[Federal Register Volume 76, Number 185 (Friday, September 23, 2011)]
[Rules and Regulations]
[Pages 59192-59235]
From the Federal Register Online via the Government Printing Office [www.gpo.gov]
[FR Doc No: 2011-24259]
[[Page 59191]]
Vol. 76
Friday,
No. 185
September 23, 2011
Part II
Federal Communications Commission
-----------------------------------------------------------------------
47 CFR Parts 0 and 8
Preserving the Open Internet; Final Rule
Federal Register / Vol. 76 , No. 185 / Friday, September 23, 2011 /
Rules and Regulations
[[Page 59192]]
-----------------------------------------------------------------------
FEDERAL COMMUNICATIONS COMMISSION
47 CFR Parts 0 and 8
[GN Docket No. 09-191; WC Docket No. 07-52; FCC 10-201]
Preserving the Open Internet
AGENCY: Federal Communications Commission.
ACTION: Final rule.
-----------------------------------------------------------------------
SUMMARY: This Report and Order establishes protections for broadband
service to preserve and reinforce Internet freedom and openness. The
Commission adopts three basic protections that are grounded in broadly
accepted Internet norms, as well as our own prior decisions. First,
transparency: fixed and mobile broadband providers must disclose the
network management practices, performance characteristics, and
commercial terms of their broadband services. Second, no blocking:
fixed broadband providers may not block lawful content, applications,
services, or non-harmful devices; mobile broadband providers may not
block lawful Web sites, or block applications that compete with their
voice or video telephony services. Third, no unreasonable
discrimination: fixed broadband providers may not unreasonably
discriminate in transmitting lawful network traffic. These rules,
applied with the complementary principle of reasonable network
management, ensure that the freedom and openness that have enabled the
Internet to flourish as an engine for creativity and commerce will
continue. This framework thus provides greater certainty and
predictability to consumers, innovators, investors, and broadband
providers, as well as the flexibility providers need to effectively
manage their networks. The framework promotes a virtuous circle of
innovation and investment in which new uses of the network--including
new content, applications, services, and devices--lead to increased
end-user demand for broadband, which drives network improvements that
in turn lead to further innovative network uses.
DATES: Effective Date: These rules are effective November 20, 2011.
FOR FURTHER INFORMATION CONTACT: Matt Warner, (202) 418-2419 or e-mail,
matthew.warner@fcc.gov.
SUPPLEMENTARY INFORMATION: This is a summary of the Commission's Report
and Order (Order) in GN Docket No. 09-191, WC Docket No. 07-52, FCC 10-
201, adopted December 21, 2010 and released December 23, 2010. The
complete text of this document is available on the Commission's Web
site at http://www.fcc.gov. It is also available for inspection and
copying during normal business hours in the FCC Reference Information
Center, Portals II, 445 12th Street, SW., Room CY-A257, Washington, DC
20554. This document may also be purchased from the Commission's
duplicating contractor, Best Copy and Printing, Inc., 445 12th Street,
SW., Room CY-B402, Washington, DC 20554, telephone (800) 378-3160 or
(202) 863-2893, facsimile (202) 863-2898, or via e-mail at http://www.bcpiweb.com.
Synopsis of the Order
I. Preserving the Free and Open Internet
In this Order the Commission takes an important step to preserve
the Internet as an open platform for innovation, investment, job
creation, economic growth, competition, and free expression. To provide
greater clarity and certainty regarding the continued freedom and
openness of the Internet, we adopt three basic rules that are grounded
in broadly accepted Internet norms, as well as our own prior decisions:
i. Transparency. Fixed and mobile broadband providers must disclose
the network management practices, performance characteristics, and
terms and conditions of their broadband services;
ii. No blocking. Fixed broadband providers may not block lawful
content, applications, services, or non-harmful devices; mobile
broadband providers may not block lawful Web sites, or block
applications that compete with their voice or video telephony services;
and
iii. No unreasonable discrimination. Fixed broadband providers may
not unreasonably discriminate in transmitting lawful network traffic.
We believe these rules, applied with the complementary principle of
reasonable network management, will empower and protect consumers and
innovators while helping ensure that the Internet continues to
flourish, with robust private investment and rapid innovation at both
the core and the edge of the network. This is consistent with the
National Broadband Plan goal of broadband access that is ubiquitous and
fast, promoting the global competitiveness of the United States.
In late 2009, we launched a public process to determine whether and
what actions might be necessary to preserve the characteristics that
have allowed the Internet to grow into an indispensable platform
supporting our nation's economy and civic life, and to foster continued
investment in the physical networks that enable the Internet. Since
then, more than 100,000 commenters have provided written input.
Commission staff held several public workshops and convened a
Technological Advisory Process with experts from industry, academia,
and consumer advocacy groups to collect their views regarding key
technical issues related to Internet openness.
This process has made clear that the Internet has thrived because
of its freedom and openness--the absence of any gatekeeper blocking
lawful uses of the network or picking winners and losers online.
Consumers and innovators do not have to seek permission before they use
the Internet to launch new technologies, start businesses, connect with
friends, or share their views. The Internet is a level playing field.
Consumers can make their own choices about what applications and
services to use and are free to decide what content they want to
access, create, or share with others. This openness promotes
competition. It also enables a self-reinforcing cycle of investment and
innovation in which new uses of the network lead to increased adoption
of broadband, which drives investment and improvements in the network
itself, which in turn lead to further innovative uses of the network
and further investment in content, applications, services, and devices.
A core goal of this Order is to foster and accelerate this cycle of
investment and innovation.
The record and our economic analysis demonstrate, however, that the
openness of the Internet cannot be taken for granted, and that it faces
real threats. Indeed, we have seen broadband providers endanger the
Internet's openness by blocking or degrading content and applications
without disclosing their practices to end users and edge providers,
notwithstanding the Commission's adoption of open Internet principles
in 2005.\1\ In light of these considerations, as well as the limited
choices most consumers have for broadband service, broadband
[[Page 59193]]
providers' financial interests in telephony and pay television services
that may compete with online content and services, and the economic and
civic benefits of maintaining an open and competitive platform for
innovation and communication, the Commission has long recognized that
certain basic standards for broadband provider conduct are necessary to
ensure the Internet's continued openness. The record also establishes
the widespread benefits of providing greater clarity in this area--
clarity that the Internet's openness will continue, that there is a
forum and procedure for resolving alleged open Internet violations, and
that broadband providers may reasonably manage their networks and
innovate with respect to network technologies and business models. We
expect the costs of compliance with our prophylactic rules to be small,
as they incorporate longstanding openness principles that are generally
in line with current practices and with norms endorsed by many
broadband providers. Conversely, the harms of open Internet violations
may be substantial, costly, and in some cases potentially irreversible.
---------------------------------------------------------------------------
\1\ In this Order we use ``broadband'' and ``broadband Internet
access service'' interchangeably, and ``broadband provider'' and
``broadband Internet access provider'' interchangeably. ``End user''
refers to any individual or entity that uses a broadband Internet
access service; we sometimes use ``subscriber'' or ``consumer'' to
refer to those end users that subscribe to a particular broadband
Internet access service. We use ``edge provider'' to refer to
content, application, service, and device providers, because they
generally operate at the edge rather than the core of the network.
These terms are not mutually exclusive.
---------------------------------------------------------------------------
The rules we proposed in the Open Internet NPRM and those we adopt
in this Order follow directly from the Commission's bipartisan Internet
Policy Statement, adopted unanimously in 2005 and made temporarily
enforceable for certain broadband providers in 2005 and 2007; openness
protections the Commission established in 2007 for users of certain
wireless spectrum; and a notice of inquiry in 2007 that asked, among
other things, whether the Commission should add a principle of
nondiscrimination to the Internet Policy Statement. Our rules build
upon these actions, first and foremost by requiring broadband providers
to be transparent in their network management practices, so that end
users can make informed choices and innovators can develop, market, and
maintain Internet-based offerings. The rules also prevent certain forms
of blocking and discrimination with respect to content, applications,
services, and devices that depend on or connect to the Internet.
An open, robust, and well-functioning Internet requires that
broadband providers have the flexibility to reasonably manage their
networks. Network management practices are reasonable if they are
appropriate and tailored to achieving a legitimate network management
purpose. Transparency and end-user control are touchstones of
reasonableness.
We recognize that broadband providers may offer other services over
the same last-mile connections used to provide broadband service. These
``specialized services'' can benefit end users and spur investment, but
they may also present risks to the open Internet. We will closely
monitor specialized services and their effects on broadband service to
ensure, through all available mechanisms, that they supplement but do
not supplant the open Internet.
Mobile broadband is at an earlier stage in its development than
fixed broadband and is evolving rapidly. For that and other reasons
discussed below, we conclude that it is appropriate at this time to
take measured steps in this area. Accordingly, we require mobile
broadband providers to comply with the transparency rule, which
includes enforceable disclosure obligations regarding device and
application certification and approval processes; we prohibit providers
from blocking lawful Web sites; and we prohibit providers from blocking
applications that compete with providers' voice and video telephony
services. We will closely monitor the development of the mobile
broadband market and will adjust the framework we adopt in this Order
as appropriate.
These rules are within our jurisdiction over interstate and foreign
communications by wire and radio. Further, they implement specific
statutory mandates in the Communications Act (``Act'') and the
Telecommunications Act of 1996 (``1996 Act''), including provisions
that direct the Commission to promote Internet investment and to
protect and promote voice, video, and audio communications services.
The framework we adopt aims to ensure the Internet remains an open
platform--one characterized by free markets and free speech--that
enables consumer choice, end-user control, competition through low
barriers to entry, and the freedom to innovate without permission. The
framework does so by protecting openness through high-level rules,
while maintaining broadband providers' and the Commission's flexibility
to adapt to changes in the market and in technology as the Internet
continues to evolve.
II. The Need for Open Internet Protections
In the Open Internet NPRM (FCC 09-93 published at 74 FR 62638,
November 30, 2009), we sought comment on the best means for preserving
and promoting a free and open Internet. We noted the near-unanimous
view that the Internet's openness and the transparency of its protocols
have been critical to its unparalleled success. Citing evidence of
broadband providers covertly blocking or degrading Internet traffic,
and concern that broadband providers have the incentive and ability to
expand those practices in the near future, we sought comment on
prophylactic rules designed to preserve the Internet's prevailing norms
of openness. Specifically, we sought comment on whether the Commission
should codify the four principles stated in the Internet Policy
Statement, plus proposed nondiscrimination and transparency rules, all
subject to reasonable network management.\2\
---------------------------------------------------------------------------
\2\ The Open Internet NPRM recast the Internet Policy Statement
principles as rules rather than consumer entitlements, but did not
change the fact that protecting and empowering end users is a
central purpose of open Internet protections.
---------------------------------------------------------------------------
Commenters agree that the open Internet is an important platform
for innovation, investment, competition, and free expression, but
disagree about whether there is a need for the Commission to take
action to preserve its openness. Commenters who favor Commission action
emphasize the risk of harmful conduct by broadband providers, and
stress that failing to act could result in irreversible damage to the
Internet. Those who favor inaction contend that the Internet generally
is open today and is likely to remain so, and express concern that
rules aimed at preventing harms may themselves impose significant
costs. In this part, we assess these conflicting views. We conclude
that the benefits of ensuring Internet openness through enforceable,
high-level, prophylactic rules outweigh the costs. The harms that could
result from threats to openness are significant and likely
irreversible, while the costs of compliance with our rules should be
small, in large part because the rules appear to be consistent with
current industry practices. The rules are carefully calibrated to
preserve the benefits of the open Internet and increase certainty for
all Internet stakeholders, with minimal burden on broadband providers.
A. The Internet's Openness Promotes Innovation, Investment,
Competition, Free Expression, and Other National Broadband Goals
Like electricity and the computer, the Internet is a ``general
purpose technology'' that enables new methods of production that have a
major impact on the entire economy. The Internet's founders
intentionally built a network that is open, in the sense that it has no
gatekeepers limiting innovation and
[[Page 59194]]
communication through the network.\3\ Accordingly, the Internet enables
an end user to access the content and applications of her choice,
without requiring permission from broadband providers. This
architecture enables innovators to create and offer new applications
and services without needing approval from any controlling entity, be
it a network provider, equipment manufacturer, industry body, or
government agency. End users benefit because the Internet's openness
allows new technologies to be developed and distributed by a broad
range of sources, not just by the companies that operate the network.
For example, Sir Tim Berners-Lee was able to invent the World Wide Web
nearly two decades after engineers developed the Internet's original
protocols, without needing changes to those protocols or any approval
from network operators. Startups and small businesses benefit because
the Internet's openness enables anyone connected to the network to
reach and do business with anyone else, allowing even the smallest and
most remotely located businesses to access national and global markets,
and contribute to the economy through e-commerce \4\ and online
advertising.\5\ Because Internet openness enables widespread innovation
and allows all end users and edge providers (rather than just the
significantly smaller number of broadband providers) to create and
determine the success or failure of content, applications, services,
and devices, it maximizes commercial and non-commercial innovations
that address key national challenges--including improvements in health
care, education, and energy efficiency that benefit our economy and
civic life.
---------------------------------------------------------------------------
\3\ The Internet's openness is supported by an ``end-to-end''
network architecture that was formulated and debated in standard-
setting organizations and foundational documents. See, e.g., WCB
Letter 12/10/10, Attach. at 17-29, Vinton G. Cerf & Robert E. Kahn,
A Protocol for Packet Network Interconnection, COM-22 IEEE
Transactions of Commc'ns Tech. 637-48 (1974); WCB Letter 12/10/10,
Attach. at 30-39, J.H. Saltzer et al., End to End Arguments in
System Design, Second Int'l Conf. on Distributed Computing Systems,
509-12 (1981); WCB Letter 12/10/10, Attach. at 49-55, B. Carpenter,
Internet Engineering Task Force (``IETF''), Architectural Principles
of the Internet, RFC 1958, 1-8 (June 1996), http://www.ietf.org/rfc/rfc1958.txt; Lawrence Roberts, Multiple Computer Networks and
Intercomputer Communication, ACM Symposium on Operation System
Principles (1967). Under the end-to-end principle, devices in the
middle of the network are not optimized for the handling of any
particular application, while devices at network endpoints perform
the functions necessary to support networked applications and
services. See generally WCB Letter 12/10/10, Attach. at 40-48, J.
Kempf & R. Austein, IETF, The Rise of the Middle and the Future of
End-to-End: Reflections on the Evolution of the Internet
Architecture, RFC 3724, 1-14 (March 2004), ftp://ftp.rfc-editor.org/in-notes/rfc3724.txt.
\4\ Business-to-consumer e-commerce was estimated to total $135
billion in 2009. See WCB Letter 12/10/10, Attach. at 81-180, Robert
D. Atkinson et al., The Internet Economy 25 Years After.com, Info.
Tech. & Innovation Found., at 24 (March 2010), available at http://www.itif.org/files/2010-25-years.pdf.
\5\ The advertising-supported Internet sustains about $300
billion of U.S. GDP. See Google Comments at 7.
---------------------------------------------------------------------------
The Internet's openness is critical to these outcomes, because it
enables a virtuous circle of innovation in which new uses of the
network--including new content, applications, services, and devices--
lead to increased end-user demand for broadband, which drives network
improvements, which in turn lead to further innovative network uses.
Novel, improved, or lower-cost offerings introduced by content,
application, service, and device providers spur end-user demand and
encourage broadband providers to expand their networks and invest in
new broadband technologies.\6\ Streaming video and e-commerce
applications, for instance, have led to major network improvements such
as fiber to the premises, VDSL, and DOCSIS 3.0. These network
improvements generate new opportunities for edge providers, spurring
them to innovate further.\7\ Each round of innovation increases the
value of the Internet for broadband providers, edge providers, online
businesses, and consumers. Continued operation of this virtuous circle,
however, depends upon low barriers to innovation and entry by edge
providers, which drive end-user demand. Restricting edge providers'
ability to reach end users, and limiting end users' ability to choose
which edge providers to patronize, would reduce the rate of innovation
at the edge and, in turn, the likely rate of improvements to network
infrastructure. Similarly, restricting the ability of broadband
providers to put the network to innovative uses may reduce the rate of
improvements to network infrastructure.
---------------------------------------------------------------------------
\6\ We note that broadband providers can also be edge providers.
\7\ For example, the increasing availability of multimedia
applications on the World Wide Web during the 1990s was one factor
that helped create demand for residential broadband services.
Internet service providers responded by adopting new network
infrastructure, modem technologies, and network protocols, and
marketed broadband to residential customers. See, e.g., WCB Letter
12/13/10, Attach. at 250-72, Chetan Sharma, Managing Growth and
Profits in the Yottabyte Era (2009), http://www.chetansharma.com/yottabyteera.htm (Yottabyte). By the late 1990s, a residential end
user could download content at speeds not achievable even on the
Internet backbone during the 1980s. See, e.g., WCB Letter 12/13/10,
Attach. at 226-32, Susan Harris & Elise Gerich, The NSFNET Backbone
Service: Chronicling the End of an Era, 10 ConneXions (April 1996),
available at http://www.merit.edu/networkresearch/projecthistory/nsfnet/nsfnet_article.php. Higher speeds and broadband's ``always
on'' capability, in turn, stimulated more innovation in
applications, from gaming to video streaming, which in turn
encouraged broadband providers to increase network speeds. WCB
Letter 12/13/10, Attach. at 233-34, Link Hoewing, Twitter, Broadband
and Innovation, PolicyBlog, Dec. 4, 2010, policyblog.verizon.com/BlogPost/626/TwitterBroadbandandInnovation.aspx.
---------------------------------------------------------------------------
Openness also is essential to the Internet's role as a platform for
speech and civic engagement. An informed electorate is critical to the
health of a functioning democracy, and Congress has recognized that the
Internet ``offer[s] a forum for a true diversity of political
discourse, unique opportunities for cultural development, and myriad
avenues for intellectual activity.'' Due to the lack of gatekeeper
control, the Internet has become a major source of news and
information, which forms the basis for informed civic discourse. Many
Americans now turn to the Internet to obtain news,\8\ and its openness
makes it an unrivaled forum for free expression. Furthermore, local,
State, and Federal government agencies are increasingly using the
Internet to communicate with the public, including to provide
information about and deliver essential services.
---------------------------------------------------------------------------
\8\ See WCB Letter 12/10/10, Attach. at 133-41, Pew Research
Ctr. for People and the Press, Americans Spend More Time Following
the News; Ideological News Sources: Who Watches and Why 17, 22
(Sept. 12, 2010), people-press.org/report/652/ (stating that ``44%
of Americans say they got news through one or more Internet or
mobile digital source yesterday''); WCB Letter 12/10/10, Attach. at
131-32, TVB Local Media Marketing Solutions, Local News: Local TV
Stations are the Top Daily News Source, http://www.tvb.org/planning_buying/120562 (estimating that 61% of Americans get news
from the Internet) (``TVB''). However, according to the Pew Project
for Excellence in Journalism, the majority of news that people
access online originates from legacy media. See Pew Project for
Excellence in Journalism, The State of the News Media: An Annual
Report on American Journalism (2010), http://www.stateofthemedia.org/2010/overview_key_findings.php (``Of news
sites with half a million visitors a month (or the top 199 news
sites once consulting, government and information data bases are
removed), 67% are from legacy media, most of them (48%)
newspapers.'').
---------------------------------------------------------------------------
Television and radio broadcasters now provide news and other
information online via their own Web sites, online aggregation Web
sites such as Hulu, and social networking platforms. Local broadcasters
are experimenting with new approaches to delivering original content,
for example by creating neighborhood-focused Web sites; delivering news
clips via online video programming aggregators, including AOL and
Google's YouTube; and offering news from citizen journalists. In
addition, broadcast networks license their full-length entertainment
programs for downloading or streaming to edge providers such as Netflix
and Apple.
[[Page 59195]]
Because these sites are becoming increasingly popular with the public,
online distribution has a strategic value for broadcasters, and is
likely to provide an increasingly important source of funding for
broadcast news and entertainment programming.
Unimpeded access to Internet distribution likewise has allowed new
video content creators to create and disseminate programs without first
securing distribution from broadcasters and multichannel video
programming distributors (MVPDs) such as cable and satellite television
companies. Online viewing of video programming content is growing
rapidly.\9\
---------------------------------------------------------------------------
\9\ See Google Comments at 28; Motorola Comments at 5; MPAA
Comments at 5-6; DISH Reply at 4-5; WCB Letter 12/10/10, Attach. at
22-23, Online Video Goes Mainstream, eMarketer, Apr. 28, 2010,
http://www.emarketer.com/Article.aspx?R=1007664 (estimating that 29%
of Internet users younger than 25 say they watch all or most of
their TV online, that as of April 2010 67% of U.S. Internet users
watch online video each month, and that this figure will increase to
77% by 2014); WCB Letter 12/10/10, Attach. at 20-21, Chris Nuttall,
Web TVs bigger for manufacturers than 3D, Financial Times, Aug. 29,
2010, http://www.ft.com/cms/s/2/0b34043a-9fe3-11df-8cc5-00144feabdc0.html (stating that 28 million Internet-enabled TV sets
are expected to be sold in 2010, an increase of 125% from 2009); WCB
Letter 12/13/10, Attach. at 291-92, Sandvine, News and Events: Press
Releases, http://www.sandvine.com/news/pr_detail.asp?ID=288
(estimating that Netflix represents more than 20% of peak downstream
Internet traffic). Cisco expects online viewing to exert significant
influence on future demand for broadband capacity, ranking as the
top source of Internet traffic by the end of 2010 and accounting for
91% of global Internet traffic by 2014. WCB Letter 12/10/10, Attach.
at 40-42, Press Release, Cisco, Annual Cisco Visual Networking Index
Forecast Projects Global IP Traffic To Increase More than Fourfold
by 2014 (June 10, 2010), http://www.cisco.com/web/MT/news/10/news_100610.html.
---------------------------------------------------------------------------
In the Open Internet NPRM, the Commission sought comment on
possible implications that the proposed rules might have ``on efforts
to close the digital divide and encourage robust broadband adoption and
participation in the Internet community by minorities and other
socially and economically disadvantaged groups.'' As we noted in the
Open Internet NPRM, according to a 2009 study, broadband adoption
varies significantly across demographic groups.\10\ We expect that open
Internet protections will help close the digital divide by maintaining
relatively low barriers to entry for underrepresented groups and
allowing for the development of diverse content, applications, and
services.\11\
---------------------------------------------------------------------------
\10\ See Pew Internet & Am. Life Project, Home Broadband
Adoption (June 2009). Approximately 14 to 24 million Americans
remain without broadband access capable of meeting the requirements
set forth in Section 706 of the Telecommunications Act of 1996, as
amended. Inquiry Concerning the Deployment of Advanced
Telecommunications Capability to All Americans in a Reasonable and
Timely Fashion, and Possible Steps to Accelerate Such Deployment
Pursuant to Section 706 of the Telecommunications Act of 1996, as
Amended by the Broadband Data Improvement Act et al., Sixth
Broadband Deployment Report, 25 FCC Rcd 9556, 9557, para. 1 (2010)
(Sixth Broadband Deployment Report).
\11\ For example, Jonathan Moore founded Rowdy Orbit IPTV, an
online platform featuring original programming for minority
audiences, because he was frustrated by the lack of representation
of people of color in traditional media. Dec. 15, 2009 Workshop Tr.
at 39-40, video available at http://www.openinternet.gov/workshops/speech-democratic-engagement-and-the-open-internet.html. The
Internet's openness--and the low costs of online entry--enables
businesses like Rowdy Orbit to launch without having to gain
approval from traditional media gatekeepers. Id. We will closely
monitor the effects of the open Internet rules we adopt in this
Order on the digital divide and on minority and disadvantaged
consumers. See generally ColorOfChange Comments; Dec. 15, 2009
Workshop Tr. at 52-60 (remarks of Ruth Livier, YLSE); 100 Black Men
of America et al. Comments at 1-2; Free Press Comments at 134-36;
Center for Media Justice et al. Comments at 7-9.
---------------------------------------------------------------------------
For all of these reasons, there is little dispute in this
proceeding that the Internet should continue as an open platform.
Accordingly, we consider below whether we can be confident that the
openness of the Internet will be self-perpetuating, or whether there
are threats to openness that the Commission can effectively mitigate.
B. Broadband Providers Have the Incentive and Ability to Limit Internet
Openness
For purposes of our analysis, we consider three types of Internet
activities: providing broadband Internet access service; providing
content, applications, services, and devices accessed over or connected
to broadband Internet access service (``edge'' products and services);
and subscribing to a broadband Internet access service that allows
access to edge products and services. These activities are not mutually
exclusive. For example, individuals who generate and share content such
as personal blogs or Facebook pages are both end users and edge
providers, and a single firm could both provide broadband Internet
access service and be an edge provider, as with a broadband provider
that offers online video content. Nevertheless, this basic taxonomy
provides a useful model for evaluating the risk and magnitude of harms
from loss of openness.
The record in this proceeding reveals that broadband providers
potentially face at least three types of incentives to reduce the
current openness of the Internet. First, broadband providers may have
economic incentives to block or otherwise disadvantage specific edge
providers or classes of edge providers, for example by controlling the
transmission of network traffic over a broadband connection, including
the price and quality of access to end users. A broadband provider
might use this power to benefit its own or affiliated offerings at the
expense of unaffiliated offerings.
Today, broadband providers have incentives to interfere with the
operation of third-party Internet-based services that compete with the
providers' revenue-generating telephony and/or pay-television services.
This situation contrasts with the first decade of the public Internet,
when dial-up was the primary form of consumer Internet access.
Independent companies such as America Online, CompuServe, and Prodigy
provided access to the Internet over telephone companies' phone lines.
As broadband has replaced dial-up, however, telephone and cable
companies have become the major providers of Internet access service.
Online content, applications, and services available from edge
providers over broadband increasingly offer actual or potential
competitive alternatives to broadband providers' own voice and video
services, which generate substantial profits. Interconnected Voice-
over-Internet-Protocol (VoIP) services, which include some over-the-top
VoIP services,\12\ ``are increasingly being used as a substitute for
traditional telephone service,'' \13\ and over-the-top
[[Page 59196]]
VoIP services represent a significant share of voice-calling minutes,
especially for international calls. Online video is rapidly growing in
popularity, and MVPDs have responded to this trend by enabling their
video subscribers to use the Internet to view their programming on
personal computers and other Internet-enabled devices. Online video
aggregators such as Netflix, Hulu, YouTube, and iTunes that are
unaffiliated with traditional MVPDs continue to proliferate and
innovate, offering movies and television programs (including broadcast
programming) on demand, and earning revenues from advertising and/or
subscriptions. Several MVPDs have stated publicly that they view these
services as a potential competitive threat to their core video
subscription service. Thus, online edge services appear likely to
continue gaining subscribers and market significance,\14\ which will
put additional competitive pressure on broadband providers' own
services. By interfering with the transmission of third parties'
Internet-based services or raising the cost of online delivery for
particular edge providers, telephone and cable companies can make those
services less attractive to subscribers in comparison to their own
offerings.
---------------------------------------------------------------------------
\12\ The Commission's rules define interconnected VoIP as ``a
service that: (1) Enables real-time, two-way voice communications;
(2) requires a broadband connection from the user's location; (3)
requires Internet protocol-compatible customer premises equipment
(CPE); and (4) permits users generally to receive calls that
originate on the public switched telephone network and to terminate
calls to the public switched telephone network.'' 47 CFR 9.3. Over-
the-top VoIP services require the end user to obtain broadband
transmission from a third-party provider, and providers of over-the-
top VoIP can vary in terms of the extent to which they rely on their
own facilities. See SBC Commc'ns Inc. and AT&T Corp. Applications
for Approval of Transfer of Control, WC Docket No, 05-65, Memorandum
Opinion and Order, 20 FCC Rcd 18290, 18337-38, para. 86 (2005).
\13\ Tel. Number Requirements for IP-Enabled Servs. Providers,
Report and Order, Declaratory Ruling, Order on Remand, and NPRM, 22
FCC Rcd 19531, 19547, para. 28 (2007); see also Vonage Comments at
3-4. In merger reviews and forbearance petitions, the Commission has
found the record ``inconclusive regarding the extent to which
various over-the-top VoIP services should be included in the
relevant product market for [mass market] local services.'' See,
e.g., Verizon Commc'ns Inc. and MCI, Inc. Application for Approval
of Transfer of Control, Memorandum Opinion and Order, 20 FCC Rcd
18433, 18480, para. 89 (2005); see also Petition of Qwest Corp. for
Forbearance Pursuant to 47 U.S.C. sec. 160(c) in the Phoenix,
Arizona Metropolitan Statistical Area, Memorandum Opinion and Order,
25 FCC Rcd 8622, 8650, para. 54 (2010) (Qwest Phoenix Order). In
contrast to those proceedings, we are not performing a market power
analysis in this proceeding, so we need not and do not here
determine with specificity whether, and to what extent, particular
over-the-top VoIP services constrain particular practices and/or
rates of services governed by Section 201. Cf. Qwest Phoenix Order,
25 FCC Rcd at 8647-48, paras. 46-47 (discussing the general approach
to product market definition); id. at 8651-52, paras. 55-56
(discussing the need for evidence that one service constrains the
price of another service to include them in the same product market
for purposes of a market power analysis).
\14\ See, e.g., WCB Letter 12/10/10, Attach. at 5763, Ryan
Fleming, New Report Shows More People Dropping Cable TV for Web
Broadcasts, Digital Trends, Apr. 16, 2010, available at http://www.digitaltrends.com/computing/new-report-shows-that-more-and-more-people-are-dropping-cable-tv-in-favor-of-web-broadcasts. Congress
recently recognized these developments by expanding disabilities
access requirements to include advanced communications services. See
Twenty-First Century Communications and Video Accessibility Act,
Public Law 111-260; see also 156 CONG. REC. 6005 (daily ed. July 26,
2010) (remarks of Rep. Waxman) (this legislation before us * * *
ensur[es] that Americans with disabilities can access the latest
communications technology.); id. at 6004 (remarks of Rep. Markey)
(``[T]he bill we are considering today significantly increases
accessibility for Americans with disabilities to the indispensable
telecommunications * * * tools of the 21st century.''); Letter from
Rick Chessen, NCTA, to Marlene H. Dortch, Secretary, FCC, GN Docket
No. 09-191 at 2 n.6 (filed Dec. 10, 2010).
---------------------------------------------------------------------------
In addition, a broadband provider may act to benefit edge providers
that have paid it to exclude rivals (for example, if one online video
site were to contract with a broadband provider to deny a rival video
site access to the broadband provider's subscribers). End users would
be harmed by the inability to access desired content, and this conduct
could lead to reduced innovation and fewer new services.\15\ Consistent
with these concerns, delivery networks that are vertically integrated
with content providers, including some MVPDs, have incentives to favor
their own affiliated content.\16\ If broadband providers had
historically favored their own affiliated businesses or those incumbent
firms that paid for advantageous access to end users, some innovative
edge providers that have today become major Internet businesses might
not have been able to survive.
---------------------------------------------------------------------------
\15\ See generally WCB Letter 12/10/10, Attach. at 23-27, Steven
C. Salop & David Scheffman, Raising Rivals' Cost, 73 Am. Econ. Rev.
267-71 (1983); WCB Letter 12/10/10, Attach. at 1-23, Steven C. Salop
& Thomas Krattenmaker, Anticompetitive Exclusion: Raising Rivals'
Costs to Achieve Power over Price, 96 Yale L.J. 214 (1986). See also
Andrew I. Gavil et al., Antitrust Law in Perspective: Cases,
Concepts and Problems in Competition Policy 1153-92 (2d ed. 2008)
(describing how policies fostering competition spur innovation). To
similar effect, a broadband provider may raise access fees to
disfavored edge providers, reducing their ability to profit by
raising their costs and limiting their ability to compete with
favored edge providers.
\16\ See Google Comments at 30-31; Netflix Comments at 7 n.10;
Vonage Reply at 4; WCB Letter 12/10/10, Attach. at 28-78, Austan
Goolsbee, Vertical Integration and the Market for Broadcast and
Cable Television Programming, Paper for the Federal Communications
Commission 31-32 (Sept. 5, 2007) (Goolsbee Study) (finding that
MVPDs excluded networks that were rivals of affiliated channels for
anticompetitive reasons). Cf. WCB Letter 12/10/10, Attach. at 85-87,
David Waterman & Andrew Weiss, Vertical Integration in Cable
Television 142-143 (1997) (MVPD exclusion of unaffiliated content
during an earlier time period); see also H.R. Rep. 102-628 (2d
Sess.) at 41 (1992) (``The Committee received testimony that
vertically integrated companies reduce diversity in programming by
threatening the viability of rival cable programming services.'').
In addition to the examples of actual misconduct that we provide,
the Goolsbee Study provides empirical evidence that cable providers
have acted in the past on anticompetitive incentives to foreclose
rivals, supporting our concern that these and other broadband
providers would act on analogous incentives in the future. We thus
disagree that we rely on ``speculative harms alone'' or have failed
to adduce ``empirical evidence.'' Baker Statement at * 1, * 4
(citing AT&T Reply Exh. 2 at 45 (J. Gregory Sidak & David J. Teece,
Innovation Spillovers and the ``Dirt Road'' Fallacy: The
Intellectual Bankruptcy of Banning Optional Transactions for
Enhanced Delivery over the Internet, 6 J. Competition L. & Econ.
521, 571-72 (2010)). To the contrary, the empirical evidence and the
misconduct that we describe below validate the economic theories
that inform our decision in this Order. Moreover, as we explain
below, by comparison to the benefits of the prophylactic measures we
adopt, the costs associated with these open Internet rules are
likely small.
---------------------------------------------------------------------------
Second, broadband providers may have incentives to increase
revenues by charging edge providers, who already pay for their own
connections to the Internet, for access or prioritized access to end
users. Although broadband providers have not historically imposed such
fees, they have argued they should be permitted to do so. A broadband
provider could force edge providers to pay inefficiently high fees
because that broadband provider is typically an edge provider's only
option for reaching a particular end user.\17\ Thus broadband providers
have the ability to act as gatekeepers.\18\
---------------------------------------------------------------------------
\17\ Some end users can be reached through more than one
broadband connection, sometimes via the same device (e.g., a
smartphone that has Wi-Fi and cellular connectivity). Even so, the
end user, not the edge provider, chooses which broadband provider
the edge provider must rely on to reach the end user.
\18\ Also known as a ``terminating monopolist.'' See, e.g., CCIA
Comments at 7; Skype Comments at 10-11; Vonage Comments at 9-10;
Google Reply at 8-14. A broadband provider can act as a gatekeeper
even if some edge providers would have bargaining power in
negotiations with broadband providers over access or prioritization
fees.
---------------------------------------------------------------------------
Broadband providers would be expected to set inefficiently high
fees to edge providers because they receive the benefits of those fees
but are unlikely to fully account for the detrimental impact on edge
providers' ability and incentive to innovate and invest, including the
possibility that some edge providers might exit or decline to enter the
market. The unaccounted-for harms to innovation are negative
externalities,\19\ and are likely to be particularly large because of
the rapid pace of Internet innovation, and wide-ranging because of the
role of the Internet as a general purpose technology. Moreover, fees
for access or prioritized access could trigger an ``arms race'' within
a given edge market segment. If one edge provider pays for access or
prioritized access to end users, subscribers may tend to favor that
provider's services, and competing edge providers may feel that they
must respond by paying, too.
---------------------------------------------------------------------------
\19\ A broadband provider may hesitate to impose costs on its
own subscribers, but it will typically not take into account the
effect that reduced edge provider investment and innovation has on
the attractiveness of the Internet to end users that rely on other
broadband providers--and will therefore ignore a significant
fraction of the cost of foregone innovation. See, e.g., OIC Comments
at 20-24. If the total number of broadband subscribers shrinks,
moreover, the social costs unaccounted for by the broadband provider
could also include the lost ability of the remaining end users to
connect with the subscribers that departed (foregone direct network
effects) and a smaller potential audience for edge providers. See,
e.g., id. at 23. Broadband providers are also unlikely to fully
account for the open Internet's power to enhance civic discourse
through news and information, or for its ability to enable
innovations that help address key national challenges such as
education, public safety, energy efficiency, and health care. See
ARL et al. Comments at 3; Google Reply at 39; American Recovery and
Reinvestment Act of 2009, Public Law 111-5, 123 Stat. 115 (2009).
---------------------------------------------------------------------------
Fees for access or prioritization to end users could reduce the
potential profit
[[Page 59197]]
that an edge provider would expect to earn from developing new
offerings, and thereby reduce edge providers' incentives to invest and
innovate.\20\ In the rapidly innovating edge sector, moreover, many new
entrants are new or small ``garage entrepreneurs,'' not large and
established firms. These emerging providers are particularly sensitive
to barriers to innovation and entry, and may have difficulty obtaining
financing if their offerings are subject to being blocked or
disadvantaged by one or more of the major broadband providers. In
addition, if edge providers need to negotiate access or prioritized
access fees with broadband providers,\21\ the resulting transaction
costs could further raise the costs of introducing new products and
might chill entry and expansion.\22\
---------------------------------------------------------------------------
\20\ See, e.g., ALA Comments at 3-4; ColorOfChange Comments at
3; Free Press Comments at 69; Google Comments at 34; Netflix
Comments at 4; OIC Comments at 29-30; DISH Reply at 10. Such fees
could also reduce an edge provider's incentive to invest in existing
offerings, assuming the fees would be expected to increase to the
extent improvements increased usage of the edge provider's
offerings.
\21\ Negotiations impose direct expenses and delay. See Google
Comments at 34. There may also be significant costs associated with
the possibility that the negotiating parties would reach an impasse.
See ALA Comments at 2 (``The cable TV industry offers a telling
example of the `pay to play' environment where some cable companies
do not offer their customers access to certain content because the
company has not successfully negotiated financial compensation with
the content provider.''). Edge providers may also bear costs arising
from their need to monitor the extent to which they actually receive
prioritized delivery.
