aktiver Portscanner weiter reduzieren.
Während der Gebrauch von Integritätsschutz mit TCP Stealth eine technische Option ist, bietet Port Knocking ohne einen solchen Schutz wenig Sicherheit gegenüber einem Angreifer, der den Datenverkehr im Netz beobachtet und Verbindungen umleitet, nachdem der TCP-Handshake passiert ist. Künftige Entwicklungen von Transportprotokollen sollten daher einen einen Schlüsselaustausch schon beim Start des Verbindungsaufbaus vorsehen. Leider passiert das auch bei SSH nicht, das sich dem Angreifer stattdessen noch vor dem kryptographischen Handshake mit einem Banner mit Versionsinformationen präsentiert. Dieser Fehler im Design von SSH macht zusätzliche Maßnahmen zur Verschleierung derzeit notwendig, wenn man den Integritätsschutz durch TCP Stealth wirkungsvoll ausnutzen möchte.
Politische Lösungen sind gefragt
Technische Lösungen wie TCP Stealth, die versuchen, mit den hochgerüsteten staatlichen Computersaboteuren Schritt zu halten, bieten einen Weg für Netzbetreiber, ihre Systeme zu härten, indem sie nicht-öffentliche TCP-Dienste gegen den Zugriff durch Angreifer schützen, seien diese nun kommerziell motiviert oder segelten unter dem offenbar alles entschuldigenden Banner der nationalen Sicherheit.
Das Rennen nur durch technische Maßnahmen zu gewinnen, ist langfristig wohl unmöglich, wie auch Linus Neumann vom CCC gerade in einem Kommentar für heise online geschrieben hat. Ohne den notwendigen politischen Willen, die Bürger rechtlich gegen die uferlosen Übergriffe zu schützen und auch in entsprechende Forschung für echte Nutzersicherheit zu investieren, wird der ungleiche Rüstungswettlauf weitergehen – und die Endnutzer, die Bürger werden die Verlierer sein.
Neumann hat nochmal darauf hingewiesen: Eigentlich sind sichere Systeme möglich, doch alle Regierungen fürchten den Kontrollverlust in einem hart gesicherten und weniger kontrollierbaren Kommunkationsnetz. Hier gibt es politisch noch viel Überzeugungsarbeit zu leisten. Vorerst müssen die Entwickler von Betriebssystemen und die Netzadministratoren das Beste aus der Situation machen, indem sie die modernsten und vor allem besten Sicherheitslösungen einsetzen, die sie bekommen können.
Die Folien sind hier:
The National Security Archive – The United States, China, and the Bomb
Become a Patron!
True Information is the most valuable resource and we ask you to give back.

Washington, D.C. – The National Security Archive has initiated a special project on the Chinese nuclear weapons program and U.S. policy toward it. The purpose is to discover how the U.S. government monitored the Chinese nuclear program and ascertain what it knew (or believed that it knew) and thought about that program from the late 1950s to the present. Besides investigating U.S. thinking about, and intelligence collection on, the Chinese nuclear program as such, the Archive’s staff is exploring its broader foreign policy significance, especially the impact on China’s relations with its neighbors and the regional proliferation of nuclear weapons capabilities. Through archival research and systematic declassification requests, the Archive is working to collect key U.S. documents on important developments in Chinese nuclear history, including weapons, delivery systems, and strategic thinking. To put the nuclear issue in the broader context of the changing relations between the United States and China, the Archive is also trying to secure the declassification of key U. S. policy papers that elucidate changes in the relationship.
In particular, the Archive’s project is exploring Washington’s thinking about the Chinese nuclear weapons program in the context of U.S. nuclear proliferation policy. The Archive is probing Washington’s initial effort to brake the development of the Chinese advanced weapons program by encouraging allies and others to abstain from the shipment of products that could have direct or indirect military applications. Moreover, the Archive is seeking the declassification of materials that shed light on an important concern since the late 1980s, China’s alleged role as a contributor to the proliferation of nuclear capabilities in South Asia and elsewhere. To the extent possible, the Archive will try to document the U.S. government’s knowledge of, and policy toward, China’s role as a nuclear proliferator and its efforts to balance proliferation concerns with a policy of cooperation with Beijing.
In the spring of 1996, the Archive began a series of Freedom of Information and mandatory review requests to the CIA, State Department, Defense Department, National Archives, and other agencies to prompt the release of relevant documents. Although this will take time, the State Department’s own systematic declassification review of central files from the 1960s has already made available some very useful material. Moreover, previous declassification requests by the Archive are beginning to generate significant material. This makes it possible for the Archive to display, on our Web site, some newly released documents on U.S. policy toward the Chinese nuclear weapons program.
The documents that follow are from 1964 when U.S. government officials recognized that China would soon acquire a nuclear weapons capability. As this material indicates, the degree of apprehension varied, with some officials truly worried that a nuclear armed China would constitute a formidable threat to the security of China’s neighbors as well as the United States. Others, however, believed that Beijing’s orientation was fundamentally cautious and defensive and that the political and psychological implications would be more immediately consequential than any military threat. Although China’s attitude toward U.S.-Soviet nonproliferation efforts was hostile, as far as can be determined, no one anticipated a development of later decades: the PRC’s apparent role as a purveyor of nuclear weapons and delivery systems technologies.
* * *
This briefing book was prepared by William Burr, the Archive’s analyst for the China nuclear weapons project and for a related project on U.S. nuclear weapons policies and programs. Currently a member of Dipomatic History‘s editorial board, he has published articles there and in the Bulletin of the Cold War International History Project. He previously directed the Archive’s project on the Berlin Crisis, 1958-1962 (published by Chadwyck-Healey in 1992).
The National Security Archive thanks the W. Alton Jones Foundation for the generous financial support that made this project possible. Anthony Wai, Duke University, and Matthew Shabatt, Stanford University, provided invaluable research assistance for this project.
THE DOCUMENTS
Document 1: “Implications of a Chinese Communist Nuclear Capability”, by Robert H. Johnson, State Department Policy Planning Staff, with forwarding memorandum to President Johnson by Policy Planning Council director Walt W. Rostow, 17 April 1964.
Source: U.S. National Archives, Record Group 59, Department of State Records, Central Foreign Policy Files, 1964-1966, file DEF 12-1 Chicom.
Robert Johnson (now associated with the National Planning Association) was one of the Department’s leading China experts. Between 1962 and 1964, he directed a number of studies on the Chinese nuclear program and its ramifications, not only for the United States but also for China’s neighbors in East and South Asia. This document is a summary of a longer study which remains classified but is undergoing declassification review. In this paper Johnson minimized the immediate military threat of a nuclear China, suggesting instead that Chinese leaders were more interested in a nuclear capability’s deterrent effect and were unlikely to engage in high-risk activities. Consistent with his relatively moderate interpretation, Johnson ruled out preemptive action against Chinese nuclear facilities except in “response to major ChiCom aggression.” Johnson explored the issue of preemption in another study: “The Bases for Direct Action Against Chinese Communist Nuclear Facilities,” also April 1964. That study is unavailable but is discussed in document 5.
Document 2: Special National Intelligence Estimate, “The Chances of an Imminent Communist Chinese Nuclear Explosion” 26 August 1964.
Source: Lyndon B. Johnson Library
The timing of a Chinese atomic test was a controversial subject during the summer and fall of 1964. As this document shows, CIA officials believed that the Chinese would not test a weapon until “sometime after the end of 1964.” State Department China specialist Allen Whiting, an official at the Bureau of Intelligence and Research, thought otherwise. Like his colleagues he was unaware that the Chinese had an operating gaseous diffusion plant which was producing weapons-grade material. Yet, he made more than the CIA of the fact that the Chinese had already constructed a 325 foot test tower at Lop Nur. Whiting was certain that the Chinese would not have taken the trouble to construct a tower unless a test was impending, although CIA technical experts were dubious. As other intelligence information becomes available, Whiting estimated a test on 1 October. (Interview with Whiting by William Burr, 13 December 1996).
Document 3: Memorandum for the Record, McGeorge Bundy, 15 September 1964
Source: Lyndon B. Johnson Library.
This report of a meeting between President Johnson’s top advisers discloses the administration’s basic approach toward the first Chinese nuclear test but nevertheless raises questions that have yet to be settled. Although it is evident that the administration had provisionally ruled out a preemptive strike, it is unclear whether Secretary of State Rusk ever had any substantive discussions of the Chinese nuclear issue with Soviet Ambassador Dobrynin during the weeks after this meeting.
Until recently, paragraph 3 of this document was entirely excised but a successful appeal by the National Security Archive led the National Archives to release all but the date of the proposed “Chinat” overflight, presumably by a U-2. The date of the overflight is unknown although a number took place in late 1964 and early 1965 to monitor Chinese nuclear weapons facilities.
Document 4: “China As a Nuclear Power (Some Thoughts Prior to the Chinese Test)”, 7 October 1964
Source: FOIA request to State Department
This document was prepared by the Office of International Security Affairs at the Department of Defense, possibly by, or under the supervision of Deputy Assistant Secretary of Defense Henry S. Rowen, who drafted other papers on the Chinese nuclear program during this period. It probably typified the “worst case” scenarios developed by those who believed that a nuclear China would become such a serious threat that it would be necessary to attack Chinese nuclear weapons facilities as a counter-proliferation measure.
Document 5: State Department Telegram No. 2025 to U.S. Embassy Paris, 9 October 1964
Source: U.S. National Archives, Record Group 59, Department of State Records, Central Foreign Policy Files, 1964-1966, file DEF 12-1 Chicom
This document provides one example of Washington’s efforts to get “hard” information on the PRC’s atomic test not long before it occurred on 16 October. In early September, several weeks before the State Department sent this cable, Allen Whiting saw a CIA report on a meeting earlier in the year between Chinese Premier Zhou Enlai and President of Mali Modibo Keita, when Zhou was visiting West Africa. Zhou told Keita that China would be testing an atomic device in October and asked him to give political support to the test when it occurred. Whiting was sure that Zhou’s statement should be taken seriously and on the basis of this and other information he convinced Secretary of State Rusk to announce, on 29 September, that a test would soon occur. (Interview with Whiting). The CIA report is unavailable but this telegram suggests that Zhou’s statement or similar comments by PRC officials to friendly governments may have leaked to the press.
Document 6: “Destruction of Chinese Nuclear Weapons Capabilities”, by G.W. Rathjens, U.S. Arms Control and Disarmament Agency, 14 December 1964.
Source: FOIA request to State Department
George Rathjens, the author of this document, was an ACDA official serving on an interagency group, directed by White House staffer Spurgeon Keeny, that assisted the President’s Task Force on the Spread of Nuclear Weapons, better known as the Gilpatric Committee after its chairman, former Deputy Secretary of Defense Roswell Gilpatric. Whether Rathjens prepared it as his own initiative or at the Committee’s request is unclear, but it may have been the latter because the Committee considered the possibility of recommending an attack on Chinese nuclear weapons facilities as part of a program to check nuclear proliferation. In this document, Rathjens summarized Roben Johnson’s still classified study of the costs and benefits of various types of attacks on the Chinese nuclear weapons complex. Apparently one of the possibilities, an “air drop of GRC [Government of the Republic of China] sabotage team” received serious consideration earlier in the year.
Taking a more bullish view of the benefits of attacking Chinese nuclear facilities, Rathjens took issue with Johnson’s conclusion that the “significance of a [Chicom nuclear] capability is not such as to justify the undertaking of actions which would involve great political costs or high military risks.” However confident Rathjens may have been that a successful attack could discourage imitators and check nuclear proliferation, that recommendation did not go into the final report, which has recently been declassified in full.
Before ACDA declassified this document in its entirety, a lightly excised version was available at the Johnson Library. Shane Maddock of the U.S. Coast Guard Academy’s History Department, published the excised version with stimulating commentary in the April 1996 issue of the SHAFR Newsletter.
Document 7: “As Explosive as a Nuclear Weapon”: The Gilpatric Report on Nuclear Proliferation, January 1965
Source: Freedom of Information Act request to State Department
Sections excised from previous releases are outlined in red.
Note: Since the Archive published this document, the Department of State has released Foreign Relations of the United States, Arms Control and Disarmament, 1964-1968, Volume XI, which includes the full text of the Gilpatric Report along with valuable background material.
Here the Archive publishes, for the first time, the complete text of the “Gilpatric Report”, the earliest major U.S. government-sponsored policy review of the spread of nuclear weapons. Largely motivated by concern over the first Chinese atomic test in October 1964, President Lyndon B. Johnson asked Wall Street lawyer and former Deputy Secretary of Defense Roswell Gilpatric to lead a special task force in investigating, and making policy recommendations on, the spread of nuclear weapons. Owing to his extensive connections in high-level corporate and governmental circles, Gilpatric was able to recruit a group of unusually senior former government officials, including DCI Allen Dulles, U. S. High Commissioner to Germany John J. McCloy, White House Science Adviser George Kistiakowsky, and SACEUR Alfred Gruenther. Johnson announced the formation of the committee on 1 November 1964. The committee completed its report in early 1965 and presented it to President Johnson on 21 January 1965.
The report came at a time when senior Johnson administration officials had important disagreements over nuclear proliferation policy. Johnson and Secretary of State Dean Rusk were already heavily committed to a Multilateral Force [MLF] designed to give the Germans and other European allies the feeling of sharing control over NATO nuclear weapons decisions while diverting them from developing independent nuclear capabilities. This complicated negotiations with Moscow which saw the MLF as incompatible with a nonproliferation treaty; nevertheless, Johnson and Rusk gave the MLF priority on the grounds that it would secure West Germany’s non-nuclear status1. Further, some senior officials thought that nuclear proliferation was inevitable and, among the right countries, potentially desirable. Thus, during a November 1964 meeting, Rusk stated that he was not convinced that “the U.S. should oppose other countries obtaining nuclear weapons.” Not only could he “conceive of situations where the Japanese or the Indians might desirably have their own nuclear weapons”, Rusk asked “should it always be the U.S. which would have to use nuclear weapons against Red China?” Robert McNamara thought otherwise: it was “unlikely that the Indians or the Japanese would ever have a suitable nuclear deterrent2.
The Gilpatric Committee tried to resolve the debate by taking an unhesitatingly strong position against nuclear proliferation, recommending that the United States “greatly intensify” its efforts to halt the spread of nuclear weapons. Besides calling for an international treaty on “non-dissemination and non-acquisition of nuclear weapons”, the report included a range of suggestions for inhibiting proliferation in specific countries in Europe, the Near East, and Asia. The latter generally involved a carrot and stick approach: inducements to discourage independent nuclear programs but a more assertive policy if inducements failed. For example, with respect to Israel, Washington would continue to offer “assurances” against Egyptian-Syrian attack; however, “make clear to Israel that those assurances would be withdrawn if she develops a nuclear weapons capability.” With respect to the MLF controversy, the report questioned Johnson administration policy by suggesting the “urgent exploration of alternatives” to permanently inhibit German nuclear weapons potential.
Spurgeon Keeny, the Committee’s staff director, believes that the report “got to LBJ that the Establishment was really worried about nuclear proliferation and that steps could be taken to do something about it”3. Yet, however Johnson may have thought about the report’s line of argument and recommendations, his immediate response appears to have been skeptical because it challenged the Administration’s emphasis on the MLF as a means to manage the German nuclear problem. Unquestionably, this contributed heavily to his decision to bar circulation of the report except at the cabinet level. Dean Rusk fully agreed, according to Glenn Seaborg’s account of a briefing for Johnson, Rusk opined that the report was “as explosive as a nuclear weapon.” Like Johnson, Rusk worried about leaks; moreover, he opposed the report’s message on Germany as well as other countries that it singled out. Uncontrolled revelations about the report would have quickly complicated U.S. relations with France, Germany, and lsrael, among others4.
One important section of the report, on possible initiatives toward the Soviet Union and their relationship to nonproliferation goals, has been declassified for some time. In it (beginning on p. 16), the Committee called for a verified fissile material cutoff (although production of tritium permitted) and strategic arms control agreements. By recommending a strategic delivery vehicle freeze (misspelled “free” in text), significant reductions in strategic force levels, and a moratorium on ABM and ICBM construction, the report presaged (and went beyond) the SALT I agreement of 1972. Elsewhere (p. 8) the Committee called for U.S. efforts to work with the Soviets in building support for a comprehensive nuclear test ban. For the Committee, U.S.-Soviet cooperation in those areas were essential because they would help create an “atmosphere conducive to wide acceptance of restraints on nuclear proliferation.”
Participants and close observers have offered conflicting analyses of the report’s impact. Some, such as Atomic Energy Commission Chairman Glenn Seaborg, downplay its significance noting that other political developments had more influence on Johnson administration policy. Others, such as Keeny and Raymond Garthoff (who represented the State Department on the Committee’s interagency staff) believe that even if the Gilpatric report did not quickly lead to tangible policy changes, it educated the President as well as its members on the significance of the nuclear proliferation issue. Keeny further argues that the report helped prepare Johnson to give strong support to a nonproliferation treaty in 1966 after the MLF approach to the German nuclear problem had lost momentum5.
No doubt owing to classification problems, the literature on the Gilpatric Committee and the early history of U.S. non- proliferation policy is sparse6. With the report fully declassified and other related information becoming available, it should now be possible for historians and social scientists to assess the Gilpatric Committee’s contribution to Lyndon Johnson’s nuclear proliferation policy. Whatever the Gilpatric report’s immediate impact may have been, the future turned out very differently than its critics anticipated. The slowing of nuclear proliferation has proven to be possible and a major goal of the Gilpatric committee–a nearly universal nonproliferation regime–came to pass. To the extent, however, that important measures supported by the Committee have yet to be acted upon–e.g., a fissile materials production cut off–or ratified, e.g., the CTBT–the report stands in harsh judgement of current international efforts to curb nuclear proliferation.
NOTES
1. For a useful overview of the MLF-NPT interrelationships, see George Bunn, Arms Control By Committee, Managing Negotiations with the Russians (Stanford University Press, 1992), 64-72.
2. Presumably, Rusk thought it better that Asians use nuclear weapons against each other rather than Euro-Americans using them against Asians. Quotations from memorandum of conversation by Herbert Scoville, ACDA, “Non-Proliferation of Nuclear Weapons- Course of Action for UNGA – Discussed by the Committee of Principals”, 23 November 1964, National Archives, Record Group 359, White House Office of Science and Technology, FOIA Release to National Security Archive.
3. Telephone conversation with Spurgeon Keeny, 24 March 1997.
4. Glenn Seaborg with Benjamin S. Loeb, Stemming the Tide: Arms Control in the Johnson Years (Lexington, MA: 1987), 143-145. This is the only generally available account of Johnson’s meeting with the committee. Neither Dean Rusk’s nor Lyndon Johnson’s memoirs mention the report.
5. Seaborg, Stemming the Tide, 148-149, although he provides a dissent from Keeny. Herbert York, Making Weapons, Talking Peace: A Physicists odyssey from Hiroshima to Geneva (New York, 1987), also downplays the report’s significance. Telephone conversation with Keeny, 24 March 1997; conversation with Raymond Garthoff, 28 March 1997. George Bunn, Arms Control by Committee, 75-81, is useful on the negotiations but does not mention the report.
6. George Perkovich’s “India’s Ambiguous Bomb” (forthcoming Ph.D. dissertation, University of Virginia), explores the impact of the Gilpatric report on Johnson’s policy, among other subjects.
For further reading:
Willis C. Armstrong et al., “The Hazards of Single-Outcome Forecasting,” in H. Bradford Westerfield, Inside ClA ‘s Private World: Declassified Articles from the Agency’s Internal Journal, 1955-1992 (New Haven, 1995), 238-254
Gordon H. Chang, Friends and Enemies: The United States, China, and the Soviet Union, 1948-1972 (Stanford, 1990)
Rosemary Foot, The Practice of Power, U.S. Relations with China Since 1949 (Oxford, 1995)
John Wilson Lewis and Xue Litai, China Builds The Bomb (Stanford, 1988)
Chris Pocock, Dragon Lady: The History of the U-2 Spyplane (Airlife, England, 1989), especially ch. 6, “Parting the Bamboo Curtain”
PI – DHS Warns of “Domestic Violent Extremists” Targeting Government Officials, Law Enforcement
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
An intelligence assessment released July 22 by the Department of Homeland Security Office of Intelligence and Analysis warns of an increasing trend of “anti-government violence” from what are described as “domestic violent extremists” inspired by the recent standoff at the Bundy Ranch in Bunkerville, Nevada. The report, titled “Domestic Violent Extremists Pose Increased Threat to Government Officials an Law Enforcement,” was originally obtained and published by Public Employees for Environmental Responsibility, a non-profit alliance of local state and federal resource professionals that has been advocating for criminal charges against Cliven Bundy and “militia snipers” involved in the April standoff with the Bureau of Land Management. In recent months, the report suggests that there has been a notable increase in violence from domestic extremists motivated by “anti-government ideologies.” Compared to the previous four years, DHS assesses that the “perceived victory by militia extremists in a show of force against the Department of Interior’s Bureau of Land Management (BLM) will likely inspire additional anti-government violence over the next year.” The report reflects a current trend in the national law enforcement community that views the rise of domestic extremist groups, variously referred to as militia or anti-government extremists as well as sovereign citizens, as a significant threat to the safety of government officials, law enforcement and first responders. In fact, a recent survey conducted by the National Consortium for the Study of Terrorism and Responses to Terrorism (START) at the University of Maryland found that law enforcement throughout the country identifies sovereign citizens as the top terrorist threat, greater even than the threat posed by Islamic extremists.
Domestic Violent Extremists and The Victory at Bunkerville
Though law enforcement agencies have been warning for years of the potential for violence perpetrated by members of the so-called sovereign citizen movement, who believe that the U.S. government is “operating outside of its jurisdiction and generally do not recognize federal, state, or local laws, policies, or governmental regulations,” the DHS’ recent assessment does not focus on members of this group. Instead, the assessment focuses on domestic violent extremists motivated by “anti-government ideologies” and a common perception of “government overreach and oppression.” Unlike sovereign citizens, these groups and individuals “recognize government authority,” however they may engage in acts of violence due to “their perception that the United States Government is tyrannical and oppressive” and “needs to be violently resisted or overthrown.” The assessment also refers repeatedly to “militia extremists” who are defined as facilitating or engaging in acts of violence “directed at federal, state, or local government officials or infrastructure in response to their belief that the government deliberately is stripping Americans of their freedoms and is attempting to establish a totalitarian regime.” These individuals often “oppose many federal and state authorities’ laws and regulations (particularly those related to firearms ownership), and often belong to paramilitary groups.”
The DHS assessment finds that a “recent spike in anti-government attacks and plots since November 2013″ is a departure from the previously sporadic occurrence of “domestic extremist violence.” The increase is believed to be motivated by “perception of government actions (or lack of action) addressing political issues such as gun control, land-use, property, and other activities as interfering with their individual rights and as oppressive measures that warrant violent reprisal against US Government entities and law enforcement.” Historically, spikes in violence have followed “high-profile confrontations” involving the U.S. government including Ruby Ridge and Waco. DHS identifies the recent standoff with BLM agents in Bunkerville, Nevada as an example of such an event that could “inspire further violence”:
(U//LES) I&A assesses that the belief among militia extremists that their threats and show of force against the BLM during the April Bunkerville standoff was a defining victory over government oppression is galvanizing some individuals-particularly militia extremists and violent lone offenders-to actively confront law enforcement officials, increasing the likelihood of violence. Additionally, this perceived success likely will embolden other militia extremists and like-minded lone offenders to attempt to replicate these confrontational tactics and force future armed standoffs with law enforcement and government officials during 2014.
Several incidents in 2014 are identified as having a “connection to the events in Bunkerville” based on news reports and information provided by law enforcement. The most significant incident discussed in the assessment is the recent murder of two Las Vegas police officers and another civilian committed by Jerad and Amanda Miller. The pair, who had attended the Bunkerville standoff, “expressed that violence was necessary to fight a perceived tyrannical US government apparatus intent on stripping Americans of their rights” according to the Southern Nevada Counterterrorism Center. The couple also left a note on the murdered police officers that “exclaimed the attack was the start of a ‘revolution,’ and a ‘new day,’ suggesting they anticipated further violence, and made statements on their social media profiles indicating their willingness to ‘shed blood,’ and ‘die fighting,’ to stop government oppression.”
In all, DHS found that there had been eight incidents of “anti-government” violence since March 2011, either in the form of an actual attack or an arrest stemming from a plot that was interrupted prior to to an attack taking place, including:
- March 2011 – Four members of the militia extremist group The Alaska Peacemakers Militia (APM) – including its leader – were arrested in March 2011 for conspiracy to kill judges and law enforcement. APM’s leader was sentenced in January 2013 to 26 years in prison. Three other members received sentences of 26, 12 and 5 years, respectively.
- November 2011 – Four militia extremists were arrested in November 2011 for planning to obtain explosives, guns and a biological toxins for attacks against government personnel, including employees of the Internal Revenue Service, the Bureau of Alcohol Tobacco Firearms and Explosives and local law enforcement. Two were convicted in 2012 for plotting to obtain explosives and two were convicted in 2014 for plotting to obtain the toxins.
- December 2011 – Georgia-based US Army soldiers – arrested in December 2011 – were convicted in 2012, 2013 and 2014 for involvement in a homicide to cover up the plans of their militia extremist group called F.E.A.R. (Forever Enduring Always Ready) that plotted to attack government and critical infrastructure targets including a hydroelectric dam and Ft. Stewart military base. According to court documents, the individuals allegedly stockpiled over $87,000 in firearms and bomb-making components.
- November 2013 – An armed lone offender extremist with an anti-government ideology entered Terminal 3 of LAX on November 1, 2013 and proceeded to the security screening area where he opened fire with an AR-15 style assault rifle. The gunman subsequently shot and killed one TSA Transportation Security Officer (TSO) and wounded two other TSOs, plus a civilian. Another individual was injured fleeing the scene. The suspected gunmen was wounded and is awaiting trial.
- February 2014 – Three militia extremists in February 2014 were arrested by federal law enforcement attempting to buy explosives in furtherance of a plot to allegedly attack the electrical grid and government targets, including DHS personnel and facilities. They are awaiting trial.
- March 2014 – A militia extremist in March 2014 was arrested by federal law enforcement for a series of plots culminating in a plan to allegedly acquire weapons and travel to Washington, D.C. to kill law enforcement and government officials. He is awaiting trial.
- April 2014 – Militia Extremists – many of whom traveled from around the country – joined peaceful protesters at a ranch in Bunkerville, NV and additionally surrounded officers with firearms during an armed standoff over grazing rights.
- June 2014 – Two violent lone offender extremists motivated by anti-government ideology ambushed and killed two Las Vegas Metropolitan Police Department officers and a civilian, wounding one more officer before dying in a shootout.
According to DHS analysis, the common link between these incidents is the targeting of “government facilities and personnel, followed by law enforcement personnel and critical infrastructure and key resources (CIKR).” Law enforcement is targeted “because these individuals perceive it as an extension of state control over individuals and CIKR is targeted to undermine the government’s perceived economic and societal power and control.”
Government and Law Enforcement are Primary Targets
Over the last few months, fusion centers around the country have issued a number of bulletins on the potential threat to law enforcement by sovereign citizens and other “domestic extremists.” In May, the Pennsylvania Criminal Intelligence Center released a bulletin to law enforcement on “Targeting First Responders” describing a number of recent incidents where individuals have sought to bring firefighters, paramedics and law enforcement to a location for the purposes of conducting a subsequent attack. In early June, the New York State Intelligence Center issued a bulletin stating that suspects “motivated by elements of a far right anti-government ideology with a particular fixation on law enforcement” had conducted attacks on government targets, including a recent incident in which Dennis Marx attempted to enter the courthouse in Forsyth County, Georgia with an an assault rifle, an assortment of grenades, body armor, and a gas mask. Marx wounded a sheriff’s deputy who returned fire, preventing him from entering the courthouse where he was scheduled to have a hearing on eleven felony drug and weapons charges. According to the bulletin, Marx had “long running issues with law enforcement and was a self-identified sovereign citizen.”
In July, the New Jersey Office of Homeland Security and Preparedness issued a bulletin to firefighters warning about the threat posed by the “anti-government sovereign citizen movement” which has been “catapulted into the forefront of public attention due to an increase in criminal activity by sovereign citizens nationwide.” The bulletin notes that while there “have been no reported incidents of fire service personnel being targeted or coming in contact with confirmed or suspected sovereign citizens” it is nonetheless important to know the indicators that one is dealing with a sovereign citizen, such as the use of “unusual language regarding self-identity, such as ‘freemen,’ state citizens, non-resident aliens, sovereign citizens, or common law citizens.”
Last August, the FBI’s San Antonio Division issued a bulletin stating that a Sovereign Citizen group was organizing youth groups to participate in door-to-door fundraising campaign with the actual intent of identifying the homes of law enforcement and first responders. The youth traveled in “small teams of at least two, traveled throughout neighborhoods knocking on doors” telling the homeowners that “they worked for a fund raising organization designed to help young individuals with public speaking.” The groups were “instructed that the information they collected counted as ‘points’” and that the “team with the most points would win a college scholarship and a large sum of money.” A yellow reference card was provided to each of the groups listing approximately fifteen professions that corresponded to a point value ranging from 500 to 2000 points. Professions listed on the card included firefighters, nurses, doctors as well as members of the military. However, the profession with the highest point value of 2000 was “police officer.” Following the release of the FBI bulletin, the New Jersey Regional Operations Intelligence Center later issued a request for information describing incidents where government officials had been threatened and instructing law enforcement to be careful when providing their personal information to unknown parties.
Matthew Aid – Changji: China’s Biggest SIGINT Site
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
I have spent the last two days going over the latest satellite imagery for a huge Chinese signals intelligence (SIGINT) out in western China, which is located eight miles east of the nondescript city of Changji and about five miles north of the provincial capital of Urumqi. Tis a dustbowl of a place, but one filled with history.
The Changji station, which I listed in my recent list of Chinese SIGINT stations, is intriguing for a number of reasons. When the CIA’s National Photographic Interpretation Center (NPIC) issued a report on the site back in 1984, there were only three parabolic satelite dish antennas on he station and a brand new operations building.
Today, there are 25 satellite dishes (none in radomes) on the station, and there ar now two separate and distinct intercept stations within the confines of the post, both of whom are intercepting communications traffic passing through U.S., Russian, and intrnational communications satellites parked in geosynchronous orbit 22,000 miles above the earth. This is a monster of a station. With 25 intercept antennas, the station can cover pretty much all of the major INTELSAT, ARABSAT etc. communications satellites parked over the Indian Ocean and Western Pacific orbital stations. If you want to take a gander at the station’s two main SATCOM intercept operations centers, see here for a site I have arbitrarily dersignated Changji #1, and here for Changji #2. There is also a big circularly-displayed antenna array (CDAA) just north of the station proper, which you can see here.
Revealed – CIA Officer Steven Roy Butler Currently stationed in Prague, Czech Republic
Video – The Islamic State: The Horrific Genocide and Eradication of Christians from Iraq
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
The Islamic State: The Horrific Genocide and Eradication of Christians from Iraq
The Islamic State is on a relentless campaign to establish a Caliphate across the Middle East, showing no mercy or tolerance for “infidels” of other faiths. Christians have been given ultimatums in conquered villages to conver, pay, or die. Raping of women and beheading of children have become common in the Islamic State’s barbaric persecution of Christians. Systematic and ruthless destruction of churches, relics, manuscripts, and ancient holy sites are erasing centuries of culture and history. In this fascinating video, learn what becomes of Qaraqosh, considered the Christian capital of Ira, a city home to around 50,000 Christians.
