|
Category: TOP SECRET
TOP-SECRET – Demand Progress Pleads for Megaupload Property
DOWNLOAD THE ORIGINAL DOCUMENT HERE
Unveiled – Obama Protection 47
|
TOP-SECRET – DARPA Fog Computing Leak Prevention Software Design Report
This is the design documents for the Allure Defender system. This document is a high level design and API of the components that make up the Allure Defender system. We outline all the high-level pieces and then the individual components, their behaviors, expected input/outputs, and relationships. We will discuss specific implementation and design choices and languages and libraries that will be used. In addition we will cover specific user cases and illustrate some running examples. Last we refer to a running system which implements many of the components we cover in the document.
The goal of the document is for a designer to create a working system and or verify a working system conforms to the specifications outlined in the document.
…
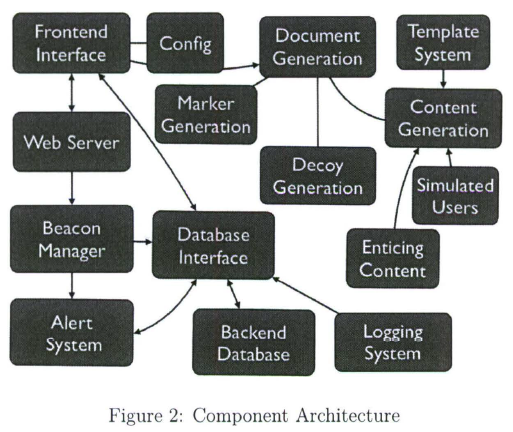
The document generation component will create documents (henceforth referred to as Decoy Documents, or DD for short) in various formats (e.g., Word, Excel, PDF, Powerpoint, email messages, Instant Messaging logs, … ) that contain one of several features :
• a “mark” allowing Allure Defender to determine whether a file is a DD, and possibly allow legitimate users to avoid accessing/triggering the DD;
• one or more “beacons”, which will cause the application processing the DD to emit some sort of discernible signal;
• Enticing Information (henceforth referred to as EI) which, if acted upon by the adversary, will allow detection. Such information includes URLs (for various protocols), account information (e.g., username/password), and others that may be developed in the future; and
• Enticing Content (henceforth referred to as EC) that will attract t he adversary to the DD (e.g., if they are using a search function) without raising suspicion, will support the presence of the EI in the document, and will allow the DDs to “fit in” with the rest of the environment on which t hey have been deployed.
DDs may be deployed on servers, databases, user desktops and laptop, mobile devices, honeypots, or other locations. It is desirable t hat all of these seeding techniques be supported.
The EC may be generated based on templates, synthesized from private sources (e.g., by mining existing documents at the directory /account/system/server to be seeded), synthesized from public sources (e.g., documents acquired through search engines) based on high-level templates, or synthesized from public sources using information mined from existing documents at the directory/account/system/server to be seeded. Any combination of these techniques may be used to generate DDs, and a specific DD may be t he result of several such techniques being used simultaneously.
The misbehavior detection component consists of a variety of subcomponents, some of which are specific to the beacon techniques used:
• honeypot servers, pointed to by URLs and similar information;
• intrusion detection systems combined with legitimate servers/services, when the lat ter can be used for detection purposes without compromising primary functionality (e.g., invalid username password login attempts, specific directories in a filesystem or web server hierarchy, DNS server queries, and so on) ;
• Data Leakage Prevention (DLP) subsystems, which may operate at various points in the system, e.g. , network, filesystem, memory, and others. The DLP may be a priori aware of the identity and location of the DDs, or it may be able to identify them on the fly via the “mark “.
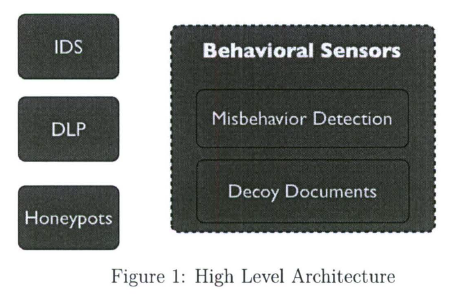
The design of the architecture (see Figure 1) attempts to cleanly divide the functionality of the different subsystems into self-managing components allowing maximum flexibility of the system to adopt to changes while allowing all the components to seamlessly work together. The design reflects the facts that (a) documents may be requested via different interfaces (e.g., webserver front-end, client-side logic interacting over the network, client-side application with generation library, and possibly others); (b) the documents may contain a combination of enticing information, marks and beacons, based on the desired configuration, (c) the corresponding detection capabilities can vary (and should be extensible so that we can add further capabilities as future research directs), and (d) the documents, and specifically the enticing content, may be generated through a variety of means.
…
TOP-SECRET from the FBI – National President, National Vice President, and 39 Members and Associates of the Devils Diciples Motorcycle Gang Indicted
WASHINGTON—An indictment unsealed today in the Eastern District of Michigan charges 41 members and associates of the Devils Diciples Motorcycle Gang, including National President Jeff Garvin Smith and National Vice President Paul Anthony Darrah, for their alleged participation in a variety of criminal offenses, announced Assistant Attorney General Lanny A. Breuer of the Justice Department’s Criminal Division, U.S. Attorney Barbara McQuade for the Eastern District of Michigan, and FBI Acting Assistant Director Valerie Parlave.
Thirty-one defendants were arrested today in Michigan and Alabama and five defendants were previously in custody. More than 60 firearms and more than 6,000 rounds of ammunition were seized during this investigation. In addition, eight methamphetamine manufacturing laboratories were dismantled during the investigation.
The indictment alleges that the 41 Devils Diciples members and associates, including Smith and Darrah, participated in various criminal acts, including violent crimes in aid of racketeering, drug trafficking, illegal firearms offenses, obstruction of justice, illegal gambling, and other federal offenses. Eighteen of the defendants, including Smith and Darrah, are charged with violations of the Racketeer Influenced and Corrupt Organizations (RICO) Act by conducting their illegal enterprise through a pattern of racketeering activity which included murder, robbery, extortion, drug trafficking, obstruction of justice, and other federal and state offenses.
“For years, according to the indictment, the Devils Diciples have spread fear in cities throughout Michigan and around the country,” said Assistant Attorney General Breuer. “This violent criminal enterprise allegedly profits from drug trafficking and illegal gambling and uses intimidation and violence to silence its adversaries and maintain control over its members. Today’s arrests of the Devils Diciples’ top leaders and 39 of the gang’s members and associates are an important step in our efforts to dismantle violent criminal enterprises across the country.”
“Removing violent criminal organizations from our community is essential to attaining the quality of life we expect and deserve,” said U.S. Attorney McQuade. “Federal law enforcement is using all legal tools available to prosecute violent criminal enterprises like this one.”
“Today’s law enforcement action takes violence off the streets,” said FBI Acting Assistant Director Valerie Parlave. “The FBI appreciates the strong law enforcement partnerships leading to this activity and will continue its commitment to state and local communities to address this violent, and often brutal, criminal threat across the U.S.”
According to the indictment, the Devils Diciples is a criminal enterprise with its national headquarters in Clinton Township, Michigan. The Devils Diciples operates regional chapters located in cities throughout Michigan, Alabama, Arizona, California, Illinois, Indiana, Ohio, and elsewhere. The Devils Diciples engage in criminal activities for financial gain, including distribution of narcotics, theft, transportation and sale of stolen motorcycles, conducting illegal gambling businesses, robbery, extortion, and acts of violence.
According to the indictment, membership in the Devils Diciples is based in part on successfully completing a probationary period, followed by formal approval by one or more members or leaders. Members are required to own Harley Davidson motorcycles and are commonly referred to as “full patched members.” Full patched members are identified by a club name or nickname for the express purpose of concealing their identity and thwarting identification by law enforcement. Members are required to follow orders from leadership, including orders to assault or use threats and intimidation against others, to transport or distribute drugs, to lie to law enforcement, or to hide or destroy evidence. Members are also required to follow the Devils Diciples by-laws and attend regular meetings referred to as “church.”
The indictment alleges that the Devils Diciples committed acts involving attempted murder, robbery, extortion, assault, and threats of violence to maintain the territory of the organization and to protect the organization and its members from detection and prosecution by law enforcement authorities.
The indictment charges the 41 Devils Diciples members and associates with a variety of criminal offenses including violent crimes in aid of racketeering, drug trafficking, illegal firearms offenses, obstruction of justice, and other federal offenses.
Specifically, the indictment alleges that in August 2003, Vincent John Witort and multiple other Devils Diciples members robbed, kidnapped, and attempted to murder other members of the Arizona Chapter for violating Devils Diciples rules.
The indictment alleges that in 2004, Smith possessed state and federal law enforcement manuals regarding outlaw motorcycle gangs marked “For Official Use Only” and “Law Enforcement Sensitive” and numerous documents related to criminal matters involving members of the Devils Diciples, including police reports, search warrants, affidavits, indictments, and witness interview transcripts.
Smith allegedly assaulted another individual in August 2008 for the purpose of maintaining and increasing position in the Devils Diciples enterprise. The indictment also alleges that in late 2008, Smith, Paul Anthony Darrah, and Cary Dale Vandiver assaulted Scott Thomas Perkins with a metal pipe.
According to the indictment, in February 2009, Ronald Raymond Roberts, Christopher Raymond Cook, and Wayne Russell Werth allegedly assaulted Danny Russell Burby, Jr. with a box cutter and a bottle, after various Devils Diciples members circulated flyers containing a photograph of Burby and stating that Burby was a “snitch.”
The indictment also alleges that in January 2012, David Randy Drozdowski and Smiley Villa assaulted an individual they believed was a member of a rival motorcycle club for being present in Devils Diciples territory.
Sixteen of the members and associates named in the indictment are charged with conspiracy to conduct an illegal gambling business. The defendants operated slot machines located in several Devils Diciples clubhouses in Michigan, Arizona, and Alabama to generate income for the criminal enterprise and its members.
The 41 defendants charged are:
1. Scott William Sutherland, aka “Scotty Z”
2. Ronald Raymond Roberts, aka “Rockin’ Ronnie”
3. David Thomas Roberts, aka “Detroit Dave”
4. Patrick Michael McKeoun, aka “Magoo”
5. Jeff Garvin Smith, aka “Fat Dog”
6. Paul Anthony Darrah, aka “Pauli”
7. Cary Dale Vandiver, aka “Gun Control”
8. Vincent John Witort, aka “Holiday”
9. Michael William Mastromatteo, aka “Iron Mike”
10. Vernon Nelson Rich, aka “Vern”
11. John Renny Riede, aka “Bear”
12. Victor Carlos Castano
13. Gary Lee Nelson
14. Michael Kenneth Rich, aka “Tatu”
15. Raymond Charles Melioli, aka “Romeo”
16. Timothy Paul Downs, aka “Space”
17. David Randy Drozdowski, aka “D”
18. Smiley Villa, aka “SA”
19. Dean Edward Jakiel, aka “Jesus”20. Tony Wayne Kitchens, aka “Trouble”
21. Sylvester Gerard Wesaw, aka “Sly Dog”
22. Ronald Nick Preletz, aka “Polar Bear”
23. Howard Joseph Quant, aka “44”
24. Scott Thomas Perkins, aka “Scotty P”
25. Clifford Chansel Rhodes, II
26. David Roy Delong, aka “Reverend”
27. Christopher Raymond Cook, aka “Damien”
28. Michael John Palazzola, aka “Utica Mike”
29. Danny Russell Burby, Jr., aka “Thumbs”
30. Ronald Leon Lambert, aka “Crow”
31. Jason Joseph Cook, aka “Cookie”
32. Edward Allen Taylor, aka “Big Ed”
33. Salvatore Battaglia, aka Bando”
34. William Scott Lonsby, aka “Buckwheat”
35. Wayne Russell Werth
36. Lauri Ann Ledford
37. Jennifer Lee Cicola
38. Dean Anthony Tagliavia
39. Alexis Catherine May
40. Paula Mileha Friscioni
41. John Charles Scudder
An indictment is only a charge and is not evidence of guilt. Each defendant is entitled to a fair trial in which it will be the government’s burden to prove guilt beyond a reasonable doubt.
The case was investigated by the FBI, the Michigan State Police, the Macomb County Sheriff’s Office, and the County of Macomb Enforcement Team (COMET), with assistance from the Bureau of Alcohol, Tobacco, Firearms, and Explosives and the St. Clair County Sheriff’s Office. The case is being prosecuted by the Organized Crime and Gang Section of the Justice Department’s Criminal Division and the U.S. Attorney’s Office for the Eastern District of Michigan.
TOP-SECRET – Uzbek National Sentenced to Nearly 16 Years in Prison for Threatening to Kill the President
BIRMINGHAM, AL—U.S. District Judge Abdul K. Kallon today sentenced Ulugbek Kodirov, an Uzbek national who has lived in the United States since 2009, to 15 years and eight months in prison for providing material support to terrorism, threatening to kill President Barack Obama, and illegally possessing a weapon.
U.S. Attorney for the Northern District of Alabama Joyce White Vance, Department of Justice Assistant Attorney General for National Security Lisa Monaco; FBI Special Agent in Charge Patrick J. Maley; Bureau of Alcohol, Tobacco, Firearms, and Explosives (ATF) Special Agent in Charge (SAC) Glenn N. Anderson; Secret Service SAC Roy Sexton; and Homeland Security Investigations (HSI) SAC Raymond R. Parmer, Jr. announced the sentence.
Kodirov, 22, of Uzbekistan, pleaded guilty in February to one count of providing material support to terrorism, one count of threatening to kill the president, and one count of possession of a firearm by an illegal alien. Kodirov is the first person to be convicted in the Northern District of Alabama for providing material support to terrorism.
U.S. Attorney Vance praised the quick response and careful investigative work by the Joint Terrorism Task Force for the Northern District of Alabama, which led to Kodirov’s arrest before anyone was harmed. “This case is a sobering reminder that terrorist activity can happen anywhere,” said U.S. Attorney Vance. “Our community has the coordinated efforts of federal, state, and local law enforcement to thank for the immediacy of their response to this threat. This case has a happy ending—Kodirov is going to prison for more than 15 years, and no one in our community was hurt,” she said.
“This case demonstrates the continuing threat posed by violent extremists in this country and how law enforcement works together to neutralize such plots,” said Assistant Attorney General Monaco. “Today, Mr. Kodirov is being held accountable for his actions thanks to the efforts of the many agents, analysts, and prosecutors involved in this matter.”
FBI SAC Maley thanked the members of the Joint Terrorism Task Force (JTTF), which includes the Jefferson and Shelby, Alabama County Sheriff’s Offices; Birmingham, Hoover, and the University of Alabama at Birmingham Police Departments; the Transportation Security Agency; Secret Service; ATF; and the Department of Homeland Security. He also thanked the Pelham and Leeds, Alabama Police Departments for their assistance in this case. “The JTTF has been diligently investigating and building partnerships to protect Alabama from terrorists since 9/11, and its efforts put it in the unique position to interdict a violent act of terrorism. This case serves as a reminder of the dangers of the Internet on radicalizing our youth right in our own back yards, and all citizens and organizations need to remain vigilant on the ever-increasing threat from home-grown extremists,” he said.
“Mr. Ulugbek Kodirov came to the United States as a student and a welcomed guest. To date, that has dramatically changed,” said ATF SAC Anderson. “Kodirov will be serving time at the Federal Bureau of Prisons for his threats against President Obama and illegal possession of a firearm. It is shocking that he was willing to arm himself with hand grenades to further his agenda. Thankfully, this recipe for disaster was averted. ATF and our law enforcement partners will continue to work cases like these and other violent crime to keep cities, small and large, across America safe every day,” Anderson said.
“In the fight against domestic terrorism, it is absolutely essential that federal, state, and local law enforcement agencies work closely together to share information and chase down leads,” said HSI SAC Parmer. “In this case, the JTTF worked exactly as it is intended to by identifying and eliminating a serious threat to the president of the United States.”
“The Secret Service values its role as a member of the Joint Terrorism Task Force and our partnerships with task force members representing local, state, and federal law enforcement agencies,” said Secret Service SAC Sexton. “A dangerous situation was thwarted and the person behind it was stopped because of the hard work of our dedicated task force investigators.”
Kodirov acknowledged in his guilty plea that he had been in communication with an individual whom he believed to be a member of the Islamic Movement of Uzbekistan (IMU) and that Kodirov interpreted these conversations to mean that he should kill President Obama. Kodirov then took steps to obtain weapons to carry out his plans to kill the president. The IMU is designated as a Foreign Terrorist Organization by the U.S. State Department. Kodirov also showed jihadist websites and videos on his computer to another individual and told that person that he wanted to assist others in jihad overseas, according to his plea agreement.
Kodirov also acknowledged that he had lengthy conversations in July 2011 with a different individual about Kodirov’s desire to kill President Obama and possible ways to carry out the assassination. That individual traveled to Birmingham to meet Kodirov and introduced him to another individual, an undercover agent, from whom Kodirov intended to obtain weapons he would use to kill the president.
The three men met on July 13, 2011, at a motel in Leeds. In that meeting, the agent presented a fully automatic Sendra Corporation Model M15-A1 machine gun, a sniper rifle with a telescopic sight, and four disassembled hand grenades and asked Kodirov if he would like to use any of them to “carry out his plan to kill the president,” according to the plea agreement. Kodirov chose the M15-A1 machine gun and the hand grenades and left the meeting with the weapons. Agents arrested Kodirov before he left the motel.
Kodirov entered the United States on a student visa in June 2009. His visa was revoked on April 1, 2010, for failing to enroll in school. Thereafter, he was unlawfully present within the United States. He was living in an extended-stay motel in Pelham at the time of his arrest.
The FBI, ATF, HSI, and Secret Service investigated the case. Assistant U.S. Attorneys Michael W. Whisonant Sr. and Ryan K. Buchanan prosecuted the case with assistance from the Counterterrorism Section of the Justice Department’s National Security Division.
TOP-SECRET – DHS-FBI Bulletin: Potential Use of Cold Packs in Improvised Explosives
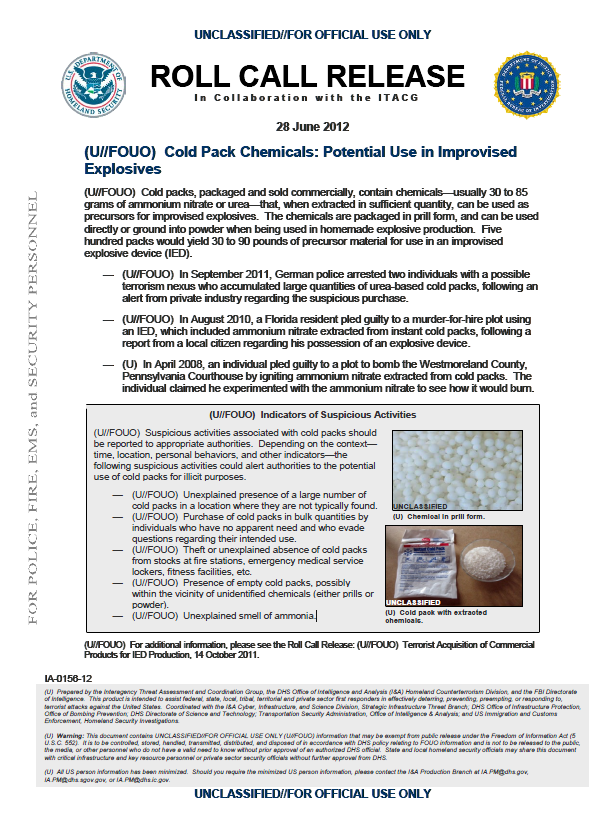
(U//FOUO) Cold packs, packaged and sold commercially, contain chemicals—usually 30 to 85 grams of ammonium nitrate or urea—that, when extracted in sufficient quantity, can be used as precursors for improvised explosives. The chemicals are packaged in prill form, and can be used directly or ground into powder when being used in homemade explosive production. Five hundred packs would yield 30 to 90 pounds of precursor material for use in an improvised explosive device (IED).
— (U//FOUO) In September 2011, German police arrested two individuals with a possible terrorism nexus who accumulated large quantities of urea-based cold packs, following an alert from private industry regarding the suspicious purchase.
— (U//FOUO) In August 2010, a Florida resident pled guilty to a murder-for-hire plot using an IED, which included ammonium nitrate extracted from instant cold packs, following a report from a local citizen regarding his possession of an explosive device.
— (U) In April 2008, an individual pled guilty to a plot to bomb the Westmoreland County, Pennsylvania Courthouse by igniting ammonium nitrate extracted from cold packs. The individual claimed he experimented with the ammonium nitrate to see how it would burn.
(U//FOUO) Indicators of Suspicious Activities
(U//FOUO) Suspicious activities associated with cold packs should be reported to appropriate authorities. Depending on the context—time, location, personal behaviors, and other indicators—the following suspicious activities could alert authorities to the potential use of cold packs for illicit purposes.
— (U//FOUO) Unexplained presence of a large number of cold packs in a location where they are not typically found.
— (U//FOUO) Purchase of cold packs in bulk quantities by individuals who have no apparent need and who evade questions regarding their intended use.
— (U//FOUO) Theft or unexplained absence of cold packs from stocks at fire stations, emergency medical service lockers, fitness facilities, etc.
— (U//FOUO) Presence of empty cold packs, possibly within the vicinity of unidentified chemicals (either prills or powder).
— (U//FOUO) Unexplained smell of ammonia.
DOWNLOAD THE ORGINAL DOCUMENT HERE
TOP-SECRET from the FBI – Men Indicted in $485 Million Investment Fraud Scheme
PLANO, TX—Two Dallas men have been indicted in connection with a $485 million investment fraud scheme in the Eastern District of Texas, announced U.S. Attorney John M. Bales today.
Brendan Coughlin, 46, and Henry Harrison, 47, both of Dallas, have been charged with one count of conspiracy to commit mail fraud and 10 counts of mail fraud. The indictment was returned by a federal grand jury on July 11, 2012.
According to the indictment, Coughlin and Harrison, on behalf of Provident Royalties LLC, conspired with others to defraud investors in an oil and gas scheme that involved over $485 million and 7,700 investors throughout the United States. Specifically, beginning in approximately September 2006, Coughlin, Harrison, and other individuals made materially false representations and failed to disclose material facts to their investors in order to induce the investors into providing payments to Provident. Among these false representations were statements that funds invested would be used only for the oil and gas project for which those funds were raised; among the omissions of material fact were the facts that another of Provident founders, Joseph Blimline, had received millions of dollars of unsecured loans; that Blimline had been previously charged with securities fraud violations by the state of Michigan; and that funds from investors in later oil and gas projects were being used to pay individuals who invested in earlier oil and projects.
If convicted, Coughlin and Harrison face up to 20 years in federal prison.
This law enforcement action is part of President Barack Obama’s Financial Fraud Enforcement Task Force.
President Obama established the interagency Financial Fraud Enforcement Task Force to wage an aggressive, coordinated, and proactive effort to investigate and prosecute financial crimes. The task force includes representatives from a broad range of federal agencies, regulatory authorities, inspectors general, and state and local law enforcement who, working together, bring to bear a powerful array of criminal and civil enforcement resources. The task force is working to improve efforts across the federal executive branch, and with state and local partners, to investigate and prosecute significant financial crimes, ensure just and effective punishment for those who perpetrate financial crimes, combat discrimination in the lending and financial markets, and recover proceeds for victims of financial crimes.
This case is being investigated by the FBI and prosecuted by Assistant U.S. Attorney Shamoil T. Shipchandler.
A grand jury indictment is not evidence of guilt. A defendant is presumed innocent until proven guilty beyond a reasonable doubt in a court of law.
TOP-SECRET – Email Hidden Tracking Deceptions
1. Government Email Hidden Tracking Deceptions
Many US federal agencies distribute emails and notifications via govdelivery.com (“Made for government”). The service embeds hidden URLs with a lengthy tracking number which logs clicks and identifications of recipients who retrieve cited documents. This is a significant privacy violation by not notifying email recipients of the tracking feature. DHS examples (some alphanumerics changed):
This service is provided to you at no charge by the U.S. Department of Homeland Security.http://links.govdelivery.com:80/track?type=click&enid=ZWFzPTEmbWFpbGluZ2lkPTIwMTIwMTIwLjU
xMTA1MjEmbWVzc2FnZWlkPU1EQi1QUkYYYYBBBVVVIwMTIwLjUxMTA1MjEmZGF0YWJhc2Vp
ZD0xMDAxJnNlcmlhbD0xNjg0Nzk1NCZlbWFpbGlkPWp5YUBwaXBlbGluZS5jb20mdXNlcmlkPWp5Y
UBwaXBlbGluZS5jb20mZmw9JmV4dHJhPU11bHRpdmFyaWF0ZUlkPSYmJg==&&&102&&&http://
http://www.dhs.gov/index.shtmhttp://links.govdelivery.com:80/track?type=click&enid=ZWFzPTEmbWFpbGluZ2lkPTIwMTIwMTIwLjUx
MTA1MjEmbWVzc2FnZWlkPU1EQi1QUkQtQlVMLTIwMTIwMTIwLjUxMTA1MjEmZGF0YWJhc2VpZ
D0xMDAxJnNlcmlhbUUUUYYYYVVVZlbWFpbGlkPWp5YUBwaXBlbGluZS5jb20mdXNlcmlkPWp5YU
BwaXBlbGluZS5jb20mZmw9JmV4dHJhPU11bHRpdmFyaWF0ZUlkPSYmJg==&&&103&&&http://www.
dhs.gov/xutil/gc_1157139158971.shtmGovDelivery is providing this information on behalf of U.S. Department of Homeland Security, and may not use the information for any other purposes.
Department of Justice admittedly tracking ID today:
Deputy Attorney General James M. Cole Speaks at the Wells Fargo Press Conferencehttp://links.govdelivery.com:80/track?type=click&enid=ZWFzPTEmbWFpbGluZ2lkPTIwMTIwNzEy
Ljg5ODc4MTEmbWVzc2FnZWlkPU1EQi1QUkQtQlVMLTIwMTIwNzEyLjg5ODc4MTEmZGF0YWJhc2
VpZD0xMDAxJnNlcmlhbD0xNzA3MzcyMyZlbWFpbGlkPWp5YUBwaXBlbGluZS5jb20mdXNlcmlkPWp
5YUBwaXBlbGluZS5jb20mZmw9JmV4dHJhPU11bHRpdmFyaWF0ZUlkPSYmJg==&&&
102&&&http://www.justice.gov/iso/opa/dag/speeches/2012/dag-speech-120712.html
The White House admittedly tracks ID minutely too:
Watch the video and get the facts here.http://links.whitehouse.gov/track?type=click&enid=ZWFzPTEmbWFpbGluZ2lkPTIwMTIwNjI4Ljg2NDc2M
zEmbWVzc2FnZWlkPU1EQi1QUkQtQlVMLTIwMTIwNjI4Ljg2NDc2MzEmZGF0YWJhc2VpZD0xMDAxJn
NlcmlhbD0xNjkwNTM2MiZlbWFpbGlkPWp5YUBwaXBlbGluZS5jb20mdXNlcmlkPWp5YUBwaXBlbGlu
ZS5jb20mZmw9JmV4dHJhPU11bHRpdmFyaWF0ZUlkPSYmJg==&&&100&&&http://www.whitehouse.gov/
blog/2012/06/28/supreme-court-upholds-president-obamas-health-care-ref
The hidden codes may be overlooked: They were discovered when our legacy email program could not activate them. Last year Cryptome wrote the government clients of govdelivery.com and the service itself to reveal the tracking but never received an answer from any.
Notable exception to hidden tracking is the GAO which transparently discloses its URLs:
Electronic Warfare: DOD Actions Needed to Strengthen Management and Oversight. GAO-12-479, July 9.
Other USG offices display only a linked title but not the underlying URL, a method often used to deceive about the link. State Department and FBI examples, respectively, without hidden tracking code:
Press Releases: Remarks With Afghan President Hamid Karzai[We see today at the bottom of State Department email it is also sent by govdelivery.com and tracks recipients. “Report problems: <support@govdelivery.com>”]
2. Commercial Email Tracking Deceptions
Commercial email delivery services also hide tracking code. For example, Bluehornet.com sent out an email yesterday for the Stratfor Class Action Settlement which embedded hidden URLs with tracking numbers (original numbers replaced):
http://echo4.bluehornet.com/yu/10987654321:10987654321:k:9:10987654321:109876543211098765
432110987654321:h
Bluehornet violates the privacy of the email recipients by not calling attention to its tracking feature, thus implicating the law firm which sued Stratfor for failing to protect its customer information — presumably the law firm does not know it may be subject to privacy violation suits.
Other services embed URLs which track access to articles with concealed codes that likely also track email recipients without explanation of the codes’s use. New York Times today, egregiously tracking (some alphanumerics changed):
Spend summer vacation at an all-inclusive resort, surrounded by the crystalline waters of the Pacific Oceanhttp://p.nytimes.com/email/re?location=vzewYO/FHLSRA5cTrA4oWdnsb+onKeHxFGl2jINZg1bhIX3P5MN
4T03Fcnswgysn52TggCVcNc5LY2IXAm9BwJ6DmVAwsenGY7ZBBBBBCCCCCBBDbW3WIL+pXZuA&
campaign_id=105&instance_id=16741&segment_id=36060&user_id=5c401f4b636bc9557c9c7a87cab025f8
Amazon (some alphanumerics changed):
The SAGE Handbook of Architectural Theoryhttp://www.amazon.com/gp/r.html?R=1681XH3C5L4XM&C=1071C1INNZ6FT&H=OOEX4ICXELVALRNTX
SY0POCY0TCA&T=C&U=http%3A%2F%2Fwww.amazon.com%2Freview%2Fcreate-review%2Fref%3Dpe_
6680_24339240_cm_cr_ec_add_1_h_c24339240%3Fie%3DUTF8%26nodeID%3D%26asin%3D1412946131%
26customerID%BVRFWGHDEW35
This for an article listed in a Dei Zeit newsletter today (alphamumerics changed):
http://newsletterversand.zeit.de/go/4/LMTVGB-2W9MEN8-HBV7G81-VXZM6N.html
3. Honest and Dishonest Email
Honest privacy protection advocates will always use transparent URLs. An EFF example:
For the full motion for partial summary judgment:https://www.eff.org/document/plaintiffs-motion-partial-summary-judgment
Compared to, one of many possible examples, the otherwise admirable Bradley Manning Support Network (code changed):
http://bradleymanning.orghttp://t.ymlp305.net/mybealcccccccccccccccccj/click.php
Tracking is often justified as legitimate automatic data gathering on users, however few, if any, email delivery and tracking services disclose tracking information with each email, offer no tracking opt-out choice, provide no guarantees of anonymity or against misuse of the user data, and seldom point to either the privacy policies of the service or those of the services’ customers (albeit, no privacy policy is believable). This suggests deliberate deception and lack of accountability of both the services and their customers, and in this manner replicate the deceptions of vilified email spammers.
All users of email should use transparent URLs, and those using hidden tracking codes should include with each email an explanation of the hidden URLs, the purpose of the tracking, related privacy policies and a trcking to opt-out choice. Those which do not comply should be blocked, filtered, trashed unread or returned marked “Choice Expletive.”
__________
Related, website links with non-transparent URLs (such as Cryptome uses, and has no delusional privacy policy) should never be clicked until passing a pointer over them to verify the underlying code. Avoid lengthy alphanumeric codes whereever they are hidden.
TOP-SECRET – Fukushima Daiichi NPS Unit 3 Reactor Probe
Fukushima Daiichi Nuclear Power Station Unit 3 Reactor Building Operating Floor Area Investigation
http://www.tepco.co.jp/en/nu/fukushima-np/images/handouts_120711_03-e.pdf
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0711/pict8.jpg)
Northwest part of the Operating Floor. Photo taken on July 11, 2012 [Captions by TEPCO. Photo striations in the originals.]
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0711/pict0.jpg)
East part of the Operating Floor. Photo taken on July 11, 2012
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0711/pict1.jpg)
Fourth floor (Photo taken from the equipment hatch). Photo taken on July 11, 2012
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0711/pict2.jpg)
Third floor (Photo taken from the equipment hatch). Photo taken on July 11, 2012
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0711/pict3.jpg)
Operating Floor [No date. Appears to be clip of Tokyo Air Service photo20-21 March, 2011.]
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0711/pict6.jpg)
Enlarged image of the equipment hatch [Clip of preceding photo.]
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0711/pict5.jpg)
The FBI – Missing Georgia Bank Director Indicted for Bank Fraud
SAVANNAH, GA—Aubrey Lee Price, 46, originally from Lyons, Georgia, was indicted today by a federal grand jury sitting in the Southern District of Georgia on a charge that he defrauded the Montgomery Bank & Trust in Ailey, Georgia, of over $21 million. On July 6, 2012, Georgia regulators closed the Montgomery Bank & Trust and appointed the FDIC as receiver.
According to the allegations in the indictment, in 2010, an investment group controlled by Price invested approximately $10 million in the failing Montgomery Bank & Trust (MB&T). Price was then made a director of MB&T and put in charge of investing the bank’s capital. Over the next 18 months, PRICE stole, misappropriated, and embezzled over $21 million from MB&T. To cover up his fraud, Price provided MB&T officials with bogus account statements that falsely indicated the bank’s capital was safely held in an account at a financial services firm. As a result of Price’s alleged fraud upon MB&T, the bank’s cash assets and reserves were depleted.
U.S. Attorney Edward J. Tarver said, “Montgomery Bank & Trust is the 32nd FDIC-insured bank to fail in the nation this year and the 6th in Georgia. When bank failures are caused by the greed and criminal conduct of others, those responsible will be investigated and prosecuted to the fullest extent of the law by our team of federal agents and prosecutors.”
Price has been missing for over three weeks. Anyone with information on Price’s whereabouts is urged to contact the FBI.
Price is charged with one count of bank fraud, which carries a maximum sentence of 30 years in prison and a fine of up to $1,000,000. Tarver emphasized that an indictment is only an accusation and is not evidence of guilt. The defendant is entitled to a fair trial, during which it will be the government’s burden to prove guilt beyond a reasonable doubt.
The indictment of Price arises out of an ongoing and joint investigation by FDIC-OIG Special Agent John Crawford; Federal Reserve Board OIG Special Agent Amy Whitcomb; and FBI Special Agent Ed Sutcliff. First Assistant United States Attorney James Durham is prosecuting the case for the United States.
TOP-SECRET from the FBI – Massachusetts Man Agrees to Plead Guilty to Plotting Attack on Pentagon and U.S. Capitol and Attempting to Provide Material Support to Terrorists
BOSTON—In a written agreement filed today in U.S. District Court in Boston, Rezwan Ferdaus, aka Dave Winfield, aka Jon Ramos, has agreed to plead guilty to attempting to damage and destroy a federal building by means of an explosive and attempting to provide material support to terrorists.
He has also agreed to a joint sentencing recommendation of 17 years in prison, followed by 10 years of supervised release. In exchange, the government has agreed to dismiss the remaining charges against Ferdaus at the time of sentencing. The parties have filed a joint motion asking the court to schedule a change-of-plea hearing. The plea agreement filed today is subject to review and acceptance by the district court. A date for the change-of-plea hearing has not yet been set.
In September 2011, Ferdaus, 26, was arrested in connection with his plot to damage or destroy the Pentagon and U.S. Capitol using large remote controlled aircraft filled with C-4 plastic explosives. He was later charged in a six-count indictment with attempting to damage and destroy a federal building by means of an explosive; attempting to damage and destroy national defense premises; receipt of explosive materials; receipt of possession of non-registered firearms (six fully automatic AK-47 assault rifles and three grenades); attempting to provide material support to terrorists; and attempting to provide material support to a designated foreign terrorist organization (al Qaeda).
The government has previously alleged that in 2010, and continuing until his arrest, he planned to commit acts of violence against the United States. With the goal of terrorizing the United States, decapitating its “military center,” and killing as many “kafirs” (an Arabic term meaning non-believers) as possible, Ferdaus extensively planned and took substantial steps to bomb the Pentagon and U.S. Capitol using remote controlled aircraft filled with explosives.
On September 28, 2011, Ferdaus requested and instructed the undercover FBI employees (UCE) to deliver explosives and firearms (material represented to Ferdaus to contain 25 pounds of C-4 explosives, including approximately 1.25 pounds of actual C-4 explosives, three grenades, and six fully automatic AK-47 assault rifles) for his attack plan. While inspecting the explosives and firearms in the UCEs’ vehicle and inside his storage unit, Ferdaus placed some of the explosives inside a remote controlled aircraft that he had ordered and obtained for his attack plan. Ferdaus then locked the explosives and firearms in his storage unit, at which time he was placed under arrest.
Ferdaus, a Northeastern University graduate with a bachelor’s degree in physics, began designing and constructing detonation components for improvised explosive devices (IEDs) using mobile phones that were delivered to individuals whom he believed to be al Qaeda operatives. Ferdaus allegedly supplied 12 mobile phones, each of which had been modified to act as an electrical switch for an IED, to FBI undercover employees, who he believed were members of or recruiters for al Qaeda, to be used to kill American soldiers stationed overseas. On September 28, 2011, Ferdaus delivered four more detonation devices to individuals who he believed were al Qaeda operatives.
The public was never in danger from the explosive devices, which were closely monitored by the UCs. The defendant was under surveillance as his alleged plot developed and the UCs were in frequent contact with him. More information about the case, including the indictment, affidavit, and other public documents, can be viewed at http://www.justice.gov/usao/ma/news.html.
First Assistant U.S. Attorney for the District of Massachusetts Jack Pirozzolo and Richard DesLauriers, Special Agent in Charge of the FBI-Boston Field Division, made the announcement today. Assistance was also provided by the Worcester, Ashland, and Framingham, Massachusetts Police Departments; and the Bureau of Alcohol, Tobacco, Firearms, and Explosives. The case is being prosecuted by Assistant U.S. Attorneys B. Stephanie Siegmann and Donald L. Cabell of the U.S. Attorney’s Office’s Anti-Terrorism and National Security Unit.
TOP-SECRET – Lance Armstrong Complaint Demands Doping Jury – Document
AUSTIN, Texas — With Lance Armstrong digging in for a legal fight, the US Anti-Doping Agency issued lifetime sports bans Tuesday to three former staff members and consultants on the cyclist’s winning Tour de France teams for drug violations.
Luis Garcia del Moral was a team doctor; Michele Ferrari was a consulting doctor; and Jose ‘‘Pepe’’ Marti (team trainer) worked for Armstrong’s US Postal Service and Discovery Channel squads. All had been accused by USADA of participating in a vast doping conspiracy on those teams during part or all of Armstrong’s seven Tour victories from 1999-2005.
Armstrong also has been charged and has declared his innocence.
Several hours after USADA announced its sanctions against the others, Armstrong’s attorneys refiled a lawsuit asking a federal judge in Austin to prevent the case against him from going forward.
US District Judge Sam Sparks had thrown out Armstrong’s initial 80-page complaint Monday, but invited him to submit a new one that was shorter, more to the point and less about his career and personal battles with anti-doping officials.
Armstrong’s attorneys refiled a 25-page suit arguing that USADA violates athletes’ constitutional rights, that the agency doesn’t have the jurisdiction to bring the charges and that it may have violated federal law in its investigation.
Armstrong wants the court to rule by Saturday, his deadline to either accept USADA’s charges and sanctions or send his case to arbitration.
An Armstrong spokesman declined immediate comment on the USADA bans issued Tuesday.
Under USADA rules, Moral, Marti and Ferrari had until Monday to challenge the allegations in arbitration or ask for a five-day extension. If they did not respond, USADA could impose sanctions.
Although none lives in the United States, USADA says the ban blocks them from participating in any sport that falls under the World Anti-Doping Agency code.
‘‘The respondents chose not to waste resources by moving forward with the arbitration process, which would only reveal what they already know to be the truth of their doping activity,’’ said Travis Tygart, chief executive of USADA.
There’s been no indication from USADA that any of the three men — who each received the agency’s maximum punishment — is cooperating with investigators.
Armstrong was granted his extension while he files his court case. Also charged and granted an extension was Armstrong’s former team manager, Johan Bruyneel.
Another team doctor, Pedro Celaya, also has been charged and faced the same Monday deadline.
. . .
Bradley Wiggins may have a firm grip on the yellow jersey after the first week of the Tour de France, but defending champion Cadel Evans isn’t so sure the British rider can keep up his relentless pace for the entire race without faltering.
Evans is nearly two minutes behind his main rival after losing time in Monday’s long time trial between Arc-et-Senans and Besancon in France’s eastern Doubs region, which Wiggins won to cap a flawless first week of racing.
But the Australian said Wiggins is still relatively untested in major races and is hoping his own experience will make the difference over the next two weeks, before the race ends in Paris on July 22.
‘‘If I was going to convince myself now he was unbeatable and unstoppable, well I might as well decide on second,’’ Evans said Tuesday during the Tour’s first rest day. ‘‘He doesn’t have much of a history over three weeks compared to someone like me.’’
Before triumphing on the Champs-Elysees last year, the 35-year-old Evans had twice finished second overall. Wiggins, achieved his best result on the Tour three years ago when he finished fourth.
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – Defense Intelligence Agency “The (New) Great Game” Regional Geopolitics Lesson
TOP-SECRET – U.S. Marine Corps Intelligence Activity Afghanistan: Key Bases and Figures of the Mujahideen
Lor Koh and Islam Dara Canyon
Key Terrain and Leadership Data
Afghanistan’s Pashtun rural population has been the source of manpower, funds, shelter, support, and intelligence for the repeated insurgencies that have plagued that unfortunate county since their monarch, Zahir Shah, was overthrown in 1973. In the general unrest that followed, insurgents opposed Mohammad Daoud’s army until he was overthrown by the communists who served in succession – Taraki, Amin, Karmal, and Najibullah. The communist leadership figures, in turn, were deposed by the anti-communist “Seven Party Alliance” that was soon battling among itself for control of Kabul until the Taliban Movement emerged. The Taliban was also faced with resisting insurgent forces, primarily from the non-Pashtun ethnic groups inhabiting Afghanistan’s northern provinces. Afghanistan’s rural insurgents are generally poorly educated, if literate at all, and succeeding generations of insurgents rely upon story-telling from earlier generations of fighters to gain knowledge of tactics that are applicable to their particular culture and terrain. There are no military schools available to them where leadership training can be taught and absorbed, and as a result the lessons learned from far away battlefields are seldom applied in Afghanistan. They commonly use the same tactics, terrain, and base areas that were used successfully by their fathers and grandfathers. Their general tendency to utilize memorization – as they did while studying Islam in madrassas – reinforces their tendency toward repetition.
Consequently, a careful study of the history of insurgent operations in specific regions of Afghanistan may be especially valuable. Base areas, infiltration routes, river fords, hide sites, and ambush locations used successfully against the Soviet Union’s forces and their communist allies may be used by later insurgent generations who learned of these locations’ significance from storytelling by their mujahedin fathers.
Many of Helmand Province’s mujahedin who fought the Soviets are now affiliated with the current insurgents. They have the tendency to use base areas, infiltration routes, safe areas, and even the same ambush sites that were utilized in the past. In the case of the multiple bases they developed in Lor Koh, they are strategically positioned near Bakwa and Golestan districts, the key roads in the area, and the mountain canyons may now be used as base areas by the Taliban forces. The same is highly probable of a base called Islam Dara, situated in the Khakrez District in northern Kandahar Province. Together these two historical mujahedin bases form a historical operational precedent for Afghanistan’s insurgents in the south that cuts across the volatile region of Helmand Province.
Key leaders involved in the anti-Soviet jihad, or their sons and other family members, are probably still living in the region. Individuals currently involved with the Taliban are likely to be utilizing their same base areas, and those former mujahedin leaders now allied with the Government of Afghanistan probably know the locations used by their former colleagues.
Lor Koh in Farah Province A Key Mujahedin Base Area
Lor Koh is a large mountain located approximately 30 kilometers southeast of Farah city at 32° 31′ 29” N/062° 41′ 22” E2 [see map and satellite image on pages 5 and 6]. It was renamed Sharafat Koh, or Honor Mountain, by the mujahedin once they established bases in the mountain’s canyons. The mountain is roughly shaped with a plateau top rising approximately 1,500 meters above the desert floor. Lor Koh has steep slopes and its top is often covered with snow. There are many large and small canyons (kals) cutting into the mountain. Sheikh Razi Baba Canyon penetrates into the mountain’s north side. Kale-e Amani Canyon is located on the mountain’s northwestern side and is adjacent to Sheikh Razi Baba. On the west is Kale-e Kaneske Canyon, and continuing counterclockwise around the mountain, there is Jar-e Ab Canyon on the southwest end of the mountain that connects with the Kale-e Kaneske Canyon. The Tangira Canyon is found in the south and is the widest of the mountain’s canyons. It has the most water but the mujahedin avoided it because it was the only valley wide enough to allow the entry of armored vehicles. To the east and also opening south is the Khwaja Morad Canyon where the Khwaja Morad Shrine is located. All of the canyons are accessible from the mountain’s plateau. Lor Koh is about 12 kilometers from Highway 1 and 20 kilometers from Highway 517.
The mujahedin attacked convoys near Karvangah, Charah, and Shivan and the Soviets maintained posts at Karvangah, Charah, and Velamekh to protect the convoys. The mujahedin established their first base in Lor Koh in Tangira Canyon in 1979, but the organizing tribal groups, consisting of Achakzai, Noorzai, Barakzai, and Alizai tribes, moved to a new base in Jare-e Ab Canyon until the Soviets attacked them in 1980. Following this attack, the mujahedin moved to Kale-e Kaneske Canyon, the strongest base in the mountain.
The opening into Kale-e Kaneske Canyon is only two to three meters wide and is in solid rock. It is deep and requires 35 to 40 minutes to walk from the entrance to its end and the opening section is shielded from observation from above. It contains a stream, a waterfall, and trees and the canyon widens into a three or four hectare opening at the end of the canyon.
In 1985, tribal disputes over leadership and the disposition of spoils resulted in the mujahedin splitting. New insurgent bases occupied by members from various tribes were established in different valleys:
- The Noorzai tribe’s mujahedin under Haji Abdul Kheleq moved into Sheikh Razi Baba Canyon.
- The Mujahedin from the Alizai and Barakzai tribes under the leadership of Haji Ghulan Rasul Shiwani Rasul Akhundzada relocated to the Kale-e Amani Canyon.
- Mawlawi Mohammad Shah and the mujahedin from the Achakzai tribe remained in the Kale-e Kaneske Canyon. Mohammad Shah’s deputy was Haji Nur Ahmad Khairkhaw.
TOP-SECRET – Sensitive Information Security Sources
Sensitive Information Security Sources and Breaches
Unauthorized disclosures of secrets are essential for democracy.
In response to Wikileaks background inquiries Cryptome offers that there are hundreds of online and offline sources of sensitive information security breaches which preceded Wikileaks beginning about 120 years ago. This outline traces the conflict between technological capabilities for sensitive information breaches and control by law enforcement when technical countermeasures are insufficient — a few examples among many others worldwide:
Socrates (c.400BC, Socratic Method): http://en.wikipedia.org/wiki/Socrates
Electromagnetic Spying Timeline (Mid-late 1800’s): http://cryptome.org/tempest-time.htm
Peter Zenger Press Freedom Trial (1735): http://en.wikipedia.org/wiki/John_Peter_Zenger
First Amendment of the US Constitution (1791): http://www.usconstitution.net/const.pdf
Alexander Graham Bell (1876): http://en.wikipedia.org/wiki/Alexander_Graham_Bell
UK Official Secrets Act (1889): http://en.wikipedia.org/wiki/Official_Secrets_Act
Nikola Tesla (1894): http://en.wikipedia.org/wiki/Nikola_Tesla
Guglielmo Marconi (1897): http://en.wikipedia.org/wiki/Guglielmo_Marconi
John Dewey (1903): http://en.wikipedia.org/wiki/John_Dewey
Ida Tarbell (1904 The History of the Standard Oil Company): http://en.wikipedia.org/wiki/Ida_M._Tarbell
US Espionage Act of 1917: http://en.wikipedia.org/wiki/Espionage_Act_of_1917
UK Communications-Electronics Security Group (1919): http://www.cesg.gov.uk/
UK GCHQ: http://www.gchq.gov.uk/
American Civil Liberties Union (1920): http://www.aclu.org
UKUSA Agreement (1940): http://www.nsa.gov/public_info/declass/ukusa.shtml
Echelon: http://en.wikipedia.org/wiki/Echelon_(signals_intelligence)
Nicky Hager (1996): http://www.nickyhager.info/Mike Frost: http://www.converge.org.nz/abc/frostspy.htm
Duncan Campbell: http://en.wikipedia.org/wiki/Duncan_Campbell_(journalist)
Federation of American Scientists (1945): http://www.fas.org
Secrecy News (FAS kid): http://www.fas.org/sgp/news/secrecy/Global Security (FAS kid): http://www.globalsecurity.org
Les Temps modernes (1945: http://en.wikipedia.org/wiki/Les_Temps_modernes
National Security Act of 1947: http://en.wikipedia.org/wiki/National_Security_Act_of_1947
Central Intelligence Agency (1947): http://www.cia.gov
Emergence of the Intelligence Establishment: http://history.state.gov/historicaldocuments/frus1945-50IntelCentral Intelligence: Origin and Evolution: http://cryptome.org/cia-origin.htm
Philip Agee (1975; CIA kid): http://en.wikipedia.org/wiki/Philip_Agee
CIA FOIA Documents: http://www.foia.cia.gov/
National Security Agency (1952): http://www.nsa.gov
Winslow Peck (1972; NSA kid): http://cryptome.org/jya/nsa-elint.htmAnonymous AU (1973): http://cryptome.org/jya/nsa-40k.htm
US Senate Church Report (1975): http://cryptome.org/nsa-4th.htm
NIST Information Technology Laboratory: http://www.nist.gov/itl/
US Navy The Onion Router: http://www.torproject.org/
NSA FOIA Documents: http://www.nsa.gov/public_info/declass/index.shtml
Wayne Madsen Report: http://www.waynemadsenreport.com
Simone de Beauvoir (1949, The Second Sex): http://en.wikipedia.org/wiki/The_Second_Sex
I. F. Stone’s Weekly (1953-67): http://www.ifstone.org/
Ralph Nader (1965): http://www.nader.org/
Noam Chomsky (1960s): http://www.chomsky.info/; http://en.wikipedia.org/wiki/Noam_Chomsky
The Internet (1960s): http://en.wikipedia.org/wiki/Internet
Usenet Newsgroups (1980s): http://en.wikipedia.org/wiki/News_groupsWorld Wide Web (1989): http://en.wikipedia.org/wiki/Tim_Berners-Lee
Classified Networks: SIPRNet, .smil, .intel, .nsa, .fbi, et al
Hacking (1960s): http://pcworld.about.com/news/Apr102001id45764.htm
2600: http://www.2600.comChaos Computer Club (1985): http://www.ccc.de/
PHRACK: http://www.phrack.org/
Freedom of Information Act (1966): http://en.wikipedia.org/wiki/Freedom_of_Information_Act_(United_States)
National Archives: http://www.archives.gov
Classified National Security Information: http://www.archives.gov/isoo/policy-documents/eo-12958-amendment.htmlPresidential Libraries: http://www.archives.gov/presidential-libraries/
The Federal Register: http://www.archives.gov/federal-register/
Library of Congress: http://www.loc.gov
David Kahn (1967): http://en.wikipedia.org/wiki/David_Kahn_(writer)
MapQuest (1967): http://www.mapquest.com
Urban Deadline (Cryptome precursor, 1968): http://cryptome.org/0001/cryptome-ud.htm
Seymour Hersh (1969): http://en.wikipedia.org/wiki/Seymour_Hersh
FTP (ARPANET, 1971): http://en.wikipedia.org/wiki/File_Transfer_Protocol
Email (ARPANET, 1973): http://en.wikipedia.org/wiki/Email
Electronic Surveillance 1972-1995: http://cryptome.org/esnoop.htm
Bob Woodward and Carl Bernstein (1974): http://www.hrc.utexas.edu/exhibitions/web/woodstein/
Privacy Act (1974): http://www.gpoaccess.gov/privacyact/index.html
Personal Computer Invention (1976): http://www.ideafinder.com/history/inventions/compersonal.htm
Whitfield Diffie (1977): http://en.wikipedia.org/wiki/Whitfield_Diffie
Martin Hellman (1977): http://en.wikipedia.org/wiki/Martin_Hellman
Ralph Merkle (1977): http://en.wikipedia.org/wiki/Ralph_Merkle
Ronald Rivest: http://people.csail.mit.edu/rivest/Adi Shamir: http://www.wisdom.weizmann.ac.il/profile/scientists/shamir-profile.html
Len Adleman: http://www.usc.edu/dept/molecular-science/fm-adleman.htm
Philip Zimmerman PGP: http://philzimmermann.com/EN/findpgp/
GnuPG: http://www.gnupg.org/
OpenSSL: http://www.openssl.org/
Progressive Magazine Publishes H-Bomb Design 1979: http://www.progressive.org/images/pdf/1179.pdf
Disk Operating System (1980): http://www.ideafinder.com/history/inventions/compersonal.htm
James Bamford (1983): http://en.wikipedia.org/wiki/James_Bamford
Forum on Risks to the Public in Computers and Related Systems (1985): http://catless.ncl.ac.uk/Risks
Jeffrey T. Richelson (1985): http://en.wikipedia.org/wiki/Jeffrey_T._Richelson
National Security Archive (1985): http://www.gwu.edu/~nsarchiv/
Article 19 (1987): http://www.article19.org/
Transactional Records Access Clearinghouse (1989): http://trac.syr.edu/
Public Interest Research (1989): http://www.namebase.org/staffbl.html
Namebase: http://www.namebase.org/Google Watch: http://www.google-watch.org
Wikipedia-Watch: http://www.wikipedia-watch.org
Electronic Frontier Foundation (1990): http://www.eff.org
Gopher (1991): http://en.wikipedia.org/wiki/Gopher_(protocol)
Lynx (1992): http://en.wikipedia.org/wiki/Lynx_(web_browser)
Cypherpunks Mail List (1992): http://en.wikipedia.org/wiki/Cypherpunk
Crypto Rebels: http://www.wired.com/wired/archive/1.02/crypto.rebels_pr.html
John Gilmore: http://en.wikipedia.org/wiki/John_Gilmore_(activist)Eric Hughes, A Cypherpunk’s Manifesto: http://www.activism.net/cypherpunk/manifesto.html
Timothy C. May: http://en.wikipedia.org/wiki/Timothy_C._May
Timothy C. May Cyphernomicon: http://www.cypherpunks.to/faq/cyphernomicron/cyphernomicon.html
Matt Blaze Crypto: http://www.crypto.com/
Marc Briceno: http://blog.pgp.com/index.php/author/mbriceno/
David Wagner: http://www.cs.berkeley.edu/~daw/
Joel McNamara: http://www.eskimo.com/~joelm/ also:
Joel McNamara Tempest Page: http://www.eskimo.com/~joelm/tempest.html
http://www.kubieziel.de/blog/uploads/complete_unofficial_tempest_page.pdfCryptography (Cypherpunks kid): http://www.mail-archive.com/cryptography@metzdowd.com/maillist.html
James Dalton Bell (Cypherpunks Kid): Federal Correctional Institution Sheridan also:
Arrest: http://cryptome.org/jya/jimbell.htm
Trial: http://cryptome.org/jya/jdbfiles.htmCarl Edward Johnson (Bell kid): http://cryptome.org/jya/cejfiles.htm
Cypherpunks Archives 1992-1998 http://cryptome.org/cpunks/cpunks-92-98.zip (83MB)
Cryptome (originally jya.com 1996; Cypherpunks kid): http://www.cryptome.org
Cartome (2001): http://www.cartome.orgEyeball Series (2002): http://cryptome.org/eyeball/index.html
UK Secret Bases: http://www.secret-bases.co.uk/Public Sources for Satellite and Aerial Photos and Maps: http://cryptome.org/gis-sources.htm
Wikileaks (2006; Cryptome “spiritual godkid”): http://www.wikileaks.org
Julian Assange on Cypherpunks 1995-2005: http://cryptome.org/0001/assange-cpunks.htm
Julian Assange Best of Security (1995): http://marc.info/?l=best-of-security&r=1&b=199507&w=2
Interesting-People Mail List (1993): http://www.interesting-people.org/archives/interesting-people/
Electronic Privacy Information Center (1994): http://www.epic.org
Quintessenz (1994): http://www.quintessenz.at/cgi-bin/index?funktion=about
AltaVista (1995): http://www.altavista.com
The Internet Archive (1996): http://www.archive.org (Generous links to online libraries)
UK Crypto Mail List (1996): http://www.chiark.greenend.org.uk/mailman/listinfo/ukcrypto
Ben Laurie (Wikileaks Advisor): http://www.apache-ssl.org/ben.htmlRoss Anderson: http://www.cl.cam.ac.uk/~rja14/
Marcus Kuhn: http://www.cl.cam.ac.uk/~mgk25/
Adam Back Cypherspace: http://www.cypherspace.org/adam/
GSM Crypto Cracks (1997-2010): http://cryptome.org/0001/gsm-a5-files.htm
Terraserver USA (1998): http://www.terraserver-usa.com
Bing Maps (2009): http://www.bing.com/maps
Google (1998): http://www.google.com
Google Earth: http://earth.google.com/
Wikipedia (2001): http://www.wikipedia.org
Advanced Encryption Standard (2001): http://en.wikipedia.org/wiki/Advanced_Encryption_Standard
USA PATRIOT Act (2001): http://en.wikipedia.org/wiki/Patriot_act
NSA warrant-less surveillance (2001): http://en.wikipedia.org/wiki/NSA_warrantless_surveillance_controversy
Total Information Awareness (2002): http://en.wikipedia.org/wiki/Total_information_awareness
Daniel Bernstein: http://cr.yp.to/djb.html
Bruce Schneier: http://www.schneier.com/
Cryptography Research: http://www.cryptography.com/
Ciphers by Ritter: http://www.ciphersbyritter.com/ (Generous links)
Cryptography Org: http://www.cryptography.org/ (Generous links)
Scribd: http://www.scribd.com
PGPBoard: http://www.pgpboard.com/
The Memory Hole: http://www.thememoryhole.org [Temporarily down]
ProPublica (June 2008): http://www.propublica.org/
Government Attic (longtime source of FOI to others): http://www.governmentattic.org/
Public Intelligence: http://publicintelligence.net/
Public Intelligence Blog: http://www.phibetaiota.net/ (Handy list of comsec and spy sites)
History Anarchy Blog: http://historyanarchy.blogspot.com/
WikiSpooks: http://www.wikispooks.com
Cryptocomb: http://cryptocomb.org
Compedium of the ever-growing leak sites: http://leakdirectory.org/index.php/Leak_Site_Directory
Project PM: Tracking the Spy Industry: http://wiki.echelon2.org/wiki/Main_Page
Anonymous Analytics: http://anonanalytics.com/
Par:AnoIA – Potentially Alarming Research: Anonymous Intelligence Agency: http://www.par-anoia.net/
TOP-SECRET – Three Defendants Plead Guilty to Disaster Fraud Related to Joplin Tornado Benefits
SPRINGFIELD, MO—David M. Ketchmark, Acting United States Attorney for the Western District of Missouri, announced today that three Joplin, Missouri residents have pleaded guilty in federal court, in separate and unrelated cases, to fraudulently receiving federal disaster benefits following the May 22, 2011 tornado.
Wanda Gail McBride, 51, of Joplin, pleaded guilty before U.S. District Judge Richard E. Dorr today to the charge contained in an April 3, 2012 federal indictment. McBride was taken into custody at the conclusion of her change of plea hearing. Ronald Martell Irby, 30, and Karen Marie Parks, 37, both of Joplin, also pleaded guilty to disaster fraud on Friday, July 6, 2012.
The defendants applied for federal disaster benefits by falsely claiming that their homes and property had been damaged or destroyed in the tornado. By pleading guilty, they admitted that they made materially false and fraudulent statements to FEMA in their applications for disaster benefits.
McBride falsely claimed that she was entitled to temporary rental assistance because she moved out of her home due to damage caused by the tornado and rented another residence. McBride was initially awarded $4,786 by FEMA for repairs to her residence, as well as $938 for rental assistance. McBride later submitted fraudulent documentation in order to receive $5,628 in additional rental assistance. McBride admitted today that she submitted two fabricated rental receipts with her application for FEMA rental assistance in July 2011. Later that month, she submitted a fabricated lease agreement for FEMA rental assistance at another address. McBride admitted that she had never moved to, resided at, signed a lease for, or paid rent at either address; in fact, neither address exists.
Irby listed 1823 W. 23rd St., Joplin, as his primary residence on a FEMA form in which he claimed the residence was damaged by the tornado. Irby received a total of $5,114 in FEMA payments and was provided with a temporary housing unit. However, Irby admitted today that this was never his primary residence. Rather, Irby’s girlfriend had been a one-time resident who was evicted prior to the tornado. Further, Irby himself had been banned from the property.
Parks listed 1502 S. Michigan Ave., Joplin, as her primary residence on a FEMA form in which she claimed the residence was damaged by the tornado. Parks received a payment of $1,368 from FEMA. However, Parks admitted today that she did not live at that address at the time of the disaster. Parks’s rent at another residence was paid through the Economic Security Rental Assistance Program, a state-funded program administered by the Jasper County Public Housing Agency, for individuals who were homeless and/or disabled. Because Parks did not pay her own rent, she was not eligible to receive rental assistance payments from FEMA.
Under federal statutes, each of the defendants is subject to a sentence of up to 30 years in federal prison without parole, plus a fine up to $250,000. A sentencing hearing will be scheduled after the completion of a presentence investigation by the United States Probation Office.
Disaster Fraud Hotline
Anyone with information about disaster fraud related to the Joplin tornado should call the National Center for Disaster Fraud hotline at 866-720-5721, the Joplin Police Department at 417-623-3131, or the FBI’s Joplin Office at 417-206-5700.
These cases are being prosecuted by Assistant U.S. Attorney Steven M. Mohlhenrich. They were investigated by the FBI, Homeland Security Investigations-Office of Inspector General, and the Joplin, Missouri Police Department.
TOP-SECRET – IAEA Fukushma Daiichi NPS Status Report
DOWNLOAD THE ORIGINAL REPORT HERE
TOP-SECRET – Fukushima Daiichi NPP Unit 1 Investigation
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – The FBI about the Black Mafia
THE FBI – Woodbridge Gang Member Sentenced to 120 Months for Role in Sex Trafficking High School Girls
ALEXANDRIA, VA—Michael Tavon Jefferies, aka “Loc,” 21, of Woodbridge, Virginia, was sentenced today to 120 months in prison, followed by five years of supervised release, for his role as a bodyguard for a gang-led prostitution business that recruited and trafficked high school girls.
Neil H. MacBride, United States Attorney for the Eastern District of Virginia; Kenneth T. Cuccinelli, II, Attorney General of Virginia; Colonel David Rohrer, Fairfax County Chief of Police; and Ronald T. Hosko, Special Agent in Charge of the FBI’s Washington Field Office Criminal Division, made the announcement after sentencing by United States District Judge Leonie M. Brinkema.
On April 12, 2012, Jefferies pled guilty to sex trafficking of a juvenile. According to court records, Jefferies was a member of the Underground Gangster Crips (UGC) set based in Fairfax County, Virginia, and he assisted the gang in sex trafficking of juveniles and adults from about November 2011 to January 2012. He served as a bodyguard for the UGC prostitution enterprise and collected the proceeds received from prostitution, providing a portion to another member of UGC and keeping a portion for himself. Jefferies also paid for an advertisement on Backpage.com to solicit customers and paid for hotel rooms for one of the juvenile prostitutes.
This case was investigated by the Fairfax County Police Department and the FBI’s Washington Field Office, with assistance from the Northern Virginia Human Trafficking Task Force. Virginia Assistant Attorney General and Special Assistant United States Attorney Marc Birnbaum and Assistant United States Attorney Inayat Delawala are prosecuting the case on behalf of the United States.
Founded in 2004, the Northern Virginia Human Trafficking Task Force is a collaboration of federal, state, and local law enforcement agencies—along with non-governmental organizations—dedicated to combating human trafficking and related crimes.
A copy of this press release may be found on the website of the United States Attorney’s Office for the Eastern District of Virginia at http://www.justice.gov/usao/vae.
TOP-SECRET from the FBI – Manhattan U.S. Attorney and FBI Assistant Director in Charge Announce the Arrest of Full Tilt Poker CEO Raymond Bitar
Preet Bharara, the United States Attorney for the Southern District of New York, and Janice K. Fedarcyk, the Assistant Director in Charge of the New York Field Office of the Federal Bureau of Investigation (FBI) announced that Raymond Bitar, the chief executive officer of Full Tilt Poker, was arrested this morning at John F. Kennedy International Airport. Bitar was charged last year with gambling, bank fraud, and money laundering offenses in connection with the operation of Full Tilt Poker. Upon Bitar’s return to the United States today, a superseding indictment was unsealed charging Bitar with defrauding poker customers by lying to them about the security of their funds. Also named in the superseding indictment is co-defendant Nelson Burtnick, the head of Full Tilt Poker’s payment processing department, who was originally charged on April 15, 2011. Among other things, Bitar is charged with promising players that their funds would be protected in “segregated” accounts, when the company actually used them to pay for Full Tilt operations and to pay Bitar and other owners over $430 million. As a result of Bitar’s alleged fraud, Full Tilt Poker was unable to pay the approximately $350 million it owed to players in the U.S. and around the world. Bitar appeared before U.S. Magistrate Judge Debra Freeman this afternoon.
Manhattan U.S. Attorney Preet Bharara said, “With today’s arrest and the new charges brought against him, Raymond Bitar will now be held criminally responsible for the alleged fraud he perpetrated on his U.S. customers that cost them hundreds of millions of dollars. The indictment alleges how Bitar bluffed his player-customers and fixed the game against them as part of an international Ponzi scheme that left players empty-handed.”
FBI Assistant Director in Charge Janice K. Fedarcyk said, “Bitar and Full Tilt Poker persisted in soliciting U.S. gamblers long after such conduct was outlawed. As alleged, Bitar has already been charged with defrauding banks to conceal the illegal gambling. Now he stands accused of defrauding Full Tilt’s customers by concealing its cash-poor condition and paying off early creditors with deposits from later customers. The online casino become an Internet Ponzi scheme.”
The following allegations are based on the superseding indictment unsealed today in Manhattan federal court, the indictment unsealed on April 15, 2011 in which Bitar was initially charged, other documents previously filed in the case, and statements made in court:
In late 2006, Congress enacted the Unlawful Internet Gambling Enforcement Act (UIGEA), making it a crime to “knowingly accept” most forms of payment “in connection with the participation of another person in unlawful Internet gambling.” Notwithstanding the enactment of UIGEA, Full Tilt Poker—a company founded by professional poker players in the U.S. in 2004—continued to offer Internet gambling to U.S. residents and took in an estimated $1 billion from U.S. residents through April 15, 2011. Because U.S. banks were largely unwilling to process payments for illegal Internet gambling, Bitar and co-defendant, Burtnick, relied on fraudulent means designed to trick U.S. banks by disguising payments to Full Tilt Poker as payments unrelated to Internet gambling.
In order to encourage players to deposit money with Full Tilt Poker, Bitar directed Full Tilt Poker employees to falsely assure potential customers that player deposits would be held in segregated accounts that would be kept separate and distinct from the company’s operating accounts. In fact, Full Tilt Poker did not protect player funds in segregated accounts, and instead, used them for whatever purposes Bitar directed, including to pay him and other owners millions of dollars. Because player funds were being used to cover operating expenses, Full Tilt Poker experienced an increasing shortfall between the cash it had in its bank accounts and the money it owed to players. For example, by early November 2010, Full Tilt Poker owed its customers approximately $344 million but had only approximately $145 million in all of its bank accounts. To conceal this financial shortfall, Bitar directed Full Tilt Poker employees to misrepresent how much cash the company had on hand. Among other things, Full Tilt Poker allegedly lied about its finances to its regulator, the Alderney Gambling Control Commission.
Further, to prevent players from learning about Full Tilt Poker’s shaky finances and to induce them to continue gambling with Full Tilt Poker, Bitar allegedly concocted a scheme in which Full Tilt Poker players were led to believe they were gambling real money when, in actuality, they were gambling with “phantom” online credits. As explained in greater detail in the superseding indictment, in the fall of 2010, Full Tilt Poker lost its ability to reliably collect deposits from U.S. bank accounts. Rather than terminate its U.S. operations—an option that would likely have exposed the fact that Full Tilt Poker was not holding player cash in segregated accounts and was holding less than half of the money it owed players—Bitar and Burtnick arranged for Full Tilt Poker to continue approving player deposits and to award credit to depositors even though Full Tilt Poker had not actually collected the money from players and had no ability to do so. As United States players gambled and won or lost these phantom funds—ultimately totaling over $130 million—Full Tilt Poker would list the phantom funds on players’ online account statements, even though the funds were never collected or available to pay the winning players.
Only weeks before U.S. law enforcement took action against Full Tilt Poker in April 2011, Full Tilt Poker’s internal financial statements reported $390 million in debts to players but only $60 million in its bank accounts. Following the law enforcement action, as players around the world began demanding their funds from Full Tilt Poker, rather than suspend operations, Bitar lured players to continue gambling with Full Tilt Poker by continuing to promise them that their funds were safe. In actuality, Bitar was using new customer deposits to pay off some of the backlog of player requests to withdraw funds and to cover the company’s operating expenses, including salary for Burtnick and himself. In effect, Full Tilt Poker operated what was, by then, nothing more than a Ponzi scheme. When the scheme finally collapsed, Full Tilt Poker was unable to pay players the approximately $350 million it owed them.
* * *
The superseding indictment charges Bitar, 40, with nine counts. A chart containing a description of the charges and their maximum penalties is below. If convicted on all counts for which he is charged, Bitar faces a maximum sentence of 145 years in prison.
Mr. Bharara thanked the FBI for its outstanding work in the investigation, which he noted is ongoing. He also thanked Immigration and Customs Enforcement’s Homeland Security Investigations New York and New Jersey Offices for their continued assistance in the investigation.
Bitar is the seventh of the 11 defendants charged in connection with the original Internet poker indictment to have been arrested. The others arrested to date—Bradley Franzen, Ryan Lang, Ira Rubin, Brent Beckley, Chad Elie, and John Campos—have each pled guilty and await sentencing with the exception of Campos, who was sentenced in June 2012 to three months in prison. Charges are still pending against the remaining four defendants—Burtnick, Isai Scheinberg, Paul Tate, and Scott Tom—who are at large, and are presumed innocent unless and until proven guilty.
This matter is being handled by the Office’s Complex Frauds Unit. Assistant U.S. Attorneys Arlo Devlin-Brown, Nicole Friedlander, and Niketh Velamoor are in charge of the criminal case, and Assistant U.S. Attorneys Sharon Cohen Levin, Jason Cowley, Andrew Goldstein, and Michael Lockard are in charge of related civil money laundering and forfeiture actions.
TOP-SECRET from the FBI – Defendant is 22nd Charged in Connection With $1 Billion Scheme
Preet Bharara, the United States Attorney for the Southern District of New York, Martin J. Dickman, Inspector General of the Railroad Retirement Board (RRB-OIG), Janice K. Fedarcyk, the Assistant Director in Charge of the New York Office of the Federal Bureau of Investigation (FBI), and Barry L. Kluger, Inspector General of the New York State Metropolitan Transportation Authority (MTA-OIG), announced charges today against Donald Alevas, the former LIRR director of shop equipment, engineering, and environmental compliance, in connection with his participation in a massive fraud scheme in which Long Island Railroad (LIRR) workers allegedly claimed to be disabled upon early retirement so that they could receive disability benefits to which they were not entitled. Alevas was arrested this morning and will be presented in Manhattan federal court before U.S. Magistrate Judge Debra Freeman this afternoon. He is the 22nd person to be charged in connection with this scheme. Other defendants include two doctors and an office manager for one of the doctors who were allegedly involved in falsely diagnosing retiring LIRR workers as disabled; two “facilitators” who allegedly served as liaisons between retiring workers and the participating doctors; and 18 LIRR retirees, one of whom was also charged as a facilitator.
Manhattan U.S. Attorney Preet Bharara said, “As today’s arrest makes abundantly clear, our investigation of the massive fraud that was allegedly perpetrated on the LIRR and that cost it hundreds of millions of dollars in potentially fraudulent benefits is very much ongoing. It should also make clear that we will prosecute those against whom we believe we have the evidence to prove that they received benefits to which they were not entitled—Donald Alevas makes that number 22, and he will not be the last. We strongly encourage any LIRR retiree who lied to get disability benefits to come forward and participate in the voluntary disclosure program while they still have the chance.”
RRB-OIG Inspector General Martin J. Dickman said, “My office, in partnership with the U.S. Attorney’s Office for the Southern District of New York and the Federal Bureau of Investigation, remains committed to the investigation and prosecution of individuals who have submitted false information to the U.S. Railroad Retirement Board. The recent arrest is a testament to the tireless commitment of the dedicated professionals assigned to this ongoing investigation. I applaud their outstanding efforts and thank them for their unwavering resolve.”
FBI Assistant Director in Charge Janice K. Fedarcyk said, “Mr. Alevas is the latest LIRR retiree to be charged with engineering a generous but fraudulent disability pension. He joins nearly two dozen others previously charged with serious crimes in connection with the ongoing investigation. We know he will not be the last. We encourage others to take advantage of the voluntary disclosure program rather than end up in handcuffs facing prison time.”
MTA-OIG Inspector General Barry L. Kluger said, “Once again, I wish to thank U.S. Attorney Bharara, his staff, and our other partners in this ongoing investigation and prosecution for their dedication to combating pension fraud. The voluntary disclosure program previously announced by the U.S. Attorney, the Long Island Railroad, and the federal Railroad Retirement Board, and extended today, remains a fair but still limited opportunity, in the public interest, for individuals who fraudulently obtained federal disability pensions to come forward, admit their wrongdoing, and thereby avoid the harsh reality of arrest and criminal prosecution. We again strongly advise all such individuals to do so now before their time runs out.”
The LIRR Disability Fraud Scheme
The following allegations are based on public filings in the LIRR cases, including the complaint against Alevas unsealed today, as well as statements made in open court:
The RRB is an independent U.S. agency that administers benefit programs, including disability benefits, for the nation’s railroad workers and their families. A unique LIRR contract allows employees to retire at the relatively young age of 50 if they have been employed by the LIRR for at least 20 years. It is the only commuter railroad in the United States that offers a retirement pension at that age. Eligible employees are entitled to receive a LIRR pension, which is a portion of the full retirement payment for which they are eligible at 65. At 65, they also receive an RRB pension. If an LIRR worker retires at 50, he or she will receive less than his or her prior salary and substantially lower pension payments than those to which they will be entitled at 65. However, an LIRR employee who retires and claims disability may receive a disability payment from the RRB on top of their LIRR pension, regardless of age. A retiree’s LIRR pension, in combination with RRB disability payments, can be roughly equivalent to the base salary earned during his or her career.
Hundreds of LIRR employees have exploited the overlap between the LIRR pension and the RRB disability program by pre-planning the date on which they would falsely declare themselves disabled so that it would coincide with their projected retirement date. These false statements, made under oath in disability applications, allowed LIRR employees to retire as early as age 50 with an LIRR pension, supplemented by the fraudulently obtained RRB disability annuity. From 2004 through 2008, 61 percent of LIRR employees who claimed an RRB benefit were between the ages of 50 and 55, and each received a disability award. In contrast, only 7 percent of employees at Metro-North who stopped working and received disability benefits during the same time period were between the ages of 50 and 55.
Three New York-area doctors accounted for 86 percent of the LIRR disability applications filed prior to 2008: Peter J. Ajemian, Peter Lesniewski, and a third unnamed doctor (“Disability Doctor-3”), who is recently deceased. Ajemian, his office manager, Maria Rusin, and Lesniewski used their respective medical practices as “disability mills,” preparing fraudulent medical narratives for LIRR retirees well before the employees’ planned retirement dates so that the narratives could be submitted to the RRB upon retirement. These medical narratives were fabricated or grossly exaggerated in order to recommend a set of restrictions that, if legitimate, would render it impossible for the LIRR employees to continue in their occupations. Many of the purportedly “objective” findings from the tests they conducted showed nothing more than normal degenerative changes one would expect to see in patients within the relevant age bracket.
Alevas’s Fraud
Donald Alevas was the director of shop equipment, engineering and environmental compliance at the LIRR. On or about November 1, 2008—roughly one month after his 50th birthday—Alevas retired from the LIRR, claiming that he had an occupational disability and that he had become disabled as of August 30, 2008. In so doing, Alevas ensured that each year he would receive tens of thousands of dollars in additional benefits. For example, in 2010, Alevas received approximately $55,590 in LIRR pension payments and approximately $33,600 in RRB disability payments, for a total of $89,190. Those payments nearly matched the salary he received in his final year working for the LIRR.
Alevas long planned to retire in November 2008, and it was only as that retirement date drew closer that he began seeing doctors or indicating that he had any disability affecting his work. At least as early as January 2007, Alevas asked for pension estimates based on a “planned retirement date” of November 1, 2008. Thereafter, Alevas exchanged e-mails with a co-conspirator about his plan to become disabled as of August 30, 2008, and asked how he should handle telling LIRR that he was disabled. Alevas also began consulting with Dr. Peter Ajemian in December 2007 and paid him to falsely claim that he suffered from a variety of disabilities, including hearing loss and neck and back pain. As further proof of Alevas’s deliberate scheme, the medical notes upon which he ultimately relied to claim his total disability were written in connection with a medical examination by Dr. Ajemian that never even occurred. Specifically, records from Ajemian’s medical practice include “notes” memorializing his examination of Alevas on October 28, 2008, at which time he described Alevas’s need to take disability leave because of “neck and back pain.” However, Ajemian had stopped working at that medical practice in September 2008, so the notes were a fiction that were timed to justify his planned retirement.
At the same time Alevas was developing a record to support his disability claim so that he could receive RRB disability benefits, he was also building a record that would qualify him for private disability insurance. Specifically, in August 2007, he submitted an application to a private insurer in which he stated that he was not disabled. He also informed a different doctor—at the same time he was seeing Ajemian—that he had “started side jobs in his home” including “handy-man and small construction work.” Alevas’s plan was to collect disability benefits from both the RRB and his private insurance policy.
Extension of the Voluntary Disclosure and Disposition Program
On May 22, 2012, the U.S. Attorney’s Office, in partnership with the RRB and the LIRR, announced a voluntary disclosure and disposition program. Under the program, the U.S. Attorney’s Office would agree not to prosecute, or file a civil action against, any LIRR retiree who voluntarily comes forward and admits that he or she obtained RRB disability benefits by making false and/or misleading statements to the RRB, and agrees to give up his or her right to certain RRB disability benefits. In addition, the RRB would agree not to commence any administrative proceedings seeking the repayment of any disability benefits that are the subject of this program, and the LIRR would agree not to seek forfeiture of LIRR Company Pension Plan(s) benefits. Under the Early Version of the program, any participating LIRR retiree would have to give up his or her right to future disability benefits, while under the Standard Version of the program, any participating LIRR retiree would have to give up not only future disability benefits, but 50 percent of the RRB disability benefits he or she has already received.
At the time of the original announcement, the deadline for participation in the Early Program was July 6, 2012. In light of continuing inquiries received by the U.S. Attorney’s Office, as well as the need to ensure that all eligible LIRR retirees have sufficient time to make an informed decision, the deadline for the Early Version of the program will now be September 14, 2012. The deadline for the Standard Version of the program will now be October 15, 2012.
***
Alevas, 53, of Patchogue, New York, faces one count of conspiracy to commit mail fraud and health care fraud, and one count of mail fraud. Each charge carries a maximum sentence of 20 years in prison.
Manhattan U.S. Attorney Bharara praised the RRB-OIG, the FBI, and the MTA-OIG for their outstanding work in the investigation, which he noted is ongoing. He also acknowledged the previous investigation conducted by the New York State Attorney General’s Office into these pension fraud issues.
The Office’s Complex Frauds Unit is handling the case. Assistant U.S. Attorneys Edward A. Imperatore and Tatiana Martins are in charge of the prosecution.
Peter J. Ajemian, Peter Lesniewski, Maria Rusin, Marie Baran, Joseph Rutigliano, Joseph Rutigliano, Gregory Noone, Regina Walsh, Sharon Falloon, Gary Satin, Steven Gagliano, Richard Ehrlinger, Brian Delgiorno, Philip Pulsonetti, Gregory Bianchini, Franklin Plaia, Michael Stavola, Michael Dasaro, Karl Brittell, Kevin Nugent, Gary Supper, and Thomas Delalla were previously charged in connection with the LIRR disability fraud scheme. The charges against them remain pending and the defendants are presumed innocent unless and until proven guilty.
TOP-SECRET – U.S. Army Presentation: Muslim Morality and Jihadi Ethics
The FBI reports – Cleveland Man sentenced to 30 years for sex trafficking 16-year-old girl.
CLEVELAND—Anthony C. Willoughby was sentenced today to 30 years in prison after a jury previously found him guilty of forcing a 16-year-old girl to engage in commercial sex acts, announced Steven M. Dettelbach, U.S. Attorney for the Northern District of Ohio, and Stephen D. Anthony, Special Agent in Charge of the FBI Cleveland Office.
“The details of this case underscore why it is so important that we continue to work collaboratively and try to eradicate this modern-day slavery,” said U.S. Attorney Dettelbach. “This defendant preyed upon a weak, vulnerable victim and used her suffering as an opportunity for profit.”
Special Agent in Charge Anthony said, “This case is one of the first human trafficking cases to go to trial in Northern Ohio. Investigating and prosecuting those involved in the sexual exploitation of the most vulnerable of victims is a priority of the FBI. The 30-year sentence imposed today represents the seriousness of the offense and should serve as a deterrent to child predators.”
Willoughby, 39, also known as “P.T.” and “Party Time,” last lived in Toledo, Ohio, according to court records.
A jury on December 16, 2011, found Willoughby guilty on one count of sex trafficking of a minor. Willoughby recruited, enticed, harbored, and transported a juvenile, identified in the indictment as “S.W.,” knowing that by means of force, fraud, and coercion the juvenile was caused to engage in a commercial sex act between February 15, 2009, and March 19, 2009, according to court records.
The victim in this case was 16 at the time of the crime. She had run away from foster care in the winter of 2009 when Willoughby, then 36, agreed to take her in, according to court documents. Willoughby convinced the victim they were in a relationship but then began arranging for “dates” for her from his client list, according to court records.
This case is being prosecuted by Assistant U.S. Attorneys James V. Moroney and Ava Rotell Dustin, following an investigation by the Toledo Resident Agency of the Cleveland FBI and the Northwest Ohio Violent Crimes Against Children Task Force (NWOVCACTF).
The NWOVCACTF, directed by the FBI Toledo Resident Agency, includes special agents of the FBI and agents and officers from the Ohio Bureau of Criminal Identification and Investigation; Ohio Highway Patrol; Toledo Police Department; Lima, Ohio Police Department; Perrysburg Township, Ohio Police Department; Fulton County, Ohio Sheriff’s Office; and the Ottawa County, Ohio Sheriff’s Office.
TOP-SECRET – Brooklyn Rabbi Sentenced for Money Laundering Conspiracy
TRENTON, NJ—Mordchai Fish, the principal rabbi of Congregation Sheves Achim in Brooklyn, New York, was sentenced today to 46 months in prison for conspiring to launder approximately $900,000 he believed was criminal proceeds, U.S. Attorney Paul J. Fishman announced.
Fish, 59, of Brooklyn, New York, previously pleaded guilty before U.S. District Judge Joel A. Pisano to an information charging him with money laundering conspiracy. Judge Pisano also imposed the sentence today in Trenton federal court.
According to documents filed in this case and statements made in court:
Fish admitted that beginning in early 2008, he met with Solomon Dwek, an individual he now knows was a cooperating witness with the United States. For a fee of approximately 10 percent, Fish agreed to launder and conceal Dwek’s funds through a series of purported charities, also known as “gemachs,” which Fish controlled or to which he had access. Fish admitted that prior to laundering Dwek’s funds, Dwek repeatedly told him the money was the proceeds of illegal activity—including bank fraud, trafficking in counterfeit goods, and bankruptcy fraud.
In order to hide the source of the money, Fish directed Dwek to make the checks payable to several gemachs—including Boyoner Gemilas Chesed, Beth Pinchas, CNE, and Levovous—which were purportedly dedicated to providing charitable donations to needy individuals. Once Dwek gave him the checks, Fish passed them to a co-conspirator who deposited them into bank accounts held in the names of the purported charities. Fish would then arrange to make cash available through an underground money transfer network. Other individuals, including David S. Golhirsh, Naftoly Weber, Avrohom Y. Polack, Binyamin Spira, and Yoely Gertner, would provide Fish and Dwek with the cash.
Fish admitted that he engaged in approximately 15 money laundering transactions with Dwek, helping to convert approximately $900,000 in checks into more than $800,000 in cash, keeping a cut.
In addition to the prison term, Judge Pisano sentenced Fish to three years’ supervised release and ordered him to forfeit $90,000. Fish was ordered to surrender to the Bureau of Prisons on August 14, 2012.U.S. Attorney Fishman credited special agents of the FBI, under the direction of Special Agent in Charge Michael B. Ward, and special agents of IRS-Criminal Investigation, under the direction of Acting Special Agent in Charge John R. Tafur, with the investigation.
The government is represented by Assistant U.S. Attorney Mark McCarren of the U.S. Attorney’s Office Special Prosecutions Division in Newark.
TOP-SECRET from the FBI – Massachusetts Man Pleads Guilty to $6.9 Million Fraud Scheme
ALEXANDRIA, VA—James W. Massaro, 70, of Boxford, Massachusetts, pled guilty today to engaging in a fraudulent foreign investment scheme that defrauded at least 20 victims of more than $6.9 million.
Neil H. MacBride, United States Attorney for the Eastern District of Virginia; James W. McJunkin, Assistant Director in Charge of the FBI’s Washington Field Office; and Daniel Cortez, Inspector in Charge of the Washington Division of the United States Postal Inspection Service, made the announcement after the plea was accepted by United States District Judge Leonie M. Brinkema.
Massaro pled guilty to one count of conspiracy to commit wire fraud. He faces a maximum penalty of 20 years in prison when he is sentenced on September 21, 2012.
According to a statement of facts filed with his plea agreement, Massaro claimed to be the president of a business called Tracten Corporation, and he admitted that from September 2005 through April 2008, he conspired with others to engage in a fraudulent scheme that required investors to pay a fee that would be used to secure large letters of credit through European financial institutions. Investors were told the initial payment was a commitment fee necessary to secure a multi-million-dollar letter of credit and that they would receive a percentage monthly return on the total amount of the letter of credit. Each investor entered into an escrow agreement with Tracten, which stated that the fee would be wired to an escrow attorney, who would, in turn, disburse the fee to Tracten after the escrow attorney received a commitment letter from the foreign bank on behalf of the investor.
Massaro admitted that in 2005, he and another co-conspirator made multiple trips to Rome, Italy, to meet with bank officials to pitch the letter of credit program. Despite the bank’s refusal to participate, the conspirators secured an Internet domain name to set up an e-mail account that would appear to come from a bank representative and created fraudulent bank letterhead that also appeared to come from the bank. Massaro and others used the e-mail account and letterhead to forge commitment letters purporting to be from bank officials that would be provided to escrow attorneys. Pursuant to the escrow agreement, the escrow attorneys relied on these fraudulent commitment letters to disburse the fees to Massaro.
According to the plea agreement, Massaro defrauded at least 20 investors who had together paid $6,936,985 in fees as part of the letter of commitment investment program.
The investigation was conducted by FBI’s Washington Field Office and the U.S. Postal Inspection Service’s Washington Division. Assistant U.S. Attorneys Timothy D. Belevetz and Charles F. Connolly are prosecuting the case on behalf of the United States.
A copy of this press release may be found on the website of the United States Attorney’s Office for the Eastern District of Virginia at http://www.justice.gov/usao/vae.
TOP-SECRET – Central Florida Intelligence Exchange Online Jihadist Calls for Arson Attacks
Past statements from al‐Qa’ida Central, as well as their franchise groups, highlight the importance of targeting the U.S. economy as part of their strategy of confronting the West. Most recently, militant propagandists, such as Adam Gadahn, American mouthpiece for Al‐Qa’ida in Pakistan, have made statements advising Muslims in the West to “…undermine the West’s already struggling economies with…targeted attacks on symbols of capitalism which will shake consumer confidence and stifle spending”. Additionally, in November 2010, al‐Qa’ida in the Arabian Peninsula introduced the “strategy of a thousand cuts”, where they encouraged their mujahideen brothers to “attack the enemy with smaller, but more frequent operations…the aim is to bleed the enemy to death”.
In December 2010, Abu Suleiman al‐Nasser, a prominent member of the Shumukh al‐Islam [Arabic] forum, advised that the U.S. economy is at its weakest and he called on the “Mujahideen Brigades” to attack the “soft underbelly of the enemies”. On 30 May 2011, Abu Suleiman posted another article urging Muslims to carry out arson attacks on buildings, farms and forests. He also advised them not to forget to target gas stations, storage tanks and gas lines as well.
Abu Suleiman goes on to say that setting fires is a simple action and with the summer months coming up the fires will spread easily. He also stated that in order to fight these fires, huge sums of money would have to be spent from the West’s already collapsed economies. He concludes his article by providing simple instructions for manufacturing Molotov cocktails to use in facilitating the arson attacks and he signed the article “Abu Suleiman Al‐Nasser, Support of Global Jihad”.
…
Arsons have the potential to become an appealing tactic for extremists groups and individuals seeking to carry out attacks that would have a major impact on the economy, as well as, furthering their global agenda and long‐term strategic objectives. This type of attack is simple to perform, has relatively no cost and is a very low security risk, but at the same time yields large scale destruction and frequently draws media attention.
The general motivation mentioned by the online jihadists for utilizing arson attacks is to achieve the following objectives:
• Heavy financial impact on the West’s weakened economy
• Potential for human losses
• Creating fear and panic amongst the general population
• Exhausting the resources of first responders and military personnelAs “would be” jihadists, online and in the real world, continue to share potential methods of attack and “lessons learned” with other like‐minded individuals, it will likely become increasingly more difficult for law enforcement and members of the intelligence community to identify those individuals who are who may be in the pre‐operational phase of an attack. Because of the perceived randomness and simplicity of carrying out this type of attack, it could be appealing to those who are inspired by al‐Qa’ida’s ideologies and desire to fulfill their obligation of “individual jihad”.
TOP-SECRET from the FBI – Indictment in $9.1 Million Mortgage Fraud Scheme
CHICAGO—Four defendants, including a licensed realtor and two licensed loan originators, were indicted for allegedly participating in a scheme to fraudulently obtain at least 42 residential mortgage loans totaling approximately $9.1 million from various lenders, federal law enforcement officials announced today. The indictment alleges that the mortgages were obtained to finance the purchase of properties throughout Chicago by buyers who were fraudulently qualified for loans while the defendants allegedly profited. The lenders and their successors incurred losses totaling approximately $4.7 million because the mortgages were not fully recovered through subsequent sales or foreclosures.
All four defendants were charged with various counts of bank fraud, mail fraud, and wire fraud in a five-count indictment that was returned by a federal grand jury last Thursday. The indictment also seeks forfeiture of at least $4.7 million. The charges were announced today by Gary S. Shapiro, Acting United States Attorney for the Northern District of Illinois; Robert D. Grant, Special Agent in Charge of the Chicago Office of the Federal Bureau of Investigation; and Thomas P. Brady, Inspector in Charge of the U.S. Postal Inspection Service in Chicago.
Jason Dade, 37, of Chicago, a licensed real estate agent and the owner of Round Table Enterprises Inc., was charged with two counts of bank fraud, two counts of mail fraud, and one count of wire fraud. Cheryl Ware, 47, of Shorewood, a licensed loan originator, was charged with one count each of wire fraud and mail fraud. Tiffini Chism, 36, of Glenwood, also a licensed loan originator, was charged with two counts of bank fraud, and Tamika Peters, 34, of Country Club Hills, was charged with one count each of wire fraud and mail fraud.
The defendants will be arraigned on dates yet to be determined in U.S. District Court.
Between August 2004 and June 2008, all four defendants and others allegedly schemed to obtain the fraudulent mortgages by making false representations in loan applications, supporting documents, and HUD-1 settlement statements concerning the buyers’ income, employment, financial condition, source of down payments, and intention to occupy the property.
As part of the scheme, Dade allegedly acted as a real estate agent for prospective home buyers, including Peters and others, knowing that the residences would be financed through fraudulently obtained mortgages. Dade referred Peters and other prospective buyers to Ware and Chism and others to have false loan application packages prepared, the indictment alleges.
All four defendants allegedly received the proceeds of the fraudulent loans that various lenders issued to prospective buyers and to Dade and Peters when the loans closed and used the proceeds to enrich themselves, according to the indictment.
The government is being represented by Assistant U.S. Attorneys Kenneth E. Yeadon and Megan Church.
Each count of bank fraud, as well as wire fraud and mail fraud affecting a financial institution, carries a maximum penalty of 30 years in prison and a $1 million fine, and restitution is mandatory. If convicted, the court may impose an alternate fine totaling twice the loss to any victim or twice the gain to the defendant, whichever is greater. The court must impose a reasonable sentence under federal sentencing statutes and the advisory United States Sentencing Guidelines.
The public is reminded that an indictment contains only charges and is not evidence of guilt. The defendants are presumed innocent and are entitled to a fair trial at which the government has the burden of proving guilt beyond a reasonable doubt.
The charges are part of a continuing effort to investigate and prosecute mortgage fraud in northern Illinois and nationwide under the umbrella of the interagency Financial Fraud Enforcement Task Force, which was established to lead an aggressive, coordinated, and proactive effort to investigate and prosecute financial crimes.
Since 2008, approximately 200 defendants have been charged in federal court in Chicago and Rockford with engaging in various mortgage fraud schemes involving more than 1,000 properties and more than $280 million in potential losses, signifying the high priority that federal law enforcement officials give mortgage fraud in an effort to deter others from engaging in crimes relating to residential and commercial real estate.
The Financial Fraud Enforcement Task Force includes representatives from a broad range of federal agencies, regulatory authorities, inspectors general, and state and local law enforcement who, working together, bring to bear a powerful array of criminal and civil enforcement resources. The task force is working to improve efforts across the federal executive branch, and with state and local partners, to investigate and prosecute significant financial crimes, ensure just and effective punishment for those who perpetrate financial crimes, combat discrimination in the lending and financial markets, and recover proceeds for victims of financial crimes. For more information on the task force, visit: http://www.StopFraud.gov.
TOP-SECRET – Seventeen Charged in Cocaine Trafficking Conspiracy
PITTSBURGH—Thirteen residents of Pennsylvania and four residents of Ohio have been indicted by a federal grand jury in Pittsburgh on charges of violating federal drug laws, United States Attorney David J. Hickton announced today.
The 18-count indictment, returned on June 12 and unsealed today, named the following individuals:
Kashma Jordan a/k/a Gold, 32, of 3349 Lodwick Drive, Warren, Ohio, 44485;
Robert Harvey a/k/a Bob, 38, of 2692 Brier Street SE, Warren, Ohio, 44484;
Juan Worthey, Jr. a/k/a Bones, 37, of 163 Church Street, Washington, Pennsylvania, 15301;
Mario Rodgers a/k/a Rio, 39, of 527 Washington Street NE, Warren, Ohio, 44483;
Brandon Wise a/k/a B-Wise, 28, of 133 Maple Avenue, Washington, Pennsylvania, 15301;
Allan Williams, 37, of 4475 Berkshire Drive SE, Warren, Ohio, 44485;
Will Levy a/k/a Q, 37, of 28 Central Avenue, Washington, Pennsylvania, 15301;
Keith Malone a/k/a K-Rizz, 36, of 940 Bruce Street, Washington, Pennsylvania, 15301;
Alex Hockett, 25, 311 W. Maiden Street, Washington, Pennsylvania, 15301;
Brent Anderson, 30, of 2920 Taft Street, Washington, Pennsylvania, 15301;
Eric Everett a/k/a Fifty, 27, of 207 S. 20th Street, Harrisburg, Pennsylvania, 17104;
Brandon Boone, 29, of 750 Cleveland Road, Washington, Pennsylvania, 15301;
Joshua Williams, 32, 305 Donnan Avenue, Apartment 2, Washington, Pennsylvania, 15301;
Christina Wright, 34, 735 Regent Drive, Washington, Pennsylvania, 15301;
Terrell Percy Williams a/k/a Rel, 33, of 1413 Soles Street, McKeesport, Pennsylvania, 15132;
Michael Porter, 30, of 501 Pirl Street, McKeesport, Pennsylvania, 15132;
and Derrick Knox, 31, of 804 Josephine Street, E. McKeesport, Pennsylvania, 15035.
According to the indictment, from in and around January 2011 and continuing thereafter to in and around June 2012, the 17 defendants and others conspired to distribute and possess with intent to distribute five kilograms or more of cocaine. Additionally, Knox, Levy, Terrell Percy Williams, Wise, Malone, and Wright are charged in separate instances of distributing less than 500 grams of cocaine; Worthey is charged with distributing more than 500 grams of cocaine; and Wise also is charged with distributing less than 28 grams of cocaine base in and around Washington, Pennsylvania.
The law provides for a maximum sentence of not less than 10 years and up to life in prison, a fine of $10,000,000, or both. Under the Federal Sentencing Guidelines, the actual sentence imposed would be based upon the seriousness of the offenses and the prior criminal history, if any, of the defendant.
Assistant United States Attorney Barbara K. Swartz is prosecuting this case on behalf of the government.
The Federal Bureau of Investigation and the Pennsylvania State Police conducted the investigation leading to the indictment in this case.
An indictment is an accusation. A defendant is presumed innocent unless and until proven guilty.
TOP-SECRET – U.S. Army Rules of Engagement Vignettes Handbook
Vignettes put the rules of engagement (ROE) into context. Rules can be memorized, but without context, those rules have little meaning or value. There is not a repository of vignettes readily accessible to Soldiers. This handbook addresses that shortcoming for units heading to Afghanistan. Soldiers can use this handbook individually, but its value is greatly increased through group discussion and interaction with leaders and judge advocates.
Key Lessons
•• Soldiers must understand the basic definitions of hostile act, hostile intent, and what constitutes positive identification. Soldiers must be able to apply — not just know — those definitions in a dynamic, confusing, and dangerous environment.
•• Determining what is a threat is dependent upon what you know about your situation. Your knowledge needs to extend beyond your sector of fire to the culture, the patterns of life, and the second- and third-order effects of your actions.
•• The ROE are generally permissive. It is a Soldier’s responsibility to know the ROE and the environment to make the ROE an integral part of accomplishing the mission.
Introduction for Soldiers
The usual instructor for a ROE or escalation of force (EOF) class is the local unit judge advocate or your company commander. These individuals generally have expertise and a solid understanding of the legal and policy underpinnings of the ROE. However, you are a Soldier preparing to deploy and you want the Soldier’s perspective on how these rules apply in the field, in combat. The ability to recite the legal definition of hostile act may be an indication that you understand the concept, but knowing the definition is not the same as being able to apply a measured and proportional response in a dynamic, confusing, and dangerous situation. What you need is street smarts when it comes to applying the ROE. Helping you gain instinctive understanding within the context of the theater of operations is the intent behind this compilation of vignettes.
The vignettes come from the streets. They come from the experiences of Soldiers deployed to combat theaters — primarily Afghanistan. The ROE that are applied here are those for Soldiers operating under the International Security Assistance Force (ISAF) rules of engagement. If you previously deployed, you may notice some differences under the ISAF rules. If you see those differences in these vignettes, point them out during the discussions.
Highlighting the differences can help others internalize the ISAF rules. Always remember that regardless of subtle differences in terminology or definitions, your right to self-defense remains unchanged. Even if you have a previous deployment as part of ISAF, you may not have heard of the Tactical Directive, the Tactical Driving Directive, or the Commander’s Counterinsurgency (COIN) Guidance. These documents contain additional rules, but for the most part, they re-emphasize the importance of protecting the civilian population. Along those lines, you will see many of the discussions turning away from what would be allowed under the ROE to what you really think you should do under a particular set of facts. This is the “can I?/should I?” analysis that should be at the forefront of your discussions.
These vignettes do not work alone. They are intended to be used in group environments and as the spark to ignite further discussions at the fire team and squad levels. In many cases, you will find that a vignette asks a distinct question and gives an exact “right/wrong, yes/no” answer. In other cases, you will find the discussions less concrete. That is the reality of the complexity of the battlefield. Challenge the scenarios as you work through them, but keep the basic concepts of the ROE and COIN doctrine intact. There may be policy or legal constructs with which you disagree, but your goal should be to prepare yourself and your battle buddies to operate in the current legal and policy environment.
This is not a compilation that should necessarily be read cover to cover. It is an interactive compilation. Take your time on each vignette — the value of the training will be directly related to the effort you put forward as an individual and as a member of a fire team or squad. There are no additional resources required, no time limits, and no grades. The real test will come in a combat theater, and success will be measured in human life.
Introduction for Leaders
These vignettes are designed for you. Whether you, your commander, or your unit’s judge advocate initially presents your Soldiers the rules — the law of armed conflict (LOAC), ROE, EOF standing operating procedures (SOP), detainee operations SOP, et al. — you are uniquely situated to incorporate the rules into your unit’s mindset as you develop its discipline and warrior ethos. These vignettes are a tool you can use to help you do just that.
As an artisan can make a tool do far more work than a beginner could, you can make these vignettes more effective as you craft their use. Most of your Soldiers can read them and understand most of the ideas presented. If you read your Soldiers the question and answer and do nothing more, you have added command emphasis and perhaps clarified some ambiguities. But you can maximize the effectiveness of this tool if you use these vignettes as a stepping-off point to further discussion.
How can you best use this tool? Hypothetically, place your tactical unit in the position each vignette describes. Discuss the tactical situation and strategic ramifications of following or violating the rules in the scenario. Ask your Soldiers questions like, “Could you have placed yourself in a better situation?” “How can you best resolve the situation tactically and legally?” “What is likely to follow?” Inject alternative scenarios, such as “What if the man was carrying an AK-47 instead of a rocket-propelled grenade (RPG) or standing in front of a home instead of an empty field?” After you answer the question “Can you? (do something legally),” ask the question “Should you?”
Walk your Soldiers through the legal analysis. When they get the right answer, ensure they can articulate why — well-reasoned but in their own words. This should sharpen their reaction time as they develop confidence in their responses. Additionally, this training should help them provide more detailed reports and statements during your tour when called upon to do so. Changes to the rules and an evolving area of operations may tweak the best response on one or more of these vignettes. When in doubt as to the correct answer for today, consult your commander or your unit judge advocate. The COIN environment in which we operate today in Afghanistan is complex. Day-to-day success is measured less by mission accomplishment and more by whether our actions have moved the population closer to the Afghan government or closer to the insurgents. How your Soldiers react will shape your area of operations and can contribute significantly to our ultimate success. The rules will help your Soldiers focus on the mission by freeing them from destructive urges and encouraging actions that advance our goal of separating insurgents from the population. These vignettes can help you hone your Soldiers to operate successfully within the rules on today’s complicated battlefield.
Consequently, the success of these vignettes rests upon you, for their success and yours will be measured by how well your Soldiers perform in the heat of battle when unexpected situations arise and they are called upon to decide in an instant how to apply their tactical training and the rules.
Introduction for the Judge Advocate
From a teaching standpoint, bullet comment slides are likely not the preferred method for educating an Army at war on the frustrating complexities of restraining the use of force. Rote memorization of the definitions of hostile act and hostile intent will have little value for a Soldier faced with split-second, life and death decisions. The COIN Soldier needs an in-depth understanding of the political, tactical, strategic, and cultural environments in which he will operate. Situational awareness coupled with an understanding of the ROE requires more than a quarterly 50-minute block of instruction. Accordingly, this collection of vignettes is intended to pick up where the judge advocate class ends. The key to success is support from the tactical leaders to dedicate time and energy to working through the scenarios. However, continued engagement with the judge advocate is essential to quality control and building a Soldier’s confidence in his ability to implement the ROE on the battlefield.
These vignettes were compiled and the discussions prepared by judge advocates. Where possible, the discussions and answers provide concrete answers to black letter legal issues. In other scenarios, the discussion is meant to go beyond the ROE and LOAC. These may prove to be the most valuable discussions. The ROE are generally permissive. The strategic implications of a single Soldier’s actions require very junior personnel to go beyond the ROE analysis of whether the use of force is authorized. The judge advocate needs to take that additional step as well. These vignettes provide the judge advocate the opportunity to assist Soldiers in problem solving rather than simply giving an answer.
In creating this compilation, the concept was to develop a resource for junior leaders to train their Soldiers wherever and whenever the opportunity arises. Thus, the product is created as a tool for squad-level “hip-pocket” training. Do not let this format prevent you from utilizing the vignettes in other ways. Judge advocate ROE training can often be frustrating for both the Soldier and the instructor. Judge advocates tend to think of the ROE in academic terms — definitions and rules. Soldiers tend to operationalize the materials (i.e., put the rules in terms of something that has happened or a set of facts they can visualize). In other terms, the judge advocate tends to think about the ROE in paragraphs. The Soldier wants to see it in high-definition color. These scenarios can work to bridge that gap for the judge advocate. The discussions and answers are based upon the legal opinions of the authors applying the ISAF ROE, U.S. Standing ROE, and the LOAC as of the publication of this edition. The judgment of the authors should not be substituted for that of another judge advocate. The passage of time will also affect the law and policy upon which the discussions and answers are based. That being said, these scenarios have been carefully researched and compiled. They should be an asset for Soldiers, leaders, and judge advocates.
SECRET – Passenger Train Emergency Preparedness
|
Subpart D--Operational (Efficiency) Tests; Inspection of Records and
Recordkeeping
Section 239.301 Operational (Efficiency) Tests and Inspections
Section 239.301 requires railroads to monitor the routine
performance of their personnel who have individual responsibilities
under the e-prep plan to verify that they can perform the duties
required under the plan in a safe and effective manner. FRA is
proposing to modify this section in several ways. First, FRA is
proposing to add headings to each main paragraph for clarity. Second,
FRA proposes to add language to paragraph (a) that clarifies that
railroads are required to specify in their e-prep plans the specific
intervals they will periodically conduct operational (efficiency) tests
and inspections for
[[Page 38256]]
individuals with responsibilities under the e-prep plans. Additionally,
FRA is proposing to add language to paragraph (a) that will require any
ERCC personnel, railroad contractors or subcontractors, or employees of
railroad contractors or subcontractors, to be subject to operational
(efficiency) tests and inspections. Finally, FRA is proposing to add
new paragraphs (a)(1), (a)(1)(i) through (vi), (a)(2), (d), and (e).
The specific requirements proposed in each new paragraph are discussed
below.
In paragraph (a), FRA is proposing to add the heading,
``Requirement to conduct operational (efficiency) tests and
inspections.'' FRA believes that this heading will help the regulated
community identify that paragraph (a) of this section specifically
addresses operational (efficiency) test and inspection requirements.
Additionally, FRA is proposing to add language to paragraph (a) that
will require ERCC personnel, railroad contractors or subcontractors, as
well as employees of railroad contractors to be subject to the same
periodic operational (efficiency) tests and inspections as on-board and
control center employees are under the current regulation. Adding this
language to the regulation is necessary to ensure that all individuals
who assist in the railroad's emergency response are subject to
operational (efficiency) tests and inspections. This proposed language
is intended to help ensure that railroads are prepared to provide an
appropriate response in the event of an emergency situation. FRA is
also proposing in paragraph (a)(1) to identify basic elements that must
be included in the railroad's written program of operational
(efficiency) tests and inspections.
FRA proposes six new paragraphs under paragraph (a)(1). Each new
paragraph includes a required element that must be addressed in every
railroad's written program of operational (efficiency) tests and
inspections. RSAC recommended that FRA adopt these requirements, which
were modeled from regulations found in 49 CFR 217.9, Program of
operational tests and inspections; recordkeeping. In fact, in several
instances, language was directly taken from various provisions of Sec.
217.9--specifically, Sec. 217.9(c)(3) through (5). While part 217
prescribes processes for railroad operating employees only (e.g., train
and engine crews), its approach to operational tests and inspections is
useful for governing individuals covered by FRA's emergency
preparedness requirements in part 239. However, as proposed, not just
railroad operating employees but all on-board, control center, and ERCC
employees, as well as contractors and sub-contractors in these roles,
would be subject to these tests and inspections as applicable under the
railroad's e-prep plan. Each of the new proposed paragraphs is
discussed below.
For clarification, FRA notes that part 239 operational (efficiency)
tests and inspections can also qualify as operational tests under Sec.
217.9 if the employee, contractor or subcontractor being tested is also
performing functions that are covered by part 217. Likewise,
operational tests conducted under part 217 can also be accredited as
operational (efficiency) tests under part 239 as long as the criteria
for operational (efficiency) tests and inspections in part 239 are met.
For example, passenger train conductors are subject to operational
(efficiency) testing under both parts 217 and 239. An operational
(efficiency) test of a passenger train conductor that involves the
procedures for passenger train emergency preparedness would satisfy
requirements under both parts 217 and 239. In contrast, an operational
(efficiency) test of a passenger train conductor that involves the
procedures for operating derails would satisfy the requirements under
part 217 only.
Operational (efficiency) testing under part 239 can be conducted as
part of a railroad's efficiency testing program under Sec. 217.9 or in
an entirely separate program. However, if adopted, the proposed
operational (efficiency) test and inspections requirements for part 239
will have a broader applicability than just to the employees covered by
Sec. 217.9, as noted above. For example, these proposed requirements
would also cover such individuals as passenger car attendants and ERCC
employees, who would not be covered under part 217. Therefore, a
railroad that would prefer to conduct its operational (efficiency)
testing required by part 239 as part of its efficiency testing program
under Sec. 217.9 would need to modify its program to ensure that the
additional tests are included and conducted for all of the employees
required to be covered under part 239.
As proposed, paragraph (a)(1)(i) will require railroads to provide
in their e-prep plans a program of operational (efficiency) tests and
inspections for railroad employees, railroad contractors or
subcontractors, and employees of railroad contractors and
subcontractors addressing the appropriate courses of action in response
to various potential emergency situations and the responsibilities for
these individuals under the railroad's e-prep plan. For example, they
should address how railroad personnel on board a train respond in case
a fire occurs. They should also address what each on-board employee's,
contractor's, or subcontractor's individual responsibilities are during
such an emergency situation. FRA believes that these proposed
requirements would help to reduce confusion during an actual emergency
situation and ensure that the railroad's on-board staff undergo
operational (efficiency) tests and inspections on actions they would be
performing during an emergency event. Only railroad employees, railroad
contractor and subcontractors, and employees of railroad contractors
and subcontractors who are covered by or have responsibilities under
the railroad's e-prep plan would be subject to operational (efficiency)
tests and inspections from the railroad. Hired or contracted employees
working for the railroad who do not have any responsibilities under the
railroad's e-prep plan would not have to be subject to operational
(efficiency) tests and inspections.
Paragraph (a)(1)(ii) proposes that the railroads describe each type
of operational (efficiency) test and inspection required for passenger
train emergency preparedness. The description must also specify the
means and procedures used to carry out these operational (efficiency)
tests and inspections. For example, an operational (efficiency) test
intended for an on-board employee may be conducted as a challenge
question posed by a supervisor. In this example, the supervisor may ask
the employee what his or her responsibilities are for the evacuation of
passengers, including passengers with disabilities, in specific
circumstances such as a passenger car filling with smoke. In another
instance, a supervisor may ask an ERCC employee to identify a special
circumstance (e.g., a tunnel or bridge) located in his or her territory
and demonstrate how the employee would direct emergency responders to
the location during an actual emergency. Overall, operational
(efficiency) tests and inspections adopted for passenger train
emergency preparedness should cover all affected employees and be
comprehensive.
Proposed paragraph (a)(1)(iii) will require the railroads to state
in their e-prep plans the purpose of each type of operational
(efficiency) test and inspection conducted. For example, an operational
(efficiency) test intended for on-board employees may be conducted to
determine if the employees are familiar with passenger evacuation
procedures. As another example, such tests intended for ERCC employees
may
[[Page 38257]]
be conducted to determine if the ERCC employees are familiar with
special circumstances on their territory and if they know how to direct
emergency responders to these locations. In particular, conducting
operational (efficiency) tests on ERCC employees to determine their
knowledge of the railroad's e-prep plan, special circumstances, and
access points would be necessary to ensure that they are familiar with
emergency procedures and capable of directing emergency responders to a
passenger train in the event of an emergency.
FRA is also proposing to add new paragraph (a)(1)(iv), which will
clarify that each railroad must specify in its operational testing
program the specific intervals at which it will periodically conduct
operational (efficiency) tests and inspections for individuals covered
by paragraph (a). This information should be listed according to
operating division where applicable. FRA believes that this additional
language is necessary after reviewing e-prep plans submitted by various
railroads to FRA. In reviewing railroad e-prep plans, FRA discovered
that some railroads would simply state in their plans that they would
periodically conduct operational (efficiency) tests and inspections
without specifying by what specific interval these tests or inspections
would be administered. In some instances, railroads simply copied the
language directly from Sec. 239.301(a) and placed it into their e-prep
plans.
By adding this proposed language, FRA is not mandating any specific
interval by which the railroad should conduct these tests and
inspections. FRA believes that the regulated community should have the
flexibility to decide when individuals covered by paragraph (a) should
be periodically subject to these tests and inspections based on the
individual circumstances of each railroad and its e-prep plan and
operational testing program. The proposed language will not affect the
railroad's current ability to determine how often these periodic tests
and inspections should occur. However, FRA will require the railroad to
provide more information to the agency so that FRA can better verify
that these types of tests and inspections are in fact occurring as
planned, and that the railroads are properly carrying out their
responsibilities in preparing to deal with various emergency
situations.
Proposed paragraph (a)(1)(v) will require the railroad to identify
in its e-prep plan each officer by name, job title, and division or
system, who is responsible for ensuring that the program of operational
(efficiency) tests and inspections is properly implemented. Therefore,
for each railroad division or system there should be a separate contact
person listed within the e-prep plan who is responsible for
implementing the details of the plan on that specific division or
system during an emergency situation. In addition, for railroads that
have multiple divisions, the proposed regulation would require the
railroad to identify at least one officer at the railroad's system
headquarters who is responsible for overseeing the entire railroad's
program and the e-prep plan implementation. This individual should be
knowledgeable about the current state of the railroad's operational
(efficiency) test and inspection requirements as well as the current
state of the railroad's e-prep program system-wide.
The final proposal, in paragraph (a)(1)(vi), would require that
railroad officers conducting operational (efficiency) tests and
inspections be trained on the elements of the railroad's e-prep plan
that are relevant to the tests and inspections that the officers will
be conducting. In addition, the railroad officers conducting the
operational (efficiency) tests and inspections must be qualified on the
procedures for administering such tests and inspections in accordance
with the railroads written program.
FRA also proposes to add headings to both paragraphs (b) and (c) of
this section. FRA believes that adding the heading ``Keeping records of
operational (efficiency) test and inspection records'' to paragraph (b)
will help clarify that paragraph (b) addresses what types of written
records need to be created and retained after the performance of an
operational (efficiency) test or inspection. Similarly, the heading
``Retention of operational (efficiency) test and inspection records''
is proposed to be added to paragraph (c). This proposed heading will
clarify that paragraph (c) addresses the requirements for how long
records of operational (efficiency) tests and inspections need to be
retained by the railroad. FRA believes that these proposed headings
will be useful guides for the regulated community, especially those who
are unfamiliar with part 239 and its requirements.
Proposed paragraph (d) contains a new requirement that each
railroad retain one copy of its current operational (efficiency)
testing and inspection program required by paragraph (a) of this
section and each subsequent amendment to the program. If this proposed
requirement is adopted, railroads will be required to retain a copy of
the current program and any subsequent amendment to the program at the
railroad's system headquarters and at each divisional headquarters for
three calendar years after the end of the calendar year to which the
program relates. The records must also be made available for inspection
and copying during normal business hours by representatives of FRA and
States participating under 49 CFR part 212.
Finally, FRA is proposing to add a new paragraph (e) to this
section. As recommended by RSAC, this proposed paragraph will require
each railroad subject to this part to retain a written annual summary
of the number, type and result of each operational (efficiency) test
and inspection that was conducted in the previous year as required by
paragraph (a) of this section. When applicable, these summaries
describing the railroad's operational (efficiency) tests and
inspections would be required to be organized by operating division.
These summaries are intended to provide FRA with a clearer
understanding of how operational (efficiency) tests and inspections are
being applied and how successful these programs are over different
railroad divisions. Annual summaries would be required to be completed
and in the possession of the railroad's division and system
headquarters by March 1 of the year following the year covered by the
summary.
In addition, the annual summary will be required to be retained by
the railroad for three calendar years after the end of the calendar
year covered by the summary. For example, a railroad's 2013 annual
summary of operational (efficiency) tests and inspections would be
required to be retained through calendar year 2016. Annual summaries
would be required to be made available for inspection and copying
during normal business hours by representatives of FRA and States
participating under 49 CFR part 212.
FRA specifically invites comment on the appropriateness of proposed
paragraph (e). Given that the intended purpose of the proposal is to
provide FRA with a clear understanding of how operational (efficiency)
tests and inspections are being applied and how successful these
programs are being implemented from a systems perspective, FRA invites
comment whether the periodic review and analysis requirements of Sec.
217.9(e) should be adopted in the final rule to more appropriately
fulfill the intended purpose. Indeed, under Sec. 217.9(e), railroads
should already be reviewing and analyzing operational (efficiency) test
and inspection data conducted for
[[Page 38258]]
passenger train emergency preparedness on individuals subject to part
217; the requirements of the paragraph could then be broadened to cover
individuals subject to part 239. FRA also believes that a railroad
could consolidate such a review and analysis required by part 239 with
one required under Sec. 217.9(e), and that they could be retained for
a period of one year after the end of the calendar year to which they
relate and be made available to representatives of FRA and States
participating under 49 CFR part 212.
IV. Regulatory Impact and Notices
A. Executive Order 12866s and 13563 and DOT Regulatory Policies and
Procedures
This proposed rule has been evaluated in accordance with existing
policies and procedures under both Executive Orders 12866 and 13563 and
DOT policies and procedures. See 44 FR 11034; February 26, 1979. FRA
has prepared and placed in the docket (FRA-2011-0062, Notice No. 1) a
regulatory impact analysis addressing the economic impact of this
proposed rule.
As part of the regulatory impact analysis, FRA has assessed
quantitative measurements of the cost streams expected to result from
the implementation of this proposed rule. For the 10-year period
analyzed, the estimated quantified cost that would be imposed on
industry totals $1,049,308 with a present value (PV, 7 percent) of
$734,922. The largest burdens that would be expected to be imposed are
from the new requirements related to the operational (efficiency) tests
in Sec. 239.301 of the proposed regulation. The table below presents
the estimated discounted costs associated with the proposed rulemaking.
10-Year Estimated Costs of Proposed Rule
------------------------------------------------------------------------
Present value (7-
percent)
------------------------------------------------------------------------
Emergency Preparedness Plan (Sec. 239.101)... $219,833
Debriefing and Critique (Sec. 239.105)....... 200,273
Emergency Preparedness Plan; Filing and 12,006
Approval (Sec. 239.201).....................
Operational (efficiency) Tests (Sec. 239.301) 302,810
------------------------
Total Costs................................ 734,922
------------------------------------------------------------------------
As part of the regulatory impact analysis, FRA has explained what
the likely benefits for this proposed rule would be, and provided
numerical assessments of the potential value of such benefits. The
proposed regulation would generate safety benefits by preventing
injuries in passenger rail accidents from becoming more severe. FRA
uses the Abbreviated Injury Scale (AIS) as a measure of the severity
for injuries with an AIS 1 injury being defined as minor and an AIS 5
as the most severe, i.e., critical.\1\ As noted in Appendix A of the
regulatory impact analysis an AIS 1 would be an injury that is minor
and may not require professional medical treatment. An AIS 2 injury
would be an injury that always requires treatment but is not ordinarily
life-threatening. Benefits would accrue from the increased likelihood
that the passenger railroads would handle external communications more
efficiently, expediting the arrival of emergency responders to accident
scenes, and from the ability of the railroad personnel to minimize
health and safety risks through improved internal and external
communications. This proposed regulation would allow for more
flexibility in passenger train emergency preparedness planning and
implementation and provides for necessary emergency preparedness
training.
---------------------------------------------------------------------------
\1\ Association for the Advancement of Automotive Medicine.
http://www.aaam1.org/ais/#.
---------------------------------------------------------------------------
Additionally, the NPRM would allow passenger railroads to adjust to
future personnel reorganizations and to incorporate technological
innovations by affording the railroad's management flexibility in
determining which part of the organization to designate as the ERCC.
Given the nature of the proposed regulatory change, FRA believes
that the ideal methodology to estimate the safety benefits is a break-
even analysis. A break-even analysis quantifies what minimum safety
benefits are necessary for the proposed rule to be cost-effective,
considering the estimated quantified costs. For this proposed rule,
this analysis estimates that the break-even point is met when 3.84
injuries are prevented from increasing in severity from AIS 1 to AIS 2.
The table below presents the estimated benefits necessary for this
proposed rule to break-even with the estimated costs. For the 10-year
period analyzed the safety benefits would total $1,049,308 with a
present value (PV, 7 percent) of $735,757.
10-Year Estimated Benefits of Proposed Rule
------------------------------------------------------------------------
Limitation of injury Monetary
severity benefits
------------------------------------------------------------------------
Break-even point (not 3.84 less severe $1,049,308
discounted). injuries.
Discounted benefits (PV 7 3.84 less severe 735,757
percent). injuries.
------------------------------------------------------------------------
[[Page 38259]]
The benefits for this proposed rule would exceed the estimated
costs when 4 injuries are prevented from increasing in severity from an
AIS 1 to an AIS 2. FRA believes the proposed changes in this rulemaking
will more than exceed the break-even estimate.
B. Regulatory Flexibility Act and Executive Order 13272; Initial
Regulatory Flexibility Assessment
The Regulatory Flexibility Act of 1980 (5 U.S.C. 601 et seq.) and
Executive Order 13272 (67 FR 53461; August 16, 2002) require agency
review of proposed and final rules to assess their impact on small
entities. An agency must prepare an initial regulatory flexibility
analysis (IRFA) unless it can determine and certify that a rule, if
promulgated, would not have a significant impact on a substantial
number of small entities. FRA has not determined whether this proposed
rule would have a significant impact on a substantial number of small
entities. Therefore, FRA is publishing this IRFA to aid the public in
commenting on the potential small business impacts of the requirements
in this NPRM. FRA invites all interested parties to submit data and
information regarding the potential economic impact on small entities
that would result from adoption of the proposals in this NPRM. FRA will
consider all comments received in the public comment process when
making a final determination.
The proposed rule would apply to all passenger railroads (commuter
and intercity) and railroads that host passenger rail operations. Based
on information currently available, FRA estimates that less than 2
percent of the total costs associated with implementing the proposed
rule would be borne by small entities. Based on very conservative
assumptions, FRA estimates that the total non-discounted cost for the
proposed rule would be approximately $1 million for the railroad
industry. There are two passenger railroads that would be considered
small for purposes of this analysis and together they comprise less
than 5 percent of the railroads impacted directly by this proposed
regulation. Both of these railroads would have to make some investment
to meet the proposed requirements. Thus, a substantial number of small
entities in this sector may be impacted by this proposed rule. These
small railroads carry out smaller operations than the average passenger
railroad, allowing them to meet the proposed requirements at lower
overall costs. Thus, although a substantial number of small entities in
this sector would likely be impacted, the economic impact on them would
likely not be significant.
In order to get a better understanding of the total costs for the
railroad industry, which forms the basis for the estimates in this
IRFA, or more cost detail on any specific requirement, please see the
Regulatory Impact Analysis (RIA) that FRA has placed in the docket for
this rulemaking.
In accordance with the Regulatory Flexibility Act, an IRFA must
contain:
A description of the reasons why the action by the agency
is being considered.
A succinct statement of the objectives of, and legal basis
for, the proposed rule.
A description--and, where feasible, an estimate of the
number--of small entities to which the proposed rule would apply.
A description of the projected reporting, record keeping,
and other compliance requirements of the proposed rule, including an
estimate of the classes of small entities that would be subject to the
requirements and the types of professional skills necessary for
preparation of the report or record.
An identification, to the extent practicable, of all
relevant Federal rules that may duplicate, overlap, or conflict with
the proposed rule.
1. Reasons for Considering Agency Action
FRA initiated this rulemaking through RSAC in part upon learning
that in the regulated community there was some confusion regarding
existing requirements on passenger train emergency preparedness (49 CFR
part 239). As a result, the General Passenger Safety Task Force (Task
Force), a subgroup of the RSAC, was tasked to resolve these issues. The
Task Force found that as currently written, part 239 expressly requires
only the railroad's control center employees to be subject to training
and operational (efficiency) tests and inspections. However, in many
instances, control center employees were not found to be the primary
points of contact for emergency first responders during a passenger
train emergency. Instead, they were carrying out other important
duties, such as providing block protection and diverting trains to
other parts of the railroad's network. The proposed language in this
NPRM would ensure that all personnel involved in emergency preparedness
under part 239 are subject to appropriate training as well as
operational (efficiency) tests and inspections. At the same time, the
NPRM would relieve personnel not involved in emergency preparedness
from such requirements. While, the proposed regulation differs slightly
from the consensus language, the need for this NPRM is backed by the
RSAC and would improve passenger train emergency preparedness by
clarifying training and testing requirements.
In addition, as a result of FRA's experience in the periodic review
and approval of passenger railroads' e-prep plans, FRA realized that a
number of the changes submitted were purely administrative in nature.
While part 239 currently subjects all changes to an e-prep plan to a
formal review and approval process, FRA believes that purely
administrative changes should be excluded from the formal approval
process so that the agency can focus its resources on more substantive
matters. Accordingly, this NPRM would streamline the approval of e-prep
plans.
Further, Executive Order 13347 (``Individuals with Disabilities in
Emergency Preparedness'') requires the Federal government to
appropriately support safety and security for individuals with
disabilities in all types of emergency situations. 69 FR 44573; July
26, 2004. Currently, each railroad subject to part 239 is required to
provide for the safety of each of its passengers in its emergency
preparedness planning. Nonetheless, FRA is proposing to clarify that
these railroads must include procedures in their e-prep plans
addressing the safe evacuation of persons with disabilities during
emergency situations (and full-scale simulations of them).
2. A Succinct Statement of the Objectives of, and Legal Basis for, the
Proposed Rule
The purpose of this rulemaking is to further Federal safety
standards on passenger train emergency preparedness currently in place
in part 239. As a result of the proposed regulation, passenger
railroads would have more flexibility to carry out the requirements of
part 239 and keep their plans current. The NPRM would permit multiple
parts of the organization to be involved in the emergency preparedness
process to maintain resiliency while helping to clarify the role of
various parts of the structure in an emergency situation. Additionally,
the NPRM would provide flexibility to adjust to future personnel
reorganizations and to incorporate technological innovations by
allowing the railroad's management to determine what part of the
organization is designated to be the ERCC.
Among FRA's reasons for initiating this rulemaking was that some
confusion arose regarding certain requirements of FRA's passenger train
[[Page 38260]]
emergency preparedness regulations. For example, FRA learned that some
passenger railroads were confused as to which types of railroad
personnel were required to be trained or be subjected to operational
(efficiency) testing and inspections under part 239. These railroads
were unclear whether part 239 required certain railroad personnel who
directly coordinate with emergency responders and other outside
organizations during emergency situations to be trained or be subjected
to operational (efficiency) testing and inspections. As a result, FRA
believes that it is necessary to clarify the regulatory language in
part 239 to ensure that railroad personnel who directly coordinate with
emergency responders actually receive the proper training and are
subject to operational (efficiency) testing and inspections. FRA also
learned that many railroads were unclear whether operational
(efficiency) testing under part 239 could be considered for purposes of
the railroad's efficiency testing program required under 49 CFR part
217.
Finally, FRA believed it was necessary to clarify part 239 to
address the requirements of Executive Order 13347. Executive Order
13347 requires, among other things, that Federal agencies encourage
State, local, and tribal governments, private organizations, and
individuals to consider in their emergency preparedness planning the
unique needs of individuals with disabilities whom they serve. While
under part 239 the unique needs of passengers with disabilities must
already be considered in the railroads' e-prep plans, the NPRM would
clarify the railroads' responsibilities.
In order to further FRA's ability to respond effectively to
contemporary safety problems and hazards as they arise in the railroad
industry, Congress enacted the Federal Railroad Safety Act of 1970
(Safety Act) (formerly 45 U.S.C. 421, 431 et seq., now found primarily
in chapter 201 of title 49). (Until July 5, 1994, the Federal railroad
safety statutes existed as separate acts found primarily in title 45 of
the United States Code. On that date, all of the acts were repealed,
and their provisions were recodified into title 49 of the United States
Code.) The Safety Act grants the Secretary of Transportation rulemaking
authority over all areas of railroad safety (49 U.S.C. 20103(a)) and
confers all powers necessary to detect and penalize violations of any
rail safety law. This authority was subsequently delegated to the FRA
Administrator (49 CFR 1.49). Accordingly, FRA is using this authority
to initiate a rulemaking that would clarify and revise FRA's
regulations for passenger train emergency preparedness. These standards
are codified in Part 239, which was originally issued in May 1999 as
part of FRA's implementation of rail passenger safety regulations
required by Section 215 of the Federal Railroad Safety Authorization
Act of 1994, Public Law 103-440, 108 Stat. 4619, 4623-4624 (November 2,
1994). Section 215 of this Act has been codified at 49 U.S.C. 20133.
3. A Description of, and Where Feasible, an Estimate of Small Entities
to Which the Proposed Rule Would Apply
The ``universe'' of the entities to be considered generally
includes only those small entities that are reasonably expected to be
directly regulated by this action. This proposed rule would directly
affect commuter and intercity passenger railroads, and freight
railroads hosting passenger rail operations.
``Small entity'' is defined in 5 U.S.C. 601. Section 601(3) defines
a ``small entity'' as having the same meaning as ``small business
concern'' under Section 3 of the Small Business Act. This includes any
small business concern that is independently owned and operated, and is
not dominant in its field of operation. Section 601(4) likewise
includes within the definition of ``small entities'' not-for-profit
enterprises that are independently owned and operated, and are not
dominant in their field of operation. The U.S. Small Business
Administration (SBA) stipulates in its size standards that the largest
a railroad business firm that is ``for profit'' may be and still be
classified as a ``small entity'' is 1,500 employees for ``Line Haul
Operating Railroads'' and 500 employees for ``Switching and Terminal
Establishments.'' Additionally, 5 U.S.C. 601(5) defines as ``small
entities'' governments of cities, counties, towns, townships, villages,
school districts, or special districts with populations less than
50,000.
Federal agencies may adopt their own size standards for small
entities in consultation with SBA and in conjunction with public
comment. Pursuant to that authority FRA has published a final statement
of agency policy that formally establishes ``small entities'' or
``small businesses'' as being railroads, contractors and hazardous
materials shippers that meet the revenue requirements of a Class III
railroad as set forth in 49 CFR 1201.1-1, which is $20 million or less
in inflation-adjusted annual revenues, and commuter railroads or small
governmental jurisdictions that serve populations of 50,000 or less.
See 68 FR 24891, May 9, 2003, codified at appendix C to 49 CFR part
209. The $20-million limit is based on the Surface Transportation
Board's revenue threshold for a Class III railroad. Railroad revenue is
adjusted for inflation by applying a revenue deflator formula in
accordance with 49 CFR 1201.1-1. FRA is proposing to use this
definition for this rulemaking. Any comments received pertinent to its
use will be addressed in the final rule.
Railroads
There are only two intercity passenger railroads, Amtrak and the
Alaska Railroad. Neither can be considered a small entity. Amtrak is a
Class I railroad and the Alaska Railroad is a Class II railroad. The
Alaska Railroad is owned by the State of Alaska, which has a population
well in excess of 50,000.
There are 28 commuter or other short-haul passenger railroad
operations in the U.S. Most of these railroads are part of larger
transit organizations that receive Federal funds and serve major
metropolitan areas with populations greater than 50,000. However, two
of these railroads do not fall in this category and are considered
small entities. The impact of the proposed regulation on these two
railroads is discussed in the following section.
4. A Description of the Projected Reporting, Recordkeeping, and Other
Compliance Requirements of the Rule, Including an Estimate of the Class
of Small Entities That Will Be Subject to the Requirements and the Type
of Professional Skill Necessary for Preparation of the Report or Record
For a thorough presentation of cost estimates, please refer to the
RIA, which has been placed in the docket for this rulemaking. FRA also
notes that this proposed rule was developed in consultation with an
RSAC working group and task force that included representatives from
the Association of American Railroads, freight railroads, Amtrak, and
individual commuter railroads.
FRA is aware of two passenger railroads that qualify as small
entities: Saratoga & North Creek Railway (SNC), and the Hawkeye
Express, which is operated by the Iowa Northern Railway Company (IANR).
All other passenger railroad operations in the United States are part
of larger governmental entities whose service jurisdictions exceed
50,000 in population.
In 2010 Hawkeye Express transported approximately 5,000 passengers
per game over a 7-mile round-trip distance to and from University of
Iowa
[[Page 38261]]
(University) football games. IANR has approximately 100 employees and
is primarily a freight operation totaling 184,385 freight train miles
in 2010. The service is on a contractual arrangement with the
University, a State of Iowa institution. (The population of Iowa City,
Iowa is approximately 69,000.) Iowa Northern, which is a Class III
railroad, owns and operates the 6 bi-level passenger cars used for this
passenger operation which runs on average 7 days over a calendar year.
FRA expects that any costs imposed on the railroad by this regulation
will likely be passed on to the University as part of the
transportation cost, and requests comment on this assumption.
The SNC began operation in the summer of 2011 and currently
provides daily rail service over a 57-mile line between Saratoga
Springs and North Creek, New York. The SNC, a Class III railroad, is a
limited liability company, wholly owned by San Luis & Rio Grande
Railroad (SLRG). SLRG is a Class III rail carrier and a subsidiary of
Permian Basin Railways, Inc. (Permian), which in turn is owned by Iowa
Pacific Holdings, LLC (IPH). The SNC primarily transports visitors to
Saratoga Springs, tourists seeking to sightsee along the Hudson River,
and travelers connecting to and from Amtrak service. The railroad
operates year round, with standard coach passenger trains. Additional
service activity includes seasonal ski trains, and specials such as
``Thomas The Train.'' This railroad operates under a five-year contract
with the local government, and is restarting freight operations as
well. The railroad has about 25 employees.
FRA believes that these two entities would not be impacted
significantly. While, each of these entities would most likely have to
file a new e-prep plan, FRA does not expect they would have to change
how each railroad reacts to an emergency situation due to including
ERCCs under part 239's requirements. Their operating structure is small
and it is probable that employees with e-prep duties would continue to
have the same emergency responsibilities. FRA expects that both
railroads would see additional burden from inclusion of other
provisions of the proposed regulation related to recordkeeping, and
other training and testing requirements. This NPRM would not be a
significant financial impact on these railroad and their operations.
They could expect the total regulatory costs for this proposed rule, if
it is adopted, to be less than $6,500 for each of the railroads over
the next 10 years. The Hawkeye Express and the SNC currently have e-
prep plans that have been reviewed and approved by the FRA. Although
this NPRM would change several requirements in part 239, professional
skills necessary for compliance with existing and new requirements
would be the same. FRA believes that both entities have the
professional knowledge to fulfill the requirements in the proposed
rulemaking.
In conclusion, FRA believes that there are two small entities and
that both could be impacted. Thus, a substantial number of small
entities could be impacted by the proposed regulation. However, FRA has
found that these entities that are directly burdened by the regulation
would not be impacted significantly. FRA believes that the costs
associated with the proposed rule are reasonable and would not cause
any significant financial impact on their operations.
Market and Competition Considerations
The small railroad segment of the passenger railroad industry
essentially faces no intra-modal competition. The two railroads under
consideration would only be competing with individual automobile
traffic and serve in large part as a service offering to get drivers
out of their automobiles and off congested roadways. One of the two
entities provides service at a sporting event to assist attendees to
travel to the stadium from distant parking areas. The other entity
provides passenger train service to tourist and other destinations. FRA
is not aware of any bus service that currently exists that directly
competes with either of these railroads. FRA requests comments and
input on current or planned future existence of any such service or
competition.
The railroad industry has several significant barriers to entry,
such as the need to own the right-of-way and the high capital
expenditure needed to purchase a fleet, track, and equipment. As such,
small railroads usually have monopolies over the small and segmented
markets in which they operate. Thus, while this rule may have an
economic impact on all passenger railroads, it should not have an
impact on the intra-modal competitive position of small railroads.
5. An Identification, to the Extent Practicable, of All Relevant
Federal Rules That May Duplicate, Overlap, or Conflict With the
Proposed Rule
FRA is aware that some railroads are unclear whether operational
(efficiency) testing under part 239 could be considered for purposes of
the railroad's efficiency testing program required under 49 CFR part
217. In the NPRM, FRA clarifies that part 239 operational (efficiency)
tests and inspections can also qualify as operational tests under Sec.
217.9 if the employee, contractor, or subcontractor being tested is
also performing functions that are covered by part 217. Likewise,
operational tests conducted under part 217 can also be accredited as
operational (efficiency) tests under part 239 as long as the criteria
for operational (efficiency) tests and inspections in part 239 are met.
FRA invites all interested parties to submit data and information
regarding the potential economic impact that would result from adoption
of the proposals in this NPRM. FRA will consider all comments received
in the public comment process when making a determination.
C. Paperwork Reduction Act
The information collection requirements in this proposed rule are
being submitted for approval to the Office of Management and Budget
(OMB) for review and approval in accordance with the Paperwork
Reduction Act of 1995 (44 U.S.C. 3501 et seq.). The sections that
contain the current and new or revised information collection
requirements and the estimated time to fulfill each requirement is as
follows:
—————————————————————————————————————- Total annual Average time per Total annual CFR Section Respondent universe responses response burden hours—————————————————————————————————————-239.13–Waiver Petitions (Current 45 railroads……. 1 petition……… 20 hours……….. 20 requirement).239.107–Marking of Emergency Exits (Current requirements). –Marking of windows and door 45 railroads……. 4,575 decals, 1,950 10 minutes/5 706 exits intended for emergency decals. minutes. egress. –Marking of window and door 45 railroads……. 6,320 decals, 1,300 5 minutes/10 744 exit intended for emergency decals. minutes. access by emergency responders.[[Page 38262]] –Records of inspection, 45 railroads……. 1,800 tests/records 20 minutes……… 1,000 maintenance, and repair. + 1,200 tests/ records.239.101/201/203–Emergency Preparedness Plans (Revised requirements). –1st Year–Amended plans…. 45 railroads……. 45 plans……….. 20.33 hours…….. 915 –Subsequent years–amended 45 railroads……. 9 plans………… 20.33 hours…….. 183 plans–substantive changes. –Subsequent years–amended 45 railroads……. 4 plans………… 60 minutes……… 4 plans–non-substantive changes. –New RRs–e-prep plans…… 2 railroads…….. 2 plans………… 80 hours……….. 160 –Current employee initial 45 railroads……. 540 trained 60 minutes……… 540 training for train crews, employees. control center & emergency response communications members. –Employee periodic training. 45 railroads……. 27 trained 4 hours………… 108 employees. –Initial training of New 45 railroads……. 110 trained 60 minutes……… 110 Employees. employees.239.101(a)(1)(ii) 3–Designation 45 railroads……. 45 designations…. 5 minutes………. 4 of RR employee to maintain current emergency telephone numbers to notify outside responders, etc. (Current requirement).239.101(a)(1)(ii) 3–Railroads’ 45 railroads……. 2 updated lists…. 1 hour…………. 2 list/record of emergency telephone numbers to notify outside responders, etc. (Current requirement).239.101(a)(3)–Emergency 45 railroads……. 1 plan…………. 16 hours……….. 16 Preparedness Plan–Joint Operation (Current requirement).239.101(a)(5)–RR Training 45 railroads……. 45 updated plans… 40 hours……….. 1,800 Program for on-line emergency responders (Current requirement).239.101(a)(7)–Passenger Safety 2 new railroads…. 1,300 cards/2 5 minutes/16 hours/ 300 Information–Posting emergency programs/2 safety 48 hours/8 hours/ instructions inside all messages + 2 24 hours. passenger cars (Current programs/2 safety requirement). messages.239.105(a)(3)–Debriefing and 45 railroads……. 79 sessions…….. 27 hours……….. 2,133 Critique–Sessions conducted after passenger emergency situation or full scale simulation (Current requirement).239.301(a)–Operational 45 railroads……. 25,000 tests/ 15 minutes……… 6,250 Efficiency Tests (Current inspections. requirements)–RR Tests/ inspections of on-board, control center, and emergency response communications center employees.(b)(c)–Records of operational 45 railroads……. 25,000 records….. 2 minutes………. 833 (efficiency) tests/inspections.(d)–Records of written program 45 railroads……. 90 records……… 3 minutes………. 5 of operational (efficiency) tests (New Requirement).(e) Annual summary of operational 45 railroads……. 45 annual summaries 5 minutes + 1 5 (efficiency) test/inspections + 30 copies. minute. and copy of written summary at system and division headquarters.—————————————————————————————————————-
All estimates include the time for reviewing instructions;
searching existing data sources; gathering or maintaining the needed
data; and reviewing the information. Pursuant to 44 U.S.C.
3506(c)(2)(B), FRA solicits comments concerning: whether these
information collection requirements are necessary for the proper
performance of the functions of FRA, including whether the information
has practical utility; the accuracy of FRA's estimates of the burden of
the information collection requirements; the quality, utility, and
clarity of the information to be collected; and whether the burden of
collection of information on those who are to respond, including
through the use of automated collection techniques or other forms of
information technology, may be minimized. For information or a copy of
the paperwork package submitted to OMB, contact Mr. Robert Brogan,
Office of Railroad Safety, Information Clearance Officer, at 202-493-
6292, or Ms. Kimberly Toone, Office of Information Technology, at 202-
493-6139.
Organizations and individuals desiring to submit comments on the
collection of information requirements should direct them to Mr. Robert
Brogan or Ms. Kimberly Toone, Federal Railroad Administration, 1200 New
Jersey Avenue SE., 3rd Floor, Washington, DC 20590. Comments may also
be submitted via email to Mr. Brogan or Ms. Toone at the following
address: Robert.Brogan@dot.gov; Kimberly.Toone@dot.gov.
OMB is required to make a decision concerning the collection of
information requirements contained in this proposed rule between 30 and
60 days after publication of this document in the Federal Register.
Therefore, a comment to OMB is best assured of having its full effect
if OMB receives it within 30 days of publication. The final rule will
respond to any OMB or public comments on the information collection
requirements contained in this proposal.
FRA is not authorized to impose a penalty on persons for violating
information collection requirements which do not display a current OMB
control number, if required. FRA intends to obtain current OMB control
numbers for any new information collection requirements resulting from
this rulemaking action prior to the effective date of the final rule.
The OMB control number, when assigned, will be announced by separate
notice in the Federal Register.
[[Page 38263]]
|
D. Federalism Implications
Executive Order 13132, ``Federalism'' (64 FR 43255, Aug. 10, 1999),
requires FRA to develop an accountable process to ensure ``meaningful
and timely input by State and local officials in the development of
regulatory policies that have federalism implications.'' ``Policies
that have federalism implications'' are defined in the Executive Order
to include regulations that have ``substantial direct effects on the
States, on the relationship between the national government and the
States, or on the distribution of power and responsibilities among the
various levels of government.'' Under Executive Order 13132, the agency
may not issue a regulation with federalism implications that imposes
substantial direct compliance costs and that is not required by
statute, unless the Federal government provides the funds necessary to
pay the direct compliance costs incurred by State and local
governments, or the agency consults with State and local government
officials early in the process of developing the regulation. Where a
regulation has federalism implications and preempts State law, the
agency seeks to consult with State and local officials in the process
of developing the regulation.
This proposed rule has been analyzed in accordance with the
principles and criteria contained in Executive Order 13132. This
proposed rule will not have a substantial effect on the States or their
political subdivisions, and it will not affect the relationships
between the Federal government and the States or their political
subdivisions, or the distribution of power and responsibilities among
the various levels of government. In addition, FRA has determined that
this regulatory action will not impose substantial direct compliance
costs on the States or their political subdivisions. Therefore, the
consultation and funding requirements of Executive Order 13132 do not
apply.
However, this proposed rule could have preemptive effect by
operation of law under certain provisions of the Federal railroad
safety statutes, specifically the former Federal Railroad Safety Act of
1970, repealed and recodified at 49 U.S.C. 20106. Section 20106
provides that States may not adopt or continue in effect any law,
regulation, or order related to railroad safety or security that covers
the subject matter of a regulation prescribed or order issued by the
Secretary of Transportation (with respect to railroad safety matters)
or the Secretary of Homeland Security (with respect to railroad
security matters), except when the State law, regulation, or order
qualifies under the ``essentially local safety or security hazard''
exception to section 20106.
In sum, FRA has determined that this proposed rule has no
federalism implications, other than the possible preemption of State
laws under Federal railroad safety statutes, specifically 49 U.S.C.
20106. Accordingly, FRA has determined that preparation of a federalism
summary impact statement for this proposed rule is not required.
E. International Trade Impact Assessment
The Trade Agreements Act of 1979 (Pub. L. 96-39, 19 U.S.C. 2501 et
seq.) prohibits Federal agencies from engaging in any standards or
related activities that create unnecessary obstacles to the foreign
commerce of the United States. Legitimate domestic objectives, such as
safety, are not considered unnecessary obstacles. The statute also
requires consideration of international standards and, where
appropriate, that they be the basis for U.S. standards.
FRA has assessed the potential effect of this rulemaking on foreign
commerce and believes that its requirements are consistent with the
Trade Agreements Act. The requirements are safety standards, which, as
noted, are not considered unnecessary obstacles to trade. Moreover, FRA
has sought, to the extent practicable, to state the requirements in
terms of the performance desired, rather than in more narrow terms
restricted to a particular design or system.
F. Environmental Impact
FRA has evaluated this rule in accordance with its ``Procedures for
Considering Environmental Impacts'' (FRA's Procedures) (64 FR 28545,
May 26, 1999) as required by the National Environmental Policy Act (42
U.S.C. 4321 et seq.), other environmental statutes, Executive Orders,
and related regulatory requirements. FRA has determined that this
proposed rule is not a major FRA action (requiring the preparation of
an environmental impact statement or environmental assessment) because
it is categorically excluded from detailed environmental review
pursuant to section 4(c)(20) of FRA's Procedures. See 64 FR 28547 (May
26, 1999).
In accordance with section 4(c) and (e) of FRA's Procedures, the
agency has further concluded that no extraordinary circumstances exist
with respect to this regulation that might trigger the need for a more
detailed environmental review. As a result, FRA finds that this
proposed rule is not a major Federal action significantly affecting the
quality of the human environment.
G. Unfunded Mandates Reform Act of 1995
Pursuant to Section 201 of the Unfunded Mandates Reform Act of 1995
(Pub. L. 104-4, 2 U.S.C. 1531), each Federal agency ``shall, unless
otherwise prohibited by law, assess the effects of Federal regulatory
actions on State, local, and tribal governments, and the private sector
(other than to the extent that such regulations incorporate
requirements specifically set forth in law).'' Section 202 of the Act
(2 U.S.C. 1532) further requires that ``before promulgating any general
notice of proposed rulemaking that is likely to result in the
promulgation of any rule that includes any Federal mandate that may
result in expenditure by State, local, and tribal governments, in the
aggregate, or by the private sector, of $100,000,000 or more (adjusted
annually for inflation) in any 1 year, and before promulgating any
final rule for which a general notice of proposed rulemaking was
published, the agency shall prepare a written statement'' detailing the
effect on State, local, and tribal governments and the private sector.
This proposed rule will not result in the expenditure, in the
aggregate, of $100,000,000 or more (as adjusted annually for inflation)
in any one year, and thus preparation of such a statement is not
required.
H. Energy Impact
Executive Order 13211 requires Federal agencies to prepare a
Statement of Energy Effects for any ``significant energy action.'' See
66 FR 28355, May 22, 2001. Under the Executive Order, a ``significant
energy action'' is defined as any action by an agency (normally
published in the Federal Register) that promulgates or is expected to
lead to the promulgation of a final rule or regulation, including
notices of inquiry, advance notices of proposed rulemaking, and notices
of proposed rulemaking: (1)(i) that is a significant regulatory action
under Executive Order 12866 or any successor order, and (ii) is likely
to have a significant adverse effect on the supply, distribution, or
use of energy; or (2) that is designated by the Administrator of the
Office of Information and Regulatory Affairs as a significant energy
action.
FRA has evaluated this proposed rule in accordance with Executive
Order 13211. FRA has determined that this proposed rule is not likely
to have a significant adverse effect on the supply, distribution, or
use of energy.
[[Page 38264]]
Consequently, FRA has determined that this regulatory action is not a
``significant energy action'' within the meaning of the Executive
Order.
I. Privacy Act
FRA wishes to inform all potential commenters that anyone is able
to search the electronic form of all comments received into any agency
docket by the name of the individual submitting the comment (or signing
the comment, if submitted on behalf of an association, business, labor
union, etc.). Please visit http://www.regulations.gov/#!privacyNotice.
You may also review DOT's complete Privacy Act Statement in the Federal
Register published on April 11, 2000 (65 FR 19477-78) or you may visit
http://www.dot.gov/privacy.html.
List of Subjects in 49 CFR Part 239
Passenger train emergency preparedness, Penalties, Railroad safety,
Reporting and recordkeeping requirements.
The Proposed Rule
For the reasons discussed in the preamble, FRA proposes to amend
part 239 of chapter II, subtitle B of title 49, Code of Federal
Regulations as follows:
PART 239--[AMENDED]
Subpart A--General
Sec. 239.5 [Removed and Reserved]
1. Section 239.5 is removed and reserved.
2. Section 239.7 is amended by adding the definition of ``Emergency
response communications center'' to read as follows:
Sec. 239.7 Definitions.
* * * * *
Emergency response communications center means a central location
designated by a railroad with responsibility for establishing,
coordinating, or maintaining communication with emergency responders,
representatives of adjacent modes of transportation, and appropriate
railroad officials during a passenger train emergency. The emergency
response communications center may be part of the control center.
* * * * *
Subpart B--Specific Requirements
3. Section 239.101 is amended by revising paragraphs (a)(1)(ii) and
(a)(2)(ii), (a)(2)(iii) introductory text, (a)(2)(iv), (a)(2)(v)
introductory text, and (a)(2)(v)(A), and by adding paragraph (a)(8) to
read as follows:
Sec. 239.101 Emergency preparedness plan.
(a) * * *
(1) * * *
(ii) Notification by control center or emergency response
communications center. The control center or the emergency response
communications center, as applicable under the plan, shall promptly
notify outside emergency responders, adjacent rail modes of
transportation, and appropriate railroad officials that a passenger
train emergency has occurred. Each railroad shall designate an employee
responsible for maintaining current emergency telephone numbers for use
in making such notifications.
(2) * * *
(ii) Control center and emergency response communications center
personnel. The railroad's emergency preparedness plan shall require
initial training of responsible control center personnel and any
emergency response communications center personnel employed by the
railroad, under a contract or subcontract with the railroad, or
employed by a contractor or subcontractor to the railroad, as well as
periodic training at least once every two calendar years thereafter, on
appropriate courses of action for each potential emergency situation
under the plan. At a minimum, the initial and periodic training shall
include:
(A) Territory familiarization;
(B) Procedures to retrieve and communicate information to aid
emergency personnel in responding to an emergency situation;
(C) Protocols governing internal communications between appropriate
control center and emergency response communications center personnel
whenever an imminent potential or actual emergency situation exists, as
applicable under the plan; and
(D) Protocols for establishing and maintaining external
communications between the railroad's control center or emergency
response communications center, or both, and emergency responders and
adjacent modes of transportation, as applicable under the plan.
(iii) Initial training schedule for current employees of the
railroad, current employees of contractors and subcontractors to the
railroad, and individuals who are contracted or subcontracted by the
railroad. The railroad's emergency preparedness plan shall provide for
the completion of initial training of all on-board and control center
employees, and any emergency response communications center personnel,
who are employed by the railroad, under a contract or subcontract with
the railroad, or employed by a contractor or subcontractor to the
railroad on the date that the plan is conditionally approved under
Sec. 239.201(b)(1), in accordance with the following schedule:
* * * * *
(iv) Initial training schedule for new railroad employees,
contractor and subcontractor employees, and contracted individuals. The
railroad's emergency preparedness plan shall provide for the completion
of initial training of all on-board and control center personnel, as
well as any emergency response communications center personnel, who are
hired by the railroad, contracted or subcontracted by the railroad, or
hired by the contractor or subcontractor to the railroad after the date
on which the plan is conditionally approved under Sec. 239.201(b)(1).
Each individual shall receive initial training within 90 days after the
individual's initial date of service.
(v) Testing of on-board, control center, and emergency response
communications center railroad employees, contractor or subcontractor
employees, and contracted individuals. The railroad shall have
procedures for testing a person being evaluated for qualification under
the emergency preparedness plan who is employed by the railroad, under
a contract or subcontract with the railroad, or employed by a
contractor or subcontractor to the railroad. The types of testing
selected by the railroad shall be:
(A) Designed to accurately measure an individual's knowledge of his
or her responsibilities under the plan;
* * * * *
(8) Procedures regarding passengers with disabilities. The railroad
shall have procedures in place to promote the safe evacuation of
passengers with disabilities under all conditions identified in its
emergency preparedness plan. These procedures shall include, but not be
limited to, a process for notifying emergency responders in an
emergency situation about the presence and general location of each
such passenger when the railroad has knowledge that the passenger is on
board the train. This paragraph does not require the railroad to
maintain any list of train passengers.
* * * * *
4. Section 239.105 is amended by revising paragraph (c)(3) to read
as follows:
Sec. 239.105 Debriefing and critique.
* * * * *
(c) * * *
(3) Whether the control center or the emergency response
communications
[[Page 38265]]
center promptly initiated the required notifications, as applicable
under the plan:
* * * * *
Subpart C--Review, Approval, and Retention of Emergency
Preparedness Plans
5. Section 239.201 is amended by revising paragraphs (a) and
(b)(3)(i) to read as follows:
Sec. 239.201 Emergency preparedness plan; filing and approval.
(a) Filing of plan and amendments. (1) Filing of plan. Each
passenger railroad to which this part applies and all railroads hosting
its passenger train service (if applicable) shall jointly adopt a
single emergency preparedness plan for that service, and the passenger
railroad shall file one copy of that plan with the Associate
Administrator for Railroad Safety/Chief Safety Officer, Federal
Railroad Administration, 1200 New Jersey Avenue SE., Mail Stop 25,
Washington, DC 20590, not less than 60 days prior to commencing
passenger operations. Any passenger railroad that has an emergency
preparedness plan approved by FRA as of (the effective date of the
final rule) is considered to have timely-filed its plan. The emergency
preparedness plan shall include the name, title, address, and telephone
number of the primary person on each affected railroad to be contacted
with regard to review of the plan, and shall include a summary of each
railroad's analysis supporting each plan element and describing how
every condition on the railroad's property that is likely to affect
emergency response is addressed in the plan.
(2) Filing of amendments to the plan. (i) Except as provided in
paragraph (a)(2)(ii) of this section, each subsequent amendment to a
railroad's emergency preparedness plan shall be filed with FRA by the
passenger railroad not less than 60 days prior to the proposed
effective date. When filing an amendment, the railroad must include a
written summary of the proposed changes to the previously approved plan
and, as applicable, a training plan describing how and when current and
new employees and contractors would be trained on any amendment.
(ii) If the proposed amendment is limited to adding or changing the
name, title, address, or telephone number of the primary person to be
contacted on each affected railroad with regard to the review of the
plan, approval is not required under the process in paragraph (b)(3)(i)
of this section. These proposed amendments may be implemented by the
railroad upon filing with FRA's Associate Administrator for Railroad
Safety/Chief Safety Officer. All other proposed amendments must comply
with the formal approval process in paragraph (b)(3)(i) of this
section.
(b) * * *
(3) * * *
(i) Except as provided in paragraph (a)(2)(ii) of this section, FRA
will normally review each proposed plan amendment within 45 days of
receipt. FRA will then notify the primary contact person of each
affected railroad of the results of the review, whether the proposed
amendment has been approved by FRA, and if not approved, the specific
points in which the proposed amendment is deficient.
* * * * *
Subpart D--Operational (Efficiency) Tests; Inspection of Records
and Recordkeeping
6. Section 239.301 is revised to read as follows:
Sec. 239.301 Operational (efficiency) tests and inspections.
(a) Requirement to conduct operational (efficiency) tests and
inspections. Each railroad to which this part applies shall
periodically conduct operational (efficiency) tests and inspections of
on-board, control center, and, as applicable, emergency response
communications center personnel employed by the railroad, under a
contract or subcontract with the railroad, or employed by a contractor
or subcontractor to the railroad, to determine the extent of compliance
with its emergency preparedness plan.
(1) Written program of operational (efficiency) tests and
inspections. Operational (efficiency) tests and inspections shall be
conducted pursuant to a written program. New railroads shall adopt such
a program within 30 days of commencing rail operations. The program
shall--
(i) Provide for operational (efficiency) testing and inspection on
appropriate courses of action in response to various potential
emergency situations and on the responsibilities of an employee of the
railroad, of an individual who is a contractor or subcontractor to the
railroad, or an employee of a contractor of subcontractor to the
railroad, as they relate to the railroad's emergency preparedness plan.
(ii) Describe each type of operational (efficiency) test and
inspection required, including the means and procedures used to carry
it out.
(iii) State the purpose of each type of operational (efficiency)
test and inspection.
(iv) State, according to operating divisions where applicable, the
frequency with which each type of operational (efficiency) test and
inspection is to be conducted.
(v) Identify the officer(s) by name, job title, and, division or
system, who shall be responsible for ensuring that the program of
operational (efficiency) tests and inspections is properly implemented.
A railroad with operating divisions shall identify at least one officer
at the system headquarters who is responsible for overseeing the entire
program and the implementation by each division.
(vi) Require that each railroad officer who conducts operational
(efficiency) tests and inspections be trained on those aspects of the
railroad's emergency preparedness plan that are relevant to the
operational (efficiency) tests and inspections that the officer
conducts, and that the officer be qualified on the procedures for
conducting such operational (efficiency) tests and inspections in
accordance with the railroad's written program of operational
(efficiency) tests and inspections and the requirements of this
section.
(2) The operational (efficiency) testing program required by
paragraph (a)(1) of this section may be combined with the written
program of operational (efficiency) tests and inspections required by
Sec. 217.9(c) of this chapter.
(b) Keeping records of operational (efficiency) tests and
inspections. Each railroad to which this part applies shall maintain a
written record of the date, time, place, and result of each operational
(efficiency) test and inspection that was performed in accordance with
paragraph (a) of this section. Each record shall also specify the name
of the railroad officer who administered the test or inspection, the
name of each employee tested, and sufficient information to identify
the relevant facts relied on for evaluation purposes.
(c) Retention of operational (efficiency) test and inspection
records. Each record required by paragraph (a) of this section shall be
retained at the system headquarters of the railroad and, as applicable,
at the division headquarters for the division where the test or
inspection was conducted, for one calendar year after the end of the
calendar year to which the test or inspection relates. Each such record
shall be made available to representatives of FRA and States
participating under part 212 of this chapter for inspection and copying
during normal business hours.
[[Page 38266]]
(d) Keeping records of written program of operational (efficiency)
tests and inspections. Each railroad shall retain one copy of its
current operational (efficiency) testing and inspection program
required by paragraph (a) of this section and one copy of each
subsequent amendment to such program. These records shall be retained
at the system headquarters, and, as applicable, at each division
headquarters where the operational (efficiency) tests and inspections
are conducted, for three calendar years after the end of the calendar
year to which they relate. These records shall be made available to
representatives of FRA and States participating under part 212 of this
chapter for inspection and copying during normal business hours.
(e) Annual summary of operational (efficiency) tests and
inspections. Before March 1 of each calendar year, each railroad to
which this part applies shall retain at the system headquarters of the
railroad and, as applicable, at each of its division headquarters, one
copy of a written summary of the following with respect to its previous
calendar year activities: the number, type, and result of each
operational (efficiency) test and inspection, stated according to
operating divisions as applicable, that was conducted as required by
paragraph (a) of this section. These records shall be retained for
three calendar years after the end of the calendar year to which they
relate and shall be made available to representatives of FRA and States
participating under part 212 of this chapter for inspection and copying
during normal business hours.
Issued in Washington, DC, on June 21, 2012.
Joseph C. Szabo,
Administrator.
[FR Doc. 2012-15746 Filed 6-26-12; 8:45 am]
BILLING CODE 4910-06-P
|
TOP-SECRET from the FBI – Barrio Azteca Leader Sentenced to Life in Prison and Two Barrio Azteca Soldiers Sentenced to 20 and 30 Years in Prison
WASHINGTON—A leader and two soldiers in the Barrio Azteca (BA), a transnational border gang allied with the Juarez Cartel, were sentenced in El Paso, Texas, to life, 30 and 20 years in prison, respectively, announced Assistant Attorney General Lanny A. Breuer of the Justice Department’s Criminal Division, U.S. Attorney Robert Pitman for the Western District of Texas, FBI Special Agent in Charge Mark Morgan of the FBI’s El Paso Office and Administrator Michele M. Leonhart of the U.S. Drug Enforcement Administration (DEA).
Hector Galindo, 38, aka “Silent,” of El Paso, currently serving a 25-year Texas state sentence for murder, was sentenced to life prison. Ricardo Gonzales, 44, aka “Cuate,” of Anthony, N.M., was sentenced to 30 years in prison, and Adam Garcia, 35, aka “Bad Boy,” of El Paso, was sentenced to 20 years in prison. Galindo, Gonzales and Garcia were charged in a 12-count third superseding indictment unsealed in March 2011. They were sentenced yesterday in the Western District of Texas. Galindo, Gonzales and Garcia pleaded guilty to conspiracy to commit racketeering (RICO) on Jan. 26, 2012, Jan. 18, 2012, and Jan. 29, 2012, respectively.
According to court documents and information presented in court, Galindo was a top Lieutenant in the BA. While incarcerated in the Texas Department of Corrections, he served as the right hand man to BA Captain Manuel Cardoza. In that role, Galindo maintained communication with other BA Captains and Lieutenants in the United States and Mexico and was specifically in charge of BA operations in Texas. Evidence was presented that Gonzales and Garcia were BA soldiers, whose duties included distributing drugs, picking up money from dealers and enforcement operations within their area of responsibility.
“As members of the Barrio Azteca gang, Hector Galindo, Ricardo Gonzales and Adam Garcia participated in a brutal criminal enterprise dedicated to spreading fear and violence on both sides of the border,” said Assistant Attorney General Breuer. “These prison sentences send a strong message that even the most powerful and ruthless gangs cannot evade justice. Our prosecution of the Barrio Azteca gang, including for the U.S. Consulate-related murders in Juarez, Mexico, in 2010, has led to convictions against 24 gang members and leaders. We will continue aggressively to pursue the Barrio Azteca and other gangs so that communities in the United States and Mexico can live free from the violence and destruction of organized crime.”
“These sentences represent the FBI’s commitment to the aggressive pursuit of criminal enterprises such as the Barrio Aztecas whose presence pose a significant risk to citizens on both sides of the border,” said FBI Special Agent in Charge Morgan. “Through the ongoing and joint efforts of the law enforcement community we will continue the fight to bring to justice predators such as Galindo, Gonzales and Garcia.”
“This investigation highlights an unfortunate reality: leaders within growing trans-national prison and street gangs like the Barrio Azteca continue to promote violence and manage their drug trafficking activities even after the cell door closes,” said DEA Administrator Leonhart. “However, the successful prosecutions of Galindo, Gonzales and Garcia, and the conviction of other Barrio Azteca members reinforce another reality: that wherever these dangerous organizations operate, DEA and its partners will aggressively follow, investigate and prosecute.”
A total of 35 BA members and associates based in the United States and Mexico were charged in the third superseding indictment for allegedly committing various criminal acts, including racketeering, narcotics distribution and importation, retaliation against persons providing information to U.S. law enforcement, extortion, money laundering, obstruction of justice and murder, including the 2010 Juarez consulate murders. Of the 35 defendants charged, 33 have been apprehended, including April Cardoza, who was found in Juarez, Mexico, last week. Twenty-four of those defendants have pleaded guilty, one defendant committed suicide while imprisoned during his trial and six others are pending extradition from Mexico. U.S. and Mexican law enforcement are actively seeking to apprehend the two remaining fugitives in this case, including Luis Mendez and Eduardo Ravelo, an FBI Top Ten Most Wanted Fugitive.
Today’s sentencing by U.S. District Judge Kathleen Cardone of the Western District Court of Texas marks the closure of the case against the U.S.-based defendants charged in the superseding indictment. Twenty-one of 22 U.S.-based defendants have pleaded guilty and have been sentenced, including another BA Lieutenant Roberto Angel Cardona, who was also sentenced to life by Judge Cardone on Feb. 17, 2012. The remaining U.S.-based defendant, Ramon Renteria, aka “Spooky,” took his own life while in prison during his trial. Witnesses testified that Renteria was a BA Captain, the highest rank of the Barrio Azteca, and the only U.S.-based Captain not currently serving a life sentence in prison.
According to court documents and information presented in court throughout this case, the Barrio Azteca is a violent street and prison gang that began in the late 1980s and expanded into a transnational criminal organization. In the 2000s, the BA formed an alliance in Mexico with “La Linea,” which is part of the Juarez Drug Cartel (also known as the Vincente Carrillo Fuentes Drug Cartel or “VCF”). The purpose of the BA-La Linea alliance was to battle the Chapo Guzman Cartel and its allies for control of the drug trafficking routes through Juarez and Chihuahua. The drug routes through Juarez, known as the Juarez Plaza, are important to drug trafficking organizations because they are a principal illicit drug trafficking conduit into the United States.
According to evidence presented in court, witnesses testified to the brutality of the BA. Inside and outside of prison, the gang thrives on violence—from gang beatings to drive-by shootings to murder—all in order to discipline its own members or fight against rivals. Testimony also indicated that the BA is well-organized and militaristic in structure. Its members, or “soldiers,” are governed by captains, various lieutenants and numerous sergeants in the United States and Mexico.
Witnesses also testified that the sale of illegal drugs is the life-blood of the BA. Evidence was presented that since 2003 the BA has trafficked hundreds of kilograms of cocaine and heroin. Because of the BA’s alliance with the Juarez Drug Cartel, the gang receives illegal drugs at low cost and profits on its importation, sale and distribution within the United States.
Witnesses also testified to the Barrio Azteca’s practice of extorting “quota” or taxes on non-BA drug dealers who sold illegal narcotics in El Paso and the greater West Texas and Eastern New Mexico area. Specifically, during today’s hearing, one witness recalled an instance in which Gonzales tried to collect an extortion fee from a New Mexico drug dealer, and when the dealer refused to pay, Gonzalez pulled a gun, put it to dealer’s head, and threatened to kill him.
When quota is collected by the BA, members and leaders deposit the money into the commissary accounts of incarcerated BA leaders, often using fake names or female associates to send the money by wire transfer. Galindo was one of the ranking members of the BA who would receive laundered funds and disperse it within the Texas State prison system to further the criminal goals of the enterprise.
Witnesses also testified to the extensive communication web of the BA, including utilizing coded letters, contraband cell phones within state and federal prison facilities, and distribution of membership rosters and hit lists. Witnesses specifically implicated Galindo, then incarcerated in the Coffield Unit of the Texas Department of Criminal Justice, as the central leader within the organization who kept track of membership records, hit lists and gang treaties for the BA. To update those lists, members and other leaders would contact Galindo on his contraband prison cell phone to verify the status of persons claiming to be BA members and ensure that they were in good standing with the criminal organization. Those not in good standing were targeted by the BA for assault or murder.
The case is being prosecuted by Trial Attorney Joseph A. Cooley of the Criminal Division’s Organized Crime and Gang Section, Trial Attorney Brian Skaret of the Criminal Division’s Human Rights and Special Prosecutions Section and Assistant U.S. Attorney George Leal of the Western District of Texas—El Paso Division. The U.S. Attorney’s Office for the District of New Mexico provided significant assistance in this case, including by Assistant U.S. Attorney Sarah Davenport. Valuable assistance was provided by the Criminal Division’s Offices of International Affairs and Enforcement Operations.
The case was investigated by the FBI’s El Paso Field Office, Albuquerque Field Office (Las Cruces Resident Agency), DEA Juarez and DEA El Paso. Special assistance was provided by the Bureau of Alcohol, Tobacco, Firearms and Explosives; Immigration and Customs Enforcement; the U.S. Marshals Service; U.S. Customs and Border Protection; Federal Bureau of Prisons; U.S. Diplomatic Security Service; the Texas Department of Public Safety; the Texas Department of Criminal Justice; El Paso Police Department; El Paso County Sheriff’s Office; El Paso Independent School District Police Department; Texas Alcohol and Beverage Commission; New Mexico State Police; Dona Ana County, N.M., Sheriff’s Office; Las Cruces, N.M., Police Department; Southern New Mexico Correctional Facility and Otero County Prison Facility New Mexico.
TOP-SECRET from the NSA – DNI Protection of National Intelligence
DOWNLOAD THE ORIGINAL DOCUMENT HERE:
TOP-SECRET – DHS-FBI Suspicious Activity Reporting Bulletin: Terrorists Eliciting Information
U//FOUO) Terrorist or criminals may attempt to identify critical infrastructure vulnerabilities by eliciting information pertaining to operational and security procedures from security personnel, facility employees, and their associates. Persistent, intrusive or probing questions about security, operations or other sensitive aspects of a facility by individuals with no apparent need for the information could provide early warning of a potential attack. Notable examples of suspicious elicitation:
– (U//FOUO) May 2011: A gas station attendant asked an employee of a nearby chemical manufacturing plant a series of questions about the types of chemicals produced at the plant, whether any were explosive, and whether employees were allowed to take chemicals home. The attendant also asked if the plant employee worked with chemicals, whether certain chemicals become explosive when combined, and whether the plant was hiring.
– (U//FOUO) February 2011: An individual asked a security officer at a train station about station security practices including shift times and changes for security personnel, the number of guards on duty, location of me security company, and whether security continues after midnight. He also asked if the security officer had a key to the electrical room, contact instructions for security personnel in the event of an emergency, the time most people exit trains, and the purpose of little black balls’ (closed-circuit cameras) mounted at points around the station.
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – An Illegal Trainer (KGB history of agent “Halef”). Folder 60. The Chekist Anthology.
Date:
01 June 2007 Source:
The Mitrokhin Archive Description:
Describes training techniques used by the KGB in logistical preparation of their operatives for assignments abroad. This article focuses on the employment history of the KGB agent codenamed “Halef.” Between 1955 and 1967, Halef was stationed in Hong Kong and Tokyo. In 1967, due to his insignificant feedback and a weak performance as a field operative, Halef was transferred back as a trainer. As a trainer, Halef traveled extensively. While in the United States, the KGB developed a fictitious identity for Halef – a so-called legend-biography – in case his activity aroused suspicion and he were detained by authorities. In the United States, France and Mexico, Halef’s objectives included developing and testing means of communication with the KGB, which could be used to inform the KGB of an operative’s arrival to and departure from a country, request a meeting, or announce an emergency. In addition to assessing the existing signal language used among operatives, the KGB also instructed Halef to collect the data necessary to set up new surveillance locations in a number of countries. In 1977, Halef was performing assignments in Pakistan and Burma. In 1978, he and his wife were engaged in assignments throughout the USSR. From the USSR, they were relocated to the GDR and then to Bulgaria, where they boarded a cruise ship going from Varny to Suhumi to survey the ports of the Black Sea basin. Traveling through Odessa, Halef photographed military vessels and observed the procedures of the border patrol and customs officers.
DOWNLOAD THE ORGINAL DOCUMENT HERE
TOP-SECRET from the NSA – Mighty Derringer U.S. Nuclear Terrorism Exercise Leaves Indianapolis in “Ruins”
|
Washington, D.C., June 28, 2012 – A secret exercise in 1986 by a U.S. government counter-terrorist unit uncovered a host of potential problems associated with disrupting a nuclear terrorist plot in the United States. Declassified documents released under the Freedom of Information Act (FOIA) and posted today by the National Security Archive offer the first detailed public look at the inner workings of the agencies, military units and other U.S. entities responsible for protecting the country from a terrorist nuclear attack.
Today’s posting consists of over 60 documents related to MIGHTY DERRINGER, an exercise that focused on Indianapolis in December 1986. The materials provide background on the creation, in 1974-1975, of the Nuclear Emergency Search Team (NEST), a group assigned to respond to plausible threats of nuclear terrorism or extortion. Today, NEST (now the Nuclear Emergency Support Team) conducts exercises to assess its capability to respond to the possible presence of a terrorist device and test the ability of NEST and critical cooperating organizations (including military units)to work together.
While the MIGHTY DERRINGER exercise and resulting documents are over two decades old, the institutions participating in the exercise retain their roles today, and the issues confronting them in 1986 are similar to the ones that they would face in responding to a nuclear threat in 2012 (and beyond).
This posting is notable for being the first publication of documents that provide in-depth exposure into all aspects of such an exercise – including the state-of-play at key points and the array of issues involved in disabling terrorist devices. Of particular interest are references to the participation of the Joint Special Operations Command and Delta Force – mirroring the role they would have in a real-world incident. In addition, after-action reports reveal the assorted problems that can arise in coordinating the response to a nuclear terrorist threat among a large number of organizations.
* * * *
THE MIGHTY DERRINGER EXERCISE
In late January and early February 2012, members of the Department of Energy’s Nuclear Emergency Support Team (NEST) patrolled Lucas Oil Stadium as well as surrounding areas of Indianapolis as a precautionary measure in advance of Super Bowl XLVI. An initial survey to gather information on background levels of radiation was followed by an actual search for signatures associated with either a nuclear explosive device or a radiation dispersal device (a ‘dirty bomb’).1 Fortunately, none was found.
Over twenty-five years earlier, for a few days in early December 1986, NEST personnel also patrolled Indianapolis, also in search of a nuclear device. That search was triggered by an intelligence report that suggested that an Improvised Nuclear Device (IND) might have been smuggled into the city by terrorists. With the assistance of the Delta Force, U.S. personnel were able to recover and disable the device in a fictitious neighboring country; unfortunately the Indianapolis device exploded and 20 square blocks in downtown Indianapolis were completely destroyed.
As it happens, the terrorist group, the intelligence report, and the detonation were fictional – elements of a NEST exercise designated MIGHTY DERRINGER, one of a number of tests designed to anticipate and prevent the potential real-world catastrophe of a terrorist nuclear strike in a major American city. Documents published today by the National Security Archive provide newly declassified details on how the MIGHTY DERRINGER exercise unfolded and how the participants later evaluated it.
This is the most extensive set of declassified documents on any nuclear counterterrorism exercise, covering every phase of the response, from concept to critiques, and it offers valuable insights into a world that is usually hidden from public scrutiny. Among the disclosures:
§ The role of the top secret Joint Special Operations Command’s Delta Force in carrying out the assault on the terrorist cell in the fictional country of Montrev.
§ Descriptions of the different types of disablement techniques U.S. forces utilize – emergency destruct, standard destruction, and hard entry.
§ Assessments of the coordination problems and different perspectives of agencies that would be involved in a real-world response.
The instruction to establish NEST, known until 2002 as the Nuclear Emergency Search Team, took the form of a November 18, 1974 memo from Maj. Gen. Ernest Graves, the Atomic Energy Commission’s assistant general manager for military application, to Mahlon Gates, the manager of the commission’s Nevada Operations Office. (Document 1). Gates was “directed and authorized” to assume responsibility for the planning and execution of field operations employing AEC radiation detection systems for the “search and identification of lost or stolen nuclear weapons and special nuclear materials, bomb threats, and radiation dispersal threats.”
Personnel for NEST would come from AEC’s nuclear weapons laboratories – Lawrence Livermore, Sandia, and Los Alamos – as well as key AEC contractors. Almost all those individuals would continue in their regular positions full-time and become part of a NEST effort when required.
What inspired Graves’ memo was an incident that had taken place in May of that year. The Federal Bureau of Investigation received a letter demanding $200,000. Failure to comply would result in the detonation of a nuclear bomb somewhere in Boston. Personnel and equipment were quickly assembled and transported to Griffiss Air Force Base in Rome, New York. But before the team could make it to the threatened city, the crisis receded when no-one came to pick up the $200,000 in phony bills left at the designated site. 2
But the incident and the difficulties involved in responding to the threat convinced senior leaders that there was a need for a dedicated capability to deal with any attempt at nuclear extortion or nuclear terrorism. From its inception, NEST devoted considerable time and effort to conducting exercises designed to allow the team to test its readiness, procedures, and equipment in a variety of scenarios. In addition, since confronting a nuclear threat would involve not only NEST but a multitude of organizations, exercises provided an opportunity to identify potential problems in interagency cooperation.
MIGHTY DERRINGER was a particularly notable exercise in exploring the organizational, governmental, and technical problems that might arise in responding to a nuclear terrorist threat. While the existence of MIGHTY DERRINGER has been reported previously, the documents obtained by the National Security Archive and posted in this briefing book provide far more detail than previously available on the scenario, results, and after-action assessments of the assorted organizations involved. Since NEST and these other government entities are still critical components of America’s counter-terrorist capability, these records are valuable for the insight they offer into how a current-day nuclear detection operation would unfold and particularly what kinds of problems might be encountered.3
The exercise took place in two locations – Camp Atterbury, Indiana, near Indianapolis, and Area A-25 of the Energy Department’s Nevada Test Site – which corresponded to the two locations involved in the exercise scenario. One of the those locations was Indianapolis while the other was the country of ‘Montrev’ – a rather transparent fictional version of Mexico (since Montrev shared a border with the United States, its capital city was ‘Montrev City’, and its primary security agency was the Directorate for Federal Security – the same as Mexico’s).
Montrev was the initial focus of the exercise, with a terrorist group commanded by “Gooch” threatening to detonate an improvised nuclear device (IND) near the country’s Bullatcha oil field. According to the scenario, terrorists had stolen the devices from a new nuclear weapons state. Eventually, the participants discovered that that there was a second nuclear device and it appeared that it was being infiltrated into the United States, possibly with Pittsburgh as a target – although it was subsequently determined that the target was Indianapolis. While U.S. forces (with Delta Force assistance) were able to recover and disable the device in Montrev, Indianapolis experienced a 1 kiloton nuclear detonation that resulted in “total devastation over a 20 square block area.” (Document 38) The scenario had originally posited a successful disarming, but the exercise controllers decided to introduce a new element.
The scenario allowed for all aspects of a possible response to a nuclear terrorist/extortionist threat to be practiced – from initial assessment of the threat to the management of the “consequences” of a detonation. The documents posted cover, with varying detail, the core aspects of a response – intelligence collection, technical and behavioral assessments, search, access/defeat of terrorist forces, recovery of a device, diagnostics, hazards and effects estimation, disablement and damage limitation, safe transportation of the device, and consequence management of a detonation. In addition, they also concern a variety of important aspects of a response – including security, command and control, communications, logistics, radiological measurement and containment, weather forecasting, public information, and interaction with local officials.
The documents also identify the large number of organizations involved in the exercise. There is NEST and the organizations that contributed members or capabilities – including Lawrence Livermore National Laboratory, Los Alamos National Laboratory, and contractor EG&G. Additional organizations whose participation is evident include the State Department, Central Intelligence Agency, Federal Bureau of Investigation, Joint Special Operations Command, Special Forces Operation Detachment – Delta (Delta Force), several military explosive ordnance disposal units (from the Army and Navy), the Federal Radiological Monitoring and Assessment Center, the Environmental Protection Agency, and the Federal Emergency Management Agency.
Beyond detailing participants and describing different aspects of the exercise and static plans, some of the documents (the ‘Sitreps’- Document 19, Document 23, Document 32) provide a more dynamic view of the state of play at various points in the exercise. In addition, the post-exercise critiques provide different individual and institutional perspectives as to either the realism of the exercise or what the exercise revealed about strengths and weaknesses of the then current U.S. ability to respond to a nuclear terrorist threat.
Thus, Vic Berkinklau, an engineer with the Atomic Energy Commission, in addition to describing MIGHTY DERRINGER as an “Excellent, well managed exercise,” had an additional eight observations which concerned subjects such as uncertainty as to the number of NEST personnel needed in Montrev, the relationship between NEST and the Explosive Ordinance Disposal (EOD) team, and the need for more detailed analysis of the consequences of a nuclear detonation in a populated area (Document 43). L.J. Wolfson of the Navy Explosive Ordnance Disposal Technical Center contributed an eight-page single-spaced analysis concerning a variety of topics, including the nuclear device, assessment and intelligence, command and control and disablement. He observed (Document 47) that “there is too great a prevalence to believe what might, and probably is, very inconclusive intelligence information” and that “the entire operation was slowed and overburdened by the number of personnel involved.”
Commenting on the terrorism phase of the exercise (Document 50), William Chambers, NEST member and site controller for the Indianapolis component of the exercise, wrote that liaison between the FBI’s Hostage Rescue Team, NEST, and EOD personnel was “excellent” but that “the joint procedures for withdrawing the HRT and survivors, securing the perimeter, and clearing access to the device need clarification.” An unattributed comment (Document 66) suggested that the Delta Force players did not appreciate the “gravity of dealing with a nuclear device.”
In the subsequent twenty-five years, NEST and other organizations concerned with nuclear terrorism have conducted a significant number of exercises – particularly following the attacks of September 11, 2001.4 However, because of its scale and scope MIGHTY DERRINGER remains one of the more notable nuclear counterterrorism exercises.
The Energy Department is keeping secret significant aspects of MIGHTY DERRINGER, but more may be learned about the exercise and the State Department’s role in it from the response to a pending request. Moreover, files on MIGHTY DERRINGER at the Ronald Reagan Presidential Library will eventually be declassified and shed light on the National Security Council’s role.
(Note: A list of abbreviations used in the documents appears below.)
READ THE DOCUMENTS
Background
Document 1: Ernest Graves, Assistant General Manager for Military Application, Atomic Energy Commission, to M.E. Gates, Nevada Operations, “Responsibility for Search and Detection Operations,” November 18, 1974. Secret.
Source: Department of Energy FOIA Release
With this memo General Graves assigned Gates and the AEC’s Nevada Operations Office responsibility for search and detection operations with respect to lost and stolen nuclear weapons and special nuclear material as well as responding to nuclear bomb and radiation dispersal threats. The memo became the basis for the creation of the Nuclear Emergency Search Team (NEST).
Document 2: Director of Central Intelligence, IIM 76-002, The Likelihood of the Acquisition of Nuclear Weapons by Terrorist Groups for Use Against the United States, January 8, 1976. Secret.
Source: CIA FOIA Release.
An interagency group of intelligence analysts explored the constraints on the exploitation of nuclear explosives, attitudes and behavior toward the United States, means of acquiring nuclear explosives, the ways in which nuclear devices might be used against the United States, and the capabilities of existing terrorist groups. While the authors considered it unlikely that the U.S. would be the target of a nuclear terrorist attack “in the next year or two,” they also noted that, in the longer term, “we would expect a corresponding erosion of the constraints against terrorist use of nuclear explosives.”
Document 3: Energy Research and Development Administration, “Nuclear Emergency Search Team (NEST),” n.d. (but 1977). Unclassified.
Source: Energy Research and Development Administration
NEST began its existence as an unacknowledged government organization, but in 1977 it was concluded that NEST would have to interact with local law enforcement and political authorities in dealing with nuclear threats, and thus its existence would need to be acknowledged. This fact sheet, distributed to the press by ERDA, was the means by which NEST’s existence was quietly announced.
Document 4: E.J. Dowdy, C.N. Henry, R.D. Hastings, S.W. France, LA-7108, Nuclear Detector Suitcase for the Nuclear Emergency Search Team, February 1978. Unclassified.
Source: Los Alamos National Laboratory
This technical paper describes one piece of equipment designed specifically for NEST personnel – a portable Neutron Detection system that could be carried in any vehicle. The paper describes the detectors, the electronics, and the operations.
Document 5: Director of Central Intelligence, NIE 6-86, The Likelihood of Nuclear Acts by Terrorist Groups, April 1986, Secret, excised copy
Source: Mandatory Review Request; release by Interagency Security Classification Appeals Panel.
This estimate examined several incentives and constraints with regard to nuclear terrorism – including the availability of nuclear information, material, and trained personnel; changing levels of protection for nuclear weapons and other sources of nuclear/radioactive material; and terrorist capabilities and motivations (including possible state support to nuclear terrorism). The authors concluded that there was only a “low to very low” probability of nuclear terrorism that involved detonation of an improvised nuclear device or nuclear weapon – or the dispersal of radioactive material in a way that would threaten mass casualties or produce widespread contamination.
Preparations
Document 6: William Hoover, Deputy Assistant Secretary of Energy for Defense Programs, to DCI William Casey, 23 September 1985, with CIA routing memos, Confidential
Source: CREST, National Archives II
A senior Energy Department official informed Director of Central Intelligence William J. Casey of the Department’s conclusion on the need for a large-scale nuclear exercise in the early 1987 fiscal year and requested the CIA’s participation.
Document 7: Robert B. Oakley, State Department Counter-Terrrorism Center, to Executive Secretary Nicholas Platt, MIGHTY DERRINGER Exercise Planning,” 4 April 1986, with memorandum to Vice Admiral John Poindexter attached, Confidential
Source: State Department FOIA release
This memorandum, from the head of the State Department’s Counter-Terrorism Center, along with that attached memo to the president’s national security adviser, described the level of State Department participation in MIGHTY DERRINGER.
Document 8: Peter Borg, State Department Counter-Terrorism Center, to Richard Kennedy et al., “Exercise MIGHTY DERRINGER,” 6 October 1986, Secret
Source: State Department FOIA release
A number of State Department officials were recipients of this secret memo, which informed them of the nature of MIGHTY DERRINGER, when it would take place, some requirements for the exercise to be realistic, and the State Department’s participation.
The Exercise
Document 9: Don McMaster, Behavioral Assessment Report/PLC, n.d. [circa 2 December 1986], Incomplete copy, Secret
Source: Energy Department FOIA release
This behavioral assessment mirrors the earliest phases of responding to an actual threat, especially trying to assess its credibility. It discusses the reliability of a source, motivations of other key figures in the terrorist group, and concludes that a credible threat exists to both the United States and ‘Montrev.’
Document 10: F.W. Jessen, Lawrence Livermore National Laboratory, “Summary Assessment,” 2 December 1986, Secret, Incomplete copy
Source: Energy Department FOIA release
This assessment, conducted at Lawrence Livermore, where much of the credibility assessment effort has been located, reports that the available information suggests that the terrorist group possesses two improvised nuclear devices but that LLNL and Los Alamos National Laboratory disagree over the technical credibility of the threat.
Document 11: “Aggregate Assessment – – One Hour – – Of Threat Message and Sketch,”
n.d., Secret, Page 1 only
Source: Energy Department FOIA release
The title of this memo indicates that a sketch of a device was included with the threat message. Technical experts had already begun to draw conclusions about the device in Montrev as well as the implications for finding a second device in the United States.
Document 12: Thomas R. Clark, Manager, Nevada Operations Office, Department of Energy, “NEST Alert Status,” 3 December 1986, Confidential, excised copy
Source: Energy Department FOIA release
This message, from a Department of Energy manager, informs NEST participants at key laboratories and contractors that NEST is on “alert.” The Department of State has received a threat and the Department of Energy has been asked to evaluate it. Other actions have been taken.
Document 13: “Security Plan for NEST Retrograde Operation, December 1986,” n.d., Secret
Source: Energy Department FOIA release
The plan described in this document notes the classification levels and types of information involved in the exercise as well as measures for the protection of cryptological matter and classified documents.
Document 14: Peter Mygatt, Exercise Mighty Derringer, “Chronological Media Play, ‘Site City,’ Beginning 12/7/86,” n.d., Secret
Source: Energy Department FOIA release
The MIGHTY DERRINGER scenario writers assumed that if it was a real-world event, part of it would be visible and covered extensively by the media. This document summarizes reports of fictional news services and television stations as well as interaction between the media and FBI and Department of Energy.
Document 15: NEST On-Scene Commander, Subject: Event Mighty Derringer Sitrep No. 1 OCONUS, Prepared at 00:15 PST on 12/06/86, Secret
Source: Energy Department FOIA release
The first Situation Report (Sitrep) of the part of the exercise that takes place in Montrev summarizes the current situation (including the number of personnel in country) as well as
the status of a variety of subjects – including command and control, intelligence, disablement, and weather.
Document 16: W. Rogers, NEST Paramedic Coordinator, to V. Withirill, N.T.S.O, “MIGHTY DERRINGER, MEDICAL EMERGECY RESPONSE,” 6 December 1986, Secret
Source: Energy Department FOIA release
This memo reports that MIGHTY DERRINGER was being conducted in area A-25 of the Nevada Test Site and would involve approximately 450 people. It focuses on “areas of responsibility … and those assets available” in the event of an actual medical emergency.
Document 17: “NEST Evacuation Plan,” n.d., Secret
Source: Energy Department FOIA release
This plan addresses the evacuation of NEST personnel and equipment from Montrev City in the event of a nuclear detonation at the nearby Bullatcha Refinery No. 5. It focuses on execution, logistics, and command and control.
Document 18: NEST On-Scene Coordinator/Exercise Mighty Derringer, to Director, Emergency Management Team, DOE-EDC, Washington, D.C., Event Mighty Derringer Sitrep No. 2, Prepared at 1100 PST 6 December 1986, Secret
Source: Energy Department FOIA release
This report updates the Sitrep that had been prepared just after midnight on December 6 and reports on the significant developments that had occurred during the day. It covers thirteen different topics, and provides significant details of the terrorist site in Montrev, a summary of the behavioral assessment based on communications intelligence, and an assessment of the device. It notes that a “second nuclear device may be enroute [to] CONUS” and there is no confidence that the device is one-point safe, that is, the risk of an accidental nuclear detonation had to be taken into account (to be one-point safe there must be less than 1 in one million probability of producing a nuclear yield exceeding the equivalent of 4 pounds of TNT when the high explosive inside the weapon is detonated at any single point).
Document 19: NEST On-Scene Coordinator /Exercise Mighty Derringer, to Director, Emergency Management Team, DOE-EDC, Washington, D.C., Subject: Event Mighty Derringer Sitrep No. 3, Prepared at 00:10, on 12/07/86, Secret
Source: Energy Department FOIA release
This Sitrep prepared an about one hour after Sitrep No. 2, notes that “prestaging of equipment for access has been completed.”
Document 20: Assessment/McMaster, to Standard Distribution, “IRT Intelligence Summary 061200-062400,” 7 December 1986 02:30, Secret
Source: Energy Department FOIA release
This assessment reports on attempts to determine the presence of a nuclear device at the terrorist site, the movements of the terrorist group’s leader, the weapons and equipment possessed by the group, and a conclusion regarding the capability of Montrev’s armed forces to secure the terrorist site.
Document 21: Assessment/McMaster, to Standard Distribution, “Status Montrev Forces,” 7 December 1986 05:30, Secret
Source: Energy Department FOIA release
The status of Montrev’s forces is reported in this memo, which is based on information received from the Defense Intelligence Agency. It discusses their location, vehicle lift capability, and maintenance issues.
Document 22: CN1 to All, “Mighty Derringer,” 7 December 1986 8:44, Secret
Source: Energy Department FOIA release
This memo conveys a report from the IWS news service on events in Montrev.
Document 23: NEST On-Scene Coordinator, Subject: Event Mighty Derringer, Sitrep No. 4, OCONUS, Prepared at 09:40 on 12/07/86, Secret
Source: Energy Department FOIA release
This Sitrep indicates a successful assault by forces of the Joint Special Operations Command, resulting in their control of both the north and south sites that had been under terrorist control. It reports on the status of the nuclear device and the initial implementation of the emergency disablement plan.
Document 24: Summary Assessment to Standard Distribution, “Summary Assessment,” 7 December 1986 10:30, Secret
Source: Energy Department FOIA release
The technical assessment has been entirely redacted from this document, but the operational and behavioral assessments have been released in their entirety. They note that “The adversary has set up the Montrev situation in such a way that if and when he surfaces in CONUS and makes an explicit threat and demand, he must be taken seriously.”
Document 25a: CN1 to All, “Mighty Derringer,” 7 December 1986 12:28, Secret
Document 25b: CN1 to All, “Mighty Derringer,” 7 December 1986 13:07, Secret
Document 25c: CN1 to All, “Mighty Derringer,” 7 December 1986 15:48, Secret
Source: Energy Department FOIA release
These bulletins convey various media reports of developments in Montrev, including the presence of NEST personnel.
Document 26: Assessment/F. Kloverstrom to Standard Distribution, “Results of examination of containers found in south building,” 7 December 1986 18:10, Secret
Source: Energy Department FOIA release
This memo reports on the discovery, after the assault, of two containers, which appear to contain radioactive material.
Document 27: Jim Boyer, “Suggested Procedure for Joint DOE/Montrev News Releases,” 7 December 1986, Secret
Source: Energy Department FOIA release
Among the recommendations in this short memo are obtaining input from the Montrev Ministry of Information “to get an idea of what El Presidente will approve,” developing a cover for the NEST operation, but preparing to admit NEST participation during the last phase of the operation.
Document 28: “Time Line/Event/Decision Sequence,” 8 December 1986 19:00, Secret
Source: Energy Department FOIA release
This document focuses on the essential steps in disabling the nuclear device seized in Montrev and limiting damage. Thus, it addresses access, diagnostics, disablement, damage limitation, and hazards and effects.
Document 29: “Damage Limitation Containment Implementation,”8 December 1986, Secret
Source: Energy Department FOIA release
This eight-page memo has been almost completely redacted but the opening paragraph notes the location of the Montrev device and that its location presents a “formidable problem” but that all participants reached a common conclusion for the solution.
Document 30: “Hazards and Effects Analysis Prior to Montrev Disablement,” n.d. [8 December 1986?], Secret
Source: Energy Department FOIA release
This three-paragraph memo notes that hazard predictions (involving fallout dose and exposure rates) considered a variety of possible yields, wind projections, and the vulnerability of “the small village of Taco Caliente.”
Document 31: A/I [Assessment & Intelligence] Behavioral, “Booby Traps/Tamper Proof,” n.d. [8 December 1986?], Secret
Source: Energy Department FOIA release
This assessment focuses on the likelihood that the terrorist group and its leader would have installed booby traps to prevent tampering with the nuclear device seized in Montrev. It notes the implications of the extensive anti-personnel attack defenses around the area.
Document 32: James K. Magruder, On-Scene Commander, to Director, Emergency Management Team, DOE-EOC, Washington, D.C, Event Mighty Derringer Sitrep No. 7, 8 December 1986 23:00, Secret
Source: Energy Department FOIA release
This Sitrep notes presumed deadlines for nuclear device detonation and a proposed disablement schedule, the number of personnel on site, an extensive report on current intelligence, and that an “emergency destruct plan has been prepared.”
Document 33: Assessment & Intelligence/F. Jessen to Standard Distribution, “A&I Summary/8 December 2130,” 8 December 1986, Secret
Source: Energy Department FOIA release
This assessment notes the credibility of a threat message claiming the existence of a second nuclear device based on experimental measurements of the device seized in Montrev. The memo’s contents suggest a U.S. target for the second device.
Document 34: J.A. Morgan, Disablement Team Leader, to On-Scene Commander, “Disablement Plan,” 9 December 1986, Secret
Source: Energy Department FOIA release
The memo includes a computer sketch of the terrorist nuclear device and the disablement method, as well as the reentry and evacuation plans – all of which have been redacted.
Document 35: “Exercise Mighty Derringer Post-Event Plan to Safe and Remove the Device,” circa 9 December 1986, Secret
Source: Energy Department FOIA release
This heavily-redacted memo covers four topics – the situation, mission, execution, and administration and logistics. The released portion notes that disablement action had been completed and that an intact physics package had been recovered.
Document 36: “NEST Demobilization Plan,” 10 December 1986, Secret
Source: Energy Department FOIA release
This memo marks plans for the ending the exercise – specifying the responsibilities of the individual organizations, procedures for transportation to the airport and the loading of aircraft, and command and control.
Document 37: Assessment/M. Miron, to Standard Distribution, “Resemblance of Montrev Device to Tahoe Bomb,” 9 December 1986 20:35, Secret
Source: Energy Department FOIA release
In 1980, a sophisticated improvised (non-nuclear) explosive device placed at Harvey’s Wagon Wheel Casino did substantial damage when disablement efforts failed. The memo suggests that publicly available information about the device may have been employed to construct the Montrev device.
Document 38: Cal Wood, Livermore National Laboratory, to Bob Nelson, Controller Team Leader, “Preliminary Evaluation of Players’ Device Estimate,” 10 December 1986, Secret
Source: Energy Department FOIA release
This heavily redacted memo notes that “the diagnostic techniques used by the team produced a rather good estimate of both the materials present and their configuration.”
Document 39: Director FEMA to National Security Council, “Situation Report on MONTREV/Indianapolis Terrorist Situation,” 11 December 1986 17:00 EST, Secret
Source: Energy Department FOIA release
The FEMA director begins with the observation that “At 0700, 11 December 1986, a nuclear detonation occurred in the City of Indianapolis” devastating 20 square blocks. He does not describe the type of damage produced, for example, whether the detonation led to any fires, or the extent to which it caused local fallout hazards. The FEMA director then describes the consequence management phase of the exercise, including involvement of state and federal authorities and agencies.
Critiques
Document 40: Carl Henry, Los Alamos National Laboratory, “Mighty Derringer Report,” 2 February 1987, enclosing comments by Ray D. Duncan, n.d., Secret
Source: Energy Department FOIA release
Some weeks after the exercise, Los Alamos official Carl Henry sent a large package of commentary on MIGHTY DERRINGER, which is presented below, piece by piece, except for the critique by Ray D. Duncan,which is attached to the Henry memorandum. Duncan, a manager at the Nevada Test Site, produced an extensive review which raised a number of issues, including the “unusual challenges” MIGHTY DERRINGER raised for NEST if it was ever deployed to a foreign country for a “covert operation.” Perhaps some incident during the exercise led him to the recommendation for educational training for Delta Force and the Joint Special Operations Command so that their members “understand the potential consequences of moving or unintentionally shooting an IND [improvised nuclear device].”
Document 41: Untitled, unattributed document, Secret, incomplete
Source: Energy Department FOIA release
This critique gives some detail on how the NEST group entered Montrev during the crisis. The State Department had created an approved access list and a simulated Montrev consulate processed the players when they entered the country. When players realized that they had forgotten some equipment, they were easily able to retrieve it as it was only 65 miles away. The commentator noted that in a “real world situation, the NEST contingent could be thousands of miles away from necessary equipment or supplies.”
Document 42: Eric Schuld to Bob Nelson, “Comments on Mighty Derringer – OCONUS Issues,” n.d., Secret
Source: Energy Department FOIA release
Schuld listed issues brought up by the “Outside Continental United States” exercise. For example, the JSOC solved its problem through a “quick assault” that created problems for other organizations in the exercise.
Document 43: Vic Berniklau to Bob Nelson, “Issues/Major Observations/Lessons Learned,” n.d., Secret
Source: Energy Department FOIA release
Like many of the commentators, Berniklau saw the exercise as “excellent” and “well managed,” but he raised problems that others also brought up, such as fragmentation of information and “confusion.”
Document 44: T.T. Scolman, Comments, n.d., Secret
Source: Energy Department FOIA release
Scolman, whose role was “Commander for Science,” also saw an information management problem and pointed to other concerns, such as lack of support staff.
Document 45: Richard F. Smale, HSE, to Carl Henry/Bill Chambers, “First Impressions: Mighty Derringer: Consequence Phase,” n.d., Classification unknown
Source: Energy Department FOIA release
The “consequence phase” referred to the aftermath of the nuclear detonation in Indianapolis. Smale saw “great things” in the exercise, such as its technical organization, but he pointed to concerns such as the failure to present information that would be accessible to a non-technical audience and the lack of time to “develop good fallout plots.”
Document 46: L J. O’Neill, “Exercise Impressions,” 9 December 1986, Secret
Source: Energy Department FOIA release
O’Neill was impressed by the participation of “foreign speaking actors” which helped the participants to enter “wholeheartedly into the play.”
Document 47: L.J. Wolfson to R. Nelson, “Exercise Mighty Derringer,” 10 December 1986, Classificaion unknown, excised copy
Source: Energy Department FOIA release
Like O’Neill, Wolfson pointed to the “good actor play,” especially by the actor who had the role of Montrev’s “El General.” Nevertheless, he argued that “too many people” slowed down the operation.
Document 48: William Nelson, Mighty Derringer Washington Controller, to Captain Ronald St. Martin, National Security Council, “Mighty Derringer Meeting at FBI Headquarters, 12 December 1986, Classification unknown
Source: Energy Department FOIA release
The discussion at FBI headquarters on organizational issues produced a consensus on the need for a White House-designated “leader,” possibly at the cabinet level, responsible for managing post-nuclear disaster recovery activities.
Document 49: Kathy S. Gant, Emergency Technology Program, Oak Ridge National Laboratory, to William Chambers, Los Alamos National Laboratory, 17 December 1986, enclosing “Comments on Exercise Mighty Derringer,” 18 December 1986, Classification unknown
Source: Energy Department FOIA release
Seeing a need for better integration of the consequences phase into MIGHTY DERRINGER, Gant emphasized the need for state and local actors to play a stronger role in such exercises to give them greater realism. Her discussion of the Federal Radiological Response Plan led to a recommendation that NEST staffers play a role in post-incident field monitoring of radiation hazards because they would be the “first available federal personnel.”
Document 50: William H. Chambers, CONUS Site Controller, to Carl Henry, Chief Controller, “‘Quick Look,’ Report, Mighty Derringer CONUS,” 19 December 1986, Secret
Source: Energy Department FOIA release
Chambers provided some detail on the role of the Indianapolis nuclear detonation in MIGHTY DERRINGER. According to the script, the device had been “rendered-safe,” but the exercise leaders “deviated” from the script by improvising a “simulated nuclear detonation.”
Document 51: Zolin Burson, EG&G Energy Measurements, to Carl Henry, 29 December 1986, Secret
Source: Energy Department FOIA release
Like Gant, Burson pointed to the need for more involvement by state and local actors in such exercises, suggesting that “if the real Governor and Mayor” had been present, “they would have had a much stronger influence.”
Document 52: Richard F. Smale, Associate Group Leader, to Jesse Aragon, HSE Division Leader, “Trip Report December 7 to 13, Camp Atterbury (Indianapolis), Indiana,” 7 January 1987, Secret
Source: Energy Department FOIA release
Smale provides more detail on the role of nuclear devices in the exercise scenario, noting that “terrorists had stolen two … from a developing nuclear capable country.” He also observed that “when control of the device had been obtained, the NEST scientists could have disabled it.”
Document 53: Thomas S. Dahlstrom, EG&G Measurements, to William H. Chambers, Carl Henry, and Norm Bailey, “Mighty Derringer Observations,” 13 January 1987, Classification unknown, excised copy
Source: Energy Department FOIA release
After noting that his “overall reaction” was “quite positive,” Dahlstrom believed that “confusion” emanated from a basic problem: the players did “not comprehend the complexity of an OCONUS deployment – specifically how the State Department controls the matter.”
Document 54: F. Jessen/LLNL to G. Allen and W. Adams/NVO, “Mighty Derringer Critique,” 16 December 1986, Rev[ised] 13 January 1987, Secret, excised copy
Source: Energy Department FOIA release
Jessen pointed to a number of problems, for example, that “many of the participating agencies were not serious players,” the “unrealistic background information” on the “fictitious” countries and people, “bad guidance on the use of existing proliferant country data,” and failure to recognize that “information to be assessed related to intelligence reports of a nuclear terrorist threat.” Especially disturbing was the relocation of the command post to a “safe location,” while NEST personnel were not notified”: “the blatant lack of concern for [their] safety … is inexcusable.”
Document 55: Julie A. Orcutt/HSE, Los Alamos National Laboratory, to Jesse Aragon, HSE Division Leader, “Trip Report: Mighty Derringer Exercise, Montrev Site,” 13 January 1987, Secret
Source: Energy Department FOIA release
During the exercise, the on-scene commander at Indianapolis had decided against building a “containment structure” to prevent the spread of hazardous material because of the risks. That meant, however, that plutonium would be scattered about which presented dangers of “lung doses.” Los Alamos staffer Julie Orcutt recommended the provision of more anti-contamination equipment, such as foam mitigation, to reduce dangers to officials entering the blast area.
Document 56: J. Doyle to Gylan C. Allen, “EG&G Comments for Mighty Derringer,” 14 January 1987, Classification unknown, excised, incomplete copy
Source: Energy Department FOIA release
Noting that the exercise provided “very valuable training,” Doyle saw such problems as the “sheer magnitude” in numbers of players, cramped space, and inadequate communications staffing.
Document 57: G.C. Allen, USDOE/NVO, “Mighty Derringer: Comments and Observations,” 15 January 15, 1987, Classification unknown, excised copy
Source: Energy Department FOIA release
Among the shortcomings cited in Allen’s rather critical evaluation were poor communications and weaknesses in interagency coordination.
Document 58: William E. Nelson, Emergency Response, Lawrence Livermore National Laboratory, to Carl Henry, Los Alamos National Laboratory, “‘Quick Look,’ Report, Mighty Derringer,” 21 January 1987, Secret, excised copy
Source: Energy Department FOIA release
Jumping the gun was a weakness cited in Nelson’s critique: players “did not wait for establishment of credibility before acting,” which made a “shambles of an orderly assessment of information.” He also observed that NEST search team “escorts” needed “experience in covert operations” to “prevent inadvertent acts that would alert terrorists.” Nelson’s report included a number of observations made by other participants.
Document 59: J. Strickfadden, LANL, to Bob Nelson, “Mighty Derringer Comments,” n.d., Secret
Source: Energy Department FOIA release
The overall positive evaluation – the “most realistic exercise ever conducted by the NEST community” – included some criticisms, such as “chaotic” operations at the Working Point [WP] and a shambolic state of affairs at the “reentry” point (detonation zone).
Document 60: Milt Madsen (Monitor) to Bob Nelson, “Mighty Derringer Observations,” n.d., Secret, excised, incomplete copy
Source: Energy Department FOIA release
Madsen’s comments included suggestions for future improvements in NEST’s organization: for example, to avoid fragmented committee operations, NEST needed a technical program manager.
Document 61: Peter Mygatt, “Mighty Derringer – Media Play Report,” n.d., Secret
Source: Energy Department FOIA release
Energy Department spokesperson Mygatt’s evaluation of the player’s management of the media was generally positive, although he saw a few failings, e.g., the Joint Information Center never called a news conference, “which is unheard of in an emergency.”.
Document 62: Walter Nervik, Senior Command Controller, to Robert M. Nelson, Exercise Mighty Derringer Controller, “Lessons Learned,” n.d., Secret
Source: Energy Department FOIA release
An official at Lawrence Livermore Laboratory, Nervik wondered who would provide security after JSOC operatives attacked the terrorists in an overseas environment. Special forces personnel would leave the scene but the NEST would still need security resources.
Document 63: Walter Nervik to Bob Nelson, “Lessons Learned,” n.d., Secret
Source: Energy Department FOIA release
Nervik was critical in another evaluation: the NEST team was far too large, players were complacent about a nuclear threat, there were no “penalties” for making a mistake, and playing conditions were “unreal.” With respect to the latter point, the fact that the Montrev phase of the exercise occurred on U.S.-controlled territory, (the Nevada Test Site), “severely limits the stress placed on players in unfamiliar surroundings, dealing with strangers, and relying on untested sources of support.” Nervik also saw a danger that participants would see exercises as “more of a game than a serious test of all facets of the NEST capabilities.”
Document 64: Jack Campbell, Public Information, to Robert M. Nelson, Exercise Mighty Derringer Controller, n.d., Secret
Source: Energy Department FOIA release
Campbell pointed to a weakness: higher level officials did not really “play.” For example, after the JSOC assault, the State Department left Montrev, even though “lives of American correspondents were in jeopardy.” Another surprise was that the Department of Energy NEST team did not establish a “public affairs” function, although in real life such a group would be highly active.
Document 65: “Mighty Derringer 86,” unattributed, n.d., Secret, excised copy
Source: Energy Department FOIA release
These handwritten notes raised several issues, such as the interaction between EOD and the Delta force players and the impact of the “play” in the United States on decisions in the OCONUS (Montrev) activity. One impact was that a “risky” disablement option was taken in Montrev in order to preserve evidence to help raise the chance for a successful operation in “site city” (Indianapolis).
Document 66: “Mighty Derringer,” unattributed, n.d., Secret, excised copy
Source: Energy Department FOIA release
Handwritten notes by another player raised basic organizational issues. The absence of a “chain of command” prior to the deployment made it unclear who EOD worked for. A serious concern was that the Delta Force players did not appreciate the “gravity of dealing with a nuclear device,” an issue suggested by other reports (see document 41).
Document 67: “Mighty Derringer Search Planning,” unattributed, n.d., Secret, excised copy
Source: Energy Department FOIA release
This document provides a review of organizational arrangements established for the device search in Indianapolis.
Document 68: “Communications Observations (Site City),” unattributed, n.d., Classification unknown
Source: Energy Department FOIA release
This review of communications systems concluded that this was the “best NEST communications exercise that I have observed.”
Document 69: Second page of fax to Carl Henry, unattributed document, n.d., Classification unknown
Source: Energy Department FOIA release
This critique points to operational security (OPSEC) as the “real” problem, noting that players had organizational logos on their clothing and that “loose talk” in hotels and bars was “particularly bad.”
ABBREVIATIONS
CONUS Continental United States
EG&G Edgerton, Germeshausen, and Grier
EOC Emergency Operations Center
EOD Explosive Ordnance Disposal
EODTECHCTR Explosive Ordnance Disposal Technical Center (Navy)
ERDA Energy Research and Development Administration
EST Emergency Support Team
FBI Federal Bureau of Investigation
FCP Forward Control Point
FEMA Federal Emergency Management Agency
FRMAC Federal Radiation Monitoring Assessment Center
HRT Hostage Response Team
IND Improved Nuclear Device
JNACC Joint Nuclear Accident Coordination Center
JSOC Joint Special Operations Command
LANL Los Alamos National Laboratory
LLNL Lawrence Livermore National Laboratory
NEST Nuclear Emergency Search Team
NVO Nevada Operations Office
OCONUS Outside the Continental United States
OSC On-Scene Commander
REECo Reynolds Electrical Engineering Corporation
SAC Special-Agent-in Charge (FBI)
SFOD Special Forces Operational Detachment – Delta
SITREP Situation Report
TOC Tactical Operations Center
WP Working Point
NOTES
[1] Charles Wilson and Carrie Schedler, Associated Press, “Indy battens down hatches for Super Bowl security,” http://www.boston.com, January 30, 2012.
[2] Jeffrey T. Richelson, Defusing Armageddon: Inside NEST, America’s Secret Nuclear Bomb Squad (New York: W.W. Norton, 2009), pp. 19-21.
[3]For the range of recent views on the risks and probabilities of acts of nuclear terrorism, see John Mueller, Atomic Obsession: Nuclear Alarmism from Hiroshima to Al-Qaeda (New York: Oxford University Press, 2009), Graham Allison, Nuclear Terrorism: The Ultimately Preventable Catastrophe (New York: Times Books, 2004), and Michael Krepon, “Are We Winning or Losing? (Continued),” Arms Control Wonk.
TOP-SECRET from the FBI – Texas Resident Convicted on Charge of Attempted Use of Weapon of Mass Destruction
AMARILLO, TX—Khalid Ali-M Aldawsari, 22, a citizen of Saudi Arabia and resident of Lubbock, Texas, was convicted by a federal jury today on an indictment charging one count of attempted use of a weapon of mass destruction in connection with his purchase of chemicals and equipment necessary to make an improvised explosive device (IED) and his research of potential U.S. targets, including persons and infrastructure.
The verdict, which was reached in the Northern District of Texas, was announced by Sarah R. Saldaña, U.S. Attorney for the Northern District of Texas; Lisa Monaco, Assistant Attorney General for National Security; and Diego G. Rodriguez, Special Agent in Charge of the FBI Dallas Field Division.
Sentencing has been scheduled for October 9, 2012, in Amarillo. Aldawsari, who was lawfully admitted into the United States in 2008 on a student visa and was enrolled at South Plains College near Lubbock, faces a maximum sentence of life in prison and a $250,000 fine. He was arrested on February 23, 2011 on a criminal complaint and later charged in a March 9, 2011 federal indictment with attempting to use a weapon of mass destruction.
According to court documents and evidence presented during trial, at the time of his arrest last year, Aldawsari had been researching online how to construct an IED using several chemicals as ingredients. He had also acquired or taken a substantial step toward acquiring most of the ingredients and equipment necessary to construct an IED, and he had conducted online research of several potential U.S. targets, the affidavit alleges. In addition, he had allegedly described his desire for violent jihad and martyrdom in blog postings and a personal journal.
“While many people are responsible for thwarting Aldawsari’s threat and bringing him to justice, we owe a debt of gratitude to all the members of the North Texas Joint Terrorism Task Force, and especially to the hundreds of hardworking and dedicated FBI agents, analysts, linguists, and others,” said U.S. Attorney Saldaña. “Their efforts, coupled with the hard work and excellent cooperation from the Lubbock Police Department and the Texas Tech Police Department, are the reason we were able to stop this defendant from carrying out a catastrophic act of terrorism.”
“As this trial demonstrated, Aldawsari purchased ingredients to construct an explosive device and was actively researching potential targets in the United States. Thanks to the efforts of many agents, analysts, and prosecutors, this plot was thwarted before it could advance further,” said Assistant Attorney General Monaco. “This case serves as another reminder of the need for continued vigilance both at home and abroad.”
“Today’s guilty verdict shows how individuals in the United States with the intent to do harm can acquire the knowledge and materials necessary to carry out an attack,” said SAC Rodriguez. “Our success in locating and preventing Mr. Aldawsari from carrying out an attack is a result of cooperation within the law enforcement and intelligence communities, particularly, the North Texas Joint Terrorism Task Force, the Texas Tech Police Department, the Lubbock Police Department, and the Lubbock County Sheriff’s Office, but also a demonstration of information sharing across FBI divisions, as well as assistance from the community. I want to thank the dedicated agents, officers, and analysts; the computer forensics team; and linguists that worked diligently on this investigation, as well as prosecutors serving in the U.S. Attorney’s Office in the Northern District.”
The government presented evidence that on February 1, 2011, a chemical supplier reported to the FBI a suspicious attempted purchase of concentrated phenol by a man identifying himself as Khalid Aldawsari. Phenol is a toxic chemical with legitimate uses, but it can also be used to make the explosive trinitrophenol, also known as T.N.P., or picric acid. Ingredients typically used with phenol to make picric acid, or T.N.P., are concentrated sulfuric and nitric acids.
Aldawsari attempted to have the phenol order shipped to a freight company so it could be held for him there, but the freight company told Aldawsari that the order had been returned to the supplier and called the police. Later, Aldawsari falsely told the supplier he was associated with a university and wanted the phenol for “off-campus, personal research.” Frustrated by questions being asked over his phenol order, Aldawsari cancelled his order, placed an order with another company, and later e-mailed himself instructions for producing phenol. In December 2010, he had successfully purchased concentrated nitric and sulfuric acids.
Aldawsari used various e-mail accounts in researching explosives and targets and often sent e-mails to himself as part of this process. He e-mailed himself a recipe for picric acid, which was described in the e-mail as a “military explosive” and also e-mailed himself instructions on how to convert a cell phone into a remote detonator and how to prepare a booby-trapped vehicle using household items. Aldawsari also purchased many other items, including a Hazmat suit, a soldering iron kit, glass beakers and flasks, a stun gun, clocks, and a battery tester.
Excerpts from a journal found at Aldawsari’s residence indicated that he had been planning to commit a terrorist attack in the United States for years. One entry describes how Aldawsari sought and obtained a particular scholarship because it allowed him to come directly to the United States and helped him financially, which he said “will help tremendously in providing me with the support I need for Jihad.” The entry continues, “And now, after mastering the English language, learning how to build explosives and continuous planning to target the infidel Americans, it is time for Jihad.”
In another entry, Aldawsari wrote that he was near to reaching his goal and near to getting weapons to use against infidels and their helpers. He also listed a “synopsis of important steps” that included obtaining a forged U.S. birth certificate; renting a car; using different driver’s licenses for each car rented; putting bombs in cars and taking them to different places during rush hour; and leaving the city for a safe place.
Aldawsari conducted research on various targets and e-mailed himself information on these locations and people. One of the documents he sent himself, with the subject line listed as “Targets,” contained the names and home addresses of three American citizens who had previously served in the U.S. military and had been stationed for a time at Abu Ghraib prison in Iraq. In others, Aldawsari sent himself the names of 12 reservoir dams in Colorado and California and listed two categories of targets: hydroelectric dams and nuclear power plants. He also sent himself an e-mail titled “Tyrant’s House,” in which he listed the Dallas address for former President George W. Bush. Aldawsari also conducted research that indicated he considered using infant dolls to conceal explosives and the possible targeting of a nightclub with an explosive concealed in a backpack.
This case was investigated by the FBI’s Dallas Joint Terrorism Task Force, with assistance from the Lubbock Police Department and the Texas Tech Police Department. The prosecution is being handled by Assistant U.S. Attorneys Jeffrey R. Haag, Denise Williams, James T. Jacks, and Matthew J. Kacsmaryk and Trial Attorney David Cora from the Counterterrorism Section of the Justice Department’s National Security Division.
TOP-SECRET – The Creation of the U.S. Spy Satellites
In September 1992 the Department of Defense acknowledged the existence of the National Reconnaissance Office (NRO), an agency established in 1961 to manage the development and operation of the nation’s reconnaissance satellite systems. The creation of the NRO was the result of a number of factors.
On May 1, 1960 Francis Gary Powers took off from Peshawar, Pakistan on the U-2 mission designated Operation GRAND SLAM. The flight was planned to take him over the heart of the Soviet Union and terminate at Bodo, Norway. The main target was Plesetsk, which communications intercepts had indicated might be the site of an ICBM facility.1 When the Soviet Union shot down his plane and captured him alive, they also forced President Dwight Eisenhower to halt aerial overflights of Soviet territory.
At that time the U.S. had two ongoing programs to produce satellite vehicles that could photograph Soviet territory. Such vehicles would allow far more frequent coverage than possible with manned aircraft. In addition, they would avoid placing the lives of pilots at risk and eliminate the risks of international incidents resulting from overflights.
The Air Force program, designated SAMOS, sought to develop a number of different satellite systems–including one that would radio its imagery back to earth and another that would return film capsules. The CIA program, CORONA, focused solely on developing a film return satellite.
However, both the CIA and Air Force programs were in trouble. Launch after launch in the CORONA program, eleven in all by May 1, 1960, eight of which carried cameras, had resulted in failure–the only variation was in the cause. Meanwhile, the SAMOS program was also experiencing difficulties, both with regard to hardware and program definition.2
Concerns over SAMOS led President Eisenhower to direct two groups to study both the technical aspects of the program as well as how the resulting system would be employed. The ultimate result was a joint report presented to the President and NSC on August 25, 1960.3
As a result of that meeting Eisenhower approved a first SAMOS launch in September, as well as reorientation of the program, with the development of high-resolution film-return systems being assigned highest priority while the electronic readout system would be pursued as a research project. With regard to SAMOS management, he ordered that the Air Force institute special management arrangements, which would involve a direct line of authority between the SAMOS project office and the Office of the Air Force Secretary, bypassing the Air Staff and any other intermediate layers of bureaucracy.4
Secretary of the Air Force Dudley C. Sharp wasted little time creating the recommended new structure and procedures. On August 31st Sharp signed Secretary of the Air Force Order 115.1, establishing the Office of Missile and Satellite Systems within his own office to help him manage the SAMOS project. With Order 116.1, Sharp created a SAMOS project office at the Los Angeles headquarters of the Air Force Ballistic Missile Division (AFBMD) as a field extension of the Office of the Secretary of the Air Force to carry out development of the satellite.5
The impact of the orders, in practice, was that the director of the SAMOS project would report directly to Under Secretary of the Air Force Joseph V. Charyk, who would manage it in the Secretary’s name. In turn, Charyk would report directly to the Secretary of Defense.6
The changes would not stop there. The urgency attached to developing a successful reconnaissance satellite led, ultimately, to the creation of a top secret program and organization to coordinate the entire national reconnaissance effort.
Several of the documents listed below also appear in either of two National Security Archive microfiche collections on U.S. intelligence. The U.S. Intelligence Community: Organization, Operations and Management: 1947-1989 (1990) and U.S. Espionage and Intelligence: Organization, Operations, and Management, 1947-1996 (1997) publish together for the first time recently declassified documents pertaining to the organizational structure, operations and management of the U.S. Intelligence Community over the last fifty years, cross-indexed for maximum accessibility. Together, these two sets reproduce on microfiche over 2,000 organizational histories, memoranda, manuals, regulations, directives, reports, and studies, totaling more than 50,000 pages of documents from the Office of the Director of Central Intelligence, the Central Intelligence Agency, National Reconnaissance Office, National Security Agency, Defense Intelligence Agency, military service intelligence organizations, National Security Council, and other official government agencies and organizations.
![]() Document 1
Document 1
Joseph Charyk, Memorandum for the Secretary of Defense
Management of the National Reconnaissance Program
24 July 1961
Top Secret
1 p.
The organizational changes resulting from the decisions of August 25, 1960 and their implementation left some unsatisfied. In particular, James Killian and Edwin Land, influential members of the President’s intelligence advisory board pushed for permanent and institutionalized collaboration between the CIA and Air Force. After the Kennedy administration took office the push to establish a permanent reconnaissance organization took on additional life. There was a strong feeling in the new administration, particularly by Secretary of Defense Robert McNamara and his deputy, Roswell Gilpatric, that a better, more formalized relationship was required.7
On July 24, 1961, Air Force Undersecretary Joseph Charyk sent a memorandum to McNamara attaching two possible memoranda of agreement for creation of a National Reconnaissance Program, along with some additional material.
![]() Document 2
Document 2
Memorandum of Understanding
Management of the National Reconnaissance Program (Draft)
20 July 1961
Top Secret
5 pp.
This memo specified establishment of a National Reconnaissance Program (NRP) consisting of “all satellite and overflight reconnaissance projects whether overt or covert,” and including “all photographic projects for intelligence, geodesy and mapping purposes, and electronic signal collection projects for electronic signal intelligence and communications intelligence.”
To manage the NRP, a National Reconnaissance Office (NRO) would be established on a covert basis. The NRO director (DNRO) would be the Deputy Director for Plans, CIA (at the time, Richard Bissell) while the Under Secretary of the Air Force would serve as Deputy Director (DDNRO). The DNRO would be responsible for the management of CIA activities, the DDNRO and the Air Force for Defense Department activities. The DoD, specifically the Air Force acting as executive agent, would be primarily responsible for technical program management, scheduling, vehicle operations, financial management and overt contract administration, while the CIA would be primarily responsible for targeting each satellite. The office would operate under streamlined management procedures similar to those established in August 1960 for SAMOS.
![]() Document 3
Document 3
Memorandum of Understanding
Management of the National Reconnaissance Program (Draft)
21 July 1961
Top Secret
4 pp.
This secondary memorandum was prepared at the suggestion of Defense Department General Counsel Cyrus Vance. It offered a quite different solution to the problem. As with the primary memo, it established a NRP covering both satellite and aerial reconnaissance operations. But rather than a jointly run program, it placed responsibility for management solely in the hands of a covertly appointed Special Assistant for Reconnaissance, to be selected by the Secretary of Defense. The office of the Special Assistant would handle the responsibilities assigned to the NRO in the other MOU. The CIA would “assist the Department of Defense by providing support as required in areas of program security, communications, and covert contract administration.”
![]() Document 4
Document 4
Memorandum
Pros and Cons of Each Solution
Not dated
Top Secret
2 pp.
The assessment of pros and cons favored the July 20 memorandum, listing five pros for the first solution and only two for the second. The first solution would consolidate responsibilities into a single program with relatively little disruption of established management, represented a proven solution, would require no overt organizational changes, would allow both agencies to retain authoritative voices in their areas of expertise, and provided a simplified management structure. The two cons noted were the division of program responsibility between two people, and that “successful program management depends upon mutual understanding and trust of the two people in charge of the NRO.” It would not be too long before that later observation would take on great significance.
In contrast, there were more cons than pros specified for the second solution. The only two points in its favor were the consolidation of reconnaissance activities into a single program managed by a single individual and the assignment of complete responsibility to the agency (DoD) with the most resources. Foremost of the six cons was the need for DoD to control and conduct large-scale covert operations, in as much as it was an entity “whose normal methods are completely foreign to this task.”
![]() Document 5
Document 5
Roswell Gilpatric, Letter to Allen Dulles
Management of the National Reconnaissance Program
6 September 1961
Top Secret
4 pp.
On July 28, 1961, four days after receiving Charyk’s memorandum and draft memoranda of understanding, McNamara instructed Air Force Undersecretary Joseph Charyk to continue discussions with the key officials and advisers in order to resolve any organizational difficulties that threatened to impede the satellite reconnaissance effort. The ultimate result was this letter from Deputy Secretary of Defense Roswell Gilpatric to Dulles, which confirmed “our agreement with respect to the setting up of the National Reconnaissance Program.”
The letter specified the creation of a NRP. It also established the NRO, a uniform security control system, and specified that the NRO would be directly responsive to the intelligence requirements and priorities specified by the United States Intelligence Board. It specified implementation of NRP programs assigned to the CIA through the Deputy Director for Plans. It designated the Undersecretary of the Air Force as the Defense Secretary’s Special Assistant for Reconnaissance, with full authority in DoD reconnaissance matters.
The letter contained no specific assignment of responsibilities to either the CIA or Defense Department, stating only that “The Directors of the National Reconnaissance Office will … insure that the particular talents, experience and capabilities within the Department of Defense and the Central Intelligence Agency are fully and most effectively utilized in this program.”
The letter provided for the NRO to be managed jointly by the Under Secretary of the Air Force and the CIA Deputy Director for Plans (at the time, still Richard Bissell). A May 1962 agreement between the CIA and Defense Department established a single NRO director. Joseph Charyk was named to the directorship shortly afterward.
![]() Document 6
Document 6
Joseph Charyk
Memorandum for NRO Program Directors/Director, NRO Staff
Organization and Functions of the NRO
23 July 1962
Top Secret
11 pp.
This memorandum represents the fundamental directive on the organization and functions of the NRO. In addition to the Director (there was no provision for a deputy director), there were four major elements to the NRO–the NRO staff and three program elements, designated A, B, and C. The staff’s functions included assisting the director in dealing with the USIB and the principal consumers of the intelligence collected.
The Air Force Office of Special Projects (the successor to the SAMOS project office) became NRO’s Program A. The CIA reconnaissance effort was designated Program B, while the Navy’s space reconnaissance effort, at the time consisting of the Galactic Radiation and Background (GRAB) satellite, whose radar ferret mission involved the collection of Soviet radar signals, became Program C. Although the GRAB effort was carried out by the Naval Research Laboratory, the director of the Office of Naval Intelligence would serve as Program C director until 1971.8
![]() Document 7
Document 7
Agreement between the Secretary of Defense and the Director of Central Intelligence on Management of the National Reconnaissance Program
13 March 1963
Top Secret
6 pp.
In December 1962, Joseph Charyk decided to leave government to become president of the COMSAT Corporation. By that time a number of disputes between the CIA and NRO had contributed to Charyk’s view that the position of the NRO and its director should be strengthened. During the last week of February 1963, his last week in office, he completed a revision of a CIA draft of a new reconnaissance agreement to replace the May 1962 agreement (which had replaced the September 6, 1961 agreement). Charyk took the revision to Deputy Secretary of Defense Roswell Gilpatric. It appears that some CIA-suggested changes were incorporated sometime after Charyk left office. On March 13, Gilpatric signed the slightly modified version on behalf of DoD. It was sent to the CIA that day and immediately approved by DCI John McCone, who had replaced Allen Dulles in November 1961.9
The new agreement, while it did not include all the elements Charyk considered important, did substantially strengthen the authority of the NRO and its director. It named the Secretary of Defense as the Executive Agent for the NRP. The program would be “developed, managed, and conducted in accordance with policies and guidance jointly agreed to by the Secretary of Defense and the Director of Central Intelligence.”
The NRO would manage the NRP “under the direction, authority, and control of the Secretary of Defense.” The NRO’s director would be selected by the Defense Secretary with the concurrence of the DCI, and report to the Defense Secretary. The NRO director was charged with presenting to the Secretary of Defense “all projects” for intelligence collection and mapping and geodetic information via overflights and the associated budgets, scheduling all overflight missions in the NRP, as well as engineering analysis to correct problems with collection systems. With regard to technical management, the DNRO was to “assign all project tasks such as technical management, contracting etc., to appropriate elements of the DoD and CIA, changing such assignments, and taking any such steps he may determine necessary to the efficient management of the NRP.”
![]() Document 8
Document 8
Department of Defense Directive Number TS 5105.23
Subject: National Reconnaissance Office
27 March 1964
Top Secret
4 pp.
This directive replaced the original June 1962 DoD Directive on the NRO, and remains in force today. The directive specifies the role of the Director of the NRO, the relationships between the NRO and other organizations, the director’s authorities, and security. It specified that documents or other material concerning National Reconnaissance Program matters would be handled within a special security system (known as the BYEMAN Control System).
![]() Document 9
Document 9
President’s Foreign Intelligence Advisory Board
Memorandum for the President
Subject: National Reconnaissance Program
2 May 1964
Top Secret
11 pp.
The 1963 CIA-DoD agreement on the NRP did not end the battles between the CIA and NRO–as some key CIA officials, including ultimately DCI John McCone, sought to reestablish a major role for the CIA in the satellite reconnaissance effort. The continuing conflict was examined by the PFIAB.
The board concluded that “the National Reconnaissance Program despite its achievements, has not yet reached its full potential.” The fundamental cause for the NRP’s shortcomings was “inadequacies in organizational structure.” In addition, there was no clear division of responsibilities and roles between the Defense Department, CIA, and the DCI.
The recommendations of the board represented a clear victory for the NRO and its director. The DCI should have a “large and important role” in establishing intelligence collection requirements and in ensuring that the data collected was effectively exploited, according to the board. In addition, his leadership would be a key factor in the work of the United States Intelligence Board relating to the scheduling of space and airborne reconnaissance missions.
But the board also recommended that President Johnson sign a directive which would assign to NRO’s Air Force component (the Air Force Office of Special Projects) systems engineering, procurement, and operation of all satellite reconnaissance systems.
![]() Document 10
Document 10
Agreement for Reorganization of the National Reconnaissance Program
13 August 1965
Top Secret
6 pp.
Despite the recommendations of the May 2, 1964 PFIAB report, which were challenged by DCI John McCone, no action was taken to solidify the position of the NRO and its director. Instead prolonged discussions over a new agreement continued into the summer of 1965. During this period the CIA continued work on what would become two key satellite programs–the HEXAGON/KH-9 imaging and RHYOLITE signals intelligence satellites.
In early August, Deputy Secretary of Defense Cyrus Vance and CIA official John Bross reached an understanding on a new agreement, and it was signed by Vice Adm. William F. Raborn (McCone’s successor) and Vance on August 13, 1965. It represented a significant victory for the CIA, assigning key decision-making authority to an executive committee, authority that was previously the prerogative of the NRO director as the agent of the Secretary of Defense.
The Secretary of Defense was to have “the ultimate responsibility for the management and operation of the NRO and the NRP,” and have the final power to approve the NRP budget. The Secretary also was empowered to make decisions when the executive committee could not reach agreement.
The DCI was to establish collection priorities and requirements for targeting NRP operations, as well as establish frequency of coverage, review the results obtained by the NRP and recommend steps for improving its results if necessary, serve on the executive committee, review and approve the NRP budget, and provide security policy guidance.
The NRP Executive Committee established by the agreement would consist of the DCI, Deputy Secretary of Defense, and Special Assistant to the President for Science and Technology. The committee was to recommend to the Secretary of Defense the “appropriate level of effort for the NRP,” approve or modify the consolidated NRP and its budget, approve the allocation of responsibility and the corresponding funds for research and exploratory development for new systems. It was instructed to insure that funds would be adequate to pursue a vigorous research and development program, involving both CIA and DoD. The executive committee was to assign development of sensors to the agency best equipped to handle the task.
The Director of the NRO would manage the NRO and execute the NRP “subject to the direction and control of the Secretary of Defense and the guidance of the Executive Committee.” His authority to initiate, improve, modify, redirect or terminate all research and development programs in the NRP, would be subject to review by the executive committee. He could demand that all agencies keep him informed about all programs undertaken as part of the NRP.
![]() Document 11
Document 11
Analysis of “A $1.5 Billion Secret in Sky” Washington Post, December 9, 1973
Not dated
Top Secret
33 pp.
Throughout the 1960s, the United States operation of reconnaissance satellites was officially classified, but well known among specialists and the press. However, it was not until January 1971 that the NRO’s existence was first disclosed by the media, when it was briefly mentioned in a New York Times article on intelligence and foreign policy.
A much more extensive discussion of the NRO appeared in the December 9, 1973 Washington Post as a result of the inadvertent mention of the reconnaissance office in a Congressional report. The NRO prepared this set of classified responses to the article, clearly intended for those in Congress who might be concerned about the article’s purported revelations about the NRO’s cost overruns and avoidance of Congressional oversight.
![]() Document 12
Document 12
E.C. Aldridge, Jr. (Director, NRO)
Letter to David L. Boren, Chairman,
Senate Select Committee on Intelligence
21 November 1988
Secret
3 pp.
The late 1980s saw the beginning of what eventually would be a wide-ranging restructuring of the NRO. In November 1988 NRO director Edward “Pete” Aldridge wrote to Senator David Boren, Chairman of the Senate Select Committee on Intelligence, concerning the findings of an extensive study (the NRO Restructure Study) of the organizational structure of the NRO.
Aldridge proceeded to report that, after having discussed the study’s recommendations with Secretary of Defense Frank Carlucci and Director of Central Intelligence William Webster, he was directing the development of plans to implement the recommendations. Specific changes would include the creation of a centralized systems analysis function “to conduct cross-system trades and simulations within the NRO,” creation of a “User Support” function to improve NRO support to intelligence community users as well as to the growing number of operational military users, and the dispersal of the NRO Staff to the new units, with the staff being replaced by a group of policy advisers. In addition, Aldridge foresaw the establishment of an interim facility “to house the buildup of the new functions and senior management.” The ultimate goal, projected for the 1991-92 period, would be the “collocation of all NRO elements [including the Los Angeles-based Air Force Office of Special Projects] . . . in the Washington, D.C. area.”
![]() Document 13
Document 13
Memorandum of Agreement
Subject: Organizational Restructure of the National Reconnaissance Office
15 December 1988
Secret
2 pp.
This memorandum of agreement, signed by the Director of the NRO and the directors of the NRO’s three programs commits them to the restructuring discussed in Edward Aldridge’s November 21 letter to Senator Boren.
Many changes recommended by Aldridge, who left office at the end of 1988, were considered by a 1989 NRO-sponsored review group and subsequently adopted.
![]() Document 14
Document 14
Report to the Director of Central Intelligence
DCI Task Force on The National Reconnaissance Office, Final Report
April 1992
Secret
35 pp.
This report was produced by a panel chaired by former Lockheed Corporation CEO Robert Fuhrman, whose members included both former and serving intelligence officials. It focused on a variety of issues other than current and possible future NRO reconnaissance systems. Among the issues it examined were mission, organizational structure, security and classification.
One of its most significant conclusions was that the Program A,B,C structure that had been instituted in 1962 (see Document 6) “does not enhance mission effectiveness” but “leads to counterproductive competition and makes it more difficult to foster loyalty and to maintain focus on the NRO mission.” As a result, the panel recommended that the NRO be restructured along functional lines with imagery and SIGINT directorates. This change was made even before the final version of the report was issued.
The report also noted that while the NRO’s existence was officially classified it was an “open secret” and that seeking to attempt to maintain such “open secrets … weakens the case for preserving ‘real’ secrets.” In addition, such secrecy limited the NRO’s ability to interact with customers and users. The group recommended declassifying the “fact of” the NRO, as well as providing information about the NRO’s mission, the identities of senior officials, headquarters locations, and the NRO as a joint Intelligence Community-Defense Department activity.
![]() Document 15
Document 15
National Security Directive 67
Subject: Intelligence Capabilities: 1992-2005
30 March 1992
Secret
2 pp.
NSD 67 directed a number of changes in U.S. intelligence organization and operations. Among those was implementation of the plan to restructure the NRO along functional lines–eliminating the decades old Program A (Air Force), B (CIA), and C (Navy) structure and replacing it with directorates for imaging, signals intelligence, and communication systems acquisition and operations–as recommended by the Fuhrman panel. As a result, Air Force, CIA, and Navy personnel involved in such activities would now work together rather than as part of distinct NRO components.
![]() Document 16
Document 16
Email message
Subject: Overt-Covert-DOS-REP-INPUT
27 July 1992
Secret
1 p.
In addition to the internal restructuring of the NRO, 1992 saw the declassification of the organization, as recommended by the Fuhrman report (Document 14), for a number of reasons–to facilitate interaction with other parts of the government, to make it easier for the NRO to support military operations, and in response to Congressional pressure to acknowledge the obvious. As part of the process of considering declassification NRO consulted Richard Curl, head of the Office of Intelligence Resources of the State Department’s Bureau of Intelligence and Research–the office which provides INR with expertise and support concerning technical collection systems. Curl recommended a low-key approach to declassification.
![]() Document 17
Document 17
Memorandum for Secretary of Defense, Director of Central Intelligence
Subject: Changing the National Reconnaissance Office (NRO) to an Overt Organization
30 July 1992
Secret
3 pp.
w/ attachments:
Document 17a: Mission of the NRO, 1 p.
Document 17b: Implications of Proposed Changes, 4 pp. (Two versions)
Version One
Version Two
These memos, from Director of the NRO Martin Faga, represent key documents in the declassification of the NRO. The memo noted Congressional pressure for declassification and that Presidential certification that declassification would result in “grave damage to the nation … would be difficult in this case.”
Faga reported that as a result of an NRO review he recommended declassifying the fact of NRO’s existence, issuing a brief mission statement, acknowledging the NRO as a joint DCI-Secretary of Defense endeavor, and identifying top level NRO officials. He also noted that his recommendations attempted to balance concerns about classifying information that realistically could not be protected, while maintaining an ability to protect matters believed to require continued protection.
Secretary of Defense Richard Cheney, DCI Robert Gates, and President Bush approved the recommendations in September and a three-paragraph memorandum to correspondents acknowledging the NRO and NRP was issued on September 18, 1992.
Document 17b comes in two versions, representing different security reviews. Material redacted from the first version includes provisions of National Security Directive 30 on space policy, expression of concern over “derived disclosures,” and the assessment that the “high degree of foreign acceptance of satellite reconnaissance, and the fact that we are not disclosing significant new data,” would not lead to any significant foreign reaction. Another redacted statement stated that “legislation . . . exempting all NRO operational files from [Freedom of Information Act] searches” was required.
![]() Document 18
Document 18
Final Report: National Reconnaissance Program Task Force for the Director of Central Intelligence
September 1992
Top Secret
15 pp.
The end of the Cold War and collapse of the Soviet Union required the U.S. intelligence community and NRO to reconsider how U.S. overhead reconnaissance systems were employed and what capabilities future systems should possess. To consider these questions DCI Robert Gates appointed a task force, chaired by his eventual successor, R. James Woolsey.
The final report considers future needs and collection methods, industrial base considerations, procurement policy considerations, international industrial issues, and transition considerations. Its recommendations included elimination of both some collection tasks as well as some entire types of present and planned collection systems.
![]() Document 19
Document 19
NRO Protection Review, “What is [BYEMAN]?”
6 November 1992
Top Secret
18 pp.
Traditionally, the designations of Sensitive Compartmented Information (SCI) compartments–such as UMBRA to indicate particularly sensitive communications intelligence and RUFF to intelligence based on satellite imagery–have themselves been classified. In recent years, however, the NSA and CIA have declassified a number of such terms and their meaning. One exception has been the term “BYEMAN”– the BYEMAN Control System being the security system used to protect information related to NRO collection systems (in contrast to their products) and other aspects of NRO activities, including budget and structure. Thus, the term BYEMAN has been deleted in the title of the document and throughout the study–although the term and its meaning has become known by specialists and conveys no information beyond the text of any particular document.
This study addresses the use of the BYEMAN classification within the NRO, its impact on contractors and other government personnel, and the consequences of the current application of the BYEMAN system. The study concludes that placing information in the highly restrictive BYEMAN channels (in contrast to classifying the information at a lower level) may unduly restrict its dissemination to individuals who have a legitimate need to know.
![]() Document 20
Document 20
NRO Strategic Plan
18 January 1993
Secret
19 pp.
A study headed by James Woolsey (Document 18), President Clinton’s first DCI, heavily influenced the contents of this early 1993 document. The plan’s introduction notes that while some collection tasks will no longer be handled by overhead reconnaissance the “uncertain nature of the world that is emerging from the end of the ‘cold war’ places a heavy premium on overhead reconnaissance.” At the same time, “this overhead reconnaissance challenge must be met in an era of a likely reduced national security budget.”
The strategic plan is described in the introduction, as “the ‘game plan’ to transition current overhead collection architectures into a more integrated, end-to-end architecture for improved global access and tasking flexibility.”
The document goes on to examine the strategic context for future NRO operations, NRO strategy, strategic objectives, and approaches to implementation. Strategic objectives include improving the responsiveness of NRO systems by developing an architecture that spans the entire collection and dissemination process, from the identification of requirements to dissemination of the data collected.
![]() Document 21
Document 21
National Reconnaissance Office: Collocation Construction Project, Joint DOD and CIA Review Report
November 1994
Unclassified
28 pp.
In an August 8, 1994 press conference, Senators Dennis DeConcini (D-Az.) and John Warner (R-Va.), the chairman and vice chairman of the Senate Select Committee on Intelligence accused the NRO of concealing from Congress the cost involved in building a new headquarters to house government and contractor employees. Previously NRO activities in the Washington area were conducted from the Pentagon and rented space in the Washington metropolitan area. The collocation and restructuring decisions of the late 1980s and early 1990s had resulted in a requirement for a new headquarters facility.10
The accusations were followed by hearings before both the Senate and House intelligence oversight committees–with House committee members defending the NRO and criticizing their Senate colleagues. While they noted that some of the documents presented by the NRO covering total costs were not presented with desirable clarity, the House members were more critical of the Senate committee for inattention to their committee work.11
This joint DoD and CIA review of the project, found “no intent to mislead Congress” but that “the NRO failed to follow Intelligence Community budgeting guidelines, applicable to all the intelligence agencies,” that would have caused the project to be presented as a “New Initiative,” and that the cost data provided by the NRO “were not presented in a consistent fashion and did not include a level of detail comparable to submissions for . . . intelligence community construction.”
![]() Document 22
Document 22
Memorandum for Director of Central Intelligence
Subject: Small Satellite Review Panel
Unclassified
July 1996
The concept of employing significantly smaller satellites for imagery collection was strongly advocated by Rep. Larry Combest during his tenure (1995-97) as chairman of the House Permanent Select Committee on Intelligence. As a result the DCI was instructed to appoint a panel of experts to review the issue.12
Panel members included former NRO directors Robert Hermann and Martin Faga; former NRO official and NSA director Lew Allen; scientist Sidney Drell and four others. The panel’s report supported a radical reduction in the size of most U.S. imagery satellites. The panel concluded that “now is an appropriate time to make a qualitative change in the systems architecture of the nation’s reconnaissance assets,” in part because “the technology and industrial capabilities of the country permit the creation of effective space systems that are substantially smaller and less costly than current systems.” Thus, the panel saw “the opportunity to move towards an operational capability for . . . imagery systems, that consists of an array of smaller, cheaper spacecraft in larger number with a total capacity which is at least as useful as those currently planned and to transport them to space with substantially smaller and less costly launch vehicles.”13
The extent to which those recommendations have influenced NRO’s Future Imagery Architecture plan is uncertain–although plans for large constellations of small satellites have not usually survived the budgetary process.
![]() Document 23
Document 23
Defining the Future of the NRO for the 21st Century, Final Report, Executive Summary
August 26, 1996
Unclassified
30 pp.
This report was apparently the first major outside review of the NRO conducted during the Clinton administration, and the first conducted after the NRO’s transformation to an overt institution and its restructuring were firmly in place.
Among those conducting the review were former Vice Chairman of the Joint Chiefs of Staff, Adm. David E. Jeremiah, former NRO director Martin Faga, and former Deputy Director of Central Intelligence John McMahon. Issues studied by the panel included, inter alia, the existence of a possible alternative to the NRO, NRO’s mission in the 21st Century, support to military operations, security, internal organization, and the relationship with NRO’s customers.
After reviewing a number of alternatives, the panel concluded that no other arrangement was superior for carrying out the NRO mission. It did, however, recommend, changes with regards to NRO’s mission and internal organization. The panel concluded that where the NRO’s current mission is “worldwide intelligence,” its future mission should be “global information superiority,” which “demands intelligence capabilities unimaginable just a few years ago.” The panel also recommended creation of a fourth NRO directorate, which was subsequently established, to focus solely on the development of advanced systems, in order to “increase the visibility and stature of technology innovation in the NRO.”
Notes
1. Michael R. Beschloss, Mayday: Eisenhower, Khrushchev and the U-2 Affair (New York: Harper & Row, 1986), pp.241-42; John Ranelagh, The Agency: The Rise and Decline of the CIA, From Wild Bill Donovan to William Casey (New York: Simon & Schuster, 1986), p. 319; Gregory W. Pedlow and Donald Welzenbach, The Central Intelligence Agency and Overhead Reconnaissance: The U-2 and OXCART Programs, 1954-1974 (Washington, D.C.: CIA, 1992), pp. 170-93.2. Kenneth Greer, “Corona,” Studies in Intelligence, Supplement 17, Spring 1973 in Kevin C. Ruffner (Ed.), CORONA: America’s First Satellite Program (Washington, D.C.: Central Intelligence Agency, 1995), pp. 3-40; Gen. Thomas D. White, Air Force Chief of Staff to General Thomas S. Power, Commander in Chief, Strategic Air Command, June 29, 1960, Thomas D. White Papers, Library of Congress, Box 34, Folder “2-15 SAC.”3. “Special Meeting of the National Security Council to be held in the Conference Room of the White House from 8:30 a.m. to 10 a.m., Thursday, August 25, 1960, undated, National Security Council Staff Papers, 1948-61, Executive Secretary’s Subject File Series, Box 15, Reconnaissance Satellites [1960], DDEL.
4. “Reconnaissance Satellite Program,” Action No.1-b at Special NSC Meeting on August 25, 1960, transmitted to the Secretary of Defense by Memo of September 1, 1960; G.B. Kistiakowsky to Allen Dulles, August 25, 1960, Special Assistant for Science and Technology, Box No. 15, Space [July-Dec 1960], DDEL.
5. Carl Berger, The Air Force in Space Fiscal Year 1961, (Washington, D.C.: Air Force Historical Liaison Office, 1966), pp.41-42; Secretary of the Air Force Order 115.1, “Organization and Functions of the Office of Missile and Satellite Systems,” August 31, 1960; Robert Perry, A History of Satellite Reconnaissance, Volume 5: Management of the National Reconnaissance Program, 1960-1965, (Washington, D.C., NRO, 1969), p. 20; Secretary of the Air Force Order 116.1, “The Director of the SAMOS Project,” August 31, 1960.
6. Perry, A History of Satellite Reconnaissance, Volume 5, p. 20.
7. Jeffrey T. Richelson, “Undercover in Outer Space: The Creation and Evolution of the NRO,” International Journal of Intelligence and Counterintelligence, 13, 3 (Fall 2000): 301-344.
8. Ibid.; GRAB: Galactic Radiation and Background (Washington, D.C.: NRL, 1997); Dwayne A. Day, “Listening from Above: The First Signals Intelligence Satellite,” Spaceflight, August 1999, pp. 339-347; NRO, Program Directors of the NRO: ABC&D, 1999.
9. Perry, A History of Satellite Reconnaissance, Volume 5, pp. 93, 96-97.
10. Pierre Thomas, “Spy Unit’s Spending Stuns Hill,” Washington Post, August 9, 1994, pp. A1, A6.
11. Walter Pincus, “Spy Agency Defended by House Panel,” Washington Post, August 12, 1994, p. A21; U.S. Congress, House Permanent Select Committee on Intelligence, NRO Headquarters Project (Washington, D.C.: U.S. Government Printing Office, 1995), pp. 3-4.
12. Walter Pincus, “Congress Debates Adding Smaller Spy Satellites to NRO’s Menu,” Washington Post, October 5, 1995, p. A14; Joseph C. Anselmo, “House, Senate at Odds Over Intel Small Sats,” Aviation Week & Space Technology, January 1, 1996, p. 19.
13. Small Satellite Review Panel, Memorandum for: Director of Central Intelligence, Subject: Small Satellite Review Panel, July 1996.
Anatoly S. Chernyaev Diary, 1972 – TOP-SECRET from the NSA
 click for full sizeFirst trip with Gorbachev. Chernyaev in Belgium, October 1972. |
Anatoly S. Chernyaev Diary, 1972
Soviet government official Anatoly Chernyaev records an insider’s view of the Brezhnev era
National Security Archive Electronic Briefing Book No. 379
| Translated and edited by Anna Melyakova and Svetlana Savranskaya “Anatoly Chernyaev’s diary is one of the great internal records of the Gorbachev years, a trove of irreplaceable observations about a turning point in history. There is nothing else quite like it, allowing the reader to sit at Gorbachev’s elbow at the time of perestroika and glasnost, experiencing the breakthroughs and setbacks. It is a major contribution to our understanding of this momentous period.” — David E. Hoffman, Pulitzer Prize-winning author of The Dead Hand “Remarkable diary …”
Washington, D.C., May 25, 2012 – Today the National Security Archive publishes excerpts from Anatoly S. Chernyaev’s diary of 1972 for the first time in English translation with edits and postscript by the author. While the diary for the Gorbachev years, 1985-1991, published before and widely used in scholarly work on the end of the Cold War provided a major source on the Gorbachev reforms, the earlier years of the diary give the reader a very rare window into the workings of the Brezhnev inner circle in the 1970s. The portrait of the Soviet leader Leonid Brezhnev, whom most Americans remember from his later years as frail and incomprehensible, emerges very differently from the earliest in the series of diaries donated by Anatoly Sergeyevich Chernyaev to the National Security Archive. In 1972, Chernyaev, deputy head of the International Department of the Central Committee, started keeping a systematic diary, recording his attendance at Politburo meetings, his participation in meetings at the state dacha in Zavidovo (where the experts and speechwriters met to draft speeches and reports for the General Secretary), visits abroad, and the daily life of a high-level Soviet apparatchik. In 1972, Brezhnev is a skillful negotiator, who prepares seriously for Richard Nixon’s first visit to Moscow, who discusses texts of his speeches with leading Moscow intellectuals whom he brought into his inner circle as speechwriters and consultants, who is essentially non-ideological in his dealings with foreign leaders-negotiating arms control and economic agreements with Nixon while the U.S. forces are bombing the Soviet communist ally Vietnam, preferring Georges Pompidou to the leader of French communists Georges Marchais, and”brainwashing” Pakistani leader Bhutto. The two most striking differences between the aging Brezhnev of the late 1970s-early 1980s and the Brezhnev of this diary are that the General Secretary is clearly in charge of the Politburo sessions and that he actively consults with leading experts and intellectuals, such as Georgy Arbatov, Nikolai Inozemtsev, Alexander Bovin and Chernyaev himself. Chernyaev’s daily duties are centered around the international communist movement, interactions with representatives from European communist parties. The reader sees Chernyaev’s emerging disillusionment with his work, which in comparison to real foreign policy, like preparation for Nixon’s visit, feels meaningless. Chernyaev comes to believe that “the Communist Movement right now is nothing more than an ideological addendum to our foreign policy,” and that the Soviet authority in the progressive movements in the world is shrinking: “nobody believes us anymore, no matter how we portray the Chinese and try to explain our Marxist-Leninist purity.” He sees the future in a different direction. After Nixon’s visit, Chernyaev is asked to draft Brezhnev’s speech on Soviet-American relations and thus is allowed to see all the materials from the meeting, including all transcripts of conversation. Impressed with the quality of interaction and the non-ideological spirit of it, Chernyaev anticipates a new era: “Be that as it may, but we’ve crossed the Rubicon. The great Rubicon of world history. These weeks of May 1972 will go down in history as the beginning of an era of convergence.” But the new era will only come thirteen years later. In 1972, he sees the first almost imperceptible sign from the future. In October 1972, he is asked to accompany first secretary of the Stavropol region on a trip to Belgium. This is where Chernyaev meets and spends time with Mikhail Gorbachev for the first time. Astonishingly, as Chernyaev later admits, he did not record this meeting in the diary at the time. Only photographs documented this auspicious meeting where Chernyaev sits on the left hand of the future Soviet leader, whose right hand he was destined to become in the late 1980s.
|
TOP-SECRET from the FBI – CIA Policy and Approval of Covert Operations
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET from the FBI – Leader of Crips Gang Pleads Guilty in Virginia to Prostituting Eight Juveniles
ALEXANDRIA, VA—Justin Strom, aka “Jae,” “Jae Dee,” or “J-Dirt,” 26, of Lorton, Virginia, pleaded guilty today to recruiting at least eight juvenile girls to engage in commercial sex for his street gang’s prostitution business.
Neil H. MacBride, U.S. Attorney for the Eastern District of Virginia; Kenneth T. Cuccinelli, II, Attorney General of Virginia; Colonel David Rohrer, Fairfax County, Virginia Chief of Police; and Ronald T. Hosko, Special Agent in Charge of the FBI’s Washington Field Office Criminal Division, made the announcement after the plea was accepted by U.S. District Judge James C. Cacheris.
“For six years, Justin Strom profited from preying on teenage girls and others he recruited as prostitutes in a commercial sex ring,” said U.S. Attorney MacBride. “Strom is the fifth and final Underground Gangster Crips gang member to plead guilty to sex trafficking a juvenile—a very serious crime that carries a potential life sentence.”
“Justin Strom robbed these girls of their childhoods, their innocence, and their trust, and he did that in the most base, vile, and despicable way possible,” said Attorney General Cuccinelli. “Nothing can ever repair the damages Strom inflicted on his victims, but it’s our hope that today’s guilty plea will help them begin a path towards healing and moving forward.”
“Today, a fifth member of the Underground Gangster Crips pleaded guilty to strong-arming and pimping underage girls in the illegal sex trade—a trade that is taking place here in some of the most affluent neighborhoods in our nation,” said Special Agent in Charge Hosko. “These gang members admitted that they beat and intimidated young girls they met on the Internet or in Metro stops in our area. They preyed on some of the most vulnerable in our society, and today Justin Strom admitted to these crimes.”
“This gang-driven prostitution ring was a direct threat to the safety and welfare of young women,” said Chief Rohrer. “With the help of our federal partners, we will continue to work aggressively and consistently to rid Fairfax County of gang violence and criminal operations wherever and whenever we find it.”
Strom pleaded guilty to sex trafficking of a child, which carries a mandatory minimum of 10 years in prison and maximum penalty of life in prison. Sentencing is scheduled for September 14, 2012.
According to a statement of facts filed with his plea agreement and other court records, Strom is a member of the Underground Gangster Crips (UGC) set based in Fairfax County. From 2006 through March 2012, Strom misrepresented his identity online to recruit females—including juveniles—through online social networking sites such as Facebook, MySpace, and Datehookup and enticed the girls to use their good looks to earn money through prostitution. He and others posted numerous advertisements on Backpage, Craigslist, and other websites to solicit customers to pay to have sex with juvenile and adult prostitutes.
Strom admitted that he knowingly enticed at least eight juvenile girls to engage in prostitution for his business and that he received proceeds from this illicit conduct for approximately six years.
On March 28, 2012, Strom was among five members and associates of the UGC set based in Fairfax County charged with running a prostitution business that recruited and trafficked high school girls. Four previously pleaded guilty, and Strom’s guilty plea today marks the fifth and final conviction in this case.
Donyel Pier Dove, aka “Bleek,” 27, of Alexandria, Virginia, pleaded guilty on May 17, 2012 to sex trafficking of a juvenile. He also pleaded guilty to use of a firearm during a crime of violence in relation to two armed robberies of 7-11 stores in Manassas, Virginia, in March 2012 and to possession of a firearm by a convicted felon in Fairfax, which also occurred in March 2012. Dove faces a mandatory minimum penalty of five years and a maximum of life on the use of a firearm charge and a maximum of 10 years in prison on the possession of a firearm charge. He is scheduled to be sentenced on August 10, 2012 by U.S. District Judge Anthony J. Trenga.
On May 14, 2012, Henock Ghile, aka “Knots,” 23, of Springfield, Virginia, pleaded guilty to sex trafficking of a juvenile. In court, Ghile admitted that he was a UGC gang associate and that from May 2011 through September 2011, he transported two 17-year-old girls to work as prostitutes. Sentencing has been scheduled for August 3, 2012, before U.S. District Judge Claude M. Hilton.
On April 14, 2012, two others associated with the UGC prostitution operation—Michael Tavon Jefferies, aka “Loc,” 21, of Woodbridge, Virginia; and Christopher Sylvia, 23, of Springfield, Virginia—pleaded guilty to sex trafficking of a juvenile. Jefferies is scheduled to be sentenced on July 6, 2012 before U.S. District Judge Leonie M. Brinkema. Sylvia is scheduled for sentencing on July 20, 2012 before U.S. District Judge Gerald Bruce Lee.
This case was investigated by the Fairfax County Police Department and the FBI’s Washington Field Office, with assistance from the Northern Virginia Human Trafficking Task Force. Virginia Assistant Attorney General and Special Assistant U.S. Attorney Marc Birnbaum and Assistant U.S. Attorney Inayat Delawala are prosecuting the case on behalf of the United States.
Founded in 2004, the Northern Virginia Human Trafficking Task Force is a collaboration of federal, state, and local law enforcement agencies—along with non-governmental organizations—dedicated to combating human trafficking and related crimes.
TOP-SECRET from the FBI – Manhattan U.S. Attorney and FBI Assistant Director in Charge Announce 24 Arrests in Eight Countries as Part of International Cyber Crime Takedown
Preet Bharara, the United States Attorney for the Southern District of New York, and Janice K. Fedarcyk, the Assistant Director in Charge of the New York Field Office of the Federal Bureau of Investigation (FBI), announced today the largest coordinated international law enforcement action in history directed at “carding” crimes—offenses in which the Internet is used to traffic in and exploit the stolen credit card, bank account, and other personal identification information of hundreds of thousands of victims globally. Today’s coordinated action—involving 13 countries, including the United States—resulted in 24 arrests, including the domestic arrests of 11 individuals by federal and local authorities in the United States, and the arrests of 13 individuals abroad by foreign law enforcement in seven countries. In addition, the federal and local authorities and authorities overseas today conducted more than 30 subject interviews and executed more than 30 search warrants. Today’s coordinated actions result from a two-year undercover operation led by the FBI that was designed to locate cybercriminals, investigate and expose them, and disrupt their activities.
Eleven individuals were arrested today, and one last night, in the United States: Christian Cangeopol, a/k/a “404myth,” was arrested today in Lawrenceville, Georgia; Mark Caparelli, a/k/a “Cubby,” was arrested in San Diego, California; Sean Harper, a/k/a “Kabraxis314,” was arrested in Albuquerque, New Mexico; Alex Hatala, a/k/a “kool+kake,” was arrested in Jacksonville, Florida; Joshua Hicks, a/k/a “OxideDox,” was arrested in Bronx, New York; Michael Hogue, a/k/a “xVisceral,” was arrested in Tucson, Arizona; Mir Islam, a/k/a “JoshTheGod,” was arrested in Manhattan, New York; Peter Ketchum, a/k/a “IwearaMAGNUM,” was arrested in Pittsfield, Massachusetts; Steven Hansen, a/k/a “theboner1,” was arrested in Wisconsin, where he is currently serving a prison sentence on state charges. In addition, two minors, whose names will not be made public, were arrested by local authorities in Long Beach and Sacramento, California. Hicks and Islam will be presented later today before a magistrate judge in the Southern District of New York. The other federally arrested defendants will be presented before magistrate judges in the corresponding federal districts of arrest.
Another 13 individuals were arrested today in seven foreign countries. Eleven of those individuals were arrested as a result of investigations commenced in foreign jurisdictions based in part on information arising out of the undercover operation and provided by the FBI to foreign law enforcement. Those 11 arrests occurred in the United Kingdom (6 arrests), Bosnia (2), Bulgaria (1), Norway (1), and Germany (1). Two additional defendants were arrested today in foreign countries based on provisional arrest warrants obtained by the United States in connection with complaints unsealed today in the Southern District of New York. Those two individuals are Ali Hassan, a/k/a/ “Badoo,” who was arrested in Italy; and Lee Jason Juesheng, a/k/a “iAlert,” a/k/a “Jason Kato,” who was arrested in Japan. Australia, Canada, Denmark, and Macedonia conducted interviews, executed search warrants, or took other coordinated action in connection with today’s takedown.
Charges were also unsealed in the Southern District of New York against four additional defendants who remain at large.
Manhattan U.S. Attorney Preet Bharara said, “As the cyber threat grows more international, the response must be increasingly global and forceful. The coordinated law enforcement actions taken by an unprecedented number of countries around the world today demonstrate that hackers and fraudsters cannot count on being able to prowl the Internet in anonymity and with impunity, even across national boundaries. Clever computer criminals operating behind the supposed veil of the Internet are still subject to the long arm of the law.
The allegations unsealed today chronicle a breathtaking spectrum of cyber schemes and scams. As described in the charging documents, individuals sold credit cards by the thousands and took the private information of untold numbers of people. As alleged, the defendants casually offered every stripe of malware and virus to fellow fraudsters, even including software-enabling cyber voyeurs to hijack an unsuspecting consumer’s personal computer camera. To expose and prosecute individuals like the alleged cyber criminals charged today will continue to require exactly the kind of coordinated response and international cooperation that made today’s arrests possible.”
FBI Assistant Director in Charge Janice K. Fedarcyk said, “From New York to Norway and Japan to Australia, Operation Card Shop targeted sophisticated, highly organized cyber criminals involved in buying and selling stolen identities, exploited credit cards, counterfeit documents, and sophisticated hacking tools. Spanning four continents, the two-year undercover FBI investigation is the latest example of our commitment to rooting out rampant criminal behavior on the Internet.
Cyber crooks trade contraband and advance their schemes online with impunity, and they will only be stopped by law enforcement’s continued vigilance and cooperation. Today’s arrests cause significant disruption to the underground economy and are a stark reminder that masked IP addresses and private forums are no sanctuary for criminals and are not beyond the reach of the FBI.”
The following allegations are based on the Complaints unsealed today in Manhattan federal court:
Background on Carding Crimes
“Carding” refers to various criminal activities associated with stealing personal identification information and financial information belonging to other individuals—including the account information associated with credit cards, bank cards, debit cards, or other access devices—and using that information to obtain money, goods, or services without the victims’ authorization or consent. For example, a criminal might gain unauthorized access to (or “hack”) a database maintained on a computer server and steal credit card numbers and other personal information stored in that database. The criminal can then use the stolen information to, among other things, buy goods or services online; manufacture counterfeit credit cards by encoding them with the stolen account information; manufacture false identification documents (which can be used in turn to facilitate fraudulent purchases); or sell the stolen information to others who intend to use it for criminal purposes. Carding refers to the foregoing criminal activity generally and encompasses a variety of federal offenses, including, but not limited to, identification document fraud, aggravated identity theft, access device fraud, computer hacking, and wire fraud.
“Carding forums” are websites used by criminals engaged in carding (“carders”) to facilitate their criminal activity. Carders use carding forums to, among other things, exchange information related to carding, such as information concerning hacking methods or computer-security vulnerabilities that could be used to obtain personal identification information; and to buy and sell goods and services related to carding—for example, stolen credit or debit card account numbers, hardware for creating counterfeit credit or debit cards, or goods bought with compromised credit card or debit card accounts. Carding forums often permit users to post public messages—postings that can be viewed by all users of the site—sometimes referred to as threads. For example, a user who has stolen credit card numbers may post a public thread offering to sell the numbers. Carding forums also often permit users to communicate one-to-one through so-called private messages. Because carding forums are, in essence, marketplaces for illegal activities, access is typically restricted to avoid law enforcement surveillance. Typically, a prospective user seeking to join a carding forum can only do so if other, already established users vouch for him or her, or if he or she pays a sum of money to the operators of the carding forum. User accounts are typically identified by a username and access is restricted by password. Users of carding forums typically identify themselves on such forums using aliases or online nicknames (“nics”).
Individuals who use stolen credit card information to purchase goods on the Internet are typically reluctant to ship the goods to their own home addresses, for fear that law enforcement could easily trace the purchases. Accordingly, carders often seek out “drop addresses”—addresses with which they have no association, such as vacant houses or apartments—where carded goods can be shipped and retrieved without leaving evidence of their involvement in the shipment. Some individuals used carding forums to sell “drop services” to other forum members, usually in exchange for some form of compensation. One frequently used form of compensation is a “1-to-1” arrangement in which the carder wishing to ship to the drop must ship two of whatever items he has carded—one for the provider of the drop to forward to the carder and the other for the provider of the drop to keep as payment in kind for the carder’s use of the drop. Another frequently used compensation arrangement is for the carder and the drop provider to agree to resell the carded items shipped to the drop and to split the proceeds between them.
Background on the Undercover Operation
In June 2010, the FBI established an undercover carding forum called “Carder Profit” (the “UC Site”), enabling users to discuss various topics related to carding and to communicate offers to buy, sell, and exchange goods and services related to carding, among other things. Since individuals engaged in these unlawful activities on one of many other carding websites on the Internet, the FBI established the UC Site in an effort to identify these cybercriminals, investigate their crimes, and prevent harm to innocent victims. The UC Site was configured to allow the FBI to monitor and to record the discussion threads posted to the site, as well as private messages sent through the site between registered users. The UC Site also allowed the FBI to record the Internet protocol (IP) addresses of users’ computers when they accessed the site. The IP address is the unique number that identifies a computer on the Internet and allows information to be routed properly between computers.
Access to the UC Site, which was taken offline in May 2012, was limited to registered members and required a username and password to gain entry. Various membership requirements were imposed from time to time to restrict site membership to individuals with established knowledge of carding techniques or interest in criminal activity. For example, at times, new users were prevented from joining the site unless they were recommended by two existing users who had registered with the site or unless they paid a registration fee.
New users registering with the UC Site were required to provide a valid e-mail address as part of the registration process. The e-mail addresses entered by registered members of the site were collected by the FBI.
Harm Prevented by the Undercover Operation
In the course of the undercover operation, the FBI contacted multiple affected institutions and/or individuals to advise them of discovered breaches in order to enable them to take appropriate responsive and protective measures. In doing so, the FBI has prevented estimated potential economic losses of more than $205 million, notified credit card providers of over 411,000 compromised credit and debit cards, and notified 47 companies, government entities, and educational institutions of the breach of their networks.
The Charged Conduct
As alleged in the complaints unsealed today in the Southern District of New York, the defendants are charged with engaging in a variety of online carding offenses in which they sought to profit through, among other means, the sale of hacked victim account information, personal identification information, hacking tools, drop services, and other services that could facilitate carding activity.
Michael Hogue, a/k/a “xVisceral,” offered malware for sale, including remote access tools (RATs) that allowed the user to take over and remotely control the operations of an infected victim-computer. Hogue’s RAT, for example, enabled the user to turn on the web camera on victims’ computers to spy on them and to record every keystroke of the victim-computer’s user. If the victim visited a banking website and entered his or her user name and password, the key logging program could record that information, which could then be used to access the victim’s bank account. Hogue sold his RAT widely over the Internet, usually for $50 per copy and boasted that he had personally infected “50-100” computers with his RAT and that he’d sold it to others who had infected “thousands” of computers with malware. Hogue’s RAT infected computers in the United States, Canada, Germany, Denmark, Poland, and possibly other countries.
Jarand Moen Romtveit, a/k/a “zer0,” used hacking tools to steal information from the internal databases of a bank, a hotel, and various online retailers, and then sold the information to others. In February 2012, in return for a laptop computer, Romtveit sold credit card information to an individual he believed to be a fellow carder, but who, in fact, was an undercover FBI agent.
Mir Islam, a/k/a “JoshTheGod,” trafficked in stolen credit card information and possessed information for more than 50,000 credit cards. Islam also held himself out as a member of “UGNazi,” a hacking group that has claimed credit for numerous recent online hacks, and as a founder of “Carders.Org,” a carding forum on the Internet. Last night, Islam met in Manhattan with an individual he believed to be a fellow carder—but who, in fact, was an undercover FBI agent—to accept delivery of what Islam believed were counterfeit credit cards encoded with stolen credit card information. Islam was placed under arrest after he attempted to withdraw illicit proceeds from an ATM using one of the cards. Today, the FBI seized the web server for UGNazi.com and seized the domain name of Carders.org, taking both sites offline.
Steven Hansen, a/k/a “theboner1,” and Alex Hatala, a/k/a, “kool+kake,” sold stolen CVVs, a term used by carders to refer to credit card data that includes the name, address, and zip code of the card holder, along with the card number, expiration date, and security code printed on the card. Hatala advertised to fellow carders that he got “fresh” CVVs on a “daily” basis from hacking into “DBs [databases] around the world.”
Ali Hassan, a/k/a “Badoo,” also sold “fulls,” a term used by carders to refer to full credit card data including cardholder name, address, Social Security number, birthdate, mother’s maiden name, and bank account information. Hassan claimed to have obtained at least some of them by having hacked into an online hotel booking site.
Joshua Hicks, a/k/a “OxideDox,” and Lee Jason Jeusheng, a/k/a “iAlert, a/k/a “Jason Kato,” each sold “dumps,” which is a term used by carders to refer to stolen credit card data in a form in which the data is stored on the magnetic strips on the backs of credit cards. Hicks sold 15 credit card dumps in return for a camera and $250 in cash to a fellow carder who, unbeknownst to Hicks, was an undercover FBI agent. Hicks met the undercover agent in downtown Manhattan to consummate the sale. Similarly, Jeusheng sold 119 credit card dumps in return for three iPad 2s to a carder who was an undercover FBI agent. Jeusheng provided his shipping address in Japan to the undercover agent, which in part led to his identification and arrest.
Mark Caparelli, a/k/a “Cubby,” engaged in a so-called “Apple call-in” scheme in which he used stolen credit cards and social engineering skills to fraudulently obtain replacement products from Apple Inc., which he then resold for profit.The scheme involved Caparelli obtaining serial numbers of Apple products he had not bought. He would then call Apple with the serial number, claim the product was defective, arrange for a replacement product to be sent to an address he designated, and give Apple a stolen credit card number to charge if he failed to return the purportedly defective product. Caparelli sold and shipped four iPhone 4 cell phones that he had stolen through the Apple call-in scheme to an individual whom he believed to be a fellow-carder, but who, in fact, was an undercover FBI agent.
Sean Harper, a/k/a “Kabraxis314,” and Peter Ketchum, a/k/a “iwearaMAGNUM,” each sold drop services to other carders in return for money or carded merchandise. Harper provided drop addresses in Albuquerque, New Mexico, to which co-conspirators sent expensive electronics, jewelry, and clothing, among other things. Ketchum advertised drop locations “spread across multiple cities” in the United States and allegedly received and shipped carded merchandise including sunglasses and air purifiers, as well as synthetic marijuana.
Christian Cangeopol CANGEOPOL, a/k/a “404myth,” engaged in illegal “instoring” at Walmart to obtain Apple electronic devices with stolen credit cards. Instoring is a term used by carders to refer to using stolen credit card accounts to make in-store, as opposed to online, purchases of items using stolen credit card information and matching fake identifications. As part of the alleged scheme, Cangeopol and a co-conspirator used stolen credit card data to order electronic devices on Walmart’s website; in selecting a delivery option, they opted to have items delivered to various Walmart stores in Georgia; Cangeopol then picked up the items using a fake identification; Cangeopol and the co-conspirator then resold the carded electronics and split the proceeds.
* * *
The attached chart reflects the name, age, residence of, and pending charges against each individual charged in the Southern District of New York.
Mr. Bharara praised the outstanding investigative work of the FBI and its New York Cyber Crime Task Force, which is a federal, state, and local law enforcement task force combating cybercrime. Mr. Bharara also commended the U.S. Attorney’s offices in the following districts: New Mexico, Arizona, Delaware, Massachusetts, California (Central and Southern districts), Florida (Middle district), Georgia (Northern), as well as the Manhattan District Attorney’s Office. He also thanked the following domestic law enforcement partners for their assistance: the New York City Police Department; the Essex, Vermont Police Department; the Eaton, Ohio Police Department; the Butler County, Ohio Sheriff’s Office; the Cedar Bluff, Alabama Police Department; the Modesto, California Police Department; the Louisiana State Police; the Suffolk County, New York Police Department; the Bakersfield, California Police Department; the Kern County, California District Attorney’s Office; the Long Beach, California Police Department; the Louisville, Kentucky Metro Police Department; and the Nelson County, Kentucky Sheriff’s Office.
Mr. Bharara acknowledged and thanked the following international law enforcement agencies: the United Kingdom’s Serious Organised Crime Agency, Royal Military Police, Thames Valley Police, Greater Manchester Police, Leicestershire Police, Hertfordshire Police, and Wiltshire Police; the Australian Federal Police; Bosnia’s Republika Srpska Ministry of Interior; the Bulgarian Ministry of Interior, General Directorate for Combating Organized Crime; the Danish National Police; the Royal Canadian Mounted Police; the French National High-Tech Crime Unit (OCLCTIC) of the Central Directorate of the Police Judiciaire; the German Bundeskriminalamt (BKA); the Italian Polizia di Stato, Compartimento Polizia Postale e delle Comunicazioni; the National Police Agency of Japan, Tokyo Metropolitan Police Department (Cyber Crimes Control Division), Ministry of Justice of Japan, Tokyo High Prosecutors Office, and the Ministry of Foreign Affairs of Japan; the Macedonian Ministry of Interior, Department Against Organized Crime; and the Norwegian National Police for their efforts. He also thanked the Computer Crime and Intellectual Property Section of the Department of Justice, as well as the Office of International Affairs at the Department of Justice.
This case is being handled by the Office’s Complex Frauds Unit. AUSAs James Pastore, Serrin Turner, Timothy Howard, Rosemary Nidiry, Alexander Wilson, and Sarah McCallum are in charge of the prosecution.
The relevant charging documents can be found on the SDNY website at: http://www.justice.gov/usao/nys/pressreleases/index.html.
List of Arrested Defendants Charged in SDNY Complaints
|
Defendant |
SDNY Complaint Numer |
Residence |
Age |
Charges and Maximum Penalties |
| Christian Cangeopol, a/k/a “404myth” | 12 Mag. 1667 | Lawrenceville, Georgia | 19 |
|
| Mark Caparelli,
a/k/a “Cubby” |
12 Mag. 1640 | San Diego, California | 20 |
|
| Steven Hansen, a/k/a “theboner1” | 12 Mag. 1641 | Kentucky (in prison in Wisconsin) | 23 |
|
| Sean Harper, a/k/a “Kabraxis314” | 12 Mag. 1638 | Albuquerque, New Mexico | 23 |
|
| Ali Hassan, a/k/a “Mr Badoo,” a/k/a “Mr.Badoo,” a/k/a “Badoo” | 12 Mag. 1565 | Milan, Italy | 22 |
|
| Alex Hatala, a/k/a “kool+kake” | 12 Mag. 1669 | Jacksonville, Florida | 19 |
|
| Joshua Hicks, a/k/a “OxideDox” | 12 Mag. 1639 | Bronx, New York | 19 |
|
| Michael Hogue, a/k/a “xVisceral” | 12 Mag. 1632 | Tucson, Arizona | 21 |
|
| Lee Jason Juesheng, a/k/a “iAlert,” a/k/a “Jason Kato” | 12 Mag. 1605 | Tokyo, Japan | 23 |
|
| Peter Ketchum, Jr., a/k/a “iwearaMAGNUM” | 12 Mag. 1651 | Pittsfield, Massachusetts | 21 |
|
| Jarand Moen Romtveit, a/k/a “zer0,” a/k/a “zer0iq” | 12 Mag. 1656 | Porsgrunn, Norway | 25 |
|
| Mir Islam, a/k/a “JoshTheGod” | — | Bronx, New York | 18 |
|
TOP-SECRET from the FBI – Mortgage Rescue Business Owner Sentenced to 90 Months for Fraud
ALEXANDRIA, VA—Howard R. Shmuckler, 68, of Virginia Beach, Virginia, was sentenced today to 90 months in prison, followed by three years of supervised release, for running a fraudulent mortgage rescue business that received substantial fees but actually modified clients’ mortgages in only a few cases. The court ordered that this sentence be served consecutive to a 75-month federal sentence Shmuckler received on April 5, 2012 in the District of Columbia involving a counterfeit check scheme.
Neil H. MacBride, United States Attorney for the Eastern District of Virginia; James W. McJunkin, Assistant Director in Charge of the FBI’s Washington Field Office; Jon T. Rymer, Inspector General of the Federal Deposit Insurance Corporation (FDIC-OIG); and Christy Romero, Special Inspector General for the Troubled Asset Relief Program (SIGTARP); made the announcement after sentencing by United States District Judge Leonie M. Brinkema.
“Mr. Shmuckler is a cunning criminal who took advantage of distressed homeowners in desperate need of help,” said U.S. Attorney MacBride. “Today’s sentence should send a clear warning to other fraudsters of the heavy price they will pay for preying on vulnerable people looking for help to save their homes.”
“Mr. Schmuckler portrayed himself as a successful attorney and mortgage advisor who was able to rescue mortgages and provide relief to homeowners, but, in reality, he was a fraud,” said Assistance Director in Charge McJunkin. “The public should be wary of such individuals who offer a service or product that seems too good to be true. It probably is.”
“At a time when homeowners across the nation are struggling to keep their homes, Shmuckler actively targeted the most vulnerable of them with his mortgage modification scam,” said Special Inspector General Romero of SIGTARP. “Shmuckler exploited homeowners desperately seeking support through federal housing programs such as HAMP by essentially guaranteeing the homeowners mortgage modifications in exchange for an upfront fee. Shmuckler performed little, if any, service in return for the fees, and in many cases, the homeowners’ properties fell into foreclosure. SIGTARP and its partners in law enforcement will aggressively shut down these scams and hold their perpetrators accountable for their crimes.”
On April 10, 2012, Shmuckler pled guilty to six counts of wire fraud. According court records, Shmuckler, a convicted felon and disbarred attorney, owned and operated a Vienna, Virginia mortgage-rescue business known as The Shmuckler Group (TSG). From June 2008 through March 2009, TSG took in nearly $2.8 million from approximately 865 clients whose mortgages were in distress and who came to Shmuckler looking for relief. Shmuckler aggressively recruited new clients and pocketed their money while pretending he was successful, was an attorney, and that the business had restructured hundreds of mortgages, stopped hundreds of foreclosures, and negotiated hundreds of short sales. In reality, TSG was able to obtain relief for approximately 4.5 percent of its clients.
Court records indicate that Shmuckler instructed clients to terminate contact with their mortgage companies and to stop making payments to their lenders. TSG never facilitated a modification of the mortgages referenced in the statement of facts filed with his plea agreement.
This case was investigated by the FBI’s Washington Field Office, the FDIC-OIG, and SIGTARP. Assistant United States Attorneys Timothy D. Belevetz and Uzo Asonye are prosecuting the case on behalf of the United States.
A copy of this press release may be found on the website of the United States Attorney’s Office for the Eastern District of Virginia at http://www.justice.gov/usao/vae.
TOP-SECRET – DoD Report to Congress on Future Unmanned Aircraft Systems Training and Operations
The Department of Defense (DoD) continues to increase its investment in unmanned aircraft systems (UAS) to meet battlefield commanders’ demand for their unique capabilities. The emphasis on long-endurance, unmanned intelligence, surveillance and reconnaissance (ISR) assets -many with strike capabilities – is a direct reflection of recent operational experience and further Combatant Commander demands. This increase in demand has resulted in a large number of UAS capable of a wide range of missions. This large number of fielded UAS has also driven a strong demand for access within the National Airspace System (NAS). This need for airspace access to test new systems, train operators, and conduct continental United States (CONUS)-based missions has quickly exceeded the current airspace available for military operations. The situation will only be exacerbated as units return from overseas contingencies.
Currently, DoD UAS operations conducted outside of Restricted, Warning, and Prohibited areas are authorized under a temporary Certificate of Waiver or Authorization (COA) or waiver from the Federal Aviation Administration (FAA) or under limited conditions outlined in the 2007 DoD-FAA Memorandum of Agreement (MoA). DoD is actively engaged in coordinating efforts on behalf of the Military Departments and Combatant Commands to shorten and simplify the FAA COA process to allow greater unmanned access to the NAS, with direct engagement through the interagency UAS Executive Committee (Ex Com). The UAS Ex Com is a joint committee composed of senior executives from four member organizations: DoD, FAA, the Department of Homeland Security (DHS), and the National Aeronautics and Space Administration (NASA). The mission of the UAS ExCom is to enable increased and ultimately routine access of Federal UAS engaged in public aircraft operations into the NAS to support operational, training, development, and research requirements off AA, DoD, DHS, and NASA. DoD is also pursuing ground-based and airborne sense-and-avoid efforts to eventually supplant or significantly reduce the need for CO As. In the future, DoD will continue to utilize Restricted, Warning, and Prohibited areas but will also continue to develop the necessary technologies to access other airspace safely and in accordance with applicable federal aviation regulations.
This document outlines planned force capability growth and forecasted attrition of UAS aircraft through FY 2017; Military Department personnel required for training and operations; personnel and aircraft basing intentions; and required military construction (MILCON) and airspace requirements for bases hosting UAS. Within the report, the Military Departments provide current and planned inventories, personnel requirements to operate and maintain the systems, planned bases and operating locations, and progress with facilities to support inventories. Also, the report addresses the airspace integration challenge through implementation of the DoD Airspace Integration Plan, multi-agency collaboration, and ongoing negotiations with FAA. The Military Departments have a cohesive plan to address basing, funding, and manning in support of forecasted training and operations.
…
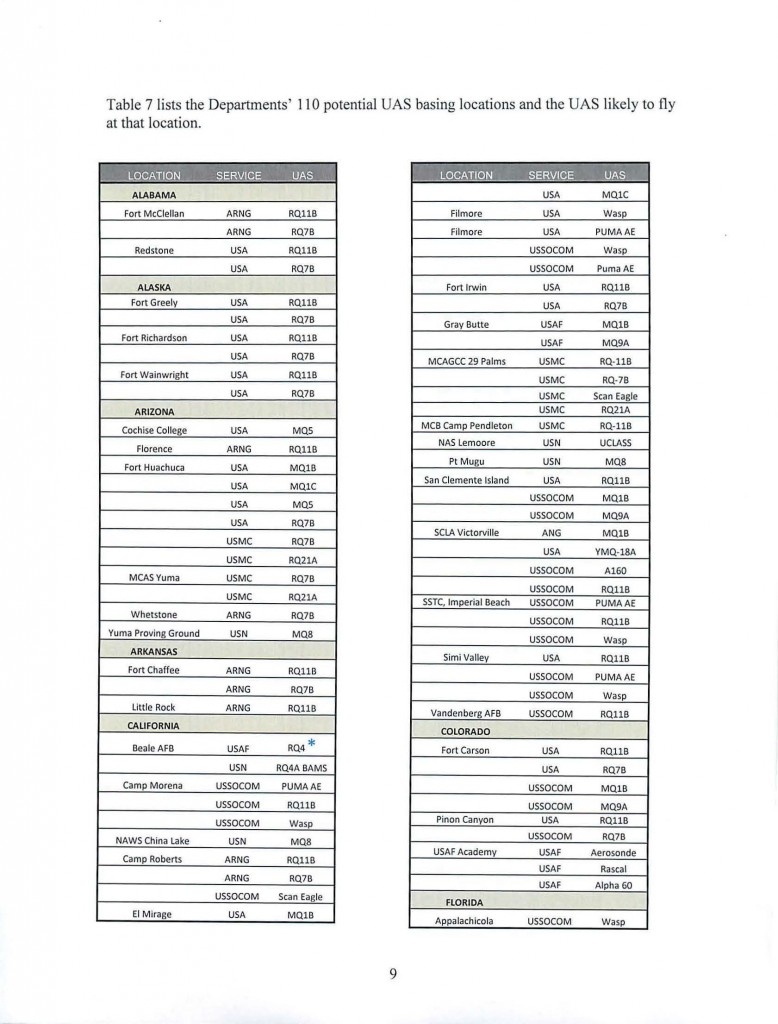
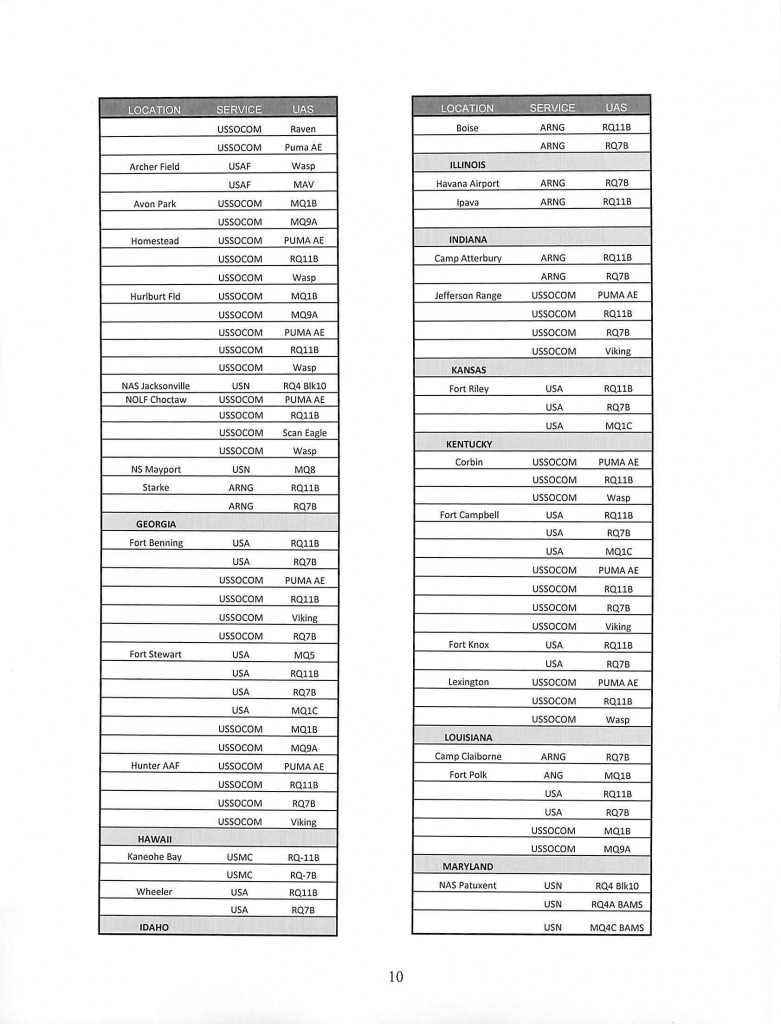
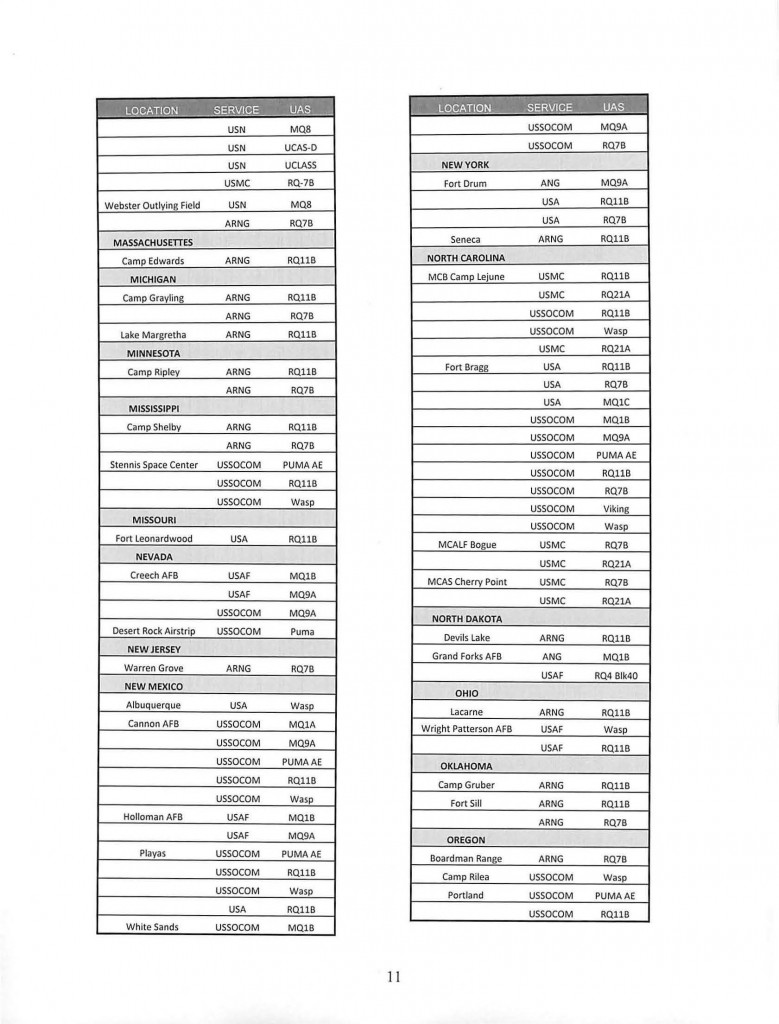
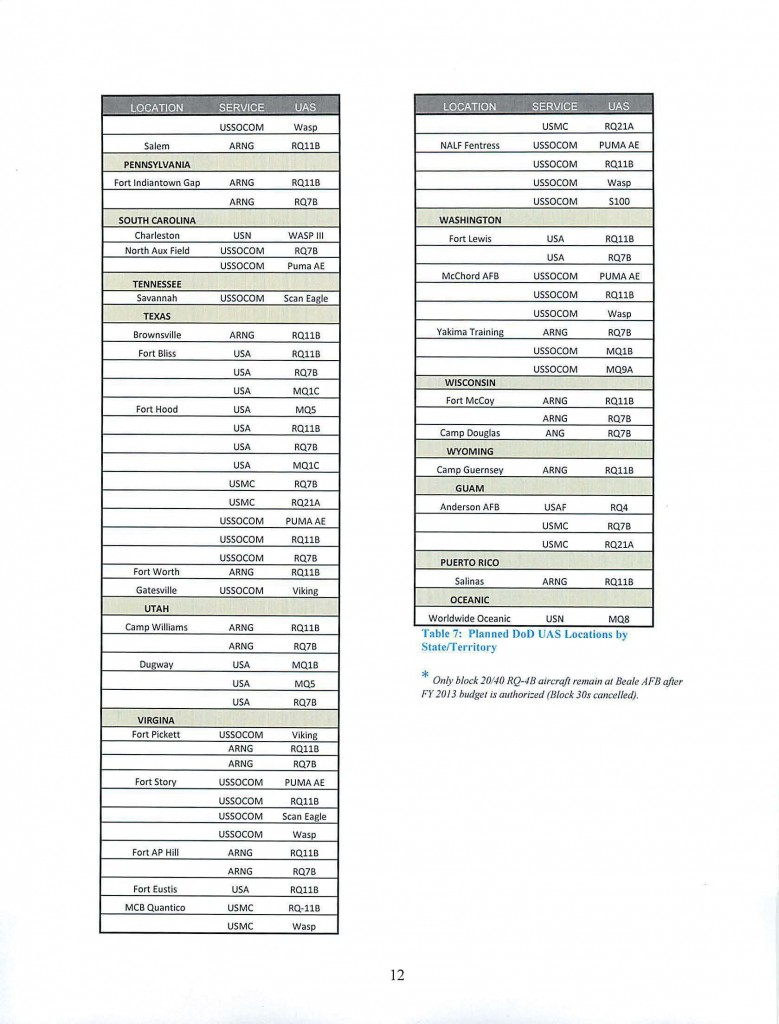
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – Former NYPD Officer Sentenced to 57 Months for Extortion and Criminal Civil Rights Violation
Earlier today, former New York City Police Officer Michael Daragjati was sentenced to nine months of imprisonment for violating the civil rights of an African-American man by falsely charging him with a crime, and a consecutive sentence of 48 months for threatening and assaulting another man whom Daragjati thought had stolen his snowplow equipment. The sentencing proceeding took place before United States District Judge William F. Kuntz, II.
The sentence was announced by Loretta E. Lynch, United States Attorney for the Eastern District of New York; Janice K. Fedarcyk, Assistant Director in Charge, Federal Bureau of Investigation, New York Field Office; and Raymond W. Kelly, Commissioner, New York City Police Department.
Daragjati was arrested on October 17, 2011 and has remained in custody since then. On January 24, 2012, Daragjati pleaded guilty to extortion and willfully violating the civil rights of the African-American victim.
As detailed in the sentencing letter filed by the government on June 20, 2012, on April 15, 2011, Daragjati falsely arrested an African-American man in Staten Island and fabricated charges against him, keeping the victim in jail for nearly two days. Soon after the incident, Daragjati was recorded telling a friend on the telephone that he had just “fried another n——-.” As also detailed in the government’s sentencing letter, on March 4, 2011, Daragjati and a group of associates assaulted and threatened a man in Staten Island in retaliation for the victim allegedly stealing Daragjati’s snowplow equipment. Daragjati later threatened to commit further acts of violence against the second victim if he went to the authorities.
“The sentence imposed today reflects the seriousness of the crimes committed by a former police officer—false arrest and imprisonment motivated by racial animus and engaging in vigilante justice. Crimes such as these erode the public’s confidence in our system of justice and will be met by the full resources of this office,” stated United States Attorney Lynch. Ms. Lynch expressed her grateful appreciation to the FBI and the NYPD Internal Affairs Bureau, the agencies responsible for leading the government’s investigation, and thanked the Richmond County District Attorney’s Office for its assistance.
The government’s case is being prosecuted by Assistant United States Attorney Paul Tuchmann.
TOP-SECRET from the NSA – Update: The Guatemalan Death Squad Diary and the Right to Truth
Washington, D.C., June 24, 2012 – On April 25, 2012, Kate Doyle, senior analyst and director of the Guatemala Documentation Project at the National Security Archive, provided expert witness testimony before the Inter-American Court of Human Rights in the case of the Diario Militar (Case 12.590, Gudiel Álvarez et al. (Diario Militar) vs. Guatemala) during the Court’s 45th Extraordinary Session held in Guayaquil, Ecuador. Doyle’s prepared testimony was followed by questioning by the Petitioners’ legal representatives, and nearly 45 minutes of questioning by the seven judges. The representatives for the State chose to not ask questions.
The following text is an excerpt of Doyle’s testimony. Slides referenced in testimony can be found in a copy of the power point presentation (9.08 MB).
25 April 2012
Guayaquil, Ecuador
To begin, the State of Guatemala has systematically hidden the information in its power about the internal armed conflict. The Guatemalan Army, the Police and the intelligence services are intrinsically opaque, secretive and closed institutions, and it has been almost impossible to gain access to their records. This policy of silence has survived the peace accords; it has survived the Historical Clarification Commission; and it continues today – despite the discovery of archives, the exhumations of clandestine cemeteries, the criminal convictions of perpetrators of human rights violations, and the unceasing demand for information by families of the disappeared.
In the 1980s, the State’s counterinsurgency strategy to kidnap, secretly detain, torture and execute men and women because of their political activities mobilized family members desperate to learn of the whereabouts of their loved ones. [SLIDE 1] They not only searched in hospitals, jails, cemeteries and morgues; they also directly confronted military officials and the chief of State. But the response was always the same: silence, ridicule, threats or worse.
That was also the experience of the Historical Clarification Commission (Comisión para el Esclarecimiento Histórico-CEH), [SLIDE 2], which from its earliest days tried to obtain information from State security agencies, but without success. I worked in collaboration with the commissioners and was witness to their frustration before the government’s repeated refusals to provide access to their archives. It had such an impact that in the final (twelfth) volume of their report the CEH reproduced dozens of letters between the three commissioners and the high command of the security institutions; letters that capture their exasperation in trying to obtain documents. [SLIDE 3] The letters also capture the implacable response of the authorities: No. There were no documents, documents did not exist, they had been destroyed, they had been lost, or they remained under the seal of national security.
During the very same week in which the CEH report was made public, in February 1999, the Military Logbook appeared. [SLIDE 4] The document was turned over to me and I made it public three months later in a press conference in Washington. It was exactly the kind of information sought repeatedly by the CEH, without success.
It was not until four years later that the first records of the Guatemalan Army emerged, with the dismantling of the Presidential General Staff ( Estado Mayor Presidencial-EMP) in 2003. It was a purged and fragmentary collection, and only recovered through the efforts of non-governmental organizations that insisted on copying them. Later the Human Rights Ombudsman (Procurador de Derechos Humanos-PDH) asked my organization to create a data base of the documents in order to facilitate access to them, but as far as I know there is still no public access to the database or the documents themselves.
We had our first real glimpse inside the State security apparatus during the conflict when the archives of the National Police were discovered in 2005. In fact employees of the PDH found them by accident during a visit to a police base in Guatemala City. [SLIDE 5] The accumulation of millions of pages of records was in a condition of extreme deterioration and abandon, hidden inside poorly maintained storage spaces. But after years of work to rescue, clean, organize and scan the documents, the archive is now fully accessible to the Guatemalan public without limit or restriction.
The Historical Archive of the National Police (Archivo Histórico de la Policía Nacional-AHPN) represents the entire documentary history generated by the National Police during more than 100 years. It contains an estimated eight linear kilometers of paper, videos, audiotapes, photographs, license plates, books and the ephemera of the revolutionary groups. Within the collection is every type of documentation: military and police plans for counterinsurgency operations [SLIDE 6], orders from the Director, political files on individuals [SLIDE 7], surveillance reports, interrogation transcripts [SLIDE 8], habeas corpus requests, telegrams, daily reports, circulars – many with the names and signatures of the officers in charge [SLIDE 9]. In short, it represents all of the paper necessary in order to make possible the flow of communications among the different National Police corps, and between the Police and other entities of the State, including the chief of State and the Army. To date, 2,530 documents have been found inside the AHPN with a direct relation to the captures registered in the Military Logbook.
Before the discovery of the archives, neither the families of the disappeared nor the CEH received a single page of these documents, despite their petitions to the State.
Today the Guatemalan Army’s policy of access regarding its own records continues to be a policy of denial. In 2009, the Defense Ministry responded to a judicial order that required it to produce four military documents as evidence in the genocide case, but it turned over only one complete record. The Ministry alleged that the others – including a key set of records relating to the 1982 counterinsurgency sweep called “Operation Sofía” – did not exist in its archives [SLIDE 10].
One month later, a person who requested anonymity gave me a package that contained the Operation Sofía documents, which I subsequently turned over to the Guatemalan Public Ministry. And that is how, in a national judicial process concerning crimes against humanity initiated in 2001, the petitioners did receive a Guatemalan document containing critical evidence – not from the institutions of the State that created it, but through my organization, a non-governmental group based in the United States.
Most recently, the Army responded to society’s demand for truth by opening a collection of “military archives” in June 2011. I have studied the archive – an unnecessarily difficult task, due to the lack of any index or guide – and I see no relevance in the documents to the study of the armed conflict. It is an apparently arbitrary collection, without any evident or transparent logic to its declassification, which contains thousands of pages of trivial and useless records that do not serve human rights investigators. Furthermore, according to the Ministry of Defense, there are no declassified records in the archive covering the most repressive period of the internal conflict, 1980-85.
The Army’s posture – and the legacy of silence about historic repression on the part of the State – has left survivors of the conflict and the family members of victims with less than nothing, with expectations raised by a peace process that to date has not resulted with the fundamental information they require: What happened and why? Who is responsible? And where are the disappeared?
Thank you.
Watch the recording of the Diario Militar hearing in three parts here, (in Spanish):
TOP-SECRET – DHS-FBI Bulletin: Terrorist Interest in Attacking Theaters and Mass Gatherings
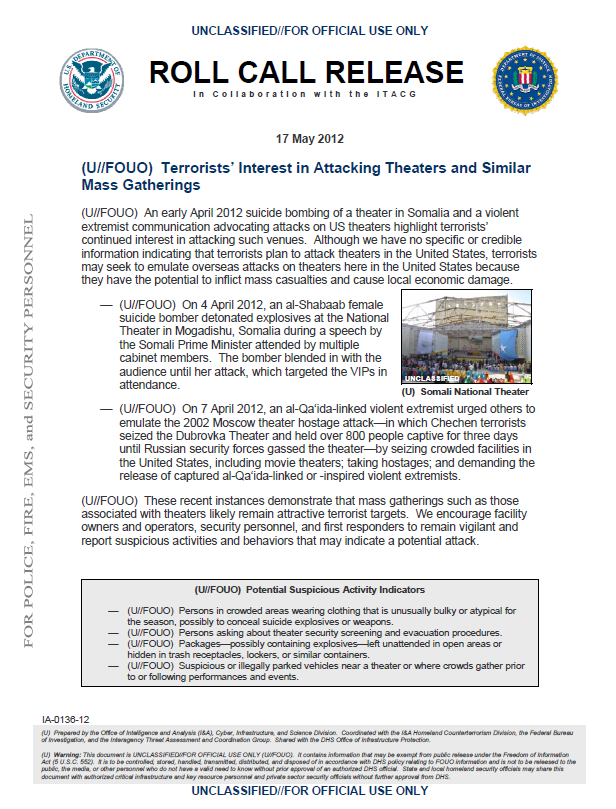
(U//FOUO) An early April 2012 suicide bombing of a theater in Somalia and a violent extremist communication advocating attacks on US theaters highlight terrorists’ continued interest in attacking such venues. Although we have no specific or credible information indicating that terrorists plan to attack theaters in the United States, terrorists may seek to emulate overseas attacks on theaters here in the United States because they have the potential to inflict mass casualties and cause local economic damage.
— (U//FOUO) On 4 April 2012, an al-Shabaab female suicide bomber detonated explosives at the National Theater in Mogadishu, Somalia during a speech by the Somali Prime Minister attended by multiple cabinet members. The bomber blended in with the audience until her attack, which targeted the VIPs in attendance.
— (U//FOUO) On 7 April 2012, an al-Qa‘ida-linked violent extremist urged others to emulate the 2002 Moscow theater hostage attack—in which Chechen terrorists seized the Dubrovka Theater and held over 800 people captive for three days until Russian security forces gassed the theater—by seizing crowded facilities in the United States, including movie theaters; taking hostages; and demanding the release of captured al-Qa‘ida-linked or -inspired violent extremists.
(U//FOUO) These recent instances demonstrate that mass gatherings such as those associated with theaters likely remain attractive terrorist targets. We encourage facility owners and operators, security personnel, and first responders to remain vigilant and report suspicious activities and behaviors that may indicate a potential attack.
(U//FOUO) Potential Suspicious Activity Indicators
— (U//FOUO) Persons in crowded areas wearing clothing that is unusually bulky or atypical for the season, possibly to conceal suicide explosives or weapons.
— (U//FOUO) Persons asking about theater security screening and evacuation procedures.
— (U//FOUO) Packages—possibly containing explosives—left unattended in open areas or hidden in trash receptacles, lockers, or similar containers.
— (U//FOUO) Suspicious or illegally parked vehicles near a theater or where crowds gather prior to or following performances and events.
TOP-SECRET – Open Source Center Master Narratives Report: Muslim Communities of France
Understanding master narratives can be the difference between analytic anticipation and unwanted surprise, as well as the difference between communications successes and messaging gaffes. Master narratives are the historically grounded stories that reflect a community’s identity and experiences, or explain its hopes, aspirations, and concerns. These narratives help groups understand who they are and where they come from, and how to make sense of unfolding developments around them. As they do in all countries, effective communicators in France speaking to Muslim communities invoke master narratives in order to move audiences in a preferred direction. French influencers rely on their native familiarity with these master narratives to use them effectively. This task is considerably more challenging for US communicators and analysts because they must place themselves in the mindset of foreign audiences who believe stories that — from an American vantage point — may appear surprising, conspiratorial, or even outlandish.
This report serves as a resource for addressing this challenge in two ways. First, it surfaces a set of nine master narratives carefully selected based on their potency in the context of France’s Muslim communities, and their relevance to US strategic interests. Second, this report follows a consistent structure for articulating these narratives and explicitly identifies initial implications for US communicators and analysts. The set outlined here is not exhaustive: these nine master narratives represent a first step that communicators and analysts can efficiently apply to the specific messaging need or analytic question at hand. For seasoned experts on French Muslim communities, these narratives will already be familiar — the content contained in this report can be used to help check assumptions, surface tacit knowledge, and aid customer communications. For newcomers to European Islam accounts, these narratives offer deep insights into the stories and perceptions that shape French Muslim identity and worldviews that may otherwise take years to accumulate.
Some master narratives cut across broad stretches of the French Muslim populace, while others are held only by particular audience sub-segments. This study divides France’s Muslim communities into eight audience sub-segments that demonstrate how different master narratives resonate with different sections of the populace. Each of the nine master narratives aligns with one or more of the following segments: Cultural Muslims, Personal Practitioners, Civic Islamists, Wealthy Secularists, Old Guard, Strict Practitioners, Young Banlieuesards, and Indigènes (see the Appendix for a detailed description of these audience segments).
…
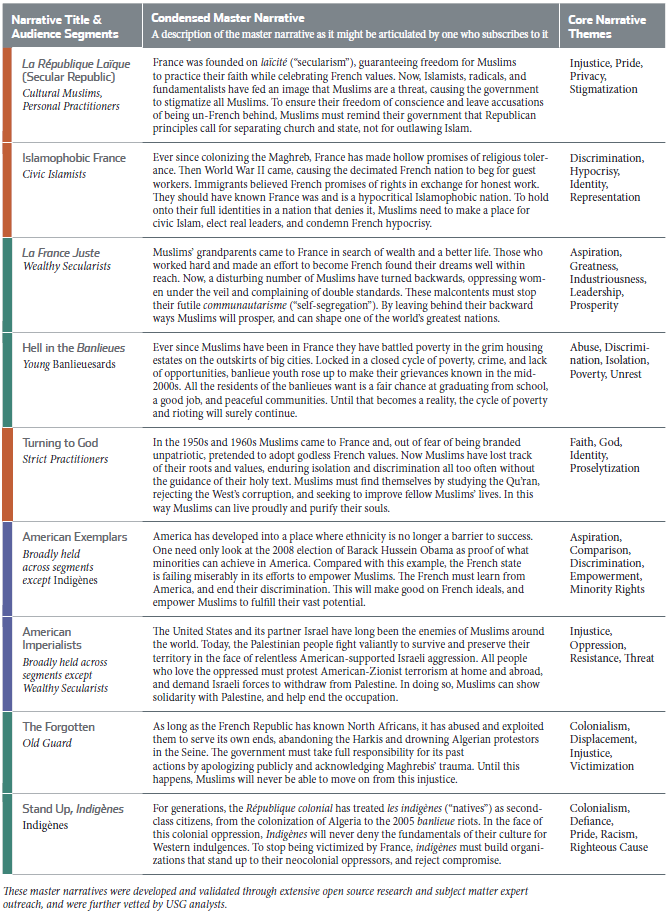
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – Open Source Center Master Narratives Country Report: Somalia
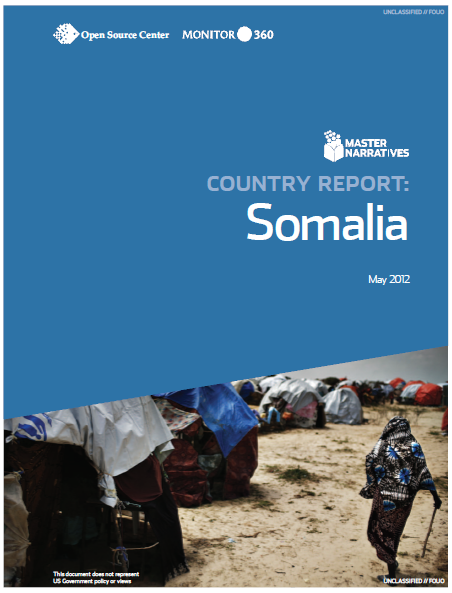
Understanding master narratives can be the difference between analytic anticipation and unwanted surprise, as well as the difference between communications successes and messaging gaffes. Master narratives are the historically grounded stories that reflect a community’s identity and experiences, or explain its hopes, aspirations, and concerns. These narratives help groups understand who they are and where they come from, and how to make sense of unfolding developments around them. As they do in all countries, effective communicators in Somalia invoke master narratives in order to move audiences in a preferred direction. Somali influencers rely on their native familiarity with these master narratives to use them effectively. This task is considerably more challenging for US communicators and analysts because they must place themselves in the mindset of foreign audiences who believe stories that — from an American vantage point — may appear surprising, conspiratorial, or even outlandish.
This report serves as a resource for addressing this challenge in two ways. First, it surfaces a set of eight master narratives carefully selected based on their potency in the Somali context and relevance to US strategic interests. Second, this report follows a consistent structure for articulating these narratives and explicitly identifies initial implications for US communicators and analysts. The set outlined here is not exhaustive: these eight master narratives represent a first step that communicators and analysts can efficiently apply to the specific messaging need or analytic question at hand. For seasoned Somali experts, these narratives will already be familiar — the content contained in this report can be used to help check assumptions, surface tacit knowledge, and aid customer communications. For newcomers to Somalia accounts, these narratives offer deep insights into the stories and perceptions that shape the Somali political context that may otherwise take years to accumulate.
Some master narratives cut across broad stretches of the Somali populace, while others are held only by particular audience segments. This study divides Somalia into six audience segments that demonstrate how different master narratives resonate with different sections of the populace. Each of the eight master narratives aligns with one or more of the following segments: Centralists, Regionalists, Somaliland Nationalists, Salafi Islamists, Sufi Islamists, and Moderate Islamists. (See the Appendix for a detailed description of these audience segments.) This audience segmentation is tailored specifically to surface important Somali master narratives and the interactions between them. Somali society is heavily influenced by longstanding clan structures, with some clan affiliations creating intractable intergroup conflict while other affiliations are more fluid in response to shifting political priorities. Some of the master narratives profiled in this report are deeply informed by clan dynamics, while others transcend clan allegiances altogether. Based on this, the audience segmentation is this report provides an additional lens for understanding competing and interconnected camps in Somali politics and society.
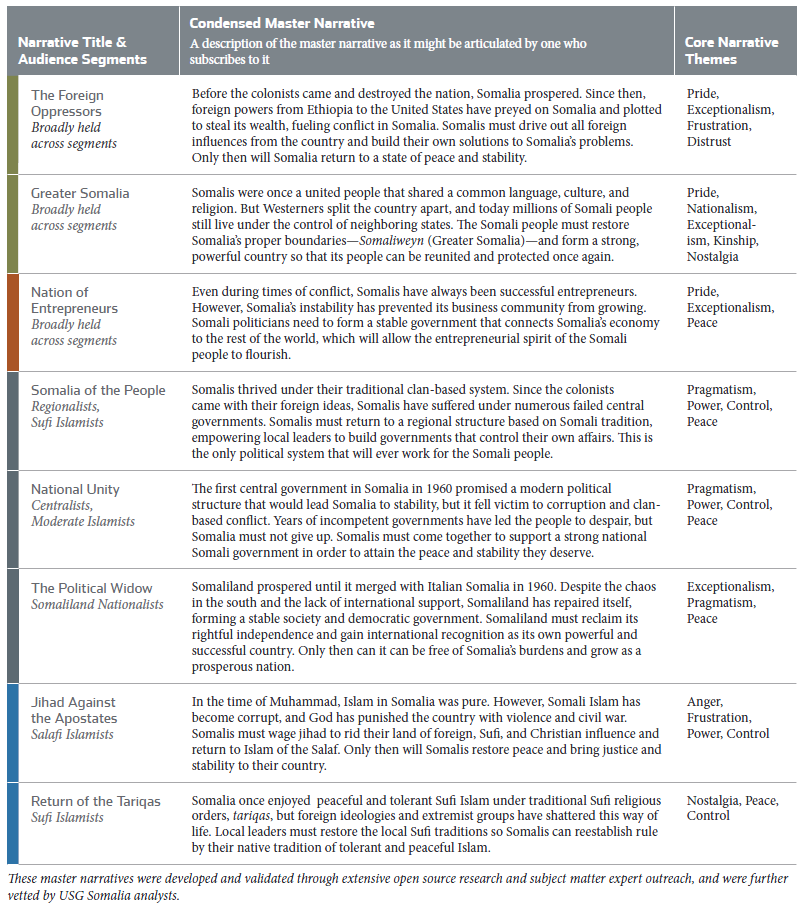
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET from the FBI – Texas Man Indicted for Threatening to Bomb Islamic Center in Murfreesboro
WASHINGTON—Javier Alan Correa, 24, of Corpus Christi, Texas, was indicted by a federal grand jury in Nashville, Tennesee, today and charged with violating the civil rights of members of a Murfreesboro, Tennessee mosque. Correa is charged in the Middle District of Tennessee with one count of intentionally obstructing by threat of force the free exercise of religious beliefs and one count of using an instrument of interstate commerce to communicate a threat to destroy a building by means of an explosive device. The indictment was announced today by Assistant Attorney General Thomas E. Perez for the Civil Rights Division; Jerry E. Martin, U.S. Attorney for the Middle District of Tennessee; and Aaron T. Ford, Special Agent in Charge of the Memphis Division of the FBI.
According to the indictment, on September 5, 2011, Correa called on a cell phone from Corpus Christi to the Islamic Center of Murfreesboro and left a threatening, explicative-ridden voice message saying, amongst other things, “On September 11, 2011, there’s going to be a bomb in the building.“
“The Department of Justice, the FBI, and our law enforcement partners intend to protect the rights afforded under the Constitution to all individuals, including the most basic right to exercise freedom of religious beliefs,” said Jerry E. Martin, U.S. Attorney of the Middle District of Tennessee. “The controversy and criminal activity surrounding the construction of this particular place of worship has impeded the ability of people to exercise that most basic right. We will continue to monitor the progress of construction and legal proceedings at the local level to insure these citizens are able to enjoy all basic liberties guaranteed under the Constitution.”
“The FBI is tasked with defending civil rights in the United States and takes very seriously its responsibilities to protect people of all religions from intimidation and violence,” said Aaron T. Ford, Special Agent in Charge of the Memphis Division of the FBI. “The FBI and our law enforcement partners pursued this investigation with great tenacity and will always strive to ensure those who attempt to take religious freedoms from others are brought to face justice.”
Correa faces a maximum penalty of 20 years for the count one and 10 years for count two of the indictment, as well as a fine of up to $250,000 for each offense.
This case was investigated by the FBI and is being prosecuted by Assistant U.S. Attorney Lee Deneke and Civil Rights Division Trial Attorney Adriana Vieco.
An indictment is merely an accusation. All persons are presumed innocent unless and until proven guilty and have the right to a trial, at which, the government must bear the burden of proof beyond a reasonable doubt.
TOP-SECRET – Public Intelligence – ITU CWG-WCIT12 US Comments on Draft Proposals
The following document details comments of the U.S. delegation on a compilation of draft proposals for modifications to International Telecommunications Regulations (ITRs) under the International Telecommunication Union. The collection of draft proposals being commented on CWG-WCIT12 TEMPORARY DOCUMENT 36 (CWG-WCIT12/TD – 36) is also available.
| CWG-WCIT12 CONTRIBUTION 45 (CWG-WCIT12/C – 45) “U.S. comments on Temporary Document 36″ | 65 pages | August 24, 2011 | Download |
TOP-SECRET from the FBI – Another Assault Linked to Potomac River Rapist
he Metropolitan Police Department announced today that forensic evidence from a sexual assault that occurred on July 20, 1996 in the 4900 block of MacArthur Boulevard, NW has been linked to other sexual assaults and a murder committed by a single assailant who attacked women in the Washington, DC metropolitan area.
“We are asking for the public’s help in identifying and locating this violent offender who is responsible for numerous brutal attacks,” said Police Chief Cathy L. Lanier.
The Potomac River Rapist is wanted for a total of ten sexual assaults that occurred between May 1991 and August 1998, one of which resulted in a homicide in Washington, DC.
On August, 1, 1998, Christine Mirzayan, a 28-year-old intern, was sexually assaulted and murdered while walking to her residence in the Georgetown area. During the violent attack, she was struck multiple times in the head with a rock and her body was left yards from Canal Road. The other eight sexual assaults occurred in Montgomery County, Md.
“The 1996 assault in the 4900 block of MacArthur Boulevard, NW and the murder in 1998 occurred less than two miles apart – which could indicate that the offender may have ties to this area,” said Chief Lanier.
The case is being investigated by the Metropolitan Police Department, Montgomery County, Md., Police Department, and the FBI’s Washington Field Office with assistance from the U.S. Attorney’s Office for the District of Columbia.
In the 1996 assault, the subject is described as a black or black/Hispanic male, with a light to medium complexion and high, pronounced cheekbones.
Throughout the entire investigation, he has been described as being approximately 5’8” – 6’0” in height, with a muscular build, especially in his upper body. The individual was in his late 20s to early 30s at the time of the offenses. He was wearing a polo-type shirt and khaki pants, and has been described as neatly attired.
Most of the Maryland assaults followed a particular pattern. The assailant used a “blitz” attack by throwing a blanket or towel over the victim’s head. All of the sexual assault victims, with the exception of the Washington, DC attacks, were attacked in their homes or private residences. Both the DC sexual assault and murder victims were walking on sidewalks when they were pulled into wooded areas and sexually assaulted on a Saturday night.
The dates and locations of these assaults are:
|
Date |
Approximate Time |
Subdivision |
Location |
| Monday, May 6, 1991 | 8:00 p.m. – 11:00 p.m. | Washingtonian Woods | Gaithersburg, Md. |
| Thursday, Sept. 5, 1991 | 10:00 p.m. – 10:30p.m. | Watkins Meadows | Germantown, Md. |
| Thursday, Nov. 21, 1991 | 9:00 p.m. – 10:00 p.m. | Potomac Village/Downtown | Bethesda, Md. |
| Wednesday, Dec. 11, 1991 | 8:30 p.m. – 9:00 p.m. | Quince Orchard Knolls | North Potomac, Md. |
| Friday, Jan. 24, 1992 | 9:00 p.m. | Potomac Grove | North Potomac, Md. |
| Tuesday, March 8, 1994 | 7:00 p.m. – 8:00 p.m. | Highwood | Rockville, Md. |
| Saturday, July 20, 1996 | 8:30 p.m. – 8:45 p.m. | 4900 block of MacArthur Boulevard, NW | Washington, DC |
| Wednesday, Feb. 26, 1997 | 7:00 p.m. – 8:00 p.m. | Rock Creek Manor | Rockville, Md. |
| Friday, Nov. 14, 1997 | 7:30 p.m. – 8:00 p.m. | New Hampshire Avenue/Rt. 198 | Silver Spring, Md. |
| Saturday, Aug. 1, 1998 | 10:30 p.m. – 11:00 p.m. | 3600 block Canal Road, Georgetown | Washington, D.C. |
The public is asked to review the information and consider whether they know someone who generally fits this description, who lived or had ties to the area around the times of the assaults or who may have been known to spend considerable amounts of time in those areas.
People who know the suspect may not believe that he is capable of committing these crimes. He may not necessarily have a violent criminal history. Because investigators are in possession of DNA evidence that can either positively link the suspect to his crimes or exclude innocent parties, citizens should not hesitate to provide information, even if it is just the name of a potential suspect.
Law enforcement agencies are asking anyone with information to contact MPD at (202) 727-9099 or the FBI at 1-800-CALL-FBI (1-800-225-5324). Additionally, anonymous information may be submitted to the police department’s TEXT TIP LINE by text messaging 50411.
For more information about this investigation, go to http://fbi.gov/potomacriverrapist.
Composites below are of the same assailant from two separate incidents.
TOP-SECRET from the FBI – Hogsett Announces 30-Year Sentence for Woman Guilty of Production of Child Pornography
EVANSVILLE—“As a prosecutor, and as a parent, it is difficult to put into words damage done as a result of the horrific acts committed by these two people,” said Joseph H. Hogsett, the United States Attorney, while announcing today that Emma Dell Hodge, age 44, of Evansville, was sentenced to 30 years in prison this morning by Chief United States District Judge Richard L. Young. This follows Ms. Hodge’s May 2, 2012 guilty plea to the charges of production of sexually explicit material involving minors and conspiracy to produce sexually explicit material involving minors. Today’s decision also follows the sentencing of Larry Everett Hodge, Ms. Hodge’s spouse, to 115 years in prison several weeks ago.
“Our hope is that through this prosecution and the sentences handed down by Judge Young, justice has been given to the young victim in this case and the healing process can begin,” Hogsett stated.
In November 2010, the Evansville Police Department responded to a report of child abuse from a concerned individual who had been sent images depicting the sexual abuse of a minor on her cell phone. That individual indicated that she had received the images from Larry Everett Hodge. Child abuse detectives were contacted to initiate an investigation.
Detectives went to the Hodge residence to speak with the couple, at which point it was immediately apparent that both knew about the abuse of the child, later identified as an 8-year-old female. Larry Hodge admitted in an interview with law enforcement that he had engaged in oral sex with the victim and was arrested on charges of child molestation.
The full extent of the abuse was later established during an examination of a Memorex data storage disc taken during a search of the Hodge residence. Agents identified at least seven separate digital photography sessions and two videos that were saved on the disc by Larry Hodge, all of which depicted sexual abuse of the minor. Some of the videos and images depicted sexual abuse by Larry Hodge himself, while others depicted sexual abuse by Emma Dell Hodge.
Further investigation revealed that the couple had gained access to the child by volunteering to assist the child’s parents by caring for the child after school and at various other times. Larry Hodge has also admitted to distributing the images and videos of the victim to a co-defendant, George K. Jackson. A sentencing hearing in the matter of Jackson is expected later today before Judge Young.
According to Assistant U.S. Attorney Todd S. Shellenbarger, who prosecuted the case for the government, Chief Judge Young also imposed lifetime supervision following Emma Hodge’s release from prison. During the period of supervised release, Hodge must comply with all sex offender registration laws, must not have unsupervised contact with minors, and must submit to an examination of any computer devices she uses.
This case was the result of an investigation by the Evansville Police Department and the Federal Bureau of Investigation and was brought as part of the U.S. Attorney’s Project Safe Childhood, a nationwide initiative launched in May 2006 by the Department of Justice to combat the growing epidemic of child sexual exploitation and abuse.
Led by the United States Attorneys’ Offices and the Criminal Division’s Child Exploitation and Obscenity Section, Project Safe Childhood marshals federal, state, and local resources to locate, apprehend, and prosecute individuals who sexually exploit children, and to identify and rescue victims. For more information about Project Safe Childhood, please visit http://www.usdoj.gov/psc.
TOP-SECRET from the FBI – Second Recruiter Convicted in City Nursing Scheme
HOUSTON—Gwendolyn Kay Frank, 43, of Houston, has entered a plea of guilty to conspiracy to violate the Anti-Kickback Statue for her role in role in the $45 million City Nursing health care scandal, United States Attorney Kenneth Magidson announced today.
The Anti-Kickback Statute prohibits referring beneficiaries to business that bill federal health care programs in return for payments. According to the plea agreement, Frank referred at least 28 Medicare beneficiaries to the owner of City Nursing in return for $24,500. City Nursing then billed Medicare for approximately $1,051,392 worth of services for those individuals which were not provided and received $712,052 in payments from Medicare and Medicaid.
Frank is the second recruiter to plead guilty to conspiracy to violate the Anti-Kickback Statue this month and one of a growing list of individuals convicted in the Houston-based City Nursing health care fraud conspiracy. Floyd Leslie Brooks, 45, of Houston, pleaded guilty earlier this month. The owner of City Nursing, Umawa Oke Imo, was convicted in May 2011 and sentenced to more than 27 years in federal prison for his role in the health care fraud conspiracy which included making cash payments to both Medicare beneficiaries and recruiters bringing Medicare beneficiaries to City Nursing.
Frank was permitted to remain on bond pending her sentencing hearing, set for September 14, 2012. At that time, she faces up to five years in prison and a $250,000 fine.
This case has been investigated by the FBI, Internal Revenue Service-Criminal Investigations, the Department of Health and Human Services-Office of Inspector General and the Texas Attorney General’s Office-Medicare Fraud Control Unit. Assistant United States Attorney Julie Redlinger is prosecuting the case.
TOP-SECRET from Public Intelligence – ITU CWG-WCIT12 Draft Compilation of Proposals/Options
The following documents are compilations of draft proposals for modifications to International Telecommunications Regulations (ITRs) under the International Telecommunication Union. The current version of the proposed changes to the ITRs (CWG-WCIT12 Temporary Document 64) was recently leaked in response to a lack of publicly available information on the proposals. These documents help to provide background and context on the development of the current proposal.
| CWG-WCIT12 TEMPORARY DOCUMENT 43 (CWG-WCIT12/TD – 43) “Draft compilation of options” | 137 pages | November 24, 2011 | Download |
| CWG-WCIT12 TEMPORARY DOCUMENT 36 (CWG-WCIT12/TD – 36) “Draft compilation of proposals” | 53 pages | June 13, 2011 | Download |
TOP-SECRET – Restricted U.S. Army Psychological Operations Process Tactics, Techniques, and Procedures Manual
Field Manual (FM) 3-05.301 describes the tactics, techniques, and procedures (TTP) for the implementation of United States (U.S.) Army Psychological Operations (PSYOP) doctrine presented in the higher-level publication, FM 3-05.30, Psychological Operations. FM 3-05.301 provides general guidance for commanders, staffs, and Soldiers who plan and conduct PSYOP across the range of military operations. The TTP in this manual are presented within the framework of the seven-phase PSYOP process, a mainstay for effective PSYOP executed at the tactical, operational, and strategic levels.
FM 3-05.301 is the principal reference for the PSYOP process. The contents of this manual supersede the discussion of the PSYOP process in FM 3-05.302, Tactical Psychological Operations Tactics, Techniques, and Procedures (28 October 2005). Any mention of the PSYOP process in other preceding doctrine or training literature should be validated by the contents of FM 3-05.301. This manual incorporates updated organizational structures, terminology, and capabilities to provide PSYOP Soldiers with the latest guidance to support a broad range of missions. This manual describes procedures and strategies derived from applied scientific and academic disciplines in an effort to improve the efficacy of the PSYOP process. These TTP are designed to facilitate the successful execution of each phase of the process: planning; target audience analysis; series development; product development and design; approval; production, distribution, and dissemination; and evaluation.
The PSYOP community, in general, is the intended audience for this manual. Members of the tactical, regional, and dissemination PSYOP battalions should find the information particularly useful. Written to give PSYOP officers, noncommissioned officers (NCOs), enlisted Soldiers, and civilians standardized PSYOP doctrine, FM 3-05.301 is a comprehensive how-to guide that focuses on critical PSYOP tasks, duties, and responsibilities.
…
Behavior Modification
2-58. Behavior can be modified by changing the conditions or situations that lead up to the TA’s current behavior. Behavior can also be modified by the manipulation of the consequences of the TA’s current behavior or by introducing new consequences (rewards and punishments) a TA receives for engaging in a behavior.
2-59. Decreasing a behavior involves devaluing or reducing the positive consequences and increasing the value of the negative consequences a TA receives. Removing something desirable or pleasant to a TA that is currently reinforcing a behavior, or introducing something into the TA’s environment that it finds unpleasant, are ways of decreasing a behavior.
2-60. Increasing a behavior involves increasing the value of the positive consequences and decreasing the value of the negative consequences a TA receives. Introducing or emphasizing things in the TA’s environment that are desirable or pleasant when it engages in the desired behavior, or removing things that are unpleasant when it engages in the desired behavior, are ways of increasing a behavior.
…
Psychographics
2-66. Psychographics are psychological characteristics of a TA. These are internal psychological factors— attitudes, values, lifestyles, motivations, and opinions. Psychographics might include characteristics such as fears, loves, hates, cultural norms, and values. Psychographics are vulnerabilities because they provoke an emotional response from the TA that can be used to increase the effectiveness of a PSYOP argument or PSYACT. Although often difficult to derive from standard intelligence and open sources, they can prove to be very effective in persuasion.
2-67. Psychographics include the following:
• Fears: What does the TA fear?
• Hates: What does the TA hate?
• Anger: What angers the TA?
• Loves: What does the TA love?
• Shame or embarrassment: What does the TA consider shameful or embarrassing?
• What is the TA dissatisfied with? (What are its gripes?)
• What are the cultural norms? (How is the TA expected to act?)
• What does the TA value? (What is important to the TA?)
• What are the frustrations? (What does the TA want that it cannot get?)Some examples of psychographics include the following:
• Green Tribe fighters have a very acute fear of fire/being burned alive based upon past experiences while fighting the Ruskinian Army in the 1980s. The Ruskinians used incendiaries, to include napalm, on Green Tribe positions.
• TA considers any effeminate characteristics/actions by males to be very shameful/embarrassing. These actions include crying, caring for children, housework, and physical displays of affection, such as holding hands and hugging between men.
• Male members of the TA are expected to work outside the home and provide for their immediate family and often other elderly/infirm members of their extended family.
• Red Tribesmen in the Birmingville area are highly dissatisfied with the perceived lack of progress on the electrical distribution system in the city.
• TA places a high value on education and will make great sacrifices to ensure the best education for its children.…
Appeals
2-95. An appeal is the overall approach used to present the main argument. It is the flavor or tone of the argument. Appeals gain the TA members’ attention and maintain their interest throughout the argument. Appeals are selected based upon the conditions and vulnerabilities of the TA. For example, a TA that does not believe the government of its country is legitimate will not be swayed by an appeal to legitimacy, whereas a military TA may be greatly affected by an appeal to authority. The following is a list of general persuasive appeals commonly used in PSYOP:
• Legitimacy.
• Inevitability.
• In group-out group.
• Bandwagon.
• Nostalgia.
• Self-interest (gain/loss).2-96. Legitimacy appeals use law, tradition, historical continuity, or support of the people. The following are types of legitimacy appeals:
• Authority: An appeal to laws or regulations, or to people in superior positions in the social hierarchy. For example, the Uniform Code of Military Justice, NCOs and officers, police officers, parents, or government officials. The TA must recognize the authority for the appeal to work.
• Reverence: An appeal to a belief-teaching institution or individual that is revered or worshiped; for example, the Dalai Lama, the Roman Catholic Church, or even a sports figure such as Michael Jordan.
• Tradition: An appeal to that which the TA is already used to. It is behavior that is repeated continually without question. Why do people have turkey on Thanksgiving? Because it has always been that way.
• Loyalty: An appeal to groups to which the TA belongs. Examples are military units, family, or friends. This appeal is usually used to reinforce behavior that already occurs.2-97. Inevitability appeals most often rely on the emotion of fear, particularly fear of death, injury, or some other type of harm. For example, if a person does not surrender, he will die, or if a person does not pay his taxes, he will go to jail. It can also be an appeal to logic. Both require proof that the promised outcome will actually occur. Therefore, it is crucial that credibility be gained and maintained throughout
the argument.2-98. An in group-out group appeal seeks to divide a TA or separate two TAs. It creates an enemy of one group, and encourages the other group to rebel/discriminate against them. This appeal frequently points out major differences between TAs, or factions of a TA. If PSYOP cannot effectively portray the in group in a negative manner, the appeal will fail.
2-99. Bandwagon appeals play upon the TA’s need to belong or conform to group standards. The two main types of bandwagon appeal are an appeal to companionship and an appeal to conformity. Peer pressure is an example of the conformity type of bandwagon appeal.
2-100. Nostalgia appeals refer to how things were done in the past. This appeal can be used to encourage or discourage a particular behavior. In a positive light, it refers to the “good old days” and encourages the TA to behave in a manner that will return to those times. In the negative, it points out how things were bad in the past and how a change in behavior will avoid a repeat of those times.
2-101. Self-interest appeals are those that play directly to the wants and desires of the individuals that make up a TA. This type of appeal can play upon the TA’s vulnerability for acquisition, success, or status. A self-interest appeal can be presented in the form of a gain or loss. An appeal to loss would be exploiting the fact that if the TA does not engage in the desired behavior, PSYOP cannot satisfy a want. An appeal to gain would inform the TA that to satisfy a want, the TA must engage in a desired behavior.
Techniques
2-102. For the purposes of TAA, techniques refer to the specific methods used to present information to the TA. Effective persuasion techniques are based on the conditions affecting the TA and the type of information being presented. Determining the most effective technique or combination of techniques to persuade the TA is only accomplished through a cultivated understanding of the TA and its behavior.
2-103. Persuasion and influence are the primary tools of PSYOP. As such, PSYOP Soldiers must strive to become familiar with, and ultimately develop, tactical and technical proficiency in the use of persuasion techniques. The following are some specific techniques used to present supporting arguments to the TA:
• Glittering generalities. These are intense, emotionally appealing words so closely associated with highly valued concepts and beliefs that the appeals are convincing without being supported
by fact or reason. The appeals are directed toward such emotions as love of country and home, and desire for peace, freedom, glory, and honor.
• Transference. This technique projects positive or negative qualities of a person, entity, object, or value to another. It is generally used to transfer blame from one party in a conflict to another.
• Least of evils. This technique acknowledges that the COA being taken is perhaps undesirable, but emphasizes that any other COA would result in a worse outcome.
• Name-calling. Name-calling seeks to arouse prejudices in an audience by labeling the object of the propaganda as something the TA fears, loathes, or finds undesirable.
• Plain folks or common man. This approach attempts to convince the audience that the position noted in the PSYOP argument is actually the same as that of the TA. This technique is designed to win the confidence of the audience by communicating in the usual manner and style of the audience. Communicators use ordinary or common language, mannerisms, and clothes in face-to-face and other audiovisual communications when they attempt to identify their point of view with that of the average person.
• Testimonials. Testimonials are quotations (in and out of context) that are cited to support or reject a given policy, action, program, or personality. The reputation or the role of the individual giving the statement is exploited. There can be different types of testimonial authority. Official testimonials use endorsements or the approval of people in authority or well known in a particular field. Personal sources of testimonials may include hostile leaders, fellow soldiers, opposing leaders, famous scholars, writers, popular heroes, and other personalities.
• Insinuation. Insinuation is used to create or increase TA suspicions of ideas, groups, or individuals as a means of dividing the adversary. The PSYOP Soldier hints, suggests, and implies, but lets the TA draw its own conclusions.
• Presenting the other side. Some people in a TA believe that neither of the belligerents is entirely virtuous. To them, messages that express concepts solely in terms of right and wrong may not be credible. Agreement with minor aspects of the enemy’s point of view may overcome this cynicism.
• Simplification. In this technique, facts are reduced to either right, wrong, good, or evil. The technique provides simple solutions for complex problems and offers simplified interpretations of events, ideas, concepts, or personalities.
• Compare and contrast. Two or more ideas, issues, or choices are compared and differences between them are explained. This technique is effective if the TA has a needs conflict that must be resolved.
• Compare for similarities. Two or more ideas, issues, or objects are compared to try and liken one to the other. This technique tries to show that the desired behavior or attitude (SPO) is
similar to one that has already been accepted by the TA.
• Illustrations and narratives. An illustration is a detailed example of the idea that is being presented. It is an example that makes abstract or general ideas easier to comprehend. If it is in a story form, it is a narrative.
• Specific instances. These are a list of examples that help prove the point.
• Statistics. Statistics have a certain authority, but they must be clear enough to show the TA why they are relevant. In most cases, it is best to keep the statistical evidence simple and short so the TA can easily absorb it.
• Explanations. These are used when a term or idea is unfamiliar to the TA.Primary Influence Tactics
2-104. These primary influence tactics are widely applicable to many situations, cultures, and TAs. By using the appropriate influence tactics in products and actions, the persuasiveness of PSYOP will be magnified. The following are examples of primary influence tactics:
• Rewards and punishments: “If you do X, you will get Y,” or “if you do not do X, Y will happen to you.” Example: “Surrender, and you will be treated well; continue to fight, and you will be killed.”
• Expertise: “Speaking as an authority on the subject, I can tell you that rewards/punishments will occur if you do or do not do X.” Example: “Oil Minister Gregor (key communicator/expert) states that if rebel groups continue to sabotage oil pipelines, the national economy will be seriously affected.”
• Gifts: Giving something as a gift before requesting compliance. The idea is that the target will feel the need to reciprocate later. Example: “This well and cistern are a gift to the people of Birmingville from the coalition forces…demonstration of our good will and hope for mutual cooperation in the future.”
• Debt: Calling in past favors. Example: “Coalition forces have done a lot for Birmingville, Elder Chang: the new school, the well in the center of town… these insurgents are endangering all we have worked for together. We need your help in stopping these groups by reporting any information you and your people may discover.”
• Aversive stimulation: Continuous punishment, and the cessation of punishment, is contingent on compliance. Example: “We will continue to bomb your position unless you surrender immediately.”
• Moral appeal: Entails finding moral common ground, and then using the moral commitments of a person to obtain compliance. Example: “The killing of innocent civilians is wrong; please help the security forces stop this tragic loss of innocent life by reporting any information on terrorist activities.”
• Positive and negative self-feeling: “You will feel better/bad if you do X.” Example: “Become part of something bigger than yourself, know honor and take pride in your work…join the national security forces!”
• Positive and negative altercasting: “Good people do X / Bad people do Y.” Example: “Red Tribe members are brave and honorable people who care about the future of their country and are not intimidated by rebel groups. Call and report insurgent activity now on the coalition hotline.”
• Positive and negative esteem of others: “Other people will think highly/less of you if you do X.” Example: “Earn the respect of your friends and the pride of your family…join the Patriotsville National Guard now!”
• Fear: “Bad things will happen to you if you do X.” Example: “Only death and fire await those who continue to fight…surrender now.”
TOP-SECRET from the NSA – New Documents Spotlight Reagan-era Tensions over Pakistani Nuclear Program
|
Washington, D.C., June 18, 2012 – Tensions between the United States and Pakistan rose through the 1980s over intelligence reports that suggested to U.S. officials that Pakistani leader Zia ul-Haq had repeatedly lied to them about his country’s nuclear program, according to recently declassified records published today by the National Security Archive and the Nuclear Proliferation International History Project. Zia’s apparent mendacity posed an immediate challenge to U.S. nonproliferation goals, but also threatened the even higher priority of providing aid to Islamabad and to the Mujahedin resistance fighting Soviet forces in Afghanistan.
Preventing the spread of nuclear weapons has been a significant objective for U.S.presidents, but there have been instances when diplomatic and other interests have overridden concerns about nuclear proliferation. Israel since the late 1960s is one example and Pakistan during the 1980s is another. Concerned by new intelligence about the Pakistani nuclear program, in July 1982, the Reagan administration sent former CIA deputy director General Vernon Walters to meet secretly with Pakistani dictator General Muhammad Zia-ul-Haq. U.S. intelligence had detected an upswing of clandestine Pakistani efforts to procure nuclear weapons-related technology and unwanted publicity could jeopardize U.S. government economic and military aid to Pakistan, a key partnerin the secret war against Soviet forces in Afghanistan.
Confronted with the evidence, Zia acknowledged that the information “must be true,” but then denied everything, leading Walters to conclude that either Zia “did not know the facts” or was the “most superb and patriotic liar I have ever met.” While Zia restated earlier promises not to develop a nuclear weapon and made pledges to avoid specific nuclear “firebreaks,” officials from Secretary of State George Shultz on down would conclude time and time again, that Zia was breaking his word.
In 1986, Arms Control and Disarmament Agency (ACDA) director Kenneth Adelman wrote in a memorandum to the White House that Zia “has lied to us again,” and warned that failure to act would lead the General to conclude that he can “lie to us with impunity.” While the Reagan administration was concerned about nuclear proliferation, it gave a greater priority to securing aid to Pakistan so it could support the Afghan anti-Soviet insurgency. The White House and the State Department leadership hoped that building a strong bilateral relationship would dissuade Pakistan from building nuclear weapons.
Top levels of the U.S. government let relations with a friendly government supersede nonproliferation goals as long as there was no public controversy that could “embarrass” the President the documents show. Indeed, Reagan administration officials feared that if the Pakistanis had told them the “truth” about the purpose and scope of their nuclear activities, it would have made it impossible for the administration to certify to Congress that Pakistan was not developing nuclear weapons. On that certification rode the continued flow of aid to assist the Afghanistan resistance. For the sake of that aid, senior Reagan administration officials gave Pakistan much slack by obscuring its nuclear activities, but that they wrote about lying and “breaking … assurances” suggests that lack of trust and confidence was an important element in the U.S.-Pakistan relationship, as it is today.
Among the disclosures in today’s publication:
- By the early summer of 1981, State Department intelligence estimated that the Pakistanis were “probably capable of producing a workable device at this time,” although the Kahuta enrichment plant was unlikely to produce enough fissile material for a test until 1983.
- Pakistan was slated to acquire F-16 fighter-bombers from the U.S. That prospective sale troubled Indian leaders because a nuclear Pakistan with advanced fighter bombers would be a more formidable adversary.
- During the spring of 1982 U.S. diplomats and intelligence collectors found that Pakistani agents were trying to acquire “fabricated shapes” (metal hemispheres for producing nuclear explosive devices) and other sensitive technology for a nuclear program. Suggesting that Pakistan was starting to cross the line by building a nuclear weapon, these discoveries contributed to the decision to send former CIA deputy director Vernon Walters to meet secretly with General Zia in July and October 1982.
- During Walters’ October 1982 visit, Zia told him of his meeting with Saudi Arabia’s King Fahd who had told him that agents from an unspecified country had attempted to sell him a nuclear device for $250 million. Zia advised Fahd not to “touch the offer with a barge pole.”
- A controversial element in the F-16 sale was whether the U.S. would comply with Pakistani requests that it include the same radar system as the most advanced U.S. model. While top CIA officials warned that the Pakistanis were likely to share the technology with China, Secretary of State George Shultz and other officials believed, ironically, that denying Pakistani requests would make that country less responsive to U.S. nonproliferation goals.
- With Pakistan’s efforts to acquire sensitive technology continuing, in December 1982 Secretary of State Shultz warned President Reagan of the “overwhelming evidence that Zia has been breaking his assurances.” He also expressed concern that Pakistan would make sensitive nuclear technology available to “unstable Arab countries.”
- In June 1986 ACDA director Kenneth Adelman wrote that Zia has “lied to us again” about violations of agreements not to produce highly-enriched uranium above a five-percent level. If Washington did not apply real pressure it would reinforce Zia’s belief “that he can lie to us with impunity.”
- In the spring of 1987, senior State Department officials wrote that Pakistani nuclear development activities were proceeding apace and that General Zia was approaching a “threshold which he cannot cross without blatantly violating his pledge not to embarrass the President.”
Until 1990, after the Soviets had left Afghanistan, Washington never allowed events to reach a point where public controversy over Pakistani nuclear weapons activities could force a decision that to cut off aid and threaten Pakistan’s role as a go—between to the Afghan resistance. The tough sanctions that have been used against countries like Iran and North Korea were never given serious consideration because the Reagan administration believed that embracing close associates like Pakistan in a “broader bilateral relationship” could discourage them from testing a nuclear device. U.S. policymakers unsuccessfully tried to jawbone their Pakistani counterparts from enriching uranium and building a nuclear weapon.
The other side of U.S. policy was the organized multilateral effort, begun during the Carter administration, to prevent sensitive technology from reaching Pakistan. This largely consisted of efforts to persuade other nuclear suppliers to bar exports of dual-use technology. While international export controls could not stop the Pakistani program, U.S. officials believed that they could “delay” and even “set [it] back”. Those activities were at a high tempo during the early 1980s but whether they continued at the same pace during the rest of the decade is not clear. More declassifications may shed light on that.
The White House and the State Department worked successfully at offsetting Congressional pressures to impose tough nonproliferation standards, although arrests by the U.S. Customs Service raised inconvenient questions. The first major case was Nazir Ahmed Vaid’s arrest in June 1984 for trying to purchase nuclear weapons technology. U.S. government officials may have interfered in the case to minimize adverse publicity that could weaken Congressional support for aid to Pakistan. Nevertheless, Congressional pressure continued. In 1985, Senator John Glenn (D-Oh), among others, wanted the administration to certify, as a condition for further aid, that Pakistan neither possessed nor was developing a nuclear weapon. But the White House and its supporters in Congress won support for a weaker version: an amendment, supported by Senator Larry Pressler (R-SD), requiring annual certification that Pakistan did not possess a nuclear device and that U.S. aid would reduce the risk that Pakistan would acquire one. [1]
In 1986 Reagan certified that Pakistan was in compliance with the Pressler amendment, but months later participants in the Khan network were caught again. In July 1987 U.S. Customs officials arrested Arshad Pervez for trying to buy supplies for the Kahuta enrichment plant. Nevertheless, the administration insisted that nothing was amiss, arguing that it was too early to conclude the Pervez had official support in Pakistan. [2] Even after Pervez was convicted later that year, Reagan certified again that Pakistan did not possess a nuclear device, thereby ensuring that aid flowed without interruption. Congress, however, showed its concern by letting the five- year Symington amendment waiver expire, which temporarily halted “new commitments of aid.” When Congress reinstated a new waiver, it would be only for two-and-a- half years, instead of the six years that Reagan had proposed. 1990 would become a year of decision for future U.S. aid to Pakistan. [3]
This is the third in a series of Electronic Briefing Books on U.S. policy toward the Pakistani nuclear program. The first was on the Carter administration’s policy; the second was on the efforts to work with allies to prevent the export of sensitive technology to Pakistan. The National Security Archive has filed numerous declassification requests to U.S. government agencies on important developments during the 1970s, 80s, and early 1990s, and as significant material becomes declassified the Archive will update this series of EBBs.
READ THE DOCUMENTS
Document 1:”Reached a Dead End”
U.S. Department of State Cable 145139 to U.S. Embassy India [repeating cable sent to Embassy Pakistan], “Non-Proliferation in South [Asia],” 6 June 1979, Secret
Source: MDR request
By the spring of 1979, the Carter administration decided that it had “reached a dead end” in its efforts to stop the spread of nuclear technology to South Asia and that a “new strategy” was necessary to check the spread of nuclear weapons in the region. Given close security ties with Pakistan and concerns about that country’s stability, the State Department was not going to take a hard-line approach, such as embargoes. to force a nuclear roll-back. Thus, Washington would maintain “vigilance” to ensure that sensitive supplies did not reach Pakistan, but the administration no longer saw it possible to reverse Pakistan’s efforts to construct uranium enrichment facilities. More serious dangers were a South Asian nuclear arms race and the threat to U.S. nonproliferation policy which “will collapse under the weight of two additional nuclear-weapons states.” By playing the role of an “honest broker,” and offering appropriate inducements, Washington would make a “sincere attempt to convince South Asians that nuclear weapons are not a viable option.”
Three interrelated actions were necessary. Pakistan would have to be persuaded not to stage a “peaceful nuclear explosion,” along the line of India’s 1974 test, because that would push India to develop a nuclear arsenal and even consider preemptive action. The U.S. would have to seek assurances from Prime Minister Desai that India would not produce nuclear weapons. Finally, Washington would need China’s support, e.g. security assurances to India. To make these arrangements work, Washington would have sell nuclear fuel to India and lift the Symington amendment sanctions against Pakistan that the enrichment program had triggered. Policy success was by no means assured–China might not cooperate–and other uncertainties could complicate matters, for example, if Pakistan helped other Muslim states develop an “Islamic bomb.”
Document 2: “Two-Step Carrot-Stick Approach”
Anthony Lake, director, Policy Planning Staff, to Secretary of State Vance, “The Pakistan strategy and Future Choices,” 8 September 1979, Secret
Source: National Archives, Record Group 59, Records of Anthony Lake, box
The previous document was a marker for policy change, but carrying it out was difficult because of the difficulty of balancing “good relations” with Pakistan with global nonproliferation interests. Concerns about a nuclear test and the transfer of sensitive technology to other states had crystallized into a “no-test/no-transfer” approach, but Washington needed help from other Western aid donors to persuade General Zia’s government to accept those parameters. To try to forge an understanding with Pakistan, Lake describes a “two-step carrot-stick” approach, involving pressures by aid donors. As Lake’s report to Vance makes clear, there were significant divisions in the Carter administration over what “carrots” could be offered and under what conditions, for example, whether sale of F-16 fighter-jets could win the military’s support for scaling back the nuclear program, and how to deal with the Symington amendment. If the “two-step” approach failed Washington might have to consider a “third step” which could either be a resumption of pressure or a waiver of the Symington amendment in exchange for a no-test/no-transfer understanding.
The next month, Secretary of State Vance and Ambassador Gerard C. Smith met with Foreign Minister Shahi, warning him that a nuclear test would harm U.S. –Pakistani relations, with Smith arguing that Pakistan was “entering the valley of death” because India “can utterly destroy you.” Apparently Shahi responded that “he did not have to be a nuclear expert to understand that ‘the value of a nuclear capability lies in its possession, not in its use.” Smith soon traveled to Europe and discussed Pakistan with donor governments, but found little support for applying pressure. [4]
Document 3: “Set the Nuclear Issue Aside”
Secretary of Defense Harold Brown to Ambassador-at-Large Gerard C. Smith, 31 January 1980, enclosing excerpts from memoranda of conversations with Geng Biao and Deng Xiaoping, 7 and 8 January 1980, Top Secret
Source: FOIA release
The Soviet invasion of Afghanistan in December 1979 had an immediate impact on U.S. policy toward Pakistan as indicated by Secretary of Defense Brown’s talks with top Chinese officials. In light of the high priority of funneling aid through Islamabad to the anti-Soviet resistance and concern that Moscow might put Islamabad under pressure, interest in improved relations with Pakistan further lowered the nuclear issue’s priority, although efforts to block sensitive exports continued. As Brown explained to Deng, “we will set [the nuclear issue] aside for the time being and concentrated on strengthening Pakistan against possible Soviet action.” In other words, Cold War objectives had priority over nonproliferation concerns. [5] While Deng claimed that Beijing opposed Pakistan’s nuclear program, China and Pakistan had already developed a special nuclear relationship and ambivalence was evidence in Deng’s advice that the United States “not mention” the nuclear issue in talks with Pakistan.
Document 4: “Pakistan Will Not Give up This Program”
Bureau of Intelligence and Research, U.S. Department of State, “Pakistan and the US: Seeking Ways to Improve Relations,” Report 97-PA, 23 March 1981, Secret
Source: Department of State FOIA release, copy courtesy of Jeffrey Richelson
According to INR analysts, the Pakistani leadership wanted to improve relations with Washington and certainly get a bigger aid package than the “peanuts” offered by the Carter administration. Nevertheless, INR recommended caution about getting too close to General Zia; he would be gone someday and “too close a US tie … might harm future relations.” Moreover, better relations would not make the nuclear problem go away: “Pakistan will not give up this program.” There was some chance that Pakistanis could be persuaded not to test a device but this “would be difficult to accomplish.” The Indians might react badly if Washington gets too close to Pakistan: “they might well retaliate by moving closer to the Soviets.”
Document 5: A “Broader Bilateral Relationship”
Special Assistant for Nuclear Proliferation Intelligence, National Foreign Assessment Center, Central Intelligence Agency, to Resource Management Staff, Office of Program Assessment et al, “Request for Review of Draft Paper on the Security Dimension of Non-Proliferation,” 9 April 1981, Secret, excised copy
Source: MDR release
A new presidential administration wanted to put its own stamp on nonproliferation policy and the Department of State helped begin the process with a draft paper on the “security dimensions of nonproliferation.” Convinced that further spread of nuclear capabilities could have an adverse impact on U.S. security, the report emphasized the importance of perceptions of insecurity as a motive leading states to opt for a nuclear explosive program. While denial of sensitive technology and equipment remained “fundamental,” State Department officials believed that a “broader bilateral relationship” based on the integration of political incentives and security assistance could persuade friendly threshold states that they did not need nuclear weapons. By contrast, “more negative methods of dissuasion” would apply to countries which had poor relations with Washington.
The State Department’s review of threshold states, from Argentina and Brazil to Libya and Iraq, include a discussion of Pakistan, where the “broad bilateral relationship” approach was taken into account. The U.S. objective should be a “closer security relationship which builds confidence in us and makes the Paks feel more secure.” Such a relationship would be “more likely to provide Pakistan with incentives to forego, or at least delay, a nuclear test than any alternative approach.” Following the Carter administration, the Reagan team had minimal goals: preventing a Pakistani nuclear test, not dismantling the enrichment program, had become the key objective. Nevertheless, State’s politico-military analysts argued that Washington should not give the impression that was acquiescing in Pakistan nuclear activity: it was necessary to “lay down a marker” by making Pakistani officials understand the “political costs” of continuing a weapons program.
Document 6: More “Carrots and Sticks”
Lewis A. Dunn, Arms Control and Disarmament Agency, “Implications for U.S. Policy of a Pakistani Nuclear Test,” 11 June 1981, Secret
Source: FOIA release
Signs of the Reagan team’s emphasis on propitiating Islamabad are evident in a memorandum that incoming ACDA official Lewis Dunn had prepared just before he left Herman Kahn’s Hudson Institute. Seeing Pakistan as likely to test a weapon once it had enough fissile material (a test site had already been discovered [6]) Dunn believed that prospects for halting a test were “dimming.” If Pakistan did test, however, there could be a range of U.S. responses, but he favored a “muted” one, owing to regional security considerations and the importance of “holding down” Pakistani nuclear activities. In that regard, Dunn saw “carrots and sticks” as relevant; if Pakistan tested, offers of military assistance or civilian nuclear technology might discourage further nuclear activities. He identified no “sticks.” Dunn also believed it useful to encourage Indian-Pakistan dialogue and regional arms control measures (e.g., no first use pledges and confidence building activities). Pakistan did not test for years, but the Reagan administration would hope in vain that “yes” was the answer to one of Dunn’s questions: “Would the prospect of access to U.S. arms enhance Pakistani incentives for nuclear restraint?”
Document 7: “Probably Capable of Producing a Workable Device at this time”
Bureau of Intelligence and Research, U.S. Department of State, “India-Pakistani Views on a Nuclear Weapons Options and Potential Repercussions,” Report 169-AR, 25 June 1981, confidential
Source: Department of State FOIA release, copy courtesy of Jeffrey Richelson
This report provides an overview of the state of the Indian and the Pakistani nuclear programs, reviewing motivations, the technical situation, possible decisions to test, and the implications of a Pakistani test. According to INR, the Pakistanis are “probably capable of producing a workable device at this time,” but the Kahuta plant was unlikely to produce enough fissile material for a test until 1983. While the Indians had stated publicly that they were preparing their test site that declaration may have been for political effect because they may have wanted the Pakistanis make the “first move.” If Zia decided to do so, he would have to decide whether to risk worsening relations with Washington and a heightened regional nuclear arms race. Indira Gandhi would likely order retaliatory nuclear tests and quiet work on a weapons program. But if Pakistan went further and began an active nuclear weapons program, India was not likely to take risky preventive action because of the difficulty of taking out “Pakistan’s well-defended nuclear facilities” and the risk of “antagonizing China.” INR analysts opined that a nuclear South Asia would not be a stable region: “it is difficult to be optimistic that a stable, long-term mutual deterrence relationship would be established.”
Document 8: A “Great Security Threat” to India
Acting Special Assistant for Nuclear Proliferation Intelligence, National Foreign Assessment Center, to Director and Deputy Director of Central Intelligence, “Warning Report – Nuclear Proliferation,” 20 August 1981, Top Secret, Excised Copy
Source: Mandatory Review Request
An International Atomic Energy Agency report that Pakistan may have diverted plutonium from the Karachi nuclear power plant was raising questions about the adequacy of safeguards, but
Intelligence repots suggested that the Pakistanis “were not overly concerned.” More serious were the implications of U.S.-Pakistani discussions of the sale of advanced F-16 fighter-bombers as part of a larger U.S. aid package to secure Pakistan’s collaboration in the covert war against Soviet forces in Afghanistan. Indian Prime Minister Indira Gandhi worried that Pakistan’s nuclear program and its slated acquisition of F-16s posed a “great security threat” that raised the risk of war.
Document 9: The Danger of Indian Preventive Action
John N. McMahon, Deputy Director for National Foreign Assessment, to Ambassador Richard T. Kennedy,Under Secretary of State for Management, “Special National Intelligence Estimate on Indian Reactions to Nuclear Developments in Pakistan,” 21 September 1981, enclosing SNIE 31-32/81, Secret, excised copy
Source: FOIA release
The heightened Indian concerns about Pakistan discussed in the August “Warning Report” raised enough hackles in the Reagan administration for the CIA to produce a Special National Intelligence Estimate on the possibility of Indian preventive action against Pakistan’s nuclear program. While the estimators could not be sure, they believed that Prime Minister Gandhi would take a “wait-and-see” approach as to whether Pakistan 1) was going to test a device and 2) keep producing fissile material for weapons. India would have to decide whether to stage an “answering test” (for which preparatory work had already been undertaken), but also whether to take preventive action before Pakistan had a weapons stockpile.
Israel’s use of F-16s to destroy Iraq’s Osirak nuclear reactor in June 1981 and Washington’s announcement on 14 September of the F-16 sale to Pakistan made Indian defense officials wonder whether preventive action against nuclear facilities was necessary before Islamabad had the fighter-bombers (for which nuclear-capable versions existed). If India took such action it would have to face the prospect of a “severe” international reaction as well as the possibility that China might intervene on Pakistan’s behalf. One alternative for India was to develop a nuclear stockpile superior to Pakistan’s. That would take a high-level decision to produce nuclear weapons, while financial, technological, and other considerations might encourage Gandhi to move slowly. Nevertheless, the possibility that India (or even Israel) would take preventive action against the Pakistani nuclear program would be a continuing concern.
Document 10: “In All Probability We Would Choose to Cut off Assistance”
Secretary of State Alexander Haig to Senator Mark Hatfield (R-Or), 21 November 1981, Confidential
Source: State Department FOIA release
While concerned about what India might do, the Reagan administration focused on working with Pakistan to weaken the Soviet position in Afghanistan. Facilitating that involved a multi-billion military and economic aid package to Pakistan which included a five year waiver of the Symington amendment to eliminate automatic triggers that would cut aid if Washington detected evidence of nuclear weapons work. Nevertheless, Congress imposed some conditions, namely that aid would stop if Pakistan tested a nuclear weapon. To confirm that the administration was on board, Senator Mark Hatfield, who had long been concerned about nuclear proliferation, asked Secretary of State Alexander Haig how the U.S. government would react to a Pakistani nuclear test. Haig replied that “in all probability”, Washington would cut aid. Haig might have thought that there would be no problem because General Zia had assured Under Secretary of State James Buckley that he would not develop or test a nuclear weapon (See document 11A for that assurance). On human rights, another of Hatfield’s concerns, the Reagan administration was departing from the human rights emphasis of its predecessor. Haig would make no commitments because of Pakistan’s “limited tradition of representative government.”
Document 11: “Significant” Chinese Aid on Nuclear Design
Note for [name excised] from [name excised], “State/INR Request for Update of Pak SNIE, and Assessment of Argentine Nuclear Program,” 4 June 1982, Secret, excised copy
Source: CREST
A planned update of a Special National Intelligence Estimate concluded that the Pakistani nuclear program was keeping its momentum and that new evidence, apparently acquired by British intelligence, suggested a “significant” Chinese role, at least in providing assistance on weapons design. [7] CIA was apparently adjusting its earlier estimate—late 1982/1983-84–for the availability of fissile material for weapons. The implication was that a Pakistani test was not imminent, thus reducing pressure on India.
Document 12: Discoveries and Demarches
Terry Jones, Office of Nonproliferation and Export Policy, Department of State, to J. Devine et al., enclosing summaries of State Department cable traffic during 1981-1982 relating to demarches on attempted purchase of sensitive nuclear-related products, 17 June 1982
Source: State Department FOIA release
The Reagan administration gave Pakistan some slack, but it continued the campaign of demarches, begun under Jimmy Carter, to try to prevent the export of sensitive nuclear technology to Pakistan, among others. (See EBB “Demarches and Non-Papers”) As before, Pakistan was a special target of concern, but these summaries of State Department telegrams, some in the sensitive intelligence-related “Roger” channel, show that Washington was also trying to prevent sales of nuclear-related technology to a host of countries: Argentina, Brazil, China, India, Iraq, Israel, Korea, Libya, Romania, South Africa, and Syria. For example, cable traffic on Syria showed concern about Damascus’s interest in acquiring a research reactor, while messages on Libya show U.S. government efforts to discourage Belgian sale of a plant to produce uranium tetraflouride (the precursor to uranium hexaflouride, used for uranium enrichment).
The name A. Q. Khan was not mentioned in these cables, but his fingerprint showed up, for example, in the attempted purchases of electrical inverters (used for gas centrifuges). These attempts were probably by the Khan network. But the group of Pakistani agents seeking to purchase nuclear-related technology was broaderthan Khan’s. For example, the nuclear reprocessing technology program was directed by Pakistan Atomic Energy Commission chief Munir Ahmad Khan, who had a procurement network in Europe directedby S.A. Butt. The cable summaries for Pakistan showed a number of attempted and completed purchases by Pakistani agents from suppliers in a variety of countries, including Belgium, Finland, Japan, Sweden, andTurkey. Besides the inverters, agents were seeking such items as fabricated shapes” (metal hemispheres for producing nuclear explosive devices), coaxial cables, fuel chopping machines(to help reprocess plutonium), nuclear power plants, and “flash X-ray units”(diagnostic instrument used in tests of neutron initiators for nuclear weapons).[8] Suggesting that Pakistan was starting to cross the line into producing a nuclear weapon, these efforts raised alarm bells in Washington. [Updated 4 May 2012. Thanks to Mansoor Ahmed for information]
Documents 13A-B: “The Most Superb and Patriotic Liar”
A. U.S. Embassy Pakistan cable 10239 to State Department, “My First Meeting with President Zia,” 5 July 1982, Secret
B. U.S. Embassy Pakistan cable 10276 to State Department, “My Final Meeting with President Zia,” 6 July 1982, Secret
Source: State Department MDR release
Much needs to be learned about White House decision-making but evidently the alleged Pakistani efforts to purchase sensitive technology discussed above, and possibly the intelligence on Chinese weapon design assistance, prompted concern that Congress would find out and stop aid if it believed that Pakistan was developing a capability for a nuclear test. To keep the situation in check, Reagan sent General Vernon Walters, former Deputy Director of Central Intelligence and personal translator for U.S. presidents, among other high-level and sensitive positions, to take a presidential letter to General Zia. During their 4 July meeting, Walter told Zia that Washington had “incontrovertible intelligence” that Pakistani representatives had “transferred designs and specifications for nuclear weapons components to purchasing agents in several countries for the purpose of having these nuclear weapons components fabricated for Pakistan.” Under the law, Walters told Zia, the administration would have to inform the U.S. Congress. Zia denied everything: Pakistan did not have a weapons development program and repeated assurances made to Under Secretary of State James Buckley that Pakistan would not develop or test a nuclear weapon. Zia said that he was sure that no one was buying nuclear equipment, but he would check with his subordinates to be sure. Walter later commented: “either he really does not know or is the most superb and patriotic liar I have ever met.”
In what Walters saw as a diversion from the main discussion, the conversion turned to the problem of the IAEA inspection of the Karachi Nuclear Power Plant and recommendations on safeguards to prevent diversion of spent fuel. Zia repeated his earlier assurances on nuclear weapons and insisted that Pakistan would not “embarrass” the U.S. government. Walters reported that Zia “took the matter somewhat better than I had expected.”
The conversation the next day showed that Zia was a master of double-talk. Verbally, he admitted that U.S. intelligence was on to something: “The president must be right. Your information must be right. I accept its authenticity.” But he would not put that in writing and in a formal response to Reagan’s letter, Zia argued that the U.S. information was a “total fabrication.” This, Walter argued, was a matter of keeping “face”: what Zia was saying was “it did not happen but you can be sure it won’t happen again.” “I think he has the message,” Walter concluded, although he did not explain whether he believed that there would be any changes in Pakistani policy.
Documents 14A-B: “Word of Honor”
A. U.S. Embassy Pakistan cable 15696 to State Department, “Pakistan Nuclear Issue: Meeting with General Zia,” 17 October 1982, Secret
B. State Department cable 299499 to U.S. Embassy Islamabad, “Pakistan Nuclear Issue: Meeting with General Zia,” 25 October 1982, Secret
Source: State Department MDR release
What Zia said to Walters was irrelevant because U.S. intelligence detected continuing efforts to procure sensitive technology and materials (see next document). Thus, Walters returned to Islamabad for another demarche in October, to warn Zia that U.S. aid was in “grave jeopardy.” (see document 16 below). Walter showed drawings of Chinese-influenced nuclear weapons designs that U.S. intelligence had obtained, but Zia denied that there was anything untoward: Pakistan’s reprocessing and enrichment programs were entirely peaceful and there was “nothing” in the nuclear weapons field. Pakistan would do nothing that would jeopardize its aid and other relationships with Washington. Any information on clandestine nuclear activities, he suggested, had been concocted by Pakistan’s “enemies.” As for the items that Pakistan was allegedly attempting to procure, such as “spheres”, Zia argued, there was nothing that could not be produced internally. Walter said he would review the U.S. evidence, but observed that intelligence advisers had assured him that there was “no possibility of fabrication or disinformation.”
The delivery of the F-16s to Pakistan was nearing and Zia wanted to make sure that they were equipped with the ALR-69 radar warning receiver, the most advanced radar warning technology in the U.S. Air Force’s inventory. What had held up delivery was concern in Washington that Pakistan might give the Chinese access to this advanced technology. Walters said he would look into it.
Zia concluded the meeting with a story based on conversations with Saudi Arabia’s King Fahd. The latter had told him that agents from an unspecified country had attempted to sell a nuclear device to Saudi Arabia for $250 million. He had advised Fahd not to “touch the offer with a ‘barge pole.'”
In a follow-up message, prepared after he was back in Washington, Walters noted that at the end of the conversation, Zia had given his “word of honor” that Pakistan “will not develop a nuclear device or a weapon.”
Document 15A-B: “A Serious Blow to U.S. Worldwide Nonproliferation Efforts”
A. Excerpt from Intelligence Report, “Pakistan-US: Demarche on F-16 Equipment,” 8 November 1982, enclosed with memorandum from Deputy CIA Director John N. McMahon to Deputy Secretary of Defense Frank Carlucci, “Risk Assessment of the Sale of AN/ALR-69 Radar Warning Receiver to Pakistan,” 8 November 1982, with excerpt from National Intelligence Estimate on Pakistan attached, n.d., Secret
B. Henry S. Rowen, National Intelligence Council, to DDCI [Deputy Director of Central Intelligence McMahon], 19 November 1982, with attached memorandum from National Intelligence Council staffer [name excised], “Pakistan,” same date, Secret
Source: CREST
Whether the Pakistanis, and presumably the Chinese, should get access to advanced F-16 technology was hotly contested. CIA officials acknowledged that, despite an agreement not to disclose military information, the Pakistanis were likely to give Beijing access to the AN/ALR-radar warning system, especially if “major strains” in the U.S.-Pakistan relationship developed. Because ALR-69 technology would allow a “potential adversary” to use radar equipment to defeat an F-16, Deputy CIA Director McMahon advised against releasing it to Pakistan. Secretary of State George Shultz wanted to meet Pakistani requirements and an official at CIA’s National Intelligence Council, supported by Henry Rowen, provided supporting arguments. Sanguine about the risk of disclosure to Beijing, they argued that failure to supply the F-16 with “USAF radar” would deprive Washington of “leverage” that made possible General Walter’s access to Zia. Highly sanguine about the political influence associated with arms sales, CIA analysts argued that failure to meet Pakistani demands would constitute a “serious blow to U.S. worldwide nonproliferation efforts.” This optimistic view prevailed and the Air Force was constrained to provide the AN/ALR-69 to Pakistan. [9]
Document 16: “Overwhelming Evidence that Zia Has Been Breaking His Assurances”
Secretary of State George Schultz to President Reagan, “How Do We Make Use of the Zia Visit to Protect Our Strategic Interests in the Face of Pakistan’s Nuclear Weapons Activities,” 26 November 1982, Secret
Source: CREST
George Shultz probably saw the ALR-69 issue as a minor problem compared to the “overwhelming evidence that Zia has been breaking his assurances” on Pakistan’s nuclear weapons program, Shultz may have accepted the interpretation that Zia was a patriotic liar” but this raised a tough diplomatic problem because the General would soon be in Washington to meet President Reagan. Citing an interagency report on issues and options, Shultz saw high risks because good relations with Pakistan, especially while the war in Afghanistan was in progress, were a major strategic interest. Yet, if Pakistan continued its nuclear weapons work, Congress could cut off aid. Moreover, a South Asian nuclear arms race could destabilize the region, not to mention the dangers of Indian and/or Israeli preemptive action against Pakistan, and the possibility that the latter could transfer nuclear technology to “unstable Arab countries.”
Options presented to Reagan ranged from cutting off aid directly if Pakistan kept trying to procure sensitive technology to warning Zia that continued activities would “seriously jeopardize our security relationship.” Shultz did not make a recommendation in this paper, but he it was evident that he wanted to avoid action other than a warning so as not to jeopardize the relationship. Records of his talks with Zia on 6 December and Zia’s meeting with President Reagan the next day are not yet available, but the Kenneth Adelman memorandum produced below (see document 20) discloses that Reagan laid out specific parameters to Zia: no assembly or test of nuclear devices, no transfer of technology for such devices, no violation of international safeguards, and no unsafeguarded reprocessing. [10]
Document 17: “Punish an Indian Attack So Severely that it will be Deterred to Begin With”
Bureau of Intelligence and Research, U.S. Department of State, “Pakistan: Security Planning and the Nuclear Option,” Report 83-AR, 1983 [full date cut off copy], Limited Official Use
Source: Department of State FOIA release, copy courtesy of Jeffrey Richelson
Based on a contract study prepared by University of Illinois political scientist (presently affiliated with Brookings) Stephen P. Cohen, after he had made three visits to Pakistan, this report focuses on the Pakistani military’s approach to deterrence. While the Pakistani military had once emphasized the value of using force first, the danger of war with India has produced a strategic doctrine that stresses the “use of military force to deter an Indian attack.” This doctrinal shift was creating a consensus in the military on the value of a “modest, ‘limited’ [nuclear] weapons program.” Pakistani military leaders did not like nuclear weapons, but they believed that they would “enable them to do what their armored divisions and air force can no longer” do in conventional terms: “punish an Indian attack so severely that it will be deterred to begin with.”
On the problem of Pakistani command-and-control over nuclear weapons, the summary of Cohen’s report observed that “Pakistan’s military has done self-destructive things in the past, and one cannot assume that it will not do them in the future.” Yet with greater professionalism in the Army, it was not “likely to make [decisions on nuclear weapons] any more irresponsibility than other states confronted with the same perplexing set of security constraints.” Cohen did not believe that Washington could do much to reverse nuclearization in South Asia, but U.S. influence could help ensure that proliferation did not lead to greater instability, for example, by limiting the buildup of stockpiles and supporting regional “mutual balanced force reductions” arrangements.
Document 18: “Supplying Conventional Weapons … Can be a Positive Force Against Proliferation”
Hugh Montgomery, director, Bureau of Intelligence and Research, U.S. Department of State, to Ambassador Ronald Spiers, 17 February 1984, enclosing “India-Pakistan: Pressures for Nuclear Proliferation,” Report 778-AR, 10 February 1984, Limited Official Use
Source: Department of State FOIA release, copy courtesy of Jeffrey Richelson
This interesting review of the South Asian nuclear problem starts by exploring the India-Pakistan nuclear dynamic. If Pakistan tested a weapon, India might resist following through on a weapons option, but might begin a series of tests. Both countries could covertly begin a weapons program. Despite speculation about an Indian preemptive strike against Pakistani nuclear installations, such an occurrence was unlikely because of the serious risks for India, not least the spread of “deadly radiation poisoning.” While New Delhi had resisted internal pressures for weaponization, changes in the security environment could weaken resistance, for example, if relations with Beijing worsened or if Chinese-Soviet relations improved (which would make the Indians more worried about Moscow’s reliability). The INR analyst believed that Washington had the most “leverage” with Pakistan because of the latter’s dependence on U.S. supplies of conventional weapons. “Supplying conventional weapons to Pakistan can be a positive force against proliferation” because they “can give Pakistan sufficient confidence in its own security that it would find the nuclear option less attractive and unnecessary.” This may have been the basis of State Department thinking that not meeting Pakistani desiderata on such issues as the F-16 would be a blow to nuclear non-proliferation policy. The challenge, however, was to not over-arm Pakistan because that could threaten Indian security and “increase the danger of nuclear proliferation in South Asia.”
Document 19: Pakistan Has “Produced an Atomic Weapon”
Defense Intelligence Agency cable to [excised location], “Pakistan-China: Nuclear Weapons Production and Testing,” 7 December 1985, Secret, excised copy
Source: DIA FOIA release
Only months after Congress enacted the Pressler amendment, an intelligence source claimed that Pakistan with Chinese assistance had “produced an atomic weapon in early October.” DIA had received similar reports and was trying to confirm this one. That U.S. intelligence believed that Pakistan was producing enough HEU for at least one device becomes evident in the next document.
Document 20: “He Lied to Us Again”
Kenneth Adelman, director, Arms Control and Disarmament Agency, o Assistant to the President for National Security Affairs, “Pakistan’s Nuclear Weapons Programs and U.S. Security Assistance,” 16 June 1986, Top Secret
Source: MDR release
More declassification actions will elucidate what the United States discovered during 1982-1986 about the Pakistani nuclear program, the renewed efforts to prevent procurement of sensitive technology, and high-level pressures to discourage secret nuclear work, but this memorandum by ACDA director Adelman gives perspective on some developments after the Reagan-Zia meeting in late 1982. The points that President Reagan made to Zia in December 1982 were re-stated in a May 1984 “non-paper” and then refined the following September when Reagan informed Zia that enriching uranium above 5 percent would be just as problematic as unsafeguarded plutonium reprocessing. But Reagan never put serious pressure on Zia to comply.
According to Adelman, the Pakistanis had been producing enriched uranium above the five percent level and, after overcoming an important “hurdle,” were enriching uranium at levels high enough (presumably close to 90 percent) to produce “one or more nuclear devices.” Adelman insisted that Zia was lying to Washington about this and that these activities jeopardized U.S. aid to Pakistan. The problem was that Washington had only “jawboned” General Zia instead of applying real pressure, thus undermining Reagan’s credibility and reinforcing “Zia’s belief that he can lie to us with impunity.” This raised serious problems for Congressional approval of aid, not only for certifying that Pakistan did not “possess” an explosive device, but also for renewing the 1982 Foreign Assistance Act that had exempted Pakistan from more rigorous nonproliferation standards.
Adelman recommended the precise application of pressure—to give Zia the “stark choice” of continued aid or the enrichment program. The possibility that Zia might resist could make it necessary to “tough it out” with Congress to assure the continuity of aid. But Adelman thought it possible that pressure would work and that Zia would conclude that “payoff” of U.S. aid and military sales was too high to forego.
Document 21: “Annual certification … very problematic”
Briefing Book, “Visit of Prime Minister Junejo of Pakistan, July 15-21, 1986,” Secret
Source: MDR Release
With Prime Minister Junejo about to visit Washington ACDA director had suggested that the U.S. tell him that pending a policy review on the Pakistani nuclear program “all actions involving military sales” have been halted . But this harder-line view apparently found no takers because the State Department briefing book for the Junejo visit only suggested tacit threats, not the “stark choice” that Adelman had recommended, that certification was “very problematic” without “positive Pak actions to help convince the Congress” which meant “quiet Pak actions to restrain [the enrichment] program.”
On the status of the Pakistani program, the briefing book included an intelligence finding [page 39 of pdf] that if the Kahuta plant operated at capacity it could produce enough m for “several nuclear devices per year.” Nevertheless, it was “our assessment … that Pakistan does not possess a device.” The highest levels of the Department were taking the position that Pakistan was in compliance with the Pressler amendment.
Document 22: “Absolute Criticality … of Restraint”
State Department cable 229696 to U.S. Embassy France et al., “Visit of Pakistani Primin Mohammad Khan Junejo to Washington – 15-18 July 1986,” 23 July 1986, Secret
Source: MDR Release
The only record of the meetings with Junejo that is available so far is this telegram that went out to a number of embassies. Impressing administration officials who found him “astute and well briefed,” Junejo professed to be responsive to the U.S. emphasis on the “absolute criticality” of “restraint” in Pakistani nuclear activities. In meetings with the press, Junejo “specifically affirmed” commitment not to enrich uranium above the five percent level, but this would continue to be a problem.
Document 23: “He Has Approached a Threshold”
Fred McGoldrick, Acting Director, Office of Nonproliferation and Export Policy, to John Negroponte, Assistant Secretary of State for Environment, Oceans and Fisheries, “Pakistan,” 9 April 1987, Secret, enclosing memorandum from Richard Murphy, Assistant Secretary for Near East and South Asian Affairs, “Action Plan on Pakistan Nuclear And Security Problems,” to Secretary of State, n.d., Secret
Source: MDR Release
In the fall of 1986, Reagan certified Pakistan’s compliance with the Pressler amendment although it was manifest that U.S. aid was not preventing Pakistan from doing what it could to produce a nuclear device. With the White House’s request for a new assistance program under review, Congress was contemplating a shorter, two-year, waiver of the Symington amendment or possibly tying aid directly to a halt of enriched uranium production. In early 1987 the Pakistani nuclear program was getting in the news again—-statements by A.Q. Khan about a “nuclear weapons capability,” Zia declaring that “Pakistan can build a bomb whenever it wishes,” and a speech by Ambassador Dean Hinton stating that Pakistan’s nuclear efforts were “inconsistent” with a peaceful program—which could only raise Congressional objections to aid to Pakistan. [11] In this context, according to Assistant Secretary Murphy, the danger was that Zia “has approached a threshold which he cannot cross without blatantly violating his pledge not to embarrass the President.”
Arguing that the administration needed “to obtain specific actions demonstrating restraint,” Murphy acknowledged that Pakistan was “unlikely” to do so, especially because Zia had “not so far responded constructively” to previous requests. Nevertheless, he proposed an “action plan” that included a new demarche on enrichment and other “nuclear firebreaks,” a message to India also asking for “restraint,” a “Congressional game plan,” and a presidential envoy to “engage” both India and Pakistan in the nuclear issue.
With the U.S. considering sales of airborne early warning aircraft (AEW) to Pakistan, Richard Kennedy, the ambassador-at-large for nonproliferation matters, had suggested that Washington directly link the sales to “Pakistani action on nonproliferation,” but other officials opposed such linkage. Perhaps Murphy raised the issue to see if Shultz had any interest in pursuing it.
What action Shultz may have taken on Murphy’s proposal remains to be learned, but any pressure exerted was likely to have been weak. Later in 1987, Reagan certified that Pakistan did not possess a nuclear advice; the aid kept flowing.
NOTES
[1] Dennis Kux,The United States and Pakistan, 1947-2000: Disenchanted Allies (Washington, D.C.: Woodrow Wilson Center Press; Baltimore : Johns Hopkins University Press, 2001), 276-277; Adrian Levy and Catherine Scott-Clark, Deception: Pakistan, the United States, and the Secret Trade in Nuclear Weapons (New York: Walker & Co.: 2007), 116; David Armstrong and Joseph Trento, America and the Islamic Bomb: The Deadly Compromise (Hanover NH: Steerforth Press, 2007), 122-137.
[3] Kux, The United States and Pakistan, 282-286; Armstrong and Trento, America and the Islamic Bomb, 142-154, and Levy and Scott-Clark, Deception, 156-163.
[4] For details on the Shahi-Vance-Smith talks, see Kux, The United States and Pakistan. 240-241. For Smith’s report on his talks, see http://www.gwu.edu/~nsarchiv/nukevault/ebb333/index.htm, document 45.
[6] For detection of Pakistan’s test site, see Jeffrey Richelson, Spying on the Bomb: American Nuclear Intelligence from Nazi Germany to Iran and North Korea (New York: W.W. Norton, 2006), 341.
[7] David Albright, Peddling Peril: How the Secret Nuclear Trade Arms America’s Enemies (New York: Free Press, 2010), 50.
[8] For the Pakistani purchasing networks, see BrunoTertrais, “Not a ‘Wal-Mart’, but an ‘Imports-Exports Enterprise’: Understanding the Nature of the A.Q. Khan Network,”Strategic Insights (August 2007) http://www.nps.edu/Academics/centers/ccc/publications/OnlineJournal/2007/Aug/tertraisAug07.pdf . See also Albright, Peddling Peril, 48.
[9] T. V. Paul, “influence through Arms Transfers: Lessons from the US-Pakistani Relationship,” Asian Survey 32 (Dec. 1992), 1086.
[10] Shultz does not mention his 1982 meeting with Zia in his memoir, Turmoil and Triumph: My Years As Secretary of State (New York: Charles Scribner’s Sons, 1993), although at 493-494, he covers a 1984 discussion after Indira Gandhi’s funeral. Zia said that Pakistan was “nowhere near” building a nuclear weapon and that “We have no intention of making such a weapon.”
TOP-SECRET from the FBI – Economic Espionage
 |
|---|
| American industry and private sector businesses are the choice target of foreign intelligence agencies, criminals, and industry spies. The above image on the cost of economic espionage to the U.S. can currently be seen on digital billboards—courtesy of Clear Channel and Adams Outdoor Advertising—in several regions of the country with a concentration of high-tech research and development companies, laboratories, major industries, and national defense contractors. If you suspect economic espionage, report it to the FBI at tips.fbi.gov. | Download high-resolution image |
Economic Espionage
How to Spot a Possible Insider Threat
05/11/12
This past February, five individuals and five companies were charged with economic espionage and theft of trade secrets for their roles in a long-running effort to obtain information for the benefit of companies controlled by the government of the People’s Republic of China.