\22\ See, e.g., Google Comments at 34-35; Shane Greenstein
Notice of Ex Parte, GN Docket No. 09-191, Transaction Cost,
Transparency, and Innovation for the Internet at 19, available at
http://www.openinternet.gov/workshops/innovation-investment-and-the-open-internet.html; van Schewick Jan. 19, 2010 Ex Parte Letter,
Opening Statement at 7 (arguing that the low costs of innovation not
only make many more applications worth pursuing, but also allow a
large and diverse group of people to become innovators, which in
turn increases the overall amount and quality of innovation). There
are approximately 1,500 broadband providers in the United States.
See Wireline Competition Bureau, FCC, Internet Access Services:
Status as of December 31, 2009 at 7, tbl. 13 (Dec. 2010) (FCC
Internet Status Report), available at http://www.fcc.gov/Daily_Releases/Daily_Business/2010/db1208/DOC-303405A1.pdf. The
innovative process frequently generates a large number of attempts,
only a few of which turn out to be highly successful. Given the
likelihood of failure, and that financing is not always readily
available to support research and development, the innovation
process in many sectors of the Internet's edge is likely to be
highly sensitive to the upfront costs of developing and introducing
new products. PIC Comments at 50 (``[I]t is unlikely that new
entrants will have the ability (both financially and with regard to
information) to negotiate with every ISP that serves the markets
that they are interested in.'').
---------------------------------------------------------------------------
Some commenters argue that an end user's ability to switch
broadband providers eliminates these problems. But many end users may
have limited choice among broadband providers, as discussed below.
Moreover, those that can switch broadband providers may not benefit
from switching if rival broadband providers charge edge providers
similarly for access and priority transmission and prioritize each edge
provider's service similarly. Further, end users may not know whether
charges or service levels their broadband provider is imposing on edge
providers vary from those of alternative broadband providers, and even
if they do have this information may find it costly to switch. For
these reasons, a dissatisfied end user, observing that some edge
provider services are subject to low transmission quality, might not
switch broadband providers (though they may switch to a rival edge
provider in the hope of improving quality).
Some commenters contend that, in the absence of open Internet
rules, broadband providers that earn substantial additional revenue by
assessing access or prioritization charges on edge providers could
avoid increasing or could reduce the rates they charge broadband
subscribers, which might increase the number of subscribers to the
broadband network. Although this scenario is possible,\23\ no broadband
provider has stated in this proceeding that it actually would use any
revenue from edge provider charges to offset subscriber charges. In
addition, these commenters fail to account for the likely detrimental
effects of access and prioritization charges on the virtuous circle of
innovation described above. Less content and fewer innovative offerings
make the Internet less attractive for end users than would otherwise be
the case. Consequently, we are unable to conclude that the possibility
of reduced subscriber charges outweighs the risks of harm described
herein.\24\
---------------------------------------------------------------------------
\23\ Economics literature recognizes that access charges could
be harmful under some circumstances and beneficial under others.
See, e.g., WCB Letter 12/10/10, Attach. at 1-62, E. Glen Weyl, A
Price Theory of Multi-Sided Platforms, 100 Am. Econ. Rev. 1642,
1642-72 (2010) (the effects of allowing broadband providers to
charge terminating rates to content providers are ambiguous); see
also WCB Letter 12/10/10, Attach. at 180-215, John Musacchio et al.,
A Two-Sided Market Analysis of Provider Investment Incentives with
an Application to the Net-Neutrality Issue, 8 Rev. of Network Econ.
22, 22-39 (2009) (noting that there are conditions under which ``a
zero termination price is socially beneficial''). Moreover, the
economic literature on two-sided markets is at an early stage of
development. AT&T Comments, Exh. 3, Schwartz Decl. at 16; Jeffrey A.
Eisenach (Eisenach) Reply at 11-12; cf., e.g., WCB Letter 12/10/10,
Attach. at 156-79, Mark Armstrong, Competition in Two-Sided Markets,
37 Rand J. of Econ. 668 (2006); WCB Letter 12/10/10, Attach. at 216-
302, Jean-Charles Rochet & Jean Tirole, Platform Competition in Two-
Sided Markets, 1 J. Eur. Econ. Ass'n 990 (2003).
\24\ Indeed, demand for broadband Internet access service might
decline even if subscriber fees fell, if the conduct of broadband
providers discouraged demand by blocking end user access to
preferred edge providers, slowing non-prioritized transmission, and
breaking the virtuous circle of innovation.
---------------------------------------------------------------------------
Third, if broadband providers can profitably charge edge providers
for prioritized access to end users, they will have an incentive to
degrade or decline to increase the quality of the service they provide
to non-prioritized traffic. This would increase the gap in quality
(such as latency in transmission) between prioritized access and non-
prioritized access, induce more edge providers to pay for prioritized
access, and allow broadband providers to charge higher prices for
prioritized access. Even more damaging, broadband providers might
withhold or decline to expand capacity in order to ``squeeze'' non-
prioritized traffic, a strategy that would increase the likelihood of
network congestion and confront edge providers with a choice between
accepting low-quality transmission or paying fees for prioritized
access to end users.
Moreover, if broadband providers could block specific content,
applications, services, or devices, end users and edge providers would
lose the control they currently have over whether other end users and
edge providers can communicate with them through the Internet. Content,
application, service, and device providers (and their investors) could
no longer assume that the market for their offerings included all U.S.
end users. And broadband providers might choose to implement
undocumented practices for traffic differentiation that undermine the
ability of developers to create generally usable applications without
having to design to particular broadband providers' unique practices or
business arrangements.\25\
---------------------------------------------------------------------------
\25\ See OIC Comments at 24; Free Press Comments at 45. The
transparency and reasonable network management guidelines we adopt
in this Order, in particular, should reduce the likelihood of such
fragmentation of the Internet.
---------------------------------------------------------------------------
All of the above concerns are exacerbated by broadband providers'
ability to make fine-grained distinctions in their handling of network
traffic as a result of increasingly sophisticated network management
tools. Such tools may be used for beneficial purposes, but they also
increase broadband providers' ability to act on incentives to engage in
[[Page 59198]]
network practices that would erode Internet openness.\26\
---------------------------------------------------------------------------
\26\ See CCIA/CEA Comments at 4; Free Press Comments at 29-30,
143-46; Google Comments at 32-34; Netflix Comments at 3; OIC
Comments at 14, 79-82; DISH Reply at 8-9; IPI Reply at 9; Vonage
Reply at 5. For examples of network management tools, see, for
example, WCB Letter 12/10/10, Attach. at 1-8, Allot Service Gateway,
Pushing the DPI Envelope: An Introduction, at 2 (June 2007),
available at http://www.sysob.com/download/AllotServiceGateway.pdf
(``Reduce the performance of applications with negative influence on
revenues (e.g. competitive VoIP services).''); WCB Letter 12/13/10,
Attach. at 289-90, Procera Networks, PLR, http://www.proceranetworks.com/customproperties/tag/Products-PLR.html; WCB
Letter 12/13/10, Attach. at 283-88, Cisco, http//:www.cisco.com/en/US/prod/collateral/ps7045/ps6129/ps6133/ps6150/prod_brochure0900aecd8025258e.pdf (marketing the ability of equipment to
identify VoIP, video, and other traffic types). Vendors market their
offerings as enabling broadband providers to ``make only modest
incremental infrastructure investments and to control operating
costs.'' WCB Letter 12/13/10, Attach. at 283, Cisco.
---------------------------------------------------------------------------
Although these threats to Internet-enabled innovation, growth, and
competition do not depend upon broadband providers having market power
with respect to end users,\27\ most would be exacerbated by such market
power. A broadband provider's incentive to favor affiliated content or
the content of unaffiliated firms that pay for it to do so, its
incentive to block or degrade traffic or charge edge providers for
access to end users, and its incentive to squeeze non-prioritized
transmission will all be greater if end users are less able to respond
by switching to rival broadband providers. The risk of market power is
highest in markets with few competitors, and most residential end users
today have only one or two choices for wireline broadband Internet
access service. As of December 2009, nearly 70 percent of households
lived in census tracts where only one or two wireline or fixed wireless
firms provided advertised download speeds of at least 3 Mbps and upload
speeds of at least 768 Kbps \28\--the closest observable benchmark to
the minimum download speed of 4 Mbps and upload speed of 1 Mbps that
the Commission has used to assess broadband deployment. About 20
percent of households are in census tracts with only one provider
advertising at least 3 Mbps down and 768 Kbps up. For Internet service
with advertised download speeds of at least 10 Mbps down and upload
speeds of at least 1.5 Mbps up, nearly 60 percent of households lived
in census tracts served by only one wireline or fixed wireless
broadband provider, while nearly 80 percent lived in census tracts
served by no more than two wireline or fixed wireless broadband
providers.
---------------------------------------------------------------------------
\27\ Because broadband providers have the ability to act as
gatekeepers even in the absence of market power with respect to end
users, we need not conduct a market power analysis.
\28\ See FCC Internet Status Report at 7, fig. 3(a). A broadband
provider's presence in a census tract does not mean it offers
service to all potential customers within that tract. And the data
reflect subscriptions, not network capability.
---------------------------------------------------------------------------
Including mobile broadband providers does not appreciably change
these numbers.\29\ The roll-out of next generation mobile services is
at an early stage, and the future of competition in residential
broadband is unclear.\30\ The record does not enable us to make a
predictive judgment that the future will be more competitive than the
past. Although wireless providers are increasingly offering faster
broadband services, we do not know, for example, how end users will
value the trade-offs between the benefits of wireless service (e.g.,
mobility) and the benefits of fixed wireline service (e.g., higher
download and upload speeds).\31\ We note that the two largest mobile
broadband providers also offer wireline or fixed service; \32\ this
could dampen their incentive to compete aggressively with wireline (or
fixed) services.\33\
---------------------------------------------------------------------------
\29\ In December 2009, nearly 60% of households lived in census
tracts where no more than two broadband providers offered service
with 3 Mbps down and 768 Kbps up, while no mobile broadband
providers offered service with 10 Mbps down and 1.5 Mbps up. Id. at
8, fig. 3(b). Mobile broadband providers generally have offered
bandwidths lower than those available from fixed providers. See
Yottabyte at 13-14.
\30\ See National Broadband Plan at 40-42. A number of
commenters discuss impediments to increased competition. See, e.g.,
Ad Hoc Comments at 9; Google Comments, at 18-22; IFTA Comments at
10-11; see also WCB Letter 12/10/10, Attach. at 9-16, Thomas Monath
et al., Economics of Fixed Broadband Network Strategies, 41 IEEE
Comm. Mag. 132, 132-39 (Sept. 2003).
\31\ See Ad Hoc Comments at 9; Google Comments at 21; Vonage
Comments at 8; IPI Reply at 14; WCB Letter 12/10/10, Attach. at 56-
65, Vikram Chandrasekhar & Jeffrey G. Andrews, Femtocell Networks: A
Survey, 46 IEEE Comm. Mag., Sept. 2008, 59, at 59-60 (explaining
mobile spectrum alone cannot compete with wireless connections to
fixed networks). We also do not know how offers by a single wireless
broadband provider for both fixed and mobile broadband services will
perform in the marketplace.
\32\ See OIC Comments at 71-72. Large cable companies that
provide fixed broadband also have substantial ownership interests in
Clear, the 4G wireless venture in which Sprint has a majority
ownership interest.
\33\ OIC Comments at 71-72; Skype Comments at 10. In cellular
telephony, multimarket conduct has been found to dampen competition.
See WCB Letter 12/10/10, Attach. at 1-24, P.M. Parker and L.H.
R[ouml]ller, Collusive conduct in duopolies: Multimarket contact and
cross ownership in the mobile telephone industry, 28 Rand J. Of
Econ. 304, 304-322 (Summer 1997); WCB Letter 12/10/10, Attach. at
25-58, Meghan R. Busse, Multimarket contact and price coordination
in the cellular telephone industry, 9 J. of Econ. & Mgmt. Strategy
287, 287-320 (Fall 2000). Moreover, some fixed broadband providers
also provide necessary inputs to some mobile providers' offerings,
such as backhaul transport to wireline facilities.
---------------------------------------------------------------------------
In addition, customers may incur significant costs in switching
broadband providers \34\ because of early termination fees; \35\ the
inconvenience of ordering, installation, and set-up, and associated
deposits or fees; possible difficulty returning the earlier broadband
provider's equipment and the cost of replacing incompatible customer-
owned equipment; the risk of temporarily losing service; the risk of
problems learning how to use the new service; and the possible loss of
a provider-specific e-mail address or Web site.
---------------------------------------------------------------------------
\34\ ARL et al. Comments at 5; Google Comments at 21-22; Netflix
Comments at 5; New Jersey Rate Counsel (NJRC) Comments at 17; OIC
Comments at 40, 73; PIC Comments at 23; Skype Comments at 12; OIC
Reply at 20-21; Paul Misener (Amazon.com) Comments at 2; see also
WCB Letter 12/10/10, Attach. at 59-76, Patrick Xavier & Dimitri
Ypsilanti, Switching Costs and Consumer Behavior: Implications for
Telecommunications Regulation, 10(4) Info 2008, 13, 13-29 (2008).
Churn is a function of many factors. See, e.g., WCB Letter 12/10/10,
Attach. at 1-53, 97-153, AT&T Comments, WT Docket No. 10-133, at 51
(Aug. 2, 2010). The evidence in the record, e.g., AT&T Comments at
83, is not probative as to the extent of competition among broadband
providers because it does not appropriately isolate a connection
between churn levels and the extent of competition.
\35\ Google Comments at 21-22. Of broadband end users with a
choice of broadband providers, 32% said paying termination fees to
their current provider was a major reason why they have not switched
service. FCC, Broadband Decision: What Drives Consumers to Switch--
Or Stick With--Their Broadband Internet Provider 8 (Dec. 2010) (FCC
Internet Survey), available at hraunfoss.fcc.gov/edocs_public/attachmatch/DOC-303264A1.pdf.
---------------------------------------------------------------------------
C. Broadband Providers Have Acted To Limit Openness
These dangers to Internet openness are not speculative or merely
theoretical. Conduct of this type has already come before the
Commission in enforcement proceedings. As early as 2005, a broadband
provider that was a subsidiary of a telephone company paid $15,000 to
settle a Commission investigation into whether it had blocked Internet
ports used for competitive VoIP applications. In 2008, the Commission
found that Comcast disrupted certain peer-to-peer (P2P) uploads of its
subscribers, without a reasonable network management justification and
without disclosing its actions. Comparable practices have been observed
in the provision of mobile broadband services. After entering into a
contract with a company to handle online payment services, a mobile
wireless provider allegedly blocked customers' attempts to use
competing services to make purchases using their mobile phones. A
nationwide mobile provider restricted the types of lawful applications
that could be accessed over its 3G mobile wireless network.
[[Page 59199]]
There have been additional allegations of blocking, slowing, or
degrading P2P traffic. We do not determine in this Order whether any of
these practices violated open Internet principles, but we note that
they have raised concerns among edge providers and end users,
particularly regarding lack of transparency. For example, in May 2008 a
major cable broadband provider acknowledged that it had managed the
traffic of P2P services. In July 2009, another cable broadband provider
entered into a class action settlement agreement stating that it had
``ceased P2P Network Management Practices,'' but allowing the provider
to resume throttling P2P traffic.\36\ There is evidence that other
broadband providers have engaged in similar degradation.\37\ In
addition, broadband providers' terms of service commonly reserve to the
provider sweeping rights to block, degrade, or favor traffic. For
example, one major cable provider reserves the right to engage,
``without limitation,'' in ``port blocking, * * * traffic
prioritization and protocol filtering.'' Further, a major mobile
broadband provider prohibits use of its wireless service for
``downloading movies using peer-to-peer file sharing services'' and
VoIP applications. And a cable modem manufacturer recently filed a
formal complaint with the Commission alleging that a major broadband
Internet access service provider has violated open Internet principles
through overly restrictive device approval procedures.
---------------------------------------------------------------------------
\36\ See RCN Settlement Agreement sec. 3.2. RCN denied any
wrongdoing, but it acknowledges that in order to ease network
congestion, it targeted specific P2P applications. See Letter from
Jean L. Kiddo, RCN, to Marlene Dortch, Secretary, FCC, GN Docket No.
09-191, WC Docket No. 07-52, at 2-5 (filed May 7, 2010).
\37\ A 2008 study by the Max Planck Institute revealed
significant blocking of BitTorrent applications in the United
States. Comcast and Cox were both cited as examples of providers
blocking traffic. See generally WCB Letter 12/10/10, Attach. at 75-
80, Marcel Dischinger et al., Max Planck Institute, Detecting
BitTorrent Blocking (2008), available at broadband.mpi-sws.org/transparency/results/08_imc_blocking.pdf; see also WCB Letter 12/
13/10, Attach. at 235-39, Max Planck Institute for Software Systems,
Glasnost: Results from Tests for BitTorrent Traffic Blocking,
broadband.mpi-sws.org/transparency/results; WCB Letter 12/13/10,
Attach. at 298-315, Christian Kreibich et al., Netalyzr:
Illuminating Edge Network Neutrality, Security, and Performance 15
(2010), available at http://www.icsi.berkeley.edu/pubs/techreports/TR-10-006.pdf.
---------------------------------------------------------------------------
These practices have occurred notwithstanding the Commission's
adoption of open Internet principles in the Internet Policy Statement;
enforcement proceedings against Madison River Communications and
Comcast for their interference with VoIP and P2P traffic, respectively;
Commission orders that required certain broadband providers to adhere
to open Internet obligations; longstanding norms of Internet openness;
and statements by major broadband providers that they support and are
abiding by open Internet principles.
D. The Benefits of Protecting the Internet's Openness Exceed the Costs
Widespread interference with the Internet's openness would likely
slow or even break the virtuous cycle of innovation that the Internet
enables, and would likely cause harms that may be irreversible or very
costly to undo. For example, edge providers could make investments in
reliance upon exclusive preferential arrangements with broadband
providers, and network management technologies may not be easy to
change.\38\ If the next revolutionary technology or business is not
developed because broadband provider practices chill entry and
innovation by edge providers, the missed opportunity may be
significant, and lost innovation, investment, and competition may be
impossible to restore after the fact. Moreover, because of the
Internet's role as a general purpose technology, erosion of Internet
openness threatens to harm innovation, investment in the core and at
the edge of the network, and competition in many sectors, with a
disproportionate effect on small, entering, and non-commercial edge
providers that drive much of the innovation on the Internet.\39\
Although harmful practices are not certain to become widespread, there
are powerful reasons for immediate concern, as broadband providers have
interfered with the open Internet in the past and have incentives and
an increasing ability to do so in the future. Effective open Internet
rules can prevent or reduce the risk of these harms, while helping to
assure Americans unfettered access to diverse sources of news,
information, and entertainment, as well as an array of technologies and
devices that enhance health, education, and the environment.
---------------------------------------------------------------------------
\38\ As one example, Comcast's transition to a protocol-agnostic
network management practice took almost nine months to complete. See
Letter from Kathryn A. Zachem, V.P., Regulatory Affairs, Comcast
Corp., to Marlene Dortch, Secretary, FCC, WC Docket No. 07-52 at 2
(filed July 10, 2008); Letter from Kathryn A. Zachem, V.P.,
Regulatory Affairs, Comcast Corp., to Marlene Dortch, Secretary,
FCC, WC Docket No. 07-52 at Attach. B at 3, 9 (filed Sept. 19, 2008)
(noting that the transition required ``lab tests, technical trials,
customer feedback, vendor evaluations, and a third-party consulting
analysis,'' as well as trials in five markets).
\39\ See, e.g., ALA Comments at 2; IFTA Comments at 14. Even
some who generally oppose open Internet rules agree that extracting
access fees from entities that produce content or services without
the anticipation of financial reward would have significant adverse
effects. See WCB Letter 12/10/10, Attach. at 35-80, C. Scott
Hemphill, Network Neutrality and the False Promise of Zero-Price
Regulation, 25 Yale J. on Reg. 135, 161-62 (2008) (``[S]ocial
production has distinctive features that make it unusually valuable,
but also unusually vulnerable, to a particular form of exclusion.
That mechanism of exclusion is not subject to the prohibitions of
antitrust law, moreover, presenting a relatively stronger argument
for regulation.''), cited in Prof. Tim Wu Comments at 9 n.22.
---------------------------------------------------------------------------
By comparison to the benefits of these prophylactic measures, the
costs associated with the open Internet rules adopted here are likely
small. Broadband providers generally endorse openness norms--including
the transparency and no blocking principles--as beneficial and in line
with current and planned business practices (though they do not
uniformly support rules making them enforceable).\40\ Even to the
extent rules require some additional disclosure of broadband providers'
practices, the costs of compliance should be modest. In addition, the
high-level rules we adopt carefully balance preserving the open
Internet against avoiding unduly burdensome regulation. Our rules
against blocking and unreasonable discrimination are subject to
reasonable network management, and our rules do not prevent broadband
providers from offering specialized services such as facilities-based
VoIP. In short, rules that reinforce the openness that has supported
the growth of the Internet, and do not substantially change this highly
successful status quo, should not entail significant compliance costs.
---------------------------------------------------------------------------
\40\ We note that many broadband providers are, or soon will be,
subject to open Internet requirements in connection with grants
under the Broadband Technology Opportunities Program (BTOP). The
American Recovery and Reinvestment Act of 2009 required that
nondiscrimination and network interconnection obligations be
``contractual conditions'' of all BTOP grants. Public Law 111-5,
sec. 6001(j), 123 Stat. 115 (codified at 47 U.S.C. sec. 1305). These
nondiscrimination and interconnection conditions require BTOP
grantees, among other things, to adhere to the principles in the
Internet Policy Statement; to display any network management
policies in a prominent location on the service provider's Web site;
and to offer interconnection where technically feasible.
---------------------------------------------------------------------------
Some commenters contend that open Internet rules are likely to
reduce investment in broadband deployment. We disagree. There is no
evidence that prior open Internet obligations have discouraged
investment; \41\ and
[[Page 59200]]
numerous commenters explain that, by preserving the virtuous circle of
innovation, open Internet rules will increase incentives to invest in
broadband infrastructure. Moreover, if permitted to deny access, or
charge edge providers for prioritized access to end users, broadband
providers may have incentives to allow congestion rather than invest in
expanding network capacity. And as described in Part III, below, our
rules allow broadband providers sufficient flexibility to address
legitimate congestion concerns and other network management
considerations. Nor is there any persuasive reason to believe that in
the absence of open Internet rules broadband providers would lower
charges to broadband end users, or otherwise change their practices in
ways that benefit innovation, investment, competition, or end users.
---------------------------------------------------------------------------
\41\ See, e.g., Free Press Comments at 4, 23-25; Google Comments
at 38-39; XO Comments at 12. In making prior investment decisions,
broadband providers could not have reasonably assumed that the
Commission would abstain from regulating in this area, as the
Commission's decisions classifying cable modem service and wireline
broadband Internet access service as information services included
notices of proposed rulemaking seeking comment on whether the
Commission should adopt rules to protect consumers. See Appropriate
Framework for Broadband Access to the Internet Over Wireline
Facilities et al., Report and Order and NPRM, 20 FCC Rcd 14853,
14929-35, paras. 146-59 (2005); Inquiry Concerning High-Speed Access
to the Internet Over Cable & Other Facilities et al., Declaratory
Ruling and NPRM, 17 FCC-- Rcd 4798, 4839-48, paras. 72-95 (2002)
(seeking comment on whether the Commission should require cable
operators to give unaffiliated ISPs access to broadband cable
networks); see also AT&T Comments at 8 (``[T]he existing principles
already address any blocking or degradation of traffic and thus
eliminate any theoretical leverage providers may have to impose
[unilateral `tolls'].'').
---------------------------------------------------------------------------
The magnitude and character of the risks we identify make it
appropriate to adopt prophylactic rules now to preserve the openness of
the Internet, rather than waiting for substantial, pervasive, and
potentially irreversible harms to occur before taking any action. The
Supreme Court has recognized that even if the Commission cannot
``predict with certainty'' the future course of a regulated market, it
may ``plan in advance of foreseeable events, instead of waiting to
react to them.'' Moreover, as the Commission found in another context,
``[e]xclusive reliance on a series of individual complaints,'' without
underlying rules, ``would prevent the Commission from obtaining a clear
picture of the evolving structure of the entire market, and addressing
competitive concerns as they arise. * * * Therefore, if the Commission
exclusively relied on individual complaints, it would only become aware
of specific * * * problems if and when the individual complainant's
interests coincided with those of the interest of the overall `public.'
''
Finally, we note that there is currently significant uncertainty
regarding the future enforcement of open Internet principles and what
constitutes appropriate network management, particularly in the wake of
the court of appeals' vacatur of the Comcast Network Management
Practices Order. A number of commenters, including leading broadband
providers, recognize the benefits of greater predictability regarding
open Internet protections.\42\ Broadband providers benefit from
increased certainty that they can reasonably manage their networks and
innovate with respect to network technologies and business models. For
those who communicate and innovate on the Internet, and for investors
in edge technologies, there is great value in having confidence that
the Internet will remain open, and that there will be a forum available
to bring complaints about violations of open Internet standards.\43\
End users also stand to benefit from assurances that services on which
they depend ``won't suddenly be pulled out from under them, held ransom
to extra payments either from the sites or from them.'' Providing clear
yet flexible rules of the road that enable the Internet to continue to
flourish is the central goal of the action we take in this Order.\44\
---------------------------------------------------------------------------
\42\ For example, AT&T has recognized that open Internet rules
``would reduce regulatory uncertainty, and should encourage
investment and innovation in next generation broadband services and
technologies.'' See WCB Letter 12/10/10, Attach. at 94, AT&T
Statement on Proposed FCC Rules to Preserve an Open Internet, AT&T
Public Policy Blog, Dec. 1, 2010, attpublicpolicy.com/government-policy/att-statement-on-proposed-fcc-rules-to-preserve-an-open-internet. Similarly, Comcast acknowledged that our proposed rules
would strike ``a workable balance between the needs of the
marketplace and the certainty that carefully-crafted and limited
rules can provide to ensure that Internet freedom and openness are
preserved.'' See David L. Cohen, FCC Proposes Rules to Preserve an
Open Internet, comcastvoices, Dec. 1, 2010, blog.comcast.com/2010/12/fcc-proposes-rules-to-preserve-an-open-internet.html; see also,
e.g., Final Brief for Intervenors NCTA and NBC Universal, Inc. at
11-13; 19-22, Comcast Corp. v. FCC, 600 F.3d 642 (DC Cir. 2010) (No.
08-1291). In addition to broadband providers, an array of industry
leaders, venture capitalists, and public interest groups have
concluded that our rules will promote investment in the Internet
ecosystem by removing regulatory uncertainty. See Free Press
Comments at 10; Google Comments at 40; PIC Comments at 28; WCB
Letter 12/10/10, Attach. at 91 (statement of CALinnovates.org), 96
(statement of Larry Cohen, president of the Communications Workers
of America), 98 (statement of Ron Conway, founder of SV Angel), 99
(statement of Craig Newmark, founder of craigslist), 105 (statement
of Dean Garfield, president and CEO of the Information Technology
Industry Council), 111 (Dec. 8, 2010 letter from Jeremy Liew,
Managing Director, Lightspeed Venture Partners to Julius
Genachowski, FCC Chairman), 112 (Dec. 1, 2010 letter from Jed Katz,
Managing Director, Javelin Venture Partners to Julius Genachowski,
FCC Chairman), 127 (statement of Gary Shapiro, president and CEO of
the Consumer Electronics Association), 128 (statement of Ram
Shriram, founder of Sherpalo Ventures), 132 (statements of Rey
Ramsey, President and CEO of TechNet, and John Chambers, Chairman
and CEO of Cisco), 133 (statement of John Doerr, Kleiner Perkins
Caufield & Byers); XO Reply at 6.
\43\ For this reason, we are not persuaded that alternative
approaches, such as rules that lack a formal enforcement mechanism,
a transparency rule alone, or reliance entirely on technical
advisory groups to resolve disputes, would adequately address the
potential harms and be less burdensome than the rules we adopt here.
See, e.g., Verizon Comments at 130-34. In particular, we reject the
notion that Commission action is unnecessary because the Department
of Justice and the Federal Trade Commission (FTC) ``are well
equipped to cure any market ills.'' Id. at 9. Our statutory
responsibilities are broader than preventing antitrust violations or
unfair competition. See, e.g., News Corp. and DIRECTV Group, Inc.,
23 FCC Rcd 3265, 3277-78, paras. 23-25 (2008). We must, for example,
promote deployment of advanced telecommunications capability, ensure
that charges in connection with telecommunications services are just
and reasonable, ensure the orderly development of local television
broadcasting, and promote the public interest through spectrum
licensing. See CDT Comments at 8-9; Comm'r Jon Liebowitz, FTC,
Concurring Statement of Commissioner Jon Leibowitz Regarding the
Staff Report: ``Broadband Connectivity Competition Policy'' (2007),
available at http://www.ftc.gov/speeches/leibowitz/V070000statement.pdf (``[T]here is little agreement over whether
antitrust, with its requirements for ex post case by case analysis,
is capable of fully and in a timely fashion resolving many of the
concerns that have animated the net neutrality debate.'').
\44\ Contrary to the suggestion of some, neither the Department
of Justice nor the FTC has concluded that the broadband market is
competitive or that open Internet rules are unnecessary. See
McDowell Statement at *4; Baker Statement at *3. In the submission
in question, the Department observed that: (1) The wireline
broadband market is highly concentrated, with most consumers served
by at most two providers; (2) the prospects for additional wireline
competition are dim due to the high fixed and sunk costs required to
provide wireline broadband service; and (3) the extent to which
mobile wireless offerings will compete with wireline offerings is
unknown. See DOJ Ex Parte Jan. 4, 2010, GN Dkt. No. 09-51, at 8, 10,
13-14. The Department specifically endorsed requiring greater
transparency by broadband providers, id. at 25-27, and recognized
that in concentrated markets, like the broadband market, it is
appropriate for policymakers to limit ``business practices that
thwart innovation.'' Id. at 11. Finally, although the Department
cautioned that care must be taken to avoid stifling infrastructure
investment, it expressed particular concern about price regulation,
which we are not adopting. Id. at 28. In 2007, the FTC issued a
staff report on broadband competition policy. See FTC, Broadband
Connectivity Competition Policy (June 2007). Like the Department,
the FTC staff did not conclude that the broadband market is
competitive. To the contrary, the FTC staff made clear that it had
not studied the state of competition in any specific markets. Id. at
8, 105, 156. With regard to the merits of open Internet rules, the
FTC staff report recited arguments pro and con, see, e.g., id. at
82, 105, 147-54, and called for additional study, id. at 7, 9-10,
157.
---------------------------------------------------------------------------
III. Open Internet Rules
To preserve the Internet's openness and broadband providers'
ability to manage and expand their networks, we adopt high-level rules
embodying four core principles: transparency, no blocking, no
unreasonable discrimination, and reasonable network management. These
rules are generally consistent with, and should not require
[[Page 59201]]
significant changes to, broadband providers' current practices, and are
also consistent with the common understanding of broadband Internet
access service as a service that enables one to go where one wants on
the Internet and communicate with anyone else online.\45\
---------------------------------------------------------------------------
\45\ The definition of ``broadband Internet access service''
proposed in the Open Internet NPRM encompassed any ``Internet
Protocol data transmission between an end user and the Internet.''
Open Internet NPRM, 24 FCC Rcd at 13128, App. A. Some commenters
argued that this definition would cover a variety of services that
do not constitute broadband Internet access service as end users and
broadband providers generally understand that term, but that merely
offer data transmission between a discrete set of Internet endpoints
(for example, virtual private networks, or videoconferencing
services). See, e.g., AT&T Comments at 96-100; Communications
Workers of America (CWA) Comments at 10-12; Sprint Reply at 16-17;
see also CDT Comments at 49-50 (distinguishing managed (or
specialized) services from broadband Internet access service by
defining the former, in part, as data transmission ``between an end
user and a limited group of parties or endpoints'') (emphasis
added).
---------------------------------------------------------------------------
A. Scope of the Rules
We find that open Internet rules should apply to ``broadband
Internet access service,'' which we define as:
A mass-market retail service by wire or radio that provides the
capability to transmit data to and receive data from all or
substantially all Internet endpoints, including any capabilities
that are incidental to and enable the operation of the
communications service, but excluding dial-up Internet access
service. This term also encompasses any service that the Commission
finds to be providing a functional equivalent of the service
described in the previous sentence, or that is used to evade the
protections set forth in this Part.
The term ``broadband Internet access service'' includes services
provided over any technology platform, including but not limited to
wire, terrestrial wireless (including fixed and mobile wireless
services using licensed or unlicensed spectrum), and satellite.\46\
---------------------------------------------------------------------------
\46\ In the Open Internet NPRM, we proposed separate definitions
of the terms ``broadband Internet access,'' and ``broadband Internet
access service.'' Open Internet NPRM, 24 FCC Rcd at 13128, App. A
sec. 8.3. For purposes of these rules, we find it simpler to define
just the service.
---------------------------------------------------------------------------
``Mass market'' means a service marketed and sold on a standardized
basis to residential customers, small businesses, and other end-user
customers such as schools and libraries. For purposes of this
definition, ``mass market'' also includes broadband Internet access
services purchased with the support of the E-rate program that may be
customized or individually negotiated. The term does not include
enterprise service offerings, which are typically offered to larger
organizations through customized or individually negotiated
arrangements.
``Broadband Internet access service'' encompasses services that
``provide the capability to transmit data to and receive data from all
or substantially all Internet endpoints.'' To ensure the efficacy of
our rules in this dynamic market, we also treat as a ``broadband
Internet access service'' any service the Commission finds to be
providing a functional equivalent of the service described in the
previous sentence, or that is used to evade the protections set forth
in these rules.
A key factor in determining whether a service is used to evade the
scope of the rules is whether the service is used as a substitute for
broadband Internet access service. For example, an Internet access
service that provides access to a substantial subset of Internet
endpoints based on end users preference to avoid certain content,
applications, or services; Internet access services that allow some
uses of the Internet (such as access to the World Wide Web) but not
others (such as e-mail); or a ``Best of the Web'' Internet access
service that provides access to 100 top Web sites could not be used to
evade the open Internet rules applicable to ``broadband Internet access
service.'' Moreover, a broadband provider may not evade these rules
simply by blocking end users' access to some Internet endpoints.
Broadband Internet access service likely does not include services
offering connectivity to one or a small number of Internet endpoints
for a particular device, e.g., connectivity bundled with e-readers,
heart monitors, or energy consumption sensors, to the extent the
service relates to the functionality of the device.\47\ Nor does
broadband Internet access service include virtual private network
services, content delivery network services, multichannel video
programming services, hosting or data storage services, or Internet
backbone services (if those services are separate from broadband
Internet access service). These services typically are not mass market
services and/or do not provide the capability to transmit data to and
receive data from all or substantially all Internet endpoints.\48\
---------------------------------------------------------------------------
\47\ To the extent these services are provided by broadband
providers over last-mile capacity shared with broadband Internet
access service, they would be specialized services.
\48\ We also note that our rules apply only as far as the limits
of a broadband provider's control over the transmission of data to
or from its broadband customers.
---------------------------------------------------------------------------
Although one purpose of our open Internet rules is to prevent
blocking or unreasonable discrimination in transmitting online traffic
for applications and services that compete with traditional voice and
video services, we determine that open Internet rules applicable to
fixed broadband providers should protect all types of Internet traffic,
not just voice or video Internet traffic. This reflects, among other
things, our view that it is generally preferable to neither require nor
encourage broadband providers to examine Internet traffic in order to
discern which traffic is subject to the rules. Even if we were to limit
our rules to voice or video traffic, moreover, it is unlikely that
broadband providers could reliably identify such traffic in all
circumstances, particularly if the voice or video traffic originated
from new services using uncommon protocols.\49\ Indeed, limiting our
rules to voice and video traffic alone could spark a costly and
wasteful cat-and-mouse game in which edge providers and end users
seeking to obtain the protection of our rules could disguise their
traffic as protected communications.\50\
---------------------------------------------------------------------------
\49\ This is true notwithstanding the increasing sophistication
of network management tools, described above in Part II.B. See
Arthur Callado et al., A Survey on Internet Traffic Identification,
11 IEEE Commnc'ns Surveys & Tutorials 37, 49 (2009).
\50\ See IETF, Reflections on Internet Transparency, RFC 4924 at
5 (Jul. 2007) (RFC 4924) (``In practice, filtering intended to block
or restrict application usage is difficult to successfully implement
without customer consent, since over time developers will tend to
re-engineer filtered protocols so as to avoid the filters. Thus over
time, filtering is likely to result in interoperability issues or
unnecessary complexity. These costs come without the benefit of
effective filtering. * * *''); IETF, Considerations on the Use of a
Service Identifier in Packet Headers, RFC 3639 at 3 (Oct. 2003) (RFC
3639) (``Attempts by intermediate systems to impose service-based
controls on communications against the perceived interests of the
end parties to the communication are often circumvented. Services
may be tunneled within other services, proxied by a collaborating
external host (e.g., an anonymous redirector), or simply run over an
alternate port (e.g., port 8080 vs port 80 for HTTP).''). Cf. RFC
3639 at 4 (``From this perspective of network and application
utility, it is preferable that no action or activity be undertaken
by any agency, carrier, service provider, or organization which
would cause end-users and protocol designers to generally obscure
service identification information from the IP packet header.'').
Our rules are nationwide and do not vary by geographic area,
notwithstanding potential variations across local markets for
broadband Internet access service. Uniform national rules create a
more predictable policy environment for broadband providers, many of
which offer services in multiple geographic areas. See, e.g., Level
3 Comments at 13; Charter Comments at iv. Edge providers will
benefit from uniform treatment of their traffic in different
localities and by different broadband providers. Broadband end users
will also benefit from uniform rules, which protect them regardless
of where they are located or which broadband provider they obtain
service from.