TOP-SECRET – The Secret List of CIA Sources – 2.619 Names and Adresses, Part 6,F,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
F
Fahey, Paul P. 1807 Calas Way, Virginia Beach, VA 23454 Fairchild, Brian 500 Wall St., No. 510, Seattle, WA 98121 Falbaum, Bertram 4921 N. Fort Verde Trail, Tucson, AZ 85715 Farmer, Jack PSC 76, Box 1671, APO, AE 09720 Farnham, David 2169 Pond View Ct., Reston, VA 22091 Farnham, Col John F. USAF 3817 Winconsin Ave., Tampa, FL 33616 Farrand, Robert K. 11 Quantum Pl., Gaithersburg, MD 20877 Farrell, Thomas 2713 W. Gum St., Rogers, AR 72756 Fascia, BrigGen John USA 115 Ann St., Clarendon Hills, IL 60514 Faulkner, David 2311 Frizzellburg Rd., Westminister, MD 21158 Faurer, LtGen Lincoln USAF 1438 Brookhaven Dr., McLean, VA 22101 Featherstone, James 319 South Pitt St., Alexandria, VA 22314 Fedor, William 9607 Westport Ln., Burke, VA 22015 Fedornak, Michael Old RR 1, Box 71E, Steuben, ME 04680 Fee, Russell 66 Douglas St SMW, Homosassa, FL 32646 Feeney, Cdr Harold USN 3442 Arkansas St., Corpus Christi, TX 78411 Feeney, William PoliSci Dept., S. Illinois University, Edwardsville, IL 62026 Feer, Frederic 22910 Portage Circle, Topanga, CA 90290 Fell, Col John USA 5550 Feltin Rd., San Jose, CA 95182 Fenyvesi, Charles 1150 15th St., NW, Washington, DC 20017 Feltman, David 705 O’Neill House Office Bldg, Washinigton, DC 20515 Ferguson, George 2515 West 14th St., Yuma, AZ 85364 Ferguson, LtCol John USA 9980 Caminito Chirimolla, San Diego, CA 92131 Ferguson, Kenneth 7021 Westbury Rd., McLean, VA 22101 Fernandez, Joseph 9542 Whitecedar Ct., Vienna, VA 22180 Ferrell, Mrs. Mary 4406 Holland Ave., Dallas, TX 75219 Ferrese, LtCol Ralph USA 2201 S. Grace St., No. 105, Lombard, IL 60148 Ferrer, Carlos Bank of Europe, Barcelona, Spain Ferrier, CWO-3 James USMC 4029 S. 70th St., Milwaukee, WI 53220 Fetterolf, Wallace 6800 Fleetwood Rd., No. 918, McLean, VA 22101 Fetzer, Clarence 14901 N. Swan Rd., Tucson, AZ 85737 Ffolkes, Rodgers P.O. Box 584, Claremont, CA 91711 Field, Mrs. Mary 4701 W. Braddock Rd., Alexandria, VA 22311 Fields, Bryan 3527 Jamestown Rd., Davidsonville, MD 21035 Fields, LtCol Thomas, USAF 135 Club Terrace, Lebanon, PA 17042 Fimbel, Richard 1311 Redwood Ln., California, MD 20619 Finder, Joseph 401 Commonwealth Ave., Boston, MA 02215 Fink, W. Gordon 1510 Knollwood Rd., Annapolis, MD 21401 Finke, Robert F. 5056 Tanaga Ct., Stone Mountain, GA 30087 Finlay, Richard 400 Balsam Dr., Severna Park, MD 21146 Finley, Irving 4369 Talmadge Trace, Lithonia, GA 300058 Firment, Conrad 204 Tapawingo Rd., SE, Vienna, VA 22180 Fischer, Addison 20 14th Ave., South, Naples, FL 33940 Fischer, Col. Howard, USAF 803 Spyglass Ln., Las Vegas, NV 89107 Fischer, Dr. Henry A. P.O. Box 780068, Sebastian, FL 32978 Fischer, Robert Hall House, Nichols College, Dudley Hill, MA 01570 Fishel, Edwin 3819 Albermale St., Arlington, VA 22207 Fisher, George 502 Grandview Dr., Sun Prarie, WI 53590 Fisher, Mrs. Renee 5003 Spring Lake Dr., Tampa, FL 33629 Fisher, W. Douglas 6721 Michaels Dr., Bethesda, MD 20817 Fisk, Nan 50 Palmetto Bay Rd., Hilton Head, SC 29928 Fitchett, James P.O. Box 1271, Harrisonburg, VA 22801 Fitzgerald, John 2 Magnolia Ave., St. Augustine, FL 32804 Flanders, Sherman 1306 Lencoe Dr., Stockton, CA 95210 Flannery, James 1812 River Rd., Elizabeth City, NC 27909 Fleming, LtCol Dennis USAF 108 W. Azalea Dr., Long Beach, MS 39560 Flowers, Earl 9704 Mantauk Ave., Bethesda, MD 20817 Flynn, Henry 31 Rowayton Woods Dr., Norwalk, CT 06854 Flynn, Michael 374 Kyle Rd., Herald Harbour, MD 21032 Flynn, MajGen Thomas USA 7813 Brookstone Ct., Ellicott City, MD 21043 Fogarty, James E. 1036 Park Ave., No. 3D, New York, NY 10028 Folensbee, Scott 3930 Kathryn Jean Ct., Fairfax, VA 22033 Foley, Charles 81 Spring Ln., Fairfax, CA 94930 Foley, Capt Robert USNR 4625 North 26th St., Arlington, VA 22207 Force, Capt Herbert USCGR 7448 Agradar Dr., Rancho Murietta, CA 95683 Ford, Harold P. 415 Russell Ave., No. 609, Gaithersburg, MD 20877 Ford, Lawrence 2737 Casa del Norte Ct., NE, Albuquerque, NM 87112 Forde, Rev. Norman 226 High Timber Ct., Gaithersburg, MD 20879 Forrette, Gerald 6142 Arctic Way, Edina, MN 54436 Fort, Bernard (Horst Gruber) P.O. Box 1690, Truckee, CA 95734 Fosmire, Thomas G. 3329 W. Lakeshore Dr., Florence, SC 29501 Fossett, Col John USA 1261 Creel Rd., NE, Palm Bay, FL 32905 Foster, Gary E. 2151 Cabots Point Ln., Reston, VA 22091 Foster, Mayhew 1006 W. Greenough Dr., Missoula, MT 59802 Fountain, Col Ernest USA 742 W. Emaus Ave., Allentown, PA 18103 Foust, CWO-4 Frank USN 2815 S. Atlantic Blvd., No. 606, Cocoa Beach, FL 32931 Fox, Thomas 2439 Villa Nova Dr., Vienna, VA 22180 Frankenfield, Capt Robert USN 1255 Madison St., Alexandria, VA 22314 Franklin, William 1836 Green Hill Rd., Virginia Beach, VA 23454 Franz, John B. P.O. Box 10568, Pompano Beach, FL 33061 Frederick, Christian 2832 Berryland Dr., Oakton, VA 22124 Frederickson, Robert 3810 Manor Dr., Greensboro, NC 27403 Freed, Mrs. Abigail Berlin 2700 Virginia Ave., NW, Washington, DC 20037 Freund, Matthew 1203 N. Quebec St., Kennewick, WA 99336 Freund, Col Philip USA N53, W14458 Aberdeen Dr., Menomonee Falls, WI 53051 Friar, James 16 The Crescent, Short Hills, NJ 07078 Frice, Gene P.O. Box 3940, San Luis Obisbo, CA 93403 Frick, LtCol William USAF P.O. Box 463/1004, Tucumcari, NM 88401 Frierson, Dr. David P.O. Box 31, Mt. Pleasant, SC 29464 Frisch, Donald 3300 Gessner, No. 200, Houston, TX 77063 Fritz, Russell P.O. Box 151282, Los Angeles, CA 90015 Frizzell, Arthur 15331 Sherwood Forest Dr., Tampa, FL 33647 Froendt, Carl 4375 Collins Rd., Spring Hill, FL 34606 Fromm, William 1104 Castle Harbour Way, No. 2B, Glen Burnie, MD 212061 Frost, Edmund 4490 Sweet Bay Ave., Melbourne, FL 32935 Fry, LtCol Clifford USA 802 Maverick Trail, SE, Albuquerque, NM 87123 Funabashi, Yoichi Ashai Shimbun, Washington, DC Furnas, Capt Wendell USN 746 19th St., Santa Monica, CA 90402 Furst, LtCol Howard USAF P.O. Box 400, El Toro, CA 92630 Fuss, David 8714 Preston Pl., Chevy Chase, MD 20815
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 15, AR,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 002086/1917 | ARABAS ZENON STANISŁAW |
| IPN 00 1043/590 | ARABCZYK STANISŁAW |
| IPN BU 0242/281 | ARABSKI ANDRZEJ |
| IPN BU 00744/1225 | ARABSKI ANDRZEJ |
| IPN BU 001134/3414 | ARABSKI ANDRZEJ |
| IPN BU 0901/1051 | ARABSKI ANDRZEJ GRZEGORZ |
| IPN BU 00945/141 | ARABSKI BRONISŁAW |
| IPN BU 0911/98 | ARABUCKI CZESŁAW |
| IPN BU 001075/183 | ARAJ WOJCIECH |
| IPN BU 00611/374 | ARAK JAN |
| IPN BU 001198/1650 | ARAK JAN |
| IPN BU 001198/5675 | ARAK JAN |
| IPN BU 0243/362 | ARAK KRZYSZTOF |
| IPN BU 0957/12 | ARAK STEFAN |
| IPN BU 0870/16 | ARAK WŁADYSŁAW |
| IPN BU 01434/233 | ARAMENT JAN |
| IPN BU 001121/317 | ARAMENT JAN |
| IPN 00 1043/1626 | ARAMENT MAREK |
| IPN BU 0833/13 | ARANDUK ALEKSANDRA |
| IPN BU 0193/1296 | ARANOWSKI ZDZISŁAW |
| IPN BU 0912/161 | ARASIMIUK STANISŁAW |
| IPN BU 01133/426 | ARASIMOWICZ EDWARD |
| IPN BU 709/723 | ARASIMOWICZ EDWARD |
| IPN BU 0911/713 | ARASIMOWICZ FRANCISZEK |
| IPN BU 0772/733 | ARASIMOWICZ MARIA |
| IPN BU 0193/8543 | ARASNIEWICZ CZESŁAW (ARAŚNIEWICZ) |
| IPN BU 00448/158 | ARASZKIEWICZ ANDRZEJ |
| IPN BU 001134/5116 | ARASZKIEWICZ ANDRZEJ |
| IPN BU 0193/7973 | ARASZKIEWICZ EUGENIUSZ |
| IPN BU 00328/659 | ARASZKIEWICZ KRZYSZTOF |
| IPN BU 001134/1486 | ARASZKIEWICZ KRZYSZTOF |
| IPN BU 02042/801 | ARASZKIEWICZ STANISŁAW |
| IPN 00 1043/137 | ARATYN HENRYK |
| IPN BU 0193/146 | ARATYN HENRYK |
| IPN BU 644/733 | ARAUCZ JAN |
| IPN BU 698/54 | ARAŹNA KATARZYNA |
| IPN BU 0242/22 | ARAŻNA ALFREDA |
| IPN BU 0604/1421 | ARAŻNIK JERZY |
| IPN BU 0988/868 | ARAŻNY ZBIGNIEW |
| IPN BU 0855/2633 | ARBATOWSKI STANISŁAW |
| IPN BU 0193/147 | ARBSZTEIN MALA |
| IPN BU 0957/13 | ARBUZIŃSKA ANNA |
| IPN BU 001121/3421 | ARCAB DOROTA ANTONINA |
| IPN BU 0958/926 | ARCHACKA WANDA |
| IPN BU 0193/1297 | ARCHACKI EDWARD |
| IPN BU 698/55 | ARCHACKI FRANCISZEK |
| IPN BU 0902/17 | ARCHACKI KAZIMIERZ |
| IPN BU 090/50 | ARCHUTOWSKA KRYSTYNA |
| IPN 00 1043/2223 | ARCHUTOWSKI VICTOR FRANCISZEK |
| IPN BU 0218/1214 | ARCIMOWICZ BARBARA ALINA |
| IPN 00 1043/2339 | ARCIMOWICZ JAN |
| IPN BU 0833/648 | ARCIMOWICZ JERZY |
| IPN BU 0242/36 | ARCIMOWICZ ROMUALDA |
| IPN BU 0951/1614 | ARCIMOWICZ SŁAWOMIR ANDRZEJ |
| IPN BU 01133/427 | ARCIŃSKI STANISŁAW |
| IPN BU 0218/2318 | ARCISZEWSKA (DUCHIŃSKA) MIROSŁAWA |
| IPN BU 0901/729 | ARCISZEWSKA EWA GRAŻYNA |
| IPN BU 0772/2143 | ARCISZEWSKA KRYSTYNA |
| IPN BU 0242/2673 | ARCISZEWSKA TERESA |
| IPN BU 0154/89 | ARCISZEWSKI BOGUSŁAW |
| IPN BU 0194/1420 | ARCISZEWSKI BOGUSŁAW |
| IPN BU 0193/23 | ARCISZEWSKI JAN |
| IPN BU 693/493 | ARCISZEWSKI JERZY |
| IPN BU 00273/550 | ARCIUCH ANATOL |
| IPN 00 1043/3483 | ARCIUCH ANATOL JÓZEF |
| IPN BU 645/6 | ARCIUCH CZESŁAWA |
| IPN BU 698/56 | ARCIUCH KRYSTYNA |
| IPN BU 00611/682 | ARCZEWSKI MARIAN |
| IPN BU 001198/1104 | ARCZEWSKI MARIAN |
| IPN BU 01133/428 | ARCZEWSKI WŁADYSŁAW |
| IPN BU 00612/1143 | ARCZEWSKI ZENON |
| IPN BU 001198/4513 | ARCZEWSKI ZENON |
| IPN BU 0193/1298 | ARCZYŃSKA (PIKLIKIEWICZ) WACŁAWA |
| IPN BU 0218/183 | ARCZYŃSKA IRENA |
| IPN BU 00234 | p.242 ARCZYŃSKI JANUSZ |
| IPN BU 0777/2 | ARCZYŃSKI JANUSZ |
| IPN 00 1052/1320 | ARCZYŃSKI TADEUSZ JAN |
| IPN BU 01000/1685 | ARCZYŃSKI WŁADYSŁAW |
| IPN BU 0194/3352 | ARCZYŃSKI ZBIGNIEW |
| IPN BU 00244/174 | ARCZYŃSKI ZBIGNIEW |
| IPN BU 644/9 | ARENDARCZYK TADEUSZ |
| IPN BU 698/57 | ARENDARSKA ZOFIA |
| IPN BU 00611/1604 | ARENDARSKI ANTONI |
| IPN BU 001198/2973 | ARENDARSKI ANTONI |
| IPN BU 00612/2066 | ARENDARSKI BOGUMIŁ |
| IPN BU 001198/5067 | ARENDARSKI BOGUMIŁ |
| IPN BU 001198/5751 | ARENDARSKI BOGUMIŁ |
| IPN BU 00612/4221 | ARENDARSKI JAROSŁAW |
| IPN BU 001198/6966 | ARENDARSKI JAROSŁAW |
| IPN BU 00283/2259 | ARENDARSKI LEOPOLD |
| IPN BU 001198/3991 | ARENDARSKI MARCIN |
| IPN BU 00249/740 | ARENDARSKI MAREK |
| IPN BU 001121/1383 | ARENDARSKI MAREK PAWEŁ |
| IPN BU 00399/47 | ARENDARSKI WITOLD |
| IPN BU 001134/4109 | ARENDARSKI WITOLD |
| IPN BU 0193/1299 | ARENDARSKI WŁADYSŁAW |
| IPN BU 00945/1104 | ARENDT – ARENT HIEROMIN – HERMAN |
| IPN BU 0193/1300 | ARENDT APOLINARY |
| IPN BU 01133/429 | ARENDT FRANCISZEK |
| IPN BU 001198/2743 | ARENDT STEFAN |
| IPN BU 01133/430 | ARENDT SZCZEPAN |
| IPN BU 01133/260 | ARENS HALINA |
| IPN BU 0194/1210 | ARENT RADZICHOWSKA JANINA |
| IPN BU 0607/68 | ARENT ANASTAZJA |
| IPN BU 0194/450 | ARENT CZESŁAW |
| IPN BU 00275/271 | ARENT JÓZEF |
| IPN BU 001134/127 | ARENT JÓZEF |
| IPN BU 698/58 | ARENT KAZIMIERZ |
| IPN BU 0777/3 | ARENT LESZEK |
| IPN BU 00323/26 | ARENT LESZEK |
| IPN BU 0912/163 | ARENT TADEUSZ |
| IPN BU 002086/1473 | ARGASIŃSKA ANNA |
| IPN BU 01133/431 | ARGASIŃSKA BOGUMIŁA |
| IPN BU 01133/432 | ARGASIŃSKA JANINA |
| IPN BU 00232/183 | ARGASIŃSKI APOLIARY |
| IPN BU 01133/433 | ARGASIŃSKI KORNEL |
| IPN BU 002152/114 | ARKABUZ WAWRZYNIEC |
| IPN BU 698/59 | ARKIN WIKTOR |
| IPN BU 0951/1954 | ARKITA (DOMINIEK / DOMINIAK) BLANDYNA |
| IPN BU 0891/108 | ARKITA EDMUND |
| IPN BU 0891/107 | ARKITA HENRYK |
| IPN BU 0891/106 | ARKITA STANISŁAW |
| IPN BU 0772/2144 | ARKUSZEWSKA JANINA |
| IPN BU 645/19 | ARKUSZEWSKA JANINA |
| IPN BU 0194/1163 | ARKUSZEWSKI ERNEST |
| IPN BU 0912/160 | ARKUSZEWSKI JÓZEF |
| IPN 00 1043/1902 | ARKUSZYŃSKI CZESŁAW |
| IPN BU 001102/203 | ARKUSZYŃSKI WOJCIECH STANISŁAW |
| IPN BU 0912/162 | ARLAK STANISŁAW |
| IPN BU 01753/53 | ARLETH LUDWIK |
| IPN 00 1043/1628 | ARMADA MAREK |
| IPN BU 698/60 | ARMATA EDWARD |
| IPN BU 001198/2690 | ARMATA TADEUSZ |
| IPN BU 0218/3178 | ARMATYS (BUDZISZEWSKA) HANNA |
| IPN BU 0193/1301 | ARMATYS EMIL |
| IPN BU 0604/1327 | ARMATYS FRANCISZEK |
| IPN BU 0901/622 | ARMIJAK MARIA |
| IPN BU 0988/1448 | ARNDT ZDZISŁAW |
| IPN BU 0993/1035 | ARNDT ZOFIA |
| IPN BU 0958/53 | ARNOL JAN |
| IPN BU 0772/734 | ARNOLD ADOLF |
| IPN BU 0912/164 | ARNOLD STANISŁAW |
| IPN BU 00200/785 | ARNOLD TERESA BARBARA |
| IPN BU 001102/288 | ARNOLD TERESA BARBARA |
| IPN BU 01133/434 | ARONOWSKI STANISŁAW |
| IPN BU 0194/789 | ARONSON JÓZEF |
| IPN BU 0193/7717 | ARSKI JÓZEF (FLAKSMAN MORDECHAJ JÓZEF) |
| IPN BU 001134/4344 | ARSZAGI HARSZAGI TADEUSZ |
| IPN BU 01256/9 | ARSZENIAK STANISŁAW |
| IPN BU 01000/1683 | ARSZENIAK WŁADYSŁAW |
| IPN BU PF | 251/197 ART EDWARD |
| IPN BU 0193/1302 | ART TADEUSZ |
| IPN BU 01250/8 | ART ZYGMUNT |
| IPN BU 0290/16 | ARTAMANOW TADEUSZ |
| IPN BU 52/55 | ARTAMONOW TADEUSZ |
| IPN BU PF | 144/85 ARTAMONOW TADEUSZ |
| IPN BU 0772/735 | ARTAMONOWICZ (ARTAMONOW) JERZY |
| IPN BU 0962/22 | ARTEMOWICZ JAN |
| IPN BU 0772/736 | ARTER HALINA |
| IPN 00 1052/111 | ARTICHOWICZ ALICJA |
| IPN BU 0242/3090 | ARTOMSKI KAZIMIERZ MAREK |
| IPN BU 00966/1645 | ARTOWICZ – UZIAK MARIA |
| IPN BU 01133/435 | ARTOWICZ MARIAN |
| IPN BU 0806/2495 | ARTYCH JERZY |
| IPN BU 0193/148 | ARTYFIKIEWICZ WOJCIECH JERZY STANISŁAW |
| IPN BU 0329/4 | ARTYMOWICZ JEFIM |
| IPN BU 01703/91 | ARTYMOWICZ MIKOŁAJ |
| IPN BU 0866/1379 | ARTYNIEW ZDZISŁAW |
| IPN BU 00328/849 | ARTYNIUK KRZYSZTOF |
| IPN BU 001134/1703 | ARTYNIUK KRZYSZTOF |
| IPN BU 0951/586 | ARTYSZ MARIAN |
| IPN BU 00612/2102 | ARWAJ STANISŁAW |
| IPN BU 0901/721 | ARYS LEOKADIA |
| IPN BU 001089/204 | ARYS TADEUSZ |
Wieder ein STASI-Spitzel enttarnt: Top-Medien-Manager als Agent
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Andreas Setzepfandt hat ein Herz für Russland. Der Leipziger lebt seit rund 15 Jahren in Moskau, wo er Vizegeneraldirektor und Personalchef von Burda Russland ist. Der Ableger des Münchner Verlags beschäftigt mehr als 400 Mitarbeiter, gibt Luxus-, Lifestyle- sowie Computer-Zeitschriften heraus. Setzepfandt engagiert sich zudem ehrenamtlich in der Deutsch-Russischen Auslandshandelskammer. Dort ist er stellvertretender Vorsitzender und leitet das Komitee für Personalfragen.
Der 44-Jährige lässt kaum eine Gelegenheit aus, um deutsche Arbeitgeber darauf hinzuweisen, dass sie ihre Angestellten in Russland pflegen sollten. Er empfiehlt, Betriebskindergärten zu gründen, eine Ausweitung der Telearbeit zu prüfen und an Klimaanlagen für die Mitarbeiter zu denken. Vor einem halben Jahr allerdings hat das Bild vom verständnisvollen Personaler einen hässlichen Kratzer erhalten.
Kritik an der Feindseligkeit auf Facebook
Es war im Februar 2014, als Setzepfandt in eine Affäre geriet und einen öffentlichen Proteststurm auslöste. Damals sagte der Moskauer Journalist Dmitri Schulgin, er habe aus politischen Gründen seinen Job bei Burdas Magazin “Computerbild Russia” verloren. Der Redakteur hatte auf seinem Facebook-Profil die Feindseligkeit gegenüber der Ukraine kritisiert: “Mein Land ist krank, wie die Deutschen in den 30er- bis 40er-Jahren des letzten Jahrhunderts.” Solche Kommentare seien ihm zum Verhängnis geworden, behauptete Schulgin anschließend.
In Deutschland ergriff die “tageszeitung” sogleich Partei für den Kollegen. “Burdas freiwillige Unterwerfung” titelte das Blatt und unterstellte damit dem Verlagshaus Duckmäusertum gegenüber dem Kreml. Der Buchautor Jürgen Roth fragte: “Burda-Verlagshaus als Handlanger des KGB/FSB in Moskau?”
Dafür gibt es keinen Beleg. Die “Welt” ist jetzt allerdings auf einen anderen Geheimdienstbezug gestoßen: Burdas Moskauer Statthalter Setzepfandt war als junger Mann hauptamtlicher Mitarbeiter des DDR-Ministeriums für Staatssicherheit (MfS) und wurde darin geschult, wie man politische Gegner effektiv bekämpft.
Keine Veranlassung, die Stasi-Tätigkeit zu melden
Über diesen Teil seiner Vergangenheit hat Setzepfandt bis zur Anfrage dieser Redaktion weder seinen Arbeitgeber Burda noch die Deutsch-Russische Auslandshandelskammer informiert. “Weil ich keine Veranlassung sah, diese Tätigkeit aus sehr frühen Jahren anzugeben”, begründet er sein Schweigen. Das Thema sei für ihn mit dem Zusammenbruch der DDR abgeschlossen gewesen. Der Sachse will auch nie seine Akte über die Zeit als MfS-Angehöriger eingesehen haben.
Die Dokumente aus dem Stasi-Unterlagenarchiv, die der “Welt” vorliegen, führen direkt zurück zu den Anfängen der Friedlichen Revolution in Leipzig. Während dieser Freiheitsbewegung stand Setzepfandt auf der falschen Seite der Geschichte. In der MfS-Kreisdienststelle Leipzig-Stadt wurde er ab Herbst 1988 an “ausgewählte Probleme der Bekämpfung der politisch-ideologischen Diversion (PID)/politischen Untergrundtätigkeit (PUT)” herangeführt, wie in seinem “Einarbeitungsplan” vermerkt ist. So wurde der Stasi-Lehrling darin geschult, “operative Ermittlungen und Beobachtungen” durchzuführen.
Exzellente Arbeit bei Ermittlungsberichten
Sein Vorgesetzter lobte in bürokratischem Deutsch, der neue Mitarbeiter habe beim “Anfertigen von Ermittlungsberichten, zusammengefassten Auskunftsberichten oder einer aus der Analyse gefertigten zusammengefassten Information” exzellente Arbeit geleistet. Setzepfandt lauschte auch Vorträgen von erfahrenen Kollegen zu Themen wie “Hauptaufgaben und Grundprinzipien der Arbeit des MfS”, “Erkennen von Anzeichen feindlicher Tätigkeit” und “Wachsamkeit, Geheimhaltung und Konspiration”.
Obwohl Stasi-Chef Erich Mielke seinerzeit in Leipzig “Provokateure, Randalierer, Rowdys und andere Kriminelle” wegen “Zusammenrottung” niederprügeln und ins Gefängnis stecken ließ, strebte Setzepfandt genau in dieser Phase eine Offizierskarriere in der Geheimpolizei an. Deshalb nahm er noch am 4. September 1989, als in seiner Heimatstadt immer mehr Bürger gegen das SED-Regime aufbegehrten, ein Studium an der MfS-eigenen Juristischen Hochschule auf. Doch schon im Januar 1990 wurde die Potsdamer Stasi-Universität abgewickelt.
Setzepfandt blieb in der Stadt und studierte Jura an einer gewöhnlichen Hochschule. “Für mich hat damals ein neues Leben begonnen”, sagt der Manager heute. Ein Leben, in dem er sich bestens etablierte: Im August 1999 wurde er in Dresden als Rechtsanwalt zugelassen. Dann ging es nach Moskau, er arbeitete dort zunächst für zwei namhafte Kanzleien, Beiten, Burkhardt, Mittl & Wegener sowie Lovells. Seine Stasi-Zugehörigkeit sieht er rückblickend als Fehler: “Heute würde ich anders entscheiden.”
Auslandshandelskammer bedauert den Vorfall
So einfach wird sich diese Sache aber nicht ad acta legen lassen. Die Deutsch-Russische Auslandshandelskammer, mit rund 850 Mitgliedsfirmen wichtigste Anlaufstelle im bilateralen Geschäft, zeigt sich überrascht von der Verstrickung ihres Vizechefs. Auf Anfrage schreibt sie: “Wir bedauern, dass Herr Setzepfandt sich nicht im Vorfeld zu seiner Vergangenheit geäußert hat”.
Rainer Seele, Präsident der Organisation und Vorstandschef des Kasseler Öl- und Gaskonzerns Wintershall, betont, Setzepfandts Stasi-Zugehörigkeit sei ihm “persönlich in keiner Weise bekannt” gewesen. Die Kammer stelle an die Kandidaten für den Vorstand sehr hohe Anforderungen. Allerdings sehe die Satzung keine Überprüfung von Personen durch Organe der Bundesrepublik Deutschland vor, schreibt Seele weiter.
Redaktionen scheuten Prozesse nicht
Für das Verlagshaus Burda ist der Vorgang besonders heikel. Magazine wie “Focus” und “Superillu” haben mehrfach Stasi-Fälle aufgedeckt. Um die Namen der Geheimdienstmitarbeiter publik machen zu können, scheuten die Redaktionen auch langwierige Prozesse nicht. Jetzt sieht sich ein Manager im eigenen Unternehmen mit seiner Stasi-Vergangenheit konfrontiert. “Wir nehmen dieses Thema sehr ernst und führen mit Herrn Setzepfandt daher auch entsprechende Gespräche”, teilt die Münchner Zentrale mit.
Allerdings sieht der Verlag keinen Grund, die Affäre um den Redakteur Schulgin neu zu bewerten. Der Journalist hat seinen Job bei “Computerbild Russia” längst verloren. Obwohl Personalchef Setzepfandt das Ende des Arbeitsverhältnisses persönlich besiegelt hat, will Burda diese Akte nicht wieder aufmachen. In Schulgins Arbeitsbuch, einem Dokument, in dem alle beruflichen Stationen von Arbeitnehmern in Russland aufgeführt werden müssen und das der “Welt” vorliegt, prangt an der entsprechenden Stelle der Stempel des Managers: “Chef der Abteilung Arbeit mit dem Personal, A. Setzepfandt”.
Nach Darstellung von Burda ist der Verlag am 20. Februar mit dem Eintrag von Schulgin auf dessen privater Facebook-Seite konfrontiert worden. Dort habe der Angestellte allerdings angegeben, bei Burda Russland zu arbeiten. Laut Verlag ist ihm in einem Gespräch mitgeteilt worden, dass sich Burda Russland von seiner privaten Meinung distanziere. Daraufhin habe Schulgin seine Kündigung eingereicht, Druck sei nicht ausgeübt worden.
Aufforderung, das Unternehmen zu verlassen
Der Betroffene hingegen sagt, er sei von seinen Vorgesetzten zunächst gedrängt worden, öffentlich zu erklären, der Eintrag stamme nicht von ihm. Er könne ja sagen, man habe seinen Account gehackt. Er sei aber nicht bereit gewesen zu lügen, sagt Schulgin. Deshalb habe man ihm gedroht, dafür zu sorgen, dass er als “Extremist” kein Visum mehr für den europäischen Schengen-Raum erhalten werde. Das empfand der Redakteur als ultimative Aufforderung, Burda zu verlassen.
Ein weiterer Facebook-Eintrag, der ihm viel Ärger einbrachte, hat folgenden Wortlaut: “Wenn ich auf der Arbeit und in der Metro die Gespräche höre, habe ich den Eindruck, dass 99,9 Prozent der Russen gleich ein Loblied auf (den Ende Februar 2014 abgesetzten ukrainischen Präsidenten) Janukowitsch singen werden und dazu aufrufen, alle Ukrainer aufzuhängen.” Diese Einschätzung wurde im Netz diskutiert, und ein Nutzer drohte Burda Russland: “,Computerbild Russia’, in diesem Fall sucht Euch einen neuen Mitarbeiter. Wir schicken einen Brief an die Staatsanwaltschaft.”
Der Ex-Vorsitzende des russischen Journalistenverbandes, Igor Jakowenko, hat jetzt im Gespräch mit dieser Redaktion angekündigt, er werde wegen der Affäre Schulgin den Deutschen Journalisten-Verband einschalten. Mit Schulgin zusammen baue er gerade eine Interessenvertretung auf. Ihr Name: “Journalistische Solidarität”.
Domestic Violent Extremists Pose Increased Threat to Law Enforcement and Government Officials
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
The following document was originally released by the Public Employees for Environmental Responsibility. For more information on the document, see our article on the subject.
DHS Office of Intelligence and Analysis (I&A) and Southern Nevada Counterterrorism Center
- 7 pages
- Law Enforcement Sensitive
- For Official Use Only
- July 22, 2014
(U//FOUO) After years of only sporadic violence from violent domestic extremists motivated by anti-government ideologies, I&A has seen a spike within the past year in violence committed by militia extremists and lone offenders who hold violent anti-government beliefs. These groups and individuals recognize government authority but facilitate or engage in acts of violence due to their perception that the United States Government is tyrannical and oppressive, coupled to their belief that the government needs to be violently resisted or overthrown. Historically, spikes in violence have followed high-profile confrontations involving the United States Government, such as Ruby Ridge and Waco. The April 2014 Bunkerville, Nevada standoff likely represents a similar event that could inspire further violence.
(U//FOUO) This assessment examines the common themes and targets of these attacks and assesses the potential for increased violence that may follow the Bunkerville standoff.
(U//FOUO) Although sovereign citizen extremist violence is also inspired by an anti-government ideology, sovereign citizen extremists are not included in this Assessment as we have detected no similar spike in this movement despite similarities in their ideologies.* In 2014, sovereign citizen extremist violence continued at roughly the same sporadic rate I&A has observed since 2010 of just over five incidents per year, as detailed in a 27 February 2014 Reference Aid, “(U//FOUO) Limited Reporting Suggests Sovereign Citizen Extremist Violence Most Common in Southern and Western United States.”
(U) Key judgments
(U//LES) I&A assesses that the perceived victory by militia extremists in a show of force against the Department of Interior’s Bureau of Land Management (BLM) in Nevada in April will likely inspire additional anti-government violence over the next year.
(UI/FOUO) I&A also assesses that the recent murders of two Las Vegas police officers is the latest and most severe incident in a growing trend of anti-government violence compared to the previous four years and inspired by perceived government overreach and oppression.
(U//FOUO) Perceived Victory at Bunkerville Likely to Prompt More Violence
(UI/LES) I&A assesses that the belief among militia extremists that their threats and show of force against the BLM during the April Bunkerville standoff was a defining victory over government oppression is galvanizing some individuals-particularly militia extremists and violent lone offenders-to actively confront law enforcement officials, increasing the likelihood of violence. Additionally, this perceived success likely will embolden other militia extremists and like-minded lone offenders to attempt to replicate these confrontational tactics and force future armed standoffs with law enforcement and government officials during 2014. At least three incidents in 2014 appear to have a connection to the events in Bunkerville based on open source and law enforcement reporting.
…
(U//FOUO) Spike in Anti-Government Violence Driven By Common Themes
(U//FOUO) I&A assesses the spike in anti-government attacks and plots since November 2013 is a departure from the random and sporadic nature of domestic extremist violence. These violent incidents are motivated by the perception of government actions (or lack of action) addressing political issues such as gun control, land-use, property, and other activities as interfering with their individual rights and as oppressive measures that warrant violent reprisal against US government entities and law enforcement, according to a body of open source reporting. These are common themes cited by attackers, but the specific motivations that drive any instance of anti-government violence vary due to the disparate beliefs and motivations of the individuals involved.
Revealed – 276 MI6 Agents
James Lloyd Baxendale: 94 Cairo (MECAS), 97 Amman; dob 1967.
James Lloyd Baxendale: dob 1967; 94 Cairo, 97 Amman, 99 Brussels, 04 Beirut (1 Sec).*
Richard Philip Bridge: 86 Warsaw, 88 Moscow; dob 1959.
Richard Philip Bridge: dob 1959; 86 Warsaw, 89 Moscow, 98 New Delhi, 04 Geneva (Cllr).*
George Benedict Joseph P Busby: 89 Bonn, 92 Belgrade; dob 1960; OBE.
George Benedict Joseph Pascal Busby: dob 1960; 89 Bonn, 92 Belgrade, 00 Vienna, 04 London.
Martin Hugh Clements: 86 Tehran, 90 Vienna; dob 1961.
Martin Hugh Clements: dob 1961; 86 Tehran, 90 Vienna, 98 Bonn, 99 Berlin, 04 Kabul (Cllr).*
Peter Salmon Collecot: 80 Khartoum, 82 Canberra, 93 Jakarta; dob 1950.
Peter Salmon Collecott: dob 1950; 85 Khartoum, 82 Canberra, 89 Jakarta, 94 Bonn, 04 Brasilia.*
Sherard Louis Cowper-Coles: 80 Cairo, 87 Washington; dob 1955; CMG, LVO.
Sherard Louis Cowper-Coles: dob 1955; 80 Cairo, 87 Washington, 97 Paris, 01 Tel Aviv, 03 Riyadh.*
John Martin Jamie Darke: 88 Cairo, 96 Dubai; dob 1953.
John Martin Jamie Darke: dob 1953; 88 Cairo, 96 Dubai, 03 Lisbon (Cllr).*
Michael Hayward Davenport: 89 Warsaw, 96 Moscow; dob 1961.
Michael Hayward Davenport: dob 1961; 90 Warsaw, 96 Moscow, 00 Warsaw, 04 Cairo (DHM).*
Robert Dominic Russell Fenn: 85 Hague, 88 Lagos, 92 New York; dob 1962.
Robert Dominic Russell Fenn: dob 1962; 85 Hague, 88 Lagos, 92 New York, 97 Rome, 04 Nicosia (DHM).*
Kevin Andrew Garvey: 81 Bangkok, 85 Hanoi, 92 Phnom Penh; dob 1960.
Kevin Andrew Garvey: dob 1960; 81 Bangkok, 85 Hanoi, 92 Phnom Penh, 93 Grand Turks, 01 Guatemala City (DHM).*
Andrew Patrick Somerset Gibbs: 79 Rio, 84 Moscow, 87 Pretoria; dob 1951; OBE.
Andrew Patrick Somerset Gibbs: dob 1951; 79 Rio, 84 Moscow, 87 Pretoria, 94 Lisbon, 02 Tel Aviv (Cllr).*
Steven John Hill: 88 Vienna, 96 New York; dob 1962.
Steven John Hill: dob 1962, 88 Vienna, 96 New York, 01 Washington (1 Sec).
Thomas Rober[t] Benedict Hurd: 95 Warsaw; dob 1964.
Thomas Robert Benedict Hurd: dob 1964; 95 Warsaw, 98 Amman, 02 Jerusalem.*
Jeremy John Legge: 87 Lusaka, 94 Vienna; dob 1961.
Jeremy John Legge: dob 1961; 87 Lusaka, 94 Vienna, 01 Paris (1 Sec).
Gareth Geoffrey Lungley: dob 1971.
Gareth Geoffrey Lungley: dob 1971; 97 Tehran, 02 Zagreb (1 Sec).
Christine Anne MacQueen: 84 Brasilia, 89 New York, 90 Paris; dob 1959.
Christine Ann MacQueen: dob 1959; 84 Brasilia, 89 New York, 90 Paris, 02 Brussels (Cllr).*
Patrick Joseph McGuinness: 88 Sanaa, 94 Abu Dhabi, 96 Cairo; dob 1963; OBE.
Patrick Joseph McGuinness: dob 1963; 88 Sanaa, 94 Abu Dhabi, 96 Cairo, 03 Rome (Cllr).*
Anthony Leopold Colyer Monckton: 90 Geneva, 96 Zagreb; dob 1960.
Anthony Leopold Colyer Monckton: dob 1960; 90 Geneva, 96 Zagreb, 98 Banja Luka, 01 Belgrade, 04 London. (See: http://cryptome.org/mi6-monckton.htm)
Richard Peter Moore: 90 Ankara, 91 Istanbul, 95 Islamabad; dob 1963.
Richard Peter Moore: dob 1963; 90 Ankara, 91 Istanbul, 95 Islamabad, 01 Kuala Lumpur (Cllr).*
Mark Scott Thomas Morgan: 84 Geneva, 88 Aden, 94 Valletta; dob 1958; MBE.
Mark Scott Thomas Morgan: dob 1958; 84 Geneva, 88 Aden, 94 Valletta, 01 Budapest (1 Sec).
Stuart Richard Morley: 89 San Jose, 90 Bridgetown, 96 Hague; dob 1959.
Stuart Richard Morley: dob 1959; 89 San Jose, 90 Bridgetown, 96 Hague, 02 New Delhi (Cllr).*
Clive Dare Newell: 79 Tehran, 82 Kabul, 86 Addis, 90 Bosnia, 94 Ankara; dob 1953.
Clive Dare Newell: dob 1953; 79 Tehran, 82 Kabul, 86 Addis Ababa, 94 Ankara, 01 Moscow, 03 Ottawa (Cllr).*
Peter James Norris: 85 Lagos, 90 Guatemala; dob 1955, Dr.
Peter James Norris: dob 1955; 85 Lagos, 90 Guatemala City, 97 Jakarta, 00 London.
Colin Douglas Partridge: 80 Delhi, 87 Hanoi, 94 Hong Kong; dob 1955.
Colin Douglas Partridge: dob 1955; 80 New Delhi, 87 Hanoi, 94 Hong Kong, 00 Seoul (Cllr).
Martin Eric Penton-Voak: 95 Moscow; dob 1965.
Martin Eric Penton-Voak: dob 1965; 95 Moscow, 01 Vienna (1 Sec).
Richard William Potter: 85 Riyadh, 88 Nicosia; dob 1960.
Richard William Potter: dob 1960; 85 Riyadh, 90 Nicosia, 95 Sarajevo, 99 Skopje, 04 Amman (Cllr).*
Michael John Regan: 86 Kabul, 89 Dubai, 95 Bangkok; dob 1955.
Michael John Regan: dob 1955; 86 Kabul, 89 Dubai, 95 Bangkok, 04 Harare (Cllr).*
Richard Paul Reynier Thompson: 91 Stockholm, 96 Geneva; dob 1960.
Richard Paul Reynier Thompson: dob 1960; 91 Stockholm, 96 Geneva, 04 Baghdad (Cllr).*
Stuart Graham Turvill: 95 Islamabad; dob 1971.
Stuart Graham Turvill: dob 1971; 95 Islamabad, 00 Accra, 03 London.
Andrew Whiteside: 95 Budapest; dob 1968.
Andrew John Whiteside: dob 1968; 95 Budapest, 02 Rome (1 Sec).*
Simon Jules Wilson: 91 Athens, 93 Zagreb; dob 1966; OBE.
Simon Jules Wilson: dob 1966; 91 Athens, 93 Zagreb, 99 New York, 02 Budapest (1 Sec).*
David John Woods: 78 Vienna, 81 Bucharest, 92 Harare, 97 Pretoria; dob 1951.
David John Woods: dob 1951; 78 Vienna, 81 Bucharest, 92 Harare, 97 Pretoria, 02 Berlin (Cllr).*
Ian Alexander Woods: 77 New York, 84 Berlin, 86 Bonn, 95 Warsaw; dob 1951.
Ian Alexander Woods: dob 1951; 77 New York, 84 Berlin, 86 Bonn, 95 Warsaw, 03 Sofia (Cllr).*
Alexander William Younger: 95 Vienna; dob 1963.
Alexander William Younger: dob 1963; 95 Vienna, 02 Dubai (1 Sec).*
311 Names on the Three Lists of MI6 Officers (including 35 duplicates above)
Madeleine Kay Alessandri: dob 1965; 90 Vienna, 96 Frankfurt, 04 Tokyo (Cllr).*
Dudley Charles Ankerson: 78 Buenos Aires, 85 Mexico, 93 Madrid; dob 1948; Dr.
Ian Nicholas Anthony: dob 1960; 88 Lisbon, 93 Brasilia, 97 London.*
Peter James Aron: dob 1946; 68 Bonn, 84 Singapore, 86 Washington, 97 Seoul,00 London.
Jeremy John Durham Ashdown (Paddy Ashdown): dob 1941; 74 Geneva (1 Sec).
Raymond Benedict Barthol Asquith: 83 Moscow, 92 Kiev; dob 1952; Viscount.
Nigel Anthony Richard Backhouse: dob 1956; 84 Kabul, 85 Kath-mandu, 89 Madrid,98 Paris, 01 London.
Kerry Charles Bagshaw: 82 Geneva, 88 Moscow; dob 1943; OBE.
Ian Walter Baharie: dob 1961; 85 Cairo, 91 Abu Dhabi, 96 Jerusalem, 99 Abuja, 03 Riyadh (Cllr).*
Anthony James Ball: dob 1968, 94 Kuwait, 99 Madrid, 03 Damascus (1 Sec).*
Ian Clive Barnard: 94 Geneva; dob 1965.
Richard Martin Donne Barrett: 83 Ankara, 88 New York, 97 Amman; dob 1949.
Nicholas Hilary Bates: dob 1949; 79 Geneva, 84 Cairo, 89 Muscat, 96 Kingston, 98 Kampala, 01 London.
James Lloyd Baxendale: 94 Cairo (MECAS), 97 Amman; dob 1967.
James Lloyd Baxendale: dob 1967; 94 Cairo, 97 Amman, 99 Brussels, 04 Beirut (1 Sec).*
Jonathan Beales.
Nicholas James Gilbert Beer: dob 1947; 77 Nairobi, 82 Madrid, 92 Hague, 99 Buenos Aires, 02 London.
Brian Maurice Bennett: dob 1948; 73 Prague, 77 Helsinki, 83 Bridgetown, 86 Vienna, 88 Hague, 97 Tunis, 03 Minsk.*
Julliette Winsome Bird: dob 1963; 92 New Delhi, 01 Brussels, 03 London.
William Hume James Blanchard: dob 1967; 92 Budapest, 98 Islamabad, 04 Ankara (1 Sec).*
Peter John William Black: 74 MECAS, 77 Kuwait, 80 Amman, 87 Dhaka; dob 1946.
Jamie Blount.
David Graeme Blunt: dob 1953; 79 Vienna, 83 Peking, 89 Canberra, 97 Oslo,02 Gibraltar (Dep.Gov.)
Rupert Bowen: 90 Windhoek, 92 Tirana.
Andrew Jonathan Corrie Boyd: 81 Accra, 88 Mexico City, 96 Islamabad; dob 1950.
Timothy Gavin Bradley: dob 1959; 86 Kuwait, 96 Belgrade, 99 London.
Julian Nicholas Braithwaite: dob 1968; 95 Zagreb, 96 Belgrade, 02 Sarajevo, 04 Washington (Cllr).*
Andrew James Brear: 94 Santiago; dob 1960.
Christopher Mark Breeze: 88 Nicosia, 94 New Delhi; dob 1963.
Alastair Breeze.
Jonathan Andrew Brewer: dob 1955; 86 Luanda, 91 Mexico, 98 Moscow, 02 London.
Richard Philip Bridge: 86 Warsaw, 88 Moscow; dob 1959.
Richard Philip Bridge: dob 1959; 86 Warsaw, 89 Moscow, 98 New Delhi, 04 Geneva (Cllr).*
Robert Edward Brinkley: dob 1954; 78 Geneva, 79 Moscow, 88 Bonn, 96 Moscow, 02 Kiev.*
Stuart Armitage Brooks: 72 Rio, 75 Lisbon, 79 Moscow, 87 Stockholm, 93 Moscow; dob 1948; OBE.
Christopher Parker Burrows: 82 East Berlin, 87 Bonn, 93 Athens; dob 1958.
George Benedict Joseph P Busby: 89 Bonn, 92 Belgrade; dob 1960; OBE.
George Benedict Joseph Pascal Busby: dob 1960; 89 Bonn, 92 Belgrade, 00 Vienna, 04 London.
Paul Brummel: dob 1965; 89 Islamabad, 95 Rome, 02 Ashgabat.*
Philippa Jane Carnall: dob 1957; 83 Beirut, 84 Damascus, 88 Hanoi, 91 Washington, 97 Cairo, 02 Islamabad (3 Sec).*
Peter Leslie Carter: dob 1956; 86 New Delhi, 94 Brussels, 01 Tel Aviv (Cllr, CG, DHM).*
David Ian Chambers: dob 1947; 94 Hong Kong, 03 Bangkok (Cllr).*
Geoff Chittenden.
Robert John Paul Church: 76 Bankok, 81 Berlin, 86 Nairobi, 89 Bangkok, 97 Nairobi; dob 1947.
Edward Clay: dob 1945; 70 Nairobi, 73 Sofia, 79 Budapest, 85 Nicosia, 93 Kampala, 94 Burundi, 99 Nicosia, 01 Nairobi.*
Timothy Clayden: 91 Warsaw, 95 Lagos; dob 1960; Wanker.
Martin Hugh Clements: 86 Tehran, 90 Vienna; dob 1961.
Martin Hugh Clements: dob 1961; 86 Tehran, 90 Vienna, 98 Bonn, 99 Berlin, 04 Kabul (Cllr).*
John Donovan Nelson Clibborn: 66 Nicosia, 72 Bonn, 72 Brussels, 88 Washington; dob 1941; CMG.
Peter Salmon Collecot: 80 Khartoum, 82 Canberra, 93 Jakarta; dob 1950.
Peter Salmon Collecott: dob 1950; 85 Khartoum, 82 Canberra, 89 Jakarta, 94 Bonn, 04 Brasilia.*
Nicholas Geoffrey Coombs: dob 1961; 87 Riyadh, 93 Amman, 00 Riyadh, 03 London.
Andrew George Tyndale Cooper: dob 1953; 84 Canberra, 88 Geneva, 95 Stockholm, 99 London.
John de Carteret Copleston: dob 1952; 75 Paris, 80 Islamabad, 87 Jakarta, 93 Lagos, 97 Canberra, 00 London.*
Andrew David Cordery: 75 Nairobi, 77 New York, 84 Lusaka, 88 Berlin, 95 Oslo; dob 1947.
Vernon Robert Court: dob 1958; 84 Bangkok, 90 Brussels, 93 Brussels, 01 Canberra (DHM).*
Sherard Louis Cowper-Coles: 80 Cairo, 87 Washington; dob 1955; CMG, LVO.
Sherard Louis Cowper-Coles: dob 1955; 80 Cairo, 87 Washington, 97 Paris, 01 Tel Aviv, 03 Riyadh.*
Anthony Evelyn Comrie Cowan: dob 1953; 78 Hong Kong, 80 Peking, 87 Brussels, 96 Hong Kong, 03 Hague (Cllr).*
Keith Craig: dob 1961.