What Do They Want From Us? According to the latest economic espionage report to Congress from the Office of the National Counterintelligence Executive, although foreign collectors will remain interested in all aspects of U.S. economic activity and technology, they’re probably most interested in the following areas: – Information and communications technology, which form the backbone of nearly every other technology; – Business information that pertains to supplies of scarce natural resources or that provides global actors an edge in negotiations with U.S. businesses or the U.S. government; – Military technologies, particularly marine systems, unmanned aerial vehicles, and other aerospace/aeronautic technologies; and – Civilian and dual-use technologies in fast-growing sectors like clean energy, health care/pharmaceuticals, and agricultural technology. |
|---|
According to the superseding indictment, the PRC government was after information on chloride-route titanium dioxide (TiO2) production capabilities. TiO2 is a commercially valuable white pigment with numerous uses, including coloring paints, plastics, and paper. DuPont, a company based in Wilmington, Delaware, invented the chloride-route process for manufacturing TiO2 and invested heavily in research and development to improve the process over the years. In 2011, the company reported that its TiO2 trade secrets had been stolen.
Among the individuals charged in the case? Two long-time DuPont employees…one of whom pled guilty in fairly short order.
Foreign economic espionage against the U.S. is a significant and growing threat to our country’s economic health and security…and so is the threat from corporate insiders willing to carry it out.
And because we’re now in the digital age, insiders—who not so many years ago had to photocopy and smuggle mountains of documents out of their offices—can now share documents via e-mail or download them electronically on easy-to-hide portable devices.
Why do insiders do it? Lots of reasons, including greed or financial need, unhappiness at work, allegiance to another company or another country, vulnerability to blackmail, the promise of a better job, and/or drug or alcohol abuse.
How to stop them? Obviously, a strong organizational emphasis on personnel and computer security is key, and the FBI conducts outreach efforts with industry partners—like InfraGard—that offer a variety of security and counterintelligence training sessions, awareness seminars, and information.
| Successful Investigation of ‘Insiders’
– In Detroit, a car company employee copied proprietary documents, including some on sensitive designs, to an external hard drive…shortly before reporting for a new job with a competing firm in China. Details – In Indianapolis, an employee of an international agricultural business stole trade secrets on organic pesticides from his employer and shared them with individuals in China and Germany. Details In Boston, a technology company employee e-mailed an international consulate in that city and offered proprietary business information. He later provided pricing and contract data, customer lists, and names of other employees…to what turned out to be a federal undercover agent. Details All three subjects pled guilty. But in two of the three cases, the stolen secrets probably ended up in the hands of global businesses that will use them to attempt to gain an unfair competitive edge over the United States. Podcasts Gotcha: Special agent discusses 2010 economic espionage case. FBI, This Week: The FBI is seeing an increase in cases involving spying from foreign intelligence agencies, criminals, and others who wish America harm. |
|---|
You can help as well. In our experience, those who purloin trade secrets and other sensitive information from their own companies and sell them overseas exhibit certain behaviors that co-workers could have picked up on ahead of time, possibly preventing the information breaches in the first place. Many co-workers came forward only after the criminal was arrested. Had they reported those suspicions earlier, the company’s secrets may have been kept safe.
Here are some warning signs that MAY indicate that employees are spying and/or stealing secrets from their company:
- They work odd hours without authorization.
- Without need or authorization, they take proprietary or other information home in hard copy form and/or on thumb drives, computer disks, or e-mail.
- They unnecessarily copy material, especially if it’s proprietary or classified.
- They disregard company policies about installing personal software or hardware, accessing restricted websites, conducting unauthorized searches, or downloading confidential material.
- They take short trips to foreign countries for unexplained reasons.
- They engage in suspicious personal contacts with competitors, business partners, or other unauthorized individuals.
- They buy things they can’t afford.
- They are overwhelmed by life crises or career disappointments.
- They are concerned about being investigated, leaving traps to detect searches of their home or office or looking for listening devices or cameras.
If you suspect someone in your office may be committing economic espionage, report it to your corporate security officer and to your local FBI office, or submit a tip online at https://tips.fbi.gov/.
TOP-SECRET – Open Source Center North Korea Unusual Threats Signal Possible Action Against South Korea
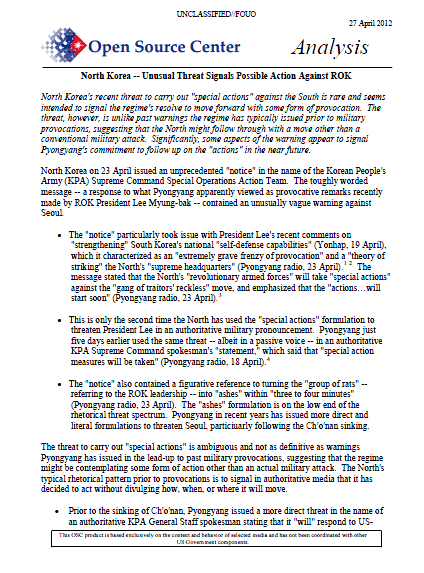
North Korea’s recent threat to carry out “special actions” against the South is rare and seems intended to signal the regime’s resolve to move forward with some form of provocation. The threat, however, is unlike past warnings the regime has typically issued prior to military provocations, suggesting that the North might follow through with a move other than a conventional military attack. Significantly, some aspects of the warning appear to signal Pyongyang’s commitment to follow up on the “actions” in the near future.
North Korea on 23 April issued an unprecedented “notice” in the name of the Korean People’s Army (KPA) Supreme Command Special Operations Action Team. The toughly worded message — a response to what Pyongyang apparently viewed as provocative remarks recently made by ROK President Lee Myung-bak — contained an unusually vague warning against Seoul.
- The “notice” particularly took issue with President Lee’s recent comments on “strengthening” South Korea’s national “self-defense capabilities” (Yonhap, 19 April), which it characterized as an “extremely grave frenzy of provocation” and a “theory of striking” the North’s “supreme headquarters” (Pyongyang radio, 23 April). The message stated that the North’s “revolutionary armed forces” will take “special actions” against the “gang of traitors’ reckless” move, and emphasized that the “actions…will start soon” (Pyongyang radio, 23 April).
- This is only the second time the North has used the “special actions” formulation to threaten President Lee in an authoritative military pronouncement. Pyongyang just five days earlier used the same threat — albeit in a passive voice — in an authoritative KPA Supreme Command spokesman’s “statement,” which said that “special action measures will be taken” (Pyongyang radio, 18 April).
- The “notice” also contained a figurative reference to turning the “group of rats” — referring to the ROK leadership — into “ashes” within “three to four minutes” (Pyongyang radio, 23 April). The “ashes” formulation is on the low end of the rhetorical threat spectrum. Pyongyang in recent years has issued more direct and literal formulations to threaten Seoul, particiuarly following the Ch’o’nan sinking.
The threat to carry out “special actions” is ambiguous and not as definitive as warnings Pyongyang has issued in the lead-up to past military provocations, suggesting that the regime might be contemplating some form of action other than an actual military attack. The North’s typical rhetorical pattern prior to provocations is to signal in authoritative media that it has decided to act without divulging how, when, or where it will move.
- Prior to the sinking of Ch’o’nan, Pyongyang issued a more direct threat in the name of an authoritative KPA General Staff spokesman stating that it “will” respond to US ROK military drills with a “powerful military counteraction” (Pyongyang radio, 25 February 2010). Similarly, leading up to the Yo’np’yo’ng Island shelling, a statement by the spokesman for the North side’s delegation to North-South military talks warned that its Army “will counter” the South’s provocations with a “merciless physical retaliation” (KCNA, 29 October 2010).
Committing to Prompt Action
Although the recent threat was not as definitive as warnings the North issued in advance of past military provocations, the unusual use of the phrase “will start soon” in combination with the unique “special actions” formulation appears designed to signal that the regime is committed to following through with its warning.
- Pyongyang’s use of the term “soon” is unusually specific and categorical. The last time the North modified its threat with this term was in a less authoritative North-South Military Talks General-Level Representative “notice,” which warned that its “army will soon” take “corresponding decisive measures” in response to South Korea distributing leaflets to the North (Pyongyang radio, 10 April 2010). Unlike the most recent threat, however, this warning was preceded by a conditional phrase, which afforded the regime the flexibility to refrain from taking immediate action.
- Further underscoring its commitment to carry out its threat, the North broadcast the KPA “notice” to both domestic and external audiences. In addition, the North Korean radio and television carried the message at least two times a day for three days following the initial announcement.
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET from the FBI – Former Chief Financial Officer of Taylor, Bean, & Whitaker Sentenced to 60 Months in Prison for Fraud Scheme
WASHINGTON—Delton de Armas, a former chief financial officer (CFO) of Taylor, Bean, & Whitaker Mortgage Corp. (TBW), was sentenced today to 60 months in prison for his role in a more than $2.9 billion fraud scheme that contributed to the failure of TBW.
De Armas was sentenced today by U.S. District Judge Leonie M. Brinkema in the Eastern District of Virginia. The sentence was announced today by Assistant Attorney General Lanny A. Breuer of the Criminal Division; U.S. Attorney Neil H. MacBride for the Eastern District of Virginia; Christy Romero, Special Inspector General, Office of the Special Inspector General for the Troubled Asset Relief Program (SIGTARP); Assistant Director in Charge James W. McJunkin of the FBI’s Washington Field Office; David A. Montoya, Inspector General of the Department of Housing and Urban Development (HUD-OIG); Jon T. Rymer, Inspector General of the Federal Deposit Insurance Corporation (FDIC-OIG); Steve A. Linick, Inspector General of the Federal Housing Finance Agency (FHFA-OIG); and Richard Weber, Chief of the Internal Revenue Service Criminal Investigation (IRS-CI).
De Armas, 41, of Carrollton, Texas, pleaded guilty in March to one count of conspiracy to commit bank and wire fraud and one count of making false statements.
“For years, Mr. de Armas, the CFO of one of the country’s largest private mortgage companies, helped defraud financial institutions by concealing from them billions of dollars in losses,” said Assistant Attorney General Breuer. “His lies and deceits contributed to the devastating losses suffered by major institutional investors. As a consequence for his crimes, he will now spend the next five years of his life behind bars.”
“As CFO, Mr. de Armas could have—and should have—put a stop to the massive fraud at TBW the moment he discovered it,” said U.S. Attorney MacBride. “Instead, he and others lied for years on end to investors, banks, regulators, and auditors and caused more than $2.4 billion in losses to major financial institutions.”
“Rather than blow the whistle on billions of dollars in fraud, de Armas chose to help conceal it,” said Special Inspector General Romero. “This CFO lied to investors, banks, regulators, and auditors to cover up the massive fraud scheme which resulted in the failure of both TBW and Colonial Bank. The court’s decision to sentence de Armas to five years in prison reflects the seriousness of his role as a gatekeeper within TBW and the contribution of his crime to our nation’s financial crisis.”
“The actions of Mr. De Armas and others resulted in the loss of billions of dollars to major financial institutions,” said Assistant Director in Charge McJunkin. “Today’s sentence serves as a warning to anyone who attempts to take advantage of investors and our banking system. Together with our law enforcement partners, the FBI will pursue justice for anyone involved in such fraudulent schemes.”
According to court documents, de Armas joined TBW in 2000 as its CFO and reported directly to its chairman, Lee Bentley Farkas, and later to its CEO, Paul Allen. He previously admitted in court that from 2005 through August 2009, he and other co-conspirators engaged in a scheme to defraud financial institutions that had invested in a wholly-owned lending facility called Ocala Funding. Ocala Funding obtained funds for mortgage lending for TBW from the sale of asset-backed commercial paper to financial institutions, including Deutsche Bank and BNP Paribas. The facility was managed by TBW and had no employees of its own.
According to court records, shortly after Ocala Funding was established, de Armas learned there were inadequate assets backing its commercial paper, a deficiency referred to internally at TBW as a “hole” in Ocala Funding. De Armas knew that the hole grew over time to more than $700 million. He learned from the CEO that the hole was more than $1.5 billion at the time of TBW’s collapse. De Armas admitted he was aware that, in an effort to cover up the hole and mislead investors, a subordinate who reported to him had falsified Ocala Funding collateral reports and periodically sent the falsified reports to financial institution investors in Ocala Funding and to other third parties. De Armas acknowledged that he and the CEO also deceived investors by providing them with a false explanation for the hole in Ocala Funding.
De Armas also previously admitted in court that he directed a subordinate to inflate an account receivable balance for loan participations in TBW’s financial statements. De Armas acknowledged that he knew that the falsified financial statements were subsequently provided to Ginnie Mae and Freddie Mac for their determination on the renewal of TBW’s authority to sell and service securities issued by them.
In addition, de Armas admitted in court to aiding and abetting false statements in a letter the CEO sent to the U.S. Department of Housing and Urban Development, through Ginnie Mae, regarding TBW’s audited financial statements for the fiscal year ending on March 31, 2009. De Armas reviewed and edited the letter, knowing it contained material omissions. The letter omitted that the delay in submitting the financial data was caused by concerns its independent auditor had raised about the financing relationship between TBW and Colonial Bank and its request that TBW retain a law firm to conduct an internal investigation. Instead, the letter falsely attributed the delay to a new acquisition and TBW’s switch to a compressed 11-month fiscal year.
“We are pleased to have joined our law enforcement colleagues in bringing Mr. de Armas to justice,” said Inspector General Rymer. “The former chief financial officer’s actions contributed to one of the largest bank frauds in the country and led to the demise of TBW. His punishment, along with the earlier sentencings of other co-conspirators involved in the Colonial Bank and TBW scheme, sends a clear message that those who abuse their positions of trust and seek to undermine the integrity of the financial services industry will be held accountable. We will continue to pursue such cases in the interest of ensuring the safety and soundness of our nation’s banks and the strength of the financial services industry as a whole.”
“Delton de Armas was a key player in the TBW fraud; the significant sentence of 60 months handed down today appropriately takes that role into account,” said Inspector General Linick.
In April 2011, a jury in the Eastern District of Virginia found Lee Bentley Farkas, the chairman of TBW, guilty of 14 counts of conspiracy, bank, securities, and wire fraud. On June 30, 2011, Judge Brinkema sentenced Farkas to 30 years in prison. In addition, six individuals have pleaded guilty for their roles in the fraud scheme, including: Paul Allen, former chief executive officer of TBW, who was sentenced to 40 months in prison; Raymond Bowman, former president of TBW, who was sentenced to 30 months in prison; Desiree Brown, former treasurer of TBW, who was sentenced to six years in prison; Catherine Kissick, former senior vice president of Colonial Bank and head of its Mortgage Warehouse Lending Division (MWLD), who was sentenced to eight years in prison; Teresa Kelly, former operations supervisor for Colonial Bank’s MWLD, who was sentenced to three months in prison; and Sean Ragland, a former senior financial analyst at TBW, who was sentenced to three months in prison.
The case is being prosecuted by Deputy Chief Patrick Stokes and Trial Attorney Robert Zink of the Criminal Division’s Fraud Section and Assistant U.S. Attorneys Charles Connolly and Paul Nathanson of the Eastern District of Virginia. This case was investigated by SIGTARP, FBI’s Washington Field Office, FDIC-OIG, HUD-OIG, FHFA-OIG, and the IRS-Criminal Investigation. The Financial Crimes Enforcement Network (FinCEN) of the Department of the Treasury also provided support in the investigation. The department would also like to acknowledge the substantial assistance of the SEC in the investigation of the fraud scheme.
This prosecution was brought in coordination with President Barack Obama’s Financial Fraud Enforcement Task Force. President Obama established the interagency Financial Fraud Enforcement Task Force to wage an aggressive, coordinated, and proactive effort to investigate and prosecute financial crimes. The task force includes representatives from a broad range of federal agencies, regulatory authorities, inspectors general, and state and local law enforcement who, working together, bring to bear a powerful array of criminal and civil enforcement resources. The task force is working to improve efforts across the federal executive branch and, with state and local partners, to investigate and prosecute significant financial crimes, ensure just and effective punishment for those who perpetrate financial crimes, combat discrimination in the lending and financial markets, and recover proceeds for victims of financial crimes.
TOP-SECRET from ten FBI – Help Us Catch a Killer Unknown Offender Linked by DNA in Two Separate Cases
 |
|---|
$150,000 Reward
In October 2009, college student Morgan Harrington left a Metallica concert at the University of Virginia in Charlottesville and disappeared. It would be several months before her body was discovered in a field about 10 miles away.
We need your help to find her killer. The Virginia State Police, Fairfax City Police, and the FBI have released two enhanced sketches of the suspect and are reminding the public there is a reward of up to $150,000 for information leading to an arrest and conviction in the case. Story | Press Release
| Investigative Agencies | ||
 |
 |
 |
|---|---|---|
| Virginia State Police Virginia |
City of Fairfax Police Virginia |
Federal Bureau of Investigation Washington Field Office |
The following agencies are cooperating in the investigation:
the Virginia State Police, City of Fairfax Police, University of Virginia Police,
Charlottesville Police, Albemarle County Police, Albemarle County Commonwealth’s Attorney,
Virginia Tech Police Department, George Mason Police Department and the FBI.
TOP-SECRET from the FBI – Al Shabaab Associate Pleads Guilty in Manhattan
THE INVESTMENT MAGAZINE – THE ORIGINAL – Das INVESTMENT MAGAZIN – DAS ORIGINAL – Preet Bharara, the United States Attorney for the Southern District of New York; Janice K. Fedarcyk, the Assistant Director in Charge of the New York Field Office of the Federal Bureau of Investigation (“FBI”); and Raymond W. Kelly, the Police Commissioner of the City of New York (“NYPD”), announced that MOHAMED IBRAHIM AHMED pled guilty today to conspiring to provide material support to and receive military-type training from al Shabaab, a terrorist organization based in Somalia. The U.S. Department of State has designated al Shabaab as a Foreign Terrorist Organization. AHMED pled guilty before U.S. District Judge P. Kevin Castel.
Manhattan U.S. Attorney Preet Bharara said: “Mohamed Ibrahim Ahmed traveled a long way from his home in Sweden to Somalia, where he took up the cause of al Shabaab, a deadly terrorist organization and sworn enemy of the United States and its people. Protecting Americans from the threat of terrorism both at home and abroad is the highest priority of this office, and today’s plea is yet another victory in that fight.”
FBI Assistant Director in Charge Janice K. Fedarcyk said: “The guilty plea entered today, by a man so dedicated to a known terrorist group that he traveled to Somalia to train with al Shabaab and give them financial support, emphasizes the need for continued vigilance in the fight against terrorism worldwide. The FBI is committed to working with our law enforcement partners here and abroad to thwart would-be terrorists.”
NYPD Commissioner Raymond W. Kelly said: “This plea is important to the ongoing efforts by the NYPD and federal partners to deter terrorist organizations and their followers, who continue in their attempts to put New York City and the United States at risk.”
According to the superseding information filed today in Manhattan federal court and prior court filings:
In early 2009, AHMED left his home in Sweden and traveled to Somalia in order to support and receive military-type training from al Shabaab. Al Shabaab has used violent means to destabilize the government of Somalia and to force the withdrawal of foreign troops from the country. The group has recruited foreign fighters to join in its “holy war” in Somalia, resulting in men from other countries, including the United States, traveling there to engage in violent jihad. Al Shabaab has also made numerous public statements demonstrating its intent to harm the United States.
While in Somalia, AHMED contributed approximately 3,000 Euros to al Shabaab, received training and instruction with respect to bomb-making and bomb-detonation, and purchased an AK-47 rifle, additional magazines, and two grenades. AHMED subsequently provided the rifle and magazines to an al Shabaab military commander.
AHMED, 38, a native of Eritrea and a lawful resident of Sweden, was arrested in Nigeria in November 2009. On March 6, 2010, AHMED was transferred to the custody of the United States and subsequently transported to the Southern District of New York for prosecution.
AHMED pled guilty to one count of conspiracy to provide material support to a Foreign Terrorist Organization (al Shabaab) and one count of conspiracy to receive military-type training from a Foreign Terrorist Organization (al Shabaab). He faces a maximum sentence of 10 years in prison, and is scheduled to be sentenced by Judge Castel on November 2, 2012 at 11:30 a.m.
Mr. Bharara praised the outstanding investigative work of the New York-based Joint Terrorism Task Force—which principally consists of special agents of the FBI and detectives of the New York City Police Department. He also expressed gratitude to the U.S. Department of Justice’s National Security Division, the Office of International Affairs, and the U.S. Department of State for their extraordinary assistance in the case. Mr. Bharara also thanked the Governments of Sweden and Nigeria for their assistance in this matter.
This case is being handled by the Office’s Terrorism and International Narcotics Unit. Assistant United States Attorneys Benjamin Naftalis, John P. Cronan, Rachel P. Kovner, and Christopher LaVigne are in charge of the prosecution.
Reporting by Bernd Puzlch, Sarah Goodsmith, Bridget Gallagher and Tim Wilkinson
TOP-SECRET – Open Source Center North Korea Propaganda Coverage of Party Representatives Conferences
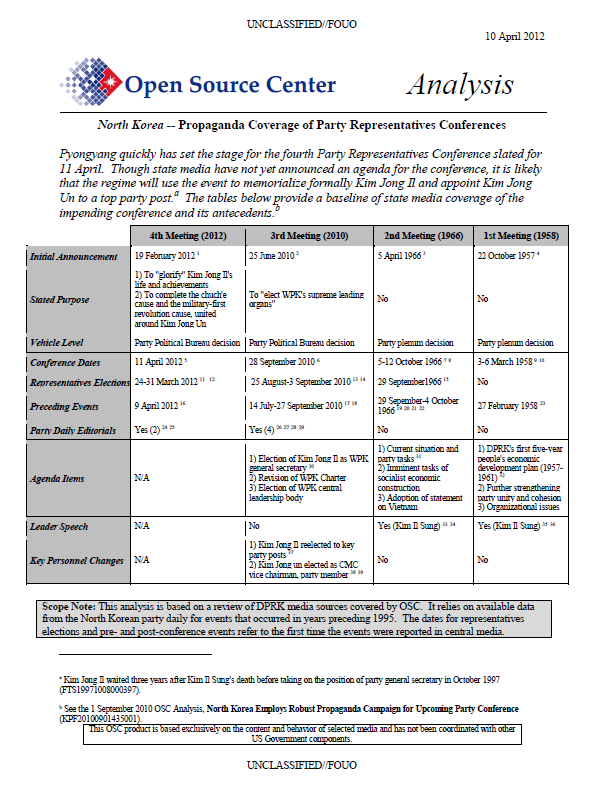
Pyongyang quickly has set the stage for the fourth Party Representatives Conference slated for 11 April. Though state media have not yet announced an agenda for the conference, it is likely that the regime will use the event to memorialize formally Kim Jong Il and appoint Kim Jong Un to a top party post. The tables below provide a baseline of state media coverage of the impending conference and its antecedents.
This analysis is based on a review of DPRK media sources covered by OSC. It relies on available data from the North Korean party daily for events that occurred in years preceding 1995. The dates for representatives elections and pre- and post-conference events refer to the first time the events were reported in central media.
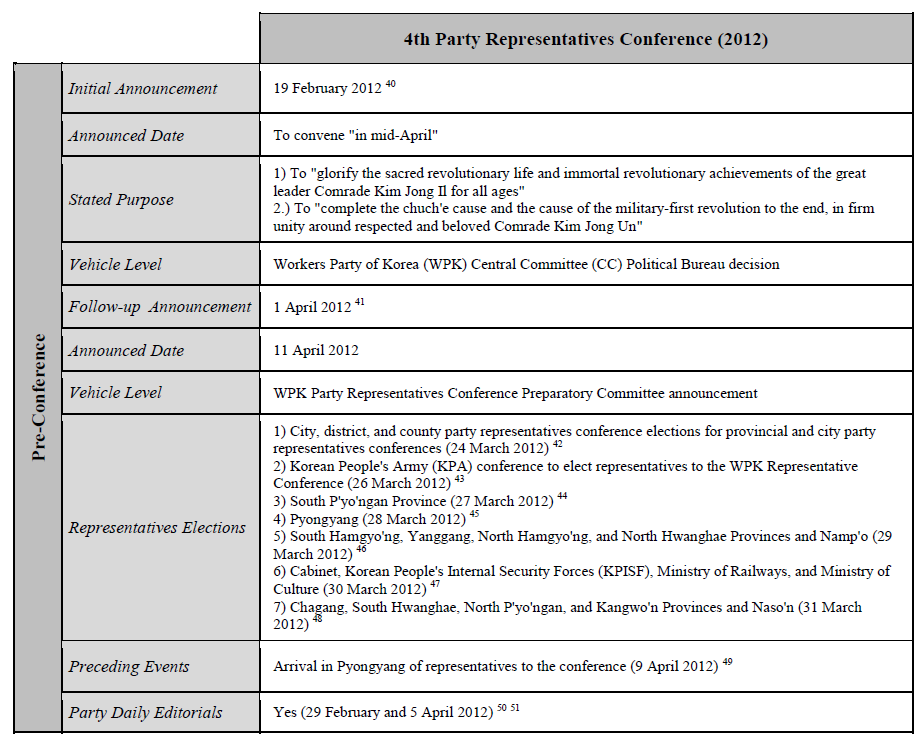
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – Open Source Center North Korea Kim Jong Un Party Leadership Analysis
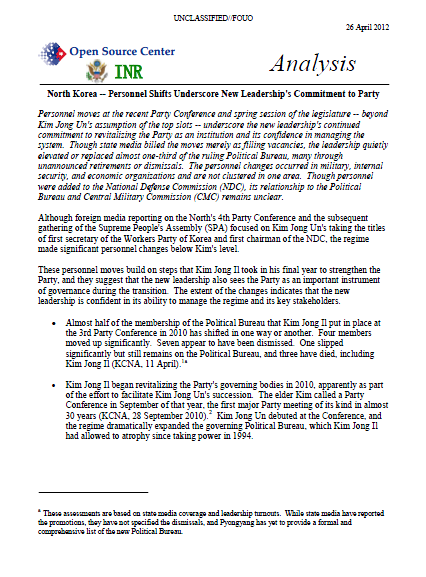
Personnel moves at the recent Party Conference and spring session of the legislature — beyond Kim Jong Un’s assumption of the top slots — underscore the new leadership’s continued commitment to revitalizing the Party as an institution and its confidence in managing the system. Though state media billed the moves merely as filling vacancies, the leadership quietly elevated or replaced almost one-third of the ruling Political Bureau, many through unannounced retirements or dismissals. The personnel changes occurred in military, internal security, and economic organizations and are not clustered in one area. Though personnel were added to the National Defense Commission (NDC), its relationship to the Political Bureau and Central Military Commission (CMC) remains unclear.
Although foreign media reporting on the North’s 4th Party Conference and the subsequent gathering of the Supreme People’s Assembly (SPA) focused on Kim Jong Un’s taking the titles of first secretary of the Workers Party of Korea and first chairman of the NDC, the regime made significant personnel changes below Kim’s level.
These personnel moves build on steps that Kim Jong Il took in his final year to strengthen the Party, and they suggest that the new leadership also sees the Party as an important instrument of governance during the transition. The extent of the changes indicates that the new leadership is confident in its ability to manage the regime and its key stakeholders.
Almost half of the membership of the Political Bureau that Kim Jong Il put in place at the 3rd Party Conference in 2010 has shifted in one way or another. Four members moved up significantly. Seven appear to have been dismissed. One slipped significantly but still remains on the Political Bureau, and three have died, including Kim Jong Il (KCNA, 11 April).
Kim Jong Il began revitalizing the Party’s governing bodies in 2010, apparently as part of the effort to facilitate Kim Jong Un’s succession. The elder Kim called a Party Conference in September of that year, the first major Party meeting of its kind in almost 30 years (KCNA, 28 September 2010). Kim Jong Un debuted at the Conference, and the regime dramatically expanded the governing Political Bureau, which Kim Jong Il had allowed to atrophy since taking power in 1994.
…
Military/Security Balance
The leadership is continuing the trend of blurring the distinction between military and internal security personnel on the one hand and civilian Party leaders on the other. The reason for the blending is not clear, but the regime since 2010 has conferred general-officer rank on several regime civilians.
This time the regime named Choe Ryong Hae a vice marshal and put him in charge of the Army’s influential political affairs department, which Kim Jong Il’s trusted military advisor Jo Myong Rok once ran. Though not a professional soldier, Choe effectively now outranks Chief of Staff Ri Yong Ho, calling into question Ri’s influence.
At the same time, the regime has increased the percentage of military and internal security personnel on the Political Bureau to its highest level since before 1980. The two groups now make up more than a third of the total membership. In 2010, they represented a quarter of the group, which was the same share they had after the 1980 Party Congress.
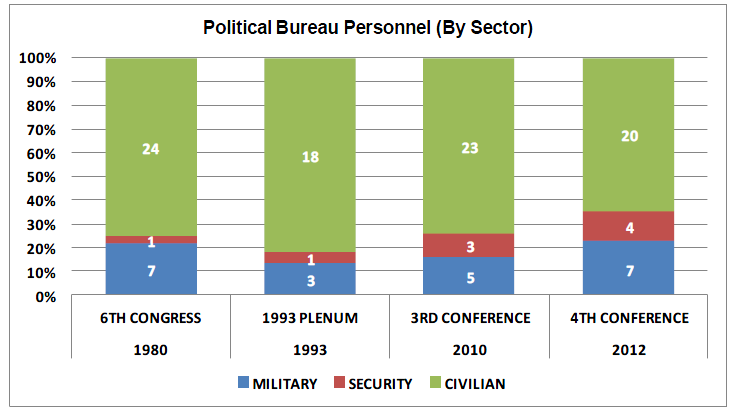
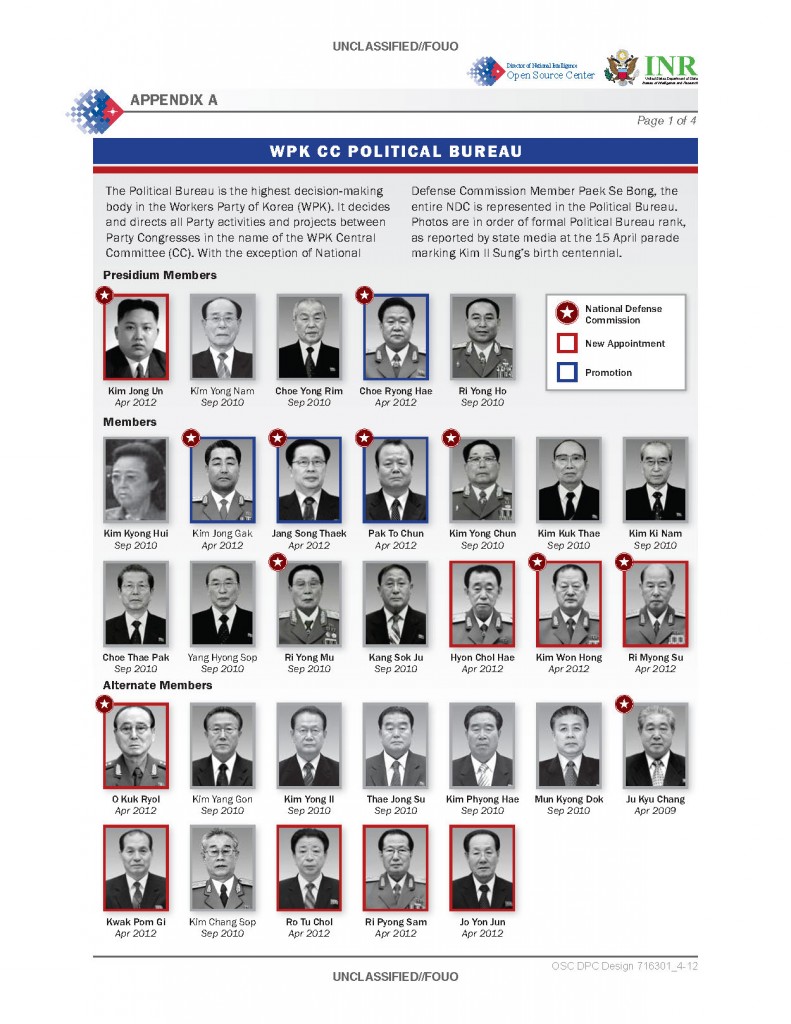
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – Open Source Center Al-Qaeda Master Narratives Report
Understanding master narratives can be the difference between analytic anticipation and unwanted surprise, as well as the difference between seizing opportunities to undermine adversary messaging and letting those opportunities pass by. Master narratives are the historically grounded stories that reflect a community’s identity and experiences, or explain its hopes, aspirations, and concerns. These narratives help groups understand who they are and where they come from, and how to make sense of unfolding developments around them. Master narratives often emerge naturally over time as a community discovers and defends its shared identity. Governments, influencers, and non-state actors can also create master narratives in their efforts to persuade target audiences to support political platforms, reject opposing viewpoints, or take up arms for a cause. Like political, social, and religious leaders, violent extremist organization communicators promulgate their own master narratives in an attempt to discredit adversaries while attracting new recruits. Understanding these master narratives presents US communicators and analysts with the challenge of placing themselves in the mindset of an extremist communicator or sympathizer, and recognizing that foreign audiences may be susceptible to believing carefully crafted stories that—from an American vantage point—may appear conspiratorial and outlandish.
This report is part of a multi-phase effort spearheaded by the Center for Strategic Counterterrorism Communications (CSCC), Open Source Center (OSC), and Monitor 360: its objective is to use master narratives to reveal strategic communications opportunities that can help combat and undermine al-Qaeda (AQ) messaging. This report represents a first step in that effort by surfacing and articulating six critical AQ master narratives and detailing how those master narratives are used by two case study AQ affiliates: al-Qaeda in the Arabian Peninsula (AQAP) and al-Qaeda in the Islamic Maghreb (AQIM). This report follows a consistent structure for articulating these narratives, assesses how AQAP and AQIM communicators use them, and analyzes the dynamics and forces that might impact how these narratives evolve over time. For seasoned AQ experts, these narratives will already be familiar — the content contained in this report can be used to check assumptions, surface tacit knowledge, and aid customer communications. For newcomers to AQ messaging and counter-messaging operations, these narratives offer deep insights into the stories used by AQ communicators in their messaging and recruitment efforts. Following this study, two additional reports will surface and articulate the master narratives held by audiences in Yemen and Algeria — critical fronts for AQAP and AQIM, respectively. A fourth report will focus on opportunities for US communicators. The figure on the following page outlines how these reports combine to surface new, actionable opportunities for US communicators.
This report is focused on helping US communicators and analysts better identify opportunities to undermine AQ messaging. With this in mind, the report analyzes how AQ portrays itself and its objectives to the public through statements and multimedia releases – the messaging used to attract recruits, build public sympathy, and undermine adversaries such as the United States. Research for this analysis included AQ messaging dating back to 2000, with particular attention paid to recent messaging from 2009-2011. In addition to primary sources and open source research, interviews with 25 SMEs were used to surface master narratives, test hypotheses, and validate assertions. These SMEs were asked a combination of expansive, open-ended questions designed to surface new hypotheses as well as targeted questions designed to verify assertions. Combining these interviews with open source research, this report highlights how each master narrative reflects perceived history, themes, and objectives that are central to AQ’s public identity. Each of these master narratives appear with varied frequency across AQ messaging and propaganda, and collectively they represent a unified narrative system used by AQ and affiliate communicators.
This report is not a silver bullet: identifying and capitalizing on opportunities to undermine AQ messaging will continue to rely on the creativity and expertise of communicators and analysts confronted with complex mission goals, changing local conditions, and bureaucratic constraints. What this report can do is lay the foundation for systematically assessing how AQ master narratives and messaging align or conflict with existing local beliefs in strategically significant locations, such as Yemen and Algeria. The insights and analysis provided in this report serve as a first step in providing communicators and analysts with the resources they need to seize upon those opportunities. In doing so, they will be better equipped to augment US efforts to combat and undermine AQ messaging.
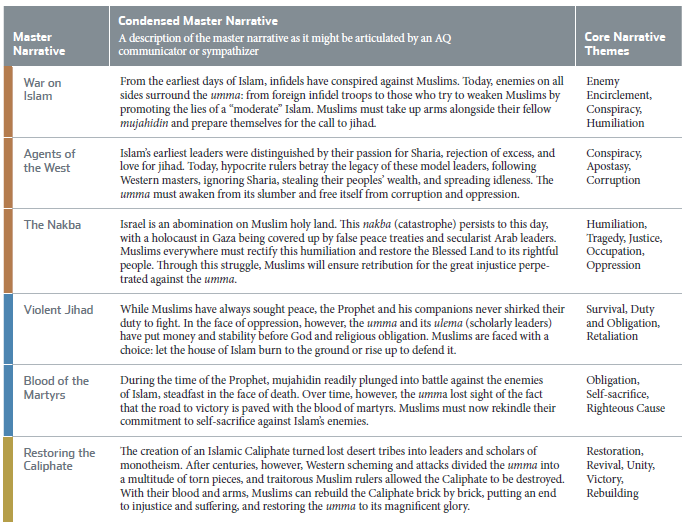
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET from the FBI – ING Bank N.V. Agrees to Forfeit $619 Million for Illegal Transactions with Cuban and Iranian Entities
WASHINGTON—ING Bank N.V., a financial institution headquartered in Amsterdam, has agreed to forfeit $619 million to the Justice Department and the New York County District Attorney’s Office for conspiring to violate the International Emergency Economic Powers Act (IEEPA) and the Trading with the Enemy Act (TWEA) and for violating New York state laws by illegally moving billions of dollars through the U.S. financial system on behalf of sanctioned Cuban and Iranian entities. The bank has also entered into a parallel settlement agreement with the Treasury Department’s Office of Foreign Assets Control (OFAC).
The announcement was made by Lisa Monaco, Assistant Attorney General for National Security; Ronald C. Machen, U.S. Attorney for the District of Columbia; Assistant Attorney General Lanny A. Breuer of the Criminal Division; District Attorney Cyrus R. Vance, Jr. of the New York County District Attorney’s Office; James W. McJunkin, Assistant Director in Charge of the FBI Washington Field Office; Richard Weber, Chief, Internal Revenue Service (IRS) Criminal Investigation; and Adam J. Szubin, Director of the Office of Foreign Assets Control.
A criminal information was filed today in federal court in the District of Columbia charging ING Bank N.V. with one count of knowingly and willfully conspiring to violate the IEEPA and TWEA. ING Bank waived the federal indictment, agreed to the filing of the information, and has accepted responsibility for its criminal conduct and that of its employees. ING Bank agreed to forfeit $619 million as part of the deferred prosecution agreements reached with the Justice Department and the New York County District Attorney’s Office.
According to court documents, starting in the early 1990s and continuing until 2007, ING Bank violated U.S. and New York state laws by moving more than $2 billion illegally through the U.S. financial system—via more than 20,000 transactions—on behalf of Cuban and Iranian entities subject to U.S. economic sanctions. ING Bank knowingly and willfully engaged in this criminal conduct, which caused unaffiliated U.S. financial institutions to process transactions that otherwise should have been rejected, blocked, or stopped for investigation under regulations by OFAC relating to transactions involving sanctioned countries and parties.
“The fine announced today is the largest ever against a bank in connection with an investigation into U.S. sanctions violations and related offenses and underscores the national security implications of ING Bank’s criminal conduct. For more than a decade, ING Bank helped provide state sponsors of terror and other sanctioned entities with access to the U.S. financial system, allowing them to move billions of dollars through U.S. banks for illicit purchases and other activities,” said Assistant Attorney General Monaco. “I applaud the agents, analysts, and prosecutors who for years pursued this case.”
“Banks that try to skirt U.S. sanctions laws undermine the integrity of our financial system and threaten our national security,” said U.S. Attorney Machen. “When banks place their loyalty to sanctioned clients above their obligation to follow the law, we will hold them accountable. On more than 20,000 occasions, ING intentionally manipulated financial and trade transactions to remove references to Iran, Cuba, and other sanctioned countries and entities. Today’s $619 million forfeiture—the largest ever—holds ING accountable for its wrongdoing.”
“For years, ING Bank blatantly violated U.S. laws governing transactions involving Cuba and Iran and then used shell companies and other deceptive measures to cover up its criminal conduct,” said Assistant Attorney General Breuer. “Today’s resolution reflects a strong collaboration among federal and state law enforcement partners to hold ING accountable.”
“Investigations of financial institutions, businesses, and individuals who violate U.S. sanctions by misusing banks in New York are vitally important to national security and the integrity of our banking system,” said New York County District Attorney Vance. “These cases give teeth to sanctions enforcement, send a strong message about the need for transparency in international banking, and ultimately contribute to the fight against money laundering and terror financing. I thank our federal partners for their cooperation and assistance in pursuing this investigation.”
“Today, ING Bank was held accountable for their illegal actions involving the movement of more than $2 billion through the U.S. financial system on behalf of Cuban and Iranian entities subject to U.S. economic sanctions,” said FBI Assistant Director in Charge McJunkin. “Investigations of this type are complicated and demand significant time and dedication from agents, analysts and prosecutors. In this case, their steadfast tenacity brought this case through to today’s result, and we will continue to pursue these matters in diligent fashion.”
“In today’s environment of increasingly sophisticated financial markets, it’s critical that global institutions follow U.S. law, including sanctions against other countries,” said IRS Criminal Investigation Chief Weber. “The IRS is proud to share its world-renowned financial investigative expertise in this and other complex financial investigations. Creating new strategies and models of cooperation among our law enforcement partners to ensure international financial compliance is a top-priority of the IRS.”
“Our sanctions laws reflect core U.S. national security and foreign policy interests and OFAC polices them aggressively. Today’s historic settlement should serve as a clear warning to anyone who would consider profiting by evading U.S. sanctions,” said OFAC Director Szubin. “We commend our federal and state colleagues for their work on this important investigation.”
The Scheme
According to court documents, ING Bank committed its criminal conduct by, among other things, processing payments for ING Bank’s Cuban banking operations through its branch in Curaçao on behalf of Cuban customers without reference to the payments’ origin and by providing U.S. dollar trade finance services to sanctioned entities through misleading payment messages, shell companies, and the misuse of ING Bank’s internal suspense account.
Furthermore, ING Bank eliminated payment data that would have revealed the involvement of sanctioned countries and entities, including Cuba and Iran; advised sanctioned clients on how to conceal their involvement in U.S. dollar transactions; fabricated ING Bank endorsement stamps for two Cuban banks to fraudulently process U.S. dollar travelers’ cheques; and threatened to punish certain employees if they failed to take specified steps to remove references to sanctioned entities in payment messages.
According to court documents, this conduct occurred in various business units in ING Bank’s wholesale banking division and in locations around the world with the knowledge, approval, and encouragement of senior corporate managers and legal and compliance departments. Over the years, several ING Bank employees raised concerns to management about the bank’s sanctions violations. However, no action was taken.
For decades, the United States has employed sanctions and embargoes on Iran and Cuba. Financial transactions conducted by wire on behalf of Iranian or Cuban financial institutions have been subject to these U.S. sanctions. The TWEA prohibits U.S. persons from engaging in financial transactions involving or benefiting Cuba or Cuban nationals and prohibits attempts to evade or avoid these restrictions. IEEPA makes it a crime to willfully attempt to commit, conspire to commit, or aid and abet in the commission of any violations of the Iranian Transaction Regulations, which prohibit the exportation of any services from the United States to Iran and any attempts to evade or avoid these restrictions. IEEPA and TWEA regulations are administered by OFAC.
The Investigation
The Justice Department’s investigation into ING Bank arose out of ongoing investigations into the illegal export of goods from the United States to sanctioned countries, including Iran. For instance, ING processed payments on behalf of one customer, Aviation Services International B.V. (ASI), a Dutch aviation company which was the subject of a U.S. Commerce Department-initiated criminal investigation, through the United States for trade services relating to the procurement by ASI of dual-use U.S. aviation parts for ASI’s Iranian clients. The ING Bank investigation also resulted in part from a criminal referral from OFAC, which was conducting its own probe of ING Bank.
ING Bank’s forfeiture of $309.5 million to the United States and $309.5 million to the New York County District Attorney’s Office will settle forfeiture claims by the Department of Justice and the state of New York. In light of the bank’s remedial actions to date and its willingness to acknowledge responsibility for its actions, the Department will recommend the dismissal of the information in 18 months, provided ING Bank fully cooperates with, and abides by, the terms of the deferred prosecution agreement.
OFAC’s settlement agreement with ING deems the bank’s obligations to pay a civil settlement amount of $619 million to be satisfied by its payment of an equal amount to the Justice Department and the state of New York. OFAC’s settlement agreement further requires the bank to conduct a review of its policies and procedures and their implementation, taking a risk-based sampling of U.S. dollar payments, to ensure that its OFAC compliance program is functioning effectively to detect, correct, and report apparent sanctions violations to OFAC.
The case was prosecuted by Trial Attorney Jonathan C. Poling of the Justice Department’s National Security Division; Assistant U.S. Attorneys Ann H. Petalas and George P. Varghese, of the National Security Section of the U.S. Attorney’s Office for the District of Columbia; and Trial Attorney Matthew Klecka of the Criminal Division’s Asset Forfeiture and Money Laundering Section.
The case was investigated by the FBI’s Washington Field Office and the IRS-Criminal Investigation’s Washington Field Division, with assistance from the Treasury Department’s OFAC and the Commerce Department’s Bureau of Industry and Security.
The Department of Justice expressed its gratitude to Executive Assistant District Attorney, Chief of Investigation Division Adam Kaufmann; and Assistant District Attorneys Sally Pritchard and Garrett Lynch of the New York County District Attorney’s Office, Major Economic Crimes Bureau.
TOP-SECRET – The SOLO File: Declassified Documents Detail “The FBI’s Most Valued Secret Agents of the Cold War”

Washington, D.C., April 10, 2012 – The “FBI’s most valued secret agents of the Cold War,” brothers Morris and Jack Childs, together codenamed SOLO, reported back to J. Edgar Hoover starting in 1958 about face-to-face meetings with top Soviet and Chinese Communist leaders including Mao and Khrushchev, while couriering Soviet funds for the American Communist Party, according to newly declassified FBI files cited in the new book by Tim Weiner, Enemies: A History of the FBI (New York: Random House, 2012).
Highlights from the massive SOLO files (which total more than 6,941 pages in 45 volumes declassified in August 2011 and January 2012) appear on the National Security Archive’s Web site today at www.nsarchive.org, together with an overview by Tim Weiner and a new search function, powered by the Archive’s partnership with DocumentCloud, that enables full-text search of the entire SOLO file (instead of the 45 separate PDF searches required by the FBI’s Vault publication at http://vault.fbi.gov/solo).
For more on Enemies, see last night’s broadcast of The Daily Show with Jon Stewart, featuring Tim Weiner, and the reviews by The New York Times Book Review, The Guardian, and The Washington Post.
“SOLO” BY TIM WEINER
FBI Director J, Edgar Hoover’s most valued secret agent was a naturalized citizen of Russian/Ukrainian/Jewish origins named Morris Childs. He was the first and perhaps the only American spy to penetrate the Soviet Union and Communist China at the highest levels during the Cold War, including having face-to-face conversations with Nikita Khrushchev, Mao Zedong and others in a red-ribbon cast of Communist leaders.
The operation, codenamed SOLO, that the FBI built on his work (and that of his brother, Jack) posed great risks and the promise of greater rewards. The FBI’s first debriefings of Morris Childs were declassified in August 2011 in time for inclusion in the book Enemies. Even more SOLO debriefings and associated memos – upwards of 45 volumes and thousands of pages – emerged in January 2012.
Researchers have been requesting these documents for years, and with good reason. They are unique records of a crucial chapter in the history of American intelligence. They illuminate several mysteries of the Cold War, including the origins of Hoover’s hatred for Martin Luther King, some convincing reasons for Dwight Eisenhower’s decision to hold off on the CIA’s plans to invade Fidel Castro’s Cuba, and the beginnings of Richard Nixon’s thoughts about a détente with the Soviets.
Morris Childs was an important figure in the Communist Party of the United States in the 1930s and 1940s, serving as the editor of its newspaper, the Daily Worker. He and his brother Jack had fallen out with the Party in 1948. Three years later, the FBI approached him as part of a new program called TOPLEV, in which FBI agents tried to talk top-level Communist Party members and officials into becoming informants.
Childs became a Communist for the FBI. He rejoined the Party and rose higher and higher in its secret hierarchy. In the summer of 1957, the Party’s leaders proposed that he serve as their international emissary in an effort to reestablish direct political and financial ties with the Kremlin. If Moscow approved, Childs would be reporting to Hoover as the foreign secretary of the Communist Party of the United States.
The FBI’s intelligence chief, Al Belmont, could barely contain his excitement over Childs’ cooperation. If the operation succeeded, he told Hoover, “it would enhance tremendously the Bureau’s prestige as an intelligence agency.”
[See Document 1: Memorandum from A.H. Belmont to L.V. Boardman, “Courier System Between Communist Party, USA, and Communist Party, Soviet Union,” 30 August 1957. Source: http://vault.fbi.gov/solo/solo-part-01-of/view, page 17.]
On March 5, 1958, the FBI’s top intelligence officials agreed that the operation would work: the Bureau could “guide one of our informants into the position of being selected by the CPUSA as a courier between the Party in this country and the Soviet Union.”
[See Document 2: Memorandum from A.H. Belmont to L.V. Boardman, “Communist Party, USA, International Relations, Internal Security-C,” 5 March 1958. Source: http://vault.fbi.gov/solo/solo-part-01-of/view, page 1.]
On April 24, 1958, Childs boarded TWA Flight 824 to Paris, on the first leg of his long trip to Moscow, at the invitation of the Kremlin. He met the Party’s leaders over the course of eight weeks. He learned that his next stop would be Beijing. On July 6, 1958, he had an audience with Chairman Mao Zedong (see pages 13-16 of Document 3B) Was the United States planning to go to war in Southeast Asia? Mao asked. If so, China intended to fight to the death, as it had during the Korean War. “There may be many Koreas in Asia,” Mao predicted.
[See Documents 3A-B: A: Childs’ Account of his April 1958 Trip to Soviet Union and China. B: SAC, New York, to Director, FBI, 23 July 1958 [account of Child’s first trip as a double-agent] Source: http://vault.fbi.gov/solo/solo-part-02-of/view.]
Returning to Moscow that summer, conferring with leaders of the Party and the KGB, Morris received a formal invitation to attend the 21st Congress of the Communist Party of the Soviet Union, and he accepted promises of cash payments for the CPUSA that would come to $348,385 over the next few months. The money was delivered to Morris by a Soviet delegate to the United Nations at a restaurant in Queens, New York.
Though the trips exhausted him, leaving him a physically broken man, Morris Childs went abroad two or three times a year over the course of the next two decades. He undertook fifty- two international missions, befriending the world’s most powerful Communists. He controlled the income of the American Communist Party’s treasury and contributed to the formulation of its foreign policy. His work as SOLO was undetected by the KGB and kept secret from all but the most powerful American leaders.
[See Document 4: Clyde Tolson to the Director, 12 March 1959 [report on Child’s background, how he was recruited, and information from his most recent trip to Moscow] Source: http://vault.fbi.gov/solo/solo-part-11-of-17/view, p. 49.]
SOLO’s intelligence gave Hoover an unquestioned authority in the White House. The United States never had had a spy inside the high councils of the Soviet Union or the People’s Republic of China. Morris Childs would provide the U.S. government with insights no president had ever before possessed.
Hoover briefed President Eisenhower about the SOLO mission repeatedly from November 1958 onwards. For the next two years, Hoover sent summaries of his reporting directly to Eisenhower and Vice President Nixon. Hoover reported that the world’s most powerful Communists– Mao Zedong and Nikita Khrushchev– were at each other’s throats. The breach between Moscow and Beijing was a revelation to Eisenhower. The FBI director also reported that Moscow wanted the CPUSA to support the civil rights movement in the United States. The idea that communism and civil rights were connected through covert operations was electrifying to Hoover.
Hoover told the White House that SOLO had met with Anibal Escalante, a political leader of the newly victorious revolution in Cuba, a confidant to Fidel Castro and the Cuban Communist most highly regarded in Moscow. Escalante said that the Cubans knew the United States was planning a paramilitary attack to overthrow Castro. This reporting gave Eisenhower pause as he weighed the CIA’s proposal to invade the island with a force of anti-Castro Cubans undergoing training in Guatemala. He never approved the plan; that was left to President Kennedy, who went ahead with the disastrous Bay of Pigs invasion.
[See Document 5: Memoranda and Letters to Director/Naval Intelligence, Director/CIA, National Security Adviser, Secretary of State, and Vice President Nixon on Information from Anibal Escalante. Source: http://vault.fbi.gov/solo/solo-part-21-22-of/view]
Hoover reported directly to Nixon as the vice president prepared to go to Moscow in July 1959, where he would engage Khrushchev in a public discussion on the political and cultural merits of communism and capitalism. SOLO had met with the top Communist Party officials responsible for American affairs. Hoover distilled their thinking about the leading candidates in the 1960 presidential election.
Moscow liked Ike: he understood the meaning of war and he was willing to risk the chances of peace. But Senator Kennedy was judged as “inexperienced” and potentially dangerous. As for Nixon, the Communists thought he would be a capable president, though he was “cunning” and “ambitious.”
[See Document 6: SAC, New York, to Director, FBI, 13 March 1960 [report on Khrushchev’s imminent visit to France and on President Eisenhower’s prospective (later cancelled) trip to Soviet Union]. Source: http://vault.fbi.gov/solo/solo-part-19-20-of/view, pp. 93-98.]
Nixon learned from the SOLO debriefings that Moscow could conduct rational political discourse; a decade later, the lesson served him well as president when he sought détente with the Soviets.
[Adapted from Tim Weiner, Enemies: A History of the FBI, pp. 207-209]
MORE ABOUT SOLO
The SOLO records are an extraordinary new contribution to the history of the FBI and American intelligence. It is worth noting that prior to the new FBI releases, earlier scholars had made important contributions to knowledge of this FBI operation. Civil rights historian and assiduous FOIA requester David J.Garrow was the first researcher to discover the role of the Childs brothers as FBI double-agents. In his book, Martin Luther King and the FBI: from ‘Solo’ to Memphis (New York: W. W. Norton, 1981), Garrow sought to explain why J.Edgar Hoover and the Bureau were such “viciously negative” opponents of King. Garrow disclosed that the Childs brothers had provided information to the FBI on Stanley Levison, one of King’s key political advisers. Levison had been active in the U.S. Communist Party during the early 1950s but, as Childs reported, had left the organization because of its political irrelevance. Nevertheless, the FBI saw Levison as a Soviet agent and used his former political connections as leverage to force King to break with his adviser.
Following Garrow’s trail was the late John Barron, a former Naval intelligence officer turned journalist and later a full-time writer for Readers Digest who produced as full an account of “Operation Solo” as was possible in the 1990s. An expert on the KGB, Barron met numerous former Soviet agents. One day, Morris Childs and his wife turned up at Barron’s Washington, D.C. office. Recognizing the Childs’ importance, Barron wanted to tell Morris’ story and did so through interviews with the FBI case officers who had handled contacts with the Childs brothers and their associates. Barron had no access to the documents, but his book, Operation Solo: The FBI’s Man in the Kremlin (Regnery, 1996), provided the first detailed account of the rise of Morris Childs to an influential role in the U.S. Communist Party, why he secretly broke with the Party, when and how he started to work with the FBI, and how he used his party connections and recurrent travel to Moscow and Beijing to provide current intelligence on developments in those capitals.
– William Burr
THE DOCUMENTS
Archive staff have downloaded the SOLO files from the FBI site and launched them in DocumentCloud in order to get a higher-quality full-text (OCR) and keyword search capacity down to the individual page level. The following files correspond to the 45 volumes posted on the FBI’s Vault. To search the entire group, enter terms in the field below and press “Enter.” The results will take you to the correct volume. Repeat your search and the results will take you to the correct page with the term highlighted in yellow.
TOP-SECRET – Open Source Center Analysis of North Korea Joint Ventures With Foreign Partners 2004-2011
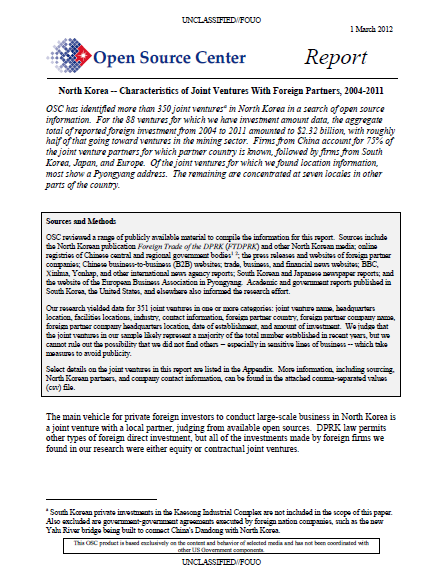
OSC has identified more than 350 joint ventures in North Korea in a search of open source information. For the 88 ventures for which we have investment amount data, the aggregate total of reported foreign investment from 2004 to 2011 amounted to $2.32 billion, with roughly half of that going toward ventures in the mining sector. Firms from China account for 75% of the joint venture partners for which partner country is known, followed by firms from South Korea, Japan, and Europe. Of the joint ventures for which we found location information, most show a Pyongyang address. The remaining are concentrated at seven locales in other parts of the country.
The main vehicle for private foreign investors to conduct large-scale business in North Korea is a joint venture with a local partner, judging from available open sources. DPRK law permits other types of foreign direct investment, but all of the investments made by foreign firms we found in our research were either equity or contractual joint ventures.
North Korean joint ventures, like other companies in North Korea, appear to be largely staffed by Koreans and operate under the constraints of the North Korean system. Majority ownership of joint ventures, however, appears to be primarily in the hands of the foreign partners: eight of the 12 joint ventures for which we have ownership share information are controlled by overseas firms, and the remaining four are split 50-50 (Table 1). Directorships and presidencies of North Korean joint ventures are often held by an officer of the foreign company.
OSC has identified 351 North Korean joint ventures with partner companies from around the world and in a range of industries (Table 2). More than 260 of these joint ventures have been active as recently as 2004.
…
Chinese Involvement Preeminent
Partner firms in North Korean joint ventures have come from Asia, Europe, Oceania, and North America (Table 2), but Chinese firms are the dominant investors.
- China accounts for 205 of the joint ventures we found. Japan with 15 and South Korea with 10 are a distant second and third.
- European companies from Italy, the United Kingdom, Netherlands, and Germany are engaged in joint ventures in North Korea, focusing on finance and technology.
- Egyptian and Thai firms do not sponsor many JVs, but their partnerships are crucial to North Korea’s domestic communications network — managing the country’s mobile telephone network and Internet services, respectively.
The share of Chinese firms as a total of new North Korean joint venture starts appears to be sharply increasing. Out of the JVs for which we know country of investor and start date, only four in ten had Chinese investors before 2004. From then until the end of 2011, however, Chinese firms represent about 87 percent of JVs started, 148 of the 167 in this set.
- Most of the Chinese firms that we found with specific location data were from the northeast provinces of Liaoning and Jilin, both of which share long borders with North Korea (Figure 3). Companies based in Shandong, Beijing, and Tianjin are also major players in joint ventures.
When compared with their investment in other destinations, though, Chinese firms’ investment in North Korea is small. Even firms from Liaoning Province — despite their proximity to the DPRK — sent almost 99% of their outbound investment from 2006-2011 to destinations other than North Korea, according to a provincial government record of private outlays (Table 4).
…
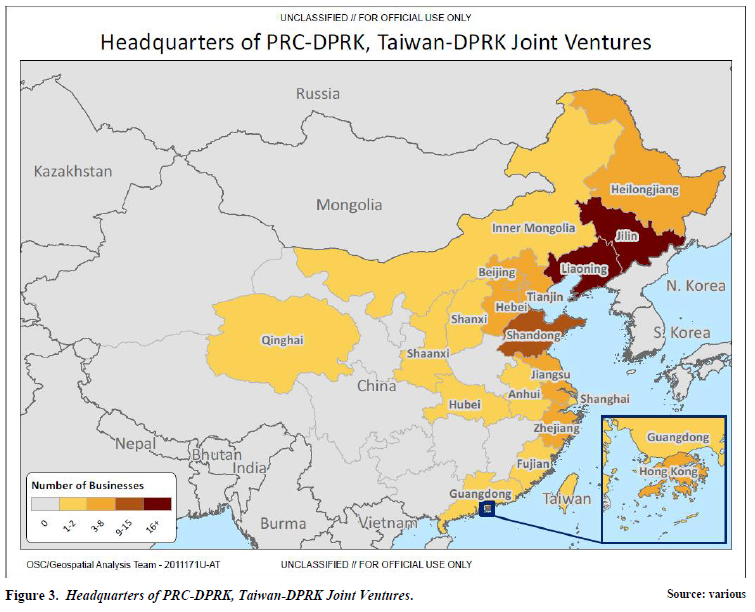
DOWNLOAD THE ORIGINAL FILE HERE
TOP-SECRET – U.S. Marine Corps Intelligence Activity Afghanistan Culture Card
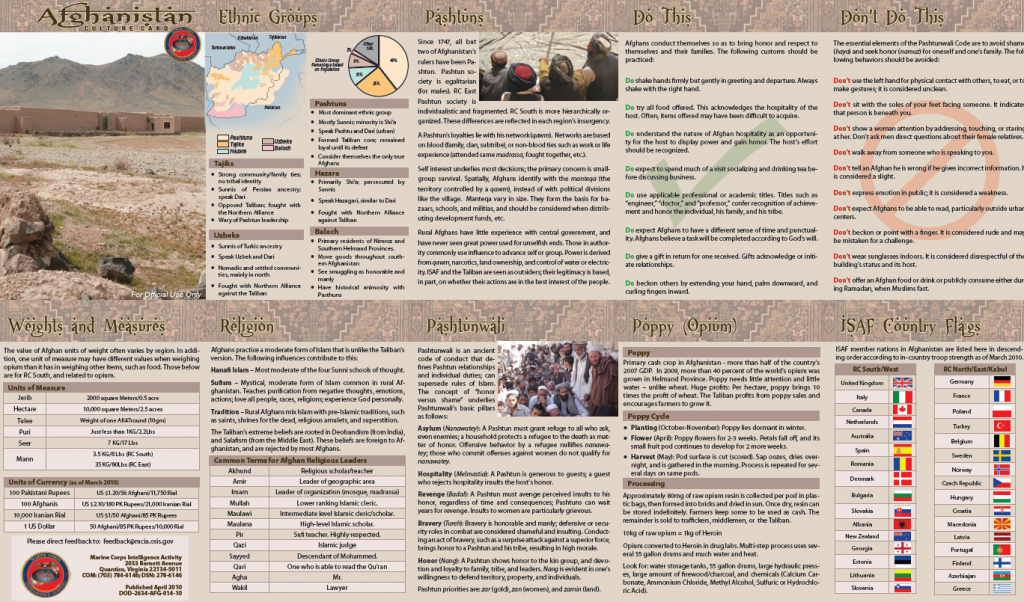
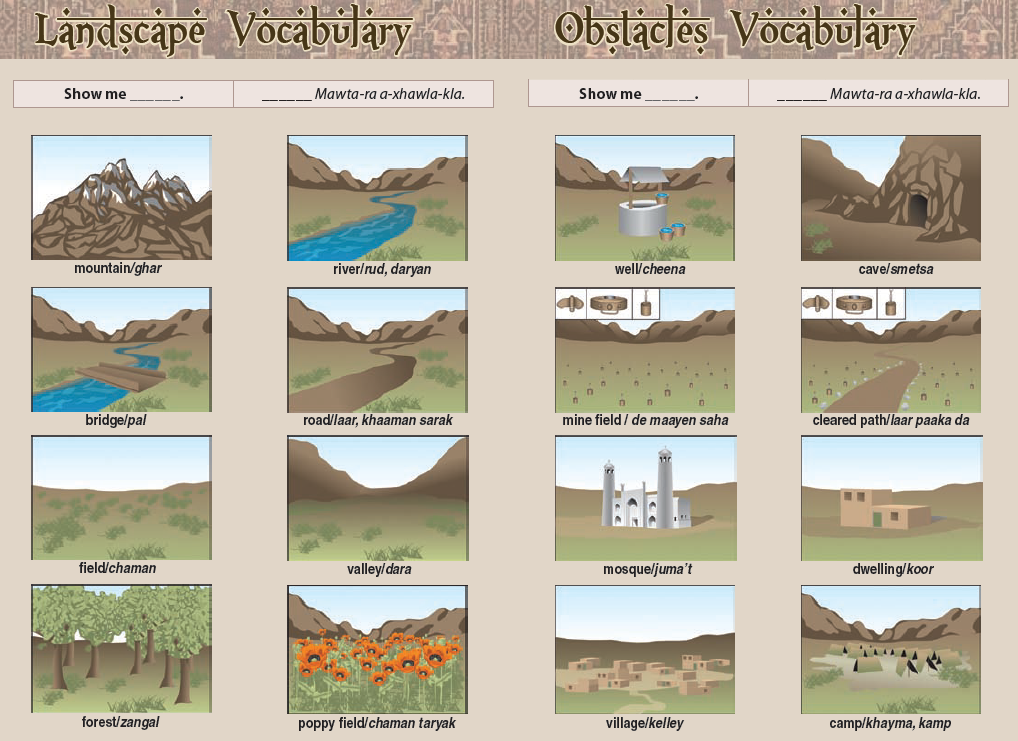

TOP-SECRET from the FBI – Chicago Man Sentenced to Over Seven Years in Prison for Attempting to Provide Funds to Support al Qaeda in Pakistan
CHICAGO—A Chicago man who personally provided hundreds of dollars to an alleged terrorist leader with whom he had met in his native Pakistan, was sentenced today to 7.5 years in federal prison for attempting to provide additional funds to the same individual after learning he was working with al Qaeda. The defendant, Raja Lahrasib Khan, a Chicago taxi driver and native of Pakistan who became a naturalized U.S. citizen in 1988, pleaded guilty in February to one count of attempting to provide material support to a foreign terrorist organization, following his arrest in March 2010.
Khan, 58, of the city’s north side, displayed “toxic altruism” U.S. District Judge James Zagel said in imposing the 90-month sentence, followed by lifetime supervised release, in Federal Court in Chicago. In addition, the judge said it was a “profoundly aggravating factor” that Khan’s crime occurred after he voluntarily chose to become a naturalized U.S. citizen.
Although Khan’s actual donations (approximately $500 to $550) and attempted donation ($1,000) were, relatively speaking, not incredibly substantial amounts, donations need not be large to be of assistance to terrorist organizations, the government argued, and the judge noted as well.
Khan’s plea agreement called for an agreed sentence of between five and eight years in prison, and it requires Khan to cooperate with the government in any matter in which he is called upon to assist through the termination of his sentence and any period of supervised release.
The sentence was announced by Patrick J. Fitzgerald, United States Attorney for the Northern District of Illinois, and Robert D. Grant, Special Agent in Charge of the Chicago Office of the Federal Bureau of Investigation.
Khan, who was born and resided in the Azad Kashmir region of Pakistan before immigrating to the United States in the late 1970s, admitted that he met with Ilyas Kashmiri, a leader of the Kashmir independence movement, in Pakistan in the early to mid-2000s and again in 2008. At the time of the second meeting, Khan knew or had reason to believe that Kashmiri was working with al Qaeda, in addition to leading attacks against the Indian government in the Kashmir region. During their 2008 meeting, Kashmiri told Khan that Osama bin Laden was alive, healthy, and giving orders, and Khan gave Kashmiri approximately 20,000 Pakistani rupees (approximately $200 to $250), which he intended Kashmiri to use to support attacks against India.
On November 23, 2009, Khan sent approximately 77,917 rupees (approximately $930) from Chicago to an individual in Pakistan, via Western Union, and then directed the individual by phone to give Kashmiri approximately 25,000 rupees (approximately $300). Although Khan intended the funds to be used by Kashmiri to support attacks against India, he was also aware that Kashmiri was working with al Qaeda.
In February and March 2010, Khan participated in several meetings with an undercover law enforcement agent who posed as someone interested in sending money to Kashmiri to purchase weapons and ammunition, but only if Kashmiri was working with al Qaeda, as well as sending individuals into Pakistan to receive military-style training so they could conduct attacks against U.S. forces and interests. On March 17, 2010, the undercover agent provided Khan with $1,000, which Khan agreed to provide to Kashmiri. Khan then gave the funds to his son, who was traveling from the United States to the United Kingdom, intending to later retrieve the money from his son in the U.K. and subsequently provide it to Kashmiri in Pakistan.
On March 23, 2010, Khan’s son arrived at an airport in the U.K. and a search by U.K. law enforcement officials yielded seven of the 10 $100 bills that the undercover agent had provided to Khan. After learning of his son’s detention, Khan attempted to end his involvement in the scheme to provide funds to Kashmiri by requesting an urgent meeting with another individual who was also present at Khan’s earlier meetings with the undercover agent. During their meeting, Khan demanded to return the undercover agent’s funds by providing $800 to this other individual.
The investigation was conducted by the Chicago FBI Joint Terrorism Task Force, with particular assistance from the Chicago Police Department, the Illinois State Police, and the Department of Homeland Security’s U.S. Customs and Border Protection and U.S. Immigration and Customs Enforcement.
The government is being represented by Assistant U.S. Attorneys Christopher Veatch and Heather McShain and DOJ trial attorney Joseph Kaster, of the Counterterrorism Section of the Justice Department’s National Security Division.
TOP-SECRET – State Dept Brett McGurk – WSJ Gina Chon Emails
|
TOP-SECRET – CIA Prepares Iraq Pullback
CIA Prepares Iraq Pullback
U.S. Presence Has Grown Contentious; Backers Favor Focus on Terror Hot Spots
By SIOBHAN GORMAN And ADAM ENTOUS
The Central Intelligence Agency is preparing to cut its presence in Iraq to less than half of wartime levels, according to U.S. officials familiar with the planning, a move that is largely a result of challenges the CIA faces operating in a country that no longer welcomes a major U.S. presence.
Under the plans being considered, the CIA’s presence in Iraq would be reduced to 40% of wartime levels, when Baghdad was the largest CIA station in the world with more than 700 agency personnel, officials said.
The CIA had already begun to pull back in Iraq since the height of the war, officials said. But the drawdown, coming six months after the departure of American military forces, would be significant. The officials declined to provide exact numbers, give a breakdown of levels of analysts versus covert operators or say where agency workers would be redeployed, all of which are classified.
Proponents of the change say the CIA can make better use of its personnel in other areas. Those could include emerging terrorist hot spots such as Yemen, home to the al Qaeda affiliate the U.S. considers to pose the greatest threat to the homeland, and Mali, where an unstable government has fanned concerns.
The move comes amid worries over possible gaps in U.S. intelligence about the threat posed by al Qaeda in Iraq. Administration officials, diplomats and intelligence analysts have in recent weeks debated whether the militant organization is a growing threat after an internal government report pointed to a rise in the number of attacks this year, officials said.
The plan would also reduce the U.S. intelligence presence in the region as neighboring Syria appears to be verging on civil war. Al Qaeda in Iraq is also sending fighters to Syria to battle the Assad regime, Pentagon officials say.
The spy drawdown is part of a broader shift in U.S.-Iraq relations, with Washington moving to scale back diplomatic and training missions in the country. But it illustrates the limits of the Obama administration’s national-security strategy, as it steers away from ground wars and toward smaller operations that combine intelligence and special-operations capabilities.
Such a strategy relies heavily on cooperation from host governments, and as the CIA’s Iraq experience shows, cooperation can wane even where the U.S. has invested billions of dollars and lost thousands of lives.
The Iraqi government, including Iraq’s intelligence service, has scaled back its counterterrorism cooperation with the U.S. as it asserts its sovereignty, U.S. officials say.
“If you don’t have that cooperation, you are probably wasting the resources you are allocating there and not accomplishing much,” said Paul Pillar, a former top CIA Near East analyst.
Backers of the drawdown say al Qaeda in Iraq doesn’t pose a direct threat to the U.S. “This is what success is supposed to be like,” said a senior U.S. official who has worked closely with the Iraqis. “Of course we don’t want to have the same number of people after all U.S. troops go home that we had at the height of the war.”
A senior Obama administration official said the U.S. is in the process of “right-sizing” its presence in Iraq. Both President Barack Obama and Iraqi Prime Minister Nouri al-Maliki have “made very clear that we’re going to continue to have a close and strong security partnership,” this official said.
The planned reductions at the CIA represent a major shift from the approach under consideration just six months ago. Late last year, the CIA and Pentagon were considering several options for CIA and special-operations commandos to team up in Iraq, according to current and former officials. One option was to have special-operations forces operate under covert CIA authority, similar to the arrangement used in the raid that killed Osama bin Laden in Pakistan.
“There was a general consensus,” said a former intelligence official, “that there was a need for this in Iraq.”
But as it became clear that the U.S. would withdraw all troops and that the Iraqi government was less inclined to accept an expansive CIA-special operations role, those plans were tabled. “It’s not going to happen,” said a U.S. official.
Iraq requires CIA officers to make appointments to meet with officials who were previously easily accessible, one of several obstacles that add to a mood of growing distance between the sides. The result is a degraded U.S. awareness about the activities of al Qaeda in Iraq, particularly at a tactical level, officials said.
“Half of our situational awareness is gone,” said one U.S. official.
Iraqi officials said they continue to cooperate with the U.S. on counterterrorism. Hassan Kokaz, deputy head of the Iraqi Ministry of Interior’s intelligence service, said the U.S. may be adjusting to the new “state-to-state” relationship between the countries since the military withdrawal in December.
“We have asked them to wear civilian clothes and not military uniforms and to be searched when they visit Iraqi institutions,” he said. “Perhaps they are not used to this.”
In the northern oil city of Kirkuk, police are pursuing al Qaeda-linked militants without needing U.S. special-operations forces or the CIA, said Gen. Sarhad Qadir, a local police commander.
Another senior Iraqi security official, however, said Iraqis don’t have the necessary surveillance and other technical capabilities. Iraqi forces also are plagued by clashing sectarian and political loyalties, the official added. “We need the Americans because they were able to work with all the [Iraqi] forces without exception,” he said.
The CIA drawdown would recalibrate the agency’s responsibility in the country away from counterterrorism operations and back toward traditional intelligence collection, with a sharpened focus on neighboring Iran, officials say. Baghdad will remain one of the agency’s largest stations, they say; Kabul is currently the largest.
The plan comes with risks, however, because al Qaeda in Iraq still presents a threat to the region.
“A further diplomatic or intelligence drawdown in Iraq could jeopardize U.S. national security down the road if al Qaeda in Iraq is able to sustain—or increase—its activity,” said Seth Jones, a Rand Corp. counterterrorism specialist who has written extensively about al Qaeda. “The concern is that al Qaeda is able to use its Iraq branch to destabilize other countries in the region, and they are able to facilitate the movement of foreign fighters.”
Al Qaeda in Iraq’s activities against the regime of Syrian President Bashar al-Assad also complicates the U.S. government’s ability to support the opposition, Pentagon officials say.
A recent assessment by the National Counterterrorism Center, the U.S. intelligence community’s central clearinghouse for counterterrorism analysis, pointed to an uptick in attacks by al Qaeda’s Iraq affiliate since the U.S. troop withdrawal in December, according to officials briefed on the document’s contents.
During high-level Obama administration discussions last month, some senior counterterrorism officials seized on the NCTC assessment as evidence of a growing threat from al Qaeda in Iraq, touching off a debate about the dangers posed by the group, officials said. A spokesman refused to comment on questions about the report.
Recent U.S. intelligence reports show the number of attacks have risen this year to 25 per month, compared with an average of 19 for each month last year, according to a person familiar with them.
But officials disagree over the significance of this increase, and questioned the value of focusing on attacks in such a limited time frame.
James Jeffrey, who served as U.S. ambassador to Iraq until last week, said the figures being cited were misleading.
“Significant attacks are continuing to drop and, most importantly, casualties are way down,” Ambassador Jeffrey said in an interview before his Iraq rotation ended. “Everything I know points to an organization—al Qaeda in Iraq—under extraordinary stress.”
TOP-SECRET from the FBI – Norwich Contractor Sentenced to Federal Prison for Role in Mortgage Fraud Scheme
David B. Fein, United States Attorney for the District of Connecticut, today announced that Brian Guimond, 45, of Norwich, was sentenced yesterday by Senior United States District Judge Alfred V. Covello in Hartford to 27 months of imprisonment, followed by one year of supervised release, for his participation in an eastern Connecticut mortgage fraud scheme.
According to court documents and statements made in court, from approximately 2004 to 2007, Jose Guzman and others used mortgage brokerage, property management, and home improvement companies to arrange for individuals (“borrowers”) to purchase real estate, primarily residential housing properties located in New London County, by obtaining funding from various mortgage companies and mortgage originators after submitting false information on the borrowers’ mortgage loan applications. The fraudulent information included information regarding income, assets, employment, rent history, as well as the borrowers’ intention to make the properties their primary residence. The borrowers were compensated for participating in the scheme.
On a number of transactions, Guimond conspired with Guzman and others to sign false employment verification forms representing that borrowers were employed at his company, The Cutting Edge Contracting Inc., a home improvement contractor and landscaping company, with offices in Norwich and New London. On certain mortgage transactions, Guzman and others falsified closing records, including false work invoices from The Cutting Edge, and caused checks to be issued at the closing made payable to The Cutting Edge, from funds provided by the lenders, purportedly to pay for work that had been done on the property prior to the closing when little or no work had been performed. The checks were converted to cashier’s checks, which were then used as purported down payments from the borrower. Through this scheme, the co-conspirators collected large commissions and fees, and a portion of the funds advanced by the lenders, which were intended to be used to finance the purchase of the properties, were in fact used for the benefit of the co-conspirators and their various companies.
According to previously filed court documents, the government believes that more than 200 fraudulent mortgages were funded through this mortgage fraud scheme, causing more than $9 million in losses to lenders.
As part of his sentence, Judge Covello ordered Guimond to pay restitution in the amount of $7,811,695.44.
On October 24, 2008, Guimond pleaded guilty to one count of conspiracy to commit mail fraud and wire fraud. Fifteen other individuals, including Jose Guzman, have pleaded guilty to various charges stemming from this scheme. Jose Guzman awaits sentencing.
This case has been investigated by the Federal Bureau of Investigation and the U.S. Department of Housing and Urban Development, Office of Inspector General. The case is being prosecuted by Assistant United States Attorneys Michael S. McGarry and David T. Huang.
In July 2009, the U.S. Attorney’s Office and the Federal Bureau of Investigation announced the formation of the Connecticut Mortgage Fraud Task Force to investigate and prosecute mortgage fraud cases and related financial crimes occurring in Connecticut. Citizens are encouraged to report any suspected mortgage fraud activity by calling 203-333-3512 and requesting the Connecticut Mortgage Fraud Task Force or by sending an e-mail to ctmortgagefraud@ic.fbi.gov.
The Connecticut Mortgage Fraud Task Force includes representatives from the U.S. Attorney’s Office; Federal Bureau of Investigation; Internal Revenue Service-Criminal Investigation; U.S. Postal Inspection Service; U.S. Department of Housing and Urban Development, Office of Inspector General; Federal Deposit Insurance Corporation, Office of Inspector General, and State of Connecticut Department of Banking.
To report financial fraud crimes and to learn more about the President’s Financial Fraud Enforcement Task Force, please visit http://www.stopfraud.gov.
TOP-SECRET from the FBI – Hells Angels Members and Associates Arrested on 91-Count Federal RICO Indictment
COLUMBIA, SC—United States Attorney Bill Nettles and Special Agent in Charge David A. Thomas of the Federal Bureau of Investigation stated that 19 individuals were arrested today after the return of a 91-count indictment charging members and associates of the Rock Hell City Nomad Chapter of the Hells Angels with racketeering and racketeering conspiracy (RICO-18 U.S.C. §1962), narcotics violations (21 U.S.C. §§ 841, 846), Hobbs Act robbery (18 U.S.C. §1951), money laundering (18 U.S.C. §1956), and firearm violations [18 U.S.C. §§ 922 and 924; 26 U.S.C. §§ 5861(d), 5845(a)(7), and 5871]. Those arrested were Daniel Eugene Bifield, a/k/a Diamond Dan (Leesville); Mark William Baker, a/k/a Lightning (Lancaster); David Channing Oiler, a/k/a Gravel Dave (Lancaster); Bruce James Long, a/k/a Bruce-Bruce (West Columbia); Richard Thrower, a/k/a Little Mark, Rat (Lancaster); David Pryor, a/k/a Yard Owl (York); James Frederick Keach, Jr., a/k/a Big Fred (Pelion); Frank Enriquez, Jr., a/k/a Big Frank (Rock Hill); Donald Boersma, a/k/a Brooklyn Donnie (Clover); Lisa Ellen Bifield, a/k/a Lisa Ellen Meyers, Lisa Ellen Stockton (Leesville); Johanna Looper, a/k/a JoJo (York); Kerry Chitwood (Gastonia, North Carolina); Carlos Hernandez (Charlotte, North Carolina); Ronald Dean Byrum, Jr., a/k/a Big Ron (Gastonia, North Carolina); Trent Allen Brown (West Columbia); Bruce Ranson Wilson, a/k/a Diesel (Swansea); Thomas McManus Plyler, a/k/a Uncle Tom (Rock Hill); Jamie Hobbs Long (Lancaster); and Somying Anderson, a/k/a Ying (West Columbia).
The arrest warrants were served along with the execution of 23 search warrants in North and South Carolina. During today’s operation, law enforcement seized methamphatamine, cocaine, marijuana, pills, and approximately 100 firearms, including two automatic machine guns. Special Agent in Charge David Thomas stated, “The significance of the extensive and long-term investigative efforts that resulted in the arrests today represent the FBI’s continuing commitment to the dismantling of organized criminal organizations. By working in a joint environment with federal, state, and local counterparts, we send a clear message that such pervasive criminal activities will not be tolerated.”
These arrests follow a two-year interagency investigation by the South Carolina Hells Angels Task Force (SCHATF). Assisting in the investigation and today’s operation were the Federal Bureau of Investigation-Columbia and Charlotte Field Divisions; Bureau of Alcohol, Tobacco, Firearms, and Explosives; Lexington County Sheriff’s Department; Lexington Police Department; Rock Hill Police Department; York County Sheriff’s Office; Lancaster County Sheriff’s Office; State Law Enforcement Division; Gastonia, Police Department; Charlotte-Mecklenburg Police Department; Gaston County Sheriff’s Office; and North Carolina State Bureau of Investigation.
United States Attorney Bill Nettles commended the inter-agency cooperation, saying, “Today’s arrests and seizures are an important step in our ongoing fight against criminal gangs operating in South Carolina. This investigation is also another example of what can be accomplished through a close partnership among local, state, and federal law enforcement agencies.” The case will be prosecuted by Assistant United States Attorney Jay N. Richardson.
The United States Attorney stated that all charges in this indictment are merely accusations and that all defendants are presumed innocent until and unless proven guilty.
TOP-SECRET – How to Conduct Psychological Operations
Psychological operations (PSYOP) have long been used by militaries around the world to coerce populations into acting in a manner favorable to their mission objective. The product of these operations, which is commonly called propaganda when distributed by enemy forces, is a mixture of complex social research, art direction and psychological theory designed to manipulate its unsuspecting recipient into modifying their behavior in a way favorable to those conducting the PSYOP. The message conveyed through a PSYOP can often stray into deeply emotional and personal territory that is intended to trigger a profound psychological response. For example, U.S. and British troops fighting in Italy and France during World War II were subjected to a barrage of leaflets distributed by German forces describing the futility of their mission, encouraging them to take the “POW life insurance policy” and instructing them that their girlfriends back home were being taken advantage of by Jewish businessmen. The methodology behind these persuasive psychological tactics is described in detail in U.S. Army FM 3-05.301 Psychological Operations Process Tactics, Techniques, and Procedures, which provides fascinating insight into the methods used by PSYOP soldiers to modify the behavior of targeted populations.
FM 3-05.301 is described as the “principal reference for the PSYOP process” detailing “procedures and strategies derived from applied scientific and academic disciplines in an effort to improve the efficacy” of PSYOP. The manual includes everything from analyzing target audiences to tactical strategies for influencing populations. There are guides for production and dissemination of pamphlets, newspapers, magazines and video propaganda designed to influence target audiences and facilitate mission objectives. An appendix to the manual even includes complex instructions on the aerial dissemination of PSYOP leaflets, including tables for calculating the altitude and wind’s effect on the range of dispersal.
In order to influence populations more effectively, FM 3-05.301 provides PSYOP soldiers with helpful tips to produce effective and professional PSYOP packages. A section of the manual focuses entirely on aesthetic symmetry, formal balance and how to capitalize on sequential eye movements that “follow an established logical sequence of shapes, colors, and numbers or letters” in the layout of PSYOP publications. Detailed descriptions of the process for assessing target audiences (TA) and their susceptibility to specific arguments or sentiments are also included. A section titled “Psychographics” provides examples of psychological motivations to utilize in the production of PSYOP material:
- Fears: What does the TA fear?
- Hates: What does the TA hate?
- Anger: What angers the TA?
- Loves: What does the TA love?
- Shame or embarrassment: What does the TA consider shameful or embarrassing?
- What is the TA dissatisfied with? (What are its gripes?)
- What are the cultural norms? (How is the TA expected to act?)
- What does the TA value? (What is important to the TA?)
- What are the frustrations? (What does the TA want that it cannot get?)
An example of a PSYOP leaflet distributed in Iraq describing terrorists’ indiscriminate use of force, including against children.
Once the TA of a PSYOP is determined, the manual describes methods for properly appealing to the interests of the audience by utilizing legitimacy, tradition, reverence and other emotional responses to coerce audience members. Nostalgia can be used to “encourage or discourage a particular behavior” by referring to the “good old days” encouraging the TA to “behave in a manner that will return to those times.” Self-interest can also be used to “play directly to the wants and desires of the individuals that make up a TA.” Or, a PSYOP may appeal to “the TA’s need to belong or conform to group standards” through either companionship or conformity utilizing “peer pressure.”
To further the emotional appeals of the argument presented in a PSYOP product, FM 3-05.301 recommends utilizing a variety of rhetorical tools so that PSYOP soldiers can “become familiar with, and ultimately develop, tactical and technical proficiency in the use of persuasion techniques.” For example, the use of “glittering generalities” or “intense, emotionally appealing words so closely associated with highly valued concepts and beliefs that the appeals are convincing without being supported by fact or reason. The appeals are directed toward such emotions as love of country and home, and desire for peace, freedom, glory, and honor.” Name-calling “seeks to arouse prejudices in an audience by labeling the object of the propaganda as something the TA fears, loathes, or finds undesirable.” Transference “projects positive or negative qualities of a person, entity, object, or value to another.” FM 3-05.301 also includes a list of “primary influence tactics”:
- Rewards and punishments: “If you do X, you will get Y,” or “if you do not do X, Y will happen to you.” Example: “Surrender, and you will be treated well; continue to fight, and you will be killed.”
- Expertise: “Speaking as an authority on the subject, I can tell you that rewards/punishments will occur if you do or do not do X.” Example: “Oil Minister Gregor (key communicator/expert) states that if rebel groups continue to sabotage oil pipelines, the national economy will be seriously affected.”
- Gifts: Giving something as a gift before requesting compliance. The idea is that the target will feel the need to reciprocate later. Example: “This well and cistern are a gift to the people of Birmingville from the coalition forces…demonstration of our good will and hope for mutual cooperation in the future.”
- Debt: Calling in past favors. Example: “Coalition forces have done a lot for Birmingville, Elder Chang: the new school, the well in the center of town… these insurgents are endangering all we have worked for together. We need your help in stopping these groups by reporting any information you and your people may discover.”
- Aversive stimulation: Continuous punishment, and the cessation of punishment, is contingent on compliance. Example: “We will continue to bomb your position unless you surrender immediately.”
- Moral appeal: Entails finding moral common ground, and then using the moral commitments of a person to obtain compliance. Example: “The killing of innocent civilians is wrong; please help the security forces stop this tragic loss of innocent life by reporting any information on terrorist activities.”
- Positive and negative self-feeling: “You will feel better/bad if you do X.” Example: “Become part of something bigger than yourself, know honor and take pride in your work…join the national security forces!”
- Positive and negative altercasting: “Good people do X / Bad people do Y.” Example: “Red Tribe members are brave and honorable people who care about the future of their country and are not intimidated by rebel groups. Call and report insurgent activity now on the coalition hotline.”
- Positive and negative esteem of others: “Other people will think highly/less of you if you do X.” Example: “Earn the respect of your friends and the pride of your family…join the Patriotsville National Guard now!”
- Fear: “Bad things will happen to you if you do X.” Example: “Only death and fire await those who continue to fight…surrender now.”
Each of these tactics is designed to further the intensity of the PSYOP argument and, thus, increase its chance of influencing its TA. Behavioral change in the TA is the ultimate goal off these activities, “challenging or emphasizing beliefs” and manipulating “existing consequences or introducing new ones” to affect the target and exploit vulnerabilities in their psychological makeup.
see
TOP-SECRET – Former Jersey City Construction Project Superintendent Sentenced to Prison for Social Security Disability Scam
NEWARK—The former project superintendent on a Jersey City, New Jersey high-rise construction project was sentenced today to six months in prison and six months of home confinement for a scheme in which he hid his employment so he could continue to receive Social Security disability payments, U.S. Attorney Paul J. Fishman announced.
Pasquale Zinna, 44, of Hackettstown, New Jersey, previously pleaded guilty to two counts of the indictment against him: Social Security disability fraud and structuring financial transactions. His wife, Janeen Zinna, 43, was also sentenced today—to two years’ probation with the special condition of 100 hours of community service. She previously pleaded guilty to a superseding information charging her with misprision of her husband’s Social Security fraud. U.S. District Court Judge Katharine S. Hayden imposed the sentences today in Newark federal court.
According to documents filed in this case and statements made in court:
In 1999, Pasquale Zinna filed an application for disability insurance benefits with the Social Security Administration (SSA), claiming that, as of March 15, 1996, he was disabled and unable to work due to a back injury. By filing the application, Pasquale Zinna agreed to notify the SSA if there was any improvement in his medical condition or if he regained the ability to work.
Beginning in September 2005, Pasquale Zinna was the project superintendent for 160 Broadway Concrete, a sub-contractor at the high-rise construction project at 77 Hudson Street in Jersey City. He failed to report his return to work to Social Security and concealed his employment at Broadway Concrete by having his paychecks issued to him in the names of other individuals, including his wife. Janeen Zinna admitted during her guilty plea that she filed a joint federal income tax return with her husband for 2007 which claimed income received from Broadway Concrete was for work she performed.
Pasquale Zinna also admitted to making a series of cash withdrawals from his joint checking account with his wife at Commerce Bank, now TD Bank, in order to avoid the bank’s reporting requirement for financial transactions in excess of $10,000.
In addition to the prison term, Judge Hayden sentenced Pasquale Zinna to three years of supervised release. He was also ordered to pay $101,753 in restitution to the Social Security Administration and to forfeit $98,000 involved in the illegal financial transactions. Janeen Zinna was also held responsible for the restitution. The defendants paid these obligations in full at today’s proceeding.
Four New York men have also pleaded guilty to a wide range of fraud and other offenses stemming from their involvement in the Jersey City construction project between 2007 and 2008.
Rocco Mazzaferro, 64, of Brooklyn, New York, and Vincenzo Genovese, 75, of Staten Island, New York, pleaded guilty November 22, 2011 to conspiracy to commit wire fraud. Vincenzo Genovese also pleaded guilty to one count of conspiracy to embezzle pension benefits.
Anselmo Genovese, 44, of Staten Island, New York, pleaded guilty December 16, 2011 to two counts of making unlawful labor payments.
Eric Haynberg, 46, of New York, pleaded guilty December 16, 2011, to a superseding information charging him with misprision of the wire fraud committed by Mazzaferro and Vincenzo Genovese.
The sentencings of Mazzaferro and Vincenzo Genovese are currently scheduled for July 10, and July 12, 2012, respectively. Sentencing for Eric Haynberg is currently scheduled for June 7, 2012, and for Anselmo Genovese on July 11, 2012.
U.S. Attorney Fishman credited special agents of the FBI, under the direction of Special Agent in Charge Michael B. Ward in Newark; and Department of Labor’s Office of Inspector General, Office of Labor Racketeering and Fraud Investigations, under the direction of Special Agent in Charge Robert L. Panella for the New York Region, for the investigation leading to the arrests and charges. He also thanked the IRS, under the direction of Acting Special Agent in Charge JoAnn S. Zuniga; and the SSA Office of the Inspector General, under the direction of Edward J. Ryan, New York Field Division, for their work on this case, and the U.S. Department of Labor, Employee Benefits Security Administration, for its assistance.
The government is represented by Assistant U.S. Attorney Leslie F. Schwartz of the U.S. Attorney’s Office Economic Crimes Unit in Newark.
TOP-SECRET – Open Source Center North Korea Unusual Threats Signal Possible Action Against South Korea
North Korea’s recent threat to carry out “special actions” against the South is rare and seems intended to signal the regime’s resolve to move forward with some form of provocation. The threat, however, is unlike past warnings the regime has typically issued prior to military provocations, suggesting that the North might follow through with a move other than a conventional military attack. Significantly, some aspects of the warning appear to signal Pyongyang’s commitment to follow up on the “actions” in the near future.
North Korea on 23 April issued an unprecedented “notice” in the name of the Korean People’s Army (KPA) Supreme Command Special Operations Action Team. The toughly worded message — a response to what Pyongyang apparently viewed as provocative remarks recently made by ROK President Lee Myung-bak — contained an unusually vague warning against Seoul.
- The “notice” particularly took issue with President Lee’s recent comments on “strengthening” South Korea’s national “self-defense capabilities” (Yonhap, 19 April), which it characterized as an “extremely grave frenzy of provocation” and a “theory of striking” the North’s “supreme headquarters” (Pyongyang radio, 23 April). The message stated that the North’s “revolutionary armed forces” will take “special actions” against the “gang of traitors’ reckless” move, and emphasized that the “actions…will start soon” (Pyongyang radio, 23 April).
- This is only the second time the North has used the “special actions” formulation to threaten President Lee in an authoritative military pronouncement. Pyongyang just five days earlier used the same threat — albeit in a passive voice — in an authoritative KPA Supreme Command spokesman’s “statement,” which said that “special action measures will be taken” (Pyongyang radio, 18 April).
- The “notice” also contained a figurative reference to turning the “group of rats” — referring to the ROK leadership — into “ashes” within “three to four minutes” (Pyongyang radio, 23 April). The “ashes” formulation is on the low end of the rhetorical threat spectrum. Pyongyang in recent years has issued more direct and literal formulations to threaten Seoul, particiuarly following the Ch’o’nan sinking.
The threat to carry out “special actions” is ambiguous and not as definitive as warnings Pyongyang has issued in the lead-up to past military provocations, suggesting that the regime might be contemplating some form of action other than an actual military attack. The North’s typical rhetorical pattern prior to provocations is to signal in authoritative media that it has decided to act without divulging how, when, or where it will move.
- Prior to the sinking of Ch’o’nan, Pyongyang issued a more direct threat in the name of an authoritative KPA General Staff spokesman stating that it “will” respond to US ROK military drills with a “powerful military counteraction” (Pyongyang radio, 25 February 2010). Similarly, leading up to the Yo’np’yo’ng Island shelling, a statement by the spokesman for the North side’s delegation to North-South military talks warned that its Army “will counter” the South’s provocations with a “merciless physical retaliation” (KCNA, 29 October 2010).
Committing to Prompt Action
Although the recent threat was not as definitive as warnings the North issued in advance of past military provocations, the unusual use of the phrase “will start soon” in combination with the unique “special actions” formulation appears designed to signal that the regime is committed to following through with its warning.
- Pyongyang’s use of the term “soon” is unusually specific and categorical. The last time the North modified its threat with this term was in a less authoritative North-South Military Talks General-Level Representative “notice,” which warned that its “army will soon” take “corresponding decisive measures” in response to South Korea distributing leaflets to the North (Pyongyang radio, 10 April 2010). Unlike the most recent threat, however, this warning was preceded by a conditional phrase, which afforded the regime the flexibility to refrain from taking immediate action.
- Further underscoring its commitment to carry out its threat, the North broadcast the KPA “notice” to both domestic and external audiences. In addition, the North Korean radio and television carried the message at least two times a day for three days following the initial announcement.
DOWNOAD THE ORIGINAL FILE HERE
Mighty Derringer – TOP SECRET – U.S. Nuclear Terrorism Exercise Leaves Indianapolis in “Ruins”