---------------------------------------------------------------------------
We recognize that there is one Internet (although it is comprised
of a multitude of different networks), and that it should remain open
and
[[Page 59202]]
interconnected regardless of the technologies and services end users
rely on to access it. However, for reasons discussed in Part III.E
below related to mobile broadband--including the fact that it is at an
earlier stage and more rapidly evolving--we apply open Internet rules
somewhat differently to mobile broadband than to fixed broadband at
this time. We define ``fixed broadband Internet access service'' as a
broadband Internet access service that serves end users primarily at
fixed endpoints using stationary equipment, such as the modem that
connects an end user's home router, computer, or other Internet access
device to the network. This term encompasses fixed wireless broadband
services (including services using unlicensed spectrum) and fixed
satellite broadband services. We define ``mobile broadband Internet
access service'' as a broadband Internet access service that serves end
users primarily using mobile stations. Mobile broadband Internet access
includes services that use smartphones as the primary endpoints for
connection to the Internet.\51\ The discussion in this Part applies to
both fixed and mobile broadband, unless specifically noted. Part III.E
further discusses application of open Internet rules to mobile
broadband.
---------------------------------------------------------------------------
\51\ We note that Section 337(f)(1) of the Act excludes public
safety services from the definition of mobile broadband Internet
access service.
---------------------------------------------------------------------------
For a number of reasons, these rules apply only to the provision of
broadband Internet access service and not to edge provider activities,
such as the provision of content or applications over the Internet.
First, the Communications Act particularly directs us to prevent harms
related to the utilization of networks and spectrum to provide
communication by wire and radio. Second, these rules are an outgrowth
of the Commission's Internet Policy Statement.\52\ The Statement was
issued in 2005 when the Commission removed key regulatory protections
from DSL service, and was intended to protect against the harms to the
open Internet that might result from broadband providers' subsequent
conduct. The Commission has always understood those principles to apply
to broadband Internet access service only, as have most private-sector
stakeholders.\53\ Thus, insofar as these rules translate existing
Commission principles into codified rules, it is appropriate to limit
the application of the rules to broadband Internet access service.
Third, broadband providers control access to the Internet for their
subscribers and for anyone wishing to reach those subscribers.\54\ They
are therefore capable of blocking, degrading, or favoring any Internet
traffic that flows to or from a particular subscriber.
---------------------------------------------------------------------------
\52\ When the Commission adopted the Internet Policy Statement,
it promised to incorporate the principles into ``ongoing
policymaking activities.'' Internet Policy Statement, 20 FCC Rcd at
14988, para. 5.
\53\ See, e.g., Appropriate Framework for Broadband Access to
the Internet over Wireline Facilities, Report and Order and Notice
of Proposed Rulemaking, 20 FCC Rcd 14853, 14976 (2005) (Wireline
Broadband Order) (separate statement of Chairman Martin); id. at
14980 (Statement of Commissioner Copps, concurring); id. at 14983
(Statement of Commissioner Adelstein, concurring); Verizon June 8,
2009 Comments, GN Docket No. 09-51, at 86 (``These principles have
helped to guide wireline providers' practices and to ensure that
consumers' expectations for their public Internet access services
are met.''). The Commission has conditioned wireline broadband
provider merger approvals on the merged entity's compliance with
these obligations. See, e.g., SBC Commc'ns Inc. and AT&T Corp.
Applications for Approval of Transfer of Control, Memorandum Opinion
and Order, 20 FCC Rcd 18290, 18392, para. 211 (2005).
\54\ We thus find broadband providers distinguishable from other
participants in the Internet marketplace. See, e.g., Verizon
Comments at 36-39 (discussing a variety of other participants in the
Internet ecosystem); Verizon Reply at 36-37 (same); NCTA Comments at
47-49 (same); NCTA Reply at 22 (same).
---------------------------------------------------------------------------
We also do not apply these rules to dial-up Internet access service
because telephone service has historically provided the easy ability to
switch among competing dial-up Internet access services. Moreover, the
underlying dial-up Internet access service is subject to protections
under Title II of the Communications Act. The Commission's
interpretation of those protections has resulted in a market for dial-
up Internet access that does not present the same concerns as the
market for broadband Internet access. No commenters suggested extending
open Internet rules to dial-up Internet access service.
Finally, we decline to apply our rules directly to coffee shops,
bookstores, airlines, and other entities when they acquire Internet
service from a broadband provider to enable their patrons to access the
Internet from their establishments (we refer to these entities as
``premise operators'').\55\ These services are typically offered by the
premise operator as an ancillary benefit to patrons. However, to
protect end users, we include within our rules broadband Internet
access services provided to premise operators for purposes of making
service available to their patrons.\56\ Although broadband providers
that offer such services are subject to open Internet rules, we note
that addressing traffic unwanted by a premise operator is a legitimate
network management purpose.\57\
---------------------------------------------------------------------------
\55\ See Communications Assistance for Law Enforcement Act and
Broadband Access and Services, First Report and Order and Further
Notice of Proposed Rulemaking, 20 FCC Rcd 14989, 15006-07, para. 36,
n.99 (2005) (CALEA Order). Consistent with the Commission's approach
in the CALEA Order, ``[w]e note * * * that the provider of
underlying [broadband service] facilities to such an establishment
would be subject to [the rules].'' Id. at 15007, para. 36.
\56\ We note that the premise operator that purchases the
Internet service remains the end user for purposes of our rules,
however. Moreover, although not bound by our rules, we encourage
premise operators to disclose relevant restrictions on broadband
service they make available to their patrons.
\57\ We also do not include within the rules free access to
individuals' wireless networks, even if those networks are
intentionally made available to others. See Electronic Frontier
Foundation (EFF) Comments at 25-28. No commenter argued that open
Internet rules should apply to individual operators of wireless
networks in these circumstances.
---------------------------------------------------------------------------
B. Transparency
Promoting competition throughout the Internet ecosystem is a
central purpose of these rules. Effective disclosure of broadband
providers' network management practices and the performance and
commercial terms of their services promotes competition--as well as
innovation, investment, end-user choice, and broadband adoption--in at
least five ways. First, disclosure ensures that end users can make
informed choices regarding the purchase and use of broadband service,
which promotes a more competitive market for broadband services and can
thereby reduce broadband providers' incentives and ability to violate
open Internet principles.\58\ Second, and relatedly, as end users'
confidence in broadband providers' practices increases, so too should
end users' adoption of broadband services--leading in turn to
additional investment in Internet infrastructure as contemplated by
Section 706 of the 1996 Act and other provisions of the communications
laws.\59\ Third,
[[Page 59203]]
disclosure supports innovation, investment, and competition by ensuring
that startups and other edge providers have the technical information
necessary to create and maintain online content, applications,
services, and devices, and to assess the risks and benefits of
embarking on new projects. Fourth, disclosure increases the likelihood
that broadband providers will abide by open Internet principles, and
that the Internet community will identify problematic conduct and
suggest fixes.\60\ Transparency thereby increases the chances that
harmful practices will not occur in the first place and that, if they
do, they will be quickly remedied, whether privately or through
Commission oversight. Fifth, disclosure will enable the Commission to
collect information necessary to assess, report on, and enforce the
other open Internet rules. For all of these reasons, most commenters
agree that informing end users, edge providers, and the Commission
about the network management practices, performance, and commercial
terms of broadband Internet access service is a necessary and
appropriate step to help preserve an open Internet.
---------------------------------------------------------------------------
\58\ Broadband providers may have an incentive not to provide
such information to end users, as doing so can lessen switching
costs for end users. Third-party information sources such as
Consumer Reports and the trade press do not routinely provide such
information. See CDT Comments at 31; CWA Comments at 21; DISH
Comments at 2; Google Comments at ii, 64-66; Level 3 Comments at 13;
Sandoval Reply at 60. Economic literature in this area also confirms
that policies requiring firms to disclose information generally
benefit competition and consumers. See, e.g., Mark Armstrong,
Interactions Between Competition and Consumer Policy, 4 Competition
Policy Int'l 97 113-16 (Spring 2008), eprints.ucl.ac.uk/7634/1/7634.pdf.
\59\ See PIC Reply at 16-18; Free Press Comments at 43-45; Ad
Hoc Comments at ii; CDT Comments at 5-7; ALA Comments at 3; National
Hispanic Media Coalition (NHMC) Comments at 8; National Broadband
Plan at 168, 174 (lack of trust in Internet is significant factor
preventing non-adopters from subscribing to broadband services); 47
U.S.C. secs. 151, 230, 254, 1302. A recent FCC survey found that
among non-broadband end users, 46% believed that the Internet is
dangerous for kids, and 57% believed that it was too easy for
personal information to be stolen online. John B. Horrigan, FCC
Survey: Broadband Adoption & Use in America 17 (Mar. 2010),
available at http://www.fcc.gov/DiversityFAC/032410/consumer-survey-horrigan.pdf.
\60\ On a number of occasions, broadband providers have blocked
lawful traffic without informing end users or edge providers. In
addition to the Madison River and Comcast-BitTorrent incidents
described above, broadband providers appear to have covertly blocked
thousands of BitTorrent uploads in the United States throughout
early 2008. See Marcel Dischinger et al.; Catherine Sandoval,
Disclosure, Deception, and Deep-Packet Inspection, 78 Fordham L.
Rev. 641, 666-84 (2009).
---------------------------------------------------------------------------
The Open Internet NPRM sought comment on what end users and edge
providers need to know about broadband service, how this information
should be disclosed, when disclosure should occur, and where
information should be available. The resulting record supports adoption
of the following rule:
A person engaged in the provision of broadband Internet access
service shall publicly disclose accurate information regarding the
network management practices, performance, and commercial terms of
its broadband Internet access services sufficient for consumers to
make informed choices regarding use of such services and for
content, application, service, and device providers to develop,
market, and maintain Internet offerings.\61\
---------------------------------------------------------------------------
\61\ For purposes of these rules, ``consumer'' includes any
subscriber to the broadband provider's broadband Internet access
service, and ``person'' includes any ``individual, group of
individuals, corporation, partnership, association, unit of
government or legal entity, however organized,'' cf. 47 CFR
54.8(a)(6). We also expect broadband providers to disclose
information about the impact of ``specialized services,'' if any, on
last-mile capacity available for, and the performance of, broadband
Internet access service.
The rule does not require public disclosure of competitively
sensitive information or information that would compromise network
security or undermine the efficacy of reasonable network management
practices.\62\ For example, a broadband provider need not publicly
disclose information regarding measures it employs to prevent spam
practices at a level of detail that would enable a spammer to defeat
those measures.
---------------------------------------------------------------------------
\62\ Commenters disagree on the risks of requiring disclosure of
information regarding technical, proprietary, and security-related
management practices. Compare, e.g., American Cable Association
(ACA) Comments at 17; AFTRA et al. Comments at ii, 16; Cox Comments
at 11; Fiber-to-the-Home Council (FTTH) Comments at 3, 27; Libove
Comments at 4; Sprint Comments at 16; T-Mobile Comments at 39, with,
e.g., Free Press Comments at 117-18; Free Press Reply at 17-19;
Digital Education Coalition (DEC) Comments at 14; NJRC Comments at
20-21. We may subsequently require disclosure of such information to
the Commission; to the extent we do, we will ensure that such
information is protected consistent with existing Commission
procedures for treatment of confidential information.
---------------------------------------------------------------------------
Despite broad agreement that broadband providers should disclose
information sufficient to enable end users and edge providers to
understand the capabilities of broadband services, commenters disagree
about the appropriate level of detail required to achieve this goal. We
believe that at this time the best approach is to allow flexibility in
implementation of the transparency rule, while providing guidance
regarding effective disclosure models. We expect that effective
disclosures will likely include some or all of the following types of
information, timely and prominently disclosed in plain language
accessible to current and prospective end users and edge providers, the
Commission, and third parties who wish to monitor network management
practices for potential violations of open Internet principles: \63\
---------------------------------------------------------------------------
\63\ In setting forth the following categories of information
subject to the transparency principle, we assume that the broadband
provider has chosen to offer its services on standardized terms,
although providers of ``information services'' are not obligated to
do so. If the provider tailors its terms of service to meet the
requirements of an individual end user, those terms must at a
minimum be disclosed to the end user in accordance with the
transparency principle.
---------------------------------------------------------------------------
Network Practices
Congestion Management: If applicable, descriptions of
congestion management practices; types of traffic subject to practices;
purposes served by practices; practices' effects on end users'
experience; criteria used in practices, such as indicators of
congestion that trigger a practice, and the typical frequency of
congestion; usage limits and the consequences of exceeding them; and
references to engineering standards, where appropriate.\64\
---------------------------------------------------------------------------
\64\ We note that the description of congestion management
practices provided by Comcast in the wake of the Comcast-BitTorrent
incident likely satisfies the transparency rule with respect to
congestion management practices. See Comcast, Network Management
Update, http://www.comcast.net/terms/network/update; Comcast,
Comcast Corporation Description of Planned Network Management
Practices to be Deployed Following the Termination of Current
Practices, downloads.comcast.net/docs/Attachment_B_Future_Practices.pdf.
---------------------------------------------------------------------------
Application-Specific Behavior: If applicable, whether and
why the provider blocks or rate-controls specific protocols or protocol
ports, modifies protocol fields in ways not prescribed by the protocol
standard, or otherwise inhibits or favors certain applications or
classes of applications.
Device Attachment Rules: If applicable, any restrictions
on the types of devices and any approval procedures for devices to
connect to the network. (For further discussion of required disclosures
regarding device and application approval procedures for mobile
broadband providers, see infra.)
Security: If applicable, practices used to ensure end-user
security or security of the network, including types of triggering
conditions that cause a mechanism to be invoked (but excluding
information that could reasonably be used to circumvent network
security).
Performance Characteristics
Service Description: A general description of the service,
including the service technology, expected and actual access speed and
latency, and the suitability of the service for real-time applications.
Impact of Specialized Services: If applicable, what
specialized services, if any, are offered to end users, and whether and
how any specialized services may affect the last-mile capacity
available for, and the performance of, broadband Internet access
service.
Commercial Terms
Pricing: For example, monthly prices, usage-based fees,
and fees for early termination or additional network services.
Privacy Policies: For example, whether network management
practices entail inspection of network traffic, and
[[Page 59204]]
whether traffic information is stored, provided to third parties, or
used by the carrier for non-network management purposes.
Redress Options: Practices for resolving end-user and edge
provider complaints and questions.
We emphasize that this list is not necessarily exhaustive, nor is it a
safe harbor--there may be additional information, not included above,
that should be disclosed for a particular broadband service to comply
with the rule in light of relevant circumstances. Broadband providers
should examine their network management practices and current
disclosures to determine what additional information, if any, should be
disclosed to comply with the rule.
In the Open Internet NPRM, we proposed that broadband providers
publicly disclose their practices on their Web sites and in promotional
materials. Most commenters agree that a provider's Web site is a
natural place for end users and edge providers to find disclosures, and
several contend that a broadband provider's only obligation should be
to post its practices on its Web site. Others assert that disclosures
should also be displayed prominently at the point-of-sale, in bill
inserts, and in the service contract. We agree that broadband providers
must, at a minimum, prominently display or provide links to disclosures
on a publicly available, easily accessible Web site that is available
to current and prospective end users and edge providers as well as to
the Commission, and must disclose relevant information at the point of
sale. Current end users must be able to easily identify which
disclosures apply to their service offering. Broadband providers'
online disclosures shall be considered disclosed to the Commission for
purposes of monitoring and enforcement. We may require additional
disclosures directly to the Commission.
We anticipate that broadband providers may be able to satisfy the
transparency rule through a single disclosure, and therefore do not at
this time require multiple disclosures targeted at different
audiences.\65\ We also decline to adopt a specific format for
disclosures, and instead require that disclosure be sufficiently clear
and accessible to meet the requirements of the rule.\66\ We will,
however, continue to monitor compliance with this rule, and may require
adherence to a particular set of best practices in the future.\67\
---------------------------------------------------------------------------
\65\ But we expect that broadband providers will make
disclosures in a manner accessible by people with disabilities.
\66\ Some commenters advocate for a standard disclosure format.
See, e.g., Adam Candeub et al. Reply at 7; Level 3 Comments at 13;
Sprint Comments at 17. Others support a plain language requirement.
See, e.g., NATOA Comments at 7; NJRC Comments at 19; IFTA Comments
at 16. Other commenters, however, argue against the imposition of a
standard format as inflexible and difficult to implement. See, e.g.,
Cox Comments at 10; National Telecommunications Cooperative
Association (NTCA) Comments at 9; Qwest Comments at 11. The approach
we adopt is similar to the approach adopted in the Commission's
Truth-in-Billing Proceeding, where we set out basic guidelines.
Truth-in-Billing and Billing Format, First Report and Order and
Further NPRM, 14 FCC Rcd 7492, 7495-96, paras. 3-5 (1999).
\67\ We may address this issue as part of a separate, ongoing
proceeding regarding transparency for communications services more
generally. Consumer Information and Disclosure, Notice of Inquiry,
FCC 09-68 (rel. Aug. 28, 2010). Relatedly, the Commission has begun
an effort, in partnership with broadband providers, to measure the
actual speed and performance of broadband service, and we expect
that the data generated by this effort will inform Commission
efforts regarding disclosure. See Comment Sought on Residential
Fixed Broadband Services Testing and Measurement Solution, Pleading
Cycle Established, Public Notice, 25 FCC Rcd 3836 (2010) (SamKnows
project); Comment Sought on Measurement of Mobile Broadband Network
Performance and Coverage, Public Notice, 25 FCC Rcd 7069 (2010)
(same).
---------------------------------------------------------------------------
Although some commenters assert that a disclosure rule will impose
significant burdens on broadband providers, no commenter cites any
particular source of increased costs, or attempts to estimate costs of
compliance. For a number of reasons, we believe that the costs of the
disclosure rule we adopt in this Order are outweighed by the benefits
of empowering end users and edge providers to make informed choices and
of facilitating the enforcement of the other open Internet rules.
First, we require only that providers post disclosures on their Web
sites and provide disclosure at the point of sale, not that they bear
the cost of printing and distributing bill inserts or other paper
documents to all existing customers.\68\ Second, although we may
subsequently determine that it is appropriate to require that specific
information be disclosed in particular ways, the transparency rule we
adopt in this Order gives broadband providers some flexibility to
determine what information to disclose and how to disclose it. We also
expressly exclude from the rule competitively sensitive information,
information that would compromise network security, and information
that would undermine the efficacy of reasonable network management
practices. Third, as discussed below, by setting the effective date of
these rules as November 20, 2011, we give broadband providers adequate
time to develop cost effective methods of compliance.
---------------------------------------------------------------------------
\68\ In a separate proceeding, the Commission has determined
that the costs of making disclosure materials available on a service
provider's Web site are outweighed by the public benefits where the
disclosure requirement applies only to entities already using the
Internet for other purposes. See Standardized and Enhanced
Disclosure Requirements for Television Broadcast Licensee Public
Interest Obligations, Report and Order, 23 FCC Rcd 1274, 1277-78,
paras. 7-10 (2008).
---------------------------------------------------------------------------
A key purpose of the transparency rule is to enable third-party
experts such as independent engineers and consumer watchdogs to monitor
and evaluate network management practices, in order to surface concerns
regarding potential open Internet violations. We also note the
existence of free software tools that enable Internet end users and
edge providers to monitor and detect blocking and discrimination by
broadband providers.\69\ Although current tools cannot detect all
instances of blocking or discrimination and cannot substitute for
disclosure of network management policies, such tools may help
supplement the transparency rule we adopt in this Order.\70\
---------------------------------------------------------------------------
\69\ See Sandoval Comments at 4-5. For example, the Max Planck
Institute analyzed data collected by the Glasnost tool from
thousands of end user, and found that broadband providers were
discriminating against application-specific traffic. See WCB Letter
12/13/10, Attach. at 235-39, Max Planck Institute for Software
Systems, Glasnost: Results from Tests for BitTorrent Traffic
Blocking, broadband.mpi-sws.org/transparency/results. Netalyzr is a
National Science Foundation-funded project that tests a wide range
of network characteristics. See International Computer Science
Institute, Netalyzer, netalyzr.icsi.berkeley.edu. Similar tools are
being developed for mobile broadband services. See, e.g., WindRider,
Mobile Network Neutrality Monitoring System, http://
www.cs.northwestern.edu/~ict992/mobile.htm.
\70\ For an example of a public-private partnership that could
encourage the development of new tools to assess network management
practices, see FCC Open Internet Apps Challenge, http://www.openinternet.gov/challenge.
---------------------------------------------------------------------------
Although transparency is essential for preserving Internet
openness, we disagree with commenters that suggest it is alone
sufficient to prevent open Internet violations. The record does not
convince us that a transparency requirement by itself will adequately
constrain problematic conduct, and we therefore adopt two additional
rules, as discussed below.
C. No Blocking and No Unreasonable Discrimination
1. No Blocking
The freedom to send and receive lawful content and to use and
provide applications and services without fear of blocking is essential
to the Internet's openness and to competition in adjacent markets such
as voice communications and video and audio programming. Similarly, the
ability to connect and use
[[Page 59205]]
any lawful devices that do not harm the network helps ensure that end
users can enjoy the competition and innovation that result when device
manufacturers can depend on networks' openness.\71\ Moreover, the no-
blocking principle has been broadly accepted since its inclusion in the
Commission's Internet Policy Statement. Major broadband providers
represent that they currently operate consistent with this principle
and are committed to continuing to do so.\72\
---------------------------------------------------------------------------
\71\ The Commission has long protected end users' rights to
attach lawful devices that do not harm communications networks. See,
e.g., Use of the Carterfone Device in Message Toll Telephone
Service, 13 FCC 2d 420, 424 (1968); Amendment of Section 64.702 of
the Commission's Rules and Regulations (Second Computer Inquiry),
Final Decision, 77 FCC 2d 384, 388 (1980); see also Michael T.
Hoeker, From Carterfone to the iPhone: Consumer Choice in the
Wireless Telecommunications Marketplace, 17 CommLaw Conspectus 187,
192 (2008); Kevin Werbach, The Federal Computer Commission, 84 N.C.
L. Rev. 1, 21 (2005).
\72\ As Qwest states, ``Qwest and virtually all major broadband
providers have supported the FCC Internet Policy Principles and
voluntarily abide by those principles as good policy.'' Qwest PN
Comments at 2-3, 5; see also, e.g., Comcast Comments at 27;
Clearwire Comments at 1; Margaret Boles, AT&T on Comcast v. FCC
Decision, AT&T Pub. Pol'y Blog (Apr. 6, 2010), attpublicpolicy.com/broadband-policy/att-statement-on-comcast-v-fcc-decision.
---------------------------------------------------------------------------
In the Open Internet NPRM, the Commission proposed codifying the
original three Internet Policy Statement principles that addressed
blocking of content, applications and services, and devices. After
consideration of the record, we consolidate the proposed rules into a
single rule for fixed broadband providers: \73\
---------------------------------------------------------------------------
\73\ As described below, we adopt a tailored version of this
rule for mobile broadband providers.
A person engaged in the provision of fixed broadband Internet
access service, insofar as such person is so engaged, shall not
block lawful content, applications, services, or non-harmful
---------------------------------------------------------------------------
devices, subject to reasonable network management.
The phrase ``content, applications, services'' refers to all
traffic transmitted to or from end users of a broadband Internet access
service, including traffic that may not fit cleanly into any of these
categories.\74\ The rule protects only transmissions of lawful content,
and does not prevent or restrict a broadband provider from refusing to
transmit unlawful material such as child pornography.\75\
---------------------------------------------------------------------------
\74\ See William Lehr et al. Comments at 27 (``While the
proposed rules of the FCC appear to make a clear distinction between
applications and services on the one hand (rule 3) and content (rule
1), we believe that there will be some activities that do not fit
cleanly into these two categories''); PIC Comments at 39; RFC 4924
at 5. For this reason the rule may prohibit the blocking of a port
or particular protocol used by an application, without blocking the
application completely, unless such practice is reasonable network
management. See Distributed Computing Industry Ass'n (DCIA) Comments
at 7 (discussing work-arounds by P2P companies facing port blocking
or other practices); Sandvine Reply at 3; RFC 4924. The rule also is
neutral with respect to where in the protocol stack or in the
network blocking could occur.
\75\ The ``no blocking'' rule does not impose any independent
legal obligation on broadband Internet access service providers to
be the arbiter of what is lawful. See, e.g., WISPA Comments at 12-
13.
---------------------------------------------------------------------------
We also note that the rule entitles end users to both connect and
use any lawful device of their choice, provided such device does not
harm the network.\76\ A broadband provider may require that devices
conform to widely accepted and publicly-available standards applicable
to its services.\77\
---------------------------------------------------------------------------
\76\ We note that MVPDs, pursuant to Section 629 and the
Commission's implementing regulations, are already subject to
similar requirements that give end users the right to attach devices
to an MVPD system provided that the attached equipment does not
cause electronic or physical harm or assist in the unauthorized
receipt of service. See Implementation of Section 304 of the
Telecommunications Act of 1996, Commercial Availability of
Navigation Devices, Report and Order, 13 FCC Rcd 14775 (1998); 47
U.S.C.. 549; 47 CFR 76.1201-03. Nothing in this Order is intended to
alter those existing rules.
\77\ For example, a DOCSIS-based broadband provider is not
required to support a DSL modem. See ACA Comments at 13-14; see also
Satellite Broadband Commenters Comments at 8-9 (noting that an
antenna and associated modem must comply with equipment and protocol
standards set by satellite companies, but that ``consumers can
[then] attach * * * any personal computer or wireless router they
wish'').
---------------------------------------------------------------------------
We make clear that the no-blocking rule bars broadband providers
from impairing or degrading particular content, applications, services,
or non-harmful devices so as to render them effectively unusable
(subject to reasonable network management).\78\ Such a prohibition is
consistent with the observation of a number of commenters that
degrading traffic can have the same effects as outright blocking, and
that such an approach is consistent with the traditional interpretation
of the Internet Policy Statement. The Commission has recognized that in
some circumstances the distinction between blocking and degrading (such
as by delaying) traffic is merely ``semantic.''
---------------------------------------------------------------------------
\78\ We do not find it appropriate to interpret our rule to
impose a blanket prohibition on degradation of traffic more
generally. Congestion ordinarily results in degradation of traffic,
and such an interpretation could effectively prohibit broadband
providers from permitting congestion to occur on their networks.
Although we expect broadband providers to continue to expand the
capacity of their networks--and we believe our rules help ensure
that they continue to have incentives to do so--we recognize that
some network congestion may be unavoidable. See, e.g., AT&T Comments
at 65; TWC Comments at 16-18; Internet Freedom Coalition Reply at 5.
---------------------------------------------------------------------------
Some concerns have been expressed that broadband providers may seek
to charge edge providers simply for delivering traffic to or carrying
traffic from the broadband provider's end-user customers. To the extent
that a content, application, or service provider could avoid being
blocked only by paying a fee, charging such a fee would not be
permissible under these rules.\79\
---------------------------------------------------------------------------
\79\ We do not intend our rules to affect existing arrangements
for network interconnection, including existing paid peering
arrangements.
---------------------------------------------------------------------------
2. No Unreasonable Discrimination
Based on our findings that fixed broadband providers have
incentives and the ability to discriminate in their handling of network
traffic in ways that can harm innovation, investment, competition, end
users, and free expression, we adopt the following rule:
A person engaged in the provision of fixed broadband Internet
access service, insofar as such person is so engaged, shall not
unreasonably discriminate in transmitting lawful network traffic
over a consumer's broadband Internet access service. Reasonable
network management shall not constitute unreasonable discrimination.
The rule strikes an appropriate balance between restricting harmful
conduct and permitting beneficial forms of differential treatment. As
the rule specifically provides, and as discussed below, discrimination
by a broadband provider that constitutes ``reasonable network
management'' is ``reasonable'' discrimination.\80\ We provide further
guidance regarding distinguishing reasonable from unreasonable
discrimination:
---------------------------------------------------------------------------
\80\ We also make clear that open Internet protections coexist
with other legal and regulatory frameworks. Except as otherwise
described in this Order, we do not address the possible application
of the no unreasonable discrimination rule to particular
circumstances, despite the requests of certain commenters. See,
e.g., AT&T Comments at 64-77, 108-12; PAETEC Comments at 13; see
also AT&T Comments at 56 (arguing that some existing agreements
could be at odds with limitations on pay for priority arrangements).
Rather, we find it more appropriate to address the application of
our rule in the context of an appropriate Commission proceeding with
the benefit of a more comprehensive record.
---------------------------------------------------------------------------
Transparency. Differential treatment of traffic is more likely to
be reasonable the more transparent to the end user that treatment is.
The Commission has previously found broadband provider practices to
violate open Internet principles in part because they were not
disclosed to end users. Transparency is particularly important with
respect to the discriminatory treatment of traffic as it is often
difficult for end users to determine the causes of slow or poor
performance of content, applications, services, or devices.
End-User Control. Maximizing end-user control is a policy goal
Congress
[[Page 59206]]
recognized in Section 230(b) of the Communications Act, and end-user
choice and control are touchstones in evaluating the reasonableness of
discrimination.\81\ As one commenter observes, ``letting users choose
how they want to use the network enables them to use the Internet in a
way that creates more value for them (and for society) than if network
providers made this choice,'' and ``is an important part of the
mechanism that produces innovation under uncertainty.'' Thus, enabling
end users to choose among different broadband offerings based on such
factors as assured data rates and reliability, or to select quality-of-
service enhancements on their own connections for traffic of their
choosing, would be unlikely to violate the no unreasonable
discrimination rule, provided the broadband provider's offerings were
fully disclosed and were not harmful to competition or end users.\82\
We recognize that there is not a binary distinction between end-user
controlled and broadband-provider controlled practices, but rather a
spectrum of practices ranging from more end-user controlled to more
broadband provider-controlled.\83\ And we do not suggest that practices
controlled entirely by broadband providers are by definition
unreasonable.
---------------------------------------------------------------------------
\81\ ``The rapidly developing array of Internet and other
interactive computer services * * * offer[ ] users a great degree of
control over the information that they receive, as well as the
potential for even greater control in the future as technology
develops.'' 47 U.S.C. 230(a)(1)-(2) (emphasis added).
\82\ In these types of arrangements ``[t]he broadband provider
does not get any particular leverage, because the ability to select
which traffic gets priority lies with individual subscribers.
Meanwhile, an entity providing content, applications, or services
does not need to worry about striking up relationships with various
broadband providers to obtain top treatment. All it needs to worry
about is building relationships with users and explaining to those
users whether and how they may want to select the particular
content, application, or service for priority treatment.'' CDT
Comments at 27; see also Amazon Comments at 2-3; SureWest Comments
at 32-33.
\83\ We note that default settings set by broadband providers
would likely be considered more broadband provider-controlled than
end-user controlled. See generally Jason Scott Johnston, Strategic
Bargaining and the Economic Theory of Contract Default Rules, 100
Yale L.J. 615 (1990); Daniel Kahneman et al., Anomalies: The
Endowment Effect, Loss Aversion, and Status Quo Bias, 5 J. Econ.
Persp. 193, 197-99 (1991).
---------------------------------------------------------------------------
Some commenters suggest that open Internet protections would
prohibit broadband providers from offering their subscribers different
tiers of service or from charging their subscribers based on bandwidth
consumed. We are, of course, always concerned about anti-consumer or
anticompetitive practices, and we remain so here. However, prohibiting
tiered or usage-based pricing and requiring all subscribers to pay the
same amount for broadband service, regardless of the performance or
usage of the service, would force lighter end users of the network to
subsidize heavier end users. It would also foreclose practices that may
appropriately align incentives to encourage efficient use of networks.
The framework we adopt in this Order does not prevent broadband
providers from asking subscribers who use the network less to pay less,
and subscribers who use the network more to pay more.
Use-Agnostic Discrimination. Differential treatment of traffic that
does not discriminate among specific uses of the network or classes of
uses is likely reasonable. For example, during periods of congestion a
broadband provider could provide more bandwidth to subscribers that
have used the network less over some preceding period of time than to
heavier users. Use-agnostic discrimination (sometimes referred to as
application-agnostic discrimination) is consistent with Internet
openness because it does not interfere with end users' choices about
which content, applications, services, or devices to use. Nor does it
distort competition among edge providers.
Standard Practices. The conformity or lack of conformity of a
practice with best practices and technical standards adopted by open,
broadly representative, and independent Internet engineering,
governance initiatives, or standards-setting organizations is another
factor to be considered in evaluating reasonableness. Recognizing the
important role of such groups is consistent with Congress's intent that
our rules in the Internet area should not ``fetter[ ]'' the free market
with unnecessary regulation,\84\ and is consistent with broadband
providers' historic reliance on such groups.\85\ We make clear,
however, that we are not delegating authority to interpret or implement
our rules to outside bodies.
---------------------------------------------------------------------------
\84\ 47 U.S.C. 230(b)(2).
\85\ Broadband providers' practices historically have relied on
the efforts of such groups, which follow open processes conducive to
broad participation. See, e.g., William Lehr et al. Comments at 24;
Comcast Comments at 53-59; FTTH Comments at 12; Internet Society
(ISOC) Comments at 1-2; OIC Comments at 50-52; Comcast Reply at 5-7.
Moreover, Internet community governance groups develop and encourage
widespread implementation of best practices, supporting an
environment that facilitates innovation.
---------------------------------------------------------------------------
In evaluating unreasonable discrimination, the types of practices
we would be concerned about include, but are not limited to,
discrimination that harms an actual or potential competitor to the
broadband provider (such as by degrading VoIP applications or services
when the broadband provider offers telephone service), that harms end
users (such as by inhibiting end users from accessing the content,
applications, services, or devices of their choice), or that impairs
free expression (such as by slowing traffic from a particular blog
because the broadband provider disagrees with the blogger's message).
For a number of reasons, including those discussed above in Part
II.B, a commercial arrangement between a broadband provider and a third
party to directly or indirectly favor some traffic over other traffic
in the broadband Internet access service connection to a subscriber of
the broadband provider (i.e., ``pay for priority'') would raise
significant cause for concern.\86\ First, pay for priority would
represent a significant departure from historical and current practice.
Since the beginning of the Internet, Internet access providers have
typically not charged particular content or application providers fees
to reach the providers' retail service end users or struck pay-for-
priority deals, and the record does not contain evidence that U.S.
broadband providers currently engage in such arrangements. Second this
departure from longstanding norms could cause great harm to innovation
and investment in and on the Internet. As discussed above, pay-for-
priority arrangements could raise barriers to entry on the Internet by
requiring fees from edge providers, as well as transaction costs
arising from the need to reach agreements with one or more broadband
providers to access a critical mass of potential end users. Fees
imposed on edge providers may be excessive because few edge providers
have the ability to bargain for lesser fees, and because no broadband
provider internalizes the full costs of reduced innovation and the exit
of edge providers from the market. Third, pay-for-priority arrangements
may particularly harm non-commercial end users, including individual
bloggers, libraries, schools, advocacy organizations, and other
speakers, especially those who communicate through video or other
content sensitive
[[Page 59207]]
to network congestion. Even open Internet skeptics acknowledge that pay
for priority may disadvantage non-commercial uses of the network, which
are typically less able to pay for priority, and for which the Internet
is a uniquely important platform. Fourth, broadband providers that
sought to offer pay-for-priority services would have an incentive to
limit the quality of service provided to non-prioritized traffic. In
light of each of these concerns, as a general matter, it is unlikely
that pay for priority would satisfy the ``no unreasonable
discrimination'' standard. The practice of a broadband Internet access
service provider prioritizing its own content, applications, or
services, or those of its affiliates, would raise the same significant
concerns and would be subject to the same standards and considerations
in evaluating reasonableness as third-party pay-for-priority
arrangements.\87\
---------------------------------------------------------------------------
\86\ The Open Internet NPRM proposed a flat ban on
discrimination and interpreted that requirement to prohibit
broadband providers from ``charg[ing] a content, application, or
service provider for enhanced or prioritized access to the
subscribers of the broadband Internet access service provider.''
Open Internet NPRM, 24 FCC Rcd at 13104-05, paras. 104, 106. In the
context of a ``no unreasonable discrimination'' rule that leaves
interpretation to a case-by-case process, we instead adopt the
approach to pay for priority described in this paragraph.
\87\ We reject arguments that our approach to pay-for-priority
arrangements is inconsistent with allowing content-delivery networks
(CDNs). See, e.g., Cisco Comments at 11-12; TWC Comments at 21-22,
65, 89-90; AT&T Reply at 49-53; Bright House Reply at 9. CDN
services are designed to reduce the capacity requirements and costs
of the CDN's edge provider clients by hosting the content for those
clients closer to end users. Unlike broadband providers, third-party
CDN providers do not control the last-mile connection to the end
user. And CDNs that do not deploy within an edge provider's network
may still reach an end user via the user's broadband connection. See
CDT Comments at 25 n.84; George Ou Comments (Preserving the Open and
Competitive Bandwidth Market) at 3; see also Cisco Comments at 11;
FTTH Comments at 23-24. Moreover, CDNs typically provide a benefit
to the sender and recipient of traffic without causing harm to
third-party traffic. Though we note disagreement regarding the
impact of CDNs on other traffic, the record does not demonstrate
that the use of CDNs has any material adverse effect on broadband
end users' experience of traffic that is not delivered via a CDN.
Compare Letter from S. Derek Turner, Free Press, to Chairman
Genachowski et al., FCC, GN Docket No. 09-191, WC Docket No. 07-52,
at 1-2 (filed July 29, 2010) with Letter from Richard Bennett, ITIF,
to Chairman Genachowski et al., FCC, GN Docket No. 09-191, WC Docket
No. 07-52, Attach. at 12 (filed Aug. 9, 2010). Indeed, the same
benefits derived from using CDNs can be achieved if an edge
provider's own servers happen to be located in close proximity to
end users. Everything on the Internet that is accessible to an end
user is not, and cannot be, in equal proximity from that end user.
See John Staurulakis Inc. Comments at 5; Bret T. Swanson Reply at 4.