Charles Graham Crawford: dob 1954; 81 Belgrade, 87 Cape Town, 93 Moscow, 96 Sarajevo, 01 Belgrade, 03 Warsaw. (* Warsaw, 05)
Michael James Crawford: dob 1954; 83 Cairo, 85 Sanaa, 86 Riyadh, 92 Warsaw, 99 Islamabad, 01 London.
Alexander John Peter Creswell: dob 1965; 95 Pretoria, 01 Kuwait (1 Sec).
John Martin Jamie Darke: 88 Cairo, 96 Dubai; dob 1953.
John Martin Jamie Darke: dob 1953; 88 Cairo, 96 Dubai, 03 Lisbon (Cllr).*
Nigel Kim Darroch: dob 1954; 80 Tokyo, 89 Rome, 97 Brussels, 03 London.
Michael Hayward Davenport: 89 Warsaw, 96 Moscow; dob 1961.
Michael Hayward Davenport: dob 1961; 90 Warsaw, 96 Moscow, 00 Warsaw, 04 Cairo (DHM).*
Peter Brian Davies: 83 Rome, 88 Peking, 96 Jakarta; dob 1954.
Elved Richard Malcolm Davies: dob 1951; 77 Jakarta, 84 Athens, 89 Nairobi, 91 Oslo, 00 Hong Kong, 04 London.
John Howard Davies: dob 1957; 83 Riyadh, 87 Damascus, 93 Riga, 99 Sofia, 03 London.
Peter Brian Davies: dob 1954; 80 Hong Kong, 83 Rome, 88 Peking, 96 Jakarta,03 Madrid (Cllr).*
John Paul Davison: dob 1950; 77 Abu Dhabi, 86 Dubai, 89 London.
Andrew John Dean: dob 1955; 84 Vienna, 90 Hanoi, 97 Sao Paolo, 00 Canberra (Cllr).*
Geoffrey Deane: dob 1950; 80 Nairobi, 88 East Berlin, 01 Munich (Consul).
Richard Billing Dearlove: 68 Nairobi, 73 Prague, 80 Paris, 87 Geneva, 91 Washington; dob 1945; OBE.
John Deerlove.
Hugh Stephen Murray Elliot: dob 1965; 91 Madrid, 99 Buenos Aires, 02 Paris (Cllr).*
Julian Ascott Evans: dob 1957; 82 Moscow, 85 Zurich, 91 New York, 02 Islamabad, 03 Ottawa (DHC).*
Stephen Nicholas Evans: dob 1950; 78 Hanoi, 83 Bangkok, 90 Ankara, 93 Islamabad, 96 Kabul, 02 Colombo.*
Keith Derek Evetts: 75 Warsaw, 77 Maputo, 83 New York, 86 Kingston, 88 Lisbon; dob 1948; OBE.
David William Fall: dob 1948; 76 Bangkok, 81 Pretoria, 90 Bangkok, 93 Canberra, 97 Hanoi, 03 Bangkok.*
Charles Blanford Farr: dob 1959; 87 Pretoria, 92 Amman, 95 London.
Michael Edward Joseph Feliks: 93 Peking; dob 1964; Dr.
Robert Dominic Russell Fenn: 85 Hague, 88 Lagos, 92 New York; dob 1962.
Robert Dominic Russell Fenn: dob 1962; 85 Hague, 88 Lagos, 92 New York, 97 Rome, 04 Nicosia (DHM).*
John Fisher: dob 1948; 76 Ankara, 82 Vienna, 93 Santiago, 99 Jakarta, 03 London.
Nicholas Bernard Frank Fishwick: 88 Lagos, 94 Istanbul; dob 1958; Dr.
Robert Dunkan Fitchett: dob 1961; 84 Dakar, 88 Bonn, 94 Paris, 03 Manila (DHM).*
Edmund Walter Fitton-Brown: dob 1962; 87 Helsinki, 93 Cairo, 98 Kuwait, 03 Cairo (Cllr).*
Richard George Hopper Fletcher: 68 Athens, 69 Nicosia, 73 Bucharest, 85 Athens; dob 1944; CMG.
Tarquin Simon Archer Folliss: dob 1957; 89 Jakarta, 95 Bucharest, 01 Copenhagen (Cllr).*
Lachlan Pelly Ferrar Forbes: dob 1970; 98 Nairobi, 02 Baku (1 Sec).*
Peter William Ford: dob 1947; 73 Beirut, 74 Cairo, 81 Paris, 87 Riyadh, 91 Singapore, 99 Bahrain, 03 Damascus.*
Nicholas John Foster: dob 1957; 86 Nicosia, 92 Moscow, 98 Athens, 03 London.
Richard Andrew Foulsham: 84 Brunei, 86 Lagos, 95 Rome; dob 1950.
Rosalind Mary Elizabeth Fowler: 90 Hong Kong; dob 1965.
Michael Roger Fox: 93 Geneva; dob 1958.
Michael Roger Fox: dob 1958; 93 Geneva, 03 Rabat (1 Sec).
Cortland Lucas Fransella: dob 1948; 73 Hong Kong, 80 Kuala Lumpur, 82 Santiago, 91 Rome, 95 London.*
Richard Ogilby Leslie Fraser-Darling: 73 Helsinki, 84 Washington; dob 1949.
Steven Alan Frost: dob 1964; 92 Islamabad, 99 Stockholm, 02 London.
Michael Adrian Fulcher: dob 1958; 85 Athens, 93 Sofia, 99 Rome, 03 London.
Robert Andrew Fulton: 69 Saigon, 73 Rome, 78 Berlin, 84 Oslo, 89 New York; dob 1944.
Stephen Peter Garner-Winship: dob 1956; 91 Rio, 93 Lisbon, 94 London.
Kevin Andrew Garvey: 81 Bangkok, 85 Hanoi, 92 Phnom Penh; dob 1960.
Kevin Andrew Garvey: dob 1960; 81 Bangkok, 85 Hanoi, 92 Phnom Penh, 93 Grand Turks, 01 Guatemala City (DHM).*
Ruppert John Addison Gaskin: dob 1974; 99 Cairo, 03 Khartoum (1 Sec).*
John Henry Cary Gerson: 69 Hong Kong, 71 Singapore, 74 Peking, 87 Hong Kong; dob 1945.
Andrew Patrick Somerset Gibbs: 79 Rio, 84 Moscow, 87 Pretoria; dob 1951; OBE.
Andrew Patrick Somerset Gibbs: dob 1951; 79 Rio, 84 Moscow, 87 Pretoria, 94 Lisbon, 02 Tel Aviv (Cllr).*
Roger James Adam Golland: dob 1955; 79 Ankara, 84 Budapest, 89 Buenos Aires, 98 Brussells, 01 London.
Sean Goodman.
Anita Goodman.
Jacqueline Goodman.
Jean Francois Gordon: dob 1953; 81 Luanda, 83 Geneva, 90 Nairobi, 96 Algiers, 01 Abidjan.
Robert Anthony Eagleson Gordon; dob 1952; 75 Warsaw, 78 Santiago, 87 Paris, 92 Warsaw, 95 Rangoon, 03 Hanoi.*
Keith Rutherford Gosling: 75 Singapore, 78 Vienna, 86 Manila, 93 Tel Aviv; dob 1944; OBE.
Matthew Steven Gould: dob 1971; 94 Manila, 02 Islamabad, 03 Tehran (DHM).*
Keith William Green: dob 1964; 92 Buenos Aires, 98 Sarajevo, 03 Santiago, 04 Baghdad (Cllr).*
Noel Joseph Guckian: dob 1955; 84 Jedda, 88 Paris, 94 Muscat, 98 Tripoli, 02 Damascus, 04 Kirkuk (CG).*
Paul Haggle: dob 1949; 76 Bangkok, 82 Islamabad, 89 Pretoria, 98 Bangkok, 01 London.
James William David Hall: dob 1965; 89 Lusaka, 91 New Delhi, 99 Vienna, 02 Pristina, 03 London.
Roger Patrick Hamilton: 78 Jakarta, 82 Tokyo, 84 Hong Kong, 89 Copenhagen; dob 1948.
Graham Stewart Hand: dob 1948; 82 Dakar, 87 Helsinki, 94 Lagos, 98 Sarajevo, 02 Algiers.
Roger John Hargreaves: 73 Hong Kong, 76 Sanaa, 85 Hong Kong, 96 Wellington; dob 1950.
William Alistair Harrison: dob 1954; 79 Warsaw, 87 New York, 95 Warsaw, 00 New York, 03 London.(* Possibly Alistair Harrison, HC, Lusaka, Zambia)
Samuel Andrew Roland Hatfield: 95 Lagos; dob 1963.
Dora Claire Sarah Healy: dob 1952; 87 Addis Ababa, 95 Nairobi, 98 London.
Steven John Hill: 88 Vienna, 96 New York; dob 1962.
Steven John Hill: dob 1962, 88 Vienna, 96 New York, 01 Washington (1 Sec).
Stephen Peter Holland: dob 1965; 00 New Delhi (1 Sec).*
Sean Christopher Erick Holt: dob 1949; 79 Havana, 82 Athens, 87 Khartoum, 91 Accra, 95 Bogota, 99 Luanda, 01 Freetown, 04 Basra (Cllr).*
Katherine Sarah-Julia Horner: 85 Moscow, 97 Moscow; dob 1952.
Thomas Rober[t] Benedict Hurd: 95 Warsaw; dob 1964.
Thomas Robert Benedict Hurd: dob 1964; 95 Warsaw, 98 Amman, 02 Jerusalem.*
Justin John Hustwitt: dob 1967; 94 Cairo, 95 Riyadh, 01 Kampala, 04 Tripoli (1 Sec).*
Nigel Norman Inkster: dob 1952; 76 Kuala Lumpur, 79 Bangkok, 83 Peking, 85 Buenos Aires, 92 Athens, 94 Hong Kong, 98 London.
Anthony John Godwin Insall: dob 1949; 75 Lagos, 82 Hong Kong, 85 Peking, 92 Kuala Lumpur, 99 Oslo, 04 London.
Andrew Michael Jackson: dob 1958; 87 Bonn, 01 Rome (1 Sec).
William Lester Jackson-Houlston: dob 1952; 80 Brussels, 82 Buenos Aires, 90 Belgrade, 99 Hague, 03 Berne (Cllr).*
Neil Marius Jacobsen: dob 1957; 86 Athens, 92 Madrid, 00 Santiago, 03 London.
John Jenkins: dob 1955; 83 Abu Dhabi, 89 Kuala Lumpur, 95 Kuwait, 99 Rangoon, 03 Jerusalem (CG).*
Richard Hugh Francis Jones: dob 1962; 86 Abu Dhabi, 94 Brussels, 03 Tirana.*
Denis Edward Peter Paul Keefe: dob 1958; 84 Prague, 92 Nairobi, 98 Prague, 04 London.
Robert Mitchell Forest Kelly: 74 Nairobi, 80 Turkey, 81 Ankara, 95 Ottowa; dob 1946.
Paul Vincent Kennedy: dob 1957; 91 Riyadh, 99 Bahrain, 04 Baghdad (1 Sec).*
Theodore Maurice Kenwrick-Pierc: 74 Brussels, 82 Nicosia, 88 Hague, 94 Athens; dob 1948.
Alex Kershaw: 97 Geneva; dob 1967.
David James Kilby: dob 1966; 01 Bangkok, 03 Cairo (1 Sec).*
Sarah-Jill Lennard Kilroy: dob 1956; 82 Montevideo, 83 Brussels, 94 Budapest, 98 London.
Richard Jonathan Knowlton: dob 1950; 78 Helsinki, 84 Harare, 91 Dubai, 97 Bridgetown, 02 Caracas, 03 Helsinki (Cllr).
Michael Anthony Kyle: dob 1948; 72 Saigon, 78 Washington, 84 Accra, 88 Dar es Salaam, 95 Berlin, 98 London.
Ian Francis Millar Lancaster: dob 1947; 75 Hanoi, 78 Prague, 83 Brussels, 91 Ankara, 95 London.(* Algiers 05)
Nicholas John Andrew Langman: 86 Montevideo, 88 New York, 94 Paris; dob 1960.
Edmund John Scott Latter: 94 Istanbul; dob 1968.
Jeremy John Legge: 87 Lusaka, 94 Vienna; dob 1961.
Jeremy John Legge: dob 1961; 87 Lusaka, 94 Vienna, 01 Paris (1 Sec).
Graham John Ley: dob 1961; 87 Cairo, 94 Nicosia, 99 Cairo, 03 London.
Barry Robert Lowen: dob 1964; 89 Kuwait, 97 New York, 03 Riyadh (Cllr).*
Gareth Geoffrey Lungley: dob 1971.
Gareth Geoffrey Lungley: dob 1971; 97 Tehran, 02 Zagreb (1 Sec).
Fiona MacCallum: dob 1962; 89 Moscow, 95 Riga, 00 Kiev, 04 Tallinn (1 Sec).
Kenneth John Alexander MacKenzie: dob 1949; 75 Brussels, 81 Buenos Aires,85 Bucharest, 92 Vienna, 97 Munich, 01 London.
John Bannerman Macpherson: dob 1951; 79 Khartoum, 80 Sanaa, 87 Sofia, 93 Cairo, 03 Stockholm (Cllr).*
Christine Anne MacQueen: 84 Brasilia, 89 New York, 90 Paris; dob 1959.
Christine Ann MacQueen: dob 1959; 84 Brasilia, 89 New York, 90 Paris, 02 Brussels (Cllr).*
Norman James MacSween: 72 Nairobi, 77 Tehran, 83 Bonn, 91 Stockholm, 95 Moscow; dob 1948.
Richard Edward Makepeace: dob 1953; 79 Muscat, 81 Prague, 89 Brussels, 95 Cairo, 99 Khartoum, 03 Abu Dhabi.*
Keith Ian Malin: dob 1953; 78 Brussels, 84 Geneva, 90 Sofia, 96 Peking, 99 London.(* Helsinki 05)
Nicholas Marden: dob 1950; 77 Nicosia, 82 Warsaw, 88 Paris, 98 Tel-Aviv, 02 London.
Rosalind Mary Marsden: dob 1950; 76 Tokyo, 85 Bonn, 93 Tokyo, 03 Kabul.*
Nicholas Jonathan Leigh Martin: dob 1948; 81 Nairobi, 87 Rome, 93 Jakarta, 00 Bridgetown (Cllr).
Iain Arthur Gray Matthewson: 81 New York, 85 Warsaw, 93 Prague; dob 1952.
Andrew David McCoch: dob 1972; 97 Istanbul, 02 Kabul, 03 Kathmandu (1 Sec).
Ian Forbes McCredie: 76f Lusaka, 79 Tehran, 83 Copenhagen, 92 New York; dob 1950; OBE.
Patrick Joseph McGuinness: 88 Sanaa, 94 Abu Dhabi, 96 Cairo; dob 1963; OBE.
Patrick Joseph McGuinness: dob 1963; 88 Sanaa, 94 Abu Dhabi, 96 Cairo, 03 Rome (Cllr).*
Justin James McKenzie Smit: 96 Moscow; dob 1969.
Sian Alexis McLean: dob 1969; 97 Hong Kong, 01 Peking (1 Sec). [*Sean McLean, Riyadh.]
Alasdair Morrell McNeill: dob 1967; 92 Istanbul, 97 Moscow, 99 London.
Peter James McQuibban: dob 1955; 82 Brasilia, 88 Warsaw, 96 Copenhagen,04 Paris (Cllr).*
William John Clovis Meath-Baker: 88 Kabul, 89 Prague, 97 Istanbul; dob 1959.
Jonathan Kenneth Milton Mitchel: dob 1959; 89 Amman, 91 Harare, 98 Bucharest, 02 London.
Andrew Jonathan Mitchell: 93 Bonn; dob 1967.
John Edward Mitchiner: dob 1951; 82 Istanbul, 87 New Delhi, 91 Berne, 97 Yerevan, 00 Calcutta, 03 Freetown.*
Anthony Leopold Colyer Monckton: 90 Geneva, 96 Zagreb; dob 1960.
Anthony Leopold Colyer Monckton: dob 1960; 90 Geneva, 96 Zagreb, 98 Banja Luka, 01 Belgrade, 04 London. (See: http://cryptome.org/mi6-monckton.htm)
Richard John Moon: dob 1959; 85 Jakarta, 93 Rome, 99 New York, 03 London.*
Richard Peter Moore: 90 Ankara, 91 Istanbul, 95 Islamabad; dob 1963.
Richard Peter Moore: dob 1963; 90 Ankara, 91 Istanbul, 95 Islamabad, 01 Kuala Lumpur (Cllr).*
Mark Scott Thomas Morgan: 84 Geneva, 88 Aden, 94 Valletta; dob 1958; MBE.
Mark Scott Thomas Morgan: dob 1958; 84 Geneva, 88 Aden, 94 Valletta, 01 Budapest (1 Sec).
Stuart Richard Morley: 89 San Jose, 90 Bridgetown, 96 Hague; dob 1959.
Stuart Richard Morley: dob 1959; 89 San Jose, 90 Bridgetown, 96 Hague, 02 New Delhi (Cllr).*
Hugh Roger Mortimer: dob 1949; 75 Rome, 78 Singapore, 83 New York, 91 Berlin, 97 Ankara, 01 Ljubljana. (* DHM, Berlin, 05)
Colin Andrew Munro: dob 1946; 71 Bonn, 73 Kuala Lumpur, 81 Bucharest, 87 East Berlin,90 Frankfurt, 97 Zagreb, 01 Mostar, 03 Vienna (OSCE, Head of UK Delegation).*
Andrew Alasdair Neil: dob 1968; 94 Nairobi, 01 Abu Dhabi (1 Sec).
Philip Raymond Nelson: dob 1950; 74 Budapest, 76 Paris, 80 Rome, 89 Manila, 91 Budapest, 94 London.
Clive Dare Newell: 79 Tehran, 82 Kabul, 86 Addis, 90 Bosnia, 94 Ankara; dob 1953.
Clive Dare Newell: dob 1953; 79 Tehran, 82 Kabul, 86 Addis Ababa, 94 Ankara, 01 Moscow, 03 Ottawa (Cllr).*
Stephen Martin Noakes: dob 1957; 90 Luanda, 96 New York, 00 London.
Richard Adam Noble: dob 1962; 87 Moscow, 93 Hague, 98 New Delhi, 03 Tashkent, 04 Hong Kong (DHM).*
Peter James Norris: 85 Lagos, 90 Guatemala; dob 1955, Dr.
Peter James Norris: dob 1955; 85 Lagos, 90 Guatemala City, 97 Jakarta, 00 London.
John Matthew O’Callaghan: dob 1966; 92 Santiago, 98 Moscow, 03 Stockholm,04 Belgrade (Cllr).*
Paul Vincent O’Connor: dob 1956; 77 Jedda, 80 Washington, 87 Istanbul, 91 Maseru, 99 St.Petersburg, 03 Berlin (1 Sec).
Stephen John O’Flaherty: dob 1951; 78 New Delhi, 81 Prague, 88 Vienna, 92 London.
Peter David Orwin: 77 Athens, 84 Brasilia, 89 Tel Aviv, 96 Hague; dob 1944; OBE, MC.
Richard Lloyd Owen: dob 1948; 78 Abu Dhabi, 80 Beirut, 83 San Jose, 86 Berlin, 93 Copenhagen, 98 London.
Simon Graham Page: dob 1961; 83 Kuala Lumpur, 88 Dublin, 92 New Delhi, 98 Riyadh, 01 London.(* 1 Sec, Bahrain, 05)
Christopher Robert Geoffrey Pagett: 78 Havana, 79 Lusaka, 88 Maputo, 97 New York; dob 1952; OBE.
Charles William Parton: dob 1956; 85 Peking, 90 Hong Kong, 03 Nicosia (Cllr).*
Colin Douglas Partridge: 80 Delhi, 87 Hanoi, 94 Hong Kong; dob 1955.
Colin Douglas Partridge: dob 1955; 80 New Delhi, 87 Hanoi, 94 Hong Kong, 00 Seoul (Cllr).
Hugh William Grant Patterson: dob 1950; 80 Berlin, 87 Guatemala City, 92 Caracas, 00 Berne, 04 London.
Martin Eric Penton-Voak: 95 Moscow; dob 1965.
Martin Eric Penton-Voak: dob 1965; 95 Moscow, 01 Vienna (1 Sec).
Geoffrey Colin Perry: 81 Hong Kong, 92 Geneva; dob 1951.
Alan Petty.
Quentin James Kitson Phillips: dob 1963; 89 Budapest, 95 Moscow, 97 Kiev, 04 Istanbul (Consul).*
Tom Richard Vaughan Phillips: dob 1950; 85 Harare, 90 Tel Aviv, 93 Washington, 00 Kampala, 02 London.
Richard William Potter: 85 Riyadh, 88 Nicosia; dob 1960.
Richard William Potter: dob 1960; 85 Riyadh, 90 Nicosia, 95 Sarajevo, 99 Skopje, 04 Amman (Cllr).*
David Herbert Powell: dob 1952; 88 Tokyo, 97 Brussels, 02 London.
Mark Precious: Buenos Aires 86; dob 1960.
Christopher Norman Russell Prentice: dob 1954; 80 Kuwait, 85 Washington, 94 Budapest, 02 Amman.*
Timothy Ian Priest: dob 1947; 75 Vienna, 81 Helsinki, 89 Athens, 99 Helsinki, 03 London.
John Andrew Raine: 88 Kuwait, 94 Damascus, 97 Riyadh; dob 1962.
Michael Charles Ramscar: 77 Lagos, 79 Brasilia, 86 Madrid, 89 San Jose, 97 Madrid; dob 1948.
John Charles Josslyn Ramsden: dob 1950; 76 Dakar, 79 Vienna, 80 Hanoi, 90 Berlin, 96 Geneva, 04 Zagreb.*
Timothy Simeon Rawlinson: 91 Lagos, 96 Stockholm; dob 1962.
Richard Robert Reeve: 73 Singapore, 77 Hong Kong, 83 Hong Kong; dob 1948.
Michael John Regan: 86 Kabul, 89 Dubai, 95 Bangkok; dob 1955.
Michael John Regan: dob 1955; 86 Kabul, 89 Dubai, 95 Bangkok, 04 Harare (Cllr).*
Peter Marius Julian Prows Reilly: 96 Khartoum; dob 1971.
Clare Louise Rickitt: dob 1964; 93 Brasilia, 96 London.
John Ridd.
Paul John Ritchie: dob 1962; 86 Nicosia, 91 New York, 99 Nicosia, 03 London.
Colin Roberts: dob 1959; 90 Tokyo, 97 Paris, 01 Tokyo, 04 Vilnius.*
David George Roberts: dob 1955; 77 Jakarta, 81 Havana, 88 Madrid, 91 Paris, 96 Santiago, 00 Berne (DHM, CG).
Michael John Wyn Roberts: dob 1960; 87 Athens, 95 Brussels, 04 Ankara (DHM).*
Philip John Barclay Roberts: dob 1949; 77 Islamabad, 82 Hanoi, 84 Tokyo,91 Lisbon, 94 Bogota, 97 Vienna, 99 London.
Elizabeth Carol Robson: dob 1955; 84 Moscow, 88 Geneva, 96 Stockholm, 02 Copenhagen (DHM).
Janet Elizabeth Rogan: 91 Peking, 98 Sarajevo; dob 1962.
Mark Alastair Runacres: dob 1959; 83 New Delhi,91 Paris, 99 New York, 02 New Delhi (DHC).*
Michael John Sanderson: dob 1948; 72 Cairo, 79 New York, 84 Oslo, 93 Hong Kong, 95 London.
William Geoffrey Sandover: dob 1955; 81 Vienna, 86 Dublin, 92 Buenos Aires, 02 Paris, 04 Islamabad (Cllr).*
John Donald William Saville: dob 1960; 83 Jakarta, 88 Warsaw, 95 Vienna, 00 Havana, 03 London. (* HC, Brunei, 05)
John McLeod Scarlett: 73 Nairobi, 76 Moscow, 84 Paris, 91 Moscow; dob 1948; OBE.
Michael William Seaman: dob 1955; 77 Jakarta, 81 Bombay, 88 Hague, 99 Athens, 02 Tbilisi (1 Sec). (* Cllr, Kabul, 05)
Richard Charles Leslie Seddon: dob 1968; 94 New Delhi, 99 Washington, 03 Islamabad (1 Sec).*
Paul Raymond Sizeland: dob 1952; 81 Brussels, 85 Doha, 88 Lagos, 96 Bangkok, 00 Shanghai, 03 London.
James Lyall Sharp: dob 1960; 89 Cairo, 96 Vienna, 02 Almaty.*
Philip Nicholas Shott: dob 1954; 83 Lagos, 87 Nicosia, 94 Lusaka, 01 Pretoria (Cllr).*
Deborah Jane Soothill: 96 Peking; dob 1969.
Andrew James Sparkes: dob 1959; 85 Ankara, 92 Bangkok, 99 Jakarta, 01 Pretoria, 04 Kinshasa.*
Richard David Spearman: 92 Istanbul, 97 Paris; dob 1960.
David Spedding.
Guy David St. John Kelso Spindler: 87 Moscow, 97 Pretoria; dob 1962.
Patrick William Sprunt: dob 1952; 78 Tokyo, 82 Brussels, 83 Bonn, 87 Tokyo, 92 New York, 99 Tokyo, 04 London.
Andrew Jeremy Stafford: 77 Stockholm, 79 Accra, 84 Prague, 91 Brussels; dob 1953.
Andrew Jeremy Stafford: dob 1953; 77 Stockholm, 79 Accra, 84 Prague, 91 Brussels, 99 Stockholm, 03 London.
Christopher David Steele: 90 Moscow; dob 1964.
Adrian Stones: dob 1960; 89 New Delhi, 92 Washington, 00 Harare (Cllr).
Christopher Rowland Charlesworth Sykes: dob 1955; 87 Hong Kong, 04 Hong Kong (Cllr, DCG).*
Mark Robert Syrett: dob 1969; 98 Oslo, 04 Riyadh (2 Sec).*
Nicholas Simon Syrett: dob 1960; 93 Luanda, 98 Bogota, 03 Nairobi (Cllr).*
Arthur David Tandy: dob 1949; 87 Riyadh, 89 London.
Anthony James Nicholas Tansley: dob 1962; 88 Riyadh, 89 Baghdad, 94 Dublin,98 Muscat, 01 London.
Geoffrey Tantum.
Duncan John Rushworth Taylor: dob 1958; 83 Havana, 92 Budapest, 00 New York (DCG).
Anthony Jonathan Terry: 70 Nairobi, 73 Havana, 79 Belgrade, 86 Santiago, 97 Geneva; dob 1946.
Harcourt Andrew Pretorius Tesoriere: dob 1950; 76 Kabul, 79 Nairobi, 81 Abidjan, 87 Damascus, 96 Tirana, 98 Kabul, 02 Riga, 05 Algiers.*[Ambassador to Latvia]
Richard Paul Reynier Thompson: 91 Stockholm, 96 Geneva; dob 1960.
Richard Paul Reynier Thompson: dob 1960; 91 Stockholm, 96 Geneva, 04 Baghdad (Cllr).*
Michael Thomson.
Daniel Vernon Thornton: 95 Brussels; dob 1969.
Damian Roderic Todd: dob 1959; 81 Pretoria, 87 Prague, 91 Bonn, 01 Bratislava.
Patrick Gilmer Topping: dob 1959; 90 Kuala Lumpur, 94 Washington, 05 Canberra (Cllr).*
Owen John Traylor: dob 1955; 81 Tokyo, 90 Berlin, 00 Istanbul, 04 London.
James Philip Tucker: dob 1966; 93 Prague, 94 Bratislava, 01 Isamabad, 03 Jakarta (Cllr).
Stuart Graham Turvill: 95 Islamabad; dob 1971.
Stuart Graham Turvill: dob 1971; 95 Islamabad, 00 Accra, 03 London.
John Venning.
Richard Vlaistow: 95 Havana.
Eric Simon Charles Wall: dob 1957; 88 Geneva, 94 Kampala, 98 Harare, 01 London.
Michael John Ward: dob 1958; 85 Istanbul, 88 Paris, 97 Brussels, 02 Budapest (DHM).*
James Wilfrid Watt: dob 1951; 80 Abu Dhabi, 85 New York, 92 Amman, 96 Islamabad, 03 Beirut.*
James Spencer Kennedy Watson: 91 Kuwait, 97 Damascus; dob 1964.
Robert Emmerson Watson: dob 1970; 98 Tel Aviv, 04 Kampala (1 Sec).*
Jonathan Michael Weldin: dob 1959; 86 Sanaa, 90 Tunis, 96 Athens, 01 London.
Andrew Ronald Whitecross: dob 1949; 81 Sanaa, 85 Baghdad, 98 Muscat, 01 London.
Andrew Whiteside: 95 Budapest; dob 1968.
Andrew John Whiteside: dob 1968; 95 Budapest, 02 Rome (1 Sec).*
Bernard Gerrard Whiteside: dob 1954; 83 Moscow, 86 Geneva, 91 Bogota, 02 Chisinau.*
Timothy Andrew Willasey-Wilsey: dob 1953; 83 Luanda, 86 San Jose, 93 Islamabad, 99 Geneva, 02 London.
Mark Williams: 95 Tehran. (Reportedly Kenneth Mark Williams)
Kenneth Mark Williams: 76 Kuala Lumpur, 79 Bridgetown, 88 Harare, 94 Delhi; dob 1944.
Simon John Williams: dob 1960; 81 Manila, 84 Mbabane, 86 Kaduna, 95 Riyadh, 98 Doha, 02 Casablanka (Consul).*
Simon Jules Wilson: 91 Athens, 93 Zagreb; dob 1966; OBE.
Simon Jules Wilson: dob 1966; 91 Athens, 93 Zagreb, 99 New York, 02 Budapest (1 Sec).*
Elizabeth Claire Wilson: dob 1974; 02 Peking (2 Sec).*[Liz Wilson, Peking]
Julian Paul Geoffrey Wiseman: 78 Geneva, 84 Dhaka, 90 Islamabad; dob 1944.
Peter Gilruth Wood: dob 1953; 84 Taiwan, 86 Peking, 95 Kuala Lumpur, 02 Peking (Cllr).*
David John Woods: 78 Vienna, 81 Bucharest, 92 Harare, 97 Pretoria; dob 1951.
David John Woods: dob 1951; 78 Vienna, 81 Bucharest, 92 Harare, 97 Pretoria, 02 Berlin (Cllr).*
Ian Alexander Woods: 77 New York, 84 Berlin, 86 Bonn, 95 Warsaw; dob 1951.
Ian Alexander Woods: dob 1951; 77 New York, 84 Berlin, 86 Bonn, 95 Warsaw, 03 Sofia (Cllr).*
Alexander William Younger: 95 Vienna; dob 1963.
Alexander William Younger: dob 1963; 95 Vienna, 02 Dubai (1 Sec).*
BILL BLUNDEN – The CIA Does Las Vegas
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
The CIA Does Las Vegas
One evening over drinks in Ethiopia, during his tour as a CIA officer back in the 1960s, John Stockwell expressed reservations about covert operations to a senior fellow officer named Larry Devlin. Stockwell worried that the CIA was infiltrating governments and corrupting leaders to no useful end. Devlin, well-known in spy circles for his work in the Congo, berated Stockwell[i]:
“You’re trying to think like the people in the NSC back in Washington who have the big picture, who know what’s going on in the world, who have all the secret information, and the experience to digest it. If they decide we should have someone in Bujumbura, Burundi, and that person should be you, then you should do your job, and wait until you have more experience, and you work your way up to that point, then you will understand national security, and you can make the big decisions. Now, get to work, and stop, you know, this philosophizing.”
It’s a compelling argument: trust me, I know secrets. In fact it’s the same sort of argument that a federal informant named Hector Xavier Monsegur used to convince an activist named Jeremy Hammond to break into a whole slew of servers belonging to foreign governments[ii]. Monsegur assured Hammond: “Trust me, everything I do serves a purpose.” Hammond didn’t realize that he was actually part of an elaborate intelligence campaign being run by the FBI. Pimped out to other American three-letter agencies as it were.
Trust Me: I’m an Insider
John Stockwell was patient. He stayed on with the CIA and rose through the ranks, ultimately garnering enough clout to sit in on subcommittee meetings of the National Security Council. What he witnessed shocked him. Stockwell saw fat old men like senior ambassador Ed Mulcahy who fell asleep[iii] and petty officials like Henry Kissinger who got into embarrassing spats when someone else sat in their chair.[iv] All the while decisions were made that would kill people.
Quelle surprise! There were no wise men making difficult decisions based on dire threats to national security. Merely bureaucrats in search of enemies whose covert programs created more problems than they solved.
There’s a lesson in this story that resonates very strongly. A security clearance is by no means a guarantee of honesty or integrity. The secrets that spies guard don’t necessarily justify covert programs. Rather the veil of the government’s classification system is often leveraged to marginalize the public, to exclude people from policy making, and conceal questionable activity that would lead to widespread condemnation and social unrest if it came to light.
Past decades offer an endless trail of evidence: Operation Gladio, Operation Mockingbird, Project MKUltra, Operation Wheeler/Wallowa, Watergate, Operation CHAOS, COINTELPRO, Operation Northwoods, P2OG (the Proactive, Preemptive Operations Group), Iran-Contra, etc.
Cryptome’s John Young describes how this dynamic literally unwinds democracy[v]:
“Those with access to secret information cannot honestly partake in public discourse due to the requirement to lie and dissimulate about what is secret information. They can only speak to one another never in public. Similarly those without access to secret information cannot fully debate the issues which affect the nation, including alleged threats promulgated by secret keepers who are forbidden by law to disclose what they know.”
The Parade of Lies
In light of Ed Snowden’s revelations, and the remarkably flat-footed response of our political leaders, society is witnessing a crisis of trust. Time after time we’ve been lied to by ostensibly credible government officials. Not little white lies, but big scandalous ones. Lies that bring into question the pluralistic assumptions about American democracy and suggest the existence of what political analysts from Turkey would call a “Deep State[vi].”
For instance, both former NSA director Keith Alexander and House Intelligence Chair Mike Rogers claimed that NSA mass interception was instrumental in disrupting over 50 terror plots, a claim that dissolved quickly upon closer scrutiny[vii].
Or contemplate an unnamed NSA spokesman who vehemently told the Washington Post that the NSA was not engaged in economic espionage[viii], only to be contradicted by leaked top-secret documents which described how the NSA broke into networks run by the Chinese telecom giant Huawei and made off with the company’s crown jewels (i.e. product source code).
When President Obama scored some air time with Charlie Rose, in soothing tones he calmly explained to viewers that the NSA doesn’t monitor American citizens without a warrant. It’s surprising that POTUS, a man with a background in constitutional law no less, would be unaware of Section 702 of the Foreign Intelligence Surveillance Act (FISA). This legal provision contains a loophole that allows just this sort of warrantless monitoring to transpire[ix]. Never mind Executive Order 12333, which is arguable an even greater threat[x].
More recently, consider Dianne Feinstein’s claim back in March that the CIA had been monitoring a network used by the Senate Intelligence Committee. John Brennan, the CIA director, told her that she was full of it and sanctimoniously replied “when the facts come out on this, I think a lot of people who are claiming that there has been this tremendous sort of spying and monitoring and hacking will be proved wrong[xi].”
Well guess what? It turns out Brennan was on the losing side of that bet. An internal investigation showed that CIA officers had indeed been watching the Senate Committee[xii]. Stop and pause for a moment. This disclosure is a serious warning sign. What, pray tell, do you think happens to the whole notion of checks and balances when the executive branch spies on the other two branches? Do you suppose there are implications for the balance of power?
Damage Control
Faced with this ever expanding dearth of credibility, spies have worked diligently to maintain the appearance of integrity.
 Specifically, industry conferences like Black Hat and DEF CON have regularly catered to the needs of U.S. Intelligence by serving as platform for the Deep State and its talking points: that Cyberwar is imminent[xiii], that cybercrime represents an existential threat[xiv], and that mass interception is perfectly normal and perfectly healthy[xv].
Specifically, industry conferences like Black Hat and DEF CON have regularly catered to the needs of U.S. Intelligence by serving as platform for the Deep State and its talking points: that Cyberwar is imminent[xiii], that cybercrime represents an existential threat[xiv], and that mass interception is perfectly normal and perfectly healthy[xv].
“If the tariff of security is paid, it will be paid in the coin of privacy. [xvi]”
In these hacker venues high-profile members of the intelligence community like Cofer Black[xvii], Shawn Henry[xviii], Keith Alexander[xix], and Dan Greer[xx] are positioned front and center in keynote slots, as if they were glamorous Hollywood celebrities. While those who value their civil liberties might opine that they should more aptly be treated like pariahs[xxi].
“Time Out” Posturing
One would hope that the gravity of Ed Snowden’s documents would have some impact. Indeed, Jeff Moss, the organizer who currently runs DEF CON and who originally founded Black Hat (and, by the way, currently sits on the Department of Homeland Security’s Advisory Council[xxii]), did attempt to make a symbolic gesture of protest in the summer of 2013. He gently requested that feds call a “time-out” and not attend DEF CON[xxiii].
To grasp the nature of this public relations maneuver is to realize that roughly 70 percent of the intelligence budget is channeled to private sector companies[xxiv]. As Glenn Greenwald observed during the 2014 Polk Award ceremony, as far as the national security state is concerned there is little distinction between the private and public sector[xxv]. Anyone who has peered into the rack space of the data broker industry knows that the NSA is an appendage on a much larger corporate apparatus[xxvi].
So asking federal employees to stay away really doesn’t change much because the driving force behind the surveillance state, the defense industry and its hi-tech offshoots, will swarm Vegas in great numbers as they normally do. Twelve months after Moss calls his halfhearted “time-out,” Black Hat rolls out the red carpet for the Deep State[xxvii], (while the government threatens to clamp down on attendance to conferences by foreign nationals[xxviii]). This is all very telling.
Bill Blunden is an independent investigator whose current areas of inquiry include information security, anti-forensics, and institutional analysis. He is the author of several books, including The Rootkit Arsenal , and Behold a Pale Farce: Cyberwar, Threat Inflation, and the Malware-Industrial Complex. Bill is the lead investigator at Below Gotham Labs.
Notes.
[i] John Stockwell, THE SECRET WARS OF THE CIA: part I, lecture given in October, 1987,
http://www.thirdworldtraveler.com/Stockwell/StockwellCIA87_1.html
[ii] Mark Mazzetti, “F.B.I. Informant Is Tied to Cyberattacks Abroad,” New York Times, April 23, 2014, http://www.nytimes.com/2014/04/24/world/fbi-informant-is-tied-to-cyberattacks-abroad.html
[iii] John Stockwell, THE SECRET WARS OF THE CIA: part I, lecture given in October, 1987,
http://www.thirdworldtraveler.com/Stockwell/StockwellCIA87_1.html
[iv] John Stockwell, The Praetorian Guard: The U.S. Role in the New World Order, South End Press, July 1, 1999.