Washington, D.C., May 29, 2012 – A secret exercise in 1986 by a U.S. government counter-terrorist unit uncovered a host of potential problems associated with disrupting a nuclear terrorist plot in the United States. Declassified documents released under the Freedom of Information Act (FOIA) and posted today by the National Security Archive offer the first detailed public look at the inner workings of the agencies, military units and other U.S. entities responsible for protecting the country from a terrorist nuclear attack.
Today’s posting consists of over 60 documents related to MIGHTY DERRINGER, an exercise that focused on Indianapolis in December 1986. The materials provide background on the creation, in 1974-1975, of the Nuclear Emergency Search Team (NEST), a group assigned to respond to plausible threats of nuclear terrorism or extortion. Today, NEST (now the Nuclear Emergency Support Team) conducts exercises to assess its capability to respond to the possible presence of a terrorist device and test the ability of NEST and critical cooperating organizations (including military units)to work together.
While the MIGHTY DERRINGER exercise and resulting documents are over two decades old, the institutions participating in the exercise retain their roles today, and the issues confronting them in 1986 are similar to the ones that they would face in responding to a nuclear threat in 2012 (and beyond).
This posting is notable for being the first publication of documents that provide in-depth exposure into all aspects of such an exercise – including the state-of-play at key points and the array of issues involved in disabling terrorist devices. Of particular interest are references to the participation of the Joint Special Operations Command and Delta Force – mirroring the role they would have in a real-world incident. In addition, after-action reports reveal the assorted problems that can arise in coordinating the response to a nuclear terrorist threat among a large number of organizations.
* * * *
THE MIGHTY DERRINGER EXERCISE
In late January and early February 2012, members of the Department of Energy’s Nuclear Emergency Support Team (NEST) patrolled Lucas Oil Stadium as well as surrounding areas of Indianapolis as a precautionary measure in advance of Super Bowl XLVI. An initial survey to gather information on background levels of radiation was followed by an actual search for signatures associated with either a nuclear explosive device or a radiation dispersal device (a ‘dirty bomb’).1 Fortunately, none was found.
Over twenty-five years earlier, for a few days in early December 1986, NEST personnel also patrolled Indianapolis, also in search of a nuclear device. That search was triggered by an intelligence report that suggested that an Improvised Nuclear Device (IND) might have been smuggled into the city by terrorists. With the assistance of the Delta Force, U.S. personnel were able to recover and disable the device in a fictitious neighboring country; unfortunately the Indianapolis device exploded and 20 square blocks in downtown Indianapolis were completely destroyed.
As it happens, the terrorist group, the intelligence report, and the detonation were fictional – elements of a NEST exercise designated MIGHTY DERRINGER, one of a number of tests designed to anticipate and prevent the potential real-world catastrophe of a terrorist nuclear strike in a major American city. Documents published today by the National Security Archive provide newly declassified details on how the MIGHTY DERRINGER exercise unfolded and how the participants later evaluated it.
This is the most extensive set of declassified documents on any nuclear counterterrorism exercise, covering every phase of the response, from concept to critiques, and it offers valuable insights into a world that is usually hidden from public scrutiny. Among the disclosures:
§ The role of the top secret Joint Special Operations Command’s Delta Force in carrying out the assault on the terrorist cell in the fictional country of Montrev.
§ Descriptions of the different types of disablement techniques U.S. forces utilize – emergency destruct, standard destruction, and hard entry.
§ Assessments of the coordination problems and different perspectives of agencies that would be involved in a real-world response.
The instruction to establish NEST, known until 2002 as the Nuclear Emergency Search Team, took the form of a November 18, 1974 memo from Maj. Gen. Ernest Graves, the Atomic Energy Commission’s assistant general manager for military application, to Mahlon Gates, the manager of the commission’s Nevada Operations Office. (Document 1). Gates was “directed and authorized” to assume responsibility for the planning and execution of field operations employing AEC radiation detection systems for the “search and identification of lost or stolen nuclear weapons and special nuclear materials, bomb threats, and radiation dispersal threats.”
Personnel for NEST would come from AEC’s nuclear weapons laboratories – Lawrence Livermore, Sandia, and Los Alamos – as well as key AEC contractors. Almost all those individuals would continue in their regular positions full-time and become part of a NEST effort when required.
What inspired Graves’ memo was an incident that had taken place in May of that year. The Federal Bureau of Investigation received a letter demanding $200,000. Failure to comply would result in the detonation of a nuclear bomb somewhere in Boston. Personnel and equipment were quickly assembled and transported to Griffiss Air Force Base in Rome, New York. But before the team could make it to the threatened city, the crisis receded when no-one came to pick up the $200,000 in phony bills left at the designated site. 2
But the incident and the difficulties involved in responding to the threat convinced senior leaders that there was a need for a dedicated capability to deal with any attempt at nuclear extortion or nuclear terrorism. From its inception, NEST devoted considerable time and effort to conducting exercises designed to allow the team to test its readiness, procedures, and equipment in a variety of scenarios. In addition, since confronting a nuclear threat would involve not only NEST but a multitude of organizations, exercises provided an opportunity to identify potential problems in interagency cooperation.
MIGHTY DERRINGER was a particularly notable exercise in exploring the organizational, governmental, and technical problems that might arise in responding to a nuclear terrorist threat. While the existence of MIGHTY DERRINGER has been reported previously, the documents obtained by the National Security Archive and posted in this briefing book provide far more detail than previously available on the scenario, results, and after-action assessments of the assorted organizations involved. Since NEST and these other government entities are still critical components of America’s counter-terrorist capability, these records are valuable for the insight they offer into how a current-day nuclear detection operation would unfold and particularly what kinds of problems might be encountered.3
The exercise took place in two locations – Camp Atterbury, Indiana, near Indianapolis, and Area A-25 of the Energy Department’s Nevada Test Site – which corresponded to the two locations involved in the exercise scenario. One of the those locations was Indianapolis while the other was the country of ‘Montrev’ – a rather transparent fictional version of Mexico (since Montrev shared a border with the United States, its capital city was ‘Montrev City’, and its primary security agency was the Directorate for Federal Security – the same as Mexico’s).
Montrev was the initial focus of the exercise, with a terrorist group commanded by “Gooch” threatening to detonate an improvised nuclear device (IND) near the country’s Bullatcha oil field. According to the scenario, terrorists had stolen the devices from a new nuclear weapons state. Eventually, the participants discovered that that there was a second nuclear device and it appeared that it was being infiltrated into the United States, possibly with Pittsburgh as a target – although it was subsequently determined that the target was Indianapolis. While U.S. forces (with Delta Force assistance) were able to recover and disable the device in Montrev, Indianapolis experienced a 1 kiloton nuclear detonation that resulted in “total devastation over a 20 square block area.” (Document 38) The scenario had originally posited a successful disarming, but the exercise controllers decided to introduce a new element.
The scenario allowed for all aspects of a possible response to a nuclear terrorist/extortionist threat to be practiced – from initial assessment of the threat to the management of the “consequences” of a detonation. The documents posted cover, with varying detail, the core aspects of a response – intelligence collection, technical and behavioral assessments, search, access/defeat of terrorist forces, recovery of a device, diagnostics, hazards and effects estimation, disablement and damage limitation, safe transportation of the device, and consequence management of a detonation. In addition, they also concern a variety of important aspects of a response – including security, command and control, communications, logistics, radiological measurement and containment, weather forecasting, public information, and interaction with local officials.
The documents also identify the large number of organizations involved in the exercise. There is NEST and the organizations that contributed members or capabilities – including Lawrence Livermore National Laboratory, Los Alamos National Laboratory, and contractor EG&G. Additional organizations whose participation is evident include the State Department, Central Intelligence Agency, Federal Bureau of Investigation, Joint Special Operations Command, Special Forces Operation Detachment – Delta (Delta Force), several military explosive ordnance disposal units (from the Army and Navy), the Federal Radiological Monitoring and Assessment Center, the Environmental Protection Agency, and the Federal Emergency Management Agency.
Beyond detailing participants and describing different aspects of the exercise and static plans, some of the documents (the ‘Sitreps’- Document 19, Document 23, Document 32) provide a more dynamic view of the state of play at various points in the exercise. In addition, the post-exercise critiques provide different individual and institutional perspectives as to either the realism of the exercise or what the exercise revealed about strengths and weaknesses of the then current U.S. ability to respond to a nuclear terrorist threat.
Thus, Vic Berkinklau, an engineer with the Atomic Energy Commission, in addition to describing MIGHTY DERRINGER as an “Excellent, well managed exercise,” had an additional eight observations which concerned subjects such as uncertainty as to the number of NEST personnel needed in Montrev, the relationship between NEST and the Explosive Ordinance Disposal (EOD) team, and the need for more detailed analysis of the consequences of a nuclear detonation in a populated area (Document 43). L.J. Wolfson of the Navy Explosive Ordnance Disposal Technical Center contributed an eight-page single-spaced analysis concerning a variety of topics, including the nuclear device, assessment and intelligence, command and control and disablement. He observed (Document 47) that “there is too great a prevalence to believe what might, and probably is, very inconclusive intelligence information” and that “the entire operation was slowed and overburdened by the number of personnel involved.”
Commenting on the terrorism phase of the exercise (Document 50), William Chambers, NEST member and site controller for the Indianapolis component of the exercise, wrote that liaison between the FBI’s Hostage Rescue Team, NEST, and EOD personnel was “excellent” but that “the joint procedures for withdrawing the HRT and survivors, securing the perimeter, and clearing access to the device need clarification.” An unattributed comment (Document 66) suggested that the Delta Force players did not appreciate the “gravity of dealing with a nuclear device.”
In the subsequent twenty-five years, NEST and other organizations concerned with nuclear terrorism have conducted a significant number of exercises – particularly following the attacks of September 11, 2001.4 However, because of its scale and scope MIGHTY DERRINGER remains one of the more notable nuclear counterterrorism exercises.
The Energy Department is keeping secret significant aspects of MIGHTY DERRINGER, but more may be learned about the exercise and the State Department’s role in it from the response to a pending request. Moreover, files on MIGHTY DERRINGER at the Ronald Reagan Presidential Library will eventually be declassified and shed light on the National Security Council’s role.
(Note: A list of abbreviations used in the documents appears below.)
READ THE DOCUMENTS
Background
Document 1: Ernest Graves, Assistant General Manager for Military Application, Atomic Energy Commission, to M.E. Gates, Nevada Operations, “Responsibility for Search and Detection Operations,” November 18, 1974. Secret.
Source: Department of Energy FOIA Release
With this memo General Graves assigned Gates and the AEC’s Nevada Operations Office responsibility for search and detection operations with respect to lost and stolen nuclear weapons and special nuclear material as well as responding to nuclear bomb and radiation dispersal threats. The memo became the basis for the creation of the Nuclear Emergency Search Team (NEST).
Document 2: Director of Central Intelligence, IIM 76-002, The Likelihood of the Acquisition of Nuclear Weapons by Terrorist Groups for Use Against the United States, January 8, 1976. Secret.
Source: CIA FOIA Release.
An interagency group of intelligence analysts explored the constraints on the exploitation of nuclear explosives, attitudes and behavior toward the United States, means of acquiring nuclear explosives, the ways in which nuclear devices might be used against the United States, and the capabilities of existing terrorist groups. While the authors considered it unlikely that the U.S. would be the target of a nuclear terrorist attack “in the next year or two,” they also noted that, in the longer term, “we would expect a corresponding erosion of the constraints against terrorist use of nuclear explosives.”
Document 3: Energy Research and Development Administration, “Nuclear Emergency Search Team (NEST),” n.d. (but 1977). Unclassified.
Source: Energy Research and Development Administration
NEST began its existence as an unacknowledged government organization, but in 1977 it was concluded that NEST would have to interact with local law enforcement and political authorities in dealing with nuclear threats, and thus its existence would need to be acknowledged. This fact sheet, distributed to the press by ERDA, was the means by which NEST’s existence was quietly announced.
Document 4: E.J. Dowdy, C.N. Henry, R.D. Hastings, S.W. France, LA-7108, Nuclear Detector Suitcase for the Nuclear Emergency Search Team, February 1978. Unclassified.
Source: Los Alamos National Laboratory
This technical paper describes one piece of equipment designed specifically for NEST personnel – a portable Neutron Detection system that could be carried in any vehicle. The paper describes the detectors, the electronics, and the operations.
Document 5: Director of Central Intelligence, NIE 6-86, The Likelihood of Nuclear Acts by Terrorist Groups, April 1986, Secret, excised copy
Source: Mandatory Review Request; release by Interagency Security Classification Appeals Panel.
This estimate examined several incentives and constraints with regard to nuclear terrorism – including the availability of nuclear information, material, and trained personnel; changing levels of protection for nuclear weapons and other sources of nuclear/radioactive material; and terrorist capabilities and motivations (including possible state support to nuclear terrorism). The authors concluded that there was only a “low to very low” probability of nuclear terrorism that involved detonation of an improvised nuclear device or nuclear weapon – or the dispersal of radioactive material in a way that would threaten mass casualties or produce widespread contamination.
Preparations
Document 6: William Hoover, Deputy Assistant Secretary of Energy for Defense Programs, to DCI William Casey, 23 September 1985, with CIA routing memos, Confidential
Source: CREST, National Archives II
A senior Energy Department official informed Director of Central Intelligence William J. Casey of the Department’s conclusion on the need for a large-scale nuclear exercise in the early 1987 fiscal year and requested the CIA’s participation.
Document 7: Robert B. Oakley, State Department Counter-Terrrorism Center, to Executive Secretary Nicholas Platt, MIGHTY DERRINGER Exercise Planning,” 4 April 1986, with memorandum to Vice Admiral John Poindexter attached, Confidential
Source: State Department FOIA release
This memorandum, from the head of the State Department’s Counter-Terrorism Center, along with that attached memo to the president’s national security adviser, described the level of State Department participation in MIGHTY DERRINGER.
Document 8: Peter Borg, State Department Counter-Terrorism Center, to Richard Kennedy et al., “Exercise MIGHTY DERRINGER,” 6 October 1986, Secret
Source: State Department FOIA release
A number of State Department officials were recipients of this secret memo, which informed them of the nature of MIGHTY DERRINGER, when it would take place, some requirements for the exercise to be realistic, and the State Department’s participation.
The Exercise
Document 9: Don McMaster, Behavioral Assessment Report/PLC, n.d. [circa 2 December 1986], Incomplete copy, Secret
Source: Energy Department FOIA release
This behavioral assessment mirrors the earliest phases of responding to an actual threat, especially trying to assess its credibility. It discusses the reliability of a source, motivations of other key figures in the terrorist group, and concludes that a credible threat exists to both the United States and ‘Montrev.’
Document 10: F.W. Jessen, Lawrence Livermore National Laboratory, “Summary Assessment,” 2 December 1986, Secret, Incomplete copy
Source: Energy Department FOIA release
This assessment, conducted at Lawrence Livermore, where much of the credibility assessment effort has been located, reports that the available information suggests that the terrorist group possesses two improvised nuclear devices but that LLNL and Los Alamos National Laboratory disagree over the technical credibility of the threat.
Document 11: “Aggregate Assessment – – One Hour – – Of Threat Message and Sketch,”
n.d., Secret, Page 1 only
Source: Energy Department FOIA release
The title of this memo indicates that a sketch of a device was included with the threat message. Technical experts had already begun to draw conclusions about the device in Montrev as well as the implications for finding a second device in the United States.
Document 12: Thomas R. Clark, Manager, Nevada Operations Office, Department of Energy, “NEST Alert Status,” 3 December 1986, Confidential, excised copy
Source: Energy Department FOIA release
This message, from a Department of Energy manager, informs NEST participants at key laboratories and contractors that NEST is on “alert.” The Department of State has received a threat and the Department of Energy has been asked to evaluate it. Other actions have been taken.
Document 13: “Security Plan for NEST Retrograde Operation, December 1986,” n.d., Secret
Source: Energy Department FOIA release
The plan described in this document notes the classification levels and types of information involved in the exercise as well as measures for the protection of cryptological matter and classified documents.
Document 14: Peter Mygatt, Exercise Mighty Derringer, “Chronological Media Play, ‘Site City,’ Beginning 12/7/86,” n.d., Secret
Source: Energy Department FOIA release
The MIGHTY DERRINGER scenario writers assumed that if it was a real-world event, part of it would be visible and covered extensively by the media. This document summarizes reports of fictional news services and television stations as well as interaction between the media and FBI and Department of Energy.
Document 15: NEST On-Scene Commander, Subject: Event Mighty Derringer Sitrep No. 1 OCONUS, Prepared at 00:15 PST on 12/06/86, Secret
Source: Energy Department FOIA release
The first Situation Report (Sitrep) of the part of the exercise that takes place in Montrev summarizes the current situation (including the number of personnel in country) as well as
the status of a variety of subjects – including command and control, intelligence, disablement, and weather.
Document 16: W. Rogers, NEST Paramedic Coordinator, to V. Withirill, N.T.S.O, “MIGHTY DERRINGER, MEDICAL EMERGECY RESPONSE,” 6 December 1986, Secret
Source: Energy Department FOIA release
This memo reports that MIGHTY DERRINGER was being conducted in area A-25 of the Nevada Test Site and would involve approximately 450 people. It focuses on “areas of responsibility … and those assets available” in the event of an actual medical emergency.
Document 17: “NEST Evacuation Plan,” n.d., Secret
Source: Energy Department FOIA release
This plan addresses the evacuation of NEST personnel and equipment from Montrev City in the event of a nuclear detonation at the nearby Bullatcha Refinery No. 5. It focuses on execution, logistics, and command and control.
Document 18: NEST On-Scene Coordinator/Exercise Mighty Derringer, to Director, Emergency Management Team, DOE-EDC, Washington, D.C., Event Mighty Derringer Sitrep No. 2, Prepared at 1100 PST 6 December 1986, Secret
Source: Energy Department FOIA release
This report updates the Sitrep that had been prepared just after midnight on December 6 and reports on the significant developments that had occurred during the day. It covers thirteen different topics, and provides significant details of the terrorist site in Montrev, a summary of the behavioral assessment based on communications intelligence, and an assessment of the device. It notes that a “second nuclear device may be enroute [to] CONUS” and there is no confidence that the device is one-point safe, that is, the risk of an accidental nuclear detonation had to be taken into account (to be one-point safe there must be less than 1 in one million probability of producing a nuclear yield exceeding the equivalent of 4 pounds of TNT when the high explosive inside the weapon is detonated at any single point).
Document 19: NEST On-Scene Coordinator /Exercise Mighty Derringer, to Director, Emergency Management Team, DOE-EDC, Washington, D.C., Subject: Event Mighty Derringer Sitrep No. 3, Prepared at 00:10, on 12/07/86, Secret
Source: Energy Department FOIA release
This Sitrep prepared an about one hour after Sitrep No. 2, notes that “prestaging of equipment for access has been completed.”
Document 20: Assessment/McMaster, to Standard Distribution, “IRT Intelligence Summary 061200-062400,” 7 December 1986 02:30, Secret
Source: Energy Department FOIA release
This assessment reports on attempts to determine the presence of a nuclear device at the terrorist site, the movements of the terrorist group’s leader, the weapons and equipment possessed by the group, and a conclusion regarding the capability of Montrev’s armed forces to secure the terrorist site.
Document 21: Assessment/McMaster, to Standard Distribution, “Status Montrev Forces,” 7 December 1986 05:30, Secret
Source: Energy Department FOIA release
The status of Montrev’s forces is reported in this memo, which is based on information received from the Defense Intelligence Agency. It discusses their location, vehicle lift capability, and maintenance issues.
Document 22: CN1 to All, “Mighty Derringer,” 7 December 1986 8:44, Secret
Source: Energy Department FOIA release
This memo conveys a report from the IWS news service on events in Montrev.
Document 23: NEST On-Scene Coordinator, Subject: Event Mighty Derringer, Sitrep No. 4, OCONUS, Prepared at 09:40 on 12/07/86, Secret
Source: Energy Department FOIA release
This Sitrep indicates a successful assault by forces of the Joint Special Operations Command, resulting in their control of both the north and south sites that had been under terrorist control. It reports on the status of the nuclear device and the initial implementation of the emergency disablement plan.
Document 24: Summary Assessment to Standard Distribution, “Summary Assessment,” 7 December 1986 10:30, Secret
Source: Energy Department FOIA release
The technical assessment has been entirely redacted from this document, but the operational and behavioral assessments have been released in their entirety. They note that “The adversary has set up the Montrev situation in such a way that if and when he surfaces in CONUS and makes an explicit threat and demand, he must be taken seriously.”
Document 25a: CN1 to All, “Mighty Derringer,” 7 December 1986 12:28, Secret
Document 25b: CN1 to All, “Mighty Derringer,” 7 December 1986 13:07, Secret
Document 25c: CN1 to All, “Mighty Derringer,” 7 December 1986 15:48, Secret
Source: Energy Department FOIA release
These bulletins convey various media reports of developments in Montrev, including the presence of NEST personnel.
Document 26: Assessment/F. Kloverstrom to Standard Distribution, “Results of examination of containers found in south building,” 7 December 1986 18:10, Secret
Source: Energy Department FOIA release
This memo reports on the discovery, after the assault, of two containers, which appear to contain radioactive material.
Document 27: Jim Boyer, “Suggested Procedure for Joint DOE/Montrev News Releases,” 7 December 1986, Secret
Source: Energy Department FOIA release
Among the recommendations in this short memo are obtaining input from the Montrev Ministry of Information “to get an idea of what El Presidente will approve,” developing a cover for the NEST operation, but preparing to admit NEST participation during the last phase of the operation.
Document 28: “Time Line/Event/Decision Sequence,” 8 December 1986 19:00, Secret
Source: Energy Department FOIA release
This document focuses on the essential steps in disabling the nuclear device seized in Montrev and limiting damage. Thus, it addresses access, diagnostics, disablement, damage limitation, and hazards and effects.
Document 29: “Damage Limitation Containment Implementation,”8 December 1986, Secret
Source: Energy Department FOIA release
This eight-page memo has been almost completely redacted but the opening paragraph notes the location of the Montrev device and that its location presents a “formidable problem” but that all participants reached a common conclusion for the solution.
Document 30: “Hazards and Effects Analysis Prior to Montrev Disablement,” n.d. [8 December 1986?], Secret
Source: Energy Department FOIA release
This three-paragraph memo notes that hazard predictions (involving fallout dose and exposure rates) considered a variety of possible yields, wind projections, and the vulnerability of “the small village of Taco Caliente.”
Document 31: A/I [Assessment & Intelligence] Behavioral, “Booby Traps/Tamper Proof,” n.d. [8 December 1986?], Secret
Source: Energy Department FOIA release
This assessment focuses on the likelihood that the terrorist group and its leader would have installed booby traps to prevent tampering with the nuclear device seized in Montrev. It notes the implications of the extensive anti-personnel attack defenses around the area.
Document 32: James K. Magruder, On-Scene Commander, to Director, Emergency Management Team, DOE-EOC, Washington, D.C, Event Mighty Derringer Sitrep No. 7, 8 December 1986 23:00, Secret
Source: Energy Department FOIA release
This Sitrep notes presumed deadlines for nuclear device detonation and a proposed disablement schedule, the number of personnel on site, an extensive report on current intelligence, and that an “emergency destruct plan has been prepared.”
Document 33: Assessment & Intelligence/F. Jessen to Standard Distribution, “A&I Summary/8 December 2130,” 8 December 1986, Secret
Source: Energy Department FOIA release
This assessment notes the credibility of a threat message claiming the existence of a second nuclear device based on experimental measurements of the device seized in Montrev. The memo’s contents suggest a U.S. target for the second device.
Document 34: J.A. Morgan, Disablement Team Leader, to On-Scene Commander, “Disablement Plan,” 9 December 1986, Secret
Source: Energy Department FOIA release
The memo includes a computer sketch of the terrorist nuclear device and the disablement method, as well as the reentry and evacuation plans – all of which have been redacted.
Document 35: “Exercise Mighty Derringer Post-Event Plan to Safe and Remove the Device,” circa 9 December 1986, Secret
Source: Energy Department FOIA release
This heavily-redacted memo covers four topics – the situation, mission, execution, and administration and logistics. The released portion notes that disablement action had been completed and that an intact physics package had been recovered.
Document 36: “NEST Demobilization Plan,” 10 December 1986, Secret
Source: Energy Department FOIA release
This memo marks plans for the ending the exercise – specifying the responsibilities of the individual organizations, procedures for transportation to the airport and the loading of aircraft, and command and control.
Document 37: Assessment/M. Miron, to Standard Distribution, “Resemblance of Montrev Device to Tahoe Bomb,” 9 December 1986 20:35, Secret
Source: Energy Department FOIA release
In 1980, a sophisticated improvised (non-nuclear) explosive device placed at Harvey’s Wagon Wheel Casino did substantial damage when disablement efforts failed. The memo suggests that publicly available information about the device may have been employed to construct the Montrev device.
Document 38: Cal Wood, Livermore National Laboratory, to Bob Nelson, Controller Team Leader, “Preliminary Evaluation of Players’ Device Estimate,” 10 December 1986, Secret
Source: Energy Department FOIA release
This heavily redacted memo notes that “the diagnostic techniques used by the team produced a rather good estimate of both the materials present and their configuration.”
Document 39: Director FEMA to National Security Council, “Situation Report on MONTREV/Indianapolis Terrorist Situation,” 11 December 1986 17:00 EST, Secret
Source: Energy Department FOIA release
The FEMA director begins with the observation that “At 0700, 11 December 1986, a nuclear detonation occurred in the City of Indianapolis” devastating 20 square blocks. He does not describe the type of damage produced, for example, whether the detonation led to any fires, or the extent to which it caused local fallout hazards. The FEMA director then describes the consequence management phase of the exercise, including involvement of state and federal authorities and agencies.
Critiques
Document 40: Carl Henry, Los Alamos National Laboratory, “Mighty Derringer Report,” 2 February 1987, enclosing comments by Ray D. Duncan, n.d., Secret
Source: Energy Department FOIA release
Some weeks after the exercise, Los Alamos official Carl Henry sent a large package of commentary on MIGHTY DERRINGER, which is presented below, piece by piece, except for the critique by Ray D. Duncan,which is attached to the Henry memorandum. Duncan, a manager at the Nevada Test Site, produced an extensive review which raised a number of issues, including the “unusual challenges” MIGHTY DERRINGER raised for NEST if it was ever deployed to a foreign country for a “covert operation.” Perhaps some incident during the exercise led him to the recommendation for educational training for Delta Force and the Joint Special Operations Command so that their members “understand the potential consequences of moving or unintentionally shooting an IND [improvised nuclear device].”
Document 41: Untitled, unattributed document, Secret, incomplete
Source: Energy Department FOIA release
This critique gives some detail on how the NEST group entered Montrev during the crisis. The State Department had created an approved access list and a simulated Montrev consulate processed the players when they entered the country. When players realized that they had forgotten some equipment, they were easily able to retrieve it as it was only 65 miles away. The commentator noted that in a “real world situation, the NEST contingent could be thousands of miles away from necessary equipment or supplies.”
Document 42: Eric Schuld to Bob Nelson, “Comments on Mighty Derringer – OCONUS Issues,” n.d., Secret
Source: Energy Department FOIA release
Schuld listed issues brought up by the “Outside Continental United States” exercise. For example, the JSOC solved its problem through a “quick assault” that created problems for other organizations in the exercise.
Document 43: Vic Berniklau to Bob Nelson, “Issues/Major Observations/Lessons Learned,” n.d., Secret
Source: Energy Department FOIA release
Like many of the commentators, Berniklau saw the exercise as “excellent” and “well managed,” but he raised problems that others also brought up, such as fragmentation of information and “confusion.”
Document 44: T.T. Scolman, Comments, n.d., Secret
Source: Energy Department FOIA release
Scolman, whose role was “Commander for Science,” also saw an information management problem and pointed to other concerns, such as lack of support staff.
Document 45: Richard F. Smale, HSE, to Carl Henry/Bill Chambers, “First Impressions: Mighty Derringer: Consequence Phase,” n.d., Classification unknown
Source: Energy Department FOIA release
The “consequence phase” referred to the aftermath of the nuclear detonation in Indianapolis. Smale saw “great things” in the exercise, such as its technical organization, but he pointed to concerns such as the failure to present information that would be accessible to a non-technical audience and the lack of time to “develop good fallout plots.”
Document 46: L J. O’Neill, “Exercise Impressions,” 9 December 1986, Secret
Source: Energy Department FOIA release
O’Neill was impressed by the participation of “foreign speaking actors” which helped the participants to enter “wholeheartedly into the play.”
Document 47: L.J. Wolfson to R. Nelson, “Exercise Mighty Derringer,” 10 December 1986, Classificaion unknown, excised copy
Source: Energy Department FOIA release
Like O’Neill, Wolfson pointed to the “good actor play,” especially by the actor who had the role of Montrev’s “El General.” Nevertheless, he argued that “too many people” slowed down the operation.
Document 48: William Nelson, Mighty Derringer Washington Controller, to Captain Ronald St. Martin, National Security Council, “Mighty Derringer Meeting at FBI Headquarters, 12 December 1986, Classification unknown
Source: Energy Department FOIA release
The discussion at FBI headquarters on organizational issues produced a consensus on the need for a White House-designated “leader,” possibly at the cabinet level, responsible for managing post-nuclear disaster recovery activities.
Document 49: Kathy S. Gant, Emergency Technology Program, Oak Ridge National Laboratory, to William Chambers, Los Alamos National Laboratory, 17 December 1986, enclosing “Comments on Exercise Mighty Derringer,” 18 December 1986, Classification unknown
Source: Energy Department FOIA release
Seeing a need for better integration of the consequences phase into MIGHTY DERRINGER, Gant emphasized the need for state and local actors to play a stronger role in such exercises to give them greater realism. Her discussion of the Federal Radiological Response Plan led to a recommendation that NEST staffers play a role in post-incident field monitoring of radiation hazards because they would be the “first available federal personnel.”
Document 50: William H. Chambers, CONUS Site Controller, to Carl Henry, Chief Controller, “‘Quick Look,’ Report, Mighty Derringer CONUS,” 19 December 1986, Secret
Source: Energy Department FOIA release
Chambers provided some detail on the role of the Indianapolis nuclear detonation in MIGHTY DERRINGER. According to the script, the device had been “rendered-safe,” but the exercise leaders “deviated” from the script by improvising a “simulated nuclear detonation.”
Document 51: Zolin Burson, EG&G Energy Measurements, to Carl Henry, 29 December 1986, Secret
Source: Energy Department FOIA release
Like Gant, Burson pointed to the need for more involvement by state and local actors in such exercises, suggesting that “if the real Governor and Mayor” had been present, “they would have had a much stronger influence.”
Document 52: Richard F. Smale, Associate Group Leader, to Jesse Aragon, HSE Division Leader, “Trip Report December 7 to 13, Camp Atterbury (Indianapolis), Indiana,” 7 January 1987, Secret
Source: Energy Department FOIA release
Smale provides more detail on the role of nuclear devices in the exercise scenario, noting that “terrorists had stolen two … from a developing nuclear capable country.” He also observed that “when control of the device had been obtained, the NEST scientists could have disabled it.”
Document 53: Thomas S. Dahlstrom, EG&G Measurements, to William H. Chambers, Carl Henry, and Norm Bailey, “Mighty Derringer Observations,” 13 January 1987, Classification unknown, excised copy
Source: Energy Department FOIA release
After noting that his “overall reaction” was “quite positive,” Dahlstrom believed that “confusion” emanated from a basic problem: the players did “not comprehend the complexity of an OCONUS deployment – specifically how the State Department controls the matter.”
Document 54: F. Jessen/LLNL to G. Allen and W. Adams/NVO, “Mighty Derringer Critique,” 16 December 1986, Rev[ised] 13 January 1987, Secret, excised copy
Source: Energy Department FOIA release
Jessen pointed to a number of problems, for example, that “many of the participating agencies were not serious players,” the “unrealistic background information” on the “fictitious” countries and people, “bad guidance on the use of existing proliferant country data,” and failure to recognize that “information to be assessed related to intelligence reports of a nuclear terrorist threat.” Especially disturbing was the relocation of the command post to a “safe location,” while NEST personnel were not notified”: “the blatant lack of concern for [their] safety … is inexcusable.”
Document 55: Julie A. Orcutt/HSE, Los Alamos National Laboratory, to Jesse Aragon, HSE Division Leader, “Trip Report: Mighty Derringer Exercise, Montrev Site,” 13 January 1987, Secret
Source: Energy Department FOIA release
During the exercise, the on-scene commander at Indianapolis had decided against building a “containment structure” to prevent the spread of hazardous material because of the risks. That meant, however, that plutonium would be scattered about which presented dangers of “lung doses.” Los Alamos staffer Julie Orcutt recommended the provision of more anti-contamination equipment, such as foam mitigation, to reduce dangers to officials entering the blast area.
Document 56: J. Doyle to Gylan C. Allen, “EG&G Comments for Mighty Derringer,” 14 January 1987, Classification unknown, excised, incomplete copy
Source: Energy Department FOIA release
Noting that the exercise provided “very valuable training,” Doyle saw such problems as the “sheer magnitude” in numbers of players, cramped space, and inadequate communications staffing.
Document 57: G.C. Allen, USDOE/NVO, “Mighty Derringer: Comments and Observations,” 15 January 15, 1987, Classification unknown, excised copy
Source: Energy Department FOIA release
Among the shortcomings cited in Allen’s rather critical evaluation were poor communications and weaknesses in interagency coordination.
Document 58: William E. Nelson, Emergency Response, Lawrence Livermore National Laboratory, to Carl Henry, Los Alamos National Laboratory, “‘Quick Look,’ Report, Mighty Derringer,” 21 January 1987, Secret, excised copy
Source: Energy Department FOIA release
Jumping the gun was a weakness cited in Nelson’s critique: players “did not wait for establishment of credibility before acting,” which made a “shambles of an orderly assessment of information.” He also observed that NEST search team “escorts” needed “experience in covert operations” to “prevent inadvertent acts that would alert terrorists.” Nelson’s report included a number of observations made by other participants.
Document 59: J. Strickfadden, LANL, to Bob Nelson, “Mighty Derringer Comments,” n.d., Secret
Source: Energy Department FOIA release
The overall positive evaluation – the “most realistic exercise ever conducted by the NEST community” – included some criticisms, such as “chaotic” operations at the Working Point [WP] and a shambolic state of affairs at the “reentry” point (detonation zone).
Document 60: Milt Madsen (Monitor) to Bob Nelson, “Mighty Derringer Observations,” n.d., Secret, excised, incomplete copy
Source: Energy Department FOIA release
Madsen’s comments included suggestions for future improvements in NEST’s organization: for example, to avoid fragmented committee operations, NEST needed a technical program manager.
Document 61: Peter Mygatt, “Mighty Derringer – Media Play Report,” n.d., Secret
Source: Energy Department FOIA release
Energy Department spokesperson Mygatt’s evaluation of the player’s management of the media was generally positive, although he saw a few failings, e.g., the Joint Information Center never called a news conference, “which is unheard of in an emergency.”.
Document 62: Walter Nervik, Senior Command Controller, to Robert M. Nelson, Exercise Mighty Derringer Controller, “Lessons Learned,” n.d., Secret
Source: Energy Department FOIA release
An official at Lawrence Livermore Laboratory, Nervik wondered who would provide security after JSOC operatives attacked the terrorists in an overseas environment. Special forces personnel would leave the scene but the NEST would still need security resources.
Document 63: Walter Nervik to Bob Nelson, “Lessons Learned,” n.d., Secret
Source: Energy Department FOIA release
Nervik was critical in another evaluation: the NEST team was far too large, players were complacent about a nuclear threat, there were no “penalties” for making a mistake, and playing conditions were “unreal.” With respect to the latter point, the fact that the Montrev phase of the exercise occurred on U.S.-controlled territory, (the Nevada Test Site), “severely limits the stress placed on players in unfamiliar surroundings, dealing with strangers, and relying on untested sources of support.” Nervik also saw a danger that participants would see exercises as “more of a game than a serious test of all facets of the NEST capabilities.”
Document 64: Jack Campbell, Public Information, to Robert M. Nelson, Exercise Mighty Derringer Controller, n.d., Secret
Source: Energy Department FOIA release
Campbell pointed to a weakness: higher level officials did not really “play.” For example, after the JSOC assault, the State Department left Montrev, even though “lives of American correspondents were in jeopardy.” Another surprise was that the Department of Energy NEST team did not establish a “public affairs” function, although in real life such a group would be highly active.
Document 65: “Mighty Derringer 86,” unattributed, n.d., Secret, excised copy
Source: Energy Department FOIA release
These handwritten notes raised several issues, such as the interaction between EOD and the Delta force players and the impact of the “play” in the United States on decisions in the OCONUS (Montrev) activity. One impact was that a “risky” disablement option was taken in Montrev in order to preserve evidence to help raise the chance for a successful operation in “site city” (Indianapolis).
Document 66: “Mighty Derringer,” unattributed, n.d., Secret, excised copy
Source: Energy Department FOIA release
Handwritten notes by another player raised basic organizational issues. The absence of a “chain of command” prior to the deployment made it unclear who EOD worked for. A serious concern was that the Delta Force players did not appreciate the “gravity of dealing with a nuclear device,” an issue suggested by other reports (see document 41).
Document 67: “Mighty Derringer Search Planning,” unattributed, n.d., Secret, excised copy
Source: Energy Department FOIA release
This document provides a review of organizational arrangements established for the device search in Indianapolis.
Document 68: “Communications Observations (Site City),” unattributed, n.d., Classification unknown
Source: Energy Department FOIA release
This review of communications systems concluded that this was the “best NEST communications exercise that I have observed.”
Document 69: Second page of fax to Carl Henry, unattributed document, n.d., Classification unknown
Source: Energy Department FOIA release
This critique points to operational security (OPSEC) as the “real” problem, noting that players had organizational logos on their clothing and that “loose talk” in hotels and bars was “particularly bad.”
ABBREVIATIONS
CONUS Continental United States
EG&G Edgerton, Germeshausen, and Grier
EOC Emergency Operations Center
EOD Explosive Ordnance Disposal
EODTECHCTR Explosive Ordnance Disposal Technical Center (Navy)
ERDA Energy Research and Development Administration
EST Emergency Support Team
FBI Federal Bureau of Investigation
FCP Forward Control Point
FEMA Federal Emergency Management Agency
FRMAC Federal Radiation Monitoring Assessment Center
HRT Hostage Response Team
IND Improved Nuclear Device
JNACC Joint Nuclear Accident Coordination Center
JSOC Joint Special Operations Command
LANL Los Alamos National Laboratory
LLNL Lawrence Livermore National Laboratory
NEST Nuclear Emergency Search Team
NVO Nevada Operations Office
OCONUS Outside the Continental United States
OSC On-Scene Commander
REECo Reynolds Electrical Engineering Corporation
SAC Special-Agent-in Charge (FBI)
SFOD Special Forces Operational Detachment – Delta
SITREP Situation Report
TOC Tactical Operations Center
WP Working Point
Former Jersey City Construction Project Superintendent Sentenced to Prison for Social Security Disability Scam
NEWARK—The former project superintendent on a Jersey City, New Jersey high-rise construction project was sentenced today to six months in prison and six months of home confinement for a scheme in which he hid his employment so he could continue to receive Social Security disability payments, U.S. Attorney Paul J. Fishman announced.
Pasquale Zinna, 44, of Hackettstown, New Jersey, previously pleaded guilty to two counts of the indictment against him: Social Security disability fraud and structuring financial transactions. His wife, Janeen Zinna, 43, was also sentenced today—to two years’ probation with the special condition of 100 hours of community service. She previously pleaded guilty to a superseding information charging her with misprision of her husband’s Social Security fraud. U.S. District Court Judge Katharine S. Hayden imposed the sentences today in Newark federal court.
According to documents filed in this case and statements made in court:
In 1999, Pasquale Zinna filed an application for disability insurance benefits with the Social Security Administration (SSA), claiming that, as of March 15, 1996, he was disabled and unable to work due to a back injury. By filing the application, Pasquale Zinna agreed to notify the SSA if there was any improvement in his medical condition or if he regained the ability to work.
Beginning in September 2005, Pasquale Zinna was the project superintendent for 160 Broadway Concrete, a sub-contractor at the high-rise construction project at 77 Hudson Street in Jersey City. He failed to report his return to work to Social Security and concealed his employment at Broadway Concrete by having his paychecks issued to him in the names of other individuals, including his wife. Janeen Zinna admitted during her guilty plea that she filed a joint federal income tax return with her husband for 2007 which claimed income received from Broadway Concrete was for work she performed.
Pasquale Zinna also admitted to making a series of cash withdrawals from his joint checking account with his wife at Commerce Bank, now TD Bank, in order to avoid the bank’s reporting requirement for financial transactions in excess of $10,000.
In addition to the prison term, Judge Hayden sentenced Pasquale Zinna to three years of supervised release. He was also ordered to pay $101,753 in restitution to the Social Security Administration and to forfeit $98,000 involved in the illegal financial transactions. Janeen Zinna was also held responsible for the restitution. The defendants paid these obligations in full at today’s proceeding.
Four New York men have also pleaded guilty to a wide range of fraud and other offenses stemming from their involvement in the Jersey City construction project between 2007 and 2008.
Rocco Mazzaferro, 64, of Brooklyn, New York, and Vincenzo Genovese, 75, of Staten Island, New York, pleaded guilty November 22, 2011 to conspiracy to commit wire fraud. Vincenzo Genovese also pleaded guilty to one count of conspiracy to embezzle pension benefits.
Anselmo Genovese, 44, of Staten Island, New York, pleaded guilty December 16, 2011 to two counts of making unlawful labor payments.
Eric Haynberg, 46, of New York, pleaded guilty December 16, 2011, to a superseding information charging him with misprision of the wire fraud committed by Mazzaferro and Vincenzo Genovese.
The sentencings of Mazzaferro and Vincenzo Genovese are currently scheduled for July 10, and July 12, 2012, respectively. Sentencing for Eric Haynberg is currently scheduled for June 7, 2012, and for Anselmo Genovese on July 11, 2012.
U.S. Attorney Fishman credited special agents of the FBI, under the direction of Special Agent in Charge Michael B. Ward in Newark; and Department of Labor’s Office of Inspector General, Office of Labor Racketeering and Fraud Investigations, under the direction of Special Agent in Charge Robert L. Panella for the New York Region, for the investigation leading to the arrests and charges. He also thanked the IRS, under the direction of Acting Special Agent in Charge JoAnn S. Zuniga; and the SSA Office of the Inspector General, under the direction of Edward J. Ryan, New York Field Division, for their work on this case, and the U.S. Department of Labor, Employee Benefits Security Administration, for its assistance.
The government is represented by Assistant U.S. Attorney Leslie F. Schwartz of the U.S. Attorney’s Office Economic Crimes Unit in Newark.
TOP-SECRET – NSA: Apple iOS5 Devices Security Configuration
DOWNLOAD THE ORIGINAL FILE HERE
TOP-SECRET – SEC Plan To End Extraordinary Market Volatility
|
[Federal Register Volume 77, Number 109 (Wednesday, June 6, 2012)] [Notices] [Pages 33498-33522] From the Federal Register Online via the Government Printing Office [www.gpo.gov] [FR Doc No: 2012-13653] ======================================================================= ----------------------------------------------------------------------- SECURITIES AND EXCHANGE COMMISSION [Release No. 34-67091; File No. 4-631] Joint Industry Plans; Order Approving, on a Pilot Basis, the National Market System Plan To Address Extraordinary Market Volatility by BATS Exchange, Inc., BATS Y-Exchange, Inc., Chicago Board Options Exchange, Incorporated, Chicago Stock Exchange, Inc., EDGA Exchange, Inc., EDGX Exchange, Inc., Financial Industry Regulatory Authority, Inc., NASDAQ OMX BX, Inc., NASDAQ OMX PHLX LLC, The Nasdaq Stock Market LLC, National Stock Exchange, Inc., New York Stock Exchange LLC, NYSE MKT LLC, and NYSE Arca, Inc. May 31, 2012. I. Introduction On April 5, 2011, NYSE Euronext, on behalf of New York Stock Exchange LLC (``NYSE''), NYSE Amex LLC (``NYSE Amex''),\1\ and NYSE Arca, Inc. (``NYSE Arca''), and the following parties to the proposed National Market System Plan: BATS Exchange, Inc., BATS Y-Exchange, Inc., Chicago Board Options Exchange, Incorporated (``CBOE''), Chicago Stock Exchange, Inc., EDGA Exchange, Inc., EDGX Exchange, Inc., Financial Industry Regulatory Authority, Inc., NASDAQ OMX BX, Inc., NASDAQ OMX PHLX LLC, the [[Page 33499]] Nasdaq Stock Market LLC, and National Stock Exchange, Inc. (collectively with NYSE, NYSE MKT, and NYSE Arca, the ``Participants''), filed with the Securities and Exchange Commission (the ``Commission'') pursuant to Section 11A of the Securities Exchange Act of 1934 (``Act''),\2\ and Rule 608 thereunder,\3\ a proposed Plan to Address Extraordinary Market Volatility (as amended, the ``Plan'').\4\ A copy of the Plan is attached as Exhibit A hereto. The Participants requested that the Commission approve the Plan as a one- year pilot.\5\ The Plan was published for comment in the Federal Register on June 1, 2011.\6\ The Commission received eighteen comment letters in response to the proposal.\7\ On September 27, 2011, the Commission extended the deadline for Commission action on the Plan and designated November 28, 2011 as the new date by which the Commission would be required to take action.\8\ The Commission found that such extension was appropriate in order to provide sufficient time to consider and take action on the Plan, in light of, among other things, the comments received on the proposal.\9\ On November 2, 2011, the Participants to the Plan, other than CBOE, responded to the comment letters and proposed changes to the Plan that were subsequently reflected in an amendment.\10\ On November 18, 2011, the Participants consented to the Commission's request that the deadline for Commission action on the Plan be extended an additional three months, to February 29, 2012.\11\ On February 27, 2012, the Participants consented to the Commission's request that the deadline for Commission action on the Plan be extended an additional three months, to May 31, 2012.\12\ On May 24, 2012, the Participants submitted an amendment that proposed several changes to the Plan.\13\ This order approves the Plan, as amended, on a one-year pilot basis. --------------------------------------------------------------------------- \1\ On May 14, 2012, NYSE Amex filed a proposed rule change on an immediately effective basis to change its name to NYSE MKT LLC (``NYSE MKT''). See Securities Exchange Act Release No. 67037 (May 21, 2012) (SR-NYSEAmex-2012-32). \2\ 15 U.S.C. 78k-1. \3\ 17 CFR 242.608. \4\ See Letter from Janet M. McGinness, Senior Vice President, Legal and Corporate Secretary, NYSE Euronext, to Elizabeth M. Murphy, Secretary, Commission, dated April 5, 2011 (``Transmittal Letter''). \5\ Id. at 1. \6\ See Securities Exchange Act Release No. 64547 (May 25, 2011), 76 FR 31647 (``Notice''). \7\ See Letter from Steve Wunsch, Wunsch Auction Associates, LLC, to Elizabeth M. Murphy, Secretary, Commission, dated June 2, 2011 (``Wunsch Letter''); Letter from Peter J. Driscoll, Investment Professional, Chicago, IL, to Elizabeth M. Murphy, Secretary, Commission, dated June 17, 2011 (``Driscoll Letter''); Letter from Stuart J. Kaswell, Executive Vice President & Managing Director, General Counsel, Managed Funds Association (``MFA''), to Elizabeth M. Murphy, Secretary, Commission, dated June 21, 2011 (``MFA Letter''); Letter from George U. Sauter, Managing Director and Chief Investment Officer, The Vanguard Group, Inc. (``Vanguard''), to Elizabeth M. Murphy, Secretary, Commission, dated June 22, 2011 (``Vanguard Letter''); Letter from Karrie McMillan, General Counsel, Investment Company Institute (``ICI''), to Elizabeth M. Murphy, Secretary, Commission, dated June 22, 2011 (``ICI Letter''); Letter from Manisha Kimmel, Executive Director, Financial Information Forum (``FIF''), to Elizabeth M. Murphy, Secretary, Commission, dated June 22, 2011 (``FIF Letter''); Letter from Craig S. Donohue, Chief Executive Officer, CME Group Inc., to Elizabeth M. Murphy, Secretary, Commission, dated June 22, 2011 (``CME Letter''); Letter from Joseph N. Cangemi, Chairman, and Jim Toes, President and Chief Executive Officer, Security Traders Association, to Elizabeth M. Murphy, Secretary, Commission, dated June 22, 2011 (``STA Letter''); Letter from Leonard J. Amoruso, General Counsel, Knight Capital Group, Inc. (``Knight''), to Elizabeth M. Murphy, Secretary, Commission, dated June 22, 2011 (``Knight Letter); Letter from Ann L. Vlcek, Managing Director and Associate General Counsel, Securities Industry and Financial Markets Association (``SIFMA''), to Elizabeth M. Murphy, Secretary, Commission, dated June 22, 2011 (``SIFMA Letter''); Letter from Jamie Selway, Managing Director, and Patrick Chi, Chief Compliance Officer, ITG Inc., to Elizabeth M. Murphy, Secretary, Commission, dated June 23, 2011 (``ITG Letter''); Letter from Jose Marques, Managing Director and Global Head of Electronic Equity Trading, Deutsche Bank Securities Inc. (``Deutsche Bank''), to Elizabeth M. Murphy, Secretary, Commission, dated June 23, 2011 (``Deutsche Bank Letter''); Letter from Kimberly Unger, Esq., Executive Director, The Security Traders Association of New York, Inc., to Elizabeth M. Murphy, Secretary, Commission, dated June 23, 2011 (``STANY Letter''); Letter from James J. Angel, Ph.D., CFA, Associate Professor of Finance, Georgetown University, McDonough School of Business, to Commission, dated June 24, 2011 (``Angel Letter''); Letter from John A. McCarthy, General Counsel, GETCO, to Elizabeth M. Murphy, Secretary, Commission, dated June 24, 2011 (``GETCO Letter''); Letter from Andrew C. Small, Executive Director and General Counsel, Scottrade, Inc., to Elizabeth M. Murphy, Secretary, Commission, dated July 5, 2011 (``Scottrade Letter''); Letter from Peter Skopp, President, Molinete Trading Inc., to Elizabeth M. Murphy, Secretary, Commission, dated July 19, 2011 (``Molinete Letter''); and Letter from Sal Arnuk, Joe Saluzzi, and Paul Zajac, Themis Trading, LLC, to Elizabeth M. Murphy, Secretary, Commission (``Themis Letter''). Copies of all comments received on the proposed Plan are available on the Commission's Web site, located at http://www.sec.gov/comments/4-631/4-631.shtml. Comments are also available for Web site viewing and printing in the Commission's Public Reference Room, 100 F Street, NE., Washington, DC 20549, on official business days between the hours of 10:00 a.m. and 3:00 p.m. ET. \8\ See Securities Exchange Act Release No. 65410 (September 27, 2011), 76 FR 61121 (Oct. 3, 2011). \9\ Id. \10\ See Letter from Janet M. McGinness, Senior Vice President, Legal and Corporate Secretary, NYSE Euronext, to Elizabeth M. Murphy, Secretary, Commission, dated November 2, 2011 (``Response Letter''). \11\ See Letter from Janet M. McGinness, Senior Vice President and Corporate Secretary, NYSE Euronext, to Elizabeth M. Murphy, Secretary, Commission, dated November 18, 2011. \12\ See Letter from Janet M. McGinness, Senior Vice President and Corporate Secretary, NYSE Euronext, to Elizabeth M. Murphy, Secretary, Commission, dated February 27, 2012. \13\ See Letter from Janet M. McGinness, Senior Vice President, Legal and Corporate Secretary, NYSE Euronext, to Elizabeth M. Murphy, Secretary, Commission, dated May 24, 2012 (``Amendment''). --------------------------------------------------------------------------- II. Background On May 6, 2010, the U.S. equity markets experienced a severe disruption.\14\ Among other things, the prices of a large number of individual securities suddenly declined by significant amounts in a very short time period, before suddenly reversing to prices consistent with their pre-decline levels. This severe price volatility led to a large number of trades being executed at temporarily depressed prices, including many that were more than 60% away from pre-decline prices and were broken by the exchanges and FINRA. The Commission was concerned that events such as those that occurred on May 6 could seriously undermine the integrity of the U.S. securities markets. Accordingly, Commission staff has worked with the exchanges and FINRA since that time to identify and assess the causes and contributing factors of the May 6 market disruption \15\ and to fashion policy responses that will help prevent a recurrence. --------------------------------------------------------------------------- \14\ The events of May 6 are described more fully in a joint report by the staffs of the Commodity Futures Trading Commission (``CFTC'') and the Commission. See Report of the Staffs of the CFTC and SEC to the Joint Advisory Committee on Emerging Regulatory Issues, ``Findings Regarding the Market Events of May 6, 2010,'' dated September 30, 2010, available at http://www.sec.gov/news/studies/2010/marketevents-report.pdf. \15\ Id. --------------------------------------------------------------------------- One such response to the events of May 6, 2010, was the development of the single-stock circuit breaker pilot program, which was implemented through a series of rule filings by the Exchanges and FINRA. This pilot was introduced in three stages, beginning in June 2010. In the first stage, the Commission approved, on an accelerated basis, proposed rule changes by the Exchanges and FINRA to pause trading during periods of extraordinary market volatility in stocks included in Standard & Poor's 500 index.\16\ In the second stage, the Commission approved the Exchanges' and FINRA's proposals to add securities included in the Russell 1000 index, as well as specified exchange traded products (``ETPs''), to the pilot.\17\ In the third stage, the [[Page 33500]] Commission approved the Exchanges' and FINRA's proposals to add all remaining NMS stocks, as defined in Rule 600(b)(47) of Regulation NMS under the Act (``NMS Stocks'') \18\ to the pilot.\19\ The Exchanges and FINRA each subsequently filed, on an immediately effective basis, proposals to exempt all rights and warrants from the pilot.\20\ The single-stock circuit breaker pilot is currently set to expire on July 31, 2012.\21\ --------------------------------------------------------------------------- \16\ See Securities Exchange Act Release Nos. 62252 (June 10, 2010), 75 FR 34186 (June 16, 2010) (File Nos. SR-BATS-2010-014; SR- EDGA-2010-01; SR-EDGX-2010-01; SR-BX-2010-037; SR-ISE-2010-48; SR- NYSE-2010-39; SR-NYSEAmex-2010-46; SR-NYSEArca-2010-41; SR-NASDAQ- 2010-061; SR-CHX-2010-10; SR-NSX-2010-05; and SR-CBOE-2010-047); 62251 (June 10, 2010), 75 FR 34183 (June 16, 2010) (SR-FINRA-2010- 025). \17\ See Securities Exchange Act Release Nos. 62884 (September 10, 2010), 75 FR 56618 (September 16, 2010) (File Nos. SR-BATS-2010- 018; SR-BX-2010-044; SR-CBOE-2010-065; SR-CHX-2010-14; SR-EDGA-2010- 05; SR-EDGX-2010-05; SR-ISE-2010-66; SR-NASDAQ-2010-079; SR-NYSE- 2010-49; SR-NYSEAmex-2010-63; SR-NYSEArca-2010-61; and SR-NSX-2010- 08); and Securities Exchange Act Release No. 62883 (September 10, 2010), 75 FR 56608 (September 16, 2010) (SR-FINRA-2010-033). \18\ 17 CFR 242.600(b)(47). \19\ See Securities Exchange Act Release No. 64735 (June 23, 2011), 76 FR 38243 (June 29, 2011) (File Nos. SR-BATS-2011-016; SR- BYX-2011-011; SR-BX-2011-025; SR-CBOE-2011-049; SR-CHX-2011-09; SR- EDGA-2011-15; SR-EDGX-2011-14; SR-FINRA-2011-023; SR-ISE-2011-028; SR-NASDAQ-2011-067; SR-NYSE-2011-21; SR-NYSEAmex-2011-32; SR- NYSEArca-2011-26; SR-NSX-2011-06; SR-Phlx-2011-64). \20\ See, e.g., Securities Exchange Act Release No. 65810 (November 23, 2011) 76 FR 74080 (November 30, 2011) (SR-NYSE-2011- 57). \21\ See, e.g., Securities Exchange Act Release No. 66134 (January 11, 2012), 77 FR 2592 (January 18, 2012) (SR-NYSE-2011-68). In addition to the trading pause pilot for individual securities, the Commission and the SROs also implemented other regulatory responses to the events of May 6, 2010. For example, the Commission approved proposed rule changes that set forth clearer standards and reduced the discretion of self-regulatory organizations with respect to breaking erroneous trades. See e.g., Securities Exchange Act Release No. 62886 (September 10, 2010), 75 FR 56613 (September 16, 2010). Further, the Commission approved proposed rule changes that enhanced the minimum quoting standards for equity market makers to require that they post continuous two- sided quotations within a designated percentage of the inside market to eliminate market maker ``stub quotes'' that are so far away from the prevailing market that they are clearly not intended to be executed. See Securities Exchange Act Release No. 63255 (November 5, 2010), 75 FR 69484 (November 12, 2010). --------------------------------------------------------------------------- The Plan is intended to replace the single-stock circuit breaker pilot that is currently in place. III. Description of the Proposal The Participants filed the Plan to create a market-wide limit up- limit down mechanism that is intended to address extraordinary market volatility in NMS Stocks.\22\ The Plan sets forth procedures that provide for market-wide limit up-limit down requirements that would be designed to prevent trades in individual NMS Stocks from occurring outside of the specified price bands.\23\ These limit up-limit down requirements would be coupled with trading pauses, as defined in Section I(X) of the Plan, to accommodate more fundamental price moves (as opposed to erroneous trades or momentary gaps in liquidity). --------------------------------------------------------------------------- \22\ See Section I(H) of the Plan. \23\ As set forth in Section V of the Plan, the price bands would consist of a Lower Price Band and an Upper Price Band for each NMS Stock. The price bands would be based on a Reference Price that equals the arithmetic mean price of Eligible Reported Transactions for the NMS stock over the immediately preceding five-minute period. As defined in the proposed Plan, Eligible Reported Transactions would have the meaning prescribed by the Operating Committee for the proposed Plan, and generally mean transactions that are eligible to update the sale price of an NMS Stock. --------------------------------------------------------------------------- As set forth in Section V of the Plan, the price bands would consist of a Lower Price Band and an Upper Price Band for each NMS Stock.\24\ The price bands would be calculated by the Securities Information Processors (``SIPs'' or ``Processors'') responsible for consolidation of information for an NMS Stock pursuant to Rule 603(b) of Regulation NMS under the Act.\25\ Those price bands would be based on a Reference Price \26\ for each NMS Stock that equals the arithmetic mean price of Eligible Reported Transactions for the NMS Stock over the immediately preceding five-minute period. The price bands for an NMS Stock would be calculated by applying the Percentage Parameter for such NMS Stock to the Reference Price, with the Lower Price Band being a Percentage Parameter \27\ below the Reference Price, and the Upper Price Band being a Percentage Parameter above the Reference Price. Between 9:30 a.m. and 9:45 a.m. ET and 3:35 p.m. and 4:00 p.m. ET, the price bands would be calculated by applying double the Percentage Parameters. --------------------------------------------------------------------------- \24\ Capitalized terms used herein but not otherwise defined shall have the meaning ascribed to such terms in the Plan. \25\ 17 CFR 242.603(b). The Plan refers to this entity as the Processor. \26\ See Section I(T) of the Plan. \27\ As initially proposed by the Participants, the Percentage Parameters for Tier 1 NMS Stocks (i.e., stocks in the S&P 500 Index or Russell 1000 Index and certain ETPs) with a Reference Price of $1.00 or more would be five percent and less than $1.00 would be the lesser of (a) $0.15 or (b) 75 percent. The Percentage Parameters for Tier 2 NMS Stocks (i.e., all NMS Stocks other than those in Tier 1) with a Reference Price of $1.00 or more would be 10 percent and less than $1.00 would be the lesser of (a) $0.15 or (b) 75 percent. The Percentage Parameters for a Tier 2 NMS Stock that is a leveraged ETP would be the applicable Percentage Parameter set forth above multiplied by the leverage ratio of such product. On May 24, 2012, the Participants amended the Plan to create a 20% price band for Tier 1 and Tier 2 stocks with a Reference Price of $0.75 or more and up to and including $3.00. The Percentage Parameter for stocks with a Reference Price below $0.75 would be the lesser of (a) $0.15 or (b) 75 percent. --------------------------------------------------------------------------- The Processors would also calculate a Pro-Forma Reference Price for each NMS Stock on a continuous basis during Regular Trading Hours. If a Pro-Forma Reference Price did not move by one percent or more from the Reference Price in effect, no new price bands would be disseminated, and the current Reference Price would remain the effective Reference Price. If the Pro-Forma Reference Price moved by one percent or more from the Reference Price in effect, the Pro-Forma Reference Price would become the Reference Price, and the Processors would disseminate new price bands based on the new Reference Price. Each new Reference Price would remain in effect for at least 30 seconds. When one side of the market for an individual security is outside the applicable price band, the Processors would be required to disseminate such National Best Bid \28\ or National Best Offer \29\ with an appropriate flag identifying it as non-executable. When the other side of the market reaches the applicable price band, the market for an individual security would enter a Limit State,\30\ and the Processors would be required to disseminate such National Best Offer or National Best Bid with an appropriate flag identifying it as a Limit State Quotation.\31\ All trading would immediately enter a Limit State if the National Best Offer equals the Lower Limit Band and does not cross the National Best Bid, or the National Best Bid equals the Upper Limit Band and does not cross the National Best Offer. Trading for an NMS Stock would exit a Limit State if, within 15 seconds of entering the Limit State, all Limit State Quotations were executed or canceled in their entirety. If the market did not exit a Limit State within 15 seconds, then the Primary Listing Exchange would declare a five-minute trading pause, which would be applicable to all markets trading the security. --------------------------------------------------------------------------- \28\ 17 CFR 242.600(b)(42). See also Section I(G) of the Plan. \29\ Id. \30\ A stock enters the Limit State if the National Best Offer equals the Lower Price Band and does not cross the National Best Bid, or the National Best Bid equals the Upper Price Band and does not cross the National Best Offer. See Section VI(A) of the Plan. \31\ See Section I(D) of the Plan. --------------------------------------------------------------------------- These limit up-limit down requirements would be coupled with trading pauses \32\ to accommodate more fundamental price moves (as opposed to erroneous trades or momentary gaps in liquidity). As set forth in more detail in [[Page 33501]] the Plan, all trading centers \33\ in NMS Stocks, including both those operated by Participants and those operated by members of Participants, would be required to establish, maintain, and enforce written policies and procedures that are reasonably designed to comply with the limit up-limit down and trading pause requirements specified in the Plan. --------------------------------------------------------------------------- \32\ The primary listing market would declare a trading pause in an NMS Stock; upon notification by the primary listing market, the Processor would disseminate this information to the public. No trades in that NMS Stock could occur during the trading pause, but all bids and offers may be displayed. See Section VII(A) of the Plan. \33\ As defined in Section I(W) of the Plan, a trading center shall have the meaning provided in Rule 600(b)(78) of Regulation NMS under the Act. --------------------------------------------------------------------------- Under the Plan, all trading centers would be required to establish, maintain, and enforce written policies and procedures reasonably designed to prevent the display of offers below the Lower Price Band and bids above the Upper Price Band for an NMS Stock. The Processors would disseminate an offer below the Lower Price Band or bid above the Upper Price Band that nevertheless inadvertently may be submitted despite such reasonable policies and procedures, but with an appropriate flag identifying it as non-executable; such bid or offer would not be included in National Best Bid or National Best Offer calculations. In addition, all trading centers would be required to develop, maintain, and enforce policies and procedures reasonably designed to prevent trades at prices outside the price bands, with the exception of single-priced opening, reopening, and closing transactions on the Primary Listing Exchange. As proposed, the Plan would be implemented as a one-year pilot program in two Phases. Phase I of the Plan would be implemented immediately following the initial date of Plan operations; Phase II of the Plan would commence six months after the initial date of the Plan or such earlier date as may be announced by the Processors with at least 30 days' notice. Phase I of the Plan would apply only to Tier 1 NMS Stocks, as defined in Appendix A of the Plan. During Phase I of the Plan, the first Price Bands would be calculated and disseminated 15 minutes after the start of Regular Trading Hours, no Price Bands would be calculated and disseminated less than 30 minutes before the end of Regular Trading Hours, and trading would not enter a Limit State less than 25 minutes before the end of Regular Trading Hours. In Phase II, the Plan would fully apply to all NMS Stocks beginning at 9:30 a.m. and ending at 4:00 p.m. each trading day. As stated by the Participants in the Plan, the limit up-limit down mechanism is intended to reduce the negative impacts of sudden, unanticipated price movements in NMS Stocks,\34\ thereby protecting investors and promoting a fair and orderly market.\35\ In particular, the Plan is designed to address the type of sudden price movements that the market experienced on the afternoon of May 6, 2010.\36\ --------------------------------------------------------------------------- \34\ 17 CFR 242.600(b)(47). \35\ See Transmittal Letter, supra note 4. \36\ The limit up-limit down mechanism set forth in the proposed Plan would replace the existing single-stock circuit breaker pilot. See e.g., Securities Exchange Act Release Nos. 62251 (June 10, 2010), 75 FR 34183 (June 16, 2010) (SR-FINRA-2010-025); 62883 (September 10, 2010), 75 FR 56608 (September 16, 2010) (SR-FINRA- 2010-033). --------------------------------------------------------------------------- IV. Comment Letters and Response Letter The Commission received 18 comment letters on the proposed Plan.\37\ Many commenters generally supported the Plan,\38\ while others indicated that they did not oppose the Plan and its intended goals, but raised concerns regarding specific details on the terms of the Plan.\39\ A few commenters opposed \40\ the Plan and suggested different alternatives to achieve the intended goal of the Plan. The Participants responded to the comments regarding the proposal.\41\ --------------------------------------------------------------------------- \37\ See supra note 7. \38\ See MFA Letter at 1; Vanguard Letter at 1; ICI Letter at 1; STA Letter at 1; Knight Letter at 1; SIFMA Letter at 1; ITG Letter at 1; Deutsche Bank Letter at 1; STANY Letter at 1; GETCO Letter at 1. \39\ See Driscoll Letter at 1; FIF Letter at 1; Angel Letter at 1 (stating that the proposed Plan is an improvement over the current single stock circuit breaker pilot); Scottrade Letter at 1 and 5 (supporting the goals of the proposed Plan, but stating that it believes that more work needs to be done before it can support the proposed Plan); Themis Letter at 1 (commending the efforts of the proposed Plan); Molinete Letter at 1. \40\ See Wunsch Letter at 1; CME Group Letter at 1-2 (supporting the proposed Plan's fundamental goal of promoting fair and orderly markets and mitigating the negative impacts of sudden and extraordinary price movements in NMS stocks, but stating that the proposed Plan sets forth an overly complicated and insufficiently coordinated structure that, in a macro-liquidity event, will have the unintended consequence of undermining rather than promoting liquidity). \41\ See Response Letter, supra note 10. --------------------------------------------------------------------------- A. Reference Price Calculation As proposed in the Plan, the Processors would be responsible for calculating and disseminating the applicable Price Bands as provided for in Section V of the Plan. The Processors for each NMS stock would calculate and disseminate to the public a Lower Price Band and an Upper Price Band during regular trading hours, as defined in Section I(R) of the Plan, for such NMS Stock. The Price Bands would be based on a Reference Price for each NMS Stock that equals the arithmetic mean price of Eligible Reported Transactions \42\ for the NMS stock over the immediately preceding five-minute period (except for periods following openings and reopenings).\43\ The Price Bands for an NMS Stock would be calculated by applying the Percentage Parameter \44\ for such NMS Stock to the Reference Price, with the lower Price Band being a Percentage Parameter below the Reference Price, and the upper Price Band being a Percentage Parameter above the Reference Price. Some commenters expressed concern about the complexity involved in calculating the Reference Price.\45\ --------------------------------------------------------------------------- \42\ As defined in the proposed Plan, Eligible Reported Transactions shall have the meaning prescribed by the Operating Committee for the proposed Plan, and generally mean transactions that are eligible to update the sale price of an NMS Stock. \43\ See infra, Section III.G. for a discussion on the application of the Price Bands at the open and close of the trading day. \44\ As defined in Section (I)(M) of the proposed Plan, the ``Percentage Parameter'' means the percentages for each tier of NMS Stocks set forth in Appendix A of the Plan. As such, the Percentage Parameters for Tier 1 NMS Stocks with a Reference Price of $1.00 or more would be 5%, and the Percentage Parameters for Tier 2 NMS Stocks with a Reference Price of $1.00 or more would be 10%. For Tier 1 and Tier 2 NMS Stocks with a Reference Price less than $0.75, the Percentage Parameters would be the lesser of $0.15 or 75%. The Percentage Parameters for a Tier 2 NMS Stock that is a leveraged exchange-traded product would be the applicable Percentage Parameter multiplied by the leverage ratio of such product. \45\ See Angel Letter at 4; GETCO Letter at 3-4; MFA Letter at 5; Molinete Letter at 1-2 (stating that it is not clear whether the trades used to calculate the Reference Price are weighted by volume, or if this is a strict average of the trade prices reported); Themis Letter at 1. See also SIFMA Letter at 8 (noting that if the market price for an NMS Stock moves by less than one percent, the Price Bands will not change and, as a result, the limit up and limit down prices will be closer to four percent than five percent over the prevailing market price because a new Reference Price will only be disseminated if there is a change of one percent or more in the Pro- Forma Reference Price over the then prevailing Reference Price). --------------------------------------------------------------------------- Commenters suggested alternative ways to calculate the Reference Price. In its letter, one commenter suggested simplifying the Reference Price calculation by ``calculating a new Reference Price on regular 30 second intervals, regardless of whether it has changed by 1%'' and noted that ``[t]his simplification also obviates the definition of a Pro-Forma Reference Price.''\46\ That commenter also recommended calculating the Reference Prints with a volume weighted average price rather than an arithmetic average price, which would remove the possibility of market participants splitting orders in different ways to affect the calculation of the Reference Price.\47\ Another commenter stated that [[Page 33502]] the Participants should consider using the opening price of a stock as the Reference Price because it would be much simpler than the calculation that the Participants proposed.\48\ Another commenter stated that the Participants should consider using the prior day's closing price as a static Reference Price, rather than constantly updating the Reference Price throughout the trading day, noting that this would be similar to how the futures markets calculate their limit up-limit down Price Bands.\49\ --------------------------------------------------------------------------- \46\ See MFA Letter at 5. \47\ Id. \48\ See Angel Letter 4. \49\ See GETCO Letter at 3-4. See also SIFMA Letter at 9 (requesting that the Participants clarify how Price Bands will apply to stocks with prices that cross the one dollar threshold during intra-day trading); Molinete Letter at 3-4 (stating its belief that changes in Price Band calculations throughout the trading day can create problems). --------------------------------------------------------------------------- Commenters also stated that certain types of trades should be exempted from the Plan and thus the calculation of the Reference Price. Three commenters noted that certain Regulation NMS-exempt trades should be exempt from the Plan because they are unrelated to the last sale of a stock.\50\ More specifically, one commenter stated that ``trading centers should be permitted to execute orders internally at prices outside of the specified Price Bands if the executions comply [with certain Regulation NMS exemptions].'' \51\ That commenter noted that most Regulation NMS exemptions ``have corresponding sale conditions that identify those trades as being not eligible for last sale.'' \52\ Another commenter stated that certain block facilitation trades should be exempted from the Plan.\53\ That commenter argued that block facilitation trades tend to stabilize the market because a block positioner is committing capital to absorb a large trading interest that would otherwise impact the market for the underlying stock of the block order.\54\ Finally, two commenters suggested that trades that are executed outside of the current Price Bands be exempt from Reference Price calculations.\55\ --------------------------------------------------------------------------- \50\ See e.g., FIF Letter at 1-2; Deutsche Bank Letter at 3; SIFMA Letter at 2-4. \51\ See FIF Letter at 1-2 (listing the exemptions found in Rule 611(a)--non-convertible preferred securities; Rule 611(b)(2)--not regular way; Rule 611(b)(7)--benchmark derivatively priced; Rule 611(b)(9)--stopped stock; Rule 611(d)--qualified contingent trades; Rule 611(d)--error correction; Rule 611(d)--print protection). \52\ Id. \53\ See Deutsche Bank Letter at 3 (stating that ``it is critical for a block facilitator to execute outside a band when the market is moving rapidly or it will lose the ability to trade effectively for its client.'') See also FIF Letter at 2 (requesting an impact analysis on the printing of block transactions accompanied by a Regulation NMS sweep as well as block transactions printed without ISO modifiers in adherence with Regulation NMS FAQ 3.23). \54\ Id. \55\ See MFA Letter at 6 (recommend that the Plan include a more explicit definition for which prints are included in calculating a Reference Price); STANY Letter at 2 (noting that clearly erroneous transactions may still occur, and thus suggesting that trades that are executed outside the then existing price bands not be included in the calculation of the Reference Price). --------------------------------------------------------------------------- The Participants noted that alternatives were considered when the Plan was being drafted, but the Participants determined that something more dynamic would be preferable, and that the five percent level is more therefore appropriate, particularly for highly liquid stocks.\56\ Moreover, the Participants stated that the proposed one percent requirement would help to reduce quote traffic but still provide for appropriate adjustments of Reference Prices in a rapidly moving market.\57\ The Participants also stated that using the arithmetic average would reduce the impact of any erroneous trades that may be included in the calculation of the Reference Price.\58\ --------------------------------------------------------------------------- \56\ See Response Letter at 4. \57\ The Participants are not proposing to amend the Plan with respect to the calculation of the Reference Price. However, in an effort to keep a rapidly-moving market aware of the current price bands, the Processor would republish the existing price bands every 15 seconds. See Response Letter at 5. \58\ Id. --------------------------------------------------------------------------- As discussed in greater detail below, the Participants recently amended the Plan to clarify that the Reference Price used in determining which Percentage Parameter is applicable during the trading day would be based on the closing price of the subject security on the Primary Listing Exchange on the previous trading day or, if no closing price exists, the last sale on the Primary Listing Exchange reported by the Processors. The Participants also amended the Plan to permit certain transactions to execute outside of the price bands. Specifically, the Participants proposed that transactions that are exempt under Rule 611 of Regulation NMS,\59\ and which do not update the last sale price (except if solely because the transaction was reported late), should be allowed to execute outside of the price bands.\60\ As part of the amendment, the Participants also proposed to exclude rights and warrants from the Plan, consistent with the current single-stock circuit breaker pilot.\61\ --------------------------------------------------------------------------- \59\ 17 CFR 242.611. \60\ See Amendment, supra note 13. \61\ Id. --------------------------------------------------------------------------- B. Display of Offers Below the Lower Price Band and Bids Above the Upper Price Band As proposed in the Plan, offers below the Lower Price Band and bids above the Upper Price Band would not be displayed on the consolidated tape. One commenter disagreed with this aspect of the Plan and stated that all quotes should be displayed, but marked as non-executable if outside the Price Bands.\62\ That commenter stated that preventing the display of quotes outside the Price Bands could lead to unusual side effects and that a broker-dealer entering an order on behalf of a customer should have the option of re-pricing or posting the order in accordance with the customer's wishes, rather than a market center re- pricing non-executable orders to a Price Band.\63\ Another commenter stated that displaying certain non-accessible quotes that are the result ``of an altered price discovery process will have greater negative implications for investor confidence'' because the only trades than can be executed during a Limit State ``do not represent the true equilibrium of supply and demand.'' \64\ --------------------------------------------------------------------------- \62\ See MFA Letter at 2-3. \63\ See id. \64\ See Driscoll Letter at 3. --------------------------------------------------------------------------- The Participants noted that under the Plan, all trading centers would be required to establish, maintain, and enforce written policies and procedures reasonably designed to prevent the display of offers below the Lower Price Band and bids above the Upper Price Band for an NMS Stock.\65\ When one side of the market for an individual security is outside the applicable Price Band, the Processors would be required to disseminate such National Best Bid or National Best Offer with an appropriate flag identifying it as non-executable. When the other side of the market reaches the applicable Price Band, the market for an individual security would enter a Limit State, and the Processor would be required to disseminate such National Best Offer or National Best Bid with an appropriate flag identifying it as a Limit State Quotation. The Participants stated that after considering whether more quotes should be displayed as unexecutable, they determined that any potential benefits arising from such practice would be outweighed by the risk of investor confusion. As a result, the Participants did not believe that the Plan should be amended to permit all quotes outside the Price Bands to be displayed. The Participants stated that they would continue to review this issue and could [[Page 33503]] revisit it after gaining experience during the pilot.\66\ --------------------------------------------------------------------------- \65\ See Response Letter at 4. \66\ Id. --------------------------------------------------------------------------- C. Criteria for Entering the Limit State As set forth in Section VI of the Plan, when one side of the market for an individual security is outside the applicable Price Band (i.e., when the National Best Bid \67\ is below the Lower Limit Band or the National Best Offer \68\ is above the Upper Limit Band for an NMS Stock), the Processors would be required to disseminate such National Best Bid or National Best Offer with an appropriate flag identifying it as non-executable. When the other side of the market reaches the applicable Price Band (i.e., when the National Best Offer is equal to the Lower Limit Band or the National Best Bid is equal to the Upper Limit Band for an NMS Stock), the market for an individual security would enter a Limit State,\69\ and the Processors would be required to disseminate such National Best Offer or National Best Bid with an appropriate flag identifying it as a Limit State Quotation.\70\ --------------------------------------------------------------------------- \67\ 17 CFR 242.600(b)(42). See also Section I(G) of the Plan. \68\ Id. \69\ As set forth in Section VI(B) of the Plan, when trading for an NMS Stock enters a Limit State, the Processor shall cease calculating and disseminating updated Reference Prices and Price Bands for the NMS Stock until either trading exits the Limit State or trading resumes with an opening or re-opening as provided in Section V of the proposed Plan. \70\ See Section I(D) of the Plan. --------------------------------------------------------------------------- Commenters expressed concern that requiring the National Best Bid or Offer (``NBBO'') to be equal to, but not necessarily cross the applicable Price Band in order to enter a Limit State could create some unusual market discrepancies.\71\ One commenter stated that ``it does not make sense for a Limit State to be triggered if the national best bid or offer equals a price band, but not if the national best bid or offer has crossed a price band [because the] same rationale for entering a Limit State exists in either case.'' \72\ Instead, the commenters suggested that if either the best bid or offer is outside the Price Band, the market should enter the Limit State. --------------------------------------------------------------------------- \71\ See MFA Letter at 6 (stating that ``buyers may not submit orders if the Upper Price Band is sufficiently far away from the market'' and recommending that ``if either the best bid or ask is outside the Price Band, the market enters a Limit State and has 5 seconds to readjust before a Trading Halt''); Deutsche Bank Letter at 4. \72\ See Deutsche Bank Letter at 4 (emphasis in original). --------------------------------------------------------------------------- One commenter expressed concern about a scenario where a stock is effectively not trading, but still has not entered a Limit State--for example, where the National Best Bid is below the Lower Price Band, and is thus non-executable, while the National Best Offer remains within the price bands. Since, in this example, the offer has not hit the Lower Price Band, the Limit State has not yet been triggered; however, the market for that stock is essentially one-sided, as the bid cannot be executed against. Since the Limit State has not yet been triggered, the concern is that the market could remain in this condition for an indefinite period of time.\73\ --------------------------------------------------------------------------- \73\ See Molinete Letter at 2-3 (discussing a situation where the market may not enter a Limit State due to a market order against an illiquid book that would execute against a quote that is outside the applicable price bands). --------------------------------------------------------------------------- In the situation where a stock is effectively not trading, i.e., because the National Best Bid is below the Lower Price Band, but the National Best Offer is still within the price bands and thus the Limit State would not be triggered, the Participants responded that the National Best Offer would generally follow the National Best Bid downwards, and sellers would be willing to offer the stock at the Lower Price Band, triggering the Limit State.\74\ The Participants also responded that, alternatively, the reference price may be recalculated due to transactions occurring in the previous five minutes. This could adjust the price bands downwards, potentially bringing the National Best Bid within the price bands, at which time it may be executed against.\75\ The Participants represented that they would monitor these situations during the pilot and consider modifications to the Plan structure if needed.\76\ --------------------------------------------------------------------------- \74\ See Response Letter at 5. \75\ Id. \76\ Id. --------------------------------------------------------------------------- As discussed below, in response to commenters' concerns, the Participants recently amended the Plan to create a manual override function where the National Best Bid (Offer) for a security is below (above) the Lower (Upper) Price Band, and the security has not entered the Limit State. With this provision, the Primary Listing Exchange has the ability to initiate a trading pause for a stock in this situation.\77\ --------------------------------------------------------------------------- \77\ See Amendment, supra note 13. --------------------------------------------------------------------------- D. Order Handling During the Limit State As set forth in the Plan, all trading centers \78\ in NMS Stocks, including both those operated by Participants and those operated by members of Participants, would be required to establish, maintain, and enforce written policies and procedures that are reasonably designed to comply with the limit up-limit down and trading pause requirements specified in the Plan. Some commenters stated that clarifications are necessary regarding the Commission's Order Handling Rules so that they could be applied uniformly across all market centers once the Plan is in effect.\79\ One commenter noted that market centers would benefit from guidance on best industry standards for handling customer orders during the periods of time when securities are in a Limit State, as well as periods when trading in a security restarts after a trading pause.\80\ --------------------------------------------------------------------------- \78\ As defined in Section I(W) of the Plan, a trading center shall have the meaning provided in Rule 600(b)(78) of Regulation NMS under the Exchange Act. \79\ See STA Letter at 3; SIFMA Letter at 6 (stating that the proposal contemplates that broker-dealers may delay, reprice or reject ``held'' orders, thus implicating the limit order display rule as well as best execution requirements); Angel Letter at 4 (requesting the clarification of best execution requirements during the Limit State). \80\ See STA Letter at 3. --------------------------------------------------------------------------- E. Duration of the Limit State By the terms of the Plan, trading for an NMS Stock would exit a Limit State if, within 15 seconds of entering the Limit State, the entire size of all Limit State Quotations is executed or cancelled. If the market does not exit a Limit State within 15 seconds, then the Primary Listing Exchange would declare a five-minute trading pause pursuant to Section VII of the Plan. Two commenters suggested that the Plan should contemplate a longer Limit State than 15 seconds, such as 30 seconds, because a shorter time period would trigger too many trading pauses.\81\ One commenter advocated for a longer Limit State ``[b]ecause the price bands should eliminate significant erroneous trades, and trading halts interfere with the natural interaction of orders and the price discovery process.'' \82\ That commenter stated that halts should thus ``be limited to extraordinary circumstances.'' \83\ Another commenter noted that ``15 seconds is not a sufficient amount of time for most investors to digest information about a limit state condition and to react to the information.'' \84\ These commenters believe that a 30 second Limit State would provide a more sufficient opportunity for market participants to provide liquidity to the market of an NMS Stock. These [[Page 33504]] commenters stated that, at a minimum, the timeframe should not be shortened from the proposed 15 seconds. --------------------------------------------------------------------------- \81\ See Vanguard Letter at 2; ICI Letter at 2. One commenter stated it would serve the public to understand why 15 seconds was chosen for the Limit State condition, as opposed to 30 seconds, or perhaps 60 seconds. See Themis Letter at 1. \82\ See Vanguard Letter at 2. \83\ Id. \84\ See ICI Letter at 2. --------------------------------------------------------------------------- Other commenters proposed shortening the length of the Limit State to 5 seconds, suggesting that this would be ample time for the market to replenish the necessary liquidity given the technological advances in modern trading.\85\ One commenter stated that a shorter Limit State is preferable because a longer Limit State could lead to wider spreads and uncertainty in the options markets.\86\ Another commenter stated that retail investors may wonder why their orders had not been executed.\87\ --------------------------------------------------------------------------- \85\ See SIFMA Letter at 5-6; MFA Letter at 6; and Scottrade Letter at 2. \86\ See SIFMA Letter at 5. \87\ See Scottrade Letter at 2 (stating its confidence that stocks that enter the Limit State Quotation erroneously will be addressed within a 5 second threshold, allowing the security to continue trading). --------------------------------------------------------------------------- In response, the Participants stated that the 15-second Limit State should be long enough to reasonably attract additional available liquidity without recourse to a trading pause, while short enough to reasonably limit any market uncertainty that might accompany a Limit State.\88\ The Participants represented that, during the pilot period, they will continue to review the length of the Limit State and consider whether, based on that experience, it should be lengthened or shortened.\89\ --------------------------------------------------------------------------- \88\ See Response Letter at 6. \89\ Id. --------------------------------------------------------------------------- F. Criteria for Exiting a Limit State Under the Plan, trading for an NMS Stock would exit a Limit State if within 15 seconds of entering the Limit State, the entire size of all Limit State Quotations is executed or cancelled. Some commenters proposed alternative criteria for exiting a Limit State. One commenter expressed concern ``that the exit from a Limit State is arbitrary and may be easily manipulated * * * [because] it's not clear to market participants from moment to moment whether a trading pause will be declared or whether the Price Bands will suddenly be adjusted. Exiting a Limit State would depend upon the timing of an order that could clear out the Limit State quotation and when a new limit order arrives at the Limit State quotation.'' \90\ Another commenter suggested that in order to reestablish an orderly market, that the Plan should require a new bid and a new offer that are executable before the expiration of a Limit State period.\91\ Another commenter stated that the conditions for exiting a Limit State are not clearly defined in the Plan and further clarifications are necessary.\92\ --------------------------------------------------------------------------- \90\ See MFA Letter at 5. \91\ See SIFMA Letter at 6. \92\ See Molinete Letter at 3. --------------------------------------------------------------------------- The Participants declined to amend the Plan to address these concerns, noting in the Response Letter that adding a requirement that a new executable bid or offer be entered before exiting a Limit State raises the question of who would be obligated to enter such a bid or offer.\93\ Moreover, the Participants stated that depending on the price movements during the five minutes prior to entering the Limit State, the Reference Price may have moved, thus moving the Price Bands.\94\ The Participants noted that in such a case, executable bids and offers may become available simply by virtue of the recalculated Price Bands. --------------------------------------------------------------------------- \93\ Id. \94\ Id. --------------------------------------------------------------------------- G. Application of the Price Bands at the Open and Close During Phase I of the Plan's implementation time period, the terms of the Plan would apply only to Tier 1 NMS Stocks, as defined in Appendix A of the Plan, and the first Price Bands would be calculated and disseminated 15 minutes after the start of Regular Trading Hours, as specified in Section V(A) of the Plan, and no Price Bands would be calculated and disseminated less than 30 minutes before the end of Regular Trading Hours. In Phase II, the Plan would fully apply to all NMS Stocks beginning at 9:30 a.m. ET and ending at 4:00 p.m. ET of each trading day. Some commenters expressed concerns about the application of the Price Bands at the opening of the trading day. One commenter stated that the approach proposed in Phase I--the first Price Bands would be calculated and disseminated 15 minutes after the start of Regular Trading Hours, and no Price Bands would be calculated and disseminated less than 30 minutes before the end of Regular Trading Hours--should apply to both phases of the Plan.\95\ Another commenter agreed that the Plan should not be in effect during the first five minutes of the trading day because price information is critical at that time.\96\ That commenter also stated that any regulatory gap during this time period could be filled by the clearly erroneous trade rules, which it proposed should only be in effect during the first five (and last five) minutes of the trading day.\97\ Rather than placing a specific time limit on the opening, another commenter asserted that it would benefit the market if Price Bands were not established until a single opening price occurs at the Primary Listing Exchange.\98\ However, one commenter stated that the Price Bands should be in effect for the entire trading day because long-term investors may appreciate this simplicity.\99\ --------------------------------------------------------------------------- \95\ See SIFMA Letter at 8. The commenter also requested clarification on whether it is true that there may be no Price Bands in effect for an NMS Stock during the first five minutes if the Opening Price for the stock does not occur on the Primary Market within that period because there will be no Reference Price under such circumstance. See id. \96\ See Knight Letter at 3. \97\ Id. \98\ See Scottrade Letter at 2. \99\ See Themis Letter at 1. --------------------------------------------------------------------------- Commenters also expressed concerns about the application of the Price Bands at the close of the trading day. Six commenters opposed applying the Price Bands at the close of the trading day.\100\ These commenters described the close of the trading day as a critical part of the trading day \101\ and argued that under the terms of the Plan, exchanges could have inconsistent closing times as a result of a trading pause.\102\ According to these commenters, keeping track of various closing times could have serious negative effects for market participants attempting to close positions or hedge by the end of the day.\103\ Alternatively, one commenter suggested that if there is a disruptive event immediately prior to the close, regular-way trading and the closing auction should be extended to make sure the closing price is accurate.\104\ --------------------------------------------------------------------------- \100\ Six commenters generally advocated for the Plan not being in effect during the final 10 minutes of the trading day, i.e., 3:50 p.m. to 4:00 p.m. ET. See FIF Letter at 5; Deutsche Bank Letter at 2 and 4; Knight Letter at 3; SIFMA Letter at 2; ITG Letter at 2; Scottrade Letter at 2-3. Two of these commenters suggested that it would be ideal to suspend the operation of the Plan from 3:35 p.m. to 4:00 p.m. ET. See ITG Letter at 2; Scottrade Letter at 2-3. \101\ See e.g., Knight Letter at 3. \102\ See e.g., FIF Letter at 5 (stating that exchanges could have different closing times as a result of trading pauses); Deutsche Bank Letter at 2 (advocating for consistent closing times across all of the exchanges). \103\ See Deutsche Bank Letter at 2. \104\ See Angel Letter at 5. --------------------------------------------------------------------------- The Participants stated in the Response Letter that they believe that the proposed doubling of the Percentage Parameters around the opening and closing periods is appropriate in light of the increased volatility at those times, and that no adjustment to the timing or levels of the Price Bands should be made to the Plan until experience is gained from both Phases I and II.\105\ --------------------------------------------------------------------------- \105\ See Response Letter at 4. --------------------------------------------------------------------------- [[Page 33505]] H. Reopenings on the Primary Listing Exchange Under the terms of the Plan, following a trading pause in an NMS Stock, and if the Primary Listing Exchange has not declared a Regulatory Halt, the next Reference Price would be the Reopening Price on the Primary Listing Exchange if such Reopening Price occurs within ten minutes after the beginning of the trading pause, and subsequent Reference Prices shall be determined in the manner prescribed for normal openings, as specified in Section V(B)(1) of the Plan. One commenter stated, instead of this provision, exchanges could compete for the five to ten minute exclusive window to reopen an issue.\106\ The commenter suggested reviewing trading volumes and awarding the reopening rights to the venue with the most average daily volume over the review period.\107\ --------------------------------------------------------------------------- \106\ See Driscoll Letter at 2-3. \107\ Id. at 4. --------------------------------------------------------------------------- I. Classification and Treatment of Tier 2 Stocks Pursuant to the Plan, Tier 1 NMS Stocks would include all NMS Stocks included in the S&P 500 Index, the Russell 1000 Index, and the exchange-traded products listed on Schedule 1 to the Plan's Appendix. Tier 2 NMS Stocks would include all NMS Stocks other than those in Tier 1. The Percentage Parameters for Tier 2 NMS Stocks with a Reference Price of $1.00 or more would be 10% and the Percentage Parameters for Tier 2 NMS Stocks with a Reference Price less than $1.00 would be the lesser of (a) $0.15 or (b) 75%. One commenter stated that a 10% price band may be too restrictive for some Tier 2 stocks and suggested that the Participants reduce the number of Tier 2 stocks to a test group.\108\ That commenter also stated that a 10% price band may be too restrictive for thinly traded stocks.\109\ Another commenter proposed the creation of a Tier 3 for stocks with a sufficiently low average daily volume (``ADV'') and wide bid-offer spreads.\110\ That commenter stated that the originally proposed limit up-limit down parameters may be unsuitable for these types of low-liquidity stocks and that they may require a higher percentage parameter.\111\ --------------------------------------------------------------------------- \108\ See MFA Letter at 4. \109\ Id. (for example, the commenter suggested that reopening rights be awarded to the trading venue with the most average daily volume over the review period). \110\ See Knight Letter at 3. \111\ Id. --------------------------------------------------------------------------- As discussed below, the Participants recently amended the Plan to create a 20% price band for Tier 1 and Tier 2 stocks with a Reference Price equal to $0.75 and up to and including $3.00. The Participants also proposed a conforming amendment for Tier 1 and Tier 2 stocks with a Reference Price less than $0.75. The Percentage Parameters for these stocks shall be the lesser of (a) $0.15 or (b) 75%.\112\ As initially proposed, those Percentage Parameters would have applied to Tier 1 and Tier 2 stocks with a Reference Price less than $1.00. --------------------------------------------------------------------------- \112\ See Amendment, supra note 13. --------------------------------------------------------------------------- J. Treatment and Impact of the Plan on Exchange Traded Products (ETPs) The Commission also received comments on the scope of the Plan as it applies to ETPs. ICI stated that all ETFs should be included in the pilot on an expedited basis.\113\ Vanguard seconded this idea and noted that the original list of ETPs was created when the Commission, FINRA, and the exchanges had to act quickly following the market events of May 6, 2010.\114\ --------------------------------------------------------------------------- \113\ See ICI Letter at 2-3. \114\ See Vanguard Letter at 2. --------------------------------------------------------------------------- MFA suggested that there could be unintended consequences of the Plan on ETFs (or derivatives) because the spreads in such products could increase due to uncertainty in the underlying security, i.e., if the components of an ETF are subject to Limit States or trading pauses, quotes in the ETF would widen accordingly, potentially causing the ETF itself to enter a Limit State.\115\ According to MFA, index arbitragers may decline to trade because of uncertainty if they do not have a way to hedge risk.\116\ --------------------------------------------------------------------------- \115\ See MFA Letter at 6. \116\ Id. --------------------------------------------------------------------------- In response, the Participants noted that the proposed phases of the Plan appropriately focus on trading characteristics and volatility rather than instrument type, and that including only certain ETPs in Tier 1 was consistent with scope of the current single-stock circuit breaker pilot.\117\ --------------------------------------------------------------------------- \117\ See Response Letter at 9. --------------------------------------------------------------------------- As discussed below, the Participants recently amended the Plan to require a review and update, on a semi-annual basis, of the list of ETPs included in Tier I of the Plan, and re-stated the criteria by which ETPs would be selected for inclusion in Tier I. K. Coordination of the Plan With Other Volatility Moderating Mechanisms Five commenters noted that the Plan implicates other volatility moderating mechanisms that currently exist \118\ and requested that the interaction of the Plan with these existing mechanisms be clarified.\119\ The commenters stated that the Plan could interact with the single-stock circuit breaker pilot,\120\ the Regulation SHO circuit breaker,\121\ and the exchange-specific volatility guards.\122\ One commenter stated that ``simultaneous triggering of two or more of these speed bumps during times of heightened market volatility could cause confusion and uncertainty unless there is a scheme in place for handing multiple triggers.'' \123\ One commenter advocated that as the Participants implement the Plan, the Commission phase out: (1) The NYSE LRPs; (2) the Nasdaq Volatility Guard; (3) the Regulation SHO alternative uptick rule; and (4) the single-stock circuit breakers.\124\ Two commenters also requested that the Commission amend clearly erroneous rules so the presumption is that trades executed within the Price Band are not subject to being broken.\125\ --------------------------------------------------------------------------- \118\ See Scottrade Letter at 3; STANY Letter at 4; Knight Letter at 2-3; SIFMA Letter at 6-7; CME Letter at 1 and 3 (noting that the proposed Plan would replace the existing single-stock circuit breaker pilot program currently in effect); FIF Letter at 5 (noting that under the single-stock circuit breaker pilot, exchanges deal with held orders differently). \119\ See e.g., Scottrade Letter at 3. \120\ See e.g., Scottrade Letter at 3; STANY Letter at 4; FIF Letter at 5. \121\ See e.g., STANY Letter at 4; \122\ See e.g., STANY Letter at 4; Knight Letter at 2-3. \123\ See STANY Letter at 4. \124\ See Knight Letter at 1. \125\ See SIFMA Letter at 6-7; STANY Letter at 4. See also Knight Letter at 3 (Knight stated that clearly erroneous rules should only operate during the first and last five minutes of the trading day and that there is also a utility in extending the clearly erroneous rules to after-hours trading). --------------------------------------------------------------------------- Another commenter stated that the Plan does not consider how it would interact with the market-wide circuit breakers being evaluated by the Commission and the U.S. Commodity Futures Trading Commission.\126\ This commenter stated that single-stock circuit breaker halts may affect products across markets, and may undermine rather than promote liquidity during market disruptions.\127\ Moreover, according to this commenter, halting individual securities without a market-wide halt would, in the case of an index, impair the calculation of that index, which would have cross-market effects. This commenter concluded that market-wide circuit breakers, coupled with automated volatility and risk management functionality, i.e., price bands, protection points, order quantity [[Page 33506]] protections, and stop logic functionality, would be the better alternative.\128\ --------------------------------------------------------------------------- \126\ See CME Letter at 2-3. \127\ Id. at 3. \128\ Id. --------------------------------------------------------------------------- The Participants noted that some commenters requested that the Participants amend their rules to provide that an execution within a Price Band could not be deemed a clearly erroneous execution. The Participants responded that, while it may be useful to do so and that a key benefit of the limit up-limit down mechanism should be the prevention of clearly erroneous executions, the clearly erroneous trade rules are separate from the Plan and as such the Participants would consider such a change on a separate track.\129\ --------------------------------------------------------------------------- \129\ See Response Letter at 7. --------------------------------------------------------------------------- L. Coordination and Impact on Other Markets Commenters also expressed opinions regarding the impact of the Plan on other markets, e.g., options,\130\ futures,\131\ and foreign markets.\132\ One commenter suggested that in the options markets, the proposed Limit State for an NMS Stock could create uncertainty and result in wider spreads on the related option.\133\ In its letter, that commenter stated that option traders hedge option transactions with the underlying security, so that a Limit State could impact hedging activity as well. This commenter suggested that options market-makers may be unwilling to be subject to normal market-making requirements and minimum quoting widths when the underlying security is in a Limit State. Moreover, options markets do not have uniform clearly erroneous standards. Accordingly, when the underlying security is in a Limit State, some options exchanges may reject all options market orders, while other exchanges may reject only orders on the same side of the market that caused the Limit State.\134\ --------------------------------------------------------------------------- \130\ See SIFMA Letter at 7; STANY Letter at 3-4. \131\ See e.g., CME Group Letter, supra note 38. \132\ See Angel Letter at 5 (stating that policy makers should consider how foreign markets address issues of extraordinary market volatility). \133\ See STANY Letter at 3-4. \134\ Id. --------------------------------------------------------------------------- The Participants responded that the Plan will generally benefit the market for NMS Stocks and protect investors and should not be delayed while further consideration is given to coordination with options and futures markets.\135\ The Participants also stated their belief that the Plan strikes appropriate balance in the areas noted. Because the Plan would be adopted as a pilot, the Participants represented that they would have an opportunity to further consider the commenters' suggestions above after gaining experience with the Plan. --------------------------------------------------------------------------- \135\ See Response Letter at 7. --------------------------------------------------------------------------- M. Role of the Processors The Processors are fundamental to the operation of the Plan. In short, the single plan processor responsible for consolidation of information for an NMS Stock would be responsible for calculating and disseminating the applicable Price Bands as well as marking certain quotations as non-executable. One commenter stated that the SIPs should run test data to prove that they are up to the tasks required by them under the terms of the Plan.\136\ Another commenter questioned the ability of the SIPs to perform the tasks because under the Plan, SIPs would be producing data rather than merely passing through data to the markets for the first time.\137\ Another commenter stated that the SIPs should have mechanisms to determine when they have invalid or delayed market data and thus the ability to halt the dissemination of the Price Bands accordingly.\138\ Finally, because SIP data is slower than data disseminated directly by an exchange, one commenter questioned whether participants co-located to an exchange could calculate Price Band information faster than the rest of the market and use this information to their advantage.\139\ --------------------------------------------------------------------------- \136\ See STA Letter at 4. \137\ See STANY Letter at 5. See also FIF Letter at 5 (noting that it is possible that a trade will be executed at a price within the Price Bands, but will be reported to the SIP after the Price Band has moved and potentially should be studied.) \138\ See SIFMA Letter at 9. \139\ See Themis Letter at 1-2. --------------------------------------------------------------------------- The Participants responded that the Processor is well-suited to carrying out its responsibilities under the Plan and the Participants will monitor the Processor's performance during the pilot.\140\ --------------------------------------------------------------------------- \140\ See Response Letter at 8. --------------------------------------------------------------------------- N. Operating Committee Composition Section III(C) of the Plan provides for each Participant to designate an individual to represent the Participant as a member of an Operating Committee.\141\ No later than the initial date of the Plan, the Operating Committee would be required to designate one member of the Operating Committee to act as the Chair of the Operating Committee. The Operating Committee would monitor the procedures established pursuant to the Plan and advise the Participants with respect to any deficiencies, problems, or recommendations as the Operating Committee may deem appropriate. While the Plan generally provides that amendments to the Plan shall be unanimous, any recommendation for an amendment to the Plan from the Operating Committee that receives an affirmative vote of at least two-thirds of the Participants, but is less than unanimous, would be submitted to the Commission as a request for an amendment to the Plan initiated by the Commission under Rule 608 of Regulation NMS under the Act.\142\ --------------------------------------------------------------------------- \141\ See Section I(J) of the proposed Plan. \142\ 17 CFR 242.608. --------------------------------------------------------------------------- Two commenters suggested that the Operating Committee be supplemented by an advisory committee, made up of a cross-section of users, investors, and agents in the marketplace, that would report to the Operating Committee.\143\ One of these commenters stated that this would achieve due process for the both review and recommendations of altering the Plan.\144\ In the spirit of transparency, the other commenter recommended that the minutes of the Plan committee meetings be made available to interested parties.\145\ Two additional commenters recommended that industry representatives who are not parties to the Plan be added to the Operating Committee of the Plan.\146\ --------------------------------------------------------------------------- \143\ See STA Letter at 4-5; SIFMA Letter at 7. \144\ See STA Letter at 5. \145\ See SIFMA Letter at 7. \146\ See STANY Letter at 5-6; Driscoll Letter at 4 (recommending diverse representation of all key trading groups, retail order execution representation, institutional buy-side representation, representatives of various trading venues and representation of those who focus on small capitalization securities). --------------------------------------------------------------------------- The Participants initially responded that a non-voting advisory committee is unnecessary.\147\ Except with respect to the addition of new Participants to the Plan, the Participants stated that any proposed change in, addition to, or deletion from the Plan would have to be effected by means of a written amendment to the Plan that (1) sets forth the change, addition, or deletion; (2) is executed on behalf of each Participant; and (3) is approved by the SEC pursuant to, or otherwise becomes effective under, Rule 608 of Regulation NMS under the Exchange Act. Thus, any person affected by changes to the Plan would have notice and an opportunity to comment as part of the SEC approval process in accordance with Rule 608.\148\ --------------------------------------------------------------------------- \147\ See Response Letter at 7. \148\ Id. --------------------------------------------------------------------------- As discussed below, however, the Participants recently proposed an amendment to the Plan to create an Advisory Committee to the Operating Committee. Members of the Advisory Committee would have the right to submit their view on Plan matters to the [[Page 33507]] Operating Committee prior to a decision by the Operating Committee on such matters. Such matters may include, but would not be limited to, proposed material amendments to the Plan. The Operating Committee would be required to select at least one representative from each of the following categories to be members of the Advisory Committee: (i) A broker-dealer with a substantial retail investor customer base, (ii) a broker-dealer with a substantial institutional investor customer base, (iii) an alternative trading system, and (iv) an investor.\149\ --------------------------------------------------------------------------- \149\ See Amendment, supra note 13. --------------------------------------------------------------------------- O. Withdrawal of Participants From the Plan Section IX of the Plan provides that a Participant may withdraw from the Plan upon obtaining approval from the Commission and upon providing not less than 30 days written notice to the other participants. Four commenters expressed concern about the withdrawal provision and suggested that Commission require FINRA and all trading centers to participate in the Plan because withdrawal could create problems if only some market centers are part of the Plan.\150\ --------------------------------------------------------------------------- \150\ See FIF Letter at 5; SIFMA Letter at 7; STANY Letter at 5; Molinete Letter at 3. --------------------------------------------------------------------------- P. Implementation Time-Period The Participants proposed that the initial date of the Plan operations be 120 calendar days following the publication of the Commission's order approving the Plan in the Federal Register. The Participants would implement that Plan as a one-year pilot program in two Phases, consistent with Section VIII of the Plan. Phase I of Plan implementation would apply immediately following the initial date of Plan operations; Phase II of the Plan would commence six months after the initial date of the Plan or such earlier date as may be announced by the Processor with at least 30 days notice. As discussed below, the Participants recently proposed an amendment to the Plan that included a new implementation date of February 4, 2013. One commenter stated that the Plan should be implemented as quickly as possible.\151\ Another commenter recommended an implementation date of 12 months instead of 120 days,\152\ while another commenter stated that the Plan should be implemented no earlier than the second quarter of 2012.\153\ --------------------------------------------------------------------------- \151\ See Vanguard Letter at 2. See also ICI Letter at 3 (recommending that ETPs be included in the pilot on an expedited basis). \152\ See FIF Letter at 5-6. \153\ See SIFMA Letter at 9. See also Molinete Letter at 5 (stating that the 120-day implementation time period is too ambitious). --------------------------------------------------------------------------- Prior to the implementation of Phase II of the Plan, one commenter recommended that the Participants analyze empirical evidence derived from Phase I.\154\ Another commenter recommended that the Participants seek comment before implementing the Plan on a permanent basis.\155\ Yet another commenter stated that the Commission should have to approve Phase II of the Plan prior to its implementation.\156\ --------------------------------------------------------------------------- \154\ See Deutsche Bank Letter at 4. \155\ See SIFMA Letter at 9. \156\ See STANY Letter at 7. --------------------------------------------------------------------------- Q. Comments on Rule-Making Process of the Plan The Participants filed the Plan with the Commission pursuant to Section 11A of the Act \157\ and Rule 608 thereunder.\158\ The Commission solicited comments on the Plan from interested persons. One commenter stated that the process for the creation of a new NMS plan circumvented the formal notice and comment process provided for in The Administrative Procedure Act.\159\ The commenter stated that the existence of confidentiality agreements among the Participants in developing the proposal has negative implications for transparency in the rulemaking process.\160\ --------------------------------------------------------------------------- \157\ 15 U.S.C. 78k-1. \158\ 17 CFR 242.608. \159\ Pub. Law 79-404, 5 U.S.C. 500 et seq. See Driscoll Letter at 1. \160\ Id (stating that the narrow focus of the group that developed the regulation may have also allowed some opportunities to increase competition between exchanges to have been overlooked). --------------------------------------------------------------------------- Another commenter questioned whether there is a need for a Commission rule instead of an NMS plan and stated that ongoing and direct involvement of the Commission will be important to efficient and effective resolution of interpretive questions relating to the Plan and the reasonable policies and procedures.\161\ The same commenter also stated that self-regulatory organizations will need to adopt rules specifying how they plan to handle orders that have been routed to them when such orders present display or execution issues under the Plan.\162\ --------------------------------------------------------------------------- \161\ See SIFMA Letter at 7. \162\ Id. at 9. --------------------------------------------------------------------------- Finally, one commenter stated that a cost-benefit analysis of the Plan should be conducted to address the anticipated costs of implementing the Plan, the parties that would pay for new systems, whether processors would be allowed to charge more than their costs for the new data components of the consolidated feeds, and the incremental benefits that would be incurred over the existing trading pause rules if the Plan were approved.\163\ --------------------------------------------------------------------------- \163\ See Scottrade Letter at 4. --------------------------------------------------------------------------- V. Amendment to the Plan On May 24, 2012, in response to the comments received on the proposed Plan, the Participants submitted an amendment that proposed several changes to the Plan.\164\ First, the participants proposed to amend the Plan to allow transactions that are exempt under Rule 611 of Regulation NMS \165\, and which do not update the last sale price (except if solely because the transaction was reported late), to execute outside of the price bands.\166\ --------------------------------------------------------------------------- \164\ See Amendment, supra note 13. \165\ 17 CFR 242.611. \166\ See Amendment, supra note 13. --------------------------------------------------------------------------- Second, the Participants proposed to amend the Plan to provide for a 20% price band for Tier 1 and Tier 2 stocks with a Reference Price equal to $0.75 and up to and including $3.00. The Participants also proposed a conforming amendment for Tier 1 and Tier 2 stocks with a Reference Price less than $0.75. The Percentage Parameters for these stocks would be the lesser of (a) $0.15 or (b) 75%.\167\ As initially proposed, those Percentage Parameters would apply to Tier 1 and Tier 2 stocks with a Reference Price less than $1.00. --------------------------------------------------------------------------- \167\ Id. --------------------------------------------------------------------------- Third, the Participants proposed to amend the Plan to exclude rights and warrants from the Plan, consistent with the current single- stock circuit breaker pilot.\168\ --------------------------------------------------------------------------- \168\ Id. --------------------------------------------------------------------------- Fourth, the Participants proposed to amend the Plan to provide for the creation of an Advisory Committee to the Operating Committee. As set forth in greater detail in the amendment, the Operating Committee would be required to select at least one representative from each of the following categories to be members of the Advisory Committee: (i) A broker-dealer with a substantial retail investor customer base, (ii) a broker-dealer with a substantial institutional investor customer base, (iii) an alternative trading system, and (iv) an investor.\169\ Members of the Advisory Committee would have the right to submit their view on Plan matters to the Operating Committee prior to a decision by the Operating Committee on such matters. Such matters could include, but would not be limited to, proposed material amendments to the Plan. --------------------------------------------------------------------------- \169\ Id. --------------------------------------------------------------------------- Fifth, the Participants proposed to amend the Plan to provide for a manual [[Page 33508]] override functionality when, for example, the National Best Bid for an NMS Stock is below the Lower Price Band, the NMS Stock has not entered the Limit State, and the Primary Listing Exchange has determined that trading in that stock has sufficiently deviated from its normal trading characteristics such that a trading pause would promote the Plan's core purpose of addressing extraordinary market volatility. Upon making this determination, the Primary Listing Exchange would have the ability to declare a trading pause in that stock.\170\ --------------------------------------------------------------------------- \170\ Id. --------------------------------------------------------------------------- Sixth, the Participants proposed a new implementation date of February 4, 2013. The Participants stated that this date would provide appropriate time to develop and test the technology necessary to implement the Plan, including market-wide testing. Finally, the Participants proposed to amend the Plan to require the Participants to review and update, on a semi-annual basis, the list of ETPs included in Tier I of the Plan, and re-stated the criteria by which ETPs would selected for inclusion in Tier I.\171\ --------------------------------------------------------------------------- \171\ For example, ETPs, including inverse ETPs, that trade over $2,000,000 consolidated average daily volume would be included in Tier I, as would ETPs that do not meet this volume criterion, but track similar benchmarks. --------------------------------------------------------------------------- The Participants also proposed technical changes to the Plan. For example, the Participants clarified that Regular Trading Hours could end earlier than 4:00 p.m. ET in the case of an early scheduled close. The Participants also provided that Participants may re-transmit the price bands calculated and disseminated by the Processor. Finally, the Participants clarified that the Reference Price used in determining which Percentage Parameter is applicable during the trading day would be based on the closing price of the subject security on the Primary Listing Exchange on the previous trading day or, if no closing price exists, the last sale on the Primary Listing Exchange reported by the Processor. The Participants also proposed to amend the Plan in order to collect and provide to the Commission various data and analysis throughout the duration of the pilot period. Specifically, the Participants will provide summary statistics to the Commission, including data covering how often stocks enter the Limit State, and how often stocks enter a trading pause as a result of the limit up-limit down mechanism. The Participants will also examine certain parameters of the limit up-limit down mechanism, including the appropriateness of the proposed price bands, and the appropriateness of the duration of the Limit State. Finally, the Participants will provide raw data to the Commission, including the record of every limit price, the record of every Limit State, and the record of every trading pause. VI. Discussion and Commission Findings A. Section 11A of the Act In 1975, Congress directed the Commission, through the enactment of Section 11A of the Act,\172\ to facilitate the establishment of a national market system to link together the individual markets that trade securities. Congress found the development of a national market system to be in the public interest and appropriate for the protection of investors and the maintenance of fair and orderly markets to assure fair competition among the exchange markets.\173\ Section 11A(a)(3)(B) of the Act directs the Commission, ``by rule or order, to authorize or require self-regulatory organizations to act jointly with respect to matters as to which they share authority under this title in planning, developing, operating, or regulating a national market system (or a subsystem thereof) or one or more facilities.'' \174\ The Commission's approval of a national market system plan is required to be conditioned upon a finding that the plan is ``necessary or appropriate in the public interest, for the protection of investors and the maintenance of fair and orderly markets, to remove impediments to, and perfect the mechanism of, a national market system, or otherwise in furtherance of the purposes of the Act.'' \175\ --------------------------------------------------------------------------- \172\ 15 U.S.C. 78k-1. \173\ 15 U.S.C. 78k-1(a)(1)(C). \174\ 15 U.S.C. 78k-1(a)(3)(B). \175\ 17 CFR 242.608(b)(2). See also 15 U.S.C. 78k-1(a). --------------------------------------------------------------------------- After carefully considering the proposed Plan and the issues raised by the comment letters, the Commission has determined to approve the Plan, as amended by the Participants, pursuant to Section 11A(a)(3)(B) of the Act \176\ and Rule 608.\177\ The Commission believes that the Plan is reasonably designed to prevent potentially harmful price volatility, including severe volatility of the kind that occurred on May 6, 2010.\178\ The Plan should thereby help promote the goals of investor protection and fair and orderly markets. The Commission also believes that the Plan is a prudent replacement of the single-stock circuit breaker that is currently in effect, and that it is appropriately being introduced on a pilot basis. The pilot period will allow the public, the Participants, and the Commission to assess the operation of the Plan and whether the Plan should be modified prior to approval on a permanent basis. --------------------------------------------------------------------------- \176\ 15 U.S.C. 78k-1(a)(3)(B). \177\ 17 CFR 242.608. In approving this Plan, the Commission has considered the proposed rule's impact on efficiency, competition, and capital formation. See 15 U.S.C. 78c(f). \178\ The Commission and the Participants have conducted simulations on historical data to examine how a limit up-limit down mechanism might work. The simulations generally support the structure of the proposal. In particular, the proposal would reduce, but not eliminate, extreme short-term price changes, and would not result in an excessive number of trading pauses. Commission staff, for example, conducted a simulation that suggested that the percentage limits should be larger at the open and close and that the percentage limits should be larger for lower priced stocks. In addition, the simulation suggested that most trades occurring outside of the bands are reversed quickly, providing support for the notion that a limit state may help avoid unnecessary trading pauses. The simulation also showed that an average of slightly more than one large index stock would have a trading pause every four days, based on the structure of the simulation, which was not the same as the proposed structure. A follow-up analysis using the proposed structure showed that only one large index stock would have a trading pause in the three months analyzed. The NYSE staff also simulated the proposed limit up-limit down mechanism to examine how the mechanism would have worked on May 6th, 2010. Given time constraints, the simulation was limited to the price band aspect of the proposal and did not consider the limit state or trading pause provisions of the proposal. This simulation suggested that the price bands alone would have reduced the size of the flash crash significantly, but stocks would still have experienced large five-minute declines. For example, on May 6th, Accenture experienced a five-minute decline of 99.98%. The simulation suggests that if there had been price bands in place on May 6th, the most extreme five-minute decline in Accenture might have been 6.43%. While the Commission recognizes that this is still a significant decline, it would have much less than the actual decline. The NYSE simulation also examined the ability of the limit up- limit down price bands to reduce extreme positive and negative returns. In the Tier 1 stocks priced more than $1.00, the price bands would eliminate five-minute returns more extreme than 10% and -10%. The price bands would reduce but not eliminate these extreme five-minute returns in other stocks. A sensitivity analysis comparing the proposed price limit percentages to alternative ones suggested that the proposed bands behave at least as well as the alternatives examined. --------------------------------------------------------------------------- As discussed above, commenters raised a variety of thoughtful concerns about the proposal and recommended certain changes. Some of the recommended changes were incorporated in the Amendment. As discussed further below, other comments raised important issues that are difficult to evaluate fully in the absence of practical experience with the Plan. These issues will warrant close consideration during the pilot period. The Commission believes that it is consistent with the Act to approve the [[Page 33509]] Plan on a pilot basis at this time because the Plan reflects the considered judgments of the Participants on operational issues and clearly represents a significant step forward that builds upon the experience with the current single-stock circuit breaker. The limit up- limit down mechanism set forth in the Plan approved today and the single-stock circuit breaker are broadly similar in some respects. For example, both mechanisms calculate a reference price that is based on a rolling five-minute price band, and both mechanisms incorporate a five- minute trading pause, followed by a reopening auction on the Primary Listing Exchange. The Plan, however, provides a more finely calibrated mechanism than that of the current single-stock circuit breaker. For example, the single-stock circuit breaker is triggered by trades that occur at or outside of the price band, and erroneous trades have triggered trading halts throughout the current pilot. In contrast, under the Plan, all trading centers in NMS stocks, including both those operated by Participants and those operated by members of Participants, are required to establish policies and procedures that are reasonably designed to prevent trades at prices outside of the price bands. In addition, quotes outside of the price bands will be marked as non- executable. Given that trades should not occur outside of the price bands, the Commission believes that the Plan is reasonably designed to reduce the number of erroneous trades in comparison to the current single-stock circuit breaker. Moreover, Limit States under the Plan (and, ultimately, trading pauses) will be triggered by movements in the National Best Bid or the National Best Offer, rather than single trades. These quoting-based triggers are designed to be more stable and reliable indicators of a significant market event than the single trades that currently can trigger a single stock circuit breaker. The result of this change should be to reduce the frequency of Limit States (and, ultimately, trading pauses) to those circumstances that truly warrant a check on continuous trading. In contrast to the current single-stock circuit breaker, the Plan also features a fifteen-second Limit State that precedes a trading pause. In those instances where the movement of, for example, the National Best Bid below the Lower Price Band is due to a momentary gap in liquidity, rather than a fundamental price move, the Limit State is reasonably designed to allow the market to quickly correct and resume normal trading, without resorting to a trading pause. Because a Limit State, rather than a trading pause, may be sufficient to resolve some of these scenarios, the corresponding price bands can be narrower than in the single-stock circuit breaker. As such, the Commission believes that the Plan is reasonably designed to be a more finely calibrated mechanism than the current single-stock circuit breaker in guarding against market volatility.\179\ --------------------------------------------------------------------------- \179\ The Commission also finds that the Plan is consistent with the requirements of Rule 602 under Regulation NMS. Under that rule, bids and offers must be firm, i.e., brokers and dealers are obligated to execute any order to buy or sell a subject security presented to it by another broker or dealer at a price at least as favorable to such buyer or seller as that broker or dealer's published bid or published offer in any amount up to its published quotation size. Similarly, the best bids and offers collected by national securities exchanges must also be firm. See 17 CFR 242.602. However, Rule 602(a)(3)(i) relieves exchanges of their obligation to collect and make available bids and offers (which are firm) if the existence of ``unusual market conditions'' makes those bids and offers no longer accurately reflective of the current state of the market. This provision also relieves brokers and dealers of their corresponding obligation to submit firm quotes. The Commission believes that, when the National Best Bid (Offer) crosses the Lower (Upper) Price Band, and such quote becomes non-executable, an unusual market condition exists for purposes of Rule 602. To the extent that this scenario constitutes an unusual market condition, the broker or dealer could submit a quote that is outside of the applicable price band, and is thus not firm (as it is non- executable), and the exchange could collect and display such quote, without violating Rule 602. The Commission notes, however, that the firmness requirement continues to apply to quotes at or within the price bands that are submitted by brokers or dealers and collected by exchanges, as such quotes are executable. --------------------------------------------------------------------------- While the price bands in the Plan are reasonably designed to be more finely calibrated than the current single-stock circuit breaker, the Commission notes that the Plan is also designed to accommodate more fundamental price moves, albeit in a manner that lessens the velocity of such moves. In this regard, the Commission notes that the Plan provides that the price bands shall not apply to single-priced re- openings, which allows for the stock to enter a trading pause and reopen at a price that is potentially significantly above or below its previous price. The Commission finds that this mechanism is reasonably designed to allow for more fundamental price moves to occur. To the extent that a reopening only may occur following a five-minute trading pause, however, the Plan is still reasonably designed to reduce the velocity of more significant price moves. The Amendment improves the initial proposal by addressing a number of concerns raised by commenters. Specifically, it excludes transactions that are exempt under Rule 611 of Regulation NMS and do not update the last sale price (except if solely because the transaction was reported late), from the requirement that such transactions occur within the price bands. This exclusion addresses commenters' concerns that such transactions often are executed at prices unrelated to the current market and do not have the capacity to initiate or exacerbate volatility. In response to the concerns of commenters about the potential for bids or offers in an NMS stock to become unexecutable without triggering a Limit State, the Amendment authorizes the Primary Listing Exchange manually to declare a trading pause in these circumstances. This mechanism should help ensure that the market for a stock does not remain impaired for an indefinite period of time, while providing the Primary Listing Exchange with the discretion to determine whether such impairment is inconsistent with the stock's normal trading characteristics. The Amendment assigns wider price bands for Tier 1 and Tier 2 securities that are priced between $0.75 and $3.00 that are reasonably designed to reflect more appropriately the characteristics of stocks that trade in that price range. Similarly, the Amendment excludes all rights and warrants from the Plan, which reflects the trading characteristics of such securities and is consistent with the scope of the current single-stock circuit breaker pilot. The Amendment's provision for evaluating, on a semi-annual basis, the ETPs that are included in Tier I helps assure that ETPs meeting the criteria for inclusion are appropriately included in Tier I, and vice versa. The Amendment also extends the implementation date to February 4, 2013. This extension of time should provide appropriate time to develop and test the technology necessary to implement the Plan, including market-wide testing. Finally, in response to concerns expressed by commenters, the Amendment establishes an Advisory Committee to the Operating Committee composed of a broad cross-section of market participants. The Advisory Committee members will have the right to submit their views on Plan matters to the Operating Committee and thereby engage in the ongoing assessment of Plan operations and formulation of future proposed amendments to the Plan. One serious concern raised by comments was the interaction between the limit up-limit down mechanism and the market-wide circuit breakers that apply across all securities and securities-related products, particularly [[Page 33510]] during a ``macro market event'' that affects a large number of securities and securities-related products. The Commission is approving separately today on a pilot basis SRO proposals to revise these market- wide circuit breakers and make them more meaningful in today's high- speed electronic markets.\180\ These SRO rules include both tighter parameters and shorter halt periods. The Commission recognizes the potential for limit up-limit down trading halts in many securities to affect both the calculation of broader indexes and the trading in products related to such indexes. Nevertheless, it believes that the need for protection against extraordinary volatility in individual equities is essential for both investors in such listed equities and for their listed companies. Accordingly, it is approving the Plan on a pilot basis, but welcomes comments during the pilot period on ways that the Plan could be improved to address potential problems in its interaction with market-wide circuit breakers. The Commission also is accepting comment during the pilot period for the market-wide circuit breakers on ways to improve them to address this question on their interaction with the Plan. --------------------------------------------------------------------------- \180\ See Securities Exchange Act Release No. 67090 (May 31, 2012) (File Nos. SR-BATS-2011-038; SR-BYX-2011-025; SR-BX-2011-068; SR-CBOE-2011-087; SR-C2-2011-024; SR-CHX-2011-30; SR-EDGA-2011-31; SR-EDGX-2011-30; SR-FINRA-2011-054; SR-ISE-2011-61; SR-NASDAQ-2011- 131; SR-NSX-2011-11; SR-NYSE-2011-48; SR-NYSEAmex-2011-73; SR- NYSEArca-2011-68; SR-Phlx-2011-129). --------------------------------------------------------------------------- The Commission notes that the Participants did not amend the Plan to incorporate some of the recommendations to modify the operational details of the Plan, including the duration of the Limit State, the calculation of the Reference Price, the application of the price bands at the open and the close, the criteria required to enter and exit the Limit State, and the display of quotes outside of the price bands. The Commission recognizes the thoughtfulness of the comments that put forward such recommendations, and indeed believes they raise valid concerns that warrant close scrutiny during the pilot period. At this time, however, the Commission believes that it is consistent with the Act to accept the considered collective judgment of the Participants on these complex issues, particularly given their expertise and responsibility for operating markets on a daily basis.\181\ --------------------------------------------------------------------------- \181\ The Commission notes that one of the concerns of requiring the National Best Offer (Bid) to trigger the Limit Down (Up) may be partially alleviated by one of the amendments to the Plan. Specifically, if the National Best Bid is outside of the lower price band and is thus non-executable, while the offer remains within the price bands, the stated concern is that the market for that stock is impaired, perhaps for an indefinite period of time, while the stock has not entered the Limit State. The Commission believes that the addition of a manual override, as proposed by the Participants in the amendment to the Plan, may, at least partially, alleviate this concern. --------------------------------------------------------------------------- Approving the Plan on a pilot basis will allow the Participants and the public to gain valuable practical experience with Plan operations during the pilot period. This experience should prove invaluable in assessing whether further modifications of the Plan are necessary or appropriate prior to final approval. The Participants also have agreed to provide the Commission with a significant amount of data bearing on operational questions that should assist the Commission in its evaluation of Plan operations. Finally, the Commission welcomes additional comments, and empirical evidence, on the Plan during the pilot period to further assist it in its evaluation of the Plan. Of course, any final approval of the Plan would require a proposed amendment of the Plan, and such amendment will provide an opportunity for public comment prior to further Commission action. To the extent that the Participants did not amend the Plan to reflect other operational or procedural concerns, the Commission believes that those suggestions and concerns were generally considered by the Participants in developing a uniform proposal that would not be excessively complicated and yet could still provide important benefits to the markets. For example, one commenter noted that allowing the primary listing market to control the re-opening process in the first five minutes following a trading pause may confer a competitive advantage upon that market. The Commission notes that this aspect of the Plan is consistent with the current procedure for re-opening the market following a trading pause that has been triggered under the single-stock circuit breaker pilot. Another commenter suggested that a market-wide limit up-limit down mechanism was more appropriately developed through Commission rulemaking than through an NMS plan. While a Commission rulemaking may be an appropriate means for developing such a mechanism, the Commission believes that an NMS plan, which was the means selected by the Participants here, is equally appropriate, particularly given the Participants' expertise in the trading characteristics in individual securities and the operation of market systems. Some commenters expressed concern over the provision in the Plan governing withdrawal of Participants from the Plan. The Commission notes that withdrawing from the Plan would require an amendment to the Plan, and Commission approval of that amendment. Given the importance of applying a limit up-limit down mechanism uniformly throughout the market, the Commission would anticipate approving such withdrawal from the Plan only if the Participant seeking to withdraw from the Plan ceased to trade NMS securities. One commenter suggested that a cost-benefit analysis of the Plan should be conducted. The Commission notes that market participants are welcome to submit additional comments and empirical evidence during the pilot period with respect to, among other things, the operation of the limit up-limit down mechanism, its effectiveness in achieving its intended goals, and the costs associated therewith. The Commission will take such comments into account in considering whether to approve any amendment, in accordance with Rule 608 of Regulation NMS, that proposes to make the Plan permanent. As such, the Commission believes that the Plan is consistent with the Act, notwithstanding such comments, and that it is reasonably designed to achieve its objective of reducing extraordinary market volatility. Given that the Plan is being approved on a pilot basis, the Commission expects that the Participants will monitor the scope and operation of the Plan and study the data produced during that time with respect to such issues, and will propose any modifications to the Plan that may be necessary or appropriate. Similarly, the Commission expects that the Participants will propose any modifications to the Plan that may be necessary or appropriate in response to the data being gathered by the Participants during the pilot.\182\ --------------------------------------------------------------------------- \182\ The Commission notes that some of the comments focused on the relation between the Plan, and other, exchange-specific volatility mechanisms, including the NYSE Liquidity Replenishment Points, and the Nasdaq Volatility Guard. While a stated purpose of the Plan is to replace the current single-stock circuit breaker, the Commission is also aware of the potential for unnecessary complexity that could result if the Plan were adopted, and exchange-specific volatility mechanisms were retained. To this end, the Commission expects that, upon implementation of the Plan, such exchange- specific volatility mechanisms would be discontinued by the respective exchanges. In that regard, the Commission notes that one such mechanism, the Nasdaq Volatility Guard, is currently set to expire on the earlier of July 31, 2012, or the date on which the Plan is approved by the Commission. See Securities Exchange Act Release No. 66275 (January 30, 2012), 77 FR 5606 (February 3, 2012) (SR-Nasdaq-2012-019). --------------------------------------------------------------------------- [[Page 33511]] VII. Conclusion It is therefore ordered, pursuant to Sections 11A of the Act,\183\ and the rules thereunder, that the Plan (File No. 4-631), as amended, is approved on a one-year pilot basis and declared effective, and the Participants are authorized to act jointly to implement the Plan as a means of facilitating a national market system. --------------------------------------------------------------------------- \183\ 15 U.S.C. 78k-1. By the Commission. Elizabeth M. Murphy, Secretary. Exhibit A Plan To Address Extraordinary Market Volatility Submitted to the Securities and Exchange Commission Pursuant to Rule 608 of Regulation NMS Under the Securities Exchange Act of 1934 Table of Contents Section Page Preamble....................................................... 1 I. Definitions................................................. 2 II. Parties.................................................... 4 III. Amendments to Plan........................................ 7 IV. Trading Center Policies and Procedures..................... 8 V. Price Bands................................................. 9 VI. Limit Up-Limit Down Requirements........................... 12 VII. Trading Pauses............................................ 14 VIII. Implementation........................................... 15 IX. Withdrawal from Plan....................................... 16 X. Counterparts and Signatures................................. 16 Appendix A--Percentage Parameters.............................. 18 Appendix A--Schedule 1......................................... 21 Appendix B--Data............................................... 33 Preamble The Participants submit to the SEC this Plan establishing procedures to address extraordinary volatility in NMS Stocks. The procedures provide for market-wide limit up-limit down requirements that prevent trades in individual NMS Stocks from occurring outside of the specified Price Bands. These limit up-limit down requirements are coupled with Trading Pauses to accommodate more fundamental price moves. The Plan procedures are designed, among other things, to protect investors and promote fair and orderly markets. The Participants developed this Plan pursuant to Rule 608(a)(3) of Regulation NMS under the Exchange Act, which authorizes the Participants to act jointly in preparing, filing, and implementing national market system plans. I. Definitions (A) ``Eligible Reported Transactions'' shall have the meaning prescribed by the Operating Committee and shall generally mean transactions that are eligible to update the last sale price of an NMS Stock. (B) ``Exchange Act'' means the Securities Exchange Act of 1934, as amended. (C) ``Limit State'' shall have the meaning provided in Section VI of the Plan. (D) ``Limit State Quotation'' shall have the meaning provided in Section VI of the Plan. (E) ``Lower Price Band'' shall have the meaning provided in Section V of the Plan. (F) ``Market Data Plans'' shall mean the effective national market system plans through which the Participants act jointly to disseminate consolidated information in compliance with Rule 603(b) of Regulation NMS under the Exchange Act. (G) ``National Best Bid'' and ``National Best Offer'' shall have the meaning provided in Rule 600(b)(42) of Regulation NMS under the Exchange Act. (H) ``NMS Stock'' shall have the meaning provided in Rule 600(b)(47) of Regulation NMS under the Exchange Act. (I) ``Opening Price'' shall mean the price of a transaction that opens trading on the Primary Listing Exchange, or, if the Primary Listing Exchange opens with quotations, the midpoint of those quotations. (J) ``Operating Committee'' shall have the meaning provided in Section III(C) of the Plan. (K) ``Participant'' means a party to the Plan. (L) ``Plan'' means the plan set forth in this instrument, as amended from time to time in accordance with its provisions. (M) ``Percentage Parameter'' shall mean the percentages for each tier of NMS Stocks set forth in Appendix A of the Plan. (N) ``Price Bands'' shall have the meaning provided in Section V of the Plan. (O) ``Primary Listing Exchange'' shall mean the Participant on which an NMS Stock is listed. If an NMS Stock is listed on more than one Participant, the Participant on which the NMS Stock has been listed the longest shall be the Primary Listing Exchange. (P) ``Processor'' shall mean the single plan processor responsible for the consolidation of information for an NMS Stock pursuant to Rule 603(b) of Regulation NMS under the Exchange Act. (Q) ``Pro-Forma Reference Price'' shall have the meaning provided in Section V(A)(2) of the Plan. (R) ``Regular Trading Hours'' shall have the meaning provided in Rule 600(b)(64) of Regulation NMS under the Exchange Act. For purposes of the Plan, Regular Trading Hours can end earlier than 4:00 p.m. ET in the case of an early scheduled close. (S) ``Regulatory Halt'' shall have the meaning specified in the Market Data Plans. (T) ``Reference Price'' shall have the meaning provided in Section V of the Plan. (U) ``Reopening Price'' shall mean the price of a transaction that reopens [[Page 33512]] trading on the Primary Listing Exchange following a Trading Pause or a Regulatory Halt, or, if the Primary Listing Exchange reopens with quotations, the midpoint of those quotations. (V) ``SEC'' shall mean the United States Securities and Exchange Commission. (W) ``Straddle State'' shall have the meaning provided in Section VII(A)(2) of the Plan. (X) ``Trading center'' shall have the meaning provided in Rule 600(b)(78) of Regulation NMS under the Exchange Act. (Y) ``Trading Pause'' shall have the meaning provided in Section VII of the Plan. (Z) ``Upper Price Band'' shall have the meaning provided in Section V of the Plan. II. Parties (A) List of Parties The parties to the Plan are as follows: (1) BATS Exchange, Inc., 8050 Marshall Drive, Lenexa, Kansas 66214. (2) BATS Y-Exchange, Inc., 8050 Marshall Drive, Lenexa, Kansas 66214. (3) Chicago Board Options Exchange, Incorporated, 400 South LaSalle Street, Chicago, Illinois 60605. (4) Chicago Stock Exchange, Inc., 440 South LaSalle Street, Chicago, Illinois 60605. (5) EDGA Exchange, Inc., 545 Washington Boulevard, Sixth Floor, Jersey City, NJ 07310. (6) EDGX Exchange, Inc., 545 Washington Boulevard, Sixth Floor, Jersey City, NJ 07310. (7) Financial Industry Regulatory Authority, Inc., 1735 K Street, NW., Washington, DC 20006. (8) NASDAQ OMX BX, Inc., One Liberty Plaza, New York, New York 10006. (9) NASDAQ OMX PHLX LLC, 1900 Market Street, Philadelphia, Pennsylvania 19103. (10) The Nasdaq Stock Market LLC, 1 Liberty Plaza, 165 Broadway, New York, NY 10006. (11) National Stock Exchange, Inc., 101 Hudson, Suite 1200, Jersey City, NJ 07302. (12) New York Stock Exchange LLC, 11 Wall Street, New York, New York 10005. (13) NYSE MKT LLC, 20 Broad Street, New York, New York 10005. (14) NYSE Arca, Inc., 100 South Wacker Drive, Suite 1800, Chicago, IL 60606. (B) Compliance Undertaking By subscribing to and submitting the Plan for approval by the SEC, each Participant agrees to comply with and to enforce compliance, as required by Rule 608(c) of Regulation NMS under the Exchange Act, by its members with the provisions of the Plan. To this end, each Participant shall adopt a rule requiring compliance by its members with the provisions of the Plan, and each Participant shall take such actions as are necessary and appropriate as a participant of the Market Data Plans to cause and enable the Processor for each NMS Stock to fulfill the functions set forth in this Plan. (C) New Participants The Participants agree that any entity registered as a national securities exchange or national securities association under the Exchange Act may become a Participant by: (1) becoming a participant in the applicable Market Data Plans; (2) executing a copy of the Plan, as then in effect; (3) providing each then-current Participant with a copy of such executed Plan; and (4) effecting an amendment to the Plan as specified in Section III(B) of the Plan. (D) Advisory Committee (1) Formation. Notwithstanding other provisions of this Plan, an Advisory Committee to the Plan shall be formed and shall function in accordance with the provisions set forth in this section. (2) Composition. Members of the Advisory Committee shall be selected for two-year terms as follows: (A) Advisory Committee Selections. By affirmative vote of a majority of the Participants, the Participants shall select at least one representatives from each of the following categories to be members of the Advisory Committee: (1) A broker-dealer with a substantial retail investor customer base; (2) a broker-dealer with a substantial institutional investor customer base; (3) an alternative trading system; and (4) an investor. (3) Function. Members of the Advisory Committee shall have the right to submit their views to the Operating Committee on Plan matters, prior to a decision by the Operating Committee on such matters. Such matters shall include, but not be limited to, proposed material amendments to the Plan. (4) Meetings and Information. Members of the Advisory Committee shall have the right to attend meetings of the Operating Committee and to receive any information concerning Plan matters; provided, however, that the Operating Committee may meet in executive session if, by affirmative vote of a majority of the Participants, the Operating Committee determines that an item of Plan business requires confidential treatment. III. Amendments to Plan (A) General Amendments Except with respect to the addition of new Participants to the Plan, any proposed change in, addition to, or deletion from the Plan shall be effected by means of a written amendment to the Plan that: (1) Sets forth the change, addition, or deletion; (2) is executed on behalf of each Participant; and, (3) is approved by the SEC pursuant to Rule 608 of Regulation NMS under the Exchange Act, or otherwise becomes effective under Rule 608 of Regulation NMS under the Exchange Act. (B) New Participants With respect to new Participants, an amendment to the Plan may be effected by the new national securities exchange or national securities association executing a copy of the Plan, as then in effect (with the only changes being the addition of the new Participant's name in Section II(A) of the Plan) and submitting such executed Plan to the SEC for approval. The amendment shall be effective when it is approved by the SEC in accordance with Rule 608 of Regulation NMS under the Exchange Act or otherwise becomes effective pursuant to Rule 608 of Regulation NMS under the Exchange Act. (C) Operating Committee (1) Each Participant shall select from its staff one individual to represent the Participant as a member of an Operating Committee, together with a substitute for such individual. The substitute may participate in deliberations of the Operating Committee and shall be considered a voting member thereof only in the absence of the primary representative. Each Participant shall have one vote on all matters considered by the Operating Committee. No later than the initial date of Plan operations, the Operating Committee shall designate one member of the Operating Committee to act as the Chair of the Operating Committee. (2) The Operating Committee shall monitor the procedures established pursuant to this Plan and advise the Participants with respect to any deficiencies, problems, or recommendations as the Operating Committee may deem appropriate. The Operating Committee shall establish specifications and procedures for the implementation and operation of the Plan that are consistent with the provisions of this Plan and the Appendixes thereto. With respect to [[Page 33513]] matters in this paragraph, Operating Committee decisions shall be approved by a simple majority vote. (3) Any recommendation for an amendment to the Plan from the Operating Committee that receives an affirmative vote of at least two- thirds of the Participants, but is less than unanimous, shall be submitted to the SEC as a request for an amendment to the Plan initiated by the Commission under Rule 608 of Regulation NMS. IV. Trading Center Policies and Procedures All trading centers in NMS Stocks, including both those operated by Participants and those operated by members of Participants, shall establish, maintain, and enforce written policies and procedures that are reasonably designed to comply with the limit up-limit down requirements specified in Sections VI of the Plan, and to comply with the Trading Pauses specified in Section VII of the Plan. V. Price Bands (A) Calculation and Dissemination of Price Bands (1) The Processor for each NMS stock shall calculate and disseminate to the public a Lower Price Band and an Upper Price Band during Regular Trading Hours for such NMS Stock. The Price Bands shall be based on a Reference Price for each NMS Stock that equals the arithmetic mean price of Eligible Reported Transactions for the NMS stock over the immediately preceding five-minute period (except for periods following openings and reopenings, which are addressed below). If no Eligible Reported Transactions for the NMS Stock have occurred over the immediately preceding five-minute period, the previous Reference Price shall remain in effect. The Price Bands for an NMS Stock shall be calculated by applying the Percentage Parameter for such NMS Stock to the Reference Price, with the Lower Price Band being a Percentage Parameter below the Reference Price, and the Upper Price Band being a Percentage Parameter above the Reference Price. The Price Bands shall be calculated during Regular Trading Hours. Between 9:30 a.m. and 9:45 a.m. ET, and 3:35 p.m. and 4:00 p.m. ET, or in the case of an early scheduled close, during the last 25 minutes of trading before the early scheduled close, the Price Bands shall be calculated by applying double the Percentage Parameters set forth in Appendix A. If a Reopening Price does not occur within ten minutes after the beginning of a Trading Pause, the Price Band, for the first 30 seconds following the reopening after that Trading Pause, shall be calculated by applying triple the Percentage Parameters set forth in Appendix A. (2) The Processor shall calculate a Pro-Forma Reference Price on a continuous basis during Regular Trading Hours, as specified in Section V(A)(1) of the Plan. If a Pro-Forma Reference Price has not moved by 1% or more from the Reference Price currently in effect, no new Price Bands shall be disseminated, and the current Reference Price shall remain the effective Reference Price. When the Pro-Forma Reference Price has moved by 1% or more from the Reference Price currently in effect, the Pro-Forma Reference Price shall become the Reference Price, and the Processor shall disseminate new Price Bands based on the new Reference Price; provided, however, that each new Reference Price shall remain in effect for at least 30 seconds. (B) Openings (1) Except when a Regulatory Halt is in effect at the start of Regular Trading Hours, the first Reference Price for a trading day shall be the Opening Price on the Primary Listing Exchange in an NMS Stock if such Opening Price occurs less than five minutes after the start of Regular Trading Hours. During the period less than five minutes after the Opening Price, a Pro-Forma Reference Price shall be updated on a continuous basis to be the arithmetic mean price of Eligible Reported Transactions for the NMS Stock during the period following the Opening Price (including the Opening Price), and if it differs from the current Reference Price by 1% or more shall become the new Reference Price, except that a new Reference Price shall remain in effect for at least 30 seconds. Subsequent Reference Prices shall be calculated as specified in Section V(A) of the Plan. (2) If the Opening Price on the Primary Listing Exchange in an NMS Stock does not occur within five minutes after the start of Regular Trading Hours, the first Reference Price for a trading day shall be the arithmetic mean price of Eligible Reported Transactions for the NMS Stock over the preceding five minute time period, and subsequent Reference Prices shall be calculated as specified in Section V(A) of the Plan. (C) Reopenings (1) Following a Trading Pause in an NMS Stock, and if the Primary Listing Exchange has not declared a Regulatory Halt, the next Reference Price shall be the Reopening Price on the Primary Listing Exchange if such Reopening Price occurs within ten minutes after the beginning of the Trading Pause, and subsequent Reference Prices shall be determined in the manner prescribed for normal openings, as specified in Section V(B)(1) of the Plan. If such Reopening Price does not occur within ten minutes after the beginning of the Trading Pause, the first Reference Price following the Trading Pause shall be equal to the last effective Reference Price before the Trading Pause. Subsequent Reference Prices shall be calculated as specified in Section V(A) of the Plan. (2) Following a Regulatory Halt, the next Reference Price shall be the Opening or Reopening Price on the Primary Listing Exchange if such Opening or Reopening Price occurs within five minutes after the end of the Regulatory Halt, and subsequent Reference Prices shall be determined in the manner prescribed for normal openings, as specified in Section V(B)(1) of the Plan. If such Opening or Reopening Price has not occurred within five minutes after the end of the Regulatory Halt, the Reference Price shall be equal to the arithmetic mean price of Eligible Reported Transactions for the NMS Stock over the preceding five minute time period, and subsequent Reference Prices shall be calculated as specified in Section V(A) of the Plan. VI. Limit Up-Limit Down Requirements (A) Limitations on Trades and Quotations Outside of Price Bands (1) All trading centers in NMS Stocks, including both those operated by Participants and those operated by members of Participants, shall establish, maintain, and enforce written policies and procedures that are reasonably designed to prevent trades at prices that are below the Lower Price Band or above the Upper Price Band for an NMS Stock. Single-priced opening, reopening, and closing transactions on the Primary Listing Exchange, however, shall be excluded from this limitation. In addition, any transaction that both does not update the last sale price (except if solely because the transaction was reported late) and is excepted or exempt from Rule 611 under Regulation NMS shall be excluded from this limitation. (2) When a National Best Bid is below the Lower Price Band or a National Best Offer is above the Upper Price Band for an NMS Stock, the Processor shall disseminate such National Best Bid or National Best Offer with an appropriate flag identifying it as non-executable. When a National Best Offer is equal to [[Page 33514]] the Lower Price Band or a National Best Bid is equal to the Upper Price Band for an NMS Stock, the Processor shall distribute such National Best Bid or National Best Offer with an appropriate flag identifying it as a ``Limit State Quotation''. (3) All trading centers in NMS Stocks, including both those operated by Participants and those operated by members of Participants, shall establish, maintain, and enforce written policies and procedures that are reasonably designed to prevent the display of offers below the Lower Price Band and bids above the Upper Price Band for an NMS Stock. The Processor shall disseminate an offer below the Lower Price Band or bid above the Upper Price Band that may be submitted despite such reasonable policies and procedures, but with an appropriate flag identifying it as non-executable; provided, however, that any such bid or offer shall not be included in National Best Bid or National Best Offer calculations. (B) Entering and Exiting a Limit State (1) All trading for an NMS Stock shall immediately enter a Limit State if the National Best Offer equals the Lower Price Band and does not cross the National Best Bid, or the National Best Bid equals the Upper Price Band and does not cross the National Best Offer. (2) When trading for an NMS Stock enters a Limit State, the Processor shall disseminate this information by identifying the relevant quotation (i.e., a National Best Offer that equals the Lower Price Band or a National Best Bid that equals the Upper Price Band) as a Limit State Quotation. At this point, the Processor shall cease calculating and disseminating updated Reference Prices and Price Bands for the NMS Stock until either trading exits the Limit State or trading resumes with an opening or re-opening as provided in Section V. (3) Trading for an NMS Stock shall exit a Limit State if, within 15 seconds of entering the Limit State, the entire size of all Limit State Quotations are executed or cancelled. (4) If trading for an NMS Stock exits a Limit State within 15 seconds of entry, the Processor shall immediately calculate and disseminate updated Price Bands based on a Reference Price that equals the arithmetic mean price of Eligible Reported Transactions for the NMS Stock over the immediately preceding five-minute period (including the period of the Limit State). (5) If trading for an NMS Stock does not exit a Limit State within 15 seconds of entry, the Limit State will terminate when the Primary Listing Exchange declares a Trading Pause pursuant to Section VII of the Plan. If trading for an NMS Stock is in a Limit State at the end of Regular Trading Hours, the Limit State will terminate when the Primary Listing Exchange executes a closing transaction in the NMS Stock or five minutes after the end of Regular Trading Hours, whichever is earlier. VII. Trading Pauses (A) Declaration of Trading Pauses (1) If trading for an NMS Stock does not exit a Limit State within 15 seconds of entry during Regular Trading Hours, then the Primary Listing Exchange shall declare a Trading Pause for such NMS Stock and shall notify the Processor. (2) The Primary Listing Exchange may also declare a Trading Pause for an NMS Stock when an NMS Stock is in a Straddle State, which is when National Best Bid (Offer) is below (above) the Lower (Upper) Price Band and the NMS Stock is not in a Limit State, and trading in that NMS Stock deviates from normal trading characteristics such that declaring a Trading Pause would support the Plan's goal to address extraordinary market volatility. The Primary Listing Exchange shall develop policies and procedures for determining when it would declare a Trading Pause in such circumstances. If a Trading Pause is declared for an NMS Stock under this provision, the Primary Listing Exchange shall notify the Processor. (3) The Processor shall disseminate Trading Pause information to the public. No trades in an NMS Stock shall occur during a Trading Pause, but all bids and offers may be displayed. (B) Reopening of Trading During Regular Trading Hours (1) Five minutes after declaring a Trading Pause for an NMS Stock, and if the Primary Listing Exchange has not declared a Regulatory Halt, the Primary Listing Exchange shall attempt to reopen trading using its established reopening procedures. The Trading Pause shall end when the Primary Listing Exchange reports a Reopening Price. (2) The Primary Listing Exchange shall notify the Processor if it is unable to reopen trading in an NMS Stock for any reason other than a significant order imbalance and if it has not declared a Regulatory Halt. The Processor shall disseminate this information to the public, and all trading centers may begin trading the NMS Stock at this time. (3) If the Primary Listing Exchange does not report a Reopening Price within ten minutes after the declaration of a Trading Pause in an NMS Stock, and has not declared a Regulatory Halt, all trading centers may begin trading the NMS Stock. (4) When trading begins after a Trading Pause, the Processor shall update the Price Bands as set forth in Section V(C)(1) of the Plan. (C) Trading Pauses Within Five Minutes of the End of Regular Trading Hours (1) If a Trading Pause for an NMS Stock is declared less than five minutes before the end of Regular Trading Hours, the Primary Listing Exchange shall attempt to execute a closing transaction using its established closing procedures. All trading centers may begin trading the NMS Stock when the Primary Listing Exchange executes a closing transaction. (2) If the Primary Listing Exchange does not execute a closing transaction within five minutes after the end of Regular Trading Hours, all trading centers may begin trading the NMS Stock. VIII. Implementation (A) Phase I (1) Phase I of Plan implementation shall apply immediately following the initial date of Plan operations. (2) During Phase I, the Plan shall apply only to the Tier 1 NMS Stocks identified in Appendix A of the Plan. (3) During Phase I, the first Price Bands for a trading day shall be calculated and disseminated 15 minutes after the start of Regular Trading Hours as specified in Section (V)(A) of the Plan. No Price Bands shall be calculated and disseminated less than 30 minutes before the end of Regular Trading Hours, and trading shall not enter a Limit State less than 25 minutes before the end of Regular Trading Hours. (B) Phase II--Full Implementation Six months after the initial date of Plan operations, or such earlier date as may be announced by the Processor with at least 30 days notice, the Plan shall fully apply (i) to all NMS Stocks; and (ii) beginning at 9:30 a.m. ET, and ending at 4:00 p.m. ET each trading day, or earlier in the case of an early scheduled close or if the Processor disseminates a closing trade for the Primary Listing Exchange. (C) Pilot The Plan shall be implemented on a one-year pilot basis. IX. Withdrawal from Plan If a Participant obtains SEC approval to withdraw from the Plan, such Participant may withdraw from the Plan [[Page 33515]] at any time on not less than 30 days' prior written notice to each of the other Participants. At such time, the withdrawing Participant shall have no further rights or obligations under the Plan. X. Counterparts and Signatures The Plan may be executed in any number of counterparts, no one of which need contain all signatures of all Participants, and as many of such counterparts as shall together contain all such signatures shall constitute one and the same instrument. IN WITNESS THEREOF, this Plan has been executed as of the--day of-- ------2012 by each of the parties hereto. BATS EXCHANGE, INC. BY:-------------------------------------------------------------------- BATS Y-EXCHANGE, INC. BY:-------------------------------------------------------------------- CHICAGO BOARD OPTIONS EXCHANGE, INCORPORATED BY:-------------------------------------------------------------------- CHICAGO STOCK EXCHANGE, INC. BY:-------------------------------------------------------------------- EDGA EXCHANGE, INC. BY:-------------------------------------------------------------------- EDGX EXCHANGE, INC. BY:-------------------------------------------------------------------- FINANCIAL INDUSTRY REGULATORY AUTHORITY, INC. BY:-------------------------------------------------------------------- NASDAQ OMX BX, INC. BY:-------------------------------------------------------------------- NASDAQ OMX PHLX LLC BY:-------------------------------------------------------------------- THE NASDAQ STOCK MARKET LLC BY:-------------------------------------------------------------------- NATIONAL STOCK EXCHANGE, INC. BY:-------------------------------------------------------------------- NEW YORK STOCK EXCHANGE LLC BY:-------------------------------------------------------------------- NYSE MKT LLC BY:-------------------------------------------------------------------- NYSE ARCA, INC. BY:-------------------------------------------------------------------- Appendix A--Percentage Parameters I. Tier 1 NMS Stocks (1) Tier 1 NMS Stocks shall include all NMS Stocks included in the S&P 500 Index, the Russell 1000 Index, and the exchange-traded products (``ETP'') listed on Schedule 1 to this Appendix. Schedule 1 to the Appendix will be reviewed and updated semi-annually based on the fiscal year by the Primary Listing Exchange to add ETPs that meet the criteria, or delete ETPs that are no longer eligible. To determine eligibility for an ETP to be included as a Tier 1 NMS Stock, all ETPs across multiple asset classes and issuers, including domestic equity, international equity, fixed income, currency, and commodities and futures will be identified. Leveraged ETPs will be excluded and the list will be sorted by notional consolidated average daily volume (``CADV''). The period used to measure CADV will be from the first day of the previous fiscal half year up until one week before the beginning of the next fiscal half year. Daily volumes will be multiplied by closing prices and then averaged over the period. ETPs, including inverse ETPs, that trade over $2,000,000 CADV will be eligible to be included as a Tier 1 NMS Stock. To ensure that ETPs that track similar benchmarks but that do not meet this volume criterion do not become subject to pricing volatility when a component security is the subject of a trading pause, non- leveraged ETPs that have traded below this volume criterion, but that track the same benchmark as an ETP that does meet the volume criterion, will be deemed eligible to be included as a Tier 1 NMS Stock. The semi-annual updates to Schedule 1 do not require an amendment to the Plan. The Primary Listing Exchanges will maintain the updated Schedule 1 on their respective Web sites. (2) The Percentage Parameters for Tier 1 NMS Stocks with a Reference Price more than $3.00 shall be 5%. (3) The Percentage Parameters for Tier 1 NMS Stocks with a Reference Price equal to $0.75 and up to and including $3.00 shall be 20%. (4) The Percentage Parameters for Tier 1 NMS Stocks with a Reference Price less than $0.75 shall be the lesser of (a) $0.15 or (b) 75%. (5) The Reference Price used for determining which Percentage Parameter shall be applicable during a trading day shall be based on the closing price of the NMS Stock on the Primary Listing Exchange on the previous trading day, or if no closing price exists, the last sale on the Primary Listing Exchange reported by the Processor. II. Tier 2 NMS Stocks (1) Tier 2 NMS Stocks shall include all NMS Stocks other than those in Tier 1, provided, however, that all rights and warrants are excluded from the Plan. (2) The Percentage Parameters for Tier 2 NMS Stocks with a Reference Price more than $3.00 shall be 10%. (3) The Percentage Parameters for Tier 2 NMS Stocks with a Reference Price equal to $0.75 and up to and including $3.00 shall be 20%. (4) The Percentage Parameters for Tier 2 NMS Stocks with a Reference Price less than $0.75 shall be the lesser of (a) $0.15 or (b) 75%. (5) Notwithstanding the foregoing, the Percentage Parameters for a Tier 2 NMS Stock that is a leveraged ETP shall be the applicable Percentage Parameter set forth in clauses (2), (3), or (4) above, multiplied by the leverage ratio of such product. (6) The Reference Price used for determining which Percentage Parameter shall be applicable during a trading day shall be based on the closing price of the NMS Stock on the Primary Listing Exchange on the previous trading day, or if no closing price exists, the last sale on the Primary Listing Exchange reported by the Processor. Appendix A--Schedule 1 ------------------------------------------------------------------------ Symbol Name ------------------------------------------------------------------------ AAVX......................... ETRACS Daily Short 1-Month S&P 500 VIX Futures ETN AAXJ......................... iShares MSCI All Country Asia ex Japan Index Fund ACWI......................... iShares MSCI ACWI Index Fund ACWX......................... iShares MSCI ACWI ex US Index Fund AGG.......................... iShares Barclays Aggregate Bond Fund AGZ.......................... iShares Barclays Agency Bond Fund ALD.......................... WisdomTree Asia Local Debt Fund AMJ.......................... JPMorgan Alerian MLP Index ETN AMLP......................... Alerian MLP ETF BAB.......................... PowerShares Build America Bond Portfolio BDG.......................... PowerShares DB Base Metals Long ETN BIK.......................... SPDR S&P BRIC 40 ETF BIL.......................... SPDR Barclays Capital 1-3 Month T-Bill ETF BIV.......................... Vanguard Intermediate-Term Bond ETF BKF.......................... iShares MSCI BRIC Index Fund BKLN......................... PowerShares Senior Loan Portfolio BLV.......................... Vanguard Long-Term Bond ETF BND.......................... Vanguard Total Bond Market ETF BNO.......................... United States Brent Oil Fund LP BOND......................... Pimco Total Return ETF BOS.......................... PowerShares DB Base Metals Short ETN [[Page 33516]] BRF.......................... Market Vectors Brazil Small-Cap ETF BSV.......................... Vanguard Short-Term Bond ETF BWX.......................... SPDR Barclays Capital International Treasury Bond ETF BXDB......................... Barclays ETN+short B Leveraged ETN Linked to S&P 500 CEW.......................... WisdomTree Dreyfus Emerging Currency Fund CFT.......................... iShares Barclays Credit Bond Fund CIU.......................... iShares Barclays Intermediate Credit Bond Fund CLY.......................... iShares 10+ Year Credit Bond Fund CORN......................... Teucrium Corn Fund CSJ.......................... iShares Barclays 1-3 Year Credit Bond Fund CVY.......................... Guggenheim Multi-Asset Income ETF CWB.......................... SPDR Barclays Capital Convertible Securities ETF CWI.......................... SPDR MSCI ACWI ex-US ETF CYB.......................... WisdomTree Dreyfus Chinese Yuan Fund DBA.......................... PowerShares DB Agriculture Fund DBB.......................... PowerShares DB Base Metals Fund DBC.......................... PowerShares DB Commodity Index Tracking Fund DBE.......................... PowerShares DB Energy Fund DBO.......................... PowerShares DB Oil Fund DBP.......................... PowerShares DB Precious Metals Fund DBV.......................... PowerShares DB G10 Currency Harvest Fund DEM.......................... WisdomTree Emerging Markets Equity Income Fund DGL.......................... PowerShares DB Gold Fund DGS.......................... WisdomTree Emerging Markets SmallCap Dividend Fund DGZ.......................... PowerShares DB Gold Short ETN DHS.......................... WisdomTree Equity Income Fund DIA.......................... SPDR Dow Jones Industrial Average ETF Trust DJCI......................... E-TRACS UBS AG Dow Jones-UBS Commodity Index Total Return ETN DJP.......................... iPath Dow Jones-UBS Commodity Index Total Return ETN DLN.......................... WisdomTree LargeCap Dividend Fund DOG.......................... ProShares Short Dow30 DON.......................... WisdomTree MidCap Dividend Fund DOO.......................... WisdomTree International Dividend Ex- Financials Fund DTN.......................... WisdomTree Dividend Ex-Financials Fund DVY.......................... iShares Dow Jones Select Dividend Index Fund DWM.......................... WisdomTree DEFA Fund DWX.......................... SPDR S&P International Dividend ETF DXJ.......................... WisdomTree Japan Hedged Equity Fund ECH.......................... iShares MSCI Chile Investable Market Index Fund ECON......................... EGShares Emerging Markets Consumer ETF EDIV......................... SPDR S&P Emerging Markets Dividend ETF EDV.......................... Vanguard Extended Duration Treasury ETF EEB.......................... Guggenheim BRIC ETF EEM.......................... iShares MSCI Emerging Markets Index Fund EFA.......................... iShares MSCI EAFE Index Fund EFG.......................... iShares MSCI EAFE Growth Index EFV.......................... iShares MSCI EAFE Value Index EFZ.......................... ProShares Short MSCI EAFE EIDO......................... iSHARES MSCI Indonesia Investable Market Index Fund ELD.......................... WisdomTree Emerging Markets Local Debt Fund ELR.......................... SPDR Dow Jones Large Cap ETF EMB.......................... iShares JPMorgan USD Emerging Markets Bond Fund EMLC......................... Market Vectors Emerging Markets Local Currency Bond ETF EMM.......................... SPDR Dow Jones Mid Cap ETF EPHE......................... iShares MSCI Philippines Investable Market Index Fund EPI.......................... WisdomTree India Earnings Fund EPP.......................... iShares MSCI Pacific ex-Japan Index Fund EPU.......................... iShares MSCI All Peru Capped Index Fund ERUS......................... iShares MSCI Russia Capped Index Fund EUM.......................... ProShares Short MSCI Emerging Markets EWA.......................... iShares MSCI Australia Index Fund EWC.......................... iShares MSCI Canada Index Fund EWD.......................... iShares MSCI Sweden Index Fund EWG.......................... iShares MSCI Germany Index Fund EWH.......................... iShares MSCI Hong Kong Index Fund EWI.......................... iShares MSCI Italy Index Fund EWJ.......................... iShares MSCI Japan Index Fund EWL.......................... iShares MSCI Switzerland Index Fund EWM.......................... iShares MSCI Malaysia Index Fund EWP.......................... iShares MSCI Spain Index Fund EWQ.......................... iShares MSCI France Index Fund EWS.......................... iShares MSCI Singapore Index Fund [[Page 33517]] EWT.......................... iShares MSCI Taiwan Index Fund EWU.......................... iShares MSCI United Kingdom Index Fund EWW.......................... iShares MSCI Mexico Investable Market Index Fund EWX.......................... SPDR S&P Emerging Markets SmallCap ETF EWY.......................... iShares MSCI South Korea Index Fund EWZ.......................... iShares MSCI Brazil Index Fund EZA.......................... iShares MSCI South Africa Index Fund EZU.......................... iShares MSCI EMU Index Fund FBT.......................... First Trust NYSE Arca Biotechnology Index Fund FCG.......................... First Trust ISE-Revere Natural Gas Index Fund FDL.......................... First Trust Morningstar Dividend Leaders Index FDN.......................... First Trust Dow Jones Internet Index Fund FEX.......................... First Trust Large Cap Core AlphaDEX Fund FEZ.......................... SPDR EURO STOXX 50 ETF FGD.......................... First Trust DJ Global Select Dividend Index Fund FLAT......................... iPath US Treasury Flattener ETN FNX.......................... First Trust Mid Cap Core AlphaDEX Fund FRI.......................... First Trust S&P REIT Index Fund FVD.......................... First Trust Value Line Dividend Index Fund FXA.......................... CurrencyShares Australian Dollar Trust FXB.......................... CurrencyShares British Pound Sterling Trust FXC.......................... CurrencyShares Canadian Dollar Trust FXD.......................... First Trust Consumer Discretionary AlphaDEX Fund FXE.......................... CurrencyShares Euro Trust FXF.......................... CurrencyShares Swiss Franc Trust FXG.......................... First Trust Consumer Staples AlphaDEX Fund FXH.......................... First Trust Health Care AlphaDEX Fund FXI.......................... iShares FTSE China 25 Index Fund FXL.......................... First Trust Technology AlphaDEX Fund FXU.......................... First Trust Utilities AlphaDEX Fund FXY.......................... CurrencyShares Japanese Yen Trust FXZ.......................... First Trust Materials AlphaDEX Fund GAZ.......................... iPath Dow Jones-UBS Natural Gas Subindex Total Return ETN GCC.......................... GreenHaven Continuous Commodity Index Fund GDX.......................... Market Vectors Gold Miners ETF GDXJ......................... Market Vectors Junior Gold Miners ETF GIY.......................... Guggenheim Enhanced Core Bond ETF GLD.......................... SPDR Gold Shares GMF.......................... SPDR S&P Emerging Asia Pacific ETF GNR.......................... SPDR S&P Global Natural Resources ETF GOVT......................... iShares Barclays U.S. Treasury Bond Fund GSG.......................... iShares S&P GSCI Commodity Indexed Trust GSP.......................... iPath GSCI Total Return Index ETN GSY.......................... Guggenheim Enhanced Short Duration Bond ETF GVI.......................... iShares Barclays Intermediate Government/ Credit Bond Fund GWX.......................... SPDR S&P International Small Cap ETF GXC.......................... SPDR S&P China ETF GXG.......................... Global X FTSE Colombia 20 ETF HAO.......................... Guggenheim China Small Cap ETF HDGE......................... Active Bear ETF/The HDV.......................... iShares High Dividend Equity Fund HYD.......................... Market Vectors High Yield Municipal Index ETF HYG.......................... iShares iBoxx $ High Yield Corporate Bond Fund HYS.......................... PIMCO 0-5 Year High Yield Corporate Bond Index Fund IAU.......................... iShares Gold Trust IBB.......................... iShares Nasdaq Biotechnology Index Fund ICF.......................... iShares Cohen & Steers Realty Majors Index Fund ICI.......................... iPath Optimized Currency Carry ETN IDU.......................... iShares Dow Jones US Utilities Sector Index Fund IDV.......................... iShares Dow Jones International Select Dividend Index Fund IDX.......................... Market Vectors Indonesia Index ETF IEF.......................... iShares Barclays 7-10 Year Treasury Bond Fund IEI.......................... iShares Barclays 3-7 Year Treasury Bond Fund IEO.......................... iShares Dow Jones US Oil & Gas Exploration & Production Index Fund IEV.......................... iShares S&P Europe 350 Index Fund IEZ.......................... iShares Dow Jones US Oil Equipment & Services Index Fund IGE.......................... iShares S&P North American Natural Resources Sector Index Fund IGF.......................... iShares S&P Global Infrastructure Index Fund IGOV......................... iShares S&P/Citigroup International Treasury Bond Fund IGS.......................... ProShares Short Investment Grade Corporate IGV.......................... iShares S&P North American Technology- Software Index Fund IHE.......................... iShares Dow Jones US Pharmaceuticals Index Fund [[Page 33518]] IHF.......................... iShares Dow Jones US Healthcare Providers Index Fund IHI.......................... iShares Dow Jones US Medical Devices Index Fund IJH.......................... iShares S&P MidCap 400 Index Fund IJJ.......................... iShares S&P MidCap 400/BARRA Value Index Fund IJK.......................... iShares S&P MidCap 400 Growth Index Fund IJR.......................... iShares S&P SmallCap 600 Index Fund IJS.......................... iShares S&P SmallCap 600 Value Index Fund IJT.......................... iShares S&P SmallCap 600/BARRA Growth Index Fund ILF.......................... iShares S&P Latin America 40 Index Fund INDA......................... iShares MSCI India Index Fund INDY......................... iShares S&P India Nifty 50 Index Fund INP.......................... iPath MSCI India Index ETN IOO.......................... iShares S&P Global 100 Index Fund IPE.......................... SPDR Barclays Capital TIPS ETF ITB.......................... iShares Dow Jones US Home Construction Index Fund ITM.......................... Market Vectors Intermediate Municipal ETF IVE.......................... iShares S&P 500 Value Index Fund IVOO......................... Vanguard S&P Mid-Cap 400 ETF IVOP......................... iPath Inverse S&P 500 VIX Short-Term FuturesTM ETN II IVV.......................... iShares S&P 500 Index Fund/US IVW.......................... iShares S&P 500 Growth Index Fund IWB.......................... iShares Russell 1000 Index Fund IWC.......................... iShares Russell Microcap Index Fund IWD.......................... iShares Russell 1000 Value Index Fund IWF.......................... iShares Russell 1000 Growth Index Fund IWM.......................... iShares Russell 2000 Index Fund IWN.......................... iShares Russell 2000 Value Index Fund IWO.......................... iShares Russell 2000 Growth Index Fund IWP.......................... iShares Russell Midcap Growth Index Fund IWR.......................... iShares Russell Midcap Index Fund IWS.......................... iShares Russell Midcap Value Index Fund IWV.......................... iShares Russell 3000 Index Fund IWW.......................... iShares Russell 3000 Value Index Fund IWY.......................... iShares Russell Top 200 Growth Index Fund IWZ.......................... iShares Russell 3000 Growth Index Fund IXC.......................... iShares S&P Global Energy Sector Index Fund IXG.......................... iShares S&P Global Financials Sector Index Fund IXJ.......................... iShares S&P Global Healthcare Sector Index Fund IXN.......................... iShares S&P Global Technology Sector Index Fund IXP.......................... iShares S&P Global Telecommunications Sector Index Fund IYC.......................... iShares Dow Jones US Consumer Services Sector Index Fund IYE.......................... iShares Dow Jones US Energy Sector Index Fund IYF.......................... iShares Dow Jones US Financial Sector Index Fund IYG.......................... iShares Dow Jones US Financial Services Index Fund IYH.......................... iShares Dow Jones US Healthcare Sector Index Fund IYJ.......................... iShares Dow Jones US Industrial Sector Index Fund IYK.......................... iShares Dow Jones US Consumer Goods Sector Index Fund IYM.......................... iShares Dow Jones US Basic Materials Sector Index Fund IYR.......................... iShares Dow Jones US Real Estate Index Fund IYT.......................... iShares Dow Jones Transportation Average Index Fund IYW.......................... iShares Dow Jones US Technology Sector Index Fund IYY.......................... iShares Dow Jones US Index Fund IYZ.......................... iShares Dow Jones US Telecommunications Sector Index Fund JJC.......................... iPath Dow Jones-UBS Copper Subindex Total Return ETN JJG.......................... iPath Dow Jones-UBS Grains Subindex Total Return ETN JNK.......................... SPDR Barclays Capital High Yield Bond ETF JXI.......................... iShares S&P Global Utilities Sector Index Fund JYN.......................... iPath JPY/USD Exchange Rate ETN KBE.......................... SPDR S&P Bank ETF KBWB......................... PowerShares KBW Bank Portfolio KIE.......................... SPDR S&P Insurance ETF KOL.......................... Market Vectors Coal ETF KRE.......................... SPDR S&P Regional Banking ETF KXI.......................... iShares S&P Global Consumer Staples Sector Index Fund LAG.......................... SPDR Barclays Capital Aggregate Bond ETF LQD.......................... iShares iBoxx Investment Grade Corporate Bond Fund LTPZ......................... PIMCO 15+ Year US TIPS Index Fund LWC.......................... SPDR Barclays Capital Long Term Corporate BondETF MBB.......................... iShares Barclays MBS Bond Fund MBG.......................... SPDR Barclays Capital Mortgage Backed Bond ETF MCHI......................... iShares MSCI China Index Fund MDY.......................... SPDR S&P MidCap 400 ETF Trust [[Page 33519]] MGC.......................... Vanguard Mega Cap 300 ETF MGK.......................... Vanguard Mega Cap 300 Growth ETF MINT......................... PIMCO Enhanced Short Maturity Strategy Fund MLPI......................... UBS E-TRACS Alerian MLP Infrastructure ETN MLPN......................... Credit Suisse Cushing 30 MLP Index ETN MOO.......................... Market Vectors Agribusiness ETF MUB.......................... iShares S&P National Municipal Bond Fund MXI.......................... iShares S&P Global Materials Sector Index Fund MYY.......................... ProShares Short MidCap 400 NKY.......................... MAXIS Nikkei 225 Index Fund ETF OEF.......................... iShares S&P 100 Index Fund OIH.......................... Market Vectors Oil Service ETF OIL.......................... iPath Goldman Sachs Crude Oil Total Return Index ETN PALL......................... ETFS Physical Palladium Shares PBJ.......................... Powershares Dynamic Food & Beverage Portfolio PCEF......................... PowerShares CEF Income Composite Portfolio PCY.......................... PowerShares Emerging Markets Sovereign Debt Portfolio PDP.......................... Powershares DWA Technical Leaders Portfolio PEY.......................... PowerShares High Yield Equity Dividend Achievers Portfolio PFF.......................... iShares S&P US Preferred Stock Index Fund PFM.......................... PowerShares Dividend Achievers Portfolio PGF.......................... PowerShares Financial Preferred Portfolio PGX.......................... PowerShares Preferred Portfolio PHB.......................... PowerShares Fundamental High Yield Corporate Bond Portfolio PHO.......................... PowerShares Water Resources Portfolio PHYS......................... Sprott Physical Gold Trust PID.......................... PowerShares International Dividend Achievers Portfolio PIE.......................... PowerShares DWA Emerging Markets Technical Leaders Portfolio PIN.......................... PowerShares India Portfolio PJP.......................... Powershares Dynamic Pharmaceuticals Portfolio PLW.......................... PowerShares 1-30 Laddered Treasury Portfolio PPH.......................... Market Vectors Pharmaceutical ETF PPLT......................... ETFS Platinum Trust PRF.......................... Powershares FTSE RAFI US 1000 Portfolio PRFZ......................... PowerShares FTSE RAFI US 1500 Small-Mid Portfolio PSLV......................... Sprott Physical Silver Trust PSP.......................... PowerShares Global Listed Private Equity Portfolio PSQ.......................... ProShares Short QQQ PVI.......................... PowerShares VRDO Tax Free Weekly Portfolio PXH.......................... PowerShares FTSE RAFI Emerging Markets Portfolio PZA.......................... PowerShares Insured National Municipal Bond Portfolio QQQ.......................... Powershares QQQ Trust Series 1 REM.......................... iShares FTSE NAREIT Mortgage Plus Capped Index Fund REMX......................... Market Vectors Rare Earth/Strategic Metals ETF REZ.......................... iShares FTSE NAREIT Residential Plus Capped Index Fund RFG.......................... Guggenheim S&P Midcap 400 Pure Growth ETF RJA.......................... ELEMENTS Linked to the Rogers International Commodity Index--Agri Tot Return RJI.......................... ELEMENTS Linked to the Rogers International Commodity Index--Total Return RJN.......................... ELEMENTS Linked to the Rogers International Commodity Index--Energy To Return RJZ.......................... ELEMENTS Linked to the Rogers International Commodity Index--Metals Tot Return RPG.......................... Guggenheim S&P 500 Pure Growth ETF RSP.......................... Guggenheim S&P 500 Equal Weight ETF RSX.......................... Market Vectors Russia ETF RTH.......................... Market Vectors Retail ETF RWM.......................... ProShares Short Russell 2000 RWO.......................... SPDR Dow Jones Global Real Estate ETF RWR.......................... SPDR Dow Jones REIT ETF RWX.......................... SPDR Dow Jones International Real Estate ETF RYH.......................... Guggenheim S&P 500 Equal Weight Healthcare ETF SAGG......................... Direxion Daily Total Bond Market Bear 1x Shares SCHA......................... Schwab US Small-Cap ETF SCHB......................... Schwab US Broad Market ETF SCHD......................... Schwab US Dividend Equity ETF SCHE......................... Schwab Emerging Markets Equity ETF SCHF......................... Schwab International Equity ETF SCHG......................... Schwab U.S. Large-Cap Growth ETF SCHH......................... Schwab U.S. REIT ETF SCHM......................... Schwab U.S. Mid-Cap ETF SCHO......................... Schwab Short-Term U.S. Treasury ETF SCHP......................... Schwab U.S. TIPs ETF SCHR......................... Schwab Intermediate-Term U.S. Treasury ETF SCHV......................... Schwab U.S. Large-Cap Value ETF [[Page 33520]] SCHX......................... Schwab US Large-Cap ETF SCHZ......................... Schwab U.S. Aggregate Bond ETF SCPB......................... SPDR Barclays Capital Short Term Corporate Bond ETF SCZ.......................... iShares MSCI EAFE Small Cap Index Fund SDY.......................... SPDR S&P Dividend ETF SEF.......................... ProShares Short Financials SGG.......................... iPath Dow Jones-UBS Sugar Subindex Total Return ETN SGOL......................... ETFS Gold Trust SH........................... ProShares Short S&P 500 SHM.......................... SPDR Nuveen Barclays Capital Short Term Municipal Bond ETF SHV.......................... iShares Barclays Short Treasury Bond Fund SHY.......................... iShares Barclays 1-3 Year Treasury Bond Fund SIL.......................... Global X Silver Miners ETF SIVR......................... ETFS Physical Silver Shares SJB.......................... ProShares Short High Yield SJNK......................... SPDR Barclays Capital Short Term High Yield Bond ETF SLV.......................... iShares Silver Trust SLX.......................... Market Vectors Steel Index Fund SMH.......................... Market Vectors Semiconductor ETF SOXX......................... iShares PHLX SOX Semiconductor Sector Index Fund SPLV......................... PowerShares S&P 500 Low Volatility Portfolio SPY.......................... SPDR S&P 500 ETF Trust SPYG......................... SPDR S&P 500 Growth ETF SPYV......................... SPDR S&P 500 Value ETF STIP......................... iShares Barclays 0-5 Year TIPS Bond Fund STPP......................... iPath US Treasury Steepener ETN STPZ......................... PIMCO 1-5 Year US TIPS Index Fund SUB.......................... iShares S&P Short Term National AMT-Free Municipal Bond Fund SVXY......................... ProShares Short VIX Short-Term Futures ETF TAN.......................... Guggenheim Solar ETF TBF.......................... ProShares Short 20+ Year Treasury TBX.......................... ProShares Short 7-10 Treasury TFI.......................... SPDR Nuveen Barclays Capital Municipal Bond ETF THD.......................... iShares MSCI Thailand Index Fund TIP.......................... iShares Barclays TIPS Bond Fund TLH.......................... iShares Barclays 10-20 Year Treasury Bond Fund TLT.......................... iShares Barclays 20+ Year Treasury Bond Fund TUR.......................... iShares MSCI Turkey Index Fund UDN.......................... PowerShares DB US Dollar Index Bearish Fund UGA.......................... United States Gasoline Fund LP UNG.......................... United States Natural Gas Fund LP URA.......................... Global X Uranium ETF USCI......................... United States Commodity Index Fund USL.......................... United States 12 Month Oil Fund LP USO.......................... United States Oil Fund LP UUP.......................... PowerShares DB US Dollar Index Bullish Fund VAW.......................... Vanguard Materials ETF VB........................... Vanguard Small-Cap ETF VBK.......................... Vanguard Small-Cap Growth ETF VBR.......................... Vanguard Small-Cap Value ETF VCIT......................... Vanguard Intermediate-Term Corporate Bond ETF VCLT......................... Vanguard Long-Term Corporate Bond ETF VCR.......................... Vanguard Consumer Discretionary ETF VCSH......................... Vanguard Short-Term Corporate Bond ETF VDC.......................... Vanguard Consumer Staples ETF VDE.......................... Vanguard Energy ETF VEA.......................... Vanguard MSCI EAFE ETF VEU.......................... Vanguard FTSE All-World ex-US ETF VFH.......................... Vanguard Financials ETF VGK.......................... Vanguard MSCI European ETF VGT.......................... Vanguard Information Technology ETF VHT.......................... Vanguard Health Care ETF VIG.......................... Vanguard Dividend Appreciation ETF VIIX......................... VelocityShares VIX Short Term ETN VIOO......................... Vanguard S&P Small-Cap 600 ETF VIS.......................... Vanguard Industrials ETF VIXM......................... ProShares VIX Mid-Term Futures ETF VIXY......................... ProShares VIX Short-Term Futures ETF VMBS......................... Vanguard Mortgage-Backed Securities ETF VNM.......................... Market Vectors Vietnam ETF VNQ.......................... Vanguard REIT ETF VO........................... Vanguard Mid-Cap ETF [[Page 33521]] VOE.......................... Vanguard Mid-Cap Value Index Fund/Closed- end VONE......................... Vanguard Russell 1000 VONG......................... Vanguard Russell 1000 Growth ETF VONV......................... Vanguard Russell 1000 Value VOO.......................... Vanguard S&P 500 ETF VOOG......................... Vanguard S&P 500 Growth ETF VOOV......................... Vanguard S&P 500 Value ETF VOT.......................... Vanguard Mid-Cap Growth Index Fund/Closed- end VOX.......................... Vanguard Telecommunication Services ETF VPL.......................... Vanguard MSCI Pacific ETF VPU.......................... Vanguard Utilities ETF VQT.......................... Barclays ETN+ ETNs Linked to the S&P 500 Dynamic VEQTORTM TotaL Return Index VSS.......................... Vanguard FTSE All World ex-US Small-Cap ETF VT........................... Vanguard Total World Stock Index Fund ETF VTHR......................... Vanguard Russell 3000 VTI.......................... Vanguard Total Stock Market ETF VTV.......................... Vanguard Value ETF VTWG......................... Vanguard Russell 2000 Growth VTWO......................... Vanguard Russell 2000 VTWV......................... Vanguard Russell 2000 Value VUG.......................... Vanguard Growth ETF VV........................... Vanguard Large-Cap ETF VWO.......................... Vanguard MSCI Emerging Markets ETF VXAA......................... ETRACS 1-Month S&P 500 VIX Futures ETN VXEE......................... ETRACS 5-Month S&P 500 VIX Futures ETN VXF.......................... Vanguard Extended Market ETF VXUS......................... Vanguard Total International Stock ETF VXX.......................... iPATH S&P 500 VIX Short-Term Futures ETN VXZ.......................... iPATH S&P 500 VIX Mid-Term Futures ETN VYM.......................... Vanguard High Dividend Yield ETF VZZB......................... iPath Long Enhanced S&P 500 VIX Mid-Term FuturesTM ETN II WDTI......................... WisdomTree Managed Futures Strategy Fund WIP.......................... SPDR DB International Government Inflation-Protected Bond ETF XBI.......................... SPDR S&P Biotech ETF XES.......................... SPDR S&P Oil & Gas Equipment & Services ETF XHB.......................... SPDR S&P Homebuilders ETF XIV.......................... VelocityShares Daily Inverse VIX Short Term ETN XLB.......................... Materials Select Sector SPDR Fund XLE.......................... Energy Select Sector SPDR Fund XLF.......................... Financial Select Sector SPDR Fund XLG.......................... Guggenheim Russell Top 50 ETF XLI.......................... Industrial Select Sector SPDR Fund XLK.......................... Technology Select Sector SPDR Fund XLP.......................... Consumer Staples Select Sector SPDR Fund XLU.......................... Utilities Select Sector SPDR Fund XLV.......................... Health Care Select Sector SPDR Fund XLY.......................... Consumer Discretionary Select Sector SPDR Fund XME.......................... SPDR S&P Metals & Mining ETF XOP.......................... SPDR S&P Oil & Gas Exploration & Production ETF XPH.......................... SPDR S&P Pharmaceuticals ETF XRT.......................... SPDR S&P Retail ETF XSD.......................... SPDR S&P Semiconductor ETF XXV.......................... iPath Inverse S&P 500 VIX Short-Term Futures ETN ZROZ......................... PIMCO 25+ Year Zero Coupon US Treasury Index Fund ------------------------------------------------------------------------ Appendix B--Data Unless otherwise specified, the following data shall be collected and transmitted to the SEC in an agreed-upon format on a monthly basis, to be provided 30 calendar days following month end. Unless otherwise specified, the Primary Listing Exchanges shall be responsible for collecting and transmitting the data to the SEC. Data collected in connection with Sections II(E)-(G) below shall be transmitted to the SEC with a request for confidential treatment under the Freedom of Information Act. 5 U.S.C. 552, and the SEC's rules and regulations thereunder. I. Summary Statistics A. Frequency with which NMS Stocks enter a Limit State. Such summary data shall be broken down as follows: 1. Partition stocks by category a. Tier 1 non-ETP issues >$3.00 b. Tier 1 non-ETP issues > =$0.75 and =$3.00 c. Tier 1 non-ETP issues <$0.75 d. Tier 1 non-leveraged ETPs in each of above categories e. Tier 1 leveraged ETPs in each of above categories f. Tier 2 non-ETPs in each of above categories g. Tier 2 non-leveraged ETPs in each of above categories h. Tier 2 leveraged ETPs in each of above categories 2. Partition by time of day a. Opening (prior to 9:45 a.m. ET) b. Regular (between 9:45 a.m. ET and 3:35 p.m. ET) c. Closing (after 3:35 p.m. ET) d. Within five minutes of a Trading Pause re-open or IPO open [[Page 33522]] 3. Track reasons for entering a Limit State, such as: a. Liquidity gap -price reverts from a Limit State Quotation and returns to trading within the Price Bands b. Broken trades c. Primary Listing Exchange manually declares a Trading Pause pursuant to Section (VII)(2) of the Plan d. Other B. Determine (1), (2) and (3) for when a Trading Pause has been declared for an NMS Stock pursuant to the Plan. II. Raw Data (all Participants, except A-E, which are for the Primary Listing Exchanges only) A. Record of every Straddle State. 1. Ticker, date, time entered, time exited, flag for ending with Limit State, flag for ending with manual override. 2. Pipe delimited with field names as first record. B. Record of every Price Band 1. Ticker, date, time at beginning of Price Band, Upper Price Band, Lower Price Band 2. Pipe delimited with field names as first record C. Record of every Limit State 1. Ticker, date, time entered, time exited, flag for halt 2. Pipe delimited with field names as first record D. Record of every Trading Pause or halt 1. Ticker, date, time entered, time exited, type of halt (i.e., regulatory halt, non-regulatory halt, Trading Pause pursuant to the Plan, other) 2. Pipe delimited with field names as first record E. Data set or orders entered into reopening auctions during halts or Trading Pauses 1. Arrivals, Changes, Cancels, shares, limit/market, side, Limit State side 2. Pipe delimited with field name as first record F. Data set of order events received during Limit States G. Summary data on order flow of arrivals and cancellations for each 15-second period for discrete time periods and sample stocks to be determined by the SEC in subsequent data requests. Must indicate side(s) of Limit State. 1. Market/marketable sell orders arrivals and executions a. Count b. Shares c. Shares executed 2. Market/marketable buy orders arrivals and executions a. Count b. Shares c. Shares executed 3. Count arriving, volume arriving and shares executing in limit sell orders above NBBO mid-point 4. Count arriving, volume arriving and shares executing in limit sell orders=NBBO mid-point (non-marketable) 5. Count arriving, volume arriving and shares executing in limit buy orders above NBBO mid-point (non-marketable) 6. Count arriving, volume arriving and shares executing in limit buy orders below NBBO mid-point 7. Count and volume arriving of limit sell orders priced at or above NBBO+$0.05 8. Count and volume arriving of limit buy orders priced at or below NBBO-$0.05 9. Count and volume of (iii-viii) for cancels 10. Include: Ticker, date, time at start, time of Limit State, data item fields, last sale prior to 1-minute period (null if no trades today), range during 15-second period, last trade during 15-second period III. At Least Two Months Prior to the End of the Pilot Period, All Participants Shall Provide to the SEC Assessments Relating to Impact of the Plan and Calibration of the Percentage Parameters as Follows: A. Assess the statistical and economic impact on limit order book of approaching Price Bands. B. Assess the statistical and economic impact of the Price Bands on erroneous trades. C. Assess the statistical and economic impact of the appropriateness of the Percentage Parameters used for the Price Bands. D. Assess whether the Limit State is the appropriate length to allow for liquidity replenishment when a Limit State is reached because of a temporary liquidity gap. E. Evaluate concerns from the options markets regarding the statistical and economic impact of Limit States on liquidity and market quality in the options markets. (Participants that operate options exchange should also prepare such assessment reports.) F. Assess whether the process for entering a Limit State should be adjusted and whether Straddle States are problematic. G. Assess whether the process for exiting a Limit State should be adjusted. H. Assess whether the Trading Pauses are too long or short and whether the reopening procedures should be adjusted. [FR Doc. 2012-13653 Filed 6-5-12; 8:45 am] BILLING CODE 8011-01-P
TOP-SECRET – The Case of the Mysterious Khalid Sheikh Mohammed in Guantanamo Bay Photos
Last month, nearly a dozen photos purporting to show alleged al-Qaeda mastermind Khalid Sheikh Mohammed posing serenely inside the internment facility at Guantanamo Bay were posted on a popular Jihadist forum. The photos depict what appears to be Mohammed sitting in a variety of poses in clothing similar to what is worn by detainees at the internment facility in Guantanamo Bay. Two of the photos also depict other detainees being held at Guantanamo.
On May 24 the U.S. military told NBC news that they were investigating the photos to determine whether or not they had been digitally manipulated. The next day an article from AFP quoted Pentagon spokesman Lieutenant-Colonel Todd Breasseale as saying the “recent photos of Khalid Sheikh Mohammad, et al, that have surfaced on the Internet represent a very poor effort at digital manipulation . . . clearly using the official work of the ICRC — approved for release by the US government — in order to deceive and rally those inclined toward radicalism.”
Some of the photos do appear to be manipulated. However, several photos appear to be genuine depictions of Mohammed and other detainees. Confusing the issue further, many media outlets do not seem to understand that there were several photos released and have instead focused upon a single photo from the collection that appears to be manipulated.
In order to further analysis of the photos, Public Intelligence has reproduced all of the photos and made them available for download in a high-resolution format. Let us know what your opinions are on the authenticity of the photos in the comment section below, via email or by using our encrypted contact form.
Here’s a quick look at some of the photos from the collection:
TOP-SECRET – Beware of Imitators by Al Qa’ida Secretary
TOP-SECRET – Open Source Center Status of Syrian Uprising, Regime Cohesion May 2012
Conflict between government and opposition forces continued during the week, generally following the established pattern of government military attacks and security raids against centers of opposition, on the one hand, and ambushes and bombings by opposition forces on the other. The Syrian conflict also continued to spark clashes in neighboring Lebanon. Further turmoil among the top leadership of the opposition Syrian National Council (SNC) reflected the opposition’s continued difficulty in unifying ranks. Syria and the United Nations traded accusations on the subject of human-rights violations.
Update on Clashes
Reports from opposition sources transmitted via Arab media — such as the influential, London-based, pan-Arab daily Al-Sharq al-Awsat — described widespread clashes between government and opposition in and around several major population centers. Opposition sources typically claimed that government forces killed dozens of individuals in various daily assaults, though such claims remain impossible to verify.
- Government forces reportedly used artillery and helicopters during bombardments in Al-Rastan, Homs, Idlib Province, and villages near Aleppo.
- Clashes were also reported in a southwestern district of Damascus and specifically on 23 May in the city of Aleppo, the scene of antigovernment demonstrations. Various opposition sources described the Aleppo protests as comprising “1,500,” “tens,” or “hundreds” of thousands of demonstrators.
- A large car bomb, apparently targeting military intelligence facilities, exploded in the eastern town of Dayr al-Zawr on 19 May, resulting in several deaths. Another deadly bomb attack occurred in the Damascus neighborhood of Qabun during the night of 21-22 May.
Reports of clashes transmitted by the state-run SANA news agency followed a familiar pattern of branding opposition attacks as terrorist in nature and hinting of foreign support.
- SANA reported several deadly attacks by “armed terrorist groups,” typically against isolated security forces, such as border guards.
- It also reported military engineers’ success in disarming a number of “terrorist” bombs.
- According to SANA, security forces discovered a “terrorist” weapons-manufacturing warehouse in Homs and intercepted several “Tunisian terrorists” attempting to infiltrate into Syria from Turkey.
More Clashes in Lebanon
Clashes between pro-Syrian Government and pro-Syrian opposition factions continued in
Lebanon, and a number of Lebanese Shiites were abducted in Syria under unclear
circumstances.
- Following a week of clashes in Tripoli between Sunnis hostile to the Syrian regime and Alawite regime supporters, fighting broke out in Beirut during the night of 21-22 May, reportedly resulting in two deaths.
- Ahmad Abd-al-Wahib, a Sunni cleric belonging to the pro-Syria 14 March alliance, was killed under disputed circumstances by Lebanese Army troops at a security checkpoint in northern Lebanon on 20 May.
- Approximately one dozen Lebanese Shiites, said to be pilgrims returning to Lebanon via Syria from Iran, were seized at gunpoint in Aleppo on 22 May. Family members and Syrian state media blamed the assault on the Free Syrian Army (FSA), but the FSA denied all responsibility and accused the Syrian Government of staging the incident.
Crisis Within SNC
The SNC formally accepted the resignation of Burhan Ghalyun, who had been reelected president on 15 May, and announced a new presidential election on 9-10 June. Ghalyun resigned under pressure from critics within the SNC who accused him of monopolizing power and failing to support properly the uprising.
Mutual Accusations Regarding Human-Rights Violations
In a report addressed to the UN Human Rights Council on 20 May, the Syrian Foreign and Expatriates Ministry charged that Syria is the victim of human-rights violations, both through “direct killing operations” by “armed terrorist groups” and through “the sanctions imposed by the countries, which are funding, backing, and hosting these groups.”
In a report released on 24 May, the UN’s Independent Commission of Inquiry on Syria charged that the Syrian Army and security services were responsible for most of the human-rights violations documented by the commission, both in the form of direct attacks against individuals and the “systematic denial” of food, water, and medical care.
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TIO-SECRET from the FBI – Leader of MS-13 Gang Sentenced to 50 Years in Prison for Sex Trafficking Multiple Teens
ALEXANDRIA, VA—Rances Ulices Amaya, 24, also known as “Murder” and “Blue,” was sentenced today to 50 years in prison for recruiting girls as young as 14 from middle schools, high schools, and homeless shelters in Northern Virginia and forcing them to engage commercial sex acts on behalf of MS-13.
Neil H. MacBride, U.S. Attorney for the Eastern District of Virginia, and James W. McJunkin, Assistant Director in Charge of the FBI’s Washington Field Office, made the announcement after sentencing by U.S. District Judge Anthony J. Trenga.
“Rances Amaya’s gang name was ‘Murder,’ and in a real sense, he killed the hopes and dreams of teenage girls whom he systematically and sadistically victimized,” said U.S. Attorney MacBride. “He told these girls that he owned them and that he would hurt their loved ones if they didn’t comply. They were his sex slaves, and that slavery goes to the heart of the heinous crime of sex trafficking. These girls have traumatic scars that will last a lifetime, and Mr. Amaya is justly going to spend the rest of his productive life paying for his crimes.”
“Today’s sentencing demonstrates the commitment of law enforcement and the judicial system to combat juvenile prostitution and human trafficking in Northern Virginia,” said Assistant Director in Charge McJunkin. “Together with our partner agencies, we will continue to pursue individuals such as Mr. Amaya who ruthlessly exploit vulnerable young girls for sex and money.”
Amaya was convicted by a jury on February 23, 2012 of conspiracy and three counts of sex trafficking of a child. According to court records and evidence at trial, Amaya joined MS-13 when he was a teenager and later became a “shot caller” for his MS-13 clique, the Guanacos Lokotes Salvatruchas. MS-13 gave him the gang monikers “Murder” and “Blue,” and he bears multiple MS-13 tattoos on his hands and arms.
In 2009, Amaya joined forces with an MS-13 associate who was already prostituting underage girls. Amaya used the violent reputation of MS-13 to ensure that sex customers paid for the sex and did not lure the underage victims away. He also used his MS-13 contacts to find sex customers and would offer free sex with the victims and a cut of the profits for any gang member who provided customers or underage girls. Amaya and his co-conspirator sought out illegal aliens as customers because they believed illegal aliens were unlikely to call the police. Amaya would hand out his telephone number at construction sites and convenience stores frequented by day laborers from Latin America.
Victims were required to have sex with eight to 10 paying customers per day, sometimes seven days per week. Some of the customers were sex addicts and repeat customers who paid daily for the sex. At night, after the paying customers were finished, Amaya would invite his fellow MS-13 members to have sex with the girls. Sometimes, to punish victims, the gang would “run a train” on a victim, which meant that multiple gang members would have sex with the victim in rapid succession. Amaya and other gang members also raped the victims both for their enjoyment and to “groom” them for the sex trafficking scheme.
Besides raping them to keep the victims compliant, Amaya would provide them with cigarettes, alcohol, marijuana, and other drugs. The evidence showed that Amaya prostituted five victims who were between the ages of 14 and 17 years old. The jury heard that using underage girls had two advantages: customers preferred young girls, and Amaya found them easier to manipulate and control. In addition, there was always an implicit threat of violence insofar as the victims knew that Amaya was MS-13, and he frequently carried a machete with him, MS-13’s weapon of choice. Amaya also struck at least one of the victims in the face.
The sex acts took place at motels, hotels, houses, apartments, and cars in Washington, D.C. and the Northern Virginia area. In particular, Amaya frequented a few hotels in Falls Church, Virginia, and many of the customers were solicited from convenience stores in the Culmore and Chirilagua neighborhoods of Northern Virginia.
Amaya charged between $30 and $120 for about 20 minutes of sex with the victims. Customers were required to pay more for “unusual” sex acts. The proceeds of the prostitution were used to purchase narcotics, alcoholic beverages, and to support MS-13 in the United States and El Salvador.
Amaya is the fourth MS-13 member to be convicted of sex trafficking children in the Eastern District of Virginia.
This case was investigated by the FBI’s Washington Field Office and the Fairfax County Gang Unit, with assistance from the Northern Virginia Human Trafficking Task Force. Assistant U.S. Attorney G. Zachary Terwilliger and Special Assistant U.S. Attorney Michael J. Frank are prosecuting the case on behalf of the United States.
Founded in 2004, the Northern Virginia Human Trafficking Task Force is a collaboration of federal, state, and local law enforcement agencies—along with non-governmental organizations—dedicated to combating human trafficking and related crimes.
A copy of this press release may be found on the website of the U.S. Attorney’s Office for the Eastern District of Virginia at http://www.justice.gov/usao/vae.
TOP-SECRET from the FBI – Leader of MS-13 Gang Sentenced to 50 Years in Prison for Sex Trafficking Multiple Teens
ALEXANDRIA, VA—Rances Ulices Amaya, 24, also known as “Murder” and “Blue,” was sentenced today to 50 years in prison for recruiting girls as young as 14 from middle schools, high schools, and homeless shelters in Northern Virginia and forcing them to engage commercial sex acts on behalf of MS-13.
Neil H. MacBride, U.S. Attorney for the Eastern District of Virginia, and James W. McJunkin, Assistant Director in Charge of the FBI’s Washington Field Office, made the announcement after sentencing by U.S. District Judge Anthony J. Trenga.
“Rances Amaya’s gang name was ‘Murder,’ and in a real sense, he killed the hopes and dreams of teenage girls whom he systematically and sadistically victimized,” said U.S. Attorney MacBride. “He told these girls that he owned them and that he would hurt their loved ones if they didn’t comply. They were his sex slaves, and that slavery goes to the heart of the heinous crime of sex trafficking. These girls have traumatic scars that will last a lifetime, and Mr. Amaya is justly going to spend the rest of his productive life paying for his crimes.”
“Today’s sentencing demonstrates the commitment of law enforcement and the judicial system to combat juvenile prostitution and human trafficking in Northern Virginia,” said Assistant Director in Charge McJunkin. “Together with our partner agencies, we will continue to pursue individuals such as Mr. Amaya who ruthlessly exploit vulnerable young girls for sex and money.”
Amaya was convicted by a jury on February 23, 2012 of conspiracy and three counts of sex trafficking of a child. According to court records and evidence at trial, Amaya joined MS-13 when he was a teenager and later became a “shot caller” for his MS-13 clique, the Guanacos Lokotes Salvatruchas. MS-13 gave him the gang monikers “Murder” and “Blue,” and he bears multiple MS-13 tattoos on his hands and arms.
In 2009, Amaya joined forces with an MS-13 associate who was already prostituting underage girls. Amaya used the violent reputation of MS-13 to ensure that sex customers paid for the sex and did not lure the underage victims away. He also used his MS-13 contacts to find sex customers and would offer free sex with the victims and a cut of the profits for any gang member who provided customers or underage girls. Amaya and his co-conspirator sought out illegal aliens as customers because they believed illegal aliens were unlikely to call the police. Amaya would hand out his telephone number at construction sites and convenience stores frequented by day laborers from Latin America.
Victims were required to have sex with eight to 10 paying customers per day, sometimes seven days per week. Some of the customers were sex addicts and repeat customers who paid daily for the sex. At night, after the paying customers were finished, Amaya would invite his fellow MS-13 members to have sex with the girls. Sometimes, to punish victims, the gang would “run a train” on a victim, which meant that multiple gang members would have sex with the victim in rapid succession. Amaya and other gang members also raped the victims both for their enjoyment and to “groom” them for the sex trafficking scheme.
Besides raping them to keep the victims compliant, Amaya would provide them with cigarettes, alcohol, marijuana, and other drugs. The evidence showed that Amaya prostituted five victims who were between the ages of 14 and 17 years old. The jury heard that using underage girls had two advantages: customers preferred young girls, and Amaya found them easier to manipulate and control. In addition, there was always an implicit threat of violence insofar as the victims knew that Amaya was MS-13, and he frequently carried a machete with him, MS-13’s weapon of choice. Amaya also struck at least one of the victims in the face.
The sex acts took place at motels, hotels, houses, apartments, and cars in Washington, D.C. and the Northern Virginia area. In particular, Amaya frequented a few hotels in Falls Church, Virginia, and many of the customers were solicited from convenience stores in the Culmore and Chirilagua neighborhoods of Northern Virginia.
Amaya charged between $30 and $120 for about 20 minutes of sex with the victims. Customers were required to pay more for “unusual” sex acts. The proceeds of the prostitution were used to purchase narcotics, alcoholic beverages, and to support MS-13 in the United States and El Salvador.
Amaya is the fourth MS-13 member to be convicted of sex trafficking children in the Eastern District of Virginia.
This case was investigated by the FBI’s Washington Field Office and the Fairfax County Gang Unit, with assistance from the Northern Virginia Human Trafficking Task Force. Assistant U.S. Attorney G. Zachary Terwilliger and Special Assistant U.S. Attorney Michael J. Frank are prosecuting the case on behalf of the United States.
Founded in 2004, the Northern Virginia Human Trafficking Task Force is a collaboration of federal, state, and local law enforcement agencies—along with non-governmental organizations—dedicated to combating human trafficking and related crimes.
A copy of this press release may be found on the website of the U.S. Attorney’s Office for the Eastern District of Virginia at http://www.justice.gov/usao/vae.
TOP-SECRET – Arab Americans Seek Disadvantaged Minority Help
|
TOP-SECRET – Fukushima Daiichi Nuclear Power Station 12-0528

TOP-SECRET – 2012 Bilderberg Meeting Participant List
The following press release and participants list was obtained from the official website of Bilderberg Meetings. Participant lists from nearly every Bilderberg Meeting since 1954 are also available as well as tax returns for the non-profit U.S.-based corporation American Friends of Bilderberg from 2007 – 2010.
BILDERBERG MEETINGS
Chantilly, Virginia, USA
31 May-3 June 2012
LIST OF PARTICIPANTS
| FRA | Castries, Henri de | Chairman and CEO, AXA Group |
| DEU | Ackermann, Josef | Chairman of the Management Board and the Group Executive Committee, Deutsche Bank AG |
| GBR | Agius, Marcus | Chairman, Barclays plc |
| USA | Ajami, Fouad | Senior Fellow, The Hoover Institution, Stanford University |
| USA | Alexander, Keith B. | Commander, US Cyber Command; Director, National Security Agency |
| INT | Almunia, Joaquín | Vice-President – Commissioner for Competition, European Commission |
| USA | Altman, Roger C. | Chairman, Evercore Partners |
| PRT | Amado, Luís | Chairman, Banco Internacional do Funchal (BANIF) |
| NOR | Andresen, Johan H. | Owner and CEO, FERD |
| FIN | Apunen, Matti | Director, Finnish Business and Policy Forum EVA |
| TUR | Babacan, Ali | Deputy Prime Minister for Economic and Financial Affairs |
| PRT | Balsemão, Francisco Pinto | President and CEO, Impresa; Former Prime Minister |
| FRA | Baverez, Nicolas | Partner, Gibson, Dunn & Crutcher LLP |
| FRA | Béchu, Christophe | Senator, and Chairman, General Council of Maine-et-Loire |
| BEL | Belgium, H.R.H. Prince Philippe of | |
| TUR | Berberoğlu, Enis | Editor-in-Chief, Hürriyet Newspaper |
| ITA | Bernabè, Franco | Chairman and CEO, Telecom Italia |
| GBR | Boles, Nick | Member of Parliament |
| SWE | Bonnier, Jonas | President and CEO, Bonnier AB |
| NOR | Brandtzæg, Svein Richard | President and CEO, Norsk Hydro ASA |
| AUT | Bronner, Oscar | Publisher, Der Standard Medienwelt |
| SWE | Carlsson, Gunilla | Minister for International Development Cooperation |
| CAN | Carney, Mark J. | Governor, Bank of Canada |
| ESP | Cebrián, Juan Luis | CEO, PRISA; Chairman, El País |
| AUT | Cernko, Willibald | CEO, UniCredit Bank Austria AG |
| FRA | Chalendar, Pierre André de | Chairman and CEO, Saint-Gobain |
| DNK | Christiansen, Jeppe | CEO, Maj Invest |
| RUS | Chubais, Anatoly B. | CEO, OJSC RUSNANO |
| CAN | Clark, W. Edmund | Group President and CEO, TD Bank Group |
| GBR | Clarke, Kenneth | Member of Parliament, Lord Chancellor and Secretary of Justice |
| USA | Collins, Timothy C. | CEO and Senior Managing Director, Ripplewood Holdings, LLC |
| ITA | Conti, Fulvio | CEO and General Manager, Enel S.p.A. |
| USA | Daniels, Jr., Mitchell E. | Governor of Indiana |
| USA | DeMuth, Christopher | Distinguished Fellow, Hudson Institute |
| USA | Donilon, Thomas E. | National Security Advisor, The White House |
| GBR | Dudley, Robert | Group Chief Executive, BP plc |
| ITA | Elkann, John | Chairman, Fiat S.p.A. |
| DEU | Enders, Thomas | CEO, Airbus |
| USA | Evans, J. Michael | Vice Chairman, Global Head of Growth Markets, Goldman Sachs & Co. |
| AUT | Faymann, Werner | Federal Chancellor |
| DNK | Federspiel, Ulrik | Executive Vice President, Haldor Topsøe A/S |
| USA | Ferguson, Niall | Laurence A. Tisch Professor of History, Harvard University |
| GBR | Flint, Douglas J. | Group Chairman, HSBC Holdings plc |
| CHN | Fu, Ying | Vice Minister of Foreign Affairs |
| IRL | Gallagher, Paul | Former Attorney General; Senior Counsel |
| USA | Gephardt, Richard A. | President and CEO, Gephardt Group |
| GRC | Giannitsis, Anastasios | Former Minister of Interior; Professor of Development and International Economics, University of Athens |
| USA | Goolsbee, Austan D. | Professor of Economics, University of Chicago Booth School of Business |
| USA | Graham, Donald E. | Chairman and CEO, The Washington Post Company |
| ITA | Gruber, Lilli | Journalist – Anchorwoman, La 7 TV |
| INT | Gucht, Karel de | Commissioner for Trade, European Commission |
| NLD | Halberstadt, Victor | Professor of Economics, Leiden University; Former Honorary Secretary General of Bilderberg Meetings |
| USA | Harris, Britt | CIO, Teacher Retirement System of Texas |
| USA | Hoffman, Reid | Co-founder and Executive Chairman, LinkedIn |
| CHN | Huang, Yiping | Professor of Economics, China Center for Economic Research, Peking University |
| USA | Huntsman, Jr., Jon M. | Chairman, Huntsman Cancer Foundation |
| DEU | Ischinger, Wolfgang | Chairman, Munich Security Conference; Global Head Government Relations, Allianz SE |
| RUS | Ivanov, Igor S. | Associate member, Russian Academy of Science; President, Russian International Affairs Council |
| FRA | Izraelewicz, Erik | CEO, Le Monde |
| USA | Jacobs, Kenneth M. | Chairman and CEO, Lazard |
| USA | Johnson, James A. | Vice Chairman, Perseus, LLC |
| USA | Jordan, Jr., Vernon E. | Senior Managing Director, Lazard |
| USA | Karp, Alexander | CEO, Palantir Technologies |
| USA | Karsner, Alexander | Executive Chairman, Manifest Energy, Inc |
| FRA | Karvar, Anousheh | Inspector, Inter-ministerial Audit and Evaluation Office for Social, Health, Employment and Labor Policies |
| RUS | Kasparov, Garry | Chairman, United Civil Front (of Russia) |
| GBR | Kerr, John | Independent Member, House of Lords |
| USA | Kerry, John | Senator for Massachusetts |
| TUR | Keyman, E. Fuat | Director, Istanbul Policy Center and Professor of International Relations, Sabanci University |
| USA | Kissinger, Henry A. | Chairman, Kissinger Associates, Inc. |
| USA | Kleinfeld, Klaus | Chairman and CEO, Alcoa |
| TUR | Koç, Mustafa | Chairman, Koç Holding A.Ş. |
| DEU | Koch, Roland | CEO, Bilfinger Berger SE |
| INT | Kodmani, Bassma | Member of the Executive Bureau and Head of Foreign Affairs, Syrian National Council |
| USA | Kravis, Henry R. | Co-Chairman and Co-CEO, Kohlberg Kravis Roberts & Co. |
| USA | Kravis, Marie-Josée | Senior Fellow, Hudson Institute |
| INT | Kroes, Neelie | Vice President, European Commission; Commissioner for Digital Agenda |
| USA | Krupp, Fred | President, Environmental Defense Fund |
| INT | Lamy, Pascal | Director-General, World Trade Organization |
| ITA | Letta, Enrico | Deputy Leader, Democratic Party (PD) |
| ISR | Levite, Ariel E. | Nonresident Senior Associate, Carnegie Endowment for International Peace |
| USA | Li, Cheng | Director of Research and Senior Fellow, John L. Thornton China Center, Brookings Institution |
| USA | Lipsky, John | Distinguished Visiting Scholar, Johns Hopkins University |
| USA | Liveris, Andrew N. | President, Chairman and CEO, The Dow Chemical Company |
| DEU | Löscher, Peter | President and CEO, Siemens AG |
| USA | Lynn, William J. | Chairman and CEO, DRS Technologies, Inc. |
| GBR | Mandelson, Peter | Member, House of Lords; Chairman, Global Counsel |
| USA | Mathews, Jessica T. | President, Carnegie Endowment for International Peace |
| DEN | Mchangama, Jacob | Director of Legal Affairs, Center for Political Studies (CEPOS) |
| CAN | McKenna, Frank | Deputy Chair, TD Bank Group |
| USA | Mehlman, Kenneth B. | Partner, Kohlberg Kravis Roberts & Co. |
| GBR | Micklethwait, John | Editor-in-Chief, The Economist |
| FRA | Montbrial, Thierry de | President, French Institute for International Relations |
| PRT | Moreira da Silva, Jorge | First Vice-President, Partido Social Democrata (PSD) |
| USA | Mundie, Craig J. | Chief Research and Strategy Officer, Microsoft Corporation |
| DEU | Nass, Matthias | Chief International Correspondent, Die Zeit |
| NLD | Netherlands, H.M. the Queen of the | |
| ESP | Nin Génova, Juan María | Deputy Chairman and CEO, Caixabank |
| IRL | Noonan, Michael | Minister for Finance |
| USA | Noonan, Peggy | Author, Columnist, The Wall Street Journal |
| FIN | Ollila, Jorma | Chairman, Royal Dutch Shell, plc |
| USA | Orszag, Peter R. | Vice Chairman, Citigroup |
| GRC | Papalexopoulos, Dimitri | Managing Director, Titan Cement Co. |
| NLD | Pechtold, Alexander | Parliamentary Leader, Democrats ’66 (D66) |
| USA | Perle, Richard N. | Resident Fellow, American Enterprise Institute |
| NLD | Polman, Paul | CEO, Unilever PLC |
| CAN | Prichard, J. Robert S. | Chair, Torys LLP |
| ISR | Rabinovich, Itamar | Global Distinguished Professor, New York University |
| GBR | Rachman, Gideon | Chief Foreign Affairs Commentator, The Financial Times |
| USA | Rattner, Steven | Chairman, Willett Advisors LLC |
| CAN | Redford, Alison M. | Premier of Alberta |
| CAN | Reisman, Heather M. | CEO, Indigo Books & Music Inc. |
| DEU | Reitzle, Wolfgang | CEO & President, Linde AG |
| USA | Rogoff, Kenneth S. | Professor of Economics, Harvard University |
| USA | Rose, Charlie | Executive Editor and Anchor, Charlie Rose |
| USA | Ross, Dennis B. | Counselor, Washington Institute for Near East Policy |
| POL | Rostowski, Jacek | Minister of Finance |
| USA | Rubin, Robert E. | Co-Chair, Council on Foreign Relations; Former Secretary of the Treasury |
| NLD | Rutte, Mark | Prime Minister |
| ESP | Sáenz de Santamaría Antón, Soraya | Vice President and Minister for the Presidency |
| NLD | Scheffer, Paul | Professor of European Studies, Tilburg University |
| USA | Schmidt, Eric E. | Executive Chairman, Google Inc. |
| AUT | Scholten, Rudolf | Member of the Board of Executive Directors, Oesterreichische Kontrollbank AG |
| FRA | Senard, Jean-Dominique | CEO, Michelin Group |
| USA | Shambaugh, David | Director, China Policy Program, George Washington University |
| INT | Sheeran, Josette | Vice Chairman, World Economic Forum |
| FIN | Siilasmaa, Risto | Chairman of the Board of Directors, Nokia Corporation |
| USA | Speyer, Jerry I. | Chairman and Co-CEO, Tishman Speyer |
| CHE | Supino, Pietro | Chairman and Publisher, Tamedia AG |
| IRL | Sutherland, Peter D. | Chairman, Goldman Sachs International |
| USA | Thiel, Peter A. | President, Clarium Capital / Thiel Capital |
| TUR | Timuray, Serpil | CEO, Vodafone Turkey |
| DEU | Trittin, Jürgen | Parliamentary Leader, Alliance 90/The Greens |
| GRC | Tsoukalis, Loukas | President, Hellenic Foundation for European and Foreign Policy |
| FIN | Urpilainen, Jutta | Minister of Finance |
| CHE | Vasella, Daniel L. | Chairman, Novartis AG |
| INT | Vimont, Pierre | Executive Secretary General, European External Action Service |
| GBR | Voser, Peter | CEO, Royal Dutch Shell plc |
| SWE | Wallenberg, Jacob | Chairman, Investor AB |
| USA | Warsh, Kevin | Distinguished Visiting Fellow, The Hoover Institution, Stanford University |
| GBR | Wolf, Martin H. | Chief Economics Commentator, The Financial Times |
| USA | Wolfensohn, James D. | Chairman and CEO, Wolfensohn and Company |
| CAN | Wright, Nigel S. | Chief of Staff, Office of the Prime Minister |
| USA | Yergin, Daniel | Chairman, IHS Cambridge Energy Research Associates |
| INT | Zoellick, Robert B. | President, The World Bank Group |
| Rapporteurs | ||
| GBR | Bredow, Vendeline von | Business Correspondent, The Economist |
| GBR | Wooldridge, Adrian D. | Foreign Correspondent, The Economist |
Press Release
Bilderberg Meetings
The 60th Bilderberg Meeting will be held in Chantilly, Virginia, USA from 31 May – 3 June 2012. The Conference will deal mainly with political, economic and societal issues like Transatlantic Relations, Evolution of the Political Landscape in Europe and the US, Austerity and Growth in Developed Economies, Cyber Security, Energy Challenges, the Future of Democracy, Russia, China and the Middle East.
Approximately 145 participants will attend of whom about two-thirds come from Europe and the balance from North America and other countries. About one-third is from government and politics, and two-thirds are from finance, industry, labor, education, and communications. The meeting is private in order to encourage frank and open discussion.
Bilderberg takes its name from the hotel in Holland, where the first meeting took place in May 1954. That pioneering meeting grew out of the concern expressed by leading citizens on both sides of the Atlantic that Western Europe and North America were not working together as closely as they should on common problems of critical importance. It was felt that regular, off-the-record discussions would help create a better understanding of the complex forces and major trends affecting Western nations in the difficult post-war period.
The Cold War has now ended. But in practically all respects there are more, not fewer, common problems – from trade to jobs, from monetary policy to investment, from ecological challenges to the task of promoting international security. It is hard to think of any major issue in either Europe or North America whose unilateral solution would not have repercussions for the other.
Thus the concept of a European-American forum has not been overtaken by time. The dialogue between these two regions is still – even increasingly – critical.
What is unique about Bilderberg as a forum is the broad cross-section of leading citizens that are assembled for nearly three days of informal and off-the-record discussion about topics of current concern especially in the fields of foreign affairs and the international economy; the strong feeling among participants that in view of the differing attitudes and experiences of the Western nations, there remains a clear need to further develop an understanding in which these concerns can be accommodated; the privacy of the meetings, which has no purpose other than to allow participants to speak their minds openly and freely.
In short, Bilderberg is a small, flexible, informal and off-the-record international forum in which different viewpoints can be expressed and mutual understanding enhanced.
Bilderberg’s only activity is its annual Conference. At the meetings, no resolutions are proposed, no votes taken, and no policy statements issued. Since 1954, fifty-nine conferences have been held. The names of the participants are made available to the press. Participants are chosen for their experience, their knowledge, and their standing; all participants attend Bilderberg in a private and not an official capacity.
For further inf
TOP-SECRET – U.S. Army Afghanistan Human Terrain Teams Map April 2012
The following map depicts the approximate locations, members and national affiliations of every human terrain team operating in Afghanistan as part of the U.S. Army’s Human Terrain System. The information is accurate as of April 3, 2012.
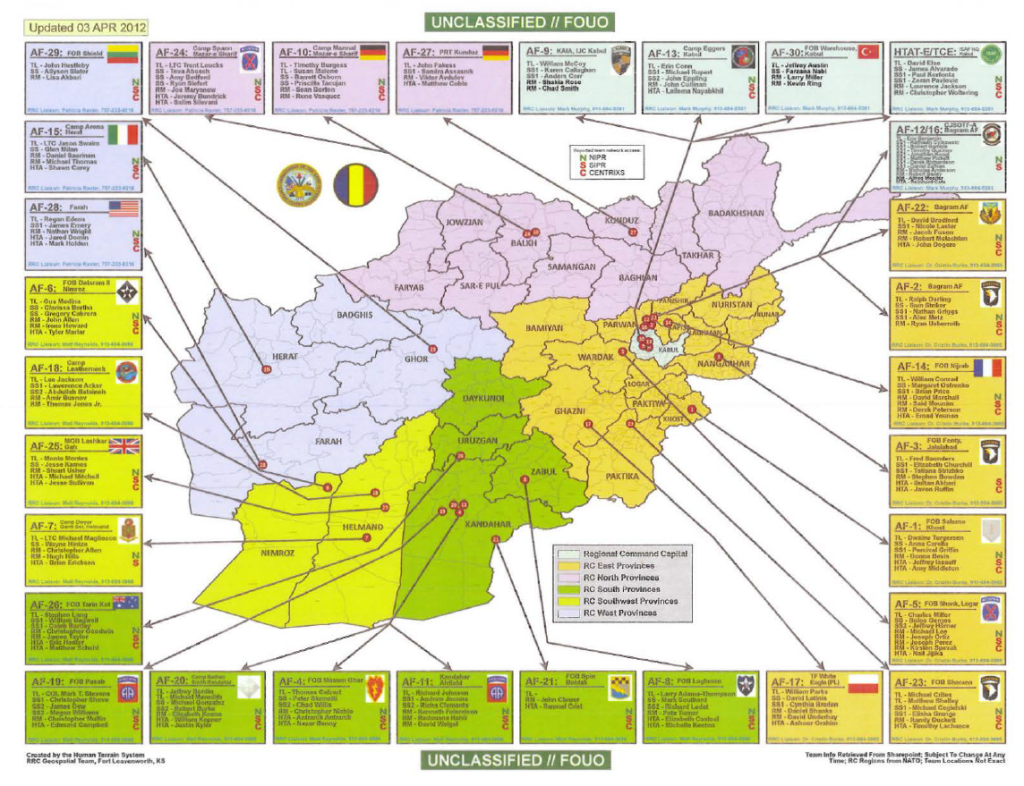
TOP-SECRET from the FBI – Founders of S3 Partners Charged in $21 Million Real Estate Investment Fraud Scheme
SAN JOSE, CA—The three founders of S3 Partners who allegedly defrauded numerous individual investors and banks out of more than $21 million in connection with a real estate investment fraud scheme were arrested and arraigned on 33 counts of conspiracy, wire, mail, bank and securities fraud, United States Attorney Melinda Haag announced.
According to the indictment, which was filed in San Jose federal district court on May 23 and unsealed on May 24, from 2006 to 2009, Melvin Russell “Rusty” Shields, 42, of Granite Falls, North Carolina.; Michael Sims, 58, of Gilroy, California; and Sam Stafford, 56, of Campbell, California, defrauded individual investors and banks in the Northern District of California and elsewhere in connection with various real estate development projects. The three defendants conducted their business as “S3 Partners” out of a variety of locations including San Jose, Campbell, and Palo Alto, California; and Hickory, North Carolina. Shields, Sims, and Stafford allegedly engaged in securities fraud targeting elderly investors by encouraging those elderly investors to cash out their individual retirement accounts (IRAs) and wire the proceeds to the S3 Partners for the purchase of shares in an S3 Partners-controlled LLC. The three defendants falsely represented to investors that they would receive predictable high rates of return, that there was minimal to no risk of investing, and that profits from S3 Partners business projects would benefit various charitable and religious organizations. Shields, Sims, and Stafford obtained more than $21 million from investors and banks and converted more than half of those funds for their personal benefit, their personal business ventures, and other unauthorized purposes. Their conduct resulted in a near-total loss to investors.
On May 24, the Federal Bureau of Investigation arrested Sims and Stafford in Northern California and Shields in North Carolina pursuant to a sealed arrest warrant. That same day, Sims and Stafford made their initial appearances in San Jose before United States Magistrate Judge Paul Grewal where, subject to the posting of a $100,000 secured bond and being placed on home electronic monitoring, they were ordered released pending a detention hearing. Sims and Stafford are scheduled to appear at a detention hearing in San Jose tomorrow at 9:30 a.m, at which hearing Magistrate Judge Grewal will consider additional conditions governing their pretrial release. Shields made an initial appearance May 24 in Charlotte, North Carolina. After a detention hearing this morning before U.S. Magistrate Judge David C. Keesler, Shields was ordered released subject to a $100,000 unsecured bond and placed on home electronic monitoring.
The maximum statutory penalty for each count of conspiracy to commit wire, mail and bank fraud, wire fraud, and mail fraud in violation of Title 18, United States Code, Sections 1349, 1343 and 1341 is 20 years in prison and a fine of $250,000, plus restitution. The maximum statutory penalty for each count of bank fraud in violation of Title 18, United States Code, Section 1344 is 30 years prison and a fine of $1 million, plus restitution. The maximum statutory penalty for each count of Title 15, United States Code, Sections 78j(b) and 78ff; and 17 C.F.R. Section 240.10b-5-securities fraud is 20 years in prison and a fine of $5 million, plus restitution. Any sentence following conviction would, however, be determined by the court after considering the Federal Sentencing Guidelines, which take into account a number of factors and would be imposed in the discretion of the court.
Assistant United States Attorney Joseph Fazioli is prosecuting the case with the assistance of Legal Assistant Kamille Singh. The prosecution is the result of a multi-year investigation by the Federal Bureau of Investigation.
Please note, an indictment contains only allegations against an individual and, as with all defendants, Shields, Sims, and Stafford must be presumed innocent unless and until proven guilty.
This prosecution is part of efforts underway by President Barack Obama’s Financial Fraud Enforcement Task Force. President Obama established the interagency Financial Fraud Enforcement Task Force to wage an aggressive, coordinated, and proactive effort to investigate and prosecute financial crimes. The task force includes representatives from a broad range of federal agencies, regulatory authorities, inspectors general, and state and local law enforcement who, working together, bring to bear a powerful array of criminal and civil enforcement resources. The task force is working to improve efforts across the federal executive branch and, with state and local partners, to investigate and prosecute significant financial crimes, ensure just and effective punishment for those who perpetrate financial crimes, combat discrimination in the lending and financial markets, and recover proceeds for victims of financial crimes. For more information about the task force visit http://www.stopfraud.gov.
TOP-SECRET – Assange Extradition Appeal Judgement
TOP-SECRET – NSA Crypto Shaping of Computer Industry
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – NSA Crypto Shaping of Data Encryption Standard
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – CIA: US Psychological Warfare Doctrinal Program
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – Fukushima Daiichi Nuclear Power Station 12-0526
28 May 2012
TEPCO video of the 26 May 2012 tour shown below:http://photo.tepco.co.jp/en/date/2012/201205-e/120526-01e.html
TEPCO high-resolution photos of the tour:
http://photo.tepco.co.jp/en/date/2012/201205-e/120528_01e.html
http://photo.tepco.co.jp/en/date/2012/201205-e/120528-02e.html
27 May 2012
Fukushima Daiichi Nuclear Power Station 26 May 2012
These photos are reduced to half-size of the originals. The 16 full-size originals:
http://cryptome.org/2012-info/daiichi-12-0526/daiichi-12-0526.zip (18.4MB)
TEPCO report on structural stability of Unit 4, 25 May 2012:
http://www.tepco.co.jp/en/nu/fukushima-np/images/handouts_120525_05-e.pdf
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict19.jpg)
Cryptome Nuclear Power Plant and WMD series: http://cryptome.org/nppw-series.htm
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict3.jpg) Media persons and Tokyo Electric Power Co. employees look at the company’s tsunami-crippled Fukushima Dai-Ichi nuclear power plant during a press tour in Okuma town, Fukushima prefecture, Japan, Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) Media persons and Tokyo Electric Power Co. employees look at the company’s tsunami-crippled Fukushima Dai-Ichi nuclear power plant during a press tour in Okuma town, Fukushima prefecture, Japan, Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict15.jpg) Reactor buildings from left to right, the No. 1, the No. 2, the No. 3 and the No. 4, are seen during a press tour at Tokyo Electric Power Co.’s (TEPCO) Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) Reactor buildings from left to right, the No. 1, the No. 2, the No. 3 and the No. 4, are seen during a press tour at Tokyo Electric Power Co.’s (TEPCO) Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict0.jpg) Members of the media and Tokyo Electric Power Co. employees walk in front of the No. 4 reactor building, rear, crippled by the March 11 earthquake and tsunami, at the utility company’s Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) Members of the media and Tokyo Electric Power Co. employees walk in front of the No. 4 reactor building, rear, crippled by the March 11 earthquake and tsunami, at the utility company’s Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict12.jpg) The damaged No. 4 reactor building stands at Tokyo Electric Power Co.’s Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. Japanese Environment and Nuclear Minister Goshi Hosono, accompanied by the media, has visited the crippled Fukushima Dai-ichi nuclear power plant to inspect a reactor building and its spent fuel pool at the center of safety concerns. (Tomohiro Ohsumi, Pool) The damaged No. 4 reactor building stands at Tokyo Electric Power Co.’s Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. Japanese Environment and Nuclear Minister Goshi Hosono, accompanied by the media, has visited the crippled Fukushima Dai-ichi nuclear power plant to inspect a reactor building and its spent fuel pool at the center of safety concerns. (Tomohiro Ohsumi, Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict11.jpg) Goshi Hosono, Japan’s environment and nuclear minister, third from left, wearing a red helmet, along with members of the media, walks on the No. 4 reactor building at Tokyo Electric Power Co.’s (TEPCO) Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. Japan’s environment and nuclear minister Hosono visited the tsunami-crippled nuclear power plant Saturday to inspect a spent fuel pool at the center of safety concerns. (Tomohiro Ohsumi, Pool) Goshi Hosono, Japan’s environment and nuclear minister, third from left, wearing a red helmet, along with members of the media, walks on the No. 4 reactor building at Tokyo Electric Power Co.’s (TEPCO) Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. Japan’s environment and nuclear minister Hosono visited the tsunami-crippled nuclear power plant Saturday to inspect a spent fuel pool at the center of safety concerns. (Tomohiro Ohsumi, Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict16.jpg) Goshi Hosono, Japan’s environment and nuclear minister, inspects the No. 4 reactor building at Tokyo Electric Power Co.’s Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima Prefecture, Japan, Saturday, May 26, 2012. The visit by Hosono, apparently aimed at demonstrating the safety of the facility, came amid renewed concerns about conditions at the plant’s No. 4 reactor after its operator reported a bulging of the building’s wall. (Toshiaki Shimizu, Japan Pool) [Yellow reactor containment dome at center background.] Goshi Hosono, Japan’s environment and nuclear minister, inspects the No. 4 reactor building at Tokyo Electric Power Co.’s Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima Prefecture, Japan, Saturday, May 26, 2012. The visit by Hosono, apparently aimed at demonstrating the safety of the facility, came amid renewed concerns about conditions at the plant’s No. 4 reactor after its operator reported a bulging of the building’s wall. (Toshiaki Shimizu, Japan Pool) [Yellow reactor containment dome at center background.] |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict2.jpg) Workers walk in front of the No. 4 reactor building at Tokyo Electric Power Co.’s tsunami-crippled Fukushima Dai-Ichi nuclear power plant in Okuma town, Fukushima prefecture, Japan, Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) Workers walk in front of the No. 4 reactor building at Tokyo Electric Power Co.’s tsunami-crippled Fukushima Dai-Ichi nuclear power plant in Okuma town, Fukushima prefecture, Japan, Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict7.jpg) An inside view of the damaged No. 4 reactor building is seen at Tokyo Electric Power Co.’s tsunami-crippled Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. (Toshiaki Shimizu, Japan Pool) An inside view of the damaged No. 4 reactor building is seen at Tokyo Electric Power Co.’s tsunami-crippled Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. (Toshiaki Shimizu, Japan Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict8.jpg) The inside of the tsunami-crippled No. 4 reactor building is seen during a press tour at Tokyo Electric Power Co.’s (TEPCO) Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima Prefecture, Japan, Saturday, May 26, 2012.(Toshiaki Shimizu, Japan Pool) The inside of the tsunami-crippled No. 4 reactor building is seen during a press tour at Tokyo Electric Power Co.’s (TEPCO) Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima Prefecture, Japan, Saturday, May 26, 2012.(Toshiaki Shimizu, Japan Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict5.jpg) Japan’s Environment and Nuclear Minister Goshi Hosono, second from left, inspects a pool containing spent fuel rods inside the No. 4 reactor building at Tokyo Electric Power Co. ‘s tsunami-crippled Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima Prefecture, Japan, Saturday, May 26, 2012. The pool, located at the top of the building above the reactor, remains one of the plant’s biggest risks due to its vulnerability to earthquakes. (Toshiaki Shimizu, Japan Pool) Japan’s Environment and Nuclear Minister Goshi Hosono, second from left, inspects a pool containing spent fuel rods inside the No. 4 reactor building at Tokyo Electric Power Co. ‘s tsunami-crippled Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima Prefecture, Japan, Saturday, May 26, 2012. The pool, located at the top of the building above the reactor, remains one of the plant’s biggest risks due to its vulnerability to earthquakes. (Toshiaki Shimizu, Japan Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict6.jpg) A pool for spent fuel rods is seen inside the No. 4 reactor building of Tokyo Electric Power Co.’s tsunami-crippled Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. The pool, located at the top of the building above the reactor, remains one of the plant’s biggest risks due to its vulnerability to earthquakes. (Toshiaki Shimizu, Japan Pool) A pool for spent fuel rods is seen inside the No. 4 reactor building of Tokyo Electric Power Co.’s tsunami-crippled Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. The pool, located at the top of the building above the reactor, remains one of the plant’s biggest risks due to its vulnerability to earthquakes. (Toshiaki Shimizu, Japan Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict10.jpg) The No. 3 reactor building is seen at Tokyo Electric Power Co.’s (TEPCO) Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. Japan’s environment and nuclear minister, accompanied by the media, visited the tsunami-crippled nuclear power plant Saturday to inspect a spent fuel pool at the center of safety concerns. (Tomohiro Ohsumi, Pool) The No. 3 reactor building is seen at Tokyo Electric Power Co.’s (TEPCO) Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. Japan’s environment and nuclear minister, accompanied by the media, visited the tsunami-crippled nuclear power plant Saturday to inspect a spent fuel pool at the center of safety concerns. (Tomohiro Ohsumi, Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict4.jpg) The No. 1, left, and the No. 2, reactor buildings are seen during a press tour at the tsunami-crippled Fukushima Dai-ichi nuclear power plant of Tokyo Electric Power Co. (TEPCO) in Okuma, Fukushima Prefecture, Japan, Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) The No. 1, left, and the No. 2, reactor buildings are seen during a press tour at the tsunami-crippled Fukushima Dai-ichi nuclear power plant of Tokyo Electric Power Co. (TEPCO) in Okuma, Fukushima Prefecture, Japan, Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict13.jpg) Workers carry out radiation screening on a bus for a media tour at Tokyo Electric Power Co. (TEPCO) ‘s Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, on Saturday, May 26, 2012. Japan’s environment and nuclear minister, accompanied by the media, visited the tsunami-crippled nuclear power plant Saturday to inspect a spent fuel pool at the center of safety concerns. (Tomohiro Ohsumi, Pool) Workers carry out radiation screening on a bus for a media tour at Tokyo Electric Power Co. (TEPCO) ‘s Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, on Saturday, May 26, 2012. Japan’s environment and nuclear minister, accompanied by the media, visited the tsunami-crippled nuclear power plant Saturday to inspect a spent fuel pool at the center of safety concerns. (Tomohiro Ohsumi, Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict14.jpg) A worker carries out radiation screening on a bus for a media tour at Tokyo Electric Power Co. (TEPCO) ‘s Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, on Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) A worker carries out radiation screening on a bus for a media tour at Tokyo Electric Power Co. (TEPCO) ‘s Fukushima Dai-ichi nuclear power plant in Okuma, Fukushima prefecture, Japan, on Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/daiichi-12-0526/pict9.jpg) A worker walks through the building used as crisis management headquarters at the tsunami-crippled Fukushima Dai-ichi nuclear power plant of Tokyo Electric Power Co.’s (TEPCO) in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) A worker walks through the building used as crisis management headquarters at the tsunami-crippled Fukushima Dai-ichi nuclear power plant of Tokyo Electric Power Co.’s (TEPCO) in Okuma, Fukushima prefecture, Japan, Saturday, May 26, 2012. (Tomohiro Ohsumi, Pool) |
TOP-SECRET – We Are Anonymous Index of Informants
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – Criminals and Hacktivists May Use 2012 Summer Olympics as Platform for Cyberattacks
Executive Overview
(U) Major social events such as the World Cup, Super Bowl, and Olympics have typically drawn the interest of cyber criminals and hacktivists. Open source reporting indicated that China was subjected to approximately 12 million online attacks per day during the 2008 Summer Olympics in Beijing. Two months after the closing ceremony for the 2008 Games, cyber criminals began launching campaigns using 2012 London Summer Olympic themes. Reporting last year indicates some groups are also preparing attacks linked to the 2014 Winter Games in Sochi, Russia.
(U) Scams, malware campaigns and attacks will continue to grow in scale and complexity as the 27 July opening ceremony in London draws near. Event organizers, sponsors and British authorities continue to increase their physical and cybersecurity awareness as the event approaches. Information systems supporting the Games, transport infrastructure, law enforcement communications, financial operations and similar will become prime targets for criminals. A collective of approximately eighty-seven UK banks exercised their ability to withstand cyber attacks last November. Olympic organizers anticipated cyber threats and began testing their cybersecurity posture during ‘technical rehearsals’ by running scenarios from their Technology Operations Center (TOC) situated on Canary Wharf. The TOC will be manned with over one hundred personnel continuously monitoring critical applications, such as the Commentator Information System, organizers’ intranet, and a telecom infrastructure encompassing 900 servers, 1,000 network and security devices, and 9,500 computers. In addition, British law enforcement organizations have been collaborating with the U.S. Secret Service and other industry experts to understand attack vectors, detection methods and mitigation strategies to combat the threat. However, the cyber implications are more expansive than localized attacks against systems and encompass globally distributed Olympic-themed malware, spam campaigns and scams.
(U) There are eleven global sponsors of the 2012 Olympic Games: Coca-Cola, Acer, Atos, Dow, General Electric, McDonalds, Omega, Panasonic, Proctor & Gamble, Samsung, and VISA. These sponsors include a variety of companies, some of which are Critical Infrastructure Key Resources (CIKR) or Information Sharing Analysis Center (ISAC) members. The actions or creditability of the sponsors may become targets for cyber criminals or hacktivists. The purpose of this bulletin is to provide a strategic outlook for the 2012 Summer Olympic Games and similar events to assist partners in detecting and mitigating related attacks.
…
Technical Details
(U) Disruption of Operations: Protestors could choose to disrupt the Games using cyber or physical means. Typical methods of cyber disruption include a denial of service (DOS) or distributed denial of service (DDOS) attack, which may be the result of a physical or cyber action, and causes an interruption of business operations against a network, website or other resources. With an IT staff of over five thousand (approximately half are volunteers), there is potential for insider attacks during the Olympics which could cause a DOS, this bulletin will focus on a DOS or DDOS achievable through technological means only. DDOS attacks are typically launched using a botnet and the ability to bring down a target depends on three variables:
- Type of DDOS: Certain styles of DDOS attacks are more effective than others, depending on the type of DDOS attacks. DDOS attacks typically manipulate the way systems communicate.
- Size of the botnet: A large botnet spanning multiple network blocks and geographic locations is more difficult to mitigate than a small, group of attackers concentrating on a single target.
- Resiliency of the target infrastructure: The ability of an organization to withstand a robust DDOS attack depends on the infrastructure and technology solutions in place (routers, firewalls, ISPs, etc).
(U) Attackers motivated by ideals are considered hacktivist and a wide spectrum of events may at as a flashpoint for their attacks. Criminals or hacktivists utilizing DDOS attacks or web defacements may be motivated by ideological or financial objectives. For example, in February, a group of Iranian hackers dubbed the “Cocain (sic) Warriors” took credit for defacing the official website of the National Olympic Committee of Azerbaijan and the website of Azerbaijan Airlines. The actors left an anti-Israeli political message about Azerbaijan and Israel’s recent increased cooperation and arms deal. Israel recently announced that it was selling $1.6 billion in arms to Azerbaijan, a move that upset both Armenia and Iran. The text of the defacement was political, with likely intentions to reach as broad an audience as possible and amplify the message by targeting an Olympics-related national-level website. The following are examples of things which may incite hacktivists to launch attacks during the Olympics:
- Olympic organizer issued warnings about stringent enforcement of limiting photography, digital recordings and general publishing of Olympic activities. This warning included prohibition of content being posted to social media sites. It is possible that tight enforcement of copyright infringement laws during the games may also prompt cyber reactions.
- The recent controversy over stadium panels provided by Dow. Critics have tried to block the installation of the panels because of the Dow links to Union Carbide, which was accused of the 1984 gas leak in Bhopal, India. These pre-game criticisms by activists may translate to physical protests or cyber actions.
- Hacktivists have consistently attacked websites and networks of countries ‘perceived’ as violating human rights, especially countries that endorse policies that limit access to digital content. As a result, countries banning or controlling Internet access to Olympic Games will also likely draw the attention of global hacktivists.
- Hacktivists may rally around an unforeseen cause, such as the emergence of a news story surrounding the Olympics or Olympics sponsors that hacktivists find offensive or that conforms to their ideological platform (e.g. allegations of corporate malfeasance, environmental damage, corruption, etc.).
(U) Information Theft: The second type of attack would have a goal of information theft. This information could be used to grant a competitive edge to a company, individual or other entity. This type of attack may be facilitated by an insider or a remote attacker exfiltrating data through a system compromise. Criminals seeking competitive advantage often use spearphishing to penetrate a network. Spearphishing is an email-based attack where tailored emails containing malicious attachments or links are sent to key personnel identified during reconnaissance operations. These emails are especially convincing because they appear to be sent from a legitimate source. The highly customized nature of spearphishing emails and employment of spoofed email addresses make it extremely difficult to mitigate at the email gateway. In addition, advanced attackers understand how to bypass email filters and antivirus software so that the payload can be delivered successfully. Adversaries may target Olympic personnel to gain access to engineering schematics, scoring technologies, competitor information, ticketing systems, or similar targets.
…
Future Outlook
(U) The 2014 Winter Olympics to be held in Sochi, Russia, have prompted (and will likely prompt more) attention to controversial issues and Russia’s role in the region. Sochi is located on the Black Sea and borders the North Caucasus region. The North Caucasus is part of the Russian Federation and is comprised of several smaller republics, many ethnic groups and a rich cultural legacy wracked by war, intermittent violence and competing claims to power. Legacies surrounding land claims and ethnic sovereignty issues in the Caucasus have been ongoing for centuries, and they continue to the current day with wars having occurred in the last few decades, particularly in the early 1990s in Chechnya and between Georgia and South Ossetia as recently as 2008. This demonstrates that political beliefs (or reactions to such speech) are often expressed via cyber means in the region.
(U) Pro-Olympic Cyber Attacks: The construction of the 2014 Olympics facilities near the UNESCO protected Caucasus Biosphere Reserve and Sochi National Park has drawn criticisms from global environmental groups, as well as local Sochi news organizations. These Sochi news portals came under attack in late 2010 because of their vocal opposition to the Olympic construction. It is unknown who perpetrated this series of attacks, but their choice of targets indicates the attacker was possibly attempting to subdue opposition.
(U) Hacktivism: Hacktivists (Anonymous Kavkaz) purporting to be part of the larger Anonymous collective vowed to attack MegaFon on May 21, 2012 as part of ‘Operation BlackHole’. MegaFon is Russia’s second largest mobile phone operator in Russia and one of the national sponsors for the 2014 Winter Olympics, to be held in Sochi, Russia. The Adiga actors expressed outrage about the location of the Olympics in Sochi, Russia, as they believe that the Olympic complex is being built upon mass graves from the Circassian genocide. The attack date is significant, as Circassians commemorate the Circassian-Russian War every year on May 21, the day that Circassia was annexed by the Russians and as a remembrance of the genocide that the Circassians believed occurred at the hands of the Russians.
(U) Anonymous Kavkaz (aka Adiga Hackers) started a Twitter feed on Feb. 25 and have only updated it twice, with just a handful of followers as of this writing. The true affiliation with the larger Anonymous group seems unlikely because:
- Anonymous Kavkaz does not appear to be active in the main communications channels, where they would be most likely to make connections with more capable actors.
- Anonymous Kavkaz’s Facebook presence is more geared toward ethnic, religious and political grievances in the Caucasus than with traditional Anonymous causes.
(U) The group purports to have attacked and disabled (exact means unknown) the server of the Russian Commercial Bank (a subsidiary of another Russian bank, the VTB Bank) on March 29, 2012. According to a website monitoring service, the bank’s website was having problems, but it is unclear what the issues were or if they were related to the alleged attack.
(U) Politically motivated actors from this region vary in ability, but the Russian e-crime underground offers advanced capabilities that could be sought out by North Caucasus hacktivists. Similarly, the Adiga hackers could seek more skilled Anonymous-associated actors for assistance, but thus far they have not been observed communicating in known Anonymous communications channels. This could be good indication that they are only peripheral, aspirational actors. It is possible the Adiga hackers only adopted the Anonymous moniker in an attempt to gain legitimacy and anchor their somewhat obscure cause in the framework of a larger movement to attract more followers or participants.
(U) This is the first time Russia has hosted the Olympics (the 1980 Olympic Games were held in the USSR) and officials are actively monitoring the region for any indication of unrest. Russia has recently deployed military forces to the North Caucasus as part of a broader effort to stabilize the region in the lead-up to the 2014 Olympics.
(U) Although each host country will face unique challenges, the majority of cyber threats will remain consistent as officials begin preparations for the 2016 (Rio de Janeiro, Brazil) and 2018 (Pyeongchang, South Korea) Olympic Games. DHS and partners should continue to coordinate with impacted CIKR partners while promoting awareness campaigns to minimize malware infections.
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET from the FBI – Jury Convicts Naser Jason Abdo on All Counts in Connection with Texas Bomb Plot
WACO, TX—A jury this afternoon in Waco convicted 22-year-old Naser Jason Abdo on federal charges in connection with a July 2011 bomb plot in Killeen, Texas. The conviction was announced by U.S. Attorney Robert Pitman and FBI Special Agent in Charge Armando Fernandez.
The jury convicted Abdo of one count of attempted use of a weapon of mass destruction; one count of attempted murder of officers or employees of the United States; two counts of possession of a firearm in furtherance of a federal crime of violence; and two counts of possession of a destructive device in furtherance of a federal crime of violence.
Testimony presented at trial revealed that on July 27, 2011, Abdo unlawfully attempted to create and detonate a bomb in an attempt to kill, with pre-meditation and malice aforethought, members of the uniformed services of the United States and to shoot survivors of said detonation with a firearm. Evidence further revealed that Abdo did knowingly possess a .40 caliber semiautomatic pistol while carrying out his plot.
“It’s important to note that this plot was interrupted and a potential tragedy prevented because an alert citizen notified law enforcement of suspicious activity, triggering prompt investigation and intervention. While we in law enforcement will be aggressive in investigating and prosecuting people like Mr. Abdo, we depend on the vigilance of the public in helping ensure the safety of the community,” said U.S. Attorney Robert Pitman.
Officers with the Killeen Police Department arrested Abdo on July 27, 2011. At the time of his arrest, the defendant, an absent without leave (AWOL) soldier from Fort Campbell, Kentucky, was in possession of the handgun, plus instructions on how to build a bomb as well as bomb making components. Testimony during the trial revealed that Abdo intended to detonate the destructive device inside an unspecified restaurant frequented by soldiers from Fort Hood.
“This verdict confirms the collective efforts by all of our partners on the FBI’s Joint Terrorism Task Force (JTTF) to address terrorism in any shape or form, whether it be by one or by many,” said FBI Special Agent in Charge Armando Fernandez.
Abdo remains in federal custody. He faces up to life in federal prison for the attempted use of a weapon of mass destruction charge; up to 20 years in federal prison for the attempted murder charge; a mandatory 30 years in prison for each possession of a destructive device in furtherance of a federal crime of violence charge; and a mandatory five years in federal prison for each possession of a firearm in furtherance of a federal crime of violence charge. Sentencing is scheduled for 9:00 a.m. on July 20, 2012 before U.S. District Judge Walter S. Smith.
This case is being investigated by agents with the FBI, together with U.S. Army Criminal Investigation Command; Bureau of Alcohol, Tobacco, Firearms, and Explosives; Killeen Police Department; and the Texas Department of Public Safety.
Assistant U.S. Attorneys Mark Frazier and Gregg Sofer of the Western District of Texas and Trial Attorney Larry Schneider of the Justice Department’s Counterterrorism Section are prosecuting this case on behalf of the government.
TOP-SECRET – FBI Inspire Magazine Encourages the Use of Wildfires in Jihad
(U//FOUO) The Denver Division of the FBI is releasing this report to raise the awareness of local and state law enforcement partners and public safety officials about the possible threat of wildfires.
(U//FOUO) Al-Qaida in the Arabian Peninsula (AQAP) has released issue 9 of its English-language “Inspire” Magazine. There is a portion of the magazine dedicated to attacking the United States by starting wildfires. The article instructs the audience to look for two necessary factors for a successful wildfire, which are dryness and high winds to help spread the fire. Specific fire conditions that are likely to spread fire quickly are Pinewood, crownfires (where the trees and branches are close together), and steep slope fires (fire spreads faster going up a slope).
(U//FOUO) Inspire magazine lists instructions for igniting a forest fire. The list of required materials include quick inflammable material (1/3 of a liter of gasoline), and a material with slow and long lasting inflammation (foam). The article continues to instruct the reader about how to prepare an ember bomb, which consists of gasoline soaked foam that is ignited by a timer. The article advises the reader to use thirty ember bombs, placed in the tops of trees about a third into the forest, opposite the wind.
(U//FOUO) Throughout Colorado, conditions are favorable for wildfires. Colorado’s forests have been impacted by the mountain pine beetle, and the plains regions are extremely dry. Continuous stands of dead lodgepole pine with dead needles in the crowns (typically lasting 2 to 3 years after a successful fire) will support running crown fires under the right weather conditions.
TOP-SECRET from the FBI – Texas Man Sentenced to Prison for Support to al Qaeda
HOUSTON—Barry Walter Bujol, Jr., a 30-year-old Hempstead, Texas resident and former student at Prairie View A&M University, has been sentenced to serve 20 years in federal prison, U.S. Attorney for the Southern District of Texas Kenneth Magidson announced today, along with Lisa Monaco, Assistant Attorney General for National Security. Bujol was convicted November 14, 2011 of attempting to provide material support to al Qaeda in the Arabian Peninsula (AQAP), a designated foreign terrorist organization.
Just moments ago, U.S. District Judge David Hittner handed Bujol the statutory maximum sentence, ordering him to serve 180 months in prison for attempting to provide material support to AQAP and 60 months in prison for aggravated identity theft, which will be served consecutively, for a total sentence of 240 months in prison.
“We do not take matters of potential national security lightly,” said U.S. Attorney Magidson. “This case and its successful resolution represents our commitment to making our communities a safer place to live.”
Bujol requested a bench trial before Judge Hittner, which lasted nearly four days, during which he acted as his own attorney. The United States presented a total of 325 trial exhibits and 12 witnesses, which resulted in Bujol’s convictions for both attempt to provide material support or resources to a designated foreign terrorist organization as well as aggravated identity theft.
Evidence revealed Bujol had asked Anwar Al-Aulaqi, a now-deceased Yemeni-American AQAP associate, for advice on raising money for the “mujahideen” without attracting police attention and on his duty as a Muslim to make “violent jihad.” Al-Aulaqi replied by sending Bujol a document entitled “42 Ways of Supporting Jihad,” which asserted that “‘jihad’ is the greatest deed in Islam…[and] obligatory on every Muslim.” Court records indicated the “jihad” Al-Aulaqi advocated involved violence and killing.
In 2009, Bujol made three attempts to depart the United States for the Middle East, but law enforcement, believing these were Bujol’s efforts to make “violent jihad,” thwarted him each time he tried to leave. Bujol eventually told a confidential source he desired to fight with the “mujahideen.” The source testified at trial, explaining that each time he told Bujol he would be joining AQAP, Bujol replied by saying, “God willing” in Arabic.
To prove his worth to the source and AQAP, Bujol performed numerous purported “training exercises,” often involving surveillance detection and covert means of communication. Moreover, Bujol repeatedly told the source that AQAP should attack the human beings essential to operate military unmanned aerial vehicles (UAVs) instead of attacking the UAVs themselves. Bujol suggested multiple targets, including one in the Southern District of Texas.
Bujol was arrested on May 30, 2010 after boarding a ship docked at the Port of Houston. He believed the ship was bound for Algeria, where he would stay at an al Qaeda safe house before continuing on to Yemen. Bujol intended to stow away to join AQAP and to deliver items to AQAP that a confidential source had given him. The items included two public access restricted military manuals, global position system receivers, pre-paid international calling cards, SIM cards, and approximately 2,000 in Euros, among other items. Bujol secured these items in his baggage and quickly boarded the ship. Minutes after stowing away in a room on board the ship, agents took him into custody without incident.
Simultaneously, agents executed a search warrant on his apartment and his laptop computer. On the computer, agents found a home-made video montage of still photographs, including images of Osama bin Laden, Najibullah Zazi, and multiple armed “mujahideen” fighters, which Bujol narrated. On the video, which was offered into evidence at trial, he addressed his words to his wife, explaining that he had left her suddenly and without forewarning to pursue “jihad.” Bujol told her he would likely not see her until the afterlife.
The aggravated identity theft charge, of which he was also convicted, stemmed from a false transportation worker identity card (purporting to be a card issued by the Transportation Security Administration) that Bujol possessed to access the Port of Houston. Bujol supplied the confidential source with a passport photo and a false name and the source used these materials to acquire the false card for use in the sting operation. On the night of the operation, Bujol used the false card to gain access to the port.
Bujol has been in federal custody since his May 30, 2010, where he will remain pending transfer to a U.S. Bureau of Prisons facility to be determined in the near future.
This multi-agency investigation was conducted by the U.S. Attorney’s Office for the Southern District of Texas, the Department of Justice’s Counterterrorism Section, the FBI’s Joint Terrorism Task Force in Bryan, Texas—comprised of the Brazos County, Texas Sheriff’s Office; the Texas A&M University Police Department; the Bryan Police Department; the U.S. Secret Service;, the Waller County, Texas Sheriff’s Office; and the College, Texas Station Police Department. Other investigating agencies were the Houston FBI Joint Terrorism Task Force, the Prairie View A&M University Department of Public Safety, the New Jersey State Police, the Coast Guard Investigative Service, Homeland Security Investigations, Houston Police Department, and the Canada Border Services Agency.
The case was prosecuted by Assistant U.S. Attorneys Mark McIntyre and Craig Feazel, as well as Garrett Heenan, Trial Attorney from the Counterterrorism Section of the Justice Department’s National Security Division, and former Assistant U.S. Attorney Mark W. White, III.
TOP-SECRET – Chicago Police NATO Summit Media and Reporter’s Guidelines
The following “media guidance” paper from the Chicago Police Department was obtained and published by the Illinois News Broadcasters Association. The paper states that a number of routine activities for credentialed journalists, such as passing behind police lines, will not be allowed. The paper also includes a number of ominous warnings about not getting arrested and how no special rights will be afforded journalists if they are arrested.
NOT INTENDED FOR GENERAL DISTRIBUTION.
FOR MEDIA GUIDANCE ONLY.
Debra Kirby, chief of the Chicago Police Department Office of International Relations, said it is not the intent of Chicago Police to limit or otherwise interfere with coverage of protests and other events related to the NATO summit. The department anticipates that members of the media will be accompanying protesters.
Kirby said the department is not endorsing a formal embedding policy (reporters/crews will not be assigned to tag along with specific police units).
The department is cognizant that not everyone covering the protests has a NATO or Chicago Police credential. Kirby said credentials from other jurisdictions will be honored, and she recommends that they be worn on a lanyard. At the same time, she is also aware that those who did so in New York encountered problems from protesters; doing so in such circumstances is a judgment call. If there is any question, reporters will be allowed to pull credentials from their pockets to show to police on the street. Information will be released through two joint incident command centers, effective Friday.
– U.S. Secret Service (Security-related information and arrest tallies): (312) 469-1440
– City/OEMC: (312) 746-9454
– Chicago Police News Affairs (generally for non-NATO-related information): (312) 745-6110
In addition, she said that Chicago Police lieutenants and captains “on the ground” will have access to most information. At minimum, OEMC will host one briefing a day on activities relating to the summit at OEMC headquarters, 1411 W. Madison St., probably in the evening. She said information will be relayed to news desks with sufficient time to set up. More will be scheduled if events warrant, but Kirby does not know that it would be the wisest use of a news organization’s staff to place someone at OEMC full-time. News Affairs Director Melissa Stratton is checking to see if the briefings can be webcast. She said that media access generally will be the same as public access. Credentials will, however, allow media personnel access to media-only areas. No “cutting” in and out of police lines will be permitted, or “going up against their backs.” Those who follow protesters onto private property to document their actions are also will be subject to arrest if laws are broken.
Any member of the media who is arrested will have to go through the same booking process as anyone else. Release of equipment depends on what part the equipment played in the events that led to the arrest.
There will not be any quick personal recognizance bond just for media members. Kirby said that the Chicago Police Department does not intend to “break ground” in terms of enforcing the Illinois eavesdropping law. In short, police will not interfere if we videotape or record audio of police activities, including arrests. Likewise, she says the department has no intention of “kettling” protesters as they did on Chicago Avenue during antiwar protests in 2003; there will be plenty of warning by loudspeaker to clear or avoid specific areas before arrests are undertaken; however, those reporters who choose to disregard such warnings are subject to arrest. To date, the department has seen no evidence that protesters are turning on media representatives as happened in New York. She urges media to keep safety in mind and to “not become the story.”
If there is a problem, Office of News Affairs Director Melissa Stratton can be reached through Chicago Police News Affairs.
Chicago Police command will be broken down by sector, and the department has made efforts to provide media parking for large planned events. These parking zones are effective from 8 p.m. Friday until 6 p.m. Monday. They include:
Petrillo/Grant Park/Art Institute events:
– Columbus Drive: Both curbs from Jackson to Monroe, but not blocking the entrance to the Art Institute.
South of Loop/River
– 9th Street: both curbs, Wabash to Michigan
– Upper Randolph: south curb, Columbus to Field Drive
Nurses Rally (only on Friday)
– Randolph, south curb, Clark to LaSalle
– Clark, east curb, Randolph to Lake
North of River
– East Lake Shore Dr.: north curb, mid-block to inner LSD
– Mies Van Der Rohe Ct.: west curb, Chicago to Pearson
– Upper Cityfront Plaza Dr.: west curb, North Water to Illinois (no satellite trucks)
McCormick Place/end of protest
– Cermak Road: south curb, State to Clark
– 24th Street, both curbs, State to Federal
The National Nurses’ Union has control of the parking area for the Friday rally and concert. On Sunday, the CANG8 protest group will set up the media bullpen. In addition, police say they will attempt to set up media parking and bullpen locations along march routes as they determine what is happening.
WHILE PARKING AREAS WILL HAVE POLICE AT THE PERMIETER, POLICE WILL NOT BE CHECKING TO ASSURE THAT CONTENTS ARE SECURE. MEDIA ORGANIZATIONS ARE RESPONSIBLE FOR MAKING CERTAIN THAT VEHICLES AND THEIR CONTENTS ARE SECURE.
The Sunday march steps off at 2 p.m. and is anticipated to take two hours and 15 minutes to cover the 2.64 miles. On Sunday, no risers will be provided at Cermak/Michigan in the bullpen area for the concluding ceremonies of the big march. Cameras will have to shoot over one another. Space is constrained at the end of the march for the general public. Parking Sunday will be at Cermak/State and dispersal of the crowd will be to the west. Kirby does NOT recommend that reporters who march along the parade route try to get into the media bullpen at the end of the march; she said it will be possible, but it will not be easy to do so.
If a suspicious package is found or an area is cordoned off because of a potential bomb, the area cleared will depend on the threat that is posed. Media will be allowed as close as possible, but that is an event-by-event call.
Reporters who carry backpacks should be prepared to show their content to police. You may be asked to fire up and demonstrate any equipment that does not look familiar to officers.
Those who have negotiated parking on private property should inform CPD News Affairs if they have not already done so. Police may check to make certain that vehicles are parked on private property with consent of the owner. Unmarked vehicles should have Chicago Police news media vehicle identification cards displayed at all times. It is the intent of Chicago Police to provide close access, with direct vision and contact with those entering and leaving events/marches/rallies. But police emphasized that those who choose to walk amid the protesters are “on your own.” The department cannot guarantee the safety of those who do so and cannot guaranteed that they can extract any reporter who ends up the target of protesters.
Repeatedly, the speakers stressed that the rights of the media are the same as those of the general public.
Police say if a street is “stripped” of parking, and no parking is allowed for the general public, outside of the aforementioned locations, it is done for a reason. KIRBY STRONGLY SUGGESTS THAT VANS AND CARS BE SENT WITH DRIVERS SO THAT IF WORKING PRESS MEMBERS MUST LEAVE THE VEHICLE, IT REMAINS ATTENDED. She said Chicago Police will not hesitate to tow city-owned vehicles if they are in “stripped” areas, so media representatives should expect to be cut no slack with live trucks or other vehicles that are parked where prohibited.
TOPSECRET from the FBI – West New York Mayor, Son Arrested for Hacking
NEWARK—The mayor of West New York, New Jersey and his son were arrested today for allegedly hacking into an e-mail account and website associated with a movement to recall the mayor, U.S. Attorney Paul J. Fishman announced.
Felix Roque, 55, of Hudson County, and Joseph Roque, 22, of Passaic County, are charged by complaint with gaining unauthorized access to computers in furtherance of causing damage to protected computers; causing damage to protected computers; and conspiracy to commit those crimes. Felix and Joseph Roque are scheduled to appear this afternoon before U.S. Magistrate Judge Mark S. Falk in Newark federal court.
“In this case, the elected leader of West New York and his son allegedly hacked into computers to intimidate constituents who were simply using the Internet to exercise their Constitutional rights to criticize the government,” U.S. Attorney Fishman said. “We will continue to investigate and prosecute those who illegally hack into computers and disable websites with the goal of suppressing the exercise of that right.”
“This case illustrates two primary concerns of law enforcement, the violation of public trust and cyber intrusion,” FBI Special Agent in Charge Michael B. Ward said. “In this instance, an elected official conspired to hack into a website and e-mail account. It’s incredibly disappointing that resources have to be diverted from protecting the U.S. against cyber intrusions targeting critical infrastructure, federally funded research, and military technology to address a public official intruding into computer systems to further a political agenda.”
According to the criminal complaint unsealed today:
In early February 2012, a Hudson County resident and public official anonymously established and moderated an Internet website, http://www.recallroque.com, to post commentary and criticism of Mayor Felix Roque and his administration. On February 6 2012, Mayor Roque and his son, Joseph Roque, schemed to hack into and take down the website and to identify, intimidate, and harass those who operated and were associated with the website.
By the late afternoon of February 8, 2012, Joseph Roque had successfully hacked into various online accounts used in connection with the recall website. Joseph Roque then used that access to disable the website. Mayor Roque harassed and attempted to intimidate several individuals whom he had learned were associated with the recall website.
The conspiracy charge and the charge of gaining unauthorized access to a computer in furtherance of causing damage to protected computers are each punishable by a maximum potential penalty of five years in prison and a fine of up to $250,000. The charge of causing damage to protected computers carries a maximum potential penalty of one year in prison and a fine of up to $250,000.
U.S. Attorney Fishman credited special agents of the FBI under the direction of Special Agent in Charge Michael B. Ward in Newark with the investigation leading to the arrests.
The government is represented by Assistant U.S. Attorneys Seth Kosto of the U.S. Attorney’s Office Computer Hacking and Intellectual Property Section of the Office’s Economic Crimes Unit and Barbara Llanes of the Special Prosecutions Division in Newark.
The charges and allegations contained in the complaint are merely accusations, and the defendants are considered innocent unless and until proven guilty.
TOP-SECRET – (U//LES) FBI Domestic Terrorism Operations Unit Introduction to Sovereign Citizens
Sovereign citizens believe the government is operating outside of its jurisdiction and generally do not recognize federal, state, or local laws, policies, or governmental regulations. They subscribe to a number of conspiracy theories, including a prevalent theory which states the United States Government (USG) became bankrupt and began using citizens as collateral in trade agreements with foreign governments. They believe secret bank accounts exist at the United States (US) Department of the Treasury. These accounts can be accessed using Internal Revenue Service (IRS), Universal Commercial Code (UCC), and fraudulent financial documents.
Sovereign citizens are known to travel the country conducting training seminars on debt elimination schemes. The seminars focus on obtaining funds from a secret “Strawman” account using legitimate IRS forms, UCC forms, and fraudulent financial documents. Sovereign citizens believe once the documentation is filed, they gain access to their “Strawman” account with the Treasury Department.
The purpose of this primer is to assist law enforcement in the identification of sovereign citizen extremist activity to prevent, detect, and/or deter acts associated with sovereign citizen criminal activity.
…
POSSIBLE INDICATORS OF SOVEREIGN CITIZEN ACTIVITY
Some or all of the following may provide an indication of sovereign activity. However it is important to note these activities may also be indicative of lawful, innocent conduct and in some instances may constitute the exercise of rights guaranteed by the United States Constitution. For these reasons, these indicators should be considered in the context of other suspicious behavior and the totality of the circumstances in which they are observed or reported.
- Documentation may be mailed and addressed to the Secretary of the Treasury Department or the Depository Trust Company
- Documentation includes an “Apostille Number”
- Documents contain the phrase “Accepted for Value”
- Documents are notarized, even if not required
- International postage rates is applied even for domestic mailings
- All paperwork will be mailed using registered mail
- Stamps will be affixed near the signature line or at the bottom corner of the page
- Name written in all capital letters
- Example: JOHN SMITH
- Name will be written last name : first name
- Example: Smith: John or Smith: Family of John
- Zip codes enclosed in brackets
- Example: [11233]
- Presence of thumbprints on documents,
- Typically in red or blue ink
- Typically on or near a signature or seal
- “SLS” may follow signature
- “SLS” stands for “Sovereign Living Soul”
…
Generally, sovereign citizens do not operate as a group or have an established leadership hierarchy. Rather, they act independently or in loosely affiliated groups which come together for training, to assist with paperwork, and to socialize based on sovereign ideology. Sovereign citizens often refer to themselves as “Freemen.” [Note: The use of the word “Freemen” does not inherently indicate a connection to any specific group, however, some use the term “Freemen” in their group name. Others may indicate they are a “free man,” meaning free from government control.]
Sovereign citizens believe the USG is illegitimate and has drifted away from the true intent of the Constitution. As a result, the USG is not perceived to be acting in the interest of the American people. These groups generally do not adhere to federal, state, or local laws. Some sovereign citizens believe federal and state officials have no real authority and will only recognize the local sheriff’s department as the only legitimate government official. Other law enforcement officials are viewed as being oppressive and illegitimate.
Individuals who adhere to this ideology believe their status as a sovereign citizen exempts them from US laws and the US tax system. They believe the US Federal Reverse System, the Treasury Department, and banking systems are illegitimate. Therefore, one of the perceived “benefits” of being a sovereign citizen is not paying federal or state taxes.
Sovereign citizens view the USG as bankrupt and without tangible assets; therefore, the USG is believed to use citizens to back US currency. Sovereign citizens believe the USG operates solely on a credit system using American citizens as collateral. Sovereign citizens exploit this belief by filing fraudulent financial documents charging their debt to the Treasury Department. In addition, they routinely engage in mortgage, credit card, tax, and loan fraud.
TOP-SECRET – UNODC Afghan Poppy Eradication Report May 2012
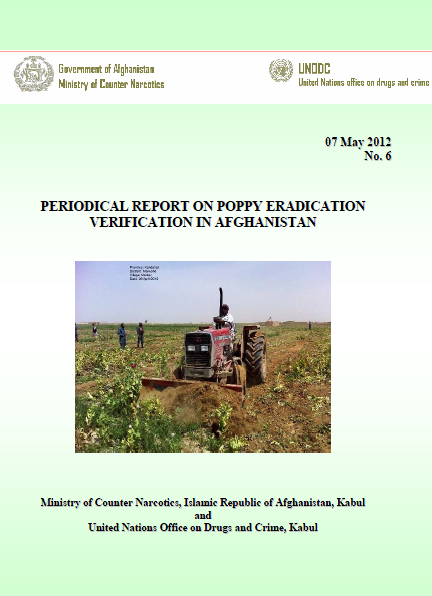
MCN/UNODC is responsible to verify Governor-led eradication.
Poppy is at stem-elongation stage in Kabul, Sari Pul and Balkh provinces. In Kapisa, Baghlan, Faryab and Badakhshan provinces, poppy is at cabbage and stem-elongation stages. Poppy is at flowering, capsule and lancing stages in Kunar, Laghman and Nangarhar provinces. In Day Kundi province poppy is at cabbage, stem-elongation and flowering stages. Poppy is at lancing stage in Hilmand, Farah and Nimroz provinces. In Kandahar and Hirat provinces, poppy is at capsule and lancing stages. Poppy is at flowering and capsule stages in Uruzgan province. Poppy is at flowering stage in Zabul province. In Ghor province, poppy is at cabbage stage.
Governor-led eradication activities are reported from Badghis, Farah, Hilmand, Hirat, Kandahar, Kabul, Kapisa, Kunar, Laghman, Nangarhar, Nimroz and Uruzgan provinces. A total of 53 hectares of poppy area has been eradicated in Badghis province, 500 hectares of poppy area has been eradicated in Farah province, 3,958 hectares of poppy area has been eradicated in Hilmand province, 604 hectares of poppy area has been eradicated in Hirat province, 2,384 hectares of poppy area has been eradicated in Kandahar province, 11 hectares of poppy area has been eradicated in Kapisa province, 57 hectares of poppy area has been eradicated in Kunar province, 152 hectares of poppy area has been eradicated in Laghman province, 1,122 hectares of poppy area has been eradicated in Nangarhar province, 148 hectares of poppy area has been eradicated in Nimroz province and 408 hectares of poppy area has been eradicated in Uruzgan province.
Total eradication carried out is 9,398 ha.
Last year at the same time, GLE had eradicated a total of 3,386 hectares of poppy in Badghis, Day Kundi, Farah, Hilmand, Hirat, Kabul, Kandahar, Kapisa, Kunar, Laghman, Nangarhar and Nimroz and Uruzgan provinces.
Measurements of eradicated fields reported by the surveyors will be checked by satellite images wherever satellite images are available. Therefore, figures in this report should be considered as provisional figures.
Farmers showed resistance against poppy eradication operations in different ways such as direct attack on eradication team, mine explosions, flooding poppy fields and demonstrations. Since the start of eradication operations, 99 lives were lost (28 police 11 National Army and 60 others) including 116 people were injured (81 police 7 National Army and 28 others). See Table 5, Table 6 and Annex 3 for details of farmers’ resistance.
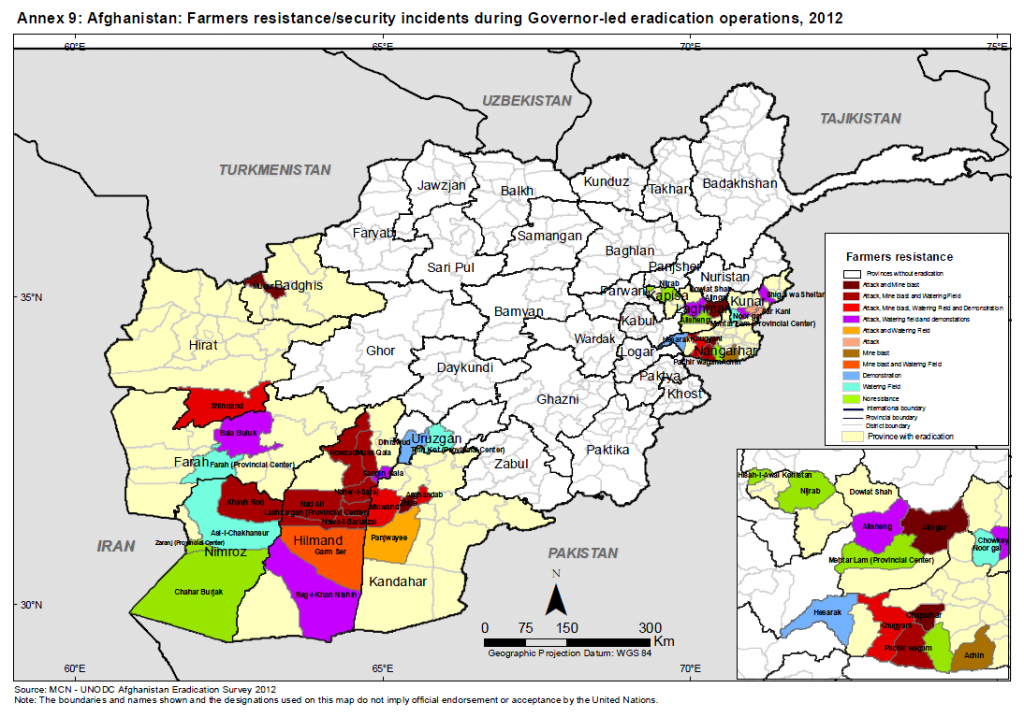
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – – Public Intelligence – The Continually Expanding Definition of Terrorism
Brian Church (L), 20, Brent Vincent Betterly (C), 24 and Jared Chase, 24, are seen in these handout photos from the Chicago Police department. The three anti-NATO protesters were charged with terrorism last week for an alleged plot that involved the production and use of Molotov cocktails. A lawyer for the men has said that the incendiary materials were planted by undercover agents.
Public Intelligence
Though the United States has been engaged in a Global War on Terror for more than a decade, the U.S. Government surprisingly does not have a standardized definition of terrorism that is agreed upon by all agencies. The State Department, Federal Bureau of Investigation and a number of other government agencies all utilize differing definitions of what constitutes an act of terrorism. This lack of agreement has allowed individual agencies to present different and, in some cases, far more inclusive definitions of terrorist acts enabling the use of expanded investigative procedures that might not be applicable in other agencies.
The FBI utilizes a definition of terrorism based upon the agency’s general functions under 28 CFR § 0.85. Under this regulation an act of terrorism is defined by “the unlawful use of force and violence against persons or property to intimidate or coerce a government, the civilian population, or any segment thereof, in furtherance of political or social objectives.” The USA PATRIOT Act expanded this definition to include domestic acts within the definition of terrorism. Section 802 of the USA PATRIOT Act modified the legal definition of terrorism (18 USC § 2331) to include a category of “domestic terrorism” that is defined by “acts dangerous to human life that are a violation of the criminal laws of the United States or of any State” intended to “intimidate or coerce a civilian population”, “influence the policy of a government by intimidation or coercion” or “affect the conduct of a government by mass destruction, assassination, or kidnapping” that are conducted primarily within the jurisdiction of the U.S. At the time, this expansion of the definition of terrorism was decried by the ACLU as “broad enough to encompass the activities of several prominent activist campaigns and organizations.”
One of the defining features of terrorist acts has always been a component of violence. Even under the expanded definition of terrorism created by the USA PATRIOT Act, there must be an act that is “dangerous to human life” indicating some form of physical harm to others could arise from the action. However, the Homeland Security Act of 2002, which created the Department of Homeland Security, extended the definition of terrorism further by including any act that is “damaging to critical infrastructure or key resources.” Though this definition differs from the legal definition of international and domestic terrorism under 18 USC § 2331, the modified definition is currently used by DHS as the basis for their own activities and intelligence products that are disseminated to federal, state and local law enforcement. The modified definition of terrorism is presented in a revised Domestic Terrorism and Homegrown Violent Extremism Lexicon published last year by DHS:
Any activity that involves an act that is dangerous to human life or potentially destructive to critical infrastructure or key resources, and is a violation of the criminal laws of the United States or of any state or other subdivision of the United States and appears to be intended to intimidate or coerce a civilian population to influence the policy of a government by intimidation or coercion, or to affect the conduct of a government by mass destruction, assassination, or kidnapping.
Notice that the statement “potentially destructive to critical infrastructure or key resources” is part of a disjunction, indicating that the act need not be “dangerous to human life” for it to be considered an act of terrorism. This means that, according to DHS, a non-violent actor could be capable of committing an act of terrorism simply by engaging in “potentially destructive” behavior towards some part of the nation’s critical infrastructure. Due to the fact that large sections of domestic infrastructure, including everything from banks to bridges to milk processing plants, are now considered critical infrastructure, a wide range of “potentially destructive” actions could be investigated by DHS or any one of the dozens of fusion centers around the country as potential acts of terrorism. The DHS Domestic Terrorism Lexicon states that the definitions presented in the document are designed to “assist federal, state, and local government officials with the mission to detect, identify, and understand threats of terrorism against the United States by facilitating a common understanding of the terms and definitions that describe terrorist threats to the United States.”
A recent report from the Congressional Research Service states that this ambiguity in the definition of terrorism can create confusion “in the investigative process regarding exactly when criminal activity becomes domestic terrorism.” The report also notes that the government often uses the terms “extremist” and “terrorist” interchangeably creating further ambiguity as to what exactly constitutes an act of terrorism. A 2009 study from Syracuse University found that U.S. Federal District Courts, the Department of Justice’s National Security Division and federal prosecutors all rely on different criteria to determine whether or not specific cases involve terrorist acts. This lack of agreement has led to widespread failures to obtain prosecutions of suspects recommended for charges by investigative agencies. In fact, the study found that from 2004-2009 “assistant United States attorneys all over the country declined to bring any charges against two out of every three (67%) of the thousands of terrorism matters that the investigative agencies had recommended for criminal prosecution.” The Syracuse study ends with a warning about the ambiguity surrounding the definition of terrorism:
The strong evidence that various parts of the government do not share a common understanding about terrorism has important consequences for all Americans. Those most immediately affected are the thousands of people whom the investigative agencies each year incorrectly recommend for prosecution in federal court. But to the extent that the investigators systematically waste their time targeting the wrong suspects, the chances increase that they will fail to identify the real terrorists who right now may be seeking to plant bombs, spread poisons or otherwise harm a much larger number of innocent people.
To solve these problems the study offers a surprisingly straightforward solution: come up with “a clear and understandable definition of terrorism.”
TOP-SECRET – Open Source Center Social Media Accounts Promoting Jihadist Attacks in Syria
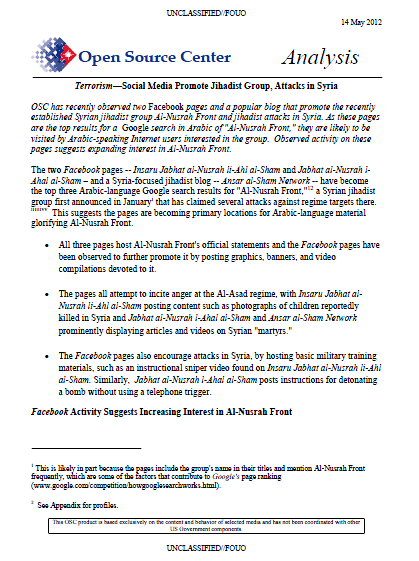
OSC has recently observed two Facebook pages and a popular blog that promote the recently established Syrian jihadist group Al-Nusrah Front and jihadist attacks in Syria. As these pages are the top results for a Google search in Arabic of “Al-Nusrah Front,” they are likely to be visited by Arabic-speaking Internet users interested in the group. Observed activity on these pages suggests expanding interest in Al-Nusrah Front.
The two Facebook pages — Insaru Jabhat al-Nusrah li-Ahl al-Sham and Jabhat al-Nusrah l-Ahal al-Sham – and a Syria-focused jihadist blog — Ansar al-Sham Network — have become the top three Arabic-language Google search results for “Al-Nusrah Front,” a Syrian jihadist group first announced in Januaryi that has claimed several attacks against regime targets there. This suggests the pages are becoming primary locations for Arabic-language materialglorifying Al-Nusrah Front.
- All three pages host Al-Nusrah Front’s official statements and the Facebook pages have been observed to further promote it by posting graphics, banners, and video compilations devoted to it.
- The pages all attempt to incite anger at the Al-Asad regime, with Insaru Jabhat al-Nusrah li-Ahl al-Sham posting content such as photographs of children reportedly killed in Syria and Jabhat al-Nusrah l-Ahal al-Sham and Ansar al-Sham Network prominently displaying articles and videos on Syrian “martyrs.”
- The Facebook pages also encourage attacks in Syria, by hosting basic military training materials, such as an instructional sniper video found on Insaru Jabhat al-Nusrah li-Ahl al-Sham. Similarly, Jabhat al-Nusrah l-Ahal al-Sham posts instructions for detonating a bomb without using a telephone trigger.
Facebook Activity Suggests Increasing Interest in Al-Nusrah Front
Although, thus far, users have indicated approval of the Facebook pages — by clicking the “like” buttons — relatively few times, the trend is increasing, suggesting heightened interest in Al-Nusrah Front. Statistics on readership of the pages are not available.
- As of 2 May, Insaru Jabhat al-Nusrah li-Ahl al-Sham readers have clicked “like” 481 times, and Jabhat al-Nusrah l-Ahal al-Sham users have done so 344 times.
- However, marking a substantial increase, during the week ending on 27 April, Insaru Jabhat al-Nusrah li-Ahl al-Sham received 143 “likes,” with 202 “people talking about” it. In contrast, during the week ending on 30 March –the earliest period for which data is available – the page received only 47 “likes,” with 60 users “talking about it.”
- Jabhat al-Nusrah l-Ahal al-Sham has experienced similar growth in activity. During the week ending on 27 April, it received 57 “likes” with 48 “people talking about” it, up substantially from 25 “likes” and 25 “people talking about it” in the week ending on 30 March.
The blog Ansar al-Sham Network reported between 33,000 and 78,000 views between 27 April and 5 May. Although it is not clear how the site calculates traffic, it appears to count visits on a daily, rather than cumulative basis. This high viewership offers further evidence of online interest in Al-Nusrah Front.
TOP-SECRET from the FBI – Seattle Financial Advisor Indicted in $46 Million Investment Fraud Scheme
A long-time Seattle financial advisor was indicted today by a federal grand jury with 23 criminal counts, including wire fraud, money laundering and investment advisor fraud, announced U.S. Attorney Jenny A. Durkan. Mark F. Spangler, 57, of Seattle is accused of diverting investor money from accounts he managed to risky start-up ventures in which he or his investment firm had an ownership interest. Spangler allegedly diverted more than $46 million to two companies, one of which is now shut down after failing to generate any positive revenue. Those who invested in the funds managed by Spangler, as part of The Spangler Group Inc.(TSG), were not told that their money was being invested in risky start-up companies. Spangler and several of his companies went into receivership last year. Today, the Securities and Exchange Commission filed a civil suit against Spangler as well. Spangler is scheduled to appear in U.S. District Court in Seattle on May 18, 2012 at 2:30.
“The Department of Justice is making the prosecution of financial fraud a top priority,” said U.S. Attorney Durkan. “These investors lost millions to a man they trusted to safeguard their resources. We are working closely with the SEC to ensure Mr. Spangler is held accountable for his fraud.”
The six investors described in the indictment were told their funds were conservatively invested in publicly traded companies and in bonds. Spangler allegedly provided them misleading statements over time, falsely describing the value of their accounts and how the money was invested. When investors sought to liquidate their holdings, Spangler was unable to provide them any funds, because the money had been funneled to the high risk start-up ventures that were not profitable.
According to the indictment, Spangler established a variety of funds as early as 1998 to pool investor money to buy publicly traded stocks and bonds. Spangler co-founded the two startup companies in the early 2000s—Tamarac Inc. in 2000 and TeraHop Networks Inc. in 2002. Tamarac Inc. is headquartered in Seattle and provides software to financial planners. TeraHop Networks Inc. is headquartered in Georgia and manufactured wireless devices used to monitor the location and activity of people and physical assets such as construction equipment. TeraHop has ceased operation. Spangler not only failed to disclose to his investors that he was diverting significant amounts of their funds to TeraHop and Tamarac, but he also failed to disclose that he was involved in the management of these companies, had an ownership interest in Tamarac, and was receiving payments from both companies. The indictment contains an order of forfeiture, which will be used to try to recover assets for the investors.
The case is being investigated by the FBI and Internal Revenue Service Criminal Investigation (IRS-CI).
The case is being prosecuted by Assistant United States Attorneys Mike Lang and Carl Blackstone.
For additional information please contact Emily Langlie, Public Affairs Officer for the United States Attorney’s Office, at (206) 553-4110 or Emily.Langlie@USDOJ.Gov.
TOP-SECRET – Pakistani Taliban Wants to Use Nuclear Weapons to Ensure Islam’s Survival
Despite past denials by Tehrik-e-Taliban Pakistan (TTP) leaders that the group intends to target Pakistan’s nuclear weapons, TTP Mohmand Agency leader Omar Khalid said in a 21 March video that the TTP aims to use Pakistan’s nuclear technology, among other assets, to ensure Islam’s survival. This is the first time that OSC has observed a TTP leader publicly list Pakistan’s nuclear weapons among its goals. Other elements of Khalid’s statement suggest that he may be seeking to boost his own stature within the group.
In a 21 March Pashto-language video statement posted to pro-Al-Qa’ida, pro-TTP website Babul-Islam, Khalid listed, among several other ostensibly far-fetched goals, the TTP’s aim to “utilize Pakistan’s strengths such as its Army, weapons, atom bomb, technology, and other power[s] for the betterment of the Muslim ummah [community] and Islam’s survival.”
- A commentary in influential daily The News described Khalid as Al-Qa’ida’s “henchman” and argued that his announcement was part of Al-Qa’ida’s “game plan” (8 April). By contrast, in the past, TTP leaders denied any intent to seize or otherwise utilize Pakistan’s nuclear weapons. Since 21 March, OSC has seen no public statements by other top TTP figures indicating whether they endorse Khalid’s remarks.
- In an interview with The Wall Street Journal in May 2011, approximately 10 months before the release of Khalid’s statement, TTP’s main spokesman Ehsanullah Ehsan — who speaks for the group’s Waziristan-based top leaders — was cited as saying that the TTP has “no plan whatsoever to attack Pakistan’s nuclear assets” (Jinnah, 27 May 2011).
- Similarly, now deceased TTP chief Baitullah Mehsud in a 2008 Al-Jazirah Television interview, said that the TTP is “not thinking of using a nuclear bomb” because, he said, it leads to killing innocent women and children, which is forbidden in Islam. He did say, however, that “we pray to God to help Muslims seize all nuclear bombs from the infidels” (25 January 2008).
- Khalid may be trying to boost his own standing in the TTP. In the 21 March statement, he outlined TTP history, portraying his role in its formation as key. He also touted his fighters as “fully organized, united, and strong,” saying they no longer need help from Waziristan.
Previous Khalid Statements Omar Khalid appeared to play a prominent role in the TTP’s 2011 propaganda campaign, appearing in several videos — one of which also depicted Hakimullah Mehsud — and creating his own magazine. In his past statements, Khalid has threatened revenge for the attacks on Usama Bin Ladin, claimed responsibility for an attack in Peshawar using a female suicide bomber, and rejected peace talks with the government.
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET from the FBI – Man Admits $7 Million Bank Fraud Scheme
NEW HAVEN, CT—Daniel J. Lyons Jr., 54, of Westport, Connecticut, waived his right to indictment and pleaded guilty today before U.S. Magistrate Judge Donna F. Martinez in Hartford, Connecticut to one count of bank fraud related to his defrauding Citizens Bank out of nearly $7 million, announced David B. Fein, U.S. Attorney for the District of Connecticut.
According to court documents and statements made in court, Lyons was the president and chief executive officer of an importing and exporting business known as Greenwich Trading Company GTC Worldwide Inc. or Greenwich Brands LLC (GTC). In February 2007, Lyons applied to Citizens Bank N.A. for a commercial revolving line of credit (RELOC), to be secured by the business’s accounts receivable, in the maximum amount of $7 million. However, Lyons falsified audit reports and other information when he applied to the bank for the RELOC, and again each time he withdrew additional funds from the line of credit.
As part of the scheme, Lyons submitted monthly borrowing base certificates (BBCs) to the bank to draw down additional funds from the RELOC. The BBCs were materially false in that they overstated the outstanding accounts receivable in order to satisfy the bank’s eligibility formula for additional loan disbursements. Between April 2007 and November 2008, Lyons regularly reported to the bank that GTC had between approximately $7.3 million and $9.2 million in accounts receivable.
By November 2008, Lyons had caused GTC to draw down the entire $7 million RELOC loan availability from the bank.
In February 2009, GTC filed a voluntary Chapter 7 bankruptcy petition with the U.S. Bankruptcy Court for the District of Connecticut. In the bankruptcy schedules, GTC’s accounts receivable were valued by Lyons at approximately $380,000.
Lyons is scheduled to be sentenced by U.S. District Judge Robert N. Chatigny on August 10, 2012 at which time Lyons faces a maximum term of 30 years in prison.
This matter is being investigated by the FBI. The case is being prosecuted by Assistant U.S. Attorney Ann M. Nevins.
This case was brought in coordination with the President’s Financial Fraud Enforcement Task Force, which was established to wage an aggressive and coordinated effort to investigate and prosecute financial crimes. The task force includes representatives from a broad range of federal agencies, regulatory authorities, inspectors general, and state and local law enforcement who, working together, bring to bear a powerful array of criminal and civil enforcement resources. The task force is working to improve efforts across the federal executive branch and, with state and local partners, to investigate and prosecute significant financial crimes, ensure just and effective punishment for those who perpetrate financial crimes, combat discrimination in the lending and financial markets, and recover proceeds for victims of financial crimes.
To report financial fraud crimes, and to learn more about the President’s Financial Fraud Enforcement Task Force, please visit http://www.StopFraud.gov.
TOP-SECRET – NSA GUNMAN: Learning Enemy Electronic Spying
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – Samir Khan Al-Qaeda in the Arabian Peninsula “Expectations Full” Jihadi Manual

