Become a Patron!
True Information is the most valuable resource and we ask you to give back.
Date: September 2015
Restriction: None
Originating Organization: National Security Agency
File Type: pdf
File Size: 1,653,564 bytes
File Hash (SHA-256): 156ED749C29E087C5698C8843C3FB39458A7F960C616EE12FE60818968DB068D
SHARKSEER
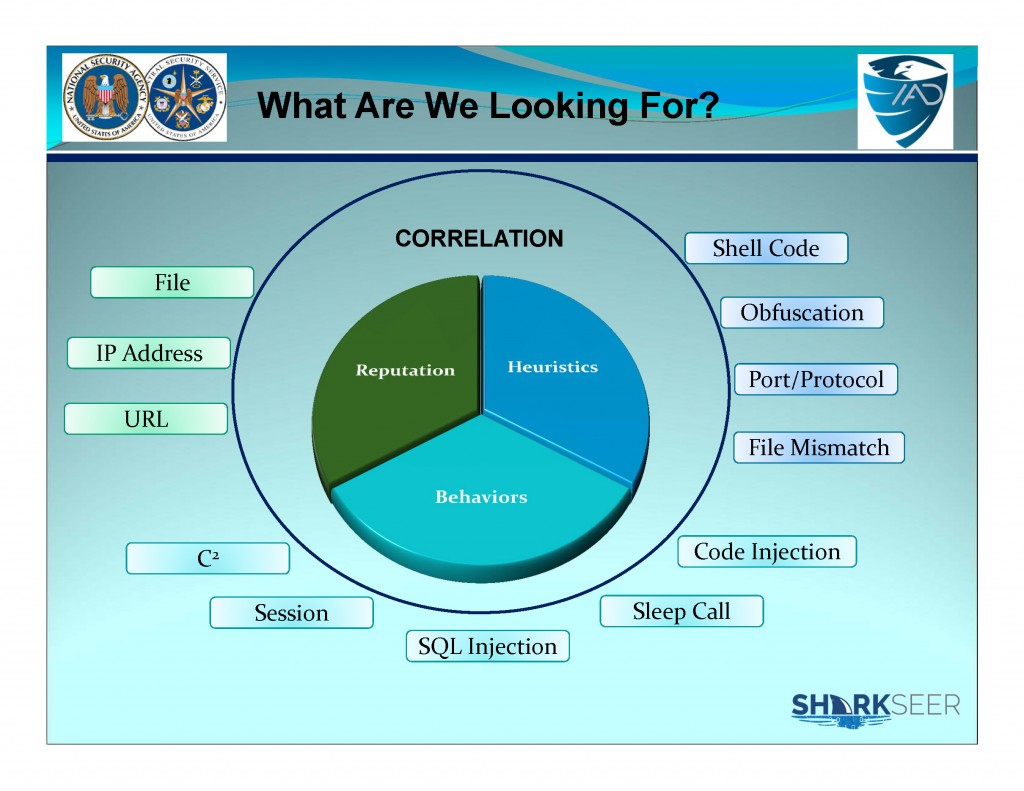