[v] John Young, “Wall Street Journal Secrecy,” Cryptome, August 22, 2014, http://cryptome.org/0002/wsj-secrecy.htm
[vi] Peter Dale Scott, “The Deep State and the Wall Street Overworld”, Asia-Pacific Journal: Japan Focus, March 10, 2014, http://japanfocus.org/-Peter_Dale-Scott/4090
[vii] Cindy Cohn and Nadia Kayyali, “The Top 5 Claims That Defenders of the NSA Have to Stop Making to Remain Credible,” Electronic Frontier Foundation, June 2, 2013, https://www.eff.org/deeplinks/2014/06/top-5-claims-defenders-nsa-have-stop-making-remain-credible
[viii] Barton Gellman and Ellen Nakashima, “, U.S. spy agencies mounted 231 offensive cyber-operations in 2011, documents show” Washington Post, August 30, 2013
[ix] Nadia Kayyali, “The Way the NSA Uses Section 702 is Deeply Troubling. Here’s Why,” Electronic Frontier Foundation, May 7, 2014, https://www.eff.org/deeplinks/2014/05/way-nsa-uses-section-702-deeply-troubling-heres-why
[x] John Napier Tye, “Meet Executive Order 12333: The Reagan rule that lets the NSA spy on Americans,” Washington Post, July 18, 2014, http://www.washingtonpost.com/opinions/meet-executive-order-12333-the-reagan-rule-that-lets-the-nsa-spy-on-americans/2014/07/18/93d2ac22-0b93-11e4-b8e5-d0de80767fc2_story.html
[xi] Mark Mazzetti And Jonathan Weisman, “Conflict Erupts in Public Rebuke on C.I.A. Inquiry,” New York Times, March 11, 2014, http://www.nytimes.com/2014/03/12/us/cia-accused-of-illegally-searching-computers-used-by-senate-committee.html
[xii]Mark Mazzetti, “C.I.A. Admits Penetrating Senate Intelligence Computers,” New York Times, July 31, 2014, http://www.nytimes.com/2014/08/01/world/senate-intelligence-commitee-cia-interrogation-report.html
[xiii] Molly Mulrain, “Former CIA Official: ‘Cyber Will Be Key Component of Any Future Conflict’”, ExecutiveBiz, August 4, 2011, http://blog.executivebiz.com/2011/08/former-cia-official-cyber-will-be-a-key-component-of-any-future-conflict/
[xiv] Gerry Smith, “Cyber-Crimes Pose ‘Existential’ Threat, FBI Warns,” Huffington Post, January 12, 2012, http://www.huffingtonpost.com/2012/01/12/cyber-threats_n_1202026.html
[xv] “U.S. Cyber Command Head General Alexander To Keynote Black Hat USA 2013,” Dark Reading, May 14, 2013, http://www.darkreading.com/risk/us-cyber-command-head-general-alexander-to-keynote-black-hat-usa-2013/d/d-id/1139741
[xvi] Daniel E. Geer, “Cybersecurity and National Policy,” Harvard Law School National Security Journal, Volume 1 – April 7, 2010, http://harvardnsj.org/2011/01/cybersecurity-and-national-policy/
[xix] Jim Finkle, “Defcon 2012 Conference: Hackers To Meet With U.S. Spy Agency Chief,” Reuters, July 20, 2012, http://www.huffingtonpost.com/2012/07/20/defcon-2012_n_1691246.html
[xx] Spencer Ackerman, “NSA keeps low profile at hacker conventions despite past appearances,” Guardian, July 31, 2014, http://www.theguardian.com/world/2014/jul/31/nsa-hacker-conventions-recruit-def-con-black-hat/print
[xxi] George Smith, “Computer Security for the 1 Percent Day,” Escape From WhiteManistan, May 19, 2014, http://dickdestiny.com/blog1/?p=18011
[xxiii] Dan Goodin, “For first time ever, feds asked to sit out DefCon hacker conference,” Ars Technica, July 11, 2013, http://arstechnica.com/security/2013/07/for-first-time-ever-feds-asked-to-sit-out-defcon-hacker-conference/
[xxiv] Tim Shorrock, “Put the Spies Back Under One Roof,” New York Times, June 17, 2013, http://www.nytimes.com/2013/06/18/opinion/put-the-spies-back-under-one-roof.html
[xxv] “”We Won’t Succumb to Threats”: Journalists Return to U.S. for First Time Since Revealing NSA Spying,” Democracy Now! April 14, 2014, http://www.democracynow.org/2014/4/14/we_wont_succumb_to_threats_journalists#
[xxvi] “Inside the Web’s $156 Billion Invisible Industry,” Motherboard, December 18, 2013, http://motherboard.vice.com/blog/inside-the-webs-156-billion-invisible-industry
[xxvii] Spencer Ackerman, “NSA keeps low profile at hacker conventions despite past appearances,” Guardian, July 31, 2014, http://www.theguardian.com/world/2014/jul/31/nsa-hacker-conventions-recruit-def-con-black-hat/print
[xxviii] Andrea Shalal and Jim Finkle, “U.S. may act to keep Chinese hackers out of Def Con hacker event,” Reuters, May 24, 2014, http://www.reuters.com/article/2014/05/24/us-cybercrime-usa-china-idUSBREA4N07D20140524
Exposed by Cryptome – Masterspy Official Style Book and Writing Guide
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Click to access ODNIstyleManual_2011_2013.pdf
Unveiled – CIA Officer Phil Raveling
Become a Patron!
True Information is the most valuable resource and we ask you to give back.

Source Sends –
1. Philip C. “Phil” Raveling, LinkedIn:
https://www.linkedin.com/pub/phil-raveling/21/97a/76b
2. From Pax Mondial:
Phil Raveling retired in 2014 after 25 years in the Central Intelligence Agency’s National Clandestine Service. He served six overseas assignments at US Embassies and CIA posts in Europe, the Middle East, and South Asia, as well as in domestic assignments in the US. From 2009–2011, Phil led the US Intelligence Community’s inter-agency Financial Intelligence Organization that was the center of excellence in the US Government for financial and counter-threat finance intelligence operations. He has broad experience in all phases of intelligence leadership, operations, collection, and reporting, with special concentration on key transnational issues such as counterterrorism, war zones, counter-threat finance, counterintelligence, and European and Middle Eastern regional issues.
Phil served over two years – in 2004 and again in 2011- in Afghanistan as the senior intelligence officer in in RC-South, leading all phases of intelligence operations in a high risk war zone environment. He executed critical intelligence collection operations against high value terrorist and insurgent networks in Afghanistan and Pakistan. In 2009, he served in Iraq, managing CIA operations in Al Anbar province. From 2012-2013, he also directed DoD intelligence collection operations across the Middle East and CENTCOM AOR, leading hundreds of officers in complex counterterrorist operations requiring extensive inter-agency coordination.
Phil Raveling holds a Master’s degree from American University and an Undergraduate degree from Texas Christian University. He speaks fluent French, Italian, and Turkish.
3. Facebook profile, username says “Phil Afghan” (heh):
https://www.facebook.com/philafghan
Pictures attached and saved for record (OSINT). FB record mentions work at “US Department of State” (typical cover)
4. He tells a friend:
“I retired from the Gov in Feb and am out on my own, very liberating! Phil.
Phil Raveling
Raven Advisory
703-531-9639
raventeam2@gmail.com
5. Wife –> Liz Steele Raveling:
https://www.facebook.com/liz.raveling
6. Daughter Alexandra Raveling, profile says went to American School of Milan (class of 2010), possibly father must have been posted to Italy:
https://www.facebook.com/alexandra.raveling
7. Son Christian Raveling, intern at Rand Construction Corp., lives in McLean VA, says he’s from “Paris, France”:
https://www.facebook.com/craveling
8. Dec 1998 issue of US State Dept magazine “State” mentions Philip C Raveling on pg 45 of 52 that Phil was transferred from Paris to European Affairs:
http://www.state.gov/documents/organization/191067.pdf
9. Property sale record:
10. Address: 2603 Faber Ct, Falls Church, VA 22046, (703) 942-8323
http://www.arivify.com/property/search/dIPxXNTki
11 Phil’s profile says “fluent in Italian and French”, among others. This proves he was posted in Italy and then France.
Video – Ebola Outbreak 2014: From the Hot Zone of this Deadly Virus Raging Out of Control
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Ebola Outbreak 2014: From the Hot Zone of this Deadly Virus Raging Out of Control
Ebola is raging out of control in Western Africa! See how quickly we went from Patient Zero in December 2013 to over a 1000 fatalities across numerous countries in just over 8 months. Fear is growing of a worldwide pandemic outbreak if the virus is not contained. Ebola is one plane ride away from reaching other countries.
TOP-SECRET – The Secret List of CIA Sources – 2.619 Names and Adresses, Part 5,E,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
E
Eames, Edward J. 4601 Cavillo Ct., SE, Rio Rancho, NM 87124 Earnest, Edwin P. 6686 Midhill Pl., Falls Church, VA 22043 Easley, LtCol Claudius USA 3601 Connecticut Ave., NW, Washington, DC 20008 East, John W. 4822 N. 15th St., Arlington, VA 22205 Eaton, BrigGen Richard USA 1448 Westlake Dr., NW, Gainesville, GA 30501 Eavenson, L. Chandler 491 Whippoorwill Ln., Sautee-Nacoochee, GA 30571 Eckels, Vernon 718 Kings Ln., Fort Washington, MD 20744 Edgar, Major Scott USAF 334 Esquina Dr., Henderson, NV 89014 Edwards, Duval 566 E. Hampton No. 238, Tucson, AZ 85712 Edwards, Henry 6412 Sewanee, Houston, TX 77005 Edwards, Capt John USN 100 E. Ocean View Ave., Norfolk, VA 23503 Egermeier, Ms Phyllis 900 E. Wilcox Dr., No. 124, Sierra Vista, AZ 85635 Eifler, Col Carl AUS 22700 Picador Dr., Salinas, CA 93901 Elder, Arthur G. 2411 Romney Rd., San Diego, CA 92109 Elkins, Allen 105 Gullane Dr. Williamsburg, VA 23188 Ellenwood, Robert 5133 Grandon Dr., Hilliard, OH 43026 Elliker, John 1054 Darrell Dr., NE, New Philadelphia, OH 44663 Elliott, Carter 640 Black Bear Run, Christiansburg, VA 24068 Elliott, Charles P. 312 La Peninsular Blvd., Naples, FL 33962 Elliott, Joe Wilson P.O. Box 74699, Los Angeles, CA 90004 Elliott, John 1655 Larchmont Ave., Lakewood, OH 44107 Ellis, John F. 1801 East 12th St., Cleveland, OH 44114 Ellis, Capt William USN 4101 Downing St., Annandale, VA 22003 Ellithrope, Major Gilbert AUS 358 Santa Margarita Dr., San Rafael, CA 94901 Ellwanger, Edward 5915 Alan Dr., Clinton, MD 20735 Elser, Cinda P.O. Box 43, North Lima, OH 44452 Elston, Paul White City 201, London W12 7TS, England Emley, Warren 936 St. Andrews Blvd., Naples, FL 33962 Encher, Cazimier V. 6745 S. Tripp Ave., Chicago, IL 60629 Endel, Max 7323 Staffordshire No. 3, Houston, TX 77030 Enkelmann, Robert 10133 Concord School Rd., St. Louis, MO 63128 Enney, MajGen James, USAF 1914 Rose Mallow Ln., Orange Park, FL 32073 Enochs, John 17316 Ash St., Fountain Valley, CA 92708 Epperson, J. B. 2440 E. 45th St., Tulsa, OK 74105 Epstein, LtCol Lawrence USAR 115 Hatteras Rd., Barnegat, NJ 08005 Epstein, Dr. Mark 9522 E. Stanhope Rd., Kensington, MD 20895 Erikson,, LtCol James USAR P.O. Box 10097, Lynchburg, VA 24506 Erkko, Aatos Helsingin Sanomat, Helsinki, Finland Erman, Dr. Seneca 7341 E. Sabino Visitia Dr., Tucson, AZ 85715 Eskes, James 1453 Montelegre Dr., San Jose, CA 95120 Esser, Mrs. Erna 1620 Wrightson Dr., McLean, VA 22101 Estey, Col Hayden USAR 5341 Westpath Way, Bethesda, MD 20816 Etheridge, Obie 138 Seaview Ln., Corpus Christi, TX 78411 Evans, James 3209 Riviera Pl., NE, Albuquerque, NM 87111 Evans, Jean 2105 Reynolds St., Falls Church, VA 22043 Evans, John RR 2, Box 1755, Arlington, VT 05250 Evans, Joseph 605 Winged Foot Ct., New Bern, NC 28562 Eye, Ralph P.O. Box 291, Bucksport, ME 04416
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 14, AQ,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 00170/693 | AQALLAL MOHAMED |
| IPN 00 1043/579 | AQALLAL MOHAMED |
| AQUALLAL GENEVIEVE |
The World At War TV – Why Russia and Ukraine Fight for Crimea
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
An informative look at Crimea’s nostalgic Russian ties and how Crimaea became a part of the Ukraine in 1954. Opening with riveting footage of the crisis in Ukraine over this small but strategic peninsula, a look back at the glory days of the Crimea and an interesting analysis of Russian strategy.
TOP-SECRET – The Secret List of CIA Sources – 2.619 Names and Adresses, Part 4,D,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
D
Dabrowski, Edmund 148-A Wallworth Park, Cherry Hill, NJ 08002 Dalby, Cranford 300 N. Washington St., No. 400, Alexandria, VA 22314 Dale, Mrs. J. Thomas 7603 North Ocean Blvd., No. 3B, Myrtle Beach, SC 29577 Dalenberg, Philip P.O. Box 7722, Fort Gordon, GA 30905 Daly, Ralph T. 99 Cloverdale Heights, Charles Town, WV 25414 Daniel, Dr. Gerard L 25 Canada St., Swanton, VT 05488 Daniluck, Serge 716 N. Belgrade Ct., Silver Spring, MD 20902 Darcy, Thomas 12821 Sunset Terrace, Clive, IA 50325 Darer, Stanley 22 Wilton Rd., Beaconfield, Bucks, IfP9 2DE, England Dann, Charles 1 Fairway Dr., Manhasset, NY 11030 Davidov, Dr. Michael 9112 Mill Pond Valley Dr., McLean, VA 22102 Davidson, Philip 83 Devon Rd., Albertson, NY 11507 Davis, Alton D. 5606 Mirror Light Place., Columbia, MD 21045 Davis, Curtis C. 10 Overhill Rd., Baltimore, MD 21210 Davis, Donald 4241 Riverside Dr., Evans, GA 30809 Davis, LtGen John USA 2346 South Mende St., Arlington, VA 22202 Davis, Mrs. Norma 4241 Riverside Dr., Evans, GA 30809 Davis, LtCol Sidney USAF 231 Greenwood Dr., Petersburg, VA 23805 Dawson, Mrs. Mary 1131 Compass Ln., No. 306, Foster City, CA 94404 Dawson, Raymond 6357 Dawson Blvd., Mentor OR 44060 Day, David W. P.O. Box 1296, Mukilteo, WA 98275 Day, Mrs. Mary Louise 4928 Sentinel Dr., No. 304, Bethesda, MD 20816 De Angelo, Mrs. Alice 2500 Virginia Ave., NW, No. 306-S, Washington, DC 20037 De Candio, LtCol Michael USA 2505 Childs Ln., Alexandria, VA 22308 de Vore, Ralph 3828 Baltimore, Shreveport, LA 71106 De Wald, LtCdr Bruce USN 5131 SE Naef Rd., Milwaukie, OR 97267 Deahl, Albert P.O. Box 277792, San Diego, CA 92128 Deahl, Warren 6125 Tamerlane Dr., South Bend, IN 46614 Dean, Mary Evelyn 1436 Woodacre Dr., McLean, VA 22101 Dean, Warren 9908 Fernwood Rd., Bethesda, MD 20817 DeBruier, Wilburn 10308 Florian Rd., Louisville, KY 40223 Deck, Mrs. Helen P. 1640 Atares Dr., No. 8, Punta Gorda, FL 33950 Dee, Col Chester H. AUS 510 S. Hi Lusi Ave., Mt. Prospect, IL 60056 Deffenbaugh, Berman 331 Ave Maria Dr., San Antonio, TX 78216 DeGenare, William 12808 Woodview Ct., Burnsville, MN 55337 DeKuyper, Frederick 4422 Underwood Rd., Baltimore, MD 21218 Del Favero, Dario 210 Southland Station Dr., No. 256, Warner Robins, GA 31088 Delaney, Col John USA 5621 Granada Blvd., Miami, FL 33146 Delanty, Timothy 8351 Forrester Blvd., Springfield, VA 22152 DeLashmit, William 2462 River Rd., Plymouth, NH 03264 Dell, George 11909 Hickory Creek Dr., Fredricksburg, VA 22407 Delia Santa, Walter 16327 Lindsay Rd., Yelm, WA 98597 De Long, Earl 1602 N. Greenbrier St., Arlington, VA 22205 DeLong, Richard 2250 East Imperial Highway, No. 323, El Segundo, CA 90245 del Olmo, Frank Los Angeles Times, Times Mirror Square, Los Angeles, CA 90053 Demich, Capt Fred USN 3106 Mereworth Ct., Oakton, VA 22124 Demello, Ronald P.O. Box 627, Hampton Falls, NH 03844 Denisevich, LtCol Peter USA 24 Heather Ct., Nashua, NH 03062 Dennett, Garland L. 1156 East Blaine Ave., Salt Lake City, UT 84105 DeNora, John 4019 Goldfinch St., No. 155, San Diego, CA 92103 Derrick, Robert 55 Atlantic Rd., Cloucester, MA 01930 Deveresuz, Robert 7423 Brad St., Falls Church, VA 22042 Devore, Dixon P.O. Box 1010, Greenville, NH 03048 Dewaid, Frank 6960 NW 6th Ct., Margate, FL 33063 de Genova, Joseph 5307 Hill Burne Way, Chevy Chase, MD 20815 Di Trolio, Jerry 1002 N. 65th St., Philadelphia, PA 19151 Dick, Herman P.O. Box 22464, Honolulu, HI 96833 Dickey, Mrs. Kiloma 29605 Chaparral Dr., Temecula, CA 92592 Dickow, Daniel P.O. Box 1470, Duxbury, MA 02332 Dickson, Philip 7800 Hidden Meadow Terrace, Potomac, MD 20854 Dietsche, Herbert 917 Teakwood Dr., Richardson, TX 75080 Diliberti, Col Angelo USA P.O. Box 295, South Elgin, IL 60177 Dillingham, RAdm Paul USN RR 2, Box 66, Roch Hall, MD 21661 Dillon, Floyd 11423 Costa Del Sol NE, Albuquerque, NM 87111 Dillon, Col Francis USA 9204 Maria Ave., Great Falls, VA 22066 Dinn, Edith P.O. Box 591330, San Francisco, CA 94118 DiNoto, Joseph 4621 Bronx Blvd, New York City, NY 10470 DiNteho, Anthony 2250 Union St., San Francisco, CA 94123 Diosdado Cesar 1774 Vale St., Chula Vista, CA 91912 Disney, Raymond 212 North Glen Ave., Annapolis, MD 21401 Ditzier, Dr. Thomas 112-4 Lauwa Pi., Khilua, HI 96734 Diver, Ms. Ruth 4339 W. Braddock Rd., No. 20, Alexandria, VA 22311 Dixon, LtCol William USA 600 Crowder Ct., Fort Walton Beach, FL 32547 Dodge, Dr. Norman 8000 Northumberland Rd., Springfield, VA 22153 Dodson, James 2005 Calvin Cliff Ln., Cincinnati, OH 45206 Doherty, George 553 Fairhaven St., Anaheim, CA 92801 Dolan, MSgt Francis USAF 2914 Caprice Dr., Corpus Christi, TX 78418 Dolan, Capt J. USMC P.O. Box 374, Garrett Park, MD 20896 Doleman, LtGen Edgar USA 1341 Pueo St, Honolulu, HI 96816 Domingos, Mrs. Agnes 188 Florida Ave., Macon, GA 31204 Donahue, Frank J. 13 Plumrose Ln., Schaumburg, IL 60194 Donahue, LtCdr Thomas USN 3704 Sprucedale Dr., Annandale, VA 22003 Donahue, William 4300 18th St West, No. 207C, Bradenton, FL 34205 Donlea, Patrick 119 Waverly Rd., Barrington, IL 60010 Donohue, Jerome 8030 McKenstry Dr., Laurel, MD 20723 Donovan, Arthur 312 Owaissa Rd., SE, Vienna, VA 22180 Dooley, Arthur 303l North Nottingham St., Arlington, VA 22207 Dorffi, Maj William USAF 497 N. Arbona Circle, Sonora, CA 95370 Dorman, E. (Viktor A. Zelenko) 350 5th Ave., New York, NY 10018 Dorr, Colgate 26290 Valley View Dr., Carmel, CA 93923 Dorsey, John P.O. Box 101, Quinton, VA 23141 Dougherty, Col Andrew USAF 10 Mile Post Ln., Pittsford, NY 14534 Dougherty, Robert 2619 S. Kihei Rd., No. 408-A, Maui, HI 96753 Douglas, Terrance 1833 Quartet Circle, Vienna, VA 22182 Douglas, Thomas (A.L Korochev) P.O. Box 381, Organ, NM 88052 Dountas, Peter P.O. Box 36647, Albuquerque, NM 87176 Douris, Charles 236 Lexington Rd., Schwenksville, PA 19473 Dowd, Capt Robert USN 3 Grouse Ln., Brevard, NC 29712 Downing, Thomas E 8 Pingree Farm Rd., Georgetown, MA 01833 Doyle, David 65 Hanapepe Loop, Honolulu, HI 96825 Doyle, Edward 19715 Ames St., Fairfax, VA 22032 Doyle, Mrs. Elizabeth 5807 Wilshire Dr., Bethesda, NM 20816 Drake, Robert 19470 Saddlebrook Ct., Fort Meyers, FL 33903 Dravis, Michael 1807 Merrimac Dr., Adelphi, NM 20783 Drawdy, Vance P.O. Box 10167, Greenville, SC 29603 Dreher, Robert 4141 N. Henderson Rd., No. 907, Arlington, VA 22203 Dreyfuss, Robert 6904 Park Terrace Dr., Alexandria, VA 22307 Dribben, Col William USA 108 East 38th St., New York, NY 10016 Drisin, David 41 Rue des Thermopyles, 75014, Paris, France Driver, Carl P.O. Box 8157 Rolling Hills, Greenville, TX 75404 Driver, Garston W. 2540 Clairemont Dr., No. 305, San Diego, CA 92117 Drum, Col James USA 311 Essex Meadows, Essex, CT 06426 Dryan, Philip 116 Calle Nivel, Los Gatos, CA 95030 DuBrul, Stephen 610 Fifth Ave., Suite 605, New York, NY 10020 Dudik, Dr. Rollie 2308 Floral Park Rd., Clinton, MD 20735 Dudley, Col Paul USAF 4606 Gaslight Circle, Las Vegas, NV 89119 Duffy, Paul 3850 Sweet Grass Ln., Chadotte, NC 28226 Dukes, Robert 10087 Windstream Dr., No. 2, Columbia, MD 21044 Duncan, Lewis 1744 Hacienda Pl., El Cajon, CA 92020 Dunlevy, Mrs. Elizabeth 4701 Willard Ave., No. 417, Chevy Chase, MD 20815 Dunlop, Cdr Edwin, USNR P.O. Box 1012, Burbank, CA 91507 DuPre, Col Paul USMC 226 E. Garden Green, Port Hueneme, CA 93041 Dupre, Robert 28 Williams St., Salem, NH 03079 Durham, Leonard 4612 Twinbook Rd., Fairfax, VA 22032 Durr, Dr. Frank 7337 Brookview Circle, Tampa, FL 33634 Duval, Thomas 77 Michael Manor Rd., Berkeley Springs, WV 25411 Dyckman, Wesley P.O. Box 301, Livermore, CA 94551 Dyer, James H 218, Capitol, Washington DC
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, Part 13, AP,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.

| IPN 00 1043/2694 | APANASEWICZ JOLANTA EWA |
| IPN BU 0833/10 | APANASIEWICZ ANNA |
| IPN BU 0242/258 | APANASOWICZ HENRYK |
| IPN BU 00249/563 | APANASOWICZ KRYSTYNA |
| IPN BU 00273/551 | APANEL WALENTY |
| IPN BU 001121/1194 | APANOSOWICZ KRYSTYNA JADWIGA STANISŁAWA |
| IPN BU 01000/1500 | APANOWICZ MIECZYSŁAW |
| IPN BU 0967/275 | APANOWICZ MIROSŁAW |
| IPN BU 0193/1295 | APEL HENRYK |
| IPN BU 0193/144 | APELMAN ROZALIA |
| IPN BU 0194/2961 | APKOWICZ JERZY |
| IPN BU 0901/1222 | APOLINARSKA IWONA (BUDZIAK) |
| IPN BU 01256/8 | APOLINARSKI WŁODZIMIERZ |
| IPN BU 683/1704 | APOLINER ABRAM |
| IPN BU 00230 | P. 52 APONOWICZ ANTONI |
| IPN BU 0242/1447 | APONOWICZ LESŁAW |
| IPN BU 00966/1731 | APOSTOLUK ANDRZEJ |
| IPN BU 00611/219 | APOSTOŁOWICZ TADEUSZ |
| IPN BU 001198/535 | APOSTOŁOWICZ TADEUSZ |
| IPN BU 0194/350 | APPEL ALEKSANDER |
| IPN BU 01000/1697 | APTACY STANISŁAW |
| IPN BU 0958/58 | APTAZY JÓZEF |
| IPN BU 0912/1639 | APTOWICZ JAN |
| IPN 00 1043/678 | APTOWICZ WINCENTY |
Video – The Inevitable Global Spread of Islam: How long before Sharia Law reaches our shores?
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Video – The Inevitable Global Spread of Islam: How long before Sharia Law reaches our shores?
A sobering analysis and news reports documenting the inevitable spread of Islam across Europe and the United States. Hear the Muslim bitter and vengeful perspective of Western society and imperialism, and the inevitable desire for Sharia Law in Europe.
TOP-SECRET – The Secret List of CIA Sources – 2.619 Names and Adresses, Part 4,D,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
D
Dabrowski, Edmund 148-A Wallworth Park, Cherry Hill, NJ 08002 Dalby, Cranford 300 N. Washington St., No. 400, Alexandria, VA 22314 Dale, Mrs. J. Thomas 7603 North Ocean Blvd., No. 3B, Myrtle Beach, SC 29577 Dalenberg, Philip P.O. Box 7722, Fort Gordon, GA 30905 Daly, Ralph T. 99 Cloverdale Heights, Charles Town, WV 25414 Daniel, Dr. Gerard L 25 Canada St., Swanton, VT 05488 Daniluck, Serge 716 N. Belgrade Ct., Silver Spring, MD 20902 Darcy, Thomas 12821 Sunset Terrace, Clive, IA 50325 Darer, Stanley 22 Wilton Rd., Beaconfield, Bucks, IfP9 2DE, England Dann, Charles 1 Fairway Dr., Manhasset, NY 11030 Davidov, Dr. Michael 9112 Mill Pond Valley Dr., McLean, VA 22102 Davidson, Philip 83 Devon Rd., Albertson, NY 11507 Davis, Alton D. 5606 Mirror Light Place., Columbia, MD 21045 Davis, Curtis C. 10 Overhill Rd., Baltimore, MD 21210 Davis, Donald 4241 Riverside Dr., Evans, GA 30809 Davis, LtGen John USA 2346 South Mende St., Arlington, VA 22202 Davis, Mrs. Norma 4241 Riverside Dr., Evans, GA 30809 Davis, LtCol Sidney USAF 231 Greenwood Dr., Petersburg, VA 23805 Dawson, Mrs. Mary 1131 Compass Ln., No. 306, Foster City, CA 94404 Dawson, Raymond 6357 Dawson Blvd., Mentor OR 44060 Day, David W. P.O. Box 1296, Mukilteo, WA 98275 Day, Mrs. Mary Louise 4928 Sentinel Dr., No. 304, Bethesda, MD 20816 De Angelo, Mrs. Alice 2500 Virginia Ave., NW, No. 306-S, Washington, DC 20037 De Candio, LtCol Michael USA 2505 Childs Ln., Alexandria, VA 22308 de Vore, Ralph 3828 Baltimore, Shreveport, LA 71106 De Wald, LtCdr Bruce USN 5131 SE Naef Rd., Milwaukie, OR 97267 Deahl, Albert P.O. Box 277792, San Diego, CA 92128 Deahl, Warren 6125 Tamerlane Dr., South Bend, IN 46614 Dean, Mary Evelyn 1436 Woodacre Dr., McLean, VA 22101 Dean, Warren 9908 Fernwood Rd., Bethesda, MD 20817 DeBruier, Wilburn 10308 Florian Rd., Louisville, KY 40223 Deck, Mrs. Helen P. 1640 Atares Dr., No. 8, Punta Gorda, FL 33950 Dee, Col Chester H. AUS 510 S. Hi Lusi Ave., Mt. Prospect, IL 60056 Deffenbaugh, Berman 331 Ave Maria Dr., San Antonio, TX 78216 DeGenare, William 12808 Woodview Ct., Burnsville, MN 55337 DeKuyper, Frederick 4422 Underwood Rd., Baltimore, MD 21218 Del Favero, Dario 210 Southland Station Dr., No. 256, Warner Robins, GA 31088 Delaney, Col John USA 5621 Granada Blvd., Miami, FL 33146 Delanty, Timothy 8351 Forrester Blvd., Springfield, VA 22152 DeLashmit, William 2462 River Rd., Plymouth, NH 03264 Dell, George 11909 Hickory Creek Dr., Fredricksburg, VA 22407 Delia Santa, Walter 16327 Lindsay Rd., Yelm, WA 98597 De Long, Earl 1602 N. Greenbrier St., Arlington, VA 22205 DeLong, Richard 2250 East Imperial Highway, No. 323, El Segundo, CA 90245 del Olmo, Frank Los Angeles Times, Times Mirror Square, Los Angeles, CA 90053 Demich, Capt Fred USN 3106 Mereworth Ct., Oakton, VA 22124 Demello, Ronald P.O. Box 627, Hampton Falls, NH 03844 Denisevich, LtCol Peter USA 24 Heather Ct., Nashua, NH 03062 Dennett, Garland L. 1156 East Blaine Ave., Salt Lake City, UT 84105 DeNora, John 4019 Goldfinch St., No. 155, San Diego, CA 92103 Derrick, Robert 55 Atlantic Rd., Cloucester, MA 01930 Deveresuz, Robert 7423 Brad St., Falls Church, VA 22042 Devore, Dixon P.O. Box 1010, Greenville, NH 03048 Dewaid, Frank 6960 NW 6th Ct., Margate, FL 33063 de Genova, Joseph 5307 Hill Burne Way, Chevy Chase, MD 20815 Di Trolio, Jerry 1002 N. 65th St., Philadelphia, PA 19151 Dick, Herman P.O. Box 22464, Honolulu, HI 96833 Dickey, Mrs. Kiloma 29605 Chaparral Dr., Temecula, CA 92592 Dickow, Daniel P.O. Box 1470, Duxbury, MA 02332 Dickson, Philip 7800 Hidden Meadow Terrace, Potomac, MD 20854 Dietsche, Herbert 917 Teakwood Dr., Richardson, TX 75080 Diliberti, Col Angelo USA P.O. Box 295, South Elgin, IL 60177 Dillingham, RAdm Paul USN RR 2, Box 66, Roch Hall, MD 21661 Dillon, Floyd 11423 Costa Del Sol NE, Albuquerque, NM 87111 Dillon, Col Francis USA 9204 Maria Ave., Great Falls, VA 22066 Dinn, Edith P.O. Box 591330, San Francisco, CA 94118 DiNoto, Joseph 4621 Bronx Blvd, New York City, NY 10470 DiNteho, Anthony 2250 Union St., San Francisco, CA 94123 Diosdado Cesar 1774 Vale St., Chula Vista, CA 91912 Disney, Raymond 212 North Glen Ave., Annapolis, MD 21401 Ditzier, Dr. Thomas 112-4 Lauwa Pi., Khilua, HI 96734 Diver, Ms. Ruth 4339 W. Braddock Rd., No. 20, Alexandria, VA 22311 Dixon, LtCol William USA 600 Crowder Ct., Fort Walton Beach, FL 32547 Dodge, Dr. Norman 8000 Northumberland Rd., Springfield, VA 22153 Dodson, James 2005 Calvin Cliff Ln., Cincinnati, OH 45206 Doherty, George 553 Fairhaven St., Anaheim, CA 92801 Dolan, MSgt Francis USAF 2914 Caprice Dr., Corpus Christi, TX 78418 Dolan, Capt J. USMC P.O. Box 374, Garrett Park, MD 20896 Doleman, LtGen Edgar USA 1341 Pueo St, Honolulu, HI 96816 Domingos, Mrs. Agnes 188 Florida Ave., Macon, GA 31204 Donahue, Frank J. 13 Plumrose Ln., Schaumburg, IL 60194 Donahue, LtCdr Thomas USN 3704 Sprucedale Dr., Annandale, VA 22003 Donahue, William 4300 18th St West, No. 207C, Bradenton, FL 34205 Donlea, Patrick 119 Waverly Rd., Barrington, IL 60010 Donohue, Jerome 8030 McKenstry Dr., Laurel, MD 20723 Donovan, Arthur 312 Owaissa Rd., SE, Vienna, VA 22180 Dooley, Arthur 303l North Nottingham St., Arlington, VA 22207 Dorffi, Maj William USAF 497 N. Arbona Circle, Sonora, CA 95370 Dorman, E. (Viktor A. Zelenko) 350 5th Ave., New York, NY 10018 Dorr, Colgate 26290 Valley View Dr., Carmel, CA 93923 Dorsey, John P.O. Box 101, Quinton, VA 23141 Dougherty, Col Andrew USAF 10 Mile Post Ln., Pittsford, NY 14534 Dougherty, Robert 2619 S. Kihei Rd., No. 408-A, Maui, HI 96753 Douglas, Terrance 1833 Quartet Circle, Vienna, VA 22182 Douglas, Thomas (A.L Korochev) P.O. Box 381, Organ, NM 88052 Dountas, Peter P.O. Box 36647, Albuquerque, NM 87176 Douris, Charles 236 Lexington Rd., Schwenksville, PA 19473 Dowd, Capt Robert USN 3 Grouse Ln., Brevard, NC 29712 Downing, Thomas E 8 Pingree Farm Rd., Georgetown, MA 01833 Doyle, David 65 Hanapepe Loop, Honolulu, HI 96825 Doyle, Edward 19715 Ames St., Fairfax, VA 22032 Doyle, Mrs. Elizabeth 5807 Wilshire Dr., Bethesda, NM 20816 Drake, Robert 19470 Saddlebrook Ct., Fort Meyers, FL 33903 Dravis, Michael 1807 Merrimac Dr., Adelphi, NM 20783 Drawdy, Vance P.O. Box 10167, Greenville, SC 29603 Dreher, Robert 4141 N. Henderson Rd., No. 907, Arlington, VA 22203 Dreyfuss, Robert 6904 Park Terrace Dr., Alexandria, VA 22307 Dribben, Col William USA 108 East 38th St., New York, NY 10016 Drisin, David 41 Rue des Thermopyles, 75014, Paris, France Driver, Carl P.O. Box 8157 Rolling Hills, Greenville, TX 75404 Driver, Garston W. 2540 Clairemont Dr., No. 305, San Diego, CA 92117 Drum, Col James USA 311 Essex Meadows, Essex, CT 06426 Dryan, Philip 116 Calle Nivel, Los Gatos, CA 95030 DuBrul, Stephen 610 Fifth Ave., Suite 605, New York, NY 10020 Dudik, Dr. Rollie 2308 Floral Park Rd., Clinton, MD 20735 Dudley, Col Paul USAF 4606 Gaslight Circle, Las Vegas, NV 89119 Duffy, Paul 3850 Sweet Grass Ln., Chadotte, NC 28226 Dukes, Robert 10087 Windstream Dr., No. 2, Columbia, MD 21044 Duncan, Lewis 1744 Hacienda Pl., El Cajon, CA 92020 Dunlevy, Mrs. Elizabeth 4701 Willard Ave., No. 417, Chevy Chase, MD 20815 Dunlop, Cdr Edwin, USNR P.O. Box 1012, Burbank, CA 91507 DuPre, Col Paul USMC 226 E. Garden Green, Port Hueneme, CA 93041 Dupre, Robert 28 Williams St., Salem, NH 03079 Durham, Leonard 4612 Twinbook Rd., Fairfax, VA 22032 Durr, Dr. Frank 7337 Brookview Circle, Tampa, FL 33634 Duval, Thomas 77 Michael Manor Rd., Berkeley Springs, WV 25411 Dyckman, Wesley P.O. Box 301, Livermore, CA 94551 Dyer, James H 218, Capitol, Washington DC
