Become a Patron!
True Information is the most valuable resource and we ask you to give back.
This is the list of the STASI Agents waiting for their call to action in Western Europe from A-Z with their real names.
We have also published on this website new documents about Stratfor and their internal discussions about the STASI.
This is part of our cooperation with Wikileaks.
The Global Intelligence files were provided by Wikileaks.
This is part of our Investigative Partnership organised by WikiLeaks – the Data was obtained by WikiLeaks.
The STASI lists stem from the STASI itself. It is the so called “Fipro” list which was made to secure the pensions of the STASI Agents in Germany after the Reunification.
Below you find an explanation in German Language:
Die Liste wurde bereits früher hier publiziert:
Vom “Stasiopfer”-Angebot führt ein Link zu einer Website in den USA (www.jya.com), die sich auch mit den Praktiken von Geheimdiensten beschäftigt. Dort findet sich die “Fipro-Liste”, das detaillierte “Finanzprojekt” der Stasi, angefertigt in den letzten Tagen der DDR, um die Rentenansprüche der rund 100 000 hauptamtlichen Mitarbeiter des MfS auch nach dem Zusammenbruch des Systems belegen zu können. Die “Fipro-Liste” ist seit langem bekannt und diente Anfang der neunziger Jahre etwa zur Identifizierung der so genannten OibE – Offiziere im besonderen Einsatz. Diese Liste „Offiziere im besonderen Einsatz“im Jahre 1991 erschien in der “taz. Die Echtheit kann beim BStU überprüft werden.
Siehe u.a. http://www.spiegel.de/spiegel/print/d-22539439.html
Auf Druck ehemaliger STASI-Leute und Ihrer Genossen wurde die Liste aus dem Verkehr gezogen.
Hier ist sie wieder:
Stasi Offiziere im besonderen Einsatz (abgekürzt OibE)
Stasi Schläfer Liste
Technische Hinweise:
Diese Daten stammen aus der OibE-Liste. Die Tabellen wurden von H.T. per OCR usw. in HTML gewandelt.
Die Datensätze sind – anders geordnet – auch Teilmenge der (‘HAMSTER’-Liste/MA_Stasi.txt). Dort sind die mit Adressen versehenen und meist gedoppelten Datensätze diejenigen der OibE.
OibE dürfen nicht mit Inoffiziellen Mitarbeitern (IM) verwechselt werden. Sie hatten im Gegensatz zu den IM [Ausnahme: HIM] ein Dienstverhältnis mit der Stasi und einen Kampfauftrag.
Die OibE sollten unter allen Umständen zum MfS stehen und mussten sich vor der “Abordnung” ins Zivilleben durch besondere ideologische Zuverlässigkeit auszeichnen. Deshalb fühlen sich viele dieser Überzeugungstäter wahrscheinlich heute noch der Stasi verpflichtet, leben aber ganz unauffällig. Man könnte sie auch als “Schläfer” bezeichnen.
Offiziere im besonderen Einsatz (abgekürzt OibE) waren hauptamtliche Mitarbeiter des Ministeriums für Staatssicherheit
Zudem kommen weitere STASI-Agenten in Westdeutschland, die noch besser getarnt wurden und deren Legenden sorgfältig aufbereitet wurden.
Viel schufen sich in den Wirren um 1989 eine neue Identität mit neuem Namen auch in Westdeutschland. Somit sind hier nur deren ALTE und RICHTIGE Namen erfasst.
Name, Vorname; Geb.-datum; DE: Zentrale, BV, KD; DE-Code; PLZ; Az. / Reg.-Nr.
Ackermann, Frank; 29.04.55; HVA; 961500; 1092; 4288/81, F
Ackermann, Kerstin; 22.02.58; HVA; 961500; 1092; 4288/81/1, F
Adelmeier, Lutz; 18.11.53; HVA; 961500; 1590; 650/75/12,
Ahrendt, Hans; 17.11.50; Abt. XI; 941100; 1092; 2382/74,
Amthor, Jürgen; 25.01.47; Abt. N; 906540; 1130; 7263/75,
Anschütz, Günter; 07.04.54; Abt. XI; 941100; 6110; 3454/86,
Antoni, Detlef; 02.06.59; HVA; 961500; 1162; 2110/84, F
Arlt, Frank; 12.03.58; HVA; 961500; 1140; 650/75/54,
Auerbach, Christel; 01.04.36; HVA; 961500; 1020; 79/74, B
Auerbach, Hans- Dieter; 25.03.37; HVA; 961500; 1020; 80/74, J
Aul, Claus; 28.09.62; HVA; 961500; 1150; 3776/85, F
Autenrieb, Eckbert; 02.06.56; Abt. N; 906540; 1095; 5785/82,
Badelt, Dieter; 17.01.37; Rostock VII; 010700; 2520; 4909/75,
Bahl, Reinhard; 10.03.48; HVA; 961500; 2800; 527/88, M
Baltruschat, Klaus; 27.07.34; HVA; 961500; 1170; 13222/60, X
Balzer, Christian; 28.10.51; Abt. N; 906540; 1115; 1690/76,
Bandermann, Hans-Rainer; 12.05.45; Abt. N; 906540; 1280; 4378/77,
Barnowsky, Wolfgang; 24.08.38; HVA; 961500; 1017; 962/83, M
Bartels, Klaus; 06.04.39; KD Stendal; 070054; 3500; BARTELS, KLAUS
Bartels, Uwe; 23.02.64; HVA; 961500; 1093; 5764/81/4, D
Barten, Günter; 27.11.38; Abt. XI; 941100; 1291; 179/78,
Barzik, Hans-Joachim; 30.08.46; HVA; 961500; 1190; 592/86, F
Barzik, Renate; 05.08.49; HVA; 961500; 1190; 592/86/1, F
Bassin, Dietrich; 28.04.34; BV Berlin XVIII; 151800; 1058; 1911/78,
Bauer, Gerhard; 29.08.47; Abt. N; 906540; 1140; 4254/77,
Bauer, Ralf; 04.06.64; HVA; 961500; 1144; 2858/84, F
Baumann, Manfred; 25.04.39; OD TU/H Dresden; 120058; 8045; XII/1353/87,
Baumann, Reinhard; 25.05.40; KD Pirna; 120052; 8300; XII/1359/87,
Bauschmann, Rolf-Jürgen; 19.04.57; Abt. N; 906540; 1095; 7575/80,
Bazyli, Dieter; 10.08.35; Frankfurt/O. IX; 050900; 1200; V/425/88,
Bäumler, Hans; 29.06.33; HVA; 961500; 1144; 21/77, F
Becker, Günter; 24.02.38; HVA; 961500; 1120; 2649/80, F
Becker, Heidrun; 30.03.52; HVA; 961500; 1090; 2850/78, J
Becker, Ralf-Ekkehard; 16.04.57; Abt. N; 906540; 1130; 5040/76,
Becke, Ronald; 07.03.57; HVA; 961500; 5062; 650/75/27,
Beier, Peter; 02.08.42; OD KKW Nord; 010050; 2200; 5678/84,
Beitz, Hans-Joachim; 07.10.37; Abt. XI; 941100; 1100; 2233/66,
Benjowski, Klaus; 22.08.35; HVA; 961500; 1162; 364/77, U
Benndorf, Roland; 11.03.57; Abt. N; 906540; 1142; 1787/81,
Berger, Andreas; 16.11.62; Abt. XI; 941100; 7065; 1713/89,
Bergmann, Holger; 23.04.60; HVA; 961500; 8291; 650/75/25,
Bergmann, Thomas; 04.04.54; HVA; 961500; 1144; 1439/89, F
Berliner, Kurt; 16.12.35; HVA; 961500; 1080; 1858/89, F
Berndt, Walter; 03.01.31; Abt. XI; 941100; 1017; 246/77,
Bernhardt, Hans; 30.05.28; HVA; 961500; 1195; 9831/61, F
Bernhardt, Hans-Joachim; 15.02.56; Abt. XI; 941100; 4370; 1709/89,
Bertholf, Manfred; 02.02.37; BV Berlin XVIII; 151800; 1055; 867/80,
Bertsch-Herzog, Herbert; 21.07.29; HVA; 961500; 1080; 3665/60/1, U
Betsch, Brigitt; 16.01.55; HVA; 961500; 1055; 5010/87, U
Betsch, Michael; 30.11.46; HVA; 961500; 1140; 2259/73,
Bettzieche, Frank; 21.10.54; HVA; 961500; 1093; 904/84, F
Bettzüge, Eberhard; 22.01.35; Abt. N; 906540; 1136; 1807/72
Beuster, Gerhard; 03.07.52; Abt. N; 906540; 1292; 7270/75,
Bevermann, Jürgen; 14.10.43; HVA; 961500; 1142; 209/81, F
Bewersdorf, Wolfram; 20.05.61; Abt. N; 906540; 1280; 3022/84,
Beyer, Alfred; 30.05.38; HVA; 961500; 1190; 528/88, M
Beyer, Andreas; 23.01.61; HVA; 961500; 1580; 650/75/55,
Bezdicek, Rolf-Dieter; 20.09.58; Abt. XI; 941100; 1120; 844/83,
Bienert, Peter; 10.08.42; Abt. N; 906540; 1020; 4110/79,
Bilke, Paul; 02.06.28; HVA; 961500; 1020; 9/76, X
Birgel, Artur; 25.01.35; HVA; 961500; 1020; 4207/84, 0
Birnbach, Steffen; 23.10.53; Karl-Marx-Stadt XX; 142000; 9081; K/3505/89,
Blank, Gerhard; 16.12.31; HVA; 961500; 1130; 3156/89, E
Blank, Monika; 12.10.39; HVA; 961500; 1130; 3156/89/1, E
Blaudzun,Alfred; 26.10.38; Rostock VI; 010600; 2500; 5011/86,
Blei, Holger; 08.05.57; HVA; 961500; 1055; 4644/80, J
Block, Gerhard; 04.11.52; Abt. XI; 941100; 3530; 5125/85,
Bloß, Rolf; 08.04.33; Dresden XVIII; 121800; 8019; XII/1344/87,
Blumenberg, Igor; 27.06.52; Abt. XI; 941100; 1130; 311/80,
Blum, Ines; 02.04.62; HVA; 961500; 1199; 2410/79, J
Blutnick, Harry; 27.01.36; HVA; 961500; 1020; 1653/87, F
Bock, Andre; 01.11.67; Abt. N; 906540; 1095; 5546/88,
Bogacz, Carsten; 10.11.58; HVA; 961500; 7513; 650/75/56,
Bohm, Peter; 24.10.45; HVA; 961500; 1144; 1671/87, F
Bohn, Detlef; 12.05.59; Abt. XI; 941100; 4070; 492/87,
Bohn, Steffi; 14.10.59; HVA; 961500; 4070; 492/87/1, F
Bohn, Wolfgang; 16.05.51; HVA; 961500; 1092; 2112/72, F
Bollmann, Lutz; 16.12.68; Abt. N; 906540; 1140; 5189/88,
Borchert, Detlef; 09.12.48; Abt. N; 906540; 1100; 255/73,
Borchert, Hans-Joachim; 19.11.54; HVA; 961500; 1142; 398/76, F
Bornschein, Horst; 20.04.30; Abt. XI; 941100; 1156; 3597/81,
Born, Joachim; 25.04.58; Abt. N; 906540; 1092; 4325/87,
Böhm, Jürgen; 22.11.44; HVA; 961500; 1142; 2660/79, M
Börnchen, Peter; 20.07.39; HVA; 961500; 1250; 30/70, A
Brada, Wolfgang; 15.11.50; HVA; 961500; 1130; 650/75/11,
Brade, Rolf; 21.07.42; Abt. XI; 941100; 1600; 271/68,
Brate, Andreas; 11.12.54; HVA; 961500; 1142; 3039/82, M
Brändel, Lothar; 19.04.35; KD Leipzig/Land; 130041; 4090; K, 4232/86,
Brendtner, Werner; 23.03.42; Rostock VII; 010700; 2520; 4733/88,
Bretschneider, Jens; 29.08.67; Karl-Marx-Stadt VIII; 140800; 9271; 182,
Bruhn, Siegfried; 28.11.50; HVA; 961500; 2520; 650/75/39,
Brunner, Manfred; 26.04.29; HVA; 961500; 1144; 1920/75, J
Bruns, Beate; 05.06.62; HVA; 961500; 1140; 6555/82, J
Brüning, Falk; 11.06.63; HVA; 961500; 1095; 4361/84, M
Burckhardt, Dietmar; 03.08.44; HVA; 961500; 1020; 3467/86, L
Burde, Hans-Joachim; 18.05.47; Abt. N; 906540; 1092; 2010/67,
Burkhardt, Marco; 12.10.59; HVA; 961500; 1142; 3887/83, E
Buschendorf, Lutz; 21.11.41; HVA; 961500; 1142; 3478/65, A
Bussin, Günter; 26.07.54; HVA; 961500; 1142; 3328/86, A
Büchner, Eckhard; 23.09.56; Abt. N; 906540; 1153; 3619/77,
Bürger, Heiderose; 05.05.50; Abt. N; 961500; 1140; 5764/81/3, D
Cantow, Hans-Gerhard; 11.01.44; HVA; 961500; 1143; 360/68, L
Christoph, Martin; 30.03.58; HVA; 961500; 9900; 650/75/26,
Claus, Werner; 29.03.26; HVA; 961500; 1017; 401/73, P
Cotte, Wolfgang; 16.11.51; HVA; 961500; 1600; 619/83, L
Czieselsky, Frank; 05.05.58; Abt. N; 906540; 1017; 2960/79,
Daum, Heinz; 09.09.35; BV Berlin VI; 150600; 1020; 4101/77,
Dau, Holger; 20.01.58; HVA; 961500; 1143; 7701/81, F
Dähn, Bernd; 23.07.48; Abt. XI; 941100; 1035; 97/75,
Degenhardt, Dieter; 12.07.31; HA VII; 970700; 1140; DEGENHARDT, DIETER
Dehmel, Wolfgang; 12.07.49; Abt. N; 906540; 1142; 7401/81,
Derlath, Bettina; 08.02.56; HVA; 961500; 1090; 5182/84, M
Deters, Frank; 10.11.67; Abt. N; 906540; 1950; 4649/87,
Deutscher, Peter; 16.07.47; HVA; 961500; 8019; 1382/89, M
Deysing, Gerd; 04.10.53; HVA; 961500; 1142; 650/75/58,
Diettrich, Günter; 06.05.53; Abt. N; 906540; 1281; 1794/80,
Dietrich, Matthias; 30.07.66; HVA; 961500; 1156; 4383/86, F
Dietrich, Reinhilde; 25.07.37; Abt. N; 906540; 1110; 5004/80,
Diettrich, Heidi; 14.11.54; Abt. N; 906540; 1281; 2002/87,
Dittrich, Michael; 09.11.46; Abt. XI; 941100; 1141; 99/75,
Dittrich, Wolfgang; 08.07.49; Abt. N; 906540; 1142; 1675/78,
Doegelsack, Uta; 20.01.63; Abt. N; 906540; 1093; 5808/84,
Donath, Martin; 03.04.51; HVA; 961500; 2520; 671/89, A
Dorgwarth, Reinhard; 10.11.48; Abt. N; 906540; 1280; 4379/77,
Dott, Bernd; 01.07.41; BV Berlin VII; 150700; 1180; 241/78,
Döbel, Holger; 07.04.61; Abt. N; 906540; 1143; 4865/81,
Döbereiner, Rene; 02.08.67; Karl-Marx-Stadt VIII; 140800; 9072; 175,
Drechsler, Peter; 06.06.57; HVA; 961500; 1136; 3594/74, F
Dreger, Uwe; 25.12.51; Abt. N; 906540; 1281; 7271/75,
Drexler, Andreas; 03.12.50; HVA; 961500; 1120; 4675/85, A
Dumke, Bodo; 21.03.51; BV Berlin VI; 150600; 1080; 1299/85,
Dybiona, Detlef; 21.05.60; Abt. XI; 941100; 3090; 494/87,
Dylla, Bernd; 07.03.57; Abt. XI; 941100; 6902; 767/86,
Ebedus, Dieter; 17.01.59; Abt. XI; 941100; 4350; 1819/87,