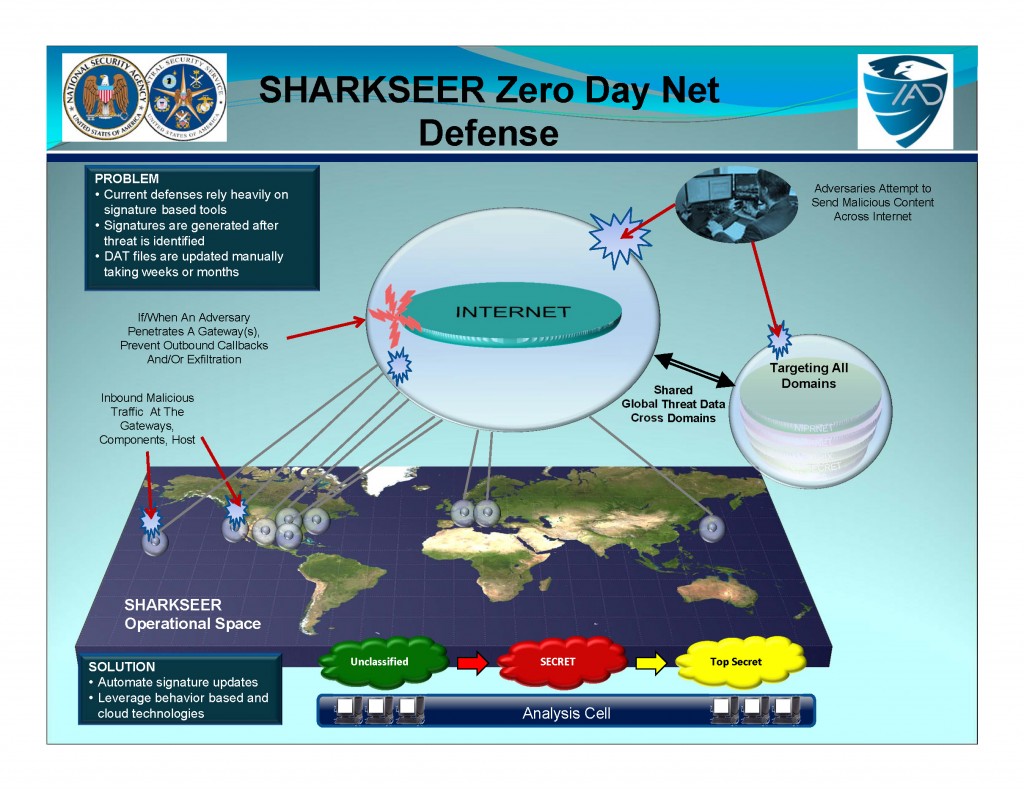
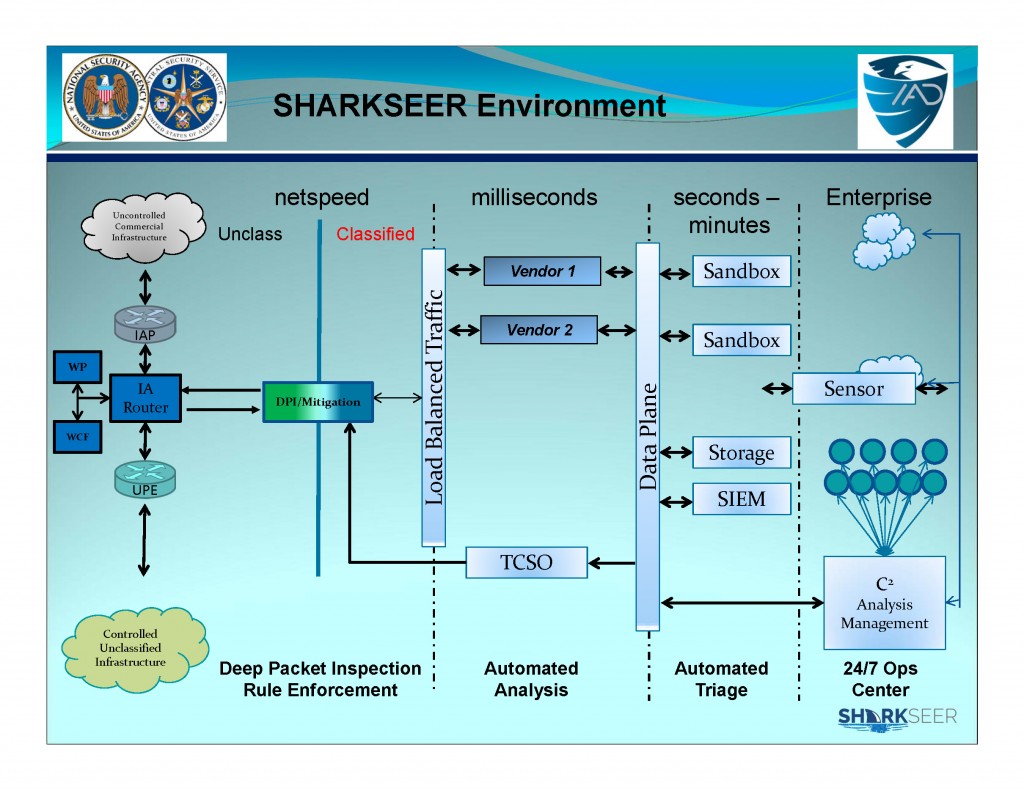
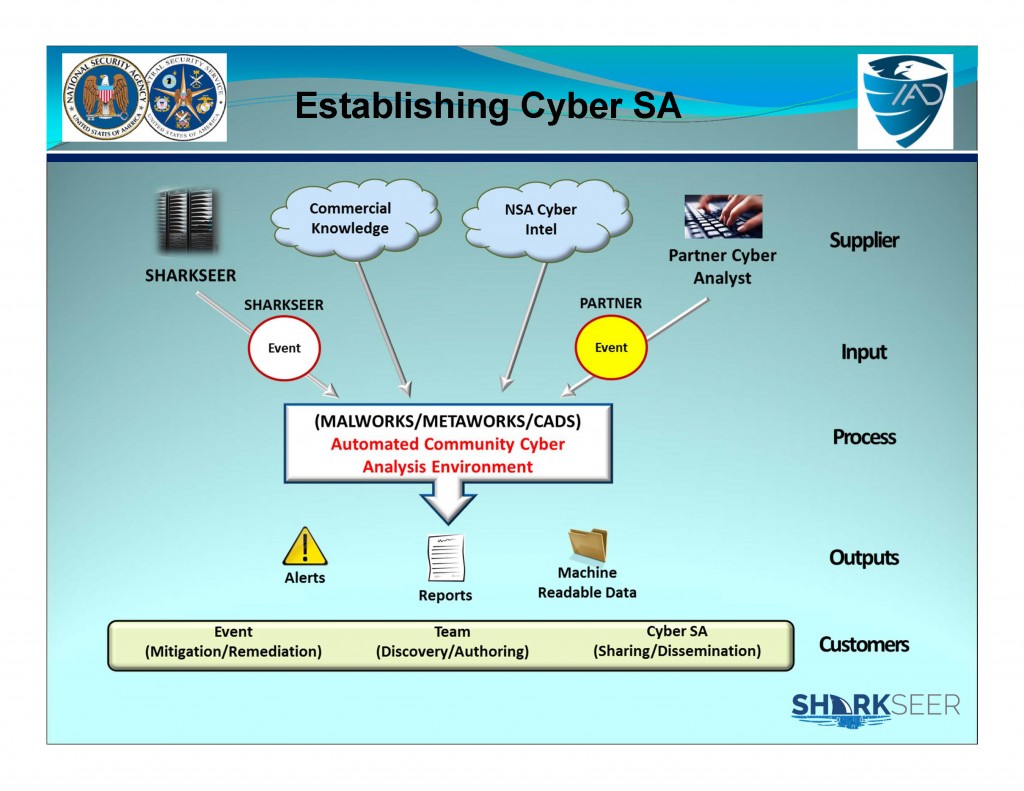
Program Definition: Detects and mitigates web-based malware Zero-Day and Advanced Persistent Threats using COTS technology by leveraging, dynamically producing, and enhancing global threat knowledge to rapidly protect the networks.