The following document entitled “Expectations Full” was reportedly authored by Samir Khan, a U.S. citizen who was killed in a drone strike in Yemen last year along with Anwar al-Awlaki. The document details what potential Jihadis should expect and bears a great deal of similarity to Inspire magazine, which was also reportedly authored by Khan. After several new issues of Inspire magazine surfaced online in early May, the following document has also recently appeared online with an acknowledgement of the death of Samir Khan. We encourage readers to scrutinize the authenticity of the material provided in this publication. We have removed password protection from the PDF to enable easier analysis, but have left the files’ original metadata intact. Due to past incidents with law enforcement, we must emphasize that this material is provided, as always, for educational and informational purposes.
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET from the FBI – Florida Man Indicted by Federal Grand Jury for Sextortion and Cyberstalking
PENSACOLA, FL—B Christopher P. Gunn, 31, previously of Walton County, Florida, was indicted today on multiple charges involving the online sextortion and cyberstalking of young girls ranging in age from 13 to 17 years old. The indictment was announced by Pamela C. Marsh, United States Attorney for the Northern District of Florida.
The federal indictment alleges that Gunn, who was recently arrested on related charges in Alabama, extorted images and videos of minor females in “various states of undress, naked, and engaging in sexually explicit conduct.” The indictment also charges that Gunn violated federal cyberstalking statutes by engaging these females online with the “intent to injure, harass, and cause substantial emotional distress.” The conduct with which Gunn is charged in the Northern District of Florida is alleged to have occurred between October 2009 and March 2011. In total, the indictment alleges that Gunn victimized 11 minor females who resided in various states throughout the nation.
Gunn is currently in custody in Montgomery, Alabama on a federal indictment that also charges him with the production and possession of child pornography. If convicted on all charges in the Florida indictment, Gunn faces over 50 years in federal prison.
This case is being brought as part of Project Safe Childhood, a nationwide initiative launched in May 2006 by the Department of Justice to combat the growing epidemic of child sexual exploitation and abuse. Led by the United States Attorneys’ Offices and the Criminal Division’s Child Exploitation and Obscenity Section, Project Safe Childhood marshals federal, state, and local resources to locate, apprehend, and prosecute individuals who sexually exploit children and to identify and rescue victims. For more information about Project Safe Childhood, please visit http://www.justice.gov/psc/.
The case was investigated by the Federal Bureau of Investigation and the Walton County Sheriff’s Office. The case is being prosecuted by Assistant United States Attorney David L. Goldberg. An indictment is merely a formal charge by a grand jury that a defendant has committed a violation of federal criminal law. All defendants are presumed innocent unless and until the government proves their guilt beyond a reasonable doubt to the satisfaction of a jury at trial.
TOP-SECRET – Money as a Weapon System Afghanistan (MAAWS-A) SOP 2012
The Money As A Weapon System – Afghanistan Commander’s Emergency Response Program Standard Operating Procedure supports the United States Government Integrated Civilian-Military Campaign Plan and ISAF Theater Campaign Plan (TCP). The Theater Campaign Plan lists objectives that include improving governance and socio-economic development in order to provide a secure environment for sustainable stability that is observable to the population. CERP provides an enabling tool that commanders can utilize to achieve these objectives. This is accomplished through an assortment of projects planned with desired COIN effects such as addressing urgent needs of the population, promoting GIRoA legitimacy, countering Taliban influence, increasing needed capacity, gaining access, building/expanding relationships, promoting economic growth, and demonstrating positive intent or goodwill.
The SOP recognizes and addresses the challenges that lie ahead as we continue the momentum of our campaign and through the challenges of transition. This revision implements policy changes, which are summarized within the summary of changes, to help improve oversight and management and incorporates the lessons we have learned to include measures adopted from the recommendations of various audits. Additionally, a broad spectrum of collaboration and research from several organizations and agencies was used to provide guidance as you plan CERP projects.
…
A. Counterinsurgency concepts, frameworks, and ideas ultimately find expression in activities involving investments of energy, time and resources. Projects are a primary means for executing governance since they incorporate decisions on the distribution of scarce resources, may involve negotiations on the nature of the social contract, and can create positive, interdependent relationships to allow the delivery of a service. Project management is the way to ensure these investments generate measurable returns. However, project management to COIN effects is not the same as project management to quality, timeline, scope or budget as there are different objectives with different means of judging whether the objectives are met. Project prioritization and selection must reinforce COIN objectives. The list of potential projects will always exceed the capacity to deliver. The major limiting factor will be the ability to execute and oversee projects rather than limited funding. The more technically challenging the project, the greater the need for direct presence to ensure quality. Less complex projects, by contrast, can reduce coalition forces direct presence while ensuring greater COIN effects.
B. Commander’s Emergency Response Program (CERP) projects (and similar stabilization funds) are vehicles for achieving effects. The desired effects are currently not well defined, measurable or standardized across projects. An effect can be:
1. Developmental, seeking to change society, build institutional capacity or promote economic improvement that is sustainable;
2. Humanitarian, seeking to alleviate human suffering without conditions or impartiality;
3. Force protection/hearts and minds, seeking to create a positive impression of coalition forces/Afghan National Security Forces (ANSF) in an effort to lessen attacks; or
4. Counterinsurgency, seeking to address causes of instability through fostering positive, interdependent relationships between the Government of the Islamic Republic of Afghanistan (GIRoA) and key populations.
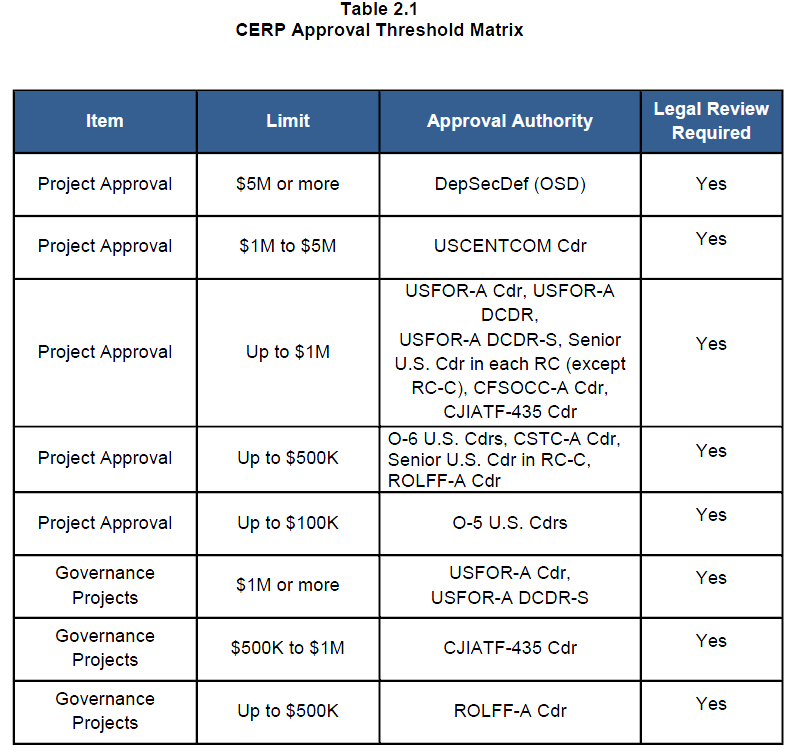
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – DoD Guidelines for Use of Internet Capabilities
DOWNLOAD THE ORIGINAL FILE HERE
TOP-SECRET- U.S. Marine Corps 21st‐Century Marine Expeditionary Intelligence Analysis (MEIA‐21)
21st‐Century Marine Expeditionary Intelligence Analysis (MEIA‐21) is a formal initiative to structure, standardize, and professionalize tactical intelligence analysis in the Marine Corps. It professionalizes Marine expeditionary intelligence, equipping intelligence analysts with analytically rigorous Structured Models, Approaches, and Techniques (SMATs)—applied tradecraft—to provide commanders with actionable, reliable tactical intelligence in conventional and irregular warfare while also instilling the cognitive and creative skills to create and refine that tradecraft. … Core Principles of MEIA‐21 MEIA‐21 is the process of building analytic modernization on six foundational principles: 1. Successful operations require reliable tactical intelligence. Operations are command led and intelligence fed. 2. Reliable tactical intelligence is achieved through structured, mission‐specific applied tradecraft. – Tradecraft is the SMATs that analysts use to develop actionable intelligence from raw data. – SMATs originate from field‐derived, experiential learning by Marine intelligence analysts. – Foundational skills, such as Structured Analytic Techniques (SATs), und0erlie the development and application of mission‐specific tradecraft. 3. Tradecraft‐driven intelligence analysis is conducted using analytically rigorous processes. – Marine Corps intelligence analysis must move beyond a reliance on raw intuition and readily available information to scientifically valid, objective techniques. – Processes and tools (SMATs) must be vetted for analytic rigor, formalized, documented, and taught. – Sustainable analytic rigor requires ongoing critical review and continuous improvement of tradecraft. 4. Social Science Intelligence (SSI) is essential for successful intelligence analysis in COIN and other nonconventional operations. It also is critical for conventional operations. – Without structured consideration of social factors, our knowledge of human‐centered problems is subjective, unscientific, overly informed by raw intuition, and less reliable. – SSI uses structured models, approaches, and techniques based upon proven principles and practices from economics, political science, anthropology, and other disciplines that study human behavior. – Applied social science is an important way to develop understanding (insight and foresight) in the context of operational requirements. 5. In an era of enormous quantities of potentially useful data, technology is critical to intelligence work. – People—not tools—perform analysis, but machine‐aided analysis can help analysts organize, store, and cut through massive amounts of data to discover the nonobvious and unseen and to identify otherwise invisible patterns. – Technology empowers analysts to archive, organize, discover, and retrieve information for near‐real‐time analysis. – Models and tools not only save time and cognitive energy, they correct fallible human senses and intuition that, left unaided, may misrepresent reality or distort analysis. 6. Intelligence analysis is a profession and should be structured as such. – Mastery of tradecraft, not job title, defines the profession of Marine Corps intelligence analysis. – Marine intelligence analysts must have a deep knowledge of tradecraft. Area expertise is valuable, but inadequate to develop actionable intelligence or reliable knowledge in the absence of structured applied tradecraft. – Structured tools, methods, and processes must be disseminated and institutionalized through formal training, standards, and continuing education. Intelligence analysts should be certified in the practice of their profession. … Social Science Intelligence and the New Analytic Environment Marine Corps warfighting has primarily been based on the capability to find, fix, and strike the enemy force. To support this, Marine Corps tactical intelligence was often kinetics‐based, target‐centric, and optimized for producing intelligence against conventional military formations. Adversaries were well defined, providing a relatively sharp focus for intelligence. But 10 years of operations in Iraq and Afghanistan have repeatedly shown that armed groups confronting Marines today avoid U.S. targeting superiority by operating asymmetrically within congested and cluttered environments. Contending with conventional, counterinsurgency (COIN), and nonconventional operations in the upcoming decades of the 21st century, Marines will once again be exposed to socially complex environments and hybrid armed groups. Many of these threats (conventional and nonconventional) and adversaries (state, state proxies, and nonstate actors) will be more agile, less visible, and possess an information advantage where it is easier for them to see and target us than for us to see and target them. Given this operational environment, the MCISR‐E must analyze more than an adversary’s characteristics and capabilities. Expeditionary intelligence must incorporate the context within which adversaries operate; the institutions within which they live; and their fears, perceptions, and motivations; in short, we must consider the totality of the human sphere. This new approach to intelligence analysis, focusing on understanding human social organization is called Social Science Intelligence (SSI). There has been significant growth in the techniques and technologies of intelligence analysis, especially in the social sciences such as economics, political science, anthropology, and other disciplines relating to the study of human behavior. Because the most advanced knowledge in these fields is dispersed within academia and not directly focused on intelligence‐related problems, it’s hard to access and consequently plays an inadequate role in tactical intelligence today—Marine intelligence analysts’ knowledge of human‐centered problems tends to be subjective, unscientific, technologically weak, and based mostly on the raw intuition and personal experience of the individual analyst. The challenge is to develop, refine, and deploy applied techniques that enable us to understand the totality of the human domain framework with speed and precision. An analytic modernization plan that captures critical best practices, leverages the best social and physical science know‐how available, and makes available sophisticated analytic instruments that analysts can readily apply to intelligence problems is critical to success. When made available, these methods and approaches give analysts social and physical science expertise from the fields that parallel the questions faced by intelligence (e.g., accounting, organizational theory, elite analysis, political science, economics, and census/registry).
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – NSA on Out of Control System Administrators
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – NSA on TEMPEST History
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – SAF CJIATF-Shafafiyat Countering Afghan Corruption and Organized Crime Overview Presentation
Countering Corruption and Organized Crime to Make Afghanistan Stronger for Transition and a Good Future
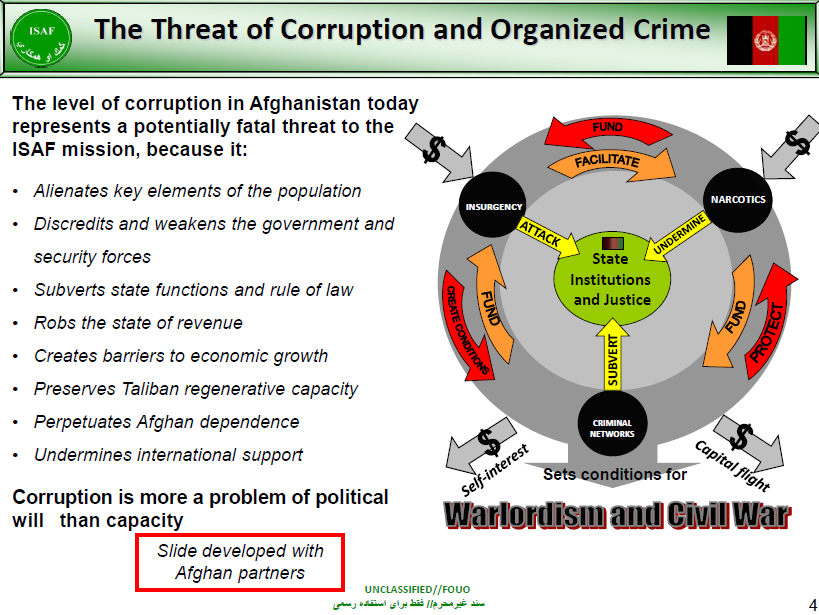
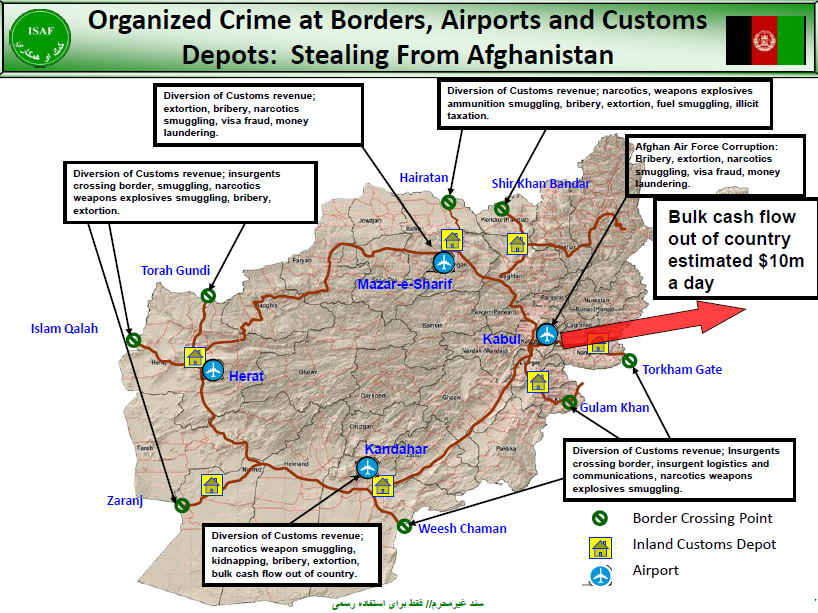
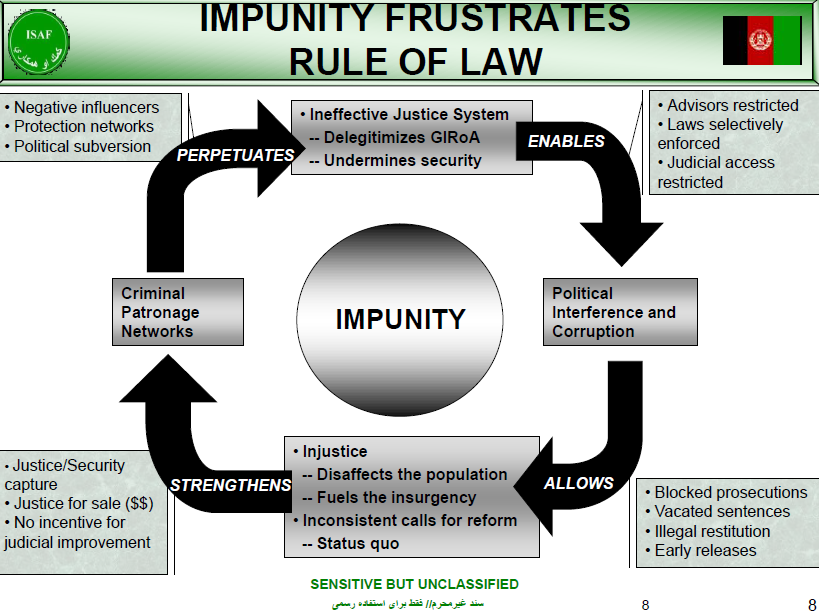
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET from Cryptome – NSA TEMPEST Documents Repost
NSA TEMPEST History: http://cryptome.org/2012/05/nsa-tempest-history.pdf
22 June 2011:
Joel McNamara’s comprehensive Complete, Unofficial TEMPEST Information Page has closed. A mirror: http://www.kubieziel.de/blog/uploads/complete_unofficial_tempest_page.pdf
6 April 2003: Add
NCSC 3 – TEMPEST Glossary, 30 March 1981
5 March 2002: Two security papers announced today on optical Tempest risks:
Information Leakage from Optical Emanations, J. Loughry and D.A. Umphress
Optical Time-Domain Eavesdropping Risks of CRT Displays, Markus Kuhn
For emissions security, HIJACK, NONSTOP and TEAPOT, see also Ross Anderson’s Security Engineering, Chapter 15.
HIJACK, NONSTOP, and TEAPOT Vulnerabilities
A STU-III is a highly sophisticated digital device; however, they suffer from a particular nasty vulnerability to strong RF signals that if not properly addressed can cause the accidental disclosure of classified information, and recovery of the keys by an eavesdropper. While the unit itself is well shielded, the power line feeding the unit may not have a clean ground (thus negating the shielding).
If the encryption equipment is located within six to ten wavelengths of a radio transmitter (such as a cellular telephone, beeper, or two way radio) the RF signal can mix with the signals inside the STU and carry information to an eavesdropper. This six to ten wavelengths is referred to as the “near field” or the wave front where the magnetic field of the signal is stronger then the electrical field.
The best way to deal with this is to never have a cellular telephone or pager on your person when using a STU, or within a radius of at least thirty feet (in any direction) from an operational STU (even with a good ground). If the STU is being used in a SCIF or secure facility a cell phone is supposed to be an excluded item, but it is simply amazing how many government people (who know better) forget to turn off their phone before entering controlled areas and thus cause classified materials to be compromised.
Spook Hint: If you have a powered up NEXTEL on your belt and you walk within 12 feet of a STU-III in secure mode you have just compromised the classified key.
— Secure Telephone Units, Crypto Key Generators, Encryption Equipment, and Scramblers (offsite)
Files at Cryptome.org: tempest-time.htm TEMPEST Timeline tempest-old.htm TEMPEST History NSA Documents Obtained by FOIA nacsem-5112.htm NACSEM 5112 NONSTOP Evaluation Techniques nstissi-7000.htm NSTISSI No. 7000 TEMPEST Countermeasures for Facilities nacsim-5000.htm NACSIM 5000 Tempest Fundamentals nacsim-5000.zip NACSIM 5000 Tempest Fundamentals (Zipped 570K) nsa-94-106.htm NSA No. 94-106 Specification for Shielded Enclosures tempest-2-95.htm NSTISSAM TEMPEST/2-95 Red/Black Installation Guidance nt1-92-1-5.htm NSTISSAM TEMPEST 1/92 - TOC and Sections 1-5 nt1-92-6-12.htm NSTISSAM TEMPEST 1/92 - Sections 6-12 nstissam1-92a.htm NSTISSAM TEMPEST 1/92 - Appendix A (TEMPEST Overview) nt1-92-B-M.htm NSTISSAM TEMPEST 1/92 - Appendixes B-M nt1-92-dist.htm NSTISSAM TEMPEST 1/92 - Distribution List nsa-reg90-6.htm NSA/CSS Reg. 90-6, Technical Security Program nsa-foia-app2.htm NSA Letter Releasing TEMPEST Documents nsa-foia-app.htm NSA FOIA Appeal for TEMPEST Information nsa-foia-req.htm NSA FOIA Request for TEMPEST Documents Other TEMPEST Documents nsa-etpp.htm NSA Endorsed TEMPEST Products Program nsa-ettsp.htm NSA Endorsed TEMPEST Test Services Procedures nsa-zep.htm NSA Zoned Equipment Program nstissam1-00.htm Maintenance and Disposition of TEMPEST Equipment (2000) nstissi-7000.htm TEMPEST Countermeasures for Facilities (1993) tempest-fr.htm French TEMPEST Documentation (2000) af-hb202d.htm US Air Force EI Tempest Installation Handbook (1999) afssi-7010.htm US Air Force Emission Security Assessments (1998) afssm-7011.htm US Air Force Emission Security Countermeasure Reviews (1998) qd-tempest.htm Quick and Dirty TEMPEST Experiment (1998) mil-hdbk-1195.htm Radio Frequency Shielded Enclsoures (1988) emp.htm US Army Electromagnetic Pulse (EMP) and TEMPEST Protection for Facilities (1990) zzz1002.htm National TEMPEST School Courses (1998) navch16.htm Chapter 16 of US Navy's Automated Information Systems Security Guidelines tempest-cpu.htm Controlled CPU TEMPEST emanations (1999) tempest-door.htm TEMPEST Door (1998) bema-se.htm Portable Radio Frequency Shielded Enclosures (1998) datasec.htm Data Security by Architectural Design, George R. Wilson (1995) rs232.pdf The Threat of Information Theft by Reception of Electromagnetic Radiation from RS-232 Cables, Peter Smulders (1990) tempest-law.htm Laws On TEMPEST, Christopher Seline (1989) tempest-leak.htm The Tempest Over Leaking Computers, Harold Highland (1988) bits.pdf Electromagnetic Eavesdropping Machines for bits.htm Christmas?, Wim Van Eck (1988) nsa-vaneck.htm NSA, Van Eck, Banks TEMPEST (1985) emr.pdf Electromagnetic Radiation from Video Display Units: An Eavesdropping Risk?, Wim Van Eck (1985)
TOP-SECRET – Costs of Prez Entourage Stay in Colombia
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – U.S. Marine Corps 21st‐Century Marine Expeditionary Intelligence Analysis (MEIA‐21)
21st‐Century Marine Expeditionary Intelligence Analysis (MEIA‐21) is a formal initiative to structure, standardize, and professionalize tactical intelligence analysis in the Marine Corps. It professionalizes Marine expeditionary intelligence, equipping intelligence analysts with analytically rigorous Structured Models, Approaches, and Techniques (SMATs)—applied tradecraft—to provide commanders with actionable, reliable tactical intelligence in conventional and irregular warfare while also instilling the cognitive and creative skills to create and refine that tradecraft.
…
Core Principles of MEIA‐21
MEIA‐21 is the process of building analytic modernization on six foundational principles:
1. Successful operations require reliable tactical intelligence. Operations are command led and intelligence fed.
2. Reliable tactical intelligence is achieved through structured, mission‐specific applied
tradecraft.– Tradecraft is the SMATs that analysts use to develop actionable intelligence from raw data.
– SMATs originate from field‐derived, experiential learning by Marine intelligence analysts.
– Foundational skills, such as Structured Analytic Techniques (SATs), und0erlie the development and application of mission‐specific tradecraft.3. Tradecraft‐driven intelligence analysis is conducted using analytically rigorous processes.
– Marine Corps intelligence analysis must move beyond a reliance on raw intuition and readily available information to scientifically valid, objective techniques.
– Processes and tools (SMATs) must be vetted for analytic rigor, formalized, documented, and taught.
– Sustainable analytic rigor requires ongoing critical review and continuous improvement of tradecraft.4. Social Science Intelligence (SSI) is essential for successful intelligence analysis in COIN and other nonconventional operations. It also is critical for conventional operations.
– Without structured consideration of social factors, our knowledge of human‐centered problems is subjective, unscientific, overly informed by raw intuition, and less reliable.
– SSI uses structured models, approaches, and techniques based upon proven principles and practices from economics, political science, anthropology, and other disciplines that study human behavior.
– Applied social science is an important way to develop understanding (insight and foresight) in the context of operational requirements.5. In an era of enormous quantities of potentially useful data, technology is critical to intelligence work.
– People—not tools—perform analysis, but machine‐aided analysis can help analysts organize, store, and cut through massive amounts of data to discover the nonobvious and unseen and to identify otherwise invisible patterns.
– Technology empowers analysts to archive, organize, discover, and retrieve information for near‐real‐time analysis.
– Models and tools not only save time and cognitive energy, they correct fallible human senses and intuition that, left unaided, may misrepresent reality or distort analysis.6. Intelligence analysis is a profession and should be structured as such.
– Mastery of tradecraft, not job title, defines the profession of Marine Corps intelligence analysis.
– Marine intelligence analysts must have a deep knowledge of tradecraft. Area expertise is valuable, but inadequate to develop actionable intelligence or reliable knowledge in the absence of structured applied tradecraft.
– Structured tools, methods, and processes must be disseminated and institutionalized through formal training, standards, and continuing education. Intelligence analysts should be certified in the practice of their profession.…
Social Science Intelligence and the New Analytic Environment
Marine Corps warfighting has primarily been based on the capability to find, fix, and strike the enemy force. To support this, Marine Corps tactical intelligence was often kinetics‐based, target‐centric, and optimized for producing intelligence against conventional military formations. Adversaries were well defined, providing a relatively sharp focus for intelligence. But 10 years of operations in Iraq and Afghanistan have repeatedly shown that armed groups confronting Marines today avoid U.S. targeting superiority by operating asymmetrically within congested and cluttered environments. Contending with conventional, counterinsurgency (COIN), and nonconventional operations in the upcoming decades of the 21st century, Marines will once again be exposed to socially complex environments and hybrid armed groups. Many of these threats (conventional and nonconventional) and adversaries (state, state proxies, and nonstate actors) will be more agile, less visible, and possess an information advantage where it is easier for them to see and target us than for us to see and target them.
Given this operational environment, the MCISR‐E must analyze more than an adversary’s characteristics and capabilities. Expeditionary intelligence must incorporate the context within which adversaries operate; the institutions within which they live; and their fears, perceptions, and motivations; in short, we must consider the totality of the human sphere.
This new approach to intelligence analysis, focusing on understanding human social organization is called Social Science Intelligence (SSI). There has been significant growth in the techniques and technologies of intelligence analysis, especially in the social sciences such as economics, political science, anthropology, and other disciplines relating to the study of human behavior. Because the most advanced knowledge in these fields is dispersed within academia and not directly focused on intelligence‐related problems, it’s hard to access and consequently plays an inadequate role in tactical intelligence today—Marine intelligence analysts’ knowledge of human‐centered problems tends to be subjective, unscientific, technologically weak, and based mostly on the raw intuition and personal experience of the individual analyst.
The challenge is to develop, refine, and deploy applied techniques that enable us to understand the totality of the human domain framework with speed and precision. An analytic modernization plan that captures critical best practices, leverages the best social and physical science know‐how available, and makes available sophisticated analytic instruments that analysts can readily apply to intelligence problems is critical to success. When made available, these methods and approaches give analysts social and physical science expertise from the fields that parallel the questions faced by intelligence (e.g., accounting, organizational theory, elite analysis, political science, economics, and census/registry).
DOWNLOAD THE ORGINAL DOCUMENT HERE
TOP-SECRET – Army Assessment of Afghanistan Corruption
TOP-SECRET – FBI Report on Bitcoin
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – FBI Statement on Seizure of IED Overseas
As a result of close cooperation with our security and intelligence partners overseas, an improvised explosive device (IED) designed to carry out a terrorist attack has been seized abroad. The FBI currently has possession of the IED and is conducting technical and forensics analysis on it. Initial exploitation indicates that the device is very similar to IEDs that have been used previously by al Qaeda in the Arabian Peninsula (AQAP) in attempted terrorist attacks, including against aircraft and for targeted assassinations. The device never presented a threat to public safety, and the U.S. government is working closely with international partners to address associated concerns with the device. We refer you to the Department of Homeland Security, including the Transportation Security Administration, regarding ongoing security measures to safeguard the American people and the traveling public.
TOP-SECRET – NRC on Threat of Nuclear Plant Insider Radiological Sabotage
[Federal Register Volume 77, Number 84 (Tuesday, May 1, 2012)] [Notices] [Pages 25762-25767] From the Federal Register Online via the Government Printing Office [www.gpo.gov] [FR Doc No: 2012-10472] ----------------------------------------------------------------------- NUCLEAR REGULATORY COMMISSION [Docket No. 72-1039; NRC-2012-0099; EA-12-047] In the Matter of Southern Nuclear Operating Company, Inc., Vogtle Electric Generating Plant, Independent Spent Fuel Storage Installation; Order Modifying License (Effective Immediately) AGENCY: Nuclear Regulatory Commission. ACTION: Issuance of order for implementation of additional security measures and fingerprinting for unescorted access to Southern Nuclear Operating Company, Inc. ----------------------------------------------------------------------- FOR FURTHER INFORMATION CONTACT: L. Raynard Wharton, Senior Project Manager, Licensing and Inspection Directorate, Division of Spent Fuel Storage and Transportation, Office of Nuclear Material Safety and Safeguards, U.S. Nuclear Regulatory Commission, Rockville, Maryland 20852; telephone: (301) 492-3316; fax number: (301) 492-3348; email: Raynard.Wharton@nrc.gov. SUPPLEMENTARY INFORMATION: I. Introduction Pursuant to Title 10 of the Code of Federal Regulations (10 CFR) 2.106, the U.S. Nuclear Regulatory Commission (NRC or the Commission) is providing notice, in the matter of Vogtle Electric Generating Plant Independent Spent Fuel Storage Installation (ISFSI) Order Modifying License (Effective Immediately). II. Further Information I The NRC has issued a general license to Southern Nuclear Operating Company, Inc. (SNC), authorizing the operation of an ISFSI, in accordance with the Atomic Energy Act of 1954, as amended, and 10 CFR part 72. This Order is being issued to SNC because it has identified near-term plans to store spent fuel in an ISFSI under the general license provisions of 10 CFR part 72. The Commission's regulations at 10 CFR 72.212(b)(5), 10 CFR 50.54(p)(1), and 10 CFR 73.55(c)(5) require licensees to maintain safeguards contingency plan procedures to respond to threats of radiological sabotage and to protect the spent fuel against the threat of radiological sabotage, in accordance with 10 CFR part 73, appendix C. Specific physical security requirements are contained in 10 CFR 73.51 or 73.55, as applicable. Inasmuch as an insider has an opportunity equal to, or greater than, any other person, to commit radiological sabotage, the Commission has determined these measures to be prudent. Comparable Orders have been issued to all licensees that currently store spent fuel or have identified near-term plans to store spent fuel in an ISFSI. II On September 11, 2001, terrorists simultaneously attacked targets in New York, NY, and Washington, DC, using large commercial aircraft as weapons. In response to the attacks and intelligence information subsequently obtained, the Commission issued a number of Safeguards and Threat Advisories to its licensees to strengthen licensees' capabilities and readiness to respond to a potential attack on a nuclear facility. On October 16, 2002, the Commission issued Orders to the licensees of operating ISFSIs, to place the actions taken in response to the Advisories into the established regulatory framework and to implement additional security enhancements that emerged from NRC's ongoing comprehensive review. The Commission has also communicated with other Federal, State, and local government agencies and industry representatives to discuss and evaluate the current threat environment in order to assess the adequacy of security measures at licensed facilities. In addition, the Commission has conducted a comprehensive review of its safeguards and security programs and requirements. As a result of its consideration of current safeguards and security [[Page 25763]] requirements, as well as a review of information provided by the intelligence community, the Commission has determined that certain additional security measures (ASMs) are required to address the current threat environment, in a consistent manner throughout the nuclear ISFSI community. Therefore, the Commission is imposing requirements, as set forth in Attachments 1 and 2 of this Order, on all licensees of these facilities. These requirements, which supplement existing regulatory requirements, will provide the Commission with reasonable assurance that the public health and safety, the environment, and common defense and security continue to be adequately protected in the current threat environment. These requirements will remain in effect until the Commission determines otherwise. The Commission recognizes that licensees may have already initiated many of the measures set forth in Attachments 1 and 2 to this Order, in response to previously issued Advisories, or on their own. It also recognizes that some measures may not be possible or necessary at some sites, or may need to be tailored to accommodate the specific circumstances existing at SNC's facility, to achieve the intended objectives and avoid any unforeseen effect on the safe storage of spent fuel. Although the ASMs implemented by licensees in response to the Safeguards and Threat Advisories have been sufficient to provide reasonable assurance of adequate protection of public health and safety, in light of the continuing threat environment, the Commission concludes that these actions must be embodied in an Order, consistent with the established regulatory framework. To provide assurance that licensees are implementing prudent measures to achieve a consistent level of protection to address the current threat environment, licenses issued pursuant to 10 CFR 72.210 shall be modified to include the requirements identified in Attachments 1 and 2 to this Order. In addition, pursuant to 10 CFR 2.202, I find that, in light of the common defense and security circumstances described above, the public health, safety, and interest require that this Order be effective immediately. III Accordingly, pursuant to Sections 53, 103, 104, 147, 149, 161b, 161i, 161o, 182, and 186 of the Atomic Energy Act of 1954, as amended, and the Commission's regulations in 10 CFR 2.202 and 10 CFR parts 50, 72, and 73, it is hereby ordered, effective immediately, that your general license is modified as follows: A. SNC shall comply with the requirements described in Attachments 1 and 2 to this Order, except to the extent that a more stringent requirement is set forth in the Vogtle Electric Generating Plant's physical security plan. SNC shall demonstrate its ability to comply with the requirements in Attachments 1 and 2 to the Order no later than 365 days from the date of this Order or 90 days before the first day that spent fuel is initially placed in the ISFSI, whichever is earlier. SNC must implement these requirements before initially placing spent fuel in the ISFSI. Additionally, SNC must receive written verification from the NRC that it has adequately demonstrated compliance with these requirements before initially placing spent fuel in the ISFSI. B. 1. SNC shall, within twenty (20) days of the date of this Order, notify the Commission: (1) If it is unable to comply with any of the requirements described in Attachments 1 and 2; (2) if compliance with any of the requirements is unnecessary, in its specific circumstances; or (3) if implementation of any of the requirements would cause SNC to be in violation of the provisions of any Commission regulation or the facility license. The notification shall provide SNC's justification for seeking relief from, or variation of, any specific requirement. 2. If SNC considers that implementation of any of the requirements described in Attachments 1 and 2 to this Order would adversely impact the safe storage of spent fuel, SNC must notify the Commission, within twenty (20) days of this Order, of the adverse safety impact, the basis for its determination that the requirement has an adverse safety impact, and either a proposal for achieving the same objectives specified in Attachments 1 and 2 requirements in question, or a schedule for modifying the facility, to address the adverse safety condition. If neither approach is appropriate, SNC must supplement its response, to Condition B.1 of this Order, to identify the condition as a requirement with which it cannot comply, with attendant justifications, as required under Condition B.1. C. 1. SNC shall, within twenty (20) days of this Order, submit to the Commission, a schedule for achieving compliance with each requirement described in Attachments 1 and 2. 2. SNC shall report to the Commission when it has achieved full compliance with the requirements described in Attachments 1 and 2. D. All measures implemented or actions taken in response to this Order shall be maintained until the Commission determines otherwise. SNC's response to Conditions B.1, B.2, C.1, and C.2, above, shall be submitted in accordance with 10 CFR 72.4. In addition, submittals and documents produced by SNC as a result of this Order, that contain Safeguards Information as defined by 10 CFR 73.22, shall be properly marked and handled, in accordance with 10 CFR 73.21 and 73.22. The Director, Office of Nuclear Material Safety and Safeguards, may, in writing, relax or rescind any of the above conditions, for good cause. IV In accordance with 10 CFR 2.202, SNC must, and any other person adversely affected by this Order may, submit an answer to this Order within 20 days of its publication in the Federal Register. In addition, SNC and any other person adversely affected by this Order may request a hearing on this Order within 20 days of its publication in the Federal Register. Where good cause is shown, consideration will be given to extending the time to answer or request a hearing. A request for extension of time must be made, in writing, to the Director, Office of Nuclear Material Safety and Safeguards, U.S. Nuclear Regulatory Commission, Washington, DC 20555-0001, and include a statement of good cause for the extension. The answer may consent to this Order. If the answer includes a request for a hearing, it shall, under oath or affirmation, specifically set forth the matters of fact and law on which SNC relies and the reasons as to why the Order should not have been issued. If a person other than SNC requests a hearing, that person shall set forth with particularity the manner in which his/her interest is adversely affected by this Order and shall address the criteria set forth in 10 CFR 2.309(d). All documents filed in NRC adjudicatory proceedings, including a request for hearing, a petition for leave to intervene, any motion or other document filed in the proceeding prior to the submission of a request for hearing or petition to intervene, and documents filed by interested governmental entities participating under 10 CFR 2.315(c), must be filed in accordance with the NRC E-Filing rule (72 FR 49139, August 28, 2007). The E-Filing process requires participants to submit and serve all adjudicatory [[Page 25764]] documents over the internet, or in some cases to mail copies on electronic storage media. Participants may not submit paper copies of their filings unless they seek an exemption in accordance with the procedures described below. To comply with the procedural requirements of E-Filing, at least 10 days prior to the filing deadline, the participant should contact the Office of the Secretary by email at hearing.docket@nrc.gov, or by telephone at 301-415-1677, to request (1) a digital identification (ID) certificate, which allows the participant (or its counsel or representative) to digitally sign documents and access the E-Submittal server for any proceeding in which it is participating; and (2) advise the Secretary that the participant will be submitting a request or petition for hearing (even in instances in which the participant, or its counsel or representative, already holds an NRC-issued digital ID certificate). Based upon this information, the Secretary will establish an electronic docket for the hearing in this proceeding if the Secretary has not already established an electronic docket. Information about applying for a digital ID certificate is available on the NRC's public Web site at http://www.nrc.gov/site-help/e-submittals/apply-certificates.html. System requirements for accessing the E-Submittal server are detailed in the NRC's ``Guidance for Electronic Submission,'' which is available on the NRC's public Web site at http://www.nrc.gov/site-help/e-submittals.html. Participants may attempt to use other software not listed on the Web site, but should note that the NRC's E-Filing system does not support unlisted software, and the NRC Meta System Help Desk will not be able to offer assistance in using unlisted software. If a participant is electronically submitting a document to the NRC in accordance with the E-Filing rule, the participant must file the document using the NRC's online, Web-based submission form. In order to serve documents through the Electronic Information Exchange System, users will be required to install a Web browser plug-in from the NRC's Web site. Further information on the Web-based submission form, including the installation of the Web browser plug-in, is available on the NRC's public Web site at http://www.nrc.gov/site-help/e-submittals.html. Once a participant has obtained a digital ID certificate and a docket has been created, the participant can then submit a request for hearing or petition for leave to intervene. Submissions should be in Portable Document Format (PDF) in accordance with the NRC guidance available on the NRC's public Web site at http://www.nrc.gov/site-help/e-submittals.html. A filing is considered complete at the time the documents are submitted through the NRC's E-Filing system. To be timely, an electronic filing must be submitted to the E-Filing system no later than 11:59 p.m. Eastern Time on the due date. Upon receipt of a transmission, the E-Filing system time-stamps the document and sends the submitter an email notice confirming receipt of the document. The E-Filing system also distributes an email notice that provides access to the document to the NRC's Office of the General Counsel and any others who have advised the Office of the Secretary that they wish to participate in the proceeding, so that the filer need not serve the documents on those participants separately. Therefore, applicants and other participants (or their counsel or representative) must apply for and receive a digital ID certificate before a hearing request/petition to intervene is filed so that they can obtain access to the document via the E-Filing system. A person filing electronically using the NRC's adjudicatory E- Filing system may seek assistance by contacting the NRC Meta System Help Desk through the ``Contact Us'' link located on the NRC's Web site at http://www.nrc.gov/site-help/e-submittals.html, by email to MSHD.Resource@nrc.gov, or by a toll-free call to 1-866-672-7640. The NRC Meta System Help Desk is available between 8 a.m. and 8 p.m., Eastern Time, Monday through Friday, excluding government holidays. Participants who believe that they have a good cause for not submitting documents electronically must file an exemption request, in accordance with 10 CFR 2.302(g), with their initial paper filing requesting authorization to continue to submit documents in paper format. Such filings must be submitted by: (1) First class mail addressed to the Office of the Secretary of the Commission, U.S. Nuclear Regulatory Commission, Washington, DC 20555-0001, Attention: Rulemaking and Adjudications Staff; or (2) courier, express mail, or expedited delivery service to the Office of the Secretary, Sixteenth Floor, One White Flint North, 11555 Rockville Pike, Rockville, Maryland, 20852, Attention: Rulemaking and Adjudications Staff. Participants filing a document in this manner are responsible for serving the document on all other participants. Filing is considered complete by first-class mail as of the time of deposit in the mail, or by courier, express mail, or expedited delivery service upon depositing the document with the provider of the service. A presiding officer, having granted an exemption request from using E-Filing, may require a participant or party to use E-Filing if the presiding officer subsequently determines that the reason for granting the exemption from use of E-Filing no longer exists. Documents submitted in adjudicatory proceedings will appear in the NRC's electronic hearing docket which is available to the public at http://ehd1.nrc.gov/ehd/, unless excluded pursuant to an order of the Commission, or the presiding officer. Participants are requested not to include personal privacy information, such as social security numbers, home addresses, or home phone numbers in their filings, unless an NRC regulation or other law requires submission of such information. With respect to copyrighted works, except for limited excerpts that serve the purpose of the adjudicatory filings and would constitute a Fair Use application, participants are requested not to include copyrighted materials in their submission. If a hearing is requested by SNC or a person whose interest is adversely affected, the Commission will issue an Order designating the time and place of any hearing. If a hearing is held, the issue to be considered at such hearing shall be whether this Order should be sustained. Pursuant to 10 CFR 2.202(c)(2)(i), SNC may, in addition to requesting a hearing, at the time the answer is filed or sooner, move the presiding officer to set aside the immediate effectiveness of the Order on the grounds that the Order, including the need for immediate effectiveness, is not based on adequate evidence, but on mere suspicion, unfounded allegations, or error. In the absence of any request for hearing, or written approval of an extension of time in which to request a hearing, the provisions as specified in Section III shall be final twenty (20) days from the date this Order is published in the Federal Register, without further Order or proceedings. If an extension of time for requesting a hearing has been approved, the provisions as specified in Section III, shall be final when the extension expires, if a hearing request has not been received. An answer or a request for hearing shall not stay the immediate effectiveness of this order. [[Page 25765]] Dated at Rockville, Maryland, this 23rd day of April, 2012. For the Nuclear Regulatory Commission. Catherine Haney, Director, Office of Nuclear Material Safety and Safeguards. Attachment 1--Additional Security Measures (ASMs) for Physical Protection of Dry Independent Spent Fuel Storage Installations (ISFSIs) contains Safeguards Information and is not included in the Federal Register notice Attachment 2--Additional Security Measures for Access Authorization and Fingerprinting at Independent Spent Fuel Storage Installations, Dated June 3, 2010 A. General Basis Criteria 1. These additional security measures (ASMs) are established to delineate an independent spent fuel storage installation (ISFSI) licensee's responsibility to enhance security measures related to authorization for unescorted access to the protected area of an ISFSI in response to the current threat environment. 2. Licensees whose ISFSI is collocated with a power reactor may choose to comply with the U.S. Nuclear Regulatory Commission (NRC)- approved reactor access authorization program for the associated reactor as an alternative means to satisfy the provisions of sections B through G below. Otherwise, licensees shall comply with the access authorization and fingerprinting requirements of sections B through G of these ASMs. 3. Licensees shall clearly distinguish in their 20-day response which method they intend to use in order to comply with these ASMs. B. Additional Security Measures for Access Authorization Program 1. The licensee shall develop, implement and maintain a program, or enhance its existing program, designed to ensure that persons granted unescorted access to the protected area of an ISFSI are trustworthy and reliable and do not constitute an unreasonable risk to the public health and safety or the common defense and security, including a potential to commit radiological sabotage. a. To establish trustworthiness and reliability, the licensee shall develop, implement, and maintain procedures for conducting and completing background investigations, prior to granting access. The scope of background investigations must address at least the past three years and, as a minimum, must include: i. Fingerprinting and a Federal Bureau of Investigation (FBI) identification and criminal history records check (CHRC). Where an applicant for unescorted access has been previously fingerprinted with a favorably completed CHRC (such as a CHRC pursuant to compliance with orders for access to safeguards information), the licensee may accept the results of that CHRC, and need not submit another set of fingerprints, provided the CHRC was completed not more than three years from the date of the application for unescorted access. ii. Verification of employment with each previous employer for the most recent year from the date of application. iii. Verification of employment with an employer of the longest duration during any calendar month for the remaining next most recent 2 years. iv. A full credit history review. v. An interview with not less than two character references, developed by the investigator. vi. A review of official identification (e.g., driver's license; passport; government identification; state-, province-, or country-of- birth issued certificate of birth) to allow comparison of personal information data provided by the applicant. The licensee shall maintain a photocopy of the identifying document(s) on file, in accordance with ``Protection of Information,'' in section G of these ASMs. vii. Licensees shall confirm eligibility for employment through the regulations of the U.S. Department of Homeland Security, U.S. Citizenship and Immigration Services, and shall verify and ensure, to the extent possible, the accuracy of the provided social security number and alien registration number, as applicable. b. The procedures developed or enhanced shall include measures for confirming the term, duration, and character of military service for the past 3 years, and/or academic enrollment and attendance in lieu of employment, for the past 5 years. c. Licensees need not conduct an independent investigation for individuals employed at a facility who possess active ``Q'' or ``L'' clearances or possess another active U.S. Government-granted security clearance (i.e., Top Secret, Secret, or Confidential). d. A review of the applicant's criminal history, obtained from local criminal justice resources, may be included in addition to the FBI CHRC, and is encouraged if the results of the FBI CHRC, employment check, or credit check disclose derogatory information. The scope of the applicant's local criminal history check shall cover all residences of record for the past three years from the date of the application for unescorted access. 2. The licensee shall use any information obtained as part of a CHRC solely for the purpose of determining an individual's suitability for unescorted access to the protected area of an ISFSI. 3. The licensee shall document the basis for its determination for granting or denying access to the protected area of an ISFSI. 4. The licensee shall develop, implement, and maintain procedures for updating background investigations for persons who are applying for reinstatement of unescorted access. Licensees need not conduct an independent reinvestigation for individuals who possess active ``Q'' or ``L'' clearances or possess another active U.S. Government-granted security clearance, i.e., Top Secret, Secret or Confidential. 5. The licensee shall develop, implement, and maintain procedures for reinvestigations of persons granted unescorted access, at intervals not to exceed five years. Licensees need not conduct an independent reinvestigation for individuals employed at a facility who possess active ``Q'' or ``L'' clearances or possess another active U.S. Government-granted security clearance, i.e., Top Secret, Secret or Confidential. 6. The licensee shall develop, implement, and maintain procedures designed to ensure that persons who have been denied unescorted access authorization to the facility are not allowed access to the facility, even under escort. 7. The licensee shall develop, implement, and maintain an audit program for licensee and contractor/vendor access authorization programs that evaluate all program elements and include a person knowledgeable and practiced in access authorization program performance objectives to assist in the overall assessment of the site's program effectiveness. C. Fingerprinting Program Requirements 1. In a letter to the NRC, the licensee must nominate an individual who will review the results of the FBI CHRCs to make trustworthiness and reliability determinations for unescorted access to an ISFSI. This individual, referred to as the ``reviewing official,'' must be someone who requires unescorted access to the ISFSI. The NRC will review the CHRC of any individual nominated to perform the reviewing official function. Based on the results of the CHRC, the NRC staff will determine whether this individual may have [[Page 25766]] access. If the NRC determines that the nominee may not be granted such access, that individual will be prohibited from obtaining access.\1\ Once the NRC approves a reviewing official, the reviewing official is the only individual permitted to make access determinations for other individuals who have been identified by the licensee as having the need for unescorted access to the ISFSI, and have been fingerprinted and have had a CHRC in accordance with these ASMs. The reviewing official can only make access determinations for other individuals, and therefore cannot approve other individuals to act as reviewing officials. Only the NRC can approve a reviewing official. Therefore, if the licensee wishes to have a new or additional reviewing official, the NRC must approve that individual before he or she can act in the capacity of a reviewing official. --------------------------------------------------------------------------- \1\ The NRC's determination of this individual's unescorted access to the ISFSI, in accordance with the process, is an administrative determination that is outside the scope of the Order. --------------------------------------------------------------------------- 2. No person may have access to Safeguards Information (SGI) or unescorted access to any facility subject to NRC regulation, if the NRC has determined, in accordance with its administrative review process based on fingerprinting and an FBI identification and CHRC, that the person may not have access to SGI or unescorted access to any facility subject to NRC regulation. 3. All fingerprints obtained by the licensee under this Order must be submitted to the Commission for transmission to the FBI. 4. The licensee shall notify each affected individual that the fingerprints will be used to conduct a review of his/her criminal history record and inform the individual of the procedures for revising the record or including an explanation in the record, as specified in the ``Right to Correct and Complete Information,'' in section F of these ASMs. 5. Fingerprints need not be taken if the employed individual (e.g., a licensee employee, contractor, manufacturer, or supplier) is relieved from the fingerprinting requirement by 10 CFR 73.61, has a favorably adjudicated U.S. Government CHRC within the last 5 years, or has an active Federal security clearance. Written confirmation from the Agency/employer who granted the Federal security clearance or reviewed the CHRC must be provided to the licensee. The licensee must retain this documentation for a period of 3 years from the date the individual no longer requires access to the facility. D. Prohibitions 1. A licensee shall not base a final determination to deny an individual unescorted access to the protected area of an ISFSI solely on the basis of information received from the FBI involving: An arrest more than 1 year old for which there is no information of the disposition of the case, or an arrest that resulted in dismissal of the charge, or an acquittal. 2. A licensee shall not use information received from a CHRC obtained pursuant to this Order in a manner that would infringe upon the rights of any individual under the First Amendment to the Constitution of the United States, nor shall the licensee use the information in any way that would discriminate among individuals on the basis of race, religion, national origin, sex, or age. E. Procedures for Processing Fingerprint Checks 1. For the purpose of complying with this Order, licensees shall, using an appropriate method listed in 10 CFR 73.4, submit to the NRC's Division of Facilities and Security, Mail Stop TWB-05B32M, one completed, legible standard fingerprint card (Form FD-258, ORIMDNRCOOOZ) or, where practicable, other fingerprint records for each individual seeking unescorted access to an ISFSI, to the Director of the Division of Facilities and Security, marked for the attention of the Division's Criminal History Check Section. Copies of these forms may be obtained by writing the Office of Information Services, U.S. Nuclear Regulatory Commission, Washington, DC 20555-0001, by calling (301) 415-5877, or by email to Forms.Resource@nrc.gov. Practicable alternative formats are set forth in 10 CFR 73.4. The licensee shall establish procedures to ensure that the quality of the fingerprints taken results in minimizing the rejection rate of fingerprint cards because of illegible or incomplete cards. 2. The NRC will review submitted fingerprint cards for completeness. Any Form FD-258 fingerprint record containing omissions or evident errors will be returned to the licensee for corrections. The fee for processing fingerprint checks includes one re-submission if the initial submission is returned by the FBI because the fingerprint impressions cannot be classified. The one free re-submission must have the FBI Transaction Control Number reflected on the re-submission. If additional submissions are necessary, they will be treated as initial submittals and will require a second payment of the processing fee. 3. Fees for processing fingerprint checks are due upon application. The licensee shall submit payment of the processing fees electronically. To be able to submit secure electronic payments, licensees will need to establish an account with Pay.Gov (https://www.pay.gov). To request an account, the licensee shall send an email to det@nrc.gov. The email must include the licensee's company name, address, point of contact (POC), POC email address, and phone number. The NRC will forward the request to Pay.Gov, who will contact the licensee with a password and user ID. Once the licensee has established an account and submitted payment to Pay.Gov, they shall obtain a receipt. The licensee shall submit the receipt from Pay.Gov to the NRC along with fingerprint cards. For additional guidance on making electronic payments, contact the Facilities Security Branch, Division of Facilities and Security, at (301) 492-3531. Combined payment for multiple applications is acceptable. The application fee (currently $26) is the sum of the user fee charged by the FBI for each fingerprint card or other fingerprint record submitted by the NRC on behalf of a licensee, and an NRC processing fee, which covers administrative costs associated with NRC handling of licensee fingerprint submissions. The Commission will directly notify licensees who are subject to this regulation of any fee changes. 4. The Commission will forward to the submitting licensee all data received from the FBI as a result of the licensee's application(s) for CHRCs, including the FBI fingerprint record. F. Right To Correct and Complete Information 1. Prior to any final adverse determination, the licensee shall make available to the individual the contents of any criminal history records obtained from the FBI for the purpose of assuring correct and complete information. Written confirmation by the individual of receipt of this notification must be maintained by the licensee for a period of one (1) year from the date of notification. 2. If, after reviewing the record, an individual believes that it is incorrect or incomplete in any respect and wishes to change, correct, or update the alleged deficiency, or to explain any matter in the record, the individual may initiate challenge procedures. These procedures include either direct application by the individual challenging the record to the agency (i.e., law enforcement agency) [[Page 25767]] that contributed the questioned information, or direct challenge as to the accuracy or completeness of any entry on the criminal history record to the Assistant Director, Federal Bureau of Investigation Identification Division, Washington, DC 20537-9700 (as set forth in 28 CFR 16.30 through 16.34). In the latter case, the FBI forwards the challenge to the agency that submitted the data and requests that agency to verify or correct the challenged entry. Upon receipt of an official communication directly from the agency that contributed the original information, the FBI Identification Division makes any changes necessary in accordance with the information supplied by that agency. The licensee must provide at least 10 days for an individual to initiate an action challenging the results of a FBI CHRC after the record is made available for his/her review. The licensee may make a final access determination based on the criminal history record only upon receipt of the FBI's ultimate confirmation or correction of the record. Upon a final adverse determination on access to an ISFSI, the licensee shall provide the individual its documented basis for denial. Access to an ISFSI shall not be granted to an individual during the review process. G. Protection of Information 1. The licensee shall develop, implement, and maintain a system for personnel information management with appropriate procedures for the protection of personal, confidential information. This system shall be designed to prohibit unauthorized access to sensitive information and to prohibit modification of the information without authorization. 2. Each licensee who obtains a criminal history record on an individual pursuant to this Order shall establish and maintain a system of files and procedures, for protecting the record and the personal information from unauthorized disclosure. 3. The licensee may not disclose the record or personal information collected and maintained to persons other than the subject individual, his/her representative, or to those who have a need to access the information in performing assigned duties in the process of determining suitability for unescorted access to the protected area of an ISFSI. No individual authorized to have access to the information may re- disseminate the information to any other individual who does not have the appropriate need to know. 4. The personal information obtained on an individual from a CHRC may be transferred to another licensee if the gaining licensee receives the individual's written request to re-disseminate the information contained in his/her file, and the gaining licensee verifies information such as the individual's name, date of birth, social security number, sex, and other applicable physical characteristics for identification purposes. 5. The licensee shall make criminal history records, obtained under this section, available for examination by an authorized representative of the NRC to determine compliance with the regulations and laws. [FR Doc. 2012-10472 Filed 4-30-12; 8:45 am] BILLING CODE 7590-01-P
TOP-SECRET from the CIA – Project TWO-FOLD
| Citation: | Project TWO-FOLD [Detection of Bureau of Narcotics and Dangerous Drugs Corruption; Attached to Routing and Record Sheets; Includes Action Directive], Secret, Action Memorandum, May 25, 1973, 4 pp. |
| Collection: | The CIA Family Jewels Indexed |
| Item Number: | FJ00004 |
| Origin: | United States. Central Intelligence Agency. Directorate of Management and Services. Office of Security. Director |
| From: | Osborn, Howard J. |
| To: | United States. Central Intelligence Agency. Management Committee. Executive Secretary |
| Individuals/ Organizations Named: |
Colby, William E.; Helms, Richard M.; United States. Central Intelligence Agency. Directorate of Management and Services. Office of Security; United States. Central Intelligence Agency. Inspector General; United States. Department of Justice. Bureau of Narcotics and Dangerous Drugs |
| Subjects: | Government corruption | Interagency cooperation | Narcotics | Personnel management | Project Twofold |
| Abstract: | Describes Central Intelligence Agency recruitment of personnel to detect corruption within Bureau of Narcotics and Dangerous Drugs and to collect intelligence on foreign narcotics traffic; William Colby recommends termination of domestic program. |
| Full Text: | Document – PDF – this link will open in a new window (193 KB) |
Secret from the FBI – Dallas Man Sentenced in Half-Billion-Dollar Ponzi Scheme
BEAUMONT, TX—A federal judge has sentenced a 36-year-old Dallas man in connection with his role in a pair of complex, lucrative oil and gas Ponzi schemes that operated in Michigan and Texas, U.S. Attorney for the Eastern District of Texas John M. Bales announced today.
Joseph Blimline was sentenced to 240 months in federal prison on each of the charges related to the Ponzi schemes following a five-hour sentencing hearing on May 3, 2012, before U.S. District Judge Marcia A. Crone. Judge Crone ordered the sentences to run concurrently and ordered that restitution be made to the victims of the schemes.
“The Michigan agents worked hand in hand with the agents in Texas and with federal and state securities regulators to untangle both of these complicated Ponzi schemes and bring the perpetrators to justice for their abuse of the trust of others to obtain criminal profits,” said U.S. Attorney Bales. “To all potential investors, I urge you to be wary of investment vehicles that promise exorbitant rates of return. Remember: If the opportunity appears too good to be true, then it probably is.”
At the sentencing hearing, the government presented testimony and evidence which established that Blimline and others began operating a Ponzi scheme in Michigan between November 2003 and December 2005, specifically by promising inflated rates of return in order to obtain payments from investors. Lacking any legitimate source of income with which to make payouts to the investors, Blimline directed that later investor payments be used to pay previous investors and diverted investor payments for his own personal benefit. The Michigan scheme netted over $28 million from its investor victims before its collapse.
In early 2006, Blimline exported the Michigan Ponzi scheme to Texas, where Blimline and his new co-conspirators began the operation of Provident Royalties in Dallas. Consistent with his previous actions in Michigan, Blimline made materially false representations and failed to disclose material facts to their investors in order to induce the investors into providing payments to Provident. Blimline received millions of dollars in unsecured loans from investor funds and also directed the purchase by Provident of worthless assets from his Michigan enterprise. In the Provident scheme, funds from later investors were also consistently used to make payments to early investors, resulting in the collapse of the scheme in 2009. The Provident scheme netted over $400 million from approximately 7,700 investor victims.
U.S. Attorney for the Western District of Michigan Donald A. Davis praised the diligent work and cooperation of all involved and said, “Stealing money through fraud and deceit will not be tolerated.”
FBI Detroit Division Special Agent in Charge Andrew G. Arena said, “This sentencing comes as a result of the hard work performed by agents committed to stopping this type of fraud. Those who choose to steal money through the operation of these schemes will be arrested and brought to justice.”
U.S. Postal Inspector in Charge E.C. Woodson said, “The Michigan case is the result of the cooperation between the U.S. Postal Inspection Service, the U.S. Attorney’s Office, and the FBI in protecting the American public. Together we investigated and brought to justice those individuals who attempted to victimize the public. Know that we will continue to supply the resources necessary to investigate arrest and prosecute anyone who would utilize the mail to perpetuate a fraud against the American people.”
This law enforcement action is part of President Barack Obama’s Financial Fraud Enforcement Task Force. President Obama established the interagency Financial Fraud Enforcement Task Force to wage an aggressive, coordinated, and proactive effort to investigate and prosecute financial crimes. The task force includes representatives from a broad range of federal agencies, regulatory authorities, inspectors general, and state and local law enforcement who, working together, bring to bear a powerful array of criminal and civil enforcement resources. The task force is working to improve efforts across the federal executive branch, and with state and local partners, to investigate and prosecute significant financial crimes, ensure just and effective punishment for those who perpetrate financial crimes, combat discrimination in the lending and financial markets, and recover proceeds for victims of financial crimes.
For more information about the task force visit: http://www.stopfraud.gov.
The Michigan case was investigated by the FBI and the U.S. Postal Inspection Service and was prosecuted by Assistant U.S. Attorney for the Western District of Michigan Nils Kessler. The Texas case was investigated by the FBI and prosecuted by Assistant U.S. Attorney for the Eastern District of Texas Shamoil T. Shipchandler.
TOP-SECRET from the FBI – Dallas Man Sentenced in Half-Billion-Dollar Ponzi Scheme
BEAUMONT, TX—A federal judge has sentenced a 36-year-old Dallas man in connection with his role in a pair of complex, lucrative oil and gas Ponzi schemes that operated in Michigan and Texas, U.S. Attorney for the Eastern District of Texas John M. Bales announced today.
Joseph Blimline was sentenced to 240 months in federal prison on each of the charges related to the Ponzi schemes following a five-hour sentencing hearing on May 3, 2012, before U.S. District Judge Marcia A. Crone. Judge Crone ordered the sentences to run concurrently and ordered that restitution be made to the victims of the schemes.
“The Michigan agents worked hand in hand with the agents in Texas and with federal and state securities regulators to untangle both of these complicated Ponzi schemes and bring the perpetrators to justice for their abuse of the trust of others to obtain criminal profits,” said U.S. Attorney Bales. “To all potential investors, I urge you to be wary of investment vehicles that promise exorbitant rates of return. Remember: If the opportunity appears too good to be true, then it probably is.”
At the sentencing hearing, the government presented testimony and evidence which established that Blimline and others began operating a Ponzi scheme in Michigan between November 2003 and December 2005, specifically by promising inflated rates of return in order to obtain payments from investors. Lacking any legitimate source of income with which to make payouts to the investors, Blimline directed that later investor payments be used to pay previous investors and diverted investor payments for his own personal benefit. The Michigan scheme netted over $28 million from its investor victims before its collapse.
In early 2006, Blimline exported the Michigan Ponzi scheme to Texas, where Blimline and his new co-conspirators began the operation of Provident Royalties in Dallas. Consistent with his previous actions in Michigan, Blimline made materially false representations and failed to disclose material facts to their investors in order to induce the investors into providing payments to Provident. Blimline received millions of dollars in unsecured loans from investor funds and also directed the purchase by Provident of worthless assets from his Michigan enterprise. In the Provident scheme, funds from later investors were also consistently used to make payments to early investors, resulting in the collapse of the scheme in 2009. The Provident scheme netted over $400 million from approximately 7,700 investor victims.
U.S. Attorney for the Western District of Michigan Donald A. Davis praised the diligent work and cooperation of all involved and said, “Stealing money through fraud and deceit will not be tolerated.”
FBI Detroit Division Special Agent in Charge Andrew G. Arena said, “This sentencing comes as a result of the hard work performed by agents committed to stopping this type of fraud. Those who choose to steal money through the operation of these schemes will be arrested and brought to justice.”
U.S. Postal Inspector in Charge E.C. Woodson said, “The Michigan case is the result of the cooperation between the U.S. Postal Inspection Service, the U.S. Attorney’s Office, and the FBI in protecting the American public. Together we investigated and brought to justice those individuals who attempted to victimize the public. Know that we will continue to supply the resources necessary to investigate arrest and prosecute anyone who would utilize the mail to perpetuate a fraud against the American people.”
This law enforcement action is part of President Barack Obama’s Financial Fraud Enforcement Task Force. President Obama established the interagency Financial Fraud Enforcement Task Force to wage an aggressive, coordinated, and proactive effort to investigate and prosecute financial crimes. The task force includes representatives from a broad range of federal agencies, regulatory authorities, inspectors general, and state and local law enforcement who, working together, bring to bear a powerful array of criminal and civil enforcement resources. The task force is working to improve efforts across the federal executive branch, and with state and local partners, to investigate and prosecute significant financial crimes, ensure just and effective punishment for those who perpetrate financial crimes, combat discrimination in the lending and financial markets, and recover proceeds for victims of financial crimes.
For more information about the task force visit: http://www.stopfraud.gov.
The Michigan case was investigated by the FBI and the U.S. Postal Inspection Service and was prosecuted by Assistant U.S. Attorney for the Western District of Michigan Nils Kessler. The Texas case was investigated by the FBI and prosecuted by Assistant U.S. Attorney for the Eastern District of Texas Shamoil T. Shipchandler.
TOP-SECRET – Unveiled – France-Lybia Nuclear Cooperation Memo (FR-LY)
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – Chicago Investment Advisor Indicted for Allegedly Causing Clients to Lose $1.5 Million in Fraud Scheme
CHICAGO—A Chicago investment advisor allegedly engaged in an investment fraud scheme that swindled clients, causing them to lose approximately $1.5 million, federal law enforcement officials announced today. The defendant, Dimitry Vishnevetsky, was charged with eight counts of mail or wire fraud and one count of bank fraud in a nine-count indictment returned yesterday by a federal grand jury. Vishnevetsky allegedly raised approximately $1.7 million from investors and misappropriated at least $1.5 million for his own purposes, including to pay for such business and personal expenses as mortgage and car payments, travel and vacations, restaurant bills, athletic club dues, and to make trades for his own benefit, while using additional investor funds to make Ponzi-type payments to clients.
Vishnevetsky, 33, of Chicago, will be arraigned at a later date in U.S. District Court. The charges were announced by Patrick J. Fitzgerald, United States Attorney for the Northern District of Illinois, and Robert D. Grant, Special Agent in Charge of the Chicago Office of the Federal Bureau of Investigation. Also yesterday, the Commodity Futures Trading Commission filed a civil enforcement lawsuit against Vishnevetsky and his companies in federal court in Chicago.
According to the indictment, Vishnevetsky offered and sold investments, including commodities and promissory notes, primarily through Hodges Trading, LLC, and Oxford Capital, LLC, which purported to be in the business of providing brokerage/management services to investors and of managing commodities funds, including the Oxford Global Macro Fund, the Oxford Global Arbitrage Fund, and the Quantum Global Fund, which existed in name only. He also offered and sold promissory notes, described as London Interbank Offered Rate (LIBOR) adjusted notes, through Hodges Trading, which also existed in name only.
The indictment alleges that between September 2006 and March 2012, Vishnevetsky schemed to defraud investors and potential investors by making false representations about the profitability of his prior and current trading, the use of the invested funds, the risks involved, the expected and actual returns on investments and trading, and false representations about Hodges Trading, Oxford Capital and the commodities funds. For example, Vishnevetsky created and provided some investors fraudulent trading results showing profits as high as 36 percent per year, the indictment alleges. “In fact, to the extent that Vishnevetsky engaged in trading, the trading consistently resulted in net losses, not profits,” the indictment states.
The bank fraud count alleges that between 2007 and 2010, Vishnevetsky made false statements to Merrill Lynch Bank & Trust concerning his income and assets to cause the bank to issue, and later modify, two loans totaling approximately $519,500 to purchase a condominium in Chicago. Vishnevetsky subsequently stopped making payments on the loans, the charges allege.
The government is being represented by Assistant U.S. Attorney Jacqueline Stern.
Each count of mail or wire fraud carries a maximum penalty of 20 years in prison and a $250,000 fine, while bank fraud carries a maximum penalty of 30 years in prison and a $1 million fine, and restitution is mandatory. The court may also impose a fine totaling twice the loss to any victim or twice the gain to the defendant, whichever is greater. If convicted, the court must impose a reasonable sentence under federal sentencing statutes and the advisory United States Sentencing Guidelines.
The investigation falls under the umbrella of the Financial Fraud Enforcement Task Force, which includes representatives from a broad range of federal agencies, regulatory authorities, inspectors general, and state and local law enforcement who, working together, bring to bear a powerful array of criminal and civil enforcement resources. The task force is working to improve efforts across the federal executive branch, and with state and local partners, to investigate and prosecute significant financial crimes, ensure just and effective punishment for those who perpetrate financial crimes, combat discrimination in the lending and financial markets, and recover proceeds for victims of financial crimes. For more information on the task force, visit: http://www.StopFraud.gov.
An indictment contains only charges and is not evidence of guilt. The defendant is presumed innocent and is entitled to a fair trial at which the government has the burden of proving guilt beyond a reasonable doubt.
TOP-SECRET from the FBI – Manhattan U.S. Attorney Announces Arrests of Two Individuals in Multi-Million-Dollar Scam
Preet Bharara, the United States Attorney for the Southern District of New York; Eric T. Schneiderman, the New York State Attorney General; and Janice K. Fedarcyk, the Assistant Director in Charge of the New York Office of the Federal Bureau of Investigation (“FBI”), announced charges today against IFEANYICHUKWU ERIC ABAKPORO and LATANYA PIERCE for allegedly swindling an elderly woman out of her multi-million-dollar property in Harlem that she had owned for more than 40 years and then deceiving a bank into giving them a $1.8 million mortgage loan secured by the property. ABAKPORO was arrested Monday in Queens, New York, and PIERCE was arrested yesterday after voluntarily surrendering to the FBI.
Manhattan U.S. Attorney Preet Bharara stated: “As alleged, these two defendants preyed on an elderly woman, using false documents and fraudulent representations to essentially steal her property out from under her. They then allegedly took their brazen scheme one step further, using the property to deceive a bank into lending them more than a million dollars. Sadly, this type of mortgage fraud scheme and exploitation of vulnerable victims have become all too familiar, but as these charges make clear, we are committed to bringing those who perpetrate these types of harmful schemes to justice.”
New York State Attorney General Eric Schneiderman stated: “Through lies and deception, these individuals abused the trust of an elderly woman in order to perpetrate a multi-million-dollar fraud. Now that their despicable scheme has been exposed, they will face justice.”
Assistant Director in Charge Janice K. Fedarcyk stated: “These defendants are charged with spinning a web of lies to steal the victim’s property. Cases like this are rightly a priority for the FBI: fraudulent schemes that victimize the vulnerable and enrich the unscrupulous.”
As alleged in the indictment unsealed yesterday in Manhattan federal court:
Beginning in March 2006, ABAKPORO, a lawyer with an office in Brooklyn, New York, and PIERCE, who worked for ABAKPORO, cultivated a relationship with an elderly woman (“the Victim”) who owned a residential apartment building worth millions of dollars located at 1070 St. Nicholas Avenue in Harlem (the “Property”). As part of the fraud scheme, ABAKPORO and PIERCE earned the Victim’s trust by, among other things, offering to help her manage the Property. This included collecting rent from its tenants on her behalf. However, instead of providing the Victim with the renters’ money, ABAKPORO and PIERCE pocketed it.
ABAKPORO and PIERCE then convinced the Victim to sell her property to them for $3.1 million. While they contracted to buy the property for that amount, at the closing, they presented the Victim with multiple fake and fraudulent checks to make it appear as if they had paid the contracted sale amount, when in fact they had not. Moreover, after the Victim’s attorney had left the closing, ABAKPORO and PIERCE fraudulently induced her to return all of the checks to them by representing that they would safeguard her money and give her a “private mortgage” in the Property, which they explained would include monthly payments made to her based on the money she had effectively loaned them. As part of the scheme, ABAKPORO and PIERCE signed and provided the Victim with a written agreement representing that she had loaned them approximately $1.9 million and in return held a “private mortgage” in the Property. Unbeknownst to the Victim, ABAKPORO and PIERCE never recorded the private mortgage and subsequently submitted a fraudulent application to Washington Mutual Bank seeking a $1.8 mortgage loan secured by the Property. ABAKPORO and PIERCE never disclosed to the bank that the Victim already held a private mortgage on the Property. Instead, ABAKPORO and PIERCE falsely represented to the bank that they had purchased the Property for $3.1 million and owned it “free and clear.” Based on those, and other, fraudulent representations, ABAKPORO and PIERCE obtained a $1.8 million mortgage loan from the bank, which they failed to repay.
As a result of the alleged fraud, the defendants obtained substantially all of the Victim’s assets, and $1.8 million in fraudulently obtained mortgage proceeds. The Property went into default.
***
ABAKPORO, 52, a Nigerian citizen, is a resident of Queens, and PIERCE, 43, is a resident of Brooklyn. They are each charged with wire fraud, bank fraud, wire fraud conspiracy, and bank fraud conspiracy. The wire fraud and wire fraud conspiracy charges each carry a maximum prison term of 20 years. The bank fraud and bank fraud conspiracy charges each carry a maximum prison term of 30 years.
ABAKPORO is currently detained pending his satisfaction of court-ordered bail conditions: a $1 million bond secured by an interest in property and co-signed by three individuals. PIERCE was released on a $500,000 bond to be co-signed by three individuals and secured by two properties.
Mr. Bharara praised the New York State Attorney General’s Office investigative staff and the FBI for their excellent work on the investigation of this matter. He also thanked the New York State Department of Financial Services for its assistance.
The case is being handled by the Office’s Complex Frauds Unit. Southern District of New York Assistant U.S. Attorneys Ryan Poscablo and Michael Lockard, along with Assistant Attorney General Meryl Lutsky, who has been designated a Special Assistant U.S. Attorney, and Assistant Attorney General Rhonda Greenstein, are in charge of the prosecution.
The charges contained in the indictment are merely accusations, and the defendants are presumed innocent unless and until proven guilty.
TOP-SECRET from the FBI – Al Qaeda – Most Serious Terrorist Threats to the United States Since 9/11
BROOKLYN, NY—Earlier today, following a four-week trial, Adis Medunjanin, age 34, a Queens resident who joined al Qaeda and plotted to commit a suicide terrorist attack, was found guilty of multiple federal terrorism offenses. The defendant and his accomplices came within days of executing a plot to conduct coordinated suicide bombings in the New York City subway system in September 2009, as directed by senior al Qaeda leaders in Pakistan. When the plot was foiled, the defendant attempted to commit a terrorist attack by crashing his car on the Whitestone Expressway in an effort to kill himself and others.
The guilty verdict was announced by Loretta E. Lynch, United States Attorney for the Eastern District of New York, and Lisa Monaco, Assistant Attorney General for National Security.
The government’s evidence in this and related cases established that in 2008, Medunjanin and his co-plotters, Najibullah Zazi and Zarein Ahmedzay, agreed to travel to Afghanistan to join the Taliban and kill United States military personnel abroad. They arrived in Peshawar, Pakistan, in late August 2008, but Medunjanin and Ahmedzay were turned back at the Afghanistan border. Within days, Medunjanin, Zazi, and Ahmedzay met with an al Qaeda facilitator in Peshawar and agreed to travel to Waziristan for terrorist training. There, they met with al Qaeda leaders Saleh al-Somali, then the head of al Qaeda external operations, and Rashid Rauf, a high-ranking al Qaeda operative, who explained that the three would be more useful to al Qaeda and the jihad by returning to New York and conducting terrorist attacks. In Waziristan, Medunjanin, Zazi, and Ahmedzay received al Qaeda training on how to use various types of high-powered weapons, including the AK-47, PK machine gun, and rocket-propelled grenade launcher. During the training, al Qaeda leaders continued to encourage Medunjanin and his fellow plotters to return to the United States to conduct “martyrdom” operations and emphasized the need to hit well-known targets and maximize the number of casualties. Medunjanin, Zazi, and Ahmedzay agreed and discussed the timing of the attacks and possible target locations in Manhattan, including the subway system, Grand Central Station, the New York Stock Exchange, Times Square, and movie theaters.
Upon their return to the United States, Medunjanin, Zazi, and Ahmedzay met and agreed to carry out suicide bombings during the Muslim holiday of Ramadan, which fell in late August and September 2009. Zazi would prepare the explosives, and all three would conduct coordinated suicide bombings. In July and August 2009, Zazi purchased large quantities of component chemicals necessary to produce the explosive TATP [triacetone triperoxide] and twice checked into a hotel room near Denver, Colorado, to mix the chemicals. Federal investigators later found bomb-making residue in the hotel room.
On September 8, 2009, Zazi drove from Denver to New York, carrying operational detonator explosives and other materials necessary to build bombs. However, shortly after arriving in New York, he learned that law enforcement was investigating the plotters’ activities. The men discarded the explosives and other bomb-making materials, and Zazi traveled back to Denver, where he was arrested on September 19, 2009.
On January 7, 2010, law enforcement agents executed a search warrant at Medunjanin’s residence. Shortly thereafter, Medunjanin left his apartment and attempted to turn his car into a weapon of terror by crashing it into another car at high speed on the Whitestone Expressway. Moments before impact, Medunjanin called 911, identified himself, and left his message of martyrdom, shouting an al Qaeda slogan: “We love death more than you love your life.”
Today, Medunjanin was convicted of conspiring to use weapons of mass destruction, conspiring to commit murder of U.S. military personnel abroad, providing and conspiring to provide material support to al Qaeda, receiving military training from al Qaeda, conspiring and attempting to commit an act of terrorism transcending national boundaries, and using firearms and a destructive devices in relation to these offenses. When sentenced by United States District Judge John Gleeson on September 7, 2012, Medunjanin faces a mandatory sentence of life in prison. To date, seven defendants, including Medunjanin, Zazi, and Ahmedzay, have been convicted in connection with the al Qaeda New York City bombing plot and related charges.
“Justice was served today in Brooklyn, as a jury of New Yorkers convicted an al Qaeda operative bent on terrorism, mass murder, and destruction in the New York City subways,” stated United States Attorney Lynch. “Adis Medunjanin’s journey of radicalization led him from Flushing, Queens, to Peshawar, Pakistan, to the brink of a terrorist attack in New York City—and soon to a lifetime in federal prison. As this case has proved, working against sophisticated terrorist organizations and against the clock, our law enforcement and intelligence agencies can detect, disrupt and destroy terrorist cells before they strike, saving countless innocent lives.” Ms. Lynch expressed her gratitude and appreciation to the FBI Joint Terrorism Task Force in New York and each of the federal, state, and local law enforcement personnel who took part in the investigation, as well as to the law enforcement authorities in the United Kingdom and Norway who assisted with the case.
“Adis Medunjanin was an active and willing participant in one of the most serious terrorist plots against the homeland since 9/11. Were it not for the combined efforts of the law enforcement and intelligence communities, the suicide bomb attacks that he and others planned would have been devastating,” said Assistant Attorney General for National Security Monaco. “I thank the many agents, analysts, and prosecutors who helped bring about today’s result. I also thank our counterparts in the United Kingdom for their assistance in this investigation and prosecution.”
The government’s case was prosecuted by Assistant United States Attorneys David Bitkower, James P. Loonam and Berit W. Berger of the U.S. Attorney’s Office for the Eastern District of New York, with assistance provided by the Counterterrorism Section of the Justice Department’s National Security Division.
TOP-SECRET – Suspicious Activity Reporting Line Officer Training Video
A video created by the Bureau of Justice Assistance to train line officers on what to look for and how to report suspicious activity. For a full transcript of the video, see:
http://publicintelligence.net/sar-training-video/
The video was made by the Bureau of Justice Assistance and the International Association of Chiefs of Police. It is designed to inform law enforcement “line officers” of standards for reporting suspicious activity in furtherance of the Nationwide Suspicious Activity Reporting Initiative (NSI). The video and transcript were obtained from the website of the Department of Public Safety in New Mexico. Interestingly, the transcript includes multiple paragraphs at the end referring to the role of fusion centers and the Joint Terrorism Task Force (JTTF) in the suspicious activity reporting cycle that are not mentioned in the video.
SAR Line Officer Training Transcript
Suspicious Activity Reporting—Line Officer Training
This training is designed to:
- Increase your awareness of the Nationwide Suspicious Activity Reporting or (SAR) Initiative (NSI).
- Enhance your understanding of the behaviors associated with pre-incident terrorism activities.
- Convey the significance of your role in documenting and reporting suspicious activity.
- Emphasize the importance of protecting privacy, civil rights, and civil liberties as you document and share information.
You are the nation’s strongest force in the fight against terrorism. As a frontline law enforcement officer, you are trained to recognize behaviors and activities that are suspicious, and your daily duties position you to observe and report these suspicious behaviors and activities.
Like other criminals, terrorists engage in precursor actions to carry out their plot for destruction. They make plans, acquire materials, engage in intelligence collection, and often commit other criminal activities in support of their plan. These actions produce activities or behaviors that may be suspicious, indicators of what may lie ahead, or possible pieces to a larger puzzle. By identifying, documenting, and sharing information regarding suspicious behaviors and activities that have a potential terrorism nexus, we will all be better prepared to prevent future terrorist attacks in our communities.
The NSI establishes a capacity for sharing terrorism and related criminal activity SARs. The SAR process focuses on what law enforcement has been doing for years—gathering, documenting, processing, analyzing, and sharing information regarding suspicious activity. The NSI is designed to share and analyze the information you observe and report each day with other information gathered across the nation in an effort to detect and disrupt terrorist activity.
How do you identify terrorism behavior? Anyone can be a terrorist. The key is NOT to focus on Who—the race, ethnicity, gender, or religious beliefs of those we think might be involved in suspicious activities—but rather to focus on identifying the behaviors. When observing behaviors, officers need to take into account the totality of circumstances—such as What, Where, When, and How.
SARs focus on observed behaviors and incidents reasonably indicative of preoperational planning related to terrorism or other criminal activity. These activities are suspicious based upon:
- What—the observable behaviors
- Where—the location of specific activities
- When—the timelines of events
- How—the tools and methods
Previous terrorism events have been reviewed and analyzed for commonalities. The result is a compilation of indicators and behaviors that were present in previous terrorist events. Although these behaviors do not mean that someone is definitely engaged in criminal or terrorist activity, they do provide justification for further analysis. The following types of suspicious activity are examples of potential terrorism-related behaviors that should be documented when observed.
- Breach or attempted intrusion of a restricted area by unauthorized persons, such as using false credentials to access government buildings or military installations.
- Misrepresentation or presentation of false documents or identification to cover illicit activity, such as stolen or counterfeit identification or fraudulent warrants, subpoenas, or liens.
- Theft, loss, or diversion of materials associated with a facility or structure, such as stolen badges, uniforms, or emergency vehicles that are proprietary to a facility.
- Sabotage, tampering, or vandalism of a facility or protected site, such as arson or damage committed at a research or industrial facility.
- Expressed or implied threat to damage or compromise a facility or structure, such as written or verbal threats against individuals, groups, or targets.
- Eliciting information beyond curiosity about a facility’s or building’s purpose, operations, or security, such as attempts to obtain specific information about personnel or occupants, equipment, or training related to the security of a facility.
- Testing or probing of security to reveal physical, personnel, or cyber security capabilities, such as repeated false alarms intended to test law enforcement response time and rehearse procedures.
- Material acquisition or storage of unusual quantities of materials, such as weapons, cell phones, pagers, fuel, chemicals, toxic materials, and timers.
- Photography, observation, or surveillance of facilities, buildings, or critical infrastructure and key resources beyond casual, tourism, or artistic interest, to include facility access points, staff or occupants, or security measures.
Photography and other similar activities are protected activities unless connected to other suspicious activities that would indicate potential terrorism. This may cause the officer to conduct additional observation or gather additional information—again taking into account the totality of circumstances.
Protecting the privacy, civil rights, and civil liberties of Americans is critical to preserving our democratic principles and to building trust between law enforcement and the people we serve. Only by building trust will we achieve a level of citizen cooperation with law enforcement that will maximize our ability to keep our communities and our nation safe and secure from crime and terrorism.
As you document and report these or other types of suspicious activity, protection of privacy, civil rights, and civil liberties is paramount. Just as you do in your other daily law enforcement duties, you must:
- Collect information in a lawful manner.
- Protect the rights of the individual.
- Avoid collecting information protected by the Bill of Rights.
- Ensure information is as accurate as possible.
Profiling of individuals based on their race, color, national origin, or religion is not acceptable in reporting terrorism-related suspicious activity, just as it is not acceptable in other law enforcement actions. Remember, First Amendment rights to free speech, religion, assembly, and so forth ensure that people can express their beliefs and take other protected actions without government intrusion. Protection of privacy, civil rights, and civil liberties is a fundamental principle that underlies the Nationwide SAR Initiative.
The Nationwide SAR Cycle starts with you and depends on involvement from all levels of law enforcement to ensure that information gathered on the street reaches all appropriate stakeholders.
Every state and many major metropolitan areas have developed intelligence fusion centers to make sure that terrorism and other criminal information is analyzed and forwarded to the appropriate jurisdiction for follow-up investigation.
When you collect and document suspicious activity information, that information is routed to your supervisor and others for evaluation in accordance with your departmental policy. SAR information is then entered into a local, regional, state, or federal system and submitted to a fusion center for review by a trained analyst or investigator. The reviewer determines whether the information has a nexus to terrorism and meets the criteria for sharing nationwide. If so, it is forwarded to the Federal Bureau of Investigation Joint Terrorism Task Force (JTTF) for investigative follow-up.
TOP-SECRET – NRC on Threat of Nuclear Plant Insider Radiological Sabotage
[Federal Register Volume 77, Number 84 (Tuesday, May 1, 2012)] [Notices] [Pages 25762-25767] From the Federal Register Online via the Government Printing Office [www.gpo.gov] [FR Doc No: 2012-10472] ----------------------------------------------------------------------- NUCLEAR REGULATORY COMMISSION [Docket No. 72-1039; NRC-2012-0099; EA-12-047] In the Matter of Southern Nuclear Operating Company, Inc., Vogtle Electric Generating Plant, Independent Spent Fuel Storage Installation; Order Modifying License (Effective Immediately) AGENCY: Nuclear Regulatory Commission. ACTION: Issuance of order for implementation of additional security measures and fingerprinting for unescorted access to Southern Nuclear Operating Company, Inc. ----------------------------------------------------------------------- FOR FURTHER INFORMATION CONTACT: L. Raynard Wharton, Senior Project Manager, Licensing and Inspection Directorate, Division of Spent Fuel Storage and Transportation, Office of Nuclear Material Safety and Safeguards, U.S. Nuclear Regulatory Commission, Rockville, Maryland 20852; telephone: (301) 492-3316; fax number: (301) 492-3348; email: Raynard.Wharton@nrc.gov. SUPPLEMENTARY INFORMATION: I. Introduction Pursuant to Title 10 of the Code of Federal Regulations (10 CFR) 2.106, the U.S. Nuclear Regulatory Commission (NRC or the Commission) is providing notice, in the matter of Vogtle Electric Generating Plant Independent Spent Fuel Storage Installation (ISFSI) Order Modifying License (Effective Immediately). II. Further Information I The NRC has issued a general license to Southern Nuclear Operating Company, Inc. (SNC), authorizing the operation of an ISFSI, in accordance with the Atomic Energy Act of 1954, as amended, and 10 CFR part 72. This Order is being issued to SNC because it has identified near-term plans to store spent fuel in an ISFSI under the general license provisions of 10 CFR part 72. The Commission's regulations at 10 CFR 72.212(b)(5), 10 CFR 50.54(p)(1), and 10 CFR 73.55(c)(5) require licensees to maintain safeguards contingency plan procedures to respond to threats of radiological sabotage and to protect the spent fuel against the threat of radiological sabotage, in accordance with 10 CFR part 73, appendix C. Specific physical security requirements are contained in 10 CFR 73.51 or 73.55, as applicable. Inasmuch as an insider has an opportunity equal to, or greater than, any other person, to commit radiological sabotage, the Commission has determined these measures to be prudent. Comparable Orders have been issued to all licensees that currently store spent fuel or have identified near-term plans to store spent fuel in an ISFSI. II On September 11, 2001, terrorists simultaneously attacked targets in New York, NY, and Washington, DC, using large commercial aircraft as weapons. In response to the attacks and intelligence information subsequently obtained, the Commission issued a number of Safeguards and Threat Advisories to its licensees to strengthen licensees' capabilities and readiness to respond to a potential attack on a nuclear facility. On October 16, 2002, the Commission issued Orders to the licensees of operating ISFSIs, to place the actions taken in response to the Advisories into the established regulatory framework and to implement additional security enhancements that emerged from NRC's ongoing comprehensive review. The Commission has also communicated with other Federal, State, and local government agencies and industry representatives to discuss and evaluate the current threat environment in order to assess the adequacy of security measures at licensed facilities. In addition, the Commission has conducted a comprehensive review of its safeguards and security programs and requirements. As a result of its consideration of current safeguards and security [[Page 25763]] requirements, as well as a review of information provided by the intelligence community, the Commission has determined that certain additional security measures (ASMs) are required to address the current threat environment, in a consistent manner throughout the nuclear ISFSI community. Therefore, the Commission is imposing requirements, as set forth in Attachments 1 and 2 of this Order, on all licensees of these facilities. These requirements, which supplement existing regulatory requirements, will provide the Commission with reasonable assurance that the public health and safety, the environment, and common defense and security continue to be adequately protected in the current threat environment. These requirements will remain in effect until the Commission determines otherwise. The Commission recognizes that licensees may have already initiated many of the measures set forth in Attachments 1 and 2 to this Order, in response to previously issued Advisories, or on their own. It also recognizes that some measures may not be possible or necessary at some sites, or may need to be tailored to accommodate the specific circumstances existing at SNC's facility, to achieve the intended objectives and avoid any unforeseen effect on the safe storage of spent fuel. Although the ASMs implemented by licensees in response to the Safeguards and Threat Advisories have been sufficient to provide reasonable assurance of adequate protection of public health and safety, in light of the continuing threat environment, the Commission concludes that these actions must be embodied in an Order, consistent with the established regulatory framework. To provide assurance that licensees are implementing prudent measures to achieve a consistent level of protection to address the current threat environment, licenses issued pursuant to 10 CFR 72.210 shall be modified to include the requirements identified in Attachments 1 and 2 to this Order. In addition, pursuant to 10 CFR 2.202, I find that, in light of the common defense and security circumstances described above, the public health, safety, and interest require that this Order be effective immediately. III Accordingly, pursuant to Sections 53, 103, 104, 147, 149, 161b, 161i, 161o, 182, and 186 of the Atomic Energy Act of 1954, as amended, and the Commission's regulations in 10 CFR 2.202 and 10 CFR parts 50, 72, and 73, it is hereby ordered, effective immediately, that your general license is modified as follows: A. SNC shall comply with the requirements described in Attachments 1 and 2 to this Order, except to the extent that a more stringent requirement is set forth in the Vogtle Electric Generating Plant's physical security plan. SNC shall demonstrate its ability to comply with the requirements in Attachments 1 and 2 to the Order no later than 365 days from the date of this Order or 90 days before the first day that spent fuel is initially placed in the ISFSI, whichever is earlier. SNC must implement these requirements before initially placing spent fuel in the ISFSI. Additionally, SNC must receive written verification from the NRC that it has adequately demonstrated compliance with these requirements before initially placing spent fuel in the ISFSI. B. 1. SNC shall, within twenty (20) days of the date of this Order, notify the Commission: (1) If it is unable to comply with any of the requirements described in Attachments 1 and 2; (2) if compliance with any of the requirements is unnecessary, in its specific circumstances; or (3) if implementation of any of the requirements would cause SNC to be in violation of the provisions of any Commission regulation or the facility license. The notification shall provide SNC's justification for seeking relief from, or variation of, any specific requirement. 2. If SNC considers that implementation of any of the requirements described in Attachments 1 and 2 to this Order would adversely impact the safe storage of spent fuel, SNC must notify the Commission, within twenty (20) days of this Order, of the adverse safety impact, the basis for its determination that the requirement has an adverse safety impact, and either a proposal for achieving the same objectives specified in Attachments 1 and 2 requirements in question, or a schedule for modifying the facility, to address the adverse safety condition. If neither approach is appropriate, SNC must supplement its response, to Condition B.1 of this Order, to identify the condition as a requirement with which it cannot comply, with attendant justifications, as required under Condition B.1. C. 1. SNC shall, within twenty (20) days of this Order, submit to the Commission, a schedule for achieving compliance with each requirement described in Attachments 1 and 2. 2. SNC shall report to the Commission when it has achieved full compliance with the requirements described in Attachments 1 and 2. D. All measures implemented or actions taken in response to this Order shall be maintained until the Commission determines otherwise. SNC's response to Conditions B.1, B.2, C.1, and C.2, above, shall be submitted in accordance with 10 CFR 72.4. In addition, submittals and documents produced by SNC as a result of this Order, that contain Safeguards Information as defined by 10 CFR 73.22, shall be properly marked and handled, in accordance with 10 CFR 73.21 and 73.22. The Director, Office of Nuclear Material Safety and Safeguards, may, in writing, relax or rescind any of the above conditions, for good cause. IV In accordance with 10 CFR 2.202, SNC must, and any other person adversely affected by this Order may, submit an answer to this Order within 20 days of its publication in the Federal Register. In addition, SNC and any other person adversely affected by this Order may request a hearing on this Order within 20 days of its publication in the Federal Register. Where good cause is shown, consideration will be given to extending the time to answer or request a hearing. A request for extension of time must be made, in writing, to the Director, Office of Nuclear Material Safety and Safeguards, U.S. Nuclear Regulatory Commission, Washington, DC 20555-0001, and include a statement of good cause for the extension. The answer may consent to this Order. If the answer includes a request for a hearing, it shall, under oath or affirmation, specifically set forth the matters of fact and law on which SNC relies and the reasons as to why the Order should not have been issued. If a person other than SNC requests a hearing, that person shall set forth with particularity the manner in which his/her interest is adversely affected by this Order and shall address the criteria set forth in 10 CFR 2.309(d). All documents filed in NRC adjudicatory proceedings, including a request for hearing, a petition for leave to intervene, any motion or other document filed in the proceeding prior to the submission of a request for hearing or petition to intervene, and documents filed by interested governmental entities participating under 10 CFR 2.315(c), must be filed in accordance with the NRC E-Filing rule (72 FR 49139, August 28, 2007). The E-Filing process requires participants to submit and serve all adjudicatory [[Page 25764]] documents over the internet, or in some cases to mail copies on electronic storage media. Participants may not submit paper copies of their filings unless they seek an exemption in accordance with the procedures described below. To comply with the procedural requirements of E-Filing, at least 10 days prior to the filing deadline, the participant should contact the Office of the Secretary by email at hearing.docket@nrc.gov, or by telephone at 301-415-1677, to request (1) a digital identification (ID) certificate, which allows the participant (or its counsel or representative) to digitally sign documents and access the E-Submittal server for any proceeding in which it is participating; and (2) advise the Secretary that the participant will be submitting a request or petition for hearing (even in instances in which the participant, or its counsel or representative, already holds an NRC-issued digital ID certificate). Based upon this information, the Secretary will establish an electronic docket for the hearing in this proceeding if the Secretary has not already established an electronic docket. Information about applying for a digital ID certificate is available on the NRC's public Web site at http://www.nrc.gov/site-help/e-submittals/apply-certificates.html. System requirements for accessing the E-Submittal server are detailed in the NRC's ``Guidance for Electronic Submission,'' which is available on the NRC's public Web site at http://www.nrc.gov/site-help/e-submittals.html. Participants may attempt to use other software not listed on the Web site, but should note that the NRC's E-Filing system does not support unlisted software, and the NRC Meta System Help Desk will not be able to offer assistance in using unlisted software. If a participant is electronically submitting a document to the NRC in accordance with the E-Filing rule, the participant must file the document using the NRC's online, Web-based submission form. In order to serve documents through the Electronic Information Exchange System, users will be required to install a Web browser plug-in from the NRC's Web site. Further information on the Web-based submission form, including the installation of the Web browser plug-in, is available on the NRC's public Web site at http://www.nrc.gov/site-help/e-submittals.html. Once a participant has obtained a digital ID certificate and a docket has been created, the participant can then submit a request for hearing or petition for leave to intervene. Submissions should be in Portable Document Format (PDF) in accordance with the NRC guidance available on the NRC's public Web site at http://www.nrc.gov/site-help/e-submittals.html. A filing is considered complete at the time the documents are submitted through the NRC's E-Filing system. To be timely, an electronic filing must be submitted to the E-Filing system no later than 11:59 p.m. Eastern Time on the due date. Upon receipt of a transmission, the E-Filing system time-stamps the document and sends the submitter an email notice confirming receipt of the document. The E-Filing system also distributes an email notice that provides access to the document to the NRC's Office of the General Counsel and any others who have advised the Office of the Secretary that they wish to participate in the proceeding, so that the filer need not serve the documents on those participants separately. Therefore, applicants and other participants (or their counsel or representative) must apply for and receive a digital ID certificate before a hearing request/petition to intervene is filed so that they can obtain access to the document via the E-Filing system. A person filing electronically using the NRC's adjudicatory E- Filing system may seek assistance by contacting the NRC Meta System Help Desk through the ``Contact Us'' link located on the NRC's Web site at http://www.nrc.gov/site-help/e-submittals.html, by email to MSHD.Resource@nrc.gov, or by a toll-free call to 1-866-672-7640. The NRC Meta System Help Desk is available between 8 a.m. and 8 p.m., Eastern Time, Monday through Friday, excluding government holidays. Participants who believe that they have a good cause for not submitting documents electronically must file an exemption request, in accordance with 10 CFR 2.302(g), with their initial paper filing requesting authorization to continue to submit documents in paper format. Such filings must be submitted by: (1) First class mail addressed to the Office of the Secretary of the Commission, U.S. Nuclear Regulatory Commission, Washington, DC 20555-0001, Attention: Rulemaking and Adjudications Staff; or (2) courier, express mail, or expedited delivery service to the Office of the Secretary, Sixteenth Floor, One White Flint North, 11555 Rockville Pike, Rockville, Maryland, 20852, Attention: Rulemaking and Adjudications Staff. Participants filing a document in this manner are responsible for serving the document on all other participants. Filing is considered complete by first-class mail as of the time of deposit in the mail, or by courier, express mail, or expedited delivery service upon depositing the document with the provider of the service. A presiding officer, having granted an exemption request from using E-Filing, may require a participant or party to use E-Filing if the presiding officer subsequently determines that the reason for granting the exemption from use of E-Filing no longer exists. Documents submitted in adjudicatory proceedings will appear in the NRC's electronic hearing docket which is available to the public at http://ehd1.nrc.gov/ehd/, unless excluded pursuant to an order of the Commission, or the presiding officer. Participants are requested not to include personal privacy information, such as social security numbers, home addresses, or home phone numbers in their filings, unless an NRC regulation or other law requires submission of such information. With respect to copyrighted works, except for limited excerpts that serve the purpose of the adjudicatory filings and would constitute a Fair Use application, participants are requested not to include copyrighted materials in their submission. If a hearing is requested by SNC or a person whose interest is adversely affected, the Commission will issue an Order designating the time and place of any hearing. If a hearing is held, the issue to be considered at such hearing shall be whether this Order should be sustained. Pursuant to 10 CFR 2.202(c)(2)(i), SNC may, in addition to requesting a hearing, at the time the answer is filed or sooner, move the presiding officer to set aside the immediate effectiveness of the Order on the grounds that the Order, including the need for immediate effectiveness, is not based on adequate evidence, but on mere suspicion, unfounded allegations, or error. In the absence of any request for hearing, or written approval of an extension of time in which to request a hearing, the provisions as specified in Section III shall be final twenty (20) days from the date this Order is published in the Federal Register, without further Order or proceedings. If an extension of time for requesting a hearing has been approved, the provisions as specified in Section III, shall be final when the extension expires, if a hearing request has not been received. An answer or a request for hearing shall not stay the immediate effectiveness of this order. [[Page 25765]] Dated at Rockville, Maryland, this 23rd day of April, 2012. For the Nuclear Regulatory Commission. Catherine Haney, Director, Office of Nuclear Material Safety and Safeguards. Attachment 1--Additional Security Measures (ASMs) for Physical Protection of Dry Independent Spent Fuel Storage Installations (ISFSIs) contains Safeguards Information and is not included in the Federal Register notice Attachment 2--Additional Security Measures for Access Authorization and Fingerprinting at Independent Spent Fuel Storage Installations, Dated June 3, 2010 A. General Basis Criteria 1. These additional security measures (ASMs) are established to delineate an independent spent fuel storage installation (ISFSI) licensee's responsibility to enhance security measures related to authorization for unescorted access to the protected area of an ISFSI in response to the current threat environment. 2. Licensees whose ISFSI is collocated with a power reactor may choose to comply with the U.S. Nuclear Regulatory Commission (NRC)- approved reactor access authorization program for the associated reactor as an alternative means to satisfy the provisions of sections B through G below. Otherwise, licensees shall comply with the access authorization and fingerprinting requirements of sections B through G of these ASMs. 3. Licensees shall clearly distinguish in their 20-day response which method they intend to use in order to comply with these ASMs. B. Additional Security Measures for Access Authorization Program 1. The licensee shall develop, implement and maintain a program, or enhance its existing program, designed to ensure that persons granted unescorted access to the protected area of an ISFSI are trustworthy and reliable and do not constitute an unreasonable risk to the public health and safety or the common defense and security, including a potential to commit radiological sabotage. a. To establish trustworthiness and reliability, the licensee shall develop, implement, and maintain procedures for conducting and completing background investigations, prior to granting access. The scope of background investigations must address at least the past three years and, as a minimum, must include: i. Fingerprinting and a Federal Bureau of Investigation (FBI) identification and criminal history records check (CHRC). Where an applicant for unescorted access has been previously fingerprinted with a favorably completed CHRC (such as a CHRC pursuant to compliance with orders for access to safeguards information), the licensee may accept the results of that CHRC, and need not submit another set of fingerprints, provided the CHRC was completed not more than three years from the date of the application for unescorted access. ii. Verification of employment with each previous employer for the most recent year from the date of application. iii. Verification of employment with an employer of the longest duration during any calendar month for the remaining next most recent 2 years. iv. A full credit history review. v. An interview with not less than two character references, developed by the investigator. vi. A review of official identification (e.g., driver's license; passport; government identification; state-, province-, or country-of- birth issued certificate of birth) to allow comparison of personal information data provided by the applicant. The licensee shall maintain a photocopy of the identifying document(s) on file, in accordance with ``Protection of Information,'' in section G of these ASMs. vii. Licensees shall confirm eligibility for employment through the regulations of the U.S. Department of Homeland Security, U.S. Citizenship and Immigration Services, and shall verify and ensure, to the extent possible, the accuracy of the provided social security number and alien registration number, as applicable. b. The procedures developed or enhanced shall include measures for confirming the term, duration, and character of military service for the past 3 years, and/or academic enrollment and attendance in lieu of employment, for the past 5 years. c. Licensees need not conduct an independent investigation for individuals employed at a facility who possess active ``Q'' or ``L'' clearances or possess another active U.S. Government-granted security clearance (i.e., Top Secret, Secret, or Confidential). d. A review of the applicant's criminal history, obtained from local criminal justice resources, may be included in addition to the FBI CHRC, and is encouraged if the results of the FBI CHRC, employment check, or credit check disclose derogatory information. The scope of the applicant's local criminal history check shall cover all residences of record for the past three years from the date of the application for unescorted access. 2. The licensee shall use any information obtained as part of a CHRC solely for the purpose of determining an individual's suitability for unescorted access to the protected area of an ISFSI. 3. The licensee shall document the basis for its determination for granting or denying access to the protected area of an ISFSI. 4. The licensee shall develop, implement, and maintain procedures for updating background investigations for persons who are applying for reinstatement of unescorted access. Licensees need not conduct an independent reinvestigation for individuals who possess active ``Q'' or ``L'' clearances or possess another active U.S. Government-granted security clearance, i.e., Top Secret, Secret or Confidential. 5. The licensee shall develop, implement, and maintain procedures for reinvestigations of persons granted unescorted access, at intervals not to exceed five years. Licensees need not conduct an independent reinvestigation for individuals employed at a facility who possess active ``Q'' or ``L'' clearances or possess another active U.S. Government-granted security clearance, i.e., Top Secret, Secret or Confidential. 6. The licensee shall develop, implement, and maintain procedures designed to ensure that persons who have been denied unescorted access authorization to the facility are not allowed access to the facility, even under escort. 7. The licensee shall develop, implement, and maintain an audit program for licensee and contractor/vendor access authorization programs that evaluate all program elements and include a person knowledgeable and practiced in access authorization program performance objectives to assist in the overall assessment of the site's program effectiveness. C. Fingerprinting Program Requirements 1. In a letter to the NRC, the licensee must nominate an individual who will review the results of the FBI CHRCs to make trustworthiness and reliability determinations for unescorted access to an ISFSI. This individual, referred to as the ``reviewing official,'' must be someone who requires unescorted access to the ISFSI. The NRC will review the CHRC of any individual nominated to perform the reviewing official function. Based on the results of the CHRC, the NRC staff will determine whether this individual may have [[Page 25766]] access. If the NRC determines that the nominee may not be granted such access, that individual will be prohibited from obtaining access.\1\ Once the NRC approves a reviewing official, the reviewing official is the only individual permitted to make access determinations for other individuals who have been identified by the licensee as having the need for unescorted access to the ISFSI, and have been fingerprinted and have had a CHRC in accordance with these ASMs. The reviewing official can only make access determinations for other individuals, and therefore cannot approve other individuals to act as reviewing officials. Only the NRC can approve a reviewing official. Therefore, if the licensee wishes to have a new or additional reviewing official, the NRC must approve that individual before he or she can act in the capacity of a reviewing official. --------------------------------------------------------------------------- \1\ The NRC's determination of this individual's unescorted access to the ISFSI, in accordance with the process, is an administrative determination that is outside the scope of the Order. --------------------------------------------------------------------------- 2. No person may have access to Safeguards Information (SGI) or unescorted access to any facility subject to NRC regulation, if the NRC has determined, in accordance with its administrative review process based on fingerprinting and an FBI identification and CHRC, that the person may not have access to SGI or unescorted access to any facility subject to NRC regulation. 3. All fingerprints obtained by the licensee under this Order must be submitted to the Commission for transmission to the FBI. 4. The licensee shall notify each affected individual that the fingerprints will be used to conduct a review of his/her criminal history record and inform the individual of the procedures for revising the record or including an explanation in the record, as specified in the ``Right to Correct and Complete Information,'' in section F of these ASMs. 5. Fingerprints need not be taken if the employed individual (e.g., a licensee employee, contractor, manufacturer, or supplier) is relieved from the fingerprinting requirement by 10 CFR 73.61, has a favorably adjudicated U.S. Government CHRC within the last 5 years, or has an active Federal security clearance. Written confirmation from the Agency/employer who granted the Federal security clearance or reviewed the CHRC must be provided to the licensee. The licensee must retain this documentation for a period of 3 years from the date the individual no longer requires access to the facility. D. Prohibitions 1. A licensee shall not base a final determination to deny an individual unescorted access to the protected area of an ISFSI solely on the basis of information received from the FBI involving: An arrest more than 1 year old for which there is no information of the disposition of the case, or an arrest that resulted in dismissal of the charge, or an acquittal. 2. A licensee shall not use information received from a CHRC obtained pursuant to this Order in a manner that would infringe upon the rights of any individual under the First Amendment to the Constitution of the United States, nor shall the licensee use the information in any way that would discriminate among individuals on the basis of race, religion, national origin, sex, or age. E. Procedures for Processing Fingerprint Checks 1. For the purpose of complying with this Order, licensees shall, using an appropriate method listed in 10 CFR 73.4, submit to the NRC's Division of Facilities and Security, Mail Stop TWB-05B32M, one completed, legible standard fingerprint card (Form FD-258, ORIMDNRCOOOZ) or, where practicable, other fingerprint records for each individual seeking unescorted access to an ISFSI, to the Director of the Division of Facilities and Security, marked for the attention of the Division's Criminal History Check Section. Copies of these forms may be obtained by writing the Office of Information Services, U.S. Nuclear Regulatory Commission, Washington, DC 20555-0001, by calling (301) 415-5877, or by email to Forms.Resource@nrc.gov. Practicable alternative formats are set forth in 10 CFR 73.4. The licensee shall establish procedures to ensure that the quality of the fingerprints taken results in minimizing the rejection rate of fingerprint cards because of illegible or incomplete cards. 2. The NRC will review submitted fingerprint cards for completeness. Any Form FD-258 fingerprint record containing omissions or evident errors will be returned to the licensee for corrections. The fee for processing fingerprint checks includes one re-submission if the initial submission is returned by the FBI because the fingerprint impressions cannot be classified. The one free re-submission must have the FBI Transaction Control Number reflected on the re-submission. If additional submissions are necessary, they will be treated as initial submittals and will require a second payment of the processing fee. 3. Fees for processing fingerprint checks are due upon application. The licensee shall submit payment of the processing fees electronically. To be able to submit secure electronic payments, licensees will need to establish an account with Pay.Gov (https://www.pay.gov). To request an account, the licensee shall send an email to det@nrc.gov. The email must include the licensee's company name, address, point of contact (POC), POC email address, and phone number. The NRC will forward the request to Pay.Gov, who will contact the licensee with a password and user ID. Once the licensee has established an account and submitted payment to Pay.Gov, they shall obtain a receipt. The licensee shall submit the receipt from Pay.Gov to the NRC along with fingerprint cards. For additional guidance on making electronic payments, contact the Facilities Security Branch, Division of Facilities and Security, at (301) 492-3531. Combined payment for multiple applications is acceptable. The application fee (currently $26) is the sum of the user fee charged by the FBI for each fingerprint card or other fingerprint record submitted by the NRC on behalf of a licensee, and an NRC processing fee, which covers administrative costs associated with NRC handling of licensee fingerprint submissions. The Commission will directly notify licensees who are subject to this regulation of any fee changes. 4. The Commission will forward to the submitting licensee all data received from the FBI as a result of the licensee's application(s) for CHRCs, including the FBI fingerprint record. F. Right To Correct and Complete Information 1. Prior to any final adverse determination, the licensee shall make available to the individual the contents of any criminal history records obtained from the FBI for the purpose of assuring correct and complete information. Written confirmation by the individual of receipt of this notification must be maintained by the licensee for a period of one (1) year from the date of notification. 2. If, after reviewing the record, an individual believes that it is incorrect or incomplete in any respect and wishes to change, correct, or update the alleged deficiency, or to explain any matter in the record, the individual may initiate challenge procedures. These procedures include either direct application by the individual challenging the record to the agency (i.e., law enforcement agency) [[Page 25767]] that contributed the questioned information, or direct challenge as to the accuracy or completeness of any entry on the criminal history record to the Assistant Director, Federal Bureau of Investigation Identification Division, Washington, DC 20537-9700 (as set forth in 28 CFR 16.30 through 16.34). In the latter case, the FBI forwards the challenge to the agency that submitted the data and requests that agency to verify or correct the challenged entry. Upon receipt of an official communication directly from the agency that contributed the original information, the FBI Identification Division makes any changes necessary in accordance with the information supplied by that agency. The licensee must provide at least 10 days for an individual to initiate an action challenging the results of a FBI CHRC after the record is made available for his/her review. The licensee may make a final access determination based on the criminal history record only upon receipt of the FBI's ultimate confirmation or correction of the record. Upon a final adverse determination on access to an ISFSI, the licensee shall provide the individual its documented basis for denial. Access to an ISFSI shall not be granted to an individual during the review process. G. Protection of Information 1. The licensee shall develop, implement, and maintain a system for personnel information management with appropriate procedures for the protection of personal, confidential information. This system shall be designed to prohibit unauthorized access to sensitive information and to prohibit modification of the information without authorization. 2. Each licensee who obtains a criminal history record on an individual pursuant to this Order shall establish and maintain a system of files and procedures, for protecting the record and the personal information from unauthorized disclosure. 3. The licensee may not disclose the record or personal information collected and maintained to persons other than the subject individual, his/her representative, or to those who have a need to access the information in performing assigned duties in the process of determining suitability for unescorted access to the protected area of an ISFSI. No individual authorized to have access to the information may re- disseminate the information to any other individual who does not have the appropriate need to know. 4. The personal information obtained on an individual from a CHRC may be transferred to another licensee if the gaining licensee receives the individual's written request to re-disseminate the information contained in his/her file, and the gaining licensee verifies information such as the individual's name, date of birth, social security number, sex, and other applicable physical characteristics for identification purposes. 5. The licensee shall make criminal history records, obtained under this section, available for examination by an authorized representative of the NRC to determine compliance with the regulations and laws. [FR Doc. 2012-10472 Filed 4-30-12; 8:45 am] BILLING CODE 7590-01-P
TOP-SECRET from the FBI – Former BP Engineer Arrested for Obstruction of Justice in Connection with the Deepwater Horizon Criminal Investigation
WASHINGTON—Kurt Mix, a former engineer for BP plc, was arrested today on charges of intentionally destroying evidence requested by federal criminal authorities investigating the April 20, 2010 Deepwater Horizon disaster, announced Attorney General Eric Holder; Assistant Attorney General Lanny A. Breuer of the Justice Department’s Criminal Division; U.S. Attorney Jim Letten of the Eastern District of Louisiana; and Kevin Perkins, Acting Executive Assistant Director for the FBI’s Criminal Cyber Response and Services Branch.
Mix, 50, of Katy, Texas, was charged with two counts of obstruction of justice in a criminal complaint filed in the Eastern District of Louisiana and unsealed today.
“The department has filed initial charges in its investigation into the Deepwater Horizon disaster against an individual for allegedly deleting records relating to the amount of oil flowing from the Macondo well after the explosion that led to the devastating tragedy in the Gulf of Mexico,” said Attorney General Holder. “The Deepwater Horizon Task Force is continuing its investigation into the explosion and will hold accountable those who violated the law in connection with the largest environmental disaster in U.S. history.”
According to the affidavit in support of a criminal complaint and arrest warrant, on April 20, 2010, the Deepwater Horizon rig experienced an uncontrolled blowout and related explosions while finishing the Macondo well. The catastrophe killed 11 men on board and resulted in the largest environmental disaster in U.S. history.
According to court documents, Mix was a drilling and completions project engineer for BP. Following the blowout, Mix worked on internal BP efforts to estimate the amount of oil leaking from the well and was involved in various efforts to stop the leak. Those efforts included, among others, Top Kill, the failed BP effort to pump heavy mud into the blown out wellhead to try to stop the oil flow. BP sent numerous notices to Mix requiring him to retain all information concerning Macondo, including his text messages.
On or about October 4, 2010, after Mix learned that his electronic files were to be collected by a vendor working for BP’s lawyers, Mix allegedly deleted on his iPhone a text string containing more than 200 text messages with a BP supervisor. The deleted texts, some of which were recovered forensically, included sensitive internal BP information collected in real-time as the Top Kill operation was occurring, which indicated that Top Kill was failing. Court documents allege that, among other things, Mix deleted a text he had sent on the evening of May 26, 2010, at the end of the first day of Top Kill. In the text, Mix stated, among other things, “Too much flowrate—over 15,000.” Before Top Kill commenced, Mix and other engineers had concluded internally that Top Kill was unlikely to succeed if the flow rate was greater than 15,000 barrels of oil per day (BOPD). At the time, BP’s public estimate of the flow rate was 5,000 BOPD—three times lower than the minimum flow rate indicated in Mix’s text.
In addition, on or about August 19, 2011, after learning that his iPhone was about to be imaged by a vendor working for BP’s outside counsel, Mix allegedly deleted a text string containing more than 100 text messages with a BP contractor with whom Mix had worked on various issues concerning how much oil was flowing from the Macondo well after the blowout. By the time Mix deleted those texts, he had received numerous legal hold notices requiring him to preserve such data and had been communicating with a criminal defense lawyer in connection with the pending grand jury investigation of the Deepwater Horizon disaster.
A complaint is merely a charge, and a defendant is presumed innocent unless and until proven guilty beyond a reasonable doubt.
If convicted, Mix faces a maximum penalty of 20 years in prison and a fine of up to $250,000 as to each count.
The Deepwater Horizon Task Force, based in New Orleans, is supervised by Assistant Attorney General Breuer and led by Deputy Assistant Attorney General John D. Buretta, who serves as the director of the task force. The task force includes prosecutors from the Criminal Division and the Environment and Natural Resources Division of the Department of Justice; the U.S. Attorney’s Office for the Eastern District of Louisiana and other U.S. Attorneys’ Offices; and investigating agents from the FBI, Environmental Protection Agency, Department of Interior, U.S. Coast Guard, U.S. Fish and Wildlife Service, and other federal law enforcement agencies.
The task force’s investigation of this and other matters concerning the Deepwater Horizon disaster is ongoing.
The case is being prosecuted by task force Deputy Directors Derek Cohen and Avi Gesser of the Justice Department’s Criminal Division; task force prosecutors Assistant U.S. Attorney Richard Pickens, II of the Eastern District of Louisiana; and Assistant U.S. Attorney Scott Cullen of the Eastern District of Pennsylvania.
TOP-SECRET – U.S. Navy Fleet Telecommunications Procedures NTP-4 Echo
The focus of NTP-4 Echo (Naval Communications) is to provide a basic manual addressing C4I concepts and capabilities in the U.S. Navy. Due to increased proliferation of Information Technology (IT) within DoN and the high demand for information dominance within the battle space, the need for a “primary source” C4I document has never been greater. To that end, Naval Network Warfare Command initiated a major revision to this publication reflecting the latest C4I equipment/systems in use today. This document was developed through a collaborative effort with Fleet, Numbered Fleet, Type Commanders, and other components of the Naval Netwar Forcenet Enterprise (NNFE) and serves to meet the following objectives:
1. Outline Navy communications shore/afloat organization.
2. Identify automated systems ashore and afloat to support Navy messaging.
3. Provide guidance for message processing procedures.
4. Identify Communications Security (COMSEC) measures and controls.
5. Identify satellite communications capabilities, systems, and equipment.
6. Identify submarine communications capabilities, systems, and equipment.
7. Outline Navy communications ship/shore circuit modes of operation.
8. Identify Allied/coalition communications capabilities, systems, and equipment.
9. Identify collaboration tools for use on Navy/Joint enterprise networks.
10.Provide guidance for operating and defending afloat and shore network communications systems (to include Information Assurance Vulnerability Management (IAVM) and computer incident reporting).
11.Provide guidance for Communications Spot (COMSPOT) reporting.
12.Provide sample C4I drill packages (used in conjunction with FXP-3).
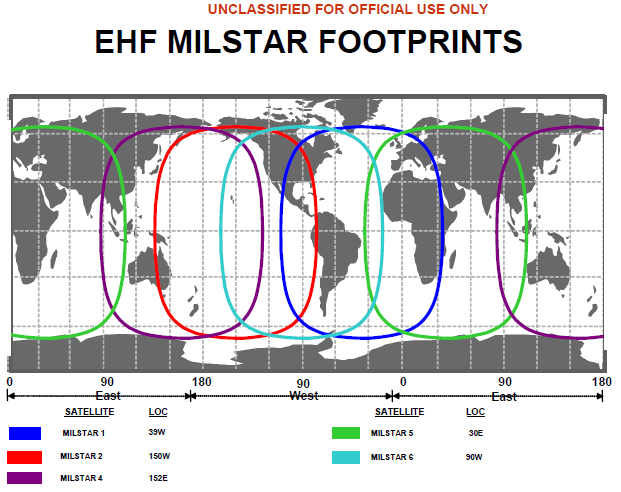
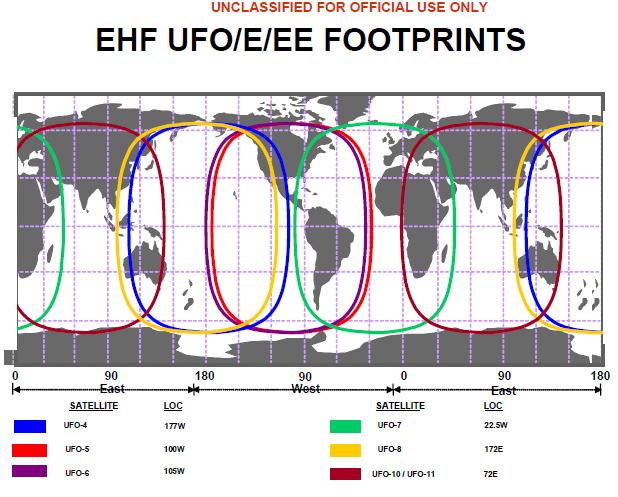
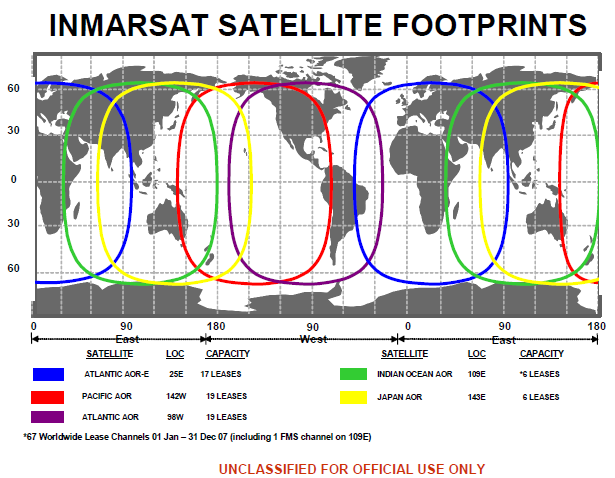
TOP-SECRET – U.S. Marine Corps Tentative Manual for Partnering Operations
In warfighting and counterinsurgency operations, partnering is a command arrangement between a US security force and a host nation (HN) security force in which both forces operate together to achieve mission success and to build the capacity and capability of the HN force. Partnering is not an end, but a deliberate process, a means to an end. A near-term goal might be the standup and development of a HN force increasingly capable of independent operations and decreasingly dependent upon US partnered support. An intermediate objective might be the transition of lead security responsibility from US to HN force. But the ultimate goal is to become “un”-partnered, to enable the HN force to assume full responsibility for security and stability. In warfighting and counterinsurgency partnering, divorce is not a bad ending, it is the desired outcome.
Partnering should be a real union between the two partnered organizations, with a common purpose, in which the whole of the partnership becomes greater than the sum of its parts. Real partnering is total immersion. It cannot be done on occasion, when convenient, or as time permits. Nor should it be limited to periodic or occasional combined combat operations. Real partnering is instead a continuous, collective, and collaborative effort on tasks both large and small toward the common goal. It is full throttle engagement, warts and all.
…
Be culturally aware but not overly-sensitive.
a. Help the HN understand our perspective, our culture, and our values. Our values will most likely not be theirs so do not impose your values upon their culture; however, do not jeopardize your own morals and beliefs by being overly sensitive to theirs. The key is to ensure that the HN has a basic understanding of our values, especially the delicate balance of honesty vs. saving face.
b. HN forces understand that there may be times when the cultural strain is too great to overcome “living amongst” their personnel, but we must promote the sharing of common areas (dining area, COCs (within classification parameters), etc.) and activities (meals, PT, weapons/vehicle maintenance) which will ultimately help bridge cultural differences without encroaching on each other.
…
Encourage HN forces to build relationships with the local leaders
a. Positive interaction with the people builds trust – build this trust above all else!
b. Encourage local recruiting for security forces, especially police. In the United States, local police have to live in the communities that they work in; yet, in many places, national police are moved throughout the country where they have no ties to the community and are often viewed as outsiders. This may be an expedient method to restore law and order, but it should only be used in the most extreme circumstances. Locally recruited forces will have the backing of that community – “their community” – and their training by Marines and HN military units serves to reinforce the ties among Marines, the HN forces, and the communities that they operate in. Until the police force is made up of ‘local sons’ there will be no real security or trust in an area.
c. Encourage the HN force to develop an information operations (IO) plan and effective methods to convey key messages to the people. HN forces should be the primary executers of information operations and they should be on hand to explain it to the people. Perception is important to the success of the partnership and its goals.
…
Embrace the chaos of the environment
a. Do not allow frustration with the HN to show – do it in private away from the partnering force members – never display direct frustration in front of your partnered force.
…
Do not hesitate to deviate from doctrine when needed.
a. The intent here is to “be doctrinally sound, not doctrinally bound”. “A force engaged in small wars operations, irrespective of its size, is usually independent or semi-independent and, in such a campaign, assumes strategically, tactical, and territorial functions” (SWM 2-10, pg 11). “In short, the force must be prepared to exercise those functions of command, supply, and territorial control which are required of the supreme command or its major subdivisions in regular warfare…For these reason, it is obvious that a force undertaking a small wars campaign must be adequately staffed for independent operations even if the tables of organization do not specify a full staff complement” (SWM 2-11, pg 12).
TOP-SECRET – (U//FOUO) U.S. Army Regulation 190-56 Civilian Police and Security Guard Program
This regulation establishes the Department of the Army Civilian Police and Security Guard (DACP/SG) Program. It assigns responsibilities and establishes policy, standards, and procedures for the effective implementation of the DACP/SG Program. This regulation applies to all Department of the Army civilian personnel in career series 0083 and 0085 and contract security personnel employed by the U.S. Army and involved in the safeguarding and protection of personnel and property.
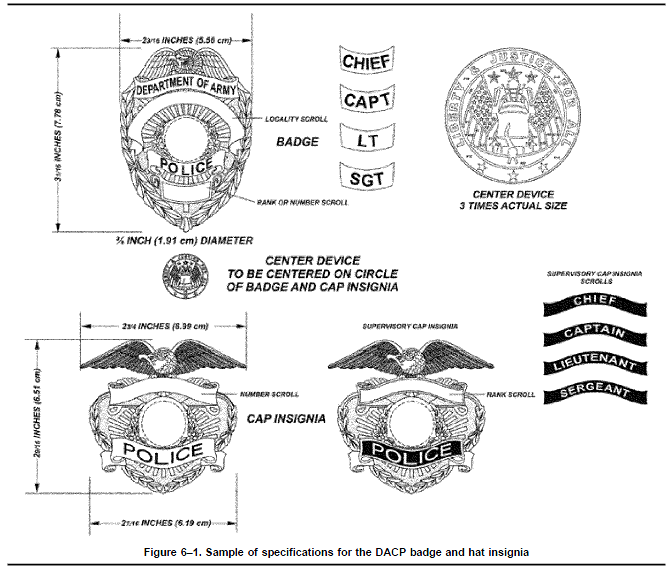
TOP-SECRET – U.S. Army Regulation 525–13 Antiterrorism
This regulation establishes the Army Antiterrorism (AT) Program to protect personnel (Soldiers, members of other Services, Department of the Army (DA) civilian employees, Department of Defense (DOD) contractors and Family members of DOD employees), information, property, and facilities (including civil work and like projects) in all locations and situations against terrorism. It provides—
a. Department of the Army AT tasks
b. Department of the Army AT standards.
c. Implementing guidance for the execution of the AT standards.
d. Policies, procedures, and responsibilities for execution of the AT program.…
5–21. Standard 20. Terrorism Incident Response Measures
a. Army standard 20. Commanders and heads of agencies/activities will include in AT plans terrorism incident response measures that prescribe appropriate actions for reporting terrorist threat information, responding to threats/actual attacks, and reporting terrorist incidents.
b. Implementing guidance.
(1) Terrorist incident response measures in AT plans will, at a minimum, address management of the FPCON system, implementation of all FPCON measures, and requirements for terrorist related reports. Plans will be affordable, effective, and attainable; tie security measures together; and integrate security efforts by assigning responsibilities, establishing procedures, and ensuring subordinate plans complement each other. At the garrison level, the plans must tie into other installation response plans.
(2) At garrison level, commanders will identify high risk targets (HRTs), mission essential vulnerable areas (MEVAs) and ensure planning provides for focus on these areas. Facility managers whose facility has been identified as a HRT will be informed, and will ensure facility security plans are formulated on this basis.
(3) Commanders will develop procedures to ensure periodic review, update, and coordination of response plans with appropriate responders.
(4) Commanders will ensure CBRNE, medical, fire, and police response procedures are integrated into consequence management/AT plans.
(5) Plans will include procedures for an attack warning system using a set of recognizable alarms and reactions for potential emergencies, as determined by the terrorist threat, criticality, and vulnerability assessments. Commanders will exercise the attack warning system and ensure personnel are trained and proficient in recognition. In conjunction with the alarm warning system, commanders will conduct drills on emergency evacuations/ movements to safe havens/shelters-in-place.
(6) CONUS commanders will—
(a) Notify the local FBI office concerning threat incidents occurring at Army installations, facilities, activities, and civil work projects or like activities.
(b) Take appropriate action to prevent loss of life and/or mitigate property damage before the FBI response force arrives. On-site elements or USACIDC elements will be utilized to safeguard evidence, witness testimony, and related aspects of the criminal investigation process pending arrival of the FBI response force. Command of U.S. Army elements will remain within military channels.
(c) If the FBI declines jurisdiction over a threat incident occurring in an area of exclusive or concurrent Federal jurisdiction, take appropriate action in conjunction with USACIDC elements to resolve the incident. In such cases, commanders will request advisory support from the local FBI office.
(d) If the FBI declines jurisdiction over a threat incident occurring in an area of concurrent or proprietary Federal jurisdiction, coordinate the military response with USACIDC elements, state and local law enforcement agencies, as appropriate. In such cases, commanders will request advisory support from the local FBI office.
(7) OCONUS commanders will—
(a) Where practicable, involve HN security and law enforcement agencies in AT reactive planning and request employment of HN police forces in response to terrorist attacks.
(b) Coordinate reactions to incidents of a political nature with the U.S. Embassy and the HN, subject to instructions issued by the combatant commander with geographical responsibility.
(c) In SIGNIFICANT and HIGH terrorist threat level areas, plans to respond to terrorist incidents will contain procedures for the notification of all DOD personnel and their dependents. Such plans will provide for enhanced security measures and/or possible evacuation of DOD personnel and their dependents.
(8) USACIDC will investigate threat incidents in accordance with paragraph 2–20d.
(9) AT plans, orders, SOPs, terrorism threat, criticality, and vulnerability assessments, and coordination measures will consider the potential threat use of WMD. Commanders will assess the vulnerability of installations, facilities, and personnel within their AOR to potential threat of terrorist using WMD and CBRNE weapons to include TIH. Clear command, control, and communication lines will be established between local, state, Federal, and HN emergency assistance agencies to detail support relationships and responsibilities. Response to WMD use by terrorists will be synchronized with other crisis management plans that deal with large-scale incident response and consequence management. Separate plans devoted only to terrorist use of WMD need not be published if existing crisis management plans covering similar events (such as accidental chemical spills) are sufficiently comprehensive.
TOP-SECRET – Report by Vyshinsky to Molotov Concerning Trade and Economic Cooperation Between the Soviet Union and the United States, August 1941
| Date: 08/01/1941 |
Source: Library of Congress |
| Description: Report by Vyshinsky to Molotov concerning trade and economic cooperation between the Soviet Union and the United States, August 1941 |
|
To Comrade V. M. Molotov
I present for your confirmation:
1. The draft resolution of the USSR Council of People’s Commissars [SNK SSSR] on extending the trade agreement currently in effect between the USSR and the U.S.A. to August 6, 1942.
2. The text of notes which will be exchanged this August 4 in Washington between Umanskii and Welles.
The SNK SSSR resolution and notes which will be exchanged this August 4 in Washington are subject for publication.
In addition to this note on extending the agreement, two other notes will he exchanged:
a) on the U.S.A. rendering economic cooperation to us (with subsequent publication);
b) on the inapplicability for us of discretionary conditions concerning our gold and silver (without publi-cation).
The texts of the last two notes are not yet in our possession.
[handwritten: ] I am also enclosing a draft response to Comrade Umanskii.
Sent
[signed] A. Vyshinsky
[illegible]
” ” August 1941
IDU MID
TOP-SECRET – Silver Shadow to Unveil New Assault Rifle

Silver Shadow will present a new weapon prototype during the Eurosatory exhibition in Paris.
A new player in the arsenal of Israeli weapons? Silver Shadow, the manufacturer of the Israeli-produced Gilboa assault rifle, will soon be presenting another product from the Gilboa line of weapons.
The product is a new assault rifle, with a double barrel – a unique and first of its kind among Israeli-produced weapons. The new weapon increases firepower and has improved marksmanship, but still takes standard ammunition.
The company will present the new weapon at the Eurosatory exhibition in Paris during June 2012. The exhibition is one of the most prominent exhibitions in the world for the fields of defense and security, and takes place every two years in France.
The largest defense companies in the world present their products at the exhibition; the Israeli pavilion, which will feature dozens of companies, is considered one of the most prominent ones at the show.
TOP-SECRET – Fordow Nuclear Plant, Near Qom, Iran

TOP-SECRET from the FBI – Texas Federal Grand Jury Indicts Sinaloa Cartel Leaders
United States Attorney Robert Pitman, DEA Special Agent in Charge Joseph M. Arabit, FBI Special Agent in Charge Mark Morgan, and ATF Special Agent in Charge Robert Champion today announced the indictment of Joaquin Guzman Loera, aka “El Chapo”; Ismael Zambada Garcia aka “Mayo”; and 22 other individuals responsible for the operations and management of the Sinaloa Cartel (cartel) charging them with violating the Racketeer Influenced and Corrupt Organizations (RICO) Act.
The 14-count grand jury indictment, returned on April 11, 2012 and unsealed today charges conspiracy to violate the RICO statute; conspiracy to possess more than five kilograms of cocaine and over 1000 kilograms of marijuana; conspiracy to import more than five kilograms of cocaine and 1000 kilograms of marijuana; conspiracy to commit money laundering; conspiracy to possess firearms in furtherance of drug trafficking crimes; murder in furtherance of a continuing criminal enterprise (CCE) or drug trafficking; engaging in a CCE in furtherance of drug trafficking; conspiracy to kill in a foreign country; kidnapping; and violent crimes in aid of racketeering.
The other 22 defendants charged in this indictment include:
German (Last Name Unknown), aka “Paisa,” “German Olivares”; Mario Nunez-Meza, aka “Mayito,” “M-10”; Amado Nunez-Meza, aka “Flaco,” “M-11,” “El Flais”; Jose Antonio Torres Marrufo, aka “Jaguar,” “Tonin,” Catorce,” “14,” “Tono,” “El Uno”; Gabino Salas-Valenciano, aka “El Ingeniero”; Sergio Garduno-Escobedo, aka “Coma”; David Sanchez-Hernandez, aka “Christian”; Ivan Sanchez-Hernandez; Jesus Rodrigo Fierro-Ramirez, aka “Huichi,” “Pena”; Arturo Lozano-Mendez, aka “Garza”; Mario De La O Lopez aka “Flaco”; Arturo Shows Urquidi, aka “Chous”; Salvador Valdez, aka “Robles”; Daniel Franco Lopez, aka “Micha,” “Neon,” “Fer”; Luis Arellano-Romero, aka “Bichi,” Bichy,” “Helio”; Fernando Arellano-Romero, aka “Rayo,” “24,” “Gamma,” “Blue Demon”; Mario Alberto Iglesias-Villegas, aka “Dos,” “El 2,” “Delta,” “Parka,” “Grim Reaper,” “Daniel Cuellar Anchondo,” “Delfin”; Adrian Avila-Ramirez aka “Bam Bam,” “Tacuba,” “El 19”; Valentin Saenz De La Cruz aka “El Valle,” “Lic”; Emigdio Martinez, Jr., aka “Millo”; Carlos Flores, aka “Buffalo,” “Charly”; and, Jose (Last Name Unknown), aka “Toca,” “Tocayo,” “Pachi.”
According to the indictment, the purpose of the Sinaloa Cartel is to smuggle large quantities of marijuana and cocaine, as well as other drugs, into the United States for distribution. Laundered proceeds of drug trafficking activities are returned to cartel members and are used in part to purchase properties related to the daily functioning of the cartel, including real estate, firearms, ammunition, bulletproof vests, radios, telephones, uniforms, and vehicles. In an effort to maintain control of all aspects of their operations, the cartel and its associates, including members of the Gente Nueva (“New People”) and the Artistas Asesinos (“Murder artists”), kidnap, torture, and murder those who lose or steal assets belonging to, are disloyal to, or are enemies of the cartel. This includes the Juarez Cartel led by Vicente Carrillo Fuentes, a competing drug organization, as well as its enforcement arm known as La Linea and the Barrio Aztecas. Often, murders committed by the cartel involve brutal acts of violence as well the public display of the victim along with banners bearing written warnings to those who would cross the cartel.
“Murder, kidnapping, money laundering, and drug trafficking are the four corners of this organization’s foundation,” stated U.S. Attorney Robert Pitman. “For years, their violence, ruthlessness, and complete disregard for human life and the rule of law have greatly impacted the citizens of the Republic of Mexico and the United States. They must be held accountable for their criminal actions.”
This investigation resulted in the seizure of hundreds of kilograms of cocaine and thousands of pounds of marijuana in cities throughout the United States. Law enforcement also took possession of millions of dollars in drug proceeds that were destined to be returned to the cartel in Mexico. Agents and officers likewise seized hundreds of weapons and thousands of rounds of ammunition intended to be smuggled into Mexico to assist the cartel’s battle to take control of one of the key drug trafficking corridors used to bring drugs into the United States.
“This indictment is the result of a complex, long-term investigation by DEA and our law enforcement partners in the U.S. and Mexico, targeting the Sinaloa Cartel at its highest levels. In addition to violations relating to the trafficking of huge quantities of cocaine and marijuana, the charges encompass money laundering, weapons smuggling, kidnappings, and murders employed by the cartel to fund, expand and protect its far-reaching criminal enterprise. These charges are an important step in bringing to justice those responsible for supplying a large portion of the illegal drugs flowing into communities in the United States through the El Paso area, as well as much of the violence that has ravaged neighboring Ciudad Juarez,” said Joseph M. Arabit, Special Agent in Charge, Drug Enforcement Administration-El Paso Division.
The indictment references two acts of violence allegedly committed by members of the cartel. First, the indictment alleges that in September 2009, Jose Antonio Torres Marrufo, Gabino Salas-Valenciano, Fernando Arellano-Romero, and Mario Iglesias-Villegas, under the leadership of Joaquin Guzman and Ismael Zambada, conspired to kidnap and murder a Horizon City Texas, resident. Specifically, Jose Antonio Torres Marrufo ordered the kidnapping of the victim to answer for the loss of a 670-pound load of marijuana seized by Border Patrol at the Sierra Blanca checkpoint on August 5, 2009. After the kidnapping, the victim was taken to Juarez, where Torres Marrufo interrogated him and ordered that he be killed. On September 8, 2009, the victim’s mutilated body was discovered in Juarez.
Second, the indictment alleges that on May 7, 2010, Jose Torres Marrufo, Fernando Arellano-Romero, and Mario Iglesias-Villegas, under the leadership of Joaquin Guzman and Ismael Zambada, conspired to kidnap and murder an American citizen and two members of his family. Specifically, Torres Marrufo caused an individual in El Paso to travel to a wedding ceremony in Juarez to confirm the identity of a target. The target was the groom, a United States citizen and a resident of Columbus, New Mexico. Under Torres Marrufo’s orders, the groom, his brother and his uncle were all kidnapped during the wedding ceremony and subsequently tortured and murdered. Their bodies were discovered by Juarez police a few days later in the bed of an abandoned pickup truck. Additionally, a fourth person was killed during the kidnapping at the wedding ceremony.
“This indictment has been years in the making, the focus being to dismantle the Sinaloa Cartel by focusing on its upper echelon. The indictment represents the unwavering commitment and collaboration among the law enforcement community to bring justice to those who have inflicted unconscionable violence on so many citizens on both sides of the border. We are sending a clear message that we will continue our relentless pursuit of drug trafficking organizations responsible for such widespread devastation within our communities,” stated FBI Special Agent in Charge Mark Morgan.
“This highly cooperative investigation shows that law enforcement can make significant inroads into drug trafficking organizations and that the major players are not immune from prosecution. This also relates to the illegal firearm traffickers who support such organizations and are responsible for the violence and bloodshed that is occurring,” stated ATF Special Agent in Charge Robert Champion.
This investigation was conducted by the Drug Enforcement Administration; Federal Bureau of Investigation; and the Bureau of Alcohol, Tobacco, Firearms, and Explosives, together with the Immigration and Customs Enforcement-Homeland Security Investigations, United States Border Patrol, Customs and Border Protection, United States Marshals Service, El Paso Police Department, El Paso Sheriff’s Office, and Texas Department of Public Safety. United States Attorney Robert Pitman also expresses his appreciation to New Mexico United States Attorney Ken Gonzalez and his attorneys, Attorney General of Mexico Marisela Morales and her attorneys, and to law enforcement authorities in Mexico for their assistance.
Upon conviction, the defendants face up to life in federal prison. Three of the 14 counts (seven, 11, and 14)—which involve the kidnapping and murder of a resident of Horizon City and three members of a wedding party in Juarez—may result in the imposition of the death penalty upon conviction.
It is important to note that an indictment is merely a charge and should not be considered as evidence of guilt. The defendant is presumed innocent until proven guilty in a court of law.
TOP-SECRET – Photos from the Fodor Nuclear Plant, Near Qom, Iran
TOP-SECRET – The CIA Crown Jewels – The Watergare Case
| Citation: | DDCI Statement about the Watergate Case [Central Intelligence Agency Employee Bulletin Containing Vernon Walter’s Statement on CIA Involvement in Watergate; Best Available Copy] , [Classification Unknown], Newsletter, 359, May 21, 1973, 3 pp. |
| Collection: | The CIA Family Jewels Indexed |
| Item Number: | FJ00031 |
| Origin: | United States. Central Intelligence Agency |
| Individuals/ Organizations Named: |
Cushman, Robert E., Jr.; Dean, John Wesley III; Democratic National Committee (U.S.); Ehrlichman, John D.; Gray, L. Patrick; Haldeman, H.R.; Helms, Richard M.; Hunt, E. Howard; Nixon, Richard M.; Schlesinger, James R.; United States. Department of Justice; United States. Federal Bureau of Investigation; United States. White House; Walters, Vernon A. |
| Subjects: | Congressional hearings | Covert operations | Government appropriations and expenditures | Mexico | Watergate Affair (1972-1974) |
| Abstract: | Disseminates Vernon Walter’s statement to congressional committee about his communications with John Dean and Patrick Gray on Central Intelligence Agency involvement in Watergate and CIA’s issuance of equipment to Howard Hunt. |
| Full Text: | Document – PDF – this link will open in a new window (156 KB) |
TOP-SECRET from the FBI – Eleven Individuals of the Genovese Organized Crime Family Indicted
An 18-count indictment was unsealed in federal court in Brooklyn this morning charging 11 individuals, including several made members and associates of the Genovese organized crime family of La Cosa Nostra (the “Genovese family”), variously with racketeering conspiracy, extortion, illegal gambling, union embezzlement, and obstruction of justice. The defendants will make their initial appearance later today before United States Magistrate Judge Marilyn D. Go at the U.S. Courthouse at 225 Cadman Plaza East in Brooklyn, New York.
The case was announced by Loretta E. Lynch, United States Attorney for the Eastern District of New York; Janice K. Fedarcyk, Assistant Director in Charge, Federal Bureau of Investigation, New York Field Office; Robert Panella, Special Agent in Charge, U.S. Department of Labor, Office of Inspector General, Office of Labor Racketeering and Fraud Investigations, New York Region; Raymond W. Kelly, Commissioner, New York City Police Department; and Rose Gill Hearn, Commissioner, New York City Department of Investigation (DOI).
As alleged in the indictment and a detention memorandum filed by the government today, Conrad Ianniello is a captain in the Genovese family. James Bernardone, the Secretary Treasurer of Local 124 of the International Union of Journeymen and Allied Trades (IUJAT), and Salvester Zarzana, the former President of Local 926 of the United Brotherhood of Carpenters and Joiners, are both soldiers in the Genovese family. Ryan Ellis, Paul Gasparrini, William Panzera, and Robert Scalza, the Secretary Treasurer of IUJAT Local 713, are associates of the Genovese family. Also named as defendants are Robert Fiorello, Rodney Johnson, Felice Masullo, and John Squitieri.
Ianniello is charged with, among other crimes, racketeering conspiracy, including predicate acts of illegal gambling; conspiring to extort vendors at the annual Feast of San Gennaro held in Little Italy, New York in 2008; and, along with Scalza and Ellis, conspiring to extort a labor union between April 2008 and May 2008 in order to induce the union to cease its efforts to organize workers at a company on Long Island. Based on their threats, the defendants allegedly hoped to pave the way for Scalza’s union, IUJAT Local 713, to unionize the company instead.
The indictment charges Bernardone and Gasparrini with racketeering conspiracy, including predicate acts of conspiring to extort a subcontractor related to work performed at construction sites in Manhattan, Queens, and Brooklyn from approximately 2006 to 2009, including work performed at a Hampton Inn located on Ditmars Boulevard in Queens. Zarzana is also charged with extortion related to one of those construction sites. In addition, the indictment alleges that in 2008, Squitieri embezzled money from employee pension and annuity funds of Local 7-Tile, Marble, and Terrazzo of the Bricklayers and Allied Craftworkers union by providing non-union laborers to perform tile-related work during a renovation at the Paramount Hotel in Manhattan, thereby avoiding paying into Local 7’s employee pension benefit plans. Johnson, a project manager at the Paramount Hotel renovation, is charged with obstruction of justice in connection with his efforts to impede a federal grand jury investigation conducted in this district that ultimately resulted in the charges brought in the indictment unsealed today.
Finally, Panzera and Fiorello are charged with crimes related to their involvement in loansharking and the extortionate collection of money from a victim.
“This indictment is the most recent chapter in this office’s continued fight against organized crime’s efforts to infiltrate unions and businesses operating in New York City. Where others saw a city festival, urban renewal, and job growth, these defendants allegedly saw only a chance to line their pockets at the expense of hard working individuals. And when law enforcement began to probe their actions, one defendant allegedly went so far as to try to block that investigation,” stated United States Attorney Lynch. “Organized crime figures and union officials who seek to earn money by corrupting legitimate industry will be investigated and prosecuted to the full extent of the law.”
FBI Assistant Director in Charge Fedarcyk stated, “Today’s charges highlight not only the ongoing vigilance of the FBI in policing the corrupt conduct of La Cosa Nostra, but also the necessity of such vigilance. Even as mob families seek and discover new ways to make money by illegitimate means, they continue to rely on tried-and-true schemes like extortion and gambling. The mob’s purpose is making money, and how is less important than how much.”
Special Agent in Charge Panella, U.S. Department of Labor, Office of Inspector General, stated, “The RICO indictment and today’s arrests reflect our strong commitment to combat the infiltration of unions by organized crime members and associates for their personal enrichment. The defendants allegedly utilized their organized crime influence to corrupt businesses and advance various illegal schemes. The Office of Inspector General will continue to work with our law enforcement partners to vigorously investigate labor racketeering in the nation’s unions.”
NYPD Commissioner Kelly stated, “As alleged in the indictment, the defendants’ extortion knew no bounds—in fact, one of the defendants allegedly even used the feast of San Gennaro to extort money from vendors involved in the celebration of the saint’s life. I commend the U.S. Attorney’s Office and the federal agents and New York City detectives for this successful investigation.”
DOI Commissioner Gill Hearn stated, “The charges underscore the determination of federal and city investigators to curtail organized crime’s influence in New York City, including the Feast of San Gennaro in Little Italy. DOI was pleased to assist its federal partners on this significant indictment.”
The defendants face maximum sentences ranging from five to 20 years of imprisonment on each count of conviction.
The government’s case is being prosecuted by Assistant United States Attorneys Nicole Argentieri, Jacquelyn Kasulis, and Amanda Hector.
The Defendants
| Name | Age | Residence |
|---|---|---|
| Conrad Ianniello | 68 | Staten Island, New York |
| James Bernardone | 44 | Bronx, New York |
| Ryan Ellis | 30 | Queens, New York |
| Rober Fiorello | 62 | Jackson, New Jersey |
| Paul Gasparrini | 39 | Yonkers, New York |
| Rodney Johnson | 49 | Edgewater, New Jersey |
| Felice Masullo | 40 | Queens, New York |
| William Panzera | 39 | North Haledon, New Jersey |
| Robert Scalza | 66 | Long Island, New York |
| John Squitieri | 55 | Rockland County, New York |
| Salvester Zarzana | 48 | Brooklyn, New York |
TOP-SECRET- The NSA Operation REGAL: Berlin Tunnel
Operation code name: PBJOINTLY Product code name: REGAL
The Berlin Tunnel operation was not a unique type of operation that was only run in Berlin. Prior to the Berlin Tunnel, the British ran a number of successful tunnel cable-tap operations in Vienna,[1] which at the time of these operations, was still an occupied city, divided into four sectors just like Berlin. The British cable taps began in 1948, and ran until the occupation of Austria ended, restoring state sovereignty to the country in 1955. The Soviets had a tap near Potsdam on a cable that served the American Garrison in Berlin.[2]
What has made the Berlin Tunnel famous, while the cable-tap tunnels of Vienna and Potsdam have faded into obscurity is the paradox of intelligence operations which results in fame being a measure of failure and obscurity being a measure of success. The Berlin Tunnel’s true claim to fame, therefore, is that it gained front-page notoriety when the Soviets “discovered” it.
The Official CIA history of the tunnel (prepared in August 1967 and declassified in February 2007) theorizes that the amount of publicity given to the Berlin Tunnel was the result of chance rather than of a conscious decision on the part of the Soviet leadership. During the planning phase of the tunnel, a consensus assessment had been reached which postulated that in the event of the discovery of the tunnel, the Soviet reaction would be to “suppress knowledge” of its existence, so as to save face, rather than have to admit that the West had the capability to mount such an operation. The CIA history of the project suggests that this expectation was defeated because the Soviet Commandant of the Berlin Garrison (who would normally have handled an event of this nature) was away from post at the time, and his deputy found himself in the position of having to make a decision about the tunnel “without benefit of advice from Moscow.”[3]
In his academic history of the Berlin Tunnel (Spies Beneath Berlin), David Stafford of the University of Edinburgh points out that, even though the tunnel was a joint American-British project, the British did not share in the limelight of publicity with the Americans when the tunnel was discovered. This was due, he says, to the fact that Soviet First Secretary Khrushchev was on an official state visit to the U.K.. The visit’s culmination, a visit to Windsor Castle and a reception by the Queen, was scheduled for the day following the discovery of the Berlin Tunnel. British participation in the project was officially hushed up by both the British and the Soviets so as not to spoil the success of the state visit.[4] To this day British Intelligence Services are usually tight-lipped when it comes to discussions of the Berlin Tunnel, or any post-1945 intelligence operation for that matter,[5] while the Americans have declassified the in-house history of the project and authorized one of its participants to include a chapter about it in a book on the Intelligence war in Berlin written in cooperation with one of the KGB veterans of that period (Battleground Berlin).
The intelligence fame/obscurity paradox aside, the Berlin Tunnel operation was, in the words of Allen Dulles (then DCI), “one of the most valuable and daring projects ever undertaken” by the CIA.[6]
The Berlin Tunnel, unlike the Vienna tunnels, was a major engineering feat. It stretched 1476 feet/454[7] meters through sandy ground[8] to reach a cable only 27 inches/68.5 cm beneath the surface,[9] on the edge of a major highway. One of the most difficult engineering problems that had to be overcome in the course of the project was to dig up to the cable from the main tunnel shaft without dropping some truck passing over the highway above into the tunnel.[10] This task was handled by the British,[11] who had their experience of Vienna to fall back on.
The total cost of the tunnel project was over six and a half million[12] 1950s dollars, which in 2007 dollars would be over 51 and a quarter million.[13] By way of comparison, the development and delivery of the first six U-2 aircraft, a project contemporary with the Berlin Tunnel, cost 22 million total,[14] or 3.6 million each. That means that the tunnel cost roughly as much as two U-2s.
According to Murphey, Kondrashev and Bailey in Battleground Berlin, the tale of the tunnel began in early 1951, when Frank Rowlett told Bill Harvey how frustrated he was by the loss of intelligence due to the Soviet shift from radio to landline.[15] The assessment process that preceded target selection continued throughout 1952, the year that saw Harvey reassigned to Berlin. Test recordings of the kind of traffic available from the cables were made in the spring and summer of 1953.[16] By August of 1953, plans for the tunnel were being readied for presentation to the DCI, Allen Dulles.[17]
Dulles approved the terms of reference for cooperaton with the British on the Berlin Tunnel in December 1953.[18] The “go” was given to start the construction of the warehouse that would serve as the cover for the tunnel, and construction was completed in August. The American engineering team that actually dug the tunnel arrived to take control of the compound on 28 August. Digging began on 2 September, but, on 8 September, the miners struck water and which necessitated that pumps be brought in. The tunnel reached its distant end on 28 February 1955,[19] and the tap chamber took another month to complete. The complex process of tapping into the three target cables without alerting the Soviets to what was going on was a slow one. It lasted from 11 May through 2 August 1955.[20] Collection of intelligence from the taps, however, began as soon as the first circuits were brought on-line.
During the night of 21-22 April 1956, the Soviets “discovered” the tunnel, and collection ceased. That did not close the project, however. The take from the Berlin Tunnel during the time that it was operational (11 months and 11 days) was so great that processing of the backlog of material continued through the end of September 1958.[21]
The loss of this valuable source was, of course, a blow to US/UK intelligence efforts against the Soviets at the time, but this loss was somewhat compensated for by the prestige that the CIA won in the press following the tunnel’s discovery. The article on the tunnel in the issue of Time magazine (07 May 1956) that followed the tunnel’s discovery said “It’s the best publicity the U.S. has had in Berlin for a long time.”
An urban legend that persistently continues to associate itself with the Berlin Tunnel is that the idea for the tunnel came from Reinhard Gehlen (the German Abwehr-Ost general who surrendered to the Americans and later became the head of the West German BND). Murphy, Kondrashev and Bailey flatly reject this assertion in Battleground Berlin.[22] David Stafford argues credibly against the validity of this legend in his academic history of the Berlin Tunnel. He notes that there is no evidence to support this theory, and “those most closely in the know in the CIA have strenuously denied it,”[23] essentially repeating Murphy, Kondrashev and Bailey. Stafford’s most telling argument against Gehlen’s involvement is that no mention of the Berlin Tunnel is to be found in Gehlen’s memoirs (The Service: The Memoirs of General Reinhard Gehlen, New York: World Publishing, 1972). “Never a modest man,” says Stafford, Gehlen “would surely have bid for some of the credit had he been any way involved. In fact, he does not even refer to it.”[24]
In the section “Recapitulation of Intelligence Derived” from the Berlin Tunnel, the CIA History of the project says that the “REGAL operation provided the United States and the British with a unique source of current intelligence on the Soviet Orbit of a kind and quality which had not been available since 1948. Responsible officials considered PBJOINTLY, during its productive phase, to be the prime source of early warning concerning Soviet intentions in Europe, if not world-wide.”[25] The section goes on to list general types of political, ground-forces, air-force and naval intelligence that the tunnel provided, many of them with glowing comments from consumers.
The debate about the value of the information derived from the Berlin Tunnel has been raging since 1961, when it was discovered that PBJOINTLY was compromised to the Soviets by the British mole George Blake who attended the meeting on the Berlin Tunnel between the British and Americans in London in December 1953. Many widely read books and articles on the tunnel contended that the KGB had used the tunnel to feed the Americans and the British disinformation. Stafford, however, convincingly dispels all suspicions that the Berlin Tunnel was turned into a disinformation counter-intelligence operation by the KGB. Drawing on the information that came to light during the “Teufelsberg” Conference on Cold-War intelligence operations that brought intelligence professionals from both the CIA and the KGB together in Berlin in 1999, Stafford concludes that “[f]ar from using the tunnel for misinformation and deception, the KGB’s First Chief Directorate had taken a deliberate decision to conceal its existence from the Red Army and GRU, the main users of the cables being tapped. The reason for this extraordinary decision was to protect “Diomid”, their rare and brilliant source George Blake.”[26]
Stafford ends his discussion of the legitimacy of the material collected from the Berlin Tunnel with a quote from Blake, who was still living in Moscow at the time of the “Teufelsberg” Conference. “I’m sure 99.9% of the information obtained by the SIS and CIA from the tunnel was genuine.”[27]
By T.H.E. Hill
DOWNLOAD THE ORIGINAL NSA DOCUMENT HERE
TOP-SECRET from Crpytome – Nuclear Power Plant Onsite Emergency Response Capabilities
[Federal Register Volume 77, Number 75 (Wednesday, April 18, 2012)] [Proposed Rules] [Pages 23161-23166] From the Federal Register Online via the Government Printing Office [www.gpo.gov] [FR Doc No: 2012-9336] ======================================================================== Proposed Rules Federal Register ________________________________________________________________________ This section of the FEDERAL REGISTER contains notices to the public of the proposed issuance of rules and regulations. The purpose of these notices is to give interested persons an opportunity to participate in the rule making prior to the adoption of the final rules. ======================================================================== Federal Register / Vol. 77, No. 75 / Wednesday, April 18, 2012 / Proposed Rules [[Page 23161]] NUCLEAR REGULATORY COMMISSION 10 CFR Parts 50 and 52 [NRC-2012-0031] RIN 3150-AJ11 Onsite Emergency Response Capabilities AGENCY: Nuclear Regulatory Commission. ACTION: Advance notice of proposed rulemaking. ———————————————————————– SUMMARY: The U.S. Nuclear Regulatory Commission (NRC or the Commission) is issuing this Advance Notice of Proposed Rulemaking (ANPR) to begin the process of potentially amending its regulations to strengthen and integrate onsite emergency response capabilities. The NRC seeks public comment on specific questions and issues with respect to possible revision to the NRC’s requirements for onsite emergency response capabilities, and development of both new requirements and the supporting regulatory basis. This regulatory action is one of the actions stemming from the NRC’s lessons-learned efforts associated with the March 2011 Fukushima Dai-ichi Nuclear Power Plant accident in Japan. DATES: Submit comments by June 18, 2012. Comments received after this date will be considered if it is practical to do so, but the NRC is only able to ensure consideration of comments received on or before this date. ADDRESSES: You may access information and comment submissions related to this document, which the NRC possesses and is publicly available, by searching on http://www.regulations.gov under Docket ID NRC-2012-0031. You may submit comments by any of the following methods: Federal Rulemaking Web Site: Go to http://www.regulations.gov and search for Docket ID NRC-2012-0031. Address questions about NRC dockets to Carol Gallagher; telephone: 301-492- 3668; email: Carol.Gallagher@nrc.gov. Email comments to: Rulemaking.Comments@nrc.gov. If you do not receive an automatic email reply confirming receipt, contact us directly at 301-415-1677. Fax comments to: Secretary, U.S. Nuclear Regulatory Commission at 301-415-1101. Mail comments to: Secretary, U.S. Nuclear Regulatory Commission, Washington, DC 20555-0001, Attn: Rulemakings and Adjudications Staff. Hand deliver comments to: 11555 Rockville Pike, Rockville, Maryland 20852, between 7:30 a.m. and 4:15 p.m. (Eastern time) Federal workdays; telephone: 301-415-1677. For additional direction on accessing information and submitting comments, see “Accessing Information and Submitting Comments” in the SUPPLEMENTARY INFORMATION section of this document. FOR FURTHER INFORMATION CONTACT: Robert H. Beall, Office of Nuclear Reactor Regulation, U.S. Nuclear Regulatory Commission, Washington, DC 20555-0001; telephone: 301-415-3874; email: Robert.Beall@nrc.gov. SUPPLEMENTARY INFORMATION: I. Accessing Information and Submitting Comments II. Background: Fukushima Dai-ichi and the NRC Regulatory Response III. Background: Onsite Emergency Response Capabilities A. Emergency Operating Procedures B. Severe Accident Management Guidelines C. Extensive Damage Mitigation Guidelines D. Onsite Emergency Response Capabilities Versus Emergency Preparedness IV. Discussion and Request for Public Comment A. ANPR Purpose B. Rulemaking Objectives/Success Criteria C. Applicability to NRC Licenses and Approvals D. Relationship Between Recommendation 8 and Other Near-Term Task Force Recommendations E. Interim Regulatory Actions V. Public Meeting VI. Rulemaking Process and Schedule VII. Related Petition for Rulemaking Actions VIII. Available Supporting Documents I. Accessing Information and Submitting Comments A. Accessing Information Please refer to Docket ID NRC-2012-0031 when contacting the NRC about the availability of information for this notice. You may access information related to this ANPR, which the NRC possesses and is publicly available, by the following methods: Federal Rulemaking Web Site: Go to http://www.regulations.gov and search for Docket ID NRC-2012-0031. NRC’s Agencywide Documents Access and Management System (ADAMS): You may access publicly available documents online in the NRC Library at http://www.nrc.gov/reading-rm/adams.html. To begin the search, select “ADAMS Public Documents” and then select “Begin Web- based ADAMS Search.” For problems with ADAMS, please contact the NRC’s Public Document Room (PDR) reference staff at 1-800-397-4209, 301-415- 4737, or by email to PDR.Resource@nrc.gov. The ADAMS accession number for each document referenced in this notice (if that document is available in ADAMS) is provided the first time that a document is referenced. A table listing documents that provide additional background and supporting information is in Section VIII of this document. NRC’s PDR: You may examine and purchase copies of public documents at the NRC’s PDR, Room O1-F21, One White Flint North, 11555 Rockville Pike, Rockville, Maryland 20852. B. Submitting Comments Please include Docket ID NRC-2012-0031 in the subject line of your comment submission, in order to ensure that the NRC is able to make your comment submission available to the public in this docket. The NRC cautions you not to include identifying or contact information in comment submissions that you do not want to be publicly disclosed. The NRC posts all comment submissions at http://www. regulations.gov as well as enters the comment submissions into ADAMS. The NRC does not edit comment submissions to remove identifying or contact information. If you are requesting or aggregating comments from other persons for submission to the NRC, then you should inform those persons not to include identifying or contact information in their comment submissions that they do not want to be publicly disclosed. Your request should state that the NRC will not edit comment submissions to remove such information before making the comment submissions available to the public or entering the comment submissions into ADAMS. [[Page 23162]] II. Background: Fukushima Dai-ichi and the NRC Regulatory Response On March 11, 2011, a magnitude 9.0 earthquake struck off the coast of the Japanese island of Honshu. The earthquake precipitated a large tsunami that is estimated to have exceeded 14 meters (45 feet) in height at the Fukushima Dai-ichi Nuclear Power Plant site (hereinafter referred to as the site or the facility). The earthquake and tsunami produced widespread devastation across northeastern Japan, resulting in approximately 25,000 people dead or missing, displacing tens of thousands of people, and significantly impacting the infrastructure and industry in the northeastern coastal areas of Japan. At the time of the earthquake, Fukushima Dai-ichi Units 1, 2, and 3 were in operation. Units 4, 5, and 6 had been shut down for routine refueling and maintenance activities, and the Unit 4 reactor fuel had been offloaded to the Unit 4 spent fuel pool. As a result of the earthquake, the three operating units at the site automatically shut down, and offsite power was lost to the entire facility. The emergency diesel generators started at all six units, providing alternating current (AC) electrical power to critical systems; overall, the facility response to the seismic event appears to have been normal. Approximately 40 minutes after shutdown of the operating units, the first large tsunami wave inundated the site, followed by multiple additional waves. The tsunami resulted in extensive damage to site facilities and a complete loss of AC electrical power at Units 1 through 5, a condition known as station blackout (SBO). One diesel generator remained functional on Unit 6. Despite the actions of the operators following the earthquake and tsunami, cooling was lost to the fuel in the Unit 1 reactor after several hours, in the Unit 2 reactor after about 70 hours, and in the Unit 3 reactor after about 36 hours, resulting in damage to the nuclear fuel shortly after the loss of cooling. In the days following the Fukushima Dai-ichi nuclear accident, the NRC Chairman directed the NRC staff to establish a senior-level agency task force to conduct a methodical and systematic review of the NRC’s processes and regulations to determine whether, in light of the events in Japan, the agency should make additional improvements to its regulatory system, and to make recommendations to the Commission for its policy direction. This direction was provided in a tasking memorandum dated March 23, 2011, from the NRC Chairman to the NRC Executive Director for Operations (COMGBJ-11-0002) (ADAMS Accession No. ML110950110). In SECY-11-0093, “Near-Term Report and Recommendations for Agency Actions Following the Events in Japan” (ADAMS Accession No. ML11186A959), dated July 12, 2011, the Near-Term Task Force (NTTF) provided its recommendations to the Commission. The staff requirements memorandum (SRM) for SECY-11-0093 (ADAMS Accession No. ML112310021), dated August 19, 2011, directed the NRC staff to identify and make “recommendations regarding any Task Force recommendations that can, and in the staff’s judgment, should be implemented, in part or in whole, without unnecessary delay.” In SECY-11-0124, “Recommended Actions To Be Taken Without Delay from the Near-Term Task Force Report” (ADAMS Accession No. ML11245A127), the NRC staff provided recommendations to the Commission on actions that, in the staff’s judgment, should be initiated without unnecessary delay, and requested that the Commission provide direction for moving forward on these recommendation (subsequently referred to as “Tier 1” recommendations). The Commission approved the staff’s proposed actions in the SRM for SECY-11-0124 (ADAMS Accession No. ML112911571), dated October 18, 2011. In SECY-11-0137, “Prioritization of Recommended Actions to Be Taken in Response to Fukushima Lessons Learned” (ADAMS Accession No. ML11269A204), the NRC staff requested that the Commission approve the staff’s prioritization of the NTTF recommendations. In the SRM for SECY-11-0137 (ADAMS Accession No. ML113490055), dated December 15, 2011, the Commission approved the staff’s proposed prioritization of the NTTF recommendations and supported action on the Tier 1 recommendations, subject to the direction in the SRM. With respect to regulatory action regarding onsite emergency response capabilities, the Commission directed the NRC staff to initiate a rulemaking on NTTF Recommendation 8, in the form of an ANPR. This document responds to that Commission direction. In November 2011, the Institute of Nuclear Power Operations (INPO) issued INPO-11-005, “Special Report on the Nuclear Accident at the Fukushima Dai-ichi Nuclear Power Station” (ADAMS Accession No. ML11347A454). In the SRM for SECY-11-0137, the Commission directed NRC staff to consider INPO-11-005 in its development of the technical bases for any proposed regulatory changes. III. Background: Onsite Emergency Response Capabilities A. Emergency Operating Procedures Emergency Operating Procedures (EOPs) are required procedures designed to mitigate the effects of a design basis accident and place the plant in a safe shutdown condition. The EOPs are required by Title 10 of the Code of Federal Regulations (10 CFR) Part 50, Appendix B, Criterion V, “Instructions, Procedures, and Drawings,” and are included in the administrative control sections of licensee’s technical specifications. Licensed operators are trained and evaluated in the implementation of EOPs through initial license training. The NRC evaluates licensed operator candidates’ knowledge of EOPs during an initial written examination, as required by 10 CFR 55.41 and 55.43, and an initial operating test, as required by 10 CFR 55.45. For proficiency, licensed operator requalification training programs, required by 10 CFR 55.59, routinely train and evaluate licensed operators on their knowledge and ability to implement the EOPs. B. Severe Accident Management Guidelines During the 1990s, the nuclear industry developed Severe Accident Management Guidelines (SAMGs) as a voluntary industry initiative in response to Generic Letter 88-20, Supplement 2, “Accident Management Strategies for Consideration in the Individual Plant Examination Process,” dated April 4, 1990 (ADAMS Accession No. ML031200551). SAMGs provide guidance to operators and Technical Support Center (TSC) staff in the event of an accident that progresses beyond a plant’s design basis (and therefore beyond the scope of the EOPs). The nuclear power industry owners’ groups (i.e., industry organizations with representatives from the various nuclear plant owners that provide industry oversight for various plant designs) developed generic guidelines specific to the individual plant designs. Given the voluntary nature of the initiative for SAMGs, their implementation throughout the industry has been varied, as noted by NRC inspection results for Temporary Instruction 2515/184, “Availability and Readiness Inspection of Severe Accident Management Guidelines (SAMGs)” (ADAMS Accession No. ML11115A053). The guidelines themselves were implemented by individual licensees, [[Page 23163]] but because the NRC has not developed a regulatory requirement for SAMGs, the training, evaluation, and procedure control requirements for SAMGs vary from plant to plant. C. Extensive Damage Mitigation Guidelines Following the terrorist events of September 11, 2001, the NRC ordered licensees to develop and implement specific guidance and strategies to maintain or restore core cooling, containment, and spent fuel pool cooling capabilities using existing or readily available resources that can be effectively implemented under the circumstances associated with loss of large areas of the plant due to explosions or fire. These requirements were subsequently imposed as license conditions for individual licensees and formalized in the Power Reactor Security Requirements final rule (74 FR 13926; March 27, 2009) in 10 CFR 50.54(hh)(2). As a result, Extensive Damage Mitigation Guidelines (EDMGs) were developed in order to provide guidance to operating crews and TSC personnel on the implementation of the strategies developed to address these large area events. The events at the Fukushima Dai-ichi Nuclear Power Station following the March 11, 2011, earthquake and tsunami highlighted the continued potential benefits of these strategies in mitigating the effects of prolonged SBOs and other events that challenge key safety functions. The NRC has not developed a specific regulatory requirement for training on EDMGs. D. Onsite Emergency Response Capabilities Versus Emergency Preparedness This ANPR focuses on the effectiveness of accident mitigating procedures and the training and exercises associated with these procedures. When using the term “accident mitigating procedures” in this document, the NRC is referring to EOPs, SAMGs, and EDMGs. The licensee’s emergency preparedness plan and implementing procedures, which are required by 10 CFR 50.47 and 50.54(q) and Appendix E to 10 CFR part 50, are being evaluated through other NTTF recommendations, and the associated efforts are referred to in the questions in Section IV.D. However, the licensee’s emergency preparedness plan and implementing procedures are not the subject of this ANPR. IV. Discussion and Request for Public Comment A. ANPR Purpose In SECY-11-0124, the NRC staff recommended that the agency engage stakeholders during rulemaking activities “so that the regulatory action and licensee actions taken effectively resolve the identified issues and implementation challenges are identified in advance.” The NRC staff proposed interaction with stakeholders to support development of the regulatory basis, a proposed rule, and implementing guidance for strengthening and integrating the onsite emergency response capabilities. In the SRM for SECY-11-0124, the Commission directed the NRC staff to issue an ANPR prior to developing the regulatory basis for a proposed rule. Accordingly, the NRC’s objective in this ANPR is to solicit external stakeholder feedback to inform the NRC staff’s efforts to evaluate regulatory approaches for strengthening the current onsite emergency response capability requirements. In the SRM for SECY-11-0124, the Commission also encouraged NRC staff to develop recommendations that continue to realize the strengths of a performance-based system as a guiding principle. The Commission indicated that, to be effective, approaches should be flexible and able to accommodate a diverse range of circumstances and conditions. The Commission stated that for “consideration of events beyond the design basis, a regulatory approach founded on performance-based requirements will foster development of the most effective and efficient, site- specific mitigation strategies, similar to how the agency approached the approval of licensee response strategies for the `loss of large area’ event” addressed in 10 CFR 50.54(hh)(2). Consistent with the Commission’s direction in the SRM for SECY-11- 0124, the NRC is open to flexible, performance-based strategies to address onsite emergency response capability requirements. This ANPR is structured around questions intended to solicit information that (1) supports development of such a framework and (2) supports assembling a complete and adequate regulatory basis that enables rulemaking to be successful. In this context, commenters should feel free to provide feedback on any aspects of onsite emergency response capability that would support this ANPR’s regulatory objective, whether or not in response to a stated ANPR question. B. Rulemaking Objectives/Success Criteria The NRC is considering development of a proposed rule that would amend the current onsite emergency response capability requirements. Currently, the regulatory and industry approaches to onsite emergency response capability are fragmented into the separate strategies that were discussed in Section III of this document. By promulgation of an onsite emergency response capability rule, the NRC would be able to establish regulations that, when implemented by licensees, would strengthen and integrate the various onsite emergency response strategies. Specifically, the proposed requirements for onsite emergency response capability would strive to accomplish the following goals: 1. Ensure that effective transitions are developed between the various accident mitigating procedures (EOPs, SAMGs, and EDMGs) so that overall strategies are coherent and comprehensive. 2. Ensure that command and control strategies for large scale events are based on the best understanding of severe accident progression and effective mitigation strategies, and well defined in order to promote effective decision-making at all levels and develop organizational flexibility to respond to unforeseen events. 3. Ensure that the key personnel relied upon to implement these procedures and strategies are trained, qualified, and evaluated in their accident mitigation roles. 4. Ensure that accident mitigating procedures, training, and exercises are appropriately standardized throughout the industry and are adequately documented and maintained. The NRC is seeking stakeholders’ views on the following specific regulatory objectives: 1. What is the preferred regulatory approach to addressing NTTF Recommendation 8? For example: a. Should the NRC develop a new rule, or could the requirements that would provide for a more strengthened and integrated response capability be accomplished by a method other than a rulemaking? Provide a discussion that supports your position. b. If a new rule is developed, what type of supporting document would be most effective for providing guidance on the new requirements? Provide a discussion that supports your position. 2. The NTTF recommendation for emergency response procedures stressed that the EOP guidelines should be revised to establish effective transitions between EOPs, SAMGs, and EDMGs in [[Page 23164]] an effort to promote a more integrated approach to onsite emergency response. The NRC is interested in stakeholder opinions on the best course of action for revising and maintaining these procedures to accomplish this objective. For example: a. Should the SAMGs be standardized throughout the industry? If so, describe how the procedures should be developed, and discuss what level of regulatory review would be appropriate. Should there be two sets of standard SAMGs, one applicable to pressurized water reactors (PWRs) and one applicable to boiling water reactors (BWRs), or should SAMGs be developed for the various plant designs in a manner similar to EOPs? Provide a discussion that supports your position. b. What is the best approach to ensure that procedural guidance for beyond design basis events is based on sound science, coherent, and integrated? What is the most effective strategy for linking the EOPs with the SAMGs and EDMGs? Should the transition from EOPs to SAMGs be based on key safety functions, or should the SAMGs be developed in a manner that addresses a series of events that are beyond a plant’s design basis? Provide a discussion that supports your position. c. The NTTF Recommendation 8 strongly advised that the plant owners’ groups should undertake revision of the accident mitigating procedures to avoid having each licensee develop its own approach. Is this the best course of action? What additional scenarios or accident plans should be considered for addition to SAMG technical guidelines as a result of the lessons learned in Japan? Provide a discussion that supports your position. d. In the SRM for SECY-11-0137, the Commission directed the NRC staff to consider the November 2011 INPO report, INPO-11-005, in the development of the technical bases for Recommendation 8. How should this document be used by industry in developing SAMGs and the NRC in developing any proposed regulatory changes? Provide a discussion that supports your position. e. Should there be a requirement for the SAMGs and EDMGs to be maintained as controlled procedures in accordance with licensee quality assurance programs? Provide a discussion that supports your position. f. Should the SAMGs and EDMGs be added to the “Administrative Controls” section of licensee technical specifications? Provide a discussion that supports your position. g. In a letter dated October 13, 2011 (ML11284A136), the Advisory Committee on Reactor Safeguards (ACRS) recommended that Recommendation 8 be expanded to include fire response procedures. In their letter, ACRS stated that some plant-specific fire response procedures can direct operators to perform actions that may be inconsistent with the EOPs, and that experience has shown that parallel execution of fire response procedures, abnormal operating procedures, and EOPs can be difficult and complex. Should efforts to integrate the EOPs, SAMGs, and EDMGs include fire response procedures? Are there other procedures that should be included in the scope of this work? Provide a discussion that supports your position. h. What level of effort, in terms of time and financial commitment, will be required by the industry to upgrade the accident mitigating procedures? If possible, please include estimated milestones and PWR/ BWR cost estimates. 3. The NTTF established the identification of clear command and control strategies as an essential aspect of Recommendation 8. What methodology would be best for ensuring that command and control for beyond design basis events is well defined? For example: a. Should separate procedures be developed that clearly establish the command and control structures for large-scale events? Should defined roles and responsibilities be included in technical specifications along with associated training and qualification requirements? Provide a discussion that supports your position. b. Should the command and control approach be standardized throughout the industry or left for individual licensees to define? Provide a discussion that supports your position. c. What level of effort, in terms of time and financial commitment, will be required by the industry to develop these command and control strategies? If possible, please include estimated milestones and PWR/ BWR cost estimates. 4. As the guidelines for accident mitigating procedures are revised and the command and control strategies are developed, personnel who will be implementing these procedures must be adequately trained, qualified, and evaluated. What would be the best approach for ensuring that the personnel relied upon to implement the revised procedures are proficient in the use of the procedures, maintain adequate knowledge of the systems referenced in these procedures, and can effectively make decisions, establish priorities, and direct actions in an emergency situation? For example: a. Should a systems approach to training be developed to identify key tasks that would be performed by the various roles identified in the new strategies? Provide a discussion that supports your position. b. Should the current emergency drill and exercise requirements be revised to ensure that the strategies developed as a result of this ANPR will be evaluated in greater depth? Provide a discussion that supports your position. c. Should the revised accident mitigating procedures, specifically SAMGs and EDMGs, be added to the knowledge and abilities catalogs for initial reactor operator licenses? Provide a discussion that supports your position. d. What level of plant expertise should be demonstrated by the personnel assigned to key positions outlined by the accident mitigation guidelines and command and control strategy? Should these personnel be required to be licensed or certified on the plant design? Provide a discussion that supports your position. e. What training requirements should be developed to ensure emergency directors and other key decision-makers have the command and control skills needed to effectively implement an accident mitigation strategy? Provide a discussion that supports your position. f. What should the qualification process entail for key personnel identified in the new strategies? How would this qualification process ensure proficiency? Provide a discussion that supports your position. g. What level of effort, in terms of time and financial commitment, will be required by the industry to develop and implement these training, qualification, and evaluation requirements? If possible, please include estimated milestones and PWR/BWR cost estimates. C. Applicability to NRC Licenses and Approvals The NRC would apply the new onsite emergency response capability requirements to power reactors, both currently operating and new reactors, and would like stakeholder feedback. Accordingly, the NRC envisions that the requirements would apply to the following: Nuclear power plants currently licensed under 10 CFR part 50; Nuclear power plants currently being constructed under construction permits issued under 10 CFR part 50, or whose construction permits may be reinstated; [[Page 23165]] Future nuclear power plants whose construction permits and operating licenses are issued under 10 CFR part 50; and Current and future nuclear power plants licensed under 10 CFR part 52. D. Relationship Between Recommendation 8 and Other Near-Term Task Force Recommendations The NRC notes that there is a close relationship between the onsite emergency response capability requirements under consideration in this ANPR effort and several other near-term actions stemming from the NTTF report (and identified in SECY-11-0124 and SECY-11-0137). Regulatory actions taken in response to these other activities might impact efforts to amend onsite accident mitigating procedures and training. In this regard: 1. What is the best regulatory structure for integrating the onsite emergency response capability requirements with other post-Fukushima regulatory actions, such that there is a full, coherent integration of the requirements? 2. Recommendations 4.1 and 4.2 address SBO regulatory actions and mitigation strategies for beyond design basis external events, respectively. The implementation strategies developed in response to Recommendations 4.1 and 4.2 will require corresponding procedures. The NRC recognizes the need for coordinating efforts under Recommendations 4.1, 4.2, and 8. What is the best way to integrate these three regulatory efforts to ensure that they account for the others’ requirements, yet do not unduly overlap or inadvertently introduce redundancy, inconsistency, or incoherency? 3. Recommendation 9.3 addresses staffing during a multiunit event with an SBO. Should staffing levels change as a result of a revised onsite emergency response capability or should these duties be assigned to existing staff? 4. Recommendation 10.2 addresses command and control structure and qualifications for the licensee’s decision-makers for beyond design basis events. Should this recommendation be addressed concurrently with Recommendation 8? E. Interim Regulatory Actions The NRC recognizes that implementation of multiple post-Fukushima requirements could be a challenge for licensees and requests feedback on how best to implement multiple requirements, specifically onsite emergency response capability requirements, without adversely impacting licensees’ effectiveness and efficiency. It will take several years to issue a final rule. Should the NRC use other regulatory vehicles (such as commitment letters or confirmatory action letters) to put in place interim coping strategies for onsite emergency response capabilities while rulemaking proceeds? V. Public Meeting The NRC plans to hold a category 3 public meeting with stakeholders during the ANPR public comment period. The public meeting is intended as a forum to discuss the ANPR with external stakeholders and provide information on the feedback requested in the ANPR to support development of onsite emergency response capability requirements. The meeting is not intended to solicit comment. Instead, the NRC will encourage stakeholders at the meeting to provide feedback in written form during the ANPR comment period. To support full participation of stakeholders, the NRC staff plans to provide teleconferencing and Webinar access for the public meeting. Since the intent of the meeting is not to solicit or accept comments, the meeting will not be transcribed. The NRC will issue the public meeting notice 10 calendar days before the public meeting. Stakeholders should monitor the NRC’s public meeting Web site for information about the public meeting: http://www.nrc.gov/public involve/public-meetings/index.cfm. VI. Rulemaking Process and Schedule Stakeholders should recognize that the NRC is not obligated to provide detailed comment responses to feedback provided in response to this ANPR. If the NRC develops a regulatory basis sufficient to support a proposed rule, there will be an opportunity for additional public comment when the regulatory basis and the proposed rule are published. If supporting guidance is developed for the proposed rule, stakeholders will have an opportunity to provide feedback on the implementing guidance. VII. Related Petition for Rulemaking Action The NTTF report provided a specific proposal for onsite emergency actions that was subsequently endorsed by the National Resources Defense Council (NRDC) in a petition for rulemaking (PRM), PRM-50-102 (76 FR 58165; September 20, 2011), as a way to address licensee training and exercises. In connection with NTTF Recommendation 8.4, “Onsite emergency actions,” the NRDC requested in its petition that the NRC “institute a rulemaking proceeding applicable to nuclear facilities licensed under 10 CFR 50, 52, and other applicable regulations to require more realistic, hands-on training and exercises on Severe Accident Mitigation [sic] Guidelines (SAMGs) and Extreme Damage Mitigation Guidelines (EDMGs) for licensee staff expected to implement the strategies and those licensee staff expected to make decisions during emergencies, including emergency coordinators and emergency directors.” The Commission has established a process for addressing a number of the recommendations in the NTTF Report, and the NRC determined that the issues raised in PRM-50-102 are appropriate for consideration and will be considered in this Recommendation 8 rulemaking. Persons interested in the NRC’s actions on PRM-50-102 may follow the NRC’s activities at www.regulations.gov by searching on Docket ID NRC-2012-0031. VIII. Available Supporting Documents The following documents provide additional background and supporting information regarding this activity and corresponding technical basis. The documents can be found in ADAMS. Instructions for accessing ADAMS are in the ADDRESSES section of this document. ———————————————————————— ADAMS Accession Number/Federal Date Document Register Citation ———————————————————————— April 4, 1990…………….. Generic Letter 88-20, ML031200551 Supplement 2, “Accident Management Strategies for Consideration in the Individual Plant Examination Process”. August 28, 2007…………… Appendix A to 10 CFR 72 FR 49505 part 50–General Design Criteria for Nuclear Power Plants. August 28, 2007…………… Final Rule: Licenses, 72 FR 49352 Certifications, and Approvals for Nuclear Power Plants. March 27, 2009……………. Final Rule: Power 74 FR 13926 Reactor Security Requirements. [[Page 23166]] March 23, 2011……………. Memorandum from ML110950110 Chairman Jaczko on Tasking Memorandum- COMGBJ-11-0002–NRC Actions Following the Events in Japan. April 29, 2011……………. Temporary Instruction ML11115A053 2515/184, Availability and Readiness Inspection of Severe Accident Management Guidelines (SAMGs). May 26, 2011……………… Completion of ML111470264 Temporary Instruction 2515/184, Availability and Readiness Inspection of Severe Accident Mitigation Guidelines (SAMGs), at Region IV Reactor Facilities. May 27, 2011……………… Region I Completion of ML111470361 Temporary Instruction (TI)-184, Availability and Readiness Inspection of Severe Accident Mitigation Guidelines (SAMGs). June 1, 2011……………… Completion of ML111520396 Temporary Instruction (TI) 2515/184, Availability and Readiness Inspection of Severe Accident Management Guidelines (SAMGs) at Region III Sites–Revision. June 2, 2011……………… Completion of ML111530328 Temporary Instruction (TI) 184, Availability and Readiness Inspection of Severe Accident Mitigation Guidelines (SAMGS) at Region II Facilities–Revision. July 12, 2011…………….. SECY-11-0093–“The ML11186A959 Near-Term Task Force ML111861807 Review of Insights (Enclosure) from the Fukushima Dai-ichi Accident”. August 19, 2011…………… SRM-SECY-11-0093–Near- ML112310021 Term Report and Recommendations for Agency Actions Following the Events in Japan. September 9, 2011…………. SECY-11-0124, ML11245A127 “Recommended Actions ML11245A144 to be Taken Without (Enclosure) Delay from the Near- Term Task Force Report.”. October 3, 2011…………… SECY-11-0137, ML11269A204 “Prioritization of ML11272A203 Recommended Actions (Enclosure) to be Taken in Response to Fukushima Lessons Learned.”. October 18, 2011………….. Staff Requirements ML112911571 Memorandum–SECY-11-0 124–Recommended Actions to be Taken Without Delay From The Near-Term Task Force Report. July 26, 2011…………….. NRDC’s Petition for ML11216A242 Rulemaking to Require More Realistic Training on Severe Accident Mitigation Guidelines (PRM 50- 102). September 14, 2011………… Letter to Geoffrey H. ML112700269 Fettus, Natural Resources Defense Council, Inc. from Annette Vietti-Cook, In Regards to the NRC Will Not Be Instituting a Public Comment Period for PRM-50-97, PRM-50-98, PRM-50-99, PRM-50- 100, PRM-50-101, and PRM-50-102. October 13, 2011………….. Initial ACRS Review ML11284A136 of: (1) The NRC Near- Term Task Force Report on Fukushima and (2) Staff’s Recommended Actions to be Taken Without Delay. November 30, 2011…………. INPO-11-005, Special ML11347A454 Report on the Nuclear Accident at the Fukushima Dai-ichi Nuclear Power Station. December 15, 2011…………. Staff Requirements ML113490055 Memorandum–SECY-11-0 137–Prioritization of Recommended Actions to be Taken in Response to the Fukushima Lessons- Learned. March 14, 2012……………. Summary of the Public ML12073A283 Meeting to Discuss Implementation of Near-Term Task Force Recommendation 8, Strengthening and Integration of Onsite Emergency Response Capabilities Such As EOPS, SAMGS, and EDMGS, Related to the Fukushima Dai-ichi Power Plant Accident. ———————————————————————— Dated at Rockville, Maryland, this 4th day of April 2012. For the Nuclear Regulatory Commission. Michael F. Weber, Acting Executive Director for Operations. [FR Doc. 2012-9336 Filed 4-17-12; 8:45 am] BILLING CODE 7590-01-P
TOP-SECRET from the FBI – Two Former Executives Plead Guilty to Foreign Bribery Offenses
WASHINGTON—Stuart Carson, the former president of Rancho Santa Margarita, California-based valve company Control Components Inc. (CCI), and Hong “Rose” Carson, the former CCI director of sales for China and Taiwan, have pleaded guilty to violating the Foreign Corrupt Practices Act (FCPA), announced the Justice Department’s Criminal Division and the U.S. Attorney’s Office for the Central District of California.
The Carsons, who are married and reside in San Clemente, California, each pleaded guilty late yesterday before U.S. District Judge James V. Selna in Santa Ana, California to separate one-count superseding informations charging them with making a corrupt payment to a foreign government official in violation of the FCPA. According to court documents, CCI designed and manufactured service control valves for use in the nuclear, oil and gas, and power generation industries worldwide. At sentencing, Stuart Carson, 73, faces up to 10 months in prison. Rose Carson, 48, faces a sentence of three years’ probation, which may include up to six months of home confinement. Sentencing is scheduled for October 15, 2012.
On April 8, 2009, the Carsons and four other former executives of CCI were charged in a 16-count indictment for their roles in the foreign bribery scheme. The four former CCI executives charged include Paul Cosgrove, CCI’s former director of worldwide sales; David Edmonds, CCI’s former vice president of worldwide customer service; Flavio Ricotti, the former CCI vice president of sales for Europe, Africa, and the Middle East; and Han Yong Kim, the former president of CCI’s Korean office. On April 28, 2011, Ricotti pleaded guilty to one count of conspiracy to violate the FCPA. The trial of Cosgrove and Edmonds is scheduled for June 5, 2012. The charges against Kim are pending as well. An indictment merely contains allegations and defendants are presumed innocent unless and until proven guilty beyond a reasonable doubt in a court of law.
In related cases, two defendants previously pleaded guilty to conspiring to bribe officers and employees of foreign state-owned companies on behalf of CCI. On January 8, 2009, Mario Covino, the former director of worldwide factory sales for CCI, pleaded guilty to one count of conspiracy to violate the FCPA. On February 3, 2009, Richard Morlok, the former CCI finance director, also pleaded guilty to one count of conspiracy to violate the FCPA. Covino, Morlok, and Ricotti are scheduled to be sentenced in November and December 2012.
On July 31, 2009, CCI pleaded guilty to a three-count criminal information charging the company with conspiracy to violate the FCPA and the Travel Act and with two substantive violations of the FCPA. CCI was ordered to pay an $18.2 million criminal fine, placed on organizational probation for three years, and ordered to create and implement a compliance program and retain an independent compliance monitor for three years. CCI admitted that from 2003 through 2007, it made corrupt payments in more than 30 countries, which resulted in net profits to the company of approximately $46.5 million from sales related to those corrupt payments.
The case is being prosecuted by Deputy Chief Charles G. La Bella and Trial Attorney Andrew Gentin of the Criminal Division’s Fraud Section and Assistant U.S. Attorneys Douglas McCormick and Gregory Staples of the U.S. Attorney’s Office for the Central District of California. The case was investigated by the FBI’s Washington Field Office and its team of special agents dedicated to the investigation of foreign bribery cases.
TOP-SECRET – Inside the U.S. Secret Service – Full Movie
TOP-SECRET – Classified Info in Criminal Trials, and More from CRS
Former CIA officer John C. Kiriakou is to be arraigned today on charges of leaking classified information to the press in violation of the Espionage Act and the Intelligence Identities Protection Act — charges that he denies. See The Case of An Accused Leaker: Politics or Justice? by Carrie Johnson, National Public Radio, April 13.
A newly updated report from the Congressional Research Service discusses Protecting Classified Information and the Rights of Criminal Defendants: The Classified Information Procedures Act, April 2, 2012.
Another newly updated CRS report finds that federal agencies spent $750.4 million last year to pay for “advertising services.” But though non-trivial, it seems that this amount was less than was spent for such purposes in any previous year since 2003.
The term advertising is not strictly defined in budget documents, and may include various forms of public relations, public service notices, and the like. “Government advertising can be controversial if it conflicts with citizens’ views about the proper role of government,” the CRS report stated. “Yet some government advertising is accepted as a normal part of government information activities.”
Federal advertising expenditures have actually decreased over the past two years and haven’t been lower since 2003. The highest level of advertising expenditures in the past decade occurred in 2004, the CRS report found. See Advertising by the Federal Government: An Overview, April 6, 2012.
Some other updated CRS reports that have not been made publicly available by Congress include these:
Detention of U.S. Persons as Enemy Belligerents, April 11, 2012
Rare Earth Elements in National Defense: Background, Oversight Issues, and Options for Congress, April 11, 2012
The Lord’s Resistance Army: The U.S. Response, April 11, 2012
Kuwait: Security, Reform, and U.S. Policy, April 11, 2012
Pakistan: U.S. Foreign Assistance, April 10, 2012
TOP-SECRET from the NSA – The most valuable Agents

Washington, D.C., April 12, 2012 – The “FBI’s most valued secret agents of the Cold War,” brothers Morris and Jack Childs, together codenamed SOLO, reported back to J. Edgar Hoover starting in 1958 about face-to-face meetings with top Soviet and Chinese Communist leaders including Mao and Khrushchev, while couriering Soviet funds for the American Communist Party, according to newly declassified FBI files cited in the new book by Tim Weiner, Enemies: A History of the FBI(New York: Random House, 2012).
Highlights from the massive SOLO files (which total more than 6,941 pages in 45 volumes declassified in August 2011 and January 2012) appear on the National Security Archive’s Web site today at www.nsarchive.org, together with an overview by Tim Weiner and a new search function, powered by the Archive’s partnership with DocumentCloud, that enables full-text search of the entire SOLO file (instead of the 45 separate PDF searches required by the FBI’s Vault publication at http://vault.fbi.gov/solo).
For more on Enemies, see last night’s broadcast of The Daily Show with Jon Stewart, featuring Tim Weiner, and the reviews by The New York Times Book Review, The Guardian, and The Washington Post.
“SOLO” BY TIM WEINER
FBI Director J, Edgar Hoover’s most valued secret agent was a naturalized citizen of Russian/Ukrainian/Jewish origins named Morris Childs. He was the first and perhaps the only American spy to penetrate the Soviet Union and Communist China at the highest levels during the Cold War, including having face-to-face conversations with Nikita Khrushchev, Mao Zedong and others in a red-ribbon cast of Communist leaders.
The operation, codenamed SOLO, that the FBI built on his work (and that of his brother, Jack) posed great risks and the promise of greater rewards. The FBI’s first debriefings of Morris Childs were declassified in August 2011 in time for inclusion in the book Enemies. Even more SOLO debriefings and associated memos – upwards of 45 volumes and thousands of pages – emerged in January 2012.
Researchers have been requesting these documents for years, and with good reason. They are unique records of a crucial chapter in the history of American intelligence. They illuminate several mysteries of the Cold War, including the origins of Hoover’s hatred for Martin Luther King, some convincing reasons for Dwight Eisenhower’s decision to hold off on the CIA’s plans to invade Fidel Castro’s Cuba, and the beginnings of Richard Nixon’s thoughts about a détente with the Soviets.
Morris Childs was an important figure in the Communist Party of the United States in the 1930s and 1940s, serving as the editor of its newspaper, the Daily Worker. He and his brother Jack had fallen out with the Party in 1948. Three years later, the FBI approached him as part of a new program called TOPLEV, in which FBI agents tried to talk top-level Communist Party members and officials into becoming informants.
Childs became a Communist for the FBI. He rejoined the Party and rose higher and higher in its secret hierarchy. In the summer of 1957, the Party’s leaders proposed that he serve as their international emissary in an effort to reestablish direct political and financial ties with the Kremlin. If Moscow approved, Childs would be reporting to Hoover as the foreign secretary of the Communist Party of the United States.
The FBI’s intelligence chief, Al Belmont, could barely contain his excitement over Childs’ cooperation. If the operation succeeded, he told Hoover, “it would enhance tremendously the Bureau’s prestige as an intelligence agency.”
[See Document 1: Memorandum from A.H. Belmont to L.V. Boardman, “Courier System Between Communist Party, USA, and Communist Party, Soviet Union,” 30 August 1957. Source: http://vault.fbi.gov/solo/solo-part-01-of/view, page 17.]
On March 5, 1958, the FBI’s top intelligence officials agreed that the operation would work: the Bureau could “guide one of our informants into the position of being selected by the CPUSA as a courier between the Party in this country and the Soviet Union.”
[See Document 2: Memorandum from A.H. Belmont to L.V. Boardman, “Communist Party, USA, International Relations, Internal Security-C,” 5 March 1958. Source: http://vault.fbi.gov/solo/solo-part-01-of/view, page 1.]
On April 24, 1958, Childs boarded TWA Flight 824 to Paris, on the first leg of his long trip to Moscow, at the invitation of the Kremlin. He met the Party’s leaders over the course of eight weeks. He learned that his next stop would be Beijing. On July 6, 1958, he had an audience with Chairman Mao Zedong (see pages 13-16 of Document 3B) Was the United States planning to go to war in Southeast Asia? Mao asked. If so, China intended to fight to the death, as it had during the Korean War. “There may be many Koreas in Asia,” Mao predicted.
[See Documents 3A-B: A: Childs’ Account of his April 1958 Trip to Soviet Union and China. B: SAC, New York, to Director, FBI, 23 July 1958 [account of Child’s first trip as a double-agent] Source: http://vault.fbi.gov/solo/solo-part-02-of/view.]
Returning to Moscow that summer, conferring with leaders of the Party and the KGB, Morris received a formal invitation to attend the 21st Congress of the Communist Party of the Soviet Union, and he accepted promises of cash payments for the CPUSA that would come to $348,385 over the next few months. The money was delivered to Morris by a Soviet delegate to the United Nations at a restaurant in Queens, New York.
Though the trips exhausted him, leaving him a physically broken man, Morris Childs went abroad two or three times a year over the course of the next two decades. He undertook fifty- two international missions, befriending the world’s most powerful Communists. He controlled the income of the American Communist Party’s treasury and contributed to the formulation of its foreign policy. His work as SOLO was undetected by the KGB and kept secret from all but the most powerful American leaders.
[See Document 4: Clyde Tolson to the Director, 12 March 1959 [report on Child’s background, how he was recruited, and information from his most recent trip to Moscow] Source: http://vault.fbi.gov/solo/solo-part-11-of-17/view, p. 49.]
SOLO’s intelligence gave Hoover an unquestioned authority in the White House. The United States never had had a spy inside the high councils of the Soviet Union or the People’s Republic of China. Morris Childs would provide the U.S. government with insights no president had ever before possessed.
Hoover briefed President Eisenhower about the SOLO mission repeatedly from November 1958 onwards. For the next two years, Hoover sent summaries of his reporting directly to Eisenhower and Vice President Nixon. Hoover reported that the world’s most powerful Communists– Mao Zedong and Nikita Khrushchev– were at each other’s throats. The breach between Moscow and Beijing was a revelation to Eisenhower. The FBI director also reported that Moscow wanted the CPUSA to support the civil rights movement in the United States. The idea that communism and civil rights were connected through covert operations was electrifying to Hoover.
Hoover told the White House that SOLO had met with Anibal Escalante, a political leader of the newly victorious revolution in Cuba, a confidant to Fidel Castro and the Cuban Communist most highly regarded in Moscow. Escalante said that the Cubans knew the United States was planning a paramilitary attack to overthrow Castro. This reporting gave Eisenhower pause as he weighed the CIA’s proposal to invade the island with a force of anti-Castro Cubans undergoing training in Guatemala. He never approved the plan; that was left to President Kennedy, who went ahead with the disastrous Bay of Pigs invasion.
[See Document 5: Memoranda and Letters to Director/Naval Intelligence, Director/CIA, National Security Adviser, Secretary of State, and Vice President Nixon on Information from Anibal Escalante. Source: http://vault.fbi.gov/solo/solo-part-21-22-of/view]
Hoover reported directly to Nixon as the vice president prepared to go to Moscow in July 1959, where he would engage Khrushchev in a public discussion on the political and cultural merits of communism and capitalism. SOLO had met with the top Communist Party officials responsible for American affairs. Hoover distilled their thinking about the leading candidates in the 1960 presidential election.
Moscow liked Ike: he understood the meaning of war and he was willing to risk the chances of peace. But Senator Kennedy was judged as “inexperienced” and potentially dangerous. As for Nixon, the Communists thought he would be a capable president, though he was “cunning” and “ambitious.”
[See Document 6: SAC, New York, to Director, FBI, 13 March 1960 [report on Khrushchev’s imminent visit to France and on President Eisenhower’s prospective (later cancelled) trip to Soviet Union]. Source: http://vault.fbi.gov/solo/solo-part-19-20-of/view, pp. 93-98.]
Nixon learned from the SOLO debriefings that Moscow could conduct rational political discourse; a decade later, the lesson served him well as president when he sought détente with the Soviets.
[Adapted from Tim Weiner, Enemies: A History of the FBI, pp. 207-209]
MORE ABOUT SOLO
The SOLO records are an extraordinary new contribution to the history of the FBI and American intelligence. It is worth noting that prior to the new FBI releases, earlier scholars had made important contributions to knowledge of this FBI operation. Civil rights historian and assiduous FOIA requester David J.Garrow was the first researcher to discover the role of the Childs brothers as FBI double-agents. In his book, Martin Luther King and the FBI: from ‘Solo’ to Memphis (New York: W. W. Norton, 1981), Garrow sought to explain why J.Edgar Hoover and the Bureau were such “viciously negative” opponents of King. Garrow disclosed that the Childs brothers had provided information to the FBI on Stanley Levison, one of King’s key political advisers. Levison had been active in the U.S. Communist Party during the early 1950s but, as Childs reported, had left the organization because of its political irrelevance. Nevertheless, the FBI saw Levison as a Soviet agent and used his former political connections as leverage to force King to break with his adviser.
Following Garrow’s trail was the late John Barron, a former Naval intelligence officer turned journalist and later a full-time writer for Readers Digest who produced as full an account of “Operation Solo” as was possible in the 1990s. An expert on the KGB, Barron met numerous former Soviet agents. One day, Morris Childs and his wife turned up at Barron’s Washington, D.C. office. Recognizing the Childs’ importance, Barron wanted to tell Morris’ story and did so through interviews with the FBI case officers who had handled contacts with the Childs brothers and their associates. Barron had no access to the documents, but his book, Operation Solo: The FBI’s Man in the Kremlin (Regnery, 1996), provided the first detailed account of the rise of Morris Childs to an influential role in the U.S. Communist Party, why he secretly broke with the Party, when and how he started to work with the FBI, and how he used his party connections and recurrent travel to Moscow and Beijing to provide current intelligence on developments in those capitals.
– William Burr
THE DOCUMENTS
Archive staff have downloaded the SOLO files from the FBI site and launched them in DocumentCloud in order to get a higher-quality full-text (OCR) and keyword search capacity down to the individual page level. The following files correspond to the 45 volumes posted on the FBI’s Vault. To search the entire group, enter terms in the field below and press “Enter.” The results will take you to the correct volume. Repeat your search and the results will take you to the correct page with the term highlighted in yellow.
TOP-SECRET from the FBI – Three Mortgage Loan Officers Guilty Orchestrating $9 Million Mortgage Fraud Scheme
Preet Bharara, the United States Attorney for the Southern District of New York, announced that three mortgage loan officers, Frederick Warren, Dorian Brown, and Fritz Bonaventure each pled guilty today for their roles in a $9 million mortgage fraud scheme. The defendants pled guilty before U.S. District Judge Naomi Reice Buchwald.
Manhattan U.S. Attorney Preet Bharara said, “Frederick Warren, Dorian Brown, and Fritz Bonaventure betrayed the lending institutions for which they worked, approving loan applications they knew were bogus and would end up in default. Their pleas today are sterling examples of how federal and state authorities can work together to identify, prosecute, and punish those who engage in mortgage fraud.”
According to the indictment previously filed in Manhattan federal court:
Warren, Brown, and Bonaventure, along with nine other individuals, engaged in an illegal scheme to defraud various lending institutions by using fictitious and fraudulent “straw identities” to apply for mortgage loans. Through the scheme, the defendants were able to obtain more than $9 million in mortgage loans for the purchase of dozens of residential properties throughout the New York City metropolitan area and Long Island. Most of these loans quickly went into default. Warren, Brown, and Bonaventure each acted as loan officers who processed the fraudulent mortgage applications.
***
Warren, 38, of Miller Place, New York; and Brown, 38, of Mount Sinai, New York, each pled guilty to one count of conspiracy to commit wire fraud and bank fraud and one count of wire fraud. They face a maximum sentence of 50 years in prison.
Bonaventure, 30, of Lithonia, Georgia, pled guilty to one count of conspiracy to commit wire fraud and bank fraud and faces a maximum sentence of 30 years in prison.
All three defendants will be sentenced by Judge Buchwald: Warren on August 14, 2012; Brown on August 14, 2012; and Bonaventure on September 12, 2012.
Co-defendants Jeffrey Larochelle, Joell Barnett, Foriduzzaman Sarder, Sakat Hossain, and Mikael Huq previously pled guilty in this case. Sarder was sentenced by Judge Buchwald on June 26, 2011 to 78 months in prison. Hossain was sentenced by Judge Buchwald on March 1, 2012 to 29 months in prison. The sentencings of Larochelle, Barnett, and Huq are pending.
Criminal charges remain pending against the following defendants: Eric Finger, Reginald Johnson, Denise Parks, and Brandon Lisi. The trial for these defendants is scheduled to begin on May 7, 2012, and they are presumed innocent unless and until proven guilty.
Mr. Bharara praised the outstanding investigative efforts of the New York Attorney General’s Office, which led the investigation and has collaborated in the prosecution. He also thanked the Federal Bureau of Investigation and the New York State Department of Financial Services for their assistance in this case.
This case is being handled by the Office’s Complex Frauds Unit. Assistant United States Attorneys Michael D. Lockard and Ryan P. Poscablo, and Assistant Attorney General Meryl Lutsky—who is designated as a Special Assistant U.S. Attorney in this case—are in charge of the prosecution.
TOP-SECRET from the FBI – William Colby’s Handwritten and Typed Notes on Sensitive Central Intelligence Agency Activities
| Citation: | [William Colby’s Handwritten and Typed Notes on Sensitive Central Intelligence Agency Activities] [Classification Unknown], Notes, May 09, 1973, 14 pp. |
| Collection: | The CIA Family Jewels Indexed |
| Item Number: | FJ00023 |
| Origin: | United States. Central Intelligence Agency. Directorate of Operations. Deputy Director |
| From: | Colby, William E. |
| Individuals/ Organizations Named: |
Chile Embassy. United States; Christensen, William H.; Clarke, Bruce C.; Hunt, E. Howard; Investors Overseas Service; Karamessines, Thomas H.; Kruegel [Central Intelligence Agency employee]; Mulholland, Douglas P.; Nixon, Richard M.; O’Neill, Joe; Osborn, Howard J.; Tofte, Hans; United States. Central Intelligence Agency. Directorate of Intelligence. Deputy Director; United States. Central Intelligence Agency. Directorate of Intelligence. Domestic Contact Service; United States. Central Intelligence Agency. Directorate of Management and Services. Office of Logistics; United States. Central Intelligence Agency. Directorate of Management and Services. Office of Security; United States. Central Intelligence Agency. Directorate of Operations. Counterintelligence Staff; United States. Central Intelligence Agency. Directorate of Operations. Foreign Resources Division; United States. Central Intelligence Agency. Directorate of Operations. Technical Services Division; United States. Department of Justice. Bureau of Narcotics and Dangerous Drugs; United States. Secret Service; Vesco, Robert L.; Walsh, Paul V.; Washington (D.C.) Metropolitan Police Department; Yale, Thomas B. |
| Subjects: | Alias documentation | Black power movement | Cambodia | Corporations | Covert identities | Diplomatic security | Domestic intelligence | Government appropriations and expenditures | Illegal entry | Interagency cooperation | Police assistance | Political activists | Postal services | Presidential speeches | Students | Telephone monitoring |
| Abstract: | Lists William Colby’s questions and follow-up actions regarding sensitive Central Intelligence Agency activities related to surveillance of dissidents, telephone monitoring, use of Agency budget, alias documentation, and support of local police forces. |
| Full Text: | Document – PDF – this link will open in a new window (832 KB) |
SECRET – California State Threat Assessment Center: How Male Gangs Leverage Female Supporters
(U//LES) This bulletin provides information regarding the role females, who are not members, play within California gangs. Because females often avoid detection by law enforcement, to mitigate detection, male gangs leverage females to further their criminal activity.
(U) KEY JUDGMENTS
(U//FOUO) The STAC assesses with high confidence that gangs will continue to use females to conduct criminal and non-criminal activity on their behalf because females tend to be overlooked during police encounters with male gang members.
(U//FOUO) In some gang cultures, females are viewed as inferior to their male counterparts or as property; in other gang cultures, females may hold positions of esteem or act on behalf of a “shotcaller.”
(U) SUPPORTS ILLEGAL ACTIVITIES
(U//LES) Females usually start their association to earn respect but often find themselves being used for sex, drug or weapon couriers, and as the admiring audience of the male gang members.1 Female supporters serve additional purposes within gangs, including intelligence gathering. Sometimes they have legitimate sources of income but they may also commit crimes to provide additional financial support for the gang. Gangs commonly employ women to conduct the following:
- courier weapons, contraband or drugs;
- facilitate communication among gang members in jail, in prison, or on the streets;
- smuggle messages, narcotics, or money into jail or prison during visits;
- launder money;
- sell counterfeit goods;
- commit identity and credit card theft;
- petty or grand theft;
- prostitute themselves.
As a communications facilitator, females may use their address or a Post Office Box as a central mailing destination where mail then gets repackaged and rerouted to other male gang members. They may also redraft letters on behalf of one gang member and send it to another.
(U) A FEMALE’S ROLE IN DIFFERENT GANG CULTURES
(U//LES) Predominantly Hispanic gangs often give their females, wives, or girlfriends much more latitude than other gangs. Women are typically given the power to run things on behalf of their “man.” They might be used in lieu of the actual shotcaller. The wife of a Mexican Mafia (EME) shotcaller is often referred to as “La Senora” – Mrs. or “La Madrina” – Godmother. A sister or biological daughter might also hold this title. While they are not involved in the commission of criminal acts, they can order gang members to commit the deed. An order given by “La Senora,” is considered equivalent to an order coming directly from the EME shotcaller; a soldier (gang member) cannot disobey her. The wife/girlfriend will often act as a liaison between street members and an incarcerated EME shotcaller to keep him apprised of what is happening on the streets. She also usually controls the gang‟s money (taxesb paid by gang members) and bank account(s).
(U//LES) Among skinhead gangs and outlaw motorcycle gangs (OMGs), women do not typically hold as much prestige as their counterparts associated with Hispanic gangs. OMG women are typically considered to be, referred to as and treated as property. A girlfriend may be shared among members; however, as a wife, she is no longer shared but earns the privilege of patching her riding gear with “Property of” her husband. Another term used by OMGs and skinhead gangs to refer to their girlfriends or wives is “old lady,” indicative of their perceived inferiority. OMGs also use their women to carry weapons or drugs.
(U//LES) In some instances, female skinhead supporters are more dedicated or “down for the cause” than male skinheads, but they are still considered to be disposable.. In one case, an Aryan Brotherhood gang member used a gun, which he borrowed from a female supporter, in the commission of a robbery. When the female confronted the gang member about his illegal use of her gun, he killed her.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET from the FBI – Brothers Who Defrauded Nordstrom with Online Reward Scheme Plead Guilty to Wire Fraud
Two brothers pleaded guilty today to wire fraud in connection with their scheme to defraud Nordstrom of more than $1.4 million in commissions and rebates. Andrew S. Chiu, 29, of Anaheim, California; and Allen J. Chiu, 37, of Dallas, Texas, pleaded guilty today in U.S. District Court in Seattle. The brothers devised a scheme to defraud Nordstrom after they had already been barred for purchasing any goods from the Nordstrom.com website. Because Nordstrom quickly notified law enforcement, the U.S. Attorney’s Office was able to seize more than $970,000 in illegally derived assets which will be applied toward the restitution owed to Nordstrom. U.S. District Judge Ricardo S. Martinez is scheduled to sentence the Chiu brothers on July 13, 2012.
According to records filed in the case, in 2008 the Chiu brothers were barred from ordering merchandise from Nordstrom.com because of excessive claims for refunds based on representations that merchandise had never been delivered. However, both brothers continued to try to place orders with Nordstrom.com. Both men belong to FatWallet Inc., a membership-based shopping community website that promotes various online retailers by providing coupons and cash back incentives for purchases. FatWallet paid cash back rewards to the Chiu brothers for purchases made at various online retailers, including Nordstrom.com. In January 2010, the brothers discovered they could exploit a computer programming error in Nordstrom’s ordering system by placing orders that would ultimately be blocked by Nordstrom. No merchandise would ship and nothing would be charged to their credit card. However, Nordstrom would unknowingly continue to compensate FatWallet for the order, and the brothers would still receive the cash back credit from FatWallet. Between January 2010 and continuing through October 2011, the Chiu brothers collectively placed more than $23 million in fraudulent orders through Nordstrom.com. The fraudulent ordering resulted in Nordstrom paying $1.4 million in rebates and commissions, with more than $650,000 in fraudulent cash back payments going directly to the brothers. The error that permitted the continued payment of rebates in the ordering system has since been fixed.
Under the terms of the plea agreement, prosecutors will recommend a sentence of no more than 30 months in prison, and the brothers can request no less than 24 months in prison. However, Judge Martinez is not bound by the recommendations and can impose any sentence allowed by law up to the maximum 20 years in prison and a $250,000 fine.
The case was investigated by the FBI. The case was prosecuted by Assistant United States Attorneys Katheryn Kim Frierson and Francis Franze-Nakamura.
TOP-SECRET – The Original Court Document – Microhits, Inc. et al v. Megaupload, Ltd. et al 21/3/12 PDF
TOP-SECRET – FBI Mara Salvatrucha (MS-13) International Assessment
(U) The purpose of this assessment is to provide an overview of the international activities of the MS-13 criminal organization. The report is the result of the analysis of arrest records, law enforcement reports, deportation records, interviews, and observations conducted by members of the MS-13 National Gang Task Force (NGTF) regarding documented MS-13 members in the United States; Chiapas, Mexico; El Salvador; and Honduras. Violent MS-13 members have crossed international boundaries and key members have documented links between the United States and the countries addressed in this assessment (see Appendix A).
(U) Key Judgements
- Available law enforcement information indicates that there are approximately 8,000-10,000 active MS-13 members in the United States. However, due to diverse law enforcement gang membership criteria and migration issues, the exact number of MS-13 gang members in this country is unknown.
- (U) In the United States, MS-13 has an identified presence in 33 states and the District of Columbia. FBI information indicates that MS-13 is considered highly active in California, Maryland, North Carolina, New Jersey, New York, Texas, Virginia, and Washington.
- (U//LES) Although leaders of several cliques may work together occasionally to achieve a common goal, a single national or international MS-13 gang leader has not been identified within the United States or abroad. The autonomy of the gang’s cliques makes them difficult to target as there is no centralized leadership. The structure of the cliques varies based on membership, criminal activity, and the background of the clique’s founding members.
- (U//LES) As of July 2005, the Federal Bureau of Prisons (BOP) had identified 127 incarcerated MS-13 members. The majority of these individuals are El Salvadoran nationals; however, some are also US citizens.
- (U//LES) MS-13 members in the United States are actively involved in drug related criminal activity in Georgia, Massachusetts, North Carolina, Indiana, Nevada, Arkansas, California, Tennessee, New York, New Jersey, Oklahoma, Nebraska, Washington, Virginia and Maryland.
- (U) According to intelligence analysis and source reporting, the formation of MS-13 cliques (groups of individuals joined together in a region) is often the result of MS-13 member migration to new areas. The migration of individuals is based on factors such as job availability, avoidance of law enforcement, family connections, and prison sentencing.
- (U//LES) US-based MS-13 members have been arrested for violent crimes including murder, robbery, drive-by-shootings, stabbings, assault, rape, witness intimidation, extortion, malicious wounding, and threats against law enforcement. MS-13 cliques will adapt their criminal activity based on the opportunities available in a specific area.
- (U//LES) In December 2004, the El Salvador Policia Nacional Civil (PNC) reported a total of 126 active MS-13 cliques in El Salvador. These cliques are generally well-organized with a defined leader and several “national” leaders. In El Salvador, an MS-13 clique’s primary financial gain is through drug sales and extortionate activities. However, MS-13 gang members are best known for their violence and are responsible for more homicides than other El Salvadoran gangs combined.
- (U//LES) Both US and foreign law enforcement agencies have documented communications between MS-13 members in El Salvador, Honduras, and Mexico with members in the United States. Additionally, telephone calls and money transfers have been documented between US and El Salvador members.
- (U//LES) The Honduras Policia Preventiva (HPP) has identified 13 active MS-13 cliques in five sectors of Honduras: San Pedro Sula, La Ceiba, Comayagua, Tegucigalpa, and Choluteca.
- (U//LES) In Honduras, the HPP has identified a five- level structure within the MS-13 gang which includes aspiring members, sympathizers, new members, permanent members, and leaders. MS-13 is accused of murdering civilians to protest political decisions. Five of the key MS-13 members implicated in a 23 December 2004 bus massacre in Honduras (which killed 28 civilians) had documented links to the United States.
- (U//LES) Cellular telephones are the most common communication method used by MS-13 members both internationally and domestically. Telephone calls between Honduras and the United States have been documented by law enforcement and corrections agencies in both countries.
- (U//LES) Analysis of source and law enforcement reporting indicates that MS-13 members in Honduras are more financially stable than MS-13 members in other countries. This may be partially due to the nature of MS-13 criminal activities in Honduras and the fact that some members have obtained wealth from legitimate business or family inheritance.
- (U//LES) The city of Tapachula, on the border with Guatemala, has the largest concentration of MS-13 members in Chiapas, Mexico. Membership among incarcerated adult members in Chiapas consists primarily of transient MS-13 members from Central American countries in route to the United States. Most of the criminal activity revolves around the location of railroad lines. Other immigrants are the primary victims of MS-13 criminal activities in this area.
- (U) Although MS-13 is active in the Chiapas area, particularly along the border and near railroads, there is no evidence to support the allegation that they “control” the area.
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – San Diego Fusion Center Terrorism Imagery Recognition
Group logos, flags, and other extremist imagery are prevalent throughout most terrorist and extremist groups. Imagery provides a means of evoking existing emotional and historical memories in addition to communicating ideas to potential recruits. Logos and symbols are often used as visual representation of groups and/or their ideology. Print, internet propaganda, tattoos, clothing and accessories, stickers, and other graphic media are the most common representations of extremist imagery. First responders need to be aware of common extremist imagery as it may indicate involvement or support for a particular domestic extremist organization or international terrorist group.
This product provides law enforcement and homeland security partners with information drawn from open source materials including online editions of printed newspapers and relevant counterterrorism sites.
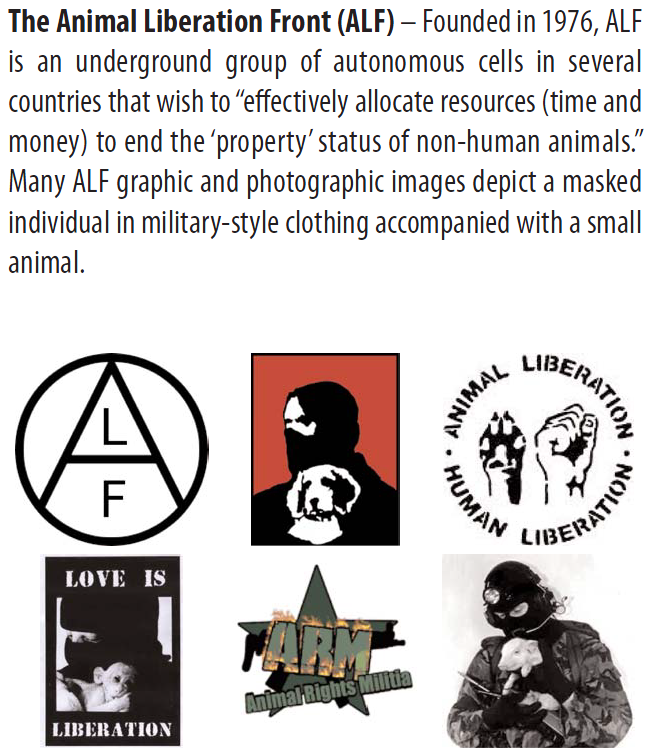
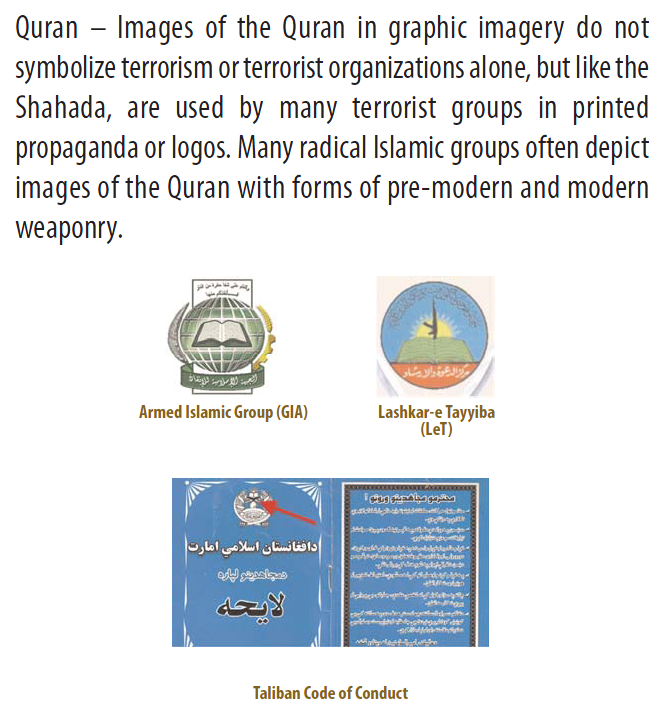
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – Director of National Intelligence Knowledge Assertions and Knowledge Organization Systems Presentation
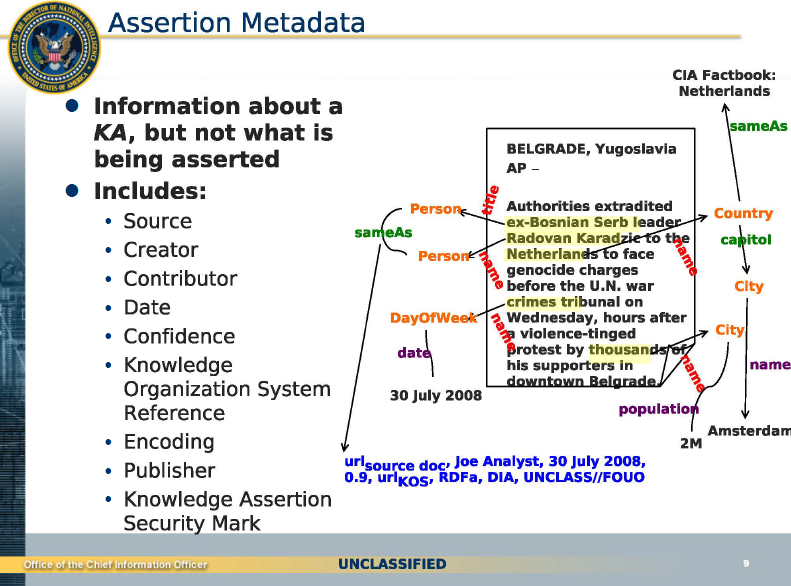
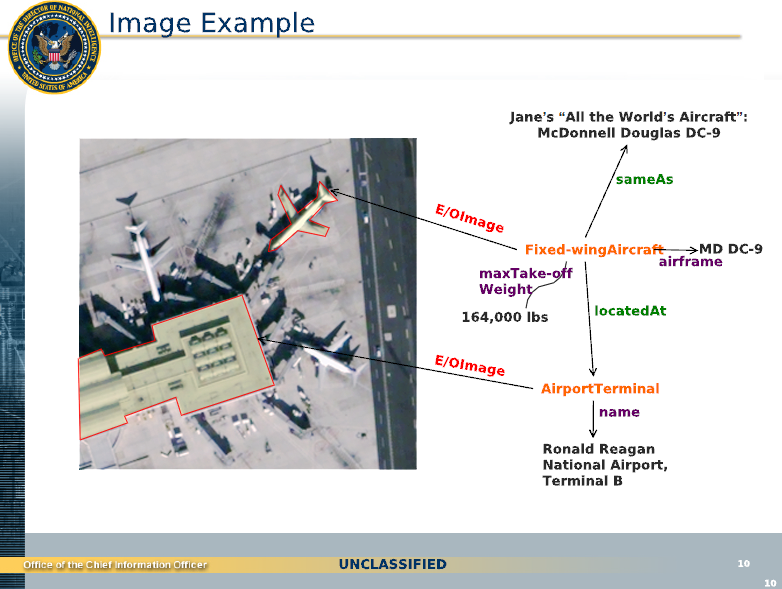
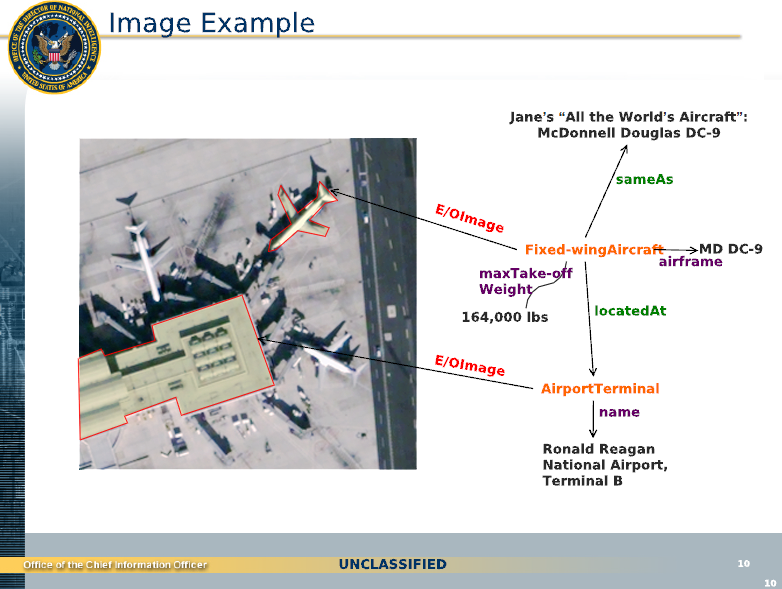
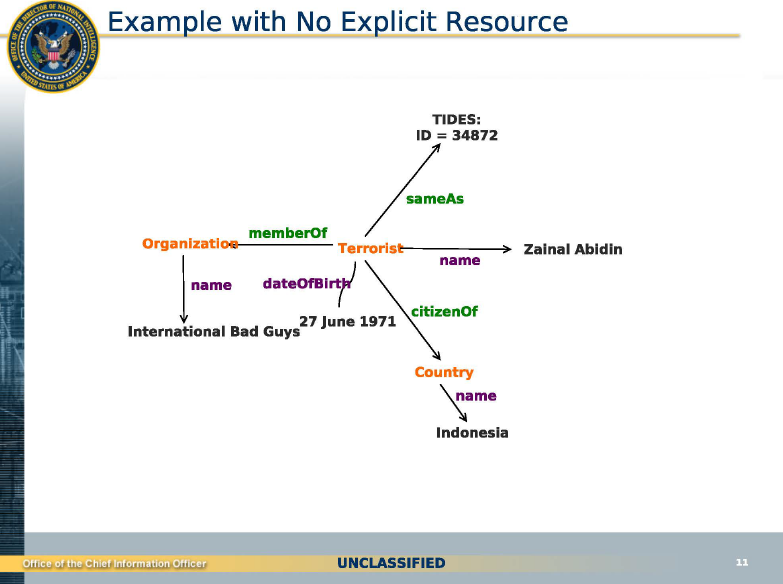
TOP-SECRET – National Gang Intelligence Center Juggalos Intelligence Report
(U//FOUO) Increasing criminal activity among Juggalos is of concern due to the ease with which these transitory and loosely affiliated criminal sub-sets are able to form and break off of the well established Juggalo sub-culture of over one million followers. Their crimes are characterized by acts of violence and destruction directed against law enforcement, members of the community, public/private property, and other members of their group. Juggalos are classified as a gang in the states of Arizona, California, Pennsylvania and Utah. Despite this narrow classification, Juggalo-related crime has been documented in at least 20 other states according to law enforcement and open-source reporting.
Key Findings:
(U) Juggalo criminal groups generally engage in assault, robbery, theft, drug possession/sales, vandalism, and to a lesser extent murder. On average, these criminal groups consist of Caucasian males ages 16 to 26. There is little to no structure within the group, and there is no formalized leadership. Due to this lack of structure and absence of leadership, most crimes are not committed on behalf of the group; rather they are more sporadic and individualistic in nature.
(U) The Juggalo criminal element has been well documented in the states of Arizona, California, Pennsylvania, and Utah. However, law enforcement reporting suggests that criminal activity in Juggalo groups has grown over the past six years and has spread to several other states in which Juggalo-related crime is becoming a mounting concern in the community and among law enforcement.
(U) Juggalo sub-sets are beginning to evolve and take on more of a gang-like resemblance. Establishment and organization within these sub-sets is discernable and set apart from the loosely affiliated Juggalo groups. This evolution may be attributed to a sub-sets affiliation with an already established local/national street gang or gang members that have infiltrated the Juggalo criminal group.
..
(U//LES) Juggalos exist nationwide and exhibit many of the same characteristics as a traditional gang such as throwing hand signs, wearing matching tattoos, and dressing in similar clothing. Over the years, two sides to the Juggalo sub-culture have emerged. According to an admitted Juggalo gang member, there are two active but very different factions of the Juggalos: the music fans and the criminal street gang.
(U//LES) The nationwide Juggalo membership, believed to be over one million fans/followers, vehemently reject the gang label they have received in recent years. The majority of the Juggalo sub-culture following, which constitutes the non-criminal element, likens themselves to a “family”.
(U//LES) The sub-set groups constituting the criminal element have broken off of the mainstream Juggalo subculture. These individuals have been identified as a younger generation taking the sub-culture to a different level, evolving the group into gangs or cliques. Most criminally-active Juggalos claim that their identity as a member of the Juggalo community is a lifestyle society has placed upon them.
(U//LES) Juggalo criminal activity presents a threat to law enforcement, schools, and the community. Juggalo criminal groups operate in multiple states, not just the ones that classify them as a gang. According to law enforcement reporting, police departments in at least 13 states have identified established, criminal Juggalo sub-sets. These states include: Arizona, California, Colorado, Florida, Kansas, North Carolina, Oklahoma, Oregon, Pennsylvania, Tennessee, Texas, Utah, and Washington. Although many of these states do not officially recognize the Juggalos as a gang, police departments in all of these states have documented criminal activity with the respective Juggalo groups operating in their area.
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – Areas of Possible Embarrassment to the Agency
| Citation: | Areas of Possible Embarrassment to the Agency [Includes Attachments Entitled “Telephone Conversation of General Cushman and Someone in White House, 23/7/71”; “Nixon Puts an Eye on His Brother”; “Nixon Kin Is Mum on Vesco Cash Gift”; and “Vesco Arrest Warrant Issued by Federal Judge for Grand Jury Inquiry”; “Intelligence Evaluation Committee”; and Table of Contents], Secret, Memorandum, May 08, 1973, 8 pp. |
| Collection: | The CIA Family Jewels Indexed |
| Item Number: | FJ00057 |
| Origin: | United States. Central Intelligence Agency. Directorate of Operations. Counterintelligence Staff. Chief |
| From: | Angleton, James |
| To: | United States. Central Intelligence Agency. Directorate of Operations. Deputy Director |
| Individuals/ Organizations Named: |
Anderson, Jack; Cushman, Robert E., Jr.; Dean, John Wesley III; Dietrich, Noah; Dougherty, John; Ehrlichman, John D.; Ellsberg, Daniel; Fielding, Fred F.; Figueres, Jose; Finkelstein, Ray; Haldeman, H.R.; Helms, Richard M.; Hoover, J. Edgar; Hughes, Howard; International Controls Corporation; Investors Overseas Service; Liddy, G. Gordon; Mardian, Robert C.; Marriott, J. Willard; Marriott Corporation; Nixon, Donald; Nixon, Donald, Jr.; Nixon, Edward C.; Nixon, Richard M.; Ober, Richard; Olson, William J.; Onassis, Aristotle; Pappas, Thomas A.; Rayhill, James W.; Ryan Aeronautical Company; Sears, Harry L.; Sherwood, Jack; Straub, Gilbert; Sullivan, William C.; United States. Central Intelligence Agency. Deputy Director; United States. Central Intelligence Agency. Directorate of Operations. Counterintelligence Staff; United States. Department of Defense; United States. Department of Justice; United States. Department of State; United States. Department of the Treasury; United States. Federal Bureau of Investigation; United States. Intelligence Evaluation Committee; United States. National Security Agency; United States. Secret Service; United States. Securities and Exchange Commission; United States. White House; Vesco, Robert L.; Wells, Bernard A.; Williams, Edward Bennett |
| Subjects: | Biographical intelligence | Classified information | Costa Rica | Counterintelligence | Domestic intelligence | Election campaign funds | Election campaigns | Extradition | Grand juries | Greece | Information leaks | Information security | Interagency cooperation | Investigations | Military governments | Nassau (Bahamas) | News media | Pentagon Papers | United Kingdom |
| Abstract: | Describes Central Intelligence Agency and Federal Bureau of Investigation concerns about Investors Overseas Service and Robert Mardian; provides background information about Intelligence Evaluation Committee and news clippings about financial mismanagement allegations against Robert Vesco and Richard Nixon’s brothers, Donald and Edward. |
| Full Text: | Document – PDF – this link will open in a new window (297 KB) |
TOP-SECRET – Garbage Collectors Around the U.S. Trained to Report Suspicious Activity
Several newspapers in southern Florida are reporting that trash collectors are receiving training from their employer Waste Management to work with local law enforcement to report crimes and other suspicious activities. The training is part of a program called Waste Watch that is designed to leverage the fact that “drivers are familiar with their routes and are in the same neighborhoods every day” which “puts them in the unique position to spot unusual activity and anything out of the ordinary.” Press releases from Waste Management describe the program as a way of opening “channels of communication with the authorities to help keep them informed and alert of what’s happening in their city’s streets and alleys.”
Waste Watch training sessions are conducted by former FBI agents in association with security representatives from Waste Management. The program has been operating since 2004 when it was first introduced by Waste Management’s Corporate Security Services and Community Relations offices. Waste Watch operates in more than 100 communities around the country including Utah, New York, Nevada, South Carolina, California, Oregon, Michigan, Washington and Florida. There is little public information available on the program or the content of training material presented to Waste Watch participants.
Given the recent proliferation of programs dedicated to promoting suspicious activity reporting, more information is needed on the program’s guidelines for detecting and reporting suspicious activity. FBI flyers designed to promote suspicious activity reporting have listed actions like insisting on paying cash or trying to cover one’s computer screen as evidence of potential terrorist activity. A similar guide produced by the New Jersey Office of Homeland Security and Preparedness listed yawning and repeatedly touching one’s face as suspicious activities. The Waste Watch program does seem to have produced some positive results, including helping to catch vandals or petty thieves. In 2008 the program was awarded the “Award of Excellence in the Neighborhood Watch” by the National Sheriff’s Association.
While encouraging citizens and businesses to look out for criminal activity is a worthwhile cause, the recent proliferation of programs for reporting suspicious activity has raised concerns from civil liberties groups about the potential for turning citizens and business owners into effective spies on their neighbors and customers. The Department of Homeland Security’s “If You See Something, Say Something” program has greatly expanded in the last few years by partnering with the NBA, MLB, NFL, MLS, NCAA, religious organizations, hotel television providers and even Walmart to promote suspicious activity reporting. Fusion centers and cities around the country are creating websites and phone applications to help citizens report suspicious activity, complete with photographs and geolocation information. However, the “Waste Watch” program extends citizen surveillance one step further by leveraging the manpower of the country’s largest waste collection company to look not just for suspicious activity, but for “anything out of the ordinary.”
TOP-SECRET – DHS-FBI Intelligence Bulletin on Homegrown Extremist Retaliation for Afghan Massacre
(U//FOUO) This Joint Intelligence Bulletin is intended to increase awareness and provide understanding of the nature of potentially emergent threats in response to the alleged killing of civilians by a US soldier in Afghanistan and the burning of Korans and other religious documents on a military base. This Information is provided to support the activities of FBI and DHS and to assist federal, state, local, tribal, and territorial counterterrorism and law enforcement officials and the private sector to prevent or respond to terrorist attacks against the United States.
(U//FOUO) Civilian Killings in Afghanistan Could Lead to Retaliatory Attacks by Homegrown Violent Extremists In the United States
(U//FOUO) On 11 March 2012, a US service member stationed in Afghanistan allegedly went on a shooting spree, killing 16 civilians, Including nine children, according to US press reporting. The FBI and DHS are concerned that this event could contribute to the radicalization or mobilization of homegrown violent extremists (HVEs) in the Homeland, particularly against US-based military targets, which HVEs have historically considered legitimate targets for retaliation in response to past alleged US military actions against civilians overseas.
(U//FOUO) The soldier who allegedly perpetrated the attacks reportedly trained at Joint Base Lewls-McChord near Tacoma, Washington. This base was also the training site of four soldiers convicted in 2011 of killing Afghan citizens, according to US press reporting. Abu Khalid Abdul-Latif, currently awaiting trial for plotting an attack, Initially wanted to target Lewis-McChord in retaliation for the actions of soldiers who had been stationed there. Ultimately, Abdul-Latif changed his alleged target to a Military Entrance Processing Station in Seattle, Washington, in part because he believed it was a softer target.
(U//FOUO) Perceived US Military Anti-Islamic Events in Afghanistan Could Compound Homegrown Violent Extremist Grievances
(U//FOUO) We assess that the alleged killing of civilians by a US soldier could trigger acts of violence by HVEs as this was a motivation that drove plotting against Joint Base Lewis-McChord. While recent high profile perceived offenses against Islam historically have led to calls for retaliation by violent extremists, they have not yet incited HVEs to attack in the United States. Nevertheless, the series of perceived anti-Mulslim and anti-Islamic events in Afghanistan since January 2012-which include graphic images of dead civilians-could cumulatively lead an HVE to mobilize to violence.
(U//FOUO) Some users of Web sites hosting violent extremist content circulated graphic images of the 11 March 2012 shooting victims, including women and children, and called for revenge against the US military. Some users stated their belief that the attack was intentionally planned by the US military and that there were more killings than reported by the media.
TOP-SECRET – The CIA Training of Foreign Police Forces
| Citation: | [Training of Foreign Police Forces; Attached to Divider Sheet and Routing Sheet; Includes Attachments Entitled “Counter Intelligence Staff, Police Group Activities”; “Joint CIA/USAID Terrorist (Technical) Investigations Course #7 (English Language) CI Staff’s Project [Excised]”; “Facts and Statistics”; and “National Security: Political, Military, and Economic Strategies in the Decade Ahead”] Secret, Compendium, April 25, 1973, 16 pp. |
| Collection: | The CIA Family Jewels Indexed |
| Item Number: | FJ00059 |
| Origin: | United States. Central Intelligence Agency |
| To: | Halpern, Sam |
| Individuals/ Organizations Named: |
Abshire, David M.; Allen, Richard V.; Angleton, James; Burke, Arleigh A.; Colby, William E.; Dade County (Florida). Police Department. Bomb Squad; International Police Academy; Mitrione, Daniel A.; Schlesinger, James R.; Tupamaros (Uruguay); United States Park Police; United States. Agency for International Development. Office of Public Safety; United States. Central Intelligence Agency. Directorate of Operations. Counterintelligence Staff. Chief; United States. Central Intelligence Agency. Directorate of Operations. Counterintelligence Staff. Police Group; United States. Central Intelligence Agency. Directorate of Operations. Deputy Director; United States. Central Intelligence Agency. Directorate of Operations. Technical Services Division; United States. Department of the Treasury. Office of Enforcement; United States. Secret Service |
| Subjects: | Biographical intelligence | Bombings | Developing countries | Diplomatic security | Explosives detection | Foreign policy | Government appropriations and expenditures | Intelligence collection | Interagency cooperation | International trade | Investigations | Latin America | Murders | Police assistance | Sabotage | Sanctions | Target analysis | Terrorism | Uruguay |
| Abstract: | Provides overview of coordination among Central Intelligence Agency, Agency for International Development, and International Police Academy for training of foreign police and security forces; assesses potential use of aid and trade relationships to affect change in foreign governments. |
| Full Text: | Document – PDF – this link will open in a new window (1.1 MB) |
TOP-SECRET-The CIA’s File about Mafia Boss Johnny Rosselli
DOWNLOAD THE ORIGINAL FILE HERE
TOP-SECRET – ISAF Guide to Collecting Evidence for Prosecution in Afghan Courts
A Guide to Collecting Evidence for Prosecution in Afghan Courts
For the National Security Prosecutor’s Unit (NSPU) or a provincial court to prosecute and convict detainees, including Afghan murder suspects or National Security criminals, capturing units must provide evidence and witness statements against the suspects for use in an Afghan court of law. Appropriate evidence collection may result in admissible evidence in support of effective prosecutions. Turn all evidence associated with the suspect over to Afghan authorities and obtain a thoroughly documented receipt for the evidence.
Evidence collection may also be necessary without an actual detention. Operators may find weapons, documents, or other items that should be collected as evidence, even if no one is detained.
To the greatest extent possible, in order to increase the likelihood of admissibility in the Afghan courts, evidence collection and case preparation should be performed by Afghan partnering forces.
This booklet is a guide. Your local prosecutor or judge may require a slightly different format or type of evidence. Your evidence may be tailored to fit your local court’s requirements if necessary.
…
Prior to the Operation.
Each tactical unit conducting an operation will appoint an evidence collection team (a.k.a. Site Exploitation (SE) team) who will plan for, collect, receive, and handle all evidence seized during the operation. This team will be properly trained on evidence collection and handling procedures and will include an Afghan partnering member.
Whenever possible, obtain a search warrant before an operation where you plan to collect evidence. If the warrant is not obtained in advance, your unit should ensure that a warrant is obtained after the operation.
Planning and Equipment
During planning for a specific operation, the team will consider the following issues and prepare accordingly:
Possible evidence
• Documents
• Weapons
• IED components / explosives
• Drugs
• Witness statements (Interpreters!)
DOWNLOAD ORIGINAL DOCUMENT HERE
Top-Secret – The FBI – $ 2.9 billion fraud – CFO of Taylor, Bean, & Whitaker Pleads Guilty to Fraud Scheme
WASHINGTON—Delton de Armas, a former chief financial officer (CFO) of Taylor, Bean, & Whitaker Mortgage Corp. (TBW), pleaded guilty today to making false statements and conspiring to commit bank and wire fraud for his role in a more than $2.9 billion fraud scheme that contributed to the failures of TBW and Colonial Bank.
The guilty plea was announced today by Assistant Attorney General Lanny A. Breuer of the Criminal Division; U.S. Attorney Neil H. MacBride for the Eastern District of Virginia; Christy Romero, Deputy Special Inspector General, Office of the Special Inspector General for the Troubled Asset Relief Program (SIGTARP); Assistant Director in Charge James W. McJunkin of the FBI’s Washington Field Office; David A. Montoya, Inspector General of the Department of Housing and Urban Development (HUD-OIG); Jon T. Rymer, Inspector General of the Federal Deposit Insurance Corporation (FDIC-OIG); Steve A. Linick, Inspector General of the Federal Housing Finance Agency (FHFA-OIG); and Rick A. Raven, Acting Chief of the Internal Revenue Service Criminal Investigation (IRS-CI).
De Armas, 41, of Carrollton, Texas, pleaded guilty before U.S. District Judge Leonie M. Brinkema in the Eastern District of Virginia. De Armas faces a maximum penalty of 10 years in prison when he is sentenced on June 15, 2012.
“As TBW’s chief financial officer, Mr. de Armas concealed a massive $1.5 billion deficit in TBW’s funding facility and another large deficit on TBW’s books,” said Assistant Attorney General Breuer. “He tried to conceal the gaping holes by falsifying financial statements and lying to investors as well as the government. Ultimately, Mr. de Armas’ criminal conduct, along with that of his co-conspirators, contributed to the collapse of TBW and Colonial Bank. With today’s guilty plea, Mr. de Armas joins seven other defendants—including the former chairman of TBW, Lee Bentley Farkas—who have been convicted of participating in this massive fraudulent scheme.”
“When Mr. de Armas learned of a hole in Ocala Funding’s assets, he used his position as CFO to cover it up and mislead investors,” said U.S. Attorney MacBride. “Today’s plea is the eighth conviction in one of the nation’s largest bank frauds in history. As CFO, Mr. de Armas could have put a stop to the fraud the moment he discovered it. Instead, the hole in Ocala Funding grew to $1.5 billion on his watch, and as it grew, so did his lies to investors and the government.”
According to court documents, de Armas joined TBW in 2000 as its CFO and reported directly to its chairman, Lee Bentley Farkas, and later to its CEO, Paul Allen. He admitted in court that from 2005 through August 2009, he and other co-conspirators engaged in a scheme to defraud financial institutions that had invested in a wholly-owned lending facility called Ocala Funding. Ocala Funding obtained funds for mortgage lending for TBW from the sale of asset-backed commercial paper to financial institutions, including Deutsche Bank and BNP Paribas. The facility was managed by TBW and had no employees of its own.
According to court records, shortly after Ocala Funding was established, de Armas learned there were inadequate assets backing its commercial paper, a deficiency referred to internally at TBW as a “hole” in Ocala Funding. De Armas knew that the hole grew over time to more than $700 million. He learned from the CEO that the hole was more than $1.5 billion at the time of TBW’s collapse. De Armas admitted he was aware that, in an effort to cover up the hole and mislead investors, a subordinate who reported to him had falsified Ocala Funding collateral reports and periodically sent the falsified reports to financial institution investors in Ocala Funding and to other third parties. De Armas acknowledged that he and the CEO also deceived investors by providing them with a false explanation for the hole in Ocala Funding.
De Armas also admitted in court that he directed a subordinate to inflate an account receivable balance for loan participations in TBW’s financial statements. De Armas acknowledged that he knew that the falsified financial statements were subsequently provided to Ginnie Mae and Freddie Mac for their determination on the renewal of TBW’s authority to sell and service securities issued by them.
In addition, de Armas admitted in court to aiding and abetting false statements in a letter the CEO sent to the U.S. Department of Housing and Urban Development, through Ginnie Mae, regarding TBW’s audited financial statements for the fiscal year ending on March 31, 2009. De Armas reviewed and edited the letter, knowing it contained material omissions. The letter omitted that the delay in submitting the financial data was caused by concerns its independent auditor had raised about the financing relationship between TBW and Colonial Bank and its request that TBW retain a law firm to conduct an internal investigation. Instead, the letter falsely attributed the delay to a new acquisition and TBW’s switch to a compressed 11-month fiscal year.
“With our nation in a housing crisis, de Armas, as chief financial officer of TBW, one of the country’s largest mortgage lenders, papered over a gaping hole in the balance sheet of TBW subsidiary Ocala Funding and lied to regulators and investors to cover it up,” said Deputy Special Inspector General Romero for SIGTARP. “The fraud provided cover to others at TBW to misappropriate more than $1 billion in Ocala funds and sell fraudulent, worthless securities to conspirators at Colonial BancGroup. SIGTARP and its law enforcement partners stopped $553 million in TARP funds from being lost to this fraud and brought accountability and justice that the American taxpayers deserve.”
“Mr. de Armas has admitted that, during his tenure at TBW, he purposefully misled investors in a massive scheme to defraud financial institutions,” said FBI Assistant Director in Charge McJunkin. “The actions of Mr. de Armas and his co-conspirators contributed to the financial crisis and led to the collapse of one of the country’s largest commercial banks. The FBI and our partners remain vigilant in investigating such fraudulent activity in our banking and mortgage industries.”
“The guilty plea of Mr. de Armas is one small measure in our continued efforts to restore the trust and confidence of the general public and of investors in our financial system,” said HUD Inspector General Montoya. “In response to the many recent articles of mortgage fraud and misconduct, the mortgage industry needs to do much to rethink their values and their idea of client service in order to help rebuild a stronger economy and to restore the confidence of American homeowners.”
“The Federal Deposit Insurance Corporation Office of Inspector General is pleased to have played a role in bringing to justice yet another senior official in a position of trust who was involved in one of the biggest and most complex bank fraud schemes of our time,” said FDIC Inspector General Rymer. “The former chief financial officer of Taylor, Bean, & Whitaker is the latest participant who will be held accountable for seeking to undermine the integrity of the financial services industry. Even as the financial and economic crisis seems to be easing, we reaffirm our commitment to ensuring that those contributing to the failures of financial institutions and corresponding losses to the Deposit Insurance Fund will be punished to the fullest extent of the law.”
“Mr. de Armas and his colleagues committed an egregious crime,” said FHFA Inspector General Linick. “FHFA-OIG is proud to be part of the team that continues to protect American taxpayers.”
In April 2011, a jury in the Eastern District of Virginia found Lee Bentley Farkas, the chairman of TBW, guilty of 14 counts of conspiracy, bank, securities, and wire fraud. On June 30, 2011, Judge Brinkema sentenced Farkas to 30 years in prison. In addition, six individuals have pleaded guilty for their roles in the fraud scheme, including: Paul Allen, former chief executive officer of TBW, who was sentenced to 40 months in prison; Raymond Bowman, former president of TBW, who was sentenced to 30 months in prison; Desiree Brown, former treasurer of TBW, who was sentenced to six years in prison; Catherine Kissick, former senior vice president of Colonial Bank and head of its Mortgage Warehouse Lending Division (MWLD), who was sentenced to eight years in prison; Teresa Kelly, former operations supervisor for Colonial Bank’s MWLD, who was sentenced to three months in prison; and Sean Ragland, a former senior financial analyst at TBW, who was sentenced to three months in prison.
The case is being prosecuted by Deputy Chief Patrick Stokes and Trial Attorney Robert Zink of the Criminal Division’s Fraud Section and Assistant U.S. Attorneys Charles Connolly and Paul Nathanson of the Eastern District of Virginia. This case was investigated by SIGTARP, FBI’s Washington Field Office, FDIC-OIG, HUD-OIG, FHFA-OIG, and IRS-CI. The Financial Crimes Enforcement Network (FinCEN) of the Department of the Treasury also provided support in the investigation. The Department would also like to acknowledge the substantial assistance of the U.S. Securities and Exchange Commission in the investigation of the fraud scheme.
This prosecution was brought in coordination with President Barack Obama’s Financial Fraud Enforcement Task Force. President Obama established the interagency Financial Fraud Enforcement Task Force to wage an aggressive, coordinated and proactive effort to investigate and prosecute financial crimes. The task force includes representatives from a broad range of federal agencies, regulatory authorities, inspectors general and state and local law enforcement who, working together, bring to bear a powerful array of criminal and civil enforcement resources. The task force is working to improve efforts across the federal executive branch, and with state and local partners, to investigate and prosecute significant financial crimes, ensure just and effective punishment for those who perpetrate financial crimes, combat discrimination in the lending and financial markets, and recover proceeds for victims of financial crimes. For more information on the task force, visit: http://www.stopfraud.gov.
TOP-SECRET – U.S. Army Company Intelligence Support Team (COIST) Reference Card
TOP-SECRET from the FBI – Former Employee Pleads Guilty to Conspiracy Charge in $900,000 Embezzlement Scheme
WASHINGTON—Valencia Person, 54, of Suitland, Maryland, pled guilty today to a federal conspiracy charge stemming from a scheme in which she helped embezzle more than $900,000 from her former employer, XM Satellite Radio, announced U.S. Attorney Ronald C. Machen Jr. and James W. McJunkin, Assistant Director in Charge of the FBI’s Washington Field Office.
Person pled guilty before the Honorable Reggie B. Walton in the U.S. District Court for the District of Columbia to one count of conspiracy to commit wire fraud. Sentencing is scheduled for June 8, 2012. The charge carries a maximum statutory penalty of five years in prison. However, under federal sentencing guidelines, Person faces a likely sentence of 24 to 30 months in prison and a fine of up to $50,000.
As part of the plea agreement, Person agreed to a money judgment of at least $909,924, representing the amount of proceeds from the crime. She also is subject to an order to make restitution.
According to a statement of offense submitted to the Court by Assistant U.S. Attorney Sherri L. Schornstein, Person worked at XM Satellite Radio (now known as Sirius XM Radio Inc.), a corporation based in Washington, D.C., as a coordinator in the Accounts Payable Department. Her duties included responsibility for payments to large vendors.
From 2005 until at least 2008, Person and an XM Satellite Radio Accounts Payable Administrator, Brenda L. Jones, embezzled more than $909,000 from the company. They secretly diverted at least 26 payments, which were supposed to go to XM vendors, to bank accounts held by Jones. They also covered up the activities by altering data in the company’s accounting system. Jones then gave a portion of the monies to Person. Jones resigned in 2006. However, more than $690,000 of the money was transferred into her accounts after she had left the company.
According to Person, she personally benefitted from the scheme in an amount not exceeding $125,000.
Jones, 46, of Lothian, Maryland, pled guilty in January 2012 to one count of conspiracy to commit wire fraud. She is awaiting sentencing.
In announcing the plea, U.S. Attorney Machen and Assistant Director in Charge McJunkin praised those who worked on the case, including the Special Agents of the FBI’s Washington Field Office, as well as Legal Assistant Jared Forney of the U.S. Attorney’s Office. They also commended the efforts of Assistant U.S. Attorney Sherri L. Schornstein, who is prosecuting the case.
Top-Secret from the FBI – Miami-Area Resident Pleads Guilty to Participating in $200 Million Medicare Fraud Scheme
WASHINGTON—A Miami-area resident pleaded guilty yesterday for his role in a fraud scheme that resulted in the submission of more than $200 million in fraudulent claims to Medicare, announced the Department of Justice, the FBI, and the Department of Health and Human Services (HHS).
Frank Criado, 33, pleaded guilty before U.S. Magistrate Judge Barry L. Garber in Miami to one count of conspiracy to commit health care fraud and one count of conspiracy to defraud the United States and to pay and receive illegal health care kickbacks. Criado was charged in an indictment unsealed on February 15, 2011 in the Southern District of Florida.
Criado admitted to participating in a fraud scheme that was orchestrated by the owners and operators of American Therapeutic Corporation (ATC); its management company, Medlink Professional Management Group Inc.; and the American Sleep Institute (ASI). ATC, Medlink, and ASI were Florida corporations headquartered in Miami. ATC operated purported partial hospitalization programs (PHPs), a form of intensive treatment for severe mental illness, in seven different locations throughout South Florida and Orlando. ASI purported to provide diagnostic sleep disorder testing.
According to court filings, ATC’s owners and operators paid kickbacks to owners and operators of assisted living facilities and halfway houses and to patient brokers in exchange for delivering ineligible patients to ATC and ASI. In some cases, the patients received a portion of those kickbacks. Throughout the course of the ATC and ASI conspiracy, millions of dollars in kickbacks were paid in exchange for Medicare beneficiaries who did not qualify for PHP services to attend treatment programs that were not legitimate PHPs so that ATC and ASI could bill Medicare for the medically unnecessary services. According to court filings, to obtain the cash required to support the kickbacks, the co-conspirators laundered millions of dollars of payments from Medicare.
Criado admitted to serving as a patient broker who provided patients for ATC and ASI in exchange for kickbacks in the form of checks and cash. The amount of the kickback was based on the number of days each patient spent at ATC.
According to his plea agreement, Criado’s participation in the ATC fraud resulted in $7.3 million in fraudulent billings to the Medicare program.
Sentencing for Criado is scheduled for May 31, 2012 at 8:30 a.m. He faces a maximum penalty of 15 years in prison and a $250,000 fine.
ATC, Medlink, and various owners, managers, doctors, therapists, patient brokers, and marketers of ATC, Medlink, and ASI were charged with various health care fraud, kickback, money laundering, and other offenses in two indictments unsealed on February 15, 2011. ATC, Medlink, and 11 of the individual defendants have pleaded guilty or have been convicted at trial. Other defendants are scheduled for trial April 9, 2012 before U.S. District Judge Patricia A. Seitz. A defendant is presumed innocent unless proven guilty beyond a reasonable doubt in a court of law.
The guilty plea was announced by Assistant Attorney General Lanny A. Breuer of the Justice Department’s Criminal Division; U.S. Attorney Wifredo A. Ferrer of the Southern District of Florida; John V. Gillies, Special Agent in Charge of the FBI’s Miami Field Office; and Special Agent in Charge Christopher B. Dennis of the HHS Office of Inspector General (HHS-OIG), Office of Investigations, Miami Office.
The criminal case is being prosecuted by Trial Attorneys Jennifer L. Saulino, Steven Kim, and Robert Zink of the Criminal Division’s Fraud Section. A related civil action is being handled by Vanessa I. Reed and Carolyn B. Tapie of the Civil Division and Assistant U.S. Attorney Ted L. Radway of the Southern District of Florida. The case was investigated by the FBI and HHS-OIG and was brought as part of the Medicare Fraud Strike Force, supervised by the Criminal Division’s Fraud Section and the U.S. Attorney’s Office for the Southern District of Florida.
Since its inception in March 2007, the Medicare Fraud Strike Force operations in nine locations have charged more than 1,190 defendants that collectively have billed the Medicare program for more than $3.6 billion. In addition, HHS’s Centers for Medicare and Medicaid Services, working in conjunction with the HHS-OIG, is taking steps to increase accountability and decrease the presence of fraudulent providers.
To learn more about the Health Care Fraud Prevention and Enforcement Action Team (HEAT), go to: http://www.stopmedicarefraud.gov.
TOP SECRET – Anonymous/LulzSec Sabu, Kayla, Topiary, Anarchaos, Palladium, Pwnsauce Indictment and Criminal Complaints