Eckert, Gerhard; 24.09.31; KD Eisenhüttenstadt; 050045; 1220; V/481/88,
Effenberger, Helga; 10.07.38; HVA; 961500; 1017; 19666/60/1, E
Effenberger, Rudolf; 13.01.33; HVA; 961500; 1017; 19666/60, E
Eggert, Asmus; 17.12.47; HVA; 961500; 1130; 2394/85, J
Eggestein, Dieter; 20.12.38; Rostock XVIII; 011800; 2520; 3862/81,
Ehrke, Hans-Jürgen; 17.01.42; Abt. N; 906540; 1090; 4025/79,
Ehrenberg, Rolland; 25.09.47; Frankfurt/O. IX; 050900; 1200; V/447/88,
Eichentopf, Marlis; 27.06.61; HVA; 961500; 5080; 5362/89, F
Eichhorn, Hans; 14.10.38; HVA; 961500; 1054; 1305/68, P
Eichner, Ulla; 02.04.42; HVA; 961500; 1092; 4218/84, F
Eisenhardt, Joachim; 05.09.58; Abt. N; 906540; 1095; 3413/78,
Elfert, Wolfgang; 08.05.56; Abt. XI; 941100; 1250; 448/80,
Elliger, Gabriele; 06.12.61; HVA; 961500; 1142; 650/75/59/1,
Elliger, Uwe; 08.05.58; HVA; 961500; 1142; 650/75/59,
Ende, Michael; 30.06.52; BV Berlin VII; 150700; 1092; 4977/79,
Engelmann, Frank; 03.08.42; HVA; 961500; 1140; 5681/86, M
Engelmann, Gabriele; 15.08.46; HVA; 961500; 1140; 3876/86, M
Englberger, Wolfgang; 24.06.43; HVA; 961500; 1020; 3760/87, U
Enke, Brigitte; 04.08.44; HVA; 961500; 1280; 650/75/50/1,
Enke, Dieter; 02.07.45; HVA; 961500; 1280; 650/75/50,
Escherich, Rolf; 18.01.40; HVA; 961500; 1156; 3039/62, F
Euen, Wolf; 19.02.44; KD Riesa; 120053; 8400; XlI/2673/87,
Ewald, Peter; 28.01.50; Abt. N; 906540; 1140; 3622/77,
Faber, Kurt; 30.07.27; Abt. XI; 941100; 1170; 8348/60,
Falkehagen, Bärbel; 10.04.56; Abt. N; 906540; 1130; 3412/78,
Falkenhagen, Ingo; 29.07.56; Abt. N; 906540; 1130; 2403/78,
Fauck, Alexa; 04.12.51; HVA; 961500; 1095; 3820/85/1, F
Fauck, Wolfgang; 21.01.50; HVA; 961500; 1095; 3820/85, F
Fähnrich, Alfred; 01.07.32; HA I; 970100; 1602; K, 4271/80
Fähnrich, Manfred; 29.03.33; Rostock XVIII; 011800; 2500; 549/60,
Fedtke, Simone; 02.03.66; HVA; 961500; 1092; 4462/81, A
Feige, Brigitte; 07.03.48; HVA; 961500; 1143; 592/88 F
Fell, Klaus; 30.05.35; Abt. N; 906540; 1092; 7259/75,
Fichtmüller, Jens; 06.03.67; HVA; 961500; 4850; 3641/88, O
Fickel, Michael; 30.01.61; HVA; 961500; 1140; 4276/83, J
Fiedler, Gunter; 16.09.51; HVA; 961500; 1034; 2113/72, F
Finsterbusch, Werner; 08.07.56; HVA; 961500; 1093; 5693/81, A
Fischer, Gerd; 21.02.61; HA VI; 970600; 1144; K, 3435/89
Fischer, Hans; 11.10.50; HVA; 961500; 1142; 505/83, O
Fischer, Hartmut; 25.04.52; HVA; 961500; 1250; 2256/73, F
Fischer, Horst; 03.02.32; HVA; 961500; 1600; 1573/85, K
Fischer, Horst; 03.05.46; KD Berlin-Köpenick; 150041; 1170; 2562/80,
Fischer, Karl-Heinz; 19.08.28; HVA; 961500; 1136; 2110/73, Z
Fischer, Klaus-Dieter; 06.12.44; Rostock XVIII; 011800; 2551; 3875/80,
Fischer, Marion; 02.08.52; HVA; 961500; 1142; 2779/84, O
Flister, Magrit; 20.02.56; HVA; 961500; 1020; 4561/87, U
Fox, Erhard; 04.12.52; Abt. XI; 941100; 2355; 5313/88,
Fraatz, Helmut; 06.07.31; HVA; 961500; 1156; 221/75, M
Franke, Lothar; 04.11.47; Abt. N; 906540; 1142; 5074/77,
Franke, Wilfried; 25.08.53; Rostock; 014300; 2500; 5952/84,
Franz, Bodo; 13.01.59; Abt. N; 906540; 1150; 1549/80,
Franz, Jürgen; 09.04.46; Abt. N; 906540; 1142; 2112/66,
Franz, Jürgen; 30.06.55; Abt. XI; 941100; 3250; 6588/81,
Frauenstein, Rolf; 14.07.52; HVA; 961500; 1143; 3166/78, J
Fränkler, Sabine; 10.02.61; HVA; 961500; 1020; 2264/86, U
Freese, Frank; 25.03.62; Abt. N; 906540; 1095; 2567/87,
Freitag, Ilona; 02.10.52; Dresden XIX; 121900; 8060; XII/2747/87,
Freund, Mario; 10.01.64; Abt. XI; 941100; 3038; 2759/89,
Freyberg, Rudolf; 23.09.35; Abt. N; 906540; 1055; 7260/75,
Freyer, Ingolf; 10.07.30; HVA; 961500; 1120; 1347/85, F
Freyer, Thorsten; 10.11.60; HVA; 961500; 1136; 650/75/40,
Frey, Rainer; 02.06.42; HVA; 961500; 7500; 1586/87, F
Frick, Dieter; 28.06.58; HVA; 961500; 1140; 4054/81, F
Friebe, Günter; 28.09.43; HVA; 961500; 1090; 1640/88, F
Friedel, Hartmut; 12.02.49; HVA; 961500; 1093; 231/78, J
Friedrich, Gerhard; 21.12.29; HA VI; 970600; 1034; K, 862/80
Friedrich, Joachim; 06.07.48; Abt. XI; 941100; 1141; 67/78,
Friedrich, Jörg; 30.06.64; HVA; 961500; 1193; 3925/86, F
Fritzsche, Harald; 14.08.57; Abt. XI; 941100; 1054;
Fruck, Gerhard; 13.05.35; Abt. N; 906540; 1136; 3706/73,
Fuchs, Eberhard; 04.10.50; HVA; 961500; 1153; 2879/78, J
Fuchs, Wolfgang; 18.11.53; HVA; 961500; 1156; 3547/82, M
Fungk, Torsten; 03.11.57; Abt. N; 906540; 1142; 2956/79,
Funke, Dieter; 20.01.38; HVA; 961500; 1080; 2929/61, F
Funk, Lutz; 22.09.57; HVA; 961500; 1095; 650/75/60,
Funk, Margret; 22.05.55; HVA; 961500; 1095; 650/75/60/1,
Füßler, Hubertus ; 10.01.56; HVA; 961500; 5080; 529/88, M
Füßl, Boris; 06.06.61; Abt. XI; 941100; 1018; 2417/88,
Fydrich, Erhard; 15.05.42; HVA; 961500; 1250; 593/86, F
Gableske, Gunther; 08.04.60; Abt. N; 906540; 1280; 7517/81,
Gallandt, Ronald; 16.08.57; Abt. N; 906540; 1280; 1788/78,
Gander, Jürgen; 31.08.47; Abt. N; 906540; 1156; 7275/75,
Gawlitza, Peter-Michael ; 07.12.46; HVA; 961500; 1142; 2505/65, G
Gäbler, Eveline; 23.08.56; Abt. N; 906540; 1281; 5155/88,
Gäbler, Ralf-Detlef ; 01.11.56; Abt. N; 906540; 1281; 3324/76,
Gehrt, Wolf-Rüdiger ; 26.01.56; Abt. N; 906540; 1090; 1840/79,
Geißenhöner, Bernd; 26.08.43; Abt. XI; 941100; 1092; 377/69,
Gerber, Jürgen; 05.05.49; Dresden XIX; 121900; 8020; XII/2666/87,
Gerber, Lutz; 19.01.61; Abt. N; 906540; 1140; 7472/80,
Gerhard, Henry; 23.02.32; KD Berlin-Köpenick; 150041; 1199; 1041/70,
Gerlach, Rainer; 25.02.53; HVA; 961500; 5080; 1477/87, F
Gerlach, Roland; 20.01.51; HVA; 961500; 1280; 4006/76, F
Gerstner, Christine; 01.07.43; HVA; 961500; 1136; 5255/85, D
Gerth, Peter; 21.05.54; Rostock XIX; 011900; 2540; 666/87,
Gielow, Hubert; 11.03.53; Abt. N; 906540; 1017; 2028/79,
Giesen, Gisela; 23.02.30; Abt. XI; 941100; 1197; 1866/69/2,
Gietl, Gottfried; 24.05.34; HVA; 961500; 1055; 18554/60, T
Gladitz, Dieter; 19.02.37; HVA; 961500; 1020; 3323/86, J
Gladitz, Edgar; 02.12.34; HVA; 961500; 1020; 2806/78, F
Gläßer, Axel; 18.07.57; Abt. N; 906540; 1020; 3100/80,
Glöckner, Hermann; 07.04.28; Dresden VI; 120600; 8060; XII/2657/87,
Goersch, Bärbel; 29.05.54; HVA; 961500; 1093; 5764/81/2, D
Golombek, Bernd; 30.07.62; Abt. XI; 941100; 1560; 5310/88,
Gompert, Dieter; 26.11.33; KD Strausberg; 050049; 1260; V/426/88,
Gorldt, Peter; 20.12.42; HVA; 961500; 9005; 530/88, M
Goutrie, Peter; 27.11.47; Abt. N; 906540; 1281; 3557/78,
Görke, Peter; 26.06.61; HVA; 961500; 1150; 921/83, F
Göthel, Jürgen ; 20.07.53; HVA; 961500; 1142; 8164/81, L
Grahmann, Dieter; 25.06.41; HVA; 961500; 1106; 5602/86, L
Gramß, Werner; 03.06.29; HVA; 961500; 1017; 2859/68, M
Grandel, Winfried; 12.03.43; KD Berlin-Köpenick; 150041; 1144; 3047/80,
Graßmann, Walter; 28.02.46; Abt. N; 906540; 1092; 2009/67,
Gräser, Rolf; 14.07.42; HVA; 961500; 1140; 662/88, M
Gräser, Ute; 24.02.63; HVA; 961500; 1140; 609/88, M
Greve, Bernd; 25.09.57; Abt. N; 906540; 1017; 5075/77,
Grieger, Angela; 11.05.63; HVA; 961500; 1185; 3973/81, O
Grigat, Alfred; 26.05.39; HVA; 961500; 2850; 3317/84, M
Grimmek, Norbert; 24.05.57; Abt. N; 906540; 1281; 4711/78,
Grimm, Peter; 03.11.41; HVA; 961500; 1156; 200/66, F
Grohmann, Achim; 15.02.54; HVA; 961500; 1100; 2518/88, F
Grohs, Michael; 19.10.53; HVA; 961500; 1143; 327/81, M
Gromes, Wilfried; 29.09.51; HVA; 961500; 1170; 1679/88, E
Großer, Jürgen; 27.01.59; HVA; 961500; 1607; 650/75/37,
Große, Hans-Peter ; 02.03.38; HVA; 961500; 1136; 2677/82, J
Großmann, Dietrich ; 24.09.41; Abt. XI; 941100; 1130; 2260/66,
Großmann, Gerald; 23.03.57; Abt. N; 906540; 1142; 1775/78,
Groß, Andreas; 29.11.55; Abt. XI; 941100; 9050; 6933/88,
Grotelüschen, Claus; 27.02.36; HVA; 961500; 1603; 2295/70, U
Grote, Konrad; 15.02.41; HVA; 961500; 1093; 1967/64, A
Groth, Rudi; 26.07.43; Abt. N; 906540; 1136; 1991/69,
Grotsch, Olaf; 21.05.63; Abt. N; 906540; 1092; 5152/88,
Gröpler, Peter; 12.06.44; HVA; 961500; 1020; 1643/68, O
Grötschel, Andrea; 28.09.57; HVA; 961500; 1540; 4463/84/1, F
Grötschel, Uwe; 28.12.58; HVA; 961500; 1540; 4463/84, F
Grube, Gerhard; 12.06.48; Abt. N; 906540; 1092; 4565/77,
Grunert, Joachim; 10.08.33; HVA; 961500; 1017; 3121/64, L
Gruner, Andreas; 22.03.58; Abt. XI; 941100; 1140; 479/83,
Gruner, Heidi; 09.09.59; HVA; 961500; 1156; 650/75/33/1,
Gruner, Michael; 28.07.55; HVA; 961500; 1156; 650/75/33,
Grünherz, Hans-Joachim; 07.04.45; Abt. XI; 941100; 1140; 3046/66,
Grütze, Regina; 18.07.55; BV Berlin XVIII; 151800; 1140; 763/86,
Gubsch, Volkmar; 19.08.52; KD Dresden/Stadt; 120040; 8038; XII/1357/87,
Gundermann, Dieter; 02.12.57; Abt. N; 906540; 1130; 2957/79,
Güntherodt, Ulrich; 28.04.46; HVA; 961500; 4090; 4273/89, M
Günther, Klaus; 06.08.55; HVA; 961500; 1130; 960/89, F
Günther, Norman; 19.11.65; HVA; 961500; 9900; 3734/88, Y
Haack, Jörg-Dieter; 06.09.52; Abt. N; 906540; 1110; 3718/76,
Haaser, Jutta; 23.11.33; Dresden VI; 120600; 8020; XII/2658/87,
Haase, Dieter; 27.06.31; Dresden IX; 120900; 8023; XII/2663/87,
Haberland, Lutz; 26.04.59; Abt. XI; 941100; 3038; 1894/87,
Hagenfeld, Wilfried; 18.02.40; HVA; 961500; 1020; 2990/76, M
Hagen, Rudolf; 24.02.39; Abt. N; 906540; 1136; 2075/76,
Hallfarth, Günter; 01.10.44; Abt. XI; 941100; 1092; 499/70/1,
Hallfarth, Renate; 20.01.48; Abt. XI; 941100; 1092; 499/70/2,
Hampel, Bärbel; 03.04.59; Abt. XI; 941100; 1280; 2563/86,
Hampel, Bernd; 23.03.56; Abt. N; 906540; 1280; 3388/76,
Hanke, Lutz; 04.02.56; HVA; 961500; 1195; 2378/88, F
Hanke, Peter; 21.10.53; HVA; 961500; 1143; 4174/88, A
Hantke, Gisela; 05.05.32; HVA; 961500; 1093; 3599/82, H
Hantke, Willi; 23.04.31; HVA; 961500; 1093; 6100/82, H
Harder, Dieter; 21.01.43; KD Riesa; 120053; 8400; XII/2674/87,
Hartmann, Andreas; 08.05.58; HVA; 961500; 1142; 650/75/52,
Hartmann, Gerd; 15.03.39; HVA; 961500; 1020; 647/87, A
Hartmann, Günter; 11.11.40; Abt. N; 906540; 1136; 1769/71,
Hasterok, Günter; 16.05.44; HVA; 961500; 1092; 1391/86, M
Hasterok, Hannelore; 07.05.50; HVA; 961500; 1092; 1737/87, F
Haude, Klaus-Dieter; 27.04.39; BV Berlin XVIII; 151800; 1020; 2978/81,
Hauschild, Dieter; 04.06.39; Rostock, Abt. Hafen; 011969; 2500; 5293/88,
Havlik, Lutz; 30.11.54; Abt. N; 906540; 1093; 5015/85,
Häber, Hermann; 02.04.48; HVA; 961500; 1143; 139/74, F
Hähn, Doris; 01.01.63; HVA; 961500; 1200; 5352/88, F
Hähn, Harald; 27.01.60; Abt. XI; 941100; 1200; 3455/86,
Härdrich, Horst; 03.07.38; Abt. XI; 941100; 1140; 3704/73,
Härtig, Uwe; 08.09.57; Abt. N; 906540; 1143; 3621/77,
Heckel, Reiner; 24.04.51; HVA; 961500; 1280; 2163/73, F
Heene, Edgar; 02.12.58; HVA; 961500; 2000; 1738/87, F
Heene, Elke; 12.02.60; HVA; 961500; 2000; 1738/87/1, F
Heerling, Frank; 01.09.62; Abt. N; 906540; 1130; 5017/85,
Heer, Carsten; 15.12.36; Abt. N; 906540; 1020; 454/73,
Heiliger, Ullrich; 20.05.57; Abt. N; 906540; 1120; 1856/86,
Heinicke, Frank; 26.05.56; Abt. N; 906540; 1017; 2564/86,
Heinrich, Guido; 26.06.66; Abt. N; 906540; 1590; 1159/89,
Heinrich, Peter; 29.04.40; HA XX; 982000; 1092; K, 3971/71
Hein, Jürgen; 20.12.54; HVA; 961500; 1152; 372/73, F
Hein, Winfried; 10.08.50; HVA; 961500; 1142; 3855/85, F
Heitfeld, Michael; 23.06.53; HVA; 961500; 1140; 4198/81, L
Hellmich, Kurt; 22.08.30; Rostock XVIII; 011800; 2520; 171/70,
Hellwig, Frank; 25.02.56; HVA; 961500; 1144; 650/75/41,
Helm, Michael; 19.04.59; Abt. XI; 941100; 9438; 589/88,