SHARKSEER’s GOALS
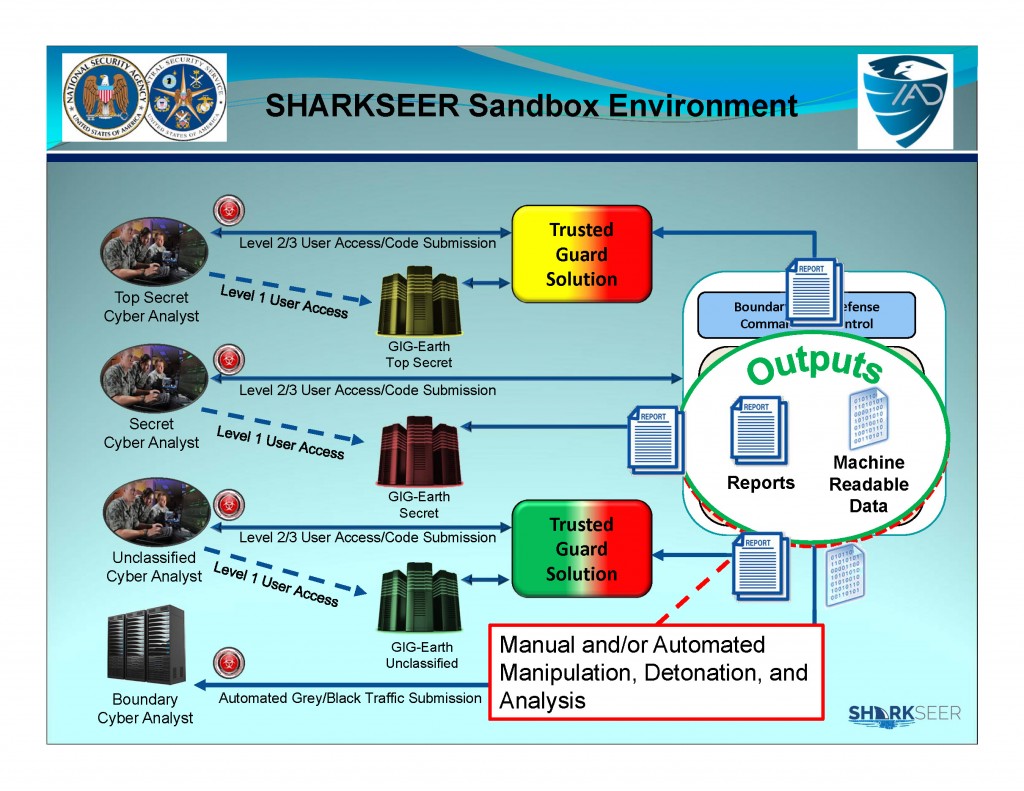
IAP Protection: Provide highly available and reliable automated sensing and mitigation capabilities to all 10 DOD IAPs. Commercial behavioral and heuristic analytics and threat data enriched with NSA unique knowledge, through automated data analysis processes, form the basis for discovery and mitigation.