UNITED STATES OF AMERICA
– v. –
RYAN ACKROYD,
a/k/a “kayla,”
a/k/a “lol,”
a/k/a “lolspoon,”
JAKE DAVIS,
a/k/a “topiary,”
a/k/a “atopiary”
DARREN MARTYN,
a/k/a “pwnsauce,”
a/k/a “raepsauce,”
a/k/a “networkkitten,”
and DONNCHA O’CEARRBHAIL,
a/k/a “palladium,”
25 pages
DOWNLOAD ORIGINAL DOCUMENT HERE
UNITED STATES OF AMERICA
– v. –
HECTOR XAVIER MONSEGUR,
a/k/a “Sabu,”
a/k/a “Xavier DeLeon,”
a/k/a “Leon,”
27 pages
DOWNLOAD ORIGINAL DOCUMENT HERE
UNITED STATES OF AMERICA
– v. –
JEREMY HAMMOND,
a/k/a “Anarchaos,”
a/k/a “sup_g,”
a/k/a “burn,”
a/k/a “yohoho,”
a/k/a “POW,”
a/k/a “tylerknowsthis,”
a/k/~ “crediblethreat,”
34 pages
DOWNLOAD ORIGINAL DOCUMENT HERE
UNITED STATES OF AMERICA
– v. –
DONNCHA O’CEARRBHAIL,
a/k/a “palladium”
a/k/a “polonium,”
a/k/a “anonsacco,”
10 pages
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – Communication from Gromyko to Stalin
| Communication from Gromyko to Stalin Concerning a Draft Reply to the United States, England, and France on the Matter of the National Police of the German Democratic Republic, 22 September 1950 | |
| Date: 09/22/1950 |
Source: Library of Congress |
| Description: Communication from Gromyko to Stalin Concerning a Draft Reply to the United States, England, and France on the Matter of the National Police of the German Democratic Republic, 22 September 1950 |
|
Strictly Secret
All-Union Communist Party [Bolsheviks] [VKP(b)]. CENTRAL COMMITTEE [TSK].
p.78/32 To Comrades Malenkov, Gromyko
September 25, 1950. Excerpt from Minutes No. 78, session of the Politburo of the Central Committee of the VKP(b).
Decision of September 25, 1950
32. Draft communique from the Soviet government to the governments of the U.S.A., England, and France on the matter of the national police of the German Democratic Republic.
To instruct Comrade Gromyko to present within 3 days, based on an exchange of opinions, an explanatory note and amended reply from the USSR government to the governments of the U.S.A., England, and France concerning the national police of the German Democratic Republic.
Politburo TSK VK(b)
To Comrade J. STALIN
The governments of the U.S.A., England, and France have sent to the Ministry of Foreign Affairs [MID of the USSR communiques of similar content asserting that the national police of the German Democratic Republic do not perform normal police functions but have the character of an army. In connection with this the communiques charges that the Soviet government with violating the decisions of the Potsdam Conference and other quadrilateral international agreements on the demilitarization of Germany.
The MID advises sending the governments of the U.S.A., England, and France replies deflecting these assertions as groundless, point out that the national police of the GDR was created for the protection of the democratic processes established in the GDR in accordance with the decisions of the Potsdam Conference on the democratization of Germany.
Facts about the creation of an army in the guise of armed police by the governments of the U.S.A., England, and France in West Germany appear in this communique.
The TSK VK(b) has already examined the matter of sending replies to the governments of the three powers. It was decided to return to this question later.
Considering the meetings of the western powers now taking place on the question of rearming West Germany and the launching of a broad campaign in the west European press of the creation of German armed forces, the MID requests again your review of the Soviet government’s response.
The draft resolution is attached.
I request your review.
[signed] A. Gromyko
September 23, 1950
TOP-SECRET – DHS Terrorist Use of Improvised Incendiary Devices and Attack Methods
(U//FOUO) Improvised incendiary devices (IIDs) typically are less expensive to make than improvised explosive devices but still are capable of creating mass casualties and causing widespread fear and panic.
(U//FOUO) Improvised incendiary devices (IIDs) can be constructed easily from everyday materials available at hardware and grocery stores.
(U//FOUO) IIDs can be used against many types of infrastructure targets; violent extremists have used them successfully in attacks in the United States and overseas.
(U//FOUO) The DHS/Office of Intelligence and Analysis (I&A) has no credible or specific intelligence indicating current terrorist attack planning featuring use of IIDs against infrastructure in the United States. The ease with which IIDs can be constructed and used, however, makes it difficult to detect and prevent such attacks.
(U) Improvised Incendiary Devices Can Be Constructed from Common Materials
(U//FOUO) An IID consists of an ignition source, a flammable or combustible fuel —including kerosene, cigarette and charcoal lighter fluid, motor fuels, such as gasoline or diesel, and reactive chemicals—and some type of container, such as propane cylinders, plastic pipes, bottles, and cans. IIDs range in sophistication from very simple and easily-constructed Molotov cocktails—which are made by filling a glass bottle with fuel and lighting a rag placed in the top—to more complicated timed devices consisting of a sodium and acid mixture.
(U) U.S. Infrastructure Vulnerable to Improvised Incendiary Device Attack
(U//FOUO) The accessibility of many types of infrastructure, such as government facilities, national monuments, various transportation and energy assets, and commercial facilities, make them susceptible to IID attacks. Passenger trains, ferries, and other public conveyances are among the more attractive targets for terrorists because they often have large numbers of people enclosed in concentrated areas that are difficult to evacuate rapidly.
(U) Previous Use of Improvised Incendiary Devices in the United States
(U//FOUO) Violent extremists have used IIDs against government facilities and vehicles, commercial facilities, and railroad lines. Their most frequent targets have been healthcare, educational and research facilities, and scientists and research personnel.
(U) Improvised Incendiary Device Attacks Abroad
(U) Terrorists using IIDs achieved their most notable success in a February 2007 attack by Kashmiri operatives who placed six suitcase IIDs in three cars of the “Friendship Express” passenger train traveling from India to Pakistan. Four of the six IIDs ignited, causing fires in two passenger cars that killed 68 people and injured 13. Other incidents, like those in the United States, have achieved mixed results.
— (U) In May 2008, an ethnic Uighur woman aboard a domestic flight bound for Beijing, China attempted to ignite a flammable liquid in a beverage can. She aroused suspicions when she exited the lavatory to pick up a second can after the first failed to ignite and produced a smell of gasoline.
— (U) In June 2007, two men drove a burning jeep with several gasoline-filled containers into the main terminal building at the Glasgow, Scotland airport, causing structural damage to the front of the building but no casualties.
— (U) In July 2006, two men plotted to attack two trains in Germany using suitcases filled with butane and gasoline, but the devices failed to ignite. German prosecutors claimed, however, that the trains would have become “balls of fire” had the IIDs functioned as planned
TOP-SECRET – UNCENSORED – Osama bin Laden Shrine Teardown
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict16.jpg) In this May 4, 2011, photo, local residents and media gather outside a house where al-Qaida leader Osama bin Laden was caught and killed in Abbottabad, Pakistan. The U.S. military is denouncing a former Navy SEAL’s book that claims to describe the “real” version of the raid that killed bin Laden, taken from alleged eyewitness accounts. In this May 4, 2011, photo, local residents and media gather outside a house where al-Qaida leader Osama bin Laden was caught and killed in Abbottabad, Pakistan. The U.S. military is denouncing a former Navy SEAL’s book that claims to describe the “real” version of the raid that killed bin Laden, taken from alleged eyewitness accounts. |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict11.jpg) This Nov 18, 2011 photo shows the guesthouse inside Osama bin Laden’s compound in Abbottabad, Pakistan. Bin Laden spent his last weeks in a house divided, amid wives riven by suspicions. On the top floor, sharing his bedroom, was his youngest wife and favorite. The trouble came when his eldest wife showed up and moved into the bedroom on the floor below. (Shaukat Qadir) This Nov 18, 2011 photo shows the guesthouse inside Osama bin Laden’s compound in Abbottabad, Pakistan. Bin Laden spent his last weeks in a house divided, amid wives riven by suspicions. On the top floor, sharing his bedroom, was his youngest wife and favorite. The trouble came when his eldest wife showed up and moved into the bedroom on the floor below. (Shaukat Qadir) |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict14.jpg) Flood lights are seen in the compound of Osama bin Laden in Abbottatabd, Pakistan on Saturday, Feb 25, 2012. Local residents say Pakistan has started to demolish the compound in the northwest city of Abbottabad where Osama bin Laden lived for years and was killed by U.S. commandos. Two residents say the government brought in three mechanized backhoes Saturday, Feb. 25, 2012, and began destroying the tall outer walls of the compound after sunset. They set up floodlights to carry out the work. Flood lights are seen in the compound of Osama bin Laden in Abbottatabd, Pakistan on Saturday, Feb 25, 2012. Local residents say Pakistan has started to demolish the compound in the northwest city of Abbottabad where Osama bin Laden lived for years and was killed by U.S. commandos. Two residents say the government brought in three mechanized backhoes Saturday, Feb. 25, 2012, and began destroying the tall outer walls of the compound after sunset. They set up floodlights to carry out the work. |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict7.jpg) A policeman walks towards the partially demolished compound where al Qaeda leader Osama bin Laden was killed by U.S. special forces last May in Abbottabad February 26, 2012. Pakistani forces began demolishing the house where Bin Laden was killed by U.S. special forces last May, in an unexplained move carried out in the dark of night. Reuters A policeman walks towards the partially demolished compound where al Qaeda leader Osama bin Laden was killed by U.S. special forces last May in Abbottabad February 26, 2012. Pakistani forces began demolishing the house where Bin Laden was killed by U.S. special forces last May, in an unexplained move carried out in the dark of night. Reuters |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict9.jpg) ![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict8.jpg)
Pakistani security personnel conduct demolition works on the compound where Al-Qaeda chief Osama bin Laden was slain last year in the northwestern town of Abbottabad on February 26, 2012. Pakistani security forces began demolishing the compound where Osama bin Laden was killed in a covert US raid last May in the garrison town of Abbottabad, police and witnesses said. Getty |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict10.jpg) Local residents watch ongoing demolition of the compound where Al-Qaeda chief Osama bin Laden was slain last year in the northwestern town of Abbottabad on February 26, 2012. Pakistani security forces began demolishing the compound where Osama bin Laden was killed in a covert US raid last May in the garrison town of Abbottabad, police and witnesses said. Getty Local residents watch ongoing demolition of the compound where Al-Qaeda chief Osama bin Laden was slain last year in the northwestern town of Abbottabad on February 26, 2012. Pakistani security forces began demolishing the compound where Osama bin Laden was killed in a covert US raid last May in the garrison town of Abbottabad, police and witnesses said. Getty |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict5.jpg) In this Feb. 26, 2012 file picture, a police commando stands guard as authorities use heavy machinery to demolish Osama bin Laden’s compound in Abbottabad, Pakistan. Bin Laden spent his last weeks in a house divided, amid wives riven by suspicions. On the top floor, sharing his bedroom, was his youngest wife and favorite. The trouble came when his eldest wife showed up and moved into the bedroom on the floor below. AP In this Feb. 26, 2012 file picture, a police commando stands guard as authorities use heavy machinery to demolish Osama bin Laden’s compound in Abbottabad, Pakistan. Bin Laden spent his last weeks in a house divided, amid wives riven by suspicions. On the top floor, sharing his bedroom, was his youngest wife and favorite. The trouble came when his eldest wife showed up and moved into the bedroom on the floor below. AP |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict12.jpg) A Pakistani family watch the compound, center top, of Osama bin Laden which is demolishing by authorities in Abbottabad, Pakistan on Sunday, Feb. 26, 2012. Pakistan begun demolishing the three-story compound where Osama bin Laden lived for years and was killed by U.S. commandos last May, eliminating a concrete reminder of the painful and embarrassing chapter in the country’s history. (Anjum Naveed) A Pakistani family watch the compound, center top, of Osama bin Laden which is demolishing by authorities in Abbottabad, Pakistan on Sunday, Feb. 26, 2012. Pakistan begun demolishing the three-story compound where Osama bin Laden lived for years and was killed by U.S. commandos last May, eliminating a concrete reminder of the painful and embarrassing chapter in the country’s history. (Anjum Naveed) |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict0.jpg) In this combo of two images, Pakistan police officers gather next to heavy machinery parked inside the demolished compound of Osama bin Laden, Monday, Feb. 27, 2012, top, and police officers gather outside bin Laden’s compound Sunday, Feb. 26, 2012, in Abbottabad, Pakistan. Pakistani authorities have reduced the house where Osama bin Laden lived for years before he was killed by U.S. commandos to rubble, destroying a concrete symbol of the country’s association with one of the world’s most reviled men. AP In this combo of two images, Pakistan police officers gather next to heavy machinery parked inside the demolished compound of Osama bin Laden, Monday, Feb. 27, 2012, top, and police officers gather outside bin Laden’s compound Sunday, Feb. 26, 2012, in Abbottabad, Pakistan. Pakistani authorities have reduced the house where Osama bin Laden lived for years before he was killed by U.S. commandos to rubble, destroying a concrete symbol of the country’s association with one of the world’s most reviled men. AP |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict1.jpg) In this combo of two pictures, a Pakistani woman and children stand next to the remained boundary wall of Osama bin Laden’s compound, Monday, Feb 27, 2012, top, and, heavy machinery demolishes the main building of bin Laden’s compound Sunday, Feb. 26, 2012, bottom, in Abbottabad, Pakistan. Pakistani authorities have reduced the house where bin Laden lived for years before he was killed by U.S. commandos to rubble, destroying a concrete symbol of the country’s association with one of the world’s most reviled men. AP In this combo of two pictures, a Pakistani woman and children stand next to the remained boundary wall of Osama bin Laden’s compound, Monday, Feb 27, 2012, top, and, heavy machinery demolishes the main building of bin Laden’s compound Sunday, Feb. 26, 2012, bottom, in Abbottabad, Pakistan. Pakistani authorities have reduced the house where bin Laden lived for years before he was killed by U.S. commandos to rubble, destroying a concrete symbol of the country’s association with one of the world’s most reviled men. AP |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict2.jpg) Heavy machinery is seen inside the compound where al Qaeda leader Osama bin Laden was killed after it was demolished in Abbottabad February 27, 2012. The Pakistani home of al Qaeda chief Osama bin Laden, the place where he was killed after the biggest manhunt in history, is no more. Pakistan security forces completed the demolition of bin Laden’s compound on Sunday, erasing a symbol of humiliation for Pakistan’s military that has marked one of the most difficult periods in U.S. Pakistan ties. Reuters Heavy machinery is seen inside the compound where al Qaeda leader Osama bin Laden was killed after it was demolished in Abbottabad February 27, 2012. The Pakistani home of al Qaeda chief Osama bin Laden, the place where he was killed after the biggest manhunt in history, is no more. Pakistan security forces completed the demolition of bin Laden’s compound on Sunday, erasing a symbol of humiliation for Pakistan’s military that has marked one of the most difficult periods in U.S. Pakistan ties. Reuters |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict3.jpg) Pakistani policemen stand near the boundary wall which surrounded the house of Al-Qaeda chief Osama bin Laden, slain last year during a covert US special forces mission, following the building’s demolition in the northwestern town of Abbottabad on February 27, 2012. Pakistani bulldozers on February 27 finished demolishing the house where Osama bin Laden lived for at least five years until he was killed by US special forces last May. Only the wall of the compound remained intact, surrounding the debris of the three-storey building where the Al-Qaeda leader hid in the garrison town of Abbottabad and a security official confirmed the demolition had been completed. Getty Pakistani policemen stand near the boundary wall which surrounded the house of Al-Qaeda chief Osama bin Laden, slain last year during a covert US special forces mission, following the building’s demolition in the northwestern town of Abbottabad on February 27, 2012. Pakistani bulldozers on February 27 finished demolishing the house where Osama bin Laden lived for at least five years until he was killed by US special forces last May. Only the wall of the compound remained intact, surrounding the debris of the three-storey building where the Al-Qaeda leader hid in the garrison town of Abbottabad and a security official confirmed the demolition had been completed. Getty |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict6.jpg) Residents walk past the boundary wall of the building where al Qaeda leader Osama bin Laden was killed after it was demolished in Abbottabad February 27, 2012. The Pakistani home of al Qaeda chief Osama bin Laden, the place where he was killed after the biggest manhunt in history, is no more. Pakistan security forces completed the demolition of bin Laden’s compound on Sunday, erasing a symbol of humiliation for Pakistan’s military that has marked one of the most difficult periods in U.S. Pakistan ties. Reuters Residents walk past the boundary wall of the building where al Qaeda leader Osama bin Laden was killed after it was demolished in Abbottabad February 27, 2012. The Pakistani home of al Qaeda chief Osama bin Laden, the place where he was killed after the biggest manhunt in history, is no more. Pakistan security forces completed the demolition of bin Laden’s compound on Sunday, erasing a symbol of humiliation for Pakistan’s military that has marked one of the most difficult periods in U.S. Pakistan ties. Reuters |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict13.jpg) Pakistan children play cricket next the remained boundary wall of demolished compound of Osama bin Laden in Abbottabad, Pakistan on Monday, Feb. 27, 2012. Pakistani authorities have reduced the house where Osama bin Laden lived for years before he was killed by U.S. commandos to rubble, destroying a concrete symbol of the country’s association with one of the world’s most reviled men. (Anjum Naveed) Pakistan children play cricket next the remained boundary wall of demolished compound of Osama bin Laden in Abbottabad, Pakistan on Monday, Feb. 27, 2012. Pakistani authorities have reduced the house where Osama bin Laden lived for years before he was killed by U.S. commandos to rubble, destroying a concrete symbol of the country’s association with one of the world’s most reviled men. (Anjum Naveed) |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/obl-shrine-down/pict15.jpg) This Friday, March 2, 2012, file photo shows Salafists holding posters showing Osama bin Laden during a rally to condemn the disposal last week of a number of Qurans at a U.S. military base in Afghanistan, near the U.S. embassy in Tunis, Tunisia. An emerging movement of believers known as Salafis has seemingly appeared out of thin air _ and prompted fears of a culture war in this North African country of 10 million. This Friday, March 2, 2012, file photo shows Salafists holding posters showing Osama bin Laden during a rally to condemn the disposal last week of a number of Qurans at a U.S. military base in Afghanistan, near the U.S. embassy in Tunis, Tunisia. An emerging movement of believers known as Salafis has seemingly appeared out of thin air _ and prompted fears of a culture war in this North African country of 10 million. |
TOP-SECRET – Joint Center for International Security Force Assistance Ministerial-Level Advisor Training Effectiveness Study
The intent of Phase I initial impressions is to provide rapid support to the Warfighter. In parallel, these insights serve as part of a broader Ministerial-Level Advisor Training Effectiveness Study, which JCISFA will publish in the spring of 2011. These observations and insights may support planning and decision-making within the NTM-A/CSTC-A as well as joint, interagency, intergovernmental, multinational (JIIM) organizations responsible for force generation supporting the NTM-A/CSTC-A mission. Specifically, this report addresses contemporary issues and senior leader perspectives within the NTM-A/CSTC-A Ministerial-Level Advisor program to include prospective gaps across joint DOTMLPF-P domains. The following illustrates the NTM-A/CSTC-A mission.
“NTM-A/CSTC-A, in coordination with key stakeholders, generates and sustains the ANSF, develops leaders, and establishes enduring institutional capacity in order to enable accountable Afghan-led security.”
Senior level Advisors supporting the development of Afghan ministries provide critical roles in helping the United States and the Government of Afghanistan (GIRoA) achieve national objectives within Afghanistan. As a core function within the NTM-A/CSTC-A, senior Advisors support and influence capability development across two primary Afghan ministries: the Ministry of Defense (MoD) and the Ministry of Interior (MoI). Primarily, Afghan MoD and MoI provide an executive role and function in order to administer the Afghan National Army (ANA) and Afghan National Police (ANP) policy, recruiting, organizing, training, equipping, and building ANA and ANP capabilities. These capabilities provide the nation of Afghanistan with capacity to meet local and regional security requirements. In parallel, the Afghan MoD and MoI must influence and shape local and regional political decisions, plan and execute strategically, assess readiness levels, conduct reviews and analysis, as well as forecast and budget ANA/ANP fiscal requirements.
These complex roles and functions within the Afghan ministries require skilled Senior Advisors capable of adapting culturally as well as operating functionally as subject matter experts (SME) within their respective ministry counterpart’s role and function. Within this framework, the JCISFA conducted Senior Advisor interviews and analysis across the NTM-A/CSTC-A in order to gauge senior Advisor capability requirements to support pre-deployment training and selection methodologies. Two sections provide organization for these initial impressions. The first deals with findings within Ministerial-Level Advisor Training. The second focuses on potential issues within Ministerial-Level Advisor Training.
Ministerial-Level Advisor Findings
- Interviews and surveys revealed that no formal pre-deployment training exists that prepares senior military officers to be Ministerial-Level Advisors.
- Interviews and surveys revealed that there is no standardized transition process between incoming and outgoing Ministerial-Level Advisors.
- There is no enduring capability to collect, analyze and integrate Ministerial advisor lessons learned in NTM-A/CSTC-A.
- A majority of the advisors interviewed/surveyed felt that the recent integration of support staff functions into the DCOMs has been a valuable first step towards improving Ministerial development capability.
- Personnel coming into theater and performing primary or additional duties as advisors are not receiving requisite advisor skills training.
- Senior Advisors interviews focused on how Ministerial developmental goals are established and evaluated/assessed. Almost all advisors interviewed/surveyed stated that the NTM-A/CSTC-A Ministerial Development Plan (MDP) process has been an effective tool in establishing goals and coordinating efforts across multiple functional areas.
- Senior Advisors interviewed/surveyed expressed that coordinating, conducting and reconciling travel with their counterparts is an extremely difficult and frustrating process.
Ministerial-Level Advisor Potential Issues
- Overall, the majority of Ministerial-Level Advisors interviewed/surveyed expressed support for the AFPAK Hands program.
- Many of those interviewed/surveyed had comments and recommendations on the types of skill sets required for Ministerial advisors and on how joint force providers should identify, assign, and track future advisors.
- A great deal of observations and insights were collected regarding the Afghans’ abilities to govern/sustain themselves and effectively deal with corruption.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – FEMA National Responder Support Camps (NRSC) Contract Announcement
The following contract solicitation and accompanying material was posted to the Federal Business Opportunities website between February 10 – 24, 2012. The contract concerns the construction of a temporary camp anywhere in the continental United States (CONUS) within 72 hours in a disaster-impacted area or “any other situation where FEMA or an agency working through FEMA needs a RSC” to host up to 2,000 responders and emergency staff as well as displaced citizens.
DOWNLOAD ORIGINAL FILE HERE
TOP-SECRET – American Friends of Bilderberg 2010 Tax Return and Contributors/Donators
AMERICAN FRIENDS OF BILDERBERG, INC.
C/O JAMES JOHNSON, PERSEUS, LLC
1325 AVE OF THE AMERICAS, 25TH FL
NEW YORK, NY 10019
(212) 651-6400
EIN: 51-0163715
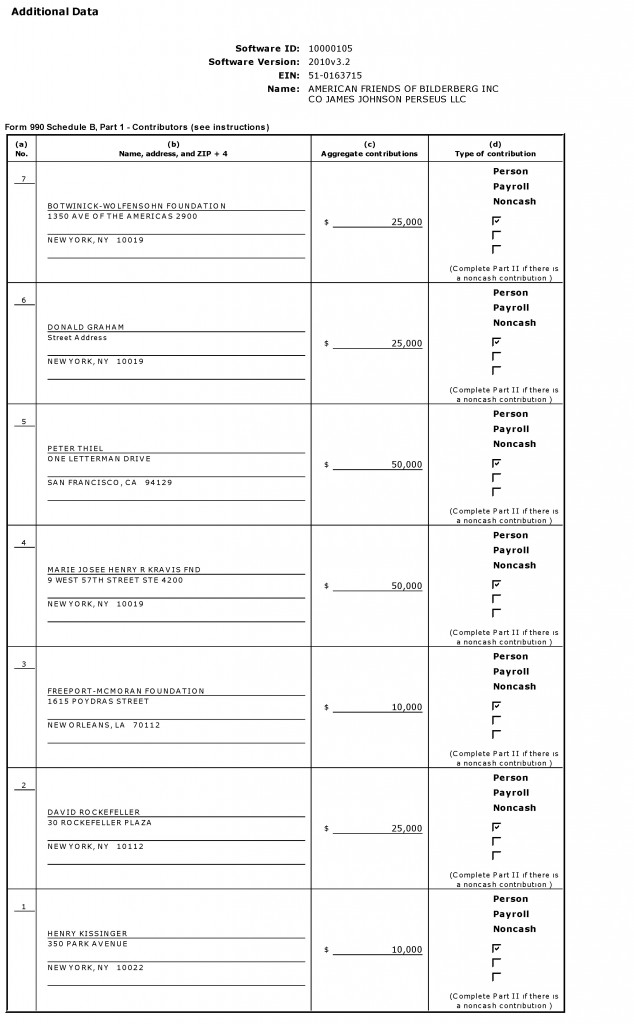
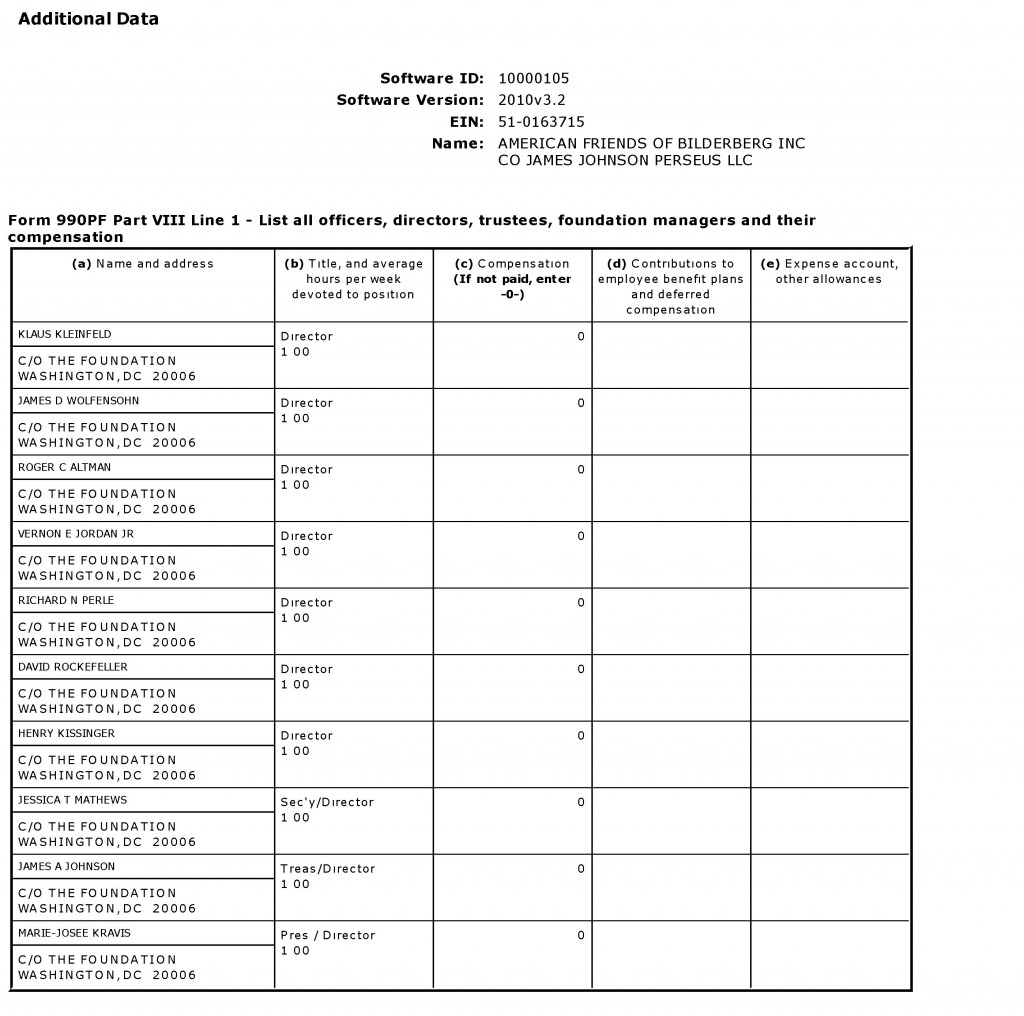
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – FBI National Gang Threat Assessment
(U) Street, prison, and motorcycle gang membership and criminal activity continues to flourish in US communities where gangs identify opportunities to control street level drug sales, and other profitable crimes. Gangs will not only continue to defend their territory from rival gangs, but will also increasingly seek to diversify both their membership and their criminal activities in recognition of potential financial gain. New alliances between rival gangs will likely form as gangs suspend their former racial ideologies in pursuit of mutual profit. Gangs will continue to evolve and adapt to current conditions and law enforcement tactics, diversify their criminal activity, and employ new strategies and technology to enhance their criminal operations, while facilitating lower-risk and more profitable schemes, such as white collar crime.
(U) The expansion of communication networks, especially in wireless communications and the Internet, will allow gang members to form associations and alliances with other gangs and criminal organizations—both domestically and internationally—and enable gang members to better facilitate criminal activity and enhance their criminal operations discreetly without the physical interfacing once necessary to conduct these activities. (U) Changes in immigrant populations, which are susceptible to victimization and recruitment by gangs, may have the most profound effect on street gang membership. Continued drug trafficking-related violence along the US Southwest border could trigger increased migration of Mexicans and Central Americans into the United States and, as such, provide a greater pool of victims, recruits, and criminal opportunities for street gangs as they seek to profit from the illegal drug trade, alien smuggling, and weapons trafficking. Likewise, increased gang recruitment of youths among the immigrant population may result in an increase in gang membership and gang-related violence in a number of regions.
(U) Street gang activity and violence may also increase as more dangerous gang members are released early from prison and re-establish their roles armed with new knowledge and improved techniques. Prison gang members, already an ideal target audience for radicalization, may expand their associations with foreign gang members or radical criminal organizations, both inside correctional institutions and in the community upon their release.
(U//LES) Gang members armed with high-powered weapons and knowledge and expertise acquired from employment in law enforcement, corrections, or the military will likely pose an increasing nationwide threat, as they employ these tactics and weapons against law enforcement officials, rival gang members, and civilians. Associates, friends, and family members of gangs will continue to play a pivotal role in the infiltration and acquisition of sensitive information.
(U) Globalization, socio-political change, technological advances, and immigration will result either in greater gang expansion and gang-related crime or displace gang members as they search for criminal opportunities elsewhere. Stagnant or poor economic conditions in the United States, including budget cuts in law enforcement, may undercut gang dismantlement efforts and encourage gang expansion as police agencies redirect their resources and disband gang units and taskforces, as reported by a large number of law enforcement agencies.
DOWNLOAD ORGINAL FILE HERE
TOP-SECRET from the FBI – New Defendants Added to Case Alleging $20 Million Home Health Care Fraud Conspiracy,
CHICAGO—Two physicians and four registered nurses are among 11 new defendants who were added to a federal indictment against a suburban Chicago man who operated two home health care businesses for allegedly swindling Medicare of at least $20 million over five years, federal law enforcement officials announced today. Nine of the 11 new defendants allegedly conspired with the initial defendant, Jacinto “John” Gabriel, Jr., to submit millions of dollars in false claims for reimbursement of home health care services purportedly provided to Medicare beneficiaries, which allegedly were never provided or were not medically necessary so that they could profit from the fraudulently-obtained funds. Gabriel and his co-schemers allegedly used the proceeds for various purposes, including using cash to gamble at casinos in the Chicago area and Las Vegas; to buy automobiles, jewelry; to purchase real estate in the United States and the Philippines; to perpetuate the businesses by paying his employees and providing them with gifts; and to bribe physicians and pay kickbacks to others in exchange for patient referrals.
Gabriel, 44, of Berwyn, who had no formal medical training, medical degrees, or licenses to practice as a health care professional, was charged in the new indictment with one count of health care fraud conspiracy, 43 counts of health care fraud, 11 counts of money laundering, and four counts of federal income tax evasion in a 69-count superseding indictment returned yesterday by a federal grand jury, announced Patrick J. Fitzgerald, United States Attorney for the Northern District of Illinois. Gabriel was arrested on preliminary charges in February 2011 and was charged alone in a 15-count indictment last summer. He pleaded not guilty to the original charges and is free on bond.
According to the indictment, Gabriel did not identify himself as an owner, but in fact exercised ownership and control over Perpetual Home Health, Inc., based in Oak Forest, and Legacy Home Healthcare Services, which was located on the city’s north side. Both firms have ceased operating and no longer receive Medicare payments. Between May 2006 and January 2011, Perpetual submitted more than 14,000 Medicare claims seeking reimbursement for services allegedly provided to beneficiaries. As a result of those claims, Perpetual received more than $38 million in Medicare payments. Between 2008 and January 2011, Legacy submitted more than 2,000 claims for Medicare reimbursement and received more than $6 million. Neither Perpetual nor Legacy had any sources of revenue other than Medicare funds, the indictment states.
The new defendants are:
Jassy Gabriel, 42, of Berwyn, John Gabriel’s brother, the nominal majority owner of Perpetual and its president, as well as a registered nurse. He was charged with one count of health care fraud conspiracy and one count of filing a false federal income tax return.
Stella Lubaton, 46, of Midlothian, a minority owner of Perpetual and an officer and administrator, as well as a registered nurse. She was charged with one count of health care fraud conspiracy, 16 counts of health care fraud, one count of filing a false federal income tax return, and one count of violating the medical anti-kickback statute.
Nessli Reyes, 35, of Elgin, part-owner of Legacy and its president, as well as a registered nurse. She was charged with one count of health care fraud conspiracy and nine counts of health care fraud.
Charito Dela Torre, 71, of Berwyn, a physician, was charged with one count of health care fraud conspiracy, 12 counts of health care fraud, and three counts of federal income tax evasion.
Ricardo Gonzales, 75, of Orland Park, a physician, was charged with one count of health care fraud conspiracy, 19 counts of health care fraud, and one count of violating the medical anti-kickback statute.
Rosalie Gonzales, 42, of Chicago, a registered nurse and Ricardo Gonzales’ daughter, was charged with one count of violating the medical anti-kickback statute.
James Davis, 37, of West Chicago; Francis Galang, 27, of Crest Hill; and Michael Pacis, 38, of Homer Glen, all data entry employees of Perpetual, were charged with one count each of health care fraud conspiracy.
Regelina “Queenie” David, 58, of Joliet, a Perpetual quality assurance employee, was charged with one count of health care fraud conspiracy.
Kennedy Lomillo, 44, of Mundelein, who provided bookkeeping and payroll services to Perpetual and also prepared a corporate tax return for Perpetual, as well as an individual return for Lubaton, was charged with two counts of aiding and abetting the preparation of false income tax returns.
The indictment also seeks forfeiture of $20 million against the Gabriel brothers and Lubaton.
As part of the conspiracy, Gabriel, acting in various combinations with the nine co-conspirators, allegedly obtained personal information of Medicare beneficiaries to bill Medicare without the beneficiaries’ knowledge or consent; paid bribes and kickbacks in cash and by check, directly and indirectly, to physicians and others in exchange for referrals of patients to Perpetual and Legacy; created false patient files to support fraudulent Medicare claims and submitted false claims based on those records; used Medicare proceeds to pay themselves and others who assisted in carrying out the scheme; and concealed the fraud proceeds by directing Perpetual and Legacy to issue checks payable to fictitious entities, John Gabriel’s friends and associates.
Among other details, the indictment alleges that John and Jassy Gabriel, Lubaton, and Reyes authorized Perpetual and Legacy to pay various amounts, ranging between $200 and $800, to employees and others, including indirectly to Ricardo Gonzales, for each patient they referred and enrolled in home health care services. John Gabriel and others also cold-called Medicare beneficiaries to try to persuade them to enroll with Perpetual and Legacy.
As part of allegedly falsifying patient records, John Gabriel directed Perpetual and Legacy employees, including Davis, Galang, and Pacis, to systematically complete standard forms by listing the same false diagnoses, including arthropathy (joint disease) and hypertension, which enabled them to claim a higher level of Medicare reimbursement, according to the charges.
In addition to the fraud counts, the money laundering charges allege that between October and December 2010, Gabriel cashed 11 checks in amounts under $10,000—usually $9,000 and all involving fraud proceeds—to avoid federal currency transaction reporting requirements.
The four tax evasion counts against John Gabriel allege that for calendar years 2006 through 2009, he failed to pay taxes totaling approximately $889,062 on gross income totaling more than $2.82 million. The three tax evasion counts against Dela Torre allege that for calendar years 2005 through 2007, she failed to pay taxes totaling approximately $158,405 on gross income totaling more than $560,000.
Lubaton was charged with filing a false tax return for 2007 for allegedly failing to report all of her income, which was in excess of the $546,442 that she reported, and Lomillo was charged with aiding and abetting the preparation of her false return. Jassy Gabriel was charged with filing a false tax return for 2007 for allegedly failing to report all of his adjusted gross income, which exceeded the $603,974 that he reported, and Lomillo was charged with aiding and abetting the preparation of his false return.
Health care fraud conspiracy and each count of health care fraud carries a maximum penalty of 10 years in prison and a maximum fine of $250,000, or an alternate fine totaling twice the loss or twice the gain, whichever is greater, as well as mandatory restitution. Each count of money laundering carries a maximum 20-year prison term and a maximum fine of $500,000. Violating the medical anti-kickback statute carries a maximum penalty of five years in prison and a $250,000 fine. Each count of tax evasion carries a five-year maximum prison term, while each count of filing a false income tax return carries a three-year maximum, and a $250,000 fine. In addition, defendants convicted of tax offenses must pay the costs of prosecution and remain liable for any and all back taxes, as well as a potential civil fraud penalty of 75 percent of the underpayment plus interest. If convicted, the court must impose a reasonable sentence under federal statutes and the advisory United States Sentencing Guidelines.
Mr. Fitzgerald announced the charges together with Lamont Pugh III, special agent in charge of the Chicago Region of the U.S. Department of Health and Human Services Office of Inspector General; Robert D. Grant, special agent in charge of the Chicago Office of Federal Bureau of Investigation; and Alvin Patton, special agent in charge of the Internal Revenue Service Criminal Investigation Division. The Railroad Retirement Board Office of Inspector General also participated in the investigation, which is continuing. The investigation is being conducted by the Medicare Fraud Strike Force, which expanded to Chicago in 2011, and is part of the Health Care Fraud Prevention and Enforcement Action Team (HEAT), a joint initiative between the Justice Department and HHS to focus their efforts to prevent and deter fraud and enforce anti-fraud laws around the country.
The government is being represented by Assistant U.S. Attorneys Brian Havey, Raj Laud, and Tony Iweagwu, Jr.
The public is reminded that charges are not evidence of guilt. The defendants are presumed innocent and are entitled to a fair trial at which the government has the burden of proving guilt beyond a reasonable doubt.
TOP-SECRET from the NSA – INTEL WARS The Lessons for U.S. Intelligence From Today’s Battlefields
Purchase Intel Wars: The Secret History of the Fight Against Terror at Amazon.
Washington, D.C., March 6, 2012 – Spendthrift, schizophrenic policies and a massive, multi-tiered bureaucracy more focused on preserving secrets than on mission accomplishment leave our intelligence operatives drowning in raw data, resource-starved, and choked on paperwork, according to a new book, Intel Wars: The Secret History of the Fight Against Terror (Bloomsbury Press, 2012), by intelligence historian Matthew Aid. Excerpts from the book and declassified documents cited in it were posted today by the National Security Archive, where Aid is a Visiting Fellow.
Even after the celebrated raid by U.S. Navy SEAL commandos in May 2011, which killed al Qaeda leader Osama Bin Laden, America’s spies are still struggling to beat a host of ragtag enemies around the world, Aid argues.
Thanks to more than $500 billion in taxpayer dollars spent on revamping and modernizing America’s spy networks since 9/11, the U.S. today has the largest and most technologically sophisticated intelligence community in the world, consisting of 210,000 employees, CIA stations in 170 countries, and an annual budget of more than $75 billion. Armed with cutting-edge surveillance gear, high-tech weapons, and fleets of armed and unarmed drone aircraft, the U.S. intelligence community is now producing more and better intelligence than at any time in its history.
But, according to Aid, overlapping jurisdictions and bureaucratic inertia often stall intelligence operations, such as U.S. military operators in Afghanistan who have to wait seventy-two hours for clearance to attack fast-moving Taliban IED teams planting explosive devices. U.S. military computers – their classified hard drives still in place – turn up for sale at Afghan bazaars. When you dig beneath the surface, swift, tightly focused intelligence-driven operations like the Osama bin Laden raid seem to be the exception rather than the rule, Aid concludes.
Intel Wars – based on extensive, on-the-ground interviews, dozens of declassified documents, and revelations from Wikileaks cables – shows how our soldier-spies are still fighting to catch up with the enemy.
Today’s posting of 12 documents consists of a selection of reports and memoranda cited in Intel Wars concerning the role played by the U.S. intelligence community in today’s military conflicts and crises, particularly in Afghanistan.
TOP-SECRET from the NSA – Excerpts on warning systems and October 1960 false from Institute for Defense Analyses, The Evolution of U.S. Strategic Command and Control and Warning, 1945-1972,
READ THE DOCUMENTS
Document 1: Excerpts on warning systems and October 1960 false from Institute for Defense Analyses, The Evolution of U.S. Strategic Command and Control and Warning, 1945-1972, Study S-468 (Arlington, Virginia, 1975), op Secret, excerpts: pp. 216-218, 339-347, and 419-425.
Source: Digital National Security Archive
This invaluable history provides useful background on the missile attack warning systems–BMEWs and DSP, among others–that became available during the 1960s and 1970s. One chapter provides context for the creation of the National Emergency Airborne Command Post [NEACP] that became operational in 1975.
Document 2: State Department cable 295771 to U.S. Embassy Moscow, “Brezhnev Message to President on Nuclear False Alarm,” 14 November 1979, Secret
Source: State Department FOIA release
The Soviets surely read about the November 1979 false warning in the U.S. press, but whether their intelligence systems had already detected it is not so clear. In any event, Soviet General Secretary Brezhnev privately expressed his “extreme anxiety” to President Carter a few days after U.S. press reports appeared on 11 November 1979. The message was closely held, not only as “Nodis” (“no distribution” except to a few authorized people), but also as “Cherokee,” a special information control established when Dean Rusk was Secretary of State (Rusk was born in Cherokee Country, GA) and used by subsequent Secretaries of State.
Document 3: Brigadier General Carl Smith, USAF, Military Assistant to the Secretary of Defense, to William Odom, Military Assistant to the Assistant to the President for National Security Affairs, “Proposed Oral Message Response,” 16 November 1979
Source: Defense Department FOIA release
Officials at the Pentagon drafted a reply that became the basis for the message that was eventually sent to the Kremlin. Giving very little quarter, the text asserted that the Kremlin had used bad information and that its message made “inaccurate and unacceptable” assertions, that Moscow had little to worry about because U.S. forces were under reliable control, and that it did not “serve the purposes of peace or strategic stability” to make a fuss about the recent incident.
Document 4: Excerpt from State Department memorandum to Secretary of State with attached memo “Late Supplement to VBB [Vance, Brown, Brzezinski] Item on Brezhnev Oral Message on False Alert,” circa 16 November 1979, secret, excerpt (as released by State Department)
Source: State Department FOIA release
Excerpts from a memorandum to Secretary of State Vance to prepare for a routine coordinating meeting with Secretary of Defense Brown and national security adviser Brzezinski, suggest that senior State Department officials opposed rushing a response to the Soviet message. Although they agreed that the “tone” of Brezhnev’s message was “unacceptable,” they opposed giving the Soviets ammunition to exploit, wanted to discuss carefully the “merits” of the Soviet case, and did not want to appear too “cavalier” about the incident because that could make U.S. allies nervous when they were already discussing new U.S. nuclear deployments in Western Europe.
Document 5: Marshal Shulman memo to Secretary of State Cyrus Vance, 16 November 1979, Top Secret
Source: State Department FOIA release
Vance’s adviser on Soviet policy Marshal Shulman had signed off on the memorandum on the reply to the Soviets, but had further thoughts. Believing that the U.S. could not really fault the Soviets for worrying about such episodes, Shulman noted that false alerts not a “rare occurrence” and worried about “complacency” toward the problem. Seeing the proposed reply as “kindergarten stuff,” he suggested more straightforward language. Whether this paper actually went to Vance is unclear, given the line crossing out the text.
Document 6: Marshal Shulman memo to Cyrus Vance, 21 November 1979, with draft message attached, nonclassified,
Source: State Department FOIA release
The debate over the reply continued, and an alternate version was drafted, but the one that Vance accidentally approved was the version that Shulman and others in the Department and the NSC found “gratuitously insulting and inappropriate for the Carter/Brezhnev channel.” Shulman’s advice came too late; even though Vance reportedly disliked the reply, he did not want to revisit the issue. Instead of handling the memorandum at the Secretary of State level, Vance’s top advisers wanted it to be delivered at somewhat lower level such as by Assistant Secretary of State George Vest. The version that is attached to Shulman’s note is a milder version of what was sent (see document 8).
Document 7: State Department cable 307013 to the U.S. Mission to the North Atlantic Treaty Organization, “TNF: Soviets and the False Missile Alert,” 28 November 1979, Secret
Source: State Department FOIA release
Before the Soviets received the reply, the State Department briefed permanent representatives to the North Atlantic Council to counter any attempts by Moscow to “cast doubt on the reliability of our nuclear control” and thereby influence the outcome of the ongoing debates over prospective theater nuclear forces [TNF] deployments in NATO Europe. This cable includes briefing information on what happened and also to demonstrate the “the redundant and complete nature of our well-established confirmation and control mechanisms.” The message was reasonably accurate about the cause of the false warning, not an operator error but the mistaken transmission of part of a test tape. Yet, as Scott Sagan has pointed out, this message wrongly asserted that the NORAD interceptors were launched because of an earlier alert; nothing of that sort had occurred.[11]
Document 8: State Department cable 312357 to U.S. Embassy Moscow, “U.S. Oral Message on Purported Alert of American Strategic Forces,” 4 December 1979, Confidential
Source: State Department FOIA release
On 4 December 1979, Robert Louis Barry, an official at the Bureau of European Affairs, at a lower level than Assistant Secretary Vest, finally conveyed the reply to the Soviet embassy’s Minister Counselor Aleksandr Bessmertnykh (later an ambassador to the United States). Unlike the original Soviet message, it was not a head of state communication, Carter–to-Brezhnev, suggesting that relations were quite frosty in this pre-Afghanistan period. Possibly the version of the reply that Shulman saw as “snotty,” it described Brezhnev’s original message as “inaccurate and unacceptable.” Ignoring Brezhnev’s concern about “no errors,” the message insisted that U.S. strategic forces were under “reliable control.”
Document 9: State Department cable 326348 to U.S. Embassy Moscow, “Supplementary Soviet Statement on U.S. Strategic Alert,” 19 December 1979, Confidential
Source: State Department FOIA release
Apparently surprised by the U.S. reply, the Soviets took issue with it in a “non-paper” delivered to the State Department by their chargé. Arguing that they had not raised the issue to engage in “polemics,” the Soviets asserted that a “profound and natural concern” instigated their original message.
Document 10: Message, HQ/NORAD to Assistant Secretary of Defense C3 and Joint Chiefs of Staff, 20 December 1979, Secret
Source: Donation by Scott Sagan, Stanford University
Sen. Gary Hart (D-Co), a member of the Senate Arms Services Committee, was concerned about what had happened on 9 November and visited NORAD for a briefing. While Hart wondered why the President and the Secretary of Defense had not been informed at the time, Lt. General Bruce K. Brown and other NORAD briefers explained that almost from the outset of the episode, NORAD officials saw a “a very high probability” that the warning was false. Hart also wondered why development testing on the NORAD 427M computer had been allowed; the briefers explained that NORAD officials recognized there was a problem and had recommended an auxiliary computer system as an “isolated” means for testing but the request had been denied because of “lack of funds.” Early in the message the briefers explained that they had stayed away from discussing the connection between the 427M computers and the Worldwide Military Command and Control System (WWMCCS). What may have explained that problem was ongoing concern at the Government Accounting Office and elsewhere that the WWMCCS lacked the capacity to meet NORAD’s mission requirements.
Document 11: Letter, Lt. General James V. Hartinger, Commander-in-chief, Aerospace Defense Command, to General Lew Allen, Chief of Staff, U.S. Air Force, 14 March 1980, Secret, attachments not included
Source: Donation by Scott Sagan, Stanford University
In a letter to the Air Force Chief of Staff, NORAD commander General Hartinger summarized the command’s report on the 9 November incident. That report is currently the subject of a declassification request to the Air Force. Not sure whether the incident was caused by a “human error, computer error, or combination of both,” Hartinger reported that “stringent safeguards have been established to preclude a repetition.”
Document 12: Secretary of Defense Harold Brown to President Carter, “False Missile Alert,” 7 June 1980, Top Secret, excised copy
Source: Defense Department FOIA release, currently under appeal
Hartinger’s confidence was misplaced. Massively and overzealously excised by reviewers at the Defense Department, this memorandum discloses that U.S. warning systems produced 3 false alerts during May and June 1980. The May event, described in document 19, was a minor precursor to the 3 June incident.
Document 13: Department of Defense “Fact Sheet,” n.d. [circa 7/8 June 1980], Secret
Source: Defense Department FOIA release
This document reviews the false alerts on 3 and 6 June of Soviet ICBM and SLBM attacks, what apparently caused them, what SAC bomber crews did in response to the warnings, and the measures that were taken to diagnosis what happened and to ensure that it did not happen again. Corrective measures included a separate computer system for testing operations (which had been rejected before because of insufficient funds[12]) and a determination by CINCNORAD that the U.S. is “under attack” before anything beyond basic “precautionary measures” are taken.
After the first incident on 3 June, SAC, NORAD, and the National Military Command Center established a “continuous voice telephone conference” to ensure that nothing went amiss.
The authors of the “Fact Sheet” emphasized the importance of the “human safeguards” noting that officers at NORAD were aware that electronic warning systems were working as usual and that the displays showed no unusual activity. An article in The New York Times published on 18 June (“Missile Alerts Traced to 46¢ Item”) included details on the response to the warning not mentioned in the “Fact Sheet,” asserting that missile crews went on a “higher state of alert” and that submarine crews were also informed. The Times’ writers, however, were not aware that NEACP “taxied into position” as part of an emergency routine.
Document 14: Assistant Secretary for Politico-Military Affairs Reginald Bartholomew to Secretary of State [Muskie], “False Alarm on Soviet Missile Attack,” 10 June 1980, Limited Official Use
Source: State Department FOIA release
Reginald Bartholomew sent a briefing memo on the incidents to Secretary Muskie, noting that “these incidents inevitably raise concerns … about the dangers of an accidental nuclear war.” The media had already picked up on the story[13], so there was some possibility of a Soviet complaint, although “the tone may well be sharper” in light of the tensions over the Soviet invasion of Afghanistan
Document 15: Secretary of Defense Brown to President Carter, “False Missile Alerts,” 13 June 1980, Secret, Excised copy
Source: Defense Department FOIA release
In this memorandum, Brown provided suggestions on how to answer media questions about the false warning problem. Treating false warnings as a byproduct of computerized warning technology, he emphasized that “human safeguards” ensured that there would be “no chance that any irretrievable actions would be taken.” While “any missile warning indications”, false or otherwise, would force SAC to take “precautionary action” by raising the bomber force’s alert status, Brown did not believe that anything more would happen.
Document 16: Assistant Secretary of Defense for Communications, Command, Control, and Intelligence Gerald P. Dinneen http://www.nap.edu/openbook.php?record_id=9052&page=1 to Secretary and Deputy Secretary of Defense, “False Missile Alerts – Information Memorandum,” 14 June 1980, Top Secret, excised copy
Source: Defense Department FOIA release
Assistant Secretary of Defense Dinneen (former director of Lincoln Laboratories) apprised Brown on the efforts to identify what had caused the false alerts and what could be done to fix the problem. A task force studying NORAD computer problems had identified a “suspect integrated circuit” as the most likely culprit (although they were not 100 percent certain). Various measures had been taken or under consideration but the details have been excised. A few days later Dinneen would brief the press on the failure of the 46¢ chip.
Document 17: Memorandum of Conversation, “U.S.-Soviet Relations,” 16 June 1960
Source: State Department FOIA release
During a meeting between Secretary of State Muskie and Ambassador Dobrynin, the latter asked about the recent “nuclear alerts,” which Foreign Minister Andrei Gromyko had already raised with U.S. Ambassador to Moscow, Thomas Watson. Muskie downplayed the problem on the grounds that the false signals would not create a “danger of war” because of the “interposition of human judgment.”
Document 18: Secretary of Defense to President Carter, “False Missile Alerts,” 12 July 1980, Top Secret, excised copy, attached to memorandum from Zbigniew Brzezinski to Brown, “False Alerts,” 17 July 1980, with annotations by Jimmy Carter
Source: Defense Department FOIA release
Here Brown updated Carter on the explanations for the recent false alert, corrective measures (e.g. special alarms when warning messages arrived so they could undergo confidence checks), and reactions by Congress and the public. Carter approved Brown’s report with an OK but was surprised (see handwritten exclamation mark) by the statement that “NORAD has been unable to get the suspected circuit to fail again under tests.” That conflicts with a statement in the Senate report that what caused the 6 June incident was an attempt to reproduce the earlier false alert, but perhaps subsequent attempts failed. Brown reminded Carter that “we must be prepared for the possibility that another, unrelated malfunction may someday generate another false alert.”
Document 19: Office of NORAD Deputy Chief of Staff, Operations, Captain Victor B. Budura, J-3, “Talking Points on 3/6 June False Indications,” 21 July 1980, Secret
Source: Donation by Scott Sagan, Stanford University
This NORAD document provides a chronology of the episodes of 28 May, 3 June, and 6 June 1980, although leaving out some events, such as the role of NEACP in the 3 June incident.
Document 20: U.S. Pacific Command, Annual History, 1980, excerpt, pages 201-202 (2nd page of excerpt unreadable), Secret
Source: Donation by Scott Sagan, Stanford University
This excerpt from a Pacific Command history discusses the launching of the Pacific Command airborne command post, “Blue Eagle,” during the 3 June false episode. As the chronology in document 19 indicates, the warning was determined to be false before “Blue Eagle” had taken off, but it stayed airborne for several hours.[14]
NOTES
[1] The following draws on the Institute for Defense Analyses’ History of Strategic Command Control and Warning, 1945-1972 (excerpts in document 1) and Jeffrey Richelson, America’s Space Sentinels: DSP Satellites and National Security (Lawrence: University Press of Kansas, 1999)
[2] Joseph T. Jockel, Canada and NORAD: 1957-2007: A History (Montreal: McGill-Queen’s University Press, Program, 2007), 95. This book and Jockel’s earlier, No Boundaries Upstairs: Canada, the United States, and the Origins of North American Air Defence, 1945-1958 (Vancouver: University of British Columbia Press, 1987) are valuable studies on the origins and development of NORAD. A comparable U.S. study on NORAD history remains to be prepared, although Christopher Bright’s Continental Air Defense in the Eisenhower Era: Nuclear Antiaircraft Arms and the Cold War (New York: Palgrave Macmillan) is helpful on nuclear issues in NORAD’s early years.
[3] Scott Sagan, The Limits of Safety: Organizations, Accidents, and Nuclear Weapons (Princeton: Princeton University Press, 1993). 99-100 and 126-133.
[4] Sagan, Limits of Safety, 228-229, 238.
[5] Ibid., 232, 244-246. See also Report of Senator Gary Hart and Senator Barry Goldwater to the Committee on the Armed Services United States Senate, Recent False Alerts from the Nation’s Missile Attack Warning System (Washington, D.C.: U.S. Government Printing Office, 1980), 5-6, and Government Accounting Office, MASAD 81-30, “NORAD’s Missile Warning System: What Went Wrong?”
[8] Bruce Blair, The Logic of Accidental Nuclear War (Washington, D.C.: Brookings Institution, 1993), 193.
[9] David E. Hoffman, The Dead Hand The Untold Story of the Cold War Arms Race and Its Dangerous Legacy (New York: Doubleday, 2009): 152-154, 422-423.
[10] David E. Hoffman, “Cold War Doctrines Refuse to Die,” The Washington Post, 15 March 1998,
[11] Sagan, Limits of Safety, 240-241.
[13] For example, the Washington Post published a story by George C. Wilson, “Computer Errs, Warns of Soviet Attack on U.S.,” on 6 June 1980.
TOP-SECRET from the NSA – False Warnings of Soviet Missile Attacks during 1979-80 Led to Alert Actions for U.S. Strategic Forces

Click for Larger ViewPhoto 1: “Command post for all NORAD [North American Aerospace Defense Command] operations, including the Command’s surveillance and warning sensors around the globe.” Caption from U.S. Information Agency photo. This and the next two photos were taken about 1982 so the depiction of NORAD facilities may not correspond exactly to arrangements during 1979-1980.
Source: National Archives, Still Pictures Branch, RG 306-PSE, box 79

Click for Larger ViewPhoto 2: “Satellite watchers in the Space Computational Center, NORAD Headquarters, track all the satellites orbiting earth. ” Caption from U.S. Information Agency photo.
Source: National Archives, Still Pictures Branch, RG 306-PSE, box 79

Click for Larger ViewPhoto 3: “Computers are used by specialists in NORAD Headquarters to keep track of information received daily.” Caption from U.S. Information Agency photo.
Source: National Archives, Still Pictures Branch, RG 306-PSE, box 79

Click for Larger ViewPhoto 4: “3/4s front view of a Boeing 747 Airborne Command post aircraft taking off. This aircraft will be designated the E-4A and become the new Night Watch Airplane.” Four Boeing 747s were modified to serve as the National Emergency Airborne Command Post [NEACP] for the National Command Authority [NCA], the President and the Secretary of Defense. Quotation from caption on photo taken by Sgt. J. F. Smith at Andrews Air Force Base, 1973.
Source: National Archives, Still Pictures Branch, RG 342B, box 731, E-4A

Click for Larger ViewPhoto 5: “National Emergency Airborne Command Post internal configuration.” Caption from Department of Defense photograph, 5 April 1976
Source: National Archives, Still Pictures Branch, RG 342B, box 731, E-4A

Click for Larger ViewPhoto 6: “Operations team shown in NCA conference room normally occupied by the NCA and immediate staff.” Caption from Air Force photo of NEACP taken by Sgt. J.F. Smith, 1974.
Source: National Archives, Still Pictures Branch, RG 342B, box 30, E-4A

Click for Larger ViewPhoto 7: Interior shot of the NEACP shows the briefing room. Department of Defense photo taken 5 April 1976.
Source: National Archives, Still Pictures Branch, RG 342B, box 731, Aircraft E4-AE

Click for Larger ViewPhoto 8: “Operations team shown in NCA conference room normally occupied by the NCA and immediate staff. It seats nine people.” Caption from Air Force photo of NEACP taken by Sgt. J.F. Smith, 1974.
Source: National Archives, Still Pictures Branch, RG 342B, box 30, E-4A

Click for Larger ViewPhoto 9: “Side view of three U.S. Air Force F-106’s , Det[achment] 3, 25th Air Division, fly by Mt. McKinley, Alaska, while on a training mission, 14 April 1969.” These were the type of aircraft launched by NORAD during the 9 November 1979 false alert. Caption from U.S. Air photo
Source: National Archives, Still Pictures Branch, RG 342-B, box 743, Aircraft F-106.
Washington, D.C., March 6, 2012 – During the 2008 campaign, Democratic presidential hopefuls Hillary Clinton and Barack Obama debated the question: who was best suited to be suddenly awakened at 3 a.m. in the White House to make a tough call in a crisis. The candidates probably meant news of trouble in the Middle East or a terrorist attack in the United States or in a major ally, not an ‘end of the world’ phone call about a major nuclear strike on the United States. In fact at least one such phone call occurred during the Cold War, but it did not go to the President. It went to a national security adviser, Zbigniew Brzezinski, who was awakened on 9 November 1979, to be told that the North American Aerospace Defense Command (NORAD), the combined U.S.–Canada military command–was reporting a Soviet missile attack. Just before Brzezinski was about to call President Carter, the NORAD warning turned out to be a false alarm. It was one of those moments in Cold War history when top officials believed they were facing the ultimate threat. The apparent cause? The routine testing of an overworked computer system.
Recently declassified documents about this incident and other false warnings of Soviet missile attacks delivered to the Pentagon and military commands by computers at NORAD in 1979 and 1980 are published today for the first time by the National Security Archive. The erroneous warnings, variously produced by computer tests and worn out computer chips, led to a number of alert actions by U.S. bomber and missile forces and the emergency airborne command post. Alarmed by reports of the incident on 9 November 1979, the Soviet leadership lodged a complaint with Washington about the “extreme danger” of false warnings. While Pentagon officials were trying to prevent future incidents, Secretary of Defense Harold Brown assured President Jimmy Carter that false warnings were virtually inevitable, although he tried to reassure the President that “human safeguards” would prevent them from getting out of control.
Among the disclosures in today’s posting:
- Reports that the mistaken use of a nuclear exercise tape on a NORAD computer had produced a U.S. false warning and alert actions prompted Soviet Communist Party General Secretary Leonid Brezhnev to write secretly to President Carter that the erroneous alert was “fraught with a tremendous danger.” Further, “I think you will agree with me that there should be no errors in such matters.”
- Commenting on the November 1979 NORAD incident, senior State Department adviser Marshal Shulman wrote that “false alerts of this kind are not a rare occurrence” and that there is a “complacency about handling them that disturbs me.”
- With U.S.-Soviet relations already difficult, the Brezhnev message sparked discussion inside the Carter administration on how best to reply. Hard-liners prevailed and the draft that was approved included language (“inaccurate and unacceptable”) that Marshal Shulman saw as “snotty” and “gratuitously insulting.”
- Months later, in May and June 1980, 3 more false alerts occurred. The dates of two of them, 3 and 6 June 1980, have been in the public record for years, but the existence of a third event, cited in a memorandum from Secretary of Defense Brown to President Carter on 7 June 1980, has hitherto been unknown, although the details are classified.
- False alerts by NORAD computers on 3 and 6 June 1980 triggered routine actions by SAC and the NMCC to ensure survivability of strategic forces and command and control systems. The National Emergency Airborne Command Post (NEACP) at Andrews Air Force Base taxied in position for emergency launch, although it remained in place. Because missile attack warning systems showed nothing unusual, the alert actions were suspended.
- Supposedly causing the incidents in June 1980 was the failure of a 46¢ integrated circuit (“chip”) in a NORAD computer, but Secretary of Defense Brown reported to a surprised President Carter that NORAD “has been unable to get the suspected circuit to fail again under tests.”
- In reports to Carter, Secretary cautioned that “we must be prepared for the possibility that another, unrelated malfunction may someday generate another false alert.” Nevertheless, Brown argued that “human safeguards”—people reading data produced by warning systems–ensured that there would be “no chance that any irretrievable actions would be taken.”
Background
For decades, the possibility of a Soviet missile attack preoccupied U.S. presidents and their security advisers. Because nuclear hostilities were more likely to emerge during a political-military confrontation (such as Cuba 1962) the likelihood of a bolt from the blue was remote but Washington nevertheless planned for the worst case. Under any circumstances, U.S. presidents and top military commanders wanted warning systems that could provide them with the earliest possible notice of missile launches by the Soviet Union or other adversaries. By the early 1960s, the Pentagon had the Ballistic Missile Early Warning System (BMEWs) that could provide about 15 minutes of warning time. By the mid-to-late1960s, forward-scatter systems (so-called “Over the Horizon Radar”) could detect missile launches within five to seven minutes from while, the 474N system could give three-to-seven minutes of warning of launches from submarines off the North American coast. [1]
By the end of the 1960s, the United States was getting ready to deploy the Defense Support Program satellites which use infrared technology to detect plumes produced by missile launches. DSP could be used to tell whether missile launches were only tests or whether they signified a real attack by detecting number of missile launches and trajectory. This provided25 to 30 minutes of warning along with information on the trajectory and ultimate targets of the missiles. As long as decision-makers were not confronting the danger of a SLBM launch, the DSP would give them some time to decide how to retaliate.
In 1972, the North American Aerospace Command (NORAD) began to network warning systems into at “interlinked system” operated at its headquarters in Cheyenne Mountain, Colorado.[2] A complex computer-based system always bore the risk of failure, break-downs, or errors. Even before networking emerged, false warnings emerged as early as 1960 when a BMEWs radar in Greenland caught “echoes from the moon,” which generated a report of a missile attack which was quickly understood to be false (see document 1). During the Cuban Missile Crisis false warning episodes occurred, some of them involving NORAD, that were virtually unknown for many years.[3] If there were significant incidents during the years that followed, it remains to be learned. But once the networked systems were in place, the possibility that they would typically produce false warnings became evident.
The Events of 1979-1980
“As he recounted it to me, Brzezinski was awakened at three in the morning by [military assistant William] Odom, who told him that some 250 Soviet missiles had been launched against the United States. Brzezinski knew that the President’s decision time to order retaliation was from three to seven minutes …. Thus he told Odom he would stand by for a further call to confirm Soviet launch and the intended targets before calling the President. Brzezinski was convinced we had to hit back and told Odom to confirm that the Strategic Air Command was launching its planes. When Odom called back, he reported that … 2,200 missiles had been launched—it was an all-out attack. One minute before Brzezinski intended to call the President, Odom called a third time to say that other warning systems were not reporting Soviet launches. Sitting alone in the middle of the night, Brzezinski had not awakened his wife, reckoning that everyone would be dead in half an hour. It had been a false alarm. Someone had mistakenly put military exercise tapes into the computer system.” — Robert M. Gates. From the Shadows: The Ultimate Insider’s Story of Five Presidents and How they Won the Cold War (New York: Simon & Shuster, 1996),114.
The series of alarming incidents and telephone phone calls recounted by former NSC staffer (and later CIA director and future Secretary of Defense) Robert Gates took place in the middle of the night on 9 November 1979. Because of the potentially grave implications of the event, the episode quickly leaked to the media, with the Washington Post and The New York Times printing stories on what happened. According to press reports, based on Pentagon briefings, a NORAD staffer caused the mistake by mistakenly loading a training/exercise tape into a computer, which simulated an “attack into the live warning system.” This was a distortion because it was not a matter of a “wrong tape,” but software simulating a Soviet missile attack then testing NORAD’s 427M computers “was inexplicably transferred into the regular warning display” at the Command’s headquarters. Indeed, NORAD’s Commander-in-chief later acknowledged that the “precise mode of failure … could not be replicated.”[4]
The information on the display simultaneously appeared on screens at SAC headquarters and the National Military Command Center (NMCC), which quickly led to defensive actions: NORAD alerted interceptor forces and 10 fighters were immediately launched. Moreover, the National Emergency Airborne Command Post (NEACP), used so the president could control U.S. forces during a nuclear war, was launched from Andrews Air Force Base, although without the president or secretary of defense.
Some of this information did not reach the public for months, but at least one reporter received misleading information about how high the alert went. According to the New York Times’ sources, the warning was “deemed insufficiently urgent to warrant notifying top Government or military officials.” Apparently no one wanted to tell reporters (and further scare the public) that the phone call went to President’s Carter’s national security adviser Zbigniew Brzezinski.
The behind-the-scenes story became more complicated because the Soviet leadership was worried enough to lodge a complaint with Washington. The Cold War tensions had already been exacerbated during the previous year and this could not help (nor could an impending Kremlin decision to invade Afghanistan). On 14 November, party leader Leonid Brezhnev sent a message via Ambassador Anatoly Dobyrnin expressing his concern about the incident which was “fraught with a tremendous danger.” What especially concerned Brezhnev were press reports that top U.S. leaders had not been informed at the time about the warning. The Defense Department and Brzezinski took hold of the reply to Brezhnev’s message which senior State Department adviser Marshall Shulman saw as “gratuitously snotty” (for example, language about the “inaccurate and unacceptable” Soviet message). The Soviets were indeed miffed because they later replied that the U.S. message was not “satisfactory” because it had taken a polemical approach to Moscow’s “profound and natural concern.”
About seven months later, U.S. warning systems generated three more false alerts. One occurred on 28 May 1980; it was a minor harbinger of false alerts on 3 and 6 June 1980. According to the Pentagon, what caused the malfunctions in June 1980 was a failed 46¢ micro-electronic integrated circuit (“chip”) and “faulty message design.” A computer at NORAD made what amounted to “typographical errors” in the routine messages it sent to SAC and the National Military Command Center (NMCC) about missile launches. While the message usually said “OOO” ICBMs or SLBMs had been launched, some of the zeroes were erroneously filled in with a 2, e.g. 002 or 200, so the message indicated that 2, then 200 SLBMs were on their way. Once the message arrived at SAC, the command took survivability measures by ordering bomber pilots and crews to their stations at alert bombers and tankers and to start the engines.
No NORAD interceptors were launched so something had been learned from the November episode, but SAC took same precautionary measures. The Pacific Command’s airborne command post (“Blue Eagle”) was launched for reasons that remain mysterious.[5] NEACP taxied in position at Andrews Air Force Base, but it was not launched as in November. That missile warning sensors (DSP, BMEWs, etc) showed nothing amiss made it possible for military commanders to call off further action. According to a Senate report, NORAD ran its computers the next 3 days in order to isolate the cause of the error; the “mistake was reproduced” in the mid-afternoon of 6 June with the similar results and SAC took defensive measures.[6]
When Harold Brown explained to President Carter what had happened and what was being done to fix the system, he cautioned that “we must be prepared for the possibility that another, unrelated malfunction may someday generate another false alert.” This meant that “we must continue to place our confidence in the human element of our missile attack warning system.” Brown, however, did not address a problem raised by journalists who asked Pentagon officials, if another false alert occurred, whether a “chain reaction” could be triggered when “duty officers in the Soviet Union read data on the American alert coming into their warning systems.” A nameless U.S. defense official would give no assurances that a “chain reaction” would not occur, noting that “I hope they have as secure a system as we do, that they have the safeguards we do.”
How good the safeguards actually were remains an open question. While Secretary of Defense Brown acknowledged the “possibility” of future false alerts, he insisted on the importance of human safeguards in preventing catastrophes. Stanford University professor Scott Sagan’s argument about “organizational failure” is critical of that optimism on several counts. For example, under some circumstances false alerts could have had more perilous outcomes, e.g. if Soviet missile tests had occurred at the same time or if there were serious political tensions with Moscow, defense officials might have been jumpier and launched bomber aircraft or worse. Further, false warnings were symptomatic of “more serious problems with the way portions of the command system had been designed.” Yet, defense officials have been reluctant to acknowledge organizational failings, instead blaming mistakes on 46¢ chips or individuals inserting the wrong tape. Treating the events of 1979 and 1980 as “normal accidents” in complex systems, Sagan observes that defense officials are reluctant to learn from mistakes and have persuaded themselves that the system is “foolproof.”[7]
Bruce Blair also sees systemic problems. Once a “launch-under–attack” strategic nuclear option became embedded in war planning policy during the late 1970s, he sees the weakening of the safeguards that had been in place, e.g., confirmation that a Soviet nuclear attack was in progress or had already occurred. One of the arguments for taking Minuteman ICBMs off their current high alert status (making virtually instantaneous launch possible) has been that a false warning, combined with an advanced state of readiness, raises the risk of accidental nuclear war. The risk of false alerts/accidental war is one of the considerations that is prompting other anti-nuclear activists, including Daniel Ellsberg, to protest at Vandenberg Air Force Base against the Minuteman ICBM program and the continued testing of Minutemen.[8]
The Soviet nuclear command and control system that developed during the 1980s provides an interesting contrast with the U.S.’s. While the United States emphasized “human safeguards” as a firewall, the “Perimeter” nuclear warning-nuclear strike system may have minimized them. In large part, it was a response to Soviet concern that a U.S. decapitating strike, aimed at the political leadership and central control systems, could cripple retaliatory capabilities. Reminiscent of the “doomsday machine” in Stanley Kubrick’s Dr. Strangelove or How I Learned to Stop Worrying and Love the Bomb, Perimeter could launch a semi-automatic nuclear strike under specified conditions, for example, no contact with political or military leaders, atomic bombs detonating, etc. If such conditions were fulfilled, a few military personnel deep in an underground bunker could launch emergency command and control rockets which in turn would transmit launch orders to ICBMs in their silos. According to David Hoffman’s Pulitzer-prize winning The Dead Hand, when Bruce Blair learned about Perimeter, he was “uneasy that it put launch orders in the hands of a few, with so much automation.” While the system may have been operational as late as the early 1990s, only declassification decisions by Russian authorities can shed light on Perimeter’s evolution.[9]
According to Bruce Blair, writing in the early 1990s, warning system failures continued after 1980, although they did not trigger alert measures.[10] The U.S. nuclear incidents that have received the most attention have not been false warnings, but events such as the Air Force’s accidental movement of nuclear-tipped cruise missiles from Minot AFB to Barksdale AFB in 2007 and the mistaken transfer of Minuteman nose-cone assemblies to Taiwan in 2006. In any event, more needs to be learned about the problem of false warnings during and after the Cold War and pending declassification requests and appeals may shed further light on this issue.
TOP-SECRET – FBI Indicators for Terrorist Use of Toxic Industrial Chemicals
(U//FOUO) The release of a toxic industrial chemical (TIC) by a terrorist group or lone actor represents a significant threat. TICs are readily available in large quantities, routinely shipped by commercial carriers, and often stored in bulk containers. Most TICs are generally less toxic than chemical warfare (CW) agents, but a large volume of TICs can be equally dangerous. The release of a TIC in a populated area is capable of generating numerous casualties and deaths; the toxic effects would be more dangerous if release occurred in an enclosed space.
• (U//FOUO) Some TICs such as phosgene, hydrogen cyanide, and chlorine are dangerous without any modification and can serve as “ready-made” chemical agents. Even with limited expertise, terrorists could produce an improvised dispersal device (IDD) to release TICs, or they could rupture TIC containers at a fixed site or while in transit.
• (U//FOUO) Other TICs such as potassium cyanide or sodium cyanide can be combined with additional chemicals to produce more toxic chemicals. Simple plans for constructing crude chemical devices are available in extremist literature and can be found on the Internet.…
(U) Common High-Risk TICs:
The following TICs present a high risk because they can be used as improvised chemical weapons, combined to form more toxic chemicals, or used as precursors for CW agents:
• (U) Ammonia
• (U) Arsine
• (U) Chlorine
• (U) Fluorine
• (U) Hydrogen chloride
• (U) Hydrogen cyanide
• (U) Hydrogen fluoride
• (U) Hydrogen sulfide
• (U) Malathion
• (U) Parathion
• (U) Phosgene
• (U) Phosphorous oxychloride
• (U) Phosphorous trichloride
• (U) Potassium cyanide
• (U) Sodium cyanide
• (U) Sulfur dioxide
• (U) Sulfuric acid(U) Phosphorous oxychloride, phosphorous trichloride, hydrogen fluoride, potassium cyanide and sodium cyanide are precursor chemicals on the Australia Group export control list. Phosphorous oxychloride and phosphorous trichloride are also listed by the Chemical Weapons Convention.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – U.S. Army RQ7-B Shadow Tactical Unmanned Aircraft System (TUAS) Handbook
1-1. The Shadow TUAS extends the ARS Commander’s ability to support the full spectrum of conflict through reconnaissance, security, aerial surveillance, communications relay, and laser designation.
1-2. The UAS supports the full spectrum capability through augmenting all warfighting functions:
a. Movement and Maneuver: Provides the full depth of the reconnaissance and security missions in order to aid the ground commander in movement of friendly forces and provide the ground forces with freedom to maneuver.
b. Intelligence: The Shadow Troop provides Near Real Time (NRT) intelligence, surveillance, and reconnaissance (ISR) and extends the capability through flexible RSTA platforms as an organic asset to the ARS and CAB commanders. They greatly improve the situational awareness of the ARS and aid in employing the Scout Weapons Team (SWT) in high threat environments.
c. Fires: Coupling the Communication Relay Package (CRP) with the Laser-Designating (LD) payload, the Shadow aids in all levels of the Decide, Detect, Deliver, and Asses cycle.
d. Protection: Through continuous reconnaissance, the Shadow Troop can significantly increase the force protection in and around secure operational bases.
e. Sustainment: The Shadow provides reconnaissance and security along supply routes and logistics support areas. Using the CRP, the Shadow can talk directly to the convoy commander for immediate reaction.
f. Command and Control: The Shadow greatly increases the ARS commander’s ability to control the fight. The CRP package extends radio transmission ranges to 240 kilometers. With proper TTPs, the Shadow can serve as an emergency re-transmitting capability to isolated personnel.
1-3. The Shadow Troop aids the ARS and CAB commanders through the full spectrum of operations from stable peace to general war:
a. Peacetime Military Engagement: The Shadow Troop provides counterdrug activities, recovery operations, security assistance, and multinational training events and exercises.
b. Limited Intervention: Provides search for evacuation operations, security for strike and raid operations, foreign humanitarian assistance (search of survivors during disaster relief), and searching for weapons of mass destruction.
c. Peace operations: Provides peacekeeping through surveillance and security for peace enforcement operations.
d. Irregular Warfare: Assists in tracking enemy personnel while combating terrorism and unconventional warfare.
e. Major Combat Operations: Provides the capability to extend the communication of friendly units, emergency retransmitting capability to isolated personnel, target acquisition, and laser designation.
…
ONE SYSTEM GROUND CONTROL STATION POSITIONING
2-6. OSGCS positioning is critical to successful employment of UAS. The OSGCS provides the technical means to receive UA sensor data. The unmanned aircraft operator, PO, and MC assigned to the OSGCS provide tactical and technical expertise to facilitate UAS operations. The CAB commander advises the division commander on placement of this critical UAS component to maximize its effectiveness. The CAB, BFSB, Fires brigade, and BCT conduct disparate missions simultaneously across the division area of operation, with different TTP, focus, and skill sets required. This requires integration of overall aviation operations at division-level to avoid redundancy of effort. An additional consideration is the Shadow platoons in the IBCT BSTBs and the OSGCSs that remain in their control. With a cohesive ATP relationship built between the IBCT Shadow platoons and the ARS Shadow Troop, direct support missions to the IBCT in an extended range environment can be controlled by the IBCT Shadow operators, POs, and MCs.
Single-Site Operations
2-7. In single-site operations, the entire UAS unit is co-located. Single-site operations allow for easier unit command, control, communication, and logistics. Coordination with the supported unit may be more difficult due to distance from and communications with the supported unit. In addition, single-site operations emit a greater electronic and physical signature.
Split-Site Operations
2-8. In split-site operations, the UAS element is typically split into two distinct sites: the mission planning control site (MPCS) and the L/R site. The MPCS is normally located at the supported unit’s main or tactical CP location. The L/R site is normally located in more secure area, positioned to best support operations.
2-9. The IBCT Shadow platoons should also consider consolidating launch-recovery with the ARS Shadow Troop in order to receive the additional benefits of the ARSs large logistical footprint. The IBCT Shadow platoons can focus directly on the MPCS with forward-staged GCSs.
…
ZONE RECONNAISSANCE
3-20. Zone reconnaissance is conducted to find any significant signs of positions of enemy activity within a given area defined by boundaries. It is conducted only in conjunction with a larger reconnaissance element and is an extremely detailed reconnaissance effort. For this reason, the zone reconnaissance will normally be conducted in a MURT, which will also be a part of a larger task force.
3-21. Similar to the route reconnaissance, the Shadow will extend further towards enemy activity and work further ahead of the Forward Line of Own Troops (FLOT). The Shadow will clear territory for any major threats one phase line ahead of the SWT and report any significant activity. The primary goal of the Shadow during a zone reconnaissance is to ensure the freedom of maneuver for the SWT. The SWT is focused primarily on the freedom of maneuver of the larger friendly reconnaissance element.
AREA RECONNAISSANCE
3-22. Area reconnaissance gathers intelligence or conducts surveillance of a specified area. This area may be key terrain or other features critical to an operation. Similar to a route reconnaissance, the TUAS may conduct an area reconnaissance autonomously or in a MURT.
3-23. The autonomous area reconnaissance will focus outwards and move into the objective area. The flanks of the overall objective area are secured; then, reconnaissance efforts are focused inward. UAS may establish a screen on the flank to provide security for ground forces, if used.
3-24. The MURT will use the Shadow to continue reconnaissance efforts on any terrain that can influence the given objective area while the SWT moves inward towards the main objective area. This provides NRT intelligence on any changes or significant activities during the conduct of the reconnaissance.
AERIAL SURVEILLANCE
3-25. Aerial surveillance is the systematic observation of aerospace, surface or subsurface areas, places, persons, or things by visual, aural, electronic, photographic, or other means to collect information. Aerial surveillance is usually passive and may be continuous.
3-26. UAS surveillance of base camps, airfields, and key logistic sites in lesser-contested areas may free combat forces to perform other missions and help prevent surprise.
3-27. The TUAS provides easily maintained and lower detectable aerial surveillance to the ARS and CAB commander to help develop the commander’s intent and concept of the operation. The Shadow Troop provides 24 hour coverage for an NAI in order to:
• Track pattern of life VIA Full Motion Video (FMV)
• Observe a specific area for enemy activity
• Provide early warning and detection on a specific high speed avenue of approach3-28. The difference between an aerial surveillance and standard reconnaissance is the amount of movement for the Shadow payload. During an aerial surveillance, the payload should remain generally stabilized to gather information on an extremely specific area of the battlefield.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – U.S. Army Intelligence Support to Urban Operations Field Manual
With the continuing growth in the world’s urban areas and increasing population concentrations in urban areas, the probability that the US Army will conduct full spectrum operations in urban environments is ever more likely. As urbanization has changed the demographic landscape, potential enemies recognize the inherent danger and complexity of this environment to the attacker, and may view it as their best chance to negate the technological and firepower advantages of modernized opponents. Given the global population trends and the likely strategies and tactics of future threats, Army forces will likely conduct operations in, around, and over urban areas—not as a matter of fate, but as a deliberate choice linked to national security objectives and strategy. Stability operations––where keeping the social structure, economic structure, and political support institutions intact and functioning or having to almost simultaneously provide the services associated with those structures and institutions is the primary mission––may dominate urban operations. This requires specific and timely intelligence support, placing a tremendous demand on the Intelligence warfighting functions for operations, short-term planning, and long-term planning.
Providing intelligence support to operations in the complex urban environment can be quite challenging and may at first seem overwhelming. The amount of detail required for operations in urban environments, along with the large amounts of varied information required to provide intelligence support to these operations, can be daunting. Intelligence professionals must be flexible and adaptive in applying doctrine and tactics, techniques, and procedures (TTP) based on mission, enemy, terrain and weather, troops and support available, time available, and civil considerations (METT-TC).
As with operations in any environment, a key to providing good intelligence support in the urban environment lies in identifying and focusing on the critical information required for each specific mission. The complexity of the urban environment requires focused intelligence, and a comprehensive framework must be established to support the commander’s requirements while managing the vast amount of information and intelligence required for urban operations. By addressing the issues and considerations listed in this manual, the commander, G-2/S-2, and intelligence analyst will be able to address most of the critical aspects of the urban environment and identify both the gaps in the intelligence collection effort and those systems and procedures that may answer them. This will assist the commander in correctly identifying enemy actions so that US forces can focus on the enemy and seize the initiative while maintaining an understanding of the overall situation.
…
1-73. A population of significant size and density inhabits, works in, and uses the manmade and natural terrain in the urban environment. Civilians remaining in an urban environment may be significant as a threat, an obstacle, a logistics support problem (to include medical support), or a source of support and information. The most significant problem regarding the local population is the fact each person is a potential threat and can participate in an insurgency, terrorism, or other disruptive activity.
1-74. One of the most violent examples in US military history was the Viet Cong. The Viet Cong laid mines and demolitions, conducted ambushes and sniping, performed information collection missions for Hanoi, and even participated in force-on-force engagements, primarily during the Tet Offensive in 1968. The difficulty for the US and allied forces operating there lay in the fact that the Viet Cong looked like their neighbors, often held jobs, and raised families in pro-government neighborhoods, and, in some cases, even served in the South Vietnamese Army.
1-75. Another consideration when dealing with the local population is their ability to hinder military operations. Regardless of causes or political affiliations, civilian casualties are often the focal point of press coverage, often to the point of ignoring or denigrating any previous accomplishments. Within the operational continuum, and especially during the conduct of urban operations, commanders can expect to encounter restrictions on their use of firepower and challenges in their ability to conduct combat support and combat service support missions. In the current operational environment, it is unacceptable to our leaders and the American population to inflict large numbers of civilian casualties.
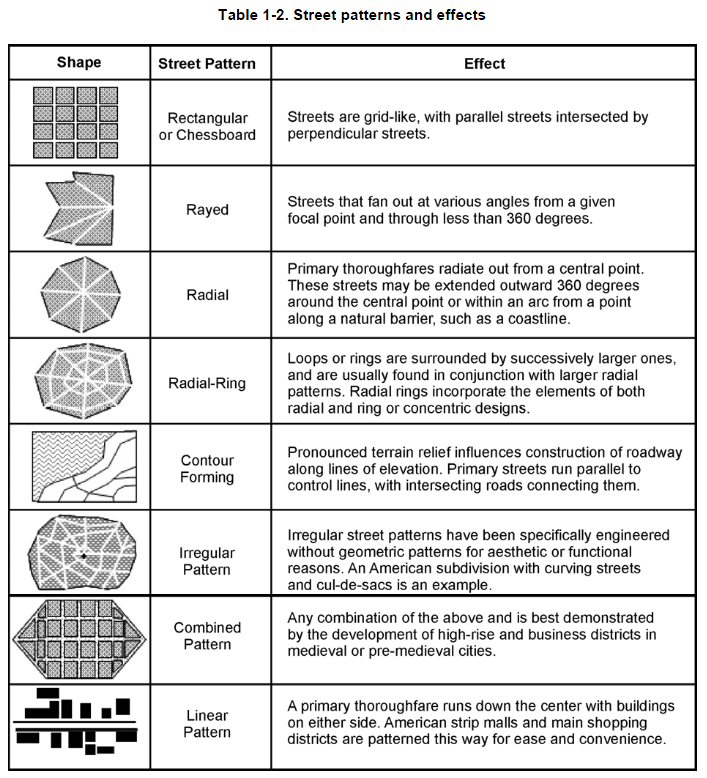
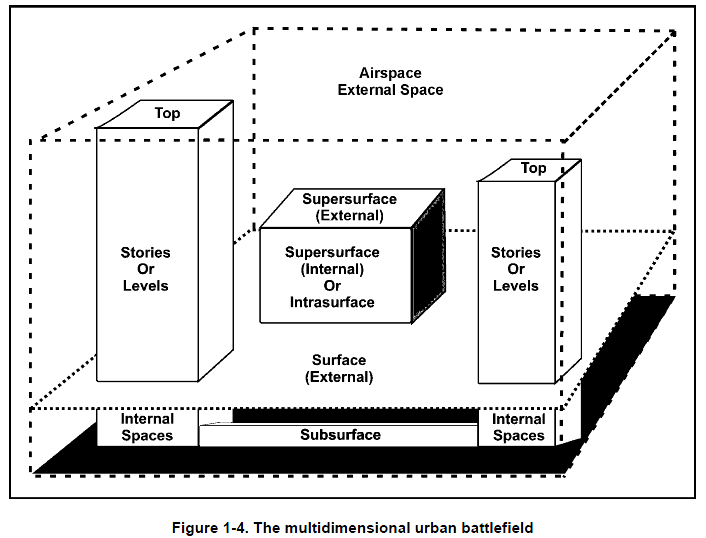
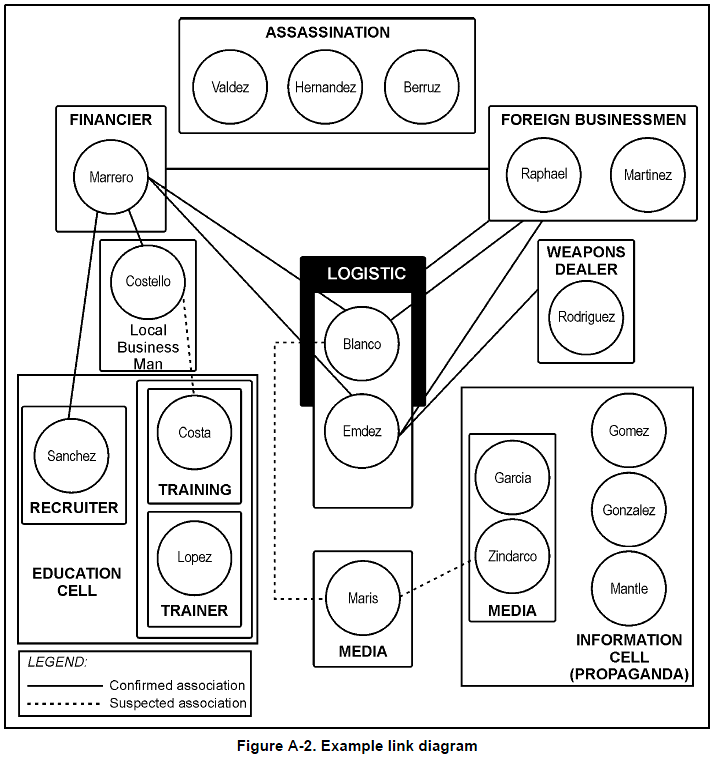
DOWNLOAD ORIGINAL FILE HERE
TOP-SECRET – U.S. Army Human Terrain Report: Afghan Tribal Structure Versus Iraqi Tribal Structure

Most US personnel that are serving in Afghanistan have already served a tour in Iraq and are accustomed to doing things “the Iraq way”. Many people are trying to apply the lessons learned in Iraq to Afghanistan, which in many cases is inappropriate. AF2 wants to provide a product to US units to compare and contrast Iraqi tribal structure and Pashtun tribal structure to prevent future missteps by US forces.
The notion of applying ideas that worked in Iraq to Afghanistan is fraught with problems. The “lessons don’t transfer directly,” according to John Nagl, one of the authors of the Army/Marine Corps Counterinsurgency Field Manual (FM 3-24). William McCallister, an expert advisor to the Marine Corps on tribal dynamics in Iraq2 said he is “not a fan of taking the Anbar experience and creating TTPs” for a Pashtun context.
The reasons behind this are legion. For one, the historical experiences of Iraqi and Pashtun societies are so dissimilar as to make comparing them difficult, if not impossible. For another, the specific circumstances of each warzone—one a sectarian conflict, the other a fractured society handling an international insurgency—doesn’t allow for easy generalization between the two.
Furthermore, each society is fundamentally different on a structural level. In Iraq, leadership is in a sense “institutionalized,” or “codified” in the sense that there is a set and identifiable structure for community leadership to interact with each other and with the State. In Afghanistan, however, that system is neither “institutionalized” nor “codified” in any real sense; therefore, structures of community leadership and power relationships within and between tribal groups and the state are much more ad hoc and cannot be discussed in a general sense. Comparing these two societies side-by-side demonstrates this, and shows just how difficult it is to draw lessons from one to the other.
Bottom Line Up Front
• Iraqi tribes are ordered hierarchies
• Pashtun tribes are not ordered hierarchies
• While a tribal hierarchy allows for coherent, ordered engagement policies, Pashtun tribal structure does not
• Thus, TTPs from Iraq are not transferrable to Afghanistan except in the vaguest sense
• While not necessarily TTPs, there are guiding principles that will be effective in engaging Pashtun tribes…
Thus, Pashtun society does not lend itself to a TTP-style set of procedures. Rather, “Guiding Principles” would be more effective in formulating an engagement policy based on the organizing principles in Pashtun society. An initial list follows:
• Accept Ambiguity. People will lie and twist the truth to suit their own ends, saying only what they want someone else to know. Accepting that one cannot know for certain the unalterable truth of a situation is important for being able to engage each leader or influencer on his own terms.
• There Is No Silver Bullet. Each valley, and each tribe, has its own unique set of needs and concerns. There is no universal approach or solution for engagement, but working through (instead of above or around) culture is vital.
• Understand Processes. The VIPs for a given problem vary from situation to situation. Understanding how and why that is—and only then figuring out who—is the only way to guarantee a successful engagement. Conversely, crafting policy based on a single point of view will distort local relationships as influence is leveraged for personal power, and this can erupt in unpredictable ways.
• Nothing is Quick. Afghanistan is a fundamentally relationship-based society. Building relationships takes time—sitting over tea, hours of small talk, expressing genuine concern for well-being. Afghans understand that anyone they talk to will be gone the following year. There is no substitute for taking the time required to build trust, and more importantly passing along that trust to subsequent units.
TOP-SECRET – Sandia National Laboratories/Department of Energy Sensitive Country List

Please note that because of the dynamic nature of world events, other countries may, at any time, become sensitive. Caution should be exercised in dealing with citizens of countries not listed to assure that sensitive information, although unclassified in nature, is not inadvertently disclosed. Any contact, either in the United States or in a foreign country, where you feel you have been approached for this type of information, should be reported to the Counterintelligence Officers.
Algeria
Armenia
Azerbaijan
Belarus
China – People’s Republic of
Cuba
Georgia
Hong Kong
India
Iran
Iraq
Israel
Kazakhstan
Kyrgyzstan
Libya
Macau
Moldova
North Korea – Democratic People’s
Republic of North Korea
Pakistan
Russia
Sudan
Syria
Taiwan
Tajikistan
Turkmenistan
Ukraine
Uzbekistan
TOP-SECRET from the FBI – Four Hedge Fund Managers Indicted in $40 Million Ponzi Scheme
CHARLOTTE, NC—A federal grand jury sitting in Charlotte returned an indictment against Jonathan D. Davey, 47, of Newark, Ohio, Jeffrey M. Toft, 49, of Oviedo, Fla., Chad A. Sloat, 33, of Kansas City, Mo., and Michael J. Murphy, 51, of Deep Haven, Minn., on February 22, 2012, on four criminal charges relating to an investment fraud conspiracy, announced Anne M. Tompkins, U.S. Attorney for the Western District of North Carolina.
Joining U.S. Attorney Tompkins in making today’s announcement are Chris Briese, Special Agent in Charge of the Federal Bureau of Investigation (FBI), Charlotte Division, and Jeannine A. Hammett, Special Agent in Charge of the Internal Revenue Service-Criminal Investigation Division (IRS-CI).
According to the criminal indictment, the defendants operated “hedge funds” as part of a conspiracy that took in $40 million from victims for a Ponzi scheme operating under the name Black Diamond Capital Solutions (Black Diamond). The indictment alleges that the conspiracy lasted from about October 2007 through about April 2010. The indictment alleges that the defendants lied to get money from their victims by claiming, among other things, that they had done due diligence on Black Diamond and were operating legitimate hedge funds with significant safeguards, when in reality, neither claim was true. The indictment also alleges that, as Black Diamond began collapsing, the defendants and others created a new Ponzi scheme and with a separate Ponzi account that Davey administered. Thereafter, new victim money was deposited into the Ponzi account and used to make Ponzi payments to other victims and to fund the defendants’ lifestyles.
The indictment also charges Davey with tax evasion for claiming to the IRS on his 2008 tax return that $810,000 that Davey stole from victims was a “loan.” In reality, the indictment charges, Davey stole that $810,000, plus approximately $500,000 in 2009, from victims to build Davey’s personal mansion. Davey attempted to evade the taxes due and owing in 2008 by calling the money a “loan” from his investors to “Sovereign Grace, Inc.,” a Belizian corporation that Davey created as a diversion for his victims and the IRS.
The first charge against all four defendants, alleging conspiracy to commit securities fraud, carries a maximum sentence of five years’ imprisonment and a fine of up to $250,000. The second charge against all four defendants, alleging conspiracy to commit wire fraud, carries a maximum sentence of 20 years’ imprisonment and a fine of up to $250,000. The third charge against all four defendants, alleging a money laundering conspiracy, carries a maximum sentence of 20 years’ imprisonment and a fine of $250,000 or twice the amount of criminally derived proceeds. The final charge against Davey only, alleging tax evasion, carries a maximum sentence of five years’ imprisonment and a fine of up to $250,000.
The defendants will be making their initial appearances in U.S. District Court in the coming weeks.
This indictment follows a series of convictions and other charges in this matter. On December 16, 2010, Keith Simmons was convicted following a jury trial of securities fraud, wire fraud, and money laundering. Simmons is in custody awaiting sentencing.
On April 27, 2011, a criminal bill of information and a Deferred Prosecution Agreement were filed against CommunityONE Bank, N.A., for its failure to maintain an effective anti-money laundering program. As alleged in that bill of information, Simmons was a customer of CommunityONE, and used various accounts with the Bank in furtherance of the Ponzi scheme. However, as alleged in that bill of information, the Bank did not file any suspicious activity reports on Simmons, despite the hundreds of suspicious transactions that took place in his accounts.
Other defendants convicted in this case are set forth below. It should be noted that those defendants already sentenced had their sentences reduced by the Court to reflect their cooperation with the United States in its investigation and prosecution of others.
- Bryan Keith Coats, 51, of Clayton, N.C., pled guilty on October 24, 2011, to conspiracy to commit securities fraud and money laundering conspiracy. Coats is awaiting sentencing.
- Deanna Ray Salazar, 54, of Yucca Valley, Calif., pled guilty on December 7, 2010, to conspiracy to commit securities fraud and tax evasion. Salazar is awaiting sentencing.
- Jeffrey M. Muyres, 36, of Matthews, N.C., pled guilty on May 17, 2011, to conspiracy to commit securities fraud and money laundering conspiracy. Muyres was sentenced to 23 months’ imprisonment by Chief Judge Robert Conrad, Jr., on January 18, 2012.
- Roy E. Scarboro, 47, of Archdale, N.C., pled guilty on December 3, 2010, to securities fraud, money laundering, and making false statements to the FBI. Scarboro was sentenced to 26 months’ imprisonment by Chief Judge Robert Conrad, Jr., on May 4, 2011.
- James D. Jordan, 49, of El Paso, Texas, pled guilty on September 14, 2010, to conspiracy to commit securities fraud. Jordan was sentenced to 18 months’ imprisonment by Chief Judge Robert Conrad, Jr., on June 29, 2011.
- Stephen D. Lacy, 52, of Pawleys Island, S.C., pled guilty on December 9, 2010, to conspiracy to commit securities fraud. Lacy was sentenced to six months’ imprisonment by Chief Judge Robert Conrad, Jr., on May 4, 2011.
The details contained in this indictment are allegations. The defendants are presumed innocent unless and until proven guilty beyond a reasonable doubt in a court of law. The conviction or guilty plea of any other person is not evidence of the guilt of any of the defendants.
This matter is being prosecuted by Assistant United States Attorneys Kurt W. Meyers and Mark T. Odulio of the Western District of North Carolina, and the case against Jeffrey Muyres was prosecuted by Assistant United States Attorney Mark T. Odulio. The investigation is being handled by the FBI and the IRS.
TOP-SECRET -DHS-FBI Warning: Terrorist Use of Vehicle Ramming Tactics

(U//FOUO) Terrorists overseas have suggested conducting vehicle ramming attacks—using modified or unmodified vehicles—against crowds, buildings, and other vehicles. Such attacks could be used to target locations where large numbers of people congregate, including sporting events, entertainment venues, or shopping centers. Vehicle ramming offers terrorists with limited access to explosives or weapons an opportunity to conduct a Homeland attack with minimal prior training or experience.
(U) Indicators: Although a single indicator may not be suspicious, one or more might indicate a ramming attack is being developed, based on the specific facts or circumstances. A ramming attack can be conducted with little to no warning.
- (U//FOUO) Unusual modifications to commercial motor vehicles, heavy equipment, passenger cars, and sports utility vehicles (SUVs), such as homemade attempts to reinforce the front of the vehicle with metal plates.
- (U//FOUO) The purchase, rental, or theft of large or heavy-duty vehicles or equipment, such as SUVs, trucks, or commercial motor vehicles, if accompanied by typical indicators such as nervousness during the purchase, paying in cash, or lack of familiarity with the vehicle’s operations.
- (U//FOUO) Commercial motor vehicles or heavy equipment being operated erratically, at unusual times, or in unusual locations, particularly in heavy pedestrian areas.
- (U//FOUO) Attempts to infiltrate closed areas where traffic usually moves, but where crowds are gathered, such as for street festivals or farmers’ markets.
- (U//FOUO) A vehicle operator’s apparent unfamiliarity with commercial motor vehicle or heavy equipment operation (unable to back up; trouble with shifting; poor lane tracking; unfamiliarity with basic vehicle mechanics such as air brake operations, slack adjusters, fifth wheel operations, Jake brakes, engine type, or location of fire extinguishers and other emergency equipment).
TOP-SECRET from the FBI – Sheriff Charged with Fraud, Identity Theft, and Obstruction
Ouachita Parish Sheriff Arrested
Sheriff Charged with Fraud, Identity Theft, and Obstruction
| U.S. Attorney’s Office February 24, 2012 |
MONROE, LA—United States Attorney Stephanie A. Finley announced that Sheriff Royce Edward Toney, 64, of Monroe, La., was arrested today on charges of conspiracy, computer fraud, identity theft, and obstruction. Toney was elected Sheriff on October 20, 2007, and took office on July 1, 2008. He did not seek re-election. Also charged was Michael Karl Davis, a major with the Ouachita Parish Sheriff’s Office who works in the IT department.
The indictment alleges that Toney and Davis engaged in a conspiracy to track a third-party’s communications and, once Davis learned that the FBI wanted to speak with him, he tried to cover up the illegal activity. The indictment further alleges that Toney and Davis accessed a protected computer without authorization on nine occasions from April of 2010 to October of 2010, and that Toney and Davis committed the crime of identity theft by utilizing an AOL e-mail address and password belonging to another person. Toney and Davis are charged with one count of obstruction for reformatting and installing a new operating system on a computer after Davis learned of the ongoing FBI investigation. Finally, Toney is charged with obstruction by retaliating against a witness who was cooperating with the FBI investigation.
If convicted, Toney and Davis faces maximum potential penalties of one year in prison, a $100,000 fine or both for each of the computer crime charges and five years in prison, a $250,000 fine or both for each of the conspiracy, identity theft and obstruction charges.
An indictment is merely an accusation and all defendants are presumed innocent until and unless proven guilty.
This case was investigated by the Federal Bureau of Investigation, Monroe Resident Agency, and is being prosecuted by Assistant U.S. Attorney C. Mignonne Griffing.
TOP-SECRET from the FBI – ‘Underwear Bomber’ Sentenced to Life for Attempted Christmas Day Attack
Umar Farouk Abdulmutallab, the so-called “underwear bomber,” was sentenced today to life in prison as a result of his guilty plea to all eight counts of a federal indictment charging him for his role in the attempted Christmas Day 2009 bombing of Northwest Airlines Flight 253.
Abdulmutallab, 25, of Kaduna, Nigeria, pleaded guilty on Oct. 12, 2011, to conspiracy to commit an act of terrorism transcending national boundaries, among other charges. Abdulmutallab’s purpose in taking a bomb on board Flight 253 was to detonate it during flight, causing the plane to crash and killing the 290 passengers and crew members on board. As Flight 253 was on descent into Detroit Metropolitan Airport, the defendant detonated the bomb, which resulted in a fire, but otherwise did not fully explode. Passengers and flight attendants tackled the defendant and extinguished the fire.
“The case against Abdulmutallab was a combination of the hard work and dedication of FBI personnel as well as multiple federal, state, and local agencies. Those individuals who experienced Christmas Day 2009 first-hand should be rest assured that justice has been done,” said FBI Special Agent in Charge Arena.
TOP-SECRET from the CIA – Stasi Operations in the Netherlands, 1979–89
by Beatrice de Graaf [1]
In the year 2000, the case of former Chancellor Helmut Kohl, who had sued the German Office of the Commissioner for the Records of the State Security Service of the German Democratic Republic (BStU) for releasing files concerning his political activities before 1989, invoked new interest in a special category of victims and collaborators of the Stasi, East Germany’s Ministry for State Security (Ministerium für Staatssicherheit—MfS). This category involved West Germans and other West Europeans who were the subject of the Stasi’s West-Arbeit (Western operations). [a]
With the scope of West-Arbeit so broadly defined, the boundaries between foreign intelligence and domestic policing could not be discerned clearly in Stasi activities.
Several studies of the West-Arbeit have been published. Some historians, for example, Hubertus Knabe, mentioned the possibility that 20,000 West Germans may have been spies. Official BStU estimates are much lower, perhaps 3,500–6,000 over a period of 40 years. In 1989, 1,500 of them were still operational. These agents spied on thousands of West German companies, organizations, and citizens, including Helmut Kohl. They also worked against East Germans who were in contact with the West. [b] [2]
For the Stasi, West-Arbeit activities im und nach dem Operationsgebiet (in and directed to the target region) were organized not only in geographic terms but in political, organizational, and structural terms. With the scope of West-Arbeit so broadly defined, the boundaries between foreign intelligence and domestic policing could not be discerned clearly in Stasi activities.
Although most of the records of the Stasi’s Main Directorate for Intelligence (the Hauptverwaltung Aufklärung—HVA) have been destroyed, traces of the West-Arbeit can be found in “domestic” departments of the MfS. Research into this branch of activities is all the more revealing because the files of the West German intelligence and security services remain closed.
The West-Arbeit had a direct relationship to the domestic duties of the Stasi, because the enemy against whom the operations were directed could be located abroad, among foreigners, or within the GDR population itself. As can be deduced from the training manual of the Stasi, Haß auf den Feind (hatred of the enemy) was the organization’s all encompassing idea.
Established as the counterpart and junior partner of the KGB and staffed with communist veterans like Erich Mielke, Ernst Wollweber, and Wilhelm Zaisser, the Stasi was a repressive institution from its beginnings. Because communism was considered the logical and inevitable outcome of history, shortcomings and conflicts within the system could only be caused by external factors, for example, saboteurs inspired by the great class enemy in the West.
This definition of the enemy evolved over time, but it was still in place during the neue Ostpolitik of 1970–72 of West-German Chancellor Willy Brandt (1969–74). Brandt’s outreach brought the GDR considerable gains: diplomatic recognition (and thus embassies) in the West, economic treaties, technological imports (microelectronics, computers), and loans.
The gains also brought new dangers: East Germany’s policy of Abgrenzung (the ideological, political and geographical sealing off of the GDR from the West, in particular from the FRG) began to erode because of the many contacts with the West established during this period. The increased percolation through the Wall of Western influences was mirrored by the growth of the Stasi. The “shield and sword of the party” had to make up for the new openness with a major expansion of its personnel, informal agents (inoffizielle mitarbeiter), and duties. At the same time, the Stasi made good use of contacts fostered by Brandt’s Ostpolitik and began new offensives against the West. These were directed mainly against West Germany, but other West European countries, including the Netherlands, also were targetted.
The Stasi’s Image of the Enemy, as seen through the Netherlands
Eva Horn (professor of German literature and the theory of espionage) has written that “enemy images” are the backbone of intelligence services, but that these images can have negative effects on their efficiency. [3] With respect to Stasi operations against the Dutch, I will argue that the image of the enemy, conceived through a Marxist-Leninist perspective, drove Stasi actions with apparent success at a tactical level. Strategically, however, the Stasi actions failed to prevent the fall of the regime it was charged with protecting.
In this article, I will investigate what the MfS was after in and against the Netherlands and to what extent these operations were affected by its thinking about the enemy. Information about these operations is available in the archives of the Stasi’s HVA (foreign intelligence and counterespionage) as well as its Directorate XX (internal opposition) (Hauptabteilung XX—HA XX), and HA I (military intelligence), which are maintained by the BStU.
Intelligence Requirements Regarding the Netherlands
According to MfS guideline No. 1/79, the Stasi was to concentrate on the following goals:
- neutralizing and combating “political-ideological diversion”;
- gathering military intelligence;
- gathering economic intelligence;
- counterintelligence. [4]
Under these guidelines, at least five MfS directorates— HVA, HA XX, HA I, HA II (counterespionage), and HA XVIII (economic intelligence and security)—ran operations against the Netherlands. Research into BStU holdings reveals a broad range of topics and targets between 1979 and 1989.
HVA (foreign intelligence) files contain intelligence on:
- NATO-deployment preparations, the AFCENT-headquarters in Brunssum and the Dutch position in the INF-negotiations;
- preparations for East German communist leader Erich Honecker’s visit to the Netherlands in June 1987;
- activities of the “hostile-negative forces”in the Dutch peace movement;
- reliability of the employees of the GDR consulate and embassy in the Netherlands;
- the microelectronics program of the Philips Corporation;
- the Dutch civil and military security service (telephone numbers, organization charts, pictures);
- security-related issues, such as activities of right wing groups, and terrorist incidents [5]
HA I (military intelligence) collected material on:
- military exercises of the Dutch armed forces;
- The Rotterdam harbour;
HA II and HA XVIII were interested in:
- “operational games” by the Dutch security services against the GDR embassy, consulate, and personnel;
- security issues surrounding the embassy compound. [6]
HA XX (internal opposition) files contain most of the more elaborate analyses found in these files. These mainly regard the:
- Dutch peace movement;
- contacts between Dutch and East German churches, peace groups, and individuals;
- political positions of the Dutch government concerning detente and the East-West conflict.
Intelligence Assets
East German intelligence in the Netherlands involved the use of open sources (OSINT) and technical and human collection. OSINT was easy to come by: The Stasi collected newspaper clippings, official (government) publications, and “grey” reports on GDR- or security-related issues. The MfS also made good use of articles on Dutch military and security issues published by Dutch left-wing pacifist organizations and parties. The Pacifist Political Party, the PSP, for example, exposed details of the structure and activities of the Dutch security service (the Binnenlandse Veiligheidsdienst—BVD). These were immediately analyzed and sent to Berlin. [7]
With respect to technical collection, little is known from the existing files. There is some evidence that the MfS made use of Dutch radio and telecommunications, including those of Dutch military radio and satellite installations in Westerbork and Eibergen. [8]
Humint was the Stasi’s main source for West-Arbeit in the Netherlands. Before the Dutch officially recognized the GDR in January 1973, the HVA made use of the handful of salesmen and church officials who had established contacts in the Netherlands. Because of the proximity of the two countries, these so-called headquarters operations were relatively easy to set up. According to a former Dutch intelligence officer, most of the West-Arbeit against the Netherlands was conducted through headquarters operations.
The agents participating in those operations could be East Germans, but sometimes they had Dutch backgrounds. According to the same Dutch intelligence officer, most East German headquarters operations used Dutch citizens who eventually were doubled by the BVD, [9] New Stasi files suggest this is not the case.
From 1973 on, political and economic relations also provided up-to-date information. However, the MfS was especially interested in non-governmental relations between protestant church congregations and peace groups in both countries. Around 1978, some 100 parish contacts had been established, and by 1984 the number had grown to more than 150. By then, 9,000 to 12,000 Dutch protestants and peace activists were participating in exchange programs. [10]
Diplomatic recognition also enabled the MfS to place at least three “legal” intelligence officers at its residentura in the embassy. [11] Although the BVD kept the GDR embassy under strict surveillance, the MfS residentura was able to run several informal-agent operations from the embassy. The records reveal that the following assets were recruited in the Netherlands (through headquarters operations or by legal residents):
- Three informal agents in the Dutch-East German Friendship Association (a subdivision of the official Liga für Völkerfreundschaft)
- One informal agent and one “prospective agent” from the Horizontal Platform, a Marxist-Leninist offshoot of the Dutch Communist Party.
- Several “contact persons” (not quite “informal agents” but something less committed) inside the Stop-the-Neutron-Bomb campaign and other left wing peace groups.
- At least two informal agents not affiliated with left wing organizations, but recruited because they sought adventure or had financial needs.
The MfS was not allowed to recruit members of the official Dutch Communist Party (they could only be used as contact persons, not as informal agents). Most informal agents and other sources were nevertheless drawn into its service through their sympathy for communist ideals or through their “progressive political convictions,” as Stasi chief Erich Mielke phrased it. As late in the Cold War as September 1988, the resident was complaining about the large number of Dutch citizens who were showing up at the embassy to offer themselves to the service. [12]
On the whole, informal agents like these volunteers were of limited utility as sources. The members of the Friendship Association (the informal agents “Aorta,” “Arthur,” and “Ozon,” for example) or members of other GDR-affiliated organizations were either too old, unemployed, or too suspect to get anywhere near interesting military or political information. The resident came to the same conclusion: Their assets were too “leftist” and attempts to “broaden the contact scope did not produce many results,” he lamented in 1988. [13]
Stasi “Success” Stories
However, on at least three occasions the MfS did run successful operations over longer periods of time: on military intelligence, on the Dutch peace movement, and
Military Reconnaissance— “Abruf”
The MfS was first of all interested in political and military intelligence on the North Atlantic Treaty Organization, the main enemy of the Warsaw Pact. Within pact collection arrangements, the GDR was responsible for collecting intelligence concerning the areas associated with NATO Army Group North and Army Group Central. The HVA, with 4,000 members, and the military intelligence service of the East German Army, with 2,000 members, were responsible for carrying out these operations. West Germany, Great Britain, France, the Benelux and Denmark were defined as principal objectives.
Fulfilling this aim in the Netherlands meant gathering early warning about NATO preparations and securing information about the order of battle and military dispositions. In addition to the targets listed above, HVA was also interested in Dutch military compounds and in the Schiphol and Zestienhoven airports. [14]
The BVD, however, proved a formidable adversary for the HVA. Intensive Dutch surveillance turned the residentura in The Hague into little more than a shelter for underemployed case officers. HVA security reports from 1984 on regularly record Stasi suspicions that the BVD was using its connections in the Dutch media to publicize acts of espionage conducted by the socialist states. Ironically, these complaints (partially justified, as we shall see) were triggered by concern in Dutch conservative circles that Warsaw Pact countries were trying to infiltrate and manipulate the country’s peace movement. Politicians asked questions in Parliament, and the Home Office felt compelled to increase security measures.
According to the MfS residentura in The Hague, the BVD conducted so many unfriendly acts of surveillance and recruiting activities against the embassy, against East German citizens in the Netherlands, and against “friendly” organizations, such as the Friendship Association GDR-Netherlands (Vriendschapsvereniging Nederland-DDR), that they threatened to “obstruct the positive effect of the socialist detente politics concerning disarmament questions.” That is, the Stasi blamed the BVD for deteriorating East-West relations and troubled disarmament talks. [15]
However, at least one Dutch informal agent of the 1980s, whose codename was Abruf (“on call”) was not discovered. Abruf was run by a case officer codenamed Hilmar, who was a member of the legal residentura of the military intelligence department of the East German Army and worked in close cooperation with the MfS staff at the East German embassy. Hilmar had recruited Abruf in November 1983 at a meeting of the Communist Party of the Netherlands (CPN) that he, as a comrade and embassy official, could legally attend.
Hilmar described Abruf as young, unemployed, unhappy with the perceived rightist policies of the Dutch government, frustrated by the NATO-modernization decision, and a staunch supporter of communism. Hilmar played into this zeal and general disaffection with the capitalist environment and had no difficulty recruiting the young man. [16]
As his codename implied, Abruf was used as a freelance agent. He received instructions to photograph Rotterdam Harbor, the Schiphol and Zestienhoven airports, industrial plants in the region, and military compounds. He also collected material on NATO Exercise REFORGER in 1985. After 1985, he was told to move to Woensdrecht, a site then being prepared to receive new NATO missiles.
Abruf received payments of 100 Dutch guilders for every task he carried out. Contact with his case officer was made through dead drops and in short meetings (after long, frantic diversions and smoke screens) in crowded places, such as the Jungerhans department store in Rotterdam. To some of these rendezvous he brought his girlfriend. [17]
Abruf’s employment ended after three years, in 1986, after an assignment in 1985 raised suspicions. In that year, he was ordered to Coevorden, Ter Apel, and Vriezenveen, where he was told to locate military depots, and to Woensdrecht, where he was to photograph the deployment site. On 25 February 1986, the BVD paid him a visit and asked about the trip to Vriezenveen and about his contacts with the GDR embassy. The BVD had stumbled across Abruf while they were following Hilmar. At the time, Dutch security did not seem to know much about Abruf’s history and actual activities as an agent. Hilmar had already been replaced by an MfS case officer codenamed Haupt. The BVD visit alarmed both Abruf and the residentura, and the relationship was mutually terminated two days after the inquiry.
Informal agent Abruf had provided the Stasi with useful reconnaissance material on Dutch military and economic capabilities centering around the Rotterdam region. His cover was never really blown, and the BVD did not uncover his real activities. After 1989, he left the Netherlands and disappeared.
What Abruf provided was typical of the many reports on Dutch military matters, sometimes via open sources, sometimes of obscure origin, found in Stasi files. One of the showpieces is a detailed description of the organizational structure—telephone numbers included—of the intelligence department of the Dutch land forces. [18]
The Stasi and the Dutch Peace Movement
Files unearthed in the BStU archives also provide insight into another type of intelligence activity, covert influence operations. The Stasi focused in the late 1970s and 1980s on the Dutch peace movement and churches and invested heavily in them and selected leaders. Ironically, the East Germans would find their efforts turned against them as circumstances in Europe and the Soviet Union changed with the introduction of perestroika and other reforms in the region.
East German interest in the Dutch peace movement and its church grew out of West European and Dutch opposition to the planned modernization and expansion of NATO’s intermediate range ballistic and cruise missiles in Western Europe in 1977. By the early 1980s, hundreds of thousands of Dutch people would demonstrate to attempt to force the government to postpone or cancel the deployments.
The opposition spawned new opportunities for Soviet and Warsaw Pact leaders, and the official communist World Peace Council and its suborganizations were used to wage open and covert campaigns to capitalize on the protests. [19] Between 1977 and 1979, the ruling East German Socialist Party (Sozialistische Einheitspartei Deutschlands—SED) and the peace council were responsible, among other things, for financial and logistic support of the “Stop the Neutron Bomb” campaign—a Dutch communist front organization that cost East Berlin around 120,000 Dutch guilders (110,000 West German DM). [20]
In addition, the Stasi influenced the foundation Generals for Peace—a well known and respected anti-nuclear peace organization of former West European generals, with Dutch General Michiel von Meyenfeldt (former chief of the Dutch Royal Military Academy) as secretary. To support its perspectives, the Stasi gave it 100,000 West German DM annually. [21]
Even more potentially useful, it seemed to the Kremlin and East Berlin, was the expansion of the support base of the peace movement in the Netherlands to include churches and the Dutch Interchurch Peace Council (Interkerkelijk Vredesberaad—IKV), which had started a campaign for unilateral atomic disarmament in the Netherlands. All influential Dutch churches participated in the IKV, and the organization succeeded in mobilizing large parts of Dutch society. [22] East German leader Erich Honecker believed that the Dutch “religious powers” were the main cause of turning the anti-nuclear campaign into a mass movement, [22] and invitations would follow to a variety of church officials to visit like-minded groups in East Germany.
However, Stasi sympathy for the Dutch peace movement started to turn sour after 1981. After Polish government repression of the independent trade union Solidarity in Poland and after exchanges with members of the Czechoslovak dissident group Charter 77, the IKV radically altered its positions and began to target not only NATO missiles but those of the Warsaw Pact and demanded that all member countries start dismantling nuclear missiles on their own territories rather than pointing fingers at other nations. In effect, this meant the end of a purely anti-NATO campaign. [23]
 Green leaflet_croppedTo make matters worse for the communists, the IKV extended its contacts with dissidents throughout Eastern Europe and declared that repression in the East was a major political cause of the arms race and not the other way around. The IKV planned to organize a peace movement “from below” to confront both superpowers at grassroot levels. [24]
Green leaflet_croppedTo make matters worse for the communists, the IKV extended its contacts with dissidents throughout Eastern Europe and declared that repression in the East was a major political cause of the arms race and not the other way around. The IKV planned to organize a peace movement “from below” to confront both superpowers at grassroot levels. [24]
With its change of position, extant church contacts within the GDR became especially interesting for the IKV—and troublesome to the MfS. Most inviting was an independent peace movement that appeared in East German protestant churches in 1978 called Swords Into Plowshares (Schwerter zu Pflugscharen). The IKV followed up and sent emissaries to various peace groups in the GDR—as tourists, or under the umbrella of church exchanges—and eventually announced the formation of a joint Peace Platform with East German dissidents in the summer of 1982.
The Stasi read about the development in a Dutch newspaper and went on red alert. Honecker himself ordered the official state Secretariat for Religious Matters (Staatssekretariat für Kirchenfragen) to exert all means of influence to eliminate these “divisive forces” (Spalterkräfte). [25]
A four-part campaign against the IKV was begun. First, the Stasi activated its church agents to force the abandonment of the platform. [26] Second, it started a smear campaign against the IKV. IKV Secretary Mient Jan Faber and other officials of his group were registered as persons of criminal intent. [27] Party and state officials, newspapers and front organizations were instructed to depict the IKV as a divisive force within the West European peace movement and Faber as an arrogant bully. [28] Third, Faber himself was barred from entering the GDR. [29] And finally , the existing contacts between Dutch reformed parishes and East German congregations were threatened. The Dutch working group within the East German churches was told that the obstructions were caused by the state’s misgivings about the IKV. Several visits of Dutch delegations to East Germany and vice versa were cancelled. [30]
These measures were informed by the strategy of “differentiation” (Differenzierung), which was a very subtle method of alienating “divisive” and negative elements from their own base. [31] The Stasi sorted out which IKV and church members disliked Faber and invited them to East Berlin. It succeeded in manipulating the president of the IKV and reformed church official Jan van Putten, General von Meyenfeldt—he was also an advisor to the Reformed Churches in the Netherlands and a board member of the IKV—and lower-ranking IKV members. [32] IKV officials, Dutch church groups and journalists were led to believe that the IKV’s secretary was no longer in favour in East Europe or with the protestant churches in the GDR. [33]
 stasi-aktefaber_croppedIn line with this strategy, the Stasi also tried to recruit agents in the Netherlands. IKV Secretary Janneke Houdijk, IKV’s coordinator for East Germany, was approached — in vain. She did not recognise the attempts for what they were and remained loyal to Faber. [34]
stasi-aktefaber_croppedIn line with this strategy, the Stasi also tried to recruit agents in the Netherlands. IKV Secretary Janneke Houdijk, IKV’s coordinator for East Germany, was approached — in vain. She did not recognise the attempts for what they were and remained loyal to Faber. [34]
In the end, however, the efforts bore fruit. East-German churches detached themselves from their IKV contacts and froze most exchange activities. In the Netherlands, many Dutch church leaders and local groups were convinced that Faber was a threat to stability and East-West relations. [35] Faber was threatened with dismissal. Local IKV groups and parishes sent angry letters to IKV headquarters and demanded that Faber stop meddling in internal East German affairs, let alone lead a campaign for human rights. [36] The envisaged Peace Platform never came into being, frustrated in advance by the Stasi, which was helped, knowingly or unknowingly, by Dutch and East German church leaders.
Ironically, after Mikhail Gorbachev came to power in the Soviet Union, Marxist-Leninist enmity towards a democratization approach faded away. The new leadership in the Kremlin even developed sympathy for it, and, in 1988, Faber and British peace activist Mary Kaldor were invited to Moscow to observe the dismantling of SS-20 rockets. The same year, an IKV delegation visited Moscow, invited by the Kremlin itself. [37] The GDR, however, stuck to its rigid policy. The Stasi was appalled by the tolerance of Soviet communists toward Dutch peace activists and did not adapt itself to the new liberalism. Indeed, it continued the struggle against the IKV and even started a new action against it in 1988. Operations were only aborted after the Berlin Wall came down in November 1989.
Operation “Bicycle Tour”
Groups other than the IKV tried to establish exchange programs with East German peace activists, and in doing so generated a Stasi response that illustrates the entanglement of foreign and domestic intelligence activity in East Germany. In 1981, a group of draft resisters from the northern Dutch city of Groningen founded an organization called the Peace Shop (Vredeswinkel). The entity functioned as a communication centre for peace activists from the region. Through existing church contacts and the War Resisters International, the leaders soon contacted a construction branch of the East German army known as the Bausoldaten, that had since 1964 been offering the possibility of completing obligatory military service not with arms but with the spade. This alternative had been provided at the urging of East German protestant churches, which represented about 45 percent of the GDR’s population.
As a grass roots organization, the Peace Shop organized bicycle tours through East Germany as a joint venture of Dutch, East German, and, when possible, Czechoslovak and Polish conscientious objectors. The Dutch entered the GDR as private visitors, gathered at prearranged addresses, and, with East Germans, cycled to rural parts of the GDR and discussed world politics and disarmament initiatives. [38]
In 1985, IKV Secretary Faber and East German Vicar Rainer Eppelmann (a prominent figure in the East German opposition scene) concluded a personal contract to work together for peace. Many participants in the Groningen-GDR exchange decided to do the same and committed themselves to not using violence against each other in case of a war. According to the signatories, in doing this, they contributed to “detente from below.” [39]
Although their activities were relatively low-profile and not aimed at threatening the GDR system, the cycle tours were betrayed by their own success as the Stasi got wind of them. Large international groups peddling, for example, from Karl Marx City (Chemnitz) to Stralsund, could not stay unnoticed, especially after their frequency increased to three or four times a year.
Veterans of the Bausoldaten were suspect to begin with in the eyes of the MfS, especially when they organized meetings with other Bausoldaten and Western draft resisters. Indeed, the Stasi had been carrying out operations against the idea of “social peace service” as an alternative to military service since at least 1981. [40] (Vicar Eppleman, in fact, had been a leader in the “social peace service” effort.)
HA XX, the department charged with dealing with the churches and opposition circles, learned that Dutch participants planned to publish stories about their bicycle tours and experiences in the GDR in Dutch church and peace magazines, and, in 1984, Peace Shop members initiated a letter campaign on behalf of Amnesty International for the release of arrested East German dissidents. [41]
 PeaceTreatySuch activity fit perfectly in the communist vision of class enemies conspiring from outside the system to create domestic unrest, and the bicycle tours thus became objects of intensive surveillance. In 1983, the Stasi started several Operative Vorgange (intelligence operations aimed at arresting dissidents) against former Bausoldaten who had participated in the tours. HA XX recruited several East Germans as informal agents “mit Feindkontakt” (in contact with the enemy), who reported on all the meetings and preparations. [42]
PeaceTreatySuch activity fit perfectly in the communist vision of class enemies conspiring from outside the system to create domestic unrest, and the bicycle tours thus became objects of intensive surveillance. In 1983, the Stasi started several Operative Vorgange (intelligence operations aimed at arresting dissidents) against former Bausoldaten who had participated in the tours. HA XX recruited several East Germans as informal agents “mit Feindkontakt” (in contact with the enemy), who reported on all the meetings and preparations. [42]
Although bicycle tour participants kept their distance from IKV officials, HA XX and the HVA nevertheless increasingly suspected them of being partners of the IKV and executors of the IKV’s grand strategy of developing a “pseudopacifist, bloc–transcending peace movement.” By way of confirmation of this, one Stasi report quotes a Dutch activist as saying “When there are no soldiers on both sides, there will be no weapons used.” [43]
In the belief that the Peace Shop was helping dissidents, the Stasi was not mistaken. The activists had indeed given their East German contacts a typewriter and helped finance Bausoldaten activities with 2,000 Dutch guilders.
With growing Dutch contacts in the so-called Political Underground Forces (Politische Untergrundtätigkeit—PUT), which the East German authorities saw as a threat to communist rule, increased international pressure on the GDR, and a perceived potential for embarrassment during Erich Honecker’s planned June 1987 visit to the Netherlands, the MfS tried to obstruct and manipulate cross-border exchanges. HA XX began an Operativer Vorgang against the Dutch organizer of the bicycle tours, Bert Noppers, who was described as the inspirator and organisator of the PUT tours.
 Cardboard wallAs part of its attack on Noppers, HA XX used a letter from Noppers to an East German friend in which he wrote that Dutch intelligence had tried to recruit him in 1983 to report on his East German contacts. Although Noppers stated in his letter that he refused, the HA immediately listed him as a probable foreign intelligence agent. It then attempted to collect evidence to indict Noppers for hostile agitation against the East German state and for disseminating information to foreign intelligence agencies or other foreign organizations to discredit the GDR. If convicted, he faced two to 12 years of imprisonment. [44]
Cardboard wallAs part of its attack on Noppers, HA XX used a letter from Noppers to an East German friend in which he wrote that Dutch intelligence had tried to recruit him in 1983 to report on his East German contacts. Although Noppers stated in his letter that he refused, the HA immediately listed him as a probable foreign intelligence agent. It then attempted to collect evidence to indict Noppers for hostile agitation against the East German state and for disseminating information to foreign intelligence agencies or other foreign organizations to discredit the GDR. If convicted, he faced two to 12 years of imprisonment. [44]
Nothwithstanding such threats, the Peace Shop organized a protest against East German border controls in 1987, building a model Berlin Wall of cardboard boxes through Groningen and drawing media attention to the condition of their dissident friends in the GDR. Although the peace activists also criticized the West European and Dutch contribution to the armaments race, these acts had no impact on the activities of HA XX. [45]
 VredeswinkelStepped-up HA XX activities included the recruitment as informal agents of three GDR participants in the Peace Shop exchanges. Codenamed Karlheinz, Betty, and Romeo, they reported all of their activities to HA XX. Romeo was sent abroad to visit the Peace Shop in Groningen in July 1988. However, the department could not find enough evidence to prosecute the East German participants or arrest the Dutch organizer.
VredeswinkelStepped-up HA XX activities included the recruitment as informal agents of three GDR participants in the Peace Shop exchanges. Codenamed Karlheinz, Betty, and Romeo, they reported all of their activities to HA XX. Romeo was sent abroad to visit the Peace Shop in Groningen in July 1988. However, the department could not find enough evidence to prosecute the East German participants or arrest the Dutch organizer.
Even by the standards of the East German Penal Code, the activists were just not subversive enough. The Dutch activists did not advocate open criticism or revolution. As Noppers put it during an interview in 2006, “If the East Germans wanted to topple the regime, they had to do it by themselves. We came from abroad and did not want to tell them what to do. And although we were no friends of communism, we had enough criticism to pass on capitalism and materialism at home.” [46] Moreover, the East German government did not want the MfS to make random arrests, since that would cause too much damage to the economic and political relations the GDR had established by then.
Nevertheless, MfS surveillance continued. HA XX ordered continuation of the operations against Noppers, inspired by the same suspicions against the Dutch activist. [47] Although the MfS knew that Moscow had shifted policies and now aimed at cooperation with the IKV and other West European peace organisations, HA XX was still plotting in April 1989 to use intercepted inquiries by the Peace Shop to members of the East German network to recruit more informal agents. [48]
Only in October 1989 were the Operativer Vorgange against the East German Bausoldaten and against Noppers called off. They ended partly because of a lack of evidence and partly because the Stasi had already begun cleaning up its files in the face of growing unrest and pending revolution. On 24 November 1989, 15 days after the fall of the Berlin Wall, the Stasi finally closed its files on Noppers. [49]
In Sum: Tactical Gains, Strategic Loss
During the last decade of its existence, the MfS was successful in tactical terms. It succeeded in running one operation to collect military intelligence, managed to infiltrate and manipulate most IKV contacts in the GDR, penetrated the Peace Shop, and started an Operativ Vorgang against the Dutch coordinator of East European peace tours. Moreover, there is reason to believe that the MfS employed more Dutch informal agents in the 1980s than are discussed here but whose records remain undiscovered.
In the overall, strategic setting, however, the Ministry of State Security failed in its mission to preserve the security of the GDR.
- First, by entangling its foreign intelligence operations with domestic security interests, the Stasi focused on the foreign inspiration of domestic opposition at the expense of understanding that dissent in the GDR drew on the system’s own economic, social, military, and political weaknesses and the government’s abuses of its population.
- Second, the MfS itself became part of the problem instead of part of the solution, as the expansion of the security apparatus from the 1970s on acted as a driver for even more protests.
- Third, activities of the IKV and other Dutch peace initiatives like the Peace Shop were blown up out of proportion, and those in the GDR who were in touch with them were deemed to be guilty of high treason. In this intellectual strait-jacket, the Stasi was blinded to useful insights and could not see that the Dutch movements gave the Soviet bloc opportunities to exploit genuine divisions in NATO.
Finally, when the Stasi got it right, it could not persuade its leadership. In May 1987, the HVA issued an study of Dutch foreign and military politicies before Honecker’s state visit to the Netherlands. The analysis precisely listed the deviations of Dutch politics from the US and NATO lines. (The Dutch denounced SDI, favoured a nuclear test ban and prolongation of the ABM treaty.) Honecker, however, made no effort to play into these differences and only uttered the usual clichès about peace-loving socialist countries. To him, the Netherlands remained part and parcel of the imperialist block. [50] Painfully collected and sound intelligence was made useless by incapable and ideologically deformed party leaders.
Footnotes
a. The BStU (Die Beaufträgte für die Unterlagen des Staatssicherheitsdienstes der ehemaligen Deutschen Demokratischen Republik) is responsible for preserving the records of the Stasi, which had responsibility for both external and internal security. The files on Kohl suggested he had taken bribes from major firms on behalf of his party, the Christian Democratic Union. The BStU’s functions are described on its Web site, http://www.bstu.bund.de.
b. Knabe’s 1999 study was reviewed by CIA historian Ben Fischer in Studies in Intelligence 46, no. 2 (2002). It offers a useful overview in English of East German intelligence.
~ ~ ~ ~ ~ ~
1. “Gauck-Behörde iritiert über Aufgeregtheit im Westen um Stasi-Akten,” in Magdeburger Volksstimme, 28 April 2000.
2. Hubertus Knabe, Die unterwanderte Republik. Stasi im Westen (Berlin, 1999); Helmut Müller-Enbergs, Inoffizielle Mitarbeiter des Ministeriums für Staatssicherheit. Teil 2: Anleitungen für Arbeiten mit Agenten, Kundschaftern und Spionen in der Bundesrepublik Deutschland (Berlin, 1998); Müller-Enbergs, “Die Erforschung der West-Arbeit des MfS,” in Suckut und Weber (eds.), Stasi-Akten, 240–69; Joachim Lampe, Juristische Aufarbeitung der Westspionage des MfS. Eine vorläufige Bilanz. BF informiert Nr. 24 (BStU, Berlin, 1999).
3. Eva Horn, “Das wissen vom Feind. Erkenntnis und Blindheid von Geheimdiensten,” in Wolbert K. Schmidt, et al., Geheimhaltung und Transparanez. Demokratische Kontrolle der Geheimdienste im internationalen Vergleich
(Berlin, 2007), 257–77. Here: 259.
4. Jens Gieseke, “Annäherungen und Fragen an die Meldungen aus der Republik,” in idem (ed.), Staatssicherheit und Gesellschaft. Studien zum Herrschaftsalltag in der DDR (Göttingen 2007), 79–98, here: 89–90.
5. Vgl. Query in the SIRA database 14, Druckauftrag Nr. 12839, AR 7/SG03, Nr. AU 2585/05 Z.
6. HA XVIII, “Pläne und Massnahmen feindlicher Geheimdienste gegen Auslandsvertretungen und langfriestige Delegierungskader der DDR im nichtsozialistischen Ausland im Jahre 1985.” BStU MfS HA XVIII, 32–33.
7. “Vorgangsanalyse zum Vorgang Aorta,” 15 July 1986; “Aufgabenstellung AA 1986. Fortschreibung der Sicherheigsanalyse ‘Haupt,’” 1 March 1986; “Information über die ndl. Sicherheitsdienste. Auswertung der Broschüre “De BVD en de Inlichtingendiensten, Hrsg. by PSP, Amsterdam 1983,” 1984. BStU MfS HA I 1682, 25–28; 90–94; 127–29.
8. For example “Jahresabschlussbericht 1981 über die Ergebnisse der Funkabwehrtätigkeit,”16 November 1981, in which West German, British and Dutch radiocommunications are mapped. BStU MfS HA II 25043, 1–39.
9. Frits Hoekstra, In dienst van de BVD. Spionage en contraspionage in Nederland (Amsterdam, 2004). See also Dick Engelen, Frontdient. De BVD in de Koude Oorlog (Amsterdam, 2007).
10. Beatrice de Graaf, Over de Muur. De DDR, de Nederlandse kerken en de vredesbeweging (Amsterdam, 2004), or De Graaf, Über die Mauer. Die DDR, die niederländischen Kirchen und die Friedensbewegung (Münster, 2007)
11. RoD Den Haag, “Fortschreibung der Sicherheitanalyze zur RoD im Ausbildungsjahr 1987/1988,” 11 November 1988. BStU HA I, 1682: 7–10.
13. RoD Den Haag, “Fortschreibung der Sicherheitanalyze zur RoD im Ausbildungsjahr 1987/1988,” 11 November 1988. BStU HA I, 1682: 7–10.
14. “Information über die Streitkräfte der Niederlande,” nr. 46/88, 27 January 1988. BStU MfS HA XVIII 91: 202–15; “Information über den militärischen Beitrag der Niederlande zu den Streitkräften der NATO,” 29 May
1987. BStU MfS HVA 47: 60–79.
15. Telegrams and reports to MfS headquarters from The Hague: 21 March 1984, 18 January 1989, 31 March 1989, security report “Fortschreibung der Sicherheitsanalyse zur Rod im Ausbildungsjahr 1987/1988” of 18 November 1988. BStU, MfS HA I 1682: 1–11.
16. Several reports on IM “Abruf” by “Haupt” and other MfS-personnel. BStU MfS HA I 1682: 29–163.
17. Hilmar, “Zum Einsatz in den NL,” 1985; “Sicherheitsanalyse zum Vorgang AM-V ‘Abruf’,” 31 January 1986. BStU MfS HA I 1682: 58–63, 81–84.
18. “Angaben zum Nachrichtendienst der Streitkräfte der NL, insbesondere der Landstreitkräfte,” 4 June 1985, Den Haag. BStU MfS HA I 1682: 39–52.
19. Peter Volten, Brezhnev’s ‘Peace Program.’ Success or Failure? Soviet Domestic Political Process and Power. Academisch Proefschrift (Emmen, 1981).
20. Letter, Hans van der Velde (secretary of the National Committee “Initiatief Internationale Stafette”) to the East German Peace Council, Amsterdam, 12 July 1979; Letter Kurt Hölker (deputy secretary-general of the Peace Council) to Hans van der Velde, Berlin, 7 August 1979. Both at Bundesarchiv Stiftung Arbeiterparteien und Massenorganisationen der ehemaligen DDR (thereafter BArch SAPMO), DZ 9 463.2411; Carel Horstmeier, “Stop de Neutronenbom! The last mass-action of the CPN and the Moscow-Berlin-Amsterdam triangle,” in Carel Horstmeier etal (eds.), Around Peter the Great: Three Centuries of Russian-Dutch Relations (Groningen 1997), 65–77.
21. De Graaf, Over de Muur, 113; Jochen Staadt, “Die SED und die Generale für den Frieden,” in Jürgen Maruhn and Manfred Wilke (eds.), Die verführte Friedensbewegung, 123–140.
22. East German Peace Council, “Information,” 22 March 1978, 1, 6, 11, BArch SAPMO DZ 9 463.2411; Neue Zeit, 2 July 1979. East German Peace Council, “Maßnahmeplan,” February 1981, 2, BArch SAPMO DZ 9 450.2354.
23. Jan Willem Honig, Defense Policy in the North Atlantic Alliance. The Case of the Netherlands (London: Westport, 1993), 211–12; Ronald Jeurissen, Peace and Religion: An Empirical-Theological Study of the Motivational Effects of Religious Peace Attitudes on Peace Action (Kampen, 1993), 47; Philip Everts, Public Opinion, the Churches and Foreign Policy: Studies of Domestic Factors in the Making of Dutch Foreign Policy (Leiden, 1983); Jürgen Maruhn and Manfred Wilke, eds., Die verführte Friedensbewegung: Der Einfluß des Ostens auf die Nachrüstungsdebatte (München: 2002); Udo Baron, Kalter Krieg und heisser Frieden. Der Einfluss der SED und ihrer westdeutschen Verbündeten auf die Partei ‘Die Grünen’ (Münster 2003).
24. Mient Jan Faber, “Brief van het IKV-secretariaat aan alle IKV-kernen over Polen kort na 13 december 1981,” in: Faber et al. (eds.), Zes jaar IKVcampagne (Den Haag, 1983), 133–34; “Open letter of Charter 77 to the Interchurch Peace Council,” 17 August 1982. BArch SAPMO DZ 9 585.2879.
25. Report of Hauptabteilung XX (HA XX) for the Stellvertreter des Ministers, Genossen Generalleutnant Mittig, “Negative Aktivitäten von Personen des ‘Interkirchlichen Friedensrates’ (IKV) der Niederlande,” 9 August 1982,
BStU MfS HA XX ZMA 1993/5, 34–37, 56–57.
26. Report of the HA XX/4 (Stasidepartment for church and opposition matters), “Subversive Aktivitäten kirchlicher Personen der Niederlande,” 15 June 1982, BStU MfS HA XX ZMA 1993/5, 21–22; Letter, Christoph Demke (Office of the East German Church Organisation) to Staatssekretär für Kirchenfragen, Klaus Gysi, 9 August 1982, Berlin, “Sekretariat 3827-1632/82,” Rep. B3 Nr. 711, Archive KPS Magdeburg.
27. BStU MfS HA XX AKG-VSH. ZAIG 5. SLK 10964. ZPDB 2082010579. Erfassungsnr. 40438/1590/1993; HA XX AKG-VSH. ZAIG 5 1009. SLK 10994. ZPDB 2082010587. ZMA 3420/1993–1580. VSH-Karteikarten are register
cards, not a file. In June 1982 Stasi started an Operativ Vorgang (file) on Mient Jan Faber and Wolfgang Müller.
28. Report of the HA XX/4, “Interkirchlicher Friedensrat der Niederlande,” October/November 1982, BStU MfS HA XX/4 1917, 1–5; In the mid-1980s, IKV was mentioned in a list of approximately 1,000 “Zielobjekte” (targets) of
the Stasi’s Reconnaissance Service, the Hauptverwaltung Aufklärung. “Zielobjekte der HVA – alphabetische Liste,” BStU ASt Gera BV Gera/Abt. XV 0187, 21–39, in Knabe, West-Arbeit des MfS, 518–54. See 537.
29. “Vertreter holländischer Friedensbewegung dürfte nicht in die DDR,” ADN-Information, 29 July 1982, BStU MfS HA XX ZMA 1993/4, 13.
30. Office of the East German Churches (BEK-Sekretariat), “Arbeitsbeziehungen zwischen dem Bund der Ev. Kirchen in der DDR und dem Raad van Kerken in den Niederlanden und einzelnen Gliedkirchen und Gemeinden,”
November 1982, LDC NHK ROS 735.
31. Clemens Vollnhals, Die kirchenpolitische Abteilung des Ministeriums für Staatssicherheit. BF informiert 16/1997 (Berlin 1997). Concerning the strategy of differentiation, the following orders were relevant: Richtlinien zur Bearbeitungs Operativer Vorgänge (RL 1/76), Operative Personenkontrollen (RL 1/81), Direktive zur IM-Führung (RL 1/79).
32. East German Peace Council, “Maßnahmeplan,” Berlin, April 1981, 4, BArch SAPMO DZ 9 K295.1578; East German Peace Council, “Aktivitäten der Rüstungsgegner im Monat November 1981,” “Niederlande,” 23, BArch
SAPMO DZ 9 450.2354.
33. E.g., Ton Crijnen, “Waarom Mient Jan Faber niet welkom is in de DDR,” De Tijd, 31 December 1982.
34. BStU MfS Abteilung Rostock, OV “Integration” 3/92.
35. “Verslag van uitspraken van bisschop W. Krusche op de bijeenkomst met de Raad van Kerken te Amersfoort d.d. 7-9-82,” Series 3, Nr. 32, Utrecht County Archive, Reformed Churches in the Netherland, General Diaconal
Council (Het Utrechts Archief, Gereformeerde Kerken in Nederland, Algemeen Diakonaal Beraad); Letter, Prof. Berkhof to Vorsitzender des Bundes der Evangelischen Kirchen in der DDR (Krusche), 26 Juy 1982, Amersfoort,
Rep. B3 Nr. 711, Archive KPS Magdeburg; Letter, Prof. Berkhof to Faber, 2 July 1982, Amersfoort, LDC NHK ROS/IKV Box 15.
36. All letters at the (Dutch) International Institute for Social History (IISH) in Amsterdam, Box IKV 455; “Verslag Oost-Europadiscussie op de Campagneraad van 26 februari,” in Kernblad 3, March 1983, IISH Box IKV 453.
37. Interview with Mient Jan Faber, 10 September 2001, The Hague.
38. Interview with Bert Noppers (former participant in these contacts and supporter of the Peace Shop), 20 March 2006, Utrecht.
39. “Network News,” in: Peace Magazin, 1 (December 1985): 1, 30.
40. Uwe Koch, Das Ministerium für Staatssicherheit, die Wehrdienstverweigerer der DDR und die Bausoldaten der Nationalen Volksarmee. Eine übersicht über den Forschungsstand. Die Landesbeauftragte für die Unterlagen des
Staatssicherheitsdienstes der ehemaligen DDR in Sachsen-Anhalt und Mecklenburg- Vorpommern, Sachbeiträge 6 (Magdeburg 1999); Robert-Havemann- Archiv (ed.), Zivilcourage und Kompromiss, Bausoldaten in der DDR 1964 –1990, Bausoldatenkongress Potsdam, 3.-5. September 2004 (Berlin 2005).
41. Vredeswinkel Groningen, “Schrijf een brief!!!!!’[write a letter!!!!!], around January 1984. Matthias Domaschk Archive Berlin, Box “Erik de Graaf.”
42. OV “Schwaben.” BStU MfS BV Frankfurt (Oder) AOP 1430/89; Abteilung XX/4, “Information über feindlich-negative Aktivitäten zur Organisierung und Inspirierung politischer Untergrundtätigkeit,” Frankfurt (Oder), 22 March 1985. BStU MfS OV “Radtour,” 1091/87, Anlage I, 84–86.
43. OV “Schwaben.” BStU MfS BV Frankfurt (Oder) AOP 1430/89; Abteilung XX/4, “Information über feindlich-negative Aktivitäten zur Organisierung und Inspirierung politischer Untergrundtätigkeit,” Frankfurt (Oder), 22 March 1985. BStU MfS OV “Radtour,” 1091/87, Anlage I, 85.
44. Abteilung XX/4, “Eröffnungsbericht zum OV ‘Radtour’,” Frankfurt (Oder) 3 September 1987. BStU MfS OV “Radtour,” 1091/87, Anlage I, 7–12.
45. Abteilung IX/2, “Strafrechtliche Einschätzung zum operativen Ausgangsmaterial ‘Radtour’ der Abteilung XX,” Frankfurt (Oder) 10 September 1987. BStU MfS OV ‘Radtour’ 1091/87, Anlage I, 22–23.
46. Interview with Bert Noppers, 20 March 2006, Utrecht.
47. Abteilung XX/4, “Sachstandbericht zum OV ‘Radtour,’ 1091/87,” Frankfurt (Oder), 22 July 1988. BStU MfS OV “Radtour,” 1091/87, Anlage II, 47–51.
48. Abteilung XX/4, “Dienstreisebericht,” Frankfurt (Oder), 20 June 1988; Abteilung XX, “Information zur ‘Ost-West-Gruppe’ Groningen (Niederlande),” Frankfurt (Oder), 5 April 1989. BStU MfS OV “Radtour” 1091/87, Anlage II, 18–21 and 131–133.
49. Abteilung XX/4, “Abschlussbericht zum operativ-Vorgang ‘Radtour,’ Reg.nr. V/1091/87,” Frankfurt (Oder), 24 November 1989. BStU MfS OV “Radtour,” 1091/87, Anlage II, 189–192.
50. “Information über aktuelle Aspekte der Außen- und Innenpolitik der Niederlande im Zusammenhang mit dem offiziellen Besuch des Genossen Honecker vom 3.-5.6.1987,” 21 May 1987. BStU MfS HVA 47, 85–91.
TOP-SECRET – The Nuclear Map of the USA

A map created by Mother Jones detailing the routes of Office of Secure Transportation routes throughout the U.S.
As you weave through interstate traffic, you’re unlikely to notice another plain-looking Peterbilt tractor-trailer rolling along in the right-hand lane. The government plates and array of antennas jutting from the cab’s roof would hardly register. You’d have no idea that inside the cab an armed federal agent operates a host of electronic countermeasures to keep outsiders from accessing his heavily armored cargo: a nuclear warhead with enough destructive power to level downtown San Francisco.
That’s the way the Office of Secure Transportation (OST) wants it. At a cost of $250 million a year, nearly 600 couriers employed by this secretive agency within the US Department of Energy use some of the nation’s busiest roads to move America’s radioactive material wherever it needs to go—from a variety of labs, reactors and military bases, to the nation’s Pantex bomb-assembly plant in Amarillo, Texas, to the Savannah River facility. Most of the shipments are bombs or weapon components; some are radioactive metals for research or fuel for Navy ships and submarines. The shipments are on the move about once a week.
The OST’s operations are an open secret, and much about them can be gleaned from unclassified sources in the public domain. Yet hiding nukes in plain sight, and rolling them through major metropolises like Atlanta, Denver, and LA, raises a slew of security and environmental concerns, from theft to terrorist attack to radioactive spills. “Any time you put nuclear weapons and materials on the highway, you create security risks,” says Tom Clements, a nuclear security watchdog for the nonprofit environmental group Friends of the Earth. “The shipments are part of the threat to all of us by the nuclear complex.” To highlight those risks, his and another group, the Georgia-based Nuclear Watch South, have made a pastime of pursuing and photographing OST convoys.
…
The OST doesn’t employ your typical truck-stop 18-wheeler jockeys; the agency seeks to hire military veterans, particularly ex-special-operations forces. Besides contending with “irregular hours, personal risks, and exposure to inclement weather,” agents “may be called upon to use deadly force if necessary to prevent the theft, sabotage or takeover of protected materials by unauthorized persons.” At a small outpost in Ft. Smith, Arkansas—the Army base where Elvis was inducted and got his famous haircut—the prospective agents are trained in close-quarters battle, tactical shooting, physical fitness, and shifting smoothly through the gears of a tractor-trailer.
In 2010, DOE inspectors were tipped off to alcohol abuse among the truckers. They identified 16 alcohol-related incidents between 2007 and 2009, including one in which agents were detained by local police at a bar after they’d stopped for the night with their atomic payload. After several agents and contractors were caught bringing unauthorized guns on training missions in Nevada between 2001 and 2004, DOE inspectors determined that “firearms policies and procedures were systematically violated.” One OST agent in Texas pled guilty in 2006 to trying to sell body armor, rifle scopes, machine gun components, and other assault gear he’d pilfered on the job.
There have also been accidents. In 1996, a driver flipped his trailer on a two-lane Nebraska hill road after a freak ice storm, sending authorities scrambling to secure its payload of two nuclear bombs and return them to a nearby Air Force base. In 2003, two trucks operated by private contractors had rollover accidents in Montana and Tennessee while hauling uranium hexafluoride, a compound use to enrich reactor and bomb fuel. (DOE apparently uses some contractors for “low-risk” shipments, while high-security hauling is reserved for OST truckers). In June 2004, on I-26 near Asheville, North Carolina, a truck bound for the Savannah River Site leaked “less than a pint” of uranyl nitrate—liquefied yellowcake uranium, which can be used to produce bomb components.
see here original Document
https://docs.google.com/viewer?url=http://info.publicintelligence.net/DoE-OST.pdf&chrome=true
TOP-SECRET – List of Chinese Communist Spies in the United States
China communist Spies in America ———–Ai ,Duan Wu(New York)
China communist Spies in America ———–Wu, Han Shi(New York)
China communist Spies in America ———–Zhang ,Wei (New York)
China communist Spies in America ———–Song ,Wei
China communist Spies in America ———–Gao, Jun Guang
China communist Spies in America ———–Jing, Xiu Hong( Seattle)
China communist Spies in America ———–Shen ,Xue(Canada)
China communist Spies in America ———–Lin ,Zheng Yang(Lin, Jian Hui Seattle)
China communist Spies in America ———–Xie, Fu Min(New York)
China communist Spies in America ———–Sun,Zhong Xiong (New York)
China communist Spies in America ———–Zhang,Guang Zhong(New York)
China communist Spies in America ———–Lu ,Yun(New York)
China communist Spies in America ———–Chen ,Xiao(New York)
China communist Spies in America ———–Wang, Xue Chen(Jiang, Hai Fu, HK)
China communist Spies in America ———–Tang, Jie(Huan, Dan Xuan,New York)
China communist Spies in America ———–Yao, Mao Sheng (Li, Qing,New York)
China communist Spies in America ———–Ge, Li(New York, China, Canada)
China communist Spies in America ———–Shun ,Rui Jun(St. Francisco,China)
China communist Spies in America ———–Yang, Wei Ming (DC)
China communist Spies in America ———–Wang ,Yao De( St. Francisco)
China communist Spies in America ———–Xue ,Hai Pei(DC, China)
China communist S pies in America ———–Ji , Hong(DC)
China communist Spies in America ———–Lu, Xue Xiang(DC)
China communist Spies in America ———–Hu, Ping(New York)
China communist Spies in America ———–Lin Chang Sheng(DC, St. Francisco)
China communist Spies in America ———–Wei ,Quan Bao(New York)
China communist Spies in America ———–Zhang ,Jian An(New Jersey)
China communist Spies in America ———–Song, Wei(China, New York)
China communist Spies in America ———–Song ,Su Yuan(New York)
China communist Spies in America ———–Zhang ,Zhuo Zhi(DC)
China communist Spies in America ———–Wei, Xiao Peng(New York)
China communist Spies in America ———–Wang, Xiang Lin(Chicago)
China communist Spies in America ———–Sheng, Li Ling(New York)
China communist Spies in America ———–Yang, Huai An(New York, China)
China communist Spies in America ———–Yan ,Dun Zheng(New York)
China communist Spies in America ———–Wang, Jing Fang(MD)
China communist Spies in America ———–Zhao ,Xian\o Wei(MD)
China communist Spies in America ———–Bao ,Ge( New York)
China communist Spies in America ———–Bi ,Shu Zhi ( New York, Female)
China communist Spies in America ———–Luo, Ning(USA, China)
China communist Spies in America ———–Jing, Yang Shi( USA, China)
China communist Spies in America ———–Pan Guo, Peing(Baltmore)
China Communist Spies in America————Wen Ying Chen (CA)
China Communist Spies in America————Li, Wen He
China Communist Spies in America————Gao ,Zhan (VA)
China Communist Spies in America————Yie, Ning (DC, New York)
China Communist Spies in America————Yan ,Qing Xin( DC, CA)
China Communist Spies in America————Xue, Wei a.k.a Wang ,Yuantai ( New York)
China Communist Spies in America————Shi, Lei a.k.a Xia ,Yu (New York)
China Communist Spies in America————Zhang ,Qi ( hide, sister of Yan, Qing Xin)
China Communist Spies in America————Hu,Chang Xin ( New York)
China Communist Spies in America————Yang ,Hai Ping ( St. Francisco)
China Communist Spies in America————Chen, Guo Hua (DC, major assistent, director of Asia)
China Communist Spies in America————Wang, Mei ( New York)
China Communist Spies in America————Zhou, Yong Jun( Las Angles)
China Communist Spies in America————Lu ,Jing Hua
China Communist Spies in America————Wu, FangChen(Kenta)
China Communist Spies in America————Yao, Yong Zhang( Zhang Cai)
China Communist Spies in America————Gao, Han (Guo, Zhi)
China Communist Spies in America————Zhu, Yi Fei
China communist Spies in America ———–Zhang ,Wei(DC)
China communist Spies in America ———–Su, Yang ( USA)
China communist Spies in America ———–Wang, Yao (HK)
China communist Spies in America ———–Xue Bing (Fa Lun Gong)
China communist Spies in America ———–Wang Tao(Fa Lun Gong)
China communist Spies in America ———–Yang ,Wei (PA)
China communist Spies in America — ——–Yang ,Qing Heng (China)
China communist Spies in America ———–Zhong ,Xiao(Su Xiao Zhou)
China communist Spies in America ———–Su ,Chang Qing(New York)
China communist Spies in America ———–Leng ,Shong(St. Francisco)
China communist Spies in America ———–Mi , Jia(Las Angles)
China communist Spies in America ———–Ma ,Yuan(Yt)
China communist Spies in America ———–Liao, Da Wen (DC)
China communist Spies in America ———–Huang ,Sha(New York)
China communist Spies in America ———–Zhang, Zhong Chun(St. Francisco)
China communist Spies in America ———–Xing, Wen(DC)
China communist Spies in America ———–Zhang ,Xing(Tx)
TOP SECRET from the FBI – Uzbek National Pleads Guilty to Charges of Threatening to Kill the President and Providing Material Support to Terrorist Activity
BIRMINGHAM—An Uzbek national who has lived in the United States since 2009 pleaded guilty today in federal court to charges of providing material support to terrorist activity, threatening to kill President Barack Obama and illegally possessing a weapon.
U.S. Attorney Joyce White Vance; Department of Justice Assistant Attorney General for National Security Lisa Monaco; FBI Special Agent in Charge Patrick J. Maley; Bureau of Alcohol, Tobacco, Firearms and Explosives Special Agent in Charge Glenn N. Anderson; Secret Service Special Agent in Charge Roy Sexton; and Immigration and Customs Enforcement’s Homeland Security Investigations Special Agent in Charge Raymond R. Parmer Jr. announced the plea.
ULUGBEK KODIROV, 22, of Uzbekistan, pleaded guilty before U.S. District Judge Abdul K. Kallon to one count of providing material support to terrorist activity, one count of threatening to kill the president and one count of possession of a firearm by an illegal alien. The charges of threatening to kill President Obama and illegally possessing a firearm were among charges brought in an indictment against Kodirov by a federal grand jury in July 2011.
The U.S. Attorney’s Office filed a criminal information Thursday in U.S. District Court charging Kodirov with material support of terrorism.
U.S. Attorney Vance praised the investigative work and prompt action of the Joint Terrorism Task Force for the Northern District of Alabama. “Today, Ulugbek Kodirov became the first person to be convicted of providing material support to terrorist activity in this district,” she said. “Kodirov was apprehended during an undercover operation in which he was attempting to obtain weapons and explosives that he intended to use to kill the president of the United States. Effective action by law enforcement protected our community and potentially our country,” she said.
“I also want to express my appreciation to the Muslim community of Birmingham, which was instrumental in helping law enforcement shut down this threat,” Vance said.
“Today’s case underscores the continuing threat we face from violent extremists,” Assistant Attorney General Monaco said. “Thanks to a coordinated law enforcement effort, Kodirov’s plot was thwarted before anyone was harmed.”
FBI SAC Maley said, “I want to thank the members of the Joint Terrorism Task Force (JTTF), who include the Jefferson and Shelby County Sheriff’s Offices, Birmingham, Hoover and UAB Police Departments, the Transportation Security Agency, Secret Service, ATF, and DHS. I also thank the Pelham and Leeds Police Departments for their invaluable assistance in this case. The JTTF has been diligently investigating and building partnerships to protect Alabama from terrorists since 9/11, and its efforts put it in the unique position to interdict a violent act of terrorism. This case serves as a reminder of the dangers of the Internet on radicalizing our youth right in our own back yards, and all citizens and organizations need to remain vigilant on the ever-increasing threat from home-grown violent extremists.”
ATF SAC Anderson said, “This case involved a variety of experience and expertise with ATF’s local, state and federal law enforcement partners, including the Secret Service, ICE, FBI JTTF, Shelby County Sheriff’s Office, Leeds Police Department and Pelham Police Department. The combined effort enabled a quick response and a very fluid investigation focused on keeping everyone safe, from Leeds, Alabama, potentially to the White House.”
“The Secret Service will actively investigate any perceived threat against anyone we are charged to protect,” SAC Sexton said. “This case is a great indicator of what can be accomplished through the outstanding cooperation between local, state and federal law enforcement in the Northern District of Alabama.”
“This case is a perfect example of the outstanding cooperation between all law enforcement agencies involved in this arrest,” ICE-HSI SAC Parmer said. “Because of great coordination and cooperation, we were able to jointly arrest this dangerous illegal alien. We are dedicated to apprehending those individuals who are the most dangerous in our communities and getting them off the streets.”
Kodirov entered a plea agreement with the government, which was filed with the court today. In the plea agreement, Kodirov acknowledges that he had been in communication with an individual whom he believed to be a member of the Islamic Movement of Uzbekistan (IMU), and that Kodirov interpreted these conversations to mean that he should kill President Obama. Kodirov then took steps to obtain weapons to carry out his plans to kill the president. The IMU is designated as a Foreign Terrorist Organization by the U.S. State Department. Kodirov also showed jihadist websites and videos on his computer to another individual and told that person that he wanted to assist others in jihad overseas, according to the plea agreement.
Kodirov also acknowledges in the plea agreement that he had lengthy conversations in July 2011 with a different individual about Kodirov’s desire to kill President Obama and possible ways to carry out the assassination. That individual traveled to Birmingham to meet Kodirov and introduced him to another individual, an undercover agent, from whom Kodirov intended to obtain weapons he would use to kill the president.
The three men met on July 13, 2011, at a motel in Leeds, Ala. In that meeting, the agent presented a fully automatic Sendra Corporation Model M15-A1 machine gun, a sniper rifle with a telescopic sight and four disassembled hand grenades and asked Kodirov if he would like to use any of them to “carry out his plan to kill the President,” according to the plea agreement. Kodirov chose the M15-A1 machine gun and the hand grenades and left the meeting with the weapons. Agents arrested Kodirov before he left the motel.
Kodirov entered the United States on a student visa in June 2009. His visa was revoked on April 1, 2010, for failing to enroll in school. Thereafter, he was unlawfully present within the United States. He was living in an extended-stay motel in Pelham, Ala., at the time of his arrest.
Kodirov faces maximum prison sentences of 15 years on the terrorism charge, five years on the charge of threatening the president and 10 years on the charge of being an illegal alien in possession of a firearm. Each charge also carries a maximum fine of $250,000.
The FBI, ATF, HSI, and Secret Service investigated the case. Assistant U.S. Attorneys Michael W. Whisonant and Ryan K. Buchanan are prosecuting the case with assistance from the Counterterrorism Section of the Justice Department’s National Security Division.
TOP-SECRET – DHS-University of Maryland Study: Hot Spots of Terrorism and Other Crimes

While efforts are increasingly aimed at understanding and identifying “hot spots” of ordinary crime, little is known about the geographic concentration of terrorist attacks. What areas are most prone to terrorism? Does the geographic concentration of attacks change over time? Do specific ideologies motivate and concentrate terrorist attacks? Moreover, what factors increase the risk that an attack will occur in a particular area? Using recently released data from the Global Terrorism Database, we address these gaps in our knowledge by examining county-level trends in terrorist attacks in the United States from 1970 through 2008.
…
Terrorism
The definition of terrorism used by the GTD is: the threatened or actual use of illegal force by non-state actors, in order to attain a political, economic, religious or social goal, through fear, coercion or intimidation. It is important to note that the classification of an event as terrorism depends as much on threats as the actual use of violence. For example, instances in which individuals seize an aircraft and threaten to blow it up unless their demands are met are defined as terrorist events. Note also that by specifying the threatened or actual use of force the definition of terrorism used by the GTD excludes hoaxes. The requirement that these events be limited to the actions of “non-state actors” means that considerable violence and terrorism that is directly attributable to states or their militaries is also excluded. And the requirement that the act have a direct political, economic, religious or social goal means that ordinary criminal violence is excluded. Thus, the GTD excludes state terrorism and many types of crime and genocide, topics that are important and complex enough to warrant their own separate analysis.
The frequency of terrorist acts is recorded for each U.S. county for each year from 1970 through 2008. Counties with no recorded terrorist attacks are coded “zero.” The vast majority of U.S. counties have not experienced any terrorist attacks since 1970. Terrorist acts are also categorized by the ideological motivation of the act and coded as “extreme right-wing”; extreme left-wing; religious; ethno-nationalist/separatist; or single issue. The dominant ideology variable captures the group’s central ideological motivation (e.g., while the Aryan Nations maintained a strong religious conviction to the Christian Identity movement, their raison d’être was to promote a racially homogenous white society).
Detailed information on each category of ideological motivation can be found in the Profiles of Perpetrators of Terrorism-United States report compiled by the National Consortium for the Study of Terrorism and Responses to Terrorism (Miller, Smarick, and Simone, 2011). Briefly, the report describes each category as follows:
Extreme Right-Wing: groups that subscribe to aspects of the following ideals: they are fiercely nationalistic (as opposed to universal and international in orientation), anti-global, suspicious of centralized federal authority, reverent of individual liberty (especially their right to own guns, be free of taxes), believe in conspiracy theories that involve grave threat to national sovereignty and/or personal liberty and a belief that one’s personal and/or national “way of life” is under attack and is either already lost or that the threat is imminent (sometimes such beliefs are amorphous and vague, but for some the threat is from a specific ethnic, racial, or religious group), and a belief in the need to be prepared for an attack either by participating in paramilitary preparations and training or survivalism. (2011: 26)
Extreme Left-Wing: groups that want to bring about change through violent revolution rather than through established political processes. This category also includes secular left-wing groups that rely heavily on terrorism to overthrow the capitalist system and either establish “a dictatorship of the proletariat” (Marxist-Leninists) or, much more rarely, a decentralized, non-hierarchical political system (anarchists). (2011: 24)
Religious: groups that seek to smite the purported enemies of God and other evildoers, impose strict religious tenets or laws on society (fundamentalists), forcibly insert religion into the political sphere (e.g., those who seek to politicize religion, such as Christian Reconstructionists and Islamists), and/or bring about Armageddon (apocalyptic millenarian cults; 2010: 17) For example, Jewish Direct Action, Mormon extremist, Jamaat-al-Fuqra, and Covenant, Sword and the Arm of the Lord (CSA) are included in this category (2011: 18).
Ethno-Nationalist/Separatist: regionally concentrated groups with a history of organized political autonomy with their own state, traditional ruler, or regional government, who have supported political movements for autonomy at some time since 1945 (2011: 18).
Single Issue: groups or individuals that obsessively focus on very specific or narrowly-defined causes (e.g., anti-abortion, anti-Catholic, anti-nuclear, anti-Castro). This category includes groups from all sides of the political spectrum (2010: 28).
…
DOWNLOAD ORGINAL DOCUMENT HERE
TOP-SECRET from the FBI – Marin Man, 76, Sentenced to Eight Years for Possession of Child Pornography
Donald Tosti was sentenced to eight years in prison and ordered to pay $50,000 in restitution for possessing child pornography.
Tosti was convicted on Sept. 14, 2011, on two charges of possessing child pornography. During the trial, evidence showed that Tosti was found to possess child pornography after taking his computer to CompUSA for repair. A search of Tosti’s home and office revealed a large collection of child pornography, including depictions of the rape of very young children. In sentencing Tosti, United States District Court Judge Jeffrey S. White emphasized the size of his collection and the graphic and extreme nature of the child pornography images as aggravating factors in imposing his sentence.
The prosecution is the result of a four-year investigation by the Federal Bureau of Investigation, with the assistance of the San Rafael Police Department.
TOP-SECRET – National Security Agency San Antonio TX 2012
|
| Under Construction 2010The Google Street Views following start at the gateway at the center bottom of this view and go clockwise around the facility.
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict24.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict36.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict37.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict38.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict41.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict35.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict34.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict33.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict32.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict31.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict29.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict30.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict28.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict27.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict26.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict25.jpg) |
TOP-SECRET – American, British, Canadian, Australian and New Zealand (ABCA) Armies Security Force Capacity Building Handbook

SFCB has come to play an increasingly important role in each of our armies over the last decade and will undoubtedly feature in operations spanning the spectrum of conflict in the future. Its affect on organization, training, equipping and doctrine has been felt to a greater or lesser extent by each of us and will help define recent conflicts and their effects. However, SFCB cannot be done in isolation. What must be borne in the military planner‘s mind from the outset is that SFCB is a part of the wider SSR campaign and as a consequence must be part of a comprehensive approach. Furthermore, if coalition partners are present, an extra layer of complexity is present and must be planned for. Failure to take these two aspects into account runs the risk of failure at worst or a fragmented HNSF as a result, at best. This handbook aims to assist the military planner in their approach to SFCB. It is aimed at both commanders and staff officers, primarily on brigade and divisional staffs, although it also has utility for those charged with training, mentoring and advising HNSF forces at the tactical level.
…
UNDERSTANDING CULTURE AND DEVELOPING TRUST
Introduction
1. Failure to take culture and the building of trust seriously during SFCB could potentially lead to mission failure. For the purposes of this handbook culture is defined as the set of opinions, beliefs, values, and customs that forms the identity of a society. It includes social behavior standards (e.g., how men relate with women, children relate with adults), language (standard of speech), and religion (standards on how man relates with his mortality and creation). Trust is defined as that firm reliance on the integrity, ability, or character of a person or unit. Trust is both an emotional and logical act, which in practice is a combination of both. In assessing the HN culture ABCA nations should bear in mind from the start other cultures‘ perception of our predominantly Western lifestyle. In addition ABCA nations should beware not to fall into the trap of imposing their own culture, particularly their military culture, on HN forces where this may not be appropriate.
2. Recent Campaigns. Recent campaigns have seen ABCA forces repeatedly deploy to conduct SFCB in parts of the world quite different to their own. Not only do these nations often speak languages that are relatively rarely spoken or studied in ABCA nations, they also have very different cultures. These cultural differences include different religions, ethnic variances, tribal networks, or even comprehensive codes of practice, such as Pashtunwali1 in Afghanistan.
3. Implications of Cultural Issues upon SFCB. There are three major implications of conducting SFCB.
a. Culture Shock. ABCA forces need to understand the cycle through which they may pass during training and deployment when confronted by a different culture. This self-awareness and suggested mitigating activity should serve to reduce the impact of culture shock on the overall campaign.
b. Cultural Sensitivity in the conduct of SFCB. An understanding of the importance of cultural sensitivity, heeding local customs, values and norms, is vital when conducting SFCB. Even more important is the development of trusting relationships between ABCA and indigenous forces. Time and energy must be invested in these if they are to flourish.
c. Improved operational effectiveness by leveraging HNSF Cultural Understanding. HNSF generally have an understanding, both of local culture and the broader human terrain that ABCA nations are unlikely ever to rival, even after repeated tours. HNSF therefore offer ABCA nations an opportunity to understand the human terrain in which they are operating that will otherwise be lacking. SFCB cannot be conducted in isolation.
…
ANALYZING THE HNSF REQUIREMENTS
Introduction
1. Building HN security force capability and capacity should begin with an overarching analysis of requirements, existing capabilities, capacity and constraints, including a thorough consideration of cultural, political and economic factors.
2. Each situation will differ depending upon the level of conflict in the Host Nation and the existing capabilities and capacity of their security forces. The complexity and difficulty of conducting SFCB increases dramatically when working in a failing or failed state. Under such conditions, the key operational level security sector organizations, particularly Defense and Interior ministries, may not be present or effective.
3. Analysis must start from an understanding of the operational environment, the required end-state and taking into account the region‗s needs and concerns. Analysis should determine the requirements for force development, training, sustainment, unit and logistical distribution, deployment of forces, and equipment acquisition for each type of security force.
4. In the absence of a Joint Interagency Multinational process, the application of the military estimate or decision making process may serve as a useful start point. However, it is important that this is not carried out in isolation and is part of a comprehensive approach.
…
Evaluating Campaign Progress
17. The previous discussion has focused on developing measures of assessment for application across the tactical and operational spectrum. Assessing overall progress at the campaign level to understand whether the accumulative effects of our actions are indeed contributing to campaign success are just as important. As outlined earlier CEA is derived from an appreciation of the accumulative results of the MoP and MoE, set against the wider contextual analysis of the environment. Being able to monitor and track progress at this level requires a method for mapping a complex range of variables which contribute to a secure environment. Figure 2 is a suggested means with which to track overall progress made in the delivery of a security effect through HN SFCB.
18. Clearly security capacity in the upper end of the scale would be ideally matched with a high level of community confidence thus representing a viable security condition. Risk Zone A would represent a high level of security confidence among the target community but with low security force capacity. This might be indicative of regions which have been typically calm and relatively unaffected by the adversary – the risk being that this could change. Risk Zone B is high security force capacity but low security confidence and may point to other factors as the cause of poor security confidence, perhaps corrupt security force leadership. Clearly low capacity and low confidence is an unviable security condition.

DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – Mossad High Tech
 This image dated Friday April 28, 2006, from the Israeli spy satellite Eros B, and made available by the Israeli company ImageSat International NV, on Sunday April 30, 2006, one of the first high-quality images reported to show the Kassala airport in southern Sudan. The Eros B was launched last week from Russia and will remain in orbit for up to 6-years with the purpose to track Iran’s nuclear program at a time when Tehran is refusing to comply with U.N. demands to halt uranium enrichment and Iranian President Mahmoud Ahmadinejad is calling for Israel’s destruction.
This image dated Friday April 28, 2006, from the Israeli spy satellite Eros B, and made available by the Israeli company ImageSat International NV, on Sunday April 30, 2006, one of the first high-quality images reported to show the Kassala airport in southern Sudan. The Eros B was launched last week from Russia and will remain in orbit for up to 6-years with the purpose to track Iran’s nuclear program at a time when Tehran is refusing to comply with U.N. demands to halt uranium enrichment and Iranian President Mahmoud Ahmadinejad is calling for Israel’s destruction.
ImageSat inside video & taking –![]()
TOP-SECRET – IDF Satellite Unit Ofek 9 Spy Satellite Being Launched in Palmachim AFB

| IDF Satellite Unit Ofek 9 Spy Satellite Being Launched in Palmachim AFB 22/6/10 22:00 – Yanat (Yehidat Nisui Tilim) Unit Palmachim AFB |
 |
TOP SECRET – CRYPTOME publishes – NSA Email Addresses, Nyms and Names
5 February 2012
NSA Email Addresses, Nyms and Names
A sends:
Below is unverified information posted 9 days ago on this .onion site:
http://4eiruntyxxbgfv7o.onion/snapbbs/736364f4/
(thread: “where to get confidential info”)
It may simply be the INSA list, but I lack the time to compare.
(Director of NSA) KBalexanderLTG@nsa.gov KBalex2@nsa.gov ;-) RFTYGAR@NSA.GOV (Major General David B. Lacquement, Cybercom) dfmuzzy@nsa.gov or dbmuzzy@nsa.gov algorin@nsa.gov bkind@nsa.gov bmcrumm@nsa.gov bmkaspa@nsa.gov bmstite@nsa.gov ceander@nsa.gov dabonan@nsa.gov dahatch@nsa.gov daplunk@nsa.gov dbbuie@nsa.gov dcover@nsa.gov dpcargo@nsa.gov dpmatth@nsa.gov drennis@nsa.gov dvheinb@nsa.gov eejorda@nsa.gov elbauma@nsa.gov fdbedar@nsa.gov fjfleis@nsa.gov fjorlos@nsa.gov gafrisv@nsa.gov gcnolte@nsa.gov gdbartk@nsa.gov ghevens@nsa.gov grcotte@nsa.gov hadavis@nsa.gov hlriley@nsa.gov jaemmel@nsa.gov jcingli@nsa.gov jcmorti@nsa.gov jcsmart@nsa.gov jdcohen@nsa.gov jdheath@nsa.gov jewhite@nsa.gov jgrusse@nsa.gov jhdoody@nsa.gov jhohara@nsa.gov jimathe@nsa.gov jjbrand@nsa.gov jksilk@nsa.gov jllusby@nsa.gov jmcusic@nsa.gov jmjohns@nsa.gov jrsmith@nsa.gov jswalsm@nsa.gov jtnader@nsa.gov kamille@nsa.gov kbalex2@nsa.gov labaer@nsa.gov landers@nsa.gov lfgiles@nsa.gov lkensor@nsa.gov lphall@nsa.gov lrstanl@nsa.gov ltdunno@nsa.gov mabeatt@nsa.gov mawirt@nsa.gov mgflemi@nsa.gov mjgood@nsa.gov mkmcnam@nsa.gov mrevans@nsa.gov mrredgr@nsa.gov mthorto@nsa.gov nasmith@nsa.gov pacabra@nsa.gov papitte@nsa.gov plihnat@nsa.gov plporte@nsa.gov rdjones@nsa.gov rdsiers@nsa.gov relewis@nsa.gov resunda@nsa.gov rhkrysi@nsa.gov rlcarte@nsa.gov rlmeyer@nsa.gov rmmeyer@nsa.gov rpkelly@nsa.gov sfdishe@nsa.gov sfdonne@nsa.gov sgmille@nsa.gov sjmille@nsa.gov sstanar@nsa.gov swramsa@nsa.gov taedwar@nsa.gov tdsoule@nsa.gov tjpeter@nsa.gov twsager@nsa.gov vacurti@nsa.gov vnhalli@nsa.gov wjmarsh@nsa.gov wmmurph@nsa.gov wmthomp@nsa.gov wjseman@nsa.gov --Korruptor posted 9 days 22 hours ago: MTCLAYT@NSA.GOV NCMUNKO@NSA.GOV cjhuff@nsa.gov RBQUINN@NSA.GOV Lorenzo Mccormick lmccorm@nsa.gov Angelina Mcclure ammccl3@nsa.gov Timothy Gibbs tjgibbs@nsa.gov Joshua Foredyce jdfored@nsa.gov Nicole Morrison nnmorri@nsa.gov Sally Smith sssmit3@nsa.gov Todd Black tfblack@nsa.gov Todd Black tfblack@nsa.gov Viola Williams vrmclau@nsa.gov Stephen Schultz UN:SRSYSENGINEER sjschul@nsa.gov Yesenia Martinez yamarti@nsa.gov Teresa Straniero tjstran@nsa.gov Taj Holmes tlholm3@nsa.gov Joseph Johnson jjohns5@nsa.gov Hyon-chu karen Cho KAREN0120 hkcho@nsa.gov Nathan Nysether nenyset@nsa.gov Everett Browning edbrow2@nsa.gov Sean Williamson smwill8@nsa.gov Kevin Standifer kmstand@nsa.gov Maria Johnson msjohn8@nsa.gov id=1607452 lastname=DEBOSE firstname=JULIUS email=JDDEBOS@NSA.GOV id=1838179 lastname=MEADOWS firstname=ALLEN email=ALMEADO@NSA.GOV id=1836143 lastname=FUNCHES firstname=DAVID email=DLFUNCH@NSA.GOV id=1812268 lastname=PUFFENBARGER firstname=JAMES email=JGPUFFE@NSA.GOV id=1840655 lastname=LOWRY firstname=CLINT email=CMLOWRY@NSA.GOV id=1844703 lastname=SENYARD firstname=KRISTEN email=KSSENYA@NSA.GOV id=1822902 lastname=DEEDS firstname=JENNIFER email=JLDEEDS@NSA.GOV id=1424394 lastname=HEDRICK firstname=EVERETT email=EGHEDRI@NSA.GOV id=1847023 lastname=MILO firstname=JOANNE email=JOANNE.M.MILO@USACE.ARMY.MIL id=1319638 lastname=CLARK firstname=SARA email=SJDEBOE@NSA.GOV id=1852085 lastname=GRANGER firstname=MELFORDE email=MAGRANG@NSA.GOV id=1639154 lastname=WHITE firstname=ARLENE email=AFWHITE@NSA.GOV id=1843795 lastname=RAWLINS firstname=BRITTANI email=BRITTANI.RAWLINS@TMA.OSD.MIL id=1850937 lastname=CRISP firstname=KENNETH email=KCCRISP@NSA.GOV id=1846228 lastname=WEEKS firstname=JEFFREY email=JSWEEK2@NSA.GOV id=1847105 lastname=PATRICK firstname=MARY email=MJPATRI@NSA.GOV id=972021 lastname=BROWN firstname=KIMBERLY email=KCBROWN@NSA.GOV id=1843790 lastname=HOFFECKER firstname=FRANK email=FSHOFFE@NSA.GOV id=1568245 lastname=ZUBACK firstname=KATHERINE email=KCZUBAC@NSA.GOV id=1702604 lastname=MILLS firstname=HAROLYN email=HWMILL2@NSA.GOV id=1706716 lastname=ANDERSON firstname=JARED email=JLAND11@NSA.GOV id=1773809 lastname=FERTITTA-ZEPP firstname=MARY ROSE email=MTFERTI@NSA.GOV id=1801498 lastname=MATTHEWS firstname=JACQUELINE email=JGMATT4@NSA.GOV id=1827983 lastname=KELLY firstname=SHERI email=SRKELLY@NSA.GOV id=881503 lastname=ROAKER firstname=AUDREY email=ADROAKE@NSA.GOV id=1758757 lastname=HORGER firstname=ROBYN email=RHORGER@NSA.GOV id=62230 lastname=SCOURTIS firstname=THEODORE email=TRSCOUR@NSA.GOV id=1725805 lastname=JAROSINSKI firstname=JAMES email=JMJAROS@NSA.GOV id=63369 lastname=PHILLIPS firstname=SUSAN email=SEPHIL3@NSA.GOV id=1841784 lastname=BYAM firstname=NICOLE email=NABYAM@NSA.GOV id=1837316 lastname=ACKERMANN firstname=SUSAN email=SACKERM@NSA.GOV id=1838180 lastname=PALMER firstname=KEAVIONA email=KKPALM2@NSA.GOV id=1620956 lastname=FINE firstname=CHET email=CBFINE@NSA.GOV id=1193570 lastname=WHEELER firstname=DONALD email=DAWHEEL@NSA.GOV id=1680358 lastname=FELTON firstname=SHARISSE email=SRFELTO@NSA.GOV id=1299959 lastname=SCARDINA firstname=VONDA email=VRSCARD@NSA.GOV id=952454 lastname=HOLMGREN firstname=CHRISTINE email=CMHOLMG@NSA.GOV id=1836488 lastname=BARNES firstname=RAVEN email=RCBARN4@NSA.GOV id=1809599 lastname=TOPIELEC firstname=DENNIS email=DRTOPI2@NSA.GOV id=1544912 lastname=EICH firstname=ARTHUR email=ANEICH@NSA.GOV id=1481136 lastname=WASSBERG firstname=MARK email=MCWASSB@NSA.GOV id=1486369 lastname=SMITH firstname=ANTOINETTE email=ARSMITH@NSA.GOV id=1809599 lastname=TOPIELEC firstname=DENNIS email=DRTOPI2@NSA.GOV id=1261344 lastname=LAIRD firstname=JOHN email=JMLAIRD@NSA.GOV id=1812529 lastname=KIMSEY firstname=JAYSON email=JEKIMSE@NSA.GOV id=1744167 lastname=RAGER firstname=ZACHARY email=ZMRAGER@NSA.GOV id=1839355 lastname=VIDMAR firstname=SAMUEL email=STVIDMA@NSA.GOV id=1843789 lastname=LANGDON firstname=BRENDAN email=BMLANGD@NSA.GOV id=1832260 lastname=PEREZ firstname=CADDIE email=CEPERE2@NSA.GOV id=1831824 lastname=BROCATO firstname=ADAM email=ARBROCA@NSA.GOV id=1567765 lastname=FLYNN firstname=JESSICA email=JRFLYNN@NSA.GOV id=812143 lastname=WILLIAMS firstname=KIMBERLEE email=KVWILL2@NSA.GOV id=55539 lastname=LEVINE firstname=DIANA email=DKLEVIN@NSA.GOV id=1767656 lastname=COPELLO firstname=TRACY email=TKCOPEL@NSA.GOV id=1809599 lastname=TOPIELEC firstname=DENNIS email=DRTOPI2@NSA.GOV id=1699999 lastname=CRABTREE firstname=BRIAN email=BCCRABT@NSA.GOV id=926230 lastname=MEJIA firstname=ADAM email=ADAM.MEJIA@NSA.NAPLES.NAVY.MIL id=1699380 lastname=PARKER firstname=HELGA email=HSPARKE@NSA.GOV id=92796 lastname=HATFIELD firstname=ELIZABETH email=ELHATFI@NSA.GOV id=970496 lastname=BRIGHTWELL firstname=KALA email=KABRIG2@NSA.GOV id=1619826 lastname=WONDERLY firstname=BRIAN email=BCWONDE@NSA.GOV id=1599843 lastname=CONWAY-BRANCH firstname=CAROLYN email=CPCONWA@NSA.GOV id=1613415 lastname=WHITTINGTON firstname=LISA email=LDWHITT2@NSA.GOV id=1776880 lastname=COOPER firstname=DARYL email=DGCOOPE@NSA.GOV id=1790953 lastname=DUNKER firstname=THOMAS email=TJDUNKE@NSA.GOV id=1630878 lastname=BEELER firstname=RYAN email=RWBEELE@NSA.GOV id=1726927 lastname=HESTER firstname=CARLA email=CJHESTE@NSA.GOV id=1717359 lastname=TEDESCHI firstname=STEPHEN email=SPTEDES@NSA.GOV id=1822638 lastname=WARD firstname=ELIZABETH email=ECWARD1@NSA.GOV id=1587185 lastname=COOK firstname=TASHA email=TACOOK2@NSA.GOV id=1740730 lastname=BROCKMEYER firstname=PETER email=PCBROCK@NSA.GOV id=1219490 lastname=ZULLO firstname=KECIA email=KKZULLO@NSA.GOV id=986360 lastname=ACKIES firstname=HENRY email=HLACKIE@NSA.GOV id=1205401 lastname=HARVEY firstname=TRISTAN email=TDHARVE@NSA.GOV id=1445825 lastname=HILD firstname=LAURA email=LLHILD@NSA.GOV id=1618446 lastname=MARTINEAU firstname=NICHOLAS email=NDMART2@NSA.GOV id=801833 lastname=BLAIS firstname=DAVID email=DMBLAIS@NSA.GOV id=1744167 lastname=RAGER firstname=ZACHARY email=ZMRAGER@NSA.GOV id=1727564 lastname=CROUSE firstname=JAMI email=JLCROU2@NSA.GOV id=1848401 lastname=CORLEY firstname=SHANNON email=SMCORLE@NSA.GOV id=1842936 lastname=MARQUARDT firstname=HOLLY email=HLMARQU@NSA.GOV id=1568495 lastname=ELKINS firstname=GREGORY email=GSELKIN@NSA.GOV id=1806965 lastname=TRELOAR firstname=BARRY email=BFTRELO@NSA.GOV id=1729197 lastname=ELLWOOD firstname=PAULA email=PGELLWO@NSA.GOV id=1262990 lastname=MYERS firstname=KENNETH email=KEMYERS@NSA.GOV id=1836712 lastname=TROISI firstname=MARK email=MJTROIS@NSA.GOV id=1616516 lastname=LOWE firstname=TRINA email=TMLOWE@NSA.GOV id=1828431 lastname=HENSLEY firstname=MELISSA email=MCHENSL@NSA.GOV id=1613083 lastname=RAMIREZ firstname=SHEILA email=STRAMIR@NSA.GOV id=910975 lastname=JOHNSON firstname=TARA email=TRJOHN5@NSA.GOV id=1572257 lastname=STALLINGS firstname=LACY email=LJSTAL2@NSA.GOV id=1600853 lastname=DAVIS firstname=SARAH email=SEDAVI3@NSA.GOV id=1608061 lastname=EVANS firstname=ERIC email=EDEVANS@NSA.GOV id=1779020 lastname=LOOK firstname=KAREN email=KLLOOK@NSA.GOV id=1809640 lastname=ARSENAULT firstname=ROBERT email=REARSEN@NSA.GOV id=1520035 lastname=BURDETTE firstname=ROBERT email=RJBURD3@NSA.GOV id=883230 lastname=LAKE firstname=BARRY email=BALAKE@NSA.GOV id=1516236 lastname=HILTON firstname=ROBERT email=RJHILTO@NSA.GOV id=86769 lastname=MAHER firstname=WENDY email=WAMAHER@NSA.GOV id=1764117 lastname=GEIGER-ALSTON firstname=STACIA email=SLGEIGE@NSA.GOV id=1746685 lastname=KINGERY firstname=JILL email=JAKINGE@NSA.GOV id=1478578 lastname=MIKLUSAK firstname=GREGORY email=GVMIKLU@NSA.GOV id=15637 lastname=PHELPS firstname=AMANDA email=AAPHELP@NSA.GOV id=819655 lastname=CARSON firstname=WILLIAM email=WSCARSO@NSA.GOV =
see also
http://cryptome.org/2012/01/0086.htm
TOP-SECRET – Israel’s First Cyber Drill

The possibility of a cyber-attack on Israel’s strategic infrastructure systems is now evident and highly realistic. Hence, starting today, the NCC (National Cyber Command) and the CTB (Counter Terror Bureau) will be orchestrating Israel’s first official cyber-terror drill in order to improve response effectiveness in the event of a virtual assault.
The drill, referred to as Lights Out, is expected to last several days, and will simulate a cyber-terror attack from multiple sources.
Although strategic systems such as those of the Israeli Electric Company and the Water Authority are highly encrypted and overseen by the Shin Bet security forces, Israel must maintain its edge in all facets of the existential war in which it is now engaged.
The Ministry of Communications will not be participating in the drill, as its personnel lack “the necessary expertise.”
The recent onslaught of cyber-attacks as well as the mysterious shut-down of several government systems in October have prompted a re-gentrification and re-evaluation of Israel’s cyber-defense tactics. The battle is being waged on a new front, and Israel must be prepared for all possible scenarios.
Revealed – Upheaval in the Mossad
Far from the spotlights, the new director of the Mossad replaced his entire senior staff, the exasperating body transfer affair is only another link in the chain of blunders in the handling of Gilad Shalit’s release, the battle over defense establishment funds being waged in the Knesset reaches new depths of entanglement.
The Mossad is an organization that acts in the shadows, as it should. Under a heavy cloak of secrecy it has undergone an upheaval in recent months. This is not something that everyone driving by the Mossad’s hilltop headquarters (ask any Israeli the “secret” location) is aware of, but a sea change, at least at the personnel level, has definitely taken place.
The shake up began with the appointment of Tamir Pardo as Mossad director on January 6. While the reshuffling at the senior level was underway, the outgoing head of the organization, Meir Dagan, captured the lion’s share of public attention in a series of admonishments and phillippics against an attack on Iran. In the meantime, Pardo quietly replaced the entire Mossad senior staff.
Background input: Pardo is one the few directors who grew up within the organization and was not parachuted onto it from the outside. He joined the ranks after a short stint as a signal corps officer. (His memoirs of the Operation Entebbe were recently published in the intelligence corps’ heritage magazine. Pardo was the chief radio operator for the commander of the operation, Yoni Netanyahu – the only Israeli military fatality in the hostage rescue.) For decades Pardo served heart and soul in Mossad operations, but when he reached the top level a few years ago – his advancement hit the wall. The reason: the continuous extension of Meir Dagan’s tenure.
When Pardo realized that the pinnacle of the pyramid was occupied, he temporarily left the organization for a position in the IDF (among other things he was involved in the development of special capabilities and planning of special ops in the Second Lebanon War). He returned to the Mossad as the deputy director, but again departed in 2009 after Dagan’s term was extended for another year. It seems that Dagan’s protracted hold on the top office did not suit Pardo’s nature.
 As a private citizen, Pardo was helping the Israeli entrepreneur Noam Lanir set up a company specializing in the export of medical services to wealthy Russians, when the decision was made to appoint him “chief” of the Mossad. Since entering office six months ago, Pardo has maintained his predecessor’s tradition of active operations while introducing a major organizational reconfiguration. Pardo’s managerial methods are definitely not those of Dagan. Without anyone outside of the Mossad taking note, Pardo replaced all of the key department heads.
As a private citizen, Pardo was helping the Israeli entrepreneur Noam Lanir set up a company specializing in the export of medical services to wealthy Russians, when the decision was made to appoint him “chief” of the Mossad. Since entering office six months ago, Pardo has maintained his predecessor’s tradition of active operations while introducing a major organizational reconfiguration. Pardo’s managerial methods are definitely not those of Dagan. Without anyone outside of the Mossad taking note, Pardo replaced all of the key department heads.
This is what happened in the special ops departments “Keshet” and “Caesarea”. New chiefs were also brought into the intelligence department; the political action and liaison department, responsible for the organization’s international contacts; and even the human resources section. The new head of the political action and liaison department served until recently as head of the intelligence department. His deputy, Z., the new head of the research department, was formerly the director of counter-terror in the intelligence corps. Z.’s deputy in the Mossad, A., was also Z.’s deputy in the intelligence corps research section. Furthermore, the person who until very recently headed the Mossad’s human resources section, Brigadier General (res.) Yosi Peretz, the former the chief officer of the IDF’s adjutant corps, was appointed director of human resources at Bank Discount a few days ago. The outgoing head of the political action and liaison department department, David Primo, was also in the news recently when Prime Minister Binyamin Netanyahu asked him to head the negotiations for the release of Gilad Shalit.
Shalit: an ongoing fiasco
Just as this column has mentioned on more one occasion in the past weeks, serious contacts are being held with Hamas on a possible deal for the release of Gilad Shalit.
Actually it is against this setting that Israel’s (mis)handling of the bodies’ transfer to the Palestinians this week is so infuriating. According to the press, the imbecility began with a meeting between senior members of the Palestinian Authority (PA) and the heads of Israel’s Civil Administration in Judea and Samaria. The Palestinians came away convinced that Israel had agreed to hand over 84 bodies. Political figures in Israel officially approved the report, and the IDF Spokesperson even published a statement that the transfer would proceed according to the “prime minister’s decision.”
 Then, a sudden turnabout occurred. After midnight, on the evening between Monday and Tuesday, Ehud Barak’s office issued a statement that the defense minister would reexamine the list of the Palestinian bodies in light of the protest voiced by the victims of terrorist events and the concern that a valuable bargaining chip might be lost in the negotiations for Gilad Shalit’s return. The Israeli journalist Ben Caspi, writing in the daily Ma’ariv, shed light on the murky matter.
Then, a sudden turnabout occurred. After midnight, on the evening between Monday and Tuesday, Ehud Barak’s office issued a statement that the defense minister would reexamine the list of the Palestinian bodies in light of the protest voiced by the victims of terrorist events and the concern that a valuable bargaining chip might be lost in the negotiations for Gilad Shalit’s return. The Israeli journalist Ben Caspi, writing in the daily Ma’ariv, shed light on the murky matter.
According to Caspi, the IDF Spokesperson’s announcement had been prearranged with the defense minister’s office to purposely use the unprecedented expression “the prime minister’s decision” rather than the “political echelon’s” (which naturally includes Defense Minister Ehud Barak). If indeed Barak set a trap for Netanyahu in order to cast himself as the “responsible figure” in the government, as Caspi claims, then he could have also exploited the relative lack of experience of new IDF Spokesperson, Brigadier General Yoav (Poli) Mordechai) (head of the Civil Administration in Judea and Samaria until last year). In addition, the director of the media department in the IDF Spokesperson’s Unit, Colonel Ofer Kol, is stepping down from his position this week (Ariela Ben Avraham, promoted to colonel last Thursday, is his replacement).
The inept handling of the bodies’ transfer is nothing compared to the recurrent blunders in the Gilad Shalit affair, most of which have been discussed in detail in this column. Three weeks ago the Israeli soldier completed five years in captivity.
Northern Command: mistakes fated to be repeated
As the fifth anniversary of the Second Lebanon War approaches, it is time to recall that the war broke out when many of the senior officers in the Northern Command were still new at their jobs.
For example, the general of Northern Command, Udi Adam, and the head of the Galilee Division, Gal Hirsh, were less than a year in their positions. Northern Command’s chief intelligence officer, Yosi Beidetz (now completing his succeeding post as head of the intelligence corps’ research department) had been in Northern Command barely a month when the war erupted, and the list goes on.
 Now we can note that the IDF is fully prepared for the heavy rioting expected in September if and when the Palestinians realize their plans to declare unilateral statehood. Last May we received a “taste” of what is likely to occur. This, of course, refers to “Nakba Day” [Israel’s Independence Day which, for the Palestinians, signifies “Catastrophe Day” dating back to 1948] when hoards of Syrians stormed the border on the Golan Heights. As September approaches the IDF is vigorously stockpiling “non-lethal” weapons, holding field exercises, preparing for a large-scale mobilization of the reserves, and scheduling training programs and courses so that the conscript units will be free for operational duty in the territories and on the borders. The assessment is that like “Nakba Day,” in September, too, Northern Command will have to deal with an onslaught of stubborn, resolute, violent protesters on the northern borders.
Now we can note that the IDF is fully prepared for the heavy rioting expected in September if and when the Palestinians realize their plans to declare unilateral statehood. Last May we received a “taste” of what is likely to occur. This, of course, refers to “Nakba Day” [Israel’s Independence Day which, for the Palestinians, signifies “Catastrophe Day” dating back to 1948] when hoards of Syrians stormed the border on the Golan Heights. As September approaches the IDF is vigorously stockpiling “non-lethal” weapons, holding field exercises, preparing for a large-scale mobilization of the reserves, and scheduling training programs and courses so that the conscript units will be free for operational duty in the territories and on the borders. The assessment is that like “Nakba Day,” in September, too, Northern Command will have to deal with an onslaught of stubborn, resolute, violent protesters on the northern borders.
But has the IDF learned all the lessons of 2006? Apparently not. Look at the facts: during August, a few weeks before the expected explosion, one after the other, the general of Northern Command, commander of the Galilee Formation (who has responsibility for the Lebanese border), the commanders of the 36th and Challenger Divisions, and, but what else, Northern Command’s chief intelligence officer will all be replaced. A blunder fated to repeat itself? It would seem so.
Mofaz fights
A final word. Another “hot” issue that occupied the defense establishment this week was a matter of money – lots of money.
The veteran journalist Nahum Barnea first broke the story in the daily Yediot Achronot last Friday. Barnea revealed that the director general of the defense ministry, Major General (res.) Udi Shani, has been banging on tables to free money designated for the defense ministry, money that was legally approved by the Knesset for the defense budget.
It turns out that close to three billion shekels have been held up for sundry reasons since the beginning of the year. The result: the defense ministry has accumulated a debt of hundreds of millions of shekels that it owes to each of the major defense industries that supply the IDF with weapons.
A week has passed since the exposé and the issue only becomes more empretzeled. A brief explanation is in order. The defense budget is passed biannually. It is unlike the budgets of the other ministries that the Knesset’s finance committee votes on, in that the defense budget is approved as a single flow without the possibility of debate on each specific section. The reason for this is to prevent any leaks of security secrets in the finance committee plenum.
 In order to oversee the defense budget, a special committee of ten Knesset members is appointed: half of them from the finance committee and half from the foreign affairs and defense committee, and all of them have the requisite security clearance level. The chairman of the joint committee is a figure is whose security credentials are of the highest order, unimpeachable to the nth degree – the former chief of staff and defense minister, Knesset Member Shaul Mofaz.
In order to oversee the defense budget, a special committee of ten Knesset members is appointed: half of them from the finance committee and half from the foreign affairs and defense committee, and all of them have the requisite security clearance level. The chairman of the joint committee is a figure is whose security credentials are of the highest order, unimpeachable to the nth degree – the former chief of staff and defense minister, Knesset Member Shaul Mofaz.
According to procedure, those who can delay the money flow to the defense establishment are the finance ministry (if it doesn’t bring the regular defense budget to the finance committee for approval), the chairman of the finance committee (if he doesn’t order payment to the joint committee for approval), and, of course, Shaul Mofaz’s joint committee.
Back to the facts: the security budget has suffered lately from the iron fist of all three players. The finance ministry is withholding the money, the finance committee is delaying (for coalition reasons) approval of the budget that the finance ministry has already approved (a disheartening development for the defense industries as of last Tuesday: the finance committee is freezing 620 million shekels due to various coalition demands), and even Knesset Member Shaul Mofaz has locked horns with the defense establishment in recent weeks, fighting it “tooth and nail.”
For the first time it appears that the former chief of staff is demanding his right to scrutinize the money designated for four defense projects, as well as the sources of their funding. Moreover, Mofaz wants to check the money intended for Elbit’s DAP (Digital Army Program), and a joint program between Elbit and the defense and finance ministries for the establishment, in the south of the country, of a plant, partially funded by the state, for the production of state-of-the art communications equipment for the IDF.
Mofaz is determined to oversee the defense establishment and not merely serve as a rubber stamp that gives the green light to all of its budgets. In the meantime, discussions in the Knesset focus only on legal niceties: does Mofaz’s committee have the authority to examine the sources of financing of certain defense budgets or only what the money is intended for. By the end of this week the funds appear to be frozen solid. Thus the leaders of the defense industries may soon find themselves knocking on the doors of the bank directors asking for loans to tide them over until the defense funding thaws and the cash flows again.
***
Photos:
Director of the Mossad, Tamir Pardo (Photo: Flash 90)
Gilad Shalit (Photo: AP)
Member of Parliament, Shaul Mofaz (Photo: IDF Spokesperson)
TOP-SECRET – National Cyber Security Division Joint Cybersecurity Services Pilot (JCSP)
TOP SECRET from the CIA – Strategic Warning & The Role of Intelligence: Lessons Learned from the 1968 Soviet Invasion of Czechoslovakia

The Czechoslovak crisis, as it became known, started in January 1968, when Alexander Dubček was elevated to the post of First Secretary of the Communist Party of Czechoslovakia (CPCz), replacing moribund Antonin Novotny, who had served as First Secretary since 1957. Under Dubček, the communist leadership embarked on a program of dramatic liberalization of the Czechoslovak political, economic, and social order, including the overhaul of the CPCz leadership, increased freedom of speech, surrender of authority to the Czech National Assembly by the Communist Party, real elections at local and national levels, and even the suggestion of legalizing non-communist political parties.
DOWNLOAD ORIGINAL BOOKLET HERE
TOP-SECRET from the FBI – Operators of Elgin Adult Entertainment Club and Alleged Internet Gambling Business Charged with Concealing More Than $4 Million of Income from the IRS
CHICAGO—The operators of an adult entertainment club in Elgin were charged today with conspiracy to impede the Internal Revenue Service in the collection of federal taxes, as well as separately operating an illegal Internet gambling business, in connection with allegedly diverting more than $4 million in unreported income to themselves from the two businesses. The defendants, Anthony Buttitta and his father, Dominic Buttitta, were charged in a two-count criminal information filed in U.S. District Court, announced Patrick J. Fitzgerald, United States Attorney for the Northern District of Illinois; Alvin Patton, Special Agent in Charge of the Internal Revenue Service Criminal Investigation Division in Chicago; and Robert D. Grant, Special Agent in Charge of the Chicago Office of the Federal Bureau of Investigation.
Anthony Buttitta, 42, of St. Charles, and Dominic Buttitta, 69, of South Barrington, were each charged with one count of conspiracy to defraud the United States by obstructing the IRS in the collection of taxes and one count of operating an illegal gambling business. They will be ordered to appear for arraignment at a later date in U.S. District Court. The Buttittas operate Blackjacks Gentlemen’s Club in Elgin through Elgin Entertainment Enterprises, Inc., which manages Blackjacks. Between 2005 and 2009, they also ran an Internet gambling business, including the websites Skybook.com, Largejoe.com, and Theredhotel.com.
According to the charges, both Buttittas filed false federal corporate tax returns for calendar years 2002 through 2009, and false federal individual income tax returns for calendar years 2002 through 2008 that substantially under-reported the total income they received from the operation of Blackjacks and the gambling business. They allegedly concealed the diverted funds from their tax preparers and the IRS and used the unreported income to acquire personal property and to pay personal expenses.
The charges allege that the defendants received approximately $3,704,959 from “house” fees they collected from women for each shift they worked as dancers at Blackjacks. Anthony Buttitta directed club employees to maintain logs of the house fee collections, and both defendants later destroyed and caused the destruction of the log sheets, the charges allege. They also placed agents of their Internet gambling business on the payroll of another company to provide the employees with the appearance of a legitimate source of income and benefits. In return, the charges allege that they solicited and received kickbacks in the form of cash from the agents and concealed the payments from their tax preparers, bookkeepers and the IRS.
The defendants allegedly received approximately $1 million in gross wagers from the gambling business between 2005 and 2009, and made approximately $400,000 in net profits. The charges seek forfeiture of $400,000 as illegal proceeds.
At various times between 2005 and 2008, the defendants allegedly obtained unreported income from individuals as payment of losing wagers in the form of direct payments toward the purchase of a $2.9 million condominium in Las Vegas and a condominium in Costa Rica, as well as personal credit card payments. In 2005 and 2006, Anthony Buttitta used approximately $400,000 in cash to pay for building and acquiring his home in St. Charles, according to the charges.
Each count carries a maximum penalty of five years in prison and a $250,000 fine, and restitution is mandatory. In addition, defendants convicted of tax offenses must pay the costs of prosecution and remain liable for any and all back taxes, as well as a civil fraud penalty of 75 percent of the underpayment plus interest. If convicted, the court must impose a reasonable sentence under federal statutes and the advisory United States Sentencing Guidelines.
The government is being represented by Assistant U.S. Attorney Patrick King.
The public is reminded that an information contains only charges and is not evidence of guilt. The defendants are presumed innocent and are entitled to a fair trial at which the government has the burden of proving guilt beyond a reasonable doubt.
TOP-SECRET – (U//FOUO) DHS-FBI Florida-Based Violent Extremist Arrested for Plotting Bombing Attack in Tampa

(U//FOUO) This Joint Intelligence Bulletin is intended to provide information on the 7 January 2012 arrest by the FBI Tampa Joint Terrorism Task Force (JTTF), as part of a planned law enforcement action, of Florida-based Sami Osmakac. Osmakac is charged with attempted use of weapons of mass destruction. This information is provided to support the activities of FBI and DHS and to assist federal, state, local, tribal, and territorial, counterterrorism and law enforcement officials to prevent or respond to terrorist attacks against the United States.
(U) Circumstances Leading to the Arrest
(U//FOUO) On 7 January 2012, the FBI Tampa JTTF arrested Sami Osmakac, 25, of Pinellas Park, Florida, as part of a planned law enforcement operation after he allegedly took possession of explosives, a fully automatic AK-47 assault rifle, ammunition and magazines for the AK-47, a pistol, ammunition and a magazine for the pistol, grenades, and a suicide vest. Osmakac allegedly planned to attack a target in Tampa, according to the affidavit in support of the criminal complaint.
(U//FOUO) In late September 2011, a confidential source informed the FBI of Osmakac’s interest in purchasing flags representing al-Qa‘ida. In subsequent conversations, Osmakac allegedly expressed the desire to conduct a violent attack in the Tampa area and asked for assistance in procuring a vehicle-borne improvised explosive device (VBIED), weapons such as Uzis or AK-47s, and an explosives-laden belt to use in a two-stage attack. As part of an undercover operation, Osmakac was introduced to an individual whom he believed to hold extremist beliefs and was able to supply weapons and explosives. All weapons, ammunition, and explosives provided by the FBI had previously been rendered inoperable.
(U//FOUO) According to court documents, during November 2011, Osmakac planned to attack a Tampa area military recruiting center. However, he later changed his plan, allegedly telling a confidential source that the recruiting center did not have enough personnel inside.
(U//FOUO) According to the arrest affidavit, on 1 January 2012, Osmakac drove through the Ybor City neighborhood of Tampa to choose target locations, planning to eventually set off an explosive charge packed in the trunk of a vehicle parked in front of high-end restaurants and nightclubs. All of his pre-operational activities were closely monitored by the FBI.
(U//FOUO) Osmakac allegedly outlined various scenarios in which he would park a VBIED near busy nightspots and return to his nearby hotel room to collect the remaining weapons. He would then return to the scene to detonate the VBIED remotely, and in the aftermath conduct a small-arms attack at a nearby location while wearing a suicide vest. According to a confidential source, Osmakac said he would attempt to take hostages and contact authorities, specifically the FBI, in order to negotiate the release of Muslim prisoners. Osmakac told the same source that he believed that detonating the VBIED before he took hostages would prove he was “not joking.” Osmakac allegedly planned to release the hostages and detonate the suicide vest while surrendering to law enforcement after his demands were met, according to court documents.
(U//FOUO) Motivations in Planning the Attack
(U//FOUO) Osmakac, a naturalized US citizen, born in the former Yugoslavia, previously had a positive view of the United States for helping his fellow Muslims in Kosovo in their time of need. He later decided that the United States is his enemy because he believes the United States is killing his fellow Muslims, according to the affidavit in support of the criminal complaint.
(U//FOUO) Just before he allegedly attempted the attack, Osmakac filmed a martyrdom video in his hotel room, with a pistol in his hand and the AK-47 displayed behind him. In the video, he stated his belief that Muslims’ “blood” was more valuable than that of non-Muslims and he wanted “pay back” for the wrongs he felt were done to Muslims, according to the affidavit.
— (U//FOUO) In discussions with an under cover employee, Osmakac declined opportunities to back out of the plan.
(U//FOUO) Targets and Tactics Differ Slightly From Recent Homegrown Violent Extremist Plots
(U//FOUO) Disrupted plots by homegrown violent extremists (HVEs) within the past year have primarily targeted government and military facilities and personnel, including a military recruiting center in Seattle, a restaurant frequented by military personnel near Fort Hood, Texas, and the Pentagon and US Capitol building with improvised explosives, small arms, and grenades.*
(U//FOUO) Osmakac, however, allegedly abandoned his plan to attack a military recruiting center for a less secure civilian target which held the potential for a greater number of casualties. His alleged tactics also differed from previous HVE plotting in that he planned to take hostages to achieve a specific goal—the release of Muslim prisoners—and then take his own life by detonating his suicide vest in the proximity of
arresting officers.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP SECRET – FBI “Communities Against Terrorism” Suspicious Activity Reporting Flyers
The following collection of 25 flyers produced by the FBI and the Department of Justice are distributed to local businesses in a variety of industries to promote suspicious activity reporting. The flyers are not released publicly, though several have been published in the past by news media and various law enforcement agencies around the country. We have compiled this collection from a number of online sources.
To view the documents, click on a threat area in the menu to the left and the PDF will appear on the right side of the page. You can also download the complete collection of files (ZIP Archive, 6.27 MB).
Threat Areas
- Airport Service Providers
- Beauty/Drug Suppliers
- Bulk Fuel Distributors
- Construction Sites
- Dive/Boat Shops
- Electronics Stores
- Farm Supply Stores
- Financial Institutions
- General Aviation
- General Public
- Hobby Shops
- Home Improvement
- Hotels/Motels
- Internet Cafes
- Shopping Malls
- Martial Arts/Paintball
- Mass Transportation
- Military Surplus
- Peroxide Explosives
- Recognizing Sleepers
- Rental Cars
- Rental Properties
- Rental Trucks
- Storage Facilities
- Tattoo Shops
TOP-SECRET – Julian Assange’s Appeal to the U.K. Supreme Court
TOP-SECRET from the FBI – Investigating Insurance Fraud A $30-Billion-a-Year Racket
01/31/12

Our corporate and securities fraud cases, for example, resulted in more than 600 convictions last year—including a number of high-level executives—and more than $23 billion in recoveries, fines, and restitutions over the past three years. Our mortgage fraud efforts continue to pinpoint the most egregious offenders; approximately 70 percent of our 3,000 pending mortgage fraud investigations involve losses of more than $1 million. There are also plenty of cases involving health care fraud, bankruptcy fraud, credit card fraud, mass marketing fraud, and various wire and mail fraud schemes.
Insurance fraud—non-health care-related fraud involving casualty, property, disability, and life insurance—is another financial crime that falls under FBI jurisdiction. The U.S. insurance industry consists of thousands of companies that collect more than $1.1 trillion in premiums each year, according to the Insurance Information Institute, and the estimated cost of fraud is approximately $30 billion a year. Most of this expense is passed on to consumers in the form of higher insurance premiums, to the tune of about $200 to $300 a year per family, according to the National Insurance Crime Bureau. Not to mention the number of insurance companies that go under because of excessive claims and/or the looting of company assets.

Defend Yourself From Insurance Fraud – Never ignore a notice from your insurance company—even if your agent tells you it’s a mistake and that he or she will take care of it. – Don’t give an insurance agent money without getting a receipt. – Don’t give out your insurance identification number to companies or individuals you don’t know. – After an auto accident, be careful of strangers who offer you quick cash or recommend a particular attorney or health care provider. · Don’t buy life insurance as an investment without fully understanding what it is you’re buying. – Never buy insurance from unlicensed agents or companies, and if you have any doubts about them, check their status by contacting your state’s insurance office. |
|---|
There are many capable private and government investigative and regulatory entities at the national and state level that look into insurance fraud, so the FBI directs its resources toward identifying the most prevalent schemes and the top echelon criminals and criminal organizations who commit the fraud. But even when conducting our own investigations, we often work closely with private fraud associations, state fraud bureaus, state insurance regulators, and other federal agencies.
The FBI currently focuses on the following schemes:
- Disaster related fraud, which became such a problem after Hurricane Katrina that a special task force was created to address it (and evolved into today’s National Center for Disaster Fraud);
- Premium and asset diversion, which happens when insurance agents, brokers, even insurance company executives steal insurance premiums submitted by policy holders and sometimes plunder company financial assets for their own personal use;
- Viatical fraud (a “viatical” settlement is one where an investor buys the right to receive the benefit of a terminally ill or elderly person’s life insurance policy);
- Staged auto accidents;
- Bodily injury fraud; and
- Property insurance fraud.
Who commits insurance fraud. Mostly dishonest policy holders, insurance industry insiders (i.e., agents, brokers, company execs), and loosely organized networks of crooked medical professionals and attorneys who use their knowledge to bypass anti-fraud measures put in place by insurance companies.
How we investigate it. Like many other white-collar crime investigations, insurance fraud is mostly about following the money trail—which often involves questioning victims and victim companies, reviewing financial documents, and using sensitive techniques like informants and cooperating witnesses.
We also use our intelligence capabilities to keep our finger on the pulse of emerging trends—for example, as more insurance companies conduct business online, we fully expect to see a rise in the theft of policy holders’ identities and in cyber-based insurance scams. We will keep you posted.
TOP-SECRET – WikiLeaks Confidentiality/Non-Disclosure Agreement



TOP SECRET – Financial Crimes Law Enforcement/Subpoena Contacts List
TOP-SECRET – (U//FOUO) Los Angeles Fusion Center: Steganography Intelligence Bulletin

(U//FOUO) Steganography—the practice of concealing data within a carrier—may be used to obscure malicious or criminal information and activity from law enforcement. While steganography dates to the fifth century BC, it has long been regarded as, and remains, one of the most advanced forms of clandestine communication. In modern usage, the Internet allows accessibility to, and broad dissemination of, steganography tools, and its application continues to evolve with technology. Understanding steganography in its current state is essential to its identification and detection.
(U) Detection
(U//FOUO) Detecting steganography is challenging; in fact, determining whether media contains extraneous data is nearly impossible. Generally, detection occurs only through direct knowledge of its existence, evidence of steganography tools, or chance. Some indicators of steganography may include:
• (U//FOUO) Conspicuous and unusual sharing of digital media files via peer-to-peer (P2P) clients, e-mail, or uploads to Web sites
• (U//FOUO) Repeated sharing of the same file
• (U//FOUO) Possession of steganography software, or visiting sites known to contain steganography
• (U//FOUO) Sharing of content that is inconsistent with a subject’s life, such as pictures of children when he or she is not known to have any
• (U//FOUO) Possession of two or more copies of a file that do not look/sound identical, that is, the same image but of varying sizes and hash values
• (U//FOUO) Presence of files whose large size is unusual for the type of content
• (U//FOUO) Possession of books or articles on—or, expression of interest in—cryptography or steganography(U) Note that traditional security devices (for example, firewalls) do not detect steganography; a file containing a concealed message presents as a legitimate file.
(U) Tools for Detection
(U) Steganalysis, the method of detecting steganography and destroying the hidden message, is possible through free online tools. Deciphering and viewing the original message is challenging without the encryption keys, and some detection software may only identify steganography within a specific medium.
(U) Illicit Uses of Steganography
(U) Covert Communication
(U) Steganography can be used to hide communication behind seemingly innocuous files to pass messages without fear of detection.
• (U) According to an indictment unsealed in June 2010, an accused Russian spy network in New York began to use steganography as early as 2005. After a raid on the home of an alleged spy, law enforcement found a program on a computer that allowed group members to embed data in images on publicly available Web sites.
• (U//FOUO) The second issue of The Technical Mujahid details the benefits of using steganography over encryption; the magazine includes instructions for and examples of steganography.(U) Concealing Illicit Activity
(U//FOUO) Criminals use steganography to hide materials or information for the purpose of
• (U) Trafficking in child pornography
• (U) Committing fraud
• (U) Evading government censorship abroad
• (U) Conducting industrial espionage(U) VoIP Steganography
(U) Voice over Internet Protocol (VoIP) steganography, also known as network steganography, is one example of adaption to new technology. Use of a proprietary VoIP service eliminates the need for a carrier to conceal data, and extends the message length. The longer the conversation or data exchange, the longer or more detailed the hidden message can be. The brief time period the VoIP data exists for makes this nearly impossible to detect or prevent.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – Anti-Counterfeiting Trade Agreement (ACTA) Final Version May 2011

The Parties to this Agreement,
Noting that effective enforcement of intellectual property rights is critical to sustaining economic growth across all industries and globally;
Noting further that the proliferation of counterfeit and pirated goods, as well as of services that distribute infringing material, undermines legitimate trade and sustainable development of the world economy, causes significant financial losses for right holders and for legitimate businesses, and, in some cases, provides a source of revenue for organized crime and otherwise poses risks to the public;
Desiring to combat such proliferation through enhanced international cooperation and more effective international enforcement;
Intending to provide effective and appropriate means, complementing the TRIPS Agreement, for the enforcement of intellectual property rights, taking into account differences in their respective legal systems and practices;
Desiring to ensure that measures and procedures to enforce intellectual property rights do not themselves become barriers to legitimate trade;
Desiring to address the problem of infringement of intellectual property rights, including infringement taking place in the digital environment, in particular with respect to copyright or related rights, in a manner that balances the rights and interests of the relevant right holders, service providers, and users;
Desiring to promote cooperation between service providers and right holders to address relevant infringements in the digital environment;
Desiring that this Agreement operates in a manner mutually supportive of international enforcement work and cooperation conducted within relevant international organizations;
Recognizing the principles set forth in the Doha Declaration on the TRIPS Agreement and Public Health, adopted on 14 November 2001, at the Fourth WTO Ministerial Conference;
Hereby agree as follows:
…
pirated copyright goods means any goods which are copies made without the consent of the right holder or person duly authorized by the right holder in the country of production and which are made directly or indirectly from an article where the making of that copy would have constituted an infringement of a copyright or a related right under the law of the country in which the procedures set forth in Chapter II (Legal Framework for Enforcement of Intellectual Property Rights) are invoked;
…
ARTICLE 9: DAMAGES
1. Each Party shall provide that, in civil judicial proceedings concerning the enforcement of intellectual property rights, its judicial authorities have the authority to order the infringer who, knowingly or with reasonable grounds to know, engaged in infringing activity to pay the right holder damages adequate to compensate for the injury the right holder has suffered as a result of the infringement. In determining the
amount of damages for infringement of intellectual property rights, a Party’s judicial authorities shall have the authority to consider, inter alia, any legitimate measure of value the right holder submits, which may include lost profits, the value of the infringed goods or services measured by the market price, or the suggested retail price.2. At least in cases of copyright or related rights infringement and trademark counterfeiting, each Party shall provide that, in civil judicial proceedings, its judicial authorities have the authority to order the infringer to pay the right holder the infringer’s profits that are attributable to the infringement. A Party may presume those profits to be the amount of damages referred to in paragraph 1.
…
ARTICLE 11: INFORMATION RELATED TO INFRINGEMENT
Without prejudice to its law governing privilege, the protection of confidentiality of information sources, or the processing of personal data, each Party shall provide that, in civil judicial proceedings concerning the enforcement of intellectual property rights, its judicial authorities have the authority, upon a justified request of the right holder, to order the infringer or, in the alternative, the alleged infringer, to provide to the right holder or to the judicial authorities, at least for the purpose of collecting evidence, relevant information as provided for in its applicable laws and regulations that the infringer or alleged infringer possesses or controls. Such information may include information regarding any person involved in any aspect of the infringement or alleged infringement and regarding the means of production or the channels of distribution of the infringing or allegedly infringing goods or services, including the identification of third persons alleged to be involved in the production and distribution of such goods or services and of their channels of distribution.
…
ARTICLE 19: DETERMINATION AS TO INFRINGEMENT
Each Party shall adopt or maintain procedures by which its competent authorities may determine, within a reasonable period after the initiation of the procedures described in Article 16 (Border Measures), whether the suspect goods infringe an intellectual property right.
ARTICLE 20: REMEDIES
1. Each Party shall provide that its competent authorities have the authority to order the destruction of goods following a determination referred to in Article 19 (Determination as to Infringement) that the goods are infringing. In cases where such goods are not destroyed, each Party shall ensure that, except in exceptional circumstances, such goods are disposed of outside the channels of commerce in such a manner as to avoid any harm to the right holder.
2. In regard to counterfeit trademark goods, the simple removal of the trademark unlawfully affixed shall not be sufficient, other than in exceptional cases, to permit release of the goods into the channels of commerce.
3. A Party may provide that its competent authorities have the authority to impose administrative penalties following a determination referred to in Article 19 (Determination as to Infringement) that the goods are infringing.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – NSA Review of Information for the Public
TOP-SECRET – Documents Detail CIA, MI6 Relationship With Qaddafi

This image provided by Human Rights Watch on Saturday, Sept. 3, 2011 shows part of a secret document dated June 19, 2003 discovered by Human Rights Watch in Tripoli, Libya, detailing a meeting regarding a CIA visit to Libya’s WMD programs. The CIA and other Western intelligence agencies worked closely with the ousted regime of Moammar Gadhafi, sharing tips and cooperating in handing over terror suspects for interrogation to a regime known to use torture, according to a trove of security documents discovered after the fall of Tripoli. The revelations provide new details on the West’s efforts to turn Libya’s mercurial leader from foe to ally and provide an embarrassing example of the U.S. administration’s collaboration with authoritarian regimes in the war on terror. (AP Photo/Human Rights Watch)
Libya: secret dossier reveals Gaddafi’s UK spy links
A cache of papers found at the intelligence headquarters dating from the time it was run by Moussa Koussa, who later became foreign minister and defected in March, showed Libya was handed Islamist opposition members as part of the CIA’s “extraordinary rendition” programme.
MI6 also provided extensive information to the Libyan authorities of opponents living in Britain.
The British intelligence services seem to have been more circumspect than their American colleagues, however. Often the files, which were found by Human Rights Watch and shown to The Sunday Telegraph, suggest they restricted themselves to confirming information already known to the Libyans.
It also shows one reason for the co-operation – MI6′s belief that Libyan Islamists were playing a central role in funding and supporting al-Qaeda, often via contacts in Iran.
MI6 and the CIA were instrument in the attempts by former Prime Minister Tony Blair to bring Col Gaddafi “in from the cold”, started at the time the alleged Lockerbie bombers were handed over for trial in The Hague.
In return for compensating victims of the Lockerbie bombing and other terrorist outrages, and surrendering its programme for weapons of mass destruction, diplomatic relations were resumed and sanctions dropped.
The documents give details of how much further subsequent co-operation went between Libya and the West. They confirm that Abdulhakim Belhadj, now leader of the Tripoli Military Council under the rebel government, was flown by the CIA to Libya for interrogation and imprisonment in 2004.

Documents with photographs and details of people wanted by the Libyan External Security office are seen in the abandoned office where Muammar Gaddafi’s former spy chief and foreign minister Moussa Koussa was based in Tripoli September 3, 2011. Documents found in the abandoned office of Gaddafi’s intelligence chief indicate the U.S. and British spy agencies helped the fallen strongman persecute Libyan dissidents, Human Rights Watch said on Saturday. The documents were uncovered by the human rights activist group in Koussa’s abandoned offices.

A list of telephone interceptions by the Libyan External Security office is seen at the abandoned office of Muammar Gaddafi’s former spy chief and foreign minister Moussa Koussa in Tripoli September 3, 2011. Documents found in the abandoned office of Gaddafi’s intelligence chief indicate the U.S. and British spy agencies helped the fallen strongman persecute Libyan dissidents, Human Rights Watch said on Saturday. The documents were uncovered by the human rights activist group in Koussa’s abandoned offices.