Finally, CDN providers unaffiliated with broadband providers
generally do not compete with edge providers and thus generally lack
economic incentives (or the ability) to discriminate against edge
providers. See Akamai Comments at 12; NASUCA Reply at 7; NCTA Reply
at 25. We likewise reject proposals to limit our rules to actions
taken at or below the ``network layer.'' See, e.g., Google Comments
at 24-26; Vonage Reply at 2; CDT Reply at 18; Prof. Scott Jordan
(Jordan) Comments at 3; see also Scott Jordan, A Layered Network
Approach to Net Neutrality, Int'l J. of Commc'n 427, 432-33 (2007)
(describing the OSI layers model and the actions of routers at and
below the network layer) attached to Letter from Scott Jordan,
Professor, University of California-Irvine, to Office of the
Secretary, FCC, GN Docket No. 09-191, WC Docket No. 07-52 (filed
Mar. 22, 2010). We are not persuaded that the proposed limitation is
necessary or appropriate in this context.
---------------------------------------------------------------------------
Because we agree with the diverse group of commenters who argue
that any nondiscrimination rule should prohibit only unreasonable
discrimination, we decline to adopt the more rigid nondiscrimination
rule proposed in the Open Internet NPRM. A strict nondiscrimination
rule would be in tension with our recognition that some forms of
discrimination, including end-user controlled discrimination, can be
beneficial. The rule we adopt provides broadband providers' sufficient
flexibility to develop service offerings and pricing plans, and to
effectively and reasonably manage their networks. We disagree with
commenters who argue that a standard based on ``reasonableness'' or
``unreasonableness'' is too vague to give broadband providers fair
notice of what is expected of them. This is not so. ``Reasonableness''
is a well-established standard for regulatee conduct.\88\ As other
commenters have pointed out, the term ``reasonable'' is ``both
administrable and indispensable to the sound administration of the
nation's telecommunications laws.''\89\
---------------------------------------------------------------------------
\88\ As recently as 1995, Congress adopted the venerable
``reasonableness'' standard when it recodified provisions of the
Interstate Commerce Act. ICC Termination Act of 1995, Public Law
104-88, sec. 106(a) (now codified at 49 U.S.C. 15501).
\89\ AT&T Reply at 33-34 (``And no one has seriously suggested
that Section 202 should itself be amended to remove the
`unreasonable' qualifier on the ground that the qualifier is too
`murky' or `complex.' Seventy-five years of experience have shown
that qualifier to be both administrable and indispensable to the
sound administration of the nation's telecommunications laws.'');
see also Comcast Reply at 26 (``[T]he Commission should embrace the
strong guidance against an overbroad rule and, instead, develop a
standard based on `unreasonable and anticompetitive discrimination.'
''); Sprint Reply at 23 (``The unreasonable discrimination standard
contained in Section 202(a) of the Act contains the very flexibility
the Commission needs to distinguish desirable from improper
discrimination.''); Thomas v. Chicago Park District, 534 U.S. 316,
324 (2002) (holding that denial of a permit ``when the intended use
would present an unreasonable danger to the health and safety of
park users or Park District employees'' is a standard that is
``reasonably specific and objective, and do[es] not leave the
decision `to the whim of the administrator' '') (citation omitted);
Cameron v. Johnson, 390 U.S. 611, 615-16 (1968) (stating that
``unreasonably'' ``is a widely used and well understood word, and
clearly so when juxtaposed with `obstruct' and `interfere' '').
---------------------------------------------------------------------------
We also reject the argument that only ``anticompetitive''
discrimination yielding ``substantial consumer harm'' should be
prohibited by our rules. We are persuaded those proposed limiting terms
are unduly narrow and could allow discriminatory conduct that is
contrary to the public interest. The broad purposes of this rule--to
encourage competition and remove impediments to infrastructure
investment while protecting consumer choice, free expression, end-user
control, and the ability to innovate without permission--cannot be
achieved by preventing only those practices that are demonstrably
anticompetitive or harmful to consumers. Rather, the rule rests on the
general proposition that broadband providers should not pick winners
and losers on the Internet--even for reasons that may be independent of
providers' competitive interests or that may not immediately or
demonstrably cause substantial consumer harm.\90\
---------------------------------------------------------------------------
\90\ For example, slowing BitTorrent packets might only affect a
few end users, but it would harm BitTorrent. More significantly, it
would raise concerns among other end users and edge providers that
their traffic could be slowed for any reason--or no reason at all--
which could in turn reduce incentives to innovate and invest, and
change the fundamental nature of the Internet as an open platform.
---------------------------------------------------------------------------
We disagree with commenters who argue that a rule against
unreasonable discrimination violates Section 3(51) of the
Communications Act for those broadband providers that are
telecommunications carriers but do not provide their broadband Internet
access service as a telecommunications service.\91\ Section 3(51)
provides that a ``telecommunications carrier shall be treated as a
common carrier under this Act only to the extent that it is engaged in
providing telecommunications services.'' \92\ This limitation is not
relevant to the Commission's actions here.\93\ The hallmark of common
[[Page 59208]]
carriage is an ``undertak[ing] to carry for all people indifferently.''
\94\ An entity ``will not be a common carrier where its practice is to
make individualized decisions, in particular cases, whether and on what
terms to deal'' with potential customers.\95\ The customers at issue
here are the end users who subscribe to broadband Internet access
services.\96\ With respect to those customers, a broadband provider may
make individualized decisions. A broadband provider that chooses not to
offer its broadband Internet access service on a common carriage basis
can, for instance, decide on a case-by-case basis whether to serve a
particular end user, what connection speed(s) to offer, and at what
price. The open Internet rules become effective only after such a
provider has voluntarily entered into a mutually satisfactory
arrangement with the end user, which may be tailored to that user. Even
then, as discussed above, the allowance for reasonable disparities
permits customized service features such as those that enhance end user
control over what Internet content is received. This flexibility to
customize service arrangements for a particular customer is the
hallmark of private carriage, which is the antithesis of common
carriage.\97\
---------------------------------------------------------------------------
\91\ See, e.g., AT&T Comments at 209-11; Verizon Comments at 93-
95; CTIA PN Reply at 20-21. We do not read the Supreme Court's
decision in FCC v. Midwest Video Corp. as addressing rules like the
rules we adopt in this Order. 440 U.S. 689 (1979). There, the Court
held that obligations on cable providers to ``hold out dedicated
channels on a first-come, nondiscriminatory basis * * * relegated
cable systems, pro tanto, to common-carrier status.'' Id. at 700-01.
None of the rules adopted in this Order requires a broadband
provider to ``hold out'' any capacity for the exclusive use of third
parties or make a public offering of its service.
\92\ 47 U.S.C. 153(51). Section 332(c)(2) contains a restriction
similar to that of sec. 3(51): ``A person engaged in the provision
of a service that is a private mobile service shall not, insofar as
such person is so engaged, be treated as a common carrier for any
purpose under this Act.'' Id. sec. 332(c)(2). Because we are not
imposing any common carrier obligations on any broadband provider,
including providers of ``private mobile service'' as defined in
Section 332(d)(3), our requirements do not violate the limitation in
Section 332(c)(2).
\93\ Courts have acknowledged that the Commission is entitled to
deference in interpreting the definition of ``common carrier.'' See
AT&T v. FCC, 572 F.2d 17, 24 (2d Cir. 1978) (citing Red Lion Broad.
Co. v. FCC, 395 U.S. 367, 381 (1969)). In adopting the rule against
unreasonable discrimination, we rely, in part, on our authority
under section 706, which is not part of the Communications Act.
Congress enacted section 706 as part of the Telecommunications Act
of 1996 and more recently codified the provision in Chapter 12 of
Title 47, at 47 U.S.C. 1302. The seven titles that comprise the
Communications Act appear in Chapter 5 of Title 47. Consequently,
even if the rule against unreasonable discrimination were
interpreted to require common carriage in a particular case, that
result would not run afoul of Section 3(51) because a network
operator would be treated as a common carrier pursuant to Section
706, not ``under'' the Communications Act.
\94\ Nat'l Ass'n of Reg. Util. Comm'rs v. FCC, 525 F.2d 630, 641
(DC Cir. 1976) (NARUC I) (quoting Semon v. Royal Indemnity Co., 279
F.2d 737, 739 (5th Cir. 1960) and other cases); see also Verizon
Comments at 93 (`` `[T]he primary sine qua non of common carrier
status is a quasi-public character, which arises out of the
undertaking `to carry for all people indifferently * * *.' ''
(quoting Nat'l Ass'n of Reg. Util. Comm'rs v. FCC, 533 F.2d 601, 608
(DC Cir. 1976) (NARUC II)). But see CTIA Reply at 57 (suggesting
that nondiscrimination is the sine qua non of common carrier
regulation referred to in NARUC II).
\95\ NARUC I, 525 F.2d at 641 (citing Semon, 279 F.2d at 739-
40). Commenters assert that any obligation that is similar to an
obligation that appears in Title II of the Act is a ``common
carrier'' obligation. See, e.g., AT&T Comments at 210-11. We
disagree. Just because an obligation appears within Title II does
not mean that the imposition of that obligation or a similar one
results in ``treating'' an entity as a common carrier. For the
meaning of common carriage treatment, which is not defined in the
Act, we look to caselaw as discussed in the text.
\96\ Even if edge providers were considered ``customers'' of the
broadband provider, the broadband provider would not be a common
carrier with regard to the role it plays in transmitting edge
providers' traffic. Our rules permit broadband providers to engage
in reasonable network management and, under certain circumstances,
block traffic and devices, engage in reasonable discrimination, and
prioritize traffic at subscribers' request. Blocking or
deprioritizing certain traffic is far from ``undertak[ing] to carry
for all [edge providers] indifferently.'' See NARUC I, 525 F.2d at
641.
\97\ See Sw. Bell Tel. Co. v. FCC, 19 F.3d 1475, 1481 (DC Cir.
1994) (``If the carrier chooses its clients on an individual basis
and determines in each particular case whether and on what terms to
serve and there is no specific regulatory compulsion to serve all
indifferently, the entity is a private carrier for that particular
service and the Commission is not at liberty to subject the entity
to regulation as a common carrier.'') (internal quotation marks
omitted). Although promoting competition throughout the Internet
ecosystem is a central purpose of these rules, we decline to adopt
as a rule the Internet Policy Statement principle regarding
consumers' entitlement to competition. We agree with those
commenters that argue that the principle is too vague to be reduced
to a rule and that the proposed rule as stated failed to provide any
meaningful guidance regarding what conduct is and is not
permissible. See, e.g., Verizon Comments at 4, 53; TPPF Comments at
7. A rule barring broadband providers from depriving end users of
their entitlement to competition does not appear to be a viable
method of promoting competition. We also do not wish to duplicate
competitive analyses carried out by the Department of Justice, the
FTC, or the Commission's merger review process.
---------------------------------------------------------------------------
D. Reasonable Network Management
Since at least 2005, when the Commission adopted the Internet
Policy Statement, we have recognized that a flourishing and open
Internet requires robust, well-functioning broadband networks, and
accordingly that open Internet protections require broadband providers
to be able to reasonably manage their networks. The open Internet rules
we adopt in this Order expressly provide for and define ``reasonable
network management'' in order to provide greater clarity to broadband
providers, network equipment providers, and Internet end users and edge
providers regarding the types of network management practices that are
consistent with open Internet protections.
In the Open Internet NPRM, the Commission proposed that open
Internet rules be subject to reasonable network management, consisting
of ``reasonable practices employed by a provider of broadband Internet
access service to: (1) Reduce or mitigate the effects of congestion on
its network or to address quality-of-service concerns; (2) address
traffic that is unwanted by users or harmful; (3) prevent the transfer
of unlawful content; or (4) prevent the unlawful transfer of content.''
The proposed definition also stated that reasonable network management
consists of ``other reasonable network management practices.''
Upon reviewing the record, we conclude that the definition of
reasonable network management should provide greater clarity regarding
the standard used to gauge reasonableness, expressly account for
technological differences among networks that may affect reasonable
network management, and omit elements that do not relate directly to
network management functions and are therefore better handled elsewhere
in the rules--for example, measures to prevent the transfer of unlawful
content. We therefore adopt the following definition of reasonable
network management:
A network management practice is reasonable if it is appropriate
and tailored to achieving a legitimate network management purpose,
taking into account the particular network architecture and
technology of the broadband Internet access service.
Legitimate network management purposes include: ensuring network
security and integrity, including by addressing traffic that is harmful
to the network; addressing traffic that is unwanted by end users
(including by premise operators), such as by providing services or
capabilities consistent with an end user's choices regarding parental
controls or security capabilities; and reducing or mitigating the
effects of congestion on the network. The term ``particular network
architecture and technology'' refers to the differences across access
platforms such as cable, DSL, satellite, and fixed wireless.
As proposed in the Open Internet NPRM, we will further develop the
scope of reasonable network management on a case-by-case basis, as
complaints about broadband providers' actual practices arise. The
novelty of Internet access and traffic management questions, the
complex nature of the Internet, and a general policy of restraint in
setting policy for Internet access service providers weigh in favor of
a case-by-case approach.
In taking this approach, we recognize the need to balance clarity
with flexibility.\98\ We discuss below certain
[[Page 59209]]
principles and considerations that will inform the Commission's case-
by-case analysis. Further, although broadband providers are not
required to seek permission from the Commission before deploying a
network management practice, they or others are free to do so, for
example by seeking a declaratory ruling.\99\
---------------------------------------------------------------------------
\98\ Some parties contend that there will be uncertainty
associated with open Internet rules, subject to reasonable network
management, which will limit provider flexibility, stifle
innovation, and slow providers' response time in managing their
networks. See, e.g., ADTRAN Comments at 11-13; Barbara Esbin (Esbin)
Comments at 7. For example, some parties express concern that that
the definition proposed in the Open Internet NPRM provided
insufficient guidance regarding what standard will be used to
determine whether a given practice is ``reasonable.'' See, e.g.,
ADTRAN Comments at 13; AT&T Comments at 13; CDT Comments at 38; PIC
Comments at 35-36, 39; Texas PUC Comments at 6-7; Verizon Reply at
8, 75, 78. Others contend that although clarity is needed, the
Commission should not list categories of activities considered
reasonable. See, e.g., Free Press Comments at 82, 85-86. We seek to
balance these interests through general rules designed to give
providers sufficient flexibility to implement necessary network
management practices, coupled with guidance regarding certain
principles and considerations that will inform the Commission's
case-by-case analysis.
\99\ See 47 CFR 1.2 (providing for ``a declaratory ruling
terminating a controversy or removing uncertainty'').
---------------------------------------------------------------------------
We reject proposals to define reasonable network management
practices more expansively or more narrowly than stated above. We agree
with commenters that the Commission should not adopt the ``narrowly or
carefully tailored'' standard discussed in the Comcast Network
Management Practices Order.\100\ We find that this standard is
unnecessarily restrictive and may overly constrain network engineering
decisions. Moreover, the ``narrowly tailored'' language could be read
to import strict scrutiny doctrine from constitutional law, which we
are not persuaded would be helpful here. Broadband providers may employ
network management practices that are appropriate and tailored to the
network management purpose they seek to achieve, but they need not
necessarily employ the most narrowly tailored practice theoretically
available to them.
---------------------------------------------------------------------------
\100\ See Comcast Network Management Practices Order, 23 FCC Rcd
at 13055-56, para. 47 (stating that, to be considered ``reasonable''
a network management practice ``should further a critically
important interest and be narrowly or carefully tailored to serve
that interest''); see also AT&T Comments at 186-87 (arguing that the
Comcast standard is too narrow); Level 3 Comments at 14; PAETEC
Comments at 17-18. But see Free Press Comments at 91-92 (stating
that the Commission should not retreat from the fundamental
framework of the Comcast standard). A ``reasonableness'' standard
also has the advantage of being administrable and familiar.
---------------------------------------------------------------------------
We also acknowledge that reasonable network management practices
may differ across platforms. For example, practices needed to manage
congestion on a fixed satellite network may be inappropriate for a
fiber-to-the-home network. We also recognize the unique network
management challenges facing broadband providers that use unlicensed
spectrum to deliver service to end users. Unlicensed spectrum is shared
among multiple users and technologies and no single user can control or
assure access to the spectrum. We believe the concept of reasonable
network management is sufficiently flexible to afford such providers
the latitude they need to effectively manage their networks.\101\
---------------------------------------------------------------------------
\101\ See Appendix A, sec. 8.11. We recognize that the standards
for fourth-generation (4G) wireless networks include the capability
to prioritize particular types of traffic, and that other broadband
Internet access services may incorporate similar features. Whether
particular uses of these technologies constitute reasonable network
management will depend on whether they are appropriate and tailored
to achieving a legitimate network management purpose.
---------------------------------------------------------------------------
The principles guiding case-by-case evaluations of network
management practices are much the same as those that guide assessments
of ``no unreasonable discrimination,'' and include transparency, end-
user control, and use- (or application-) agnostic treatment. We also
offer guidance in the specific context of the legitimate network
management purposes listed above.
Network Security or Integrity and Traffic Unwanted by End Users.
Broadband providers may implement reasonable practices to ensure
network security and integrity, including by addressing traffic that is
harmful to the network.\102\ Many commenters strongly support allowing
broadband providers to implement such network management practices.
Some commenters, however, express concern that providers might
implement anticompetitive or otherwise problematic practices in the
name of protecting network security. We make clear that, for the
singling out of any specific application for blocking or degradation
based on harm to the network to be a reasonable network management
practice, a broadband provider should be prepared to provide a
substantive explanation for concluding that the particular traffic is
harmful to the network, such as traffic that constitutes a denial-of-
service attack on specific network infrastructure elements or exploits
a particular security vulnerability.
---------------------------------------------------------------------------
\102\ In the context of broadband Internet access service,
techniques to ensure network security and integrity are designed to
protect the access network and the Internet against actions by
malicious or compromised end systems. Examples include spam,
botnets, and distributed denial of service attacks. Unwanted traffic
includes worms, malware, and viruses that exploit end-user system
vulnerabilities; denial of service attacks; and spam. See IETF,
Report from the IAB workshop on Unwanted Traffic March 9-10, 2006,
RFC 4948, at 31 (Aug. 2007), available at http://www.rfc-editor.org/rfc/rfc4948.txt.
---------------------------------------------------------------------------
Broadband providers also may implement reasonable practices to
address traffic that a particular end user chooses not to receive.
Thus, for example, a broadband provider could provide services or
capabilities consistent with an end user's choices regarding parental
controls, or allow end users to choose a service that provides access
to the Internet but not to pornographic Web sites. Likewise, a
broadband provider serving a premise operator could restrict traffic
unwanted by that entity, though such restrictions should be disclosed.
Our rule will not impose liability on a broadband provider where such
liability is prohibited by Section 230(c)(2) of the Act.\103\
---------------------------------------------------------------------------
\103\ See 47 U.S.C. 230(c)(2) (no provider of an interactive
computer service shall be held liable on account of ``(A) any action
voluntarily taken in good faith to restrict access to or
availability of material that the provider or user considers to be
obscene, lewd, lascivious, filthy, excessively violent, harassing,
or otherwise objectionable, whether or not such material is
constitutionally protected; or (B) any action taken to enable or
make available to information content providers or others the
technical means to restrict access to material described in
[subparagraph (A)]'').
---------------------------------------------------------------------------
We note that, in some cases, mechanisms that reduce or eliminate
some forms of harmful or unwanted traffic may also interfere with
legitimate network traffic. Such mechanisms must be appropriate and
tailored to the threat; should be evaluated periodically as to their
continued necessity; and should allow end users to opt-in or opt-out if
possible.\104\ Disclosures of network management practices used to
address network security or traffic a particular end user does not want
to receive should clearly state the objective of the mechanism and, if
applicable, how an end user can opt in or out of the practice.
---------------------------------------------------------------------------
\104\ For example, a network provider might be able to assess a
network endpoint's posture--see IETF, Network Endpoint Assessment
(NEA): Overview and Requirements, RFC 5209 (Jun. 2008); Internet
Engineering Task Force, PA-TNC: A Posture Attribute (PA) Protocol
Compatible with Trusted Network Connect (TNC), RFC 5792 (Mar.
2010)--and tailor port blocking accordingly. With the posture
assessment, an end user might then opt out of the network management
mechanism by upgrading the operating system or installing a suitable
firewall.
---------------------------------------------------------------------------
Network Congestion. Numerous commenters support permitting the use
of reasonable network management practices to address the effects of
congestion, and we agree that congestion management may be a legitimate
network management purpose. For example, broadband providers may need
to take reasonable steps to ensure that heavy users do not crowd out
others. What constitutes congestion and what measures are reasonable to
address it may vary depending on the technology platform for a
particular broadband Internet access service. For example, if cable
modem subscribers in a particular neighborhood are experiencing
congestion, it may be reasonable for a broadband provider to
temporarily limit
[[Page 59210]]
the bandwidth available to individual end users in that neighborhood
who are using a substantially disproportionate amount of bandwidth.
We emphasize that reasonable network management practices are not
limited to the categories described here, and that broadband providers
may take other reasonable steps to maintain the proper functioning of
their networks, consistent with the definition of reasonable network
management we adopt. As we stated in the Open Internet NPRM, ``we do
not presume to know now everything that providers may need to do to
provide robust, safe, and secure Internet access to their subscribers,
much less everything they may need to do as technologies and usage
patterns change in the future.'' Broadband providers should have
flexibility to experiment, innovate, and reasonably manage their
networks.
E. Mobile Broadband
There is one Internet, which should remain open for consumers and
innovators alike, although it may be accessed through different
technologies and services. The record demonstrates the importance of
freedom and openness for mobile broadband networks, and the rationales
for adopting high-level open Internet rules, discussed above, are for
the most part as applicable to mobile broadband as they are to fixed
broadband. Consumer choice, freedom of expression, end-user control,
competition, and the freedom to innovate without permission are as
important when end users are accessing the Internet via mobile
broadband as via fixed. And there have been instances of mobile
providers blocking certain third-party applications, particularly
applications that compete with the provider's own offerings; relatedly,
concerns have been raised about inadequate transparency regarding
network management practices. We also note that some mobile broadband
providers affirmatively state they do not oppose the application of
openness rules to mobile broadband.
However, as explained in the Open Internet NPRM and subsequent
Public Notice, mobile broadband presents special considerations that
suggest differences in how and when open Internet protections should
apply. Mobile broadband is an earlier-stage platform than fixed
broadband, and it is rapidly evolving. For most of the history of the
Internet, access has been predominantly through fixed platforms--first
dial-up, then cable modem and DSL services. As of a few years ago, most
consumers used their mobile phones primarily to make phone calls and
send text messages, and most mobile providers offered Internet access
only via ``walled gardens'' or stripped down Web sites. Today, however,
mobile broadband is an important Internet access platform that is
helping drive broadband adoption, and data usage is growing rapidly.
The mobile ecosystem is experiencing very rapid innovation and change,
including an expanding array of smartphones, aircard modems, and other
devices that enable Internet access; the emergence and rapid growth of
dedicated-purpose mobile devices like e-readers; the development of
mobile application (``app'') stores and hundreds of thousands of mobile
apps; and the evolution of new business models for mobile broadband
providers, including usage-based pricing.
Moreover, most consumers have more choices for mobile broadband
than for fixed (particularly fixed wireline) broadband.\105\ Mobile
broadband speeds, capacity, and penetration are typically much lower
than for fixed broadband, though some providers have begun offering 4G
service that will enable offerings with higher speeds and capacity and
lower latency than previous generations of mobile service.\106\ In
addition, existing mobile networks present operational constraints that
fixed broadband networks do not typically encounter. This puts greater
pressure on the concept of ``reasonable network management'' for mobile
providers, and creates additional challenges in applying a broader set
of rules to mobile at this time. Further, we recognize that there have
been meaningful recent moves toward openness in and on mobile broadband
networks, including the introduction of third-party devices and
applications on a number of mobile broadband networks, and more open
mobile devices. In addition, we anticipate soon seeing the effects on
the market of the openness conditions we imposed on mobile providers
that operate on upper 700 MHz C Block (``C Block'') spectrum,\107\
which includes Verizon Wireless, one of the largest mobile wireless
carriers in the U.S.
---------------------------------------------------------------------------
\105\ Compare National Broadband Plan at 37 (Exh. 4-A) with 39-
40 (Exh. 4-E). However, in many areas of the country, particularly
in rural areas, there are fewer options for mobile broadband. See
Fourteenth Wireless Competition Report at para. 355, tbl. 39 & chart
48. This may result in some consumers having fewer options for
mobile broadband than for fixed.
\106\ Some fixed broadband providers contend that current mobile
broadband offerings directly compete with their offerings. See
Letter from Michael D. Saperstein, Jr., Director of Regulatory
Affairs, Frontier Communications, to Marlene Dortch, Secretary, FCC,
GN Docket No. 09-191 (filed Dec. 15, 2010) (discussing entry of
wireless service into the broadband market and its effect on
wireline broadband subscribership) and Attach. at 1 (citing reports
that LTE is ``a very practical and encouraging substitution for DSL,
particularly when you look at rural markets''); Letter from Malena
F. Barzilai, Federal Government Affairs, Windstream Communications,
Inc., to Marlene Dortch, Secretary, FCC, GN Docket No. 09-191 (filed
Dec. 15, 2010). As part of our ongoing monitoring, we will track
such competition and any impact these rules may have on it.
\107\ The first network using spectrum subject to these rules
has recently started offering service. See Press Release, Verizon
Wireless, Blazingly Fast: Verizon Wireless Launches The World's
Largest 4G LTE Wireless Network On Sunday, Dec. 5 (Dec. 5, 2010),
available at news.vzw.com/news/2010/12/pr2010-12-03.html.
Specifically, licensees subject to the rule must provide an open
platform for third-party applications and devices. See 700 MHz
Second Report and Order, 22 FCC Rcd 15289; 47 CFR 27.16. The rules
we adopt in this Order are independent of those open platform
requirements. We expect our observations of how the 700 MHz open
platform rules affect the mobile broadband sector to inform our
ongoing analysis of the application of openness rules to mobile
broadband generally. 700 MHz Second Report and Order, 22 FCC Rcd at
15364-65, 15374, paras. 205, 229. A number of commenters support the
Commission's waiting to determine whether to apply openness rules to
mobile wireless until the effects of the C Block openness
requirement can be observed. See, e.g., AT&T PN Reply, at 32-37;
Cricket PN Reply at 11. We also note that some providers tout
openness as a competitive advantage. See, e.g., Clearwire Comments
at 7; Verizon Reply at 47-52.
---------------------------------------------------------------------------
In light of these considerations, we conclude it is appropriate to
take measured steps at this time to protect the openness of the
Internet when accessed through mobile broadband. We apply certain of
the open Internet rules, requiring compliance with the transparency
rule and a basic no-blocking rule.\108\
---------------------------------------------------------------------------
\108\ We note that section 332(a) requires us, ``[i]n taking
actions to manage the spectrum to be made available for use by the
private mobile service,'' to consider various factors, including
whether our actions will ``improve the efficiency of spectrum use
and reduce the regulatory burden,'' and ``encourage competition.''
47 U.S.C. 332(a)(2), (3). To the extent section 332(a) applies to
our actions in this Order, we note that we have considered these
factors.
---------------------------------------------------------------------------
1. Application of Openness Principles to Mobile Broadband
a. Transparency
The wide array of commenters who support a disclosure requirement
generally agree that all broadband providers, including mobile
broadband providers, should be required to disclose their network
management practices. Although some mobile broadband providers argue
that the dynamic nature of mobile network management makes meaningful
disclosure difficult, we conclude that end users need a clear
understanding of network management practices, performance, and
commercial terms, regardless of the broadband platform they use to
access the Internet. Although a number of mobile broadband
[[Page 59211]]
providers have adopted voluntary codes of conduct regarding disclosure,
we believe that a uniform rule applicable to all mobile broadband
providers will best preserve Internet openness by ensuring that end
users have sufficient information to make informed choices regarding
use of the network; and that content, application, service, and device
providers have the information needed to develop, market, and maintain
Internet offerings. The transparency rule will also aid the Commission
in monitoring the evolution of mobile broadband and adjusting, as
appropriate, the framework adopted in this Order.
Therefore, as stated above, we require mobile broadband providers
to follow the same transparency rule applicable to fixed broadband
providers. Further, although we do not require mobile broadband
providers to allow third-party devices or all third-party applications
on their networks, we nonetheless require mobile broadband providers to
disclose their third-party device and application certification
procedures, if any; to clearly explain their criteria for any
restrictions on use of their network; and to expeditiously inform
device and application providers of any decisions to deny access to the
network or of a failure to approve their particular devices or
applications. With respect to the types of disclosures required to
satisfy the rule, we direct mobile broadband providers to the
discussion in Part III.B, above. Additionally, mobile broadband
providers should follow the guidance the Commission provided to
licensees of the upper 700 MHz C Block spectrum regarding compliance
with their disclosure obligations, particularly regarding disclosure to
third-party application developers and device manufacturers of criteria
and approval procedures (to the extent applicable).\109\ For example,
these disclosures include, to the extent applicable, establishing a
transparent and efficient approval process for third parties, as set
forth in Section 27.16(d).\110\
---------------------------------------------------------------------------
\109\ 700 MHz Second Report and Order, 22 FCC Rcd at 15371-72,
para. 224 (``[A] C Block licensee must publish [for example, by
posting on the provider's Web site] standards no later than the time
at which it makes such standards available to any preferred vendors
(i.e., vendors with whom the provider has a relationship to design
products for the provider's network). We also require the C Block
licensee to provide to potential customers notice of the customers'
rights to request the attachment of a device or application to the
licensee's network, and notice of the licensee's process for
customers to make such requests, including the relevant network
criteria.'').
\110\ See 47 CFR 27.16(d) (``Access requests. (1) Licensees
shall establish and publish clear and reasonable procedures for
parties to seek approval to use devices or applications on the
licensees' networks. A licensee must also provide to potential
customers notice of the customers' rights to request the attachment
of a device or application to the licensee's network, and notice of
the licensee's process for customers to make such requests,
including the relevant network criteria. (2) If a licensee
determines that a request for access would violate its technical
standards or regulatory requirements, the licensee shall
expeditiously provide a written response to the requester specifying
the basis for denying access and providing an opportunity for the
requester to modify its request to satisfy the licensee's
concerns.'').
---------------------------------------------------------------------------
b. No Blocking
We adopt a no blocking rule that guarantees end users' access to
the Web and protects against mobile broadband providers' blocking
applications that compete with their other primary service offering--
voice and video telephony--while ensuring that mobile broadband
providers can engage in reasonable network management:
A person engaged in the provision of mobile broadband Internet
access service, insofar as such person is so engaged, shall not
block consumers from accessing lawful Web sites, subject to
reasonable network management; nor shall such person block
applications that compete with the provider's voice or video
telephony services, subject to reasonable network management.
We understand a ``provider's voice or video telephony services'' to
include a voice or video telephony service provided by any entity in
which the provider has an attributable interest.\111\ We emphasize that
the rule protects any and all applications that compete with a mobile
broadband provider's voice or video telephony services. Further,
degrading a particular Web site or an application that competes with
the provider's voice or video telephony services so as to render the
Web site or application effectively unusable would be considered
tantamount to blocking (subject to reasonable network management).
---------------------------------------------------------------------------
\111\ For the purposes of these rules, an attributable interest
includes equity ownership interest in or de facto control of, or by,
the entity that provides the voice or video telephony service. An
attributable interest also includes any exclusive arrangement for
such voice or video telephony service, including de facto exclusive
arrangements.
---------------------------------------------------------------------------
End users expect to be able to access any lawful Web site through
their broadband service, whether fixed or mobile. Web browsing
continues to generate the largest amount of mobile data traffic, and
applications and services are increasingly being provisioned and used
entirely through the Web, without requiring a standalone application to
be downloaded to a device. Given that the mobile Web is well-developed
relative to other mobile applications and services, and enjoys similar
expectations of openness that characterize Web use through fixed
broadband, we find it appropriate to act here. We also recognize that
accessing a Web site typically does not present the same network
management issues that downloading and running an app on a device may
present. At this time, a prohibition on blocking access to lawful Web
sites (including any related traffic transmitted or received by any
plug-in, scripting language, or other browser extension) appropriately
balances protection for the ability of end users to access content,
applications, and services through the Web and assurance that mobile
broadband providers can effectively manage their mobile broadband
networks.
Situations have arisen in which mobile wireless providers have
blocked third-party applications that arguably compete with their
telephony offerings.\112\ This type of blocking confirms that mobile
broadband providers may have strong incentives to limit Internet
openness when confronted with third-party applications that compete
with their telephony services. Some commenters express concern that
wireless providers could favor their own applications over the
applications of unaffiliated developers, under the guise of reasonable
network management. A number of commenters assert that blocking or
hindering the delivery of services that compete with those offered by
the mobile broadband provider, such as over-the-top VoIP, should be
prohibited. According to Skype, for example, there is ``a consensus
that at a minimum, a `no blocking' rule should apply to voice and video
applications that compete with broadband network operators' own service
offerings.'' Clearwire argues that the Commission should restrict only
practices that appear to have an element of anticompetitive intent.
Although some commenters support a broader no-blocking rule, we believe
that a targeted prophylactic rule is appropriate at this
[[Page 59212]]
time,\113\ and necessary to deter this type of behavior in the future.
---------------------------------------------------------------------------
\112\ See, e.g., Letter from James W. Cicconi, AT&T Services,
Inc., to Ruth Milkman, Chief, Wireless Telecommunications Bureau,
FCC, RM-11361, RM-11497 at 6-8 (filed Aug. 21, 2009); DISH PN Reply
at 7 (``VoIP operators such as Skype have faced significant
difficulty in gaining access across wireless Internet
connections.''). Mobile providers blocking VoIP services is an issue
not only in the United States, but worldwide. In Europe, the Body of
European Regulators for Electronic Communications reported, among
other issues, a number of cases of blocking or charging extra for
VoIP services by certain European mobile operators. See European
Commission, Information Society and Media Directorate-General Report
on the Public Consultation on ``The Open Internet and Net Neutrality
in Europe'' 2, (Nov. 9, 2010), ec.europa.eu/information--society/
policy/ecomm/library/public--consult/net--neutrality/index--en.htm.
\113\ See Letter from Jonathan Spalter, Chairman, Mobile Future,
to Marlene H. Dortch, Secretary, FCC, GN Docket Nos. 09-191 & 10-
127, at 3 n.16 (filed Dec. 13, 2010) (supporting tailored
prohibition on blocking applications), citing AT&T Comments at 65;
T-Mobile Comments, Declaration of Grant Castle at 4. The no blocking
rule that we adopt for mobile broadband involves distinct treatment
of applications that compete with the provider's voice and video
telephony services, whereas we have adopted a broader traffic-based
approach for fixed broadband. We acknowledge that this rule for
mobile broadband may lead in some limited measure to the traffic-
identification difficulties discussed with respect to fixed
broadband. We find, however, that the reasons for taking our
cautious approach to mobile broadband outweigh this concern,
particularly in light of our intent to monitor developments
involving mobile broadband, including this and other aspects of the
practical implementation of our rules.
---------------------------------------------------------------------------
The prohibition on blocking applications that compete with a
broadband provider's voice or video telephony services does not apply
to a broadband provider's operation of application stores or their
functional equivalent. In operating app stores, broadband providers
compete directly with other types of entities, including device
manufacturers and operating system developers,\114\ and we do not
intend to limit mobile broadband providers' flexibility to curate their
app stores similar to app store operators that are not subject to these
rules.
---------------------------------------------------------------------------
\114\ For example, app stores are operated by manufacturers and
operating system developers such as Nokia, Apple, RIM, Google,
Microsoft, and third parties such as GetJar. See also AT&T PN
Comments at 63-66 (emphasizing the competitiveness of the market for
mobile apps, including the variety of sources from which consumers
may obtain applications); T-Mobile PN Comments at 21 (``The
competitive wireless marketplace will continue to discipline app
store owners * * * that exclude third-party apps from their app
stores entirely, eliminating the need for Commission action.''). We
note, however, that for a few devices, such as Apple's iPhone, there
may be fewer options for accessing and distributing apps.
---------------------------------------------------------------------------
As indicated in Part III.D above, the reasonable network management
definition takes into account the particular network architecture and
technology of the broadband Internet access service. Thus, in
determining whether a network management practice is reasonable, the
Commission will consider technical, operational, and other differences
between wireless and other broadband Internet access platforms,
including differences relating to efficient use of spectrum. We
anticipate that conditions in mobile broadband networks may necessitate
network management practices that would not be necessary in most fixed
networks, but conclude that our definition of reasonable network
management is flexible enough to accommodate such differences.
2. Ongoing Monitoring
Although some commenters support applying the no unreasonable
discrimination rule to mobile broadband,\115\ for the reasons discussed
above, we decline to do so, preferring at this time to put in place
basic openness protections and monitor the development of the mobile
broadband marketplace. We emphasize that our decision to proceed
incrementally with respect to mobile broadband at this time should not
suggest that we implicitly approve of any provider behavior that runs
counter to general open Internet principles. Beyond those practices
expressly prohibited by our rules, other conduct by mobile broadband
providers, particularly conduct that would violate our rules for fixed
broadband, may not necessarily be consistent with Internet openness and
the public interest.
---------------------------------------------------------------------------
\115\ See, e.g, Free Press Comments at 125-26; OIC Comments at
36-39. See also, e.g., Leap Comments at 17-22; Sprint Reply at 24-
26. A number of commenters suggest that openness rules should be
applied identically to all broadband platforms. See, e.g.,
CenturyLink Comments at 22-23; Comcast Comments at 32; DISH Network
PN Comments at 17; NCTA PN Comments at 11; Qwest PN Comments at 12-
19; SureWest PN Comments at 18-20; TWC PN Comments at 33-35; Vonage
PN Comments at 10-18; Windstream PN Comments at 6-19.
---------------------------------------------------------------------------
We are taking measured steps to protect openness for mobile
broadband at this time in part because we want to better understand how
the mobile broadband market is developing before determining whether
adjustments to this framework are necessary. To that end, we will
closely monitor developments in the mobile broadband market, with a
particular focus on the following issues: (1) The effects of these
rules, the C Block conditions, and market developments related to the
openness of the Internet as accessed through mobile broadband; (2) any
conduct by mobile broadband providers that harms innovation,
investment, competition, end users, free expression or the achievement
of national broadband goals; (3) the extent to which differences
between fixed and mobile rules affect fixed and mobile broadband
markets, including competition among fixed and mobile broadband
providers; and (4) the extent to which differences between fixed and
mobile rules affect end users for whom mobile broadband is their only
or primary Internet access platform.\116\ We will investigate and
evaluate concerns as they arise. We also will adjust our rules as
appropriate. To aid the Commission in these tasks, we will create an
Open Internet Advisory Committee, as discussed below, with a mandate
that includes monitoring and regularly reporting on the state of
Internet openness for mobile broadband.