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, 120.000 Spies, 12, AN,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 0194/1798 | ANALEWICZ ALEKSANDER |
| IPN BU 0218/2624 | ANANIN KRZYSZTOF |
| IPN BU 00611/2006 | ANAŃKO JAN |
| IPN BU 001198/3635 | ANAŃKO JAN |
| IPN BU 0772/2129 | ANASZEWSKA MARIA |
| IPN BU 0772/730 | ANASZEWSKA ZOFIA |
| IPN BU 0958/60 | ANATOLIUSZ ZYGMUNT |
| IPN BU 0891/111 | ANCEROWICZ TADEUSZ |
| IPN BU 698/31 | ANCEWICZ JADWIGA |
| IPN BU 0901/2314 | ANCHIM ELŻBIETA |
| IPN BU 00334/621 | ANCYPA JANUSZ RYSZARD |
| IPN BU 001134/3530 | ANCYPA JANUSZ RYSZARD |
| IPN BU 001102/2179 | ANCYPA JERZY |
| IPN BU 0951/675 | ANCYPAROWICZ RYSZARD |
| IPN BU 710/201 | ANCYPAROWICZ ALBERT |
| IPN BU 0218/1784 | ANCYPAROWICZ JADWIGA |
| IPN BU 02042/207 | ANCYPAROWICZ JERZY |
| IPN BU 0866/9 | ANCZAREK KRYSTYNA |
| IPN 00 1043/3026 | ANCZARSKI MARIAN |
| IPN BU 0951/765 | ANCZEWSKA ANTONINA |
| IPN BU 00200/356 | ANCZEWSKI IGNACY |
| IPN 00 1052/1198 | ANCZEWSKI IGNACY |
| IPN BU 0193/132 | ANCZEWSKI JÓZEF |
| IPN BU 0942/304 | ANCZEWSKI RYSZARD |
| IPN BU 0912/856 | ANCZEWSKI TADEUSZ |
| IPN 00 1043/2563 | ANCZUKÓW MAREK JAN |
| IPN BU 0604/423 | ANCZURA JÓZEF |
| IPN BU 0218/2392 | ANCZURA SABINA |
| IPN BU 0951/1792 | ANCZYK EDMUND |
| IPN BU 636/1823 | ANCZYK JÓZEFA |
| IPN BU 636/1824 | ANCZYK JÓZEFA |
| IPN BU 698/32 | ANCZYKOWSKA JADWIGA |
| IPN BU 0193/7402 | ANCZYKOWSKI ZYGMUNT |
| IPN BU 01000/1675 | ANDERMAN JANINA |
| IPN BU 0988/569 | ANDERMAN ZYGMUNT |
| IPN BU 01133/409 | ANDERS JAN |
| IPN BU 644/5 | ANDERS LUDWIK |
| IPN BU 002086/1241 | ANDERS PAWEŁ MAREK |
| IPN BU 00277/1306 | ANDERSON EDWARD |
| IPN BU 001121/3457 | ANDERSON EDWARD |
| IPN BU 002086/730 | ANDERSON EDWARD IVAR |
| IPN BU 693/1436 | ANDERSON IZABELA |
| IPN BU 00328/1413 | ANDERSSON (ANDERSON) TERESA |
| IPN BU 001134/2356 | ANDERSSON TERESA |
| IPN BU 00945/723 | ANDERSZ STANISŁAW |
| IPN BU 00456/6 | ANDLER ZBIGNIEW |
| IPN 00 1043/3279 | ANDRAKA HENRYK |
| IPN BU 0806/2083 | ANDRAKA JAN |
| IPN BU 0806/2082 | ANDRAKA ZOFIA |
| IPN BU 00191/447 | ANDRALKA HENRYK |
| IPN BU 0806/2914 | ANDRASIAK JERZY |
| IPN BU 0591/4 | ANDRASIK TOMASZ |
| IPN BU 0591/5 | ANDRASIK WOJCIECH |
| IPN BU 00612/4192 | ANDRASZ STANISŁAW |
| IPN BU 001198/6944 | ANDRASZ STANISŁAW |
| IPN BU 698/66 | ANDRASZ ZYGMUNT |
| IPN BU 0242/1935 | ANDRASZ) NYCZ ALEKSANDRA |
| IPN BU 00966/1473 | ANDRASZEK KRYSTYNA |
| IPN BU 00611/1616 | ANDRASZEK ZBIGNIEW |
| IPN BU 001198/2985 | ANDRASZEK ZBIGNIEW |
| IPN BU 00200/86 | ANDREARCZYK EWARYST |
| IPN 00 1052/447 | ANDREARCZYK EWARYST |
| IPN BU 00234 | p.242 ANDREARCZYK FRANCISZEK |
| IPN BU 693/494 | ANDREASIK JAN |
| IPN BU 00433/140 | ANDRECKI MACIEJ |
| IPN BU 00611/976 | ANDREJAS JÓZEF |
| IPN BU 001198/1392 | ANDREJAS JÓZEF |
| IPN BU 0901/1665 | ANDREJEK STEFANIA |
| IPN BU 0243/104 | ANDREJEW ALICJA |
| IPN BU 00611/1153 | ANDREJEW BOHDAN |
| IPN BU 001198/1566 | ANDREJEW BOHDAN |
| IPN BU 0772/478 | ANDREJEW LESZEK |
| IPN BU 0902/9 | ANDREJUK ANATOL |
| IPN BU 001134/4781 | ANDREOTTI DANUTA |
| IPN BU 00399/436 | ANDREOTTI DANUTA JANINA |
| IPN BU 685/239 | Andres Zbigniew |
| IPN BU 01000/1703 | ANDRONOW ALEKSANDER |
| IPN BU 01000/1674 | ANDRONOW MIKOŁAJ |
| IPN BU 00244/119 | ANDROSIUK EUGENIUSZ |
| IPN BU 0218/961 | ANDROSIUK JADWIGA |
| IPN BU 645/2 | ANDROSIUK JADWIGA |
| IPN BU 0772/2 | ANDROSIUK KRZYSZTOF |
| IPN BU 001134/3676 | ANDROSIUK PAWEŁ |
| IPN BU 0218/356 | ANDROSIUK WŁODZIMIERZ |
| IPN BU 0902/10 | ANDROSIUK WŁODZIMIERZ |
| IPN BU 01000/1673 | ANDRUCHEWICZ EUGENIUSZ |
| IPN 00 1052/1097 | ANDRUCZYK MIECZYSŁAW |
| IPN BU 0806/3033 | ANDRUK ELŻBIETA |
| IPN BU 00966/372 | ANDRUKIEWICZ STANISŁAW |
| IPN BU 0772/2130 | ANDRUSIEWICZ (RUDNICKA) MARIA |
| IPN BU 0193/1283 | ANDRUSIEWICZ TADEUSZ |
| IPN BU 0218/2964 | ANDRUSKA (KARWOWSKA) JADWIGA |
| IPN BU 00225/77 | ANDRUSYSZYN KAZIMIERZ |
| IPN BU 001121/200 | ANDRUSYSZYN KAZIMIERZ |
| IPN BU 0911/1 | ANDRUSYSZYN MIROSŁAW |
| IPN BU 0290/10 | ANDRUSZCZAK KRYSTYNA |
| IPN BU 01000/1676 | ANDRUSZCZYK EUGENIA |
| IPN BU 0193/7977 | ANDRUSZEWSKI JÓZEF |
| IPN BU 0218/3461 | ANDRUSZKIEWICZ (MOCH) MIECZYSŁAWA |
| IPN BU 00744/427 | ANDRUSZKIEWICZ ADAM |
| IPN BU 001121/4063 | ANDRUSZKIEWICZ ADAM |
| IPN BU 0242/395 | ANDRUSZKIEWICZ ANDRZEJ |
| IPN BU 01133/410 | ANDRUSZKIEWICZ BRONISŁAW |
| IPN 00 1052/365 | ANDRUSZKIEWICZ EUGENIUSZ WALDEMAR |
| IPN BU 00234 | p.254 ANDRUSZKIEWICZ FRANCISZEK |
| IPN BU 698/33 | ANDRUSZKIEWICZ JAN |
| IPN BU 698/34 | ANDRUSZKIEWICZ JERZY |
| IPN BU 644/722 | ANDRUSZKIEWICZ JÓZEF |
| IPN BU 698/35 | ANDRUSZKIEWICZ JÓZEF |
| IPN BU 649/1 | ANDRUSZKIEWICZ KRZYSZTOF |
| IPN BU 636/1850 | ANDRUSZKIEWICZ LEOKADIA |
| IPN BU 0193/4727 | ANDRUSZKIEWICZ PAWEŁ |
| IPN BU 0218/2222 | ANDRUSZKIEWICZ STANISŁAW |
| IPN BU 685/3 | ANDRUSZKIEWICZ WANDA |
| IPN BU 001164/361 | Andruszkiewicz Wojciech |
| IPN BU 0290/13 | ANDRUSZKIEWICZ ZBIGNIEW |
| IPN BU 698/36 | ANDRUSZKIEWICZ ZDZISŁAW |
| IPN BU 0193/133 | ANDRUSZKIEWICZ ZOFIA |
| IPN BU 0902/11 | ANDRUSZKÓW STANISŁAW |
| IPN BU PF | 125/150 ANDRUSZUK BARBARA |
| IPN BU 00751/51 | ANDRUSZUK JANUSZ |
| IPN BU 001102/1535 | ANDRUSZUK JANUSZ |
| IPN BU 00200/1099 | ANDRYCH KRZYSZTOF |
| IPN BU 001102/695 | ANDRYCH KRZYSZTOF |
| IPN BU 01250/263 | ANDRYCH ZOFIA |
| IPN BU 0772/2131 | ANDRYCHOWICZ JAN |
| IPN BU 00966/1197 | ANDRYCHOWICZ RAFAŁ JAN |
| IPN BU 685/238 | Andrychowska Maria |
| IPN BU 0910/54 | ANDRYCHOWSKI JAN |
| IPN BU 0193/4782 | ANDRYKA FELIKS |
| IPN BU 00244/58 | ANDRYKA MARIAN |
| IPN BU 00200/65 | ANDRYS WIESŁAW |
| IPN 00 1052/415 | ANDRYS WIESŁAW |
| IPN BU 0772/731 | ANDRYSIAK JÓZEF |
| IPN BU 00448/386 | ANDRYSIAK KATARZYNA |
| IPN BU 001134/5366 | ANDRYSIAK KATARZYNA |
| IPN BU 698/38 | ANDRYSIAK KRYSTYNA |
| IPN BU 00328/1093 | ANDRYSIAK RENATA |
| IPN BU 001134/1965 | ANDRYSIAK RENATA |
| IPN BU 644/6 | ANDRYSIAK STANISŁAW |
| IPN BU 00244/58 | ANDRYSIAK TADEUSZ |
| IPN BU 0194/1094 | ANDRYSIAK WOJCIECH |
| IPN BU 0892/66 | ANDRYSIEWICZ BOLESŁAW |
| IPN BU 00945/583 | ANDRYSKOWSKI – BRZOZOWSKI – BNOROWSKI JAN – JERZY |
| IPN BU 0902/12 | ANDRYSZAK CZESŁAW |
| IPN 00 1052/315 | ANDRYSZCZAK BOGDAN JERZY |
| IPN BU 0951/1951 | ANDRYSZCZAK JADWIGA |
| IPN BU 01000/1691 | ANDRYSZCZAK JERZY |
| IPN BU 644/723 | ANDRYSZCZAK ROMAN |
| IPN BU 0242/688 | ANDRYSZCZAK TADEUSZ |
| IPN BU 00249/445 | ANDRYSZCZYK KAZIMIERZ |
| IPN BU 001121/1075 | ANDRYSZCZYK KAZIMIERZ |
| IPN BU 645/10 | ANDRYSZEK JADWIGA |
| IPN BU 644/724 | ANDRYSZEK STANISŁAW |
| IPN BU 0193/135 | ANDRYSZEWSKI STANISŁAW PIOTR |
| IPN BU 0193/8010 | ANDRYSZEWSKI ZBIGNIEW |
| IPN BU 0912/154 | ANDRZEJACZEK CZESŁAW |
| IPN BU 698/39 | ANDRZEJAK BOLESŁAW |
| IPN BU 01000/1680 | ANDRZEJAK DANUTA |
| IPN BU 01133/411 | ANDRZEJAK EUGENIUSZ |
| IPN BU 0988/568 | ANDRZEJAK FRANCISZEK |
| IPN BU 698/40 | ANDRZEJAK JAN |
| IPN BU 0194/1400 | ANDRZEJAK RYSZARD |
| IPN BU 0993/1036 | ANDRZEJAK RYSZARD |
| IPN BU 980/184 | ANDRZEJAK STANISŁAW |
| IPN BU 01133/412 | ANDRZEJAK TADEUSZ |
| IPN BU 0243/462 | ANDRZEJCZAK (KRASUCKA) BEATA |
| IPN BU 644/7 | ANDRZEJCZAK ALFRED |
| IPN BU 0951/1120 | ANDRZEJCZAK BARBARA |
| IPN BU 0891/2547 | ANDRZEJCZAK BERNARD |
| IPN BU 0891/285 | ANDRZEJCZAK CZESŁAW |
| IPN BU 00945/1825 | ANDRZEJCZAK CZESŁAW – WŁODZIMIERZ – WIKTOR |
| IPN BU 00234 | p.190 ANDRZEJCZAK HALINA |
| IPN BU 0193/1284 | ANDRZEJCZAK JAN |
| IPN BU 0772/732 | ANDRZEJCZAK JAN |
| IPN BU 0891/110 | ANDRZEJCZAK JÓZEF |
| IPN BU 01133/413 | ANDRZEJCZAK KAZIMIERZ |
| IPN BU PF | 280/57 ANDRZEJCZAK LUDW. |
| IPN BU 00335/156 | ANDRZEJCZAK LUDWIK |
| IPN BU 0305/84 | ANDRZEJCZAK LUDWIK |
| IPN 00 1043/3014 | ANDRZEJCZAK LUDWIK ZBIGNIEW |
| IPN BU 0866/10 | ANDRZEJCZAK MARIAN |
| IPN BU 644/8 | ANDRZEJCZAK MARIAN |
| IPN BU 0891/104 | ANDRZEJCZAK MIECZYSŁAW |
| IPN BU 0193/137 | ANDRZEJCZAK MIECZYSŁAW |
| IPN BU 001121/758 | ANDRZEJCZAK MIROSŁAW |
| IPN BU 0891/286 | ANDRZEJCZAK STANISŁAW |
| IPN BU 00244/58 | ANDRZEJCZAK STANISŁAW |
| IPN BU 0806/2485 | ANDRZEJCZAK STANISŁAW JERZY |
| IPN BU 01133/414 | ANDRZEJCZAK TADEUSZ |
| IPN BU 0993/679 | ANDRZEJCZAK WIESŁAWA |
| IPN BU 0891/130 | ANDRZEJCZAK ZYGMUNT |
| IPN BU 01000/1681 | ANDRZEJCZUK HALINA |
| IPN BU 0218/3360 | ANDRZEJCZUK PIOTR |
| IPN BU 01000/1433 | ANDRZEJCZUK PIOTR |
| IPN BU 00283/238 | ANDRZEJCZYK CEZARY |
| IPN BU 01000/2096 | ANDRZEJCZYK JADWIGA |
| IPN BU 0891/131 | ANDRZEJCZYK JAN |
| IPN BU 01079/135 | ANDRZEJCZYK JAN |
| IPN BU 01256/5 | ANDRZEJCZYK SABINA |
| IPN BU 0193/6354 | ANDRZEJCZYK WŁADYSŁAW |
| IPN BU 00249/1296 | ANDRZEJCZYK ZOFIA |
| IPN BU 001121/1907 | ANDRZEJCZYK ZOFIA BARBARA |
| IPN BU 644/725 | ANDRZEJEWISKI STANISŁAW |
| IPN BU 00283/1857 | ANDRZEJEWSJU RYSZARD |
| IPN BU 0772/3735 | ANDRZEJEWSKA (JAROSZ) ALICJA JOLANTA |
| IPN BU 0243/46 | ANDRZEJEWSKA (ZWALIŃSKA) LIDIA |
| IPN 00 1043/2265 | ANDRZEJEWSKA ANNA |
| IPN BU 0242/62 | ANDRZEJEWSKA BOGUMIŁA |
| IPN BU PF | 498/13 ANDRZEJEWSKA ELŻBIETA |
| IPN BU 002086/1449 | ANDRZEJEWSKA ELŻBIETA DANUTA |
| IPN BU 0218/650 | ANDRZEJEWSKA EWA |
| IPN BU 0833/646 | ANDRZEJEWSKA JADWIGA |
| IPN BU 0194/1752 | ANDRZEJEWSKA JOLANTA |
| IPN BU 698/41 | ANDRZEJEWSKA MARIA |
| IPN BU 0193/8081 | ANDRZEJEWSKA MARTA |
| IPN BU 0194/146 | ANDRZEJEWSKA OLGA |
| IPN BU 0942/386 | ANDRZEJEWSKA RÓŻA |
| IPN BU 0772/23 | ANDRZEJEWSKA STANISŁAWA |
| IPN BU 645/21 | ANDRZEJEWSKA TAMARA |
| IPN BU 0772/24 | ANDRZEJEWSKA WACŁAWA LEONARDA |
| IPN BU 0772/2132 | ANDRZEJEWSKA WALERIA |
| IPN BU 01000/1695 | ANDRZEJEWSKA WANDA |
| IPN BU 0193/8156 | ANDRZEJEWSKA ZOFIA |
| IPN BU 002086/996 | ANDRZEJEWSKA-STAROSZ KRYSTYNA BARBARA |
| IPN BU 0891/272 | ANDRZEJEWSKI ADAM |
| IPN BU PF | 1021/2 ANDRZEJEWSKI ADAM |
| IPN BU 0958/54 | ANDRZEJEWSKI BRONISŁAW |
| IPN BU 00945/1793 | ANDRZEJEWSKI BRONISŁAW |
| IPN BU 00744/597 | ANDRZEJEWSKI DARIUSZ |
| IPN BU 001121/4321 | ANDRZEJEWSKI DARIUSZ |
| IPN BU 0957/15 | ANDRZEJEWSKI EUGENIUSZ |
| IPN BU 01250/5 | ANDRZEJEWSKI FELIKS |
| IPN BU 0194/1541 | ANDRZEJEWSKI FRANCISZEK |
| IPN BU 0912/155 | ANDRZEJEWSKI HENRYK |
| IPN BU 0958/55 | ANDRZEJEWSKI HENRYK |
| IPN BU 01000/1677 | ANDRZEJEWSKI HENRYK |
| IPN BU 01000/406 | ANDRZEJEWSKI HENRYK |
| IPN BU 01000/654 | ANDRZEJEWSKI HENRYK |
| IPN BU 0772/2133 | ANDRZEJEWSKI HENRYK |
| IPN BU 00334/22 | ANDRZEJEWSKI JACEK |
| IPN BU 001134/2641 | ANDRZEJEWSKI JACEK |
| IPN BU 0218/3227 | ANDRZEJEWSKI JAN |
| IPN 00 1043/1104 | ANDRZEJEWSKI JAN |
| IPN BU 685/242 | Andrzejewski Janusz |
| IPN BU 710/429 | ANDRZEJEWSKI JERZY |
| IPN BU 00249/1115 | ANDRZEJEWSKI JERZY |
| IPN BU 001121/1731 | ANDRZEJEWSKI JERZY |
| IPN BU 0772/2134 | ANDRZEJEWSKI JÓZEF |
| IPN BU 0806/2192 | ANDRZEJEWSKI JÓZEF |
| IPN BU 0951/359 | ANDRZEJEWSKI JÓZEF |
| IPN BU 001089/37 | ANDRZEJEWSKI JÓZEF |
| IPN BU 698/42 | ANDRZEJEWSKI JÓZEF |
| IPN BU 01000/1678 | ANDRZEJEWSKI KAZIMIERZ |
| IPN BU 0872/69 | ANDRZEJEWSKI LEON |
| IPN BU 00945/1092 | ANDRZEJEWSKI LEON |
| IPN BU 01753/6 | ANDRZEJEWSKI LEON |
| IPN BU 0194/2505 | ANDRZEJEWSKI MARIAN |
| IPN BU 0772/26 | ANDRZEJEWSKI MARIAN |
| IPN 00 1043/3958 | ANDRZEJEWSKI MARIAN |
| IPN BU 002086/1483 | ANDRZEJEWSKI MARIAN ROMAN |
| IPN BU 0942/491 | ANDRZEJEWSKI MIECZYSŁAW |
| IPN BU 0957/11 | ANDRZEJEWSKI MIECZYSŁAW |
| IPN BU 698/43 | ANDRZEJEWSKI SŁAWOMIR |
| IPN BU 0912/255 | ANDRZEJEWSKI STANISŁAW |
| IPN BU 0958/56 | ANDRZEJEWSKI STANISŁAW |
| IPN BU 0218/2537 | ANDRZEJEWSKI STANISŁAW |
| IPN BU 0218/3175 | ANDRZEJEWSKI STANISŁAW |
| IPN BU 0942/129 | ANDRZEJEWSKI STANISŁAW |
| IPN BU 001121/431 | ANDRZEJEWSKI WACŁAW |
| IPN BU 0604/1237 | ANDRZEJEWSKI WIESŁAW |
| IPN BU 00283/2208 | ANDRZEJEWSKI WIESŁAW |
| IPN BU 0891/287 | ANDRZEJEWSKI WŁADYSŁAW |
| IPN BU 01000/199 | ANDRZEJEWSKI WŁADYSŁAW |
| IPN BU 002082/406 | ANDRZEJEWSKI WŁODZIMIERZ |
| IPN BU 002086/1104 | ANDRZEJEWSKI WŁODZIMIERZ |
| IPN BU 644/726 | ANDRZEJEWSKI ZBIGNIEW |
| IPN BU 01000/1694 | ANDRZEJEWSKI ZDZISŁAW |
| IPN BU 0892/68 | ANDRZEJEWSKI ZYGMUNT |
| IPN BU 0892/77 | ANDRZEJEWSKI ZYGMUNT |
| IPN BU 0772/3778 | ANDRZEJEWSKI) JĘDRZEJEWSKI PIOTR |
| IPN BU 645/20 | ANDRZEJKIEWICZ WŁADYSŁAW |
| IPN BU 0242/798 | ANDRZEJUK BOLESŁAW |
| IPN BU 0951/520 | ANDRZEJUK JADWIGA TERESA |
| IPN BU 001102/224 | ANDRZEJUK MARIA |
| IPN BU 0242/601 | ANDRZEJUK MARZENA HELENA |
| IPN BU 00612/1324 | ANDUŁA WŁADYSŁAW |
| IPN BU 00750/30 | ANDUSZKIEWICZ WOJCIECH |
| IPN BU 776/144 | ANDZELMAN REGINA |
| IPN BU 0242/2605 | ANDZIAK (RYBACZYK) HALINA |
| IPN BU 01256/6 | ANDZIAK ADAM |
| IPN BU 0193/9035 | ANDZIAK APOLONIA |
| IPN BU 0772/2135 | ANDZIAK FRANCISZKA |
| IPN BU 0193/2313 | ANDZIAK HENRYK |
| IPN BU PF | 299/108 ANDZIAK JANUSZ |
| IPN BU 645/17 | ANDZIAK JERZY |
| IPN 00 1043/2479 | ANDZIAK JERZY JAN |
| IPN BU 645/14 | ANDZIAK JÓZEF |
| IPN BU 00191/501 | ANDZIAK KRYSTYNA |
| IPN 00 1043/3569 | ANDZIAK KRYSTYNA |
| IPN BU 0193/1285 | ANDZIAK LEWANDOWSKA IRENA |
| IPN BU 0194/2286 | ANDZIAK LILIANA |
| IPN BU 0218/1932 | ANDZIAK RYSZARD |
| IPN BU 01079/195 | ANDZIAK STANISŁAW |
| IPN BU 01133/415 | ANDZIAK TADEUSZ |
| IPN BU 00744/670 | ANDZIAK ZBIGNIEW |
| IPN BU 001134/3 | ANDZIAK ZBIGNIEW |
| IPN BU 0193/1304 | ANDZIEJCZYK KAZIMIERZ |
| IPN BU 01000/156 | ANECKI ADAM |
| IPN BU 0193/1282 | ANEFAL ALEKSANDER |
| IPN BU 00448/435 | ANGELARD ANDRZEJ |
| IPN BU 001134/5415 | ANGELARD ANDRZEJ STANISŁAW |
| IPN BU 00200/1003 | ANGELUS WŁODZIMIERZ |
| IPN BU 001102/579 | ANGELUS WŁODZIMIERZ |
| IPN BU 0772/21 | ANGER HALINA |
| IPN BU 0772/539 | ANGER JANUSZ |
| IPN BU 0193/139 | ANGIEL LUCJAN |
| IPN BU 0218/1553 | ANGIELCZYK ANDRZEJ |
| IPN BU 001089/39 | ANGIELCZYK WACŁAW |
| IPN BU 0988/2 | ANGIELEWSKA WACŁAWA |
| IPN BU 00611/1796 | ANGIELSKI JÓZEF |
| IPN BU 001198/5698 | ANGIELSKI JÓZEF |
| IPN BU 0866/11 | ANGIELSKI MIECZYSŁAW |
| IPN BU 00328/1505 | ANGIELSKI MIROSŁAW |
| IPN BU 001134/2472 | ANGIELSKI MIROSŁAW |
| IPN BU 0951/1952 | ANGIER JAN |
| IPN BU 001089/36 | ANGRECKI WITOLD |
| IPN BU 0218/3608 | ANIELAK (GAWROŃSKA) HANNA |
| IPN BU 00966/548 | ANIELAK JAN |
| IPN BU 00966/194 | ANIELAK MARIAN |
| IPN BU 0218/3043 | ANIELAK TADEUSZ |
| IPN BU 02042/78 | ANIELAK ZDZISŁAW |
| IPN BU 01133/416 | ANIELSKA KRYSTYNA |
| IPN BU 01133/341 | ANIELSKI TADEUSZ |
| IPN BU 0891/2159 | ANIOŁ ANTONI |
| IPN BU 01000/1682 | ANIOŁ FRANCISZEK |
| IPN BU 980/2 | ANIOŁ HELENA |
| IPN BU 0772/2136 | ANIOŁ IRENA |
| IPN BU 00612/870 | ANIOŁ IRENA |
| IPN BU 00612/680 | ANIOŁ JAN |
| IPN BU 001198/4371 | ANIOŁ JAN |
| IPN BU 00328/673 | ANIOŁ MAREK |
| IPN BU 001134/1504 | ANIOŁ MAREK |
| IPN BU 00612/3171 | ANIOŁ TADEUSZ |
| IPN BU 001198/6267 | ANIOŁ TADEUSZ |
| IPN BU 00611/1241 | ANIOŁ WŁADYSŁAW |
| IPN BU 001198/2114 | ANIOŁ WŁADYSŁAW |
| IPN BU 00230 | P. 169 ANIOŁ ZDZISŁAW |
| IPN BU 00230 | P. 81 ANIOŁ ZDZISŁAW |
| IPN BU 0870/315 | ANIOŁEK JÓZEF |
| IPN BU 0988/1231 | ANIOŁEK STANISŁAW |
| IPN BU 52/60 | ANIOŁEK STEFAN |
| IPN BU 0194/1070 | ANIOŁKOWSKA DANUTA |
| IPN BU 01133/417 | ANIOŁKOWSKI FELIKS |
| IPN BU 00744/818 | ANIOŁKOWSKI MAREK |
| IPN BU 001134/408 | ANIOŁKOWSKI MAREK |
| IPN 00 1043/2115 | ANIOŁOWSKA JANINA |
| IPN BU 0218/2433 | ANIOŁOWSKI ANDRZEJ |
| IPN BU 0951/1869 | ANIOŁOWSKI TOMASZ |
| IPN BU 710/456 | ANISEROWICZ IRENA |
| IPN BU 0902/14 | ANISIEWICZ ANDRZEJ |
| IPN BU 0806/1136 | ANISIEWICZ HALINA |
| IPN BU 980/189 | ANISIEWICZ IRENA |
| IPN BU 0242/1532 | ANISIEWICZ MICHAŁ |
| IPN BU 980/190 | ANISIEWICZ TADEUSZ |
| IPN BU 0772/567 | ANISIEWICZ WANDA |
| IPN BU 0866/1378 | ANISIEWICZ ZBIGNIEW |
| IPN BU 0902/15 | ANISIMOW TADEUSZ |
| IPN BU 0193/6518 | ANISZEWSKA (MACUGA) ALICJA |
| IPN BU 0772/2137 | ANISZEWSKA BERNADA |
| IPN BU 0892/69 | ANISZEWSKA HENRYKA |
| IPN BU 0772/2138 | ANISZEWSKA ZOFIA |
| IPN BU 01137/81 | ANISZEWSKI CZESŁAW |
| IPN BU 0951/1688 | ANISZEWSKI JÓZEF |
| IPN BU 01000/1679 | ANISZEWSKI JULIAN |
| IPN BU 01250/6 | ANISZEWSKI MARIAN |
| IPN BU 00966/1242 | ANISZEWSKI SYLWESTER ANTONI |
| IPN BU 01079/316 | ANISZEWSKI TADEUSZ |
| IPN BU 0193/140 | ANIŚKIEWICZ WIKTOR |
| IPN BU 090/150 | ANKIEL ZENON |
| IPN BU 00288/208 | ANKIERSZTEJN KAZIMIERZ |
| IPN BU 01133/418 | ANKIEWICZ IGNACY |
| IPN BU 02042/342 | ANKLEWICZ ANDRZEJ |
| IPN BU 0912/843 | ANKOWSKI JÓZEF |
| IPN BU 0912/156 | ANKOWSKI STEFAN |
| IPN BU 001198/1196 | ANKUDOWICZ IGNACY |
| IPN BU 0194/2621 | ANKUDOWICZ JERZY |
| IPN 00 1043/2957 | ANKUDOWICZ JERZY MARIA |
| IPN BU 00945/1855 | ANONIEWSKA BERNARD |
| IPN BU 0193/141 | ANPIŁOW ALEKSANDER |
| IPN BU 698/37 | ANRYCHOWICZ KAZIMIERA |
| IPN BU 00945/1556 | ANSELM JAN |
| IPN BU 01137/5 | ANSZYN MARIA |
| IPN BU 01000/32 | ANTAS JAN |
| IPN BU 01000/200 | ANTAS STANISŁAWA |
| IPN BU 00200/123 | ANTCZAK – KURZYNA DANUTA EWA |
| IPN BU 0242/2075 | ANTCZAK (NOWAKOWSKA) KRYSTYNA |
| IPN BU 0901/1479 | ANTCZAK (STAŚKIEWICZ) ALICJA |
| IPN BU 0833/9 | ANTCZAK ALEKSANDER |
| IPN BU 0218/2579 | ANTCZAK BARBARA |
| IPN BU 698/44 | ANTCZAK CECYLIA |
| IPN BU 0912/157 | ANTCZAK DANIELA |
| IPN BU 0193/1286 | ANTCZAK EDMUND |
| IPN BU 00328/1056 | ANTCZAK EDWARD |
| IPN 00 1043/2359 | ANTCZAK EDWARD |
| IPN BU 001134/1919 | ANTCZAK EDWARD |
| IPN BU 0891/279 | ANTCZAK FRANCISZEK |
| IPN BU 001198/3513 | ANTCZAK HALINA |
| IPN BU 0604/1401 | ANTCZAK HENRYK |
| IPN BU 0891/280 | ANTCZAK IGNACY |
| IPN BU 710/22 | ANTCZAK IGNACY |
| IPN BU 0891/281 | ANTCZAK JAN |
| IPN BU 0806/1384 | ANTCZAK JAN |
| IPN BU 002082/109 | ANTCZAK JERZY |
| IPN 00 1043/57 | ANTCZAK JERZY |
| IPN BU 002086/302 | ANTCZAK JERZY KAZIMIERZ |
| IPN BU 0891/109 | ANTCZAK JÓZEF |
| IPN BU 0772/2139 | ANTCZAK KAZIMIERA |
| IPN BU 0891/113 | ANTCZAK KAZIMIERZ |
| IPN BU 0891/282 | ANTCZAK KAZIMIERZ |
| IPN BU 0218/2203 | ANTCZAK KRYSTYNA |
| IPN BU 0902/16 | ANTCZAK LUCJAN |
| IPN BU 0772/3476 | ANTCZAK MARIA |
| IPN BU 002086/846 | ANTCZAK MARIA |
| IPN BU 01000/522 | ANTCZAK MARIAN |
| IPN BU 001134/2535 | ANTCZAK MARIUSZ |
| IPN BU 0242/3034 | ANTCZAK MARZENA |
| IPN BU 00966/794 | ANTCZAK PIOTR |
| IPN BU 644/727 | ANTCZAK RYSZAD |
| IPN BU 0604/1345 | ANTCZAK RYSZARD |
| IPN BU 0912/1561 | ANTCZAK STANISŁAW |
| IPN BU 0193/142 | ANTCZAK STANISŁAW |
| IPN BU 001102/2010 | ANTCZAK STANISŁAW |
| IPN BU 0891/133 | ANTCZAK TADEUSZ |
| IPN BU 0242/1297 | ANTCZAK TADEUSZ JAN |
| IPN BU 0604/254 | ANTCZAK WIKTOR |
| IPN BU 00249/607 | ANTCZAK WOJCIECH |
| IPN BU 001121/1249 | ANTCZAK WOJCIECH |
| IPN BU 0910/55 | ANTCZAK ZOFIA |
| IPN 00 1052/560 | ANTCZAK-KURZYNA EWA DANUTA |
| IPN BU 636/1823 | ANTCZYK WIKTORIA |
| IPN BU 0901/1397 | ANTECKA MAŁGORZATA WICH WĘCH WECH |
| IPN BU 0951/1934 | ANTEPOWICZ JÓZEF |
| IPN BU 0911/5 | ANTKIEWICZ STEFAN |
| IPN BU 0912/158 | ANTKIEWICZ WŁADYSŁAW |
| IPN BU 0193/1287 | ANTKIEWICZ ZYGFRYD |
| IPN BU 0942/73 | ANTKOWIAK ANNA |
| IPN BU 00234 | p.249 ANTKOWIAK BRONISŁAW |
| IPN BU 0772/2141 | ANTKOWIAK CECYLIA |
| IPN BU 644/728 | ANTKOWIAK DIONIZY |
| IPN BU 01312/2 | ANTKOWIAK DOROTA |
| IPN BU 644/729 | ANTKOWIAK EDWARD |
| IPN BU 0193/1288 | ANTKOWIAK JAN |
| IPN BU 636/1801 | ANTKOWIAK JAN |
| IPN BU 00249/418 | ANTKOWIAK LECH |
| IPN BU 001121/1044 | ANTKOWIAK LECH |
| IPN BU 0193/6083 | ANTKOWIAK MIECZYSŁAW |
| IPN BU 0604/90 | ANTKOWIAK STANISŁAW |
| IPN BU 645/13 | ANTKOWSKA HELENA |
| IPN BU 0591/6 | ANTKOWSKI ARNOLD |
| IPN 00 1043/1720 | ANTO ANTOSZKIEWICZ MARIA TERESA |
| IPN BU 0772/2140 | ANTOLAK (CABAN) MONIKA |
| IPN BU 0968/16 | ANTOLAK DANUTA |
| IPN BU 0993/289 | ANTOLAK ELŻBIETA |
| IPN BU 683/220 | ANTOLAK KAZIMIERA |
| IPN BU 683/221 | ANTOLAK STANISŁAW |
| IPN BU 01133/419 | ANTOLAK WACŁAW |
| IPN BU 0193/1289 | ANTOLEWSKI STANISŁAW |
| IPN BU 0194/1274 | ANTONAW WŁODZIMIERZ |
| IPN BU 00170/883 | ANTONIAK – SKONECKA HALINA |
| IPN BU 698/46 | ANTONIAK ARKADIUSZ |
| IPN 00 1043/1708 | ANTONIAK BOGUSŁAWA SABINA |
| IPN BU 0951/1595 | ANTONIAK HELENA |
| IPN BU 0604/346 | ANTONIAK HENRYK |
| IPN BU 0894/19 | ANTONIAK IRENA |
| IPN BU 0193/5453 | ANTONIAK JAN |
| IPN BU 02063/18 | ANTONIAK JANUSZ |
| IPN BU 0193/1290 | ANTONIAK JERZY EUGENIUSZ |
| IPN BU 00612/1472 | ANTONIAK JÓZEF |
| IPN BU 001164/20 | Antoniak Julian |
| IPN BU 0806/1348 | ANTONIAK KRYSTYNA |
| IPN BU 0951/740 | ANTONIAK KRZYSZTOF |
| IPN BU 0854/1003 | ANTONIAK MIECZYSŁAW |
| IPN BU 0193/1291 | ANTONIAK MIECZYSŁAW JÓZEF |
| IPN BU 0242/666 | ANTONIAK MIROSŁAW |
| IPN BU 02042/555 | ANTONIAK PIOTR |
| IPN BU 0194/3638 | ANTONIAK RYSZARD JULIAN |
| IPN 00 1043/1044 | ANTONIAK SKONECKA HALINA |
| IPN BU 0901/1450 | ANTONIAK TOMASZ |
| IPN BU 01434/280 | ANTONIAK WIESŁAW |
| IPN BU 0194/3275 | ANTONIAK WIKTOR |
| IPN BU 0194/917 | ANTONIAK WŁADYSŁAW |
| IPN BU 0901/2495 | ANTONIAK ZYGMUNT |
| IPN BU 0967/1 | ANTONIAK ZYGMUNT |
| IPN BU 0967/1 | ANTONIAK ZYGMUNT |
| IPN BU 0194/39 | ANTONIENKO TADEUSZ |
| IPN BU 0604/1822 | ANTONIEWICZ ANDRZEJ |
| IPN BU 696/1346 | ANTONIEWICZ FRANCISZEK |
| IPN BU 696/1347 | ANTONIEWICZ FRANCISZEK |
| IPN BU 698/47 | ANTONIEWICZ FRANCISZEK |
| IPN BU PF | 97/35 ANTONIEWICZ JAN |
| IPN BU 0194/2964 | ANTONIEWICZ KAROL |
| IPN BU 01133/420 | ANTONIEWICZ MARIAN |
| IPN 00 1043/1867 | ANTONIEWICZ OLGIERD JAN |
| IPN BU 01000/1690 | ANTONIEWICZ STANISŁAW |
| IPN 00 1043/1230 | ANTONIEWICZ TOMASZ |
| IPN BU 0305/374 | ANTONIEWICZ WACŁAW |
| IPN BU 0194/2804 | ANTONIEWICZ ZBIGNIEW |
| IPN BU 698/49 | ANTONIEWICZ-STRAUS IRENA |
| IPN BU 0242/1752 | ANTONIEWSKA (MOŚCICKA. BAZYL) MAŁGORZATA |
| IPN BU 01270/1 | ANTONIEWSKA CZAPKOWICZ TERESA |
| IPN BU 01133/421 | ANTONIEWSKI ANTONI |
| IPN BU 00168/301 | ANTONIEWSKI BERNARD |
| IPN BU 00257/326 | ANTONIEWSKI BERNARD JAN |
| IPN BU 001102/1393 | ANTONIEWSKI BERNARD JAN |
| IPN BU 0329/3 | ANTONIEWSKI FRANC |
| IPN BU 0891/1775 | ANTONIEWSKI WŁADYSŁAW |
| IPN BU 0194/682 | ANTONIEWSKI ZYGMUNT |
| IPN BU 0218/2025 | ANTONIEWSKI ZYGMUNT |
| IPN BU 01000/1684 | ANTONIK TADEUSZ |
| IPN BU 00611/2003 | ANTONIK WACŁAW |
| IPN BU 001198/3626 | ANTONIK WACŁAW |
| IPN BU 0218/2252 | ANTONISZCZAK TADEUSZ |
| IPN BU 0870/17 | ANTONISZCZAK-PACHNOWSKA MARIA |
| IPN BU 01133/422 | ANTONIUK FRANCISZEK |
| IPN BU 0772/22 | ANTONIUK FRANCISZEK ANTONI |
| IPN BU 645/3 | ANTONIUK MARIA |
| IPN BU 0591/7 | ANTONIUK WŁODZIMIERZ |
| IPN BU 00464/126/61 | ANTONKIEWICZ IRENEUSZ |
| IPN BU 00689/104 | ANTONKIEWICZ IRENEUSZ |
| IPN BU 0305/86 | ANTONKIEWICZ IRENEUSZ |
| IPN BU 001198/3815 | ANTONKIEWICZ TADEUSZ |
| IPN BU 0892/26 | ANTONOW MIKOŁAJ |
| IPN BU 0604/1213 | ANTONOWICZ ALINA |
| IPN BU 001089/43 | ANTONOWICZ AURELIA |
| IPN BU 0902/13 | ANTONOWICZ EUGENIUSZ |
| IPN BU 02042/112 | ANTONOWICZ JAN |
| IPN BU 0772/740 | ANTONOWICZ JÓZEF |
| IPN BU 0833/8 | ANTONOWICZ RYSZARD |
| IPN BU 698/50 | ANTONOWICZ SABINA |
| IPN BU 698/51 | ANTONOWICZ WIKTOR |
| IPN BU 644/730 | ANTOŃ LEOPOLD |
| IPN BU 00399/325 | ANTOŃCZAK WACŁAW |
| IPN 00 1043/2018 | ANTOŃCZAK WACŁAW |
| IPN BU 001134/4674 | ANTOŃCZAK WACŁAW |
| IPN BU 698/45 | ANTOŃCZYK STANISŁAW |
| IPN BU 0993/606 | ANTOS ANDRZEJ |
| IPN BU 00249/546 | ANTOS CZESŁAW |
| IPN BU 001121/1178 | ANTOS CZESŁAW |
| IPN 00 1043/915 | ANTOS JULIAN |
| IPN BU 0242/1866 | ANTOS KAZIMIERZ |
| IPN BU 0951/1949 | ANTOS KRYSTYNA |
| IPN BU 00191/117 | ANTOS ZDZISŁAW |
| IPN 00 1043/2122 | ANTOS ZDZISŁAW |
| IPN BU 02184/1 | ANTOSIAK TERESA |
| IPN BU PF | 2077/51 ANTOSIAK WŁADYSŁAW |
| IPN BU 01133/423 | ANTOSIEWICZ BARBARA |
| IPN BU 0951/1569 | ANTOSIEWICZ BOŻENA URSZULA |
| IPN BU 645/7 | ANTOSIEWICZ DANUTA |
| IPN BU 01310/1 | ANTOSIEWICZ EWA |
| IPN BU 645/15 | ANTOSIEWICZ FELIKS |
| IPN BU 0193/8382 | ANTOSIEWICZ GRABOWSKA ANNA |
| IPN BU 698/48 | ANTOSIEWICZ HELENA |
| IPN BU 00275/335 | ANTOSIEWICZ IRENEUSZ |
| IPN BU 001134/190 | ANTOSIEWICZ IRENEUSZ |
| IPN BU 00966/196 | ANTOSIEWICZ JAN |
| IPN BU 0193/143 | ANTOSIEWICZ JAN ANTOŚIEWICZ ANTONIEWICZ ANTOŃIEWICZ |
| IPN BU 00744/184 | ANTOSIEWICZ JERZY |
| IPN BU 001121/3819 | ANTOSIEWICZ JERZY |
| IPN BU 00399/7 | ANTOSIEWICZ PAWEŁ |
| IPN BU 001134/4046 | ANTOSIEWICZ PAWEŁ |
| IPN BU 001134/2811 | ANTOSIEWICZ PIOTR |
| IPN BU 01250/7 | ANTOSIEWICZ STANISLAW |
| IPN BU 001075/66 | ANTOSIEWICZ STANISŁAW |
| IPN BU 645/4 | ANTOSIEWICZ STANISŁAWA |
| IPN BU 0866/12 | ANTOSIEWICZ STANISŁAWA |
| IPN BU 0218/2075 | ANTOSIEWICZ STEFAN |
| IPN BU 00744/888 | ANTOSIEWICZ SYLWESTER |
| IPN BU 001134/642 | ANTOSIEWICZ SYLWESTER |
| IPN BU 698/52 | ANTOSIEWICZ WACŁAW |
| IPN BU 0604/981 | ANTOSIK CZESŁAW |
| IPN BU 0806/908 | ANTOSIK EUGENIA |
| IPN BU 01133/424 | ANTOSIK HENRYK |
| IPN BU 00200/54 | ANTOSIK JADWIGA |
| IPN 00 1052/400 | ANTOSIK JADWIGA |
| IPN BU 0193/6246 | ANTOSIK JÓZEF |
| IPN BU 0951/1955 | ANTOSIK JÓZEF |
| IPN BU 001164/25 | Antosik Mieczysław |
| IPN BU 0218/2422 | ANTOSIK STANISŁAW |
| IPN BU PF | 498/14 ANTOSIK ZAREMBA ZOFIA |
| IPN BU 01133/425 | ANTOSIK ZYGMUNT |
| IPN BU 0242/2855 | ANTOSIK(OGAŃSKA)ANGELA |
| IPN BU 0193/1292 | ANTOSZ ADAM |
| IPN 00 1043/3103 | ANTOSZ ROMUALDA WIESŁAWA |
| IPN BU 001198/3604 | ANTOSZ STANISŁAW |
| IPN BU 698/53 | ANTOSZAK CZESŁAW |
| IPN BU 0958/927 | ANTOSZCZUK FRANCISZEK |
| IPN BU 00169/35 | ANTOSZCZUK TADEUSZ |
| IPN 00 1043/3046 | ANTOSZCZUK TADEUSZ |
| IPN BU 0772/2142 | ANTOSZEWSKA ANIELA |
| IPN BU PF | 970/79 ANTOSZEWSKA BARBARA |
| IPN 00 1043/1763 | ANTOSZEWSKI ANDRZEJ LEON |
| IPN BU 644/731 | ANTOSZEWSKI FELIKS |
| IPN BU 0872/1 | ANTOSZEWSKI HENRYK |
| IPN BU 0872/68 | ANTOSZEWSKI JÓZEF |
| IPN BU 644/751 | ANTOSZEWSKI KAZIMIERZ |
| IPN BU 00945/1857 | ANTOSZEWSKI RYSZARD – JÓZEF |
| IPN BU 00168/303 | ANTOSZEWSKI RYSZARD JÓZEF |
| IPN BU 0193/1293 | ANTOSZEWSKI STANISŁAW |
| IPN BU 0951/1939 | ANTOSZEWSKI STANISŁAW |
| IPN BU 00328/474 | ANTOSZKIEWICZ ANDRZEJ |
| IPN BU 001134/1257 | ANTOSZKIEWICZ ANDRZEJ |
| IPN BU 0951/1311 | ANTOSZKIEWICZ CZESŁAW |
| IPN BU 0951/1610 | ANTOSZKIEWICZ JAN |
| IPN BU 0951/1950 | ANTOŚ STANISŁAWA |
| IPN BU 0912/159 | ANTOŚKIEWICZ ZYGMUNT |
| IPN BU 0951/1944 | ANTOWILSKA JANINA |
| IPN BU 01000/1698 | ANTOWSKA HALINA |
| IPN BU 0242/2139 | ANTUSZEWICZ EJSMONT DANUTA |
| IPN BU 636/1822 | ANTYPOROWICZ ALFREDA |
| IPN BU 644/732 | ANTYPOROWICZ KONSTANTY |
| IPN BU 0772/739 | ANUCIŃSKI STANISŁAW |
| IPN BU 0958/57 | ANULEWICZ ALEKSANDER |
| IPN BU 00257/431 | ANULEWICZ JACEK |
| IPN BU 001102/1498 | ANULEWICZ JACEK |
| IPN BU 00283/1519 | ANUS EDWARD |
| IPN BU 00768/853 | ANUS EDWARD |
| IPN BU 001198/3209 | ANUS EDWARD |
| IPN BU 00612/2333 | ANUSIAK ANDRZEJ |
| IPN BU 001198/5468 | ANUSIAK ANDRZEJ |
| IPN BU 00966/1955 | ANUSIEWICZ HENRYK |
| IPN BU 0193/1294 | ANUSIK STEFAN |
| IPN BU 0772/4528 | ANUSZEWSKI JAN |
| IPN BU 00750/214 | ANUSZEWSKI JAN |
| IPN BU 0193/7436 | ANUSZEWSKI STEFAN |
| IPN BU 0218/2128 | ANUSZKIEWICZ CZESŁAW |
| IPN BU 01000/1710 | ANUSZKIEWICZ STANISŁAW |
| IPN BU 01000/2091 | ANUSZKIEWICZ STANISŁAW |
| IPN BU 00328/1431 | ANUSZKIEWICZ TADEUSZ |
| IPN BU 001134/2373 | ANUSZKIEWICZ TADEUSZ |
| IPN BU 093/2 | ANUSZKIEWICZ Z |
| IPN BU 0806/2576 | ANUSZKIEWICZ ZOFIA |
| IPN BU 0866/13 | ANUSZKIEWICZ ZYGMUNT |
| IPN BU 0988/3 | ANYSZEWSKI ROMAN |
| IPN BU 0242/1898 | ANYSZKIEWICZ FRANCISZKA |
| IPN BU 0891/170 | ANYŻ JAN |
| IPN BU 696/1188 | ANYŻ WANDA |
| IPN BU 0218/1029 | ANYŻEWSKI JAN |
| IPN BU 00249/736 | ANZELEWICZ JANINA |
| IPN BU 00200/1396 | ANZORGE KAZIMIERZ |
| IPN BU 001102/997 | ANZORGE KAZIMIERZ |
Journalists feel like ‘spies and criminals’ under surveillance
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
|
|
|
The Rise of the Islamic State – IS – Film
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
The Islamic State, formerly known as ISIL and then ISIS, is rapidly and ruthlessly taking increasing control of Iraq. See Abu Bakr al-Baghdadi, the leader of this terrifying Caliphate call upon Sunni Muslims to join his Jihad to conquer land for a vast empire that knows no bounds. Strict Sharia law, the eradication of Christianity, with no mercy and no compromise, the Islamic State may already have weapons of mass destruction as this video shows. Watch the whole video for the prophetic and obvious prediction in which we were warned about the rise of the Islamic State.