Hempel, Günter; 25.04.34; KD Eisenhüttenstadt; 050045; 1220; V/1001/88,
Hempel, Reinhard; 28.06.51; HVA; 961500; 1153; 1746/89, E
Hempel, Wolfgang; 02.07.53; Abt. N; 906540; 1020; 5015/77,
Henckel, Peter; 04.05.58; Abt. N; 906540; 1144; 3891/77,
Henke, Frank; 25.12.56; Abt. N; 906540; 1071; 3891/76,
Hennemann, Lutz; 29.09.50; Abt. N; 906540; 1100; 7269/75,
Hennig, Dietmar; 07.01.52; HVA; 961500; 1090; 1226/70, F
Henning, Friedrich; 11.05.35; HVA; 961500; 1017; 440/87, U
Henrion, Lothar; 07.01.41; KD Plauen; 140054; 9900; 1435/89,
Hentschke, Angelika; 19.07.51; HVA; 961500; 1153; 4189/89/1, F
Hentschke, Günther ; 08.01.51; HVA; 961500; 1153; 4189/89, F
Herbert, Roland; 10.10.43; HVA; 961500; 1020; 494/69, F
Herbst, Manfred; 09.10.33; HVA; 961500; 1156; 1087/84, U
Herder, Edeltraut; 27.07.31; HVA; 961500; 1020; 867/61, O
Herer, Erhard; 18.06.40; HVA; 961500; 1130; 4010/70, E
Herkendell, Karl-Heinz; 31.01.43; Abt. N; 906540; 1020; 3894/77,
Herkendell, Martha; 01.03.46; Abt. N; 906540; 1020; 4053/85,
Herold, Gerhard; 29.05.53; HVA; 961500; 1250; 4484/84, F
Herold, Monika; 28.08.52; HA VI; 970600; 1040; K, 3315/86
Herrmann, Alexander; 08.03.51; Abt. N; 906540; 1140; 3077/71,
Herrmann, Dietmar; 30.08.38; HA I; 970100; 8060; K, 5235/86
Herrmann, Günther; 28.01.30; HVA; 961500; 1020; 3627/74, A
Herschel, Steffen; 14.11.52; Abt. N; 906540; 1130; 1607/76,
Hertel, Ralf; 12.04.59; Abt. N; 906540; 1040; 2958/79,
Hertzsch, Wilfried; 10.07.43; HVA; 961500; 2591; 3906/83, M
Herzog, Peter; 08.04.47; HVA; 961500; 8600; 2872/87, M
Herz, Rudolf; 16.05.35; HVA; 961500; 1136; 4391/83, M
Hesse, Christina; 25.12.50; HVA; 961500; 1560; 4040/88, F
Hesse, Klaus; 09.09.47; HVA; 961500; 1136; 2032/72, J
Hesse, Rainer; 24.04.48; Abt. XI; 941100; 1560; 4484/87,
Hexamer, Rene; 10.04.57; HVA; 961500; 1197; 8082/81, F
Hielscher, Dirk; 26.01.56; HVA; 961500; 1092; 417/86, O
Hiersche, Eveline; 16.06.36; HVA; 961500; 1110; 3073/89, K
Hildebrandt, Fred; 23.12.57; HVA; 961500; 6060; 650/75/31,
Hildebrandt, Marion; 28.09.51; HVA; 961500; 1140; 3721/88/1, F
Hildebrandt, Michael; 03.08.52; HVA; 961500; 1140; 3721/88, F
Hildebrandt, Sonja; 07.02.54; HVA; 961500; 1165; 3020/76/26, M
Hildebrand, Hans-Jürgen ; 09.05.39; Frankfurt/O. VI; 050600; 1200; V/427/88,
Hildebrand, Norbert; 23.05.55; Abt. XI; 941100; 5600; 480/83,
Hille, Thomas; 27.04.61; Abt. N; 906540; 1055; 1356/84,
Hinterthan, Bernd; 25.11.41; Rostock VI; 010600; 2551; 1748/89,
Hinz, Hans-Jürgen; 18.01.43; Abt. XI; 941100; 1115; 410/70,
Hirsch, Jürgen; 31.07.54; Abt. XI; 941100; 1195; 2740/77,
Hirt, Sigurd; 05.07.42; Abt. XI; 941100; 1130; 1601/68,
Hitschler, Helmut; 22.07.58; ZAIG; 995300; 8010; K/4402/88,
Hofert, Michael; 02.09.59; HVA; 961500; 1093; 947/84, F
Hoffmann, Frank; 28.02.44; HVA; 961500; 1120; 1587/87, F
Hoffmann, Gunter; 03.11.54; HVA; 961500; 1140; 650/75/17,
Hoffmann, Hartmut; 06.08.51; Abt. XI; 941100; 1095; 6732/80,
Hoffmann, Ines; 03.11.61; HVA; 961500; 1140; 650/75/17/1,
Hofmann, Dieter; 18.04.39; HVA; 961500; 1162; 2607/84, F
Hofmann, Ellen; 03.10.54; Abt. N; 906540; 1280; 1680/81,
Hofmann, Udo; 20.02.41; HVA; 961500; 6019; 1492/86, F
Hohlfeld, Hartmut; 14.05.55; HVA; 961500; 1141; 2596/79, J
Hohnhold, Ulrich; 02.05.52; KD Fürstenwalde; 050047; 1240; V/453/88,
Hommel, Klaus; 14.09.52; HVA; 961500; 1142; 2503/77, F
Hoppe, Werner-Michael; 18.06.44; Abt. N; 906540; 1055; 2900/66,
Hornauer, Uwe; 16.08.46; HVA; 961500; 1092; 65/76, A
Hornemann, Rainer; 29.01.47; HVA; 961500; 1156; 1529/87, M
Hornig, Udo; 04.06.59; Abt. XI; 941100; 1140; 5850/84,
Horn, Jochen; 22.06.59; HVA; 961500; 1297; 2613/84, E
Höhl, Volker; 15.10.60; Abt. N; 906540; 1140; 1153/86,
Höhne, Siegfried; 10.10.39; KD Eisenhüttenstadt; 050045; 1220; V/1013/88,
Höhn, Marina; 22.03.60; HVA; 961500; 1150; 3022/89, A
Hölzel, Manfred; 29.05.39; Dresden VI; 120600; 8060; XII/1339/87,
Höppner, Matthias; 03.01.58; Abt. XI; 941100; 1143; 1710/89,
Hörnig, Klaus; 21.01.45; Abt. XI; 941100; 1092; 1903/72
Hösel, Karl; 08.11.35; Abt. XI; 941100; 1130; 434/68,
Hubatsch, Klaus; 02.12.55; HVA; 961500; 1143; 668/72, F
Hugel, Hans-Georg; 26.05.54; HVA; 961500; 1152; 4055/88, O
Huhn, Bernd; 02.12.52; HVA; 961500; 1142; 1565/86, M
Hundt, Thomas; 20.03.61; HVA; 961500; 1142; 650/75/62,
Hunger, Werner; 23.02.40; HVA; 961500; 1017; 415/81, F
Husung, Peter; 28.11.37; HVA; 961500; 1017; 2111/73, A
Huth, Andreas; 20.04.59; Dresden XIX; 121900; 8036; XII/2748/87,
Hübner, Henri; 18.11.58; Abt. N; 906540; 1034; 3892/79,
Hübner, Ina; 23.10.64; BV Berlin VI; 150600; 1090; K/4166/88,
Hübsch, Bernd; 20.09.43; HVA; 961500; 1080; 47/73, F
Hückel, Tino; 20.03.64; Abt. N; 906540; 1195; 3507/86,
Hühr, Bruno; 02.06.55; Abt. N; 906540; 1140; 3558/78,
Hüter, Rolf; 01.01.37; HVA; 961500; 1144; 2148/74, F
Ibold, Manfred; 10.08.51; HVA; 961500; 1100; 1904/73, F
Ickert, Winfried; 23.07.56; HVA; 961500; 1153; 650/75/8,
Ide, Hans-Heinrich; 27.09.41; Abt. N; 906540; 1156; 1611/76,
Illig, Gerald; 22.02.58; Abt. N; 906540; 1140; 2959/79,
Immermann, Gunter; 15.11.53; HVA; 961500; 1071; 959/89, F
Irmscher, Frank; 20.07.59; HVA; 961500; 1034; 2912/78, F
Jaenicke, Uwe; 23.06.53; HVA; 961500; 1156; 3057/89, F
Jahn, Heinz; 04.11.35; Rostock XIX; 011900; 2300; 3335/75,
Jahn, Klaus; 04.11.50; Abt. XI; 941100; 1120; 1515/75,
Jakowlow, Manfred; 29.03.50; Abt. N; 906540; 1281; 1058/86,
Janietz, Eberhard; 04.08.51; HVA; 961500; 1120; 2570/79, O
Janke, Erwin; 22.06.43; HVA; 961500; 7500; 3972/86, M
Jarchow, Hans-Jürgen; 06.04.44; HVA; 961500; 4850; 2355/88, M
Jasmann, Hans-Peter; 25.06.38; Rostock XIX; 011900; 2355; 4081/86,
Jautze, Stephan; 19.08.53; HVA; 961500; 1054; 2164/73, F
Jäger, Bernd; 04.11.47; Abt. XI; 941100; 1142; 245/77,
Jäger, Monika; 13.04.44; HVA; 961500; 1147; 618/86, M
Jäger, Siegfried; 10.01.43; HVA; 961500; 1147; 619/86, M
Jähne, Karsten; 24.06.57; HVA; 961500; 8060; 650/75/42,
Jähn, Rolf; 01.04.32; HVA; 961500; 1183; 187/61, J
Jedicke, Jürgen; 16.10.55; Abt. XI; 941100; 5060; 2415/88,
Jesse, Jan; 18.11.63; HVA; 961500; 1150; 503/82, M
John, Werner; 12.01.45; HVA; 961500; 9005; 2124/89, F
Jost, Rainer; 22.03.55; Karl-Marx-Stadt VIII; 140800; 9050; 167,
Jung, Herbert; 04.10.51; Abt. XI; 941100; 1600; 69/76,
Junkereit, Dieter; 14.05.62; Karl-Marx-Stadt VIII; 140800; 9050; 172,
Junkereit, Monika; 01.12.64; Karl-Marx-Stadt VIII; 140800; 9050; 173,
Jurisch, Hans; 11.08.32; HVA; 961500; 1130; 3730/66, K
Jürgens, Karl; 30.01.52; Abt. N; 906540; 1141; 1692/76,
Jürgens, Monika; 16.06.41; HVA; 961500; 3580; 2969/87, M
Jürgens, Peter; 13.03.41; HVA; 961500; 3580; 2968/87, M
Kaden, Horst; 13.01.35; Frankfurt/O. VI; 050600; 1200; V/430/88,
Kahl, Frank; 19.02.50; HVA; 961500; 8017; 2224/86, O
Kaiser, Karl; 16.12.36; Abt. N; 906540; 1136; 4568/77,
Kalbaß, Herbert; 21.10.34; Abt. XI; 941100; 1071; 8569/60,
Kappelmann, Jens; 08.07.53; HVA; 961500; 1160; 2972/76, F
Kappis, Peter; 14.12.49; KD Berlin-Treptow; 150046; 1093; 5320/88,
Karasch, Klaus-Dieter; 02.10.51; Abt. N; 906540; 1142; 5044/76,
Karlstedt, Manfred; 27.09.51; HVA; 961500; 1150; 1635/84, O
Kasper, Hans-Hendrik; 03.05.51; HVA; 961500; 1150; 2784/72, U
Kasper, Reiner; 16.01.56; Abt. N; 906540; 1130; 3472/76,
Kathert, Klaus; 03.06.49; Abt. N; 906540; 1292; 1354/71,
Keindorf, Thomas; 09.05.66; HVA; 961500; 1156; 3732/87, O
Kellermann, Harald; 26.04.51; HVA; 961500; 1140; 4691/89, L
Keller, Hans-Joachim; 22.10.38; HVA; 961500; 1020; 2245/73, M
Keller, Klaus; 25.01.36; HVA; 961500; 1600; 2332/73, M
Keller, Rolf; 25.10.57; HVA; 961500; 2000; 5743/84, M
Kellner, Axel; 05.01.40; Abt. XI; 941100; 1140; 759/66,
Kerlisch, Werner; 23.04.36; OD KKW Nord; 010050; 2200; 3477/73,
Kernchen, Eckehardt; 01.10.50; Abt. N; 906540; 1020; 5041/76,
Kettner, Bernd; 28.05.47; Rostock, Abt. Hafen; 011969; 2520; 4080/86,
Keyselt, Klaus; 30.04.51; HVA; 961500; 1142; 1938/75, F
Kießig, Horst; 02.05.37; HVA; 961500; 1156; 307/82, J
Kießling, Dirk; 11.03.69; Abt. N; 906540; 1092; 5156/88,
Kirchbach, Rene; 05.04.64; HVA; 961500; 8010; 5865/84, F
Kirchhof, Jens; 04.12.61; HVA; 961500; 1020; 650/75/72,
Kirchner, Marianne; 18.10.43; HVA; 961500; 1130; 4718/88/1, F
Kirchner, Wolfgang; 23.08.39; HVA; 961500; 1130; 4718/88, F
Kirmse, Udo; 24.02.39; HVA; 961500; 1136; 2824/84, X
Kirsten, Falko; 11.02.50; HVA; 961500; 1600; 2511/77, M
Kirst, Alfred; 08.03.34; HA VI; 970600; 1080; K/4428/87,
Kißig, Jochen; 11.05.53; KD Löbau; 120049; 8700; KISSIG, JOCHEN
Kittler, Manfred; 13.03.33; Dresden XVIII; 121800; 8251; XII/1346/87,
Kittler, Roland; 25.01.58; Abt. XI; 941100; 4020; 5311/88,
Klarner, Volkmar; 23.03.54; Abt. XI; 941100; 9900; 2305/85,
Kleiber, Thomas; 02.01.55; HVA; 961500; 1020; 4365/86, U
Kleinhempel, Heinz; 04.07.57; Leipzig XVIII; 131800; 7050; K/5409/88,
Klemcke, Hermann; 15.11.51; KD Schwedt; 050050; 1330; V/446/88,
Klemens, Leo; 25.03.27; HVA; 961500; 1532; 19522/60, X
Klemme, Jan; 03.02.67; Abt. N; 906540; 1142; 2976/86,
Klenz, Henry; 03.12.56; Abt. XI; 941100; 1130; 409/81,
Klingsieck, Ralf; 10.10.47; HVA; 961500; 1092; 1644/69, F
Klotzke, Jürgen; 05.07.48; HVA; 961500; 6908; 3914/85, A
Klutznik, Axel; 11.07.61; Abt. XI; 941100; 1580; :
Kluwe, Frank; 11.10.49; HVA; 961500; 1142; 465/74, F
Knackstedt, Hans-Jürgen; 02.03.41; Abt. XI; 941100; 1162; 40/69,
Knaupe, Henk; 14.10.65; HVA; 961500; 1090; 423/88, M
Knieling, Annelie; 09.11.50; HVA; 961500; 1115; 3167/78, U
Knobloch, Angelika; 11.07.49; Abt. N; 906540; 1281; 1997/77,
Knobloch, Hans-Uwe; 23.10.57; Abt. N; 906540; 1092; 2487/77,
Knorr, Hans-Joachim; 25.04.38; HVA; 961500; 1615; 304/80, M
Knoth, Uwe; 08.04.57; Abt. XI; 941100; 1100; 6461/82,
Knöller, Sergej; 24.10.63; HVA; 961500; 1095; 5000/87, F
Knötel, Ronald; 14.10.63; BV Magdeburg, Abt. XV; 071500; 3080; :
Kobel, Werner; 07.03.38; HVA; 961500; 1600; 4710/80, L
Kobuch, Norbert; 22.12.51; HVA; 961500; 1058; 4980/88, O
Kochanek, Wolfgang; 14.09.41; HVA; 961500; 1055; 389/74, A
Kochsiek, Jürgen; 15.03.41; Karl-Marx-Stadt VIII; 140800; 9050; 178,
Koch, Arno; 18.02.37; KD Görlitz; 120047; 8903; XII/2406/88,
Koch, Bernhard; 12.02.44; HVA; 961500; 1142; 1566/86, M
Koch, Helmut; 20.12.49; Abt. N; 906540; 1153; 5340/84,
Koch, Jutta; 16.06.32; Abt. XI; 941100; 1162; 2390/70,
Koch, Paul; 09.05.44; HVA; 961500; 1910; 4651/85, M
Koch, Wilhelm; 22.08.41; Abt. XI; 941100; 1115; 416/70,
Koderhold, Dieter; 25.06.47; Abt. N; 906540; 1140; 447/74,
Koglin, Mario; 11.08.66; HVA; 961500; 1110; 3900/85, M
Kohoutek, Sepp; 10.03.54; HVA; 961500; 1090; 4998/87, F
Kokscht, Thomas; 10.07.58; HVA; 961500; 1035; 836/77, F
Kolasinski, Helge; 04.04.63; Abt. N; 906540; 1054; 2220/83,
Kolleßer, Klaus; 11.03.51; HVA; 961500; 7072; 612/89, F
Kolleßer, Regina; 11.11.48; HVA; 961500; 7072; 6763/88, F
Kolletzky, Olaf; 08.07.54; Abt. XI; 941100; 9900; 862/83,
Konieczny, Frank; 04.09.44; HVA; 961500; 1600; 1762/89, N
Konnopka, Frank; 11.04.48; Abt. N; 906540; 1280; 5003/80,
Konnopka, Gudrun; 27.12.48; Abt. N; 906540; 1280; 4038/79,
Konschel, Peter; 30.03.49; Abt. N; 906540; 1280; 4054/85,
Kopius, Elke; 24.04.51; Abt. N; 906540; 1140; 1885/81,