---------------------------------------------------------------------------
\116\ We note that mobile broadband is the only or primary
broadband Internet access platform used by many Americans.
---------------------------------------------------------------------------
Further, we reaffirm our commitment to enforcing the open platform
requirements applicable to upper 700 MHz C Block licensees. The first
networks using this spectrum are now becoming operational.
F. Other Laws and Considerations
Open Internet rules are not intended to expand or contract
broadband providers' rights or obligations with respect to other laws
or safety and security considerations, including the needs of emergency
communications and law enforcement, public safety, and national
security authorities. Similarly, open Internet rules protect only
lawful content, and are not intended to inhibit efforts by broadband
providers to address unlawful transfers of content. For example, there
should be no doubt that broadband providers can prioritize
communications from emergency responders, or block transfers of child
pornography. To make clear that open Internet protections can and must
coexist with these other legal frameworks, we adopt the following
clarifying provisions:
Nothing in this part supersedes any obligation or authorization
a provider of broadband Internet access service may have to address
the needs of emergency communications or law enforcement, public
safety, or national security authorities, consistent with or as
permitted by applicable law, or limits the provider's ability to do
so.
Nothing in this part prohibits reasonable efforts by a provider
of broadband Internet access service to address copyright
infringement or other unlawful activity.
1. Emergency Communications and Safety and Security Authorities
Commenters are broadly supportive of our proposal to state that
open Internet rules do not supersede any obligation a broadband
provider may have--or limit its ability--to address the needs of
emergency communications or law enforcement, public safety, or homeland
or national security authorities (together, ``safety and security
authorities''). Broadband providers have obligations under statutes
such as the Communications Assistance for Law Enforcement Act, the
Foreign Intelligence Surveillance Act, and the Electronic
Communications Privacy Act that could in some circumstances intersect
with open Internet protections, and most commenters recognize the
benefits of clarifying that these obligations are not inconsistent with
open Internet rules. Likewise, in connection with an emergency, there
[[Page 59213]]
may be Federal, state, Tribal, and local public safety entities;
homeland security personnel; and other authorities that need guaranteed
or prioritized access to the Internet in order to coordinate disaster
relief and other emergency response efforts, or for other emergency
communications. In the Open Internet NPRM we proposed to address the
needs of law enforcement in one rule and the needs of emergency
communications and public safety, national, and homeland security
authorities in a separate rule. We are persuaded by the record that
these rules should be combined, as the interests at issue are
substantially similar.\117\ We also agree that the rule should focus on
the needs of ``law enforcement * * * authorities'' rather than the
needs of ``law enforcement.'' The purpose of the safety and security
provision is first to ensure that open Internet rules do not restrict
broadband providers in addressing the needs of law enforcement
authorities, and second to ensure that broadband providers do not use
the safety and security provision without the imprimatur of a law
enforcement authority, as a loophole to the rules. As such, application
of the safety and security rule should be tied to invocation by
relevant authorities rather than to a broadband provider's independent
notion of law enforcement.
---------------------------------------------------------------------------
\117\ See PIC Comments at 42-44. We intend the term ``national
security authorities'' to include homeland security authorities.
---------------------------------------------------------------------------
Some commenters urge us to limit the scope of the safety and
security rule, or argue that it is unnecessary because other statutes
give broadband providers the ability and responsibility to assist law
enforcement. Several commenters urge the Commission to revise its
proposal to clarify that broadband providers may not take any voluntary
steps that would be inconsistent with open Internet principles, beyond
those steps required by law. They argue, for example, that a broad
exception for voluntary efforts could swallow open Internet rules by
allowing broadband providers to cloak discriminatory practices under
the guise of protecting safety and security.\118\
---------------------------------------------------------------------------
\118\ See EFF Comments at 20-22. EFF would require a pre-
deployment waiver from the Commission if the needs of law
enforcement would require broadband providers to act inconsistently
with open Internet rules. Id. at 22.
---------------------------------------------------------------------------
We agree with commenters that the safety and security rule should
be tailored to avoid the possibility of broadband providers using their
discretion to mask improper practices. But it would be a mistake to
limit the rule to situations in which broadband providers have an
obligation to assist safety and security personnel. For example, such a
limitation would prevent broadband providers from implementing the
Cellular Priority Access Service (also known as the Wireless Priority
Service (WPS)), which allows for but does not legally require the
prioritization of public safety communications on wireless networks. We
do not think it necessary or advisable to provide for pre-deployment
review by the Commission, particularly because time may be of the
essence in meeting safety and security needs.\119\
---------------------------------------------------------------------------
\119\ The National Emergency Number Association (NENA) would
encourage or require network managers to provide public safety users
with advance notice of changes in network management that could
affect emergency services. See NENA Comments at 5-6. Although we do
not adopt such a requirement, we encourage broadband providers to be
mindful of the potential impact on emergency services when
implementing network management policies, and to coordinate major
changes with providers of emergency services when appropriate.
---------------------------------------------------------------------------
2. Transfers of Unlawful Content and Unlawful Transfers of Content
In the NPRM, we proposed to treat as reasonable network management
``reasonable practices to * * * prevent the transfer of unlawful
content; or * * * prevent the unlawful transfer of content.'' For
reasons explained above we decline to include these practices within
the scope of ``reasonable network management.'' However, we conclude
that a clear statement that open Internet rules do not prohibit
broadband providers from making reasonable efforts to address the
transfer of unlawful content or unlawful transfers of content is
helpful to ensure that open Internet rules are not used as a shield to
enable unlawful activity or to deter prompt action against such
activity. For example, open Internet rules should not be invoked to
protect copyright infringement, which has adverse consequences for the
economy, nor should they protect child pornography. We emphasize that
open Internet rules do not alter copyright laws and are not intended to
prohibit or discourage voluntary practices undertaken to address or
mitigate the occurrence of copyright infringement.\120\
---------------------------------------------------------------------------
\120\ See, e.g., Stanford University--DMCA Complaint Resolution
Center; User Generated Content Principles, http://www.ugcprinciples.com (cited in Letter from Linda Kinney, MPAA, to
Marlene H. Dortch, Secretary, FCC, GN Docket Nos. 09-191, 10-137, WC
Docket No. 07-52 at 1 (filed Nov. 29, 2010)). Open Internet rules
are not intended to affect the legal status of cooperative efforts
by broadband Internet access service providers and other service
providers that are designed to curtail infringement in response to
information provided by rights holders in a manner that is timely,
effective, and accommodates the legitimate interests of providers,
rights holders, and end users.
---------------------------------------------------------------------------
G. Specialized Services
In the Open Internet NPRM, the Commission recognized that broadband
providers offer services that share capacity with broadband Internet
access service over providers' last-mile facilities, and may develop
and offer other such services in the future. These ``specialized
services,'' such as some broadband providers' existing facilities-based
VoIP and Internet Protocol-video offerings, differ from broadband
Internet access service and may drive additional private investment in
broadband networks and provide end users valued services, supplementing
the benefits of the open Internet. At the same time, specialized
services may raise concerns regarding bypassing open Internet
protections, supplanting the open Internet, and enabling
anticompetitive conduct. For example, open Internet protections may be
weakened if broadband providers offer specialized services that are
substantially similar to, but do not meet the definition of, broadband
Internet access service, and if consumer protections do not apply to
such services. In addition, broadband providers may constrict or fail
to continue expanding network capacity allocated to broadband Internet
access service to provide more capacity for specialized services. If
this occurs, and particularly to the extent specialized services grow
as substitutes for the delivery of content, applications, and services
over broadband Internet access service, the Internet may wither as an
open platform for competition, innovation, and free expression. These
concerns may be exacerbated by consumers' limited choices for broadband
providers, which may leave some end users unable to effectively
exercise their preferences for broadband Internet access service (or
content, applications, or services available through broadband Internet
access service) over specialized services.
We agree with the many commenters who advocate that the Commission
exercise its authority to closely monitor and proceed incrementally
with respect to specialized services, rather than adopting policies
specific to such services at this time. We will carefully observe
market developments to verify that specialized services promote
investment, innovation, competition, and end-user benefits without
undermining or threatening the open Internet.\121\ We note also that
our rules
[[Page 59214]]
define broadband Internet access service to encompass ``any service
that the Commission finds to be providing a functional equivalent of
[broadband Internet access service], or that is used to evade the
protections set forth in these rules.'' \122\
---------------------------------------------------------------------------
\121\ Our decision not to adopt rules regarding specialized
services at this time involves an issue distinct from the regulatory
classification of services such as VoIP and IPTV under the
Communications Act, a subject we do not address in this Order.
Likewise, the Commission's actions here do not affect any existing
obligation to provide interconnection, unbundled network elements,
or special access or other wholesale access under Sections 201, 251,
256, and 271 of the Act. 47 U.S.C. 201, 251, 256, 271.
\122\ Some commenters, including Internet engineering experts
and analysts, emphasize the importance of distinguishing between the
open Internet and specialized services and state that ``this
distinction must continue as a most appropriate and constructive
basis for pursuing your policy goals.'' Various Advocates for the
Open Internet PN Reply at 3; see also id. at 2.
---------------------------------------------------------------------------
We will closely monitor the robustness and affordability of
broadband Internet access services, with a particular focus on any
signs that specialized services are in any way retarding the growth of
or constricting capacity available for broadband Internet access
service. We fully expect that broadband providers will increase
capacity offered for broadband Internet access service if they expand
network capacity to accommodate specialized services. We would be
concerned if capacity for broadband Internet access service did not
keep pace. We also expect broadband providers to disclose information
about specialized services' impact, if any, on last-mile capacity
available for, and the performance of, broadband Internet access
service. We may consider additional disclosure requirements in this
area in our related proceeding regarding consumer transparency and
disclosure. We would also be concerned by any marketing, advertising,
or other messaging by broadband providers suggesting that one or more
specialized services, taken alone or together, and not provided in
accordance with our open Internet rules, is ``Internet'' service or a
substitute for broadband Internet access service. Finally, we will
monitor the potential for anticompetitive or otherwise harmful effects
from specialized services, including from any arrangements a broadband
provider may seek to enter into with third parties to offer such
services. The Open Internet Advisory Committee will aid us in
monitoring these issues.
IV. The Commission's Authority To Adopt Open Internet Rules
Congress created the Commission ``[f]or the purpose of regulating
interstate and foreign commerce in communication by wire and radio so
as to make available, so far as possible, to all people of the United
States * * * a rapid, efficient, Nation-wide, and world-wide wire and
radio communication service with adequate facilities at reasonable
charges, for the purpose of the national defense, [and] for the purpose
of promoting safety of life and property through the use of wire and
radio communication.'' Section 2 of the Communications Act grants the
Commission jurisdiction over ``all interstate and foreign communication
by wire or radio.'' As the Supreme Court explained in the radio
context, Congress charged the Commission with ``regulating a field of
enterprise the dominant characteristic of which was the rapid pace of
its unfolding'' and therefore intended to give the Commission
sufficiently ``broad'' authority to address new issues that arise with
respect to ``fluid and dynamic'' communications technologies.\123\
Broadband Internet access services are clearly within the Commission's
subject matter jurisdiction and historically have been supervised by
the Commission. Furthermore, as explained below, our adoption of basic
rules of the road for broadband providers implements specific statutory
mandates in the Communications Act and the Telecommunications Act of
1996.
---------------------------------------------------------------------------
\123\ Nat'l Broad. Co., Inc. v. United States, 319 U.S. 190,
219-20 (1943) (Congress did not ``attempt[] an itemized catalogue of
the specific manifestations of the general problems'' that it
entrusted to the Commission); see also FCC v. Pottsville Broad. Co.,
309 U.S. 134, 137, 138 (1940) (the Commission's statutory
responsibilities and authority amount to ``a unified and
comprehensive regulatory system'' for the communications industry
that allows a single agency to ``maintain, through appropriate
administrative control, a grip on the dynamic aspects'' of that
ever-changing industry).
---------------------------------------------------------------------------
Congress has demonstrated its awareness of the importance of the
Internet and advanced services to modern interstate communications. In
Section 230 of the Act, for example, Congress announced ``the policy of
the United States'' concerning the Internet, which includes
``promot[ing] the continued development of the Internet'' and
``encourag[ing] the development of technologies which maximize user
control over what information is received by individuals, families, and
schools who use the Internet,'' while also ``preserv[ing] the vibrant
and competitive free market that presently exists for the Internet and
other interactive computer services'' and avoiding unnecessary
regulation. Other statements of congressional policy further confirm
the Commission's statutory authority. In Section 254 of the Act, for
example, Congress charged the Commission with designing a Federal
universal program that has as one of several objectives making
``[a]ccess to advanced telecommunications and information services''
available ``in all regions of the Nation,'' and particularly to
schools, libraries, and health care providers. To the same end, in
Section 706 of the 1996 Act, Congress instructed the Commission to
``encourage the deployment on a reasonable and timely basis of advanced
telecommunications capability to all Americans (including, in
particular, elementary and secondary schools and classrooms)'' and, if
it finds that advanced telecommunications capability is not being
deployed to all Americans ``on a reasonable and timely basis,'' to
``take immediate action to accelerate deployment of such capability.''
This mandate provides the Commission both ``authority'' and
``discretion'' ``to settle on the best regulatory or deregulatory
approach to broadband.'' As the legislative history of the 1996 Act
confirms, Congress believed that the laws it drafted would compel the
Commission to protect and promote the Internet, while allowing the
agency sufficient flexibility to decide how to do so.\124\ As explained
in detail below, Congress did not limit its instructions to the
Commission to one Section of the communications laws. Rather, it
expressed its instructions in multiple Sections which, viewed as a
whole, provide broad authority to promote competition, investment,
transparency, and an open Internet through the rules we adopt in this
Order.
---------------------------------------------------------------------------
\124\ S. Rep. No. 104-23, at 51 (1995) (``The goal is to
accelerate deployment of an advanced capability that will enable
subscribers in all parts of the United States to send and receive
information in all its forms--voice, data, graphics, and video--over
a high-speed switched, interactive, broadband, transmission
capability.'').
---------------------------------------------------------------------------
A. Section 706 of the 1996 Act Provides Authority for the Open Internet
Rules
As noted, Section 706 of the 1996 Act directs the Commission (along
with state commissions) to take actions that encourage the deployment
of ``advanced telecommunications capability.'' ``[A]dvanced
telecommunications capability,'' as defined in the statute, includes
broadband Internet access.\125\
[[Page 59215]]
Under Section 706(a), the Commission must encourage the deployment of
such capability by ``utilizing, in a manner consistent with the public
interest, convenience, and necessity,'' various tools including
``measures that promote competition in the local telecommunications
market, or other regulating methods that remove barriers to
infrastructure investment.'' For the reasons stated in Parts II.A, II.D
and III.B, above, our open Internet rules will have precisely that
effect.
---------------------------------------------------------------------------
\125\ 47 U.S.C. 1302(d)(1) (defining ``advanced
telecommunications capability'' as ``high-speed, switched, broadband
telecommunications capability that enables users to originate and
receive high-quality voice, data, graphics, and video
telecommunications using any technology''). See National Broadband
Plan for our Future, Notice of Inquiry, 24 FCC Rcd 4342, 4309, App.
para. 13 (2009) (``advanced telecommunications capability'' includes
broadband Internet access); Inquiry Concerning the Deployment of
Advanced Telecomms. Capability to All Americans in a Reasonable and
Timely Fashion, 14 FCC Rcd 2398, 2400, para. 1 (Section 706
addresses ``the deployment of broadband capability''), 2406 para. 20
(same). Even when broadband Internet access is provided as an
``information service'' rather than a ``telecommunications
service,'' see Nat'l Cable & Telecomm. Ass'n v. Brand X Internet
Servs., 545 U.S. 967, 977-78 (2005), it involves
``telecommunications.'' 47 U.S.C. 153(24). Given Section 706's
explicit focus on deployment of broadband access to voice, data, and
video communications, it is not important that the statute does not
use the exact phrase ``Internet network management.''
---------------------------------------------------------------------------
In Comcast, the DC Circuit identified Section 706(a) as a provision
that ``at least arguably * * * delegate[s] regulatory authority to the
Commission,'' and in fact ``contain[s] a direct mandate--the Commission
`shall encourage.' '' \126\ The court, however, regarded the Commission
as ``bound by'' a prior order that, in the court of appeals'
understanding, had held that Section 706(a) is not a grant of
authority. In the Advanced Services Order, to which the court referred,
the Commission held that Section 706(a) did not permit it to encourage
advanced services deployment through the mechanism of forbearance
without complying with the specific requirements for forbearance set
forth in Section 10 of the Communications Act. The issue presented in
the 1998 proceeding was whether the Commission could rely on the broad
terms of Section 706(a) to trump those specific requirements. In the
Advanced Services Order, the Commission ruled that it could not do so,
noting that it would be ``unreasonable'' to conclude that Congress
intended Section 706(a) to ``allow the Commission to eviscerate
[specified] forbearance exclusions after having expressly singled out
[those exclusions] for different treatment in Section 10.'' The
Commission accordingly concluded that Section 706(a) did not give it
independent authority--in other words, authority over and above what it
otherwise possessed \127\--to forbear from applying other provisions of
the Act. The Commission's holding thus honored the interpretive canon
that ``[a] specific provision * * * controls one[ ] of more general
application.''
---------------------------------------------------------------------------
\126\ See Comcast, 600 F.3d at 658; see also 47 U.S.C. 1302(a)
(``The Commission * * * shall encourage the deployment on a
reasonable and timely basis of advanced telecommunications
capability to all Americans * * * by utilizing * * * price cap
regulation, regulatory forbearance, measures that promote
competition in the local telecommunications market, or other
regulating methods that remove barriers to infrastructure
investment.''). Because Section 706 contains a ``direct mandate,''
we reject the argument pressed by some commenters (see, e.g., AT&T
Comments at 217-18; Verizon Comments at 100-01; Qwest Comments at
58-59; Letter from Rick Chessen, Senior Vice President, Law and
Regulatory Policy, NCTA, to Marlene H. Dortch, Secretary, FCC, GN
Docket Nos. 09-191 & 10-127, WC Docket No. 07-52, at 7 (filed Dec.
10, 2010) (NCTA Dec. 10, 2010 Ex Parte Letter)) that Section 706
confers no substantive authority.
\127\ Consistent with longstanding Supreme Court precedent, we
have understood this authority to include our ancillary jurisdiction
to further congressional policy. See, e.g., Amendment of Section
64.702 of the Commission's Rules and Regulations (Second Computer
Inquiry), Final Decision, 77 FCC 2d 384, 474 (1980), aff'd, Computer
& Commc'ns Indus. Ass'n. v. FCC, 693 F.2d 198, 211-14 (DC Cir. 1982)
(CCIA).
---------------------------------------------------------------------------
While disavowing a reading of Section 706(a) that would allow the
agency to trump specific mandates of the Communications Act, the
Commission nonetheless affirmed in the Advanced Services Order that
Section 706(a) ``gives this Commission an affirmative obligation to
encourage the deployment of advanced services'' using its existing
rulemaking, forbearance and adjudicatory powers, and stressed that
``this obligation has substance.'' The Advanced Services Order is,
therefore, consistent with our present understanding that Section
706(a) authorizes the Commission (along with state commissions) to take
actions, within their subject matter jurisdiction and not inconsistent
with other provisions of law, that encourage the deployment of advanced
telecommunications capability by any of the means listed in the
provision.\128\
---------------------------------------------------------------------------
\128\ To the extent the Advanced Services Order can be construed
as having read Section 706(a) differently, we reject that reading of
the statute for the reasons discussed in the text.
---------------------------------------------------------------------------
In directing the Commission to ``encourage the deployment on a
reasonable and timely basis of advanced telecommunications capability
to all Americans * * * by utilizing * * * price cap regulation,
regulatory forbearance, measures that promote competition in the local
telecommunications market, or other regulating methods that remove
barriers to infrastructure investment,'' Congress necessarily invested
the Commission with the statutory authority to carry out those acts.
Indeed, the relevant Senate Report explained that the provisions of
Section 706 are ``intended to ensure that one of the primary objectives
of the [1996 Act]--to accelerate deployment of advanced
telecommunications capability--is achieved,'' and stressed that these
provisions are ``a necessary fail-safe'' to guarantee that Congress's
objective is reached. It would be odd indeed to characterize Section
706(a) as a ``fail-safe'' that ``ensures'' the Commission's ability to
promote advanced services if it conferred no actual authority. Here,
under our reading, Section 706(a) authorizes the Commission to address
practices, such as blocking VoIP communications, degrading or raising
the cost of online video, or denying end users material information
about their broadband service, that have the potential to stifle
overall investment in Internet infrastructure and limit competition in
telecommunications markets.
This reading of Section 706(a) obviates the concern of some
commenters that our jurisdiction under the provision could be
``limitless'' or ``unbounded.'' To the contrary, our Section 706(a)
authority is limited in three critical respects. First, our mandate
under Section 706(a) must be read consistently with Sections 1 and 2 of
the Act, which define the Commission's subject matter jurisdiction over
``interstate and foreign commerce in communication by wire and radio.''
\129\ As a result, our authority under Section 706(a) does not, in our
view, extend beyond our subject matter jurisdiction under the
Communications Act. Second, the Commission's actions
[[Page 59216]]
under Section 706(a) must ``encourage the deployment on a reasonable
and timely basis of advanced telecommunications capability to all
Americans.'' Third, the activity undertaken to encourage such
deployment must ``utilize[e], in a manner consistent with the public
interest, convenience, and necessity,'' one (or more) of various
specified methods. These include: ``price cap regulation, regulatory
forbearance, measures that promote competition in the local
telecommunications market, or other regulating methods that remove
barriers to infrastructure investment.'' Actions that do not fall
within those categories are not authorized by Section 706(a). Thus, as
the DC Circuit has noted, while the statutory authority granted by
Section 706(a) is broad, it is ``not unfettered.'' \130\
---------------------------------------------------------------------------
\129\ 47 U.S.C. 151, 152. The Commission historically has
recognized that services carrying Internet traffic are
jurisdictionally mixed, but generally subject to Federal regulation.
See, e.g., Nat'l Ass'n of Regulatory Util. Comm'rs Petition for
Clarification or Declaratory Ruling that No FCC Order or Rule Limits
State Authority to Collect Broadband Data, Memorandum Opinion and
Order, 25 FCC Rcd 5051, 5054, paras. 8-9 & n. 24 (2010). Where, as
here, ``it is not possible to separate the interstate and intrastate
aspects of the service,'' the Commission may preempt state
regulation where ``Federal regulation is necessary to further a
valid Federal regulatory objective, i.e., state regulation would
conflict with Federal regulatory policies.'' Minn. Pub. Utils.
Comm'n v. FCC, 483 F.3d 570, 578 (8th Cir. 2007); see also La. Pub.
Serv. Comm'n v. FCC, 476 U.S. 355, 375 n. 4 (1986). Except to the
extent a state requirement conflicts on its face with a Commission
decision herein, the Commission will evaluate preemption in light of
the fact-specific nature of the relevant inquiry, on a case-by-case
basis. We recognize, for example, that states play a vital role in
protecting end users from fraud, enforcing fair business practices,
and responding to consumer inquiries and complaints. See, e.g.,
Vonage Order, 19 FCC Rcd at 22404-05, para. 1. We have no intention
of impairing states' or local governments' ability to carry out
these duties unless we find that specific measures conflict with
Federal law or policy. In determining whether state or local
regulations frustrate Federal policies, we will, among other things,
be guided by the overarching congressional policies described in
Section 230 of the Act and Section 706 of the 1996 Act. 47 U.S.C.
230, 1302.
\130\ Ad Hoc Telecomms. Users Comm., 572 F.3d at 906-07 (``The
general and generous phrasing of sec. 706 means that the FCC
possesses significant albeit not unfettered, authority and
discretion to settle on the best regulatory or deregulatory approach
to broadband.'').
---------------------------------------------------------------------------
Section 706(a) accordingly provides the Commission a specific
delegation of legislative authority to promote the deployment of
advanced services, including by means of the open Internet rules
adopted in this Order. Our understanding of Section 706(a) is,
moreover, harmonious with other statutory provisions that confer a
broad mandate on the Commission. Section 706(a)'s directive to
``encourage the deployment [of advanced telecommunications capability]
on a reasonable and timely basis'' using the methods specified in the
statute is, for example, no broader than other provisions of the
Commission's authorizing statutes that command the agency to ensure
``just'' and ``reasonable'' rates and practices, or to regulate
services in the ``public interest.'' Indeed, our authority under
Section 706(a) is generally consistent with--albeit narrower than--the
understanding of ancillary jurisdiction under which this Commission
operated for decades before the Comcast decision.\131\ The similarities
between the two in fact explain why the Commission has not heretofore
had occasion to describe Section 706(a) in this way: In the particular
proceedings prior to Comcast, setting out the understanding of Section
706(a) that we articulate in this Order would not meaningfully have
increased the authority that we understood the Commission already to
possess.\132\
---------------------------------------------------------------------------
\131\ In Comcast, the court stated that `` `[t]he Commission * *
* may exercise ancillary jurisdiction only when two conditions are
satisfied: (1) The Commission's general jurisdictional grant under
Title I [of the Communications Act] covers the regulated subject and
(2) the regulations are reasonably ancillary to the Commission's
effective performance of its statutorily mandated responsibilities.'
'' 600 F.3d at 646 (quoting Am. Library Ass'n v. FCC, 406 F.3d 689,
691-92 (DC Cir. 2005)) (alterations in original). The court further
ruled that the second prong of this test requires the Commission to
rely on specific delegations of statutory authority. 600 F.3d at
644, 654.
\132\ Ignoring that Section 706(a) expressly contemplates the
use of ``regulating methods'' such as price regulation, some
commenters read prior Commission orders as suggesting that Section
706 authorizes only deregulatory actions. See AT&T Comments at 216
(citing Petition for Declaratory Ruling that pulver.com's Free World
Dialup is Neither Telecomm. Nor A Telecomms. Serv., Memorandum
Opinion and Order, 19 FCC Rcd 3307, 3319, para. 19 n. 69 (2004)
(Pulver Order)); Esbin Comments at 52 (citing Inquiry Concerning
High-Speed Access to the Internet Over Cable and Other Facilities et
al., Declaratory Ruling and Notice of Proposed Rulemaking, 17 FCC
Rcd 4798, 4801, 4826, 4840, paras. 4, 47, 73, (2002) (Cable Modem
Declaratory Ruling) and Appropriate Framework for Broadband Access
to the Internet Over Wireline Facilities et al., Report and Order
and Notice of Proposed Rulemaking, 20 FCC Rcd 14853, 14894 para. 77
(2005) (Wireline Broadband Report and Order)). They are mistaken.
The Pulver Order stated only that Section 706 did not contemplate
the application of ``economic and entry/exit regulation inherent in
Title II'' to information service Internet applications. Pulver
Order, 19 FCC Rcd at 3379, para. 19 n. 69 (emphasis added). The open
Internet rules that we adopt in this Order do not regulate Internet
applications, much less impose Title II (i.e., common carrier)
regulation on such applications. Moreover, at the same time the
Commission determined in the Cable Modem Declaratory Ruling and the
Wireline Broadband Report and Order that cable modem service and
wireline broadband services (such as DSL) could be provided as
information services not subject to Title II, it proposed new
regulations under other sources of authority including Section 706.
See Cable Modem Declaratory Ruling, 17 FCC Rcd at 4840, para. 73;
Wireline Broadband Report and Order, 20 FCC Rcd at 14929-30, 14987,
para. 146. On the same day the Commission adopted the Wireline
Broadband Report and Order, it also adopted the Internet Policy
Statement, which rested in part on Section 706. 20 FCC Rcd 14986,
para. 2 (2005). Our prior orders therefore do not construe Section
706 as exclusively deregulatory. And to the extent that any prior
order does suggest such a construction, we now reject it. See Ad Hoc
Telecomms. Users Comm., 572 F.3d at 908 (Section 706 ``direct[s] the
FCC to make the major policy decisions and to select the mix of
regulatory and deregulatory tools the Commission deems most
appropriate in the public interest to facilitate broadband
deployment and competition'') (emphasis added).
---------------------------------------------------------------------------
Section 706(b) of the 1996 Act provides additional authority to
take actions such as enforcing open Internet principles. It directs the
Commission to undertake annual inquiries concerning the availability of
advanced telecommunications capability to all Americans and requires
that, if the Commission finds that such capability is not being
deployed in a reasonable and timely fashion, it ``shall take immediate
action to accelerate deployment of such capability by removing barriers
to infrastructure investment and by promoting competition in the
telecommunications market.'' In July 2010, the Commission ``conclude[d]
that broadband deployment to all Americans is not reasonable and
timely'' and noted that ``[a]s a consequence of that conclusion,''
Section 706(b) was triggered. Section 706(b) therefore provides express
authority for the pro-investment, pro-competition rules we adopt in
this Order.
B. Authority To Promote Competition and Investment in, and Protect End
Users of, Voice, Video, and Audio Services
The Commission also has authority under the Communications Act to
adopt the open Internet rules in order to promote competition and
investment in voice, video, and audio services. Furthermore, for the
reasons stated in Part II, above, even if statutory provisions related
to voice, video, and audio communications were the only sources of
authority for the open Internet rules (which is not the case), it would
not be sound policy to attempt to implement rules concerning only
voice, video, or audio transmissions over the Internet.\133\
---------------------------------------------------------------------------
\133\ Many broadband providers offer their service on a common
carriage basis under Title II of the Act. See Framework for
Broadband Internet Serv., Notice of Inquiry, 25 FCC Rcd 7866, 7875,
para. 21 (2010). With respect to these providers, the rules we adopt
in this Order are additionally supported on that basis. With the
possible exception of transparency requirements, however, the open
Internet rules are unlikely to create substantial new duties for
these providers in practice.
---------------------------------------------------------------------------
1. The Commission Has Authority To Adopt Open Internet Rules To Further
Its Responsibilities Under Title II of the Act
Section 201 of the Act delegates to the Commission ``express and
expansive authority'' to ensure that the ``charges [and] practices * *
* in connection with'' telecommunications services are ``just and
reasonable.'' As described in Part II.B, interconnected VoIP services,
which include some over-the-top VoIP services, ``are increasingly being
used as a substitute for traditional telephone service.''\134\ Over-
the-top services therefore do, or will, contribute to the marketplace
discipline of voice telecommunications services regulated under Section
201.\135\ Furthermore,
[[Page 59217]]
companies that provide both voice communications and broadband Internet
access services (for example, telephone companies that are broadband
providers) have the incentive and ability to block, degrade, or
otherwise disadvantage the services of their online voice competitors.
Because the Commission may enlist market forces to fulfill its Section
201 responsibilities, we possess authority to prevent these
anticompetitive practices through open Internet rules.\136\
---------------------------------------------------------------------------
\134\ Tel. No. Requirements for IP-Enabled Servs. Providers,
Report and Order, Declaratory Ruling, Order on Remand, and NPRM, 22
FCC Rcd 19531, 19547, para. 28 (2007). By definition, interconnected
VoIP services allow calls to and from traditional phone networks.
\135\ See NCTA Dec. 10, 2010 Ex Parte Letter (arguing that the
Commission could exercise authority ancillary to several provisions
of Title II of the Act, including Sections 201 and 202, ``to ensure
that common carrier services continue to be offered on just and
reasonable terms and conditions'' and to ``facilitate consumer
access to broadband-based alternatives to common carrier services
such as Voice over Internet Protocol''); Vonage Comments at 11-12
(``The Commission's proposed regulations would help preserve the
competitive balance between providers electing to operate under
Title II and those operating under Title I.''); Google Comments at
45-46 (``The widespread use of VoIP and related services as cheaper
and more feature-rich alternatives to Title II services has
significant effects on traditional telephone providers' practices
and pricing, as well [as] on network interconnection between Title
II and IP networks that consumers use to reach each other, going to
the heart of the Commission's Title II responsibilities.'')
(footnotes and citations omitted); Letter from Devendra T. Kumar,
Counsel to Skype Communications S.A.R.L., to Marlene H. Dortch,
Secretary, FCC, GN Docket No. 09-191, WC Docket No. 07-52 (filed
Nov. 30, 2010) (arguing that the Commission has authority ancillary
to Section 201 to protect international VoIP calling); XO Comments
at 20 (noting the impact of, inter alia, VoIP on the Commission's
``traditional framework'' for regulating voice services under Title
II); Letter from Alan Inouye et al., on behalf of ALA, ARL and
EDUCAUSE, to Chairman Julius Genachowski et al., GN Docket No. 09-
191, WC Docket No. 07-52 at 4-5 (filed Dec. 13, 2010) (citing
examples of how libraries and higher education institutions are
using broadband services, including VoIP, to replace traditional
common carrier services). In previous orders, the Commission has
embraced the use of VoIP to avoid or constrain high international
calling rates. See Universal Serv. Contribution Methodology et al.,
Report and Order and Notice of Proposed Rulemaking, 21 FCC Rcd 7518,
7546, para. 55 & n.187 (2006) (``[I]nterconnected VoIP service is
often marketed as an economical way to make interstate and
international calls, as a lower-cost substitute for wireline toll
service.''), rev'd in part sub nom. Vonage Holdings Corp. v. FCC,
489 F.3d 1232 (DC Cir. 2007); Reporting Requirements for U.S.
Providers of Int'l Telecomms. Servs., Notice of Proposed Rulemaking,
19 FCC Rcd 6460, 6470, para. 22 (2004) (``Improvements in the
packet-switched transmission technology underlying the Internet now
allow providers of VoIP to offer international voice transmission of
reasonable quality at a price lower than current IMTS rates.'')
(footnote omitted); Int'l Settlements Policy Reform, Notice of
Proposed Rulemaking, 17 FCC Rcd 19954, 19964, para. 13 (2002)
(``This ability to engage in least-cost routing, as well as
alternative, non-traditional services such as IP Telephony or Voice-
Over-IP, in conjunction with the benchmarks policy have created a
market dynamic that is pressuring international settlement rates
downward.''). In addition, NCTA has explained that, ``[b]y enabling
consumers to make informed choices regarding broadband Internet
access service,'' the Commission could conclude that transparency
requirements ``would help promote the competitiveness of VoIP and
other broadband-based communications services'' and ``thereby
facilitate the operation of market forces to discipline the charges
and other practices of common carriers, in fulfillment of the
Commission's obligations under Sections 201 and 202'' of the Act.
NCTA Dec. 10, 2010 Ex Parte Letter at 2-3.
\136\ We reject the argument asserted by some commenters (see,
e.g., AT&T Comments at 218-19; Verizon Comments at 98-99) that the
various grants of rulemaking authority in the Act, including the
express grant of rulemaking authority in Section 201(b) itself, do
not authorize the promulgation of rules pursuant to Section 201(b).
See AT&T Corp. v. Iowa Utils. Bd., 525 U.S. 366, 378 (1999) (``We
think that the grant in sec. 201(b) means what it says: The FCC has
rulemaking authority to carry out the `provisions of this Act.' '').
---------------------------------------------------------------------------
Section 251(a)(1) of the Act imposes a duty on all
telecommunications carriers ``to interconnect directly or indirectly
with the facilities of other telecommunications carriers.'' Many over-
the-top VoIP services allow end users to receive calls from and/or
place calls to traditional phone networks operated by
telecommunications carriers. The Commission has not determined whether
any such VoIP providers are telecommunications carriers. To the extent
that VoIP services are information services (rather than
telecommunications services), any blocking or degrading of a call from
a traditional telephone customer to a customer of a VoIP provider, or
vice-versa, would deny the traditional telephone customer the intended
benefits of telecommunications interconnection under Section 251(a)(1).
Over-the-top VoIP customers account for a growing share of telephone
usage. If calls to and from these VoIP customers were not delivered
efficiently and reliably by broadband providers, all users of the
public switched telephone network would be limited in their ability to
communicate, and Congress's goal of ``efficient, Nation-wide, and
world-wide'' communications across interconnected networks would be
frustrated. To the extent that VoIP services are telecommunications
services, a broadband provider's interference with traffic exchanged
between a provider of VoIP telecommunications services and another
telecommunications carrier would interfere with interconnection between
two telecommunications carriers under Section 251(a)(1).\137\
---------------------------------------------------------------------------
\137\ See also 47 U.S.C. 256(b)(1) (directing the Commission to
``establish procedures for * * * oversight of coordinated network
planning by telecommunications carriers and other providers of
telecommunications service for the effective and efficient
interconnection of public telecommunications networks used to
provide telecommunications service''); Comcast, 600 F.3d at 659
(acknowledging Section 256's objective, while adding that Section
256 does not `` `expand[ ] * * * any authority that the Commission'
otherwise has under law'') (quoting 47 U.S.C. 256(c)).
---------------------------------------------------------------------------
2. The Commission Has Authority To Adopt Open Internet Rules To Further
Its Responsibilities Under Titles III and VI of the Act
``The Commission has been charged with broad responsibilities for
the orderly development of an appropriate system of local television
broadcasting,'' \138\ which arise from the Commission's more general
public interest obligation to ``ensure the larger and more effective
use of radio.'' \139\ Similarly, the Commission has broad jurisdiction
to oversee MVPD services, including direct-broadcast satellite
(DBS).\140\ Consistent with these mandates, our jurisdiction over video
and audio services under Titles III and VI of the Communications Act
provides additional authority for open Internet rules.
---------------------------------------------------------------------------
\138\ See United States v. Sw. Cable Co., 392 U.S. 157, 177
(1968); see also id. at 174 (``[T]hese obligations require for their
satisfaction the creation of a system of local broadcasting
stations, such that `all communities of appreciable size (will) have
at least one television station as an outlet for local self-
expression.' ''); 47 U.S.C. 307(b) (Commission shall ``make such
distribution of licenses, * * * among the several States and
communities as to provide a fair, efficient, and equitable
distribution of radio service to each of the same''), 303(f) & (h)
(authorizing the Commission to allocate broadcasting zones or areas
and to promulgate regulations ``as it may deem necessary'' to
prevent interference among stations) (cited in Sw. Cable, 392 U.S.
at 173-74).