TOP-SECRET – The Secret List of CIA Sources – 2.619 Names and Adresses, Part 3,C,
C
Cacioppo, Anthony J. Reported deceased Cahill, Edward 8433 Hollins Ln., Vienna, VA 22182 Cahill, Capt William USN 3039 Dick Wilson Dr., Sarasota, FL 34240 Cake, Ms. Patricia A. 3242 Atlanta St., Fairfax, VA 22030 Calder, James D. 13330 Blanco Rd., No. 1113, San Antonio, TX 78216 Calderon, Mrs. Priscilla 2506 Vancouver Ave., San Diego, CA 92104 Calese, Donald J. 22015 N. Morage Ln., Sun City West, AZ 85375 Callaghan, Richard 173 Pascack Ave., Emerson, NJ 07630 Callahan, Maj Harold USA 508 Apple Grove Rd., Silver Spring, MD 20904 Callahan, Patrick 9110 Belvoir Woods Pkway, No. 221, Fort Belvoir, VA 22060 Callahan, Richard A. P.O. Box 239, Pebble Beach, CA 93953 Caminer, Gerald 1723 Powell Dr., Ventura, CA 93004 Cammarota, Armand 32 Valencia Ln., Clifton Park, NY 12065 Camp, Peter 272 1st Ave., New York, NY 10009 Campbell, Gretchen 6701 Corner Ln., McLean, VA 22101 Campbell, James E. 7002 River Oake Dr., McLean, VA 22101 Campbell, Dr. Kenneth 3701 S. George Mason Dr., No. 103N, Falls Church, VA 22041 Campbell, Wesley G. Hoover Institute, Stanford University, Palo Alto, CA Campos, Anthony 9125 Dickens Ave., Surfside, FL 33154 Canoy, Mariano 50 Rizal St., No. 805, San Francisco, CA 94107 Cantergiani, Col Joseph USAF 685 Blackhawk Dr., NE, Albuquerque, NM 87122 Canton, Col John USMC 16 Massanuttten Dr., Fort Royal, VA 22630 Caracristi, Ms Ann 1222 28th St., NW, Washington, DC 20007 Carino, LtCol James P. USAF 1142 Stony Ln., Gladwyne, PA 19035 Carley, LtCol Ronald AUS Rt 2, Lemars, IA 51031 Carley, Wayne H. 311 Rollins St., Falls Church, VA 22046 Carlson, Col Stan USA 6219 Baker Ave., NE, Minneapolis, MN 55432 Carmody, LtCol James USA 8514 Lancashire Dr., Springfield, VA 22151 Carmoy, Herve’ Banque Industraile Mobiliere, Paris, France Carnes, Cdr Calland USN 11078 Saffold Way, Reston, VA 22090 Carosia, Cdr Joseph J. USN 1608 Fort Duquesne Dr., Cherry Hill, NJ 08003 Carroll, Charles L. 11710 Parliment St., No. 510, San Antonio, TX 78213 Carroll, Edward 106 Bradock Rd., Williamsburg, VA 23185 Carson, Edward M. First Interstate Bancorp, Los Angeles, CA Carter, James H. 712 Samuel Chase Ln., W. Melbourne, FL 32904 Carter, William R. 5600 Ridgefield Rd., Bethesda, MD 20816 Cartwright, Cecil J. P.O. Box 227, Yazoo City, MS 39194 Cary, George L. 6900 Breezewood Terrace, Rockville, MD 20852 Casanova, Jean-Claude Economic Institute for Policy Studies, Paris, France Casey, Col Edmund AUS 7702 Twinleaf Trail, Orange, CA 92669 Casey, Robert M. 1245 Cresthaven Dr., Silver Spring, MD 20903 Cash, CWO John USN 10514 Greenford Dr., San Diego, CA 92126 Caspersen, LtCol Ralph AUS 5109 S. Washburn Ave., Minneapolis, MN 55410 Castorani, Samuel 10026 Sageglow, Houston, TX 77089 Caswell, John F. 2801 New Mexico Ave, NW, No. 605, Washington, DC 20007 Cater, Col Maurice USMC 240 Calle De Sereno, Leucadia, CA 92024 Caton, Col Edward USAF 300 Bayview Dr, NE, St. Petersburg, FL 33704 Cavadine, John O. 10708 Norman Ave., Fairfax, VA 22030 Cavalier, SgtM William USA 2826 Huntngton Park Dr., Waterford, MI 48329 Cavanaugh, Joseph M 3310 Fish Canyon Rd., Duarte, CA 91010 Cecchini, Col Louis USA 16200 Laurel Ridge Dr., Laurel, MD 20707 Cesare, Donald J. 2729 Alteza Ln., Colorado Springs, CO 80917 Chaffin, C. Wayne 6714 Northport, Dallas, TX 75230 Chaffin, Richard 1051 9th Ave., Huntington, WV, 25701 Chalker, William R. Jr. 5 South Trail, Arden, DE 19810 Chamberlain, Gary J. 755 Shaker Dr., Medina, OH 44254 Chambers, Gregory 19 Bailey Rd., Millburn, NJ 07041 Chambers, John A. 421 West 5th Ave., Columbus, OH 43201 Champlin, Malcom M 485 Ellita Ave., Oakland, CA 94610 Chapin, Capt A. Winfield USNR P.O. Box 789, Palm Beach, FL 33480 Chapman, LtCol Gerald S. USAF 13822 Via Alto Ct., Saratoga, CA 95070 Chapman, LtCdr William USN 888 Canyon View Loop, Hamilton, MT 59840 Charriere, Robert F. 332 Waldo Rd., Arlington, MA 02174 Chase, Col Harold B. USAF 3112 N. Rosser St., Alexandria, VA 22311 Cherry, Maj Donald USAF 2166 Northam Rd., Columbus, OH 43221 Chesnut, George L. 2306 N. Vernon St., Arlington, VA 22207 Chigos, Dr. David 651 Silvergate Ave., San Diego, CA 92106 Chillemi, Richard L. 15436 Snowhill Ln., Centreville, VA 22020 Chin, Robert 10509 Tyler Terace, Potomac, MD 20854 Chino, Yoshitoki Daiwa Securities Ltd., Tokyo, Japan Chizewsky, Nicholas A. 125 Highway 80, Bisbee, AZ 85603 Chizum, David G. 476 Whitetail Dr., Franktown, CO 80116 Choate, Art 117 Pine Valley, Williamsburg, VA 23188 Christiansen, Ms. Kathleen 1022 Simas Ave., Pinole, CA 94564 Christie, Col William USAF 6409 Seven Oaks Dr., Falls Church, VA 22042 Christman, John H. 2055 Oxford Ave., Cardiff, CA 92007 Christopher, Col Stone USAF 5100 John D. Ryan Blvd., No. 315., San Antonio, TX 78245 Chron, Dr. Gustav 7110 N. McAlpin Ave., Chicago, IL 60646 Chu, Kirby P. P.O. Box 26418, San Francisco, CA 94126 Cianci, Salvatore 1704 Glenkarney Pl., Silver Spring, MD Cieri, Paul P. CMR 416, Box 251, APO, AE 09613 Cinnamon, LeRoy 1208 Spicewood Dr., Schertz, TX 78154 Cioci, Mario 8038 Glendale Rd., Chevy Chase, MD 20815 Claar, Richard 86 Hancock Pl., NE, Leesburg, VA 22075 Clapper, LtGen James USAF 5366 Ashleigh Rd., Fairfax, VA 22030 Clare, Kenneth 1600 North Oak St., No. 320, Arlington, VA 22209 Clark, MajGen Arthur USAF 3540 Rugby Rd., Durham, NC 27707 Clark, Donald D. 17 W. 514 Victory Parkway, Addison, IL 60101 Clark, Galen L. 30 Holly Way, Parachute, CO 81635 Clark, J. Ransom PoliSci Dept., Muskingum College, New Concord OH 43762 Clark, John M. 40 Santa Macia Dr., Novato, CA 94947 Clark, Ned 8701 Contee, Rd., Laurel, MD 20708 Clarke, Charles R. P.O. Box 22121, Santa Clara, CA 95055 Clarke, LtCol Robert F. USAF 5846 S. Wilshire Dr., Tucson, AZ 85711 Clary, Carter P.O. Box 80074, Albuquerque, NM 87198 Cline, Dr. Raymond 3027 N. Pollard St., Arlington, VA 22207 Clinton, Babes van Dillen 131 Sycamore Ave., San Mateo, CA 94402 Clontz, Col Ralph C. USA 2229 Queens Rd., East, Charlotte, NC 28207 Clothier, William J. 215 S. 16th St., Philadelphia, PA 19102 Clough, Herbert D. Jr. 14315 Riverside Dr., No. 106, Sherman Oaks, CA 91423 Clutter, LtCol Roderick USAF 121 N. 7th St., Boonville, IN 47601 Coats, LtCol J. C. USAF 1409 Camino Cerrito, SE, ALbuquerque, NM 87123 Cochran, Farrett 1619 Greenbrier Ct., Reston, VA 22090 Coco, John J. 695 Johnson St., North Andover MA 01845 Coffee, Edward 226 N. Oakland St., Arlington, VA 22203 Coffey, Raymond 28 Harbor View Ct, NE, Decatur, AL 35601 Coffin, Charles E. 260 S. 300 W, Lebanon, IN 46052 Colby, Maj George USAF 1422 Cypress, St. Cloud, FL 32769 Colby, William E. 3028 Dent Place, NW, Washington, DC 20007 Cole, John D. 420 South Alexandria, Los Angeles, CA 90020 Cole, Michael R. 12020 Sunrise Valley Dr., No. 100, Reston, VA 22091 Coleman, Dr. Robert P.O. Box 1101, Lake Elsinore, CA 92531 Coleman, Francis I.G. 1807 Kalorama Square, SE, Washington, DC 20008 Coleman, Col John USA 191 Folsom Dr., Dayton, OH 45405 Colgan, Frederick R. 1543 Longfellow Ct., McLean, VA 22101 Collazo, Jose P.O. Box 12142, Loiza Station, Santurce, PR 00914 Collie, David W. 242 Portland, Houston, TX 77006 Collier, Col Daniel USAR 1199 Park Ave., No. 7F, New York, NY 10028 Collin, Barry C. 1325 Howard Ave., No. 301, Burlingame, CA 94010 Collingwood, Dr. Ronald 10615 G Tierrasanta Blvd., No. 344, San Diego, CA 92124 Collins, Edward M. 816 Eagle Ln., Apollo Beach, FL 33572 Collins, Col Frank USAF 7362 Rebecca Dr., Hollin Hills, VA 22307 Collins, J. Foster 6804 Sorrell St., Mclean, VA 22101 Collins, LtCol James USAR 3420 Eliot Rd., Erie, PA 16508 Collomb, Bertrand Lafarge Coppee, Paris, France Collins, Ms. Mary Rose 5688 Bayberry Dr., Cincinatti, OH 45242 Combemalle, Jean-Loup RR 1, Box 309, Fainsville, VA 22065 Comras, Peter 2431 Del Air Blvd., Apt. D, Delray Beach, FL 33445 Conaty, Joseph 11519 Bucknell Dr., Silver Spring, MD 20902 Condon, Joseph P.O. Box 10231, Naples, FL 33941 Conner, William E. 46911 Bushwood Ct., Sterling, VA 20914 Connolly, Col George USA 681 Village Rd., North Palm Beach, FL 33408 Connolly, LtCol Philip USAF 7115 11th Ave., West, Badenton, FL 34209 Connor, John 91 Richardson Rd., Coventry, RI 02816 Connors, John J. 6912 Clemson Dr., Alexandria, VA 22307 Conway, Donald 13003 Melville Ln., Fairfax, VA 22033 Cook, Arie 20275 Quesada Ave., Port Charlotte, FL 33952 Cook, RAdm Ralph USN 153 Nawilliwili St., Honolulu, HI 96825 Cook, R. W. 762 Lunallio Home Rd., Honolulu, HI 96825 Cooke, Richard K. RR 4, Box 129, Keyser, WV 26726 Colley, Ms Laura 424 Heron Pt., Chestertown, MD 21620 Coombe, G.W. 555 California St., San Francisco, CA 94104 Cooper, C.E. 11623 46th Ave., NE, Marysville, WA 98217 Cooper, Capt David USN 3805 Winterset Dr., Annandale, VA 22003 Cooper, Mrs. Lucille V. 6635 Montarbor Dr., Colorado Spings, CO 80918 Cooper, Paul 4417 Lowell St., NW, Washington, DC 20016 Copher, Paul B. 9032 E. 33rd Pl., Tuscon, AZ 85710 Corn, Milton W. 300 N. State St., No. 5417, Chicago, IL 60610 Corry, Cecil 625 N. Lincoln St., Arlington, VA 22201 Corsa, Richard 2819 Moselle Ct., Walnut Creek, CA 94598 Corson, William, Col USMC 9550 River Rd., Potomac, MD 20554 Costanzo, Christopher RR 1, Box 74, Randolph, VT 05060 Coster, Dr. Abraham 3541 West Braddock Rd., Alexandria, VA 22302 Cosialle, Bertrand BNP, 5 Place Massena, Nice 06000 France Coti, Col William USMC 8247 Clifton Farm Ct., Alexandria, VA 22306 Courtney, John 12012 Valleywood Dr., Wheaton, MD 20902 Covault, Ms Grace 3309 Canningate Rd., No. 102, Fairfax, VA 22031 Cowan, Bruce 17 Washinigton St., Rutland, VT 05701 Cowgill, Col Ralph USAF 3610 Crede Dr., Charleston, WV 25302 Cowles, Floyd R. 3945 S.W. Marigold St., Portland, OR 97219 Crabb, LtCol Merle USMC 8110 Kings Point Dr., Springfield, VA 22153 Craig, CWO-4 Joseph USMCR P.O. Box 30005, Chicago, IL 60630 Craig, Robert J. P.O. Box 74, St. Michaels, MD 21663 Craigmile, Dr. James 810 Forest Hill Ct., Columbia, MO 65203 Cramer, Martin G. 5205 Benton Ave., Bethesda, MD 20814 Cramer, Col William USAF 817 San Marcos Ln., Bedford, TX 76021 Crampton, Kevin 22 Rancho Novato Dr., Pomona, CA 91766 Crandall, Dr. Maureen 5100 38th St., NW, Washington, DC 20016 Crandall, LtCol Walter M. USA 4802 Tara Woods Dr., East, Jacksonville, FL 32210 Creighton, John 1116 Fernwood Dr., Millbrae, CA 94030 Cremins, Patrick J. 3253 Chrisland Dr., Annapolis, MD 21403 Crilly, Cdr Eugene USNR 276 J St., Coronado, CA 92118 Crippen, Roy E. 801 Peterson Dr., Silver City, NM 88061 Critchfield, Col James USA 1552 Harbor Rd., Williamsburg, VA 23185 Critchfield, Lois 1552 Harbor Rd., Williamsburg, VA 23185 Critides, A. Byron 439-16 Camille Circle, San Jose, CA 95134 Crivelli, Capt Joseph USAR 18 Hastings Ln., Hicksville, NY 11801 Cronin, Paul E. 2512 K St., NW, No. 12, Washington, DC 20037 Cronin, Peter 36 Concord Dr., Madison, CT 06443 Crosby, Kenneth M. 3000 K St., NW, Suite 620, Washington, DC 20007 Cross, Richard L. RR 14, Box 2549, Kennewick, WA 99337 Crouter, Cdr Robert W. USN 18 Foundry St., Box 573, Amherst, NH 03031 Crow, Col Robert S. USAR 2205 Ryan Dr., Alvin, TX 77511 Crowley, Henry 1003 Devere Dr., Silver spring, MD 20903 Crowley, Robert 2818 Cathedral Ave., NW, Washington, DC 20008 Crumpler, Hugh 17205 Montero Dr., Silver Spring, MD 20903 Culp, Dr. Mildred 3313 39th Ave., W, Seattle, WA 981888 Cummings, Richard Strassburgerstr. 10, D-800809, Munich, Germany Cummings, Richard M P.O. Box 349, Bridgehampton, NY 11932 Cunningham, Robert P.O. Box 588, Pawleys Island, SC 29585 Curley, Cdr E. Patrick USN 7501 Maritime Ln., Springfield, VA 22153 Currie, Clare-Adair 7580 Dunwood Way, San Diego, CA 92114 Curry, Thomas H. 2613 Steeplechase Dr., Reston, VA 22091 Curtis, Gerald L. Columbia University, New York, NY 10027 Curts, Robert I. 5755 W. Ada Ln., Larkspur, CO 80118 Cwiek, Mitchell S. 1926 Bernardo Ave., Escondido, CA 92025
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, 120.000 Spies, Part 11, AM,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 0892/739 | AMAŁOWICZ ANDRZEJ |
| IPN BU 00611/1650 | AMANOWICZ FRANCISZEK |
| IPN BU 001198/3016 | AMANOWICZ FRANCISZEK |
| IPN BU 00283/2043 | AMANOWICZ JAN |
| IPN BU 00334/526 | AMANOWSKA MAGDALENA |
| IPN BU 001134/3408 | AMANOWSKA MAGDALENA |
| IPN BU 0951/1953 | AMANOWSKI FRANCISZEK |
| IPN BU 0242/2979 | AMAROWICZ JERZY |
| IPN BU 01000/1693 | AMBIK JANINA |
| IPN BU 00277/486 | AMBORSKI KRZYSZTOF |
| IPN BU 001121/2701 | AMBORSKI KRZYSZTOF |
| IPN BU 00328/1406 | AMBROĄ HANNA |
| IPN BU 0864/114 | AMBROCH MARIAN |
| IPN BU 00945/2264 | AMBROS ALEKSANDRA – MARIA |
| IPN BU 00170/161 | AMBROS ALEKSANDRA MARIA |
| IPN BU 0218/1607 | AMBROSZCZYK HALINA |
| IPN BU 0242/804 | AMBROSZCZYK JAN |
| IPN BU 00249/87 | AMBROSZKIEWICZ-KESSLER DANUTA |
| IPN BU 001121/670 | AMBROSZKIEWICZ-KESSLER DANUTA |
| IPN BU 001198/3337 | AMBROZ JAN |
| IPN BU 0855/2632 | AMBROZIAK ANDRZEJ |
| IPN BU 0942/119 | AMBROZIAK ANDRZEJ |
| IPN BU 52/54 | AMBROZIAK ANDRZEJ |
| IPN BU 01753/156 | AMBROZIAK ANIELA |
| IPN BU 0870/122 | AMBROZIAK BOGUSŁAW-JAN |
| IPN BU 0891/127 | AMBROZIAK CZESŁAW |
| IPN BU 0892/25 | AMBROZIAK FRANCISZEK |
| IPN BU 01133/405 | AMBROZIAK HENRYK |
| IPN BU 644/721 | AMBROZIAK HENRYK |
| IPN BU 00328/855 | AMBROZIAK HENRYK JÓZEF |
| IPN BU 001134/1709 | AMBROZIAK HENRYK JÓZEF |
| IPN BU 0891/1783 | AMBROZIAK JAN |
| IPN BU 01000/621 | AMBROZIAK JAN |
| IPN BU 644/4 | AMBROZIAK JAN |
| IPN BU 0891/129 | AMBROZIAK JAN JERZY |
| IPN BU 0772/2127 | AMBROZIAK JANINA |
| IPN BU 00273/200 | AMBROZIAK JANUSZ |
| IPN BU 01000/1709 | AMBROZIAK JERZY |
| IPN BU 0242/783 | AMBROZIAK KAZIMIERZ |
| IPN BU 0242/2330 | AMBROZIAK KOWALCZYK ELIZA |
| IPN BU 645/1434 | AMBROZIAK MAŁGORZATA |
| IPN BU 00249/1215 | AMBROZIAK MAŁGORZATA |
| IPN BU 001121/1828 | AMBROZIAK MAŁGORZATA |
| IPN BU 00230 | P 48 AMBROZIAK MARIA |
| IPN BU 0912/153 | AMBROZIAK MIECZYSŁAW |
| IPN BU 00744/672 | AMBROZIAK MIECZYSŁAW |
| IPN BU 001134/5 | AMBROZIAK MIECZYSŁAW |
| IPN BU PF | 125/149 AMBROZIAK ROMAN |
| IPN BU 0958/29 | AMBROZIAK STANISŁAW |
| IPN BU 0193/8926 | AMBROZIAK STANISŁAW |
| IPN BU 0772/2128 | AMBROZIAK STANISŁAW |
| IPN BU 01133/406 | AMBROZIAK STEFAN |
| IPN BU 093/4 | AMBROZIAK T |
| IPN BU 0193/1280 | AMBROZIAK TADEUSZ |
| IPN BU 0218/1487 | AMBROZIAK TADEUSZ |
| IPN BU 001164/164 | Ambroziak Tadeusz |
| IPN BU 0242/1904 | AMBROZIAK WACŁAWA (KISIEL) |
| IPN BU 0901/1627 | AMBROZIAK WALDEMAR |
| IPN BU 0772/474 | AMBROZIAK WIESŁAWA |
| IPN BU 0604/317 | AMBROZIAK WITOLD |
| IPN BU 0967/160 | AMBROZIAK WŁADYSŁAW |
| IPN BU 00277/1158 | AMBROZIAK WŁADYSŁAW |
| IPN BU 0193/130 | AMBROZIAK-SOMMERFELD BOŻENA |
| IPN BU 00191/137 | AMBROZIEWICZ JERZY JAN |
| IPN 00 1043/2170 | AMBROZIEWICZ JERZY JAN |
| IPN BU 698/28 | AMBROZIEWICZ MARIA |
| IPN BU 001089/34 | AMBROZIEWICZ RYSZARD |
| IPN BU 00191/256 | AMBROZIEWICZ-WITCZYK BARBARA |
| IPN BU 00612/3899 | AMBROZIK ANDRZEJ |
| IPN BU 001198/6727 | AMBROZIK ANDRZEJ |
| IPN BU 0901/1676 | AMBROZIK JANINA |
| IPN BU 698/29 | AMBROZIŃSKA JANINA |
| IPN BU 0218/1610 | AMBROZIŃSKA WIESŁAWA HALINA |
| IPN BU 0604/265 | AMBROZIŃSKI EDWARD |
| IPN 00 1043/2680 | AMBROZY JÓZEF |
| IPN BU 01133/407 | AMBROZY KAZIMIERZ |
| IPN BU 0243/361 | AMBROŻ (INDYK) GRAZYNA |
| IPN BU 00966/1430 | AMBROŻ ANNA |
| IPN BU 0901/2179 | AMBROŻ URSZULA |
| IPN BU 0243/189 | AMBROŻ ZBIGNIEW |
| IPN 00 1043/2556 | AMBROŻEWICZ WITCZAK BARBARA |
| IPN BU 00751/246 | AMBROŻKIEWICZ KAZIMIERZ |
| IPN BU 001102/2247 | AMBROŻKIEWICZ SŁAWOMIR |
| IPN 00 1052/1597 | AMBROŻKIEWICZ-AMBROZIEWICZ-WIELUŃSKA TELIMENA MARIA |
| IPN BU 00612/4443 | AMBROŻY EDWARD |
| IPN BU 001198/7130 | AMBROŻY EDWARD |
| IPN 00 1052/1109 | AMBROŻY JACEK |
| IPN 00 1043/203 | AMBROŻY JÓZEF ALBIN |
| IPN BU 0193/6611 | AMBROŻY MARIAN |
| IPN BU 698/30 | AMBROŻY PIOTR |
| IPN BU 0951/928 | AMBRYSZEWSKA BRONISŁAWA |
| IPN BU 0772/25 | AMBRYSZEWSKA IRENA |
| IPN BU 00312 | AMBRZYKOWSKI MIROSŁAW |
| IPN BU 00312/140 | AMBRZYKOWSKI MIROSŁAW |
| IPN BU 0806/1154 | AMEL STEFAN |
| IPN BU 0951/1937 | AMEL WALENTY |
| IPN BU 01000/1700 | AMEREK KAZIMIERZ |
| IPN BU 00945/2440 | AMEREK KRYSTYNA |
| IPN BU 706/616 | AMEREK MARIAN |
| IPN 00 1043/3688 | AMEREK MARIAN |
| IPN BU 00612/4933 | AMEREK MIECZYSŁAW |
| IPN BU 00612/2809 | AMERYK ANDRZEJ |
| IPN BU 001198/6032 | AMERYK ANDRZEJ |
| IPN BU 00170/196 | AMIELIS WALERY |
| IPN BU 00945/2247 | AMIELIS WALERY |
| IPN BU 00448/719 | AMIRIAN RAFIK |
| IPN BU 001134/5696 | AMIRIAN RAFIK RAFAEL |
| IPN BU 093/1 | AMIZOW CZESŁAWA |
| IPN BU 0993/692 | AMMOL MARIA |
| IPN BU 01133/408 | AMPT JADWIGA |
| IPN BU 0193/1281 | AMPT KAZIMIERZ |
| IPN BU 0988/621 | AMPULSKI STANISŁAW |
| IPN BU 0951/1941 | AMROZIAK (BRUDZIŃSKA) ZOFIA |
| IPN BU 0772/729 | AMROZIAK ANNA MARIA |
| IPN BU 0806/822 | AMRYSZEWSKA MARIANNA |
| IPN BU 01000/1135 | AMRYSZEWSKA MARIANNA |
| IPN BU 01000/1672 | AMRYSZEWSKI STANISŁAW |
| IPN BU 0604/347 | AMZEL BOGUSŁAW |
| IPN BU 0194/1251 | AMZEL MICHŁ |
| IPN BU 0193/6517 | AMZEL MIROSŁAWA (MANSFELD MINA) |
| IPN BU 02042/518 | AMZEL WALDEMAR |
TOP-SECRET – The Secret List of CIA Sources – 2.619 Names and Adresses, Part 2,B,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
B
Babbitt, Capt Franklin USN 10713 Miller Rd., Oakton, VA 22124 Babcock, Fenton 106 Elderberry Dr., Winchester, VA 22603 Babcock, James H. 11500 Fairway Dr., No. 307, Reston, VA 22090 Bachman, Lawrence W. 3419 Valewood Dr. Oakton, VA 22124 Baclawski, Dr. Joseph A. 11226 Mitscher St., Kensington, MD 20895 Bacot, John C. Bank of New York Co., New York, NY Baczynski,John L. 4 Romero Ct., Novato, CA 94945 Baer, Richard T. 12104 Foxhill Ln., Bowie, MD 20715 Bailey, LtCdr George USN 1028 Isabella, No. A, Coronado, CA 92118 Bailey, Paul L. 3640 Windjammer Dr., Colorado Springs, CO 30920 Bailey, Cdr William B. USN 3802 Kendale Rd., Annandale, VA 22003 Baird, Dane E. 9 Park Ave., Belmont, MA 02178 Baker, Ms Margaret E. 4100 Massachusetts, Ave., NW, No. 806, Washington, DC 20016 Baker, LtCol Paul D. AUS P.O. Box 83, Rockridge Baths, VA 24473 Balaban, Rudolph J. 522 Charles Ave., New Kensington, PA 15068 Balch, John W. 178 Thomas Johnson Dr., No. 200, Frederick, MD 21701 Baldwin, Thomas 202 SE 1st St., Evansville, IN 47713 Ball, Ms Virginia J. 1101 New Hampshire Ave., NW, No. 821, Washington, DC 20037 Ballew, Frank B. P.O. Box 7641, St. Thomas, VI 00801 Ballow, CW4 Jearl E. USA 83 Roundtable Rd., Springfield, IL 62704 Balserio, Aldo E. 1216 Kennedy Blvd., Union City, NJ 07087 Bane, Howard T. 10232 Confederate Lane, Fairfax, VA 22030 Bangs, Lawrence C. 4725 San Pedro Dr., NE, No. 16, Albuquerque, NM 87109 Bannerman, Robert L. P.O. Box 1132, Santa Rosa Beach, FL 32459 Barber, Hubert H. Jr. 913 Allegro Ln., Apollo Beach, FL 33572 Barber, William H. 19504 Gallitin Ct., Gaithersburg, MD 20879 Barclay, John G. L. Virgin Del Pilar 8, Cabrils, Spain Barker, LtCol Wayne G USA 23995 Carrillo Dr., Mission Viejo, CA 92691 Barlow, William J. 11402 Chapel Rd., Clifton, VA 22024 Barndt, Walter D. Jr. P.O. Box 1155, Grantham, NH 03753 Barnhart, James M. 3310 Baltimore, Lawton, OK 73505 Barnwell, Michael J. P.O. Box 914, Union Lake, MI 48387 Barrett, Col Frederick T. USA 4936 N. 33rd Rd., Arlington, VA 22207 Barrios, LtCol Jose Alberto 1140 NE 110 Terrace, Miami, FL 33161 Barrow, Lonnie M. 12401 North 22nd St., No. F 706, Tampa, FL 33612 Barry, John J. 2300 Pimmit Dr., No. 614, Falls Church, VA 22043 Barton, Donald E. 46-075 Meheanu Pl., No. 3331, Kaneohe, HI 96744 Bartreau, William L. 4402 Wind River Ln., Garland, TX 75042 Basher, William E. 12504 Buckley Dr., Silver Spring, MD 20904 Basil, William 41-48 171st, Flushing, NY 11358 Bass, W. Streeter 3005 Willow Springs Ct., Williamsburg, VA 23185 Batcho, David G. 5611 Desert Star, Las Cruces, NM 88005 Bates, Mrs. Constance N. 660 S. Jefferson St., Arlington, VA 22204 Bath, Capt Alan H. USN 2502 Watts, Houston, TX 77030 Bathke, Burton C. 4909 Piedra Rosa NE, Albuquerque, NM 87111 Bauer, Clyde W. 1652 North Oriole Place, Orange, CA 92667 Beach, Jenny L. 3906 Walt-Ann Dr., Ellicot City, MD 212042 Bean, Harold 3820 N. Chesterbrook Rd. Arlington, VA 22207 Beasey, Mrs. Anita H. 9737 Ashbourn Dr., Burke, VA 22015 Beasley, Robert S. 17911 Pond Rd., Ashton, MD 20816 Bechtel, George 14070 Sandy Hook Rd., NE, Poulsbo, WA 98370 Beck, Capt Donald A USN 5770 Arbolada Dr., Lake Don Pedro, La Grange, CA 95329 Beckman, Charles J. 10412 El Capitan Circle, Sun City, AZ 85351 Beed, Douglas K. 9081 Ocean Pines, Berlin, MD 21811 Beidleman, Edward B. 937 Kului Pl., Honolulu, HI 96821 Belferman, Herman 9508 Milstead Dr., Bethesda, MD 20817 Bell, Maj James R USA 1929 Clubhouse Way, No. 1, Billings, MT 59105 Bell, Jean S. 1104 Cresthaven Dr., Silver Spring, MD 20903 Bellak, LtCdr Theodore USN 21 Craigside Pl No. 8D, Honolulu, HI 96817 Bello, Roberto 8701 Bergenline Ave., No. B8, North Bergen, NJ 07047 Belt, Charles V. 3330 N. Leisure World Blvd., No. 530, Silver Spring, MD 20906 Belt, William G. 330 Riola Pl., Pensacola, FL 32506 Bembry, Al G. RR 1, Box 216C, Whittier, NC 28789 Benchea, Hortenziu 3543 Tanglewood Trail, Palm Harbour, FL 34586 Benjamin, Capt Albert USNR 40 Old Farm Rd., Bellair, Charlottsville, VA 22903 Bennett, Robert S. 9521 Purcell Dr., Potomac, MD 20854 Bennett, Ms. Shelly Lea 75-B Pelham St., Newport, RI 02840 Bennett, William P.O. Box 4264, Civic Centre, San Rafael, CA 94913 Benson, Howard F. Jr. 8086 S. Niagara Way, Englewood, CO 80112 Beran, Miles P.O. Box 40282, Bay Village, OH 44140 Bercovitz, George E. 195-40F Peck Ave., Fresh Meadows, NY, 11365 Berejkoff, George R. 3715 Wood Plaza Way, Kelseyville, CA 95451 Berent, LtCol Mark E. USAF RR 1, Box 25, Remington, VA 227334 Berger, Col George C. USAF 9713 Rhapsody Dr., Vienna, VA 22181 Berglund, Mrs. Ruth L. 319 Rolling Mountain Rd., Bentonville, VA 22610 Berkaw, Ernest de Mun Jr. Southporte 103, 3322 Casseekey Island, Jupiter, FL 33477 Berkeley, Roy G. RR 1, Box 318, Shaftsbury, VT 05262 Berlin, Capt Richard G. AUS 690 55th Ave., NE, St. Petersburg, FL 33703 Berman, Dr. Stanley J. 1575 Soquel Dr., Santa Cruz, CA 95065 Bernabel, Anthony A. 512 Main St., No. 1011, Ft. Worth, TX 76102 Bernard, Richard L. 10009 Renfrew Rd., Silver Spring, MD 20901 Berrey, Michael D. 37340 Clubland Dr., Marietta, GA 30067 Berry, LtCol Clyde M. USA 13505 Kingscross Ct., Midlothian, VA 23113 Bessac, Frank B. 1826 Traynor, Missoula, MT 59802 Bessette, LtCol Carol S. USAF 8351 Taunton Pl., Springfield, VA 22152 Betts, John 5416 Canterbury Rd., Fairway, KS 66205 Betts, Capt Roger S. USN 110 Gulfview Rd., Punta Gorda, FL 33950 Beya, BGen Richard S. USAF 7831 Lee Ave., Alexandria, VA 22308 Beyrle, Joseph R. 1782 Columbus Ave., Norton Shores, MI 49441 Biddle, Delbert W. P.O. Box 860, Sausalito, CA 94966 Bidwell, Richard F. 204 Needlewood Dr., Rt. 1, Huddleston, VA 24104 Biggs, Sgt Darryl G. USA P.O. Box 578, Newton, AL 36352 Billings, John M. 4101 Nellie Custis Ct., Alexandria, VA 22309 Billingsley, RAdm Edward USN 12401 N. 22nd St., No. A-510, Tampt, FL 33612 Birnbaum, Cdr P.O. USN 1621 Inlet Ct., Reston, VA 22090 Bishop, Maj Lynn R. USA 209 Alder St., Liverpool, NY 13088 Bishop, Maurice 102 Bear Gulch Rd., Woodside, CA 94062 Bizic, Peter Jr. 7786 Turlock Rd., Springfield, VA 22135 Blackwood, Anna M. 13 Largo Vista Pl., Palm Coast, FL 32164 Blair, Joseph W. 3404 American Dr., No. 3204, Lago Vista, TX 78645 Blake, Cochran 1500 S. Fern St., No. 618, Arlington, VA 22202 Blanche, James A. 405 Calavaras Ct., Las Vegas, NV 89110 Blank, LtCol Donald USAF 4500 W. 210th St., Fairview Park, OH 44126 Blank, William D. 1830 Avenieda Del Mundo, No. 510, Coronado, CA 92118 Blas, Raymond H. 4789 E. Monticeto Ave., Fresno, CA 93702 Blaufarb, Douglas S. 601 Green St., Winchester, VA 22601 Blaylock, LtCol Norman R. USA 7305 Lake Tree Dr., Fairfax Station, VA 22039 Block, Ralph D. 707 Holy Rood Ln., Houston, TX 77024 Bly, Herman O. 5315 Shalley Circle, Ft. Meyers, FL 33919 Boak, David G. RR 2, Box 125, Vineyard Haven, MA 02568 Boardman, Col William USA P.O. Box 445, Monument, CO 80132 Bock, Col Charles USAF 21 North Edison St., Arlington, VA 22203 Bodroghy, Col Robert AUS 131 Kingsley Rd., SW, Vienna, VA 22180 Boginis, James W. P.O. Box 1167, Purceville, VA 22132 Boland, Arthur F. 6415 Wilcox Ct., Alexandria, VA 22310 Boland, Mira L. 714 St. Johns Rd., Baltimore, MD 21210 Bolson, Mrs. Elizabeth B. 43155 Portola Ave., SP 73, Palm Desert, CA 92260 Bon, Michel Agence Nationale pour l’Emploi, Paris, France Boner, William C. Jr. 8504 Quaint Ln., Vienna, VA 22180 Bonin, Mrs. Mildred A. 711 N. Church St., Hazleton, PA 18201 Bonner, Col William USAF 101 Londonderry Rd., Gooze Circle, SC 29445 Borel, Paul A. 188 Hunter Trail, Southern Pines, NC 28387 Borland, Ms Harriet 3900 Watson Pl., NW, No. 8 CA, Washington, DC 20016 Borrego, Eugene T. 6608 Seneca Farm Rd., Columbia, MD 21046 Borrmann, Donald A. 10154 Sterling Terrace, Rockville, MD 20850 Bort, Col Edward H. USA RR 1, Box 2085, Manchester Center, VT 05255 Boss, Hollis J. 444 Via Colinas, Thousand Oaks, CA 91632 Boswell, Dale E. 31 Karen Lee Lane, Manitou Springs, CO 80825 Botsford, LtCol Norman USA 15107 Interlachen Dr., No. 412, Silver Spring, MD 20906 Bottom, Dr. Norman R. P.O. Box 164509, Miami, FL 33116 Boublik, Mrs. Irene U. 8470 Greensboro Dr., No. 522, McLean, VA 22102 Boushee, Capt. Frank L. USN 1937 Brookhaven Rd., Wilmington, NC 28403 Bowen, James R. 12502 Millstream Sr., Bowie, MD 20715 Bowers, Hollis 116A Windsor Knot Rd., Edinburgh, VA 22824 Bowie, LtCol W. Russell 8330 Loveland Dr., Omaha, NE 68124 Bowman, Harold W. 531-A West Alton Ave., Santa Ana, CA 92707 Bowman, Capt Marion E. USN 10314 Royal Rd., Silver Spring, MD 20903 Boyd, Fredrick H. 19683 Spencer, Detroit, MI 48234 Boyd, Robert N. 8 Wild Turkey Run, Hilton Head Island, SC 29928 Boyer, Maj Charles R. DMASC PSC 821, Box 117, FPO, AE 09421 Boyes, Dr. Joseph H. 220 Coast Boulevard, La Jolla, CA 92037 Boyes, William W. Jr. 2214 McAuliffe Dr., Rockville, MD 20815 Boyle, Mrs. Barbara 5101 River Rd., No. 707, Bethesda, MD 20816 Boyle, Raymond E. 326 Markley Ct., Indian Harbour Beach, FL 32937 Boyles, Bruce 871 Hunt St., Akron, OH 44306 Brackett, Dewey 853 Armada Way, West Union, SC 29696 Bradish, Warren A. 4841 Foxshire Circle, Tampa, FL 33624 Braeuninger, A. Dale 7 Northport Ave., Belfast ME 04915 Brandner, Robert T. 6475 Cedarbrook Dr., New Albany, OH 43054 Brandon, Harry B. 227 Forest Dr., Falls Church, VA 22046 Brandstetter, Col Frank USA Las Brisas, Box 1807, Acapulco, Mexico Brandt, Dr. John H. P.O. Box 5003, Alamosa, CO 81101 Brannan, Ms. Mildred S. 6380 Lakewood Dr., Falls Church, VA 22041 Brass, Robin B. 242 Lake Plymouth Blvd, Plymouth, CT 06782 Bratcher, Steven K. 1390 Chain Bridge Rd., McLean, VA 22101 Bray, Wayne D. 250 E. Alameda, No. 307, Santa Fe, NM 87501 Brazas, Edward S. 7726 Lisle Ave., Falls Church, VA 22043 Breaw, Richard 1053 Jeff Ryan Dr., Herndon, VA 22070 Breckinridge, Scott D. 395 Redding Rd., No. 13, Lexington, KY 40517 Breitweiser, Paul B. 25042 Shaver Lake Circle, Lake Forest, CA 93630 Breitweiser, LtGen R. USAF P.O. Box 2454, New Bern, NC 28560 Brennan, Ms. Elinor L. 3154 Siron St., Falls Church, VA 22042 Brennan, Raymond J. 2129 W, New Haven Ave., No. 124, W. Melbourne, FL 32940 Brent, I. D’Arcy 16 Monocan Dr., Nellysford, VA 22958 Brewer, Charles V. 8912 Ridge Pl., Bethesda, MD 20817 Brewer, Joseph G. 36 Pine Ln., Douglassville, PA 19518 Brewer, Mary O. 8912 Ridge Pl., Bethesda, MD 29817 Briggs, Charles A. 1752 Brookside Ln., Vienna, VA 22182 Briggs, Ms. Katherine 8102 Highwood Dr., Bloomington, MN 55438 Briggs, Ralph T. 5224 D. Annie Oakley Dr., Las Vegas, NV 89120 Bright, Maj George USA P.O. Box 47, Keene Valley, NY 12943 Brinegar, LtCol Maurine USA 98-351 Koauka LP, No. 1908, Alea, HI 96701 Britton, Theodore R. 310 Somerlane Pl., Avondale Estates, GA 30002 Brockwell, Dr. Robert L. 150 E. Hartsdale Ave., No. 4D, Hartsdale, NY 10530 Broder, James 245 W. Bonita Ave., San Dimas, CA 91773 Brodie, Earl D. 4031 Happy Valley Rd., Lafayette, CA 94549 Broe, William V. 111 Indian Trail, North Scituate, MA 12060 Bronson, Col Howard USAF 5034 New Forest Dr., No. 5309, San Antonio, TX 78229 Bronson, Lynwood F. P.O. Box 1801, Carmel, CA 93921 Brooke, MajGen James USA 32 Bark Mill Terrace, Montville, NJ 07045 Brooks, RAdm Thomas USN 7125 Game Lord Dr., Springfield, VA 22153 Brophy, Gilbert T. 810 Saturn St., No. 15, Jupiter, FL 33458 Browitt, James W. 1128 Old Chisholm Trail, Dewey, AZ 86327 Brown, A. Freeborn 114 Glenwood Rd., Bel Air, MD 21014 Brown, F. Reese P.O. Box 411, New York, NY 10021 Brown, Fravel S. 836 Kennebeck Ct., San Diego, CA 92109 Brown, Frederick 6427 Pima St., Alexandria, VA 22312 Brown, Capt Jeffery USAR 315 First St., Ste U-82, Encinitas, CA 92024 Brown, Cdr Lyle C. USNR RR 2, Box 97, Waco, TX 76708 Brown, Marcus 270 Matterhorn Dr., Sautee-Nacoochee, GA 30571 Brown, Ralph 11911 Lomica Dr., San Diego, CA 92128 Brown, Robert K. P.O. Box 693, Boulder, CO 80306 Brown, Cdr Ronald USN 10926 Middlegate Dr., Fairfax, VA 22032 Brown, Susanne 208 Main St., No. 45, Medford, MA 02155 Brown, Ted F. P.O. Box 26508, Albuquerque, NM 87125 Brown, Thomas R. 9519 Center St., Vienna, VA 22180 Brown, Mrs. Virginia 1330 Torrance St., San Diego, CA 92103 Brown, William T. 2502 Rocky Branch Rd., Vienna VA 22181 Browne, Mrs. Jane 3921 Palo Verde Ave., Bonita, CA 92002 Breummer, Russell 4024 N. 40th St., Arlington, VA 22207 Brugioni, Dino 301 Storck Rd., Hartwood, VA 22405 Brumbaugh, Granville RR 1, Box 301, Waitsfield, VT 05673 Brumfiel, LtCol Robert USAF 12212 St. James Rd., Potomac, MD 20854 Brumm, Maj Steven USAF 5002 Ivy Rd., Panama City, FL 32405 Brune, Louis J. 12516 Over Ridge Rd., Potomac, MD 20854 Brunelle, Crd William T. USN 4325 Willow Woods Dr., Annandale, VA 22003 Brunson, LtCol Jack USA 5604 Farmwood Ct., Alexandria, VA 22310 Brustolon, Mark 3 Riversedge, Ivoryton, CT 06442 Buchanan, LtCol Charles AUS Howard Ct., RD No. 3, Pottsville, PA 17901 Buchanan, Edwin A. 3400 N. Venice St., Arlington, VA 22207 Buchanan. Phillip G. 3861 Gals Island Ave., St. James City, FL 33956 Buck, Frederick 6441 Rainbow Heights Rd., Fallbrook, CA 92028 Buckelew, Alvin 2742 Las Gallinas Ave., San Rafael, CA 94903 Buddenbaum Dennis 8923 Hendon Ln., Houston, TX 77036 Budenbach, Mrs Mary 21 Calibogue Cay Rd., Hilton Head, SC 29928 Buffham, Benson K. 3750 Galt Ocean Dr., No. 1505, Ft. Lauderdale, FL 33308 Buford, William N. 6355 Moccasin Pass Ct., Colorado Spings, CO 80919 Bugliarello, George Polytechnical University, Brooklyn, NY Bullock, Roy E. 3674 16th St., No. 5, San Francisco, CA 94114 Bunton, Gerald P. 2088 Gillen Ln., Falls Church, VA 22043 Burbach, Robert T. 2673 Barnstone Ln., Laguna Hills, CA 92653 Burdick, Dr. Charles, P.O. Box 205, Ferndale, CA 95536 Burhans, LtCol William USAF P.O. Box 225, Marshall, TX 75671 Burke, Gerard P. 1117 Spotswood Dr., Silver Spring, MD 20904 Burke, John M. 1522 Sudden Valley, Bellingham, WA 98226 Burke, Dr. Robert L. 2409 NE 37th St., Ft. Lauderdale, FL 33308 Burkhalter, Col Michael USAF 401 100th Ave., NE, Bellevue, WA 98004 Burks, A. Roy 57 Flints Grove Dr., Gaithersburg, MD 20878 Burks, Martin P.O. Box 8932, Horseshoe Bay, TX 78564 Burmeister, Mrs. Josephine 652 Doral Ln., Melbourne, FL 323940 Burnham, William 1005 Main St., Murray, KY 42071 Burnette, Capt Oliver USN 4004 Moss Pl., Alexandria, VA 22304 Burns, Robert F. 5463 Fox Hollow Dr., Naples, FL 33942 Burt, LtCol Joseph USAF 4534 N, 15th St., Arlington, VA 22207 Busch, Richard 34 Remsen St., Brooklyn Heights, NY 11201 Bush, George H.W. P.O. Box 79798, Houston, TX 77297 Bush, Col James O. USAF 8420 Masters Ct., Alexandria, VA 22308 Bush, Lester E. 2004 Michigan Ave., NE, St. Petersburg, FL 33703 Busic, Merle 225 Bowie Trail, Lusby, MD 20657 Bussey, Col Donald AUS 350 Graham St., Carlisle, PA 17013 Bussey, Col Henry M. USAF 2610 Chestnut Bend, San Antonio, TX 78232 Butcher, Clifton 810 Hendrickson St., Clinton, TN 37716 Buterbaugh, Brian 2321 Old Trail Dr., Reston, VA 22091 Buttleman, Col Leslie USA 1812 Birch Rd., McLean, VA 22101 Butts, RAdm John USN 20 Manor Dr. Pensacola, FL 32507 Byrne, James 7229 Timber Ln., Falls Church, VA 22046 Byrom, Cecil L. 1101 Edgewood Dr., Greenville, TX 75401