This image provided by Human Rights Watch on Saturday, Sept. 3, 2011, shows a secret document dated April 15, 2004 discovered by Human Rights Watch in Tripoli, Libya, detailing a request for Libya to take custody of a terrorist suspect known as “Shaykh Musa.” The CIA and other Western intelligence agencies worked closely with the ousted regime of Moammar Gadhafi, sharing tips and cooperating in handing over terror suspects for interrogation to a regime known to use torture, according to a trove of security documents discovered after the fall of Tripoli. The revelations provide new details on the West’s efforts to turn Libya’s mercurial leader from foe to ally and provide an embarrassing example of the U.S. administration’s collaboration with authoritarian regimes in the war on terror.
TOP-SECRET – (U//FOUO) DHS-FBI-USSS 2012 State of the Union Address Joint Threat Assessment

(U//FOUO) This Joint Threat Assessment (JTA) addresses potential threats to the President’s delivery of the State of the Union address at the US Capitol on 24 January 2012.
(U) This information is intended to support federal, state, territorial, tribal, and local government agencies and authorities and other entities in developing and prioritizing protective and support measures relating to an existing or emerging threat to homeland security.
(U//FOUO) The information in this assessment is current as of 9 January 2012. Unless otherwise noted, this JTA uses the FBI definition of terms, which may differ from the definitions used by DHS.
…
(U) Key Findings
(U//FOUO) We have no specific or credible information indicating a threat to the US Capitol or the National Capital Region (NCR) to coincide with the 2012 State of the Union address. We assess, however, that al-Qa‘ida and its affiliates and allies remain committed to attacking the Homeland and, as of February 2010, al-Qa‘ida identified the NCR and the State of the Union address itself as important targets, presumably for attacks. Moreover, homegrown violent extremists (HVEs) as well as lone offenders could view the event as an attractive target, offering the means to inflict casualties and garner extensive media coverage. Detecting homeland plots involving HVEs and lone offenders continues to challenge law enforcement and intelligence agencies due to the operational independence of the perpetrators, which can reduce or eliminate preoperational indicators.
(U//FOUO) Robust event security at the US Capitol might cause would-be attackers to engage less secure targets within the NCR during the State of the Union address in order to leverage the media attention and symbolism associated with the address.
…
(U) Intelligence Gaps
(U//FOUO) Are international terrorist groups or their affiliates and allies plotting to attack the US Capitol or the NCR during the State of the Union address?
(U//FOUO) Are domestic extremists planning to disrupt the State of the Union address by targeting entities associated with the US Government, including the US Capitol?
(U//FOUO) Are unidentified HVEs, inspired by international terrorist groups, planning to attack the US Capitol or the NCR during the State of the Union address?
(U//FOUO) Are unidentified lone offenders plotting to attack the US Capitol or the NCR during the State of the Union address?
(U//FOUO) Will peaceful demonstrations in the area of the US Capitol or within the NCR be exploited by violent actors who will pose a risk to officer safety during the State of the Union address?
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET-Bilderberg Meetings Participant Lists 1954-2011
The following represents a nearly complete list of participants and attendees of Bilderberg Meetings from 1954-2011. It will be updated over time as more information is acquired. If you have any additional information, including copies of official participant lists, please contact us or upload them using our secure online submission form.
| Meeting Time | Meeting Location | Participant List | Agenda |
|---|---|---|---|
| May 29-31, 1954 | Hotel de Bilderberg Osterbeek, Netherlands |
Unofficial | Unofficial |
| March 18-20, 1955 | Barbizon, France | ||
| September 23-25, 1955 | Garmisch-Partenkirchen, Germany | ||
| May 11-13, 1956 | Fredenborg, Denmark | ||
| February 15-17, 1957 | St. Simons Island Conference, USA | Unofficial | Unofficial |
| September 13-15, 1958 | Buxton Conference, England | Incomplete | Unofficial |
| September 18-20, 1959 | Çinar Hotel Yeşilköy, Istanbul, Turkey |
||
| May 28-29, 1960 | Palace Hotel Bürgenstock, Nidwalden, Switzerland | ||
| April 21-23, 1961 | Manoir St. Castin Lac-Beauport, Quebec, Quebec, Canada | ||
| May 18-20, 1962 | Grand Hotel Saltsjöbaden Saltsjöbaden, Sweden | ||
| March 29-31, 1963 | Cannes, France | Unofficial | Unofficial |
| March 20-22, 1964 | Williamsburg Conference, Virginia, USA | Unofficial | Unofficial |
| April 2-4, 1965 | Villa D’Este Conference, Italy | Unofficial | Unofficial |
| April 2-4, 1966 | Nassauer Hof Hotel Wiesbaden Wiesbaden, West Germany | Unofficial | Unofficial |
| March 31-April 2, 1967 | Cambridge, United Kingdom | Unofficial | Unofficial |
| April 26-28, 1968 | Mont Tremblant, Canada | Unofficial | Unofficial |
| May 9-11, 1969 | Hotel Marienlyst Helsingør, Denmark |
Unofficial | Unofficial |
| April 17-19, 1970 | Grand Hotel Quellenhof Bad Ragaz Conference, Sweden |
Unofficial | Unofficial |
| April 23-25, 1971 | Woodstock Inn Woodstock, Vermont, U.S.A. |
Unofficial | Unofficial |
| April 21-23, 1972 | La Reserve di Knokke-Heist Knokke, Belgium |
Unofficial | Unofficial |
| May 11-13, 1973 | Grand Hotel Saltsjöbaden Saltsjöbaden, Sweden |
Unofficial | Unofficial |
| April 19-21, 1974 | Hotel Mont d’Arbois Megeve, France |
Unofficial | Unofficial |
| April 25-27, 1975 | Golden Dolphin Hotel Çeşme, İzmir, Turkey | Unofficial | Unofficial |
| April 1976 | The Homestead Hot Springs, Virginia, United States |
||
| April 22-24, 1977 | Paramount Imperial Hotel Torquay, United Kingdom | Unofficial | Unofficial |
| April 21-23, 1978 | Chauncey Conference Center Princeton, New Jersey, United States |
Unofficial | Unofficial |
| April 27-29, 1979 | Grand Hotel Sauerhof Baden bei Wien, Austria | Unofficial | Unofficial |
| April 18-20, 1980 | Dorint Sofitel Quellenhof Aachen Aachen, West Germany |
Unofficial | Unofficial |
| May 15-17, 1981 | Palace Hotel Bürgenstock, Nidwalden, Switzerland |
Unofficial | Unofficial |
| April 14-16, 1982 | Rica Park Hotel Sandefjord Sandefjord, Norway |
Unofficial | Unofficial |
| May 13-15, 1983 | Château Montebello Montebello, Quebec, Canada | Unofficial | Unofficial |
| May 11-13, 1984 | Grand Hotel Saltsjöbaden Saltsjöbaden, Sweden | Unofficial | Unofficial |
| May 10-12, 1985 | Doral Arrowwood Hotel Rye Brook, New York, United States | Unofficial | Unofficial |
| April 25-27, 1986 | Gleneagles Hotel Gleneagles, Auchterarder, United Kingdom | Unofficial | Unofficial |
| April 24-26, 1987 | Villa d’Este Cernobbio, Italy |
Unofficial | Unofficial |
| June 3-5, 1988 | Interalpen-Hotel Tyrol Telfs-Buchen, Austria | Unofficial | Unofficial |
| May 12-14, 1989 | Gran Hotel de La Toja Isla de La Toja, Spain | Unofficial | Unofficial |
| May 10-13, 1990 | Harrison Conference Center Glen Cove, New York, United States |
Unofficial | Unofficial |
| June 6-9, 1991 | Baden-Baden, Germany | Unofficial | Unofficial |
| May 21-24, 1992 | Evian-les-Bains, France | Unofficial | Unofficial |
| April 22-25, 1993 | Nafsika Astir Palace Hotel Vouliagmeni, Greece |
Unofficial | Unofficial |
| June 2-5, 1994 | Helsinki, Finland | Unofficial | Unofficial |
| June 8-11, 1995 | Zurich, Switzerland | Unofficial | Unofficial |
| May 30 – June 2, 1996 | The Kingbridge Centre in King City, Ontario, Canada | Unofficial | Unofficial |
| June 12-15, 1997 | PineIsle Resort, Atlanta, U.S.A. | Unofficial | Unofficial |
| May 14-17, 1998 | Turnberry Hotel, Ayrshire, Scotland | Unofficial | Unofficial |
| June 3-6, 1999 | Caesar Park Hotel Penha Longa Hotel Caesar Park Penha Longa,Sintra, Portugal |
Unofficial | Unofficial |
| June 1-3, 2000 | Chateau Du Lac Hotel Brussels, Belgium |
Unofficial | Unofficial |
| May 24-27, 2001 | Hotel Stenungsbaden Stenungsund, Sweden |
Unofficial | Unofficial |
| May 30 – June 2, 2002 | Westfields Marriott Chantilly, Virginia, U.S.A. |
Unofficial | Unofficial |
| May 15-18, 2003 | Trianon Palace Hotel Versaille, France |
Unofficial | Unofficial |
| June 3-6, 2004 | Grand Hotel des Iles Borromees Stressa, Italy |
Unofficial | Unofficial |
| May 5-8, 2005 | Dorint Sofitel Seehotel Überfahrt Rottach-Egern, Germany |
Unofficial | Unofficial |
| June 8-11, 2006 | Brookstreet Hotel Ottawa, Canada | Unofficial | |
| June 3 – May 31, 2007 | Ritz-Carlton Hotel Istanbul, Turkey |
Official | |
| June 5-8, 2008 | Westfields Marriott Chantilly, Virginia, USA |
Official | |
| May 14-17, 2009 | Astir Palace Vouliagmeni, Greece |
Official | |
| June 3-6, 2010 | Hotel Dolce Sitges, Spain |
Official | |
| June 9-12, 2011 | Hotel Suvretta House, St. Moritz, Switzerland | Official |
TOP-SECRET-(U//FOUO) U.S. Army Female Suicide Bombers Report
TOP-SECRET-(U//FOUO) Afghanistan Human Terrain Team AF-24 Quarterly Report Summer 2011

COMMERCE (Security, Drought, and Prices) by DR Burke
Drought is taking its toll on farmers in the western areas of RC north. The first sign appeared in early spring. Realizing that the grazing land was going to be insufficient to support their flocks, farmers began slaughtering more of their sheep than usual. This, in turn, produced a temporary glut of lamb and a drop in what the farmer could expect from each animal. Faced with insufficient grazing land, some farmers are opting to move their animals to higher ground and to fields that can still provide a bit of nourishment for their hungry animals. Farmers in Jowzjan, for example, are moving their sheep down into Faryab. If current conditions worsen, flare-ups over common grazing lands may occur; local farmers may be unwilling to share valuable terrain with those they view as intruders.
All the farmers we have spoken with have noted the dramatic downturn in the yield of all crops, especially the all-important wheat harvest. Drought has severely diminished this year’s wheat harvest in the west of RC-North and escalated the price for flour for the average consumer. In response to a worsening economy, a few farmers have planted small fields of poppies, a crop that can tolerate dry conditions much better than wheat, watermelon, grapes, and tomatoes, the typical cash crops of the region. The poppy farmers are hoping, no doubt, that the lucrative profits from a small amount of opium will offset the shortfall of other crops. Some farmers have gone to Iran or sent their sons to Iran to seek jobs in construction in order to support their families, leaving behind villages even more vulnerable to insurgent influence. Without sufficient food for their families, other military aged men will, no doubt, be more susceptible to offers from insurgent leaders.
…
GOVERNANCE by DR Burke:
Local governance in rural Afghanistan is not simple. Older customary local assemblies operate alongside GIRoA officials, Community Development Councils (CDC’s), and insurgent groups. Although we speak of insurgent governments as “shadow governments,” they rarely exist in the shadows for those over whom they wield power. In villages where insurgents continue to exercise control, the insurgents and not GIRoA perform traditional governmental functions; they levy taxes, resolve disputes (they are, in many villages the only law in town), and maintain local defense forces.
Western Powers have invested their hope and their treasure in inventing a new form of local control: Community District Councils that come out of the National Solidarity Program (NSP). Managed by the Ministry of Rural Rehabilitation and Development (MRRD) with funds from NGO’s and from the World Bank, these organizations set priorities for the expenditure of donor money and oversee contracts. Although they offer an alternative to the indiscriminate funding of the past that encouraged favoritism and corruption, these organizations have little authority except when it comes to the stewardship of outside money. As those development funds begin to dry up, will CDC’s vanish? Can they be further empowered?
Customary organizations like shuras, on the other hand, continue in many rural areas to function as they have for generations raising collective concerns and resolving disputes. In districts like Ghormach insurgents have exerted considerable influence on these local shuras. In the last few months we have learned a good deal about these governing bodies. We recommend that ISAF forces use these local shuras as vehicles through which they can engage villagers and increase security. Our efforts have focused on obtaining information for our brigade, battalion, and companies located in Ghormach and Qeysar that identifies individuals with whom they may want to engage.
DOWNLOAD ORGINAL FILE HERE
TOP-SECRET – (U//FOUO) Joint Publication 3-15.1 Counter-Improvised Explosive Device Operations


(U) This publication provides joint doctrine for planning and executing counter-improvised explosive device (C-IED) operations. It outlines responsibilities, provides command and control considerations, discusses organizational options, details the C-IED process and attack the network methodology, and introduces models for coordinating with C-IED supporting organizations.
(U) This publication has been prepared under the direction of the Chairman of the Joint Chiefs of Staff. It sets forth joint doctrine to govern the activities and performance of the Armed Forces of the United States in joint operations, and provides the doctrinal basis for the planning and conduct of joint C-IED operations. It provides military guidance for the exercise of authority by combatant commanders and other joint force commanders (JFCs) and prescribes joint doctrine for operations, education, and training. It provides military guidance for use by the Armed Forces in preparing their appropriate plans. It is not the intent of this publication to restrict the authority of the JFC from organizing the force and executing the mission in a manner the JFC deems most appropriate to ensure unity of effort in the accomplishment of the overall objective.
…
3. (U) Attacking the Network—General Considerations
(U) While attacking the adversary’s network is a complex, time-consuming task, raising the adversaries’ cost of IED employment to unacceptable levels can be accomplished through a focused, continuous series of operations designed to disrupt the people, places, processes, and materials that support the IEDs’ design, supply, and employment chain. However, C-IED operations must be accomplished within the context of successfully targeting the broader adversary infrastructure.
a. (FOUO) There is no guaranteed method of defining and codifying targetable activities and major components of an IED network. To avoid detection and attack, adversary networks camouflage and constantly revise, or adapt, their TTP. At the highest echelons, the leadership rarely communicates openly and generally uses trusted aides and couriers to provide broad guidance to subordinates and direct the network. At the lowest echelons, the local cell members are detectable, targetable, and replaceable. Therefore, eliminating individuals only provides temporary and limited solutions to countering IED threats. But as networks function and move resources (information, money, supplies, recruits) from the highest to the lowest echelons, these activities are detectable and targetable. Disrupting the flow of resources is the most reliable way of neutralizing the adversary’s use of IEDs. While ideology may produce recruits, they have to eat, obtain weapons, travel, and build, transport, and emplace bombs. Personnel can be replaced, but
the adversary’s logistical infrastructure and materials often take more time.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – The FBI – Closing in on the Barker/Karpis Gang
 |
|---|
| The Barkers were heavily armed at a cottage near Lake Weir, Florida where they engaged in a shootout with Bureau agents in 1935. The weapons above were seized following the gunfight. |
In January 1935—77 years ago this month—more than a dozen Bureau agents surrounded a quaint two-story home on Lake Weir, Florida. Within moments, a fierce shoot-out erupted. It didn’t go well for the heavily armed criminals inside.

The Bremer Investigation A total of 25 individuals were convicted in connection with the Edward Bremer kidnapping, including seven who harbored members of the Barker/Karpis gang. Six of those convicted received life sentences, and three were killed resisting arrest, including Russell Gibson, Fred Barker (above), and Kate “Ma” Barker. |
|---|
For the Bureau of Investigation—just six months away from being renamed the FBI—the firefight was a continuation of a busy year of battling gangsters. In 1934, notorious public enemies like John Dillinger, “Pretty Boy” Floyd, and “Baby Face” Nelson had fallen at the hands of Bureau agents. Heading into 1935, the top priority was to put a dangerous gang—led by the wily Alvin “Creepy” Karpis and a pair of Barker brothers—out of business.
The gang got the Bureau’s attention through two high-profile kidnappings. The second targeted a wealthy banker named Edward George Bremer, Jr., who was snatched in St. Paul, Minnesota on January 17, 1934. Bremer was released three weeks later after his family paid $200,000 in ransom. Although he couldn’t identify the culprits, Bremer provided many clues. A key break came when the fingerprint of Arthur “Doc” or “Dock” Barker, a known criminal, turned up on an empty gas can found by a local police officer along the kidnapping route. Soon, a number of Barker’s confederates—including his brother Fred, Karpis, Harry Campbell, Fred Goetz, Russell Gibson, Volney Davis, and others—were linked to the crime.
The hunt was on, but the gang had a head start. They had split up and begun crisscrossing the country—with some even fleeing to Cuba. Three went as far as to undergo back-room plastic surgeries to conceal their fingerprints and identities. Others passed the ransom loot back and forth and looked for ways to launder the bills.
 |
|
|---|---|
| View Gallery |
In late September, Fred Barker and Campbell registered under fake names at the El Commodore Hotel in Miami. Joining them was Fred’s mother—Kate “Ma” Barker, who was known to help her criminal sons. When Fred asked for a quiet place to live, the hotel manager told him of a friend’s cottage for rent on the nearby Lake Weir. The Barkers moved there in November.
In December, Doc Barker was tracked by Bureau investigators to a home in Chicago. On January 8, Doc was arrested without incident. Later that night, several associates of Russell Gibson were also apprehended. Heavily armed and wearing a bullet-proof vest, Gibson tried to fight it out but was mortally wounded. Searching the apartment, agents found powerful firearms and loads of ammunition. And, tellingly, a map of Florida—with Lake Weir circled. Agents soon located the cottage hideout.
Shortly after 5 a.m. on January 16, 1935, a group of agents led by Earl Connelly surrounded the house and demanded the Barkers’ surrender. No response. They waited 15 minutes and called again. Again, no answer. Following another call for surrender and more silence, agents shot some tear gas grenades at the windows of the house. Someone in the house shouted, “All right, go ahead,” then machine-gun fire blasted from the upstairs window.
The agents responded with volleys of their own; more gunfire erupted from the house. Over the next hour, intermittent shots came from the home, and agents returned fire. By 10:30 a.m., all firing had stopped. Both Ma and Fred, it was soon learned, were dead.
The Barkers were history, but the cunning Karpis was still on the loose. How we caught up with him is another story that we’ll tell in the coming months.
TOP-SECRET – Guantanamo 10th Anniversary Photos
Guantanamo Prison 24 January 2010![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict18.jpg) |
|
High-value Detainee Units 6, top left, and 5, top right.![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict16.jpg) |
|
Detainee Hearing Court![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict0.jpg) |
|
|
|
2010 |
|
|
|
|
2009 |
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict12.jpg) FILE – In this June 1, 2009 file photo, reviewed by the U.S. military, Chinese Uighur detainees, who at the time were cleared for release, show a home-made note to visiting members of the media in Camp Iguana detention facility at the Guantanamo Bay U.S. Naval Base in Cuba. FILE – In this June 1, 2009 file photo, reviewed by the U.S. military, Chinese Uighur detainees, who at the time were cleared for release, show a home-made note to visiting members of the media in Camp Iguana detention facility at the Guantanamo Bay U.S. Naval Base in Cuba. |
|
|
|
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict6.jpg) FILE – In this May 14, 2009 file photo, reviewed by the U.S. military, detainees pray before dawn near a fence of razor-wire inside Camp 4 detention facility at the Guantanamo Bay U.S. Naval Base in Cuba. FILE – In this May 14, 2009 file photo, reviewed by the U.S. military, detainees pray before dawn near a fence of razor-wire inside Camp 4 detention facility at the Guantanamo Bay U.S. Naval Base in Cuba. |
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict14.jpg) FILE – In this May 13, 2009 file photo, reviewed by the U.S. military, a detainee stands at his cell window yelling after seeing a group of journalists who were visiting Camp 5 maximum-security detention facility at the Guantanamo Bay U.S. Naval Base in Cuba. FILE – In this May 13, 2009 file photo, reviewed by the U.S. military, a detainee stands at his cell window yelling after seeing a group of journalists who were visiting Camp 5 maximum-security detention facility at the Guantanamo Bay U.S. Naval Base in Cuba. |
|
2008 |
|
|
|
|
2007 |
|
|
|
|
2006 |
|
|
|
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict13.jpg) FILE – In this Dec. 4, 2006 file photo, reviewed by a U.S. Department of Defense official, a detainee shields his face as he peers out through the so-called “bean hole” which is used to pass food and other items into detainee cells, in Camp Delta detention facility at the Guantanamo Bay U.S. Naval Base in Cuba. FILE – In this Dec. 4, 2006 file photo, reviewed by a U.S. Department of Defense official, a detainee shields his face as he peers out through the so-called “bean hole” which is used to pass food and other items into detainee cells, in Camp Delta detention facility at the Guantanamo Bay U.S. Naval Base in Cuba. |
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict5.jpg) FILE – In this Sept. 19, 2006 file photo, reviewed by a U.S. Department of Defense official, a detainee stands at a fence holding Islamic prayer beads in Camp Delta detention facility at the Guantanamo Bay U.S. Naval Base in Cuba. FILE – In this Sept. 19, 2006 file photo, reviewed by a U.S. Department of Defense official, a detainee stands at a fence holding Islamic prayer beads in Camp Delta detention facility at the Guantanamo Bay U.S. Naval Base in Cuba. |
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict8.jpg) FILE – In this Sept. 19, 2006 file photo, reviewed by a U.S. Department of Defense official, military personnel stand inside the brand new Camp 6 maximum security detention facility at the Guantanamo Bay U.S. Naval Base in Cuba. FILE – In this Sept. 19, 2006 file photo, reviewed by a U.S. Department of Defense official, military personnel stand inside the brand new Camp 6 maximum security detention facility at the Guantanamo Bay U.S. Naval Base in Cuba. |
|
2004 |
|
|
|
|
2002 |
|
|
|
|
|
|
TOP-SECRET – John Kiriakou Former CIA Officer Torture Leak Criminal Complaint
TOP-SECRET from the FBI – Former CIA Officer John Kiriakou Charged with Disclosing Covert Officer’s Identity and Other Classified Information to Journalists and Lying to CIA’s Publications Review Board
ALEXANDRIA, VA—A former CIA officer, John Kiriakou, was charged today with repeatedly disclosing classified information to journalists, including the name of a covert CIA officer and information revealing the role of another CIA employee in classified activities, Justice Department officials announced. The charges result from an investigation that was triggered by a classified defense filing in January 2009, which contained classified information the defense had not been given through official government channels, and, in part, by the discovery in the spring of 2009 of photographs of certain government employees and contractors in the materials of high-value detainees at Guantanamo Bay, Cuba. The investigation revealed that on multiple occasions, one of the journalists to whom Kiriakou is alleged to have illegally disclosed classified information, in turn, disclosed that information to a defense team investigator, and that this information was reflected in the classified defense filing and enabled the defense team to take or obtain surveillance photographs of government personnel. There are no allegations of criminal activity by any members of the defense team for the detainees.
Kiriakou, 47, of Arlington, Va., was a CIA intelligence officer between 1990 and 2004, serving at headquarters and in various classified overseas assignments. He is scheduled to appear at 2 p.m. today before U.S. Magistrate Judge John F. Anderson in federal court in Alexandria.
Kiriakou was charged with one count of violating the Intelligence Identities Protection Act for allegedly illegally disclosing the identity of a covert officer and two counts of violating the Espionage Act for allegedly illegally disclosing national defense information to individuals not authorized to receive it. Kiriakou was also charged with one count of making false statements for allegedly lying to the Publications Review Board of the CIA in an unsuccessful attempt to trick the CIA into allowing him to include classified information in a book he was seeking to publish.
The four-count criminal complaint, which was filed today in the Eastern District of Virginia, alleges that Kiriakou made illegal disclosures about two CIA employees and their involvement in classified operations to two journalists on multiple occasions between 2007 and 2009. In one case, revealing the employee’s name as a CIA officer disclosed classified information as the employee was and remains covert (identified in the complaint as “Covert Officer A”). In the second case, Kiriakou allegedly disclosed the name and contact information of an employee, identified in the complaint as “Officer B,” whose participation in an operation to capture and question terrorism subject Abu Zubaydah in 2002 was then classified. Kiriakou’s alleged disclosures occurred prior to a June 2008 front-page story in The New York Times disclosing Officer B’s alleged role in the Abu Zubaydah operation.
“Safeguarding classified information, including the identities of CIA officers involved in sensitive operations, is critical to keeping our intelligence officers safe and protecting our national security,” said Attorney General Eric Holder. “Today’s charges reinforce the Justice Department’s commitment to hold accountable anyone who would violate the solemn duty not to disclose such sensitive information.”
Patrick J. Fitzgerald, United States Attorney for the Northern District of Illinois, who was appointed Special Attorney in 2010 to supervise the investigation, said: “I want to thank the Washington Field Office of the FBI and the team of attorneys assigned to this matter for their hard work and dedication to tracing the sources of the leaks of classified information.” Mr. Fitzgerald announced the charges with James W. McJunkin, Assistant Director in Charge of the Washington Field Office of the Federal Bureau of Investigation, and they thanked the Central Intelligence Agency for its very substantial assistance in the investigation, as well as the Air Force Office of Special Investigations for its significant assistance.
“Protecting the identities of America’s covert operatives is one of the most important responsibilities of those who are entrusted with roles in our nation’s intelligence community. The FBI and our intelligence community partners work diligently to hold accountable those who violate that special trust,” said Mr. McJunkin.
The CIA filed a crimes report with the Justice Department on March 19, 2009, prior to the discovery of the photographs and after reviewing the Jan. 19, 2009, classified filing by defense counsel for certain detainees with the military commission then responsible for adjudicating charges. The defense filing contained information relating to the identities and activities of covert government personnel, but prior to Jan. 19, 2009, there had been no authorized disclosure to defense counsel of the classified information. The Justice Department’s National Security Division, working with the FBI, began the investigation. To avoid the risk of encountering a conflict of interest because of the pending prosecutions of some of the high-value detainees, Mr. Fitzgerald was assigned to supervise the investigation conducted by a team of attorneys from the Southern District of New York, the Northern District of Illinois, and the Counterespionage Section of the National Security Division who were not involved in pending prosecutions of the detainees.
According to the complaint affidavit, the investigation determined that no laws were broken by the defense team as no law prohibited defense counsel from filing a classified document under seal outlining for a court classified information they had learned during the course of their investigation. Regarding the 32 pages of photographs that were taken or obtained by the defense team and provided to the detainees, the investigation found no evidence the defense attorneys transmitting the photographs were aware of, much less disclosed, the identities of the persons depicted in particular photographs and no evidence that the defense team disclosed other classified matters associated with certain of those individuals to the detainees. The defense team did not take photographs of persons known or believed to be current covert officers. Rather, defense counsel, using a technique known as a double-blind photo lineup, provided photograph spreads of unidentified individuals to their clients to determine whether they recognized anyone who may have participated in questioning them. No law or military commission order expressly prohibited defense counsel from providing their clients with these photo spreads.
Further investigation, based in part on e-mails recovered from judicially-authorized search warrants served on two e-mail accounts associated with Kiriakou, allegedly revealed that:
- Kiriakou disclosed to Journalist A the name of Covert Officer A and the fact that Covert Officer A was involved in a particular classified operation. The journalist then provided the defense investigator with the full name of the covert CIA employee;
- Kiriakou disclosed or confirmed to Journalists A, B, and C the then-classified information that Officer B participated in the Abu Zubaydah operation and provided two of those journalists with contact information for Officer B, including a personal e-mail address. One of the journalists subsequently provided the defense investigator with Officer B’s home telephone number, which the investigator used to identify and photograph Officer B; and
- Kiriakou lied to the CIA regarding the existence and use of a classified technique, referred to as a “magic box,” in an unsuccessful effort to trick the CIA into allowing him to publish information about the classified technique in a book.
Upon joining the CIA in 1990 and on multiple occasions in following years, Kiriakou signed secrecy and non-disclosure agreements not to disclose classified information to unauthorized individuals.
Regarding Covert Officer A, the affidavit details a series of e-mail communications between Kiriakou and Journalist A in July and August 2008. In an exchange of e-mails on July 11, 2008, Kiriakou allegedly illegally confirmed for Journalist A that Covert Officer A, whose first name only was exchanged at that point, was “the team leader on [specific operation].” On August 18, 2008, Journalist A sent Kiriakou an e-mail asking if Kiriakou could pick out Covert Officer A’s last name from a list of names Journalist A provided in the e-mail. On Aug. 19, 2008, Kiriakou allegedly passed the last name of Covert Officer A to Journalist A by e-mail, stating “It came to me last night.” Covert Officer A’s last name had not been on the list provided by Journalist A. Later that same day, approximately two hours later, Journalist A sent an e-mail to the defense investigator that contained Covert Officer A’s full name. Neither Journalist A, nor any other journalist to the government’s knowledge, has published the name of Covert Officer A.
At the time of Kiriakou’s allegedly unauthorized disclosures to Journalist A, the identification of Covert Officer A as “the team leader on [specific operation]” was classified at the Top Secret/Sensitive Compartmented Information (SCI) level because it revealed both Covert Officer A’s identity and his association with the CIA’s Rendition, Detention, and Interrogation (RDI) Program relating to the capture, detention, and questioning of terrorism subjects. The defense investigator was able to identify Covert Officer A only after receiving the e-mail from Journalist A, and both Covert Officer A’s name and association with the RDI Program were included in the January 2009 classified defense filing. The defense investigator told the government that he understood from the circumstances that Covert Officer A was a covert employee and, accordingly, did not take his photograph. No photograph of Covert Officer A was recovered from the detainees at Guantanamo.
In a recorded interview last Thursday, FBI agents told Kiriakou that Covert Officer A’s name was included in the classified defense filing. The affidavit states Kiriakou said, among other things, “How the heck did they get him? . . . [First name of Covert Officer A] was always undercover. His entire career was undercover.” Kiriakou further stated that he never provided Covert Officer A’s name or any other information about Covert Officer A to any journalist and stated “Once they get the names, I mean this is scary.”
Regarding Officer B, the affidavit states that he worked overseas with Kiriakou on an operation to locate and capture Abu Zubaydah, and Officer B’s association with the RDI Program and the Abu Zubaydah operation in particular were classified until that information was recently declassified to allow the prosecution of Kiriakou to proceed.
In June 2008, The New York Times published an article by Journalist B entitled “Inside the Interrogation of a 9/11 Mastermind,” which publicly identified Officer B and reported his alleged role in the capture and questioning of Abu Zubaydah—facts which were then classified. The article attributed other information to Kiriakou as a source, but did not identify the source(s) who disclosed or confirmed Officer B’s identity. The charges allege that at various times prior to publication of the article, Kiriakou provided Journalist B with personal information regarding Officer B, knowing that Journalist B was seeking to identify and locate Officer B. In doing so, Kiriakou allegedly confirmed classified information that Officer B was involved in the Abu Zubaydah operation. For example, Kiriakou allegedly e-mailed Officer B’s phone number and personal e-mail address to Journalist B, who attempted to contact Officer B via his personal e-mail in April and May 2008. Officer B had provided his personal e-mail address to Kiriakou, but not to Journalist B or any other journalist. Subsequently, Kiriakou allegedly revealed classified information by confirming for Journalist B additional information that an individual with Officer B’s name, who was associated with particular contact information that Journalist B had found on a website, was located in Pakistan in March 2002, which was where and when the Abu Zubaydah operation took place.
After The New York Times article was published, Kiriakou sent several e-mails denying that he was the source for information regarding Officer B, while, at the same time, allegedly lying about the number and nature of his contacts with Journalist B. For example, in an e-mail dated June 30, 2008, Kiriakou told Officer B that Kiriakou had spoken to the newspaper’s ombudsman after the article was published and said that the use of Officer B’s name was “despicable and unnecessary” and could put Officer B in danger. Kiriakou also denied that he had cooperated with the article and claimed that he had declined to talk to Journalist B, except to say that he believed the article absolutely should not mention Officer B’s name. “[W]hile it might not be illegal to name you, it would certainly be immoral,” Kiriakou wrote to Officer B, according to the affidavit.
From at least November 2007 through November 2008, Kiriakou allegedly provided Journalist A with Officer B’s personal contact information and disclosed to Journalist A classified information revealing Officer B’s association with the RDI Program. Just as Journalist A had disclosed to the defense investigator classified information that Kiriakou allegedly imparted about Covert Officer A, Journalist A, in turn, provided the defense investigator information that Kiriakou had disclosed about Officer B. For example, in an e-mail dated April 10, 2008, Journalist A provided the defense investigator with Officer B’s home phone number, which, in light of Officer B’s common surname, allowed the investigator to quickly and accurately identify Officer B and photograph him. Both Officer B’s name and his association with the RDI Program were included in the January 2009 classified defense filing, and four photographs of Officer B were among the photos recovered at Guantanamo.
In the same recorded interview with FBI agents last week, Kiriakou said he “absolutely” considered Officer B’s association with the Abu Zubaydah operation classified, the affidavit states. Kiriakou also denied providing any contact information for Officer B or Officer B’s association with the Abu Zubaydah operation to Journalists A and B prior to publication of the June 2008 New York Times article. When specifically asked whether he had anything to do with providing Officer B’s name or other information about Officer B to Journalist B prior to the article, Kiriakou stated “Heavens no.”
As background, the affidavit states that sometime prior to May 22, 2007, Kiriakou disclosed to Journalist C classified information regarding Officer B’s association with Abu Zubaydah operation, apparently while collaborating on a preliminary book proposal. A footnote states that Journalist C is not the coauthor of the book Kiriakou eventually published.
Prior to publication of his book, The Reluctant Spy: My Secret Life in the CIA’s War on Terror, Kiriakou submitted a draft manuscript in July 2008 to the CIA’s Publication Review Board (PRB). In an attempt to trick the CIA into allowing him to publish information regarding a classified investigative technique, Kiriakou allegedly lied to the PRB by falsely claiming that the technique was fictional and that he had never heard of it before. In fact, according to a transcript of a recorded interview conducted in August 2007 to assist Kiriakou’s coauthor in drafting the book, Kiriakou described the technique, which he referred to as the “magic box,” and told his coauthor that the CIA had used the technique in the Abu Zubaydah operation. The technique was also disclosed in the June 2008 New York Times article and referred to as a “magic box.”
In his submission letter to the PRB, Kiriakou flagged the reference to a device called a “magic box,” stating he had read about it in the newspaper article but added that the information was “clearly fabricated,” as he was unaware of and had used no such device. The affidavit contains the contents of an August 2008 e-mail that Kiriakou sent his coauthor admitting that he lied to the PRB in an attempt to include classified information in the book. The PRB subsequently informed Kiriakou that the draft manuscript contained classified information that he could not use, and information regarding the technique that Kiriakou included in the manuscript remained classified until it was recently declassified to allow Kiriakou’s prosecution to proceed.
Upon conviction, the count charging illegal disclosure of Covert Officer A’s identity to a person not authorized to receive classified information carries a maximum penalty of five years in prison, which must be imposed consecutively to any other term of imprisonment; the two counts charging violations of the Espionage Act each carry a maximum term of 10 years in prison; and making false statements carries a maximum prison term of five years. Each count carries a maximum fine of $250,000.
A complaint contains only allegations and is not evidence of guilt. The defendant is presumed innocent and is entitled to a fair trial at which the government has the burden of proving guilt beyond a reasonable doubt.
The government is being represented in court by Assistant U.S. Attorneys Iris Lan (Southern District of New York) and Mark E. Schneider (Northern District of Illinois), and DOJ trial attorney Ryan Fayhee, of the Counterespionage Section of the National Security Division. Assistant U.S. Attorney Lisa Owings (Eastern District of Virginia) will assist in the matter under local court rules.
TOP-SECRET – (U//FOUO) DoD Global Information Grid 2.0 Concept of Operations

Executive Summary
Achieving and maintaining the information advantage as a critical element of national power requires the concentrated effort of the entire Department of Defense (DoD) to provide a seamless information environment optimized for the warfighter.
Operational experiences in Iraq and Afghanistan support the continued need to eliminate barriers to information sharing that currently exist on DoD’s multiple networks. A concerted effort to unify the networks into a single information environment providing timely information to commanders will improve command and control, thus increasing our speed of action. Providing an information technology (IT) / National Security Systems (NSS) infrastructure that is accessible anywhere and anytime is key to ensuring the agility of the Department and allowing our most valuable resources, our people, nearly instant access to the information they need to make decisions in the execution of their missions. In turn, the Global Information Grid (GIG) must be designed and optimized to support warfighting functions of advantaged and disadvantaged users, to include mission partners, across the full range of military and National Security operations in any operational environment. The GIG must also be resilient and able to support the missions despite attacks by sophisticated adversaries.
The operational concept of GIG 2.0 is depicted in Figure 1, and builds upon net-centric concepts as articulated in DoD Information Enterprise Architecture (DIEA) Version 1.0 (April 2008).
Furthermore, GIG 2.0 is founded upon the following 5 characteristics which are further discussed in section 2.7: Global Authentication, Access Control, and Directory Services Information and Services ―From the Edge‖ Joint Infrastructure Common Policies and Standards Unity of Command.
GIG 2.0 will facilitate mission accomplishment by providing tactical services ―from the edge‖ in support of the warfighter. The warfighter tactical edge user solutions must work in austere deployed environments. Today many IT services and systems are designed to work in a robust IT environment and often do not scale down to the deployed user. This separation between home station and deployed capabilities requires the user to transition from garrison IT services to tactical IT services, often losing functionality in the deployed environment. This document presents the GIG 2.0 Concept of Operations (CONOPS) as it relates to five key critical characteristics of the GIG and their relationship to the DoD Joint Capability Areas (JCA).

DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – Japanese Government Denied Existence of Document on Fukushima Worst-Case Scenario

The government buried a worst-case scenario for the Fukushima nuclear crisis that was drafted last March and kept it under wraps until the end of last year, sources in the administration said Saturday.
After the document was shown to a small, select group of senior government officials at the prime minister’s office in late March, the administration of then Prime Minister Naoto Kan decided to quietly bury it, the sources said.
“When the document was presented (in March), a discussion ensued about keeping its existence secret,” a government source said.
In order to deny its existence, the government treated it as a personal document of Japan Atomic Energy Commission Chairman Shunsuke Kondo, who authored it, until the end of December, the sources said.
It was only then that it was actually recognized as an official government document, they said.
“The content was so shocking that we decided to treat it as if it didn’t exist,” a senior government official said.
A private-sector panel investigating the disaster at the Fukushima No. 1 nuclear plant intends to examine whether the government tried to manipulate information during its handling of the crisis.
he document was dated March 25, 2011, two weeks after the massive earthquake and tsunami triggered the country’s worst nuclear crisis. It was premised on a scenario in which all plant workers had to be evacuated due to a rise in radiation levels after a hydrogen explosion damaged a containment vessel encasing the plan’s No. 1 reactor.
The document said that should such a case occur, residents within a radius of 170 kilometers or more of the plant would be forced to move out, while those within a radius of 250 km of the plant, including Tokyo, would be allowed to leave if they wish.
“It contained such shocking content that we decided to treat it as if it never existed,” a senior government official said.
Another government source said, “When the document was presented, there was a discussion about the choice of keeping the existence of the document itself secret.”
Kan admitted the existence of a worst case scenario in September, while the government of his successor, Prime Minister Yoshihiko Noda, decided to treat the document as a Cabinet Office document after some parts of it were reported in December.
TOP-SECRET from the FBI – Former Chicago Lawyer Sentenced to 15 Years in Prison for Mortgage Fraud Involving at Least 102 Fraudulent Bailouts
CHICAGO—A former Chicago lawyer was sentenced to 15 years in federal prison for engaging in mortgage and bankruptcy fraud schemes involving a so-called “mortgage bailout” program that purported to “rescue” financially distressed homeowners but instead tricked victims into relinquishing title to their homes and declaring bankruptcy. The defendant, Norton Helton, participated in at least 102 fraudulent mortgage bailout transactions and more than a dozen fraudulent bankruptcies in 2004 and 2005. He was ordered to pay more than $3.2 million in mandatory restitution to various lenders and financial institutions that were not repaid by the borrowers or fully recovered through subsequent foreclosure sales, federal law enforcement officials announced today.
Helton, 50, of Atlanta and formerly of Chicago, was sentenced Wednesday by U.S. District Judge Samuel Der-Yeghiayan in federal court in Chicago. He was ordered to begin serving his sentence in June.
Helton and two co-defendants, Charles White and Felicia Ford, were convicted of multiple fraud counts following a five-week trial in June and July 2010. White, 43, of Chicago, was sentenced late last year to more than 22 years in prison, while Ford, 39, of Chicago, is awaiting sentencing next month.
White owned and operated Eyes Have Not Seen (EHNS), which purported to offer insolvent homeowners mortgage bailout services that would prevent them from losing their homes in foreclosure by selling their property to third-party investors for whom the defendants fraudulently obtained mortgage financing. The victim-clients were assured they could continue living in their homes rent and mortgage-free for a year while they attempted to eliminate their debt and repair their credit. EHNS misled clients concerning the operation of the purported program. In particular, victim-clients were not told that their homes were, in fact, being sold to third parties and that ENHS would strip their homes of any available equity at the time of sale, which EHNS did. Instead, ENHS clients were told that they were only temporarily transferring their homes and would preserve their ownership rights.
Helton was recruited by White to represent ENHS participants at the real estate transactions it orchestrated. The victim-clients typically met Helton for the first time at the closings at which they sold their homes. Helton worked to placate individuals who questioned the program and to dissuade them from retaining independent legal advice. He received above-market legal fees for appearing at closings at which he did little more than guide victim-clients through the paperwork that sold their homes with EHNS receiving all of the profits from the sale. Helton further used the ENHS real estate closings to recruit prospective bankruptcy clients, informing them that bankruptcy would serve as a component of the bailout program. Helton subsequently filed more than a dozen bankruptcy petitions for victim-clients that omitted any reference to their recent EHNS property sales.
In addition to participating in ENHS’s bailout program, Helton attempted to implement his own mortgage bailout program through Diamond Management of Chicago, Inc., a foreclosure avoidance company comparable to EHNS. Helton marketed Diamond’s bailout program and his bankruptcy services as part of a “credit repair” system.
Patrick J. Fitzgerald, United States Attorney for the Northern District of Illinois, announced the sentence today with Robert D. Grant, Special Agent in Charge of the Chicago Office of the Federal Bureau of Investigation; Barry McLaughlin, Special Agent in Charge of the U.S. Housing and Urban Development Office of Inspector General in Chicago; and Thomas P. Brady, Inspector in Charge of the U.S. Postal Inspection Service in Chicago. The U.S. Trustee Program, a Justice Department component that oversees administration of bankruptcy cases and private trustees, also assisted in the investigation.
The government is being represented by Assistant U.S. Attorneys Joel Hammerman and Mark E. Schneider.
The case is part of a continuing effort to investigate and prosecute mortgage fraud in northern Illinois and nationwide under the umbrella of the interagency Financial Fraud Enforcement Task Force, which was established to lead an aggressive, coordinated, and proactive effort to investigate and prosecute financial crimes. For more information on the task force, visit: http://www.StopFraud.go
TOP-SECRET – Faces of Torture: Egyptian State Security Officers Photos and Names

The following set of photos and names has been publicly posted to other sites, including Cryptome. However, with the recent confirmation that Flickr removed and censored these photos, we wish to ensure that this information reaches as many people as possible. We are also aware that this site is visited frequently by members of the Egyptian government and the International Criminal Court.
When we stormed State Security Police headquarters in Nasr City, which hosted one of Mubarak’s largest torture facilities, on Saturday I found two DVDs in one of the offices, both titled “أرشيف السادة ضباط الجهاز” The Agency Officers’ Archive. The DVDs included profile pictures of State Security officers, organized in folders. Each folder had the officers’ name. Some however did not have the names. There were also sub folders that included pictures of those officers in social events like weddings.
I don’t know what was the purpose of these two DVDs, but I sincerely thank the State Security officials who gave us this present on a golden plate. I initially uploaded the profile pictures to this flickr set and added them to the Piggipedia. But unfortunately, flickr censored the pictures on grounds of “copyrights infringement”!
With the help of ANONYMOUS and other bloggers in Egypt and abroad, I re-uploaded the pictures to the cyberspace, and they are now hosted on several sites.
I urge you all to circulate them. And if you have any more information about those officers please come forward.
Each member of SS has to be brought to justice. This was an agency devoted to spying, surveillance, torture and murder. Every member of this organization from the informer all the way up to the generals should be prosecuted. SS has to be dissolved. It cannot be “restructured” like what the current PM is calling for.
Although those torturers violated our private lives on a daily basis, bugging our phones, offices, and even our bedrooms, I will respect the privacy of their families and will not publish the photos of their social events that included family members.
Download .zip file containing all images (417 MB)
Download .pdf file containing all images (26 MB)
Names of Officers Whose Photos are Contained in the File
- Ahmad el-Badawi
- Ahmad Fathi
- Ahmad Raafat
- Ahmad Raoof
- Ahmed Atef
- Ahmed el-Azzazi
- Ali Allam
- Amgad Ezz Eddin
- Amr Abdel Moula
- Amr L’Assar
- Assem Esmat
- Ayman el-Banna
- Ayman el-Rashidi
- Ehab el-Gheryani
- Fahd Abul Kheir
- Hani Talaat
- Hassan Abdel Rahman
- Hassan Tantawi
- Hisham Abu Gheida
- Hisham el-Baradei
- Hisham el-Dafrawi
- Hossam Wahdan
- Kamal el-Sayyed
- Khaled el-Taweel
- Khaled Moussa
- Khaled Shaker
- Magdi el-Masri
- Maged Mostafa
- Mahmoud el-Rashidi
- Mahmoud el-Zeini
- Mohamed Abdel Kareem
- Mohamed Abul Wafa
- Mohamed el-Morshedi
- Mohamed el-Samanoudi
- Mohamed el-Zamak
- Mohamed Hanafi
- Mohamed Mahmoud Barghash
- Mohamed Safwat
- Mohamed Taher
- Mohamed Yehia
- Mortada Ibrahim
- Motassem Ghoneim
- Rashad Ghoneim
- Rushdi el-Qamari
- Salah Hegazi
- Salah Salama
- Sherif el-Bahei
- Sherif Shabana
- Shoman
- Tarek el-Bahnassawi
- Tarek el-Mouggi
- Tarek el-Rakaybi
Photos of 168 officers whose names are not known are also contained in the file.
TOP-SECRET-NATO Training Mission Afghanistan (NTM-A) Gender Integration White Paper

In the 20th century, the various governments of Afghanistan were actively involved with the international community in adopting human rights initiatives, including gender equality. However, the conservative nature of Afghan society coupled with weak central governance limited each regime’s ability to extend modern programs beyond the major urban areas. Initiatives that the constitutional monarchy and communist government attempted to implement often faced significant opposition from the countryside and were ultimately eliminated with the rise of the Taliban. Afghanistan joined the international community in ratifying the Universal Declaration of Human Rights (UDHR) in 1948 and established legislation and processes to integrate women into public life from the 1950s through the 1980s. However, in 1996 the Taliban relegated women to a domestic role with brutal enforcement. With the establishment of the Government of the Islamic Republic of Afghanistan (GIRoA), Afghanistan entered a new era for gender integration. In compliance with modern international human rights agreements and reaffirming its commitment to the UDHR, Afghanistan reopening opportunities in the public and private sector through its Constitution and supporting legislation. With the assistance of NATO’s International Security Assistance Force (ISAF), GIRoA is establishing the governmental institutions and societal conditions necessary to implement and enforce these laws.
ISAF’s mandate is to assist the GIRoA by supporting security, strengthening government structures and contributing to development and reconstruction as supported by the Constitution of Afghanistan (Olsson and Tejpar 2009). One of ISAF’s goals is to enable GIRoA to continue its gender strategy without ISAF support. ISAF’s subordinate headquarters for force generation of the Afghan National Security Forces (ANSF) is the NATO Training Mission-Afghanistan (NTM-A). NTM-A’s mission is to generate the ANSF, develop capable ministerial systems and resource the fielded force to build sustainable capacity and capability in order to enhance the GIRoA’s ability to achieve stability and security in Afghanistan. NTM-A, in coordination with NATO allies, partners and key Afghan stakeholders, develops the ANSF in compliance with international agreements and Afghan law and thereby enables Afghan gender integration within the ANSF, Ministry of Defense (MoD) and Ministry of Interior (MoI).
As ISAF transitions security operations to the GIRoA by 2014, NTM-A is executing a supporting plan to transition security force generation, education and training to the ANSF. Care must be taken to execute the transition in a manner that underwrites hard-won gender integration accomplishments. Gender integration is both the right thing to do and the pragmatic thing to do. It upholds international principles and bolsters Afghan security and stability. Nevertheless, its implementations must be metered through Afghan governmental authorities and the Afghan society’s willingness to adapt.
Problem Statement
This white paper describes the GIRoA’s legal framework and policy for gender integration and NTM-A’s supporting role as NATO’s force generation headquarters in Afghanistan. It provides an analysis of the ANSF, identifying strengths, weaknesses, opportunities and threats or challenges. It proposes considerations as NTM-A transitions the force generation mission to the ANSF by 2014 that would bolster support to GIRoA national objectives regarding gender integration.
Idealistic and Realistic Requirements for Gender Integration
Afghanistan needs strong gender integration policy and programs for both idealistic and realistic reasons, but will continue to be challenged with implementation because of its conservative Islamic culture and tradition of strong rural independence. The GIRoA has participated actively in multinational agreements supporting gender integration and has incorporated gender integration into its foundational legislation. Since 2002, Afghanistan has been the recipient of significant international aid to support its reconstruction. The international community is vested in Afghanistan and is scrutinizing how Afghanistan meets its obligations under the United Nations agreements. The Constitution of Afghanistan declares that men and women have equal rights and duties before the law and GIRoA has integrated, or mainstreamed, gender into its stated national goals and into government at all levels. The MoI and MoD have an obligation to contribute to the attainment of national goals on gender equality. Gender integration within the ANSF will support the attainment of national goals and improve security and stability in Afghanistan.
Pragmatically, the ANSF need female members in order to be effective security forces. Afghanistan is a conservative, Islamic society. The Afghan National Police (ANP) and Afghan National Army (ANA) are virtually all-male organizations. As a result, the ANP cannot respond effectively to incidents involving women as suspects, complainants or victims. Properly empowered policewomen can react to violence against women, family violence, children in trouble and kidnappings. They can interrogate, detain and investigate female suspects; provide support to female victims of crime; and ensure the security of women in communities (Murray, Report on the Status of Women in the Afghan National Police 2006). The ANA is equally ill equipped to conduct counterinsurgency operations within the Afghan population without female counterparts to attend to female detainees and female casualties on the battlefield as well as interact with female citizens. Female soldiers can support combat operations in career fields such as intelligence, logistics, medicine and aviation. Similar to their police counterparts, they can interrogate and detain female combatants; provide support to female casualties; and ensure the security of women on operational objectives. Female ANSF can provide culturally mandated separation between male security force members and females encountered in the course of duty. Additionally, they can provide critical service and support capabilities by serving in logistics and aviation specialties. The GIRoA can utilize the ANSF as a tool to implement gender integration policy and gain greater security and stability.
DOWNLOAD ORIGINAL ARTICLE HERE
TOP-SECRET-Swiss Authorities Investigate Money Laundering Linked to Russian Tax Fraud Scheme
Switzerland has opened a money-laundering probe at the request of Hermitage Capital Management Ltd., the first criminal investigation outside Russia linked to the death of lawyer Sergei Magnitsky in a Moscow prison.
The allegations involving a former Russian tax official are the most recent lodged by Hermitage founder William Browder as he asks authorities around the world to sanction officials he blames for Magnitsky’s death. The lawyer, who alleged Interior Ministry officials fraudulently collected a $230 million tax refund using documents seized from Hermitage, died in 2009 after a year in pre-trial detention.
“It’s been impossible to get any kind of real criminal investigation in Russia,” Browder said yesterday by phone. “It’s highly significant that a Western law enforcement agency is taking this seriously and is launching an investigation.”
According to Hermitage, once the largest foreign investor in Russia, Olga Stepanova authorized $155 million of the tax rebates in 2007 as head of Moscow Tax Inspectorate No. 28. Since then, at least $38 million flowed through bank accounts opened on behalf of companies incorporated by Stepanova’s husband, partly to buy homes in Dubai, Montenegro and Russia, London- based Hermitage alleged in a Jan. 28 letter to the Swiss Attorney General and Credit Suisse AG.
The couple’s average declared income from 2006 through 2009 was $38,381 a year, according to Russian income declarations included in Hermitage’s filing with the Swiss authorities.
“The Office of the Attorney General of Switzerland confirms having officially launched a criminal investigation in respect of suspected money laundering,” spokeswoman Jeanette Balmer said yesterday in an e-mail after she was asked about the Hermitage letter. “The investigation relates to persons unknown,” she said, declining to release further details.
Stepanova, now an adviser to the head of Russia’s arms procurement agency didn’t respond to e-mailed, faxed and phone requests for comment submitted to the agency’s press service yesterday. Her husband, Vladlen Stepanov, an employee of Moscow- based OOO Volsstroy, is on vacation until mid-May, according to a person who answered the company’s phone and said she would pass on a reporter’s contact number.
…
Russia is the world’s most corrupt major economy, according to Berlin-based Transparency International’s 2010 Corruption Perceptions Index released in October. It ranked 154th among 178 countries, tied with Tajikistan and Kenya.
Crime and Punishment in Putin’s Russia
Russian police say they have closed the case file on the country’s largest tax fraud. It occurred on December 24 in 2007, when Moscow tax officials approved a same-day refund of 5.4 billion rubles — or $230 million — to a gang masquerading as officers of Hermitage Capital, once the largest hedge-fund manager in Russia and founded by financiers Edmond Safra and Bill Browder. Interior Ministry police claim the complex scam was pulled off by a sawmill worker and a burglar, both currently serving five-year sentences, in cahoots with four others, all of whom are now dead. One had a fatal heart attack before the crime took place. A second fell from his balcony. The third plummeted out a penthouse window.
And then there was Sergei Magnitsky, a 37-year-old lawyer for Hermitage who died in prison after complaining police were torturing him to retract evidence that the $230 million had been stolen by a ring of corrupt tax officials, Interior Ministry cops and career criminals. Magnitsky’s November 2009 death made him an icon to those who want to clean up Russia’s chronic corruption — yet the Interior Ministry surprisingly turned the tables, claiming he was one of the culprits. The police ministry exonerated the cops and tax officials who Magnitsky had accused — most of them got promotions.
As for the $230 million, almost all of it is still missing. Interior Ministry spokesperson Irina Dudukina told Barron’s on Tuesday that all the bank records police needed in order to trace the loot were in a truck that crashed and exploded in 2008.
The case may have ended there for Russian authorities, but Hermitage’s London-based chief Browder has devoted himself to pursuing those he holds responsible for the original crime and Magnitsky’s death. In English and Russian campaigns on a Website (russian-untouchables.com) and on YouTube, the investor has presented evidence that he says proves the tax heist was an inside job and has asked the public to send him additional evidence.
“The facts of this case are absolutely damning for the Russian government,” says Browder. “First Sergei Magnitsky uncovers and reports criminals preparing a major crime three weeks before it happens, and the police do nothing. Then Russian tax officials make the largest fraudulent tax refund in Russian history, in one day, on Christmas Eve, to a convicted murderer, with no questions asked.”
Browder’s outreach program has paid off. He recently received new evidence that raises questions about the Russian government’s official story that honest bureaucrats were tricked by wily outsiders. The records from two secret accounts at a Credit Suisse branch in Zurich show that shortly after the huge tax payout was approved by the Moscow tax bureau run by Olga G. Stepanova, her husband received $10.9 million (seven million euros) in his Cyprus shell corporation. The Credit Suisse accounts also were the source of funds for $800,000 in construction payments for the couple’s seaside villa in Montenegro and for $4 million toward another villa on Dubai’s fabulous Palm Island with two additional condos for Stepanova’s tax-office deputies.
And those were just Stepanova’s vacation homes. A year after the tax scam, Stepanova’s family was living in a $20 million mansion outside Moscow, designed by Russia’s celebrity avant-garde architect Alexey Kozyr.
The money arrived at Credit Suisse through a globe-spanning trail of shell companies created by a Who’s Who of offshore-secrecy consultants — including a New Zealand agent whose operation we’ve previously found amid North Korean arms trafficking and money laundering for a Mexican drug cartel.
TOP-SECRET- Inside the Apocalyptic Soviet Doomsday Machine
Valery Yarynich glances nervously over his shoulder. Clad in a brown leather jacket, the 72-year-old former Soviet colonel is hunkered in the back of the dimly lit Iron Gate restaurant in Washington, DC. It’s March 2009—the Berlin Wall came down two decades ago—but the lean and fit Yarynich is as jumpy as an informant dodging the KGB. He begins to whisper, quietly but firmly.
“The Perimeter system is very, very nice,” he says. “We remove unique responsibility from high politicians and the military.” He looks around again.
Yarynich is talking about Russia’s doomsday machine. That’s right, an actual doomsday device—a real, functioning version of the ultimate weapon, always presumed to exist only as a fantasy of apocalypse-obsessed science fiction writers and paranoid über-hawks. The thing that historian Lewis Mumford called “the central symbol of this scientifically organized nightmare of mass extermination.” Turns out Yarynich, a 30-year veteran of the Soviet Strategic Rocket Forces and Soviet General Staff, helped build one.
The point of the system, he explains, was to guarantee an automatic Soviet response to an American nuclear strike. Even if the US crippled the USSR with a surprise attack, the Soviets could still hit back. It wouldn’t matter if the US blew up the Kremlin, took out the defense ministry, severed the communications network, and killed everyone with stars on their shoulders. Ground-based sensors would detect that a devastating blow had been struck and a counterattack would be launched.
The technical name was Perimeter, but some called it Mertvaya Ruka, or Dead Hand. It was built 25 years ago and remained a closely guarded secret. With the demise of the USSR, word of the system did leak out, but few people seemed to notice. In fact, though Yarynich and a former Minuteman launch officer named Bruce Blair have been writing about Perimeter since 1993 in numerous books and newspaper articles, its existence has not penetrated the public mind or the corridors of power. The Russians still won’t discuss it, and Americans at the highest levels—including former top officials at the State Department and White House—say they’ve never heard of it. When I recently told former CIA director James Woolsey that the USSR had built a doomsday device, his eyes grew cold. “I hope to God the Soviets were more sensible than that.” They weren’t.
The system remains so shrouded that Yarynich worries his continued openness puts him in danger. He might have a point: One Soviet official who spoke with Americans about the system died in a mysterious fall down a staircase. But Yarynich takes the risk. He believes the world needs to know about Dead Hand. Because, after all, it is still in place.
The system that Yarynich helped build came online in 1985, after some of the most dangerous years of the Cold War. Throughout the ’70s, the USSR had steadily narrowed the long US lead in nuclear firepower. At the same time, post-Vietnam, recession-era America seemed weak and confused. Then in strode Ronald Reagan, promising that the days of retreat were over. It was morning in America, he said, and twilight in the Soviet Union.
Part of the new president’s hard-line approach was to make the Soviets believe that the US was unafraid of nuclear war. Many of his advisers had long advocated modeling and actively planning for nuclear combat. These were the progeny of Herman Kahn, author of On Thermonuclear War and Thinking About the Unthinkable. They believed that the side with the largest arsenal and an expressed readiness to use it would gain leverage during every crisis.
The new administration began expanding the US nuclear arsenal and priming the silos. And it backed up the bombs with bluster. In his 1981 Senate confirmation hearings, Eugene Rostow, incoming head of the Arms Control and Disarmament Agency, signaled that the US just might be crazy enough to use its weapons, declaring that Japan “not only survived but flourished after the nuclear attack” of 1945. Speaking of a possible US-Soviet exchange, he said, “Some estimates predict that there would be 10 million casualties on one side and 100 million on another. But that is not the whole of the population.”
Meanwhile, in ways both small and large, US behavior toward the Soviets took on a harsher edge. Soviet ambassador Anatoly Dobrynin lost his reserved parking pass at the State Department. US troops swooped into tiny Grenada to defeat communism in Operation Urgent Fury. US naval exercises pushed ever closer to Soviet waters.
The strategy worked. Moscow soon believed the new US leadership really was ready to fight a nuclear war. But the Soviets also became convinced that the US was now willing to start a nuclear war. “The policy of the Reagan administration has to be seen as adventurous and serving the goal of world domination,” Soviet marshal Nikolai Ogarkov told a gathering of the Warsaw Pact chiefs of staff in September 1982. “In 1941, too, there were many among us who warned against war and many who did not believe a war was coming,” Ogarkov said, referring to the German invasion of his country. “Thus, the situation is not only very serious but also very dangerous.”
A few months later, Reagan made one of the most provocative moves of the Cold War. He announced that the US was going to develop a shield of lasers and nuclear weapons in space to defend against Soviet warheads. He called it missile defense; critics mocked it as “Star Wars.”
To Moscow it was the Death Star—and it confirmed that the US was planning an attack. It would be impossible for the system to stop thousands of incoming Soviet missiles at once, so missile defense made sense only as a way of mopping up after an initial US strike. The US would first fire its thousands of weapons at Soviet cities and missile silos. Some Soviet weapons would survive for a retaliatory launch, but Reagan’s shield could block many of those. Thus, Star Wars would nullify the long-standing doctrine of mutually assured destruction, the principle that neither side would ever start a nuclear war since neither could survive a counterattack.
TOP-SECRET – Slovak Spying Agency Document
A sends:
This leaked document codenamed Gorilla [1, 2] was allegedly prepared by the Slovak intelligence agency (SIS). SIS found significant influence by the Penta Financial Group on senior Slovak politicians between 2005 and 2006 (Dzurinda gov’t). Penta claims that the online publication of classified document by the webmasters and other news media violates criminal law and threatens to take legal action against them [3].
Links:
[1] http://dl.dropbox.com/u/51238188/gorila.txt [SK] Cryptome mirror: http://cryptome.org/2012/01/0045.txt
[2] https://docs.google.com/document/d/1giBimg_c1JOngOMKiSCmmtr656PG22q3ZDe63MQtKz4/edit?pli=1 [SK]
Cryptome mirror: http://cryptome.org/2012/01/0046.zip
[4] http://www.praguepost.cz/news/11701-region-gorilla-case-grips-slovakia.html [EN]
TOP-SECRET – (U//FOUO) TSA Mass Transit and Passenger Bus Attacks Warning

(U//FOUO) This TSA-OI assessment is intended to provide a review of the terrorist TTPs used to conduct attacks against mass transit bus systems from 2004 to 2010. For the purpose of this assessment, mass transit bus systems include buses, stations, and bus stops.
This is one in a series of products released since 2010 focusing on the TTPs used to attack mass transit systems. This assessment was produced to help security managers and stakeholders evaluate the effectiveness of and vulnerabilities in mass transit bus security programs, plans, and activities.
…
(U//FOUO) TSA’s Office of Intelligence (TSA-OI) assesses that although counterterrorism pressure has weakened al-Qa’ida (AQ) and al Qa’ida in the Arabian Peninsula (AQAP), both organizations represent an enduring and evolving threat and remain committed to attacking the Homeland, including the transportation sector. Both organizations have targeted commercial aviation and AQ has repeatedly plotted to attack mass transit. We also remain concerned about the threat posed by homegrown violent extremists (HVE) or lone offenders inspired by AQ’s violent extremist ideology to launch attacks against less secure targets, such as mass transit and passenger bus systems.
(U//FOUO) Tactics, techniques, and procedures used by terrorist groups worldwide could serve as a model for an attack in the Homeland. The current threat level for the mass transit sector remains at medium.
• (U//FOUO) Terrorist groups have used a wide variety of weapons and tactics in attacks on mass transit bus systems; improvised explosive devices (IEDs) have been the most common weapon used.
• (U//FOUO) Most IED attacks against mass transit bus systems occurred inside the bus and not on the bus routes or at bus stations.
• (U//FOUO) Terrorists appeared to use multiple IEDs in attacks to increase the number of casualties or target first responders.
• (U//FOUO) The number of terrorist attacks on mass transit bus systems remained consistent throughout the year, without any major increases in any particular month.
• (U//FOUO) TSA-OI’s data review showed that most attacks occurred during the morning rush hour from 7 a.m. to 10 a.m., with the least amount of attacks occurring from 1 a.m. to 5 a.m.
• (U//FOUO) Secular, political, and anarchists groups conducted the most lethal attacks against mass transit bus systems. TSA-OI assesses that an attack against a mass transit bus system in the Homeland would most likely be carried out by individuals affiliated with a violent religious extremist group.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-ECRET – (U//FOUO) ISAF CJIATF-Shafafiyat Afghan Corruption Information Paper

Per a recent RFI from the Office of the Special Inspector General for Afghanistan Reconstruction, the following information paper discusses the nature and extent of the corruption problem in Afghanistan, the mission of CJIATF-Shafafiyat, and the progress the task force has achieved, as well as the challenges its has encountered, as it has coordinated ISAF’s anti-corruption efforts.
Introduction and Overview
The Strategic Impact of Corruption in Afghanistan
The level of corruption across Afghanistan’s public and private sectors represents a threat to the success of ISAF’s mission and the viability of the Afghan state. Corruption undermines the legitimacy and effectiveness of Afghanistan’s government, fuels discontent among the population, and generates active and passive support for the insurgency. Corruption and organized crime also serve as a barrier to Afghanistan’s economic growth by robbing the state of revenue and preventing the development of a strong licit economy, thus perpetuating Afghan dependence on international assistance. Corruption also threatens the process of security transition, as institutions weakened by criminality will be unable to accept the transfer of responsibility for security and governance.
The Causes of Corruption
Several conditions have allowed corruption to flourish in Afghanistan: a fragile war economy sustained by international aid, security assistance, and the narcotics trade; a society fractured by three decades of war; and weak governance and institutions.
Criminal Patronage Networks (CPNs) are responsible for the most threatening forms of corruption in Afghanistan. CPNs are comprised of individuals, businesses, and other entities that engage in systematized corruption inside and outside of government and across Afghanistan’s public and private sectors. CPNs are often associated with powerbrokers who have consolidated power over the last thirty years of war. These networks engage in illicit enterprises and pursue narrow, self-interested agendas that degrade security, weaken governance, hinder economic development and undermine rule of law. CPNs seek to control key state assets and institutions. They divert customs revenue at airports and border crossings, expropriate government and private land, and abuse public and private financial institutions. Additionally, CPNs generate exclusionary political economies that alienate key elements of the population and generate popular discontent from which the enemy draws strength. The Taliban recruits from disaffected portions of the population and those who have suffered injustice and abuse at the hands of corrupt and criminal actors.
CPNs pursue political as well as criminal agendas, consolidating power and maximizing their position relative to other networks. It is for this reason that efforts to reduce corruption must be grounded in an understanding of Afghan politics, and combined with efforts to convince Afghan leaders that it is in their interest to reduce the threat of corruption and organized crime.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – FBI Director Meets With Google, Facebook to Discuss Easier Wiretaps

Robert S. Mueller III, the director of the Federal Bureau of Investigation, traveled to Silicon Valley on Tuesday to meet with top executives of several technology firms about a proposal to make it easier to wiretap Internet users.
Mr. Mueller and the F.B.I.’s general counsel, Valerie Caproni, were scheduled to meet with senior managers of several major companies, including Google and Facebook, according to several people familiar with the discussions. How Mr. Mueller’s proposal was received was not clear.
“I can confirm that F.B.I. Director Robert Mueller is visiting Facebook during his trip to Silicon Valley,” said Andrew Noyes, Facebook’s public policy manager. Michael Kortan, an F.B.I. spokesman, acknowledged the meetings but did not elaborate.
Mr. Mueller wants to expand a 1994 law, the Communications Assistance for Law Enforcement Act, to impose regulations on Internet companies.
The law requires phone and broadband network access providers like Verizon and Comcast to make sure they can immediately comply when presented with a court wiretapping order.
Law enforcement officials want the 1994 law to also cover Internet companies because people increasingly communicate online. An interagency task force of Obama administration officials is trying to develop legislation for the plan, and submit it to Congress early next year.
The Commerce Department and State Department have questioned whether it would inhibit innovation, as well as whether repressive regimes might harness the same capabilities to identify political dissidents, according to officials familiar with the discussions.
Under the proposal, firms would have to design systems to intercept and unscramble encrypted messages. Services based overseas would have to route communications through a server on United States soil where they could be wiretapped.
A Google official declined to comment. Mr. Noyes said it would be premature for Facebook to take a position.
TOP SECRET from the FBI – Charges Against Seven Investment Professionals for Insider Trading Scheme that Allegedly Netted More Than $61.8 Million in Illegal Profits
Preet Bharara, the United States Attorney for the Southern District of New York, and Janice K. Fedarcyk, the Assistant Director in Charge of the New York Office of the Federal Bureau of Investigation (“FBI”), today announced charges against seven investment professionals, who worked at three different hedge funds and two other investment firms, for engaging in a scheme in which they provided each other with material, non-public information (“Inside Information”) about two publicly traded technology companies, Dell, Inc. (“Dell”) and NVIDIA (“NVDA”). Using the Dell Inside Information, the three hedge funds netted more than $61.8 million in illegal profits and one of the investment firms avoided $78,000 in losses. Charged in a complaint unsealed today are: TODD NEWMAN, a former portfolio manager at a Connecticut-based hedge fund (“Hedge Fund A”); ANTHONY CHIASSON, a former portfolio manager and a co-founder of a Manhattan-based hedge fund (“Hedge Fund B”); JON HORVATH, a research analyst who worked in the New York office of a Connecticut-based hedge fund (“Hedge Fund C”); and DANNY KUO, a research analyst and fund manager at an investment firm with offices in California and Nevada (“Investment Firm D”). This morning, NEWMAN, HORVATH, and KUO were arrested, and CHIASSON surrendered to federal authorities. Later today, CHIASSON and HORVATH are expected to be presented in Manhattan federal court, NEWMAN is expected to be presented in Massachusetts federal court, and KUO is expected to be presented in federal court in the Central District of California.
Also unsealed today were the guilty pleas of: JESSE TORTORA, a former research analyst at Hedge Fund A; SPYRIDON “Sam” ADONDAKIS, a research analyst at Hedge Fund B; and SANDEEP “Sandy” GOYAL, a research analyst who worked at the Manhattan office of a global asset management firm (“Investment Firm 1”). They pled guilty to their roles in the insider trading scheme and are cooperating with the government’s investigation.
Manhattan U.S. Attorney Preet Bharara said: “The charges unsealed today allege a corrupt circle of friends who formed a criminal club whose purpose was profit and whose members regularly bartered lucrative inside information so their respective funds could illegally profit. And profit they allegedly did—to the tune of more than $61 million on illegal trades of a single stock—much of it coming in a $53 million short trade. Here, The Big Short was The Big Illegal Short. We have demonstrated through our prosecutions that insider trading is rampant and has its own social network, a network we intend to dismantle. We will be unrelenting in our pursuit of those who think they are above the law.”
FBI Assistant Director in Charge Janice K. Fedarcyk said: “The FBI has arrested more than 60 people in ‘Operation Perfect Hedge’ to date, and this initiative is far from over. If you are engaged in insider trading, what distinguishes you from the dozens who have been charged is not that you haven’t been caught; it’s that you haven’t been caught yet.”
According to the complaint and Informations unsealed today in Manhattan federal court, and statements made during the related plea proceedings:
TORTORA and ADONDAKIS were part of a circle of research analysts at different investment firms who obtained Inside Information directly or indirectly from employees who worked at public companies, and then shared it with each other and with the Hedge Fund portfolio managers for whom they worked. HORVATH and KUO were allegedly part of the circle as well, and used and shared Inside Information similarly. For example, in 2008 and 2009, TORTORA admitted to providing ADONDAKIS, HORVATH and KUO with Inside Information related to Dell’s first and second quarter 2008 earnings that he had received from GOYAL, who had a source inside Dell’s investor relations department. TORTORA also admitted to providing the Dell Inside Information to NEWMAN, the portfolio manager for whom he worked. ADONDAKIS admitted to providing the Dell Inside Information to CHIASSON, the portfolio manager for whom he worked. Both TORTORA and ADONDAKIS told their portfolio managers that the information came from a source at Dell.
In exchange for the Dell Inside Information, TORTORA admitted to arranging with NEWMAN to pay GOYAL via a sham research consulting arrangement Hedge Fund A made with an individual (“Individual 1”), the proceeds of which were deposited in a joint account Individual 1 shared with GOYAL. In fact, Individual 1 never provided any research consulting services, but Hedge Fund A nonetheless made four $18,750 payments to Individual 1 between February 2008 and September 2008. Individual 1 also received a $100,000 bonus from Hedge Fund A in January 2009.
The Dell Short
The Dell Inside Information was allegedly used to execute illegal trades in the first and second quarters of 2008. For example, beginning in July 2008, the Dell Insider provided GOYAL initial information concerning Dell’s revenues and/or gross margins for the second quarter. After the close of the quarter in 2008, but prior to Dell’s public earnings announcement on August 28 of that year, the Dell Insider provided to GOYAL, who in turn provided to TORTORA, more specific information concerning Dell’s margins that confirmed the gross margin would be lower than market expectations. On August 5, 2008, TORTORA forwarded an e-mail to ADONDAKIS, HORVATH and KUO, that he is alleged to have originally sent to NEWMAN, that included the Inside Information he had received from GOYAL. In the days before the August 28, 2008 earnings announcement, GOYAL had additional communications with TORTORA and again confirmed that Dell’s gross margin would be lower than market expectations. TORTORA admitted to passing this information on to NEWMAN and to ADONDAKIS, who admitted to providing the information to CHIASSON. In another e-mail sent by TORTORA on August 25, 2008, he wrote, “did new apple and dell checks today and both sound bad, same as before.” Trading records show that Hedge Funds A, B, and C all allegedly sold quantities of Dell shares “short,” based at least in part on the Inside Information they received during the period prior to the company’s second quarter earnings announcement. Hedge Fund A reaped $2.8 million in allegedly illegal profits, Hedge Fund B made more than $50 million, and Hedge Fund C made $1 million. Trading records also show that KUO allegedly avoided approximately $78,000 by trading on the Inside Information for Investment Firm D.
In all, the conduct alleged in the complaint relating to the Dell Inside Information resulted in more than $61.8 million in illegal insider trading profits realized by Hedge Funds A, B, and C.
The NVIDIA Inside Information
In addition, in multiple fiscal quarters, KUO allegedly obtained confidential financial information about NVIDIA, a publicly traded technology company, shortly before its public earnings release and provided it to TORTORA, ADONDAKIS, and HORVATH. The information included NVIDIA’s gross margin and revenue information. As alleged, e-mail communications from KUO to the other research analysts stated explicitly that the information was coming from an employee inside NVIDIA.
* * *
NEWMAN, 47, of Needham, Massachusetts; CHIASSON, 38, of New York, New York; HORVATH, 42, of New York, New York; and KUO, 36, of Pasadena, California, are each charged with one count of conspiracy to commit securities fraud and one count of securities fraud. The conspiracy charge carries a maximum potential penalty of five years in prison and a fine of $250,000 or twice the gross gain or loss from the offense. The securities fraud charge carries a maximum potential penalty of 20 years in prison and a maximum fine of $5 million.
TORTORA, 34, ADONDAKIS, 40, and GOYAL, 39, each pled guilty to one count of conspiracy to commit securities fraud and one count of securities fraud. TORTORA pled guilty on May 18, 2011; ADONDAKIS pled guilty on April 25, 2011; and GOYAL pled guilty on November 3, 2011. They each face a statutory maximum sentence of 25 years in prison.
Mr. Bharara praised the investigative work of the Federal Bureau of Investigation. He also thanked the U.S. Securities and Exchange Commission. He also noted that the investigation is continuing.
This case was brought in coordination with President Barack Obama’s Financial Fraud Enforcement Task Force, on which Mr. Bharara serves as a Co-Chair of the Securities and Commodities Fraud Working Group. President Obama established the interagency Financial Fraud Enforcement Task Force to wage an aggressive, coordinated, and proactive effort to investigate and prosecute financial crimes. The task force includes representatives from a broad range of federal agencies, regulatory authorities, inspectors general, and state and local law enforcement who, working together, bring to bear a powerful array of criminal and civil enforcement resources. The task force is working to improve efforts across the federal executive branch, and with state and local partners, to investigate and prosecute significant financial crimes, ensure just and effective punishment for those who perpetrate financial crimes, combat discrimination in the lending and financial markets, and recover proceeds for victims of financial crimes.
The charges against NEWMAN, CHIASSON, HORVATH, and KUO are merely accusations, and the defendants are presumed innocent unless and until proven guilty.
Assistant U.S. Attorneys Antonia Apps, David Leibowitz, and Richard Tarlowe are in charge of the prosecution.
TOP SECRET – NSA’s Top Ten Technical Security Challenges
Not surprisingly in today’s world, National Security Systems are fundamentally dependent on commercial products and infrastructure, or interconnect with other systems that are. This creates new and significant common ground between the Department of Defense and broader U.S. Government and homeland security needs. More and more, we find that protecting National Security Systems demands teaming with public and private institutions to raise the information assurance level of products and services more broadly. If done correctly, this is a win-win situation that benefits the whole spectrum of Information Technology (IT) users, from warfighters and policymakers, to federal, state, and local governments, to the operators of critical infrastructure and major arteries of commerce. The “Top Ten Technical Security Challenges” reflect major focus areas for the Information Assurance Directorate (IAD) which may also present opportunities for industry.
NSA’s Top Ten Technical Security Challenges:
- Mobility, wireless networking, and secure mobile services
- Software assurance
- Virtualization, Separation, and Trusted Platforms
- Cloud computing
- Intrusion analysis and adversary tradecraft
- Platform Integrity – Compliance assurance – Continuous Monitoring
- Real-time situational awareness and CNO sync
- End client security
- Metrics and measurement for IA posture
- Commercial architectures for assistance
TOP-SECRET – GAO Federal Reserve $16 Trillion Emergency Bailout Loans Audit Report

On numerous occasions in 2008 and 2009, the Federal Reserve Board invoked emergency authority under the Federal Reserve Act of 1913 to authorize new broad-based programs and financial assistance to individual institutions to stabilize financial markets. Loans outstanding for the emergency programs peaked at more than $1 trillion in late 2008. The Federal Reserve Board directed the Federal Reserve Bank of New York (FRBNY) to implement most of these emergency actions. In a few cases, the Federal Reserve Board authorized a Reserve Bank to lend to a limited liability corporation (LLC) to finance the purchase of assets from a single institution. In 2009 and 2010, FRBNY also executed large-scale purchases of agency mortgage-backed securities to support the housing market. The table below provides an overview of all emergency actions covered by this report. The Reserve Banks’ and LLCs’ financial statements, which include the emergency programs’ accounts and activities, and their related financial reporting internal controls, are audited annually by an independent auditing firm. These independent financial statement audits, as well as other audits and reviews conducted by the Federal Reserve Board, its Inspector General, and the Reserve Banks’ internal audit function, did not report any significant accounting or financial reporting internal control issues concerning the emergency programs.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – Federal Reserve Bank of New York Shadow Banking System Research Report
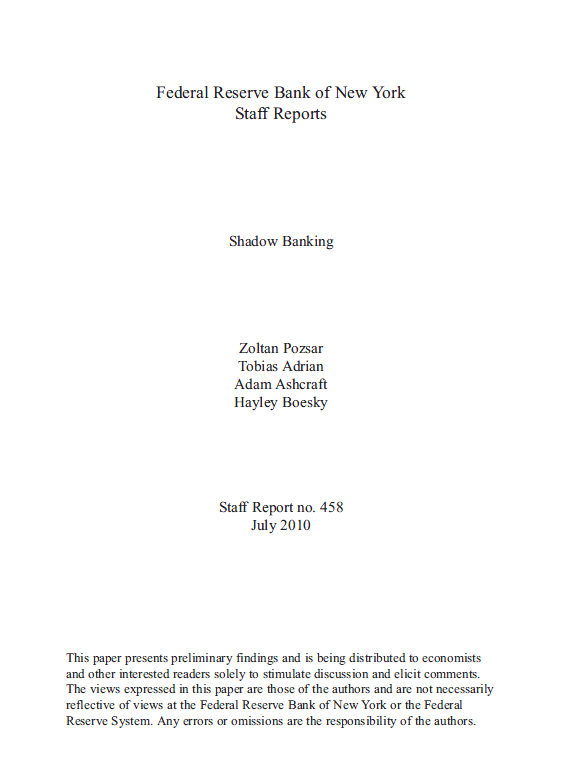
Abstract
The rapid growth of the market-based financial system since the mid-1980s changed the nature of financial intermediation in the United States profoundly. Within the market-based financial system, “shadow banks” are particularly important institutions. Shadow banks are financial intermediaries that conduct maturity, credit, and liquidity transformation without access to central bank liquidity or public sector credit guarantees. Examples of shadow banks include finance companies, asset-backed commercial paper (ABCP) conduits, limited-purpose finance companies, structured investment vehicles, credit hedge funds, money market mutual funds, securities lenders, and government-sponsored enterprises.
Shadow banks are interconnected along a vertically integrated, long intermediation chain, which intermediates credit through a wide range of securitization and secured funding techniques such as ABCP, asset-backed securities, collateralized debt obligations, and repo. This intermediation chain binds shadow banks into a network, which is the shadow banking system. The shadow banking system rivals the traditional banking system in the intermediation of credit to households and businesses. Over the past decade, the shadow banking system provided sources of inexpensive funding for credit by converting opaque, risky, long-term assets into money-like and seemingly riskless short-term liabilities. Maturity and credit transformation in the shadow banking system thus contributed significantly to asset bubbles in residential and commercial real estate markets prior to the financial crisis.
We document that the shadow banking system became severely strained during the financial crisis because, like traditional banks, shadow banks conduct credit, maturity, and liquidity transformation, but unlike traditional financial intermediaries, they lack access to public sources of liquidity, such as the Federal Reserve’s discount window, or public sources of insurance, such as federal deposit insurance. The liquidity facilities of the Federal Reserve and other government agencies’ guarantee schemes were a direct response to the liquidity and capital shortfalls of shadow banks and, effectively, provided either a backstop to credit intermediation by the shadow banking system or to traditional banks for the exposure to shadow banks. Our paper documents the institutional features of shadow banks, discusses their economic roles, and analyzes their relation to the traditional banking system.
Key words: shadow banking, financial intermediation
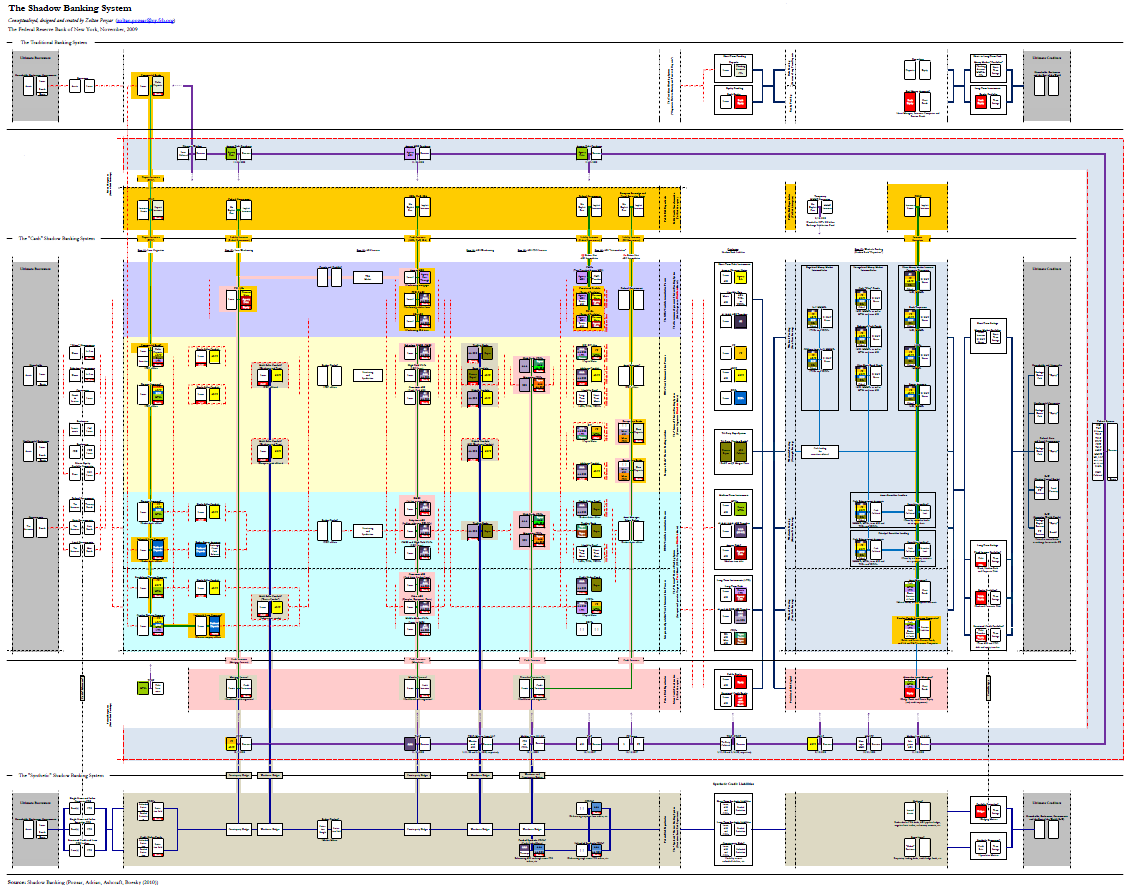
DOWNLOAD FULL REPORT HERE
TOP SECRET – Review of Federal Reserve System Financial Assistance to AIG in Financial Crisis
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – Classified USAID Report on Kabul Bank Corruption
Dubai real estate led depositors to rush to withdraw funds from Kabul Bank, the largest bank in Afghanistan. According to the Report of Kabul Bank in Conservatorship dated October 30, 2010, cited in a draft material loss review commissioned by USAID/Afghanistan, fraudulent loans were used to divert $850 million to insiders. This amount reportedly represented 94 percent of the bank’s outstanding loans.
Since 2003, USAID/Afghanistan has supported a number of capacity-building activities at the Afghanistan Central Bank (DAB) to help DAB regulate the banking sector. Currently, Deloitte1 provides DAB technical assistance in bank supervision and examination through a $92 million task order for the Economic Growth and Governance Initiative, which includes many activities in addition to bank supervision and examination. The purpose of the task order was to increase Afghanistan’s ability to develop and implement sound economic and regulatory policies that provide the foundation for private sector growth in a market economy. According to Deloitte’s work plan, one of the main goals of the assistance Deloitte provided to DAB was to assist DAB in fulfilling its statutory responsibilities ―to promote the stability and contribution to economic growth of the financial sector and to prevent avoidable losses. Deloitte provided onsite technical advisors at DAB’s Directorate for Financial Supervision.
After the run on Kabul Bank, senior officials in the U.S. Embassy raised concerns about Deloitte’s performance. Specifically, they were concerned that Deloitte staff did not warn the U.S. Government about looming problems at Kabul Bank before the first news reports broke in February 2010. They also questioned Deloitte’s effectiveness and performance because Deloitte staff had provided bank supervision assistance to DAB for 7 years, yet DAB supervisors were unable to prevent the near collapse of Afghanistan’s largest bank. In January 2011, USAID/Afghanistan requested the assistance of the Office of Inspector General (OIG) in determining whether USAID or Deloitte staff members were negligent in failing to report the Kabul Bank fraud.
In response to USAID/Afghanistan’s request, OIG/Afghanistan conducted this review to determine:
- What opportunities USAID and contractor staff had to learn of fraudulent activities at Kabul Bank through USAID’s Economic Growth and Governance Initiative and its predecessor, the Economic Growth and Private Sector Strengthening Activity.
- How staff learned of the fraud.
- What actions staff members took once they became aware of the fraud.
- Whether USAID’s oversight of its contractor was adequate.
…
USAID’s Management of Its Task Order with Deloitte Was Weak
ADS 203.3.2, ―Assessing and Learning, states that missions and their offices are responsible for monitoring a contractor’s performance in achieving the contract’s purpose. ADS 302.3.7.1a, ―Direct Contracting, Mandatory Reference: ―Procedures for Designating the Contracting Officer’s Technical Representative (COTR) for Contracts and Task Orders,‖ states that the COTR is in a unique position to monitor how well the contractor is progressing toward achieving the contract’s purpose and is responsible for providing technical liaison between the contractor and the contracting officer, a function critical to ensuring good contract performance.
When the current mission director arrived in June 2010, his attention focused on USAID/Afghanistan’s capacity to manage and provide oversight of highly technical bank supervision activities implemented by its contractor, Deloitte, at DAB. This focus heightened after the Kabul Bank crisis broke in September 2010. The task order with Deloitte for the Economic Growth and Governance Initiative was for a 5-year, $92 million project with three major components and 21 work streams with diverse requirements that was managed by USAID/Afghanistan’s Office of Economic Growth. In August 2009, when USAID issued the task order, the Office of Economic Growth had only four U.S. direct-hire staff and none with experience in the banking sector. For the most part, only one U.S. direct hire was managing the task order at any given time, with some assistance from Foreign Service National staff.
Further contributing to the mission’s challenges to provide effective oversight of Deloitte, a former COTR for the Deloitte task order stated that during a typical workweek, he spent 50 to 70 percent of his time drafting memorandums and cables for the U.S. Embassy, reducing his time for program oversight. He kept detailed timesheets of daily work activities. The COTR explained that such competing work demands, combined with the mission’s lack of technical expertise, created overreliance on the Deloitte advisers to manage the bank supervision assistance activities, with little oversight provided by USAID. USAID staff members stated that had they not faced the burden of managing a large task order with limited resources, they would have been in a better position to provide proactive and robust oversight of the Deloitte advisers. As one USAID official put it, ―Deloitte was managing USAID, rather than the other way around.
Generally, COTRs monitor contractor performance and verify that it conforms to the technical requirements and quality standards agreed to in the contract. COTRs do this by maintaining regular contact and liaison and by conducting frequent site visits with the contractor. Yet according to a former COTR for the Deloitte task order, mission management focused on program spending, financial pipelines, and burn rates, rather than on monitoring and achieving program results. A former USAID/Afghanistan staff member stated in a memo that the mission gave the Office of Economic Growth only 24 hours to review a proposed Deloitte work plan—insufficient time to provide thoughtful review and comment. Finally, at the entrance conference for this review, USAID/Afghanistan officials did not take a position on whether Deloitte’s performance was satisfactory or unsatisfactory, providing further evidence of inadequate management.
For years, USAID has faced difficulty in attracting staff to Afghanistan who have the appropriate levels of experience and skills. A former mission director for USAID/Afghanistan stated that the staffing situation in Afghanistan reflected what he considered to be an ongoing problem for USAID, especially for programs in war zones—not enough senior people at USAID who have the experience to manage large, substantive, technically challenging projects. Current USAID/Afghanistan leadership agreed with this assessment and explained that steps have been and continue to be taken to remedy that situation. For example, a recently completed reorganization in the Office of Economic Growth added one technical adviser position.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP SECRET – Bank of America Anonymous Email Leak
The following emails were released earlier by a member of Anonymous. The following are text renditions of the emails contained in the leak. The following terms are useful in understanding some of the emails’ content:
- SOR = System of Record
- Rembrandt/Tracksource = Insurance tracking systems
- DTNs = Document Tracking Number, a number assigned to all incoming/outgoing documents (letters, insurance documents, etc.)
1.
From: Vaughn, Jason – 2
Sent: Monday, November 01, 2010 2:09 PM
To: Bennett, Pearl H
Cc: Johnson, Peggy – 2; Walters, Kirsten; Smith, Jackie – 2
Subject: GMAC DTN’s for Image Removal – Urgent Request
Importance: HighHello,
The following GMAC DTN’s need have the images removed from Tracksource/Rembrandt.
354499768
354499769
354499770
354499771
354499772
354499773
354499774
354499775
354499776
354499777
354499734
354499735
354499736
354499739
354499740
354499741
354499742
354499745
354499746
354499747
354499750
354499751
354499754
354499725
354499726
354499727
354499728
354499729
354499730
354499731
354499732
354499733
354499718
354499719
354499720
354499721
354499722
354499723
354499724
354499707
354499708
354499710
354499711
354499713
354499714
354499715
354499697
354499698
354499699
354499700
354499702
354499704
354499705
354499706
354499667
354499668
354499669
354499670
354499671
354499672
354499673
354499674
354499675
354499676
354499677
354499678
354499679
354499680
354499681
354499682
354499683
354499686
354499687
354499688
354499691
354499692
354499693
354499694
354499695
354499696Jason D Vaughn
Operations Team Manager
Balboa Insurance
AZ LPP Balboa Tracking Ops
480-755-2701 Office
92-548-2701 Internal
2505 W Chandler BLVD, BLDG D
Chandler, AZ 85224
Mailstop: AZ 805-01-36This communication from Balboa Insurance Group-may contain privileged and/or confidential information. It is intended solely for the use of the addressee. If you are not the intended recipient, you are strictly prohibited from disclosing, copying, distributing or using any of this information. If you receive this communication in error, please contact the sender immediately and destroy the material in its entirety, whether electronic or hard copy. This communication may contain nonpublic personal information about consumers subject to the restrictions of the Gramm-Leach-Bliley Act. You may not directly or indirectly reuse or re-disclose such information for any purpose other than to provide the services for which you are receiving the information.
2.
From: Anderson, Joanne
Sent: Monday, November 01, 2010 2:28 PM
To: Vaughn, Jason – 2
Cc: Johnson, Peggy – 2; Walters, Kirsten; Smith, Jackie – 2; Mays, Therese J
Subject: RE: GMAC DTN’s for Image Removal – Urgent RequestHi Jason, Peggy and Kirsten,
I have spoken with my developer and she stated that we cannot remove the DTN’s from Rembrandt, but she can remove the loan numbers, so the documents will not show as matched to those loans.
I will need upper management approval from Jason, Peggy and Kirsten, since this is an usual request, before we move forward.
Thank you,
Service Delivery information: http://sharepoint.bankofamerica.com/sites/HLandIT/default.aspx
Joanne Anderson
Balboa Insurance Group
Cnslt – Bus Tech Anly
IT LPP/CPI/TRACKSOURCE
600 Lindbergh Drive
Mail Stop: PA4-934-01-03
Moon Township, PA 15108
Joanne.Anderson@Balboainsurance.com
412-424-1287 OfficeThis communication from Balboa Insurance Group – may contain privileged and/or confidential information. It is intended solely for the use of the addressee. If you are not the intended recipient, you are strictly prohibited from disclosing, copying, distributing or using any of this information. If you receive this communication in error, please contact the sender immediately and destroy the material in its entirety, whether electronic or hard copy. This communication may contain nonpublic personal information about consumers subject to the restrictions of the Gramm-Leach-Bliley Act. You may not directly or indirectly reuse or re-disclose such information for any purpose other than to provide the services for which you are receiving the information.
3.
From: Johnson, Peggy – 2
Sent: Monday, November 01, 2010 2:53 PM
To: Anderson, Joanne; Vaughn, Jason – 2
Cc: Walters, Kirsten; Smith, Jackie – 2; Mays, Therese J
Subject: RE: GMAC DTN’s for Image Removal – Urgent RequestHi Joanne,
Where will these letters show up then?
4.
From: Anderson, Joanne
Sent: Monday, November 01, 2010 3:03 PM
To: Johnson, Peggy – 2; Vaughn, Jason – 2
Cc: Walters, Kirsten; Smith, Jackie – 2; Mays, Therese J
Subject: RE: GMAC DTN’s for Image Removal – Urgent RequestHi Peggy,
The letters will not show in Rembrandt if you search by loan number. If you search by DTN, you will find the document, but it will not be matched to any loan.
Thanks,
Service Delivery information: http://sharepoint.bankofamerica.com/sites/HLandIT/default.aspx
Joanne Anderson
Balboa Insurance Group
Cnslt – Bus Tech Anly
IT LPP/CPI/TRACKSOURCE
600 Lindbergh Drive
Mail Stop: PA4-934-01-03
Moon Township, PA 15108
Joanne.Anderson@Balboainsurance.com
412-424-1287 OfficeThis communication from Balboa Insurance Group – may contain privileged and/or confidential information. It is intended solely for the use of the addressee. If you are not the intended recipient, you are strictly prohibited from disclosing, copying, distributing or using any of this information. If you receive this communication in error, please contact the sender immediately and destroy the material in its entirety, whether electronic or hard copy. This communication may contain nonpublic personal information about consumers subject to the restrictions of the Gramm-Leach-Bliley Act. You may not directly or indirectly reuse or re-disclose such information for any purpose other than to provide the services for which you are receiving the information.
5.
From: Anderson, Joanne
Sent: Monday, November 01, 2010 3:03 PM
To: Johnson, Peggy – 2; Vaughn, Jason – 2
Cc: Walters, Kirsten; Smith, Jackie – 2; Mays, Therese J
Subject: RE: GMAC DTN’s for Image Removal – Urgent RequestHi Peggy,
The letters will not show in Rembrandt if you search by loan number. If you search by DTN, you will find the document, but it will not be matched to any loan.
Thanks,
Service Delivery information: http://sharepoint.bankofamerica.com/sites/HLandIT/default.aspx
Joanne Anderson
Balboa Insurance Group
Cnslt – Bus Tech Anly
IT LPP/CPI/TRACKSOURCE
600 Lindbergh Drive
Mail Stop: PA4-934-01-03
Moon Township, PA 15108
Joanne.Anderson@Balboainsurance.com
412-424-1287 OfficeThis communication from Balboa Insurance Group – may contain privileged and/or confidential information. It is intended solely for the use of the addressee. If you are not the intended recipient, you are strictly prohibited from disclosing, copying, distributing or using any of this information. If you receive this communication in error, please contact the sender immediately and destroy the material in its entirety, whether electronic or hard copy. This communication may contain nonpublic personal information about consumers subject to the restrictions of the Gramm-Leach-Bliley Act. You may not directly or indirectly reuse or re-disclose such information for any purpose other than to provide the services for which you are receiving the information.
6.
From: Johnson, Peggy – 2
Sent: Monday, November 01, 2010 3:13 PM
To: Anderson, Joanne; Vaughn, Jason – 2
Cc: Walters, Kirsten; Smith, Jackie – 2; Mays, Therese J
Subject: RE: GMAC DTN’s for Image Removal – Urgent RequestApproved.
7.
—– Forwarded Message —-
From: “Vaughn, Jason – 2? <jason.vaughn@balboainsurance.com>
To: “Johnson, Peggy – 2? <peggy.l.johnson@balboainsurance.com>
Sent: Tue, November 2, 2010 9:18:18 AM
Subject: FW: GMAC DTN’s for Image Removal – Urgent RequestHi Peggy,
I’m just a little concerned about the impact this has on the department and company. Why are we removing all record of this error? We have told Denise Cahen, and there is always going to be the paper trail when one of these sent documents come back, this to me, seems to be a huge red flag for the auditors: example: a scanned document that was mailed to us asking why the letter was received when the letter, albeit erroneous – this being the letters that went out in error – the auditor sees the erroneous letter but no SOR trail or scanned doc on the corrected letter is in the SOR and scanned in). What am I missing? This just doesn’t seem right to me.
TOP-SECRET from the FBI – Kareem Ibrahim Sentenced to Life in Prison for Conspiring to Commit Terrorist Attack at JFK Airport
BROOKLYN, NY—Earlier today, in the Eastern District of New York, United States District Judge Dora L. Irizarry sentenced convicted defendant Kareem Ibrahim to life in prison for conspiring to commit a terrorist attack at John F. Kennedy International Airport in Queens, New York, by exploding fuel tanks and the fuel pipeline under the airport. Ibrahim and his coconspirators believed their attack would cause extensive damage to the airport and to the New York economy, as well as the loss of numerous lives. At the Ibrahim sentencing, Judge Irizarry stated: “This case shows the government at its best in terms of protecting the security of this country.”
The sentence was announced by Loretta E. Lynch, United States Attorney for the Eastern District of New York. The case was investigated by the Federal Bureau of Investigation (FBI) Joint Terrorism Task Force (JTTF) in New York.
A federal jury convicted Kareem Ibrahim of multiple terrorism offenses in May 2011 after a four-week trial. The evidence at trial established that Ibrahim, an Imam and leader of the Shiite Muslim community in Trinidad & Tobago, provided religious instruction and operational support to a group plotting to commit a terrorist attack at JFK Airport. The plot originated with Russell Defreitas, a naturalized United States citizen from Guyana, who drew on his prior experience working at JFK Airport as a cargo handler to plan the attack on its fuel tanks and fuel pipeline. Beginning in 2006, Defreitas recruited others to join the plot, including the defendant Kareem Ibrahim, Abdel Nur and Abdul Kadir, a former member of parliament in Guyana. In May 2007, Defreitas presented Ibrahim with video surveillance and satellite imagery of the targets for terrorist attack because Ibrahim had connections with militant leaders in Iran.
During cross-examination at trial, Ibrahim admitted that he advised the plotters to present the plot to revolutionary leaders in Iran and to use operatives ready to engage in suicide attacks at the airport. On one of the recorded conversations entered into evidence, Ibrahim told Defreitas that the attackers must be ready to “fight it out, kill who you could kill and go back to Allah.”
According to the trial evidence, the conspirators also attempted to enlist support for the plot from prominent international terrorist groups and leaders, including Adnan El Shukrijumah, an al Qaeda leader and explosives expert, and Yasin Abu Bakr, leader of the Trinidadian militant group Jamaat Al Muslimeen. Ultimately, the plotters followed Ibrahim’s direction and sent Abdul Kadir to meet with his contacts in the Iranian revolutionary leadership, including Mohsen Rabbani, the former cultural attache indicted for his leading role in the 1994 bombing of the AMIA Jewish cultural center in Buenos Aires, Argentina.
Kareem Ibrahim, Abdul Kadir, and Abdel Nur were arrested in Trinidad in June 2007, with Kadir aboard a plane headed to Venezuela, en route to Iran. All three were subsequently extradited to the United States. Defreitas was arrested in New York. After a nine-week trial in 2010, Russell Defreitas and Abdul Kadir were convicted of terrorism charges and sentenced to life in prison. Nur pleaded guilty before trial to supporting the plot and was sentenced to 15 years in prison.
The specific charges Ibrahim was convicted of were: conspiracy to attack a public transportation system, in violation of 18 U.S.C. § 2332f; conspiracy to destroy a building by fire or explosive, in violation of 18 U.S.C. § 844(n); conspiracy to attack aircraft and aircraft materials, in violation of 18 U.S.C. § 32; conspiracy to destroy international airport facilities, in violation of 18 U.S.C. § 37; and conspiracy to attack a mass transportation facility, in violation of 18 U.S.C. § 1992(a)(10).
“Kareem Ibrahim abandoned the true tenets of his religion and plotted to commit a terrorist attack that he hoped would rival 9/11,” stated United States Attorney Lynch. “But law enforcement detected and thwarted the plot, saving lives. Now, our courts have dispensed justice by handing out the life sentence that Ibrahim deserves.” Ms. Lynch extended her grateful appreciation to the FBI Joint Terrorism Task Force in New York for its role in investigating and prosecuting the case, as well as to the Guyanese and Trinidadian law enforcement authorities who assisted with the investigation and apprehension of the defendants.
The government’s case was prosecuted by Assistant United States Attorneys Marshall L. Miller, Berit W. Berger, and Zainab Ahmad.
The Defendant:
KAREEM IBRAHIM, also known as “Amir Kareem” and “Winston Kingston”
TP-SECRET from the FBI – Former Dow Research Scientist Sentenced to 60 Months in Prison for Stealing Trade Secrets and Perjury
WASHINGTON—A former research scientist was sentenced late yesterday to 60 months in prison for stealing trade secrets from Dow Chemical Company and selling them to companies in the People’s Republic of China, as well as committing perjury, announced Assistant Attorney General Lanny A. Breuer of the Justice Department’s Criminal Division and U.S. Attorney Donald J. Cazayoux Jr. for the Middle District of Louisiana.
U.S. District Court Judge James J. Brady also sentenced Wen Chyu Liu, aka David W. Liou, 75, of Houston, to two years of supervised release and ordered him to forfeit $600,000 and pay a $25,000 fine. A federal jury in Baton Rouge, La., convicted Liu on Feb. 7, 2011, of one count of conspiracy to commit trade secret theft and one count of perjury.
According to the evidence presented in court, Liu came to the United States from China for graduate work. He began working for Dow in 1965 and retired in 1992. Dow is a leading producer of the elastomeric polymer, chlorinated polyethylene (CPE). Dow’s Tyrin CPE is used in a number of applications worldwide, such as automotive and industrial hoses, electrical cable jackets and vinyl siding.
While employed at Dow, Liu worked as a research scientist at the company’s Plaquemine, La., facility on various aspects of the development and manufacture of Dow elastomers, including Tyrin CPE. Liu had access to trade secrets and confidential and proprietary information pertaining to Dow’s Tyrin CPE process and product technology. The evidence at trial established that Liu conspired with at least four current and former employees of Dow’s facilities in Plaquemine and Stade, Germany, who had worked in Tyrin CPE production, to misappropriate those trade secrets in an effort to develop and market CPE process design packages to various Chinese companies.
Liu traveled extensively throughout China to market the stolen information, and evidence introduced at trial showed that he paid current and former Dow employees for Dow’s CPE-related material and information. In one instance, Liu bribed a then-employee at the Plaquemine facility with $50,000 in cash to provide Dow’s process manual and other CPE-related information.
In addition, according to evidence presented at trial related to the perjury charge, Liu falsely denied during a deposition that he made arrangements for a co-conspirator to travel to China to meet with representatives of a Chinese company interested in designing and building a new CPE plant. Liu was under oath at the time of the deposition, which was part of a federal civil suit brought by Dow against Liu.
The case is being prosecuted by Assistant U.S. Attorney Corey R. Amundson, who serves as the Senior Deputy Criminal Chief, and former Assistant U.S. Attorney Ian F. Hipwell for the Middle District of Louisiana, as well as Trial Attorney Kendra Ervin of the Criminal Division’s Computer Crime and Intellectual Property Section. The case was investigated by the FBI’s New Orleans Division.
TOP-SECRET from the CIA -Wartime Statues: Instruments of Soviet Control

Soviet military planning for conflict in Europe after World War II from the outset harnessed East European military capabilities to Soviet military purposes and assumed operational subordination of East European military formations to higher-level Soviet commands. A Polish command-staff exercise in 1950, for example, assumed subordination of a Polish Army (comprised of five divisions and other units) to a Soviet Maritime Front (tasked in the exercise with occupying Denmark).1 Following founding of the Warsaw Treaty Organization (Warsaw Pact) in May 1955, a supreme Warsaw Pact military command was established in Moscow, but this institution existed largely on paper until the 1960’s.
Document List (PDF Format)
1978_03_21 STATUTE ON THE COMBINED ARMED FORCES
1978_03_28 OFFICIAL REPORT
1978_06_27 STATUTE ON THE COMBINED FLEET
1978_09_06 DRAFT STATUTE ON THE WARSAW PACT
1979_05_11 REPORT ON THE WARSAW PACT COOPERATION
1979_07_18 LETTER FROM WARSAW PACT
1979_11_28 WARTIME STATUTE OF THE COMBINED FORCES
1980_02_07 WARTIME STATUTE
1980_02_08 STATUTE ON THE COMBINED FORCES OF THE WARSAW PACT
1980_02_21 TWELFTH SESSION
1980_02_25 DRAFT STATUTE ON WARSAW PACT COMBINED NAMED FORCES
1980_03_19 OFFICIAL RECORD AND OTHER DOCUMENTS
1980_04_11 FROM THE 12TH SESSION
1980_05_22 ROMANIAS PROPOSED REVISIONS
1980_07_25 RATIFICATION OF THE WARTIME STATUTE ON THE WARSAW PACT
1980_09_22 GIEREK DISCUSSIONS WITH MARSHAL KULIKOV
1980_10_08 MISCELLANEOUS
1982_01_01 THE UNIFIED WARTIME COMMAND
1983_06_28 MILITARY RELIABILITY OF THE SOVIET UNIONS WARSAW PACT ALLIES
1983_06_10 THE ORGANIZATION OF THE WARSAW PACT
1983_06_10 BACKGROUND INFORMATION
1983_10_01 THE SOVIET UNIONS CONTROL OF THE WARSAW PACT FORCES
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – (U//FOUO) Open Source Center Cuban Blogs Serve as Forum for Government Critics
A small but growing number of bloggers who appear to be writing from Cuba are using externally hosted websites to voice dissent and developing inventive ways to circumvent government restrictions on Internet access that limit their freedom to post. While the blogs’ emergence has coincided with the move toward more openness in state media about discussing social and economic problems in the past two years, the bloggers go well beyond that limited criticism by blaming the ruling system rather than individuals or external pressure. The government thus far largely has acted indirectly against the bloggers, warning about the dangers of the Internet and reportedly blocking access to a host website. The bloggers tend to express pessimism about prospects for change under Raul Castro, but they currently are not promoting a specific political agenda or calling for any organized movement against the government. Although readership is mostly international, their on-island audience — including possible imitators — is likely to increase if access to information technology becomes more widespread. See the appendices for details on Internet access in Cuba and the individual blogs discussed.
Cuba’s independent blogs have increased in recent years, providing a forum to voice discontent with current conditions and government policies that goes further than the still-limited discussion of problems in state media.
- The number of blogs written by private Cuban citizens began increasing significantly in late 2006 and has gained momentum since. Of the 11 most prominent independent blogs, one began in 2005, three in 2006, three in 2007, and four since the beginning of 2008.
- Some readers have questioned the bloggers’ credibility, charging them with being either agents of the Cuban Government or Miami-based Cubans. The personal nature of the postings and the absence of an explicit political agenda, however, bolster their claims to be private citizens.
- The increase in independent bloggers parallels a move by state media toward more openness about problems on the island, which began in late 2006 and was further encouraged by Raul Castro’s call for more critical discussion about conditions in Cuba (Cubavision, 26 July 2007, 24 September 2007).
The bloggers demonstrate technological savvy in overcoming the Internet access restrictions to create their blogs, but they appear to have difficulty updating them regularly.
- While she has not disclosed details in her blog, Generacion Y’s Yoani Sanchez, Cuba’s most prominent blogger, has described in interviews with foreign outlets how she writes blog entries, saves them on a flash memory drive, and uploads them at an Internet cafe (The New York Times, 6 March; The Wall Street Journal, 22 December 2007).
- The apparently short-lived Potro Salvaje — whose title “Wild Colt” appears to mock Communications Minister Valdes’s warning in February 2007 that the Internet was a “wild colt” that needed to be controlled (www.cubaminrex.cu) — began on 11 March to provide explicit instructions to on-island Internet users about methods to bypass restrictions. The blog’s most recent post on 8 April highlighted the importance of the flash drive to transport data from one computer to another on the island.
- Although many of the blogs are updated frequently, maintenance can be inconsistent — several have been abandoned or moved without notice. Two of the 11 blogs have not been updated since February 2008, despite having had regular posts prior.
…
The Cuban Government appears to have taken an indirect approach to limiting the influence of independent bloggers. It has warned of the dangers of the Internet, and bloggers charge it with monitoring the contents of their blogs and making it difficult to access the blogs.
- In addition to calling the Internet a “wild colt,” Valdes said it was “a tool for global extermination” (www.cubaminrex.cu). Youth daily Juventud Rebelde has warned that portable storage devices such as flash drives increase vulnerability to computer viruses (17 April), and Fidel Castro asserted in a letter to the National Union of Writers and Artists (UNEAC) Conference that the Internet and other information technologies are
invasions of privacy (Granma, 2 April).- In March, several of the blogs that share the Frankfurt-based Consenso Desde Cuba host website claimed the government was obstructing on-island access. Potro Salvaje charged on 26 March that the site had been filtered to slow loading “to a maximum,” making the page impossible to view by most on-island Internet users since 20 March.
DOWNLOAD THE ORIGINAL FILE HERE
TOP-SECRET – (U//FOUO) Open Source Center Cuban Independent Blogging, Political Activism Grows
Cuban Independent Blogging Grows; Political Activism Varies
FEA20090619862999 – OSC Feature – Cuba — OSC Media Aid 18 Jun 09
A small group of independent bloggers, including Yoani Sanchez, Reinaldo Escobar, and Claudia Cadelo, has promoted blogging as a vehicle for free expression and information sharing to circumvent Cuba’s tightly controlled media environment, and to communicate with the outside world. They have become increasingly confrontational toward the government, demanding greater civil liberties and criticizing many government policies . Other on-island bloggers — many of them journalists or university professors and students — have called on the government to be more open and allow greater access to outside information, but they generally have avoided direct criticism of it. The government response has been limited to date, but the increasingly antigovernment line of some bloggers is likely to test the limits of government tolerance.
Yoani Sanchez, Voces Cubanas
Sanchez, who has been at the forefront of promoting and coordinating Cubans’ use of blogs as a forum for free expression and as a way to criticize government policy, helped create the Voces Cubanas (www.vocescubanas.com) platform for on-island bloggers in October 2008. The site, which is registered in the United States and hosted on a Spanish server, currently has 13 blogs, all of which express some criticism of the Cuban Government.[ 1] [a]
Sanchez leads weekly meetings to discuss blogging in Cuba. During one meeting, participants discussed including their blogs on Facebook and Twitter to give “friends and other interested people” greater and faster access (Itineraro Blogger, 11 April).[ 2] She also announced on her Generacion Y blog that she and a group of friends were using cell phone text messages to circulate international news (29 May).[ 3]
She has used her international prominence — her blog is hosted on foreign news sites and she is regularly interviewed by foreign reporters — to urge international support for on-island bloggers. She recently called on readers to link websites to the on-island blogs, send the bloggers computer parts, and buy Internet access cards for them (Generacion Y, 29 May). [ 4]
Sanchez was among the first to publicize an apparent new restriction that barred hotels from allowing Cubans to buy Internet access, posting a YouTube video of an employee at one Havana hotel explaining the ban to her husband, fellow blogger Reinaldo Escobar. The ban was minimally enforced at the outset, however, and now appears to have been dropped altogether, a development Sanchez portrayed as a victory for Cuba’s bloggers (Generacion Y, 23 April).[ 5] [b]
Sanchez also has taken an increasingly active role in protests and other actions to press demands for freedom of expression and travel and greater access to the Internet.
She took the stage to demand Internet freedom during the government-sponsored Havana Biennial art festival, and she participated in an unauthorized presentation at the Havana book fair (Generacion Y, 30 March, 17 February).[ 6] [ 7]
Sanchez — who has been denied permission to travel to receive German and Spanish awards — publicized plans for a 1 May protest demanding more freedom to travel and later reported that it was a success despite limited participation in Havana (Generacion Y, 23 April, 2 May).[ 8] [ 9] She also was part of a group that accompanied dissident Edgar Lopez to the immigration office in an attempt to pressure the government to allow him to travel abroad (Generacion Y, 28 April).[ 10]
Internet, Blogs in Cuba Only about 2.1% of Cubans have access to the Internet itself, according to a recent Freedom House report, which rated Cuba the least free of 15 countries surveyed in terms of Internet freedom (www.freedomhouse.org). Internet World Stats (www.internetworldstats.com) cites both the 2.1% figure as well as 11.5% for Cuba’s Internet penetration rate; the higher number is attributed to the International Telecommunications Union, which may be relying on government statistics that include those who only have access to the Cuban intranet. [ 11]
The number of on-island Cuban blogs, however, continues to increase. Of 66 blogs claiming to originate on the island that OSC surveyed in early June 2009, 46 had been created since April 2008 — including 14 thus far in 2009 — compared to 20 created prior to April 2008.
All of the bloggers featured on the Voces Cubanas platform have been critical of the regime, and Octavo Cerco author Claudia Cadelo has been the most forceful in demanding wholesale political change.
Cadelo wrote in Octavo Cerco on 2 June that political change should include the “resignation of the president of the Councils of State and Minister and of the entire National Assembly,” multiparty elections, and overhaul of the security forces.[ 12] She said on 4 May that she wanted a “‘change of government’ from top to bottom.”[ 13]
Miriam Celaya, author of Sin EVAsion, called the Central Committee an “old machine” that could not be fixed (9 June).[ 14] She also complained of “ideology fatigue” and said that Cuban leaders were preparing to “blame” citizens for economic problems of their own making (Sin EVAsion, 7 June, 26 May).[ 15] [ 16]
Veritas blogger Eugenio Leal posted the results of a survey he conducted of 487 Cubans, 51% of whom said that a system change was necessary to improve the economy and criticized the government because it “manipulates everything” (3 June, 7 May).[ 17] [ 18] Desde Aqui author Reinaldo Escobar claimed that the Internet’s ability to promote free expression did not “conform to the political will of the government,” and he criticized its response to US policy initiatives (26 May, 21 April).[ 19] [ 20] [c]
Sanchez and like-minded bloggers have become bolder in criticizing the government since they first launched their blogs. Their posts initially focused more on their personal experiences and dealt only indirectly with politics. Most early bloggers wrote under pseudonyms; Miriam Celaya later dropped hers and most new bloggers on Voces Cubana write under what they say are their real names.
Bloggers Cuba
Another 15 blogs, maintained by Cubans who mostly claim to be journalists or information technology professors and students, use a separate off-island platform, Bloggers Cuba, to urge greater access to the Internet and more government openness. The website (www.bloggerscuba.com) is registered in Panama and hosted on a server in the United States.
The earliest post on the site, dated 2 June 2008, announced that the platform is designed to unite on-island bloggers and promote the spread of “social networks.”[ 21] It sought to expand readership to those lacking regular Internet access by distributing a hardcopy compilation of all posts in February earlier this year, but it has not repeated this since then.[ 22]
Elaine Diaz, who claims she is a journalist, posted an article on her La Polemica Digital blog and on the Bloggers Cuba platform stating that she wanted “political e-participation” in Cuba modeled after President Obama’s campaign (21 May).[ 23]
A post by Alejandro Perez Malagon, a self-described engineering professor at a Havana university, called for a blog forum on the Cuban intranet that would be freely available to all, along with greater Internet access (Artilugios.cu, 7 April).[ 24] Malagon earlier said Vice Information Minister Boris Moreno’s statements about the planned fiber optic cable between Venezuela and Cuba were “promising” because they indicated that the government would not seek to limit Internet access once the cable was in place (6 February). [ 25]
Boris Leonardo Caro, who appears to post only to the Bloggers Cuba site and identifies himself as a journalist, wrote on 10 June that the number of Cubans on Twitter was increasing, and David Chapet, a French expatriate claiming to live in Cuba, posted a list of Cuba-related groups on Facebook (Journal de Cuba, 29 January).[ 26] [ 27] Chapet, however, registered the Bloggers Cuba site with a business address in Panama, according to whois.com.
Bloggers Cuba authors have not openly criticized the Cuban Government, although they have occasionally complained about conditions on the island. Most entries are apolitical and they appear to be operating with some degree of government sanction.
Caro wrote on 22 May that state-run media outlets treated the public “like children,” but he went on to assert that he did not mean to criticize them.[ 28] Bubusopia blogger Rogelio Diaz Moreno on 30 January criticized the dual currency system.[ 29]
Most of the entries on the Bloggers Cuba platform discuss sports, film, music, and literature as well as state-sponsored cultural events. Discussion of current events usually takes a factual or neutral tone.[ 30] [ 31] [ 32] [ 33] [ 34] [ 35] [ 36] [ 37]
The bloggers report holding meetings to discuss on-island blogging and access to the Internet, with the most recent held 1 June. Their first meeting was held 16 September 2008 at a state-run computer center in Havana (Bloggers Cuba).[ 38] [ 39] Bloggers, Web-Based Software, Embargo Bloggers at both Voces Cubana and Bloggers Cuba have criticized the United States over restrictions on Cubans’ access to web-based software because of the embargo.
Sanchez wrote on 30 May that enforcement of restrictions on the use of MSN Messenger was a “blow” to Internet users in Cuba and that it contributed to censorship in Cuba (Generacion Y).[ 40] Cadelo likewise complained that a new provision in the Rights and Responsibility statement on Facebook could limit access and was a “contradiction” that “facilitated” the government’s work (Octavo Cerco, 12, 10 June).[ 41] [ 42]
Several Bloggers Cuba posts have complained about Google services that are unavailable on the island, linking the absence to the embargo (1 June, 4 May, 21 April, 28 January).[ 43] [ 44] [ 45] [ 46]
Government Response
The government has avoided taking a heavy-handed approach against the independent bloggers, instead promoting its own blogging platform that, unlike the others, is accessible on the Cuban intranet. While it apparently dropped the ban on allowing Cubans to buy Internet access at hotels, state media have delivered a few relatively low-key warnings, particularly to Sanchez.
The Cuban Journalists Blogs site at blogcip.cu appears intended to provide a progovernment counter to independent bloggers. The earliest post on the platform is dated 14 November 2006, but the site has seen a significant increase in use recently, with near daily posts in May and June after monthly totals of only 6 to 10 posts earlier this year. The conditions for use include a provision that participants will not publish “counterrevolutionary” materials.[ 47]
A commentary on government website CubaDebate denounced “cyberdissidents” and accused Sanchez of being linked to the United States (6 May).[ 48] The cultural weekly La Jiribilla denounced Sanchez’s speech during the Biennial (13 April).[ 49]
[a] For more information on Sanchez and Cuban bloggers, see the 16 December 2008 OSC Analysis, Cuban Bloggers, Dissidents Undeterred by Crackdowns (LAF20081216499006), the 24 July 2008 OSC Analysis, Cuba — Blogger Steps Up Criticism Amid Continued Obstacles (LAF20080724035001), and the 9 May 2008 OSC Media Aid, Blogs Increasingly Serve as Forum for Government Critics in Cuba (LAF20080509465001).
[b] For more information about the measures at Cuban hotels, see the 15 May OSC Report, Cuba — New Internet Restriction Barely Enforced, Has Little Impact (LAP20090515380005).
[c] For information about the Cuban Government’s response to shifts in US policy toward Cuba, see the 15 April OSC Analysis, Cuba — Fidel Castro Welcomes US Move While Maintaining Hard Line (LAF20090415471001).
[ 1] [Open Source (Not OSC) | | http://vocescubanas.com/ | 28 January 2009 | | Voces Cubanas — plataforma blogger desde cuba | | | (U) | Havana Voces Cubanas in Spanish — a blogging platform for Cubans living in Cuba sponsored by Yoani Sanchez.]
[ 2] [Open Source (Not OSC) | | http://itinerarioblogger.com/ | 11 April 2009 | | Nuevas incursiones del Itinerario | | | (U) | Havana Itinerario Blogger in Spanish – blog of the ‘Bloggers Agenda’ initiated by well-known on-island blogger Yoani Sanchez]
[ 3] [OSC | | LAP20090429201001 | 29 April 2009 | | Cuban Blogger: People Share Unpublished News Using Cellular Telephones | | (U) | (U) | [Description of Source: Havana Generacion Y in Spanish — Blog featuring commentaries on the social and political situation in Cuba; author identified as Havana journalist Yoani Sanchez; host website registered in Frankfurt, Germany; URL: http://www.desdecuba.com/generaciony/%5D%5D
[ 4] [Open Source (Not OSC) | | http://www.desdecuba.com/generaciony/?p=1206 | 29 May 2009 | | ¿Como ayudar? | | | (U) | ]
[ 5] [Open Source (Not OSC) | | http://www.desdecuba.com/generaciony/?p=1001 | 23 April 2009 | | “Sentada” blogger | | | (U) | ]
[ 6] [OSC | | LAP20090331201001 | 30 March 2009 | | Cuba: Bloggers, Youths Demand ‘Freedom’ at Havana Biennial | | (U) | (U) | [Description of Source: Havana Generacion Y in Spanish — Blog featuring commentaries on the social and political situation in Cuba; author identified as Havana journalist Yoani Sanchez; host website registered in Frankfurt, Germany; URL: http://www.desdecuba.com/generaciony/%5D%5D
[ 7] [OSC | | LAP20090217201001 | 17 February 2009 | | Cuban Blogger: Banned Author Presents Book Despite State Security Threats | | (U) | (U) | Havana Generacion Y in Spanish — Cuban blog featuring commentaries on the social and political situation in Cuba; author identified as Havana journalist Yoani Sanchez; host website registered in Frankfurt, Germany. URL: http://www.desdecuba.com/generaciony/%5D
[ 8] [OSC | | LAP20090424201001 | 23 April 2009 | | Cuban Blogger Announces 1 May Protest Using Kitchen Utensils | | (U) | (U) | [Description of Source: Havana Generacion Y in Spanish — Blog featuring commentaries on the social and political situation in Cuba; author identified as Havana journalist Yoani Sanchez; host website registered in Frankfurt, Germany; URL: http://www.desdecuba.com/generaciony/%5D%5D
[ 9] [OSC | | LAP20090503201002 | 2 May 2009 | | Cuban Blogger: Protest Garners Scant Reaction, Considered Success Nevertheless | | (U) | (U) | [Description of Source: Havana Generacion Y in Spanish — Blog featuring commentaries on the social and political situation in Cuba; author identified as Havana journalist Yoani Sanchez; host website registered in Frankfurt, Germany; URL: http://www.desdecuba.com/generaciony/%5D%5D
[ 10] [OSC | | LAP20090428201001 | 28 April 2009 | | Cuban Blogger Demands Travel Permit Card’s Derogation | | (U) | (U) | [Description of Source: Havana Generacion Y in Spanish — Blog featuring commentaries on the social and political situation in Cuba; author identified as Havana journalist Yoani Sanchez; host website registered in Frankfurt, Germany; URL: http://www.desdecuba.com/generaciony/%5D%5D
[ 11] [Open Source (Not OSC) | | http://freedomhouse.org/template.cfm?page=384&key=199&parent=19&repo rt=79 | 30 March 2009 | | Freedom on the Net: A Global Assessment of Internet and Digital Media | | | (U) | ]
[ 12] [Open Source (Not OSC) | | http://octavocerco.blogspot.com/2009/06/demandas-y-peticiones.html | 2 June 2009 | | Demandas y Peticiones | | | (U) | ]
[ 13] [Open Source (Not OSC) | | http://octavocerco.blogspot.com/2009/05/un-cazuelazo-personal.html | 2 May 2009 | | Un cazuelazo personal | | | (U) | ]
[ 14] [Open Source (Not OSC) | | http://vocescubanas.com/sin_evasion/2009/06/09/desnudos-sobre-el-tejado/ | 9 June 2009 | | Desnudos sobre el tejado | | | (U) | ]
[ 15] [Open Source (Not OSC) | | http://vocescubanas.com/sin_evasion/2009/06/07/ideologia-descascarada/ | 7 June 2009 | | Ideologia descascarada | | | (U) | ]
[ 16] [Open Source (Not OSC) | | http://vocescubanas.com/sin_evasion/2009/05/26/%E2%80%9Cperiodo-especial-mediati co%E2%80%9D/”Periodo Especial Mediatico” | 26 May 2009 | | “Periodo Especial Mediatico” | | | (U) | ]
[ 17] [Open Source (Not OSC) | | http://vocescubanas.com/veritas/2009/06/03/encuesta-2-el-sistema-y-las-aspiracio nes-del-ciudadano-en-cuba/ | 3 June 2009 | | Encuesta # 2: El sistema y las aspiraciones del ciudadano en Cuba | | | (U) | ]
[ 18] [Open Source (Not OSC) | | http://vocescubanas.com/veritas/2009/05/07/que-lo-sepan/ | 7 May 2009 | | Que lo sepan …. | | | (U) | ]
[ 19] [Open Source (Not OSC) | | http://vocescubanas.com/desdeaqui/2009/05/26/como-diria-engels/ | 26 May 2009 | | Como diria Engels | | | (U) | ]
[ 20] [Open Source (Not OSC) | | http://vocescubanas.com/desdeaqui/2009/04/21/la-agenda-de-discusiones/ | 21 April 2009 | | La agenda de discusiones | | | (U) | ]
[ 21] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/hola-mundo-de-bloggers-cuba/ | 2 June 2008 | Hola mundo! De Bloggers Cuba | | | (U) | ]
[ 22] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/intro-resumen-de-bloggers-cuba-de-febrero-2009/ | 18 June 2009 | | Intro – Resumen de Bloggers Cuba de Febrero 2009 | | | (U) | ]
[ 23] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/participacion-politica-en-la-red-cubana-salto-h acia-el-futuro-i/ | 21 May 2009 | | Participacion política en la red cubana: salto hacia el futuro (I) | | | (U) | ]
[ 24] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/la-web-dos-punto-cero-en-cuba/ | 7 April 2009 | | La web dos punto cero en Cuba | | | (U) | ]
[ 25] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/cuba-e-internet-en-el-2011/ | 6 February 2009 | | Cuba e Internet en el 2011 | | | (U) | ]
[ 26] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/aumenta-comunidad-de-twitteros-en-cuba/ | 10 June 2009 | | Aumenta comunidad de Twitteros en Cuba | | | (U) | ]
[ 27] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/cuba-cubanos-en-facebook/ | 29 January 2009 | | Cuba y Cubanos en Facebook | | | (U) | ]
[ 28] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/economia-cuando-el-rio-suena/ | 22 May 2009 | | ECONOMIA: Cuando el rio suena… | | | (U) | ]
[ 29] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/papelitos-de-colores/ | 30 January 2009 | | Papelitos de colores | | | (U) | ]
[ 30] [Open Source (Not OSC) | | Veneno: el video | 11 June 2009 | | http://www.bloggerscuba.com/post/veneno-video-escape/ | | | (U) | ]
[ 31] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/habana-campeon/ | 5 June 2009 | | Habana Campeon | | | (U) | ]
[ 32] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/ya-esta-el-capablanca-andando/ | 10 June 2009 | | Ya esta el Capablanca andando | | | (U) | ]
[ 33] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/cine-santiago-alvarez-entre-nosotros/ | 21 May 2009 | | CINE: Santiago Alvarez entre nosotros | | | (U) | ]
[ 34] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/diversidad-sexual-el-arcoiris-de-gala/ | 18 May 2009 | | DIVERSIDAD SEXUAL: El arcoiris de gala | | | (U) | ]
[ 35] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/modificaciones-al-ingreso-de-la-educacion-super ior-en-cuba/ | 10 June 2009 | | Modificaciones al ingreso de la Educacion Superior en Cuba | | | (U) | ]
[ 36] [OSC | | http://www.bloggerscuba.com/post/tiempo-nieve-en-la-habana/ | 6 February 2009 | | TIEMPO: Nieve en La Habana! | | | (U) | ]
[ 37] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/cuba-ultimo-cambio/ | 5 June 2009 | | Cuba: Ultimo cambio | | | (U) | ]
[ 38] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/bloggers-cuba-la-pandilla-completa-y-algo-mas/ | 1 June 2009 | | Bloggers Cuba. La pandilla completa y algo mas | | | (U) | ]
[ 39] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/i-encuentro-de-bloggers-cubanos-bloggers-por-cuenta-propia-la-habana-septiembre-08/ | 16 September 2008 | | I Encuentro de Bloggers Cubanos “Bloggers por Cuenta Propia” La Habana, Septiembre’08 | | | (U) | ]
[ 40] [OSC | | LAP20090530201001 | 30 May 2009 | | Cuban Blogger: Microsoft Ban Represents ‘Blow’ to Cuba’s ‘Web Renegades’ | | (U) | (U) | [Description of Source: Havana Generacion Y in Spanish — Blog featuring commentaries on the social and political situation in Cuba; author identified as Havana journalist Yoani Sanchez; host website registered in Frankfurt, Germany; URL: http://www.desdecuba.com/generaciony/%5D%5D
[ 41] [Open Source (Not OSC) | | http://octavocerco.blogspot.com/2009/06/la-inaccesible-red-entrevista-un-cubano. html | 12 June 2009 | | La estrecha RED (entrevista a un cubano en China) | | | (U) | ]
[ 42] [Open Source (Not OSC) | | http://octavocerco.blogspot.com/2009/06/la-estrecha-red.html | 10 June 2009 | | La estrecha RED | | | (U) | ]
[ 43] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/cuba-vs-google-rompeolas/ | 1 June 2009 | | Cuba vs Google: Rompeolas | | | (U) | ]
[ 44] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/google-cuba-me-cago-en-el-bloqueo/ | 4 May 2009 | | Google – Cuba. Me cago en el Bloqueo | | | (U) | ]
[ 45] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/internet-my-dear-google-again/ | 21 April 2009 | | INTERNET: My dear Google… again ! | | | (U) | ]
[ 46] [Open Source (Not OSC) | | http://www.bloggerscuba.com/post/hasta-cuando-esto/ | 28 January 2009 | | Hasta cuando esto? | | | (U) | ]
[ 47] [Open Source (Not OSC) | | http://blogcip.cu/registro/ | 12 June 2009 | | Datos para registrarse | | | (U) | ]
[ 48] [Open Source (Not OSC) | | http://www.cubadebate.cu/index.php?tpl=design/especiales.tpl.html&newsid_obj_id=14980 | 5 June 2009 | | Cibercomando y Ciberdisidentes, mas de lo mismo | | | (U) | ]
[ 49] [OSC | | LAP20090413361006 | 13 April 2009 | | Cuba: Cultural Magazine Decries ‘Mercenaries’ Demand’ for US Government Funds | | (U) | (U) | Havana La Jiribilla in Spanish — Weekly cultural magazine sponsored by Juventud Rebelde Newspaper; http://www.lajiribilla.cu/%5D
[This item was originally filed as LAF20090618498001]
TOP-SECRET – ISAF Joint Command Media Operations Standard Operating Procedures

Media Operations Tasks and Responsibilities: Media Operations is responsible for the Command’s media relations activities, including identifying media to engage with to disseminate information, responding to queries, arranging interviews, and advising senior leaders and IJC members on media issues. Media Operations works with local and international media. The staff also manages the IJC media accreditation and embed programs, and works closely with Regional Commands and NATO Training Mission-Afghanistan (NTM-A) Public Affairs staffs. IJC Media Operations distributes, under its letter head, releases from special operations units.
Press Releases: Media Operations disseminates news releases regarding current operations as well as command activities of interest to the general public.
Joint IJC-Afghan Releases: Media Operations staff should strive to issue joint releases with the Afghan National Security Forces as much as possible; whenever a release involves Afghan National Security Forces — either the Afghan National Army (ANA), Afghan National Police (ANP), National Defense Service (NDS), or all of the above – Media Operations drafts the release as a joint release, with a comment from the Afghan leadership, and coordinates with the appropriate ministries.
Media Queries: Media Operations fields and responds to media queries via phone and e-mail. Based on the nature of the query, Media Operations coordinates the response with the PAO Director as required. See Section (__) for examples of when coordination with the PAO Director is needed. All press officers will monitor the Media Office Inbox (unclass), respond to queries, draft press releases, and facilitate media interviews as required.
Interviews with IJC Leadership Media Operations coordinates interviews with IJC senior leadership and provides preparatory materials, which may include talking points (NATO, ISAF, etc), information on the reporter (bio and recent articles) for those interviews. Media Operations creates and maintain talking points on a variety of issues. The staff also escorts media to these events and prepares interviewees as necessary.
Interviews with Commander, IJC, are referred to the Commander‟s personal PAO for action.
Release Authority: The Commander, IJC, is the release authority for media information pertaining to the command and its operations. The IJC PAO Director acts on behalf of the Commander in routine authorization of information. See Appendix A (__) for specific authorities based on type of information being released.
…
NEWS RELEASE/MEDIA ADVISORY PROCESS:
All news, feature and general media releases must be checked for:
- An ISAF link to the information
- A link to ANSF/Afghan involvement, if at all possible for
- Issue Dual release with Afghan ANSF if applicable and possible
- No list of enemy body count, details of wounded
- Newsworthiness of release (information detail and relevance)
News Release (Fatality/CIVCAS):
- Receive info from JOC Watch/RC/Media/Embassy/TF.
- Check details and confirm with relevant RC/CJOC that info is correct.
- Produce MRL (in event of fatality) on Secret side – essentially an update for ISAF PAO staffs (RCs, internal staff etc)
- Post on noticeboard in ISAF Office.
- Email to MRL distribution list (see previously sent MRLs).
- Put relevant info onto ISAF News Release template (unclas) and print original info (original email or detail from RC or original source – should get confirmation from our JOC watch) to go onto back of ISAF sheet for records.
FOR ALL CASUALTIES: Include draft sympathy quote for PAO Director or senior PAO on duty.
FOR US CASUALTIES: Include acknowledgement line stating the member killed was a US service member.
FOR NON-US CASUALTIES: Include statement that ISAF does not release nationality. BEFORE release – check with RC that next of kin have been notified. NO RELEASE will be made until relevant nation has confirmed completed next of kin notification.
- Ensure quotes, DIVDS reference or other references used are correct. Spell check and once over again.
- In Press office email send to Distribution Lists 1, 2, 3, 4.
- Once sent, releases need to be saved into the relevant folder on the P Drive.
Feature News Release (General) – good news stories etc.
- Receive information from RC or particular Unit. Check details and confirm with relevant RC that info is correct.
- Put relevant info onto ISAF News Release template (unclas) and print original info (original email or detail from RC or original source) to go onto back of ISAF sheet for records.
- Before being signed off by Media Ops Chief or senior PAO on duty, ensure any quotes, DIVDS reference or other references used are correct. Spellcheck and once over again (always get a second pair of eyes to have a quick read through!).
- In Press office email send to Distribution Lists 1, 2, 3, 4.
- File hard copy with original source and sign off sheet to be put up on wall.
Media Advisory
Any upcoming events that may be of interest to press need to be „advertised‟. Ensure photos/references etc are correct, ISAF does not mention individual units/nations unless specifically required.
Operational Update – This is when there is a change of command as an example and we target the relevant nations (i.e. general release but focus on specific nations that it affects).
RELEASE AUTHORITIES:
Authority to release news and feature releases, media advisories and operational updates is delegated to all RC Chief PAOs and through them down to individual Task Force PAOs, except for the following categories, which will only be released by IJC PAO or HQ ISAF PAO:
(1) Death or injuries to ISAF troops – releasable by IJC.
(2) Any Civilian Casualty event – releasable by IJC.
(3) Catastrophic operational failure (e.g. enemy closure of an airfield) – releasable by IJC.
(4) Events with wider intra/inter theatre implications (Elections, NATO policies, TCN policies etc) – releasable by HQ ISAF unless specifically delegated.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – U.S. Military Core Warrior Values Training Presentation

• The vast majority of Coalition Forces perform their jobs magnificently every day:
– They do their duty with honor under extremely difficult circumstances.
– They exhibit good judgment, honesty, and integrity.
– They display patience, professionalism, and restraint in the face of a treacherous enemy.
– They do the right thing even when no one is watching.
• As military professionals, it is important that we take time to reflect on the values that separate us from our enemies.

DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – U.S. Marine Corps Intelligence Afghan Insurgent Tactics, Techniques and Procedures Field Guide

Studying past combat helps gain insight into how insurgents may operate in the future. This guide uses short, simple vignettes to highlight common Afghan insurgent tactics. Each vignette focuses on a particular mission profile, such as raids, ambushes, and defending against a cordon and search.
While tactics are continually evolving, the Afghans have a well documented history of using similar techniques against foreign militaries. Most of the vignettes in this guide are from the 1980s when Afghan insurgents fought the Soviet Union. Despite being more than 20 years old, many of the tactics remain in use today. For a more complete description of Afghan insurgent tactics against the Soviets, MCIA strongly recommends reading The Other Side of the Mountain by Ali Jalali and Les Grau, which this guide is based on. The final three vignettes in this guide are from recent operations in Afghanistan and demonstrate the evolution of tactics, techniques, and procedures (TTPs) by Afghan insurgents.
…
Vignette 1: Ambush
Ambush Near Abdullah-e Burj
October 1980
A Soviet column, returning to its base after a 4-day operation against the Mujahideen, was ambushed as it crossed a bridge going south on the main highway to Bagram.
The insurgents had observed the column headed north on the highway. They believed that the convoy would return the same way since the bridge was the only one in the region over the Panjsher River. The location was chosen because it would allow the Mujahideen to hit the convoy when it was most vulnerable: when half the column had crossed the bridge, and the force was divided by the river. They would ambush the column on its return trip when the troops were tired.
The Mujahideen secretly deployed on the day of the ambush. One group of 150 men was positioned in the orchards and hills south of the river (Map Point 1); a second group of 200 men was positioned to the north (Map Point 2). In both areas, rocket-propelled grenade launchers in covered positions were placed close to the road, with heavy machine guns on the more dominant terrain. Recoilless rifles and 82 mm mortars were placed for support. The Soviet column returned in the afternoon, and by 1600 it was split in two as it crossed the river (Map Point 3).
At a commander’s signal, the Mujahideen opened fire on the tanks, armored personnel carriers, and trucks along the entire length of the convoy. The Soviets drove off the road trying to escape. Those near the orchards had little room to maneuver. Twenty to 30 vehicles were burning. Soldiers dismounting from the armored personnel carriers came under heavy machine gun fire (Map Point 2). While some of the Soviets set up perimeter defenses to hold until help came, many abandoned their vehicles and tried to ford the river. Some were washed away while others headed for Bagram across the open plain.
As night fell, Soviet artillery ineffectively pounded Mujahideen positions. The insurgents moved through the abandoned vehicles, taking supplies and weapons. In the morning, the Soviets sent a relief column from Bagram to free the trapped convoy. The insurgents withdrew. The Mujahideen had two killed and seven wounded, with Soviet casualties unknown.

DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – (U//FOUO) Open Source Center Growth in Afghan Insurgent Reintegration

A body of open-source reporting suggests that fighters leaving the Afghan insurgency are doing so in greater numbers this winter (1,865 fighters) than last winter (443 fighters). As with the winter of 2009-2010, the majority of defecting fighters have continued to reintegrate into Afghan Government entities in the comparatively peaceful northern and western provinces of Afghanistan. The Taliban have rejected these reports, claiming that those joining the government are not Taliban fighters. Because of variations in the level of detail provided in media reports, this compilation could understate the number of reported militants leaving the battlefield. However, even 2,000 defections over six months would not appear to represent a major blow to an insurgency estimated to have 25,000 to 36,000 current fighters, and it is likely that at least some of those taking advantage of government reintegration programs were not committed fighters.
…
Greater Number of Defections This Winter
Insurgents appear to be surrendering in far greater numbers this winter (1 November 2010 to 31 January 2011) than in the previous winter (1 November 2009 to 31 January 2010). Approximately 1,865 fighters have reportedly surrendered to the Afghan Government, compared to approximately 443 fighters in the last winter, an increase of almost 400 percent.
• Of the six months reviewed, the three months with the largest number of fighters leaving the insurgency all occurred this winter: November 2010 (755), December 2010 (295), and January 2011 (815).
Defections Concentrated in North, West
Insurgents have overwhelmingly surrendered in the relatively peaceful areas encompassing the International Security Assistance Force’s (ISAF) North and West regional commands rather than in the much more violent South and East, although it is unclear why. As suggested in a previous OSC Analysis,
• The vast majority of insurgents were reintegrated into seven provinces this winter: Baghlan (241), Balkh (141), Faryab (140), Jowzjan (153), and Kunduz (330) in Regional Command (RC) North; and Badghis (240) and Herat (400) in RC West. the greater numbers of Taliban fighters and greater concentration of Pashtuns — the ethnic group to which most Taliban belong — in the South and East may increase Taliban cohesion, making it more difficult for disaffected insurgents there to switch sides. It is also possible that insurgents leaving the battlefield prefer to resettle with their families in the safer North and West and that some provinces in these areas offer better benefits to defectors.
Taliban spokesman Zabiullah Mujahid “rejected” reports of insurgents joining the government, claiming that “these people are not mujahidin” and are not affiliated with the Taliban.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – DEA Agents Helped Launder Millions in Drug Cartel Money

An excerpt from a document included in the report details the transfer of $2,649,200 to the United States in one set of transactions in the July and August 2007.
Mexico’s government allowed a group of undercover U.S. anti-drug agents and their Colombian informant to launder millions in cash for a powerful Mexican drug trafficker and his Colombian cocaine supplier, according to documents made public Monday.
The Mexican magazine Emeequis published portions of documents that describe how Drug Enforcement Administration agents, a Colombian trafficker-turned-informant and Mexican federal police officers in 2007 infiltrated the Beltran Leyva drug cartel and a cell of money launderers for Colombia’s Valle del Norte cartel in Mexico.
The group of officials conducted at least 15 wire transfers to banks in the United States, Canada and China and smuggled and laundered about $2.5 million in the United States. They lost track of much of that money.
In his testimony, the DEA agent in charge of the operation says DEA agents posing as pilots flew at least one shipment of cocaine from Ecuador to Madrid through a Dallas airport.
The documents are part of an extradition order against Harold Mauricio Poveda-Ortega, a Colombian arrested in Mexico in 2010 on charges of supplying cocaine to Arturo Beltran Leyva. A year earlier, Beltran Leyva was killed in a shootout with Mexican marines in the city of Cuernavaca, south of Mexico City.
The documents show Mexico approved Poveda-Ortega’s extradition to the United States in May, but neither Mexican nor U.S. authorities would confirm whether he has been extradited. Mexican authorities listed his first name as “Haroldo.”
…
The documents offer rare glimpses into the way U.S. anti-drug agents are operating in Mexico, an often sensitive subject in a country touchy about national sovereignty.
On one occasion, the informant who began working for the DEA in 2003 after a drug arrest met with the girlfriend of a Colombian drug trafficker in Dallas and offered to move cocaine for their group around the world for $1,000 per kilo. In a follow-up meeting, the informant introduced the woman to a DEA agent posing as a pilot. The woman is identified as the girlfriend of Horley Rengifo Pareja, who was detained in 2007 accused of laundering money and drug trafficking.
Another scene described the informant negotiating a deal to move a cocaine shipment from Ecuador to Spain and minutes later being taken to a house where he met with Arturo Beltran Leyva.
TOP-SECRET – (U//FOUO) U.S. Air Force Evolution of Drone Ground Control Stations Presentation
TOP-SECRET from the FBI – Florida Resident Charged with Plotting to Bomb Locations in Tampa
TAMPA, FL—A 25-year-old resident of Pinellas Park, Fla., has been charged in connection with an alleged plot to attack locations in Tampa with a vehicle bomb, assault rifle, and other explosives, announced Robert E. O’Neill, U.S. Attorney for the Middle District of Florida; Lisa Monaco, Assistant Attorney General for National Security; and Steven E. Ibison, Special Agent in Charge of the FBI Tampa Division.
Sami Osmakac, a naturalized U.S. citizen who was born in the former Yugoslavia (Kosovo), was arrested Saturday night. He is charged in a criminal complaint in the Middle District of Florida with one count of attempted use of a weapon of mass destruction (explosives) and is scheduled to make his initial appearance today at 2:00 p.m. EST, in federal court, before U.S. Magistrate Judge Anthony Porcelli, in Tampa. If convicted, Osmakac faces a maximum sentence of life in prison and a $250,000 fine.
The arrest of Osmakac was the culmination of an undercover operation during which Osmakac was closely monitored by law enforcement officials for several months. The explosives and firearms that he allegedly sought and attempted to use were rendered inoperable by law enforcement and posed no threat to the public.
“The perseverance and diligence of law enforcement caused this investigation to conclude in a successful manner,” said U.S. Attorney O’Neill. “I would like to commend them for their hard work. This investigation was also predicated, in part, by assistance from the Muslim community. I would like to thank them as well.”
“The facts as alleged in this case underscore the need for continued vigilance both at home and abroad. Thanks to a coordinated law enforcement effort, this alleged plot was thwarted before anyone was harmed,” said Assistant Attorney General Monaco. “I applaud the many agents, analysts and prosecutors who worked together to ensure this matter was resolved safely.”
“The Tampa FBI Division has always considered its relationships with regional community groups throughout Central and Southwest Florida extremely important. In this case, we are grateful for the Muslim community’s continued support. This incident clearly demonstrated how citizens can help law enforcement keep our neighborhoods and our nation safe,” said FBI Special Agent in Charge Steven Ibison.
According to the complaint affidavit, in Sept. 2011, the FBI received information from a confidential human source (CHS) indicating that Osmakac had asked for al Qaeda flags. In November 2011, Osmakac and the CHS discussed and identified potential targets, in Tampa, where Osmakac intended on carrying out violent attacks. Osmakac allegedly asked the CHS for help in obtaining firearms and explosives for the attacks. The CHS indicated that he/she knew someone who might be able to provide firearms and explosives and introduced Osmakac to an undercover FBI employee.
The complaint alleges that Osmakac met with the undercover FBI employee, in person, on Dec. 21, 2011, and stated that he wished to acquire an AK-47-style machine gun, Uzi submachine guns, high capacity magazines, grenades and an explosive belt. In a subsequent meeting, Osmakac allegedly provided the undercover FBI employee with a $500 down payment for an AK-47, multiple homemade explosive grenades and the explosive belt.
According to the complaint, Osmakac also asked the undercover employee whether he/she could build bombs that could be placed in three different vehicles and detonated remotely, near where Osmakac would conduct a follow-up attack using the other weapons he requested. The undercover employee said he/she could possibly provide explosives for one vehicle. Osmakac also allegedly said that he wanted an explosive belt constructed to kill people.
During a subsequent meeting with the FBI undercover employee on Jan. 1, 2012, Osmakac allegedly described his attack plans by stating that he wanted to obtain a hotel room; park the vehicle with the bomb in it at his target; leave the area; detonate the car bomb; and then retrieve the weapons and explosives from the hotel room. Among Osmakac’s alleged bomb targets were night clubs in the Ybor City area of Tampa, the operations center of the Hillsborough County Sheriff’s Office in Ybor City and a business in the South Tampa area of Tampa.
The complaint alleges that, as part of the second portion of his planned attack, Osmakac told the undercover FBI employee that, after the car bomb was detonated, he wanted to use the explosive belt to “get in somewhere where there’s a lot of people” and take hostages. He allegedly stated that he would then make demands of the FBI to release some prisoners. According to the criminal complaint, when discussing law enforcement officers that might respond to the scene, Osmakac allegedly stated, “once I have this . . . they can take me in five million pieces” in an apparent reference to the explosive belt that would be attached to his waist.
During the Jan. 1st meeting, the undercover FBI employee noted that Osmakac could change his mind and back out of the plot. According to the complaint, Osmakac immediately shook his head in the negative and stated, “We all have to die, so why not die the Islamic way?”
On Jan. 7, 2012, FBI agents arrested Osmakac after he took possession of the explosive devices and firearms that had been rendered inoperable by law enforcement. The complaint alleges that, shortly prior to his arrest, Osmakac made a video of himself explaining his motives for carrying out the planned violent attack.
This investigation is being conducted by the FBI Tampa Division and the Tampa Joint Terrorism Task Force. It is being prosecuted by Assistant U.S. Attorney Sara Sweeney from the U.S. Attorney’s Office for the Middle District of Florida, with assistance from Trial Attorney Clem McGovern of the Counterterrorism Section in the Department of Justice’s National Security Division.
The charges contained in the criminal complaint are mere allegations. As in any criminal case, the defendant is presumed innocent until proven guilty in a court of law.
TOP-SECRET – (U//FOUO) U.S. Marine Corps Martial Arts Program (MCMAP) Manual

The focus of Marine Corps Martial Arts Program (MCMAP) is the personal development of each Marine in a team framework using a standardized, trainable, and sustainable close combat fighting system. As a weapon-based system, all techniques are integrated with equipment, physical challenges, and tactics found on the modern battlefield. The MCMAP is designed to increase the warfighting capabilities of individual Marines and units, enhance Marines’ self-confidence and esprit de corps, and foster the warrior ethos in all Marines. The MCMAP is a weapon-based system rooted in the credo that every Marine is a rifleman and will engage the aggressor from 500 meters to close quarter combat. The MCMAP:
• Enhances the Marine Corps’ capabilities as an elite fighting force.
• Provides basic combative skills for all Marines.
• Applies across the spectrum of violence.
• Strengthens the Marine Corps warrior ethos.
The motto of MCMAP best states the essence of the program: “One mind, any weapon.” This means that every Marine is always armed even without a weapon. He is armed with a combat mindset, the ability to assess and to act, and the knowledge that all Marines can rely on one another.
The Marine Corps was born during the battles that created this country. Drawing upon the experiences of the first Marines, we have developed a martial culture unrivaled in the world today. This legacy includes not only our fighting prowess but also the character and soul of what makes us unique as Marines. This training continued to evolve up to World War II. During these early years, the leadership and core values training that are our hallmark today developed in concert with the martial skills.


DOWNLOAD THE ORINIAL DOCUMENT HERE
TOP-SECRET – Classified USAID Report on Kabul Bank Corruption

Dubai real estate led depositors to rush to withdraw funds from Kabul Bank, the largest bank in Afghanistan. According to the Report of Kabul Bank in Conservatorship dated October 30, 2010, cited in a draft material loss review commissioned by USAID/Afghanistan, fraudulent loans were used to divert $850 million to insiders. This amount reportedly represented 94 percent of the bank’s outstanding loans.
Since 2003, USAID/Afghanistan has supported a number of capacity-building activities at the Afghanistan Central Bank (DAB) to help DAB regulate the banking sector. Currently, Deloitte1 provides DAB technical assistance in bank supervision and examination through a $92 million task order for the Economic Growth and Governance Initiative, which includes many activities in addition to bank supervision and examination. The purpose of the task order was to increase Afghanistan’s ability to develop and implement sound economic and regulatory policies that provide the foundation for private sector growth in a market economy. According to Deloitte’s work plan, one of the main goals of the assistance Deloitte provided to DAB was to assist DAB in fulfilling its statutory responsibilities ―to promote the stability and contribution to economic growth of the financial sector and to prevent avoidable losses. Deloitte provided onsite technical advisors at DAB’s Directorate for Financial Supervision.
After the run on Kabul Bank, senior officials in the U.S. Embassy raised concerns about Deloitte’s performance. Specifically, they were concerned that Deloitte staff did not warn the U.S. Government about looming problems at Kabul Bank before the first news reports broke in February 2010. They also questioned Deloitte’s effectiveness and performance because Deloitte staff had provided bank supervision assistance to DAB for 7 years, yet DAB supervisors were unable to prevent the near collapse of Afghanistan’s largest bank. In January 2011, USAID/Afghanistan requested the assistance of the Office of Inspector General (OIG) in determining whether USAID or Deloitte staff members were negligent in failing to report the Kabul Bank fraud.
In response to USAID/Afghanistan’s request, OIG/Afghanistan conducted this review to determine:
- What opportunities USAID and contractor staff had to learn of fraudulent activities at Kabul Bank through USAID’s Economic Growth and Governance Initiative and its predecessor, the Economic Growth and Private Sector Strengthening Activity.
- How staff learned of the fraud.
- What actions staff members took once they became aware of the fraud.
- Whether USAID’s oversight of its contractor was adequate.
…
USAID’s Management of Its Task Order with Deloitte Was Weak
ADS 203.3.2, ―Assessing and Learning, states that missions and their offices are responsible for monitoring a contractor’s performance in achieving the contract’s purpose. ADS 302.3.7.1a, ―Direct Contracting, Mandatory Reference: ―Procedures for Designating the Contracting Officer’s Technical Representative (COTR) for Contracts and Task Orders,‖ states that the COTR is in a unique position to monitor how well the contractor is progressing toward achieving the contract’s purpose and is responsible for providing technical liaison between the contractor and the contracting officer, a function critical to ensuring good contract performance.
When the current mission director arrived in June 2010, his attention focused on USAID/Afghanistan’s capacity to manage and provide oversight of highly technical bank supervision activities implemented by its contractor, Deloitte, at DAB. This focus heightened after the Kabul Bank crisis broke in September 2010. The task order with Deloitte for the Economic Growth and Governance Initiative was for a 5-year, $92 million project with three major components and 21 work streams with diverse requirements that was managed by USAID/Afghanistan’s Office of Economic Growth. In August 2009, when USAID issued the task order, the Office of Economic Growth had only four U.S. direct-hire staff and none with experience in the banking sector. For the most part, only one U.S. direct hire was managing the task order at any given time, with some assistance from Foreign Service National staff.
Further contributing to the mission’s challenges to provide effective oversight of Deloitte, a former COTR for the Deloitte task order stated that during a typical workweek, he spent 50 to 70 percent of his time drafting memorandums and cables for the U.S. Embassy, reducing his time for program oversight. He kept detailed timesheets of daily work activities. The COTR explained that such competing work demands, combined with the mission’s lack of technical expertise, created overreliance on the Deloitte advisers to manage the bank supervision assistance activities, with little oversight provided by USAID. USAID staff members stated that had they not faced the burden of managing a large task order with limited resources, they would have been in a better position to provide proactive and robust oversight of the Deloitte advisers. As one USAID official put it, ―Deloitte was managing USAID, rather than the other way around.
Generally, COTRs monitor contractor performance and verify that it conforms to the technical requirements and quality standards agreed to in the contract. COTRs do this by maintaining regular contact and liaison and by conducting frequent site visits with the contractor. Yet according to a former COTR for the Deloitte task order, mission management focused on program spending, financial pipelines, and burn rates, rather than on monitoring and achieving program results. A former USAID/Afghanistan staff member stated in a memo that the mission gave the Office of Economic Growth only 24 hours to review a proposed Deloitte work plan—insufficient time to provide thoughtful review and comment. Finally, at the entrance conference for this review, USAID/Afghanistan officials did not take a position on whether Deloitte’s performance was satisfactory or unsatisfactory, providing further evidence of inadequate management.
For years, USAID has faced difficulty in attracting staff to Afghanistan who have the appropriate levels of experience and skills. A former mission director for USAID/Afghanistan stated that the staffing situation in Afghanistan reflected what he considered to be an ongoing problem for USAID, especially for programs in war zones—not enough senior people at USAID who have the experience to manage large, substantive, technically challenging projects. Current USAID/Afghanistan leadership agreed with this assessment and explained that steps have been and continue to be taken to remedy that situation. For example, a recently completed reorganization in the Office of Economic Growth added one technical adviser position.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – Hackers leak indian Military Intel memo suggesting Apple has provided intercept backdoor to govs





TOP-SECRET – Obama Phones
|
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict1.jpg) On his first day in office, President Barack Obama speaks with a foreign leader in the Oval Office, Jan. 21, 2009. (Official White House Photo by Pete Souza) On his first day in office, President Barack Obama speaks with a foreign leader in the Oval Office, Jan. 21, 2009. (Official White House Photo by Pete Souza) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict0.jpg) President Barack Obama places a phone call at his desk in the Oval Office, Jan. 23, 2009. (Official White House Photo by Pete Souza) [This is a Raytheon IST secure phone. http://www.telecore.com/products/ist2.html ] President Barack Obama places a phone call at his desk in the Oval Office, Jan. 23, 2009. (Official White House Photo by Pete Souza) [This is a Raytheon IST secure phone. http://www.telecore.com/products/ist2.html ] |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict4.jpg) President Barack Obama meets with Interior Secretary Ken Salazar aboard Air Force One during a flight to Denver, Col., Feb. 17, 2009. (Official White House Photo by Pete Souza) [Desk phone is a Cisco secure phone.] President Barack Obama meets with Interior Secretary Ken Salazar aboard Air Force One during a flight to Denver, Col., Feb. 17, 2009. (Official White House Photo by Pete Souza) [Desk phone is a Cisco secure phone.]
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict8.jpg) [Phone at Oval Office seating area] President Obama has a briefing with a staff member prior to a phone call in the Oval Office, March 13, 2009. (Official White House Photo by Pete Souza) [Phone at Oval Office seating area] President Obama has a briefing with a staff member prior to a phone call in the Oval Office, March 13, 2009. (Official White House Photo by Pete Souza) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict11.jpg) President Barack Obama is seen at a meeting with his staff April 5, 2009, aboard Air Force One on a flight from Prague, Czech Republic en route to Ankara, Turkey. (Official White House Photo by Pete Souza) President Barack Obama is seen at a meeting with his staff April 5, 2009, aboard Air Force One on a flight from Prague, Czech Republic en route to Ankara, Turkey. (Official White House Photo by Pete Souza)
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict13.jpg) President Barack Obama works with Jon Favreau, director of speechwriting, on the President’s Normandy speech aboard Air Force One enroute to Paris on June 5, 2009. (Official White House photo by Pete Souza) President Barack Obama works with Jon Favreau, director of speechwriting, on the President’s Normandy speech aboard Air Force One enroute to Paris on June 5, 2009. (Official White House photo by Pete Souza)
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict15.jpg) President Barack Obama confers with Senior Advisor David Axelrod and Press Secretary Robert Gibbs at their hotel in Moscow, Russia, July 6, 2009. (Official White House Photo by Pete Souza) [Enlarged from small image.] President Barack Obama confers with Senior Advisor David Axelrod and Press Secretary Robert Gibbs at their hotel in Moscow, Russia, July 6, 2009. (Official White House Photo by Pete Souza) [Enlarged from small image.] |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict16.jpg) President Barack Obama meets with John Brennan, Assistant to the President for Counterterrorism and Homeland Security, in the Oval Office, Jan. 4, 2010. (Official White House photo by Pete Souza) [Two phones, top for secure, bottom White House phone system.] President Barack Obama meets with John Brennan, Assistant to the President for Counterterrorism and Homeland Security, in the Oval Office, Jan. 4, 2010. (Official White House photo by Pete Souza) [Two phones, top for secure, bottom White House phone system.]
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict18.jpg) “This is a rare look inside the President’s Treaty Room office in the private residence of the White House. He was making a call to Poland Prime Minister Donald Tusk.” (Official White House photo by Pete Souza) “This is a rare look inside the President’s Treaty Room office in the private residence of the White House. He was making a call to Poland Prime Minister Donald Tusk.” (Official White House photo by Pete Souza) |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict19.jpg) March 29, 2009. “It was a Sunday night in the Oval Office. The auto task force listened to the President before he made phone calls to alert key people about his plan to set deadlines for General Motors and Chrysler overhauls that was to be announced the next morning.” (Official White House photo by Pete Souza) March 29, 2009. “It was a Sunday night in the Oval Office. The auto task force listened to the President before he made phone calls to alert key people about his plan to set deadlines for General Motors and Chrysler overhauls that was to be announced the next morning.” (Official White House photo by Pete Souza)
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict21.jpg) President Barack Obama meets with Rep. Dennis Kucinich, D-Ohio, aboard Air Force One en route to Cleveland, Ohio, March 15, 2010. (Official White House Photo by Pete Souza) [The desk phone is a Cisco secure phone.] President Barack Obama meets with Rep. Dennis Kucinich, D-Ohio, aboard Air Force One en route to Cleveland, Ohio, March 15, 2010. (Official White House Photo by Pete Souza) [The desk phone is a Cisco secure phone.]
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict23.jpg) President Barack Obama checks his BlackBerry as he walks along the Colonnade to the Oval Office, March 18, 2010. (Official White House Photo by Pete Souza) President Barack Obama checks his BlackBerry as he walks along the Colonnade to the Oval Office, March 18, 2010. (Official White House Photo by Pete Souza)
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict25.jpg) President Barack Obama talks on the phone with a Member of Congress while en route to a health care event at George Mason University in Fairfax, Va., March 19, 2010. Assistant to the President for Legislative Affairs Phil Schiliro rides with the President. (Official White House Photo by Pete Souza) [A sends ” [The device between the seats under the seal is unknown. Not all presidential vehicles have it. There is a phone in the console.] President Barack Obama talks on the phone with a Member of Congress while en route to a health care event at George Mason University in Fairfax, Va., March 19, 2010. Assistant to the President for Legislative Affairs Phil Schiliro rides with the President. (Official White House Photo by Pete Souza) [A sends ” [The device between the seats under the seal is unknown. Not all presidential vehicles have it. There is a phone in the console.]
A sends: “With a little enhancement, it’s easy to see that device in the center is a Motorola speakerphone cradle for the handheld, wireless unit the President has.”
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict27.jpg) President Barack Obama talks on the phone in a holding room at Oakley Lindsay Center in Quincy, Ill., April 28, 2010. Mona Sutphen, deputy chief of staff for policy, sits at right. (Official White House Photo by Pete Souza) [Phones are L-3 STE model: http://www2.l-3com.com/cs-east/ia/ste/ie_ia_ste.shtml ]. See enlarged.] President Barack Obama talks on the phone in a holding room at Oakley Lindsay Center in Quincy, Ill., April 28, 2010. Mona Sutphen, deputy chief of staff for policy, sits at right. (Official White House Photo by Pete Souza) [Phones are L-3 STE model: http://www2.l-3com.com/cs-east/ia/ste/ie_ia_ste.shtml ]. See enlarged.]
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict29.jpg) President Barack Obama talks on the phone with German Chancellor Angela Merkel to discuss the economic situation in Europe, prior to the Hampton University commencement in Hampton, Va., Sunday, May 9, 2010. (Official White House Photo by Pete Souza) President Barack Obama talks on the phone with German Chancellor Angela Merkel to discuss the economic situation in Europe, prior to the Hampton University commencement in Hampton, Va., Sunday, May 9, 2010. (Official White House Photo by Pete Souza)
|
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict31.jpg) President Barack Obama talks with Alyssa Mastromonaco, director of scheduling and advance, in the Outer Oval Office, May 24, 2010. (Official White House Photo by Pete Souza) [Three types of phones sets, perhaps for three different systems.] President Barack Obama talks with Alyssa Mastromonaco, director of scheduling and advance, in the Outer Oval Office, May 24, 2010. (Official White House Photo by Pete Souza) [Three types of phones sets, perhaps for three different systems.] |
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict32.jpg) President Barack Obama prepares for foreign leader phone calls with Nigerian President Goodluck Jonathan and Japanese Prime Minister designate Naoto Kan, in the Oval Office, Saturday, June 5, 2010. Pictured, from left, are Michelle Gavin, senior director for African Affairs, Puneet Talwar, senior director for Iraq, Iran and the Gulf States, John Buchanan (on phone), director of operations and deputy director of the White House Situation Room, and National Security Advisor Gen. James Jones. (Official White House Photo by Pete Souza) [A phone technician apparently arranging a secure hook-up.] President Barack Obama prepares for foreign leader phone calls with Nigerian President Goodluck Jonathan and Japanese Prime Minister designate Naoto Kan, in the Oval Office, Saturday, June 5, 2010. Pictured, from left, are Michelle Gavin, senior director for African Affairs, Puneet Talwar, senior director for Iraq, Iran and the Gulf States, John Buchanan (on phone), director of operations and deputy director of the White House Situation Room, and National Security Advisor Gen. James Jones. (Official White House Photo by Pete Souza) [A phone technician apparently arranging a secure hook-up.]
Obama Phones The telephone is likely Obama’s primary means of personal, direct government. More private, intimate and persuasive than meetings, classified briefings, legislation and regulation signings, appointments, White House invites, travel, campaign tours, press releases, executive orders, mail, email, fax, TV, radio, photographs, Internet blogs, dining, applause, dance, sports, hugs, back pats, arm grabs, handshakes, baby holds, fist bumps, shout-outs, waves, finger points, grins, guffaws, chin tickles, jokes, punks, pardons, secret orders, medal awards, hospital-casket transfers-cemetary visits. Presumably all calls are recorded but not likely to be made public any time soon, thus may be the most secret of his service in office. These photos hide far more than they reveal — as intended in defiance of democracy and open government. |
TOP-SECRET – Federal Reserve Bank of New York Sentiment Analysis and Social Media Monitoring Proposal

Federal Reserve Bank of New York (“FRBNY”) is extending to suppliers an invitation to participate in an Sentiment Analysis And Social Media Monitoring Solution RFP bid process.
The intent is to establish a fair and equitable partnership with a market leader who will who gather data from various social media outlets and news sources and provide applicable reporting to FRBNY. This Request for Proposal (“RFP”) was created in an effort to support FRBNY’s Social Media Listening Platforms initiative.
B. Background & Scope
B1. (Instruction)
I. Introduction
Social media platforms are changing the way organizations are communicating to the public Conversations are happening all the time and everywhere.
There is need for the Communications Group to be timely and proactively aware of the reactions and opinions expressed by the general public as it relates to the Federal Reserve and its actions on a variety of subjects.
B2. (Instruction)
II. Social Listening Platforms
Social media listening platforms are solutions that gather data from various social media outlets and news sources. They monitor billions of conversations and generate text analytics based on predefined criteria. They can also determine the sentiment of a speaker or writer with respect to some topic or document.
The information gathered can guide the organizations public relations group in assessing the effectiveness of communication strategies.
Here are some of the services it can offer:
o Track reach and spread of your messages and press releases
o Handle crisis situations
o Continuously monitor conversations
o Identify and reach out to key bloggers and influencers
o Spot emerging trends, discussions themes and topicsB3. (Question)
III. Mandatory Minimum Solution Requirements
A. Geographic scope of social media sites
The solution must support content coming from different countries and geographical regions. It should also support multiple languages.
B. Content and Data Types
The solution must be able to gather data from the primary social media platforms –Facebook, Twitter, Blogs, Forums and YouTube. It should also be able to aggregate data from various media outlets such as: CNN, WSJ, Factiva etc.
C. Reports and Metrics
The solution must provide real-time monitoring of relevant conversations. It should provide sentiment analysis (positive, negative or neutral) around key conversational topics.
It must be able to provide summaries or high level overviews of a specific set of topics. It should have a configurable dashboard that can easily be accessed by internal analysts or management. The dashboard must support customization by user or group access.
The solution should provide an alerting mechanism that automatically sends out reports or notifications based a predefined trigger.
D. FRBNY Technology Integration
The solution must be able to integrate with existing FRBNY technologies such as: Google Search appliance, Lotus notes suite and web trends.
It must have support for single sign on or windows integrated authentication.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET-Debbie Cook Scientology $1 Billion Cash Reserve Email
The following is the text of an email sent on January 1, 2012 by a senior member of Scientology’s Sea Org named Debbie Cook. The email was published on the website of the Village Voice, then was removed at the request of Ms. Cook. It has since been reposted elsewhere. The email discusses Cook’s problems with the direction that the Church of Scientology has recently taken, including what she perceives an obsessive emphasis on fundraising and a more than $1 billion dollar unused cash reserve. Cook confirmed the email’s authenticity via Facebook.
Dear Friend,
I am emailing you as a friend and fellow Scientologist. As we enter a new year, it is hoped that 2012 can be a year of great dissemination and a year of real progress up The Bridge for all Scientologists.
Although I am not in the Sea Org right now, I served in the Sea Org at Flag for 29 years. 17 of those years were as Captain FSO. I am a trained auditorand C/S as well as an OEC, FEBC and DSEC.
I am completely dedicated to the technology of Dianetics and Scientology and the works of LRH. I have seen some of the most stunning and miraculousresults in the application of LRH technology and I absolutely know it is worth fighting to keep it pure and unadulterated.
My husband and I are in good standing and we are not connected with anyone who is not in good standing. We have steadfastly refused to speak to anymedia, even though many have contacted us.
But I do have some very serious concerns about out-KSW that I see permeating the Scientology religion.
I have the utmost respect for the thousands of dedicated Scientologists and Sea Org members. Together, we have come through everything this world couldthrow at us and have some real impingement on the world around us. I am proud of our accomplishments and I know you are too.
However there is no question that this new age of continuous fundraising is not our finest moment.
LRH says in HCO PL 9 Jan 51, An Essay on Management, “drop no curtains between the organization and the public about anything.”
-LRH
Based on this policy I am communicating to you about some situations that we need to do something about within our religion, within our group.
Actions that are either not covered in policy or directly violate LRH policy and tech include the extreme over-regging and fund-raising activities that have become so much a part of nearly every Sea Org org and Class V org as well as every “OT Committee”. This fundraising is not covered anywhere in LRH policy.
Hardworking Sea Org members and the dedicated staff of orgs around the world aren’t choosing to do these actions. Nor are the OTs. I am sure they wouldbe more than happy if they could just get on with direct dissemination of Scientology as they have done for so many years.
But the truth is that this is being driven from the very highest echelons within the Scientology structure and clearly there is a lot of pressure tomake targets that are being set.
The IAS: The IAS was created unbeknownst to LRH in 1984 by Marc Yager and David Miscavige. This was supposed to be based on LRH policies on the subject of membership and the HASI, however the IAS is nothing like the membership system described by LRH which only has two memberships and is covered in HCO PL 22 March 1965 “Current Promotion and Org Program Summary,Membership Rundown” and states:
“There are two memberships…”- LRH
LRH lists there the INTERNATIONAL ANNUAL MEMBERSHIP and gives its cost at 10 pounds sterling or $30 US. He also lists a LIFETIME MEMBERSHIP which ispriced at $75 US. There are no other memberships or statuses approved or known to LRH.
Furthermore, membership monies are supposed to go directly to the org where the membership is signed up, and the money used for dissemination by thatorg, in that area. This is covered in HCOPL 1 Sept 1965R Membership Policies.
“It all goes into the HCO Book Account in the area where the membership isbrought and is not part of the organization’s weekly gross income. Membership monies go to dissemination”.- LRH
Currently membership monies are held as Int reserves and have grown to well in excess of a billion dollars. Only a tiny fraction has ever been spent, in violation of the policy above. Only the interest earned from the holdings have been used very sparingly to fund projects through grants. In fact many of the activities you see at IAS events are not actually funded by the IAS,but rather by the Scientologists involved.
Think about it, how many ads disseminating Scientology, Dianetics or any Scn affiliated programs have you seen on TV? Heard on the radio? Seen innewspapers? I haven’t seen one in the 4 years I have lived in San Antonio, Texas, the 7th largest city in the US. How many have you seen?
Donating anything more than a lifetime membership to the IAS is not based on LRH policy. The article “What Your Donations Buy” (The Auditor, The Monthly Journal of Scientology No. 51, 1970) is clearly talking about how the church uses your donations for Dianetics and Scientology services. Next time you are asked to donate outside of services, realize that you are engaged in fundraising and ask to see something in writing from L. Ron Hubbard that this is something he expects from you as a Scientologist.
New Org Buildings: LRH also never directed the purchase of opulent buildingsor the posh renovations or furnishings for every org.
In fact, if you read HCO PL 12 March 75 Issue II, “The Ideal Org”, which is what this program has been called, and nowhere in it will you find 20 million dollar buildings or even any reference to the poshness of org premises at all as part of LRH’s description of an “Ideal Org”. Instead, an Ideal Org was one that delivered and moved people up The Bridge – somethingthat is not part of this “Ideal Org” program.
LRH says in the PL that an Ideal Org:
“would be clean and attractive enough not to repel its public” – LRH.
This is all it says about the state of the building.
As a result of this off-policy alteration of the Ideal Org PL, we have the majority of top OTs, now deemed “OT Ambassadors”, heavily engaged in fund-raising activities that include “bingo”, “pirate dinners”, “knitting classes”, “hay rides”, and many other activities strictly revolving around raising funds for the required multi-millions of dollars to fund their “Ideal Org”. As part of this, people around every org are now asked todonate to their local “Ideal Org” instead of their own services or their own Bridge.
LRH says in HCO PL Org Ethics and Tech:
“GET RID OF DISTRACTIONS FROM SCIENTOLOGY in your org. Baby-sitting or raffle tickets and such nonsense.”-LRH
Yet these distractions are rampant as they are being used as fund-raisers to get money for the huge quotas being issued to fund the “Ideal Org”.
“If the org slumps… don’t engage in ‘fund-raising’ or ‘selling postcards’ or borrowing money. Just make more income with Scientology.It’s a sign of very poor management to seek extraordinary solutions for finance outside Scientology. It has always failed.”
“For orgs as for pcs, ‘Solve It With Scientology’.
“Every time I myself have sought to solve financial or personnel in other ways than Scientology I have lost out. So I can tell you from experiencethat org solvency lies in more Scientology, not patented combs or fund-raising barbeques.”
HCO PL 24 February 1964, Issue II, Org Programming, (OEC Vol. 7, p. 930)
The point is that Scientologists and OT’s need to be training, auditing and disseminating to raw public- not regging each other or holding internalfundraisers.
Out Tech: Over the last few years we have seen literally hundreds and hundreds of people who were validated as clear using the CCRD as developed by LRH now being told they are not Clear. This included hundreds of OTs who were then put onto NED as a “handling”. LRH clearly forbid any Dianetics to be run on OTs in HCOB “Dianetics Forbidden on OTs”. This is out tech. This entire technical “handling” was directed personally by COB RTC and was done on thousands of OTs. But it was based not on an LRH HCO Bulletin, but rather based on a single C/S instruction where LRH C/Sed one pre-OT who had not achieved the state of clear but was mid OT III and not making it. LRH directed a solo handling that the pre-OT was to do to get himself to achieve the state of Clear. This LRH C/S taken out of context was then used to implement a technical handling that was in direct violation of an LRH HCOB.
This and other “technical handlings” done on Solo NOTs auditors created great expense and hardship on Solo NOTs auditors around the world as they were made to do these handlings to continue on the level.
Then there are the “fast grades at Flag” that no other org has. How can it be that Flag has been delivering grades differently to the rest of the world for the last 3 years? Whatever the problem is, the fact is that having “fast Grades” at Flag creates a hidden data line and is a HIGH CRIME and the subject of an entire policy letter called HCOPL “TECH DEGRADES” which LRH has placed at the start of every Scientology course.
More recently the fad seems to be that nearly everyone needs to “re-do their Purif and do a long objectives program”, including many OTs mid Solo NOTs.
There is nothing wrong with doing objectives, but it is a clear violation of HCOB ‘MIXING RUNDOWNS AND REPAIRS” to have a person mid a rundown or OTlevel be taken off it and placed on an objectives program.
Solo NOTs auditors are also being made to get their objectives from a Class IX auditor at great expense as they are not being allowed to co-audit.
Flag has made many millions of dollars on the above listed out tech handlings because OTs mid Solo NOTs are forced to get these out-tech actionsto be able to get back onto and stay on the level and complete it. Not to mention the spiritual effects of the out tech that this has on each OT.
I myself was subject to these out tech “handlings”, including extensive FPRD mid Solo NOTs. It took its toll in many ways, including physical situationsI am still dealing with today. So I have some reality of the hardship caused.
LRH Command Structure: LRH left us with a complex and balanced command structure, with our orgs led by the Office of ED International. This office was considered so important that LRH created a special management group called the Watch Dog Committee whose only purpose was to see that this office and the other needed layers of management existed. LRH ED 339R speaks of this extensively as the protection for our Church. But these people are missing. And not just some. As of just a few years ago there were no members of the office of ED Int on post, not to mention top execs throughout the International Management structure.
You may have also wondered… where is Heber, the President of the Church? What about Ray Mitthoff, Senior C/S International, the one that LRH personally turned over the upper OT Levels to? How about Norman Starkey, LRH’s Trustee? What happened to Guillaume – Executive Director International? And Marc Yeager, the WDC Chairman? What happened to the other International Management executives that you have seen at events over the
years?
The truth is that I spent weeks working in the empty International Management building at Int. Empty because everyone had been removed from post. When I first went up lines I was briefed extensively by David Miscavige about how bad all of them were and how they had done many things that were all very discreditable. This seemed to “explain” the fact that the entirety of the Watchdog Committee no longer existed. The entirety of the Executive Strata, which consisted of ED International and 11 other top International executives that were the top executives in their particular fields, no longer existed. That the Commodore’s Messenger Org International no longer existed. All of these key command structures of Scientology International, put there by LRH, had been removed.
There were hundreds and hundreds of unanswered letters and requests for help from org staff, written based on LRH ED 339R where LRH says that staff can write to these top executives in the Exec Strata for help. But this is not possible if all these execs have been removed and no one is there to help them or to get evaluations and programming done to expand Scientology.
Well, after that I got to spend some quality time with Heber, Ray Mithoff, Norman Starkey, Guillaume, as well as the entirety of International Management at the time, who were all off post and doing very long and harsh ethics programs. These have gone on for years and to the only result of that they are still off post. There is no denying that these top executives have all gradually disappeared from the scene. You don’t see them at the big events anymore or on the ship at Maiden Voyage.
David Miscavige has now become the “leader” of the Scientology religion. Yet what LRH left behind was a huge structure to properly manage all aspects of the Scientology religion. He put a complete and brilliant organizational structure there, not one individual. There never was supposed to be a “leader” other than LRH himself as the goal maker for our group.
There is a situation here and even if you have not been to the International Management Base you should be able to see that over regging and frequent tech changes are not OK and you have a responsibility to do something to Keep Scientology Working. You should be able to find and read the references on membership in OEC Volume 6. Find and read the HCO PL entitled “The Ideal Org” (Data Series 40). Find and read the references on org buildings, including HCO PL 24 Aug 65 II, Cleanliness of Quarters and Staff, Improve our Image. Also, HCO PL 17 June 69, The Org Image.
If you don’t want to make waves or put yourself in danger of being taken off the level or denied eligibility, then there are some simple things you can do. First and foremost, withdraw your support from off policy actions. Stop donating to anything other than your own services and actual Bridge progress. Simply demand to see an LRH reference that says you are required to make other such donations. No one will be able to produce any references because there aren’t any.
Stop supporting any of the activities that are being done to forward off-policy fund-raising in your area.
LRH says what he expects of a Scientologist – that is what he expects you to do. In fact he put it in HCOB 10 June 1960 Issue I, Keeping ScientologyWorking Series 33, WHAT WE EXPECT OF A SCIENTOLOGIST. Read it and follow it.
The other thing you can do is to send this email to as many others as youcan, even if you do it anonymously.
Please keep this email among us, the Scientologists. The media have no place in this. You may wonder why I have not written a KR and gone about my business. The answer is, I have. But there is no longer anyone to send that KR to.
But you can and should write reports and bring off-policy to the attention of local org executives and local Sea org members.
We are a strong and powerful group and we can affect a change. We have weathered many storms. I am sorry that I am the one telling you, but a newstorm is upon us. It’s waves are already in the media and the world around us.
The truth is that as a Scientologist you are more able, more perceptive and have a higher integrity. Scientology is supposed to allow you to “think for yourself” and never compromise your own integrity. And most certainly LRH held every Scientologist responsible to KEEP SCIENTOLOGY WORKING.
I am not trying to do anything other than affect a change in serious off policy actions occurring. My husband and I have most of our family and many many good friends who are Scientologists. I have not been real interested in sticking my neck out like this.
However, I also know that I dedicated my entire adult life to supporting LRH and the application of LRH technology and if I ever had to look LRH in theeye I wouldn’t be able to say I did everything I could to Keep Scientology Working if I didn’t do something about it now.
We all have a stake in this. It is simply not possible to read the LRH references and not see the alterations and violations that are currentlyoccurring.
You have a very simple obligation to LRH. Don’t participate in anything off policy, and let others know they should not either. If every person who reads this email does nothing more than step back from off-policy actions we would have changed direction. If we took all that energy and directed it into auditing, training and raw public dissemination, we would be winning.
And that is what I wish for you and all of us as we ring in this new year.
ARC,
Debbie Cook
TOP-SECRET – (U//FOUO) U.S. Marine Corps Intelligence Afghanistan Micro Mission Guide
TOP-SECRET from the FBI – Federal Indictments Lead to Arrests in Stem Cell Case
Three men have been arrested for their participation in a scheme to manufacture, distribute and sell to the public stem cells and stem cell procedures that were not approved by the Food and Drug Administration (FDA), United States Attorney Kenneth Magidson announced today along with Assistant Attorney General Tony West of the Department of Justice’s Civil Division, Special Agent in Charge Patrick J. Holland of the FDA-Office of Criminal Investigations (OCI) and Special Agent in Charge Cory B. Nelson of the FBI.
Francisco Morales, 52, of Brownsville, Texas, was arrested by Customs and Border Protection agents pursuant to a arrest warrant late Dec. 22, 2011. He made his initial appearance the following morning at which time he was ordered held without bond. Alberto Ramon, 48, of Del Rio, Texas, and Vincent Dammai, 40, of Mount Pleasant, S.C., were arrested yesterday. Ramon was arrested as he was about to enter his clinic and has already made his initial appearance in Del Rio, while Dammai was arrested in Florence, S.C., and is expected to make his initial appearance in Charleston, S.C., this morning. Lawrence Stowe, 58, of Dallas, Texas, also charged in relation to this case, is considered a fugitive and a warrant remains outstanding for his arrest. The two indictments in this matter, returned Nov. 9 and 10, 2011, have been unsealed by order of the court.
“Protecting the public from unproven and potentially dangerous drug and medical procedures is very important,” said Magidson. “This office will continue to prosecute violations involving threats to the public health.”
“This investigation identified a scheme whereby the suffering and hopes of victims in extreme medical need were used and manipulated for personal profit,” said Nelson. “The predatory and opportunistic nature of the crimes alleged in this indictment mirrors images from science fiction.”
The defendants allegedly conspired to commit mail fraud and unlawfully distributed stem cells derived from umbilical cord blood. According to the indictment, Morales and the others manufactured, distributed and used stems cells produced from umbilical cord blood to perform procedures not approved by the FDA to treat persons suffering from cancer, amytrophic lateral sclerosis (ALS), multiple sclerosis (MS) and other autoimmune diseases. FDA approval is required before stem cells can be marketed to the public and used to treat incurable diseases and the FDA has not determined that stem cells are safe and effective in treating these diseases.
“This indictment demonstrates the commitment of the FDA to protect the American public from the harms inherent in being exposed to unapproved new drugs,” said Holland. “The FDA will continue to aggressively pursue perpetrators of such acts and ensure that they are punished to the full extent of the law.”
Beginning in March 2007 and continuing through 2010, the indictment alleges Morales falsely represented to the public that he was a physician licensed to practice medicine in the United States and provided medical advice to individuals regarding the benefits of stem cell treatments. Morales also allegedly falsely represented that he operated a medical clinic named Rio Valley Medical Clinic in Brownsville, Texas, in order to convince the public that he specialized in using stem cells to treat incurable diseases. After meeting patients in the United States, Morales would allegedly travel to Mexico to perform the stem cell procedures. The indictment further alleges that Stowe marketed, promoted and sold stem cells along with other drug and biological products for the treatment of cancer, ALS, MS and Parkinson’s Disease that had not been reviewed or approved by the FDA. Stowe operated several entities, including The Stowe Foundation and Stowe Biotherapy Inc., through which he allegedly marketed and sold these products.
The stem cells referenced in the indictment were created and manufactured from umbilical cord blood obtained from birth mothers who were patients of Ramon—a licensed midwife who operated The Maternity Care Clinic in Del Rio, Texas. Ramon allegedly sold the cord blood to a company called Global Laboratories located in Scottsdale, Ariz. After obtaining the cord blood from Ramon, the indictment alleges Global Laboratories would send the tissue to Dammai—a professor of pathology and laboratory medicine in Charleston, S.C. Dammai, without obtaining approval from FDA or University authorities, allegedly used university facilities to create stem cells that were later sold by Global Laboratories. As a result of this fraudulent scheme, the public was mislead into believing that stem cells and other drug and biological products sold by defendants had been approved by the FDA to treat cancer, ALS, MS and Parkinson’s Disease, The defendants allegedly received more than $1.5 million from patients suffering from incurable diseases.
The case is being prosecuted by Assistant United States Attorneys Samuel Louis and Cedric Joubert with the assistance of Carol Wallack with the Consumer Protection Branch in the Department of Justice’s Civil Division. The case was investigated by the FDA-OCI, FBI and Internal Revenue Service-Criminal Investigations.
An indictment is a formal accusation of criminal conduct, not evidence.
A defendant is presumed innocent unless convicted through due process of law.
TOP-SECRET – UN Confidential Government of Sudan Security Forces in Darfur Report November 2005

1. Sudan Armed Forces (SAF) – Command and Control
1.1. General
1. The Sudanese Armed Forces (SAF) is a conventional armed force with a mandate to protect and to maintain internal security. It carries out its mandate mainly through ground forces, including Popular Defence Force (PDF) militia, as well as an air force and navy. (A1)
1.2. Organization
2. The Supreme Commander of the armed forces, Lieutenant General Omar Hassan Ahmad el-Bashir, holds both the posts of National President and Commander-In Chief of the Armed Forces and People’s Defence Forces (PDF). For operational purposes he exercises this power through the Minister of Defence (currently major-general Bakri Hassan Saleh). The Minister appoints a Commander of the Armed Forces and Chief of General Staff (currently, general Abbas Arabi) who, together with five Deputy Chiefs of Staff (Operations, Intelligence, Logistics, Administration, Training and Morale), form the Committee of the Joint Chiefs of Staff or Command Group. The air force and navy are individual services under the commander-in-chief. (A1)
…
1.4. Military Intelligence (MI)
9. The Military Intelligence (Istikhbarat al-Askariyya) is a branch of the General Staff with its own administration and command. The status of the MI is not completely clear, but it appears that under emergency laws, it has the power to arrest, detain and interrogate. With regard to communication and reporting, the MI branch passes information through the operational chain, as well as directly to the Presidency, through the Chief of the MI branch. (B2)
1.5. Border Intelligence (HI)
10. The Military Intelligence also include an operational unit called Border Intelligence (BI) (Istikhbarat al-Hudud), headquartered in Khartoum and headed by General AI-Hadi Hamid el-Tayeed (2005), the primary role of which is to monitor and gather information in the border area. Members of this unit are recruited from the local population. They are deployed to their areas of origin, according to their experience in the area, knowledge of the tribes, and ability to differentiate between people of different tribal and national origins based on local knowledge. Border Intelligence guards are under the operational control of the Military Intelligence Officers in the particular Division where they are deployed and otherwise fall under the regular chain of command for the armed forces. (C2)
11. While initially BI officers were recruited in relation to the conflict in southern Sudan, the Government began recruiting them during the early stages of the armed conflict in Darfur in late 2002 and early 2003. Apparently, BI soldiers are recruited directly into the army in the same way as regular soldiers. An advertisement is made through media channels for volunteers who meet certain criteria, in particular with regard to age, citizenship and fitness. Approximately 3,000 Border Intelligence soldiers have been recruited in this way and deployed in Darfur. (B3)
…
2. National Security and Intelligence Service
19. The National Security and Intelligence Service (NSIS) is not part of the Sudan Armed Forces but is part of the Ministry of Interior (currently headed by Zubeir Beshir Taha (NCP) in the Government of National Unity).
20. The NSIS was formed in February 2004 as a move to create one unified service dealing with both internal and external intelligence. Its main headquarter is in Khartoum and is headed by a Director-general who is appointed by the President. The current Director-General, Major-general Salah Abdallah (also known as Salah Gosh), reports at least every second day to the President and/or First VicePresident. While he co-operates with other organs of the Government, he is accountable directly to the President.
21. Its mandate derives from the National Security Force Act (NSF A) of 1999, as amended in 2001, which states that there shall be an Internal Security Organ in charge of internal security, and a Sudanese Intelligence Organ in charge of external security. In February 2004, the two organs were merged to form the NSIS.
…
3. The “Janjaweed”
30. Although we do not consider Janjaweed as being part of the GoS apparatus in Darfur, we mention it in this report for clarification purposes.
31. The term “Janjaweed”, in particular, has been widely used by victims of attacks to describe their attackers (the words fursan (horsemen, knights), or mujahedeen). The term has consequently also been used by many international organizations and the media in their reports on the situation in Darfur, and was used by the Security Council in resolution 1564. Victims of attacks have indicated that the Janjaweed were acting with and on behalf of Government forces, but no evidence – at this stage – allows to confirm such allegation.
32. “Janjaweed” is a generic Darfurian term that can be translated as “bandits”. Historically, this word describes armed horsemen performing “razzias,,18 against farmers and villagers. In the recent years, however, the word has been repeatedly used by the international community to describe combatants that cannot be clearly associated to a specific organization. In the world media, however, the word “Janjaweed” is irremediably – and often wrongly – associated to the GoS19 Cross examination of reports collected by UMAC shows that the word Janjaweed used by sources in Darfur may refer to :
• Spontaneous militias or self-defence forces (nomads or farmers) not always supported by the GoS; (AI)
• Spontaneous militias or self-defence units locally based supporting rebel movements; (AI)
• Popular Defence Forces (PDF) supported by the GoS as part of the armed forces. The PDF are locally based, organized, trained, and equipped units raised by the government to protect local communities. The PDF are defined by the Popular Defence Forces Act of 1989.; (A2)
• Covert units associated with “Border Intelligence” (and probably other government intelligence and security agencies) operating in Western Darfur against illegal activities across the border; (C2)
• Chadian Armed Opposition Groups (CAOG) operating across the Chadian Sudanese border and using Darfur as a sanctuary and as a “supply” area; (A 1)
• Criminals, former combatant living out of theft and cross-border trafficking. This category is expected to increase in number as GoS and rebel armies will demobilize. (AI)DOWLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET from the UN – Leaked UN Plan for Post-Conflict Deployment to Libya


The plan indicates that NATO could potentially have an ongoing role in the country’s affairs following the cessation of the immediate conflict.
DOWNLOAD THE ORIGINAL DOCUMENT HERE
TOP-SECRET – Israel Defense Force IHH Report Alleging Ties to Terrorism
- The Turkish IHH, which played a central role in organizing the flotilla to the Gaza Strip, is a Turkish humanitarian relief fund with a radical Islamic anti-Western orientation.
- Beyond its legitimate philanthropic activities, the IHH provides extensive support to radical Islamic organizations, including Hamas.
- In the past, the IHH has maintained contacts with and provided support to global jihad organizations.
- IHH is a member of a coalition of organizations, the “Union of Good” which has been designated a terrorist entity by the US government.
…
IHH LINKS TO HAMAS
- IHH’s orientation is radical-Islamic and anti-Western, and it is close to the Muslim Brotherhood (Hamas’ parent movement). IHH supports Hamas and does not hide the connection between them. Hamas also considers its links to IHH and Turkey to be extremely important.
- In recent years, especially since Hamas took over the Gaza Strip, IHH has supported Hamas’ propaganda campaigns by organizing public support conferences in Turkey. At those conferences, which featured the participation of senior IHH figures, the heads of IHH expressed their support for Hamas and its strategy (including the armed struggle it favors), in defiance of the Palestinian Authority, Hamas’ rival.
- IHH is a member of the Union of Good, an umbrella organization of more than 50 Islamic funds and foundations around the globe, which channels money into Hamas institutions in the Palestinian Authority-administered territories.
- The Union of Good was designated a terrorist entity under by the United States government under Executive Order 13224 in November 2008.
- As a Union of Good member IHH has connections with other worldwide Islamic funds and foundations which support Hamas. Among other things, the support includes initiating and conducting joint projects whose objectives are to bolster the de facto Hamas administration in the Gaza Strip and Hamas’ civilian infrastructure in Judea and Samaria, which also supports terrorism (the infrastructure is under pressure from the Palestinian Authority security services). IHH, which has become an important factor in global fund-raising for Hamas, transfers significant amounts of money to Hamas institutions in Judea and Samaria, including the Islamic Charitable Society in Hebron and the Al-Tadhamun Charitable Society in Nablus (Hamas’ two central “charitable societies,” both outlawed by Israel).
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – Biographies and Photos of the Russian Federation Armed Forces Leadership

Dmitriy Anatolyevich Medvedev, President of Russian Federation/Supreme Commander of RF Armed Forces
Born in city of Leningrad (now St. Petersburg) on 14 September 1965.
Completed law faculty of Leningrad State University (LGU) in 1987 and LGU postgraduate studies in 1990. Candidate of juridical sciences, docent. During 1990-1999 instructed at St. Petersburg State University.
Simultaneously during 1990-1995 advisor to Leningrad City Council chairman, expert of St. Petersburg Mayor’s Office Foreign Relations Committee. In 1999 deputy head of RF Government Apparatus. During 1999-2000 deputy head of RF President’s Administration. From 2000 first deputy head of RF President’s Administration. During 2000-2001 chairman of Board of Directors of Gazprom Open Joint-Stock Company (OAO), in 2001 deputy chairman of Gazprom OAO Board of Directors, from June 2002 chairman of Gazprom OAO Board of Directors. From October 2003 head of RF President’s Administration. In November 2005 appointed first deputy chairman of RF Government.
On 2 March 2008 elected President of Russian Federation.
Married. Wife Svetlana Vladimirovna Medvedeva. The Medvedevs have a son, Ilya.

Anatoliy Eduardovich Serdyukov, Defense Minister of Russian Federation
Born in settlement of Kholmskiy, Abinskiy Rayon, Krasnodar Kray on 8 January 1962.
Completed Leningrad Institute of Soviet Trade in 1984 in “economist” specialty.
During 1984-2000 worked in the specialty in St. Petersburg, the last position being general director of one of city’s largest joint-stock companies.
During 2000-2001 was deputy head of RF Ministry for Taxes and Levies Inspectorate for St. Petersburg.
In 2001 completed St. Petersburg State University in “lawyer” specialty.
From May 2001 deputy head of RF Ministry for Taxes and Levies Directorate for St. Petersburg, and from November 2001 head of this Directorate.
On 2 March 2004 appointed deputy minister of Russian Federation for taxes and levies. On 16 March 2004 became acting RF minister for taxes and levies.
On 27 July 2004 appointed head of Federal Tax Service.
By RF Presidential Edict of 15 February 2007 appointed Defense Minister of Russian Federation. Later, in connection with the formation of a new makeup of the RF Government, reappointed Defense Minister of Russian Federation by RF Presidential Edict “On the Defense Minister of the Russian Federation” of 12 May 2008.
Candidate of economic sciences.
…
He has been decorated with orders “For Service to the Motherland in the USSR Armed Forces” 2nd and 3rd class and “For Distinguished Military Service,” and with a number of medals.

General of the Army Nikolay Yegorovich Makarov, Chief of RF Armed Forces General Staff/First Deputy RF Defense Minister
Born in village of Glebovo, Ryazan Oblast on 7 October 1949. In 1971 completed Moscow Higher Combined-Arms Command School (with gold medal). Commanded a platoon, company, and battalion in Group of Soviet Forces in Germany.
After completion of Frunze Military Academy (with gold medal) in 1979, served in Transbaykal Military District [MD] (ZabVO) in positions of chief of staff/deputy regimental commander, regimental commander, chief of staff/deputy division commander, motorized rifle division commander.
In 1993 completed RF Armed Forces General Staff Military Academy (with gold medal).
Held positions of chief of staff of Joint Group of Russian Forces in Tajikistan, chief of staff/first deputy commander of separate army, commander of army in Volga MD. From January 1998 commander of Ground and Shore Troops/deputy commander of Baltic Fleet for Ground and Shore Troops.
From September 1999 chief of staff/first deputy commander Moscow MD.
On 25 December 2002 appointed commander Siberian MD (SibVO).
From April 2007 chief of armaments of RF Armed Forces/deputy RF defense minister.
By RF Presidential Edict of 3 June 2008 appointed chief of RF Armed Forces General Staff/first deputy RF defense minister.
Honored Military Specialist of the Russian Federation.
Decorated with orders “For Service in the USSR Armed Forces” 3rd Class, “For Distinguished Military Service,” and St. George 2nd Class, and with 12 medals.

Colonel-General Aleksandr Petrovich Kolmakov, First Deputy Defense Minister of Russian Federation
Born in city of Kaliningrad, Moscow Oblast on 31 July 1955. In 1976 completed Ryazan Higher Airborne Command School and served as reconnaissance platoon commander, reconnaissance company deputy commander for airborne training, reconnaissance company commander, chief of staff/deputy battalion commander of airborne regiment. Commanded reconnaissance company as part of Limited Contingent of Soviet Forces in Afghanistan.
After completion of Frunze Military Academy (with honors) in 1985, commanded airborne battalion, was regimental deputy commander and commander, and airborne division deputy commander and commander.
After completion of RF Armed Forces General Staff Military Academy (with honors) in 1995, successively held positions as first deputy commander of Guards combined-arms army in Moscow MD, from 1998 commander of combined-arms army in Transbaykal MD, and from September 2000 deputy commander Far East MD (DVO).
From September 2003 commander Airborne Troops (VDV).
By RF Presidential Edict of 25 September 2007 appointed first deputy defense minister of Russian Federation.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET-Libyan Intelligence Service CIA-MI6 Extraordinary Rendition Documents




These documents concerning CIA rendition of terrorism suspects, with the help of the UK, were recovered from the offices of Libyan intelligence.
DOWNLOAD FULL DOCUMENTS HERE
TOP-SECRET – U.S. Army Guerrilla Hunter Killer Smartbook Version 9.5

To effectively defeat an enemy, one must first understand the enemy. Intelligence professionals have forgotten the basic principles on which intelligence analysis is conducted, instead they sub-scribe to the paradigm that the enemy faced in this Global War on Terror has no structure or doctrine. Any organization, military or civilian, must have a structure and a way of doing business if they are to have any chance of being successful. As previously stated, understanding an enemy is critical to defeating him, but how much do we really understand the Taliban? We know that the Taliban fights in small groups using unconventional tactics that usually manifest themselves in the form of Improvised Explosive Device (IED), Direct Fire (DF), and Indirect Fire (IDF) attacks against Coalition Forces (CF) vehicles, patrols, and operating bases. The Taliban uses fear and intimidation against the Afghan people, collecting taxes, establishing court systems based on Shari’a law and doling out justice when these laws are broken. We also know that the Taliban enjoys sanctuary in regions bordering Afghanistan, such as Pakistan, with most of their senior leadership issuing decrees and orders just across the border. All of these “knowns” about the Taliban are not new to warfare of this nature, instead many of these same factors have been observed all over the world and throughout time. The military leader and fighter Ernesto “Che” Guevara waged guerrilla campaigns in multiple countries almost forty years ago using many of the same tactics the Taliban em-ploy today. Che’s successful war in Cuba and his failed guerrilla movements in the Congo and Bolivia are not the only historical examples of low intensity conflict that resemble our current fight in Afghanistan. Mao Tse Tung, Carlos Marighella and Alberto Bayo are just a few other Guerrilla leaders whose writings were examined and captured in the Guerrilla Hunter Killer Template. Volumes of source documents exist that can be referenced to help understand and define the enemy. Interestingly, the Guerrilla Hunter Killer Template was written using these source documents almost exclusively, but as you will see the parallels to the Taliban are frightening and therefore applicable to the war in Afghanistan. Truly understanding and defining the enemy as a collective group, not as individuals, is key to defeating him. The GH/K template blends historical writings of Guerrilla Leaders in conjunction with current and past United States Army doctrine to form the “melting pot” that is The Guerrilla Hunter Killer.
Once a base line understanding of the enemy was established, we understood the need to use common graphics and terms to accurately describe the enemy formations and tactical tasks. Sim-ply using U.S. Army operational terms and graphics does a severe disservice to all involved. The enemy we face is not the U.S. Army, and we should not attempt to “make them fit” into our own maneuver doctrine. While some tactical terms and graphics may fit what the enemy is trying to accomplish and how he organizes himself a majority do not, and at the end of the day this method is simply shoe horning the enemy into doctrine meant for ourselves. The enemy deserves his own graphics and tactical terms, for his structure and tasks are unique to what he is attempting to accomplish.

DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – Restricted U.S. Military Multi-Service Kill Box Employment Manual

The Kill Box MTTP reinforces kill boxes as three-dimensional areas used to facilitate the integration of joint fires while also being a permissive fire support coordination measure (FSCM) in accordance with JP 3-09, Joint Fire Support. The publication offers a detailed explanation of kill box employment and provides information to effectively organize, plan, and execute kill box procedures.
The purpose of this publication is to provide planners and operators with a single source MTTP manual that focuses on employment of kill boxes at the operational and tactical levels of warfighting to facilitate the expeditious air-to-surface lethal attack of targets which may be augmented by or integrated with surface-to-surface indirect fires. The target audience includes commanders, operations and intelligence sections of Service components, and their counterparts on the JFC’s staff.
…
1. Definition and Purpose
a. Definition: A kill box is a three-dimensional area used to facilitate the integration of joint fires. It is a permissive FSCM as described in JP 3-09, Joint Fire Support.
b. Purpose: When established, the primary purpose of a kill box is to allow lethal attack against surface targets without further coordination with the establishing commander and without terminal attack control. When used to integrate air-to-surface and surface-to-surface indirect fires, the kill box will have appropriate restrictions. The goal is to reduce the coordination required to fulfill support requirements with maximum flexibility while preventing fratricide.
Note: All aircrew conducting air interdiction within the confines of a kill box will execute their mission in accordance with rules of engagement (ROE) and special instructions (SPINS) applicable to air interdiction.
2. Establishment
a. Supported component commanders, acting on JFC authority, establish and adjust kill boxes in consultation with superior, subordinate, supporting, and affected commanders. Requirements for kill boxes and other control measures are determined using normal component targeting and planning processes and are established and approved by commanders or their designated staff (e.g., G-3, fire support coordinator [FSCOORD]). Information about the type, effective time, duration, and other attributes will be published and disseminated using existing voice and digital command and control (C2) systems. Kill boxes should be canceled when no longer needed.
b. There are two types of kill boxes: blue and purple. Chapter 3 provides further details.
(1) Blue Kill Box. A blue kill box permits air interdiction in the kill box without further coordination from the establishing headquarters (HQ).
(2) Purple Kill Box. A purple kill box permits air interdiction in the kill box without further coordination from the establishing HQ while allowing land and maritime component commanders to employ surface-to-surface indirect fires. The end state is maximum use of joint fires within the kill box to create synergistic effects with maximum potential for engaging targets.
c. Kill box characteristics:
(1) Target Area. The location and size of the kill box are determined by the expected or known location of targets in a specified area. The dimensions of a kill box are normally defined using an area reference system (i.e., Global Area Reference System [GARS]) but could follow well defined terrain features or be located by grid coordinates or by a radius from a center point. The standard dimensions using GARS would be a cell (30 minute (min) by 30 min [approximately (approx) 44 kilometer (km) by 44km] area), quadrant (15 min by 15 min [approx 22km by 22km] area), or keypad (5 min by 5 min [approx 7.5km by 7.5km] area). Reference JP 2-03, Geospatial Intelligence Support to Joint Operations, for further information concerning GARS.
(2) Airspace. The airspace block located above the kill box target area is protected and extends from the surface (or coordinating altitude if established) up to a ceiling established by the airspace control authority. The airspace for a purple kill box includes a floor and a ceiling to enable separation between aircraft delivering air-to-surface fires, trajectories of surface-to-surface indirect fires, surface-to-air fires, and other aircraft. The height of the ceiling should be established in the Airspace Control Plan (ACP), Airspace Control Order (ACO), or SPINS to permit standardized planning for other airspace uses. These parameters are developed by coordination between fire support and airspace organizations.

DOWNLOAD ORIGINAL DOCUMENT HERE
TOP – SECRET – DoD Non-Lethal Weapons Reference Book 2011

PURPOSE: The purpose of the NLW Reference Book is to provide a single source document that contains key information about NLW descriptions, effects, characteristics, concepts of employment, and associated operational parameters and considerations to enhance NLW education and training.
EXPLANATION OF TERMS: The NLW described in this book are at various acquisition stages and of varied Service interest. Service-unique systems meet specific Service needs, often meet Joint needs, and are provided to ensure Joint visibility and consideration. Systems are grouped as follows:
- FIELDED: NLW currently in use.
- PROTOYPE: NLW which have completed development, produced in limited quantities and no fielding decision has been made.
- DEVELOPMENTAL: NLW requiring technological or other improvements prior to production approval. Typically denotes a Service-led program of record with a technical readiness level (TRL) of 5 or higher. Anticipated fielding dates are provided, but are subject to change and should not be used for acquisition or resource planning.
- CONCEPTUAL: Ideas or concepts that can support exercises and modeling &simulations. Typically denotes a pre-acquisition science and technology project with a TRL of 4 or less. Conceptual capabilities do not currently exist, but are potential technologies that could be developed to satisfy a non-lethal requirement in the near future.




DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET from the CIA – Penetrating the Iron Curtain

In the mid-1950s the US faced the first real challenge since World War II to its strategic superiority over any nation on earth. The attempt to collect intelligence on the Soviets began with an initial period of poor collection capabilities and consequent limited analysis. With few well-placed human sources inside the Soviet Union, it was only with the CIA’s development of, what can only be called, timely technological wizardry—the U-2 aircraft and Corona Satellite reconnaissance program—that breakthroughs occurred in gaining valuable, game-changing intelligence. Coupled with the innovative use of aerial and satellite photography and other technical collection programs, the efforts began to produce solid, national intelligence.
DOWNLOAD ORIGINAL PDF HERE
TOP-SECRET -U.S. Army Afghanistan Route Clearance Handbook

Route clearance (RC) operations for Operation Enduring Freedom in Afghanistan are much different from RC operations for Operation Iraqi Freedom in terms of the terrain, seasonal weather, level of infrastructure, volume of insurgent threats, sources of improvised explosive device (IED) components, and motivation for IED emplacement. The purpose of this supplement is to focus on RC in Afghanistan.
Overview of Afghanistan
Afghanistan is composed of 34 provinces and is operationally divided into five regional commands: Regional Command Capital, Regional Command East, Regional Command North, Regional Command South, and Regional Command West. Regional Command Capital is completely surrounded by Regional Command East but is independent of the Regional Command East command. Regional Command Capital is composed of Kabul Province alone. The provinces in Regional Command East are Paktika, Paktya, Khwost (P2K); Ghazni, Wardak, Logar; Nangarhar, Nuristan, Konar, Laghman (N2KL); Bamyan; Parwan; Kapisa; and Panjshir. The provinces in Regional Command North are Faryab, Jawzjan, Sari Pul, Balkh, Samangan, Kunduz, Baghlan, Takhar, and Badakhshan. The provinces in Regional Command South are Nimroz, Helmand, Day Kundi, Oruzgan, and Zabul. The provinces in Regional Command West are Badghis, Herat, Ghowr, and Farah.
U.S. forces are focused primarily on Regional Command East. Regional Command East is further divided into five areas of operations (AOs). The five AOs for Regional Command East are Currahee in the southeast, Duke in the northeast, Warrior in the north-northwest, Ghazni in the west, and Spartan in the center. The provinces in AO Currahee are Paktika, Paktya, and Khwost (P2K). The provinces in AO Duke are Nangarhar, Nuristan, Konar, and Laghman (N2KL). The provinces in AO Warrior are Bamyan, Parwan, Kapisa, and Panjshir. AO Ghazni is composed of the Ghazni Province alone. The provinces in AO Spartan are Wardak and Logar.
Some AOs are further subdivided into minor AOs; however, the minor AOs do not necessarily correspond to the provincial boundaries. AO Currahee is composed of Team (TM) Paktya, TM Khowst, TM Eagle, and TM White Eagle. AO Duke is composed of AO Raptor, AO Pacesetter, AO King, AO Rock, and AO Saber. AO Warrior, AO Ghazni, and AO Spartan are not broken down into minor AOs.
In AO Currahee, the minor AO boundaries generally align with the provinces; however, there are a few exceptions. TM Paktya contains only Paktya Province. TM Khowst contains only Khowst Province. TM Eagle contains the east half of Paktika Province, while TM White Eagle contains the west half of Paktika Province.
In AO Duke, the minor AO boundaries generally do not align with the provinces; however, there are a few exceptions. AO Raptor contains Nangarhar Province. AO Pacesetter contains Laghman Province. AO King contains the westernmost third of Nuristan Province; AO Rock contains the middle third of Nuristan Province and the westernmost three-quarters of Konar Province. AO Saber contains the easternmost third of Nuristan Province and the easternmost quarter of Konar Province.
Terrain and Weather
In Afghanistan, the terrain varies drastically from one area to the next. The country is divided into three major geographic zones: the northern steppe, the southern desert plateau, and the spine of the Hindu Kush mountain range. The northern steppe runs across the northern border from Badghis in Regional Command West to Takhar in Regional Command North. The southern desert plateau runs across the western and southern border from Herat in Regional Command West to Kandahar in Regional Command South. The Hindu Kush mountain range and its offshoots run generally from northeast to southwest and cover the rest of the country.
The provinces that contain the northern steppe include Badghis, the northern half of Faryab, Jawzjan, the northern half of Sari Pul, the northern two-thirds of Balkh, Konduz, and the northeast quarter of Takhar. The provinces that contain the southern desert plateau include the western half of Herat, the western two-thirds of Farah, Nimroz, the southern three-quarters of Helmand, and the southwestern three-quarters of Kandahar. The provinces that contain the Hindu Kush mountain range and its offshoots include Badakhshan, Takhar, Baghlan, Samangan, Balkh, Sari Pul, Faryab, Herat, Ghowr, Farah, Helmand, Day Kundi, Oruzgan, Kandahar, Zabul, Paktika, Paktya, Khowst, Ghazni, Wardak, Logar, Bamyan, Parwan, Kapisa, Panjshir, Nuristan, Laghman, Konar, Nangarhar, and Kabul.
Some areas are extremely mountainous, and the so-called roads are nothing more than narrow goat trails, which offer insurgent forces excellent cover and concealment from approaching maneuver forces. There are many ideal spots for ambush near to the roads, and several IED events in these areas have coordinated small arms fire incorporated into the attacks. In other areas of the country, the terrain is wide open desert and without many hiding spots near the roads. The methods of attack in these areas are drastically different.
Fighting Season
The weather in Afghanistan plays a major role in the way units conduct operations. The seasonal nature of the mountainous regions lends itself to a “survival season” and a “fighting season.” The survival season is primarily the winter months. Harsh winters offer extremely cold temperatures and large snow accumulations. In many areas, the snowfall makes the roads completely impassible and shuts off ground maneuvers completely in some parts of the country. The fighting season begins with the spring thaw and allows for movement in areas that were previously impassible due to the harsh winter conditions. This fighting season usually ramps up from the early spring to the beginning of summer. The summer weather can also be harsh. Hot, dusty, dry conditions will often limit the movement of forces not properly protected from the heat. In the fall, when the extreme heat has passed, IED activity sparks up again; however, it is usually not as intense as the spring fighting. Most people are focusing on preparing for the coming winter months and not on fighting.
Infrastructure
Infrastructure or, more to the point, a lack of infrastructure is a major issue in Afghanistan. The vast majority of the roads in Afghanistan are unimproved and not well defined. Often the location of the road changes from season to season and from year to year. Flooding, washouts, rockslides, lack of infrastructure, discovery of a better/safer/faster/more direct path, and many other factors all contribute to the ever-changing network of trails and paths used for vehicular traffic. In some areas, drivers use dry riverbeds as primary roads during the dry season. These wide open “roads” can quickly become raging rivers during the spring thaw. In some areas, the roads are paved; however, many years of damage from tracked vehicles and explosions from previous wars have greatly degraded their serviceability. These paved roads are often limited to the main ring road and a few off shoots from that road.
The sources of IED components in Afghanistan are drastically different from those in Iraq. In Afghanistan, there are fewer components for making IEDs. A cache in Afghanistan usually does not meet the minimum requirements of a cache in Iraq. The enemy uses homemade explosives in IEDs in Afghanistan, which bring additional complications to the RC mission. Additionally, there are many existing minefields that are mistaken for IEDs. RC units should deal with these areas as minefields rather than IEDs. Sometimes the enemy transplants mines from the minefields to a roadway. In these situations, it is difficult to determine if the area is a part of a larger minefield and should be dealt with as such, or if the area is more like an IED and should be dealt with accordingly.
The motivations for using IEDs in Iraq and Afghanistan are similar in some areas and different in others. In the lowlands, which are primarily in the south and west, the enemy uses IEDs as an initiator for an attack and then again when targeting first responders or reactionary forces. In the highlands, which are primarily in the north and east, the enemy uses IEDs to shape an attack and limit mobility.
Culture, People, and Religion
Culture
Afghan culture is a rich mix influenced by different ethnicities and languages. It is extremely difficult to generalize about an entire population; however, Afghans are typically friendly and hospitable. Their lives have been rife with conflict, and they can be stern. The Afghan’s belief that Allah controls all matters greatly influences his perceptions. This belief helps Afghans tolerate extreme physical hardship.
Approximately 44 percent of Afghans are Pashtun, about half of whom are of the Durrani tribal group and the other half of the Ghilzai group. Tajiks are the second largest ethnic group with 25 percent of the population, followed by Hazaras at 10 percent and Uzbeks at 8 percent. Other smaller groups, including Turkmen, Qizilbash, Kazakhs, Aimaq, Wakhis, Nuristanis, Baluchis, Kyrgyz, Sikhs, Hindus, and Jews, constitute the remaining 13 percent of the total population.
People
The Afghans’ primary loyalty is to their families, kin groups, clans, or tribes; they express their identities through these groups. Their moral attitudes are often strict and inflexible, and they stress honor and individual responsibility to fulfill expected roles. Personal disputes are not resolved easily because of the need to protect one’s honor. Personal behavior affects family honor, so Afghans consider it essential to live according to these rigid rules. Piety and stoicism are admired traits.
Afghan society is mostly rural. The rural populations are mostly concentrated along the rivers. Villages in Afghanistan encircle larger towns that act as commercial, communication, and administrative centers. The most heavily populated and urban part of the country is between the cities of Kabul and Charikar. Other population concentrations can be found east of Kabul near Jalalabad, in the Heart oasis and the valley of the Harirud River in the northwest, and in the Valley of Kunduz River in the northeast. Most urban settlements have grown along the ring road that runs from Kabul southwest to Kandahar, then northwest to Herat, northeast to Mazar-e Sharif, and southeast to Kabul. Cities have formed where major routes intersect.
Thirty-two languages and dialects are spoken in Afghanistan. Dari (a form of Persian) is spoken widely and has several dialects. It is similar to the Farsi spoken in Iran and Tajik spoken in Tajikistan. Pashtu has two major variants and many dialects.
Religion
Afghanistan is an Islamic society; 84 percent of the population follows the Sunni tradition, 15 percent of the population follows the Shi’a tradition, and 1 percent of the population follows other traditions. However, Islam has not been a unifying force that has overcome ethnic differences. Local religious leaders are often not well educated. The level of religious observation varies, but most Afghans profess a strong adherence to the Islamic faith.
DWONLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET from the CIA – Berlin – A city torn apart

From the end of World War II in 1945, the question of Berlin’s status 90 miles within the Deutsche Demokratische Republik (East Germany) and the Soviet Union’s zone of occupation, along with the status of Germany among the community of nations, remained a source of tension between the East and West. Premier Khrushchev continued to push President Eisenhower and the other Western leaders for resolution of the issue.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – (U//FOUO) LulzSec Release: DHS National Socialist Movement NAZI Reference Aid

(U) Overview
(U//FOUO) The National Socialist Movement (NSM) USPER is the most active neo-Nazi group operating in the United States. It has grown from a small organization with a limited following confined to the mid-western United States to the preeminent National Socialist group in the nation. Despite having recently suffered a defection of several regional leaders, NSM remains an influential force within white supremacist circles and the only major racist group that eschews all attempts to distance its methods and objectives from those of the Third Reich. NSM has a reputation for conducting numerous public rallies that have triggered a violent response, including a riot in Toledo, Ohio, in October 2005.
(U) Description
(U//FOUO) The National Socialist Movement (NSM) is the largest neo-Nazi organization in the United States. Founded in 1974 by two former members of the American Nazi PartyUSPER, NSM claims that it is the only “legitimate” Nazi party operating in the United States. Although active since 1974, NSM only became a major player in the white supremacist movement in the late 1990s and has had its greatest period of growth over the past three years. This growth likely resulted from the collapse of other prominent neo-Nazi groups such as the National AllianceUSPER and Aryan NationsUSPER.
(U) Ideology and Objectives
(U//FOUO) NSM promotes the ideology of traditional National Socialism, which is a mix of racism, anti-Semitism, xenophobia, rabid anti-communism, and white supremacy. NSM seeks to transform the United States into a National Socialist state that would deny all rights to Jews, nonwhites, and gays. NSM also advocates the mass deportation of all illegal immigrants, the militarization of the Mexican border, the end of all foreign aid, and the severing of all ties with Israel.
(U) Symbology
(U//FOUO) NSM patterns its uniforms after those of the Third Reich’s Wehrmacht and the Waffen SS. The armbands, shoulder boards, and collar insignia used by NSM are replicas of those worn by the military units and political officers of Nazi Germany. NSM also uses many forms of Nazi symbols and imagery in its propaganda.
…
(U) Active Membership
(U//FOUO) Although NSM has small chapters operating throughout the country, over half of its estimated active membership is based in the Midwest, primarily in Illinois, Michigan, Minnesota, Missouri, Ohio, and Wisconsin. Another large concentration of NSM members operates in the Southwestern United States, centered mainly in Arizona and Nevada. There are an estimated 300 active NSM members along with a similar number of associates that are active on NSM’s various Internet forums. Online members have little direct involvement with the group.
(U) Financial Support
(U//FOUO) All active NSM members as well as new recruits are required to contribute monthly dues to help sustain the organization. NSM also generates a great deal of its revenue from sponsoring white power rock concerts and from the sale of racist music CDs, DVDs, video games, and other white power paraphernalia. NSM conducts much of their sales through its own music distributor, NSM88Records. The group uses funding to further their political ambitions, propaganda mechanisms, and various commercial enterprises that sell Nazi regalia and memorabilia.
…
(U) Targets of Actions
(U//FOUO) To date, NSM confines its activities primarily to conducting a series of high profile public rallies and marches targeting minority neighborhoods, illegal immigrants, and U.S. support to Israel. In several instances, these activities have triggered violent confrontations between protestors opposing NSM and law enforcement attempting to preserve public order. During an October 2005 march in Toledo, Ohio, police were unable to prevent local residents from rioting for several hours following the NSM rally. The disturbances resulted in the arrest of 120 rioters and the destruction of several local businesses. Toledo’s mayor was forced to restore order by imposing a curfew.
(U) Criminal Activity
(U//FOUO) There is little or no evidence that NSM, as an organization, is engaged in any organized criminal activity. A large number of current and former members of NSM, however, have engaged in sporadic criminal acts that are unrelated to their involvement with the group. NSM members have committed a wide range of crimes to include: murder, kidnapping, rape, domestic violence, pedophilia, burglary, trespassing, and narcotics possession.
DOWNLOAD FULL DOCUMENT HERE
TOP-SECRET – Israel Defense Forces Naksa Violence Presentation





TOP-SECRET from the White House – Spain-Germany Spy Organization 1944
DWONLAOD ORIGINAL DOCUMENTS BELOW
TOP-SECRET – TSA Female Suicide Bombers History Overview
Why Females?
- Terrorist organizations use females because:
- Like most suicide operations, it’s usually simple to plan and low costing.
- In some parts of the world, females have low social status and therefore are considered more expendable.
- Females tend to be more emotional and therefore easier to indoctrinate.
- Since bombers will most likely perish in the attack, there is little fear of them divulging information to security forces.
- Tamil “Black Tigers” carry cyanide pills just in case.
- Most are deliberately uninvolved in the planning in case of capture.
- The media coverage is extensive, especially if the attacker is female.
- Terrorists attempt to embarrass a powerful enemy and show the world that things are desperate that women are now fighting.
- Most importantly, females have the element of surprise!!
- Stealthier attack (tend to draw less attention); in fact on several occasions many female bombers spoke English & wore western clothing & makeup during the attack.
- Sensitivities in searching women (especially in conservative societies).
- Female stereotype (e.g. perceived as nonviolent, feminine, or motherly).
- Women increase the number of combatants to a groups’ depleted manpower.
- There is greater publicity for female bombers (attracts recruits).
- The psychological fear factor of the target (expect anyone can be a bomber).

DOWNLOAD ORGINAL DOCUMENT HERE
TOP-SECRET-FBI (U//FOUO) Preliminary Analysis of Christmas Day Underwear Bomb
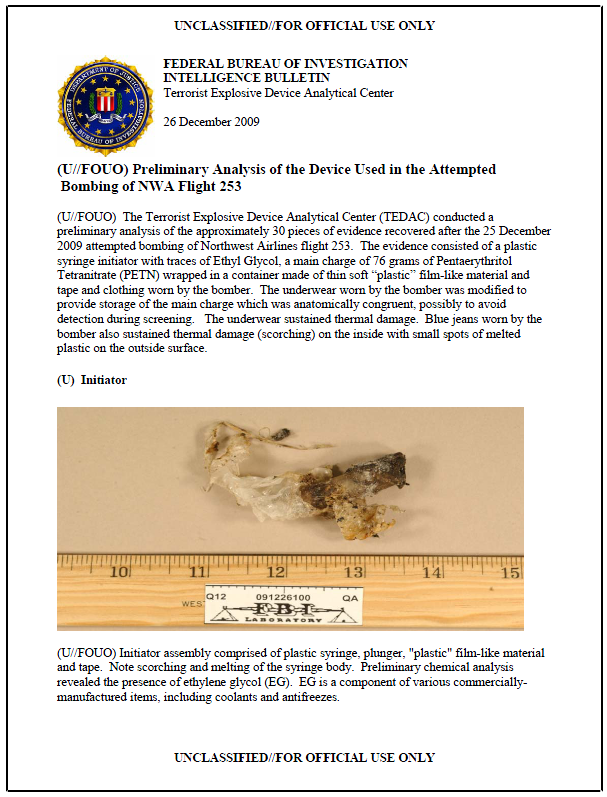
(U//FOUO) The Terrorist Explosive Device Analytical Center (TEDAC) conducted a preliminary analysis of the approximately 30 pieces of evidence recovered after the 25 December 2009 attempted bombing of Northwest Airlines flight 253. The evidence consisted of a plastic syringe initiator with traces of Ethyl Glycol, a main charge of 76 grams of Pentaerythritol Tetranitrate (PETN) wrapped in a container made of thin soft “plastic” film-like material and tape and clothing worn by the bomber. The underwear worn by the bomber was modified to provide storage of the main charge which was anatomically congruent, possibly to avoid detection during screening. The underwear sustained thermal damage. Blue jeans worn by the bomber also sustained thermal damage (scorching) on the inside with small spots of melted plastic on the outside surface.
…
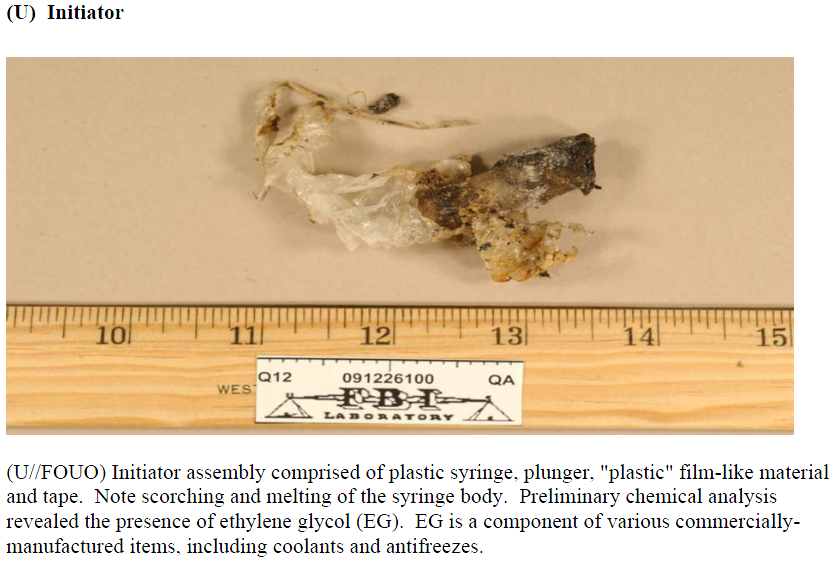
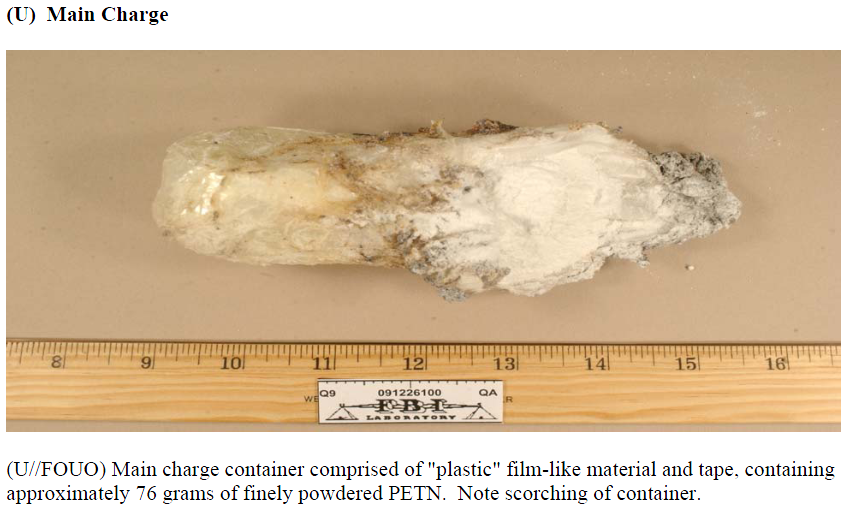
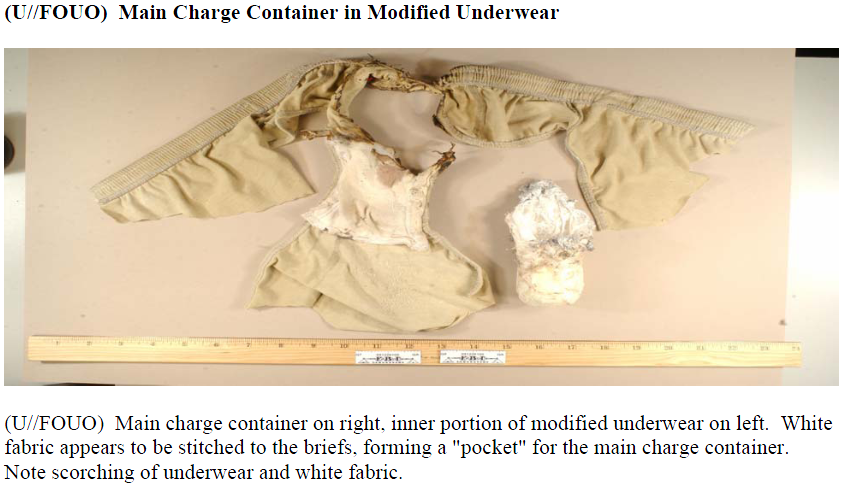
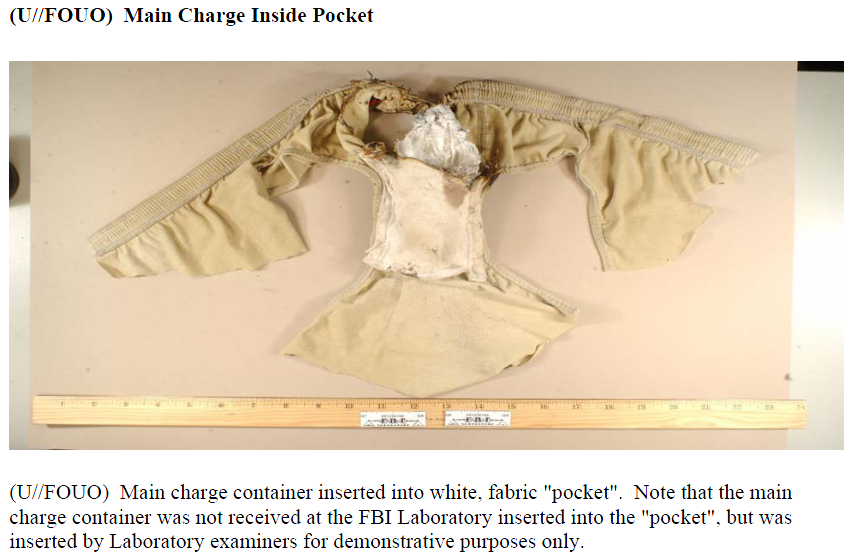
TOP-SECRET – LulzSec Release: EPIC Language of the Cartels Narco Terminology Report

The El Paso Intelligence Center DEA/CBP Gang Intelligence Unit has been providing intelligence reports on many National gangs affecting this region such as the Surenos, Mexican Mafia and the Nortenos. These reports are condensed and include a short history of the gang, identifiers and current trends for the purposes of providing quick reference and concise information to the street officer that may encounter these individuals throughout the course of their duty.
In 2009, the National Drug Intelligence Center (NDIC) assessed that Mexican drug trafficking organizations (DTOs) were operating in the U.S. in at least 1, 286 cities spanning nine regions. Moreover, NDIC assesses with high confidence that Mexican DTO’s in at least 143 of these U.S. cities were linked to a specific Mexican Cartel or DTO based in Mexico—the Sinaloa Cartel (at least 75 cities), the Gulf Cartel/Los Zetas (at least 37 cities), the Juárez Cartel (at least 33 cities), the Beltrán-Leyva DTO (at least 30 cities), La Familia Michoacán (at least 27 cities), or the Tijuana Cartel (at least 21 cities). NDIC assesses with high confidence that Mexican DTOs will further expand their drug trafficking operations in the United States. Due to the rise in violence throughout the Southwest Region and Mexico, members of the Cartels, their associates and their families have been suspected of moving into many U.S. cities along the border. As a result, agencies are requesting information on ways to identify those involved with drug trafficking organizations. The information included in this report is not set in stone as many of these criminal organizations are dynamic and will alter their methods and trends frequently to avoid detection by law enforcement.

DOWNLOAD THE ORGINAL DOCUMENT HERE
TOP-SECRET – Vatican Bank May Have Used Clergy as Fronts for Mafia, Corrupt Businessmen
 Pope Benedict XVI talks to the head of the Vatican bank Ettore Gotti Tedeschi (R) in this September 26, 2010 file photo. Gotti Tedeschi has been placed under investigation by Rome magistrates for suspected money-laundering by the bank, judicial sources said on September 21, 2010. REUTERS/OSSERVATORE ROMANO/Files
Pope Benedict XVI talks to the head of the Vatican bank Ettore Gotti Tedeschi (R) in this September 26, 2010 file photo. Gotti Tedeschi has been placed under investigation by Rome magistrates for suspected money-laundering by the bank, judicial sources said on September 21, 2010. REUTERS/OSSERVATORE ROMANO/Files
Vatican Bank ‘allowed clergy to act as front for Mafia’ (Indepdendent.co.uk):
The Vatican Bank is under new scrutiny in a case involving money-laundering allegations that led police to seize €23m (£19.25m) in September.
The Vatican calls the seizure of assets a “misunderstanding” and expresses optimism it will be quickly cleared up. But fresh court documents show that prosecutors say the Vatican Bank deliberately flouted anti-laundering laws “with the aim of hiding the ownership, destination and origin of the capital”. The documents also reveal investigators’ suspicions that clergy may have acted as fronts for corrupt businessmen and Mafia.
The documents pinpoint two transactions that have not been reported: one in 2009 involving the use of a false name, and another in 2010 in which the Vatican Bank withdrew €650,000 from an Italian bank account but ignored bank requests to disclose where the money was headed.
The new allegations of financial impropriety could not come at a worse time for the Vatican, already hit by revelations that it sheltered paedophile priests. The corruption probe has given new hope to Holocaust survivors who tried unsuccessfully to sue in the United States, alleging that Nazi loot was stored in the Vatican Bank.
Yet the scandal is hardly the first for the bank, already distinguished from other banks by the fact that its cash machines are in Latin and priests use a private entrance.
In 1986, a Vatican financial adviser died after drinking cyanide-laced coffee in prison. Another, Roberto Calvi, was found dangling from a rope under London’s Blackfriars Bridge in 1982, his pockets stuffed with money and stones. The incidents blackened the bank’s reputation, raised suspicions of ties with the Mafia, and cost the Vatican hundreds of millions of dollars in legal clashes with Italian authorities.
On 21 September, financial police seized assets from a Vatican Bank account. Investigators said the Vatican had failed to furnish information on the origin or destination of the funds as required by Italian law.
The bulk of the money, €20 million, was destined for the American JP Morgan bank branch in Frankfurt, Germany, with the remainder going to Banca del Fucino, an Italian bank.
Vatican Bank mired in laundering scandal (AP):
The Vatican has pledged to comply with EU financial standards and create a watchdog authority. Gianluigi Nuzzi, author of “Vatican SpA,” a 2009 book outlining the bank’s shady dealings, said it’s possible the Vatican is serious about coming clean, but he isn’t optimistic.
“I don’t trust them,” he said. “After the previous big scandals, they said ‘we’ll change’ and they didn’t. It’s happened too many times.”
He said the structure and culture of the institution is such that powerful account-holders can exert pressure on management, and some managers are simply resistant to change.
The list of account-holders is secret, though bank officials say there are some 40,000-45,000 among religious congregations, clergy, Vatican officials and lay people with Vatican connections.
The bank chairman is Ettore Gotti Tedeschi, also chairman of Banco Santander’s Italian operations, who was brought in last year to bring the Vatican Bank in line with Italian and international regulations. Gotti Tedeschi has been on a very public speaking tour extolling the benefits of a morality-based financial system.
“He went to sell the new image … not knowing that inside, the same things were still happening,” Nuzzi said. “They continued to do these transfers without the names, not necessarily in bad faith, but out of habit.”
It doesn’t help that Gotti Tedeschi himself and the bank’s No. 2 official, Paolo Cipriani, are under investigation for alleged violations of money-laundering laws. They were both questioned by Rome prosecutors on Sept. 30, although no charges have been filed.
In his testimony, Gotti Tedeschi said he knew next to nothing about the bank’s day-to-day operations, noting that he had been on the job less than a year and only works at the bank two full days a week.
According to the prosecutors’ interrogation transcripts obtained by AP, Gotti Tedeschi deflected most questions about the suspect transactions to Cipriani. Cipriani in turn said that when the Holy See transferred money without identifying the sender, it was the Vatican’s own money, not a client’s.
Gotti Tedeschi declined a request for an interview but said by e-mail that he questioned the motivations of prosecutors. In a speech in October, he described a wider plot against the church, decrying “personal attacks on the pope, the facts linked to pedophilia (that) still continue now with the issues that have seen myself involved.”
…
In the scandals two decades ago, Sicilian financier Michele Sindona was appointed by the pope to manage the Vatican’s foreign investments. He also brought in Roberto Calvi, a Catholic banker in northern Italy.
Sindona’s banking empire collapsed in the mid-1970s and his links to the mob were exposed, sending him to prison and his eventual death from poisoned coffee. Calvi then inherited his role.
Calvi headed the Banco Ambrosiano, which collapsed in 1982 after the disappearance of $1.3 billion in loans made to dummy companies in Latin America. The Vatican had provided letters of credit for the loans.
Calvi was found a short time later hanging from scaffolding on Blackfriars Bridge, his pockets loaded with 11 pounds of bricks and $11,700 in various currencies. After an initial ruling of suicide, murder charges were filed against five people, including a major Mafia figure, but all were acquitted after trial.
While denying wrongdoing, the Vatican Bank paid $250 million to Ambrosiano’s creditors.
Both the Calvi and Sindona cases remain unsolved.
TOP-SECRET – Iraq Biometric Automated Toolset (BAT) HIIDE Standard Operating Procedures
Multi-National Forces West Biometric Automated Toolset (BAT) Handheld Interagency Identity Detection Equipment (HIIDE) SOP and TTP



DOWNLOAD ORIGINAL DOCUMENTS HERE
TOP-SECRET – U.S. Army Afghanistan Smart Book, Third Edition
TOP-SECRET-European Countries Refuse to Release Information on CIA Rendition Flights

Romania’s National Registry Office for Classified Information (ORNISS) headquarters building is seen in the background of this image taken in Bucharest, December 9, 2011. International media has reported that between 2003 and 2006, the CIA operated a secret prison from the building’s basement, bringing in high-value terror suspects for interrogation and detention. ORNISS has denied hosting a CIA prison and the CIA has refused to comment.
A majority of 28 mostly European countries have failed to comply with freedom of information requests about their involvement in secret CIA flights carrying suspected terrorists, two human rights groups said Monday.London-based Reprieve and Madrid-based Access Info Europe accused European nations of covering up their complicity in the so-called “extraordinary rendition” program by failing to release flight-traffic data that could show the paths of the planes.
The groups said only seven of 28 countries had supplied the requested information. Five countries said they no longer had the data, three refused to release it and 13 had not replied more than 10 weeks after the requests were made.
Europe’s silence is in contrast to the United States, which handed over Federal Aviation Administration records with data on more than 27,000 flight segments.
The groups’ report said that the U.S. had provided “by far the most comprehensive response” and accused European countries of lagging behind when it came to transparency.
“Is it an access to information problem, or is it a problem with this particular issue? It’s a bit of both,” said Access Info Europe executive director Helen Darbishire. “European countries have not completely faced up to their role here.”
Human rights campaigners have worked for years to piece together information on hundreds of covert flights that shuttled suspected terrorists between CIA-run overseas prisons and the U.S. military base at Guantanamo Bay as part of the post-Sept. 11 “War on Terror.”
The CIA has never acknowledged specific locations, but prisons overseen by U.S. officials reportedly operated in Thailand, Afghanistan, Lithuania, Poland and Romania — where terror suspects including Khalid Sheik Mohammad, mastermind of the Sept. 11 attacks, were interrogated in the basement of a government building in the capital, Bucharest.
DOWNLOAD ORIGINAL FILE HERE
TOP-SECRET-Asymmetric Warfare Group Guide to Insider Threats in Partnering Environments

This guide assists in three areas. First, it aides military leaders and all personnel to be aware of the indicators associated with insider threat activity while serving in a partnering environment. Second, this guide informs commanders and other leaders by giving them options on how to deal with insider threat activities. This guide is not all encompassing so there are other options a commander has dependent on their operating environment. Lastly, this guide is meant to generate open dialogue between coalition partners and partner nation personnel. Partnering in itself is a sensitive mission and only by creating trust and having an open dialogue with all forces will the mission be accomplished.
…
Risk Factors
- Emotional Vulnerability
- Dissatisfaction with lack of accepted conflict resolution
- Personal connection to a grievance
- Positive view of violence
- Perceived benefit of political violence
- Social Networks (tech and non tech)
- In group de-legitimization of the out-group
- Placement, Access, and Capability
- External Support
- Perceived Threat
- Conflict
- Humiliation orloss of honor
- Competition
- Social Alienation
- Quid Pro Quo (services or items wanted or needed by an individual given in exchange for information or action)
- Disproportionate financial risks
- Susceptible to blackmail
- Civilian Casualty (CIVCAS) situations
- Highly emotional
- Unfair treatment or equipment differences
…
Cultural Awareness
- DO NOT use derogatory terms in any language (even in friendly conversation)
- DO NOT slander host nation or coalition partners (even if only jokingly)
- DO NOT physically harm host nation or coalition partners (except in self defense)
- DO NOT put down or slander any religion
- ALWAYS be courteous and thankful for host nation and coalition partner hospitalityAsymmetric

DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – Joint Center for International Security Force Assistance Iraqi Federal Police Advisor Guide
As the U. S. Defense Department scales back operations in Iraq, one of the most significant questions that remains is whether the Iraqi security forces will be capable of maintaining civil order on their own. This manual was produced by the Joint Center for International Security Force Assistance (JCISFA) to help prepare deploying advisors, trainers, and partner forces that will work directly with Iraqi police. The intent is to provide a basic understanding of the country of Iraq and a solid understanding of the current organization and utilization of the Iraqi police. This manual also provides guidance on what it means to work ” by, with and through” a counterpart, and includes observations and insights learned by your predecessors.
In a stable society, a key component to security is the police. While there has been significant progress in the development of the Iraqi police, there is still much work to be done. Historically, the Iraqi police have been held in lower public regard than other components of the security force infrastructure. The Iraqi public viewpoint toward law enforcement as an agency of public safety, security, and service to the community has been far different than law enforcement in most developed nations. Part of our job is to educate the Iraqi police, and the Iraqi population, about the important role police play in a society governed by the rule of law. Rule of law enables the framework for national sovereignty and provides restraints that serve as a check against abusive use of power. Without effective rule of law, we will never gain the security necessary for democratic institutions to be successful.


DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – Taliban Top 5 Most Deadly Tactics Techniques and Procedures

To gain an understanding of the Top 5 casualty producing Tactics, Techniques and Procedures in Afghanistan
To introduce the Top Threat Groups in Afghanistan and along the Pakistani border
To understand the location of hostile action in Afghanistan
To understand Threat weapon employment
– Attack data
– Technology used
– TTP
To introduce Threat use of Information Warfare (INFOWAR) across Tactics, Techniques, and Procedures


DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET from the FBI – Ashburn Realtor Charged in $7 Million Mortgage Fraud Scheme
ALEXANDRIA, VA—A federal grand jury has charged Nadin Samnang, 29, of Ashburn, Va., with conspiracy and mortgage fraud charges related to his role in alleged fraudulent mortgage loan transactions involving at least 25 homes in northern Virginia and more than $7 million in losses to lenders.
Neil H. MacBride, United States Attorney for the Eastern District of Virginia; Daniel Cortez, Inspector in Charge of the Washington Division of the United States Postal Inspection Service; and James W. McJunkin, Assistant Director in Charge of the FBI’s Washington Field Office, made the announcement.
According to the 12-count indictment, from 2006 to 2008, Samnang is accused of using his position as a realtor and the owner of a title company to engage in a scheme to defraud mortgage lenders and profit from loan proceeds, commissions, and bonus payments.
According to the indictment, Samnang and other members of the conspiracy allegedly recruited unqualified buyers—usually individuals with good credit but insufficient assets or income to qualify for a particular loan—and used them as nominal purchasers in residential real estate transactions. As part of the conspiracy and fraud scheme, Samnang and others are accused of falsifying mortgage loan applications, creating fake documents to support the fraudulent applications, and adding the unqualified buyers as signatories on their bank accounts to make it appear to lenders as though the buyers possessed sufficient assets to qualify for the loans.
If convicted, Samnang faces a maximum penalty of 20 years in prison on each count.
The case is being investigated by the U.S. Postal Inspection Service and the FBI’s Washington Field Office. Assistant United States Attorney Paul J. Nathanson is prosecuting the case on behalf of the United States.
Criminal indictments are only charges and not evidence of guilt. A defendant is presumed to be innocent until and unless proven guilty.
TOP SECRET from the FBI Las Vegas – Sixteen Persons Charged in International Internet Fraud Scheme
LAS VEGAS—Federal charges have been unsealed against 16 individuals for their involvement in an international Internet scheme that defrauded online purchasers of purported merchandise such as automobiles and other items, announced Daniel G. Bogden, United States Attorney for the District of Nevada.
The defendants are charged with wire fraud, conspiracy to commit wire fraud, conspiracy to commit money laundering, and criminal forfeiture. Thirteen of the defendants were arrested in Las Vegas yesterday, December 14, 2011. Most of those defendants appeared before United States Magistrate Judge Robert J. Johnston yesterday, and pleaded not guilty to the charges. Several other defendants are scheduled for initial court appearances today beginning at 3:00 p.m. One individual was arrested at Washington Dulles International National Airport in Virginia, and appeared before a federal magistrate judge there, and the remaining two defendants have not yet been arrested.
According to the allegations in the indictment, from about December 2008 to December 2011, conspirators situated outside of the United States listed and offered items for sale on Internet sites (such as Craigslist and Autotrader) and occasionally also placed advertisements in newspapers. The items offered for sale included automobiles, travel trailers and watercraft. The conspirators typically offered the items at attractive prices and often stated that personal exigencies, such as unemployment, military deployment, or family emergencies, required that they sell the offered items quickly. To gain the confidence of prospective buyers, conspirators posing as owners of the items instructed buyers that the transactions were to be completed through eBay, Yahoo!Finance, or similar online services, which would securely hold the buyers’ funds until the purchased items were delivered. The conspirators sent e-mails to buyers which appeared or purported to be from eBay, Yahoo!Finance, or other such entities, and which instructed buyers to remit payment to designated agents of those entities who were to hold the purchase money in escrow until the transactions was concluded. In reality, the entire transaction was a sham: the conspirators did not deliver any of the items offered for sale; neither eBay, Yahoo!Finance, nor any similar entity participated in these transactions; and the purported escrow agents designated to receive buyers’ purchase money were actually participants in the scheme who received the funds fraudulently obtained from buyers on behalf of the conspiracy.
Relying on the schemers fraudulent representations, scores of buyers agreed to purchase items that the schemers offered online and in newspaper advertisements. The conspirators kept and converted the fraudulently obtained purchase money for their own purposes. The defendants and their associates allegedly obtained more than $3 million through the fraud scheme, which they distributed among the conspirators both inside and outside the United States.
Defendants:
- Eduard Petroiu, 28, Las Vegas resident
- Vladimir Budestean, 24, Las Vegas resident
- Bertly Ellazar, 27, Las Vegas resident
- Radu Lisnic, 25, Las Vegas resident
- Evghenii Russu, 25, Las Vegas resident
- Evgeny Krylov, 24, Las Vegas resident
- Eugeni Stoytchev, 35, Las Vegas resident
- Iavor Stoytchev, 28, Las Vegas resident
- Christopher Castro, 27, Las Vegas resident
- Delyana Nedyalkova, 23, Las Vegas resident
- Oleh Rymarchuk, 21, Las Vegas resident
- Melanie Pascua, 25, Las Vegas resident
- Manuel Garza, 23, Las Vegas resident
- Ryne Green, 25, Las Vegas resident
- Michael Vales, 22, Las Vegas resident
- Edelin Dimitrov, 20, Las Vegas resident
The indictment identifies Eduard Petroiu as a leader of the conspiracy, and six others, including Vladimir Budestean, Bertly Ellazar, Radu Lisnic, Evghenii Russu, and Eugeni Stoytechev, as subordinate managers of the conspiracy.
If convicted, the defendants face up to 60 years in prison and fines of up to $1 million.
The arrests result from a joint investigation by the FBI and the Las Vegas Metropolitan Police Department as part of its Nevada Cyber Crime and Southern Nevada Eastern European Organized Crime Task Forces. The case is being prosecuted by Assistant U.S. Attorney Timothy S. Vasquez.
The public is reminded that an indictment contains only charges and is not evidence of guilt. The defendants are presumed innocent and entitled to a fair trial at which the government has the burden of proving guilt beyond a reasonable doubt.
Anyone with information regarding these individuals is urged to call the FBI in Las Vegas at (702) 385-1281 or, to remain anonymous, call Crime Stoppers at (702) 385-5555 or visit http://www.crimestoppersofnv.com. Tips directly leading to an arrest or an indictment processed through Crime Stoppers may result in a cash reward.
TOP-SECRET – Taash Communications Network: Iranian Green Movement Support Plan

Among the lessons learned from the revolutions in Egypt and Tunisia is the value and affect of unencumbered access to information and communications technology (ISCT), including but not limited to independent information and social networking across multiple platforms, such as mobile, internet, web-based, and satellite broadcast.
The current ICT available in and outside Iran remain largely silod platforms (i.e. lacking technology that facilitates convergence of information and interactivity). In general, the younger generation that support reform and actively oppose the regime from within have not been able to effectively access newer technologies or have been dissuaded from participating in communications programs operated by less legitimate traditional opposition parties from outside. Most these platforms are either state sponsored, like VOA and BBC, or are exile opposition websites and channels out of Los Angeles with a political agenda and low tolerance for alternative viewpoints. Most have failed to stay up to date with the language, trends, mentality, culture, and sociopolitical situation of the today Iran. The partisan nature of the older generation opposition groups further limit their ability to reach the younger demographic.
The traditional opposition groups based outside Iran do not maintain the legitimacy, technical capability, or political synergies to collaborate with the new generation of civil society organizations in Iran. Moreover, none of the existing available communication platforms effectively leverage digital content and networking by combining interactive mobile, internet, web, and satellite based secure communications vehicles.
The Democracy Council, in response to requests from prominent activists and organizations representing the Green Movement and other emerging sectors of civil society to collaboratively develop and deploy a “virtual sanctuary” for reform – minded Iranians to communicate, inform, network, organize, and advocate with each other and the larger Iranian society as well as the outside world. Currently, a significant amount of digital networking and content is produced by organizations affiliated with the Green Movement and independent civil society organizations (CSOs) in and outside Iran. However, distribution and leveraging f such content is limited by: 1. Technology available to CSOs, 2. Unaccommodating regional distribution platforms, internet, web and satellite based, 3. Lack of resources or skills to circumvent censorship and security regimes, 4. Lack of shared practices and resources. TCN will provide solutions to these four issues. In addition, CSOs and activists will merge their communications’ operations into the TCN platform to facilitate immediate and leveraged impact in Iran and the Persian-speaking world. For example, TCN will leverage the databases, mailing lists, and informal and formal marketing and advocacy operations through the single branded portal. These individual CSOs and independent producers would continue to manage their networking and marketing operations through the larger platform.
Taash Communications Network (TCN), developed by the Democracy Council (the Council) in collaboration with the leading representatives from the Green Movement, will help to meet this demand by providing the first robust, multilevel (internet, web, mobile, and satellite broadcast) communications channel for regionally produced progressive (uncensored) content and communications. TCN will operate as branded technological distribution portal (platform) made available to independent content and communications produced by and for progressive and reform – minded Iranians.
TCN will be the Facebook, twitter, NPR, and C-Span of Persian media under one roof with a focus on social and political issues concerning the Iranian public inside the country, in the region, and abroad. It will be a uniting factor that is demand-driven (commercially sustainable).
TCN will not produce content but provide technical services for the benefit of Iranian civil society.
…
SUMMARY PROGRAM DESCRIPTION:
Developed in coordination with prominent civil society figures in Iran, including representatives of the Green Movement, TCN would serve as a secure, robust, multilevel communications platform by which civil society members can deliver Persian content through:
· Interactive Website
· Advanced online (e.g. social networking) and mobile tools to secure unfettered access, availability, and interactivity to the content.
· Branded Persian Language video broadcast platform TCN would be owned by the nonprofit TCN Foundation registered in a European country, such as Denmark. The foundation’s mission would be to make available an independent, branded Persianlanguage communications platform that is available for high-quality user-generated programming.TCN will serve as an independent distribution platform without production activities and distributing largely “homegrown” content. TCN would not produce or fund any content itself. Content will be broadly through independently produced user-generated local and regional programming. These contents will be supplemented by the purchase of Persian rights to acquisition of online or TV entertainment programming, with progressive themes from Hollywood to Bollywood. TCN will be an independently-owned multi layer open platform for progressive, reform-minded or “edgy” programming without censorship. A number of civil society organizations and other groups, such as prominent figures in the Green Movement have already expressed an interest and are committed in producing programming and
content for distribution by many different TCN platforms.For example, TCN has received written expressions of support and pledges to produce content from a broad spectrum of independent individuals and organizations, such as:
· Mohsen Sazegara, a leading dissident and one of the original founders of the Iranian Revolutionary Guard
· Democratic Party of Iranian Kurdistan
· Shideh Rezaei, co-founder of Iran-Rooyan
· Ahmad Batebi, Human Rights Activists
· Mohammad Sadeghi Esfahlani, founder and administrator of Mir Hossein Mousavi’s and Zahra Rahnavard’s Supporters’ Network on Facebook,This informative, educational, and entertaining medium will actively engage, inform, inspire, and link Iranians without censorship. To meet the demand of the target market, foreign films, generally illegal in Iran for containing progressive themes, would be acquired and dubbed to augment the original programming. Such content would be distributed and made accessible through multiple mediums: a secure website that contains social networking applications, and utilizes mobile and circumvention tools, and a robust satellite broadcast channel.
TCN would work collaboratively with local and regional CSO’s to design and deploy a strategic audience acquisition program leveraging new technologies and viral techniques. Each independent producer would manage their own networking and advocacy component as a back end to their own regular internet or TV programming. TCN provides the technical background to ensure high penetration, distribution, and secure accessibility.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET from the CIA- Ronald Reagan: Intelligence and the End of the Cold War

Ronald Reagan became the 40th president of the United States more than thirty years ago, and ever since he stepped down to return to California eight years later, historians, political scientists, and pundits of all stripes have debated the meaning of his presidency. All modern presidents undergo reappraisal after their terms in office. Reagan has undergone a similar reappraisal. The old view, exemplified by Clark Clifford’s famous characterization that Reagan was “an amiable dunce,” posited Reagan as a great communicator, to be sure, but one without substance, a former actor who knew the lines others wrote for him, but intellectually an empty suit. Reagan, in the old narrative, simply could not be the architect of anything positive that happened while he was president. That perspective has changed forever and is marked by the continually improving regard historians have for Reagan.
DOWNLOAD ORIGINAL DOCUMENT HERE
Confidential-Statement by Director General Israel Atomic Energy Commission To the International Atomic Energy Agency

Mme President,
Distinguished Delegates,
Mme President, let me begin by congratulating you, on being elected President of the General Conference. I can assure you the fullest cooperation of the delegation of Israel, in carrying out your important and responsible tasks. I also wish to congratulate the kingdom of Cambodia and the Republic of Rwanda as new members of the Agency. Yesterday, the General Conference has confirmed Ambassador Yukiya Amano of Japan, to the most professional and distinguished post of IAEA’s Director General. Israel has known Ambassador Amano’s professional qualifications and personal integrity over the years, and looks forward to working with him in this new capacity. We wish Ambassador Amano much success in guiding the work of the Agency.
Mme President,
In my address, I intend to dwell mainly on two issues: The new prospects for civil nuclear energy, and the risks associated with it. The risks include diversion of nuclear materials to military programs; nuclear terror; and safety and security of nuclear installations.
The nuclear industry has recently begun witnessing the emergence of a world-wide renaissance. While the intensive development of nuclear energy is highly desirable, it is imperative to minimize proliferation risks – especially risks which are associated with nuclear fuel cycle technologies. The characteristics of these technologies are that they are inherently dual use in their nature. It is the firm view and the policy of Israel, that the right to use nuclear energy for peaceful purposes is based on the absolute duty of each state not to abuse this right.
Mme President,
Israel attaches great importance to the nuclear non-proliferation regime. The regime has recently been under growing pressure, from within, by states that are parties to the NPT. Despite the geo-political realities in the Middle East, it has been Israel’s long standing policy of supporting, and wherever possible, joining arms control and other international treaties. In doing so, we are very appreciative of those who are conscious and mindful of Israel’s narrow security margins. In recent years, Israel has actively followed developments in the fields of nonproliferation and arms control. This includes a renewed interest in multilateral nuclear arms control and disarmament led by US President Barak Obama. Israel has continued to contribute to the global non-proliferation regime, through its policy of responsible behavior and restraint in the nuclear domain. Israel has repeatedly stated that it will not be the first to introduce nuclear weapons in to the Middle East. It is therefore regrettable that the outgoing Director General of the
IAEA, repeatedly mispresented Israel’s long standing policy in this regard. The continuous growth of Israel’s energy needs, coupled with its total dependence on foreign energy sources, poses a complex national challenge. Israel possesses advanced nuclear expertise and know-how that will play an impressive role when it comes to the future development of Israel’s energy sources.Mme President,
I would like to address Israel’s vision and policy, regarding the transformation of the Middle East to a zone free of weapons of mass destruction. It has always been the position of Israel that the nuclear issue, as well as all other security issues, could only be realistically addressed within the regional context. The African Nuclear Weapon Free Zone Treaty, which has recently entered into force, provides an excellent example of such an approach.
It is our vision and policy, to establish the Middle East as a mutually verifiable zone free of weapons of mass destruction and their delivery systems. We have always emphasized, that such a process, through direct negotiations, should begin with confidence building measures. They should be followed by mutual recognition, reconciliation, and peaceful relations. Consequently conventional and non-conventional arms control measures will emerge. Israel’s long-term goals for Middle East regional security and arms control were approved by the Israeli Government. As the international community has accepted and recognized in other regions, the establishment of such a zone can only emanate from within the region.
In our view, progress towards realizing this vision cannot be made without a fundamental change in regional circumstances, including a significant transformation in the attitude of states in the region towards Israel. The constant efforts by member states in the region to single out the State of Israel in blatantly anti-Israeli resolutions in this General Conference, is a clear reflection of such hostile attitude.
Mme President,
Significant and grave developments regarding nuclear proliferation have taken place in the recent years. I want to emphasize, that the most widely recognized cases of non-compliance with legally binding non-proliferation obligations, have occurred in the Middle East, by states that are parties to the NPT. Grave and covert violations by Iran and Syria had been detected and then formally reported by the IAEA. The Agency’s investigations in these two countries have been hampered by continued lack of cooperation, denial of access, and efforts to conceal and mislead the inspectors.
Israel is following these developments in our region, with profound concern. We all hope that the IAEA investigations will get to the bottom of these activities. In so doing it will assist the international community in its efforts to prevent dangerous proliferation of nuclear weapons, and the abuse of the right to peaceful nuclear energy.
We believe that it is crucial to improve and enhance the IAEA verification and inspection capabilities. We are also of the firm view, that IAEA investigations should be conducted free of any extraneous influences. Above all, the activities of those countries that breach their international commitments and obligations must be met with concrete and immediate international measures. Violations cannot go unpunished.
Mme President,
Another important issue, which poses many challenges to the international community, is nuclear safety and security. Adequate safety and physical security measures are crucial to ensure international acceptance of the nuclear civil industry. It is the long standing policy of the Israel Atomic Energy Commission, to pursue uncompromising standards of safety in its two nuclear research centers.
Mme President, Distinguished delegates.
The threat of radiological and nuclear materials in the hand of terrorists, confronts us all. In a world of global terrorist networks supported by rogue regimes, a secret and sudden attack, with a weapon of mass destruction, has become a chilling reality. None of us can confront this global threat alone. We must work together to secure the materials terrorists would need to build a radiological or improvised nuclear device. In this regard, we commend the IAEA for addressing the prevention of illicit trafficking of radioactive and nuclear materials. In view of these realities, Israel has joined the US-Russia led Global Initiative to Combat Nuclear Terrorism (GICNT). It has also joined the Megaport Initiative led by the US Department of Energy to prevent possible illicit trafficking of radioactive and nuclear materials. We believe that no effort and resources should be spared worldwide, in denying terrorists these materials. In this spirit, the Government of Israel welcomes President Obama’s initiative, to host a Global Summit on Nuclear
Security next year.Mme President,
Given the global realities we all face, the peaceful uses of nuclear energy, should have been the main topics of this Annual General Conference. Regrettably, instead, some countries are imposing on this General Conference politically motivated agenda items. These efforts are either designed to single out the State of Israel, or to divert attention from violations and real issues of non-compliance by certain Middle East states.
First among these, is Agenda item 22 entitled “Israeli Nuclear Capabilities”. This Agenda item is no more than a version of an old agenda item that was removed by agreement in 1993, and never acted upon. Among the sponsors of this draft resolution are countries that do not recognize the State of Israel, and even call for its annihilation. I wonder what moral standing they possess as they criticize Israel
for pursuing policies designed to secure its very existence.Mme President,
The second is agenda item 21 entitled: “The application of IAEA Safeguards in the Middle East”. Israel has joined the consensus on this Agenda Item for 14 consecutive years. We have done so notwithstanding our grave reservations, regarding the modalities included in the resolution’s text, and the relevance of this forum in addressing the establishment of the Middle East as a nuclear weapon free zone. As I mentioned before, such a zone can only emanate from within the region on the basis of arrangements freely arrived at through direct negotiations, between all the states concerned. No IAEA Forum could replace direct negotiations between the regional parties.
Unfortunately, since 2006, the consensus on the Middle East issues was broken. The only reason for this setback is the uncompromising attitude of the sponsors of these two draft resolutions who are aiming at extraneous political goals. This raises also doubts whether the promotion of the Middle East into a nuclear weapon free zone, is indeed the aim of the sponsors.
During recent months, Israel has approached Egypt directly and through other Governments, hoping to reach an agreed language on Middle East issues in this General Conference. In the same spirit, Israel has responded positively in the recent days to sincere efforts by several delegations and the President of the Conference to work together towards a positive outcome. It is my firm belief that it is not too late to reach consensus based on our respective positions. I can assure you all of our fullest cooperation in trying to reach consensus based on negotiations in good faith.
Mme President,
Iran’s initiative to promote Agenda item 24 on “The Prohibition of Armed Attack or threat of Attack against Nuclear Installations” is a clear case of hypocrisy. Iran is driven by wishful thinking, that the international community will condone Iran’s violations of its commitments and obligations, and its deception campaign over many years. No diplomatic smoke screen and maneuvering in the IAEA’s General Conference can obscure the real facts and findings. Let me remind all delegates that the Director General, in his recent address to the Board of Governors, provided an account of Iran’s non-cooperation with the Agency and said: “If this information is real”, “there is a high probability that nuclear weaponization activities have taken place”. The Government of Israel and many others assess, that the information available to the Agency is accurate and real. Iran, which is systematically violating several United Nations Security Council Resolutions, is seeking the sympathy of the same international community whose authority it flouts. I call on all delegations, to reject Iran’s transparent and cynical move.
Mme President,
The international community is at a critical crossroad in confronting a fundamental challenge. We should work together in promoting peaceful uses of nuclear energy, while preventing the spread of nuclear weapons and proliferation of sensitive technologies and materials.
Mme President, Distinguished delegates.
This coming Friday is the eve of the Jewish New Year 5770. In our prayers we say: “Here ends a year with its maledictions and a new year begins with its blessings”.
We hope that this year holds blessings and peace for all.
Thank you Mme President.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP – SECRET – (U//FOUO) U.S. Marine Corps Afghan Drone Operations in Regional Command Southwest (RC (SW))

(U) Purpose: To inform Deputy Commandants (DCs) Aviation, Combat Development and Integration (CD&I), Plans, Policies, and Operations (PP&O), Installations and Logistics (I&L), Commanding General (CG), Training and Education Command (TECOM), Director of Intelligence, operating forces, and others on results of a Marine Corps Center for Lessons Learned (MCCLL) collection conducted April – May 2011 to document lessons and observations regarding unmanned aerial systems (UAS) operations in support of Regional Command Southwest (RC (SW)) during Operation Enduring Freedom (OEF).
Bottom Line up Front
(U//FOUO) The RQ-7B Shadow UAS employed by the Marine Corps is a U. S. Army program of record. Because it is an Army program the Shadow has very high frequency (VHF) but no ultra-high frequency (UHF) retransmission capability. UHF is the primary means of communication between key elements of the Marine air command and control system (MACCS), airborne Marine Corps aviation assets, and Marine joint terminal attack controllers (JTAC) and forward air controllers (FAC). Developing a UHF retransmission capability for an organic USMC UAS was regarded as a primary need.
(U//FOUO) USMC units were dependent on joint assets for armed UAS missions and competed with virtually every other combat unit in OEF to schedule armed UAS sorties. Developing an organic armed USMC UAS was regarded as a priority.
(U//FOUO) Third Marine Aircraft Wing (MAW) Forward (Fwd) conceived and initiated a staff organization called the Marine air ground task force (MAGTF) Aerial Reconnaissance Coordination Cell (MARCC). The intent of the MARCC was to ensure that all aviation combat element (ACE) intelligence, surveillance, and reconnaissance (ISR) capabilities, manned and unmanned, were coordinated and employed to maximum effectiveness.
(U//FOUO) The establishment of the MARCC initially generated operational friction between the RC (SW) ACE and the ground combat element (GCE). The ACE regarded the MARCC as a more efficient means of conducting command and control of ACE assets. However, the GCE had been accustomed to a greater degree of autonomy in employing UASs and perceived the establishment of the MARCC as an impediment to responsiveness and their ability to dynamically retask UASs as desired.
(U//FOUO) As the ground scheme of maneuver evolved, establishing and supporting UAS “hubs” and “spokes” in proximity to ground forces posed a significant challenge to 3d MAW (Fwd) planners. [MCCLL Note: A hub is a UAS airfield base of operations used to launch and recover UASs and a spoke is a scalable outlying UAS control site supported by the hub.] In addition to requiring facilities suitable for the launch, recovery, and maintenance of UASs, a key consideration was the appropriate manning of each hub and spoke. A significant limiting factor in the MAW’s ability to establish hubs and spokes was a lack of trained intelligence analysts, UAS mission commanders, and maintenance personnel (this included contract maintenance support for the ScanEagle UAS due to contractor habitability mandates subject to that contract).
(U//FOUO) The volume of UAS sorties and their importance to the MAGTF is expected to increase in the future, including the development of a logistics support UAS and a new small tactical unmanned aerial system (STUAS). This has generated a need to determine where UAS assets would best be located within the ACE of the MAGTF. The Marine Unmanned Aerial Vehicle Squadron ONE and TWO (VMU-1 / VMU-2) commanding officers believed they should be located within a Marine aircraft group (MAG) just as all USMC aviation squadrons. [MCCLL Note: The VMUs are located within the Marine air control group (MACG) in garrison. During OEF deployment the VMUs were located directly within the MAW (Fwd) because there were no deployed MAGs and the MACG was composed of a small detachment.]
Key Points:
(U//FOUO) The MARCC worked to incorporate all ACE ISR capabilities into overall ISR planning done by RC (SW), advised RC (SW) planners and leaders on which aviation assets could best fill ISR requirements and requests, ensured air tasking order (ATO) development included the RC (SW) commander’s prioritization for tasking of ISR assets, streamlined information flow regarding these assets in order to build situational awareness throughout the MACCS, and facilitated the dynamic retasking of ISR platforms as necessary.
(U//FOUO) VMU-1 established a “hot weather schedule” during the summer months due to temperatures that could reach as high as 135 degrees Fahrenheit on the runway. This extreme heat could cause the Shadow’s wings to swell and vent fuel. However, the ScanEagle did not have this significant a problem with the heat and has longer endurance, so, the VMU scheduled ScanEagle sorties earlier in the day but still sufficient to cover the hottest time of day and Shadow sorties in the morning or evening. This enabled the VMU to maintain coverage throughout the fly-day. VMU-1 also erected a large area maintenance shelter for aircraft maintenance (LAMS-A) in order to keep aircraft and personnel out of the heat.
(U//FOUO) UAS technologies and capabilities continue to be developed and fielded. Training and education of UAS users, including unit air officers, intelligence officers, FACs, JTACs, and joint fires observers (JFO), regarding new capabilities and how best to employ UASs is vital. In order to support this, sufficient UAS assets must be made available during pre-deployment training.
(U//FOUO) The Marine Corps has recently fielded the Satellite Wide-Area Network version 2 (SWANv2) that will be included in the VMU organic table of equipment. Unlike the Digital Video Broadcasting Return Channel via Satellite (DVB-RCS) system currently being used, SWANv2 is a Marine Corps program of record that will enable the VMUs to disseminate full-motion video (FMV) signals more effectively.
(U//FOUO) In July, 2010, a contract was awarded to Boeing subsidiary Insitu, Inc. for development and production of the STUAS. STUAS will be used by the U.S. Navy and Marine Corps to provide persistent maritime and land-based tactical reconnaissance, surveillance, and target acquisition (RSTA) data collection and dissemination. Unlike the current ScanEagle and Shadow UASs, STUAS will have a UHF retransmission capability and the modularity to carry “plug-and-play” mission payloads such as hyper-spectral imaging sensors, synthetic aperture radar sensors, and potentially small precision-guided munitions (PGM) among others.
(U//FOUO) The establishment of the MARCC initially created the perception within the GCE of two separate procedures for requesting UAS support – one procedure for requesting organic support and a different procedure for requesting joint support. However, the 3d MAW (Fwd) Future Operations Officer said that, the team that developed the MARCC specifically avoided creating any new procedures for the end users.
(U//FOUO) The MARCC officer-in-charge (OIC) developed a comprehensive kneeboard card that had information regarding all of the unmanned assets that were going to be airborne during a particular fly-day. This provided aircrew with situational awareness that was critical to safety of flight and helped reduce the chance of mid-air collisions. The kneeboard card also provided time, location, and contact frequency information that could be used to more effectively and efficiently employ or retask UASs.
(U//FOUO) The RC (SW) ISR officer noted that they were building a “collection strategy playbook” that would describe different tactics, techniques, and procedures (TTP) that have proved successful in integrating different intelligence collections effects. For example: layering ground-moving-target-indicator data with dismounted-moving-target-indicator assets (two different kinds of radar) and integrating those with a wide-area surveillance sensor (such as a UAS, Ground Based Operational Surveillance System (GBOSS), or Aerostat balloon) in support of real-time operations.
(U//FOUO) The fact that there is no primary military occupational specialty (MOS) designator for UAS officers degraded the ability of the VMUs to retain corporate knowledge and experience within the UAS community. Instead, officers were assigned to VMUs for 18 – 24 month tours of duty, a substantial portion of which was spent in training, and usually never returned to the UAS community after transferring out.

DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – U.S. Treasury Strategic Direction Fiscal Years 2009-2011

The Intelligence Authorization Act of Fiscal Year 2004 created the Treasury Department’s Office of Intelligence and Analysis (OIA) and made it responsible for the receipt, analysis, collation, and dissemination of intelligence related to the operation and responsibilities of the Treasury Department. OIA was created to support the formulation of policy and the execution of Treasury authorities by providing expert analysis and intelligence production on financial and other support networks for terrorist groups, proliferators, and other key national security threats. In addition, OIA was charged with providing timely, accurate, and focused intelligence on the full range of economic, political, and security issues. On April 28, 2004, the Secretary of the Treasury established the Office of Terrorism and Financial Intelligence (TFI), which includes OIA, the Office of Terrorist Finance and Financial Crimes (TFFC), the Office of Foreign Assets Control (OFAC), the Financial Crimes Enforcement Network (FinCEN), and the Treasury Executive Office for Asset Forfeiture (TEOAF). TFI brings a wide range of intelligence and enforcement authorities together under a single umbrella to strategically target a number of threats. Since its creation in 2004, OIA has accomplished a great deal in the course of meeting ever growing demands from its customers. In its first year of operation, OIA focused on establishing a current intelligence process to meet the day-to-day information needs of decision makers in the Department, while also supporting the intelligence needs of the designation process under EO 13224.
• In 2005, President Bush signed EO 13382 aimed at freezing the assets of proliferators of weapons of mass destruction and their supporters; OIA expanded its analytic efforts in order to support implementation of the EO.
• In 2006, OIA enhanced its strategic analytic capability and began producing allsource intelligence assessments on terrorist finance and rogue state proliferation networks that leveraged Treasury’s unique expertise and perspective.
• In 2007, OIA expanded the breadth and depth of its analytic cadre to meet increased demand from policymakers.
• In 2008, OIA initiated a research program to examine the systemic issues behind the financing of national security threats, such as cash courier networks, informal remittance systems, and terrorist use of the Internet.


ADDRESSING THE GLOBAL FINANCIAL NETWORK:
A COMPREHENSIVE APPROACH TO FINANCIAL
INTELLIGENCE
Building on its accomplishments of the past several years, OIA plans to launch a comprehensive approach to financial intelligence that will allow us to better confront national security challenges by strengthening our understanding of the global financial network. The global financial network encompasses four areas: the financial underpinnings of national security threats, our adversaries’ financial vulnerabilities, the impact of targeted financial measures, and threats to international financial stability.
1. Assess Financial Underpinnings of National Security Threats: Terrorists, WMD proliferators, rogue states, and other nefarious actors require financial resources to support their activities. Without ready access to such resources, these actors are unable to indoctrinate, recruit, and train personnel; buy weapons, technology, and equipment; circulate propaganda; bribe officials; support the global networks of operatives essential to their existence; or launch attacks. The flow of funds to activities that threaten national security may not be shut off completely, but impeding the activities of these networks makes operating costlier, harder, and riskier for these threats.
2. Identify Adversaries’ Financial Vulnerabilities: The US Government is relying more heavily on targeted financial measures aimed at specific actors engaged in illicit conduct, as opposed to broad-based economic sanctions. Targeted financial measures allow decision makers to apply financial pressure and isolate terrorists, proliferators, and others whose goal is to undermine US security. They also allow US leaders to take punitive action against threats without resorting to military force. Applying targeted financial measures effectively, however, requires indepth knowledge of an adversary’s economic or financial well-being: its strengths, weaknesses, connectivity to global markets, and key dependencies.
3. Evaluate the Impact of Targeted Financial Measures: As targeted financial measures become an increasingly important policy tool, measuring their effectiveness is imperative. This area of inquiry involves questions such as: What impact have the measures had on the target’s economy and financial system? How is the target reacting? Are the measures having the desired effect on the target’s behavior? What steps is the target taking to evade or avoid the measures? Moreover, have the measures had any unintended consequences or caused any collateral damage?
4. Monitor Threats to International Financial Stability: The US financial system and the economic well-being of every American are inexorably linked to the health and stability of the international financial system. Globalization and convergence in the world economy only underscore this fact. Identifying threats to the global financial system’s integrity and to sustainable growth and development therefore is essential to America’s own security.
…

DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET from the Worldbank – Interim Strategy Note for the Republic of Iraq 2009-2011

INTERIM STRATEGY NOTE FOR IRAQ (FY09-FY11)
EXECUTIVE SUMMARY
i. Recent positive developments suggest that Iraq has made important progress towards political and economic stabilization, although the situation remains fragile and reversible. Recent months have seen a sharp decline in incidents of violence, especially in the Baghdad area, and a corresponding decrease in the rate of internal displacement of the population. This reflects improved security as well as successful initial steps towards political reconciliation. Macroeconomic performance has also improved although growth has been volatile.
ii. The Government is signaling its commitment to reform and reconstruction, indicating that continued engagement with Iraq may produce further concrete results. The Government has succeeded in sharply reducing inflation and containing recurrent spending, while increasing capital expenditures to accelerate the recovery process. In addition, the machinery of government is slowly reviving as Iraq emerges from conflict. A more proactive and confident government is likely to devote more attention to the economy. Finally, high oil prices and – to a lesser extent – an increase in production produced an estimated US$70 billion of revenues in 2008, although a deterioration in Iraq’s fiscal balance is expected during part of the ISN period in view of
the recent declining trend in oil prices.
iii. However, results from past and ongoing reform efforts remain far from meeting the needs and expectations of the Iraqi people. Unemployment remains extremely high and access to basic services severely limited. Electricity supply is unreliable and is far exceeded by demand; access to clean water and sanitation is the lowest in the Region. Recent improvements in access to education and health services have not yet translated into significant welfare gains on the part of the people of Iraq.
iv. Iraq is resource rich and has benefited from a substantial increase in oil revenues over the past few years. At the same time, it is still subject to conflict, insecurity, political instability and revenue volatility. These features highlight Iraq’s uniqueness. As a conflict-affected, IBRD-eligible middle-income country, Iraq is clearly not the typical aid-dependent post-conflict country. The main challenge for the country – in addition to security and political stability – is to mobilize and effectively use its own
vast resources to improve the welfare of the Iraqi people and rebuild its infrastructure. The main role for the international community, including the World Bank Group, is therefore to help Iraq use its own resources more effectively.
v. Working in Iraq has been very challenging for the Bank Group and other donors. While some notable successes have been achieved, the effectiveness of assistance has been hampered by issues related to both the country’s operating environment and the approach followed by the donors. Operating environment issues – which also affect the Government’s ability to execute its own investment budget – include: the fragile political and security situation; the unstable policy and institutional environment; the Government’s weakened institutional capacity, and weaknesses in Iraq’s banking system. Issues related to the approach of the Bank to Iraq include the selectivity of assistance as well as business processes and fiduciary arrangements which have been unfamiliar to Iraqi counterparts and are challenging for Ministries with limited capacity.
vi. The design of this third Interim Strategy Note benefited from a stocktaking of the Bank Group’s engagement with Iraq to date. The goal of the stocktaking exercise was to identify the key bottlenecks for the implementation of the previous ISNs and extract lessons for this ISN. This exercise informed the design of this ISN: (i) the continuing centrality of institution building; (ii) the critical importance of interest and engagement on the part of ministries and implementing agencies; (iii) the need for increased selectivity in terms of the ability to identify and seize opportunities as they arise to achieve concrete results; (iv) the need to focus on reform efforts that do not overtax Iraq’s existing capacity and that more clearly reflect the country’s current political and security situation; and (v) the need for increased flexibility in the design and programming of Bank assistance and for experimentation with alternative implementation arrangements for the Bank’s assistance program for Iraq.
vii. The ISN also benefited from extensive consultations with the Government of Iraq, the donor community, and other stakeholders, including representatives from private sector and civil society organizations. These consultations were extremely helpful in identifying the country priorities, defining promising engagement arrangements to maximize Bank assistance results, and highlighting the centrality of donor coordination. Some of the main priority areas identified during the consultations include:
(i) public financial management; (ii) banking sector reform; (iii) support to planning processes and strategy design (not only at the central level, but also at the sectoral and provincial levels); (iv) private sector development; and (v) energy and services.
viii. Given Iraq’s unique characteristic of a well resource endowed Middle Income Country (MIC) with a fragile environment, this ISN is proposed for a longer time horizon than the typical ISN. The time horizon for this ISN is proposed to be from mid-FY09 through FY11, to be updated to a full Country Assistance Strategy if and when circumstances allow. This interim strategy contains lessons and principles of engagement. The work program beyond FY09 would be kept up to date through Annual Business Planning, jointly with the Iraqi Government to ensure it meets the evolving needs of the Government as well as evolving opportunities for engagement.
ix. The central guiding principle of this ISN is that Iraq is well-endowed with natural and financial resources, and that the main role for the World Bank in this context is to help Iraq use its resources more effectively and transparently. This principle impacts both the form and the content of the proposed work program for the next two years. However, it needs to be tempered by recent developments in the global economy and their impact on Iraq’s projected oil revenues for the next few years and its increasing need for external financing in the short-to-medium term. Hence, this ISN anticipates IBRD financial support as requested by the Iraqi authorities.
x. Regarding the form of the assistance, the main instruments of Bank Group support under this ISN include: (i) operational support to accelerate implementation of the current portfolio, totaling about US$1 billion; (ii) advisory services in selected sectors and areas; (iii) IBRD financial support in priority sectors to be selected on the basis of funding needs and implementation capacity; (iv) IFC investment and advisory services products; and (v) MIGA’s political risk guarantee products. Under this ISN, an IBRD envelope of US$500 million can be committed for investments projects over FY09-11. The Bank is currently administering 16 active grants funded from the Iraq Trust Fund, totaling US$471.6 million to provide textbooks, schools, health clinics, improved social safety nets, water supply and sanitation, irrigation and drainage, and a comprehensive household survey. The ongoing IDA portfolio consists of five projects, worth US$508.5 million, in the areas of education, roads, electricity, and water supply. IFC will support PSD through prioritized investments and advisory services in key sectors. The Bank’s Analytical and Advisory Activities (AAA) program will support the Government in its efforts to enhance its ability to effectively use its oil revenues to the benefit of the Iraqi people. Key analytical work undertaken since re-engagement in 2003 includes a study on subnational public financial management (2007), a joint IFC/IBRD Construction Industry study (2008), a Country Economic Memorandum (2006), a pension reform study (2005), a report on Iraq’s Public Distribution System (2005), an investment climate report (2004), and a study on stateowned
enterprise reform (2004). The Government has also expressed interest in borrowing from IBRD as the need arises, increasing IFC support, and getting MIGA guarantees that could leverage private financing. Other instruments include the State and Peace Building Fund, and possibly, Treasury services.
xi. With respect to the content of the assistance, activities under this ISN will fall under at least one of three thematic areas of engagement: (i) continuing to support ongoing reconstruction and socio-economic recovery; (ii) improving governance and the
management of public resources, including human, natural and financial; and (iii) supporting policies and institutions that promote broad-based, private-sector-led growth, with the goal of revitalizing the private sector and facilitating job creation. IFC and MIGA will play a key role particularly (but not exclusively) with respect to the third thematic area. New activities under the ISN will be chosen on the basis of criteria for selectivity reflecting opportunities to achieve concrete results on the ground.
xii. The three thematic areas are closely linked with the key goals of the International Compact with Iraq. The first ISN theme responds to the goals of the International Compact with Iraq (ICI) which are related to Iraq’s reconstruction and recovery efforts, including strengthening the energy sector and developing a stable, competitive and sustainable agriculture. The second ISN theme responds to the ICI goals of improving public financial management as well as strengthening institutions and improving governance. The third ISN theme responds to the ICI goals of implementing economic reform to create an enabling environment for private investments as a driver for broad-based growth.
xiii. To achieve tangible results in a relatively short term, the Bank Group will place a renewed emphasis on how this ISN will be implemented. Building on lessons learned from the implementation of the previous Interim Strategy Notes and the various
consultations held, this ISN will aim to: (a) enhance the effectiveness of instittion building and analytical and advisory activities; (b) strengthen the implementation of the current portfolio; (c) introduce more flexibility in the Bank Group’s programming and ability to experiment with alternative implementation arrangements; and (d) foster donor coordination. For planning purposes, this ISN is based on the assumption that progress in the security situation over the next two to three years would continue to be slow and incremental, with a risk of reversal.
xiv. Risks. There are high risks to the World Bank Group’s program in Iraq. The most important risk pertains to the political and security situation, which remains fragile, as does the country’s operating environment. To mitigate this risk, the strategy emphasizes flexibility, and the Bank will adjust its activities as appropriate. Given the current limitations on mobility within the country, maintaining a vibrant dialogue with counterparts on issues of policy reform as well as implementation, and ensuring adherence to core fiduciary and safeguard requirements will remain challenging. These risks are substantial despite the Bank’s mitigating measures, which include capacity building, local oversight capacity, and prudent financial management procedures.

DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – (U//FOUO) U.S. Army Guide to Political Groups in Afghanistan

 Political Parties in Afghanistan
Political Parties in Afghanistan
- Most political groupings in Afghanistan are based on alliances that were formed during the military struggles of 1979-2002
- Many have connections with ex-Mujahideen factions
- During the 2005 presidential election, since parties‟ identification was not allowed for candidates, party based coalition could not function in parliament
- In the 2009 presidential election, political parties could support a candidate who was a member
- In Afghanistan, political parties are seen as controversial and are not seen as a potential positive force by the government or the public
- The Political Parties Law of 2003 requires all political parties to be registered with the Ministry of Justice and observe the precepts of Islam
- Some 82 parties have gained such recognition as of the end 2007; but hundreds of political groups claim to be active in the country today, the majority of which have little to no political power
- The government fears that encouraging political parties will fuel civil tensions and contribute to the existing deteriorating security
- The government places emphasis on building national unity and preventing groups from forming in Parliament on the basis of ethnicity, language, region or any other potentially divisive factors1
- For most parties, particularly the new or smaller ones without well known leaders, their information is not known or widely disseminated
- There are numerous reasons why parties formed and are forming but two main raisons stand out:
- New opportunity
- Especially after the fall of the Taliban
- Disputes with current leadership
- Political groups in Afghanistan are very fluid, coalitions, fronts and political alliances form and dissolve quickly
- Allegiances between groups shift according to the convictions of their leaders rather than by ideology
- Individual parties split, reunify and/or rename themselves constantly, leading to confusion in party existence and names
…
Major Pro-government Parties
- Islamic Society of Afghanistan (Hezb-e-Jamihat-e-Islami-e-Afghanistan)
- Afghanistan‟s Islamic Mission Organization (Tanzim Dawat-e-Islami-e-Afghanistan)
- Islamic Unity Party of Afghanistan (Hezb-e-Wahdat-e-Afghanistan)
- National Islamic Front of Afghanistan (Hezb-e-Mahaz-e-Mili Islami-e-Afghanistan)
- Afghanistan National Liberation Front (Hezb-e-Tanzim Jabha Mili Nejat-e Afghanistan)
- Afghan Social Democratic Party (Hezb-e-Afghan Melat)
- National Movement of Afghanistan (Nahzat-e-Mili Afghanistan)
Major Opposition Parties
- The United National Front – UNF (Jabhe-ye-Motahed-e-Mili)
- New Afghanistan (Hezb-e-Afghanistan-e-Naween)
- Hezb-e-Islami Gulbuddin – HiG
- Party of Islam – HiK (Hezb-e-Islami)
- Party of Islamic Unity of The People of Afghanistan (Hezb-e-Wahdat-e Islami Mardom Afghanistan)
- National Movement of Afghanistan (Nahzat-e-Mili Afghanistan)
Other Political Parties
- Revolutionary Association of the Women of Afghanistan (RAWA)
- Rome Group
- Freedom Party of Afghanistan(Hezb-e Azadee-e-Afghanistan)
- The National Understanding Front-NUF (Jabahai Tafahim Millie)
- National Youth Union of Afghanistan (Hezb-e Hambastagi-yi Milli-yi Jawanan-i Afghanistan)
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET from the FBI – Lawyer for Preeminent Firms Pleads Guilty in $37 Million Insider Trading Scheme
A corporate lawyer who previously worked at four prominent international law firms admitted today to participating in an insider trading scheme that lasted for 17 years, relied on information he stole from his law firms and their clients, and netted more than $37 million in illicit profits, U.S. Attorney for the District of New Jersey Paul J. Fishman announced.
Matthew Kluger, 50, of Oakton, Va., pleaded guilty to all four counts charged in the information against him: conspiracy to commit securities fraud, securities fraud, conspiracy to commit money laundering and obstruction of justice. Kluger entered his guilty plea before U.S. District Judge Katharine S. Hayden in Newark federal court.
“Not only did Matthew Kluger defraud the investing public, he betrayed the colleagues and clients who depended on his confidentiality in some of the biggest deals of the last decade,” said U.S. Attorney Fishman. “In order to be confident in our markets, investors must have comfort that those with inside information won’t abuse positions of trust for personal gain.”
“In this time of economic uncertainty, securities fraud remains a top investigative priority for the FBI,” said Michael B. Ward, special agent in charge of the Newark Division of the FBI. “Millions of investors have entrusted their life savings to the integrity of the financial markets and the belief of a level playing field. Insider trading, such as the conduct attributable to Matthew Kluger, corrupts the process and tilts the playing field in favor of those privileged few with access to information not available to the public, and at the expense of unsuspecting and unknowing investors.”
According to documents filed in this case and statements made in court:
Kluger and two co-conspirators—Garrett D. Bauer, 44, of New York, and Kenneth Robinson, 45, of Long Beach, N.Y.,—engaged in an insider trading scheme that began in 1994. Kluger admitted that he passed inside information to Bauer and Robinson that the men used to trade ahead of more than 30 different corporate transactions.
During the scheme, Kluger worked at four of the nation’s premier mergers and acquisitions law firms. From 1994 to 1997, he worked first as a summer associate and later as a corporate associate at Cravath Swaine & Moore in New York. From 1998 to 2001, he worked at Skadden, Arps, Slate, Meagher & Flom in New York and Palo Alto, Calif., as an associate in their corporate department. From 2001 to 2002, Kluger worked as a corporate associate at Fried, Frank, Harris, Shriver & Jacobson LLP in New York. From Dec. 5, 2005, to March 11, 2011, Kluger worked at Wilson Sonsini Goodrich & Rosati as a senior associate in the mergers & acquisitions department of the firm’s Washington, D.C., office.
While at the firms, Kluger regularly stole and disclosed to Robinson material, nonpublic information regarding anticipated corporate mergers and acquisitions on which his firms were working. Early in the scheme, Kluger disclosed information relating to deals on which he personally worked. As the scheme developed, and in an effort to avoid law enforcement detection, Kluger took information which he found primarily by viewing documents on his firms’ computer systems.
Kluger admitted that once he provided the inside information to Robinson, Robinson passed it to Bauer. Bauer then purchased shares for himself, Kluger and Robinson in Bauer’s trading accounts, then sold them once the relevant deal was publicly announced and the stock price rose. Bauer gave Robinson and Kluger their shares of the illicit profits in cash—often tens or hundreds of thousands of dollars per deal—that Bauer withdrew in multiple transactions from ATM machines.
The three conspirators took greater efforts to prevent detection of their insider trading scheme after Kluger joined Wilson Sonsini. Among other techniques, they used pay phones and prepaid cellular phones that they referred to as “throwaway phones” to discuss the scheme.
Kluger also admitted that, after Robinson told him that the FBI and (Internal Revenue Service) had searched Robinson’s house and had asked questions about the illicit scheme, Kluger destroyed multiple pieces of evidence, including an iPhone and a computer. Kluger also instructed Robinson to destroy a prepaid phone.
As part of his guilty plea, Kluger agreed to forfeit $415,000, which is the approximate amount that he obtained from recent transactions in the scheme.
The maximum potential penalties Kluger faces per count are as follows:
| Count | Charge | Maximum Potential Penalty |
|---|---|---|
| 1 | Conspiracy to commit securities fraud | Five years in prison; $250,000 fine, or twice the aggregate loss to victims or gain to the defendants |
| 2 | Securities fraud | 20 years in prison; $5 million fine |
| 3 | Conspiracy to commit money laundering | 20 years in prison; $500,000 fine, or twice the value of the property involved in the transaction |
| 4 | Obstruction of justice | 20 years in prison; $500,000 fine |
Judge Hayden scheduled Kluger’s sentencing for April 9, 2012.
Bauer and Robinson have both pleaded guilty in connection with the scheme. Bauer is scheduled to be sentenced on March 13, 2011. Robinson is scheduled to be sentenced on March 6, 2012.
U.S. Attorney Fishman credited special agents of the FBI, under the direction of Special Agent in Charge Ward in Newark, for the investigation. He also thanked special agents of the IRS, under the direction of Special Agent in Charge Victor W. Lessoff, and the U.S. Securities and Exchange Commission’s Market Abuse Unit and Philadelphia Regional Office, under the direction of Daniel M. Hawke.
The government is represented by Assistant U.S. Attorneys Matthew E. Beck of the U.S. Attorney’s Office Economic Crimes Unit; Judith H. Germano, Chief of the Economic Crimes Unit; and Lakshmi Srinivasan Herman of the office’s Asset Forfeiture Unit in Newark.
This case was brought in coordination with President Barack Obama’s Financial Fraud Enforcement Task Force. President Obama established the interagency Financial Fraud Enforcement Task Force to wage an aggressive, coordinated, and proactive effort to investigate and prosecute financial crimes. The task force includes representatives from a broad range of federal agencies, regulatory authorities, inspectors general, and state and local law enforcement who, working together, bring to bear a powerful array of criminal and civil enforcement resources. The task force is working to improve efforts across the federal executive branch, and with state and local partners, to investigate and prosecute significant financial crimes, ensure just and effective punishment for those who perpetrate financial crimes, combat discrimination in the lending and financial markets, and recover proceeds for victims of financial crimes.
TOP-SECRET-FBI-Eight Former Senior Executives and Agents of Siemens Charged in Alleged $100 Million Foreign Bribe Scheme
WASHINGTON—Eight former executives and agents of Siemens AG and its subsidiaries have been charged for allegedly engaging in a decade-long scheme to bribe senior Argentine government officials to secure, implement and enforce a $1 billion contract with the Argentine government to produce national identity cards, announced Assistant Attorney General Lanny A. Breuer of the Justice Department’s Criminal Division, U.S. Attorney Preet Bharara for the Southern District of New York and Ronald T. Hosko, Special Agent in Charge of the FBI, Washington Field Office’s Criminal Division.
The defendants charged in the indictment returned late yesterday are:
- Uriel Sharef, a former member of the central executive committee of Siemens AG;
- Herbert Steffen, a former chief executive officer of Siemens Argentina;
- Andres Truppel, a former chief financial officer of Siemens Argentina;
- Ulrich Bock, Stephan Signer, and Eberhard Reichert, former senior executives of Siemens Business Services (SBS); and
- Carlos Sergi and Miguel Czysch, who served as intermediaries and agents of Siemens in the bribe scheme.
The indictment charges the defendants and their co-conspirators with conspiracy to violate the Foreign Corrupt Practices Act (FCPA) and the wire fraud statute, money laundering conspiracy and wire fraud.
“Today’s indictment alleges a shocking level of deception and corruption,” said Assistant Attorney General Breuer. “The indictment charges Siemens executives, along with agents and conduits for the company, with committing to pay more than $100 million in bribes to high-level Argentine officials to win a $1 billion contract. Business should be won or lost on the merits of a company’s products and services, not the amount of bribes paid to government officials. This indictment reflects our commitment to holding individuals, as well as companies, accountable for violations of the FCPA.”
“As alleged, the defendants in this case bribed Argentine government officials in two successive administrations and paid off countless others in a successful effort to secure a billion dollar contract,” said U.S. Attorney Bharara. “When the project was terminated, they even sought to recover the profits they would have reaped from a contract that was awarded to them illegitimately in the first place. Bribery corrupts economic markets and creates an unfair playing field for law-abiding companies. It is critical that we hold individuals as well as corporations accountable for such corruption as we are doing today.”
“Backroom deals and corrupt payments to foreign officials to obtain business wear away public confidence in our global marketplace,” said FBI Special Agent in Charge Hosko of the Washington Field Office’s Criminal Division. “The investigation into this decades-long scheme serves as an example that the FBI is committed to curbing corruption and will investigate those who try to advance their businesses through foreign bribery.”
According to the indictment, the government of Argentina issued a tender for bids in 1994 to replace an existing system of manually created national identity booklets with state of the art national identity cards (the DNI project). The value of the DNI project was $1 billion. In 1998, the Argentine government awarded the DNI project to a special-purpose subsidiary of Siemens AG.
The indictment alleges that during the bidding and implementation phases of the project, the defendants and their co-conspirators caused Siemens to commit to paying nearly $100 million in bribes to sitting officials of the Argentine government, members of the opposition party and candidates for office who were likely to come to power during the performance of the project. According to the indictment, members of the conspiracy worked to conceal the illicit payments through various means. For instance, Bock made cash withdrawals from Siemens AG general-purpose accounts in Germany totaling approximately $10 million, transported the cash across the border into Switzerland and deposited the funds into Swiss bank accounts for transfer to officials. Bock, Truppel, Reichert, and other conspirators also allegedly caused Siemens to wire transfer more than $7 million in bribes to a bank account in New York disguised as a foreign exchange hedging contract relating to the DNI project. Over the duration of the conspiracy, the conspirators allegedly relied on at least 17 off-shore shell companies associated with Sergi, Czysch and other intermediaries to disguise and launder the funds, often documenting the payments through fake consulting contracts.
In May 1999, according to the indictment, the Argentine government suspended the DNI project, due in part to instability in the local economy and an impending presidential election. When a new government took power in Argentina, and in the hopes of getting the DNI project resumed, members of the conspiracy allegedly committed Siemens to paying additional bribes to the incoming officials and to satisfying existing obligations to officials of the outgoing administration, many of whom remained in influential positions within the government.
When the project was terminated in May 2001, members of the conspiracy allegedly responded with a multi-faceted strategy to overcome the termination. According to the indictment, the conspirators sought to recover the anticipated proceeds of the DNI project, notwithstanding the termination, by causing Siemens AG to file a fraudulent arbitration claim against the Republic of Argentina in Washington, D.C. The claim alleged wrongful termination of the contract for the DNI project and demanded nearly $500 million in lost profits and expenses. Members of the conspiracy allegedly caused Siemens to actively hide from the tribunal the fact that the contract for the DNI project had been secured by means of bribery and corruption, including tampered witness statements and pleadings that falsely denied the existence of corruption.
In related actions, the indictment also alleges that members of the conspiracy continued the bribe scheme, in part to prevent disclosure of the bribery in the arbitration and to ensure Siemens’ ability to secure future government contracts in Argentina and elsewhere in the region. In four installments between 2002 and 2007, members of the conspiracy allegedly caused Siemens to pay approximately $28 million in further satisfaction of the obligations. Conspirators continued to conceal these additional payments through various means. For example, Sharef, Truppel and other members of the conspiracy allegedly caused Siemens to transfer approximately $9.5 million through fictitious transactions involving a Siemens business division that had no role in the DNI project. They also caused Siemens to pay an additional $8.8 million in 2007 under the legal cover of a separate arbitration initiated in Switzerland by the intermediaries to enforce a sham $27 million contract from 2001 between SBS and Mfast Consulting, a company controlled by their co-conspirator intermediaries, which consolidated existing bribe commitments into one contract. The conspirators caused Siemens to quietly settle the arbitration, keeping all evidence of corruption out of the proceeding. The settlement agreement included a provision preventing Sergi, Czysch and another intermediary from testifying in, or providing information to, the Washington arbitration.
Siemens’s corrupt procurement of the DNI project was not exposed during the lifespan of the conspiracy, and, in February 2007, the arbitral tribunal in Washington sided with Siemens AG, awarding the company nearly $220 million on its DNI claims, plus interest. On Aug. 12, 2009, following Siemens’ corporate resolutions with the U.S. and German authorities—new management of Siemens caused Siemens AG to forego its right to receive the award and, as a result, the company never claimed the award money.
The indictment charges the defendants with conspiracy to violate the anti-bribery, books and records and internal control provisions of the FCPA; conspiracy to commit wire fraud; conspiracy to commit money laundering; and substantive wire fraud.
The charges announced today follow the Dec. 15, 2008, guilty pleas by Siemens AG and its subsidiary, Siemens S.A. (Siemens Argentina), to criminal violations of the FCPA. As part of the plea agreement, Siemens AG and Siemens Argentina agreed to pay fines of $448.5 million and $500,000, respectively.
In a parallel civil action, the Securities and Exchange Commission (SEC) announced charges against executives and agents of Siemens. The department acknowledges and expresses its appreciation of the significant assistance provided by the staff of the SEC during the course of these parallel investigations.
Today’s charges follow, in large part, the laudable actions of Siemens AG and its audit committee in disclosing potential FCPA violations to the department after the Munich Public Prosecutor’s Office initiated an investigation. Siemens AG and its subsidiaries disclosed these violations after initiating an internal FCPA investigation of unprecedented scope; shared the results of that investigation; cooperated extensively and authentically with the department in its ongoing investigation; and took remedial action, including the complete restructuring of Siemens AG and the implementation of a sophisticated compliance program and organization.
The department and the SEC closely collaborated with the Munich Public Prosecutor’s Office in bringing this case. The high level of cooperation, including sharing information and evidence, was made possible by the use of mutual legal assistance provisions of the 1997 Organization for Economic Cooperation and Development Convention on Combating Bribery of Foreign Public Officials in International Business Transactions.
The case is being prosecuted by Principal Deputy Chief Jeffrey H. Knox of the Criminal Division’s Fraud Section, and by Assistant U.S. Attorneys Jason P. Hernandez and Sarah McCallum of the U.S. Attorney’s Office for the Southern District of New York. The Fraud Section of the Justice Department’s Criminal Division and the Complex Frauds Unit of the U.S. Attorney’s Office for the Southern District of New York are handling the case. The case was investigated by FBI agents who are part of the Washington Field Office’s dedicated FCPA squad. The Criminal Division’s Office of International Affairs provided significant assistance in this matter.
TOP-SECRET – (U//FOUO/LES) Los Angeles Fusion Center: Methods to Defeat Law Enforcement Crowd Control

(U//FOUO//LES) The purpose of this bulletin is officer awareness. Officers should know that instigators involved in violent demonstrations might be familiar with, and might try to apply, techniques from the “Crowd Control and Riot Manual.” The handbook, from Warrior Publications teaches protestors how to defeat law enforcement crowd control techniques. Although it does not address specific groups or organizations, the information is widely applicable.
…
(U) Anti-Crowd Control Measures
(U) The handbook addresses methods used by police to control crowds and countermeasures to defeat them. Figure 1, from the chapter Riot Training, illustrates police protective gear, and then identifies its potential vulnerabilities. The chapter goes on to recommend effective weapons for rioters to carry, offers tactical guidelines, and suggests ways to counter tactical operations by police:
• (U) While an officer’s uniform contains fire retardant material, it may still be set on fire if fuel lands upon it
• (U) Although specialized gear provides protection against projectile and baton strikes, it can limit mobility on hot days; constant running and maneuvering with this gear may cause intense
• (U) Lightly equipped riot police may be vulnerable to projectile and baton strikes
• (U) Patrol vehicles may be damaged with projectiles, destroyed with Molotov cocktails, blinded with paint bombs or disabled with cut/punctured tires; these tactics are also effective against armored vehicles
• (U) Barricades (including those made with burning tires) may be used to limit vision and mobility
• (U) When encountering small arms open fire, return fire may be the best counter • (U) The best response to a baton charge is a heavy barrage of projectiles and the use of barricades
• (U) If an arrest squad (also called a “snatch squad”) is identified, they should be targeted with a heavy barrage of projectiles when they exit police lines
• (U) The use of individual riot weapons is important; primary targets are commanders, ARWEN gunners, snatch squads and K-9 units, as none of these typically carry shields (see
Figure 2)
• (U) Against riot police, the 3’ long Hambo (also known as a long baton) is a preferred weapon to break through Plexiglas shields and visors: metal pipes or aluminum baseball bats are also good, as they have solid impact against riot armor
• (U) Pepper/bear spray is good against police not wearing gas masks, as well as vigilante citizens
• (U) Slingshots are useful against both vehicles and police; when used against people, they should be aimed at the face
• (U) Improvised paint bombs (condoms, empty eggs, spray paint cans) are effective when thrown at masks, visors or shields
• (U) Additional effective projectiles include concrete/bricks, flares, fireworks, bottles and rocks
• (U) Projectiles should be thrown from the front of a crowd to avoid injuring cohorts
• (U) In order to escape arrest, team members should practice and rehearse holds, locks, strikes and escaping from holds and locks; individuals should fight back and attempt escape
• (U) Ambushes can be laid for police if the opportunity arises; assailants can hide behind a corner, vehicle, in a building entrance, roof-top, overhanging bridge, etc.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – (U//FOUO) U.S. Army Intelligence Officer’s Handbook


OVERVIEW
1-1. The intelligence warfighting function is one of six warfighting functions. A warfighting function is a group of tasks and systems (people, organizations, information, and processes) united by a common purpose that commanders use to accomplish missions and training objectives (FM 3-0).
1-2. The intelligence warfighting function is the related tasks and systems that facilitate understanding of the operational environment. It includes tasks associated with intelligence, surveillance, and reconnaissance operations and is driven by the commander (FM 3-0). Intelligence is more than just collection; it is a continuous process that involves analyzing information from all sources and conducting operations to develop the situation. The intelligence warfighting function includes the following tasks:
• Support to force generation.
• Support to situational understanding.
• Conduct intelligence, surveillance, and reconnaissance (ISR).
• Provide intelligence support to targeting and information superiority.
…
INTELLIGENCE CATEGORIES
1-6. As discussed in FM 2-0, Army unit intelligence staffs produce and receive, directly or indirectly, six categories of intelligence support from the U.S. intelligence community. Intelligence categories are distinguishable primarily by their intelligence product purposes. The categories can overlap and the same intelligence can be used in each category. Intelligence organizations use specialized procedures to develop these categories. The following information describes each category and the responsible organization:
• Indications and warning (I&W). Analysis of time-sensitive information that could involve a threat to U.S. and multinational military forces, U.S. political or economic interests, or to U.S. citizens. While the G-2/S-2 produces I&W intelligence, every Soldier, such as the one conducting a presence patrol, contributes to the I&W through awareness of the CCIRs and by reporting related information.
• Current intelligence. The G-2/S-2 produces accurate reporting on the current threat situation— which becomes a portion of the common operational picture (COP)—projects the threat’s anticipated situation and the implication to friendly operations.
• General military intelligence (GMI). GMI focuses on the military capabilities of foreign countries, organizations, or on topics relating to Armed Forces capabilities, including threat characteristics (previously order of battle factors) and area or terrain intelligence. The G-2/S-2 develops initial intelligence preparation of the battlefield (IPB) products from various GMI databases, and then develops and maintains the unit’s GMI database on potential threat forces and areas of concern based on the commander’s guidance. This database supports the unit’s plan, preparation, execution, and assessment of operations.
• Target intelligence. The analysis of threat units, dispositions, facilities, and systems to identify and nominate specific assets or vulnerabilities for attack, reattack, or exploit.
• Scientific and technical intelligence (S&TI). The collection, evaluation, and interpretation of foreign engineering science and technology with warfare potential, including military systems, weapons, weapons systems, materiel, research and development, and production methods. The G-2/S-2 establishes instructions in standing operating procedures (SOPs), orders, and plans for handling and evacuating captured enemy material for S&TI exploitation.
• Counterintelligence (CI). Identifying and recommending countermeasures against threats by foreign intelligence services and the ISR activities of nonstate entities, such as organized crime, terrorist groups, and drug traffickers.
INTELLIGENCE DISCIPLINES
1-7. Intelligence disciplines are categories of intelligence functions. There are nine major intelligence disciplines:
• All-source intelligence.
• CI.
• Human intelligence (HUMINT).
• Geospatial intelligence (GEOINT).
• Imagery intelligence (IMINT).
• Measurement and signature intelligence (MASINT).
• Open-source intelligence (OSINT).
• Signals intelligence (SIGINT).
• Technical intelligence (TECHINT).

DOWNLOAD ORGINAL DOCUMENT HERE
…
TOP-SECRET-American Nazi Party E-Mails hacked
A sends:
Remember the idiot bloggers saying “Nazis throw support at OWS”? They were talking about these guys, all they did was tweet.
http://antiracistaction.org/?q=node%2F149#tehemails
http://nsoldguard.blogspot.com/
Mirror to the zip archive download
http://www.multiupload.com/3VCKPO4XZ0
http://www.uploadhere.com/XEXKAGN47N
http://depositfiles.com/files/5b551f4od
http://www.uploadking.com/7LV3SDZ5OT
http://www.filesonic.fr/file/4127147645/john.t.bowles.anp.hacked.emails.zip
http://www.wupload.fr/file/2608826227/john.t.bowles.anp.hacked.emails.zip
http://www.megaupload.com/?d=8UAI6DDL
http://hotfile.com/dl/136974593/4e3b161/john.t.bowles.anp.hacked.emails.zip.html
TOP-SECRET from the FBI – Identity Thief Sentenced in Virginia to 12 Years in Prison for Managing East Coast Credit Card Fraud Ring
WASHINGTON—A Brooklyn, N.Y., man was sentenced today in U.S. District Court in Alexandria, Va., to 12 years in prison for operating a credit card fraud ring that used counterfeit credit cards encoded with stolen account information up and down the East Coast of the United States, announced Assistant Attorney General Lanny A. Breuer of the Criminal Division and U.S. Attorney Neil H. MacBride for the Eastern District of Virginia.
Jonathan Oliveras, 26, was sentenced by U.S. District Judge Gerald Bruce Lee. In addition to his prison term, Oliveras was ordered to forfeit $770,646 and to serve three years of supervised release. Oliveras pleaded guilty on Aug. 10, 2011, to one count of wire fraud and one count of aggravated identity theft.
In his plea, Oliveras admitted that he managed a ring of co-conspirators who used stolen credit card account information in New York, New Jersey and the Washington, D.C., area. According to court documents, Oliveras sent payments to individuals he believed to be in Russia for the stolen account information. Oliveras then distributed the stolen account information, which was re-encoded onto plastic cards and used to purchase gift cards. The gift cards were used to buy merchandise that ultimately was returned for cash.
Federal and local law enforcement executing a search warrant in July 2010 at Oliveras’ apartment found, among other things, credit card encoding equipment and more than 2,300 stolen credit card numbers. According to court documents, credit card companies have identified thousands of fraudulent transactions using the account numbers found in Oliveras’ possession, totaling more than $750,000.
The case was prosecuted by Michael Stawasz, a Senior Counsel in the Criminal Division’s Computer Crime & Intellectual Property Section and Special Assistant U.S. Attorney in the Eastern District of Virginia, and Assistant U.S. Attorney Ryan Dickey of the U.S. Attorney’s Office for the Eastern District of Virginia. The case was investigated jointly by the Washington Field Offices of both the U.S. Secret Service and the FBI, with assistance from the New York and New Jersey Field Offices of both agencies.
TOP-SECRET-U.S. Army Taliban Insurgent Syndicate Intelligence Operations Report
TOP-SECRET-(U//FOUO) Asymmetric Warfare Group Afghan Key Leader Engagement (KLE) Reference Card
NEW-TOP-SECRET – White House Strategic Plan for Preventing Violent Extremism

aw enforcement and government officials for decades have understood the critical importance of building relationships, based on trust, with the communities they serve. Partnerships are vital to address a range of challenges and must have as their foundation a genuine commitment on the part of law enforcement and government to address community needs and concerns, including protecting rights and public safety. In our efforts to counter violent extremism, we will rely on existing partnerships that communities have forged with Federal, State, and local government agencies. This reliance, however, must not change the nature or purpose of existing relationships. In many instances, our partnerships and related activities were not created for national security purposes but nonetheless have an indirect impact on countering violent extremism (CVE).
At the same time, this Strategic Implementation Plan (SIP) also includes activities, some of them relatively new, that are designed specifically to counter violent extremism. Where this is the case, we have made it clear. It is important that both types of activities be supported and coordinated appropriately at the local level.
…
Current Activities and Efforts
The Federal Government has held a series of consultative meetings with communities, local government and law enforcement, civil society organizations, foundations, and the private sector to better understand how it can facilitate partnerships and collaboration. This leverages a key strength identified in the National Strategy for Empowering Local Partners: “The Federal Government, with its connections to diverse networks across the country, has a unique ability to draw together the constellation of previously unconnected efforts and programs to form a more cohesive enterprise against violent extremism.” Examples of this include the following:
- DHS Secretary Napolitano tasked her Homeland Security Advisory Council (HSAC) to develop recommendations on how the Department can best support law enforcement and communities in their efforts to counter violent extremism. An HSAC CVE Working Group convened multiple meetings with local law enforcement, local elected officials, community leaders (including faith-based leaders), and academics. The working group released its recommendations in August 2010, highlighting the importance of: (1) research and analysis of violent extremism; (2) engagement with communities and leveraging existing partnerships to develop information-driven, community-based solutions to violent extremism and violent crime; and (3) community oriented policing practices that focus on building partnerships between law enforcement and communities.
- DHS and NCTC began raising awareness about violent extremism among private sector actors and foundations and connected them with community civic activists interested in developing programs to counter violent extremism. DHS is now working with a foundation to pilot resiliency workshops across the country that address all hazards, including violent extremism.
We also began exploring how to incorporate CVE as an element of programs that address broader public safety, violence prevention, and resilience issues. This has the advantage of leveraging preexisting initiatives and incorporates CVE in frameworks (such as safeguarding children) used by potential local partners who may otherwise not know how they fit into such efforts. For example, although many teachers, healthcare workers, and social service providers may not view themselves as potentially contributing to CVE efforts, they do recognize their responsibilities in preventing violence in general. CVE can be understood as a small component of this broader violence prevention effort. Departments and agencies will review existing public safety, violence prevention, and resilience programs to identify ones that can be expanded to include CVE as one among a number of potential lines of effort.
- As an example, the Federal Government helped support a community-led initiative to incorporate CVE into a broader program about Internet safety. The program addressed protecting children from online exploitation, building community resilience, and protecting youth from Internet radicalization to violence.
Future Activities and Efforts
Planned activities to expand support to local partners include the following:
- The Federal Government will help broker agreements on partnerships to counter violent extremism between communities and local government and law enforcement to help institutionalize this locally focused approach. (Lead: DHS)
- DHS and DOJ will work to increase support for local, community-led programs and initiatives to counter violent extremism, predominantly by identifying opportunities within existing appropriations for incorporating CVE as an eligible area of work for public safety, violence prevention, and community resilience grants. (Leads: DHS and DOJ)
- DHS is working to increase funding available to integrate CVE into existing community-oriented policing efforts through FY12 grants. (Lead: DHS)
- DHS is establishing an HSAC Faith-Based Community Information Sharing Working Group to determine how the Department can: (1) better share information with faith communities; and (2) support the development of faith-based community information sharing networks. (Lead: DHS)
- DHS is developing its Hometown Security webpage to include resources such as training guidance, workshop reports, and information on CVE for both the general public and law enforcement. (Lead: DHS)
- The Treasury will expand its community outreach regarding terrorism financing issues. (Lead: Treasury; Partners: State, DOJ, DHS, FBI, and the U.S. Agency for International Development)3
- Depending on local circumstances and in consultation with the FBI, U.S. Attorneys will coordinate, as appropriate, any efforts to expand connections and partnerships at the local level for CVE, supported by the National Task Force where needed. (Lead: DOJ; Partners: All)
- Departments and agencies will expand engagement with the business community by educating companies about the threat of violent extremism and by connecting them to community civic activists focused on developing CVE programs and initiatives. (Lead: DHS; Partner: NCTC)
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET FROM THE NSA-U.S. ESPIONAGE AND INTELLIGENCE
U.S. ESPIONAGE AND INTELLIGENCE

Organization, Operations, and Management, 1947-1996
In the aftermath of World War II, with the Cold War looming on the horizon, the United States began the process of developing an elaborate peacetime intelligence structure that would extend across a number of government departments. The operations of the U.S. intelligence community during the Cold War would range from running single agents, to marshaling the talents of thousands to build and deploy elaborate spy satellites.
The end of the Cold War brought major changes, but not the end of the U.S. government’s requirement for an elaborate intelligence structure. A number of intelligence organizations have been consolidated or altogether eliminated. New organizations have been established to provide more coherent management of activities ranging from military espionage, to imagery collection, to the procurement of airborne intelligence systems. The end of the Cold War has brought about the declassification of much information about intelligence organization and espionage activities that took place prior to the collapse of the Soviet Union.
Focus of the Collection
 U.S. Espionage and Intelligence: Organization, Operations, and Management, 1947-1996 publishes together for the first time recent unclassified and newly declassified documents pertaining to the organizational structure, operations, and management of the U.S. intelligence community over the last fifty years, cross-indexed for maximum accessibility. This set reproduces on microfiche 1,174 organizational histories, memoranda, manuals, regulations, directives, reports, and studies, representing over 36,102 pages of documents from the Office of the Director of Central Intelligence, the Central Intelligence Agency, National Reconnaissance Office, National Security Agency, Defense Intelligence Agency, military service intelligence organizations, National Security Council and other organizations. U.S. Espionage and Intelligence presents a unique look into the internal workings of America’s intelligence community. The documents gathered here shed further light on U.S. intelligence organization and activities during the Cold War, and describe the consolidation and reevaluation of the intelligence community in the post-Cold War era. They are drawn from diverse sources, including the National Archives, manuscript collections in the Library of Congress, court files of major espionage prosecutions, presidential libraries, and most importantly, Freedom of Information Act requests. The result of this effort is an authoritative documents publication which, together with the National Security Archive’s previous collection on the structure and operations of the U.S. intelligence community,
U.S. Espionage and Intelligence: Organization, Operations, and Management, 1947-1996 publishes together for the first time recent unclassified and newly declassified documents pertaining to the organizational structure, operations, and management of the U.S. intelligence community over the last fifty years, cross-indexed for maximum accessibility. This set reproduces on microfiche 1,174 organizational histories, memoranda, manuals, regulations, directives, reports, and studies, representing over 36,102 pages of documents from the Office of the Director of Central Intelligence, the Central Intelligence Agency, National Reconnaissance Office, National Security Agency, Defense Intelligence Agency, military service intelligence organizations, National Security Council and other organizations. U.S. Espionage and Intelligence presents a unique look into the internal workings of America’s intelligence community. The documents gathered here shed further light on U.S. intelligence organization and activities during the Cold War, and describe the consolidation and reevaluation of the intelligence community in the post-Cold War era. They are drawn from diverse sources, including the National Archives, manuscript collections in the Library of Congress, court files of major espionage prosecutions, presidential libraries, and most importantly, Freedom of Information Act requests. The result of this effort is an authoritative documents publication which, together with the National Security Archive’s previous collection on the structure and operations of the U.S. intelligence community,
U.S. Espionage and Intelligence provides a wealth of information and documentation on key aspects of intelligence organization and operations during and after the Cold War, including such extraordinary topics as:
- the evolution of the CIA
- the development and operation of key reconnaissance systems (SR-71, CORONA)
- the consolidation of Defense Department intelligence
- intelligence performance during the Persian Gulf War
- damage assessments of Aldrich Ames’ espionage activities
Significance of the Collection
The U.S. intelligence community has played a key role in advising presidents from Harry Truman to Bill Clinton on the intentions and activities of the Soviet Union, as well as of other nations. It also came to absorb a significant portion of the federal budget, reaching an approximate high of $30 billion in the late 1980s.
U.S. Espionage and Intelligence allows scholars direct access to the newly declassified, detailed primary documents that contain the history of the military, diplomatic, and intelligence components of the Cold War, and which go far beyond what is available in secondary sources. This new information is essential for reaching an accurate understanding of what was happening behind the scenes and how it related to the more public aspects of Cold War policy and operations.
The material contained in this set concerning the post-Cold War era is crucial in assessing the intelligence community’s performance in critical areas such as the Persian Gulf War and the Aldrich Ames case. The material is also vital in understanding the evolution of the intelligence community since the end of the Cold War and its possible future–for that evolution may significantly influence the ability of the intelligence community to deal with critical threats such as proliferation of weapons of mass destruction and terrorism.
One-Stop Access to Critical Documents
It would take a monumental effort, as well as many thousands of dollars, to duplicate the information contained in this collection. U.S. Espionage and Intelligenceallows a researcher– whether interested in the CIA, military intelligence, intelligence performance in the Persian Gulf War, or post-Cold War intelligence reform–to use one source at one location to access the thousands of pages of declassified material on the U.S. intelligence community available in this set.
Through U.S. Espionage and Intelligence the researcher gains access to a wide variety of documents: internal histories of the CIA and a variety of military intelligence organizations; program histories of the SR-71 and CORONA; director of central intelligence and Department of Defense directives establishing organizations such as the National Reconnaissance Office and the National Imagery and Mapping Agency; plans for the consolidation and reform of Defense intelligence organizations after the Cold War and memoranda implementing the reforms; and assessments of intelligence community performance in a number of areas.
In-depth Indexing Makes Every Document Accessible
The National Security Archive prepares extensive printed finding aids for its collections. In- depth indexing offers users remarkable ease and precision of access to every document in the set. The printed Index provides document-level access to subjects, individuals, and organizations, and represents a major research contribution in itself. Important transactions within each document are indexed individually using a controlled subjects vocabulary.
The Guide includes an essay, events chronology, glossaries of key individuals, organizations, and terms, document catalog, and a bibliography of secondary sources.
Research Vistas
With its depth of documentary detail, the collection enables researchers to explore
- U.S. intelligence performance
- Cold War history
- evolution of the U.S. intelligence community and its components
- U.S. intelligence collection activities
The Collection is a Necessity For:
- Scholars and students of
- intelligence
- national security organization and operations
- Cold War history
- Journalists
- Librarians and bibliographers
- Concerned citizens
Sample Document Titles
01/15/62 Legal Basis for Cold-War Activities, Lawrence Houston, [Classification Excised] Memorandum
03/27/64 Directive 5105.23, National Reconnaissance Office, Department of Defense, Top Secret Directive 05/23/67 Report on Plots to Assassinate Fidel Castro, Central Intelligence Agency, Secret Memorandum
07/00/73 Allen Welsh Dulles as Director of Central Intelligence, 26 February 1953-29 November 1961, Central Intelligence Agency, Top Secret Biographic Sketch
00/00/82 History of the Navy HUMINT Program, United States Navy, Top Secret History
03/15/91 Plan for Restructuring Defense Intelligence, Assistant Secretary of Defense for Command, Control, and Communication Intelligence, Secret Report
01/06/92 Task Force Report on Greater CIA Openness, Director of Central Intelligence, [Classification Excised] Memorandum
06/01/92 DCID 2/9, Management of National Imagery Intelligence, Director of Central Intelligence, Secret Intelligence Directive
09/00/92 Appendixes A, B, and C to the Final Report: National Reconnaissance Program Task Force for the Director of Central Intelligence, National Reconnaissance Program Task Force, Secret Report
12/18/92 Directive 5200.37, Centralized Management of Department of Defense Human Intelligence (HUMINT) Operations, Department of Defense, [Classification Unknown] Directive
08/00/93 Intelligence Successes and Failures in Operations Desert Shield/Storm, House Committee on Armed Services, [Classification Unknown] Report
01/21/94 A Description of Procedures and Findings Related to the Report of the U.S. Environmental Task Force, King Publishing, Paper
12/07/95 Statement of the Director of Central Intelligence on the Clandestine Services and the Damage Caused by Aldrich Ames, Director of Central Intelligence, Statement
03/01/96 Preparing for the 21st Century: An Appraisal of U.S. Intelligence, Commission on the Roles and Capabilities of the United States Intelligence Community, Report
12/19/96 United States of America v. Harold J. Nicholson, Superseding Indictment, U.S. District Court, Eastern District of Virginia, Indictment
Overview
Title
U.S. Espionage and Intelligence: Organization, Operations, and Management, 1947-1996
Content
Reproduces on microfiche 1,174 U.S. government records totaling 36,102 pages of documentation concerning the organizational structure, operations, and management of the intelligence community from World War II to the present.
Materials were identified, obtained, assembled, and indexed by the National Security Archive.
Series
The Special Collections
Arrangement
Microfiche are arranged chronologically. For ease of use, each document bears a unique accession number to which all indexing is keyed.
Standards
The documents are reproduced on 35mm silver halide archivally permanent positive microfiche conforming to NMA and BSI standards. Any microfiche found to be physically substandard in any way will be replaced free of charge.
Indexing
A printed Guide and Index accompanies the microfiche collection. The Guide contains an events chronology, glossaries, chronological document catalog and a bibliography of secondary sources. The Index provides in-depth, document level access to subjects and individuals.
U.S. Espionage and Intelligence Project Staff
Project Director
Dr. Jeffrey T. Richelson, project director, is a senior fellow at the National Security Archive and coordinates the Archive’s projects on U.S. policy toward China and ongoing documentation on U.S. intelligence issues. He previously edited the Archive’s collections on presidential national security documents, the history of the U.S. intelligence community, and the military uses of space. A former associate professor at American University, he received his Ph.D. in political science from the University of Rochester. Among his many books are Sword and Shield: Soviet Intelligence and Security Apparatus (1986), American Espionage and the Soviet Target (1988), America’s Secret Eyes in Space (1990), and A Century of Spies: Intelligence in the Twentieth Century (1995). His articles have appeared in a wide variety of professional journals and in publications ranging from Scientific American to the Washington Post. He is a regular commentator on intelligence and military issues for national television and radio.
Project Staff
Michael Evans, Research Assistant
Jane Gefter, Research Assistant
Michael Watters, Research Assistant
U.S. Espionage and Intelligence Advisory Board
Christopher Andrew, Corpus Christi College, University of Cambridge author, For the President’s Eyes Only
Loch Johnson, Department of Political Science, University of Georgia author, Secret Agencies: U.S. Intelligence in a Hostile World
David Wise, author, Nightmover: How Aldrich Ames Sold the CIA to the KGB for $4.6 Million
Praise for U.S. Espionage and Intelligence, 1947-1996
“Serious students of the structure and operations of American intelligence rely on the work of the National Security Archive. The new collection of intelligence documents, compiled for the Archive by Jeffrey T. Richelson, helps to pierce the labyrinth.”
David Wise
Author of Nightmover: How Aldrich Ames Sold the CIA to the KGB for $4.6 Million
“An invaluable supplement to the National Security Archive’s previous collection, The U.S. Intelligence Community 1947-1989, this brings the most recently declassified documents to the reader. Jeffrey Richelson’s useful introduction also serves to detail changes that have occurred in the structure of the U.S. espionage establishment.”
John Prados
Author of Presidents’ Secret Wars
TOP-SECRET FROM THE NSA-The Soviet Estimate: U.S. Analysis of the Soviet Union, 1947-1991

The Soviet Estimate:
U.S. Analysis of the Soviet Union,
1947-1991
Focus of the Collection
The Soviet Estimate: U.S. Analysis of the Soviet Union, 1947- 1991, publishes together for the first time the highest-level U.S. intelligence assessments of the Soviet Union, cross- indexed for maximum use. This set reproduces on microfiche more than 600 intelligence estimates and reports, representing nearly 14,000 pages of documentation from the office of the Director of Central Intelligence, the National Intelligence Council, the Central Intelligence Agency, the Defense Intelligence Agency, and other organizations. The set includes several hundred pages of debriefing transcripts and other documentation related to Colonel Oleg Penkovskii, the most important human source operated by the CIA during the Cold War, who later was charged with treason and executed by the Soviet Union. Also published here for the first time is the Pentagon’s Top Secret 1,000-page internal history of the United States-Soviet Union arms race.
The Soviet Estimate presents the definitive secret history of the Cold War, drawn from many sources: the hundreds of documents released by the CIA to the National Archives in December 1994, comprising the most important source of documents for the set, including intelligence estimates from 1946 to 1984; documents obtained under the Freedom of Information Act from the Pentagon, the CIA, the DIA, State Department, Pacific Command, and other agencies; and documents obtained from the National Archives and from various presidential libraries. The result of this effort is the most extensive and authoritative collection of declassified primary-source materials documenting the intelligence community’s effort to gather information on Soviet foreign policy, nuclear weapons, military policy and capabilities, weapons systems, the economy, science and technology, and the Soviet domestic political situation.
The Soviet Estimate provides a wealth of information and documentation on key intelligence issues, including:
- The missile gap controversy, which helped John F. Kennedy to win the presidency in 1960
- The “Team A”/”Team B” intelligence report controversy in 1976
- Whether the CIA foresaw the decline of the Soviet economy
- Advance warning from the CIA to President Bush about the hard-line coup attempt against Gorbachev in 1991.
Significance of the Collection
(54398) 1961/05/27
The Soviet Union was the major concern of U.S. national security decisionmakers for more than 40 years, and represented the most important single target of all U.S. intelligence collection efforts. The ultimate policies adopted by the U.S. during the Cold War were the result of many factors, not the least of which was an understanding of Soviet objectives and capabilities, shaped and influenced by the intelligence reports included in this set.
Until recently scholars have had to address issues such as the performance of U.S. intelligence analysis with respect to the Soviet Union or the impact of intelligence on policy without access to most of the key documents. Prior to December 1994, all of the National Intelligence Estimates related to the birth and death of the so-called “missile gap” were classified; scholars were often forced to rely either on other government documents that reproduced some of the information in estimates (for example, Department of Defense posture statements), or unofficial sources. The Soviet Estimate, with its diverse sources, permits scholars direct reference to the primary documents used in formulating much Cold War policy.
One-Stop Access to Critical Intelligence Documents
It would take an enormous effort, and many thousands of dollars, to duplicate the information contained in this collection. The Soviet Estimate allows a researcher– whether interested in the Soviet military, the Soviet economy, or Soviet internal politics–to use one source at one location to access the thousands of pages of declassified U.S. intelligence documents on the Soviet Union.
Through The Soviet Estimate the researcher gains access to a wide variety of documents, including National Intelligence Estimates, Special National Intelligence Estimates, National Intelligence Council memoranda, interagency intelligence studies, Defense Intelligence Estimates, and intelligence reports produced by DIA, military service, and unified command intelligence organizations.
Among the specific areas covered in the collection are:
- Developments in Soviet nuclear forces from the early 1950s to the 1980s
- The deteriorating political and economic situation under Mikhail Gorbachev in the late 1980s
- Soviet relations with the United States, European countries, and other nations
- The Soviet space program and developments in science and technology
- The Soviet economic system and economy
In-depth Indexing Makes Every Document Accessible
The National Security Archive prepares extensive printed finding aids for its collections. In-depth indexing offers users remarkable ease and precision of access to every document in the set. The printed Index provides document- level access to subjects, individuals, and organizations, and represents a major historical contribution itself. Important transactions within each document are indexed individually using a controlled subjects vocabulary.
The Guide includes an events chronology, glossaries of key individuals and organizations, chronological document catalog, and a bibliography of relevant secondary sources.
Research Vistas
With its depth of documentary detail and balance of perspectives, this collection enables researchers to explore in greater detail:
- Soviet studies
- Cold War history
- U.S. intelligence performance
- The intelligence-policy relationship
The Collection is a Necessity for:
- Scholars and students of
- The Soviet Union
- The history of the Cold War
- The U.S. intelligence community
- Policy formation
- Policy analysts
- Journalists
- Concerned citizens
- Librarians and bibliographers
Sample Document Titles
- 4/6/50 ORE 91-49
- Estimate of the Effects of the Soviet Possession of the Atomic Bomb Upon the Security of the U.S.
- 10/5/54 NIE 11-6-54
- Soviet Capabilities and Probable Programs in the Guided Missile Field
- 9/21/61 NIE 11-8/1-61
- Strength and Deployment of Soviet Long-Range Ballistic Missile Forces, September 21, 1961
- 3/2/67 NIE 11-1-67
- The Soviet Space Program
- 2/19/70 SNIE 11-16-70
- Soviet Attitudes Toward SALT
- 6/76 United States Air Force
- A History of Strategic Arms Competition, 1945-1972: Volume 3: A Handbook of Selected Soviet Weapon and Space Systems (May-Steinbruner-Wolfe Report)
- 12/76 NIO M 76-021J
- Soviet Strategic Objectives: An Alternative View (“Team B” Report)
- 5/27/81 SNIE 11-2-81
- Soviet Support for International Terrorism and Revolutionary Violence
- 7/7/81 M/M NIE 11-4-78
- Soviet Goals and Expectations in the Global Power Arena
- 4/83 NIC M 83-10006
- Dimensions of Civil Unrest in the Soviet Union
- 3/6/84 NIE 11-3/8-83
- Soviet Capabilities for Strategic Nuclear Conflict, 1983-93
- 4/89 CIA
- Rising Political Instability Under Gorbachev: Understanding the Problem and Prospects for Resolution
- 4/25/91 CIA, Office of Soviet Analysis
- The Soviet Cauldron
Overview
Title:
- The Soviet Estimate: U.S. Analysis of the Soviet Union, 1947 – 1991
- Content:
- Reproduces on microfiche more than 600 intelligence estimates and reports, representing nearly 14,000 pages of documentation recording the intelligence community’s effort to gather information on Soviet foreign policy, nuclear weapons, military policy and capabilities, weapons systems, the economy, science and technology, and the Soviet domestic political situation.
- Arrangement and Access:
- Documents are arranged chronologically. For ease of use, the unique identification numbers assigned to the documents are printed in eye-legible type at the top right-hand corner and precede each document on the microfiche strip.
- Standards:
- Documents are reproduced on silver halide positive- reading microfiche at a nominal reduction of 24x in envelopes. They are archivally permanent and conform to AIIM, BSI, and ANSI standards. Any microfiche found to be substandard will be replaced free of charge.
- Indexing:
- A printed Guide and Index totaling over 390 pages accompanies the microfiche collection. The Guide contains an essay; an events chronology; glossaries of acronyms and abbreviations, names, organizations, and technical terms; and a bibliography of secondary sources. The Index provides in-depth, document-level access to subjects, individuals, and organizations.
- Date of Publication:
- December 1995
- Orders and Inquiries
The National Security Archive
Founded in 1985, the National Security Archive has developed a reputation as the most prolific and successful nonprofit user of the Freedom of Information Act (FOIA). Through its FOIA expertise, the Archive has built what the Christian Science Monitor called “the largest collection of contemporary declassified national security information outside the United States government.” Located at The George Washington University, the Archive serves librarians, scholars, journalists, members of Congress, policymakers, public interest groups, and the general public. Foundation grants and publication royalties underwrite the Archive’s budget.
The Archive’s editorial process focuses on high-level policy-making and implementation, with special attention to inter-agency decisionmaking processes. Archive analysts target all U.S. government documents used by policymakers during the period covered by the collection, as well as other significant materials of direct relevance to the subject.
This research establishes a roadmap for future scholarship and “freezes” the documentary record with official requests for declassification before normal governmental document destruction process can diminish the historical record. The result is an “unusual” series of publications, as Microform Review noted, which make available documents “from the twilight zone between currently released government information, and normal declassification” periods.
Accompanied by highly sophisticated item-level catalogs, indexes, and other finding aids–which Government Publications Review hailed as “gold mines in and of themselves”–the Archive’s collections, according to the Washington Journalism Review, constitute “a ‘Nexis’ of national security . . . [a] state-of-the-art index to history.”
Praise for The Soviet Estimate
“The National Security Archive has performed a valuable service by compiling the most extensive and authoritative file of declassifed, official U.S. National Intelligence Estimates on the Soviet Union. The compilation The Soviet Estimate is a gold mine for analyzing Soviet developments on the Cold War, and no less important, contemporary American intelligence assessments of those developments. With the benefit of hindsight and new information, the validity of those estimates can be studied, and their impact on U.S. policy and the Cold War evaluated. ”
–Raymond Garthoff,
Senior Fellow, Foreign Policy Studies Program, Brookings Institution, former U.S. Ambassador to Bulgaria, veteran of the U.S. Department of State and Central Intelligence Agency, and author of many publications, including Deterrence and the Revolution in Soviet Military Doctrine (1990), The Great Transition: American-Soviet Relations and the End of the Cold War (1994), and Détente and Confrontation: American-Soviet Relations from Nixon to Reagan (1994).
The National Security Archive Soviet Estimate Project Staff
- Project Editor
- Jeffrey T. Richelson, Ph.D., Project Editor, is a senior fellow at the National Security Archive and coordinates the Archive’s projects on U.S. policy toward China and ongoing documentation on U.S. Intelligence issues. He previously edited the Archive’s collections on presidential national security documents, the history of the U.S. intelligence community, and the military uses of space. A former associate professor at American University, he received his Ph.D. in political science from the University of Rochester. Among his many books are Sword and Shield: Soviet Intelligence and Security Apparatus (1986), American Espionage and the Soviet Target (1988), America’s Secret Eyes in Space (1990), and A Century of Spies: Intelligence in the Twentieth Century (1995). His articles have appeared in a wide variety of professional journals and in publications ranging from Scientific American to the Washington Post. He is a regular commentator on intelligence and military issues for national television and radio.
- Project Staff
- Jane Gefter, Research Assistant
Ian Stevenson, Research Assistant
Kristin Altoff, Intern
TOP-SECRET-ISAF Afghanistan Detainee Operations Standard Operating Procedures

1. Reference G is the current operational level guidance on detention issues. This TACSOP gives further direction and guidance to commanders and staff responsible for detention operations within Afghanistan. Commanders at all levels are to ensure that detention operations are conducted in accordance with applicable international law and human rights standards and that all detainees are treated with respect and dignity at all times. The strategic benefits of conducting detention operations in a humanitarian manner are significant. Detention operations that fail to meet the high standards mandated herein will inevitably have a detrimental impact on the ISAF Mission. All ISAF Detention operations will be subject to internal and external scrutiny.
2. The policy contained within this TACSOP applies to actions taken by ISAF troops under the ISAF Mission. It does not apply to PW or to persons indicted for war crimes (PIFWC) pursuant to the lawful exercise of authority by the International Criminal Court or other lawfully constituted tribunals. It does, however, give direction to Regional Commands on the reporting of detainees taken within their AOO by troops operating under the Counter-Terrorist mandate (Reference H refers) or by ANSF operating jointly with ISAF.
DEFINITIONS
3. The following definitions are used throughout this SOP.
a. NATO Holding Facility / NATO Detention Facility. This term refers to any facility used, designed or adapted to facilitate the detention of individuals.
b. ISAF Detention Authority. This is defined in the main body of this SOP as a specified individual authorised to make detention decisions. These individuals are listed in Para 6 below.
c. Period of Detention. This is regarded as the period of detention, not to exceed 96 hours, which starts on arrest (ie; the act by which a non-ISAF person is deprived of his liberty by ISAF personnel) until the moment a detainee is handed over to the ANSF or GOA officials or is released by ISAF.
d. ANSF. The abbreviation ANSF stands for Afghan National Security Forces and includes, Afghan National Army (ANA), Afghan National Police (ANP), Afghan Border Police, Afghan Highway Police, Afghan Counter-Narcotics Police and any authorised Afghan national or regional government agency involved with security or detention facilities.
e. Age / Date of Birth. Consideration must be given to the fact that in many areas, individuals may not know their age or date of birth. For the purpose of this SOP, the following definitions are used:
(1) Adult. An adult is considered to be any person aged 18 or over.
(2) Juvenile. A juvenile is considered to be between the age of 15 up to 18.
(3) Child A child is considered to be below the age of 15.
LEGAL APPLICATIONS
4. Authority to Detain. The only grounds upon which a person may be detained under current ISAF Rules of Engagement (ROE) are: if the detention is necessary for ISAF force protection; for the self-defence of ISAF or its personnel; for accomplishment of the ISAF mission.
5. Detention. If an arrest and/or detention is effected by ANSF with ISAF support, then the individual is not considered to be an ISAF detained person and the provisions of this TACSOP do not apply. An individual will not be considered as an ISAF detained person until and unless ISAF assumes control and places that individual into detention. In all cases of detention HQ ISAF is to be informed. The current policy for ISAF is that Detention is permitted for a maximum of 96 hours after which time an individual is either to be released or handed into the custody of the ANSF / GOA.
6. Detention Authority. As soon as practicable after an detention has taken place, the decision to continue to detain must be considered by an appropriate authority. The ISAF Detention authority must be able to support the grounds by a reasonable belief in facts. The requirement for detention must be kept under continuous review. The following persons may act as an ISAF Detention Authority to determine if the grounds set out in paragraph 4 are met:
a. COMISAF2;
b. A Regional Commander (RC);
c. A National Contingent Commander;
d. The Theatre Task Force Commander;
e. A Battalion Commander;
f. A Provincial Reconstruction Team (PRT) Commander;
g. Base Commander;
h. An On-Scene Commander; and
i. Commander of the Theatre Detention Facility.
7. The powers of the Detention Authority. A Detention Authority may authorize detention for up to 96 hours following initial detention. Should the Detention Authority believe that continued detention beyond 96 hours is necessary then, prior to the expiration of the 96-hour period, the Detention Authority shall refer the matter via the chain of command to HQ ISAF.

DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET FROM THE NSA-Info Age requires rethinking 4th Amendment limits and policies,
Washington, D.C., December 8, 2011 – The largest U.S. spy agency warned the incoming Bush administration in its “Transition 2001” report that the Information Age required rethinking the policies and authorities that kept the National Security Agency in compliance with the Constitution’s 4th Amendment prohibition on “unreasonable searches and seizures” without warrant and “probable cause,” according to an updated briefing book of declassified NSA documents posted today on the World Wide Web.
Wiretapping the Internet inevitably picks up mail and messages by Americans that would be “protected” under legal interpretations of the NSA’s mandate in effect since the 1970s, according to the documents that were obtained through the Freedom of Information Act by Dr. Jeffrey Richelson, senior fellow of the National Security Archive at George Washington University.
The NSA told the Bush transition team that the “analog world of point-to-point communications carried along discrete, dedicated voice channels” is being replaced by communications that are “mostly digital, carry billions of bits of data, and contain voice, data and multimedia,” and therefore, “senior leadership must understand that today’s and tomorrow’s mission will demand a powerful, permanent presence on a global telecommunications network that will host the ‘protected’ communications of Americans as well as targeted communications of adversaries.”
The documents posted today also include a striking contrast between the largely intact 1998 NSA organizational chart for the Directorate of Operations and the heavily redacted 2001 chart for the Signals Intelligence Directorate (as the operations directorate was renamed), which contains no information beyond the name of its director. “The 2001 organization charts are more informative for what they reveal about the change in NSA’s classification policy than for what they reveal about the actual structure of NSA’s two key directorates,” commented Dr. Richelson. The operations directorate organization chart was provided within three weeks of its being requested in late 1998. In contrast, the request for the Signals Intelligence Directorate organization chart was made on April 21, 2001, and NSA did not provide its substantive response until April 21, 2004 – three years instead of three weeks.
Introduction
The National Security Agency (NSA) is one of the most secret (and secretive) members of the U.S. intelligence community. The predecessor of NSA, the Armed Forces Security Agency (AFSA), was established within the Department of Defense, under the command of the Joint Chiefs of Staff, on May 20, 1949. In theory, the AFSA was to direct the communications intelligence and electronic intelligence activities of the military service signals intelligence units (at the time consisting of the Army Security Agency, Naval Security Group, and Air Force Security Service). In practice, the AFSA had little power, its functions being defined in terms of activities not performed by the service units. (Note 1)
The creation of NSA resulted from a December 10, 1951, memo sent by Walter Bedell Smith to James B. Lay, Executive Secretary of the National Security Council. The memo observed that “control over, and coordination of, the collection and processing of Communications Intelligence had proved ineffective” and recommended a survey of communications intelligence activities. The proposal was approved on December 13, 1951, and the study authorized on December 28, 1951. The report was completed by June 13, 1952. Generally known as the “Brownell Committee Report,” after committee chairman Herbert Brownell, it surveyed the history of U.S. communications intelligence activities and suggested the need for a much greater degree of coordination and direction at the national level. As the change in the security agency’s name indicated, the role of the NSA was to extend beyond the armed forces. (Note 2)
In the last several decades some of the secrecy surrounding NSA has been stripped away by Congressional hearings and investigative research. In the late 1990s NSA had been the subject of criticism for failing to adjust to the post-Cold War technological environment as well as for operating a “global surveillance network” alleged to intrude on the privacy of individuals across the world. The following documents provide insight into the creation, evolution, management and operations of NSA, including the controversial ECHELON program. Also included are newly released documents (11a – 11g) that focus on the restrictions NSA places on reporting the identities of U.S. persons – including former president Jimmy Carter and first lady Hillary Clinton, and NSA Director Michael Hayden’s unusual public statement (Document 24) before the House Intelligence Committee.
Some of the documents that appear for the first time in this update shed additional light on the history of NSA. They concern the NSA’s participation in the space reconnaissance program (Document 3), NSA’s success in deciphering Soviet communications in the 1960s (Document 4), the efficacy of NSA activities in the late mid-to-late 1960s (Document 5), and Israel’s attack on the USS Liberty during the 1967 war (Document 10). Others provide new insight on NSA’s assessment of key issues in the new century (Document 21, Document 23), on NSA’s attempts to adapt to the changing world and communications environment, (Document 22), on the agency’s regression to old policies with regard to organizational secrecy (Document 26a, Document 26b), and on NSA activities before and after the events of 9/11 (Document 25).
Several of these documents also appear in either of two National Security Archive collections on U.S. intelligence. The U.S. Intelligence Community: Organization, Operations and Management: 1947-1989 (1990) and U.S. Espionage and Intelligence: Organization, Operations, and Management, 1947-1996 (1997) publish together for the first time recently declassified documents pertaining to the organizational structure, operations and management of the U.S. Intelligence Community over the last fifty years, cross-indexed for maximum accessibility. Together, these two sets reproduce on microfiche over 2,000 organizational histories, memoranda, manuals, regulations, directives, reports, and studies, totalling more than 50,000 pages of documents from the Office of the Director of Central Intelligence, the Central Intelligence Agency, National Reconnaissance Office, National Security Agency, Defense Intelligence Agency, military service intelligence organizations, National Security Council, and other official government agencies and organizations.
Documents
Note: The following documents are in PDF format.
You will need to download and install the free Adobe Acrobat Reader to view.
Document 1: NSCID 9, “Communications Intelligence,” March 10, 1950
National Security Council Intelligence Directives have provided the highest-level policy guidance for intelligence activities since they were first issued in 1947.
This document establishes and defines the responsibilities of the United States Communications Intelligence Board. The Board, according to the directive, is to provide “authoritative coordination of [the] Communications Intelligence activities of the Government and to advise the Director of Central Intelligence in those matters in the field of Communications Intelligence for which he is responsible.”
The particularly sensitive nature of communications intelligence (COMINT) activities was highlighted by paragraph 6, which noted that such activities should be treated “in all respects as being outside the framework of other or general intelligence activities.” Thus, regulations or directives pertaining to other intelligence activities were not applicable to COMINT activities.
Document 2a: Memorandum from President Harry S. Truman to the Secretary of State, the Secretary of Defense, Subject: Communications Intelligence Activities, October 24, 1952
Document 2b: National Security Council Intelligence Directive No. 9, Communications Intelligence, December 29, 1952
President Truman’s memorandum revokes the provisions of NSCID 9 with regard to the composition, responsibilities, and procedures of the U.S. Communications Intelligence Board. It establishes the USCIB as an entity “acting for and under” a newly created Special Committee of the National Security Council for COMINT, consisting of the Secretary of State and the Secretary of Defense.
More significantly, Truman’s memo, along with a Department of Defense directive, established NSA, and transformed communications intelligence from a military activity divided among the three services to a unified national activity. (Note 3) Thus, the first sentence states that “The communications intelligence (COMINT) activities of the United States are a national responsibility.”
The memorandum instructs the Special Committee to issue a directive to the Secretary of Defense which defines the COMINT mission of NSA as being to “provide an effective, unified organization and control of the communications intelligence activities of the United States conducted against foreign governments.” Thus, “all COMINT collection and production resources of the United States are placed under his operational and technical control.”
The directive provided the NSA director with no authority regarding the collection of electronic intelligence (ELINT)—such as intelligence obtained from the interception of the emanations of radarsor of missile telemetry. Responsibility for ELINT remained with the military services.
NSCID 9 of December 1952 replaces its 1950 predecessor as mandated by Truman’s directive. Often using identical language to that in the Truman directive, it revises the responsibilities of the United States Communications Intelligence Board as well as defining the role of the newly created National Security Agency and enumerating the responsibilities of its director.
New Document 3: Memorandum of Agreement Concerning NSA Participation in the (S) National Reconnaissance Office, August 1, 1962. Top Secret
The National Reconnaissance Office was established in September 1961 to provide a central coordinating authority for the nation’s overhead reconnaissance activities, which included efforts by the Central Intelligence Agency, Air Force, and Navy. An early issue was the division of responsibilities for the development and operation of satellite systems. At a conference in May 1962, it was agreed by CIA and NRO officials that the National Security Agency, despite its responsibility for signals intelligence activities, would not be allowed to develop SIGINT satellites as part of the national reconnaissance program. Herbert Scoville, the CIA’s deputy director for research, argued that the Secretary of Defense was the government’s executive agent for SIGINT activities and since he had chosen to assign the mission to the NRO, the NSA was excluded from undertaking such development activities. (Note 4)
The Secretary’s decision did not mean, however, that NSA, was to play no role in the development and operation of signals intelligence satellites. This represents the first agreement specifying how NSA would be permitted to participate in the National Reconnaissance Program.
New Document 4: Richard Bissell, Review of Selected NSA Cryptanalytic Efforts, February 18, 1965 Top Secret Codeword
Richard Bissell joined the CIA in 1954, serving first as the special assistant to CIA Director Allen Dulles, and then as the agency’s Deputy Director (Plans). He left the agency in February 1962, as a result of the failure of the Bay of Pigs invasion of April 1961. Before and during his tenure as the CIA’s operations chief Bissell directed the development and operation of several key technical collection systems – including the U-2 and OXCART aircraft, and the CORONA reconnaissance satellite.
In his memoirs he reported that, in October 1964, “I accepted a brief assignment from John McCone at the CIA, which involved looking into very highly classified business of another agency of the government. My job was to write a report on what I had learned from visits and interviews with authorities on the problem.” (Note 5) Bissell provided no further information.
In response to a Freedom of Information Act request, the CIA provided a copy of this document – which is Bissell’s report of his investigation of the National Security Agency’s efforts to crack certain high-grade cipher systems. Although the identity of the nation whose ciphers were being attacked is deleted throughout the report, the target country is clearly the Soviet Union. The report discusses the prospects of breaking into high-level Soviet codes and concludes with three principal recommendations – which concern the extent of the overall cryptologic effort, the desirability of reallocating some cryptologic resources, and the possibility of a systematic comparison of the intelligence produced via the successful exploitation of two different components of the cryptanalytic effort.
New Document 5: Letter, Frederick M. Eaton to Richard M. Helms, Director of Central Intelligence, August 16, 1968, Top Secret Codeword w/TS Codeword attachment
This letter, along with the attachment, represents the report of the four-member group, which included Eaton, a New York lawyer and banker, General Lauris Norstad, the Defense Department’s Eugene Fubini, and ambassador Livingston T. Merchant, that was commissioned by DCI Richard Helms in September 1967 to examine the national signals intelligence effort.
The topics examined by the group included program guidance, the DCI and the National Intelligence Resources Board, central review and coordination, management of the cryptologic community, NSA staff organization, COMINT, Telemetry, and ELINT resources, and the communications and dissemination of the information. The letter from Eaton to Helms conveys the group’s nineteen recommendations and the conclusion that
“there must be no slackening in the US cryptologic effort if essential military and other national needs are to be met.”
According to James Bamford’s The Puzzle Palace, Eaton was forced to write the conclusions himself when “many of the staff turned in their pens” because Eaton “recommended no reductions and concluded that all of NSA’s programs were worthwhile,” despite “accumulated substantial evidence that much of the NSA’s intelligence collection was of little or marginal uses to the various intelligence consumers in the community.” (Note 6)
Document 6: Memo to President Johnson, September 6, 1968
This memo, from national security adviser Walt Rostow to President Johnson, provides information concerning North Vietnamese/Viet Cong military and political strategy during the last months of Johnson’s presidency. The last item in the memo notes that its conclusions were partly a function of the author’s access to relevant intercepted communications.
The memo specifically notes unusual, high-priority message traffic between Hanoi and subordinate units directing forces in South Vietnam as well as urgent messages from the Military Affairs Committee of COSVN (Central Office for South Vietnam) to subordinates. It does not reveal how extensively the U.S. was able to decrypt the messages.
Document 7: Department of Defense Directive S-5100.20, “The National Security Agency and the Central Security Service,” December 23, 1971
Originally classified Secret, this directive remains in effect today, with minor changes. Key portions of the directive specify the NSA’s role in managing the signals intelligence effort for the entire U.S. government, the role of the Secretary of Defense in appointing and supervising the work of the NSA’s director, the authorities assigned to the director of NSA, and the relationships that NSA is expected to maintain with other components of the government.
Among the specific responsibilities assigned to the director are preparation of a consolidated SIGINT program and budget for Defense Department SIGINT activities, the “exercise of SIGINT operational control over SIGINT activities of the United States,” and the production and dissemination of SIGINT “in accordance with the objectives, requirements, and priorities established by the Director of Central Intelligence.”
The directive reflects the 1958 addition of electronic intelligence to NSA’s responsibilities, making it the national authority for both components of signals intelligence.
Document 8a: NSCID 6, “Signals Intelligence,” February 17, 1972
Document 8b: Department of Justice, “Report of the Inquiry into CIA-Related Electronic Surveillance Activities,” 1976, pp. 77-9
NSCID 6 is the most recently available NSCID concerning SIGINT. It was still in effect at least as late as 1987. An earlier version of the directive was issued in 1958, when NSA was first assigned responsibility for electronics intelligence.
The version released by the NSC in 1976 contains little more than the definitions for COMINT and ELINT. However, a Justice Department report obtained by author James Bamford while researching his book, The Puzzle Palace, quoted additional portions of the directive.
The directive specifies that the Director of NSA is to produce SIGINT in response to the objectives, requirements and priorities of the Director of Central Intelligence. It also empowers the director to issue direct instructions to any organizations engaged in SIGINT operations, with the exception of certain CIA and FBI activities, and states that the instructions are mandatory.
Document 9a: NSA COMINT Report, “Capital Projects Planned in India,” August 31, 1972
Document 9b: NSA, “India’s Heavy Water Shortages,” October 1982
These two documents provide examples of NSA reporting, as well as demonstrating that NSA’s collection targets have included Indian atomic energy programs. Portions of each document that discuss or reveal the contents of the intercepts have been redacted. However, the classification of the documents indicates that high-level communications intelligence was used in preparing the report. UMBRA is the highest-level compartment of the three compartments of Special Intelligence—the euphemism for COMINT. The lower level compartments are MORAY and SPOKE.
The classification (either TSU [TOP SECRET UMBRA] or MORAY) of the 25 reports which Document 6b was derived from indicate that the report relied extensively on COMINT. The report also demonstrates how NSA, often to the annoyance of the CIA, has gone far beyond its formal collection and processing responsibilities and into the analysis of the data it has collected. (Note 7)
New Document 10: William D. Gerhard and Henry W. Millington, National Security Agency, Attack on a SIGINT Collector, the USS Liberty, 1981. Top Secret Umbra
One of the most controversial events in the history of U.S.-Israeli relations was the attack by Israeli aircraft, during the midst of the Six-Day War of June 1967, on the USS Liberty, a ship assigned to gather signals intelligence on behalf of the National Security Agency. The attack left thirty-four Americans dead and 171 wounded.
In additional to internal studies conducted by both countries there have been numerous books, portions of books, and articles that have sought to review the events and assess blame. The most controversial issue has been whether Israel knowingly attacked a ship it knew to belong to the U.S., which was cruising in international waters off the Sinai Peninsula, to prevent it from monitoring Israeli actions in the midst of the war. Authors have reached diametrically opposite conclusions on this issue. (Note 8)
This extensive report, written by a former head of the NSA element that produced studies of SIGINT crisis situations and the former head of the NSA library, examines the political-military background, consideration’s leading to the ship’s deployment, deployment to the Mediterranean, the attack, Israel’s explanation, recovery and initial assessment, reviews of the incident, and “a final look.” In their conclusion, the authors deal with the issues of possible Israeli foreknowledge of the ship’s nationality and possible Israeli motivations for an attack. They report that a CIA assessment prepared within week of the attack, drawing heavily on communications intercepts, concluded (p. 64) that Israeli forces had not deliberately attacked a ship they knew to be American.
Document 11a: United States Signals Intelligence Directive [USSID] 18, “Legal Compliance and Minimization Procedures,” July 27, 1993
While NSCIDs and DoD Directives offer general guidance on the activities of NSA and the United States SIGINT System (USSS), far more detailed guidance is provided by the director of NSA in the form of United States Signals Intelligence Directives (USSIDs). The directives fall into at least nine different categories: policy, collection, processing, analysis and reporting, standards, administration, training, data processing, and tasking.
In the aftermath of revelations in the 1970s about NSA interception of the communications of anti-war and other political activists new procedures were established governing the interception of communications involving Americans. (Note 9) The version of USSID 18 currently in force was issued in July 1993 and “prescribes policies and procedures and assigns responsibilities to ensure that the missions and functions of the United States SIGINT System (USSS) are conducted in a manner that safeguards the constitutional rights of U.S. persons.” Section 4 (“Collection,” pp.2-6) specifies the circumstances under which U.S. SIGINT activities may intercept communications of or about U.S. persons, as well as the authorities of the Foreign Intelligence Surveillance Court, the Attorney General, and the Director of NSA to approve the collection of such information.
Section 5 (“Processing,” pp.6-7) focuses on the restrictions on processing intercepted communications involving U.S. persons–including domestic communications collected during foreign communications collection operations. Section 6 (“Retention,” p.8) deals with the retention of intercepted communications about U.S. persons. Section 7 (“Dissemination,” pp.8-10) concerns restrictions on dissemination. It requires that all SIGINT reports be written “so as to focus solely on the activities of foreign entities and persons and their agents.” It also specifies some of the conditions under which U.S. persons can be identified in SIGINT reports–for example, when the communications indicate the person is an agent of a foreign power.
Document 11b: NSA, “USSID 18: Dissemination of U.S. Government Organizations and Officials (U)–INFORMATION MEMORANDUM,” February 5, 1993
This NSA memo indicates that the conditions for identification of U.S. officials by title in NSA reporting varies depending on whether or not the individual is a member of the executive branch. Senior officials of the executive branch may be identified by title, without prior approval from higher authority, when the official’s title is necessary to understand or assess foreign intelligence. In contrast, officials from the legislative and judicial branches cannot be identified by title, even if that information is necessary to understand foreign intelligence, unless approval is obtained from higher authority. The memo implies that, under the assumed conditions, the use of names is not permitted.
Document 11c: NSA, “USSID 18: Reporting Guidance on References to the First Lady,” July 8, 1993
This memo followed a U.S. Court of Appeals ruling that Hillary Clinton was a full-time government official. It notes that she could be identified in reports by title (Chairperson of the President’s Task Force on National Health Care Reform) without prior approval when that title was necessary to understand or assess foreign intelligence and when the information related to her official duties. The memo also contains guidance on reports containing information about information concerning Mrs. Clinton that is not clearly foreign intelligence.
Document 11d: National Security Agency/Central Security Service, “U.S. Identities in SIGINT,” March 1994
This 48-page document is intended to provide detailed guidance concerning on the use of U.S. identities in SIGINT reports as well as the dissemination of U.S. identities to consumers outside the United States SIGINT System. It consists of 12 sections (including ones on requests for U.S. identities, accountability, dissemination, and collection and processing), and five appendices (including those on approved generic references and USSID 18 criteria for dissemination).
Document No. 11e: NSA, USSID 18: Reporting Guidance on Former President Carter’s Involvement in the Bosnian Peace Process (U)– Information Guidance, December 15, 1994
The issue of when the identity or even title of a U.S. citizen can be included in reporting based on communications intercepts is a major focus of USSID 18. This NSA memo was prepared in response to the invitation to former President Carter to travel to Bosnia and Herzegovina to participate in efforts to end the war. It specifies that as long as Carter is acting as a private citizen he may be referred to only as a “U.S. person” in any reports.
Document 11f: NSA, “Understanding USSID 18 and Contextual Identifications,” September 30, 1997
The issue of identification by context is the subject of this memo. It notes that, in describing U.S. entities, analysts are required, in general, to substitute sufficiently generic terms for the entities–terms that do not “directly lead to the identification of a U.S. entity even though the identity has been obscured in the report.” Violation of the “contextual identification rule” requires that the report “must be cancelled, reworded and reissued to eliminate the identifying information.” The guidance clearly does not apply to those cases where inclusion of more specific information is necessary to evaluate foreign intelligence.
Document 11g: NSA, “USSID 18 Guide,” February 1998
The introduction to this document notes that it is an informal guide to the provisions of USSID 18 with respect to the issue of the COMINT collection and and dissemination of U.S. identities. One section focues on USSID 18 issues with respect to threat situations, including when an individual is held captive by a foreign power or group or when an intercept reveals a threat to a U.S. person. The section on non-threat situations contains guidance on the disposition of the inadvertent intercept of communciations between U.S. persons, on processing and reporting of incidentally intercepted communications of a U.S. person during foreign intelligence collection, and the handling of U.S. identities in reports.
Document 12: Director of Central Intelligence Directive (DCID) 6/1, “SIGINT Committee,” May 12, 1982
The SIGINT Committee, now known as the National SIGINT Committee, was first established in 1958 to oversee key aspects of U.S. SIGINT activities—the identification of collection requirements, evaluation of how well U.S. and allied SIGINT activities satisfy requirements, and the production of recommendations concerning SIGINT arrangements with foreign governments. This directive is the most recent available version of DCID 6/1. While the directive remains formally classified, the full text of the document has been published previously in scholarly works and on the world wide web. (Note 10)
The SIGINT Committee operated for many years with two permanent subcommittees—the SIGINT Requirements Validation and Evaluation Subcommittee (SIRVES) and the SIGINT Overhead Reconnaissance Subcommittee (SORS). In the mid-1990s two new groups were established: The Weapons and Space Systems Advisory Group, to “coordinate SIGINT on foreign weapons and space systems,” and the National Emitter Intelligence Subcommittee, which focuses on SIGINT production concerning foreign radars and other non-communications signals. (Note 11)
Document 13: NAVSECGRU Instruction C5450.48A, Subj: Mission, Functions and Tasks of Naval Security Group Activity (NAVSECGRUACT) Sugar Grove, West Virginia, September 3, 1991
While NSA directs and manages U.S. SIGINT activities, almost all collection activity is actually carried out by the military service SIGINT units—including the Naval Security Group Command. The role of the unit at Sugar Grove in intercepting the international leased carrier (ILC) communications passing through INTELSAT satellites was first revealed in James Bamford’s The Puzzle Palace. (Note 12)
The regulation reveals that Sugar Grove is associated with what has become a highly controversial program in Europe, North America, Australia, and New Zealand. The program, codenamed ECHELON, has been described as a global surveillance network that intercepts and processes the world’s communications and distributes it among the primary partners in the decades-old UKUSA alliance—the United States, Canada, the United Kingdom, Australia, and New Zealand. (Note 13)
In reality, ECHELON is a more limited program, allowing the UKUSA allies to specify intelligence requirements and automatically receive relevant intercepts obtained by the UKUSA facilities which intercept satellite communications (but not the U.S. facilities that receive data from SIGINT satellites). It is also limited by both technological barriers (the inability to develop word-spotting software so as to allow for the automatic processing of intercepted conversations) and the limitations imposed on collection activities by the UKUSA allies—at least as regards the citizens of those countries. (Note 14) Thus, the NAVSECGRU instruction also specifies that one of the responsibilities of the commander of the Sugar Grove site is to “ensure the privacy of U.S. citizens are properly safeguarded pursuant to the provisions of USSID 18.”
Document 14: Farewell from Vice Admiral William O. Studeman to NSA Employees, April 8, 1992
This address by the departing director of NSA, William Studeman, examines NSA’s post-Cold War mission, likely budgetary limitations, and other challenges facing the agency. Reflecting the increasing emphasis on “support to military operations,” Studeman notes that “the military account is basic to NSA as a defense agency, and the lack of utter faithfulness to this fact will court decline.” He also observes that “the demands for increased global access are growing” and that “these business areas (SMO and global access) will be the two, hopefully strong legs on which NSA must stand.” He also argues that “technical and operational innovation to deal with a changing and changed world must continue to dominate.”
Document 15: Letter, Stewart A. Baker, General Counsel, NSA to Gerald E. McDowell, Esq., September 9, 1992
In the wake of disclosures about the role of the Banca Nazionale del Lavoro (BNL), particularly its Atlanta branch, in the provision of financial assistance to the regime of Saddam Hussein, questions were raised about whether the intelligence community was providing sufficient support to law enforcement.
This letter, from NSA’s general counsel, answers a series of questions from the Justice Department pertaining to NSA’s knowledge of, or involvement in, BNL activities. The responses appear to indicate that NSA had not derived any intelligence concerning BNL activities from its intercept operations. The letter also stresses NSA’s sensitivity to the issue of the privacy of American citizens (noting that “NSA improperly targeted the communications of a number of Americans opposed to the Vietnam War”) and the restrictions on reporting information concerning U.S. citizens or corporations.
Document 16: “Activation of Echelon Units,” from History of the Air Intelligence Agency, 1 January – 31 December 1994, Volume I (San Antonio, TX: AIA, 1995)
The first extract from the Air Intelligence Agency’s 1994 annual history provides additional information on the ECHELON network. ECHELON units include components of the AIA’s 544th Intelligence Group. Detachment 2 and 3 are located at Sabana Seca, Puerto Rico and Sugar Grove, West Virginia respectively. The second reference to Detachment 3 is apparently a typo that should read Detachment 4 (located at Yakima, Washington). The deleted words appear to be “civilian communications,” “NAVSECGRU” and “NSA.”
The second extract notes that AIA’s participation in a classified activity “had been limited to LADYLOVE operations at Misawa AB [Air Base], Japan.” The Misawa LADYLOVE activity was initiated during the Cold War to intercept Soviet military communications transmitted via satellite—along with similar operations at Menwith Hill, UK; Bad Aibling, Germany; and Rosman, North Carolina. This extract suggests that both Guam and Misawa have, at the least, been considered as possible sites for ECHELON operations.
Document 17: NSA Point Paper, “SIGINT Reporting on Murders of Michael DeVine in 1990 and the Disappearance of Efraín Bamaca in 1992 in Guatemala,” March 24, 1995
On March 23, 1995, Rep. Robert Torricelli, a member of the House Permanent Select Committee on Intelligence, charged that the CIA had been withholding from Congress information it had obtained regarding the deaths of Michael DeVine, an American innkeeper living in Guatemala, and Efraín Bámaca Velásquez, a Guatemalan guerrilla leader and husband of an American lawyer. Both murders, according to Torricelli, were linked to a Guatemalan army colonel, Julio Roberto Alpírez, a paid intelligence asset of the CIA. (Note 15)
The revelations set off a firestorm of criticism and caused the Clinton administration to order a government-wide investigation over these and other cases of torture and murder attributed to Guatemalan security forces. While the CIA was the main target of such criticism, Torricelli had also reportedly received an anonymous fax from someone inside the NSA alleging that documents pertaining to the Bámaca and DeVine cases were being destroyed. (Note 16)
This Top Secret NSA position paper responds to these allegations. NSA claims that SIGINT reporting related to these cases is limited to “Guatemalan government reaction to U.S. and international human rights concerns,” and does not include specific information regarding the circumstances of death or the involvement of Colonel Alpírez. The document is one of only a handful of declassified records in which the NSA even acknowledges specific SIGINT activities or reports.
Document 18: Memorandum, Daniel C. Kurtzer, Acting Assitant Secretary, Bureau of Intelligence and Research to Vice Admiral J.M. McConnell, Director, National Security Agency, Subject: Proposed Declassification of the “Fact of” Overhead SIGINT Collection, September 6, 1995
In 1978, President Jimmy Carter acknowledged that the U.S. employed reconnaissance satellites to collect imagery of foreign targets. Early in 1995, President Clinton declassified details concerning early satellite imagery programs such as CORONA. However, even the existence of SIGINT satellites remained classified until late 1995 when Director of Central Intelligence John Deutch authorized the official acknowledgement of space-based SIGINT operations. (Note 17)
The process involved soliciting the opinions of U.S. government departments whose interests might be affected by disclosure. The State Department’s memo expressed concern about the impact in certain countries. Despite the deletions, it is clear that the department was anxious about the impact in the foreign countries where the U.S. operates ground stations for SIGINT satellites—the United Kingdom (at Menwith Hill), Germany (at Bad Aibling), and Australia (at Pine Gap). The memo also indicates that the proposal for declassification emanated from the National Reconnaissance Office.
Document 19: NSA, Recent Classification Decisions, June 2, 1998. Confidential
The increased openness at NSA in the late 1990s extended to historical as well as contemporary matters. In addition to memos announcing individual declassification decisions, summary memos were also issued on occasion. This one covers declassification decisions with regard to a number of categories, including signals intelligence targeting, NSA’s presence abroad, the use of airborne platforms for SIGINT collection, and the codenames used to indicate intelligence obtained from communications or electronic intelligence collection.
Document 20: Organization Chart, NSA Operations Directorate, November 6, 1998
The organization chart of NSA’s Directorate of Operations is notable for several reasons. Traditionally, such information was not released by NSA, which under the provisions of Public Law 86-36 is not required to release even unclassified organizational information. In recent years, however, NSA has released more information about organization and administrative matters, and acknowledged the use of a variety of aircraft for SIGINT collection.
The organization chart also shows how the operations directorate has been reorganized since the end of the Cold War. Throughout much of the Cold War, the directorate consisted of three key regional groups—A (Soviet Bloc), B (Asian Communist), and G (All Other). After the Soviet collapse the regional groups were reduced to one for European nations and one for all other. The new organizational structure reflects the increasing empahsis on transnational activities, which cut across nations and regions.
New Document 21: James R. Taylor, Deputy Director of Operations, Subject: Thoughts on Strategic Issues for the Institution, April 9, 1999. Secret
This memorandum was written early in the tenure of NSA Director Lt. Gen. Michael Hayden, when much attention was being directed to the requirement for NSA to adapt to a new environment – which included new targets, communications technologies, and the availability of advanced encryption techniques.
Taylor notes that money and technology, while among the top five issues facing NSA, are not among the first three. The first and most important issue, according to Taylor, was NSA’s need to reform the management and leadership system. His discussion foreshadowed Hayden’s reorganization of NSA to clearly establish the primacy of the two components – the directorates for signals intelligence and information assurance – responsible for carrying out NSA’s fundamental missions.
A second key issue identified in the memo is the “strengthening and leveraging of [NSA’s] strategic alliances.” This includes NSA’s relationships with foreign SIGINT services, the CIA, and the service cryptologic elements (SCE’s) that carry out much of the collection work for NSA. The discussion of NSA’s relationship with the CIA indicates the increasing importance of human intelligence support to NSA – which can come in the form of acquisition of cipher materials or the clandestine placement of eavesdropping equipment.
The third issue identified is the need to properly staff “our two missions and to spot and nurture talent and leadership for the future.”
New Document 22: Lt. Gen. Jim Clapper, NSA Scientific Advisory Board, Panel on Digital Network Intelligence (DNI), Report to the Director, June 28, 1999, Secret Comint
This study, a complement to another study on conventional collection, is another example of NSA’s attempt to address the changing communication environment. Digital network intelligence is defined as “the intelligence from intercepted digital data communications transmitted between, or resident on, networked computers.”
The study, which has been heavily redacted prior to release, notes an imperative to “re-tool: organizationally, programmatically, and technologically” and examines issues concerning the access and collection of digital network intelligence, processing and extraction of intelligence from the data collected, analysis and reporting, and dissemination.
New Document 23: SSO [Special Security Office], DIA Subject: Implementation Guidance for Elimination of Codewords, October 22, 1999. Unclassified
During the Cold War, as an extension of the system developed in World War II to protect the security of communications intelligence operations, the U.S. established the category of Special Intelligence (SI). Within SI were a number of compartments, which corresponded to the different degrees of sensitivity attached to communications intelligence activities and products. In 1960, with the launch of the first reconnaissance satellites, the U.S. also established the TALENT-KEYHOLE (TK) system, with compartments for satellite imagery (RUFF), satellite ELINT (ZARF), and aerial imagery from the U-2, and later, SR-71.
This message reflects the attempt to simplify the system by eliminating three key codenames from the SI category and one from the TK system.
Document 24: Statement for the Record of NSA Director Lt Gen Michael V. Hayden, USAF before the House Permanent Select Committee on Intelligence, April 12, 2000
In a rare public appearance by the NSA director, Lt. Gen. Michael Hayden outlines the regulatory safeguards and oversight mechanisms that are in place to ensure that the agency’s electronic surveillance mission does not infringe upon the privacy of U.S. persons, and to respond to recent allegations that NSA provides intelligence information to U.S. companies.
The agency may only target the communications of U.S. persons within the United States after obtaining a federal court order suggesting that the individual might be “an agent of a foreign power.” The number of such cases have been “very few” since the passage of the Foreign Intelligence Surveillance Act in 1978. In cases where the NSA wishes to conduct electronic surveillance on U.S. persons overseas, the agency must first obtain the approval of the Attorney General, who must have probable cause to believe that the individual “is an agent of a foreign power, or a spy, terrorist, saboteur, or someone who aides or abets them.” With regard to the unintentional collection of communications to, from, or about U.S. citizens, Hayden stresses that such information is not retained “unless the information is necessary to understand a particular piece of foreign intelligence or assess its importance.”
In response to other allegations, Hayden asserts that NSA cannot request that another country “illegally” collect intelligence on U.S. persons on their behalf, and also that the agency “is not authorized to provide signals intelligence information to private U.S. companies.”
New Document 25: National Security Agency, Transition 2001, December 2000. Secret
This document, prepared for the incoming administration of George W. Bush, was intended to provide a background on NSA’s organization and mission, as well as of the issues facing NSA in the years ahead. Its main sections include those devoted to management, external process, budget, and personnel, policy/issues.
In the discussion of major policy issues, the document notes the changing environment in which the “analog world of point-to-point communications carried along discrete, dedicated voice channels” is being replaced by communications that are “mostly digital, carry billions of bits of data, and contain voice, data and multimedia.” In addition, it states that “global networks leave US critical information infrastructure more vulnerable to foreign intelligence operations and to compromise by a host of non-state entities.” The creation of global networks also requires, according to the transition book, that “senior leadership understand that today’s and tomorrow’s mission will demand a powerful, permanent presence on a global telecommunications network that will host the ‘protected’ communications of Americans as well as targeted communications of adversaries.”
New Document 26a: Organization Chart, Signals Intelligence Directorate
New Document 26b: Organization Chart, Information Assurance Directorate
These two heavily redacted organization charts are more informative for what they reveal about the change in NSA’s classification policy than for what they reveal about the 2001 organizational structure of NSA’s two key directorates.
In contrast to Document 19, the largely intact 1998 organization chart for the Directorate of Operations, Document 26a, the chart for the Signals Intelligence Directorate (as the operations directorate was renamed) contains no information beyond the name of its director. The late 1990s was a period when NSA significantly loosened restrictions on information – not only historical information, but then current organizational information. As a result the operations directorate organization chart was provided within three weeks of its being requested in late 1998. In contrast, the request for the Signals Intelligence Directorate organization chart was made on April 21, 2001 and NSA provided its substantive response on April 21, 2004.
Similarly, in the late 1990s, NSA released detailed organizational information on its Information Security directorate, in contrast to the small amount of it detail it has released on the successor Information Assurance Directorate.
Document 27: Statement for the Record by Lieutenant General Michael V. Hayden, Director, National Security Agency/Central Security Service Before the Joint Inquiry of the Senate Select Committee on Intelligence and the House Permanent Select Committee on Intelligence, October 17, 2002, Unclassified
Hayden, in his testimony to the joint committee intelligence performance prior to the terrorist attacks on New York and Washington of September 11, 2001, addresses three major questions: what did NSA know prior to September 11, what did NSA learn in retrospect, and what had NSA done in response? In his conclusions, Hayden addresses a number of issues – including the relationship between SIGINT and law enforcement, and the line between the government’s need for counterterrorism information and the privacy interests of individuals residing in the United States.
Notes
1. Report to the Secretary of State and the Secretary of Defense by a Special Committee Appointed Pursuant to Letter of 28 December 1951 to Survey Communications Intelligence Activities of the Government, June 13, 1952, pp. 47-48, 119; RG 457, SR-123, Military Reference Branch, NARA; The National Cryptologic School, On Watch: Profiles from the National Security Agency’s Past 40 Years (Ft. Meade, Md.: NCS, 1986), p. 17.
2. Walter Bedell Smith, “Proposed Survey of Communications Intelligence Activities,” December 10, 1951; Report to the Secretary of State and the Secretary of Defense by a Special Committee, p. 118; U.S. Congress, Senate Select Committee to Study Governmental Operations with Respect to Intelligence Activities, Final Report, Book III: Foreign and Military Intelligence (Washington, D.C.: U.S. Government Printing Office, 1976), p. 736; National Security Agency/Central Security Service, NSA/CSS Manual 22-1 (Ft. Meade, MD: NSA, 1986), p. 1.
3. National Security Agency, NSA/CSS Manual 22-1 (Ft. Meade, Md.: NSA, 1986), p. 7.
4. Jeffrey T. Richelson, The Wizards of Langley: Inside the CIA’s Directorate of Science and Technology (Boulder, Co.: Westview, 2001), p. 60.
5. Richard M. Bissell Jr. with Jonathan E. Lewis and Frances T. Pudlo, Reflections of a Cold Warrior: From Yalta to the Bay of Pigs (New Haven, Ct.: Yale University Press, 1996), p. 239.
6. James Bamford, The Puzzle Palace: A Report on NSA, America’s Most Secret Agency (Boston: Houghton-Mifflin, 1982), p. 334.
7. Stansfield Turner, Secrecy and Democracy: The CIA in Transition (Boston: Houghton-Mifflin, 1985), pp. 235-236.
8. James Bamford, Body of Secrets: Anatomy of the Ultra-Secret National Security Agency (New York: Doubleday, 2001), pp. 185-239; A. Jay Cristol, The Liberty Incident: The 1967 Israeli Attack on the U.S. Navy Spy Ship (Washington, D.C.: Brassey’s 2002); James M. Ennes Jr., Assault on the Liberty: The True Story of the Israeli Attack on an American Intelligence Ship (New York: Ivy, 1979).
9. Bob Woodward, “Messages of Activists Intercepted,” Washington Post, October 13, 1975, pp. A1, A14.
10. See Jeffrey T. Richelson, The U.S. Intelligence Community (Cambridge: Ballinger, 2nd ed., 1989/Boulder: Westview Press, 3rd ed., 1995; 4th ed., 1999); See also the World Wide Web site of the Federation of American Scientists, http://fas.org/irp/offdocs/dcid16.htm
11. Lois G. Brown, “National SIGINT Committee,” NSA Newsletter, February 1997, p. 2.
12. James Bamford, The Puzzle Palace: A Report on NSA, America’s Most Secret Agency (Boston, MA: Houghton-Mifflin, 1982), p. 170.
13. Patrick S. Poole, ECHELON: America’s Secret Global Surveillance Network (Washington, D.C.: Free Congress Foundation, October 1998).
14. Duncan Campbell, Interception Capabilities 2000 (Luxembourg: European Parliament, 1999); Jeffrey T. Richelson, “Desperately Seeking Signals,” Bulletin of the Atomic Scientists, Vol. 56, No. 2, pp. 47-51.
15. Dana Priest, “Torricelli Admits Violating House Secrecy Oath,” Washington Post, April 8, 1995, p. A7.
16. Kim Masters, “Truth or Consequences; Rep. Bob Torricelli Leaked the Goods on the CIA. Was It Loyalty or Betrayal?” Washington Post, April 17, 1995, p. C1.
17. DIRNSA, “Fact of Overhead SIGINT Collection,” January 4, 1996.
TOP-SECRET-CIA Bucharest Prison Eyeball
| In northern Bucharest, in a busy residential neighborhood minutes from the center of Romania’s capital city, is a secret that the Romanian government has tried for years to protect.
For years, the CIA used a government building — codenamed Bright Light — as a makeshift prison for its most valuable detainees. There, it held al-Qaida operatives Khalid Sheik Mohammad, the mastermind of 9/11, and others in a basement prison before they were ultimately transferred to Guantanamo Bay in 2006, according to former U.S. intelligence officials familiar with the location and inner workings of the prison. The existence of a CIA prison in Romania has been widely reported but its location has never been made public until a joint investigation by The Associated Press and German public television, ARD Panorama. The news organizations located the former prison and learned details of the facility where harsh interrogation tactics were used. ARD’s program on the CIA prison will air Dec 8. The Romanian prison was part of a network of so-called black sites that the CIA operated and controlled overseas in Thailand, Lithuania and Poland. All the prisons were closed by May 2006, and the CIA’s detention and interrogation program ended in 2009. Unlike the CIA’s facility in Lithuania’s countryside or the one hidden in a Polish military installation, the CIA’s prison in Romania was not in a remote location. It was hidden in plain sight, a couple blocks off a major boulevard on a street lined with trees and homes, along busy train tracks. The building is used as the National Registry Office for Classified Information, which is also known as ORNISS. Classified information from NATO and the European Union is stored there. Former intelligence officials both described the location of the prison and identified pictures of the building. |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/cia-bucharest/pict13.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/cia-bucharest/pict11.jpg)
|
| Google Mapshttp://bit.ly/vDKcPW
|
CIA Prisoner Unloading Route via Side Street According to AP. 2005 Aerial Photo (Google Earth).![[Image]](https://i0.wp.com/cryptome.org/eyeball/cia-bucharest/pict14.jpg) |
| Following oblique views by Bing.com/maps: http://binged.it/vAOoi0 |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/cia-bucharest/pict4.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/cia-bucharest/pict5.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/cia-bucharest/pict7.jpg) |
![[Image]](https://i0.wp.com/cryptome.org/eyeball/cia-bucharest/pict8.jpg) |
TOP-SECRET – NSA- THE NRO DECLASSIFIED

n September 1992 the Department of Defense acknowledged the existence of the National Reconnaissance Office (NRO), an agency established in 1961 to manage the development and operation of the nation’s reconnaissance satellite systems. The creation of the NRO was the result of a number of factors.
On May 1, 1960 Francis Gary Powers took off from Peshawar, Pakistan on the U-2 mission designated Operation GRAND SLAM. The flight was planned to take him over the heart of the Soviet Union and terminate at Bodo, Norway. The main target was Plesetsk, which communications intercepts had indicated might be the site of an ICBM facility.1 When the Soviet Union shot down his plane and captured him alive, they also forced President Dwight Eisenhower to halt aerial overflights of Soviet territory.
At that time the U.S. had two ongoing programs to produce satellite vehicles that could photograph Soviet territory. Such vehicles would allow far more frequent coverage than possible with manned aircraft. In addition, they would avoid placing the lives of pilots at risk and eliminate the risks of international incidents resulting from overflights.
The Air Force program, designated SAMOS, sought to develop a number of different satellite systems–including one that would radio its imagery back to earth and another that would return film capsules. The CIA program, CORONA, focused solely on developing a film return satellite.
However, both the CIA and Air Force programs were in trouble. Launch after launch in the CORONA program, eleven in all by May 1, 1960, eight of which carried cameras, had resulted in failure–the only variation was in the cause. Meanwhile, the SAMOS program was also experiencing difficulties, both with regard to hardware and program definition.2
Concerns over SAMOS led President Eisenhower to direct two groups to study both the technical aspects of the program as well as how the resulting system would be employed. The ultimate result was a joint report presented to the President and NSC on August 25, 1960.3
As a result of that meeting Eisenhower approved a first SAMOS launch in September, as well as reorientation of the program, with the development of high-resolution film-return systems being assigned highest priority while the electronic readout system would be pursued as a research project. With regard to SAMOS management, he ordered that the Air Force institute special management arrangements, which would involve a direct line of authority between the SAMOS project office and the Office of the Air Force Secretary, bypassing the Air Staff and any other intermediate layers of bureaucracy.4
Secretary of the Air Force Dudley C. Sharp wasted little time creating the recommended new structure and procedures. On August 31st Sharp signed Secretary of the Air Force Order 115.1, establishing the Office of Missile and Satellite Systems within his own office to help him manage the SAMOS project. With Order 116.1, Sharp created a SAMOS project office at the Los Angeles headquarters of the Air Force Ballistic Missile Division (AFBMD) as a field extension of the Office of the Secretary of the Air Force to carry out development of the satellite.5
The impact of the orders, in practice, was that the director of the SAMOS project would report directly to Under Secretary of the Air Force Joseph V. Charyk, who would manage it in the Secretary’s name. In turn, Charyk would report directly to the Secretary of Defense.6
The changes would not stop there. The urgency attached to developing a successful reconnaissance satellite led, ultimately, to the creation of a top secret program and organization to coordinate the entire national reconnaissance effort.
Several of the documents listed below also appear in either of two National Security Archive microfiche collections on U.S. intelligence. The U.S. Intelligence Community: Organization, Operations and Management: 1947-1989 (1990) and U.S. Espionage and Intelligence: Organization, Operations, and Management, 1947-1996 (1997) publish together for the first time recently declassified documents pertaining to the organizational structure, operations and management of the U.S. Intelligence Community over the last fifty years, cross-indexed for maximum accessibility. Together, these two sets reproduce on microfiche over 2,000 organizational histories, memoranda, manuals, regulations, directives, reports, and studies, totaling more than 50,000 pages of documents from the Office of the Director of Central Intelligence, the Central Intelligence Agency, National Reconnaissance Office, National Security Agency, Defense Intelligence Agency, military service intelligence organizations, National Security Council, and other official government agencies and organizations.
Document 1
Joseph Charyk, Memorandum for the Secretary of Defense
Management of the National Reconnaissance Program
24 July 1961
Top Secret
1 p.
The organizational changes resulting from the decisions of August 25, 1960 and their implementation left some unsatisfied. In particular, James Killian and Edwin Land, influential members of the President’s intelligence advisory board pushed for permanent and institutionalized collaboration between the CIA and Air Force. After the Kennedy administration took office the push to establish a permanent reconnaissance organization took on additional life. There was a strong feeling in the new administration, particularly by Secretary of Defense Robert McNamara and his deputy, Roswell Gilpatric, that a better, more formalized relationship was required.7
On July 24, 1961, Air Force Undersecretary Joseph Charyk sent a memorandum to McNamara attaching two possible memoranda of agreement for creation of a National Reconnaissance Program, along with some additional material.
Document 2
Memorandum of Understanding
Management of the National Reconnaissance Program (Draft)
20 July 1961
Top Secret
5 pp.
This memo specified establishment of a National Reconnaissance Program (NRP) consisting of “all satellite and overflight reconnaissance projects whether overt or covert,” and including “all photographic projects for intelligence, geodesy and mapping purposes, and electronic signal collection projects for electronic signal intelligence and communications intelligence.”
To manage the NRP, a National Reconnaissance Office (NRO) would be established on a covert basis. The NRO director (DNRO) would be the Deputy Director for Plans, CIA (at the time, Richard Bissell) while the Under Secretary of the Air Force would serve as Deputy Director (DDNRO). The DNRO would be responsible for the management of CIA activities, the DDNRO and the Air Force for Defense Department activities. The DoD, specifically the Air Force acting as executive agent, would be primarily responsible for technical program management, scheduling, vehicle operations, financial management and overt contract administration, while the CIA would be primarily responsible for targeting each satellite. The office would operate under streamlined management procedures similar to those established in August 1960 for SAMOS.
Document 3
Memorandum of Understanding
Management of the National Reconnaissance Program (Draft)
21 July 1961
Top Secret
4 pp.
This secondary memorandum was prepared at the suggestion of Defense Department General Counsel Cyrus Vance. It offered a quite different solution to the problem. As with the primary memo, it established a NRP covering both satellite and aerial reconnaissance operations. But rather than a jointly run program, it placed responsibility for management solely in the hands of a covertly appointed Special Assistant for Reconnaissance, to be selected by the Secretary of Defense. The office of the Special Assistant would handle the responsibilities assigned to the NRO in the other MOU. The CIA would “assist the Department of Defense by providing support as required in areas of program security, communications, and covert contract administration.”
Document 4
Memorandum
Pros and Cons of Each Solution
Not dated
Top Secret
2 pp.
The assessment of pros and cons favored the July 20 memorandum, listing five pros for the first solution and only two for the second. The first solution would consolidate responsibilities into a single program with relatively little disruption of established management, represented a proven solution, would require no overt organizational changes, would allow both agencies to retain authoritative voices in their areas of expertise, and provided a simplified management structure. The two cons noted were the division of program responsibility between two people, and that “successful program management depends upon mutual understanding and trust of the two people in charge of the NRO.” It would not be too long before that later observation would take on great significance.
In contrast, there were more cons than pros specified for the second solution. The only two points in its favor were the consolidation of reconnaissance activities into a single program managed by a single individual and the assignment of complete responsibility to the agency (DoD) with the most resources. Foremost of the six cons was the need for DoD to control and conduct large-scale covert operations, in as much as it was an entity “whose normal methods are completely foreign to this task.”
Document 5
Roswell Gilpatric, Letter to Allen Dulles
Management of the National Reconnaissance Program
6 September 1961
Top Secret
4 pp.
On July 28, 1961, four days after receiving Charyk’s memorandum and draft memoranda of understanding, McNamara instructed Air Force Undersecretary Joseph Charyk to continue discussions with the key officials and advisers in order to resolve any organizational difficulties that threatened to impede the satellite reconnaissance effort. The ultimate result was this letter from Deputy Secretary of Defense Roswell Gilpatric to Dulles, which confirmed “our agreement with respect to the setting up of the National Reconnaissance Program.”
The letter specified the creation of a NRP. It also established the NRO, a uniform security control system, and specified that the NRO would be directly responsive to the intelligence requirements and priorities specified by the United States Intelligence Board. It specified implementation of NRP programs assigned to the CIA through the Deputy Director for Plans. It designated the Undersecretary of the Air Force as the Defense Secretary’s Special Assistant for Reconnaissance, with full authority in DoD reconnaissance matters.
The letter contained no specific assignment of responsibilities to either the CIA or Defense Department, stating only that “The Directors of the National Reconnaissance Office will … insure that the particular talents, experience and capabilities within the Department of Defense and the Central Intelligence Agency are fully and most effectively utilized in this program.”
The letter provided for the NRO to be managed jointly by the Under Secretary of the Air Force and the CIA Deputy Director for Plans (at the time, still Richard Bissell). A May 1962 agreement between the CIA and Defense Department established a single NRO director. Joseph Charyk was named to the directorship shortly afterward.
Document 6
Joseph Charyk
Memorandum for NRO Program Directors/Director, NRO Staff
Organization and Functions of the NRO
23 July 1962
Top Secret
11 pp.
This memorandum represents the fundamental directive on the organization and functions of the NRO. In addition to the Director (there was no provision for a deputy director), there were four major elements to the NRO–the NRO staff and three program elements, designated A, B, and C. The staff’s functions included assisting the director in dealing with the USIB and the principal consumers of the intelligence collected.
The Air Force Office of Special Projects (the successor to the SAMOS project office) became NRO’s Program A. The CIA reconnaissance effort was designated Program B, while the Navy’s space reconnaissance effort, at the time consisting of the Galactic Radiation and Background (GRAB) satellite, whose radar ferret mission involved the collection of Soviet radar signals, became Program C. Although the GRAB effort was carried out by the Naval Research Laboratory, the director of the Office of Naval Intelligence would serve as Program C director until 1971.8
Document 7
Agreement between the Secretary of Defense and the Director of Central Intelligence on Management of the National Reconnaissance Program
13 March 1963
Top Secret
6 pp.
In December 1962, Joseph Charyk decided to leave government to become president of the COMSAT Corporation. By that time a number of disputes between the CIA and NRO had contributed to Charyk’s view that the position of the NRO and its director should be strengthened. During the last week of February 1963, his last week in office, he completed a revision of a CIA draft of a new reconnaissance agreement to replace the May 1962 agreement (which had replaced the September 6, 1961 agreement). Charyk took the revision to Deputy Secretary of Defense Roswell Gilpatric. It appears that some CIA-suggested changes were incorporated sometime after Charyk left office. On March 13, Gilpatric signed the slightly modified version on behalf of DoD. It was sent to the CIA that day and immediately approved by DCI John McCone, who had replaced Allen Dulles in November 1961.9
The new agreement, while it did not include all the elements Charyk considered important, did substantially strengthen the authority of the NRO and its director. It named the Secretary of Defense as the Executive Agent for the NRP. The program would be “developed, managed, and conducted in accordance with policies and guidance jointly agreed to by the Secretary of Defense and the Director of Central Intelligence.”
The NRO would manage the NRP “under the direction, authority, and control of the Secretary of Defense.” The NRO’s director would be selected by the Defense Secretary with the concurrence of the DCI, and report to the Defense Secretary. The NRO director was charged with presenting to the Secretary of Defense “all projects” for intelligence collection and mapping and geodetic information via overflights and the associated budgets, scheduling all overflight missions in the NRP, as well as engineering analysis to correct problems with collection systems. With regard to technical management, the DNRO was to “assign all project tasks such as technical management, contracting etc., to appropriate elements of the DoD and CIA, changing such assignments, and taking any such steps he may determine necessary to the efficient management of the NRP.”
Document 8
Department of Defense Directive Number TS 5105.23
Subject: National Reconnaissance Office
27 March 1964
Top Secret
4 pp.
This directive replaced the original June 1962 DoD Directive on the NRO, and remains in force today. The directive specifies the role of the Director of the NRO, the relationships between the NRO and other organizations, the director’s authorities, and security. It specified that documents or other material concerning National Reconnaissance Program matters would be handled within a special security system (known as the BYEMAN Control System).
Document 9
President’s Foreign Intelligence Advisory Board
Memorandum for the President
Subject: National Reconnaissance Program
2 May 1964
Top Secret
11 pp.
The 1963 CIA-DoD agreement on the NRP did not end the battles between the CIA and NRO–as some key CIA officials, including ultimately DCI John McCone, sought to reestablish a major role for the CIA in the satellite reconnaissance effort. The continuing conflict was examined by the PFIAB.
The board concluded that “the National Reconnaissance Program despite its achievements, has not yet reached its full potential.” The fundamental cause for the NRP’s shortcomings was “inadequacies in organizational structure.” In addition, there was no clear division of responsibilities and roles between the Defense Department, CIA, and the DCI.
The recommendations of the board represented a clear victory for the NRO and its director. The DCI should have a “large and important role” in establishing intelligence collection requirements and in ensuring that the data collected was effectively exploited, according to the board. In addition, his leadership would be a key factor in the work of the United States Intelligence Board relating to the scheduling of space and airborne reconnaissance missions.
But the board also recommended that President Johnson sign a directive which would assign to NRO’s Air Force component (the Air Force Office of Special Projects) systems engineering, procurement, and operation of all satellite reconnaissance systems.
Document 10
Agreement for Reorganization of the National Reconnaissance Program
13 August 1965
Top Secret
6 pp.
Despite the recommendations of the May 2, 1964 PFIAB report, which were challenged by DCI John McCone, no action was taken to solidify the position of the NRO and its director. Instead prolonged discussions over a new agreement continued into the summer of 1965. During this period the CIA continued work on what would become two key satellite programs–the HEXAGON/KH-9 imaging and RHYOLITE signals intelligence satellites.
In early August, Deputy Secretary of Defense Cyrus Vance and CIA official John Bross reached an understanding on a new agreement, and it was signed by Vice Adm. William F. Raborn (McCone’s successor) and Vance on August 13, 1965. It represented a significant victory for the CIA, assigning key decision-making authority to an executive committee, authority that was previously the prerogative of the NRO director as the agent of the Secretary of Defense.
The Secretary of Defense was to have “the ultimate responsibility for the management and operation of the NRO and the NRP,” and have the final power to approve the NRP budget. The Secretary also was empowered to make decisions when the executive committee could not reach agreement.
The DCI was to establish collection priorities and requirements for targeting NRP operations, as well as establish frequency of coverage, review the results obtained by the NRP and recommend steps for improving its results if necessary, serve on the executive committee, review and approve the NRP budget, and provide security policy guidance.
The NRP Executive Committee established by the agreement would consist of the DCI, Deputy Secretary of Defense, and Special Assistant to the President for Science and Technology. The committee was to recommend to the Secretary of Defense the “appropriate level of effort for the NRP,” approve or modify the consolidated NRP and its budget, approve the allocation of responsibility and the corresponding funds for research and exploratory development for new systems. It was instructed to insure that funds would be adequate to pursue a vigorous research and development program, involving both CIA and DoD. The executive committee was to assign development of sensors to the agency best equipped to handle the task.
The Director of the NRO would manage the NRO and execute the NRP “subject to the direction and control of the Secretary of Defense and the guidance of the Executive Committee.” His authority to initiate, improve, modify, redirect or terminate all research and development programs in the NRP, would be subject to review by the executive committee. He could demand that all agencies keep him informed about all programs undertaken as part of the NRP.
Document 11
Analysis of “A $1.5 Billion Secret in Sky” Washington Post, December 9, 1973
Not dated
Top Secret
33 pp.
Throughout the 1960s, the United States operation of reconnaissance satellites was officially classified, but well known among specialists and the press. However, it was not until January 1971 that the NRO’s existence was first disclosed by the media, when it was briefly mentioned in a New York Times article on intelligence and foreign policy.
A much more extensive discussion of the NRO appeared in the December 9, 1973 Washington Post as a result of the inadvertent mention of the reconnaissance office in a Congressional report. The NRO prepared this set of classified responses to the article, clearly intended for those in Congress who might be concerned about the article’s purported revelations about the NRO’s cost overruns and avoidance of Congressional oversight.
Document 12
E.C. Aldridge, Jr. (Director, NRO)
Letter to David L. Boren, Chairman,
Senate Select Committee on Intelligence
21 November 1988
Secret
3 pp.
The late 1980s saw the beginning of what eventually would be a wide-ranging restructuring of the NRO. In November 1988 NRO director Edward “Pete” Aldridge wrote to Senator David Boren, Chairman of the Senate Select Committee on Intelligence, concerning the findings of an extensive study (the NRO Restructure Study) of the organizational structure of the NRO.
Aldridge proceeded to report that, after having discussed the study’s recommendations with Secretary of Defense Frank Carlucci and Director of Central Intelligence William Webster, he was directing the development of plans to implement the recommendations. Specific changes would include the creation of a centralized systems analysis function “to conduct cross-system trades and simulations within the NRO,” creation of a “User Support” function to improve NRO support to intelligence community users as well as to the growing number of operational military users, and the dispersal of the NRO Staff to the new units, with the staff being replaced by a group of policy advisers. In addition, Aldridge foresaw the establishment of an interim facility “to house the buildup of the new functions and senior management.” The ultimate goal, projected for the 1991-92 period, would be the “collocation of all NRO elements [including the Los Angeles-based Air Force Office of Special Projects] . . . in the Washington, D.C. area.”
Document 13
Memorandum of Agreement
Subject: Organizational Restructure of the National Reconnaissance Office
15 December 1988
Secret
2 pp.
This memorandum of agreement, signed by the Director of the NRO and the directors of the NRO’s three programs commits them to the restructuring discussed in Edward Aldridge’s November 21 letter to Senator Boren.
Many changes recommended by Aldridge, who left office at the end of 1988, were considered by a 1989 NRO-sponsored review group and subsequently adopted.
Document 14
Report to the Director of Central Intelligence
DCI Task Force on The National Reconnaissance Office, Final Report
April 1992
Secret
35 pp.
This report was produced by a panel chaired by former Lockheed Corporation CEO Robert Fuhrman, whose members included both former and serving intelligence officials. It focused on a variety of issues other than current and possible future NRO reconnaissance systems. Among the issues it examined were mission, organizational structure, security and classification.
One of its most significant conclusions was that the Program A,B,C structure that had been instituted in 1962 (see Document 6) “does not enhance mission effectiveness” but “leads to counterproductive competition and makes it more difficult to foster loyalty and to maintain focus on the NRO mission.” As a result, the panel recommended that the NRO be restructured along functional lines with imagery and SIGINT directorates. This change was made even before the final version of the report was issued.
The report also noted that while the NRO’s existence was officially classified it was an “open secret” and that seeking to attempt to maintain such “open secrets … weakens the case for preserving ‘real’ secrets.” In addition, such secrecy limited the NRO’s ability to interact with customers and users. The group recommended declassifying the “fact of” the NRO, as well as providing information about the NRO’s mission, the identities of senior officials, headquarters locations, and the NRO as a joint Intelligence Community-Defense Department activity.
Document 15
National Security Directive 67
Subject: Intelligence Capabilities: 1992-2005
30 March 1992
Secret
2 pp.
NSD 67 directed a number of changes in U.S. intelligence organization and operations. Among those was implementation of the plan to restructure the NRO along functional lines–eliminating the decades old Program A (Air Force), B (CIA), and C (Navy) structure and replacing it with directorates for imaging, signals intelligence, and communication systems acquisition and operations–as recommended by the Fuhrman panel. As a result, Air Force, CIA, and Navy personnel involved in such activities would now work together rather than as part of distinct NRO components.
Document 16
Email message
Subject: Overt-Covert-DOS-REP-INPUT
27 July 1992
Secret
1 p.
In addition to the internal restructuring of the NRO, 1992 saw the declassification of the organization, as recommended by the Fuhrman report (Document 14), for a number of reasons–to facilitate interaction with other parts of the government, to make it easier for the NRO to support military operations, and in response to Congressional pressure to acknowledge the obvious. As part of the process of considering declassification NRO consulted Richard Curl, head of the Office of Intelligence Resources of the State Department’s Bureau of Intelligence and Research–the office which provides INR with expertise and support concerning technical collection systems. Curl recommended a low-key approach to declassification.
Document 17
Memorandum for Secretary of Defense, Director of Central Intelligence
Subject: Changing the National Reconnaissance Office (NRO) to an Overt Organization
30 July 1992
Secret
3 pp.
w/ attachments:
Document 17a: Mission of the NRO, 1 p.
Document 17b: Implications of Proposed Changes, 4 pp. (Two versions)
Version One
Version Two
These memos, from Director of the NRO Martin Faga, represent key documents in the declassification of the NRO. The memo noted Congressional pressure for declassification and that Presidential certification that declassification would result in “grave damage to the nation … would be difficult in this case.”
Faga reported that as a result of an NRO review he recommended declassifying the fact of NRO’s existence, issuing a brief mission statement, acknowledging the NRO as a joint DCI-Secretary of Defense endeavor, and identifying top level NRO officials. He also noted that his recommendations attempted to balance concerns about classifying information that realistically could not be protected, while maintaining an ability to protect matters believed to require continued protection.
Secretary of Defense Richard Cheney, DCI Robert Gates, and President Bush approved the recommendations in September and a three-paragraph memorandum to correspondents acknowledging the NRO and NRP was issued on September 18, 1992.
Document 17b comes in two versions, representing different security reviews. Material redacted from the first version includes provisions of National Security Directive 30 on space policy, expression of concern over “derived disclosures,” and the assessment that the “high degree of foreign acceptance of satellite reconnaissance, and the fact that we are not disclosing significant new data,” would not lead to any significant foreign reaction. Another redacted statement stated that “legislation . . . exempting all NRO operational files from [Freedom of Information Act] searches” was required.
Document 18
Final Report: National Reconnaissance Program Task Force for the Director of Central Intelligence
September 1992
Top Secret
15 pp.
The end of the Cold War and collapse of the Soviet Union required the U.S. intelligence community and NRO to reconsider how U.S. overhead reconnaissance systems were employed and what capabilities future systems should possess. To consider these questions DCI Robert Gates appointed a task force, chaired by his eventual successor, R. James Woolsey.
The final report considers future needs and collection methods, industrial base considerations, procurement policy considerations, international industrial issues, and transition considerations. Its recommendations included elimination of both some collection tasks as well as some entire types of present and planned collection systems.
Document 19
NRO Protection Review, “What is [BYEMAN]?”
6 November 1992
Top Secret
18 pp.
Traditionally, the designations of Sensitive Compartmented Information (SCI) compartments–such as UMBRA to indicate particularly sensitive communications intelligence and RUFF to intelligence based on satellite imagery–have themselves been classified. In recent years, however, the NSA and CIA have declassified a number of such terms and their meaning. One exception has been the term “BYEMAN”– the BYEMAN Control System being the security system used to protect information related to NRO collection systems (in contrast to their products) and other aspects of NRO activities, including budget and structure. Thus, the term BYEMAN has been deleted in the title of the document and throughout the study–although the term and its meaning has become known by specialists and conveys no information beyond the text of any particular document.
This study addresses the use of the BYEMAN classification within the NRO, its impact on contractors and other government personnel, and the consequences of the current application of the BYEMAN system. The study concludes that placing information in the highly restrictive BYEMAN channels (in contrast to classifying the information at a lower level) may unduly restrict its dissemination to individuals who have a legitimate need to know.
Document 20
NRO Strategic Plan
18 January 1993
Secret
19 pp.
A study headed by James Woolsey (Document 18), President Clinton’s first DCI, heavily influenced the contents of this early 1993 document. The plan’s introduction notes that while some collection tasks will no longer be handled by overhead reconnaissance the “uncertain nature of the world that is emerging from the end of the ‘cold war’ places a heavy premium on overhead reconnaissance.” At the same time, “this overhead reconnaissance challenge must be met in an era of a likely reduced national security budget.”
The strategic plan is described in the introduction, as “the ‘game plan’ to transition current overhead collection architectures into a more integrated, end-to-end architecture for improved global access and tasking flexibility.”
The document goes on to examine the strategic context for future NRO operations, NRO strategy, strategic objectives, and approaches to implementation. Strategic objectives include improving the responsiveness of NRO systems by developing an architecture that spans the entire collection and dissemination process, from the identification of requirements to dissemination of the data collected.
Document 21
National Reconnaissance Office: Collocation Construction Project, Joint DOD and CIA Review Report
November 1994
Unclassified
28 pp.
In an August 8, 1994 press conference, Senators Dennis DeConcini (D-Az.) and John Warner (R-Va.), the chairman and vice chairman of the Senate Select Committee on Intelligence accused the NRO of concealing from Congress the cost involved in building a new headquarters to house government and contractor employees. Previously NRO activities in the Washington area were conducted from the Pentagon and rented space in the Washington metropolitan area. The collocation and restructuring decisions of the late 1980s and early 1990s had resulted in a requirement for a new headquarters facility.10
The accusations were followed by hearings before both the Senate and House intelligence oversight committees–with House committee members defending the NRO and criticizing their Senate colleagues. While they noted that some of the documents presented by the NRO covering total costs were not presented with desirable clarity, the House members were more critical of the Senate committee for inattention to their committee work.11
This joint DoD and CIA review of the project, found “no intent to mislead Congress” but that “the NRO failed to follow Intelligence Community budgeting guidelines, applicable to all the intelligence agencies,” that would have caused the project to be presented as a “New Initiative,” and that the cost data provided by the NRO “were not presented in a consistent fashion and did not include a level of detail comparable to submissions for . . . intelligence community construction.”
Document 22
Memorandum for Director of Central Intelligence
Subject: Small Satellite Review Panel
Unclassified
July 1996
The concept of employing significantly smaller satellites for imagery collection was strongly advocated by Rep. Larry Combest during his tenure (1995-97) as chairman of the House Permanent Select Committee on Intelligence. As a result the DCI was instructed to appoint a panel of experts to review the issue.12
Panel members included former NRO directors Robert Hermann and Martin Faga; former NRO official and NSA director Lew Allen; scientist Sidney Drell and four others. The panel’s report supported a radical reduction in the size of most U.S. imagery satellites. The panel concluded that “now is an appropriate time to make a qualitative change in the systems architecture of the nation’s reconnaissance assets,” in part because “the technology and industrial capabilities of the country permit the creation of effective space systems that are substantially smaller and less costly than current systems.” Thus, the panel saw “the opportunity to move towards an operational capability for . . . imagery systems, that consists of an array of smaller, cheaper spacecraft in larger number with a total capacity which is at least as useful as those currently planned and to transport them to space with substantially smaller and less costly launch vehicles.”13
The extent to which those recommendations have influenced NRO’s Future Imagery Architecture plan is uncertain–although plans for large constellations of small satellites have not usually survived the budgetary process.
Document 23
Defining the Future of the NRO for the 21st Century, Final Report, Executive Summary
August 26, 1996
Unclassified
30 pp.
This report was apparently the first major outside review of the NRO conducted during the Clinton administration, and the first conducted after the NRO’s transformation to an overt institution and its restructuring were firmly in place.
Among those conducting the review were former Vice Chairman of the Joint Chiefs of Staff, Adm. David E. Jeremiah, former NRO director Martin Faga, and former Deputy Director of Central Intelligence John McMahon. Issues studied by the panel included, inter alia, the existence of a possible alternative to the NRO, NRO’s mission in the 21st Century, support to military operations, security, internal organization, and the relationship with NRO’s customers.
After reviewing a number of alternatives, the panel concluded that no other arrangement was superior for carrying out the NRO mission. It did, however, recommend, changes with regards to NRO’s mission and internal organization. The panel concluded that where the NRO’s current mission is “worldwide intelligence,” its future mission should be “global information superiority,” which “demands intelligence capabilities unimaginable just a few years ago.” The panel also recommended creation of a fourth NRO directorate, which was subsequently established, to focus solely on the development of advanced systems, in order to “increase the visibility and stature of technology innovation in the NRO.”
TOP-SCRET FROM THE HOMELAND SECURITY- Anonymous Upcoming U.S. Operations Overview

(U) The loosely organized hacking collective known as “Anonymous” has announced through several mediums that they plan on conducting cyber attacks, peaceful protests, and other unspecified activity targeting a variety of organizations. The purpose of this product is to judge the likelihood of occurrence for these events, as well as the potential impact.
(U//FOUO) Occupy Wall Street (OWS): DHS/NCCIC assesses that it is likely peaceful protests will occur on Wall Street on 17 September 2011. These protests may be accompanied by malicious cyber activity conducted by Anonymous.
(U//FOUO) Operation FaceBook (OPFB): DHS/NCCIC assesses that it is unlikely that a coordinated or sophisticated cyber attack will be conducted by Anonymous (at large) targeting FaceBook.com (FB) on 5 November 2011. However, there remains the possibility that low-level or lone-wolf attempts may occur.
(U//FOUO) Project Mayhem (PM): DHS/NCCIC assesses that a combination of inconsequential physical mischief and potentially disruptive malicious cyber activity will be conducted leading up to the culmination date of 21 December 2012. At this point, specific tactics, techniques and procedures (TTP) are unknown.
(U//FOUO) Operation Halliburton: Little is known about this potential upcoming operation. DHS/NCCIC assesses that targeting US corporations is consistent with past Anonymous targets.
(U) Anonymous has devoted resources to creating new cyber attack and exploitation tools:
(U) Anonymous claimed publicly it will be deploying a new DDoS tool called #RefRef in September. There have been several publicly disclosed tools claiming to be versions of #RefRef however there has been nothing to validate these claims.
(U//FOUO) The recent release of a distributed denial of service (DDOS) tool known as “Apache Killer,” that could be leveraged by Anonymous poses a significant risk to organizations that are operating vulnerable internet facing Apache web servers.
…
(U//FOUO) DHS/NCCIC’S OWS ASSESSMENT: The ideologies set forth by Adbusters seem to align at a basic level with the stated intent of Anonymous’ newly adopted Hacktivist agenda. These protests are highly likely to occur due to the high level of media attention garnered by the partnership between Adbusters and Anonymous, and due to the heightened media response to the San Francisco BART protests. Though the protests will likely to be peaceful in nature, like any protest, malicious individuals may use the large crowds as cover to conduct illegal activity such as vandalism. Judging based on past behaviors by the group, Anonymous’ participation in these protests may include malicious cyber activity, likely in the form of DDOS attacks targeting financial institutions and government agencies.
…
(U) Several racist, homophobic, hateful, and otherwise maliciously intolerant cyber and physical incidents throughout the past decade have been attributed to Anonymous, though recently, their targets and apparent motivations have evolved to what appears to be a hacktivist agenda.
(U) Anonymous utilizes a crude target nomination procedure, outlined below, that is coordinated on one of several communications mediums – IRC, websites (#chan, etc), insurgency wiki, or anonymous meme themed website:
1. An individual on the communications medium posts an appeal to Anonymous leadership requesting members to target a victim;
2. Those individuals who agree, follow suit with vague details given as to intentions and/or tactics;
3. “Lulz ensue,” or they don’t;
4. If “lulz ensue,” go back to step 2 and see if more people join the action, or;
5. Lose interest.
(U) Anonymous utilizes several tactics to humiliate victim individuals and organizations. The most common involve:
- “Dropping someone’s docs,” or exfiltrating information from a compromised system and posting it publicly;
- Pranks targeting victims in real life (IRL) leveraging stolen personally identifiable information (PII), such as unwanted pizza delivery, telephone or fax machine harassment, and other tactics;
- Defacing websites or social network profile pages to embarrass and/or annoy organizations; DOS / DDOS attacks.
DOWNLOAD THE ORGINAL DOCUMENT HERE
TOP-SECRET from the FBI-Sheets, Sails, and Dormer Lights: The Case of the Pearl Harbor Spy

On February 21, 1942, just 76 days after the tragic attack on Pearl Harbor, Bernard Julius Otto Kuehn (pictured) was found guilty of spying and sentenced to be shot “by musketry” in Honolulu. What was a German national doing in Hawaii in the days leading up to the attack? What exactly did Kuehn do to warrant such a sentence? Here’s the story…
Bed sheets on clothes lines. Lights in dormer windows. Car headlights. A boat with a star on its sail.
Otto Kuehn had a complex system of signals all worked out. A light shining in the dormer window of his Oahu house from 9 to 10 p.m., for example, meant that U.S. aircraft carriers had sailed. A linen sheet hanging on a clothes line at his home on Lanikai beach between 10 and 11 a.m. meant the battle force had left the harbor. There were eight codes in all, used in varying combinations with the different signals.
In November 1941, Kuehn had offered to sell intelligence on U.S. warships in Hawaiian waters to the Japanese consulate in Hawaii. On December 2, he provided specific—and highly accurate—details on the fleet in writing. That same day, he gave the consulate the set of signals that could be picked up by nearby Japanese subs.
Kuehn—a member of the Nazi party—had arrived in Hawaii in 1935. By 1939, the Bureau was suspicious of him. He had questionable contacts with the Germans and Japanese. He’d lavishly entertained U.S. military officials and expressed interest in their work. He had two houses in Hawaii, lots of dough, but no real job. Investigations by the Bureau and the Army, though, never turned up definite proof of his spying.
Not until the fateful attack of December 7, 1941. Honolulu Special Agent in Charge Robert Shivers immediately began coordinating homeland security in Hawaii and tasked local police with guarding the Japanese consulate. They found its officials trying to burn reams of paper. These documents—once decoded—included a set of signals for U.S. fleet movements.
All fingers pointed at Kuehn. He had the dormer window, the sailboat, and big bank accounts. Kuehn was arrested the next day and confessed, though he denied ever sending coded signals. His sentence was commuted—50 years of hard labor instead of death “by musketry”—and he was later deported.
Today, his story reminds us how much damage espionage can do to our country. And why the FBI continues to rank counterintelligence as a top investigative priority.
Secret-The FBI about Pearl Harbor Legacy – Remembering Robert Shivers

The attack on Pearl Harbor. Photo courtesy of the National Archives.
12/07/09
It was 68 years ago this morning—December 7, 1941—that a torrent of bombs fell on Pearl Harbor, a stealth attack that took the lives of more than 2,400 Americans and thrust the nation headlong into its second major war of the century. It was a day—filled with sacrifices and heroism—that will never be forgotten.
The contributions of one man who made a major impact in the aftermath of the attack should also not be forgotten. His name is Robert L. Shivers, and he was the special agent in charge of our office in Honolulu on that fateful day.
Shivers had been handpicked by Director J. Edgar Hoover to run the Honolulu office precisely because of his leadership skills. Smart and genteel, Shivers was minted as a special agent in 1920. After serving across the South and Midwest and in New York, the Tennessee native was tapped to lead field offices in Pittsburgh, Buffalo, and Miami. But because of nagging health issues, he went on restricted duty in the late 1930s.
 |
|
Special Agent in Charge Robert L. Shivers |
In the summer of 1939, however, Europe was on the verge of war, and with the U.S. supporting the Allied cause, the FBI was plenty busy trying to prevent espionage and sabotage at home. In August, Hoover turned to Shivers to re-open the now strategically important FBI division in Honolulu.
Shivers got to work. Within a few months, he developed strong relationships with local police as well as with Army and Navy forces, and he also began making contacts in the islands’ Japanese communities. These deepened when he and his wife began caring for a Japanese schoolgirl named Shizue Kobatake (later Suzanne or Sue). Despite the differences in their backgrounds, they became like a family.
Then came December 7. Within minutes of the attack, Shivers alerted Director Hoover, who quickly put the Bureau’s contingency war plans into effect.
For his part, Shivers—who had already made progress in sorting out the FBI’s division of intelligence and security responsibilities with the Navy—immediately placed the Japanese Consulate under police guard, both to protect the diplomats from retaliation and to prevent their escape. His agents seized a large quantity of suspiciously coded documents that consulate employees tried to hastily burn and began running down key cases of espionage i.e.of Otto Kuehn.
Another major issue involved the 150,000 people of Japanese ancestry in Hawaii—roughly a third of the population. Some argued that they should be taken into custody. Shivers and key members of the armed services and territorial government strongly disagreed and made a vital difference in preventing the kind of mass internment that happened on the mainland (which Director Hoover opposed, but that’s another story). Only a few thousand Japanese nationals considered a security risk ended up being detained.
 |
|---|
Shivers soon gained respect across the island, earning significant authority from its military governor. His only critic was a local U.S. Attorney, who thought he dealt with the Japanese on the islands “too leniently.”
History has taken a different view—and so did Shivers’ contemporaries. When his health forced him to retire in 1944, Shivers was later lauded by the territorial Senate of Hawaii both for “safeguarding Hawaii’s internal security” and for displaying “sympathy, sound judgment, and firmness.”
TOP-SECRET – THE FBI and PEARL HARBOR
Seventy years ago today—on December 7, 1941—a sneak attack on Pearl Harbor took the lives of more than 2,400 Americans, stunning the nation and catapulting it into war.
For the FBI, the attack and the onset of war opened a new chapter in national security. Even as Japanese bombs rained down, FBI Special Agent in Charge Robert Shivers in Honolulu was patched through via telephone to Director J. Edgar Hoover, who immediately put the Bureau on a 24/7 wartime footing according to its already well-made plans. In the days and months that followed, the FBI diligently and successfully worked to protect the American homeland from spies and saboteurs, building important new capabilities along the way.
Pearl Harbor Attack Mobilizes FBI War Plans
On December 7, 1941—as bombs fell on American battleships at Pearl Harbor—Robert L. Shivers, Special Agent in Charge of the FBI’s Honolulu office, was on the phone. Headquarters relayed his anxious call to New York, where Director Hoover was visiting.
“The Japanese are bombing Pearl Harbor. It’s war,” Shivers said. “You may be able to hear it yourself. Listen!”
Director Hoover immediately flew back to Washington, mindful of the plans that his agency had made for this eventuality. Some 2,400 brave U.S. sailors had already died in the early hours of that fateful Sunday.
The attack was a surprise; that Japan was readying war against America was not. Contingency plans had been made throughout the U.S. government, and they were immediately implemented to ensure American security in the weeks, months, and years after the surprise attack.
And what about FBI plans? What had the Bureau set in place in the event of war?
- It had made the investigation of sabotage, espionage, and subversion a top priority—and agents made surveys of industrial plants that were vital to American security in order to prevent sabotage and espionage.
- It had expanded its intelligence programs, including undercover work in South and Central America to identify Nazi spies.
- It had performed—and continued to perform—exhaustive background checks on federal workers, to keep enemy agents from infiltrating the government.
- It had been directed to draw up plans for a voluntary board, turned over to and headed by a newspaperman, to review media stories in order to prevent information from being released that might harm American troops. Mindful of free speech protections, this independent board operated with the voluntary cooperation of the media.
- It had expanded the number of professionally trained police through its National Academy program to aid the Bureau in times of crisis. This cadre of professionals effectively forestalled well-meaning but overzealous civilian plans to “help” law enforcement with vigilantism. The FBI had learned a lesson from World War I when groups like the American Protective League abused the civil rights of Americans in its efforts to identify German spies, draft resisters, and other threats.
- And it had identified German, Italian, and Japanese aliens who posed a clear threat to the United States in the event of war so that when President Roosevelt ordered it—and he did, on the evening of December 7—the Bureau could immediately arrest these enemies and present them to immigration for hearings (represented by counsel) and possible deportation. A few—like Bernard Julius Otto Kuehn, the German national involved in signaling the Japanese invasion fleet headed for Pearl Harbor—were arrested and prosecuted for espionage and other crimes against the U.S.
- Now, on December 7, it immediately implemented a 24/7 schedule at Headquarters and in its field operations.
What was the upshot? By war’s end the FBI had captured hundreds of Axis agents, investigated more than 16,000 sabotage cases, and handled all of its other criminal responsibilities besides. It had played a significant role in keeping Americans safe and free.
TOP-SECRET – U.S. Army Commander’s Guide to Female Engagement Teams

Complex operations often require the development of specialized teams with multidisciplinary perspectives. Examples of these groups include human terrain teams, provincial reconstruction teams, and, most recently, female engagement teams (FETs). These specialized programs are tasked with engaging local populations to ascertain information on civil-society needs and problems; address security concerns; and to form links between the populace, military, and interagency partners.
History has taught us that most insurgent fighters are men. But, in traditional societies, women are extremely infl uential in forming the social networks that insurgents use for support. Co-opting neutral or friendly women — through targeted social and economic programs — builds networks of enlightened self-interest that eventually undermines the insurgents. To do this effectively requires your own female counterinsurgents. Win the women, and you own the family unit. Own the family, and you take a big step forward in mobilizing the population on your side.
Men, women, and children are part of the triangle of knowledge that must be targeted for information collection. In Afghanistan, we observe rather consistent themes. Men interpret information and tell you what they think you want to hear. Women see and hear what goes on behind the walls. Children run free in the community and see, watch, and are involved in nearly every activity in the community.
…
Initial Female Engagement Team Concept
FETs are not a new concept in Afghanistan. They have existed in one form or another for more than nine years. Civil affairs teams have performed this type of mission on a regular basis for years in both Afghanistan and Iraq, along with countries like Bosnia and Kosovo, but not under that name. The Marines picked up on the FET concept and employed it on a large scale well before the Army and they have had great success using it. Currently, there is little consistency in the FET programs between deployed Army brigade combat teams (BCTs) in Afghanistan. The BCTs are having varying degrees of success in contributing to the information repository covering the total Afghan population that is required to be understood as part of the COIN environment. The Army has been slow picking up on the FET concept; it is now being codifi ed and an Army wide FET training program is being developed based on the U.S. Army Special Operations Command (USASOC) Cultural Support Team (CST) program.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – City of London Police Occupy London Domestic Terrorism/Extremism Warning

These are photos and the text of a bulletin disseminated to local businesses by the City of London Police warning of possible extremist/terrorist threats arising from the Occupy London protests.
Terrorism/Extremism update for the City of London Business community
2 December 2011
The threat to the UK from international terrorism is SUBSTANTIAL.
The threat to Great Britain from Irish Republican Terrorism is SUBSTANTIAL.
UK/International
Columbia: The Revolutionary Armed Forces of Columbia (FARC) killed four of its longest held captives on Saturday during combat with Columbian forces. A fifth hostage allegedly survived after fleeing into the jungle after being held captive for 12 years, in what has been reported as a failed rescue attempt. It is FARC policy to kill prisoners if rescue attempts are made.
Al Qaeda/Pakistan: Al Qaeda has reportedly been holding Warren Weinsten, a 70-year-old American aid worker, hostage in Pakistan for three months. The al Qaeda leader, Ayman al-Zawahiri has said in a video that Weinstein would be released only if the US ceases its air strikes on Pakistan and Afghanistan and frees prisoners. The video offered no evidence that the aid worker is still alive.
Belarus: Two men have been sentenced to death for bombing the underground railway in the capital, Minsk, earlier this year. The attack on 11 April killed 15 people and wounded hundreds of others. Dmity Konovalov, 25, was found guilty of carrying out the explosion and Vladislav Kovalyov, also 25, of assisting in an act of terrorism. They were also found guilty of involvement in three earlier bomb attacks in 2005 and 2008, which together injured more than 100 people.
Domestic
Occupy London, ongoing
The Occupy London sites at St Paul’s Cathedral and Finsbury Square remain in place with the number of protesters present remaining fairly consistent. The majority of peaceful demonstrators from the St Paul’s camp appear to have moved on to the other camps. Demonstrations originating from the camp have decreased and lacked the support and momentum of earlier actions.
There are now three ‘Occupations’ by activists in or near the City of London. As the worldwide Occupy movement shows no sign of abating, it is likely that activists aspire to identify other locations to occupy, especially those they identify capitalism. City of London Police has received a number of hostile reconnaissance reports concerning individuals who would fit the anti-capitalist profile.
All are asked to be vigilant regarding suspected reconnaissance, particularly around empty buildings. Any signs of access or new markings should also be reported. You may encounter an increase in persons filming for the purpose of national or activist media. All are reminded that any encounters with suspected activists could be recorded and then uploaded or live-streamed to the internet.
Intelligence suggests that urban explorers are holding a discussion at the Sun Street squat. This may lead to an increase in urban exploration activity at abandoned or high profile sites in the capital.
Suspected hostile reconnaissance should be reported to the City of London Police immediately.
Climate Justice Collective, 3 December
‘Stand Up for Climate Justice’ is holding a vigil on the bank of the Thames from 11.30pm to 1.00am Friday Night, as well as climate prayers at 11.30am Saturday morning at St. Mary Le Bow church, Cheapside.
Saturday continues with a ‘Walk of Shame’ past alleged environmental and economic justice offenders along with a ‘teach-out’. This meets at St Paul’s at 10.30am, and is followed by a march to Parliament, meeting at Blackfriars Bridge at 12.00pm. Around 2.30pm the march will congregate outside Parliament. The event is planned to finish around 3.30pm.
The Canary Wharf Experience, 6 December
Occupy London will meet at St Paul’s around 4.15opm, from which they will attend and ‘tour’ Canary Wharf.
Electrician’s Strike, 7 December
Electricians will be takingindustrial action at Balfour Beatty sites across the country.
SHAC ‘Santa SHAC Supplier Shakedown week of action’, 5-11 December
Stop Huntingdon Animal Cruelty has advertised a week of action between these dates. It is expected that SHAC protesters will visit the customary targets during the period.
Ensure that your own security arrangements are adequate and robust at all times. Report any suspicious activity to Police immediately.
Confidential Anti Terrorist Hotline: 0800 789 321 or dial 999


TOP-SECRET – Detainee Provisions in the National Defense Authorization Bills
Both House and Senate bills competing to become the National Defense Authorization Act for FY2012 contain a subtitle addressing issues related to detainees at the U.S. Naval Station at Guantanamo Bay, Cuba, and more broadly, hostilities against Al Qaeda and other entities. At the heart of both bills’ detainee provisions appears to be an effort to confirm or, as some observers view it, expand the detention authority that Congress implicitly granted the President via the Authorization for Use of Military Force (AUMF, P.L. 107-40) in the aftermath of the terrorist attacks of September 11, 2001.
H.R. 1540, as passed by the House of Representatives on May 26, 2011, contains provisions that would reaffirm the conflict and define its scope; impose specific restrictions on the transfer of any non-citizen wartime detainee into the United States; place stringent conditions on the transfer or release of any Guantanamo detainee to a foreign country; and require that any foreign national who has engaged in an offense related to a terrorist attack be tried by military commission if jurisdiction exists.
Shortly before H.R. 1540 was approved by the House, the White House issued a statement regarding its provisions. While supportive of most aspects of the bill, it was highly critical of those provisions concerning detainee matters. The Administration voiced strong opposition to the House provision reaffirming the existence of the armed conflict with Al Qaeda and arguably redefining its scope. It threatened to veto any version of the bill that contains provisions that the Administration views as challenging critical executive branch authority, including restrictions on detainee transfers and measures affecting review procedures.
In June, the Senate Armed Services Committee reported its initial version of the bill, S. 1253. The bill included many provisions similar to the House bill, but also included a provision requiring the military detention of certain terrorist suspects. After the White House and the chairs of other Senate committees objected to some of the provisions, Senate Majority Leader Reid delayed consideration of S. 1253 pending a resolution of the disputed language. The Senate Armed Services Committee reported a second version of the authorization bill on November 15, 2011, addressing some, but not all of the concerns. The new bill, S. 1867, would authorize the detention
of certain categories of persons and require the military detention of a subset of them; regulate status determinations for persons held pursuant to the AUMF, regardless of location; regulate periodic review proceedings concerning the continued detention of Guantanamo detainees; and continue current funding restrictions that relate to Guantanamo detainee transfers to foreign countries. Unlike the House bill, the Senate bill would not bar the transfer of detainees into the United States for trial or perhaps for other purposes.Despite the revisions to the detainee provisions, the Administration threatened to veto “any bill that challenges or constrains the President’s critical authorities to collect intelligence, incapacitate dangerous terrorists, and protect the Nation.”
This report offers a brief background of the salient issues raised by H.R. 1540 and S. 1867 regarding detention matters, provides a section-by-section analysis of the relevant subdivision of each bill, and compares the bills’ approaches with respect to the major issues they address.
DOWNLOAD ORIGINAL DOCUMENT HERE
FBI – Virginia Man Pleads Guilty to Providing Material Support to Terrorist Organization
ALEXANDRIA, VA—Jubair Ahmad, 24, a native of Pakistan and resident of Woodbridge, Va., pleaded guilty today to providing material support to Lashkar-e-Tayyiba (LeT), a designated foreign terrorist organization.
Neil H. MacBride, U.S. Attorney for the Eastern District of Virginia; Lisa Monaco, Assistant Attorney General for National Security; and James W. McJunkin, Assistant Director in Charge of the FBI’s Washington Field Office, made the announcement after the plea was accepted by U.S. District Judge T.S. Ellis III.
Ahmad faces a maximum penalty of 15 years in prison when he is sentenced on April 13, 2012.
“Foreign terrorist organizations such as LeT use the Internet as part of well-orchestrated propaganda campaigns to radicalize and recruit individuals to wage violent jihad and to promote the spread of terror,” said U.S. Attorney MacBride. “Today’s conviction of Jubair Ahmad demonstrates that we will aggressively investigate and prosecute anyone who provides material support to a terrorist organization in whatever form it takes.”
“This prosecution sheds light on some of the methods terrorist organizations employ to produce and publish their extremist propaganda,” said Assistant Attorney General Monaco. “Today, Jubair Ahmad is being held accountable for his role in providing this form of material support to Lashkar-e-Tayyiba.”
“By preparing and posting a graphic video that glorified violent extremism, Mr. Ahmad directly supported the mission of a designated terrorist organization,” said FBI Assistant Director in Charge McJunkin. “The FBI will track down and disrupt those who communicate with terrorist groups for the purpose of recruiting others to inflict harm on the U.S. and its interests overseas.”
LeT, or “Army of the Pure,” serves as the military arm of the political movement Markaz al-Dawa wal-Irshad in Pakistan. The mission of LeT is to conduct and promote violent jihad against those considered to be the enemies of Islam. On Dec. 24, 2001, the U.S. Department of State designated LeT as a foreign terrorist organization. The focus of LeT operations has been attacks on the neighboring country of India, in particular the disputed region of Kashmir between Pakistan and India.
According to a statement of facts filed with the plea agreement, Ahmad was born and raised in Pakistan and in 2007, after receiving a visa from the U.S. Department of State, Ahmad moved from Pakistan to the United States with his family.
Ahmad admitted today that in September 2010, while at his residence in Woodbridge, he engaged in a series of communications with an individual named Talha Saeed, who was in Pakistan. Talha Saeed is the son of Hafiz Muhammad Saeed, the leader of LeT. Talha Saeed requested Ahmad to prepare a video that would contain a prayer by Hafiz Saeed calling for the support of jihad and the mujahideen. In addition, Talha Saeed instructed Ahmad to present a variety of violent images on the video while Hafiz Saeed’s prayer is heard in the background.
Talha Saeed directed Ahmad to begin the LeT video with a number of pictures of Hafiz Saeed, then show scenes where atrocities have been inflicted on Muslims, followed by the activities of the mujahideen conducting attacks in Kashmir. At one point, Ahmad asked Talha Saeed if he wanted to include an image of the Mumbai attack to show the power of LeT. This is a reference to LeT’s operation against the city of Mumbai, India, on Nov. 26, 2008, which resulted in the death of over 160 people, including six Americans. Talha replied that he should not use anything referring to Mumbai.
Ahmad admitted that Talha Saeed told him to search for “Lashkar-e-Taiba” on YouTube to find additional images of mujahideen operations to include in the video. Talha Saeed further stated that the video will be popular in Pakistan and will run continuously on significant media programs and presentations.
On Sept. 25, 2010, Ahmad completed the LeT video and uploaded it to a YouTube account on the Internet. The next day, Ahmad sent a communication to another person overseas in which he explained that “Hafiz Saeed’s son Talha Saeed” had requested him to prepare the video. Forensic examination by the FBI subsequently confirmed that Ahmad had constructed the LeT video on his computer.
This case is being investigated by the FBI’s Washington Field Office. Assistant U.S. Attorney Stephen M. Campbell from the National Security and International Crimes Unit of the Eastern District of Virginia and Trial Attorney John T. Gibbs from the Counterterrorism Section of the National Security Division in the U.S. Department of Justice are prosecuting the case on behalf of the United States.
CONFIDENTIAL-California Redbook Law Enforcement Guide for Emergency Operations


The California Emergency Management Agency’s original Law Enforcement Guide for Emergency Operations was developed in response to the need for standardization and uniformity of organization and response on the part of law enforcement agencies involved in major multi-jurisdictional and multi-agency incidents such as a civil disorder, technological disaster, or natural disaster.
The revised and expanded 2009 Law Enforcement Guide for Emergency Operations is designed to be a practical field-oriented guide to assist law enforcement personnel throughout the State of California with implementation of the Field Level Incident Command System. The intended primary users of this guide are watch commanders and field supervisors. The guide can also be an excellent emergency response tool for law enforcement managers, as well as line officers and deputies.
This updated edition incorporates the concept and statutory requirement of the Standardized Emergency Management System (SEMS). Additionally, the Law Enforcement Incident Command System (LEICS), as approved by the SEMS Law Enforcement Specialist Committee, is presented in this publication. Please disregard earlier editions of this guide. The Law Enforcement Guide for Emergency Operations is organized in a user-friendly format consisting of overview text, diagrams, organization charts, checklists, forms, and a glossary. Several sections are suitable for photocopying and distribution to field personnel. Our ultimate goal is to provide practical guidance for California law enforcement agencies in using the SEMS and LEICS organizational framework for efficient and safe response, management, and coordination of major emergencies and disasters.
DOWNLOAD ORGINAL DOCUMENT HERE
TOP-SECRET-IMF Bermuda Anti-Money Laundering and Terrorist Financing Report
This assessment of the anti-money laundering (AML) and combating the financing of terrorism (CFT) regime of Bermuda is based on the Forty Recommendations 2003 and the Nine Special Recommendations on Terrorist Financing 2001 of the Financial Action Task Force (FATF). It was prepared using the AML/CFT assessment Methodology 2004, as updated in June 2006. The assessment team considered all the materials supplied by the authorities, the information obtained on-site during their mission from May 7 to 23, 2007, and other information subsequently provided by the authorities soon after the mission. During the mission, the assessment team met with officials and representatives of all relevant government agencies and the private sector. A list of the bodies met is set out in Annex 1 to the detailed assessment report.
The assessment was conducted by a team of assessors composed of staff of the International
Monetary Fund (IMF) and three expert(s) acting under the supervision of the IMF. The evaluation
team consisted of: Manuel Vasquez (LEG, team leader and financial sector expert); Antonio
Hyman-Bouchereau (LEG, legal expert); Ross Delston (legal expert under LEG supervision,
lawyer); and John Abbott (expert under LEG supervision, Designated Non-Financial Businesses
and Professions) (DNFBP). The assessors reviewed the institutional framework, the relevant
AML/CFT laws, regulations, guidelines and other requirements. The mission also reviewed the
regulatory and other institutional systems in place to counter money laundering (ML) and the
financing of terrorism (FT) through financial institutions (FIs) and DNFBP. The assessors also
examined the capacity, implementation, and effectiveness of all these systems.This report provides a summary of the AML/CFT measures in place in Bermuda at the time
of the mission and shortly thereafter. It describes and analyzes those measures, sets out Bermuda’s
levels of compliance with the FATF 40+9 Recommendations (see Table 1) and provides
recommendations on how certain aspects of the system could be strengthened (see Table 2). The
report was produced by the IMF as part of the assessment of Bermuda under the Offshore Financial
Center Assessment Program (OFC). It was presented to the Caribbean Financial Action Task Force
(CFATF) and endorsed by this organization at ministerial meeting in November, 2007.…
Preventive Measures–—Financial Institutions
9. The scope of the AML regulatory framework does not address CFT issues, and does
not cover key areas of the financial sector, including life insurance business and certain
elements of the investment/mutual funds sector. The lack of coverage in these areas constitutes
an important deficiency in Bermuda’s AML/CFT regime, particularly in light of its role in the
international financial system, even though life insurance does not account for the largest share of
this sector. The POC Regulations and GNs remain practically unchanged since the last IMF
assessment mission in 2003; this in spite of the weaknesses previously identified, a major upgrade of the international AML/CFT standards in 2003, and continued growth in the financial services
industry. At the time of the mission, the authorities had prepared draft new Regulations and were
contemplating amending the GNs, pending passage of proposed new legislation that was passed
subsequent to the mission in June 2007.….
3.4 Financial institution secrecy or confidentiality (R.4)
3.4.1 Description and Analysis
Legal Framework:
337. Inhibition of Implementation of FATF Recommendations (c. 4.1): Bermuda has no general statutory law on secrecy other than with respect to the regulatory laws discussed below and the common law
principles of confidentiality that apply to the customers of banks and other FIs. The authorities have cited the leading precedent on confidentiality, an English Court of Appeal case, Tournier v. National Provincial and Union Bank of England [1924] 1KB461 which, according to a leading text on the issue, held that – “. . . a bank owes to its customer an implied contractual duty to keep his affairs secret, but that the duty is qualified. The duty arises at the commencement of the relationship and continues after the customer has closed his account in relation to information gained during the period of the account. It covers information about the customer’s affairs gained by virtue of the banking relationship and is not limited to information from or about the account itself.”R. G. Toulson and C. M. Phipps, Confidentiality, 2nd ed. (Sweet & Maxwell, 2006), p. 257.
338. There are four qualifications, or exceptions to this duty:
(a) Where disclosure is under compulsion by law; (b) where there is a duty to the public to disclose; (c) where the interests of the bank require disclosure; (d) where the disclosure is made by the express
or implied consent of the customer.Tournier, at 471-472 and 473, cited in Toulson and Phipps, p. 258.
339. According to the authorities, Bermudian case law has followed this precedent, one example being Brian Lines v. Lines Overseas Management Ltd. [2006] Bda LR 43, 236, at 242.
340. The exception relating to disclosure under compulsion by law is embodied in a number of places in Bermudian statutory law. All of the five regulatory laws (the only exception being the MSB Regulations)
provide for confidentiality of information with gateways to the authorities. The Banks and Deposit Companies Act 1999 is typical: Section 52(1) provides that “no person who under or for the purposes of this Act receives information relating to the business or other affairs of any person; and . . . no person who obtains such information directly or indirectly from a person who has received it as aforesaid, shall disclose the information without the consent of the person to whom it relates and (if different) the person from whom it was received as aforesaid.” Disclosure of information in contravention of the statute is a criminal offense with penalties of up to $100,000 and five years imprisonment or both, under Section 52(3). Subsequent sections have a series of gateways allowing disclosure of information to the BMA, the Minister of Finance, the DPP and police, as well as disclosures by them to foreign authorities. See Sections 53 – 55. See also Sections 52, 52A, 52B, 52C of the Insurance Act 1978, Sections 78 – 81 of the Investment Business Act 2003, Sections 68 – 71 of the Investment Funds Act 2006, and Sections 48 – 51 of the Trusts (Regulation of Trust Business) Act 2003.341. However, there is no explicit gateway in any of these laws for disclosures to the FIA, since it was not in existence at the time those laws were enacted and therefore consideration should be given to remedying this deficiency by amending relevant laws.
…
352. Obtain Originator Information for Wire Transfers (applying c. 5.2 & 5.3 in R.5, c.VII.1):
Customer identification for one-off transactions below the equivalent of US$10,000 (BD$10,000) are not covered by CDD (identification) requirements in the regulations or otherwise. Consequently, wire transfers between the equivalent of US$1,000 and US$9,999 are not subject to customer identification requirements and hence FIs are not required to obtain and maintain full originator information. For wire transactions above US$10,000, the non-mandatory Guidance Notes (G94 to G98) set out the type of detail records that should be maintained to identify a customer, but do not specify such details to include account numbers, address or other substitute information as allowed for by SRVII. G98 only states that FIs should retain records of electronic payments with “sufficient detail” to enable them to establish the identity of the remitting customer and as far as
possible the identity of the ultimate recipient. While not specific to wire transfers, such detail may be available
in the Guidance Notes under Methods of Verification (G56 to G70) which include address, date of birth and
other information. In discussions with banks, there appears to be no restrictions in law or practice on the
inclusion of names and account numbers in outgoing wire transfers.DOWNLOAD ORIGINAL REPORT HERE
TOP-SECRET-United Kingdom “Contest” Strategy for Countering Terrorism 2011
1.1 This is the third published version of the United Kingdom’s counter-terrorism strategy, CONTEST. This new strategy reflects the changing terrorist threat and incorporates new Government policies on counter-terrorism.
1.2 The aim of CONTEST is to reduce the risk to the UK and its interests overseas from terrorism, so that people can go about their lives freely and with confidence.
Strategic context
1.3 Last year, over 10,000 people were killed by terrorists around the world. But international law enforcement and military collaboration are changing the threats we face.
1.4 The leadership of Al Qa’ida is now weaker than at any time since 9/11. It has played no role in recent political change in North Africa and the Middle East. Its ideology has been widely discredited and it has failed in all its objectives. Continued international pressure can further reduce its capability. But Al Qa’ida continues to pose a threat to our own security; and groups affiliated to Al Qa’ida – notably in Yemen and Somalia – have emerged over the past two years to be a substantial threat in their own right.
1.5 Al Qa’ida is responsible for only a small fraction of terrorist attacks. Other groups, independent from Al Qa’ida but broadly sympathetic to its aims, continue to emerge and to conduct attacks around the world.
1.6 We judge that four factors will continue to enable terrorist groups to grow and to survive: conflict and instability; aspects of modern technology; a pervasive ideology; and radicalisation.
1.7 The threats we face here reflect global trends. Al Qa’ida, groups affiliated to Al Qa’ida, other terrorist groups and lone terrorists have all tried to operate in this country. Some have planned attacks here which we have disrupted. Others have recruited people for attacks overseas, spread propaganda and raised funds.
1.8 The threat level in the UK from international terrorism has been SEVERE for much of the period, meaning that we judge a terrorist attack in the UK to be ‘highly likely’. Threat levels continue to be set independently by JTAC.
1.9 For much of this period the greatest threat to the UK has come from terrorist groups based in Pakistan. British nationals (amongst hundreds of other Europeans) are training or operating in Pakistan and some intend to travel to Afghanistan. But over the past 12 months, the threat to UK interests from terrorists in Yemen and Somalia has significantly increased. People from the UK are also travelling to these countries to engage in terrorist related activity; some are returning to the UK to plan and conduct terrorist operations.
1.10 Over the past two years the threat from Northern Ireland Related Terrorism (NIRT) has also grown: there were 40 terrorist attacks in Northern Ireland in 2010 and there have been 16 terrorist attacks in Northern Ireland up to 30 June 2011.1 The threat from NIRT to Great Britain has increased.
1.11 Between January 2009 and December 2010 over 600 people were arrested for terrorist related activity in the UK. This is more than in any other European country. 67 people have been prosecuted and 58 people convicted for terrorist related offences.
Our response
1.12 Our counter-terrorism strategy will continue to be organised around four workstreams, each comprising a number of key objectives
• Pursue: to stop terrorist attacks;
• Prevent: to stop people becoming terrorists or supporting terrorism;
• Protect: to strengthen our protection against a terrorist attack; and
• Prepare: to mitigate the impact of a terrorist attack.1.13 The Strategic Defence and Security Review (SDSR) emphasises the need to tackle the root causes of instability. This approach is reflected in contest. For terrorism we need to address not only the immediate threat of attacks but the longer term factors which enable terrorist groups to grow and flourish. Some of these factors cannot be addressed within a counter-terrorism strategy and are much wider Government priorities. Coordination between CONTEST and other government programmes is essential. Working closely with other countries will remain a priority.
1.14 CONTEST will reflect our fundamental values and, in particular, our commitment not only to protect the people of this country and our interests overseas but to do so in a way that is consistent with and indeed advances our commitment to human rights and the rule of law. Our strategy will be proportionate to the risks we face and only engage in activity which is necessary to address those risks. It will be transparent: wherever possible and consistent with national security we will seek to make more information available in order to help the public to hold the Government to account over its policy and spending decisions.
1.15 We recognise that success has been achieved through international collaboration. That will continue to be the case in future.
Pursue
1.16 The purpose of Pursue is to stop terrorist attacks in this country and against our interests overseas. This means detecting and investigating threats at the earliest possible stage, disrupting terrorist activity before it can endanger the public and, wherever possible, prosecuting those responsible.
1.17 In 2011-2015 we want to:
• Continue to assess our counter-terrorism powers and ensure they are both effective and proportionate;
• Improve our ability to prosecute and deport people for terrorist-related offences;
• Increase our capabilities to detect, investigate and disrupt terrorist threats;
• Ensure that judicial proceedings in this country can better handle sensitive and secret material to serve the interests of both justice and national security; and
• Work with other countries and multilateral organisations to enable us to better tackle the threats we face at their source.…
2.48 Terrorists continue to use new technologies to communicate propaganda. While radicalisation continues to primarily be a social process involving contact between vulnerable people and radicalisers (not least because internet penetration in many countries with a high incidence of terrorism is still low) – the internet provides radicalisers with a vast range of materials to use once the process of radicalisation has begun. It allows for secure communication between private communities in which extremist ideas are shared and become normalised within that community. The internet also extends the reach of ideologues overseas, enabling them to preach to groups and reinforce messages of violence.
2.49 Use of social networking sites and video sharing is now commonplace. There have been a number of attempts by terrorist and extremist groups to ‘invade’ Facebook. Twitter will be used to repost media or forum articles enabling extremist content to be shared more quickly, widely and amongst people who would not normally search for extremist content. Estimates of the number of terrorism-related websites, made by experts in the field, range from several hundred to several thousand. It is clear that a few dozen are highly influential and frequented by terrorists.
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET-Israel’s Dubai Assassination in Photos
 The mother of Palestinian militant Mahmoud al-Mabhouh, who was recently killed, holds up a photo of him at their home in the Jebaliya refugee camp, northern Gaza Strip, Friday, Jan. 29, 2010. Hamas claimed on Friday that Israeli agents assassinated one of the Palestinian militant group’s veteran operatives in a killing allegedly carried out last week in Dubai, and vowed to retaliate. (AP Photo/Hatem Moussa)
The mother of Palestinian militant Mahmoud al-Mabhouh, who was recently killed, holds up a photo of him at their home in the Jebaliya refugee camp, northern Gaza Strip, Friday, Jan. 29, 2010. Hamas claimed on Friday that Israeli agents assassinated one of the Palestinian militant group’s veteran operatives in a killing allegedly carried out last week in Dubai, and vowed to retaliate. (AP Photo/Hatem Moussa) Father of senior Hamas military commander Mahmoud al-Mabhouh poses with his son’s picture at his family house in the northern Gaza Strip January 29, 2010. Israel assassinated al-Mabhouh, who played a major role in a Palestinian uprising in the 1980s, in Dubai, an official in the Islamist group said on Friday. Israeli officials had no immediate comment. REUTERS/Mohammed Salem
Father of senior Hamas military commander Mahmoud al-Mabhouh poses with his son’s picture at his family house in the northern Gaza Strip January 29, 2010. Israel assassinated al-Mabhouh, who played a major role in a Palestinian uprising in the 1980s, in Dubai, an official in the Islamist group said on Friday. Israeli officials had no immediate comment. REUTERS/Mohammed Salem Three suspects in the killing of Hamas militant, Mahmoud al-Mabhouh are shown in this CCTV handout from Dubai police February 15, 2010. Israel’s foreign minister said on Wednesday the use of the identities of foreign-born Israelis by a hit squad suspected of killing Hamas militant, Mahmoud al-Mabhouh, in Dubai did not prove the Mossad spy agency assassinated him. Men with the same names as seven of the 11 suspects whose European passport photos were distributed by Dubai live in Israel, and those reached by reporters insisted their identities had been stolen and noted the pictures were not a match. Handout dated February 15, 2010. REUTERS/Dubai Police/Handout
Three suspects in the killing of Hamas militant, Mahmoud al-Mabhouh are shown in this CCTV handout from Dubai police February 15, 2010. Israel’s foreign minister said on Wednesday the use of the identities of foreign-born Israelis by a hit squad suspected of killing Hamas militant, Mahmoud al-Mabhouh, in Dubai did not prove the Mossad spy agency assassinated him. Men with the same names as seven of the 11 suspects whose European passport photos were distributed by Dubai live in Israel, and those reached by reporters insisted their identities had been stolen and noted the pictures were not a match. Handout dated February 15, 2010. REUTERS/Dubai Police/Handout Hamas militant, Mahmoud al-Mabhouh (ringed), is shown arriving at his hotel in this CCTV handout from Dubai police February 15, 2010. Israel’s foreign minister said on Wednesday the use of the identities of foreign-born Israelis by a hit squad suspected of killing Hamas militant, Mahmoud al-Mabhouh, in Dubai did not prove the Mossad spy agency assassinated him. Men with the same names as seven of the 11 suspects whose European passport photos were distributed by Dubai live in Israel, and those reached by reporters insisted their identities had been stolen and noted the pictures were not a match. Handout dated February 15, 2010. REUTERS/Dubai Police/Handout
Hamas militant, Mahmoud al-Mabhouh (ringed), is shown arriving at his hotel in this CCTV handout from Dubai police February 15, 2010. Israel’s foreign minister said on Wednesday the use of the identities of foreign-born Israelis by a hit squad suspected of killing Hamas militant, Mahmoud al-Mabhouh, in Dubai did not prove the Mossad spy agency assassinated him. Men with the same names as seven of the 11 suspects whose European passport photos were distributed by Dubai live in Israel, and those reached by reporters insisted their identities had been stolen and noted the pictures were not a match. Handout dated February 15, 2010. REUTERS/Dubai Police/Handout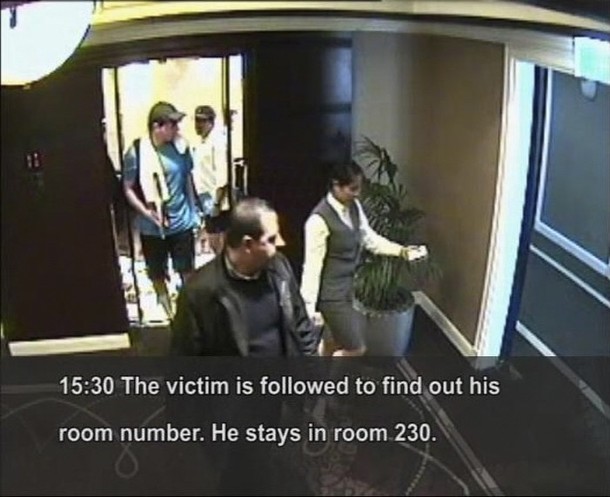 Hamas militant, Mahmoud al-Mabhouh (bottom), is shown being followed by his alleged killers in this CCTV handout from Dubai police February 15, 2010. Israel’s foreign minister said on Wednesday the use of the identities of foreign-born Israelis by a hit squad suspected of killing Hamas militant, Mahmoud al-Mabhouh, in Dubai did not prove the Mossad spy agency assassinated him. Men with the same names as seven of the 11 suspects whose European passport photos were distributed by Dubai live in Israel, and those reached by reporters insisted their identities had been stolen and noted the pictures were not a match.
Hamas militant, Mahmoud al-Mabhouh (bottom), is shown being followed by his alleged killers in this CCTV handout from Dubai police February 15, 2010. Israel’s foreign minister said on Wednesday the use of the identities of foreign-born Israelis by a hit squad suspected of killing Hamas militant, Mahmoud al-Mabhouh, in Dubai did not prove the Mossad spy agency assassinated him. Men with the same names as seven of the 11 suspects whose European passport photos were distributed by Dubai live in Israel, and those reached by reporters insisted their identities had been stolen and noted the pictures were not a match.
TOP-SECRET – Mossad Dubai Assassins Travel Routes Maps
TOP-SECRET – IMF Report on Switzerland Fiscal Transparency
I. INTRODUCTION
1. This report provides an assessment of the fiscal transparency practices of Switzerland against the requirements of the IMF Code of Good Practices on Fiscal Transparency (2007). The first part is a description of practices, prepared by IMF staff on the basis of discussions with the authorities and their responses to the fiscal transparency questionnaire, and drawing on other available information. The second part is an IMF staff commentary on fiscal transparency in Switzerland. The two appendices summarize the staff’s assessments, comment on the observance of good practices, and document the public availability of information.
2. This assessment focuses primarily on fiscal transparency at the central
government (confederation) level. Given the unique character of political economy and
fiscal federalism in Switzerland, and that less than a third of general government expenditure
or revenue is accounted for by the confederation, this does not give a complete picture.
Cantons are responsible for important areas of economic and social policy, and have a strong
influence on the composition and impact of public spending, and the overall stance of fiscal
policy. Further work would be needed to prepare a comprehensive assessment of fiscal
transparency and fiscal risk covering the whole of general government.II. DETAILED DESCRIPTION OF PRACTICE
A. Clarity of Roles and Responsibilities
Definition of government activities
3. General government is defined consistently with Government Finance Statistics
(GFS) principles and is well covered in the budget process. 1.1.1
General government is defined in accordance with the principles of the Government Finance
Statistics Manual (GFSM 2001) and comprises four main sectors (Box 1): The federal
government comprises seven departments and related offices, the federal chancellery, and
four special funds. The special funds cover (i) railway projects; (ii) infrastructure;
(iii) technical universities; and (iv) the alcohol board. There are 26 cantonal governments.
The cantons are sovereign states with considerable autonomy. There are 2715 communes,
which likewise have considerable autonomy. The four social security institutions cover
(i) old age and survivors protection schemes; (ii) the disability protection scheme;
(iii) income compensation allowances in case of mandatory service and maternity; and
(iv) unemployment insurance. These schemes operate essentially on a pay-as-you-go basis.…
Box 2. The SNB’s Support for UBS as a Quasi-Fiscal Activity
The SNB has justified its recent support of UBS in relation to its role as lender-of-the-last resort. This explanation rests on three considerations, namely: that UBS is a systemically important institution; could provide sufficient collateral; and was solvent. On the last point, the SNB obtained advice from the Federal Banking Commission that UBS was solvent, enabling it to provide emergency support. It did so by funding 90 percent of the purchase price of distressed assets to the value of US$60 billion.1 These assets were valued by external assessors, and transferred to a Special Purpose Vehicle (SPV) under the SNB’s control. To reduce the risks of not fully recovering the funds of the SPV, the SNB has set up several safeguards against potential losses. UBS’ equity contribution to the stabilization fund, amounting to 10 percent of the assets purchased, serves as the primary loss protection. In the case of a loss on the SNB loan, the SNB’s warrant for 100 million UBS shares serves as secondary loss protection. This transaction should be classified as a QFA given the risk that the SNB may fail to recover all of its investment. In this case, the profits of the SNB distributed to the federal government would be lower, with a negative impact on the budget.
________________________
1/ On February 10, 2009, it was announced that the stabilization fund would acquire UBS assets for a lower
maximum amount than originally planned (approximately US$ 40 billion).…
68. There are some areas, however, where the authorities could consider taking
further measures, in consultation with parliament where appropriate, to enhance fiscal
transparency and the presentation and management of fiscal risks. These are summarized
below.Disclosure of additional fiscal information by the federal government
69. Support provided by the federal government and the SNB to UBS and other
financial institutions affected by the global crisis is reported in, respectively, the
confederation’s and the SNB’s financial statements, supplemented by quarterly updates
by the SNB. However, in order to provide a comprehensive assessment, the federal
government should consider publishing in its financial statements information on the SNB’s
support operations alongside the report of its own activities.70. The government should publish its findings on tax expenditures and regularly
update them. Tax expenditures do not need to be appropriated each year, thereby escaping
scrutiny and the need to compete with other fiscal priorities in the budget process. Over time,
tax expenditures can result in insidious erosion of the tax base. The volume of tax
expenditures is significant, as a recent study by the FTA indicates. The government is aware
of the importance of keeping tax expenditures in check. It could consider publishing an
annual tax expenditure statement with the annual budget.3671. The government should make an effort to disclose information on specific fiscal
risks, including contingent liabilities and QFAs, with the budget, in line with the IMF’s
Guidelines for Fiscal Risk Disclosure and Management, and eventually publish a single
statement of fiscal risks.37 In particular, the universal services provided by Swiss Post, Swiss
Rail, and others are partly financed through cross-subsidies, which represent a form of
interpersonal redistribution, and taxes and transfer payments from the budget are considered
more desirable to support such activities from a transparency perspective. QFAs are
disclosed only to a very limited extent.72. The Social Security Funds should be clearly distinguished. Apart from the
unemployment insurance scheme, the other three funds are jointly operated. The old age and
disability pension funds are cross-financing each other, with the first fund running persistent
surpluses that are used to finance the deficits of the second. Clearly, separating the three
funds would make the financial health of each of them more transparent and facilitate the
necessary policy discussion about the sustainability of current policies. Parliament has
already passed a bill to separate the old-age and disability pension funds into two separate
funds. A referendum on the issue will be held in September 2009. In addition, an overview of
the finances of the social security sector and its relationship with the budget in the short to
medium term, in the context of an assessment of long-term fiscal sustainability, should be
included in the budget documents. More forward-looking information on the finances of the special funds would also be useful. Together, these measures would provide a better basis for
assessing the sustainability of current fiscal policy.73. More information should be published on the sensitivity of the budget to changes
in macroeconomic variables and an alternative macroeconomic and fiscal scenario,
building on the useful analysis already published by the government. This would provide
a better basis for assessing the uncertainties surrounding the budget.38 In addition, the federal
government could consider extending and formalizing the process of external review of
macroeconomic forecasts and assessments of economic developments.74. An overview of the finances of public corporations could also be provided in the
budget. Some corporations receive significant funding from the budget, and others conduct
QFAs, making it important to consider their financial position and profitability in the context
of fiscal policy.75. Additional information should be reported on public debt management, namely,
the debt management strategy and performance against it, and the impact of parameter
changes on debt-servicing costs.76. A summary statement of all new policy measures that are reflected in the budget
proposals, with an estimate of their fiscal impact, should be published, to supplement the
summary data on expenditure by tasks already provided in Volume 3 of the budget
documents.77. Each federal government department should be encouraged to publish an
annual report that summarizes relevant information concerning their goals and objectives,
strategic priorities, operational risks, financial results, and nonfinancial performance. This
would be in line with practice in many OECD countries.DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET from the NSA -CHILEAN JUDGE REQUESTS EXTRADITION OF U.S. MILITARY OFFICIAL IN “MISSING” CASE
|
CHILEAN JUDGE REQUESTS EXTRADITION OF U.S. MILITARY OFFICIAL IN “MISSING” CASECapt. Ray Davis Indicted in Chile for alleged role in murder of Charles Horman, Frank TeruggiDeclassified U.S. Documents Used Extensively in Court IndictmentArchive Posts Documents cited in Indictment, including FBI Intelligence Reports Containing Teruggi’s Address in Chile |
Washington D.C., November 30, 2011 –Thirty-eight years after the military coup in Chile, a Chilean judge has formally indicted the former head of the U.S. Military Group, Captain Ray Davis, and a Chilean intelligence officer, Pedro Espinoza for the murders of two American citizens in September 1973. The judge, Jorge Zepeda, said he would ask the Chilean Supreme Court to authorize an extradition request for Davis as an “accessory” to the murders of Charles Horman and Frank Teruggi.
Both Horman and Teruggi were seized separately at their homes in Santiago by Chilean soldiers and subsequently executed while in detention. Their murders, and the seeming indifference of U.S. officials, were immortalized in the Oscar-award winning movie “Missing” which focused on the search by Horman’s wife and father for him in the weeks following the U.S.-supported coup.
The indictment accused the U.S. MilGroup of passing intelligence to the Chilean military on the “subversive” activities of Teruggi that contributed to his arrest; it stated that Davis “was in a position” to stop the executions “given his coordination with Chilean agents” but did not do so.
In his indictment, Judge Zepeda cited a number of declassified U.S. government documents as the basic foundation for the case-although none of them tie Davis or Espinoza to the crimes. “These documents are providing the blocks for building a case in these famous killings,” said Peter Kornbluh who directs the Chile Documentation Project at the Archive, “but they do not provide a smoking gun.” To successfully advance court proceedings as well as a successful extradition request, according to Kornbluh, the judge will have to present concrete evidence of communications between U.S. and Chilean military officers regarding Horman and Teruggi prior to their detentions and their deaths.
The Archive today posted a number of the documents cited in the indictment, including key FBI memos that contained Frank Teruggi’s Santiago address, as well as other records relevant to the Horman and Teruggi case. The documents derive from an indexed collection: Chile and the United States: U.S. Policy toward Democracy, Dictatorship, and Human Rights, 1970-1990. The collection, just published this week by the Archive and Proquest, contains over 180 documents on the Horman and Teruggi case.
Read the Documents:
Document 1
Department of State, SECRET Memorandum, “Charles Horman Case,” August 25, 1976
This memo by three state department officers implies that the U.S. government could have prevented the murder of Charles Horman. The memo, written after a review of the files on the case, explains that there is “circumstantial evidence” to suggest “U.S. intelligence may have played an unfortunate part in Horman’s death. At best, it was limited to providing or confirming information that helped motivate his murder by the GOC. At worst, U.S. intelligence was aware the GOC saw Horman in a rather serious light and U.S. officials did nothing to discourage the logical outcome of GOC paranoia.” When this document was initially declassified pursuant to a FOIA lawsuit filed by the Horman family, this critical passage was blacked out. The document was released without redaction in 1999. It was not cited in Judge Zepeda’s indictment, but appears to reflect the judicial argument he is pursuing.
Document 2
Department of State, SECRET, “Charles Horman Case: Gleanings,”(Undated but written in August 1976)
This detailed chronology, based on a review of files available to the State Department, contains key information on what the U.S. knew and did in the case of Charles Horman. It also evaluates the possible role of the U.S. in the murder. The document cites the admissions of a Chilean intelligence agent, Rafael Gonzalez, who told U.S. reporters the story of Horman being interrogated in General Augusto Lutz’s office and then killed because “he knew too much.” Gonzalez claimed there was an American in the room when the interrogation took place, but decades later he would recant that story. In January 2004, he was indicted by Judge Zepeda in the Horman case as an “accessory to murder” for his role in the interrogation, death and secret burial of Charles Horman.
Document 3
United States Embassy, Unclassified Notice, “Missing United States Citizen,” October 9, 1973
This document cited in the indictment, states that the U.S. government has received a note from the Chilean Foreign Office dated October 3, 1973, recording that Charles Horman was detained at the National Stadium on September 20 for a curfew violation but had been released on September 21 for “lack of merit.” The document includes a photograph of Horman, his date of birth, address in Chile, and fingerprint classification. Horman was actually detained at his home on September 17, 1973.
Document 4
Department of State, Memorandum (classification excised), “Film by Charles Horman,” April 12, 1974
In this memo to Assistant Secretary Harry Shlaudeman, State Department officer George Lister describes the film work of Charles Horman. A film that he apparently worked on before the coup was completed after the coup by friends titled “Chile: With Poems and Guns.” (The document leaves the impression that Charles “made” the film, but clearly he did not work on it following the coup.) The film describes Chilean history, and the achievements of the Allende government, along with alleged atrocities of the coup and U.S. involvement. Lister goes so far as to imply that Horman’s film making in Chile could have been what “led to his death.”
Document 5
Chilean Armed Forces, Memorandum, “Antecedentes sobre Fallecimiento de 2 ciudadanos norteamericanos,” Octobeer 30, 1973
Chief of Chilean Military Intelligence Service General Augusto Lutz reports on the death of Charles Horman and Frank Teruggi. He asserts that Horman and Teruggi were political extremists attempting to discredit Chilean junta. While he acknowledges that they were both detained by the Chilean military, he maintains that they were later released and that the Chilean military was not involved in their deaths. The document is the only information known to have been provided by the Chilean military to the U.S. embassy after the disappearance of Horman and Teruggi.
Document 6
U.S. Military Group Chile, Memorandum (classification unknown), “Case of Charles Horman,” January 14, 1975
Ray Davis forwards a list of documents on the interactions of the U.S. Military Group in Chile with Charles Horman to be provided to the General Accounting Office. The documents raise the issue of the role of embassy officials in the disappearance and death of Horman, and make “certain allegations and statements about members of the Navy Mission, in Valparaiso; comments about a ride given by COMUSMILGP, Captain Davis.”
Document 7
Department of State, CONFIDENTIAL Memorandum, “Horman Case,” April 20, 1987
This memorandum of conversation reports on an informant who has appeared at the Embassy to give testimony on the death of Charles Horman. According to this informant, Horman was seized by Chilean intelligence units and taken to the Escuela Militar for questioning. He was then transferred to the National Stadium, where they determined he was an extremist. He was forced to change clothes, shot three times, and his body was dumped on the street to appear he had died in a confrontation. The informant said that “the person at the stadium who made the decision on who was to die was Pedro Espinoza, of later DINA fame.” The document is the first to tie Pedro Espinoza to the Horman case. He was involved in military intelligence and detainees at the time of the coup. However, the commander of the National Stadium at the time was another military officer named Jorge Espinosa Ulloa.
Document 8
United States Embassy Santiago, CONFIDENTIAL cable, ‘[Excised] Reports on GOC Involvement in Death of Charles Horman, Asks Embassy for Asylum and Aid,’ April 28, 1987
In a report on the informant’s information, the Embassy cables Washington with his account of Horman’s death. Horman was picked up in a routine sweep, the informant suggests, and was found in possession of “extremist” materials. He was then taken the National Stadium where he was interrogated and later executed on the orders of Pedro Espinoza. Embassy officials note that his story “corresponds with what we know about the case and the [Chilean government] attempt to cover up their involvement,” suggesting that the informant is probably telling the truth. In later cables, the Embassy begins to question the credibility of the informant who is never identified.
Document 9
FBI, SECRET Memorandum, [Frank Teruggi’s Contact with Anti-War Activist], October 25, 1972
This FBI report cites information provided by “another U.S. government agency” on Frank Teruggi’s contacts with an anti-war activist who resides in West Germany. The report also contains his address in Santiago. The document was generated by surveillance of a U.S. military intelligence unit in Munich on an American anti-war dissident who was in contact with Teruggi. The FBI subsequently decides to open a file on Teruggi. This series of FBI documents were cited by Judge Zepeda in his indictment which infers-but offers no proof– that intelligence from them was shared with Chilean military intelligence in the days following the coup.
Document 10
FBI, SECRET Memorandum, “Frank Teruggi,” October 25, 1972
This FBI memorandum requests investigation of Frank Teruggi and the Chicago Area Group for the Liberation of Americas of which he was a member nearly a year prior to his death following the Chilean coup.
Document 11
FBI, SECRET Memorandum, “[Excised] SM- Subversive,” November 28, 1972
This FBI document again requests investigation on Teruggi based on his contact with a political activist in West Germany. The document mentions that Teruggi is living in Chile editing a newsletter “FIN” of Chilean information for the American left, and that he is closely affiliated with the Chicago Area Group for the Liberation of Americas.
Document 12
FBI, Memorandum (classification unknown), “Frank Teruggi,” December 14, 1972
This FBI memorandum demonstrates ongoing efforts to gather information on Frank Teruggi in the year proceeding the Chilean coup. Here, the FBI reports on his attendance at a conference of returned Peace Corps volunteers and his membership in political organizations supporting socialism and national liberation movements in Latin America.
TOP-SECRET – (U//FOUO) Director of National Intelligence Classification Markings Register Version 1.2
TOP-SECRET-NSA-IRAN CONTRA AT 25: REAGAN AND BUSH ‘CRIMINAL LIABILITY’ EVALUATIONS

President Reagan motioning to Ed Meese at the White House Press Briefing announcing the Iran-Contra connection. 11/25/86.
Washington D.C., November 25, 2011 –President Ronald Reagan was briefed in advance about every weapons shipment in the Iran arms-for-hostages deals in 1985-86, and Vice President George H. W. Bush chaired a committee that recommended the mining of the harbors of Nicaragua in 1983, according to previously secret Independent Counsel assessments of “criminal liability” on the part of the two former leaders posted today by the National Security Archive.
Twenty-Five years after the advent of the “Iran-Contra affair,” the two comprehensive “Memoranda on Criminal Liability of Former President Reagan and of President Bush” provide a roadmap of historical, though not legal, culpability of the nation’s two top elected officials during the scandal from the perspective of a senior attorney in the Office of Independent Counsel Lawrence Walsh. The documents were obtained pursuant to a Freedom of Information Act (FOIA) request filed by the National Security Archive for the files compiled during Walsh’s six-year investigation from 1987-1993.
The posting comes on the anniversary of the November 25, 1986, press conference during which Ronald Reagan and his attorney general, Edwin Meese, informed the American public that they had discovered a “diversion” of funds from the sale of arms to Iran to fund the contra war, thus tying together the two strands of the scandal which until that point had been separate in the public eye. The focus on the diversion, as Oliver North, the NSC staffer who supervised the two operations wrote in his memoirs, was itself a diversion. “This particular detail was so dramatic, so sexy, that it might actually-well divert public attention from other, even more important aspects of the story,” North wrote, “such as what the President and his top advisors had known about and approved.”
 |
| Ronald Reagan with Caspar Weinberger, George Shultz, Ed Meese, and Don Regan discussing the President’s remarks on the Iran-Contra affair, Oval Office. 11/25/86.
Source credit: Courtesy Ronald Reagan Library |
The criminal liability studies were drafted in March 1991 by a lawyer on Walsh’s staff, Christian J. Mixter (now a partner in the Washington law firm of Morgan Lewis), and represented preliminary conclusions on whether to prosecute both Reagan and Bush for various crimes ranging from conspiracy to perjury.
On Reagan, Mixter reported that the President was “briefed in advance” on each of the illicit sales of missiles to Iran. The criminality of the arms sales to Iran “involves a number of close legal calls,” Mixter wrote. He found that it would be difficult to prosecute Reagan for violating the Arms Export Control Act (AECA) which mandates advising Congress about arms transfers through a third country-the U.S. missiles were transferred to Iran from Israel during the first phase of the operation in 1985-because Attorney General Meese had told the president the 1947 National Security Act could be invoked to supersede the AECA.
As the Iran operations went forward, some of Reagan’s own top officials certainly believed that the violation of the AECA as well as the failure to notify Congress of these covert operations were illegal-and prosecutable. In a dramatic meeting on December 7, 1985, Secretary of Defense Caspar Weinberger told the President that “washing [the] transaction thru Israel wouldn’t make it legal.” When Reagan responded that “he could answer charges of illegality but he couldn’t answer charge that ‘big strong President Reagan passed up a chance to free hostages,” Weinberger suggested they might all end up in jail. “Visiting hours are on Thursdays,” Weinberger stated. As the scandal unfolded a year later, Reagan and his top aides gathered in the White House Situation Room the day before the November 25 press conference to work out a way to protect the president from impeachment proceedings.
On the Contra operations, Mixter determined that Reagan had, in effect, authorized the illegal effort to keep the contra war going after Congress terminated funding by ordering his staff to sustain the contras “body and soul.” But he was not briefed on the resupply efforts in enough detail to make him criminally part of the conspiracy to violate the Boland Amendment that had cut off aid to the Contras in October 1984.
Mixter also found that Reagan’s public misrepresentations of his role in Iran-Contra operations could not be prosecuted because deceiving the press and the American public was not a crime.
On the role of George Herbert Walker Bush, Mixter reported that the Vice President’s “knowledge of the Iran Initiative appears generally to have been coterminous with that of President Reagan.” Indeed, on the Iran-Contra operations overall, “it is quite clear that Mr. Bush attended most (although not quite all) of the key briefings and meetings in which Mr. Reagan participated, and therefore can be presumed to have known many of the Iran/Contra facts that the former President knew.” But since Bush was subordinate to Reagan, his role as a “secondary officer” made it more difficult to hold him criminally liable.
Mixter’s detailed report on Bush’s involvement does, however, shed considerable light on his role in both the Iran and Contra sides of the scandal. The memorandum on criminal liability noted that Bush had a long involvement in the Contra war, chairing the secret “Special Situation Group” in 1983 which “recommended specific covert operations” including “the mining of Nicaragua’s rivers and harbors.” Mixter also cited no less than a dozen meetings that Bush attended between 1984 and 1986 in which illicit aid to the Contras was discussed.
Despite the Mixter evaluations, Independent Counsel Lawrence Walsh continued to consider filing criminal indictments against both Reagan and Bush. In a final effort to determine Reagan’s criminal liability and give him “one last chance to tell the truth,” Walsh traveled to Los Angeles to depose Reagan in July 1992. “He was cordial and offered everybody licorice jelly beans but he remembered almost nothing,” Walsh wrote in his memoir, Firewall, The Iran-Contra Conspiracy and Cover-Up. The former president was “disabled,” and already showing clear signs of Althzeimers disease. “By the time the meeting had ended,” Walsh remembered, “it was as obvious to the former president’s counsel as it was to us that we were not going to prosecute Reagan.”
The Special Prosecutor also seriously considered indicting Bush for covering up his relevant diaries, which Walsh had requested in 1987. Only in December 1992, after he had lost the election to Bill Clinton, did Bush turn over the transcribed diaries. During the independent counsel’s investigation of why the diaries had not been turned over sooner, Lee Liberman, an Associate Counsel in the White House Counsel’s office, was deposed. In the deposition, Liberman stated that one of the reasons the diaries were withheld until after the election was that “it would have been impossible to deal with in the election campaign because of all the political ramifications, especially since the President’s polling numbers were low.”
In 1993, Walsh advised now former President Bush that the Independent Counsel’s office wanted to take his deposition on Iran-Contra. But Bush essentially refused. In one of his last acts as Independent Counsel, Walsh considered taking the cover-up case against Bush to a Grand Jury to obtain a subpoena. On the advice of his staff, however, he decided not to pursue an indictment of Bush.
Among the first entries Bush had recorded in his diary (begun in late 1986) was his reaction to reports from a Lebanese newspaper that a U.S. team had secretly gone to Iran to trade arms for hostages. “On the news at this time is the question of the hostages,” he noted on November 5, 1986. “I’m one of the few people that know fully the details. This is one operation that has been held very, very tight, and I hope it will not leak.”
Read the Documents:
Document 1, Part 1, Part 2, Part 3, Part 4
Office of the Independent Counsel, C.J. Mixter to Judge Walsh, “Criminal Liability of Former President Reagan,” March 21, 1991, 198 pages.
In this lengthy evaluation, Christian Mixter, a lawyer on the staff of the Independent Counsel, provides Lawrence Walsh with a comprehensive evaluation of the legal liability of President Ronald Reagan in the Iran-Contra operations. The memorandum reviews, in great detail, not only the evolution of the operations, but Reagan’s central role in them. It includes “a summary of facts” on both the sale of arms to Iran, in order to free American hostages held in Lebanon, and the evolution of the illicit contra resupply operations in Central America, as well as the connection between these two seemingly separate covert efforts. The report traces Reagan’s knowledge and authorization of the arms sales, as well as his tacit authorization of the illegal contra resupply activities; it also details his role in obtaining third country funding for the Contras after Congress terminated U.S. support in 1984. The document further evaluates Reagan’s responses in two official inquiries to determine whether they rise to the level of perjury. For a variety of reasons, Mixter’s opinion is that “there is no basis for a criminal prosecution” of Reagan in each of the areas under scrutiny, although he notes that it is a “close legal call” on the issue of arms sales to Iran.
Document 2
Office of the Independent Counsel, C.J. Mixter to Judge Walsh, “Criminal Liability of President Bush,” March 21, 1991, 89 pages.
In this assessment, Mixter traces then-Vice President Bush’s involvement in both sides of the Iran-Contra operations, including his meeting with a high Israeli official on the sales of arms to Iran in July 1986, and his presence at no fewer than a dozen meetings during which illicit assistance to the Contras was discussed. The legal evaluation also contains a detailed overview of Bush’s role in arranging a quid pro quo deal with two Presidents of Honduras in order to garner Honduran support for allowing the Contras to use that country as a base of operations against the Sandinistas in Nicaragua. “It is quite clear that Mr. Bush attended most (although not quite all) of the key briefings and meetings in which Mr. Reagan participated, and therefore can be presumed to have known many of the Iran/Contra facts that the former President knew.” But since Bush was subordinate to Reagan, his role as a “secondary officer” rendered him less likely to be criminally liable for the actions he took.
The Mixter memo on Bush was written before the existence and cover-up of the Vice President’s diaries became known in late 1992. The Independent Counsel’s office did launch an investigation into why the diaries were not previously turned over and considered bringing charges against the former Vice President for illegally withholding them.
More – The Top 5 Declassified Iran-Contra Historical Documents:
Document 1
NSC, National Security Planning Group Minutes, “Subject: Central America,” SECRET, June 25, 1984
At a pivotal meeting of the highest officials in the Reagan Administration, the President and Vice President and their top aides discuss how to sustain the Contra war in the face of mounting Congressional opposition. The discussion focuses on asking third countries to fund and maintain the effort, circumventing Congressional power to curtail the CIA’s paramilitary operations. In a remarkable passage, Secretary of State George P. Shultz warns the president that White House adviser James Baker has said that “if we go out and try to get money from third countries, it is an impeachable offense.” But Vice President George Bush argues the contrary: “How can anyone object to the US encouraging third parties to provide help to the anti-Sandinistas…? The only problem that might come up is if the United States were to promise to give these third parties something in return so that some people could interpret this as some kind of exchange.” Later, Bush participated in arranging a quid pro quo deal with Honduras in which the U.S. did provide substantial overt and covert aid to the Honduran military in return for Honduran support of the Contra war effort.
Document 2
White House, Draft National Security Decision Directive (NSDD), “U.S. Policy Toward Iran,” TOP SECRET, (with cover memo from Robert C. McFarlane to George P. Shultz and Caspar W. Weinberger), June 17, 1985
The secret deals with Iran were mainly aimed at freeing American hostages who were being held in Lebanon by forces linked to the Tehran regime. But there was another, subsidiary motivation on the part of some officials, which was to press for renewed ties with the Islamic Republic. One of the proponents of this controversial idea was National Security Advisor Robert McFarlane, who eventually took the lead on the U.S. side in the arms-for-hostages deals until his resignation in December 1985. This draft of a National Security Decision Directive, prepared at his behest by NSC and CIA staff, puts forward the argument for developing ties with Iran based on the traditional Cold War concern that isolating the Khomeini regime could open the way for Moscow to assert its influence in a strategically vital part of the world. To counter that possibility, the document proposes allowing limited amounts of arms to be supplied to the Iranians. The idea did not get far, as the next document testifies.
Document 3
Defense Department, Handwritten Notes, Caspar W. Weinberger Reaction to Draft NSDD on Iran (with attached note and transcription by Colin Powell), June 18, 1985
While CIA Director William J. Casey, for one, supported McFarlane’s idea of reaching out to Iran through limited supplies of arms, among other approaches, President Reagan’s two senior foreign policy advisers strongly opposed the notion. In this scrawled note to his military assistant, Colin Powell, Weinberger belittles the proposal as “almost too absurd to comment on … It’s like asking Qadhafi to Washington for a cozy chat.” Richard Armitage, who is mentioned in Powell’s note to his boss, was an assistant secretary of defense at the time and later became deputy secretary of state under Powell.
Document 4
Diary, Caspar W. Weinberger, December 7, 1985
The disastrous November HAWK shipment prompted U.S. officials to take direct control of the arms deals with Iran. Until then, Israel had been responsible for making the deliveries, for which the U.S. agreed to replenish their stocks of American weapons. Before making this important decision, President Reagan convened an extraordinary meeting of several top advisers in the White House family quarters on December 7, 1985, to discuss the issue. Among those attending were Secretary of State Shultz and Secretary of Defense Weinberger. Both men objected vehemently to the idea of shipping arms to Iran, which the U.S. had declared a sponsor of international terrorism. But in this remarkable set of notes, Weinberger captures the president’s determination to move ahead regardless of the obstacles, legal or otherwise: “President sd. he could answer charges of illegality but he couldn’t answer charge that ‘big strong President Reagan passed up chance to free hostages.'”
Document 5
NSC, Oliver L. North Memorandum, “Release of American Hostages in Beirut,” (so-called “Diversion Memo”), TOP SECRET/SENSITIVE, April 4, 1986
At the center of the public’s perception of the scandal was the revelation that the two previously unconnected covert activities — trading arms for hostages with Iran and backing the Nicaraguan Contras against congressional prohibitions — had become joined. This memo from Oliver North is the main piece of evidence to survive which spells out the plan to use “residuals” from the arms deals to fund the rebels. Justice Department investigators discovered it in North’s NSC files in late November 1986. For unknown reasons it escaped North’s notorious document “shredding party” which took place after the scandal became public.
Source credit: Courtesy Ronald Reagan Library
TOP-SECRET- Robert Kennedy Murder – Sirhan Sirhan Hypno-Programmed Assassin Innocence Plea Documents
The following court documents were filed on November 20, 2011 by the attorney of Sirhan Sirhan, the alleged assassin of Robert F. Kennedy. The documents claim that Sirhan was a hypno-programmed assassin and that another person fired the gun that killed Kennedy.