\139\ Nat'l Broad. Co., 319 U.S. at 216 (public interest to be
served is the ``larger and more effective use of radio'') (citation
and internal quotation marks omitted).
\140\ See 47 U.S.C. 303(v); see also N.Y. State Comm'n on Cable
Television v. FCC, 749 F.2d 804, 807-12 (DC Cir. 1984) (upholding
the Commission's exercise of ancillary authority over satellite
master antenna television service); 47 U.S.C. 548 (discussed below).
---------------------------------------------------------------------------
First, such rules are necessary to the effective performance of our
Title III responsibilities to ensure the ``orderly development * * * of
local television broadcasting'' \141\ and the ``more effective use of
radio.'' \142\ As discussed in Parts II.A and II.B, Internet video
distribution is increasingly important to all video programming
services, including local television broadcast service. Radio stations
also are providing audio and video content on the Internet. At the same
time,
[[Page 59218]]
broadband providers--many of which are also MVPDs--have the incentive
and ability to engage in self-interested practices that may include
blocking or degrading the quality of online programming content,
including broadcast content, or charging unreasonable additional fees
for faster delivery of such content. Absent the rules we adopt in this
Order, such practices jeopardize broadcasters' ability to offer news
(including local news) and other programming over the Internet, and, in
turn, threaten to impair their ability to offer high-quality broadcast
content.\143\
---------------------------------------------------------------------------
\141\ Sw. Cable, 392 U.S. at 177; see 47 U.S.C. 303(f) & (h)
(establishing Commission's authority to allocate broadcasting zones
or areas and to promulgate regulations ``as it may deem necessary''
to prevent interference among stations) (cited in Sw. Cable, 392
U.S. at 173-74).
\142\ Nat'l Broad. Co., 319 U.S. at 216; see also 47 U.S.C.
303(g) (establishing Commission's duty to ``generally encourage the
larger and more effective use of radio in the public interest''),
307(b) (``[T]he Commission shall make such distribution of licenses
* * * among the several States and communities as to provide a fair,
efficient, and equitable distribution of radio service to each of
the same.'').
\143\ NCTA has noted that ``[t]he Commission could decide that,
based on the growing importance of broadcast programming distributed
over broadband networks to both television viewers and the business
of broadcasting itself, ensuring that broadcast video content made
available over broadband networks is not subject to unreasonable
discrimination or anticompetitive treatment is necessary to preserve
and strengthen the system of local broadcasting.'' NCTA Dec. 10,
2010 Ex Parte Letter at 3; see also id. (``Facilitating the
availability of broadcast content on the Internet may also help to
foster more efficient and intensive use of spectrum, thereby
supporting the Commission's duty in Section 303(g) to `generally
encourage the larger and more effective use of radio in the public
interest.' '') (quoting 47 U.S.C. 303(g)).
---------------------------------------------------------------------------
The Commission likewise has authority under Title VI of the Act to
adopt open Internet rules that protect competition in the provision of
MVPD services. A cable or telephone company's interference with the
online transmission of programming by DBS operators or stand-alone
online video programming aggregators that may function as competitive
alternatives to traditional MVPDs \144\ would frustrate Congress's
stated goals in enacting Section 628 of the Act, which include
promoting ``competition and diversity in the multichannel video
programming market''; ``increase[ing] the availability of satellite
cable programming and satellite broadcast programming to persons in
rural and other areas not currently able to receive such programming'';
and ``spur[ring] the development of communications technologies.''
\145\
---------------------------------------------------------------------------
\144\ The issue whether online-only video programming
aggregators are themselves MVPDs under the Communications Act and
our regulations has been raised in pending program access complaint
proceedings. See, e.g., VDC Corp. v. Turner Network Sales, Inc.,
Program Access Complaint (Jan. 18, 2007); Sky Angel U.S., LLC v.
Discovery Commc'ns LLC, Program Access Complaint (Mar. 24, 2010).
Nothing in this Order should be read to state or imply any
determination on this issue.
\145\ 47 U.S.C. sec. 548(a). The Act defines ``video
programming'' as ``programming provided by, or generally considered
comparable to programming provided by, a television broadcast
station.'' 47 U.S.C. sec. 522(20). Although the Commission stated
nearly a decade ago that video `` `streamed' over the Internet'' had
``not yet achieved television quality'' and therefore did not
constitute ``video programming'' at that time, see Cable Modem
Declaratory Ruling, 17 FCC Rcd at 4834, para. 63 n.236, intervening
improvements in streaming technology and broadband availability
enable such programming to be ``comparable to programming provided
by * * * a television broadcast station,'' 47 U.S.C. sec. 522(20).
This finding is consistent with our prediction more than five years
ago that ``[a]s video compression technology improves, data transfer
rates increase, and media adapters that link TV to a broadband
connection become more widely used, * * * video over the Internet
will proliferate and improve in quality.'' Ann. Assessment of the
Status of Competition in the Mkt. for the Delivery of Video
Programming, Notice of Inquiry, 19 FCC Rcd 10909, 10932, para. 74
(2004) (citation omitted).
---------------------------------------------------------------------------
When Congress enacted Section 628 in 1992, it was specifically
concerned about the incentive and ability of cable operators to use
their control of video programming to impede competition from the then-
nascent DBS industry.\146\ Since that time, the Internet has opened a
new competitive arena in which MVPDs that offer broadband service have
the opportunity and incentive to impede DBS providers and other
competing MVPDs--and the statute reaches this analogous arena as well.
Section 628(b) prohibits cable operators from engaging in ``unfair or
deceptive acts or practices the purpose or effect of which is to
prevent or hinder significantly the ability of an MVPD to deliver
satellite cable programming or satellite broadcast programming to
consumers.'' An ``unfair method of competition or unfair act or
practice'' under Section 628(b) includes acts that can be
anticompetitive.\147\ Thus, Section 628(b) proscribes practices by
cable operators that (i) can impede competition, and (ii) have the
purpose or effect of preventing or significantly hindering other MVPDs
from providing consumers their satellite-delivered programming (i.e.,
programming transmitted to MVPDs via satellite for retransmission to
subscribers).\148\ Section 628(c)(1), in turn, directs the Commission
to adopt rules proscribing unfair practices by cable operators and
their affiliated satellite cable programming vendors. Section 628(j)
provides that telephone companies offering video programming services
are subject to the same rules as cable operators.
---------------------------------------------------------------------------
\146\ See Cable Act of 1992, Public Law 102-385, sec. 2(a)(5),
106 Stat. 1460, 1461 (``Vertically integrated program suppliers * *
* have the incentive and ability to favor their affiliated cable
operators over nonaffiliated cable operators and programming
distributors using other technologies.''); H.R. Rep. No. 102-862, at
93 (1992) (Conf. Rep.), reprinted in 1992 U.S.C.C.A.N. 1231, 1275
(``In adopting rules under this section, the conferees expect the
Commission to address and resolve the problems of unreasonable cable
industry practices, including restricting the availability of
programming and charging discriminatory prices to non-cable
technologies.''); S. Rep. No. 102-92, at 26 (1991), reprinted in
1992 U.S.C.C.A.N. 1133, 1159 (``[C]able programmers may simply
refuse to sell to potential competitors. Small cable operators,
satellite dish owners, and wireless cable operators complain that
they are denied access to, or charged more for, programming than
large, vertically integrated cable operators.'').
\147\ Review of the Commission's Program Access Rules and
Examination of Programming Tying Arrangements, First Report and
Order, 25 FCC Rcd 746, 779, para. 48 & n. 190 (2010) (citing
Exclusive Contracts for Provision of Video Serv. in Multiple
Dwelling Units and Other Real Estate Devs., Report and Order and
Further Notice of Proposed Rulemaking, 22 FCC Rcd 20235, 20255,
para. 43, aff'd, NCTA, 567 F.3d 659); see also NTCA, 567 F.3d at
664-65 (referring to ``unfair dealing'' and ``anticompetitive
practices'').
\148\ See 47 U.S.C. 548(b); NCTA, 567 F.3d at 664. In NCTA, the
court held that the Commission reasonably concluded that the ``broad
and sweeping terms'' of Section 628(b) authorized it to ban
exclusive agreements between cable operators and building owners
that prevented other MVPDs from providing their programming to
residents of those buildings. The court observed that ``the words
Congress chose [in Section 628(b)] focus not on practices that
prevent MVPDs from obtaining satellite cable or satellite broadcast
programming, but on practices that prevent them from `providing'
that programming `to subscribers or consumers.' '' NCTA, 567 F.3d at
664 (emphasis in original).
---------------------------------------------------------------------------
The open Internet rules directly further our mandate under Section
628. Cable operators, telephone companies, and DBS operators alike are
seeking to keep and win customers by expanding their MVPD offerings to
include online access to their programming.\149\ For example, in
providing its MVPD service, DISH (one of the nation's two DBS
providers) relies significantly on online dissemination of programming,
including video-on-demand and other programming, that competes with
similar offerings by cable operators.\150\
[[Page 59219]]
As DISH explains, ``[a]s more and more video consumption moves online,
the competitive viability of stand-alone MVPDs depends on their ability
to offer an online video experience of the same quality as the online
video offerings of integrated broadband providers.'' The open Internet
rules will prevent practices by cable operators and telephone
companies, in their role as broadband providers, that have the purpose
or effect of significantly hindering (or altogether preventing)
delivery of video programming protected under Section 628(b).\151\ The
Commission therefore is authorized to adopt open Internet rules under
Section 628(b), (c)(1), and (j).\152\
---------------------------------------------------------------------------
\149\ DISH Reply at 4-5 (``Pay-TV services continue to evolve at
a rapid pace and providers increasingly are integrating their vast
offerings of linear channels with online content,'' while
``consumers are adopting online video services as a complement to
traditional, linear pay-TV services'' and ``specifically desire
Internet video as a complement to * * * [MVPDs'] traditional TV
offerings.'') (footnotes and citations omitted). We find
unpersuasive the contention that this Order fails to ``grapple with
the implications of the market forces that are driving MVPDs * * *
to add Internet connectivity to their multichannel video
offerings.'' McDowell Statement at *24 (footnote omitted). Our
analysis takes account of these developments, which are discussed at
length in Part II.A, above.
\150\ Id. at 5-8 & n. 20 (discussing ``DishOnline service,''
which ``allows DISH to offer over 3,000 movies and TV shows through
its `DishOnline' Internet video service,'' and noting that ``the
success of DishOnline is critically dependent on broadband access
provided and controlled by DISH's competitors in the MVPD market'');
DISH PN Comments at 2-3; DISH Network, Watch Live TV Online OR
Recorded Programs with DishOnline, http://www.dish-systems.com/products/dish_online.php (`` `DISHOnline.com integrates DISH
Network's expansive TV programming lineup with the vast amount of
online video content, adding another dimension to our `pay once,
take your TV everywhere' product platform.' ''). Much of the regular
subscription programming that DISH offers online is satellite-
delivered programming. See DISH Network, Watch Live TV Online OR
Recorded Programs with DishOnline, http://www.dish-systems.com/products/dish_online.php (noting that customers can watch content
from cable programmers such as the Discovery Channel and MTV). Thus,
we reject NCTA's argument that ``[t]here is no basis for asserting
that any cable operator or common carrier's practices with respect
to Internet-delivered video could * * * `prevent or significantly
hinder' an MVPD from providing satellite cable programming.'' NCTA
Dec. 10, 2010 Ex Parte Letter at 5.
\151\ Notwithstanding suggestions to the contrary, the
Commission is not required to wait until anticompetitive harms are
realized before acting. Rather, the Commission may exercise its
ancillary jurisdiction to ``plan in advance of foreseeable events,
instead of waiting to react to them.'' Sw. Cable, 392 U.S. at 176-77
(citation and internal quotation marks omitted); see also Star
Wireless, LLC v. FCC, 522 F.3d at 475.
\152\ See Open Internet NRPM, 24 FCC Rcd at 13099, para. 85
(discussing role of the Internet in fostering video programming
competition and the Commission's authority to regulate video
services).
---------------------------------------------------------------------------
Similarly, open Internet rules enable us to carry out our
responsibilities under Section 616(a) of the Act, which confers
additional express statutory authority to combat discriminatory network
management practices by broadband providers. Section 616(a) directs the
Commission to adopt regulations governing program carriage agreements
``and related practices'' between cable operators or other MVPDs and
video programming vendors.\153\ The program carriage regulations must
include provisions that prevent MVPDs from ``unreasonably restrain[ing]
the ability of an unaffiliated video programming vendor to compete
fairly by discriminating in video programming distribution,'' on the
basis of a vendor's affiliation or lack of affiliation with the MVPD,
in the selection, terms, or conditions of carriage of the vendor's
programming.\154\ MVPD practices that discriminatorily impede competing
video programming vendors' online delivery of programming to consumers
affect the vendors' ability to ``compete fairly'' for viewers, just as
surely as MVPDs' discriminatory selection of video programming for
carriage on cable systems has this effect. We find that discriminatory
practices by MVPDs in their capacity as broadband providers, such as
blocking or charging fees for termination of online video programming
to end users, are ``related'' to program carriage agreements and within
our mandate to adopt regulations under Section 616(a).\155\
---------------------------------------------------------------------------
\153\ An MVPD is ``a person such as, but not limited to, a cable
operator, a multichannel multipoint distribution service, a direct
broadcast satellite service, or a television receive-only satellite
program distributor, who makes available for purchase, by
subscribers or customers, multiple channels of video programming.''
47 U.S.C. 522(13). A ``video programming vendor'' is any ``person
engaged in the production, creation, or wholesale distribution of
video programming for sale.'' 47 U.S.C. 536(b). A number of video
programming vendors make their programming available online. See,
e.g., Hulu.com, http://www.hulu.com/about; Biography Channel, http://www.biography.com; Hallmark Channel, http://www.hallmarkchannel.com.
\154\ 47 U.S.C. 536(a)(1)-(3); see also 47 CFR 76.1301
(implementing regulations to address practices specified in Section
616(a)(1)-(3)).
\155\ The Act does not define ``related practices'' as that
phrase is used in Section 616(a). Because the term is neither
explicitly defined in the statute nor susceptible of only one
meaning, we construe it, consistent with dictionary definitions, to
cover practices that are ``akin'' or ``connected'' to those
specifically identified in Section 616(a)(1)-(3). See Black's Law
Dictionary 1158 (5th ed. 1979); Webster's Third New Int'l Dictionary
1916 (1993). The argument that Section 616(a) has no application to
Internet access service overlooks that the statute expressly covers
these ``related practices.''
---------------------------------------------------------------------------
C. Authority To Protect the Public Interest Through Spectrum Licensing
Open Internet rules for wireless services are further supported by
our authority, under Title III of the Communications Act, to protect
the public interest through spectrum licensing. Congress has entrusted
the Commission with ``maintain[ing] the control of the United States
over all the channels of radio transmission.'' Licensees hold
Commission-granted authorizations to use that spectrum subject to
conditions the Commission imposes on that use.\156\ In considering
whether to grant a license to use spectrum, therefore, the Commission
must ``determine * * * whether the public interest, convenience, and
necessity will be served by the granting of such application.'' \157\
Likewise, when identifying classes of licenses to be awarded by auction
and the characteristics of those licenses, the Commission ``shall
include safeguards to protect the public interest'' and must seek to
promote a number of goals, including ``the development and rapid
deployment of new technologies, products, and services.'' Even after
licenses are awarded, the Commission may change the license terms ``if
in the judgment of the Commission such action will promote the public
interest, convenience, and necessity.'' The Commission may exercise
this authority on a license-by-license basis or through a rulemaking,
even if the affected licenses were awarded at auction.
---------------------------------------------------------------------------
\156\ 47 U.S.C. 304, 316(a)(1). We thus disagree with commenters
who suggest in general that there is nothing in Title III to support
the imposition of open Internet rules. See, e.g., EFF Comments at 6
n. 13.
\157\ 47 U.S.C. 309(a); see also 47 U.S.C. 307(a) (``The
Commission, if public convenience, interest, or necessity will be
served thereby, subject to the limitations of this [Act], shall
grant to any applicant therefor a station license provided for by
this [Act].'').
---------------------------------------------------------------------------
The Commission previously has required wireless licensees to comply
with open Internet principles, as appropriate in the particular
situation before it. In 2007, when it modified the service rules for
the 700 MHz band, the Commission took ``a measured step to encourage
additional innovation and consumer choice at this critical stage in the
evolution of wireless broadband services.'' Specifically, the
Commission required C block licensees ``to allow customers, device
manufacturers, third-party application developers, and others to use or
develop the devices and applications of their choosing in C Block
networks, so long as they meet all applicable regulatory requirements
and comply with reasonable conditions related to management of the
wireless network (i.e., do not cause harm to the network).'' The open
Internet conditions we adopt in this Order likewise are necessary to
advance the public interest in innovation and investment.\158\
---------------------------------------------------------------------------
\158\ In addition, the use of mobile VoIP applications is likely
to constrain prices for CMRS voice services, similar to what we
described earlier with regard to VoIP and traditional phone
services.
---------------------------------------------------------------------------
AT&T contends that the Commission cannot apply ``neutrality''
regulations to wireless broadband services outside the upper 700 MHz C
Block spectrum because any such regulations ``would unlawfully rescind
critical rulings in the Commission's 700 MHz Second Report and Order on
which providers relied in making multi-billion dollar investments,''
\159\ and that adopting these regulations more broadly to all mobile
providers would violate the Administrative Procedure Act. We disagree.
As explained above, the Commission retains the statutory authority to
impose new requirements on existing licenses beyond those that were in
place at the time of grant, whether the licenses were assigned by
[[Page 59220]]
auction or by other means.\160\ In this case, parties were made well
aware that the agency might extend openness requirements beyond the C
Block, diminishing any reliance interest they might assert.\161\ To the
extent that AT&T argues that application of openness principles reduced
auction bids on the C Block spectrum, we find that the reasons for the
price differences between the C Block and other 700 MHz spectrum blocks
are far more complex. A number of factors, including unique auction
dynamics and significant differences between the C Block spectrum and
other blocks of 700 MHz spectrum contributed to these price
differences. In balancing the public interest factors we are required
to consider, we have determined that adopting a targeted set of rules
that apply to all mobile broadband providers is necessary at this time.
---------------------------------------------------------------------------
\159\ AT&T PN Reply at 32. AT&T asserts that winners of non-C-
Block licenses paid a premium for licenses not subject to the open
platform requirements that applied to the upper 700 MHz C Block
licenses. Id. at 33-34.
\160\ The Commission may act by rulemaking to modify or impose
rules applicable to all licensees or licensees in a particular
class; in order to modify specific licenses held by particular
licensees, however, the Commission generally is required to follow
the modification procedure set forth in 47 U.S.C. 316. See Comm. for
Effective Cellular Rules v. FCC, 53 F.3d 1309, 1319-20 (DC Cir.
1995).
\161\ See generally 700 MHz Second Report and Order, 22 FCC Rcd
at 15358-65. In the 700 MHz Second Report and Order, the Commission
stated that its decision to limit open-platform requirements to the
C Block was based on the record before it ``at this time,'' id. at
15361, and noted that openness issues in the wireless industry were
being considered more broadly in other proceedings. Id. at 15363.
The public notice setting procedures for the 2008 auction advised
bidders that the rules governing auctioned licenses would be subject
to ``pending and future proceedings'' before the Commission. See
Auction of 700 MHz Band Licenses Scheduled for January 24, 2008,
Public Notice, 22 FCC Rcd 18141, 18156, para. 42 (2007).
---------------------------------------------------------------------------
D. Authority To Collect Information To Enable the Commission To Perform
Its Reporting Obligations to Congress
Additional sections of the Communications Act provide authority for
our transparency requirement in particular. Section 4(k) provides for
an annual report to Congress that ``shall contain * * * such
information and data collected by the Commission as may be considered
of value in the determination of questions connected with the
regulation of interstate * * * wire and radio communication'' and
provide ``recommendations to Congress as to additional legislation
which the Commission deems necessary or desirable.'' \162\ The
Commission has previously relied on Section 4(k), among other
provisions, as a basis for its authority to gather information.\163\
The Comcast court, moreover, ``readily accept[ed]'' that ``certain
assertions of Commission authority could be `reasonably ancillary' to
the Commission's statutory responsibility to issue a report to
Congress. For example, the Commission might impose disclosure
requirements on regulated entities in order to gather data needed for
such a report.'' \164\ We adopt such disclosure requirements here.
---------------------------------------------------------------------------
\162\ 47 U.S.C. 154(k). In a similar vein, Section 257 of the
Act directs the Commission to report to Congress every three years
on ``market entry barriers'' that the Commission recommends be
eliminated, including ``barriers for entrepreneurs and other small
businesses in the provision and ownership of telecommunications
services and information services.'' 47 U.S.C. 257(a) & (c); see
also Comcast, 600 F.3d at 659; NCTA Dec. 10, 2010 Ex Parte Letter at
3 (``[S]ection 257's reporting mandate provides a basis for the
Commission to require providers of broadband Internet access service
to disclose the terms and conditions of service in order to assess
whether such terms hamper small business entry and, if so, whether
any legislation may be required to address the problem.'') (footnote
omitted).
\163\ See, e.g., New Part 4 of the Commission's Rules Concerning
Disruptions to Commc'ns, Report and Order and Further Notice of
Proposed Rulemaking, 19 FCC Rcd 16830, 16837, paras. 1, 12 (2004)
(extending Commission's reporting requirements for communications
disruptions to certain providers of non-wireline communications, in
part based on Section 4(k)); DTV Consumer Educ. Initiative, Report &
Order, 23 FCC Rcd 4134, 4147, paras. 1, 2, 28 (2008) (requiring
various entities, including broadcasters, to submit quarterly
reports to the Commission detailing their consumer education efforts
related to the DTV transition, in part based on section 4(k));
Review of the Commission's Broad. Cable and Equal Emp't Opportunity
Rules and Policies, Second Report and Order and Third Notice of
Proposed Rulemaking, 17 FCC Rcd 24018, 24077, paras. 5, 195 (2002)
(promulgating recordkeeping and reporting requirements for broadcast
licensees and other regulated entities to show compliance with equal
opportunities hiring rules, in part based on section 4(k)).
\164\ 600 F.3d at 659. All, or nearly all, providers of
broadband Internet access service are regulated by the Commission
insofar as they operate under certificates to provide common
carriage service, or under licenses to use radio spectrum.
---------------------------------------------------------------------------
Finally, the Commission has broad authority under Section 218 of
the Act to obtain ``full and complete information'' from common
carriers and their affiliates. To the extent broadband providers are
affiliated with communications common carriers, Section 218 allows the
Commission to require the provision of information such as that covered
by the transparency rule we adopt in this Order.\165\ We believe that
these disclosure requirements will assist us in carrying out our
reporting obligations to Congress.
---------------------------------------------------------------------------
\165\ Cf. US West, Inc. v. FCC, 778 F.2d 23, 26-27 (DC Cir.
1985) (acknowledging Commission's authority under Section 218 to
impose reporting requirements on holding companies that owned local
telephone companies).
---------------------------------------------------------------------------
E. Constitutional Issues
Some commenters contend that open Internet rules violate the First
Amendment and amount to an unconstitutional taking under the Fifth
Amendment. We examine these constitutional arguments below, and find
them unfounded.
1. First Amendment
Several broadband providers argue that open Internet rules are
inconsistent with the free speech guarantee of the First Amendment.
These commenters generally contend that because broadband providers
distribute their own and third-party content to customers, they are
speakers entitled to First Amendment protections. Therefore, they
argue, rules that prevent broadband providers from favoring the
transmission of some content over other content violate their free
speech rights. Other commenters contend that none of the proposed rules
implicate the First Amendment, because providing broadband service is
conduct that is not correctly understood as speech.
In arguing that broadband service is protected by the First
Amendment, AT&T compares its provision of broadband service to the
operation of a cable television system, and points out that the Supreme
Court has determined that cable programmers and cable operators engage
in speech protected by the First Amendment. The analogy is inapt. When
the Supreme Court held in Turner I that cable operators were protected
by the First Amendment, the critical factor that made cable operators
``speakers'' was their production of programming and their exercise of
``editorial discretion over which programs and stations to include''
(and thus which to exclude).
Unlike cable television operators, broadband providers typically
are best described not as ``speakers,'' but rather as conduits for
speech. The broadband Internet access service at issue here does not
involve an exercise of editorial discretion that is comparable to cable
companies' choice of which stations or programs to include in their
service. In this proceeding broadband providers have not, for instance,
shown that they market their services as benefiting from an editorial
presence.\166\ To the contrary, Internet end users expect that they can
obtain access to all or substantially all content that is available on
the Internet, without the editorial
[[Page 59221]]
intervention of their broadband provider.\167\
---------------------------------------------------------------------------
\166\ See, e.g., AT&T, AT&T U-verse, http://www.att-services.net/att-u-verse.html (AT&T U-verse: ``Customers can get the
information they want, when they want it''); Verizon, FiOS Internet,
http://www22.verizon.com/Residential/FiOSInternet/Overview.htm and
Verizon, High Speed Internet, http://www22.verizon.com/Residential/HighSpeedInternet (Verizon FiOS and High Speed Internet: ``Internet,
plus all the free extras'').
\167\ See Verizon Comments at 117 (``[B]roadband providers today
provide traditional Internet access services that offer subscribers
access to all lawful content and have strong economic incentives to
continue to do so.'') (emphasis added).
---------------------------------------------------------------------------
Consistent with that understanding, broadband providers maintain
that they qualify for statutory immunity from liability for copyright
violations or the distribution of offensive material precisely because
they lack control over what end users transmit and receive.\168\ In
addition, when defending themselves against subpoenas in litigation
involving alleged copyright violations, broadband providers typically
take the position that they are simply conduits of information provided
by others.\169\
---------------------------------------------------------------------------
\168\ See 17 U.S.C. 512(a) (a ``service provider shall not be
liable * * * for infringement of copyright by reason of the
provider's transmitting, routing, or providing connections for''
material distributed by others on its network); 47 U.S.C. 230(c)(1)
(``[N]o provider or user of an interactive computer service shall be
treated as the publisher or speaker of any information provided by
another information content provider''); see also Recording Indus.
Ass'n of Am., Inc. v. Verizon Internet Servs., Inc., 351 F.3d 1229,
1234 (DC Cir. 2003) (discussing in context of subpoena issued to
Verizon under the Digital Millennium Copyright Act Section 512(a)'s
``four safe harbors, each of which immunizes ISPs from liability
from copyright infringement''), cert. denied, 543 U.S. 924 (2004).
For example ``Verizon.net, the home page for Verizon Internet
customers, contains a notice explicitly claiming copyright over the
contents of the page. In contrast, the terms of service of Verizon
Internet access explicitly disclaim any affiliation with content
transmitted over the network.'' PK Reply at 22.
\169\ See, e.g., Charter Commc'ns, Inc., Subpoena Enforcement
Matter, 393 F.3d 771, 777 (8th Cir. 2005) (subpoenas served on
Charter were not authorized because ``Charter's function'' as a
broadband provider ``was limited to acting as a conduit for the
allegedly copyright protected material'' at issue); Verizon Internet
Servs., 351 F.3d at 1237 (accepting Verizon's argument that Federal
copyright law ``does not authorize the issuance of a subpoena to an
ISP acting as a mere conduit for the transmission of information
sent by others'').
---------------------------------------------------------------------------
To be sure, broadband providers engage in network management
practices designed to protect their Internet services against spam and
malicious content, but that practice bears little resemblance to an
editor's choosing which programs, among a range of programs, to
carry.\170\ Furthermore, this Order does not limit broadband providers'
ability to modify their own Web pages, or transmit any lawful message
that they wish, just like any other speaker. Broadband providers are
also free under this Order to offer a wide range of ``edited''
services. If, for example, a broadband provider wanted to offer a
service limited to ``family friendly'' materials to end users who
desire only such content, it could do so under the rules we promulgate
in this Order.
---------------------------------------------------------------------------
\170\ We recognize that in two cases, Federal district courts
have concluded that the provision of broadband service is ``speech''
protected by the First Amendment. In Itasca, the district court
reasoned that broadband providers were analogous to cable and
satellite television companies, which are protected by the First
Amendment. Ill. Bell Tel. Co. v. Vill. of Itasca, 503 F. Supp. 2d
928, 947-49 (N.D. Ill. 2007). And in Broward County, the district
court determined that the transmission function provided by
broadband service could not be separated from the content of the
speech being transmitted. Comcast Cablevision of Broward Cnty., Inc.
v. Broward Cnty., 124 F. Supp. 2d 685, 691-92 (S.D. Fla. 2000). For
the reasons stated, we disagree with the reasoning of those
decisions.
---------------------------------------------------------------------------
AT&T and NCTA argue that open Internet rules interfere with the
speech rights of content and application providers to the extent they
are prevented from paying broadband providers for higher quality
service. Purchasing a higher quality of termination service for one's
own Internet traffic, though, is not speech--just as providing the
underlying transmission service is not. Telephone common carriers, for
instance, transmit users' speech for hire, but no court has ever
suggested that regulation of common carriage arrangements triggers
First Amendment scrutiny.
Even if open Internet rules did implicate expressive activity, they
would not violate the First Amendment. Because the rules are based on
the characteristics of broadband Internet access service, independent
of content or viewpoint, they would be subject to intermediate First
Amendment scrutiny.\171\ The regulations in this Order are triggered by
a broadband provider offering broadband Internet access, not by the
message of any provider. Indeed, the point of open Internet rules is to
protect traffic regardless of its content. Verizon's argument that such
regulation is presumptively suspect because it makes speaker-based
distinctions likewise lacks merit: Our action is based on the
transmission service provided by broadband providers rather than on
what providers have to say. In any event, speaker-based distinctions
are permissible so long as they are ```justified by some special
characteristic of' the particular medium being regulated''--here the
ability of broadband providers to favor or disfavor Internet traffic to
the detriment of innovation, investment, competition, public discourse,
and end users.
---------------------------------------------------------------------------
\171\ See Turner I, 512 U.S. at 642. Regulations generally are
content neutral if justified without reference to content or
viewpoint. Id. at 643; BellSouth Corp. v. FCC, 144 F.3d 58, 69 (DC
Cir. 1998); Time Warner Entm't Co., L.P. v. FCC, 93 F.3d 957, 966-67
(DC Cir. 1996).
---------------------------------------------------------------------------
Under intermediate scrutiny, a content-neutral regulation will be
sustained if ``it furthers an important or substantial government
interest * * * unrelated to the suppression of free expression,'' and
if ``the means chosen'' to achieve that interest ``do not burden
substantially more speech than is necessary.'' The government interests
underlying this Order--preserving an open Internet to encourage
competition and remove impediments to infrastructure investment while
enabling consumer choice, end-user control, free expression, and the
freedom to innovate without permission--ensure the public's access to a
multiplicity of information sources and maximize the Internet's
potential to further the public interest. As a result, these interests
satisfy the intermediate-scrutiny standard.\172\ Indeed, the interest
in keeping the Internet open to a wide range of information sources is
an important free speech interest in its own right. As Turner I
affirmed, ``assuring that the public has access to a multiplicity of
information sources is a governmental purpose of the highest order, for
it promotes values central to the First Amendment.'' \173\ This Order
protects the speech interests of all Internet speakers.
---------------------------------------------------------------------------
\172\ These interests are consistent with the Communications
Act's charge to the Commission to make available a ``rapid and
efficient'' national communications infrastructure, 47 U.S.C. 151;
to promote, consistent with a ``vibrant and competitive free
market,'' ``the continued development of the Internet and other
interactive computer services''; and to ``encourage the development
of technologies which maximize user control over what information is
received,'' 47 U.S.C. 230(b)(1)-(3). Indeed, AT&T concedes that
``[t]here is little doubt that preservation of an open and free
Internet is an `important or substantial government interest.' ''
AT&T Comments at 237 (quoting Turner I, 512 U.S. at 662).
\173\ 512 U.S. at 663. The Turner I Court continued: ``Indeed,
it has long been a basic tenet of national communications policy
that the widest possible dissemination of information from diverse
and antagonistic sources is essential to the welfare of the
public.'' Id. (internal quotation marks omitted). See also FCC v.
Nat'l Citizens Comm. for Broad., 436 U.S. 775, 795 (1978) (NCCB)
(quoting Associated Press v. United States, 326 U.S. 1, 20 (1945)).
---------------------------------------------------------------------------
Time Warner and Verizon contend that the government lacks important
or substantial interests because the harms from prohibited practices
supposedly are speculative. This ignores actual instances of harmful
practices by broadband providers, as discussed in Part II.B. In any
event, the Commission is not required to stay its hand until
substantial harms already have occurred. On the contrary, the
Commission's predictive judgments as to the development of a problem
and likely injury to the public interest are entitled to great
deference.
In sum, the rules we adopt are narrowly tailored to advance the
important government interests at stake.
[[Page 59222]]
The rules apply only to that portion of the end user's link to the
Internet over which the end user's broadband provider has control. They
forbid only those actions that could unfairly impede the public's use
of this important resource. Broadband providers are left with ample
opportunities to transmit their own content, to maintain their own Web
sites, and to engage in reasonable network management. In addition,
they can offer edited services to their end users. The rules are
narrowly tailored because they address the problem at hand, and go no
farther.\174\
---------------------------------------------------------------------------
\174\ AT&T contends (AT&T Comments at 219-20) that our rules
would conflict with prohibitions contained in Section 326 of the Act
against ``censorship'' of ``radio communications'' or interference
with ``the right of free speech by means of radio communication.''
47 U.S.C. 326. For the same reasons that our rules do not violate
the First Amendment, they do not violate Section 326's statutory
prohibition.
---------------------------------------------------------------------------
2. Fifth Amendment Takings
Contrary to the claims of some broadband providers, open Internet
rules pose no issue under the Fifth Amendment's Takings Clause. Our
rules do not compel new services or limit broadband providers'
flexibility in setting prices for their broadband Internet access
services, but simply require transparency and prevent broadband
providers--when they voluntarily carry Internet traffic--from blocking
or unreasonably discriminating in their treatment of that traffic.
Moreover, this Order involves setting policies for communications
networks, an activity that has been one of this Commission's central
duties since it was established in 1934.
Absent compelled permanent physical occupations of property,\175\
takings analysis involves ``essentially ad hoc, factual inquiries''
regarding such factors as the degree of interference with ``investment-
backed expectations,'' the ``economic impact of the regulation'' and
``the character of the government action.'' In this regard, takings law
makes clear that property owners cannot, as a general matter, expect
that existing legal requirements regarding their property will remain
entirely unchanged. As discussed in Part II, the history of broadband
Internet access services offers no basis for reasonable reliance on a
policy regime in which providers are free to conceal or discriminate
without limit, and the rules we adopt in this Order should not impose
substantial new costs on broadband providers.\176\ Accordingly, our
Order does not raise constitutional concerns under regulatory takings
analysis.
---------------------------------------------------------------------------
\175\ Verizon contends that ``[t]o the extent the proposed rules
would prohibit the owner of a broadband network from setting the
terms on which other providers can occupy its property, the rule
would give those providers the equivalent of a permanent easement on
the network--a form of physical occupation.'' Verizon Comments at
119 (citing Loretto v. Teleprompter Manhattan CATV Corp., 458 U.S.
419, 430 (1982)). Not so. Such transmissions are neither
``occupations'' nor ``permanent.'' See Loretto, 458 U.S. at 435
n.12; see also Cablevision Sys. Corp. v. FCC, 570 F.3d 83, 98 (2d
Cir. 2009) (upholding Commission's finding that a must-carry
obligation did not constitute a physical occupation because ``the
transmission of WRNN's signal does not involve a physical occupation
of Cablevision's equipment or property''). In addition, to the
extent broadband providers voluntarily allow any customer to
transmit or receive information, the imposition of reasonable non-
discrimination requirements would not be a taking under Loretto. See
Hilton Washington Corp. v. District of Columbia, 777 F.2d 47 (DC
Cir. 1985); Yee v. City of Escondido, 503 U.S. 519, 531 (1992).
\176\ This history likewise refutes the assertion that prior
Commission decisions ``engendered serious reliance interests'' that
would be unsettled by our adoption of open Internet rules. Baker
Statement at *11 n.41 (citation and internal quotation marks
omitted).
---------------------------------------------------------------------------
V. Enforcement
Prompt and effective enforcement of the rules adopted in this Order
is crucial to preserving an open Internet and providing clear guidance
to stakeholders. We anticipate that many of the disputes that will
arise regarding alleged open Internet violations--particularly those
centered on engineering-focused questions--will be resolvable by the
parties without Commission involvement. We thus encourage parties to
endeavor to resolve disputes through direct negotiation focused on
relevant technical issues, and to consult with independent technical
bodies. Many commenters endorse this approach.\177\
---------------------------------------------------------------------------
\177\ See, e.g., Bright House Networks Comments at 10; CCIA
Comments at 2, 34; Google-Verizon Joint Comments at 4 (``A robust
role for technical and industry groups should be encouraged to
address any challenges or problems that may arise and to help guide
the practices of all players. * * *''); WISPA Comments at 14-16;
DISH Network Reply at 24-26; Qwest Reply at 32.
---------------------------------------------------------------------------
Should issues develop that are not resolved through private
processes, the Commission will provide backstop mechanisms to address
such disputes.\178\ In the Open Internet NPRM, the Commission proposed
to enforce open Internet rules through case-by-case adjudication, a
proposal that met with almost universal support among commenters. The
Commission also sought comment on whether it should adopt complaint
procedures specifically governing alleged violations of open Internet
rules, and whether any of the Commission's existing rules provide a
suitable model.
---------------------------------------------------------------------------
\178\ Providers and other parties may also seek guidance from
the Commission on questions about the application of the open
Internet rules in particular contexts, for instance by requesting a
declaratory ruling. See 47 CFR 1.2.