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, 120.000 Spies, Part 10, AL,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 001121/2481 | AL KADHI GAWA |
| IPN BU 00277/255 | AL. KADHI GAWA |
| IPN BU 00275/372 | AL. KHOURI FARAJ |
| IPN BU 00448/503 | AL. SAHAF MOHAMMED |
| IPN BU 001134/223 | AL.-KHOURI FARAJ |
| IPN 00 1052/1531 | AL.-SAAD HUSAIN-IDAN |
| IPN BU 001134/5479 | AL.-SAHAF MOHAMMED RIDHA |
| IPN BU 00750/7 | ALABA MIECZYSŁAW |
| IPN BU 00966/371 | ALABA STANISŁAW |
| IPN BU 698/21 | ALABRUDZIŃSKI JAKUB |
| IPN BU 01133/400 | ALABRUDZIŃSKI STANISŁAW |
| IPN BU 0901/199 | ALAMA HIERONIM JÓZEF |
| IPN BU 002085/328 | ALAME MOHAMAD HASSAN |
| IPN BU 002081/262 | ALAME MOHAMED |
| IPN BU 01133/401 | ALBEKIER TADEUSZ |
| IPN BU 00415/182 | ALBERA EDMUND |
| IPN BU 00283/991 | ALBERA KRZYSZTOF |
| IPN BU 00768/681 | ALBERA KRZYSZTOF |
| IPN BU 00415/463 | ALBERA ZDZISŁAW |
| IPN BU 00768/420 | ALBERSKI ANDRZEJ |
| IPN BU 00283/560 | ALBERSKI ANDZREJ |
| IPN BU 001134/2948 | Alberski Jan |
| IPN BU 00611/851 | ALBERSKI MARIAN |
| IPN BU 001198/1292 | ALBERSKI MARIAN |
| IPN BU 0993/669 | ALBERSKI TADEUSZ |
| IPN 00 1043/1173 | ALBIN KAZIMIERZ |
| IPN BU 00277/1391 | ALBINIAK JÓZEF |
| IPN BU 001121/3541 | ALBINIAK JÓZEF |
| IPN BU 02042/362 | ALBINIAK MARIA |
| IPN BU 00168/330 | ALBINOWSKI STANISŁAW |
| IPN BU 01434/40 | ALBINOWSKI STANISŁAW |
| IPN BU 00945/1887 | ALBINOWSKI STANISŁAW – JÓZEF |
| IPN BU 00275/596 | ALBOSZTA JAN |
| IPN BU 001134/531 | ALBOSZTA JAN |
| IPN BU 0305/479 | ALBOSZTA ZBIGNIEW |
| IPN BU 748/168 | ALBRECHCIŃSKI ROBERT |
| IPN BU 698/22 | ALBRECHCIŃSKI STANISŁAW |
| IPN BU 002086/1195 | ALBRECHT ANDRZEJ TADEUSZ |
| IPN BU PF | 125/148 ALBRECHT DANUTA |
| IPN BU 0772/2090 | ALBRECHT HELENA |
| IPN BU 01000/1708 | ALBRECHT HENRYK |
| IPN BU 01133/402 | ALBRECHT JAN |
| IPN BU 00611/514 | ALBRECHT JAN |
| IPN BU 001198/918 | ALBRECHT JAN |
| IPN BU 698/23 | ALBRECHT JANUSZ |
| IPN BU 01000/1699 | ALBRECHT JOANNA |
| IPN BU 0604/568 | ALBRECHT KRZYSZTOF |
| IPN BU 001102/1933 | ALBRECHT STANISŁAW |
| IPN BU 698/24 | ALBRECHT STEFAN |
| IPN BU 00611/2016 | ALBRYCHT LEONARD |
| IPN BU 00257/369 | ALCHIMOWICZ ANDRZEJ WOJCIECH |
| IPN BU 001102/1436 | ALCHIMOWICZ ANDRZEJ WOJCIECH |
| IPN BU 0218/667 | ALCHIMOWICZ STEFAN |
| IPN BU 0193/125 | ALCHIMOWICZ WACŁAW KAZIMIERZ |
| IPN BU 0604/888 | ALCZYSZYN ZYGFRYD |
| IPN BU 0806/3196 | ALDONA EKIERT |
| IPN 00 1043/2984 | ALDRIDGE KONOPASEK KRYSTYNA BARBARA |
| IPN BU 698/25 | ALEF GUSTAW |
| IPN BU 00244/58 | ALEF-BOLKOWIAK GUSTAW |
| IPN BU 00945/1687 | ALEJSKI ANTONI |
| IPN BU 00168/237 | ALEJSKI STANISŁAW |
| IPN BU 00945/1687 | ALEJSKI STANISŁAW – WACŁAW |
| IPN BU 0891/171 | ALEKS ZYGMUNT |
| IPN BU 0193/128 | ALEKSADROWICZ WACŁAWA |
| IPN BU 0951/1936 | ALEKSANDER HELENA |
| IPN BU 0901/2337 | ALEKSANDER LUBOMIR JERZY |
| IPN BU 00283/2128 | ALEKSANDEREK DARIUSZ |
| IPN BU 0951/1943 | ALEKSANDEREK STANISŁAWA |
| IPN BU 0329/1 | ALEKSANDROW PIOTR |
| IPN BU 0772/2091 | ALEKSANDROWICZ GENOWEFA |
| IPN BU 00277/326 | ALEKSANDROWICZ ALICJA |
| IPN BU 001121/2548 | ALEKSANDROWICZ ALICJA KAMILA |
| IPN BU 0193/126 | ALEKSANDROWICZ ANASTAZJA |
| IPN BU 0993/1037 | ALEKSANDROWICZ ANNA |
| IPN BU 0287/329 | ALEKSANDROWICZ CZESŁAW |
| IPN BU PF | 251/155 ALEKSANDROWICZ DARIUSZ |
| IPN BU PF | 251/189 ALEKSANDROWICZ DARIUSZ |
| IPN BU 00283/1027 | ALEKSANDROWICZ EWA |
| IPN BU 00191/632 | ALEKSANDROWICZ FRANCISZEK |
| IPN 00 1052/23 | ALEKSANDROWICZ FRANCISZEK |
| IPN BU 00169/137 | ALEKSANDROWICZ GRZEGORZ |
| IPN BU 001102/2009 | ALEKSANDROWICZ GRZEGORZ |
| IPN BU 0193/127 | ALEKSANDROWICZ HENRYK |
| IPN BU 698/65 | ALEKSANDROWICZ IRENA |
| IPN BU PF | 251/194 ALEKSANDROWICZ IZABELA |
| IPN BU 980/190 | ALEKSANDROWICZ JANINA |
| IPN BU 00277/885 | ALEKSANDROWICZ JANUSZ |
| IPN BU 001121/3072 | ALEKSANDROWICZ JANUSZ |
| IPN BU 01133/403 | ALEKSANDROWICZ JERZY |
| IPN BU 0864/3 | ALEKSANDROWICZ JÓZEF |
| IPN BU 00611/1538 | ALEKSANDROWICZ KAZIMIERZ |
| IPN BU 001198/2864 | ALEKSANDROWICZ KAZIMIERZ |
| IPN BU 0218/2428 | ALEKSANDROWICZ KRYSTYNA |
| IPN BU 1161/89 | ALEKSANDROWICZ PIOTR |
| IPN BU 0891/44 | ALEKSANDROWICZ ROMAN |
| IPN BU 0833/649 | ALEKSANDROWICZ WANDA |
| IPN BU 01133/444 | ALEKSANDROWICZ WIESŁAWA |
| IPN BU 001134/2329 | ALEKSANDROWICZ WŁADYSŁAW |
| IPN BU 0958/59 | ALEKSANDROWICZ ZYGMUNT |
| IPN BU 644/719 | ALEKSANDROWICZ ZYGMUNT |
| IPN BU 0806/949 | ALEKSANDROWSKA BARBARA |
| IPN BU 0194/2265 | ALEKSANDROWSKA TERESA |
| IPN BU 0193/1279 | ALEKSANDROWSKI LEON |
| IPN BU 00249/1564 | ALEKSANDROWSKI WACŁAW |
| IPN BU 001121/2165 | ALEKSANDROWSKI WACŁAW |
| IPN BU 0591/3 | ALEKSANDRUK WOJCIECH |
| IPN BU 0891/276 | ALEKSANDRZAK JÓZEF |
| IPN BU 0951/1932 | ALEKSIEJCZUK MARIA |
| IPN BU 002082/451 | ALEKSIEJEW GRZEGORZ |
| IPN BU 002086/1268 | ALEKSIEJEW GRZEGORZ |
| IPN BU 001121/244 | ALEKSIEJEW GRZEGORZ |
| IPN BU 0329/2 | ALEKSIEJEW WIACZESLAW |
| IPN BU 0951/1791 | ALEKSIEJUK ELŻBIETA |
| IPN BU 01000/1707 | ALEKSIEWICZ STEFAN |
| IPN BU 0902/8 | ALEKSIN JEFREM |
| IPN BU 0957/567 | ALEKSIŃSKI AUGUSTYN |
| IPN BU 001075/271 | ALEKSIUK MAREK |
| IPN BU 00234 | p.249 ALEKSNIN CZESŁAW |
| IPN BU 0604/535 | ALEKSY ANDRZEJ |
| IPN BU 0287/133 | ALEKSY MARIANNA |
| IPN BU 0193/6247 | ALENOWICZ EDWARD |
| IPN BU 0218/1952 | ALESZCZYK ROBERT |
| IPN BU 710/239 | ALETUROWICZ RYSZARD |
| IPN 00 1052/1643 | ALEXANDROWICZ MAŁGORZATA MARIA |
| IPN BU 001198/850 | ALF RYSZARD |
| IPN BU 644/720 | ALGIERT RYSZARD |
| IPN BU 002085/297 | ALI ZUHIR |
| IPN BU 0833/12 | ALICH MARCELI |
| IPN BU 001121/3709 | ALICKI TADEUSZ |
| IPN BU 0194/3714 | ALIŃSKA PELAGIA |
| IPN BU 093/5 | ALIŃSKA ST |
| IPN BU 0772/2092 | ALIŃSKI ALEKSANDER |
| IPN BU 0193/8209 | ALIZARCZYK MIKOŁAJ |
| IPN BU 002086/522 | AL-JAWACHIRI IBRAHIM-KADHIM |
| IPN BU 00169/38 | ALLGEYER MARIA |
| IPN BU 00945/646 | ALLGEYER MARIA |
| IPN BU 00170/852 | ALLINA FELIKS |
| IPN 00 1043/992 | ALLINA FELIKS |
| IPN BU 00688/83 | ALOKSA WŁADYSŁAW |
| IPN BU 0951/1938 | ALPERT RUTA |
| IPN BU 0806/1875 | ALSTER HELENA |
| IPN BU 0855/2935 | ALSZER LIDIA |
| IPN BU 0194/1110 | ALTENBERG HELENA |
| IPN BU 645/16 | ALTENBERGER INGEBORGA |
| IPN BU 00334/692 | ALTERMAN BOGDAN |
| IPN BU 00200/18 | ALTMAN JÓZEF |
| IPN 00 1052/279 | ALTMAN JÓZEF |
| IPN BU 0242/1023 | ALTRYCH JANUSZ |
| IPN BU 698/26 | ALUCHNA IRENA |
| IPN BU 01133/404 | ALWIN HIERONIM |
| IPN 00 1052/775 | ALWIN HIERONIM |
| IPN BU 0870/312 | ALZAK KAZIMIERZ |
| IPN BU 001198/410 | ALZAK WACŁAW |
SECRET-House Oversight Committee Report: Pseudo-Classification of Executive Branch Documents
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
PSEUDO-CLASSIFICATION OF EXECUTIVE BRANCH DOCUMENTS: PROBLEMS WITH THE TRANSPORTATION SECURITY ADMINISTRATION’S USE OF THE SENSITIVE SECURITY INFORMATION (SSI) DESIGNATION
- 29 pages
- July 24, 2014
Under the Air Transportation Security Act of 1974, the Federal Aviation Administration (FAA) created a category of sensitive but unclassified information, frequently referred to as “Sensitive Security Information” (SSI), and issued regulations that prohibit the disclosure of any information that would be detrimental to transportation security. These regulations restrict disclosure of SSI, exempting information properly marked as SSI from release under the Freedom of Information Act.
After the 1988 bombing of a commercial airliner that crashed in Lockerbie, Scotland, the FAA made significant changes in aviation security, expanding the definition of SSI to include any information the FAA Administrator determined may reveal systemic vulnerabilities within the aviation system, or vulnerabilities of aviation facilities to attacks. Other definitional expansions included details of inspections and investigations, as well as alleged violations and certain agency findings. The SSI regulation was later expanded in order to limit access to protected information to those persons who have a “need-to-know.”
While the SSI designation can protect sensitive information, it is also vulnerable to misuse. Bipartisan concerns about the use of the SSI designation by the Transportation Security Administration (TSA), an agency of the Department of Homeland Security (DHS), have existed since the promulgation of the SSI regulations in 2004. Through its investigation, the Committee obtained witness testimony and documents that show possible misuse of the SSI designation by TSA. Witnesses detailed instances in which TSA barred the release of SSI documents against the advice of TSA’s SSI Office. TSA also released SSI documents against the advice of career staff in the SSI Office. The Committee’s investigation revealed that coordination challenges exist among the TSA Administrator, TSA’s Office of Public Affairs (OPA), and TSA’s SSI Office.
Witnesses testified that many of the problems related to the SSI designation process emanate from the structure of the SSI regulation itself. TSA’s SSI Office is staffed with career employees tasked with assisting in the SSI designation process. The final authority on SSI designation, however, rests with the TSA Administrator. Pursuant to the regulation, the TSA Administrator must provide certain documentation supporting his SSI designations. Yet, witnesses interviewed by the Committee stated that there were multiple incidents in which the SSI Office was not consulted or where TSA took actions against the advice of SSI Office officials. Further, such actions occurred without the TSA Administrator providing required written documentation supporting the action.
Due to this contentious relationship and the failure to follow proper procedures, the SSI Office struggled to carry out its statutory obligations effectively. While the TSA Administrator has the final authority to determine whether information is SSI, he is also required under the regulations to submit written explanations of his decisions to the SSI Office in a timely fashion. Unfortunately, the repeated failure to submit written determinations before taking actions on SSI caused a rift between senior TSA leadership and the SSI Office. This rift resulted in inconsistencies, which could be detrimental to the process for protecting sensitive information.
This report explores issues related to the current TSA SSI designation process and recommends improvements to ensure that sensitive information is properly protected while non-sensitive information is properly released to the public. TSA’s use of SSI reveals a broader problem of pseudo-classification of information in federal departments and agencies. Limits on such labeling of information are needed to provide greater transparency and accountability to the public while promoting information security.
…
SSI is not classified national security information and therefore not afforded the same protections as classified information. SSI is defined in the Homeland Security Act of 2002 as information obtained or developed during security activities, “if the Under Secretary decides that disclosing the information would (A) be an unwarranted invasion of personal privacy; (B) reveal a trade secret or privileged or confidential commercial or financial information, or (C) be detrimental to the security of transportation.” In order for information to be SSI, it must be related to transportation security, and it must fall under one of the 16 categories of SSI as defined in the SSI regulation.
Although SSI is not subject to the handling requirements governing classified national security information, it is subject to the handling procedures required by TSA’s SSI regulation. Restrictions on access to SSI and penalties for unauthorized disclosure of SSI are much less severe. A security clearance is not required to gain access to SSI, and criminal penalties may not be imposed in the event of unauthorized disclosure of SSI. Unauthorized disclosure of SSI may, however, result in civil penalties and/or other enforcement or corrective actions.
…
VI. Inappropriate Use of the SSI Designation to Prevent FOIA Releases
FINDING: TSA improperly designated certain information as SSI in order to avoid its public release.
Witnesses interviewed by the Committee testified about instances in which TSA inappropriately withheld documents from FOIA requesters because it was deemed SSI. Former SSI Office Director Andrew Colsky testified that TSA used the SSI designation to prevent the release of documents to FOIA requesters related to Whole Body Imagers (WBIs). He stated:
There’s certain public interest groups out there that do a lot of FOIA requests over these types of things, and one of them did a FOIA request about information related to those scanners, I guess, and their ability to store images or not store images or whatever. And now this is being—you know, coming secondhand, but from a significant number of highly reliable sources, and — I don’t want to say anything to get anybody in trouble — and things that I personally overheard where there was information in the responsive documents that was not by any stretch of the imagination at all SSI, but was either embarrassing or was something that they just didn’t want the other side to know. And there was extreme pressure from again I’ll use the term ‘front office’ to mark it as SSI.
Colsky also discussed other ways that TSA may be withholding information from disclosure under FOIA. He stated:
[C]urrently I sit in the Freedom of Information Act office. And one of the first things I was told when I got there from both attorneys and FOIA processors was, oh, yeah, don’t worry about it, because if you come across embarrassing information or whatever, [the Chief Counsel] will just hide it and come up with an exemption; because if you cover it with a FOIA exemption, it’s so hard for the other person to challenge it, and it will be costly and difficult for them to challenge it, and they’re probably never going to see it anyway, so you just get away with it. That’s the way it’s done.
TOP-SECRET – The Secret List of CIA Sources – 2.619 Names and Adresses Part 1,A,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
A
Abbott, Alfred P.O. Box 10205, Albuquerque, NM 87184 Abbott, Dr. Preston S. 1305 Namassin Rd., Alexandria, VA 22308 Abernathy, John W. 7601 W. Charleston Blvd., No. 60, Las Vegas, NV 89117 Abernathy, Thomas B. 1815 Beulah Rd., Vienna, VA 22180 Absher, Kenneth M. P.O. Box 6150, San Antonio, TX 78209 Achilles, Barbara H. 1014 Aponi Rd., SE, Vienna, VA 22180 Adams, Fred H. 509 Fourth Ave., New Kensington, PA 15068 Adams, Nathan M. 321 S. Piff St., Alexandria, VA 22314 Adams, Capt Robert E. USN 5127 North 37th Rd., Arlington, VA 22207 Addicott, Kenneth F. General Delivery, Carmel, CA 93921 Adkisson, Capt Hubert USN 840 North Atlantic Ave., No. C 402, Cocoa Beach, FL 32931 Adler, David B. 2300 Old Spanish Trail, No. 2014, Houston, TX 77054 Adnet, Jacques J. 4515 Diamondback Dr., Colorado Springs, CO 80921 Aiello, Ms. Phyllis 2207 Wagner Ave., Erie, PA 16510 Albers, Capt Steven C. USN 8340 Greensboro Dr., No. 707, McLean, VA 22102 A Albert, Garret L. 9002 Glenbrook Rd., Fairfax, VA 22031 Albertson, John P. 367 Main St., Old Saybrook, CT 06475 Albitz, Ben F. 7924 Inverness Ridge Rd., Potomac, MD 20854 Albrecht, LtCol Walter USAF 15 Gardens Corner Ct., Charleston, SC 29407 Alden, Sygmund P.O. Box 611374, Miami, FL 33161 Alderman, Col Nathaniel USA P.O. Box 20772, St. Petersburg, FL 33742 Algrant, James J. P.O. Box 1047, Camden, ME 04843 Alkek, Lt James USA 4107 Solway, Houston, TX 77025 Allen, Andrew E. 122 Pepper Ave,, Larkspur, CA 94939 Allen, Charles J. 50 Holden St., Shrewsbury, MA 01545 Allen, George W. 5520 N. 23rd St., Arlington, VA 22205 Allen, Herbert L. P.O. Box 1291, Dunedin, FL 34697 Allen, John K. 3339 Military Rd., NW, Washington. DC 20015 Allen, LtCdr Scott, USN 1457 Aunsuna St., Kailua, HI 96734 Allison, Ms. E.T. Flandro Grossmont Gardens, 5480 Maringo Ave., La Mesa, CA 91942 Allner, Frederick A. Jr. 5225 Pooks Hill Rd., No. 1016 South, Bethesda, MD 20814 Althausen, William 1305 Marlin Dr., Naples, FL 33962 Altobelli, Louis U. 1680 NW 133rd St., Miami, FL 33167 Altomare, Gasper R. 600 Amherst Dr., SE, Albuquerque, NM 87106 Amargo, Carlos A. 8802 SW 52nd Ct., Ocala, FL 34476 Amato, Joseph 3716 Ramsgate Dr., Annapolis, MD 21403 Amazeen, Col Charles P. 2108 Penfield Ln., Bowie, MD 20716 Ames, Aldrich 2512 N. Randolph St., N. Arlington, VA 22207 Anderegg, Richard 103 G St.,SW, No. B 203, Washington, DC 20024 Anderson, Bruce 900 Allied Bank Plaza, Houston, TX 77002 Anderson, David 5703 West Hearn Rd., Glendale, AZ 85306 Anderson, Lt Douglas USNR 27 Meadow Wood Dr., Greenwich, CT 06830 Anderson, Dwayne S. 2637 DePaul Dr., Vienna, VA 22180 Anderson, James A. 4400 East West Hiway, No. 903, Bethesda, MD 20814 Anderson, Major Karl USAF 5886 Scripps St., San Diego, CA 92122 Anderson, Ms. Mary Louise 26 Anchorage Rd., Sausalito, CA 94965 Anderson, Robert C. 2 Fenway, Derry, NH 03038 Anderson, Mrs. Sally 7 Lexington Ave., No. 7A, New York, NY 10010 Anderson, Thomas D. 3925 Del Monte, Houston, TX 77019 Anderson, Dr. William H. 34 Coolidge Hill Rd., Cambridge, MA 02138 Andraitis, LtCol Arthur USAF 11707 Flemish Miff Ct., Oakton, VA 22124
Putin’s War: Riveting Raw Footage from the Front Lines – Video
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Front line footage from Ukraine as brave civilians stand up to tanks and gunfire. Warning! Some footage can be disturbing!
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, 120.000 Spies, Part 9, AK,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 00168/44 | AKACKI ZENOBIUSZ |
| IPN BU 00945/1345 | AKACKI ZENOBIUSZ – ZBIGNIEW |
| IPN BU 0193/1278 | AKERMAN (ROZENBLUM) EWA |
| IPN 00 1043/728 | AKERMAN ELŻBIETA |
| IPN BU 0194/1626 | AKERTOWICZ TEODOR |
| IPN BU 0958/67 | AKIER EUGENIUSZ |
| IPN BU 0193/123 | AKININA HALINA |
| IPN BU 00945/598 | AKOLIŃSKI STANISŁAW – JAN |
| IPN BU 01000/291 | AKONOM WACŁAW |
| IPN BU 0193/7659 | AKORT WANDA |
| IPN BU 02042/703 | AKSAMIT HENRYK |
| IPN BU PF | 109/94 AKSAMIT HENRYK |
| IPN BU 0604/841 | AKSAMIT JAN |
| IPN BU 0242/2704 | AKSAMIT MAREK |
| IPN BU 52/61 | AKSAMIT TADEUSZ |
| IPN BU 0951/1790 | AKSAMITOWSKI HENRYK |
| IPN BU 0866/1377 | AKSAMITOWSKI ROMAN |
| IPN BU 01000/1704 | AKSAMITOWSKI STANISŁAW |
| IPN BU 00334/537 | AKSAMITOWSKI ZBIGNIEW |
| IPN BU 001134/3423 | AKSAMITOWSKI ZBIGNIEW |
| IPN BU 0772/728 | AKSIENOW TEODOR (FIEDOR) |
| IPN BU 00312 | AKTABOWSKI |
| IPN BU 00312/16 | AKTABOWSKI |
| IPN BU 00168/304 | AKTONOROWICZ HENRYK |
| IPN BU 00945/1860 | AKTONOROWICZ HENRYK |
| IPN BU 001134/3873 | AKUTOWICZ RYSZARD |
Putin’s World War IIII started already in Ukraine – more to come
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, 120.000 Spies, Part 8, AJ,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 0194/969 | AJCHLER CZESŁAW |
| IPN BU 0833/7 | AJEWSKI ALEKSANDER |
| IPN BU 00234 | p.97 AJEWSKI HENRYK |
| IPN BU 0305/85 | AJEWSKI HENRYK |
| IPN BU 0866/8 | AJEWSKI STANISŁAW |
| IPN BU 00232/78 | AJNENKIEL JERZY |
| IPN BU 001164/92 | Ajnenkiel Jerzy |
| IPN BU 698/18 | AJZEMAN GENOWEFA |
| IPN BU 0772/727 | AJZENBERG JADWIGA |
| IPN BU 698/19 | AJZENBERG JÓZEF |
| IPN BU 0772/2089 | AJZENSZTEIN LEON |
| IPN BU 698/20 | AJZNER MARIA |
Identifying Mexican Mafia Members and Associates
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
The following document was obtained from a website associated with the Regional Information Sharing Systems Program.
IDENTIFYING MEXICAN MAFIA MEMBERS AND ASSOCIATES
- 1 page
- Law Enforcement Sensitive
- April 8, 2014
(U//LES) Humming bird and Marilyn Monroe tattoos may have a nexus to the Mexican Mafia, while “G Shields” (Aztec warrior shields) and mariposas (butterflies) may be decreasing in popularity. As certain tattoos sported by Mexican Mafia members and supporters become mainstream, and because California Department of Corrections is known to use certain tattoos as validation points, Mexican Mafia members may introduce new tattoos to make it difficult for law enforcement and correctional officers to identify membership or affiliation with the group. Tattoos are also increasingly disguised within other tattoos, which can make them more difficult to easily identify.
(U) INDICATION OF MEXICAN MAFIA MEMBERSHIP
(U) Black Hand
(U//LES) Only la EME brothers are allowed to obtain the black hand tattoo. It is considered an honored privilege, but not a requirement, to display the black hand. Inspired by La Costra Nostra’s (Italian Mob) Black Hand of Death.
(U) la EME
(U//LES) Translates to the letter “M” in Spanish; a shorthand or secretive way of displaying allegiance to the Mexican Mafia.
NOTE: “EME-SA” indicates membership to MS-13, not Mexican Mafia.(U) MM
(U//LES) Abbreviation can be potential indication of association or membership to the Mexican Mafia without directly identifying the organization.
(U) INDICATION OF POSSIBLE MEXICAN MAFIA ASSOCIATION
(U) 13 (and variations)
(U//LES) Signifies the 13th letter of the alphabet, M, which is pronounced “la EME” in Spanish. Can also be spelled out as “trece.”
(U) Aztec Numbering and Kanpol
(U//LES) Kanpol—directly translating as “south great”—references Aztec numbering and “Sureño.” Lines in Aztec numbering represent 5, and dots represent 1; two lines and three dots add to 13. Tattoos of the Aztec word “matlactomei,” which translates as thirteen, may also be used.
(U) Aztec Warrior Shield
(U//LES) Both Norteños and Sureños identify with Aztec culture and beliefs, but the Aztec warrior shield is most commonly found on Sureños. Advocates an ideology that Sureños are warriors or soldiers, rather than criminals, participating in a worthy cause for their race and culture.
(U) Lips
(U//LES) Possibly a covert method that may signify 13 and loyalty to Mexican Mafia: the bottom lip is similar in shape to 1 while the top lip is similar in shape to 3. The color blue is an indication of loyalty to Mexican Mafia.
(U) Marilyn Monroe
(U//LES) May indicate association with or membership to Mexican Mafia, as Marilyn Monroe’s initials represent “MM.” Recent reporting suggests this tattoo is most likely found on non-validated associates.
(U) Hummingbird and Mariposa
(U//LES) Emerging reporting suggests a shift toward using hummingbird tattoos to portray Huitzilopochtli, an Aztec god of war, to represent being a soldier of Mexican Mafia. Mariposas may also indicate association or membership to Mexican Mafia. Curving of butterfly wings may represent “MM.” Most likely to be seen on “first generation” Mexican Mafia associates.
Cryptome unveils Moshe Feiglin Final Solution for Gaza
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
A sends:
Moshe Feiglin is Deputy Speaker of the Israeli Knesset.
On August first, on Facebook[1], he proposed a solution to the Gaza conflict that can only be called genocide. (May it never come to pass, and that he, and his ideas be repudiated. )
The main points are these:
* Concentration camps, he calls them tent cities.
* Mass deportations, any remaining required to publicly sign loyalty oaths to Israel. He proposes to pay Gazans to emigrate, though doesn’t specify actual amounts.
* Near total annihilation of Gaza
* Settlement of the ethnically cleansed areas (which is 100% of Gaza).
It is worth noting, and a hopeful sign that several replies, in Hebrew, to his masterplan call it genocide, and accuse him of being a Nazi, delusional, and/or stoned. The ones who agree with him, and/or want him to become the next Prime Minister, however, are discouraging and terrifying. A few even advocate for more extreme measures than the above.
I will end on a note, tweeted by none other the United States Holocaust Memorial Museum[2], in response to similar sentiments from Yochanan Gordon[3] (who at least later apologized[4]). “Genocide is NEVER permissible.”
Translation of his proposal from Dena Shunra[5]
(Note on the comments: they were translated by Google Translate, but the Hebrew ones are still identifiable, the text is aligned to the right margin.)
—-
With God’s Help
Attention
Prime Minister Benjamin Netanyahu
Mr. Prime Minister,
We have just heard that Hamas has used the ceasefire to abduct an officer. It turns out that this operation is not about to be over any too soon.
The failures of this operation were inherent to it from the outset, because:
a) It has no proper and clear goal;
b) there is no appropriate moral framework to support our soldiers.
What is required now is that we internalize the fact that Oslo is finished, that this is our country – our country exclusively, including Gaza.
There are no two states, and there are no two peoples. There is only one state for one people.
Having internalized this, what is needed is a deep and thorough strategic review, in terms of the definition of the enemy, of the operational tasks, of the strategic goals, and of course, of appropriate necessary war ethics.
(1) Defining the enemy:
The strategic enemy is extremist Arab Islam in all its varieties, from Iran to Gaza, which seeks to annihilate Israel in its entirety. The immediate enemy is Hamas. (Not the tunnels, not the rockets, but Hamas.)
(2) Defining the tasks
Conquest of the entire Gaza Strip, and annihilation of all fighting forces and their supporters.
(3) Defining the strategic goal:
To turn Gaza into Jaffa, a flourishing Israeli city with a minimum number of hostile civilians.
(4) Defining war ethics: “Woe to the evildoer, and woe to his neighbor”
In light of these four points, Israel must do the following:
a) The IDF [Israeli army] shall designate certain open areas on the Sinai border, adjacent to the sea, in which the civilian population will be concentrated, far from the built-up areas that are used for launches and tunneling. In these areas, tent encampments will be established, until relevant emigration destinations are determined.