Korn, Robert; 11.09.37; HVA; 961500; 1195; 43/63, L
Kosch, Bärbel; 07.08.60; HVA; 961500; 6500; 3153/89, F
Kosch, Gunter; 31.01.53; Abt. XI; 941100; 6500; 2414/88,
Kosin, Heinz; 07.03.26; HVA; 961500; 1020; 2148/72, U
Kowatzkl, Fred; 15.05.55; Abt. N; 906540; 1150; 4712/78,
Köhler, Erwin; 06.10.40; Frankfurt/O. XVIII; 051800; 1200; V/442/88,
Köhler, Klaus; 20.02.52; HVA; 961500; 1020; 2565/88, O
Köhler, Petra; 20.03.51; HVA; 961500; 1017; 318/78, E
Köhler, Wolfgang; 29.06.51; HVA; 961500; 1017; 3254/84, E
König, Hans; 23.05.36; Abt. N; 906540; 1136; 7261/75,
Körner, Manfred; 26.01.43; Dresden VI; 120600; 8019; XII/414/89,
Köster, Sven; 18.04.66; Abt. N; 906500; 1150; 4732/87,
Köster, Ulrich; 20.11.42; Abt. N; 906540; 1292; 1687/76,
Kraatz, Jens-Peter; 27.09.60; Abt. N; 906540; 1090; 7603/81,
Krahl, Frank-Michael; 03.03.50; Abt. N; 906540; 1130; 1614/75,
Krahmüller, Uwe; 14.12.65; HVA; 961500; 6018; 5265/85, Q
Krahn, Charlotte; 22.04.30; HVA; 961500; 1020; 46/72, U
Kramer, Bernd; 20.10.41; Karl-Marx-Stadt, BKG; 142900; 9005; K/6104/88
Krannich, Matthias; 20.03.57; Abt. XI; 941100; 1144; 5798/84,
Kranz, Herbert; 17.12.39; Abt. N; 906540; 1092; 9805/61,
Kranz, Rosmarie; 21.12.40; Abt. N; 906540; 1092; 4354/77,
Krause, Johannes; 24.10.49; Abt. XI; 941100; 1600; 3702/73,
Krauße, Günter; 25.05.37; HVA; 961500; 8360; 1498/87, F
Kraus, Bert; 03.03.61; HVA; 961500; 1143; 813/83, P
Kraus, Rudolf; 23.07.37; HVA; 961500; 1140; 340/81, F
Kreher, Ralf; 28.02.67; Abt. N; 906540; 9300; 1160/89,
Kreinberger, Rolf; 25.05.29; HVA; 961500; 1121; 2637/77, S
Krenz, Bianca; 23.12.62; HVA; 961500; 1120; 3899/86, U
Kresse, Lutz; 12.10.54; HVA; 961500; 2090; 2354/88, M
Krietsch, Sabine; 10.11.49; Abt. N; 906540; 1280; 1922/76,
Kringler, Paul; 02.07.28; KD Stralsund; 010047; 2300; 1110/73,
Krohn, Heinz Günter; 28.01.56; Abt. XI; 941100; 7033; 493/87,
Krone, Reinhard; 23.07.48; HVA; 961500; 4090; 3823/86, M
Kröpelin, Detlef; 01.11.56; HVA; 961500; 1142; 51/80, F
Krumpfert, Joachim; 15.02.49; Abt. N; 906540; 1034; 1763/76,
Kruse, Gerlinde; 02.10.54; Abt. XI; 941100; 1142; 4701/89,
Kruse, Peter; 07.01.46; Abt. N; 906540; 1142; 1989/76,
Krüger, Andreas; 11.04.61; Abt. N; 906540; 1130; 7148/81,
Krüger, Brigitte; 11.02.37; HVA; 961500; 1130; 3419/84/1, O
Krüger, Hans; 15.06.37; HVA; 961500; 1130; 3419/84, O
Krüger, Holger; 26.04.57; Abt. N; 906540; 1280; 3389/76,
Krüger, Horst; 05.10.43; Abt. N; 906540; 1034; 1622/76,
Krüger, Reinhard; 26.04.33; Abt. N; 906540; 1017; 7257/75,
Krüger, Uwe; 22.08.60; Abt. XI; 941100; 7513; 3385/84,
Krzebeck, Siegfried; 05.02.52; Abt. N; 906540; 1035; 1689/76,
Krzyzanowski, Claus; 28.11.53; Abt. N; 906540; 1130; 1926/76,
Kudernatsch, Matthias; 18.03.65; Abt. N; 906540; 1150; 5032/89,
Kulitzscher, Manfred; 30.05.32; Rostock XVIII; 011800; 2555; 1530/70,
Kunisch, Frank; 20.02.59; Abt. N; 906540; 1150; 4107/79,
Kunze, Alfred; 30.03.32; KD Eberswalde; 050044; 1298; V/429/88,
Kunze, Heinz; 08.05.37; Dresden XVIII; 121800; 8101; XII/1345/87,
Kunze, Wilfried; 01.04.45; BV Berlin XVIII; 151800; 1145; 2809/88,
Kunzmann, Frank; 08.06.53; HVA; 961500; 9050; 650/75/64,
Kupferschmidt, Erich; 23.07.52; Abt. N; 906540; 1140; 2808/79,
Kupferschmidt, Gudrun; 03.05.52; Abt. XI; 941100; 1140; :
Kupsch, Michael; 28.04.58; HVA; 961500; 1090; 2686/79, F
Kurjuweit, Karlheinz; 27.03.50; KD Angermünde; 050041; 1330; V/439/88,
Küchenmeister, Hartmut; 31.03.54; HVA; 961500; 1144; 5042/86, N
Kücken, Werner; 31.08.28; BV Berlin XVIII; 151800; 1421; 1143/70,
Kynast, Klaus; 29.04.55; HVA; 961500; 1150; 1043/84, A
Ladebeck, Bernd; 22.05.56; Abt. N; 906540; 1140; 4952/77,
Lagemann, Jürgen; 22.08.48; Abt. XI; 941100; 1140; 7/76,
Lamberz, Ulrich; 02.07.52; HVA; 961500; 1092; 234/73, F
Lamm, Hans-Joachim; 03.01.42; Dresden VI; 120600; 8020; XII/2655/87,
Langer, Achim; 09.03.56; Abt. N; 906540; 1130; 1864/78,
Langer, Karl; 06.10.34; Abt. N; 906540; 1297; 1796/80,
Lange, Frank; 31.12.50; Abt. XI; 941100; 1143; 2745/79,
Lange, Gerd; 15.12.60; HVA; 961500; 4300; 650/75/19,
Lange, Harald; 03.01.34; HVA; 961500; 1147; 2367/73, U
Lange, Karl-Heinz; 31.12.52; HVA; 961500; 1058; 107/75, F
Lange, Kathlen; 23.05.62; HVA; 961500; 4300; 1763/88, E
Lange, Matthias; 07.10.56; Abt. N; 906540; 1141; 3503/87,
Lange, Ralf; 15.08.60; HVA; 961500; 1100; 1433/85, J
Lange, Reiner; 12.06.36; HVA; 961500; 1017; 1046/67, M
Lauenroth, Hans-Peter; 08.08.61; HVA; 961500; 1136; 1078/81, F
Laue, Lutz; 25.02.53; Abt. N; 906540; 1143; 2528/82,
Laupert, Andrea; 16.09.61; HVA; 961500; 1140; 2816/80, O
Lätzer, Eberhard; 03.12.48; Abt. XI; 941100; 1140; 3700/73,
Lechelt, Arno; 24.06.44; Abt. XI; 941100; 1140; 8511/81,
Lehmann, Frank; 11.07.66; HVA; 961500; 7580; 3170/89, Q
Lehmann, Holger; 14.10.62; Abt. N; 906540; 1144; 6082/82,
Lehmann, Rainer; 08.03.49; HVA; 961500; 1150; 2987/77, J
Leibscher, Axel; 26.03.54; HVA; 961500; 7301; 650/75/65/,
Leinweber, Manfred; 04.03.42; HVA; 961500; 1136; 166/77, M
Leirich, Bernd; 02.06.55; Abt. XI; 941100; 2500; 2796/87,
Leistner, Dieter; 23.05.42; HVA; 961500; 1250; 3478/84, J
Lemke, Frank; 09.11.60; Abt. N; 906540; 1071; 3021/84,
Lemke, Sabine; 15.09.65; Abt. N; 906540; 1071; 969/86,
Lenhard, Peter; 27.09.51; Abt. N; 906540; 1140; 1906/71,
Leonhardt, Heiko; 12.01.66; Abt. N; 906540; 1130; 5391/86,
Lerche, Ruth; 12.03.33; HVA; 961500; 1092; 3899/63, U
Leuschner, Harald; 01.10.39; HVA; 961500; 1020; 3713/87, F
Leymann, Jan; 30.03.61; HVA; 961500; 1092; 3020/76/9, M
Liebholz, Gisela; 09.01.30; HVA; 961500; 1055; 225/78, U
Liedke, Peter; 04.12.50; HVA; 961500; 1140; 1476/87, F
Lieniger, Bruno; 01.11.31; Abt. XI; 941100; 1140; 4167/83,
Ließneck, Walter; 12.10.37; HVA; 961500; 1115; 1990/72, M
Lietz, Peter; 13.02.54; Abt. N; 906540; 1280; 1990/76,
Linck, Joachim; 27.02.48; HVA; 961500; 2330; 1528/87, M
Linck, Rita; 27.11.51; Abt. XI; 941100; 2330; 1533/87, M
Lindig, Hans-Dieter; 11.01.30; Rostock VI; 010600; 2540; 1397/86,
Lindner, Dietmar; 09.06.51; Abt. N; 906540; 1140; 1988/76,
Lindner, Steffen; 18.04.68; HVA; 961500; 1035; 3948/86, M
Linke, Gerald; 29.06.39; HVA; 961500; 6504; 3871/87, F
Linke, Marga; 01.09.39; HVA; 961500; 6504; 3871/87/1, F
Linke, Reinhard; 18.07.30; HVA; 961500; 1199; 153/72, J
Lippert, Bodo; 04.01.62; Abt. N; 906540; 1071; 7402/81,
Lißke, Birgit; 13.03.55; Karl-Marx-Stadt VIII; 140800; 9050; 177,
Lißke, Gerhard; 17.01.51; Karl-Marx-Stadt VIII; 140800; 9050; 176,
Lobedan, Gerd; 21.05.54; HVA; 961500; 1143; 3961/83, M
Lode, Harald; 06.10.53; HVA; 961500; 8036; 2429/88, M
Lohse, Gerd; 24.07.46; Abt. N; 906540; 1144; 2007/67,
Loos, Siegfried; 30.06.40; HVA; 961500; 9061; 1750/72, M
Lorenz, Jörg; 21.05.62; HVA; 961500; 1017; 5026/84, F
Lorenz, Werner; 01.01.34; HVA; 961500; 1595; 4626/79, F
Lorenz, Wolfgang; 03.05.54; HVA; 961500; 1143; 95/76, F
Loudovici, Armin; 12.10.39; HVA; 961500; 1190; 4331/86, F
Löbnitz, Wolfram; 26.08.57; HVA; 961500; 1195; 1371/77, F
Löwa, Werner; 30.05.54; HVA; 961500; 1093; 425/79, F
Lubs, Bodo; 14.03.53; Abt. XI; 941100; 2103; 2026/86,
Lucas, Karl-Heinz; 27.02.57; Abt. N; 906540; 1090; 3705/77,
Ludwig, Horst; 27.08.31; HVA; 961500; 1017; 2588/77, P
Ludwig, Lutz; 15.10.53; HVA; 961500; 1143; 2113/89, E
Lux, Klaus; 19.08.43; KD Wolgast; 010049; 2220; 5577/81,
Lübke, Brigitte; 22.04.41; Rostock XVIII; 011800; 2500; 1119/79,
Lübke, Klaus; 27.03.52; HVA; 961500; 1220; 650/75/22,
Lücke, Karl-Ernst; 17.10.37; Abt. XI; 941100; 1035; 769/86,
Lück, Michael; 16.07.60; Abt. XI; 941100; 7260; 3814/85,
Lüdecke, Olaf; 15.06.48; Abt. XI; 941100; 1092; 2747/79,
Lüneburg, Karsten; 31.07.60; Abt. N; 906540; 1142; 3079/83,
Maaske, Gudrun; 11.11.42; HVA; 961500; 1162; 1351/89, N
Maaske, Klaus; 26.07.39; HVA; 961500; 1162; 3997/85, N
Maaß, Uwe; 20.07.61; HVA; 961500; 1100; 1680/88, F
Maget, Gerhard; 18.12.51; HVA; 961500; 1142; 2576/77, F
Maigatter, Tino; 21.02.62; HVA; 961500; 1054; 2766/84, F
Malchow, Dieter; 19.07.54; HVA; 961500; 1110; 2730/89, F
Manikowski, Jürgen; 30.07.54; Abt. XI; 941100; 2540; 1607/88,
Maretzki, Peter; 27.03.57; HVA; 961500; 1093; 235/79, M
Marks, Stefan; 20.09.52; HVA; 961500; 1250; 2501/77, F
Marnitz, Andreas; 01.10.56; HVA; 961500; 1150; 3498/86, F
Marr, Donald; 10.04.37; Abt. XI; 941100; 1250; 8/74,
Masula, Jens; 23.08.64; HVA; 961500; 1152; 5863/84, F
Matros, Jürgen; 04.06.53; HVA; 961500; 1160; 4049/88, O
Mattner, Susanne; 02.12.61; Abt. N; 906540; 1140; 3966/82,
Matusch, Klaus-Dieter; 20.09.56; Abt. N; 906540; 1090; 3685/82,
Maudrich, Peter; 10.02.58; Abt. XI; 941100; 6502; 4705/85,
Maune, Monika; 16.06.59; Dresden VI; 120600; 8023; XII/1334/89,
May, Jürgen; 19.04.57; Abt. N; 906540; 1156; 1508/80,
Märkel, Günter; 01.06.41; Abt. N; 906540; 1130; 3325/76,
Märkel, Sigrid; 02.06.41; Abt. N; 906540; 1130; 5272/76,
Mehlhorn, Lutz-Rainer; 15.11.40; HVA; 961500; 1020; 1029/67, J
Meichsner, Matthias; 03.09.58; HVA; 961500; 1090; 4416/80, F
Meier, Bernd; 08.08.54; Dresden XIX; 121900; 8020; XII/2749/87,
Meier, Detlef; 23.09.51; Abt. N; 906540; 1150; 448/74,
Meilick, Bernd; 11.06.47; HVA; 961500; 1092; 419/81, M
Mekelburg, Michaela; 21.03.61; HVA; 961500; 1140; 1346/85/1, F
Menzel, Harri; 27.01.35; Rostock VII; 010700; 2520; 5951/84,
Menz, Harry; 27.05.38; HVA; 961500; 1136; 12487/60, A
Merkel, Thomas; 19.01.59; HVA; 961500; 1055; 424/82, M
Messerle, Peter; 05.06.53; HVA; 961500; 1195; 2784/73, F
Metelmann, Bernd; 16.05.56; Abt. N; 906540; 1130; 3390/76,
Meyer, Detlef; 09.08.52; KD Rostock; 010040; 2540; 379/88,
Meyer, Horst; 23.08.33; HVA; 961500; 1100; 1348/85, F
Meyer, Jürgen; 04.01.42; Abt. N; 906540; 1140; 2587/65,
Michaelis, Holger; 20.10.58; HVA; 961500; 1152; 2611/84, F
Michel, Günther; 07.06.51; Abt. N; 906540; 1093; 2407/77,
Mieley, Siegfried; 30.07.36; Frankfurt/O. VII; 050700; 1200; V/431/88,
Mielke, Klaus; 11.07.39; Abt. XI; 941100; 1055; 2899/68,
Miersch, Harald; 26.11.51; HVA; 961500; 1142; 174/79, M
Mihm, Guido; 11.07.70; HVA; 961500; 1035; 4666/89,
Milde, Jörg; 16.11.54; BV Berlin XVIII; 151800; 1136; 4199/80,
Mirtschink, Jürgen; 09.01.48; HVA; 961500; 1034; 1902/72, F
Mischner, Jörg; 24.11.64; HVA; 961500; 1150; 1716/89, I
Mittelberger, Andreas; 15.02.65; Abt. N; 906540; 1020; 5221/84,
Mitzscherling, Peter; 27.02.36; Abt. XI; 941100; 1136; 410/81,
Monatsch, Jörg; 17.12.67; Schwerin II; 020200; 2755; :
Montwill, Frank; 25.04.54; HVA; 961500; 1144; 5630/86, A
Möckel, Joachim; 12.02.45; HVA; 961500; 9050; 3757/87, F
Mrosk, Dieter; 01.11.43; Abt. XI; 941100; 1140; 211/74,
Muth, Rolf; 31.01.29; HVA; 961500; 1017; 269/68, P
Mutscher, Monika; 01.12.53; Abt. N; 906540; 1130; 3684/82,
Mühlbauer, Dietmar; 02.06.47; Abt. N; 906540; 1092; 374/75,
Mühle, Dieter; 07.03.40; KD Dresden/Stadt; 120040; 8010; XII/2671/87,
Müller, Bärbel; 12.03.41; HVA; 961500; 1170; 1675/84/1, C
Müller, Barbara; 22.09.52; Abt. XI; 941100; 2356; 1608/88/1,
Müller, Detlef; 04.02.58; HVA; 961500; 1020; 650/75/43,
Müller, Ernst-Peter; 24.07.40; HVA; 961500; 1170; 1675/84, C
Müller, Erwin; 19.07.44; Abt. N; 906540; 2081; 2626/65,
Müller, Hannelore; 22.06.46; Abt. N; 906540; 2081; 3339/78,
Müller, Heinz-Jürgen; 24.09.48; HVA; 961500; 2520; 499/87, F