---------------------------------------------------------------------------
A. Informal Complaints
Many commenters urge the Commission to adopt informal complaint
procedures that equip end users and edge providers with a simple and
cost-effective option for calling attention to open Internet rule
violations. We agree that end users, edge providers, and others should
have an efficient vehicle to bring potential open Internet violations
to the Commission, and indeed, such a vehicle is already available.
Parties may submit complaints to the Commission pursuant to Section
1.41 of the Commission's rules. Unlike formal complaints, no filing fee
is required. We recommend that end users and edge providers submit any
complaints through the Commission's Web site, at http://esupport.fcc.gov/complaints.htm. The Consumer and Governmental Affairs
Bureau will also make available resources explaining these rules and
facilitating the filing of informal complaints. Although individual
informal complaints will not typically result in written Commission
orders, the Enforcement Bureau will examine trends or patterns in
complaints to identify potential targets for investigation and
enforcement action.\179\
---------------------------------------------------------------------------
\179\ As with our other complaint rules, the availability of
complaint procedures does not bar the Commission from initiating
separate and independent enforcement proceedings for potential
violations. See 47 CFR 0.111(a)(16).
---------------------------------------------------------------------------
B. Formal Complaints
Many commenters propose that the Commission adopt formal complaint
procedures to address open Internet disputes. We agree that such
procedures should be available in the event an open Internet dispute
cannot be resolved through other means. Formal complaint processes
permit anyone--including individual end users and edge providers--to
file a claim alleging that another party has violated a statute or
rule, and asking the Commission to rule on the dispute. A number of
commenters suggest that existing Commission procedural rules could
readily be utilized to govern open Internet complaints.
We conclude that adopting a set of procedures based on our Part 76
cable access complaint rules will best suit the needs of open Internet
disputes that may arise.\180\ Although similar to the
[[Page 59223]]
complaint rules under Section 208, we find that the part 76 rules are
more streamlined and thus preferable.\181\
---------------------------------------------------------------------------
\180\ The Commission is authorized to resolve formal
complaints--and adopt procedural rules governing the process--
pursuant to Sections 4(i) and 4(j) of the Act. 47 U.S.C.. 154(i),
154(j). In addition, Section 403 of the Act enables the Commission
to initiate inquiries and enforce orders on its own motion. 47
U.S.C. 403. Inherent in such authority is the ability to resolve
disputes concerning violations of the open Internet rules.
\181\ The Part 76 rules were promulgated to address complaints
against cable systems. See 1998 Biennial Regulatory Review--Part
76--Cable Television Service Pleading and Complaint Rules, Report
and Order, 14 FCC Rcd 418, 420, para. 6 (1999) (``1998 Biennial
Review''). For example, a local television station may bring a
complaint, pursuant to the Part 76 rules, claiming that it was
wrongfully denied carriage on a cable system. See 47 CFR 76.61. Some
complaints alleging open Internet violations may be analogous, such
as those brought by a content or application provider claiming that
broadband providers--many of which are cable companies--are
unlawfully blocking or degrading access to end users.
---------------------------------------------------------------------------
Under the rules we adopt in this Order, any person may file a
formal complaint. Before filing a complaint, a complainant must first
notify the defendant in writing that it intends to file a complaint
with the Commission for violation of rules adopted in this Order.\182\
After the complaint has been filed, the defendant must submit an
answer, and the complainant may submit a reply. In some cases, the
facts might be uncontested, and the proceeding can be completed based
on the pleadings. In other cases, a thorough analysis of the challenged
conduct might require further factual development and briefing.\183\
Based on the record developed, Commission staff (or the Commission
itself) will issue an order determining the lawfulness of the
challenged practice.
---------------------------------------------------------------------------
\182\ As with other formal complaint procedures, a filing fee
will be required. See 47 CFR 1.1106.
\183\ The rules give the Commission discretion to order other
procedures as appropriate, including briefing, status conferences,
oral argument, evidentiary hearings, discovery, or referral to an
administrative law judge. See 47 CFR 8.14(e) through (g).
---------------------------------------------------------------------------
As in other contexts, complainants in open Internet proceedings
will ultimately bear the burden of proof to demonstrate by a
preponderance of the evidence that an alleged violation of the rules
has occurred. A number of commenters propose, however, that once a
complainant makes a prima facie showing that an open Internet rule has
been violated, the burden should shift to the broadband provider to
demonstrate that the challenged practice is reasonable. This approach
is appropriate in the context of certain open Internet complaints, when
the evidence necessary to apply the open Internet rules is
predominantly in the possession of the broadband provider. Accordingly,
we require a complainant alleging a violation of the open Internet
rules to plead fully and with specificity the basis of its claims and
to provide facts, supported when possible by documentation or
affidavit, sufficient to establish a prima facie case of an open
Internet violation. In turn, the broadband provider must answer each
claim with particularity and furnish facts, supported by documentation
or affidavit, demonstrating the reasonableness of the challenged
practice. At that point, the complainant will have the opportunity to
demonstrate that the practice is not reasonable. Should experience
reveal the need to adjust the burden of proof in open Internet
disputes, we will do so as appropriate.
Several commenters urge the Commission to adopt timelines for the
complaint process. We recognize the need to resolve alleged violations
swiftly, and accordingly will allow requests for expedited treatment of
open Internet complaints under the Enforcement Bureau's Accelerated
Docket procedures.\184\
---------------------------------------------------------------------------
\184\ See 47 CFR 1.730. Furthermore, for good cause, pursuant to
47 CFR 1.3, the Commission may shorten the deadlines or otherwise
revise the procedures herein to expedite the adjudication of
complaints.
---------------------------------------------------------------------------
In resolving formal complaints, the Commission will draw on
resources from across the agency--including engineering, economic, and
legal experts--to resolve open Internet complaints in a timely manner.
In addition, we will take into account standards and best practices
adopted by relevant standard-setting organizations, and such
organizations and outside advisory groups also may provide valuable
technical assistance in resolving disputes. Further, in order to
facilitate prompt decision-making, when possible we will resolve open
Internet formal complaints at the bureau level, rather than the
Commission level.\185\
---------------------------------------------------------------------------
\185\ The rules adopted in this Order explicitly authorize the
Enforcement Bureau to resolve complaints alleging open Internet
violations.
---------------------------------------------------------------------------
C. FCC Initiated Actions
As noted above, in addition to ruling on complaints, the Commission
has the authority to initiate enforcement actions on its own motion.
For instance, Section 403 of the Act permits the Commission to initiate
an inquiry concerning any question arising under the Act, and Section
503(b) authorizes us to issue citations and impose forfeiture penalties
for violations of our rules. Should the Commission find that a
broadband Internet provider is engaging in activity that violates the
open Internet rules, we will take appropriate enforcement action,
including the issuance of forfeitures.
VI. Effective Date, Open Internet Advisory Committee, and Commission
Review
Some of the rules adopted in this Order contain new information
collection requirements subject to the Paperwork Reduction Act (PRA).
Our rules addressing transparency are among those requiring PRA
approval. The disclosure rule is essential to the proper functioning of
our open Internet framework, and we therefore make all the rules we
adopt in this Order effective November 20, 2011.
To assist the Commission in monitoring the state of Internet
openness and the effects of our rules, we intend to create an Open
Internet Advisory Committee. The Committee, to be created in
consultation with the General Services Administration pursuant to the
Federal Advisory Committee Act, will be an inclusive and transparent
body that will hold public meetings. It will be comprised of a balanced
group including consumer advocates; Internet engineering experts;
content, application, and service providers; network equipment and end-
user-device manufacturers and suppliers; investors; broadband service
providers; and other parties the Commission may deem appropriate. The
Committee will aid the Commission in tracking developments with respect
to the freedom and openness of the Internet, in particular with respect
to issues discussed in this Order, including technical standards and
issues relating to mobile broadband and specialized services. The
Committee will report to the Commission and make recommendations it
deems appropriate concerning our open Internet framework.
In light of the pace of change of technologies and the market for
broadband Internet access service, and to evaluate the efficacy of the
framework adopted in this Order for preserving Internet openness, the
Commission will review all of the rules in this Order no later than two
years from their effective date, and will adjust its open Internet
framework as appropriate.
VII. Procedural Matters
A. Final Regulatory Flexibility Analysis
As required by the Regulatory Flexibility Act of 1980, as amended
(RFA), an Initial Regulatory Flexibility Analysis (IRFA) was included
in the Open Internet NPRM in GN Docket No. 09-191 and WC Docket No. 07-
52. The Commission sought written public
[[Page 59224]]
comment on the proposals in these dockets, including comment on the
IRFA. This Final Regulatory Flexibility Analysis (FRFA) conforms to the
RFA.
Need for, and Objectives of, the Rules
In this Order the Commission takes an important step to preserve
the Internet as an open platform for innovation, investment, job
creation, economic growth, competition, and free expression. To provide
greater clarity and certainty regarding the continued freedom and
openness of the Internet, we adopt three basic rules that are grounded
in broadly accepted Internet norms, as well as our own prior decisions:
i. Transparency. Fixed and mobile broadband providers must disclose
the network management practices, performance characteristics, and
terms and conditions of their broadband services;
ii. No blocking. Fixed broadband providers may not block lawful
content, applications, services, or non-harmful devices; mobile
broadband providers may not block lawful Web sites, or block
applications that compete with their voice or video telephony services;
and
iii. No unreasonable discrimination. Fixed broadband providers may
not unreasonably discriminate in transmitting lawful network traffic.
We believe these rules, applied with the complementary principle of
reasonable network management, will empower and protect consumers and
innovators while helping ensure that the Internet continues to
flourish, with robust private investment and rapid innovation at both
the core and the edge of the network. This is consistent with the
National Broadband Plan goal of broadband access that is ubiquitous and
fast, promoting the global competitiveness of the United States.
In late 2009, we launched a public process to determine whether and
what actions might be necessary to preserve the characteristics that
have allowed the Internet to grow into an indispensable platform
supporting our nation's economy and civic life, and to foster continued
investment in the physical networks that enable the Internet. Since
then, more than 100,000 commenters have provided written input.
Commission staff held several public workshops and convened a
Technological Advisory Process with experts from industry, academia,
and consumer advocacy groups to collect their views regarding key
technical issues related to Internet openness.
This process has made clear that the Internet has thrived because
of its freedom and openness--the absence of any gatekeeper blocking
lawful uses of the network or picking winners and losers online.
Consumers and innovators do not have to seek permission before they use
the Internet to launch new technologies, start businesses, connect with
friends, or share their views. The Internet is a level playing field.
Consumers can make their own choices about what applications and
services to use and are free to decide what content they want to
access, create, or share with others. This openness promotes
competition. It also enables a self-reinforcing cycle of investment and
innovation in which new uses of the network lead to increased adoption
of broadband, which drives investment and improvements in the network
itself, which in turn lead to further innovative uses of the network
and further investment in content, applications, services, and devices.
A core goal of this Order is to foster and accelerate this cycle of
investment and innovation.
The record and our economic analysis demonstrate, however, that the
openness of the Internet cannot be taken for granted, and that it faces
real threats. Indeed, we have seen broadband providers endanger the
Internet's openness by blocking or degrading content and applications
without disclosing their practices to end users and edge providers,
notwithstanding the Commission's adoption of open Internet principles
in 2005. In light of these considerations, as well as the limited
choices most consumers have for broadband service, broadband providers'
financial interests in telephony and pay television services that may
compete with online content and services, and the economic and civic
benefits of maintaining an open and competitive platform for innovation
and communication, the Commission has long recognized that certain
basic standards for broadband provider conduct are necessary to ensure
the Internet's continued openness. The record also establishes the
widespread benefits of providing greater clarity in this area--clarity
that the Internet's openness will continue; that there is a forum and
procedure for resolving alleged open Internet violations; and that
broadband providers may reasonably manage their networks and innovate
with respect to network technologies and business models. We expect the
costs of compliance with our prophylactic rules to be small, as they
incorporate longstanding openness principles that are generally in line
with current practices and with norms endorsed by many broadband
providers. Conversely, the harms of open Internet violations may be
substantial, costly, and in some cases potentially irreversible.
The rules we proposed in the Open Internet NPRM and those we adopt
in this Order follow directly from the Commission's bipartisan Internet
Policy Statement, adopted unanimously in 2005 and made temporarily
enforceable for certain providers in 2005 and 2006; openness
protections the Commission established in 2007 for users of certain
wireless spectrum; and a notice of inquiry in 2007 that asked, among
other things, whether the Commission should add a principle of
nondiscrimination to the Internet Policy Statement. Our rules build
upon these actions, first and foremost by requiring broadband providers
to be transparent in their network management practices, so that end
users can make informed choices and innovators can develop, market, and
maintain Internet-based offerings. The rules also prevent certain forms
of blocking and discrimination with respect to content, applications,
services, and devices that depend on or connect to the Internet.
An open, robust, and well-functioning Internet requires that
broadband providers have the flexibility to reasonably manage their
networks. Network management practices are reasonable if they are
appropriate and tailored to achieving a legitimate network management
purpose. Transparency and end-user control are touchstones of
reasonableness.
We recognize that broadband providers may offer other services over
the same last-mile connections used to provide broadband service. These
``specialized services'' can benefit end users and spur investment, but
they may also present risks to the open Internet. We will closely
monitor specialized services and their effects on broadband service to
ensure, through all available mechanisms, that they supplement but do
not supplant the open Internet.
Mobile broadband is at an earlier stage in its development than
fixed broadband and is evolving rapidly. For that and other reasons
discussed below, we conclude that it is appropriate at this time to
take measured steps in this area. Accordingly, we require mobile
providers to comply with the transparency rule, which includes
enforceable disclosure obligations regarding device and application
certification and approval processes; we prohibit providers from
blocking lawful Web sites; and we prohibit providers from blocking
applications that compete with providers' voice and video telephony
services. We will closely
[[Page 59225]]
monitor the development of the mobile broadband market and will adjust
the framework we adopt in this Order as appropriate.
These rules are within our jurisdiction over interstate and foreign
communications by wire and radio. Further, they implement specific
statutory mandates in the Communications Act (``Act'') and the
Telecommunications Act of 1996 (``1996 Act''), including provisions
that direct the Commission to promote Internet investment and to
protect and promote voice, video, and audio communications services.
The framework we adopt in this Order aims to ensure the Internet
remains an open platform--one characterized by free markets and free
speech--that enables consumer choice, end-user control, competition
through low barriers to entry, and the freedom to innovate without
permission. The framework does so by protecting openness through high-
level rules, while maintaining broadband providers' and the
Commission's flexibility to adapt to changes in the market and in
technology as the Internet continues to evolve.
Summary of the Significant Issues Raised by the Public Comments in
Response to the IRFA and Summary of the Assessment of the Agency of
Such Issues
A few commenters discussed the IRFA from the Open Internet NPRM.
The Center for Regulatory Effectiveness (CRE) argued that the Open
Internet NPRM's IRFA was defective because it ineffectively followed 5
U.S.C. secs. 603(a) (``Such analysis shall describe the impact of the
proposed rule on small entities.'') and 603(c) (``Each initial
regulatory flexibility analysis shall also contain a description of any
significant alternatives to the proposed rule which accomplish the
stated objectives of applicable statutes and which minimize any
significant economic impact of the proposed rule on small entities.'').
CRE does not provide any case law to support its interpretation that
the Commission is in violation of these aspects of the statute, nor
does CRE attempt to argue that SBEs have actually or theoretically been
harmed. Rather, CRE is concerned that by not following its reading of
these parts of the law, the Commission is being hypocritical by not
being transparent enough. CRE recommends that the Commission publish a
revised IRFA for public comment. We disagree: we believe that the IRFA
was adequate and that the opportunity for SBEs to comment in a publicly
accessible docket should remove any potential harm to openness that CRE
is concerned with, as well as any harms to SBEs that could occur by not
following CRE's interpretation of the law.
The Smithville Telephone Company (Smithville) notes that many ILECs
have vastly fewer employees than the 1500 or less that is required to
be recognized as a small business under the SBA. For instance,
Smithville states that it has seven employees. Smithville also observes
that some other small ILECs in Mississippi have staffs of 8, 4, 2, 3,
and 21. Smithville argues that companies of this size do not have the
resources to fully analyze issues and participate in Commission
proceedings. Smithville would like the Commission to use the data that
it regularly receives from carriers to set a carrier size where
exemptions from proposed rules and less complex reporting requirements
can be set. In the present case, however, we determine that this is not
necessary. We expect the costs of compliance with these rules to be
small, as the high-level rules incorporate longstanding openness
principles that appear to be generally in line with most broadband
providers' current practices. We note that Smithville does not cite any
particular source of increased costs, or attempt to estimate costs of
compliance. Nonetheless, the Commission attempts to ease any burden
that the transparency rule may cause by only requiring disclosure on a
Web site and at the point of sale, making the transparency rule
flexible. In addition, by setting the effective date of these rules as
November 20, 2011, the Order gives broadband providers adequate time to
develop cost-effective methods of compliance. Finally, to the extent
that the transparency rule imposes a new obligation on small
businesses, we find that the flexibility built into the rule addresses
any compliance concerns.
The American Cable Association (ACA) notes that the Commission has
an obligation to ``include in the FRFA a comprehensive discussion of
the economic impact its actions will have on small cable operators.''
The ACA cites its other comments, which ask the Commission to clarify
that the codified principles would not obligate broadband service
providers to (1) ``employ specific network management practices,'' (2)
``impose affirmative obligations dealing with unlawful content or the
unlawful transfer of content,'' (3) ``accommodate lawful devices that
are not supported by a broadband provider's network,'' and (4)
``provide information regarding a company's network management
practices through any reporting, recordkeeping, or means other than
through a company's Web site or Web page.'' Addressing ACA's arguments
with regard to cable operators, and fixed broadband providers in
particular, (1), the Commission is not requiring specific network
management practices. The Commission only requires that any network
management be reasonable; the Commission does not require that any
specific practice be employed. Regarding (2), the rules do not impose
affirmative obligations dealing with unlawful content or the unlawful
transfer of content. We state that the ``no blocking'' rule does not
prevent or restrict a broadband provider from refusing to transmit
material such as child pornography. In response to (3), the Order
clarifies that the ``no blocking'' rule protects only devices that do
not harm the network and only requires fixed broadband service
providers to allow devices that conform to publicly available industry
standards applicable to the providers' services. Directly addressing
ACA's concern, the Order notes that a DOCSIS-based provider is not
required to support a DSL modem. In response to (4), the disclosure
requirement in this Order does not require additional forms of
disclosure, other than, at a minimum, requiring broadband providers to
prominently display or provide links to disclosures on a publicly
available, easily accessible Web site that is available to current and
prospective end users and edge providers as well as to the Commission,
and disclosing relevant information at the point of sale.
Description and Estimate of the Number of Small Entities to Which the
Rules Apply
The RFA directs agencies to provide a description of, and, where
feasible, an estimate of, the number of small entities that may be
affected by the rules adopted herein. The RFA generally defines the
term ``small entity'' as having the same meaning as the terms ``small
business,'' ``small organization,'' and ``small governmental
jurisdiction.'' In addition, the term ``small business'' has the same
meaning as the term ``small business concern'' under the Small Business
Act. A ``small business concern'' is one which: (1) Is independently
owned and operated; (2) is not dominant in its field of operation; and
(3) satisfies any additional criteria established by the Small Business
Administration (SBA).
1. Total Small Entities
Our action may, over time, affect small entities that are not
easily categorized at present. We therefore
[[Page 59226]]
describe here, at the outset, three comprehensive, statutory small
entity size standards. First, nationwide, there are a total of
approximately 27.2 million small businesses, according to the SBA. In
addition, a ``small organization'' is generally ``any not-for-profit
enterprise which is independently owned and operated and is not
dominant in its field.'' Nationwide, as of 2002, there were
approximately 1.6 million small organizations. Finally, the term
``small governmental jurisdiction'' is defined generally as
``governments of cities, towns, townships, villages, school districts,
or special districts, with a population of less than fifty thousand.''
Census Bureau data for 2002 indicate that there were 87,525 local
governmental jurisdictions in the United States. We estimate that, of
this total, 84,377 entities were ``small governmental jurisdictions.''
Thus, we estimate that most governmental jurisdictions are small.
2. Internet Access Service Providers
Internet Service Providers. The 2007 Economic Census places these
firms, whose services might include voice over Internet Protocol
(VoIP), in either of two categories, depending on whether the service
is provided over the provider's own telecommunications facilities
(e.g., cable and DSL ISPs), or over client-supplied telecommunications
connections (e.g., dial-up ISPs). The former are within the category of
Wired Telecommunications Carriers, which has an SBA small business size
standard of 1,500 or fewer employees. These are also labeled
``broadband.'' The latter are within the category of All Other
Telecommunications, which has a size standard of annual receipts of $25
million or less. These are labeled non-broadband. The most current
Economic Census data for all such firms are 2007 data, which are
detailed specifically for ISPs within the categories above. For the
first category, the data show that 396 firms operated for the entire
year, of which 159 had nine or fewer employees. For the second
category, the data show that 1,682 firms operated for the entire year.
Of those, 1,675 had annual receipts below $25 million per year, and an
additional two had receipts of between $25 million and $ 49,999,999.
Consequently, we estimate that the majority of ISP firms are small
entities.
The ISP industry has changed since 2007. The 2007 data cited above
may therefore include entities that no longer provide Internet access
service and may exclude entities that now provide such service. To
ensure that this FRFA describes the universe of small entities that our
action might affect, we discuss in turn several different types of
entities that might be providing Internet access service.
3. Wireline Providers
Incumbent Local Exchange Carriers (Incumbent LECs). Neither the
Commission nor the SBA has developed a small business size standard
specifically for incumbent local exchange services. The appropriate
size standard under SBA rules is for the category Wired
Telecommunications Carriers. Under that size standard, such a business
is small if it has 1,500 or fewer employees. According to Commission
data, 1,311 carriers have reported that they are engaged in the
provision of incumbent local exchange services. Of these 1,311
carriers, an estimated 1,024 have 1,500 or fewer employees and 287 have
more than 1,500 employees. Consequently, the Commission estimates that
most providers of incumbent local exchange service are small businesses
that may be affected by our proposed action.
Competitive Local Exchange Carriers (Competitive LECs), Competitive
Access Providers (CAPs), Shared-Tenant Service Providers, and Other
Local Service Providers. Neither the Commission nor the SBA has
developed a small business size standard specifically for these service
providers. The appropriate size standard under SBA rules is for the
category Wired Telecommunications Carriers. Under that size standard,
such a business is small if it has 1,500 or fewer employees. According
to Commission data, 1005 carriers have reported that they are engaged
in the provision of either competitive access provider services or
competitive local exchange carrier services. Of these 1005 carriers, an
estimated 918 have 1,500 or fewer employees and 87 have more than 1,500
employees. In addition, 16 carriers have reported that they are
``Shared-Tenant Service Providers,'' and all 16 are estimated to have
1,500 or fewer employees. In addition, 89 carriers have reported that
they are ``Other Local Service Providers.'' Of the 89, all have 1,500
or fewer employees. Consequently, the Commission estimates that most
providers of competitive local exchange service, competitive access
providers, Shared-Tenant Service Providers, and other local service
providers are small entities that may be affected by our action.
We have included small incumbent LECs in this present RFA analysis.
As noted above, a ``small business'' under the RFA is one that, inter
alia, meets the pertinent small business size standard (e.g., a
telephone communications business having 1,500 or fewer employees), and
``is not dominant in its field of operation.'' The SBA's Office of
Advocacy contends that, for RFA purposes, small incumbent LECs are not
dominant in their field of operation because any such dominance is not
``national'' in scope. We have therefore included small incumbent LECs
in this RFA analysis, although we emphasize that this RFA action has no
effect on Commission analyses and determinations in other, non-RFA
contexts.
Interexchange Carriers. Neither the Commission nor the SBA has
developed a small business size standard specifically for providers of
interexchange services. The appropriate size standard under SBA rules
is for the category Wired Telecommunications Carriers. Under that size
standard, such a business is small if it has 1,500 or fewer employees.
According to Commission data, 300 carriers have reported that they are
engaged in the provision of interexchange service. Of these, an
estimated 268 have 1,500 or fewer employees and 32 have more than 1,500
employees. Consequently, the Commission estimates that the majority of
IXCs are small entities that may be affected by our action.
Operator Service Providers (OSPs). Neither the Commission nor the
SBA has developed a small business size standard specifically for
operator service providers. The appropriate size standard under SBA
rules is for the category Wired Telecommunications Carriers. Under that
size standard, such a business is small if it has 1,500 or fewer
employees. According to Commission data, 33 carriers have reported that
they are engaged in the provision of operator services. Of these, an
estimated 31 have 1,500 or fewer employees and 2 has more than 1,500
employees. Consequently, the Commission estimates that the majority of
OSPs are small entities that may be affected by our proposed action.
4. Wireless Providers--Fixed and Mobile
For reasons discussed above in the text of the Order, the
Commission has distinguished wireless fixed broadband Internet access
service from wireless mobile broadband Internet access service.
Specifically, the Commission decided that fixed broadband Internet
access service providers, whether wireline or wireless, must disclose
their network management practices and the performance characteristics
and commercial terms of their broadband services; may not block lawful
content, applications, services or non-harmful
[[Page 59227]]
devices; and may not unreasonably discriminate in transmitting lawful
network traffic. Also for the reasons discussed above, the Commission
decided that wireless mobile broadband Internet access service
providers must disclose their network management practices and
performance characteristics and commercial terms of their broadband
service and may not block lawful Web sites or block applications that
compete with their voice or video telephony service. Thus, to the
extent the wireless services listed below are used by wireless firms
for fixed and mobile broadband Internet access services, the actions in
this Order may have an impact on those small businesses as set forth
above and further below. In addition, for those services subject to
auctions, we note that, as a general matter, the number of winning
bidders that claim to qualify as small businesses at the close of an
auction does not necessarily represent the number of small businesses
currently in service. Also, the Commission does not generally track
subsequent business size unless, in the context of assignments and
transfers or reportable eligibility events, unjust enrichment issues
are implicated.
Wireless Telecommunications Carriers (except Satellite). Since
2007, the Census Bureau has placed wireless firms within this new,
broad, economic census category. Prior to that time, such firms were
within the now-superseded categories of ``Paging'' and ``Cellular and
Other Wireless Telecommunications.'' Under the present and prior
categories, the SBA has deemed a wireless business to be small if it
has 1,500 or fewer employees. For the category of Wireless
Telecommunications Carriers (except Satellite), preliminary data for
2007 show that there were 11,927 firms operating that year. While the
Census Bureau has not released data on the establishments broken down
by number of employees, we note that the Census Bureau lists total
employment for all firms in that sector at 281,262. Since all firms
with fewer than 1,500 employees are considered small, given the total
employment in the sector, we estimate that the vast majority of
wireless firms are small.
Wireless Communications Services. This service can be used for
fixed, mobile, radiolocation, and digital audio broadcasting satellite
uses. The Commission defined ``small business'' for the wireless
communications services (WCS) auction as an entity with average gross
revenues of $40 million for each of the three preceding years, and a
``very small business'' as an entity with average gross revenues of $15
million for each of the three preceding years. The SBA has approved
these definitions. The Commission auctioned geographic area licenses in
the WCS service. In the auction, which commenced on April 15, 1997 and
closed on April 25, 1997, seven bidders won 31 licenses that qualified
as very small business entities, and one bidder won one license that
qualified as a small business entity.
1670-1675 MHz Services. This service can be used for fixed and
mobile uses, except aeronautical mobile. An auction for one license in
the 1670-1675 MHz band commenced on April 30, 2003 and closed the same
day. One license was awarded. The winning bidder was not a small
entity.
Wireless Telephony. Wireless telephony includes cellular, personal
communications services, and specialized mobile radio telephony
carriers. As noted, the SBA has developed a small business size
standard for Wireless Telecommunications Carriers (except Satellite).
Under the SBA small business size standard, a business is small if it
has 1,500 or fewer employees. According to Trends in Telephone Service
data, 413 carriers reported that they were engaged in wireless
telephony. Of these, an estimated 261 have 1,500 or fewer employees and
152 have more than 1,500 employees. Therefore, more than half of these
entities can be considered small.
Broadband Personal Communications Service. The broadband personal
communications services (PCS) spectrum is divided into six frequency
blocks designated A through F, and the Commission has held auctions for
each block. The Commission initially defined a ``small business'' for
C- and F-Block licenses as an entity that has average gross revenues of
$40 million or less in the three previous calendar years. For F-Block
licenses, an additional small business size standard for ``very small
business'' was added and is defined as an entity that, together with
its affiliates, has average gross revenues of not more than $15 million
for the preceding three calendar years. These small business size
standards, in the context of broadband PCS auctions, have been approved
by the SBA. No small businesses within the SBA-approved small business
size standards bid successfully for licenses in Blocks A and B. There
were 90 winning bidders that claimed small business status in the first
two C-Block auctions. A total of 93 bidders that claimed small business
status won approximately 40 percent of the 1,479 licenses in the first
auction for the D, E, and F Blocks. On April 15, 1999, the Commission
completed the reauction of 347 C-, D-, E-, and F-Block licenses in
Auction No. 22. Of the 57 winning bidders in that auction, 48 claimed
small business status and won 277 licenses.
On January 26, 2001, the Commission completed the auction of 422 C
and F Block Broadband PCS licenses in Auction No. 35. Of the 35 winning
bidders in that auction, 29 claimed small business status. Subsequent
events concerning Auction 35, including judicial and agency
determinations, resulted in a total of 163 C and F Block licenses being
available for grant. On February 15, 2005, the Commission completed an
auction of 242 C-, D-, E-, and F-Block licenses in Auction No. 58. Of
the 24 winning bidders in that auction, 16 claimed small business
status and won 156 licenses. On May 21, 2007, the Commission completed
an auction of 33 licenses in the A, C, and F Blocks in Auction No. 71.
Of the 12 winning bidders in that auction, five claimed small business
status and won 18 licenses. On August 20, 2008, the Commission
completed the auction of 20 C-, D-, E-, and F-Block Broadband PCS
licenses in Auction No. 78. Of the eight winning bidders for Broadband
PCS licenses in that auction, six claimed small business status and won
14 licenses.
Specialized Mobile Radio Licenses. The Commission awards ``small
entity'' bidding credits in auctions for Specialized Mobile Radio (SMR)
geographic area licenses in the 800 MHz and 900 MHz bands to firms that
had revenues of no more than $15 million in each of the three previous
calendar years. The Commission awards ``very small entity'' bidding
credits to firms that had revenues of no more than $3 million in each
of the three previous calendar years. The SBA has approved these small
business size standards for the 900 MHz Service. The Commission has
held auctions for geographic area licenses in the 800 MHz and 900 MHz
bands. The 900 MHz SMR auction began on December 5, 1995, and closed on
April 15, 1996. Sixty bidders claiming that they qualified as small
businesses under the $15 million size standard won 263 geographic area
licenses in the 900 MHz SMR band. The 800 MHz SMR auction for the upper
200 channels began on October 28, 1997, and was completed on December
8, 1997. Ten bidders claiming that they qualified as small businesses
under the $15 million size standard won 38 geographic area licenses for
the upper 200 channels in the 800 MHz SMR band. A second auction for
the 800 MHz band was held
[[Page 59228]]
on January 10, 2002 and closed on January 17, 2002 and included 23 BEA
licenses. One bidder claiming small business status won five licenses.
The auction of the 1,053 800 MHz SMR geographic area licenses for
the General Category channels began on August 16, 2000, and was
completed on September 1, 2000. Eleven bidders won 108 geographic area
licenses for the General Category channels in the 800 MHz SMR band and
qualified as small businesses under the $15 million size standard. In
an auction completed on December 5, 2000, a total of 2,800 Economic
Area licenses in the lower 80 channels of the 800 MHz SMR service were
awarded. Of the 22 winning bidders, 19 claimed small business status
and won 129 licenses. Thus, combining all four auctions, 41 winning
bidders for geographic licenses in the 800 MHz SMR band claimed status
as small businesses.
In addition, there are numerous incumbent site-by-site SMR licenses
and licensees with extended implementation authorizations in the 800
and 900 MHz bands. We do not know how many firms provide 800 MHz or 900
MHz geographic area SMR service pursuant to extended implementation
authorizations, nor how many of these providers have annual revenues of
no more than $15 million. In addition, we do not know how many of these
firms have 1,500 or fewer employees, which is the SBA-determined size
standard. We assume, for purposes of this analysis, that all of the
remaining extended implementation authorizations are held by small
entities, as defined by the SBA.
Lower 700 MHz Band Licenses. The Commission previously adopted
criteria for defining three groups of small businesses for purposes of
determining their eligibility for special provisions such as bidding
credits. The Commission defined a ``small business'' as an entity that,
together with its affiliates and controlling principals, has average
gross revenues not exceeding $40 million for the preceding three years.
A ``very small business'' is defined as an entity that, together with
its affiliates and controlling principals, has average gross revenues
that are not more than $15 million for the preceding three years.
Additionally, the lower 700 MHz Service had a third category of small
business status for Metropolitan/Rural Service Area (MSA/RSA)
licenses--``entrepreneur''--which is defined as an entity that,
together with its affiliates and controlling principals, has average
gross revenues that are not more than $3 million for the preceding
three years. The SBA approved these small size standards. An auction of
740 licenses (one license in each of the 734 MSAs/RSAs and one license
in each of the six Economic Area Groupings (EAGs)) commenced on August
27, 2002, and closed on September 18, 2002. Of the 740 licenses
available for auction, 484 licenses were won by 102 winning bidders.
Seventy-two of the winning bidders claimed small business, very small
business or entrepreneur status and won a total of 329 licenses. A
second auction commenced on May 28, 2003, closed on June 13, 2003, and
included 256 licenses: 5 EAG licenses and 476 Cellular Market Area
licenses. Seventeen winning bidders claimed small or very small
business status and won 60 licenses, and nine winning bidders claimed
entrepreneur status and won 154 licenses. On July 26, 2005, the
Commission completed an auction of 5 licenses in the Lower 700 MHz band
(Auction No. 60). There were three winning bidders for five licenses.
All three winning bidders claimed small business status.
In 2007, the Commission reexamined its rules governing the 700 MHz
band in the 700 MHz Second Report and Order. An auction of 700 MHz
licenses commenced January 24, 2008 and closed on March 18, 2008, which
included, 176 Economic Area licenses in the A Block, 734 Cellular
Market Area licenses in the B Block, and 176 EA licenses in the E
Block. Twenty winning bidders, claiming small business status (those
with attributable average annual gross revenues that exceed $15 million
and do not exceed $40 million for the preceding three years) won 49
licenses. Thirty three winning bidders claiming very small business
status (those with attributable average annual gross revenues that do
not exceed $15 million for the preceding three years) won 325 licenses.
Upper 700 MHz Band Licenses. In the 700 MHz Second Report and
Order, the Commission revised its rules regarding Upper 700 MHz
licenses. On January 24, 2008, the Commission commenced Auction 73 in
which several licenses in the Upper 700 MHz band were available for
licensing: 12 Regional Economic Area Grouping licenses in the C Block,
and one nationwide license in the D Block. The auction concluded on
March 18, 2008, with 3 winning bidders claiming very small business
status (those with attributable average annual gross revenues that do
not exceed $15 million for the preceding three years) and winning five
licenses.
700 MHz Guard Band Licensees. In 2000, in the 700 MHz Guard Band
Order, the Commission adopted size standards for ``small businesses''
and ``very small businesses'' for purposes of determining their
eligibility for special provisions such as bidding credits and
installment payments. A small business in this service is an entity
that, together with its affiliates and controlling principals, has
average gross revenues not exceeding $40 million for the preceding
three years. Additionally, a very small business is an entity that,
together with its affiliates and controlling principals, has average
gross revenues that are not more than $15 million for the preceding
three years. SBA approval of these definitions is not required. An
auction of 52 Major Economic Area licenses commenced on September 6,
2000, and closed on September 21, 2000. Of the 104 licenses auctioned,
96 licenses were sold to nine bidders. Five of these bidders were small
businesses that won a total of 26 licenses. A second auction of 700 MHz
Guard Band licenses commenced on February 13, 2001, and closed on
February 21, 2001. All eight of the licenses auctioned were sold to
three bidders. One of these bidders was a small business that won a
total of two licenses.
Air-Ground Radiotelephone Service. The Commission has previously
used the SBA's small business size standard applicable to Wireless
Telecommunications Carriers (except Satellite), i.e., an entity
employing no more than 1,500 persons. There are fewer than 10 licensees
in the Air-Ground Radiotelephone Service, and under that definition, we
estimate that almost all of them qualify as small entities under the
SBA definition. For purposes of assigning Air-Ground Radiotelephone
Service licenses through competitive bidding, the Commission has
defined ``small business'' as an entity that, together with controlling
interests and affiliates, has average annual gross revenues for the
preceding three years not exceeding $40 million. A ``very small
business'' is defined as an entity that, together with controlling
interests and affiliates, has average annual gross revenues for the
preceding three years not exceeding $15 million. These definitions were
approved by the SBA. In May 2006, the Commission completed an auction
of nationwide commercial Air-Ground Radiotelephone Service licenses in
the 800 MHz band (Auction No. 65). On June 2, 2006, the auction closed
with two winning bidders winning two Air-Ground Radiotelephone Services
licenses. Neither of the winning bidders claimed small business status.
AWS Services (1710-1755 MHz and 2110-2155 MHz bands (AWS-1); 1915-
[[Page 59229]]
1920 MHz, 1995-2000 MHz, 2020-2025 MHz and 2175-2180 MHz bands (AWS-2);
2155-2175 MHz band (AWS-3)). For the AWS-1 bands, the Commission has
defined a ``small business'' as an entity with average annual gross
revenues for the preceding three years not exceeding $40 million, and a
``very small business'' as an entity with average annual gross revenues
for the preceding three years not exceeding $15 million. For AWS-2 and
AWS-3, although we do not know for certain which entities are likely to
apply for these frequencies, we note that the AWS-1 bands are
comparable to those used for cellular service and personal
communications service. The Commission has not yet adopted size
standards for the AWS-2 or AWS-3 bands but proposes to treat both AWS-2
and AWS-3 similarly to broadband PCS service and AWS-1 service due to
the comparable capital requirements and other factors, such as issues
involved in relocating incumbents and developing markets, technologies,
and services.