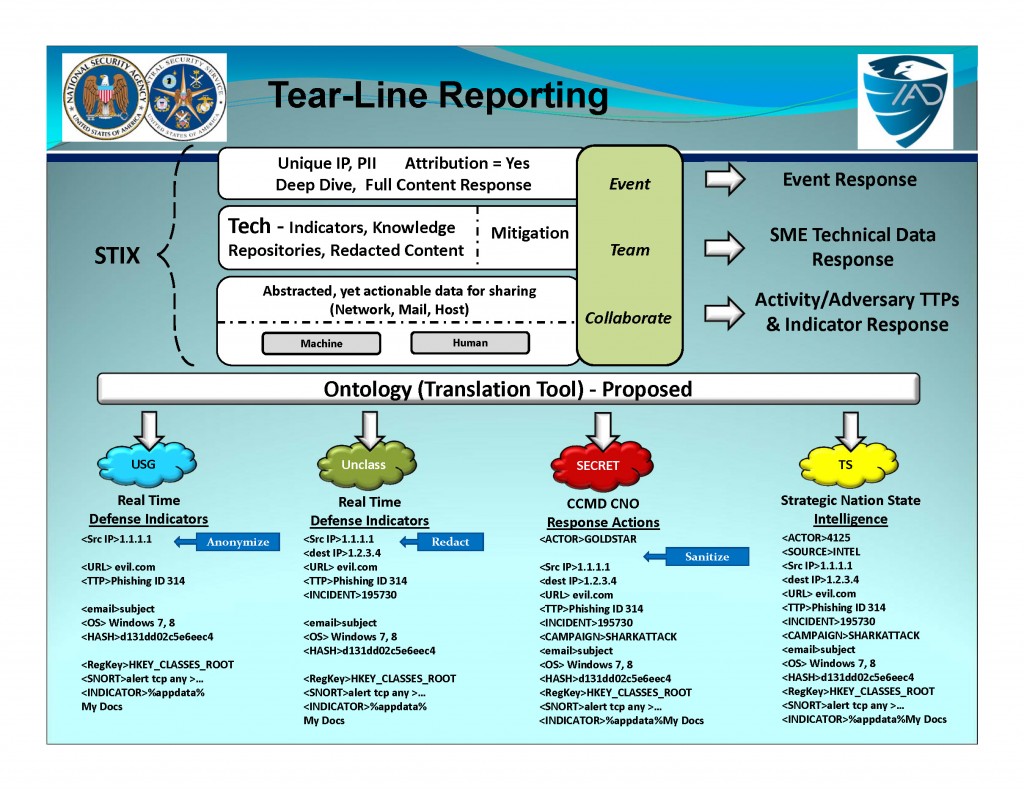
Cyber Situational Awareness and Data Sharing: Consume public malware threat data, enrich with NSA unique knowledge and processes. Share with partners through automation systems, for example the SHARKSEER Global Threat Intelligence (GTI) and SPLUNK systems. The data will be shared in real time with stakeholders and network defenders on UNCLASSIFIED, U//FOUO, SECRET, and TOP SECRET networks.
…


You must be logged in to post a comment.