Müller, Helga; 15.11.37; HVA; 961500; 1144; 5009/87, D
Müller, Helmut; 07.01.40; BV Berlin XVIII; 151800; 1080; 608/83,
Müller, Irina; 19.09.62; HVA; 961500; 1020; 650/75/43/1,
Müller, Johannes; 09.08.46; Abt. N; 906540; 1140; 2006/67,
Müller, Jürgen; 07.08.59; HVA; 961500; 7930; 650/75/23,
Müller, Jürgen; 25.07.53; Abt. N; 906540; 1090; 3490/83,
Müller, Matthias; 03.06.53; HVA; 961500; 7840; 4729/89, M
Müller, Peter; 06.06.37; Dresden XVIII; 121800; 8023; XII/1348/87,
Müller, Uwe; 02.12.63; HVA; 961500; 1136; 3791/85, F
Müller, Uwe; 07.10.54; Abt. XI; 941100; 2356; 1608/88,
Münchow, Frank; 19.02.61; Abt. XI; 941100; 2830;
Münzel, Heinz; 20.07.47; HVA; 961500; 1020; 167/78, K
Mütschard, Peter; 28.01.52; HVA; 961500; 7060; 650/75/35,
Nareike, Kurt; 28.09.37; Rostock VI; 010600; 2520; 5283/78,
Nathe, Rolf; 27.09.30; HVA; 961500; 1170; 8/75, J
Naue, Rainer; 14.03.56; Abt. N; 906540; 1130; 3077/83,
Naumann, Gerhard; 25.02.49; Cottbus XIX; 061900; 7500; K3504/89,
Naumann, Uwe; 15.07.56; HVA; 961500; 8321; 650/75/36,
Näther, Frank; 08.09.50; HVA; 961500; 1140; 2257/70, F
Neff, Gertrud; 25.04.31; Abt. XI; 941100; 1156; 8510/81,
Nehls, Jörg; 08.07.58; HVA; 961500; 1143; 2592/80, F
Nennhaus, Detlef; 30.06.47; Abt. N; 906540; 1140; 7264/75,
Nestler, Olaf; 26.05.63; Abt. N; 906540; 1040; 2080/82,
Neumann, Klaus-Dieter; 24.07.47; Abt. XI; 941100; 1400; 3386/71,
Nicicky, Stephan; 23.04.55; Abt. N; 906540; 1092; 1999/77,
Nier, Herbert; 28.08.54; HVA; 961500; 1100; 2477/75, F
Noculak, Johannes; 27.05.41; HVA; 961500; 1162; 113/74, L
Noetzel, Peter; 27.02.40; Abt. N; 906540; 1136; 1608/76,
Noffke, Bernd; 11.10.59; Abt. N; 906540; 1197; 5016/85,
Nöbel, Manfred; 29.11.32; BV Berlin XVIII; 151800; 1020; 1341/83,
Nölte, Joachim; 11.11.48; HVA; 961500; 1017; 2553/80, P
Nücklich, Horst; 03.06.35; Dresden, BKG; 122900; 8010; XII/2753/87,
Oelschlaeger, Wolfgang; 06.03.39; Abt. XI; 941100; 1162; 9802/61,
Oertel, Hans-Joachim; 07.12.54; HVA; 961500; 1120; 3561/88, E
Oertel, Ulrich; 12.01.51; HVA; 961500; 1156; 19/76, F
Ola, Heinz; 25.06.34; Abt. N; 906540; 1092; 3705/73,
Ondrej, Detlev; 31.01.52; Abt. XI; 941100; 1136; 3763/88,
Ondrej, Ilona ; 24.07.54; HVA; 961500; 1136; 3763/88/1, F
Ondrusch, Aribert; 11.06.52; HVA; 961500; 7063; 6372/81, U
Ostoike, Harry; 14.05.57; Abt. N; 906540; 1140; 6979/80,
Otto, Hans; 03.06.50; HVA; 961500; 1144; 4692/89, L
Paasch, Uwe; 26.02.58; Abt. XI; 941100; 7280; 2794/87,
Pach, Detlef; 08.03.44; Dresden VII; 120700; 8101; XII/1342/87,
Pahlke, Lothar; 30.07.42; HVA; 961500; 6850; 650/75/18,
Pahlke, Gudrun; 15.08.49; HVA; 961500; 6850; 650/75/18/1,
Pangsy, Reiner; 12.11.40; Abt. N; 906540; 1280; 2437/60,
Parke, Kerstin; 26.01.62; Abt. XI; 941100; 3018; 1894/87/1,
Paulick, Gunter; 30.06.57; HVA; 961500; 7513; 650/75/44,
Paul, Gerhard; 11.08.53; HVA; 961500; 1100; 2639/79, J
Paul, Werner; 28.04.52; Abt. N; 906540; 1150; 3893/77,
Pawlak, Norbert; 01.10.47; BV Berlin XX; 152000; 1140; 3005/84,
Päsler, Knut; 15.07.65; HVA; 961500; 2000; 5196/84, F
Pecher, Rudolf; 27.09.55; Abt. N; 906540; 1020; 7272/75,
Perschon, Andreas; 01.11.58; HVA; 961500; 1055; 1233/80, F
Petermann, Walter; 28.01.50; HVA; 961500; 1130; 4216/84, F
Peters, Joachim; 15.02.55; Abt. XI; 941100; 1580; 2797/87,
Petzold, Frank; 24.04.60; Abt. XI; 941100; 7840; 1711/89,
Pfarr, Wilfried; 04.09.38; HVA; 961500; 1080; 180/73, M
Philipp, Siegfried; 19.10.49; Abt. N; 906540; 1017; 3078/83,
Pieritz, Reiner; 10.06.49; Abt. XI; 941100; 1600; 3701/73,
Pierschel, Bernd; 25.02.40; HVA; 961500; 1280; 128/68, F
Pietschmann, Hans; 26.05.40; Dresden XVIII; 121800; 8010; XII/2665/87,
Piletzki, Doris; 20.04.54; Abt. N; 906540; 1120; 1603/76,
Pingel, Jürgen; 14.04.34; HVA; 961500; 1020; 250/81, M
Plogas, Lutz-Ulrich; 14.04.50; HVA; 961500; 1092; 3974/87, J
Plomann, Michael; 31.03.61; Abt. N; 906540; 1100; 3501/85,
Ploner, Ekhard; 08.06.30; HVA; 961500; 1020; 1041/67, M
Plumbohm, Ilona; 26.02.59; Abt. XI; 941100; 1092; 1844/88,
Pohl, Bernd; 07.11.52; Cottbus, Abt. KuSch; 064000; 7500; 1587/87,
Pohl, Heinrich; 05.10.53; ZAIG; 995300; 8036; K, 4401/88
Polcuch, Konrad; 03.12.53; HVA; 961500; 1055; 3671/88, M
Polcuch, Marion; 06.11.53; HVA; 961500; 1055; 3670/88, F
Polster, Claus; 07.07.50; HVA; 961500; 7034; 1530/87, M
Popp, Rudolf; 21.09.36; HVA; 961500; 1136; 4283/88, F
Porges, Brigitte; 09.06.49; HVA; 961500; 1280; 3137/89, F
Porges, Manfred; 18.12.45; HVA; 961500; 1280; 3136/89, F
Pötsch, Hans; 03.11.41; HVA; 961500; 1197; 112/76, M
Prade, Reiner; 19.09.56; HVA; 961500; 1145; 4527/87, A
Pratsch, Klaus; 21.07.39; HVA; 961500; 1017; 1331/63, T
Preißler, Steffen; 05.06.66; Abt. N; 906540; 8017; 1161/89,
Prestin, Uwe; 03.11.40; Abt. N; 906540; 1150; 7399/81,
Preusche, Dieter; 07.12.43; HVA; 961500; 1142; 6977/75, A
Proft, Andre; 09.10.63; HVA; 961500; 1017; 760/88, D
Prokop, Adolf; 02.02.39; AGM, Arbeitsgebiet R; 956024; 5066; K, 187/71
Propf, Ulrich; 12.06.57; HVA; 961500; 4350; 650/75/4,
Puchner, Albrecht; 05.07.53; Abt. N; 906540; 1200; 2319/84,
Puchta, Gerdt; 09.01.51; HVA; 961500; 2540; 1864/89, M
Pufe, Rainer; 21.02.52; Abt. N; 906540; 1140; 1514/75,
Püstel, Brigitte; 27.04.43; Abt. XI; 941100; 1100; 239/85,
Püwick, Heinz; 01.08.28; HVA; 961500; 1280; 330/85, T
Pyritz, Frank; 08.10.58; Abt. N; 906540; 1092; 2128/78,
Radke, Bernd; 29.09.46; Abt. N; 906540; 1280; 1604/76,
Radke, Gudrun; 24.06.47; Abt. N; 906540; 1280; 2286/74,
Radtke, Peter; 27.08.62; HVA; 961500; 1140; 2637/84, M
Radünz, Christine; 26.09.53; HVA; 961500; 1136; 2758/78, J
Rahn, Winfried; 25.04.57; Abt. N; 906540; 1090; 4142/79,
Ramme, Alwin; 12.03.32; HVA; 961500; 1017; 3321/71, U
Ramminger, Uwe; 04.01.54; Abt. XI; 941100; 8245; 3256/84,
Rasel, Klaus; 30.05.42; HVA; 961500; 1532; 650/75/45,
Rasmus, Hartmut; 04.02.43; Abt. XI; 941100; 5500; 702/86,
Ratschke, Lutz-Dieter; 04.12.53; Abt. N; 906540; 1034; 5042/76,
Ratzmann, Ingrid; 18.04.37; HVA; 961500; 1035; 1672/84, A
Rauch, Benno; 25.09.53; Abt. N; 906540; 1136; 4146/79,
Rauch, Hannelore; 24.12.50; HVA; 961500; 2794; 650/75/30/1,
Rauch, Helmut; 09.01.53; HVA; 961500; 1092; 574/72, F
Rauch, Lothar; 04.11.53; HVA; 961500; 2794; 650/75/30,
Redlich, Hans-Joachim; 27.09.41; BV Berlin XIX; 151900; 1150; 1091/79,
Redlinghöfer, Ilse; 28.07.37; HA III; 940300; 1162; K, 1858/88,
Regner, Karsten; 19.03.63; HVA; 961500; 1092; 4311/84, M
Reichelt, Werner; 10.12.35; Abt. XI; 941100; 1020; 2046/64,
Reichelt, Wolfgang; 24.04.38; Rostock XVIII; 011800; 2520; 189/71,
Reichel, Joachim; 06.07.44; HVA; 961500; 2500; 1863/89, M
Reichel, Manfred; 14.04.59; HVA; 961500; 1093; 3062/78, F
Reichel, Reinhard; 20.09.45; Abt. XI; 941100; 1080; 17/71,
Reichert, Bernd; 11.06.50; Abt. N; 906540; 1093; 2094/72,
Reif, Frank; 05.10.58; HVA; 961500; 6016; 650/75/20,
Reiß, Alfred; 06.10.34; HVA; 961500; 1020; 4242/60, J
Reiter, Hermann; 11.10.37; HVA; 961500; 1100; 186/77, J
Renner, Andreas; 16.04.59; HVA; 961500; 1153; 19/81, F
Renner, Lothar; 05.06.45; HVA; 961500; 1054; 136/71, J
Rennhack, Lutz-Peter; 12.11.54; HVA; 961500; 4730; 650/75/46,
Retzlaff, Gerd; 06.07.39; HVA; 961500; 1142; 2756/84, G
Reuter, Simone; 19.06.67; HVA; 961500; 1140; 4274/89, M
Ribbecke, Horst; 19.04.25; HA XVIII; 981800; 1017; RIBBECKE, HORST
Richter, Andre; 21.09.61; Abt. N; 906540; 1143; 5786/82,
Richter, Detlef; 02.05.57; Abt. N; 906540; 1093; 7135/80,
Richter, Norbert; 24.09.47; KD Freiberg; 140047; 9200; K/1724/89,
Richter, Reinhard; 27.02.52; HVA; 961500; 1035; 4349/84, O
Richter, Willi; 21.06.32; HVA; 961500; 1130; 3776/87, F
Riedel, Dieter; 24.11.52; HVA; 961500; 1140; 3848/81, M
Riedel, Dietmar; 19.02.52; HVA; 961500; 1020; 2970/87, M
Riedel, Erhard; 26.03.46; HA III; 940300; 1136; K, 2963/89
Riedel, Winfried; 27.05.40; HVA; 961500; 1017; 777/65, M
Riemer, Rudi; 04.03.32; Frankfurt/O. XVIII; 051800; 1200; V/443/88,
Riesner, Wolfgang; 12.06.50; Abt. N; 906540; 1136; 2279/74/1,
Riewe, Hartmut; 16.08.42; KD Wismar; 010048; 2402; 4910/75,
Ritzmann, Hartmut; 23.01.56; HVA; 961500; 1140; 1715/89, M
Roeßler, Jochen; 13.03.41; KD Dresden/Stadt; 120040; 8060; XII/2670/87,
Rolfs, Raimund; 16.10.57; HVA; 961500; 1136; 3891/83, F
Roll, Gerd; 05.09.55; HVA; 961500; 2200; 650/75/28,
Roloff, Herbert; 16.02.36; HVA; 961500; 1144; 1611/69, Q
Rosenkranz, Rudolf; 23.11.30; Rostock XVIII; 011800; 2565; 680/70,
Rosenthal, Ralf; 19.12.64; HVA; 961500; 1140; 5423/88, S
Rostek, Horst; 26.05.29; HVA; 961500; 1156; 18500/60, F
Rost, Andrea; 23.11.57; HVA; 961500; 1150; 4298/89, F
Rost, Dieter; 31.05.57; Abt. N; 906540; 1150; 7214/81,
Rothbauer, Edmund; 04.08.30; Frankfurt/O., SED-PO-Ltg.; 054100; 1200; V/432/88,
Roth, Andreas; 31.03.52; HVA; 961500; 1140; 121/69/35, AB
Roth, Hans-Jochen; 12.07.43; HVA; 961500; 1800; 1381/89, M
Rödel, Johannes; 05.07.33; HVA; 961500; 1614; 650/88, D
Röder, Detlev; 12.06.56; Abt. N; 906540; 1130; 744/88, N
Röder, Siegmar; 03.05.37; HVA; 961500; 1156; 18/67, S
Röhling, Thomas; 30.04.59; Abt. XI; 941100; 1035; 1649/82,
Röhl, Gerhard; 26.07.52; Abt. N; 906540; 1142; 1883/81,
Röhner, Bernd; 07.01.57; HVA; 961500; 1040; 4700/89, F
Römer, Heinz; 11.02.32; HVA; 961500; 1250; 5192/86, M
Römer, Lutz; 09.08.59; HVA; 961500; 1055; 3400/89, F
Rörster, Hans; 29.05.30; HVA; 961500; 1147; 1593/86, U
Rösch, Klaus; 28.04.41; Abt. XI; 941100; 1100; 9797/61,
Rösner, Andreas; 16.06.51; ZAIG; 995300; 8020; K, 2964/89
Rudolph, Peter; 05.10.29; HVA; 961500; 2520; 7095/60, A
Ruschel, Dietger; 15.08.43; HVA; 961500; 1140; 2111/72, F
Russ, Wolfgang; 08.01.48; HVA; 961500; 1153; 6983/75, M
Ruthenberg, Gerd-Wolfram; 08.11.53; HVA; 961500; 1093; 5714/81, L
Rücker, Frank; 20.01.63; HVA; 961500; 1130; 5361/89, F
Rücker, Ricarda; 21.05.66; HVA; 961500; 1130; 5361/89/1, F
Sacher, Hans; 06.11.26; HVA; 961500; 1162; 252/74, U
Sachse, Ingrid; 15.12.40; HVA; 961500; 1020; 580/89, F
Sachse, Manfred; 15.04.34; BV Berlin XX; 152000; 1193; 219/76,
Sahling, Frank; 12.07.50; HVA; 961500; 1136; 6908/82, F
Salm, Rainer; 11.05.58; HVA; 961500; 1143; 44/81, F
Salomon, Walter; 12.11.29; HVA; 961500; 1273; 2142/73, L
Salomo, Gerhard; 08.01.30; Dresden XX; 122000; 8023; XII/2667/87,
Salomo, Günther; 21.05.41; Dresden VI; 120600; 8060; XII/1885/89,
Sander, Gerhard; 25.05.52; HVA; 961500; 1093; 157/85, M
Sander, Rudolf; 14.11.33; HVA; 961500; 1188; 790/88, F
Sasse, Klaus-Jürgen; 01.12.42; Abteilung XI; 941100; 1092; 1339/68,
Sauer, Uwe; 09.05.58; Abt. N; 906540; 1150; 4551/77,
Sawatzki, Paul-Eckhard; 06.03.56; HVA; 961500; 1054; 2963/78, F
Schaarschmidt, Steffen; 06.10.58; Karl-Marx-Stadt VIII; 140800; 9001; 181,
Schade, Detlef; 10.11.57; Abt. N; 906540; 1090; 2195/82,
Schaffrath, Hans-Martin; 26.03.44; BV Berlin VI; 150600; 1156; 1352/75,
Scharfenberg, Anette; 02.12.63; Abt. N; 906540; 1093; 5559/83,
Schellenberger, Gerd; 11.11.50; BV Berlin XX; 152000; 1080; 3003/84,
Schemmel, Manfred; 18.02.54; Abt. XI; 941100; 7270; 2795/87,
Schering, Norbert; 24.03.55; HVA; 961500; 1195; 2729/89, A
Schiecke, Dieter; 12.10.54; HVA; 961500; 1153; 1960/75, M
Schiemann, Peter; 04.01.43; HVA; 961500; 1017; 693/86, E