3650-3700 MHz band. In March 2005, the Commission released a Report
and Order and Memorandum Opinion and Order that provides for
nationwide, non-exclusive licensing of terrestrial operations,
utilizing contention-based technologies, in the 3650 MHz band (i.e.,
3650-3700 MHz). As of April 2010, more than 1270 licenses have been
granted and more than 7433 sites have been registered. The Commission
has not developed a definition of small entities applicable to 3650-
3700 MHz band nationwide, non-exclusive licensees. However, we estimate
that the majority of these licensees are Internet Access Service
Providers (ISPs) and that most of those licensees are small businesses.
Fixed Microwave Services. Microwave services include common
carrier, private-operational fixed, and broadcast auxiliary radio
services. They also include the Local Multipoint Distribution Service
(LMDS), the Digital Electronic Message Service (DEMS), and the 24 GHz
Service, where licensees can choose between common carrier and non-
common carrier status. At present, there are approximately 31,428
common carrier fixed licensees and 79,732 private operational-fixed
licensees and broadcast auxiliary radio licensees in the microwave
services. There are approximately 120 LMDS licensees, three DEMS
licensees, and three 24 GHz licensees. The Commission has not yet
defined a small business with respect to microwave services. For
purposes of the IRFA, we will use the SBA's definition applicable to
Wireless Telecommunications Carriers (except satellite)--i.e., an
entity with no more than 1,500 persons. Under the present and prior
categories, the SBA has deemed a wireless business to be small if it
has 1,500 or fewer employees. For the category of Wireless
Telecommunications Carriers (except Satellite), preliminary data for
2007 show that there were 11,927 firms operating that year. While the
Census Bureau has not released data on the establishments broken down
by number of employees, we note that the Census Bureau lists total
employment for all firms in that sector at 281,262. Since all firms
with fewer than 1,500 employees are considered small, given the total
employment in the sector, we estimate that the vast majority of firms
using microwave services are small. We note that the number of firms
does not necessarily track the number of licensees. We estimate that
virtually all of the Fixed Microwave licensees (excluding broadcast
auxiliary licensees) would qualify as small entities under the SBA
definition.
Broadband Radio Service and Educational Broadband Service.
Broadband Radio Service systems, previously referred to as Multipoint
Distribution Service (MDS) and Multichannel Multipoint Distribution
Service (MMDS) systems, and ``wireless cable,'' transmit video
programming to subscribers and provide two-way high speed data
operations using the microwave frequencies of the Broadband Radio
Service (BRS) and Educational Broadband Service (EBS) (previously
referred to as the Instructional Television Fixed Service (ITFS)). In
connection with the 1996 BRS auction, the Commission established a
small business size standard as an entity that had annual average gross
revenues of no more than $40 million in the previous three calendar
years. The BRS auctions resulted in 67 successful bidders obtaining
licensing opportunities for 493 Basic Trading Areas (BTAs). Of the 67
auction winners, 61 met the definition of a small business. BRS also
includes licensees of stations authorized prior to the auction. At this
time, we estimate that of the 61 small business BRS auction winners, 48
remain small business licensees. In addition to the 48 small businesses
that hold BTA authorizations, there are approximately 392 incumbent BRS
licensees that are considered small entities. After adding the number
of small business auction licensees to the number of incumbent
licensees not already counted, we find that there are currently
approximately 440 BRS licensees that are defined as small businesses
under either the SBA or the Commission's rules. In 2009, the Commission
conducted Auction 86, the sale of 78 licenses in the BRS areas. The
Commission offered three levels of bidding credits: (i) A bidder with
attributed average annual gross revenues that exceed $15 million and do
not exceed $40 million for the preceding three years (small business)
will receive a 15 percent discount on its winning bid; (ii) a bidder
with attributed average annual gross revenues that exceed $3 million
and do not exceed $15 million for the preceding three years (very small
business) will receive a 25 percent discount on its winning bid; and
(iii) a bidder with attributed average annual gross revenues that do
not exceed $3 million for the preceding three years (entrepreneur) will
receive a 35 percent discount on its winning bid. Auction 86 concluded
in 2009 with the sale of 61 licenses. Of the ten winning bidders, two
bidders that claimed small business status won 4 licenses; one bidder
that claimed very small business status won three licenses; and two
bidders that claimed entrepreneur status won six licenses.
In addition, the SBA's Cable Television Distribution Services small
business size standard is applicable to EBS. There are presently 2,032
EBS licensees. All but 100 of these licenses are held by educational
institutions. Educational institutions are included in this analysis as
small entities. Thus, we estimate that at least 1,932 licensees are
small businesses. Since 2007, Cable Television Distribution Services
have been defined within the broad economic census category of Wired
Telecommunications Carriers; that category is defined as follows:
``This industry comprises establishments primarily engaged in operating
and/or providing access to transmission facilities and infrastructure
that they own and/or lease for the transmission of voice, data, text,
sound, and video using wired telecommunications networks. Transmission
facilities may be based on a single technology or a combination of
technologies.'' The SBA has developed a small business size standard
for this category, which is: all such firms having 1,500 or fewer
employees. To gauge small business prevalence for these cable services
we must, however, use the most current census data that are based on
the previous category of Cable and Other Program Distribution and its
associated size standard; that size standard was: all such firms having
$13.5 million or less in annual receipts. According to Census Bureau
data for 2002, there were a total of 1,191 firms
[[Page 59230]]
in this previous category that operated for the entire year. Of this
total, 1,087 firms had annual receipts of under $10 million, and 43
firms had receipts of $10 million or more but less than $25 million.
Thus, the majority of these firms can be considered small.
5. Satellite Service Providers
Satellite Telecommunications Providers. Two economic census
categories address the satellite industry. The first category has a
small business size standard of $15 million or less in average annual
receipts, under SBA rules. The second has a size standard of $25
million or less in annual receipts. The most current Census Bureau data
in this context, however, are from the (last) economic census of 2002,
and we will use those figures to gauge the prevalence of small
businesses in these categories.
The category of Satellite Telecommunications ``comprises
establishments primarily engaged in providing telecommunications
services to other establishments in the telecommunications and
broadcasting industries by forwarding and receiving communications
signals via a system of satellites or reselling satellite
telecommunications.'' For this category, Census Bureau data for 2002
show that there were a total of 371 firms that operated for the entire
year. Of this total, 307 firms had annual receipts of under $10
million, and 26 firms had receipts of $10 million to $24,999,999.
Consequently, we estimate that the majority of Satellite
Telecommunications firms are small entities that might be affected by
our action.
The second category of All Other Telecommunications comprises,
inter alia, ``establishments primarily engaged in providing specialized
telecommunications services, such as satellite tracking, communications
telemetry, and radar station operation. This industry also includes
establishments primarily engaged in providing satellite terminal
stations and associated facilities connected with one or more
terrestrial systems and capable of transmitting telecommunications to,
and receiving telecommunications from, satellite systems.'' For this
category, Census Bureau data for 2002 show that there were a total of
332 firms that operated for the entire year. Of this total, 303 firms
had annual receipts of under $10 million and 15 firms had annual
receipts of $10 million to $24,999,999. Consequently, we estimate that
the majority of All Other Telecommunications firms are small entities
that might be affected by our action.
6. Cable Service Providers
Because Section 706 requires us to monitor the deployment of
broadband regardless of technology or transmission media employed, we
anticipate that some broadband service providers may not provide
telephone service. Accordingly, we describe below other types of firms
that may provide broadband services, including cable companies, MDS
providers, and utilities, among others.
Cable and Other Program Distributors. Since 2007, these services
have been defined within the broad economic census category of Wired
Telecommunications Carriers; that category is defined as follows:
``This industry comprises establishments primarily engaged in operating
and/or providing access to transmission facilities and infrastructure
that they own and/or lease for the transmission of voice, data, text,
sound, and video using wired telecommunications networks. Transmission
facilities may be based on a single technology or a combination of
technologies.'' The SBA has developed a small business size standard
for this category, which is: all such firms having 1,500 or fewer
employees. To gauge small business prevalence for these cable services
we must, however, use current census data that are based on the
previous category of Cable and Other Program Distribution and its
associated size standard; that size standard was: all such firms having
$13.5 million or less in annual receipts. According to Census Bureau
data for 2002, there were a total of 1,191 firms in this previous
category that operated for the entire year. Of this total, 1,087 firms
had annual receipts of under $10 million, and 43 firms had receipts of
$10 million or more but less than $25 million. Thus, the majority of
these firms can be considered small.
Cable Companies and Systems. The Commission has also developed its
own small business size standards, for the purpose of cable rate
regulation. Under the Commission's rules, a ``small cable company'' is
one serving 400,000 or fewer subscribers, nationwide. Industry data
indicate that, of 1,076 cable operators nationwide, all but eleven are
small under this size standard. In addition, under the Commission's
rules, a ``small system'' is a cable system serving 15,000 or fewer
subscribers. Industry data indicate that, of 7,208 systems nationwide,
6,139 systems have under 10,000 subscribers, and an additional 379
systems have 10,000-19,999 subscribers. Thus, under this second size
standard, most cable systems are small.
Cable System Operators. The Communications Act of 1934, as amended,
also contains a size standard for small cable system operators, which
is ``a cable operator that, directly or through an affiliate, serves in
the aggregate fewer than 1 percent of all subscribers in the United
States and is not affiliated with any entity or entities whose gross
annual revenues in the aggregate exceed $250,000,000.'' The Commission
has determined that an operator serving fewer than 677,000 subscribers
shall be deemed a small operator, if its annual revenues, when combined
with the total annual revenues of all its affiliates, do not exceed
$250 million in the aggregate. Industry data indicate that, of 1,076
cable operators nationwide, all but ten are small under this size
standard. We note that the Commission neither requests nor collects
information on whether cable system operators are affiliated with
entities whose gross annual revenues exceed $250 million, and therefore
we are unable to estimate more accurately the number of cable system
operators that would qualify as small under this size standard.
7. Electric Power Generators, Transmitters, and Distributors
Electric Power Generators, Transmitters, and Distributors. The
Census Bureau defines an industry group comprised of ``establishments,
primarily engaged in generating, transmitting, and/or distributing
electric power. Establishments in this industry group may perform one
or more of the following activities: (1) Operate generation facilities
that produce electric energy; (2) operate transmission systems that
convey the electricity from the generation facility to the distribution
system; and (3) operate distribution systems that convey electric power
received from the generation facility or the transmission system to the
final consumer.'' The SBA has developed a small business size standard
for firms in this category: ``A firm is small if, including its
affiliates, it is primarily engaged in the generation, transmission,
and/or distribution of electric energy for sale and its total electric
output for the preceding fiscal year did not exceed 4 million megawatt
hours.'' According to Census Bureau data for 2002, there were 1,644
firms in this category that operated for the entire year. Census data
do not track electric output and we have not determined how many of
these firms fit the SBA size standard for small, with no more than 4
million megawatt hours of electric output. Consequently, we
[[Page 59231]]
estimate that 1,644 or fewer firms may be considered small under the
SBA small business size standard.
Description of Projected Reporting, Recordkeeping, and Other Compliance
Requirements for Small Entities
As indicated above, the Internet's legacy of openness and
transparency has been critical to its success as an engine for
creativity, innovation, and economic development. To help preserve this
fundamental character of the Internet, the Order requires that
broadband providers must, at a minimum, prominently display or provide
links to disclosures on a publicly available, easily accessible Web
site that is available to current and prospective end users and edge
providers as well as to the Commission, and at the point of sale.
Providers should ensure that all Web site disclosures are accessible by
persons with disabilities. We do not require additional forms of
disclosure. Broadband providers' disclosures to the public include
disclosure to the Commission; that is, the Commission will monitor
public disclosures and may require additional disclosures directly to
the Commission. We anticipate that broadband providers may be able to
satisfy the transparency rule through a single disclosure, and
therefore do not require multiple disclosures targeted at different
audiences. This affects all classes of small entities mentioned in
Appendix B, part C, and requires professional skills of entering
information onto a Web page and an understanding of the entities'
network practices, both of which are easily managed by staff of these
types of small entities.
Steps Taken To Minimize the Significant Economic Impact on Small
Entities, and Significant Alternatives Considered
The RFA requires an agency to describe any significant alternatives
that it has considered in reaching its proposed approach, which may
include (among others) the following four alternatives: (1) The
establishment of differing compliance or reporting requirements or
timetables that take into account the resources available to small
entities; (2) the clarification, consolidation, or simplification of
compliance or reporting requirements under the rule for small entities;
(3) the use of performance, rather than design, standards; and (4) an
exemption from coverage of the rule, or any part thereof, for small
entities.
The rules adopted in this Order are generally consistent with
current industry practices, so the costs of compliance should be small.
Although some commenters assert that a disclosure rule will impose
significant burdens on broadband providers, no commenter cites any
particular source of increased costs, or attempts to estimate costs of
compliance. For a number of reasons, we believe that the costs of the
disclosure rule we adopt in this Order are outweighed by the benefits
of empowering end users to make informed choices and of facilitating
the enforcement of the other open Internet rules. First, we require
only that providers post disclosures on their Web sites and at the
point of sale, not that they bear the cost of printing and distributing
bill inserts or other paper documents to all existing customers.
Second, although we may subsequently determine that it is appropriate
to require that specific information be disclosed in particular ways,
the transparency rule we adopt in this Order gives broadband providers
flexibility to determine what information to disclose and how to
disclose it. We also expressly exclude from the rule competitively
sensitive information, information that would compromise network
security, and information that would undermine the efficacy of
reasonable network management practices. Third, by setting the
effective date of these rules as November 20, 2011, we give broadband
providers adequate time to develop cost effective methods of
compliance. Thus, the rule gives broadband providers--including small
entities--sufficient time and flexibility to implement the rules in a
cost-effective manner. Finally, these rules provide certainty and
clarity that are beneficial both to broadband providers and to their
customers.
Report to Congress
The Commission has sent a copy of the Order, including this FRFA,
in a report to Congress and the Government Accountability Office
pursuant to the Congressional Review Act. In addition, the Commission
will send a copy of the Order, including this FRFA, to the Chief
Counsel for Advocacy of the SBA.
B. Paperwork Reduction Act of 1995 Analysis
This document contains new information collection requirements
subject to the Paperwork Reduction Act of 1995 (PRA), Public Law 104-
13.
C. Congressional Review Act
The Commission has sent a copy of this Report and Order to Congress
and the Government Accountability Office pursuant to the Congressional
Review Act, see 5 U.S.C. 801(a)(1)(A).
D. Data Quality Act
The Commission certifies that it has complied with the Office of
Management and Budget Final Information Quality Bulletin for Peer
Review, 70 FR 2664, January 14 (2005), and the Data Quality Act, Public
Law 106-554 (2001), codified at 44 U.S.C. 3516 note, with regard to its
reliance on influential scientific information in the Report and Order
in GN Docket No. 09-191 and WC Docket No. 07-52.
E. Accessible Formats
To request materials in accessible formats for people with
disabilities (braille, large print, electronic files, audio format),
send an e-mail to fcc504@fcc.gov or call the Consumer & Governmental
Affairs Bureau at 202-418-0530 (voice), 202-418-0432 (tty). Contact the
FCC to request reasonable accommodations for filing comments
(accessible format documents, sign language interpreters, CARTS, etc.)
by e-mail: FCC504@fcc.gov; phone: (202) 418-0530 (voice), (202) 418-
0432 (TTY).
VIII. Ordering Clauses
Accordingly, it is ordered that, pursuant to Sections 1, 2, 3, 4,
201, 218, 230, 251, 254, 256, 257, 301, 303, 304, 307, 309, 316, 332,
403, 503, 602, 616, and 628, of the Communications Act of 1934, as
amended, and Section 706 of the Telecommunications Act of 1996, as
amended, 47 U.S.C. secs. 151, 152, 153, 154, 201, 218, 230, 251, 254,
256, 257, 301, 303, 304, 307, 309, 316, 332, 403, 503, 522, 536, 548,
1302, this Report and Order is adopted.
It is further ordered that Part 0 of the Commission's rules is
amended as set forth in Appendix B.
It is further ordered that Part 8 of the Commission's Rules, 47 CFR
Part 8, is added as set forth in Appendix A and B.
It is further ordered that this Report and Order shall become
effective November 20, 2011.
It is further ordered that the Commission's Consumer and
Governmental Affairs Bureau, Reference Information Center, shall send a
copy of this Report and Order, including the Final Regulatory
Flexibility Analysis, to the Chief Counsel for Advocacy of the Small
Business Administration.
List of Subjects
47 CFR Part 0
Cable television, Communications, Common carriers, Communications
common carriers, Radio, Satellites, Telecommunications, Telephone.
[[Page 59232]]
47 CFR Part 8
Cable television, Communications, Common carriers, Communications
common carriers, Radio, Satellites, Telecommunications, Telephone.
Federal Communications Commission.
Marlene H. Dortch,
Secretary.
For the reasons discussed in the preamble, the Federal
Communications Commission amends 47 CFR part 0 to read as follows:
PART 0--COMMISSION ORGANIZATION
0
1. The authority citation for part 0 continues to read as follows:
Authority: Sec. 5, 48 Stat. 1068, as amended; 47 U.S.C. 155,
225, unless otherwise noted.
0
2. Section 0.111 is amended by adding paragraph (a)(24) to read as
follows:
Sec. 0.111 Functions of the Bureau.
(a) * * *
(24) Resolve complaints alleging violations of the open Internet
rules.
* * * * *
0
3. Add part 8 to read as follows:
PART 8--PRESERVING THE OPEN INTERNET
Sec.
8.1 Purpose.
8.3 Transparency.
8.5 No Blocking.
8.7 No Unreasonable Discrimination.
8.9 Other Laws and Considerations.
8.11 Definitions.
8.12 Formal Complaints.
8.13 General pleading requirements.
8.14 General formal complaint procedures.
8.15 Status conference.
8.16 Confidentiality of proprietary information.
8.17 Review.
Authority: 47 U.S.C. secs. 151, 152, 153, 154, 201, 218, 230,
251, 254, 256, 257, 301, 303, 304, 307, 309, 316, 332, 403, 503,
522, 536, 548, 1302.
Sec. 8.1 Purpose.
The purpose of this part is to preserve the Internet as an open
platform enabling consumer choice, freedom of expression, end-user
control, competition, and the freedom to innovate without permission.
Sec. 8.3 Transparency.
A person engaged in the provision of broadband Internet access
service shall publicly disclose accurate information regarding the
network management practices, performance, and commercial terms of its
broadband Internet access services sufficient for consumers to make
informed choices regarding use of such services and for content,
application, service, and device providers to develop, market, and
maintain Internet offerings.
Sec. 8.5 No Blocking.
(a) A person engaged in the provision of fixed broadband Internet
access service, insofar as such person is so engaged, shall not block
lawful content, applications, services, or non-harmful devices, subject
to reasonable network management.
(b) A person engaged in the provision of mobile broadband Internet
access service, insofar as such person is so engaged, shall not block
consumers from accessing lawful Web sites, subject to reasonable
network management; nor shall such person block applications that
compete with the provider's voice or video telephony services, subject
to reasonable network management.
Sec. 8.7 No Unreasonable Discrimination.
A person engaged in the provision of fixed broadband Internet
access service, insofar as such person is so engaged, shall not
unreasonably discriminate in transmitting lawful network traffic over a
consumer's broadband Internet access service. Reasonable network
management shall not constitute unreasonable discrimination.
Sec. 8.9 Other Laws and Considerations.
(a) Nothing in this part supersedes any obligation or authorization
a provider of broadband Internet access service may have to address the
needs of emergency communications or law enforcement, public safety, or
national security authorities, consistent with or as permitted by
applicable law, or limits the provider's ability to do so.
(b) Nothing in this part prohibits reasonable efforts by a provider
of broadband Internet access service to address copyright infringement
or other unlawful activity.
Sec. 8.11 Definitions.
(a) Broadband Internet access service. A mass-market retail service
by wire or radio that provides the capability to transmit data to and
receive data from all or substantially all Internet endpoints,
including any capabilities that are incidental to and enable the
operation of the communications service, but excluding dial-up Internet
access service. This term also encompasses any service that the
Commission finds to be providing a functional equivalent of the service
described in the previous sentence, or that is used to evade the
protections set forth in this part.
(b) Fixed broadband Internet access service. A broadband Internet
access service that serves end users primarily at fixed endpoints using
stationary equipment. Fixed broadband Internet access service includes
fixed wireless services (including fixed unlicensed wireless services),
and fixed satellite services.
(c) Mobile broadband Internet access service. A broadband Internet
access service that serves end users primarily using mobile stations.
(d) Reasonable network management. A network management practice is
reasonable if it is appropriate and tailored to achieving a legitimate
network management purpose, taking into account the particular network
architecture and technology of the broadband Internet access service.
Sec. 8.12 Formal Complaints.
Any person may file a formal complaint alleging a violation of the
rules in this part.
Sec. 8.13 General pleading requirements.
(a) General pleading requirements. All written submissions, both
substantive and procedural, must conform to the following standards:
(1) A pleading must be clear, concise, and explicit. All matters
concerning a claim, defense or requested remedy should be pleaded fully
and with specificity.
(2) Pleadings must contain facts that, if true, are sufficient to
warrant a grant of the relief requested.
(3) Facts must be supported by relevant documentation or affidavit.
(4) The original of all pleadings and submissions by any party
shall be signed by that party, or by the party's attorney. Complaints
must be signed by the complainant. The signing party shall state his or
her address and telephone number and the date on which the document was
signed. Copies should be conformed to the original. Each submission
must contain a written verification that the signatory has read the
submission and to the best of his or her knowledge, information and
belief formed after reasonable inquiry, it is well grounded in fact and
is warranted by existing law or a good faith argument for the
extension, modification or reversal of existing law; and that it is not
interposed for any improper purpose. If any pleading or other
submission is signed in violation of this provision, the Commission
shall upon motion or upon its own initiative impose appropriate
sanctions.
(5) Legal arguments must be supported by appropriate judicial,
Commission, or statutory authority.
[[Page 59233]]
Opposing authorities must be distinguished. Copies must be provided of
all non-Commission authorities relied upon which are not routinely
available in national reporting systems, such as unpublished decisions
or slip opinions of courts or administrative agencies.
(6) Parties are responsible for the continuing accuracy and
completeness of all information and supporting authority furnished in a
pending complaint proceeding. Information submitted, as well as
relevant legal authorities, must be current and updated as necessary
and in a timely manner at any time before a decision is rendered on the
merits of the complaint.
(7) Parties seeking expedited resolution of their complaint may
request acceptance on the Enforcement Bureau's Accelerated Docket
pursuant to the procedures at Sec. 1.730 of this chapter.
(b) Copies to be Filed. The complainant shall file an original copy
of the complaint, accompanied by the correct fee, in accordance with
part 1, subpart G (see Sec. 1.1106 of this chapter) and, on the same
day:
(1) File three copies of the complaint with the Office of the
Commission Secretary;
(2) Serve two copies on the Market Disputes Resolution Division,
Enforcement Bureau;
(3) Serve the complaint by hand delivery on either the named
defendant or one of the named defendant's registered agents for service
of process, if available, on the same date that the complaint is filed
with the Commission.
(c) Prefiling notice required. Any person intending to file a
complaint under this section must first notify the potential defendant
in writing that it intends to file a complaint with the Commission
based on actions alleged to violate one or more of the provisions
contained in this part. The notice must be sufficiently detailed so
that its recipient(s) can determine the specific nature of the
potential complaint. The potential complainant must allow a minimum of
ten (10) days for the potential defendant(s) to respond before filing a
complaint with the Commission.
(d) Frivolous pleadings. It shall be unlawful for any party to file
a frivolous pleading with the Commission. Any violation of this
paragraph shall constitute an abuse of process subject to appropriate
sanctions.
Sec. 8.14 General formal complaint procedures.
(a) Complaints. In addition to the general pleading requirements,
complaints must adhere to the following requirements:
(1) Certificate of service. Complaints shall be accompanied by a
certificate of service on any defendant.
(2) Statement of relief requested--(i) The complaint shall state
the relief requested. It shall state fully and precisely all pertinent
facts and considerations relied on to demonstrate the need for the
relief requested and to support a determination that a grant of such
relief would serve the public interest.
(ii) The complaint shall set forth all steps taken by the parties
to resolve the problem.
(iii) A complaint may, on request of the filing party, be dismissed
without prejudice as a matter of right prior to the adoption date of
any final action taken by the Commission with respect to the petition
or complaint. A request for the return of an initiating document will
be regarded as a request for dismissal.
(3) Failure to prosecute. Failure to prosecute a complaint, or
failure to respond to official correspondence or request for additional
information, will be cause for dismissal. Such dismissal will be
without prejudice if it occurs prior to the adoption date of any final
action taken by the Commission with respect to the initiating pleading.
(b) Answers to complaints. Unless otherwise directed by the
Commission, any party who is served with a complaint shall file an
answer in accordance with the following requirements:
(1) The answer shall be filed within 20 days of service of the
complaint.
(2) The answer shall advise the parties and the Commission fully
and completely of the nature of any and all defenses, and shall respond
specifically to all material allegations of the complaint. Collateral
or immaterial issues shall be avoided in answers and every effort
should be made to narrow the issues. Any party against whom a complaint
is filed failing to file and serve an answer within the time and in the
manner prescribed by these rules may be deemed in default and an order
may be entered against defendant in accordance with the allegations
contained in the complaint.
(3) Facts must be supported by relevant documentation or affidavit.
(4) The answer shall admit or deny the averments on which the
adverse party relies. If the defendant is without knowledge or
information sufficient to form a belief as to the truth of an averment,
the defendant shall so state and this has the effect of a denial. When
a defendant intends in good faith to deny only part of an averment, the
answer shall specify so much of it as is true and shall deny only the
remainder, and state in detail the basis of that denial.
(5) Averments in a complaint are deemed to be admitted when not
denied in the answer.
(c) Reply. In addition to the general pleading requirements,
replies must adhere to the following requirements:
(1) The complainant may file a reply to a responsive pleading that
shall be served on the defendant and shall also contain a detailed full
showing, supported by affidavit, of any additional facts or
considerations relied on. Unless expressly permitted by the Commission,
replies shall not contain new matters.
(2) Failure to reply will not be deemed an admission of any
allegations contained in the responsive pleading, except with respect
to any affirmative defense set forth therein.
(3) Unless otherwise directed by the Commission, replies must be
filed within ten (10) days after submission of the responsive pleading.
(d) Motions. Except as provided in this section, or upon a showing
of extraordinary circumstances, additional motions or pleadings by any
party will not be accepted.
(e) Additional procedures and written submissions. (1) The
Commission may specify other procedures, such as oral argument or
evidentiary hearing directed to particular aspects, as it deems
appropriate. In the event that an evidentiary hearing is required, the
Commission will determine, on the basis of the pleadings and such other
procedures as it may specify, whether temporary relief should be
afforded any party pending the hearing and the nature of any such
temporary relief.
(2) The Commission may require the parties to submit any additional
information it deems appropriate for a full, fair, and expeditious
resolution of the proceeding, including copies of all contracts and
documents reflecting arrangements and understandings alleged to violate
the requirements set forth in the Communications Act and in this part,
as well as affidavits and exhibits.
(3) The Commission may, in its discretion, require the parties to
file briefs summarizing the facts and issues presented in the pleadings
and other record evidence.
(i) These briefs shall contain the findings of fact and conclusions
of law which that party is urging the Commission to adopt, with
specific citations to the record, and supported by relevant authority
and analysis.
(ii) The schedule for filing any briefs shall be at the discretion
of the Commission. Unless ordered otherwise
[[Page 59234]]
by the Commission, such briefs shall not exceed fifty (50) pages.
(iii) Reply briefs may be submitted at the discretion of the
Commission. Unless ordered otherwise by the Commission, reply briefs
shall not exceed thirty (30) pages.
(f) Discovery. (1) The Commission may in its discretion order
discovery limited to the issues specified by the Commission. Such
discovery may include answers to written interrogatories, depositions,
document production, or requests for admissions.
(2) The Commission may in its discretion direct the parties to
submit discovery proposals, together with a memorandum in support of
the discovery requested. Such discovery requests may include answers to
written interrogatories, admissions, document production, or
depositions. The Commission may hold a status conference with the
parties, pursuant to Sec. 8.15, to determine the scope of discovery,
or direct the parties regarding the scope of discovery. If the
Commission determines that extensive discovery is required or that
depositions are warranted, the Commission may advise the parties that
the proceeding will be referred to an administrative law judge in
accordance with paragraph (g) of this section.
(g) Referral to administrative law judge. (1) After reviewing the
pleadings, and at any stage of the proceeding thereafter, the
Commission may, in its discretion, designate any proceeding or discrete
issues arising out of any proceeding for an adjudicatory hearing before
an administrative law judge.
(2) Before designation for hearing, the Commission shall notify,
either orally or in writing, the parties to the proceeding of its
intent to so designate, and the parties shall be given a period of ten
(10) days to elect to resolve the dispute through alternative dispute
resolution procedures, or to proceed with an adjudicatory hearing. Such
election shall be submitted in writing to the Commission.
(3) Unless otherwise directed by the Commission, or upon motion by
the Enforcement Bureau Chief, the Enforcement Bureau Chief shall not be
deemed to be a party to a proceeding designated for a hearing before an
administrative law judge pursuant to this paragraph (g).
(h) Commission ruling. The Commission (or the Enforcement Bureau on
delegated authority), after consideration of the pleadings, shall issue
an order ruling on the complaint.
Sec. 8.15 Status conference.
(a) In any proceeding subject to the part 8 rules, the Commission
may in its discretion direct the attorneys and/or the parties to appear
for a conference to consider:
(1) Simplification or narrowing of the issues;
(2) The necessity for or desirability of amendments to the
pleadings, additional pleadings, or other evidentiary submissions;
(3) Obtaining admissions of fact or stipulations between the
parties as to any or all of the matters in controversy;
(4) Settlement of the matters in controversy by agreement of the
parties;
(5) The necessity for and extent of discovery, including objections
to interrogatories or requests for written documents;
(6) The need and schedule for filing briefs, and the date for any
further conferences; and
(7) Such other matters that may aid in the disposition of the
proceeding.
(b) Any party may request that a conference be held at any time
after an initiating document has been filed.
(c) Conferences will be scheduled by the Commission at such time
and place as it may designate, to be conducted in person or by
telephone conference call.
(d) The failure of any attorney or party, following advance notice
with an opportunity to be present, to appear at a scheduled conference
will be deemed a waiver and will not preclude the Commission from
conferring with those parties or counsel present.
(e) During a status conference, the Commission may issue oral
rulings pertaining to a variety of matters relevant to the conduct of
the proceeding including, inter alia, procedural matters, discovery,
and the submission of briefs or other evidentiary materials. These
rulings will be promptly memorialized in writing and served on the
parties. When such rulings require a party to take affirmative action,
such action will be required within ten (10) days from the date of the
written memorialization unless otherwise directed by the Commission.
Sec. 8.16 Confidentiality of proprietary information.
(a) Any materials filed in the course of a proceeding under this
part may be designated as proprietary by that party if the party
believes in good faith that the materials fall within an exemption to
disclosure contained in the Freedom of Information Act (FOIA), 5 U.S.C.
552(b). Any party asserting confidentiality for such materials shall so
indicate by clearly marking each page, or portion thereof, for which a
proprietary designation is claimed. If a proprietary designation is
challenged, the party claiming confidentiality will have the burden of
demonstrating, by a preponderance of the evidence, that the material
designated as proprietary falls under the standards for nondisclosure
enunciated in FOIA.
(b) Submissions containing information claimed to be proprietary
under this section shall be submitted to the Commission in confidence
pursuant to the requirements of Sec. 0.459 of this chapter and clearly
marked ``Not for Public Inspection.'' An edited version removing all
proprietary data shall be filed with the Commission for inclusion in
the public file within five (5) days from the date the unedited reply
is submitted, and shall be served on the opposing parties.
(c) Except as provided in paragraph (d) of this section, materials
marked as proprietary may be disclosed solely to the following persons,
only for use in the proceeding, and only to the extent necessary to
assist in the prosecution or defense of the case:
(1) Counsel of record representing the parties in the proceeding
and any support personnel employed by such attorneys;
(2) Officers or employees of the parties in the proceeding who are
named by another party as being directly involved in the proceeding;
(3) Consultants or expert witnesses retained by the parties;
(4) The Commission and its staff; and
(5) Court reporters and stenographers in accordance with the terms
and conditions of this section.
(d) The Commission will entertain, subject to a proper showing, a
party's request to further restrict access to proprietary information
as specified by the party. The other parties will have an opportunity
to respond to such requests.
(e) The persons designated in paragraphs (c) and (d) of this
section shall not disclose information designated as proprietary to any
person who is not authorized under this section to receive such
information, and shall not use the information in any activity or
function other than the prosecution or defense of the case before the
Commission. Each individual who is provided access to the information
by the opposing party shall sign a notarized statement affirmatively
stating, or shall certify under penalty of perjury, that the individual
has personally reviewed the Commission's rules and understands the
limitations they impose on the signing party.
(f) No copies of materials marked proprietary may be made except
copies
[[Page 59235]]
to be used by persons designated in paragraphs (c) and (d) of this
section. Each party shall maintain a log recording the number of copies
made of all proprietary material and the persons to whom the copies
have been provided.
(g) Upon termination of the complaint proceeding, including all
appeals and petitions, all originals and reproductions of any
proprietary materials, along with the log recording persons who
received copies of such materials, shall be provided to the producing
party. In addition, upon final termination of the proceeding, any notes
or other work product derived in whole or in part from the proprietary
materials of an opposing or third party shall be destroyed.
Sec. 8.17 Review.
(a) Interlocutory review. (1) Except as provided below, no party
may seek review of interlocutory rulings until a decision on the merits
has been issued by the Commission's staff, including an administrative
law judge.
(2) Rulings listed in this paragraph are reviewable as a matter of
right. An application for review of such ruling may not be deferred and
raised as an exception to a decision on the merits.
(i) If the staff's ruling denies or terminates the right of any
person to participate as a party to the proceeding, such person, as a
matter of right, may file an application for review of that ruling.
(ii) If the staff's ruling requires production of documents or
other written evidence, over objection based on a claim of privilege,
the ruling on the claim of privilege is reviewable as a matter of
right.
(iii) If the staff's ruling denies a motion to disqualify a staff
person from participating in the proceeding, the ruling is reviewable
as a matter of right.
(b) Petitions for reconsideration. Petitions for reconsideration of
interlocutory actions by the Commission's staff or by an administrative
law judge will not be entertained. Petitions for reconsideration of a
decision on the merits made by the Commission's staff should be filed
in accordance with Sec. Sec. 1.104 through 1.106 of this chapter.
(c) Application for review. (1) Any party to a part 8 proceeding
aggrieved by any decision on the merits issued by the staff pursuant to
delegated authority may file an application for review by the
Commission in accordance with Sec. 1.115 of this chapter.
(2) Any party to a part 8 proceeding aggrieved by any decision on
the merits by an administrative law judge may file an appeal of the
decision directly with the Commission, in accordance with Sec. Sec.
1.276(a) and 1.277(a) through (c) of this chapter.
[FR Doc. 2011-24259 Filed 9-22-11; 8:45 am]
BILLING CODE 6712-01-P







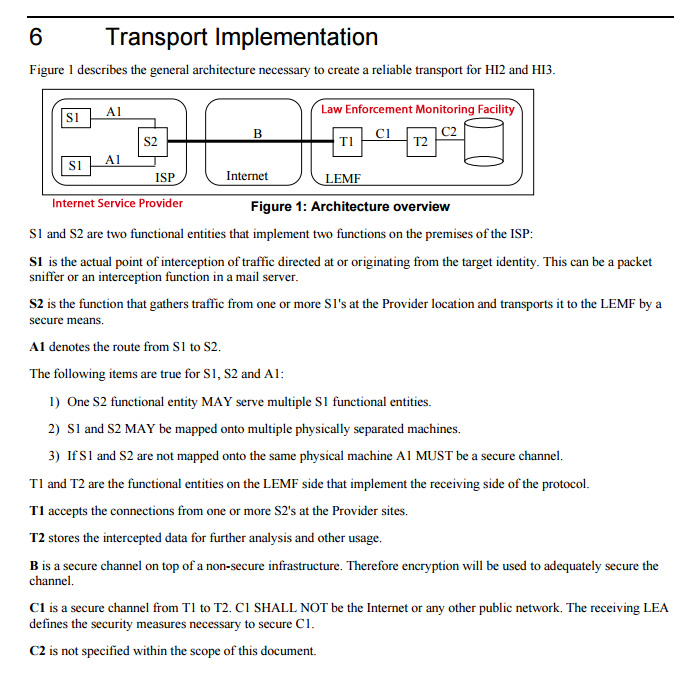
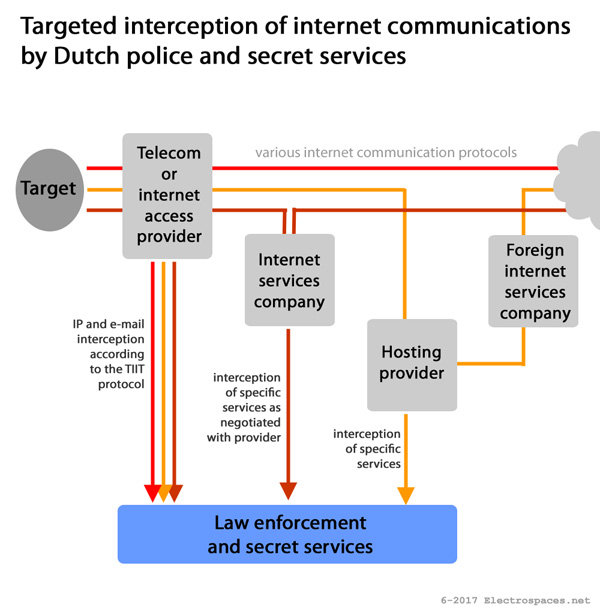



4 comments:
Anonymous said…
Anonymous said…
see here said…
cyberzon said…
Post a Comment