The supply of electricity and water to the formerly populated areas will be disconnected.
b) The formerly populated areas will be shelled with maximum fire power. The entire civilian and military infrastructure of Hamas, its means of communication and of logistics, will be destroyed entirely, down to their foundations.
c) The IDF will divide the Gaza Strip laterally and crosswise, significantly expand the corridors, occupy commanding positions, and exterminate nests of resistance, in the event that any should remain.
d) Israel will start searching for emigration destinations and quotas for the refugees from Gaza. Those who wish to emigrate will be given a generous economic support package, and will arrive at the receiving countries with considerable economic capabilities.
e) Those who insist on staying, if they can be proven to have no affiliation with Hamas, will be required to publicly sign a declaration of loyalty to Israel, and receive a blue ID card similar to that of the Arabs of East Jerusalem.
f) When the fighting will end, Israeli law will be extended to cover the entire Gaza Strip, the people evicted from the Gush Katif will be invited to return to their settlements, and the city of Gaza and its suburbs will be rebuilt as true Israeli touristic and commercial cities.
Mr. Prime Minister,
This is the a fateful hour of decision in the history of the State of Israel.
All metastases of our enemy, from Iran and Hizballah through ISIS and the Muslim Brotherhood, are rubbing their hands gleefully and preparing themselves for the next round.
I am warning that any outcome that is less than what I defined here means encouraging the continued offensive against Israel. Only when Hizballah will understand how we have dealt with Hamas in the south, it will refrain from launching its 100,000 missiles from the north.
I call on you to adopt the strategy proposed here.
I have no doubt that the entire Israeli people will stand to your right with its overwhelming majority, like myself – if only you will adopt it.
With high regards, respectfully,
Moshe Feiglin
—-
![[Image]](https://i0.wp.com/cryptome.org/2014/08/moshe-feiglin-0.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2014/08/moshe-feiglin-1.jpg)
References:
[1] https://www.facebook.com/MFeiglin/posts/695450140534104
[2] https://twitter.com/HolocaustMuseum/status/495292357596966912
[3] https://archive.today/RPf3M
[4] http://5tjt.com/apology-from-yochanan-gordon/
[5]
See also:
Russian Spies – Deceitfull Beauties – Film
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, 120.000 Spies,Part 7, AI,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 0772/2088 | AICHEN ALEKSANDRA |
| IPN BU 0193/7057 | AICHEN LIPA |
Das Stalin-Putin-KGB-Stasi-Büro West Folge 1 Scheinwelten Putin und “GoMoPa” & Genossen
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Die “GoMoPa”-Genossen und IM:
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, 120.000 Spies, Part 6, AH,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 00200/879 | AHMAD SARWAR MOHAMMAD |
| IPN BU 001102/416 | AHMAD SARWAR MOHAMMAD |
| IPN BU 00945/1773 | AHMED – MOHAMED – SAED – EL – ASAD AHMED |
| IPN BU 01434/232 | AHMED MOHAMED SAED EL ASAD |
The Shevardnadze File by The National Security Archive
Become a Patron!
True Information is the most valuable resource and we ask you to give back.

Eduard Shevardnadze. (photographer unknown)
| Compiled and edited by Svetlana Savranskaya and Thomas Blanton
For more information contact: |
Related Links
Eduard Shevardnadze, Foreign Minister Under Gorbachev, Dies at 86
|
 Eduard Shevardnadze (seated second from right, next to George Shultz) listens to conversation between President Reagan and General Secretary Gorbachev at Geneva, November 20, 1985. (Source: Ronald Reagan Presidential Library) Washington, DC, July 24, 2014 – Former Soviet foreign minister Eduard Shevardnadze, who passed away on July 7, brought a new diplomatic style and candor to bear in changing U.S.-Soviet relations in the late 1980s and ending the Cold War, according to Soviet and U.S. declassified documents posted today by the National Security Archive at George Washington University (www.nsarchive.org). The posting includes the 1985 Politburo minutes of Shevardnadze’s surprise selection as foreign minister, contrasted with the behind-the-scenes account from senior Central Committee official Anatoly Chernyaev in his diary. The e-book also includes the transcripts of Shevardnadze’s remarkable first conversations with his American counterparts, George Shultz (in the Reagan administration) and James Baker (in the George H.W. Bush administration); other memcons featuring Shevardnadze’s leading role in summit meetings between Soviet leader Mikhail Gorbachev and American presidents Ronald Reagan and George H.W. Bush, and Shevardnadze’s last conversation with Bush before the end of the Soviet Union in 1991.  President Ronald Reagan and Soviet Foreign Minister Eduard Shevardnadze in the Oval Office, September 23, 1988. (photographer unknown) Shevardnadze’s rise to leadership of the Foreign Ministry in 1985, only months after Gorbachev became general secretary, was a “bolt from the blue,” in Chernyaev’s words. Shevardnadze’s talks with Shultz brought a whole new tone to U.S.-Soviet discourse, while the Soviet minister’s growing friendship with Baker, including 1989’s fly-fishing outing in Wyoming, led to actual partnership between the former Cold War adversaries by the time of Iraq’s invasion of Kuwait in 1990. But the memcons also reflect Shevardnadze’s frustration with American “pauses” and missed opportunities for dramatic arms reductions across the board, and for earlier domestic political transformation in the Soviet Union. The National Security Archive obtained the Shevardnadze documents through Freedom of Information Act requests to the Reagan and Bush presidential libraries and to the U.S. State Department, and through generous donations from Anatoly Chernyaev. Additional material comes from the files of the Gorbachev Foundation, the Russian State Archive of Contemporary History, and the former Communist Party (SED) archives in Germany.  General Secretary Mikhail Gorbachev and Foreign Minister Eduard Shevardnadze at a meeting of European leaders, November 21, 1990. (photographer unknown) Two key aides to Shevardnadze played leading roles in developing the new Soviet foreign policy during the 1980s, and deserve mention for helping scholars afterwards understand the end of the Cold War. Experienced diplomat Sergei Tarasenko had already served in the Soviet embassy in Washington and provided Shevardnadze with expert advice on relations with the U.S., including in most of the U.S.-Soviet meetings transcribed here. Tarasenko also participated in the seminal 1998 Musgrove discussion published in the award-winning book, Masterpieces of History: The Peaceful End of the Cold War in Europe, 1989 (Budapest/New York: Central European University Press, 2010). Teimuraz Stepanov-Mamaladze served as Shevardnadze’s chief of staff, having come with him from Georgia to the Foreign Ministry, and subsequently donated his invaluable diaries and notes of the period to the Hoover Institution Archives at Stanford University.
THE DOCUMENTSDOCUMENT 1: Excerpt of Official Minutes of the Politburo CC CPSU Session, June 29, 1985 Source: Russian State Archive of Contemporary History (RGANI), Fond 89. Translated by Svetlana Savranskaya. Perhaps the most audacious personnel change made by Gorbachev came very early, only four months into his leadership, when longtime Foreign Minister Andrei Gromyko (known to the Americans as “Mr. Nyet”) retired upwards to the job of chairman of the Presidium of the Supreme Soviet — the titular head of state— as part of the deal that earlier had featured Gromyko advocating for Gorbachev’s election as general secretary. Gromyko understood that his successor would be his carefully-groomed deputy, Georgi Kornienko — so there was shock-and-awe throughout the Central Committee and the Foreign Ministry when Gorbachev instead proposed as foreign minister the ambitious first secretary of the Georgian Communist Party, Eduard Shevardnadze. During the Politburo session on June 29, 1985, Gorbachev stepped down from his position as chairman of the Presidium of the Supreme Soviet, which he held together with his position as general secretary (Leonid Brezhnev had merged the two jobs in 1977). By kicking Gromyko upstairs, Gorbachev opened a key position-Minister of Foreign Affairs — where he wanted to place his close ally, whom he already knew shared his reformist thinking on both international and domestic policy. This official record of the Politburo session shows Gorbachev nominating Shevardnadze, ostensibly after discussing several alternative candidates with Gromyko and jointly coming to the conclusion that Shevardnadze was the best choice. All Politburo members express their full support for Gorbachev’s candidate— testament to the power of the general secretary.
 Secretary of State James Baker and Foreign Minister Eduard Shevardnadze fly-fishing in Wyoming, September 24, 1989. (photographer unknown) DOCUMENT 2: Diary of Anatoly Chernyaev, July 1, 1985 Source: Diary of Anatoly S Chernyaev, donated to the National Security Archive. Translated by Anna Melyakova. Anatoly Chernyaev, who at the time was first deputy head of the International Department of the Central Committee (CC CPSU), describes in his diary the nominations of Gromyko and Shevardnadze as they were announced at the CC CPSU Plenum. The Plenum had to approve the nominations that the Supreme Soviet would confirm the next day. Shevardnadze’s nomination was like a “bolt from the blue,” Chernyaev writes. The diary relates how Boris Ponomarev, head of the International Department, told Chernyaev what had actually happened at the Politburo, an account that differs substantially from the official minutes (see Document 1). According to Ponomarev, the Shevardnadze nomination was a total surprise to other Politburo members, and Gromyko and Ponomarev tried to protest by suggesting career diplomat Yuli Vorontsov as a candidate, but Gorbachev disregarded their protest completely. Chernyaev concludes that Gorbachev’s nomination of Shevardnadze is “very indicative of the end of Gromyko’s monopoly and the power of the MFA’s staff over foreign policy.”
DOCUMENT 3: Record of Conversation between George Shultz and Eduard Shevardnadze in Helsinki, July 31, 1985 Source: Freedom of Information Act (FOIA) request to the Department of State. This U.S. State Department memcon records the meeting with the U.S. secretary of state during Shevardnadze’s first foreign trip in office — to Helsinki for a meeting of CSCE foreign ministers on the tenth anniversary of the Helsinki Final Act. In this first meeting with George Shultz, the Soviet foreign minister mainly reads from his notes, giving the American a tour d’horizon of the Soviet positions on arms control. However, his tone is strikingly different from previous meetings when Andrei Gromyko had represented the Soviet side. Even on questions of human rights, Shevardnadze reacts not with “indignation or rage” (as Shultz comments in his memoirs) but asks Shultz jokingly, “When I come to the United States, should I talk about unemployment and blacks?” In the second part of the conversation, where Shultz and Shevardnadze are accompanied only by translators, Shevardnadze urges his counterpart to move fast on arms control, indicating that the Soviets are willing to reassess their positions — “there is no time now to postpone solutions.” He ends the conversation with the statement: “you have experience but we have the truth,” a remark that would win him some positive points from the Politburo.
DOCUMENT 4: Minutes of Politburo discussion of Shultz-Shevardnadze talks in Vienna, November 13, 1986 Source: Archive of the Gorbachev Foundation. Translated by Svetlana Savranskaya. Shevardnadze was an active participant at the historic summit between Gorbachev and Reagan in Reykjavik in October 1986, where the two leaders almost agreed to abolish nuclear weapons. Just after the summit, the Soviets, trying to build on the momentum of Reykjavik, tried to offer the U.S. side concessions on laboratory testing for the missile defense program so close to Reagan’s heart – a change in position that might have made a difference at Reykjavik. But it was too late. Enmeshed in the growing Iran-contra scandal and under attack from allies like Margaret Thatcher for nuclear heresy, the Reagan administration had already retreated from the Reykjavik positions. Here the Politburo reviews the results of the November Shevardnadze-Shultz talks in Geneva, where Shultz refused even to discuss Shevardnadze’s new proposals concerning what testing would be allowed and not allowed under the ABM treaty. Shultz’s position notwithstanding, Gorbachev emphasizes the need to press the U.S. to move forward on the basis of Reykjavik. He stresses that “we have not yet truly understood what Reykjavik means,” referring to its significance as a new level of disarmament dialogue and reduction of the sense of nuclear threat.
DOCUMENT 5: Record of Shultz-Shevardnadze Conversation in Moscow, April 21, 1988 Source: FOIA request to the Department of State. This State Department memorandum of conversation records the third set of negotiations between the U.S. secretary of state and the Soviet foreign minister leading up to the 1988 Moscow summit (February in Moscow, March in Washington, now April back in Moscow). Shevardnadze presses for progress on the START treaty aimed at reducing nuclear weapons, but Shultz responds that still-unresolved issues like sea-launched cruise missiles (SLCMs) would not “reach full closure during the next month,” so agreement would be unlikely for the summit. Arguments over these nuclear-armed cruise missiles would hold up START negotiations for years, pushed by the parochial interests of the U.S. Navy rather than a consideration of the national interest, but by 1991 their lack of strategic value would lead to President George H. W. Bush’s unilateral decision to withdraw all tactical nuclear weapons from U.S. ships. The bulk of the discussion here concerns human rights issues, including an interesting exchange about the Vienna follow-up meeting on the Helsinki Final Act. Shultz raises his “disappointment with the performance of the Soviet delegation” at Vienna, which “was not prepared to go as far in its statements as what the Soviet leadership was saying in Moscow.” Shevardnadze responds, “We have a hard delegation” in Vienna; we tell them one thing, “They do something different.”
DOCUMENT 6: Minutes of the Politburo discussion of Mikhail Gorbachev’s United Nations speech, December 27-28, 1988 Source: RGANI. Published in “Istochnik” 5-6, 1993. Translated by Vladislav Zubok. The December 27-28 Politburo meeting was the first following Gorbachev’s return from the United States after his historic announcement at the United Nations of massive unilateral Soviet withdrawals of forces from Eastern Europe. Observers in the United States ranging from Sen. Daniel Moynihan to Gen. Andrew Goodpaster hailed the speech as marking the end of the Cold War; but incoming Bush administration “hawks” such as Brent Scowcroft did not agree (as Gorbachev would only find out later, with the 1989 “pause”). Part of the context here in the Politburo for Gorbachev’s lengthy monologues and Shevardnadze’s proposals for a “businesslike” withdrawal of Soviet troops from Eastern Europe is the growing bewilderment of certain military and KGB leaders who were not fully informed in advance about the scale and tempo of Gorbachev’s announced unilateral arms cuts. Still, there is no trace of real opposition to the new course. The Soviet party leader has learned a lesson from the military’s lack of a strong reaction to previous discussions of “sufficiency” as a national security strategy, and he is now ramming change down their throats. Ever obedient, Defense Minister Dmitri Yazov states, “everyone reacted with understanding,” even after Shevardnadze’s aggressive attacks against the military for retrograde thinking, for directly contradicting the U.N. speech, and for proposing only “admissible” openness rather than true glasnost. Ironically, however, when Shevardnadze and Ligachev suggest announcing the size of Soviet reductions “publicly,” it is Gorbachev who objects: if the Soviet people and party learn how huge Soviet defense expenditures really are, it will undermine the propaganda effect of his U.N. speech.
DOCUMENT 7: Record of Conversation between Erich Honecker and Eduard Shevardnadze, June 9, 1989 Source: Stiftung Archiv der Parteien und Massenorganisationen der DDR-Bundesarchiv, SED, ZK, JIV2/2A/3225. Translated by Christiaan Hetzner. This is one of many documents that became available in the Communist party archives of the former East Germany (GDR) after the fall of the Berlin Wall and the unification of Germany. Less than a week after Solidarity had swept the Polish elections, to the dismay of the Polish Communists, the hard-line GDR leader Erick Honecker is rapidly becoming a dinosaur on the verge of extinction. At this moment in mid-1989, only Nicolae Ceausescu of Romania surpasses Honecker in his resistance to Gorbachev’s perestroika and the new thinking in Moscow represented in this meeting by Shevardnadze. Honecker has even banned some of the new Soviet publications from distribution in the GDR. The conversation reveals Honecker’s deep ideological concerns, and his understanding of the geostrategic realities in Central Europe. He reminds Shevardnadze that “socialism cannot be lost in Poland” because through Poland run the communications lines between the Soviet Union and the Soviet troops in the GDR facing NATO’s divisions. This same consideration led Honecker and his predecessor, Walter Ulbricht, to urge Soviet military intervention to suppress previous East European uprisings such as the Prague Spring in 1968 or the strikes in Poland in 1980-1981. But here Honecker is most dismayed by Gorbachev’s upcoming trip to West Germany (FRG), which threatens Honecker’s own political “balancing act,” which in turn depends on poor relations between the Soviets and the West Germans. Shevardnadze has an impossible mission here, to assuage the East German leader’s concerns about all the changes taking place in Poland, Hungary and inside the Soviet Union. Shevardnadze’s opening words — “our friends in the GDR need not worry” — sound more than ironic today. In fact, Shevardnadze does not believe in Honecker’s concept of East German “socialism,” and in only a few months, the Moscow leadership would signal to Honecker’s colleagues it was time for him to go.
DOCUMENT 8: Memorandum of Conversation between George Bush and Eduard Shevardnadze in Washington, September 21, 1989 Source: FOIA request to the George H.W. Bush presidential library. This meeting in Washington marks the start of Shevardnadze’s trip to the United States that will culminate with his fly-fishing expeditions with James Baker in Wyoming, where the two men established a close personal connection. This was also Shevardnadze’s first meeting with George H.W. Bush as president of the United States. He tells Bush about the progress of domestic perestroika and democratization in the Soviet Union, the work on economic reform, and the new tenor of U.S.-Soviet relations. However, Shevardnadze laments that the desired progress toward a 50% reduction in strategic nuclear weapons is not on the horizon, and he urges his U.S. counterparts to pick up the pace. He also enumerates other Soviet arms control proposals, including banning fissionable materials and eliminating short-range nuclear weapons.
DOCUMENT 9: Memorandum of Conversation between George Bush and Eduard Shevardnadze in Washington, April 6, 1990 Source: FOIA request to the George H.W. Bush presidential library. Shevardnadze is in Washington for this meeting, working out arrangements for the long-planned summit meeting between Bush and Gorbachev that will take place at the end of May. The Lithuania crisis has created a rift in U.S.-Soviet relations, “lost momentum” in Bush’s phrase, as the independence demands of Lithuanian nationalists build on the long-standing American position of non-recognition of Soviet incorporation of the Baltics, as well as domestic U.S. political pressures from émigré groups. Gorbachev’s own lack of understanding for Baltic nationalism has produced an inconsistent Soviet policy alternating between crackdowns, threats of an embargo, and attempts at dialogue. Shevardnadze tries to explain to the Americans why the Soviets needed “Presidential authority” to deal with the problems between ethnic groups in Lithuania, not to mention Soviet claims to ownership of the factories there. But when Bush says the Soviets have backtracked on arms control agreements (such as how to count air-launched cruise missiles, or ACLMs), Shevardnadze is quick to point out how the Americans have reneged on their on-site inspection pledges. Perhaps most remarkably, Shevardnadze describes the Soviet argument for a nuclear test ban as based on domestic political pressures from mass demonstrations (such as in Kazakhstan against the Semipalatinsk test range). The Soviet foreign minister also makes a plea for partnership in international financial institutions such as the European Bank for Reconstruction and Development, saying the Soviets are “not looking for your help.” This would change within a year. On the American side, the conversation reveals a clear expression of Bush’s vision when he reports he is often asked, “Who is the enemy?” Bush’s answer: “unpredictability.” And perhaps it is just diplo-speak, but it is all the same music to Shevardnadze’s ears, when the American president combines his own “Europe whole and free” phrase with Gorbachev’s “common European home” and remarks that the latter idea is “very close to our own.”
DOCUMENT 10: Memorandum of Conversation between George Bush and Eduard Shevardnadze in Washington, May 6, 1991 Source: FOIA request to the George H.W. Bush presidential library. This is Shevardnadze’s last meeting with President Bush, and he appears only in his unofficial capacity as president of the Moscow-based Foreign Policy Association. Shevardnadze resigned as foreign minister in December 1990, warning against the coming dictatorship, and protesting Gorbachev’s turn toward the hard-liners. But here Shevardnadze comes to Washington asking for support for the embattled reform still underway in the Soviet Union. He describes the dismal situation in his country, pointing specifically to economic instability, the nationalities crisis, and the rising conservative opposition. He regrets delays on every important issue, especially the Union treaty that would precipitate the hard-line coup in August 1991: “if we had offered this treaty in 1987 or even 1988, all would have signed it.” But most of all, the former foreign minister is “concerned, indeed frightened, by the pause in our relations.” He urges Bush not to delay the planned Moscow summit (it would ultimately happen at the very end of July) and to keep engaging with Gorbachev. In effect, progress in U.S.-Soviet relations has become the only strong card Gorbachev has left to play in the context of his domestic crises. Bush and Shevardnadze talk about Gorbachev’s relationship with Russian leader Boris Yeltsin and wonder why they cannot find a way to work together. Shevardnadze appeals to Bush to move fast on reductions in conventional forces (CFE) and in nuclear weapons (START) because “demilitarization is the best way to help the Soviet Union.” For Bush, however, completing these two treaties remains a precondition for even holding the 1991 summit. Shevardnadze’s plea for farm credits is especially poignant; a year earlier, he sought economic partnership, but now he says, “We must let people [in the Soviet Union] feel something tangible. I know it is hard, but if it is possible, give the credits.” Prophetically, Shevardnadze remarks, “Even if we can’t maintain a single Soviet Union, reform will continue.” |
Revealed – Marine Corps Intelligence Activity Malaysia Country Handbook
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
The following guide is part of a series of handbooks covering basic information and statistics about countries around the world produced by the Marine Corps Intelligence Activity. The handbooks are not released to the public.
| Malaysia Country Handbook |
October 2002 | 180 pages | Download (PDF 1.25 MB) |
1. This handbook provides basic reference information on Malaysia, including its geography, history, government, military forces, and communications and transportation networks. This information is intended to familiarize military personnel with local customs and area knowledge to assist them during their assignment to Malaysian.
2. This product is published under the auspices of the U.S. Department of Defense Intelligence Production Program (DoDIPP) with the Marine Corps Intelligence Activity designated as the community coordinator for the Country Handbook Program. This product reflects the coordinated U.S. Defense Intelligence Community position on Malaysia.
3. Dissemination and use of this publication is restricted to official military and government personnel from the United States of America, United Kingdom, Canada, Australia, NATO member countries, and other countries as required and designated for support of coalition operations.
4. The photos and text reproduced herein have been extracted solely for research, comment, and information reporting, and are intended for fair use by designated personnel in their official duties, including local reproduction for training. Further dissemination of copyrighted material contained in this document, to include excerpts and graphics, is strictly prohibited under Title 17, U.S. Code.
…
Unveiled – CIA-DoD Chabelly Djibouti Drone Base
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
|
Docu Film – The Spy Who Went Into The Cold: Kim Philby, Soviet KGB Super Spy
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Documentary exploring the murky circumstances behind the escape of one of Britain’s most notorious spies.
In 1963, at the height of the Cold War, a well-educated Englishman called Kim Philby boarded a Russian freighter in Beirut and defected to Moscow from under the nose of British Intelligence. For the best part of thirty years he had been spying for the Soviet Union, much of that time while holding senior jobs in MI6.
Fifty years on, more questions than answers still surround his defection. Had he really confessed before he went? Was his escape from justice an embarrassing mistake or part of the plan? This film, shot in Beirut, London and Moscow, sets out to find the answers, revealing the blind spots in the British ruling class that made it so vulnerable to KGB penetration.
Read more about Kim Philby and the Cambridge Five:
https://www.goodreads.com/book/show/5…
https://www.goodreads.com/book/show/5…
https://www.goodreads.com/book/show/5…
https://www.goodreads.com/book/show/1…
https://www.goodreads.com/book/show/5…
https://www.goodreads.com/book/show/8…
https://www.goodreads.com/book/show/2…
https://www.goodreads.com/book/show/2…
TOP-SECRET – The Secret List of KGB Spies in Eastern Europe, 120.000 Spies, Part 5, AG,
Become a Patron!
True Information is the most valuable resource and we ask you to give back.
| IPN BU 002086/1601 | AGACIAK ANNA MARIA |
| IPN BU 001198/2787 | AGIJEWICZ STEFAN |
| IPN BU 00612/970 | AGNEŻA JAN |
| IPN BU 001198/4468 | AGNEŻA JAN |
| IPN BU 0772/20 | AGNIESZCZAK STANISŁAW |
| IPN BU 0951/982 | AGNYZIAK ROMAN ANDRZEJ |


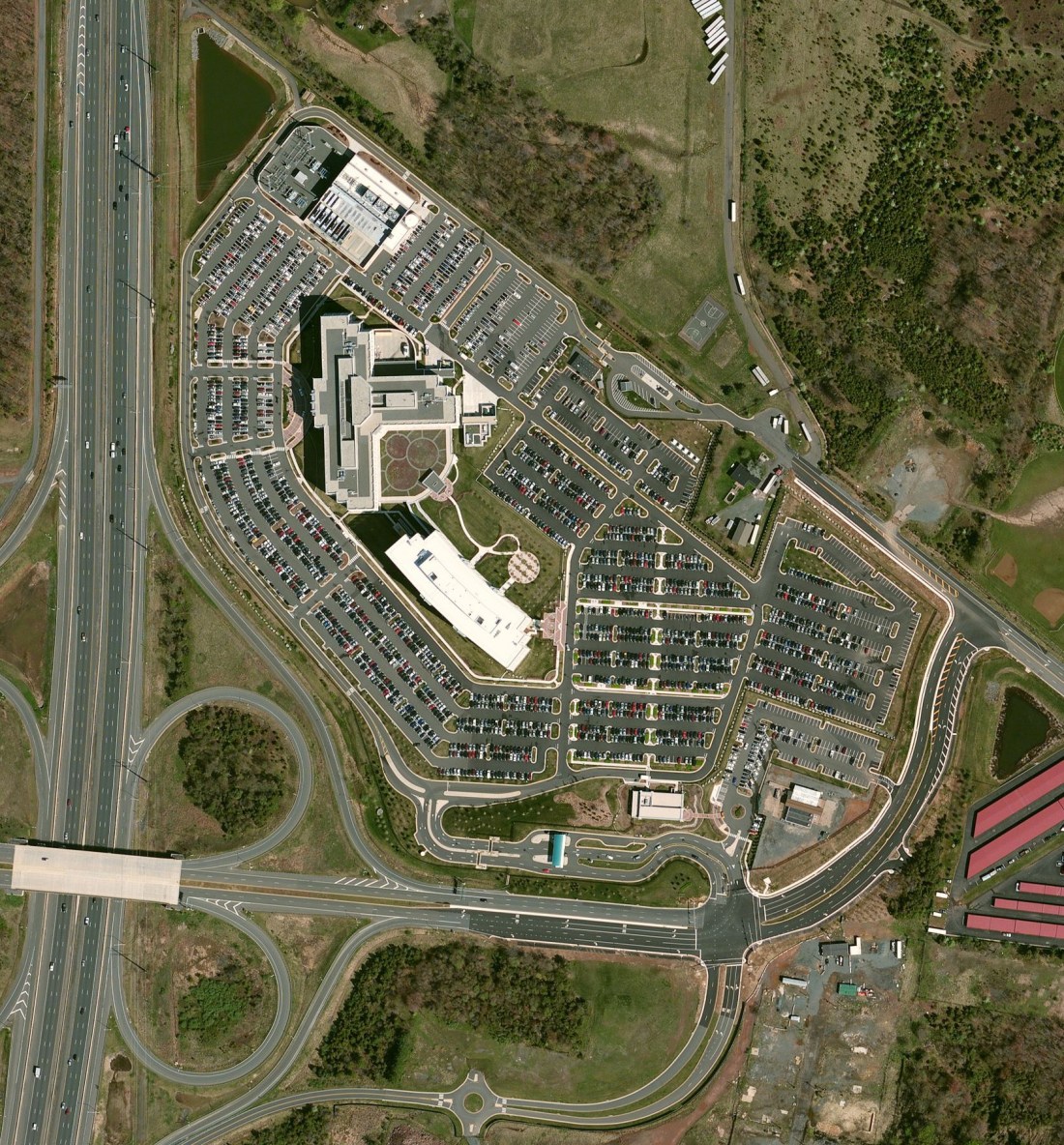






















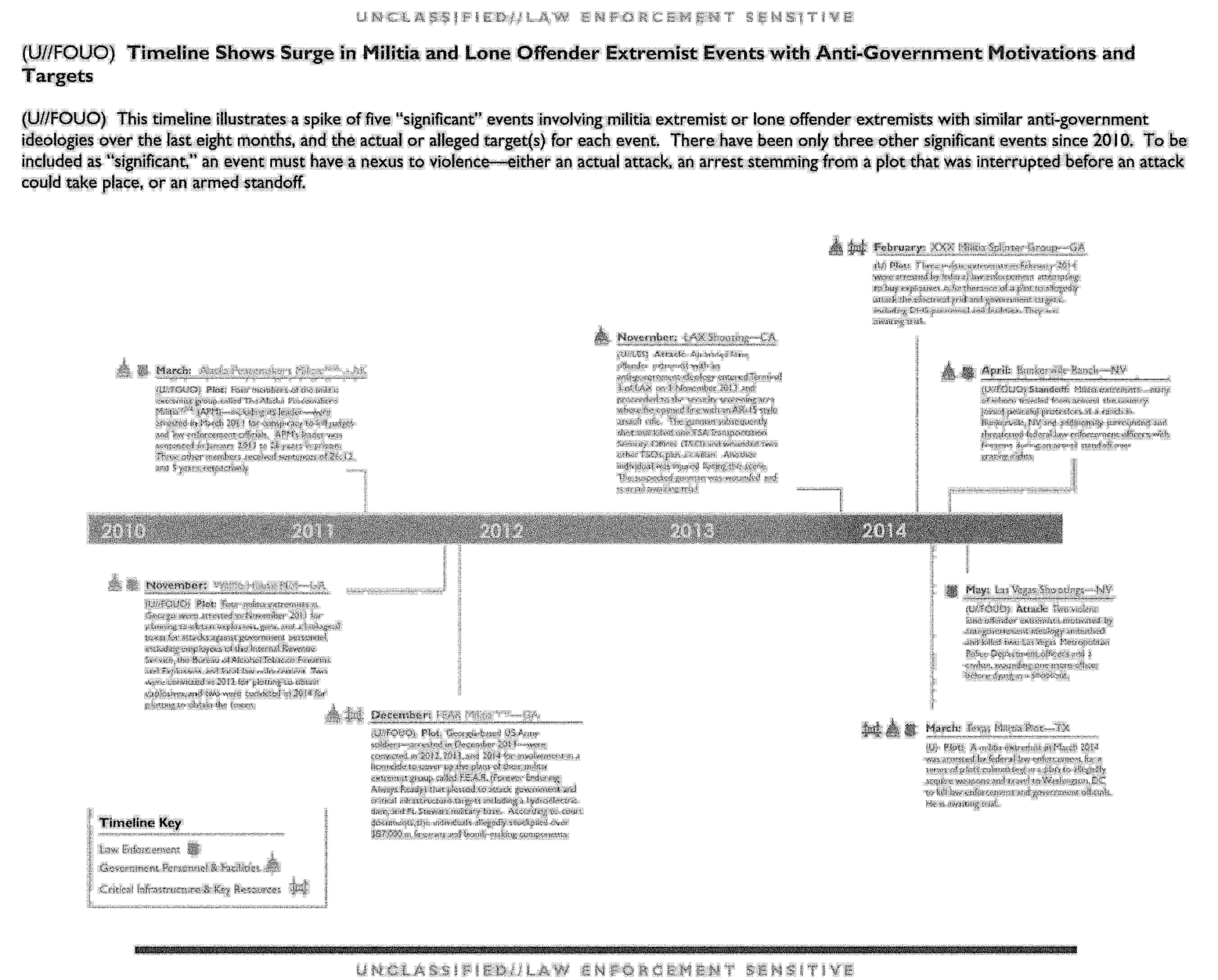













 Translation: A land / Where the air / Is like honey, / You can leave / And speed away carefree, — / But a land, / With which / You suffered together / Is in your heart permanently. [Vladimir Mayakovsky, “Good”] Happy Birthday!
Translation: A land / Where the air / Is like honey, / You can leave / And speed away carefree, — / But a land, / With which / You suffered together / Is in your heart permanently. [Vladimir Mayakovsky, “Good”] Happy Birthday!











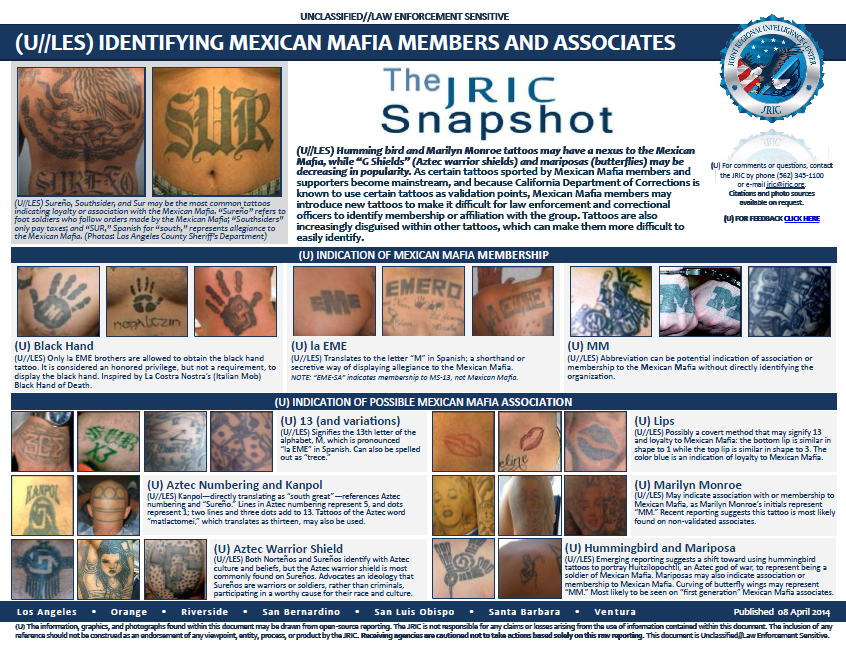





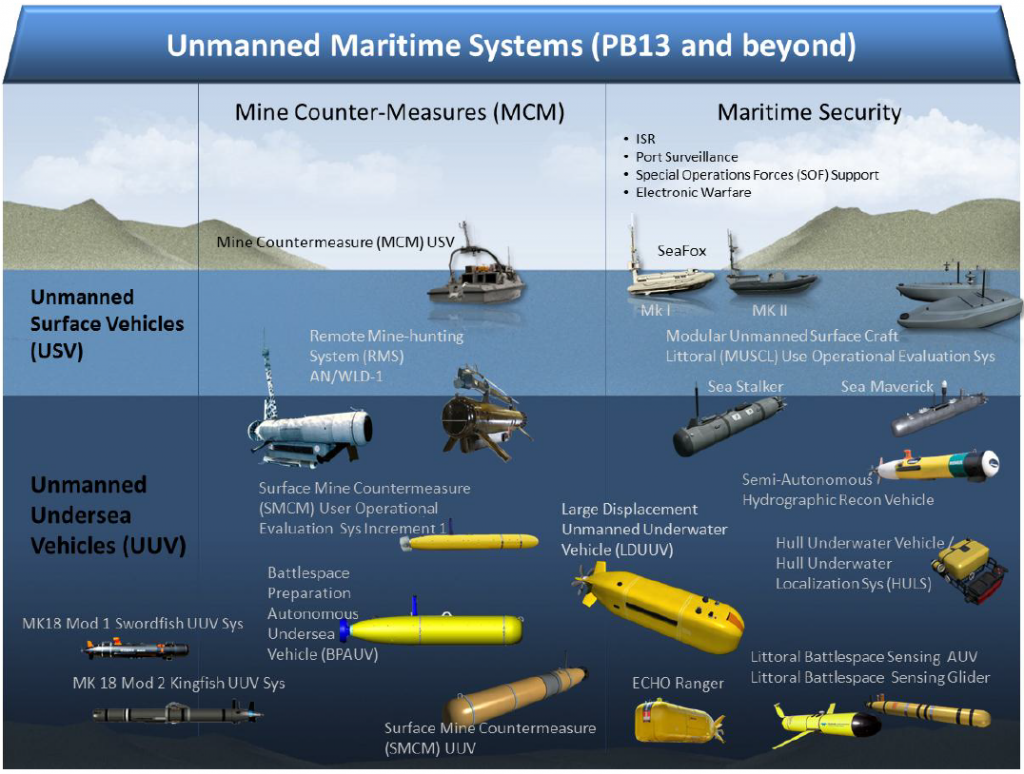
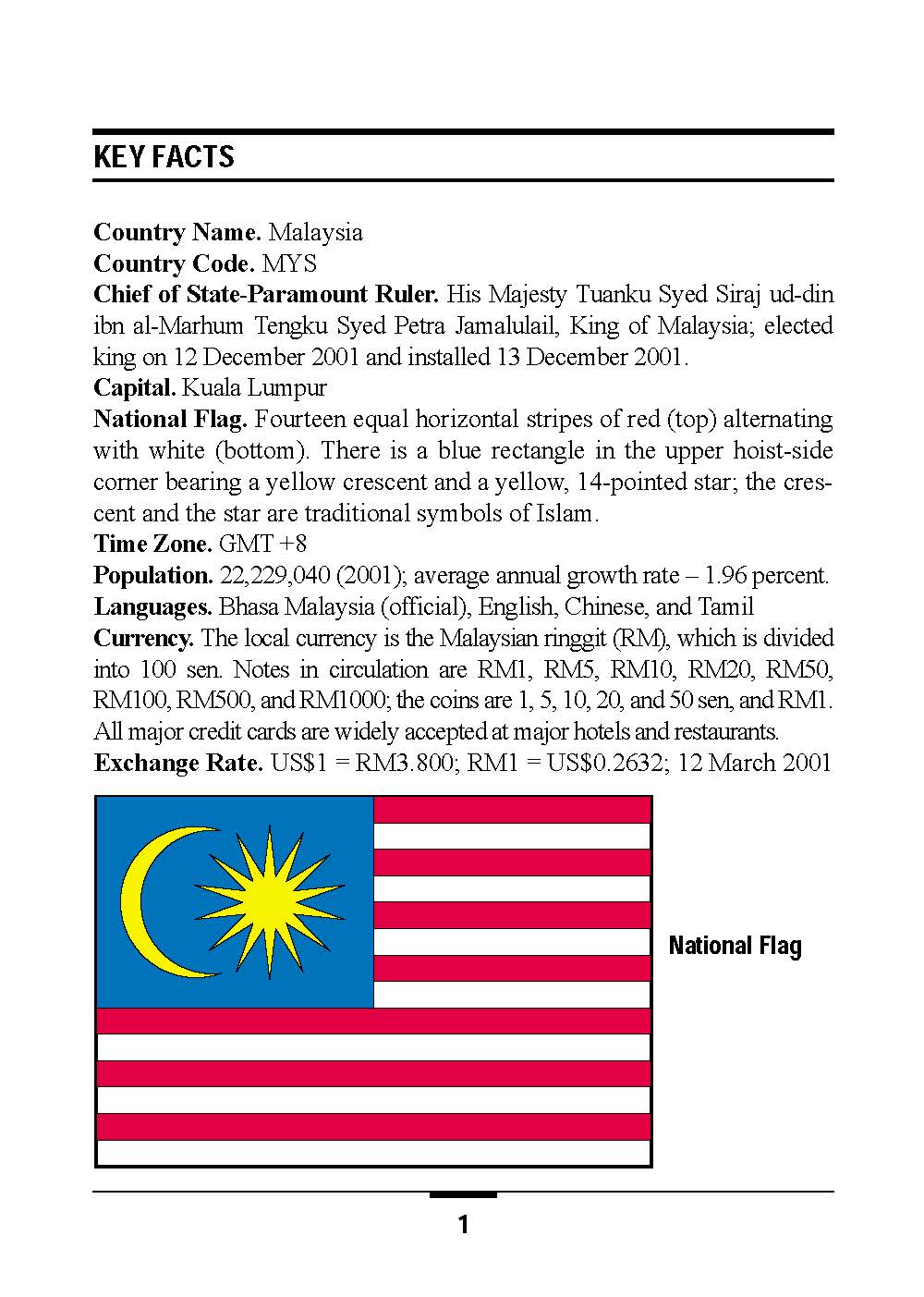

![[Image]](https://i0.wp.com/cryptome.org/2014-info/chabelly/pict17.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2014-info/chabelly/pict18.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2014-info/chabelly/pict70.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2014-info/chabelly/pict76.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2014-info/chabelly/pict78.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2014-info/chabelly/pict69.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2014-info/chabelly/pict71.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2014-info/chabelly/pict72.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2014-info/chabelly/pict73.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2014-info/chabelly/pict74.jpg)

You must be logged in to post a comment.