Schiemann, Renate; 09.04.45; HVA; 961500; 1017; 693/86/1, E
Schierz, Rolf-Jörg; 13.02.61; Karl-Marx-Stadt VIII; 140800; 9050; 180,
Schilling, Aribert; 07.04.51; Abt. N; 906540; 1093; 3618/77,
Schilling, Klaus; 29.09.41; Leipzig VI; 130600; 7060; K, 1043/87
Schink, Peter; 30.12.55; HVA; 961500; 1130; 6659/80, M
Schlauß, Hannelore; 17.10.52; Abt. N; 906540; 1298; 5153/88,
Schleicher, Gerhard; 22.06.43; HVA; 961500; 1250; 36/77, M
Schlenkrich, Dieter; 07.05.41; Abt. N; 906540; 1092; 1253/65,
Schlesinger, Harald; 10.10.62; Abt. N; 906540; 1142; 5558/83,
Schliebe, Edda; 25.07.39; Abt. XI; 941100; 1130; 2758/89,
Schliesch, Erhard; 30.03.28; Dresden VII; 120700; 8060; XII/2660/87,
Schlinsog, Helfried; 16.06.44; HVA; 961500; 7022; 544/88, F
Schlinsog, Regina; 05.02.47; HVA; 961500; 7022; 544/88/02, F
Schlögl, Thomas; 01.08.64; Abt. N; 906540; 1141; 3020/84,
Schmidt-Bock, Peter; 04.05.56; Abt. N; 906540; 1142; 2962/79,
Schmidt, Andreas; 16.01.63; Abt. N; 906540; 1140; 5787/82,
Schmidt, Dietmar; 12.06.44; Abt. XI; 941100; 1093; 1276/73,
Schmidt, Eberhard; 22.09.47; HVA; 961500; 1280; 231/75, M
Schmidt, Gerd; 29.07.39; HVA; 961500; 5900; 551/86, F
Schmidt, Gudrun; 08.12.44; HVA; 961500; 4050; 1532/87, M
Schmidt, Hans-Dieter; 03.01.32; Dresden XVIII; 121800; 8019; XII/2664/87,
Schmidt, Hans-Dieter; 30.07.36; Frankfurt/O. XIX; 051900; 1200; V/449/88,
Schmidt, Hartmut; 10.02.62; Abt. N; 906540; 1136; 4050/82,
Schmidt, Joachim; 19.12.43; HVA; 961500; 4050; 1531/87, M
Schmidt, Klaus-Peter; 28.03.56; Abt. XI; 941100; 1600; 407/78,
Schmidt, Kuno; 10.01.37; Abt. XI; 941100; 1020; 1868/69,
Schmidt, Manfred; 04.08.54; HVA; 961500; 1100; 2616/80, U
Schmidt, Werner; 18.07.36; Kreisdienststelle [KD] Bautzen; 120042; 8609; XII/1355/87,
Schmidt, Wilfried; 14.10.52; HVA; 961500; 1093; 237/73, F
Schmiedke, Günter; 04.10.33; Frankfurt/O., BKG; 052900; 1200; V/436/88,
Schneider, Astrid; 24.03.51; HVA; 961500; 1140; 3353/86, F
Schneider, Günter; 08.10.54; HVA; 961500; 5800; 3470/85, M
Schneider, Günter; 26.07.41; Abt. N; 906540; 1136; 9806/61,
Schneider, Harald; 26.01.48; HVA; 961500; 1140; 4128/83, M
Schneider, Karl-Heinz; 24.12.34; HVA; 961500; 9900; 6857/82, M
Schneider, Lothar; 16.11.56; HVA; 961500; 1280; 1525/75, F
Schneider, Siegfried; 06.09.33; Frankfurt/O. XVIII; 051800; 1136; V/450/88,
Scholz, Gisela; 15.03.39; HVA; 961500; 1093; 5478/88, F
Schömann, Bodo; 12.12.61; Abt. XI; 941100; 1200; 5312/88,
Schönau, Lothar; 07.08.34; HVA; 961500; 1095; 3127/78, H
Schönau, Ruth; 23.02.33; HVA; 961500; 1095; 3127/78/1, H
Schönberg, Klaus; 27.12.51; Abt. XI; 941100; 9931; 3457/86,
Schönfeld, Dieter; 15.12.58; Abt. XI; 941100; 7570; 2806/89,
Schönfeld, Klaus; 14.09.41; HVA; 961500; 1136; 596/86, F
Schreyer, Harry; 16.01.38; HA I; 970100; 1185; K, 741/89
Schröder, Horst; 12.06.51; Abt. XI; 941100; 4090; 3458/86,
Schröter, Helmut; 14.08.35; KD Rostock; 010040; 2520; 552/75,
Schubert, Harry; 05.07.51; Abt. N; 906540; 1130; 3693/78,
Schubert, Thomas; 10.05.57; HVA; 961500; 1090; 4848/80, F
Schulke, Klaus-Peter; 06.12.41; Abt. N; 906540; 1092; 3953/76,
Schultze, Ralf; 30.04.56; HVA; 961500; 1150; 2306/74, F
Schulze, Alfred; 07.07.37; Abt. N; 906540; 1093; 4324/87,
Schulze, Frank; 09.07.60; HVA; 961500; 1197; 650/75/69,
Schulz, Dorelies; 11.03.49; HVA; 961500; 1136; 4640/89, M
Schulz, Michael; 03.03.65; Abt. N; 906540; 1140; 4909/86,
Schulz, Ronald; 22.08.61; HVA; 961500; 7700; 650/75/68,
Schulz, Udo; 30.03.58; HVA; 961500; 1143; 113/75, F
Schulz, Werner; 09.02.35; Frankfurt/O. XIX; 051900; 1200; V/437/88,
Schumacher, Michael; 13.04.57; Abt. N; 906540; 1090; 3819/79,
Schurz, Günter; 25.03.33; KD Dresden/Stadt; 120040; 8060; XII/2669/87,
Schuster, Bernd; 29.01.42; HVA; 961500; 1140; 61/67, M
Schußmann, Heike; 18.05.58; Abt. XI; 941100; 2000; 1712/89/1,
Schußmann, Klaus; 10.01.60; Abt. XI; 941100; 2000; 1712/89,
Schübel, Andreas; 03.10.61; HVA; 961500; 6301; 650/75/67,
Schütz, Harald; 19.09.32; HVA; 961500; 1153; 2580/65, K
Schwabe, Karl Heinz; 01.07.54; HVA; 961500; 1150; 234/79, J
Schwalbe, Manfred; 04.08.33; Frankfurt/O. XVIII; 051800; 1200; V/454/88,
Schwarzbach, Walter; 01.04.44; HVA; 961500; 1092; 5018/87, F
Schwarze, Lothar; 19.09.35; Dresden XVIII; 121800; 8020; XII/1352/87,
Schwarz, Frank; 19.01.56; Abt. N; 906540; 1093; 5327/80,
Schwarz, Stefan; 26.02.65; HVA; 961500; 1152; 1656/69/2, P
Schwenk, Wilfried; 03.02.55; HVA; 961500; 2620; 650/75/48,
Schwoch, Gerth; 28.06.51; Abt. N; 906540; 1140; 7274/75,
Schwunteck, Harald; 26.08.57; Abt. N; 906540; 8010; 2966/79,
Seckel, Peter; 11.09.60; HVA; 961500; 1143; 3543/81, F
Seckel, Wolfgang; 01.02.39; Karl-Marx-Stadt XX; 142000; 9005; K/3430/89,
Seeger, Regina; 22.03.51; HVA; 961500; 1140; 109/78, J
Seelig, Werner; 11.04.14; HVA; 961500; 1140; 1472/87, F
Seel, Ingolf; 31.07.57; HVA; 961500; 1035; 368/78, F
Seel, Uwe; 06.09.57; HVA; 961500; 1143; 3962/83, N
Seel, Werner; 28.12.32; HVA; 961500; 1142; 3502/61, T
Seibt, Eberhard; 31.08.36; Dresden VII; 120700; 8060; XII/1340/87,
Seibt, Rudolf; 15.09.30; Abt. N; 906540; 1092; 350/73,
Seibt, Siegfried; 24.04.34; Dresden II; 120200; 8021; XII/1338/87,
Seidel, Knut; 02.10.66; Karl-Marx-Stadt VIII; 140800; 9050; 174,
Seidel, Marga; 07.07.36; HVA; 961500; 1092; 2310/88/1, E
Seidel, Matthias; 15.08.59; HVA; 961500; 1017; 491/80, F
Seidel, Michael; 21.07.52; HVA; 961500; 1092; 581/89, U
Seidel, Wolfgang; 24.05.31; HVA; 961500; 1092; 2310/88, E
Seiffert,Reimar; 12.11.29; KD Eisenhüttenstadt; 050045; 1220; V/433/88,
Sellig, Dieter; 11.07.34; Abt. N; 906540; 1020; 7258/75,
Sell, Andreas; 28.06.54; HVA; 961500; 1095; 2311/88, O
Sendsitzky, Peter; 10.09.47; Abt. N; 906540; 1092; 3723/80,
Seyfarth, Stephan; 22.12.60; HVA; 961500; 1040; 4609/80, J
Siegert, Gerhard; 31.05.48; Abt. N; 906540; 1140; 3883/76,
Siegler, Werner; 01.11.52; HVA; 961500; 1400; 1485/87, O
Sievers, Reinhard; 14.10.49; Abt. N; 906540; 1140; 3822/77,
Siggelkow, Wolfgang; 03.11.60; Abt. XI; 941100; 2823; 590/88,
Sikorski, Joachim; 16.01.58; Abt. N; 906540; 1130; 5261/82,
Sikorski, Wolfgang; 27.11.49; Abt. N; 906540; 1156; 2309/73,
Simbrick, Joachim; 21.12.51; Abt. XI; 941100; 1153; 6462/82,
Sitte, Jutta; 06.08.38; HVA; 961500; 1055; 4139/88, M
Sitte, Kurt; 08.09.38; HVA; 961500; 1055; 3009/89, M
Skibinski, Udo; 24.11.42; HVA; 961500; 1020; 326/73, F
Skirde, Udo; 18.01.38; HVA; 961500; 1130; 890/82, T
Smetana, Rüdiger; 18.02.39; BV Berlin XVIII; 151800; 1136; 417/79,
Smiejczak, Jan-Peter; 16.04.64; HVA; 961500; 1156; 2833/87, M
Smolinski, Hans-Joachim; 21.05.53; Abt. N; 906540; 9300; 4070/79,
Sodann, Peter; 23.09.39; HVA; 961500; 7060; 3932/87, M
Sommerfeld, Dirk; 20.06.50; HVA; 961500; 1280; 1555/87, F
Sonnenfeld, Kurt; 25.04.44; Abt. N; 906540; 1017; 2262/87,
Sonntag, Peter; 18.03.55; HVA; 961500; 1092; 2817/80, M
Spangenberg, Heinz; 09.10.56; Abt. XI; 941100; 6550; 6665/82,
Spenke, Günter; 24.01.32; Abt. N; 906540; 1020; 4550/77,
Sperling, Achim; 29.10.56; HVA; 961500; 1130; 4681/79, F
Sprenger, Gisela; 01.06.54; HVA; 961500; 1020; 2633/88, J
Springer, Dieter; 23.06.34; KD Schwedt; 050050; 1330; V/435/88,
Staigies, Artur; 26.10.30; OD KKW Nord; 010050; 2220; 1022/84,
Standke, Michael; 04.11.54; Karl-Marx-Stadt VIII; 140800; 9023; 179,
Stange, Detlef; 20.02.59; Abt. N; 906540; 1115; 5547/88,
Stapff, Dirk; 08.03.63; HVA; 961500; 1090; 2612/84, F
Starick, Hartmuth; 02.08.52; Abt. XI; 941100; 1080; 8509/81,
Städtke, Hartmut; 20.05.56; Abt. N; 906540; 1140; 4029/79,
Steffin, Peter; 09.08.41; Rostock IX; 010900; 2520; 3762/82,
Steger, Ralph; 28.08.65; HVA; 961500; 1180; 2778/76/1, T
Stehr, Gerd; 29.03.58; Abt. XI; 941100; 1200; 3957/83,
Steinert, Joachim; 27.11.36; KD Rügen; 010046; 2355; 4028/86,
Steinmetz, Gerhard; 08.04.48; Abt. XI; 941100; 1017; 1904/72,
Steinmüller, Peter; 07.03.56; HVA; 961500; 1142; 1881/88, A
Stein, Peter; 05.02.61; Dresden XX; 122000; 8019; XII/2405/88,
Stein, Werner; 01.08.37; KD Berlin-Friedrichshain; 150040; 1197; 5579/88,
Stephan, Wolfgang; 29.06.37; KD Dresden/Stadt; 120040; 8060; XII/1358/87,
Sternberger, Dieter; 02.12.34; Abt. N; 906540; 1195; 1474/65/1,
Sternberger, Erika; 08.02.41; Abt. XI; 941100; 1195; 4586/85,
Steuding, Werner; 24.07.42; HA VI; 970600; 1190; K, 1042/87
Steyskal, Richard; 12.11.45; HVA; 961500; 1806; 650/75/53,
Stichler, Christian; 15.06.57; HVA; 961500; 1040; 3462/79, F
Stirzel, Werner; 10.06.34; KD Bautzen; 120042; 8600; XII/1354/87,
Stollmayer, Sabine; 10.03.51; HVA; 961500; 1293; 338/81, J
Stoll, Dietrich; 10.06.36; Rostock XVIII; 011800; 2551; 417/71,
Stopp, Helmar; 01.07.57; Abt. N; 906540; 1123; 5218/84,
Storbeck, Lutz; 30.09.59; HVA; 961500; 1095; 2769/84, F
Stoye, Andre; 28.11.60; HVA; 961500; 1152; 3261/84, F
Straube, Jost; 18.09.58; HVA; 961500; 1058; 3573/82, F
Strauhs, Rüdiger; 05.03.55; Abt. XI; 941100; 1017; 6370/81,
Strähler, Gisela; 28.02.42; Abt. N; 906540; 1281; 5150/88,
Strähler, Siegbert; 05.05.39; Abt. N; 906540; 1281; 5151/88,
Streda, Sylvia; 06.10.54; KD Schwedt; 050050; 1330; V/440/88,
Striegler, Ralf; 14.07.64; Abt. N; 906540; 1142; 1642/85,
Strischek, Erika; 11.11.49; HVA; 961500; 1035; 4270/78/1, N
Strischek, Rudolf; 23.08.45; HVA; 961500; 1035; 4270/78, N
Strobel, Günter; 02.04.36; HA I; 970100; 8312; K, 5809/82,
Stroth, Elke; 28.06.59; Abt. XI; 941100; 2760; 498/86/1,
Stroth, Heiko; 15.06.58; Abt. XI; 941100; 2760; 498/86,
Strutz, Reiner; 01.06.52; HVA; 961500; 2861; 309/76, F
Stuhl, Diethard; 02.03.61; Abt. XI; 941100; 6018; 591/88,
Stüdemann, Robert; 14.11.50; HVA; 961500; 1071; 1870/87, L
Stümer, Hans; 18.03.31; HVA; 961500; 1156; 3032/82, J
Stürmer, Gerlinde; 24.01.60; Abt. N; 906540; 1140; 2015/80,
Suhm, Rüdiger; 24.02.60; Abt. XI; 941100; 2831; 5346/85,
Swienty, Gerald; 25.03.51; Abt. XI; 941100; 1600; 2093/72,
Switalla, Heinz-Joachim; 12.01.46; HVA; 961500; 1017; 2105/73, O
Taubert, Gerald; 05.07.59; Abt. N; 906540; 1130; 5326/80,
Tausend, Klaus; 06.04.47; Abt. XI; 941100; 1142; 6987/75/1,
Teichmeyer, Lutz; 28.10.50; HVA; 961500; 1144; 1603/75, M
Tellbrun, Wolfgang; 09.07.47; Abt. N; 906540; 1140; 5133/76,
Telschow, Lieselotte; 24.03.35; HVA; 961500; 1136; 5181/84, U
Teuter, Maik; 21.12.64; Abt. N; 906540; 1280; 2729/86,
Thale, Klaus; 06.04.44; Abt. N; 906540; 1136; 666/66,
Thäter, Wolfgang; 23.02.45; KD Berlin-Weißensee; 150047; 1140; 1484/82,
Thiele, Horst; 26.09.34; HVA; 961500; 1093; 2481/88, F
Thiele, Ingrid; 04.08.38; HVA; 961500; 1093; 2481/88/1, F
Thiel, Manfred; 12.04.39; Abt. N; 906540; 1093; 9804/61,
Thomas, Heinz; 07.06.42; HVA; 961500; 6902; 3672/88, M
Thomas, Karsten; 18.02.62; HVA; 961500; 1153; 3407/84, F
Thomas, Manfred; 23.03.57; Abt. N; 906540; 1280; 3475/76,
Thomas, Nikita; 18.06.51; HVA; 961500; 1092; 650/75/32,
Thümmel, Elke; 25.12.56; HVA; 961500; 8060; 2528/88/1, F
Thümmel, Volker; 16.01.59; Abt. XI; 941100; 8060; 2528/88,
Thürasch, Carola; 01.11.59; HVA; 961500; 1597; 3849/86, F
Thürasch, Werner; 06.06.50; Abt. XI; 941100; 1597; 4417/84,
Tiede, Lars; 16.02.67; HVA; 961500; 2560; 2767/89, F
Tietsche, Frank; 25.06.55; HVA; 961500; 1141; 361/74, F
Tietz, Gisa; 14.03.47; HVA; 961500; 1092; 2428/79, O.