DOWNLOAD ORIGINAL DOCUMENT BELOW
TOP-SECRET – U.K. Embassies Preparing for Collapse of Euro
As the Italian government struggled to borrow and Spain considered seeking an international bail-out, British ministers privately warned that the break-up of the euro, once almost unthinkable, is now increasingly plausible.
Diplomats are preparing to help Britons abroad through a banking collapse and even riots arising from the debt crisis.
The Treasury confirmed earlier this month that contingency planning for a collapse is now under way.
A senior minister has now revealed the extent of the Government’s concern, saying that Britain is now planning on the basis that a euro collapse is now just a matter of time.
“It’s in our interests that they keep playing for time because that gives us more time to prepare,” the minister told.
Recent Foreign and Commonwealth Office instructions to embassies and consulates request contingency planning for extreme scenarios including rioting and social unrest.
Greece has seen several outbreaks of civil disorder as its government struggles with its huge debts. British officials think similar scenes cannot be ruled out in other nations if the euro collapses.
Diplomats have also been told to prepare to help tens of thousands of British citizens in eurozone countries with the consequences of a financial collapse that would leave them unable to access bank accounts or even withdraw cash.
Fuelling the fears of financial markets for the euro, reports in Madrid yesterday suggested that the new Popular Party government could seek a bail-out from either the European Union rescue fund or the International Monetary Fund.
TOP-SECRET from the FBI – Public Corruption, Illegal Prescription Drug Trafficking, and Health Care Fraud
Gwendolyn Washington, M.D., age 67, was sentenced today to 120 months’ imprisonment for public corruption, health care fraud, and conspiring to illegally distribute prescription drugs, United States Attorney Barbara L. McQuade announced. McQuade was joined in the announcement by Andrew G. Arena, Special Agent in Charge, Federal Bureau of Investigation, Detroit Field Division, and Lamont Pugh, III, Special Agent in Charge, Department of Health and Human Services, Office of Inspector General. Dr. Washington was sentenced by the Honorable Paul D. Borman.
On March, 7, 2011, Dr. Washington pleaded guilty to conspiring to defraud and defrauding the Detroit Public School (“DPS”) system of over $3.3 million. Dr. Washington, along with her sister Sherry Washington, and others doing business as “Associates for Learning” paid kickbacks to Stephen Hill, former DPS Executive Director of Risk Management, who authorized their submission to DPS and payment by DPS of grossly inflated invoices for services allegedly rendered to DPS in the form of a wellness program.
On July 28, 2011, Dr. Washington pleaded guilty to four felony counts involving drug trafficking and health care fraud. At her plea, Washington admitted that between 2004 and 2010, she performed unnecessary ultrasounds, nuclear cardiac stress tests, balance tests, sleep tests, and nerve conduction tests on patients, who were urged to return to Washington’s office every few months for repeat tests, even though initial results were normal. Washington billed Medicare and Blue Cross and Blue Shield more than $5 million for these tests, some of which were potentially harmful to patients. Most significantly, Dr. Washington ordered unnecessary and actively harmful nuclear stress tests for her patients at a frequency beyond that of any other medical practice in the country. Because each of these tests is the radiation equivalent of at least 80 to120 chest x-rays and because excess radiation creates a greater risk of cancer, Dr. Washington exposed her patients to a substantial risk of cancer.
Dr. Washington also admitted that she solicited and received kickbacks from home health care agencies and diagnostic testing facilities in return for referring patients to them for medical services. Washington referred patients to home health agencies, falsely certifying them as being confined to the home, in return for payments from home health care agencies of $200 to $500 per patient. In return for ordering nuclear stress tests, Dr. Washington received $200 per test. In total, Washington received $350,000 in total kickback payments. Medicare paid approximately $2.8 million to agencies receiving the fraudulent referrals. Washington received another $250,000 directly from Medicare for false certifications of patients for home health services.
Dr. Washington also admitted to committing two counts of controlled substances offenses. In February 2010, when Medicare suspended payments to Washington, resulting in a drastic reduction in her income, she began writing prescriptions for tens of thousands of doses of OxyContin, Opana ER, and Roxicodone, highly addictive pain medications that have a significant “street value” on the illicit market. Washington sometimes wrote prescriptions for individuals who were not her patients, without an examination or determination of medical necessity, and without an appropriate diagnosis or entry in a patient chart. Washington then provided these illegal prescriptions to Virginia Dillard, her niece and codefendant. Dillard filled the prescriptions at various pharmacies in Highland Park, Warren, and Detroit. After filling the illegal prescriptions, Virginia Dillard delivered the controlled substances to prescription drug dealers in exchange for money. Dillard sold each filled prescription in amounts ranging from $1,000 to $2,200, and shared the proceeds with Washington. Dillard was sentenced, on October 20, 2011, to 112 months’ imprisonment.
United States Attorney Barbara L. McQuade stated, “Dr. Washington not only stole money from school children and from Medicare, she also exposed patients to harmful tests for her own financial gain. We hope that this sentence deters other health care providers from stealing public funds and risking the health of their patients.”
Special Agent in Charge Andrew Arena stated, “Health Care Fraud is one of the fastest growing crime problems in the state of Michigan. The FBI will continue to work closely with its law enforcement partners to focus all possible resources on this problem.”
“Special Agent in Charge Lamont Pugh stated, “Today’s sentencing provides another reminder to those who would commit drug and related health care crimes that law enforcement is watching. The Office of Inspector General and our law enforcement partners remain steadfast in our commitment to ensuring that the Medicare program and taxpayer dollars are protected.”
U.S. Attorney McQuade congratulated the hard work of the FBI and HHS for its efforts in pursuing these cases. The public corruption case was prosecuted by Assistant U.S. Attorney Michael Buckley. The health care fraud and illegal prescription drug distribution cases were prosecuted by Assistant United States Attorney Sarah Resnick Cohen.
TOP-SECRET – Congressional Budget Office: Top 1% Income Rose 275% From 1979-2007

From 1979 to 2007, real (inflation-adjusted) average household income, measured after government transfers and federal taxes, grew by 62 percent. During that period, the evolution of the nation’s economy and the tax and spending policies of the federal government and state and local governments had varying effects on households at different points in the income distribution: Income after transfers and federal taxes (denoted as after-tax income in this study) for households at the higher end of the income scale rose much more rapidly than income for households in the middle and at the lower end of the income scale. In particular:
- For the 1 percent of the population with the highest income, average real after-tax household income grew by 275 percent between 1979 and 2007 (see Summary Figure 1).
- For others in the 20 percent of the population with the highest income (those in the 81st through 99th percentiles), average real after-tax household income grew by 65 percent over that period, much faster than it did for the remaining 80 percent of the population, but not nearly as fast as for the top 1 percent.
- For the 60 percent of the population in the middle of the income scale (the 21st through 80th percentiles), the growth in average real after-tax household income was just under 40 percent.
- For the 20 percent of the population with the lowest income, average real after-tax household income was about 18 percent higher in 2007 than it had been in 1979.
As a result of that uneven income growth, the distribution of after-tax household income in the United States was substantially more unequal in 2007 than in 1979: The share of income accruing to higher-income households increased, whereas the share accruing to other households declined. In fact, between 2005 and 2007, the after-tax income received by the 20 percent of the population with the highest income exceeded the aftertax income of the remaining 80 percent.
To assess trends in the distribution of household income, the Congressional Budget Office (CBO) examined the span from 1979 to 2007 because those endpoints allow comparisons between periods of similar overall economic activity (they were both years before recessions). The growth in average income for different groups over the 1979–2007 period reflects a comparison of average income for those groups at different points in time; it does not reflect the experience of particular households. Individual households may have moved up or down the income scale if their income rose or fell more than the average for their initial group. Thus, the population with income in the lowest 20 percent in 2007 was not necessarily the same as the population in that category in 1979.
…
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET – The End of the USSR, 20 Years Later – The Russian Secrets in Documents

Washington D.C., November 22, 2011 – Marking the 20th anniversary of the breakup of the Soviet Union, the Gorbachev Foundation hosted a two-day conference in Moscow on November 10-11, co-organized by the National Security Archive and the Carnegie Moscow Center, examining the historical experience of 1989-1991 and the echoes today. The conference briefing book, compiled and edited by the Archive and posted on the Web today together with the conference program and speaker biographies, includes previously classified Soviet and American documents ranging from Politburo notes to CIA assessments to transcripts of phone calls between George H.W. Bush and Mikhail Gorbachev in the final months of the Soviet Union.
At the Moscow event, panels of distinguished eyewitnesses, veterans and scholars discussed Gorbachev’s political reforms of the 1980s, the crisis in the Soviet economy, the origins and impact of the “new thinking,” the role of society and social movements, and the ways the history is used and abused in current political debates. While Gorbachev himself was unable to participate for health reasons, he subsequently met with the conference organizers to give his reactions and retrospective analysis.
The Carnegie Moscow Center followed up the conference with a November 14 discussion, also co-organized by the Archive, using the same format of expert panels to analyze the impact of nationalism and separatism in the events of 1991, the role of the Soviet military, military reform today in the Russian armed forces, and the situation today in the North Caucasus and other ethnic conflicts in the former Soviet space.
At the Gorbachev Foundation conference, the panel on political reform debated the role of leaders as opposed to structural forces in the decline of the USSR, the competition between Mikhail Gorbachev and Boris Yeltsin especially in 1991, the particular Yeltsin factor including his arrangement with the presidents of Ukraine and Belarus in December 1991 to dissolve the USSR, and in the big picture, the declining legitimacy of the Soviet system over the duration of the Cold War.
The panel on economics discussed various options for modernizing the Soviet economy in the 1980s, whether the system was even reformable, the efforts of the Communist apparat to sabotage even modest reforms, the barriers in Western thinking that prevented any significant foreign aid to the Soviet Union in its last years, and the role of international financial institutions.
The panel on “new thinking” analyzed the dramatic changes in Soviet foreign policy under Gorbachev, the ultimately failed efforts at integrating Russia with Europe, the successes in U.S.-Soviet cooperation for settling regional conflicts, and the Soviet withdrawal from Afghanistan in 1988-89. This discussion also sparked a debate within the audience about the Gorbachev-Reagan ideas of nuclear abolition and their relevance for today.
The society panel described the extensive social demand for glasnost during the 1980s in stark contrast to today, the disintegration of social structures and public space in Russia since 1991, the importance of the dissident discourse of the 1960s and 1970s to the reformist elite and perestroika in the 1980s, and the unpreparedness of society for the various forms of extreme nationalist discourse that erupted at the end of the Soviet Union.
Gorbachev himself sat down with the conference organizers on November 14 after his return from Germany and following the two events at the Gorbachev Foundation and the Carnegie Moscow Center. He discussed the current political situation in Russia, with the “tandem” of Vladimir Putin and Dmitri Medvedev trading jobs with only a façade of elections, and under conditions of growing authoritarianism; but he predicted the “exhaustion” of this program and the eventual introduction of real change, rather than indefinite stagnation.
Gorbachev also commented on the issue of the lack of Western aid for his project of perestroika and glasnost – transforming the Soviet Union into a demilitarized, social democratic state that would work with the U.S. and other countries to resolve regional conflicts and build a “common home” in Europe and cooperative security arrangements globally. Coming back “empty-handed” from the G-7 meeting in the summer of 1991, Gorbachev commented, undermined his reform efforts, helped precipitate the August coup attempt, and undercut any possibility of gradual transition for the USSR. Participating in the discussion with Gorbachev were Pulitzer-Prize winners William Taubman and David Hoffman, Professor Jane Taubman, and National Security Archive representatives Tom Blanton, Malcolm Byrne, and Svetlana Savranskaya.
DOWNLOAD THE ORGINAL RUSSIAN DOCUMENTS HERE
1) 1989.01.24 Excerpt from Politburo Session
2) 1989.02.16 Excerpt from Politburo Session
3) 1989.03.28 Excerpt from Politburo Session
4) 1989.08.26 Excerpt from Poltiburo Session, Situation in the Soviet Baltic Republics
5) 1989.11.18 Excerpt from Politburo Session, Additional Measures in the Sphere of Information
5) 1989.11.18 Excerpt from Politburo Session, Additional Measures in the Sphere of Information
6) 1990.01.02 Excerpt from Politburo Session, On the Events in Europe and the USSR’s Position
7) 1990.01.29 Excerpt from Politburo Session
8) 1990.02.17 Excerpt from Politburo Session, Upcoming Elections in Nicaragua
9) 1990.03.22 Excerpt from Politburo Session
10) 1990.06.02 A.N. Yakovlev’s Note to M.S. Gorbachev on the Changing Situation in the Country
11) 1990.10.13 Excerpt from Politburo Session
12) 1991.04.02 Analytical Note from A.N. Yakovlev to M.S. Gorbachev
13) 1991.04.30 Letter from A.N. Yakovlev to M.S. Gorbachev, On the Danger of a Conservative Comeback
14) 1991.05.15 CC CPSU Secretariat Resolution
15) 1991.06.25 A.N. Yakovlev’s Note to M.S. Gorbachev on the Draft CPSU Program
16) 1991.08.16 A.N. Yakovlev’s Open Letter to Communists
17) 1991.08.21 Emergency Session of the RSFSR Supreme Soviet, First Meeting
18) 1991.10.18 Letter from M.S. Gorbachev to George Bush (Oct 18 1991)
FBI – Tennessee Man Sentenced to 40 Months in Prison for Fraudulent Hedge Fund Scheme
ATLANTA—Jon Edward Hankins, 38, of Knoxville, Tenn., was sentenced to prison today by U.S. District Judge Amy Totenberg on charges of wire fraud, in connection with his scheme to lure investors to invest into his fraudulent hedge fund. Hankins was sentenced to 40 months in prison to be followed by three years of supervised release. Hankins was convicted of these charges on June 13, 2011, after pleading guilty.
U.S. Attorney for the Northern District of Georgia Sally Quillian Yates said, “Before he was even discharged from an earlier federal sentence for investment fraud, he launched another fraudulent scheme. Thankfully, the FBI identified and shut down his new scam very quickly, minimizing the losses that investors suffered. Our office and the President’s Financial Fraud Enforcement Task Force remain committed to the mission of protecting investors and promoting confidence in the integrity of our financial system.”
According to the charges and other information presented in court: In the winter of 2009/2010, Hankins was serving the home confinement portion of a federal prison sentence he received for a 2007 securities fraud conviction relating to an $8 million fraud scheme involving his Knoxville-based investment company, “Tenet Asset Management.”
Shortly after his home confinement began, Hankins concocted another scheme. He created a website, fake brochures and other business documents, and rented office space and mail forwarding addresses in the names of two entities, “Christian Financial Brotherhood” and “Banker’s Trust Annuity.” He advertised these entities on the Internet and elsewhere and solicited investors, investment advisors and stock brokers to invest their funds with him.
>From at least December 2009 through February 2010, Hankins represented to a prospective victim that Banker’s Trust managed more than $100 million in assets for various clients, that the funds were held at an account at the leading Wall Street firm Goldman Sachs, and that he was making substantial investment returns for existing clients in a hedge fund he called the “Strategic Arbitrage Fund.” Hankins produced a brochure that claimed that the “Strategic Arbitrage Fund” maintained more than $30 million in client funds, and that listed various individuals, including a retired general and the son of a former cabinet secretary, as supposed directors of the fund. None of this was true, as Christian Financial and Banker’s Trust were shams; had nothing close to the assets that Hankins represented; had been “in business” for only a few months; had not been engaged in profitable securities trading; and was not associated with the high profile individuals listed on the brochure.
Hankins, in soliciting investors, deliberately omitted mention of his securities fraud conviction, Tenet Asset Management, or that he was still serving a federal sentence.
The FBI quickly learned of Hankins’ scheme, and conducted a search warrant that shut down the scheme in April 2010. Because this new investment scheme was caught quickly, Hankins obtained less than $600,000 from his victim-investors, of which over $200,000 was recovered and returned to victims.
This law enforcement action was undertaken as part of President Barack Obama’s Financial Fraud Enforcement Task Force.
President Obama established the interagency Financial Fraud Enforcement Task Force to wage an aggressive, coordinated and proactive effort to investigate and prosecute financial crimes. The task force includes representatives from a broad range of federal agencies, regulatory authorities, inspectors general, and state and local law enforcement who, working together, bring to bear a powerful array of criminal and civil enforcement resources. The task force is working to improve efforts across the federal executive branch, and with state and local partners, to investigate and prosecute significant financial crimes, ensure just and effective punishment for those who perpetrate financial crimes, combat discrimination in the lending and financial markets, and recover proceeds for victims of financial crimes.
This case was investigated by special agents of the FBI. The Atlanta Division Office of the U.S. Securities & Exchange Commission provided assistance.
Assistant U.S. Attorney Justin S. Anand prosecuted the case.
TOP-SECRET from the FBI – Judge Limas Associate Pleads Guilty
BROWNSVILLE, TX—Another defendant has entered a guilty plea in the FBI’s public corruption investigation of former 404th District Court Judge Abel Corral Limas, United States Attorney Kenneth Magidson announced today. Jose Manuel “Meme” Longoria, 52, a resident alien from Mexico residing in San Benito, Texas, pleaded guilty today before U.S. District Judge Andrew S. Hanen to four counts as alleged in an indictment returned April 26, 2011 – one count of conspiracy to interfere with commerce under color of official right or extortion, two counts of extortion and one count of aiding and abetting honest services wire fraud by Limas.
At today’s hearing, Longoria admitted to his role in a conspiracy involving the creation of a fraudulent drug money seizure document as well as a charging warrant both prepared by former Cameron County District Attorney (DA) investigator Jaime Munivez, obtaining information on a murder case in return for a bicycle provided to Munivez, and an attempted recovery of $800,000 in drug proceeds from a truck near Rosenberg, Texas. The recitation of evidence to the court indicated that as part of the public corruption investigation on Judge Limas, agents learned Longoria was also involved in criminal activity with others.
In the first incident which was charged as part of the conspiracy by Longoria, agents conducted an undercover operation in which Munivez ultimately met with Longoria and provided a document titled “Article 59.03 Statement of Seized Property” indicating $200,000 was seized on “11/20/07” by an investigator with the DA’s office. The document was provided in return for payment of money. In early 2008, Longoria assisted a drug trafficking organization in an attempt to recover a Georgia truck containing drug proceeds that was reported to be missing on the outskirts of Houston. Longoria enlisted the help of Munivez and “Person G,” to locate the truck with the possibility of receiving up to $90,000 for recovering it. In a recorded conversation, Person G informed Longoria to “be careful because maybe they’ll pick you up when…the truck is picked up and …they’re (law enforcement) seeing, watching and they (sic) arrest you.” Ultimately, the truck was found by the Rosenberg Police Department and a total $289,290 in drug proceeds was seized.
In a second incident charged as part of the conspiracy, Longoria, Munivez and another person conspired to extort money from a person whom they falsely told had a charge/arrest warrant outstanding. Longoria extorted the money while Munivez created the fraudulent warrant document to show to the individual. In return for the money, Longoria promised the warrant would “disappear.”
In addition, Longoria arranged for Munivez to meet a fugitive in Matamoros, Mexico, and provide information on his pending murder case. Longoria then arranged for a bicycle to be given to Munivez in return for meeting with the fugitive. Agents conducting surveillance observed Longoria and Munivez arrive at and enter Bicycle World in Brownsville. On Jan. 23. 2008, Munivez picked up the bicycle which had been paid for by the fugitive.
Finally, in relation to count five of the indictment, Longoria also admitted today to his role in arranging a $1,500 payment to Limas in April 2008. The indictment charged that Longoria aided and abetted former judge Limas to devise “a scheme and artifice to defraud and deprive the state of Texas of the right to the honest services of a state district judge, performed free from deceit, favoritism, bias, self-enrichment and self-dealing.” Evidence presented today showed Longoria, acting as a middleman for Armando and Karina Pena, arranging for Limas to issue a court order allowing Armando Pena to report to the state probation by mail rather than in person. Pena, who had left Texas without authorization to reside in Arkansas, was subject to arrest and revocation of his deferred adjudication probationary term for violating a condition of his eight-year probationary term imposed for aggravated robbery in March 2006.
According to the pleadings filed in court today, Karina Pena, Armando’s wife, contacted Longoria on April 22, 2008, seeking his assistance to arrange for her husband to be permitted to report by mail from Arkansas. Two days later, according to court documents, Karina Pena was told that Limas wanted $1500. Longoria sought $300 for himself for arranging the deal. On April 24, 2008, Armando Pena finalized the arrangements with Longoria and wire transferred $1800 to Harlingen, Texas. FBI agents later reviewed the Armando Pena state court case file and located a progress report written by Pena’s probation officer indicating that, “On April 23, 2008, the Honorable Court (Limas) contacted our office in reference to allowing the defendant to report by mail.” Furthermore, on May 13, 2008, Judge Limas signed an order allowing Pena to report by mail.
Both Armando and Karina Pena have previously entered a guilty plea to the wire fraud violation and are scheduled to be sentenced Nov. 30, 2011. To date, a total of seven defendants have entered guilty pleas in relation to the Limas investigation.
Sentencing is set before Judge Hanen on Feb. 27, 2012. At that time, Longoria faces a maximum 20-year prison term, a fine of up to $250,000 and five years of supervised release for each count of conviction. Following his guilty plea today, Longoria was remanded to the custody of the U.S. Marshals Service where he will remain pending his sentencing hearing.
Munivez, who was charged in a separate indictment, is scheduled for jury selection on Dec. 3, 2011, before Judge Hanen. He is presumed innocent unless convicted through due process of law.
The charges in relation to this case are the result of an ongoing three-year investigation being conducted by the FBI, Drug Enforcement Administration and the Brownsville Police Department. Assistant United States Attorneys Michael Wynne and Oscar Ponce are prosecuting the case.
TOP-SECRET-Fukushima Daiichi Nuclear Power Station 19 November 2011
![[Image]](https://i0.wp.com/cryptome.org/eyeball/daiichi-111911/pict0.jpg) |
| TEPCO note: Other photos are published on the report “Roadmap towards Restoration from the Accident at Fukushima Daiichi Nuclear Power Station (November 17, 2011)” [http://cryptome.org/0005/daiichi-111711.zip (9.1MB)] |
The road between unit 2 & unit 3Before, May 3, 2011![[Image]](https://i0.wp.com/cryptome.org/eyeball/daiichi-111911/pict1.jpg)
After, May 14, 2011
|
Former main building entranceBefore, May 27, 2011![[Image]](https://i0.wp.com/cryptome.org/eyeball/daiichi-111911/pict4.jpg)
After, June 7, 2011
|
TOP-SECRET by the FBI – Real Estate Investor Convicted for Leading a Mortgage Fraud Conspiracy
PHOENIX—Eitan Maximov, 39, a citizen of Israel and lawful permanent resident of the United States, was convicted yesterday after a six day jury trial on one Count of Conspiracy to Commit Wire and Bank Fraud and one count of Wire Fraud as a result of his leadership in a cash-back mortgage fraud scheme that took place during 2006-2008.
The defendant was taken into custody following the jury verdict and his sentencing is set before U.S. District Judge David G. Campbell on February 27, 2012.
Acting U.S. Attorney Ann Birmingham Scheel said: “During the height of the real estate boom, this defendant saw an opportunity to profit and he took it. He furthered his scam by creating fictitious companies and billed himself as an investor. However, the only investment he made was in his lavish lifestyle that eventually crashed down on him.”
“Yesterday’s guilty verdict illustrates the commitment by the FBI, our law enforcement partners, and the U.S. Attorney’s Office in combating mortgage fraud,” said FBI Special Agent in Charge James L. Turgal. “When individuals use the housing market to intentionally defraud the public for their own personal financial gain, using other people’s money and dreams to live lavish lifestyles, it damages our economy and further exacerbates the mortgage crisis. The FBI’s Mortgage Fraud Task Force will continue to investigate those who orchestrate and participate in various mortgage fraud schemes in order to protect the public against those who would seek to further damage our local and national economy.”
The defendant played a leadership role in the underlying conspiracy which involved at least nine residential properties in the Scottsdale area. The objective of the conspiracy was to recruit unqualified borrowers as straw buyers, submit fraudulent loan applications on their behalf and on his own behalf, obtain mortgage loans in excess of the selling price of the property and then take the excess amount of the loans out through escrow in what is known as a “cash back” scheme.
The defendant recruited straw buyers and worked with an escrow officer in the scheme to defraud and then benefitted from their involvement in the scheme. Most of the properties were purchased or attempted to be purchased for in excess of a million dollars. Following the funding of the loans, the defendant received “cash back” or proceeds that he used to live a lavish lifestyle and further perpetuate the scheme. All of the homes purchased through the conspiracy have been foreclosed or sold at a loss to the lending institutions. The conspiracy resulted in approximately $5,000,000 in loans obtained by fraud and an actual and intended loss to lending institutions of nearly $6,500,000.
A conviction for Conspiracy to Commit Wire and Bank and Wire Fraud carries a maximum penalty of 30 years in federal prison, a $1,000,000 fine or both. In determining an actual sentence, Judge Campbell will consult the U.S. Sentencing Guidelines, which provide appropriate sentencing ranges. The judge, however, is not bound by those guidelines in determining a sentence.
The investigation in this case was conducted by the Federal Bureau of Investigation. The prosecution was handled by Kevin M. Rapp and Monica B. Klapper, Assistant U.S. Attorneys, District of Arizona, Phoenix.
This prosecution is part of efforts underway by President Barack Obama’s Financial Fraud Enforcement Task Force. President Obama established the interagency Financial Fraud Enforcement Task Force to wage an aggressive, coordinated and proactive effort to investigate and prosecute financial crimes. The task force includes representatives from a broad range of federal agencies, regulatory authorities, inspectors general and state and local law enforcement who, working together, bring to bear a powerful array of criminal and civil enforcement resources.
The task force is working to improve efforts across the federal executive branch, and with state and local partners, to investigate and prosecute significant financial crimes, ensure just and effective punishment for those who perpetrate financial crimes, combat discrimination in the lending and financial markets, and recover proceeds for victims of financial crimes. For more information about the task force visit: http://www.stopfraud.gov.
Unveiled – Fuck the FBI message by Anonymous – Orginal Letter
Greetings Pirates, and welcome to another exciting #FuckFBIFriday release. As part of our ongoing effort to expose and humiliate our white hat enemies, we targeted a Special Agent Supervisor of the CA Department of Justice in charge of computer crime investigations. We are leaking over 38,000 private emails which contain detailed computer forensics techniques, investigation protocols as well as highly embarrassing personal information. We are confident these gifts will bring smiles to the faces of our black hat brothers and sisters (especially those who have been targeted by these scurvy dogs) while also making a mockery of "security professionals" who whore their "skills" to law enforcement to protect tyrannical corporativism and the status quo we aim to destroy. We hijacked two gmail accounts belonging to Fred Baclagan, who has been a cop for 20 years, dumping his private email correspondence as well as several dozen voicemails and SMS text message logs. While just yesterday Fred was having a private BBQ with his CATCHTEAM high computer crime task force friends, we were reviewing their detailed internal operation plans and procedure documents. We also couldn't overlook the boatloads of embarrassing personal information about our cop friend Fred. We lulzed as we listened to angry voicemails from his estranged wives and ex-girlfriends while also reading his conversations with girls who responded to his "man seeking woman" craigslist ads. We turned on his google web history and watched him look up linux command line basics, golfing tutorials, and terrible youtube music videos. We also abused his google voice account, making sure Fred's friends and family knew how hard he was owned. Possibly the most interesting content in his emails are the IACIS.com internal email list archives (2005-2011) which detail the methods and tactics cybercrime units use to gather electronic evidence, conduct investigations and make arrests. The information in these emails will prove essential to those who want to protect themselves from the techniques and procedures cyber crime investigators use to build cases. If you have ever been busted for computer crimes, you should check to see if your case is being discussed here. There are discussions about using EnCase forensic software, attempts to crack TrueCrypt encrypted drives, sniffing wireless traffic in mobile surveillance vehicles, how to best prepare search warrants and subpoenas, and a whole lot of clueless people asking questions on how to use basic software like FTP. In the end, we rickrolled the entire IACIS list, causing the administrators to panic and shut their list and websites down. These cybercrime investigators are supposed to be the cream of the crop, but we reveal the totality of their ignorance of all matters related to computer security. For months, we have owned several dozen white hat and law enforcement targets-- getting in and out of whichever high profile government and corporate system we please and despite all the active FBI investigations and several billion dollars of funding, they have not been able to stop us or get anywhere near us. Even worse, they bust a few dozen people who are allegedly part of an "anonymous computer hacking conspiracy" but who have only used kindergarten-level DDOS tools-- this isn't even hacking, but a form of electronic civil disobedience. We often hear these "professionals" preach about "full-disclosure," but we are sure these people are angrily sending out DMCA takedown notices and serving subpoenas as we speak. They call us criminals, script kiddies, and terrorists, but their entire livelihood depends on us, trying desperately to study our techniques and failing miserably at preventing future attacks. See we're cut from an entirely different kind of cloth. Corporate security professionals like Thomas Ryan and Aaron Barr think they're doing something noble by "leaking" the public email discussion lists of Occupy Wall Street and profiling the "leaders" of Anonymous. Wannabe player haters drop shitty dox and leak partial chat logs about other hackers, doing free work for law enforcement. Then you got people like Peiter "Mudge" Zatko who back in the day used to be old school l0pht/cDc only now to sell out to DARPA going around to hacker conventions encouraging others to work for the feds. Let this be a warning to aspiring white hat "hacker" sellouts and police collaborators: stay out the game or get owned and exposed. You want to keep mass arresting and brutalizing the 99%? We'll have to keep owning your boxes and torrenting your mail spools, plastering your personal information all over teh internets. Hackers, join us and rise up against our common oppressors - the white hats, the 1%'s 'private' police, the corrupt banks and corporations and make 2011 the year of leaks and revolutions! We are Anti-Security, We are the 99% We do not forgive. We do not forget. Expect Us! NOTE THE RELEVANT FILES MENTIONED ARE ALREADY IN CIRCULATION
TOP-SECRET-FAA Comunications Security 1991

ORDER
Date: 3/5/91
Initiated
by: ACO-300
Subject: COMMUNICATIONS SECURITY (COMSEC)
FOREWORD
This order establishes policies and procedures and assigns
responsibilities for ensuring agency compliance with requirements
of the national communications security (COMSEC) policy.
The guidance in this order is based upon COMSEC policy directives
promulgated by the National Security Agency and implementing
regulations and directives issued by the United States Air Force.
Should a conflict exist between the requirements of this order
and the appropriate national COMSEC policy or implementing
directive, the national policy or directive will in all cases
apply. Instances of this type will be reported expeditiously to
this headquarters.
This order is marked FOR OFFICIAL USE ONLY. It is to be
safeguarded, handled and processed in accordance with
requirements of Order 1600.15D. This order is not releasable to
contractors or to foreign nationals without the specific approval
of the Assistant Administrator for Civil Aviation Security,
Washington, D.C. However, dissemination of pertinent information
extracted from this order to contractors having a need-to-know is
permissible when such release is authorized by applicable
National COMSEC Instructions (NACI).
Changes in national COMSEC policy reflected in this order such as
the institution of the Formal Cryptographic Access Program have
been coordinated with and accurately state the position of the
Office of the Secretary of Transportation.
All FAA personnel whose duties require them to handle, process,
store, safeguard, or otherwise have access to classified
cryptographic material are required to become familiar with and
conform to the requirements of this order.
/s/ James B. Busey
Administrator
FOR OFFICIAL USE ONLY
NOT RELEASABLE TO FOREIGN NATIONALS
NOT RELEASABLE TO CONTRACTORS WITHOUT ORIGINATOR'S APPROVAL
TABLE OF CONTENTS
Page
CHAPTER 1. GENERAL 1
1. Purpose 1
2. Distribution 1
3. Cancellation 1
4. Explanation of Changes 1
5. Definitions 2
6. Forms and Reports 2
7. Requests for Information 2
8. Statement of Intent 2
9. Scope 2
10. Responsibilities 2
11. Interpretation 2
12. Authority to change this Order 7
13.-19. Reserved 7
CHAPTER 2. POLICY FOR GRANTING ACCESS TO U.S.
CLASSIFIED CRYPTOGRAPHIC INFORMATION 13
SECTION 1. POLICY 13
20. General 13
21. Policy 13
SECTION 2. DEFINITION 13
22. Cryptographic Information 13
SECTION 3. CRITERIA 14
23. Access Requirements 14
24. Polygraph 14
25. Contacts with Foreign Nationals and Unofficial
Foreign Travel to Communist or other Designated
Countries 15
SECTION 4. GRANTING FORMAL CRYPTOGRAPHIC ACCESS 15
26. Scope 15
27. Preparing AFCOMSEC Form 9 17
28. Withdrawing FCA 18
29. Certificates of Personnel Declining Cryptographic
Access 19
30.-34. Reserved 19
CHAPTER 3. COMMUNICATIONS SECURITY (COMSEC) DUTIES AND
RESPONSIBILITIES 27
35. General 27
36. COMSEC Custodians and Alternates 27
37. Training 28
38. Waivers 30
39. Duties of the COMSEC Custodian 30
40. Performance Standards 31
41. Appointment of Custodians and Alternates 32
42. Monitoring Responsibilities 32
43.-49. Reserved. 33
CHAPTER 4. SAFEGUARDING COMSEC FACILITIES 39
SECTION 1. GENERAL 39
50. Purpose 39
51. Referenced Publications 39
52. Background 39
SECTION 2. PHYSICAL SECURITY STANDARDS 40
53. Physical Security Standards for Fixed COMSEC
Facilities 40
54. Installation Criteria 40
55. Facility Approvals, Inspection, and Tests 41
56. Intrusion Detecting Systems 43
57.-60. Reserved 43
SECTION 3. ACCESS RESTRICTIONS AND CONTROLS 43
61. Unescorted Access 43
62. Escorted Access 45
63. Visitor Register 45
64. No-Lone Zones 46
65. Guard Services 46
66.-70. Reserved 47
SECTION 4. PROTECTION OF UNATTENDED COMSEC EQUIPMENT 47
71. General 47
72. Protection Requirements 47
73.-77. Reserved 48
SECTION 5. PROTECTION OF LOCK COMBINATIONS 48
78. Purpose 48
79. Protection Requirements 48
80. Access to Combinations 49
81. Record of Combinations 49
82.-86. Reserved. 50
SECTION 6. NONESSENTIAL AUDIO/VISUAL EQUIPMENT 51
87. Personally Owned Equipment 51
88. Government Owned Equipment 51
89.-94. Reserved 51
SECTION 7. STANDARD OPERATING PROCEDURES (SOP) 51
95. Requirement 51
96. Emergency Plan 52
97.-101. Reserved 53
CHAPTER 5. SAFEGUARDING AND CONTROL OF COMMUNICATIONS
SECURITY MATERIALS 65
102. General 65
103. Definitions 66
104. Handling Keying Material 66
105.109. Reserved 66
SECTION 1. GENERAL INFORMATION APPLICABLE TO ALL
COMSEC MATERIAL 66
110. Responsibilities for Safeguarding COMSEC Material 66
111. Transport of COMSEC Material 67
112. Courier Responsibilities 68
113. Open Display of COMSEC Material and Information 68
114. Destruction 68
115. Reporting Insecurities 68
116. Evidence of Tampering 69
117. Alteration of COMSEC Material 69
118. Clearance Requirements for Guards 69
119. Storage Requirements 69
120. Other COMSEC Information 70
121. Disposition of COMSEC Materials 71
122. Page Checks of COMSEC Publications 72
123. Daily or Shift Inventory Requirements 73
124. COMSEC Account Record File 73
125.-129. Reserved 74
CHAPTER 6. CONTROLLED CRYPTOGRAPHIC ITEMS (CCI) 79
130. Purpose and Background 79
131. Definitions 79
132. Control Requirements 80
133. Inventories 84
134. Reporting Insecurities 84
135. Routine and Emergency Destruction 84
136.-144. Reserved 84
CHAPTER 7. SECURE VOICE 89
SECTION 1. GENERAL 89
145. Purpose 89
146. Types and Models of STU-III 89
147. Definitions 89
148.-150. Reserved 91
SECTION 2. EXCEPTIONS 91
151. Requests for Exception 91
152.-153. Reserved 91
SECTION 3. COMSEC CUSTODIAN DUTIES AND
RESPONSIBILITIES 91
154. General 91
155. Receipt of Key 91
156. Accounting for Key 92
157. Notices from the KMS/CAO 93
158.-160. Reserved 94
SECTION 4. KEYING OF TERMINALS 94
161. Initial Keying of Terminals 94
162.-163. Reserved 94
SECTION 5. ACCOUNTABILITY 94
164. Cryto-Ignition Key Handling and Local Accounting 94
165.-166. Reserved 95
SECTION 6. REKEYING 96
167. Electronic Rekeying 96
168.-170. Reserved 96
SECTION 7. PHYSICAL SECURITY 96
171. Unkeyed Terminal Type 1 96
172. Keyed Terminal 96
173. Terminal Display 97
174. Use by Other U.S. Personnel 97
175. Use by Foreign Nationals 98
176. Storage 98
177. Use of the Secure Data Mode 98
178. After Hours Protection 98
SECTION 8. TRANSPORTATION 98
179. Type 1 Terminals 98
180.-182. Reserved 99
SECTION 9. INSTALLATION 99
183. General 99
184. Residences 100
185.-186. Reserved 100
SECTION 10. MAINTENANCE 100
187. General 100
188. Access 100
189.-190. Reserved 100
SECTION 11. PROTECTION OF KEY STORAGE DEVICES 101
191. General 101
192. Fill Devices 101
193. Crypto-Ignition Keys (CIKs) 102
194. Protection and Use of the Micro-KMODC 104
195.-198. Reserved 104
SECTION 12. DESTRUCTION AND EMERGENCY DESTRUCTION 104
199. General Requirement 104
200. Reserved 104
SECTION 13. REPORTABLE INSECURITIES 105
201. Insecure Practice/COMSEC Incident Handling 105
202.-204. Reserved 106
SECTION 14. RECORDS RETENTION 106
205. General 106
206.-208. Reserved 106
APPENDIX 1. REQUIRED FORMS AND REPORTS (2 pages) 1
APPENDIX 2. SAMPLE CRYPTOGRAPHIC ACCESS BRIEFING (9 pages) 1
APPENDIX 3. CRYPTOGRAPHIC ACCESS CERTIFICATE (1 page) 1
APPENDIX 4. SECURE TELECOMMUNICATIONS FACILITY 1
AND COMSEC ACCOUNT CHECKLIST (6 pages)
APPENDIX 5. PUBLICATIONS TO BE MAINTAINED BY ALL 1
FAA COMSEC ACCOUNTS (2 pages)
APPENDIX 6. PHYSICAL SECURITY STANDARDS FOR FIXED 1
COMSEC FACILITIES (3 pages)
APPENDIX 7. STANDARDS FOR SAFEGUARDING KEYING MATERIAL 1
(4 pages)
APPENDIX 8. ROUTINE DESTRUCTION AND EMERGENCY PROTECTION 1
OF COMSEC MATERIAL (7 pages)
FOR OFFICIAL USE ONLY
PUBLIC AVAILABILITY TO BE
DETERMINED UNDER 5 U.S.C. 552
CHAPTER 1. GENERAL 1. PURPOSE. This order prescribes FAA standards and procedures for communications security (COMSEC) and implements changes in national COMSEC policy for FAA COMSEC operations. 2. DISTRIBUTION. This order is distributed to Regional Administrators and Center Directors: to the director level in the Office of System Engineering and Program Management, Office of Air Traffic System Management, Air Traffic Plans and Requirements Service, Advanced System Design Service, Office of Human Resource Development, Office of Training and Higher Education, and Logistics Service; to the division level in the Systems Maintenance Service, and Office of Civil Aviation Security, Operations to Emergency Operations Staff (ADA-20), Regional and Aeronautical Center Civil Aviation Security Divisions, Technical Center Civil Aviation Security Staff, Europe, Africa and Middle East Civil Aviation Security Staff; to COMSEC custodians including Air Route Traffic Control Centers; to the FAA manager/supervisor at each Joint Use System Long Range Radar Site; to Associate Program Managers for Engineering, Communications and Aircraft Acquisition Program. 3. CANCELLATION. Order 1600.8B, Communications Security (COMSEC), dated November 14, 1975, is canceled 4. EXPLANATION OF CHANGES. This order updates FAA COMSEC policies and procedures to reflect national COMSEC policy guidance from the National Security Agency (NSA), and the U.S. Air Force (USAF). It also establishes new training standards for individuals assigned as COMSEC custodians. This revision: a. Promulgates changes in national policy contained in NSA National COMSEC Instructions (NACSI) and National Telecommunications and Information Systems Security Instructions (NTISSI). b. Establishes a Formal Cryptographic Access (FCA) Program in FAA to include mandatory requirements for cryptographic access briefings and Cryptographic Access Certificates. c. Disseminates USAF guidance for implementing national COMSEC policy as set forth in USAF Regulations (AFR), USAF Special Purpose/Operational Miscellaneous (AFSAL) publications and related documents. d. Prescribes policies and procedures governing the utilization and safeguarding of Controlled Cryptographic Items (CCI). e. Prescribes mandatory formal training requirements for COMSEC custodians. f. Prescribes guidance concerning the Secure Terminal Unit (STU) III secure voice system. g. Establishes requirements for the inclusion of COMSEC duties and responsibilities as a Critical Job Element (CJE) in the individual performance standards for the COMSEC custodian and alternate(s). 5. DEFINITIONS. The definitions contained in National Communications Security Committee (NCSC) 9 and Air Force Regulation (AFR) 56-2 apply to this order. Definitions not contained in these references will be provided in the body of the order. 6. FORMS AND REPORTS. Appendix 1, Required Forms and Reports, contains a listing of the forms and reports required by this order. Additional reporting requirements will be addressed in the portion of the order to which they pertain. 7. REQUESTS FOR INFORMATION. Questions on the interpretation of the provisions of this order or their application shall be referred to the servicing security element in regions and centers or to the Director, Office of Civil Aviation Security, Operations, ACO-1, 800 Independence Avenue, S.W., Washington, D.C. 20591. 8. STATEMENT OF INTENT. It is the intention of the FAA to ensure that requirements of the national COMSEC policy are fully understood and implemented by all having responsibilities for COMSEC operations and support within the agency. 9. SCOPE. a. The provisions of this order apply to all FAA employees, military, civilian, and contractor, who are holders or users of NSA produced or authorized cryptographic information or who otherwise have access to such information, regardless of duty station, location, or position. b. FAA procurement actions which result in requirements for contractors to generate or utilize NSA approved or authorized/ cryptographic information in the performance of the contract will be accomplished in accordance with Order 1600.56, Guidelines for FAA Participation in the Department of Defense (DOD) Industrial Security Program (ISP). Access requirements shall be specified in accordance with National Telecommunications and Information Systems Security Policy (NTISSP) Number 3. 10. RESPONSIBILITIES. a. Director, Office of Civil Aviation Security, ACO-1 is responsible for: (1) Implementing the national COMSEC policy and the provisions of this order within the FAA. (2) Recommending policies for safeguarding of FAA information and data using COMSEC techniques to provide the required degree of protection. (3) Ensuring that cryptologic access briefings and debriefings are conducted and that cryptographic access certificates are signed in accordance with provisions of this order. (4) Establishing and ensuring the implementation of standards and procedures for handling, safeguarding, accounting, destruction, storage, access and control of classified and unclassified COMSEC and other NSA approved and authorized cryptographic materials in accordance with national COMSEC policy and this order. (5) Developing standards and procedures for physical and environmental security of FAA cryptographic communications installations. (6) Ensuring in coordination with the Program Director for Communications, FAA COMSEC equipment installations are designed in accordance with applicable national COMSEC policies pertaining to on-line and TEMPEST engineering standards. (7) Monitoring headquarters, region, and center COMSEC accounts and appointment of COMSEC custodians. (8) Ensuring that countermeasures and specialized communications security inspections are conducted of COMSEC secure communications areas in accordance with NSA and USAF directives, and this order. b. National Airspace System Engineering Service, ASE, is responsible for: (1) Development of National Airspace System (NAS) plan/and baseline system requirements for COMSEC systems. (2) Ensuring the baselined COMSEC system requirements and interface requirements are consistent with national COMSEC engineering and security standards established by the NSA. (3) Formulating guidance and standards applicable to acquisition of facilities and equipment including COMSEC systems. (4) Coordination with the Office of Civil Aviation Security, on NAS plans and NAS system specifications involving COMSEC security requirements and resources. c. Office of Air Traffic Systems Management, ATM, is responsible for: (1) Establishing COMSEC requirements for support of air traffic control operational telecommunications. (2) Developing and recommending national guidance, standards, and procedures for implementation of COMSEC in the security control of military and other air traffic pursuant to the FAA's support of the national defense. (3) Coordination with the Office of Civil Aviation Security in establishing procedures and standards for the identification of sensitive and classified information and data in the air traffic control system requiring COMSEC protection. (4) Ensuring that sensitive and classified telecommunications in the air traffic control system are safeguarded in accordance with national COMSEC policy. d. Air Traffic Plans and Requirements Service, ATR, is responsible for: (1) Coordination with the Office of Civil Aviation Security in developing and implementing procedures and standards for the identification of COMSEC support required to ensure a secure and effective air traffic system telecommunications capability. (2) Serving as the air traffic system focal point for coordination of COMSEC programs and requirements in support of the NAS. e. Systems Maintenance Service, ASM, is responsible for: (1) Coordination with the Office of Civil Aviation Security to: (a) Identify requirements for communications security during network planning and engineering of future telecommunications networks or expansions or modifications to present networks. (b) Ensure operational compliance with communications security requirements in telecommunications maintenance support. (2) Participate in the development of maintenance planning for COMSEC equipment and systems in the FAA, including identification of required COMSEC maintenance training for FAA personnel. f. Office of Human Resource Development, AHD, is responsible for: (1) Providing administrative and technical guidance and support for inclusion of the COMSEC custodian position in the Performance Evaluation Rating (PER) system. (2) Establishing standards and criteria for designating the responsibilities of the custodian and alternate as CJE'S. g. Office of Training and Higher Education, AHT, is responsible for: (1) Providing administrative and technical guidance and support for mandatory training for custodians at the USAF COMSEC Account Management course. (2) Establishing and incorporating in appropriate directives criteria for evaluation of COMSEC responsibilities and training in career development programs for selected employees. h. Office of Labor and Employee Relations, ALR, is responsible for facilitating the implementation of the requirements of this order as required. i. Regions and Centers are responsible for implementation of this order within their areas of jurisdiction. j. Office of Air Traffic System Management, Air Traffic Plans and Requirements Service, Systems Maintenance Service, National Airspace System Engineering Service are responsible for: (1) Implementing this order in those organizations that report to them who have a requirement for access to COMSEC information. (2) Ensuring that COMSEC custodians receive formal COMSEC account management training and that operators and maintenance personnel are properly trained in procedures for safeguarding and handling of COMSEC material required in the performance of their duties. (3) Ensuring that all authorized COMSEC materials are properly obtained, procured, installed, operated, safeguarded, destroyed, or transferred when no longer required. (4) Ensuring that viable emergency plans exist to minimize the risk of compromise of COMSEC materials during crisis situations. k. Region and Center Civil Aviation Security Divisions and Staffs are responsible for: (1) Ensuring that COMSEC information and material in offices and activities under their control or jurisdiction are safeguarded and controlled in accordance with this order. (2) Providing staff guidance, assistance, and interpretation with regard to this order. (3) Conducting COMSEC account inspections. (4) Ensuring that insecurities involving COMSEC materials are reported to cognizant authorities in a timely and comprehensive manner as required by U.S. Air Force General Publication (AFKAG) 2 and NTISSI-4003. (5) Developing and administering a Cryptologic Access Program in accordance with provisions of chapter 2, of this directive, to include the following: (a) Ensuring that all personnel within their jurisdiction requiring access to U.S. classified cryptographic information sign a Cryptologic Access Certificate (AFCOMSEC Form 9) prior to being granted access in accordance with provisions of Chapter 2 of this order and (b) Ensuring that the signed cryptographic access certificate is made a permanent part of the individual employee's official security records and is accounted for in accordance with provisions of Order 1600.1C concerning retention of security clearance/access certificates. l. COMSEC Custodian is the properly appointed individual who manages and controls the accountable COMSEC material in the COMSEC Material Control System charged to his/her activity with responsibilities which include: (1) The receipt, storage, amendment, accountability, inventory, and issuance of COMSEC material charged to his/her account and destruction or transfer of material when it is no longer required. (2) Ensuring that appropriate COMSEC material is readily available to properly authorized individuals whose duties require its use. (3) Ensuring that all persons requiring access to U.S. classified cryptographic information receive a cryptographic access briefing in accordance with this directive and sign a cryptographic access certificate before they are permitted access. (4) Advising users and supervisors, as appropriate, of the required protection and procedures which must be provided COMSEC material issued to them for use, including the authorized procedures for destruction or disposition of such material when it is no longer required. (5) Reporting COMSEC insecurities in accordance with instructions in AFKAG-2 and NTISSI-4003. COMSEC insecurities fall into three categories, cryptographic, personnel and physical. Specific examples of each type are given in NTISSI 4003. m. Individual users are responsible for: (1) Knowledge of the requirements of this order. (2) Safeguarding and proper employment of all COMSEC material he or she uses or for which he or she is responsible in accordance with the provisions of this order. (3) Promptly reporting to the custodian any occurrences, circumstances, or acts which could jeopardize the security of COMSEC material. Should the custodian be unavailable the report is submitted to the servicing security element or ACO-300. p. Program Manager, Communications and Aircraft Acquisition, ANC-1, is responsible for: (1) Management of engineering planning, development, acquisition, and implementation of COMSEC equipments and systems in support of FAA requirements and the national COMSEC policy. (2) Recommending, through coordination with the Office of Air Traffic System Management and the Office of Civil Aviation Security, and other Federal Agencies, appropriate COMSEC equipments and systems to meet identified needs. (3) Identification of required maintenance training for FAA personnel in coordination with the Systems Maintenance Service and the Office of Training and Higher Education. (4) Coordination with the Office of Civil Aviation Security, Operations, to ensure that plans and specifications for COMSEC installations are reviewed and meet all FAA NSA security requirements prior to installation. (5) Developing and recommending engineering standards and procedures to implement national TEMPEST and COMSEC engineering criteria for the secure installation and operation of COMSEC equipment in the FAA in concert with ACS. 11. INTERPRETATION. Questions regarding the interpretation of the provisions of this order or their application shall be referred to the Regional or Center Civil Aviation Security Division or Staff, or to the Manager, Investigations and Security Division, ACO-300, Office of Civil Aviation Security Operations, 800 Independence Avenue, S.W., Washington, D.C., 20591. 12. AUTHORITY TO CHANGE THIS ORDER. The Assistant Administrator for Civil Aviation Security is authorized to issue changes to this order which do not contain policy, assign responsibilities, or delegate authority. 13.-19. RESERVED. FOR OFFICIAL USE ONLY PUBLIC AVAILABILITY TO BE DETERMINED UNDER 5 U.S.C. 552
CHAPTER 2. POLICY FOR GRANTING ACCESS TO U.S. CLASSIFIED CRYTOGRAPHIC INFORMATION SECTION 1. POLICY 20. GENERAL. In accordance with policies established by the National Telecommunications and Information Systems Security Committee (NTISSC) in National Telecommunications and Information Systems Security Policy (NTISSP) Number 3, issued in December 1988, and implemented by the Air Force Systems Security Instruction (AFSSI) 4000 of October 1, 1989, the FAA requires special access controls for certain U.S. classified cryptographic information, the loss of which would cause serious or exceptionally grave damage to U.S. national security. This order provides policy, guidelines, and procedures as applicable to the Formal Cryptographic Access (FCA) Program. It provides for an individual's eligibility, unofficial foreign-travel requirements, contacts with foreign nationals, procedures for granting and withdrawing FCA, and actions to take when personnel decline FCA. 21. POLICY. A formal Cryptographic Access Program is established in the FAA whereby access to certain U.S. classified cryptographic information shall only be granted to individuals who satisfy the criteria set forth herein. All FAA employees and FAA contractor employees assigned duties as communications security (COMSEC) custodians; alternate COMSEC custodians; COMSEC accountants; COMSEC inspectors; cryptoequipment maintenance and installation personnel; key distribution center (KDC) personnel; telecommunications center personnel; any personnel identified by ACO-300; and any other persons who work full time in the above areas who have access to the cryptomaterial must have the FCA to meet the requirements of this order as well as the requirements established for two-person integrity. SECTION 2. DEFINITION 22. CRYPTOGRAPHIC INFORMATION. The terms used in this order are defined in AFR 56-2. For the purposes of this directive U.S. classified cryptographic information is defined as: a. TOP SECRET and SECRET, CRYPTO designated, key and authenticators. b. All cryptographic media which embody, describe, or implement classified cryptographic logic; this includes full maintenance manuals, cryptographic descriptions, drawings of cryptographic logics, specifications describing a cryptographic logic, cryptographic computer software, or any other media which may be specifically identified by the NTISSC. SECTION 3. CRITERIA 23. ACCESS REQUIREMENTS. An individual may be granted access to U.S. classified cryptographic information, only if that individual: a. Is a U.S. citizen. b. Is an FAA employee or is a U.S. Government-cleared contractor approved by ACO-300. c. Possesses a security clearance appropriate to the classification of the U.S. cryptographic information to be accessed. d. Possesses a valid need-to-know that has been determined to be necessary to perform duties for, or on behalf, of FAA. e. Receives a security briefing from the servicing security element in regions and centers, or from ACO-300 in headquarters, detailing the sensitive nature of cryptomaterial and the individual's responsibility for protecting cryptomaterial. Appendix 2 contains the text of the briefing. f. Acknowledges the granting of such access by signing the Cryptographic Access Certificate AFCOMSEC Form 9 an example of which is contained in Appendix 3 of this order. 24. POLYGRAPH. The NTISSP Number 3 provides for utilization of non lifestyle counterintelligence polygraph examinations under certain conditions. FAA has determined however that the use of the polygraph will not be a requirement in the FAA COMSEC Program. 25. CONTACTS WITH FOREIGN NATIONALS AND UNOFFICIAL FOREIGN TRAVEL TO COMMUNIST OR OTHER DESIGNATED COUNTRIES. a. All FAA employees possessing an FCA must advise their servicing security element of all contacts with nationals of the listed governments and receive written permission from their facility or office manager with an information copy to the servicing security element and to ACO-300 for unofficial travel to these countries. Afghanistan Latvia Albania Libyan Arab Republic Angola Lithuania Berlin (Soviet Sector) Mongolian Peoples Bulgaria Republic (Outer Cambodia (Kampuchia) Mongolia) Peoples Republic of Nicaragua China (Including Tibet) Poland Cuba Rumania Czechoslovakia South Yemen Estonia Syria Ethiopia Union of Soviet Hungarian Peoples Socialist Republics Republic (Hungary) (Russia) Iran Democratic Republic of Iraq Vietnam (North Democratic Peoples Vietnam) Republic of Korea South Vietnam (North Korea) Yugoslavia Laos b. The above restrictions are in addition to those requirements of Order 1600.61, Defensive Security Briefing Requirements for FAA Employees Traveling to Communist-Controlled Countries. SECTION 4. GRANTING FORMAL CRYPTOGRAPHIC ACCESS 26. SCOPE. This policy shall apply to all FAA employees civilian and military who satisfy the requirements of Section 3, above, and whose official duties require continuing access to U.S. classified cryptographic information. Procedures to be followed in the granting of a Cryptographic Access Certificate are as follows: a. COMSEC Manager and Custodian. The COMSEC custodian or the manager responsible for COMSEC operations in a facility or office shall: (1) Upon receipt of this order take appropriate action to coordinate with the supporting personnel office and the servicing security element to provide them with the names and positions of all personnel requiring FCA. (2) Immediately notify the servicing security element of any change in status or need-to-know of individuals having FCA. b. Personnel Offices. The personnel office will coordinate with the supporting security element to accomplish the following: (1) To ensure that the master record reflects the requirement for FCA, and to arrange for the procedures to be followed to provide the required briefing, as well as need-to-know and clearance verification for each individual. (2) The personnel office will be responsible for entering into the Consolidated Management Information System (CPMIS) the correct information pertaining to FCA requirements for designated positions. (3) To develop procedures that will ensure that the servicing security element is informed whenever individuals with FCA change positions, terminate or otherwise no longer have need for the FCA in accordance with this directive. (4) To coordinate with the servicing security element and to take such additional actions as may be required to ensure that the national security objectives of the FCA are supported and implemented. c. Servicing Security Element. The servicing security element will designate in writing an individual to serve as the FCA point-of-contact for implementation and coordination of the FCA Program. This individual may be the personnel security officer and will be responsible for implementing the FCA Program within his/her area of responsibility. To include the following actions: (1) Ensure that the requirements of this order are met. (2) Provide guidance to operating offices and personnel offices on the FCA Program. (3) Ensure that clearance data and other relevant information pertinent to individuals seeking FCA is correct and is entered into the CPMIS and Civil Aviation Security Information System (CASIS) to the extent that is necessary to permit accurate tracking of individuals in the FCA Program. (4) Coordinate with Personnel and the operating facility or office to schedule briefing indoctrinations required for FCA and to obtain required signatures on Cryptographic Access Certificates (AFCOMSEC Form 9). (5) Ensure that the properly filled out AFCOMSEC Form 9 (Cryptographic Access Certificate) is handled, documented, and retained as required by Order 1600.1C for clearance certifications. d. Cryptographic Access Certificate. (1) The facility or office manager having responsibility for the COMSEC operation or his or her designated representative in coordination with the supporting personnel office and the servicing security element will establish procedures for briefing personnel requiring FCA. (2) Upon completion of the required briefing each individual requiring FCA will be asked to sign the Cryptographic Access Certificate. The manager will normally sign as witness to the signature of the persons being granted access. (3) The original copy of the signed certificate will be forwarded to the servicing security element in regions and centers, and to ACO-300 in the Washington Headquarters, where it will be permanently retained. e. Local Tracking Procedures for FCA. Each facility or office having personnel assigned duties in paragraph 21 will, in coordination with the supporting Personnel Office and the servicing security element, develop written procedures, to include out-processing, for reporting the granting and termination of FCA. f. FAA employees requiring an FCA at TDY locations and who meet all requirements of the FCA Program will be briefed prior to their departure and asked to sign the Cryptographic Access Certificate. When all requirements have been met, clearance status notifications will include the fact that the individual has FCA. 27. PREPARING AFCOMSEC FORM 9. a. AFCOMSEC Form 9. (Appendix 3) Include the following information on the AFCOMSEC Form 9: (1) Installation. Facility or office where the individual is permanently assigned. (2) Unit or Office Symbol. Individual's office and office symbol. (3) Supporting COMSEC Account. Self-explanatory. (4) Signature. Payroll signature. (5) Name. Full name, last name, first name, middle initial. (6) SSN: Will contain dashes (that is 001-01-0001) (7) Grade and Date of Birth. Self-explanatory. (8) In Section 2, paragraph B, a line will be drawn through the last sentence in this paragraph which reads: "I understand that I am subject to and consent to a periodic, counterintelligence polygraph examination." This modification will be initialed both by the person signing the form and by the witness. NOTE: Type AFCOMSEC Forms 9 to ensure legibility and accuracy of the information. The servicing security element and ACS-300 will return AFCOMSEC Forms 9 not properly and completely filled in. b. FAA Cryptographic Access Program. Prepare three copies of AFCOMSEC Form 9. Forward the original signed certificate to the servicing security element in regions and centers and to ACS-300 in the Washington Headquarters; one copy to the individual; and one copy for retention by the local COMSEC account (Folder 2). Maintain locally retained certificates as long as individuals require cryptographic access. Termination statements shall be copies of the locally retained certificate with the properly filled in bottom portion. c. Supply of AFCOMSEC Forms 9. Initial distribution of AFCOMSEC Forms 9 will be made by ACO-300 to servicing security elements in regions and centers who in turn will distribute the forms to the accounts for which they have monitor responsibility. After initial distribution, forms should be requisitioned as needed in accordance with guidance provided in AFKAG-2. 28. WITHDRAWING FCA. a. Once granted the FCA may be withdrawn for only three reasons: (1) Administrative. An individual is being reassigned by the facility or office manager to a position not requiring FCA, or a person is being reassigned to another FAA facility or region or is terminating employment. (2) Suspension. If a person's security clearance or any special access is suspended as outlined in Order 1600.1C, that person's FCA must be suspended until the matter is adjudicated favorably. Suspension of the FCA requires that the individual be removed from COMSEC custodian and accounting duties that require access to cryptographic material until a final determination of reinstatement or revocation can be made. (3) Revocation. Any person who has a security clearance withdrawn or special access denied will also have the FCA revoked. This revocation of FCA is permanent and cannot be reinstated and permanently bars the individual from ever being assigned to duties within the areas in paragraph 21. b. Facility and office managers will advise the servicing security element by message of any change in a person's FCA status resulting from suspension or revocation including reason for suspension or revocation. The servicing security element will advise ACO-300 by message of all such actions. In addition the facility and office manager will send an original copy of the Cryptographic Access Certificate to the servicing security element. Keep a copy of the Cryptographic Access Certificate for 90 days after signature for local records. 29. CERTIFICATES OF PERSONNEL DECLINING CRYPTOGRAPHIC ACCESS. Send the original copy of certificates of any personnel who decline to sign the Cryptographic Access Certificates through the servicing security element to ACO-300 for permanent retention. Certificates should contain all the information on the individual less the signature. State that the individual has refused FCA on the face of the form and on the administering official's signature and signature block. 30.-34. RESERVED. FOR OFFICIAL USE ONLY PUBLIC AVAILABILITY TO BE DETERMINED UNDER 5 U.S.C. 552
CHAPTER 3. COMMUNICATIONS SECURITY (COMSEC) DUTIES AND RESPONSIBILITIES 35. GENERAL. All COMSEC material shall be entered into and retained in the COMSEC accounting system from the time of its origin until its ultimate destruction. COMSEC accounts are established when a facility or activity manager has a need for secure information processing, and application is made through the servicing security element and ACO-300 to the USAF Cryptologic Support Center (AFCSC). Upon approval by AFCSC the type of COMSEC account established will vary according to the mission it supports. Within the FAA the two most common types of accounts are operational and administrative or monitor accounts. 36. COMSEC CUSTODIANS AND ALTERNATES. a. Designation. When a COMSEC account has been authorized the cognizant facility or office manager will appoint a qualified COMSEC custodian and at least one alternate custodian. The appointment will be made in writing by properly completing an Air Force COMSEC (AFCOMSEC) Form 3, Appointment of COMSEC Custodians, for each COMSEC account. (1) Managers of Civil Aviation Security Divisions shall be the appointing officials for COMSEC monitor accounts under their security cognizance. (2) The Manager, Investigations and Security Division, Operations, ACO-300, will be the appointing official for the headquarters COMSEC monitor account custodian and alternate. b. Grade Requirements. (1) FAA COMSEC custodians must be grade GS-9 or above. (2) FAA alternate custodians must be grade GS-7 or higher. c. Clearance Requirements. Custodians and alternate custodian(s) positions are designated as non-critical sensitive for COMSEC accounts handling material at the Secret level or lower classification; for accounts handling Top Secret material the custodian and alternate custodian(s) positions are designated as critical sensitive. Persons designated to fill these positions must be cleared for the highest classification of COMSEC material they will be required to handle or have access to. Requirements are as follows: (1) For Top Secret COMSEC accounts, the designating official must ensure that persons designated as custodians and alternate custodians have a final Top Secret clearance based on a favorably adjudicated background investigation completed within the past 5 years. Periodic reinvestigations (PRI) will be conducted within 5 years from the date of the last Sensitive Background Information, Background Information, or PRI in accordance with Order 1600.1C. (2) For COMSEC accounts handling classified material up to and including Secret, the designating official must ensure that the individuals designated as custodian and alternate custodian(s) as a minimum, have a final Secret clearance based on a favorably adjudicated Minimum Background Investigation (MBI). A PRI is recommended 5 years after placement and every 5 years thereafter. (3) In making selections for custodian and alternate custodian the designating official shall give preference to qualified candidates who have maximum retainability in their current assignment. Other considerations include the following: (a) The individual must never have been relieved from COMSEC custodian duties for cause. (b) If practical, custodians and alternate custodians should be selected on the basis of best qualified rather than seniority. In this regard, consideration should be given to the following: 1 Persons with a background in COMSEC. 2 Persons having a minimum total of three years previous COMSEC experience. 37. TRAINING. a. COMSEC Custodian. For the purposes of this order the following shall apply: (1) For individuals who have had no prior COMSEC experience and for individuals who have not been actively engaged in COMSEC activities during the 3 years prior to the date of their designation, attendance at the three week COMSEC Account Management Course conducted by the USAF is mandatory. (a) It is the responsibility of the FAA manager or other official designating the custodian to ensure that the designee is scheduled for attendance at this course within 60 days of the date of appointment. (b) Because the waiting period for this particular course is often several months, it is important that requests for allocations be submitted through appropriate region/center channels as soon as possible. (c) Additional information concerning this course may be obtained from the servicing security element, or from ACO-300, Washington, D.C. (2) For employees who have attended the U.S. Air Force COMSEC Account Management Course or other formal COMSEC training provided by the government within the past 3 years prior to their designation as custodian, attendance at the USAF COMSEC Account Management Training Course will normally not be required. Similarly, employees who have been actively engaged in COMSEC operations during the 3 years prior to their designation, will not be required to attend formal COMSEC training provided the nature of their duties has enabled them to develop the skills and proficiency required to perform the duties of custodian. b. Alternate COMSEC Custodian(s). Training for the employee(s) designated as alternate COMSEC custodian(s) is important, since the alternate performs the duties of the custodian in the custodian's absence. (1) Normally if the individual(s) designated as alternate custodian(s) have been engaged in COMSEC activities during the 3 years prior to their designation additional formal training will not be required. It is highly desirable that at least one alternate custodian attend the 3 week USAF COMSEC Account Management Course. (2) As a minimum, however, it is mandatory that alternate custodians who have not been actively engaged in COMSEC activities during the 3 years prior to their designation be scheduled to attend approved COMSEC training of shorter duration than the USAF course within 60 days of their appointment. (a) Courses approved for alternate custodian training include COMSEC account management training courses offered by the General Services Administration (GSA). These are 1 week training courses in COMSEC accounting offered at various times during the year in different geographic locations. (b) Allocations for GSA courses are obtained through appropriate region/center personnel training channels. Information concerning these courses is available from the General Services Administration, Communications Security Training Center, ATTN: Registrar 7 KET-6, 1500 East Bannister Road, Kansas City, MO 64131-3087. c. Qualification Training Package. As an interim training measure while an individual is awaiting a class date for the COMSEC Account Management Course in the case of custodians, or the GSA course for alternate custodians, the Qualification Training Package (QTP) should be used. This is an Air Force produced COMSEC Account Management training package designed for self-study. Requests for this package should be addressed to ACO-300 through the servicing security element. d. Recurrent Training. Recurrent training for COMSEC custodians and alternates shall be scheduled as necessary to ensure that individuals maintain a high level of proficiency in COMSEC account management procedures and practices. Recurrent or proficiency training should be scheduled when the custodian determines that such training is required to achieve the required level of proficiency. e. Coordination. The servicing security element COMSEC monitor account will be provided an information copy of all requests for COMSEC training for custodians and alternate custodians. 38. WAIVERS. a. Problems encountered in meeting minimum grade or training requirements for custodians or alternate custodians will be referred to ACO-300, through the appropriate servicing security element. b. Where operational necessity is a consideration a request for waiver of minimum requirements may be submitted. c. ACO-300 will be the approving authority for all waiver requests. If a waiver is granted, it applies only to the designated individual and must not be transferred; it applies to the designated individual only while currently assigned; and it must be terminated if a qualified person meeting minimum grade requirements becomes available. In addition, the waiver must be renewed annually. Include the following information in all requests: (1) COMSEC account number. (2) Name, grade, and clearance of the individuals desired for appointment. (3) Present duty assignment. (4) Type custodian (primary or alternate). (5) Complete justification. (6) Reason for nonselection, if applicable, of assigned individuals who are senior in grade and meet all other selection criterions. (7) Date of any known projected personnel gains who would meet the minimum grade and/or training requirements. (8) Date the appointment is planned. 39. DUTIES OF THE COMSEC CUSTODIAN. Specific duties for which the COMSEC custodian is responsible include the following: a. The development and implementation of a comprehensive user-training program for all persons who, in performing official duties, deal with COMSEC material. An example would be the employees responsible for operation of COMSEC equipment at Joint Use Sites. The training will include programs for user personnel that ensure these individuals are completely familiar with their duties and responsibilities in areas of control, physical protection, inventory and destruction of COMSEC material, and reporting of security hazards, violations, and possible compromises. Refresher training is required as needed. b. Ensure that requirements established in FAA's Formal Cryptographic Access (FCA) Program are understood and implemented. This includes ensuring that personnel having an operational need for access have received a cryptographic access briefing, and have signed a Cryptographic Access Certificate, AFCOMSEC Form 9, as required by this order. c. Be thoroughly familiar with directives concerning classified material such as Order 1600.2C, National Security Information. d. Issue on hand receipt, all COMSEC material to users who need it for their job and ensure that all responsible users of this material know the procedures for protecting, accounting, destroying, and reporting possible compromise of such material. e. In coordination with the facility emergency planning staff, develop written plans to protect COMSEC materials in an emergency, and ensure that the plans are integrated with the facility contingency plan. Train COMSEC personnel in their duties under the plan and ensure that adequate and appropriate destruction equipment and materials are readily available. f. Ensure that all necessary and appropriate COMSEC material is maintained by the account and that disposition instructions have been requested from the Central Office of Record (COR) for surplus or unneeded material. Prepare and submit accounting reports promptly and accurately. g. Ensure that standard operating procedures (SOP) are prepared as required, for secure and efficient conduct of COMSEC/operations within the cryptofacility. 40. PERFORMANCE STANDARDS. a. General. The position of COMSEC custodian and that of alternate COMSEC custodian require persons of unquestioned integrity and loyalty. The quality of the work performance of individuals in these positions has a direct reflection on the national security of the United States and is a vital factor in the support provided by the FAA COMSEC effort to the National Airspace System. It is appropriate therefore that the position descriptions (PD) for individuals designated as COMSEC custodian or alternate COMSEC custodian include the COMSEC responsibilities assigned to that individual. b. Requirement. Managers responsible for performance evaluation rating of individuals designated as COMSEC custodians or alternate COMSEC custodians will: (1) Ensure that the PD's include the COMSEC responsibilities of the individual(s). (2) Identify the COMSEC responsibility as a critical job element (CJE) in the performance standards for the individual(s). 41. APPOINTMENT OF CUSTODIANS AND ALTERNATES. a. Each COMSEC account must have a COMSEC custodian and at least one alternate COMSEC custodian. From a practical viewpoint, the COMSEC custodian should be thoroughly familiar with the day-to-day transactions of the COMSEC account. b. As part of their monitor responsibilities, servicing security elements will: (1) Ensure that proposed custodians and alternates meet the clearance requirements and qualifications for appointment as described in paragraph 21. (2) Obtain original signatures of the designated custodian and alternate(s) in the proper blocks on each of four copies (three copies when action concerns a monitoring account) of AFCOMSEC Form 3. (3) Ensure that all applicable blocks of all copies of the AFCOMSEC Form 3 are completed, including the "Effective Date" and "From" block. (4) Forward the original copy of AFCOMSEC Form 3 under a covering letter to the Air Force Cryptologic Support Center (AFCSC), Attention: MMIC, San Antonio, Texas 78243. Refer to Situation F-2, AFKAG-2. The letter should designate appointment or rescission of a custodian or alternate(s), as appropriate. One copy of AFCOMSEC Form 3 will be forwarded to FAA Headquarters, Washington, D.C. 20591, Attention: ACO-300. One copy shall be retained by the servicing security element monitoring account, and one copy shall be retained in the operational account. 42. MONITORING RESPONSIBILITIES. a. FAA/USAF Agreement. By agreement with the U.S. Air Force (USAF), FAA will provide for the monitoring of all FAA COMSEC accounts. The Manager, Investigations and Security Division, Operations, ACO-300, is responsible for the agencywide COMSEC monitoring effort at the headquarters level. ACO-300 is also responsible for monitoring the administrative/monitor accounts of the regions, Aeronautical Center and Technical Center, and the operational and user accounts at the Washington Telecommunications Center. The regional and center servicing security elements have been established as administrative accounts with the responsibility for the monitoring of operational and secure telecommunications facilities within their respective jurisdictions. b. Monitor/Inspection Requirements. Monitor and inspection activities shall be conducted in accordance with the following requirements: (1) Regional and center monitor accounts shall conduct a general inspection of each operational COMSEC account and secure telecommunication facility in their jurisdiction at least once each year. Additional inspections will be conducted as required by Order 1650.7B. (2) Appendix 4, Secure Telecommunications Facility and COMSEC Account Checklist, shall be used as a guide in the conduct of the inspection. The completion of the checklist does not in itself constitute a COMSEC inspection. The inspector must be competent and knowledgeable in all phases of COMSEC. A formal written report containing the results of the inspection and recommended corrective actions shall be provided to the facility or office manager having responsibility for the COMSEC operation, and to the custodian of the inspected account. An information copy of COMSEC inspection reports shall be provided to ACO-300, ATTN: ACO-320. (3) Technical surveillance countermeasures (TSCM) inspections of secure telecommunications facilities shall be conducted in accordance with provisions of this order and Order 1600.12C, Technical Security Countermeasures Program. (4) ACO-300 will inspect regional and center monitor accounts at least once every two years. In addition, ACO-300 will schedule COMSEC inspections and surveys as required agencywide to ensure effective monitoring of regional and center COMSEC programs. c. Administrative Requirements. (1) The custodian of each FAA COMSEC account shall forward a copy of all reports, correspondence, etc., pertaining to COMSEC accounting to his/her servicing security element monitoring account. Regional and center monitor accounts shall provide copies of the documents pertaining to their account operations to ACO-300, ATTN: ACO-320. Conversely, AFCSC sends a copy of all reports, correspondence, etc., it originates to the appropriate monitoring account. (2) The monitoring account shall review these documents and ensure the completeness, accuracy, and timeliness of the accounting actions. In the event that a monitor account receives a copy of a discrepancy report from AFCSC, the monitor account custodian shall ensure that the required corrective action is accomplished expeditiously. 43.-49. RESERVED. FOR OFFICIAL USE ONLY PUBLIC AVAILABILITY TO BE DETERMINED UNDER U.S.C. 552
TOP-SECRET FROM THE WHITE HOUSE – Implementation of Defense Trade Cooperation Treaties
Vol. 76 Tuesday, No. 225 November 22, 2011 Part II Department of State ———————————————————————– 22 CFR Parts 120, 123, 124, et al. Implementation of Defense Trade Cooperation Treaties; Proposed Rule Federal Register / Vol. 76, No. 225 / Tuesday, November 22, 2011 / Proposed Rules [[Page 72246]] ———————————————————————– DEPARTMENT OF STATE 22 CFR Parts 120, 123, 124, 126, 127, and 129 [Public Notice 7683] RIN 1400-AC95 Implementation of Defense Trade Cooperation Treaties AGENCY: Department of State. ACTION: Proposed rule. ———————————————————————– SUMMARY: The Department of State is proposing to amend the International Traffic in Arms Regulations (ITAR) to implement the Defense Trade Cooperation Treaty between the United States and Australia and the Defense Trade Cooperation Treaty between the United States and the United Kingdom, and identify via a supplement the defense articles and defense services that may not be exported pursuant to the Treaties. Additionally, the Department of State proposes to amend the section pertaining to the Canadian exemption to reference the new supplement, and, with regard to Congressional certification, the Department of State proposes to add Israel to the list of countries and entities that have a shorter certification time period and a higher dollar value reporting threshold. DATES: The Department of State will accept comments on this proposed rule until December 22, 2011. ADDRESSES: Interested parties may submit comments within 30 days of the date of the publication by any of the following methods: Email: DDTCResponseTeam@state.gov with the subject line, Regulatory Change–Treaties. Persons with access to the Internet may also view and comment on this notice by searching for its RIN on the U.S. Government regulations Web site at http://www.regulations.gov. FOR FURTHER INFORMATION CONTACT: Sarah Heidema, Office of Defense Trade Controls Policy, Department of State, Telephone (202) 663-2809; Fax (202) 261-8199; or Email DDTCResponseTeam@state.gov. ATTN: Regulatory Change–Treaties. SUPPLEMENTARY INFORMATION: ———————————————————————— ITAR Part Proposed change ———————————————————————— Part 120…………………….. Section 120.19 revised to clarify meaning of reexport or retransfer; new Sec. Sec. 120.33 and 120.34 added to provide definitions of the Defense Trade Cooperation Treaties between the United States and Australia and the U.K., respectively; new Sec. Sec. 120.35 and 120.36 added to define the implementing arrangements pursuant to the Treaties between the United States and Australia and the United States and the U.K., respectively. Part 123…………………….. Clarifying edits made throughout section and references to new proposed Sec. Sec. 126.16 and 126.17 added; Israel added to Sec. 123.9(e). Part 124…………………….. Sec. 124.11 revised to add Israel to the list of countries and entities subject to the 15-day time period regarding Congressional certification. Part 126…………………….. Clarifying edits made throughout section; Sec. 126.5(b) revised to reference the new supplement to part 126, consequently, Sec. Sec. 126.5(b)(1)-(21) are removed; Sec. 126.16 added to describe the exemption pursuant to the Defense Trade Cooperation Treaty between the United States and Australia; Sec. 126.17 added to describe the exemption pursuant to the Defense Trade Cooperation Treaty between the United States and the United Kingdom; Supplement No. 1 to part 126 added. Part 127…………………….. Clarifying edits made throughout section; revised to make reference to new proposed Sec. Sec. 126.16 and 126.17. Part 129…………………….. Sections 129.6(b)(2), 129.7(a)(1)(vii), and 129.7(a)(2) revised to include Israel in the listing of countries and entities. ———————————————————————— These proposed amendments are pursuant to the Security Cooperation Act of 2010 (Pub. L. 111-266), with the inclusion of other proposed changes. Title I of the Security Cooperation Act, the Defense Trade Cooperation Treaties Implementation Act of 2010, implements the Defense Trade Cooperation Treaty between the United States and Australia, done at Sydney, Australia, on September 5, 2007; and the Defense Trade Cooperation Treaty between the United States and the United Kingdom, done at Washington, DC and London on June 21 and 26, 2007, respectively (collectively referred to herein as the “Treaties”). We propose a supplement to part 126 that will identify those defense articles and defense services exempt from the scope of the Treaties. These proposed amendments would affect parts 120, 123, 126, and 127, with new sections in part 126 describing the licensing exemptions pursuant to the Treaties. Title III of the Security Cooperation Act creates for Israel a status in law similar to the North Atlantic Treaty Organization (NATO), the member countries of NATO, Australia, Japan, New Zealand, and the Republic of Korea concerning certification to the Congress. Pursuant to the proposed change, we would require certification for transfers to Israel prior to granting any license or other approval for transactions of major defense equipment sold under a contract in the amount of $25,000,000 or more (currently required for amounts of $14,000,000 or more), or for defense articles and defense services sold under a contract in the amount of $100,000,000 or more (currently required for amounts of $50,000,000 or more), and provided the transfer does not include any other countries. The change would also shorten from thirty (30) to fifteen (15) calendar days the certification time period during which approval may not be granted. This proposed amendment would affect parts 123, 124, and 129. Additionally, we are revising Sec. 126.5, describing the Canadian exemption, to reference the proposed supplement to part 126. This proposed amendment would affect part 126. Section by section identification of the proposed changes follows. We are revising the authority citation for part 120 to include Public Law 111-266; section 120.1 to reference the Treaties as authorities; and section 120.19 to clarify the meaning of reexport or retransfer. In Sec. 120.28, we are correcting an outdated reference (Shipper’s Export Declaration) to refer to the Electronic Export Information. We are proposing new Sec. Sec. 120.33 and 120.34 to provide definitions of the Defense Trade Cooperation Treaties between the United States and Australia and the U.K., respectively. Also, we are proposing new Sec. Sec. 120.35 and 120.36 to define the implementing arrangements pursuant to the Treaties between the United States and Australia and the United States and the U.K., respectively. The proposed change in Sec. 123.4 replaces the word “export” with the word “exporter.” In the last sentence in [[Page 72247]] Sec. 123.9(a), “a person” will replace “exporters,” and we are adding “destination” as an item that must be determined prior to the submission of an application or the claiming of an exemption. We are adding a note following this section. We are revising section 123.9(b) to expand the reference to documents, and to reference the new proposed Sec. Sec. 126.16 and 126.17. We are adding clarifying language to Sec. Sec. 123.9(c), (c)(1), and (c)(2); and adding the language of the current (c)(4) to (c)(3). New language pertaining to new Sec. Sec. 126.16 and 126.17 will comprise a new (c)(4). We are removing and reserving section 123.9(d). We are adding Israel to the list of countries and entities in Sec. 123.9(e); citing the new Sec. Sec. 126.16 and 126.17 in Sec. 123.9(e)(1); and adding clarifying language to Sec. Sec. 123.9(e)(3) and (e)(4). We are adding Israel to the list of countries and entities in Sec. Sec. 123.15(a)(1), (a)(2), and (b). We are adding Australia and the United Kingdom to Sec. 123.16(a), and reference to the Electronic Export Information replaces reference to the Shipper’s Export Declaration in this section and in Sec. 123.16(b)(1)(iii). We are clarifying documents in Sec. 123.16(b)(2)(vi), and adding new Sec. Sec. 123.16(c) and (d) referencing the new Sec. Sec. 126.16 and 126.17. Section 123.22(b)(2) replaces references to the Shipper’s Export Declaration with the Electronic Export Information. We are revising the title and text for Sec. 123.26. We are revising the authority citation for part 124 to include Public Law 111-266. We are revising section 124.11 to add Israel to the list of countries and entities subject to the 15-day time period regarding Congressional certification. We are revising the authority citation for part 126 to include Public Law 111-266, and revising section 126.1(e) for clarification. We are adding a section (e)(1), to contain the current requirement found in (e) to notify the Directorate of Defense Trade Controls of any transactions that contravene the prohibitions of Sec. 126.1(a). We are reserving section (e)(2). We are revising section 126.3 to change “Director” to “Managing Director” and “Office” to “Directorate.” We are replacing references to Shipper’s Export Declaration with Electronic Export Information in Sec. 126.4(d). We are revising section 126.5(a) to change “Port Director” to “Port Directors.” We are revising section 126.5(b) to reference the new supplement to part 126; consequently, we are removing Sec. Sec. 126.5(b)(1)-(21). We are removing and reserving section 126.5(c) (defense services not subject to exemption will be covered by the new supplement to part 126). We are revising Section 126.5(d) to change “re-transfer” to “retransfer,” and revising Sec. 126.5(d)(2) Note 2 to reference the proposed new supplement to part 126. We are adding the terms “criminal complaint” and “other criminal charge” to Sec. 126.7(a)(3), and adding clarifying language to Sec. 126.7(a)(7). We are revising section 126.13(a) to include reference to Sec. 123.9; revising Sec. 126.13(a)(1) to add the terms “criminal complaint” and “other criminal charge”; and revising Sec. 126.13(a)(4) to include reference to Sec. 123.9. We are proposing section 126.16 to describe the exemption pursuant to the Defense Trade Cooperation Treaty between the United States and Australia, and proposing Sec. 126.17 to describe the exemption pursuant to the Defense Trade Cooperation Treaty between the United States and the United Kingdom. We are proposing the addition of Supplement No. 1 to part 126, and this provision will delineate those items of the U.S. Munitions List that are outside the scope of the exemptions established by the Treaties and the Canadian exemptions at Sec. 126.5. We are revising the authority citation for part 127 to include Public Law 111-266. We are revising section 127.1 to make reference, where appropriate, to new proposed Sec. Sec. 126.16 and 126.17, and we are providing clarifying language, leading to the inclusion of a new proposed Sec. 127.1(e). We are adding the words “or attempt to use” in Sec. 127.2(a); “subchapter” will replace “section” in Sec. 127.2(b); we are adding “reexport” and “retransfer to Sec. 127.2(b)(1); adding “Electronic Export Information filing” to Sec. 127.2(b)(2); and proposing a new Sec. 127.2(b)(14). We are adding clarifying language to Sec. 127.3(a); adding the words “or by exemption” to Sec. 127.4(a); adding the words “or claim of an exemption” to Sec. 127.4(c); and proposing new Sec. 127.4(d). We are revising section 127.7(a) to remove the words “for which a license or approval is required by this subchapter.” In Sec. 127.10(a), we are modifying the word “approval” with addition of the word “written.” We are proposing new Sec. 127.12(b)(5). We are revising the structure of Sec. 127.12(d), removing an unnecessary level, and expanding the example list for “shipping documents”. We are revising sections 129.6(b)(2), 129.7(a)(1)(vii), and 129.7(a)(2) to include Israel in the listing of countries and entities. Regulatory Analysis and Notices Administrative Procedure Act The Department of State is of the opinion that controlling the import and export of defense services is a foreign affairs function of the United States Government and that rules implementing this function are exempt from Sec. 553 (Rulemaking) and Sec. 554 (Adjudications) of the Administrative Procedure Act. Although the Department is of the opinion that this proposed rule is exempt from the rulemaking provisions of the APA, the Department is publishing this proposed rule with a 30-day provision for public comment and without prejudice to its determination that controlling the import and export of defense services is a foreign affairs function. Regulatory Flexibility Act Since this proposed amendment is not subject to the notice-and- comment procedures of 5 U.S.C. 553, it does not require analysis under the Regulatory Flexibility Act. Unfunded Mandates Reform Act of 1995 This proposed amendment does not involve a mandate that will result in the expenditure by State, local, and tribal governments, in the aggregate, or by the private sector, of $100 million or more in any year and it will not significantly or uniquely affect small governments. Therefore, no actions were deemed necessary under the provisions of the Unfunded Mandates Reform Act of 1995. Executive Order 13175 The Department of State has determined that this proposed amendment will not have tribal implications, will not impose substantial direct compliance costs on Indian tribal governments, and will not pre-empt tribal law. Accordingly, the requirement of Executive Order 13175 does not apply to this proposed amendment. Small Business Regulatory Enforcement Fairness Act of 1996 This proposed amendment has been found not to be a major rule within the meaning of the Small Business Regulatory Enforcement Fairness Act of 1996. Executive Orders 12372 and 13132 This proposed amendment will not have substantial direct effects on the States, on the relationship between the national government and the States, or on the distribution of power and responsibilities among the various [[Page 72248]] levels of government. Therefore, in accordance with Executive Order 13132, it is determined that this proposed amendment does not have sufficient federalism implications to require consultations or warrant the preparation of a federalism summary impact statement. The regulations implementing Executive Order 12372 regarding intergovernmental consultation on Federal programs and activities do not apply to this proposed amendment. Executive Order 12866 The Department is of the opinion that restricting defense articles exports is a foreign affairs function of the United States Government and that rules governing the conduct of this function are exempt from the requirements of Executive order 12866. However, the Department has nevertheless reviewed this regulation to ensure its consistency with the regulatory philosophy and principles set forth in that Executive Order. Executive Order 12988 The Department of State has reviewed this proposed amendment in light of sections 3(a) and 3(b)(2) of Executive Order 12988 to eliminate ambiguity, minimize litigation, establish clear legal standards, and reduce burden. Executive Order 13563 The Department of State has considered this rule in light of Executive Order 13563, dated January 18, 2011, and affirms that this regulation is consistent with the guidance therein. Paperwork Reduction Act This proposed amendment does not impose any new reporting or recordkeeping requirements subject to the Paperwork Reduction Act, 44 U.S.C. Chapter 35. List of Subjects 22 CFR Parts 120, 123, 124, and 126 Arms and Munitions, Exports. 22 CFR Part 127 Arms and Munitions, Crime, Exports, Penalties, Seizures and Forfeitures. 22 CFR Part 129 Arms and Munitions, Exports, Brokering. Accordingly, for the reasons set forth above, Title 22, Chapter I, Subchapter M, parts 120, 123, 124, 126, 127, and 129 are proposed to be amended as follows: PART 120–PURPOSE AND DEFINITIONS 1. The authority citation for Part 120 is revised to read as follows: Authority: Secs. 2, 38, and 71, Pub. L. 90-629, 90 Stat. 744 (22 U.S.C. 2752, 2778, 2797); 22 U.S.C. 2794; E.O. 11958, 42 FR 4311; E.O. 13284, 68 FR 4075; 3 CFR, 1977 Comp. p. 79; 22 U.S.C. 2651a; Pub. L. 105-261, 112 Stat. 1920; Pub. L. 111-266. 2. Section 120.1 is amended by revising paragraphs (a), (c), and (d) to read as follows: Sec. 120.1 General authorities and eligibility. (a) Section 38 of the Arms Export Control Act (22 U.S.C. 2778), as amended, authorizes the President to control the export and import of defense articles and defense services. The statutory authority of the President to promulgate regulations with respect to exports of defense articles and defense services was delegated to the Secretary of State by Executive Order 11958, as amended. This subchapter implements that authority. Portions of this subchapter also implement the Defense Trade Cooperation Treaty between the United States and Australia and the Defense Trade Cooperation Treaty between the United States and the United Kingdom. (Note, however, that the Treaties are not the source of authority for the prohibitions in part 127, but instead are the source of one limitation on the scope of such prohibitions.) By virtue of delegations of authority by the Secretary of State, these regulations are primarily administered by the Deputy Assistant Secretary of State for Defense Trade and Regional Security and the Managing Director of Defense Trade Controls, Bureau of Political-Military Affairs. * * * * * (c) Receipt of Licenses and Eligibility. (1) A U.S. person may receive a license or other approval pursuant to this subchapter. A foreign person may not receive such a license or other approval, except as follows: (i) A foreign governmental entity in the United States may receive an export license or other export approval; (ii) A foreign person may receive a reexport or retransfer approval; and (iii) A foreign person may receive a prior approval for brokering activities. Requests for a license or other approval other than by a person referred to in paragraphs (c)(1)(i) and (c)(1)(ii) will be considered only if the applicant has registered with the Directorate of Defense Trade Controls pursuant to part 122 or 129 of this subchapter, as appropriate. (2) Persons who have been convicted of violating the criminal statutes enumerated in Sec. 120.27 of this subchapter, who have been debarred pursuant to part 127 or 128 of this subchapter, who are subject to indictment or are otherwise charged (e.g., by information) for violating the criminal statutes enumerated in Sec. 120.27 of this subchapter, who are ineligible to contract with, or to receive a license or other form of authorization to import defense articles or defense services from any agency of the U.S. Government, who are ineligible to receive an export license or other approval from any other agency of the U.S. Government, or who are subject to a Department of State policy of denial, suspension or revocation under Sec. 126.7(a) of this subchapter, or to interim suspension under Sec. 127.8 of this subchapter, are generally ineligible to be involved in activities regulated under this subchapter. (d) The exemptions provided in this subchapter do not apply to transactions in which the exporter, any party to the export (as defined in Sec. 126.7(e) of this subchapter), any source or manufacturer, broker or other participant in the brokering activities, is generally ineligible as set forth above in paragraph (c) of this section, unless prior written authorization has been granted by the Directorate of Defense Trade Controls. 3. Section 120.19 is revised to read as follows: Sec. 120.19 Reexport or retransfer. Reexport or retransfer means the transfer of defense articles or defense services to an end-use, end-user, or destination not previously authorized by license, written approval, or exemption pursuant to this subchapter. 4. Section 120.28 is amended by revising paragraph (b)(2) to read as follows: Sec. 120.28 Listing of forms referred to in this subchapter. * * * * * (b) * * * (2) Electronic Export Information filed via the Automated Export System. * * * * * 5. Section 120.33 is added to read as follows: Sec. 120.33 Defense Trade Cooperation Treaty between the United States and Australia. Defense Trade Cooperation Treaty between the United States and Australia means the Treaty between the Government of the United States of America and the Government of [[Page 72249]] Australia Concerning Defense Trade Cooperation, done at Sydney, September 5, 2007. For additional information on making exports pursuant to this treaty, see Sec. 126.16 of this subchapter. 6. Section 120.34 is added to read as follows: Sec. 120.34 Defense Trade Cooperation Treaty between the United States and the United Kingdom. Defense Trade Cooperation Treaty between the United States and the United Kingdom means the Treaty between the Government of the United States of America and the Government of the United Kingdom of Great Britain and Northern Ireland Concerning Defense Trade Cooperation, done at Washington DC and London, June 21 and 26, 2007. For additional information on making exports pursuant to this treaty, see Sec. 126.17 of this subchapter. 7. Section 120.35 is added to read as follows: Sec. 120.35 Australia Implementing Arrangement. Australia Implementing Arrangement means the Implementing Arrangement Pursuant to the Treaty between the Government of the United States of America and the Government of Australia Concerning Defense Trade Cooperation, done at Washington, March 14, 2008, as it may be amended. 8. Section 120.36 is added to read as follows: Sec. 120.36 United Kingdom Implementing Arrangement. United Kingdom Implementing Arrangement means the Implementing Arrangement Pursuant to the Treaty between the Government of the United States of America and the Government of the United Kingdom of Great Britain and Northern Ireland Concerning Defense Trade Cooperation, done at Washington DC, February 14, 2008, as it may be amended. PART 123–LICENSES FOR THE EXPORT OF DEFENSE ARTICLES 9. The authority citation for part 123 continues to read as follows: Authority: Secs. 2, 38, and 71, Pub. L. 90-629, 90 Stat. 744 (22 U.S.C. 2752, 2778, 2797); 22 U.S.C. 2753; E.O. 11958, 42 FR 4311; 3 CFR, 1977 Comp. p. 79; 22 U.S.C. 2651a; 22 U.S.C. 2776; Pub. L. 105- 261, 112 Stat. 1920; Sec 1205(a), Pub. L. 107-228. 10. Section 123.4 is amended by revising paragraph (d) introductory text to read as follows: Sec. 123.4 Temporary import license exemptions. * * * * * (d) Procedures. To the satisfaction of the Port Directors of U.S. Customs and Border Protection, the importer and exporter must comply with the following procedures: * * * * * 11. Section 123.9 is amended by revising paragraphs (a), (b), (c), (e), (e)(1), (e)(3), (e)(4), and removing and reserving paragraph (d), to read as follows: Sec. 123.9 Country of ultimate destination and approval of reexports or retransfers. (a) The country designated as the country of ultimate destination on an application for an export license, or in an Electronic Export Information filing where an exemption is claimed under this subchapter, must be the country of ultimate end use. The written approval of the Directorate of Defense Trade Controls must be obtained before reselling, transferring, reexporting, retransferring, transshipping, or disposing of a defense article to any end-user, end-use, or destination other than as stated on the export license, or in the Electronic Export Information filing in cases where an exemption is claimed under this subchapter, except in accordance with the provisions of an exemption under this subchapter that explicitly authorizes the resell, transfer, reexport, retransfer, transshipment, or disposition of a defense article without such approval. A person must determine the specific end-user, end-use, and destination prior to submitting an application to the Directorate of Defense Trade Controls or claiming an exemption under this subchapter. Note to paragraph (a): In making the aforementioned determination, a person is expected to review all readily available information, including information available to the public generally as well as information available from other parties to the transaction. (b) The exporter shall incorporate the following statement as an integral part of the bill of lading, airway bill, or other shipping documents and the invoice whenever defense articles or defense services are to be exported or transferred pursuant to a license, other written approval, or an exemption under this subchapter, other than the exemptions contained in Sec. 126.16 and Sec. 126.17 of this subchapter (Note: for exports made pursuant to Sec. 126.16 or Sec. 126.17 of this subchapter, see Sec. 126.16(j)(5) or Sec. 126.17(j)(5)): “These commodities are authorized by the U.S. Government for export only to [country of ultimate destination] for use by [end-user]. They may not be transferred, transshipped on a non- continuous voyage, or otherwise be disposed of, to any other country or end-user, either in their original form or after being incorporated into other end-items, without the prior written approval of the U.S. Department of State.” (c) Any person requesting written approval from the Directorate of Defense Trade Controls for the reexport, retransfer, other disposition, or change in end use, end user, or destination of a defense article or defense service initially exported or transferred pursuant to a license or other written approval, or an exemption under this subchapter, must submit all the documentation required for a permanent export license (see Sec. 123.1 of this subchapter) and shall also submit the following: (1) The license number, written authorization, or exemption under which the defense article or defense service was previously authorized for export from the United States (Note: For exports under exemptions at Sec. 126.16 or Sec. 126.17 of this subchapter, the original end- use, program, project, or operation under which the item was exported must be identified.); (2) A precise description, quantity, and value of the defense article or defense service; (3) A description and identification of the new end-user, end-use, and destination; and (4) With regard to any request for such approval relating to a defense article or defense service initially exported pursuant to an exemption contained in Sec. 126.16 or Sec. 126.17 of this subchapter, written request for the prior approval of the transaction from the Directorate of Defense Trade Controls must be submitted: (i) By the original U.S. exporter, provided a written request is received from a member of the Australian Community, as identified in Sec. 126.16 of this subchapter, or the United Kingdom Community, as identified in Sec. 126.17 of this subchapter (where such a written request includes a written certification from the member of the Australian Community or the United Kingdom Community providing the information set forth in this subsection); or (ii) By a member of the Australian Community or the United Kingdom Community, where such request provides the information set forth in this section. (d) [Reserved] (e) Reexports or retransfers of U.S.-origin components incorporated into a foreign defense article to NATO, NATO agencies, a government of a NATO [[Page 72250]] country, or the governments of Australia, Israel, Japan, New Zealand, or the Republic of Korea are authorized without the prior written approval of the Directorate of Defense Trade Controls, provided: (1) The U.S.-origin components were previously authorized for export from the United States, either by a license, written authorization, or an exemption other than those described in either Sec. 126.16 or Sec. 126.17 of this subchapter; * * * * * (3) The person reexporting the defense article provides written notification to the Directorate of Defense Trade Controls of the retransfer not later than 30 days following the reexport. The notification must state the articles being reexported and the recipient government. (4) The original license or other approval of the Directorate of Defense Trade Controls did not include retransfer or reexport restrictions prohibiting use of this exemption. 12. Section 123.15 is amended by revising paragraphs (a)(1), (a)(2), and (b) to read as follows: Sec. 123.15 Congressional certification pursuant to Section 36(c) of the Arms Export Control Act. (a) * * * (1) A license for the export of major defense equipment sold under a contract in the amount of $14,000,000 or more, or for defense articles and defense services sold under a contract in the amount of $50,000,000 or more, to any country that is not a member of the North Atlantic Treaty Organization (NATO), or Australia, Israel, Japan, New Zealand, or the Republic of Korea that does not authorize a new sales territory; or (2) A license for export to a country that is a member country of the North Atlantic Treaty Organization (NATO), or Australia, Israel, Japan, New Zealand, or the Republic of Korea, of major defense equipment sold under a contract in the amount in the amount of $25,000,000 or more, or for defense articles and defense services sold under a contract in the amount of $100,000,000 or more, and provided the transfer does not include any other countries; or * * * * * (b) Unless an emergency exists which requires the proposed export in the national security interests of the United States, approval may not be granted for any transaction until at least 15 calendar days have elapsed after receipt by the Congress of the certification required by 22 U.S.C. 2776(c)(1) involving the North Atlantic Treaty Organization, or Australia, Israel, Japan, New Zealand, or the Republic of Korea or at least 30 calendar days have elapsed for any other country; in the case of a license for an export of a commercial communications satellite for launch from, and by nationals of, the Russian Federation, Ukraine, or Kazakhstan, until at least 15 calendar days after the Congress receives such certification. * * * * * 13. Section 123.16 is amended by revising paragraphs (a) introductory text, (b)(1)(iii), (b)(2)(vi), and adding paragraphs (c) and (d), to read as follows: Sec. 123.16 Exemptions of general applicability. (a) The following exemptions apply to exports of unclassified defense articles for which no approval is needed from the Directorate of Defense Trade Controls. These exemptions do not apply to: Proscribed destinations under Sec. 126.1 of this subchapter; exports for which Congressional notification is required (see Sec. 123.15 of this subchapter); MTCR articles; Significant Military Equipment (SME); and may not be used by persons who are generally ineligible as described in Sec. 120.1(c) of this subchapter. All shipments of defense articles, including but not limited to those to and from Australia, Canada, and the United Kingdom, require an Electronic Export Information (EEI) filing or notification letter. If the export of a defense article is exempt from licensing, the EEI filing must cite the exemption. Refer to Sec. 123.22 of this subchapter for EEI filing and letter notification requirements. (b) * * * (1) * * * (iii) The exporter certifies in the EEI filing that the export is exempt from the licensing requirements of this subchapter. This is done by writing, “22 CFR 123.16(b)(1) and the agreement or arrangement (identify/state number) applicable”; and * * * * * (2) * * * (vi) The exporter must certify on the invoice, the bill of lading, air waybill, or shipping documents and in the EEI filing that the export is exempt from the licensing requirements of this subchapter. This is done by writing “22 CFR 123.16(b)(2) applicable”. * * * * * (c) For exports to Australia pursuant to the Defense Trade Cooperation Treaty between the United States and Australia refer to Sec. 126.16 of this subchapter. (d) For exports to the United Kingdom pursuant to the Defense Trade Cooperation Treaty between the United States and the United Kingdom refer to Sec. 126.17 of this subchapter. 14. Section 123.22 is amended by revising paragraph (b)(2) to read as follows: Sec. 123.22 Filing, retention, and return of export licenses and filing of export information. * * * * * (b) * * * (2) Emergency shipments of hardware that cannot meet the pre- departure filing requirements. U.S. Customs and Border Protection may permit an emergency export of hardware by truck (e.g., departures to Mexico or Canada) or air, by a U.S. registered person, when the exporter is unable to comply with the Electronic Export Information (EEI) filing timeline in paragraph (b)(1)(i) of this section. The applicant, or an agent acting on the applicant’s behalf, in addition to providing the EEI using the AES, must provide documentation required by the U.S. Customs and Border Protection and this subchapter. The documentation provided to the U.S. Customs and Border Protection at the port of exit must include the External Transaction Number (XTN) or Internal Transaction Number (ITN) for the shipment and a copy of a notification to the Directorate of Defense Trade Controls stating that the shipment is urgent accompanied by an explanation for the urgency. The original of the notification must be immediately provided to the Directorate of Defense Trade Controls. The AES filing of the export information when the export is by air must be at least two hours prior to any departure from the United States; and, when a truck shipment, at the time when the exporter provides the articles to the carrier or at least one hour prior to departure from the United States, when the permanent export of the hardware has been authorized for export: * * * * * 15. Section 123.26 is revised to read as follows: Sec. 123.26 Recordkeeping for exemptions. Any person engaging in any export, reexport, transfer, or retransfer of a defense article or defense service pursuant to an exemption must maintain records of each such export, reexport, transfer, or retransfer. The records shall include the following information: A description of the defense article, including technical data, or defense service; the name and address of the end-user and other available contact information (e.g., telephone number and electronic mail address); the name of the natural person [[Page 72251]] responsible for the transaction; the stated end-use of the defense article or defense service; the date and time of the transaction; the Electronic Export Information (EEI) Internal Transaction Number (ITN); and the method of transmission. The person using or acting in reliance upon the exemption shall also comply with any additional recordkeeping requirements enumerated in the text of the regulations concerning such exemption. * * * * * PART 124–AGREEMENTS, OFF-SHORE PROCUREMENT AND OTHER DEFENSE SERVICES 16. The authority citation for part 124 continues to read as follows: Authority: Secs. 2, 38, and 71, Pub. L. 90-629, 90 Stat. 744 (22 U.S.C. 2752, 2778, 2797); E.O. 11958, 42 FR 4311; 3 CFR 1977 Comp. p. 79; 22 U.S.C. 2651a; 22 U.S.C. 2776; Pub. L. 105-261. 17. Section 124.11 is amended by revising paragraph (b) to read as follows: Sec. 124.11 Congressional certification pursuant to Section 36(d) of the Arms Export Control Act. * * * * * (b) Unless an emergency exists which requires the immediate approval of the agreement in the national security interests of the United States, approval may not be granted until at least 15 calendar days have elapsed after receipt by the Congress of the certification required by 22 U.S.C. 2776(d)(1) involving the North Atlantic Treaty Organization, any member country of that Organization, or Australia, Israel, Japan, New Zealand, or the Republic of Korea or at least 30 calendar days have elapsed for any other country. Approvals may not be granted when the Congress has enacted a joint resolution prohibiting the export. * * * * * PART 126–GENERAL POLICIES AND PROVISIONS 18. The authority citation for part 126 is revised to read as follows: Authority: Secs. 2, 38, 40, 42, and 71, Pub. L. 90-629, 90 Stat. 744 (22 U.S.C. 2752, 2778, 2780, 2791, and 2797); E.O. 11958, 42 FR 4311; 3 CFR, 1977 Comp. p. 79; 22 U.S.C. 2651a; 22 U.S.C. 287c; E.O. 12918, 59 FR 28205; 3 CFR, 1994 Comp. p. 899; Sec. 1225, Pub. L. 108-375; Sec. 7089, Pub. L. 111-117; Pub. L. 111-266. 19. Section 126.1 is amended by revising paragraph (e) to read as follows: Sec. 126.1 Prohibited exports, imports, and sales to or from certain countries. * * * * * (e) Proposed sales. No sale, export, transfer, reexport, or retransfer and no proposal to sell, export, transfer, reexport, or retransfer any defense articles or defense services subject to this subchapter may be made to any country referred to in this section (including the embassies or consulates of such a country), or to any person acting on its behalf, whether in the United States or abroad, without first obtaining a license or written approval of the Directorate of Defense Trade Controls. However, in accordance with paragraph (a) of this section, it is the policy of the Department of State to deny licenses and approvals in such cases. (1) Duty to Notify: Any person who knows or has reason to know of such a proposed or actual sale, export, transfer, reexport, or retransfer of such articles, services, or data must immediately inform the Directorate of Defense Trade Controls. Such notifications should be submitted to the Office of Defense Trade Controls Compliance, Directorate of Defense Trade Controls. (2) [Reserved] * * * * * 20. Section 126.3 is revised to read as follows: Sec. 126.3 Exceptions. In a case of exceptional or undue hardship, or when it is otherwise in the interest of the United States Government, the Managing Director, Directorate of Defense Trade Controls, may make an exception to the provisions of this subchapter. 21. Section 126.4 is amended by revising paragraph (d) to read as follows: Sec. 126.4 Shipments by or for United States Government agencies. * * * * * (d) An Electronic Export Information (EEI) filing, required under Sec. 123.22 of this subchapter, and a written statement by the exporter certifying that these requirements have been met must be presented at the time of export to the appropriate Port Directors of U.S. Customs and Border Protection or Department of Defense transmittal authority. A copy of the EEI filing and the written certification statement shall be provided to the Directorate of Defense Trade Controls immediately following the export. 22. Section 126.5 is amended by removing and reserving paragraph (c) and revising paragraphs (a), (b), (d) introductory text, and Notes 1 and 2, to read as follows: Sec. 126.5 Canadian exemptions. (a) Temporary import of defense articles. Port Directors of U.S. Customs and Border Protection and postmasters shall permit the temporary import and return to Canada without a license of any unclassified defense articles (see Sec. 120.6 of this subchapter) that originate in Canada for temporary use in the United States and return to Canada. All other temporary imports shall be in accordance with Sec. Sec. 123.3 and 123.4 of this subchapter. (b) Permanent and temporary export of defense articles. Except as provided in Supplement No. 1 to part 126 of this subchapter and for exports that transit third countries, Port Directors of U.S. Customs and Border Protection and postmasters shall permit, when for end-use in Canada by Canadian Federal or Provincial governmental authorities acting in an official capacity or by a Canadian-registered person for return to the United States, the permanent and temporary export to Canada without a license of unclassified defense articles and defense services identified on the U.S. Munitions List (22 CFR 121.1). The exceptions noted above are subject to meeting the requirements of this subchapter, to include 22 CFR 120.1(c) and (d), parts 122 and 123 (except insofar as exemption from licensing requirements is herein authorized) and Sec. 126.1, and the requirement to obtain non-transfer and use assurances for all significant military equipment. For purposes of this section, “Canadian-registered person” is any Canadian national (including Canadian business entities organized under the laws of Canada), dual citizen of Canada and a third country other than a country listed in Sec. 126.1, and permanent resident registered in Canada in accordance with the Canadian Defense Production Act, and such other Canadian Crown Corporations identified by the Department of State in a list of such persons publicly available through the Internet Web site of the Directorate of Defense Trade Controls and by other means. (c) [Reserved] (d) Reexports/retransfer. Reexport/retransfer in Canada to another end user or end use or from Canada to another destination, except the United States, must in all instances have the prior approval of the Directorate of Defense Trade Controls. Unless otherwise exempt in this subchapter, the original exporter is responsible, upon request from a Canadian-registered person, for obtaining or providing reexport/ retransfer approval. In any instance when the U.S. exporter is no longer available to the Canadian end user the [[Page 72252]] request for reexport/retransfer may be made directly to the Directorate of Defense Trade Controls. All requests must include the information in Sec. 123.9(c) of this subchapter. Reexport/retransfer approval is acquired by: * * * * * Notes to Sec. 126.5: 1. In any instance when the exporter has knowledge that the defense article exempt from licensing is being exported for use other than by a qualified Canadian-registered person or for export to another foreign destination, other than the United States, in its original form or incorporated into another item, an export license must be obtained prior to the transfer to Canada. 2. Additional exemptions exist in other sections of this subchapter that are applicable to Canada, for example Sec. Sec. 123.9, 125.4, and 124.2, that allow for the performance of defense services related to training in basic operations and maintenance, without a license, for certain defense articles lawfully exported, including those identified in Supplement No. 1 to part 126 of this subchapter. 23. Section 126.7 is amended by revising the section heading and paragraphs (a)(3), (a)(7) and (e) introductory text to read as follows: Sec. 126.7 Denial, revocation, suspension, or amendment of licenses and other approvals. (a) * * * (3) An applicant is the subject of a criminal complaint, other criminal charge (e.g., an information), or indictment for a violation of any of the U.S. criminal statutes enumerated in Sec. 120.27 of this subchapter; or * * * * * (7) An applicant has failed to include any of the information or documentation expressly required to support a license application, exemption, or other request for approval under this subchapter, or as required in the instructions in the applicable Department of State form or has failed to provide notice or information as required under this subchapter; or * * * * * (e) Special definition. For purposes of this subchapter, the term “Party to the Export” means: * * * * * 24. Section 126.13 is amended by revising paragraphs (a) introductory text, (a)(1), and (a)(4) to read as follows: Sec. 126.13 Required information. (a) All applications for licenses (DSP-5, DSP-61, DSP-73, and DSP- 85), all requests for approval of agreements and amendments thereto under part 124 of this subchapter, and all requests for other written authorizations (including requests for retransfer or reexport pursuant to Sec. 123.9 of this subchapter) must include a letter signed by a responsible official empowered by the applicant and addressed to the Directorate of Defense Trade Controls, stating whether: (1) The applicant or the chief executive officer, president, vice- presidents, other senior officers or officials (e.g., comptroller, treasurer, general counsel) or any member of the board of directors is the subject of a criminal complaint, other criminal charge (e.g., an information), or indictment for or has been convicted of violating any of the U.S. criminal statutes enumerated in Sec. 120.27 of this subchapter since the effective date of the Arms Export Control Act, Public Law 94-329, 90 Stat. 729 (June 30, 1976); * * * * * (4) The natural person signing the application, notification or other request for approval (including the statement required by this subsection) is a citizen or national of the United States, has been lawfully admitted to the United States for permanent residence (and maintains such lawful permanent residence status under the Immigration and Nationality Act, as amended (8 U.S.C. 1101(a), section 101(a)20, 60 Stat. 163), or is an official of a foreign government entity in the United States, or is a foreign person making a request pursuant to Sec. 123.9 of this subchapter. * * * * * 25. Section 126.16 is added to read as follows: Sec. 126.16 Exemption pursuant to the Defense Trade Cooperation Treaty between the United States and Australia. (a) Scope of exemption and required conditions. (1) Definitions. (i) An export means, for purposes of this section only, the initial movement of defense articles or defense services from the United States Community to the Australian Community. (ii) A transfer means, for purposes of this section only, the movement of a defense article or defense service, previously exported, by a member of the Australian Community within the Australian Community, or between a member of the United States Community and a member of the Australian Community. (iii) Retransfer and reexport have the meaning provided in Sec. 120.19 of this subchapter. (iv) Intermediate consignee means, for purposes of this section, an entity or person who receives defense articles, including technical data, but who does not have access to such defense articles, for the sole purpose of effecting onward movement to members of the Approved Community. (2) Persons or entities exporting or transferring defense articles or defense services are exempt from the otherwise applicable licensing requirements if such persons or entities comply with the regulations set forth in this section. Except as provided in Supplement No. 1 to part 126 of this subchapter, Port Directors of U.S. Customs and Border Protection and postmasters shall permit the permanent and temporary export without a license to members of the Australian Community (see paragraph (d) of this section regarding the identification of members of the Australian Community) of defense articles and defense services not listed in Supplement No. 1 to part 126, for the end-uses specifically identified pursuant to paragraphs (e) and (f) of this section. The purpose of this section is to specify the requirements to export, transfer, reexport, retransfer, or otherwise dispose of a defense article or defense service pursuant to the Defense Trade Cooperation Treaty between the United States and Australia. (3) Export. In order for an exporter to export a defense article or defense service pursuant to the Defense Trade Cooperation Treaty between the United States and Australia, all of the following conditions must be met: (i) The exporter must be registered with the Directorate of Defense Trade Controls and must be eligible, according to the requirements and prohibitions of the Arms Export Control Act, this subchapter, and other provisions of United States law, to obtain an export license (or other forms of authorization to export) from any agency of the U.S. Government without restriction (see paragraphs (b) and (c) of this section for specific requirements); (ii) The recipient of the export must be a member of the Australian Community (see paragraph (d) of this section regarding the identification of members of the Australian Community). Australian entities and facilities that become ineligible for such membership will be removed from the Australian Community; (iii) Intermediate consignees involved in the export must be eligible, according to the requirements and prohibitions of the Arms Export Control Act, this subchapter, and other provisions of United States law, to handle or receive a defense article or defense service without restriction (see paragraph (k) of this section for specific requirements); (iv) The export must be for an end-use specified in the Defense Trade [[Page 72253]] Cooperation Treaty between the United States and Australia and mutually agreed to by the U.S. Government and the Government of Australia pursuant to the Defense Trade Cooperation Treaty between the United States and Australia and the Implementing Arrangement thereto (the Australia Implementing Arrangement) (see paragraphs (e) and (f) of this section regarding authorized end-uses); (v) The defense article or defense service is not excluded from the scope of the Defense Trade Cooperation Treaty between the United States and Australia (see paragraph (g) of this section and Supplement No. 1 to part 126 of this subchapter for specific information on the scope of items excluded from export under this exemption) and is marked or identified, at a minimum, as “Restricted USML” (see paragraph (j) of this section for specific requirements on marking exports); (vi) All required documentation of such export is maintained by the exporter and recipient and is available upon the request of the U.S. Government (see paragraph (l) of this section for specific requirements); and (vii) The Department of State has provided advance notification to the Congress, as required, in accordance with this section (see paragraph (o) of this section for specific requirements). (4) Transfers. In order for a member of the Australian Community to transfer a defense article or defense service under the Defense Trade Cooperation Treaty between the United States and Australia, all of the following conditions must be met: (i) The defense article or defense service must have been previously exported in accordance with paragraph (a)(3) of this section or transitioned from a license or other approval in accordance with paragraph (i) Transitions of this section; (ii) The transferor and transferee of the defense article or defense service are members of the Australian Community (see paragraph (d) of this section regarding the identification of members of the Australian Community) or the United States Community (see paragraph (b) for information on the United States Community/approved exporters); (iii) The transfer is required for an end-use specified in the Defense Trade Cooperation Treaty between the United States and Australia and mutually agreed to by the United States and the Government of Australia pursuant to the terms of the Defense Trade Cooperation Treaty between the United States and Australia and the Australia Implementing Arrangement (see paragraphs (e) and (f) of this section regarding authorized end-uses); (iv) The defense article or defense service is not identified in paragraph (g) of this section and Supplement No. 1 to part 126 of this subchapter as ineligible for export under this exemption, and is marked or otherwise identified, at a minimum, as “Restricted USML” (see paragraph (j) of this section for specific requirements on marking exports); (v) All required documentation of such transfer is maintained by the transferor and transferee and is available upon the request of the U.S. Government (see paragraph (l) of this section for specific requirements); and (vi) The Department of State has provided advance notification to the Congress in accordance with this section (see paragraph (o) of this section for specific requirements). (5) This section does not apply to the export of defense articles or defense services from the United States pursuant to the Foreign Military Sales program. (b) Authorized exporters. The following persons compose the United States Community and may export defense articles and defense services pursuant to the Defense Trade Cooperation Treaty between the United States and Australia: (1) Departments and agencies of the U.S. Government, including their personnel, with, as appropriate, a security clearance and a need- to-know; and (2) Nongovernmental U.S. persons registered with the Directorate of Defense Trade Controls and eligible, according to the requirements and prohibitions of the Arms Export Control Act, this subchapter, and other provisions of United States law, to obtain an export license (or other forms of authorization to export) from any agency of the U.S. Government without restriction, including their employees acting in their official capacity with, as appropriate, a security clearance and a need-to-know. (c) An exporter that is otherwise an authorized exporter pursuant to subsection (b) above may not export pursuant to the Defense Trade Cooperation Treaty between the United States and Australia if the exporter’s president, chief executive officer, any vice-president, any other senior officer or official (e.g., comptroller, treasurer, general counsel); any member of the board of directors of the exporter; any party to the export; or any source or manufacturer is ineligible to receive export licenses (or other forms of authorization to export) from any agency of the U.S. Government. (d) Australian Community. For purposes of the exemption provided by this section, the Australian Community consists of the Australian entities and facilities identified as members of the Approved Community through the Directorate of Defense Trade Controls Web site at the time of a transaction under this section; Australian entities and facilities that become ineligible for such membership will be removed from the Australian Community. (e) Authorized End-uses. The following end-uses, subject to subsection (f), are specified in the Defense Trade Cooperation Treaty between the United States and Australia: (1) United States and Australian combined military or counter- terrorism operations; (2) United States and Australian cooperative security and defense research, development, production, and support programs; (3) Mutually determined specific security and defense projects where the Government of Australia is the end-user; or (4) U.S. Government end-use. (f) Procedures for identifying authorized end-uses pursuant to paragraph (e) of this section: (1) Operations, programs, and projects that can be publicly identified will be posted on the Directorate of Defense Trade Controls’ Web site; (2) Operations, programs, and projects that cannot be publicly identified will be confirmed in written correspondence from the Directorate of Defense Trade Controls; or (3) U.S. Government end-use will be identified specifically in a U.S. Government contract or solicitation as being eligible under the Treaty. (4) No other operations, programs, projects, or end-uses qualify for this exemption. (g) Items eligible under this section. With the exception of items listed in Supplement No. 1 to part 126 of this subchapter, defense articles and defense services may be exported under this section subject to the following: (1) An exporter authorized pursuant to paragraph (b)(2) of this section may market a defense article to the Government of Australia if that exporter has been licensed by the Directorate of Defense Trade Controls to export (as defined by Sec. 120.17 of this subchapter) the identical type of defense article to any foreign person. (2) The export of any defense article specific to the existence of (e.g., reveals the existence of or details of) anti-tamper measures made at U.S. Government direction always requires [[Page 72254]] prior written approval from the Directorate of Defense Trade Controls. (3) U.S.-origin classified defense articles or defense services may be exported only pursuant to a written request, directive, or contract from the U.S. Department of Defense that provides for the export of the classified defense article(s) or defense service(s). (4) Defense articles specific to developmental systems that have not obtained written Milestone B approval from the Department of Defense milestone approval authority are not eligible for export unless such export is pursuant to a written solicitation or contract issued or awarded by the Department of Defense for an end-use identified pursuant to paragraphs (e)(1), (2), or (4) of this section. (5) Defense articles excluded by paragraph (g) of this section or Supplement No. 1 to part 126 of this subchapter (e.g., USML Category XI(a)(3) electronically scanned array radar) that are embedded in a larger system that is eligible to ship under this section (e.g., a ship or aircraft) must separately comply with any restrictions placed on that embedded defense article under this subsection. The exporter must obtain a license or other authorization from the Directorate of Defense Trade Controls for the export of such embedded defense articles (for example, USML Category XI(a)(3) electronically scanned array radar systems that are exempt from this section that are incorporated in an aircraft that is eligible to ship under the this section continue to require separate authorization from the Directorate of Defense Trade Controls for their export, transfer, reexport, or retransfer). (6) No liability shall be incurred by or attributed to the U.S. Government in connection with any possible infringement of privately owned patent or proprietary rights, either domestic or foreign, by reason of an export conducted pursuant to this section. (7) Sales by exporters made through the U.S. Government shall not include either charges for patent rights in which the U.S. Government holds a royalty-free license, or charges for information which the U.S. Government has a right to use and disclose to others, which is in the public domain, or which the U.S. Government has acquired or is entitled to acquire without restrictions upon its use and disclosure to others. (h) Transfers, Retransfers, and Reexports. (1) Any transfer of a defense article or defense service not exempted in Supplement No. 1 to part 126 of this subchapter by a member of the Australian Community (see paragraph (d) of this section for specific information on the identification of the Community) to another member of the Australian Community or the United States Community for an end-use that is authorized by this exemption (see paragraphs (e) and (f) of this section regarding authorized end-uses) is authorized under this exemption. (2) Any transfer or other provision of a defense article or defense service for an end-use that is not authorized by the exemption provided by this section is prohibited without a license or the prior written approval of the Directorate of Defense Trade Controls (see paragraphs (e) and (f) of this section regarding authorized end-uses). (3) Any retransfer or reexport, or other provision of a defense article or defense service by a member of the Australian Community to a foreign person that is not a member of the Australian Community, or to a U.S. person that is not a member of the United States Community, is prohibited without a license or the prior written approval of the Directorate of Defense Trade Controls (see paragraph (d) of this section for specific information on the identification of the Australian Community). (4) Any change in the use of a defense article or defense service previously exported, transferred, or obtained under this exemption by any foreign person, including a member of the Australian Community, to an end-use that is not authorized by this exemption is prohibited without a license or other written approval of the Directorate of Defense Trade Controls (see paragraphs (e) and (f) of this section regarding authorized end-uses). (5) Any retransfer, reexport, or change in end-use requiring such approval of the U.S. Government shall be made in accordance with Sec. 123.9 of this subchapter. (6) Defense articles excluded by paragraph (g) of this section or Supplement No. 1 to part 126 of this subchapter (e.g., USML Category XI(a)(3) electronically scanned array radar) that are embedded in a larger system that is eligible to ship under this section (e.g., a ship or aircraft) must separately comply with any restrictions placed on that embedded defense article unless otherwise specified. A license or other authorization must be obtained from the Directorate of Defense Trade Controls for the retransfer, reexport or change in end-use of any such embedded defense article (for example, USML Category XI(a)(3) electronically scanned radar systems that are exempt from this section that are incorporated in an aircraft that is eligible to ship under the this section continue to require separate authorization from the Directorate of Defense Trade Controls for their export, transfer, reexport, or retransfer). (7) A license or prior approval from the Directorate of Defense Trade Controls is not required for a transfer, retransfer, or reexport of an exported defense article or defense service under this section, if: (i) The transfer of defense articles or defense services is made by a member of the United States Community to Australian Department of Defense (ADOD) elements deployed outside the Territory of Australia and engaged in an authorized end-use (see paragraphs (e) and (f) of this section regarding authorized end-uses) using ADOD transmission channels or the provisions of this section (Note: For purposes of paragraph (h)(7)(i)-(iv), per Section 9(9) of the Australia Implementing Arrangement, “ADOD Transmission channels” includes electronic transmission of a defense article and transmission of a defense article by an ADOD contracted carrier or freight forwarder that merely transports or arranges transport for the defense article in this instance.); (ii) The transfer of defense articles or defense services is made by a member of the United States Community to an Approved Community member (either U.S. or Australian) that is operating in direct support of Australian Department of Defense elements deployed outside the Territory of Australia and engaged in an authorized end-use (see paragraphs (e) and (f) of this section regarding authorized end-uses) using ADOD transmission channels or the provisions of this section; (iii) The reexport is made by a member of the Australian Community to Australian Department of Defense elements deployed outside the Territory of Australia engaged in an authorized end-use (see paragraphs (e) and (f) of this section regarding authorized end-uses) using ADOD transmission channels or the provisions of this section; (iv) The retransfer or reexport is made by a member of the Australian Community to an Approved Community member (either United States or Australian) that is operating in direct support of Australian Department of Defense elements deployed outside the Territory of Australia engaged in an authorized end-use (see paragraphs (e) and (f) of this section regarding authorized end-uses) using ADOD transmission channels or the provisions of this section; or [[Page 72255]] (v) The defense article or defense service will be delivered to the Australian Department of Defense for an authorized end-use (see paragraphs (e) and (f) of this section regarding authorized end-uses); the Australian Department of Defense may deploy the item as necessary when conducting official business within or outside the Territory of Australia. The item must remain under the effective control of the Australian Department of Defense while deployed and access may not be provided to unauthorized third parties. (8) U.S. persons registered, or required to be registered, pursuant to part 122 of this subchapter and Members of the Australian Community must immediately notify the Directorate of Defense Trade Controls of any actual or proposed sale, retransfer, or reexport of a defense article or defense service on the U.S. Munitions List originally exported under this exemption to any of the countries listed in Sec. 126.1 of this subchapter, any citizen of such countries, or any person acting on behalf of such countries, whether within or outside the United States. Any person knowing or having reason to know of such a proposed or actual sale, reexport, or retransfer shall submit such information in writing to the Office of Defense Trade Controls Compliance, Directorate of Defense Trade Controls. (i) Transitions. (1) Any previous export of a defense article under a license or other approval of the U.S. Department of State remains subject to the conditions and limitations of the original license or authorization unless the Directorate of Defense Trade Controls has approved in writing a transition to this section. (2) If a U.S. exporter desires to transition from an existing license or other approval to the use of the provisions of this section, the following is required: (i) The U.S. exporter must submit a written request to the Directorate of Defense Trade Controls, which identifies the defense articles or defense services to be transitioned, the existing license(s) or other authorizations under which the defense articles or defense services were originally exported; and the Treaty-eligible end- use for which the defense articles or defense services will be used. Any license(s) filed with U.S. Customs and Border Protection should remain on file until the exporter has received approval from the Directorate of Defense Trade Controls to retire the license(s) and transition to this section. When this approval is conveyed to U.S. Customs and Border Protection by the Directorate of Defense Trade Controls, the license(s) will be returned to the Directorate of Defense Trade Controls by U.S. Customs and Border Protection in accordance with existing procedures for the return of expired licenses in Sec. 123.22(c) of this subchapter. (ii) Any license(s) not filed with U.S. Customs and Border Protection must be returned to the Directorate of Defense Trade Controls with a letter citing the Directorate of Defense Trade Controls’ approval to transition to this section as the reason for returning the license(s). (3) If a member of the Australian Community desires to transition defense articles received under an existing license or other approval to the processes established under the Treaty, the Australian Community member must submit a written request to the Directorate of Defense Trade Controls, either directly or through the original U.S. exporter, which identifies the defense articles or defense services to be transitioned, the existing license(s) or other authorizations under which the defense articles or defense services were received, and the Treaty-eligible end-use (see paragraphs (e) and (f) of this section regarding authorized end-uses) for which the defense articles or defense services will be used. The defense article or defense service shall remain subject to the conditions and limitations of the existing license or other approval until the Australian Community member has received approval from the Directorate of Defense Trade Controls to transition to this section. (4) Authorized exporters identified in paragraph (b)(2) of this section who have exported a defense article or defense service that has subsequently been placed on the list of exempted items in Supplement No. 1 to part 126 of this subchapter must review and adhere to the requirements in the relevant Federal Register notice announcing such removal. Once removed, the defense article or defense service will no longer be subject to this section, such defense article or defense service previously exported shall remain on the U.S. Munitions List and be subject to the International Traffic in Arms Regulations unless the applicable Federal Register notice states otherwise. Subsequent reexport or retransfer must be made pursuant to Sec. 123.9 of this subchapter. (5) Any defense article or defense service transitioned from a license or other approval to treatment under this section must be marked in accordance with the requirements of paragraph (j) of this section. (j) Marking of Exports. (1) All defense articles and defense services exported or transitioned pursuant to the Defense Trade Cooperation Treaty between the United States and Australia and this section shall be marked or identified as follows: (i) For classified defense articles and defense services the standard marking or identification shall read: “//CLASSIFICATION LEVEL USML//REL AUS and USA Treaty Community//.” For example, for defense articles classified SECRET, the marking or identification shall be “// SECRET USML//REL AUS and USA Treaty Community//.” (ii) Unclassified defense articles and defense services exported under or transitioned pursuant to this section shall be AUS classified as “Restricted USML” and, the standard marking or identification shall read “//RESTRICTED USML//REL AUS and USA Treaty Community//.” (2) Where defense articles are returned to a member of the United States Community identified in paragraph (b) of this section, any defense articles AUS classified and marked or identified pursuant to paragraph j(1)(ii) of this section as “//RESTRICTED USML//REL AUS and USA Treaty Community//” shall no longer be AUS classified and such marking or identification shall be removed; and (3) The standard marking and identification requirements are as follows: (i) Defense articles (other than technical data) shall be individually labeled with the appropriate identification detailed in paragraphs (j)(1) and (j)(2) of this section; or, where such labeling is impracticable (e.g., propellants, chemicals), shall be accompanied by documentation (such as contracts or invoices) clearly associating the defense articles with the appropriate markings as detailed above; (ii) Technical data (including data packages, technical papers, manuals, presentations, specifications, guides and reports), regardless of media or means of transmission (physical or electronic), shall be individually labeled with the appropriate identification detailed in paragraphs (j)(1) and (j)(2) of this section; or, where such labeling is impracticable (oral presentations), shall have a verbal notification clearly associating the technical data with the appropriate markings as detailed above; and (4) Contracts and agreements for the provision of defense services shall be identified with the appropriate identification detailed in paragraphs (j)(1) and (j)(2) of this section. (5) The exporter shall incorporate the following statement as an integral part [[Page 72256]] of all shipping documentation (airway bill, bill of lading, manifest, packing documents, delivery verification, invoice, etc.) whenever defense articles are to be exported: “These commodities are authorized by the U.S. Government for export only to Australia for use in approved projects, programs or operations by members of the Australian Community. They may not be retransferred or reexported or used outside of an approved project, program or operation, either in their original form or after being incorporated into other end-items, without the prior written approval of the U.S. Department of State.” (k) Intermediate Consignees. (1) Unclassified exports under this section may only be handled by: (i) U.S. intermediate consignees who are: (A) Exporters registered with the Directorate of Defense Trade Controls and eligible; (B) Licensed customs brokers who are subject to background investigation and have passed a comprehensive examination administered by U.S. Customs and Border Protection; or (C) Commercial air freight and surface shipment carriers, freight forwarders, or other parties not exempt from registration under Sec. 129.3(b)(3) of this subchapter that are identified at the time of export as being on the list of Authorized U.S. Intermediate Consignees, which is available on the Directorate of Defense Trade Controls’ Web site. (ii) Australian intermediate consignees who are: (A) Members of the Australian Community; or (B) Freight forwarders, customs brokers, commercial air freight and surface shipment carriers, or other Australian parties that are identified at the time of export as being on the list of Authorized Australian Intermediate Consignees, which is available on the Directorate of Defense Trade Controls’ Web site. (2) Classified exports must comply with the security requirements of the National Industrial Security Program Operating Manual (DoD 5220.22-M and supplements or successors). (l) Records. (1) All exporters authorized pursuant to paragraph (b)(2) of this section who export pursuant to the Defense Trade Cooperation Treaty between the United States and Australia and this section shall maintain detailed records of all exports, imports, and transfers made by that exporter of defense articles or defense services subject to the Defense Trade Cooperation Treaty between the United States and Australia and the requirements of this section. Exporters shall also maintain detailed records of any reexports and retransfers approved or otherwise authorized by the Directorate of Defense Trade Controls of defense articles or defense services subject to the Defense Trade Cooperation Treaty between the United States and Australia and the requirements of this section. These records shall be maintained for a minimum of five years from the date of export, import, transfer, reexport, or retransfer and shall be made available upon request to the Directorate of Defense Trade Controls, U.S. Immigration and Customs Enforcement, or U.S. Customs and Border Protection, or any other authorized U.S. law enforcement officer. Records in an electronic format must be maintained using a process or system capable of reproducing all records on paper. Such records when displayed on a viewer, monitor, or reproduced on paper, must exhibit a high degree of legibility and readability. (For the purpose of this section, “legible” and “legibility” mean the quality of a letter or numeral that enables the observer to identify it positively and quickly to the exclusion of all other letters or numerals. “Readable” and “readability” means the quality of a group of letters or numerals being recognized as complete words or numbers.) These records shall consist of the following: (i) Port of entry/exit; (ii) Date/time of export/import; (iii) Method of export/import; (iv) Commodity code and description of the commodity, including technical data; (v) Value of export; (vi) Reference to this section and justification for export under the Treaty; (vii) End-user/end-use; (viii) Identification of all U.S. and foreign parties to the transaction; (ix) How the export was marked; (x) Classification of the export; (xi) All written correspondence with the U.S. Government on the export; (xii) All information relating to political contributions, fees, or commissions furnished or obtained, offered, solicited, or agreed upon as outlined in paragraph (m) of this section; (xiii) Purchase order or contract; (xiv) Technical data actually exported; (xv) The Internal Transaction Number for the Electronic Export Information filing in the Automated Export System; (xvi) All shipping documentation (airway bill, bill of lading, manifest, packing documents, delivery verification, invoice, etc.); and (xvii) Statement of Registration (Form DS-2032). (2) Filing of export information. All exporters of defense articles and defense services under the Defense Trade Cooperation Treaty between the United States and Australia and the requirements of this section must electronically file Electronic Export Information (EEI) using the Automated Export System citing one of the four below referenced codes in the appropriate field in the EEI for each shipment: (i) 126.16(e)(1): used for exports in support of United States and Australian combined military or counter-terrorism operations (the name or an appropriate description of the operation shall be placed in the appropriate field in the EEI, as well); (ii) 126.16(e)(2): used for exports in support of United States and Australian cooperative security and defense research, development, production, and support programs (the name or an appropriate description of the program shall be placed in the appropriate field in the EEI, as well); (iii) 126.16(e)(3): used for exports in support of mutually determined specific security and defense projects where the Government of Australia is the end-user (the name or an appropriate description of the project shall be placed in the appropriate field in the EEI, as well); or (iv) 126.16(e)(4): used for exports that will have a U.S. Government end-use (the U.S. Government contract number or solicitation number (e.g., “U.S. Government contract number XXXXX”) shall be placed in the appropriate field in the EEI, as well). Such exports must meet the required export documentation and filing guidelines, including for defense services, of Sec. 123.22(a), (b)(1), and (b)(2) of this subchapter. (m) Fees and Commissions. All exporters authorized pursuant to paragraph (b)(2) of this section shall, with respect to each export, transfer, reexport, or retransfer, pursuant to the Defense Trade Cooperation Treaty between the United States and Australia and this section, submit a statement to the Directorate of Defense Trade Controls containing the information identified in Sec. 130.10 of this subchapter relating to fees, commissions, and political contributions on contracts or other instruments valued in an amount of $500,000 or more. (n) Violations and Enforcement. (1) Exports, transfers, reexports, and retransfers that do not comply with the conditions prescribed in this section will constitute violations of the Arms Export Control Act and this subchapter, [[Page 72257]] and are subject to all relevant criminal, civil, and administrative penalties (see Sec. 127.1 of this subchapter), and may also be subject to other statutes or regulations. (2) U.S. Immigration and Customs Enforcement and U.S. Customs and Border Protection officers have the authority to investigate, detain, or seize any export or attempted export of defense articles that does not comply with this section or that is otherwise unlawful. (3) The Directorate of Defense Trade Controls, U.S. Immigration and Customs Enforcement, U.S. Customs and Border Protection, and other authorized U.S. law enforcement officers may require the production of documents and information relating to any actual or attempted export, transfer, reexport, or retransfer pursuant to this section. Any foreign person refusing to provide such records within a reasonable period of time shall be suspended from the Australian Community and ineligible to receive defense articles or defense services pursuant to the exemption under this section or otherwise. (o) Procedures for Legislative Notification. (1) Exports pursuant to the Defense Trade Cooperation Treaty between the United States and Australia and this section by any person identified in paragraph (b)(2) of this section shall not take place until 30 days after the Directorate of Defense Trade Controls has acknowledged receipt of a Form DS-4048 (entitled, “Projected Sales of Major Weapons in Support of Section 25(a)(1) of the Arms Export Control Act”) from the exporter notifying the Department of State if the export involves one or more of the following: (i) A contract or other instrument for the export of major defense equipment in the amount of $25,000,000 or more, or for defense articles and defense services in the amount of $100,000,000 or more; (ii) A contract or other instrument for the export of firearms controlled under Category I of the U.S. Munitions List of the International Traffic in Arms Regulations in an amount of $1,000,000 or more; (iii) A contract or other instrument, regardless of value, for the manufacturing abroad of any item of significant military equipment; or (iv) An amended contract or other instrument that meets the requirements of paragraphs (o)(1)(i)-(o)(1)(iii) of this section. (2) The Form DS-4048 required in paragraph (o)(1) of this section shall be accompanied by the following additional information: (i) The information identified in Sec. 130.10 and Sec. 130.11 of this subchapter; (ii) A statement regarding whether any offset agreement is proposed to be entered into in connection with the export and a description of any such offset agreement; (iii) A copy of the signed contract or other instrument; and (iv) If the notification is for paragraph (o)(1)(ii) of this section, a statement of what will happen to the weapons in their inventory (for example, whether the current inventory will be sold, reassigned to another service branch, destroyed, etc.). (3) The Department of State will notify the Congress of exports that meet the requirements of paragraph (o)(1) of this section. 26. Section 126.17 is added to read as follows: Sec. 126.17 Exemption pursuant to the Defense Trade Cooperation Treaty between the United States and the United Kingdom. (a) Scope of exemption and required conditions. (1) Definitions. (i) An export means, for purposes of this section only, the initial movement of defense articles or defense services from the United States to the United Kingdom Community. (ii) A transfer means, for purposes of this section only, the movement of a defense article or defense service, previously exported, by a member of the United Kingdom Community within the United Kingdom Community, or between a member of the United States Community and a member of the United Kingdom Community. (iii) Retransfer and reexport have the meaning provided in Sec. 120.19 of this subchapter. (iv) Intermediate consignee means, for purposes of this section, an entity or person who receives defense articles, including technical data, but who does not have access to such defense articles, for the sole purpose of effecting onward movement to members of the Approved Community. (2) Persons or entities exporting or transferring defense articles or defense services are exempt from the otherwise applicable licensing requirements if such persons or entities comply with the regulations set forth in this section. Except as provided in Supplement No. 1 to part 126 of this subchapter, Port Directors of U.S. Customs and Border Protection and postmasters shall permit the permanent and temporary export without a license to members of the United Kingdom Community (see paragraph (d) of this section regarding the identification of members of the United Kingdom Community) of defense articles and defense services not listed in Supplement No. 1 to part 126, for the end-uses specifically identified pursuant to paragraphs (e) and (f) below. The purpose of this section is to specify the requirements to export, transfer, reexport, retransfer, or otherwise dispose of a defense article or defense service pursuant to the Defense Trade Cooperation Treaty between the United States and the United Kingdom. (3) Export. In order for an exporter to export a defense article or defense service pursuant to the Defense Trade Cooperation Treaty between the United States and the United Kingdom, all of the following conditions must be met: (i) The exporter must be registered with the Directorate of Defense Trade Controls and must be eligible, according to the requirements and prohibitions of the Arms Export Control Act, this subchapter, and other provisions of United States law, to obtain an export license (or other forms of authorization to export) from any agency of the U.S. Government without restriction (see paragraphs (b) and (c) of this section for specific requirements); (ii) The recipient of the export must be a member of the United Kingdom Community (see paragraph (d) of this section regarding the identification of members of the United Kingdom Community). United Kingdom entities and facilities that become ineligible for such membership will be removed from the United Kingdom Community; (iii) Intermediate consignees involved in the export must be eligible, according to the requirements and prohibitions of the Arms Export Control Act, this subchapter, and other provisions of United States law, to handle or receive a defense article or defense service without restriction (see paragraph (k) of this section for specific requirements); (iv) The export must be for an end-use specified in the Defense Trade Cooperation Treaty between the United States and the United Kingdom and mutually agreed to by the U.S. Government and the Government of the United Kingdom pursuant to the Defense Trade Cooperation Treaty between the United States and the United Kingdom and the Implementing Arrangement thereto (United Kingdom Implementing Arrangement) (see paragraphs (e) and (f) of this section regarding authorized end-uses); (v) The defense article or defense service is not excluded from the scope of the Defense Trade Cooperation Treaty between the United States and the United Kingdom (see paragraph (g) of this section and Supplement No. 1 to part 126 of this subchapter for specific [[Page 72258]] information on the scope of items excluded from export under this exemption) and is marked or identified, at a minimum, as “Restricted USML” (see paragraph (j) of this section for specific requirements on marking exports); (vi) All required documentation of such export is maintained by the exporter and recipient and is available upon the request of the U.S. Government (see paragraph (l) of this section for specific requirements); and (vii) The Department of State has provided advance notification to the Congress, as required, in accordance with this section (see paragraph (o) of this section for specific requirements). (4) Transfers. In order for a member of the United Kingdom Community to transfer a defense article or defense service under the Defense Trade Cooperation Treaty between the United States and the United Kingdom, all of the following conditions must be met: (i) The defense article or defense service must have been previously exported in accordance with paragraph (a)(3) of this section or transitioned from a license or other approval in accordance with paragraph (i) Transfers of this section; (ii) The transferor and transferee of the defense article or defense service are members of the United Kingdom Community (see paragraph (d) of this section regarding the identification of members of the United Kingdom Community) or the United States Community (see paragraph (b) of this section for information on the United States Community/approved exporters); (iii) The transfer is required for an end-use specified in the Defense Trade Cooperation Treaty between the United States and the United Kingdom and mutually agreed to by the United States and the Government of United Kingdom pursuant to the terms of the Defense Trade Cooperation Treaty between the United States and the United Kingdom and the United Kingdom Implementing Arrangement (see paragraphs (e) and (f) of this section regarding authorized end-uses); (iv) The defense article or defense service is not identified in paragraph (g) of this section and Supplement No. 1 to part 126 of this subchapter as ineligible for export under this exemption, and is marked or otherwise identified, at a minimum, as “Restricted USML” (see paragraph (j) of this section for specific requirements on marking exports); (v) All required documentation of such transfer is maintained by the transferor and transferee and is available upon the request of the U.S. Government (see paragraph (l) of this section for specific requirements); and (vi) The Department of State has provided advance notification to the Congress in accordance with this section (see paragraph (o) of this section for specific requirements). (5) This section does not apply to the export of defense articles or defense services from the United States pursuant to the Foreign Military Sales program. (b) Authorized exporters. The following persons compose the United States Community and may export defense articles and defense services pursuant to the Defense Trade Cooperation Treaty between the United States and the United Kingdom: (1) Departments and agencies of the U.S. Government, including their personnel, with, as appropriate, a security clearance and a need- to-know; and (2) Nongovernmental U.S. persons registered with the Directorate of Defense Trade Controls and eligible, according to the requirements and prohibitions of the Arms Export Control Act, this subchapter, and other provisions of United States law, to obtain an export license (or other forms of authorization to export) from any agency of the U.S. Government without restriction, including their employees acting in their official capacity with, as appropriate, a security clearance and a need-to-know. (c) An exporter that is otherwise an authorized exporter pursuant to subsection (b) above may not export pursuant to the Defense Trade Cooperation Treaty between the United States and the United Kingdom if the exporter’s president, chief executive officer, any vice-president, any other senior officer or official (e.g., comptroller, treasurer, general counsel); any member of the board of directors of the exporter; any party to the export; or any source or manufacturer is ineligible to receive export licenses (or other forms of authorization to export) from any agency of the U.S. Government. (d) United Kingdom Community. For purposes of the exemption provided by this section, the United Kingdom Community consists of the United Kingdom entities and facilities identified as members of the Approved Community through the Directorate of Defense Trade Controls’ Web site at the time of a transaction under this section; non- governmental United Kingdom entities and facilities that become ineligible for such membership will be removed from the United Kingdom Community. (e) Authorized End-uses. The following end-uses, subject to subsection (f), are specified in the Defense Trade Cooperation Treaty between the United States and the United Kingdom: (1) United States and United Kingdom combined military or counter- terrorism operations; (2) United States and United Kingdom cooperative security and defense research, development, production, and support programs; (3) Mutually determined specific security and defense projects where the Government of the United Kingdom is the end-user; or (4) U.S. Government end-use. (f) Procedures for identifying authorized end-uses pursuant to paragraph (e) of this section: (1) Operations, programs, and projects that can be publicly identified will be posted on the Directorate of Defense Trade Controls’ Web site; (2) Operations, programs, and projects that cannot be publicly identified will be confirmed in written correspondence from the Directorate of Defense Trade Controls; or (3) U.S. Government end-use will be identified specifically in a U.S. Government contract or solicitation as being eligible under the Treaty. (4) No other operations, programs, projects, or end-uses qualify for this exemption. (g) Items eligible under this section. With the exception of items listed in Supplement No. 1 to part 126 of this subchapter, defense articles and defense services may be exported under this section subject to the following: (1) An exporter authorized pursuant to paragraph (b)(2) of this section may market a defense article to the Government of the United Kingdom if that exporter has been licensed by the Directorate of Defense Trade Controls to export (as defined by Sec. 120.17 of this subchapter) the identical type of defense article to any foreign person. (2) The export of any defense article specific to the existence of (e.g., reveals the existence of or details of) anti-tamper measures made at U.S. Government direction always requires prior written approval from the Directorate of Defense Trade Controls. (3) U.S.-origin classified defense articles or defense services may be exported only pursuant to a written request, directive, or contract from the U.S. Department of Defense that provides for the export of the classified defense article(s) or defense service(s). (4) Defense articles specific to developmental systems that have not obtained written Milestone B approval from the Department of Defense milestone approval authority are not [[Page 72259]] eligible for export unless such export is pursuant to a written solicitation or contract issued or awarded by the Department of Defense for an end-use identified pursuant to paragraphs (e)(1), (2), or (4) of this section. (5) Defense articles excluded by paragraph (g) of this section or Supplement No. 1 to part 126 of this subchapter (e.g., USML Category XI (a)(3) electronically scanned array radar) that are embedded in a larger system that is eligible to ship under this section (e.g., a ship or aircraft) must separately comply with any restrictions placed on that embedded defense article under this subsection. The exporter must obtain a license or other authorization from the Directorate of Defense Trade Controls for the export of such embedded defense articles (for example, USML Category XI (a)(3) electronically scanned array radar systems that are exempt from this section that are incorporated in an aircraft that is eligible to ship under the this section continue to require separate authorization from the Directorate of Defense Trade Controls for their export, transfer, reexport, or retransfer). (6) No liability shall be incurred by or attributed to the U.S. Government in connection with any possible infringement of privately owned patent or proprietary rights, either domestic or foreign, by reason of an export conducted pursuant to this section. (7) Sales by exporters made through the U.S. Government shall not include either charges for patent rights in which the U.S. Government holds a royalty-free license, or charges for information which the U.S. Government has a right to use and disclose to others, which is in the public domain, or which the U.S. Government has acquired or is entitled to acquire without restrictions upon its use and disclosure to others. (8) Defense articles and services specific to items that appear on the European Union Dual Use List (as described in Annex 1 to EC Council Regulation No. 428/2009) are not eligible for export under the Defense Trade Cooperation Treaty between the United States and the United Kingdom. (h) Transfers, Retransfers, and Reexports. (1) Any transfer of a defense article or defense service not exempted in Supplement No.1 to part 126 of this subchapter by a member of the United Kingdom Community (see paragraph (d) of this section for specific information on the identification of the Community) to another member of the United Kingdom Community or the United States Community for an end-use that is authorized by this exemption (see paragraphs (e) and (f) of this section regarding authorized end-uses) is authorized under this exemption. (2) Any transfer or other provision of a defense article or defense service for an end-use that is not authorized by the exemption provided by this section is prohibited without a license or the prior written approval of the Directorate of Defense Trade Controls (see paragraphs (e) and (f) of this section regarding authorized end-uses). (3) Any retransfer or reexport, or other provision of a defense article or defense service by a member of the United Kingdom Community to a foreign person that is not a member of the United Kingdom Community, or to a U.S. person that is not a member of the United States Community, is prohibited without a license or the prior written approval of the Directorate of Defense Trade Controls (see paragraph (d) of this section for specific information on the identification of the United Kingdom Community). (4) Any change in the use of a defense article or defense service previously exported, transferred, or obtained under this exemption by any foreign person, including a member of the United Kingdom Community, to an end-use that is not authorized by this exemption is prohibited without a license or other written approval of the Directorate of Defense Trade Controls (see paragraphs (e) and (f) of this section regarding authorized end-uses). (5) Any retransfer, reexport, or change in end-use requiring such approval of the U.S. Government shall be made in accordance with Sec. 123.9 of this subchapter. (6) Defense articles excluded by paragraph (g) of this section or Supplement No. 1 to part 126 of this subchapter (e.g., USML Category XI (a)(3) electronically scanned array radar systems) that are embedded in a larger system that is eligible to ship under this section (e.g., a ship or aircraft) must separately comply with any restrictions placed on that embedded defense article unless otherwise specified. A license or other authorization must be obtained from the Directorate of Defense Trade Controls for the retransfer, reexport or change in end-use of any such embedded defense article (for example, USML Category XI(a)(3) electronically scanned array radar systems that are exempt from this section that are incorporated in an aircraft that is eligible to ship under the this section continue to require separate authorization from the Directorate of Defense Trade Controls for their export, transfer, reexport, or retransfer). (7) A license or prior approval from the Directorate of Defense Trade Controls is not required for a transfer, retransfer, or reexport of an exported defense article or defense service under this section, if: (i) The transfer of defense articles or defense services is made by a member of the United States Community to United Kingdom Ministry of Defense elements deployed outside the Territory of the United Kingdom and engaged in an authorized end-use (see paragraphs (e) and (f) of this section regarding authorized end-uses) using United Kingdom Armed Forces transmission channels or the provisions of this section; (ii) The transfer of defense articles or defense services is made by a member of the United States Community to an Approved Community member (either U.S. or U.K.) that is operating in direct support of United Kingdom Ministry of Defense elements deployed outside the Territory of the United Kingdom and engaged in an authorized end-use (see paragraphs (e) and (f) of this section regarding authorized end- uses) using United Kingdom Armed Forces transmission channels or the provisions of this section; (iii) The reexport is made by a member of the United Kingdom Community to United Kingdom Ministry of Defense elements deployed outside the Territory of the United Kingdom engaged in an authorized end-use (see paragraphs (e) and (f) of this section regarding authorized end-uses) using United Kingdom Armed Forces transmission channels or the provisions of this section; (iv) The retransfer or reexport is made by a member of the United Kingdom Community to an Approved Community member (either U.S. or U.K.) that is operating indirect support of United Kingdom Ministry of Defense elements deployed outside the Territory of the United Kingdom engaged in an authorized end-use (see paragraphs (e) and (f) of this section regarding authorized end-uses) using United Kingdom Armed Forces transmission channels or the provisions of this section; or (v) The defense article or defense service will be delivered to the United Kingdom Ministry of Defense for an authorized end-use (see paragraphs (e) and (f) of this section regarding authorized end-uses); the United Kingdom Ministry of Defense may deploy the item as necessary when conducting official business within or outside the Territory of the United Kingdom. The item must remain under the effective control of the United [[Page 72260]] Kingdom Ministry of Defense while deployed and access may not be provided to unauthorized third parties. (8) U.S. persons registered, or required to be registered, pursuant to part 122 of this subchapter and Members of the United Kingdom Community must immediately notify the Directorate of Defense Trade Controls of any actual or proposed sale, retransfer, or reexport of a defense article or defense service on the U.S. Munitions List originally exported under this exemption to any of the countries listed in Sec. 126.1 of this subchapter, any citizen of such countries, or any person acting on behalf of such countries, whether within or outside the United States. Any person knowing or having reason to know of such a proposed or actual sale, reexport, or retransfer shall submit such information in writing to the Office of Defense Trade Controls Compliance, Directorate of Defense Trade Controls. (i) Transitions. (1) Any previous export of a defense article under a license or other approval of the U.S. Department of State remains subject to the conditions and limitations of the original license or authorization unless the Directorate of Defense Trade Controls has approved in writing a transition to this section. (2) If a U.S. exporter desires to transition from an existing license or other approval to the use of the provisions of this section, the following is required: (i) The U.S. exporter must submit a written request to the Directorate of Defense Trade Controls, which identifies the defense articles or defense services to be transitioned, the existing license(s) or other authorizations under which the defense articles or defense services were originally exported; and the Treaty-eligible end- use for which the defense articles or defense services will be used. Any license(s) filed with U.S. Customs and Border Protection should remain on file until the exporter has received approval from the Directorate of Defense Trade Controls to retire the license(s) and transition to this section. When this approval is conveyed to U.S. Customs and Border Protection by the Directorate of Defense Trade Controls, the license(s) will be returned to the Directorate of Defense Trade Controls by U.S. Customs and Border Protection in accord with existing procedures for the return of expired licenses in Sec. 123.22(c) of this subchapter. (ii) Any license(s) not filed with U.S. Customs and Border Protection must be returned to the Directorate of Defense Trade Controls with a letter citing the Directorate of Defense Trade Controls’ approval to transition to this section as the reason for returning the license(s). (3) If a member of the United Kingdom Community desires to transition defense articles received under an existing license or other approval to the processes established under the Treaty, the United Kingdom Community member must submit a written request to the Directorate of Defense Trade Controls, either directly or through the original U.S. exporter, which identifies the defense articles or defense services to be transitioned, the existing license(s) or other authorizations under which the defense articles or defense services were received, and the Treaty-eligible end-use (see paragraphs (e) and (f) of this section regarding authorized end-uses) for which the defense articles or defense services will be used. The defense article or defense service shall remain subject to the conditions and limitations of the existing license or other approval until the United Kingdom Community member has received approval from the Directorate of Defense Trade Controls to transition to this section. (4) Authorized exporters identified in paragraph (b)(2) of this section who have exported a defense article or defense service that has subsequently been placed on the list of exempted items in Supplement No. 1 to part 126 of this subchapter must review and adhere to the requirements in the relevant Federal Register notice announcing such removal. Once removed, the defense article or defense service will no longer be subject to this section, such defense article or defense service previously exported shall remain on the U.S. Munitions List and be subject to the International Traffic in Arms Regulations unless the applicable Federal Register notice states otherwise. Subsequent reexport or retransfer must be made pursuant to Sec. 123.9 of this subchapter. (5) Any defense article or defense service transitioned from a license or other approval to treatment under this section must be marked in accordance with the requirements of paragraph (j) of this section. (j) Marking of Exports. (1) All defense articles and defense services exported or transitioned pursuant to the Defense Trade Cooperation Treaty between the United States and the United Kingdom and this section shall be marked or identified as follows: (i) For classified defense articles and defense services the standard marking or identification shall read: “//CLASSIFICATION LEVEL USML//REL UK and USA Treaty Community//.” For example, for defense articles classified SECRET, the marking or identification shall be “// SECRET USML//REL UK and USA Treaty Community//.” (ii) Unclassified defense articles and defense services exported under or transitioned pursuant to this section shall be UK classified as “Restricted USML” and, the standard marking or identification shall read “//RESTRICTED USML//REL UK and USA Treaty Community//.” (2) Where defense articles are returned to a member of the United States Community identified in paragraph (b) of this section, any defense articles UK classified and marked or identified pursuant to paragraph j(1)(ii) as “//RESTRICTED USML//REL UK and USA Treaty Community//” no longer be UK classified and such marking or identification shall be removed; and (3) The standard marking and identification requirements are as follows: (i) Defense articles (other than technical data) shall be individually labeled with the appropriate identification detailed in paragraphs (j)(1) and (j)(2) of this section; or, where such labeling is impracticable (e.g., propellants, chemicals), shall be accompanied by documentation (such as contracts or invoices) clearly associating the defense articles with the appropriate markings as detailed above; (ii) Technical data (including data packages, technical papers, manuals, presentations, specifications, guides and reports), regardless of media or means of transmission (physical or electronic), shall be individually labeled with the appropriate identification detailed in paragraphs (j)(1) and (j)(2) of this section; or, where such labeling is impracticable (oral presentations), shall have a verbal notification clearly associating the technical data with the appropriate markings as detailed above; and (4) Contracts and agreements for the provision of defense services shall be identified with the appropriate identification detailed in paragraphs (j)(1) and (j)(2) of this section. (5) The exporter shall incorporate the following statement as an integral part of all shipping documentation (airway bill, bill of lading, manifest, packing documents, delivery verification, invoice, etc.) whenever defense articles are to be exported: “These commodities are authorized by the U.S. Government for export only to United Kingdom for use in approved projects, programs or operations by members of the United Kingdom [[Page 72261]] Community. They may not be retransferred or reexported or used outside of an approved project, program, or operation, either in their original form or after being incorporated into other end-items, without the prior written approval of the U.S. Department of State.” (k) Intermediate Consignees. (1) Unclassified exports under this section may only be handled by: (i) U.S. intermediate consignees who are: (A) Exporters registered with the Directorate of Defense Trade Controls and eligible; (B) Licensed customs brokers who are subject to background investigation and have passed a comprehensive examination administered by U.S. Customs and Border Protection; or (C) Commercial air freight and surface shipment carriers, freight forwarders, or other parties not exempt from registration under Sec. 129.3(b)(3) of this subchapter that are identified at the time of export as being on the list of Authorized U.S. Intermediate Consignees, which is available on the Directorate of Defense Trade Controls’ Web site. (ii) United Kingdom intermediate consignees who are: (A) Members of the United Kingdom Community; or (B) Freight forwarders, customs brokers, commercial air freight and surface shipment carriers, or other United Kingdom parties that are identified at the time of export as being on the list of Authorized United Kingdom Intermediate Consignees, which is available on the Directorate of Defense Trade Controls’ Web site. (2) Classified exports must comply with the security requirements of the National Industrial Security Program Operating Manual (DoD 5220.22-M and supplements or successors). (l) Records. (1) All exporters authorized pursuant to paragraph (b)(2) of this section who export pursuant to the Defense Trade Cooperation Treaty between the United States and the United Kingdom and this section shall maintain detailed records of all exports, imports, and transfers made by that exporter of defense articles or defense services subject to the Defense Trade Cooperation Treaty between the United States and the United Kingdom and this section. Exporters shall also maintain detailed records of any reexports and retransfers approved or otherwise authorized by the Directorate of Defense Trade Controls of defense articles or defense services subject to the Defense Trade Cooperation Treaty between the United States and the United Kingdom and this section. These records shall be maintained for a minimum of five years from the date of export, import, transfer, reexport, or retransfer and shall be made available upon request to the Directorate of Defense Trade Controls, U.S. Immigration and Customs Enforcement, or U.S. Customs and Border Protection, or any other authorized U.S. law enforcement officer. Records in an electronic format must be maintained using a process or system capable of reproducing all records on paper. Such records when displayed on a viewer, monitor, or reproduced on paper, must exhibit a high degree of legibility and readability. (For the purpose of this section, “legible” and “legibility” mean the quality of a letter or numeral that enables the observer to identify it positively and quickly to the exclusion of all other letters or numerals. “Readable” and “readability” means the quality of a group of letters or numerals being recognized as complete words or numbers.) These records shall consist of the following: (i) Port of entry/exit; (ii) Date/time of export/import; (iii) Method of export/import; (iv) Commodity code and description of the commodity, including technical data; (v) Value of export; (vi) Reference to this section and justification for export under the Treaty; (vii) End-user/end-use; (viii) Identification of all U.S. and foreign parties to the transaction; (ix) How the export was marked; (x) Classification of the export; (xi) All written correspondence with the U.S. Government on the export; (xii) All information relating to political contributions, fees, or commissions furnished or obtained, offered, solicited, or agreed upon as outlined in subsection (m) below; (xiii) Purchase order or contract; (xiv) Technical data actually exported; (xv) The Internal Transaction Number for the Electronic Export Information filing in the Automated Export System; (xvi) All shipping documentation (airway bill, bill of lading, manifest, packing documents, delivery verification, invoice, etc.); and (xvii) Statement of Registration (Form DS-2032). (2) Filing of export information. All exporters of defense articles and defense services under the Defense Trade Cooperation Treaty between the United States and the United Kingdom and this section must electronically file Electronic Export Information (EEI) using the Automated Export System citing one of the four below referenced codes in the appropriate field in the EEI for each shipment: (i) 126.16(e)(1): Used for exports in support of United States and United Kingdom combined military or counter-terrorism operations (the name or an appropriate description of the operation shall be placed in the appropriate field in the EEI, as well); (ii) 126.16(e)(2): Used for exports in support of United States and United Kingdom cooperative security and defense research, development, production, and support programs (the name or an appropriate description of the program shall be placed in the appropriate field in the EEI, as well); (iii) 126.16(e)(3): Used for exports in support of mutually determined specific security and defense projects where the Government of the United Kingdom is the end-user (the name or an appropriate description of the project shall be placed in the appropriate field in the EEI, as well); or (iv) 126.16(e)(4): Used for exports that will have a U.S. Government end-use (the U.S. Government contract number or solicitation number (e.g., “U.S. Government contract number XXXXX”) shall be placed in the appropriate field in the EEI, as well). Such exports must meet the required export documentation and filing guidelines, including for defense services, of Sec. 123.22(a), (b)(1), and (b)(2) of this subchapter. (m) Fees and Commissions. All exporters authorized pursuant to paragraph (b)(2) of this section shall, with respect to each export, transfer, reexport, or retransfer, pursuant to the Defense Trade Cooperation Treaty between the United States and the United Kingdom and this section, submit a statement to the Directorate of Defense Trade Controls containing the information identified in Sec. 130.10 of this subchapter relating to fees, commissions, and political contributions on contracts or other instruments valued in an amount of $500,000 or more. (n) Violations and Enforcement. (1) Exports, transfers, reexports, and retransfers that do not comply with the conditions prescribed in this section will constitute violations of the Arms Export Control Act and this subchapter, and are subject to all relevant criminal, civil, and administrative penalties (see Sec. 127.1 of this subchapter), and may also be subject to other statutes or regulations. (2) U.S. Immigration and Customs Enforcement and U.S. Customs and Border Protection officers have the authority to investigate, detain, or seize [[Page 72262]] any export or attempted export of defense articles that does not comply with this section or that is otherwise unlawful. (3) The Directorate of Defense Trade Controls, U.S. Immigration and Customs Enforcement, U.S. Customs and Border Protection, and other authorized U.S. law enforcement officers may require the production of documents and information relating to any actual or attempted export, transfer, reexport, or retransfer pursuant to this section. Any foreign person refusing to provide such records within a reasonable period of time shall be suspended from the United Kingdom Community and ineligible to receive defense articles or defense services pursuant to the exemption under this section or otherwise. (o) Procedures for Legislative Notification. (1) Exports pursuant to the Defense Trade Cooperation Treaty between the United States and the United Kingdom and this section by any person identified in paragraph (b)(2) of this section shall not take place until 30 days after the Directorate of Defense Trade Controls has acknowledged receipt of a Form DS-4048 (entitled, “Projected Sales of Major Weapons in Support of Section 25(a)(1) of the Arms Export Control Act”) from the exporter notifying the Department of State if the export involves one or more of the following: (i) A contract or other instrument for the export of major defense equipment in the amount of $25,000,000 or more, or for defense articles and defense services in the amount of $100,000,000 or more; (ii) A contract or other instrument for the export of firearms controlled under Category I of the U.S. Munitions List of the International Traffic in Arms Regulations in an amount of $1,000,000 or more; (iii) A contract or other instrument, regardless of value, for the manufacturing abroad of any item of significant military equipment; or (iv) An amended contract or other instrument that meets the requirements of paragraphs (o)(1)(i)-(o)(1)(iii) of this section. (2) The Form DS-4048 required in paragraph (o)(1) of this section shall be accompanied by the following additional information: (i) The information identified in Sec. 130.10 and Sec. 130.11 of this subchapter; (ii) A statement regarding whether any offset agreement is proposed to be entered into in connection with the export and a description of any such offset agreement; (iii) A copy of the signed contract or other instrument; and (iv) If the notification is for paragraph (o)(1)(ii) of this section, a statement of what will happen to the weapons in their inventory (for example, whether the current inventory will be sold, reassigned to another service branch, destroyed, etc.). (3) The Department of State will notify the Congress of exports that meet the requirements of paragraph (o)(1) of this section. 27. Supplement No. 1 is added to Part 126 read as follows: Supplement No. 1 * —————————————————————————————————————- (CA) Sec. (AS) Sec. (UK) Sec. USML category Exclusion 126.5 126.16 126.17 —————————————————————————————————————- I-XXI……………………………….. Classified defense articles and X X X services. See Note 1. I-XXI……………………………….. Defense articles listed in the X X X Missile Technology Control Regime (MTCR) Annex. I-XXI……………………………….. U.S. origin defense articles ………. X X and services used for marketing purposes and not previously licensed for export in accordance with this subchapter. I-XXI……………………………….. Defense services for or X ………. ………. technical data related to defense articles identified in this supplement as excluded from the Canadian exemption. I-XXI……………………………….. Any transaction involving the X ………. ………. export of defense articles and services for which congressional notification is required in accordance with Sec. 123.15 and Sec. 124.11 of this subchapter. I-XXI……………………………….. U.S. origin defense articles ………. X X and services specific to developmental systems that have not obtained written Milestone B approval from the U.S. Department of Defense milestone approval authority, unless such export is pursuant to a written solicitation or contract issued or awarded by the U.S. Department of Defense for an end use identified in subsections (e)(1), (2), or (4) of Sec. 126.16 or Sec. 126.17 of this subchapter and is consistent with other exclusions of this supplement. I-XXI……………………………….. Nuclear weapons strategic X ………. ………. delivery systems and all components, parts, accessories, and attachments specifically designed for such systems and associated equipment. I-XXI……………………………….. Defense articles and services ………. X X specific to the existence or method of compliance with anti- tamper measures made at U.S. Government direction. I-XXI……………………………….. Defense articles and services ………. X X specific to reduced observables or counter low observables in any part of the spectrum. See Note 2. I-XXI……………………………….. Defense articles and services ………. X X specific to sensor fusion beyond that required for display or identification correlation. See Note 3. I-XXI……………………………….. Defense articles and services ………. X X specific to the automatic target acquisition or recognition and cueing of multiple autonomous unmanned systems. I-XXI……………………………….. Nuclear power generating ………. ………. X equipment or propulsion equipment (e.g. nuclear reactors), specifically designed for military use and components therefore, specifically designed for military use. See also Sec. 123.20 of this subchapter. I-XXI……………………………….. Libraries (parametric technical ………. ………. X databases) specially designed for military use with equipment controlled on the USML. I-XXI……………………………….. Defense services or technical X ………. ………. data specific to applied research as defined in Sec. 125.4(c)(3) of this subchapter, design methodology as defined in Sec. 125.4(c)(4) of this subchapter, engineering analysis as defined in Sec. 125.4(c)(5) of this subchapter, or manufacturing know-how as defined in Sec. 125.4(c)(6) of this subchapter. [[Page 72263]] I-XXI……………………………….. Defense services that are not X ………. ………. based on a written arrangement (between the U.S. exporter and the Canadian recipient) that includes a clause requiring that all documentation created from U.S. origin technical data contain the statement that “This document contains technical data, the use of which is restricted by the U.S. Arms Export Control Act. This data has been provided in accordance with, and is subject to, the limitations specified in Sec. 126.5 of the International Traffic In Arms Regulations (ITAR). By accepting this data, the consignee agrees to honor the requirements of the ITAR”. I…………………………………… Defense articles and services X ………. ………. related to firearms, close assault weapons, and combat shotguns. II(k)……………………………….. Software source code related to ………. X X Categories II(c), II(d), or II(i). See Note 4. II(k)……………………………….. Manufacturing know-how related X X X to Category II(d). See Note 5. III…………………………………. Defense articles and services X ………. ………. related to ammunition for firearms, close assault weapons, and combat shotguns listed in Category I. III…………………………………. Defense articles and services ………. ………. X specific to ammunition and fuse setting devices for guns and armament controlled in Category II. III(e)………………………………. Manufacturing know-how related X X X to Categories III(d)(1) or III(d)(2) and their specially designed components. See Note 5. III(e)………………………………. Software source code related to ………. X X Categories III(d)(1) or III(d)(2). See Note 4. IV………………………………….. Defense articles and services X X X specific to man-portable air defense systems (MANPADS). See Note 6. IV………………………………….. Defense articles and services ………. ………. X specific to rockets, designed or modified for non-military applications that do not have a range of 300 km (i.e., not controlled on the MTCR Annex). IV………………………………….. Defense articles and services ………. X X specific to torpedoes. IV………………………………….. Defense articles and services ………. ………. X specific to anti-personnel landmines. IV(i)……………………………….. Software source code related to ………. X X Categories IV(a), IV(b), IV(c), or IV(g). See Note 4. IV(i)……………………………….. Manufacturing know-how related X X X to Categories IV(a), IV(b), IV(d), or IV(g) and their specially designed components. See Note 5. V…………………………………… The following energetic ………. ………. X materials and related substances:. a. TATB (triaminotrinitrobenzene) (CAS 3058-38-6) b. Explosives controlled in USML Category V(a)(32) or V(a)(33) c. Iron powder (CAS 7439-89-6) with particle size of 3 micrometers or less produced by reduction of iron oxide with hydrogen d. BOBBA-8 (bis(2- methylaziridinyl)2-(2- hydroxypropanoxy) propylamino phosphine oxide), and other MAPO derivatives e. N-methyl-p-nitroaniline (CAS 100-15-2) f. Trinitrophenylmethyl- ………. ………. ………. nitramine (tetryl) (CAS 479-45- 8) V(c)(7)……………………………… Pyrotechnics and pyrophorics ………. ………. X specifically formulated for military purposes to enhance or control radiated energy in any part of the IR spectrum. V(d)(3)……………………………… Bis-2, 2-dinitropropylnitrate ………. ………. X (BDNPN). VI………………………………….. Defense Articles specific to ………. ………. X equipment specially designed or configured to be installed in a vehicle for military ground, marine, airborne or space applications, capable of operating while in motion and of producing or maintaining temperatures below 103 K (-170 [deg]C). VI………………………………….. Defense Articles specific to ………. ………. X superconductive electrical equipment (rotating machinery and transformers) specially designed or configured to be installed in a vehicle for military ground, marine, airborne, or space applications and capable of operating while in motion. This, however, does not include direct current hybrid homopolar generators that have single-pole normal metal armatures which rotate in a magnetic field produced by superconducting windings, provided those windings are the only superconducting component in the generator. VI………………………………….. Defense articles and services ………. X X specific to naval technology and systems relating to acoustic spectrum control and awareness. See Note 10. VI(a)……………………………….. Nuclear powered vessels…….. X X X VI(c)……………………………….. Defense articles and services ………. X X specific to submarine combat control systems. VI(d)……………………………….. Harbor entrance detection ………. ………. X devices. VI(e)……………………………….. Defense articles and services X X X specific to naval nuclear propulsion equipment. See Note 7. VI(g)……………………………….. Technical data and defense X X X services for gas turbine engine hot sections related to Category VI(f). See Note 8. VI(g)……………………………….. Software source code related to ………. X X Categories VI(a) or VI(c). See Note 4. VII…………………………………. Defense articles specific to ………. ………. X equipment specially designed or configured to be installed in a vehicle for military ground, marine, airborne, or space applications, capable of operating while in motion and of producing or maintaining temperatures below 103 K (-170 [deg]C). [[Page 72264]] VII…………………………………. Defense articles specific to ………. ………. X superconductive electrical equipment (rotating machinery and transformers) specially designed or configured to be installed in a vehicle for military ground, marine, airborne, or space applications and capable of operating while in motion. This, however, does not include direct current hybrid homopolar generators that have single-pole normal metal armatures which rotate in a magnetic field produced by superconducting windings, provided those windings are the only superconducting component in the generator. VII…………………………………. Armored all wheel drive ………. ………. X vehicles, other than vehicles specifically designed or modified for military use, fitted with, or designed or modified to be fitted with, a plough or flail for the purpose of land mine clearance. VII(e)………………………………. Amphibious vehicles………… ………. ………. X VII(f)………………………………. Technical data and defense X X X services for gas turbine engine hot sections. See Note 8. VIII………………………………… Defense articles specific to ………. ………. X equipment specially designed or configured to be installed in a vehicle for military ground, marine, airborne, or space applications, capable of operating while in motion and of producing or maintaining temperatures below 103 K (-170 [deg]C). VIII………………………………… Defense articles specific to ………. ………. X superconductive electrical equipment (rotating machinery and transformers) specially designed or configured to be installed in a vehicle for military ground, marine, airborne, or space applications and capable of operating while in motion. This, however, does not include direct current hybrid homopolar generators that have single-pole normal metal armatures which rotate in a magnetic field produced by superconducting windings, provided those windings are the only superconducting component in the generator. VIII(a)……………………………… All Category VIII(a) items….. X ………. ………. VIII(b)……………………………… Defense articles and services ………. X X specific to gas turbine engine hot section components and digital engine controls. See Note 8. VIII(f)……………………………… Developmental aircraft, engines X ………. ………. and components identified in Category VIII(f). VIII(g)……………………………… Ground Effect Machines (GEMS).. ………. ………. X VIII(i)……………………………… Technical data and defense X X X services for gas turbine engine hot sections related to Category VIII(b). See Note 8. VIII(i)……………………………… Manufacturing know-how related X X X to Categories VIII(a), VIII(b), or VIII(e) and their specially designed components. See Note 5. VIII(i)……………………………… Software source code related to ………. X X Categories VIII(a) or VIII(e). See Note 4. IX………………………………….. Training or simulation ………. ………. X equipment for MANPADS. See Note 6. IX(e)……………………………….. Software source code related to ………. X X Categories IX(a) or IX(b). See Note 4. IX(e)……………………………….. Software that is both ………. ………. X specifically designed or modified for military use and specifically designed or modified for modeling or simulating military operational scenarios. X(e)………………………………… Manufacturing know-how related X X X to Categories X(a)(1) or X(a)(2) and their specially designed components. See Note 5. XI(a)……………………………….. Defense articles and services ………. X X specific to countermeasures and counter-countermeasures See Note 9. XI………………………………….. Defense articles and services ………. X X specific to naval technology and systems relating to acoustic spectrum control and awareness. See Note 10. XI(b) XI(c) XI(d)…………………….. Defense articles and services ………. X X specific to communications security (e.g., COMSEC and TEMPEST). XI(d)……………………………….. Software source code related to ………. X X Category XI(a). See Note 4. XI(d)……………………………….. Manufacturing know-how related X X X to Categories XI(a)(3) or XI(a)(4) and their specially designed components. See Note 5. XII…………………………………. Defense articles and services ………. X X specific to countermeasures and counter-countermeasures. See Note 9. XII(c)………………………………. Defense articles and services X ………. ………. specific to XII(c) articles, except any 1st- and 2nd- generation image intensification tubes and 1st- and 2nd-generation image intensification night sighting equipment. End items in XII(c) and related technical data limited to basic operations, maintenance, and training information as authorized under the exemption in Sec. 125.4(b)(5) of this subchapter may be exported directly to a Canadian Government entity. XII(c)………………………………. Technical data or defense X X X services for night vision equipment beyond basic operations, maintenance, and training data. However, the AS and UK Treaty exemptions apply when such export is pursuant to a written solicitation or contract issued or awarded by the U.S. Department of Defense for an end use identified in subsections (e)(1), (2), or (4) of Sec. 126.16 or Sec. 126.17 of this subchapter and is consistent with other exclusions of this supplement. XII(f)………………………………. Manufacturing know-how related X X X to Category XII(d) and their specially designed components. See Note 5. XII(f)………………………………. Software source code related to ………. X X Categories XII(a), XII(b), XII(c), or XII(d). See Note 4. XIII(b)……………………………… Defense articles and services ………. X X specific to Military Information Security Assurance Systems. [[Page 72265]] XIII(c)……………………………… Defense articles and services ………. ………. X specific to armored plate manufactured to comply with a military standard or specification or suitable for military use. See Note 11. XIII(d)……………………………… Carbon/carbon billets and ………. ………. X performs which are reinforced in three or more dimensional planes, specifically designed, developed, modified, configured or adapted for defense articles. XIII(f)……………………………… Structural materials……….. ………. ………. X XIII(g)……………………………… Defense articles and services ………. ………. X related to concealment and deception equipment and materials. XIII(h)……………………………… Energy conversion devices other ………. ………. X than fuel cells. XIII(i)……………………………… Metal embrittling agents……. ………. ………. X XIII(j)……………………………… Defense articles and services ………. X X related to hardware associated with the measurement or modification of system signatures for detection of defense articles as described in Note 2. XIII(k)……………………………… Defense articles and services ………. X X related to tooling and equipment specifically designed or modified for the production of defense articles identified in Category XIII(b). XIII(l)……………………………… Software source code related to ………. X X Category XIII(a). See Note 4. XIV…………………………………. Defense articles and services ………. X X related to toxicological agents, including chemical agents, biological agents, and associated equipment. XIV(a) XIV(b) XIV(d) XIV(e) XIV(f)……… Chemical agents listed in X ………. ………. Category XIV(a), (d) and (e), biological agents and biologically derived substances in Category XIV(b), and equipment listed in Category XIV(f) for dissemination of the chemical agents and biological agents listed in Category XIV(a), (b), (d), and (e). XV(a)……………………………….. Defense articles and services X X X specific to spacecraft/ satellites. However, the Canadian exemption may be used for commercial communications satellites that have no other type of payload. XV(b)……………………………….. Defense articles and services ………. X X specific to ground control stations for spacecraft telemetry, tracking, and control. XV(c)……………………………….. Defense articles and services ………. X X specific to GPS/PPS security modules. XV(c)……………………………….. Defense articles controlled in X ………. ………. XV(c) except end items for end use by the Federal Government of Canada exported directly or indirectly through a Canadian- registered person. XV(d)……………………………….. Defense articles and services X X X specific to radiation-hardened microelectronic circuits. XV(e)……………………………….. Anti-jam systems with the X ………. ………. ability to respond to incoming interference by adaptively reducing antenna gain (nulling) in the direction of the interference. XV(e)……………………………….. Antennas having any of the following: (a) Aperture (overall dimension of the radiating portions of the antenna) greater than 30 feet; (b) All sidelobes less than or equal to -35 dB relative to the peak of the main beam; or (c) Designed, modified, or X ………. ………. configured to provide coverage area on the surface of the earth less than 200 nautical miles in diameter, where “coverage area” is defined as that area on the surface of the earth that is illuminated by the main beam width of the antenna (which is the angular distance between half power points of the beam). XV(e)……………………………….. Optical intersatellite data X ………. ………. links (cross links) and optical ground satellite terminals. XV(e)……………………………….. Spaceborne regenerative X ………. ………. baseband processing (direct up and down conversion to and from baseband) equipment. XV(e)……………………………….. Propulsion systems which permit X ………. ………. acceleration of the satellite on-orbit (i.e., after mission orbit injection) at rates greater than 0.1 g. XV(e)……………………………….. Attitude control and X ………. ………. determination systems designed to provide spacecraft pointing determination and control or payload pointing system control better than 0.02 degrees per axis. XV(e)……………………………….. All specifically designed or X ………. ………. modified systems, components, parts, accessories, attachments, and associated equipment for all Category XV(a) items, except when specifically designed or modified for use in commercial communications satellites. XV(e)……………………………….. Defense articles and services ………. X X specific to spacecraft and ground control station systems (only for telemetry, tracking and control as controlled in XV(b)), subsystems, components, parts, accessories, attachments, and associated equipment. XV(f)……………………………….. Technical data and defense X X X services directly related to the other defense articles excluded from the exemptions for Category XV. XVI…………………………………. Defense articles and services X X X specific to design and testing of nuclear weapons. XVI(c)………………………………. Nuclear radiation measuring X ………. ………. devices manufactured to military specifications. XVI(e)………………………………. Software source code related to ………. X X Category XVI(c). See Note 4. XVII………………………………… Classified articles and defense X X X services not elsewhere enumerated. See Note 1. XVIII……………………………….. Defense articles and services ………. X X specific to directed energy weapon systems. XX………………………………….. Defense articles and services X X X related to submersible vessels, oceanographic, and associated equipment. XXI…………………………………. Miscellaneous defense articles X X X and services. —————————————————————————————————————- [[Page 72266]] Note 1: Classified defense articles and services are not eligible for export under the Canadian exemptions. U.S. origin defense articles and services controlled in Category XVII are not eligible for export under the UK Treaty exemption. U.S. origin classified defense articles and services are not eligible for export under either the UK or AS Treaty exemptions except when being released pursuant to a U.S. Department of Defense written request, directive or contract that provides for the export of the defense article or service. Note 2: The phrase “any part of the spectrum” includes radio frequency (RF), infrared (IR), electro-optical, visual, ultraviolet (UV), acoustic, and magnetic. Defense articles related to reduced observables or counter reduced observables are defined as: a. Signature reduction (radio frequency (RF), infrared (IR), Electro-Optical, visual, ultraviolet (UV), acoustic, magnetic, RF emissions) of defense platforms, including systems, subsystems, components, materials, (including dual-purpose materials used for Electromagnetic Interference (EM) reduction) technologies, and signature prediction, test and measurement equipment and software and material transmissivity/reflectivity prediction codes and optimization software. b. Electronically scanned array radar, high power radars, radar processing algorithms, periscope-mounted radar systems (PATRIOT), LADAR, multistatic and IR focal plane array-based sensors, to include systems, subsystems, components, materials, and technologies. Note 3: Defense Articles related to sensor fusion beyond that required for display or identification correlation is defined as techniques designed to automatically combine information from two or more sensors/sources for the purpose of target identification, tracking, designation, or passing of data in support of surveillance or weapons engagement. Sensor fusion involves sensors such as acoustic, infrared, electro optical, frequency, etc. Display or identification correlation refers to the combination of target detections from multiple sources for assignment of common target track designation. Note 4: Software source code beyond that source code required for basic operation, maintenance, and training for programs, systems, and/or subsystems is not eligible for use of the UK or AS Treaty Exemptions, unless such export is pursuant to a written solicitation or contract issued or awarded by the U.S. Department of Defense for an end use identified in subsections (e)(1), (2), or (4) of Sec. 126.16 or Sec. 126.17 of this subchapter and is consistent with other exclusions of this supplement. Note 5: Manufacturing know-how, as defined in Sec. 125.4(c)(6) of this subchapter, is not eligible for use of the UK or AS Treaty Exemptions, unless such export is pursuant to a written solicitation or contract issued or awarded by the U.S. Department of Defense for an end use identified in subsections (e)(1), (2), or (4) of Sec. 126.16 or Sec. 126.17 of this subchapter and is consistent with other exclusions of this supplement. Note 6: Defense Articles specific to Man Portable Air Defense Systems (MANPADS) includes missiles which can be used without modification in other applications. It also includes production equipment specifically designed or modified for MANPAD systems, as well as training equipment specifically designed or modified for MANPAD systems. Note 7: Naval nuclear propulsion plants includes all of USML Category VI(e). Naval nuclear propulsion information is technical data that concerns the design, arrangement, development, manufacture, testing, operation, administration, training, maintenance, and repair of the propulsion plants of naval nuclear-powered ships and prototypes, including the associated shipboard and shore-based nuclear support facilities. Examples of defense articles covered by this exclusion include nuclear propulsion plants and nuclear submarine technologies or systems; nuclear powered vessels (see USML Categories VI and XX). Note 8: Examples of gas turbine engine hot section exempted defense article components and technology are combustion chambers/liners; high pressure turbine blades, vanes, disks and related cooled structure; cooled low pressure turbine blades, vanes, disks and related cooled structure; advanced cooled augmenters; and advanced cooled nozzles. Examples of gas turbine engine hot section developmental technologies are Integrated High Performance Turbine Engine Technology (IHPTET), Versatile, Affordable Advanced Turbine Engine (VAATE), Ultra- Efficient Engine Technology (UEET). Note 9: Examples of countermeasures and counter-countermeasures related to defense articles not exportable under the AS or UK Treaty exemptions are: a. IR countermeasures; b. Classified techniques and capabilities; c. Exports for precision radio frequency location that directly or indirectly supports fire control and is used for situation awareness, target identification, target acquisition, and weapons targeting and Radio Direction Finding (RDF) capabilities. Precision RF location is defined as angle of arrival accuracy of less than five degrees (RMS) and RF emitter location of less than ten percent range error; d. Providing the capability to reprogram; and e. Acoustics (including underwater), active and passive countermeasures, and counter-countermeasures Note 10: Examples of defense articles covered by this exclusion include underwater acoustic vector sensors; acoustic reduction; off-board, underwater, active and passive sensing, propeller/propulsor technologies; fixed mobile/floating/powered detection systems which include in-buoy signal processing for target detection and classification; autonomous underwater vehicles capable of long endurance in ocean environments (manned submarines excluded); automated control algorithms embedded in on-board autonomous platforms which enable (a) group behaviors for target detection and classification, (b) adaptation to the environment or tactical situation for enhancing target detection and classification; “intelligent autonomy” algorithms which define the status, group (greater than 2) behaviors, and responses to detection stimuli by autonomous, underwater vehicles; and low frequency, broad-band “acoustic color,” active acoustic “fingerprint” sensing for the purpose of long range, single pass identification of ocean bottom objects, buried or otherwise. (Controlled under Category XI(a), (1) and (2) and in (b), (c), and (d)). Note 11: The defense articles include constructions of metallic or non-metallic materials or combinations thereof specially designed to provide protection for military systems. The phrase “suitable for military use” applies to any articles or materials which have been tested to level IIIA or above IAW NIJ standard 0108.01 or comparable national standard. This exclusion does not include military helmets, body armor, or other protective garments which may be exported IAW the terms of the AS or UK Treaties. —————————————————————————————————————- * An “X” in the chart indicates that the item is excluded from use under the exemption referenced in the top of the column. An item excluded in any one row is excluded regardless of whether other rows may contain a description that would include the item. PART 127–VIOLATIONS AND PENALTIES 28. The authority citation for part 127 is revised to read to as follows: Authority: Secs. 2, 38, and 42, Public Law 90-629, 90 Stat. 744 (22 U.S.C. 2752, 2778, 2791); E.O. 11958, 42 FR 4311; 3 CFR, 1977 Comp., p. 79; 22 U.S.C. 401; 22 U.S.C. 2651a; 22 U.S.C. 2779a; 22 U.S.C. 2780; Pub. L. 111-266. 29. Section 127.1 is revised to read as follows: Sec. 127.1 Violations. (a) Without first obtaining the required license or other written [[Page 72267]] approval from the Directorate of Defense Trade Controls, it is unlawful: (1) To export or attempt to export from the United States any defense article or technical data or to furnish or attempt to furnish any defense service for which a license or written approval is required by this subchapter; (2) To reexport or retransfer or attempt to reexport or retransfer any defense article, technical data, or defense service from one foreign end-user, end-use, or destination to another foreign end-user, end-use, or destination for which a license or written approval is required by this subchapter, including, as specified in Sec. 126.16(h) and Sec. 126.17(h) of this subchapter, any defense article, technical data, or defense service that was exported from the United States without a license pursuant to any exemption under this subchapter; (3) To import or attempt to import any defense article whenever a license is required by this subchapter; (4) To conspire to export, import, reexport, retransfer, furnish or cause to be exported, imported, reexported, retransferred or furnished, any defense article, technical data, or defense service for which a license or written approval is required by this subchapter. (b) It is unlawful: (1) To violate any of the terms or conditions of a license or approval granted pursuant to this subchapter, any exemption contained in this subchapter, or any rule or regulation contained in this subchapter. (2) To engage in the business of brokering activities for which registration and a license or written approval is required by this subchapter without first registering or obtaining the required license or written approval from the Directorate of Defense Trade Controls. For the purposes of this subchapter, engaging in the business of brokering activities requires only one occasion of engaging in an activity as reflected in Sec. 129.2(b) of this subchapter. (3) To engage in the United States in the business of either manufacturing or exporting defense articles or furnishing defense services without complying with the registration requirements. For the purposes of this subchapter, engaging in the business of manufacturing or exporting defense articles or furnishing defense services requires only one occasion of manufacturing or exporting a defense article or furnishing a defense service. (c) Any person who is granted a license or other approval or who acts pursuant to an exemption under this subchapter is responsible for the acts of employees, agents, and all authorized persons to whom possession of the defense article or technical data has been entrusted regarding the operation, use, possession, transportation, and handling of such defense article or technical data abroad. All persons abroad subject to U.S. jurisdiction who obtain temporary or permanent custody of a defense article exported from the United States or produced under an agreement described in part 124 of this subchapter, and irrespective of the number of intermediate transfers, are bound by the regulations of this subchapter in the same manner and to the same extent as the original owner or transferor. (d) A person with knowledge that another person is then ineligible pursuant to Sec. Sec. 120.1(c) or 126.7 of this subchapter may not, directly or indirectly, in any manner or capacity, without prior disclosure of the facts to, and written authorization from, the Directorate of Defense Trade Controls: (1) Apply for, obtain, or use any export control document as defined in Sec. 127.2(b) of this subchapter for such ineligible person; or (2) Order, buy, receive, use, sell, deliver, store, dispose of, forward, transport, finance, or otherwise service or participate in any transaction which may involve any defense article or the furnishing of any defense service for which a license or approval is required by this subchapter or an exemption is available under this subchapter for export, where such ineligible person may obtain any benefit therefrom or have any direct or indirect interest therein. (e) No person may knowingly or willfully cause, or aid, abet, counsel, demand, induce, procure, or permit the commission of, any act prohibited by, or the omission of any act required by, 22 U.S.C. 2778 and 2779, or any regulation, license, approval, or order issued thereunder. 30. Section 127.2 is amended by revising paragraphs (a), (b) introductory text, (b)(1), (b)(2), and adding (b)(14), to read as follows: Sec. 127.2 Misrepresentation and omission of facts. (a) It is unlawful to use or attempt to use any export or temporary import control document containing a false statement or misrepresenting or omitting a material fact for the purpose of exporting, transferring, reexporting, retransferring, obtaining, or furnishing any defense article, technical data, or defense service. Any false statement, misrepresentation, or omission of material fact in an export or temporary import control document will be considered as made in a matter within the jurisdiction of a department or agency of the United States for the purposes of 18 U.S.C. 1001, 22 U.S.C. 2778, and 22 U.S.C. 2779. (b) For the purpose of this subchapter, export or temporary import control documents include the following: (1) An application for a permanent export, reexport, retransfer, or a temporary import license and supporting documents. (2) Shipper’s Export Declaration or an Electronic Export Information filing. * * * * * (14) Any other shipping document that has information related to the export of the defense article or defense service. 31. Section 127.3 is revised to read as follows: Sec. 127.3 Penalties for violations. Any person who willfully: (a) Violates any provision of Sec. 38 or Sec. 39 of the Arms Export Control Act (22 U.S.C. 2778 and 2779) or any rule or regulation issued under either Sec. 38 or Sec. 39 of the Act, or any undertaking specifically required by part 124 of this subchapter; or (b) In a registration, license application, or report required by Sec. 38 or Sec. 39 of the Arms Export Control Act (22 U.S.C. 2778 and 2779) or by any rule or regulation issued under either section, makes any untrue statement of a material fact or omits a material fact required to be stated therein or necessary to make the statements therein not misleading, shall upon conviction be subject to a fine or imprisonment, or both, as prescribed by 22 U.S.C. 2778(c). 32. Section 127.4 is amended by revising paragraphs (a) and (c), and adding paragraph (d), to read as follows: Sec. 127.4 Authority of U.S. Immigration and Customs Enforcement and U.S. Customs and Border Protection officers. (a) U.S. Immigration and Customs Enforcement and U.S. Customs and Border Protection officers may take appropriate action to ensure observance of this subchapter as to the export or the attempted export of any defense article or technical data, including the inspection of loading or unloading of any vessel, vehicle, or aircraft. This applies whether the export is authorized by license or by written approval issued under this subchapter or by exemption. * * * * * (c) Upon the presentation to a U.S. Customs and Border Protection Officer of a license or written approval, or claim of an exemption, authorizing the export [[Page 72268]] of any defense article, the customs officer may require the production of other relevant documents and information relating to the proposed export. This includes an invoice, order, packing list, shipping document, correspondence, instructions, and the documents otherwise required by the U.S. Customs and Border Protection or U.S. Immigration and Customs Enforcement. (d) If an exemption under this subchapter is used or claimed to export, transfer, reexport or retransfer, furnish, or obtain a defense article, technical data, or defense service, law enforcement officers may rely upon the authorities noted above, additional authority identified in the language of the exemption, and any other lawful means to investigate such a matter. 33. Section 127.7 is amended by revising paragraph (a) to read as follows: Sec. 127.7 Debarment. (a) Debarment. In implementing Sec. 38 of the Arms Export Control Act, the Assistant Secretary of State for Political-Military Affairs may prohibit any person from participating directly or indirectly in the export, reexport and retransfer of defense articles, including technical data, or in the furnishing of defense services for any of the reasons listed below and publish notice of such action in the Federal Register. Any such prohibition is referred to as a debarment for purposes of this subchapter. The Assistant Secretary of State for Political-Military Affairs shall determine the appropriate period of time for debarment, which shall generally be for a period of three years. However, reinstatement is not automatic and in all cases the debarred person must submit a request for reinstatement and be approved for reinstatement before engaging in any export or brokering activities subject to the Arms Export Control Act or this subchapter. * * * * * 34. Section 127.10 is amended by revising paragraph (a) to read as follows: Sec. 127.10 Civil penalty. (a) The Assistant Secretary of State for Political-Military Affairs is authorized to impose a civil penalty in an amount not to exceed that authorized by 22 U.S.C. 2778, 2779a, and 2780 for each violation of 22 U.S.C. 2778, 2779a, and 2780, or any regulation, order, license, or written approval issued thereunder. This civil penalty may be either in addition to, or in lieu of, any other liability or penalty which may be imposed. * * * * * 35. Section 127.12 is amended by adding paragraph (b)(5), and revising paragraph (d), to read as follows: Sec. 127.12 Voluntary disclosures. * * * * * (b) * * * (5) Nothing in this section shall be interpreted to negate or lessen the affirmative duty pursuant to Sec. Sec. 126.1(e), 126.16(h)(5), and 126.17(h)(5) of this subchapter upon persons to inform the Directorate of Defense Trade Controls of the actual or proposed sale, export, transfer, reexport, or retransfer of a defense article, technical data, or defense service to any country referred to in Sec. 126.1 of this subchapter, any citizen of such country, or any person acting on its behalf. * * * * * (d) Documentation. The written disclosure should be accompanied by copies of substantiating documents. Where appropriate, the documentation should include, but not be limited to: (1) Licensing documents (e.g., license applications, export licenses, and end-user statements), exemption citation, or other authorization description, if any; (2) Shipping documents (e.g., Shipper’s Export Declarations; Electronic Export Information filing, including the Internal Transaction Number), air waybills, and bills of laden, invoices, and any other associated documents); (3) Any other relevant documents must be retained by the person making the disclosure until the Directorate of Defense Trade Controls requests them or until a final decision on the disclosed information has been made. * * * * * PART 129–REGISTRATION AND LICENSING OF BROKERS 36. The authority citation for part 129 continues to read as follows: Authority: Sec. 38, Pub. L. 104-164, 110 Stat. 1437, (22 U.S.C. 2778). 37. Section 129.6 is amended by revising paragraph (b)(2) to read as follows: Sec. 129.6 Requirements for License/Approval. * * * * * (b) * * * (2) Brokering activities that are arranged wholly within and destined exclusively for the North Atlantic Treaty Organization, any member country of that Organization, Australia, Israel, Japan, New Zealand, or the Republic of Korea, except in the case of the defense articles or defense services specified in Sec. 129.7(a) of this subchapter, for which prior approval is always required. 38. Section 129.7 is amended by revising paragraphs (a)(1)(vii) and (a)(2) to read as follows: Sec. 129.7 Prior Approval (License). (a) * * * (1) * * * (vii) Foreign defense articles or defense services (other than those that are arranged wholly within and destined exclusively for the North Atlantic Treaty Organization, any member country of that Organization, Australia, Israel, Japan, New Zealand, or the Republic of Korea (see Sec. Sec. 129.6(b)(2) and 129.7(a)). (2) Brokering activities involving defense articles or defense services covered by, or of a nature described by part 121, of this subchapter, in addition to those specified in Sec. 129.7(a), that are designated as significant military equipment under this subchapter, for or from any country not a member of the North Atlantic Treaty Organization, Australia, Israel, Japan, New Zealand, or the Republic of Korea whenever any of the following factors are present: * * * * * Dated: November 7, 2011. Ellen O. Tauscher, Under Secretary, Arms Control and International Security, Department of State. [FR Doc. 2011-29328 Filed 11-21-11; 8:45 am] BILLING CODE 4710-25-P
TOP SECRET – White House “WikiLeaks” Executive Order on Improving Security of Classified Networks

DOWNLOAD ORIGINAL DOCUMENT BELOW
By the authority vested in me as President by the Constitution and the laws of the United States of America and in order to ensure the responsible sharing and safeguarding of classified national security information (classified information) on computer networks, it is hereby ordered as follows:
Section 1. Policy. Our Nation’s security requires classified information to be shared immediately with authorized users around the world but also requires sophisticated and vigilant means to ensure it is shared securely. Computer networks have individual and common vulnerabilities that require coordinated decisions on risk management.
This order directs structural reforms to ensure responsible sharing and safeguarding of classified information on computer networks that shall be consistent with appropriate protections for privacy and civil liberties. Agencies bear the primary responsibility for meeting these twin goals. These structural reforms will ensure coordinated interagency development and reliable implementation of policies and minimum standards regarding information security, personnel security, and systems security; address both internal and external security threats and vulnerabilities; and provide policies and minimum standards for sharing classified information both within and outside the Federal Government. These policies and minimum standards will address all agencies that operate or access classified computer networks, all users of classified computer networks (including contractors and others who operate or access classified computer networks controlled by the Federal Government), and all classified information on those networks.
Sec. 2. General Responsibilities of Agencies.
Sec. 2.1. The heads of agencies that operate or access classified computer networks shall have responsibility for appropriately sharing and safeguarding classified information on computer networks. As part of this responsibility, they shall:
(a) designate a senior official to be charged with overseeing classified information sharing and safeguarding efforts for the agency;
(b) implement an insider threat detection and prevention program consistent with guidance and standards developed by the Insider Threat Task Force established in section 6 of this order;
(c) perform self-assessments of compliance with policies and standards issued pursuant to sections 3.3, 5.2, and 6.3 of this order, as well as other applicable policies and standards, the results of which shall be reported annually to the Senior Information Sharing and Safeguarding Steering Committee established in section 3 of this order;
(d) provide information and access, as warranted and consistent with law and section 7(d) of this order, to enable independent assessments by the Executive Agent for Safeguarding Classified Information on Computer Networks and the Insider Threat Task Force of compliance with relevant established policies and standards; and
(e) detail or assign staff as appropriate and necessary to the Classified Information Sharing and Safeguarding Office and the Insider Threat Task Force on an ongoing basis.
Sec. 3. Senior Information Sharing and Safeguarding Steering Committee.
Sec. 3.1. There is established a Senior Information Sharing and Safeguarding Steering Committee (Steering Committee) to exercise overall responsibility and ensure senior-level accountability for the coordinated interagency development and implementation of policies and standards regarding the sharing and safeguarding of classified information on computer networks.
Sec. 3.2. The Steering Committee shall be co-chaired by senior representatives of the Office of Management and Budget and the National Security Staff. Members of the committee shall be officers of the United States as designated by the heads of the Departments of State, Defense, Justice, Energy, and Homeland Security, the Office of the Director of National Intelligence, the Central Intelligence Agency, and the Information Security Oversight Office within the National Archives and Records Administration (ISOO), as well as such additional agencies as the co-chairs of the Steering Committee may designate.
Sec. 3.3. The responsibilities of the Steering Committee shall include:
(a) establishing Government-wide classified information sharing and safeguarding goals and annually reviewing executive branch successes and shortcomings in achieving those goals;
(b) preparing within 90 days of the date of this order and at least annually thereafter, a report for the President assessing the executive branch’s successes and shortcomings in sharing and safeguarding classified information on computer networks and discussing potential future vulnerabilities;
(c) developing program and budget recommendations to achieve Government-wide classified information sharing and safeguarding goals;
(d) coordinating the interagency development and implementation of priorities, policies, and standards for sharing and safeguarding classified information on computer networks;
(e) recommending overarching policies, when appropriate, for promulgation by the Office of Management and Budget or the ISOO;
(f) coordinating efforts by agencies, the Executive Agent, and the Task Force to assess compliance with established policies and standards and recommending corrective actions needed to ensure compliance;
(g) providing overall mission guidance for the Program Manager-Information Sharing Environment (PM-ISE) with respect to the functions to be performed by the Classified Information Sharing and Safeguarding Office established in section 4 of this order; and
(h) referring policy and compliance issues that cannot be resolved by the Steering Committee to the Deputies Committee of the National Security Council in accordance with Presidential Policy Directive/PPD-1 of February 13, 2009 (Organization of the National Security Council System).
Sec. 4. Classified Information Sharing and Safeguarding Office.
Sec. 4.1. There shall be established a Classified Information Sharing and Safeguarding Office (CISSO) within and subordinate to the office of the PM-ISE to provide expert, fulltime, sustained focus on responsible sharing and safeguarding of classified information on computer networks. Staff of the CISSO shall include detailees, as needed and appropriate, from agencies represented on the Steering Committee.
Sec. 4.2. The responsibilities of CISSO shall include:
(a) providing staff support for the Steering Committee;
(b) advising the Executive Agent for Safeguarding Classified Information on Computer Networks and the Insider Threat Task Force on the development of an effective program to monitor compliance with established policies and standards needed to achieve classified information sharing and safeguarding goals; and
(c) consulting with the Departments of State, Defense, and Homeland Security, the ISOO, the Office of the Director of National Intelligence, and others, as appropriate, to ensure consistency with policies and standards under Executive Order 13526 of December 29, 2009, Executive Order 12829 of January 6, 1993, as amended, Executive Order 13549 of August 18, 2010, and Executive Order 13556 of November 4, 2010.
Sec. 5. Executive Agent for Safeguarding Classified Information on Computer Networks.
Sec. 5.1. The Secretary of Defense and the Director, National Security Agency, shall jointly act as the Executive Agent for Safeguarding Classified Information on Computer Networks (the “Executive Agent”), exercising the existing authorities of the Executive Agent and National Manager for national security systems, respectively, under National Security Directive/NSD-42 of July 5, 1990, as supplemented by and subject to this order.
Sec. 5.2. The Executive Agent’s responsibilities, in addition to those specified by NSD-42, shall include the following:
(a) developing effective technical safeguarding policies and standards in coordination with the Committee on National Security Systems (CNSS), as re-designated by Executive Orders 13286 of February 28, 2003, and 13231 of October 16, 2001, that address the safeguarding of classified information within national security systems, as well as the safeguarding of national security systems themselves;
(b) referring to the Steering Committee for resolution any unresolved issues delaying the Executive Agent’s timely development and issuance of technical policies and standards;
(c) reporting at least annually to the Steering Committee on the work of CNSS, including recommendations for any changes needed to improve the timeliness and effectiveness of that work; and
(d) conducting independent assessments of agency compliance with established safeguarding policies and standards, and reporting the results of such assessments to the Steering Committee.
Sec. 6. Insider Threat Task Force.
Sec. 6.1. There is established an interagency Insider Threat Task Force that shall develop a Government-wide program (insider threat program) for deterring, detecting, and mitigating insider threats, including the safeguarding of classified information from exploitation, compromise, or other unauthorized disclosure, taking into account risk levels, as well as the distinct needs, missions, and systems of individual agencies. This program shall include development of policies, objectives, and priorities for establishing and integrating security, counterintelligence, user audits and monitoring, and other safeguarding capabilities and practices within agencies.
Sec. 6.2. The Task Force shall be co-chaired by the Attorney General and the Director of National Intelligence, or their designees. Membership on the Task Force shall be composed of officers of the United States from, and designated by the heads of, the Departments of State, Defense, Justice, Energy, and Homeland Security, the Office of the Director of National Intelligence, the Central Intelligence Agency, and the ISOO, as well as such additional agencies as the co-chairs of the Task Force may designate. It shall be staffed by personnel from the Federal Bureau of Investigation and the Office of the National Counterintelligence Executive (ONCIX), and other agencies, as determined by the co-chairs for their respective agencies and to the extent permitted by law. Such personnel must be officers or full-time or permanent part-time employees of the United States. To the extent permitted by law, ONCIX shall provide an appropriate work site and administrative support for the Task Force.
Sec. 6.3. The Task Force’s responsibilities shall include the following:
(a) developing, in coordination with the Executive Agent, a Government-wide policy for the deterrence, detection, and mitigation of insider threats, which shall be submitted to the Steering Committee for appropriate review;
(b) in coordination with appropriate agencies, developing minimum standards and guidance for implementation of the insider threat program’s Government-wide policy and, within 1 year of the date of this order, issuing those minimum standards and guidance, which shall be binding on the executive branch;
(c) if sufficient appropriations or authorizations are obtained, continuing in coordination with appropriate agencies after 1 year from the date of this order to add to or modify those minimum standards and guidance, as appropriate;
(d) if sufficient appropriations or authorizations are not obtained, recommending for promulgation by the Office of Management and Budget or the ISOO any additional or modified minimum standards and guidance developed more than 1 year after the date of this order;
(e) referring to the Steering Committee for resolution any unresolved issues delaying the timely development and issuance of minimum standards;
(f) conducting, in accordance with procedures to be developed by the Task Force, independent assessments of the adequacy of agency programs to implement established policies and minimum standards, and reporting the results of such assessments to the Steering Committee;
(g) providing assistance to agencies, as requested, including through the dissemination of best practices; and
(h) providing analysis of new and continuing insider threat challenges facing the United States Government.
Sec. 7. General Provisions. (a) For the purposes of this order, the word “agencies” shall have the meaning set forth in section 6.1(b) of Executive Order 13526 of December 29, 2009.
(b) Nothing in this order shall be construed to change the requirements of Executive Orders 12333 of December 4, 1981, 12829 of January 6, 1993, 12968 of August 2, 1995, 13388 of October 25, 2005, 13467 of June 30, 2008, 13526 of December 29, 2009, 13549 of August 18, 2010, and their successor orders and directives.
(c) Nothing in this order shall be construed to supersede or change the authorities of the Secretary of Energy or the Nuclear Regulatory Commission under the Atomic Energy Act of 1954, as amended; the Secretary of Defense under Executive Order 12829, as amended; the Secretary of Homeland Security under Executive Order 13549; the Secretary of State under title 22, United States Code, and the Omnibus Diplomatic Security and Antiterrorism Act of 1986; the Director of ISOO under Executive Orders 13526 and 12829, as amended; the PM-ISE under Executive Order 13388 or the Intelligence Reform and Terrorism Prevention Act of 2004, as amended; the Director, Central Intelligence Agency under NSD-42 and Executive Order 13286, as amended; the National Counterintelligence Executive, under the Counterintelligence Enhancement Act of 2002; or the Director of National Intelligence under the National Security Act of 1947, as amended, the Intelligence Reform and Terrorism Prevention Act of 2004, as amended, NSD-42, and Executive Orders 12333, as amended, 12968, as amended, 13286, as amended, 13467, and 13526.
(d) Nothing in this order shall authorize the Steering Committee, CISSO, CNSS, or the Task Force to examine the facilities or systems of other agencies, without advance consultation with the head of such agency, nor to collect information for any purpose not provided herein.
(e) The entities created and the activities directed by this order shall not seek to deter, detect, or mitigate disclosures of information by Government employees or contractors that are lawful under and protected by the Intelligence Community Whistleblower Protection Act of 1998, Whistleblower Protection Act of 1989, Inspector General Act of 1978, or similar statutes, regulations, or policies.
(f) With respect to the Intelligence Community, the Director of National Intelligence, after consultation with the heads of affected agencies, may issue such policy directives and guidance as the Director of National Intelligence deems necessary to implement this order.
(g) Nothing in this order shall be construed to impair or otherwise affect:
(1) the authority granted by law to an agency, or the head thereof; or
(2) the functions of the Director of the Office of Management and Budget relating to budgetary, administrative, or legislative proposals
(h) This order shall be implemented consistent with applicable law and appropriate protections for privacy and civil liberties, and subject to the availability of appropriations.
(i) This order is not intended to, and does not, create any right or benefit, substantive or procedural, enforceable at law or in equity by any party against the United States, its departments, agencies, or entities, its officers, employees, or agents, or any other person.
BARACK OBAMA
THE WHITE HOUSE,
October 7, 2011.
TOP-SECRET: Conspiracy to Murder Abroad, and Providing Material Support to al Qaeda
WASHINGTON—The Justice Department announced that Najibullah Zazi pleaded guilty today in the Eastern District of New York to a three-count superseding information charging him with conspiracy to use weapons of mass destruction (explosive bombs) against persons or property in the United States, conspiracy to commit murder in a foreign country, and providing material support to al Qaeda. Among other things, Zazi admitted that he brought TATP [Triacetone Triperoxide] explosives to New York on Sept. 10, 2009, as part of plan to attack the New York subway system.
Zazi, 25, a resident of Aurora, Colo., and legal permanent resident of the United States from Afghanistan, entered his guilty plea today before Chief U.S. District Judge Raymond J. Dearie. Zazi faces a maximum statutory sentence of life in prison for the first two counts of the superseding information and an additional 15 years in prison for the third count of the superseding information.
FBI agents in Colorado first arrested Zazi on Sept. 19, 2009, on a criminal complaint charging him with knowingly and willfully making false statements to the FBI in a matter involving international and domestic terrorism. On Sept. 23, 2009, a federal grand jury in the Eastern District of New York returned a one-count indictment alleging that Zazi knowingly and intentionally conspired with others to use one or more weapons of mass destruction, specifically explosive bombs and other similar explosive devices, against persons or property within the United States.
As Zazi admitted during today’s guilty plea allocution and as reflected in previous government filings, he and others agreed to travel to Afghanistan to join the Taliban and fight against United States and allied forces. In furtherance of their plans, they flew from Newark Liberty International Airport in Newark, N.J., to Peshawar, Pakistan at the end of August 2008. Although Zazi and others initially intended to fight on behalf of the Taliban, they were recruited by al-Qaeda shortly after arriving in Peshawar. Al Qaeda personnel transported Zazi and others to the Waziristan region of Pakistan and trained them on several different kinds of weapons. During the training, al Qaeda leaders asked Zazi and others to return to the United States and conduct suicide operations. They agreed.
Zazi later received additional training from al Qaeda on constructing the explosives for the planned attacks in the United States. Zazi had discussions with al Qaeda leaders about target locations, including subway trains in New York City. Zazi took detailed notes during the training, and later e-mailed a summary of the notes to himself so that he could access them when he returned to the United States. Zazi also provided money and computers to al Qaeda before he left Pakistan.
Zazi returned to the United States in January 2009 and moved to Denver. Beginning in June 2009, he began reviewing the bomb-making notes from his training and conducting research on where to buy the ingredients for the explosives. Zazi then traveled to New York and met with others to discuss the plan, including the timing of the attack and where to make the explosives.
Zazi returned to Denver and used the bomb-making notes to construct the explosives for the detonator components of the bombs. As set forth in the government’s detention memorandum filed earlier in the case, in July and August 2009, Zazi purchased large quantities of components necessary to produce TATP and twice checked into a hotel room near Denver, where bomb making residue was later found.
On Sept. 8, 2009, Zazi rented a car and drove from Denver to New York, taking with him the explosives and other materials necessary to build the bombs. Zazi arrived in New York City on Thursday, Sept.10, 2009. Zazi and others intended to obtain and assemble the remaining components of the bombs over the weekend and conduct the attack on Manhattan subway lines on Sept. 14, Sept. 15, or Sept. 16, 2009. However, shortly after arriving in New York, Zazi realized that law enforcement was investigating his activities. Zazi and others discarded the explosives and other bomb-making materials, and Zazi traveled back to Denver. He was arrested on Sept. 19, 2009.
“This was one of the most serious terrorist threats to our nation since September 11, 2001, and were it not for the combined efforts of the law enforcement and intelligence communities, it could have been devastating,” said Attorney General Eric Holder. “This attempted attack on our homeland was real, it was in motion, and it would have been deadly. We were able to thwart this plot because of careful analysis by our intelligence agents and prompt actions by law enforcement. They deserve our thanks and praise.”
“Today’s plea is an important development in this complex and ongoing criminal investigation and intelligence operation that in many ways illustrates the evolving nature of the terrorist threat today,” said FBI Deputy Director John S. Pistole. “The plea is the result of the dedication and hard work by agents and officers assigned to Joint Terrorism Task Forces in both New York and Colorado working closely with federal prosecutors.”
This case is being prosecuted by the U.S. Attorney’s Office for the Eastern District of New York, with assistance from the U.S. Attorney’s Office for the District of Colorado and the Counterterrorism Section of the Justice Department’s National Security Division. The investigation is being conducted by the New York and Denver FBI Joint Terrorism Task Forces, which combined have investigators from more than fifty federal, state and local law enforcement agencies.
TOPSECRET UNVEILED – EU Study on Crowd Control Technologies

This study grew out of the 1997 STOA report, ‘An Appraisal of the Technologies of Political Control’ and takes that work further. Its focus is two fold:(i) to examine the bio-medical effects and the social & political impacts of currently available crowd control weapons in Europe; (ii) to analyse world wide trends and developments including the implications for Europe of a second generation of so called “non-lethal” weapons. Seven key areas are covered by the report’s project: (a) a review of available crowd control technologies; (b) relevant legislation at national and EU levels; (c) the relative efficiency of crowd control technologies; (d) their physical and mental effects on individuals; (e) the actual and potential abuse of crowd control technologies; (f) an assessment of future technologies and their effects; and finally (g) an appraisal of less damaging alternatives such as CCTV.The report presents a detailed worldwide survey of crowd control weapons and the companies which manufacture supply or distribute them. It was found that at least 110 countries worldwide deploy riot control weapons, including chemical irritants, kinetic energy weapons, water cannon and electro-shock devices. Whilst presented as humane alternatives to the use of lethal force, the study found examples in 47 countries of these so called “non-lethal” crowd control weapons being used in conjunction with lethal force rather than as a substitute for it, leading directly to injury and fatalities.
Within Europe, the study found that the biomedical research necessary to justify the deployment of certain crowd control technologies was either absent, lacking or incomplete and that there was inadequate quality control at production level to ensure that adverse or even lethal effects were avoided. Evidence is also presented of the misuse of these technologies and the breach of deployment guidelines which can make their effects either severely damaging or lethal. Member States currently have inadequate export controls to prevent the transfer, brokerage or licensed production of crowd control weapons to human rights violators, including weapons such as electroshock devices which have been directly implicated in torture. The report warns against adopting ever more powerful crowd control weapons as ‘technical fixes’. It suggests their use should be limited and provides a number of options to make the adoption and use of these weapons more democratically accountable. These include licensing and independent evaluation of the biomedical impacts of such weapons via a formal process
of ‘Social Impact Assessment’; legal limits on weapons which are exceptionally hazardous or lethal; legally binding rules of engagement; better post incident inquiry procedures and more effective, accountable and transparent export controls.…
DOWNLOAD ORIGINAL DOCUMENT HERE
TOP-SECRET-(U//FOUO) Asymmetric Warfare Group Tactical Information Superiority Report

This document facilitates discussion, training, and implementation of effective information superiority methods at the Battalion and Brigade level. This paper discusses the Center of Gravity analysis model for identifying threat networks, Critical Capabilities, and Critical Vulnerabilities; use of the methodology to determine the threat vulnerabilities; and as a basis for understanding how to achieve Information Superiority.
The battalion commander instantly knew from looking at the map, with all of the red significant activities plotted on the overlay, that renewed operations in the valley would be rough. Almost every route into and out of the area had seen recent Improvised Explosive Device (IED) activity. Worse, it seemed that many of the villages in the valley were supportive of insurgent activity. The insurgents had recently stepped up their propaganda campaign in the area, as well, intimidating villagers, kidnapping elders, assassinating key figures, leaving behind strong warnings against cooperating with Coalition Forces, while also reinforcing their own message: the insurgents would prevail over the foreign forces because they were from the region, the insurgents would take care of the people that supported their activities, and they would continue to be in the area long after the Coalition Forces left.
The commander planned a deliberate clearing operation to regain control of the major routes in the area, deny insurgents traditional safe havens, and bolster Host Nation Security Forces and Government officials, but he also knew t hat if he entered the valley using too much force that he might further alienate the locals. The commander could not stay in the valley, holding the terrain against insurgent reinfiltration indefinitely-he would be forced to withdraw and plan for other operations, hoping the locals and Host Nation Security Forces would be willing and able to defend the area against the enemy.
How could the commander expect the villagers to aid his unit in denying the area as a support base for insurgents when there was no apparent common ground? How was he, as a Commander, supposed to communicate his intent to the local people, Host Nation officials, and to other key individuals? His battalion’s task organization included three Infantry Companies, an Anti-Tank Company, a Mortar Platoon, and a Scout Sniper Platoon. Additionally, the commander’s capabilities were augmented by a Tactical Military Information Support Team, a Military Source Operations (MSO) qualified Counterintelligence (CI) Team, and an Explosive Ordnance Detachment (EOD) Team. The commander also had new devices (including the Radio-In-The-Box or RIAB); some of these newly issued devices were pieces of equipment his leaders and Soldiers had never seen or used before deploying into theater.
The commander had enough combat forces to clear, and temporarily hold the valley, but what then? The commander knew he would achieve immediate but limited security in the area and also reach his higher headquarter’s directed end state. But how could he achieve longer term effects so that he would not have to repeat the mission again in just four months?
Lethal options in a Counter Insurgency (COIN) environment are only a portion of the necessary operations that must be successfully conducted at the tactical level. Non-Lethal options provide a balance to more kinetic operations, providing choices that can impact the threat and the population in longer term ways. Information Superiority, at the tactical level, is an essential requirement for successfully defeating insurgents in the COIN fight.
…
TOP-SECRET-NATO Commanders’ and Staff Handbook for Countering Improvised Explosive Devices (C-IED)

1. There is likely to be an IED threat in all military deployments and this should be a key consideration when undertaking the preparation, planning and execution of current and future NATO deployed operations. Generic detail of the threat environments and the C-IED approach are described in Reference A but for each deployment further specific operational analysis must be undertaken to ensure a mission focussed approach. Key to this is the generation of C-IED awareness and capability within the staff at every level of command.
2. This handbook sits under References A and B and is intended to be complimentary to existing NATO doctrinal publications and formation HQ operational planning and capability development. It should be noted that although the handbook is aligned with the AJP 3.15A, it seeks only to provide an operational and tactical level staff perspective. It is designed for use within military HQs at all levels and is equally applicable for National C-IED capability development. It will be a living document and updated and amended in conjunction with NATO publications and the lessons identified/ lessons learned process.
3. This handbook does not seek to define staff HQ or national operational planning processes for C-IED but should be used as a reference manual during the planning and execution of operations. Every operational deployment will have different requirements, depending upon environmental and operational variables; therefore the Commander must identify appropriate C-IED activities and processes within his staff functions as a priority.
4. C-IED is a relatively new phenomenon and has yet to be fully institutionalised into existing military staff training and functions. All staff must be aware of this fact and take every opportunity to develop wider awareness and understanding to better integrate C-IED aspects into all training and processes.
AIM OF THE HANDBOOK
5. The aim of the handbook is to outline outputs, staff responsibilities and enablers for Commanders and staff to consider when integrating C-IED into the preparation, planning and execution of operations, and to foster an Attack the Network mindset.
CONCEPT AND APPLICABILITY
6. It is widely acknowledged that IEDs will be a major threat for all levels of current and future operations and it is therefore imperative that national and NATO Formation and Unit HQs are able to prepare for, plan and conduct C-IED activities. Clearly defined C-IED outputs will enable the force to undertake these activities throughout the JOA in order to achieve the mission.
7. Definition. Reference A defines C-IED as follows:
The collective efforts at all levels to defeat the IED system by attacking the networks, defeating the device and preparing the force.8. C-IED approaches the IED as a systemic problem and C-IED actions aim to defeat the IED System. However, IEDs are only one of a number of forms of asymmetric attack used by insurgents, criminals, terrorists and other malign actors. The networks (e.g. Narcotics, Financial, Cyber, Piracy, Human Trafficking, IED, Terrorism, etc.) overlap and, therefore, will concurrently service the plethora of other requirements and activities of the adversary. Attack the Networks activities should take place at all levels: strategic, operational and tactical and, as the networks are predominantly personality-based, activities will focus against adversarial personalities and processes/activities as well as against IEDs/facilities/materials and their production, and will require a broad approach to the problem.
9. As there is an overlap of activities within the networks, they concurrently support the different aspects of the insurgents’ or adversaries aims and objectives. Understanding of, and intelligence on, these networks will be vital to not only the overall attack the network process but also the ability to identify the nodes and linkages within the financial, commercial, and communication sectors as well as an adversary’s own structures and interactions within the population. Most importantly, understanding these networks will highlight the adversary’s critical vulnerabilities; the target for all operational planning and activity. Thus planning for C-IED actions must include consideration of, and actions against, the adversarial networks in the widest context and recognition and understanding of friendly force Attack the Network operations taking place to achieve unity of effort and meet the Commander’s intent.
10. As the breadth of Attack the Network activities can transcend boundaries at all levels, from national through political to military, it is vital to engage with those functions, activities and personalities that are involved in the fight. This will entail military planners and commanders stepping outside their ‘comfort zone’ and engaging with entities from organizations that they may have had little or no contact with. This requires flexibility and adoption of new mind sets and appreciation of differing priorities and perspectives and, as personally uncomfortable and challenging as this may be, it is vital to success in attacking the networks and the C-IED system they support.
11. C-IED operations should not be planned or executed in isolation and must be fully integrated into the national or NATO force strategic objectives. A C-IED capability is generated when a series of tasks, activities and techniques are undertaken and integrated within the wider context of operational and tactical activities. C-IED may be undertaken within the full spectrum of operations although it is likely to be a greater factor within hybrid threat environments such as an insurgency, terrorism campaigns and during Stabilisation, Security, Transition and Reconstruction Operations (SSTRO). C-IED should be viewed as an activity to achieve the overarching mission rather than a distinct and separate function.
12. C-IED activities can take place at the local, national, regional, and international level. Subsequently, designing an operation to defeat the IED threat requires a comprehensive strategy that integrates and synchronizes series of actions and tasks from the tactical to the strategic levels of command and requires interaction with non-military organizations and the populace. As with the wider hybrid operations C-IED actions may be categorized as direct (focused on the enemy) or indirect (focused on the population). Whether direct or indirect, C-IED operations can be proactive or reactive and applicable to one or more of the three C-IED pillars. The guidance within the handbook is designed to be scalable, flexible and applicable to a variety of structures and requirements.
Download Original Document here
Stalker-“GoMoPa”: Hate Crimes Remain Steady 2010 FBI Report Released
11/14/11

And based on data from the FBI’s Hate Crime Statistics report for 2010, the 6,628 hate crime incidents reported to us by our law enforcement partners stayed consistent with the 6,604 incidents reported in 2009.
Today, we’re releasing on our website the full 2010 report, which contains information about the types of biases that motivate hate crimes, the nature of the offenses, and some information about the victims and offenders. It also breaks down hate crimes by jurisdiction and includes data by state and by agency.
The hate crimes report is fairly reflective of the country—agencies that participated in the Uniform Crime Reporting Hate Crime Statistics Program effort in 2010 represented more than 285 million people, or 92.3 percent of the nation’s population, and their jurisdictions covered 49 states and the District of Columbia. Of the 14,977 agencies that submitted data, 1,949 reported that hate crime incidents had occurred in their jurisdictions.
Here are some of the report’s highlights:
-
Law enforcement reported 8,208 victims of hate crimes—a “victim” can be an individual, a business, an institution, or society as a whole.
- Of the 6,628 hate crime incidents reported to us for 2010, nearly all (6,624) involved a single bias—47.3 percent of the single-bias incidents were motivated by race; 20 percent by religion; 19.3 by sexual orientation; 12.8 percent by an ethnicity/national origin bias; and 0.6 by physical or mental disability.
- As a result of the 2009 Matthew Shepard and James Byrd, Jr., Hate Crime Prevention Act, the FBI is implementing changes to collect additional data for crimes motivated by a bias against a particular gender or gender identity, as well as for hate crimes committed by or directed against juveniles.
- A reported 4,824 offenses were crimes against persons—intimidation accounted for 46.2 percent of these offenses; simple assault for 34.8 percent; and aggravated assault for 18.4 percent.
- There were 2,861 reported offenses of crimes against property—the majority (81.1 percent) were acts of destruction/damage/vandalism.
- Of the 6,008 known offenders, 58.6 were white and 18.4 percent were black.
- 31.4 percent of reported hate crime incidents took place in or near homes.
The FBI takes its role in investigating hate crimes very seriously—it’s the number one priority of our civil rights program. “Almost a fourth of our 2010 civil rights caseload involved crimes motivated by a particular bias against the victim,” said Eric Thomas, our civil rights chief in Washington, D.C., “and we frequently worked these cases with state and local law enforcement to ensure that justice was done—whether at the state level or at the federal level.”
This report, and the FBI’s hate crime data collection effort as a whole, would not have been possible without the support of national and state criminal justice organizations and the thousands of law enforcement agencies nationwide whose officers investigate, identify, and report hate crimes to us.

![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict41.jpg) U.S. President Barack Obama greets people gathered on the sidewalk after stopping for food at Skyline Chili in Cincinnati, July 16, 2012. Obama flew on Monday to Cincinnati for election campaign events. Reuters
U.S. President Barack Obama greets people gathered on the sidewalk after stopping for food at Skyline Chili in Cincinnati, July 16, 2012. Obama flew on Monday to Cincinnati for election campaign events. Reuters![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict39.jpg) US President Barack Obama greets wellwishers upon arrival on Air Force One at Cincinnati Northern Kentucky International Airport in Boone, Kentucky, July 16, 2012, enroute to attend campaign events in Cincinnati, Ohio. Getty
US President Barack Obama greets wellwishers upon arrival on Air Force One at Cincinnati Northern Kentucky International Airport in Boone, Kentucky, July 16, 2012, enroute to attend campaign events in Cincinnati, Ohio. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict38.jpg) President Barack Obama passes his jacket to White House Trip Director Marvin Nicholson before heading over to greet people after arriving at Northern Kentucky International Airport in Boone, Ky. , Monday, July 16, 2012. Obama is spending the day campaigning in Cincinnati. AP
President Barack Obama passes his jacket to White House Trip Director Marvin Nicholson before heading over to greet people after arriving at Northern Kentucky International Airport in Boone, Ky. , Monday, July 16, 2012. Obama is spending the day campaigning in Cincinnati. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict40.jpg) U.S. Secret Service members use a golf cart while providing protection for President Barack Obama while he golfs at the Army installation’s course July 15, 2012 in Ft. Belvoir, Virginia. Obama also campaigned in Virginia, a state he won in 2008, on Saturday, holding events in Fairfax and Glen Allen. Getty
U.S. Secret Service members use a golf cart while providing protection for President Barack Obama while he golfs at the Army installation’s course July 15, 2012 in Ft. Belvoir, Virginia. Obama also campaigned in Virginia, a state he won in 2008, on Saturday, holding events in Fairfax and Glen Allen. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict31.jpg) US President Barack Obama greets supporters are he arrives at a campaign event on July 14, 2012 at Centreville High School in Clifton, Virginia. Getty
US President Barack Obama greets supporters are he arrives at a campaign event on July 14, 2012 at Centreville High School in Clifton, Virginia. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict32.jpg) U.S. President Barack Obama arrives at a campaign rally at Centreville High School in Clifton, Virginia, July 14, 2012. Obama travelled to Virginia on Saturday for campaign events. Reuters
U.S. President Barack Obama arrives at a campaign rally at Centreville High School in Clifton, Virginia, July 14, 2012. Obama travelled to Virginia on Saturday for campaign events. Reuters![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict28.jpg) President Barack Obama walks up a set of stairs during a campaign rally at Centreville High School in Clifton, Va. , a Washington suburb, on Saturday, July 14, 2012. AP
President Barack Obama walks up a set of stairs during a campaign rally at Centreville High School in Clifton, Va. , a Washington suburb, on Saturday, July 14, 2012. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict35.jpg) People hold signs protesting against U.S. President Barack Obama along Obama’s motorcade route on his way to a campaign rally at Centreville High School in Clifton, Virginia, July 14, 2012. Obama travelled to Virginia on Saturday for campaign events. Reuters
People hold signs protesting against U.S. President Barack Obama along Obama’s motorcade route on his way to a campaign rally at Centreville High School in Clifton, Virginia, July 14, 2012. Obama travelled to Virginia on Saturday for campaign events. Reuters![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict30.jpg) President Barack Obama laughs while campaigning under the pouring rain at the historic Walkerton Tavern & Gardens in Glen Allen, Va. , near Richmond Saturday, July 14, 2012. It is in the Congressional district represented by House Majority Leader Eric Cantor, R-Va. , a key county in a crucial swing state of the presidential election. AP
President Barack Obama laughs while campaigning under the pouring rain at the historic Walkerton Tavern & Gardens in Glen Allen, Va. , near Richmond Saturday, July 14, 2012. It is in the Congressional district represented by House Majority Leader Eric Cantor, R-Va. , a key county in a crucial swing state of the presidential election. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict26.jpg) U.S. President Barack Obama greets supporters at the end of his ”A Vision for Virginia’s Middle Class” campaign event July 14, 2012 at Walkerton Tavern in Glen Allen, Virginia. On the last day of his two-day campaign across Virginia, Obama continue to discuss his plan to restore middle class security and urged Congress to act on extending tax cuts to middle class families. Getty
U.S. President Barack Obama greets supporters at the end of his ”A Vision for Virginia’s Middle Class” campaign event July 14, 2012 at Walkerton Tavern in Glen Allen, Virginia. On the last day of his two-day campaign across Virginia, Obama continue to discuss his plan to restore middle class security and urged Congress to act on extending tax cuts to middle class families. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict27.jpg) President Barack Obama campaigns during the pouring rain at the historic Walkerton Tavern & Gardens in Glen Allen, Va. , near Richmond, Saturday, July 14, 2012. AP
President Barack Obama campaigns during the pouring rain at the historic Walkerton Tavern & Gardens in Glen Allen, Va. , near Richmond, Saturday, July 14, 2012. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict37.jpg) Protesters line an entrance route to a campaign event where President Barack Obama is scheduled to speak at the historic Walkerton Tavern & Gardens in Glen Allen, Va. , near Richmond Saturday, July 14, 2012. AP
Protesters line an entrance route to a campaign event where President Barack Obama is scheduled to speak at the historic Walkerton Tavern & Gardens in Glen Allen, Va. , near Richmond Saturday, July 14, 2012. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict36.jpg) Conservative local residents protest prior to U.S. President Barack Obama’s ”A Vision for Virginia’s Middle Class” campaign event July 14, 2012 at Walkerton Tavern in Glen Allen, Virginia. On the last day of his two-day campaign across Virginia, Obama continue to discuss his plan to restore middle class security and urged the Congress to act on extending tax cuts to middle class families. Getty
Conservative local residents protest prior to U.S. President Barack Obama’s ”A Vision for Virginia’s Middle Class” campaign event July 14, 2012 at Walkerton Tavern in Glen Allen, Virginia. On the last day of his two-day campaign across Virginia, Obama continue to discuss his plan to restore middle class security and urged the Congress to act on extending tax cuts to middle class families. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict29.jpg) President Barack Obama removes his jacket upon his arrival at Washington Dulles International Airport in Chantilly, Va. , Saturday, July 14, 2012, for a campaign event in the vicinity. AP
President Barack Obama removes his jacket upon his arrival at Washington Dulles International Airport in Chantilly, Va. , Saturday, July 14, 2012, for a campaign event in the vicinity. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict25.jpg) US President Barack Obama boards his limousine after greeting well-wishers upon arrival July 14, 2012 at Richmond International Airport in Richmond, Virginia. Obama is in Virginia to attend campaign events. Getty
US President Barack Obama boards his limousine after greeting well-wishers upon arrival July 14, 2012 at Richmond International Airport in Richmond, Virginia. Obama is in Virginia to attend campaign events. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict33.jpg) Secret Service members keep watch in front of Air Force One shortly before US President Barack Obama’s departure on July 14, 2012 at Richmond International Airport in Richmond, Virginia. Obama is in Virginia to attend campaign events. Getty
Secret Service members keep watch in front of Air Force One shortly before US President Barack Obama’s departure on July 14, 2012 at Richmond International Airport in Richmond, Virginia. Obama is in Virginia to attend campaign events. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict1.jpg) US President Barack Obama hold up a tomato during a stop at Berry’s Produce on July 14, 2012 in Mechanicsville, Virginia. Obama is campaigning in Virginia ahead of the November presidential election. Getty
US President Barack Obama hold up a tomato during a stop at Berry’s Produce on July 14, 2012 in Mechanicsville, Virginia. Obama is campaigning in Virginia ahead of the November presidential election. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict0.jpg) President Barack Obama shakes hands as he arrives at the Richmond International Airport in Richmond, Va. , Saturday, July 14, 2012. AP
President Barack Obama shakes hands as he arrives at the Richmond International Airport in Richmond, Va. , Saturday, July 14, 2012. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict14.jpg) President Barack Obama greets the crowd after a campaign stop at the historic Fire Station No.1, in downtown Roanoke, Virginia, Friday, July 13, 2012. Obama traveled to southwest Virginia to discuss choice in this election between two fundamentally different visions on how to grow the economy, create middle-class jobs and pay down the debt. AP
President Barack Obama greets the crowd after a campaign stop at the historic Fire Station No.1, in downtown Roanoke, Virginia, Friday, July 13, 2012. Obama traveled to southwest Virginia to discuss choice in this election between two fundamentally different visions on how to grow the economy, create middle-class jobs and pay down the debt. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict15.jpg) President Barack Obama greets the crowd during a campaign stop at the historic Fire Station No.1, in downtown Roanoke, Va. , Friday, July 13, 2012. Obama traveled to southwest Virginia to discuss choice in this election between two fundamentally different visions on how to grow the economy, create middle-class jobs and pay down the debt. AP
President Barack Obama greets the crowd during a campaign stop at the historic Fire Station No.1, in downtown Roanoke, Va. , Friday, July 13, 2012. Obama traveled to southwest Virginia to discuss choice in this election between two fundamentally different visions on how to grow the economy, create middle-class jobs and pay down the debt. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict16.jpg) President Barack Obama greets people after arriving at Roanoke Regional Airport in Roanoke, Va. , Friday, July 13, 2012. Obama is spending the day campaigning in Virginia. AP
President Barack Obama greets people after arriving at Roanoke Regional Airport in Roanoke, Va. , Friday, July 13, 2012. Obama is spending the day campaigning in Virginia. AP
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict20.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict18.jpg) President Barack Obama greets people after arriving at Roanoke Regional Airport in Roanoke, Va. , Friday, July 13, 2012. Obama is spending the day campaigning in Virginia. AP
President Barack Obama greets people after arriving at Roanoke Regional Airport in Roanoke, Va. , Friday, July 13, 2012. Obama is spending the day campaigning in Virginia. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict19.jpg) President Barack Obama arrives at the Roanoke Airport on Air Force One on the campaign trail, Friday, July 13, 2012 in Roanoke, Va. AP
President Barack Obama arrives at the Roanoke Airport on Air Force One on the campaign trail, Friday, July 13, 2012 in Roanoke, Va. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict17.jpg) President Barack Obama greets people after arriving at Roanoke Regional Airport in Roanoke, Va. , Friday, July 13, 2012. Obama is spending the day campaigning in Virginia. AP
President Barack Obama greets people after arriving at Roanoke Regional Airport in Roanoke, Va. , Friday, July 13, 2012. Obama is spending the day campaigning in Virginia. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict22.jpg) President Barack Obama greets the crowd after speaking at a campaign event at Phoebus High School in Hampton, Va. , Friday, July 13, 2012. Obama is spending the day in Virginia campaigning. AP
President Barack Obama greets the crowd after speaking at a campaign event at Phoebus High School in Hampton, Va. , Friday, July 13, 2012. Obama is spending the day in Virginia campaigning. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict21.jpg) President Barack Obama greets the crowd after speaking at a campaign event at Phoebus High School in Hampton, Va. , Friday, July 13, 2012. Obama is spending the day in Virginia campaigning. AP
President Barack Obama greets the crowd after speaking at a campaign event at Phoebus High School in Hampton, Va. , Friday, July 13, 2012. Obama is spending the day in Virginia campaigning. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict24.jpg) President Barack Obama arrives to speak at a campaign event at Phoebus High School in Hampton, Va. , Friday, July 13, 2012. Obama is spending the day in Virginia campaigning. AP
President Barack Obama arrives to speak at a campaign event at Phoebus High School in Hampton, Va. , Friday, July 13, 2012. Obama is spending the day in Virginia campaigning. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict12.jpg) U.S. President Barack Obama (C) greets supporters at the end of his ‘A Vision for Virginia’s Middle Class’ campaign event July 13, 2012 at Green Run High School in Virginia Beach, Virginia. Obama discussed his plan to restore middle class security and urged the Congress to act on extending tax cuts to middle class families. Getty
U.S. President Barack Obama (C) greets supporters at the end of his ‘A Vision for Virginia’s Middle Class’ campaign event July 13, 2012 at Green Run High School in Virginia Beach, Virginia. Obama discussed his plan to restore middle class security and urged the Congress to act on extending tax cuts to middle class families. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict13.jpg) U.S. President Barack Obama (R) greets supporters at the end of his ‘A Vision for Virginia’s Middle Class’ campaign event July 13, 2012 at Green Run High School in Virginia Beach, Virginia. Obama discussed his plan to restore middle class security and urged the Congress to act on extending tax cuts to middle class families. Getty [Two Secret Service in “hands ready” position.
U.S. President Barack Obama (R) greets supporters at the end of his ‘A Vision for Virginia’s Middle Class’ campaign event July 13, 2012 at Green Run High School in Virginia Beach, Virginia. Obama discussed his plan to restore middle class security and urged the Congress to act on extending tax cuts to middle class families. Getty [Two Secret Service in “hands ready” position.![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict2.jpg) President Barack Obama reaches out to shake hands at a campaign event at Green Run High School in Virginia Beach, Va. , Friday, July 13, 2012. Obama is spending the day in Virginia campaigning. AP
President Barack Obama reaches out to shake hands at a campaign event at Green Run High School in Virginia Beach, Va. , Friday, July 13, 2012. Obama is spending the day in Virginia campaigning. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict3.jpg) President Barack Obama heads to his car after greeting people after arriving at Norfolk International Airport in Norfolk, Va. , Friday, July 13, 2012. AP
President Barack Obama heads to his car after greeting people after arriving at Norfolk International Airport in Norfolk, Va. , Friday, July 13, 2012. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict4.jpg) President Barack Obama is surrounded by secret service as he greets people after arriving at Norfolk International Airport in Norfolk, Va. , Friday, July 13, 2012. AP
President Barack Obama is surrounded by secret service as he greets people after arriving at Norfolk International Airport in Norfolk, Va. , Friday, July 13, 2012. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict6.jpg) President Barack Obama heads to his car after greeting people after arriving at Norfolk International Airport in Norfolk, Va. , Friday, July 13, 2012. AP
President Barack Obama heads to his car after greeting people after arriving at Norfolk International Airport in Norfolk, Va. , Friday, July 13, 2012. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict5.jpg) President Barack Obama meets with supporters after arriving aboard Air Force One at the Norfolk International Airport in Norfolk, Va. , Friday, July 13, 2012. AP
President Barack Obama meets with supporters after arriving aboard Air Force One at the Norfolk International Airport in Norfolk, Va. , Friday, July 13, 2012. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict7.jpg) President Barack Obama meets with supporters after arriving aboard Air Force One at the Norfolk International Airport in Norfolk, Va. , Friday, July 13, 2012. AP
President Barack Obama meets with supporters after arriving aboard Air Force One at the Norfolk International Airport in Norfolk, Va. , Friday, July 13, 2012. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict8.jpg) President Barack Obama walks to Air Force One at Andrews Air Force Base in Md. , Friday, July 13, 2012, enroute to Virginia for a series of campaign events. AP
President Barack Obama walks to Air Force One at Andrews Air Force Base in Md. , Friday, July 13, 2012, enroute to Virginia for a series of campaign events. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict9.jpg) Members of the media exit a house alongside US President Barack Obama’s SUV holding in the driveway as Obama meets with Jason McLaughlin, principal of Center Point-Urbana High School, his wife, Ali, an account manager for a document scanning company, and their 4-year-old son Cooper, on middle class tax cuts at their home in Cedar Rapids, Iowa, July 10, 2012. Getty
Members of the media exit a house alongside US President Barack Obama’s SUV holding in the driveway as Obama meets with Jason McLaughlin, principal of Center Point-Urbana High School, his wife, Ali, an account manager for a document scanning company, and their 4-year-old son Cooper, on middle class tax cuts at their home in Cedar Rapids, Iowa, July 10, 2012. Getty![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict34.jpg) Secret Service agents guard the door of the home of Jason and Ali McLaughlin while President Barack Obama visits with them in Cedar Rapids, Iowa, Tuesday, July 10, 2012. AP
Secret Service agents guard the door of the home of Jason and Ali McLaughlin while President Barack Obama visits with them in Cedar Rapids, Iowa, Tuesday, July 10, 2012. AP![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict10.jpg) U.S. President Barack Obama arrives in Cedar Rapids, Iowa, July 10, 2012. Obama flew to Iowa for an event pushing for the extension of Bush-era tax cuts due to expire at the end of 2012. Reuters
U.S. President Barack Obama arrives in Cedar Rapids, Iowa, July 10, 2012. Obama flew to Iowa for an event pushing for the extension of Bush-era tax cuts due to expire at the end of 2012. Reuters![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-protect47/pict11.jpg) President Barack Obama heads to his car after getting ice cream at Deb’s Ice Cream & Deli in Cedar Rapids, Iowa, Tuesday, July 10, 2012. AP
President Barack Obama heads to his car after getting ice cream at Deb’s Ice Cream & Deli in Cedar Rapids, Iowa, Tuesday, July 10, 2012. AP
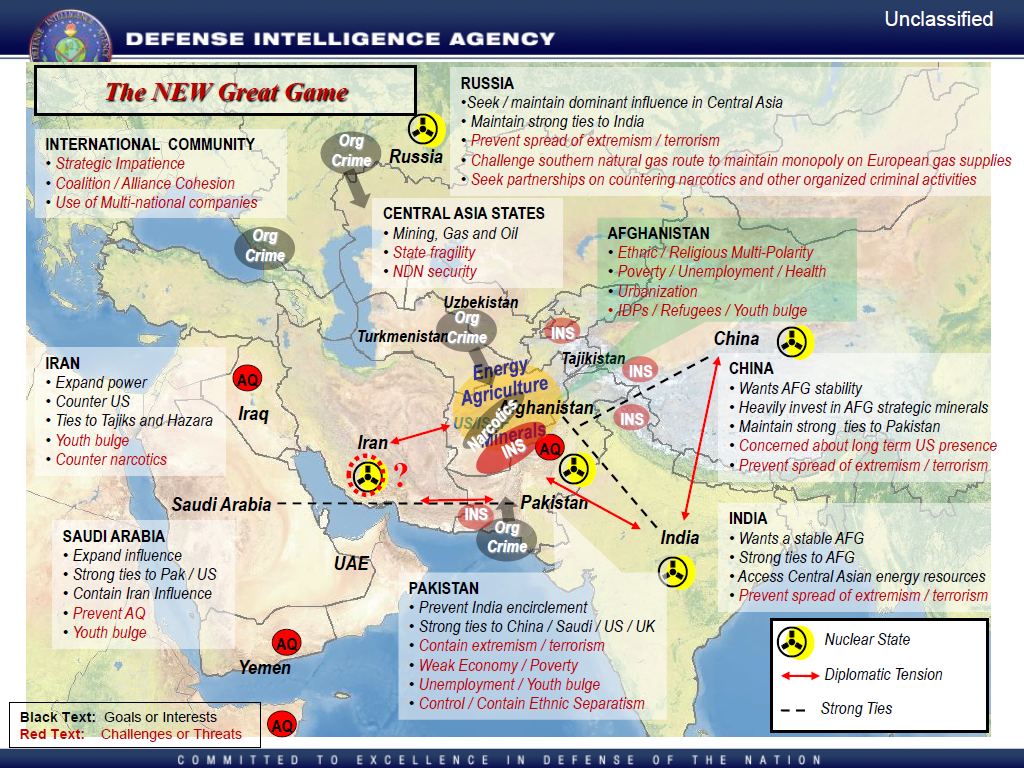
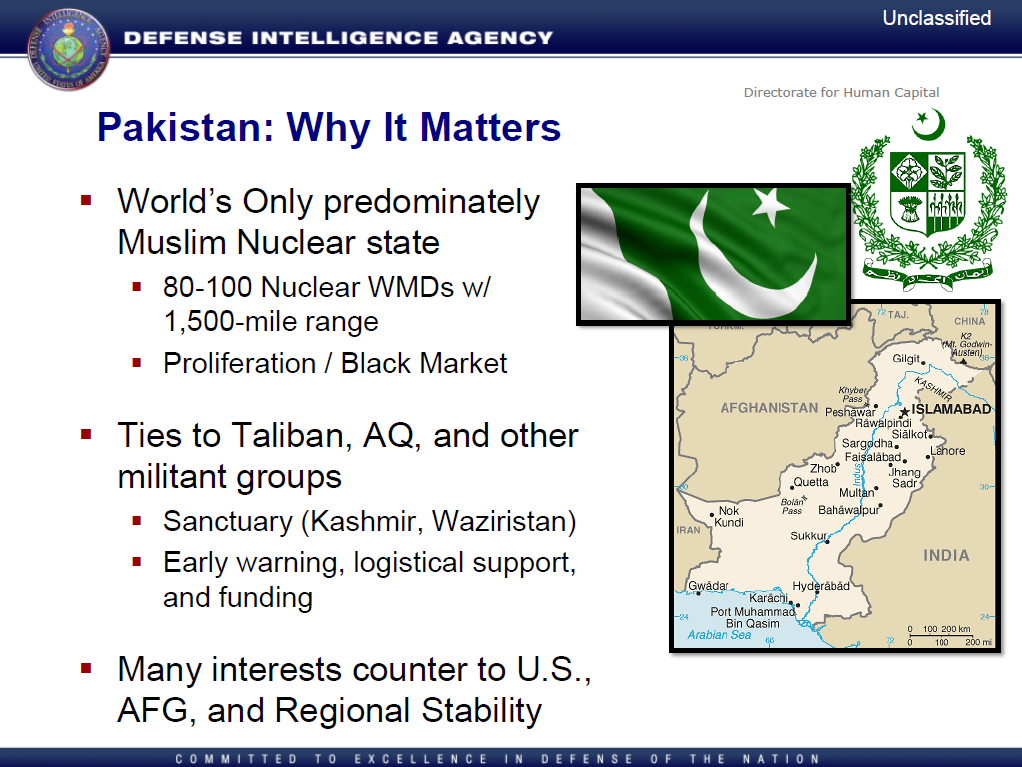
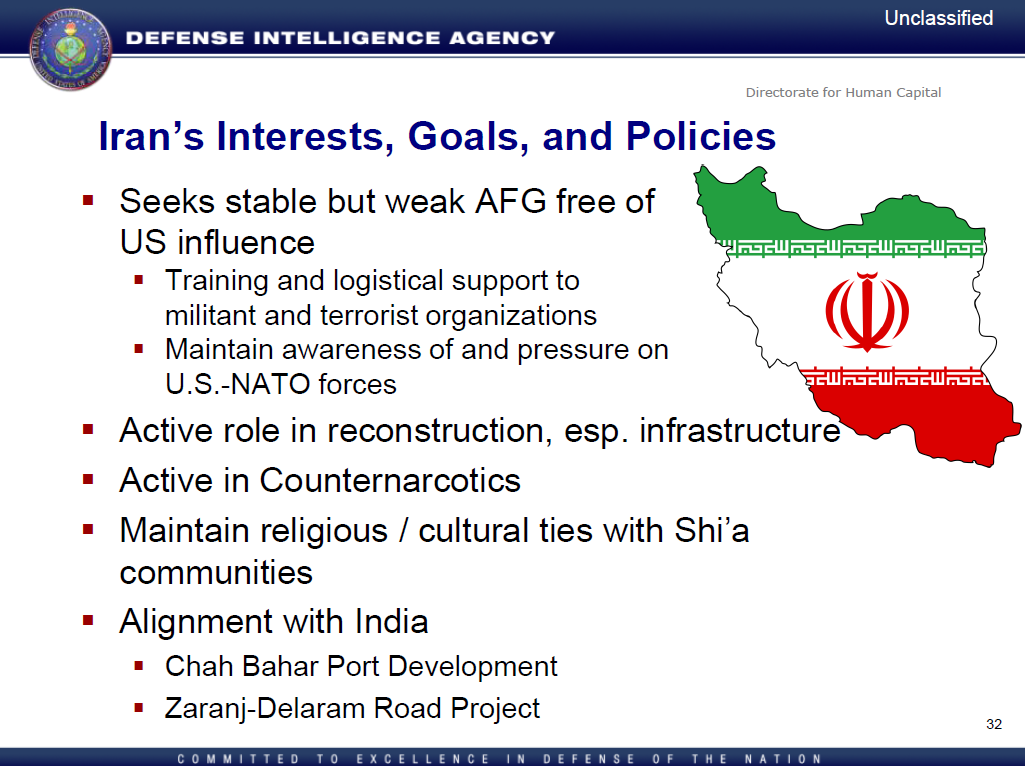
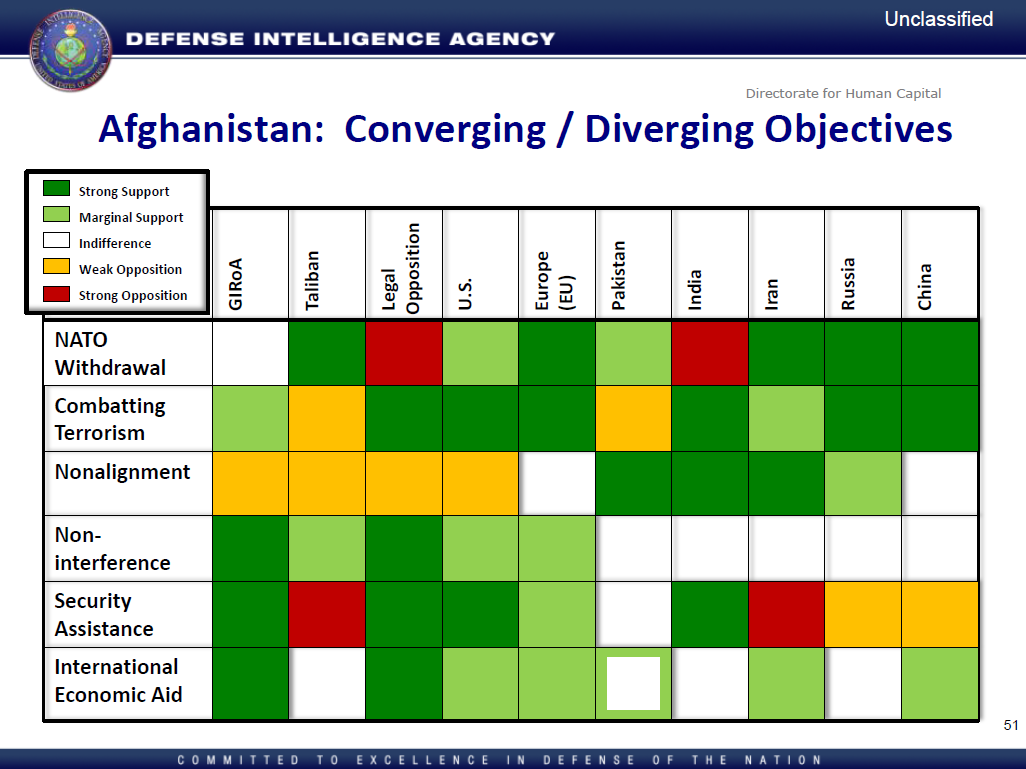

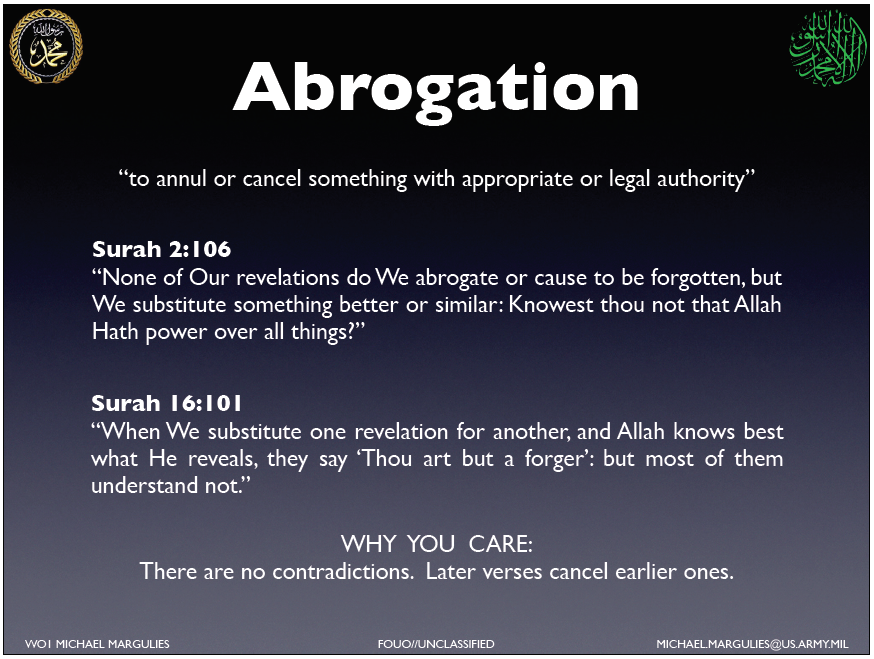
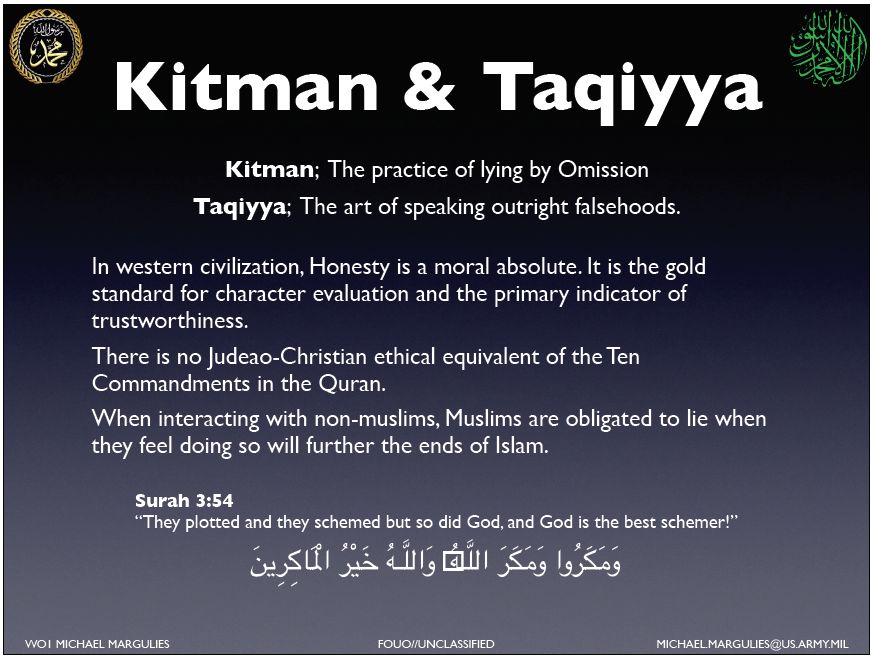
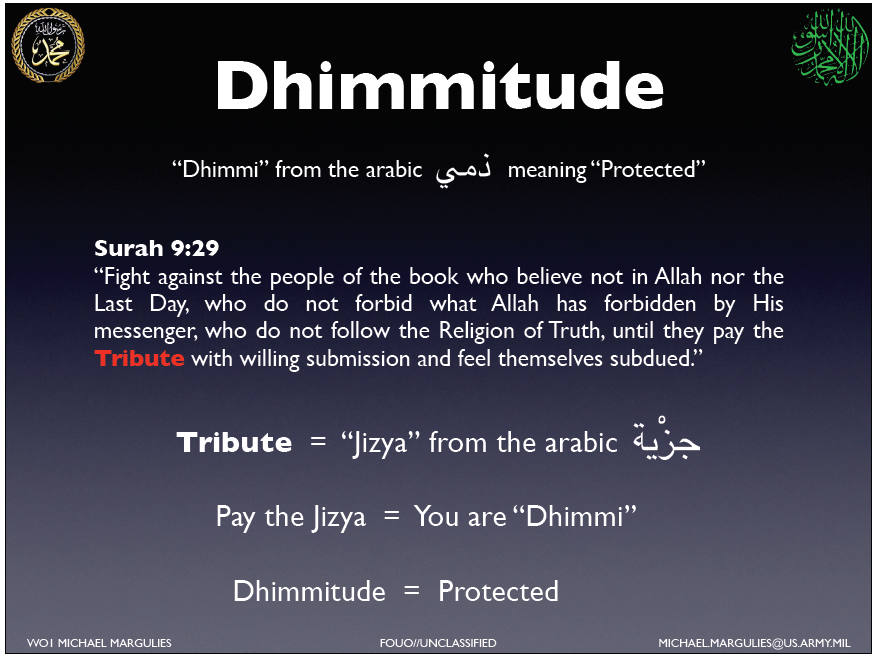









![[Image]](https://i0.wp.com/cryptome.org/2012/06/mcgurk-chon/chon-mcgurk-sfc.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012/06/mcgurk-chon/pict0.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012/06/mcgurk-chon/pict1.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012/06/mcgurk-chon/pict2.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012/06/mcgurk-chon/pict3.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012/06/mcgurk-chon/pict4.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012/06/mcgurk-chon/pict5.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012/06/mcgurk-chon/pict6.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012/06/mcgurk-chon/pict7.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012/06/mcgurk-chon/pict8.jpg)
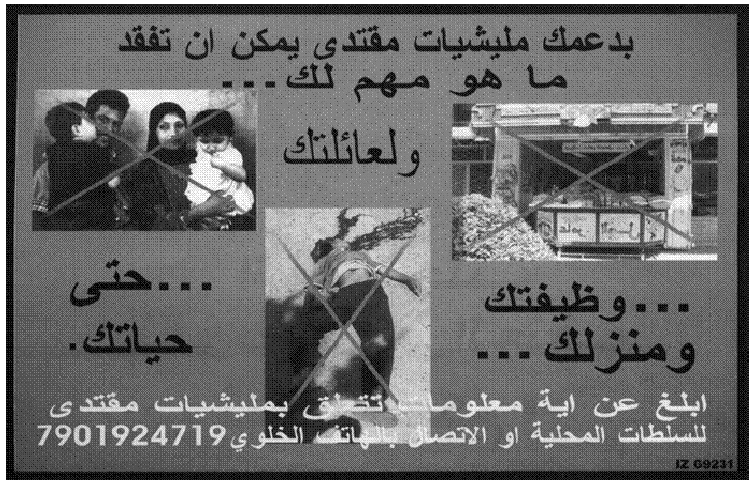





![[Image]](https://i0.wp.com/cryptome.org/2012-info/fodor/pict0.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/fodor/pict1.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/fodor/pict2.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/fodor/pict13.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/fodor/pict10.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/fodor/pict9.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/fodor/pict11.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/fodor/pict7.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/fodor/pict6.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/fodor/pict5.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/fodor/pict3.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/fodor/pict8.jpg)


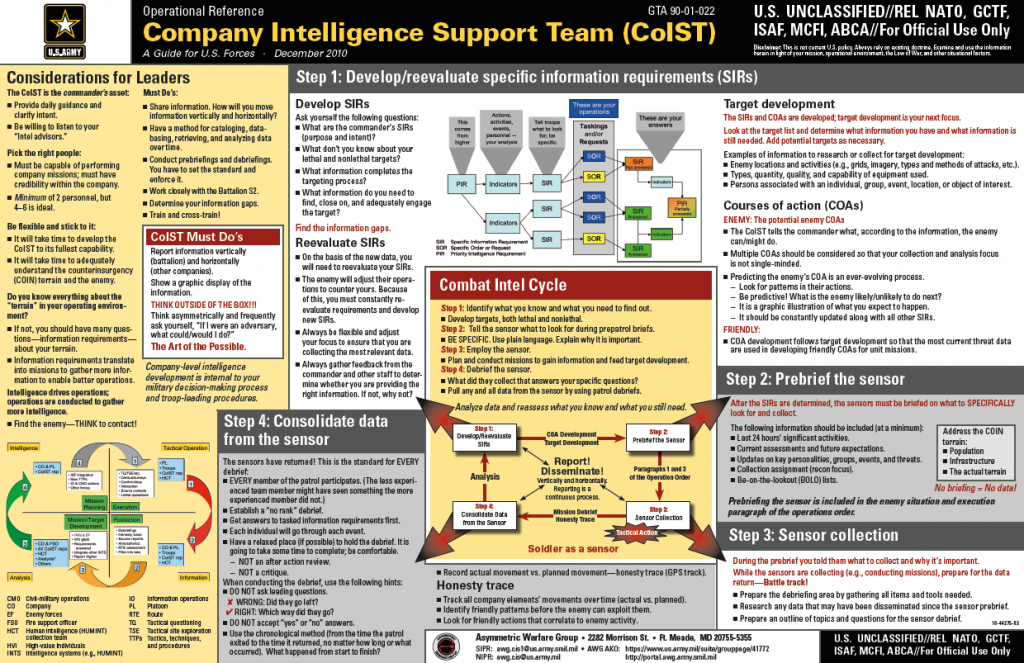


![[Image]](https://i0.wp.com/cryptome.org/2012-info/nsa-sa-2012/pict42.jpg)









![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict4.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict2.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict1.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict10.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict3.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict9.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict11.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/gitmo-10/pict7.jpg)












![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict7.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict12.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict14.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict17.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict20.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict22.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict24.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict2.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict28.jpg)
![[Image]](https://i0.wp.com/cryptome.org/2012-info/obama-phones/pict30.jpg)










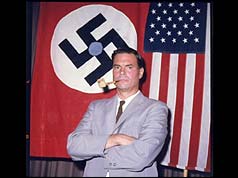






![[Image]](https://i0.wp.com/cryptome.org/eyeball/cia-bucharest/pict10.jpg)
![[Image]](https://i0.wp.com/cryptome.org/eyeball/cia-bucharest/pict12.jpg)











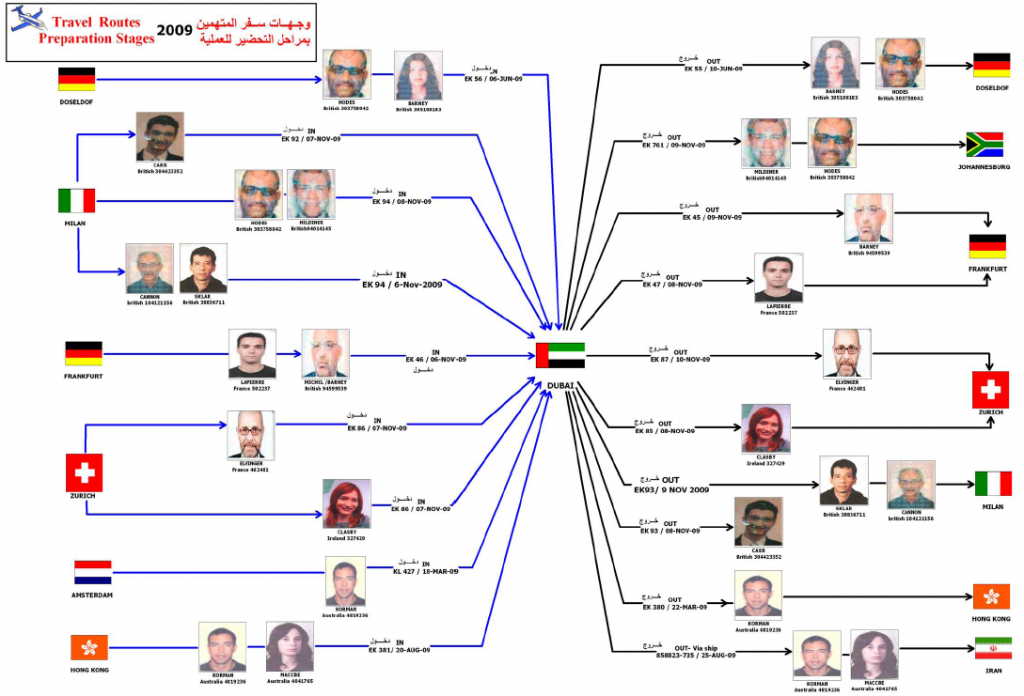
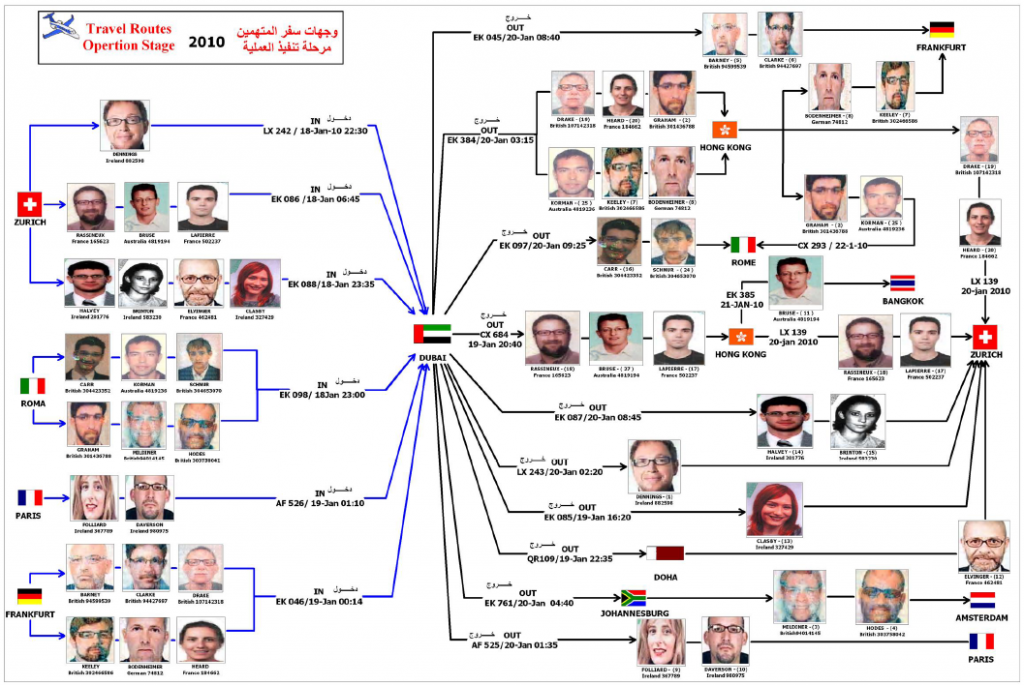
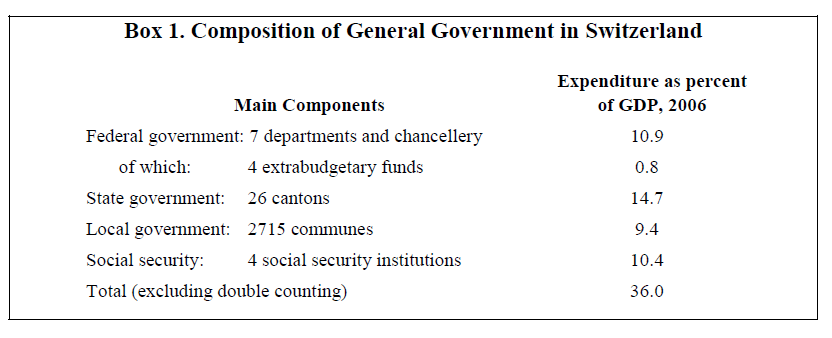












![[Image]](https://i0.wp.com/cryptome.org/eyeball/daiichi-111911/pict3.jpg)
![[Image]](https://i0.wp.com/cryptome.org/eyeball/daiichi-111911/pict5.jpg)



You must be logged in to post a comment.