Tietz, Hans-Joachim; 27.01.47; HVA; 961500; 2000; 514/87, F
Tippmann, Falk; 12.06.53; Karl-Marx-Stadt VIII; 140800; 9050; 169,
Tkatsch, Ingo; 06.11.66; HVA; 961500; 1150; 2143/86, A
Tondock, Heinz; 08.02.30; HVA; 961500; 1156; 1601/75, M
Tornau, Andre; 15.10.65; Schwerin II; 020200; 2755; :
Treder, Gerd; 30.06.40; Rostock , Abt. Hafen; 011969; 2520; 3062/85,
Trenkmann, Ute; 20.09.52; HVA; 961500; 1156; 3904/86/1, F
Trenkmann, Wolfgang; 10.07.51; HVA; 961500; 1156; 3904/86, F
Triegel, Rainer; 17.01.62; Abt. N; 906540; 1034; 5788/82,
Trinks, Hartmut; 24.07.55; Abt. N; 906540; 1150; 3474/76,
Troisch, Andreas; 15.11.57; HVA; 961500; 1020; 2691/80, F
Trommler, Werner; 28.02.51; HVA; 961500; 1156; 957/89, F
Tschiharz, Ute; 03.05.58; HVA; 961500; 3540; 650/75/49/1,
Tschiharz, Wolfgang; 12.06.51; HVA; 961500; 3540; 650/75/49,
Tusche, Hans-Jürgen; 11.07.43; Abt. XI; 941100; 1020; 288/67,
Uher, Edgar; 09.11.52; HVA; 961500; 1142; 175/75, F
Uhlig, Andrea; 01.05.57; HVA; 961500; 1250; 2664/84, J
Uhlig, Gerd; 16.11.46; Abt. N; 906540; 1130; 2114/66,
Uhlig, Gunter; 17.10.52; Karl-Marx-Stadt VIII; 140800; 9044; 163,
Ulbrich, Fritz; 11.12.36; Abt. XI; 941100; 1095; 922/82,
Ullmann, Klaus; 16.10.51; Karl-Marx-Stadt VIII; 140800; 9001; 168,
Unger, Dieter; 29.12.52; HVA; 961500; 1156; 2427/74, F
Unger, Peter; 18.06.56; Abt. N; 906540; 1130; 5095/77,
Unmack, Franz; 01.08.48; HVA; 961500; 1055; 177/79, M
Unseld, Werner; 26.05.28; HVA; 961500; 4500; 18264/60, Y
Unterlauf, Diethard; 05.04.46; HVA; 961500; 9999; 337/77, O
Urban, Hartmut; 08.04.45; Abt. N; 906540; 1162; 1346/68,
Van Rossum, Ralf; 20.03.43; HVA; 961500; 9999; 2856/80, M
Vieweg, Jens-Uwe; 27.12.58; Abt. XI; 941100; 1200; 4706/85,
Vogel, Michael; 25.10.56; Abt. N; 906540; 1093; 1551/80,
Vogler, Reinhard; 15.07.49; HVA; 961500; 5820; 650/75/70,
Vogl, Hansjochen; 09.07.37; HVA; 961500; 1100; 6183/82/1, L
Vogt, Ditmar; 02.05.38; Abt. N; 906540; 1199; 5073/77,
Voigtländer, Christian; 03.12.47; HVA; 961500; 4090; 476/88, A
Voigtländer, Gunter; 25.06.52; HVA; 961500; 1055; 2769/87, F
Voigt, Armin; 22.10.51; Abt. XI; 941100; 1600; 412/77,
Voigt, Helmut; 15.02.50; HVA; 961500; 1017; 2482/88, F
Voigt, Knut; 01.08.48; HVA; 961500; 1156; 1430/85, M
Vollmeyer, Wolfgang; 10.10.50; HA VI; 970600; 1054; K, 4427/87
Vopel, Dieter; 03.01.35; HVA; 961500; 1090; 4083/81, M
Vopel, Elke; 26.03.47; Abt. XI; 941100; 1600; 417/70/2,
Vopel, Hans; 11.08.45; Abt. XI; 941100; 1600; 417/70/1,
Vorberg, Horst; 10.04.53; KD Zwickau; 140061; 9561; K/1436/89,
Voßwinkel, Hartmut; 29.04.50; HVA; 961500; 1140; 353/77, A
Völkel, Alfred; 20.06.31; HVA; 961500; 1113; 18556/60, E
Völkel, Heiko; 23.03.62; HVA; 961500; 1020; 2859/84, U
Völz, Andreas; 29.12.56; Abt. XI; 941100; 9900; 4170/83,
Vtelensky, Rainer; 04.11.44; OD KKW Nord; 010050; 2200; 2678/70,
Wadewitz, Volker; 04.08.57; HVA; 961500; 1034; 2472/79, F
Wagenknecht, Bernd; 20.12.40; HA IX; 990900; 1020; K, 5799/82
Wagner, Michael; 28.08.61; Abt. XI; 941100; 7065; 6932/88,
Wagner, Silke; 28.12.64; HVA; 961500; 7065; 6932/88/1, F
Walter, Isolde; 27.02.48; Rostock VIII; 010800; 1153; 2832/85,
Warncke, Claus-Dieter; 06.04.44; Abt. XI; 941100; 1140; 2496/74,
Warnecke, Siegfried; 27.12.59; Abt. N; 906540; 1142; 1985/79,
Warzel, Franz; 14.05.28; HVA; 961500; 1020; 181/73, M
Wächter, Wolfgang; 28.09.49; HVA; 961500; 9270; 650/75/16,
Wäckerle, Andrej; 03.04.50; HVA; 961500; 1092; 4683/79, M
Wähner, Jürgen; 28.04.56; Abt. N; 906540; 1093; 3473/76,
Weber, Dieter; 16.06.49; HVA; 961500; 1120; 1779/71, F
Weber, Frank; 06.10.50; KD Dresden/Land; 120041; 8270; XII/2668/87,
Weber, Gerd; 02.07.65; HVA; 961500; 1090; 3383/85, Q
Weber, Hans; 11.07.43; HVA; 961500; 1130; 192/73, X
Weber, Rainer; 06.11.45; HVA; 961500; 1110; 6794/82, O
Weber, Ulrich; 09.03.45; Abt. N; 906540; 1280; 1990/69,
Wedel, Kay; 07.03.64; Abt. N; 906540; 1144; 4933/86,
Weichman, Jürgen; 22.02.48; Abt. XI; 941100; 1156; 3212/77,
Weidehase, Jörg; 25.10.54; Abt. N; 906540; 1142; 3392/76,
Weigand, Andre; 09.04.68; HVA; 961500; 7024; 3118/89, S
Weigelt, Lutz; 22.01.56; Abt. N; 906540; 1280; 3391/76,
Weigel, Jens-Friedrich; 28.06.50; Abt. N; 906540; 1291; 7268/75,
Weigold, Dieter; 13.02.41; Abt. N; 906540; 1058; 2901/66,
Weihrauch, Heike; 11.07.59; HVA; 961500; 2050; 650/75/71/1,
Weinert, Gerhard; 06.10.39; KD Grimmen; 010044; 2300; 1608/70,
Weirich, Manfred; 11.06.38; Abt. N; 906540; 1020; 9798/61,
Weller, Jörg; 11.01.63; HVA; 961500; 1092; 1047/82, M
Welzel, Herbert; 30.04.44; Abt. N; 906540; 1281; 7265/75,
Welzel, Jürgen; 12.05.54; KD Greifswald; 010042; 2200; 617/83,
Wenzel, Joachim; 04.01.53; HVA; 961500; 1142; 5693/83, F
Wenzel, Joachim; 10.12.41; Abt. XI; 941100; 1400; 182/70,
Wenzel, Rolf; 13.05.47; Abt. XI; 941100; 1144; 1748/75,
Werner, Dietmar; 12.04.47; Abt. N; 906540; 1017; 376/69,
Werner, Günter; 31.01.37; HVA; 961500; 1160; 4553/85, H
Werner, Hartmut; 19.01.45; Abt. XI; 941100; 1156; 176/72,
Werner, Uwe; 04.08.61; HVA; 961500; 1143; 1577/86, F
Werner, Wolfgang; 17.11.35; HA VI; 970600; 1140; K, 505/87
Werner, Wolfgang; 24.08.56; Abt. N; 906540; 1020; 3884/76,
Wernicke, Günter; 10.07.49; Abt. XI; 941100; 1157; 98/75,
Wessendorf, Volker; 09.12.51; HVA; 961500; 1190; 1478/87, F
Wesser, Andrea; 20.04.64; HVA; 961500; 1100; 661/86, J
Westland, Jürgen; 08.01.51; Abt. XI; 941100; 1156; 2895/77,
Wetzel, Katrin; 29.03.60; HVA; 961500; 1145; 475/78, J
Wiedemann, Günther; 12.07.56; Abt. N; 906540; 1280; 5219/84,
Wiertelorz, Horst; 05.07.49; Abt. N; 906540; 1136; 3892/77,
Wiesel, Bernd; 20.04.58; Abt. N; 906540; 1143; 2129/78,
Wiesner, Erhard; 31.07.36; HVA; 961500; 1140; 3659/64, M
Wilde, Dirk; 24.12.63; Abt. XI; 941100; 2300; :
Wilde, Hans-Heinz; 27.07.32; Rostock XVIII; 011800; 2300; 5749/79,
Wilhelm, Ralf; 15.07.51; HVA; 961500; 1142; 23/77, F
Wilke, Hartmut; 09.05.60; Abt. N; 906540; 1092; 5019/85,
Winderlich, Jens; 10.10.67; HVA; 961500; 1093; 3453/86, O
Winkler, Anton; 22.03.42; HVA; 961500; 1156; 4674/89, M
Winkler, Georg; 07.08.30; Dresden XVIII; 121800; 8250; XII/1347/87,
Winkler, Günter; 30.04.45; HVA; 961500; 1142; 1996/73, A
Winter, Marina; 26.11.60; HVA; 961500; 1130; 4293/84, J
Witte, Dieter; 23.11.37; Abt. N; 906540; 1140; 5039/76,
Wittstock, Manfred; 31.03.32; Rostock VII; 010700; 2500; 936/64,
Witzel, Rainer; 19.04.64; HVA; 961500; 1090; 3581/88, M
Witzmann, Helmar; 06.08.54; Abt. XI; 941100; 1142; 3959/83,
Wokurka, Ulf; 31.10.62; HVA; 961500; 1055; 4228/83, F
Wolfsteller, Roland; 11.11.59; Abt. N; 906540; 2080; 1598/81,
Wolf, Barbara; 11.02.45; HVA; 961500; 1595; 804/83/1, F
Wolf, Jürgen; 15.10.51; Abt. XI; 941100; 1140; 2741/77,
Wolf, Klaus; 30.03.55; Abt. N; 906540; 1095; 2012/78,
Wolf, Matthias; 24.11.60; HVA; 961500; 1090; 3051/89, E
Wolf, Rainer; 22.02.59; Abt. N; 906540; 1130; 1548/80,
Wolf, Ulrich; 13.03.43; HVA; 961500; 1595; 804/83, F
Wolkenstein, Dietrich; 09.03.35; HVA; 961500; 1281; 962/64, M
Wolkenstein, Hubertus; 25.12.63; HVA; 961500; 1142; 6480/82, M
Wolkenstein, Renate; 23.08.33; HVA; 961500; 1281; 962/64/1, M
Worsch, Jürgen; 28.09.48; Abt. XI; 941100; 1140; 339/73,
Worsch, Ursula; 04.02.49; HVA; 961500; 1140; 339/73/2, E
Wotzka, Jörg-Michael; 27.07.47; KD Rostock; 010040; 2520; 3391/89,
Wöller, Klaus; 31.12.30; HVA; 961500; 1020; 2953/77, J
Wunderlich, Uwe; 06.05.60; Abt. N; 906540; 1140; 4037/79,
Würzburg, Gerd; 10.06.57; HVA; 961500; 1157; 421/79, F
Zapke, Helge-Jens; 01.10.67; Abt. N; 906540; 1156; 953/87,
Zech, Jürgen; 16.07.51; HVA; 961500; 1055; 4598/87, F
Zehl, Klaus; 07.01.38; Rostock VI; 010600; 2510; 553/75,
Zeiseweis, Ralf; 11.11.62; BV Berlin XX; 152000; 1140; 3299/88,
Zeiske, Tino; 27.07.61; HVA; 961500; 1143; 2614/84, F
Zellmer, Bernd; 04.12.55; Abt. N; 906540; 1136; 3620/77,
Zentsch, Peter; 28.08.41; Rostock, BKG; 012900; 2500; 2254/84,
Zetzsche, Jürgen; 16.10.52; Abt. N; 906540; 1144; 1753/80,
Ziegler, Frank; 15.11.63; HVA; 961500; 7010; 3341/86, S
Ziesche, Hans-Dieter; 16.01.60; HVA; 961500; 1017; 205/84, F
Ziese, Elvira; 09.10.54; Frankfurt/O. VI; 050600; 1200; V/441/88,
Zilm, Klaus; 03.03.51; HVA; 961500; 1601; 422/87, F
Zimmermann, Bernd; 07.08.39; HVA; 961500; 1080; 458/63, A
Zimmermann, Peter; 09.11.38; Frankfurt/O. XVIII; 051800; 1203; V/445/88,
Zimmermann, Werner; 05.03.46; Dresden VI; 120600; 8080; XII/1165/88,
Zobel, Frank; 03.04.67; HVA; 961500; 2003; 2842/89, J
Zobler, Günter; 06.09.36; HVA; 961500; 1120; 1826/88, A
Zurflüh, Joachim; 24.12.35; Abt. XI; 941100; 1150; 237/70,
Zwetz, Axel; 13.05.38; Abt. N; 906540; 1136; 958/65,







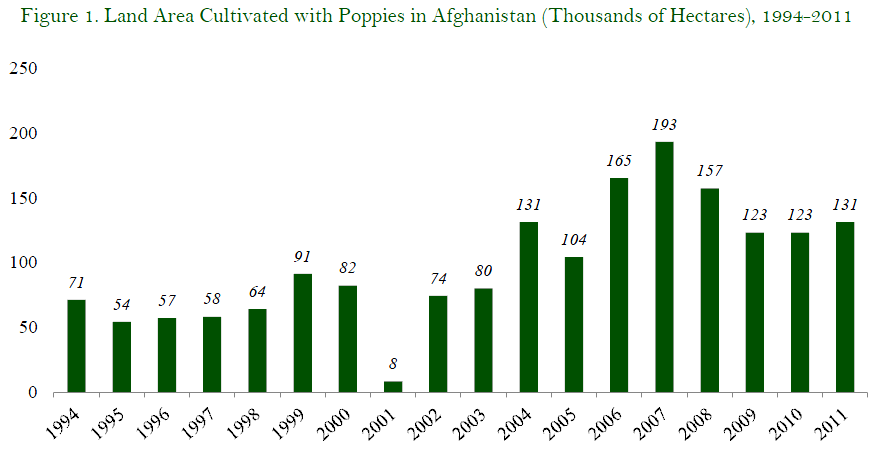
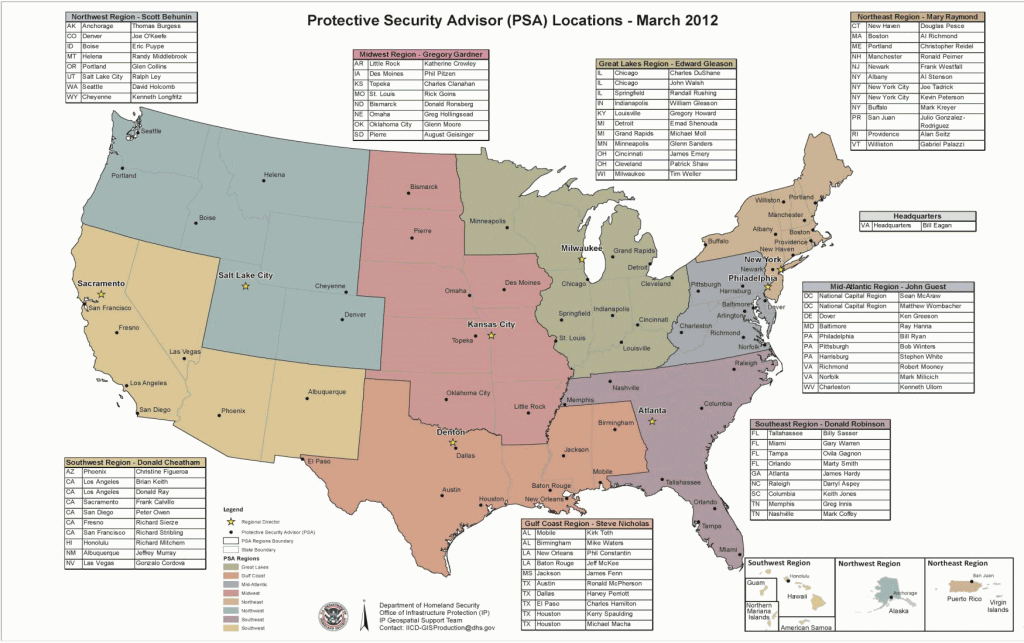

![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict2.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict3.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict62.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict63.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict0.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict71.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict1.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict4.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict64.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict65.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict5.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict66.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict67.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict70.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict68.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict69.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict6.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict7.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict8.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict9.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict10.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict11.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/camp-bastion/pict12.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/uk-drones/pict52.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/uk-drones/pict59.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/uk-drones/pict60.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/uk-drones/pict53.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/uk-drones/pict58.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/uk-drones/pict54.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/uk-drones/pict55.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/uk-drones/pict57.jpg) A soldier of Bravo Company, 1 Rifles launches a Desert Hawk UAV (Unmanned Aerial Vehicle) from a WMIK Landrover during an operation near Garmsir, Afghanistan. Desert Hawk is a portable UAV surveillance system which provides aerial video reconnaissance. It has a flight time of approximately one hour, and can fly anywhere within a 10km radius of its ground control station. It has both day and night time (thermal imaging) capability. The equipment can be used for a variety of tasks, such as force protection for convoys and patrols, route clearance, base security, reconnaissance or target tracking. March 20, 2009. MoD
A soldier of Bravo Company, 1 Rifles launches a Desert Hawk UAV (Unmanned Aerial Vehicle) from a WMIK Landrover during an operation near Garmsir, Afghanistan. Desert Hawk is a portable UAV surveillance system which provides aerial video reconnaissance. It has a flight time of approximately one hour, and can fly anywhere within a 10km radius of its ground control station. It has both day and night time (thermal imaging) capability. The equipment can be used for a variety of tasks, such as force protection for convoys and patrols, route clearance, base security, reconnaissance or target tracking. March 20, 2009. MoD![[Image]](https://i0.wp.com/cryptome.org/2012-info/uk-drones/pict56.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/uk-drones/pict61.jpg)





![[Image]](https://i0.wp.com/cryptome.org/2012-info/benghazi/pict8.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/benghazi/pict10.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/benghazi/pict7.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/benghazi/pict9.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/benghazi/pict15.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/benghazi/pict16.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/benghazi/pict12.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/benghazi/pict13.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/benghazi/pict14.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/benghazi/pict18.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/benghazi/pict17.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/benghazi/pict11.jpg)
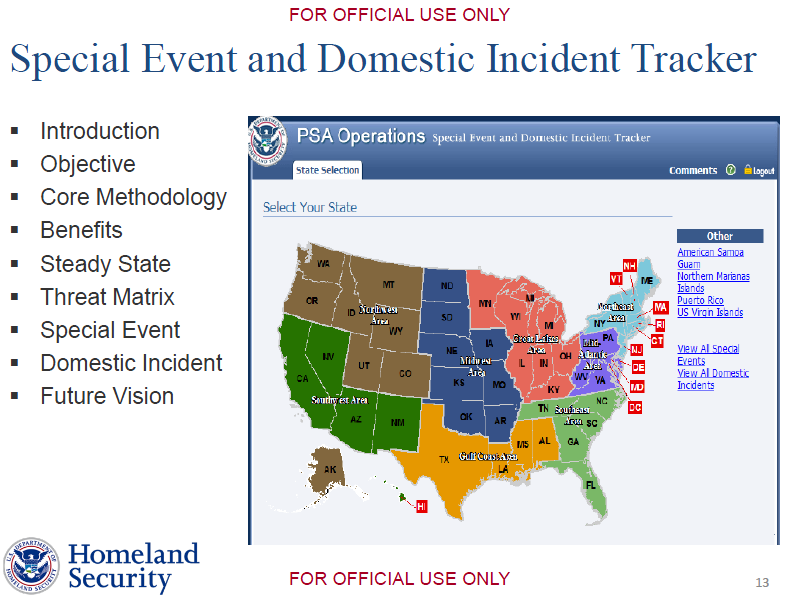
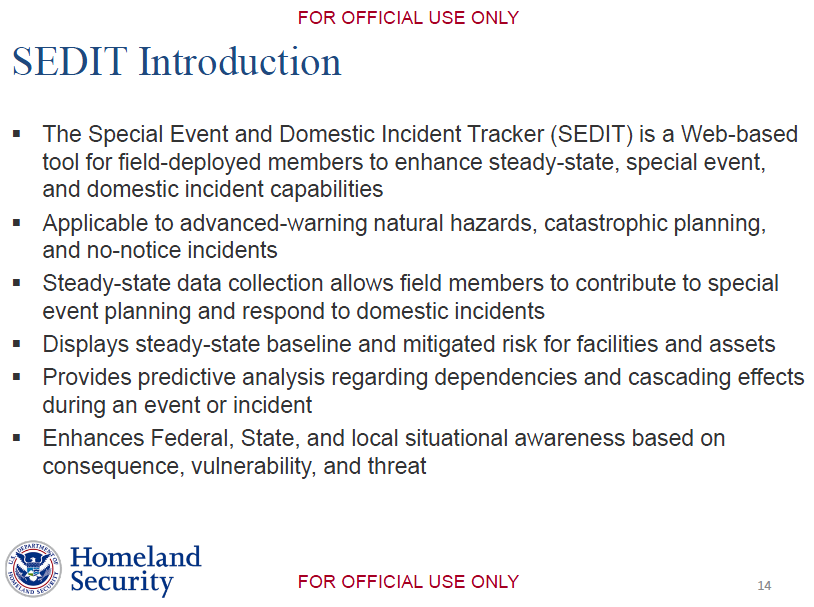

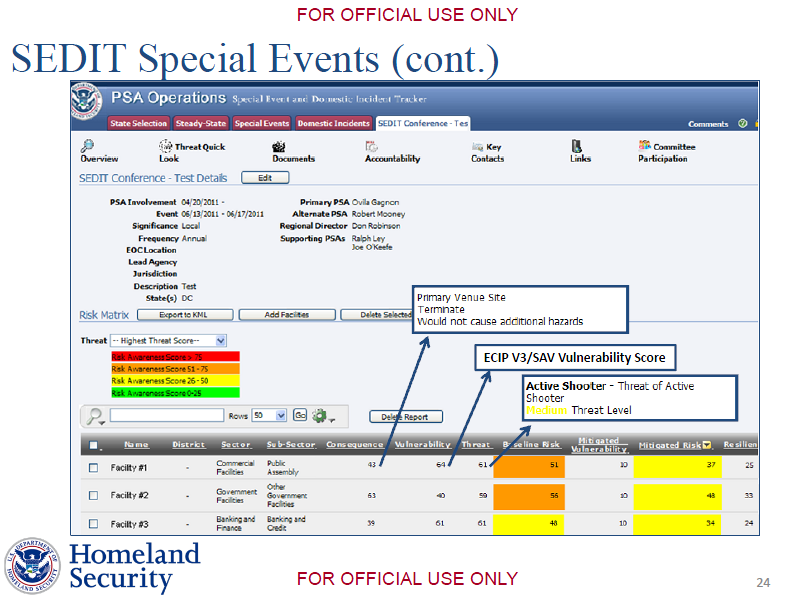






 In den Akten der Staatssicherheit findet sich zum Fall Günter Litfin auch ein undatiertes Foto: Gedenkstein für Günter Litfin am Friedrich-List-Ufer, aufgestellt am 24.8.1962. Heute befindet sich der Gedenkstein an der Sandkrugbrücke in der Berliner Invalidenstraße. Quelle: BStU, MfS, HA IX, Fo 1673, Bild 88
In den Akten der Staatssicherheit findet sich zum Fall Günter Litfin auch ein undatiertes Foto: Gedenkstein für Günter Litfin am Friedrich-List-Ufer, aufgestellt am 24.8.1962. Heute befindet sich der Gedenkstein an der Sandkrugbrücke in der Berliner Invalidenstraße. Quelle: BStU, MfS, HA IX, Fo 1673, Bild 88




Na ja, Fakt ist, dass Wirecard ein Zahlungsdienstleister ist, der gut und gerne 60% seiner Umsätze mit Onlineglücksspielanbietern macht. Die Frage ist doch wer hinter dieser Bluetool Ltd steckt und der International Payment Systems die die Gelder über die Wirecard zu Schuett geschleust haben. Diese Nameh müssen der Wirecard ja bekannt sein. Solange hier keine Aufklärung passiert, denke ich stimmt bei der Wirecard was nicht. Und zum Nachdenken – wenn Schuett all dies nur erfunden hat und eine Story um die Wirecard strickt, dann müssten die Richter in USA doch sehr leichtgläubig sein. Wenn jemand nach einem Geständnis in USA gegen Kaution von 100K auf freien Fuss kommt, dann hat er kooperiert und die Hosen runter gelassen. Anzunhemen, der tanzt den Amis auf der Nase rum und bindet ihnen einen Bären auf, fällt mir schwer zu glauben. Die Amis kämpfen rigeros gegen illegales Online Glücksspiel, und ich denke, dass gegen Nennung der wahren Hintergründe der Zahlungen und deren Auftraggeber diese Kaution gewährt wurde. Auch machen die US Behörden keine Strafanzeige in DE wenn sie sich ihrer Sache nicht sicher sind. Und nochmals, wer sich nicht sicher ist, lässt seinen Hauptverdächtigen nicht frei. Ich denke wir sehen noch ordentlich “Bewegung” bei der Wirecard in den nächsten Wochen. Vielleicht auch ein paar plötzliche personelle Wechsel…
Cantaloop –
I’ve been looking into this story and am wondering where you get your information regarding Wirecards revs (60% onling gambling). Would you mind pointing me in the right direction?
Thanks!
Sarah
Warum kommt denn niemand darauf das Gomopa auch Informanten hat? Vielleicht drückte sich auch der Deinst nur falsch aus? Vielleicht hat auch die Journalistin in Florida am Telefon etwas anderes erzählt als sie es dem Handelsblatt berichtete? Jedenfalls ist die Pressemeldung bei Gomopa etwas geändert worden. Dass liest sich jetzt so:
eil er gegenüber dem Richter ein umfassendes Geständnis ablegte. Darin soll Schütt massiv die Wirecard AG beschuldigen.
Schütt soll nach Informationen eines Informanten ausgesagt haben: Er sei nur ein kleiner Geldbote. Einer von insgesamt fünf. Er habe lediglich im Auftrag und als Treuhänder für die Wirecard AG, insbesondere der Wirecard Bank AG, gearbeitet. Beauftragt wurde er hierzu direkt vom Vorstand der Wirecard AG, Herrn Rüdiger Trautmann (er hat den Vorstand am 31. Januar 2010 aus persönlichen Gründen inzwischen verlassen) und Herrn Dr. Markus Braun, Vorstandschef und zugleich Vertriebsvorstand der Wirecard AG.
Die Einzahlungen erfolgten dabei über Mastercard und Visacard und seien über die Wirecard Bank abgewickelt worden. Die Wirecard Bank hat bei beiden Karteninstituten den Status des Aquirierers. Wirecard habe ein “institutionelles System zur Abwicklung illegaler Zahlungen im Internet entwickelt”.
Konjunktiv ist angesagt! Schütt soll. Doppelte Absicherung bei Informationen eines Informanten. Gomopa ist also schon etwas zurückgerudert. Wie dem auch sei. Wo Rauch ist ist auch Feuer! Ich glaube das die Wircard da bis über beide Ohren drinn steckt! Vielleicht nicht gerade der Boss, aber die lassen machen.
Naja, das mag ja wohl sein, dass Gomopa Informanten hat, aber es lässt sich nirgendwo belegen, dass Schuett diese Aussagen gemacht haben soll. Ich bekomme in den nächsten Tagen/Wochen das genaue Gerichtsprotokoll, sobald es vom Gericht veröffentlich wurde, werde ich es hier online stellen.
Es kann schon sein, dass Schuett diese Aussagen gegenüber den Bundesbehörden gemacht, vor Gericht soll er das jedenfalls nicht gesagt haben.
Ich persönlich glaube nicht an eine Verwicklung von Wirecard, dann könnten Sie genauso auch alle anderen Banken verdächtigen. Viel mehr sollte mal hier ermittelt werden, wer sich hinter der Bluetool Ltd. bzw. deren Gesellschafter (sind Offshorefirmen) befindet. Zumindest muss es ja auch bei der Wirecard Aufzeichnungen geben, wer Zeichnungsberechtigter für das Bluetool Konto bei der Wirecard war. Wahrscheinlich nur ein Strohmann, aber hier kann die Staatsanwaltschaft ihre Ermittlungen ausweiten.
Momentan kommt es mir allerdings vor, als bewegt sich bisher keine deutsche Staatsanwaltschaft in dem Fall, nicht gegen Schuett und auch nicht gegen Bluetool.
http://www.usag24-betrug.com/index.php/gomopas-wirecard-behauptungen-zweifelhaft-schuett-hat-keinerlei-behauptungen-zu-wirecard-gemacht/
und in der FAZ:
Wirtschaftskriminalität Großrazzia wegen Verdachts auf Insiderhandel
Schlag gegen mutmaßliche Anlagebetrüger: Die Staatsanwaltschaft München hat in einer Großrazzia Dutzende Büros und Wohnungen nach Beweisen für Insiderhandel durchsucht. Drei Verdächtige wurden verhaftet. Durchsucht wurde auch die Schutzgemeinschaft der Kapitalanleger.
Von Henning Peitsmeier
24.09.2010 2010-09-24T08:31:05+0200
//
© Wolfgang Eilmes / F.A.Z.
Betrugsverdacht: An der Börse sollen fast wertlose Papiere gekauft, die Kurse durch gezielt positive Nachrichten nach oben getrieben und dann wieder verkauft worden sein
Die Münchner Staatsanwaltschaft hat in einer Großrazzia umfangreiches Beweismaterial gegen mutmaßliche Anlagebetrüger sichergestellt. Ermittelt wird gegen ein Netzwerk von Investoren, Zockern und Gerüchtestreuern, die seit Jahren gemeinsame Sache gemacht haben sollen. Die Vorwürfe lauten auf Marktmanipulation und Insiderhandel mit Aktien, sagte die Sprecherin der Anklagebehörde, Barbara Stockinger. „Wir ermitteln gegen 31 Beschuldigte, und es besteht erheblicher Tatverdacht.“ Dabei laufen die Ermittlungen bereits seit 2007, und sie reichen bis hin zur Schutzgemeinschaft der Kapitalanleger (SdK), deren Redner gern auf den Hauptversammlungen von Dax-Konzernen auftreten.
Nach Informationen der F.A.Z. sitzen die früheren SdK-Sprecher Markus Straub und Tobias Bosler in Untersuchungshaft. Sie gehören zum Kreis der Verdächtigen, die in windigen Börsenbriefen und Internetportalen Gerüchte über Aktien von Unternehmen wie Wirecard oder Nascacell verbreitet haben sollen. Erschwert würden die Untersuchungen, weil die Beschuldigten oft Namen und Firmenadressen wechselten und internationale Durchsuchungsbeschlüsse notwendig gewesen seien, sagte eine mit der Angelegenheit befasste Person dieser Zeitung. Die Masche selbst ist nach ihren Angaben leicht durchschaubar, aber schwer nachzuweisen. Vermutlich haben sämtliche Verdächtige Gerüchte über mindestens 20 kleine Aktiengesellschaften gestreut und an den Kursausschlägen der jeweiligen Aktien kräftig verdient. Gegenstand dieser Geschäfte waren bevorzugt im unregulierten Freihandel notierte und meist wertlose Aktien, sogenannte Pennystocks. Die Kurse dieser Werte sind wegen ihres hohen Streubesitzes leicht zu manipulieren.
Gezielt Gerüchte gestreut
Nach Informationen der F.A.Z. sollen unter anderem gezielt über den Finanznachrichtendienst Gomopa im Internet Gerüchte über Pennystocks gestreut worden sein. Gomopa steht für Goldman Morgenstern & Partners Consulting LLC. Auf ihrer Internetseite hat Gomopa „Transparenz in Sachen Finanzen, Vorsorge und Geldanlage“ versprochen, doch ihr Chef Klaus Maurischat saß als mutmaßlicher Betrüger schon in Untersuchungshaft.
Seit einigen Tagen ist die Internetseite http://www.gomopa.net offline, und es kursieren Gerüchte über finanzielle Unregelmäßigkeiten. Immer wieder ist Gomopa in juristische Streitigkeiten verwickelt. In einer einstweiligen Verfügung des Landgerichts Berlin vom 31. August (Az.: 27 O 658/10) ist das Unternehmen aufgefordert worden, nicht länger Falschinformationen über den Kasseler Immobilienhändler Immovation AG und seinen Finanzvorstand Lars Bergmann zu verbreiten. „Gomopa hat seinen Firmensitz bewusst in New York, weil die Firma dort presserechtlich nicht belangt werden kann“, sagte ein Kenner des Unternehmens der F.A.Z.
Die SdK räumte am Freitag ein, dass auch ihre Geschäftsräume durchsucht wurden. Es gebe jedoch „aus der Sicht der SdK keinerlei neue Vorwürfe gegen den Verein“. Die alten Vorwürfe gegen die SdK stehen im Zusammenhang mit Kursmanipulationen bei Aktien der Unternehmen Thielert und Wirecard. Staatsanwaltschaft und Allfinanzaufsicht Bafin ermittelten seinerzeit gegen den damaligen stellvertretenden SdK-Vorsitzenden Straub. Dieser hatte eingeräumt, Verkaufsoptionen auf das Zahlungsunternehmen Wirecard zu halten, dessen Kurs durch heftige Kritik der SdK unter Druck geraten war. Später trat Straub, der offenbar in kurzer Zeit ein Vermögen verdient hatte, zurück. Wirecard hatte Anzeige wegen Insiderhandels und Kursmanipulation gegen sechs Personen erstattet, darunter auch aktuelle und frühere SdK-Vorstände.
und das HANDELSBLATT:
Finanzaufsicht untersucht Kursachterbahn bei Wirecard
exklusiv Die Bundesanstalt für Finanzdienstleistungsaufsicht BaFin hat aufgrund der merkwürdigen Kursturbulenzen der Wirecard-Aktie eine förmliche Untersuchung des Falles eingeleitet. BaFin prüft mögliche Marktmanipulationen nach Falschbericht des Internetdienstes Gomopa. Zwei der Gomopa-Gründer wurden schon 2006 wegen Betrugs verurteilt
FRANKFURT. Die Bundesanstalt für Finanzdienstleistungsaufsicht BaFin hat aufgrund der merkwürdigen Kursturbulenzen der Wirecard-Aktie eine förmliche Untersuchung des Falles eingeleitet. “Wir prüfen, ob es Anhaltspunkte für Marktmanipulation in Aktien der Wirecard AG gibt”, sagte eine BaFin-Sprecherin. Zu Details könne sie sich jedoch nicht äußern.
Der Kurs des Münchener Zahlungsabwicklers Wirecard war am vergangenen Dienstag um mehr als 30 Prozent eingebrochen. Am Abend zuvor hatte der Internetdienst Goldman, Morgenstern & Partners (Gomopa) berichtet, der in den USA wegen illegalen Online-Glücksspiels verhaftete Deutsche Michael Schütt habe in einem Geständnis Wirecard schwer belastet. Gomopa bezog sich auf einen Bericht der Lokalzeitung “Naples News”. Schütt habe ausgesagt, er sei bei illegalen Geldgeschäften direkt vom Wirecard-Vorstand beauftragt worden.
Das Problem an dem Gomopa-Bericht: Er war falsch. Wie Nachfragen des Handelsblattes ergaben, hat die Reporterin, die für die “Naples News” über Schütt schreibt, Wirecard nie erwähnt. Gomopa reagierte auf Nachfragen zögerlich. Erst löschte der Dienst den Hinweis auf die Lokalzeitung, hielt aber den Vorwurf aufrecht, Schütt habe Wirecardbelastet. Danach änderte man den Bericht erneut. Nun hieß es, ein Informant von Gomopa verfüge über die fraglichen Details aus Schütts Geständnis.
Dem Handelsblatt liegt inzwischen das amtliche Protokoll von Schütts Geständnis am 23. März vor. Schütt bekennt sich darin schuldig, illegale Geldgeschäfte im Zusammenhang mit Online-Glücksspiel abgewickelt zu haben. Das Wort Wirecard kommt nicht vor. Gomopa hatte zu Wochenbeginn seinen Text erneut geändert und nun behauptet, Schütt belaste “eine Bank”. Auf erneute Nachfragen des Handelsblattes war der Bericht dann ganz verschwunden.
Der Kurs von Wirecard hat sich inzwischen fast vollständig erholt. Ein Frankfurter Analyst sagte, für ihn sei klar, dass die Aktie seit Wochen manipuliert werde. Erst verteure sich die Leihe der Aktie, dann komme es zu außergewöhnlichem Handel, danach tauchten plötzlich desaströse Gerüchte auf. Dazu gehöre auch die Anzeige, die vor kurzem bei der Staatsanwaltschaft München einging und Wirecard der Geldwäsche bezichtigt. Es sei offensichtlich, dass Short Seller mit der Wirecard-Aktie Jojo spielen.
Mark Vornkahl, einer der Gründer von Gomopa wies den Vorwurf der Kursmanipulation gestern zurück. Man wolle nur die Wahrheit aufdecken. Es ist allerdings nicht das erste Mal, dass Gomopa-Vertreter ins Zwielicht geraten. 2006 wurden Vornkahl und Mitgründer Klaus Maurischat wegen Betrugs an einem Anleger verurteilt. Maurischat gab gestern gegenüber dem Handelsblatt weitere Verurteilungen zu. Es habe sich dabei jedoch nicht um Anlagebetrug gehandelt.